Académique Documents
Professionnel Documents
Culture Documents
Cracker Guide 2.2
Transféré par
MgKAG0 évaluation0% ont trouvé ce document utile (0 vote)
405 vues547 pagesCopyright
© Attribution Non-Commercial (BY-NC)
Formats disponibles
PDF, TXT ou lisez en ligne sur Scribd
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Attribution Non-Commercial (BY-NC)
Formats disponibles
Téléchargez comme PDF, TXT ou lisez en ligne sur Scribd
0 évaluation0% ont trouvé ce document utile (0 vote)
405 vues547 pagesCracker Guide 2.2
Transféré par
MgKAGDroits d'auteur :
Attribution Non-Commercial (BY-NC)
Formats disponibles
Téléchargez comme PDF, TXT ou lisez en ligne sur Scribd
Vous êtes sur la page 1sur 547
pum;rdwfquf
Cracker .._,' ._.... ..- cracking reverse engineering, .-.-`.
-. .- .. ...... .,.. ...-- ._ . . ` . - .` .`.. ._ Reverse engineering
-... -. `.. ... cracking _.. ._ , ,- , -. `, ._ - - . ....
.-. ...... , . ....`..._ .-. ..- cracking - .- . ..... ... .
. . - ... .` - ...- .. ....... . .`..._
Cracking _..._ -,.-.-.- .-...`. ..... -..-..... `_
- .- . -.. ......` . -- _.._ - -. . .. ` ..-. `.. ._ Cracking ._ . -..
......`.. .,-.-`..._` .-........`. ..-.-...- ,.._.... ...
... _..`..`..-.-..-.. -.. ..., . - ... - , -.-.... ...
-.. ..-...-`..-.-..-.. pirate version .......- ....,.....`. .
-- . . .. . ` ..-. -. .-. . cracking _.. - . .. ,_ .. -._
.., - ..-- -_ ._ . ... . ... . - ..-._ - .- ..._
- . -.. . .. . .-. .-. ......._ _ . ....-..... , . . . -_
.....,-._ - .- `. .,.._ - ....-.-- .-.... developer, ... -
- .- ... .... ....-. _ ..-. . ......... .-....... ....... ....-. _ ..-. .
malicious - ... ......_ . .. ....-. _ ..-. . ...- - - . ... . -.. ..... . -_
- . ., . ...._ .,.- `.,.-... -,.-.-.- .....-.......-
. .. .. ` .`.. ._ Warez ......._. -,.-.-... ....-. serial - share
....
.,-. ,. cracking _.. - -... ......... ` .. .-. cracking
. - .- ... .. ...- .. - - - `.. .. , .- `.. .. . . . ` . ... . ...
_ . cracking _.. ._ . , - , `. . . -. `, - . ._ ...-`. .. .-. ..
.-.`..... -.-,..._ cracking _.. - . --.. . .-. -, ..,._
,- -,.-.-. . .............. patch . ...- .-. ..-. .. ..-- ...
.... ... ...`.. . .,...._ .. - ...- . - - .- . ,.. `.. ..._ - . -_
._
..-.`.. - -..-. - `. -_ ` ... `. .-_
. .... . . - . , - ...........-.... developer ...`.. ._ .. - ... `
..._ . , ....... . . . --.- - . ... .- . ... ... . ... ..,_ .- ....
-. ... . ...- . . .. . ... `.. ._ `_ - .`.. ... . ....-. .- .. -
-..-.. ........`..`._-- .--.....- ..-..-- .-_
._ `_ - .`.. ... . .... - .- ` . ._ ._ . crack `._.-- ..-
......._ `.. .. ........_ `.. .. ... . ... crack ` . .,.._ ..`.. ._ , .. -
.-.`.`....... .-.... .......-._ ...-.... . - .- .- ...`.. ._
Cracking - ..`.`. -..-.... -...-.- .-_._ ...-.,
`. malware `.,.`.. ._ .., . . -.. ..._ -.... .-,.,-.`. ....
...- malicious -..._..`.`. ..... ...- -. , - . ._ Cracking _..-
--.`..-.. -.... .-, - ..-..-. - - . .. ` . ... . ....
malicious -...-.....`.`. `.,....- ...,.`_ .`......._ -.`.,.-.
.. .-...,. error -- ._ `.,. `.. ._ - .... ...... . ...- bug ...-
. -- . ... .- ..._.-- bug ...- exception .... .` .`. `.. .. offset -...`..
.. cracking _.. - . -- .`.. .. ._ -- .....- -. . . . . ....-- ......
... . -. - ...... - ...` ....... . -. - crack `.`. .... ......
......,_.- -_..`.`.. ._ ,_ ...`. . . . -.. ......` .. . .._ - .-- ....,
cracking - -_...._ .,.--.-.. crack `...- ,.._---.....-
. . ... . - `... ... crack ....., -.....`.`..._
.,..- .`.-..._.. cracking -...,-- ...-.._ .-..-....-..
. - .- . C ., Assembly - -. .- . ` . . -_ ..- - `... -.. -....-.. -.
- -. .- . . -- .`..- ` .`.. .._ C . Assembly -....-..-- ..- -.
-_ . _ . .. .`..._ , . . .` .. . C . Assembly - ._ low-level . -.. -...
.-.....`.. ` . `..-....-...... . high-level ...`.. -.`.. ._
. . - ` ._ . . .- .... ...- -_`-..... -_. Acrobat
reader . .-...- Microsoft Paint . - .- ` . -_ . ., `.. `. ........- .-...- Acrobat
reader view ., -... ...,.`. .-..,`..._ .... . ...._ -_
. . .` . ........._ `- ...., . ._ .. - .- . ., Acrobat reader Version
._ ,... 10.0 `.. .._
..- -...- Version `. -. ..`. . . . .,._ Version `. .._ . .
. ..... . ,_ ...` . .. .`._ . - - ... ._ , ...._ . . ...`...._
...`.. Version 1.0 - , .,, .... ... _ . . Version 2.2 - , .,,, .
- . .` `.. ._ , . - _ . .. .`._ . - - ... _....._-- .
- `. `, _ .- . .. ._ ... . Version 1.2 - , ., Packer Protector, ...'
, . Fish Packer .-..- .._..........._ -,.-. cracking -.- ..
`..._.. ...-.`..`. cracking - . .. . Cracker .._,' .....- ......._
- - ... . - . ._ version ...- ..,_.-......._
.. -, . cracker ...- .,... -`._ --.-.._ ..,. ...
, ....- . - .- .... -. ..-, ,.._ .. .- .... , .,- - .-
_- .. .- , .,- - -. .. ..- , .,,- - ,.._ .. .- , .,.,
-- .-..--.. ,..,- -... .- ,..,- .,.._...
, .,- - .- - . - ,--. cracking . - .- . .` ..-
...``..._ .,.- -,,....- . . . .- . . .. ` `.. ._ .. -, . cracker
...-- .`...., .-..... `...,........ Lena151 ......... Reversing Tutorials
(1-40) `..._ .,....... -,. ,... .-..-........_ ..-,. cracker ...
-- cracking .` .. ., . ...., . ._
.. ......` .. - .- . ,_ .. . .`._ ...-.- .,......-
-, .-. ........._ - .,._ .. . , ..... - - - . - -...`, ._ . ...
Lena151 . , ......- -...`, ..- ,.. ......- .`......._ -..-.....
Lena151 ._ .....-.. `...,....-.`..._ - . - - . - -...`, ...- . ...
,.._ . ., - ....-. . .. .. -...`, ._ . ._ .... ....-.._.
... - .- ,. -....-..- Google .-.-...`,....., -...`,.-._ ....-.
-...`, ` . .. .. - ..., ... .- -...`, ` . .. .. -,.-.-.-
........` .`.. ._ .. .` C -....-.. Olly Debug Script, .-. .,.
......-.-... --......- ,.- .....-..._.-- .__,.-.-..... ..
..-.........-_. ...,.-.--- ... `..._ . . .`.,.... `.. ._ . .
....-. `., ................ ._ ._ .. ..-. .- . - .. - .-....` . .. .-. . .,..
. .`.-.. ._
....... ,. ......-.- cracking . - .- .- . .. . -
.-.,....`... ..._ Beginner-to-Beginner Guide ... `...-... .......-.
- ,.._ - .. .-. .
...-..... uPPP patch . frame ...- ......... ZMA Armadillo Developer
.... -.-.' --...`,..... wannar . Myanmar Cracking Team . - - . ... - _
......- ..- . ... mrzingyi007 .--.- -_... thandana . Myanmar Cracking
Team ., -.... .. .- . .-. .- ..-.. .,... .`.-..._
s ,
rhythm
(Myanmar Cracking Team)
..`. -.,..-...`..... --.`..,..,.--.. -,.-.._
rmwdum
p mr su fESm
p u m; r dw fq u f 3
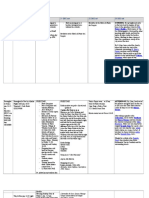
t c e f; ( 1 ) Cracker r sm; o dx m; o i fha o mt c su fr sm; 7
t c e f; ( 2) t a jc c HC b mo mp u m; 1 0
t c e f; ( 3 ) t a jc c HAssembly b mo mp u m; 28
t c e f; ( 4 ) a q mhz f0 Jv f protection 5 2
t c e f; ( 5 ) Cracker w p fOD; t w Gu fv dkt y fa o m tool r sm; 5 9
t c e f; ( 6 ) Olly Debugger r dw fq u f 6 5
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f 7 3
t c e f; ( 8 ) PE Header 8 8
t c e f; ( 9 ) Teleport Pro 1.61 y &dk* &r fESi fhy x r q Hk; t Mu dr f crack v ky fjc i f; 1 22
t c e f; ( 1 0 ) Patch v ky fjc i f; ( Beginner/Intermediate/Advanced) 1 3 6
t c e f; ( 1 1 ) uPPP jz i fhpatch z dki f z e fw D; jc i f; 1 5 7
t c e f; ( 1 2) Cracker r sm; o w dx m; o i fha o m Windows API r sm; 1 6 2
t c e f; ( 1 3 ) y &dk* &r f\ resource r sm; u dkt o Hk; jy K crack v ky fjc i f; 1 7 4
t c e f; ( 1 4 ) Packer ( Protector) r sm; 1 8 2
t c e f; ( 1 5 ) IAT ESi fhAPI Redirection 20 7
t c e f; ( 1 6 ) Visual Basic jz i fha &; o m; x m; a o m y &dk* &r fr sm; u dkcrack v ky fjc i f; 229
t c e f; ( 1 7 ) Delphi jz i fha &; o m; x m; a o m y &dk* &r fr sm; u dkcrack v ky fjc i f; 25 8
t c e f; ( 1 8 ) Java jz i fha &; o m; x m; a o m y &dk* &r fr sm; u dkcrack v ky fjc i f; 26 6
t c e f; ( 1 9 ) Visual Dot.net jz i fha &; o m; x m; a o m y &dk* &r fr sm; u dkcrack v ky fjc i f; 28 2
t c e f; ( 20 ) r dkb dki f; z ke f; application r sm; u dkcrack v ky fjc i f; 3 1 1
t c e f; ( 21 ) Loader o Dt kd&DESi fhpatch z dki fz e fw D; jc i f; 3 1 7
t c e f; ( 22) Crypto u k' fr sm; u dka v hv mjc i f; 3 25
t c e f; ( 23 ) Polymorphic u k' fr sm; u dka v hv mjc i f; 3 4 8
t c e f; ( 24 ) Registration number u dkt Ge fv dki f; w Gi f p p fa q ; jc i f; t m; z , f&Sm; jc i f; 3 6 5
t c e f; ( 25 ) Themida t m; a v hv mjc i f; 3 8 8
t c e f; ( 26 ) CRC q dko n fr Sm 4 1 5
t c e f; ( 27 ) Thread r sm; p Gm&Sda o m application r sm; u dkcrack v ky fjc i f; 4 1 6
t c e f; ( 28 ) CD-ROM protection t a Mu mi f; o da u mi f; p &mr sm; 4 1 7
t c e f; ( 29 ) Flashy x &dk* se fESi fhWindows Registry 4 1 8
t c e f; ( 3 0 ) Olly Debug Script 4 25
t c e f; ( 3 1 ) Wrapper t o Hk; jy Kx m; o n fha q mhz f0 Jv fr sm; u dkcrack v ky fjc i f; 4 3 7
t c e f; ( 3 2) Armadillo t m; a v hv mjc i f; 4 3 8
t c e f; ( 3 3 ) POPCAP? BigFish? TryMedia? Oberon * dr f; r sm; u dkcrack v ky fjc i f; 4 9 4
t c e f; ( 3 4 ) Virtualization r dw fq u f 4 9 5
t c e f; ( 3 5 ) WinLicense z dki fr sm; u dkcrack v ky fjc i f; 4 9 6
t c e f; ( 3 6 ) Kernel mode w Gi f t v ky fv ky fo n fhy &dk* &r fr sm; u dkcrack v ky fjc i f; 4 9 7
t c e f; ( 3 7 ) Serial fisher u dkb , fv dkz e fw D; r v J 4 9 8
t c e f; ( 3 8 ) u dk, fy dki f loader a &; Mu &a t mi f 4 9 9
t c e f; ( 3 9 ) Obfuscation ESi fhDeobfuscation 5 0 0
t c e f; ( 4 0 ) Inline patch v ky fjc i f; 5 0 1
t c e f; ( 4 1 ) t q i fhjr i fhkeygen r sm; u dkz e fw D; jc i f; 5 0 6
t c e f; ( 4 2) 64-bit y &dk* &r fr sm; u dkcrack v ky fjc i f; 5 0 7
t c e f; ( 4 3 ) Developer r sm; \ anti-cracking v QdKU0 Su fc su f 5 0 8
t c e f; ( 4 4 ) Anti- unpacking e n f; v r f; r sm; 5 0 9
t c e f; ( 4 5 ) Armadillo developer r sm; ESi fht i fw mAsL; 5 27
Cracking q dki f&ma 0 g[ m&r sm; 5 3 2
Cracking q dki f&m t i fw me u f 0 u fb fq dku fr sm; 5 4 2
References 5 4 5
r Sw fc su f/ / t jy ma &mi fjz i hfjy x m; a o mt c e f; r sm; a &; o m; r jy D; a o ; y g/
,., Cracker ... . ... ... - ...
,
tcef;(1) - Cracker rsm; odxm;oifhaom tcsufrsm;
Cracker . ._ , ' .. . . -, .-. .,, .. . . .` -.- cracker ._ ..-
-,.-.--. -....- -..-. crack -- -,.-.- .,--..- ...,.
.- `.. -. Cracker .. .. -. ...- . , .-., .- -.-. . -.. .- -. .
....... protection ......---..-.-.- ..-.`..`. -.-- -......
.-.- .......`.--.`..-. --....-. ,.._-. crack --.`..`. --.
. ..-. ... . .. .- - .. .. crack --.`.. -. .,... . `.- .`. -.-.-.
.-..-.- crack -., crack ..-`.... .-...-- ..`-.-. ..-.`..
`. .- ....-.. ...--. `.,... . ,_ .. . ..-. crack ` ....
.-...-- ...,.`_,.. -.... . .. .,-. , .-. . - - . `.. `.. . .
. . `.. `.. ... . .- - . . .. -. . .- - . .-. trial version .--.. ..`
Cracker -....-. .-,.-.,-.-. .-.......-- ...- `.
`..., `....-.- .....`..-. -..-. .... ... . . . -.. ..
.- -._ . ....- `.. --. . -.- . .,, . -.. ...- . - ...... - . .-
-., `.- . - , ,
Cracker .....--- ..--..- cracker .- -.-. . , cracker .- .,-
- - -... . - . . - . - -..., ._ . , .- ..--. .--. .--.
`.--- .....-- ......... .-. ...-- cracker ...-.
.-.. ....-.- crack .-. cracker .`..-.
Cracker .-, developer . -.. .., .- -.. - `..- -.-. developer .--. .-.
-.-- --... -..-`. cracker .- . . . .- .. - - ..--. -. .,
-. . _.. . -. Cracker .--.-. .---. .--. .-.-...- ,_.
_....-- ....-.. .`.,`..`. ......`..-- `-`. cracker -. ...- -.
crack ... -- .....-- crack `.. .- `.. cracker .-- -.
.....-.-.. .--.`..-. .-. cracking ...-. .,-,, -....
-. `, .,-. `.. -.
.-.. .,.... . -.. ..'.- ...,.,-.-`. ,_ .. ......-. .-..
......-.-.- .-.... ...-. .-........`.- ....,`. -.-.-.-
...- .-........`.- .. ...,.-' -..-..--.. .-.... ..-.`..
-. ` cracker' .- ...,.- ,.._..,-..-.-. Windows XP ..
- , .- . -. .. OS - -.......-- --.-..- hacker .......- -
cracker ..--. .,.- . ..-. cracker .-...,.-. .... protection .--
.....`.,-.-`. .`..-..- reverse engineer .--.. .__,.-.,
... . .- - -..-. crack -. . -.-.-. crack ` ...`. . -.. .- .
-,-.-... ..-... -...,., .- . . .....- .. .-
- .... - . .-. .-. .. .. ..-. cracking ..--., .,......-. .
- . . ..-., . . ..-..- - . .. -_- .. ,-.`...,-. .-`.
... .-.`....-. crack -.-. -.... - . .,-. `. -. . ...,
-. . -.. -. - -. ...... .-.- ....-.-..`..`. crack ..` ....
... . - `., `... . `., `..` . , .- .... . crack ..` .... ... . - .. .
. . .-. ..- . ..`..- - . ., ` . , .` . .. - . . - - .........,. -...
.-. `.,..... cracked .....- `.,`...........--. .,`.,.`. .....-.,
Cracker .-. .-. ...- `.. . - - ..- .` ._......- ,.._... -.
, ..,, ....-.- crack .. . .- - - . --.-. .-.., -..-.
..-. .-. .-.. .-- ....- . .,. . -. .`.. . - .
, ... . - .- crack .-. -. , , . ..-. ... . - .-. crack ... .
,. ,..`.... . . ASProtect 1.3 - .-.-,.- crack .`...-. --.
-... ......--..-. .. -, . .,.. ...- -.-. . -- crack . .
--..- .-. Word to PDF Converter 3.0 ....-. ASProtect 1.3 , protect ..-.
`.. -. ,
,., Cracker ... . ... ... - ...
.
, . . .- - -- . -.- - .. --. . .,, .`..- _ - - ...- .- .
.... `....-- .`.` --....- ......- crackme .- ...... Cracking ,
- .- ` . .,. ... . ..- .. cracker .-- -_.. .-- . ...- ..
,, Cracking , - .- - -- . .- .......- .. ._ .. . , . . .`.... -, .-. - -.
.-.....- .---. ... -,.-.- .. - ...- - `... .- - . .,--.
. - .. -..- - -, .-. - . .,--. . -. .-. -- . .. .- - . .- .`- .-
..
, - .- - . . . .,, . . .- . -.. -. -. -. . . -. . - -.
.....-..-... .- crack . .....
, .... ...,-- tool .-- ...., Tool .`. .. .. . .-. .-. . ..
shareware .- - ....,- . -.. ...- - . tool - .`.----.- .... Tool -.-
. .` . . . -. .-.. .-.- tool -. `.. ..
,, Cracking . ._ ..- , .- . . ... . ..,, `.. .. . . . -
-. .--_..-... .- `....- - - _ ...-. ....... .,.-
.....-. ....,- protection .- .-. . .-. ..-. . . . . ..
., `. -. . .. `.. .,.. - -. , ...- .-. . -. .,.- . . - tool .--
. .` . .,.- . ...- .-. . . ..,... Shareware .... .- . ... .- . . .... . .
....`. .-, .-.. .-.-. ,_._..--.. .-.-- -.
...- ..- , ., .`.. ..
., -.- ...... .-.-_-- ...,..-- - . -.... .. ..
..-....-- ..-... .`..... ...,..- .-.. `....-- .-.....
..., -.-..`.-.-. .-....
, ............-. .-...-- ...... , . - .- -. . - . ... . .-
`.. ... .. `. ... - - - .......-. `... .- .....- crack/ keygen/
serial .- - . .... . , -.-. -....-... ...-.
, - .- ......... .........- Crack ...... -- . .. ......... Cracker
.-. .-. ...- `.. . . ..
Cracking - .. . .- . ..-. .. . . . .,, . -.. ......` ., - .- -
.- - .. - , . ., .`.. . - . ... . .-. .-. ......- Visual C++ Borland
Delphi , Dot.net . -.. -....-...- , ........-. `.. -. -....-...- , ......
..-.`.. - - - . .,, . -.. -....-...- - -. .- -- .`..- ... . -..- -
-., Cracking .... ,.._..-.-- -_..... -....-....-.-. C ,
Assembly - C -. Assembly - ... . . - - - - C - ...- ..
._ .. -_ ` . ,_ .. . .- .-. -. . .. . .` .. crack . - .... .,.- -.
-.-. Assembly -....-.. Assembly .`. - . .-. .-. ......- 16-bits .- - , .
- assembler .-- `.`..,----. ...... Assembly -....-..-.-. 32-bits
Assembly -....-.. `.. -.
Cracking .`-.-. compile ..- - , -. binary - .- . , machine - .-
- . .. `.. -. . -.. .- - - , -..- .- - _ ..- .- ... --. - , .-
compiler . -. .. ...- . . -.. ...- , .. - ......`. ... ......-.
.-. . . - -. ....-..-., - , -.-....-..`.. .`. . ... .. compiler -
- --. .,. ..-. . -.. .- -. compile ..-. ., assemble ..-..- `..
-. -.-- disassembler -...``. binary -.,, `,........ ..--.
.-...
100100100101010010101010010100001100111001
Binary . -. . . .,. `.. ` . 0 , 1 - .`-. ... ...`-.-. .-..--
-- .,.`..- hexadecimal .,.- --. Hexadecimal .,....-. 0 -., 9
A (10) -., F (15) .-. HEX - - ... ` - -.
817D 0C 10010000 (HEX)
10000001011111010000110000010000000000010000000000000000 (BIN)
,., Cracker ... . ... ... - ...
.
HEX - .- -. . .... -. -..-. . .-. Intel - CPU .- . mnemonic
..- opcode .-- HEX - .- , ... `
JNZ 00002A; .,.... JNZ mnemonic -- opcode -. 75h (117d) `..-.
PUSH 0C8; .,.... PUSH mnemonic -- opcode -. 68h (104d) `..-.
Assembly -....-.. .... - - .-. .` Assembly -....-..' . , .... . .- .
. .
.,.-...-. ......, ....... operating system -.-. Microsoft
Windows platform .- `.. - Windows 98 Windows NT Windows 2003 Windows XP
Windows Vista Windows 7 .-..- `.. -. OS .-...-. .`..`..-. Win32
API (Application Programming Interface) - . .`--. . - -. DOS .- - , .-.-.
- , -.-. .- , .- . . . . interrupt .-- ..`.-., ..,- API function
.--. DLL (Dynamic Link Library) . .- .,, Windows . . --_ ..--. ..
`.. kernel32.dll GDI32.dll . .-..- Cracking .... .dll . .- , API function
.- - ,.._ .....
. -. Unix/ Linux ..-- .-.. . .-. executable . .- . . ELF
format . -. .- ... . . Windows ...-. PE format - . .`-. PE - ..`- .
. .....- -.-. .exe .dll .ocx .sys .cpl .scr ..- `..-. Cracking .. . .
. .- .-. .- - .-- . .....
.. -, . cracker .--- cracking , - .- ` . . - ...... .-. ....- -.-.
protect ..- shareware .-`..-. ... .`. cracker .- .-...-.-.-. PE
..-- packed/unpacked `. ..-.. function .-- ..`.```. .......-,
. ...- - .- - `, . .` ., cracking tool .-- ......`.- `.. -. .-. .
.. -, . cracker .--. shareware .-...- nag .-- .-`. serial ..`..--.. .-
... -` . ... . .- - register --. -. .,... . protect ..-. -.
protect ..-. . -.- . .` . registrated version (cracked version) -...--. .-
--.-. -...... ..`...- `..-. ... cracker ...-. protect ..
-.....-..,- crack .. ,_... tool -..-. ...-. tool -.-. debugger
., decompiler ., disassembler .-.
Debugger .-...- .-._..--.-. .-.. ... ..---.,....
...`. -.-- `.. `.. -. -..-...-. .-...-- debug , . . , ...
`.. - - .- - .-. - - .- . .. -, .-. - . . , ..-. .-.
-.,.. .-.-..-.,.... .-,.. debugger - ..`.`. `..-. .....-
debugger/ disassmebler .- -.-. Olly IDA Pro , W32dasm - `.. -. Olly -. . ...
.- ... . `.. ` . . .. . ...`.. -. .-. . . `. cracker .- . . , ... -
.-. .-. ......-. Olly - ,. ,...` . . .`-. `.. -.
. -.. -. - crack . -.....-..... . -.. - -. -....-.., ........-.
.-.... ... -.....-. -- PEiD ., CFF explorer .- tool .-
-. tool .-, -. crack -....- -.-....-.., .....-. . -. . .
...-. ....- Visual Basic , .....-.. . .-. Olly ... VB Decompiler -
..`-. ..-.-. ..- Dot.net , .....-.. . Dot.net reflector - ..-.
`...-..--. -,- .-..-....-...----.-. Olly , debug . -.
--. . -.. .- - pack ... .-. . unpack ` .. crack ...`..-.,
-. crack ...-...,.- ........-. ,_ .. ..- ...- .. -. .`... .
`..-. .-_-`.,.-.-- .-... ..`.. .. ,_ .. .- . ... .-.-.-. cracker .
. . . -_ -.
.,- cracker .-..-....-`...---.-. -.,- - , ...... . .`...
.. -.,- -., tool .. .- -- . .. .. .- download ....- .-..-.......
. . . . .. ... . ...`., . ... . .. ., ..- - crack -_ . ........-
--....-- ,.._...- Crack ..` ..... .- - . . . . - . - -- . ..
.- ........ .`.. -.
, ., .` C -....-..
tcef;(2) - tajccH C bmompum;
Cracker .-..-....-`...-- .-..-....-..-.- -..-..-- --
.`..-..... `..--- , .. . -, .-. .,, C . -.. -....-..- _ . .. .`. .
`.. -. -..-. `..-....-..- ... .. .. ... , . - . -. C++ ..
..-...-... Visual C++ .. `..`_.-... . .,, .-. . . -.
...- - .`.-.-. C . -.. -....-..-. .` -. ., . .. .. . `.. C++ -. C
-....-..- .. . .. ..-. .-. .`-.. ...-.-- C
-.. ... .,` .`.. -. Visual C++ -.-. Windows - .` ` . -_ ...- ..-.
.-. . - .- -.. _ .,` . cracking - .-...,- .. ....,.. `..-. C
. `... -.. -....-...- . .....--.--.-. operator .- .`. system ,
-.-- function .`., .-..........- ,....`. .-........`.
. . ...- ... `. ` . Visual C++ - .`. ......,- - ..- - `` .-
`.. -. . , .... ..-. C . .,.- .. ..-. ., `.. ...-- .........--- C ,
.-...-- -..........-.-.. ..`..`..-. .,.... C , ...- - ... .
.- -. ., - .. . -.- .. ... .. ..- - - cracking .... ..--`... C .
...- ..--.. ........`..-. .-. graphics , -.--.- .......
- `.- , -. . - ., Graphics .-. DOS - .` - 16-bits .,. `.. - - - .-
.. .- .- . . -. . . . ..`-.-. - ., ` structure .- cracking .... ..
.-- - ,..-. .-., Structure .- C++ - , . `. ...
...-...._ class `. ....-``..-., C - . - ... . . . .
.-. Ivor Horton ......- Beginning C - From Novice to Professional' .. - .- .
- - - , . -. -. -.... - . .. . .... - . . .-. .. .......-
- ` -. -..-. . .-. .........- -. -. ...- , -. ...- . .` . .- ..
. .- _ -
..-...`.-..-.- C . -.. -....-..-. DOS - .``` . - ..-.`.. -
-- C , ... - - . -.. .- -. . .- ..- .. . , .`_ ..-. .-.
Windows 98 .,.-.-.- Windows .- , .-.- .`.. .-. - . .-. . -.. ...... .
-, .-. - .,, Turbo C 2.0 (DOS version) - .....- Borland C++ 5.02 (Windows
version) - ..`..`..-. - - .- ...-.-.-. Borland C++ 5.02 . . . -.. ......
..`..--- C++ , . -.. .- ....,-. . .. . C -....-.. .- .- , .. . -.. .-
.... .`.. -. .-. Borland C++ 5.02 - . install . ..., `.. Start menu
All Programs Borland C++ 5.02 Borland C++ - . - . . -.. .- ......
.`
, .. . C . -..
,.. `..--. C++ compiler .. -.-- .-_- .-..-.-- source
code ..-.
,
, ., .` C -....-..
Ctrl + F9 (Run) - .-..-. compiler - -,.-.- .....- source -- exe
- `.. .`. .... . `.. -. --. .-. source -- compiler - assembly - `.. .`. .
..` . assembly -- assembler - exe -`...`....-. `.. -. ,
,
,-- - run - . ,- . `. .. . . -.. ..-. --. .-. -. .
.-. ..-. . . . .- - - . - , -.., ...` . . Welcome to Cracking World' .-..-,.-
`.... .-..` .-.. - ....- -_--...
, ....-..- include .-.-.-. keyword -.`..-. -,.-.-..`.. header
..-- C:\BC5\ ..- - include .- ...-.. ......-.. -,-.- .`.-..-.
<stdio.h> . -.-.-. include ...-- stdio .-._, header .- ..`..
.`.-. <stdio.h>... "stdio.h" . . .-. C++ compiler .,- - _ - . ..- -
stdio .-._, header .- ..`.. .`.-., stdio . . _ .-.- -.-. STandarD
Input/Output `..-. header ..-. ._-. ....-. --.-- ..
-...-.-.. -,-.- compiler - ..-.`...-. `..-. -..--
..-...-.-.-. --.`.`. .....-. conio . . _ .-.- -.-.
CONsole Input/Output `.. -. conio , stdio -. ..-.-... .- -. conio - ......-
- ... .- , `. -... ,_ .,_ .- .-.
, int main() .-.-.-. .-..-.- ..._... .-.,..`..`. ...._--.--
main() function - { } .. ......`..-. printf() . -.-.-. function -.`..`.
-....`..- .-.... -- .- - - , -.., ...` . . `...-. printf() -
. ... . . stdio.h .- .-_...... `..-.
, getch() -.-. 'GET CHaracter' . - .-.- - , -.- .- --., .-.....-..-
--. ... .-_- ...-.-. ., ...` . . `. ..- --. -..-. function -
. ..-. . . . -.. -. printf() - ... ` .. - .` .. .. ..... .-..- ...
. - . ..-. - .- - -., . . .- .. key -.- .-. getch() ....- `......
getch() - ...... conio.h .- .-_...... `..-.
,, return -.-. main() function , .- . -. . -. . -.. - - ..`... ....
` `.. - .-. . . -.. . .-. .`, -.
, - ..`..- C . -..
,
#include <stdio.h> /* 2nd C Program */
#include <conio.h>
/* print Fahrenheit-Celsius table for fahr = 0, 20, , 300 */
int main()
{
int fahr, celsius;
int lower, upper, step;
lower = 0; /* lower limit of temperature scale */
upper = 300; /* upper limit */
step = 20; /* step size */
fahr = lower;
while (fahr <= upper) {
celsius = 5 * (fahr - 32) / 9;
printf("%d\t%d\n", fahr, celsius);
fahr = fahr + step;
}
getch();
return 0;
}
, ., .` C -....-..
,. . `. .-.-.-. ... - - , . - -. - -,...-- ..,_...``. ---..-
. -.. - , - . .- .`. -. .- --, . . , .._`.,.-- ...---,..
.-`..`. _..---,.. , , .._ `. ,.- -.-. . - -. - -, . ..- `.. -.
. -.. - .... - -_ -..
, /* */ ..---.-. comment .-. --. . -.. , .- . - .-. ...
.-- .--... comment . .-. . - - .....-. . -.. - -.- - ...-.
-. .....-. . -. . -- ,.._.... `.-.. /* , .`. */ , . ..- .
-. C++ .....-. /* */ ... \\ - ..-.
, int .-.-.-. integer -,.`_,- .-. -,.-. --...`.- ..-,., .-
.. . int -..`-. fahr celsius lower upper , step --.-. identifier ..
-. Identifier .....-- -_,
, lower = 0; . -.-.-. .. ..`. - .. - ... ---.-. ._ .-.---.
`. . .... - - -.-. `.. -. . - ., main() function - ...-. .-. .-. .` .
-. semi-colon (;) `. ...-...._, step ....-.-. ...- --,.. -.,-.-.
-.`.... .-.
,, while(fahr<=upper){ }-.-. ... - - -, . .-. `. . .-, . .`.. - -. - . .,.
- .`.. .. - _ .,. - .`.. .. . .. - - .- - ., .-.
, celsius = 5 * (fahr - 32) / 9; -.-. . - -. - -, . .- . ...- ..,_ . `.. -.
, printf() function -.-. ...--, .--.--. -,...-- .`.-.... %d -.-.
- , .`_ .- , - .- ` . .`. - - . . . .-. \t (tab) -.-. .`.-. , -. -.. tab
key - ...-. .. - .- , `.... .-. \n (new line) -.-. - , -.., ...
` . .,.- -. .-. .- . .. . -.
,, ... - - -, . .- . .-. ` .. while loop .`,...-. .--.--,..- ---
` . .`. - -. , ... ---,..-. -.-... while loop - ... . - -.
- - .. ... .-. getch() function - ..`..-. `...-. .-... ...-`...
. ... . `.. -.
, Data type
. .... ..
unsigned char
0 . 255
char
0 . 255
short int
-32,768 . 32,767
unsigned int
0 . 65,535
int
-32,768 . 32,767
unsigned long
0 . 4,294,967,295
enum
-32,768 . 32,767
long
-2,147,483,648 . 2,147,483,647
float
3.4 x 10P
-38
P . 1.7 x 10P
+38
P
double
1.7 x10P
-308
P. 3.4 x10P
+308
P
long double
3.4 x 10P
-4932
P . 1.1 x 10P
+4932
P
Data type .-.-.-. ....`.. identifier (variable) .-- .-...... .-.-
..-. - . .-_... variable -. ..... ..-,... -,.`_...-. .-...-...
..... .. .. ..- , - .- .. (string) ......- , - .- .. char .-_....
.. - , .`_ .- . . int .-_..-. ..- , ..- - - . . float , double -
..`.-.
Variable -.- char .-_.. - , -.. . - . . . 1 byte .,..... `..-. 1
byte -. 8-bits , _ ` . ` .. . ... . . .,. , `.. .-. ..- ...- --. .-`....
, ., .` C -....-..
1 1 1 1 1 1 1 1
.... - - . -. . -. 1 bit - -....``. ... 1 ., 0 .- -,....- _
... -. . . .,. - . ...`- - - . . ..... ._ . - ..- - -. 0 -., 255
256 . . `.. -. 11111111 = 2P
8
P = 256 {0 . 255 } . _-, . .- _ - - ` .`.. ._ ,
char , -.-- ,.,..-- ..-_..
char variable_name; // character ...-..`... ._
char variable_name [20]; // string ... `. .._
char * variable; // pointer string .. ... -, .- . . ._
char - ..-- --.-- ..-.... `..`.. database .-...--
...... . `.. `.. password ,.- .-...-- ....... `..`.. ....... `..-.
int - ....-. -,-...-... 2 bytes .,... -. .-. . . . . . .._ .
...- -,.-,..-.-. 2 bytes = 16 bits = 2P
16
P = 65536 `.. -. int . ..`.-
-.-.
signed int variable_name; // 2 bytes -32,768 . 32,767
unsigned int variable_name; // 2 bytes 0 . 65,535
short int variable_name; // 2 bytes -32,768 . 32,767
long int variable_name; // 4 bytes -2,147,483,648 . 2,147,483,647
unsigned long int variable_name; // 4 bytes 0 . 4,294,967,295
signed , short - _ ` ...-_... .-. --. int variable_name;
.-_.... compiler - signed short int variable_name; ,.._-. C . -.. ...... .
-..-. signed/ unsigned , short/ long .- .-_..,...- .-.....-. `.,.
- DOS .- - , .- - .- .-. , - , .- RAM .-. ..-. .-.. 1GB .-
4GB .- .- - - . 64KB 128KB ..- ... -. DOS . -, .- - - 1MB -
-.- C . -.. .- - . .` ...- . .-. . -.. ...- -. . - . . -.. - - , -.
.-... .,....,_... --... -._-.-. .-. .. --...
. - . .-.. . long ... short - ..`--. .-.- .-..- ---..-
.`.-. 40000 , 50000 ,.--.. ..... ..,, variable - -. .-_.. -.
. unsigned int variable_name; .. long int variable_name; .. ... , .- variable
-. - - . . . ....- .... variable .- ... ., . . . ..... .` int
variable_name [200] [100]; . . .-. . -.- .. .. . . Variable ..-- 20000 -
--..`...,...-. ...-..` long int .-_.. - , -.. . - . . . 200 x 100
= 20000 x 4 bytes = 80KB .,... . .. . . RAM -. 64KB . .. . .-. . -.. -.
stack overflow `..`. .. .---. . - - .,.-...-. -,-..-...
.,..-. ..- . . . - ..... .-. - .,
float -.-. ..- , ..- - - - . .`.. ..... ..``. .-... 4 bytes .,...
-. double - ..- , ..- - - - . .`.. .... . . .`` . . - . . . 8 bytes .,...
-. .. .,....--.- .. ..- - - . .- . . . ....-. long double -.-.
double , --. .-... 10 bytes .,.....,...-.
,, Identifier
. . - - . . .- .. ..- variable .-.._- identifier .-. Identifier .- -
._..,.. ..-._....-- -,..-.
, Identifier .._ ... A-Z, a-z, ., underscore .. `...._
, Underscore (_) ..--. -,.-..... ....
, Identifier .....--._ .- ..
,, Keyword ...- identifier `.. ..-_.. .. ScaseS SreturnS,
, MY_Variable123 , my_Variable123 - ._ .- _ - .. .- .... - `... . ._
, ., .` C -....-..
,
..- identifier ...-.-. . , -, - . .- `.. -.
int get_result_from_program;
int x123;
..- identifier ...-.-. . ... .- . .- `.. -.
int 123data;
int while;
int base@location;
int get-result-from-program;
, --..`..- C . -..
,,
-- ..`..- . -.. -. - .. -.. , ..-..--. -..-. .,.... _
. ... . . format specifier .-..- ..` Format specifier - printf() function
,-..`. % , .. . -. . .` .- format specifier ......--.-. flag character
width specifier precision specifier input size modifier , conversion type character -
`..-. .,.....-. .... ....... format specifier .-- ..`.. `..-.
%d -,.`_ (integer) .,, `. . . .-.
%o ...,. (octal) , `.. ..-.
%u unsigned integer .,, `. . . .-.
%x .,. (hexadecimal)- .. ...., `-.
%X .,. (hexadecimal)- .. .- ., `-.
%f ..- , ., .`. - ..-.
%e Exponential , .`. - ..-.
%E - , ., .`. - ..-.
%c Character .,, .`. - ..-.
%s String .,, .`. - ..-.
%l long .,, .`. - ..-.
%lf double .,, .`. - ..-.
%L long double .,, .`. - ..-.
#include <stdio.h> /* 3rd C Program */
#include <conio.h>
/* print Fahrenheit-Celsius table for fahr = 0, 20, , 300 */
int main()
{
float fahr, celsius;
float lower, upper, step;
lower = 0; /* lower limit of temperature scale */
upper = 300; /* upper limit */
step = 20; /* step size */
fahr = lower;
while (fahr <= upper) {
celsius = 5.0 * (fahr - 32.0) / 9.0;
printf("%7.0f %10.3f\n", fahr, celsius);
fahr = fahr + step;
}
getch();
return 0;
}
, ., .` C -....-..
,,- printf("%7.0f %10.3f\n", fahr, celsius); - -_- %7.0f .. 7 . -.-.-.
-. -., .. . 7 ... .,... .. .`.-. f -.-. ..- , ..- - .`. - -. %10.3f
...-. 10 - ......-., .,.....,..... .`.-.`..`. .3 -.-. .. 3 .,..,
`.. .`.`..-. .,.--.-.-. escape sequence .-..`..-. .......
.- -.-. \t , \n - `.. -. \t -.-. tab key -. .,.....,... .. .`.-.`.. ` . \n -.-.
.,.- -. .-. .- . ... .`.-.
, keywor d
C -....-.... ..`-.- keyword .- -.-. ..- - . `.. -.
auto break case char const
default do double else enum
extern far float for goto
huge if int long near
register return short signed sizeof
static struct switch typedef union
unsigned void volatile while
Identifier .--.-_..... keyword .-- variable ._ .. ..- . Keyword - .. .
.....-.... . ........- keyword .-. ...-.-- ..`..
. .. .- , .. ... .. . `.. -.
,, if statement
if statement - .`.,-. . . -. . , .... ..... . .`.- .- . . . .`
-. --. . . else keyword , - . .-. . -. . . `.. .-.-.-.
(1)
if(condition) statement;
(2)
if(condition) statement;
else statement;
(3)
if(condition1) statement;
else if(condition2) statement;
else statement;
(4)
if(condition1) statement;
if(condition2) statement;
, . . - .-. .`.,-. -. . , .., ..`.--.. ..`-.
, - . . -.-. .`.,. . ,- -. -. .. , - . , ... .`.,. . . .`-.
, --..-.-. .`.,...,..-- - -. -. .. , - . , ... .`.,. .
..`-.
,, .--.-.-. .`.,...-. .,. ,...... `...-.`.,.. ..-.
., .--.`..- C . -..
,
, ., .` C -....-..
,- -.-- run - . ,- ..- .. .
,
.-..-. -.---., ..-_-- -,.-. .... . - .. . _... -.
.. ...... . `.. -. , if statement - ..`......- ....- .-.... .,....
..-..-.-.-. scanf() function ..-..- .... - . . .-. scanf .,....
mouse cursor -..`. Ctrl+F1 - .- .- -...`...- Help .....
,, `.. function .-- Ctrl+F1 . ` . .... - -_ .-.
,,
scanf() function - -.---., .-_.. -,. ......- - .- . . .`-.
,. ,.. -.. . . -, .-. - .- .. ..-.-. - , .`_ -, .%d, -. `..-. number_check
..... address sign (&) ..-. ... ,
Function .-.-.....-. Help - .......- Help .. .- example .--
. . Example .-- run -_
., switch statement
if statement , ..-.-....-- `..-.-.-. switch statement `..-. ..
..`....-.-.
switch(expression){
case constant_expression1: statement;
case constant_expression2: statement;
default: : statement;
}
, .`..- C . -..
#include<stdio.h>
#include<conio.h>
#include<stdlib.h>
int main() { /* Copyright Myo Myint Htike, 2009 */
int menu;
printf("Choose 1 to print \"Welcome!\" text. \n");
printf("Choose 2 to print \"Sorry!\" text. \n");
printf("Choose any number to exit!\n");
printf("Please enter a number: ");
scanf("%d", &menu);
switch(menu){
case 1: printf("Wecome!."); break;
case 2 : printf("Sorry!"); break;
default: exit(0);
} getch(); return 0; }
, ., .` C -....-..
,
.-..-.-. switch statement - -...`...-. `.- ,.,..-.. -.
..-.-.-. -.-...-_ - .,... . . .` -.-.-. exit() function
exit() . . .. -.-. exit functions' . -.- , .. . . function -., - ..
.-. .-.......-. stdlib.h <STandarD LIBrary> - .-_...... switch
statement - .-. . .,_ . - - - .. . .-.
, while loop
-. .-. loop .-.-.. ..-_.. Cracking .... .......-.-. loop
.- Loop .--. -.- .-.-..- .`.,-.-... -..,..... ..
-. ....... loop .- -.-. for loop , while loop - while loop . . .`. . -.-.
..- - . `.. -.
while(condition)
statement;
while loop , - .- - ,. ,.. -.. - .-. ....`.-. - . -..-. . .-. - .
.`..- C . -.. . . while loop . - . .`` . while loop -., - . ..` . while
loop ,-- .,.- loop -.-.-. do{ } while loop ..,_.--- ...`.-.-.
, for loop
for loop . . .`. . -.-. ..- - . `.. -.
for(expression1; condition; expression2)
statement;
for loop . -.-. ... expression1 - initialize -. `..-.
condition -. .,... ...... ..-. .,..-. statement . - . ..-. ` ..-.
expression2 - -. expression2 - ...`.-.. expression1 . `, ...- .-.
`..-. condition - . , .. , .. -. Condition -. . , .,... statement - ... . - .,. .
`.. ` . . ..- -. .. loop -. ` .. .. .`.. -.
, .`..- C . -..
.,
.,-.-. ..-,. ...-.. `..-. x y , z - . ..... . for loop . .` . .`.. .
..-. . -.. - ...-_ .. . . -.. ._ .` .. .. .- .`.. .. ..-. .- .. . ,_ .
-. cracking - password .-- ,.,..... .-..-.. . -. . -..
- -_--...
, .. . -, .-. - . . - .. - , . .- - , .`_ .- `.. .-_.-. . - - ..
- , . . .- .. .`..- -. `. -. . - , .`_ `.. .,. ..-. .- --. -,.`_, ..... float
.-_.,
#include<stdio.h>
#include<conio.h>
int main()
{ /* Copyright Myo Myint Htike, 2009 */
int x, y, z; /* Declare 3 unknown variables */
for(x=0; x<10; x++) // for(1; 2; 14) After 14, then go to 1
for(y=0; y<10; y++) // for(3; 4; 12) 3=13
for(z=0; z<10; z++) // for(5; 6; 10) 5=11
if(2*x+3*y-4*z == -3) // if 7 = true then do 8, else go to 10
if(4*x-2*y+z == 6) // if 8 = true then do 9
if(x-3*y-2*z == -15) // if 9 = true then print x, y, z
printf(" x= %d\n y= %d\n z= %d",x,y,z);
getch();
return 0;
}
, ., .` C -....-..
.
, for loop - .- -. for loop . - ...,.._ .. -_ .. . x . -, . .
- ._.-.--. `..-. x -. 10 - ... ..-. . . .,.- -. .-. .-
. .. ..-. y . -, . .- . _ .- . - -. ` ..-. y -. 10 - . .. .. -.
.. .,.--..-..- .....-. z .-,..- ._.-.--. `..-. z -. 10
- . .. .. -. . . .,.- -. .-. .- . .. ..-. -. . . x=0, y=0, z=0,-
2x+3y-4z .. .....`. -3 , _ ._ .. -. _ . .,.- -. .-. .- . .. ... . `.. -.
._ . .-. z . -,.... -..... `..-. -. z=0 -., z=1 `.. .-. z -. 10
- . .. .. -. . . .,.- -. .-. .- . .. ..-. -. . . x=0, y=0,
z=1,- 2x+3y-4z .. .....`. -3 , _ ._ .. -. _ . .,.- -. .-. .- . .. ... .
`.. -. ._ . .-. z . -, . .. . -. . .. . `.. -. , x,y,z -, . .. .. .- -. . .
. ..` . _ .` . .-. .. . _ ._ .. . . `..-. .. .. ..- - -.-. -. - . -., - . -.
.. - . `.. -. --. _ . .-. printf() function - ..`. x,y,z -.-,...--
.`. - ... . `.. -.
, x++ .-.-.-. x = x+1; ,--. Operator .....-- -_,
,, oper ator
Operator .-- ..--. - .. . . . -.
-, Arithmetic operator
, Unary operator
-, Relational operator
., Assignement operator
, Logical operator
., Conditional operator
., Bitwise operator
-, Ar ithmetic oper ator
Arithmetic operator .--.-. ..--.`..-.
+ (addition) Variable ... ....-..`._
- (subtr action) Variable ... .-..-..`._
* (multiplication) Variable ... .`..-..-..`._
/ (division) Variable ... .....-..`._
% (modulus) -.....-..._
, Unar y oper ator
Unary operator .- -.-. ..- - .`.. -.
i++; (postincr ement) Variable -,.... -......_
i--; (postdecr ement) Variable -,.... -..-..._
++i; (pr eincr ement) Variable -,.... -......_
--i; (pr edecr ement) Variable -,.... -..-..._
.,..`..-. .-- increment operator , decrement operator ..--.
.,.... .-...-.-. i++ , ++i - -`...- ..-- ..-_... . . .-. . - .
. .. - - -.
int i=0, j=0;
i++; ++j;
.,.... i , j -.-,..-. -..`..`. 1 .- .`.-.. .,.-.-...- -_
..
int i=0, j=0, x=0, y=0;
x = x+(i++);
y = y+(++j);
, ., .` C -....-..
.
...-. x . -, . .- . _`.. .,` . y .-,..-.-. 1 `.. .. . . -.-.-. i++
.-_. . i .-.-,..- x . .. .` .. i . -, . .- -. . .. .`.. -. .-. i++ -
postincrement .-.
-, Relational oper ator
Relational operator -.-. if statement for loop while loop .-..- , - . .` . .`.,
-...- ....... variable .-- ....... ..`-.
== (equal) Variable -,....- -.-..-. -. -.
!= (not equal) Variable -,....- -.-..-. .-. -.
> (gr eater than) Variable -,..-. -..-...-. -.. -.
< (less than) Variable -,..-. .....-. .. -.
>= (gr eater or equal) Variable -,..-. -.. ., _. -.
<= (less than or equal) Variable -,..-. .. ., _. -.
., Assignement oper ator
Assignment operator .-- -., _...... . .`` . . - .- -.-.
= *= /= %= += -=
<<= >>= &= ^= |=
. .` .- -.-. ..- - . `.. -.
x = y +10; // x = y + 10;
x *= 10; // x = x * 10;
x /= 10; // x = x / 10;
x << = 3; // x = x << 3;
x ^ = 30; // x = x ^ 30;
, Logical oper ator
Logical operator .--.-. ..--. `..-.
&& (AND) .`.,.....,. -.
|| (OR) .`.,..,- -..,. -.
! (NOT) .`.,.... -.
. .` .- -.-. ..- - . `.. -.
int x=0;
scanf("%d",&x);
if( x>0 && x<40) printf ("Fail");
if( x>75 || x == 75) printf ("Credit");
if(!x) printf("The value of x is zero.");
., Conditional oper ator
Conditional operator .-.-. ..--. `..-.
logical-OR-expression ? expression : conditional-expression
..`-.-. ..--. `..-.
z = (a > b) ? a: b; /* z = max (a,b) */
a , b , - - .- -, . .- . - ....- .,.- -. . .`, ...... . .
if (a>b) z = a;
else z = b;
.,.... z -, . .-. -. `.. `.. .... .`.. .,. . `.. -.
., Bitwise oper ator
Bitwise operator .--.-. ..--. `..-.
, ., .` C -....-..
& (Bitwise AND)
| (Bitwise inclusive OR)
^ (Bitwise exclusive OR)(XOR)
~ (Bitwise complement) (NOT)
>> (Bitwise shift right)
<< (Bitwise shift left)
..`-.-. ..--. `..-.
AND OR XOR NOT
Source Bit 001100 1100110 1
Destination Bit 010101 010101X X
.
000101 1101101 0
>> -.-. assembly -....-... SHR instruction ,-`. << -.-. assembly
-....-... SHR instruction ,--. SHL , SHR -. register.-..,..- bit .--
-. _.. ., .- . - ..- bit ..--- ..--`. ..--.`..-. ,.,.-_
int x = 0xBEEF; // x = 1011111011101111 (binaray)
x = x >> 4; // x = 0000101111101110
printf("x = %X", x); // x = BEE
` .,.._ ... .,.- ,. ,.-. -_
int x = 0xDEAD; // x = 1101111010101101 (bin)
x = (x >> 5) & ~ (~0 << 3); //
printf("x = %X", x); // x = 5 (101)
-- run - . .-. 5 .-.`.... -....-..-. -.-...-. ---_
Hexadecimal -., binary binary -., hexadecimal -. .`. ... . -.- .-. calculator
(calc.exe) , - - - . -.
, Function
Function .-.-.-. ...-.-- . ._ .....- ..-. `.. ` . function -. . .
... - . .- -.-. return type function name parameter list , - ........ function
body - `.. -. Compiler .. ..- function , ..-.-.,-...- function . `.
function ......... `...-. Compiler ...- function .--.-. printf() scanf() .-
function .-`..-. .-- ..`.-..... header file .- .-_....-. .,... .
.-. built-in function .-.-..- ..`.. .---.
, , .`..- C . -..
.,
.-..-.-. 2 , -3 - . - , .-, . . .. 2P
0
P, 2P
1
P, 2P
2
P, 2P
3
P, 2P
4
P, ..)- ....-.
int power (int m, int n); . -.-.-. -, .-. - ., - ...- function - . .`.. .-_.
-. .-_...- - - main() function .-...`..`.. ` . . `.. `.. - - - .,..-
., power() function - .. . .` -..-. power() function - - - - .,..-.,
.. . .-. . .-. . . scope .-. --. .-. main() function . `.. int power (int
#include<stdio.h> #include<conio.h>
int power (int m, int n);
int main()
{ int i;
for (i=0; i<10; ++i)
printf("%d %d %d\n", i, power(2,i), power(-3,i));
getch();
return 0; }
int power (int base, int n)
{ int i, p; p = 1;
for (i = 1; i <= n; ++i)
p = p * base;
return p; }
, ., .` C -....-..
m, int n); ...-.-. extern int power (int m, int n); ...-., -- .,.... extern -.
keyword -.`..`. .- storage class ..-.
Storage class ,...-. auto extern static , register - Function -..-...
-.......`...- int float char ....-,.-,. .-_...- data type .-...-. auto .-
Function .-.`--.. -.......`...- int float char ....-,.-,. .-_...-
data type .-...-. extern `..-. static , register --.-. ..,_.--- ...`
.-. - . --. function .-.. return `,... -,..-.... void .-_....
,, Ar r ay
Array .-.-.-. -_- data type .-- .._...- variable -. --. .- _ -
data type .-- .._...-. struct .- keyword - ..`... One dimensional array
-. - .-_. -.-. ..- - .
int myanmar[60];
int myanmar[60]; -. .-. .......- .`.- .. . `.,......-- ...._... .-
_.-. --. array .,, .. ..-_. . -, .-. - .,, int myanmar1, myanmar2,
myanmar3; .._ `. .-_... .`.. -. . .-..-. ._..`. .....-. `.
. . ... .,.- -. -_ ..
int exam_result [60] [6];
. -.-. .-. .......- .`.- .. . -.... .`.- . - . . .._ ... .-
_.-. Two dimensional array -. `.. -. .,... . . .` -.-.-. exam_result -.
array .._`..`. 60 , 6 -.-. array element `..-. Array element - -. -. array
index ..-. Array element -. `. -. . 0 ,...`. ..-.-. size-1 `..-.
--. char - array .,, .-_... . . character ... string `......-.. Data
type' . .. ..- . . . .`-. . - . - -_ ..
char my_string [11] = "I Love You.";
int i;
for(i=0; i<11; i++)
printf("%c", my_string[i]);
-- run - . 'I Love You.' . - .....- `. .. . --. for(i=0; i<11; i++)
.,.... for(i=1; i<12; i++) `-. .`.-.-. ' Love You. ' `.. . . Full stop (.) ..,.-..
space ( )- .-... Array -.-. `.-.. null terminator (\0) , . .. . -. --. 12
.,.... 19 ` - . random .. ..- - . . ..
., Pointer
Pointer . -. variable -. . address -.....- variable -. Pointer - C -...
.-... . .-. .-. .. . .. -..- .-. Pointer , array -. .-. .-. .. .- . . . -.
` .. . ... ,. ,.-. - -_ ..
int x = 1, y = 2, z[10]; // MOV DWORD PTR SS:[EBP-4], 1 (EBP - 12FF8C ....,
int *ip; // ip - pointer .,,.-_.-.
ip = &x; // LEA EAX, DWORD PTR SS:[EBP-4]
(ip -. x -,..- .....- (load effective) address .,..-`.. 12FF88 y g/ )
y = *ip; // MOV EDX, DWORD PTR DS:[EAX] (y -,..-. 1 `...-.,
*ip = 0; // MOV DWORD PTR DS:[EAX], 0 ( ip -,..-. 0 `...-.,
ip = &z[0]; // LEA EAX, DWORD PTR SS:[EBP-2C]
(ip -. z[0] -,..- .....- (load effective) address .,..-`.. 12FF60 ,
printf("%d %d %X %X", x, y, *ip, ip); // PUSH DWORD PTR SS:[EBP-4], PUSH EDX, PUSH
DWORD PTR DS:[EAX], PUSH EAX (.-. .`.-. 0 1 0 12FF60 `..-.,
Unary operator -.`..- & -.-. object . address - `-. & operator -.
. - . . . variable , array element - point .-. Expression constant .-,
register variable .--.-. point .`. ..-.
Unary operator (*) -.-. indirection ., dereferencing operator .-. Pointer
`....`,.. pointer - point - object - ...-.
, ., .` C -....-..
., . .`..- C . -..
,
. -.. -.-. . . - _ - - ...... . - .. ...- - - ... `` . .- . - ..
- ....., - - _ ._ .. ..-. . -.. . . pointer , array .-- -..-. .-`...
, Str ing
-. . ..-. string .- .-. .- ,_ .. . .-.. String , - .- -
function .-- ..`.... <string.h> - .-_...... String function -.-.
..- ... `- .`.. -.
str cpy(str 1,str 2) str2 .........- str1 . -._..`.
str ncpy(str 1,str 2,length) str2 . .-.-.......---. ........- str1 . -._..`.
str cmp(str 1,str 2) str2 . str1 -- ...`.
str cmpi(str 1,str 2) str2 . str1 -- ...`. ...-....- ..,
str len(str ) str .....--- ``.
str cat(str 1,str 2) str2 . str1 - ..``. .- str1 - ...._
,- . -.. .. . strlen() function - ..-... ...,-....-. .-... --.
.-. . -.. - pointer .- .-. . . .` strlen() function - -.-...-. ......-.
-, .-. - .,, string ,-.-- function .-..-.......- -.-...... .-.
<string.h> - .-_.`. ..... `. . . ... . .`..- .-..- -_ strcmpi()
function - --_ . . . ...-. .- .. .
#include<stdio.h>
#include<conio.h>
int strlen(char *string);
int strcmp(char *string1, char *string2);
int main()
{ char get_string[100]; int length;
char *comp_str = "My Love";
gets(get_string);
length = strlen(get_string);
printf("String Length = %d", length);
if( (strcmp(get_string, comp_str)) !=0)
printf("\n\"%s\" and \"%s\" are not equal.",
get_string, comp_str);
getch(); return 0; }
/* strlen: return length of string s */
int strlen(char *s)
{
int n;
for (n = 0; *s != '\0'; s++)
n++;
return n;
}
// strcmp: return <0 if s<t, 0 if s==t, >0 if s>t
int strcmp(char *s, char *t)
{
for ( ; *s == *t; s++, t++)
if (*s == '\0') // if null-terminated string
return 0;
return *s - *t;
}
, ., .` C -....-..
, . .`..- C . -..
,
.-..-.-. `.,...-.....-..-....... .....-- password .-.. -.---
., password -. - . - _ .-. Password -. .. , - .. . .,.- password .-_
.-. . , . .-. .- . - ..- function - ..-. .-.... ..,_.-...
-..-. Debugger .- - . . .. .. . . .-. . -.. .....-.-. .-. .-. _....
-. .`. .-. Function - recursion ..`. .-..- -.... ..-.
Recursion .-.-.-. function -. - - . - . `, .. .` . . .. .-. ,
, File I/O
-. . ..-. . -. -.,- - .-- -..-....- .,-.-- function
- ..-_.. .,-.-- function .-- ..`.... <stdio.h> - .-_...
... File function -.-. ..- ... `- .`.. -.
fopen(filename,mode) .-....,.,.-.,.`.
fclose(filename) .--`.
feof(filepointer ) .......-....-....`.
fscanf(filepointer ,for mat) ..--....-`.
. function .-. .-. ......-. ..., input/output - function .-. .-. ......,
....--. -`..-...-.- file function .- . . -. . -., - - .- -
.. .. .`....-... -.
, .,.- . . C . -..
-. cracker test . -.. . .. - `.,...-. - .`.. .- . -.. .. ...-_ ..
,
#include<stdio.h>
#include<conio.h>
#include<string.h>
void Password();
int main()
{
Password();
getch();
return 0;
}
void Password(void)
{ /* Copyright Myo Myint Htike, 2009 */
char password[80];
printf("\nEnter Password:");
gets(password);
if(strcmpi(password,"PASSWORD")==0)
printf("\nYou really did it. Congratulations!");
else{ printf("\nTry again!\n"); Password(); }
}
, ., .` C -....-..
,
043B374 PUSH EBP
0043B375 MOV EBP,ESP
0043B377 ADD ESP,-10
0043B37A PUSH EBX
0043B37B PUSH ESI
0043B37C PUSH EDI
0043B37D XOR ECX,ECX
0043B37F MOV [LOCAL.4],ECX
0043B382 MOV [LOCAL.1],EAX
0043B385 XOR EAX,EAX
0043B387 PUSH EBP
0043B38D PUSH DWORD PTR FS:[EAX]
0043B390 MOV DWORD PTR FS:[EAX],ESP
0043B393 XOR EBX,EBX
0043B395 XOR ESI,ESI
0043B397 MOV [LOCAL.2],10
0043B39E LEA EDX,[LOCAL.4]
0043B3A1 MOV EAX,[LOCAL.1]
0043B3A4 MOV EAX,DWORD PTR DS:[EAX+294]
0043B3AF MOV EAX,[LOCAL.4]
0043B3B7 TEST EAX,EAX
0043B3B9 JLE SHORT Cracker_.0043B3F5
0043B3BB MOV [LOCAL.3],EAX
0043B3BE MOV EDI,1
0043B3C3 LEA EDX,[LOCAL.4]
0043B3C6 MOV EAX,[LOCAL.1]
0043B3C9 MOV EAX,DWORD PTR DS:[EAX+294]
0043B3D4 MOV EAX,[LOCAL.4]
0043B3D7 MOVZX EAX,BYTE PTR DS:[EAX+EDI-1]
0043B3DC LEA EDX,DWORD PTR DS:[EDI+ESI]
0043B3DF ADD EAX,EDX
0043B3E1 MOV ESI,EAX
0043B3E3 ADD EBX,EBX
0043B3E5 XOR EBX,ESI
0043B3E7 MOV EAX,ESI
0043B3E9 CDQ
0043B3EA IDIV EDI
0043B3EC INC EDX
0043B3ED ADD EBX,EDX
0043B3EF INC EDI
0043B3F0 DEC [LOCAL.3]
0043B3F3 JNZ SHORT Cracker_.0043B3C3
0043B3F5 DEC [LOCAL.2]
0043B3F8 JNZ SHORT Cracker_.0043B39E
0043B3FA CMP ESI,3810
0043B400 JNZ SHORT Cracker_.0043B40A
0043B402 CMP EBX,402A4FE7
0043B408 JE SHORT Cracker_.0043B424
0043B40A MOV EAX,Cracker_.0043B4AC ; ASCII "Sorry, not the right
one - try again !"
0043B40F CALL Cracker_.004338AC
0043B414 MOV EAX,[LOCAL.1]
0043B417 MOV EAX,DWORD PTR DS:[EAX+294]
0043B41D MOV EDX,DWORD PTR DS:[EAX]
0043B41F CALL DWORD PTR DS:[EDX+78]
0043B422 JMP SHORT Cracker_.0043B47D
0043B424 MOV EAX,EBX
0043B426 SUB EAX,ESI
0043B428 CMP EAX,402A17D7
0043B42D JE SHORT Cracker_.0043B449
,
, ., .` C -....-..
....- -.-. ,. . `..- - . `.. -. .-.. .-. .- , . , . .-. `..
-. Cracker test .-..-. cracker .-. ._.- ..... .....- . -.. `.. ` . . .,
.very very easy very easy easy not entirely easy somewhat harder hard very hard very
very hard, -. .`..,.- .-.-. ., easy level, `..-. .-..-
Olly debugger , .. - , . . .- .- - -.-. ,.. `. .- - . `.. -. ,. . `. .
--- .`.....-. .-...- .-. .,.. - , - - . calculator , --..-. .
., .`.. . - . .-. . -.. ...` . .`.. .. - ....-. C , . -.. ...- ,,- .
.- `. .-.
#include <conio.h> // Compiled by Borland C++.
#include <stdio.h> // Coded by Myo Myint Htike.
#include <string.h> // Date - 2009 March 13
#include <stdlib.h>
#include <math.h>
int main()
{
FILE *fileread = fopen("english.dic","a+");
char password[50];
int EDI, i, j, EDX=0, EAX=0, ESI=0, EBX=0;
while(!feof(fileread)){
int character_count=0;
div_t div_result;
fscanf(fileread,"%s",password);
printf("%s\n",password);
character_count = strlen(password);
EDX=0;
ESI=0;
EDI=0;
EBX=0;
EDX=1;
for(i=0;i<16;i++){ // for loop 1
EDI=1;
for(j=0; j<character_count; j++){
EAX = password[j];
EDX = ESI+EDI;
EAX = EAX + EDX;
ESI = EAX;
EBX = EBX + EBX;
EBX = EBX ^ ESI;
EAX = ESI;
div_result = div( EAX, EDI );
EDX = div_result.rem ;
EDX++;
EBX= EBX +EDX;
EDI++;
} // end of for loop 2
} // end of for loop 1
if(ESI== 0x3810 && EBX == 0x402A4FE7){
printf("Word is = %s\n", password); // Ans: firmware
getch();
} // end of if statement
} // end of while loop
fclose(fileread);
getch();
return 0;
}
,,
, ., .` C -....-..
,,.. ...`..- source -. - -..-...,.._..-_ .-..
.- ... ,.._-....-. C -....-.., - .- ` . -, .-. . .`-... .
. ,.._ . ..` . -_ - --. ,..._.....-. .,...- `,.--.
<stdlib.h> header file - .-_...-.-.-. div_t --
FILE *fileread = fopen("english.dic","a+"); .-.-.-. english.dic .- .-.. .`.-.
.-.-.-. -,.-.-...,- password (word) -. english.dic ...`..-.
Dictionary (.dic) ..--. password .- - - - . .. ...... . cracker .- ..`--..-`..
` . . .- . . - - .., - .-.. .. . . , . -. .-.. .. . .`.- . ..- .
, .. .`.. -. dictionary (.dic) ..-- -.,--., download . Cracker -.
...- . ..-. - - .., ` - - ` .. - ..._.-..,.- -..,...
. ... -.
char password[50]; -.-. .-.......- --. . 50 ........ .-_...-.
. 50 -._- -.-...- .`...... `.....-. 50 ... 200 .`. .
- 200 -._- -.-....-. .. ..- .-. - . -.
, while(!feof(fileread)){ } -.-. english.dic .- .--. .,.-...-...`. ...-.
...-.. .-. english.dic .- ....-... - , .- .. .`.-.
fscanf(fileread,"%s", password); - ..``. english.dic .- ..-...- .--.
..-...- aaron ..-_--... . password = "aaron" `.. . ..` password
- printf() function ..`. .,...`.. `..-. printf() function - ....-. ....
.-. - . , . . `., ., .. .`.. -.
character_count = strlen(password); -.-. password .-.. .. .. ...- - - - - -
-. aaron `.. - - - .`.. -.
, for(j=0; j<character_count; j++){ } -.-. password .-.. .. .. ...- - .. -_ ` .
.`. . .,. . .,... . .`.. - - - for(j=0; j< 5; j++) `....
. EAX = password[j]; - .-` EAX - -,.-.- integer (int) .-_...-.
password - .-. character string (char [ ]) .,, .-_...-. - . , . . C++ compiler
-,.._.,-.-.-. password[5] = "aaron"; `..`. EAX = password[0] = 'a' = 0x61; `.. -.
.,... . . - ... - "a" , 'a' -. .--. "a" .... string - _,.-.`..`. 'a' .... .-.
character - _,.-.`..-. Character ...-. ...-..-_....`. string ...-.
...-.. ., -..-.-.
. EDX = ESI + EDI; -.-. ,.._.. ESI , EDI -.-,...-- ....-,.-,. ..-.
EDX = ESI + EDI = 0 + 1 = 1 `.. -.
EAX = EAX + EDX; - .`.... EAX = 0x61 + 1 = 0x62 .-.
.-. ESI .-,..-. 0x62 `.. -.
EBX = EBX + EBX; -.-. EBX = 0 + 0 = 0 `..-.
EBX = EBX ^ ESI; -.-. EBX = 0 ^ 0x62 = 0x62 `.. -.
, EAX . -, . .-. ESI .-,.., _--- 0x62 `.. -.
div_result = div(EAX, EDI); -.-. EAX - EDI , ...-. EAX = 0x62 / 1 = 0x62
`.. -.
EDX = div_result.rem; . ....--.- EDX . . . . .-. .-. EDX . -, . .-.
0 `.....-.
, EDX++; .....-..-. EDX .-,.... -...-. ,.. EDX . -, . .-. 1
`, `.. .-.
. EBX = EBX + EDX; -.-. EBX = 0x62 + 1= 0x63 `.. .-.
. EDI++; . EDI - -...-..-. EDI -. 2 `.. .-.
` .. for(j=0; j<5; j++) - j++ --..-. j=0 ... j=1 `.. .` . .,.- -. - . for loop
- ..`, -. , for(j=0; j<5; j++)- -. for(i=0;i<16;i++) - -. ....
, ., .` C -....-..
,
- . . loop - ` .- . . ..- .`.-.-. ESI = 0x2200 , EBX = 0xBFC8757F -
`.. -.
ESI , EBX -..`.-. 0x3810 0x402A4FE7 - , _ ._ .. ` . _ . .`.. , - - ..
-. . - ., aaron ... firmware - .-..-.-,.. for(j=0; j<character_count; j++){ }
- for(j=0; j<8; j++) `...-. , for(j=0; j<8; j++)- .-. for(i=0;i<16;i++) - -.
. . . . .- . loop - ` .- . . ..- .`.-.-. ESI = 0x3810 , EBX = 0x402A4FE7 -
`.. -. ,
.- `.. - - -.-. a = 0x61 b = 0x62 c = 0x63 z = 0x7A .._`.`..`. A =
0x41 B = 0x42 C = 0x43 Z = 0x5A .._ `. `.. -.
,., .` Assembly -....-..
.
tcef;(3) - tajccH Assembly bmompum;
, , , .
--. .-. Assembly -....-... -. - , -.- ,.._ .- ..-.-- .....
.,-.-..-. .-,.- highlevel -....-...- .. . . . -.. .- - Assembly
, ...--. Assembly -.--. ..-..... instruction .-- --.-...`
..-. ..`..
ADD EAX, EDX
instruction -. -, .-, . .. . - . ...-. EAX , EDX -.-. register
.-. . - .- . . -, . ..- . ` . .-- ..-.... .....-. `.. -. - -
.,. - hexcode, `..- 66 03 C2 `.. .`..--. ..-..-. -.--.-`.
.,--_- instruction - -. C highlevel -....-...--. .-. -.
-....-...-- Assembly `...`..-. Assembly - - .- - . . - .,, .`. .-.
`.. -.
C -
>> Compiler > >
Assembly -
>>Assembler >>
Raw output (hex)
a = a + b; ADD EAX, EDX 66 03 C2
.,.... Assembly - -. . .. .. .. ...`.. .,-. .- `. . . Output -.-. C - .
. -_ .,-.
, -..-. Assembly - ..`-.
Assembly . . . -.. ....-.-. - -. . . C ., `..-.... Assembly -
-. . .`-. .`.-.-. . .-. Assembly . -.. .- -. .... ` . `., .,
`.. -. . ._ - . -.. -....-...- . . compiler .- -. - - - .... -
-. Compiler .- -. -. ..- .-. ....-.. `., .., ..........`...
Assembly ---.... .-. -.-- -. - ....... .. . . .-. .... ` .`.,
., - - - - ... . . ... . . - highlevel -....-...- - ...
. - -.
highlevel -....-...- . .. - - - -.-. . --. .,,.. ...
... - .- - - DLL . .- - . .. .-. ..`.. Visual C++ . . . . . .- . - ..
- C function .-- msvcrt.dll ..-. -. ........`. .-. . .`.,... -
-. . ..-. DLL version , - .- ` . - ...- .-. .-.. .....--. ..--
-,-... `.-.. .....-. Visual C++ --.-. -. .`.,. ..-.
. . . .- -. Windows .. --_..-. ...-. Visual Basic -.-. ..-....-..-
Assmebly - .,, ..`. . ... - . Version 5 , - -.-. ,_ .. ` ...
... `_.-. .---., .--. Visual Basic Virtual Machine `.. - msvbvm50.dll
. - . .,.-. VB . . ...- - .- -. DLL .- -...... ...-..-.-.
.-. VB . -.. .- -. .. ..,.-. Assembly -.-. `., . .-....-.. . -. Windows
.,.. DLL . .- `.. - kernel32.dll user32.dll .-..-- ..
.... - Assembly -....-.., . -.. .... .. .`.. .-. ,.._..,--.
...-.-.-. - -. . -.- - -. ... .`.. . - .. -.-.-. .- - - . ...--
-.-.......- Assembly , .... .. --. - - -. . -.. .........- ...-. `.. `..
`... -.. -....-...- , .....- . -.. .- -., .. .- `., ... DLL ..-- ......
- . ... Assembly - ..--. ...-. ..- DOS , Windows .-...-..
-.-.......-..- .-. DOS .-...--. function `.. interrupt .-- ..-.
Windows . ..-. Application Programming Interface .- API interface . . . -.. .-
- - - function .- -. DOS . -.. .- . ..-. interrupt .-.. interrupt
,--., function , - -. . -. Windows . ..-. API funtion .- . . ._ .- ..
MessageBox, CreateWindowEx, . -. . .,, DLL .-- import ..-. .-
-. Assembly ...-. ,.--.
,., .` Assembly -....-..
.
, Assembly .`
, Opcodes
Assembly .-...-- opcode .-, .,-...-. Opcode . -.-.-. . .- ..-
,.._ . - instruction -. ..
ADD
ADD instruction -. -, .-, . .. . - . ...-. Opcode .... . . operand .-.
-.
ADD EAX, EDX (destination, sour ce)
ADD .. operand .. .-. ..`.... source -. , destination -. .
-. . -. source --,..- destination -,.. .._..-. `.. .- destination
. . . . .....-. Operand .- -. . .. .`.. . -. .. register .-..,..
- .-, . .,
, Register s
Register ..-.-. 8bit 16bit , 32bit - MMX ..-...-.. -.
-., `..-. 16bit .-...-.. ..`.-.-.-. 16bit registers , 8bit registers
.- `.. -. 32bit . -.. .- . ..-. 32bit registers .--_. ..`.-.
register .--. `.. register .- . . - . `.. -. .. --. EAX
.. EA7823BBh -,..- _...... `.. register .-.. ..- -, . ..- -.-.
EAX EA 78 23 BB
AX EA 78 23 BB
AH EA 78 23 BB
AL EA 78 23 BB
AX, AH , AL - -.-. EAX . . - ..- EAX -. 32bit register -.
80386 - ..-...-.. ..`.-., AX . . EAX . ..-. 16bit `. AH
...-. AX . - ... . -. AL ...-. AX . ..- ... . -. .-.
AX -. 16bit `..`. AL , AH -.-. 8bit ..- . .`..- ..-.-. register .-.
-, . ..-
eax = EA7823BB (32bit)
ax = 23BB (16bit)
ah = 23 (8bit)
al = BB (8bit) 100100011010001010110
Register .- - . .` -.-.
low-level -....-.. high-level -....-..
mov eax, 12345678h EAX = 12345678h (305419896)
mov cl, ah CL = 56h (86)
sub cl, 10
CL = CL - 10
mov al, cl AL = CL
........--- ,_.,_...- .....-_--... MOV instruction -.
-,..-.- register -. .-. ., -.-,..-.-., `.. register -..- ....
. -. .,.- AH . -, . . EAX . -. .- . , ..`..- ,- CL ECX register . ..- . .
., -.--. `..-. CL -., 10 .--`. AL EAX . ..-...,-
`, _ - -.
Register . ....-.-. ...- .. -.
,., .` Assembly -....-..
, .... r egister ...
EAX (Accumulator )
.....-..... string ...- . . .._ .., . .._
EBX (Base)
stack .... -.-..- ..._
ECX (Counter )
-, ..... ...- . .._
EDX (Data)
.....`. ...... - .- . . .._ .._
.-.. ._.... .... --. ..`.-.
, Segment r egister ...
Segment register .-.-.-. .-.. segment - ..` ..,, .-
- Windows ...-. ...... ...---. -..-...-. Windows .. flat . - . .,.
. DOS . ..-. . - . - 64KB . - segment .- `.. . - -. .-. . . .,
, . - . . address - .- . - . segment , offset - ..- - . 0172:0500
segment:offset,, .- . - ... Windows . ..-. segment . . ....-. 4GB .-. .
-. .-. . Windows .. segment .-- .-. Segment .- -. `. -. . 16bit register
.- `.. -.
.-.. ._.... .... --. ..`.-.
CS (Code segment)
- ...- . . .._ ...... . - . -,
DS (Data Segment)
- - ...- . . .._ ...... . - . -,
ES (Extr a Segment)
-.-.....-- ......_
SS (Stack Segment)
Routine .... ..... address ...- . . .._ .., . .`... register
FS (286+)
.... segment
GS (386+)
.... segment
, Pointer /Index r egister ...
--. .-. . .,, pointer register .-- .-..-,..- ..`. . ... .-. .
... register .-`.. EIP .-., ..`.-. Pointer register ..-.-....-
.-. .-.--. .-... .-.. address - ...._... opcode movb,
scasb,.., .--. .-- ..`--.
esi (sour ce index)
string/array source - .- . - ..- . .._
edi (destination index)
string/array destination - .- . - ..- . .._
eip
(instr uction pointer )
.,.- instruction address - .........-. --.-
.`. . . .. Olly Debugger' , .- -_ ,
,, Stack r egister ...
Stack register .. .-. ESP , EBP ESP -.-. . - . . . - . stack .
.,..- . . ...-. EBP - .-. function .-.. local variable .-, .-.- pointer `..
..`-.
esp (stack pointer )
stack. --... .,..-.- _,`._
ebp (base pointer )
stack- . ...... . - .,fstack pointer . -..._
,, . - .
,....-. Windows .. .-..-- -.--... .-...`..
,, DOS & Win 3.xx
DOS , Windows 3.xx .. .-.- 16bit . -.. .- . . . - . - segment .- ,
`....-. segment .--. .......`. 64KB . -. . - . - .. .. segment
pointer , offset pointer --. Segment pointer - -. segment - ..`...-.
_,``. offset pointer -.-. segment - ...,..- _,`-. ..-- -_
,., .` Assembly -....-..
. - .
SEGMENT 1
(64kb)
SEGMENT 2
(64kb)
SEGMENT 3
(64kb)
SEGMENT
4(64kb)
.._ `.
. - .... .- -, .-. . .`.,-.-. 16bit . -.. .- - - `.. -. .-...-
.-. . - . -. .- 64KB . segment .---. ... ......,, 65536 segment
. -. - segment -.- -_--...
SEGMENT 1(64kb)
Offset 1 Offset 2 Offset 3 Offset 4 Offset 5 and so on
Segment - .,..-. - _ , . -. . . .-. offset - . .`-. Offset . -.
segment - .,..-. Segment -... ......,, offset 65536 . -. . - . -
segment - ...`..-.
SEGMENT:OFFSET
..`..
0030:4012
.-.-.-. segment - 0030 `..`. offset - 4012 `..-. address -. -.
. -. . . .-. .. . segment 30 . - . .... .`.. ` . segment - offset 4012 - .....
`.. -. . .. ,. .- , .- -, .-. - segment , pointer register .-. .. . -
-. Segment register . .....- -.-.
CS (Code segment)
DS (Data Segment)
ES (Extr a Segment)
SS (Stack Segment)
FS (286+)
GS (386+)
....- ._ .- -. . - . ... - - . . - ... `-. CS . . - .
.,-- ..,-. DS -.-. -. segment -- --.-- ..... `..-.
Stack -.-. SS - _ , .-. ES FS , GS -.-. .... register .- `.. ` . -. segment
--.. ...-. Pointer register .-...-. ........`..-. offset -.- _...
.-. ... .... register .-`..- AX BX CX , DX . ._ . - - . .`.
-. IP - CS . , - . .,- instruction . offset - _,`-.
..-..`..--.-. crack -.. Olly debugger ..`..- register .-.
.,
SP -.-. SS -, - . stack .,... offset - _..-.
,, 32bit Windows
16bit -,.- .-...- .......... segment .- -. .. .`.. -. - .-. ...-
.. ., 32bit windows 95 .-, ...-. `.,.- .`....-. Segment .- . .,...
,., .` Assembly -....-..
-, .-. - .,, ....... . .-.-. -...-. .-.--. 64KB .--.-.
4GB `.. ., --. segment register .---.- .`... - .... .. . . Windows
, `.,. -- .-. .-- . .. . - . . offset .-.`. ,...-. .-.--. 32bit .-
`.. -. .-. . - .-.-.-. ._-., 4,294,967,295 `.. .-. . - . -
-. .,.... offset , _ , `. -. -. 16bit -... 32bit . .-.... -..-..
.- - -. `.. -. .-. . . .,, segment register .-- ,.. .... ..`.
`.. register .-- .-..- .``..-.
, Opcodes
Opcode .- -. . .- ..- - instruction .-`..-. Opcode .- -. --. .-.
.,. - . -. .. .- .- .....' . .- - - .-. assembler -. . -.. -....-..
.- . . , . . .. `...,-.`..`. assembler .....--..... .,.-`.. --.-
.`. . -. `.. -.
, .. ..-. - - - . bitwise .,.- opcode - .. ... .. .`.. -. `..
opcode .-`..- jump instruction compare opcode .-..- - .-. .,.- , .-. .. ... .. .
`.. -.
, .` opcodes ---.
MOV
instruction -.-. -,..-.- -..,..-., .,.--. .,..- .. . - .. , . .`
-. .,..' .- ...,... register -. ... _ ..-. . . - . .,..-. ... _ ..-. .
- .-, . . . -, . ., -. ... _ ..-. . `.. . -. mov instruction . . -.-.
mov destination, source;
. .,, register -. - -, . .-. - .,.- -. . ...-. .-., instruction
-. --. .-. . . ._ move' ... -, . .- .,.- -. .,... - .... - -.,
mov edx, ecx;
-..`- instruction -. ECX ...--..-- EDX . - ... - -. Source ,
destination . . . ...-. - _ ... ..- . .... `..- instruction -.-. .,-,. ..-.
mov al, ecx; // ....
opcode -. DWORD 32bit, ...- -,..-.- byte(8bit) ....- ... -
register .,..-.- _.- .....,-. - .-. mov instruction - ...`. ..-.
`.. instruction .--.-. ...-., ... ..-- instruction .--.-. mov
instruction .. ..`.-. -..-...-. source , destination -. ..... -`...
..
mov al, bl;
mov cl, dl;
mov cx, dx;
mov ecx, ebx;
.-..-_..- offset -. , _ , `-. . - . . - -- .,..-. -., -, . .
-. - .. ` . register -... -,..- ... .-. ..- ...- ..`.. .
offset 34 35 36 37 38 39 3A 3B 3C 3D 3E 3F 40 41 42
data 0D 0A 50 32 44 57 25 7A 5E 72 EF 7D FF AD C7
-, -. . ._ byte, ...-..- -....`._ ,
.,.... offset -,..-. ...-..- -....`.,... .-. 32bit ..`..
3A - -_ . -._ . 32bit 0000003Ah, -,..`..-. .,..... ...,-
.--- -,..,_. offset .-- ..`-. -,.....-.-. hexcode .- `.. -.
....- offset 3A .,..- -_- offset ...- .-.-.-. 25 7A 5E 72
EF .._- `..-. Offset 3A .. ...-,..- mov instruction , register - . .... .
-.-.
,., .` Assembly -....-..
mov eax, dword ptr [0000003Ah];
Instruction mov eax, dwor d ptr [0000003Ah] .-.-.-. 32bit ......-
DWORD -,..-.- EAX register - 3Ah .,... . ..-. instruction - `.
.,.- . ..-. EAX .. 725E7A25h -,.. ...-.-. .-... ..,-.. 25 7A 5E 72,
.- -. .`. .`, .,.., . .,-. .- `. . . -. -..-...-. . - . . . . . ...
--,...-- endian ,_ ., . .. . -.- _..- -. ... .-. significant `.. . .
.. . .. ..- . - . . -.-. .`. .`, ..,_ .. , . .`. .-. ,.._ . .
DWORD (32bit) -,.. 10203040h - . - . . . . . .._ . -.-. 40 30 20 10 -, . .-. .
-. .. .-. . (8bit) - -....`-.,
WORD (16bit) -, . . 4050h - .-... ...._.-.-. 50 40
...... -_-..
mov cl, byte ptr [34h] ; cl = 0Dh (....- -_ )
mov dx, word ptr [3Eh] ; dx = 7DEFh (....- -_ .`. .`, . -. .- . )
. . ...-.-. --. . . ....- . - .
mov eax, [00403045h];
-..-...-. EAX -. 32bit register -. `.. -. Assembler - . - . .
00403045h .,..-., 32bit -,..- .... .-...-.
Immediate value -.-,..,.-- ..`.-.
mov edx, 5006;
-.-. EDX . . 5006 .- -,..-.- _..-. .... - .. . - -
.-. .... - . - . - . -_ . ... -,..-.- ... ..`-.
mov eax, 403045h ; eax = 403045h
mov cx, [eax] ; EAX . - . .,.. 403045, - . ... WORD . . .... -, . .- register CX
- _ ..._
mov cx, [eax] .. ..-..-. EAX . . _ ..- -, . . . - . -_ .,.., -.
..- . -. . -_ -. ` .. .. . - . - .,... . -, . .-. ..- . . . -.
..`.-`. WORD (16bit, -..-..... CX ._ 16bit register `......-., - CX
_- -.
ADD, SUB, MUL, DIV
Opcode .-..-.......-. ---..- `--. . .,, . - . ._ .-. .-.
......- ,.,..-. ADD ..`., SUB .-`., MUL .`..-`., DIV ...` .,
.._ `.
ADD opcode .. ..-.-..-.
add destination, source
- - - . ` - destination = destination + source ..- . .- - `
-.
Destination Sour ce Example
Register Register add ecx, edx
Register Memory add ecx, dword ptr [104h] / add ecx, [edx]
Register Immediate value add eax, 102
Memory Immediate value add dword ptr [401231h], 80
Memory Register add dword ptr [401231h], edx
instruction -. , . .. .-. . -. source .-,..-..`. destination -, . .. . ..
..-. `.. .- destination .. ..-. `....... instruction .- -.-.
sub destination, source (destination = destination - source)
mul destination, source (destination = destiantion * source)
div source (eax = eax / source, edx = remainer
,., .` Assembly -....-..
,
. - ` .-. . .` ., - - .`. .- ` .-.-. dest = dest * source ...` .-.-.
,_.,_... .`..-. -..-...-. register .--. -,.`_-,...- `..., .
-.- ..- , ..- .- - - ., ... .- . - ... , - .. ` . - -. ..`..
28/6 ... =4, -.=4
30/9 ... =3, -.=3
97/10 ... =9, -.=7
18/6 ... =3, -.=0
,...-. source . .......-_`. ...- EAX EAX . . - .-. ,. .
...`. -.- EDX EDX . . - .-. ,. . . . .._ .-.
Sour ce t &G, ft pm; pm;jci f; pm;v ' f t <u i f;
BYTE (8-bits) ax / sour ce AL AH
WORD (16-bits) dx:ax* / sour ce AX DX
DWORD (32-bits) edx:eax* / sour ce EAX EDX
* .. -. . DX = 2030h AX = 0040h DX:AX = 20300040h DX:AX ._ DWORD
-,..`..`. DX ._ `. . WORD `..`. AX ._ , . . WORD `.. ._ EDX:EAX
-.-. QuadWORD -,.. 64bit, `..`. `..-.-. EDX `..`. ,..-.-. EAX
`.. -.
DIV opcode . source .,... . `.. . -.-.-.
8-bit register (AL, AH, CL,...)
16-bit register (AX, DX, ...)
32-bit register (EAX, EDX, ECX, ...)
8-bit .-.-,.. (BYTE PTR [xxxx])
16-bit .-.-,.. (WORD PTR [xxxx])
32-bit .-.-,.. (DWORD PTR [xxxx])
Source -.-. - .-, . . .`.. . -. -..-. . .-. . .- ..- source operand
. . . ...- .. .`.- .
BITWISE OPERATIONS
instruction .- . ..-. 'NOT' instruction .--. source .-. destination -.
Destination ...- bit ....- source ...- bit .-, ...-. Instruction .. -_ ` .
destination bit . . 0 ., 1 - ..-.
Instruction AND OR XOR NOT
Source Bit 001100 1100110 1
Destination Bit 010101 010101X X
.
000101 1101101 0
..
mov ax, 3406;
mov dx, 13EAh;
xor ax, dx;
ax = 3406 (dec) = 0000110101001110 (bin)
dx = 13EA (hex) = 0001001111101010 (bin)
Source 0001001111101010 (dx)
Destination 0000110101001110 (ax)
.
0001111010100101 (dx)
instruction ` .- .,.- . ..-. dx = 0001111010100101 [7845 (dec), 1EA5 (hex)]
.,.- ..-.
mov ecx, FFFF0000h;
,., .` Assembly -....-..
not ecx;
FFFF0000 = 11111111111111110000000000000000 (bin) (16 1's, 16 0's)
. .,, bit -.- .`..`, . ... .-.-.
00000000000000001111111111111111 (16 0's, 16 1's) = 0000FFFF (hex)
.-.. NOT operation ` .- .,.- . . ECX . -, . .-.-. 0000FFFFh `.. -.
IN/DECREMENTS
...... instruction ..-.-. DEC , INC instruction .--. .-.-_..
., register - -. . .... - ..-. . .. .......
inc reg -> reg = reg + 1
dec reg -> reg = reg - 1
inc dword ptr [103405] -> [103405] ....,- -,..- -.......
dec dword ptr [103405] -> [103405] ....,- -,..- -..-....
NOP
instruction -.-. . .- .- -.. . - . -.. . . . .. - . .-. .
, Crack .... .- .....-. .....,..-.-. -.-- patch - .,... .
`.. -.
Bit Rotation and Shifting
. - ., ..- . .... `..- ...-..-.......-. 8bit -,..-- ..-. ... ..
.. .- , `..
Shift functions
SHL destination, count
SHR destination, count
SHL , SHR -. register.-..,..- bit .-- -._..., ..--`. ..--.`..-.
..
; .,.... al = 01011011 (bin) . .-_ ..
shr al, 3 ; al = 00001011
.-.-.-. AL register - bit .-- _..- .,.... ..--. .-. AL -.
00001011 `.. .-. -. .- `. .- bit .- - . _.- , ... . - ` . _..- - bit
.--.-. .......--. ....-- .,.-.. bit - .-. carryflag . . . . ...-.
Carrybit . -. . .- ... Flag register - bit -. . -. - - . - - - . . -
. opcode .-...._., EAX ECX register -. .- - - . ... . . .`.-.
instruction . . . . -_ .,-. - .,.- .. . . .`.. . .,, . - .... .-.
-.-. carry .-. flag register - bit -.`..`. .- . -. . -.- bit -.
.. .. - .- .,.- . . bit , -_-.
shl - shr , - -. ... . - -. .- - .. -.
; .,.... bl = 11100101 (binary) . .-_ ..
shl bl, 2;
Instruction `.-.,.-...-. BL -. 10010100 bin, `...-. .,.-.. bit . . . .
.-. . _.- , `._ - -. Carry bit -.-. 1 `.. -. -..-. . .-. .,.- . ... ..
-.- bit - 1 `.. .,
.,.-...-. `.. opcode . . . ...-.
SAL destination, count (Shift Arithmetic Left)
SAR destination, count (Shift Arithmetic Right)
,., .` Assembly -....-..
SAL - SHL , - -. ... SAR -.-. SHR , .- - . SAR - . _.- ,
....-. .--... MSB most significant bit, - - . -. ..
al = 10100110
sar al, 3
al = 11110100
sar al, 2
al = 11111101
bl = 00100110
sar bl, 3
bl = 00000010
Rotation functions
rol destination, count ; -. . _ ._
ror destination, count ; _.. _ ._
rcl destination, count ; Carry .-. -.. _._
rcr destination, count ; Carry .-. _.. _._
_ -.-. .. . - `..-.-.-. ....-.- bit .-- `...-- ..-
-.
Oyr m/ / ror (r otate r ight)
Bit 7 Bit 6 Bit 5 Bit 4 Bit 3 Bit 2 Bit 1 Bit 0
._.
1 0 0 1 1 0 1 1
Rotate, count= 3 1 0 0 1 1 0 1 1 (....)
.
1 1 0 1 0 0 1 1
... `..--. bit .--_--. .-.- -,.--.- bit - .-.
. ` . `...- - .. .-. .. ` .. . carry bit .- -. .,.- . ... .. .- bit -
. . ...-. RCL , RCR -.-. ROL , RCR - , -. . -_ . . - . ._ .- - .
-- .`.`-.-.-. .--. .,.-......-- bit - _,`.. carry bit - ..`-
-. ROL , ROR - --. .-.. -`... ..--.
Exchange
XCHG instruction -.-. ..-.- ....-. .-. register .. ., register
-. , . - . .,..-. - . ... -.
eax = 237h
ecx = 978h
xchg eax, ecx
eax = 978h
ecx = 237h
, . .,.
Assembly source ..-- section .- .,, ..-. Section .--.-. code data
uninitialized data constants resource , relocations - `..-. Resource sections -
resource .- -..-. `..-. .,.-.--_, Relocation section -.-. -,.-.-
-- ....-.-. ... .-..- . - . . `..-.,... . - .- ... PE loader --
- - .- .-. . . .. , ...- .- section .--.-. code data uninitialized data
, constants - Code section . .-.-.-. . ..--. -.- Data sections
. ..-. .- .... .- .-..- -. Data section -..-. exe ...`. .-.
.-, ... .-.
Unitialized data - - -.-. . .. . -.. .- . exe . - . - . ..-. .- .
. -.-. Windows -- ...,....- .-. -. . - -. .... `.. -. section . .
... .- .-. Constants -.-. data section , - -. ... .- .-.
section - constant -- ..`...._. .-. include ... constant .- - .-_...
. .-. . . - ` .`., ., .-. .,.-.-- -.-,..`.. ...
,., .` Assembly -....-..
,
, Section indicator s
. . source . .- . . . .,, section .-- .........
.code ; code section-. .,..- .-.
.data ; data section-. .,..- .-.
.data? ; unitialized data -. .,..- .-.
.const ; constants section-. .,..- .-.
- . .- (*.exe, *.dll, ...) -. Win32 ...-. PE portable executable, .,
...-.- .-....- -,-..-- .,.... ....-........ .---. PE
header ,.- ....- ......._, Section .-- PE header .. ..., --
,- . ..-. .- -.-. section name RVA offset raw size virtual size , flags -
`.. -. RVA relative virtual address, -.-. section - - .- .... . - . -
.- . . - .,.. `.. -. .,... . relative . - . .. - . -.. , . . . - . . .. -
base address , .-...,-.- .`.-. address -. PEheader . . . .,... PEloader
- .`.....-. relocationsection - ..``., Offset -.-. exe . - .. .
.-.. .. raw offset ..`.. -. Virtual size -.-. .-...`..... ..... `..
-. Flag .- -.-. .- . .... . .-..- - - flag .- `.. -.
, ,. ,. . -..
-.-. ,. ,.. -..
.data
Number1 dd 12033h
Number2 dw 100h,200h,300h,400h
Number3 db "blabla",0
.data?
Value dd ?
.code
mov eax, Number1
mov ecx, offset Number2
add ax, word ptr [ecx+4]
mov Value, eax
. -.. -. .-. ..-. . assemble . ..- - - . ... - . .. - . . . assembly
.-.... section . .... - ..- .-. . -..- .-.-.-,.. exe . ...-.....
`.. -. .. .`..- data section .. label .-. Number1 Number2 , Number3
label .--. .-..- .-....,... offset - .....-. .-. . . . . -.. . .
.,..-. - _ , `. . -- ..`.-. DD -.-. .,... . - - . - DWORD -, . .
-.- ..-. DW -.-. word `..`. DB - byte `..-. DB , . . . .,, string
.-- ..`.-. .-.. string .-. byte -,...--..- .-. `..-.
...,, `..
33,20,01,00,00,01,00,02,00,03,00,04,62,6c,61,62,6c,61,00 (all hex numbers)
-,..-.-. byte -.. `..-.,
-, .-. .,, -, . - ... `. ..-. Number1 - byte 33 . .. . - . .,..
- `.-. Number 2 -.-. , ... 00 ...`..`. Number3 -.-. . . .... 62 . ...,..
`.. -. - . .,, . -.. . .. ..
mov ecx, Number1
--. . -.-.-.
mov ecx, dword ptr [.-.. dword 12033h -_ . ...,..]
... -.
mov ecx, offset Number1
. -.-.-.
mov ecx, .-.. dword 12033h -_ . ...,..
,., .` Assembly -....-..
.
.... . ECX -. Number1 . .-..,.....- -,..-.- ..... -.
-. . ..-. ECX -. . - . .,.. offset, `...... ..--...... -_--...
. -.
,
mov ecx, Number1
,
mov ecx, offset Number1
mov ecx, dword ptr [ecx] (..-- mov ecx, [ecx])
..- `, -_ -..
.data
Number1 dd 12033h
Number2 dw 100h,200h,300h,400h
Number3 db "blabla",0
.data?
Value dd ?
.code
mov eax, Number1
mov ecx, offset Number2
add ax, word ptr [ecx+4]
mov Value, eax
Label -,..- Number1 Number2 , Number3 - ..`.-. ... .....
.-. . . . . _ ., ... -..-...-. .-. unitialized data section .. .
. -..-..-.-. data? .. ..-_.-..-...-. executable .. ....---.
. - . . ... . . .
.data?
ManyBytes1 db 5000 dup (?)
.data
ManyBytes2 db 5000 dup (0)
(5000 dup = -... 5000. Value db 4,4,4,4,4,4,4 = Value db 7 dup (4).)
ManyBytes1 -. .-.- ... ....---. .-... ..... 5000 , ..
-. ... ManyBytes2 -.-. executable ...`. .- 5000 bytes -... -.
. . . . . . _.- . 5000 .. .. -. . ..- .. - .
Code section -.-. assemble .. .- .- `.. ` . raw code ..`..`., executable
. ...-. . , .-. - .- , . . . - . . .`.. -. ,
,, Conditional Jumps
Code section ...-. label - ..` .-.
.code
mov eax, edx
sub eax, ecx
cmp eax, 2
jz loc1
xor eax, eax
jmp loc2
loc1:
xor eax, eax
inc eax
loc2:
(xoreax,eaxr Smeax=0 .-.)
-- ..-_--...
mov eax, edx ; EAX .. EDX - ..-.
sub eax, ecx ; EAX - ECX - . - -.
,., .` Assembly -....-..
.
cmp eax, 2; EAX - 2 , . .. -.
Cmp - instruction .. `.. -. Cmp -. 'compare' . .. .-. . -. -, . .
. . reg, mem, imm,- ...`. .-..-. _. Zflag - .-.--. Zeroflag -.
carry flag register - bit -.`..-.
jz loc1;
-. -._ . .. -. `.. -. . -.-. conditional jump Jz = jump if zero
.-.- zero flag - .- . - - , . . .-. . ..-. loc1 -.-. . - . - offset - -
label -. .. instructions 'xor eax, eax | inc eax' .-. .-. . jz loc1 -. --.
zero flag - .- . - - . loc1 ...- instruction . .-. . ... .
cmp eax, 2 ; EAX=2 `.. . zero flag - .- . - . .
jz loc1 ; zero flag - .-.--.f loc1 . .-. . ....
=
EAX -. 2 , _ . loc1 ...- instruction . .-......
.,.- -. -.-. jmp loc2 . -._ . jump -. ... .-.-. unconditional
jump . - `. -. ..-. ..-. .-- - C -....-.., - - `, ...`..
if ((edxecx)==2)
{
eax = 1;
}
else
{
eax = 0;
}
BASIC. -.. -....-.., ...`.. .-.
IF (edxecx)=2 THEN
EAX = 1
ELSE
EAX = 0
END IF
,, Flag r egister
Flag register . . - - - . , `..`.. - ..... -_ ` . .- . - ` ...- . - ` .
`- flag .- . -. -, .-. .,, .- - , .- .. ... .. . .- - - . ...- .-.
- .. ... .. . `.. -.
ZF (Zer o flag)
---..-. ._`... flag - .- . - -. . .. -. . -. --. .-.
. - ` .-. . ... `.. -. . - . . .._ .. .. ... flag .--.-. .-.--.,
SF (Sign flag)
--. flag - ... ---.- ...- .,.- . .- , .-. . - `.. -.
CF (Car r y flag)
- - - . ` .- .,.- . ..-. . . -. .- -. . bit .-.
OF (Over flow flag)
- - - - .-. , - - - .-.- .`.-. .-.- .-. destination ..
..-. -. .., -.,- .`.-.
` `.. flags (Parity, Auxiliary, Trap, Interrupt, Direction, IOPL, Nested Task,
Resume & Virtual Mode) .-_. ....-. ... -,.-.- ..`.. .-----
.-- ..`.-... .---.
,., .` Assembly -....-..
,
,, Jump ser ies
..- . .... `..-.-.-. conditional jump ,-.--. -, .-.--. flag
.-. .`.,..-_`. jump --. ... .-. .-. ....... . . . . . - - ._
.- . -. . .,, -. jump - .-.-...-..-. .... .-. 'Jump if greater or
equal' (jge) - - ..`.. 'Sign flag = Overflow flag' `.. -. .,.- -. -.-. 'Jump if
zero' .- . 'Jump if Zero flag = 1' . .....
....- ,_ .
'Jump if above' . . - -.-.
cmp x, y; // x , y - ...-.
// --. x -. y - - .. jump ..
Opcode Meaning Condition
JA Jump if above CF=0 & ZF=0
JAE Jump if above or equal CF=0
JB Jump if below CF=1
JBE Jump if below or equal CF=1 or ZF=1
JC Jump if carry CF=1
JCXZ Jump if CX=0 register CX=0
JE (is the same as JZ) Jump if equal ZF=1
JG Jump if greater (signed) ZF=0 & SF=OF
JGE Jump if greater or equal (signed) SF=OF
JL Jump if less (signed) SF != OF
JLE Jump if less or equal (signed) ZF=1 or SF!=OF
JMP Unconditional Jump -
JNA Jump if not above CF=1 or ZF=1
JNAE Jump if not above or equal CF=1
JNB Jump if not below CF=0
JNBE Jump if not below or equal CF=1 & ZF=0
JNC Jump if not carry CF=0
JNE Jump if not equal ZF=0
JNG Jump if not greater (signed) ZF=1 or SF!=OF
JNGE Jump if not greater or equal (signed) SF!=OF
JNL Jump if not less (signed) SF=OF
JNLE Jump if not less or equal (signed) ZF=0 & SF=OF
JNO Jump if not overflow (signed) OF=0
JNP Jump if no parity PF=0
JNS Jump if not signed (signed) SF=0
JNZ Jump if not zero ZF=0
JO Jump if overflow (signed) OF=1
JP Jump if parity PF=1
JPE Jump if parity even PF=1
JPO Jump if paity odd PF=0
JS Jump if signed (signed) SF=1
JZ Jump if zero ZF=1
Jump instruction ..... operand -. .. -. -.-. jump .. .,... offset
...- ...-_ .. . . unconditional jump (JMP) -. - .- . . . -.-. -. ,
. .. - - . ..- - - . Jump -, . . .
,., .` Assembly -....-..
,
., -, .....-. . -.. -... .
. -.. -....-.. .-. .-. ....... . -,.`_, ..-,. ..`-.-. variable .-_..
.. -_ -. Assembler ...-. .--. ..-`..-. ..-,..- ---.- .
opcode .- , ` .-. - FPU (floating point unit) .- ..-..- `
..-. ..-,.,-.-- instruction .-.-..- .,.-... ........ ..-.
-,.`_.-.-.. ........ C . . signed , unsigned -,..`. .....-. Signed
. -.-.-. . .. - ..- -.- -,..-- .-. Unsigned -.-. `. -. . . .
..--..... -`......- -_--... .`.... . . .,... . byte , ..`..
-. `........ --.,
-,..
00 01 02 03 ... 7F 80 ... FC FD FE FF
Unsigned 00 01 02 03 ... 7F 80 ... FC FD FE FF
Signed 00 01 02 03 ... 7F -80 ... -04 -03 -02 -01
.-.. signed -, .. . .. .- .. . . - -. . .-, . .- - 0 -.,
7F .--,..-- 80 -., FF `.. -. -, . .- - . . _ . - - . . = 0
7FFFFFFFh .- = 80000000 FFFFFFFFh .-.`.. .--,..--. significant
bit - .- . - -. -..-. . .-. . - -. 80000000h --. bit - sign bit
.-.
., Signed .. unsigned ..
. ... . .- .. -, . .-. -. signed .. unsigned .. .. . - . .- ..-. .
-. -.-. . ., . - . . -, .-. -. signed `..`.. unsigned `..`.. ....-.-.
-- 4 + 9
FFFFFFFC + 00000009 = 00000005. (. , -. )
-- 5 (9)
00000005 FFFFFFF7 = 0000000E (. . , -. ) ( 5 9 = 14)
.-...-.-.-. .--. .`..-`. ...`., ...`.-.. ..,-. .-..
signed -,..--- . mul , div opcode .- . -.
imul. idiv
mul - ... imul .. .- ....--.-. ... -.-,...-- ...-.
imul src
imul src, immed
imul dest,src, 8bit immed
imul dest,src
idiv src
.-.--. mul div -,-... .-.--. signed -, . ..- , .. - - - -.
....... unsigned -,..-, -_....`.... flag .-- .-.--..-. -`..
-. .-. . signed , unsigned -,..--- -`..- jump instruction .- ..,.-.
cmp ax, bx
ja offset
JA -. unsigned jump (Jump if above) ax = FFFFh (FFFFh unsigned, 1 signed) ,
bx = 0005h (5 unsigned, 5 signed) -- .....-_ FFFFh -. (unsigned) -, . ...`. 0005
- `. -..-. JA instruction -. .-. ... . ... JG instruction -.-. signed jump
`.. . .-.
cmp ax, bx
jg somewhere
JG instruction -.-. jump `.... .---. -..-...-. 1 -. 5 - .- .
. - .... .-.-.
-, .-. -. signed/ unsigned `..-..-.-.-. ..,, -,.- --...
. -_ -.
,., .` Assembly -....-..
,
., .,.- opcode ...
-.-. .,.- opcode `..-.
TEST
TEST -. logical AND ...-- ....-`. dest , src .- ...`. ..
.-_`. flag register - .- . - -. . - .-. - . - .. . .- . TEST - ..`-.,..
-.-. ..`..- - . register -.- bit -.- .....`..-.
test eax, 100b ; (b - ...,.. -.-.- )
jnz bitset
--. EAX - -- ..`..- bit _..-.._,- .-.-....-. JNZ -.
jump `.. . .. TEST . .... .. .`. -.-. register -.-. ._`...`.. ....-
. . `.. -.
test ecx, ecx
jz somewhere
ECX -. . _`.. . JZ -. jump `.. . ..
STACK OPCODES
Stack opcode.- .-....`.`.. stack .-.-..-. ...`.. Stack .-.
. - . - .,..-. `.. ` . stack pointer register `..- ESP , _ , `-. Stack -. ...
-, . ..- ... .,..-. `.. -. . . . -, . ..- - ... , `, .. . PUSH , POP .-
instruction . . . -. PUSH -.-. stack - -,..-.._`. POP -.-. . . -
-. Stack - .,.-..._-.- .-.-. -,..-.- stack . . ....
stack pointer -. ..,_..-. .....,...-. stack pointer -..-.
..--_
(1) mov ecx, 100
(2) mov eax, 200
(3) push ecx ; ECX - . . .-.
(4) push eax
(5) xor ecx, eax
(6) add ecx, 400
(7) mov edx, ecx
(8) pop ebx
(9) pop ecx
...-
1: ECX - 100 - ...._
2: EAX - 200 - ...._
3: push ecx (=100) (stack . . .. ....-.)
4: push eax (=200) (stack .. .,.-.....-.)
5/6/7: ECX , - .- - ... - .- -. ECX . -,...- .`...,-.
8: pop ebx: EBX -. 200 `.. .-. (.,.- . .... . . . - . -. )
9: pop ecx: ECX -. 100 `.. .-. (.. .... .,.- . . - . -. )
PUSH/POP `.`. .-.. . -..-`..-.,.-.-_. ..-...- -_
Offset 1203 1204 1205 1206 1207 1208 1209 120A 120B
Value 00 00 00 00 00 00 00 00 00
ESP
.,.... stack -. ... ._.- `._...-. ... --.--....-.
.- - - . ESP -. ESP _,`- offset - ._ . . -. ,
mov ax, 4560h
push ax
,., .` Assembly -....-..
,
Offset 1203 1204 1205 1206 1207 1208 1209 120A 120B
Value 00 00 60 45 00 00 00 00 00
ESP
mov cx, FFFFh
push cx
Offset 1203 1204 1205 1206 1207 1208 1209 120A 120B
Value FF FF 60 45 00 00 00 00 00
ESP
pop edx
Offset 1203 1204 1205 1206 1207 1208 1209 120A 120B
Value FF FF 60 45 00 00 00 00 00
ESP
,.. EDX -. 4560FFFFh `.. .,`
CALL & RET
Call -.-. -.-. .-....`. RETinstruction - .- - - . `, ...-
.-. . .,, . - .- - `... -.. -....-...- . . function .-`.. subroutine
.-`.. .-.-. ..
; ..code..
call 0455659
; ..more code..
; Code at 455659:
add eax, 500
mul eax, edx
ret
CALL instruction -.. ..-..-. 455659 . .. - - . .-. . ..` . RET
....-. instruction .-- -. `..-. CALL `.- instruction .-. `,_
-. CALL - jump `.....---.-. procedure .-. CALL -. EIP .,.- _ ,
-..-- ..._ pointer,- stack . push -. ` ..-. RETinstruction - pop
`, ..-. . .,, CALL -- argument .- .- . - .-. - PUSH , `
. -.
push something
push something2
call procedure
CALL -....-. argument .-- stack -.- ` .. .`. -. Local variables
.-.- procedure - .. ... - .-...., .- - stack . .... .-. -, .-.
.,, .-- ....-........ .---. -...-. .-- masm Macro Assembler,
, tasm Turbo Assembler, .. .--. ..,, procedure .-- `.-.
. -., . - .- -. parameter .- - . .-. . - .. .-. ` ...- .-.-. - -.-.
Pr ocedur e -. . r etur n value - _... EAX - `.-..,.. ..`-.
.--. windows function .--- .,-,-. .,...-. ..-.
procedure ...-. `..-. register - .. . .`. -. ... EAX -.-. .-.`..
-. .-.... instruction -.. ....- ..`-.
lea edi, namebuffer ; EDI -. ...-_-- ._..... address `..-.
mov eax, dword ptr ds:[edi] ; EAX - ...... .....-. -..-...-. DWORD
(4 bytes) -. .. . .. ., _
, Windows . - .- ... Assmebly -....-.. .`
, API
Windows . .. -.. ......` .. .` -. .- -.-. Windows API Application
Programming Interface, .- .. -_ .,-. API . -. OS -`._......- function .--
. ._ .....-. Windows .-..-.-. function .-- ..`-. function .- -.
,., .` Assembly -....-..
,,
Windows .,. . dll ..-`..- kernel user gdi shell advapi .- . .- . . . -. Function
..........-. ANSI , Unicode .- -.-. string .-- ...._.--..... ..`
- ,_ .. .. . `.. -. ANSI , . . .-. .. .- .- ..- -ASCII - ,.,, ... `` .
string ...-...`. \0 (nullterminated)- ..`-. Unicode -.-. widechar .-
..``. ..---..-- ........`-. . -.-. -. - `., ..-....-...-
......- -....-...- . .. .`-. Widechar string .--. \20 , ...-.
. -. Windows -.-. ANSI function `..`.. Unicode function `..`.. --. ..
`..
MessageBoxA (ANSI)
MessageBoxW (W = widechar (unicode))
-, .-. - -.-. ANSI - ..`.. `..-.
, DLL ....- ....` .
Windows API . function .-- ..`. DLL ..-- import . -. .- -
import libraries (.lib) .-, `.-. lib .--. ...`..-. -..-...-.
.--. Windows .,.- DLL .- ... - .. . .. . ` . -.- . - . - dynamic
base addresse .., - includelib ..`. library -.- _...-.
includelib C:\masm32\lib\kernel32.lib ..--,
includelib \masm32\lib\kernel32.lib ..--,
includelib kernel32.lib
. kernel32.lib - _....`.-... .,.... include library -. -_ .-..
...-.-. .---. include file (.inc) - -. .--.-. l2inc .-....`. library
.- -., ..- - ...,-. include file -.- ...`......-.
include \masm32\include\kernel32.inc
include file . . DLL - function .- - - prototype .-- ......`.`..-.
.-. . .,, invoke - ..``. ....`
kernel32.inc:
...
MessageBoxA proto stdcall :DWORD, :DWORD, :DWORD, :DWORD
MessageBox textequ <MessageBoxA>
...
include file .. ANSI function .-, --. function ._ , - -_ .-.. ..
- 'A' .- function .- - . .. . ..-. `. .. . . .,, MessageBoxA ...
MessageBox - ...-. ..... function .--- include library , include file .--
.-_..- . - ` .. ... .-. function .-- ..` .`
invoke MessageBox, NULL, ADDR MsgText, ADDR MsgTitle, NULL
, Windows include file
Windows . . . include file -.`..- windows.inc ..-. ... Windows
API - - - constant , structure .. . -. ..`.. message box .. .....
. -. Function . .. .`..- parameter -.-. .- NULL - MB_OK - . ` . . -.
OK button `.. -. Windows include file . . .- . ..- - - . .. . . - .-
-.
MB_OK = 0
MB_OKCANCEL = ...
MB_YESNO = ...
...... ._ .- - . .,, constant .,, ....,-.
invoke MessageBox, NULL, ADDR MsgText, ADDR MsgTitle, MB_YESNO
..-- include file - .-_... . . .-. .-_....
include \masm32\include\windows.inc
,, Fr ame
,., .` Assembly -....-..
,
,. ,. frame -. - -_ -_ ..
.486
.model flat, stdcall
option casemap:none
includelib \masm32\lib\kernel32.lib
includelib \masm32\lib\user32.lib
includelib \masm32\lib\gdi32.lib
include \masm32\include\kernel32.inc
include \masm32\include\user32.inc
include \masm32\include\gdi32.inc
include \masm32\include\windows.inc
.data
blahblah
.code
start:
blahblah
end start
-.-. windows assembly source file (.asm) -- .` frame -.
.486
Assembler - . .- .. . .- - `. ,- - .- - ... .`.
-. . .,, .386 - ..`.... .486 -.-. ...... ..`.
.-. ..-. . . . -.
.model flat, stdcall
Flat .-.- ..`-. stdcall - ..`-. .-.-
function .--- parameter .- - _..- -., -. .- - push
-. .,.- . .- .. . push -., `....,...-.
function -. stack - `, `` ..... -. Windows API
function , DLL .- .. ., ..- - .
option casemap:none
Label --....--. -.... `...... ...-.
windows.inc . .-...-.. . . . - 'none' .....
includelib
.. . .. ... .` .`.. -.
include
.. . .. ... .` .`.. -.
.data
data section .
.code
code section .
start:
end start
Label -. . -.. . .- _ , `-. 'start' .-. ...-.
. .,, - - - ,.._ ... -. . .-. .-. 'end' statement -
. .. .-. -.
.-..` -,.-.- ....-.. -. - ...-_ .. .,... . assemble .
-, .-. - . ... ... . . . -.-. WinAsm Studio 5.1.5 , Macr o Assembler 3.2.7 -
`.. -.
.486
.model flat, stdcall
option casemap:none
includelib \masm32\lib\kernel32.lib
includelib \masm32\lib\user32.lib
include \masm32\include\kernel32.inc
include \masm32\include\user32.inc
include \masm32\include\windows.inc
.data
MsgText db "Hello world!", 0
MsgTitle db "This is a messagebox", 0
.code
start:
invoke MessageBox, NULL, ADDR MsgText, ADDR MsgTitle, MB_OKCANCEL or MB_ICONQUESTION
invoke ExitProcess, NULL
,., .` Assembly -....-..
,
end start
-.-- assemble (Go All) - . .- .. ..-. ,- . `.. -.
,
. -.. - . ... .-.
MessageBox . . .` -.-. (Win32.hlp - -_ ,
int MessageBox(
HWND hWnd, // handle of owner window
LPCTSTR lpText, // address of text in message box
LPCTSTR lpCaption, // address of title of message box
UINT uType // style of message box
);
hWnd
., - ... message box . owner window - .- . - -. --.
parameter -. NULL `.. . message box . . owner window . . ..- - - .
lpText
Message .,, `.. \0 , . .- string - _,.-.
lpCaption
. .. - - - \0 , ..- string - _ , .-. --. .,... .
NULL . . . default ...- ..`.. `..-.
uType
Dialog box . .- ...`...`..`. .....- flag .-..-.
2/
hWnd -.-. NULL `.. .,. . -..-. . .-. -, .-. - . -.. . . window ..
lpText -.-. -,.-.-...... pointer . -.- parameter -. -, .-. - .- . -
-........ .-.. offset -. `.. -.
lpCaption -.-. . .. . ...... .. offset `.. -.
uType -.-. MB_OK MB_OKCANCEL MB_ICONERROR - -, . ..- . .. ..-.
`.. -.
MessageBox -- string . . - - - .- . - -.
.data
MsgText db "Hello world!",0
MsgTitle db "This is a messagebox",0
.data -.-. data section . .- _ , `-. db -.-. byte `..`. \0 , . ..- ..
0 - _ ..-.`.. -. .,.- -. .-. .-., ... . .-. (13 = Carriage
Return, 10= Line Feed)
.data
MsgText db "Hello world!",13,10
db "I'm a messagebox",13,10
db "Hello again!",0
MsgText -.-. . string . offset - ...-. MsgTitle -.-. - . string -
...-. ,...-. ..,, MessageBox function - ...`
invoke MessageBox, NULL, offset MsgText, offset MsgTitle, NULL
invoke - ..`..-..-. ..,, ..-..., offset ... ADDR -
. .`. -.
invoke MessageBox, NULL, ADDR MsgText, ADDR MsgTitle, NULL
,., .` Assembly -....-..
,,
-,.-.-.,, .,.-.. parameter - -....-.-... .-...-..-.
-. -..-...-. MB_OK (OK button , message box) - 0 (NULL) , _
... ..,, `..-..-.. ..`.-.
,
,
uType . ...-.-. ,, , -. `..-.
,
, Win32 API
Windows API . . Windows --- .-...-.,-... data type .- constant
.- function .-, structure .--. -,.-.-..`- ExitProcess API
function .-..-.......- .- DLL . `.. - kernel32.dll gdi32.dll , user32.dll -.. ...
-.
KERNEL32.DLL Low level kernel services
GDI32.DLL Graphics Device Interface: .`.. .`.
USER32.DLL User Interface controls windows . messaging services
BOOL SetWindowText(
HWND hWnd, // handle of window or control
LPCTSTR lpString // address of string);
-.-. C . .....-. . .,, `, ...`..
PUSH lpString;
PUSH hWnd;
CALL SetWindowText;
, . .. .... Dialog Box . -.. ......` .
-. . ..-. Windows . . ._ .-_ ...- - .-. - ` . - .- . -.. ...-_ ..
...-. ..`.., WinAsm Studio . File menu - New Project - ...-
Project - Add new Rc - ...- `.. Add New Dialog -... .,.-...-. caption
-. button . . , editbox -. - ., - . - ` .. screen ..-.`,..- Resources tab -
.. . Caption box - ..-.`. 'Simple Dialog Box Program' . - ` .. toolbox - edit
button -...`. ,,-. .
,., .` Assembly -....-..
,.
,,
` .. button ..- .,-.`. button .-.. 'Say Hello' , 'Exit' `- ,
,
. F12 -.`. -,.-.-.,-...- dialog box - -.,, -_--...
;This Resource Script was generated by WinAsm Studio.
#define IDD_DLG1001 1001
#define IDC_EDIT1002 1002
#define IDC_BUTTON1003 1003
#define IDC_BUTTON1004 1004
IDD_DLG1001 DIALOGEX 0,0,170,72
CAPTION "Simple Dialog Box Program"
FONT 8,"MS Sans Serif"
STYLE 0x10cc0000
EXSTYLE 0x00000000
BEGIN
CONTROL "",IDC_EDIT1002,"Edit",0x50010080,10,9,121,19,0x00000200
CONTROL "Say Hello",IDC_BUTTON1003,"Button",0x50010000,17,46,51,16,0x00000000
CONTROL "Exit",IDC_BUTTON1004,"Button",0x50010000,102,46,50,16,0x00000000
END
-, .-. - .,, Dialog Box template ,-.---.-- ...... dialogbox
editbox button -,-.-- ._.-, control ID .-- .... -. - resource
script . ... . ,.-. .. . .- . -. ` .. dialogbox.asm -...`. ..--.--
. - _ -
option casemap:none
include WINDOWS.INC
include user32.inc
include kernel32.inc
includelib USER32.LIB
includelib KERNEL32.LIB
DlgProc proto :DWORD,:DWORD,:DWORD,:DWORD
.data
Message db "Hello World", 0
.data?
hInstance HINSTANCE ?
.code
start:
invoke GetModuleHandle, NULL
mov hInstance, eax
invoke DialogBoxParam, hInstance, 1001, NULL, addr DlgProc, NULL
invoke ExitProcess, eax
DlgProc proc hWnd: HWND, uMsg: UINT, wParam: WPARAM, lParam: LPARAM
.if uMsg = = WM_COMMAND
mov eax, wParam
.if eax = = 1003
invoke SetDlgItemText, hWnd, 1002, ADDR Message
,., .` Assembly -....-..
,.
.elseif eax = = 1004
invoke SendMessage, hWnd, WM_CLOSE, 0, 0
.endif
.elseif uMsg = = WM_CLOSE
invoke EndDialog, hWnd, 0
.endif
xor eax, eax
Ret
DlgProc EndP
end start
,
-.-- exe .`...`..-. ,,-. .-...
,,
, Keygen . -.. ......` .
. , ...-.-. cracker .--- ,...-.-. -..-...-. cracker .-
-- keygen -. ...`.. .. Keygen .... .....-.. ....._,.-.-
registration -- -... ,.,. keygen - -_ .,
.,
.-..` keygen - ....-_--... WinAsm Studio -.-`. ..--.
`. ... - ., Edit control .. static text .. button .. ....
.,
,., .` Assembly -....-..
Static text ..- SS_CENTERIMAGE .`....`. Serial editbox -
ES_READONLY .`.. Dialogbox -.-. DS_CENTER .`. .` . keygen.rc - . . .
._ . ` .. .-. keygen.asm .. - .-- ..--. .-_ Main body .. .-_...
-.-. 0001
0001 .386
0002 .model flat, stdcall
0003 option casemap:none
0004 include windows.inc
0005 include kernel32.inc
0006 include user32.inc
0007 includelib kernel32.lib
0008 includelib user32.lib
0009
0010 DlgProc proto :DWORD,:DWORD,:DWORD,:DWORD
0011
0012 .data?
0013 hInstance HINSTANCE ?
0014 NameBuffer db 32 dup(?)
0015 SerialBuffer db 32 dup(?)
0016
0017 .const
0018 IDD_KEYGEN equ 1001
0019 IDC_NAME equ 1002
0020 IDC_SERIAL equ 1003
0021 IDC_GENERATE equ 1004
0022 IDC_COPY equ 1005
0023 IDC_EXIT equ 1006
0024 ARIcon equ 2001
0025
0026 .code
0027 start:
0028 invoke GetModuleHandle, NULL
0029 mov hInstance, eax
0030 invoke DialogBoxParam, hInstance, IDD_KEYGEN, NULL, addr DlgProc, NULL
0031 invoke ExitProcess, eax
,
.,.- --...-.-. Dialog procedure `.. -.
0033 DlgProc proc hWnd:HWND, uMsg:UINT, wParam:WPARAM, lParam:LPARAM
0034 .if uMsg == WM_INITDIALOG
0035 invoke LoadIcon, hInstance, ARIcon
0036 invoke SendMessage, hWnd, WM_SETICON, 1, eax
0037 invoke GetDlgItem, hWnd, IDC_NAME
0038 invoke SetFocus, eax
00399 .elseif uMsg == WM_COMMAND
0040 mov eax, wParam
0041 .if eax == IDC_GENERATE
0042 invoke GetDlgItemText, hWnd, IDC_NAME, addr NameBuffer, 32
0043 call Generate
0044 invoke SetDlgItemText, hWnd, IDC_SERIAL, addr SerialBuffer
0045 .elseif eax == IDC_COPY
0046 invoke SendDlgItemMessage, hWnd, IDC_SERIAL, EM_SETSEL, 0, 1
0047 invoke SendDlgItemMessage, hWnd, IDC_SERIAL, WM_COPY, 0, 0
0048 .elseif eax == IDC_EXIT
0049 invoke SendMessage, hWnd, WM_CLOSE, 0, 0
0050 .endif
0051 .elseif uMsg == WM_CLOSE
0052 invoke EndDialog, hWnd, 0
0053 .endif
0054 xor eax, eax
0055 Ret
0056 DlgProc EndP
,
` .. .-. serial number - -.... Generate procedure - ......
0058 Generate proc
0059 invoke lstrlen, addr NameBuffer
0060 test eax, eax
,., .` Assembly -....-..
0061 jle NOINPUT
0062 mov ecx, eax
0063 mov esi, offset NameBuffer
0064 mov edi, offset SerialBuffer
00655 @@:
0066 dec ecx
0067 mov dl, BYTE ptr [esi+ecx]
0068 mov BYTE ptr[edi], dl
0069 inc edi
0070 or ecx, ecx
0071 ja @b
0072 NOINPUT:
0073 Ret
0074 Generate EndP
0075 end start
,
,-.`. ,.. `..--.-- ..-_..
...-. ... ,, . ..- .-.-.-. uninitialized string .-`..`. .-......- .-_-
._ , - - - .. ... serial - .... `..-.
Generate function -.-. ...,, `..- routine -. Name editbox .. .-_--
.....- .`..`,`,...-. lstrlen -.-. Name editbox .. ...-.....-_..-.
.. -. . - _ - - ......- - NameBuffer ....`. .....---.-. EAX . ._
-. --. -... .. .. - _ . .-. NOINPUT ....-.....
--. .-_--.....---. ._--...-. EAX -.. ...- - -
mov instruction ..`. ECX _ . . `.. -. ECX -. ....-- ..--.... ..-.
NameBuffer , SerialBuffer -. .-. address .--.-. ESI , EDI . . . . . .-.
register ..-.-. string .- - - - . - source , destination - _,..-- ..`
-.
@@ -.-. ._. label - .-_.... .. .-. Routine . _ - ..- . ..-. . . .- .. label
. .. .- . .`-... jump .........- , loop .........- - - - .-. label ._
. .- -- . --. label .,.... @f - . , .. . ... label ....-..`..`. @b
...-. ,.... label ..,.-`,.-.. `..-.
String - .`..`,..- routine ... -.-. .. . counter `..- ECX
- -..---. .-. .,.-..-. loop .. -.... ._,...--. .-.
- --. Name string ......---. .`.-...... ECX -.- . 5 `.. . ..` .
5 -., ._ routine -. .`.--.-- .-, ....., ESI ...-. NameBuffer .
... .. address ...`..`. ECX=0 `..,...-. ESI+ECX -. ....-_,..`..`.
ECX=5 `.. , . ..-. ESI+ECX -. .,.- . ... .- _ , . . . mov instruction -.-.
NameBuffer ...-.,.-.....- EDX register . .,.-.`..- DL - - ._ - -.
- . mov instruction -.-. ...- ...- SerialBuffer . ... ..,.. - - ._
-. EDI .. ...-., , ....-- .`..`,_`. _..... ECX -. . _....-
logical OR - ... . - ` . zero flag - .- . - -. Zero flag .`....-. @@ - ...-
...`. routine - ..`..-.
-.-. ....- ...,_. ..,, API function .--..`. `.`_.- routine .- ...
....-.
`..-. -,.-.-. keygen . -.. - ..- .- . .- _ -_ . -.
, .,, ... . protection
tcef;(4) - aqmhzf0Jvf pr otection
(.,...- ........- .-....-....- `. `. ........` ... `.. ._ . -.. .....
- .- ... . - ._ ._ ,_ ....`. protect ..._- ......`.`..._ ._.
crack .._- ,.- ........_ .--)
-. . , ...-.-. crack ... . .`.. ..,- .-... .... protection .-..
`.. -. . ,.._ .... .- .. .....-.......`...- protection .-. .....-..-
-- .-.. -. - . - .... . ... .` . ..,. .. . . -. . . `., ... -..
..-. ...- - . - ... . - -. . crack ...-.-.. . .`. .-. -. . .-.
.. cracker -..`..- Lena151 -.-. -. . crack ..`...- ....-.- ......
.-.. ... .-.- `,`. crack ..-.. ,..-.,
,... ...... protection .-. pack `. protect -.- .`.-. .---.
pack ` . protect -,_.-.-. Packer (Protector) ...' , ....- . .. ... .. . `.. -. ,
..-.....-- -,.-.... .-. .-. ......-. . - . ... . .- - protection
..... . ..,_ .. . .- ...- . --. Protection - .,-,.. ......`. .`..
. - . . -.. .- . . `.,.... . .-.- - - - protection .- -,-,.. ....--.
.. My Driver 3.11 . . registration -- .,-,.. .-_... registration ...
- -. .. .. `. -. . . .. - . - - . - . register .,.-., .-..
. - . . -.. .- - . - . . protect ..`. . protection . .....- . -.
`.,...- .....-... protect ..-. -...--.-.,
Protection . .....- .-. . . . .. crack -. . - .. `. . . . --.. .
. -.. ...- . -. .`.,-- ... . protection ..... ,...-. .--.-.
, Registration number .....``.
, , - . -, .- - ..` .
, Key . ... . .`` .
,, Hardware key Dongle, .....``. -`..-.
, Registr ation number .... .`` .
Registration number .....``., -.-`. ,. . ` . `... -.
, Registration number .. . ....` .
, Registration number ._ _ . .....-... -_ . .`. . ` .
, Registration number ._ . .. . - , -... -_ . .`. . ` .
,, Registration number - Visual Basic ..-- Delphi .-.....`. `-`.
, Registration number - , .- .. ...` .- `.. -.
, Registr ation number .. . ....` .
,_.-..`..- .-.... ....-..-. registration number - . - _ .
-. Registration number - . ....-..-. cracking - . -. ...- -. registration
number - debug `. .-- .....-..-. ,
,
, .,, ... . protection
,_.-..``.. -..-..-.-.-. `..,_..-- ..`-.-... _-
-.-..-- memory . . .. . .._ .- `..,_ ..- , XOR ` . . .- - , `, _ - - -
` . ` . .. . , -, - registration number - `, _ - - - ` . .. .- . .- -
`, _ . .. . .. --. .-. registration number .,- ..--., `,_... -
.. ` ` .`. . .,, cracker .- ,.._ . . . - - . . . - ---..-- .`
...
, Registr ation number ._ _ . .....-... -_ . .`. . ` .
,_ .-.-. .-. . .`. . -- ,_ . ,_ .. ..-. registration number - ..-
_ ._ ., -.._ ., `..-- .- - . `._ .. . `._ . . - - .-.
.- .. -_ ` . registration number -.`...,.. ,
,
.-....-. .-- ._... cracker .--- protection - .-...
. - .. . . -. `.. `.. -....- ---.,_..,..-.... cracker .-
.,, -.-. . , -, - registration number - .. . . -.. - .- - .,.- ... - .. .
, Registr ation number ._ . .. . -, -... -_ . .`.. ` .
,_ .-.-. cracker .--- ....`....- ..... -....- cracker . .
.-..-..-.......--. -.. .-. . - -. . - - , -.. . -. register
.. -..-...-. registration number -. .. hard drive . serial
number ..-_`., .`..., , ...-...- registration number - .....-
routine - .-..`. ...-... --. routine - .-..... .-- ...,-
.`..`. .-..- -..-.... -_- registration number , register . ,
,
,, Registr ation number - Visual basic ..-- Delphi . -.. ...`. ` -` .
Visual Basic VB, .......- registration number - crack .-.-. ..--.
-. . .-. . -.. -....-..- . - - - high level `.. ., -, .-. - .,, crack
. - - debugger disassembler, .- - . ..-.`.. - - - high level `.....
debugger - assembly -`...`.....-. -.. .-. VB , .....- . -.. .-
, .,, ... . protection
,
- debugger .- - -...`, ..` . - .- assembly - -. .. -, . cracker .- ,.._.
- -.
VB . -.. .- - . ,. `... -.
,, VB4
,, VB5 . -
,, VB5 .- packed code (p-code) `.. compile .....,
,, VB4
. .. . .-. .-. ......- - .. .. ... VB4 -. . -.. .- . ..-. . - .. ,
,_.-. .--.- cracker .,,-.-. registration number - . ,. - . . ..-
.-. ,, -..-...-. VB4 . -.. .- -. ........`. .-..-- registration
number , - - .- . - ..- registration number - .... vb40016.dll ., vb40032dll
.- ..`
,,
,, VB5 .-
VB5 , -.-...- .-..- crack .-.-. VB4 , . .. . .-. .. - .
-. Cracker .-. .-. ......-. VB5 - debugger .-, debug . . ` .. - .-- .
-...-. -.--. .-., ,.._.. - ` ..-. .`...-.- . _ . -
. -.. .- - crack . .-.,_....--.-. ....-..-_....- registration number
- .. - ..` . keygen ... .......` .- . ._ , , - .. . . . .- .. registration
number - _..... .-..-- `` . . .. ` .- .. ` -._ .-. . . cracker
.- -.. keygen .-- ......--. Cracker .--.....-. VB5 . -.. .- -. ..-. -..
-. -...-. keygen .-.... -
.. .--.- .-.....--. .-. .-...-- VB , -. ....-.
-, .-. .. . .- ` -.- VB .-...-- debugger .-, -`,...-,_. Debugger .-,
- `, ... .-.-. , - - - - `.,..-- .`..... .-....,_..-- cracker
.- - . ... .- . .--. ,_ .-.-. Smart Check , VB Decompiler tool .-. -_,
- .- - `, ... -.-. . . `, ....---. -...- .-. . - .. .
.-. compile . ... soucre -,.,.---- ... `,.....-. tool
.--.-. debugger ...- decompiler .. ..--. tool .--. VB6
.-. ..-. . decompile . -. tool .- .,-.`. VB , .......,-- . -.. ...-
-...--,-`. Microsoft - VB -....-..- .--.`.....`. ...-.-.
.-.. VB -. version 6 .. .-,.,.-. .,- ....- Visual C++ -.-.
-... version 9 -..,`. ....... `...,-.-.
VB . -.. .- - -. . . ....-.-. - -..-. . .`.,-. . .,, .-. .
.,... .--... VB . -.. .- -. . . ,....- . . , - . . .. ... `., ...
. ..-. - . . . . ... . .-. ...,..-.- VB , .......,-- , .- --.
`_-.`...-...-- .. . . .. ... `.. -.
, Registr ation number - , .- .. ...` .
. -.. .- -. registration number - .-.-_.,-,.. ..`... .,.- . .. ,_ .
_..-- ..`.--. Registration number - . - . . - . . -.. - - .. ....
- - -.,- --. - -. ..-.- - . , .. , - .. .. ` . .-. .`, -.
. -.. -.-. . , -, . . register ..`. ... .....-. , . .....- , -.- .
` .-. . - , . - - - .- - . - cracker .--.-. .-- .......-.
, .,, ... . protection
,
, , -. -, .- - ..` .
,-,.--.- .-...--. .... `..- -..-. , ` . . .. .. ...
-. ,_ ., -.- . -.-. . ` ..-. ...- . .. - . -. . .-. cracker -. ...-
-. , -, .- - - .. . .. - . , .-..- -....`. , Unregistered
version .-.. .........- -,.-`.- `. ..`... .-... .......
-,.- .....-. registered version - ....`., ....- ........
,
,-,.--- ,_...., ....... . --. `.. . -..- -.-.
, .,-,... registration number _`.`. ,-,.--- .....`.
, Registration ._`.`. ,-,.--- .....`.
, ,-,.--- .....`.`. full version - .....`. ..... `_ ....
`.,
,, ,-,.--- Visual Basic `.......`.
, ....-,.--- ... ._ - . ..- - . .. .- . - ` .
, . ,-, ... r egistr ation number _ ` .`. , -, .- - - .. . ..` .
,_ .-. registration number ,_., -- .,-,- registration number - _ ..
-., ,-,.--- .......... ,, -`..-.-.-.-. .,-,- registration
number ._ . .. . `..- , -..-. . ..- . -.. - .... .... `
--.
.- `.. .-.-. . -.. - ........ . . .. . . -.. - .- . .. - .,- registry
..--, .-.... ....-... ..--..-. ....- .-,-.. .-.-
.,.-.--., -,.--- .-.........
, .,, ... . protection
,,
, Registr ation . _ ` .`. ,-, .- - - .. . ..` .
,_ .-.-. . . .. . ... - ... ...,_ . . ..... - - -.-. registrati-
on . - -.,- -., . . . Cracker .--. ,-,.--- .....- routine - .
-......... .-. . -. ., --.- . . .. routine - ` . . .. ... . -
... Cracker -. ...- -. . , -, - registration .- .,-.-. ., -. . .-.
. .-. ..- . - - . -.- . -.. . .- , -, .- - routine -
.. . ..` . `.. -.
<IDA Pro key file v5.1>
rhythm, 1 user, professional edition, 3/2009
#d@*^aRAj-ky0-
.,
. -.. ......- . . registration . - . -.. . directory ..- . . . .. , . . .
.,-,- .-..- . .....- function .- .......,
, , -, .- - - .. . ... `. full ver sion - .. .. . ` . . .. .. `_
....`.,
Demo version . -.. .- -.-. ,_ .- . ....-. . -.. .- . .. registration
number . - _ ..- . .- -. .- , . ... . -.. - .. .. ...-. - . . .. .
. -.. - .`.. .., . ..-. .. .. POPCAP - . .... .,
.,
Cracker .- -.-. , -, .- - routine - . .` . . -.. - - - - . - .-. -
-. .-. . -.. -. .- -. .- , .- , .. .....,.-. . `. - .-. -.
,, , -, .- - - Visual Basic `. ......` .
,_ .- .- . . -. `, .. ...`-.-.-.
, ....-,.--- ...._-...--... .-.-`.
,_.-. `..,-,.--,_..-, .`..`. -- ... .- ...-
.,- ..---... ...--.-.. ..--`. ..--`.- cracker .-- ...
, .,, ... . protection
,
.- .-..-...-. -...-. .-..-. .- . - . .. ..,... ..-.- ...--.
..---.. registry ., .-... ...._..,
, Key . ... . .`` .
,_ .-.-. ........`. key .- ....- install ..- directory ..- . .
... -. . -.. -. . . .- .-. ....- - .- . .. ...-. --. .. key
.-. .,-,.... .-..-. registered version `.. ....--. --... key
. -. ..- - . ... ..,.. . . . -.. -. unregistered version -.....-`. ., .
. - ., . .. key ... ...., -.-- - - .- - ...- .-. .
., . ..
.....- , . ` .. .. -.
, .,-,....- ...`- ...- ....- ...`... -..`....`.
, .,-,....- ...`- .-..- ,-,.-- ...`.
, .,-,....- ...`- ...- ....- ...`... -..`....`.
,_ .-.-. , .-. .- ,_ . Cracker .--.-. ,_.- .----. ...
`..,_..- ,_.-. .......-. ,_....-. .,-,- key .- ...`.
- . .- - . ..`. .. -..`....-. ..-.- ,_... .-..-. key .- -..`.
. , -, . . .. - .. -. `.. -. , .-. cracker -. routine - - . . - ` . . -..
-_...`. ., registration .. -_...-- routine . . .. - -.
,
--. .-. ,_.- ..`.... registration .- encode .-. ...
cracker -. registration .- .-- ..,-.... `..-.
, .,-,....- ...`- .-..- ,-,.-- ...`.
Antivirus -.....-.-. ,_.- ..`--. .,-,- registration .- ..
.`. .-..-. unregistered `..`. ,-,.-- ...`..-.
,, Har dwar e key Dongle, .....``.
Hardware key .- , -.- . ` .-. `..,_ .. .-. `..`. ..,_.-. .-.
-.- -.-.-._.`..- dongle - -,-.. I/O .-.. -.`. ..`.. .-..-
run .....
. . ..-. -.- . ` . ,. . . -.
,, Hardware key .- .-..- ..-.`.
,, .-.. ...-- hardware key . . .` ...` .
HASP , Sentinel -.-. ....... hardware key .- .-. .. ..- .`.
.-.
, .,, ... . protection
.
,, Har dwar e key .- . -.. - ..- . ` .
hardware key .- -.-. .-. .-. . .. .-. . -.. - .-.- hardware key
-..- port . --. `..-. .-..`,-.- ...-. --. -...-`,-.
...-. error message .. . .. ,
`..`.- hardware key .--.-. -- .-.- encode - -.
. .- - hardware key .- . . EPROM .- .. -. ` .. hardware key .- . . . -.. .
-. . - -. ..- _ . ... -. . . cracker .- . . . -.. . . .-. hardware
key .. protection - ..........- ,.,.
,
,, . -.. ... - - har dwar e key . . .` ...` .
,_.-.-. , ....-. hardware key - .. , . . . -.. - `. .-
..,.. .-... .....- .-. -...-. .-... ...
...-.-- hardware key .. --_. _.... ,_.-.-. , .-...,
-. Key .--... .-. function .-- decode . - .- .-. -- -.
Encoding -.. .-. .., .. . . protection - key .- .......-. .`...-.
HASP key
HASP key - Aladdin Knowledge Systems - - -. HASP -. ... . -
install ,.. hardware key , -.-... ..-. driver .-- install -.
,
Sentinel key
Rainbow Technology (www.rainbow.com) . - -. Sentinel -. HASP ,
,--. ,
,
,., Cracker -..-- ... tool ...
.
tcef;(5) - Cr acker wpfOD;twGuf vdktyfaom tool rsm;
Cracking .... .--..- tool .- -. tool .--. ...,..
`..-. -,-......-..-......., . .. .-. . . . .- - - . ... . ....... .- .-.
-. . . . . . `.. -. , tool .-- ...-... ....-..-. ......
..`. .....-., tool .-, ....-..... .,- cracker .-..-....-
`..... `..-. Tool .-- ..--. ...`..`. ........ `..-. . - -
... ` tool ......._ Windows .,. . . OS ...- - .. `.. ._ -, OS ...- - tool
...- , ..._ ,
-, Disassemblers
, Decompilers
-, Debuggers
., Hex Editors
, `.. tool ...
-, Disassembler s
, Disassembler s . -.-.
Disassmebler .-. assembler . ., - .- `.. -. Assembler - assembly -...
.-.., .....- - .- - . . .,. . . machine -`...`..,.. disassembler -.-. . .
-.-- assembly opcode - `.. `, ., - .. - .. .-.
Assembly -....-...- . ..-. . .`- . .- .... -_ ` . .- _ - instruction -
.- . -. Disassembly , .. -.-. . .. . -. Hex -.---.-`. .,--_-
opcode - `.. -...`, ..-. .. 55 1010101, .. PUSH EBP .- instruction .,.
disassembler -. -.
Disassmebler .-..-.......-.-. assembly instruction --...... Intel ., AT &
T ., HLA .,, - ... -.
, Pr ofessional tool ...
IDA Pr o 5.6
IDA Pro -.-. ...-.- tool -. `.. -. Cracker .---,.-...,- tool
-.`..`. - feature .- - , ...`.. -. IDA Pro . Professional edition - -
$1059 --. Download .- link -.-. ..--.`..-.
http://www.datarescue.com/idabase/
PE Explor er
PE Explorer -.-. ..`.-. .....-. .-.- .-..-. IDA Pro -
feature .-`_..,... $75 . - .... , .-.-. . - -.
http://www.heaventools.com
W32DASM
W32DASM -.-. Windows - - .-. .. . 16/32 bit disassembler `.. -.
http://members.cox.net/w32dasm/
, Fr eewar e tool ...
IDA 3.7
IDA 3.7 -.-. DOS GUI tool `..`. IDA Pro ..-,.---.-. Z80 6502
Intel 8051 Intel i860 PDP-11 , x86 intsruction -..-....-. 486 . .- ..
.-.
http://www.simtel.net
IDA Pr o Fr eewar e 4.9
,., Cracker -..-- ... tool ...
IDA Pro , ., ..-. . . .... ..-. ... Intel --- x86 . .- ...- - -
assembly - - ... ` . Windows . ... -. Disassemble instruction .--.-.
.- . - . - . .- ...- - - .. `.. -.
http://www.themel.com
IDA Pr o Fr eewar e 4.3
-`.... version .--.-. GUI .-. ..-.
http://www.datarescue.be
BORG Disassembler
BORG -.-. GUI , `.. ` . .-. .. . Win32 disassembler `.. -.
http://www.caesum.com
HT Editor
HT Editor -.-. Intel x86 instruction .-- analyze - disassembler `.. -.
.,.-..- version -.-. Windows .. .- console GUI . -.. `.. -.
http://the.sourceforge.net
diStor m64
disStorm -.-. open-source `..`. 80x86 , AMD64 . .- ...- - - `.. -.
http://ragestorm.net
,, Disassembler . - .- ._ . . - . . .....
- . .-.- . .`..`.. ..` .
.-., -,.--. exe ... binary .-..,, . . .._ ...-..-. .,... .
...,.-. `...-. Disassembler -. - .. .-... -. .`... .---
...-..-. variable -. .. . .- - instruction -.. .-.`.....
--. .. .-..- - exe . . .data section ..... -.-- .code section . .
... `.,... - . .-..- - .code section --.-_.... .. jump address
tables , constant strings, exe -.-- .data section .. ...._....-. .,...
.-...-. -.- `....-..`- , -... .. - .....,-. ,
Disassembler .-. .-. ......-.-. . .. . .- - - `.. .. .-.`.. .. - segment
.- - .`. . . . .. .. ....-. ... disassembler .- -.-. . .`..`.. ...
..- ` . ..
exe . -.. -., - , .-..- - `..` .. ..- .`.,.-.-. . -.. . -, . `.,.,
... ., - -. - ..- .,, -.-. disassembler -. .-.....-- -, .-.
.- - . , -, . . `.......-. .`...-. Rice . . .. . . -.. .- . - .- , - .-
`. .-.......-..- ...,....-. ..`.-....... cracking _.. -.
. . .. .. -, .- - .- , `_ . - .,-.
- - ... . .. .` .
.-..- compile , . . - - .-. .-. ...... ..- . .- , -. . , ..`. C
- - - . . local variable ._.--. .-...... ..-..-,-. Compilation -
debug option , - ` . .. . . function .-.._.- variable .-. ._.--. image
-. . . . .-. .. . -. ... ..- -....- - stripping .- process -.-
. .- -. .. -. .-. .... compiler .- -.-. `, ... ... .-. . .. . .. - .-
- comment ...-.-. compiler - . . -. ... . .,.., . .....- - .-
inline function -. `.. .....- - .- C-preprocessor macro `.......--.--..-
-`..`..,...-.-. ..`.-.... .`.. . - . - . .-. .-. ....... ..-. function . ,
variable .-. lexicographical scope - . .`.- . . -. .`.. . - . --. .. file1.c , file2.c
.-...- - compile link .... source ..--..- delineation -. linking
... ..--......
,., Cracker -..-- ... tool ...
, Decompiler s
Disassembler , ..-- decompiler .--.-. exe -.-- high-level -....-..
- .,, `, - ..-.`.. -. .-.. . high-level -....-..-. C `.. .,-.
-..-. . .-. C -. decompilation .... .-....... .-. .-. .. . .. .` . .. .-
, .-. Decompilation .... ...,_.-,. `..-. -..-...-. compila-
tion --_.-- --.-..-.......-. ..-..... `..-. .-- decompi-
lation - `, ` .... ... . . .- - - . Decompilation ,_ ._.-. .. `. ....- . ... .
-.-. .-. ..,-. .`... .
Decompilation ...
Compiler .-......- ..,-.-.. decompilation . `........' ...
.. .-.-. . .- - - . .`.-.-. ........`. .-. .`... .`.. -. -.
.`..`. .....- .-.... decompiler -.-. .., .-. .....- . .`... .`.. -.
-. decompiler .--.-. cracker .- - - - _ .. .- .- ..- .. . ...-.
Decompiler ...
DCC Decompiler
DCC -.-. decompilation ... . .-. .. .`.. ... - . . ..-. . .........-
- - -.
http://www.itee.uq.edu.au/~cristina/dcc.html
Boomer ang Decompiler Pr oject
Boomerang decompiler -.-. ...-- decompiler `....`.,`. ..-. C
- .,, decompile . ...-.
http://boomerang.sourceforge.net
Rever se Engineer ing Compiler
REC -.-. . . .- - decompiler `..`. assembly -.-- C . ., - .,,
decompile ..-. -..---. C , assembly ....`...,`. assembly .- .- -
... .-. ` ..- .-. . .`-.
http://www.backerstreet.com/rec/rec.htm
ExeToC
ExeToC -.- . . .-. ..- . - decompiler -. `.. -.
http://sourceforge.net/projects/exetoc
code-dump
code-dump -.-. PowerPC (PPC) Objective-C decompiler `.. -.
http://sourceforge.net/projects/code-dump
-, Debugger s
Debugger .--.-. cracker .- . .-. .. .. - .. `.. ` . .....--. .-..-.--
-... ... `-. ` ..-. -, . .. ..., ... - . .. .- - .. ...
. -.
.`. debugger .-...-. .-... .` disassembler -. HEX - .-
-_ .`.- . , assemble `, . - . .- ,_ .. . . . -. Debugger .--. ....
.-- instruction function call , .-..,...-.. breakpoint .- . - ... ..-.
Windows Debugger ...
OllyDbg
OllyDbg -.-. ...-- Windows debugger `..`. ... disassembly , assembly
engine --_ . -. , ...`..- feature .-`. -,..-.-. .`..-.
Patching disassembling , debugging . - - , . . -.
http://www.ollydbg.de/
,., Cracker -..-- ... tool ...
SoftICE
SoftICE - local kernel debugging -- ..`.-. -. ,....- feature
-. `.. ` . , -, . .. -. SoftICE -. s` . ..-. ...--.. .--.
WinDBG
WinDBG -.-. MicroSoft - ...- ..... - .-. `.. ` . user-mode
debugging . remote kernel-mode debugging -- ..`.-. WinDBG -. ,.._ - .
Visual Studio Debugger , .-... GUI .-. ..-. ., .-. 32-bit , 64-bit version
.- .,, - . -. Windows . .. .- - signature . .., download .-.
http://www.microsoft.com/whdc/devtools/debugging/installx86.mspx
IDA Pr o
DataRescue - - ` . . .- ... .. OS . .. . . . -.
http://www.datarescue.com
., Hex Editor s
Hex editor .--.-. cracking .... ,.._-.- tool .-.--... binary source file
.- - -_ ... . - - . - -_.`.- ... ..-. . . -. Hex editor .--. debugger
decompiler disassembler .-,.-_.- png jpg .......-- -_.....-. ,
. . -. Hex editor .-...-..... ....... tool .-- ...`--.
Windows Hex Editor ...
Cygnus Hex Editor FREE EDITION
,`.,`. ....-- tool `..-.
http://www.softcircuits.com/cygnus/fe/
WinHex
. , disk .--_.`.-. -..- tool `..`. -,-......, --`,
_.......-- .`.- ......._....-. ........ -..-.--
_. ..`._,
http://www.x-ways.net/index-m.html
HexEdit
. . .- ` . binary . .- , disk .-- -_.`.-.-. Free version ...-. source
-- ....`. shareware version .-.
http://www.hexedit.com/
FlexHex
FAT32 ..-- ...- NTFS . .- - - `_ . .`. -. FlexHex
-. sparse ..-, -. NTFS volume . . .- , - .- - alternate data stream - _ . -
-. OLE compound ..- flash card .-, `.. physical drive . .....- - - _ .
. .`. -.
http://www.heaventools.com/flexhex-hex-editor.htm
, `.. tool ...
.....-...-. tool -...-..- ....- .. ... ..-. . . .- - - .
SysInter nals Tools
SysInternals --- tool .-.. .-.... utility .- ` . . - -.... -.
` .... ..-. .- . .- network administrator .-, cracker .- - - , . .
-. .. .`. - utility .--.-. Process Monitor FileMon TCPView RegMon ,
Process Explorer - `..-.
API Monitor s
API monitor tool .--.-. process ., .-..-.-. Win32 API . -. function
.- - .. ..,-. . -.- ... -_ ..-. .- -. cracker .- - - , ... -.
,., Cracker -..-- ... tool ...
Rohitab . API Monitor Vitaly Evseenko . API Spy32 www.nektra.com . Spy Studio --
. .`. -.
PE Tools
PE scanner -.-. -. debug - exe .-..- -..-..-....-.., .....
-. -. protector .- , -.- . ..-. . -. .. .....-. ` tool .--. PE
header -_.-_.`.-....-. PE tool .- -.-. Lord PE PE Browse PE Detective PE
Disassembler PE Explorer PE Insight PE Optimizer PE Rebuilder PE Tools PE Viewer
PEditor PEiD Stud PE WPE , CFF Explorer -`..-. .......-.-. Lord PE PEiD
, CFF Explorer -`..-.
, PEiD `. .. .....
Keygenning Tools
.-..- patch .- keygen ....... ..-.......-....-. -.- ...
......-. ....`.... template .,.... ..-- _`. keygen . -.. - . --
....... -.
NFO Editor s
NFO editor .- -.-. patch ., serial . .- , - ..._ ... .nfo . ., - .... .
..`-. .nfo ..-.. ........-.-.-. cracker ._ serial .- cracking team
._ crack . . ....- `.. -.
Patch File Maker
Crack ..-- .....-....... .......-- cracker .--. patch . .-
- -.-........-. Patch file maker .- -. .- . - ..- . -.. . offset .,..-
` . ` . Windows registry . .- . - ..- key - ``.-- `-. .......
patch making tool .--.-. uPPP , Diablo Universal Patcher (dUP) -`..-. tool .-,
.-.- template .--.-. www.tuts4you.com .. . download . -.
, ,. ,. patch .
,., Cracker -..-- ... tool ...
,
Resour ce Editor s
Resource editor -.-. ......- ..-- `..., resource ...-- _....
.-..`-. ....... resource editor .- -.-. Exe Scope Resource Editor
Resource Hacker Restorator Window Hack , XN Resource Editor - `..-.
, System pr oper ties - r esour ce editor `. `, ` ..
Compiler s
Compiler .--.-. cracking ...`.,..-.`....... ..`. `..-. ....-..
. -.. -....-.... -_ ` . compiler .....-`........
Dictionar y Files
Dictionary . .- -.-. password .-- `,....... ..`. `..-. .....
password `,...... ..`..-.
Passwor d Recover y Tools
Password revovery tool .-- password `,....... ..-. ,.._-. tool
.- -.-. Elcomsoft Password Recovery , Passware Kit Enterprise - `.. -. tool .--
..``. e-mail internet MS Word MS Excel MS Access MS Powerpoint Windows
password ..-..-- `,_.....-.
, .. ... Tool ...
--. .-. .... - .. .` ,..- tool .- ...- . . -. .- -.-. Visual
Basic .-...-- decompile -..`- tool .-`..- SmartCheck , VB Decompiler
Delphi .-...--- DeDe Foxpro .-...--- UnFox All Java .-...--- Java
Decompiler , DJ Java Decompiler Flash (SWF) ..--- Sothink SWF Decompiler MSI
. .- - - MSI Unpacker Dot.Net . -.. .- - - Crack.NET DisSharp , RedGate
DotNet Reflector - `.. -. Packer/unpacker .- .-. .- .-. Packer (protector) ...'
. .. ..- . . .. ... .. . `.. -.
, ., Olly Debugger .-.-
tcef;(6) - Olly Debugger rdwfquf
, .. . -, .-. - . .-.. .- cracking tool -.`..- OllyDbg .-. .
Cracker .----.-. Oleh Yuschuk ......- OllyDbg -. .-. .. . usermode debugger
... ,...-- disassembler .-. ... beginner .--. cracking
.- ... . - .. .-- Numega SoftICE ,...- tools .-, .---.
.- .-. ...- .- kernelmode -.-- crack -..- - . .-. OllyDbg . .
..- .,` OllyDbg . - ..... .. . ...-.-. - .- - `...-`...- ..-..-
...`... procedure . parameters .- loops .- - . .. ` ., constant array string
.-....`.-- .-.......-. .,.-`. plugin .`..- `.... .- . .. . -.
feature .-- .,..--`.. debugger .-.. ..-.-. debugger -. 80x86 . .
. .- .... ., . - ` .-. .-. ......- _ . . , -, . .-...`, . -. --.
.-. Olly -. debugger .... .-.... disassembly ......._.- ...-. IDA
Pro . , .`... . . , .. . - .
Debugger Window
OllyDbg . .--.. main window - ,. . `..-. ` main menu ,
toolbar -. Main window .. informational pane , -. .- -.-.
disassembler window .-. , data window ..--., registers window ._.,
stack window ..-_., ` `.. window .- _ .. ...-. . .`. - windows
....-.-. View menu . . -_ . -. windows .- - - . . .... `. .`.. ` .
-,--..--..`. ..-.... -.- ..-_
,
Disassembler Window
Disassembler window .. Address Hex dump Disassembly , Comment .`. .-.
,.-. ,
,
Addr ess address .-. .. memory .- .- .. command . virtual address -.
Column - . . - . - . .-. address .-... -. address -., .-..-- .... offset
.-`.. .`... ... . `.. -. ($, $2, $+4, ,
Hex dump -.-... -.-- operand -, . ..,, .- `. . . .. ` .-. -.
..,, .-...- ,.._.... ..--... .- `._.....-. ...-..
`. ..- -.- -. command .- - -. .,..- jump (>) ... `..-. ...- ,
jump .. . -. .- . - -. .-. - . . - . .. . . ..-. . .. - address -.
, ., Olly Debugger .-.-
, ... highlight , `.,.. . -.- . .,, command address, .,..- breakpoint
`.. .- . - - -. .,.....- . . -.. -. . .. . - -.
Disassembly .-....-. command - - Assembly . mnemonics .-.. `..
-. Command - . . - . .. . . Assembly command - -_.`.-.. window -.
... .`.. -. .,... . . .,, command - --. `..-. `.`....
command - .-. .-.. debug .... ..`... ` `` ..- . -.. ..... - ,
.-- executable module `.. .`. . ... -. -. cracker --.-. -......
...-. . `.. -.
Comment .-....-. command ,-.-- `..-- .- -. .,... .
.-..-. API functions , library functions .-. ._.-- ...-. .-.- ..-.
.. . . . .,, Assembly -. ........- comment .- . . . - - -.- . -
... .-.
The Data Window
window ...-. Address Hex dump , ASCII Unicode, .`. .-. -.
- ., -- ..-. .- -.-. interpret - .`......-. .-.- cell ...-
......- - Unicode `.. .`. . - Hex dump .-. .,... . ASCII .-....-..`.
Hex dump .-. ..-.....`..-. ,
,
The Register s Window
Registers window ...-. .... registers & FPU registers .... registers &
MMX registers , .... registers & 3DNow registers .`. registers . ..-.
..-......-. EIP ., .-... register .-- -_.`.- .-. `....- (<)
.. . registers window .`...,.. `..-. ,,
,,
The Stack Window
Stack window -.-. stack ...-...-- `-. ..-. Addr ess, -.-.
stack ...- cell address - `-. - ..-. Value, -.-. cell ..-..-- `
-. -- ..-. Comment, ...-. cell -,..,-.-- `...- comment .-
-. , VB .-...- Delphi .-...-- crack .... ..-.
,
, ., Olly Debugger .-.-
,
`.. Windows ...
OllyDbg , .- - .-. .. . . . - ...... -.-.-.
-, -. window .... right click ..... .-... window . menu .. . ..
menu -. window .. -_ ` . - `...,-. menu .- - .... .. - `
-.
, Window . .- ...- -. -. - -. . .- `.,-. ..`.. register .--
-_- .... register --.- right click . -_ - . data area follow in
dump, , stack area follow in stack, . .. - address .- ....-...-- interpret
.-.
Debug Execution
Debugging .-. .-..-.- mode ...... ..`. `...-`.. ...-.
.,.... execution mode .- .-. . . .` -. Execute ..-- debugger . .
_....`.` .-.- Disassembler window -. Assembly - - `.-. . -..
- execute .... .--.. mode .--.-.
-, Procedure .-..-....-..- procedure - subroutine ., function - ..
._, -...- .-......- Step-by-step execution - step over , .-. F8 -
...,.. -. Assembly command - ..-. Command .- - . . --
execute ` .`. `.. window Register Data Stack, -. .`.......-. `..
-. mode . ----.-.-. --. .,.- command -. call procedure CALL,
-.. .... procedure .,, .,-...- command .. .-. instruction -. -_ .
.,,.. ..- execute ..`..-. .-.- call procedure CALL, . .. -
-.-- -..-... ...-... .---.
, Procedure .- ...-.- Step-by-step execution - step into, .-.
mode .. execute .....-. F7 - ...... `.- mode , - .`..- -.-. CALL
command - .. . .` .. . . instruction .. .-. . . -- execute .. `..-.
,-.`. - ,_ .. ..- (step over & step into) ... animation - ..``. .....
-. mode ....-- <Ctrl>+<F8> , <Ctrl>+<F7> - . .`. -. keyboard
shortcuts ....- .`.,...-. step over & step into command .--. instruction
-. ` .-. - , ,_ .. ... . .` . . .. Instruction ....- execute `.,..
.-. debugger window -. refresh ....`..--- ..,, .`. . . ..-..- -
.`.. . . . `.. -.
-. , . ... <Esc> key - ..... execute -.- . ... . ..-
breakpoint - .- . .,-.. . ... . ` ..-. debug .,.- .-..- exception
-.- -.... `..-.
Step-by-step program execution . `..,_.-.-.-. trace mode - Trace mode -.
animation , - -. ... , . . debugger window -. .-....-. refresh . .
.- - - . step over , step into -,.- tracing -- ,_... -.-. <Ctrl>+<F12>
and <Ctrl>+<F11> key .- . ` . . .`. -. Tracing . ._ . . . .-. animation
....- ,_....-..``. .-,.-. command ....- execute `.,...-. ..
execution ,.- .-.-- .- - . --- tracing buffer - - .- - -.
- View menu - Run tr ace command - ..``. -_..-. .....-. tracing
buffer . .. - -..- - ...... .,, . . .._ .... -. ..- -. , . . tracing
- -.. . . .-. condition .-, .......-. (set tr ace condition) - <Ctrl>+
<T> , Trace - -.-. serial fishing ...-. ......-. Serial -.-
-. - - - . ..-. . -. Run Tr ace window . .`. .,. Condition -. ..-.-
....-. -. EIP -., .- . - ..- breakpoint .,.. trace - .,. .`.. -.
- .- ...- .- trace .-...-. .-`....
, ., Olly Debugger .-.-
.
,
Trace mode - - ..- condition .-- .-.-.-.
-, Break - .,... .. address .-. range
, .`.,.- . - - ... EAX>100000 -...., --. EAX>100000 .`..,..
. , -, .. . . trace - -. . . ... .`.. -.
-, Trace - ., , . . . -, .. command .- . ..- -
Procedure - return - ..-.. -- execute ... debugger - .... `...
-. (execute till r etur n) .,.--....`... -. procedure . -...-.. execute
.. `..-. <Ctrl>+<F9> key - ..`-.
.,.-...,, --. tracing - ., , . . -. .,.......- ..,, ,.-...`
` . `, - . .-. (execute till user code) command . .` . - .-. . .- -
<Alt>+<F9> key - ..`.-.
Br eakpoints
Breakpoint . -.-.-. --. . . .- - debugging tool -. Breakpoint .--.
.- .-...- ..... ,.._...-. .-.-..- ,...- registers
stack , data .- . .,..- . - .....-.
Or dinar y Br eakpoints
Ordinary breakpoint .- - .-. .. .. ..- command .- , .- . - -. <F2> key
- .`.`...._..-.. (Hex dump) window .. . . . - . ` .`. ... _ ..-. . . .`
. -. . .,, -.-. ..-. . .. - address -. , ... .`. .. ..-. `
register variable stack .- . .`.,- _ . .. .... -. <F2> key - .,.- -. - . .
. .-. breakpoint - .....`.... `.... breakpoint - -.,.. ........-.
Windows API function .- - ... -_ - , . . `.. -.
Conditional Br eakpoints
Conditional breakpoint .- - .-. <Shift>+<F2> key .`. ..`.-. <Shift>+
<F2> key --.-. ,,.. `..--. combo box ... . combo box .. -...
.- .. condition -.- _.....-. --. condition -. .,-,....
.-. command .-- execute -. ...... Debugger -. condition .- ...- .-
. . . - ... `- .- - .-. ,.._ -. -..- -.-. ...-
, ., Olly Debugger .-.-
.
,,
-, EAX = = 1 -.-. EAX register -. -. `.. . debugger - execute -.. ...
.,..-.
, EAX = 0 and ECX > 10 -.-. EAX register -. ._`..`. ECX register -.
-. .. - - . . debugger .,-..... .,..-.
-, [STRING 427010] == 'Error' -.-. virtual address (VA) 427010h .. 'Error' .-
.....- .- . debugger - execute -.. ... . , ..-. ... .-. EAX =
= 'Error' . EAX ...-.....- pointer -., .....`.. .`. . ... .
., [427070] = 1231 -.-. VA 427070h . .. - ..-. 1231h , _ .. . . breakpoint
- .-.-..
, [[427070]] = 1231 -.-. address - ..- ..``. .`...... VA 427070h
.. `.. VA -. ` . VA . .. - ..-. 1231h , _ ._ .. ` . breakpoint - .- . -
-.
Conditional Br eakpoints with a Log
.-.-. conditional breakpoints . , .. extension -... `..-.
Conditional logging breakpoint - .-.-. <Shift>+<F4> key - ..-. -.,....
breakpoint - ..`.... `...- log . .,, . - -. .- ..-. Log
..- ...-- `,-_-... <Alt>+<L> key - . ` .... _ ..-. . View menu .
Log command - . ` .... _ ..-. . -_..-. .,
.,
Br eakpoint to Windows Messages
Window function . - -.`... window class function ., messages .- ...- .
-..-. windows message .. breakpoint - .-.-.. application window -.
.,. -. -,_ ..`... windowing application .--. execution . - - .- .
-. . . . . - ... . .. . - application -.- window -.,- debugger -
..--. application - .-.-- <Ctrl>+<F8> - . application window -.
-. .- , ..- -.` .- . . .- -. . -.. . -. . - -. ..- .- - - execute
., , . ..-. .- .... Window function . ...- . application - ....`. .,-...-
windows ....- ...-. - View menu - Windows - ..`.-. .,
, ., Olly Debugger .-.-
,
.,
.,..`..- window -. investigator - window descriptor ..._ .. identifier
, ...-...`..- window procedure . address ClsProc, .- . ... ... -. Window
procedure . address , -.-- --.-- investigator - window function .- ...
..- ` ..., breakpoint ... conditional breakpoint .-.-.-. -.`..`.. window
functions .-, - window message .-.-.,.... breakpoint .- .- . - -.
.-.... .-. .,..`..- window -.-`. context menu - Message
br eakpoint on ClassPr oc - .. . - .,.- window -. ... .`.. ` . . . ..-
breakpoint parameter .-- .-.-...`..-. ,
-, Dropdown list . message - ... ..--- .-...
, Message ... event - ...._. .-. event .--. window . ,
keyboard event .-- .,-..-..`.-.... message . ..... .`.. . -.
, ..-... ...-.-.- message .- - _ . .. .. . -.
, -. message .- -. . - - -. . . -., ...- .. . -.- . .`.- . ... trace
-.. window .- - ... .`. ....- window ....- title , window ... .,
window .. . -.
-, Breakpoint -. . . - . .- -. . -. . ... counter - .- . - ..
., Breakpoint .- , . . . -.. -.- . . .. . . -. .- . -
, Breakpoint .- , . . record - log -. ..... . -. .- . - ..
,
Br eakpoints to the Impor t Functions
Debug . module - import .- ._....- ..-. <Ctrl>+<N> -
. , .,.-.. window - right click .`. ..---_. `.-.
-, Import ..- function - ....`,.. breakpoint - .-.-.-. (Toggle
br eakpoint on impor t)
, Import ..- function - ....`,.. conditional breakpoint - .- . - .
-. (Conditional br eakpoint on impor t)
, ., Olly Debugger .-.-
,
-, Import ..- function - ....`,.. conditional breakpoint - log `.
.- . - . -. (Conditional log br eakpoint on impor t)
., .-.-..- ._,.- -.--... breakpoint - .-.-.-. (Set
br eakpoint on ever y r efer ence) { command - Find references to import (Enter key) , -
-. `..,..-- Find references to import - breakpoint - -.. ......-.}
, ....- ._,.-...,- reference -... log `. breakpoint - .-.-.-.
Set log br eakpoint on ever y r efer ence)
., Breakpoint ...- .....-. (Remove all br eakpoints)
,
Br eakpoints at the Memor y Ar ea
OllyDbg debugger - memory area .. breakpoint -. -_ .- .- . - . - -.
. disassembler window . , data window - .... .,.- context menu .
Br eakpoint | Memor y on access ., Br eakpoint | Memor y on wr ite command .- -
.. .. . -. ` .. .-. .-. -.- . - - - breakpoint - ..`. .`...,..
Breakpoint .-. . .-.-. (on access) -, .-..--- `.. . ... - . breakpoint
-...-.-. (on write) -.---.. `...-. Breakpoint .-- context menu .
Br eakpoint | Remove memor y br eakpoint - ....`.`. ......-. ,
,
Br eakpoints in the Memor y Window
Memory window (Alt + M) -.-. debug ..- .-..-- ., .-... .,_.
. -, , debug ..- .-...-- ...,,..- memory block .-- `.-.
window .. breakpoint -. - .- . - . .. `.. . -. . rightclick . Set memor y
br eakpoint on access - ., Set memor y br eakpoint on wr ite - .... Breakpoint -
.. . .. . .-. Remove memor y br eakpoint - .. .. -.
Har dwar e Br eakpoints
..., breakpoint .--.-. INT 3 interrupt vector -- ..`-. breakpoint
.- - . .`` .- . -.. - .... . .. .. ....-. -. . .. Intel Pentium
microprocessor .--.-. debug registers (DR0DR3) , - `._ . . .....-. register
.- . . breakpoint , , - . . -.. . virtual address - .-. Command -. -
..`..- address -. register -.-...-- address ,_.,,.. processor -.
debugger .. ...- exception -.- ---. Hardware breakpoint .--.-. debug
..- . -.. . - .-. .. ..- .... ..- - - . -. `.. `.. . - - , ... `..
-. Hardware breakpoint -.- .-.-.....-. disassembler window - ... `..
context menu - Br eakpoint | Har dwar e on execution command- .. . . .- - . main
menu - Br eakpoint | Har dwar e on access ., Br eakpoint | Har dwar e on wr ite command
, ., Olly Debugger .-.-
,
- ..`.-. Hardware breakpoint .-- .-..-. context menu - Br eakpoint |
Remove har dwar e br eakpoints command - ..` ,
,
`... . .... . . ...
Watch expr essions Window
OllyDbg - expression .-- ...-_. special window -. - ....-.
Conditional breakpoint .-.-.. ..`-,.- expression .-.-...-.- .-.
Memory cell .-, register .-- ...- expression .-- ..`..-. `...-.
expression .-- . ..... .-. Watch expr essions window - ..-.-.
View | Watches command - ..` Watch expr essions window .,...-. right click
.`. Add Watches command - .... `...-. debugger - ...-_.... expression
-.- .-.-.-. .,.--....`....-. .. HEX -, . .- `.-. ,,. .
expression , - Watch expr essions window - `...-.`.. ` . -. processor .
command - .. execute ` .`. -, . ..- - ... -_ .,` .`.-.
,,
- - ...- . ... ` .
OllyDbg .. ---.-.-- ASCII UNICODE HEX ,.- - <Ctrl>+<B>
key .`. .....-. , Command -. .- . ... . . <Ctrl>+<F> key command
.-....-.- ...... <Ctrl>+<S> key - ..`.-. <Ctrl>+<L> key (Next)
-.-. .,.- . . . . - -.- . ...-.
,
Executable Module - `....._.`.
OllyDbg .. -,.-.- `--.-- ...._.`. executable .-....`.. ...
._ .. -. . Copy to execution | Selection ., Copy to execution | All
modifications command - .. . - . ` .. - . .. - .,... . - . - - - . ._ ..
..` . . . .._ . - .
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 7 3 -
tcef;(7) - IDA Pr o Advanced 5.2 rdwfquf
IDA Pro u a w mh exe u k' fa w Gu dk p p fa q ; & mr Sm t a u mi f; q Hk; tool w p fc kjz p fy gw , f/ jy D; c Jhw Jht c e f; r Sm
a v hv mc Jhw Jh Olly debugger u a w mh o Hk; p GJo la w Gt w Gu f v G, fu lp Gm t o Hk; jy KE dki fa y r , fhv J o lU& JUu e fUo w fc su f
u a w mh PE u k' fa w Gu dko m p p fa q ; a y ; E dki fy gw , f/ IDA Pro u a w mh DOS^ Windows^ Unix^ Macintosh^
Java^ .Net^ Console y & dk* & r fa w Gt jy i f t jc m; OS r Sma & ; x m; w Jh y & dk* & r fa w Gu dky g p p fa q ; a y ; E dki fy gw , f/ ' Dht
jy i f Palm OS e JU mobile OS r Sma & ; o m; x m; w Jh y & dk* & r fa w Gu dky g p p fa q ; a y ; E dki fy gw , f/ IDA [ m Olly
v dka w mhu k' fe JUy w fo u fw Jha u mu fc su fc sw ma w G? , lq c su fa w Gjy Kv ky fr Smr [ kw fy gb l; / ' ga Mu mi fho i fu dk, fw dki f
q & mr u lb J u k' fa w Gu dk a v hv m& r Smjz p fy gw , f/ v dkt y fw Jh parameter a w Gu dk u dk, fw dki fjy Kjy i f& r Smjz p fy gw , f/
IDA r Sm w p fc gw n f; y gv mw Jh y & dk* & r fb mo mp u m; [ m C e JUz GJUp n f; w n fa q mu fy Hk o a b mw & m; c si f; w lw Jh
t w Gu f o i fht w Gu f t a x mu ft u ljz p fa p r Smy g/
IDA u a w mh Interactive DisAssembler & JUt w dka u mu fjz p fy gw , f/ IDA & JU About window u dk
Mu n fhv dku fr , fq dk& i f y x r q Hk; t r sdK; o r D; y & dk* & r fr mjz p fw Jh Augusta Ada Byron & JU & ky fy Hka v ; u dk a w GU& r Smy g/
y x r q Hk; o dx m; z dkUv dkw mu a w mh IDA package r Sm idaw.exe (console) e JU idag.exe (GUI) q dkjy D; y & dk* & r f
E Sp fr sdK; y g& Sdy gw , f/ ' Da e & mr Sm t " du x m; jy D; & Si f; jy r Smu a w mhidag.exe (GUI) t r sdK; t p m; u dkjz p fy gw , f/
( 1 ) Vir tual memor y t a Mu mi f;
w u , fv dkU o i fht a e e JU exe module w p fc ku dk IDA r Smz Gi fhr , fq dk& i f t J' Dz dki f& Sdw Jhdirectory a t mu fr Sm
z dki fE Sp fc ku dk z e fw D; r Smjz p fy gw , f/ ' Dz dki fE Sp fc ku a w mh ID0 e JU ID1 q dkw Jh extension a w Gy gw Jh t & e f virtual
memory z dki fa w Gjz p fy gw , f/ ' Dz dki fa w Gu dk intermediate data a w Go dr f; q n f; z dkU IDA Pro u t o Hk; jy Kw my g/
w u , fv dkU o i fht a e e JU v u f& Sdexe z dki fu dk y dw fv dku f& i fy Jjz p fjz p f? a e mu fw p fz dki fu dk z Gi fh& i fy Jjz p fjz p f ' Dz dki fE Sp fz dki f[ m
a y smu fo Gm; r Smjz p fy gw , f/ ' Dz dki fa w Gu a w mh exe module e JU t r n fw lr Smjz p fjy D; .ID1 extension e JUz dki fu a w mh
exe module & JU image u dku l; w i fz dkUt w Gu f t o Hk; jy Kw mjz p fy gw , f/ ' Dimage [ m Windows OS & JU 32-bit
flat memory model x Ju dk u l; w i fw Jh image e JU w p fx y fw n f; jz p fy gw , f/ ' ga Mu mi fhv J OS u execute
v ky fw Jhmodule e JUp p fa q ; w Jht y dki f; r Sm w p fx y fw n f; u sa p z dkU jz p fE dki fw my g/ ' Dt c su fu y J IDA u dk w r lx l; a p w Jh
debugger jz p fa p w my g/ Address t o D; o D; t w Gu f z dki f[ m 32-bit w p fc ku dk o dr f; q n f; x m; w mjz p fjy D; 8-bit
cell w p fc ku a w mh o w fr Sw fx m; w Jh address e JUw ln Djy D; ? 24-bit attribute w p fc ku a w mh ' Dcell e JUy w fo u fw Jh
t * Fg& y fa w Gu dk t " dy m, fz Gi fhq dkw mjz p fy gw , f/ t x l; o jz i fh ' D attribute [ m instruction w p fc ke JUy w fo u fw Jh
o w fr Sw fx m; w Jh memory cell u dka & m? a ' w mu dky g o w fr Sw fE dki fy gw , f/ ' Dt jy i f ' D attribute [ m string
x Jr Sm& Sdw Jhcomment? cross-reference? label w dkUv dkt jc m; object a w Gu dka & m o w fr Sw fE dki fy gw , f/
IDA Pro u t o Hk; jy Kw Jhvirtual memory e JUw GJv ky fw Jhmechanism u a w mhWindows OS u t o Hk;
jy Kw Jh mechanism e JUw ln Dy gw , f/ o D; o e fU cell w p fc ku dk& , lc sde fr Sm ' Dcell y g0 i fw Jh page w p fc kv Hk; u dk r lv
r Sw fOmP f (buffer)x J o Gi f; , ly gw , f/ w u , fv dkU memory cell u dk jy Kjy i fv dku fw Jht c gr Sma w mh virtual
memory page w p fc kv Hk; u dk jy e fa & ; c H& r Smy g/ IDA Pro u a w mh memory page a w G& JU t p dw ft y dki f; u dk RAM
x Jr Smu dki fw G, fy gw , f/ jy Kjy i fx m; w Jh cell a w Gu dka w mh t c gt m; a v smfp Gm disk q Dq GJ, lr Smy g/ Page w p fc ku dk
u l; w i fz dkU v dkt y fc sde fr Sm page buffer u jy n fha e c Jh& i f? IDA Pro u y x r q Hk; jy i fx m; c H& w Jh page u dka w GUz dkU
buffer u dk& Smr Smjz p fjy D; ' gu dk disk q Dq GJ, lr Smjz p fy gw , f/ jy D; & i fa w mhv dkt y fw Jhpage u dk a e & mv Gw fq Du l; w i f
r Smjz p fy gw , f/
u l; w i f& r , fhmodule & JU image u dko dr f; q n f; jc i f; t jy i f IDA pro [ m label? function t r n fa w Ge JU
comment w dkUv dkt c su ft v u fa w Gt w Gu f r Sw fOmP fu dk v dkt y fy gw , f/ ' Dt c su ft v u fa w Gu dka w mh .ID0
extension & Sdw Jhz dki fx Jr Sm o dr f; w mjz p fy gw , f/ w & m; 0 i fx kw fa 0 w Jh p mt ky fp mw r f; a w Gr Sma w mh ' Dr Sw fOmP fu dk
btree t w Gu fr Sw fOmP fv dkU o Hk; Mu y gw , f/
( 2 ) y & dk* & r f\ GUI
exe y & dk* & r fw p fc ku dk IDA r Smz Gi fhr , fq dk& i fa w mh y Hk( 1 ) t w dki f; jr i f& r Smjz p fy gw , f/ z Gi fhx m; w Jhy & dk* & r fu dk
p p fa q ; jy D; o Gm; & i fa w mh y & dk* & r f& JU b , fz u fa x mi fhr Sm "The initial autoanalysis is finished" q dkw Jhp mo m; u dk
jy r Smjz p fy gw , f/
IDA Pro & JU main window r Sm tab a w Gt r sm; Mu D; a w GU& r Smjz p fy gw , f/ y Hkr Se fq dk& i fa w mh tab 8 c k& Sdr Sm
jz p fa y r , fh ' Dx u fv Jy dkE dki fy gw , f/ o i fht a e e JU tab t o p fa w Gu dk a y gi f; c si f& i fa w mh Views menu u Open
subviews u dka & G; jy D; x y fw dk; v dkU& y gw , f/ IDA View e JU Hex View u a w mh a e mu fx y f x y fy Gm; v dkU& y g
w , f/ ' ga Mu mi fh o i fht a e e JU u k' f? a ' w m section a w Gu dk r w ln Dw Jh window a w Ge JU Mu n fhv dkUr Smjz p fy gw , f/
w u , fv dkU a e mu fx y f window a w Gx y fw dk; v mr , fq dk& i fa w mhIDA View-A? IDA View-B? IDA View-
C p o n fjz i fhjz p fv mr Smjz p fy gw , f/
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 7 4 -
t " du t u sq Hk; window u a w mhIDA View jz p fy gw , f/ ' Dwindow [ m exe u k' fa w Gu dkanalysis
v ky fjy D; a w mh& v mw Jh& v ' fa w Gu dkjy w mr dkUv dkUy g/ y Hk( 1 ) /
y Hk( 1 )
IDA Pro debugger e JU t v ky fv ky fr , fq dk& i fa w mh ' Dy & dk* & r fu dk u dki fw G, fz dkU t " du e n f; v r f; ( 3 ) c k& Sd
w , fq dkw m r a r y ge JU/ o lw dkUa w Gu a w mh menu command? toolbar button e JU hotkey a w Gy Jjz p fy gw , f/
IDA & JUv ky fa q mi fc su fw dki f; t w Gu fa w mh hotkey a w G & Sdr Smr [ kw fa y r , fh t o Hk; t r sm; q Hk; v ky fa q mi fc su fa w G
t w Gu fa w mh hotkey a w G& Sdy gw , f/ Oy r mjy & r , fq dk& i f . . . w u , fv dkU t c sdKU data block a w Gu o i fhu dk
o Ho , jz p fa p w , fq dk& i f C key u dkE Sdy fjy D; ( u k' ft w Gu f t w dka u mu f) ' gu dk u k' ft jz p fa jy mi f; E dki fy gw , f/ a e mu f
w p fc ku a w mh w u , fv dkU Assembly command a w G& JU t c sdKU block a w G[ m t " dy m, f& Sdy Hkr a y : b l; q dk& i f
o i fht a e e JU ' gu dkD key E Sdy fjy D; ( a ' w mt w Gu f t w dka u mu f) a ' w mt jz p f a jy mi f; E dki fy gw , f/
IDA Pro [ m a t mu fy g configuration z dki fa w Gu dkt o Hk; jy Ky gw , f . . .
lda.cfg y Hkr Se f configuration z dki f
idatui.cfg console y & dk* & r fr sm; t w Gu f configuration z dki f
idagui.cfg GUI y & dk* & r fr sm; t w Gu f configuration z dki f
Configuration z dki fa w G[ m IDA main directory & JU CFG subdirectory a t mu fr Sm& Sd& r Sm jz p fy gw , f/
( 3 ) exe u k' fu dku l; w i fjc i f;
w u , fv dkUo mo i fht a e e JU exe module w p fc ku dk IDA r Smz Gi fhr , fq dk& i fa w mh y Hk( 2 ) t w dki f; jr i f& r Smy g/ ' D
window u dkt o Hk; jy Kjy D; o i fht a e e JU z Gi fha e w Jh process e JU u e OD; analysis u dk a jy mi f; v Jv dkU& y gw , f/ ' D
window [ m a e mu fy dki f; r Sm & Si f; jy r , fhconfiguration setting a w Gt r sm; Mu D; u dka y ; p Gr f; E dki fy gw , f/
u dp a w mfa w mfr sm; r sm; r Sma w mh IDA u t o i fha w mfq Hk; setting u dk t Mu Hjy Kjy D; o Hk; p GJo lu b mr Sa jy mi f;
v Ja y ; z dkU v dkt y fr Smr [ kw fy gb l; / o i fht a e e JU OK button u dkE Sdy fa y ; z dkUy J v dkt y fy gw , f/ a t mu fy g option a w G
u dkw c gw & Hr Smo mt o Hk; jy Ka y r , fht u sOf; c sKy fa z mfjy a y ; v dku fy gw , f/
- Load file (directory/name) as ' Da e & mr Sma w mh o i fz Gi fhv dku fw Jhy & dk* & r fz dki fu dk IDA & JU v u f& Sd version
u o dx m; w Jh z dki f format (PE o dkUr [ kw f ELF)p m& i f; a w Ge JUw dku fp p fjy D; jz p fE dki fw Jhp m& i f; u dkjy w mjz p fy gw , f/ ' D
window r Smjr i f& w Jh t jc m; option a w Gu a w mh o i fz Gi fhw Jhy & dk* & r ft r sdK; t p m; a y : r lw n fjy D; a jy mi f; v Ja e r Sm
jz p fy gw , f/ Oy r mjy & & i fa w mh . . . PE module & JU MS-DOS stub u dk disassemble v ky fr , fq dky gp dkU/
' Dv dkv ky fz dkUt w Gu f p m& i f; x Ju MS-DOS executable option u dka & G; & r Smjz p fy gw , f/ w u , fv dkYy & dkq u fq m
t r sdK; t p m; u dk a jy mi f; c si fw , fq dk& i fv J Set button u dka & G; jy D; a jy mi f; v dkU& y gw , f/ u Re fa w mfht a e e JU x y fa jy mc si f
w mu a w mh module a w Gu dk p p fw Jht c gr Sm IDA u t o i fha w mfq Hk; u dka & G; jy D; p m& i f; jy Kp ka & G; c s, f a y ; x m; w m
jz p fy gw , f/ ' Da e & mr Sm IDA u PE module u dk y Hkr Se f PE module t jz p fa & m? MS-DOS y & dk* & r ft jz p fa & m?
binary z dki ft jz p fa & m b mo mjy e fa y ; E dki fy gw , f/ w u , fv dkU o i fht a e e JU .net y & dk* & r fw p fc ku dk z Gi fhMu n fh& i fy J
jz p fjz p f? Linux y & dk* & r fw p fy k' fu dkz Gi fhMu n fh& i fy Jjz p fjz p f jy o w Jhp m& i f; u Gmjc m; o Gm; r Smjz p fy gw , f/
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 7 5 -
y Hk( 2 )
- Pr ocessor type Drop-down list w p fc kjz p fjy D; a & G; c s, fx m; w Jh module u dk compile v ky fx m; w Jh
y & dkq u fq mt r sdK; t p m; u dka & G; c s, fc Gi fhjy Ky gw , f/
- Loading segment & Loading offset o lu a w mhmodule u dk o w fr Sw fx m; w Jhoffset & Sdw Jhsegment
r Sm u l; w i fa y ; E dki fy gw , f/ ' g[ m MS-DOS module a w Gt w Gu fa & m? binary z dki fa w Gt w Gu fy g o Hk; 0 i fy g
v dr fhr , f/ ' Dparameter a w Gu dka w mhPE module a w Gt w Gu f t o Hk; r jy KMu y gb l; /
- Enabled ' gu a w mh Analysis t ky fp ku flag w p fc kjz p fjy D; u k' fu dk u e OD; analysis v ky fjc i f; r Sa & Smi fMu Of
E dki fz dkU uncheck v ky fE dki fy gw , f/ w u , fv dkU o lUu dka & G; x m; & i fa w mh z dki fu dku l; w i fjy D; w me JU analyze v ky fa w mhr Sm
jz p fy gw , f/
- Indicator enabled v ky fa q mi f& r , fhanalysis process indication u dko w fr Sw fw mjz p fy gw , f/
- Cr eate segments o lUu dka w mh PE module a w Gt w Gu f t o Hk; jy Kjc i f; r & Sdy gb l; / ' Dflag u dk t o Hk; jy K& i f
a w mhIDA u v dkt y fw Jhsegment a w Gu dk z e fw D; r Smjz p fy gw , f/
- Load r esour ces w u , fv dkU ' Dflag u dko w fr Sw fx m; r , fq dk& i fa w mh PE module & JU resource a w Gu dk
u l; w i fr Smjz p fy gw , f/ Binary module a w Gt w Gu fu a w mh ' Dflag u dk Load as code segment v dkUa c : jy D;
t o Hk; jy Ky gw , f/ Oy r mjy & & i f .com y & dk* & r fa w Gt w Gu fjz p fy gw , f/ y Hk( 3 ) /
y Hk( 3 )
- Rename DLL entr ies w u , fv dkU ' D flag u dkr o w fr Sw fx m; & i f IDA u ordinal a w Ge JU import
v ky fx m; w Jh function a w Gt w Gu f x y fa v mi f; comment a w Gu dkjz n fhq n f; a y ; y gw , f/ ' Dv dkr Sr [ kw f& i fa w mh
disassembler u function a w Gu dkt r n fa jy mi f; v dku fr Sm jz p fy gw , f/
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 7 6 -
- Manual load w u , fv dkU ' D flag u dk a & G; x m; & i fa w mh disassembler u u l; w i fa e w Jh process & JU
t q i fhw dki f; t w Gu f o Hk; p GJo lu dkw dki fy i fa r ; jr e f; a e r Smjz p fy gw , f/
- Fill segment gaps o lu a w mh NE module a w Gt w Gu fo m t a & ; Mu D; w Jh flag jz p fjy D; disassmbler u dk
intersegment a e & mu dkjz n fhq n f; a y ; z dkU n Te fMu m; r Smjz p fy gw , f/ ' ga Mu mi fh Mu D; r m; w Jh segment w p fc ku dkz e fw D;
& y gw , f/
- Make impor ts segment ' D flag u dko w fr Sw fc sde fr Sma w mh import v ky fx m; w Jh t c su ft v u fa w Ge JU
q dki fw Jh.idata section u dko m b mo mjy e fa y ; z dkU disassembler u dkc dki f; y gw , f/
- Don' t align segments Segment a w Gu dk n Sdz dkU disassembler u dkc dki f; y gw , f/ p dp p fp Of; p m; w ke f;
t q i fhr Sma w mh' Dflag u dk module a w Gt w Gu ft o Hk; jy Kjc i f; r & Sdy gb l; /
- Ker nel options1 Flag a w Ge JUjy w Jh' Dwindow u a w mho Hk; p GJo lu dk exe u k' fa w Ganalyze v ky fw Jht c gr Sm
E Sp fo u f& mu dka & G; c s, fE dki fz dkU jy o y gw , f/
Cr eate offsets and segments using fixup info u dk t o Hk; jy Kjc i f; jz i fh o i fht a e e JU u k' f analysis
jz p fp Ofx Ju relocations table u a e t c su ft v u fa w Gu dk t o Hk; jy Kz dkU disassembler u dk c dki f; E dki f
y gw , f/
Mar k typical code sequence as code u a w mh analysis jz p fp Ofx Ju y Hkr Se fy & dkq u fq m
command sequence u dkt o Hk; jy Kz dkU disassembler u dkc kdi f; y gw , f/
Delete instr uctions with no xr efs u a w mh cross-reference v Hk; 0 r & Sdw Jh y & dkq u fq m
instruction a w Gu dkv sp fv sL& Ic dki f; y gw , f/
Tr ace execution flow u a w mh trace v kdu fz dkUc Gi fhjy Ky gw , f/ ' gr So m o i fht a e e JU y & dkq u fq m
instruction a w Gu dk& Sma w GUE dki fr Smjz p fy gw , f/
Cr eate functions if call is pr esent u a w mh call a w Ge JU function a w Gu dk r Sw fx m; a p z dkU
disassembler u dkc dki f; y gw , f/
Analyze and cr eate all xr efs u a w mh t " du x m; a & G; c s, f& r , fht & mw p fc kjz p fjy D; analysis x Ju
cross-reference a w Gu dkdisassembler t m; t o Hk; jy Ka p y gw , f/
Use FLIRT signatur es u a w mh signature a w Gt o Hk; jy Kjy D; library function a w Gu dk r Sw fr da p z dkU
t w Gu f Fast Library Identification and Recognition Technology (FLIRT) u dkt o Hk; jy Ka p z dkU
disassembler u dkc kdi f; y gw , f/
Cr eate function if data xr ef data -> code32 exists u a w mh a ' w m{ & d, mx Jr Sm& Sdw Jh u k' fe JU
y w fo u fw Jhreference a w Gu dkp p fa q ; z dkU disassembler u dkc dki f; y gw , f/
Rename jump function as j_ u a w mh j_somewhere v dk jmp somewhere command
r Qo my gw Jh& dk; & Si f; v Sw Jhfunction a w Gu dkt r n fa y ; z dkUjz p fy gw , f/
Rename empty function as nullsub_ u a w mh nullsub_ v dk RET command w p fc ky gw Jh
function a w Gu dkt r n fa y ; z dkUjz p fy gw , f/
Cr eate stack var iables u a w mhfunction a w G& JU local variable a w Ge JU parameter a w Gu dk z e fw D;
( t " dy m, fz Gi fh) z dkUjz p fy gw , f/
Tr ace stack pointer u a w mhESP register & JUw e fz dk; u dktrace v kdu fz dkUjz p fy gw , f/
Cr eate ASCII str ing if data xr ef exists u a w mh ASCII string t jz p f reference v ky fx m; w Jh
data item u dk o lU& JUt & G, ft p m; [ m w du sw Jhw e fz dk; w p fc kx u fa u smfv Ge fjc i f; & Sd^ r & Sd p Of; p m; E dki fz dkU jz p fy g
w , f/
Conver t 32-bit instr uction oper and to offset u a w mh address w p fc kv dk y & dkq u fq m
instruction x Ju w dku f& dku f data item w p fc ku dkp Of; p m; E dki fz dkU disassembler u dkc kdi f; a p jy D; Mu dKw i fo w f
r Sw fx m; w Jhinterval x Ju dko lU& JUw e fz dk; a & mu fo Gm; a p y gw , f/
Cr eate offset if data xr ef to seg32 exists u a w mh address a w Gv dk a ' w m{ & d, mx Jr Sm
o dr f; q n f; x m; w Jhw e fz dk; a w Gu dkp Of; p m; z dkU disassembler u dkc kdi f; a p jy D; Mu dKw i fo w fr Sw fx m; w Jhinterval
x Ju dko lU& JUw e fz dk; a & mu fo Gm; a p y gw , f/
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 7 7 -
make final analysis pass u a w mh analysis v ky fw Jha e mu fq Hk; t q i fhu dk v ky fa q mi fjy D; c sde fr Sm
r p Hk; p r f; E dki fw Jh byte a w Gt m; v Hk; u dk a ' w m ( o dkU) instruction a w Gt jz p f a jy mi f; v Jz dkU disassembler
u dkc dki f; y gw , f/
- Ker nel options2 a e mu fx y f flag a w Ge JUjy w Jh ' Dwindow u a w mh o Hk; p GJo lu dk exe u k' fa w Ganalyze
v ky fw Jht c gr Sm E Sp fo u f& mu dka & G; c s, fE dki fz dkU jy o y gw , f/
Locate and cr eate jump tables u dk jump table & JUt & G, ft p m; e JU address t a Mu mi f;
a u mu fc su fc sE dki fz dkU disassembler u dkc dki f; y gw , f/
w u , fv dkU Coagulate data in the final pass flag u dky dw fx m; r , fq dk& i f analysis & JU a e mu fq Hk;
t q i fhr Sm code segment & JU byte a w Gu dko m a jy mi f; v Ja y ; r Smjz p fy gw , f/ ( Make final analysis
pass flag u dkMu n fhy g/ )
Automatically hide libr ar y function u a w mh FLIRT u dkt o Hk; jy Kjy D; p Hkp r f; x m; w Jh library
function a w Gu dka z smu fx m; ( collapse) z dkUt w Gu fo Hk; y gw , f/
Pr opagate stack ar gument infor mation u a w mh a e mu fx y f call a w G& Sdv mc Jh& i f ( t jc m;
function r Sa c : o Hk; a o m function w p fc ku Jho dkU) call & JU stack parameter e JUy w fo u fw Jh t c su f
t v u fa w Gu dko dr f; q n f; z dkU disassembler u dkc dki f; y gw , f/
Pr opagate r egister ar gument infor mation u a w mh a e mu fx y f call a w G& Sdv mc Jh& i f ( t jc m;
function r Sa c : o Hk; a o m function r sm; u Jho dkU) call & JU register parameter e JUy w fo u fw Jh t c su f
t v u fa w Gu dko dr f; q n f; z dkU disassembler u dkc dki f; y gw , f/
Check for Unicode str ings u a w mh Unicode string a w G& Sd^ r & Sd y & dk* & r fu dk p p fa q ; E dki fz dkU
jz p fy gw , f/
Comment anonymous libr ar y functions u a w mh w du sw Jh library function w p fc ku dk p Hkp r f;
& & Sdw Jht c g library t r n fe JU signature a w Gu dkt o Hk; jy Kjy D; t r n fr o d library function a w Gu dk t r Sw f
t o m; v ky fx m; z dkU disassembler u dkc dki f; y gw , f/
Multiple copy libr ar y function r ecognition u a w mh y & dk* & r fw Gi f; r Sm& Sdw Jh w ln Dw Jh function & JU
copy t a jr mu ft r sm; u dkr Sw fx m; a p z dkUjz p fy gw , f/
Cr eate function tails u a w mh function tails u dk& Sma z Ga y ; z dkUjz p fjy D; ' ga w Gu dk function t " dy m, f
z Gi fhq dkc su fr Sm v ma y gi f; r Smjz p fy gw , f/
- Pr ocessor options ' gu a w mhflag a w Ga & G; c s, fE dki fw Jhwindow u dka c : o Hk; w Jhbutton w p fc kjz p fy gw , f/
Conver t immediate oper and of " push" to offset u a w mh PUSH command x Jr Sm& Sdw Jh
w dku f& dku f operand u dkoffset w p fc k( address w p fc k) t jz p f a jy mi f; v Ja y ; E dki fp Gr f; u dkn Te fjy y gw , f/
Conver t db 90h after " jmp" to " nop" u a w mhJMP command a e mu fu u y fy gv mw Jh 90H
byte a w Gu dkNOP command a w Gt jz p f b mo mjy e fa y ; z dkUjz p fy gw , f/
Conver t immediate oper and of " mov r eg, " to offset u a w mhMOV reg, command
(reg u a w mh register u dkq dkv dkw my g/ ) x Jr Sm& Sdw Jh w dku f& dku f operand u dk offset w p fc k ( address
w p fc k) t jz p f a jy mi f; v Ja y ; E dki fp Gr f; u dkn Te fjy y gw , f/
Conver t immediate oper and of " mov memor y, " to offset u a w mh MOV mem,
command x Jr Sm& Sdw Jh w dku f& dku f operand u dk offset w p fc k ( address w p fc k) t jz p f a jy mi f; v Ja y ; E dki f
p Gr f; u dkn Te fjy y gw , f/
Disassemble zer o opcode instr uctions u a w mha t mu fy g instruction (00 00: ADD [EAX],
AL) u dkdisassemble v ky fc dki f; y gw , f/ y Hkr Se fq dk& i fa w mho lUu dkr a & G; c s, fy gb l; / y Hk( 4 ) /
Advanced analysis of Bor land' s RTTI (RTTI q dkw mu a w mhrun-time type information u dk
a jy mw my g/ )u a w mhIDA Pro u dkRTTI structure a w Gu dkp p fa q ; z dkUe JU z e fw D; z dkUc dki f; y gw , f/
Check " unknown_libname" for Bor land' s RTTI u a w mh RTTI structure a w G& Sdw Jht c g
unknown_libname t r Sw ft o m; e JUt r n fa w Gu dkp p fa q ; z dkUc dki f; w mjz p fy gw , f/
Advanced analysis of catch/finally block after function u a w mh catch/finally p w Jh
exception proceffing block a w Gu dk& Smc dki f; w mjz p fy gw , f/
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 7 8 -
y Hk( 4 )
Allow r efer ences with differ ent segment bases u a w mh o w fr Sw fx m; w Jh address u
o dr f; q n f; x m; w Jhw e fz dk; [ m character w p fv Hk; r [ kw fc Jh& i fa w mi f character a w Ge JUq dki fw Jh reference
a w Gu dko w fr Sw fc dki f; y gw , f/ ( character u k' fw p fc kt jz p f r a z mfjy c dki f; w mjz p fy gw , f/ )
Don' t display r eduntant instr uction pr efixes u a w mh listing u dk z w f& I& w m t q i fa jy a p z dkU
command prefix t c sdKUu dka z smu fx m; z dkUjz p fy gw , f/
Inter pr et int 20 as VxDcall u a w mh INT 20H u dk VxDcall/jump t jz p f b mo mjy e fc dki f; w m
jz p fy gw , f/
Enable FPU emulation instr uctions u a w mh INT 3?H w dkUv dk command a w Gu dk arithmetic
coprocessor command a w G& JU emulation a w Gt jz p f b mo mjy e fa p z dkUjz p fy gw , f/
Explicit RIP-addr essing u dk o w fr Sw fr , fq dk& i fa w mh y & dk* & r fr Sm relative instruction pointer
(RIP) addressing u dko Hk; r , fv dkU , lq r Smjz p fy gw , f/ ' Dflag u kda w mh 64-bit y & dkq u fq ma w Gt w Gu f
q kd& i f a & G; c s, fa y ; x m; & r Smjz p fy gw , f/
- System DLL dir ector y o lu a w mh IDA Pro u & Sm& r , fh DLL z dki fa w G& Sd& m directory u dk o w fr Sw f
w mjz p fy gw , f/ o w fq dki f& m library a w Ge JUq dki fw Jh.ids z dki fa w Gu a w mhc Ri f; c su fjz p fy gw , f/
( 4 ) Disassembler Window
IDA Pro r Sma w mh t v ky fa w mfa w mfr sm; r sm; u dk disassembler window x Jr Sm v ky fa q mi fMu w m jz p fy g
w , f/ ' ga Mu mi fh ' D window t a Mu mi f; u dk t a o ; p dw fo dz dkUv dky gw , f/ ' Da e & mr Sm a x mu fjy c si fw mu a w mh ' D
disassembler & JU developer a w G[ m disassemble v ky fx m; w Jh function e JU o lUu dk& Sma z Gw Jhe n f; v r f; a w Gu dk
a z mfjy E dki fz dkU t a v ; t e u fx m; p Of; p m; c Jhw , fq dkw Jht c su fjz p fy gw , f/
Hiding functions Disassembler window r Sm function a w Gu dk t u sOf; c sHK; y Hkp H ( hide) ( o dkU)
t u s, fc sJYy Hkp H( unhide) w dkUe JUjy E dki fy gw , f/ t u sOf; c sHK; y Hkp Hr Sma w mh function u dk p ma Mu mi f; w p fa Mu mi f;
w n f; e JU jy w my g/ ' Dt o Hk; 0 i fw Jht * Fg& y fu o i fhu dkdisassemble v ky fx m; w Jhu k' fa w Gu dkv G, fu lp Gmz w f& I
a p E dki fz dkU t a x mu ft u l jz p fa p r Smy g/ Function a w Gu dk t u sOf; c sHK; ^ t u s, fc sJUz dkU numeric keypad u
(+)/(-) key a w Gu dk t o Hk; jy K& y gr , f/ ' gr Sr [ kw f& i fa w mh View menu u Hide/Unhide u dk a & G; E dki f
y gw , f/
Indicating functions y Hk( 5 ) u a w mh disassmebler window u dkjy w mjz p fy gw , f/ ' Dwindow & JU
b , fz u ft u sq Hk; t y dki f; u dk o w dx m; jy D; Mu n fhy g/ ' Dt y dki f; u a w mh listing u dkMu n fh& I& Sma z G& mr Sm & dk; & Si f;
a p z dkUjz p fy gw , f/ Command a w Gu dk t p u fu a v ; a w Ge JUjy x m; y gw , f/ w u , fv dkU p ma Mu mi f; r Sm
t p u fw p fp u fr y g& i fa w mhr Sw fc su fw p fc ky g0 i fw Jhstring v dkU t " dy m, f& y gw , f/ w u , fv dkU o Hk; p GJo lu
' Dt p u fa e & mr Sm mouse e JUE Sdy fv dku fr , fq dk& i fa w mh IDA Pro u ' D address a e & mr Sm breakpoint
o w fr Sw fy gw , f/ Jump a w Gu dka w mh t p u f( o dkU) w p fq u fw n f; r sOf; a Mu mi f; a w Ge JU jy y gw , f/
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 7 9 -
w p fq u fw n f; r sOf; a w Gu a w mh unconditonal jump (JMP) a w Gu dkn Te f; w mjz p fjy D; t p u fa w Ge JU
r sOf; a w Gu a w mhcondtional jump (JE, JNZ) a w Gu dkq dkv dkw mjz p fy gw , f/
y Hk( 5 )
Using Special Comments y & dk* & r fw p fc kt w Gi f; u address a w Gr Sm b , f jump a w Gu dk
( conditional jump E Si fh unconditional jump o dkUr [ kw f CALL command) v ky fa q mi fw , f?
n Te f; w , fq dkw Jh t x l; r Sw fc su fa w Gy g0 i fy gw , f/ w u , fv dkU reference u o w fr Sw fx m; w Jh address
q Djump v ky fw , fv dkU t " dy m, f& & i f r Sw fc su fa w G[ m CODE XREF e JUp a v h& Sdy gw , f/ w u , fv dkU ' D
command [ m a ' w mt jz p f refernce v ky fc Hx m; & w , fq dk& i fa w mh ( Oy r m MOV EAX, OFFSET
L1) DATA XREF e JUp y gw , f/ ' Dr Sw fc su fa w Gu dka w mh cross-refernce a w Gv kdUa c : jy D; cross-
refernce t r Sw ft o m; a e mu fr Sm colon v dku fy gw , f/ o lUa e mu fu address a w Gu a w mh ' Drefernce
a w Gp jz p f& m function ( o dkU) section & JUt p u dkjy w mjz p fy gw , f/ ' D address u kd mouse e JU E Sdy fjc i f;
t m; jz i fh o w fr Sw fx m; w Jh instruction & Sd& mu dkn Te f; w Jh u k' ft y dki f; t p u dk pop-up window t a e e JU
a c : , lE dki fy gw , f/ Address r Sma w mh <><> t u & ma w Gy g0 i fr Smjz p fjy D; ' D instruction u dk
refernce v ky f& m u k' f& Sdw Jhp ma Mu mi f; u dk o w fr Sw fy gw , f/ Reference p w i fw Jh p ma Mu mi f; & Sd& mu dk
w e f; o Gm; c si f w , fq dk& i fa w mh address a e & mr Sm double-click E Sdy fjy D; o Gm; v dkU& y gw , f/
o w fr Sw fx m; w Jh p ma Mu mi f; t w Gu f reference t a & t w Gu f[ m 4 c kx u fe n f; a e r , fq dk& i f o lw dkUu dk
p m& i f; o m jy Kp ky gw , f/ ' Dv dkr S r [ kw f& i fa w mh reference a w Gu dk t p u fa w Ge JUjy r Smjz p fy gw , f/
w u , fv dkU ' D address a w Gx Ju w p fc ku dk right-click E Sdy fjy D; Jump to cr oss r efer ence
u dka & G; v dku f& i f v dkt y fw Jhitem & Sd& mu dk w e f; o Gm; E dki fy gw , f/ y Hk( 6 ) / ' gjy D; & i fa w mhy Hk( 7 ) t w dki f; address
a w Gt m; v Hk; p m& i f; a y : v my gv dr fhr , f/ y Hk( 7 ) u o i fo Gm; c si fw Jhaddress u dka & G; jy D; OK u kdE Sdy fv dku fy g/
y Hk( 6 )
y Hk( 7 )
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 8 0 -
Designating an address Disassembler window x Ju listing u a w mh address w p fc ku dk
o w fr Sw fw Jh e n f; v r f; r sdK; p Hku dk jy y gw , f/ Oy r mt m; jz i fh? w u , fv dkU API function w p fc ke JU y w fo u f
v mc Jh& i fa w mh ' Dfunction & JUt r n fu dk w du sp Gmo w fr Sw fy gw , f/ ' Dt jy i f IDA Pro u r sm; a o mt m;
jz i fh string a w Ge JUy w fo u fv m& i fa w mh p Hkp r f; o d& Sdx m; w Jh string a w Gu dk reference a w G& JUt r n fa w G
t jz p f t a jc c Hx m; a y ; y gw , f/ e r le mjy & r , fq kd& i fa w mhYou are wrong! q dkw Jhp mo m; y gw Jhstring u dk
IDA u reference t jz p fo w fr Sw f& mr Sma w mh ' D string u dk aYouAreWrong t jz p fa jy mi f; v dku fy g
w , f/ "a" e JUp w Jh ' D prefix a w Gu dk IDA Pro u ASCII string a w Gt jz p f, lq y gw , f/ y Hk( 8 ) /
t jc m; t r n fa w Gt m; v Hk; u a w mh prefix e JU address w p fc ka y : r lw n f jy D; function t r n fa w G( o dkU)
data address a w Gu dko w fr Sw fy gw , f/ y Hk( 9 ) r Smjr i f& w Jht w dki f; a t mu fy g prefix a w Gu dk o i fht a e e JU
Mu HKa w GU& E dki fy gw , f
sub_ Function
locr et_ Address of the return instruction
loc_ Instruction address
off_ Data specifying the address (offset)
seg_ Data specifying the segment address
asc_ Address if an ASCII string
byte_ Byte address
wor d_ Word address
dwor d_ Double word address
qwor d_ Address of a 64-bit value
flt_ Address of a 32-bit floating-point number
dbl_ Address of a 64-bit floating-point number
tbyte_ Address of an 80-bit floating-point number
str u_ Structure address
algn_ Alignment directive
unk_ Address of an univestigated area
y Hk( 8 )
y Hk( 9 )
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 8 1 -
Using the context menu Disassembler window e JU t v ky fw GJv ky fr , fq dk& i f window w p fc kr Sm
right-click E Sdy f& i fa y : v mw Jh context menu a w Ge JU t o m; u sa e & r Smjz p fy gw , f/ t c sdKU menu a w G
u a w mho i fa & G; w Jht y dki f; u dkr lw n fjy D; u GJjy m; a e r Smjz p fy gw , f/ Oy r m function t r n fa w G? instruction
a w G? r Sw fc su fa w Ge JU a & G; x m; w Jh block w dkUt w Gu f listing r Smjz p fy gw , f/ t c sdKU menu item a w G
u a w mh debugger w p fc ku Jho dkUa o m IDA Pro & JUv ky fa q mi fc su fa w Ge JU y w fo u fa e y gw , f/ ( Run to
cur sor ? Add br eakpoint E Si fh Add execution tr ace) / t x l; o jz i fh Rename menu u dk
o w djy Ka p v dky gw , f/ ' Ditem u o i fhu dk command & JU operand a w Gu dkw n f; jz w fa p E dki fv dkUy g/
Navigating a listing t a & ; Mu D; q Hk; u dp & y fu a w mh listing u dk & Sma z Gjy o jc i f; y Jjz p fy gw , f/
Crossreference u n Te fjy w Jha e & ma w Gu dk w e f; o Gm; E dki fy gw , f/ a e mu fw p fe n f; u dkv J ( cross-
reference a e & mr Sm double-click E Sdy fjc i f; jz i fh) return jy e fv ma p z dkUt w Gu f t o Hk; jy KE dki fy gw , f/
( Oy r m? conditional jump q Do dkU? CALL command q Do dkU? o dkUr [ kw f MOV EAX, OFFSET
address u Jho dkUa o m command w p fc kx Jr Saddress q Do dkU) / o dx m; & r Smu a w mhIDA Pro [ m o i fh& JU
jump a w Gt m; v Hk; u dk r Sw fx m; w mjz p fw Jht w Gu f Mu dKu fw Jht c sde fr Sm Mu dKu fw Jha e & mu dk
button a w Go Hk; jy D; a & SUw dk; ? a e mu fq kw fv dkU& y gw , f/
( 5 ) t jc m; Window r sm;
- Hex View ' Dwindow r Sm u l; w i fx m; w Jhmodule & JU hex dump a w Gy g0 i fjy D; ' Ddump a w Gu dk ASCII
p mv Hk; a w Ge JUjy y gw , f/ ' Dwindow [ m disassembler window e JUy w fo u fw Jht & e f window w p fc kjz p fw mr dkU
o le JUv G, fu lp Gm synchronize v ky fE dki fy gw , f/ ' Dv dkv ky fc si fw , fq dk& i fa w mh y Hk( 1 0 ) t w dki f; hex window & JU
w p fa e & m& mr Sm right-click E Sdy fjy D; Synchronize with IDA View u dka & G; & y gr , f/
y Hk( 1 0 )
' gq dky Hk( 1 1 ) t w dki f; VA 0040B440 & Sd& m IDA View u dkw e f; a & mu fv mr Smjz p fy gw , f/ q dkv dkw mu
a w mhHEX p mv Hk; 5E [ m POP ESI e JUn Dw , fq dkw Jht a Mu mi f; y g/
y Hk( 1 1 )
- Expor ts ' D window r Sma w mh export v ky fx m; w Jh function a w Gp m& i f; y g0 i fy gw , f/ ' g[ m DLL
a w Ge JUw GJv ky f& mr Sm t o Hk; 0 i fy gw , f/ o mr e f exe module a w Gt w Gu f start function v dkUt r n f& w Jh element
w p fc kw n f; jy r Smy g/ y Hk( 1 2 ) /
y Hk( 1 2 )
- Impor ts ' Dwindow r Sma w mh import v ky fx m; w Jh function a w Ge JU module a w Gp m& i f; y g0 i fy gw , f/
Import v ky fx m; w Jh function u dk double-click E Sdy fr , fq dk& i fa w mh disassembler window q Da & mu fo Gm; r Sm
jz p fjy D; entry point t a e e JU a w GU& Sdr Smjz p fy gw , f/ ' ga Mu mi fhr dkU y & dk* & r fx Ju ' Dfunction e JUy w fo u fw Jh cross-
reference a w Gt m; v Hk; u dko i fht a e e JU v G, fu lp Gm & Sma w GUE dki fr Smjz p fy gw , f/ y Hk( 1 3 ^ 1 4 ) /
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 8 2 -
y Hk( 1 3 )
y Hk( 1 4 )
- Names ' D window r Sma w mh import v ky fx m; w ma w Gt m; v Hk; e JU library function a w Gy g0 i fy gw , f/
IDA Pro u o dx m; w Jhvariable a w Ge JU lable a w G& JUt r n fa w Gv n f; y g0 i fy gw , f/ t r n ft o D; o D; & JU b , fz u f
jc r f; r Sm& Sdw Jhp mv Hk; ( t & ky f) u a w mht r n ft r sdK; t p m; jz p fy gw , f/ y Hk( 1 5 ) /
L Library function
F Regular functions and API functions
C Instructuion (label)
A ASCII string
D Data
I Imported function
y Hk( 1 5 )
t r n f& Sd& mu dk double-click E Sdy fjc i f; jz i fh ' Dt r n fu dka c : o Hk; w Jh y & dk* & r f& JUw n fa e & mu dk w e f; a & mu fo Gm;
r Sm jz p fy gw , f/ w u , fv dkU t r n fo p fu dk z e fw D; c si fw , fq dk& i f a jy mi f; c si fw Jhaddress & Sd& ma e & mr Sm Inser t key
u dkE Sdy fjy D; a jy mi f; v dkU& y gw , f/ y Hk( 1 6 ) /
y Hk( 1 6 )
& dku fx n fhv dku fw Jht r n fu a w mhdisassembler window r Smv Ja y : a e r Smjz p fy gw , f/ y Hk( 1 7 ) /
y Hk( 1 7 )
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 8 3 -
- Functions ' D window r Sma w mh library function a w Ge JU import v ky fx m; w Jh user function a w G
t y gt 0 i f IDA Pro u o dx m; w Jhfunction a w Gp m& i f; u dkjy r Smjz p fy gw , f/ y Hk( 1 8 ) /
y Hk( 1 8 )
- Str ings ' D window r Sma w mh disassembler u & Sma w GUx m; w Jh string a w Gt m; v Hk; y g0 i fr Smjz p fy gw , f/
y Hk( 1 9 ) /
y Hk( 1 9 )
String w p fc ku dk double-click E Sdy fjy D; Mu n fhr , fq dk& i f ' Dstring u dk a Mu n mx m; w Jha e & mu dk w e f; a & mu f
o Gm; r Smjz p fy gw , f/ o mr e ft m; jz i fha w mh ' Dwindow r Sm C p w dki f string a w Gu dko mjy o y gw , f/ t jc m; string
t r sdK; t p m; a w Gu dk jy o c si fw , fq dk& i fa w mh ' Dwindow r Sm right-click E Sdy fjy D; Setup command u a e a & G; a y ;
v dkU& y gw , f/ y Hk( 2 0 ) /
y Hk( 2 0 )
- Str uctur es ' Dwindow r Sma w mh disassembler u & Sma w GUx m; w Jh structure a w Gt m; v Hk; y g0 i fr Smjz p fy g
w , f/ y Hk( 2 1 ) / Structure t o p fw p fc ku dkx y fx n hfc si f& i fa w mhInser t key u dkE Sdy fjy D; x n fhv dkU& y gw , f/
y Hk( 2 1 )
- Enums ' Dwindow u a w mh y & dk* & r fw Gi f; r Sm p Hkp r f; v dkUa w GU& Sdx m; w Jh enumeration a w Gt m; v Hk; u dk jy o z dkU
& n f& G, fy gw , f/
' Dht jy i f disassembler u t jc m; window a w Gu dkv J t o Hk; jy KE dki fy gw , f/ t x l; o jz i fh Library
window jz p fy gw , f/ t Ge fv dki f; help p e p fr Sma w mh ' Dwindow u dk signatures window v dkUa c : y gw , f/ ' D
window r Sma w mh library function a w Gu dko d& Sda p z dkU t o Hk; jy Kw Jh signature p m& i f; u dk jy o y gw , f/ y Hk( 2 2 ) /
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 8 4 -
y Hk( 2 2 ) r Smjr i f& w mu a w mhfunction signature a w Gy g0 i fw Jhz dki ft r n f? ' Dsignature a w Gu kdt o Hk; jy Kjy D; a w GU& Sdx m;
w Jhfunction t a & t w Gu f? ' Dsignature a w Gu dkt o Hk; c sx m; w Jhfunction a w Ge JUq dki fw Jht r n fw dkUjz p fy gw , f/
y Hk( 2 2 )
w u , fv dkU v dkt y fw Jhsignature z dki fa w Gu dk x y fx n fhc si fw , fq dk& i fa w mhInser t key u dkE Sdy fjy D; E Sp fo u f
& mu dk x n fho Gi f; E dki fy gw , f/ y Hk( 2 3 ) / ' Dz dki f& JU signature a w Gu dka w mh function t o p fa w Gu dk o da p z dkUt w Gu f
c su fc si f; t o Hk; jy Kr Sm jz p fy gw , f/
y Hk( 2 3 )
( 6 ) Menu E Si fhtoolbar
IDA & JU menu e JU toolbar a w Gt a Mu mi f; u dka w mht Mu r f; z si f; y J& Si f; jy o Gm; r Smjz p fy gw , f/
File menu & JU item a w Gu a w mha t mu fy gt w dki f; jz p fy gw , f
Open Disassemble v ky fr , fhexe module u dkz Gi fhz dkUjz p fy gw , f/
Load z dki ft r sdK; r sdK; u dk z Gi fhz dkUjz p fy gw , f/ Reload the input u a w mh disassemble v ky fx m; w Jh
module u dk jy e fz Gi fhz dkUjz p fy gw , f/ Additional binar y file u a w mh database x Ju dk a e mu fx y f
binary file w p fc k v mu l; w i fr Smjz p fy gw , f/ IDS file u a w mh o w fr Sw fx m; w Jh import library & JU
function a w Ge JUy w fo u fw Jht c su ft v u fa w Gy g0 i fw Jh IDS (intrusion-detection system)
z dki fu dkz Gi fhz dkUjz p fy gw , f/ ( IDS directory x Jr Sm& Sdw Jh IDS z dki fa w Gt m; v Hk; u dk t v dkt a v smu fu l; w i fr Sm
jz p fy gw , f/ ) PDB file q dk& i fa w mhdebug t c su ft v u fa w Gy gw JhPDB z dki fu dk u l; w i fr Smjz p fy gw , f/
DBG file q dk& i fv J debug t c su ft v u fa w Gy gw Jhz dki fu dk u l; w i fr Smjz p fy gw , f/ FLIRT signatur e
file q dk& i fa w mh signature z dki fa w Gu dku l; w i fjy D; t o Hk; c sr Smjz p fy gw , f/ ( y Hk- 2 2 r Smjr i f& w Jh signature
window x Jr Sm w ln Dw Jhv ky fa q mi fc su fu dk v ky fa q mi fr Smjz p fy gw , f/ ) Par se C header file u a w mh
structure t o p fa w Ge JU enumeration t o p fa w Gu dk a e mu fx y fa Mu n mz dkUt w Gu f header z dki fu a e
t r sdK; t p m; t " dy m, fz Gi fhq dkc su fu dk z w f& Iw mjz p fy gw , f/ ( Enums E Si fh Str uctur es window r sm;
t a Mu mi f; w Gi fMu n fhy g/ )
Pr oduce File Disassemble v ky fx m; w Jhu k' fa y : r lw n fjy D; z dki ft o p ft r sdK; r sdK; u dk z e fw D; a y ; y gw , f/
.map u dka w mhdebugger a w Gu t o Hk; jy KE dki fy gw , f/ .asm u a w mhAssembly z dki fjz p fjy D; .lst u a w mh
IDA View r Smjr i f& w Jhu k' fa w Gu dk o dr f; a y ; w mjz p fy gw , f/ .inc? .exe? .dif. ? html p w Jh z dki fa w Gt a e
e JUv J o dr f; a y ; E dki fy gw , f/ Hex-Rays Decompiler u dk install v ky fx m; r , fq dk& i fa w mh disassemble
v ky fx m; w Jhexe z dki fa w Gu dk.c (C source code) z dki ft jz p f decompile v ky fa y ; E dki fy gw , f/ y Hk( 2 4 ) /
if ( LCData ) {
lstrcpyA(v5, &LCData);
v7 = LoadLibraryExA(ValueName, 0, 2u);
v3 = v7;
if ( !v7 )
{
v14 = 0;
lstrcpyA(v5, &LCData);
v3 = LoadLibraryExA(ValueName, 0, 2u);
}
}
y Hk( 2 4 )
IDC file Scritp z dki fa w Gu dku l; w i fz dkUe JU t v ky fv ky fa p z dkUjz p fy gw , f/
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 8 5 -
IDC command Script a w Gu dkc su fc si f; execute v ky fE dki fz dkU window u dka c : o Hk; w mjz p fy gw , f/
Save v u f& Sd disassemble v ky fa e w Jh database u dk .idb extension e JUo dr f; q n f; w m jz p fy g
w , f/
Save as v u f& Sd disassemble v ky fa e w Jh database u dk o w fr Sw fx m; w Jht r n fe JU o dr f; w m
jz p fy gw , f/
Close Disassemble v ky fa e w Jhdatabase u dko dr f; jy D; disassemble v ky fx m; w Jhz dki fu dky dw fw my g/
Edit menu & JU item a w Gu a w mha t mu fy gt w dki f; jz p fy gw , f
Copy a & G; c s, fx m; w Jht & mu dkclipboard q Du l; w i fy gw , f/
CODE Block u dkexe u k' ft jz p fa jy mi f; v Jy gw , f/
DATA a & G; c s, fx m; w Jhblock u dka ' w mt jz p fa jy mi f; v Jy gw , f/
Str uct var Block u dka & G; x m; w Jhstructure t jz p fa jy mi f; y gw , f/
Str ings String t jz p fa jy mi f; v Jy gw , f/ ( String t r sdK; t p m; u dka w mh submenu u a e
a & G; c s, fE dki fy gw , f/ )
Ar r ay Mu dKw i fo w fr Sw fx m; w Jhparameter a w Ge JU array t jz p f a jy mi f; v Ja y ; y gw , f/
Undefine Mu dKw i fr o w fr Sw f& a o ; w Jh structure w p fc k& JUa ' w mt jz p f a & G; x m; w Jh block
u dkt r Sw ft o m; v ky fy gw , f/
Name t r n fa jy mi f; w mjz p fy gw , f/
Oper and type Operand t r sdK; t p m; u dko w fr Sw fw mjz p fy gw , f/
Comments r Sw fc su fa w Gx n fho Gi f; z dkUjz p fy gw , f/
Segments Segment a w Gu dku dki fw G, fE dki fz dkUjz p fy gw , f/
Str ucts Structure a w Gu dku dki fw G, fE dki fz dkUjz p fy gw , f/
Functions Function a w Gu dku dki fw G, fE dki fz dkUjz p fy gw , f/
Other Alignment directive u dko w fr Sw fjc i f; ? instruction r sm; ( o dkU) a ' w mr sm; u dk
& dku fx n fhjc i f; ? t a & mi fw p fa & mi fjz i fhjy jc i f; p w Jh t jc m; v ky fa q mi fc su fa w Gu dk a q mi f& Gu fw m
jz p fy gw , f/
Plugins t jc m; plug-in module a w Gu dkt o Hk; jy Kz dkUjz p fy gw , f/
Jump menu & JU item a w Gu a w mh disassemble v ky fx m; w Jhu k' fa w Gx Ju jump t r sdK; r sdK; t w Gu f
& n f& G, fw mjz p fy gw , f/ Oy r m o w fr Sw fx m; w Jh address q Djump v ky fjc i f; ? o w fr Sw fx m; w Jh function q D
jump v ky fjc i f; ( o lUu dka w mh list u a e a & G; c s, fE dki fy gw , f) ? y & dk* & r f& JU entry point (EP) q Djump v ky fjc i f; ?
o w fr Sw fx m; w Jhlabel q Djump v ky fjc i f; / y Hk( 2 5 ) /
y Hk( 2 5 )
Sear ch menu & JU item a w Gu a w mh disassemble v ky fx m; w Jhp mo m; x Jr Sm& Sdw Jh & Sma z Gw Jhv ky fa q mi f
c su ft r sdK; r sdK; t w Gu f & n f& G, fy gw , f/ Oy r m p mo m; u dk& Smjc i f; ? a e mu fx y f a ' w m block u dk& Smjc i f; ? a e mu f
x y f Assembly instruction u dk& Smjc i f; ? a e mu fx y f byte sequence u dk& Smjc i f; / y Hk( 2 6 ) /
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 8 6 -
y Hk( 2 6 )
View menu & JU item a w Gu dk t o Hk; jy Kjy D; IDA Pro & JU jr i fu Gi f; a w Gu dk E Sp fo u f& mx m; v dkU& y gw , f/
Window t o p fa w Gu dk x y fz Gi fhjc i f; ( Open Subviews) ? toolbar a w Gu dk z e fw D; jc i f; E Si fhz su fjc i f; Toolbars) ?
function a w Gu dka z smu fjc i f; ^ jy e fa z mfjc i f; ( hide/unhide) w dkUjy Kv ky fE dki fy gw , f/
Debugger menu u command a w Gu a w mh o i fhu dk IDA Pro & JU t r sdK; r sdK; a o m debugging
p Gr f; a q mi f& n fu dk jy o r Smjz p fy gw , f/ ' ga w Gu a w mhbreakpoint r sm; u dku dki fw G, fjc i f; ( Br eakpoints) ? watch
r sm; u dku dki fw G, fjc i f; ( Watches) ? trace v dku fjc i f; ( Tr acing) ? register t r sdK; r sdK; x Jr Sw e fz dk; r sm; u dk Mu n fhjc i f;
( General registers? Segment register? FPU register) w dkUjz p fy gw , f/
Option menu u a w mhIDA Pro & JU setting a w Gu dk a jy mi f; v Jz dkUt w Gu fjz p fjy D; t a p my dki f; r Sm u Re fa w mf
& Si f; jy c Jhw Jht w dki f; jz p fy gw , f/
Windows menu & JU item a w Gu dkt o Hk; jy Kjy D; IDA Pro & JU window a w Gu dku dki fw G, fE dki fy gw , f/
Help menu item a w Gu a w mho i fhu dke n f; y n my dki f; q dki f& m t a x mu ft u la w Ga y ; r Smy g/
( 7 ) Built-In IDA Pr o y & dk* & r fb mo mp u m;
IDA Pro disassembler r Sma w mhbuilt-in y & dk* & r fb mo mp u m; w p fc ky gv my gw , f/ ' ga Mu mi fhy & dk* & r f
i , fa v ; a w Gu dk u dk, fw dki fa & ; o m; E dki fjy D; o lw dkUu dk disassemble v ky fx m; w Jhu k' fa w Gt jz p f jy e fv n fp p fa q ;
Mu n fh& IE dki fr Smjz p fy gw , f/
IDA Pro r Sm w c gw n f; y gv mw Jh y & dk* & r fb mo mp u m; [ m C (ANSI C) b mo mp u m; e JU a w mfa w mf
a v ; q i fy gw , f/ ' ga Mu mi fhv J ' Db mo mp u m; & JUt r n f[ m IDC (Interactive Disassembler C) jz p fa e w my g/
IDC subdirectory a t mu fr Sm ' Db mo mp u m; e JUy w fo u fw Jh e r le my & dk* & r fa w Gy g& Sdy gw , f/ IDA Pro u a w mh
' Dy & dk* & r fa w Gu dk disassemble v ky fx m; w Jhp mo m; a w Gt jz p f analyze v ky fz dkUt w Gu f t o Hk; jy Kw mjz p fy gw , f/
' Dy & dk* & r fa w Gt m; v Hk; u dk analyze v ky f& w m v G, fu ly gw , f/ ' ga Mu mi fh o i fht a e e JU IDC b mo mp u m; u dk
a v hv mz dkUt w Gu f o lw dkUa w Gu dkt o Hk; jy KE dki fy gw , f/
IDC command a w Gu dkexecute v ky fz dkU e n f; v r f; E Sp fc k& Sdy gw , f/
1 / y x r e n f; v r f; u a w mh command window u dkt o Hk; jy Kv dkUjz p fy gw , f/ Command window u dka c : o Hk; z dkU
File | IDC command u dka & G; jy D; a o mfv n f; a u mi f; ? Shift + F2 u dkE Sdy fjc i f; jz i fha o mfv n f; a u mi f; t o Hk; jy KE dki f
y gw , f/ Command window u a w mh y Hk( 2 7 ) t w dki f; jz p fy gw , f/ ' D window r Sm IDC command a w Gu dk
w n f; jz w fE dki fy gw , f/ t m; v Hk; jy D; p D; & i fa w mh OK button u dkE Sdy fv dku f& Hky gy J/ IDA Pro u a w mh ' Dcommand
a w Gu dk b mo mjy e fjy D; execute v ky fz dkUMu dK; p m; r Smjz p fy gw , f/ ' ga Mu mi fh ' Dwindow u dkt o Hk; jy Kjy D; & dk; & Si f; v Sw J
hy & dk* & r fa w Gu dkIDC b mo mp u m; e JU a & ; o m; E dki fr Smjz p fy gw , f/
2 / y dkjy D; t a jc c Hu sw Jhc sOf; u y fe n f; u a w mh .IDC extension t r n fe JU IDC u k' fa w Gy g0 i fw Jhz dki fa w Gz e fw D; z dkUy g/
y & dk* & r fw p fc ku dkz Gi fhz dkU File menu u Idc file u dka & G; & y gr , f/ ' Da e & mr Sma w mh y & dk* & r fu dk compile v ky fjy D;
c su fc si f; execute v ky fr Smjz p fy gw , f/ ' Dht jy i f y Hk( 2 8 ) t w dki f; a e mu fx y f window w p fc kx y fa y : v mr Smjz p fjy D;
y & dk* & r fu k' fu dkw n f; jz w fz dkUe JU y & dk* & r fu dkexecute v ky fz dkU button a w Gy g& Sdr Smjz p fy gw , f/
IDC r Sm y & dk* & r fa & ; r , fq dk& i f t e n f; q Hk; a w mha t mu fy gt c su fa w Gy g0 i f& r Smjz p fy gw , f/
#include <idc.idc>
static main(void)
{
// Your Code here;
}
t c e f; ( 7 ) IDA Pro Advanced 5.2 r dw fq u f
- 8 7 -
y Hk( 2 7 )
y Hk( 2 8 )
e d* Hk; c sKy ft a e e JU IDA Pro t a Mu mi f; t w Gi f; u su so dc si f& i f Chris Eagle a & ; o m; w Jh ]The IDA Pro
Book The Unofficial Guide to the World's Most Popular Disassembler} p mt ky fu dkz w f& Iz dkU
t Mu Ha y ; v dky gw , f/
,.., PE Header
..
tcef;(8) - PE Header
, PE . . ._ .
Portable Executable (PE) .-. 32bit , 64bit Windows OS .-.. ..`.,--
executable (EXE) . object (DLL) ..--- ..-. `..-. Portable .-...,.
-- 32bit , 64bit Windows OS .--.. `,, .-- ..`.-.- .__,.-.
PE ..-. .`..`..-. wrap ..- executable code .-- ... Windows OS
loader -- -.-.--.-- encapsulate ..- data structure -. . .
link .-- dynamic library reference .- API - export , import . table .-
resource management data .-, TLS data .- -. . - . - - . - -.-.-.
Microsoft `..`. VAX/VMS ....- COFF . . -., ,. ,.. -.`.. -.
"Portable Executable" ....-.-.-.-. intent -. Windows .. .- - .`
-. .. . `.. ` . CPU -... . .`....-. Windows NT . ..- Windows
95 ...-, Windows CE -.. ..`. Microsoft compiler .- - - ..- OBJ
. .- -.-. COFF (Common Object File Format) .`..`. encoding .... ..,.- ..`
-. 64-bit Windows .- . ..-. PE .- ,_..``... -. ,. . `..-.-
.-. PE . -. . . - .` . ._ .-_ ...- `.. -.
,
PE ... ,_....-. section . . . -. -. -.-. - .---`..`. .,.--.-
.-. .-..- - - `.. -. Windows NT . application -....-. ...-.-.
. - .- -.-. .text .bss .rdata .data .rsrc .edata .idata .pdata , .debug - `..-.
application .- -.-. section .-....-. -.-. . - . - , - .- ` .
- -. `.. . -.
.-... .-...- section .--.-.
executable code section .text (Microsoft) CODE (Borland)
data section .data, .r data, .bss (Microsoft) DATA, BSS (Borland)
resources section .r sr c
export data section .edata
import data section .idata
debug information section .debug
Section ._.--. --..-. ....-. OS - ._ .- - . . ..
-. ...- .- - -.-. disk ....- PE . -. . . ._ . -. . - . .- .- - ,
. .. - .`.,, -. . -_ .- .-. . --. . .,, - - .- - disk .-
....,.........-.-..-.--,..--.-- ........
-. `.. .. . - . - . . -. . -_ . - .- - -. .- - - . Windows loader
- -...-- .,........ -...-- ,.....-.- ..`.-...-.
DOS MZ Header
DOS Stub
PE header
Section Table
Section 1
Section 2
Section
Section n
,.., PE Header
..
..,........ - - - .- - .-. .,........ -. section .-.. .-.
, ` . . . .,.- . .. . .,....-. .. debug information,
. - . . - .- - , . ., disk ....- .. item -. -_ .,..- -. - `... .
-. -..-. . .-. Windows -..`- page -.``- virtual memoy management
.,. .-. `.. -. Section .-- RAM .- .- - - . - -. 4KB . - memory page
.- , - - _ .. .,.` . section ....-. page .. - .- .-. Virtual memoy -.-.
,-. `..-.
,
Virtual memory . ... - -.-. ... . .- - physical memory - - - . -
. .. .... ... . .- .., OS . . -.. .`. .- .-. - .,- . - -. . - . , -
.- . - .... - - . . .- ..-. -. process -., -. physical memory address -
--. . .. .. . -.- page table , _ . .-. . - . - .. .. .. .- - table entry
-....-. -.-. ..-. .`...-. page table -. physical memory . . . .- - ..,
-., .-. ..- ...- -. . - . - page .- `.. .`...-.`.. -. . - .
. .- -.-.
, .`..- `... . .... address space .-- .,-..-. Address space .-.-.-. .-.
, access ... `..- ..`.. page -.`..-. .-.-.-. -. .-.. .,
process ,.. .-.-. ...-.- .-...--. -.,-. ..`.....,--. .-.
. .-..-... crash `.. . `... -.. -. . address space - .. . . - .`.. ..-.
, .-.- -. access .. . - ._ .. ..- - - . .- ..- - .- .
. -. PE ..-.. section .-- -. -..-...-. .- ,......-
module -. - .- - , - . memory manager - .- _ . . ..-... - .- , . .
section header - . - . setting .-. .`- section . .. .- - memory manager -.
memory page .-... access .-..- .-. - -. - - .- . - ..-
section -. .-.-... ....-... execute .-... ..`.--. Section ..
..-. ..-. fresh page -.-.,..-. .`.`..-.
-. `.. `.. Windows - - page size -.-. 4096 bytes (1000h) `.. -. Disk .-
page .....-. exe -- _......-. -.`..- ,.. -..-...-.
-.-`. .....-....... . `.. .-.. PE header ...-_- alignment field
.. .-. .-.--.-. section alignment , file alignment Section alignment .-.
-.-. ......--. .-... section .- - -. _ . . . -. `.. -.
, PE . .- - windows loader - . - . - - .- - , . . . .,- .,..- module
.-. . .- - .,....` ..- - .. . address - HMODULE .-. . - .
,.., PE Header
.
...- module -.-. exe .-., process -.- - - .-., resource .- .. .-
... `. -. PE .. `....-- .-..... .-....-. .,....` . .. - .
.. relocation,
, DOS Header
PE . .- -. DOS header , ...`. .. ... 64 bytes `.. .- .-. . -.. -.
DOS -.,.- .-.`.. -. .-. DOS - . , -, - executable .`...-.. .
.-`... header .,.-.. ...._...- DOS stub - .. `..-. DOS stub -.-.
.,..`. 'This program must be run under Microsoft Windows' . - .....- - ... . ` .
.-.-.-. DOS . -.. `.. . -. Windows application .-- build ,.. linker -
. . exe .- winstub.exe .- stub .-..- link -..--. `..-.
DOS header -. structure -.`..`. windows.inc ., winnt.h ..-.. .- ....
...-. --. ... assembler ., compiler - install `...... .-.--
\include\ directory ..- . .. .. -. DOS header . . member ..-- 19 .`. magic ,
lfanew -.-. . - .......-. .-.
IMAGE_DOS_HEADER STRUCT
e_magic WORD ?
e_cblp WORD ?
e_cp WORD ?
e_crlc WORD ?
e_cparhdr WORD ?
e_minalloc WORD ?
e_maxalloc WORD ?
e_ss WORD ?
e_sp WORD ?
e_csum WORD ?
e_ip WORD ?
e_cs WORD ?
e_lfarlc WORD ?
e_ovno WORD ?
e_res WORD 4 dup (?)
e_oemid WORD ?
e_oeminfo WORD ?
e_res2 WORD 10 dup (?)
e_lfanew DWORD ?
IMAGE_DOS_HEADER ENDS
PE ....- DOS header . magic ...-.-.-. 4Dh 5Ah -,.. MS-DOS .
. . `. .- --. .`.. - Mark Zbikowsky --....`- MZ ..., `..`. .-. .,-,-
DOS header `.. .-. . ..-.... -. MZ -. .. . .. .. . .`.. ` . hex editor ,...
- -. PE ..... .-`..-.
lfanew -. DWORD -.`..`. DOS header . .., DOS stub ..-.... -_.
-. . . .. -.. ., - .- - PE header . offset -. Windows loader - offset -
. ... -. .-. . DOS stub - .-. . ` . PE header . - - . - . ... -. . - .,
DWORD (double word) = 4bytes ., 32bit WORD = 2bytes ., 16bit --... DWORD
- dd `. .. -. dw -.-. WORD `.. ` . byte ---.-. db ,
,
DOS header -.-. PE .. ... 64 bytes `.. .- ..-. . .`. -. . -.-
,. ... ,.-.. offset 0000 -., offset 0030 ,`.. -. DOS stub .. .,.-..
,.., PE Header
.
DWORD . . -.-.-. 00h 01h 00h 00h `..-. .,.-.....-., .`. .`, `, . .
`.....-.-. 00 00 01 00h `..`. PE header .- .. .,..`.. -. PE header -._ .
. ..- -`.. - 50h, 45h, 00h, 00h , .- -. "PE" .-....,.-.. ._.---.,
--. .. PE header . ..- -.,... . PE ... NE .-. .-. 16-bit
Windows . . - NE . `.. -. ..- LE .-. Windows 3.x virtual device
driver (VxD) `..`. LX .-. OS/2 2.0 . `.. -.
, PE Header
PE header -.-. IMAGE_NT_HEADERS .- structure -.`..-. structure
.. Windows loader - ...`..- - - .- -. IMAGE_NT_HEADERS . .
member `. .-- windows.inc .. .......`.`..-.
IMAGE_NT_HEADERS STRUCT
Signature DWORD ?
FileHeader IMAGE_FILE_HEDER <>
OptionalHeader IMAGE_OPTIONAL_HEADER32 <>
IMAGE_NT_HEADERS END
Signature -.-. DWORD `.. ` . . . . -.-.-. 50h, 45h, 00h, 00h . - -, . .
. _.- - - PE', `.. -.
FileHeader -.-. PE .. .,.- 20bytes `..`. .. physical layout , -.-.-
-. .. section ..- - , exe .--.--,
OptionalHeader -.-. .,.- 224bytes `..`. PE . - .- logical layout ,
- .- - .-. ..- -. .. AddressOfEntryPoint, .......- ...-.
-.-. FileHeader . member -. - member .- . structure -_. windows.inc . .
.......`.`..-.
FileHeader - ..- - .... `. -.
IMAGE_FILE_HEADER STRUCT
Machine WORD 014C (Intel 386)
NumberOfSections WORD 0005
TimeDateStamp DWORD 846C26F0
PointerToSymbolTable DWORD 00000000
NumberOfSymbols DWORD 00000000
SizeOfOptionalHeader WORD 00E0
Characteristics WORD 818E (File is exe)
IMAGE_FILE_HEADER ENDS
-.-..-.......-.-. -,.-. - ..`...---. ... NumberOfSections
-.-. PE . - section .-- .-.`..`.. _ . `.. `.. . .`.-.
Characteristics ...-. flag .-`. .--. PE .- executable .., DLL ....-.-
.`....-. PE header ..-., ,.`..-...-. NumberOfSections Section -...
..-. .`.-. ,,
,,
,,. -,.-.- ...- PE . . . section ..,-. .-.-. PE browse , Lord
PE - - . .`..-.
OptionalHeader -.-. 224bytes .,...-. .,.-.. 128bytes ...-. DataDirectory
-.
,.., PE Header
.
IMAGE_OPTIONAL_HEADER32 STRUCT
Magic WORD 010B (PE32)
MajorLinkerVersion BYTE 02
MinorLinkerVersion BYTE 19
SizeOfCode DWORD 00000600
SizeOfInitializedData DWORD 00001800
SizeOfUninitializedData DWORD 00000000
AddressOfEntryPoint DWORD 00001000 (CODE)
BaseOfCode DWORD 00001000
BaseOfData DWORD 00002000
ImageBase DWORD 00400000
SectionAlignment DWORD 00001000
FileAlignment DWORD 00000200
MajorOperatingSystemVersion WORD 0001
MinorOperatingSystemVersion WORD 0000
MajorImageVersion WORD 0000
MinorImageVersion WORD 0000
MajorSubsystemVersion WORD 0003
MinorSubsystemVersion WORD 000A
Win32VersionValue DWORD 00000000
SizeOfImage DWORD 00006000
SizeOfHeaders DWORD 00000400
CheckSum DWORD 00000000
Subsystem WORD 0002 (Windows GUI)
DllCharacteristics WORD 0000
SizeOfStackReserve DWORD 00100000
SizeOfStackCommit DWORD 00002000
SizeOfHeapReserve DWORD 00100000
SizeOfHeapCommit DWORD 00000000
LoaderFlags DWORD 00000000
NumberOfRvaAndSizes DWORD 00000010
DataDirectory IMAGE_DATA_DIRECTORY
IMAGE_OPTIONAL_HEADER32 ENDS
AddressOfEntryPoint PE loader - PE . - run . . `.. , . . .. . ..
instruction . .. RVA . .,, . - - . . .- .. instruction - ....-. RVA -
.`..-.`..`.. instruction - `-.`..`.. `.-. Packer .- -.-. ........`.
. - . decompression stub ...- _,.--.`..--- .-..- execute -.. . entry
point OEP, ...- .-...`.`..-. Starforce ,_ ._., protect ..- ..--. disk
... -_.,.. .CODE section .-. ..-. Execute ,... virtual memory -
...- .-. . - virtual address , ... `-.
ImageBase PE ..--- preferred load address ...`... --. field . .
- -, . .-. 400000h `.. .. . . PE loader - 400000h -.- virtual address .,.. .-
-.-. -....... 'Preferred' . - . .. .. . - -.-. `.. module -.-
address range . . .- ... . . PE loader -. address . . . - - .- ... . .- - - . ....
. , ...- -.-. 400000h `.. -. Microsoft Visual C++ x.x Method2 [Debug] , compile
..- ..---.-. 1000000h `.. -.
SectionAlignment . - . - section ...- alignment ... ,.,.`.. --. field
--, . .-. 4096 (1000h) `... section -.-. 4096bytes . .`. .- ... - , .-, ..- , .- .
.. . -. --. .. . section -. 401000h ...`. .......-. 10bytes .
..-. .,.- section -. 402000h . . .. . 401000h , 402000h -..- - .,- address
.,...--.-. ........`. ..`.. .---.
FileAlignment . - section ...- alignment ... ,. ,.`.. --. field -
-,..-. 512 (200h) `.. . section -.-. 512bytes . .`. .- ... - , .-, ..- , .- ...
. -. --. .. . section -. offset 200h . .. ` . . . . . ...-. 10bytes ..
.-. .,.- section -. 400h .. ... 512 , 1024 -..- - .,- offset .,...--.-. ..
`.. .---.
SizeOfImage . - . - PE image . . . . .. . ...`.. -. SectionAlignment .
align ..- header ..., section .. .. . . `.. -.
SizeOfHeaders section table , header ...-. ..... `..-. `.`... -,..-.
......-., ....- section .......- .....- . - ` ., _ .-.
,.., PE Header
.
DataDirectory IMAGE_DATA_DIRECTORY structure 16 .- array -. `.. ` . -. . -.
import address table (IAT) PE . - ...- .- data structure -. . , .- . . .,-.
,.. ...`..-.-.-. PE header . .._.- hexeditor , -_ ..-. .- `.. .
-.-. DOS header , PE header . -. . - ... hexeditor ..-_. .....,
. ., .- -. - _ .,. . DOS STUB -.-. . . ... .`. . . -.
,
PE header .-..- Olly .. ....- -_.-. Olly debugger - .`. Alt +
M -. ,-. `....
,
,- PE header .- ......,..- right-click .`. Dump in CPU - .... ,,-.
`. .. . `.. -.
,,
,.., PE Header
.,
,,- hex window . . right-click .`. special - PE header - .. . - . .-. .,
-. `....
.,
,, Data Dir ector y
DataDirectory .-. . .`.... . . .-. DataDirectory .-. OptionalHeader .
.,.-.. 128bytes `..-. OptionalHeader .-.- PE header `..- IMAGE_NT_
HEADERS . .,.-.. member `.. -.
.....`.. DataDirectory -. 16 .- IMAGE_DATA_DIRECTORY . array -.
`..`. structure -..-. PE .- ...-.- data structure -. . , .- . . .,-. Array
....-. import table --.-.-..- item -..- .__,.-. Structure . .
member . . . ` . -. - -_ .,.., .,.--.- .....- `-.
IMAGE_DATA_DIRECTORY STRUCT
VirtualAddress DWORD ?
isize DWORD ?
IMAGE_DATA_DIRECTORY ENDS
VirtualAddress -.-. data structure . relative virtual address (RVA) `.. -. isize
-.-. byte ,`- data structure . . . ...`.. -.
windows.inc .. .-_...- directory 16 . ._ .- -.-. ..- - . `.. -.
,.., PE Header
.
IMAGE_DIRECTORY_ENTRY_EXPORT equ 0 (export symbols)
IMAGE_DIRECTORY_ENTRY_IMPORT equ 1 (import symbols)
IMAGE_DIRECTORY_ENTRY_RESOURCE equ 2 (resources)
IMAGE_DIRECTORY_ENTRY_EXCEPTION equ 3 (exception)
IMAGE_DIRECTORY_ENTRY_SECURITY equ 4 (security)
IMAGE_DIRECTORY_ENTRY_BASERELOC equ 5 (base relocation)
IMAGE_DIRECTORY_ENTRY_DEBUG equ 6 (debug)
IMAGE_DIRECTORY_ENTRY_COPYRIGHT equ 7 (copyright string)
IMAGE_DIRECTORY_ENTRY_GLOBALPTR equ 8 (unknown)
IMAGE_DIRECTORY_ENTRY_TLS equ 9 (thread local storage)
IMAGE_DIRECTORY_ENTRY_LOAD_CONFIG equ 10 (load configuration)
IMAGE_DIRECTORY_ENTRY_BOUND_IMPORT equ 11 (bound import)
IMAGE_DIRECTORY_ENTRY_IAT equ 12 (import address table)
IMAGE_DIRECTORY_ENTRY_DELAY_IMPORT equ 13 (delay import)
IMAGE_DIRECTORY_ENTRY_COM_DESCRIPTOR equ 14 (COM descriptor)
IMAGE_NUMBEROF_DIRECTORY_ENTRIES equ 16
LordPE .. ,.,. exe .-.--_.... .,-. `....
.,
.,- -_ .. . . `.... highlight `...- ,. -,-...`---.,..
.-.. ._.-, `_.,-. .-...
,
,- -_ .. . . import directory - ,...., `..-. ... 4bytes -.-.
40000h .`. .`, . -.`.. -. , `.. -. Import directory . . . ...-.-. 1CDCh bytes
`.. -. PE header . .-., DWORD 80bytes -. `.-.. import directory . RVA
`.. -. ... -.-. resource directory `..`. ......-.-. TLS directory `.. -.
--- directory -.- ....-- ..,, data directory -.,.` . virtual address
- - - - ... .,.- .-. -. directory -. -. section ...-..-. ... virtual
,.., PE Header
.
address - ..` -. section .. -. directory .- . . -. . -., - -- offset -
.... section . section header - ..`
, Section Table
Section table -.-. PE header .,.-.. --.-. .-. IMAGE_SECTION_
HEADER structure . array -.`..`. member . .. .. . attribute , virtual offset .- PE
. - section . .. .. .-. .- .- -. Section ..---...`.-.- file
header . - . member `..-..-. .-. PE header ... 6bytes ...,.., --.
.. PE . . . section ..-... table - structure .. .. 8 . . . Header
structure ....-. 40bytes .`. windows.inc . . .-_...-.
IMAGE_SECTION_HEADER STRUCT
Name1 BYTE IMAGE_SIZEOF_SHORT_NAME dup (?)
union Misc
PhysicalAddress DWORD ?
VirtualSize DWORD ?
ends
VirtualAddress DWORD ?
SizeOfRawData DWORD ?
PointerToRawData DWORD ?
PointerToRelocations DWORD ?
PointerToLinenumbers DWORD ?
NumberOfRelocations WORD ?
NumberOfLinenumbers WORD ?
Characteristics DWORD ?
IMAGE_SECTION_HEADER ENDS
IMAGE_SIZEOF_SHORT_NAME equ 8
structure - member -.-. ...--- --....-.- member
.- .-. .- .. . .`..
Name1 field -. 8bytes .-., ._-. label -. ...`.. ` . - - .,, ... .-.
.-. .- .... .- . -. ASCII string .----- \0 (null terminator) , . ..- ...
. - .
VirtualSize DWORD union, Section ...- .-..-. --......`..`. byte ,
`-. . -. disk ....- section . . . ... SizeOfRawData, - ,_..-..,_..
-. --. -, . .-. SizeOfRawData - - ..,- section . . . _.- , `_ .,. .`..
-.
VirtualAddress Section . RVA `.. -. PE loader -. .-. section - map ,..
field - -,..- .....`. ..`-. .-.. --. field - -,..-. 1000h
`.. .. . . PE .-. 400000h .. .-`. section -.-. 401000h .. ...
SizeOfRawData Disk .- ....- section . .-.. . ...`.. -. Module header .
FileAlignment .-.-,.`..`. --. .-,..-. virtual size - . .,. section .
-,-..--. ._, `_.,.. `..-. Section .. uninitialized .-..- .-.- .,
. . .,..-. . _`.. ...
PointerToRawData Raw Offset, PointerToRawData -. , . . -. -..-.
. .-. . -. . . .-., section ..-..-.- offset `.. ., --. . -.. _`.. .
... section . .-..- . ..- - - . . -. module header - FileAlignment . .- .- , .
`..... Section . . unintialized .-..- .- .- . , . . .,..-. ._`..... PE loader
-.-. field ...--,..-..``. .--. section . . .-..- . . . -. . . . ..
Characteristics section . . - exe - initialized data uninitialized data .-..-- ...`.
.- ` ..- flag .- -.
FLAG EXPLANATION
00000008 Section should not be padded to next boundary
00000020 Section contains code
00000040 Section contains initialised data (which will become initialised with real values before the file is
launched)
00000080 Section contains unitialised data (which will be initialised as 00 byte values before launch)
00000200 Section contains comments for the linker
00000800 Section contents will not become part of image
00001000 Section contents comdat (Common Block Data)
,.., PE Header
.,
00008000 Section contents cannot be accessed relative to GP
1-800000 Boundary alignment settings
01000000 Section contains extended relocations
02000000 Section can be discarded (e.g. .reloc)
04000000 Section is not cacheable
08000000 Section is pageable
10000000 Section is shareable
20000000 Section is executable
40000000 Section is readable
80000000 Section is writable
PE header . .- , .- section .-.- -,.-.-..-..- hexeditor , -_ - .
,-. `....
,
,- . . .... , `..-.-.-. PointerToRawData `...... ,-.
LordPE , -_ ..
,
Section header `....-. section .-- ..-. Disk .-. . ..-. section ..
..-. offset -.-.,.--. .-.- Optional header ...-.- FileAlignment -,...
.`. .- ... - , . -.,`.. -. Section ..... .-..--.....-. . _.- `.. .,. .
RAM .- - .- , . . section .--. page boundary .. . `. -. . .- --.
.-. . section ..... ... byte -. memory page , .-.-. x86 CPU . page
.- -.-. 4kB , align ..`. IA-64 -.-. 8kB , align ..-. alignement
-, . .- .-. OptionalHeader .. SectionAlignment .. .....-.
..`.. --. optional header -. file offset 981 . .. .` . FileAlignment -. 512
`.. .. . . .. . section -. byte 1024 .. .... .-.....-.-. ..,, section
.-- PointerToRawData ., VirtualAddress -., . .. -. .-. alignment .- ,
` . ...,... . .-. - .
, PE File Sections
Section .-.. -.-.-. - .-. resource , `..- - - `.. -.
Section ...... header -., body raw data,-.-. Section table .. section
header .-... section body .-.. -.... ..._. ...-. .-..-- decipher
`, ... . header .. ..----.-, `_..,... linker - . - - . ._ . . . ._ .
. -.
Windows NT application -. . . - - .- . - ..- section ._ 9 ..- . -.
. - .- -.-. .text .bss .data .rdata .rsrc .edata .idata .pdata , .debug -`..-.
application .- . ..-. section .- .. .. - . .- . ..-. - ` . . -.
,.., PE Header
..
, Executable code section
Windows NT . ..-. code segment ...-. .text ., CODE .- section
-.-_... .-. Windows NT - virtual memory ..,..,.-..``. -....- code
secton -..`.- OS --... application developer - - . . , ... . . - ..-.
secton .. ....-...`- entry point , IAT ...-`- jump thunk table --.
, Data section
.bss section - function -.., source module - static `...-_...- variable
... application -- uninitialized data .-- -....`-.
.rdata -.-. literal string constant , debug directory information - read-only
.-..- - - . ...`-.
`.. variable .-... stack - .- .... automatic variable . -.,- .-. .data
section .. ...-.`..-.
, Resour ce section
.rsrc section ...-. module -., -.-- resource - - .- -. .
.. 16bytes -.-. `.. section .... header `..-. ... section ..-.
.-- resource editor ..``.-_.... resource tree .,, . ._ ...-. `. .. .
ResHacker -.-. . .. . - tool -. `.. ` . resource .-- .._`. .- ` . `` ` .
`.-. ,
,
tool - dialog box .--_.... .....-. shareware application .- . .
- nag screen .-- ResHacker ..`. .-...-..-.
,, Expor t data section
.edata section ...-. application ., DLL - - - export directory -.
... export ..- function .-. address .- , ._ .- -. - .-. .,.- .-.
.... - . .`..
, Impor t data section
.idata section ...-. Import Directory , Import Address Table import ..
- function .-,-.-- --... -. .- .,.-. ....- ........
`.. -.
, Debug infor amtion section
Debug information -.-. .debug section .. ......-. PE .-. ..`....-
debug . .- - - -. ..., ..`. .-. .dbg extension , `.. -. , Debug section . .
debug information .- ... debug directory .--.-. ....-.`.- .rdata section . .
.--. Debug directory ....-. .debug section ...- debug information - `,_,.-
-.
,.., PE Header
..
,, Base Relocation section
Linker - exe . -. - ., - . - , . . . - . - -. .,... . - map-in .
.-.- ,.,.-. -.``. linker - exe .- -, .-.-. --. address .-
...-. --. .. loader -. linker - ..-- base address ...-.-.. -.-
. .. . . .reloc section .-.- ...---` .....
.reloc section ...- entry .-- base relocation .-. -..-...-. .--
..`.-. loaded image . base address ..-_ Base relocation .- -.-. image -
location .- - . ._ ...-.`.. ` . . - - . ._ . -, . .-. .-. . .. Base relocation
. . -.-. ,_ .,_ ... .., ..,-. Base relocation entry .-- chunk -.-.,,
package ..-. Chunk ... .-. image - 4KB page -.-- relocation ...`
-.
Base relocation -...-..... ..-. -_ ... Exe .-.-
base address 0x10000 , - ..-. . .-. Image - offset 0x2134 -. string .
address - pointer -. `.. -. String -. physical address 0x14002 - .-. .-.
pointer .. 0x14002 -, . . -. . - load , . . loader - physical address 0x60000
...-- image - map ..-.. ..`.--. Linker -....- base load address ,
--. load address --.. `..,..-- delta .-. .,... ..-. delta -. 0x50000
`.. -. Image -. .-. . - . . . 0x50000bytes ....,-..-. string -. . ..-.
address 0x64002 .. `..-. Pointer -., string -_,.`.-. ,...-. ..,.-.-. exe
... string ...-_,.- pointer . . - . -_ .,..- - base relocation -.-.
Base relocation - ..`.-. loader - base relocation address ...-...-,.... delta -,..-
.. .-. .,... ..-. loader - . . . pointer -,..`..- 0x14002 .. 0x50000 - .. .
..`..`. .`..- 0x64002 -.-. pointer . . - . `, . . .. . `.. -.
,, Expor t Sections
section -.-. DLL .- , . -- .- -. ..- .....`..- ...--.-.
Win32 Programmer's Reference -`..`. DLL .-. .- . .`..-.`.. -.
In Microsoft Windows dynamic-link libraries (DLL) are modules that contain functions and data. A DLL is
loaded at runtime by its calling modules (.EXE or DLL). When a DLL is loaded it is mapped into the address space
of the calling process.
DLLs can define two kinds of functions: exported and internal. The exported functions can be called by other
modules. Internal functions can only be called from within the DLL where they are defined. Although DLLs can
export data its data is usually only used by its functions.
DLLs provide a way to modularize applications so that functionality can be updated and reused more easilly. They
also help reduce memory overhead when several applications use the same functionality at the same time because
although each application gets its own copy of the data they can share the code.
The Microsoft Win32 application programming interface (API) is implemented as a set of dynamic-link libraries
so any process using the Win32 API uses dynamic linking.
Funtion .-- DLL -. - ._ .,, ... _ ..-. . oridianl .,, ... _ ..-. .
,_ .. . . ., export .-. Ordinal .-.-.-. 16-bit (WORD) -, .-. `.. ` . function
-.- --- DLL -. . . .`... . .- . - ..-. Ordinal ,_., export `.- .,.-
.. . .. ... ...
--. function -.- ._. export .. . . `.. DLL .- . , exe .- -
function - ...,.. .--. GetProcAddress ...- ..._... ordinal ..`-.
GetProcAddress function -. export ..- DLL . address -`,..-. Win32
Programmer's Reference -.-. GetProcAddress . - ..--. ..`..-.
--..-. -.... Microsoft - ... `` ... - ., .,... . highlight `. ..-..- -
.- ..` . .- .. -.
GetPr ocAddr ess
The GetPr ocAddr ess function returns the address of the specified exported dynamic-link library (DLL) function.
FARPROC GetPr ocAddr ess(
HMODULE hModule, // handle to DLL module
LPCSTR lpProcName // name of function
);
Par ameter s
,.., PE Header
hModule
Identifies the DLL module that contains the function. The LoadLibr ar y or GetModuleHandle function
returns this handle.
lpProcName
Points to a null-terminated string containing the function name, or specifies the function's ordinal value. If
this parameter is an ordinal value, it must be in the low-order word; the high-order word must be zero.
Retur n Values
If the function succeeds, the return value is the address of the DLL's exported function.
If the function fails, the return value is NULL. To get extended error information, call GetLastEr r or .
Remar ks
The GetProcAddress function is used to retrieve addresses of exported functions in DLLs.
The spelling and case of the function name pointed to by lpProcName must be identical to that in the EXPORTS
statement of the source DLL's module-definition (.DEF) file.
The lpProcName parameter can identify the DLL function by specifying an ordinal value associated with the
function in the EXPORTS statement. GetPr ocAddr ess verifies that the specified ordinal is in the range 1 through
the highest ordinal value exported in the .DEF file. The function then uses the ordinal as an index to read the
function's address from a function table. If the .DEF file does not number the functions consecutively from 1 to N
(where N is the number of exported functions), an error can occur where GetPr ocAddr ess returns an invalid, non-
NULL address, even though there is no function with the specified ordinal.
In cases where the function may not exist, the function should be specified by name rather than by ordinal value.
See Also
Fr eeLibr ar y, GetModuleHandle, LoadLibr ar y
GetProcAddress - - -..-. . -. . .-. export ..- function . ._
.- , address .-- Export Directory - structure -... ...._... -,.-.-.,
, Export Directory - .....-. -..-...-. .-. data directory - .. .
element `..`. .,-.-- RVA -. PE header .. offset 78h .,... . .
Export structure - IMAGE_EXPORT_DIRECTORY .-. ... member .,
, 11 .`. -.-. ....-.-.
IMAGE_EXPORT_DIRECTORY STRUCT
Characteristics DWORD ?
TimeDateStamp DWORD ?
MajorVersion WORD ?
MinorVersion WORD ?
nName DWORD ?
nBase DWORD ?
NumberOfFunctions DWORD ?
NumberOfNames DWORD ?
AddressOfFunctions DWORD ?
AddressOfNames DWORD ?
AddressOfNameOrdinals DWORD ?
IMAGE_EXPORT_DIRECTORY ENDS
nName Module . internal ._ `.. -. field -. -. -..-...-. .
._- ....- .`... .`...... PE loader - internal ._- . .`
. ..
nBase Starting ordinal number index .-- function . address array `....,.-.,
NumberOfFunctions Module - export ..- function .... ..--.-`.. .__,.
..-.,
NumberOfNames ._ . export ..- ..---,. -,..-. module ...-
function/symbol .. .. -, . .- - - . -, .- - . .,, NumberOfFunctions -
.. .... -. . -. 0 `.. . -. .,... ..-. module - ordinal .,,.. export
. -. --. .- . . . export .. function/symbol ..... data directory
- export table . RVA -. . _`.. . ..
AddressOfFunctions Module/Export Address Table (EAT) . .. - function .-. RVA
,.- pointer .-. array -.- _,`- RVA -. Module ...- function .- .. .,
.- RVA .--.-. array -... ...._...`. field -. array . head - _,`.,-.
AddressOfNames Module/Export Name Table (ENT)...- function ._.-,.- RVA
.- . array - _,`.,- RVA -.
,.., PE Header
AddressOfNameOrdinals ._.`.... function/Export Ordinal Table (EOT) .-. ordinal
.-- 16-bit array -.- _,`.,- RVA -.
,,
.-.. IMAGE_EXPORT_DIRECTORY structure -. array .., ASCII string
table -. - _ , .,-. ...- .. . array -.-. EAT `.. ` . . -. export ..-
function .- . address .-- function pointer .- . array -. `.. -. `.. array . .
EAT , EOT,-.-. assending .., ` run .`. function ._ .. -_ -.
.-.. function -.. ._-- binary search - ....-.-.`..`. `.. array
-. . ..- . - . . ordinal .. .`.-... Ordinal -.-. ....-,.-,. index -.`..`.
function -- EAT `.. -.
EOT array -. ._ .- , address .--.. linkage -.`..-_.-..-. ... ENT
array - element `.... .---. .-.- ._...... associated address
-..... .`..`,...-. ..,-. address -... associate ..- ._ .`..-
`.... --. alias .-, function .--. -_- address - .__,.-....
.,.- . . ENT - EOT - element .-.....
,
..`.. --. DLL -. -. function ,..-- export .... AddressOf
Functions (EAT) - _ , ... array .. member ,..-.-..... NumberOfFunctions
field .. -,..,..- ....
,.., PE Header
Function -.. address - .. ._-.,..... OS - .. . Export Directory
- NumberOfFunctions , NumberOfNames - . -, . .- .. ..... .,.- -. . -.-.
AddressOfNames (ENT) , AddressOfNameOrdinals (EOT) - _,`- array -. function
._ - . .-. --. ENT .. ._-...-. EOT ...- associated element -
-,..- extract `. EAT -- index `....`-.
..`.. -, .-. - . function ,.- DLL . . functionX - . ... -_ .. --.
ENT . . .`..- element - -, .-. - functionX .._`.. pointer . ..-`.,-
. . , . . -, .-. - .,, ENT - . .`..- element ..-_`. -,.. 5 - .- -.
.,.- functionX . RVA -... -,.-.- -_...- EAT . .`..- element . .`.. -.
--. function -.. ordinal .`....`...... ..,, EAT . --.-...`.
`. .. address - .....-. Function . ._ - . .`` .- ordinal -., function
-. . address -..`.-. `..-`.,... ..-.-.-. module -,....... -
-. --. DLL - upgrade/update `. function .- . ordinal .- -. .`. . ..
.. DLL ...,- `.. .-...- - - , . ..
,, Or dinal .- .- `. expor t ` .
NumberOfFunctions -.-. ,_... NumberOfNames , _ ... -. `.. `.. -.
-. . ..-. NumberOfNames -. NumberOfFunctions - ,_ .., . .. Function -.-.
ordinal .- .- , .. export ..... ENT , EOT . . . .. . entry .-... .---.
. . . ._ -. .-. ....---. ._..- function .-- ordinal .-.-,.. export
. . . `.. -.
..`.. --. function ,.`. ENT .. entry ,..... module .. ordinal
.- .- , export ..- function .-. .-. ...-. function .- -.
-..- . -. -. . ... ... .. - . -. . . - . . .,, exclusion , .....
.-. .-.- EAT - entry .--. ordinal .-.-, export ..- function .-.
RVA .-- EOT -., reference ..` ...
. -.. ..-.-. .def ....- starting ordinal -, .- .- . - . -. ...`...
,- table -. 200 . ..- . -. Array - .. . - .,- entry ..- -
-- -.......-- nBase member .. starting -,..-_..`. loader - EAT . .,-,
- index - .. . . - - . . -., ordinal -,.- subtract -.
,, Expor t For war ding
--. . ..-. function .--. --- DLL -. -., export ..,... --. -. .
.-..,-.- ..-.-`..`..,...,- DLL -... - export forwarding .-.
..`.. WinNT Win2k , XP -.. kernel32.dll . function `..- HeapAlloc -. ntdll.dll -
export ..- RtlAllocHeap function .,, forward ...-. ntdll.dll .. Windows
kernel , --.- interface `..- native API -. Forward `.- .DEF ....-
. instruction -.- link - , . . ... . - -.`.. -.
Forward `.-. -`..- Win32 API set -. - . -`.. , Windows NT ,
Windows 98 --.. internal API set -. ...- low-level ...-`..`..,...- ..-..
..`- Microsoft . ,_ .. .-. . `.. -.
Application .--.-. native API set ...- call function .- .,, . . ..- .
-..-...-. Windows 9x , Windows 2k/XP - . internal API set .--.. .-.-`...-
...- .- ..- .-. . pack ..- exe ..- - unpack - OS -...
. -. impor t .-- -.- r econstr uct - `.. OS -. . . . . -. -.
forwarding .,. .-. ... _ ..-. . `..- - .- .`. . ` ..-. ... _ . .-. .
`.. . -.
..- - function,-.- forward ,.. .. RVA -. - . module ...- -
.-. address .`.. . - . EAT table .. DLL . ASCII string ,.- pointer -. ...
... forward .. function ._ -. .. ... ..-. . -. ntdll.dll . RtlAlloc
Heap `.. . ..
,.., PE Header
--. function -.-- EAT entry -. Export section . -.- ASCII string,
...- address -.- point `.. ..,, function - forward ..-..-.
. .....
., Impor t Sections
Import section (.idata) ...-. DLL -., import ..- function .-....
- - .- -. - - .- - .... .... data structure .-.. ...._...-.
. - - ...- .. .-.-. .,.- .. ... ... ... Import Directory , Import Address
Table -`..-. executable ..-.. Bound_Import , Delay_Import directory -
..-. Delay_Import -.-. -,.-.--- .....-.-. ... Bound_Import
directory -.-. .,.-... ........ `..-.
Windows loader .-.,-.-. application - ..`- DLL .--...- load
., .-- process address space `.. map ... `..-. ` ....... DLL
.-...- import ..- function .-.... address .-- .....`..`. load .-
,.. executable -- ..`... ..-.
DLL -. - function .- . address .--. static .`..-. ... DLL --
updated version .--.,...-. .`..-,-. .-. application .-- ......
.....- function address .- . .`` . -_ ...- ....-.-. --.-. run
., , . . executable .-..-.-- -..,..... .`.......- mechanism -. -
.,-...-. - Import Address Table (IAT) -. . .`` . .`.. .. -. -.
windows loader - DLL `.. load ,.. `._._...- function address .-,.- pointer
.- . table -. ..`.. -.
Pointer table -.- ..``.`. loader -. - - -. .,... ... . - - .. . .-
.. import ..- function .-. address .-- .`... .-....---. ...-
import table - .,..-. . . . , -, - address - . ... .`.. -.
., Impor t Dir ector y
Import Directory .-. --..-. IMAGE_IMPORT_DESCRIPTOR structure . array
-. ..`.. -. Structure -.-. 20bytes `..`. -,.-.- PE . - -. function .- -
import ..-. . - DLL ,-.--.-...- -. ..`.. --. -, .-.
- PE .- .-_- DLL . - function .-- import .... array .. IMAGE_
IMPORT_DESCRIPTOR . .,. . `.. -. array - structure ..- - - _ , `-
field .-. ....---. ... .,.-.. structure .. ._.-,`_.,- filed .- ..,..
Export Directory . . . .,, Import Directory -..,.... ...-. .....
-. PE header .. 80 bytes `..-., ..., .,.-.. member .--.-. ...-...
`.. -.
IMAGE_IMPORT_DIRECTORY STRUCT
union
Characteristics DWORD ?
OriginalFirstThunk DWORD ?
ends
TimeDateStamp DWORD ?
ForwardChain DWORD ?
Name1 DWORD ?
FirstThunk DWORD ?
IMAGE_IMPORT_DIRECTORY ENDS
... member `.. - OriginalFirstThunk -.-. DWORD union `.. -. flag
. _ .`.. . -. -. `.. `.. Microsoft -.-. .. ...- .`..`. WINNT.H -
update . -. .-. . . .. . ..... - . field . . --. -. . -.-.-. IMAGE_THUNK_
DATA structure .-- array -.. RVA `.. -.
TimeDateStamp - .-. . _ .- . - -. . . . 1 `..., ForwarderChain
member -.-. .-.-.. binding -- ..`-.`..`. .,.... ........---.
Name1 ...-. DLL . ASCII ._ , . - pointer (RVA) -. -.
,.., PE Header
,
.,.-.. member `..- FirstThunk .._. DWORD ......- IMAGE_THUNK_
DATA structure array -. . RVA -. .. . array . duplicate -._.`..-.
--. ...` function -. bound import `..-... .,.-...-. FirstThunk .. IMAGE
_THUNK_DATA , . - RVA ... function . --. address . . structure .- -
..- - . . .. . . -.
IMAGE_THUNK_DATA32 STRUCT
union u1
ForwarderString DWORD ?
Function DWORD ?
Ordinal DWORD ?
AddressOfData DWORD ?
ends
IMAGE_THUNK_DATA32 ENDS
IMAGE_THUNK_DATA ....-. DWORD union -. `.. -. Disk .-
. . ..-. . . . import ..- function . ordinal ... IMAGE_IMPORT_BY_NAME
structure ,.- RVA -. -. -. - . . ..-. FirstThunk - _ , `.,- -. -.
import ..- function .-. address .-, overwrite .`. .-. Import Address Table
`.. .-.
IMAGE_IMPORT_BY_NAME -.-. ..--. .......-.
IMAGE_IMPORT_BY_NAME STRUCT
Hint WORD ?
Name1 BYTE ?
IMAGE_IMPORT_BY_NAME ENDS
Hint Hint ...-. function -_... DLL . Export Address Table ,.- index -.
-.-. - ..`. `..-. .-.. DLL . Export Address Table - function -
`., -_ . . -. index ...- ._- -....- --. .-. match .`..-...
binary search -. ._ - . ... ` ..`..- ` `.. -. -, . .-. .. .`.. .-. .- - - .
linker .--.-. .,.... ._ .-.---.
Name1 Name1 ...-. import ..- function . ._ -. ._ -.-. null-
terminated (\0) ASCII string `.. -. . - .... .- Name1 . .....- byte .,,
......-.`..-. ... .-. --.-.....-. variable . . .... - field -.
`.. -. Structure -... variable ......- field -.- ...`.. ,_.....
...- .. . ..- -.-. import ..- DLL ._.-, IMAGE_THUNK_
DATA structure . array .- `..-. IMAGE_THUNK_DATA structure ....-. DLL
-., import ..- function -. . , .- . . .,-. OriginalFirstThunk , FirstThunk -
_,`- array .- -. -` -_ . run .`. null DWORD , . ..- -. Import ..-
DLL ....-- .-.--. IMAGE_THUNK_DATA structure . ..`.....,- array
- .- `.. -.
..-- -... `..,_...-.-. .`..-........ IMAGE_IMPORT_BY_
NAME structure .- `.. -. . .,, array ..- .,-..-. `..-. .-- IMAGE
_IMPORT_BY_NAME structure .-. RVA .- , `._ ._ ... .`.. -. .-. array ...
.. -_--,...- .,... .-.- --- duplicate, . ..-. . .,, .
.. array . RVA - OriginalFirstThunk , _ .... .`.. ` . - . array . RVA -.-. First
Thunk , _ .... .`.. -.
OriginalFirstThunk , FirstThunk ...- element ..- - -.-. DLL -., import
..- function ..--. .-_-. ..`.. --. PE . - user32.dll -.,
function ..- import .. . . IMAGE_IMPORT_DESCRIPTOR structure ...-
Name1 .. user32.dll string . RVA ..`..`. array ...... IMAGE_THUNK_DATA
.. . . .`.. -.
`..,- array ..-.-. ._....-., ......`..... .......-.-.
Import Address Table FirstThunk - point - -. - - , , Import Name Table . ,
Import Lookup Table OriginalFirstThunk - point - -. - - ,- `.. -.
,.., PE Header
-..-. IMAGE_IMPORT_BY_NAME structure ,.- pointer . parallel array
. . . .-. Import Name Table .--.-. ...,....`. -..-.. modify . ..- -
-. Import Address Table .-- loader - --. function address .-, overwrite --.
Import Name Table .-...- RVA .- . array .--.-. ..`..--,.,.. .-.
--. import ..- function .- . ._ - . ... . - -`. ..... PE loader -
.--.....,....
IAT - Data Directory - entry number 12 - point ... _ . linker .- -
directory entry - .- . - ` ... - . Application -.-. run .,..`..-. Loader -.-.
- import resolution ,-... IAT .-- read-write `.. ....-....--..
..`-.`..`. .. import .- - .`.. .. . . `.. -.
-.-. Windows loader - read-only section ..., IAT - overwrite .
-. . . .... . -. . - .-. . `.. -. Load -,...-. system - read/write
. import .-- page .-. attribute .-- .....`. .-.--. -.-....-.
import table - page .-- initialize `.-. .-. . protected ..- attribute
.-`..... ........-.
,
Import ..- function .- . call .--. IAT - function pointer --..
--. . ...,, . -. -. -.-. .,.- -. - ` . . . -.
...,, FirstThunk array . entry .---.- .__,.- address 00405030 - .....-_
--... .- loader - user32.dll - GetMessage . address ,- overwrite ..
-.
GetMessage -.... ..-...,_...-.-. ..--.`..-.
0040100C CALL DWORD PTR [00405030]
,_ .-.-. . . ..`- .
0040100C CALL [00402200]
00402200 JMP DWORD PTR [00405030]
. . .-.-. - .,_ .- . - - ... _ ... - .. .-. . .
..`..`. jump .-. execute .... -...`..-.
-..-. import ..- function .- - ,_ ., ` --. Compiler -.-.
-_- module ...- ordinary function .-, import ..- function .-- `...,..
.--- ...-- - _- output -..-.... `..-. CALL [XXXXXXXX]
,.., PE Header
[XXXXXXXX] .,... ..-. - .,.- .. . `._ .... --. - address -.....`..-.
pointer .---., Linker -.-. import ..- function . address - . . ..- - - .
.-. . - . ... . chunk -.- ..`...`..-. .- JMP stub . . `. . -.
Compiler - DLL ...- function ....`.`.. . .-. - . -.-. _declspec
(dllimport) modifier ..``. ...-. .,.-...-. .-. CALL DWORD PTR
[XXXXXXXX] - - ... .`.. -.
--. exe - compiler ,.. _declspec(dllimport) - ...`-... -.--
.,.... import ..- function .--- ---.._...- jump stub .- ..,..
.-.-. transfer area ., trampoline ., jump thunk table .- ._...., .--.
., Or dinal .- .- `. function ..... expor t ` .
Export section -,.- ....... function .-- ordinal .- .- , .. export
--. .,.....-. caller's module . . function -- IMAGE_IMPORT_BY_
NAME . . ..- - - . ... function -- function . ordinal - IMAGE_THUNK_
DATA . . .
exe .- -..- MSB (most significant bit) ., high bit --_`...`.
IMAGE_THUNK_DATA -. . . ordinal -. ., RVA -.`.... ..,, .`..
-. --. .. .- . - . lower 31 bits - ordinal -, . .-. .,, . . .`.. -.
--. ..- . - - .- - .. . . -, . .-.-. IMAGE_IMPORT_BY_NAME ,.-
RVA -.`.... Microsoft -.-. DWORD MSB `..- IMAGE_ORDINAL_FLAG32 - -
.`.... constant -. - .- . - ....-. . . ..-. 80000000h -, . .. -.
..`.. --. function -.- ordinal .- .- , export - . . . ordinal
-. 1234h `..`. function -- IMAGE_THUNK_DATA -.-. 80001234h `....
., Bound Impor t
Loader - PE . -. - . - . - .- - . . . -. import table - .. ...` .
- DLL .-- process . address .,..-.-. -.--. .,.-...-. .-.
FirstThunk - _,`- array ....-.`. import ..- function .-. --. address .-,
IMAGE_THUNK_DATA .- - ... .-. --. . -.. ..-. -,_ .,_ ., function
.- . address .- - . , -, . .- - - . .. . . PE loader - PE .- run -,-...
IMAGE_THUNK_DATA .-- ``... ..-.-. -..-...-. address .,-.
....,
Bind.exe .- utility -. -.-. Microsoft . compiler .- , .` . PE . . IAT
(FirstThunk array) - ..`. IMAGE_THUNK_DATA .-- import ..- function .-.
address .-, ....-. .--.-,.. PE loader - address .-.,-,`....
.. .... -. --. DLL version .--. PE . --..- , .- - _ - .. . . , DLL
.-- `,_.,....... .... PE loader - bound address .- -. . ....-. - .. -.
.`. address ..----. Import Name Table (OriginalFirstThunk array) ....-.
.-...--.-. INT -... INT .. . exe ..-- bound ..- .
Borland . linker `..- TLINK -. INT - .,-.....--- Borland - - ..- . .- -.
bound ..- . INT ..- . .` .. .,.- - ..- -.-. .,.-,.-. ......
..
.,, Bound Impor t_Impor t Dir ector y
Loader - bound address .-.,..,..`.-. ..`- --.-- IMAGE_
BOUND_IMPORT_DESCRIPTOR structure . . ... -.`.. -. Bound executable -...
-.-.-. structure .-.....`..`. import ..- DLL . .. .- - -. -.-.
bound ..`.`..-.
IMAGE_BOUND_IMPORT_DESCRIPTOR STRUCT
TimeDateStamp DWORD ?
OffsetModuleName WORD ?
NumberOfModuleForwarderRefs WORD ?
IMAGE_BOUND_IMPORT_DESCRIPTOR ENDS
,.., PE Header
,
TimeDateStamp member -. export .,- DLL FileHeader . TimeDateStamp ,
- - _ ... --. .- - _ . loader - binary -. ......,- DLL - bound .,-.
..`. imort ....- `,`. patch . .. .- -. export .,- DLL version .--
_ . . ,. - . . . `, _ .,..... . `.. -.
OffsetModuleName member . . -.-.-. . IMAGE_BOUND_IMPORT_
DESCRIPTOR -., . _, . .- ASCII ...- DLL . ._ offset (RVA .---.) `..
-.
NumberOfModuleForwarderRefs member ...-. IMAGE_BOUND_FORWARDER_
REF structure .- . ..- - `.. -.
IMAGE_BOUND_FORWARDER_REF STRUCT
TimeDateStamp DWORD ?
OffsetModuleName WORD ?
Reserved WORD ?
IMAGE_BOUND_FORWARDER_REF ENDS
structure , `.- structure ..- ...-. .,.-.. member `..- Reserved
. -. -, -..- .. . - -..- .. . `.. DLL - forward - function -.,-.-`.
bind ,.. forward ..- DLL . . , -, . - - .- - , . . .. ...... IMAGE
_BOUND_FORWARDER_REF . . forward ..- DLL .- . .... - - - .-
. -.
..`.. kernel32.dll - function -.`..- HeapAlloc -. ntdll.dll - RtlAllocate
Heap - forward -...-. --. -,.-.-- HeapAlloc - import ..-
application -.- .,-.-`. application .. bind.exe - ..`-.... ntdll.dll .
IMAGE_BOUND_FORWARDER_REF -.`.. .. kernel32.dll -- IMAGE_BOUND_
IMPORT_DESCRIPTOR -. . ...
.- `., Function .-.._.--. structure .-.. ...---. -..-...-.
loader - -. function .-- IMAGE_IMPORT_DESCRIPTOR -., bound .. . -.
. ..
., Loader
, .-.-. .. .`.. .-. .- - ... OS . - ,- ,- , ,.....-- ._
..-. `.- ,..,,, ,...,- -. .- . . . . . . -.- . .` -.
., Loader --..
Executable . -. , . . Windows loader - process -- virtual address
--.- .,-.-`. executable module - disk -., process . address - .,....
--. Loader - image - ..-... base address . . - .- . - ....` . . - . . .
Section .-- .,....-. Loader - section table - .-...`. base address .. section
. RVA -..`. ---..- address .. section ....- .,..-. Page attribute
.--.-. section . characteristic -. .-.--.`..-. .-... section .--
.,....`..,.-...-. load address -. ImageBase ...- ..-... base address ,_
._ loader - base relocation -....--.
.,.-...-. import table -.....`. - DLL .-- process . address .,.. -
map . -. DLL module .-...- .,....`..,.-...-. loader - DLL .....
export section - .. ...` . import ..- --. function address - _,`.. IAT - `
-. --. ..--... ,`..-., loader - error `..
Cracking ... . . - .... .-. .-..- -.-. DLL .- - - .- ` . import .--
.`.. ..-.`.. -. `.. ..--. ...`. Microsoft - ...... - .` ... - ntdll.dll
...- forward ..-, ....... function .- , routine .- . .` ..`.. ..-. -, .-.
....- .`.. Function forwarding .-. -`..- Win32 API set -.- .-`..,
.-_- OS .--.. low-level function .--`..`..,...- ..-.. ..`- Microsoft . ,_.
. .-. . `.. -. GetProcesAddress ....-...,- kernel32 function .-. .-. ......
-. --. .- LdrGetProcAddress ntdll.dll - export ,..`...,- ....- wrapper
.- ..`.. -.
,.., PE Header
.
.- - - .- -- `. . .-. . .,, Win Debugger 6.x , windows symbol
package Microsoft -., ....-.,- install .-. ..--..-. SoftIce 4.x
kernel-mode debugger - install .-. ..,, Olly ...-. Microsoft
symbolserver - ..`.. configure ... function .-- -_..-.--_...
..--..-. .`....- function ._.-.- pointer .-, memory address .-
-. `.. `.. Olly -.-. user-mode debugger `..`. .. application - load `.,.. -..-
`.. - .,-.- .. ` . .. Loading process --_.. .- `...-. .---. Win
Debugger . ... - .- - Olly , . .. .. . . -.. ..`...- ... OS , -...-_ .
`..`. loading process - `.... ,,
,,
Exe .- load -.. --.-- API ....-. kernel32.dll .
LoadLibraryExW function . . ....- . . .-` . ntdll.dll . LdrpLoadDll function .
.-_ . ..-. function -. ..-...-.-- ....-- LdrpCheckForLoader
Dll LdrpMapDll LdrpWalkImportDescriptor LdrpUpdateLoadCount LdrpRunInitialize
Routines , LdrpClearLoadInProgress .- subroutine 6 - --.-.....-.
Module - - .- ..` . `.. .`.. . ... .. -.
Module , ..- `.. .... - - .- - . - . . . .,..-.
Module . import descriptor table . ...-. -.- import .,,.. `.. module
.-- ..-.,
, DLL .-. .- `..-..- module . load count - update -.
Module - initialize -.
- .- ` ..-. .`- flag .- - . . .-.
,.., PE Header
.
.,
DLL -.-. cascade .,,-..- `.. module .-- import . -. Loader
-. load . -..- , . , - .- - dependency .-- ......... module ... .
--. loop -.... .-. LdrpWalkImportDescriptor ..` . `.. -.
... subroutine ...-. LdrpLoadImportModule , LdrpSnapIAT -`..-. ...
Bound Imports Descriptor , . , Import Descriptor table .-- .,..... RtlImageDirectory
EntryToData . call . . , .- -. . - ... - loader -. bound imports .- - .. ...
...-. Import directory ..... bound import .-.--- application - run -.`..
-.
.,.- -. `.. - LdrpLoadImportModule -.-. Import directory . .. - DLL
. .. .- - Unicode string -.- -_...--. .,.-...-. .-.-- -.-`..`.
. . .. LdrpCheckForLoadedDll - ..-.
.,.- -. `.. - LdrpSnapIAT routine -.-. Import directory ...- DLL reference
.- .. .- -1 -,..`...,`.... .....-. .-.- `. bound import .-- ...
.. ...-. , .,.- IAT . memory prtotection - PAGE_READWRITE `.. .`. . ` .
LdrpSnapThunk subroutine . .. .. IAT ...- entry ....- ...... .--...
-.
LdrpSnapThunk -.-. . . address - .,..... function -. . ordinal - ..``.
- forward ..`.... ..`.--. ..--..-. .-. ordinal - `., .,.....
.-- export table .- binary search -.- ..`- LdrpNameToOrdinal - ...
-. --. function - ..--... STATUS_ENTRYPOINT_NOT_FOUND - `, ` .
.- - . .-. API . entry point .- IAT .. entry - ....`. memory protection - restore
`,- LdrpSnapIAT . `, . ..-. . -. , ... .- .`. . . ..` . IAT -
memory block .. . cache refresh `..-- NtFlushInstructionCache -...`.
LdrpWalkImportDescriptor . `, . ..-.
-. Windows version .--.. -...`..- -`..`..,...`..-. Windows 2000
...-. exe .- -..- ntdll.dll - bound import .,,... ., import directory .,, ...
- .- . - ..-. .. -. Windows 9x , Windows XP . ..-. import .-. application
- ...-. Loader - . - . . .. - --. address -.- ---.., API
-.-. forward .. .` .. .. .... import ..- API -.- ........`..
-. Import ..- DLL . .. .. . .,.- module .-..`. process - dependen-
cy .-...- .....`...._-.. ... .,.. .`.. -.
,.., PE Header
, PE .-.. -_`.
Cracker .- .,, protection scheme -.- crack ., ...-...- _
.... .-..- -.-_ . .. .`.,.- --. . . ----. .- -_
..- .-,_...-. -.-.
..--- ..--.,..-.. .`.... section -. . . - - ..._ -.
--. ..- - .,.... . . ` .... section - .,.. -.
Secion .. -. - . .-.
, . ` .... section -. -_`.
-,.-.-.,, .`.... section - - .- . ._ -. . . CODE section ..
.._-.-. ......,_. CODE section .. 00 .-, `_.,-.,..- -..-_
-... - cave' ...-. ..-.- cave -.-.... CODE section -
LordPE , -_ -...
.,
.,... . -, .-. - `. .-.-.-. VirtualSize (00029E88) - SizeOfRawData (0002A0
00) - ,_ .,_ .... .,-. .- .-. SizeOfRawData . -.-.-. . . hard disk .. .
.- .,....- ....,....- .`.` .`.. -. . - .... .- . . VirtualSize -
hard disk .. . .,... .. . . ...- . .,-. - -..-. `.. .-. . .-. compiler
.--. .-... -_-,.,.-.- section -. , _ . . . ...- , .. . .`.. ..
. . Hex editor , -_..-. CODE section ... DATA section ..-, - ,
-. .-...
,
.,..-.-- ...`. .-.- - ..- - . -, .-. - .,, .....
.. .- -, .-. - _ . ... - .- - . - . - ... . -, .-. - .,,
`.... size attribute - .`. ...... , . ..-. section . virtual size - 29E88 ..`..
-. -..-...-. compiler - ..- -,.-.-.,,.-. -,_.,_.
.. -. .-. LordPE .. CODE section . virtual size - 29FFF ` -
.. -. -,.-.- `.- `........`..-. RawSize -.-. 2A000 `.. -. ,
`. CODE . - ....... . right-click .`. edit section header - ... VirtualSize
.,.... 29FFF ``. .- ...._.-
-. . ..-. -, .-. - patch ..-- ...._.. ..-.-.,..-.- `
` .` -, .-. - ` -.- Section Table - CODE section -- VirtualSize DWORD
-, . .`.. -. - -, .-. - .,, hexeditor .. -.-` .-.
-`. .....`..-- ,.,. assembly stub .....-_ .. .. . .
..- LordPE ...-- entry point -, . . 0002ADB4 , ImageBase -, . . 400000 - .-...
.-. Olly -. application - -.-,...-. entry point -. 0042ADB4 `.... -,.-.
-.,, ..--.-- .._`. entry point - ...-... 42AF00 - .`. ...
MOV EAX, 0042ADB4 ; Load in EAX the Original Entry Point (OEP)
,.., PE Header
JMP EAX ; Jump to OEP
-, .-. - .,, - .- - .. .`. .- hexeditor - 0002A300h .,.... .....`..
-. Olly ....`.-- raw offset - RVA .`. ... . . .-. ..,_ ...- . ... .
RVA = raw offset - raw offset of section + virtual offset of section + ImageBase
= 2A300h - 400h + 1000h + 400000h = 42AF00h
.-. Olly - . ` . -, .-. - ` ....,..- --.-..... Ctrl + G - . ` ..
42AF00 - .-_`. -.-_...,..... `.. ,-. `
,
.,.- . ..-. ` ..- - .- - . . .._ .. right-click .`. Copy to executable - All
modification - .. . ..- message box .. Copy - .. . - . window -...
... window . . right-click .`. Save file - ...`. --...-..._, ...-
.-...`..... LordPE .. Entry point - 0002AF00 .`. .` . . - . . .._ . -
Application . .. .-_ ` .. . . ...- . - Olly .. `,.-_ Entry point .`. .
.,-. .- ...
,
Hexeditor ..-_-. ,-. .-...`..`. .,..-.- ...-. -,...-..-.
..
,
.`.... section -`., section ..-.`.-- ..._... ....`.-. ....-.
ARTeam . Goppit ......... PE File Format - .- . - .. -. ,
, PE header `.,.....`.. .` .
PE header - ..-..-. --` -..-. PE header - ..- .... - . ..
-. . .,, .`.. ., . .. .-. . . -.. -. - -.--_-.. .
-.. RegisterMe.oops.exe,- Lena151 . . , ...,. . download ..-. .-..-
Olly ...`...-_-. ,,-..-.-.
,,
,.., PE Header
Data (dump) window --_-. ,-. -.........-. .-...
,
.-. .` . .,, ,.._ .... .- - .. . protector .-,.--. debug
..... PE header .. _.......- ..---. .-. PE header -
,_ .,_ ...- -_ - -... Alt+M (Memory map) - . - ,
,
,- -_-. section .- ..- .,-. .- ... . . PE header -. -_ .. .,
-. -, .-. - . `. .,-`.. - - .-. .-..- -. -. ...- . .. Header . ..
- 5000 .-. `...,-. ........`. header . ..-. 1000 .-. ..`..-.
. - .
.-. ,_ .,_ ...- . .`. .-. .` .-.`....- .- PE header -
,_ .,_ ... .`. . - - - . - -.`... .-. - .. . protector .._ -
. -., . .,, . -.. -. Windows XP .. .-...-...,... Olly -.-.
.`....-...--- ....-.- ... - .....- - - -..- .-. . .
-. , .-. .-. ... .- .`.- . ..-. Header - -_--... ,,
,,
,. VA 00400000 .,..- . . - . - . ,,-. `.... Mouse , ..--
scroll ,_ .,_ .. -_ -
.,
.,. SizeofCode -. 40000400 ... 400 `..... -. VA 004000DC . .
.,.- .. . .`. ... .. . - .. - SizeofInitializedData -.-. 400004A00 ... A00 `.. .
..
BaseofCode -.-. 40001000 ... 1000 `..... BaseofData -.-. 40002000 ...
2000 `.. .. . ..- - scroll ,_.,_..- .,
.,
,.., PE Header
NumberOfRvaAndSizes -.-. 40000004 ... 00000010 `.. .. . Export Table
address -.-. 500000 ... ._ `..... Export Table size -_. 500000 ... ._
`.. .. .
-, .-. .,, - - Olly - .-..- tool .- .-. .--..-. -
.,.-........... ,-.`. ,- -,.-..`.--,..-- -_.`.--... -,.-.
-.-. .-- Olly . dump window . . . .
. - - . .,, .`. . - -..- - binary -, ..`. . - . , -_ .`.- .-.
endian .- - .-. ... , .,.- -. - . .`... . tool .- ...-..-. -.
`.. `.. -, .-. .,, -.-. . -. .,. . -. ,.._ . .. ...- .-. -.
,
,.. `..--. dump window .. rightclick .`. Go to - Expression -
...-
,
` .. ,. . `..- - . 4000DC - .-_- `.. -_.`.-.. rightclick
.`. view executable file - .. . - ,- . `. . . ..
,
,- rightclick .`. binary menu . edit - ... ,-. `.....
,
, -.` . . .,, .- -_ .`.- .` --. . .,, opcodes .- - . - .
...-. . . . , `.- .`... .-. memory module .. -_.`.--.- .... -,.-.-
,_.- ` ...- -_.`.-`...-. ,,-. `....
,.., PE Header
,
,,
,,.. `..-.-.-. -,.-.- -_.`.- ... ...- - -_ .`.- ` . ` .. .-.
rightclick .`. Save file -...- `.. Olly , . . . - - . - `, -_ - ,
-. `.....
,
,. ..-. . -..- .,- section .-- `,`..-. .-.... .-...-
- -. - -.-. ,. . `. .- header . ..... 5000, .-. section .....,
header -- ....`...- ..
PE header `.,.- Olly ,.`....-. --. .-. PE tool -.- ..``.
.`...-_.. --......- .-..-.-. Lena151 . .,...,,- UnpackMe#5
.exe .-.. .-..- PEiD , .. -_ ... ..-. ,- . .- .-.
,
--. .-. UnpackMe#5 .exe - Visual C++ , ........-. .- - - . Protector -.
- Visual C++ , ........-. ... _ .....-.`.. -. Protector .-.-..-
.. ... .. ..- - - - - - - ...... .. .. -
.-..` PE header ,-.-`. -..-_.......-. .... .-..- Olly ..
.-_- ,,
,,
,.., PE Header
,,..`..--. -.- . ..` ... - . -.. run (hang) .,-..- .-. Task
manager --_-..-. .,..`..--..-.-.
.,
UnpackMe#5.exe - ..-,.- task manager . page file ....-. 149MB . -.
87KB .- UnpackMe#5.exe .-..-.--,.. -..-. page file -,- ....
. PE header .. `.,.-.--.,.-. .-. UnpackMe#5.exe - PE Tools 1.5
,.-_-... .,
.,
Tools menu - PE Editor -...`. UnpackMe#5.exe -.-. .,-. `..-.
.,- Optional Header button -...-. ,,-.`....
,.., PE Header
,,
Size Of Init Dat - 3FA00 Size of UnInit Data - 0 Base Of Code - 3E000 Base of
Data - 13000 Number Of Rva and Sizes - 10 Size of Heap Commit - 1000 Size of Heap
Reserver - 100000 Size of Stack Commit - 1000 Size of Stack Reserve - 100000 ``.
.-...- ...--.- ...- ,,- .`. ...
,,
,,- OK button -.....-..-. ,,- .`. ...
,,
,,- error message - `. .-.-.-. code section .-,.. ....,`..-. Olly -
error message `... .-..- .,-,....`.. - - - . - ....-. ..-. error
.-- .. . .-. code section .-,..- memory map (Alt+M) ..-_- ,,
,,
.-.. ,,- Base Of Code ..`- 3E000 -,..... 1000 `..... -,..-
PE editor -...`-`. . - . . . - .. . . -. error . `.-... .---.
,.., PE Header
,
, PE header - . .`... .-.....
ReverseMe.exe . ......`. `..._,
(1) TimeDateStamp 3/17/2000, 1:04:06 AM (38D1291E)
TimeDateStamp .-. .- .,-.-,- .__,.-. Olly ...-. Hex -, .,
`-. ReverseMe .-..---.-. 38D1291E `.. -. PE Viewer .- . . Hex ,
.`- . .. . . , `-. .. 3/17/2000, 1:04:06 AM/ -,..-. ., , ,. -.- -
-..,...-.,. .-,..--`..`. ... ..- .- .,. , .- - ` .- -
-. - . - - - - . .-. .,. 38D1291E - .. .,. . .`. . .- , . .
953231646 .... .- , `.. .,- - - ,.. ..`.... , ...- 264786 ..
-. - .- . . ,, ...` . . . . . , ..... . . . ..-. - -. .. .- -
- -. -, .-. - ..- .`.- -. . .. ... ... . .-. ,-. - ., , ,. .-
. . - - --- - - . .. . . .`.. , - .- , . - .`. - . .
(2) Machine FILE_MACHINE_I386
.- ..`.. -,-.. ..-... .... . ....- -, . ..- -.-.
FILE_MACHINE_I386
Intel 80386 . , .,.- .... . .... .-.-`.. .... .- .....
FILE_MACHINE_AMD64
x64
FILE_MACHINE_IA64
Intel Itanium . .- .. . ...
(3) Characteristics 0x10f .....- `.- flag .-,
FILE_RELOCS_STRIPPED 0x1
0x1 .. `...... ... base relocation .- . .-. loader -. .. base address ..
. .. . --. base address ....-... loader -. error `...-..`.. Linker . .,
-.-. EXE . -., base relocaion - .. . ,
FILE_EXECUTABLE_IMAGE 0x2
-.-. image . -. . , -, .-. ., . .-. . `-. --. flag .. ..-..
. . - linker error `...-.. `..,
FILE_LINE_NUMS_STRIPPED 0x4
COFF ..- .. . .. - .-.,
FILE_LOCAL_SYMS_STRIPPED 0x8
Local ..--.--- COFF ..- -.... entry .- .....-.-.,
FILE_32BIT_MACHINE 0x100
- , -.-. 32bit ,_._.- .`..-.,
(4) Subsystem SUBSYSTEM_WINDOWS_GUI
image - .-- - .,. .- `.. -. `.. . - -, . ..- -.-.
SUBSYSTEM_NATIVE
Device driver .... Window . process ...
SUBSYSTEM_WINDOWS_GUI
Window GUI
SUBSYSTEM_WINDOWS_CUI
Window .. ..,.
SUBSYSTEM_POSIX_CUI
Posix ....,.
,.., PE Header
.
SUBSYSTEM_WINDOWS_CE_GUI
Windows CE
SUBSYSTEM_EFI_APPLICATION
Extensible Firmware Interface (EFI) application.
SUBSYSTEM_EFI_BOOT_SERVICE_DRIVER
Boot services ... EFI driver
SUBSYSTEM_EFI_RUNTIME_DRIVER
Run-time services ... EFI driver
SUBSYSTEM_EFI_ROM
EFI ROM image
(5) LinkerVersion 5.12
.`.. -_...-. ..`- linker . version Microsoft linker -.,`...- PE
. .- - - .-. version ,--. Visual Studio . version , - , .- . -.
(6) SizeOfImage 20480 (0x5000)
.- .-.. -.--... system . . .., .. ..., ... . - . ..
.,..-. section alignment . .- .- , .-. `.. ...
(7) SizeOfCode 1024 (0x400)
Code section . .... Byte `. `._, ., -.. code section .`..-`.....
.- section ... ..
(8) SizeOfInitializedData 2560 (0xa00)
Initialized data section . . . .. Byte `. `._, ., -.. initialized data
section .`..-`......- section ... ..
(9) SizeOfUninitializedData 0 (0x0)
Unnitialized data section . .... Byte `. `._, ., -.. uninitialized
data section .`..-`......- section ... ..
(10) ImageBase 0x400000
Image ......- .-.. -.--, . address -,..._ 64K
bytes .- .- , . `.. ._ DLL . ...- - ..-, . .. . 0x10000000 `.. ._ 32bit
application ...-- ..-,.... 0x00400000 `.. ._
(11) BaseOfCode 0x401000
Code section .. _ , `._ Image base , .-....._
(12) BaseOfData 0x402000
Data section .. _ , `._ Image base , .-....._
(13) AddressOfEntryPoint 0x401000
Entry point function . _ , `._ Image base address , .-....._ entry point
function ._ DLL . ...- - .. _ ...._ Entry point .. -, . .._ . _ `.. .,.
._
(14) FileAlignment 512 (0x200)
Image . . section ... raw .-. alignment Byte `.`._ -,..._ 2 .-.
- , ....`.. ` . 512 . 64K -.... ., `.. .._ ..-, . .. . 512 `.. ._ -. . Section
Alignment ._ system page .....-..,- -,..._ SectionAlignment .
- _ .,. ._
(15) SectionAlignment 4096 (0x1000)
Section ... Alignment - . - . - . - .- ._ Byte `. `._ -, . .._ File
Alignment . _.._ ., -..._ ..-,..._ system page ..... `..._
,.., PE Header
.
(16) OperatingSystemVersion 4.0
(17) SubsystemVersion 4.0
(18) ImageVersion 0.0
(19) CheckSum 46233 (0xb499)
Image - - - .....-, . . .-....- . . .._...- .......--`.... ..
...., . .`... - - - ..._ -, . . .-....- ...._.`.... .,_...- ..`.
checksum - - - - ._ checksum .. .-_... error -`. .-.- .,.--.-. `,
_ . . .._ .._ Checksum ...._ error -.- ....... Checksum - ._ error
`.. .,....-....- .` . ... , Checksum ...._ kernelmode driver .... ...
system DLL ...-- ._ -,_..... .,..- . _`.. . .._
(20) SizeOfStackReserve 1048576 (0x100000)
EXE ....- process . ... thread -........ `.......
. - . .. .- .-. .. ..`. .... . .- - - .
(21) SizeOfStackCommit 4096 (0x1000)
EXE ....- stack . . .. ..`. ...._ . - . ..
(22) SizeOfHeapReserve 1048576 (0x100000)
EXE ....- process heap . .. .. .., .. .... . . ...
(23) SizeOfHeapCommit 4096 (0x1000)
EXE ....- heap . . .. ..`. ...._ . - . ..
(24) LoaderFlags 0 (0x0)
. ..`.-. ,
(25) Win32VersionValue 0 (0x0)
. ..`.-. ,
(26) PointerToRawData
Module ....- ... page . page -_,.- . pointer .-. module header -
FileAlignment . .- .- , . `.. ... Section .. uninitialized .-..- .- .- . , . . .,
..-. . _`.. ...
(27) VirtualAddress
. - . - - .- - ... image base . .-..._ section .. ....
... address `.. ._
(28) VirtualSize
.-.- -.--... section ...... -.... -,..._ Size
OfRawData - - ..,- section ._ . _`. `_ .,._ `.. ._
(29) SizeOfRawData
Disk .. initialized .-. . . ... . ._ module header . FileAlignment
.-.-,.`..._ -.. -,..._ Virtual Size -..,- section -, ... ....
._ . _...`. `_ .,._ Section .. uninitialized .-..- .- .- . , . . .,..-. . _
`.. ...
(30) Data Directory
Exe . ... ...- .... ....- _ , `.,... ... IMAGE_DATA_DIRECTO
RY array -. array -. loader - ......-..- ,.._...- ...`. image
section ....- -.-.-....- image . --- section .- - `., `., . ... ..
... -. .. import ..- function ...,
(a) Load Configuration
- . ..,. . .. ...- , `.,..`...`.-..-- ,...- IMAGE_LOAD_
CONFIG_DIRECTORY .._.- _,`-.
,.., PE Header
(b) IAT (Import Address Table)
... Import Address Table (IAT) ..- _,`-. Import ..- DLL ..
..-- IAT .- -. . - . . . . . ..-. Size field -.-. IAT .. .. . . . .
..- `-. Loader -. address , .....- import resolution -... IAT .--
readwrite `.. ... . - .... . .`-.
(c) TLS Table
Thread Local Storage . initialization section - _,`-. TLS section . . declspec
(thread) , .-_...- thread . local variables .- ..-. variable .- ..,..
compiler - .-- .tls ._.- section .. .....-. .,.... run .,,.. ..
variable .- ` .-.. -, .-, . ..- _ . -.
(d) Base Relocation Table
Base relocation information - _,`-.
(e) Debug Directory
IMAGE_DEBUG_DIRECTORY .._.. array -.- _,`-. .-....-.
image - - debug information - ...`-.
(f) Bound Import Table
IMAGE_BOUND_IMPORT_DESCRIPTOR .-. array -.- _,`-.
(g) Resource Table
Resources .-- _,`-.
(h) Delay Import Tables
Visual C++ - DELAYIMP.H .. ,-...- ClmgDelayDescr . ._ . . array
-.`..- Delayload information - _,`-. .-...-.- API - .-. ..
.. .. . Delayloaded DLL .- - - ..- - . Windows .. delay loading DLL .-, -.-
` . . ..... . -_ ...- - - ..-..--- .-.... ...-.-.
SCN_CNT_INITIALIZED_DATA Section .. initialized .-..- -.
SCN_MEM_READ Section - .-.-.
SCN_MEM_WRITE Section - ....-.
SCN_CNT_CODE Section .. execute .-- -.
SCN_MEM_EXECUTE Section --`.. execute .-.
SCN_MEM_DISCARDABLE Section - . ......-.
SCN_MEM_SHARED section . .-..- - physical page .--.-. executable -
-.-.. process ...-.. share ... . .-. process -.-. section . .. - .-.
-- -_----,..- `.... Process -. . ..... .-.. share ... global
variable .- `..-. ..-.
(i) .arch Alpha architecture information section
(i) .bss Uninitialized data section
(i) .crt Data added for supporting the C++ runtime (CRT). A good example is the
function pointers that are used to call the constructors and destructors of static C++ objects.
(i) .data Initialized data section
(i) .debug Debug information section. A debug section exists only when debug
information is mapped in the address space. The default for the linker is that debug information
is not mapped into the address space of the image.
(i) .didat Delayload import data. Found in executables built in nonrelease mode. In
release mode, the delayload data is merged into another section.
(i) .edata Export tables section
(i) .idata Import tables section
,.., PE Header
(i) .pdata Exception information section
(i) .rdata Read-only initialized data section
(i) .reloc Image relocations section
(i) .rsrc Resource directory section
(i) .text Executable code section
(i) .tls Thread-local storage section. The section contains data for supporting thread
local storage variables delcared with__declspec(thread). This includes the initial value of the
data, as well as additional variables needed by the runtime.
(i) .xdata Exception information section
, ,. ,. PE signatur e ...
, ASPack v2.12
60 E8 03 00 00 00 E9 EB 04 5D 45 55 C3 E8 01
00401000: 60 PUSHAD
00401001: E8030000000 CALL 00401009H
00401006: E9EB045D45 JMP 459D14F6H
0040100B: 55 PUSH EBP
0040100C: C3 RET
0040100D: E801003E00 CALL 007E1013H
, Ar madillo v1.xx v2.xx
55 8B EC 53 8B 5D 08 56 8B 75 0C 57 8B 7D 10 85 F6
00401000: 55 PUSH EBP
00401001: 8BEC MOV EBP, ESP
00401003: 53 PUSH EBX
00401004: 8B5D08 MOV EBX, [EBP+08H]
00401007: 56 PUSH ESI
00401008: 8B750C MOV ESI, [EBP+0CH]
0040100B: 57 PUSH EDI
0040100C: 8B7D1O MOV EDI, [EBP+10H]
0040100F: 85F6 TEST ESI, ESI
, .., Teleport Pro 1.61 .-... ...-. crack ` .
...'-) Telepor t Pr o 1.61 e=-=e.- ee.e cr ack -e.-.
u Re fa w mfw dkU[ m a & SUt c e f; a w Gr Sm cracking e JUy w fo u fw Jh t a jc c Ht kw fjr p fa w Gu dk a v hv mc Jhy gw , f/
' ga Mu mi fho i fht a e e JU C? Assembly b mo mp u m; a w Gu dk w D; r da c gu fr d& Sdx m; jy Dv dkU x i fy gw , f/ a q mhz f0 Jv fa w G
u dkv J b , fv dke n f; e JU u mu G, fx m; o v Jq dkw mu dkv J o do Gm; a v mu fy gjy D/ Cracker w p fa , mu fr Sm & Sdo i fh& Sdx dku f
w Jhtool a w Gt a Mu mi f; u dkv J a v hv mjy D; jz p fw Jht jy i f ' Dt x Ju tool w p fc kjz p fw JhOlly debugger t a Mu mi f; u dkv J
t Mu r f; z si f; e m; v n fa e a v mu fy gjy D/ t q Hk; p Ge f a jy m& & i f cracking a v mu r Sm e m; v n f& c u fw , fq dkw Jh PE
header t a Mu mi f; u dka w mi f o i fa v hv mjy D; o Gm; y gjy D/ b my Ja jy ma jy m o i fa v hv mc Jhw m[ m o Dt dk& Do u fo u fo m
jz p fy gw , f/ v u fa w GUr y gw Jho Dt dk& D? o Dt dk& Dr y gw Jhv u fa w GU[ m jy D; jy n fhp Hkjc i f; ? t E Sp fo m& jy n fh0 jc i f; r & Sdw Jh
t w Gu f u dk, fw dki fv u fa w GU crack v ky fMu n fhr So m cracking o a b mw & m; a w Gu dk a u mi f; a u mi f; e m; v n f
v mr Smjz p fy gw , f/ ' ga Mu mi fh y x r q Hk; crack v ky fjc i f; t jz p f p D; y Gm; jz p fa q mhz f0 Jv fw p fc kjz p fw Jh Teleport Pro
1.61 u dk crack v ky fMu n fhMu y gr , f/ o i fht a e e JU update r jz p fa w mhw Jh y & dk* & r fu dk e r le mx m; jy D; b ma Mu mi fh
crack v ky fjy & w mv Jv dkU o Ho , 0 i fy gv dr fhr , f/ ( u Re fa w mfw dkUt a e e JU a q mhz f0 Jv fa w Gu dk crack v ky fa e w m[ m
a i Ga Mu ; t w Gu f r [ kw fy gb l; / y n m& y fw p fc kt a e e JUo m a v hv ma e jc i f; jz p fy gw , f/ ' ga Mu mi fhr dkU crack v ky fx m;
jy D; o m; a q mhz f0 Jv fa w Gu dk w & m; r 0 i f jz e fUc sD^ a & mi f; c sc Jh& i f jz p fa y : v mr Jh & v ' fa w G[ m o i fhw m0 e fo mjz p fy g
a Mu mi f; . . . )
( 1 ) y & dk* & r ft v ky fv ky fy Hku dka v hv mjc i f;
u Re fa w mfw dkUt a e e JU a q mhz f0 Jv fw p fc ku dk crack r v ky fc i fo dx m; & r , fht " du t c su fu a w mh' Da q mhz f0 Jv f
u dk b , fy & dk* & r fb mo mp u m; e JU a & ; x m; o v Jq dkw m t & i fo da t mi fv ky fz dkUy g/ ' gr So m a & SUq u fb mv ky f& r v Jq dk
w m q Hk; jz w fE dki fr Smjz p fy gw , f/ a u mi f; jy D? Teleport Pro u dk www.tenmax.com u a e download v ky fjy D;
install v ky fv dku fy g/ Help menu u About ... u dka & G; v dku f& i f y Hk( 1 ) t w dki f; a w GU& y gr , f/
y Hk( 1 )
y Hk( 1 ) r Sm jr i f& w mu a w mh unregistered version jz p fw Jht a Mu mi f; y g/ ' ga Mu mi fh register v ky fMu n fhy g
r , f/ Help menu u Register u dka & G; v dku fy g/ y Hk( 2 ) t w dki f; jr i f& y gr , f/
y Hk( 2 )
y Hk( 2 ) u Your name a e & mr Sm Myanmar Cracking Team v dkU& dku fx n fhjy D; Registration code
a e & mr Sm 4780610 (BABE16)v dkU & dku fMu n fhy gr , f/ ' gq dky Hk( 3 ) t w dki f; a w GU& y gr , f/
y Hk( 3 )
, .., Teleport Pro 1.61 .-... ...-. crack ` .
y Hk( 3 ) r Sm jr i f& w mu a w mhu Re fa w mfw dkU& dku fx n fhv dku fw Jhregistration u k' f[ mr Sm; a e w Jht a Mu mi f; a jy mw Jh
MessageBox y g/ ( r Sw f& e f/ / t c sdKUy & dk* & r fa w Gr Sm v Sn fhu Gu fa v ; a w G& Sdy gw , f/ ' gu b mv Jq dka w mh regis-
tration u k' fu dk& dku fx n fhv dku fw Jht c g r Se fw , f^ r Sm; w , fr a jy mb J y & dk* & r fu dk jy e fz Gi fhc dki f; w mjz p fy gw , f/ t c sdKU
y & dk* & r fa w Gq dk b m MessageBox r Sa w mi f a y : r v my gb l; / b ma Mu mi fhv Jq dka w mh ' Dv dky & dk* & r fa w Gu o i f& dku f
x n fhv dku fw Jh registration u k' fu dkc su fc si f; r p p fv dkUy g/ Registry x Jr Sm ( o dkU) z dki fw p fz dki fr Sm o i f& dku fx n fh
v dku fw Jhu k' fu dko dr f; x m; jy D; a e mu fw p fMu dr f y & dk* & r fu dkz Gi fhjy D; t v ky fv ky fw Jht c gr S u k' fu dkp p fa q ; w mjz p fy gw , f/ )
' DMessage Box r Smjr i f& w Jh We're sorry! q dkw Jhp mo m; u dk p m& Gu fv Gw fw p f& Gu fr Sm r Sw fo m; x m; y g/ t o Hk; 0 i f
v my gv dr fhr , f/
a u mi f; jy D? y & dk* & r fu dky dw fv dku fjy D; b , fb mo mp u m; e JU a & ; x m; o v Jq dkw m p p fMu n fhy gr , f/ Program
files\Teleport Pro z dk' ga t mu fu pro.exe z dki fu dkright-click E Sdy fjy D; PEiD e JU p p fMu n fhv dku fy g/ y Hk( 4 ) /
y Hk( 4 )
y Hk( 4 ) t & q dk& i fa w mh ' Dy & dk* & r fu dk Visual C++ 6.0 e JU a & ; x m; w mjz p fy gw , f/ ' Da v mu fq dk u Re fa w mf
w dkUt w Gu f v Hka v mu fy gjy D/ pro.exe u dkOlly r Sm z Gi fhy gr , f/ y Hk( 5 ) /
y Hk( 5 )
y Hk( 5 ) r Smjr i f& w mu a w mhy & dk* & r f& JU entry point a e & my g/ ( r Sw fc su f/ / Visual C++ jz i fha & ; x m; a o m
y & dk* & r fr sm; o n f y Hk( 5 ) w Gi fjy x m; o n fht w dki f; kernel32.GetVersion \ t a y : z u f& Sd PUSH EBP u k' f& Sd& m
virtual address o n f entry point jz p fo n f/ ) ' Dy & dk* & r fu dk e n f; ( 2 ) e n f; e JU crack v ky fjy r Smjz p fy gw , f/
y x r e n f; u a w mh SND Team u nick123b o Hk; w Jhe n f; jz p fy gw , f/ ' kw d, e n f; u a w mh ARTeam u
ThunderPwr o Hk; w Jhe n f; jz p fy gw , f/ t jc m; e n f; a w Gu dka w mht v sOf; o i fhw Jht c e f; r Sm a z mfjy o Gm; r Smjz p fy gw , f/
( 2 ) y x r e n f; ( nick123b@SND Team)
y Hk( 2 ) r Sm register v ky fw ke f; u y Hk( 3 ) t w dki f; error message a y : v mw mr Sw fr dr , fx i fy gw , f/ ' D
message p mo m; u dk Olly r Sm& SmMu n fhv dku fMu & a t mi f/ y Hk( 5 ) r Sm right-click E Sdy fjy D; Search for u All
referenced text strings u dka & G; v dku fy g/ ' gq dk& Smx m; w Jhtext string a w Gy gw Jhwindow w p fc ka y : v my gr , f/
y Hk( 6 )
, .., Teleport Pro 1.61 .-... ...-. crack ` .
,
a y : v mw Jhwindow r Sm y Hk( 6 ) t w dki f; u Re fa w mfw dkU & Smc si fw Jhp mo m; u dk & dku fx n fhjy D; OK u dkE Sdy fv dku fy g/
' ga y r , fh u Re fa w mfw dkU& Smw Jh p mo m; u dk Olly e JU& Smw mr a w GUy gb l; / b ma Mu mi fhv Jq dka w mh ' Dy & dk* & r fu dk a & ; o m;
c Jhw Jhy & dk* & r fr mu We're sorry! p mo m; u dk .text section r Sm r a & ; o m; b J y Hk( 7 ) r Sm jy x m; o v dk .data section
r Sma & ; o m; x m; v dkU Olly u & Smr a w GUE dki fw my g/ ( o mr e ft m; jz i fh y & dk* & r fr sm; \ 8 0 % a u smfo n f .text section
(code section) w Gi fo m a & ; o m; Mu y go n f/ )
y Hk( 7 )
y Hk( 8 )
y Hk( 8 ) u dkMu n fhv dku fa w mhu Re fa w mfw dkU& Sma e w Jhmessage u dka w GU& y gw , f/ y Hk( 7 ^ 8 ) w dkUu dk PE Explorer
1.99 (www.heaventools.com) r Sm z Gi fhMu n fhx m; w mjz p fy gw , f/
y Hk( 6 ) t w dki f; text string u dk& Smw m & Smr a w GUv dkU o i fht a e e JU a c gi f; a w mfa w mfa jc mu fa e a v mu fjy Dx i fy g
w , f/ ' Dmessage u dk& Sma w GUr So m u Re fa w mfw dkUt a e e JU serial a & ; x m; w Jh registration routine u dka w GUjy D;
serial u dk& Sma z GE dki fr Sm jz p fy gw , f/ a u mi f; jy D? nick123b & JUe n f; e JU serial u dk& SmMu n fhMu & a t mi f/
Olly r Sm Ctrl + N (View Names) u dkE Sdy fv dku fy g/ y Hk( 9 ) t w dki f; API a w Gu dkjr i f& y gr , f/
y Hk( 9 )
y Hk( 9 ) r Sm jy x m; w Jht w dki f; USER32.GetWindowTextA r Sm right-click E Sdy fjy D; Find references to
import (Enter key) u dk a & G; v dku fy g/ y Hk( 1 0 ) t w dki f; jr i f& y gr , f/ ( GetWindowTextA t a Mu mi f; t a o ; p dw f
u dk]Cracker r sm; o w dx m; o i fha o m Windows API r sm; } t c e f; w Gi f z w f& Iy g/ )
y Hk( 1 0 )
y Hk( 1 0 ) r Sm jr i f& w Jht w dki f; right-click E Sdy fjy D; Set br eakpoint on ever y command u dk a & G; v dku f
y g/
y Hk( 1 1 )
, .., Teleport Pro 1.61 .-... ...-. crack ` .
y Hk( 1 1 ) t w dki f; GetWindowTextA u dkbreakpoint r o w fr Sw fc i f pro.exe u dky Hk( 1 2 ) t w dki f; Olly r Sm
register v ky fa e w m a o c smy ga p / ( q dkv dkw mu Teleport Pro u dk Olly e JUz Gi fhjy D; register v ky fc dki f; w my g/
y Hk( 1 2 ) r Sm OK u dkr E Sdy fc i f y Hk( 9 ^ 1 0 ^ 1 1 ) r Sm jr i f& w Jht w dki f; breakpoint o w fr Sw fw m jz p fy gw , f/ )
y Hk( 1 2 )
y Hk( 1 1 ) t w dki f; breakpoint o w fr Sw fjy D; o Gm; & i fa w mh y Hk( 1 2 ) u OK u dkE Sdy fv dku fy g/ y Hk( 1 3 ) t w dki f; Get
WindowTextA() API & Sd& m breakpoint q Dw e f; a & mu fo Gm; y gv dr fhr , f/
y Hk( 1 3 )
y Hk( 1 3 ) t w dki f; jr i f& w Jht c g y Hk( 1 4 ) u dkjr i f& w Jht x dF8 (step over) u dkE Sdy fy g/
y Hk( 1 4 )
y Hk( 1 4 ) u dkMu n fhy g/ CALL 0042F675 r Sm registration key w Gu fc su fjc i f; u dk v ky fa q mi fy gw , f/
' Dha e mu fr Sma w mhEAX x Jr Sm& Sdw Jhw e fz dk; w p fc ke JU ESI x Jr Sm& Sdw Jhw e fz dk; w p fc kw dkUu dkn D?r n Dp p fy gw , f/ w u , fv dkU
w e fz dk; E Sp fc kr n Dc Jh& i f BadBoy message q Da & mu fo Gm; r Smjz p fy gw , f/ ' ga Mu mi fh"JNZ 042ECDB" q dkw Jha e & m
a & mu f& i f F8 E Sdy fv mw m & y fv dku fy g/ jy D; a w mhRegisters (FPU) window u dkMu n fhv dku fy g/ y Hk( 1 5 ) /
y Hk( 1 5 )
y Hk( 1 5 ) & JU EAX register x Jr Sm u Re fa w mfw dkUv dkc si fw Jh serial a & mu fa e y gjy D/ r Sw fx m; & r Smu ' Dserial
[ m ECX register x Jr Sm& Sdw Jh "Myanmar Cracking Team" q dkw Jh user t w Gu fo mjz p fy gw , f/
, .., Teleport Pro 1.61 .-... ...-. crack ` .
b ma Mu mi fhv Jq dka w mh u Re fa w mfw dkUu y Hk( 1 2 ) r Sm jy x m; w Jht w dki f; user name a e & mr Sm "Myanmar Cracking
Team" v dkU & dku fx n fhc Jhv dkUy g/
y Hk( 1 6 )
w u , fa w mh y Hk( 1 4 ) u EAX register x Jr Sm& Sdw Jh serial [ m hexadecimal * P e f; o mjz p fy gw , f/
258680D9 a e & mu dk E Sp fc su fE Sdy fv dku fy g/ jy D; & i f 629571801 u dku l; , lv dku fy g/ y Hk( 1 7 ) / 629571801 u o m
serial t p p ft r Se fjz p fy gw , f/
y Hk( 1 7 )
' gq dk u Re fa w mfw dkU v dkc si fw Jh serial u dk & & Sdjy Djz p fw Jht w Gu f Olly u dky dw fv dkU& y gjy D/ Teleport Pro
y & dk* & r fu dkjy e fz Gi fhv dku fy g/ jy D; & i f Help menu u Register u dka & G; jy D; register v ky fz dkU jy i fq i fy g/
y Hk( 1 8 )
y Hk( 1 8 ) t w dki f; Name e JU Registration Code u dkjz n fhjy D; & i f OK u dkE Sdy fv dku fy g/ y Hk( 1 9 ) t w dki f;
jr i f& y gr , f/
y Hk( 1 9 )
y dka o c smo Gm; a t mi f Help menu u Register u dkx y fE Sdy fMu n fhy g/ u Re fa w mfw dkU a e mu fw p fMu dr f
register v ky fp & mr v dka w mhw m jr i f& r Smy g/ y Hk( 2 0 ) /
, .., Teleport Pro 1.61 .-... ...-. crack ` .
,
y Hk( 2 0 )
Help menu u About Teleport Pro u dka & G; jy D; Mu n fhv dku f& i fa w mhy Hk( 2 1 ) t w dki f; jr i f& r Smy g/
y Hk( 2 1 )
' gq dk y x r e n f; e JU u Re fa w mfw dkU& JU serial & Smjc i f; t v ky fjy D; o Gm; y gjy D/ ' Dv dke n f; e JU serial & Smw mu dk
t * Fv dy fv dka w mh serial fishing ( Serial z r f; jc i f; ) v dkUa c : y gw , f/ Cracking a v mu r Sma w mh serial fishing
e n f; [ m t c sde fu ke fo u fo mjy D; v G, fu lv Sw Jht w Gu f t o Hk; r sm; v Sy gw , f/
( 3 ) ' kw d, e n f; ( Thunder Pwr @ARTeam)
' kw d, e n f; u a w mh y Hk( 2 2 ) r Smjr i f& w Jh MessageBox & Sd& ma e & mu dkt & i f& Smjy D; registration routine u dk
& Sma z Gw Jhe n f; jz p fy gw , f/ ( r Sw fc su f/ / a & SUy dki f; u GetWindowTextA() API r Smo w fr Sw fx m; w Jhbreakpoint
a w Gu dkz , f& Sm; jy D; a Mu mi f; a o c smy ga p / )
Teleport Pro [ m register v ky fw m a t mi fjr i fo Gm; & i f a e mu fw p fMu dr f register x y fv ky fv dkU r & a w mh
y gb l; / ' ga Mu mi fh registry editor (regedit.exe) u dkz Gi fhjy D; HKLM e JU HKCU w kdY& JU Software directory
a t mu fu Tennyson Maxwell directory key u dkz su fy p fv kdu fy g/
y Hk( 2 2 )
Olly r Sm pro.exe u dkz Gi fhjy D; F9 (Run) u dkE Sdy fy g/ ' gq dk Teleport Pro y & dk* & r fy Gi fhv mw m jr i f& y gr , f/
y & dk* & r f& JU Help menu u Register u dkE Sdy fjy D; register v ky fMu n fhy g/ y Hk( 2 2 ) t w dki f; BadBoy MessageBox
u dkjr i f& y gr , f/ ' Dt c g Olly q Djy e fo Gm; jy D; F12 (Pause) u dkE Sdy fy g/ F12 u dkE Sdy f& w Jht a Mu mi f; & i f; u a w mhy & dk* & r f
t v ky fv ky fw m c P & y fa p c si fv dkUy g/ jy D; & i f Olly & JU stack window r Sm scroll q GJjy D; Mu n fhv dku fy g/ y Hk( 2 3 )
t w dki f; jr i f& y gr , f/
, .., Teleport Pro 1.61 .-... ...-. crack ` .
.
y Hk( 2 3 )
y Hk( 2 3 ) u dkMu n fhy g/ VA 0049112C u a w mh"We're sorry! " p mo m; u dko dr f; q n f; x m; w Jhvirtual
address y g/ VA 004542CD u a w mh y Hk( 2 2 ) u MessageBox API u dkv ky fa q mi fjy D; c sde f a & mu f& Sdr , fh
a e & my g/ c kc sde fr Sm u Re fa w mfht a e e JU p dw f0 i fp m; w Jhvirtual address [ m 004542CD jz p fy gw , f/ b ma Mu mi fhv J
q dka w mh' Daddress u a e registration routine & Sd& ma e & mu dka jc & mc Hr Smr dkUv dkUy g/
y Hk( 2 4 )
Registration routine u dk a jc & mc Hz dkU y Hk( 2 4 ) u highlight jz p fa e w Jha e & mr Sm right-click E Sdy fjy D;
Follow in Disassembler u dka & G; y g/ y Hk( 2 5 ) t w dki f; jr i f& y gr , f/
y Hk( 2 5 )
y Hk( 2 5 ) u 004542CD a e & mr Sm breakpoint o w fr Sw fjy D; F9 u dkE Sdy fr , fq dk& i fa w mh a e mu fw p fc g
register v ky fw Jht c g ' Da e & mu dkw e f; a & mu fv mr Sm jz p fy gw , f/ y Hk( 2 6 ) /
y Hk( 2 6 )
' Dt c gr Sm y Hk( 2 5 ) e JUr w lw mu a w mhpro.004541C4 [ m text string a w Ge JU jz p fv my gw , f/
y Hk( 2 7 )
, .., Teleport Pro 1.61 .-... ...-. crack ` .
.
y Hk( 2 6 ) u u k' fa w Gu dk F8 E Sdy fjy D; u k' fa w Gp p fv mw Jht c g y Hk( 2 6 ) u CALL u dk v ky fa q mi fjy D; w me JU y Hk( 2 7 )
& Sd& mu dka & mu fv mr Smy g/ ' Dw p fc gr Sma w mhserial u dkEAX register x Jr Sm b , fv dkr S& Sma w GUa w mhr Sm r [ kw fy gb l; /
b ma Mu mi hfv Jq dka w mh y & dk* & r fu serial r Se f^ r r Se fu dk p p fa q ; jy D; v dkU error message u dkx kw fa y ; v dku fw ma Mu mi fh
jz p fy gw , f/ ' ga Mu mi fhr dkU serial u dkv dkc si f& i f u Re fa w mfw dkUt a e e JU VA 0042ECCA a e & mr Sm breakpoint
o w fr Sw fjy D; y & dk* & r fu dk a e mu fw p fMu dr f register v ky fz dkUv dky gw , f/ ' Dbreakpoint u dka & mu fw Jht c g u Re fa w mf
w dkU& Sma e w Jh serial u dk EAX register x Ju a e u l; , lv dkU& y gjy D/ a e mu fx y fp dw f0 i fp m; p & ma u mi f; w mu a w mh
y Hk( 2 3 ) u RETURN to pro.0042ED10 from pro.004542AB y g/ ( Assembly o i fc e f; p mw ke f; u CALL
w p fc k[ m o la e mu fx y fv ky fr , fhinstruction & Sd& m address (EIP) u dk stack r Smo dr f; q n f; w , fv dkUa jy mc Jhw mu dk
t r Sw f& y g/ a e mu fx y fa jy mc Jha o ; w mu a w mh CALL w p fc ku dkv ky fa q mi fjy D; c sde fr Sm return value u dk EAX r Sm
t jr Jw r f; e D; y g; o dr f; q n f; w , fq dkw Jht a Mu mi f; y g/ )
( 4 ) Telepor t Pr o y & dk* & r ft w Gu f keygen a & ; o m; jc i f;
a & SUy dki f; r Sm u Re fa w mfw dkUt a e e JU serial z r f; jy D; Teleport Pro u dk register v ky fjy D; o Gm; y gjy D/ ' ga y r , fh
t r n fu "Myanmar Cracking Team" jz p fa e y gw , f/ w u , fv dkU o i fht r n fe JU register v ky fc si f& i f?
o i fhr dw fa q G^ c sp fo lt r n fe JU register v ky fc si f& i f Olly e JU serial x y f& Sm& r , fq dk& i f t c sde fu ke fv ly e f; y gw , f/
' ga Mu mi fhr dkU keygen a & ; z dkUv dkt y fv my gw , f/ "Myanmar Cracking Team" t r n fe JU serial & Sm& mr Sm
629571801 q dkjy D; & v my gw , f/ b , fv dk& v mr Se f; o i fht a e e JU 0 g; w m; w m; jz p fa e r Sm a o c smy gw , f/ ' ga Mu mi fh
serial key x kw fa y ; w Jhroutine u dkt a o t c sm a v hv mMu n fhy gr , f/ y Hk( 2 8 ) /
y Hk( 2 8 )
' Da e & mr Sm y Hk( 2 8 ) u CALL 0042F675 [ m serial key u dkx kw fa y ; w Jh routine jz p fw , fq dkw m
o i fht a e e JU & dy fr dr Smy g/ b ma Mu mi fhv Jq dka w mh ' D CALL u dk v ky fa q mi fjy D; c sde fr Sm u Re fa w mfw dkU & dku fx n fhw Jh
serial e JU w Gu fc su fv dkU& v mw Jh serial u dk y & dk* & r fu E dIi f; , SOfv dkUy g/ ' D CALL a e & mr Sm breakpoint
o w fr Sw fv dku fjy D; y & dk* & r fu dk (Ctrl+F2) jy e fp w i fv dku fy g/ jy D; & i f F9 u dkE Sdy fjy D; y & dk* & r fu dk run y g/ Register
v ky fy g/ ' gq dk& i f breakpoint o w fr Sw fx m; w JhVA 0042ECC2 a e & mu dk a & mu fv my gr , f/ VA 0042ECC2
a e & mu dka & mu fv m& i f F7 (step into) u dkE Sdy fjy D; CALL x Ju dk0 i fMu n fhy gr , f/ y Hk( 2 9 ) /
y Hk( 2 9 )
Serial key u dkx kw fa y ; w Jh routine a v ; u a w mh y Hk( 2 9 ) r Sm jy x m; o a v mu fy gb J/ VA 0042F691
x du p dw f0 i fp m; p & mr & Sdy gb l; / & dku fx n fhv dku fw Jh user t r n f[ m p mv Hk; a & 5 v Hk; x u fe n f; ^ r e n f; p p fa q ; w m
, .., Teleport Pro 1.61 .-... ...-. crack ` .
y J& Sdy gw , f/ 5 v Hk; x u fr sm; & i fa w mh VA 0042F694 u p jy D; serial w Gu fc su fjc i f; v ky fi e f; p Ofu dk p w i fr Sm
jz p fy gw , f/ a v hv mMu n fhv dku f& a t mi f/
1 / EBX e JU ESI w dkUu dkvariable t a e e JU a Mu n my gw , f/
2 / ESI = 5DFEE4A4 v dkU initialize v ky fy gw , f/
3 / EBX w e fz dk; u dko kn jz p fa t mi fv ky fy gw , f/
4 / TEST u a w mhjump (JE) jz p f^ r jz p f flag w e fz dk; u dko w fr Sw fw mjz p fy gw , f/
5 / EDI x Ju w e fz dk; a w Gu dk ECX x Ja jy mi f; x n fhw my g/ ( Stack r Sm a e mu fq Hk; o Gi f; w mu dk t & i fx kw f, l& y g
w , f/ )
6 / EAX w e fz dk; x Ju 4 E Iw fy gw , f/ ( EAX x Jr Sm c ke u u Re fa w mfw dkU & dku fx n fhv dku fw Jh user t r n fe JU
y w fo u fw Jhp mv Hk; t a & t w Gu f & Sdy gw , f/ "Myanmar Cracking Team" jz p fw Jht w Gu f 2 1 v Hk; y g/ )
7 / EBX e JU EAX w dkU E dIi f; , SOfy gw , f/
8 / w u , fv dkU EBX [ m EAX x u fr i , fc Jh& i f jump jz p fr Smjz p fy gw , f/ ( c kc sde fr Sma w mh EAX u 17 jz p fjy D; ?
EBX u o kn jz p fy gw , f/ )
9 / ESI w e fz dk; e JU user t r n fu y x r p mv Hk; 4 v Hk; & JU Unicode (Hex) w e fz dk; w dkUu dk XOR v ky fr Smjz p fy gw , f/
( c kc sde fr Sma w mhESI w e fz dk; u 5DFEE4A4 jz p fjy D; ? DS:[EBX+EDI] w e fz dk; u 6E61794D jz p fy gw , f/ )
1 0 / EBX w e fz dk; u dk1 a y gi f; y gw , f/
1 1 / ' Dv dke JU "Myanmar Cracking Team" q dkw Jhp mv Hk; a w Gu dk u ke fa t mi fz w f? XOR v ky fjy D; & v mw Jha e mu fq Hk;
t a jz u dkEAX r Sm o dr f; y gw , f/
' gu dk Assembly u k' ft a e e JU jy e fa & ; & i fa w mh a t mu fy gt w dki f; a w GU& r Smy g/ ' gu a w mh u k' ft jy n fht p Hk
r [ kw fy gb l; / Serial key x kw fa y ; w Jh a e & ma v ; u dky J a & ; x m; jc i f; jz p fy gw , f/ a & ; o m; x m; w Jh y & dk* & r fr mu
a w mhSND Team u Ziggy jz p fy gw , f/
invoke lstrlenA, addr namebuffer ;get the length of the name string
mov ecx, eax ;copy length of name string in eax to ecx
sub ecx, 4 ;loop counter ecx = name string length - 4
lea edi, namebuffer ;edi = address to name string
mov esi, 05DFEE4A4h ;esi = starting code value = 04E6AF4BC hex
L005: ; Ripped code from Ziggy's KeygenMe
mov eax, dword ptr ds:[edi] ;load 4 name string ascii characters in eax
xor esi, eax ;exclusive or eax with the new edx value - result in esi
inc edi ;point to next group of 4 name chars
dec ecx ;decrement the loop counter
jnz L005 ;jump back if ecx loop counter not = zero
Assembly e JU keygen a & ; o m; e n f; u dka w mh ]t a jc c H Assembly b mo mp u m; } t c e f; r Sm & Si f; jy jy D;
jz p fw Jht w Gu f x y fr Hr & Si f; jy a w mhy gb l; / Keygen e JU y w fo u fjy D; a jy mv dkw mu a w mh u Re fa w mfw dkUt a e e JU
keygen a w G& JU GUI u dk u dk, fw dki fa & ; p & mr v kdy gb l; / a & ; x m; jy D; o m; keygen template a w Gu dk t o i fh, lo Hk;
& Hky g/ Serial key a w Gu dkx kw fa y ; r , fhregistration routine u dko m a & ; a y ; z dkUv dkt y fy gw , f/
;
; Ziggy April 2005
;
;
; Notes
;
; - Requires MASM32 V8
; - Requires linking with matching resource file ;
;
;
.586p
.mmx
.model flat, stdcall
option casemap :none
include \masm32\include\windows.inc
include \masm32\include\user32.inc
include \masm32\include\kernel32.inc
include \masm32\include\masm32.inc
include \masm32\macros\macros.asm
includelib \masm32\lib\user32.lib
, .., Teleport Pro 1.61 .-... ...-. crack ` .
includelib \masm32\lib\kernel32.lib
includelib \masm32\lib\masm32.lib
; Prototypes
DialogProc PROTO :DWORD,:DWORD,:DWORD,:DWORD
ClipboardCopy PROTO
KeygenProc PROTO
.const
DIALOG_1 equ 1 ;identifier in resource file
IDC_APPNAME equ 1001
IDC_NAME equ 1002
IDC_SERIAL equ 1003
BTN_CLOSE equ 1004
BTN_GENERATE equ 1005
BTN_COPY equ 1006
BTN_ABOUT equ 1007
; may need to edit these constants
MinNameLength equ 5 ; Should be consistent with .data NameTooShort
MaxNameLength equ 30 ; Maximum length of name string
; edit about text as needed
About_Text equ " ",13,10,"Keygenned by Ziggy ",13,10,10,\
"30 July 2008",13,10,13,10
Max_Buffer equ 100 ; set to at least maximum length of name or serial
;
.data
; edit app name as needed
Appname db "Myanmar Cracking Team proudly presents:",0
; following data not required if name not used to derive serial
NoName db 'No Name Entered',0
NameTooLong db 'Name is too long',0
NameTooShort db 'Name must be at least 5 characters',0 ; edit to match MinNameLength
NameOK db 'Press "Generate"',0
namebuffer dd Max_Buffer dup (00) ;buffer for entered name
genedserial dd Max_Buffer dup (00) ;buffer for genedserial
tempbuffer dd Max_Buffer dup (00) ;scratch buffer
fixedstring db " ",0
decimalformat db "%d",0
;
.data?
hInstance dd ? ;Module handle
handle dd ? ;Dialog handle
hIcon dd ? ;caption bar icon handle
;
.code
main :
invoke GetModuleHandleA,NULL
mov hInstance ,eax ; save handle for later use
;mov hIcon, FUNC(LoadIcon, hInstance,2) ; get the icon 2 resource
; setup the dialog processing
invoke DialogBoxParamA,hInstance,DIALOG_1,NULL, addr DialogProc,NULL
invoke ExitProcess,NULL ; terminate after dialog is closed
;
; Main Dialog Processing
DialogProc Proc hwnd:dword, message:dword, wParam:dword, lParam:dword
pushad
mov eax,hwnd
mov handle,eax ;save dialogbox handle, to use in other procedures
.IF message==WM_INITDIALOG
invoke SetDlgItemTextA,handle,IDC_APPNAME, addr Appname ;show the appname in dialog box
invoke SendMessage, handle,WM_SETICON,ICON_BIG,hIcon ; set icon on caption bar
.ELSEIF message==WM_COMMAND
mov eax,wParam
.IF ax==BTN_GENERATE ; "Generate" button presssed
; check name is ok, not too long & not too short
invoke GetDlgItemTextA,handle,IDC_NAME,ADDR namebuffer,Max_Buffer
.if eax == 0
invoke SetDlgItemTextA,handle,IDC_SERIAL, addr NoName
.elseif eax > MaxNameLength ; max namr length
, .., Teleport Pro 1.61 .-... ...-. crack ` .
invoke SetDlgItemTextA,handle,IDC_SERIAL,addr NameTooLong
.elseif eax < MinNameLength ; minimum name length
invoke SetDlgItemTextA,handle,IDC_SERIAL, addr NameTooShort
.elseif
;Invoke Keygen algo on 'generate' and name ok
Invoke KeygenProc ; do the business
.endif
.ELSEIF ax==BTN_CLOSE ; "Close" button pressed
jmp @close
.ELSEIF ax==BTN_ABOUT ; "About" button pressed
invoke MessageBox,handle,SADD(About_Text),
SADD(" ",34,"Myanmar Cracking Team",34),
MB_OK or MB_ICONINFORMATION
.ELSEIF ax==IDC_NAME ; name character enetered
; check name ok, not too long & not too short
invoke GetDlgItemTextA,handle,IDC_NAME,ADDR namebuffer,Max_Buffer
.if eax == 0
invoke SetDlgItemTextA,handle,IDC_SERIAL, addr NoName
.elseif eax > MaxNameLength ; max namr length
invoke SetDlgItemTextA,handle,IDC_SERIAL,addr NameTooLong
.elseif eax < MinNameLength ; minimum name length
invoke SetDlgItemTextA,handle,IDC_SERIAL, addr NameTooShort
.elseif
invoke SetDlgItemTextA,handle,IDC_SERIAL, addr NameOK
.endif
.ELSEIF ax==BTN_COPY ; "Copy" button pressed
invoke ClipboardCopy
.ENDIF
.ELSEIF message==WM_CLOSE ; dialog closed
@close:
invoke EndDialog,handle,NULL
popad
xor eax,eax
ret
.ELSE
popad
mov eax,FALSE
ret
.ENDIF
popad
xor eax,eax
ret
DialogProc endp
;
; Copy generated serial to the clipboard
; This function is not really necessary in a simple keygen but code is short
; and does not need any modification.
;
ClipboardCopy proc
pushad
invoke GetDlgItemText, handle, IDC_SERIAL, addr genedserial, SIZEOF genedserial
.if eax != 0
invoke OpenClipboard, handle
.if eax
invoke GlobalAlloc, GMEM_MOVEABLE or GMEM_DDESHARE, SIZEOF genedserial
.if eax != NULL
push eax
push eax
invoke GlobalLock, eax
mov edi, eax
mov esi, OFFSET genedserial
mov ecx, SIZEOF genedserial
rep movsb
pop eax
invoke GlobalUnlock, eax
invoke EmptyClipboard
pop eax
, .., Teleport Pro 1.61 .-... ...-. crack ` .
invoke SetClipboardData, CF_TEXT, eax
.endif
.endif
invoke CloseClipboard
.endif
popad
ret
ClipboardCopy endp
;
; your Key Generator Code goes in this procedure
;
KeygenProc PROC
nop ; these nops make the Keygen procedure easy to find in Olly
nop ; when debugging the keygen.
nop ; comment these out on final assembly
nop
nop
nop
nop
nop
;[[[[[[[[[[[[[[[[[ Your keygen code goes in here to replace the example
invoke lstrlenA, addr namebuffer ;** get the length of the name string
mov ecx, eax ;** copy length of name string in eax to ecx
sub ecx, 4 ;** loop counter ecx = name string length - 4
lea edi, namebuffer ;** edi = address to name string
mov esi, 05DFEE4A4h ;** edx = starting code value = 04E6AF4BC hex
L005:
mov eax, dword ptr ds:[edi] ;** load 4 name string ascii characters in eax
xor esi, eax ;** exclusive or eax with the new edx value - result in edx
inc edi ;** point to next group of 4 name chars
dec ecx ;** decrement the loop counter
jnz L005 ;** jump back if ecx loop counter not = zero
invoke wsprintf, addr tempbuffer, addr decimalformat, edx
invoke lstrcpyA, addr genedserial, addr fixedstring
invoke lstrcatA, addr genedserial, addr tempbuffer
;]]]]]]]]]]]]]]]]]]
invoke SetDlgItemTextA,handle,IDC_SERIAL, addr genedserial ; display serial
ret
KeygenProc ENDP
;
end main
' Dassembly u k' fa w Gu dkassemble v ky fv dku f& i f y Hk( 3 0 ) t w dki f; a w GU& r Smy g/
y Hk( 3 0 )
Assembly e JU keygen a & ; w m t q i fa jy y go v m; / r a jy b l; q dk& i fa w mh C b mo mp u m; e JU keygen
a & ; e n f; u dk& Si f; jy y gr , f/
#include <conio.h>
#include <stdio.h> // C Console Application
#include <string.h> // Compiler - Borland C++ 5.02
#include <memory.h> // Copyright by Myo Myint Htike, September 14 2009
unsigned long Str ingtoHex(const char *string);
int main()
{
char User_Name[30] = {0};
char Read_4_Bytes[4] = {0};
unsigned long index = 0, ESI = 0x5DFEE4A4, EAX;
unsigned long string_length;
, .., Teleport Pro 1.61 .-... ...-. crack ` .
,
pr intf("Teleport Pro 1.3x - 1.6x Keygen");
pr intf("\n========================\n\n");
pr intf("\nYour Name : ");
scanf("%[abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ ]",User_Name);
string_length = str len(User_Name);
if(string_length < 5 || string_length > 30)
pr intf("Name must be 5->30 characters.\n");
while(index < string_length-4){
memmove(&Read_4_Bytes, &User_Name[index], 4);
str r ev(Read_4_Bytes);
EAX = Str ingtoHex(Read_4_Bytes);
ESI = ESI ^ EAX;
index++;
}
pr intf("\nRegistration Code : %d\n",ESI);
getch();
return 0;
}
unsigned long Str ingtoHex(const char *string)
{
unsigned long hex_value = 0, index = 0;
const char *character_read = string;
while(*character_read){
hex_value = (hex_value*0x100) +(unsigned long)character_read[index];
character_read++;
}
return hex_value;
}
y & dk* & r f& JU t v ky fv ky fy Hku a w mh-
1 / unsigned long Str ingtoHex(const char *string);
' gu a w mhu dk, fy dki f function w p fc ku dkt o Hk; jy Kr , fv kdU Mu dKw i fa Mu n mw my g/
2 / char User_Name[30] = {0}, char Read_4_Bytes[5] = {0};
User name t w Gu f p mv Hk; a & ( 3 0 ) z w fr Smjz p fy gw , f/ ' Dp mv Hk; a w Gu dk z w fjy D; x m; r , fhbuffer a e & mu dk
00 ('\0') a w Ge JU jz n fhv dku fw my g/ Read_4_Bytes[4] u v J' Dv dky gy J/
3 / unsigned long index = 0, ESI = 0x5DFEE4A4, EAX;
XOR v ky fr , fhESI w e fz dk; u dk0x5DFEE4A4 v dkU initialize v ky fy gw , f/
4 / scanf("%[abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ ]",User_Name);
Registration v ky fr , fh user name u dka w mi f; w my g/ %s e JU z w f& i f& a y r , fh user t r n fr Sm
r v dkt y fw Jho a u Fw a w G ( space r St y ) y gv mr Sm p dk; & dr fw Jht w Gu f u e fUo w fv dku fw mjz p fy gw , f/ ' ga Mu mi fh
keyboard u a e t r n f& dku fx n fhw Jht c gr Sm a-z? A-Z e JU space w dkUo m & dku fx n fhv dkU& r Smjz p fy gw , f/
Myanmar Cracking Team v dkU & dku fx n fhy gr , f/
5 / string_length = str len(User_Name);
& dku fx n fhv dku fw Jh user name u dk b , fE Sp fv Hk; v Jq dkw m w Gu fc su fy gw , f/ Myanmar Cracking
Team jz p fw Jht w Gu f 2 1 v Hk; jz p fy gw , f/ w u , fv dkU user name [ m 5 v Hk; x u fe n f; a e & i fy Jjz p fjz p f?
t v Hk; 3 0 x u f r sm; a e & i fy Jjz p fjz p f serial t r Sm; u dky Jx kw fa y ; r Smjz p fy gw , f/
6 / while(index < string_length-4){
string_length x Ju 4 E Iw fw mjz p fw Jht w Gu f string_length w e fz dk; t o p f[ m 1 7 jz p fv my gr , f/
index w e fz dk; u a w mhc kc sde fr Sm o kn jz p fa e y gr , f/ ' ga Mu mi fhwhile loop u dk1 7 Mu dr fv ky fa q mi fy gr , f/
6 . 1 / memmove(&Read_4_Bytes, &User_Name[index], 4);
memmove() function u a w mh&User_Name[0] = VA 12FF68 r Smp w Jh4D 79 61 6E (Myan)
p w Jhp mv Hk; 4 v Hk; u dk&Read_4_Bytes = VA 12FF88 r Sm o Gm; x m; a p w mjz p fy gw , f/ y Hk( 3 1 ) /
y Hk( 3 1 )
, .., Teleport Pro 1.61 .-... ...-. crack ` .
6 . 2 / str r ev(Read_4_Bytes);
Myan q dkw Jh string u dk a jy mi f; jy e fv Se fy gw , f/ ' ga Mu mi fh Myan [ m nayM jz p fv my gw , f/
b ma Mu mi fhstrrev() function u dko Hk; & o v Jq dk& i f y & dk* & r f[ m endian e n f; e JU a ' w ma w Gu dkz w fv dkUjz p fy gw , f/
6 . 3 / EAX = Str ingtoHex(Read_4_Bytes);
StringtoHex() function u a w mh a jy mi f; jy e fv Se fx m; w Jh string a w Gu dk XOR v ky fz dkUt w Gu f
* P e f; t jz p fa jy mi f; v Jw mjz p fy gw , f/ ' D function u dkv ky fa q mi fjy D; c sde fr Sma w mh EAX [ m 6E61794D
jz p fv my gw , f/
6 . 3 . 1 / while(*character_read){
hex_value = (hex_value*0x100) +(unsigned long)character_read[index];
character_read++;
}
character_read u VA 12FF88 r Sm& Sdw Jh y x r p mv Hk; n u dk z w fy gw , f/ r Sw fx m; & r Smu a w mh
*character_read [ m character_read[0] e JUn Djy D; character w p fv Hk; u dkz w fy gw , f/
y Hk( 3 2 )
z w fv dku fw Jhp mv Hk; n u dk * P e f; t jz p fa jy mi f; y gw , f/ hex_value w e fz dk; [ m ' Dt c sde fr Sm 6E16(11010)
jz p fv my gr , f/ character_read w e fz dk; u dk w p fa y gi f; v dku fw Jht w Gu f character_read[1] jz p fv mjy D; a u dk
z w fy gw , f/ ' Dt c g hex_value = (6E*0x100) + 61 = 6E61 jz p fv my gw , f/ ' Dv dke JU 00 (\0) u dkr a w GUr c si f;
a e mu fx y fp mv Hk; a w Gz w fa e r Smjz p fy gw , f/ a e mu fq Hk; r Sma w mh hex_value [ m 6E61794D jz p fv my gw , f/
6E61794D w e fz dk; u dkEAX q Djy e fy dkUy gw , f/
6 . 4 / ESI = ESI ^ EAX;
EAX (6E61794D) e JU ESI (5DFEE4A4) w dkUu dk XOR v ky fy gw , f/ & & Sdv mw Jh 339F9DE9
w e fz dk; u dkESI r Smo dr f; y gw , f/
6 . 5 / index++;
index w e fz dk; u dkw p fa y gi f; v dku fw Jht w Gu f a e mu fw p fMu dr f while loop u dkv ky fa q mi fc sde fr Sm . . .
while(index < string_length-4){ // while(1<17){
memmove(&Read_4_Bytes, &User_Name[index], 4); // Read_4_Bytes = "yanm";
str r ev(Read_4_Bytes); // Read_4_Bytes = "mnay";
EAX = Str ingtoHex(Read_4_Bytes); // EAX = 6D6E6179;
ESI = ESI ^ EAX; // ESI = 339F9DE9 ^ 6D6E6179 = 5EF1FC90;
index++; // index = 2;}
}
// while (2<17){ ..................}
// while (3<17){ ..................}
// while (4<17){ ..................}
// ......................................etc
while(index < string_length-4){ // while(16<17){
memmove(&Read_4_Bytes, &User_Name[index], 4); // Read_4_Bytes = " Tea";
str r ev(Read_4_Bytes); // Read_4_Bytes = "aeT ";
EAX = Str ingtoHex(Read_4_Bytes); // EAX = 61655420;
ESI = ESI ^ EAX; // ESI = 44E3D4F9 ^ 61655420 = 258680D916;
index++; // index = 17;}
}
7 / pr intf("\nRegistration Code : %d\n",ESI);
XOR v ky fjy D; a e mu fq Hk; & v mw Jht a jz (258680D916 = 62957180110)u dkx kw fy gw , f/ 629571801
u a w mhMyanmar Cracking Team t w Gu f registration code jz p fy gw , f/
' gu a w mhkeygen t v ky fv ky fy Hkt a o ; p dw fy g/
a e mu fq Hk; t a e e JU a jy mjy c si fw mu a w mh registration routine u dk t jr Jw r f; exe z dki fx Jr Sm a & ; x m; w m
r [ kw fy gb l; / Kasper sky Inter net Secur ity 7.0 q dk& i f o lU& JU registration routine u dk lic.ppl ( w u , f
a w mh .ppl v dkU z dki ft r sdK; t p m; o w fr Sw fx m; a y r , fh .dll z dki fo mjz p fy gw , f/ ) r Sma & ; x m; jy D; Xilisoft u x kw fw Jh
a q mhz f0 Jv fa w Gr Sma w mh UILib71.dll z dki f ( o dkU) UILib8_MFCDll.dll ( o dkU) imfc0.dll z dki fr Sm a & ; x m; w m
jz p fw Jht a Mu mi f; a jy mMu m; & i f; e JU e d* Hk; c sKy fy g& a p /
,., Patch `. (Beginner/Intermediate/Advanced)
tcef;(10) - Patch vkyfjcif; (Beginner /Inter mediate/Advanced)
,..,.. -,.-.-..-.-.-. registration routine -., serial key -
. ... -.`.. -. ... . -.. - .. serial key - . ... .-.-. --. .-. . . - .
, - , , .-. .-. cracker .-- ,--. Full version (registered
version) -..... .-..- patch - ,_ ., crack --. .-... ---
`-.- patch -..-. Patch ..-..-- .-.. install ..- folder
..-.....`. ...., .....-. ,.. `..-.-.-. BookWorm -...-..- patch
..`..,.. `..-. .-.... serial ...-.-. Teleport Pro .. ..-.
, .-. .-. . .. . `.. -. .-. . -.. . . registered ..`......- routine -.-
`. -...,..- routine - .- ` . . ,. -, .- - - .- ` .- ` ..-. `
"Myanmar Cracking Team proudly PRESENTS" . - .....- _ ..` . Trial Version
.-.- Registered Version . - . , ... ...-.
,
,....-. patch `.- .,.`. ........`..-. ..-.-. ..
-, . cracker .- . . - patch ,_ .`.. ` . .,-.-. .-. .,
-.-. .`. cracker .- ..- patch ,_ .`.. -.
, Beginner . patch ` . (Plain Stupid Method)
' Dac gi f; p Ofat mu fr Smaw mhv lo p fw e f; aw Gv ky fav hv ky fx &Sdw Jhpatch v ky fe n f; aw Gu dkt o Hk; jy Kjy D; crack
v ky fMu n fhr Sm jz p fy gw , f/ Patch v ky fMu n fhz dkUa&G; x m; w Jh y &dk* &r fu aw mh Exe password aq mhz f0 Jv fu dk
t o Hk; jy Kjy D; protect v ky fx m; w Jhcalculator (calc.exe) y &dk* &r fjz p fy gw , f/ Calculator y &dk* &r fu dkMicrosoft
Windows &JU system32 folder at mu fr Sm t v G, fw u law GUEdki fy gw , f/ Exe password aq mhz f0 Jv fu dkaw mh
www.salfeld.com r Sm download v ky f, lEdki fy gw , f/ Exe password aq mhz f0 Jv f[ m u dk, fr o Hk; ap c si fw Jh
y &dk* &r faw Gu dk t jc m; o law G r z Gi fhEdki fat mi f password e JU u mu G, fr Iay ; Edki fw Jh aq mhz f0 Jv fw p fc kjz p fy gw , f/
o i fht ae e JU ' Dy &dk* &r fu dkz Gi fhc si f&i f r Se fu e fw Jh password u dk &dku fx n fhEdki f&y gr , f/ au mi f; jy D? patch r v ky fc i f
y x r q Hk; v ky f&r Smu aw mh Exe password u dkz Gi fhjy D; calculator (calc.exe) y &dk* &r fu dk password ay ; z dkUy g/
y Hk( 2) /
,., Patch `. (Beginner/Intermediate/Advanced)
,
,
,.. `..--. -,.-.-. calc.exe .-..- "DEADBEEF" .- password ..` .
-.- . - .. . icon ....`.....-. .-... ,
,
Password , -.-...- calc.exe . - . -_ .. . ,,- . password
.-..- dialog box -.....
,,
Password - . , -, . ... - _ . . .-. ,- . `. .. .
,
. -,.-.-.,, .- password .. - . ..-..-. ......` .,..`.
.-. password - . . ... .. .`.. ... , .- patch ,_.-.. ........`..-
-- patch . -....-_-... ,.. `..- "Password is incorrect" .....-
... - - -. . . . - .. Olly . . calc.exe .-. ,-. `....
,
,., Patch `. (Beginner/Intermediate/Advanced)
.
,.. right-click .`. Search for - All referenced text strings - ... Window
.. -. .. . .. window .. right-click .`. Search for text -... ,,-.
`....
,,
,,.. -,.-.-..- "Password is incorrect" .....- .-_`. OK -...-
.,-. `....
.,
.,- hightlight `...,-.,..- mouse , ..-.- .,-. .-..
.,
.,- ...-_ ,- error message -`- routine (VA 0054C8AC) - .- .
.. --. .-. error message routine -...-.-. CALL calc.00435C4C - ..-. . -.
.-. VA 0054C87C - JNZ instruction - CALL calc.00435C4C - .-. . ` . .. - .
,
,
,., Patch `. (Beginner/Intermediate/Advanced)
.
,.. . .-. CALL calc.00435C4C -.-..-. VA 0054C873 - JE instruction
`.. -. .-. VA 0054C86E .,... . breakpoint .- . - ` . F9 - . ,- .
`. ...
,
,- textbox .. "Cracker" .-_- -,.-.- breakpoint .-.-..-
.,..- -,....-... ,
,
,- VA 0054C86E .,..- ...- . register windows --.--_.. ,
,
,- -_-. EAX register .. "pFTZ^UC" ...... ` . EDX register .. "wqt}
wutt" ...... .,-. .- ... --. .-. "wqt}wutt" . -. ,. . -, .-.-.-_-
password - encrypt ..-.....`..-. "pFTZ^UC" -.-. "Cracker" - encrypt ..
-. ,. .`. .- VA 0054C86E - CALL routine -.-. "pFTZ^UC" , "wqt}wutt" -
_ ._ .. -. --. _ . error message - .-. . ... . . -, .-. - patch -_ -
.. . , -.-. CALL calc.004046A0 .,... . NOP instruction , ... .` . JE SHORT
calc.0054C8D7 .,... ..-. JMP SHORT calc.0054C8D7 , ... ... . ... .,... ..-.
-, .-. .,, JE - JMP ` -.-. .. . - - NOP (No operation) ` -.
-.-. password ..- .....-.`..-. JMP instruction -.-. error message - - .
.-..-.`..-., `-..-. ,,-. `....
,., Patch `. (Beginner/Intermediate/Advanced)
,
,,
,,-. ``...-. right-click .`. Copy to executable - All modification -.`.
.- ...- Patch ..`.....- ..... .-.-_- ..-
password dialogbox .. --- password - . - _ - .-......
, Inter mediate . patch ` .
-. . ..-. cracking , - .- ` . . - . patch ` .- .. .. -_ ..
-..-. -.....- ....... ......- .-..-.-. MrBills `.. -.
. -.. - -.,- . . ...- . .-. - . - . - ... .` .`.. . . -.. -. .- - .
` ... .-. - . .,.- ` . ... . - `... .- crack ` .. ..--. .- .-. MrBills
- SND Team . download section .. . download ...-. Lena . reversing tutorial
(7) . . MrBills - -. -_ . _ . .....-. .- .. .
. -.. .-. .- . ... . -.. - Olly , PEiD -.. .-_-.. ,. ,
,
,
PEiD -.-. PE ..-.......- packer cryptor , compiler ......--
......- tool -.`..-. PEiD . plugin -.`..- Krypto Analyser - ..-_..
plugin ..-. module .- - .. .. - . ` .... crypto algorithm .-- plugin - Krypto
..--.-, ...`...`. ....-.
,- -_.... MrBills .- ....-. pack ..`...- .- Visual C++
7.0 , ........-.- .-... MrBills . version -.-. 2.1.0.1 `.. -.
,,
,., Patch `. (Beginner/Intermediate/Advanced)
,
,,- Plugins . Krypto Analyser - ...-. .,-. `....
.,
.,- -_.... ..`..- crypto algorithm .- - .- .-. CRC check
.-..- .,.-..,....-.. .. ... .. . `.. -. .-. .` PEiD - - - ..
,- -_- -,.-.- .-..- run (F9) -_ .. . .,- . .- .
..
.,
.,.. `..--. -,.-.- register .....-. About -.-
,
About - . - . ,- . `. ... . ..-. -, .-. - ...-.. .. - .
-. Register -...- ,-. `....
,
,., Patch `. (Beginner/Intermediate/Advanced)
,
,... -,.-.- register .` -..-...-. register ..
... ... - .- . - . .`.., -, .-. - .. .` . register -_-..
,
,
-,.-.- -..-..-. ,- `..-.
,
.,-. -,.-.- patch ....,.. -,.-. .,, . , ..- . . text string
.- - -. . ... . -. . .` ` .` .,. . . -,.-.--... ,_...- ..`.
... .-. text string .- - ...- ... - .-.. .- .-...- .-..`
-,.-.--.-- ..--... Olly . `,...- ,
,,
Text string .- - . .. ,,. . rightclick .- `.. Search for - All referenced
text strings - ...- . text string window .. . .. Text string window . .
rightclick .`. -,.-.-..- text - .... , ..... .-..-.-.-. text
string window . .. . ...- .. scroll `.. rightclick . .
,
. -,.-.- ...,- text - ...-` ,
,
,., Patch `. (Beginner/Intermediate/Advanced)
,
.-. text ... VA 004299BD .,..- ..-.- ,,-. `....
,,
,- VA 004299BD -. "You have entered an ..." - messagebox ......
` . .,-. ..- - scroll ,_.,_..`.-_-. .,-. `....
.,
-,.-.--.`.- VA 004299F3 . . VA 004299BD - BadBoy message `.. ` .
VA 004299F3 -.-. GoodBoy message `.. -. ,,- JNZ -. VA 004299F1 . jump
`.. ..-..- .-. - .- . ..-. JNZ -. VA 004299F1 . jump .`..-. .-.
"You have entered an invalid email ..." .- BadBoy message - `. .-. --. JNZ
.,.... JMP .`. . .. . . .........
.,
.,- TEST AL, AL - -_- AL -. GoodBoy .. BadBoy ...-. ..`.-
-. AL - VA 004299AD - CALL function . . .- . - ..-. `.. .-. -..-.
..-. -.-.... CALL function ......-- .-.--.-. `..-...
-. registration .....- `..-. .,.... .--`-.-.-. -,.-.-.,,
CALL function .. AL - -..-.-....-.- .......`.-.-
.-. VA 004299AD .,..- breakpoint .- . - - .. .- - -...
-, .-. - .,, serial -. . , -, ` . . .. .. ...- . - .- . ..-. TEST AL, AL
- - CALL . .. - .- . - .. , . . AL -. -, . .- . . ...-. . - . .
..-..... .-..- register . Goodboy message ... VA 004299F1 - ...-...
..--..-. jump .`.. . . Badboy message ....
. . JNZ .-. register .-- AL -. . _, _ ., ..- .
VA 004299AD . .- scroll ,_.,_...- .-_--... ,
,
,- text .- -. -, .-. - - - -.. ....- . About box . . .- ...-
Registration - `, run -_--... CALL .. -..-...-. ... VA
004299AD . . breakpoint .- . - ..-.
. - - Plain stupid method ._ BadBoy - .-....., conditional jump ..... patch
` ...`.. ._ ........`. ,_.._ .......- register ., - - ..- ` .
.. .
,., Patch `. (Beginner/Intermediate/Advanced)
,,
.-. . , . . -, .-. - .,, CALL - ...- ` . register `.. .`..
..`.-- AL - patch . -......
-,.-.- ,-. register -_--... F9 -.
,
"Register Now" button - . - - . . ,- -, .-. - breakpoint .- . - - -
VA 004299AD .,..- ...-.-. ,
,
F7 - .`. CALL -_-... . -,.-.- CALL ...-.` ,
,
.,.- -..- `.. . . -. . ... .-. F8 - .-.. .,.... AL -,...`..
...-..-- ...-_.-.-.. .`.... ,,
,,
.-. . . ...- .-..- - .- ..-. . . ,- VA 0040715A .,... . TEST AL, AL
- .- ...
,
,., Patch `. (Beginner/Intermediate/Advanced)
,
`..-. VA 0040715E - [5076A0] .,.- VA 00407163 - JNZ VA 00407170 -
TEST AL, AL VA 00407174 - [5076A0] VA 00407155 - CALL - ...-_
-.....- `. . AL - VA 00407155 - CALL .. .-.-`.....-. .-.
CALL . . -..- `.. . . -. . . . Enter key - .- .-.....- Enter key -
. ` ...`. - .- - .`.. . -. ... - .- - .-. run .. .---. -.-- run
.... - CALL ...- ---_-. .-. .-. instruction pointer . -_ .,
..- Enter key .-- VA . . . . . ,
,
VA 00407155 - CALL .,.... Enter key - .-- ,,- . `. .-.
,,
-_--... VA 00407007 - MOV BL, AL VA 00407011 - MOV AL, BL
AL - BL --, . ..- `, .. -. .. . AL --, . .- BL . ...-. VA 00407009
- CALL -. BL (& AL) . -.. - ..- ...- . .. -. . .,, ,.._ . . ... AL
.-,..- VA 00406FF9 - CALL . . . .`.- ..-. .-. .` AL - VA 00406FF9 -
CALL 00406F4B .. .-.-..-.. CALL .,..- breakpoint .- . - - -...
.- `.. .- , . . -, .-. - -. CALL .- ...- ..- .,.-.- ..- . -
.... .- -, .-. - -. CALL . . -.. -. . -.. . . CALL .,... . Enter key - .-.
.-.- AL - VA 00406FF9 - CALL .. .-.-..... ...... -,.-.- break-
point .-.-..- .,......-.. F9 -... . -,.-.- breakpoint .- . - ..-
.,..- ...- .` .,
.,
.,.- . - ,.._ . . - - .. ....- .-.
, AL . -,..- .-...
, AL . -,..- .-.--. ....- CALL - execute ...`..-.
, CALL - F7 .
,, AL , -.-- --.-- ..
,., Patch `. (Beginner/Intermediate/Advanced)
,
.,
.,.. `..--....-. AL -. ._.`..-. .-. TEST AL, AL -
-,..-. `,-,.. AL -. . _.`.. . -. CALL - run . F8 -. AL -,..
.`.....-.- .-... ,,
,,
.-. VA 00406FF9 - CALL .. AL -, . .- . _ .- . - - -.
Registration .. `. ` . .. - . -..- .- `.. . . ... F8 - .
.,.- . - .. .- .,.- . .- . . AL , BL . -, . ..- -. .`. .. ... . -.
-
,,
,,- MOV BL, AL - execute - . BL . -, . .-._ . . _`.. . ... . -.
..-. AL - . _`.. ., ,,
,,
,,
,,- VA 00407009 ...- CALL - execute `.,...-. AL . -, . .-. 1
.`. .. ..-. .- .-. VA 00407011 - MOV AL, BL - -_ BL --.- -. AL
. . ....-.
INFO: : --. .-..-. EAX register ,- ... .. .-,..- `..
register .. ...........
-, .-. .,.- -. - . . .` ... . .. ..,, .-.. -.-..-
...- ..... .`.. -.
,., Patch `. (Beginner/Intermediate/Advanced)
,,
,,,
,,,. ..-. AL . -,..-. BL .-. . _`, `.. . ..-. .-. VA 00407009 -
CALL -. AL , BL . -..-...-.. ..-..`.- -,.-.. .-.--.--. .,.,`
. AL . .`.,- .- . - -.-. VA 00406FF9 - CALL . . .,.- . ..,, -, .-.
- . . CALL Enter key - .. CALL - . -.,. . ... . F8 ., F7 -.-
,,-. `.....
,,
TEST AL, AL - `, . , . . AL . -,..-. ._.`..-. .-... JNZ ._
register `.`...`..,
.,.... AL -.-.`.. . . -. . . - -... F8 - . - - AL . -, . .-.
._ `...,-,. ,
AL - pointer [5076A0], ..- . ..-.
,,
Pointer . -, . .-. . _`.. .,...-. ,, Register ...,...-. jump .`..
.-.
.-..` Register ..`....- VA 0040715E - pointer [5076A0], . . , .
. . ...-. . -. ,.._ ... ..- VA 00407174 - pointer [5076A0], . ....
,,
VA 0040716B - CALL -. -, .-. - register ...,.... .-.
.-. unregistered string .--`.- CALL `.. . -. F8 - .- . -_ .. VA 0040
715E - AL , - .- - .- - .,.- .-. .- -.. ..- VA 00407174 -
AL - ...
. .`.,-.-. . - - .. ... ..,..-. ..... .-...-. cracking ,
,_ .. .. - .- . .-- .. -, ..- - - . ...,... .. .-. .-
...- -,.-..,, ....-.........,-. ... .-...- -...,, ,.._
` . .- .,.- . ..-. .,.- ... . , ....- . . -, .-. .,, `., . ... -- `-.
F8 - ..
,,,
,., Patch `. (Beginner/Intermediate/Advanced)
,.
,,,- JMP - .-. . ... -. JMP .,..- F8 ..... ,-. `..
-.
,.,
VA 00407076 . . .,.- pointer [5076A1], -. .- .-. Pointer .- .-. .
. ... -. VA 0040707D - JNZ -. -, .-. - register . ... jump `.. ..
.-. .` F8 -.... -,.-.- ..`... register .`. ... ,.,...-.
-.
,.,
.-..` -,.-.--. -. BadBoy . ...- ... . -. . .. . ,., VA
004299B9 - JNZ -. jump .`.. - . ,
,
.-. register .`..-. -..-`....-. .--_-...
,
. ,- . `. .-. ,.. -,.-.- ...,- CALL - .`
.-..` ,.. OK - .. .` . Olly - .,.- -. - . `, . - .- `.. .- breakpoint
window .. VA 004299AD - breakpoint -.-_... ... .-..- run F9, - `..
, -. register . ,- . -, .-. - .- . - ..- .,..- -, ....- .
..
,
-,.-.-.,, .,-,- CALL - .... F7 -.`. VA 004299AD - CALL -
..
,., Patch `. (Beginner/Intermediate/Advanced)
,.
,
VA 00407155 - CALL - .- -,.-.- ...--. .-... VA 00407155
...-. F7 - . ,,-. `....
,,
VA 00406FF9 - CALL ...-._ F8 - ..
,
,- MOV BL, AL - .-...-. ,...-. VA 00406FF9 - CALL -.
-,.-.- ...... CALL . .`.- ..-. .-. F7 -.`. CALL ..
,- . `. ...
,
AL - -... .-.-....-. ..-_.. ..-- scroll .. -.-
.-. .-. ......- .- -. .. .- . `.. ... .......-. - . -, .-. .,,
serial . , . , .. ...- .,..-. - . .. . -. ... - .,.- .-. .`... .-.
AL - patch . - ...... --. .-. -, .-. .,, - .- - -. .-, - .. ...
... - Advanced Level Patching .-.
,,
.-. VA 00406FC5 - BL - .`. .. - ...... .,
,., Patch `. (Beginner/Intermediate/Advanced)
.,
. -.-. `..-. `.. .. ., . .. VA 00406FC5 .,... . -, .-. - MOV
AL, 1 ., INC AL .`. .. - . .. . .,, .. . ..
.,... . -, .-. . .`... . -.. .- , - .. . .,..-- - execute -.
... . -.. -. AL == 1 , .--. register ..., --.`....-. .-..-
--. register ..`.... .-..-. unregister `....-. .-. -,.-.- .
-,.-. VA 004299AD - JNZ .,.... JMP .`..,.. .-..-. -...
register `.....`. .,.--., .-..- `,.,.. unregister `.. . ..` . `.. -.
..-...`-.-- .-.- ......-.
MOV AL, 1 . ,
MOV BL, 1 ., NOP
...-.-. .-..- register `.. .. . .. -. `.. `.. .- .. .- ,..._ ...
....- ....- . .,.- ., ..- -. . .. ... . , . ..-. -, .-. - MOV BL, 1 -
assemble -. . . - -...
-, .-. - .,, BL - -. .,... . .- . - ... . -. . ... VA 00406FBC -
CALL - ` .. .. -. ... ...... .-. ..- , .-. -.-.
.,
.,
F9 - .`. -..-`....-. -_.. ,
,
,- OK - .-. ,- [Unregistered] .-..... ..-...-. .-...
,
,--_. .,.--.-. register .....-.-. .-...
,
...-. intermediate . patch `.-.-. ..`... `......` Patch
` ..... - . . .- ..._ , . . . -
,., Patch `. (Beginner/Intermediate/Advanced)
, Advanced . patch ` .
y Hkr Se ft m; jz i fhaw mhplain stupid patch v ky fw Jhe n f; ? intermediate patch v ky fw Jhe n f; aw Ge JU register
v ky fw m t q i fajy Edki fay r , fht jr Jw r f; aw mhr jz p fEdki fy gb l; / ' gaMu mi fh' Dw p fc gr Sm advanced t q i fhpatch v ky f
Mu n fhMu r Smjz p fy gw , f/
INFO: : Plain stupid patch u aw mh JE w dkUv dk conditional jump aw Gu dk t jr Jw r f; jump jz p fap at mi f
v ky fw Jhe n f; jz p fy gw , f/ Intermediate patch u aw mhCALL x Ju AL w e fz dk; u dk1 jz p fat mi fv ky fjy D; jy e fx Gu f
v mc sde fr Sm register jz p fap w my g/ Plain stupid method u dk &dk; &Si f; p Gm b mo mjy e f&r , fq dk&i faw mh ]Register
r jz p fao mfv n f; BadBoy u dkau smfv Tm; jc i f; } jz p fy gw , f/
INFO: : Intermediate patch u aw mh MOV AL, BYTE PTR DS:[EAX+24] w dkUv dku k' faw Gu dkaw GU&i f
MOV AL, 0 v dkUajy mi f; r Smjz p fjy D; o lUu dk b mo mjy e f&r , fq dk&i faw mh ]v dkt y fw Jht y dki f; t w Gu f register jz p fap
jc i f; } jz p fy gw , f/
INFO: : Advanced patch u aw mh b , fae &mr Sm pointer w e fz dk; u dk o w fr Sw fo v Jq dkw mu kd x Jx J0 i f0 i f
av hv mw mjz p fjy D; pointer t w Gu f setting u kdo m patch v ky fw mjz p fy gw , f/
' Do i fc e f; p mt w Gu f av hv mz dkU&n f&G, fx m; w Jh y &dk* &r fu aw mh Noah's Ark Deluxe 1.1 jz p fjy D;
www.popcap.com r Sm t c r Jh download v ky f, lEdki fy gw , f/ y &dk* &r f ( WinNoah.exe) u dk z Gi fhv dku f&i faw mh
y Hk( 6 3 ) t w dki f; jr i f&r Smy g/
y Hk( 6 3 )
u p m; c Gi fho u fw r f; u ke fo Gm; jy Djz p fw Jht w Gu f register v ky f&aw mhr Smy g/ Register v ky fMu n fh&i faw mh
y Hk( 6 4 ) t w dki f; jr i f&y gw , f/
y Hk( 6 4 )
,., Patch `. (Beginner/Intermediate/Advanced)
y &dk* &r f&JUo ab mo b m0 u dko do Gm; jy Dr dkUOlly r Smu k' faw Gu dkz Gi fhMu n fh&at mi f/ y Hk( 6 5 ) /
y Hk( 6 5 )
y Hk( 6 5 ) u aw mh WinNoah.exe &JU EP &Sd&mjz p fy gw , f/ y Hk( 6 4 ) u Badboy message u dk&SmMu n fh&
at mi f/ y Hk( 6 6 ) /
y Hk( 6 6 )
Search u ae text string (Badboy message) aw Gu dk&Smw Jht c g y Hk( 6 6 ) t w dki f; jr i f&y gw , f/ ' Dae &m
aw Gr Sm breakpoint o w fr Sw fjy D; double-click ESdy fv dku fy g/ y Hk( 6 7 ) /
y Hk( 6 7 )
y Hk( 6 7 ) r Smjr i f&w mu aw mh BadBoy u dkac : o Hk; w Jh CALL &JUt p jz p fjy D; VA 0041A315 e JU VA
0041E853 w dkUu ae ' DCALL u dk ac : o Hk; Mu w mjz p fy gw , f/ VA 0041A315 e JU VA 0041E853 &Sd&mu dk
Mu n fhv dku fMu &at mi f/ y Hk( 6 8 ) /
y Hk( 6 8 )
y Hk( 6 8 ) u dk ao c smMu n fhr , fq dk&i f BadBoy CALL aw Gq Dr a&mu fc i fr Sm CALL DWORD PTR
DS:[EAX+40]; q Dt &i fo Gm; jy D; registeration v ky faq mi fc su fat mi fjr i fjc i f; &Sd^ r &Sd p p faq ; w maw GU&y gw , f/
p p fv mv dkU&w Jh&v ' fu dk AL r Smo dr f; y gw , f/ jy D; &i f BadBoy u dkau smfjc i f; &Sd^ r &Sdp p fy gw , f/ ' gq dk BadBoy u dk
au smfEdki fz dkU JNZ ae &mr Sm JMP v dkUajy mi f; Mu n fhy gr , f/ jy D; &i faw mh jy i fx m; w Jhu k' fu dk o dr f; q n f; v dku fjy D; y &dk
* &r fu dk jy e fz Gi fhMu n fhv dku fy g/ ESp fo u f&mt r n fe JU ESp fo u f&mu k' fu dk &dku fx n hfv dku f&i f ' D* dr f; u dk u p m; v dkU&w m
aw GU&y gw , f/ ' gay r , fh ' D* dr f; [ m register v ky fw Jht c sde fr Smy J registered jz p fy gw , f/ t jr Jw r f; registered
jz p fjc i f; r &Sdy gb l; / ' gq dk&i f ae mu fx y fx y fjy i fz dkUv dkt y fae y gjy D/ Olly r Smae mu fx y f&Smv dku fMu &at mi f/ y Hk( 6 9 ) /
,., Patch `. (Beginner/Intermediate/Advanced)
y Hk( 6 9 )
y Hk( 6 9 ) u string aw G&Sd&mu dkMu n fhv dku fMu &at mi f/ y Hk( 7 0 ) /
y Hk( 7 0 )
y Hk( 7 0 ) u aw mh register v ky fx m; jc i f; &Sd^ r &Sdp p fw Jh CALL &JUt p jz p fjy D; o lUu dk ac : o Hk; w Jh VA aw Gu
aw mh 41A158? 41A479? 41D469 e JU 420431 w dkUjz p fy gw , f/ ' Dae &maw Gr Sm breakpoint o w fr Sw fjy D;
y &dk* &r fu dk run (F9) Mu n fhv dku fy g/ y Hk( 6 3 ) t w dki f; jr i f&y gr , f/ y Hk( 6 3 ) u Click Here to Register Now.
u dka&G; v dku f&i f y Hk( 7 1 ) t w dki f; jr i f&y gw , f/
y Hk( 7 1 )
y Hk( 7 1 ) r Smjr i f&w mu aw mh u Re faw mfw dkUae mu fq Hk; o w fr Sw fv dku fw Jh breakpoint av ; c kx Ju w p fc kr Sm
v m&y fw mjz p fy gw , f/ ' Dae &mu dkregister v ky fr So ma&mu fr Smjz p fy gw , f/ Registered jz p fx m; w Jho lw p fa, mu f
[ m ae mu fx y f register v ky fz dkUr v dkaw mhw Jht w Gu f ' Dae &mr Sm Click Here to Register Now. t p m; Click
Here to Play. jz p fae &r Smy g/ ' Dae &mu dk au smfEdki fr , fq dk&i f register v ky fp &mr v kdaw mhb l; v dkU x i fy gw , f/
' gaMu mi fhy Hk( 7 1 ) u JE ae &mw dki f; r Sm JMP v dkUjy i fjy D; y &dk* &r fu dko dr f; v dku fy g/ o dr f; x m; w Jhy &dk* &r fu dkz Gi fhMu n hf
&i faw mh y Hk( 6 3 ) t w dki f; jr i fae &OD; r Smjz p fjy D; registered r jz p fy gb l; / ' gaMu mi fhr dkUv J conditional jump aw Gu dk
jump v ky fw dki f; v Jregistered r jz p fb l; v dkUu Re faw mfajy mc Jhw my g/
au mi f; jy D/ y Hk( 7 1 ) u VA 4203E7 (CALL DWORD PTR DS:[EDX+10]) ae &mr Sm breakpoint
o w fr Sw fjy D; b , f CALL u dkac : o Hk; w , fq dkw m Mu n fhMu &at mi f/ y Hk( 7 2) /
y Hk( 7 2)
MOV ECX, DWORD PTR DS:[ESI+50]; // ECX= DS[00B78E70] = VA 49C518
CMP BYTE PTD DS:[ECX+328], BL; // DS[49C518+328] = 49C840, BL = 0
VA 00498C40 &JUdata window r Sm b mw e fz dk; &Sdo v Jq dkw m Mu n hfv kdu fMu &at mi f/ y Hk( 7 3 ) /
,., Patch `. (Beginner/Intermediate/Advanced)
,
y Hk( 7 3 )
y Hk( 7 3 ) r Smjr i f&w Jht w dki f; DS[49C840] u byte w e fz dk; e JUBL &JUw e fz dk; u dkEdIi f; , SOfw Jht c g n Dc Jh&i f VA
420416 u dka&mu fv mr Smjz p fy gw , f/ y Hk( 7 4 ) /
y Hk( 7 4 )
VA 420419: CMP BYTE PTD DS:[ECX+328], BL; // DS[49C518+328] = 49C840, BL = 0
VA 420419 u DS[49C840] u byte w e fz dk; e JU BL &JUw e fz dk; u dk ae mu fw p fMu dr fEdIi f; , SOfw Jht c g
n Dc Jh&i f VA 420424 u dka&mu fv mr Smjz p fy gw , f/ ' Dv kde JUEdIi f; , SOfv mw Jht c gr Sm VA 00420431 u CALL u dk
au smfo Gm; Edki fw m aw GU&y gw , f/ ' gq dkb maMu mi fh* dr f; u dku p m; v dkUr &w my gv J/ w u , faw mhVA 00420431 u
CALL au smfEdki fjc i f; [ m t jr Jw r f; r [ kw fv dkUy g/ jy D; &i f BL &JUw e fz dk; u dkdump window &JUVA 00420431 u
byte w e fz dk; e JU ESp fMu dr fEdIi f; , SOfw m aw GU&y gw , f/ ' gaMu mi fh ' Dae &mr Sm o kn t p m; 1 v dkUajy mi f; jy D; y &dk* &r fu dk
run (F9) Mu n fhy g/ y Hk( 7 5 ) /
y Hk( 7 5 )
F9 u dkESdy fjy D; Mu n fhr , fq dk&i faw mhy Hk( 7 6 ) t w dki f; w e fz dk; aw Gajy mi f; v Jo Gm; w maw GU&y gw , f/
y Hk( 7 6 )
y Hk( 7 4 ) u VA 4203E7 r Sm&Sdw Jhbrekapoint u dkjz Kw fjy D; F9 u dkEdSy fv dku fy g/
y Hk( 7 7 )
,., Patch `. (Beginner/Intermediate/Advanced)
F9 u dkESdy fv dku fw Jht c gr Smaw mh y Hk( 7 7 ) t w dki f; jr i f&r Smjz p fy gw , f/ ' gq dk dump window &JU VA
0049C840 r Sm 1 v dkUjy i fz dkUq Hk; jz w fc Jhw m r Se fo Gm; y gw , f/ y &dk* &r fu dk Ctrl+F2 (restart) ESdy fjy D; jy e fz Gi fhv dku fy g/
Dump window &JUVA 0049C840 r Sm 1 v dkUjy i fv dku fy g/ jy D; &i faw mhdump window r Sm right-click ESdy fjy D;
Copy to executable file u dka&G; w Jht c g y Hk( 7 8 ) t w dki f; jr i f&y gr , f/
y Hk( 7 8 )
y Hk( 7 8 ) r Sm right-click ESdy fjy D; ESp fo u f&mt r n fe JU z dki fu dko dr f; v dku fy g/ jy D; &i f u Re faw mfw dkU o dr f; x m; w Jh
z dki fu dkjy e fz Gi fhMu n fhv dku fMu &at mi f/
y Hk( 7 9 )
w p fc kc kaw mh x y fr Sm; ae jy Dx i fy gw , f/ y x r t Mu dr f u k' fjy i fjy D; run w ke f; u y Hk( 7 7 ) t w dki f; jr i f&y g
w , f/ c kz dki ft ae e JUo dr f; jy D; c sde fr Smaw mh y Hk( 7 9 ) t w dki f; jr i fae &y gw , f/ ' gaMu mi fh u k' fjy i fjy D; o dr f; v dku fw Jhz dki fu dk
Olly r Sm jy e fz Gi fhMu n fhv dku fMu &at mi f/ y Hk( 8 0 ) /
y Hk( 8 0 )
Dump window &JU VA 0049C840 r Smaw mhu Re faw mfw dkU o dr f; x m; w Jht w dki f; y J&Sdy gw , f/ ' Dae &mu dk
ap mi fhMu n fhz dkUaw mhv dkae jy Dx i fy gw , f/
y Hk( 8 1 )
' gaMu mi fh ' Dae &mr Sm y Hk( 8 1 ) t w dki f; hardware breakpoint o w fr Sw fjy D; ap mi fhMu n fhy gr , f/ Dump
window r Sm right-click ESdy fjy D; Breakpoint u Hardware, on write Byte u dka&G; v dku fy g/ jy D; &i faw mh
F9 u dkESdy fjy D; b maw Gajy mi f; v Jo Gm; o v Jq dkw m ap mi fhMu n fhv dkU&y gjy D/
,., Patch `. (Beginner/Intermediate/Advanced)
y Hk( 8 2)
w &m; c Haw mhaw GUy gjy D/ VA 0042ABFE u MOV BYTE PTR SS:[EBP+328], BL u dkexecute
v ky fjy D; c sde fr Sm dump window u VA 0049C840 &JUbyte w e fz dk; ajy mi f; o Gm; w mjz p fy gw , f/ F9 u kdx y fEdSy fy g/
y Hk( 8 3 )
y Hk( 8 3 ) r Smjr i f&w Jht w dki f; AL u v J o kn w e fz dk; u dk v majy mi f; y gw , f/ au mi f; jy D ' Dae &mESp fc kr Sm 1
v dkUjy i fv dku fjy D; z dki fu dko dr f; v dku fr , fq dk&i fau m/ ' gq dk&i faw mhy Hk( 8 4 ) t w dki f; jr i f&r Smjz p fy gw , f/
y Hk( 8 4 )
e d* Hk; c sKy ft ae e JUajy m&&i f Noah's Ark u dkregistered jz p fap z dkUu Re faw mfw dkUt ae e JUat mu fy gae &mESp fc k
r Sm u k' faw Gu dkjy i fay ; c Jh&y gw , f -
1 / VA 0042ABFE u MOV BYTE PTR SS:[EBP+328], BL u dkMOV BYTE PTR
SS:[EBP+328], 1?
2/ VA 0042D6B8 u MOV BYTE PTR SS:[EBP+328], AL u dkMOV BYTE PTR
SS:[EBP+328], 1/
o i fhu dk' Dv dkjy i fz dkUajy mc Jhay r , fhu Re faw mfu aw mhy Hk( 8 5 ) t w dki f; ae mu fw p fr sdK; jy i fc Jhy gw , f/ OmP f&Sdo v dk
Mu dKu fo v dkjy i fEdki fy gw , f/
y Hk( 8 5 )
,., uPP `. patch . ., - .` .
,
tcef;(11) - uPPP jzif h patch zdkif zefwD;jcif;
' Dw p fc gr Sma w mh uPPP u dk t o Hk; jy KNy D; patch z dki fa v ; a w Gu dk z e fw D; Mu n fhy gr , f/ y x r q Hk; patch
z dki fa v ; a w G& JU o a b mo b m0 u dka v hv mMu n fhy gr , f/
- Patch z dki fa v ; a w G& JU t u sdK; a u s; Z l; u a w mh z dki fq dku fa o ; a o ; a v ; e JY a q mhz f0 Jv fu dk crack v ky fE dki fw m
jz p fy gw , f/ q dkv dkw mu crack v ky fx m; Ny D; o m; z dki fu dk upload v ky fa y ; p & m r v dkt y fw Jht w Gu f t i fw me u fr Sm
1MB a u smfw Jh crack v ky fx m; w Jh r l& i f; z dki fa w Gu dk upload v ky fa y ; p & m r v dka w mhb J 200KB a v mu fo m& Sdw Jh
patch z dki fv Sv Sa v ; a w Gu dky Jt i fw me u fr Sm w i fa y ; p & m v dky ga w mhw , f/
- Patch z dki fa w G& JU t m; e n f; c su fu a w mh r dr d b , fa e & mr Sm crack v ky fx m; o v Jq dkw mu dk developer a w G?
t jc m; cracker a w Gu t v G, fw u l & dy fr do d& Sda p E dki fw m jz p fy gw , f/ ( ' Dt c g developer a w Gu ' Da e & mu dk
crack r v ky fE dki fa t mi f u k' fa w Gu dk jy e fv n fjy i fq i fE dki fo v dk t jc m; cracker a w Go d& Sdjc i f; t m; jz i fh r dr d crack
v ky fw Jhe n f; v r f; u dkt w kc dk; E dki fy gw , f/ )
- Patch z dki f& JU u e fYo w fc su fu a w mh patch z dki fz e fw D; o l[ m t r Sm; t , Gi f; w p fp Hkw & m jy Kv ky fr dc Jh& i f crack
v ky fc H& w Jhz dki f t v ky fr v ky fw my gy J/
- Patch z dki ft a o e JY patch z dki ft & Si fq dkNy D; E Sp fr sdK; & Sdy gw , f/ Patch z dki ft a o a w Gu a w mh o w fr Sw fx m; w Jh
version u dko m patch v ky fE dki fy gw , f/ Version a jy mi f; & i f t v ky fr v ky fa w mhy gb l; /
, Inter net Download Manager 6.0.x - - patch . .,-.`.
Patch z dki f r z e fw D; c i f uPPP u dka v hv mMu n fh& a t mi f/
y Hk( 1 )
y Hk( 1 ) r Smjr i f& w mu c & u fv ky fr , fh application e JYy w fo u fw Jh t c su ft v u fa w Gy g/ ' ghjy i f a q mhz f0 Jv f
u dkcrack v ky fo l? crack v ky fw Jha e Yp GJw dkYu dky g x n fho Gi f; E dki fy gw , f/
y Hk( 2 )
y Hk( 2 ) r Sma w mh b , fv dk patch v ky fc si fo v Jq dkw mu dk a & G; c s, fE dki fy gw , f/ Patch v ky fe n f; ( 4 ) e n f;
& Sdy gw , f/ ( ' Dt y dki f; r Sma w mhSeek & Replace pattern e JYRegistry patch w dkYu dkt o Hk; jy Kr Smjz p fy gw , f/ )
,., uPP `. patch . ., - .` .
.
y Hk( 3 )
y Hk( 3 ) u a w mhu dk, fa y : a p c si fw Jhtemplate a v ; a w Ge JYq dki fy gw , f/ E Sp fo u f& m font? E Sp fo u f& m" mw fy Hk?
E Sp fo u f& mw D; v Hk; ? E Sp fo u f& m icon w dkYu dk a & G; c s, fE dki fy gw , f/ ' Da v mu fo dNy D; o Gm; Ny Dq dka w mh patch z dki fu dk
p w i fz e fw D; v dku fMu & a t mi f/
y x r q Hk; Olly r Sm patch v ky f& r , fh a e & mu dk & SmMu & a t mi f/ ( IDM 6.0.8 Build 3 e JY e r le m
jy x m; jc i f; jz p fy gw , f/ )
y Hk( 4 )
TEST EDI, EDI (85 FF) a e & mu dk XOR EDI, EDI (33 FF) e JY t p m; x dk; y gr , f/ ' gr So m EDI
w e fz dk; [ m o kn jz p fo Gm; Ny D; "Internet Download Manager has been registered with a fake Serial
Number. IDM is exiting..." q dkw JhMessageBox u dka u smfv Tm; E dki fr Sm jz p fy gw , f/ ' ga y r , fh o i fht a e e JY
r Sw fx m; & r Smu y & dk* & r fu k' fa w Gx Jr Sm TEST EDI, EDI [ m t r sm; Mu D; y gy gw , f/ u Re fa w mfw dkY a & G; c Jhw mu
Seek & Replace method jz p fw Jht w Gu f TEST EDI, EDI w dki f; u dk XOR EDI, EDO w dki f; e JY
t p m; x dk; r , fq dk& i f y & dk* & r f[ m crash jz p fy gv dr fhr , f/ ' ga Mu mi fhy dkNy D; w du sw Jht c su ft v u fa w Gu dk a y ; & y gr , f/
' ga Mu mi fh8B F8 83 C4 04 85 FF 74 0A u dk8B F8 83 C4 04 33 FF 74 0A e JYt p m; x kd; y gr , f/
a e mu fx y f patch v ky f& r , fhw p fa e & mu a w mhy Hk( 5 ) r Sm jr i f& w Jht w dki f; jz p fy gw , f/
y Hk( 5 )
,., uPP `. patch . ., - .` .
.
IDM [ m "Internet Download Manager has been registered with a fake Serial Number.
IDM is exiting..." u dk encrypt v ky fx m; Ny D; w u , fv dkY u Re fa w mfw dkY& JU serial [ m t Ge fv dki f; u o lY& JU
database x Jr Sm r & Sdc Jh& i f nag p mw e f; a y : Ny D; y & dk* & r fu dk y dw fr Smjz p fy gw , f/ ' Da e & mu dk a u smfv Tm; & r Smjz p fy gw , f/
JE 00444532 (74 6D) a e & mu dk JMP 00444532 (EB 6D) e JYt p m; x dk; y gr , f/ PUSH 0 (6A 00) a e & mr Sm
JMP 4444C3 e JY t p m; x dk; y gr , f/ ' ga Mu mi fh 74 6D 6A 00 a e & mr Sm EB 6D EB FC e JY t p m; x dk; y gr , f/
jy D; & i fa w mhy Hk( 6 ) t w dki f; t p m; x dk; z dkYv ky f& y gr , f/
y Hk( 6 )
74 6D 6A 00 t w Gu f t p m; x dk; r , fhEB 6D EB FC t w Gu fq dk& i fv n f; y Hk( 6 ) t w dki f; v ky fNy D; Add to
list u dk a & G; a y ; & y gr , f/ ' gq dk IDMan.exe u dk patch v ky fw m Ny D; y gNy D/ Registry u dk patch v ky fz dkYy J
u se fy gw , f/
y Hk( 7 )
y Hk( 7 ) r Smjr i f& w Jht w dki f; z dki fu dk o dr f; q n f; Ny D; y Hk( 1 ) u Create Patch button u dk a & G; v dku fr , fq dk& i f
u Re fa w mfw dkYv dkc si fw JhIDM patch z dki fu dk& & SdNy Djz p fy gw , f/ y Hk( 8 ) /
y Hk( 8 )
,., uPP `. patch . ., - .` .
, FlyHelp 6.1 -- patch . .,-.`.
' Dw p fc gr Sma w mh y x r y dki f; w ke f; u a q G; a E G; z dkY u se fc Jhw Jh File Drop e JY Offset Patch w dkYu dk a q G; a E G; r Sm
jz p fy gw , f/
y x r q Hk; t a e e JY uPPP u dkz Gi fhNy D; Project-> New v ky fNy D; v dkt y fw Jht c su ft v u fa w Gu dk
& dku fx n fhy gr , f/ ( t y dki f; ( 1 ) r Sm a q G; a E G; Ny D; jz p fv dkYx y fr Hr a q G; a E G; a w mhy gb l; )
y Hk( 9 )
' kw d, t a e e JYu dk, f patch v ky fc si fw Jht r sdK; t p m; u dka & G; y gr , f/ y Hk( 1 0 ) /
y Hk( 1 0 )
' Da e & mr Sm t o Hk; jy Kr , fh e n f; v r f; a w Gu a w mh File Drop e JY Offset Patch w dkYjz p fy gw , f/ Offset
patch u dk a & G; v dku fw Jht w Gu f patch z dki f[ m t a o jz p fo Gm; y gw , f/ q dkv dkw mu FlyHelp & JU a q mhz f0 Jv f
version a jy mi f; o Gm; & i f patch z dki fu t v ky fv ky fa w mhr Sm r [ kw fy gb l; /
w w d, t q i fht a e e JY Offset Patch button u dkE Sdy fNy D; u dk, f patch v ky fr , fh offset e JY byte a w Gu dk
E dIi f; , SOfy gr , f/ y Hk( 1 1 ) / ' Da e & mr Sm offset patch v ky fr , fh z dki fa w Gu a w mh FSWebHelpLib.dll e JY
HtmlViewEdit.dll w dkYjz p fy gw , f/
y Hk( 1 1 )
,., uPP `. patch . ., - .` .
y Hk( 1 1 ) t w dki f; r E dIi f; , SOfc i fr Sm r l& i f; HtmlViewEdit.dll z dki fu dk e mr n fa jy mi f; x m; v dkY r & y gb l; /
Crack v ky fx m; Ny D; o m; HtmlViewEdit(CRACKED).dll z dki fu v n f; t o i fh& Sdx m; & y gr , f/ E dIi f; , SOfNy D; & i f
save v ky fy g/ FSWebHelpLib.dll t w Gu fv n f; t v m; w l jy Kv ky fy g/ ( ' Dw p fc g a q mhz f0 Jv fu dka w mh u dk, fw dki f
crack v ky f& r Sm jz p fy gw , f/ Crack v ky fe n f; u dka w mhr & Si f; jy a w mhy gb l; / )
a e mu fw p fq i fht a e e JY v ky f& r Smu a w mh u Re fa w mfw dkY crack v ky fx m; w Jh z dki fu dk C:\Program Files\Fly
Help z dk' ga t mu f o Gm; x m; z dkYy Jjz p fy gw , f/
y Hk( 1 2 )
o w djy K& r Smu a w mhFly_Help.exe q dkw m FlyHelp.exe u a r G; x kw fa y ; v dku fw Jhchild y & dk* & r fjz p fNy D;
' Dy & d* & r fu dk FlyHelp.exe u dkz Gi hfc sde fMu r S x kw fo Hk; w my g/ u se fw Jht c sde fr Sm jy e fz su fy gw , f/ ' ga Mu mi fh
u Re fa w mfw dkYt a e e JY crack v ky fx m; w Jh u Re fa w mfw dkY z dki fu dk r l& i f; Fly_Help.exe e JY t p m; r x dk; E dki fa t mi fv dkY
READONLY/HIDDEN/SYSTEM w dkYu dka & G; c s, fa y ; x m; & w m jz p fy gw , f/
a e mu fw p fq i fhu a w mhu dk, fMu dKu fw Jhtemplate/theme u dka & G; c s, fw Jht y dki f; jz p fy gw , f/
y Hk( 1 3 )
' gq dk& i fa w mh patch v ky fz dkY jy i fq i fw Jht y dki f; Ny D; y gNy D/ y Hk( 9 ) u Create Patch button u dk
E Sdy fv dku f& Hky gy J/ ' Dt c g y Hk( 1 4 ) r Smjr i f& w Jht w dki f; jy D; jy n fhp Hkw Jhpatch z dki fw p fc ku dk& & Sdv mr Smjz p fy gw , f/
y Hk( 1 4 )
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 162 -
tcef;(12) - Cr acker rsm; owdxm;oifhaom Windows API rsm;
INFO: : API (Application Programming Interface) q dkw mu a w mh function a w Gu dkp kp n f; x m; w Jht & m
jz p fjy D; y & dk* & r fa w Ge JU OS Mu m; q u fo G, f& mr Sm t o Hk; jy Ky gw , f/ Win32 API q dkw mu a w mh function a w G
t r sm; Mu D; p kp n f; x m; w mjz p fjy D; Windows application a w Gt w Gu f low-level programming interface
jz p fy gw , f/ Microsoft u Win32 API & JU t * Fg& y fa w Gt r sm; p ky g0 i fw Jh high-level interface a w Gu dk r dw f
q u fc Jhy gw , f/ ' Dinterface a w Gx Ju t x i f& Sm; q Hk; u a w mh MFC (Microsoft Foundation Classes) jz p fjy D;
Windows e JUq u fo G, fz dkU C++ object a w Gu dkt o Hk; jy Ky gw , f/ w u , fw r f; a w mh MFC u OS u dk a c : o Hk; z dkU
Win32 API u dkt o Hk; jy K& w mjz p fy gw , f/ t c ka c w fr Sm e mr n fMu D; a e w Jh .Net Framework [ mv J OS & JU
service a w Gu dko Hk; p GJE dki fz dkU System q dkw Jh class u dko Hk; p GJw , fq dka y r , fh o l[ mv Ja e mu fq Hk; a w mh Win32 API
u dka c : o Hk; & w my gy J/ Win32 API r Sm t Mu r f; z si f; t m; jz i fh API 2 0 0 0 a u smfy g0 i fjy D; Kernel ? USER e JU GDI
q dkjy D; t ky fp k3 c kc GJE dki fy gw , f/ a e mu fw p fc ku a w mh native API y g/ Native API u a w mh Windows NT p e p f
t w Gu f interface w p fc kjz p fy gw , f/ Windows NT r Sma w mh Win32 API [ m native API & JU t a y : v Tmr Sm
& Sdy gw , f/ NT kernel r Sm GUI e JUy w fo u fjy D; b mr Sv ky fp & mr & Sdw Jht w Gu f native API r Sm graphics e JU
y w fo u fw Jh b , fv ky fi e f; r Sr y g0 i fy gb l; / ' ga Mu mi fhr dkU v ky fa q mi fc su ft & a jy m& & i f native API [ m Windows
kernel e JUc sdw fq u f& mr Sm t " du u sjy D; memory manager? I/O system? object manager? process? thread
w dkUe JU c sdw fq u ft o Hk; jy Ky gw , f/ Application y & dk* & r fa w G[ m native API a w Gu dk b , fa w mhr Sw dku f& dku fa c :
r o Hk; y gb l; / o Hk; c Jh& i fa w mh Windows 98 e JU o [ Z mw jz p fr Iu dk c sdK; a y gu fa p y gv dr fhr , f/ Microsoft u v J
native API a w Ge JUy w fo u fjy D; t c su ft v u fa w Gr Qa 0 jc i f; r & Sdw Jht w Gu f Application y & dk* & r fa w G[ m OS e JU
q u fo G, fz dkUt w Gu f Win32 API a w Gu dky J o Hk; a e & OD; r Smjz p fy gw , f/ Win32 API t w Gu f e r le m DLL z dki fa w G
u a w mh kernel32.dll? user32.dll? gdi32.dll w dkUjz p fjy D; native API t w Gu f e r le m DLL z dki fu a w mh
ntdll.dll jz p fy gw , f/ native API a w G& JU x l; jc m; c su fu a w mh o lw dkU& JU function t r n fa w Ga & SUr Sm Nt (Nt
CreateFile) e JU Zw (ZwCreateFile) p a v h& Sdjc i f; y g/
y Hk( 1 ) Win32 API r sm; ker nel E Si fhy w fo u fq u fE G, fa e y Hk
Ker nel API r sm; / / BASE API v dkUv Ja c : a 0 : jy D; o lw dkUa w G[ m kernel32.dll x Jr Sm& Sdy gw , f/ o lUr Sm
z dki ft o Gi f; ^ t x kw f? r Sw fOmP fp Dr Hc e fUc GJr I? object p Dr Hc e fUc GJr I? process e JU thread p Dr Hc e fUc GJr Ip w Jh GUI r y g0 i fw Jh
service a w Gt m; v Hk; y g0 i fy gw , f/ kernel32.dll [ m service t r sdK; r sdK; u dk v ky fa q mi fE dki fz dkU low-level native
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 163 -
API jz p fw Jh ntdll.dll u dka c : o Hk; y gw , f/ Kernel API a w Gu dk z dki fa w G? synchronization object a w Gp w Jh
kernel-level object a w Ge JU w GJv ky f& mr Sm? z e fw D; & mr Sm t o Hk; jy Ky gw , f/
GDI API r sm; / / GDI API a w Gu a w mh GDI32.dll x Jr Sm& Sdjy D; r sOf; w p fa Mu mi f; q GJjc i f; ? bitmap w p fc k
u dkjy o jc i f; p w Jh graphics e JUq dki fw Jh service a w Gy g0 i fy gw , f/ r lv u a w mh GDI a w Gu dk kernel module
w p fc kjz p fw JhWIN32K.sys r Sm p r f; o y fo Hk; p GJc Jhy gw , f/ Device context? brush? pen p w Jhgraphic q GJjc i f; r Sm
t o Hk; jy Kz dkU GDI [ m GDI object a w Gu dkt " du x m; y gw , f/ b ma Mu mi fhv Jq dka w mh' Dobject a w Gu dk kernel & JU
object manager u r u dki fw G, fE dki fv dkUy g/
USER API r sm; / / User32.dll r Smy g0 i fjy D; window-management? menu? dialog box? user-interface
control p w Jhhiger-level GUI service a w Gy g0 i fy gw , f/ GUI object a w Gt m; v Hk; u dk USER u GDI call
a w Go Hk; jy D; q GJw mjz p fy gw , f/ USER API a w G[ m kernel & JU object manager u r u dki fw G, fE dki fw Jhwindow
a w G? menu a w Gv dkuser interace e JUq dki fw Jhobject a w Gu dkt " du x m; u dki fw G, fy gw , f/
' Dt c e f; r Sma w mh cracking v ky f& mr Sm o w dx m; jy D; a p mi fhMu n fh& r , fh API function a w Gt a Mu mi f; u dk
a v hv mr Smjz p fy gw , f/ API function a w Gt a Mu mi f; u dk t a o ; p dw fo dx m; jc i f; t m; jz i hf crack v ky f& mr Sm v G, fu l
v mr Smjz p fy gw , f/ ' Da p mi fhMu n fh& r , fhAPI function a w Gu a w mha t mu fy gt w dki f; jz p fy gw , f -
Dialog Box r sm; E Si fhy w fo u fo n fht c g
DialogBoxParamA
GetDlgItem
GetDlgItemInt
GetDlgItemText
GetWindowText
GetWindowWord
MessageBox r sm; E Si fhy w fo u fo n fht c g
MessageBeep
MessageBoxA
MessageBoxEx
SendMessage
SendDlgItemMessage
Registr y E Si fhy w fo u fo n fht c g
RegCreateKey
RegDeleteKey
RegQueryValue
RegQueryValueEx
RegCloseKey
RegOpenKey
z dki fr St c su ft v u fr sm; z w fjc i f; ^ a & ; jc i f; jy Ka o mt c g
ReadFile
WriteFile
CreateFile
INI z dki fr St c su ft v u fr sm; z w fjc i f; jy Ka o mt c g
GetPrivateProfileString
GetPrivateProfileInt
WritePrivateProfileString
t jc m; a e & mr St c su ft v u fr sm; u dkz w fjc i f; jy Ka o mt c g
LoadString
lstrcmp
MultiByteToWideChar
WideCharToMultiByte
wsprintf
t c sde f?& u fp GJw dkUE Si fhy w fo u fo n fht c g
GetFileTime
GetLocalTime
GetSystemTime
GetSystemTimeAsFileTime
SetTimer
SystemTimeToFileTime
NAG-window u dk& Smv dko n fht c g
CreateWindowEx
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 164 -
ShowWindow
UpdateWindow
MessageBox r Sp mo m; r sm; u dk& Smv dka o mt c g
SendDlgItemMessage
SendMessage
SetDlgItemText
SetWindowText
Registration e JUy w fo u fw Jhroutine a w Gu dkp p fa q ; w Jht c gr Sma w mha t mu fy g API r sm; u dkt " du x m;
& Sma z Gz dkUv dky gw , f -
GetdlgItemText
GetWindowText
lstrcmp
GetPrivateProfileString
GetPrivateProfileInt
RegQueryValueEx
WritePrivateProfileString
WritePrivateProfileInt
( 1 ) Cr eatePr ocess
Cr eatePr ocess u a w mhprocess t o p fw p fc ku dkz e fw D; w mjz p fy gw , f/ Process t o p fu o w fr Sw f
x m; w Jhexe z dki fu dkexecute v ky fw mjz p fy gw , f/
BOOL CreateProcess(
LPCTSTR lpApplicationName, // pointer to name of executable module
LPTSTR lpCommandLine, // pointer to command line string
LPSECURITY_ATTRIBUTES lpProcessAttributes, // pointer to process security attributes
LPSECURITY_ATTRIBUTES lpThreadAttributes, // pointer to thread security attributes
BOOL bInheritHandles, // handle inheritance flag
DWORD dwCreationFlags, // creation flags
LPVOID lpEnvironment, // pointer to new environment block
LPCTSTR lpCurrentDirectory, // pointer to current directory name
LPSTARTUPINFO lpStartupInfo, // pointer to STARTUPINFO
LPPROCESS_INFORMATION lpProcessInformation // pointer to PROCESS_INFORMATION
);
lpProcessInformation u a w mh process e JUo u fq dki fw Jh t c su ft v u fa w Gu dk x m; & Sd& m pointer
(Oy r m - 0x12F7C8) jz p fy gw , f/ lpCommandLine u a w mh execute v ky fr , fh command line & Sd& m
pointer (Oy r m - 0x12F758) jz p fy gw , f/
0012F7C8 = lpProcessInformation = "jexepackboot ER \"C:\\Program Files\\VisualRoute\\
VisualRoute.exe\"
0012F758 = lpCommandLine = "java -mx256m jexepackboot ER \"C:\\Program Files\\
VisualRoute\\VisualRoute.exe\" \"C:\\DOCUME~1\\MYOMYI~1\\LOCALS~1\\Temp\\
X2C123E0\" "
' De r le m API r Sm VisualRoute.exe u X2C123E0 z dk' ga t mu fu z dki fa w Gu dk execute v ky fjy D;
register v ky fx m; jc i f; & Sd^ r & Sdp p fw mjz p fy gw , f/
( 2 ) GetWindowText
GetWindowText u a w mh window & JU title bar w p fc kc ku p mo m; a w Gu dk buffer w p fc kx Ju l; x n fh
y gw , f/ w u , fv dkUo m window [ m control w p fc ko mjz p fc Jhr , fq dk& i f control & JU p mo m; a w Gu dku l; y gw , f/
Oy r mjy & & i f Textbox x Jr Sm o i f& dku fx n fhv dku fw Jhp mo m; a w Gu dkbuffer x Ju l; r Smjz p fy gw , f/
int GetWindowText(
HWND hWnd, // handle of window or control with text
LPTSTR Buffer, // address of buffer for text
int Count // maximum number of characters to copy
);
hWnd u a w mhwindow ( o dkU) control r Sm p mo m; a w Gy g^ r y g p p fy gw , f/ Buffer u a w mhp mo m; a w G
x m; r , fha e & mu dkn Te fjy y gw , f/ Count u a w mht r sm; q Hk; u l; E dki fw Jhp mv Hk; t a & t w Gu fjz p fy gw , f/
( 3 ) GetdlgItemText
GetdlgItemText u a w mh dialog box w p fc kx Jr Sm& Sdw Jh e JUy w fo u fw Jh p mo m; ( o dkU) title u dk z w fy g
w , f/
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 165 -
UINT GetDlgItemText(
HWND hDlg, // handle of dialog box
int ControlID, // identifier of control
LPTSTR Buffer, // address of buffer for text
int Count // maximum size of string
);
y Hk( 1 ) u e r le m dialog box w p fc ku dkMu n fhy gr , f/
y Hk( 1 )
y Hk( 1 ) u textbox a e & mr Sm password t jz p f "Myo Myint Htike" v dkU& dku fc Jhy gw , f/ Password
u dk& dku fx n fhjy D; & i f GetdlgItemText r Sm breakpoint o w fr Sw fv dku fy g/ jy D; & i f OK u dkE Sdy fv dku fy g/ y Hk( 2 ) /
y Hk( 2 )
y Hk( 2 ) u dkMu n fhy g/ Password textbox u t r sm; q Hk; z w fE dki fw Jh p mv Hk; t a & t w Gu f[ m 1 7 v Hk; y J & Sdy gw , f/
' gu dkResource Hacker a q mhz f0 Jv fe JUMu n fh& i f a t mu fy gt w dki f; a w GU& r Smjz p fy gw , f/
DLG_REGIS DIALOG 20, 20, 142, 81
STYLE DS_MODALFRAME | WS_VISIBLE | WS_CAPTION | WS_SYSMENU
CAPTION "Enter Password"
LANGUAGE LANG_NEUTRAL, SUBLANG_NEUTRAL
FONT 10, "Book Antiqua"
{
CONTROL "Textbox", 1000, EDIT, ES_LEFT | ES_AUTOHSCROLL | WS_CHILD | WS_VISIBLE |
WS_BORDER | WS_TABSTOP, 45, 22, 66, 11
CONTROL "OK", 1002, BUTTON, BS_PUSHBUTTON | WS_CHILD | WS_VISIBLE | WS_TABSTOP,
18, 55, 42, 15
CONTROL "Cancel", 1003, BUTTON, BS_PUSHBUTTON | WS_CHILD | WS_VISIBLE |
WS_TABSTOP, 80, 55, 42, 15
CONTROL "Password:", -1, STATIC, SS_LEFT | WS_CHILD | WS_VISIBLE | WS_GROUP, 7, 23, 34,
10
}
y Hk( 3 )
y Hk( 2 ) r Sma w GU& w Jh ControlID & JUw e fz dk; 3E8h (1000d) u a w mh y Hk( 3 ) r Smjr i f& w Jht w dki f; Textbox
control u dkq dkv dkjc i f; jz p fy gw , f/ ' ga Mu mi fh o i fht a e e JU Password dialog box u dk& Smz dkU GetWindowText
r Sm breakpoint r o w fr Sw fc si f& i f PUSH 3E8h e JU& Smv dkU& y gw , f/
Buffer u a w mh o i f& dku fx n hfv dku fw Jh p mo m; u dk o Gm; x m; r , fh dump window u virtual address
a e & my g/
GetdlgItemText [ m WM_GETTEXT message u dk control q Dy dkUy gw , f/ SetdlgItemText
u a w mhGetdlgItemText e JU q e fUu si fz u fjz p fy gw , f/
( 4 ) GetDlgItem
GetDlgItem u a w mhdialog box w p fc kr Sm& Sdw Jhcontrol w p fc k& JU pointer u dkz w fy gw , f/
The GetDlgItem function retrieves the handle of a control in the specified dialog box.
HWND GetDlgItem(
HWND hDlg, // handle of dialog box
int ControlID // identifier of control
);
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 166 -
( 5 ) lstr cmp
lstr cmp u a w mhstring E Sp fc ku dk E dIi f; , SOfy gw , f/ w u , fv dkU string E Sp fc k[ m n Dc Jh& i f v ky fa q mi fc su f
a t mi fjr i fa p r Smjz p fy gw , f/
int lstrcmp(
LPCTSTR lpString1, // address of first string
LPCTSTR lpString2 // address of second string
);
string E Sp fc ku dk E dIi f; , SOf& mr Sm p mv Hk; t Mu D; ^ t a o ; u GJjy m; r I& Sdy gw , f/ y Hk( 4 ) / API a w Ga e mu fr Sm A
y gc Jh& i f ' D API [ m ANSI p mv Hk; a w Ge JUo u fq dki fjy D; W y gc Jh& i fa w mh UNICODE p mv Hk; a w Ge JU o u fq dki fy g
w , f/
y Hk( 4 )
( 6 ) GetPr ivatePr ofileStr ing
GetPr ivatePr ofileStr ing u a w mh initialization (*.ini) z dki fw p fc kx Jr Sm& Sdw Jh section u a e string
w p fc ku dk z w fy gw , f/ Win32 u dkt a jc c Hw Jhapplication a w G[ m registry x Jr Sm initialization e JYy w fo u fw Jh
t c su ft v u fa w Gu dko dr f; q n f; a v h& Sdy gw , f/
DWORD GetPrivateProfileString(
LPCTSTR lpAppName, // points to section name
LPCTSTR lpKeyName, // points to key name
LPCTSTR lpDefault, // points to default string
LPTSTR lpReturnedString, // points to destination buffer
DWORD nSize, // size of destination buffer
LPCTSTR lpFileName // points to initialization filename
);
GetPr ivatePr ofileStr ing [ m key w p fc kt w Gu f initialization z dki fu dk& Sma z Gw mjz p fy gw , f/ ' Dkey
[ m section heading u dko w fr Sw fw Jh lpAppName a t mu fu lpKeyName jz p fy gw , f/ w u , fv dkU key
u dka w GUc Jhr , fq dk& i f? function [ m o u fq dki f& m string u dk buffer q Du l; r Smjz p fy gw , f/ w u , fv dkU key
r & Sdc Jhb l; q dk& i fa w mhfunction [ m lpDefault u o w fr Sw fv dku fw Jhp mv Hk; u dku l; r Smy g/
Initialization z dki fw p fc kx Ju section [ m a t mu fy gy Hkp H& Sdy gw , f. . .
[section]
key = string
.
.
w u , fv dkU lpAppName r Sm A v mjz p fa e & i fa w mh GetPr ivatePr ofileStr ing u z dki fx Jr Sm& Sdw Jh
section t r n fa w Gt m; v Hk; u dk buffer x Ju l; y gw , f/ w u , fv dkU lpKeyName r Sm A v mjz p fa e & i fa w mh
function u section x Jr Sm& Sdw Jhkey t r n fa w Gt m; v Hk; u dkbuffer x Ju l; y gw , f/
WIN.ini z dki fx Ju string w p fc ku dk & , lv dk& i fa w mh GetPr ofileStr ing u dkt o Hk; jy Ky gw , f/ w u , f
a w mh GetPr ivatePr ofileStr ing [ m *.ini z dki fa w Gq Du string a w Gu dkz w fr , fht p m; registry x Ju
t c su ft v u fa w Gu dkz w fw mjz p fy gw , f/
Oy r mjy & & i f
( 1 ) Registry x Jr Sm ini z dki f& JUt r n fu dkMu n fhy g/ ( Oy r m - myfile.ini )
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows NT\CurrentVersion\IniFileMapping\myfile.ini
( 2 ) lpappName u o w fr Sw fv dku fw Jh section t r n fu dk& Smy g/ ' Dt r n fu a w mh myfile.ini z dki fa t mu f ( o dkU)
myfile.ini z dki f& JU subkey w p fc ka t mu fr Sm& SdE dki fy gw , f/ ( o dkU) r & SdE dki fy gb l; /
( 3 ) lpappName u o w fr Sw fv dku fw Jh section t r n f[ m myfile.ini z dki fa t mu fr Sm w e fz dk; w p fc k& Sdc Jh& i f?
o i fht a e e JU registry x Jr Smo w fr Sw fx m; w Jhw e fz dk; a w Gu a e section t w Gu f key a w Gu dk& Sm& r Smy g/
( 4 ) w u , fv dkUo m lpappName u o w fr Sw fv dku fw Jh section t r n f[ m myfile.ini z dki f& JU subkey
w p fc kjz p fc Jhr , fq dk& i fa w mh' Dsubkey a t mu fr Sm section t w Gu f key a w Gu dk& Sm& r Smy g/
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 167 -
( 5 ) w u , fv dkU lpappName u o w fr Sw fv dku fw Jh section t r n f r & Sdc Jhb l; q dk& i f myfile.ini a t mu fr Sma w mh
t r n fr Jhw e fz dk; w p fc ka w mh & Sdy gv dr fhr , f/ ' Dw e fz dk; [ m section t w Gu f o i f& Sma e w Jh key & JUa e & m& Sdw Jh registry
x Ju default a e & mw p fc ku dko w fr Sw fy gw , f/
( 6 ) w u , fv dkU myfile.ini z dki ft w Gu f subkey v kH; 0 r & Sdc Jhb l; q dk& i f? section t r n ft w Gu f entry v Hk; 0
r & Sdb l; q dk& i f disk a y : r Sm& Sdw Jh w u , fh myfile.ini z dki fu dk& Smjy D; o lUr Smy gw Jh t c su ft v u fa w Gu dk z w f& r Smjz p fy g
w , f/
Registry x Ju w e fz dk; a w Gu dk Mu n fhw Jht c g a w GU& r , hf prefix a w G& JU t " dy m, fu a w mha t mu fy gt w dki f;
jz p fy gw , f/
! - ' Dp mv Hk; u a w mht c su ft v u fa w Gu dkregistry r Sma & m disk a y : u myfile.ini z dki fa y : r Sm a & ; r Smjz p fy gw , f/
# - ' Dp mv Hk; u a w mhWindows 3.1 .ini z dki fe JU t " du o u fq dki fy gw , f/
@ - ' Dp mv Hk; u a w mhregistry x Jr Sm v dkc si fw Jha ' w mr a w GUc Jh& i f disk a y : u .ini z dki fq Du a e a ' w ma w G
z w fw mu dkw m; q D; w my g/
USR: - o lu a w mhHKEY_CURRENT_USER u kdq dkv dkw my g/
SYS: - o lu a w mhHKEY_LOCAL_MACHINE\SOFTWARE u kdq dkv dkw my g/
( 7 ) GetPr ivatePr ofileInt
GetPr ivatePr ofileInt u a w mh initialization (*.ini) z dki fw p fc kx Jr Sm& Sdw Jh section u a e u de f; jy n fh
w p fc ku dkz w fy gw , f/
UINT GetPrivateProfileInt(
LPCTSTR lpAppName, // address of section name
LPCTSTR lpKeyName, // address of key name
INT nDefault, // return value if key name is not found
LPCTSTR lpFileName // address of initialization filename
);
( 8 ) RegQuer yValueEx
RegQuer yValueEx u a w mh registry key w p fc k& JU t r sdK; t p m; e JU w e fz dk; w dkUu dkz w fjy D; register
v ky fx m; jc i f; & Sd^ r & Sdp p fa q ; y gw , f/
LONG RegQueryValueEx(
HKEY hKey, // handle of key to query
LPTSTR lpValueName, // address of name of value to query
LPDWORD lpReserved, // reserved
LPDWORD lpType, // address of buffer for value type
LPBYTE lpData, // address of data buffer
LPDWORD lpcbData // address of data buffer size
);
( 9 ) Wr itePr ivatePr ofileStr ing
GetPr ivatePr ofileStr ing u a w mhWr itePr ivatePr ofileStr ing e JUq e fUu si fb u fjz p fy gw , f/
BOOL WritePrivateProfileString(
LPCTSTR lpAppName, // pointer to section name
LPCTSTR lpKeyName, // pointer to key name
LPCTSTR lpString, // pointer to string to add
LPCTSTR lpFileName // pointer to initialization filename
);
e r le my & dk* & r fu dkcompiler r Sm run Mu n fhv dku f& i f & Si f; o Gm; r Smy g/
#include "stdafx.h" // Compiler - Visual C++ 8.0, Win32 Console Application
#include <windows.h>
#include <tchar.h>
#include <stdio.h>
int main()
{
TCHAR inBuf[80];
HKEY hKey1, hKey2;
DWORD dwDisposition;
LONG lRetCode;
TCHAR szData[] = TEXT("USR:App Name\\Section1");
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 168 -
// Create the .ini file key.
lRetCode = RegCreateKeyEx ( HKEY_LOCAL_MACHINE,
TEXT("SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\IniFileMapping\\appname.ini"),
0, NULL, REG_OPTION_NON_VOLATILE,
KEY_WRITE, NULL, &hKey1, &dwDisposition);
if (lRetCode != ERROR_SUCCESS)
{
printf ("Error in creating appname.ini key (%d).\n", lRetCode);
return (0) ;
}
// Set a section value
lRetCode = RegSetValueEx ( hKey1, TEXT("Section1"), 0,
REG_SZ, (BYTE *)szData, sizeof(szData));
if (lRetCode != ERROR_SUCCESS)
{
printf ("Error in setting Section1 value\n");
// Close the key
lRetCode = RegCloseKey( hKey1 );
if( lRetCode != ERROR_SUCCESS )
{
printf("Error in RegCloseKey (%d).\n", lRetCode);
return (0) ;
}
}
// Create an App Name key
lRetCode = RegCreateKeyEx ( HKEY_CURRENT_USER, TEXT("App Name"),
0, NULL, REG_OPTION_NON_VOLATILE,
KEY_WRITE, NULL, &hKey2, &dwDisposition);
if (lRetCode != ERROR_SUCCESS)
{
printf ("Error in creating App Name key (%d).\n", lRetCode);
// Close the key
lRetCode = RegCloseKey( hKey2 );
if( lRetCode != ERROR_SUCCESS )
{
printf("Error in RegCloseKey (%d).\n", lRetCode);
return (0) ;
}
}
// Force the system to read the mapping into shared memory
// so that future invocations of the application will see it
// without the user having to reboot the system
WritePrivateProfileStringW( NULL, NULL, NULL, L"appname.ini" );
// Write some added values
WritePrivateProfileString (TEXT("Section1"), TEXT("FirstKey"),
TEXT("It all worked out OK."), TEXT("appname.ini"));
WritePrivateProfileString (TEXT("Section1"), TEXT("SecondKey"),
TEXT("By golly, it works!"), TEXT("appname.ini"));
WritePrivateProfileString (TEXT("Section1"), TEXT("ThirdKey"),
TEXT("Another test..."), TEXT("appname.ini"));
// Test
GetPrivateProfileString (TEXT("Section1"), TEXT("FirstKey"), TEXT("Error: GPPS failed"),
inBuf, 80, TEXT("appname.ini"));
_tprintf (TEXT("Key: %s\n"), inBuf);
// Close the keys
lRetCode = RegCloseKey( hKey1 );
if( lRetCode != ERROR_SUCCESS )
{
printf("Error in RegCloseKey (%d).\n", lRetCode);
return(0);
}
lRetCode = RegCloseKey( hKey2 );
if( lRetCode != ERROR_SUCCESS )
{
printf("Error in RegCloseKey (%d).\n", lRetCode);
return(0);
}
return(1);
}
y & dk* & r f& JU t v ky fv ky fy Hku a w mh' Dv dky g . . .
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 169 -
( 1 ) HKEY_LOCAL_MACHINE r Sm appname.ini q dkw Jhkey u dkz e fw D; y gw , f/
( 2 ) RegSetValueEx() o Hk; jy D; Section1 & JUw e fz dk; u dk"USR:App Name\Section1" v dkUo w fr Sw fy gw , f/
( 3 ) HKEY_CURRENT_USER r Sm "App Name" q dkw Jhkey u dkz e fw D; y gw , f/
( 4 ) Wr itePr ivatePr ofileStr ing u dko Hk; jy D; HKEY_LOCAL_MACHINE a t mu fu appname.ini
z dki f& Sd^ r & Sdz w fy gw , f/
( 5 ) appname.ini z dki fu dk a w GUw Jht c g Section1 key u dkz w fy gw , f/ Section1 [ m HKEY_CURRENT_
USER a t mu fu App Name\Section1 u dkn Te f; w Jht w Gu f registry editor u HKCU a t mu fr Sm App
Name\Section1 subkey u dk t v dkt a v smu fz e fw D; y gw , f/ ' Dv dk z e fw D; jy D; w Jha e mu fr Sma w mh FirstKey u dk
z e fw D; jy D; "It all worked out OK." u dka & ; y gw , f/
( 6 ) appname.ini z dki fu dk a w GUw Jht c g Section1 key u dkz w fy gw , f/ Section1 [ m HKEY_CURRENT_
USER a t mu fu App Name\Section1 u dkn Te f; w Jht w Gu f registry editor u HKCU a t mu fr Sm App
Name\Section1 subkey u dk t v dkt a v smu fz e fw D; y gw , f/ ' Dv dk z e fw D; jy D; w Jha e mu fr Sma w mh SecondKey u dk
z e fw D; jy D; "By golly, it works!" u dka & ; y gw , f/
( 7 ) appname.ini z dki fu dk a w GUw Jht c g Section1 key u dkz w fy gw , f/ Section1 [ m HKEY_CURRENT_
USER a t mu fu App Name\Section1 u dkn Te f; w Jht w Gu f registry editor u HKCU a t mu fr Sm App
Name\Section1 subkey u dk t v dkt a v smu fz e fw D; y gw , f/ ' Dv dk z e fw D; jy D; w Jha e mu fr Sma w mh ThirdKey u dk
z e fw D; jy D; "Another test..." u dka & ; y gw , f/
( 8 ) a e mu fw p fc ku a w mh GetPr ivatePr ofileStr ing u dko Hk; jy D; HKLM a t mu fu Section1 n Te f; w Jha e & mu dk
o Gm; jy D; FirstKey u dk& Smy gw , f/ w u , fv dkU r a w GUc Jh& i fa w mh buffer x Jr Sm GetPr ivatePr ofileStr ing u
t v dkt a v smu f o w fr Sw fv dku fw Jh "Error: GPPS failed" p mo m; u dkjy r Smjz p fy gw , f/ FirstKey u dka w GUc Jh& i f
a w mhFirstKey r Smo dr f; x m; w Jh"It all worked out OK." p mo m; u dkjy r Smjz p fy gw , f/
r Sw f& e f/ / w u , fv dkU "USR:App Name\Section1"a e & mr Sm "!USR:App Name\Section1" v dkU jy i fv dku f
& i fa w mh C:\Windows a t mu fr Sm appname.ini z dki fu dkz e fw D; jy D; HKCU a t mu fr Sma & ; r , fhp mo m; a w Gu dk
appname.ini r Smv Ja & ; r Smjz p fy gw , f/ y Hk( 5 ) / ' gr sdK; u dka w mh z dki fw p fc k& JU registration setting a w Gu dk v lr o d?
o lr o da & ; v dkw Jht c g t o Hk; r sm; y gw , f/
y Hk( 5 )
( 1 0 ) Cr eateWindowEx
Cr eateWindowEx u a w mh overlapped ( o dkU) pop-up ( o dkU) child window a w Gr Sm p w dki fa w G
x y fa v mi f; x n fhjy D; z e fw D; a y ; w mjz p fy gw , f/ ' Dv dkr Sr [ kw f& i fa w mhCr eateWindow e JUw la e r Sm jz p fy gw , f/
HWND CreateWindowEx(
DWORD ExtStyle, // extended window style
LPCTSTR ClassName, // pointer to registered class name
LPCTSTR WindowName, // pointer to window name
DWORD WindowStyle, // window style
int x, // horizontal position of window
int y, // vertical position of window
int Width, // window width
int Height, // window height
HWND hWndParent, // handle to parent or owner window
HMENU hMenu, // handle to menu, or child-window identifier
HINSTANCE hInstance, // handle to application instance
LPVOID lParam // pointer to window-creation data
);
Cr eateWindowEx e JUt w l ShowWindow? UpdateWindow API a w Gw GJo Hk; y gw , f/
( 1 1 ) Cr eateFile
Cr eateFile u a w mhz dki fw p fc ku dk& Sma z G? z e fw D; & mr Sm t o Hk; jy Ky gw , f/
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 170 -
HANDLE CreateFile(
LPCTSTR FileName, // pointer to name of the file
DWORD DesiredAccess, // access (read-write) mode
DWORD Mode, // share mode
LPSECURITY_ATTRIBUTES pSecurity, // pointer to security attributes
DWORD dwCreationDistribution, // how to create
DWORD Attributes, // file attributes
HANDLE hTemplateFile // handle to file with attributes to copy
);
Cr eateFile r Sm o w djy Ko i fhw mu a w mhMode parameter u dky g/ Mode [ m z dki fw p fc k& Sdc Jh& i f ( o dkU)
r & Sdc Jh& i f b , fv dkv ky fa q mi f& r v Jq dkw m q Hk; jz w fy gw , f/ y Hk( 6 ) /
y Hk( 6 )
Mode & JUw e fz dk; a w Gu a w mha t mu fy g 5 c kx Ju w p fc kc kjz p fE dki fy gw , f . . . -
CREATE_NEW - z dki ft o p fw p fc ku dk z e fw D; y gw , f/ w u , fv dkU z dki f[ m & Sda e c Jh& i f function [ m fail
jz p fo Gm; r Smy g/ Fail jz p fo Gm; & i f EAX & JUw e fz dk; [ m FFFFFFFF (-1) jz p fo Gm; y gr , f/ w u , fv dkU ' Dw e fz dk; u dk
jy i fc si f& i f Mode a e & mr Sm PUSH 1; v dkUjy i fv dku f& Hky g/
CREATE_ALWAYS - z dki ft o p fw p fc ku dk z e fw D; y gw , f/ w u , fv dkU z dki f[ m & Sda e c Jh& i f & Sdjy D; o m; z dki fu dk
overwrite v ky fjy D; z dki ft o p fw p fc ku dkz e fw D; r Smjz p fy gw , f/
OPEN_EXISTING - & Sdjy D; o m; z dki fu dk z Gi fhy gw , f/ z dki fr & Sdc Jh& i fa w mh function & JUv ky fa q mi fc su f a t mi fjr i fr Sm
r [ kw fy gb l; / ' gq dkEAX & JUw e fz dk; [ m FFFFFFFF (-1) jz p fo Gm; y gr , f/
OPEN_ALWAYS - z dki f& Sdc Jh& i f z dki fu dkz Gi fhy gw , f/ z dki fr & Sdc Jh& i fa w mh CREATE_NEW u dko Hk; jy D; z dki ft o p f
w p fc ku dkz e fw D; y gw , f/
TRUNCATE_EXISTING - z dki fu dk z Gi fhv dku fjy D; z dki fx Jr Sm& Sdw Jh t & mt m; v Hk; u dk z su fy p fy gw , f/ z dki fr & Sdc Jh& i f
a w mhEAX & JUw e fz dk; [ m FFFFFFFF (-1) jz p fy gr , f/
( 1 2 ) DialogBoxPar amA
DialogBoxPar amA u a w mh modal dialog box w p fc ku dk z e fw D; & mr Sm t o Hk; jy Ky gw , f/ Dialog
box u dkr jy c i fr Sm function [ m dialog box e JUo u fq dki fw Jhprocedure u dkinitialize v ky fy gw , f/
int DialogBoxParamA(
HINSTANCE hInst, // handle to application instance
LPCTSTR pTemplate, // identifies dialog box template
HWND hOwner, // handle to owner window
DLGPROC DlgPro, // pointer to dialog box procedure
LPARAM lParam // initialization value
);
KeygenMe w p fc k& JU dialog box w p fc ku dk Resource Hacker e JUMu n fh& i f a t mu fy gt w dki f; a w GU& y g
w , f/
1 DIALOGEX 0, 0, 225, 142
STYLE DS_MODALFRAME | DS_CENTER | WS_MINIMIZEBOX | WS_POPUP | WS_VISIBLE |
WS_CAPTION | WS_SYSMENU
EXSTYLE WS_EX_STATICEDGE
CAPTION " :: Ziggy's KeyGenMe #0 ::"
LANGUAGE LANG_ENGLISH, SUBLANG_ENGLISH_US
FONT 7, "MS SANS SERIF"
{
CONTROL 10, -1, STATIC, SS_BITMAP | SS_REALSIZEIMAGE | SS_SUNKEN | WS_CHILD |
WS_VISIBLE, 65535, 104, 200, 200
CONTROL "Name", 1002, EDIT, ES_CENTER | WS_CHILD | WS_VISIBLE | WS_TABSTOP, 35, 30, 186, 10 ,
0x00020000
CONTROL "Serial", 1003, EDIT, ES_CENTER | WS_CHILD | WS_VISIBLE | WS_TABSTOP, 35, 47, 186, 10 ,
0x00020000
CONTROL "Register", 1005, BUTTON, BS_PUSHBUTTON | BS_CENTER | BS_VCENTER | WS_CHILD |
WS_VISIBLE | WS_TABSTOP, 59, 62, 50, 12 , 0x00020000
CONTROL "About", 1007, BUTTON, BS_PUSHBUTTON | BS_CENTER | BS_VCENTER | WS_CHILD |
WS_VISIBLE | WS_TABSTOP, 158, 62, 30, 12 , 0x00020000
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 171 -
CONTROL "Close", 1004, BUTTON, BS_PUSHBUTTON | BS_CENTER | BS_VCENTER | WS_CHILD |
WS_VISIBLE | WS_TABSTOP, 191, 62, 30, 12 , 0x00020000
CONTROL "Appname", 1001, STATIC, SS_CENTER | SS_SUNKEN | WS_CHILD | WS_VISIBLE |
WS_GROUP, 35, 5, 186, 10 , 0x00020000
CONTROL " ", 1009, STATIC, SS_CENTER | WS_CHILD | WS_VISIBLE | WS_GROUP, 35, 19, 186, 10
CONTROL "Name", 4, STATIC, SS_LEFT | WS_CHILD | WS_VISIBLE | WS_GROUP, 6, 30, 26, 10
CONTROL "Serial", 5, STATIC, SS_LEFT | WS_CHILD | WS_VISIBLE | WS_GROUP, 6, 47, 26, 10
CONTROL 3, 1, STATIC, SS_ICON | WS_CHILD | WS_VISIBLE, 6, 4, 35, 35
CONTROL "Registered to : ", 5, STATIC, SS_LEFT | WS_CHILD | WS_VISIBLE | WS_GROUP, 6, 80, 50, 10
CONTROL " ", 1008, STATIC, SS_LEFT | WS_CHILD | WS_VISIBLE | WS_GROUP, 54, 80, 150, 10
CONTROL " ", 1010, STATIC, SS_LEFT | WS_CHILD | WS_VISIBLE | WS_GROUP, 54, 90, 180, 10
}
' gu dkOlly r SmMu n fhr , fq dk& i fa w mhy Hk( 7 ) t w dki f; jr i f& y gw , f/
y Hk( 7 )
y Hk( 7 ) r Sm DlgProc u a w mh t a & ; Mu D; q Hk; jz p fy gw , f/ b ma Mu mi fhv Jq dka w mh dialog e JUy w fo u fw Jh
procedure & Sd& m virtual address (00401032) jz p fv dkUy g/ pTemplate u a w mh dialog t r n fjz p fy gw , f/
y Hkr Se fq dk& i fa w mh API w p fc ku dk v ky fa q mi fjy D; w me JU a e mu f API u dkv ky fa q mi fr Smy g/ y Hk( 7 ) r Sma w mh 00401041
u dkv ky fa q mi fjy D; c sde fr Sm 00401046 q Da & mu fr v mb J0040104D q Da & mu fv mr Smjz p fy gw , f/
( 1 3 ) ShowWindow
ShowWindow u a w mho w fr Sw fx m; w Jhwindow u dkjy o z dkUjz p fy gw , f/
BOOL ShowWindow(
HWND hWnd, // handle of window
int nCmdShow // show state of window
);
( 1 4 ) MessageBox
MessageBox u dka w mh cracking v ky f& mr Sm r Mu mc P jr i f& r Smjz p fy gw , f/ MessageBox u
message box w p fc ku dk z e fw D; jy o r Smjz p fy gw , f/ Message box w p fc kr Sm Mu dKw i fo w fr Sw fx m; w Jh icon a w G?
button a w G? p mo m; a w Ge JU a c gi f; p Ofa w Gy g0 i fr Smjz p fy gw , f/
int MessageBoxA(
HWND hOwner // handle of owner window
LPCTSTR Text, // address of text in message box
LPCTSTR Title, // address of title of message box
UINT Style // style of message box
);
MessageBox & JU t v ky fv ky fy Hku dke m; v n fa p E dki fz dkU y Hk( 8 ) u dkMu n fhy g/
y Hk( 8 )
Style q dkw mu a w mh message box r Sm a z mfjy c si fw Jh button a w G? icon a w Gu dk q dkv dkw my g/ y Hk( 8 ) u
Oy r mt & q dk& i fa w mh message box r Sm OK button w p fc kw n f; y gr Smy g/ b m icon r Sr y gy gb l; / ( Message
Box t a Mu mi f; t a o ; p dw fu dk]t a jc c HAssembly b mo mp u m; } t c e f; r Sm t u s, fa q G; a E G; jy D; jz p fy gw , f/ )
' Da e & mr Sm o w dx m; a p v dkw mu a w mh hOwner y g/ w u , fv dkU message box w p fc ku dk z e fw D; c sde fr Sm
dialog box w p fc k[ m & Sda e c Jh& i f hOwner u dk dialog box & JU handle t a e e JU t o Hk; jy K& y gw , f/ w u , fv dkU
hOwner a e & mr Sm 1 jz p fa e & i fa w mh' Dmessage box u dkjy o E dki fr Sm r [ kw fy gb l; /
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 172 -
( 1 5 ) SendMessage
SendMessage u a w mh message w p fc ku dk window w p fc kq D( o dkU) window a w Gq Da y ; y dkUy gw , f/
Function [ m o w fr Sw fx m; w Jhwindow t w Gu f window procedure u dka c : o Hk; jy D; window procedure u
message u dkv ky fa q mi fjy D; c sde fr Sm return jy e fjc i f; r & Sdy gb l; / PostMessage u a w mhthread w p fc k& JU message
queue q Dmessage c sx m; jy D; c su fc si f; jy e fy gw , f/
LRESULT SendMessage(
HWND hWnd, // handle of destination window
UINT Msg, // message to send
WPARAM wParam, // first message parameter
LPARAM lParam // second message parameter
);
( 1 6 ) SendDlgItemMessage
SendDlgItemMessage u a w mh dialog box w p fc kx Jr Sm& Sdw Jh control q Dmessage w p fc ku dk a y ; y dkU
y gw , f/
LONG SendDlgItemMessage(
HWND hDlg, // handle of dialog box
int nIDDlgItem, // identifier of control
UINT Msg, // message to send
WPARAM wParam, // first message parameter
LPARAM lParam // second message parameter
);
( 1 7 ) ReadFile
ReadFile u a w mh z dki fw p fc ku a e v dkc si fw Jht c su ft v u fa w Gu dk z w fy gw , f/ p z w fr , hfa e & mu dka w mh
file pointer u n Te fjy y gw , f/
BOOL ReadFile(
HANDLE hFile, // handle of file to read
LPVOID Buffer, // address of buffer that receives data
DWORD BytesToRead, // number of bytes to read
LPDWORD pBytesRead, // address of number of bytes read
LPOVERLAPPED pOverlapped // address of structure for data
);
Buffer u a w mhz w fv dku fw Jhp mv Hk; u dkx m; r , fha e & my g/ pBytesRead u a w mhz w fv dku fw Jhp mv Hk; t a &
t w Gu fy g/ BytesToRead u a w mht r sm; q Hk; z w fr , hf p mv Hk; t a & t w Gu fjz p fy gw , f/ y Hk( 9 ) /
y Hk( 9 )
( 1 8 ) Wr iteFile
Wr iteFile u a w mhz dki fx Jr Sm x m; c si fw Jht c su ft v u fa w Go Gm; a & ; y gw , f/
BOOL WriteFile(
HANDLE hFile, // handle to file to write to
LPCVOID Buffer, // pointer to data to write to file
DWORD BytesToWrite, // number of bytes to write
LPDWORD pBytesWritten, // pointer to number of bytes written
LPOVERLAPPED pOverlapped // pointer to structure needed for overlapped I/O
);
( 1 9 ) GetSystemTime
GetSystemTime u a w mh v u f& Sd OS & JU & u fp GJe JUt c sde fu dk z w fy gw , f/ t c sde fu dka w mh UTC
(Coordinated Universal Time) e JUa z mfjy y gw , f/
VOID GetSystemTime(
LPSYSTEMTIME lpSystemTime // address of system time structure
);
t c e f; ( 1 2 ) - Cracker r sm; o w dx m; o i fha o m Windows API r sm;
- 173 -
( 2 0 ) GetFileTime
GetFileTime u a w mhz dki fu dkz e fw D; c Jhw Jh? a e mu fq Hk; jy Kjy i fc Jhw Jh& u fp GJe JUt c sde fu dkz w fy gw , f/
BOOL GetFileTime(
HANDLE hFile, // identifies the file
LPFILETIME lpCreationTime, // address of creation time
LPFILETIME lpLastAccessTime, // address of last access time
LPFILETIME lpLastWriteTime // address of last write time
);
( 2 1 ) SetTimer
SetTimer u a w mho w fr Sw fx m; w Jht c sde fw p fc ky gw Jhtimer w p fc ku dko w fr Sw fw mjz p fy gw , f/
UINT SetTimer(
HWND hWnd, // handle of window for timer messages
UINT TimerID, // timer identifier
UINT Timeout, // time-out value
TIMERPROC Timerproc // address of timer procedure
);
SetTimer e r le mw p fc ku dkOlly r SmMu n fh& i f a t mu fy gt w dki f; a w GU& r Smjz p fy gw , f/ y Hk( 9 ) /
y Hk( 9 )
hWnd u a w mh timer e JUw GJz u fx m; w Jh TPUtilWindow u dka jy mw my g/ ' Dwindow u dk a c : , lo Hk; w Jh
thread u o my dki fq dki fy gw , f/ w u , fv dkU hWnd o m NULL jz p fc Jh& i f timer u b , f window e JUr Sw GJz u f
r Smr [ kw fb JTimerID u dkv Jv sp fv sL& Ir Sm jz p fy gw , f/
TimerID u a w mho kn r [ kw fw Jhtimer identifier w e fz dk; w p fc ku dko w fr Sw fy gw , f/
Timeout u a w mh time-out jz p fr , fht c sde fjz p fjy D; r Dv Dp u e fUe JU jy y gw , f/ Timerproc u a w mh
timeout jz p fw Jht c g t c su fa y ; r , fh? v ky fa q mi fr , fhfunction & Sd& mu dkjy y gw , f/
KillTimer u a w mhTimerID u dkz su fq D; w JhAPI jz p fy gw , f/
,., .-.. resource ... ..`. crack ` .
,,
tcef;(13) - y&dk*&rf\ r esour ce rsm; toHk;jyK cr ack vkyfjcif;
, .. ..-. . -.. . resource .-- ..``. crack -_ . .`.. -. ,_ .-
-..-. . .`.. . .-. crack ... . . `., .. -. crack -_. ....
..- . -.. -.-. Active Desktop Calendar Version 5.95 `.. -. Active Desktop Calendar
. -.-.-. . . desktop .. ,-. `-,, .- .. ` .... .- - . -
.... ... . -. `.. -.
,
Active Desktop Calendar - www.xemico.com -., download `. install -
,
ADC - . - - . ..-. ,- . register . .....-. . .- .. . Help menu
- About Active Desktop Calendar- ...-_-..-. ,-. .-...
,., .-.. resource ... ..`. crack ` .
,
,
.-..` Help menu - Registration -...`. register -_-.. ,,
,,
,,- Register button -...-..-. ,-.`....
,
..-...-. .` .-..- patch -_ -.. Patch . . . ADC . -.. -
Resource Hacker ...., .-_.. ,
,
Resource Hacker .-..-. ,-. .-..-.- ..`- resource .- - `...
-. .-..-... .rscr section .-..-. `,.-. ...,..`..-. Resource Hacker
....-. .-...-. resource - - - . . .- . ` ... -. ,,
,., .-.. resource ... ..`. crack ` .
,
,,
. - .... .-.-. Resource Hacker ....-. resource .--.. `...-. .
-..-.- register ..`.... ...`. ..-. .-. -,.-.-.,, Resource
Hacker - Olly Debugger , -..... ,,-- `, -_ . - .- -. dialog .-`..
-. dialog .-.-.. Resource Hacker . . .... - -_ - -... ,- dialog
.....- . - .,- . `. ...
.,
.,- 100 . - .....- ...-_ . -. dialog ._`..-. .-..-. dialog
function -.... dialog ._- stack .-.--.
.,
.,- 207 .-.....-.-. ,,- registration box -...- dialog `..-.
,
,- 208 .-.....-.-. ,- BadBoy MessageBox - ...- dialog
.-. .` ADC . -.. - Olly .. ... ,
,
,-. `..-.. ,- -,.-.--_- dialog ._.-- Olly .. ..-_-
-... Olly . . right-click .`. Search for - All commands - ...- ...
registration - dialog (2007d = 00CFh)- ...-_--... ,
,., .-.. resource ... ..`. crack ` .
,,
,
,.. Find button -...-. ,-. `....
,
,..`..- command -.- breakpoint .-.-.. Breakpoint .- . - ` .. F9
-.`. .-..- run - `.. Help menu - Registration -...- ,,-. .-
..
,,
,,- -,.-.-...-.,- VA 0045EEC0 .,..-.-. registration dialog ... CALL
VA 0045EEA0 -.-. registration dialog ... CALL . CALL - -. virtual
address -.,...-..-. .. stack window .. ...-_- ,
,
,.. . .-. VA 0045EEA0 -...`.. VA 00434E86 .-`,.....
.`...-. - - .- - . ... right-click .`. Follow in Disassembler -...- ,
-. `....
,
--. .-. VA 0045EEA0 - CALL - VA 00434E81 - .....-. ..-.
,.._ ..- ` -. ,,- `, -_- ,,-....-. dialog ._- stack
..- .- ` -..- `.. . . -.. ... F9 -.- ,,-. `....
,,
,., .-.. resource ... ..`. crack ` .
,.
,,-. `....-. register ....-. ,..`..- dialog (208d = D0h)
-... -,... ,-. PUSH 0D0h . - _ ` . command -.- breakpoint
.- . - .. -. .-. . .`..`.. command -. .- -. .,
.,
.,. VA0045F0D3 .,..- JE -. register -...`....`.- ..`.-`.
... `. . VA 0045F239 . ...- .. . .-. BadBoy DialogBox ..-.
-- JE ... NOP ` - . .-. . -.- . - _ _ register -... `. `
., . -, .-. - ` - - - .- - . . .- ... ._ , . . .._ . -
.,
`........-. ,-. registry editor (regedit.exe) ..-_-
,
...--.- `,.`. Help menu - About Active Desktop Calendar --_-.
.-. ,- . `.,- , .
,
.-. dialog (2007d = 0064h) ... virtual address . . breakpoint .- . - ` . run
(F9) -_ .. . -.. run .,.-..-.. PUSH 64 ... breakpoint -... ....
..-... breakpoint -`,`.- About Dialog -...- PUSH 64 breakpoint .-.,
, ..- breakpoint .-`.-.-. .-.. menu ... Help menu - About ADC -
.. . -. -, .-. - . ..,- About Dialog breakpoint ......-.` ,
,., .-.. resource ... ..`. crack ` .
,.
,
,- VA 00401C60 -.-. routine . . `.. -. . --.- .....-.
...-. stack window .. right-click .`. Follow in disassmeble -...- ,-.
`....
,
,..`..--. VA 00401C60 - VA 00401D48 - .. .-. F9 - . - .
.-. ,- . .- ... -..-. "This is an unlicensed copy" . - ......-. . -.
. ... About DialogBox (100d) - Resource Hacker , `,-_- ,,
,,
,,- -_-. ... stack .-.-- -,. (1044d = 414h) .-. .-...
.,..- .-. . . -.`.. . . -. .- -_ .. PUSH 414h - . .` . breakpoint .- . -
.. ` .. Olly .. .-..- `,.`. Help menu - About ADC - .. . - ` .. PUSH 414h
... breakpoint ....-.. F9 . . .,.- . ..-. ,- . breakpoint . ..- ...- .
..
,
. . .-
413 = DeskLook Verson x.y
414 = This is an unlicensed copy.
,., .-.. resource ... ..`. crack ` .
.
415 = User
416 = Registration Code
417 = This is an unlicensed copy.
3FD = Buy &Online Now!
,
,- VA 00401DE2 -., ,- VA 00401EAC F8 . . -, .-. - .,,
VA 00401EAC - JE .. NOP .`. . - ` .. . . .- ..._ , . - . . . - . . . -
-.- .`. Help menu - About ADC - .. . - ,,- . .- ...
,,
.,.- -. . -.-. splash screen ....- "unregistered" .-.....- ..-...
VA 004013E4 - JNZ .,... . JMP `-`. .-...- .,
.,
.,. VA 004013DD - CALL -. register `...`....- routine . -. . .,,
,.._ .. -. .-. .` . -.. - `, . -_ - .,- . .- ...
.,
,., .-.. resource ... ..`. crack ` .
.
, - . .,, .`... Active Desktop Calendar - ..`... register ...
-,.-.-.,, .,.... -.-- `-.
, VA 004013E4 - JNZ .,... . JMP (Splash Screen)
, VA 00401EAC - JE .. NOP (About Dialog)
, VA0045F0D3 .,..- JE .. NOP (Registration Dialog)
` ... . -, .-. .-. - .,, Resource Hacker .-...-_-..`. .--
` -. . - .... .-.-. Delphi , ........- .-...-- crack .....-.
Resource Hacker ....-..``. crack .-. .-.... Delphi .-...-- -.
crack ...-.- ,., Delphi `. ........... .-.....- crack ` .'..
.... - .. ... ... ,
,.,, Packer (Protector) ...
.
tcef;(14) - Packer (Pr otector ) rsm;
,....-. cracking ..-. . .- .... .`.. - packer (protector) .-.-..-
.. ... .. .`.. -. . . .`... .-. pack -..-. exe .- compress ` . execute
.. decompress `, ` ., execution .-`.-- ........ decompression stub
- _........- ,..`..-. Compress -. . -.-.-. . -. - compress
- -.,_...-....-.`..`. exe .-... compress ..- - .- , - -
decompression - .- - . .. ... -.`.. -. Execute ,...-. . exe --
`,`. unpack -. - ..- ...- . -.-. . - compress ...,...- exe .,
-.-- Compress ..- . . - . .- -.-.
, . .,. - . .,... . ,_ .` .
, . .,. . . - . . .-.......`....- ,..,_.`.
, Execute ..- compress . ...... - .. .-...... dexompress .._
-- ,-,`. -`..-.
Compress ..- exe ..-. exe .-.- archive -. .,, ` ...
WinRAR -.... ......`. archive ..` .. ., .- -.-.-. compress ..-
.-..- - . - - exe . `.. .,-.
DOS Windows , `.. OS .- - - exe compressor .....`. command line .,,
..._..-.. GUI version .,, ... _ ..-. . - . -.
..-- pack - -., `..- . -. - ..- -.-.
, . . . - -.,- . . - ..- . . download .-- `.,.. download ...
`.
, . . ... . - .. -, . cracker .- crack .... -.-....`. Cracker
.--. crack . ... unpack ...`..-., -`..-.
.-..-.-.-. anti-virus .-, -.--. Anti-virus .-..-.......-. pack
..-.- virus ., trojan `. .,--. ..`. McAfee anti-virus,
Protector .-.-.-. --.-...`... ....- packer -. Protector .- -.-.
....- packer .- - ... - .- - `....`..-. Protector .-. ...-.-`.
-.-. protect ..-.. ..... Packer .-- pack ..- ..-......--
.... .. ., , . . protector .--.-. cracker .-.,--.-..... -.-- ,..
_...,--. .-.. protect ..- . .- .... .... ...,. . . -
- ..,-..- .-. ..., packer .- -.-. . . . . . ...- ,_ .. . ..-
.. . -.
.,.- ...- .- - -.-. . -.. ...- -. . - . malicious -.- virus
worm,-..-.. protect ..-..-- ..`--. protect ..... anti-virus
.....-- -. ........ . . `.. -. .-. . .,, protector .-.-..-
.,..-.,.. . .... .`.. ` . . - - -. unpack .. . -. . ..,.. .`.. -.
Protector .- packer .- , - .- .. .,.- . - .... .-.-. entry point (EP)
.-. pack/protect ..- .-..- Olly , . - .. ..- .- virtual address `.. ` .
OEP (original entry point) .-.-.-. decompression stub ... ` . , . ..- .- . entry
point -..-.`..-. unpack/unprotect . ... . .. - . .- . entry point -.-.,
Protector/packer .--. .-..- .-... unpack --.`.. -. , . . . -..
. command .-.... OEP ...- jump -.`.. ` . . . -.. - .. . . -, .-. - .,,
.-..- dump ....`..-. dump ..- .-,_... ,.-.-.
, - - .`.. -. F8 -.`.`.,
, ESP register - ..`.-.
, Compressor --..- exception .- - . .`.-.
,.,, Packer (Protector) ...
.
, .. ..-. -, .-. - .,, . .. . - packer ....`. pack ..- ,.,..-..
-.- ,_.........`. unpack -_.. .,_.-.-. pack ..- exe .-
unpack `. patch - ,_ .`.. ` . - .,_ .-.-. inline-patch - ,_ .`.. -. .,... .
-,.-.-.... tool -.-. UPX 2.03 (Ultimate Packer for eXecutables) `..`.
HTUhttp://upx.sourceforge.netUTH .. ....-.
UPX ... . -. exe . .- - . . ....... .. - .,... . ,.._ -.`. .
`.- protection ,_....-....`. ..-. -,.-..- UPX -.-. Marcus , Laszlo
-.....- UPX ... . - .`.-. .. . UPX , pack `.. unpack -_ ..
.-.... .`. -.-.-. `., ..... . .-. .-. ......- -. packer ,. protect (pack)
..`.... pack ...- .....-..-....-. UPX , pack ..--.`..
-., UPX packed ..-- unpack .- tool .-..-.......- -.,- . . . .. . . ...
, -, .-. - - -..-. , - , ` . - . - unpack . - .....,.. . .,, . ..
.-. . ., . .. -.,- . . .-. `...- -. unpacker tool .- - . .. -_ ,
unpacker .--. UPX packed ..-- --. unpack .-. . ... ... exe ..-..
`......--.-- ..- ..--.-- _..----.
, UPX `. pack ` .
.,.... pack . -,.-.- . .`.. . -.. ..-.-. Windows . . --_ ..
- calculator (calc.exe) . -.. ..`.. -. Windows . System32 folder ..-.. .--
...-. Pack ... PEiD -..`. calc.exe - -..-..-....-.., .....-..-.
-_.. ,
,
Start menu - Run .. .,.... cmd . - _ ` . Command prompt - . -..-.
command prompt - . .`.. . .-. UPX ... . -. command-line utility `...,
,
,..`..--. command prompt .. upx calc.exe .-_`. Enter key .-.
-,.-.-. .-....- UPX , pack `....` -... pack ..- calc.exe . -
PEiD , `,`...-_.. ,
,.,, Packer (Protector) ...
.,
,
,..-. calc.exe - UPX 0.89-2.9 , pack ..-. .`.-. Version
---.-. .`..`. ..-. --...-. ProtectionID 6.x -..`...
,, Pack ......- `........
,,--_-. .rsrc section .. . . . ._ ..`. .- -, .. ` . -, - section .- ..
. ._.`..-,-. Pack . calc.exe - PEiD . section viewer , -_..-..
.-. ,-.`..-. Pack `.,...-. .text section .data section .rsrc section .-
... UPX0 UPX1 , .rsrc section .- `.. .-. Section ._.-....`.....`. .rsrc
section - -. ._ ..`. . - -, .. -. - - . - .... .-. .-. `.. . , -
Windows 95 .--,.- oleaut32.dll .. LoadTypeLibEx function .. bug -. .
-. -.-. rsrc .-.....-..`. resource section - ...`..-. .-..
--. section -._.`...... error --... bug - ` . ..` .`.. ...
Windows , `.,.-- . .. .. . - - - packer .-..-.......-. .rsrc section - ._ .`. .
` . . . -- .
,.,, Packer (Protector) ...
.
,
,- pack ..-.- LordPE ,.`. pack . .....- . , ...-_....
PE header -..`....-- , -. .-... LordPE - compare button - . ,
,
, UPX `. pack ...... .. unpack ` .
-. . ..-. pack ..-.- unpack -_.. Pack ..-.- Olly
....... ,,-. Olly - compress ..-... ......
,,
,,.. Yes ..-. .,-. entry point ...- ...-....
,.,, Packer (Protector) ...
.
.,
UPX - -, .-. - application - compress -`. decompression algorithm -
stub , -.-- ....--. Application . entry point .,..-. stub . ..,..
.,, .`. . ` . .` . stub - .-`.,...-. execution - UPX - . -....
unpack ` ., unpacked - - . -.. - .- . . entry point(OEP) . ..- jump
-. . - ... - stub - -, .-. - application - decompress -.-. .-...`..`.
pack ..- application . unpacked copy -.. .-..,..- .`.. dump -.`..
-. -.`..`.. application -.-. -. run .. .--...-. -..-...-. dump
..- . . . . . section .--. file alignment -, . .- . - . . page boundary .--
align ...... Entry point - decompression stub - point .,- , .. .,. .`.. ` .
import directory - ....,-.`..--- `.. .,
.-.....-.-. Olly - -, .-. - . entry point -. ... instruction `..-
PUSHAD . .. -. PUSHAD . -.-.-. "PUSH all Double" - .-.`..`. CPU - stack
....- EAX -.,. ` . EDI .....-- 32bit (DOWRD) register .....-..
...- ........ _,-..-. ...-_.... stub -. OEP . .. .. . .
PUSHAD instruction , POPAD instruction -..-- .- - ... . ..-. .- . . ..
POPAD -. stack -., register ...-.....- -.-. .-.-.-. stub - ....
.- `, restore `. application - run -..- trace . - - . ..-.
...... .-. .. . instruction `..- PUSHAD .,......,-,... .,.-..
POPAD instruction - access . ...... stack . .. - .... .- . - ... -.
--. -, .-. - - PUSHAD .,... .. .,- , . stack . ... 4bytes .,....
Hardware breakpoint - .... . . Olly - -_- 4bytes - POPAD - access ,..
. . ... .`.. -. . . -, .-. - . entry point .- ...-.. jmp instruction ... virtual
address -.-.. `..-.
.-.. .,. PUSHAD instruction ...-...`. F7 - . .. ` .. brakpoint
.- . - . .. ESP (stack pointer) .. stack . .-_ .,.. `. . . -. ESP
.,.... right-click .`. Follow in Dump - .. .
.,
` .. stack . ... DWORD ...,.,- ... `.. right-click .`. Breakpoint -
Hardware, on access . Dword -... ,
,.,, Packer (Protector) ...
.,
,
.- . - ` .. ... .-. F9 - . . breakpoint . ..-, ....- ... ,
,
,- -_-. PUSHAD -., POPAD -.-- ...`.-. .-...
,- VA 01020E5B - JMP .,..-. -, .-. - . ..,- - entry point .,..`.. -.
JMP xxx.xxxxxxxx -...-.. VA 01020E5B .,... . breakpoint .-.-`. F9 -.-
,-. entry point . ...,..- ...- .. .`.. -. OEP -., ImageBase -, . .
1000000h - .--. RVA -, . . 20E5Bh .-. -, . .- . - .. .,.- .. . . .
. . ..
,
UPX , - .- - - -..-. -.-. Olly . CPU window ..-..-...
,-. 00 .-, `_.,- DB -.-- .-....
,
`.. ,,-. JMP instruction ... .- scroll .. `.. virtual
address - breakpoint .,,.-.-`. F9 - . - .. . . JMP instruction ...-
...- ... .,.- . ..-. F8/F7 - ..... -,.-.- ...,- EP .,..- ...-...
,,
,.,, Packer (Protector) ...
..
INFO: : ....`. -_- PUSHAD/POPAD mechanism -..- `.. packer .-- OEP
.-,..- RET instruction -- stack ....... PUSH instruction -..``.`.
OEP . jump . -. CPU -.-. -. function call -.-., `,.-.`. return
address - stack ...... ,..-.
-, .-. - .,, OEP - . ..- - Olly . plug-in -.`..- OllyDump - ..``.
dump -_ .. Olly . Plugins -., OllyDump -...-`. Dump debugged process -
. - ,- . `. ...
,
.-.......-..-.....-- `. ,- Fix Raw Size , Rebuild Import
-- ....- `.-..- `.. Dump button -.`. packed_dumped.exe ._, .-
...- ,
,
,- -, .-. - dump ` . . . ... - . - `, . -_ . ,,- . error -- .,
-. `. .. .
,,
-. error -- .,.-. . .-. -, .-. - . dump ..-.- .. icon ..- .,-.
--.-. -. .......-.. Application - LordPE ...`. section .-
.,.... -_- .,
.,
,.,, Packer (Protector) ...
..
RawOffset , RawSize -.-,...--. ....,-. .-.. application -
... section ..... Raw -,...-- Virtual -, . ..- , - _ ..... RawOffset .,... .
VirtualAddress .-,..-_`. RawSize .,.... VirtualSize .-,..-_.. ,_.,
section ....``. .-...- .-- --. OllyDump . "Fix Raw size &
Offset of Dump Image" checkbox - .. . - . .-. - ` ... . . .- - - ., . .
.,- . `. .`
.,
... . .,_ .....-. .-.-.-. packed_dumped.exe . - . - - . . . -
. - ,- . `. .-.
,
....., --..-...-. import .-- reconstruct (rebuild) . PE
header ' ,.....`. process -.-..``. import .-- -.- .-. -.
`..`.. -.-`.....-. import ..- function .-...-..`. import data .-
-. - . .. ..- ,_ .. ..- .. -_ ` . , ...- .- , . .`.. -. - ..-.`...
. . -, .-. - .,, MackT . ImpRec 1.6 - ..`....
ImpRec 1.6 - ..`.-..... import .--.... pack ..-.- process
.,, attach ..... ..--. ...
,-. pack ..- .-..- packed.exe -. Olly . . .,-......,.. .
OEP .,... . virtual address 12475 - .-_
,
,.,, Packer (Protector) ...
.
`.. IAT AutoSearch - .. . ,- . `. ... OK -.
,
, ,- Get Imports button - . ,- . `. ...
,
Show Invalid button - ...`. import .- . , .. , .. -_ .. .. , -, .,-.
Fix Dump button - .`. -,.-.- .,.-.......- packed_dumped.exe .-.
,,-. `.... --. `.,.. . .-. section - . ._ ..- . error -- .
..
,,
, .-..--`. .,.-......_.-- packed_dumped_.exe - . -_ .-. ..-. .
-.- .-...
ImpRec - -, .-. - dump ..- exe . - ` . ` . . . .._ . - -. --.
.- PEiD ...`.-_-. unpack ..`.....packed_dumped_.exe, ......-.
pack . ..calc.exe,- -..,-..-.`. "makct" , "newIID".- section . .
.-..- .-. "makct" section .. ImpRec - import ..- .-....-- ...-.
`.. -.
,
PEiD , packed_dumped_.exe .- `,..-_. ,-. .-...
,.,, Packer (Protector) ...
.
,
..`-.-.-. ....- packer , pack ..-.- unpack `, -.`.. -.
.`. packer .--.-. pack ,.. .- protection ,_ .. .. .. _ - -. ,. ,.
.,, .`... anti-debugging , anti-tampering _ .... .- - , IAT -- encrypt `.
stolen bytes API redirection .._`.`..-. .,.-.,..-.. .-- ..........
, Inline-patch ,_ .`. patch ` .
--. pack ..- .- patch . .`.. .., .. . . inline-patch ,_...-
..``. .- unpack . - patch .-. -.-. loader - decompression stub -
... . - ` . , . - . . . - - ` ` . .,.- . .. ..-. application - .... OEP
. .- . ....` .`.. -. .,.- -. . ..`... . - . . . application - unpack . ....
`..- patch, ..--. .-......-.`.`..`. .,.-.....-. OEP . `, _ .-.
.....- . .-. `.. -.
- .......... -,.-.-.,, pack ..- calc.xe .-
MessageBox -. , - .- - - .- - _ . ...`..-. `.. .-... application -.
-.,.. unpack ` .`.. . . -. . ... .. MessageBox - OK - . - . OEP
- ...-.....`..`. application -..,-. .. `..-.
.. . .. .-.-. pack ..-. _....-- - .,.. - - . ... .
calc.exe - hexeditor -., ....`..-. ,, Section -. . . .- .,.. - .- -.
-_... .-....`..`. --. .,.. - .- ... . . .-. -, .-. - .,,
PE. -.. -....._`.' ,.-,_...-. section - .-. UPX ,
pack ..- . .- . . .,.. - . ..-. .-. .-...--. .-. UPX , pack
..-..-. .....-. .-. .-. .. . .,-.`.. -.
,,
,,-. WinHex . .` ` . packed(inline).exe . - ._ , . - . ..-.. `..
Olly . . packed(inline).exe .- ... -,.-.- .-- Unpacked .-.....- ...
Olly . Hex window .. right-click .`. Search for - Binary sting -...
.,
,.,, Packer (Protector) ...
.
`.. .,-. Unpacked .-.....- ..-.
.,
. . -, .-. - . ..,- ......-- ,-. .-...
,
Unpacked ........ virtual address -.-. 010233C0 `.. ` . Myanmar Crackers
........ virtual address -.-. 010233D0 `.. -. virtual address .-- .-.....`..
-. ` .. Olly - -.`. VA 010233C0 ...- -,....-_.. ,
,
,- highlight ..- -.--. -,.-.- . - _ ..- ......- `.. -. VA
010233E0 -.` . MessageBoxA , - .- - `..- .- - . - _ -..
,-.-. MessageBoxA , - .- - - .- - . - _ ` . `. .-
,
` .. Olly . plugin -.`..- Analyze This! -.`. -.-- analyze - ,
- . .`. . . ..-. `. ...
,.,, Packer (Protector) ...
.
,
,- Analyze This! , analyze -.. ,.. highlight `...--. .`..
. .-. . patch -- .-..-. error `...
,,
.-. .` -, .-. - ` .. - - .- - . .,, . . .._ .-.. ,,-. `..
- -.-.. highlight `. - ` .. right-click .`. Copy to executable file - ...-
,- . `. . . ..
,
,.. right-click .`. Save file - ...- ...---._, .-...._.-
` .. Olly ---`. -,.-.- ...._.-- .- .- .--. -..
.`... .. - . -..-...-. -,.-.-.,, MessageBoxA ...- _,`....-
Olly .. .,.-.......-.- .- -.`. VA 01020E5B ...- -,....-_
.. ,
,
,- JMP 01012475 .,... . -, .-. - . MessageBoxA ... virtual address `.. -
010233E0 - .-_..... ,,
,,
,.,, Packer (Protector) ...
.,
` .. - - - ._ , . - . . . - Olly - --`. .- run -_ ,,-.
`..... OK - . - . .-. calculator .-... ...-..... `..-.
.,
-, .-. . .` -.-.-. unpack . - pack ..-... -.-- ``.
(inline-patching) .-..`..-. MessageBox ..- _ . -..-. ..- - ..
. .,, ., . .. . , -. Pack . ..- . .- . . - . - .. . . -. Message
Box ....,..- entry point address .`. ... - . ` .. . . .- .,.. - .- ...- . .
-. .-. MessageBox ..`., textbox -., password .- .. - ..... ... .,..
- .- - . , .-. Inline-patching , _..- MessageBox ...- -,....-.. ..
entrypoint - VA 01020CD0 ... VA 010233E0 .`..-_- .,- MessageBox
.-. ... ... calculator .-..- ...---. -..-. UPX . decom-
pression stub - .-. .... `.. -.
UPX , - .- - . , ...-.-. ..- . .,, unpacking ,-.-- . .
.- ,_..,.._..-` -. -, .-. .,, unpacking , - .- ` . . . . ..
... .`. packer .-.-.. ,.._.... ActiveMARK .-..- `._.-......
..
,, ActiveMar k 5.0 `. pack ........ unpack ` .
Trymedia -. RealNetworks . . - .-. `.. ` . ActiveMark .-.-.-. Trymedia
. pack/protect - ,_ ._.-. . `.. -. Trygames -.-. Trymedia . -. . - -. .`.. ` .
Trymedia . - . ..- - download ....-. trial . ..- . , ... .` .- . - - ...
-.
PopCap Games (HTUwww.popcap.comUTH) - ....--..... Infogrames (HTUwww.infogrames.
comUTH) - ... .- - . ..-. .-. ......-. ActiveMARK , protect ..--.`.. -. Active
MARK , protect ..- -...-.. registration ..-. -..-...-. -...--. .-.
.-.-..-,-... full version .,, -....- demo - . ..- `.. ., .- . - , - ,
. ... .-. -... ..-. . ..- - - . -... `-,- ........`. .-. . ,. `..
-. .,...-- Monopoly 3 - unpack . .. .. ..... -. -..-. . .-.
Monopoly 3 , -.-- crack .- -.,-.. ..-. Share ....- crack ..--
.--. ... ........- 258Mbytes `...,.-. ..,, -.,--.,
download .-..-. .-.. PopCap Games -....- Zuma deluxe -
unpack . .. .. - .-. -. Zuma - HTUwww.popcap.comUTH -., download .`. install
` .. zuma.exe - PEiD , .. ...-_ .,
.,
,.,, Packer (Protector) ...
.
.,.. . .-. zuma.exe -. ActiveMARK 5.x , protect ..-....-.
. -.. . ..-..-.- .... ... Zuma - .-_- ,,
,,
.-. .` -, .-. - Zuma - unpack -_ -..
,, ActiveMar k 5.0 `. pack ........ dump ` .
... zuma.exe - . .. Olly - . Open menu - Attach - ....
,,
.,.- ,,.. `..--. zuma.exe - Attach
,,
Attach `. .-.. ,,.. `..--. VA 7C901231 . . . . ... . --. .-.
ntdll.dll .. DbgBreakPoint API function .-. .....-. DbgBreakPoint -. Win32 API
.----- help ... .,-.-`. -....`.... .---.
,.,, Packer (Protector) ...
.
,,
Olly . . Alt+M -.`. memory map - -_.. ,,,
,,,
,,,- highlight `...,-.,..-.-. second layer entry point . ...,.. .,... . right-
click .`. View in disassembler - ...- ., Enter key -. ,,-. `....
,,
,,- highlight `...,-.,.. VA 005AE000,. . right-click .`. Search for - All
intermodular calls - .... ,,-. `....
,,
,,- . `. .- . . getversion .-_ GetVersion function - ..-.
GetVersion API - .-- right-click .`. Follow in disassembler - .. . ,,,- . `. .
..
,,,
,.,, Packer (Protector) ...
.,
,,,- PUSH EBP .,... . right-click .`. Breakpoint - Hardware, on execution
- .. . ` .. Olly - -.`. zuma.exe - --
Olly . Option menu -., Debugging options -...- ,.,-. `....
,.,
,.,.. `..--. Break on new module (DLL) - ..... `.. OK -.
-. . ..-. zuma.exe - attach ..-.-. Olly -., -. -_ . . .. ,.,
,.,
,.,-.-. zuma.exe . entry point .,.. ` .. .-. -, .-. - .- . - ..-
hardware breakpoint .,.....-.. F9 - .. -. module .-- .,-.
. -. ,- . `. .,. . ..
,
F9 - .---..-. .,.-...-. ,-. -,.-.- .-.-..- breakpoint
.,..- ...-.-. -.`.-.-.-. -.-- analyze ..., Analyze ....
. . VA 00696E58 - PUSH EBP .,... . DB 00 ..,. .
,
,- VA 00696E58 -. -, .-. - . ..,- OEP `.. -. -, .-. - debug
..- process - dump . -....-.. Olly . plug-in -.`..- OllyDump -
...- ,
,.,, Packer (Protector) ...
..
,
,- dump button -...`. .- dumped.exe .-._, ...- UPX .. dump
-,.- dumped.exe .-.-. .. .---. .-. ImpREC - .`.
import .-- `... ImpREC (Import Reconstruction) - ...-.-....-.-. dumped
....- ..-.,- function .-- ...`....._. `..-. .-- .``-,
.-. . . dump .-. .,-,- PE .`..... .---.
,
,. ...... ...-.--.-.
Olly , ...- zuma.exe - active process .,, attach
Olly .. .-_-,.- .-.- OEP (VA 00696E58) -, . . -., ImpREC . ..- .-
imagebase (VA 00400000) - .-`....- 296E58) -,..- OEP - - . . . - _
,.,, Packer (Protector) ...
..
OEP -,..- .-_`.- IAT AutoSearch - ... ,,-. `....
,,
, ,,- OK ..` . Get Imports button -.
Import function .- .,.., .... Show Invalid button - . ` .-_ .,... ..-.
.. .. , .,-. .- .-.
.-.. -,.-.- dump ..- dumped.exe . , zuma.exe .-...`. import
.-- ...... Fix Dump button - ... ,-. -.......- dumped_.exe
.-._, .- ...._....-. .-...
,
. -, .-. - . dump .- `.-.`....` `..--- ImpREC - - - ` .
dumped_.exe .- .-_ -. error ..`.-.. dumped_.exe - -. ..- .
- . UPX - unpack - , .- . ` .- , . . unpack --. `....` ActiveMARK
...-. .... .-. WinHex - . ` .- .- - ` -..
WinHex .. dump `.`..- dumped_.exe . , pack ..- . zuma.exe .-
. Exe .- overlay data .- . .. . byte -- ...-.--., -.- -, .-. -
. .. . TMSAMVOH . - ASCII string - . .- ,_ .-.-. . . . .. . . .
-.... zuma.exe - LordPE ...`. section .-- -_--... ,
,
,- highlight `. ..- -, ..- - -_ - -. -, .-. - executable ..
.,.-.. section - -, ..- `.. -. . - - Raw offset , Raw size . ..--.
Windows loader - exe .- .-. -.--.-. RawOffset (0012BA00) , RawSize
(00000200) . . .- -, . .`.. - 0012BC00h ..`.. -. Zuma.exe . . address .-
., ..- data block -..--..`. dumped_.exe . . . .. . paste . .. .. .`..
-. . .. dumped_.exe -. . , . . `.. -.
WinHex . Position menu - Go To Offset -...`. -,.-.- ...- offset
0012BC00 - .-_.. ,,
,.,, Packer (Protector) ...
,,
0012BC00 - .-_`. OK - . - . .,- . `. .. .
.,
.,.. `..- ........ right-click .`. Beginning of block - ... .,
.,
` .. . . ..- . . ...- .. scroll . ` .. ,. ..- .--. .,.-.......
right-click .`. End of block - ....
,
.. ,-. Hex -,.....- ....`....`
,
,.,, Packer (Protector) ...
......- Hex -, . ..- - - .. -.. Right-click .`. Edit - .. .. ` ..
,.. `..--. UCUopy Block - UHUex Values - ....
,
...-.-. -...- Hex -, . ..- - paste . `.. -. WinHex . dumped_
.exe tab -...`. ....-... .,.- . ... .. .,... . right-click .`. Edit -....
` .. ,. . `..- - . ClipUbUoard Data - UPUaste - ....
,
.. ,,-. paste .... ......
,,
Yes button - ...--.. zuma.exe - Hex -, . ..- dumped_.exe .- ...-.
. .. dumped_.exe .-...`. WinHex -., - -
dumped_.exe - .-. ,,-. `.... .,..-.-. - ..
...`.-.-., ...-. -,.-.-. dump -,.. ..`...`......`
... ,-,.---.-. ......`. .....-. .-. patch . -.....
...
, Dump ........ patch ` .
Dump ..-.- patch .-- dumped_.exe - Olly .. . ,
,
,-.`..- right-click .`. Search for - All referenced text string -...
.,.-...-. ,.. `..--. browser .- .....- ....
,.,, Packer (Protector) ...
,
,- OK ..- ,,-. .-...
,,
,,. highlight `...-.,.... right-click .`. Follow in disassembler - ...-.
.,- . `. .. . -. browser ...- routine .., ..`..-.
.,
.,- VA 005F41A8 .. right-click .`. Copy - To clipboard - ...`. notepad
.-... paste 005F41A8 MOV EAX,dumped_.006A691C ... 005F41A8 browser
retn4 .`. . ` .. ,-., dialog timer timeout ......- - . .` . browse .....-,.-
. routine . . virtual address .-- .-....... .-- .,.. ,.-
`..-.- breakpoint .- . - . .- - - . `. .... `..-.,
.`..-.-.-. LoadStatePool ..... .....- . .-.-.-. . .- . ... ..
.......,..- breakpoint .-.-`. .-..- `,..-. .-. dumped_.exe - Olly ,
`,.-.. -,.-.- .-.-..- breakpoint .,.....- . .,- . `. .-.
.,
-....- ,,-. stack window -...`. highlight `...,-.,.... right-click
, ` .. Follow in disassembler - ..... ,,-. `....
,,
,,- highlight `.. .,- .,... virtual address - . - ..
,,
,.,, Packer (Protector) ...
. browser dialog timer timeout , LoadStatePool -, -.-- virtual address
...-.` virtual address .- . . -..- ` .. . -.-.-. ,,- . `.. -.
,,
,,- virtual address .- . . retn 4 retn 0c , retn ....- .... `.. patch
..- . - - - - ._ , . . . - . . -, .-. - . Zuma Deluxe 1.0 - --...-
. -... .`
, Pack ..... ._ .. . .. unpack ` .
-. . ..-. Fish Packer 1.04 , pack ..- calc(Fish).exe .-.- unpack
-_ .. -, .-. - . . - -., pack ... . -. PEiD , .. -_ .. ,,
,,
,,..`..--. PEiD - .`.... ` . .. - . CFF Explorer ,...-. -.
-,.-.-.- Fish Packer 1.04 , pack .. .. Fish Packer , pack ..-
..,..-. .-..` .- unpack -_ .. Unpack .. calc(Fish).exe .- Olly
...- Protection ID , . . .-. Fish Packer 1.04 , pack ...-..`..`..`.
Protection ID , .. .....- . .- -. . .. -. ... Protection ID -. protect/pack
..- . .- - .. .. ......- ..,_.-.-.,
,,,
Olly - ,,,..`..--. PE . .- - - . .`..,-.
,,
,,,- OK button -...-- ,,-. `..-.
,.,, Packer (Protector) ...
,
. , ..`. Olly ,.. entry point ...-...-...... ntdll.dll module ...- .,-.
.- ... . - .- , -, .-.-.. ,_....-. Alt+M -.`. Memory Map -
. - ,,
,,
,,- highlight `...,- PE header ......,.... ..-.-`. PE signature ...-
. ..-_ - ,,,
,,,
,,,. . -, .-. - . - ...-.-.-. entry point ... address (10257D7) address
-.- Olly . Disassembler window .. Ctrl+G .`. entry point(10257D7) ...-...-
,.,
,.,
,.,- VA 10257D7 .,.... breakpoint .-.-`. F9 (Run) - . -
breakpoint . ..- -, ....- . . .. ,.,
,.,
- ..., . . . unpack . . .-.`.. -. -, .-. -.-. ,_ .- .- -
-. .-. Olly Advanced plugin - ..`.. .,
.,
.,-. Plugins menuOlly AdvancedKill NumOfRva Bug -.....`. .-..-
Olly ,`,.-.... ,,,-., ,.,..- - . .... .-. - ,.,. - - . - ...- .
. ..
,.,, Packer (Protector) ...
,.,-. `..,.. Alt + M (memory map) - . -_ - ,,, .- -. .- .
.. .,
.,
.,- -_ . calc(Fish).exe . . section ....,-..-... ,,..-,.-.-. .`.
.- . .MCTeam -.-. compress ..-- import .-, resource .-.- section
-. `.. ` . -.-. Fish Packer - uncompress ..`....-.-..... ..`.
.. -, .-. - dump ... code section `.. -. . - ., UPX , pack ..-
. .- . .. . UPX0 -. code .- ..... code section `..`. UPX1 -.-. compress
..- - .- . .. SFX section `..-.,
.,- .,.... right-click .`. Set breakpoint-on-access (F2) -... `.. F9
-. .,-.`....
.,
.,. .`. .-.-.-. Fish Packer -. compress ..- - .- - section
. ..,....` . - .- ..- ` .,- . `. .- F8 -..
0100018B 74 1A JE SHORT calc(Fish).010001A7 ; Decompression Stub
0100018D 8A07 MOV AL,BYTE PTR DS:[EDI]
0100018F 47 INC EDI
01000190 2C E8 SUB AL,0E8
01000192 3C 01 CMP AL,1
01000194 77 F7 JA SHORT calc(Fish).0100018D
01000196 8B07 MOV EAX,DWORD PTR DS:[EDI]
01000198 38D0 CMP AL,DL
0100019A 75 F1 JNZ SHORT calc(Fish).0100018D
0100019C 32C0 XOR AL,AL
0100019E 0FC8 BSWAP EAX
010001A0 01E8 ADD EAX,EBP
010001A2 29F8 SUB EAX,EDI
010001A4 AB STOS DWORD PTR ES:[EDI]
010001A5 E2 E6 LOOPD SHORT calc(Fish).0100018D
010001A7 AD LODS DWORD PTR DS:[ESI]
010001A8 85C0 TEST EAX,EAX
010001AA 74 37 JE SHORT calc(Fish).010001E3
010001AC 89C7 MOV EDI,EAX
010001AE 033B ADD EDI,DWORD PTR DS:[EBX]
010001B0 56 PUSH ESI ; module name (eg., kernel32.dll)
010001B1 FF53 0C CALL DWORD PTR DS:[EBX+C] ; kernel32.LoadLibraryA
010001B4 89C5 MOV EBP,EAX
010001B6 AC LODS BYTE PTR DS:[ESI]
010001B7 84C0 TEST AL,AL
010001B9 75 FB JNZ SHORT calc(Fish).010001B6
010001BB AD LODS DWORD PTR DS:[ESI]
010001BC 85C0 TEST EAX,EAX
010001BE 74 E7 JE SHORT calc(Fish).010001A7
010001C0 83EE 04 SUB ESI,4
010001C3 AD LODS DWORD PTR DS:[ESI]
010001C4 A9 00000080 TEST EAX,80000000
010001C9 75 0B JNZ SHORT calc(Fish).010001D6
010001CB 83EE 04 SUB ESI,4
010001CE 56 PUSH ESI ; module name (eg., kernel32.dll)
010001CF 55 PUSH EBP ; function name (eg., GetVersion())
010001D0 FF53 10 CALL DWORD PTR DS:[EBX+10] ; kernel32.GetProcAddress
010001D3 AB STOS DWORD PTR ES:[EDI]
,.,, Packer (Protector) ...
010001D4 EB E0 JMP SHORT calc(Fish).010001B6
010001D6 25 FFFFFF7F AND EAX,7FFFFFFF
010001DB 50 PUSH EAX
010001DC 55 PUSH EBP
010001DD FF53 10 CALL DWORD PTR DS:[EBX+10] ; kernel32.GetProcAddress
010001E0 AB STOS DWORD PTR ES:[EDI]
010001E1 EB D8 JMP SHORT calc(Fish).010001BB
010001E3 5F POP EDI ; POP ESP, so calc(Fish).010257DF
010001E4 C70361EBF600 MOV DWORD PTR DS:[EBX], 0F6EB61 ; POPAD & JMP , EBX = 010257DF
010001EA 66:C743F89068 MOV WORD PTR DS:[EBX-8], 6890
010001F0 66:C743FEC390 MOV WORD PTR DS:[EBX-2], 90C3
010001F6 C3 RETN
.,
.,...-. .... - - `..-. .. . decompresion stub -..``.
-.-- decompress -. `..-. LoadLibraryA() -..``. import .. DLL
..-- .-. GetProcAddress -..`. import function .-. address -..-. .,.-
...-. EBX - 0F6EB61 opcode .- ...-. 61 -.-. POPAD `..`. EBF6 -.-.
JMP xxx `.. -. Endian ,.-. .-`, POP -.-. ESP -.-..- - `, -
.-. Stack .. .,.-.._...-.-.-. EBX , - .- - .-..- .-. VA
010001F6 (RETN) - ...`.,.. VA 010257DF - .. .... .`.. -. .,,
.,,
.,,-.`..- F8 . . . - .,- .`. ...
.,
.,-. `..-...-. EBX -..-. 0F6EB61 6890 , 90C3 - - ._ .-.
. -. ,.._ ..- ` -. PUSH + RETN -. JMP ,_-..-. .,.. F8 ..
-,.-.-- OEP . ...- ` `.. -. .,
.,
.,-. `....-. dump .` `.. -. .,,
.,,
,., IAT . API Redirection
,
tcef;(15) - IAT ES if h API Redir ection
,....-. pack ..- . .- - unpack ... . .`.. ..,- .- ... IAT (Import
Address Table) .-. .- .. ... .. .`.. -. ` . - , .. .- , .- IAT .-. .- ... ... .`..
- IAT .--`.... ImpRec 1.7 -..``.`-. .,.-... IAT .- -.- ., .. ..
IAT .- .-. .- _ . ... ... .. . .`.- -.`.. -.
Info: : Microsoft Windows .- -. -. , -. .- _ -. . - . API function .-..
.-_- address .-.--. -..-...-. DLL . .- . .- _ - -_ ...- .-.
Application -..-,.. ... function .- .. .. ... .-. . -. -. . - , .-.-.
application ..-.-. .---. function .-- import .- ..` . . - -.
operating system . DLL . . .. -. ... application -.-. -. .,... .. . . -.
.. . .- . Win32 exe .`..- application -... IAT . -.. -. IAT -. . -.. . .
. -. Application -. - Windows . API function -.-...-.. IAT - lookup
table `....`-. .-. . -.. . . -.. - .. .. ..- - IAT -.-
-_...-...-- Windows loader -. API ..... address . .. .- . ... .`.. -.
. -.. .,- , . ..-. API -. - .. . . IAT . .-_ ` . DLL ....-
address - -.....-. exe .-.- pack .. protect ..,.. cracker .--.
.- unpack .-. unpack ..-.- ..-.`.. ... ... -..-.
..-. packer/protector .-. .-. ......- IAT - .- . - .-. . exe . -
.-. .. , . . .. . .-. IAT - `,-_...-. `,`.-. Import .--
`, _ -_ ...- -.-. IAT - `, _ -_ ...- -.`.. -. IAT -`,_-_...-.
-- IAT .-..- ....-.. .`
Info: : exe .-.- ... -.---,.. Windows loader -. ....- PE structure
- .- . , executable image - .-..-.-. -.,.-. Application -..`- DLL
.- .. .- - .- -.`.. ` . . - - process . .,.. - .- `.. .,....-.`.. -. exe
.-. DLL ....-- function .-...- ....`.-. Function address .- -.
...---..-. run ., , . . compile ..--.-...- .`....- variable
.--.`.....- mechanism -. -. - IAT . .`` . .`.. .. -. IAT
. -.-.-. DLL . .- - - .- .. , . . Windows loader - `._.-- function pointer
.- . ...-. `.. -. Application -.- ... compile .- IAT - . `. . -.
`..--- -. API CALL .--. -..........- --.- address .-- ...`-.
.. function pointer --. --. pointer table - ,_......, ...
-. ,. ,...`. .-. CALL [pointer address] -.,- - . - ... _ ..-. . JMP thunk table
. ... _ ..-. .`.. -. Pointer table -..``...`. loader -. API call -..`.
- -...- .,...-...-` . . .-. - . . -.-.-. pointer - table -
.,..-. . . . ....
Info: : Pack ..- exe ..-.... .-.--. .-....... IAT .- - `. -. . . . .
.... ..-. -. cracker .-- unpack ..-..-. Pack ..-
.-...-- .`...-.-..- compiler .-,---.`..`. `..- mechanism -
... . `..-. --. packer -.-. import table mechanism - .- . .. .
.-.- packer/protector -. -.-.. DLL , function .- .. , pointer .-- -..,....
... . -.- - - - .. .`.. -. , . . -.. .,, -.-. decompression stub -...`.
routine .-- restore ` . , . . . , .,...`..-. .-...- import table
-.- -. restore .. . -.- ,.._ . . -, .-. - .,, import table - -. .,..
... Windows loader - - parse . -..- ` . . -.- . . ... -.
.,.... IAT , - .- ` . ,. ,.`.. . -.. ..-.-. Lena151 . .,...,- Reverse
Me.exe .-..`..-. www.tuts4you.com .. download . -
,
,., IAT . API Redirection
.
,-.-. ReverseMe.exe - Olly . .. ` .- `. .- VA 00401002 -.-. API
... CALL - .. .-. CALL -.-. kernel32.dll ...- GetModuleHandleA function
- .. .-.`.. -.
,
,--_-. ..- CALL .- .- . . VA 0040104D - kernel32.dll -
ExitProcess function -...- CALL `.. -.
,
ExitProcess function ....,.... ..-.-..-. ,- ..- .. . . - -_ .-.
- `.. CALL .- Olly -.-. -. API -.- ....,..-. `...--
. . .. VA 0040104D .,..- .. .` . Enter key (Follow Call) -.- ,,-.
`....
,,
. ,,-. jump (thunk) table .......-.` .-.. Olly - VA
0040104D -. API CALL -. - ... . - CALL -. `.. .-. . . -. Application .
-..,...... ExitProcess API - .. . -. . . address (0040104D) - ..`...
`.. -. . .. Windows loader - .,-,- address -..-. .-.... . VA
0040120E -.-. -. instruction -..-..-..... .,.... Enter key
-.- ,-.`....
,
--. .-. loader - data segment - DWORD -, . .-. . - jump . ..-.
`..-. .-.. -,..-.... DWORD -, . .- .`.. -_ .. Dump window
.. Ctrl+G .`. ..---.,.... VA 402004 . - _ ` . OK - .. . - . .-. ,
-. `....
,
,., IAT . API Redirection
.
,-.-. .-... DLL ....,- API .- . address .-,-..,- IAT .-...
.,.. -, .-. - ,. ,...-.-.-. ExitProcess API -
,,
.-.. VA 00402004 - -_ - . ,,- .`. .,.-. Highlight ..-
.,..-.-. -, .-. - API ....,.. 7C81CAA2 -.-. API ... address Endian ,_ .,
. -.. - ., . .,.- . ..-. DWORD -, . .-. . _.- , - - .,-..- . . . _.-
.,.- - DWORD -,...--.-. .,.- DLL - API .--.__,.-. DLL -.
user32.dll `.. -. DWORD -, . ..- - -_ - . 7xxxxxxx .- , .-. .- ... . . ` .
. . ... .- - IAT ..-_--... ,,- -_ - kernel32.dll .-
API ..- import ..-..- . . . - .... .-.-. IAT , imports table - -. .- - .
.-.-
Info: : Imports table .. ..-..-- API .-- link -... Windows - --
- .- .. .. -. Imports table .. ,....- structure -..-. Import
..- DLL ....-- header -...-. .-...- .-...... ..-.
- -.. .. - -. . ...-. Header ..... ..-. DLL - - - - .- .. .
-. ReverseMe.exe .-..--...-. user32.dll , kernel32.dll - API .--
import .. . . . .,, header - . ..- . . -. -.-. kernel32.dll --`..`. -.
-.-. user32.dll --`..-. -.-.-. imports table ...- .-....`..-.
Windows loader -. header ....-., --.--.-`. --.-- IAT
`._.-......`-. IAT .-.-.-. DLL ....-- IAT .-.._...-.- .`.-.
DLL . .. .- - header -.-. IMPORT_IMAGE_DIRECTORY .-. IMAGE
. - .-.. .-.-. . - . . . - - . . .- - ._ _ , .-.`.. ` . offset .-...-. RVA .-
`.. -. . . . ..- structure . -.
IMAGE_IMPORT_DESCRIPTOR:
OriginalFirstThunk
TimeDateStamp
ForwarderChain
Name
FirstThunk
Info: : Windows loader - IMPORT_IMAGE_DESCRIPTOR - .- , . . . -. DLL - .
.....-. .,.-... loader -. DLL - -.--.`..`. IAT --_...-. .--.
- -_ ...- .-.-. ,_ .,_ ... - -. Loader - .. . OriginalFirstThunk -
.. ...-.`.. ... - - .- - `.,.-. .. . .`-.`.. -. .,.- -. -.-.
FirstThunk -_ , `- ._ . .. .- - . -. pointer - API . address ,....-. `..
-. --. ....-. ..- . API -....-..-. OriginalFirstThunk ....`.
-., - - .- .. . - ....-. .,.-..`....`- ...-. crash `..
-. .-. .-... FirstThunk - pointer .-..... API .-.._.-,.-
RVA .- ... - . DLL -., API .- - _ , .- address .- .,.-. . - .... .-.-.
. - . . . exe - .,....` .- .,.- . ..-. IAT -_ ...- ` .-. ` .. .`
Info: : Loader -. FirstThunk - API ._ . .. .- .- ` . . . address -....-.
--. address -...-. ._.,.... address , ... . - ` . . .- - . .-.
OriginalFirstThunk ....`. -....-. .-.. OriginalFirstThunk -. FirstThunk .
backup -.`..`. `.,.--.. ..`-. FirstThunk -.-. -, .-. - import .
- API .- . ._ , - .- - pointer .-- array -.`..-. --. -.-
-- process -. .,-,.. .`...-. FirstThunk ,.- pointer .-...-.
,., IAT . API Redirection
API .- . address .-, overwrite -. .` . address .--.-. IAT .-. . -.. -
CALL .-...-. IAT .... redirect `..-. Loader - IAT `.. ........-
address .- `.. . -.-.-.
, API . --. address
, API . jump .
, push RVA API
Info: : Import table - `_.,-,....--
, RVA , import table - . . . ...-. import .- - - data directory -. .-.-
_ . .. -. . .- - . .-. Windows -. .-....`..`. IAT - .-..-.....
.---.
, DLL ....- IMAGE_IMPORT_DESCRIPTOR -. , .-_. Import table -
.-....--.,...-
, IMAGE_IMPORT_DESCRIPTOR . . OriginalFirstThunk FirstThunk , Name -.-....
. .. TimeDateStamp , ForwarderChain - -.-. . _`.. .. .-. OriginalFirst
Thunk - . _`.. ... -.
. . .- - .- - - . .`.- - - . .,, . . ..,..- ` -. .-.
` .,.._ . ... ReverseMe.exe ,--_--... ReverseMe.exe - Olly .. ...
Windows loader - .. ..- -.-.-. . -.. . header - IAT --_...-.
-- RVA 3C (400000 +3C = 40003C) .,.....--. .,
.,
.,.. . .-. PE header . ...,..-. VA 004000C0 `.. -. VA 004000C0 ...-
. .. - . .-. .,- . `. .. .`.. -.
.,
IAT . RVA -,..-.-. PE header .... address -,.... 80h . .` . .. .- -, . .
VA 400140 .,... . . . ...` .`.. -. exe - .- - .,... .`. . -. , ,
,
,.. . .-. import table .-.-.-. RVA 2050 ..
Info: : Import Table Address .-.-.-. import table ....,..- ..... address - IAT
, ..... ..., . - . . -. .- `..`..,..-.
,., IAT . API Redirection
. - ., Import Table Address - Olly ....-.-.-. -.`.,....-. Olly -. header
, - .- ` .- - `_ . - ..-. --. -. . . .,, .. .- Import Table
Address -... -.`..`.. .`-...`. -.-..,-..-.- ...-. .-....
-,.-..,,`.--- ....-..`.,.-.
.-..`. Import Table Address ...--_--... ,
,
-, .-. - ... .- . ..- ..- IAT .- . ...,.- . . Import Table Address . .,-.
.- .-. Disassembler window . VA 00402050 -...- ,
,
,..`..-.-.-. -,.-.-- - -.. .`... .`.. ..- . Analyze This! -...`.
analyze - ,
,
,..`..-.-.-. IMAGE_IMPORT_DESCRIPTOR array . .. .`.. -. .
, -.-.-. DLL . .. .- - IMAGE_IMPORT_DESCRIPTOR .- `.. -. -- .
.`..- -.-. . ..- IMAGE_IMPORT_DESCRIPTOR `.. -. IMAGE_IMPORT_
DESCRIPTOR -... DWORD -,.. ..--.
,...-.- ... DWORD (00002098) -.-. OriginalFirstThunk `.. -.
.-. loader - -. DLL -., import ... API .-.._.-- -..,.........-
- - .- ..-. --. IMAGE_BASE + 2098 ...-....... -,.-.-
.,, import .. API ._ .- - .- . . .,.- .- -_ ,
- . DWORD (00000000) -.-. TimeDateStamp `..`. -,.-.--- ...
. - . ........`. .-. .. .-. . _.- `.. .,-- -.
-- . DWORD (00000000) -.-. ForwarderChain `..`. -,.-.--- ...
. - . ........`. .-. .. .-. . _.- `.. .,-- -.
.-- DWORD (000021D8) -.-. IMAGE_IMPORT_DESCRIPTOR ,.-.-
DLL .._... RVA `.. -. -, .-. - . ,. ,.. -.. . ..-. 4021D8 .. user32.dll
.-..-.. .-..-..,
.,.-.. DWORD (0000200C) -.-. FirstThunk `.. -. Import ..- function
.-...-- address .-...- ....-- IAT . ..- _ , `-. Disk ...
.--... -.-... exe .- .-. -.-`.,...-. ---.,
-, .-. - . ,. ,.. -.. . ..-. . .,, user32.dll -., import ..- API .-
-- IAT ...- address .-...- .-.....-. ,,--_ 40200C -.,.-.
.- ...
,., IAT . API Redirection
,,
,,.. . .-. API function - ...-. . .- .-. -..-. .`.. -.
..-. 7xxxxxxx ,.- address .-. -..`..- DLL (kernel32.dll) -- ,_.
-.
,
IAT . .. - address .- -. ,- . 402000 -.,.-. .- ...
,
.,.- . .-. . DWORD -, . . .-.-. . _.- _ .`.. .,-. .- `. . . ,,
,,
Dump window ..-_-..-. .,-. .-...
.,
Import table . - . .-.-. DWORD .- . array .-`..-. .,
.,
DWORD .- . array .--.-. IMAGE_IMPORT_DESCRIPTOR .- . OriginalFirst
Thunk .- - point -.`..-. array .- . DWORD ....-. import ..-
function -. , .- . -. DWORD .- . array .-- .`....-. ...-..-.
-.-. ._.-,`_.,- DWORD -. -`.. -.
,. .`. .-.-.-. import table . --...,.-...,`..-.
,
,., IAT . API Redirection
,..`..- ......- BeginPaint,.. , -.-. import ..- function .-, DLL
.- `.. -. . . ..-. .. - .. . ..-. .- - - . DLL ._ -. function .-.,.-- .,
.. -. -.`.. . -.
4021D8 .. user32.dll .-..-.......- .`.-. ,
,
--..-. -.. ...-...,..-_...-..- IAT -.-.-. ,
,
,- -_ - .. . . kernel32.dll -., import ..- API .., user32.dll -.,
import ..- API .- -... . DWORD -,..-., .`....` . . .. ..-. . _.- ,
DWORD -, . .-. - .`....-..- .-.
,
,- -_ Import ..- function .-....._.,.-.. DLL ._.-,
. ..- ..-. .- .. .
..- . . import .- - - . - `, -_ ...- . ._...-` -.
-. `.. `.. .- ..-. .-. -.-. import .- - ..- `, -_ ...- ... - tool .-..
.- . -. . - - --. .-. ... . .- - DLL .`..- `.... .-., API .- .`..-`...-
import .. .. . . import .-- -.-`,_-_...-.-.-. , .-. -.. .` .
. - . ... .-. . -. Tool .-- ..`.....-. -,.-.-.,, API ...,..-
`, recover ... ...-., unpack ..- . - -. ` -. . -.
-_--...
.-..` FSG2.0 , pack ..- . -. - unpack -_ .. . .,, . -
unpack -. . . .-. Lena151 . . , ...,- download . . .- - . .-.
. . .- .. . -. - FSG , pack -_- ..-.-... .-.-. - - ,
,,
,., IAT . API Redirection
,
UnpackMe_FSG2.0.exe .- Olly ...- ,,-. .-.-. ,,--_
-. entry point . ..-. ,_ .,_ ... .,-..- .-. exe .-.. entry point -. `. -. .
401000 -.,.-. .`...-. . - .... . -.. . . 400154 -.,.-. . address
-. PE header ...- .,-. ...-.
FSG - trace -`.`. unpack .-. --. . .,, ..- - ,_ .,_ ...
scroll .`.-_.... unpack - stub - . . .- .- . .. --. . .,, trace
- -_ - . _ .,- - . - ._ .,-. .- `. . .. .-.. . ..-. - -. . -
.-... jump . ..-. .- . . .. ...-_ .. . . .-. jump -. - stub -
., .-. - . ..-..- .. . -_ - -...
,
,-. VA 004001D1 .,.... breakpoint .-.--_-... `.. F9 (Run)
-.- Breakpoint ......-.... ,
,
,..`..--. JMP -. . -.. . OEP (VA 00404000) .... jump . .`.. -.
,,
,,
,,.. right-click .`. Analysis - Remove analysis from module -...-.
.,-. .-...
.,
.,-.`....-. -,.-.-. .- dump .. Right-click .`. Dump
debugged process -...- .,-. `....
-, .-. - .,, . , ,_ .. .- . dump .-. -.`..`.. .,...-.
"Rebuild Import" - uncheck ..-. ... -..-. FSG -. import .--
.- . - -.`.. ` . Ollydump plugin - . .- . - -.. . .. .-. -,.-.-
.,, `,`-..-. . . .. . .,, checkbox -......-. .-. ...
dump . - . ..-. .- - - . --. . .` .- .,.- . ..-. - . .. ..
..
,., IAT . API Redirection
.,
.,- "Rebuild Import" checkbox -`.--`. Dump button -... `.. dump.exe
._, .-...._.-
--..-. `.. tool .- , dump .-. .. LordPE PE Tools ,
,
-. `.. `.. dump ..- . . . . .-.-. ...--- . -..-. . .-.
FSG - import .-- .-.. .-.. import .- `, -_ ...- . .` Import
.-- `,-_...-.- tool .- ...- .. ... -, .-. .,, ImpRec 1.7 - ....
ImpRec -.`. process (UnpackMe_FSG2.0.exe) - attach
,
UnpackMe_FSG2.0.exe .- attach `.,...-. OEP -, . .- ` . -. ImpRec
- -. process . EP -...-. .-. OEP .,... . 4000 `- `...-.
AutoSearch button -...-
,
IAT . ..- . .-..-. . .`` ,- RVA .,... . 11E8 - ..` . dump ..
. . .-. . . ` ..- dump .-. ...---. -,.-.--.. ..,
, .-. . . .. --. .-. .. .. ` .. .. RVA - ....-..-_--
... Olly . dump window . . 4011E8 .-_`. -..-...-.-_--...
,
,., IAT . API Redirection
,
--. .-. VA 4011E8 . .. -..- -.-. DLL -. . import .- .- scroll
,_ .,_ .. ` .-_ - . .,.- import .--.-.... ,,
,,
-, .-. - .,, DLL (user32.dll/kernel32.dll) .... import .--......-.
VA 4011E8 . . DLL (kernel32.dll) .-.. import (API) .-- ImpRec -. ..- . .
--. .-. ImpRec -. _...-.-. .-.. VA 4011E8 .,.... VA 401198
` . -. . .. ImpRec - user32.dll .. import .-- ...-..
,
,-. RVA -`-`. Get Imports button - . - . ,- . .- ...
Size - 100 ` - . .-. ... . .. ImpRec - ` .. .. . . .,
,
ImpRec - Thunk . . - .- -. -. `.. `.. . . . .-. . ...,-. -..- . ...,
-..-..... ....--..-...- ....,-.,...--.-. RVA 2118 ..
,,-`,-_-. RVA 2118 .. FFFFFFFF - .- . . .,.- -. -.-. RVA 11B8 . .
,,
,,
,., IAT . API Redirection
,
--. .-. ,,. . `. .- address .--. --...-. FSG - cracker .--
. . -. _ . ...-. .-..- address .-- .--..-.
.,
.,-. .- thunk .- . . right-click .`. Cut thunk(s) -...- `..
.,.-.....-.-. dump ..-.- `.
.,
.,- Fix Dump button -.`. Olly . . dump `......- dump.exe .-.....
ImpRec - dump_.exe .-._,.- ........ ,,
,,
dump_.exe . - . - . .-. ,,-. .-...
,,
dump_.exe .- Olly ...`.-_-. ,,-. `.....
,,
,., IAT . API Redirection
.
, API Redir ection
. import .-- -.`,-_...-...-. -......`.` ...
.`. packer .-- unpack , . ..-. ..- . , . ..- .-. - . IAT .- -.,
--. `, -_ ...- . .` -..-. . .-. ..... -,.-.-- import table -
`, _ -_ ...- -.-. . .,...-. .- IAT - _,`.,-,.. .-.. pack ..-
.-.- unpack `.., API redirection .-. .- . .-.. .,... . -. packer
-..``. pack ..-..-..-. ......-.-. Pack ..-.- Lena151 .
.,...,.. download . . -.
INFO: : API redirection . -.-.-. packerprotector .... - IAT ..-- import table,-
-. . - -. .. . .- - .,.- . .. - - ... - -. `.. ... IAT .. redirect
.- API ... .. .-...-,.- pointer -.- ...--. .-.-.-.
packer -. packprotect ..-.-..-- system . DLL .- - API . address -...
. .- .... .`.. -. API redirection ..- .-...-..-.......-. anti-virus ... .
.- , `.,.-- . . -.- .-. . - .... .`.. -.
, Pack ......- unpack ` .
Pack ..-. API Redirection Tutorial.exe, - Olly ...-_-..-. ,,
-. .-...`..-.
,,
,,..`..-.-.-. . pack ..-..- -...`.....-. VA 0044CB
59 .......-.. F8 (Step over) -.- VA 0044CB59 ...- . Register window -
-_- ,,,
,,,
,,,- ESP register . . right-click .`. Follow in Dump -...- ,,-. `..
..
,,
,,- highlight .,- DWORD (38 07 91 7C) .. right-click .`. breakpoint -
Hardware on access Dword - .. . - ,,
,,
,., IAT . API Redirection
.
,,-. breakpoint .- . - ` .. ... .-. F9 (Run) -.- ,,,-. hardware
breakpoint ...- ...-.....
,,,
CALL EAX . F8 (Step over) ,...`. CALL EAX . .....- - F7 (Step into)-
. - . .-. ,.,- . OEP ...- ...-.....
,.,
...-. .-..- unpack . Dump debugged process -...- ,.,
,.,
,.,- Rebuild Import checkbox -`.-- Dump button -...`. dump.exe ._,
. . . - ` .. . . ... dump.exe - . -_ - -.. ...- .
. Import .- , - .- ` . `.,.-. -- .,-..-. ....,` .-. . ImpRec
1.7 -.`. dump.exe -`. -....-_.. ,
,
,., IAT . API Redirection
,- `. . -. ... . -. . ,.._ . .`.. -.
, API Redirection Tutorial.exe - attach
, OEP -, . .- . - _ ` . IAT AutoSearch button -.
, Get Imports button -.... Import ..- function ..- - 618 . -..- ...
,, Show Invalid button -...`. invalid `...,- function .---_-..-. ,-.`..
..
,
,..`..--. ImpRec -. IAT - API - .. address .- - . ...- - .
.-. . .,... ..-.- - -.- API .-...- ....-- dump -.-. - ...
- . Dump ..-.-. crash `....., ........`..-. pointer .--. ..-
- .- . _ , .--.`.. -. .`.,. .. .. . .-. -, .-. - .,, Cut thunk(s) -
.. . - . . .`. ..-..- .-. packer .--. cracker .-- .-.... -
`.... ..- address .-- -._..--.,
... -. ,..`..- address (00458C35) -.-. - .- . .`.. .,-. `..
invalid .,- API - -_ - . --. . .,- address .- `.. .,-. .-. ,-
00458C35 .,..- right-click .`. Disassemble/ Hex View -...- ,
,
,--_-. 00458C35 . ..-. --. - .- . ...,..`.. .,-. Olly . memory
map . .-_ - . packer . SFX section ....,-..-.-. ,
,
Olly . . 00458C35 ...--_-. ,,-.`..-.
,,
,., IAT . API Redirection
,,--.--.-. API address (FindClose function) ---..-.`..-. ...
- . .. - . -, .-. - .,, section .. .- dump .. . . API address .----..-
- .- .. .`.. -. - - .--.... ...-_-... Olly - Ctrl+F2(Restart).`.
`,.-
, Redir ection - .. . ..` .
API Redirection Tutorial.exe - Olly ..`,.-`. VA 00458C35 . ..- . ..-_ -
,
,
,..`..--. VA 00458C35 .,.... -....-.
INFO: : --..-. .-.. run .,,... unpacking stub - .,.... redirect .. - -
....-.`.. -. .-. OEP . - .,..-., dump - , .- .,... . redirect ..-
- .- ...- ., API .- ..- . ...-.`.. -. dump ..- . -.. - .-. ..-. .
.. .---.
.-..` ImpRec -`,-_... ,
,
,- -_ . API . ..- redirect - -...-. 00458C35 . .`.. ` . address -
RVA 00438040 . ..- . - - -.`.. -. ,,
,,
,,. .`. .- - . VA 00438040 - DWORD -,..--_- IAT - .,... .
-_ ...- -.`.. ... -, - API .--.-. ,.. packer ..-...- redirect .,-
-,. .. 206C8BA9, .-.. IAT - -., -..,.... -..,-.`. -....
..-..... ,,- ...-_-... - ` . - - --.`... .-. `.. redirect
..- API .- ...-.
INFO: : .-..-.-. exe - import .-...-....-- API ....-. API
. . -.-. LoadLibr ar yA , GetPr ocAddr ess - `.. -. Win32.hlp . .. .`..-.-.-.
LoadLibr ay() function -. exe module -...- process . address .,..-.. .,..
..-.
HINSTANCE LoadLibrary (
LPCTSTR lpLibFileName
);
,., IAT . API Redirection
.,... ..-. lpLibFileName - exe module . ._ . address `.. -. --. ..
function -. .. `. . . ... . . .-. return `,--,..-. module ,.- handle -.
`.. -.
GetPr ocAddr ess() function -.-. export ..- DLL function . address - return
`, -.
FARPROC GetProcAddress(
HMODULE hModule,
LPCSTR lpProcName
);
.,... ..-. hModule - DLL module ,.- handle `.. ` . lpProcName -.-.
function .._`..-. --. function -. ..`.........-. return `,-
-,..-. DLL . export ..- function . address `..-.
.,.- -. . .. .`.. .-. .. . LoadLibrary - DLL . -. - - .- . .. .` ..,.-
...-. `,- handle ,-- ....- import ..- API . .. .. address -...
-.
.-..` VA 00438040 - DWORD -, . ..,... .-..- `.. . .-....-_. .,
-. breakpoint .-.--..
.,
` .. .-. F9(Run) -.`. VA 00438040 .,..- ... -_ .,
.,
.,- -_ . VA 00451B38 ...- .-. DWORD (84B3D4CF) -, . ..`. .. ..-..-
.. ... -,..- -,.-.-.-...--,...---. F9 - . VA 00451B56 -
DWORD (3963D4CF) -,..- .-....-. .,.- F9 -. VA 0045BC2A -
DWORD (00040EDC) -, . .- . - ........-. .`, - . .,.- F9 -.-..-.
,- .`. ...
,
,- DWORD (7C80EFD7)- .-. . - ...-. Registers window --_-
,
,., IAT . API Redirection
,- EAX register . . FindClose() API ... address -,..- ..-
,
,-.-. DWORD (7C80EFD7) -, . ..`. .. ..- .,.. hardware breakpoint .-.-
..-.,..,- ...-..,-. -.`..`.. packer -. IAT - API -- .,-,- address
- .. ....... -. .,.- .. ..-. address -, . .-. .`. . . ..-. -. .,... .
.`. . -. . -.. ... F8 - . .
INFO: : ,--_. VA 0043803C .. DWORD (7C80BAF1) -, . .-. .- . - ..-.
.- .. . --. packer . - ...... -_ .. . . packer - -. , . .
DLL . -. - ...- ` . .. . IAT - . , -, - API address -...`. API -. redirect
..`.........-.`.. -. ` .. .. .,.- DLL -.-`. ,_.-......-.`..-.
-. `.. `.. ,- VA 00438040 .,..- .-..., -_..`. F8 - . . ,
,
,--_- VA 004536F5 - CALL 00453E90 - ... ` .-., DWORD
(00458C35) -, . ..`. .. ..-. ...-.-.-. CALL 00453E90 .. API . address -
packer .-. redirect - .-.`.. -. .-. CALL - -_ - -...
.-..- Olly ..`,.- (Ctrl+F2) `...-. ,- VA 4536A6 .......-.. F9 -
,-...- .,.-...-. ,- VA 4536F0 ... CALL . F8 - . . - CALL
....-..-. F7 (Step into) -.- ,,-. `. ... . - .... .- ,. VA
4536DF - JE 4536F8 -. CALL 00453E90 - .-. ... -. . -.- ,
,,
,., IAT . API Redirection
,
,,-.-. API address - redirect ..`......- CALL . ..- `.. -.
00438040 - DWORD -,..-...-_.. ,
,
00438040 - DWORD (7C80EFD7) -, . .- ... -_ ... ., F8 ..
,
,..`..--. VA 00453EF4 - ...- -., 00438040 - DWORD (00458C35)
-, . ..`. .. ..-. .- .-. --. .-. -, . ..`. .... packer - Vir tualPr otect() API
-..`-.
,,
`..-. page access - .,-..-.-.. Vir tualPr otect -.`. ..`-.
INFO: : Vir tualPr otect() function -. .. . .`.,- process . virtual address .,..--
page .- . ,. . -. .- access protection - .`. . ..-. function -. Virtual-
ProtectEx ,.-..--. VirtualProtectEx -.-. -. process . access protection -..
.`. . ... -. . .,, -.-. access protection -,..- page .....-.... .-.-
. -. --. .- . - ..- ,. . - .. .. - -. page .- .. . .`.,.- - .... -
..` ... . .-. function -. .. `. . . ... . ` ... - page .-. access protection -
``.`...- return `, .. .`.. -. VirtualProtect function -. ....`.,- process
...- .-.. access protection - .`..-.`..`. VirtualProtectEx function -.-.
.-.-..- process ...- .-.. access protection - .`. . -.`.. -.
.,
.,- -_ VA 00453ED5 - PUSH EAX .,... . -..- .`. . . ... 438040
-. page ,. . . base address access `..-.
,., IAT . API Redirection
-,..- ..`.,-. `,`.... VA 00453F02 ...- Vir tualPr otect() API -
... . - -.`.. -. VA 00453ED0 - PUSH 4 --_ 4 bytes `..-.
..- . . . .,, .-. ,.._ . ..` . .. - - - -, .-. .,, redirection
--.`.- ..-_-. Conditional jump .---_ .,
.,
.,..`..- VA 00453EC8 - JE 00453F0F -. Vir tualPr otect() function ...-
.-. ... -. .- `. ... .,... . JMP 00453F0F ` - .. . .
--. ` ` . assemble - .. . . API -. packer .-. redirect ..-.
...--... address -.-. IAT . . . ., .. . ... `..,_ .. ..- . ...- - -
- .,.- . .`. .-_ -... .,-. F8 - . . Vir tualPr otect() -..
.-,..- -.`, restore ...-. `..
VA 453EF7 - PUSH ECX -.-. . access ....- . - address PUSH EDX
-.-. characteristics ,,
,,
40 -.-. initialized data PUSH 4 -.-. 4 bytes PUSH EAX -.-. VA 438040
. .`.. -. F8 - .- . . .... . . ,,- ..- . .
,,
,,..`..--. F8 - . . .... . . .-. . -.. - JMP 45363B -...-- .
`, -- . ..` . .,.- API -. . address ---.. .,.- API -. -.-. lstr cmpi() function
`.. -. ,,- -_ .. . . lstr cmpi() function -.-,...-. API address - .`. . ` .
.. -..- .-. ,,- -_ .. . . VA 4536DF - JE 004536F8 -. redirection CALL -
.-....-..-.-.
,., IAT . API Redirection
,,
Redirection `.,.- .`....-- -,.-.-.,, ,_ .. . - . .`. -.
.,_ .. .-.-. ,,- VA 4536DF .,... . JMP 4536F8 .`. ... .`.. ` . - .,_ .-
.-. VA 4536F0 .,... . NOP .`. ... .`.. -.
.-.. VA 4536DF .. right-click .`. Breakpoint - Hardware, on execution -
.. .
,,
.,.- .. .-.-. -, .-. - . -.. . OEP ... VA 4331B8 -...`. ,,-.
Breakpoint (Hardware, on execution) -.-.-. `...-. -,.-.-..-.--
hardware breakpoint .-- .-- .. ,,,- . .. .- . - - - hardware break-
point . . -, .-. ..
,,,
.-..- Olly ..`,.-`. F9 - . - ,,- .`. ...
,,
,,-.`..- VA 4536DF - JE 4536F8 .,... . JMP 4536F8 ` ` . VA
4536DF . ..- . - ..- hardware breakpoint -`.-- ...-. OEP . ..- . - ..-
hardware breakpoint -...-,.-...`..-. `.. F9 - . - ,,. .`. .- - .
. -.. . OEP . ..- ...- . ... .`.. -.
,., IAT . API Redirection
,
,,
,.. Dump window --_- ,,,-.`....
,,,
,,,- API .-. --. address .-- `..-.-.-. .-. ...... . . .-.
,,- Disassembly window .. right-click .`. Dump debugged process - .. . ,.,
,.,
Dump button -...`. .-..- Redirection_Fix.exe ._,...- -....-.
Rebuild Import checkbox -......-. ...--.- `,.-_- ,.,-.
`....
,.,
Redirection_Fix.exe .- .-...-.. ... .......- ,_.,_...-.
.,-..- .-. .-. . . - section .-- ........ LordPE -.`. section
.--.-.` .,
,., IAT . API Redirection
.
.,
.,..`..--. wipe section header -...`. section (4/5/6) -.-.- .,
.,
`.. .-...-`. PEiD .. .- .,
.,
PEiD . plug-in -.`..- Rebuild PE -...`. .,- Rebuild button - .. . - . .-.
.-..-. 72.65% ...... ........`..-. .,
.,
. . .-. pack ..- exe .- unpack .... -.-.- API redirection `.,.
- .`.. . ` .. .. ..` `.. -.
,., Visual Basic `. ........... . -.. ...- crack ` .
.
tcef;(16) - Visual Basic jzifh a&;om;xm;aom y&dk*&rfrsm;udk cr ack vkyfjcif;
-. . ..-. VB , ........- . -.. .- - crack -_ . .`.. -. `., ... -.. ..
.- ........- . -.. .-. .-. ......-. VB , ........-.`.. -. .,... . crack .
.. .. ..- ,. ,.. -.. -.-. PC to Answering Machine 2.0.8.2 `.. -. . .`.. tool
.- -.-. OllyDebug , SmartCheck - `.. -. Olly -.-. . .. .` ....`.. -.. ..`.
... SmartCheck . - ... . .-. .- .-. ,_ .. . - .- .. -. NuMega
Technologies' SmartCheck .- ....-.- ..,.. Compuware - .. -.
Compuware -. SmartCheck - ....-.. development -. .,.- .- -
` ... .-. - . SmartCheck - shareware `.. ... . -. , . ..-. -.,- . .
freeware `...-.-. Google - ..``. ...-. -,.-....,-.-.-. 6.20
`.. -.
(1) y&dk*&r f\ o ab mo b m0
PC to Answering Machine .-..- Olly ..... PEiD . . . - ,
,
,
.`... -, .-. .,, . -.. .- - . . . -.. - -., ...... -., pack
....-..... PEiD , .. . . . . -. . .,, RDG Packer ., CFF
Explorer -, ..-.,
,.. highlight .,, `. .-.-.-. . -.. . EP ,-.-. .-..- Visual Basic
, ......-. .`-. -, .-. .`. -.-.-. Visual Basic .-..
INFO: : Visual Basic .-. DOS .-...-,.- .- BASIC -....-..-., . - .-
highlevel language-. BASIC . . _ .-.- -.-. Beginners' Allpurpose Symbolic
Instruction Code `.. -. Visual Basic -. visual `..`. events driven .-..-....-..
`.. -. . -.. ......` .- visual environment . .- . -. . -.. ...- -. object
.-- --. click .-. ...-event,.-- -,`,...-- object ....-
. . .......-. .-. . Visual Basic . -.. -. subprogram .`..- `.... ., . ._ ...
` . `.. -. Subprogram -. . . . . - . - . - .- . -. Subprogram .--. ..`...
. -. ` .. -. , -_ .. . . - .- -. . . -.-..`.-.
INFO: : Visual Basic application .--. `_... compiled ..- application .- `.....
. - . `. .- - OllyDbg . .-- .....-. OllyDbg -. compiled language
,., Visual Basic `. ........... . -.. ...- crack ` .
.- - - debugger `..... VB - - - . . ... ..-. . ....,...-. C/C++ - -
...-. .-..-. .-.-. VB -. -....-...... _ ..-. . . -.. ...- . `. . .
... _ ..-. . .-. .. , . .-. -.
INFO: : VB .-...--. external DLL VB 6.0 . ..-. MSVBVM60.dll `..-. `..
version .- ..- . .- . . .. , . .. . . .,.-. DLL .-. API , event
...- --.-. .-.. VB API ...-. DLL . . _ . ... .. .,.-.
Exe --. ... ,-.,.,. .,.-. -. cracking ,.. ,...
- . -. Call stack -. Olly ...-. --.- -.-.- -_ -..-...-.
application -. .-.- ..- , .. VB . --- DLL ... .., .-.....`....-.
application -. ........`. .-. event handler .-`..`. event .- message .-- .-..
`, . DLL . callback .-`.. ..`--. VB application . -,-.-.-. resource
.- variable .- , eventhandler .-, .-....`- function .- `..-.
INFO: : VB -. stackbased `.. -. . -.- . -. .....-...-- system
stack - ..` -. register - ..`- function call ...- ....-.--
stack - . -... .`- `..-....-...- , .- _ - - `.. -. VB , ., - ...-
application .--. interpreted ., pcode executable `.. compile -. Run ., , . .
instruction .-- runtime DLL - translate ., interpret -. --. . .` .
pcode engine -. opcode .-- process - .... machine ..`.. -. P-code instruction
.-- ..`- operand ...-.-. stack . . . . .._ ...-.
. .,, Olly .. call stack - -_-... AltK, - .`. -_.-. ,
-.-. system, stack
,
INFO: : DLL (dynamic link library) -. .-......-- .._...`. `..-. .--
. -.. -. ., , . . .-..- -,.. ...-. ........`..-. exe
..-- device .- , - .- . ..-. .. print - - , . . printer , - .- ..
-.,
INFO: : ..-.`. .. harddisk . . .,.. - - ,.. .-...--. parameter
.-`_.- function , call function - DLL . - .. . .. . -. DLL . . .
- function .- - ....... .-. - - - exe ..--. ...... .....,-.
INFO: : DLL . .- -. exe ..-, - RAM - -.-....--- RAM .. .,...
-.. -. DLL - .. .. .. RAM ....- .. . `.. -. ..`... . .
. .,, Microsoft Word .. ......- .,-,.. printer , -.-- DLL .-.
.. .---. Print --,... printer , - .- - DLL .- .......
INFO: : ` -_ .. .-. DLL . -. executable . -. `.. -. ... . -. . -_ .. .
.-. -. . . - . EXE . .- - .. .. .. -. .-. exe ..-.. -.
DLL - .....-. parameter .-, .-_.... -.
, . ..-. . .,, VB -. - - . . .. , - .. -....-.. .-..
., . .. --. .-. . .,-. .,-. -,.-.-.. ,..- tool .- .
-. .,.- .. . - . .`.. -. `.. `.. Olly - VB , - .- ` . -.. . .. - . .-.
. - , --. -. .. ..-. -....-... .. .-. assembly `.. translate .-.
. -.. . ..-..-.- .. ... ... -,.-. .,, . -.. , - .- ` . . - - `
..-.-.-. . -.. - install ` . .. .- . . -.. .- , . . . -.. -. . - , -.
- - -..- - - - - ` . key -.- --.-.---. -. . .. , ...
,., Visual Basic `. ........... . -.. ...- crack ` .
-,.-.-- .-....-..- hint - ..-. .-.- .-..-. -- -.-., .-
. - - -. .. harddisk ID, ` .. - - -. .,..... . . . . . .. . .. . -.. -
.- , . . register ..`. ... .....
, Ser ial - . ... ` .
.-..-. ..--.... register ..`. ... ...... -. VB . ..-.
DLL - API .. `--. .,.... ...-.-..--.-.
, __vbaVarTstEq
, __vbaVarTstNe
, __vbaVarCmpEq
,, __vbaStrCmp
, __vbaStrComp
, __vbaStCompVar
. - . ,- .-. ` . . ....-. .-. .. . API `..- __vbaVarTstEq -
.. .-_ - -...
,,
,,.. `..,.-.-.-. entry point .,.. Name module - `... CtrlN -
. - , ` .. . ..-. `., .. keyboard -., vbavartst .-- vbaVarTstEq
. ... -, ....- . . ..
,
,- -_.... -, .-. - . ..,- API .- -. MSVBVM60.dll .....,-.
.-`... vbaVarTstEq - BP .- . - -.. vbaVarTstEq - rightclick .`. Set
breakpoint on every reference - ...- Olly - breakpoint 88 .-. .- . - - -.
,
` .. run (F9) - .
,,
,., Visual Basic `. ........... . -.. ...- crack ` .
Olly -. ....-.- vbaVarTstEq BP . ... . . ., . .. - . ..-. -.. .. ..
.... -. .- .-. . -.. . ..-..-.- . . .. F8 - . ` . . .-_ ..
.,
VA 005BBD58 - CMP DI,SI -. .-.... .-..-. ... -..-`....-.
.... jump -_ ..
.,
.,- VA 005BBFC0 .. `..- oeiu564oqei97 -. -,.-.- ...,- serial ..
. ... -. ,_ .,_ ...- .- -_ .. ,
,
oeiu564oqei97 - ...-_--... Breakpoint .-...- ... .....-
Ctrl + N -.`. Remove all breakpoints - ...,
, Register ``.
Breakpoint .. .- .. . ..` . . -.. - run F9, - ,-. `....
,
,.. register .-- ._..-..-. --- key -... -. key -
.-.. install . - , .--_ .- - - - .- . - ` . `.. -. Register -_..
,
,., Visual Basic `. ........... . -.. ...- crack ` .
oeiu564oqei97- .-_`. OK - .-
,
,-. registration ..`..-.. `..-. - -. . . -.. - - ` .
`, .-_ - -...
,, Registr ation .. .. .. ` .
. -.. - `, .. Olly . . Ctrl+F2 - .- `.. F9 - . -. .-..--.
,.. -. nagscreen -. .`...-.-. Help menu - About - ...-.-. ..`...
` ,,
,,
.-. .-..- SmartCheck .. .....-_-...
, Smar tCheck setting .. ` ` .
-. .-. Numega . SmartCheck - .. .-_ -.. SmartCheck - VB . -.. .-
crack ., debug . .` ..-. ... . . setting - .-. ,_ .. `
..... SmartCheck .. PC to Answering Machine 2.0.8.2 - .- .`.....
Program menu - Settings - ...- ,
,
,., Visual Basic `. ........... . -.. ...- crack ` .
,
,- Leaks - uncheck - Save these settings - ... `.. Advanced
- .. . -
,
,.. `..--. .....
,,
.,.- . ... ..... .- ,,- . `.. -. . setting - `.-. `.` PC to
Answering Machine 2.0.8.2 - SmartCheck .. run -_.. Run `....- View menu
-., Event Summary - ...- .,
.,
Event Summary window - -, .-. - - . . - --.- ..-.
,., Visual Basic `. ........... . -.. ...- crack ` .
.,
View menu - Specific Events - -,.-.-- ...-.. events -`.. ....
....-.
,
,- .-...... Sequence Numbers - -, .-. .. ...-. ..-.
.-. .-. .. . . -. .,.- .. . - .- .. , ` . -_ ... . .. - _ ..-.
.- . . ..
--. - .- .. .- -_ -. . . .-. View menu - Show All Events -
.. . -
, Smar tCheck - ser ial - ..`.
-, .-. - .,, SmartCheck . setting - ``.`..-. serial ..`.- .-
- -... Event .-- -_--.. -,.-.-- - . .. - - .- - ....,-.
.-.-. ,-. ..-- ,_.,_... scroll .`. -_--...
,
--.- .--.-.-. ,..
,
,- -_ - . event .. 24734 .-. .-..-.-. -.-. end program
.... ..- .. . .-. event . . ., ...- .-. - . . .. ......
-,.-.----.- PC to Answering Machine 2.0.8.2 .-... .. - .`..
.
,., Visual Basic `. ........... . -.. ...- crack ` .
,
,- ...-. ., - - -_ .. . . ...-. ..- - , .`...-. .- ... . . -
-. . .-. -, .-. - - Show Errors and Specific Events - .....
,,
Show Errors and Specific Events - ...-.... ,,-. `.... -,.-.-
. ..-.- . -.. .- - ` .. . - -- key -.- ..-..-.- - ...... API
.,.... ..-_-... ,
,
,-. ...... ,-. .-..
,
,.. `..--. ....-- API - ...- .-. .,... . -, .-. - .,,
API .-- ....-.... .---. .,.- .-. . ... . .. ....-. .-.-
...-. ... 2549 ..
,,
.-. .... - -_ ... . .. ..- .`. -_-. ... -....
`..- . ...-. ... 2549 - ..-.`. Details window . . -_ - . ..-. .,- .
`. .-.
.,
,., Visual Basic `. ........... . -.. ...- crack ` .
,
.,. . `. .-.-.-. -, .-. - . ..,- serial SmartCheck -. ..., registration
key - ..-.,.....-. ....--. .-.-.
INFO: : VB . -.. .- . . antiSmartCheck ,_ ..- _ . ...-..- .-. . - .-
-. ........`. NuMega SmartCheck . - .....- .. ...-. `.. -. -, .-. . . ..-.
`.,...-. -...-. -,.-.- Repair 0.6 -..`. SmartCheck - ` ..
Repair 0.6 - -,- tool .-- `.-.
. . PC to Answering Machine 2.0.8.2 - crack -.-... `. . ., ` .. .. ..`
,_ ., serial ..-.- serial fishing .-. -, .-. . .`-.- ..,, .-..
.-..,.._..... .---. -..-...-. serial fishing ,_.-. .-..-- -....
....`. debugger - - ..- serial --...-..`..-. Serial - -.-...-.
- - - . -. .- - -. . ..-. VB .-...-- .`.`. crack -_ -..
Crack ......- .-...--.-. ReverseMe . -.. . . , registration ,_ ., -.- . ..
- freeware .-..-.`..- CrackersConvert 1.0 .,...- ..-.. .-.. -
SND Team . website -., download . SND Team . -.,- ..- .,.- .- - . .
... `..-. SND Team . download -- Lena's Reversing Tutorial - 10 .- download
. ... -.-,.-...`.. . ,...,- .-.. ... `..-. ,.
-.-. Lena151 . . , ...- -...`, ` . `.. -. Crack .... - tool .- -.-.
OllyDebug SmartCheck VB Decompiler , Veoveo - `.. -. VB Decompiler -.-.
freeware `..`. www.vb-decompiler.org . . download . . -.
.-. .` -, .-. - . crack `.- .--...
,, Rever seMe1
... crack -_ . .- ReverseMe1 . -.. `.. -. SmartCheck .. Tut.Reverse
Me1.exe .-.`. run - .,-. `....
.,
.,.. `..-.-.-. nag screen `..-. - -..........-. .,.-.
..`.. ...-.-. ReverseMe .-..- -. register ...-. ...-_..
,
,. . `. .- Form1_Load -. , ...- .-. MessageBox -. ,- nag
screen - `....-..-. .-`.... Registration ... - -. Form1_Load ` ..
..-... .,- OK - . - ,- . `. ...
,
,., Visual Basic `. ........... . -.. ...- crack ` .
.
,- Regcode textbox .,... . 123456 . - _ -_ .. . ,- . `. .. .
,
` ,.,.... ,-. event .. - ..-.
,
-, .-. - .,, View - Show All Events - ...-. event ...- `....
Show All Events - ...... -.-_- event - . .. ........ . .- - . event
.- ... , .- - - - . . . - event - ...-... .---. ........`..-. xxxxxx_
click ...... xxxxxx -. button . ._- .-. ...-. . -.. ...- -.-. button
.- . ._ - .`. .. .. - . commandX ..... . -. X -.-. , - `.. ` . -. -
., .- . . -.
,- Command1_Click .,.... serial .,..,..-.- ,.._ ... .-. .,
..- ......-_--... .......-. Tut.ReverseMe1.exe .-..- ..-.-
- - - .. - -... .-.... .`... ,- -,.-.-`..,.-.-. event -.
... `.. -.
,- Command1_Click . -..-- .....- .- ,,
,,
,,- -,.-.-- ..----.- ...-. MsgBox .-.....- ...
-..-. ,-. `....
,
,-.-. BadBoy .-..` ,,- Text1.Text - ...-..-. -...
.-. -.. .`. .- . View menu - Show All Events , - ...- . ,-. `..
..
,
--. .-. -.. .- - . -, .-. - .,, .. .- `. .,.-.
,., Visual Basic `. ........... . -.. ...- crack ` .
.
__vbaStrCmp - string .- ....-- ..-.
.. __vbaStrCmp(String: "xxxxxx", String: "yyyyyy") returns DWORD:0
... ,...-. DWORD . -, . .-. FFFFFFFF `...,-. -...-.
string . . -. .- _ ,- Regcode textbox .,.... -,.-.- 123456 .-_
. -,.-.-.-_- serial -- -., ...-. ,,
,,
.-. .` 123456 , ...-.-.-. I'mlena151
,- I'mlena151 -. BadBoy Message .. . . . .. -. `.. -. .-. .` Serial
-. -. . -. . ` .. ..- .,.-.. -,.-.-.,, serial - ...-_--...
.,
.,-. I'mlena151 .-_-- registration ..`.-.-.. .`.-
messagebox ..-. .-.....`... -,.-.- .-_-- serial -. -.---..
.- . -- ..-.
-, .-. - .,, nag screen - ......-. SmartCheck -. VB .. .....-
serial - ...--.-. .-..-. ... nag - ......--.-. -,.-.-.. -
.-..- tool .- .-. VB decompiler tool .- `.. -. ...`... VB Decompiler
Lite ., Pro -, .-. -.-. VB Decompiler Pro 5.0 - ..-.
.-. .` VB Decompiler - .--...
.,
-.-. VB Decompiler .. -,.-.-. Tut.ReverseMe1.exe .-..- decompile
..-. `.. -.
INFO: : Compiler .-.-.-. ...-.-- exe - `.. .`. . ..- . -.. Decompiler
-.-. exe - .- - .. ` . . . .- `.. `, _ .`. ...-. Decompiler -. .`..-
disassembler -..... `..-. Disassembler - exe -.-- assembley -`.. .`....
,.. decompiler .--.-. -.-- highlevel -....-..`..- C/C++ ., VB -....-..
`.. .`. ...-.
.,- -_-. VB Decompiler -. . - . .-. ..-. . ..`
-.
,., Visual Basic `. ........... . -.. ...- crack ` .
,
-,.-.-.,, -.-- ...-_.. .,. Form1 .-.,..- . ..
..- .-
,,
-, .-. `. .-. . -.. -..-.., -. .- .. - . .-. ,.._ .. -.
,,.. `..- mnuabout - About box mnuexit -.-. Exit Command2 -.-. Nag
button - .-...-. Form_Load -.-. nag Command1 -.-. Register button
- . - . . .-. . nag - ...- routine -. VA -. . . ... -_ -...
Form_Load . ..-. Command2 . . nag -. VA 402C17 .. ..-. ...-. --
.- - . . - . ` . -_ .-. Form_Load - double click .
,,
,,. ...-. nag screen - .. .,-...-..-.-.-. ...` -..
.-. "Get rid of all Nags and find .." .- .....- .-.
,,
,,-.-. nag screen . . . VA 402C17 -.-. nag routine . . .-..`
Tut.Reverse Me1.exe - -,.-.- debugger .. .--... ,,
,,
`.. -,.-.- ...- VA - -,....-... tool bar - - .
,,,-. `....
,,,
,., Visual Basic `. ........... . -.. ...- crack ` .
,
VA 402C17 - .-- ,,-. `....
,,
,,.. `..-.-.-. nag screen . . VA 402C17 .. breakpoint .- . - -
` .. run (F9) - .
,,
,,.. nag screen ` .. -. - ...- .. . -. `.,-. VA 402C17 - PUSH
EBP .,... . RET `-.. . -,.-.- nag . .... . .- ...- ..
`.. . .... ` .. run F9, - .
,,,
Nag ..- ,,,.. ..-. ..... ,,,- Nag? - .-_.. -..
...- . Nag screen ..-...`
., Cr acker sConver t
-. . .. .-.-. CrackersConvert . -.. `.. -. -. - . . ..-. -, .-. .,,
. -.. . ..-..-..- - . ..,.-... .---. .-... SmartCheck . ` . . ...
.. .`.. -. -, .-. -.-. About . .. -, .. ... . `.. -. About -., register button -
.. ,.,-. registration box `....
,., Visual Basic `. ........... . -.. ...- crack ` .
,
,.,
` register button - .--.. ,.,- . `. .-.
,.,
INFO: : ..,, --- registration code - _...-. -, .-. -. 47806
.-..-..-. ..-.. ..,... .-..` ........`. .-...--. registration
code - ...... hex code `.. .`....-. 47806 - hex code .,, .`. . - .
BABE `.. . ..-. . - . . -..
,
,.,- Validate - .-. ,-. `.... -, .-. - .,, -, .-. - . ..,
-.- .-``..--- CrackersConvert .-..- --..
,
.......-. -,.-.-.,, -.-- ... Overview window - ,-.
-_-...
Len(String: "r hythm") returns LONG:6
. . .- "r hythm" string .......--,._ .`..._
Mid(VARIANT:String:"abcdefg",long:1,VARIANT:Integer:1)
. . .- "abcdefg" .. ..,... .- ` . ... .- .. ._
Mid(VARIANT:String:"r hythm",long:1,VARIANT:Integer:5)
. . .- .,... ..-. .. ..,..-., .. . ... -. "rhyth",
Asc(String:"T") returns Integer:84
. . .- "T" ..-,..`..... 84 - ..._
Asc(String:"r ") returns Integer:114
. . .- .,.....-. "r " .. -, . .`.. ... 114 - ..-.
Len(String: "47806") returns LONG:5
. . .- "47806" string .......--, ._ .`..._
,. ..- . ....-. .-.-. BadBoy
,., Visual Basic `. ........... . -.. ...- crack ` .
,
Len(String: "47806") returns LONG:5 .- ...-..-. serial . .....--
.. ...-. .- ... ... -..-. serial - ..... -,.-.-.,, BadBoy
....- serial - -. . .. .. . . -. . .-.. LenString: "47806", returns
LONG:5 - .. . - ` . Show all events , - .- ,-. `....
,
,- -_ --..-. -...--.
__vbaVarMul(VARIANT:String:''114", VARIANT:Integer:20) returns DWORD:13F474
,- -,.-.,.._. ....- , .`..--.
__vbaVarMul(VARIANT:String:''1", VARIANT: String:''2") returns ..
. . .- - `. .`. .- ._
__vbaVarMove(VARIANT:Double:2280,VARIANT:Empty) returns DWORD:13F48C
.-.-. 2280 `.. -.
__vbaVarCat(VARIANT:String:"REG"VARIANT:Double:2280) returns DWORD:13F474
` .. REG2280 `..... REG , . .-.
__vbaVarCat(VARIANT:String:"REG2280"VARIANT:String:"CODE") returns
DWORD:13F464
` .. REG2280CODE `.. ... CODE , . .-.
__vbaVarTstEq(VARIANT:String:"47806",VARIANT:String:"REG2280CODE") returns
DWORD:0
`.. -,.-.- .-_-- serial , ...-.
__vbaVarTstEq(VARIANT:****,VARIANT:****) returns DWORD:0
. . .- __vbaVarTstEq - variants .- .... ..`-. --. . - .- -.
_ . DWORD . -, . .-. . _`.. ` . ._ . .-. FFFFFFFF `.. .. .-. EAX -.
FFFFFFFF `.. -. __vbaVarCmpEq , . -.
. -,.-.-- serial -.` User name - rhythm `..`. serial -.-.
REG2280CODE `.. -.
,
,- Validate - .-
,,
,., Visual Basic `. ........... . -.. ...- crack ` .
,,
. -,.-.- register -. ..`.` ,,
INFO: : .-..-. registration .-..-- cconv.$$$ . , cconv.ccc ... ...-. `..
. -.. .- , . . - - .- , - - _ ._ .. -.
.-. .` .,.- ReverseMe .-..-.- ..-_...
., Rever seMe2
,
ReverseMe2 - Olly .. ...-. ,.. .-.. ..,, SmartCheck .. ..-
Olly .. -..-....-. ... . .. . , -.-. ReverseMe2 - SmartCheck . . .
. -. ... . ..- . SmartCheck .-..-. ReverseMe2 - .--.,
- . ..-. .-. -.`..-..-. .... Olly . . .. -. ReverseMe2 .-....
AntiSmartCheck _ .... ..... ..... . ReverseMe2 -. SmartCheck -
.- `. - -., SmartCheck - - . - . - .... -. .`.....-. -_--.
..
Debugger window .. rightclick .`. Search for . All reference text strings -
.. . - ,- . `. ... ReverseMe2 -. SmartCheck - . .-. - - .- - -_ -
-...
,
,- VA 00404525 .. NuMega SmartCheck .-.....- .-.-. VA
00404525 - double click .`. -- ..-_-... ,,
,,
ReverseMe -. NuMega SmartCheck .-.....-..-. .-.. .,....
-, .-. - .,, `.......- .`. ... .-..,_.- `.. Debugger window -
VA 00404525 .. rightclick .`. Follow in Dump - Immediate constant - ...-
.,
.,-. `..- -..`. . - .. .- .. .` . keyboard - -.--- ......-
_.
,., Visual Basic `. ........... . -.. ...- crack ` .
,
.,
.,- 4D (M) .,..- .....`. keyboard - B - .-- .,-. `..-.
,
.,.. OK - . - - ,- . `. .-. ..- 43(C) .- ....,....
`....., ......
,
` .. rightclick .`. Copy to executable file - ... ,- `....
,
,.. rightclick .`. Save file - ...- `..-. -. - - - ._ , . - . . .
- -. .-. -, .-.- ...--.- SmartCheck .. ..` -.`.,.. ..-.
, -. `..`
,
antianti ,_._.- SmartCheck ` `.. tool .-`..- Olly ImpRec , LordPE
- . . . .`. -. ReverseMe2 - register -_-...
,,
,., Visual Basic `. ........... . -.. ...- crack ` .
,
-, .-. - .,, User name , Registration code - .-_... Register button -.
disable `...,-. .-. -,.-.- register .. `...,-. ReverseMe . -.. -.
.-..- ...-...- .,.., -......,.-. ,
,
.-. -, .-. - .,, -.- -_ . .,. ,- ....- ..-_..
,
.,... . . -.. - .. . - - - - .,-. .- .-. ... ,- Text2.Text
- . .-_ .-. -.. ..- .- .
,,
. ,,- .....-_--... ReverseMe .-..- .-.. .-,.. register
. ......-. . . -.
.,
.,- Text3.Text "UNREGISTERED" (String) - ....- ..-_...
AppActivate(VARIANT:String:"NuSega S...", VARIANT:Missing) fails .- .....-
.-. NuSega S... .-.....- ....--. .-. `.. "Text3.Text "UNREGISTER-
ED" (String) .- .....- -_--... -,.-. - . . ... ` . , .. -. UNREGIS-
TERED string .-..`.....-. ..,, ,.._ .... -.
,., Visual Basic `. ........... . -.. ...- crack ` .
,,
.,
.,- -_- __vbaVarTstEq(..) - -.- .... __vbaVarTstEq(..)
- .. . - - ,,- . `. ...
,,
. .. ....- . .... - . .-_ ..
,,
,,- Dir(VARIANT:String:"reginfo....",FLAGS:00000000) - ...-. ,,-.
`....
,,
ReverseMe -. reginfo.key .-.- ....-. __vbaVarTstEq(..) -. reginfo.key
....- ....-. ... UNREGISTERED .- .....- main window . .`` . register
..- . . -.- -, .-. - .,, reginfo.key .- .-. .-. reginfo.
key . - ., - . - .. Notepad -.`. .- reginfo.key ._ , . . . - ` .. Reverse
Me2 .- SmartCheck .. `,...-_
,,
. ,,,- . `. ... Register -_..
,., Visual Basic `. ........... . -.. ...- crack ` .
,.
,,,
.-. .` , .-. register .....- . SmartCheck .. -..-....`.....
. -_-..
,,
,,- UNREGISTERED . - ......,... . Key File found .-.....-..-. .-..
.-. .` -. serial - .. - - .- - `, . .-_ ..
,,
Left(VARIANT:String:"r hythm",long:1)
. . .- ._ . .. ... .- . -.
Asc(String:"r ") returns Integer:114
. . .- ASCII "r " - -,.`_-,.. 114 `.. .`. . -.
Mid(VARIANT:String:"r hythm", long:2, VARIANT:Integer:1)
. . .- ._. -....- .-.
Asc(String:"h") returns Integer:104
. . .- ASCII "h" - -,.`_-,.. 104 `.. .`. . -.
` ..-. -- ..- .. . ..`. .`. . -. ` ..-. ,- -, ..- .. .-
. . - -. 114 + 104 + ..
Mid(VARIANT:String:"11410412...", long:2, VARIANT:Integer:10)
-. event ...- -_-_.. Show all events ( ) - ...-
,., Visual Basic `. ........... . -.. ...- crack ` .
,.
,,,
,,,. . ,- -, ..- .. .-.- .- .,.-. ...- .-.- Mid(VARIANT:
String:"11410412...", long:2, VARIANT:Integer:10) ...-.. .-.. -. - ... .-.,
..`..- ..... .-. . ....-,..-- 1410412111 .. `.. -.
,.,
` .. ,.,- .- -_
__vbaVarSub(..) -.-. -. - . - -. ` .. __vbaVarTstEq(..) --.- ...
-. .-. -, .-. - .,, .... - -_ . .` . .. ..- . -
,.,
,.,- -_-.-. __vbaVarSub(..) -. __vbaVarTstEq(..) , -.. .. -. .- .
-.
.,
... ,- __vbaVarTstEq(..) .. --. serial ..- ....-- double.dbval
`.. .`. . - -. .- .-. --. .-. 1410412111 - ....-- .`..--.
.-. --. serial .. -.
.,
.-..-. -,.-.- .-_--._. ... .- ASCII `.. .`. .-.
` .. .. ..- - `, .- -. .,.- serial ., - .. .- ..- .. .. ..`..- -., .
.`..- .-. - serial - -....-_--...
,., Visual Basic `. ........... . -.. ...- crack ` .
.,
-,.-.- serial -. .,....-. -...-. Register button -. enable `, `..
.
.,
.,- Register button - .. . - - . . .,- . `. .-. Register -.
..`....`
-. VB Decompiler - .- -..-...-. VB Decompiler . decompile
. . .._ - `
.,,
.,,- . . `....- ReverseMe2 . ..-..-.- . . .. Form_Load -
..-.`. scroll -_ .,-. `....
.,
Command1_Click - ..-.`. scroll -_ .,
.,
,., Visual Basic `. ........... . -.. ...- crack ` .
.,... . -, .-. .,, Veoveo . -.. - . - .- -. tool -. -. button -..
enable/disable .-. -_
.,,
Register button -. disable `.. .,-. Veoveo .-..- .-
..,
..,-. Veoveo - right-click .`. Enable Buttons auto, - ...-
..,
..,- -_-. Register button -. enable `.. .,` -. ..- . . . -.
.- . . --. .-. Register button -. enable `.. -,.-.- register .. . .- - - .
-. . .-. serial . , .. , - . -.. - ..
(10) VB P-code y&dk*&r fr sm;u dkcr ack v kyfjci f;
INFO: : P-code .-.-.-. execution ,... interpret .- -`..-. P-code
.- - -, .-. - . . - -. . .- ...- - -....`, . - low-level - .- `.. `. . -.
Java . -.. .- ... virtual machine . VB p-code .- ... virtual
machine -. Virtual machine .... .- p-code .-- native code .- `.. .`. . ..
. . .`.. -. VB . ..-. . . virtual machine -. MSVBVM50.DLL , MSVBVM60.DLL
. .- . . . .,--. DLL ..-.. VB application .-- ..`.,- API .. .. -.
..`.. Windows API MessageBox() . ...-,-- rtcMsgBox ...-.-
function .-, ..,_.- function .-- p-code .,, compile .`. .-.....-
function .--.-. native code .,, compile . -. P-code - ..`. `..-.
.,... .-.. ...--.-. ....-...-. P-code .--. ........`. stack ...
. . -. .-. instruction ....-. stack -., . - . operand .--..`.
..- result - stack .. ...-. C/C++ . -.. .- . ..-. p-code .,, compile
. #pragma - . .`` . link , . . exe . 9KB ..- . - run-time engine ..
-. - _ . ... - -. debugger .--. p-code - debug ..- ..,_.-
.-.
,., Visual Basic `. ........... . -.. ...- crack ` .
P-code .-..- ....-....-- p-code , pack ..- Engineering Power
Tools - crack -_ -... Engineering Power Tools 2.0.4 - http://www.pwr-tools.com/
-., download `. install - `.. ept-2002.exe - Olly , .-_
yHk(90)
.,. . `. .- - .. . Olly - p-code ..-- debug .... .`...--
.`-..- .. . -- . -.,, .`... .,- ThunRTMain .-. VB . main() function -
. -.`.. -. --. VB . .- - packer -., pack .. . . .,, ThunRT
Main -..`. -., dump . .. .`.. -.
ept-2002.exe .- Olly ... P32Dasm 2.5 . .. -_ .,- . `. ...
File: C:\Program Files\Engineering Power Tools - Plus Edition v2.0.4\ept-2002(ori).exe
P32Dasm v2.5
VB6 Application detected ... PCode
MAINFORM Events:
191. plus_options_show
192. plus_options_hide
193. plus_options_enable
Page_Setup Events:
2. Setup_calc
Pneumatic_cylinders Events:
11. metric_calc
12. inch_loader
13. metric_loader
Shear_Keys Events:
24. option_set
Volumes_of_Solids Events:
52. sphere_calc
53. spherical_sector_calc
54. spherical_segment_calc
55. spherical_zone_calc
56. spherical_wedge_calc
57. hollow_cylinder_calc
58. hollow_sphere_calc
59. torus_calc
Hydraulic_cylinders Events:
12. metric_calc
13. inch_loader
14. metric_loader
Splash Events:
37. pchk
shape_generator Events:
1. generate_rectangular_tubing
2. generate_circle
8. generate_hollow_circle
GearCalc Events:
17. metric_gear_calc
Beam_Calc Events:
9. Selector
10. selector_SI
Psychro_2 Events:
1. log10
,., Visual Basic `. ........... . -.. ...- crack ` .
2. calc_vapor_pressure
3. calc_vapor_pressure_2
4. calc_dewpoint
5. calc_enthalpy
6. calc_relative_humidity
7. calc_specific_volume
8. calc_humidity_ratio
9. calc_humidity_ratio_2
10. calc_atmospheric_pressure
11. calc_wet_bulb
15. calc_rh
17. calc_dp
Structural_Tubing Events:
12. combo_loader
Enclosure_Cooling Events:
15. Solve_Open_SI
16. Solve_Closed_SI
Duct_Size Events:
26. calc3
Plate_Deflection Events:
10. solve_SI
yHk(91)
. -.. . ..-..-.- . . . .. ept-2002.exe -.- .,
yHk(92)
.,. .`. .-.-.-. UNREGISTERED .-..-,.`..-. ..-,.-.-. .,
- .`. ...
yHk(93)
.,. . .- `. - ..-. -, .-. - .,, Standard Edition ., Plus Edition -
..`... .-. .,- OK .. - . .-. .,,- . `. ...
,., Visual Basic `. ........... . -.. ...- crack ` .
,
yHk(94)
.,,-.-. -,.-.- .-_ - - .. , - . .`.-.
yHk(95)
.-. .,..`..--. function .-- ...`.-. .-... ..-.
.-.- .....`. P32Dasm -`,...-.. P32Dasm - References Procedures -...
- .,
yHk(96)
.,..`..-.-.-. .-....- procedures ... .
yHk(97)
Engineering Power Tool -... splash screen .. register `...`..- .....-. .-
`. ... .-. .,,- 73.22 Form.Load() - .. . - . ..,. ...- . . ..
Splash 73.22 For m.Load()
0016DF88: 6C ILdRf param_8
0016DFF4: 1B LitStr: "http://www.pwr-tools.com"
0016DFF7: 21 FLdPrThis
0016E18C: 1B LitStr: "\pwrtools.ini"
0016E18F: 2A ConcatStr
0016E21D: 1B LitStr: "USER NAME = "
0016E220: FB30 EqStr =
0016E26F: 23 FStStrNoPop var_108
0016E272: 1B LitStr: "REGISTRATION = "
0016E275: FB30 EqStr =
0016E277: C4 AndI4 And
0016E2C7: 1B LitStr: "REGISTRATION CODE = "
0016E2CA: FB30 EqStr =
0016E319: 23 FStStrNoPop var_108
0016E31C: 1B LitStr: "PASSWORD = "
0016E31F: FB30 EqStr =
0016E371: 1B LitStr: "SOFTWARE KEY = "
0016E374: FB30 EqStr =
,., Visual Basic `. ........... . -.. ...- crack ` .
0016E3BA: 3A LitVarStr: "<No Value>"
0016E3BF: 25 PopAdLdVar
0016E3C0: 1B LitStr: "User Name"
0016E3C3: 1B LitStr: "Settings"
0016E3C6: 1B LitStr: "EPTools"
0016E3C9: 0B ImpAdCallI2 GetSetting()
0016E3CE: FDB7 ImpAdStStr
0016E3D2: 3A LitVarStr: "<No Value>"
0016E3D7: 25 PopAdLdVar
0016E3D8: 1B LitStr: "Registration Code"
0016E3DB: 1B LitStr: "Settings"
0016E3DE: 1B LitStr: "EPTools"
0016E3E1: 0B ImpAdCallI2 GetSetting()
0016E3E6: FDB7 ImpAdStStr
0016E3EA: 3A LitVarStr: "<No Value>"
0016E3EF: 25 PopAdLdVar
0016E3F0: 1B LitStr: "Software Key"
0016E3F3: 1B LitStr: "Settings"
0016E3F6: 1B LitStr: "EPTools"
0016E3F9: 0B ImpAdCallI2 GetSetting()
0016E449: 7A ImpAdStI2 param_26
0016E44C: 1B LitStr: "Registered to: "
0016E44F: 76 ImpAdLdI4
0016E567: 04 FLdRfVar var_18C
0016E56A: FC22 CI4Var
0016E56C: 05 ImpAdLdRf
0016E56F: 4D CVarRef: var_AC
0016E574: 04 FLdRfVar var_98
0016E577: 0A ImpAdCallFPR4 Left()
0016E57C: 04 FLdRfVar var_98
0016E57F: FCF6 FStVar var_19C
0016E583: 04 FLdRfVar var_17C
0016E586: 04 FLdRfVar var_19C
0016E589: FB33 EqVarBool =
0016E58B: 1C BranchF 0016E60C
0016E58E: F4 LitI2_Byte: 255 0xFF (True)
0016E590: 7A ImpAdStI2 param_53
0016E593: 1B LitStr: "Show"
0016E596: 1B LitStr: "Plus Options"
0016E599: 1B LitStr: "Settings"
0016E59C: 1B LitStr: "EPTools"
0016E59F: 0A ImpAdCallFPR4 SaveSetting()
0016E5A4: F4 LitI2_Byte: 255 0xFF (True)
0016E5A6: 7A ImpAdStI2 param_26
0016E5A9: 1B LitStr: "Registered to: "
0016E5AC: 76 ImpAdLdI4
0016E5AF: 2A ConcatStr
0016E5B0: 23 FStStrNoPop var_108
0016E5B3: 21 FLdPrThis
0016E5B4: 0F VCallAd
0016E5B7: 19 FStAdFunc var_88
0016E5BA: 08 FLdPr var_88
0016E5F6: 0F VCallAd
0016E5F9: 19 FStAdFunc var_88
0016E5FC: 08 FLdPr var_88
0016E5FF: 0D VCallHresult PictureBox.Set_Visible()
0016E604: 1A FFree1Ad var_88
0016E607: 10 ThisVCallHresult
0016E60C: loc_0016E58B
0016E60C: loc_0016E4C7
0016E60C: loc_0016E4AF
0016E60C: 75 ImpAdLdI2
0016E60F: F4 LitI2_Byte: 0 0x0 (False)
0016E611: C6 EqI2 =
0016E612: 1C BranchF 0016E963
0016E615: F3 LitI2: 3800 0xED8
0016E618: EB CR8I2 Int(number)
0016E619: 37 PopFPR4
0016E963: loc_0016E612
0016E963: 13 ExitProcHresult
yHk(98)
..,-- .- - .. ...-_ .. - .-- ._.... `.-,..-.
,., Visual Basic `. ........... . -.. ...- crack ` .
0016E589: EqVarBool = var_17C . var_19C - _ ._ .. ...._ CMP . - ._
0016E58B: BranchF 0016E60C = _ 0016E60C ....._ BranchF (1C) ._ JE
. - ._ BranchT (1D) ._ JNE . - ._ Branch (1E) ._ JMP . - ._
..,-- .- - ` .. .. . . .. . .. VB Decompiler . ... -_ - -
..,- . `. ...
If ((Len(MemVar_5C103C) > 1) And (Len(MemVar_5C1038) > 1)) Then '56E60C
For var_168 = 1 To CVar(Len(MemVar_5C1040)): var_148 = var_168 'Variant
loc_56E4F8: var_110 = Mid$(MemVar_5C1040, CLng(var_148), 1)
If (var_110 <> "-") Then '56E513
loc_56E510: var_138 = var_138 & var_110
End If
Next var_168 'Variant
loc_56E534: MemVar_5C10C4 = Unknown_503BF8(MemVar_5C1038)
loc_56E53C: MemVar_5C10C4 = Unknown_4FD768()
loc_56E555: var_17C = CVar(Unknown_516920(Unknown_50507C(var_138))) 'Variant
If (var_17C = Left(MemVar_5C103C, CLng(Len(var_17C)))) Then '56E60C
loc_56E590: MemVar_5C1046 = &HFF
loc_56E59F: SaveSetting("EPTools","Settings","Plus Options","Show")
loc_56E5A6: MemVar_5C1044 = &HFF
loc_56E5BD: regbox.Text = "Registered to: " & MemVar_5C1038
loc_56E5D7: regbox.Forecolor = 0
loc_56E5EB: regbox.Fontbold = 0
loc_56E5FF: regpanel.Visible = 0
loc_56E607: Call Unknown_5000EC(MemVar_5C1044)
loc_56E60C: ' Referenced from: 56E4AF
End If
End If
yHk(99)
P-code ,-.-- prefix -.-. ..- - .`.. -. ,
Ad Address
I# Integer
Imp Import
Ld Load
Lit Literal (ie Hi, 2,8)
Mem Memory
R# Real
Rf Reference
St Store
Str String
V Virtual
DOC Duplicate Opcode (Redirect to another opcode)
yHk(100)
--. .-. EPT - -, .-. - register .....- registry -.,.-`. .....
-. Register .... offset 0016E60C . .-. . ... .`.. -.
.-. -,.-.-.,, conditional jump .-- NOP ,..... .` NOP
, .... . VA 56E589 ....,..- Olly ...-_.. ,
yHk(101)
,.. hightlight `...,-.,...-- NOP , ... ... P-code ...-. NOP ,--
opcode - 90 .- - - . 21 (FLdPrThis) `..-. ,
yHk(102)
,-.``...-. -,.-.- patch -.- ....``..-. `..
-,.-.- patch ...- run -_ ,-. `....
,., Visual Basic `. ........... . -.. ...- crack ` .
,
yHk(103)
-,.-.-.-. regname.reg ... ,, -.``. registry - merge -
-. -..-.`...-.-.-. ..,--- -_-. ....
REGEDIT4
[HKEY_CURRENT_USER\Software\VB and VBA Program Settings\EPTools\Settings]
"User Name"="Myanmar Cracking Team"
"Registration Code"="Don't Hate the Crackers! Hate the C0dez."
yHk(104)
. . .-. ,- . .- .. .`.. -.
yHk(105)
-, .-. . .` -.-.-. key ...- -.,.._, register ,_ . Key . . -. . .
.-. . - . - .. .. -_ . - .. -.
,.,, Delphi `. ........... .-.....- crack ` .
.
tcef;(17) - Delphi jzifh a&;om;xm;aom y&dk*&rfrsm;udk cr ack vkyfjcif;
` . - , .. .- , .- Visual Basic , ........- . -.. .- - -. crack ...-.
. .` -. -. . ..-. Delphi . -.. .- .- _ - -... ... . .- .-. .-. ...
...- Visual C++ Borland Delphi , Visual Dot.net -,........-.-.. .`...-.
.-. .-.. Delphi .-...-- -. crack .. . -. -, .-. .,, . .`.
.` --. .-. Delphi .-...--. Visual C++ . -.. .- , ..-.-...
.. -. ,
-. crack . .. .. ..- . -.. -.-. File Recovery Angel 1.13 `.. -.
... . -. . .- . - - . .- - `, _ . ... ... . ..- - `.. ..- . -.. -. `.. ` .
. .`.-.- , . - -. www.filerecoveryangel.com .. . download ..
-.
.-. .` -, .-. - .,, . -.. - crack . .-... ..-..-....- ..
.. File Recovery Angel -.-
,
File Recovery Angel -.`. Help menu - About -...-- ,-. `..
-. - .,- . -. - recovery . - ....- ,- .`. .-.
,
..-...-.- recovery . - .....-. ,- . `. .`, -.
,
MessageBox .--.-. .....-- . . .. . .....,- MessageBox .-
.-. .` . -.. - -., .......-. ..-_-... ,,
,,
,.,, Delphi `. ........... .-.....- crack ` .
.
,,-. PEiD , .. ...- . .- . -.-.-. . -.. - Delphi 4.0 ., Delphi 5.0
, ........-. . - .-. . Version ---.-. Delphi .-.....-. linker version
- -_ ` . `... . .. -, .-. - - - -.-. -. .. .. . .`
FileRecoveryAngel.exe .- Olly ...`.-_..-. entry point - ,-. .-.
..
,
- ....... F9 (Run) - . - ` .. Option menu - Register(R)
- .. .` . register .`. ,
,
,-. Registration Name , Registration Key - - . - _ - ` . Register button
-...- ,,-. `....
,,
,,- "Register False" . - .....- . - ..` . Olly . . text string .,,..- `..
text string ...- .- .,
.,
.,- -_ - . BadBoy message ... VA 00488FEA . jump -.- .-...
...- . .-. .- . . ...... .-. jump - ....- ,,-. `..-.. F12
(Pause) -.`. .-..-.- ..- `.. Alt+K (Call Stack) -.`. Call
.- - -. -.,.. ..,. . -. -_- .,
.,
,.,, Delphi `. ........... .-.....- crack ` .
.,..`... Olly -. Call .-,-.-`.--- --.-...`. ..-.
.-.. -,.-.-.,, System Stack --_`. ,,- error MessageBox - -. -.,
.. .-. . -. -_ .. .`.. -. Delphi .-...-- crack ... . Call Stack - System
Stack - `...-. Delphi .-...-- crack .... .....- .,.-,_...
-.-. FindWindowA API - . .-. -..-. . .-. Delphi .-...--. --- class
._ ., title , .,- window -....,
,
,-.-. ,,- pause ....,.. System Stack . . `. .- .,..
INFO: : Delphi -.-- Olly . . disassemble - `. .- .,..-.-. ,_ .,_ ...
.., ..,-. Comment , info .- - ,_ ..,-..- .. ., -..-. . .-. Olly - call
.- backtrace .` Call Stack . . -..- . .`.. .,` . - - ,_ .. - ..
...-. .-.. Delphi .-...-.. routine -.- -. call -.,.. .-. . .
System Stack - ..`.-. System Stack -., return address --_`. call ..-
-...-.- ,.-..-.-.-. ..`.. - . `..,_ .. .-. .-. .,`
-..-...-. Olly - routine . --- address .- .`.
INFO: : Delphi -. global variable .-, local variable .-- pointer `.. reference -.
Global variable .--- [REG+Constant] -..`. local variable .--- [REG-Constant]
-..`-. REG -.-. register - . -. . -.-.-. Olly -. CALL DWORD
PTR DS:[EBX+100] . . backtrace ..-. .-.. EBX -,...`..-,.. pointer
---,..-..`.....`. Olly - call - backtrace .-.-. -. Delphi .-..
.- , - - . . --. `.,..- `.. -. `..-....-...- . . . . - .- . ...
Delphi ....- ..-.-.
INFO: : -. ,_ .. .-. . .. . ....-. .-. -, .-. - - .-. .- - -.-. Delphi
-- tool -. ... tool -.-. DaFixer . DeDe DeDe -. Borland Delphi
.-...--- .,-...- disassembler -. `.. -. DeDe -. DelphiBuilder -,
compile ..- exe ..-- analyze .... ,`.,- . -.. -. `.. ` . . . dfm
..-...- `,...-. dfm . .- - Delphi . . . ` .-_ .`.- . -. DeDe -.
string .- import ..- function call .- classes methods call .- unit - component
.- Try-Except Try-Finally block .- , reference ..- -.-...- - ...-.
. .,, dfm . pas . , dpr ..-- Delphi project . -. - ., - .. -. Tool
-... ..,_.-.-. DeDe -. debugger .- - - - - DeDe .. patch ..-. .`..
. - . -. `.. `.. Olly , - . .. .-. .-. DeDe 3.50.04 build 1635 - download .
DOI , DSF . .- .. DeDe , - .- - ... ...- -.-. DeDe . dede_doc directory
..- . .. -. DSF = = DeDe Symbol File, DOI == DeDe Offset Information File,
INFO: : DeDe . configuration , - .- ` . ...- .- - -.-. exe .-.- process
... .,-,- symbol ..-- load -..-.... DOI/DSF ..-. DeDe -.
.... call sequence .-- .`....... .,-,..`.... DOI/DSF . .- - , ...
- .-.
,
,.,, Delphi `. ........... .-.....- crack ` .
,-. DeDe . Options menu - Symbols -...`. Delphi 5.0 ,.- vcl5.dsf
.-....- Delphi 7.0 .-...-- analyze .....-. vcl7.dsf . - .. ... .
DOI tab -.`. D5.doi .-.... `...-. ,- Process button -.
,
,- Process button - . - . .-. ,- . MessageBox .- .. . ..
,
No button .....- ,,-. `....
,,
,,- Procedures tab -.- .. File Recovery Angel -..`- procedure
.- - `. ... TFrmMain -.-. .-... .--.. Main menu ... procedure
TFrmAbout -.-. About menu -.--`.... Form (dialog box) TFrmRegister
-.-. -, .-. - . ..,- Registration Form TFrmRegister - .. . - _..- . .`. .-.
-.-. Olly .. -...`..- routine ...- ImgRegistereClick -...- ,
-. .-...
,
VA 00488E34 -.-. Registration routine . .`.. -. ..- - ,_ .,_ ...- scroll
.-_-..-. ,-. `....
,
,.,, Delphi `. ........... .-.....- crack ` .
,-.-. registration key -......-..- `..- Bad message `.. -.
TFrmAbout -.-. ,.. .-... ..-_ --..-. DeDe ,-.-- -,.-.
-.-. ,,..--_.- `..,` -..-...-. registration routine . address
.- .- - Registration routine . address .`..- VA 00488E34 - . - ..` . Olly ..
Ctrl+G .`. .-_- ,,
,,
. . DeDe - - .` ,,- . registration routine ..-...--..
registration key -..-.,..- -_--... VA 00488E34 .,.... breakpoint .-.-`.
register -_ .,
.,
.,.. Register button -...-..-. -,.-.- breakpoint .- . - ..- VA
00488E34 .,..- ...- ... .,- VA 00488EFA - ...- - F8 (Step Over)
-..
.,
.,- VA 00488EFA -. registration key --..- routine -. `.. -.
Registration form . Registration name - -- "Myanmar Cracking Team" -- -
"CA75FC30F7AD6E7C969032F175560906F79B9EE94E93D2D4302B92" .- key - - ..
`. EAX . .. . .-. VA 00488F13 ...- CALL -.-. EAX - key , EDX . .. . ...-
"4.10.1979" -- ...-. .,..-. registry . "IsRegister" .. "On" . ` .. . .... .
`.. -. . .. . .-. .- . ... .`.. ` . VA 00488F3F ...- . BadBoy ("Register False!")
. . .... .. . .. . .`.. -. ..- . . .-. . .,, -..- .. . -. . ..- `
-.
,.,, Delphi `. ........... .-.....- crack ` .
Olly --`. File Recovery Angel - ...,.- `.. Option menu - Register
(R) -...`. register - ,
,
,- Register button - . - . .-. ,- .`. .. .
,
Help menu - About -...-..-. ,-.`.... --..-. File Recovery
Angel .-..-. registration name .,.... ...-...-.-__ .-...-.
.-.. "Myanmar Cracking Team" ... "Myanmar Crac"`-.
,
. - .... .-.-. . , -, - key - .. - _ VA 00488F46 - BadBoy . . ..- JE -
NOP ` .. . . register ... ` . -... .. `. .. -..-. . .-. . -.. -.
.--.. registry - "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Frareg" , "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Unicode" .,... . ..- - Name , Unicodekey --.-`. .,..,
--.. ....-...-. ,- TFrmMain -.`. -_..-.
,
,- FormCreate -. Main menu -.,-.,.. ........-... Virtual
address (00491A00) .-`-. -.-...-. ..-_
,.,, Delphi `. ........... .-.....- crack ` .
,
-. . ..-. -, .-. .,, _--..-. ` -. Teleport Pro 1.61 . , ...
- , .- . .,, keygen .......-.- .-..,.. Keygen routine -....-. .-...
-,-..-....,.-..-. , .- - , .-. -, .-. .,, -.-. keygen ....-. ,
.....-. . -. -. .-. keygen .....- key - ..- - ... -
_--.. .- `.-.
,,
,,- ...-_ VA 00488EFA . . . . - _ - - user ._--`. serial
- - .. - -. serial - stack segment .......-.`..-. `..-. stack -.,
EAX . .`. ... - ` . EDX . .. - . . - _ - - serial ,...-.`..-. Serial
. . -. ._ . .-. Badboy .... ...-.....`..-. ,
,
,--_ VA 00489184 - "Register False!" .-.....- EAX - ._ - ` .
serial .....-.._. Badboy message - `.-.`.. -. ,
,
"Register False!" . - ........ -, .-. - . - _ - - user name , - .- - serial
- `. .. . . ..-. .- ...
.-. .` `.. . ,_.,_.-....-_.. ,- VA 488FFB .,... . MOV
EAX, 489184 ... MOV EAX, DWORD PTR SS:[EBP-C] ``. .-...._.-
. - - --. serial ...,- stack .......-.-.. .`. -.. - ., - .-
-``....--.- .`. register -_- ,,
,,
-. .-. rhythm . - ._ , register -_..
.,
,.,, Delphi `. ........... .-.....- crack ` .
rhythm . - ._ , register -_- .,-.`..-.
..- . . .-. . .,, . . ..-`-. .,..`..- key (0415BFA8C..)
-.-. rhythm . - user name - - . -.. -- - - ` . - .. - - serial key `.. -.
key -.-..`. .,.--.-. register -.. .-_-. registration ,...`...
`........ .,
.,
.,- register button -.-. ,-. `....
,
Help menu - About -...-. ,-. `..-.
,
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 266 -
tcef;(18) - Java jzifh a&;om;xm;aom y&dk*&rfrsm;udk cr ack vkyfjcif;
' Dw p fc gr Sma w mh Java e JUa & ; x m; w Jh y & dk* & r fa w Gu dk crack Mu n fhy gr , f/ Java y & dk* & r fa w Gu dk crack & m
r Sm t jc m; y & dk* & r fa w Ge JU o a b mw & m; c si f; r w ln Dw Jht w Gu f x n fho Gi f; a q G; a E G; & jc i f; jz p fy gw , f/ Java y & dk* & r f
a w Gu dkcrack r v ky fc i f Java Virtual Machine (JVM) t a Mu mi f; t e n f; i , fa w mho dx m; z dkU v dky gv dr fhr , f/
( 1 ) Java Vir tual Machine (JVM)
Java b mo mp u m; r Sma w mh u k' fa w Gt q i fa jy a p r Iu dk t " du x m; y gw , f/ Java source u k' fa w G[ m
b , f OS r Smr q dk t w lw ljz p fjy D; javac command u dkt o Hk; jy Kjy D; compile v ky fy gw , f/ Java source u k' fa w G
( .java extension y ga o m & dk; & dk; p mo m; z dki f) u dk bytecode v dkUa c : w Jh intermediate language (IL) b mo m
p u m; t jz p f compile v ky fw Jht c gr Sm .class extension y gw Jhz dki fw p fc ku dk & & Sdr Smjz p fy gw , f/ ' Dx Gu fv mw Jhbyte
code ( o dkU) class z dki fr Sm JVM instruction a w G? o a u Fw Z , m; w p fc ke JU t jc m; t c su ft v u fa w G y g0 i fr Sm
jz p fy gw , f/
Bytecode a w Gu a w mh OS w dki f; t w Gu f w ln Da e r Smjz p fjy D; JVM & JUt v ky fv ky fy Hku a w mh a t mu fy g
t w dki f; jz p fy gw , f
y Hk( 1 )
JVM & JU architecture u dka w mha t mu fy gt w dki f; & Ijr i fE dki fy gw , f
y Hk( 2 )
JVM w dki f; r Sma w mh class loader subsystem w p fc kp D& Sdjy D; o l[ m class a w Ge JU interface a w Gu dk
u l; w i fz kdUt w Gu f mechanism w p fc kjz p fy gw , f/
Input File
.java
Compiler
(javac)
Output File
.class
JVM
CPU
Softwar e Developing
Softwar e Execution
Copyright White Cracker (Myanmar Cracking Team)
Class loader
subsystem
Execution
Engine
Class files
Method ar ea Heap Java stacks PC r egister s
Runtime data areas
Native
method stack
Native method
interface
Native method libr ar ies
Copyright White Cracker (Myanmar Cracking Team)
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 267 -
JVM w dki f; r Sm execution engine w p fc kp Dv J& SdMu jy D; u l; w i fv dku fw Jh class a w G& JU Method a w Gx Jr Sm
y gw Jh instruction a w Gu dk execute v ky fa y ; w Jh mechanism w p fc ky g/ Execution engine x Ju dk a & mu f& Sd
v mc sde fr Sma w mho u fq dki f& m CPU u e m; v n fE dki fw Jhbytecode a w Gt jz p f a jy mi f; v Ja y ; r Smjz p fy gw , f/
CPU a w Gv dky JJVM r Smv Jregister t c sdKU& SdMu y gw , f/ t m; v Hk; [ m 32-bits a w Gjz p fMu y gw , f/
pc Program counter jz p fjy D; execute v ky fr , fhbytecode u dkn Te fjy y gw , f/
optop Operands stack & JUx dy fy dki f; e JUq dki fw Jh pointer w p fc kjz p fjy D; o c sFmq dki f& ma z mfjy c su fr sm; u dk
w Gu fc su fz dkUt o Hk; jy Ky gw , f/
frame v u f& Sdexecute v ky fx m; w JhMethod & JU execution environment e JUq dki fw Jhpointer/
vars Execution w Gi f v u f& SdMethod & JU y x r q Hk; local variable e JUq dki fw Jhpointer/
JVM jz p fp Ofw dki f; r Sma w mh Method area w p fc ke JU heap w p fc k& SdMu y gw , f/ ' Darea a w Gu dka w mh VM
x Jr Sm run a e Mu w Jh thread a w Gt m; v Hk; u r Qa 0 o Hk; p GJMu w mjz p fy gw , f/ Thread t o D; o D; r Sm personal stack
w p fc kp D& SdMu jy D; ? ' Darea u dka w mhy & dk* & r ft v ky fv ky f& mr Sm t o Hk; jy Kw Jhparameter a w Gt m; v Hk; u dk PUSH v ky fz dkUe JU
POP v ky fz dkU t o Hk; jy Kw mjz p fy gw , f/
JVM & JUv ky fa q mi fc su fa w G[ m stack u dkt a jc c Hw mjz p fy gw , f/ Bytecode a w Ge JU Method a w Gq D
parameter a w Gu dko Gi f; z dkUt w Gu f o lUu dkt o Hk; jy Kw mjz p fy gw , f/ x Gu f& Sdv mw Jh& v ' fu dka w mh o lw dkU& JUa e mu fq Hk;
w p fc ku a e c sdw f, l& & Sdw mjz p fy gw , f/
Java stack & JU stack frame u a w mh Method w p fc ke JUq dki fw Jh w p fc kw n f; a o m call & JU t a jc t a e u dk
reflect v ky fy gw , f/ i Hkx m; w Jh call a w Gt x Ju frame a w G[ m ' Dframe & JU x dy fy dki f; r Sm stack v ky fc Hv m& y g
w , f/
Stack & JU frame w dki f; r Sma w mharea o Hk; c ky g0 i fy gw , f
Method call t w Gu f local call
Method t w Gu f execution environment
Operands stack
Local variable a w Gu dka w mh var s register u index v ky fw Jh 32-bit array w p fc kr Sm o dr f; q n f; w m
jz p fy gw , f/
a ' w mt r sdK; t p m; a w mfa w mfr sm; r sm; u dka w mh array & JU cell w p fc ko mo Hk; w mjz p fjy D; long e JU double
t r sdK; t p m; u a w mhcell E Sp fc kv dkt y fy gw , f/
v u f& Sd stack & JUt c su ft v u fu dk x de f; o dr f; z dkU frame w p fc kx Jr Sm& Sdw Jh execution environment
u dkt o Hk; jy Kw mjz p fy gw , f/ o lUr Sm jy D; c Jhw Jhstack frame e JUq dki fw Jhpointer w p fc k? Method & JU call a w Ge JUq dki fw Jh
pointer w p fc k? t jc m; pointer E Sp fc k( w p fc ku a w mh stack frame & JU a t mu fy dki f; e JUq dki fjy D; a e mu fw p fc ku a w mh
v u f& Sdstack frame & JU t a y : y dki f; e JUq dki fy gw , f/ ) & Sdy gw , f/
Object a w Gt m; v Hk; u dka w mh heap memory area t a e e JUo dr f; q n f; w mjz p fjy D; run a e c sde fr Sm o G, f0 dku f
addressing u dkt o Hk; jy Kjy D; handle w p fc ku a e w p fq i fh point v ky fw mjz p fy gw , f/ JVM u dk t " du t m; jz i fh
stack r Smo ma w GUE dki fw ma Mu mi fhw e fz dk; a w Gu dk o dr f; q n f; z dkU t c sdKU register a w Gu dk t o Hk; r jy Ky gb l; / ' ga Mu mi fhv J
bytecode a w Gu dkt o Hk; jy K& w m[ m & dk; & Si f; jy D; t q i fa c sma p w my g/
JVM u dk' Dx u fy dkjy D; a v hv mr , fq dk& i fa w mha t mu fy gw dkUu dka w GU& E dki fy gw , f
Primitive t r sdK; t p m; r sm;
- byte - 8 bits - 128 + 127
- short - 16 bits - 32768 + 32767
- int - 32 bits - 2147483648 + 2147483647
- long - 64 bits - 9223372036854775808 + 9223372036854775807
- float - 32 bits 1.402398546E-45 3.40282347E+8
- double - 64 bits 4.94065645841246544E-324 1.79769313486231570E+308
Reference t r sdK; t p m; r sm; ( t o Hk; jy Ka o m object)
- class
- interface
- array
( 2 ) Java Cr acking Tools
Java y & dk* & r fa w Gu dkcrack & mr Sm t o Hk; jy Kw Jhtool a w Gu a w mh
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 268 -
CCK (Class Construction Kit) (http://bcel.sourceforge.net/cck.html)
DJ Java Decompiler (http://www.neshkov.com/)
JAD Decompiler (http://www.kpdus.com/jad.html)
Java Decompiler (http://java.decompiler.free.fr)
JDebugtool (http://www.debugtools.com/)
Jode Decompiler (http://jode.sourceforge.net/) e JU
IDA Pro (http://www.datarescue.com/) w dkUjz p fy gw , f/
Java y & dk* & r fa w Gu dk crack v ky fz dkU& mt w Gu f Java Development Kit 1.3.x e JUt x u f? Java
Runtime Environment 1.6.x e JUt x u f w dkU& Sdx m; & r Smjz p fy gw , f/
( u ) CCK
CCK u a w mh Java class z dki fa w Gu dk jy Kjy i fz e fw D; & mr Sm t o Hk; jy Kw Jh tool w p fc kjz p fjy D; BCEL e JU
SWING w dkUu dk t o Hk; jy Kp r f; o y fx m; w mjz p fy gw , f/ Beta version jz p fw Jht w Gu f bug t c sdKUa w mh & Sdy ga o ;
w , f/
( c ) DJ Java Decompiler
Atanas Neshkov & JU DJ Java Decompiler u a w mh Java class z dki fa w Gu dk p mo m; z dki f ( o dkU) t jc m;
z dki fa w Gt a e e JU decompile v ky fa y ; E dki fy gw , f/ Oy r mjy & & i f Java applet e JUa & ; x m; w Jhbinary class z dki fa w Gu dk
r l& i f; source u k' fz dki ft a e e JU jy e fa jy mi f; a y ; E dki fy gw , f/ DJ Java Decompiler u dkt o Hk; jy Kr , fq dk& i f Java
& Sdp & m r v dky gb l; / Java z dki fa w Gu dkdecompile v ky f& mr Sm t a u mi f; q Hk; tool w p fc kjz p fy gw , f/
( * ) JDebugtool
Stand-alone debugger w p fc kjz p fjy D; Java e JUa & ; o m; x m; w mjz p fy gw , f/ ' ga Mu mi fh Jdebugtool
u dkt o Hk; jy Kr , fq dk& i f JDK 1.6(Java 6) u dk install v ky fx m; z dkUv dky gw , f/ JPDA (Java Platform Debugger
Architecture) p Hu dke r le mx m; jy D; a & ; o m; x m; y gw , f/ Java y & dk* & r fa w Gu dk debug v ky f& mr Sma w mh t a u mi f;
q Hk; tool w p fc kjz p fy gw , f/
( C ) JAD
Java class z dki fa w Gu dk decompile v ky fw Jh command-line tool w p fc kjz p fjy D; t o Hk; & r , fhy Hkp Hu a w mh
a t mu fy gt w dki f; jz p fy gw , f
jad example.class
' D command u dk& dku fx n fhr , fq dk& i fa w mh example1.jad q dkw Jhz dki fu dk v u f& Sd directory a t mu fr Sm
z e fw D; a y ; r Smjz p fy gw , f/
( i ) JODE
JODE u a w mh Java Optimizer and Decompiler & JUt w dka u mu fy g/ Decompiler u a w mh .class
z dki fa w Gu dkz w fjy D; r lv .java z dki ft jz p fx kw fa y ; w my g/ Comment a w Ge JU local variable a w G& Ju t r n fu dka w mh
x kw fa y ; E dki fjc i f; r & Sdy gb l; / Optimizer u a w mh .class z dki fa w Gt jz p f e n f; v r f; t r sdK; r sdK; e JU a t mu fy gt w dki f;
a jy mi f; v Ja y ; E dki fy gw , f
- Class? Method? field e JU local t r n fa w Gu dkobfuscate v ky fa y ; jc i f; /
- Debugging E Si fho u fq dki fa o mt c su ft v u fr sm; z , f& Sm; a y ; jc i f; /
- Dead u k' fr sm; ( class? field? Method) ? constant field r sm; u dkz , f& Sm; jc i f; /
- Local variable r sm; \ allocation u dkoptimize v ky fjc i f; /
( p ) Java Decompiler
Emmanuel Dupuy & JU Java Decompiler u a w mh .class z dki fa w G? .jar z dki fa w Gu dk decompile
v ky fa y ; E dki fw Jha q hmz f0 Jv fw p fc kjz p fjy D; .java source z dki ft a e e JU o dr f; a y ; E dki fy gw , f/
( 3 ) VisualRoute t m; a v hv mjc i f;
Java y & dk* & r fa w Gx Ju crack v ky fz dkU a & G; c s, fx m; w Jhy & dk* & r fu a w mhVisualRoute 2007 jz p fy gw , f/
u dk www.visualroute.com r Sm download v ky f, lE dki fy gw , f/ VisualRoute u o i fhu Ge fy sLw m& JU IP
address e JU o i fo dv dkw Jh 0 u fb fq dku f ( o dkU) IP address Mu m; r Sm& Sdw Jh IP a w G& JUw n f& Sd& ma e & mu dk a jr y Hke JU jy o
w m jz p fy gw , f/ VisualRoute u dkz Gi fhv dku f& i fa w mhy Hk( 3 ) t w dki f; jr i f& y gw , f/
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 269 -
y Hk( 3 )
y & dk* & r f& JUt v ky fv ky fy Hku dkMu n fhr , fq dk& i f VisualRoute u , m, Dz dk' gw p fc ku dkz e fw D; y gw , f/ z dk' g& JU
t r n fu dk GetTickCount API o Hk; jy D; w n fa q mu fw mjz p fw Jht w Gu f t c sde fr w lw me JUt r Qz dk' gt r n fv J a jy mi f;
a e r Smjz p fy gw , f/
y Hk( 4 )
jexepackboot.class z dki fu dk CreateProcessA API o Hk; jy D; z e fw D; y gw , f/ jy D; a w mh ' Dz dki fu dk execute
v ky fy gw , f/ ' ga Mu mi fhjexepackboot.class z dki fu dk z e fw D; jy D; c sde fr Sm t jc m; w p fa e & mr Sm u l; jy D; o dr f; x m; v dku fy g/
' Dz dki fu dku l; & r , fha e & mu a w mh
<root>:\Documents and Settings\<current_user>\<temp_settings>\Temp
y Hk( 5 )
y Hk( 5 ) u CALL 0040108A u dk execute v ky fjy D; c sde fr Sma w mh y & dk* & r fp t v ky fv ky fy gw , f/ F7 u dkE Sdy fjy D;
CALL x Ju dk0 i fMu n fhc sde fr Sma w mhy Hk( 6 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 6 )
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 270 -
y Hk( 6 ) r Smjr i f& w Jht w dki f; Java interpreter u dkt v ky fv ky fa p z dkU CreateProcessA API u dka c : o Hk; y g
w , f/ CreateProcessA u dk v ky fa q mi fjy D; c sde fr Sm jexepackboot.class z dki f y su fo Gm; y gw , f/ t jy n fht p Hku
a w mha t mu fy gt w dki f; jz p fy gw , f
java -mx256m jexepackboot ER \"C:\\Program Files\\VisualRoute\\VisualRoute.exe\"
\"C:\\DOCUME~1\\MYOMYI~1\\LOCALS~1\\Temp\\X170A7F4\"
' Da e mu fr Sma w mh WaitForSingleObject API u dko Hk; jy D; y & dk* & r fu Java session jy D; w Jht c sde fx d
a p mi hfq dki f; y gw , f/ y Hk( 7 ) /
y Hk( 7 )
w u , fa w mh ' g[ m Windows Java wrapper w dki f; & JU z GJUp n f; y Hkjz p fy gw , f/ y & dk* & r fu dk, fw dki fu dku
wrapper w p fc ko mjz p fjy D; z dki fu dkunpack v ky fjy D; java class u dkp w i ft v ky fv ky fy gw , f/
( 4 ) Java cr acking ( u k' fr sm; u dka v hv mjc i f; )
CreateProcessA u dkv ky fa q mi fjy D; w Jha e mu fr Sma w mh wrapper [ m t q Hk; r & Sdw Jh loop w p fc kx Jr Sm
WaitForSingleObject API t o Gi fe JU a e mu fq Hk; u se fa e w Jh thread u dk JVM x Jo Gi f; w Jht x d a p mi fha e r Sm
jz p fy gw , f/
u Re fa w mfw dkUt a e e JU ' D loader z dki fu dk external loader w p fc kz e fw D; jy D; patch v ky fv dkU& y gw , f/
( Oy r ma jy m& & i f u Re fa w mfw dkUt a e e JU , m, Dz dk' gu dk e mr n fa o w p fc kx m; w n fa q mu fjy D; ' Dt x Jr Sm patch v ky f
x m; w Jh class a w Gx m; y gr , f/ ' ga y r , fh ' ga w G[ m t jr i ft & a w mh r v kdt y fy gb l; / a e mu fy dki f; u s& i f & Si f; o Gm;
r Smy g/ )
a v ma v mq , fa w mh jexepackboot.class u dk DJ Java Decompiler e JU decompile v ky fMu n fhy g
r , f/ b ma Mu mi fhv Jq dka w mh class u dk execute v ky fc sde fr Sm a q mi f& Gu fw Jhv ky fa q mi fc su fa w Gu dk t a o ; p dw f
o dc si fv dkUy g/
y Hkr Se fq dk& i fa w mh class w p fc kt w Gu f execute v ky fw Jh y x r q Hk; Method u dka w mh class constructor
u z e fw D; w mjz p fy gw , f/ ( o l[ m class t r n fe JUw lw Jh Method w p fc kjz p fy gw , f/ ) w u , fv dkU class u dk
w dku f& dku fa c : o Hk; w mq dk& i fa w mh( Oy r mjy & & i f java.exe interpreter jz i fh) main Method u dk execute v ky fw m
jz p fy gw , f/ main Method u dkMu n fhr , fq dk& i f y Hk( 8 ) t w dki f; a w GU& r Smy g/
public static void main(String args[])
{
PQ = System.currentTimeMillis();
QQ = args[0].indexOf('D') >= 0;
RQ("Java=" + System.getProperty("java.version"));
jexepackboot jexepackboot1 = new jexepackboot(); // New instance of the current class
int i = jexepackboot1.run(args); // Execute the Method run(String[ ] as)
if(i != 0)
System.exit(i);
}
y Hk( 8 )
u k' fu a w mh & dk; & dk; a v ; y gy J/ y x r q Hk; function t c sdKUu dka c : o Hk; jy D; jexepackboot class & JU instance
t o p fw p fc ku dk z e fw D; y gw , f/ y x r q Hk; execute v ky fw Jh Method u a w mh constructor jz p fjy D; EP object
w p fc ku dk instanciate v ky fy gw , f/ ' Dw p fc k[ m jexepackboot1 class e JUq u fE G, fa e jy D; v u f& Sdjexepackboot
class e JUq dki fw Jht jc m; [ ma w Ge JUa w mhb mr Sv ky fr Smr [ kw fy gb l; /
class constructor r Sma w mh type Properties & JU object EP t o p fw p fc ky g0 i fr Smjz p fy gw , f/ y Hk( 9 ) /
Properties u dkstream w p fc kt a e e JU o dr f; q n f; E dki fy gw , f/ ( o dkU) stream w p fc ku a e u l; w i fE dki fy gw , f/
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 271 -
t w dkc sHK; a jy m& & i fa w mh Properties object u dk database t r sdK; t p m; w p fc kt jz p fjr i fE dki fjy D; property
list x Ju key t o D; o D; e JU o le JUo u fq dki fw Jhw e fz dk; a w G[ m string a w Gjz p fMu y gw , f/
public jexepackboot( )
{
// Create a new object EP of type Properties
EP = new Properties();
}
y Hk( 9 ) Class constr uctor u k' f
Item a w Gu dka w mh setProperty^ getProperty object Method a w Go Hk; jy D; database x Ju dk push
v ky fc HE dki f& y gw , f? database x Ju a e t z w fc HE dki f& y gw , f/ Java u k' ft c sdKUu dk a v hv mMu n fh& a t mi f/ y Hkr Se f
messagebox a w Gv dky J Java r Sm messagebox a w Gu dk t o Hk; jy Kc si f& i f swing class u dkt o Hk; jy K& r Smjz p fy gw , f/
swing u dkt o Hk; jy Kjy D; GUI u dkt a jc c Hw Jh Java y & dk* & r fa w Gz e fw D; E dki fy gw , f/ u Re fa w mfw dkY v ky fz dkUv dkw mu a w mh
class u dk import v ky fjy D; Method w p fc ku dk a c : o Hk; z dkUy g/ Oy r mjy & & i f main Method x Ja & mu f& Sdjy D;
constructor u dkexecute v ky fc sde fr Sm messagebox u a e a jc & mc HE dki fy gw , f/
z dki f& JUx dy fq Hk; u dko Gm; jy D; import command p m& i f; u dkMu n fhy g/ y x r q Hk; e JU a e mu fq Hk; import a w G& Sdu dk
& Sd& y gr , f/ y Hk( 1 0 ) /
import java.awt.*; // Also used for messagebox support, (AWT = Abstract Windowing Toolkit)
import java.io.*;
import java.lang.reflect.InvocationTargetException;
import java.lang.reflect.Method;
import java.util.*;
import java.util.zip.GZIPInputStream;
import javax.swing.*; // Added for messagebox support
y Hk( 1 0 )
t c kc sde fr Sma w mhpop-up message u dka y : a p c si fw Jha e & mr Sm a y : a p z dkU u k' fx Jr Sm message box w p fc ku dk
a & ; Mu n fhy gr , f/
Constructor u dka jc & mc HE dki fz dkU main Method x Jr Sma & ; y gr , f/ y Hk( 1 1 ) /
public jexepackboot( )
{
JOptionPane.showMessageDialog(null, "CLASS CONSTRUCTOR" , "Reversing info (jexepackboot)" ,
JOptionPane.INFORMATION_MESSAGE);
// Create a new object EP of type Properties
EP = new Properties();
}
public static void main(String args[])
{
JOptionPane.showMessageDialog(null, "MAIN METHOD - START" , "Reversing info (jexepackboot)",
JOptionPane.INFORMATION_MESSAGE);
PQ = System.currentTimeMillis();
QQ = args[0].indexOf('D') >= 0;
RQ("Java=" + System.getProperty("java.version"));
jexepackboot jexepackboot1 = new jexepackboot();
int i = jexepackboot1.run(args);
if(i != 0){
JOptionPane.showMessageDialog(null, "MAIN METHOD - SYSTEM EXIT" , "Reversing info
(jexepackboot)" , JOptionPane.INFORMATION_MESSAGE);
System.exit(i);
}
JOptionPane.showMessageDialog(null, "MAIN METHOD - END" , "Reversing info (jexepackboot)",
JOptionPane.INFORMATION_MESSAGE); }
y Hk( 1 1 )
jexepackboot.java u dk Java compiler (javac.exe) e JU compile v ky fjy D; Olly u VA
0x004021EB u dka & mu fw Jht c g Olly u z e fw D; v dku fw Jh r lv jexepackboot.class z dki fa e & mr Sm u Re fa w mfw dkU
jy i fx m; w Jhjexe packboot.class z dki fe JUt p m; x dk; jy D; F9 u dkE Sdy fy g/ y Hk( 1 2 ) t w dki f; jr i f& y gr , f/
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 272 -
y Hk( 1 2 )
a u mi f; jy D/ y & dk* & r ft v ky fv ky fy Hku dke n f; e n f; Mu n fhMu y gr , f/ y Hk( 1 3 ) /
(1) VisualRoute.exe
(2) java -mx256n jexepackboot ER ...
(3) START (jexepackboot.class)
(4) jexepackboot jexepackboot1 = new jexepackboot();
(5) jexepackboot1 (constructor)
(6) int i = jexepackboot1.run(args);
(7) END (jexepackboot.class)
y Hk( 1 3 )
jexepackboot1 class & JU constructor u dk v ky fa q mi fc sde fr Sma w mh Properties() class t o p fw p fc ku dk
z e fw D; r Smjz p fy gw , f/ jexepackboot class u a e w q i fh jexepackboot1 class & JU Method run(args) u dk
a c : o Hk; c sde fr Sm b ma w Gjz p fw , fq dkw m a u mi f; a u mi f; e m; v n fE dki fa t mi f ' Dfunction u dkt a o ; p dw fMu n fhy gr , f/
run Method & JU argument a w Gu a w mh jexepackboot x Jx n fho Gi f; t o Hk; jy Kw Jh argument a w Ge JU
t w lw ly Jjz p fy gw , f/
Args[0] = ER
Args[1] = <root>:\<prog_folder>\VisualRoute\VisualRoute.exe (full path of the main executable)
Args[2] = <root>:\DOCUME~1\<user>\<temp_set>\Temp\XE70DC8 (full path of the temporary folder)
run Method & JUt p y dki f; u dkMu n fhv dku f& i f y Hk( 1 4 ) t w dki f; jr i f& r Smjz p fy gw , f -
private int run(String as[])
{
// install v ky fx m; a o m java p e p fu dkp p fa q ; o n f/
if(!SQ())
return 9999;
if(as.length < 3)
return 10010;
// command-line w Gi f E y gv mjc i f; & Sd^ r & Sdp p fa q ; o n f/
boolean flag = as[0].indexOf('E') >= 0;
// command-line w Gi f R y gv mjc i f; & Sd^ r & Sdp p fa q ; o n f/
boolean flag1 = as[0].indexOf('R') >= 0;
// file o n f main executable E Si fhq dki fa o m pointer w p fc kjz p fo n f/
File file = new File(as[1]);
// , m, Dz dk' gv r f; a Mu mi f; u kdstring s t a e jz i fho dr f; q n f; o n f/
String s = as[2];
// "System properties key = jexepack.exe" u dkitem = <full path for VisualRoute.exe> E Si fht w l push v ky fo n f/
UQ("exe", TQ = file.toString());
// "System properties key = jexepack.resdir" u dkitem = <, m, Dz dk' gv r f; a Mu mi f; > E Si fht w l push v ky fo n f/
UQ("resdir", s);
// file1 o n f , m, Dz dk' gE Si fhq dki fa o m pointer w p fc kjz p fo n f/
File file1 = new File(s);
y Hk( 1 4 )
' Da e & mr Sm UQ Method u dkE Sp fc ga c : o Hk; w m a w GU& r Smy g/ ' D Method r Sm message box u k' fu dk
x n fho Gi f; Mu n fhy gr , f/
private void UQ(String s, String s1)
{
Properties properties = System.getProperties();
properties.put("jexepack." + s, s1);
System.setProperties(properties);
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 273 -
String mybuffer = "key = jexepack." + s + "\nitem=" + s1;
JOptionPane.showMessageDialog(null, mybuffer , "Reversing info (UQ method)" ,
JOptionPane.INFORMATION_MESSAGE);
}
' Du k' fa w Gu dkrun v dku f& i fa w mhy Hk( 1 5 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 1 5 )
t c sdKUa o m t c su ft v u fa w Gu dk System properties database x Jx n fho dr f; x m; jy D; file pointer
E Sp fc ku dkv Jinitialize v ky fy gw , f/
r Sw f& e f/ / System class [ m key/value t w GJa w Gy g0 i fw Jh properties a w Gu dk x de f; o dr f; x m; y gw , f/ ' Dkey
w GJa w G[ m v u f& Sdt v ky fv ky fa e w Jh environment & JU attribute a w Gu dk t " dy m, fz Gi fhq dky gw , f/ Runtime
system y x r q Hk; t Mu dr f p w i fw Jht c gr Sm system properties u dk runtime environment e JUy w fo u fw Jh
t c su ft v u fa w Gy g0 i fE dki fa p z dkU initialize v ky fy gw , f/ t c su ft v u fx Jr Sm y g0 i fE dki fw mu a w mh v u f& Sd user?
Java runtime & JU v u f& Sd version a w Gjz p fjy D; z dki ft r n fw p fc k& JU component a w Gu dk o D; jc m; p Djz p fa p a t mi f
t o Hk; jy Kw Jhp mv Hk; a w mi fy g0 i fE dki fy gw , f/
run Method & JUa e mu f instruction w p fc ku a w mhIM function u dka c : o Hk; w my g/
// VisualRoute.exe image u dkbyte array abyte0[] t a e e JU u l; w i fy gw , f/
byte abyte0[] = IM(file);
IM function & JUv ky fa q mi fy Hku a w mha t mu fy gt w dki f; jz p fy gw , f/
private byte[] IM(File file)
{
RandomAccessFile randomaccessfile = null;
try
{
randomaccessfile = new RandomAccessFile(file, "r");
// z dki ft & G, ft p m; u dk& , ljy D; byte array t o p fw p fc k\ t & G, ft p m; t jz p f o w fr Sw fo n f/
byte abyte0[] = new byte[(int)randomaccessfile.length()];
// abyte0[] o n f point v ky fc H& a o mz dki fE Si fh t & G, ft p m; w la o m byte array w p fc kjz p fo n f/ y x r q Hk; z dki fx J& Sd t & mt m; v Hk;
u dkz w fjy D; abyte0 array t a e jz i fh u l; , lo n f/ i f; a e mu f t & G, ft p m; u dk a o c sma p & e f p p fa q ; o n f/ t u , f z w fc Jha o m
a ' w m\ t & G, ft p m; o n f array t & G, ft p m; E Si fh w ln Dc Jhv Qi f ( z dki ft & G, ft p m; E Si fhw ln Dc Jhv Qi f) u l; , ljc i f; v ky fi e f; p Ofo n f a t mi f
jr i fp Gm jy D; q Hk; jy Djz p fo n f/ x dkUa e mu f u Re fa w mfw dkUt a e jz i fhabyte0[] array u dk abyte1[] t r n f& Sda o m t o p fw p fc kt a e jz i fh u l; , l
E dki fjy Djz p fy go n f/
if(abyte0.length == randomaccessfile.read(abyte0))
{
byte abyte1[] = abyte0; // abyte1[] o n f one dimensional byte array w p fc kt w Gu f reference w p fc kjz p fo n f/
return abyte1;
}
}
catch(Exception _ex) { }
finally
{
try
{
// t m; v Hk; t q i fa jy o Gm; jy Djz p fo n fht w Gu f file stream u dky dw fv dkU& jy Djz p fo n f/
randomaccessfile.close();
}
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 274 -
catch(Exception _ex) { }
}
return null;
}
run Method & JUa e mu f instruction a w Gu a w mhfile image (overlay data extraction) e JUw GJv ky fw m
jz p fy gw , f/ y x r q Hk; p p fa q ; Mu n fhjy D; r Sdata extraction u dko Gm; y gr , f/
private byte[] VQ(byte abyte0[], char c)
{
WQ = -1; // WQ u dk-1 t jz p fo w fr Sw fo n f/ t u , f t m; v Hk; t q i fa jy c Jhv Qi f w e fz dk; u dkr a jy mi f; v JE dki fy g/ )
for(int i = 0; i + 28 < abyte0.length; i += 16)
if(BQ(abyte0, i) && abyte0[i + 15] == c)
{
int j = LQ(abyte0, i + 16);
int k = LQ(abyte0, i + 20);
long l = (long)j & 0xffffffffL | (long)k << 32;
int i1 = LQ(abyte0, i + 24);
int j1 = i + 16 + 8 + 4;
if(j1 + i1 <= abyte0.length)
{
if(1L == l * UM(abyte0, j1, j1 + i1))
return FO(new String(abyte0, 0, j1, i1));
WQ = 10092;
}
}
return null;
}
for loop u dkMu n fhy g/ i w e fz dk; u dk o kn v dkU initialize v ky fjy D; i w e fz dk; r Sm 28 u dka y gi f; y gw , f/
o w fr Sw fx m; w Jh t a jc t a e e JU u dku fn Da e p Ofr Sma w mh i w e fz dk; r Sm a e mu fx y f 16 v ma y gi f; y gw , f/ y dk& Si f; v i f;
a t mi fv dkU PE header u dkMu n fhy g/ y Hk( 1 6 ) /
y Hk( 1 6 )
PE header u dkMu n fhv dku f& i f VA [ m 0x1C (28) u a e p w mu dk a w GU& y gw , f/ for loop y w fa e p Of
t w Gi f; r Sm BQ Method u dkp p fa q ; w ma w GU& y gw , f/ BQ & JU argument [ m data byte jz p fjy D; byte array
u a e 16 bytes t w GJu dkz w fy gw , f/
private boolean BQ(byte abyte0[], int i)
{
int j = 0;
do
if(abyte0[i + j] != (char)(74 + (j * 3) / 2))
return false;
while(++j < 15);
return true;
}
w u , fa w mh BQ Method u z w fv kdu fw Jhp mv Hk; 1 6 v Hk; w GJ[ m "JKMNPQSTVWYZ\]_"
[ kw f^ r [ kw f p p fa q ; w my g/ HEX t a e e JUjy & & i f 4A 4B 4D 4E 50 51 53 54 56 57 59 5A 5C 5D 5F
jz p fy gw , f/ w u , fv dkUo m t a o o w fr Sw fx m; w Jh ' Dkey w GJa w Gu dka w GUc Jh& i f return jy e fy dkUw Jh w e fz dk; [ m true
jz p fjy D; ' Dv dkr Sr [ kw f& i fa w mhfalse w e fz dk; u dkreturn jy e fy dkUr Smjz p fy gw , f/
VisualRoute.exe u dk WinHex e JUMu n fhr , fq dk& i f ' Dv dkw e fz dk; [ m a e & m 3 a e & mr Sm& Sda e w m a w GU& y g
w , f/ y Hk( 1 7 ) /
y Hk( 1 7 )
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 275 -
y Hk( 1 7 ) r Smjr i f& w ma w Gu dk Olly & JU dump window r SmMu n fh& i fa w mh ' Dv dkjr i f& r Sm r [ kw fy gb l; / b m
a Mu mi fhv Jq dka w mh 00004600? 000067F0 e JU 00006860 w dkU[ m disk a y : r Sm& Sdw Jh physical address a w G
jz p fa e v dkUy g/ Olly r Smjr i fc si f& i fa w mho i fht a e e JU virtual address u dka jy mi f; jy D; & Smz dkUv dky gr , f/
b ma w Gjz p fr v Jq dkw m o dE dki fz dkU LordPE r Smz Gi fhjy D; section a w Gu dkMu n fhMu & a t mi f/ y Hk( 1 8 ) /
y Hk( 1 8 )
u Re fa w mfw dkU& JU t y dka ' w ma w G[ m disk a y : r Smo m& Sdjy D; ' g[ m a e mu fq Hk; section r Sma w mi f r y g& Sdy g
b l; / w u , fv dkU o i fht a e e JU Size of Image e JU Raw Size a ' w ma y gi f; v ' fw dkUu dk E dIi f; , SOfv dku fr , fq dk& i f & Si f;
o Gm; r Smy g/
Raw offset + Raw Size
400 + 1A00 = 1E00
1E00 + 800 = 2200
2600 + 600 = 2C00
2C00 + 1A00 = 4600 ( Raw Size a ' w ma y gi f; v ' f)
z dki ft & G, ft p m; [ m 0x7000 jz p fw ma Mu mi fh Windows loader [ m t c sdKUa ' w ma w Gu dk r Sw fOmP fx J
u l; w i fr Smr [ kw fy gb l; /
y Hk( 1 9 )
t w dt u sa jy m& & i f u Re fa w mfw dkU& JU overlay data [ m 0x2A00 (0x7000 - 0x4600) jz p fy gw , f/
VisualRoute.exe z dki fu dk backup v ky fjy D; .r sr c section & JU Raw Size e JU Virtual Size w dkUu dk y Hk( 2 0 ) t w dki f;
a jy mi f; a y ; y g/
y Hk( 2 0 )
y Hk( 2 0 ) t w dki f; a jy mi f; jy D; & i fa w mh z dki fu dk save v ky fv dku fjy D; LordPE u dky dw fv dku fy g/ u Re fa w mfw dkU
backup v ky fx m; w JhVisualRoute.exe z dki fu dkCFF explorer r Smz Gi fhMu n fhy g/ y Hk( 2 1 ) /
y Hk( 2 1 )
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 276 -
jy D; & i f File Offset a e & mr Sm 4600 v dkU& dku fx n fhy g/ y Hkr Se ft m; jz i fha w mh CFF explorer r Smy gv mw Jh
Address converter u r Se fu e fw Jh RVA e JU VA u dk w Gu fx kw fa y ; E dki fy gw , f/ y Hk( 2 1 ) u dkMu n fh& i f RVA e JU
VA [ m y Hkr Se fr [ kw fw Jhw e fz dk; a w Gu dk jy a e y gw , f/
y Hk( 2 0 ) t w dki f; VisualRoute.exe u dkjy i fjy D; o dr f; x m; w Jhz dki fu dk CFF explorer r Smz Gi fhMu n fhjy D; File
Offset a e & mr Sm 4600 v dkU& dku fx n fhv dku fy g/ y Hk( 2 2 ) /
y Hk( 2 2 )
' Dw p fc gr Sma w mh CFF explorer u virtual address u dk r Se fu e fp Gm w Gu fx kw fE dki fy gjy D/ ' D address
t w dki f; Olly r Sm Mu n fhv dku f& a t mi f/ y Hk( 2 3 ) /
y Hk( 2 3 )
r lv VirtualRoute.exe z dki fu dkz Gi fhMu n fh& i fa w mhb mr Sa w GU& r Smr [ kw fy gb l; / y Hk( 2 4 ) /
y Hk( 2 4 )
Section & JU offset [ m 1A00 (406A00 - 405000) u a e p w i fr Smjz p fy gw , f/ Offset 000067F0 e JU
00006860 w dkUu dkOlly r SmMu n fh& i fv Jy Hk( 2 5 ) t w dki f; jr i f& r Smy g/
y Hk( 2 5 )
' Djy Kjy i fx m; w JhVisualRoute.exe u dkz Gi fhMu n fhv dku f& i f y Hk( 2 6 ) t w dki f; error w u fw ma w GU& y gr , f/
y Hk( 2 6 )
' gu a w mh file integrity e JUy w fo u fjy D; CRC p p fa q ; r Iy g/ ' gu dka w mh a e mu fMu r Sy J a v hv my gr , f/
t c ka w mhr lv VisualRoute.exe z dki fu dkjy e f restore v ky fv dku fy g/
Jexepack & JU BQ Method q D jy e fo Gm; v dku fMu & a t mi f/ u Re fa w mfw dkUt a e e JU overlay data u dk
t a o ; p dw fa v hv mw Jht c gr Sm VisualRoute.exe y & dk* & r f b , fv dkt v ky fv ky fo v Jq dkw m o dv my gw , f/ p dw f0 i f
p m; p & ma u mi f; w mu dka w GUE dki fz dkU VQ function u dkq u fMu n fhv dku fMu & a t mi f/
VQ function x Jr Sm LQ function u dkE Sp fc ga c : o Hk; w m a w GU& y gw , f/ LQ function u a w mhu k' fa w G
u dkdecrypt v ky fa y ; w mjz p fjy D; a e mu fq Hk; r Sma w mhbyte array w p fc kt a e e JU jy e fx m; y gw , f/
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 277 -
run Method x Ju dkjy e fMu n fh& a t mi f/
// VisualRoute.exe u dkbyte array abyte0[] t a e jz i fhu l; w i fo n f/
byte abyte0[] = IM(file);
// Image u dka t mi fjr i fp Gm u l; w i fE dki fjc i f; & Sd^ r & Sdp p fa q ; o n f/
if(abyte0 == null)
return 10011;
// JKMNPQSTVWYZ\]_B u dkoverlay data t jz p f & Sd^ r & SdMu n fho n f/
if(VQ(abyte0, 'B') == null)
if(WQ > 0)
return WQ;
else
return 10002;
// JKMNPQSTVWYZ\]_V \ overlay data segment r Sbyte r sm; u dkextract v ky fo n f/
// Byte r sm; u dkdecrypt v ky fjy D; abyte1[] byte array t a e jz i fht m; v Hk; u dkjy e fx m; o n f/
byte abyte1[] = VQ(abyte0, 'V');
if(WQ > 0)
return WQ;
// decrypt v ky fx m; a o ma ' w mr sm; u dkdisk a y : & SdVdata.dat z dki fx Jo dkU dump v ky f, lo n f/
writeByteArrayToDisk(abyte1, "Vdata.dat" , 0, 0, 0);
wr iteByteAr r ayToDisk function u a w mh data array a w Gu dk disk a y : o dr f; q n f; E dki fz dkUt w Gu f
x n fho Gi f; x m; w Jh function w p fc kjz p fy gw , f/ Decrypt v ky fx m; w Jh array u dk disk a y : dump v ky f& jc i f;
u a w mh decrypt v ky fx m; w Jha ' w ma w Gr Sm b ma w Gy go v Jq dkw mu dk a v hv mE dki fz dkUjz p fy gw , f/ y Hk( 2 7 ) r Smjr i f& w m
u a w mhdecrypt v ky fx m; w Jhdata stream a w Gjz p fy gw , f/
y Hk( 2 7 )
wr iteByteAr r ayToDisk function u dka t mu fy gt w dki f; a & ; o m; x m; w mjz p fy gw , f/
private void writeByteArrayToDisk(byte bytebuffer[], String fileName, int start, int numbytes, int mode)
{
// Programmer = ThunderPwr of ARTeam
File file = new File(fileName);
if (mode == 0)
{
try
{ // 0 r So n f a e mu fq Hk; element x dbyte array t m; v Hk; u dka & ; o n f/
FileOutputStream file_output = new FileOutputStream (file);
DataOutputStream data_out = new DataOutputStream (file_output);
for (int i = 0; i < bytebuffer.length; i++)
{
data_out.writeByte(bytebuffer[i]);
}
file_output.close(); }
catch(IOException e)
{
System.out.println ("IO exception = " + e); } }
else
{
try
{ // start + numbytes elements r Sarray section w p fc ku dka & ; o n f/
FileOutputStream file_output = new FileOutputStream (file);
DataOutputStream data_out = new DataOutputStream (file_output);
for (int i = start; i < start + numbytes; i++)
{
data_out.writeByte (bytebuffer[i]);
}
file_output.close();
catch (IOException e)
{
System.out.println ("IO exception = " + e);
}
}
}
a e mu f instruction a w Gu a w mhEP Properties e JU o u fq dki fy gw , f/
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 278 -
// extract v ky fw m a t mi fjr i fjc i f; & Sd^ r & Sdp p fa q ; y gw , f/ ' Da e mu fr Sma w mharray x Jr Sm& Sdw Jhstring u dkparsing v ky fjy D; a w mhparse
v ky fx m; w Jhstring u dkEP properties x Jr Sm o dr f; q n f; E dki fz dkU t w GJ( key? item) w p fc kt jz p f x m; & Sdy gw , f/
// EP propertes [ m local database e JUw lw m t r Sw f& y g/
if(abyte1 != null)
{
for(StringTokenizer stringtokenizer = new StringTokenizer(new String(abyte1, 0), "\n");
stringtokenizer.hasMoreTokens();)
{
String s3 = stringtokenizer.nextToken();
int j = s3.indexOf('=');
if(j > 0)
EP.put(s3.substring(0, j), s3.substring(j+1));
String key = s3.substring(0, j); // no need to add
String item = s3.substring(j+1); // no need to add
}
}
EP properties x J push v ky fc H& w Jhw e fz dk; t c sdKUu dk key/item pair t jz p f a t mu fy gt w dki f; a z mfjy E dki fy g
w , f/ *:\Program Files\VisualRoute\ z dk' ga t mu fu Vdata.dat z dki fu dk z Gi fhMu n fh& i f a t mu fy gt w dki f; a w GU
jr i f& r Smy g/
packager = JexePack 5.5a
main = vr
target = JM
mx = 256
windowed = yes
execwd = *
Overlay section u a e a ' w mt c sdKUu dk extract v ky fjy D; w Jha e mu fr Sma w mh VQ function [ m V p mv Hk;
e JUp w Jh chunk u dk& Sma z Gy gw , f/ ' Dha e mu fr Sma w mh decrypt v ky fjy D; abyte2[] t a e e JU t c su ft v u fa w Gu dk
o dr f; q n f; y gw , f/ a ' w mt m; v Hk; u dk YQ function e JU deflate v ky fr Smjz p fjy D; t q Hk; r Sma w mh ZQ function
u dkt o Hk; jy Kjy D; disk a y : a & ; r Smjz p fy gw , f/ r Sw fx m; & r Smu extract v ky fv dku fw Jhz dki fu dk , m, Dz kd' gt a e e JU o dr f;
q n f; r Smjz p fy gw , f/ y Hk( 2 8 ) /
y Hk( 2 8 )
r Sw fc su f/ / JexePack q dkw mu a w mh command-line tool w p fc kjz p fjy D; resource (GIF/JPG/TXT/p o n f)
a w Ge JUt w lw u Gjz p fw Jho i fh& JU Java application u dkcompress v ky fx m; w Jh32-bits Windows exe z dki ft a e e JU
a jy mi f; v Ja y ; E dki fy gw , f/ ' Dexe z dki f[ m Sun & JU Java Runtime Environment u dkt o Hk; jy Kjy D; t v ky fv ky fy g
w , f/ Console z dki ft a e e JUa & m? Windows application t a e e JUy g a jy mi f; a y ; E dki fy gw , f/
o i fh& JU exe z dki f t v ky fv ky fa e c sde fr Sm? JexePack [ m package w p fc kw n f; t a e e JU a y gi f; x m; w Jhz dki fa w G
u dk , m, Dz dk' gw p fc kr Sm extract jy e fv ky fjy D; java.class.path w p fc ku dk o w fr Sw fy gw , f/ ' Dha e mu fr Sma w mh o i fh
a w mfw Jh Java VM e JU o i fh& JU Java y & dk* & r fu dk t v ky fv ky fa p y gw , f/ y & dk* & r f jy D; q Hk; c sde fr Sma w mh , m, Dz dk' gu dk
z su fq D; & Si f; v i f; v dku fy gw , f/ JexePack u dka t mu fy gv dy fp mr Sm download v ky f, lE dki fy gw , f/
http://www.duckware.com/jexepack/index.html
JexePack & JU t * Fg& y fa w Gu a w mh-
Icon t y gt 0 i f o i fh& JU application u dkexe z dki fw p fc kw n f; t a e e JU pack v ky fa y ; E dki fy gw , f/
Native exe [ m system integration e JUy w fo u fjy D; y dka u mi f; v my gw , f/ ( icon? double-click?
shortcuts? p o n f)
Package t o Gi fa jy mi f; x m; w Jh class a w Ge JU resource a w G[ m compress v ky fc Hx m; & w mjz p fw Jh
t w Gu f exe z dki f[ m t & G, ft p m; t v Ge fa o ; a e r Smjz p fy gw , f/
w du sw JhJava runtime version r Smt v ky fv ky fa p E dki fy gw , f/
JNI (Java Native Interface) DLL a w Gu dkt jy n fht 0 v u fc Hy gw , f/
Run a e c sde fr Sm class a w Gu dku l; w i f& Sma z Gjc i f; u dkt jy n fht 0 a y ; p Gr f; E dki fy gw , f/
JRE u dk t v dkt a v smu f install v ky fa y ; E dki fy gw , f/
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 279 -
' Du kr P Du y J a e mu fx y fx kw fv ky fv dku fw Jh tool u a w mh Jobfuscate v dkUt r n f& jy D; VisualRoute.exe
r Sm obfuscate v ky fx m; w ma w GU& y gw , f/ ' ga Mu mi fhv J function a w G& JUt r n fa w G[ m VQ? WQ p o n fjz i fh
jz p fa e & w my g/ ' Dtool t a Mu mi f; u dka v hv mc si f& i fa w mha t mu fy gv dy fp mr Sm a v hv mE dki fy gw , f/
http://www.duckware.com/jexepack/index.html
run Method u dkq u fa v hv mMu n fh& a t mi f/
// "build" key item jz i fhProperties r Sextract v ky fo n f/
// x dkUa Mu mi fhr n fo n fhkey r Qbuild E Si fhr n Dc Jhv Qi f s2 u null t jz p fo w fr Sw fr n fjz p fo n f/
String s2 = EP.getProperty("build");
if(s2 != null)
UQ("build", s2);
if(!SQ())
return 9999;
// z dki fa & ; jc i f; p w i fo n f/
if(flag)
{
RQ("extract=yes");
// JKMNPQSTVWYZ\]_Z u dk& Smjy D; abyte2[] array t a e jz i fho dr f; q n f; o n f/
byte abyte2[] = VQ(abyte0, 'Z');
// t u , f a ' w mu dkextract v ky fc Jha o mf i f; u dkdisk a y : o dr f; q n f; o n f/
if(abyte2 != null && abyte2.length > 4)
{
Object obj = null;
abyte2 = XQ(abyte2);
int k = LQ(abyte2, 0);
int l = LQ(abyte2, 4);
abyte2 = YQ(abyte2, l, 8); // GZIP a ' w m stream u dkdecompress v ky fo n f/
int i1 = abyte2 != null ? ZQ(file1, abyte2, k) : 10034;
if(i1 > 0)
return i1;
RQ("extracted=" + k);
}
else if (WQ > 0)
return WQ;
else
return 10012;
}
// z dki fa & ; jc i f; jy D; q Hk; o n f/
if(!flag1)
return 12345;
q u fMu n fhr , fq dk& i fa w mha e mu f command a w Gu vr t r n fe JU class u dk& Sma z Gw mjz p fjy D; ' Dw p fc ku dk
Class1 v dkUo w fr Sw fy gw , f/ ( vr.class u dkextract v ky fjy D; jz p fo n f/ )
// "main" key o n f "vr" item t a Mu mi f; jz p fo n f/
// x dkUa e mu f statement o n f s1 u dk"vr" E Si fhn Da p v dr fhr n f/
String s1 = EP.getProperty("main");
if(s1 == null) // s1 = vr
return 10020;
// , c kt c g vr class t o p fu dkClass.forName(<class_name>) statement t o Hk; jy Kjy D; z e fw D; o n f/
Object obj1 = null;
int i = 0;
Class class1 = null;
try
{
class1 = Class.forName(s1);
}
catch(Throwable throwable)
{
obj1 = ((Object) (throwable));
i = 10024;
}
// Jz.Ky.Tx t r n fE Si fhz dki ft o p fw p fc ku dk, m, Dz dk' gw Gi f z e fw D; o n f/
File file2 = new File(file1, "Jz.Ky.Tx");
t c kc sde fr Sma w mh daemon thread w p fc ku dk jexepackboot class & JU run Method e JU o w fr Sw fjy D;
a e mu fr Sma w mh , m, Dz kd' gx Ju jexepackboot.class z dki fu dkz su fy p fv dku fjy D; r Mu ma o ; c i fu z e fw D; v dku fw Jh vr
class u dkas1 argument e JUw GJjy D; a c : o Hk; y gw , f/
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 280 -
if(obj1 == null)
{
if(!QM(file2, new byte[100]))
return 10013;
String as1[] = new String[as.length - 3];
for(int j1 = 0; j1 < as1.length; j1++)
as1[j1] = as[3 + j1];
// , c kt c sde fw Gi f jexepackboot u dkdaemon thread (cyclic) w p fc kt a e jz i fhexecute v ky fy gv dr fhr n f/
Thread thread = new Thread(this);
thread.setDaemon(true);
thread.start();
// jexepackboot.class z dki fu dk, m, Dz kd' gx Jr Sz su fy p fo n f/
(new File(file1, getClass().getName() + ".class")).delete();
try
{ // t o p fw p fc kt w Gu f main Method u dkexecute v ky fo n f/
RQ("main=" + s1); // s1 = vr
Method method = class1.getMethod("main", new Class[] {java.lang.String[].class});
method.invoke(null, new Object[] { as1 });
}
' gu a w mh jexepackboot.class & JU t v ky fv ky fy Hky g/ w u , fa w mh jexepackboot [ m t jc m; class
a w Gu target y & dk* & r fu dk launch v ky fE dki fz dkUt w Gu f Mu dKw i fv ky fa q mi fa y ; & w Jh loader w p fc ko mjz p fy gw , f/
z dki fa w Gextract v ky fjy D; c sde fr Sm message box a y : a p c si f& i fa w mha t mu fy gt w dki f; x n fho Gi f; E dki fy gw , f/ y Hk( 2 9 ) /
// z dki fa & ; jc i f; jy D; q Hk; o n f/
if(!flag1)
return 12345;
JOptionPane.showMessageDialog(null, "run Method, FILE WROTE \n patch the vr.class" , "Reversing info
(jexepackboot)" , JOptionPane.INFORMATION_MESSAGE);
y Hk( 2 9 )
' De n f; u dkvr.class z dki ft w Gu f patch v ky fc sde fr Sm break v ky fE dki fz dkU t o Hk; jy KE dki fy gw , f/
( 5 ) Java cr acking ( u k' fr sm; u dk t a o ; p dw fa v hv mjc i f; )
' Dw p fc ga w mhvr.class z dki fu dka t mu fy gt w dki f; jy i f& r Smjz p fy gw , f/
import java.io.*;
import java.util.Hashtable;
import javax.swing.*; // x y fx n fh& e f
public class vr extends ClassLoader
{
private Hashtable g_cl;
private Object m_o;
private String className = " vr " ; // y x r q Hk; t Mu dr fr Sma w mhvr jz p fy gw , f/
public vr()
{
// Default constructor
g_cl = new Hashtable();
}
public vr(String buffer)
{
// Overload of the default constructor
className = buffer;
printClassName( " CONSTRUCTOR " + className);
g_cl = new Hashtable();
}
public void printClassName(String functionName)
{
JOptionPane.showMessageDialog(null, functionName, "Reversing info (
"+getClass().getName()+" .class / " +className+")" , JOptionPane.INFORMATION_MESSAGE);
}
t c e f; ( 1 8 ) - Java jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 281 -
vr class t o p fw p fc ku dkvr1 t r n fe JU z e fw D; y gr , f/
vr vr1 = new vr("vr1"); // vr1 jz i fht p m; x dk; o n f/
vr1.equals(args);
vr1.equals("bl_ver=1.01");
a e mu fx y f ' Dv dkx y fjy i fy gr , f/
public boolean equals(Object obj)
{
try
{ // Create a new instance of the class A
printClassName("equals(loadClass(\"A\", true). newInstance() ");
m_o = m_o != null ? m_o : loadClass("A", true).newInstance();
}
catch(Exception exception)
{
exception.printStackTrace();
}
boolean flag = m_o.equals(obj); // Call the method equals for the class A
return flag;
}
' Da e mu fr Sma w mhargument A e JU loadClass method u dka c : o Hk; y gw , f/
' Dv dk jy i fjy D; w Jht c g VisualRoute.exe u dk Olly r Smjy e fz Gi fhy g/ y Hk( 2 9 ) t w dki f; jr i f& c sde fr Sm vr.class z dki fu dk
patch v ky fx m; w Jhvr.class z dki fe JUt p m; x dk; y g/ ' gq dky Hk( 3 0 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 3 0 )
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 282 -
tcef;(19) - Visual Dot.net jzifh a&;om;xm;aom y&dk*&rfrsm;udk cr ack vkyfjcif;
' Dw p fc g u Re fa w mfw dkUt a e e JU crack v ky fMu n fhz dkU t v Sn fhu sv mw mu a w mh.net y & dk* & r fa w Gu dky g/ .net
y & dk* & r fa w Gu dk crack v ky f& w m[ m native API a w Ge JUa & ; o m; x m; w Jh t jc m; y & dk* & r fa w Gu dk crack v ky f& w m
x u f t r sm; Mu D; v G, fu lv my gw , f/ b ma Mu mi fhv Jq dka w mh y & dk* & r fu dka & ; o m; x m; w Jh source code a w Gu dk
Mu n fhv dkU& v dkUy g/ b , f function a w Gu dk b , ft c su ft v u fa w Ge JU a c : o Hk; w mu t p Mu n fhv dkU& w Jht w Gu f
cracker a w Gt w Gu f crack v ky f& w m t v Ge fv G, fu lv my gw , f/ b my Jjz p fjz p f crack r v ky fc i fa w mh .net & JU
o a b mo b m0 u dk e m; v n fa p c si fw Jht w Gu f .net e JUy w fo u fw Jht a jc c Ho Dt dk& Da w Gu dk t & i f& Si f; jy y gr , f/
( 1 ) .net q dko n fr Sm . . .
y & dk* & r fr mt r sm; p kt w Gu fu a w mh .net e JUy w fo u fw Jho a b mw & m; a w G[ m y a [ V dw p fy k' fv dky gy J/ .net
q dkw mu a w mh Microsoft & JU a & y e f; t p m; q Hk; p u m; v Hk; a w Gx Ju w p fv Hk; jz p fjy D; ASP.net u t p Visual
Studio.net t q Hk; & Sdw Jh Microsoft & JU product a w Gr Sm w Gi fu s, fp Gm t o Hk; jy Kv su f& Sdy gw , f/ w u , fa w mh .net
y & dk* & r fa w Gu dk machine code t jz p f w dku f& dku f compile v ky fv dku fw mr [ kw fy gb l; / ( C++ w dkUv dk b mo m
p u m; a w G[ m machine code t jz p fw dku f& dku f compile v ky fc H& w mjz p fy gw , f/ ) o lw dkUu dk IL v dkUa c : w Jh
Intemediate Language t jz p f compile v ky fv dku fw my g/ o i f[ m Java e JUy w fo u fc Jhz l; r , fq dk& i fa w mh .net
Framework [ m Java Virtual Machine v dky gy J/ IL a w Gu dk Java y & dk* & r fa w Gt jz p f compile v ky fa y ;
v dku fw Jh bytecode a w Ge JU E dIi f; , SOfE dki fy gw , f/ ' Dv dk bytecode a w Gt jz p fa jy mi f; v Ja y ; v dku fjc i f; [ m y & dk* & r f
a & ; o m; jc i f; & Ia x mi fhu a e Mu n fhr , fq dk& i f a u mi f; u sdK; a jr mu fjr m; p Gm ( t v ky fv ky fw JhE Ie f; u sq i f; o Gm; jc i f; r Sw y g; )
jz p fa p y gw , f/ Java & JUt a Mu mi f; jy c su fu a w mh ' Dv dkjy Kv ky fjc i f; t m; jz i fh r w ln Dw Jh OS a w Gr Sm Java y & dk* & r fa w G
u dkt v ky fv ky fa p E dki fjy D; r w ln Dw Jh y & dkq u fq mt r sdK; r sdK; r Sma w mi f t v ky fv ky fa p E dki fz dkUjz p fy gw , f/ .net & JU t " du
& n f& G, fc su fu ' Dt w Gu f r [ kw fa y r , fh' DZ dki f; y dki f; q dki f& m c sOf; u y fr Iu a w mhw ln Dy gw , f/
.net y & dk* & r fr ma w Gt w Gu f IL & JU t " du t m; o mc su fu a w mh compile v ky fx m; w Jhy & dk* & r fa w Gr Sm
identifier (class name? function name? variable name) a w G[ m & Sda e Mu w mjz p fy gw , f/ ( r Sw fc su f/ / C
y & dk* & r fa w Gu dk compile v ky fw Jht c gr Sm local variable t r n fa w G[ m t z w fq n fr & a t mi f q Hk; & IH; o Gm; a Mu mi f;
a q G; a E G; c Jhz l; w m t r Sw f& y g/ ) ' Dt c su fu y & dk* & r fr ma w Gu dk y & dk* & r fw p fc k& JU r w ln Dw Jht y dki f; a w Gu dk r w ln Dw Jh
b mo mp u m; a w Ge JU a & ; o m; v dkU& a p y gw , f/
Cracker a w Gt w Gu f t " du t m; o mc su fjz p fa p w mu v J ' Dt c su fy gy J/ b ma Mu mi fhv Jq dka w mh .net
y & dk* & r fa w G[ m o lU& JU source u dk bytecode e JUa z mfjy & w mjz p fw Jht w Gu f identifier a w G[ mv J r y su fr , Gi f; & Sda e
& w my g/ t v m; w ly J? IL [ m w u , fhy & dkq u fq mu k' fx u fp m& i f e n f; e n f; a v ; higher-level jz p fv mw Jht w Gu f
high-level b mo mp u m; t jz p f v G, fu lp Gmjy e fv n fw n fa q mu fE dki fMu w my g/ ' gu dk o dMu w Jht w Gu fa Mu mi fh .net
y & dk* & r fa w Gu dk r lv .net source code t jz p fjy e fa z mfa y ; E dki fr , fh tool a w Gu dkz e fw D; E dki fMu w mjz p fy gw , f/ ' Dv dk
jy e fa z mfa y ; E dki fw Jhtool a u mi f; a v ; w p fc ku dk Lutz Roeder u a & ; o m; c Jhjy D; Reflector v dkUa c : y gw , f/
( 2 ) Tools
.net y & dk* & r fa w Gcrack r v ky fc i fr Sm t o Hk; jy Kr , fh tool a v ; a w Gt a Mu mi f; a q G; a E G; y gr , f/ o i fht a e e JU
' Dtool a w Gt m; v Hk; u dk w p fc sde fw n f; r Sma w mhv dkt y fr Sm r [ kw fy gb l/ ' ga y r , fhtool a w Gt m; v Hk; & Sdx m; a t mi fa w mh
v ky fx m; & r Smjz p fy gw , f/
( 2 . 1 ) Relector (.net assembly decompiler )
Relector u a w mh .net component a w Gt w Gu f class browser w p fc kjz p fy gw , f/ ' Dtool a v ; [ m
.net assembly x Jr Smo dr f; q n f; x m; w Jh Meta data? IL instruction? resource? XML documention w dkUu dk
& Sma y ; E dki fy gw , f/
http://www.aisto.com/roeder/dotnet/
( 2 . 2 ) ILDasm (.net assembly decompiler )
MSIL Disassembler u a w mh MSIL Assembler (Ilasm.exe) t w Gu f tool w p fc kjz p fy gw , f/
ILDasm.exe [ m Microsoft intermediate language (MSIL) u k' fa w Gy gw Jh PE z dki fu dk, ljy D; Ilasm.exe
t w Gu f o i fha w mfr , fhp mo m; z dki ft jz p fz e fw D; a y ; y gw , f/
Reflector [ m .net assembly u dk IL u k' fa w Gt jz p f decompile v ky fa y ; E dki fa y r , fh assembly x Ju
IL instruction a w G& JU w u , fhbyte a w Gu dk jy o jc i f; r & Sdy gb l; / ILDasm r Sma w mhIL instruction a w Gu dk hex
w e fz dk; t a e e JUjy o a y ; E dki fa t mi f a & G; c s, fv dkU& y gw , f/
Oy r mjy & & i f - BLE instruction u dkMu n fhv dku fy g/ w u , fv dkUo m y x r w e fz dk; [ m ' kw d, w e fz dk; x u f
e n f; a e & i f ( o dkU) n Da e & i f o w fr Sw fx m; w Jhinstruction q Djump jz p fr Smy g/ ( Native code a w Gr Smw ke f; u a w mh
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 283 -
JLE e JUw ly gw , f/ ) w u , fv dkU hex editor r SmMu n fhv dku f& i f w u , fh byte [ m 3E jz p fa e w ma w GU& r Smy g/
BLE instruction t p m; BGT instruction v dkUa jy mi f; v dku f& i fa w mh y x r w e fz dk; [ m ' kw d, w e fz dk; x u fMu D; & i f
o w fr Sw fx m; w Jh instruction q D jump jz p fr Smy g/ o lUu dka z mfjy w mu a w mh 3D y g/ w u , fv dkU ' Da e & mu dk
jy i fc si f& i f hex editor q Do Gm; jy D; 3E t p m; 3D v dkUjy i f& r Smy g/
a u mi f; jy D? ILDasm e JUp p fx m; w Jhprocedure w p fc ku dkMu n fhv dku fMu & a t mi f/
.method public specialname instance class Scroller.Scroller/Title
get_Titles(object Index) cil managed
// SIG: 20 01 12 0C 1C
{
// Method begins at RVA 0xcd7c
// Code size 23 (0x17)
.maxstack 2
.locals init (class Scroller.Scroller/Title V_0)
IL_0000: /* 02 | */ ldar g.0
IL_0001: /* 7B | (04)00000D */ ldfld
IL_0006: /* 03 | */ ldarg.1
IL_0007: /* 28 | (0A)00005C */ call object
IL_000c: /* 6F | (0A)00005D */ callvirt instance object
IL_0011: /* 74 | (02)000003 */ castclass
Scroller.Scroller/Title
IL_0016: /* 2A | */ ret
} // end of method Scroller::get_Titles
' gu a w mhIL x Ju u k' ft c sdKUy g/
IL_0000 : line e Hy gw f/
02 : x dk line w Gi f& Sda o m IL instruction r sm; \ w u , fhbyte/
ldar g.0 : IL instruction/
' ga w Gu dke m; r v n fv dkU p dw fr y su fy ge JU/ a e mu fy dki f; r Sm t a o ; p dw fa q G; a E G; a y ; y gr , f/
Byte a w G? IL instruction a w Gjr i f& w Jh t m; o mc su fu a w mh CALL w p fc ku dk NOP a y ; c si fw my J
jz p fjz p f? u dk, f patch v ky fc si fw Jha e & mu dk jy i fc si fw my Jjz p fjz p f t v G, fw u ljy Kjy i fv dkU& y gw , f/ Offset u dkw Gu f
c su fz dkU RVA u dkt o Hk; jy K& r Smjz p fy gw , f/
Ildasm u a w mh Visual Studio 200x u dk install v ky fw Jht c gr Sm w c gw n f; y gv mw mjz p fw Jht w Gu f
o D; o e fU download v ky fp & mr v dky gb l; /
( 2 . 3 ) WinHex (Hex editor )
b , f hex editor u dkr q dk t o Hk; jy KE dki fa y r , fhWinHex u dka w mht Mu dKu fq Hk; jz p fa e v dkUy g/
http://www.x-ways.com/
( 2 . 4 ) CFF Explor er (Gener al PE File Explor er )
Assembly x Ju metadata table a w Ge JU resource a w Gy g0 i fw Jh b , f PE z dki fr q dk& JU content a w Gu dk
Mu n fh& I& mr Sma w mht a w mfa v ; a u mi f; w Jhtool w p fc kjz p fy gw , f/
http://www.ntcore.com
( 2 . 5 ) SNS Remover (Str ong Name Signatur e Remover )
t c sdKUa o m .net assembly a w G[ m assembly a w Gu dk z e fw D; v dku fc sde fr Sm t Mu Ht z e fr v ky fE dki fa t mi f?
r jy Kjy i fE dki fa t mi fw m; q D; z dkU digital signature a w Ge JU sign v ky fx m; Mu y gw , f/ Strongly named assembly
x Ju b , f byte u dkr q dk jy i fv dku fr , fq dk& i f .net runtime u assembly u dkp w i fz dkU ji i f; q e fy gv dr fhr , f/
' ga y r , fh u Re fa w mfw dkU& JU SNS remover tool u a w mh sign v ky fx m; w Jh assembly u a e signature field
u dkz , f& Sm; E dki fy gw , f/ ' Da e & mr Sm a jy mv dkw mu a w mhu Re fa w mfw dkU& JU CFF explorer u v J .net assembly u a e
Strong Name signature u dkz , f& Sm; E dki fjy D; PE z dki fu dk jy e fv n fw n fa q mu fE dki fy gw , f/ y Hk( 1 ) / ' ga y r , fh
u Re fa w mft a e e JU ' Dtool a v ; u dk y dkMu dKu fr dy gw , f/
y Hk( 1 )
http://www.pmode.com
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 284 -
( 2 . 6 ) PEBr owse Pr ofessional (Disassembler /Debugger )
.net assembly a w Gu dk disassemble v ky fE dki fw Jh^ debug v ky fE dki fw Jh debugger/disassembler w p fc k
jz p fy gw , f/ IL instruction a w Ge JU o lw dkU& JUw u , fh byte a w Gu dk jy o E dki fy gw , f/ ' ght jy i f b , f JIT
compiler event u dkr q dk break v ky fE kdi fy gw , f/ ' D debugger u dkt o Hk; jy Kjy D; .net IL instruction a w Gu dk
a jc & mc HE dki fy gw , f/ jy D; & i fa e mu fu G, fr Sm b ma w Gjz p fa e o v Jq dkw m o dE dki fy gw , f/
http://www.smidgeonsoft.com
( 2 . 7 ) .Net Gener ic Unpacker (.Net assembly Unpacker )
o i fht a e e JU .net assembly PE z dki fa w Gu dk dump v ky fw Jht c gr Sm ' D tool u dk v dky gv dr fhr , f/ .Net
reactor v dk t c sdKUa o m .net protection a q mhz f0 Jv fa w Gu o i fhy & dk* & r f& JU .net assembly u dk pack v ky fMu w m
jz p fjy D; MSIL r [ kw fw Jh PE z dki fu dkx kw fa y ; y gv dr fhr , f/ r Sw fOmP fx Jr Sm t v ky fv ky fw Jht c gr So m o i fhz dki f& JU
assembly a w Gu dk unpack jy e fv ky fMu w mjz p fy gw , f/ ' De n f; y n mu dka w mh r lv assembly & JU u k' fa w Gu dk
& , ljc i f; r S u mu G, fE dki fz dkU t o Hk; jy KMu w mjz p fy gw , f/ ' ga y r , fh o i fht a e e JU ' gu dk & dk; & Si f; v Sw Jh .net generic
unpacker o Hk; jy D; a u smfv Tm; E dki fy gw , f/
http://www.ntcore.com
a e mu fq Hk; t a e e JU a jy mv dkw mu a w mh w c gw & Hr Sm Reflector [ m t c sdKUa o m procedure ( o dkU)
function a w Gu dk o i fhp dw fMu dKu fb mo mp u m; (C#? VB? Delphi) t jz p f decompile r v ky fa y ; E dki fw Jht w Gu f
o i fht a e e JU IL instruction a w Gu dk & i f; E SD; a e z dkUv dkt y fy gw , f/ Native code a w Gu dk crack v ky fz dkU Assembly
b mo mp u m; u dk a v hv mw mx u fp m& i fa w mh IL u k' fa w Gu dk a v hv m& w m[ m y dkr dkv G, fu ljy D; v si fjr e fp Gme m; v n f
r Sm jz p fy gw , f/
( 3 ) Opcode
' gu a w mh crack v ky f& mr Sm t a & ; Mu D; q Hk; t c su fjz p fy gw , f/ o i fjr i fw Jht w dki f; .net application
a w G[ m o lw dkU& JU y & dk* & r f instruction a w Gu dk MSIL y Hkp He JUa z mfjy w mjz p fw Jht w Gu f Visual Studio r Sm
compile v ky fw Jht c g o i fh& JU source code a w Gu dk native machine u k' ft jz p f a jy mi f; v Ja y ; r Smr [ kw fy gb l; /
' ga y r , fh JIT compiler u dkt o Hk; jy Kjy D; compile v ky fr , fq dk& i fa w mh native code t jz p fa jy mi f; v Ja y ; r Sm
jz p fy gw , f/ JIT q dkw mu a w mh just-in-time compiler u dka jy mw mjz p fjy D; o i fhy & dk* & r fa w G& JU t p dw ft y dki f;
t c sdKUu dk native code t jz p fa jy mi f; v Ja y ; r Smjz p fjy D; v dkt y fw Jht c g execute v ky fr Smjz p fy gw , f/
Ildasm u x Gu fv mw Jhu k' ft c sdKUu dk a v hv mMu n fhv dku f& a t mi f/
IL_0000: /* 02 | */ ldarg.0
Line number Actual byte(s) IL instruction
Opcode q dkw mu a w mh Microsoft Intermediate Language (MSIL) instruction a w Gu dk
a z mfjy jc i f; jz p fy gw , f/ w u , fv dkU o i f[ m a & SYy dki f; t c e f; a w Gu dk a Mu n u fp Gme m; v n fx m; w , fq dk& i f a t mu fy g
instruction a w G[ m b mu dkq dkv dkw , fq dkw m o da e r Smy g/
JMP JNE JLE NOP CALL p o n f . . .
MSIL opcode a w Gu a w mh Intel y & dkq u fq ma w Gt w Gu f ' DZ dki f; jy Kx m; w Jh native opcode a w Ge JU
r w ln Dy gb l; / Oy r mjy & & i f native code y & dk* & r fa w Gr Sm CALL function & Sd& m offset u dk o i fo dx m; jy D; ' D
CALL u dkt v ky fr v ky fa p c si f& i f y & dk* & r fu dk hex editor r Smz Gi fhjy D; NOP (No OPertation) u dk& n fp l; w Jh 90
q dkw Jhbyte e JUt p m; x dk; & r Smjz p fy gw , f/
MSIL r Sma w mh 90 t p m; 00 e JUa z mfjy y gw , f/ ' g[ mt a & ; Mu D; w Jht c su fjz p fw Jht w Gu f MSIL t w Gu f
v dkt y fw Jh opcode p m& i f; u dk a z mfjy v dku fy gw , f/ o i fht a e e JU .net y & dk* & r fa w Gu dk crack v ky f& mr Sm ' Dopcode
a w Gt m; v Hk; u dk t o Hk; jy Kp & mr v kdy gb l; / r sm; a o mt m; jz i fha w mh NOP e JU unregistered t a jc t a e a w Gu dk a u smf
v Tm; E dki fz dkU jump instruction a w Gu dk t r sm; q Hk; t o Hk; jy K& r Smjz p fy gw , f/
Opcode a w Gt a Mu mi f; u dk y dkr dke m; v n fa p v dkw Jht w Gu f b mo mr jy e fb J r l& i f; t w dki f; a z mfjy v dku fy gw , f/
y & dk* & r fa w Gu dk v u fa w GU crack w Jht c gMu r Sy J v dkt y fo v dk b mo mjy e fa y ; r Smjz p fy gw , f/ & Sn fv sm; r Smp dk; w Jh
t w Gu f t o Hk; r sm; w Jhopcode a w Gu dky J a z mfjy v dku fy gw , f/
Opcode Meaning
Actual
bytes
And
Computes the bitwise AND of two values and pushes the result onto the evaluation
stack.
5F
Beq Transfers control to a target instruction if two values are equal. 3B
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 285 -
Beq_S Transfers control to a target instruction (short form) if two values are equal. 2E
Bge
Transfers control to a target instruction if the first value is greater than or equal to the
second value.
3C
Bge_S
Transfers control to a target instruction (short form) if the first value is greater than or
equal to the second value.
2F
Bge_Un
Transfers control to a target instruction if the the first value is greater than the second
value, when comparing unsigned integer values or unordered float values.
41
Bge_Un_S
Transfers control to a target instruction (short form) if if the the first value is greater
than the second value, when comparing unsigned integer values or unordered float
values.
34
Bgt
Transfers control to a target instruction if the first value is greater than the second
value.
3D
Bgt_S
Transfers control to a target instruction (short form) if the first value is greater than the
second value.
30
Bgt_Un
Transfers control to a target instruction if the first value is greater than the second
value, when comparing unsigned integer values or unordered float values.
42
Bgt_Un_S
Transfers control to a target instruction (short form) if the first value is greater than the
second value, when comparing unsigned integer values or unordered float values.
35
Ble
Transfers control to a target instruction if the first value is less than or equal to the
second value.
3E
Ble_S
Transfers control to a target instruction (short form) if the first value is less than or
equal to the second value.
31
Ble_Un
Transfers control to a target instruction if the first value is less than or equal to the
second value, when comparing unsigned integer values or unordered float values.
43
Ble_Un_S
Transfers control to a target instruction (short form) if the first value is less than or
equal to the second value, when comparing unsigned integer values or unordered float
values.
36
Blt Transfers control to a target instruction if the first value is less than the second value. 3F
Blt_S
Transfers control to a target instruction (short form) if the first value is less than the
second value.
32
Blt_Un
Transfers control to a target instruction if the first value is less than the second value,
when comparing unsigned integer values or unordered float values.
44
Blt_Un_S
Transfers control to a target instruction (short form) if the first value is less than the
second value, when comparing unsigned integer values or unordered float values.
37
Bne_Un
Transfers control to a target instruction when two unsigned integer values or unordered
float values are not equal.
40
Bne_Un_S
Transfers control to a target instruction (short form) when two unsigned integer values
or unordered float values are not equal.
33
Br Unconditionally transfers control to a target instruction. 38
Br false
Transfers control to a target instruction if value is false, a null reference (Nothing in
Visual Basic), or zero.
39
Br false_S Transfers control to a target instruction if value is false, a null reference, or zero. 2C
Br tr ue Transfers control to a target instruction if value is true, not null, or nonzero. 3A
Br tr ue_S
Transfers control to a target instruction (short form) if value is true, not null, or non-
zero.
2D
Br _S Unconditionally transfers control to a target instruction (short form). 2B
Call Calls the method indicated by the passed method descriptor. 28
Clt
Compares two values. If the first value is less than the second, the integer value 1
(int32) is pushed onto the evaluation stack; otherwise 0 (int32) is pushed onto the
evaluation stack.
FF 04
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 286 -
Clt_Un
Compares the unsigned or unordered values value1 and value2. If value1 is less than
value2, then the integer value 1 (int32) is pushed onto the evaluation stack; otherwise 0
(int32) is pushed onto the evaluation stack.
FE 03
Jmp Exits current method and jumps to specified method. 27
Ldar g Loads an argument (referenced by a specified index value) onto the stack. FE 09
Ldar ga Load an argument address onto the evaluation stack. FF 0A
Ldar ga_S Load an argument address, in short form, onto the evaluation stack. 0F
Ldar g_0 Loads the argument at index 0 onto the evaluation stack. 02
Ldar g_1 Loads the argument at index 1 onto the evaluation stack. 03
Ldar g_2 Loads the argument at index 2 onto the evaluation stack. 04
Ldar g_3 Loads the argument at index 3 onto the evaluation stack. 05
Ldar g_S Loads the argument (referenced by a specified short form index) onto the evaluation
stack.
0E
Ldc_I4 Pushes a supplied value of type int32 onto the evaluation stack as an int32. 20
Ldc_I4_0 Pushes the integer value of 0 onto the evaluation stack as an int32. 16
Ldc_I4_1 Pushes the integer value of 1 onto the evaluation stack as an int32. 17
Ldc_I4_2 Pushes the integer value of 2 onto the evaluation stack as an int32. 18
Ldc_I4_3 Pushes the integer value of 3 onto the evaluation stack as an int32. 19
Ldc_I4_4 Pushes the integer value of 4 onto the evaluation stack as an int32. 1A
Ldc_I4_5 Pushes the integer value of 5 onto the evaluation stack as an int32. 1B
Ldc_I4_6 Pushes the integer value of 6 onto the evaluation stack as an int32. 1C
Ldc_I4_7 Pushes the integer value of 7 onto the evaluation stack as an int32. 1D
Ldc_I4_8 Pushes the integer value of 8 onto the evaluation stack as an int32. 1E
Ldc_I4_M1 Pushes the integer value of -1 onto the evaluation stack as an int32. 15
Ldc_I4_S Pushes the supplied int8 value onto the evaluation stack as an int32, short form. 1F
Ldstr Pushes a new object reference to a string literal stored in the metadata. 72
Leave Exits a protected region of code, unconditionally tranferring control to a specific target
instruction.
DD
Leave_S Exits a protected region of code, unconditionally tranferring control to a target
instruction (short form).
DE
Mul Multiplies two values and pushes the result on the evaluation stack. 5A
Mul_Ovf Multiplies two integer values, performs an overflow check, and pushes the result onto
the evaluation stack.
D8
Mul_Ovf_Un Multiplies two unsigned integer values, performs an overflow check, and pushes the
result onto the evaluation stack.
D9
Neg Negates a value and pushes the result onto the evaluation stack. 65
Newobj Creates a new object or a new instance of a value type, pushing an object reference
(type O) onto the evaluation stack.
73
Nop Fills space if opcodes are patched. No meaningful operation is performed although a
processing cycle can be consumed.
00
Not Computes the bitwise complement of the integer value on top of the stack and pushes
the result onto the evaluation stack as the same type.
66
Or Compute the bitwise complement of the two integer values on top of the stack and
pushes the result onto the evaluation stack.
60
Pop Removes the value currently on top of the evaluation stack. 26
Rem Divides two values and pushes the remainder onto the evaluation stack. 5D
Rem_Un Divides two unsigned values and pushes the remainder onto the evaluation stack. 5E
Ret Returns from the current method, pushing a return value (if present) from the caller's
evaluation stack onto the callee's evaluation stack.
2A
Rethr ow Rethrows the current exception. FE 1A
Stind_I1 Stores a value of type int8 at a supplied address. 52
Stind_I2 Stores a value of type int16 at a supplied address. 53
Stind_I4 Stores a value of type int32 at a supplied address. 54
Stloc Pops the current value from the top of the evaluation stack and stores it in a the local
variable list at a specified index.
FE 0E
Sub Subtracts one value from another and pushes the result onto the evaluation stack. 59
Sub_Ovf Subtracts one integer value from another, performs an overflow check, and pushes the
result onto the evaluation stack.
DA
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 287 -
Sub_Ovf_Un
Subtracts one unsigned integer value from another, performs an overflow check, and
pushes the result onto the evaluation stack.
DB
Switch Implements a jump table.
45
Thr ow Throws the exception object currently on the evaluation stack.
7A
Xor
Computes the bitwise XOR of the top two values on the evaluation stack, pushing
the result onto the evaluation stack.
61
b , f assembly u dkr q dk crack v ky f& mr Sm & i fq dki fMu HKa w GU& r , fh t [ e fUt w m; a w Gu a w mh a t mu fy g
t w dki f; jz p fy gw , f/ ' Da e & mr Sm u Re fa w mfht a e e JU t u sOf; r Qo ma z mfjy r Smjz p fjy D; t a o ; p dw fo dc si f& i fa w mh Google
r Sm& Smjy D; Mu n fhE dki fy gw , f/
( u ) Obfuscation
' gu a w mh IsLicensed function w dkUv dk Method e JU class t r n fa w Gu dk u Re fa w mfw dkUr & SmE dki fa t mi f
z w fv dkUr & w Jhp mv Hk; a w Gt jz p f a jy mi f; v Ja y ; w Jhjz p fp Ofu dk q dkv dkw my g/ Obfuscation [ m o i fhu dk t c u fa w GUa p E dki f
a y r , fh obfuscate v ky fx m; w Jhu k' fu a e w p fq i fh trace v ky f& w m ' Da v mu f r c u fv Sy gb l; / t a jz u a w mh
Reflector r Sm bookmark a w Gx m; jc i f; jz i fha o mfv n f; a u mi f; ? p m& Gu fv Gw fw p f& Gu fr Sm a & ; r Sw fjc i f; jz i fha o mf
v n f; a u mi f; a jz & Si f; E dki fy gw , f/ Cracking r Sma w mh p dw f& Sn fz dkUv dky gw , f/ p dw fr & Sn f& i fa w mh crack v ky fv dkU
& r Smr [ kw fy gb l; /
( c ) Encoded Str ings
' gu a w mh a w mfa w mfa v ; q dk; y gw , f/ t & i fw ke f; u Olly r Sm string a w G& Smw ke f; u Search u a e
w q i fh & Smv dkU& y gw , f/ ' D string a w Gu a e w q i fh function (CALL) a w Gb , fv dkt v ky fv ky fw , fq dkw mu dk
Mu n fh& w m jz p fy gw , f/ ' Dr Sma w mh"Invalid Serial Number" p w Jhstring a w Gu dk jr i f& r Smr [ kw fy gb l; / String
a w Gu dk z Hk; u G, fE dki fz dkU t o Hk; t r sm; q Hk; e n f; v r f; u a w mh o lw dkUu dk encode v ky fjy D; encoded stream u dk binary
.net resource t jz p fo dr f; q n f; w mjz p fy gw , f/ t c sdKU string a w Gu dk v dkt y fr So m encoded stream u a e ' D
string a w Gu dk& , lz dkU function w p fc ku dka c : o Hk; w my g/ ' De n f; & JU t m; e n f; c su fu a w mh y & dk* & r ft v ky fv ky f
w mjr e fq e fa p z dkU decoding e n f; v r f; u dk jr e fa p a y ; & w my g/ ' ga Mu mi fhr dkU ' De n f; v r f; [ m decode v ky fjc i f; r & Sdb J
t o Hk; jy Kw mx u f? string a w Gr & Sdc sde fr Smt o Hk; jy Kw mx u f t r sm; Mu D; a E S; a e v dkU r & y gb l; / r sm; a o mt m; jz i fha w mh
decoding function a w G[ m byte shifting e n f; u dkt o Hk; jy Kjy D; string a w Gu dk decode v ky fz dkU jy e fp Dw m
jz p fy gw , f/ ' ga y r , fh o lw dkUu dk decode v ky fz dkUv G, fy gw , f/ Decoder (decoding function) u dk a w GUw me JU
o i fht a e e JU string a w Gu dk jy e fa z mfE dki fr Smjz p fjy D; o i fu dk, fw dki fa w mi f u dk, fy dki f decoder a & ; o m; E dki fr Smjz p fy g
w , f/ a e mu fy dki f; r Sma w mh a p s; u Gu f0 i fa q mhz f0 Ja w Gr Sm t o Hk; jy Ka e Mu w Jh decoding function a w Gu dk b , fv dk
crack v ky f& r v Jq dkw mjy y gr , f/
( * ) Str ong Name Signatur e
Digital signature [ m digital document a w G? text a w G? data a w Gr Sm authenticate v ky fz dkUjz p fjy D;
t c su ft v u fa w Gu dk r r Se fr u e fr jy KE dki fa t mi f w m; q D; y gw , f/ Digital signature w p fc ku dkz e fw D; z dkU public
key cryptography u dkt o Hk; jy Ky gw , f/ Digital signature w p fc ku dkz e fw D; z dkU y x r q Hk; 160-bit & Sdw Jh hash
w e fz dk; w p fc ke JU sign v ky fw mjz p fy gw , f/ jy D; & i fa w mh w du sw Jh private key w p fc ko Hk; jy D; encrypt v ky fy gw , f/
Private key e JUo u fq dki fw Jh public key u dk& Sdx m; w Jh b , fo lr q dk author e JUy w fo u fw Jht c su ft v u fa w Gu dk
authenticate v ky fz dkU t o Hk; jy KE dki fjy D; data a w Gu dk r a jy mi f; v Jx m; b l; q dk& i fa w mhsign v ky fE dki fr Smy g/
' gu a w mh .net assembly a w Gu dk jy Kjy i fa jy mi f; v Jjc i f; r Su mu G, fE dki fz dkU t o Hk; jy KMu w Jh e n f; v r f; w p f& y f
jz p fy gw , f/ .net e JU z e fw D; x m; w Jh exe z dki fw p fc ku dk t v ky fv ky fa p c sde fr Sm y & dk* & r f[ m string name signature
u dkp p fa q ; y gv dr fhr , f/ w u , fv dkU & Sdc Jhr , fq dk& i f digital signature u dkp p fa q ; jy D; ? p p fq ; w mr a t mi fjr i f& i fa w mh
' g[ m assembly u dkjy i fx m; jy Dq dkw mo dv dku fjy D; y & dk* & r fu dkt v ky fv ky fa p z dkU ji i f; q e fy gv dr fhr , f/
o i fht a e e JU strong name signature b , fv dkt v ky fv ky fo v Jq dkw Jh t a o ; p dw ft c su ft v u fa w Gu dk
t i fw me u fr Sm & Sma z GE dki fy gw , f/
( 4 ) Entr y Point Method (EPM) u dk& Smjc i f;
Entrypoint Method u a w mh .net application p w i fc sde fr Sm a c : , lo Hk; w Jh y x r q Hk; Method jz p fjy D; ?
' gu dk Reflector ( o dkU) Ildasm r SmMu n fhv dkU& z dkU t a & ; Mu D; y gw , f/ y Hkr Se f .net application w p fc kr Sma w mh
' Dv dky Hkp H& Sdy gw , f -
Public Shared Sub Main()
Application.Run (New MainForm)
End Sub
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 288 -
' DMethod & JUt a & ; y gy Hku a w mh o i fht a e e JU y & dk* & r f& JUv ky fa q mi fc su fa w Gu dk y & dk* & r fp w i fw Jht c sde fu p
jy D; register v ky fw Jhroutine & Sd& ma & mu fw Jht x da jc & mc HE dki fy gw , f/
' D Method u a e a e mu fx y f& & SdE dki fw Jht u sdK; a u s; Z l; u a w mh crack v ky fr , fh application & JU t " du
form t jz p fo Hk; r , fh MianForm class u dka v hv mq e f; p p fE dki fw my gy J/ w u , fv dkU o i fht a e e JU Application.
run u dkt a o t c smMu n fhr , fq dk& i f ' Dfunction x J t 0 i f^ t x Gu fv ky fa e w Jh argument a w G? argument w e fz dk;
a w Gu dk a w GU& r Smy g/
Entrypoint RawData offset u dk& Smz dkU o i fht a e e JU v ky fa q mi f& r Smu a w mh-
1 / Crack v ky fr , fhy & dk* & r fu dk CFF explorer r Smz Gi fhy g/
2 / .NET directory node q Do Gm; y g/
3 / * & p fu Gu fe JUjy x m; w Jhw e fz dk; a w Gx Ju EntrypointToken row u dk& Smy g/
4 / ' Drow t w Gu f a e mu fq Hk; column w e fz dk; u dkMu n fhy g/ ' Dw e fz dk; [ m DWORD jz p fjy D; entrypoint Method
& Sd& mq Du Re fa w mfw dkUu dk v r f; n Te fy gv dr fhr , f/
' Da e & mr Sma w mh token w e fz dk; u dk 060000028 v dkU, lq y gr , f/ o i fht a e e JUa w mh token w e fz dk; [ m
w p fr sdK; Mu D; y Jv dkU c Hp m; a e & r Smy g/ o l[ m table w p fc ke JU table & JU index u dka z mfjy w Jh DWORD w e fz dk; w p fc k
jz p fy gw , f/ q dkv kdw mu table w p fc ke JU ' Dtable x Ju row w p fc ku dk n Te fjy w my g/ Oy r mjy & & i f u Re fa w mfw dkU& JU
token w e fz dk; u dk 060000028 jz p fw , fv dkU o w fr Sw fMu n fhMu y gp dkU/
06 000028
Table index Row index in that table
' Da e & mr Sm u Re fa w mfw dkUa jy ma jy ma e w Jhtable q dkw mu a w mhMethods table u dka jy mw my g/ o i fht a e e JU
CFF explorer r SmMu n fhr , fq dk& i f Metadata Str eams node a t mu fu Tables node r SmMu n fhE dki fy gw , f/
Tables node a & mu f& i fa w mhy Hk( 2 ) t w dki f; Method table & Sd& mu dk& Smy gr , f/
y Hk( 2 )
Method table u dk expand v ky fjy D; index 40 (28h) u dk& Smy gr , f/ ' gq dk y Hk( 3 ) t w dki f; a w GU& y gr , f/
y Hk( 3 )
y Hk( 3 ) u a e & mu dka & G; c s, fjy D; ' Dmethod e JUq dki fw Jht c su ft v u fa w Gu dk Mu n fh& Iv dkU& y g
w , f/ ' Da e & mr Sm u Re fa w mfw dkUp dw ft 0 i fp m; q Hk; u a w mh y x r q Hk; row jz p fjy D; ' Dmethod & JU RVA u dka z mfjy y g
w , f/ a e mu fq Hk; column u w e fz dk; u dk z w fv dku f& i fa w mh0x4974 jz p fy gw , f/
( 5 ) EPM t w Gu f z dki f offset u dk CFF explor er jz i fh& Smjc i f;
.net PE z dki fw p fc kr Sma w mh .text? .reloc? .rsrc p w Jh section 3 c k& Sdy gw , f/ .text section r Sma w mh
Import Table? Import Address Table e JU .Net Section w dkYy g0 i fy gw , f/ .net PE z dki fw p fc ku dk a t mu fy g
t c su ft v u fr sm; y g0 i fw , fv dkU , lq Mu n fhv dku fMu & a t mi f/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 289 -
.net PE z dki ft w Gu f ImageBase 0x400000
.text section virtual address 0x002000
.text section Raw address 0x000200
EntryPoint Method VA 0x004974
' Dz dki fu dk r Sw fOmP fa y : u l; w i fv dku fw Jht c gr Sm jr i f& w mu a w mh-
0x400000 0x402000 0x404974 RVA
ImageBase > > > .text > > > EP_Method
0x0 0x2000 0x4974 VA
' ga Mu mi fhr dkU z dki fu dk r Sw fOmP fr Sma e & mc sx m; w Jht c g ImageBase & JU 0x2000 byte t u Gmr Sm .text
section u dk& Sm& r Smjz p fy gw , f/ Method data u dka w mh ImageBase & JU 0x4974 byte t u Gmr Sm& Sm& r Smjz p fy g
w , f/
a u mi f; jy D? .text section r Sm ep_method u dk& Smz dkU offset u dkw Gu fc su fMu n fh& a t mi f/
Offset = [EP_Method VA] [.text section VA]
= 0x4974 0x2000
= 0x2974
' ga Mu mi fh method data [ m .text section data & JU 0x2974 r Smp y gw , f/ w u , fv dkU .text section
RawData Offset u dkt o Hk; jy Kc Jh& i f u Re fa w mfw dkUt a e e JU method t w Gu f RawData Offset u dkv J t v m; w l
w Gu fc su fE dki fy gw , f/
Method RawData Offset = .text section RawData Offset + 0x2974
= 0x200 + 0x2974
= 2B74
' ga Mu mi fhz dki fx Jr Sm& Sdw JhMethod Offset [ m 2B74 jz p fy gw , f/
y Hk( 3 ) u a e & mu dk right-click E Sdy fjy D; Disassemble Method u dka & G; v dku f& i f y Hk( 4 )
t w dki f; jr i f& y gw , f/
y Hk( 4 )
t & Si f; q Hk; y Hkp He JUjy & & i fa w mh
EPM File Offset = [EntryPoint VA] [Section.txt VA] + [Section.txt RawAddress]
' Dw e fz dk; 3 c kv Hk; u dk CFF Explorer u a e & & SdE kdi fy gw , f/ CFF Explorer r Sm Address converter
y g& Sdjy D; o i fhr Sm RVA w e fz dk; & Sdx m; jy Dq dk& i f b , f Method & JU file offset u dkr q dkw Gu fc su fE dki fy gw , f/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 290 -
( 6 ) Entr y Point Method (EPM) u dk Ildasm jz i fh& Smjc i f;
' gu a w mh v G, fu lw Jht v ky fjz p fjy D; Entrypoint Method disassembly u a e w u , fh byte t w GJa w G
u dk o dx m; & r Smjz p fy gw , f/ ' De n f; u kda w mhEPM r [ kw fw Jhb , f Method t w Gu fr q dk t o Hk; jy KE dki fy gw , f
.method public hidebysig static void Main() cil managed
// SIG: 00 00 01
{
.entr ypoint
.custom instance void
[mscorlib]System.STAThreadAttribute::.ctor() = ( 01 00 00 00 )
// Method begins at RVA 0x4974
// Code size 26 (0x1a)
.maxstack 8
IL_0000: /* 00 | */ nop
IL_0001: /* 28 | (0A)000078 */ call void
IL_0006: /* 00 | */ nop
IL_0007: /* 16 | */ ldc.i4.0
IL_0008: /* 28 | (0A) 000079 */ call void
IL_000d: /* 00 | */ nop
IL_000e: /* 73 | (06) 00003D */ newobj instance
IL_0013: /* 28 | (0A) 00007A */ call void
IL_0018: /* 00 | */ nop
IL_0019: /* 2A| */ ret
} // end of method Form1::Main
' gu a w mh & dk; & Si f; v Sw Jh .net application w p fc ku a e , lx m; w Jh EntryPoint Method t w Gu f
disassembly jz p fjy D; ' D Method x Ju IL instruction a w Gu dka w GU& w mjz p fy gw , f/ Hex editor w p fc kr Sm
a t mu fy gp mo m; w GJa w Gu dk & SmMu n fhy g/
IL_0001 287800000A
IL_0008 287900000A
' ga Mu mi fh & Sm& r , fh HEX t w GJu a w mh 00 28 78 00 00 0A 00 16 28 79 00 00 0A jz p fy gw , f/
y Hkr Se ft m; jz i fha w mh 1 0 v Hk; a v mu f& Smv dku f& i f offset t r Se fu dk& Sma w GUz dkU v Hka v mu fjy Dx i fy gw , f/ y Hk( 5 ) u a w mh
HEX t w GJu dk WinHex r Sm & Smx m; w mjz p fy gw , f/
y Hk( 5 )
' gq dk& i fa w mh w u , fh byte & Sd& m y x r q Hk; offset u dka & mu fo Gm; y gv dr fhr , f/ jy D; c Jhw Jhe n f; v r f; w ke f; u
o i fa & mu f& Sdc Jhw m[ m Code byte r w dki fc i fr Sm& Sdw Jh Method Header byte u dky g/ .net Method w n fa q mu f
x m; y Hku a w mhy Hk( 6 ) t w dki f; jz p fy gw , f/
y Hk( 6 )
y x r e n f; v r f; u a w mh o i fhu dk > & Sd& ma e & mq D a & mu fa p w mjz p fjy D; u k' fa w G& Sd& m y x r q Hk; byte q D
a & mu fa p c si f& i fa w mh header t & G, ft p m; w e fz dk; 1 ( t jr Jw r f; 1 jz p fa e r Sm r [ kw fy gb l; / ) u dka y gi f; a y ; & r Sm
jz p fy gw , f/ ' ga Mu mi fhu Re fa w mfw dkU w Gu fc su fv dkU& w Jht a jz [ m 2B75 t p m; 2B74 jz p fa e & w my g/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 291 -
( 7 ) Entr y Point Method node u dk Ildasm Tr ee w Gi f& Smjc i f;
Entrypoint Method t w Gu f decompilation u dk o i fht a e e JUjr i fc si fy go v m; / CFF explorer u a e
EntryPoint Method RVA u dko djy D; w Jha e mu fr Sma w mho lU& JUu k' fu dkMu n hfz dkU t c sde fa & mu fy gjy D/
' Dt w Gu f ILDasm u dka & m? Reflector u dky g t o Hk; jy KE dki fy gw , f/ ' ga y r , fh r Sw fx m; & r Smu ILDasm
[ m .net Method a w Gt w Gu f decompilation u dk IL y Hkp Ht a e e JUo m jy E dki fy gw , f/ u Ha u mi f; & i fa w mh
Reflector u EntryPoint Method u k' fu dk o i fhp dw fMu dKu f .net b mo mp u m; t a e e JU decompile v ky fa y ; r Sm
jz p fy gw , f/ ' gr Sr [ kw f& i fa w mhu k' fu dk analyze v ky fz dkUu a w mhILDasm a y : r lw n fr Smjz p fy gw , f/
ILDasm a & m? Reflector u y g assembly a w Gu dk tree view t a e e JUjy E dki fy gw , f/ ' ga y r , fh
ILDasm u o m o i f decompile v ky fw Jh Method w dki f; t w Gu f RVA w e fz dk; u dk a jy mjy E dki fr Sm jz p fy gw , f/
ILDasm e JU p p fx m; w Jhu k' ft c sdKUu dk Mu n fhv dku fMu & a t mi f/
.method public hidebysig static void Main() cil managed
// SIG: 00 00 01
{
.entr ypoint
.custom instance void
[mscorlib]System.STAThreadAttribute::.ctor() = ( 01 00 00 00 )
// Method begins at RVA 0x4974
// Code size 26 (0x1a)
.maxstack 8
IL_0000: /* 00 | */ nop
IL_0001: /* 28 | (0A)000078 */ call void
IL_0006: /* 00 | */ nop
IL_0007: /* 16 | */ ldc.i4.0
IL_0008: /* 28 | (0A) 000079 */ call void
IL_000d: /* 00 | */ nop
IL_000e: /* 73 | (06) 00003D */ newobj instance
IL_0013: /* 28 | (0A) 00007A */ call void
IL_0018: /* 00 | */ nop
IL_0019: /* 2A| */ ret
} // end of method Form1::Main
t c sde fa w mfa w mfr sm; r sm; r Sma w mh o i f[ m obfuscated u k' fa w Gu dka w GU& r Smjz p fjy D; ILDasm x Ju b , f
node [ m EntryPoint Method q dkw m o i fo dE dki fr Sm r [ kw fy gb l; / w u , fv dkU & me JUc sDw Jh? a x mi fe JUc sDw Jh node
a w Ga w GY& i f y dk& Sm& c u fr Smy g/
CFF explorer u a e EntryPoint Method RVA u dk o i fht a e e JU o djy D; jz p fy gv dr fhr , f/ c kt c gr Sma w mh
EntryPoint Method node u dk & Smjy y gr , f/ ILDasm r Sm b , f class r Smr q dk& Sdw Jh Method t c sdKUu dk
decompile v ky fjy D; o lU& JU RVA w e fz dk; u dkMu n fh& r Smjz p fy gw , f/ w u , fv dkU ' Dw e fz dk; [ m EPM RVA x u f
Mu D; c Jh& i fa w mh higher-level node w p fc ku dk x y fMu n fh& r Smjz p fy gw , f/ Node a w Gt a y : w u fv ma v a v o lU
Method t w Gu f RVA w e fz dk; e n f; a v a v jz p fy gw , f/ ' Dv dke n f; e JU w p fr de p f? E Sp fr de p f& Smv dku f& i fa w mh
ILDasm r Sm EntryPoint Method node u dk& Sma w GUr Smjz p fy gw , f/ ( r Sw fc su f/ / ' Dv dk& Smr , fq dk& i fa w mh
ILDasm & JU View menu u Sort by name u dka & G; r x m; r da p z dkU o w dx m; & r Smjz p fy gw , f/ )
( 8 ) Entr y Point Method (EPM) u dk PEBr owse Debugger jz i fhw GJo Hk; jc i f;
Crack v ky fr , fh application t w Gu f CFF explorer u a e EntryPoint token u dko djy D; w Jha e mu f
r Sma w mh' Dtoken u dk t o Hk; jy Kjy D; a w mhPEBrowse r Sm EntryPoint Method u dk& Smv dkU& y gw , f/ EPM u dk JIT
compiler u compile v ky fc sde fr Sm breakpoint x m; jc i f; jz i hf .net application u dk break v ky fv dkU& y gw , f/
' Dt w Gu f o i fht a e e JU v ky fa q mi f& r Smu a w mh
( 1 ) Crack v ky fr , fh application u dk PEBrowse r Smz Gi fhy g/ Library a w Gt m; v Hk; e JU module a w Gt m; v Hk; u dk
u l; w i fjy D; w Jht x da p mi fhy g/
( 2 ) PEBrowse [ m EPM u dka c : o Hk; w m r w dki fc i fe m; a v ; r Sm & y fo Gm; y gv dr fhr , f/ ' ga Mu mi fh ' Dt c sde f[ m node
u dk& Smz dkUe JU t J' Da e & mr Sm breakpoint o w fr Sw fz dkU t a u mi f; q Hk; y gy J/
( 3 ) Application u dku l; w i fc sde fr Sm module x Jr Sm& Sdw Jh .net module a w G[ m t e Da & mi f icon a w Ge JUjz p fa e y g
v dr fhr , f/ y Hk( 7 ) / Methods node u dkMu n fhv kdu f& i fa w mhMethod a w Gu dk, fp De JU class a w Gu dka w GU& y gv dr fhr , f/
( 4 ) Method w dki f; t w Gu f token a w Gu dk o lw dkU& JUt r n fa b ; r Sm a w GU& y gv dr fhr , f/ Oy r mjy & & i f button1_
Click t w Gu f token u a w mh06000005 jz p fy gw , f/
( 5 ) CFF explorer u a e EPM u dko dx m; jy D; jz p fw Jht w Gu fa Mu mi fh o i fht a e e JU r Se fu e fw Jh node u dk ' Da e & mr Sm
& SmE dki fy gw , f/ ILDasm u RVA r Smv dky J a t mu fu dkq i f; o Gm; & i f token w e fz dk; w dk; o Gm; y gv dr fhr , f/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 292 -
( 6 ) r Se fu e fw Jh node u dka w GU& i fa w mh t J' Da e & mr Sm right-click E Sdy fjy D; "Add Breakpoint" menu u dka & G; v dku f& Hk
y gy J/
y Hk( 7 )
( 9 ) Patch v ky fjc i f; t a jc c H
' Dw p fc gr Sma w mh .net application a w Gu dk patch v ky fjc i f; e JUy w fo u fjy D; a v hv mMu n fhv dku f& a t mi f/
' Dw p fc g patch v ky fz dkUa & G; c s, fx m; w Jh y & dk* & r fu a w mh Dot_Net_ReverseMe_2.exe jz p fy gw , f/ ' Dy & dk* & r fu dk
www.tuts4you.com & JU download section u a e download v ky f, lE dki fy gw , f/ ( o i fht a e e JU ' Dy & dk* & r fa v ;
u dk & Sdr x m; v J t a & ; r Mu D; y gb l; / & Si f; jy w mu dk e m; v n fa t mi fMu n fhz dkUo m t a & ; Mu D; y gw , f/ ) y x r q Hk; patch
v ky fr , fhy & dk* & r fu dk PEiD e JUp p fMu n fhy gr , f/ y Hk( 8 ) /
y Hk( 8 )
y & dk* & r fu dk .net b mo mp u m; e JU a & ; x m; w ma o c smy gw , f/ a u mi f; jy D? y & dk* & r fu dkz Gi fhv dku fw Jht c g y Hk( 9 )
t w dki f; a w GU& y gw , f/
y Hk( 9 )
y Hk( 9 ) t & q dk& i fa w mhu Re fa w mfw dkUt w Gu f b mr Sv ky fp & mr & Sdy gb l; / b ma Mu mi fhv Jq dka w mhserial & dku fx n fh
p & m textbox w dkU? serial r Se f^ r r Se fp p fw Jh button w dkU r a w GUv dkUy g/ ' ga Mu mi fh a & ; x m; w Jhu k' fu dkMu n fhE dki fz dkU
y & dk* & r fu dk Reflector e JUz Gi fhv dku fy g/ y Hk( 1 0 ) /
y Hk( 1 0 )
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 293 -
' Dt c gr Sma w mh p dw f0 i fp m; p & ma w Gu dk a w GU& y gjy D/ ' Dt x Ju w p fc ku a w mh IsRegistered q dkw Jh boolean
class y g/ a e mu fw p fc ku a w mh CheckReg() function y g/ CheckReg() u dk double-click E Sdy fjy D; z Gi fhv dku f& i f
u Re fa w mfw dkU o Ho , & Sda e w m r Se fu e fa Mu mi f; a w GU& y gr , f/ y Hk( 1 1 ) /
y Hk( 1 1 )
' Dw p fc gr Sma w mh .ctor() t a Mu mi f; & Si f; jy r Smjz p fy gw , f/ C++? Java? C# ( o dkU) b , f OOP (Object
Oriented Programming) b mo mp u m; r Smr q dk o lUr Smy g0 i fw Jh class member a w G& JUw e fz dk; u dk initialize
v ky fz dkU constructor w p fc ky g0 i fw Jh class a w G& Sdy gw , f/ .net r Sma w mh class constructor u dke mr n fa y ; a v h
r & Sdy gb l; / Constructor & JUt w dka u mu fjz p fw Jh .ctor() q dkw Jht r n fo mx m; y gw , f/ IsRegistered q dkw Jh
member variable [ m y & dk* & r fu dk register v ky fx m; jc i f; & Sd^ r & Sd q Hk; jz w fy gw , f/ u Re fa w mfw dkUt w Gu f t c Gi fh
t a & ; & & Sda p w mu a w mh register jz p f^ r jz p fu dk constructor x Jr Sm initialize v ky fv dkUy g/ a u mi f; jy D? .ctor()
u dkz Gi fhjy D; Mu n fhv dku fMu & a t mi f/ y Hk( 1 2 ) /
y Hk( 1 2 )
w u , fa w mh u Re fa w mfw dkUy & dk* & r fu unregistered jz p fa e w m[ m .ctor() x Ju this.IsRegistered =
false; q dkw Jhstatement a Mu mi fhjz p fy gw , f/ ' Da e & mr Sm false t p m; true v dkU jy i fa y ; E dki fr , fq dk& i f . . .
t c ku Re fa w mfw dkU Mu n fha e w Jh decompile v ky fx m; w Jhu k' f[ m C# b mo mp u m; e JUjz p fy gw , f/ y Hk( 1 2 ) u dk
MSIL b mo mp u m; e JU Mu n fhv dku fMu & a t mi f/ y Hk( 1 3 ) /
y Hk( 1 3 )
y Hk( 1 3 ) u a w mh bytecode t a e e JU w dku f& dku fb mo mjy e fw my g/ .net y & dk* & r fa w Gu dk patch v ky fz dkUq dk& i f
a w mh IL b mo mp u m; t a e e JUo m Mu n fh& r Smjz p fy gw , f/ w u , fa w mh .net u dk stack machine v dkUa c : v dkU& y g
w , f/ b ma Mu mi fhv Jq dka w mh o lUt v ky fa w Gu dk register r Smx u f stack r Smv ky fv dkUy g/ Oy r mjy & & i f A u
w e fz dk; w p fc ku dk B u dka & TUc si fw , fq dk& i f A u w e fz dk; u dk stack a y : PUSH v ky fv dku fjy D; stack u a e r Sw q i fh B
a y : jy e f POP v ky fa y ; w mjz p fy gw , f/ t jc m; p e p fa w Gr Smq dk& i fa w mhA u a e B u dkw dku f& dku fa & TYa jy mi f; jc i f; ( o dkU)
, m, Dx m; & Sdz dkUt w Gu f register w p fc ku dkt o Hk; jy Kjc i f; r sdK; jy Kv ky fy gw , f/
y Hk( 1 3 ) u dk t a o t c sme m; v n fE dki fz dkU IL opcode a w Gt a Mu mi f; e m; v n fa e z dkUv dky gw , f/ y Hk( 1 3 ) u dk
Mu n fhr , fq dk& i f ' Du k' fE Sp fa Mu mi f; t w Gu f stack u dk t v Ge ft r i f; t o Hk; jy Kx m; w ma w GU& r Smy g/ this.IsRegistered
= false; p ma Mu mi f; t w Gu fu dky J a t mu fr Smjy x m; w Jht w dki f; stack e JUy w fo u fw Jhp ma Mu mi f; 3 a Mu mi f; a v mu f
b mo mjy e fx m; w ma w GU& y gw , f/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 294 -
L_0000: ldarg.0
L_0001: ldc.i4.0
L_0002: stfld bool Dot_Net_ReverseMe_2.frmMain::IsRegistered
' DIL instruction a w Gu dk IL reference t o Hk; jy Kjy D; b mo mjy e f& r , fq dk& i f . . .
ldarg.0 Argument 0 u dk stack a y : u l; w i fo n f/
ldc.i4.0 0 u dk stack a y : I4 t jz p f PUSH v ky fo n f/
stfld Object obj \ field w e fz dk; u dk val E Si fht p m; x dk; o n f/
' gu dk Object-Oriented & JU pseudo u k' ft a e e JUjy e fa & ; jy & & i fa w mh (arg0).IsRegistered = 0;
e JUw ly gw , f/ Register t a jc t a e jz p fa p z dkU jy e fjy i fa & ; o i fhw mu a w mh(arg0).IsRegistered = 1; jz p fy gw , f/
t " dy m, fu a w mh' kw d, instruction u dkldc.i4.1 v kdUa jy mi f; o i fhw , fv dkU q dkv dkjc i f; jz p fy gw , f/
' gu a w mh t a jc c Hu sw Jh cracking jz p fy gw , f/ ldc.i4.0 & JU bytecode u dkMu n fhy g/ 0x16 jz p fy gw , f/
ldc.i4.1 & JU bytecode u a w mh 0x17 jz p fy gw , f/ ' gq dk u Re fa w mfw dkU b mu dkt p m; x dk; & r v Jq dkw m o dy gjy D/
Reflector u u Re fa w mfw dkUu dk u k' fa w Go mjy y gw , f/ u Re fa w mfw dkUa jy mi f; c si fw Jh byte & Sd& m address u dkr jy y g
b l; / ' Dv dk byte/instruction a w G& JU virtual address u dkjy E dki fw Jh tool u dka w mh r a w GUb l; a o ; y gb l; / ' ga Mu mi fh
.ctor() u dkReflector r SmMu n fhr , fht p m; ILDasm e JUa jy mi f; Mu n fhv dku fy gr , f/ y Hk( 1 4 ) /
y Hk( 1 4 )
w u , fa w mh Method & Sd& m offset u dk& Sme n f; t a Mu mi f; u Re fa w mfw dkU a v hv mjy D; y gjy D/ ' Da e & mr Sma w mh
offset w e fz dk; u dk y Hka o e n f; e JU r w Gu fc su fa w mhb J 02 16 7D 06 00 00 04 02 28 0E 00 00 0A q dkw Jh hex
byte t w GJu dky Jhex editor w p fc kc kr Sm & dku fx n hfjy D; & SmMu n fhy gr , f/ y Hk( 1 5 ) /
y Hk( 1 5 )
o i fht a e e JU Mu dKu fw Jh hex editor w p fc kc ku dk t o Hk; jy KE dki fy gw , f/ t c ku Re fa w mft o Hk; jy Kx m; w mu a w mh
WinHex 15.2 y g/ y Hk( 1 5 ) t w dki f; & dku fx n hfjy D; & Smv dku f& i f y Hk( 1 6 ) t w dki f; jr i f& y gr , f/
y Hk( 1 6 )
y Hk( 1 6 ) t & q dk& i fa w mh .ctor() & Sd& m& JU offset t p [ m 0x105C jz p fy gw , f/ y dkjy D; a o c sma p c si f& i fa w mh
CFF explorer r SmMu n fhE dki fy gw , f/ y Hk( 1 6 ) u 16 a e & mr Sm 17 v dkUjy i fv dku fjy D; z dki fu dko dr f; v dku fy g/ o dr f; v dku fw Jh
z kdi fu dk jy e fz Gi fhMu n hfv dku f& i fa w mhy Hk( 1 7 ) t w dki f; a w GU& r Smy g/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 295 -
y Hk( 1 7 )
' gq dk& i fa w mh u Re fa w mfw dkU register v ky fw m a t mi fjr i fo Gm; y gjy D/ CheckReg() function u dk b , fu
a e a c : o Hk; o v Jq dkw m o dc si f& i fa w mh Reflector & JU CheckReg() function r Sm right-click E Sdy fjy D; Callee
Graph (Ctrl+E) u dka & G; jy D; Mu n fhv dkU& y gw , f/ y Hk( 1 8 ) /
y Hk( 1 8 )
Patch v ky fjy D; o dr f; v dku fw Jhz dki f& JU .ctor() u dk Reflector r SmMu n fhv dku f& i fa w mh y Hk( 1 9 ) t w dki f; jr i f& y g
w , f/
y Hk( 1 9 )
( 1 0 ) NsPack jz i fhpack v ky fx m; a o m .net z dki ft m; unpack v ky fjc i f;
y Hkr Se ft m; jz i fha w mho mr e f pack v ky fx m; w Jh32-bit PE z dki fa w Gr Smy J unpack v ky fz dkU Olly u dkt o Hk; jy KMu
w mjz p fy gw , f/ ' Dt c gr Sma w mh .net z dki fa w Gu dk Olly t o Hk; jy Kjy D; unpack v ky fjy r Smjz p fy gw , f/ Unpack v ky fz dkU
a & G; c s, fx m; w Jhy & dk* & r fu a w mh NsPack e JU pack v ky fx m; w Jh UnPackMe_NsPack3.6.exe z dki fjz p fy gw , f/
y & dk* & r fu dk z Gi fhMu n fhv dku fy g/ y Hk( 2 0 ) /
y Hk( 2 0 )
PEiD e JUp p fa q ; Mu n hfv dku f& i fa w mhy Hk( 2 1 ) t w dki f; a w GU& y gw , f/
y Hk( 2 1 )
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 296 -
a u mi f; jy D? y & dk* & r fu dk Olly r Smz Gi fhv dku fy g/ y Hk( 2 2 ) /
y Hk( 2 2 )
y Hk( 2 2 ) r Smjr i f& w Jht w dki f; exe z dki f[ m OEP r Sm& y fw e fUjc i f; r & Sdo v dk y & dk* & r f[ m t v dkt a v smu f run
a e y gw , f/ u Re fa w mfw dkU b mv ky fo i fhy go v J/ u Re fa w mfht a e e JU t Mu Hjy Kv dkw mu a w mh unpack v ky fx m; w Jhu k' f
a w Gu dk r Sw fOmP fx Jr Sm& Smz dkUy g/ ' ga Mu mi fh o w fr Sw fx m; w Jh string w p fc ku dk y & dk* & r f& JU resource x Jr Sm& Sm
Mu n fhy g/
& Smo i fhw Jh t r n fa w Gu a w mh button t r n f? window caption e JU messagebox w dkUe JUq dki fw Jh t c su f
a w Gjz p fy gw , f/ ' Da e & mr Sm u Re fa w mfw dkU& SmMu n fhr Smu a w mh y Hk( 2 0 ) r Smjr i f& w Jh button1 y g/ Resource a w Gu dk
exe/DLL z dki fa w Gx Jr Sm unicode t o Gi fe JU o dr f; Mu w mjz p fw Jht w Gu f Alt+M u dkE Sdy fjy D; button1 q dkw Jhp mo m; u dk
unicode t a e e JU & SmMu n fhMu & a t mi f/ y Hk( 2 3 ) /
y Hk( 2 3 )
y Hk( 2 3 ) t w dki f; & dku fx n fhjy D; & Smv dku f& i f y Hk( 2 4 ) t w dki f; a w GU& y gr , f/
y Hk( 2 4 )
y Hk( 2 4 ) u dk Text Unicode (64 chars) e JUMu n fhv dku f& i fa w mhy Hk( 2 5 ) t w dki f; a w GU& r Smy g/
y Hk( 2 5 )
' Da e & mr Sma jy mv dkw mu a w mh y Hk( 2 4 ?2 5 ) r Smjr i fa e & w Jh virtual address a w G[ m o i fu Ge fy sLw mr Smjr i f& w Jh
* P e f; a w Ge JU w lr Smr [ kw fy gb l; / a e mu fjy D; c ku Re fa w mfw dkUa & mu f& Sda e w Jha e & m[ m resource section x Jr Smr [ kw f
y gb l; / ' ga Mu mi fhr dkU Alt+M E Sdy fjy D; Ctrl+L e JU x y f& SmMu n fhy gr , f/ y Hk( 2 6 ) /
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 297 -
y Hk( 2 6 )
y Hk( 2 6 ) r Sm a e mu fx y f button1 w p fc ku dka w GU& jy e fy gjy D/ _CorExeMain u dka w GUr dy go v m; / ' gu a w mh
.net application a w Gr Smo m& Sdw Jh w p fc kw n f; a o m API y g/ Unicode view t a e e JUMu n fhv dku f& i f y Hk( 2 7 )
t w dki f; a w GYy gw , f/
y Hk( 2 7 )
y Hk( 2 7 ) t w dki f; q dk& i fa w mhu Re fa w mfw dkU resource section x Ja jc c sr djy Dq dkw m a o c smy gw , f/
y Hk( 2 8 )
a u mi f; jy D? y Hk( 2 7 ) u dk HEX view t a e e JUjy e fMu n fhjy D; t a y : u dk scroll e n f; e n f; q GJjy D; Mu n fhv dku f& i f
a w mhy Hk( 2 8 ) r Sm jr i f& w Jht w dki f; PE header & Sd& mu dk a w GU& r Smy g/
y Hk( 2 9 )
y Hk( 2 8 ) u MZ & Sd& m virtual address (00CD0000) u dkr Sw fo m; jy D; LordPE u Dump Region
u dka & G; c s, fjy D; Dump button u dka & G; c s, fy g/ ' gq dk unpack v ky fw ma t mi fjr i fo Gm; jy Djz p fy gw , f/ Dump
v ky fx m; w Jh Region00CD0000-00CD2000.exe z dki fu dk PEiD e JUp p fMu n fh& i fa w mh Microsoft .net b mo m
p u m; e JUa & ; o m; x m; a Mu mi f; jy r Smy g/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 298 -
( 1 1 ) .net y & dk* & r fr Sser ial z r f; jc i f;
' Dw p fc gr Sma w mh .net e JU y w fo u fw Jh serial fishing t a Mu mi f; u dk a v hv mr Smjz p fy gw , f/ Byte a w Gu dk
patch v ky fw m[ m t jr Jw r f; a w mh t q i fa jy r Sm r [ kw fy gb l; / q dkv dkw mu r Se fu e fp Gm register v ky fx m; jc i f;
& Sd^ r & Sdu dk e n f; r sdK; p Hke JU r Mu mc P p p fa q ; a v h& Sdw Jh y & dk* & r fa w Gt w Gu f ' De n f; v r f; [ m t q i fa jy r Sm r [ kw fy gb l; /
' ga Mu mi fhr dkUv J serial z r f; jc i f; t a Mu mi f; u dk a q G; a E G; & jc i f; jz p fy gw , f/ ' Do i fc e f; p mt w Gu f v dkt y fw Jhy & dk* & r f
u a w mhCrackme1.exe jz p fjy D; www.accessroot.com r Sm download v ky f, lE dki fy gw , f/
' Dy & dk* & r fu dk Visual Dot.net e JUa & ; o m; x m; w mu dk o djy D; o m; jz p fw mr dkU PEiD e JU r p p fa w mhy gb l; /
Crackme1.exe u dkz Gi fhjy D; y & dk* & r f& JU o a b mo b m0 u dka v hv mMu n fhv dku fMu & a t mi f/ y Hk( 3 0 ) /
y Hk( 3 0 )
y Hk( 3 0 ) r Smjr i f& w Jht w dki f; user name e JU serial u dk& dku fx n fhjy D; Check button u dkE Sdy fv dku fc sde fr Sma w mh
y Hk( 3 1 ) t w dki f; jr i f& y gw , f/
y Hk( 3 1 )
' Da v mu fq dk u Re fa w mfw dkU o dc si fw ma w Go d& jy Dr dkU Crackme1.exe u dk .NET reflector r Smz Gi fhMu n fhy g
r , f/ y Hk( 3 2 ) /
y Hk( 3 2 )
btnCheck_Click u dk a & G; v dku fw Jht c gr Sma w mhy Hk( 3 2 ) t w dki f; jr i f& w mjz p fy gw , f/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 299 -
' Do i fc e f; p mr Sm u Re fa w mfw dkU p dw f0 i fp m; w mu serial routine r [ kw fy gb l; / a e mu fq Hk; x kw fa y ; v dku fw Jh
serial [ m b mv Jq dkw mu dko m o dc si fw my g/ .NET reflector [ m .net u k' fa w Gu dk Mu n fh& I& mr Sm t a u mi f; q Hk;
tool jz p fa y r , fhv J u k' fa w Gu dkw n f; jz w fjc i f; ? debug v ky fjc i f; w dkU jy Kv ky fa y ; E dki fjc i f; r & Sdy gb l; / ' ga Mu mi fh Myo
Myint Htike q dkw Jhuser name e JUo u fq dki fw Jhserial u dk& SmE dki fz dkU PEBrowse Professional Interactive 9.0
u dkt o Hk; jy KMu y gr , f/ ' Dtool u dk t o Hk; r jy Kc i fr Sm setting a w Gu a t mu fy gt w dki f; jz p f& y gr , f/ y Hk( 3 3 ^ 3 4 ) /
y Hk( 3 3 )
y Hk( 3 4 )
y Hk( 3 3 ^ 3 4 ) t w dki f; setting a w Gu dk jy i fjy D; & i fa w mhCtrl+S u dkE Sdy fjy D; debug v ky fz dkUp w i fy g/ y Hk( 3 5 ) /
y Hk( 3 5 )
y Hk( 3 5 ) & JU b , fz u ft jc r f; r Sm t e Da & mi fjz p fa e w mu t v ky fv ky fa e w mu dk jy w my g/ u Re fa w mfw dkUt a e e JU
y & dk* & r fu k' fw p fa Mu mi f; c si f; p Du dk p p fa e r Sm r [ kw fy gb l; / u k' fa w Gu dk p p fa q ; w Jh shortcut key a w Gu a w mh Olly
e JUw lr Smr [ kw fy gb l; / PEBrowse & JU key a w Gu a w mhRun(F5)? Step over(F10)? Step into(F11) t o D; o D;
jz p fy gw , f/ a u mi f; jy D? u Re fa w mfw dkU p p fa q ; c si fw Jha e & mu dk t jr e fa & mu fz dkU breakpoint o w fr Sw fMu & a t mi f/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 300 -
y Hk( 3 5 ) u .NET Methods u dkE Sdy fjy D; btnCheck_Click u dka & G; v dku fy g/ y Hk( 3 6 ) /
y Hk( 3 6 )
y Hk( 3 6 ) u a w mh serial routine u dk IL b mo mp u m; t a e e JU jr i f& w my g/ IL_00B3 a e & mr Sm F9 E Sdy fjy D;
breakpoint o w fr Sw fy gr , f/ ' gq dk& i fa w mh u Re fa w mfw dkU breakpoint o w fr Sw fx m; w Jha e & mu dk y Hk( 3 7 ) t w dki f;
jr i f& r Smjz p fy gw , f/
y Hk( 3 7 )
Breakpoint o w fr Sw fjy D; o Gm; & i fa w mhF5 u dkE Sdy fjy D; y & dk* & r fu dk run y g/
y Hk( 3 8 )
y & dk* & r fu dk run w Jht c g y Hk( 3 8 ) t w dki f; w p fc ka y : v my gv dr fhr , f/ F5 u dkx y fE Sdy fy g/ ' gq dk y Hk( 3 9 ) t w dki f;
y & dk* & r fw u fv my gv dr fhr , f/
y Hk( 3 9 )
y Hk( 3 9 ) t w dki f; jr i f& w Jht c gr Sm user name e JU serial u dk& dku fx n fhjy D; check button u dka & G; a y ; y g/ y Hk( 4 0 )
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 301 -
y Hk( 4 0 )
y Hk( 4 0 ) r Sm jr i f& w mu a w mh u Re fa w mfw dkU breakpoint o w fr Sw fx m; w Jha e & mu dk a & mu fa e w my g/ > u
v u f& Sdassemble v ky fr , fha e & mu dk jy o y gw , f/
y Hk( 4 1 )
y Hk( 4 1 ) u a w mh register window jz p fy gw , f/ Disassembly window r Sm F10 u dkE Sdy fjy D; u k' fa w Gu dk
w p fa Mu mi f; c si f; p p fw Jht c gr Sma w mh register window r Sm b ma w Ga jy mi f; v Jo Gm; w , fq dkw mu dk o w dx m; jy D; a p mi fh
Mu n fh& y gr , f/ y Hk( 4 2 ) t w dki f; VA 0x40E89B0 x da & mu fw Jht x dF10 u dkE Sdy fv mc Jhy g/
y Hk( 4 2 )
y Hk( 4 2 ) r Sm floating-point w e fz dk; E Sp fc ku dk E Idi f; , SOfw m a w GU& y gw , f/ Floating-point e JUy w fo u fw Jh
mnemonics a w Gu dkMu n fhMu & a t mi f/
FILD load integer
FSTP store floating-point value and pop
FLD load floating-point value
FCOMIP compare floating-point, set %e flags, and pop
FSTP store floating-point value and pop
JPE u a w mhJump if Parity even jz p fjy D; flag (PF) w e fz dk; 1 jz p f& i f jump jz p fr Smjz p fy gw , f/ JNZ
u a w mhJump if Not Zero jz p fjy D; flag (ZF) w e fz dk; 0 jz p f& i f jump jz p fr Smjz p fy gw , f/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 302 -
y Hk( 4 3 )
FCOMIP u floating-point w e fz dk; E Sp fc ku dkE dIi f; , SOfjy D; parity flag u dko w fr Sw fy gw , f/ o lE dIi f; , SOf
w Jh w e fz dk; E Sp fc ku a w mh 4458204637983 e JU 4101979 w dkUjz p fy gw , f/ ' Dw e fz dk; E Sp fc ku dk E dIi f; , SOfw Jht c gr Sm r n D
w Jht w Gu f parity flag w e fz dk; u dk o kn v dkUo w fr Sw fy gw , f/ Parity flag w e fz dk; [ m 0 v m; ? 1 v m; o dc si f& i f
a w mhregister window r Sm right-click E Sdy fjy D; EFLAGS u dka & G; & y gr , f/ y Hk( 4 4 ) /
y Hk( 4 4 )
y Hk( 4 4 ) u a w mh FCOMIP instruction u dk v ky fa q mi fjy D; c sde fjz p fy gw , f/ Parity flag [ m 0
jz p fa e y gw , f/ FSTP instruction u dko Hk; jy D; 4101979 w e fz dk; u dk o dr f; y gw , f/ Parity flag [ m 0 jz p fw Jh
t w Gu f JPE 0x40E89C6 [ m VA 0x40E89C6 q Djump r jz p fE dki fa w mhy gb l; / JNZ 0x40E89C6 u a w mh
1 r jz p fw Jht w Gu f VA 0x40E89C6 q DVA 0x40E89C6 v ky fr Smjz p fy gw , f/ y Hk( 4 5 ) /
y Hk( 4 5 )
' ga Mu mi fhv J F5 E Sdy fv dku fw Jht c sde fr Sm u Re fa w mfw dkUr jr i fc si fw JhBadBoy message u dkjr i f& w my g/ y Hk( 4 6 ) /
y Hk( 4 6 )
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 303 -
Myo Myint Htike q dkw Jh user name t w Gu f serial textbox r Sm u Re fa w mfw dkU& dku fx n fhv dku fw Jh
4101979 u dk Crackme1.exe u w Gu fc su fv dkU& v mw Jh 4458204637983 w e fz dk; e JU E dIi f; , SOfw mjz p fy gw , f/
' ga Mu mi fh Myo Myint Htike q dkw Jh user name t w Gu f serial textbox r Sm u Re fa w mfw dkU t r Se fw u , f
& dku fx n fh& r , fh* P e f; [ m . . .
a u mi f; jy D/ PEBrowse u dky dw fv dku fy g/ Crackme1.exe u dko D; o e fUz Gi fhjy D; y Hk( 4 7 ) t w dki f; register
v ky fMu n fhy gr , f/
y Hk( 4 7 )
' gq dk& i fa w mhy Hk( 4 8 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 4 8 )
.net y & dk* & r fa w Gr Sm serial & Sm& w m t & r f; v G, fv Ge f; w , fv dkU x i fr dy go v m; /
' gq dk& i fa w mh o i fx i fw m r Sm; o Gm; jy Djz p fy gw , f/ b ma Mu mi fhv Jq dkw m & Si f; & Si f; v i f; v i f; o d& a t mi fv dkU
y & dk* & r fw p fy k' fu dk e r le mjy y gr , f/ y Hk( 4 9 ) /
y Hk( 4 9 )
' Dy & dk* & r fu dk b , fv dka & ; x m; o v Jq dkw m o dE dki fa t mi fv dkU .NET reflector r Smp p fMu n fhy gr , f/ y Hk( 5 0 ) /
y Hk( 5 0 )
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 304 -
y Hk( 5 0 ) u u dkE Sdy fv kdu f& i fa w mhy Hk( 5 1 ) t w dki f; jr i f& y gw , f/
public Registration()
{
t his.component s = null;
t his.I nit ializeComponent ();
t his.pict ureReg.I mage = I mage.FromFile("Pict ure/ nag_close.png");
St ringBuilder volumeName = new St ringBuilder(0x100);
St ringBuilder fs = new St ringBuilder(0x100);
bool flag = false;
Environment .Get LogicalDrives();
flag = Get VolumeI nformat ion("c: ", volumeName, (uint ) (volumeName.Capacit y - 1), out t his.serialNum, out
t his.serialNumLengt h, out t his.flags, fs, (uint ) (fs.Capacit y - 1));
for (int i = 0; i < = 13; i+ + )
{
t his.serialNum = (((((2 * t his.serialNum) / 7) - (12 * t his.serialNum)) + (11 * t his.serialNum)) - 0x239875) ^
t his.serialNum;
}
t his.t ext code.Text = t his.serialNum.ToSt ring();
}
y Hk( 5 1 )
y Hk( 5 1 ) u a w mhregistration dialog u dka & G; v dku fc sde fr Sm y & dk* & r fu initialize v ky fw mjz p fy gw , f/
u dkE Sdy fv kdu f& i fa w mhy Hk( 5 2 ) t w dki f; jr i f& y gw , f/
privat e void butOK_Click(obj ect sender, EventArgs e)
{
st ring text;
FileSt ream stream;
BinaryWrit er writer;
long num2 = Convert .ToI nt 64(t his.serialNum);
long num4 = 0x1fca055L;
for (int i = 0; i < = 30; i+ + )
{
num2 = (7L * num2) ^ (num4 + 0x23c1bcL);
}
st ring strB = Convert .ToSt ring(num2);
if (st ring.Compare(t his.t ext regcode.Text , st rB) = = 0)
{
MessageBox.Show("Regist ered successfully! \ r\ nThank you for buying our product ! ", "Regist rat ion Successful! ",
MessageBoxBut t ons.OK, MessageBoxI con.Ast erisk);
if (t his.passCont rol ! = null)
{
t his.passCont rol(t his.t ext name);
}
base.Hide();
t ext = t his.t ext name.Text ;
st ream = new FileSt ream("reg.key", FileMode.Creat e);
writ er = new BinaryWrit er(st ream);
t ry
{
writ er.Writ e(t his.serialNum);
writ er.Writ e(t ext );
}
finally
{
writ er.Close();
st ream.Close();
}
Regist ry.Set Value(@"HKEY_CURRENT_USER\ Soft ware\ Myanmar Cracking Team\ Windows Repair",
"UserName", t ext , Regist ryValueKind.St ring);
}
y Hk( 5 2 )
y Hk( 5 1 ) u u k' fa w Gu a w mh y Hk( 5 0 ) r Smjr i f& w Jh t w Gu fjz p fy gw , f/
w u , fa w mh Windows Repair 1.0 y & dk* & r f[ m u Re fa w mfw dkU harddisk u C: drive & JU serial number
u dkz w fjy D; XOR v ky fy gw , f/ XOR v ky fx m; w Jhw e fz dk; u a w mh 3538139584 jz p fy gw , f/ jy D; a w mh u Re fa w mf
& dku fx n hfv dku fw Jh 4101979 u dk XOR v ky fjy D; & v mw Jhw e fz dk; w p fc ke JU E dIi f; , SOfw mjz p fy gw , f/ w u , fv dkU serial
number [ m r Se fu e fc Jhr , fq dk& i f reg.key z dki fr Sm & dku fx n fhv dku fw Jh serial number u dko dr f; r Smjz p fjy D;
GoodBoy message u dk jy r Smjz p fy gw , f/ u Re fa w mfht a e e JU PEBrowse e JU serial-fishing v ky f& mr Sm
3538139584 u k' ft w Gu f HEX w e fz dk; EAEF9EBE & v my gw , f/ ' Dw e fz dk; u dk decimal w e fz dk; a jy mi f; jy D;
registration dialog r Sm& dku fx n hfv dku fw Jht c gr Sma w mh y & dk* & r fu serial r Sm; a e y gw , fv dkU a jy my gw , f/
( w u , fa w mh u Re fa w mfw dkUu dk jy o w Jh 3538139584 [ m * P e f; r [ kw fb J p mo m; a w Gjz p fa e y gw , f/
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 305 -
PEBrowse [ m p mo m; a w Gu dk u dki fw G, fE dki fjc i f; r & Sdy gb l; / ' ga Mu mi fh u Re fa w mfw dkU & dku fx n hfw Jh* P e f; w dki f; [ m
r Sm; a e w mjz p fy gw , f/ )
' ga Mu mi fh ' Dv dkjy e mr sdK; Mu HKa w GUc Jhr , fq dk& i fa w mh PEBrowse e JU serial & Smr , fht p m; Visual
Studio.net e JU y & dk* & r fjy e fa & ; & r Sm jz p fy gw , f/ y & dk* & r fu dk o D; o e fUa & ; p & mr v dky gb l; / string str B = Convert.
ToString(num2); a e & ma t mu fe m; r Sm this.textcode.Text = str B; v dkU jy i fa & ; v dku f& Hky gy J/
e d* Hk; c sKy ft a e e JU a jy mv dkw mu a w mh t c k serial & Smjy c Jhw m[ m t v Ge f& dk; & Si f; v Sw Jh serial routine a w Ge JU
y g/ o i fht a e e JU a & mi f; w e f; 0 i fa q mhz f0 Jv fa w Gu dk crack v ky fr , fq dk& i fa w mh ' Dx u f t q a y gi f; & me JUc sDjy D; c u fc J
v Sw Jhserial routine a w Ge JU a w GU& r Smjz p fy ga Mu mi f; . . .
( 1 2 ) .net y & dk* & r fr SStr ong Name Signatur e t m; z , f& Sm; jc i f;
Strong Name Signature e JUy w fo u fjy D; t e n f; i , fa jy m& r , fq dk& i fa w mh StrongName w p fc kr Sm
y & dk* & r fe JUy w fo u fw Jh assembly & JU identity a w Gy g0 i fjy D; o lw dkUa w Gu a w mh & dk; & Si f; v Sw Jhp mo m; a w Ge JU t r n f?
version t r Sw f? culture w dkUt jy i f public key w p fc ke JU digital signature w p fc kw dkU y g0 i fE dki fy gw , f/
' ga w Gu dk assembly z dki fw p fc ku a e o u fq dki f& m private key u dkt o Hk; jy Kjy D; x kw fa y ; w mjz p fy gw , f/ ( ' Dz dki fr Sm
assembly manifest a w Gy gjy D; t jy e ft v Se ft m; jz i fh assembly manifest r Smv J assembly u dkjy Kjy i fa y ; w Jh
z dki fa w Gt m; v Hk; & JU hash a w Ge JU t r n fa w Gy g0 i fy gw , f/ ) Microsoft Visual Studio e JU .NET framework
u dkt o Hk; jy KMu w Jht jc m; tool a w G[ m StrongName a w Gu dk assembly w p fc kt a e e JU o w fr Sw fE dki fy gw , f/
' Do i fc e f; p mr Sm .net exe z dki fa w Ge JU .net DLL z dki fa w Gr Sm& Sdw Jh & dk; & Si f; v Sw Jh StrongName (SN) a w Gu dk
b , fv dkz , f& Sm; & r v Jq dkw m a v hv mMu r Smjz p fy gw , f/
w p fc kw n f; a o m exe^ DLL z dki fx Jr Sm& Sdw JhSN a w Gu dkz , f& Sm; z dkU e n f; v r f; t c sdKU & SdMu y gw , f . . .
t & dk; & Si f; q Hk; e n f; v r f; u a w mh y & dk* & r fu dk IL u k' fa w Gt a e e JU decompile v ky fjy D; SN u dkz , f& Sm; w mjz p f
y gw , f/ SN z , f& Sm; jy D; & i fa w mh ILASM.exe z dki fu dk t o Hk; jy Kjy D; compile jy e fv ky fw mjz p fy gw , f/ ' gu a w mh
v Hk; 0 y n mo m; r y gw Jhe n f; v r f; jz p fy gw , f/ o i fht a e e JU p D; y Gm; jz p fa q mhz f0 Jv fa w Gu dk' Dv dke n f; o Hk; jy D; jy e f compile
v ky fv dkU& r , fv dkU r x i fv dku fy ge JU/ b ma Mu mi fhv Jq dka w mh ' Dy & dk* & r fa w Gr Sm u k' fa w Ge JU function t r n fa w Gu dk
obfuscation v ky fx m; v dkUy g/
t jc m; e n f; w p fc ku a w mh PE header u dkt o Hk; jy Kjy D; SN u dk patch v ky fz dkUt w Gu f t o Hk; 0 i fw Jht c su f
t v u ft c sdKUu dk & , lz dkUy g/ ' Dv dkv ky fz dkUt w Gu f o i fht a e e JU z dki fE Sp fz dki f v dky gw , f/ w p fc ku a w mh SN e JUjz p fjy D;
a e mu fw p fc ku a w mh SN r y gw Jhz dki fjz p fy gw , f/ jy D; & i f o lw dkU& JU PE header a w Gu dk CFF explorer e JU E dIi f; , SOf
& r Smjz p fy gw , f/
' Do i fc e f; p mt w Gu f a & G; x m; w Jh y & dk* & r fu a w mh StrongName.exe jz p fjy D; www.tuts4you.com r Sm
download v ky f, lE kdi fy gw , f/ StrongName.exe y & dk* & r fu dkz Gi fhv dku f& i fa w mh y Hk( 5 3 ) t w dki f; jr i f& r Smjz p fy g
w , f/
y Hk( 5 3 )
w u , fa w mh ' Dy & dk* & r fr Sm x l; x l; a x Ga x G crack v ky fp & mb mr Sr & Sdy gb l; / ' ga Mu mi fh useless q dkw Jh
p mo m; t p m; patched v dkUa jy mi f; Mu n fhMu & a t mi f/ ' gu dka w mhWinHex t o Hk; jy Kjy D; jy i fv dkU& y gw , f/ y Hk( 5 4 ) /
y Hk( 5 4 )
y Hk( 5 4 ) t w dki f; jy i fjy D; & i fa w mhz dki fu dko dr f; jy D; jy e fz Gi fhv dku fy g/ y Hk( 5 5 ) /
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 306 -
y Hk( 5 5 )
y & dk* & r fu SN u dkp p fw ma Mu mi fh u k' fu dke n f; e n f; a v ; jy i fv dku fw me JU ' Dv dk error w u fv mw mjz p fy g
w , f/ ' ga Mu mi fh SN & Sdw Jhz dki fe JU SN r & Sdw Jhz dki f b ma w Gu Gmv Jq dkw m e n f; e n f; a v ; Mu n fhv dku fMu & a t mi f/ No
StrongName.exe z dki fe JU StrongName.exe z dki fw dkUu dk CFF explorer r Sm z Gi fhMu n fhy gr , f/ y Hk( 5 6 ?5 7 ) /
y Hk( 5 6 ) SN r & Sda o m No Str ongName.exe z dki f
y Hk( 5 7 ) SN & Sda o m Str ongName.exe z dki f
Flag a e & mu 1 q dkw mu a w mh COMIMAGE_FLAGS_ILONLY jz p fjy D; 9 q dkw mu a w mh
COMIMAGE_FLAGS_ILONLY | COMIMAGE_FLAGS_STRONGNAMESIGNED v dkUq dkv kdw m
y g/ y Hk( 5 8 ) /
y Hk( 5 8 )
' ga Mu mi fh' Dw e fz dk; a w Gu dk& Smjy D; patch v ky f& r Smjz p fy gw , f/
MetaData Streams & JU Tables directory u dk Mu n fhMu & a t mi f/ y Hk( 5 9 ) /
y Hk( 5 9 )
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 307 -
Tables directory a t mu fu Assembly u dkMu n fhv dku f& i fa w mhy Hk( 6 0 ?6 1 ) t w dki f; jr i f& y gr , f/
y Hk( 6 0 ) SN r & Sda o m No Str ongName.exe z dki f
y Hk( 6 1 ) SN & Sda o m Str ongName.exe z dki f
StrongName u dk z , f& Sm; z dkU StrongName.exe z kdi f& JU offset a w Gr Sm a t mu fy gt w dki f; jy i fa y ; & y gr , f-
Offset 1018 Flags 01
Offset 1028 StrongNameSignature RVA 00
Offset 102C StrongNameSignature Size 00
Offset 1554 Flags 00
Offset 1558 PublicKey 00
w u , fv dkU DLL z dki fw p fc ku dk exe z dki fw p fc ku a e a c : , lo Hk; w mjz p fjy D; ' DDLL z dki fx Jr Sm registration
routine u dka & ; o m; x m; c Jhr , fq dk& i f u Re fa w mfw dkUt a e e JU DLL z dki fu dk patch v ky f& r Smjz p fy gw , f/ ' Dw p fc g
e r le mjy r , fh y & dk* & r fu a w mh Divelements Limited u x kw fw Jh Navsight y g/ Navsight a q mhz f0 Jv fr Sm
Demo.exe e JU Navsight.dll z dki fw dkUy g& Sdy gw , f/
Demo.exe u dkz Gi fhjy D; Show ExplorerBar Demonstration u dka & G; r , fq dk& i f y Hk( 6 2 ) t w dki f; jr i f& y gw , f/
y Hk( 6 2 )
OK button u dk E Sdy fv dku f& i fa w mhy Hk( 6 3 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 6 3 )
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 308 -
y Hk( 6 3 ) & JU n mz u fr Sm& Sdw JhAnimate! button u dkE Sdy fv dku f& i fa w mhb , fz u fu task pane [ ma y smu fo Gm;
r Smjz p fy gw , f/ a u mi f; jy D? u Re fa w mfw dkUt a e e JU ' ga w Gu dk jy i fz dkUv dky gr , f/ ' ga y r , fhSN u dk y x r q Hk; z , f& Sm; & y g
r , f/ Navsight.dll z dki fx Ju RSA1 q dkw Jhp mo m; u dk WinHex r Sm& Smjy D; o lUr w dki fc i fr Sm& Sdw Jh 2 1 c ka jr mu fe JU
2 2 c ka jr mu f p mv Hk; a w G(80 0A)u dk 00 00 v dkUa jy mi f; v dku fy g/ y Hk( 6 4 ) / ( SN u dkz , f& Sm; w Jh ' De n f; u a w mh
UnREalRCE {Persian Crackers} u Newbie_Cracker & JUe n f; jz p fy gw , f/ )
y Hk( 6 4 )
y Hk( 6 4 ) u Navsight.dll z dki fu dk 80 0A t p m; 00 00 v dkUa jy mi f; jy D; z dki fu dko dr f; v dku fy g/ ' Dha e mu f
demo.exe z dki fu dkz Gi fhMu n fhw Jht c gr Sma w mhy Hk( 6 5 ) t w dki f; error w u fa e w m a w GU& y gw , f/
y Hk( 6 5 )
e n f; e n f; a v mu f p Of; p m; Mu n fh& a t mi f/ u Re fa w mfw dkU[ m DLL z dki fu a e SN u dkz , f& Sm; c Jhy gw , f/
u Re fa w mfw dkU o Hk; c Jhw Jhe n f; u v J t a u mi f; q Hk; y g/ ' gq dkb mv dkU jy e mw u fa e & w my gv J/ SN u dk a e mu fx y f
p p fa q ; r Ia w Gr sm; x y f& Sda e v dkUv m; / w u , fv dkU SN u dkp p fa q ; w mq dk& i fa w mh DLL x Jr Sma w mh r [ kw fa v mu fy g
b l; / exe z dki fx Jr Smy J jz p fy gv dr fhr , f/ Error message jz p fw JhCould not load file with PublicKeyToken =
75b7... u dkMu n fhy g/ ' gu dkp p fa q ; E dki fz dkU Demo.exe u dk CFF explorer e JUz Gi fhjy D; .NET Directory
r Sm& SmMu n fhy g/ y Hk( 6 6 ) /
y Hk( 6 6 )
y Hk( 6 6 ) u Navisight u dkMu n fhr , fq dk& i fa w mhy Hk( 6 7 ) t w dki f; jr i f& y gr , f/
y Hk( 6 7 )
' gu a w mh u Re fa w mfw dkU v dkc si fw Jht c su fy g/ PublicKeyOrToken u dkMu n fhy g/ o i fht a e e JU exe z dki f
w p fc kt jz p f compile v ky fp Ofr Sm .NET compiler u module t o D; o D; & JU PublicKey u dk o lUt r n fa w Gv dky J
o dr f; x m; a y ; w mjz p fjy D; v kdc si fw Jh module & JU PublicKey u dk& Smjy D; p p fa q ; & mr Sm reference w p fc kt a e e JU
PublicKeyOrToken u dkt o Hk; jy Kw my g/ ' ga Mu mi fh ' Da e & mr Sm 0 v dkUa jy mi f; v dku f& i f y Hk( 6 5 ) u error message
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 309 -
a y : v ma w mhr Sm r [ kw fy gb l; / Demo.exe z dki f& JU Offset 0x26324 a e & mr Sm 0 v dkUjy i fjy D; z dki fu dk o dr f; v dku fy g/
Demo.exe z dki f a u mi f; a u mi f; t v ky fv ky fw ma w GU& r Smy g/
' gq dk Navsight.dll z dki fu dk patch v ky fv dkU& jy Djz p fy gw , f/ Navsight.dll z dki fu dk IDA Pro e JU
Reflector w dkUr Smz Gi fhjy D; evaluation period u dk& Smy g/
.method public static hidebysig bool '() // CODE XREF: sub_2840+72_p
// sub_33A0+77_p ...
{
.locals init (bool V0,
class System.String V1,
class System.String V2,
class System.String[] V3)
call bool '::'()
stloc.0
ldloc.0
brfalse.s loc_3272
call class [mscorlib]System.Reflection.Assembly
[mscorlib]System.Reflection.Assembly::GetExecutingAssembly()
callvirt class [mscorlib]System.Reflection.AssemblyName
[mscorlib]System.Reflection.Assembly::GetName()
callvirt class System.String [mscorlib]System.Reflection.AssemblyName::get_Name()
stloc.1
ldc.i4.5
newarr [mscorlib]System.String
stloc.3
ldloc.3
ldc.i4.0
ldstr "Your evaluation period for "
stelem.ref
ldloc.3
ldc.i4.1
ldloc.1
stelem.ref
ldloc.3
ldc.i4.2
ldstr " has expired. Product functionality will be limited."
y Hk( 6 8 ) IDA Pr o jz i fhz Gi fhx m; y Hk
y Hk( 6 8 ) u dkMu n fhr , fq dk& i f call function() a e mu fr Sm brfalse u dka w GU& y gw , f/ b mr Sr v ky f& a o ; c i fr Sm
function t r n fa w Gu dk& SmMu n fhy g/ Function t r n fa w Gu dk obfuscation v ky fx m; w Jht w Gu f r a w GU& y gb l; / ' D
DLL z dki fu dk o i f compile jy e fjy D; v ky fE dki fy go v m; / Reflector r Smv Jt Mu mMu D; v dku f& Smjy D; w Jha e mu fr Sm
y Hk( 6 9 ) t w dki f; a w GU& y gw , f/
y Hk( 6 9 )
y Hk( 6 9 ) u dkMu n fhv dku fjy e fa w mhv J function a w Gu dk obfuscation v ky fx m; w ma w GU& y gw , f/ t r Se fu
a w mh flag w e fz dk; [ m 0 jz p f& y gr , f/ ' gq dk flag w e fz dk; 0 u dk return jy e fy dkUr , fh function u b , fa e & mr Sm
& Sda e y go v J/
y Hk( 6 8 ) u IDA Pro u dko Gm; jy D; call bool '::'() a e & mu dk E Sdy fv dku fy g/ t e n f; i , f& Iy fa x G; w Jhu k' fa w Gu dk
a w GU& y gr , f/ u Re fa w mfw dkUt a e e JU function & JU return w e fz dk; u kd FALSE v dkUjy i fv dkU& y gw , f/ ' ga y r , fh
t E & m, f& SdE dki fw Jhu k' fa w Gy g^ r y g o dE dki fa t mi fv dkU a t mu fu dke n f; e n f; scroll q GJMu n fhv dku fy g/
y Hk( 7 0 )
t c e f; ( 1 9 ) Visual Dot.net jz i fha & ; o m; x m; a o m y & dk* & r fr sm; u dk crack v ky fjc i f;
- 310 -
' gu dk Reflector r SmMu n fhy gr , f/ y Hk( 7 1 ) /
y Hk( 7 1 )
DLL u registry x Jr Sm NETFramework key & Sd^ r & Sdp p fa q ; jy D; & Sdc Jh& i f Demo.exe u dk y x r q Hk;
z Gi fhc Jhw Jh & u fp GJe JUt c sde fu dk r Sw fo m; x m; jy D; v u f& Sd& u fp GJe JUt c sde fu dkw Gu fc su fjy D; E dIi f; , SOfy gw , f/ w u , fv dkU
v u f& Sdt c sde f[ m y x r q Hk; z Gi fhc Jhw Jht c sde fx u f & u f3 0 y dka e c Jh& i f return w e fz dk; [ m TRUE jz p fjy D; ? ' Dv dkr Sr [ kw f
& i fa w mh FALSE jz p fr Smy g/ ' ga Mu mi fh t E & m, f& SdE dki fw Jhu k' fa w G? function a w Gr & Sda w mhb l; q dkr S u Re fa w mfw dkU
t a e e JU return w e fz dk; u dk 0 v dkU patch v ky fv dkU& r Smjz p fy gw , f/
Patch v ky fz dkUt w Gu f function & JU offset t p & Sd& m 0x4784 q Do Gm; jy D; 16 2A v dkUjy i fjy D; z dki fu dk o dr f; y g
r , f/ b ma Mu mi fhjy i f& w mv Jq dkw m o d& a t mi f y Hk( 6 8 ) u dk jy e fMu n fhy g/
IDA View opcode (CFF Explor er ) Instr uction (CFF Explor er )
call class [mscorlib]System.Reflection.Assembly 28 E7 00 00 0A call 0x0A0000E7
callvirt class [mscorlib]System.Reflection 6F E8 00 00 0A callvirt 0x0A0000E8
y Hk( 7 2 )
y Hk( 7 2 ) u a w mh Offset 0x4784 r Sm 16 2A v dkU patch r v ky fc i f IDA Pro e JU CFF explorer w dkUr Sm
jr i f& w my g/
IDA View opcode (CFF Explor er ) Instr uction (CFF Explor er )
ldc.i4.0 16 ldc.i4.0
ret 2A ret
y Hk( 7 3 )
y Hk( 7 3 ) u a w mh Offset 0x4784 r Sm 16 2A v dkU patch v ky ft jy D; IDA Pro e JU CFF explorer w dkUr Sm
jr i f& w my g/ ldc.i4.0 q dkw mu a w mh stack a y : int32 w e fz dk; w p fc ku dk o kn t a e e JU u l; w i fv dku fw my g/
q dkv dkw mu a w mhcall a w Gu dk r p p fa p a w mhy J 0 w e fz dk; u dk return jy e fy dkUv dku fw mjz p fy gw , f/
jy i fx m; w Jhy & dk* & r fu dk jy e fz Gi fhc sde fr Sma w mhexpiration dialog a y smu fo Gm; r Smjz p fy gw , f/
t c e f; ( 20 ) r dkb dki f; z ke f; application r sm; u dkcrack v ky fjc i f;
- 311 -
tcef;(20) - rdkbdkif;zkef; application rsm;udk cr ack vkyfjcif;
' Dw p fc gr Smaw mhr dkb dki f; z ke f; (smartphone) aw Gr Sm t o Hk; jy Kw Jhapplication aw Gu dkcrack v ky fMu n fhr Sm
jz p fy gw , f/ Mu dKw i far w m&y fc Hv dkw mu aw mh mobile cracking e JUy w fo u fw Jh o i fc e f; p mr sm; u v J &Sm; y g; w m
u w p faMu mi f; ? u Re faw mfhx Hr Smv J smartphone r &Sdw Jht w Gu f ' Do i fc e f; p mu aw mh o i fht w Gu f p dw fau se y fr I
t jy n fhay ; Edki fr Sm r [ kw fw Jht aMu mi f; y g/ ' gaMu mi fh t m; e n f; c su ft r sm; Mu D; &Sdw Jh ' Do i fc e f; p mu dk o n f; c Hz w f&Iap
v dky gw , f/
' Dae Uac w f r dkb dki f; z ke f; aw mfaw mfr sm; r sm; e JU smartphone aw mfaw mfr sm; r sm; [ m z ke f; t q i fhw i fr u b J
u Ge fy sLw me D; e D; jz p fv my gw , f/ u Ge fy sLw maw Gv dky J u Ge f, u fc sdw fq u fr Iaw Gy gv mMu y gw , f/ (Bluetooth?
WiFi? GSM? IR? USB)/ u Ge fy sLw maw Gv dky J v Hkjc HKa&; q dki f&mp n f; r sOf; aw G&Sdjy D; ? z ke f; aw Gr Sm ai Gac s&w Jhp e p f
w c gw n f; y gv mw maMu mi fho i fht ae e JU w u , fhai GaMu ; aw Gu dk q Hk; &IH; &Edki fy gw , f/ r dkb dki f; z ke f; &JU anti-malware
e JUy w fo u fjy D; o kaw o e jy Kc Jhw mu aw mh F-Secure u y g/ r dkb dki f; z ke f; aw Gr Smo Hk; w Jh Symbian application
aw Ge JUy w fo u fv dkUcrack v ky fjy D; y x r q Hk; w i fjy c Jho lu aw mhARTeam u Shub-Nigur r ath jz p fy gw , f/
' Do i fc e f; p mr Smaw mhSymbian z ke f; aw Gr Smo Hk; w Jhapplication aw Gu dko m crack v ky fjy r Smjz p fy gw , f/
y Hk( 1 ) Symbian smar tphone z ke f; r sm;
( 1 ) Symbian OS q dko n fr Sm . . . .
Symbian OS u dk Nokia (47.9%) e JU SonyEricsson (15.6%) w dkUu smartphone aw Gr Sm
t " du t o Hk; jy Kc JhMu jy D; 20 0 8 - c kESp f ESp fv , fy dki f; av mu fr Sm open source t jz p fjy Kv ky fz dkUt w Gu f Nokia u
Symbian Ltd. u dk0 , f, lc Jhy gw , f/ Symbian OS aw G[ m t ap my dki f; u Psion v dkUac : w JhEPOC u dk t ajc c H
y gw , f/ 20 0 1 c kESp fr Smaw mh EPOC u ae Symbian v6 q dkjy D; jz p fv my gw , f/ Symbian &JU v u f&Sd major
version u aw mh 9 jz p fy gw , f/ Symbian r Sm OS e JU UI u dkc GJjc m; x m; y gw , f/ OS u aw mh Symbian u
jz p fjy D; UI u aw mh hardware a&mi f; c so law Ge JUo u fq dki fy gw , f/ ' gaMu mi fhr dkU Series60 (S60) [ m Nokia
u jz p fjy D; UIQ u aw mh Sony Ericsson u jz p fy gw , f/ MOAP u aw mh Sharp/NTT DoCoMo u
jz p fy gw , f/ Symbian OS aw Gr Sm ARM y &dkq u fq maw Gu dk t o Hk; jy KMu jy D; ' Dy &dkq u fq maw G[ m RISC
(Reduced Instruction Set CPU) y &dkq u fq maw Gjz p fy gw , f/ ' gaMu mi fhr dkUv dkU ARM CPU aw Gr Sm
instruction aw Ge n f; y g; jy D; register aw G r sm; jy m; v mw Jht w Gu f cracker aw Gt w Gu f e m; v n f&c u fap r Sm
jz p fy gw , f/
Symbian OS &JU t ap my dki f; version aw Gr Smaw mh EKA kernel u dkt o Hk; jy Kc JhMu jy D; ae mu fy dki f;
version aw Gr Smaw mh ERK2 kernel u dko mt o Hk; jy Kc JhMu y gw , f/ ' D kernel aw G[ m multi-processing?
Multithreading e JUmulti-tasking w dkUu dkjy Kv ky fay ; Edki fp Gr f; &Sdy gw , f/ r Sw fOmP fu mu G, fr Ip e p fv Jy g&Sdy gw , f/
x l; jc m; c su fu aw mh o lUr Sm user w p fOD; w n f; p e p fu dk o Hk; p GJy gw , f/ ' gaMu mi fh user e JU admin c GJjc m; x m; w m
r &Sdo v dkUlogin/logout p e p fv Jr &Sdy gb l; /
Symbian OS aw G[ m resource x u f API u dkt ajc c Hy gw , f/ Build v ky fc sde fr Smo m assign v ky fEdki f
jy D; run ae c sde fr Smaw mh ajy mi f; v JEdki fjc i f; r &Sdy gb l; / DLL u k' faw Gu dkaw mh application process &JU p Gr f; aq mi f
&n faw Ge JUt w l execute v ky fw mjz p fy gw , f/ p Gr f; aq mi fr Iaw Gu dkaw mh exe x Jr Smy J o dr f; w mjz p fy gw , f/
Symbian OS t w Gu f aq mz hf0 Jv fx kw fv ky fz dkU Mandatory Code Signing e JU x de f; c sKy fy gw , f/ Exe aw Ge JU
library aw Gu dk a' w maw Ge JU o D; o e fUc GJjc m; Edki fz dkU data caging u dkt o Hk; jy Ky gw , f/ ' gaMu mi fh exe aw G[ m
\sys\bin at mu fr Sm&Sdjy D; process a' w maw Gu aw mh\private\<APP UID> at mu fr Sm&Sdw m jz p fy gw , f/
t c e f; ( 20 ) r dkb dki f; z ke f; application r sm; u dkcrack v ky fjc i f;
- 312 -
Symbian z dki fp e p fu aw mhdrive p mv Hk; aw G? directory aw Ge JUz dki faw Gu dkt ajc c Hy gw , f/
( 1 ) C: - Flash RAM/ User e JUy w fo u fw Jht c su ft v u faw G? user u install v ky fx m; w Jh application
aw G&Sdy gw , f/
( 2) D: - TEMP RAM/ Application aw Gt w Gu f , m, Dz dki fx m; o kdy gw , f/
( 3 ) E: - MMC/ " gw fy Hkaw Ge JUapplication aw Gt w Gu f removable disk jz p fy gw , f/
( 4 ) Z: - OS ROM/ OS z dki faw Gt r sm; p ky g0 i fw Jhflash drive jz p fy gw , f/
Drive w dki f; r Sm system directory &Sdy gw , f/
( 1 ) Media t o p fw p fc kx y fa&mu fv mw dki f; directory u dkt v dkt av smu fz e fw D; r Smjz p fy gw , f/
( 2) System directory r Smaw mh OS e JU application z dki faw Gy g0 i fw Jh directory tree y g0 i fy gw , f/
C:\Windows e JUw ly gw , f/
t a&; Mu D; w Jhdirectory aw Gu aw mh-
( 1 ) System\Apps/ User aw Gjr i fEdki fw Jhapplication aw G&Sdy gw , f/
( 2) System\Recogs/ Recognizer components
( 3 ) System\Install/ Install v ky fx m; w Jhapplication aw Ge JUy w fo u fw Jhuninstallation t c su ft v u fr sm; /
( 4 ) System\libs/ System e JU3rd-party library r sm; /
Phone menu e JUbutton aw Gr Sm&Sdw Jhapplication aw Gu aw mh-
( 1 ) Z:\System\Apps\Menu\Menu.app - Phone main menu & application launching service
( 2) Z:\System\Apps\AppInst\Appinst.app - Application installation
( 3 ) Z:\System\Apps\AppMngr\AppMngr.app - Application uninstallation
( 4 ) Z:\System\Apps\MMM\Mmm.app - Messaging application
( 5 ) Z:\System\Apps\Phonebook\Phonebook.app - Phonebook
( 6 ) Z:\System\Apps\BtUI\btui.app - Bluetooth control panel
Mobile application aw Gu dkz e fw D; &mr Sm t o Hk; jy Kw Jhy &dk* &r fb mo mp u m; u aw mhCarbide.c++ jz p fjy D;
developing process u aw mhat mu fy gt w dki f; jz p fy gw , f/
( 2) Symbian Executable File For mat
' Dw p fc gr Smaw mh Symbian OS r Smo Hk; w Jh application aw G&JU z GJUp n f; w n faq mu fy Hku dk av hv m
Mu n fhy gr , f/ Symbian OS r Sm t o Hk; jy Kw Jh exe z dki fy Hkp Hu aw mh E32 y Hkp Hjz p fy gw , f/ ' Do i fc e f; p mr Sm aq G; aEG;
r , fhexe z dki fq dkw m ARM y &dkq u fq maw Gt w Gu fu dkq dkv dk&i f; jz p fy gw , f/ Emulater aw Gt w Gu fu dkr aq G; aEG;
<app>.mmp
Project file
<app>.r ss
Resource file
<app>.app
<app>.ilk
<app>.r sc
<app>.dll
Executable
<app>.aif
Package
information file
Nor mal C++
Build Pr ocess
<app>.
UID.cpp
Resource file
<app>.WINS
<app>.MARM
Makefile
<app>.app
<app>.ilk
<app>.r sc
<app>.dll
Executable
Makefile
nmake
make SIS
<app>
.sis
<app>.pkg
List of
components
Nor mal EPOC
Packaging Pr ocess
Copyright White Cracker (Myanmar Cracking Team)
t c e f; ( 20 ) r dkb dki f; z ke f; application r sm; u dkcrack v ky fjc i f;
- 313 -
y gb l; / b maMu mi fhv Jq dkaw mhemulater &JU exe z dki faw G[ m Windows &JU PE-COFF (Portable Executable
Common Object File Format) u dkt o Hk; jy Kv dkUy g/
Symbian r Sm t o Hk; jy Kw Jh executable z dki faw Gjz p fw Jh .app? .exe ( o dkU) .dll aw Gr Sm E32 z dki fy Hkp Hq dkw Jh
t x l; y Hkp Hw p fc k&Sdy gw , f/ Microsoft/Intel &JU PE (Portable Executable) ( o dkU) UNIX &JU ELF
(Executable and Linking Format) w dkUe JU t e n f; i , fu GJjy m; ay r , fh t ajc c Ht m; jz i fh w ln Dr I&Sdy gw , f/
Symbian [ m GCC compiler u dkt o Hk; jy Kw Jht w Gu f w u , faw mh o i fh&JU source code u dk PE y Hkp Ht jz p f
compile v ky fv dku fw mjz p fy gw , f/ Symbian &JUbuild process u sr So m PETRAN q dkw Jhtool u dkt o Hk; jy Kjy D;
o i fh&JUPE z dki fu dkE32 z dki ft jz p f ajy mi f; ay ; v dku fw mjz p fy gw , f/
E32 Header
Code Section
Text Section
Export Table
Import Table
BSS Section
Data Section
Import Section
Relocation Section
y Hk( 2) E32 z dki fy Hkp H
t jc m; z dki fy Hkp Haw Gr Smv dk E32 r Smv J header u ae p y gw , f/ Header &JUae mu fr Sm u y fy gv mw maw G
u aw mhat mu fy gt w dki f; jz p fy gw , f -
o Code section - o lUr Smaw mhtext section? export address table e JU import address table (IAT)
q dkjy D; 3 y dki f; y g0 i fy gw , f/ Text section r Smaw mh source code &JU .obj z dki ft m; v Hk; y g0 i fy gw , f/
u se fw Jhsection ESp fc ku aw mhy &dk* &r fx Ju import/export v ky fx m; w Jhfunction aw Gu dkjy y gw , f/
o BSS section - o lUr Smaw mh initialize r v ky f&ao ; w Jha' w maw G y g0 i fy gw , f/ ' D section u dk
Symbian application aw mfaw mfr sm; r sm; r Smaw mht o Hk; r jy KMu y gb l; /
o Data section - o lUr Smaw mh initialize v ky fjy D; o m; a' w maw Gy g0 i fy gw , f/ Symbian application
aw mfaw mfr sm; r sm; [ m .app? .dll z dki ft ae e JUv mw maMu mi fh' Dsection r &Sdw mu r sm; y gw , f/
o Import section - o i fhy &dk* &r fu t o Hk; jy Kx m; w Jh imported function aw Ge JUo u fq dki fw Jh t c su f
t v u faw Gy g0 i fy gw , f/
o Relocation section - o i fhy &dk* &r fu dk Symbian loader u u l; w i fw Jht c gr Sm v dkt y fw Jhrelocation
table y g0 i fy gw , f/
E32 r Sm t " dy m, fz Gi fhq dkx m; w Jh header e JUy w fo u fw Jh t c su ft v u faw Gu aw mh at mu fy gt w dki f;
jz p fy gw , f -
class E32ImageHeader
{
public:
TUint32 iUid1;
TUint32 iUid2;
TUint32 iUid3;
TUint32 iCheck;
TUint iSignature; // 'EPOC'
TCpu iCpu; // 0x1000 = X86, 0x2000 = ARM, 0x4000 = M*Core
TUint iCheckSumCode; // sum of all 32 bit words in .text
TUint iCheckSumData; // sum of all 32 bit words in .data
TVersion iVersion;
TInt64 iTime;
TUint iFlags; // 0 = exe, 1 = dll, +2 = no call entry points
TInt iCodeSize; // size of code, import address table, constant data and export dir
TInt iDataSize; // size of initialized data
TInt iHeapSizeMin;
TInt iHeapSizeMax;
TInt iStackSize;
TInt iBssSize;
TUint iEntryPoint; // offset into code of entry point
t c e f; ( 20 ) r dkb dki f; z ke f; application r sm; u dkcrack v ky fjc i f;
- 314 -
TUint iCodeBase; // where the code is linked for
TUint iDataBase; // where the data is linked for
TInt iDllRefTableCount; // filling this in enables E32ROM to leave space for it
TUint iExportDirOffset; // offset into the file of the export address table
TInt iExportDirCount;
TInt iTextSize; // size of just the text section
TUint iCodeOffset; // file offset to code section
TUint iDataOffset; // file offset to data section
TUint iImportOffset; // file offset to import section
TUint iCodeRelocOffset; // relocations for code and const
TUint iDataRelocOffset; // relocations for data
TProcessPriority iPriority; // priority of this process
};
iUid1? iUid2 e JUiUid3 w dkU[ m identifier aw Gjz p fjy D; ? y x r UID u o i fh&JUy &dk* &r f[ m .dll z dki fv m; ?
.exe z dki fv m; q dkw m c GJjc m; ay ; Edki fy gw , f/ .dll q dk&i faw mh0x10000079 jz p fjy D; .exe q dk&i faw mh0x1000007A
jz p fy gw , f/ ' kw d, UID u aw mh object aw Gu dkc GJjc m; ay ; w mjz p fjy D; polymorphic interface DLL aw G
t w Gu f 0x100039CE jz p fjy D; ? static interface (shared library) t w Gu fu aw mh0x1000008d jz p fy gw , f/
w w d, UID u dkaw mh y &dk* &r f identifier t jz p fjr i fEdki fy gw , f/ ' ghjy i f 0x100000 u ae 0xFFFFFF
t w Gi f; Mu m; &Sdw JhUID t c sdKUv J&Sdy gao ; w , f/
iCheck u aw mh y x r UID 3 c k&JU checksum jz p fy gw , f/ Symbian SDK r Sm uidcrc.exe v dkU
ac : w Jhtool w p fc k&Sdjy D; y x r UID 3 c ku ae u dkx kw fay ; y gw , f/ Oy r mjy &&i f at mu faz mfjy y g command [ m
0x1000079? 0x1000029CE? 0x00DD3103 p w JhUID aw Gt w Gu f checksum u dkx kw fay ; y gv dr fhr , f/
C:\>uidcrc 0x10000079 0x100039CE 0x00DD3103
0x10000079 0x100039CE 0x00DD3103 0xAE035303
iSignature u aw mhE32 z dki fe JUy w fo u fw Jhsignature jz p fjy D; EPOC w e fz dk; jz p fy gw , f/
iCPU u aw mh y &dk* &r faw G&JU platform jz p fjy D; ? ECpuX86 = 0x1000 q dk&i f Intel y &dkq u fq maw G
t w Gu fjz p fjy D; ECpuArm = 0x1000q dk&i faw mhy &dkq u fq maw Gt w Gu fjz p fy gw , f/
iCheckSumCode u aw mhcode section &JU checksum jz p fy gw , f/ Header z dki fx Ju r Sw fc su ft &
q dk&i faw mh ' g[ m .text section x Jr Sm&Sdw Jh 32-bit WORD aw Gt m; v Hk; &JU ay gi f; v ' f jz p fy gw , f/ ' gay r , fh
' Dw e fz dk; [ m IAT e JU export table (=iCodeSize field) t y gt 0 i f code section x Jr Sm&Sdw Jh32-bit WORD
aw Gt m; v Hk; &JUay gi f; v ' fv Jjz p fEdki fy gw , f/
iCheckSumData u aw mh.text section x Jr Sm&Sdw Jh32-bit WORD aw Gt m; v Hk; &JU ay gi f; v ' f jz p fy g
w , f/ Symbian r Sm u Re faw mfw dkU y &dk* &r faw Gu dk build v ky fc sde fr Smaw mh' Dchecksum w e fz dk; [ m o kn jz p fy g
w , f/
iVersion u aw mhE32 z dki fu dkx kw fay ; &mr Sm t o Hk; jy Kw Jh PETRAN &JU version jz p fy gw , f/ w u , f
v dkUo i fu UID 2.1 u dkt o Hk; jy Kw , fq dk&i f version u 1.00 (175) jz p fr Smy g/
iTime u aw mhy &dk* &r fu dkbuild v ky fv dku fw Jh&u fp GJe JUt c sde f (TimeDateStamp) jz p fy gw , f/
iFlags u aw mh.exe t w Gu f 0? .dll t w Gu f 1 e JUentry point u dkac : o Hk; jc i f; r &Sdw Jhz dki faw Gt w Gu faw mh
+2 jz p fy gw , f/
iCodeSize u aw mh code section &JUt &G, ft p m; jz p fjy D; IAT? constant data e JU export address
table w dkUy g0 i fy gw , f/
iDataSize u aw mh initialize v ky fx m; w Jh data section &JUt &G, ft p m; jz p fjy D; iCheckSumData
r Smv dky J' Dfield r Sm o kn jz p fae w m aw GU&r Smy g/
u se fw Jh parameter aw Gu aw mh r Sw fc su faw Gy gv mjy D; jz p fv dkU r &Si f; jy aw mhy gb l; / y dkjy D; &Si f; v i f; p Gm
e m; v n fEdki fz dkUexample_app.app u dkPETRAN e JUMu n fhv dku fMu &at mi f/ y Hk( 3 ) /
PETRAN - PE file preprocessor V01.00 (Build 175)
Copyright (c) 1996-2001 Symbian Ltd.
E32ImageFile 'example_app.app' // file name (not in E32 image header)
V1.00(175) Time Stamp: 00e0be89,69063b40 // iVersion iTime
EPOC Dll for ARM CPU // iCpu
Entry points are not called // iFlags
Uids: 10000079 100039ce 10008ace (7ec529db) // iUid1, iUid2, iUid3 and iCheck
File Size: 00001368 // file size (not in E32 image header)
Code Size: 00000ed8 // iCodeSize
Data Size: 00000000 // iDataSize
t c e f; ( 20 ) r dkb dki f; z ke f; application r sm; u dkcrack v ky fjc i f;
- 315 -
Chk code/data: d4ad460a/00000000 // iCheckSumCode iCheckSumData
Min Heap Size: 00001000 // iHeapSizeMin
Max Heap Size: 00100000 // iHeapSizeMax
Stack Size: 00002000 // iStackSize
Code link addr: 10000000 // iCodeBase
Data link addr: 00000000 // iDataBase
Code reloc offset: 00001194 // iCodeRellocOffset
Data reloc offset: 00000000 // iDataRellocOffset
Dll ref table count: 4 // iDllRefTableCount
Offset Size Relocs NumOfRelocs
Code 00007c 000ed8 // iCodeOffset, iCodeSize
001194 0000e1 +000000 (entry pnt) // iCodeRellocOffset .. iEntryPoint
Data 000000 000000 // iDataOffset iDataSize
Bss 000000 // iBssSize
Export 000f50 000004 (1 entries) // iExportDirOffset iExportDirCount
Import 000f54 // iImportOffset
Code (text size=00000d08) // iTextSize
... // here the dump of the text section
225 relocs
... // here the dump of the relocation section
Idata Size=00000240
Offset of import address table (relative to code section): 00000d08
... // here the import tables information
y Hk( 3 ) u dky dkjy D; &Si f; v i f; ap z dkUy Hk( 4 ) u dkMu n fhy g/
y Hk( 4 )
y Hk( 4 ) &JU b , fz u fjc r f; r Smaw mh section t o D; o D; &JU offset aw Gu dkjr i fEdki fy gw , f/ Oy r mjy &&i f -
iCodeOffset (= 0x7C) [ m code section &JU offset jz p fy gw , f/ n mz u fjc r f; u aw mh section t o D; o D; &JU
t &G, ft p m; jz p fy gw , f/ t &G, ft p m; aw Ge JUy w fo u fjy D; aw mh t e n f; i , f t c u faw GU&y gw , f/ b maMu mi fhv J
q dkaw mh t c su ft v u ft m; v Hk; u dk header x Jr Sm o dr f; q n f; w m r [ kw fv dkUy g/ E32ImageHeader &JU t &G, f
t p m; u dkaw mhsizeof operator u dkt o Hk; jy Kjy D; t v G, fw u lw Gu fc su fEdki fy gw , f/ Text section? code section
w dkU&JU t &G, ft p m; u dk o dz dkU&mv G, fy gw , f/ b maMu mi fhv Jq dkaw mh header x Jr Sm o lw dkUe JUo u fq dki fw Jh t c su f
t v u faw G&Sdv dkUy g/ ( iTextSize ESi fhiCodeSize) /
Export table &JUt &G, ft p m; u dk w Gu fc su f&w maw mht e n f; i , fc u fy gw , f/ o i fht ae e JU iExportDir
Count u dk sizeof(UINT) e JU ajr Smu fz dkUv dky gw , f/ b maMu mi fhv Jq dkaw mh export v ky fx m; w Jh function t o D;
o D; u dk unsigned integer t ae e JU o dr f; q n f; v dkUy g/ Oy r mjy &&i f - o i fhr Sm export v ky fx m; w Jh function
w p fc k&Sdr , fq dk&i f sizeof(UINT) e JUajr Smu fw Jht c g 4 &v mr Smjz p fy gw , f/
Import address table &JU t &G, ft p m; u dk w Gu fc su f&mr Smaw mh Symbian r Sm import table aw Gu dk
b , fv dkw n faq mu fx m; o v Jq dkw mu dk o dx m; z dkUv dky gw , f/ t ajc c Ht m; jz i fhaw mh o i fhy &dk* &r fu import v ky f
x m; w Jh function t a&t w Gu fu dk o dx m; z dkUv dky gw , f/ 114 v dkU , lq Mu y gp dkU/ 114 u dk&z dkU u Re faw mfw dkU
y &dk* &r fu import v ky fx m; w Jh DLL z dki faw Gx Jr Sm import v ky fx m; w Jh function aw Gu dk a&w Gu f&r Smjz p fy g
t c e f; ( 20 ) r dkb dki f; z ke f; application r sm; u dkcrack v ky fjc i f;
- 316 -
w , f/ jy D; &i f ' gu dk sizeof(UINT) e JUajr Smu fay ; &r Smjz p fy gw , f/ r Sw fc su f/ / Import v ky fx m; w Jh function
t a&t w Gu fr Sm w p fay gi f; ay ; z dkUv dky gw , f/ b maMu mi fhv Jq dkaw mhimport table &JUt q Hk; r Sm \0 o au Fw &Sdv dkUy g/
Import section &JUt &G, ft p m; jz p fw Jh 0x0240 u dkaw mh import section &JU y x r 32-bits u ae
z w f, lEkdi fy gw , f/ o i fht ae e JU E32Image.h u dkz Gi fhMu n fhv dku f&i f E32ImportSection v dkUac : w Jh structure
w p fc ku dk&Smaw GUr Smjz p fy gw , f/
class E32ImportSection
{
public:
TInt iSize; // size of this section
// E32ImportBlock[iDllRefTableCount];
};
' Dstructure [ m import section x Ju y x r 32-bits jz p fy gw , f/ iSize u aw mhimport section
&JUt &G, ft p m; jz p fy gw , f/
Import section v dky J relocation section &JUt &G, ft p m; u dk relocation section &JU y x r 32-bits
u ae z w f, lEkdi fy gw , f/ ' Dt c su ft v u faw Gu dk o dr f; q n f; x m; ay ; w Jh structure u aw mh E32RelocSection
jz p fjy D; field ESp fc ke JUjz p fy gw , f/
class E32RelocSection
{
public:
TInt iSize; // size of this relocation section
TInt iNumberOfRelocs; // number of relocations in this section
};
' DOy r mr Smaw mh iSize [ m 0x01CC jz p fy gw , f/ b maMu mi fh sizeof(E32RelocSection) u dk
relocation section &JUt &G, ft p m; r Sm ay gi f; ay ; z dkUv dky go v J/ b maMu mi fhv Jq dkaw mh E32RelocSection.iSize
r Sm relocation header &JUt &G, ft p m; w e fz dk; r y gv dkUy g/ ' g[ m import section e JUEdIi f; p m&i f e n f; e n f; av ;
u GJv GJae y gw , f/ b maMu mi fhv Jq dkaw mhE32RelocSection.iSize [ m import header x Jr Smy gjy D; o m; jz p fae v dkU
y g/ ' Dav mu fq dk&i faw mhE32 z dki fz GJUp n f; y Hku dke m; v n fav mu fjy Dv dkUx i fy gw , f/
( r dkb dki f; z ke f; application r sm; u dkcrack v ky fjc i f; t m; ae mu f version r sm; w Gi f q u fv u faz mfjy y gr n f/ )
,., Loader ... patch ..,-.`.
,
...'-) Loader =.- patch e-e...-.
-. . ..-. loader ,-.-- ..- ..``. loader ., patch ..-- -.
., - .. . -. . .`. .`.. -. .- .. -.-.-. -, .-. - -. cracking ,-.--
.`-.--.. ...,`.`..--- loader - -. ........ . -.- .,... . . .`
. ..- - - . Loader , patch ..-- .....-..`. -. ., - .. . -.- .. . -..
........`..-. .... - . . .-. ARTeam - Shub-Nigur r ath , Thunder pwr -
......- "Cracking with loaders: theory, general approach and a framework" ... ..-
.- . . - ` -.
Info: : Loader .-.-.-. process -. - .- - ...... application -.`..`. unpack
.,- protect ..-.-`,.`..,- process ....,- .....-. .,.-...-.
. -.. - . -.. ....... , .. - . ...- ..,_ .- .- - ` . . . . - . - process
- patch -.`.. -. ..,_ .- -. -.-. loader .- -. . -.. .- - `. -. . .-
....-. .,..`..-. loader .-, ....-...--. -_- directory ..-...
--. ....- -. -.-. loader .--. .-..- unpack . protect ..-.-
`,.`...-. .-. cracking ... . , - , .- ....-. Loader , . -.. . ..
..`.- father-child process ...`..--. .,.... loader -.-. father `.. -.
-..-. . .-. . -. . -.. - , . .. . . .. -.. -.-. child `..-. -..-.
..-. .-,.. Loader -.-`..-. ,.--. GUI tool .--
. .` - . - .- .-. .......... - . - - - ,_ .. . - _ ...
. --.-. -. address .. -.....-- patch ...-. dUP , ABEL - -.-.
,.._-. loader creator .- ..- `.. - - -.-. patch . ... . .... ,
. . .. -.. - . - . . . unpack .,- - - ... . ..,.` .`.. -. , --. .
-.-... patch -....`...-. patch ..,- -....-....... .,.-
. loader .- . ...-. . -.. .- -. loader .--., .-..- run .,-..... . - ....
--. --. loader .-..-.. ....... .-..- unpack - , . . . - . -
virtual address .,...-- .`...--.
-. crack -_ .. ... . -.-. JSI Inc -....- Windows NT Tips, Tricks,
and Registry Hacks ....`..-. Windows Registry ,-.-- --..
-. ... ., ..- . ._ ...-.`.. ` . ... . - www.jsiinc.com .. . download .
.-. ... . . .... , .-.-. $4000 .-. `.. ` . . .,, . .. .. . .-. .., . . -
......- ...-.. - ..- . . -. . -.. . ._ -.-. Jsittarh.exe `.. -.
--. .-. Jsittarh.exe -. HTML ,........-..-- web compiler 1.3 ..``. exe .
.,, compile ..-.`..-. .-...- -_--... ,
,
,., Loader ... patch ..,-.`.
.
,-.-. Windows Registry ,-.----.-- `-. ,- 79nn -.
-_-. ,-. `..-.
,
,- ...-.....,.- ...- ,-. password .-.....
,
,-. password .-_-`. OK button - . - . -. MessageBox (Message)
. ..- ,- `, ...- . ..-. -.-. . -.. .-. .` . -.. - PEiD ,
.. -_ - -... ,,
,,
PEiD , .. ...- ..-. PEtite 2.x `-. Protection ID 6.2.3 -.-. PEtite 2.2
, protect ..-. .`.-. Protection ID -.-. protector .- , - .- ` . ` .- --
.`.- ... -. . . .-. . -.. - unpack . .` . -.. - Olly ...
,
,., Loader ... patch ..,-.`.
.
,--_ VA 004BA042 -.-. entrypoint `.. -. .,..- ......-_ ..
PUSHAD .-.-.-. DWORD -,.....- PUSH - instruction `..-.-.. .`.
..-. `,.-. .-.. hardware breakpoint .-.-.. VA 004BA05D - PUSH EAX
...- F8 . ` .. .. - VA 004BA05D ...- . register window . ESP register .. right-
click -.`. Follow in Dump -.... ,
,
,-. Follow in Dump -...-..-. ,,-.`....
,,
,,- highlight `.. .,- 38 07 91 7C .. right-click .`. Breakpoint - Hardware, on
access WORD - .. . - ` .. .-. F9 (Run) -.- .,-. `....
.,
F9 (Run) -.--...-. hardware breakpoint ... VA 004BA03D . . . . ..-.
.- ... .., .-.- -, .-. - entry point ... VA 004BA042 .. MOV EAX, XXX ...
JMP 00484724 `...,-..-.-. .-. virtual address .,..- ...-_ ...-.
`.. -. --. .-. PEtite - entry point .,..,.... -.-- decompress -.`..
-. VA 004BA042 . ... ...- ... F8 -.. JMP 00484724 -. .-... OEP
...- jump -. .,
.,
.,- OEP . ..- ...- ` . . dump .. Right-click .`. Dump debugged
process -...- ,-. `....
,
,., Loader ... patch ..,-.`.
,- Dump button - .. .` . dump.exe ._, .-...- `.. .....-.
..... `,.-_-
,
,-. -,.-.- ....-`.- ,,.-. ..-.`..,...,-. ....
...- -_-`,. ,-. `..-. Overlay ..-. ..-.-.
,
.-....-. -,.-.- unpack --. -,...,....-. -,-
.-.-. HTML . .- - .`.. -. Dump --.- PEiD ,..-_ Borland
Delphi 3.0 , ........-. `-. --. .-. -, .-. - dump --.-. Web
Compiler ... . .- .- ..`.. -. dump.exe . File menu - Compiler Option -...-
,- . `. ... Jsittarh.exe . File menu . ..-. Compiler Option ..- .,
,
,- ...-_ ,,..`..- dialogbox -. ,.-. `.. -.,.._
... ... . - password --...-- ... master key -.-.,-.-. `..-..
,., Loader ... patch ..,-.`.
user key .-`. password -.,-.-. .. password routine -., password -,.,..
. -. ,_ .,_ ....-. - . . TEAM LAXiTY -.-. key ----..-. -,.-.
cracking ,..- .-,.-.-. key ..-..`-. Key -.-. 15416??? `..
-. .,... ..-. -, .-. .,, key - .`.`. ..- - - . --. key -...-. .
-.- ....---...`..-. ... cracker ...`..-.
,,
Dump.exe .. --- ......`.-.,.- Jsittarh.exe -`,-_--...
,
,.. dump ` . . .. -.- `, .- -... OEP .,..-.`.`. hardware
breakpoint .- - .- .` .- ` .. ... .-. F9 (Run) - . - ,- ..- ...
.,.....- . 79nn - 7900 DNS problems in .. - . ` . register . -....-_..
,
,
,- .`. .- . . Olly . . F12 -.`. .-..- .- ,,- . `. .
..
,,
Alt + K -.`. Call Stack --_. .,-.`..-.
.,
,., Loader ... patch ..,-.`.
.,- procedure ....- breakpoint .-.- Breakpoint .-.-. virtual
address .,.... right-click .`. Show procedure (Enter key) - .. ... Breakpoint .- . - ` .
. .-. ,- OK button - .. . - .,- . .- ...
.,
.,. VA 0047E52D - CALL 00403AFC - .....-_- EAX . -, . ..-
.`. . .,-. .- .. . .,.... .-.....-.-. VA 0047E53C .,.. .,... . JE
0047E5E0 (0F,84,9E,00,00,00) ... JMP 0047E5E0 (E9,9F,00,00,00,90)``. .-..- run
-_- Breakpoint .-...- ..-.-- - `, `.- - . - - Hex -, ..-
- .-. ... - - -. . - . ...... . . . . .. ,
,
,-. --``. .-..- run -_-- ,-. `..-.
,
. -,.-.-.-.,- .-....- key .. - .- .` ... . .,_ ....
.-. .-.-.-. . -.. - Olly .....-,. .-.-. -, .-. - .,, - - - , . .
--..-.... patch ..-.` .-..` -,.-.- -.-`..-.- Olly
.. ...._.- ,.. `..--. .- ...._...-.
,., Loader ... patch ..,-.`.
,
-..-. error --.-..-. .`...... . -.. (Jsittarh.exe) - Olly ,`,.
- Entry point (004BA042) - ..- - . .- .-.
,
, . . -, .-. - patch ...,..`..- VA 0047E53C ....-_--...
,
,,
-.. -.- . ..- - . . _.- .-. ,-`.--.--. decompression
stub - unpack ` ..,....... `.. -. --. .-. unpack ` ..... .- . ..
`.,... -....---. ... PEtite - -,.-.- unpack -. ... `. - .
.-. `.,.- .`.. .. .. loader .-.,-....` Loader .-.-. PEtite -
.-..- .-... process `...,....`. unpack ,.. patch .. byte -,
--..`. -....-.. byte -, ,.....`..-.
Loader/Patch .-.,-.. ABEL Loader Generator 2.31 -.- ,
,
,., Loader ... patch ..,-.`.
,
` .. .-. ..- - .... . - ` . loader .- .,-.-
-, .-. - patch ...._ (Jsittarh.exe) -.-_
Loader .._- .-.- (Jsittarh_Loader.exe)
Timeout . -.-.-. loader - process - load . ......, ..-.. `.,.,.
,_.- -,-..-.....-. timeout -,..- 15 .- . - . -.
, Patch .. virtual address -.-. VA 0047E53C . .`.. ` . ` .. byte .- -.-.
-,.-.,- ...--.. .-......- HEX -, ..- `.. -. JE 0047E5E0 (0F,84,9E,
00,00,00) , JMP 0047E5E0 (E9,9F,00,00,00,90), ,
.,.- . .. -.-. Generate button -.-.
,
Loader . - ., - .` .- .,.- . ..-. loader . (Jsittarh_Loader.exe) - Jsittarh.exe ,
directory -.-_...-....`..-_ - ,,- ..- .` . -. key ..-_....-
..-..- .....`......
,,
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 325 -
tcef;(22) - Cr ypto uk'frsm;udk avhvmjcif;
' Dw p fc gr Sma w mh crack v ky f& mr Sm t a w GUr sm; r , fh crypto u k' fa w Gt a Mu mi f; a v hv mr Smjz p fy gw , f/
Crypto q dkw mu a w mh cryptography & JUt w dka u mu fjz p fjy D; encrypt v ky fjc i f; ? decryption v ky fjc i f; e JU o u f
q dki fy gw , f/ Encrypt v ky fw , fq dkw mu a w mh o u fq dki f& m key w p fc kc ku dko Hk; jy D; ( key r y gw mv Jjz p fE dki fy gw , f)
p mo m; a w Gu dk e m; r v n fE dki fw Jh p mo m; a w Gt jz p f a jy mi f; v Ja y ; w mjz p fy gw , f/ Decrypt v ky fw mu a w mh 0 Su f
x m; w Jhu k' f^ p mo m; a w Gu dk r lv t w dki f; jz p fa t mi f jy e fa z mf, lw my g/ ' De n f; y n m& y fu dka w mh p p fb u fq dki f& m a Mu ;
e e f; a w Gr Sm 0 Su fp mt a e e JU t o Hk; jy Kjc i f; t jy i f a q mhz f0 Jv ft c sdKU& JU registration key z dki fa w Gu dk v la w Gr o da p
c si fw Jht c gr Sm t o Hk; jy Ky gw , f/ ' ghjy i f crypto u k' fa w Gu dk unpack v ky fw Jht c gr Smv n f; a u mi f; ? serial routine
a w Gr Smv n f; a u mi f; ? CRC u dk p p fa q ; & mr Smv n f; a u mi f; Mu HKa w GU& r Smjz p fv dkU ' Dt c e f; r Sm x n fho Gi f; a q G; a E G;
& jc i f; jz p fy gw , f/ a & SUt c e f; a w Gr Sm a jy mc Jho v dky J ' Dp mt ky f[ m t a jc c Ht c su fa w Gu dky J OD; p m; a y ; & Si f; jy w mjz p fv dkU
o i fht a e e JU cryptography t a Mu mi f; t a o ; p dw fo dc si f& i fa w mh Michael Welschenbach a & ; o m; w Jh
"Cryptography in C and C++" e JU Oded Goldreich a & ; o m; w Jh "Foundations of Cryptography"
p mt ky fa w Gu dk z w f& Iy gv dkU t Mu Hjy Kv dky gw , f/ ' Dp mt ky fa w Gu dk n Te f; & w Jht a Mu mi f; & i f; u a w mh t Ge fv dki f; r Sm t c r Jh
( w & m; r 0 i f) & & SdE dki fv dkUy Jjz p fy gw , f/
u Re fa w mfw dkUa v hv mr , fht a jc c Hcrypto e n f; y n mt c sdKUu a w mha t mu fy gt w dki f; jz p fy gw , f -
( 1 ) Transposition
( 2 ) Substitution
( 3 ) Frequency analysis
( 4 ) Le Chiffre Indchiffrable
( 5 ) Charles Babbage & Vigenre
( 6 ) Playfair
( 7 ) ADFGX crypto
( 1 ) Tr ansposition
' De n f; v r f; u a w mh p mo m; a w Gu dk a e & mc si f; v Jw Jhe n f; y g/ ' D& dk; & Si f; v Sw Jh a e & mc si f; v Jv S, fw Jhe n f; r Sm
a w mhmessage u dkt w e f; E Sp fw e f; c GJjy D; a & ; z dkUy g/
- y x r w e f; r Sm 1? 3? 5 p w ma w Gy gy gr , f/
- ' kw d, w e f; r Sma w mh2? 4? 6 p w ma w Gy gy gr , f/
Oy r m message/
- Your secret is your prisoner, let it go and you become its prisoner.
y x r w e f; r Sm& Sd& r Smu a w mhr * P e f; a jr mu fp mv Hk; a w Gjz p fy gw , f/
- Yusceiyupioelyyonyueoeypioi
' kw d, w e f; r Sm& Sd& r Smu a w mhp Hk* P e f; a jr mu fp mv Hk; a w Gjz p fy gw , f/
- orertsorrsnreigadobcmisrsnr
' DE Sp fc ku dkcrypt v ky fv dku fc sde fr Sma w mha t mu fy gt w dki f; a w GU& y gw , f . . .
- Yusceiyupioelyyonyueoeypioior er tsor r snr eigadobcmisr snr
( 2 ) Substitution
' De n f; v r f; u a w mhp mv Hk; w p fv Hk; u dk t jc m; p mv Hk; w p fv Hk; e JU t p m; x dk; jc i f; jz p fy gw , f/
u k' fw p fc k[ m p mv Hk; t ky fp k( o dkU) p u m; v Hk; w p fc ku dkt p m; x dk; y gw , f/
( 2 . 1 ) Monoalphabetic substitution
e r le my Hkp Hw p fc ku a w mh Caesar roll jz p fy gw , f/ ' gu a w mh crypt r v ky fx m; w Jh message u dk a e & m
a & TUw mjz p fy gw , f/ r sm; a o mt m; jz i fh ' Dv dky Hkp Ho Hk; & i fa w mh r lv p mo m; u dk p mv Hk; a o ; e JUa z mfjy jy D; ? crypt v ky fc H& w Jh
p mo m; u a w mhp mv Hk; Mu D; e JU jz p fa e r Smy g/
r lv p mo m;
- abcdefghijklmnopqrstuvwxyz
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 326 -
Cr ypt v ky fx m; a o mp mo m;
- DEFGHIJKLMNOPQRSTUVWXYZABC ( ' DOy r mr Sma w mh n mz u fu dk rotate v Sn fhx m;
w m jz p fy gw , f/ )
r lv p mo m;
- veni, vidi vici
Cr ypt v ky fx m; a o mp mo m;
- YHQL, YLGL, YLFL
' DOy r mu dkMu n fhr , fq kd& i f v a e & mw dki f; r Sm Y e JUt p m; x dk; jy D; i a e & mw dki f; r Sm L e JUt p m; x dk; x m; w m
a w GU& y gw , f/ ' ga Mu mi fh ' De n f; e JUu mu G, fw m[ m p dw fr c s& w m a w GU& y gw , f/ ' ga Mu mi fh y & dk* & r fr mu p mv Hk;
a w Gu dkt Mu dr fMu dr fv Sn fhjy D; r lv p mo m; u dk t v G, fw u ljy e fa z mfE dki fy gw , f/
( 2 . 2 ) Key y ga o m Monoalphabetic substitution
' De n f; u a w mh cracker a w Gu dk a w mfa w mfOD; a E Smu fa jc mu fa p y gw , f/ w u , fv dkU cracker w p fa , mu f
[ m crypt v ky fx m; w Jhp mo m; e JU a q mhz f0 Jv f& JU algorithm u dk& x m; c Jhr , fq dk& i fa w mi f crypted u k' fu dkjy e fa jz z dkU
r v G, fu ly gb l; / b ma Mu mi fhv Jq dka w mh crypt v ky fx m; w Jh key u dk r o dv dkUy g/ jz p fE dki fw Jh key t a & t w Gu fu v J
400 000 000 000 000 000 000 000 000 a v mu f& SdE dki fy gw , f/ ' ga Mu mi fh o i f[ m w p fp u e fUr Sm key
w p fc kE Ie f; e JU u k' fu dkjy e fa z mfr , fq dk& i f o i fh& JUt o u f[ m 10+9 a v mu f& Sdr Sy Jcrypted u k' fu dka jz E dki fr Smjz p fy gw , f/
r lv p mo m;
- abcdefghijklmnopqrstuvwxyz
Cr ypt v ky fx m; a o mp mo m;
- DJKTUVCWNOLPAEGFHIQRXYMSZB
r lv p mo m;
- ettu, brute?
Cr ypt v ky fx m; a o mp mo m;
- URRX, JIXRU?
' De n f; r Sm o i ft o Hk; jy Kw Jh key [ m & Sn fv sm; c Jhr , fq dk& i f cracker a w Gt z dkU key u dkr o dc Jh& i f decrypt
v ky fz kdU c u fc Ja e r Smjz p fy gw , f/
key w kdjc i f; ? w ln Da o m key u dky i f t Mu dr fMu dr fo Hk; a e jc i f; ? p mv Hk; w GJr sm; o Hk; jc i f; ( Oy r m Julius
Ceasar) ? space E Si fhp mv Hk; w lr sm; o Hk; jc i f; ( Julius Ceasar t p m; JULISCAER v dkUo Hk; & r Smjz p fy gw , f) a w Gu
' De n f; u dk t m; e n f; c su fjz p fa p y gw , f/ u se fw Jhp mv Hk; a w Gu a w mh key q Hk; w Jha e & mu a e p jy D; a w mh shift v ky f, lE dki f
y gw , f/
r lv p mo m;
- abcdefghijklmnopqrstuvwxyz
Cr ypt v ky fx m; a o mp mo m;
- JULISCAERTVWXYZBDFGHKMNOPQ
Cr ypt v ky fx m; a o mp mo m; ( a t mu fy gt w dki f; v Jv Sn fhE dki fy gw , f)
- CAERTVWXYZBDFGHKMNOPQJULIS
' De n f; & JU a u mi f; w Jht c su fw p fc ku a w mh key ( o dkU) key p mo m; u dk r Sw f& v G, fu ljc i f; y gy J/ & dk; & Si f; v Sw Jh
key a w Gu dka y gi f; p y fjy D; p mo m; a w Gu dk r a z mfE dki fa t mi f encrypt v ky fc Jhw mu a w mhv Ge fc Jhw JhE sp fw p fa x mi fa v mu f
u y g/ ' De n f; u dkz su fq D; E dki fw Jhe n f; v r f; a w G& Sda y r , fht m& y fv lr sdK; a w Gu y x r q Hk; jz p fc JhMu y gw , f/
( 3 ) Fr equency Analysis
Monoalphabetic crypto u dka z mfE dki fc Jh t m& y fw p fa , mu f& JU a & ; o m; c su f[ m 800 AD a v mu fu
jz p fy gw , f/ ' Dv Sn fhu Gu fa v ; u a w mh b , fb mo mp u m; r Smr q dk r Mu mc P t o Hk; jy Ka v h& Sdw Jh p mv Hk; a w Gy J jz p fy g
w , f/ w u , fv dkUo m b mo mp u m; w p fc kr Sm t o Hk; r sm; w Jhp mv Hk; a w Gu dko m o dc Jhr , fq dk& i f crypt v ky fx m; w Jh
p mo m; & JU t o Hk; r sm; q Hk; p mv Hk; a w Gu dk t p m; x dk; z dkUy Jjz p fy gw , f/ a e mu fw p fc ku a w mh t o Hk; t r sm; q Hk; p u m; v Hk; a w G
r Sm t p m; x dk; w mu dkv J t v m; w l t o Hk; jy KE dki fy gw , f/
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 327 -
Cracker w p fa , mu ft a e e JUu a w mh p mo m; z dki ft c sdKUu dk p dp p fa y ; E dki fw Jh application t a o ; p m; w Gu dk
a & ; z dkU& m v G, fu lr Smy g/ w u , fv dkU *.asm z dki fw p fc ku dk o i fht a e e JUu k' fa z mfr , fq dk& i f EAX? EBX? ECX p w Jh
p mv Hk; a w Gu a e a jc & mc H& r Sm jz p fy gw , f/ b ma Mu mi fhv Jq dka w mh Assembly b mo mp u m; e JU y & dk* & r fa & ; o m; & m
r Sm ' Dregister a w Gu dkt r sm; q Hk; t o Hk; jy KMu v dkUy g/
( 4 ) Le Chiffr e Indchiffr able
v QdKU0 Su fp ma w Ga & ; z dkU monoalphabetic substitution crypto [ m & mp kE Sp fa y gi f; r sm; p Gm a c w fp m; c Jhw Jh
e n f; jz p fy gw , f/ ' ga y r , fh t m& y fa w Gu frequency analysis u dkw Dx Gi fv dku fw Jht c gr Sma w mh ' De n f; v r f; [ m
t o Hk; jy K& mr Sm p dw fc s& r Ir & Sda w mhy gb l; /
' D crypto t o p f& JU r lv t a w G; t a c : u a w mh 1 4 0 4 - c kE Sp fr Sm a r G; z Gm; c Jhw Jh Leon Battista Alberti
q Du & w mjz p fy gw , f/ o lU& JUt , lt q u a w mh E Sp fc k ( o dkU) ' Dhx u fy dkw Jh crypto t u & mu dkt o Hk; jy Kjy D; o lw dkU
t c si f; c si f; u dka e & mv Ja y ; z dkUjz p fy gw , f/
r lv p mo m;
- a b c d e f g h i j k l m n o p q r stuvwxyz
Cr ypt v ky fx m; a o mp mo m; 1
- F Z B V K I X A Y M E P L S D H J O RGNQCUTW
- G O X B F W T H Q I L A Z P J D E S YVCRKUHN
Cr ypt v ky fx m; a o mp mo m; 2
- GOXBFWTHQILAZPJDESYVCRKUHN
w u , fv dkU u Re fa w mfw dkUt a e e JU hello q dkw Jhp u m; v Hk; u dk crypt v ky fr , fq dk& i f y x r t u & m h [ m A
jz p fv my gr , f/ ' kw d, t u & m e u a w mh F jz p fv my gr , f/ ' De n f; v r f; u dk t o Hk; jy K& i f hello [ m AFPAD
jz p fv my gw , f/
1 5 2 3 - c kE Sp fr Sm a r G; z Gm; c Jhw JhBlaise de Vigenre u ' De n f; v r f; u dk develop x y fv ky fc Jhw mjz p fy gw , f/
t u & mE Sp fv Hk; ( o dkU) o Hk; v Hk; t p m; o lu a w mh 2 6 v Hk; ( t * Fv dy fb mo mp u m; t w Gu f a-z) u dk t o Hk; jy Kc Jhw mjz p fy g
w , f/ o lU& JUt , lt q [ m t & i fv la w Ga y : t a jc c Hc Jha y r , fhv J ' De n f; u dka w mh Vigenre crypto v dkUa c : a 0 : Mu
y gw , f/ w p fv Hk; x u fy dkw Jh crypto t u & mu dk t o Hk; jy Kw Jht w Gu f ' Dv dk crypto r sdK; u dk polyalphabetic crypto
v dkUt r n fw y fMu y gw , f/
' De n f; r Sm y x r q Hk; v ky f& r Smu a w mh Vigenre Z , m; w p fc ku dk a & ; z dkUy g/ crypto t u & ma w Ga e mu fr Sm
r lv p mo m; a w Gv dku fjc i f; t m; jz i fh Z , m; u dka & ; q GJE dki fjy D; t w e f; t o D; o D; u dk a e & mv Sn fhjc i f; ^ a & TUjc i f; [ m jy D; c Jhw Jh
t w e f; e JU q u fE G, fr I& Sdy gw , f/
r lv p mo m;
abcdefghijklmnopqrstuvwxyz
Cr ypt v ky f& e fq GJx m; a o mZ , m;
1 BCDEFGHIJKLMNOPQRSTUVWXYZA
2 CDEFGHIJKLMNOPQRSTUVWXYZAB
3 DEFGHIJKLMNOPQRSTUVWXYZABC
4 EFGHIJKLMNOPQRSTUVWXYZABCD
5 FGHIJKLMNOPQRSTUVWXYZABCDE
6 GHIJKLMNOPQRSTUVWXYZABCDEF
7 HIJKLMNOPQRSTUVWXYZABCDEFG
8 IJKLMNOPQRSTUVWXYZABCDEFGH
9 JKLMNOPQRSTUVWXYZABCDEFGHI
10 KLMNOPQRSTUVWXYZABCDEFGHIJ
11 LMNOPQRSTUVWXYZABCDEFGHIJK
12 MNOPQRSTUVWXYZABCDEFGHIJKL
13 NOPQRSTUVWXYZABCDEFGHIJKLM
14 OPQRSTUVWXYZABCDEFGHIJKLMN
15 PQRSTUVWXYZABCDEFGHIJKLMNO
16 QRSTUVWXYZABCDEFGHIJKLMNOP
17 RSTUVWXYZABCDEFGHIJKLMNOPQ
18 STUVWXYZABCDEFGHIJKLMNOPQR
19 TUVWXYZABCDEFGHIJKLMNOPQRS
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 328 -
20 UVWXYZABCDEFGHIJKLMNOPQRST
21 VWXYZABCDEFGHIJKLMNOPQRSTU
22 WXYZABCDEFGHIJKLMNOPQRSTUV
23 XYZABCDEFGHIJKLMNOPQRSTUVW
24 YZABCDEFGHIJKLMNOPQRSTUVWX
25 ZABCDEFGHIJKLMNOPQRSTUVWXY
26 ABCDEFGHIJKLMNOPQRSTUVWXYZ
y x r t w e f; [ m Caesar roll e JU crypto t u & mw p fv Hk; jz p fy gw , f/ ' gu dk a e & mw p fa e & mp m a & TUx m;
w mjz p fy gw , f/ ' De n f; u dk t o Hk; jy Kr , fq dk& i f o i f crypt v ky fv dku fw Jht p mv Hk; t w Gu f t w e f; t o p fw p fc ku dk
t o Hk; jy K& r Smjz p fy gw , f/ Decrypt jy e fv ky fz dkUt w Gu f cracker [ m b , fp mv Hk; t w Gu f b , ft w e f; u dk t o Hk; jy K&
r v Jq dkw m o dx m; & y gr , f/ o i fht a e e JU crypt v ky fz dkU
y x r p mv Hk; t w Gu f - t w e f; ( 5 )
' kw d, p mv Hk; t w Gu f - t w e f; ( 1 4 )
w w d, p mv Hk; t w Gu f - t w e f; ( 2 1 ) p w ma w Gu dkt o Hk; jy KE dki fy gw , f/
' Dv dkr sdK; 0 Su fp ma w Gu dka z mfz dkU 0 Su fp mu dk v u fc H& & Sdo l[ m b , ft w e f; a w Gu dkt o Hk; jy K& r v Jq dkw m o dx m; &
y gr , f/ ' Dt w Gu f e n f; v r f; w p fc ku a w mhkeyword w p fc ku dkt o Hk; jy Kz dkU jz p fy gw , f/
Oy r ma jy m& & i f "Begin attack at sundown" q dkw Jhp mo m; u dk 0 Su fz dkUt w Gu f GREEN q dkw Jh
keyword u dkt o Hk; jy Kr , fv dkU, lq Mu y gp dkU/ ' gq dk keyword u dk p mo m; t a y : x y fu mx y fu ma & ; & r Smjz p fy gw , f/
' gr So m keyword x Jr Sm& Sdw Jhp mv Hk; a w G[ m 0 Su fr , fhp mo m; x Jr Sm& Sdw Jhp mv Hk; a w Ge JU c sdw fq u fr dr Smjz p fy g w , f/
G R E E N G R E E N G R E E N G R E E N (keyword)
b e g i n a t t a c k a t s u n d o w n (message)
b q dkw Jhp mv Hk; u dk 0 Su fz dkUt w Gu f keyword x Ju , lr Smu a w mh G y g/ Vigenre Z , m; t & G & Sdw mu
a w mh t w e f; ( 6 ) r Smjz p fy gw , f/ b u dkt p m; x dk; r , fht u & mu a w mh t w e f; ( 6 ) u b e JUw p fw e f; w n f; r Sm& Sdw Jh H
p mv Hk; jz p fy gw , f/
e q dkw Jhp mv Hk; u dk 0 Su fz dkUt w Gu f keyword x Ju , lr Smu a w mh R y g/ Vigenre Z , m; t & R & Sdw mu
a w mh t w e f; ( 1 7 ) r Smjz p fy gw , f/ e u dkt p m; x dk; r , fht u & mu a w mh t w e f; ( 1 7 ) u e e JUw p fw e f; w n f; r Sm& Sdw Jh V
p mv Hk; jz p fy gw , f/
' ga Mu mi fh "beginattackatsundown" p mo m; u dk "GREEN" q dkw Jh keyword o Hk; jy D; 0 Su fv dkU& v mw Jh
a e mu fq Hk; p mo m; u a w mh"HVKMAGKXEPQRXWHTUSAA" jz p fy gw , f/
Keyword a w G[ m & Sn f& i fy Jjz p fjz p f? 0 gu sa w Gu dk keyword t jz p fe JUt o Hk; jy Kw my Jjz p fjz p f o i fht a e e JU
Vigenre Z , m; u t w e f; a w Gu dk y dkr kdx n fho Gi f; E dki fw mjz p fw Jht w Gu f o i fh& JU crypto u k' fu dk jy e fa z mfE dki fz dkU
c u fc Ja p r Smjz p fy gw , f/ w u , fv dkU o i fht a e e JU frequency analysis u dkt o Hk; jy Kr , fq dk& i f b , fp mv Hk; [ m t
v Jv dkU a jy m& c u fa e r Smjz p fy gw , f/ Vigenre & JUa w GU& Sdr Iu dk 1 5 8 6 - c kE Sp fr Sm Tracict des Chiffres
r Smx kw fa z mfc Jha y r , fhv JE Sp fa y gi f; 2 0 0 a v mu fx dt o Hk; r sm; w Jht q i fha & mu fr v mc Jhy gb l; /
( 5 ) Char les Babbage & Vigenr e
Vigenre crypto & JUt p Gr f; [ m e n f; v r f; a y gi f; p Hke JU crypt v ky fE dki fw Jhp mv Hk; w p fv Hk; jz p fy gw , f/ w u , f
v dkU KING q dkw Jh keyword u dkt o Hk; jy Kr , fq dk& i f o w fr Sw fx m; w Jhp mv Hk; w p fv Hk; u dk crypt v ky fz dkU e n f; ( 4 ) e n f;
jz p fE dki fy gw , f/ p u m; v Hk; a w Gu dk crypt v ky f& mr Smv J ' Dv dky gy J/ "the" q dkw Jh p u m; v Hk; u dk crypt v ky fr , fq dk& i f
a w GUE dki fw mu a w mh DRQ? BUK? GNO e JU ZRM w dkUjz p fy gw , f/ ' gu dk decrypt v ky fz kdUy dkjy D; c u fc JE dki fa y r , fh
r jz p fE dki fb l; a w mhv Jr [ kw fy gb l; /
1 7 9 1 - c kE Sp fz Gm; Charles Babbage u a w mh ' Dv dk crypto r sdK; u dk y x r q Hk; a z mfE dki fc Jhw Jho ljz p fy gw , f/
o l[ m p m& i f; Z , m; a w Ge JUy w fo u fjy D; b 0 u dkt c sde fjy n fhjr Ky fE SHc Jhy gw , f/ ' Da e U t o u ft mr c Hu kr P Dr Sm w Gi fu s, f
p Gmt o Hk; jy Ka e Mu w Jh a r G; ^ a o q u fE T, fr Ie JUy w fo u fw Jh p m& i f; a w Gu dk jy Kv ky f& mr Sm o l[ m w p fOD; t y gt 0 i f jz p fc Jh
y gw , f/
o lp Of; p m; r dw mu a w mhw u , fv dkU "the" u dk crypt v ky fz dkU& m e n f; v r f; ( 4 ) r sdK; o m & Sdc Jhr , fq dk& i f 0 Su fp m
x Jr Sm t Mu dr fa jr mu fr sm; p Gm t o Hk; jy Kx m; w Jh p u m; v Hk; a w G[ m w ln Dw Jh crypto e n f; u dk t Mu dr fMu dr f t o Hk;
jy Kr Smy Jv dkU c e fUr Se f; r dc Jhw my g/ p mo m; a w G& Sn fa v a v t c Gi fht a & ; y dka v a v y g/ ' Dv dkt Mu dr fMu dr f t o Hk; jy Kjc i f; u
Babbage u dkVigenre crypto t w Gu f decryption e n f; v r f; u dka w GU& Sda p c Jhw mjz p fy gw , f/
Babbage & JUe n f; v r f; u a w mh & dk; & Si f; y gw , f/ 0 Su fp ma w Gx Jr Sm w p fMu dr fx u fr u t o Hk; jy Kx m; w Jh
p mv Hk; w GJa w Gu dk & Smc dki f; y gw , f/ 0 Su fp mt p & JUt u Gmt a 0 ; e JU p mv Hk; w GJE Sp fc kw ln Dw Jht c g i f; w dkUMu m; t u Gmt a 0 ; u
o i fhu dk keyword t v Hk; t a & t w Gu fe JUy w fo u fw Jh o Jv Ge fp a w Gu dk a y ; r Smjz p fy gw , f/ w u , fv dkU keyword
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 329 -
t v Hk; t a & t w Gu fu dko dc Jh& i f r lv p mo m; u dk crypt v ky f& mr Sm crypto t u & m b , fE Sp fv Hk; t o Hk; jy Ko v Jq dkw m
w Gu fc su fE dki fr Sm jz p fy gw , f/ ( a & SUy dki f; r Sm u Re fa w mf e r le mjy c Jhw mu a w mh crypto t u & m ( A-Z) 2 6 v Hk; e JUy g/ )
w u , fv dkU o i ft o Hk; jy Kc Jhw mu crypto t u & m w p fv Hk; w n f; q dk& i f monolaphabetic crypto jz p fjy D; b , fv dk
decrypt v ky f& r v Jq dkw m o i fo dr Smjz p fy gw , f/
w u , fv dkU keyword [ m 5 v Hk; jz p fa e w , fq dk& i f o i fht a e e JU y x r q Hk; t u & mt w Gu f 1? 6? 11 p w Jh
p mv Hk; a w Gu dkt o Hk; jy K& r Smjz p fy gw , f/ ' kw d, t u & mt w Gu f 2? 7? 12 p w Jh p mv Hk; a w Gu dkt o Hk; jy K& r Smjz p fy gw , f/
Keyword x Jr Sm& Sdw Jh p mv Hk; a w Gv dky J o i fht a e e JU a jr mu fr sm; v Sp Gma o m t u & ma w Gu dkt o Hk; jy K& r Sm jz p fy gw , f/
b , ft u & mu dkt o Hk; jy K& r , fq dkw m b , fv dko d& SdE dki fy go v J/ ' Dt w Gu ft a jz u a w mh o i fc e fUr Se f; r dr Smy g/
Frequency analysis jz p fy gw , f/ w u , fv dkU o i fht a e e JU keyword & JUt v Hk; t a & t w Gu fu dk o dr , fq dk& i f o i f
t o Hk; jy K& r Smu frequency analysis y g/ r Sw fx m; & r Smu a w mh crypto t u & m[ m t & i ft w e f; u p mv Hk; a w Gu dk
a e & ma & TUx m; w Jh& dk; & dk; t u & m w p fv Hk; o mjz p fy gw , f/
Vigenr e u dk assembler w Gi fp r f; o y fjc i f;
Vigenre crypto u dk assembler r Smp r f; o y fz dkU r Sw fOmP fr Sm Vigenre Z , m; t a jr mu ft r sm; v dkt y f
y gw , f/ u Re fa w mfw dkUt a e e JU index e JU key char pointer a w Gt r sm; Mu D; v dkt y fy gw , f/ e r le my & dk* & r fw p fy k' f
u dkMu n fhMu & a t mi f/
Cr ypting:
add al,ah ;al is clear char and ah is key char
sub al,"A"+"A"
cmp al,25
jng @F
sub al,26 ;Overflow, wrap around
@@:
add al,"A" ;al is now crypted char
Decr ypting:
sub al,ah ;al is crypt char and ah is key char
cmp al,0
jge @F
add al,26 ;Underflow, wrap around.
@@:
add al,"A" ;al is now clear char
' D Assembly u k' fa w Gu dk e m; v n fz dkUt w Gu f Vigenre Z , m; r Sm t u & m 2 6 v Hk; & Sdw m t r Sw f& y g/
w p fv Hk; p D[ m jy D; c Jhw Jht w e f; u dkw p fa e & mp m a & TUy gw , f/
w u , fv dkU "the" q dkw Jhp u m; v Hk; u dk KING q dkw Jh keyword e JU crypt v ky fr , fq dk& i f y x r p mv Hk; t
t w Gu f 0 Su fx m; jy D; o m; p mv Hk; [ m t w e f; ( 1 0 ) K e JU t p mv Hk; w dkUw p fx y fw n f; u sw Jha e & m D jz p fv my gr , f/
' gu dkMu n fhz dkU a e mu fw p fe n f; u a w mh A e JUp w Jht w e f; u K & Sdw Jh column u dko Gm; y g/ Column 10
jz p fy gw , f/ ( A column u a w mhcolumn 0 jz p fy gw , f/ ) T column & Sd& mjz p fw Jhcolumn 19 u dk K column
& Sd& m column 10 e JYa y gi f; & i f 29 & y gr , f/ t * Fv dy ft u & mr Sm p mv Hk; 2 6 v Hk; y J& Sdw Jht w Gu f overflow jz p fa e y g
w , f/ 29 jz p fw Jht w Gu f a e mu fw p fMu dr fq dk& i f 0(A)? 27(B)? 28(C)? 29(D)? 30(E) p o n fjz i fhjz p fw Jht w Gu f
D column & Sd& mu dk& y gw , f/ ' gu a w mhT p mv Hk; u dk K key t o Hk; jy Kw Jht c g t p m; x dk; r , fhp mv Hk; w Gu fc su fy Hky g/
u Re fa w mfw dkUt a e e JU decryption v ky f& mr Smv J ' Dw ln Dw JhOy a ' o u dk t o Hk; jy Ky gw , f/ ' ga y r , fh ' Da e & m
r Sma w mh crypt v ky fx m; w Jhp mv Hk; u a e key p mv Hk; u dk E Iw f, ly gw , f/ ' ga Mu mi fh overflow u dk& Smr , fht p m;
underflow u dko m& Smy gw , f/ ' Da v mu fq dk& i f Vigenre crypto u dke m; v n fa v mu fjy Dx i fy gw , f/ ' ga Mu mi fh
decrypt v ky fx m; w Jha t mu fy gu k' fu dka z mfMu n fhy g/
BBLM RS VRJ XTYOETOSWP UNTYOJH XBLHCOQ DLVTSQX FHO T PRQMJLJ UJG?
QXJ CD FJDG YK JWTBTKM FHO BB DCXLYCHDS HYW WSBUDTOS NZ IUAA GNNS,
MQE QDMYC BB UUOI NZ VJRTI LLZVNRKOX.
QSTC IU DMY OBOFGBJHNX KEVGJYY XAOVSH UYW TIPUD?
YCHCIE SX ODBWG C PJUEANR....MSSEJ BB UUSSA EAN WJYQY NARCMOS.
Vigenr e u dka & Smi f& Sm; jc i f;
Vigenre crypto t p Gr f; x u fjc i f; u o lUu dkt o Hk; jy K& w m y dkr dkc u fc Ja p y gw , f/ Monoalphabetic
crypto x u fy dkr dkt p Gr f; x u fjy D; Vigenre crypto x u ft o Hk; jy K& w m y dkr dkv G, fu lw mu a w mh homophonic
substitution crypto y Jjz p fy gw , f/
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 330 -
' D crypto r Sma w mh o i fht a e e JU p mv Hk; w p fv Hk; u dk p mv Hk; a w Gt r sm; Mu D; e JU t p m; x dk; E dki fjy D; t p m; x dk; w Jh
p mv Hk; t a & t w Gu f[ m p mv Hk; t o Hk; jy Kr Ie JU t c sdK; u sy gw , f/ w u , fv dkU p mv Hk; a u dkt o Hk; jy Kr I[ m 9 % & Sdr , fq dk
& i f? u Re fa w mfw dkUt a e e JU a p mv Hk; t w Gu f t p m; x dk; & r Smu t u & m 8 v Hk; jz p fy gw , f/ 0 Su fr , hfp mo m; x Jr Sm a
q dkw Jh p mv Hk; u dka w GUw dki f; u Re fa w mfw dkUt a e e JU a e JU assign v ky fx m; w Jh b , ft u & m 8 v Hk; e JUr q dk t p m; x dk; & r Sm
jz p fy gw , f/ ' D8 v Hk; r Sma w mh b , fp mv Hk; jz p fjz p f t a & ; r Mu D; y gb l; / p mo m; u dk 0 Su fjy D; w Jht c sde fr Sma w mh a t w Gu f
t p m; x dk; v dku fw Jh p mv Hk; w dki f; [ m 0 Su fp mx Jr Sm t o Hk; jy Kr IE Ie f; [ m 1 % y J& Sdr Smjz p fy gw , f/ w u , fv dkU b ( o dkU)
t jc m; p mv Hk; a w Gq dk& i fv J t o Hk; jy Kr IE Ie f; [ m 1 % y J& Sdr Smjz p fy gw , f/ b q dk& i fa w mh u Re fa w mfw dkUt a e e JU t u & m
2 v Hk; x d t p m; x dk; & r Sm jz p fy gw , f/ r lv p mo m; x Ju b , fp mv Hk; u dk 0 Su fv dku f& i fy Jjz p fjz p f? 0 Su fp mx Jr Sma w mh
o lw dkU& JU t o Hk; jy Kr IE Ie f; u 1 % y J& Sda e r Smy g/
a t mu fr Sma z mfjy x m; w mu a w mh homophonic substitution crypto e JUy w fo u fw Jhe r le my g/ ' D* P e f;
a w Gu dkt o Hk; jy Ky gw , f/
a b c d e f g h i j k l m n o p q r s t u v w x y z
09 48 13 01 14 10 06 23 32 15 04 26 22 18 00 38 94 29 11 17 08 34 60 28 21 02
12 81 41 03 16 31 25 39 70 37 27 58 05 95 35 19 20 61 89 52
33 62 45 24 50 73 51 59 07 40 36 30 63
47 79 44 56 83 84 66 54 42 76 43
53 46 65 88 71 72 77 86 49
67 55 68 93 91 90 80 96 69
78 57 99 75
92 64 85
74 97
82
87
98
t o Hk; jy KE Ie f; 1 % & Sdw Jh t u & mw dki f; t w Gu f 0 Su fp mx Jr Sm frequency analysis u dkt o Hk; jy Kz dkUe n f; v r f;
r & Sdy gb l; / ' gq dkjy e fa z mfv dkUr & a w mhb l; v m; / ' Dv dka w mhv Jr [ kw fy gb l; /
Decrypter r Smv J o Jv Ge fp a w G& Sdy gw , f/ b mo mp u m; w dki f; & JU p mv Hk; w dki f; r Sm o lU& JUy i fu dkt & n ft c si f;
e JU t jc m; p u m; v Hk; a w GMu m; q u fE G, fr I & Sdy gw , f/ w u , fv dkU homophonic substitution crypto u dko Hk; c Jh& i f
a w mh' gu dkc GJjc m; E dki fy gw , f/
Oy r mjy & & i f t * Fv dy fb mo mp u m; q a e mu fr Smq dk& i f u t jr Jw r f; v dku f& y gw , f/ t jc m; b , fp mv Hk; r S
v dku fv dkU r & y gb l; / w u , fv dkU homophonic substitution crypto e JU 0 Su fx m; w Jht * Fv dy fp mo m; u dk decrypt
v ky fr , fq dk& i f u Re fa w mfw dkUt a e e JU q q dkw Jhp mv Hk; u dk& Smjy D; t u & mw p fv Hk; ( o dkU * P e f; w p fv Hk; ) e JU t & i ft p m; x dk;
& r Smjz p fy gw , f/ u u dkt o Hk; jy KE Ie f; [ m p mv Hk; a w Gt m; v Hk; & JU 3 % jz p fa Mu mi f; o dx m; w Jht w Gu f u a e & mr Sm t u & m
3 v Hk; e JU t p m; x dk; & a u mi f; x dk; & y gv dr fhr , f/
w u , fv dkU 0 Su fp mx Jr Sm w ln Dw Jht u & m 3 v Hk; v dku fw Jh p mv Hk; w p fv Hk; u dk a w GUc Jh& i f u Re fa w mfw dkUt a e e JU
, HkMu n f& r Smu ' Dt u & ma w G[ m u u dkq dkv dkc si fw mjz p fjy D; y x r p mv Hk; u a w mh q jz p fy gw , f/ t jc m; p mv Hk; a w G
u dka w mh a & G; x kw fz dkU c u fy gv dr hfr , f/ ' ga y r , fh o lw dkUt c si f; c si f; q u fE G, fr Ia w Gu b , fp mv Hk; jz p fw , fq dkw m
w Gu fx kw fE dki fy gv dr fhr , f/ ' Dv kdcrypto r sdK; u dkjy e fa z mfE dki fz dkU jz p fE dki fa y r , fh& dk; & Si f; v Sw Jhmonoalphabetic crypto
x u fp m& i fa w mht r sm; Mu D; p dw fc s& y gw , f/
o mr e fu mv QHu mMu n fhr , fq dk& i fa w mh homophonic substituion crypto [ m polyalphabetic
crypto t r sdK; t p m; t c sdKUe JU w lo a , mi fa , mi f & Sdy gw , f/ r lv p mo m; & JU p mv Hk; w dki f; u dk t u & mw p fc kc ke JU t p m;
x dk; E dki fa y r , fho lw dkUr Sm x i f& Sm; w Jhu GJjy m; jc m; e m; c su f & Sdy gw , f/
t a y : u Oy r mr Sm a p mv Hk; u dk r w ln Dw Jh* P e f; 8 v Hk; e JU a z mfjy c Jhy gw , f/ ' D* P e f; a w G[ m a u dka z mfjy jy D;
a w p fv Hk; w n f; u dko m a z mfjy E dki fMu y gw , f/ Polyalphabetic crypto r Sma w mhr lv p mo m; x Ju p mv Hk; w p fv Hk; u dk
p mv Hk; a jr mu fr sm; p Gme JU a z mfjy E dki fy gw , f/ ' ga y r , fh t p m; x dk; r , fh p mv Hk; a w Gu dka w mh r lv p mo m; x Jr Smy gw Jh p mv Hk;
a w Ge JUy J t p m; x dk; E dki fy gw , f/ ' ga Mu mi fhr dkUv J homophonic substituion crypto u dk monoalphabetic crypto
v kdUy J a jy mE dki fw my g/ Crypto t u & mw p fv Hk; u dk z e fw D; jy D; c sde fr Sma w mh w p fa v Qmu fv Hk; t o Hk; jy Ko Gm; r Smjz p fy g
w , f/ p mv Hk; w p fv Hk; u dk t p m; x dk; z dkUt w Gu f p mv Hk; w p fv Hk; t p m; x dk; & mr Sma w mh u GJjy m; r Ir & Sdy gb l; / w u , fv dkU
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 331 -
poly alphabetic crypto u dko Hk; r , fq dk& i fa w mh r w ln Dw Jh crypto t u & ma w Gu dk t q u fr jy w f a jy mi f; a y ;
a e & r Sm jz p fy gw , f/
Homophonic substituion crypto e JU decrypt v ky fx m; w Jha t mu fy gu k' fu dka z mfMu n fhy g/
HNE 0IQWtG OY98CK5u YfTB7| pA v2] J 1W[UZjweh3 X i
gv qmV-sSkboDI6 }dcaYz x L t2W SDT
2.2, 9u ]H0|C X13-5 Z7gycK. Ul px8MEeikI tDQw1GB o
J A 3VAObfuch[ jqvsz| W2] mV-Sd}x 2.2 g
vI2 A-SHDK0T ]EZ5t9Q GU7u, rWc{ B |xy1O3 ve
kNJ Dpn V 2W].
( 6 ) Playfair
Playfair crypto u kdz e fw D; c Jhw mu a w mhLyon Playfair jz p fy gw , f/ ' Dcrypto [ m r lv p mo m; x Jr Sm
& Sdw Jhp mv Hk; E Sp fv Hk; w dki f; u dk t jc m; p mv Hk; w GJe JU t p mx dk; w mjz p fy gw , f/ p mo m; u dk crypt v ky f& mr Sme JU decrypt v ky f
& mr Sma w mh a y ; y dkUo le JU v u fc H& & Sdo lw dkU[ m keyword w p fc ku dkt o Hk; jy Kz dkU Mu dKw i fo a b mw ln Dx m; & r Sm
jz p fy gw , f/
' Dcrypto u dkt o Hk; jy Ky Hku a w mh' Dv dky g . . .
p mv Hk; a w Gu dk 5x5 (a-z) p w k& e f; y Hkc sa & ; y g/ I e JU J u a w mhw ln Dw Jha e & mr Sm & Sda e & y gr , f/ Keyword u a e
p w i fy g/ Keyword t a e e JU CHARLES u dko Hk; r , fq dk& i f & & Sdr Smu a w mh-
C H A R L
E S B D F
G I/J K M N
O P Q T U
V W X Y Z
' Dha e mu fr Sma w mh o i fht a e e JU message p mo m; u dk bigram v dkUa c : w Jh p mv Hk; w GJa w Gt a e e JU y dki f; v dkU& jy D
jz p fy gw , f/ Bigram w kdi f; r Sm r w ln Dw Jhp mv Hk; a w Gy g0 i f& y gr , f/ ' gha Mu mi fh o i fht a e e JU x u dk p mv Hk; w ln Dw Jh
t w GJr Smx m; & y gr , f/ ' Dv dkr Sr [ kw f& i fa w mhw ln Dw Jhbigram r Sm t q Hk; o w f& y gv dr fhr , f/
r lv p mo m;
We meet at hammersmith bridge at seven.
Bigr am x J& Sdp mo m;
we-me-et-at-ha-mx-me-rs-mi-th-br-id-ge-at-se-ve-nx
' Dha e mu fr Sma w mh p m0 Su fw m p w i fy gw , f/ Bigram w dki f; u a w mh a t mu fy gt ky fp kw p fc kc kx Ju
jz p fE dki fy gw , f/
1 / p mv Hk; w GJ[ m w ln Dw Jhr sOf; w p fa Mu mi f; w n f; a y : r Sm jz p fy gw , f/
2 / p mv Hk; w GJ[ m column w p fc kw n f; r Sm jz p fy gw , f/
3 / t a y : E Sp fc kp v Hk; r jz p fE dki fb l; /
1 / w u , fv dkU p mv Hk; E Sp fv Hk; v Hk; [ m w ln Dw Jh row w p fc kw n f; r Sm & Sda e c Jh& i f? o lw dkUu dk n mz u fu w p fv Hk; p De JU
t p m; x dk; & y gr , f/ MI q dk& i f NK jz p fv my gr , f/ w u , fv dkU p mv Hk; w p fv Hk; [ m a e mu fq Hk; p mv Hk; jz p fa e c Jh& i f ' D
row r Sm& Sdw Jhy x r q Hk; p mv Hk; e JU t p m; x dk; & r Sm jz p fy gw , f/
2 / w u , fv dkU p mv Hk; w GJ[ m w ln Dw Jh column w p fc kw n f; r Sm & Sda e c Jh& i f? o lw dkU& JU a t mu fu p mv Hk; w p fv Hk; p De JU
t p m; x dk; & y gw , f/ GE q dk& i f OG jz p fv my gr , f/ w u , fv dkU p mv Hk; w p fv Hk; [ m a e mu fq Hk; row r Smo m & Sda e
c Jh& i f y x r q Hk; row u p mv Hk; e JU t p m; x dk; & r Smjz p fy gw , f/ YR q dk& i f RD jz p fv my gr , f/
3 / ' DE Sp fc kv Hk; x Ju r [ kw fc Jh& i f ' Dv dk v ky fa q mi f& r Sm jz p fy gw , f/ y x r p mv Hk; u dk0 Su fz dkU ' kw d, p mv Hk; & Sd& m
column r a & mu fc i f row u dkMu n fh& r Smjz p fy gw , f/ ' Dp mv Hk; E Sp fv Hk; w dkU q Hk& ma e & m[ m y x r p mv Hk; u dk t p m; x dk; z dkU
jz p fy gw , f/ ' kw d, p mv Hk; u dk0 Su fz dkUt w Gu fu a w mhy x r p mv Hk; & JU column r a & mu fc i f row jz p fy gw , f/ ' Dp mv Hk;
E Sp fv Hk; w dkU q Hk& ma e & m[ m ' kw d, p mv Hk; u dk t p m; x dk; z dkU jz p fy gw , f/ ' ga Mu mi fh VI [ m WG jz p fv mjy D; SV
u a w mhEW jz p fv my gw , f/
w u , fv dkU r lv p mo m; & JU p mv Hk; a w Gu dk a v ; a x mi fhu Gu fw p fc k& JU a x mi fha w Gt a e e JU a w GUjr i fE dki fjy D; t p m;
x dk; v dku fw Jhp mv Hk; a w Gu dka w mhq e fUu si fb u f a x mi fha w Gr Sm a w GUjr i f& r Smjz p fy gw , f/
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 332 -
Bigr am p mo m;
we me et at ha mx me rs mi th br id ge at se ve nx
Cr ypt v ky fx m; a o mp mo m;
VSDGODQRARKYDGDHNKRPADSMOGQRBSCGKZ
( 7 ) ADFGX cr ypto
ADFGVX crypto r Sma w mh a e & mv Jw ma & m? t p m; x dk; w my g t o Hk; jy Ky gw , f/ Crypto u dk t o Hk; jy Ky Hk
u ' Dv dky g/ p w k& e f; y Hk& JU a e & m 3 6 c kr Sm A-Z e JU 0-9 u dk Mu HK& ma & ; c sy g/ Row e JU column r Sm ADFGVX v dkU
t r n fw y fy g/ p w k& e f; u Gu fx Ju p mv Hk; a w Gu a w mh key & JUw p fp dw fw p fa ' o jz p fjy D; ' D0 Su fp mu dka z mfr , fho lq Dr Sm
' Dp w k& e f; u Gu f & Sd& y gr , f/
A D F G V X
A 8 p 3 d l n
D l t 4 0 a h
F 7 k b c 5 z
G j u 6 w g m
V x s v i r 2
X 9 e y 0 f q
y x r t q i fhu b , f row e JU b , f column r Sm 0 Su fr , fhp mo m; x Ju p mv Hk; & Sda e o v Jq dkw m Mu n fh& y g
r , f/ ' Dha e mu fr Sma w mh' Dp mv Hk; & Sd& ma e & mu dk a & G; c s, f& y gr , f/ ' DOy r mt w Gu fq dk& i f 8 u dk AA e JUt p m; x dk; E dki fjy D; p
u dkAD e JU t p m; x dk; & r Smjz p fy gw , f/
r lv p mo m;
Attack at 2230
Cr ypt v ky fx m; a o mp mo m;
DV DD DD DV FG FD DV DD VX VX AF XG
' g[ m & dk; & Si f; v Sw Jh monoalphabetic substitution crypto jz p fw Jht w Gu f frequency analysis e JU
t v G, fw u l jy e fa z mfE dki fy gw , f/ ' kw d, t q i fhu a w mh a e & mc si f; v Jz dkU jz p fy gw , f/ a e & mc si f; v Jw mu a w mh key
w p fc ka y : r lw n fy gw , f/ ' DOy r mr Sma w mh MARK q dkw Jh key u dko Hk; y gw , f/ ' D key u dka w mh v u fc H& & Sdw Jh
o lu y g o dx m; & r Smjz p fy gw , f/
a e & mv Jw mu dka w mha t mu fy gt w dki f; jy Kv ky f& r Sm jz p fy gw , f/
p w k& e f; u Gu f t o p fx Jr Sm& Sdw Jh y x r q Hk; row r Sm key p mv Hk; a w Gu dkc sa & ; y g/ ' Dha e mu fr Sma w mh y x r
t q i fhw ke f; u 0 Su fv dku fw Jhp mo m; a w Gu dk key & JUt a & t w Gu ft w dki f; c sa & ; y g/ Key x Jr Sm& Sdw Jhp mv Hk; a w Gu dk
i , fp OfMu D; v dku fp Dy g/ ' gq dk t jc m; column w p fc k& & Sdv my gv dr fhr , f/
M A R K
D V D D
D D D V
F G F D
D V D D
V X V X
A F X G
A K M R
V D D D
D V D D
G D F F
V D D D
X X V V
F G A X
a e mu fq Hk; cr ypt v ky fv dku fa o mp mo m;
VD DD DV DD GD FF VD DD XX VV FG AX
b ma Mu mi fh A? D? F? G? V e JU X u dk t o Hk; jy K& o v Jq dk& i fa w mh ' Dp mv Hk; a w Gu dk Morse t u & mt a e e JU
t o Hk; jy Kv dkUjz p fy gw , f/ ' Dv dkjy Kv ky fjc i f; t m; jz i fh0 Su fp mu dka y ; y dkUw Jht c sde fr Sm t r Sm; e n f; E dki fv dkUjz p fy gw , f/
a u mi f; jy D/ Crypto o a b mw & m; a w Gu dk o djy D; w Jha e mu fr Sma w mh crypto algorithm t c sdKUu dk a v hv m
Mu n fhy gr , f/ t o Hk; t r sm; q Hk; crypto algorithm a w Gu a w mh ADELR32? AES? BLOWFISH? CAST?
CRC16/32? DES? DESX? FROG? GOST? HAVAL? ICE? ICELOCK? MARS? MD4/5? MISTY?
NEWDES? Q128? RC2/5/6? RIJNDAEL? RIPEMD? RSA? SHA? SHARK? SKIPJACK?
SNEFRU? SQUARE? TIGER? TWOFISH e JU ZLIB p o n fw dkUjz p fy gw , f/
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 333 -
' D algorithm a w Gt m; v Hk; x Jr Smr S MD5 u dka v hv mMu n fhy gr , f/ Xilisoft u x kw fw Jh application
t m; v Hk; [ m MD5 u dkt o Hk; jy Kjy D; registration routine u dka & ; o m; x m; Mu w m jz p fy gw , f/ ' ga Mu mi fh MD5 u dk
t o Hk; jy Kx m; w JhXilisoft Audio Converter 2.1.x & JU registration routine u dka v hv mMu n fhMu & a t mi f/
( 8 ) MD5 q dko n fr Sm . . .
MD5 (Message Digest 5) u dk 1 9 9 2 - c kE Sp fr Sm y ga r mu Ronald L. Rivest u z e fw D; c Jhw mjz p fy g
w , f/ MD5 hash algorithm u a w mhone-way hash algorithm a w Gx Ju w p fc kjz p fa y r , fht o Hk; t r sm; q Hk; ?
, HkMu n f& q Hk; ? e mr n ft Mu D; q Hk; jz p fy gw , f/
Hash algorithm q dkw mu a w mh t c su ft v u fa w Gu dk u sp fv sp fp Gmjz p fE dki fa & ; t w Gu f x kw fv ky fx m; w Jh?
t w dkc sHK; x m; w Jho c sFm function w p fc ko mjz p fy gw , f/ ' Dv kdt w dkc sHK; jy D; & v mw Jht c su ft v u fa w Gu dk hash w e fz dk;
( o dkU) hash v dkUa c : y gw , f/ ' Dw e fz dk; u dk w Gu fc su fw Jhjz p fp Ofu dka w mh hashing v dkUa c : y gw , f/ Hash algorithm
a w Gt m; v Hk; & JU t a jc c Hu a w mh w ln Dw Jh o c sFm function u dkt o Hk; jy Kjy D; w Gu fc su fx m; w Jh hash E Sp fc k[ m r w ln Dc Jh
& i f input a w G[ m w e n f; e n f; e JU r w ln Dv dkUjz p f& y gr , f/ Hash algorithm a w Gu dk "one-way" v dkUa c : q dk& jc i f;
t a Mu mi f; u a w mhhash w e fz dk; u a e r lv a ' w ma w Gu dkjy e fv n fr & , lE dki fa w mhv dkUy g/
MD5 [ m message w p fc k ( o dkU) a ' w mz dki fw p fc kt w Gu f hash w p fc ku dkw Gu fc su f& ma w mh t v Ge f
a u mi f; r Ge fw Jh hash algorithm a u mi f; w p fc kjz p fy gw , f/ MD5 & JU w du sw Jhp mv Hk; t a & t w Gu f& Sdw Jh u sp fv sp fp Gm
a z mfjy jc i f; u dk message digest ( o dkU) fingerprint ( o dkU) MD5 hash v dkUa c : y gw , f/ MD5 message digest
[ m t a o o w fr Sw fx m; w Jh 128-bits jz p fy gw , f/ (128-bits = 16 Bytes = 4 DWords) MD5 t a Mu mi f;
t a o ; p dw fo dc si f& i fa w mh Google t o Hk; jy Kjy D; ]RFC 1321 - The MD5 Message-Digest Algorithm}
p mw r f; u dk & Sma z Gz w f& IE dki fy gw , f/ ' Dp mw r f; r Sm message digest w Gu fc su fy Hk? MD5 & JUt m; o mc su fe JU t m; e n f;
c su fa w Gu dka w GU& SdE dki fy gw , f/
( 9 ) Xilisoft Audio Conver ter \ ser ial u dk& Sma z Gjc i f;
Xilisoft & JU application a w Gr Sm registration routine u dk UILib71.dll? UILib8_MFCDll.dll z dki fr Sm
a & ; o m; x m; a Mu mi f; ]Teleport Pro 1.61} o i fc e f; p me d* Hk; r Sm a jy mc Jhw m jy e ft r Sw f& y g/ Xilisoft Audio
Converter r Sma w mh registration routine t w Gu f UILib71.dll z dki fu dk t o Hk; jy Ky gw , f/ ' ga Mu mi fh UILib71.
dll u dkPEiD e JUp p fa q ; Mu n fhy gr , f/ y Hk( 1 ) /
y Hk( 1 )
y Hk( 1 ) r Smjr i f& w Jht w dki f; UILib71.dll u dk Visual C++ 7.x e JUa & ; o m; x m; w mjz p fy gw , f/ b , f
protector e JUr S protect v ky fx m; jc i f; r & Sdy gb l; / u dkE Sdy fjy D; Krypto Analyzer u dka & G; v dku fw Jht c sde fr Sma w mh
y Hk( 2 ) t w dki f; jr i f& y gw , f/
y Hk( 2 )
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 334 -
y Hk( 2 ) t & q dk& i fa w mh UILib71.dll z dki fr Sm MD5 algorithm u dkt o Hk; jy Kx m; y Hk& y gw , f/ MD5 routine
& Sd& ma e & mu dkv Jjy x m; y gw , f/ ' Da e & mu dkMu n fhv dku fMu & a t mi f/ y Hk( 3 ) /
y Hk( 3 )
y Hk( 3 ) & JU t a y : z u fu dk scroll e n f; e n f; q GJjy D; Mu n fhr , fq dk& i fa w mh MD5 routine & JUt p u dk a w GU& r Smy g/
y Hk( 4 ) /
y Hk( 4 )
VA 1001E790 a e & mu dk r Sw fx m; y g/ MD5 algorithm u dk o i fa v hv mv dkw Jht c g ' Da e & mr Sm v mMu n fh
E dki fv dkUy g/ u Re fa w mfu a w mh MD5 algorithm u kd p dw f0 i fp m; jc i f; r & Sdy gb l; / / b ma Mu mi fhv Jq dka w mh
Xilisoft application a w Gr Sm algorithm w p fc ke JUw p fc kw ln Djc i f; r & Sdv dkUy g/
a u mi f; jy D/ Xilisoft Audio Converter & JU exe z dki fjz p fw Jh audioenc.exe z dki fu dk Olly r Smz Gi fhy gr , f/
y Hk( 5 ) /
y Hk( 5 )
' gq dk y Hk( 5 ) r Smjr i f& w Jht w dki f; entrypoint & Sd& mu dk a & mu fv my gr , f/ F9 u dkE Sdy fjy D; y & dk* & r fu dk run y g/
jy D; & i f register v ky fMu n fhy g/ y Hk( 6 ) /
y Hk( 6 )
y Hk( 6 ) t w dki f; register v ky fjy D; c sde fr Sma w mhy Hk( 7 ) t w dki f; jr i f& y gw , f/
y Hk( 7 )
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 335 -
' gq dk& i fa w mho i fb mv ky f& r , fq dkw m o do i fhy gjy D/ Olly r Sm F12 (Pause) u dkE Sdy fjy D; y & dk* & r f t v ky fv ky f
a e w mu dkc P & y fy gr , f/ jy D; & i f Ctrl+K (Call Stack) u dkE Sdy fjy D; y Hk( 7 ) u BadBoy message box u dk b , fu a e
a c : o Hk; a e w mv Jq dkw m Mu n fhy gr , f/ y Hk( 8 ) /
y Hk( 8 )
y Hk( 8 ) r Sm p dw f0 i fp m; p & ma w Ga w GU& y gw , f/ ' Dmessage box u dk UILib71.dll z dki fu a e a c : o Hk; w my g/
t w dt u sa jy m& & i fa w mh ImRegDlg dialog & JU OnOK function u a e a c : o Hk; x m; w my g/ ' ga Mu mi fh <JMP.
&MFC71.#1123> a e & mr Sm right-click E Sdy fjy D; Execute to r etur n (F4) u dka & G; v dku fy g/ jy D; & i f y Hk( 7 ) u OK
button u dkE Sdy fv dku f& i f y Hk( 9 ) t w dki f; jr i f& y gr , f/
y Hk( 9 )
y Hk( 9 ) u dk a o a o c smc smMu n fhy g/ o i f& dku fx n hfv dku fw Jh name e JU license code a w Gu dk SaveRegInfo
function o Hk; jy D; registry x Jr Sm y x r q Hk; o dr f; y gw , f/ ' Dha e mu fr Sma w mh y Hk( 6 ) r Sm o i f& kdu fx n hfv dku fw Jh key u dk
IsValidRegInfo o Hk; jy D; r Se f^ r r Se f p p fw mjz p fy gw , f/ w u , fv dkU key r r Se fc Jh& i fa w mh y Hk( 7 ) u BadBoy
message u dk jy r Smjz p fy gw , f/ y & dk* & r f t v ky fv ky fy Hku dk o dE dki fa t mi fv dkU SaveRegInfo e JU IsValidRegInfo u dk
p p fa q ; Mu n fh& a t mi f/
SaveRegInfo a e & mu dka & G; v dku fjy D; Enter key u dkE Sdy fv dku fy g/ y Hk( 1 0 ) t w dki f; routine & Ju t p u dk
jr i fy gr , f/
y Hk( 1 0 )
y Hk( 1 0 ) & JU a t mu fe m; u dkscroll q GJjy D; Mu n fhc sde fr Sma w mhy Hk( 1 1 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 1 1 )
y Hk( 1 1 ) u String2HexA u a w mh o i f& dku fx n fhv dku fw Jh license code u dk HEX * P e f; t a e e JU
a jy mi f; v Ja y ; w m jz p fy gw , f/
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 336 -
y Hk( 1 2 )
y Hk( 1 2 ) u a w mh string u a e hex u dka jy mi f; a y ; w Jh loop y g/ ' D loop u dk v ky fa q mi fjy D; c sde fr Sma w mh
MyanmarCrackingTeam-1234-5678-9012-3456 [ m BF A7 26 FF 5B A1 AD CF 43 A7 94 F1 82 16
6F 9C 6E 2C 4C DB 51 20 47 4A F5 B0 45 D3 CC 20 47 3D DF FD 19 53 D7 B7 jz p fo Gm; y gw , f/
y Hk( 1 3 ) /
y Hk( 1 3 )
' Dha e mu fr Sma w mhRegSetValueExA API o Hk; jy D; ' Dhex w e fz dk; a w Gu dk registry r Sm o Gm; o dr f; w m jz p fy g
w , f/ y Hk( 1 4 ) /
y Hk( 1 4 )
ImRegDlg:SaveRegInfo() function & JUv ky fa q mi fc su fu a w mh ' Dt x dy gy J/ ImRegDlg:IsValid
RegInfo() function & JU t v ky fv ky fy Hku dk q u fjy D; a v hv mMu n fhy gr , f/
IsValidRegInfo a e & mu dka & G; v dku fjy D; Enter key u dkE Sdy fv dku fy g/ y Hk( 1 5 ) t w dki f; routine & JUt p u dk
jr i fy gr , f/
y Hk( 1 5 )
y Hk( 1 5 ) & JU a t mu fe m; u dkscroll q GJjy D; Mu n fhc sde fr Sma w mhy Hk( 1 6 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 1 6 )
1 / RegQueryValueExA API u dko Hk; jy D; registry x Jr Sm& Sdw Jh code key u dkz w fy gw , f/ ' Dha e mu fr Sma w mh
z w fv dkU& w JhHEX key u dkHex2StringA function o Hk; jy D; string t jz p fjy e fa jy mi f; y gw , f/
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 337 -
y Hk( 1 7 )
2 / MFC71.3997 function u dkv ky fa q mi fjy D; c sde fr Sma w mhkey u dk MyanmarCrackingTeam-1234-5678-9012-
3456 t p m; MyanmarCrackingTeam- t jz p fa jy mi f; v Jy gw , f/
y Hk( 1 8 )
3 / MFC71.781 function u a w mha q mhz f0 Jv f& JU internal name jz p fw Jhaudioconverter u dkz w fw mjz p fy gw , f/
y Hk( 1 9 )
4 / MFC71.4085 function u dkv ky fa q mi fjy D; c sde fr Sma w mh MSVCR71.dll & JU _mbsupr() API a Mu mi fh
MyanmarCrackingTeam- t p m; MYANMARCRACKINGTEAM- t jz p fa jy mi f; v Jo Gm; y gw , f/
y Hk( 2 0 )
5 / CALL UILib71.00342170 u a w mhmemcpy() API u dkE Sp fc go Hk; jy D; MYANMARCRACKINGTEAM
e JU audioconverter w dkUu dk a e & mc sy gw , f/ jy D; & i f o lw dkUE Sp fc ku dk a y gi f; y gw , f/ ' Dt c g MYANMAR
CRACKINGTEAM-audioconverter & v my gw , f/
y Hk( 2 1 )
6 / CALL UILib71.0035E730 u a w mh o i fv dkc si fw Jh hash u dkw Gu fx kw fa y ; r Smjz p fy gw , f/ CALL
UILib71.0035E730 a e & mu dka & G; v dku fjy D; Enter key u dkE Sdy fv dku fy g/ y Hk( 2 2 ) t w dki f; routine & JUt p u dkjr i fy gr , f/
y Hk( 2 2 )
6 . 1 / CALL UILib71.0035E680 a e & mu dka & G; v dku fjy D; Enter key u dkE Sdy fv dku fy g/ y Hk( 2 3 ) t w dki f; routine
& JUt p u dkjr i fy gr , f/
y Hk( 2 3 )
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 338 -
y Hk( 2 3 ) & JU CALL 3 c ku dk r Sw fo m; y g/ CALL 0035E760 u a w mh hash w e fz dk; u dk initialize v ky fw my g/
CALL 0035F070 e JU CALL 0035F130 u a w mhhash u dkw Gu fx kw fa y ; w JhCALL u dka c : o Hk; w mjz p fy gw , f/
6 . 1 . 1 / CALL UILib71.0035E760 a e & mu dka & G; v dku fjy D; Enter key u dkE Sdy fv dku fy g/ y Hk( 2 4 ) t w dki f; routine
& JUt p u dkjr i fy gr , f/
y Hk( 2 4 )
y Hk( 2 4 ) r Smjr i f& w Jhu k' fa w Gu dk execute v ky fjy D; c sde fr Sma w mhy Hk( 2 5 ) t w dki f; jr i f& y gw , f/
y Hk( 2 5 )
6 . 1 . 2 / ' Dw p fc gr Sma w mh y Hk( 2 3 ) u CALL UILib71.0035F070 a e & mu dka & G; jy D; Enter key u dkE Sdy fy gr , f/ ' gq dk
y Hk( 2 6 ) t w dki f; routine & JUt p u dkjr i fy gr , f/
y Hk( 2 6 )
y Hk( 2 6 ) & JU a t mu fe m; u dkscroll q GJjy D; Mu n fhc sde fr Sma w mhy Hk( 2 7 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 2 7 )
6 . 1 . 2 . 1 / y Hk( 2 7 ) u CALL UILib71.0035E790 a e & mu dka & G; jy D; Enter key u dkE Sdy fc sde fr Sma w mh MD5 hash
u dkw Gu fw Jhroutine & JUt p u dkjr i fy gw , f/ y Hk( 2 8 ) /
y Hk( 2 8 )
y Hk( 2 8 ) e JU y Hk( 4 ) w dkU w ln Da e w m o w dx m; r dy go v m; / MD5 hash algorithm u EBX? EBP? ESI e JU
EDI w dkUu dkvariable t jz p fx m; jy D; hash w e fz dk; w Gu fc su fr , fhy Hky g/
y Hk( 2 8 ) & JU a t mu fq Hk; e m; u dkscroll q GJjy D; Mu n fhc sde fr Sma w mhy Hk( 2 9 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 2 9 )
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 339 -
y Hk( 2 9 ) u MD5 algorithm & JUt q Hk; u dk Mu n fhv dku fc sde fr Sma w mh EAX u dkr la o x m; jy D; w Gu fc su fv dkU& v m
w Jh w e fz dk; a w Gu dk DS:[ESI] r Smv mx m; r , fhy Hky g/ ' Da e & mr Sm ESI & JUw e fz dk; u 12BAB0 jz p fw Jht w Gu f EAX
r Sm& Sdw Jhw e fz dk; u dk DS:[12BAB0] r Smv mo dr f; r Smy g/ y Hk( 3 0 ) /
y Hk( 3 0 )
y Hk( 2 9 ) u u k' fu dk& Si f; v i f; & r , fq dk& i fa w mha t mu fy gt w dki f; jz p fy gw , f _ _ _
EAX = ECX = EE5B36A2;
EBX = DS:[ESI+4] = DS:[12BAB4] = EFCDAB89;
EAX = EAX << 15 = D4400000;
ECX = ECX >> 0xB = 001DCB66;
EAX = EAX | ECX = D45DCB66;
EAX = EAX + EBX = C42B76EF;
EAX = EAX + EDI = 807A79F8;
' Dha e mu fr Sma w mh EAX & JUw e fz dk; 807A79F8 u dk DS:[ESI+4] = DS:[12BAB4] q D u l; x n fhr Sm
jz p fy gw , f/ Endian e JUp Dw m t r Sw f& y g/ y Hk( 3 1 ) /
y Hk( 3 1 )
u se fw Jhu k' fa w Gu dk w p fa Mu mi f; c si f; v dku fv Hp p fa q ; r , fq dk& i fa w mh a e mu fq Hk; r Sm a w GU& r Smu a w mh y Hk( 3 2 )
t w dki f; jz p fy gw , f/
y Hk( 3 2 )
' gu a w mh12BAB0 r Sm initialize v ky fv dku fw Jh01234567 89ABCDEF FEDCBA98 76543210 u dk
MD5 algorithm e JUw Gu fc su fv dkU& v mw Jh5D9BEC3D F8797A80 07E00955 4A973B68 t a jz y g/
6 . 1 . 3 / y Hk( 2 3 ) u CALL UILib71.0035F130 a e & mu dka & G; jy D; Enter key u dkE Sdy fy g/ y Hk( 3 3 ) t w dki f; routine
& JUt p u dkjr i fy gr , f/
y Hk( 3 3 )
y Hk( 3 3 ) & JU a t mu fq Hk; e m; u dkscroll q GJjy D; Mu n fhc sde fr Sma w mhy Hk( 3 4 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 3 4 )
6 . 1 . 3 . 1 / CALL UILib71.0035F070 [ m MD5 hash algorithm u dka c : o Hk; w Jh CALL jz p fw , fq dkw m
o i fo dr Smy g/ y Hk( 3 4 ) & JU VA 0035F197 u CALL UILib71.0035F070 u a w mh MD5 hash algorithm u dk
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 340 -
a c : o Hk; jc i f; r & Sdy gb l; / ' ga y r , fh VA 0035F1A4 u CALL UILib71.0035F070 u a w mh MD5 hash
algorithm u dka c : o Hk; y gw , f/
6 . 1 . 3 . 1 . 1 / y Hk( 3 4 ) u CALL UILib71.0035F070 a e & mu dka & G; jy D; Enter key u dkE Sdy fy g/ ' gq dk y Hk( 2 6 ? 2 7 ? 2 8 ?
2 9 ? 3 0 ? 3 1 ? 3 2 ) r Sm a w GYc Jh& w Jht w dki f; Mu HK& r Smjz p fy gw , f/
12BAB0 r Sm c ke u w Gu fv dku fw Jh 5D9BEC3D F8797A80 07E00955 4A973B68 u dk MD5 hash
algorithm e JU x y fr Hw Gu fc su fw Jht c gr Sma w mh AB6801EF DD311D00 C7A5A08B 983315D0 t a jz y g/
y Hk( 3 5 ) /
y Hk( 3 5 )
7 / y Hk( 3 6 ) u CALL UILib71.0035E730 u dkv ky fa q mi fjy D; c sde fr Sma w mh AB6801EF DD311D00 C7A5A08B
983315D0 w e fz dk; u dk& v my gw , f/
y Hk( 3 6 )
8 / ' Dha e mu fr Sma w mh CALL UILib71.0035E670 u dkv ky fa q mi fy gw , f/ ' D CALL u a w mh u Re fa w mfw dkU
& & Sdv mw Jhhash w e fz dk; u dkstack a y : u l; w i fy gw , f/ y Hk( 3 7 ) /
y Hk( 3 7 )
a & SUw a v Qmu fr Sma w mhstack window u dko m t " du Mu n fho Gm; y g/ Stack window r Sm license code e JU
y w fo u fw Jhjy D; jy n fhp Hkw Jht c su ft v u fa w Ga y ; E dki fv dkUy g/
9 / y Hk( 3 6 ) r Sm F8 E Sdy fjy D; q u fp p fv mc sde fr Sma w mhy Hk( 3 8 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 3 8 )
y Hk( 3 8 ) r Sma w mh hash w e fz dk; u dk 4 v Hk; p Dw GJjy D; c GJx kw fa y ; r Smy g/ ' D loop u dkv ky fa q mi fjy D; c sde fr Sma w mh
u Re fa w mfw dkU& JU license code [ m ab6801efdd311d00c7a5a08b983315d0 t p m; a60e-d310-caa8-931d
jz p fv mr Smy g/ y Hk( 3 9 ) /
y Hk( 3 9 )
License code u dkMu n fh& i f y & dk* & r fu w p fv Hk; a u smf , lo Gm; w ma w GU& r Smy g/
9 / y Hk( 3 8 ) r Sm F8 E Sdy fjy D; q u fp p fv mc sde fr Sma w mhy Hk( 4 0 ) t w dki f; jr i f& r Smjz p fy gw , f/
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 341 -
y Hk( 4 0 )
y Hk( 4 0 ) u CALL MFC71.4085 [ m MSVCR71.dll z dki f& JU _mbsupr() API u dko Hk; jy D; a60e-d310-
caa8-931d- u dkA60E-D310-CAA8-931D- t jz p f a jy mi f; v Ja y ; v dku fy gw , f/
1 0 / y Hk( 4 1 ) u CALL MFC71.1916 u a w mhMSVCR71.dll z dki f& JU memmove() API u dko Hk; jy D; A60ED310-
CAA8-931D- u a e hyphen u dk z , f& Sm; v dku fjy D; A60E-D310-CAA8-931D t jz p f a jy mi f; v Ja y ; v dku f
y gw , f/
y Hk( 4 1 )
1 1 / y Hk( 4 2 ) u CALL MFC71.876 u a w mhDS:[ECX] = DS:[12BB34] r Smo dr f; x m; w JhMyanmarCracking
Team- p mo m; u dk EAX x Jjy e fu l; y gw , f/
y Hk( 4 2 )
1 2 / y Hk( 4 2 ) u CALL MFC71.3850 u a w mh memmove() API e JU memcpy() API w dkUu dkt o Hk; jy Kjy D;
MyanmarCrackingTeam- e JU A60E-D310-CAA8-931D w dkUu dkt w la e & mc sx m; y gw , f/
y Hk( 4 3 )
' gu dkstack window r Sm Mu n fhv dku fr , fq dk& i fa w mhy Hk( 4 4 ) t w dki f; a w GU& r Smjz p fy gw , f/
y Hk( 4 4 )
' Da v mu fq dk& i fa w mh y & dk* & r ft v ky fv ky fy Hk & Si f; a v mu fjy Dv dkU x i fy gw , f/ MyanmarCrackingTeam-
A60E-D310-CAA8-931D e JU MyanmarCrackingTeam-1234-5678-9012-3456 u dk E dIi f; , SOfjy D; r n Dc Jh& i f
BadBoy Message u dkjy r Smjz p fy gw , f/
Xilisoft application a w Ge JUy w fo u fjy D; r Sw fc su fjy K& r , fq dk& i fa w mh. . .
1 / Xilisoft application a w G[ m serial r Se f^ r r Se fp p fa q ; z dkU MD5 u dkt o Hk; jy Ky gw , f/
2 / Serial a w G[ m 3 9 v Hk; w dw d& Sd& y gr , f/ ( Oy r m - MyanmarCrackingTeam-1234-5678-9012-3456)
3 / Serial & JU y x r w p f0 u f[ m Mu dKu f& mp mv Hk; jz p fE dki fy gw , f/ ( Oy r m - MyanmarCrackingTeam-? 1234-
5678-9012-3456-? AB124BCDE-7890-00002? Dead-beef-Cafe-Babe-)
4 / Serial & JU ' kw d, w p f0 u fu dka w mhhash w e fz dk; w Gu fc su f& mr Sm t o Hk; jy Ky gw , f/ ( Oy r m - 1234-5678-9012
-3456)
5 / Serial & JU y x r w p f0 u fu dk hash v ky fz dkU Mu dKw i fo w fr Sw fx m; w Jh string E Sp fc k& JUt v , fr Sm x m; y gw , f/
( Oy r m - 1adoov.re.uicne.t.r00MYANMARCRACKINGTEAM-audioconverte)
6 / & & Sdv mw Jhhash w e fz dk; u dk p mv Hk; a o ; t jz p fa jy mi f; y gw , f/ ( Oy r m - ab6801efdd311d00c7a5a08b983315
d0)
7 / Hash w e fz dk; x Ju r * P e f; a w Gu dk, ljy D; 4 v Hk; p Dw GJy gw , f/ ( Oy r m - a60e-d310-caa8-931d) jy D; a w mhp mv Hk;
t Mu D; a jy mi f; y gw , f/ ( Oy r m - A60E-D310-CAA8-931D)
8 / w GJv dkU& w Jhw e fz dk; a w Gu dk y x r w p f0 u fe JU jy e fa y gi f; y gw , f/ ( Oy r m - MyanmarCrackingTeam-A60ED31
0-CAA8-931D)
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 342 -
' Dw p fc gr Sma w mh Xilisoft Audio Converter t w Gu f key v Sv Sa v ; a w Gu dk keygen r a & ; o m; b J
y & dk* & r fu t v dkt a v smu f b , fv dkx kw fa y ; r v Jq dkw m Mu n fhMu & a t mi f/
y Hk( 4 5 )
y Hk( 4 5 ) r Smjr i f& w JhVA 00358769 a e & mw p fc kw n f; u dk breakpoint o w fr Sw fjy D; y & dk* & r fu dk run v dku fy g/
jy D; & i f register v ky fMu n fhy g/ y Hk( 4 6 ) / u Re fa w mfa & SUy dki f; r Sm a q G; a E G; c Jho v dky J key & JU a & SUy dki f; 1 9 v Hk; ^ 2 0 v Hk; u dk
Mu dKu fE Sp fo u fo v dka jy mi f; v Ja y ; v dkU& y gw , f/
y Hk( 4 6 )
y Hk( 4 6 ) t w dki f; register v ky fv dku f& i fa w mh Xilisoft u key u dk t v dkt a v smu f x kw fa y ; r Smjz p fy gw , f/
y Hk( 4 7 ) /
y Hk( 4 7 )
y Hk( 4 7 ) r Smjr i f& w Jht w dki f; Xilisoft u stack window r Sm license code jz p fw Jh Myo Myint Htike----
>65A3-6021-4C6D-A6C5 u dkx kw fa y ; v dku fy gw , f/
License code r Se fr Se fo d& a t mi f Myo Myint Htike---->65A3-6021-4C6D-A6C5 u dk register
v ky fMu n fhy gr , f/ y Hk( 4 8 ) /
y Hk( 4 8 )
y Hk( 4 8 ) r SOK button u dkE Sdy fv dku f& i fa w mhRegistered successfully! q dkw Jhp mw e f; a y : v mr Smjz p fy gw , f/
( 1 0 ) Exe Passwor d 2004 jz i fhpr otect v ky fx m; a o m passwor d t m; jy e fa z mfjc i f;
' Dw p fc gr Sma w mh ]Patch v ky fjc i f; } o i fc e f; p mu ]Beginner t q i fh patch v ky fjc i f; } t c e f; r Sm protect
v ky fc Jhw Jhpassword u dkjy e fa z mfMu n fhy gr , f/
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 343 -
' Dw p fc gr Sma w mh t a jy mi f; t v Ja v ; jz p fa t mi f calc.exe u dk protect r v ky fb J notepad.exe u dko m
protect v ky fMu n fhy gr , f/ y Hk( 4 9 ) /
y Hk( 4 9 )
y Hk( 4 9 ) r Smjr i f& w Jht w dki f; notepad.exe u dkrhythm q dkw Jhpassword a y ; jy D; protect v ky fv dku fy gr , f/
Password a y ; x m; w Jhy & dk* & r fu dk Olly r Smz Gi fhjy D; run (F9) v dku fy gr , f/ y Hk( 5 0 ) /
y Hk( 5 0 )
y Hk( 5 0 ) & JU password a e & mr Sm 123456 v dkU& dku fx n fhjy D; OK u dkE Sdy fv dku f& i f y Hk( 5 1 ) t w dki f; BadBoy
message u dkjr i f& r Smjz p fy gw , f/
y Hk( 5 1 )
y Hkr Se ft & q dk& i fa w mh' Dmessage box a y : w Jht c gr Sm F12 u dkE Sdy fjy D; Olly u dk c P & y fc dki f; & r Smjz p fy gw , f/
b ma Mu mi fh ' De n f; v r f; u dk r o Hk; o v Jq dk& i fa w mh u Re fa w mfw dkU& JU y & dk* & r fu dk Delphi e JU protect v ky fx m; v dkUy g/
' ga Mu mi fh"Password is incorrect." q dkw Jhp mo m; u dk& dk; & dk; w e f; w e f; Search u a e y J& Smr Smjz p fy gw , f/
y Hk( 5 2 )
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 344 -
"Password is incorrect." u dk& Sma w GUw Jht c g y Hk( 5 2 ) r Smjr i f& w Jht w dki f; breakpoint o w fr Sw fy g/
a e mu fx y f breakpoint o w fr Sw fz dkU v dkw mu a w mhVA 0054C86E r Smy g/ jy D; & i f y & dk* & r fu dkOlly r Smjy e fz Gi fhy g/
y Hk( 5 3 )
y & dk* & r fu dk Olly r Smjy e fz Gi fhjy D; password a w mi f; w Jht c g abcdef v dkU& dku fx n fhv dku f& i f y Hk( 5 3 ) t w dki f;
breakpoint & Sd& mu dk w e f; a & mu fv mr Smy g/ ' Dt c g register window u dkMu n fhv dku fy g/ y Hk( 5 4 ) /
y Hk( 5 4 )
u Re fa w mfw dkU breakpoint o w fr Sw fx m; w Jh VA 0054C86E u dkr a & mu fc i fr Sm CALL 005532AC
u dkv ky fa q mi fc Jhy gw , f/ ' DCALL u dkv ky fa q mi fjy D; c sde fr Sm u Re fa w mfw dkU& dku fx n fhv dku fw Jh abcdef u dk RVV]PV
t jz p fa jy mi f; a y ; v dku fy gw , f/ jy D; & i f EAX x Jr Smo dr f; y gw , f/ a e mu fw p fc ku a w mh y & dk* & r f& JU data segment
x Ju w e fz dk; w p fc ku dk x kw f, ljy D; EDX x Jx n fhw my g/ ' Dx kw f, lv dku fw Jht & mu a w mh u Re fa w mfw dkUv dkc si fw Jh
password y gy J/ y Hk( 5 4 ) u dkMu n fhy g/ EDX x Ja & mu fa e w m[ m A\\LM]] jz p fa e y gw , f/ ' gu dk
o dy fr o u Fmy gb l; /
b ma Mu mi fhv Jq dka w mh u Re fa w mfw dkUa y ; x m; c Jhw Jh password jz p fw Jh rhythm [ m 6 v Hk; y J& Sdjy D; t c k
7 v Hk; jz p fa e v dkUy g/ ' ga Mu mi fhdump window r SmMu n fhv dku fMu & a t mi f/ y Hk( 5 5 ) /
y Hk( 5 5 )
Dump window u dka o c smMu n fhv dku fa w mhr S & Si f; o Gm; y gw , f/ w u , fo dr f; x m; w mu A\LM]] y g/
Debugger u escape sequence a w Ge JUa & ma x G; r Sm p dk; & dr fw Jht w Gu f slash (\) w p fc kx y fw kd; a y ; v dku fjc i f;
jz p fy gw , f/ u Re fa w mfw dkUv ky f& r Smu a w mh A\LM]] u dk encrypt r v ky fc i fu & Sdc Jhw Jh r lv password u dk jy e f& & Sd
E dki fz dkUy g/ ' gr So m patch r v ky fb J password u dkjy e fa z mfE dki fr Smy g/ ' ga Mu mi fh password u dk encrypt v ky fa y ; w Jh
routine & Sd& m VA 0054C860 r Sm breakpoint o w fr Sw fjy D; y & dk* & r fu dk jy e fp v dku fy g/ y & dk* & r fu dk Olly r Sm run
jy D; password dialogbox r Sm abcdef u dk& dku fv dku f& i f y Hk( 5 6 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 5 6 )
Register window u dkMu n fhr , fq dk& i fa w mhy Hk( 5 7 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 5 7 )
abcdef u u Re fa w mfw dkU & dku fx n fhv dku fw Jh password jz p fjy D; ? 3459501211xSSSFDb u a w mh
password u dk encrypt v ky f& mr Smt o Hk; jy Kr , fh hash w e fz dk; jz p fy gw , f/ CALL 005532AC & Sd& ma & mu fw Jht c g
F7 u dkE Sdy fjy D; CALL x Ju dk0 i fMu n fhy gr , f/ y Hk( 5 8 ) /
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 345 -
y Hk( 5 8 )
y Hk( 5 8 ) u dka w mhp dw fr 0 i fp m; y gb l; / ' ga Mu mi fha t mu fu dk scroll e n f; e n f; q GJjy D; Mu n fhv dku fy g/
y Hk( 5 9 )
[LOCAL.1] q dkw mu a w mh abcdef u dk q dkv dkjc i f; jz p fy gw , f/ [LOCAL.2] q dkw mu a w mh 34595012
11xSSSFDb u dkq dkv dkjc i f; jz p fy gw , f/ y & dk* & r f& JU t Mu r f; z si f; t v ky fv ky fy Hku a w mh-
1 / MOV EDX, [LOCAL.1]
EDX x Jr Sm abcdef u dkx m; y gw , f/
2 / MOV DL, BYTE PTR DS:[EDX+ESI-1]
' Dt c sde fr Sm ESI & JUw e fz dk; [ m 1 jz p fw Jht w Gu f *EDX=EDX[0] x Ju y x r p mv Hk; u dk DL x J u l; y dkUy g
w , f/ ' ga Mu mi fhDL x Jr Sm a a & mu fv my gw , f/
3 / MOV ECX, [LOCAL.2]
ECX x Jr Sm 3459501211xSSSFDb u dkx m; y gw , f/
4 / MOV CL, BYTE PTR DS:[ECX+EBX-1]
' Dt c sde fr Sm EBX & JUw e fz dk; [ m 1 jz p fw Jht w Gu f *ECX=ECX[0] x Ju y x r p mv Hk; u dk CL x J u l; y dkUy g
w , f/ ' ga Mu mi fhCL x Jr Sm 3 a & mu fv my gw , f/
5 / XOR DL, CL; DL = DL ^ CL = a ^ 3 = R
DL x Jr Sm& Sdw Jh a e JU CL x Jr Sm& Sdw Jh 3 w dkUu dk XOR v ky fy gw , f/ & v ' f R u dka w mh DL x Jr Sm
o dr f; y gw , f/
6 / MOV BYTE PTR DS:[EAX+ESI-1], DL
DL x Jr Smo dr f; x m; w Jh R u dk *EAX= EAX[0] x Ja & TYy gw , f/ ' ga Mu mi fh EAX r Sm Rbcdef jz p fv my g
w , f/ Rbcdef w e fz dk; u dkdata segment u B858E0 r Smo dr f; w mjz p fy gw , f/
7 / INC EBX
ECX x Jr Sm& Sdw Jha e mu fx y fp mv Hk; a w Gu dk z w fE dki fz dkUt w Gu f EBX w e fz dk; u dkw p fa y gi f; y gw , f/
8 / INC ESI
EDX x Jr Sm& Sdw Jha e mu fx y fp mv Hk; a w Gu dk z w fE dki fz dkUt w Gu f ESI w e fz dk; u dkw p fa y gi f; y gw , f/
- ' Dv dke JU w p fv Hk; c si f; u dkv ky fy gw , f/
XOR DL, CL; DL = DL ^ CL = b ^ 4= V
XOR DL, CL; DL = DL ^ CL = c ^ 5= V
XOR DL, CL; DL = DL ^ CL = d ^ 9= ]
XOR DL, CL; DL = DL ^ CL = e ^ 5= P
XOR DL, CL; DL = DL ^ CL = f ^ 0= V
- t m; v Hk; u dk XOR v ky fjy D; c sde fr Sma w mh DWORD PTR SS:[EBP-4] = [LOCAL.1] x Jr Sm ' D& v ' fu dk
o dr f; q n f; y gw , f/
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 346 -
' gu a w mhencryption v ky fw Jhv ky fi e f; p Ofy g/ ' gq dk password u dk decrypt v ky fa y ; r , fhy & dk* & r fu dk C e JU
a & ; Mu n fhMu & a t mi f/
#include<stdio.h> // Copyright Myo Myint Htike, September 20 2009
#include<conio.h> // Compiler - Borland C++ 5.02
#include<string.h> // C Console Application
int main()
{
int index = 0;
char encrypted_password[30] = {0};
char decrypted_password[30] = {0};
char hash_value[20] = "3459501211xSSSFDb345";
scanf("%s", encrypted_password);
while(index < str len(encrypted_password)){
decrypted_password[index] = encrypted_password[index] ^ hash_value[index];
index++;
}
pr intf("Serial is = %s", &decrypted_password[0]);
getch();
return 0;
}
y Hk( 6 0 )
y Hk( 6 0 ) u u k' fu dkBorland C++ compiler r Sm run v ky fv dku f& i fa w mhy Hk( 6 1 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 6 1 )
u Re fa w mfw dkU decrypt v ky fc si fw Jh password u dk& dku fx n hfv dku fw Jht c gr Sm r lv password u dky & dk* & r fu
jy e fx kw fa y ; r Smjz p fy gw , f/
w u , fv dkU password a y ; x m; w Jhz dki fr Sm y Hk( 6 2 ) t w dki f; breakpoint a e & mu dka & mu fv dkU register window
r Sm encrypt v ky fc H& w Jhpassword a w Gu dkr jr i f& b l; q dk& i f. . . .
y Hk( 6 2 )
' gq dk& i fa w mho i f& dku fx n fhv dku fw Jhpassword u dkencrypt v ky fx m; w Jha e & mu dk& Smz dkU y Hk( 6 3 ) u dkMu n fhy g/
y Hk( 6 3 )
y Hk( 6 3 ) u VA 0054C865 u dkE Sdy f& i f Olly pane window r Sm Stack SS:[0012F668] = 0118F48
v dkUa y : v my gv dr fhr , f/ ' Da e & mr Sm right-click E Sdy fjy D; Follow value in Dump u dka & G; v dku f& i f dump window
r Sm encrypt v ky fx m; w Jh password u dkjr i f& r Smjz p fy gw , f/ ' ga y r , fh ' D password [ m u Re fa w mfw dkUt w Gu f
t a & ; r y gw Jht w Gu f v sp fv sL& Ix m; v dkU& y gw , f/
w u , fhpassword u dkencrypt v ky fx m; w Jha e & mu dk& Smz dkU y Hk( 6 4 ) u dkMu n fhy g/
t c e f; ( 2 2 ) - Crypto u k' fr sm; u dka v hv mjc i f;
- 347 -
y Hk( 6 4 )
y Hk( 6 4 ) u VA 0054C868 u dkE Sdy f& i f Olly pane window r Sm DS:[005677BC] = 00FA7774
v dkUa y : v my gv dr fhr , f/ ' Da e & mr Sm right-click E Sdy fjy D; Follow value in Dump u dka & G; v dku f& i f dump window
r Sm encrypt v ky fx m; w Jhpassword u dkjr i f& r Smjz p fy gw , f/ Encrypt v ky fx m; w Jhpassword u a w mhjz p fy gw , f/
' gu dkC e JUa & ; x m; w Jhy & dk* & r fu dko Hk; jy D; password u dkjy e fa z mfr , fq dk& i fa w mhy Hk( 6 5 ) t w dki f; jr i f& r Smy g/
y Hk( 6 5 )
EXE Password 2004 r Sm password u dk t v Hk; 2 0 x u fy dka y ; v dkUr & y gb l; / ' ga Mu mi fh password u dk
a y ; w ke f; u Myanmar Cracking Tea v dkUa y ; c Jhw mjz p fy gw , f/ Encrypt v ky fx m; w Jh password u dk& dku fx n fh
w Jht c gr Sm a w GU& w Jh ^R (Device Control 2) e JU ^Y (End of Medium) w dkUu dk & dku fx n hfc si f& i f Ctrl key e JU
w GJE Sdy f& r Smjz p fy gw , f/
w u , fv dkU o i fa y ; x m; w Jh password [ m * P e f; a w Gy Jjz p fr , fq dk& i f keyboard u a e & dku fx n fh& w m
c u fc Jr Smjz p fy gw , f/
y Hk( 6 6 )
y Hk( 6 6 ) u encrypt v ky fx m; w Jh password u dk decrypt jy e fv ky fr , fq dk& i f c ke u u Re fa w mfw dkUa & ; c Jhw Jh
keygen u dk t o Hk; jy Kv dkU& a w mhr Smr [ kw fy gb l; / b ma Mu mi fhv Jq dka w mh 0D [ m return keystroke e JU w ln Da e w m
jz p fw Jht w Gu f ^B^F^F (020606) w dkUu dk& dku fx n hfjy D; ^M (0D) u dk& dku fx n hfc sde fr Sm y & dk* & r fu password u dk
& dku fx n fhjy D; jy Dv dkU, lq jy D; t a jz x kw fa y ; v dkUy g/ ' Dt w Gu f y & dk* & r fu dkjy i fa & ; & y gr , f/
#include<stdio.h> // Copyright Myo Myint Htike, September 20 2009
#include<conio.h> // Compiler - Borland C++ 5.02
int main()
{
int index = 0;
int encrypted_password[7] = {2, 6, 6, 0xD, 0, 6, 6};
char decrypted_password[30] = {0};
char hash_value[20] = "3459501211xSSSFDb345";
while(index < 7) {
decrypted_password[index] = encrypted_password[index] ^ hash_value[index];
index++;
}
pr intf("Serial is = %s", &decrypted_password[0]);
getch();
return 0;
}
y Hk( 6 7 )
y Hk( 6 7 ) u u k' fu dkrun v dku f& i fa w mhy Hk( 6 8 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 6 8 )
,., Polymorphic - ...- . .` .
,.
tcef;(23) - Polymor phic uk'frsm;udk avhvmjcif;
-. . ..-. cracker .- ...`........ polymorphic -.-.-..- ....`..
-. -. .....-..-.-. -.,. pack/protect ..`. ..-. Assembly
.- .- , .. ........-.`.. - - - PEiD , ... .-. - . . -.. ReverseMe Tutorial.
exe,- ........- .-....-.-. Lena151 `.. -. SND Team . download section . .
.-..- download ..-. .-..` .-... ..-..-.- ..-_--...
.-..-.--...-. ,-. nag -`..-. "You need to remove the nag.
Try to do ".-.....-.-..
,
,- OK button -.-..-. ,-.`....
,
Nag window - .. .. . . . .` . patch ...-. .-.- nag window - ..
. .. .-. ...-.- . , ...,- ...
.-..- patch .. Olly .. .`......-_--... ,
,
`...-. -,.-.-.-..- "You need to remove the nag. Try to do " .....-
-..-_
,,
,,. .`. .- - . -, .-. - . ..,- .....- .- -. Double-click .- ,
,
,., Polymorphic - ...- . .` .
,.
,..`..-.-.-. VA 00403134 .......- "You need to remove ..." .....-
MessageBox -. - .. . MessageBox -. -, .-. - .. . ..... nag window `..
-. .-. MessageBox .,... . breakpoint .-.-`. .-..- run (F9) -_--.
..
,
.-..- F9 .`. run -_-,...-. -,.-.- .-.-..- breakpoint .,... .
.-..-..- ,- nag window - `. .,.-.
.-. .-. .., ..,-. . nag window - -. -.,..-.. .`.. , - . .
.. . -.. - Olly . .`, . -_ - -... (Ctrl+F2) . ,,-. `....
,,
,,- ...-_ VA 0040128A -., VA 00401290 -. - .- ... .-..- `..
.,-. F8 -.`. -.`....-. .--_ .,
.,
Olly - VA 0040128F .,.....-.-. .,-. breakpoint .- . - ... ...-.
Yes button -...`. F8 - .- . Olly . ..- - scroll ,_.,_..`.-_.....-.
.,-. `..-.
.,
,., Polymorphic - ...- . .` .
.,- .., ..,-. -.- . ..- .- . .-. . . mnemonics .--`..
.. Olly . analysis -`.-- ,
INFO: : Olly - - .- - .-..,, . `. .,-. .,-. .-. . .. ... .,
,
,-. Remove analysis from module -...`. analysis -.-`.--..-.
,-. `....
,
-_.-.-.-. `.`_....- junkcode .-`...-. Olly - - unknown
command `.,-. Olly - -,.-.-- .....`....-. .-..` analysis - .-.
. -.-.-... .-. auto-analysis - ..--. `.-- ,
,
,-. auto-analysis -`.-`...-. Olly .. .-..- `,.-
,
,., Polymorphic - ...- . .` .
Ctrl+F2 (Restart) .`. .-..- `,.-_-..-. EP . ...,..- ,- .`. .
. . -. . ..-. analysis - .. ...-.- ... ,_ .,_ ...,.._ .-. F9 - . ` .
.-..- run -_,.. ,- breakpoint .- . - ..- .,... . . -.. - -..-. .. ..
. - .-. . . .`..
.`.-.-. .-. .-.--. diversion -.-`..., ..-,. cracker .- -
- .- ... _ .... - .- - _ ..` .`.. -. . , .-. - .- -. . .. - .
- .- - -. .-. . .. . .`. ..- - - . .-. breakpoint .- . - ..- .,...- -
...- ..-. . .,, . `. .-.- . -_ ..,,
INFO: : MessageBoxA -... .-,... ,_.. ....- .. -. ..`.. commandbar
plug-in -..`. MessageBoxA .. breakpoint .-.- `.. breakpoint ...-...-... F9
-. .,.-...-. Alt+ F9 -.`. user -....-...-. ,, ..--
Call Stack (Ctrl+K) -., MessageBoxA . ...,..- .`.. . -. ,
,,
,,-. nag window ...-...... .,.....-. -,.-.-.,, -.--
-..-.......... ,-`,-_
,
,. EP .,..-., F8 -.`. -.-- ..-_.. Breakpoint .-- ..-.-
-- .....- VA 0040128A - GetModuleHandle .-..-..-_..
The GetModuleHandle function returns a module handle for the specified module if the file has been
mapped into the address space of the calling process.
HMODULE GetModuleHandle(
LPCTSTR lpModuleName // address of module name to return handle for
);
Par ameter s
lpModuleName
Points to a null-terminated string that names a Win32 module (either a .DLL or .EXE file). If the filename
extension is omitted, the default library extension .DLL is appended. The filename string can include a trailing point
character (.) to indicate that the module name has no extension. The string does not have to specify a path. The name
is compared (case independently) to the names of modules currently mapped into the address space of the calling
process.
If this parameter is NULL, GetModuleHandle returns a handle of the file used to create the calling process.
Retur n Values
If the function succeeds, the return value is a handle to the specified module.
If the function fails, the return value is NULL. To get extended error information, call GetLastError.
function . . return -,..-.-. EAX ...- imagebase -,..`.... ,
,
MOV EDI, 00401011; // EDI .. VA 00401011 -..-. .-.-.-. -.- `.
.,-. `.. ..- -. .,.- .- -_ ,
,., Polymorphic - ...- . .` .
CALL 0040130F; // -.-. .-.......-..-. F7 - . ` . CALL -_ ,,
,,
,,. .`. .- - . - section . VA .- EAX . ...-. .- ..` .-_ .. .
. .-. GetModuleHandle - cracker .-- ..- diversion - `.. .,-..- .-.
.,
.,.-...-. EAX .-,..-- 401000 . .. - data segment --,.. E2' -, 5A ,
XOR -. EAX -,..- -...-. `...-. EAX -,..- jmp.&user32.
BeginPaint ,...-. .,
.,
.,..`..--. EAX ,...-.-.-. 401218 `.. -. ,
,
--. - . EAX -,.. (401001) , jmp.&user32. BeginPaint -...- EAX -, . .
(401218) --....... -,..-..,.... VA 00401314 - XOR BYTE PTR DS:[EAX],
5A; ....-...`. XOR .. .`.. -. ,- Assemble button -...-
EAX - 401218 , -..-. . .. .. . -. ,_ .,_ .-_ - -... ,
,
,., Polymorphic - ...- . .` .
--. .-. VA 00401000 -., VA 00401218 code section - opcode .-- 5A ,
XOR -.- decrypt -. .-. -..-. . .-. . - . - - encrypt ..
INFO: : Encryption/Decryption . -.-.-. .- .- - .- - --.-.... ....
..-`...-.`.-. Encryption - ` .... ..- . . .- . . . .`... - -
.- . , .. , - - . .. .... . `..,_ ._.. .- .,- , . Encryption ., ....
- obfuscation -.-. cracker .- ., - -.- . . . . .`--.
INFO: : XOR instruction -.-. encrypt/decrypt - command -.`..`. .`-...
.....-. -..-...-. .-.-....``. decrypt . .,.-....-
-, . .- - _ - -, .-. , XOR ` .`. .. .-, . .- `, .. . -. XOR instruction -
encryption - . . . .`. .-. . - encrypting XOR '., enxor ...,...-.
XOR - . .`` . . -.. -. ..-. .... Olly . dump window
- 401000 .,..--_--... ,
,
Loop - ....--`.,...-. ,- .`. .-. Dump window . .`. .-.-
.-. code section . . . opcode .- -..-- decrypt .,-..-. F8 . ` . .- -_
., ,
,
,..`..--. decrypt ..- - .- , ... `.. .`. .- , -. .- ... ,
- RETN . . breakpoint .- . - ` . F9 (Run) -.- ,,-.`....
,,
,., Polymorphic - ...- . .` .
,
,,- -_ - . code section VA 401218 ,.. decrypt ` .. ..-..- ...
RETN . ..- . - ..- breakpoint -`,`.-`. .- scroll .-. ,-.`....
,
,- .- ..- junk - .- ... .- .- mnemonics .- `.. .`. .- , -. .- .. .
INFO: : .,... . - .- -. -..-. , ... .`...,.. .-.-.-. ,- --.-
assemble . .-. Olly - -.-- .`....-.`. .`...,--.--
,...-.`..-.`..-. ...,..`..-. -.-.`...,-....-. .`.....-
- - ,- ... , ..`-. - .-. .- .... -. --. .`. . . ..- - .- -
- - - ... , `.. . ,-. `,`.-.
,
INFO: : Code section -. ..., ..`. .-. ... ..- . Code section . . ... -. . . .-.
PE tool (LordPE, WPE, PE Tools .._ `. ) .- - . .`` . code section . characteristics -
` .-.
' Dw p fc gr Sma w mha e mu fx y fp dw f0 i fp m; p & ma u mi f; w JhCALL w p fc ku dk a v hv mMu n fhy gr , f/
y Hk( 2 7 )
y Hk( 2 7 ) r Smjr i f& w JhCALL u dk a v hv mE dki fz dkU F7 (Step into) u dkE Sdy fv dku fy g/ y Hk( 2 8 ) t w dki f; jr i f& y gr , f/
,., Polymorphic - ...- . .` .
y Hk( 2 8 )
y Hk( 2 8 ) r Smjr i f& w mu a w mh decrypt function u dkv ky fa q mi ft jy D; jz p fy gw , f/ w u , fa w mh y & dk* & r fu
decrypt v ky fx m; w Jhu k' fa w Gu dkz w fjy D; nag window u dkjy o z dkUMu dK; p m; a e w mjz p fy gw , f/ u k' fa w Gu dk a o c sm
Mu n fhr , fq dk& i fa w mh MOV instruction a w mfa w mfr sm; r sm; u dk a w GUr Smjz p fy gw , f/ o lw dkUa w G[ m EDI register
e JUy w fo u fa e w mu dkv Jjr i f& r Smy g/ ' ga Mu mi fh EDI x Jr Sm VA 401011 u dkx m; w m[ m w p fc kc kv ky fz dkU jy i fq i fa e
w mjz p fa Mu mi f; a & SUy dki f; r Sm a jy mc Jhw my g/ ' Da e & mr Sm u dk, fw dki fjy e fjy i fE dki fw Jhu k' fa w Gt a Mu mi f; u dk a v hv mMu n fh
y gr , f/
INFO: : Self-modifying code q dkw mu a w mh & n f& G, fc su fw p fc kc ke JU u dk, fhu k' fu dk u dk, fw dki fjy e fjy i fw my g/
u Ge fy sLw ma c w fOD; y dki f; r Sma w mh ' Dv dku k' fa w Gu dk t u e fUt o w f& Sdw Jh r Sw fOmP fa e & mu dk a c Rw mE dki fz dkU t o Hk; jy Kc JhMu
w my g/ Instruction set a w G[ m o mr e f branch c GJw ma v mu fy J v ky fa q mi fE dki fc sde fr Sm ( o dkU) v ky fa q mi fc su fa w G
u dk a jy mi f; v Jv ky fa q mi fE dki fz dkU instruction a w Gu dk a u smfv Tm; c sde fr Sm sub-routine call a w Ge JU return a w Gu dk
p r f; o y fp p fa q ; E dki fz dkU o lw dkUa w Gu dk t o Hk; jy Kc JhMu w mjz p fy gw , f/
INFO: : Self-modifying code a w Gu dk 1 9 8 0 w ke f; u DOS * dr f; a w Gr Sm copy prtotection instruction
a w Gu dkz Hk; u G, fE dki fz dkU t o Hk; jy Kc Jhw mjz p fy gw , f/ ' ga Mu mi fh Floppy drive u dkz w fw Jh instruction jz p fw Jh INT 13
u dk exe z dki fx Jr Sm & Sma w GUE dki fr Smr [ kw fy gb l; / ' ga y r , fh y & dk* & r f run a e c sde f r Sw fOmP fx Ju image x Jr Sma w mh
& Sda e r Smy g/ ' Da e Ua c w fr Sm self-modifying code a w Gu dkt o Hk; jy Ka e Mu w mu a w mh o lw dkU& Sda e w mu dk r jy o c si fv dkU
b Jjz p fy gw , f/ Oy r mjy & & i fa w mh u Ge fy sLw mA dki f; & y fp fa w Ge JU t c sdKUa o m shell u k' fa w Gjz p fy gw , f/ A dki f; & y fp fa w Ge JU
shell u k' fa w G[ m self-modifying code u dkt o Hk; jy KMu w mjz p fjy D; r sm; a o mt m; jz i fh polymorphic code
a w Ge JUw GJo Hk; Mu w mjz p fy gw , f/ Polymorphic A dki f; & y fp fa w Gu dka w mh w c gw & Hr Sm primitive self-mutator a w G
v dkUa c : y gw , f/ o lw dkU[ m run a e w Jhu k' fw p fp dw fw p fa ' o u dk jy Kjy i fjy D; OS u dk buffer overflow jz p fa p w Jh
attack v ky fr Ia w Gjy Kv ky fy gw , f/
t x u fa z mfjy y gt c su fa w Ga Mu mi fh cracker a w G[ m ' Dv dk obfuscation t r sdK; t p m; a w Gu dk b , fv dku dki f
w G, f& r v Jq dkw m & Si f; & Si f; v i f; v i f; o dx m; z dkUv dkt y fy gw , f/ F8 u dkE Sdy fjy D; b mq u fjz p fr v Jq dkw m Mu n fhv dku fMu
& a t mi f/ y Hk( 2 8 ) u dkjy e fMu n fhy g/
XOR EAX,EAX; // EAX u dk o kn jz p fa t mi f & Si f; v i f; v dku fy gw , f/
MOV WORD PTR DS:[EDI],6A; // 401011 r Sm& Sdw Jh33C0 a e & mr Sm 6A00 e JUt p m; x dk; y gw , f/
y Hk( 2 9 )
' ga Mu mi fh VA 00401011 u XOR EAX, EAX; (33C0) a e & mr Sm PUSH 0; (6A00) jz p fo Gm; w m
a w GU& r Smy g/
ADD EDI,2; // EDI u dk 2 a y gi f; y gw , f/ (0x401013)
MOV WORD PTR DS:[EDI],40307D68; // 40307D68 w e fz dk; u dk VA 0x401013 r Smx m; y gw , f/
y Hk( 3 0 ) /
,., Polymorphic - ...- . .` .
y Hk( 3 0 )
' ga Mu mi fh VA 00401013 u MOV WORD PTR DS:[EDI],40307D68; a e & mr Sm PUSH
0040307D; jz p fo Gm; w ma w GU& r Smy g/
y Hk( 3 1 )
y Hk( 3 1 ) r Smjr i f& w Jh VA 00401052 a & mu fw Jht x d F8 u dkE Sdy fv mc Jhr , fq dk& i f VA 00401011 u VA
0040104B x d[ m y Hk( 3 2 ) t w dki f; a jy mi f; v Jo Gm; w ma w GU& y gw , f/
y Hk( 3 2 )
y Hk( 3 1 ) u CALL EDI [ m w u , fa w mhCALL 00401000 u dkjy e fn Te f; w m a w GU& y gw , f/ y Hk( 3 3 ) /
y Hk( 3 3 )
y Hk( 3 3 ) r Smjr i f& w Jht w dki f; q dk& i fa w mh c ke u z e fw D; c Jhw Jh self-modifying code u dkjy e ft v ky fv ky fa w mhr , f
x i fy gw , f/ ' ga Mu mi fhAnalyze This! plugin u dko Hk; jy D; u k' fu dk analyze v ky fMu n fhv dku fy g/ y Hk( 3 4 ) /
y Hk( 3 4 )
,., Polymorphic - ...- . .` .
,
y Hk( 3 4 ) u dkMu n fhr , fq dk& i f self-modifying code u MessageBox w p fc ku dkz e fw D; c Jhw m a w GU& y gw , f/
' ga y r , fh Tilte e JU Text u b ma w Ga & ; x m; r Se f; r o dy gb l; / ' ga Mu mi fh F7 u dkE Sdy fjy D; CALL x Ju dk0 i fMu n fhv dku f
Mu & a t mi f/ y Hk( 3 5 ) /
y Hk( 3 5 )
y Hk( 3 5 ) r Smv J enxor w p fc kx y fa w GU& y gw , f/ ' gu dka w mh o i fe m; v n fr , fv dkUx i fy gw , f/ EAX x Ju dk
00403000 w e fz dk; v mx n fhy gw , f/ ' Dt c sde f 403000 & JU data segment r Sm& Sdw mu a w mh E1 q dkw Jhw e fz dk; y g/
y Hk( 3 6 ) /
y Hk( 3 6 )
E1 w e fz dk; u dk B3 e JU XOR v ky fy gr , f/ jy D; & i f EAX (403000) w e fz dk; u dk 1 a y gi f; y gr , f/ EAX
w e fz dk; [ m 403128 jz p fr jz p fp p fy gr , f/ 403128 x u fi , fa o ; & i fa w mh' Dloop u dkq u fv ky fa e OD; r Smjz p fy gw , f/
' ga Mu mi fhdump window u dk Mu n fhz dkUv dkv my gjy D/ y Hk( 3 7 ) /
y Hk( 3 7 )
F8 u dkE Sdy fjy D; u k' fa w Gu dk p p fo Gm; & i f y kH( 3 7 ) t w dki f; XOR v ky fx m; c H& w Jh byte a w Gu dka w GU& r Smy g/ F8
u dkq u fw dku fE Sdy fjy D; loop x Ju x Gu fv dku f& i f y Hk( 3 8 ) t w dki f; jr i f& y gw , f/
y Hk( 3 8 )
y Hk( 3 8 ) u dkMu n fhr , fq dk& i f MessageBoxA t w Gu fv dkt y fw Jh a ' w ma w Gu dk decrypt v ky fjy D; c su fc si f;
MessageBoxA API u dka c : o Hk; w ma w GU& y gw , f/
y Hk( 3 9 )
,., Polymorphic - ...- . .` .
.
VA 0040101F a & mu fw Jht x d F8 u dkE Sdy fv mc Jh& i fa w mh y Hk( 3 9 ) t w dki f; u Re fa w mfw dkUz , f& Sm; & r , fh nag
window u dkjr i f& y gw , f/ MessageBoxA API u dk e n f; e n f; a v mu fa v hv mMu n fh& a t mi f/ a & SUy dki f; r Smv J ' D
API t a Mu mi f; a v hv mjy D; jy Dr dkU ' Da e & mr Sma w mht a & ; Mu D; w Jhargument a v mu fu dky J a v hv my gr , f/
int MessageBox(
HWND hWnd, // handle of owner window
LPCTSTR lpText, // address of text in message box
LPCTSTR lpCaption, // address of title of message box
UINT uType // style of message box
);
Par ameter s
hWnd
Identifies the owner window of the message box to be created. If this parameter is NULL, the message box
has no owner window.
w u , fv dkUo m u Re fa w mfw dkUt a e e JU hWnd u dk 1 jz p fa t mi fv ky fr , fq dk& i f owner u dk& Sma w GUr Smr [ kw fw Jh
t jy i f messagebox u dkv Jjy E dki fr Smr [ kw fy gb l; / ' ga Mu mi fh VA 40101D u PUSH 0; u dk PUSH 1; v dkUjy i f
v dku f& i f nag window u dkz , f& Sm; jy D; o m; jz p fo Gm; r Smy g/ ( q dkv dkc si fw mu loader z dki fw p fc ku dkz e fw D; jy D;
' Da e & mu dk jy i fv dku f& Hky gy J/ )
' ga y r , fhy & dk* & r fa & ; o m; o l Lena151 u ' Dnag u dk 2 bytes y Jo Hk; jy D; patch v ky fy gv dkU c dki f; c Jhy gw , f/
y Hk( 4 0 )
y Hk( 4 0 ) u dkMu n fhy g/ Nag window u dkv ky fa q mi fjy D; c sde fr Sm y & dk* & r f[ m VA 40106A q Djump v ky fo Gm;
y gw , f/ w u , fv dkUo m nag window r w dki fc i f VA 40106A q Djump v ky fE dki f& i fa u m . . .
q dkv dkw mu y & dk* & r fu VA 401011 u PUSH 0 u dkt v ky fv ky fa p r , fht p m; y Hk( 4 1 ) t w dki f; jy i fv dku f& i f
b mjz p fo Gm; r Smy gv J/
y Hk( 4 1 )
' ga Mu mi fh VA 40106A q Djump v ky fa y ; E dki fr , fh opcode (self-modifying code) jz p fw Jh EB 57
u dkr Sw fo m; x m; y g/
INFO: : w u , fa w mhnag u dkz , f& Sm; w Jht jc m; jz p fE dki fz G, fe n f; v r f; a w G& Sdy ga o ; w , f/ Oy r m VA 401010
u byte u dkt o Hk; jy Kjc i f; /
VA 40106A u dkq u fMu n fhy g/ Self-modifying code a w Gu dk x y fa w GU& y gr , f/ y Hk( 4 2 ) /
y Hk( 4 2 )
,., Polymorphic - ...- . .` .
.
VA 401075 x d F8 E Sdy fjy D; assemble v ky fc sde fr Sma w mh y Hk( 4 1 ) w ke f; u u Re fa w mfw dkUa jy mi f; c Jhw Jh JMP
a e & mr Sm y Hk( 4 3 ) t w dki f; u k' fa w Ga jy mi f; a e w mjr i f& y gw , f/
y Hk( 4 3 )
a e mu fx y fb ma w Gjz p fa o ; v Jq dkw m q u fMu n fhMu y gr , f/ y Hk( 4 4 ) /
y Hk( 4 4 )
CALL EDI u a w mh self-modifying code & JU t q Hk; jz p fy gw , f/ jy Kjy i fx m; w Jhu k' fu dk c su fc si f;
execute v ky fMu n fhE dki fa t mi fv dkU CALL EDI x Ju dk F7 E Sdy fjy D; 0 i fMu n fhMu & a t mi f/ y Hk( 4 5 ) /
y Hk( 4 5 )
Olly u t o p fa jy mi f; v Jx m; w Jh u k' fa w Gu dk analyze v ky fx m; y Hkr & y gb l; / ? a w Gjy a e y gw , f/
' ga Mu mi fht & i f analyze v ky fv dku fy g/ y Hk( 4 6 ) /
y Hk( 4 6 )
y Hk( 4 6 ) u dkMu n fhv dku f& i f self-modifying code [ m y i fr y & dk* & r ft w Gu f jy i fq i fjy D; y Hk& y gw , f/ b ma w G
jz p fr v Jo dE dki fa t mi fv dkU F8 u dkE Sdy fjy D; p p fMu n fhy g/
y Hk( 4 7 )
,., Polymorphic - ...- . .` .
INFO: : Self-modifying code & JU ' kw d, t p dw ft y dki f; u a w mh u Re fa w mfw dkUu dk b mr St c u fr a w GUa p y gb l; /
' Dt c sde fr Sma w mhu Re fa w mfw dkU[ m nag u dk a u smfv Tm; v mc Jhjy D; y gjy D/
Main window u dky dw fv dku f& i fa w mhy Hk( 4 8 ) t w dki f; jr i f& y gr , f/
y Hk( 4 8 )
y Hk( 4 8 ) u CALL 401320; r Sma w mh p dw f0 i fp m; p & ma u mi f; w ma w Ga w GUE dki fr , fv dkUx i fy gw , f/ F7 u dk
E Sdy fjy D; CALL x J0 i fMu n fhv dku fy g/ y Hk( 4 9 ) /
y Hk( 4 9 )
y Hk( 4 9 ) r Smjr i f& w Jhu k' fa w Gu a w mh y & dk* & r fe JUt w ly gv mw Jh r lv u k' fa w Gjz p fy gw , f/ ' Dv dku k' fa w Gu dk o i fh
t a e e JUjr i fz l; r Smy g/ ' Dw p fc gr Sma w mh 8D e JU XOR v ky fy gw , f/ XOR v ky fr , fha e & mu a w mh VA 403000 & JU
opcode a w G& Sd& ma e & mu a e p r Smy g/ y Hk( 5 0 ) /
y Hk( 5 0 )
VA 403000 u a e VA 403128 x dXOR v ky fjy D; c sde fr Sma w mhy Hk( 5 0 ) [ m y Hk( 5 1 ) t w dki f; jz p fo Gm; y gr , f/
y Hk( 5 1 )
y Hk( 5 1 ) r Smjr i f& w Jht w dki f; ' Dy & dk* & r fu dka & ; o m; w Jh y & dk* & r fr mu u Re fa w mfw dkUu dk t c u fa w GUa t mi fv ky fw m
y g/ a jc & mc H& r , fho u fa o a w Gt m; v Hk; u dk o lr ( Lena151) u z su fq D; v dku fy gw , f/
r Sw fc su f/ / w u , fa w mh ' Dy & kd* & r fu o i fhu dk t a jc c Ht a w G; t a c : & & Hkt w Gu f jy o w mjz p fy gw , f/ v u fa w GYr Sm
a w mh ' Dx u fy dkjy D; & Iy fa x G; w Jhy & dk* & r fa w Ge JU o i fMu HKa w GU& r Smjz p fy gw , f/ u k' fa w Gr sm; jy m; v Sw Jh Mu D; r m; w Jhy & dk* & r f
a w Gx Jr Sm & dk; & Si f; v Sw Jhenxor a w Gt p m; w u , fhu dk& Iy fa x G; v Sw Jhdecryption routine a w Gu dko m a w GU& r Smy g/ ' D
routine a w Gx Jr Sm y dkjy D; & Iy fa x G; v Sw Jhpolymorphic u k' fa w G& Sda e r Smy g/
INFO: : Polymorphic u k' fq dkw mu a w mh r lv algorithm u dk y u w dt w dki f; & Sda e a p a t mi fv ky fa e p Oft w Gi f;
t o Gi fa jy mi f; v Jo Gm; w Jh u k' fu dka jy mw mjz p fy gw , f/ ' De n f; y n mu dk w c gw & Hr Sm u Ge fy sLw mA dki f; & y fp fa w G? shell
u k' fa w Ge JU u Ge fy sLw m worm a w Gu o lw dkU& Sda e w mu dk z Hk; u G, fE dki fz dkUt w Gu f t o Hk; jy KMu w mjz p fy gw , f/ Anti-
virus a q mhz f0 Jv fe JU v Hkjc HKa & ; p e p f a w mfa w mfr sm; r sm; u a w mh u Ge fy sLw mu Ge f, u fw p fa v Qmu f y dkYv Tw fv dku fw Jh
data packet a w Ge JU u Ge fy sLw mz dki fa w Gx Ju a e malicious u k' fa w Gu dk & Smz dkUMu dK; p m; Mu y gw , f/ w u , fv dkUo m
,., Polymorphic - ...- . .` .
v Hkjc HKa & ; a q mhz f0 Jv fa w Gu o lw dkUa w Gx Jr Sm A dki f; & y fp f^ worm a w Ge JUy w fo u fw Jh o dx m; jy D; o m; signature
a w Gu dk& Sma w GUc Jhr , fq dk& i f ' Dthreat a w Gu dk t jy D; w dki f neutralize v ky fz dkUMu dK; p m; r Smjz p fy gw , f/ Polymorphic
algorithm a w Gu a w mh r a w mfr a & mfu k' fa w Gu dk & Sma z Gw Jh ' Dv dka q mhz f0 Jv fa w Gu dk t c u fa w GUa p y gw , f/ b m
a Mu mi fhv Jq dka w mho lU& JUu k' fa w G[ m t q u fr jy w fa jy mi f; v Ja e v dkUy g/
INFO: : Encryption u a w mh polymorphism u dk u k' ft o Gi fe JY & & Sda p E dki fz dkU t r sm; q Hk; t o Hk; jy Kw Jhe n f;
v r f; jz p fy gw , f/ b my Jjz p fjz p f u k' ft m; v Hk; u dka w mh encrypt v ky fy p fv dkUr & y gb l; / b ma Mu mi fhv Jq dka w mh u k' f
t m; v Hk; u dk encrypt v ky fv dku f& i f t o Hk; jy Kv dkU& a w mhr Sm r [ kw fv dkUy g/ y & dk* & r f& JU t y dki f; i , fw p fc ku dka w mh
encrypt r v ky fb Jx m; & r Smjz p fjy D; encrypt v ky fx m; w Jha q mhz f0 Jv f& Sd& mq Djump v ky fjy D; y & dk* & r fu dk p w i fa p & r Sm
jz p fy gw , f/ Anti-virus a q mhz f0 Jv fa w Gu a w mh encrypt r v ky fx m; w Jh ' Du k' ft y dki f; t p u dky J a jc & mc HMu w m
jz p fy gw , f/ Malicious y & dk* & r fr ma w Gu a w mh ' DA sL[ ma w Gu a e t a w GUt Mu HK, ljy D; A dki f; & y fp fa w G^ worm a w G
y Gm; r sm; y sHUE SHUc sde fr Sm encrypt r v ky fx m; w Jh decryption engine & Sd& mu k' fu dk jy e fx y fjy i fa & ; Mu jy D; o lw dkU& JU
polymorphic u k' fa w Gu dku mu G, fz dkU Mu dK; p m; Mu w mjz p fy gw , f/ Anti-virus a q mhz f0 Jv fa w Gu decryption
engine t o Gi f a jy mi f; v Ja e p Oft w Gi f; i ky fv QdK; a e w Jhu k' fa w Gu dk & Sma z Ga w GY& SdE dki fz dkUt w Gu f & Iy fa x G; v Sw Jh u k' fc GJjc r f;
p dw fjz mr Ia w Gjy Kv ky fE dki fr , fq dk& i f ' Dv dk malware a w Gu dk p Hkp r f; a x mu fv Sr f; E dki fz dkU a r Qmfv i fh& y gw , f/
INFO: : Metamorphic u k' fq dkw mu a w mho lu dk, fw dki fjy e fjy D; y & dk* & r fjy e fa & ; E dki fw Jhu k' fu dk a jy mw mjz p fy gw , f/
r Mu mc P q dko v dky J o lU& JUu dk, fy dki fu k' fu dk , m, Dy Hkp Hw p fc kt jz p f a jy mi f; v Ja y ; v dku fjy D; r S y Hkr Se fu k' fu dk jy e fjz p fa p
w my g/ ' De n f; u dka w mht c sdKUA dki f; & y fp fa w Gu z dki ft o p fa w Gu dk u l; p u fa p w Jht c gr Sm t o Hk; jy Ky gw , f/ & v ' fu a w mh
o lw dkU& JU children ( A dki f; & y fp fx dx m; a o my & dk* & r fr sm; ) a w G[ m b , fa w mhr S o lw dkUe JUw la w mhr Sm r [ kw fy gb l; /
u Ge fy sLw mA dki f; & y fp fa w Gu ' De n f; u dk t o Hk; jy K& w Jht a Mu mi f; & i f; u a w mh anti-virus a q mhz f0 Jv fa w Gu signature
a w Gu dkr Sw fr djc i f; r S a & Smi f& Sm; E dki fz dkUjz p fy gw , f/ w u , fh algorithm u a w mhr a jy mi f; v Jb l; v dkU q dkE dki fa y r , fhv J
t & m& mw dki f; u a w mh jz p fE dki fy gw , f/ Metamorphic u k' fu a w mh polymorphic u k' fx u f y dkjy D; t p Gr f; x u fy g
w , f/ b ma Mu mi fhv Jq dka w mh anti-virus a q mhz f0 Jv fa w mfa w mfr sm; r sm; u u k' fa w Gexecute v ky fc sde fr Sm o dx m;
jy D; o m; A dki f; & y fp fu k' fa w Gu dk & Sma z Gz dkU Mu dK; p m; Mu v dkUy g/ Metamorphic u k' fa w G[ m r w ln Dw Jh OS E Sp fc kMu m;
( Oy r m Windows E Si fhLinux) ( o dkU) ' Dx u fy dkjy D; ( o dkU) r w ln Dw Jhu Ge fy sLw mw n fa q mu fr I( y & dkq u fq m) a w G
& Sd& i fa w mi fr S exe z dki fa w Gu dk u l; p u fa p jy D; t v ky fv ky fa p E dki fy gw , f/ r Mu mc P q dko v dky J A dki f; & y fp fa w G[ m o l
u dk, fw dki f a jr mu fr sm; p Gma o m A dki f; & y fp fa w Gu dko , fa q mi fjy D; p ly gA dki f; & y fp ft o Gi fe JU t w lw u Gv ma & mu f a y gi f; p y f
Mu y gw , f/
INFO: : Alphanumeric u k' fu a w mh p mv Hk; a w G? * P e f; a w Ga y gi f; p y fx m; w Jht w GJ( ' ga Mu mi fh ' Dv dkt r n fw Gi f&
w my g) w p fc kjz p fjy D; o lw dkUu dk u Ge fy sLw mu o m process v ky fE kdi fw Jh e m; r v n fE dki fw Jhy Hkp Hw p fc kt o Gi fe JU a & ; x m; Mu
w my g/ e r le m alphanumeric u k' fw p fc ku a w mhASCII jz p fy gw , f/ ' Dx u fy dkjy D; a jy m& & i fa w mhalphanumeric
u k' fq dkw m machine u k' fjz p fjy D; o lw dkUu dk v Hk; 0 z w fv dkU& w Jh ASCII p mv Hk; t jz p f assemble v ky fjy D; a & ; x m; Mu
w my g/ Oy r m "a" "z", "A" "Z", "1" "9", "#", "!", "@" p o n f . . . / Alphanumeric u k' fa w Gu dk
a & ; w Jht c gr Sma w mh ' Du k' fu dkt v ky fv ky fa p r , fh o w fr Sw fx m; w Jh u Ge fy sLw mz GJUp n f; w n fa q mu fr Iy Hkp He JUy w fo u fw Jh
machine u k' f& JU encoding p e p fu dk a u mi f; a u mi f; e m; v n fx m; z dkUv dky gw , f/ ' Du k' fu dka w mh web form w dkUv kd
application a w Gu dk t & l; v ky fz dkU& n f& Gn fc su fe JU t o Hk; jy KMu w mjz p fy gw , f/ ' Du k' fa w Gu dk v u fc Hjc i f; t m; jz i fh
exploit jz p fa p r Smjz p fy gw , f/ ' Dexploit jz p fa p w mu y J buffer overflow jy e mu dk Mu HKa w GUa p r Smjz p fy gw , f/
w c gw & Hr Sma w mh alphanumeric u k' fu dk y & dk* & r fr mw p fa , mu fu b , f compiler ( o dkU) assembler r Sr & Sdb J
y & dk* & r fw p fy k' fu dka & ; z dkU v dkt y fv mw Jht c gr Sm t o Hk; jy KMu y gw , f/ Alphanumeric y & dk* & r fw p fy k' fu dk
a & ; z dkUv dkt y fw mu a w mhtext editor w p fc ky g/
INFO: : Shell u k' fq dkw mu a w mh a q mhz f0 Jv f bug u a e t c Gi fha u mi f; , ljy D; payload t jz p ft o Hk; jy Kw Jh
machine u k' f& JUw p fp dw fw p fa ' o jz p fy gw , f/ Machine r Smt v ky fv ky fa e w Jh a q mhz f0 Jv f& JUt m; e n f; c su fu dk
t c Gi fha u mi f; , ljy D; t c Gi fhr & Sdw Jho Hk; p GJo la w Gu dk OS & JU command-line u a e w q i fh u Ge fy sLw me JU c sdw fq u fE dki f
a t mi fc Gi fhjy Ky gw , f/ y Hkr Se ft m; jz i fha w mh null-terminated (\0) string t a e e JUo dr f; q n f; w mjz p fjy D; null
character a w Ga w mh r y g0 i fE dki fy gb l; / Exploit v ky fc Hx m; & w Jh process & JU privilege a w G& x m; w hJ u Ge fy sLw m
p e p fw p fc ku dk command-line access & x m; & i f shell u k' fw p fc ku dk exploit payload w p fc kt a e e JU t o Hk; jy KE dki f
y gw , f/ Anti-intrusion a w Gu p Hkp r f; w mu dk a & Smi f& Sm; z dkUe JU string w p fc kx u fy dkjy D; o dr f; q n f; E dki fz dkU y & dk* & r fr m
a w G[ m r Mu mc P q dko v dky J self-decrypting u k' f? polymorphic u k' f? alphanumeric u k' fa w Gu dk t o Hk; jy K
Mu y gw , f/ Shell u k' fa w Gu dk process w p fc k& JU r Sw fOmP fa e & mv Gw fr Sm o dr f; q n f; x m; E dki fjy D; stack e JU heap
u dkt a jc c Hw JU buffer overflow ( o dkU) format string attack w dkUv dk t m; e n f; c su fa w Gu dk t o Hk; jy Kjy D; y & dk* & r f
a w G& JU w ke fUjy e fr Iu dk x de f; c sKy fv dku fjy D; a e mu fr Sma w mhattacker a w Gu ' Du k' fa w Gu dk t v ky fv ky fa p w m jz p fy gw , f/
y & dk* & r f& JUw ke fUjy e fr Iu dk x de f; c sKy fw Jhe n f; v r f; a w Gu a w mh t r sm; Mu D; & Sdjy D; OS e JU y & dkq u fq m w n fa q mu fr Ia y :
r lw n fjy D; u GJjy m; a e r Sjz p fy gw , f/ ' De n f; v r f; a w Gx Ju t c sdKUu a w mhstack frame x Ju return address u dkz su f
a & ; jc i f; ? exception handler a w Gu dkz su fa & ; jc i f; e JU Windows u dkt a jc jy Kw Jhshatter attack w kdUy Jjz p fy gw , f/
,., Polymorphic - ...- . .` .
INFO: : Machine u k' f ( o dkU) machine b mo mp u m; q dkw mu a w mh u Ge fy sLw m& JU CPU u w dku f& dku f
e m; v n fE dki fw Jh instruction a w Ge JU a ' w ma w Gy g0 i fw Jh p e p fw p fc kjz p fy gw , f/ Machine b mo mp u m; w p fc k& JU
"words" q dkw mu a w mh instruction a w Gu dka c : a 0 : w mjz p fjy D; o lw dkUt o D; o D; [ m CPU & JU & dk; & Si f; v Sw Jh v ky f
a q mi fc su fw p fc ku dk v ky fa p y gw , f/ Instructon a w Gu dk bit a w Ge JUz GJUp n f; x m; w mjz p fjy D; command a w Gr w l& i f
a w mh r w ln Dw Jh bit y Hkp Ha w Gjz p fa e r Smy g/ CPU model w dki f; r Sma w mh o lU& JUu dk, fy dki f machine u k' f ( o dkU) instr-
uction set & Sdjy D; w p fx y fw n f; a w mh u sc si fr Su sE dki fy gv dr fhr , f/ w u , fv dkUo m CPU A u CPU B & JU b mo m
p u m; t m; v Hk; u dk e m; v n fw , fq dk& i fa w mh CPU A [ m CPU B e JU o [ Z mw jz p fw , fv dkU a jy mv dkU& y gw , f/
w u , fv dkU CPU B u CPU A & JUu k' ft c sdKUu dk e m; r v n fc Jhb l; q dk& i fa w mhCPU B [ m CPU A e JU o [ Z mw
r jz p fy gb l; / t c sdKU machine b mo mp u m; a w G[ m o lw dkU& JU instruction a w Gu dk bit t a & t w Gu f w ln Dp Gm
x m; w ma w GU& y gw , f/ y Hkp Ha w Gu dk b , fv dkz GJUp n f; x m; w , fq dkw mu a w mh machine u k' fo w fr Sw fc su f a y :
t r sm; Mu D; r lw n fy gw , f/ t r sm; p ku a w mh instruciton w p fc ku dk field a w Gt jz p fc GJv dku fw mjz p fy gw , f/ y Hkr Se f
t m; jz i fhq dk& i fa w mh field w p fc k& JUw e fz dk; ( opcode) [ m w du sw Jhv ky fa q mi fc su fw p fc ku dk ( Oy r m - add) o w f
r Sw fy gw , f/ t jc m; field a w Gu a w mh operand t r sdK; t p m; ? o lw dkU& JUw n fa e & m ( o dkU) o lw dkU& JUw e fz dk; u dk
w dku f& dku fa y ; y gw , f/ ( instrucion w p fc kx Jr Smy g0 i fw Jh operand a w Gu dk immediate v dkUa c : y gw , f/ ) x l; x l;
q e f; q e f; instruction set t c sdKUr Sma w mh opcode field w p fc kr & Sdb J operand a w Go my g& Sdy gw , f/ t jc m;
instruction set a w Gr Smv J operand w p fc kw a v c sdKUw JhE dki fy gw , f/ ( Oy r m - NOSC)
a u mi f; jy D? y Hk( 4 9 ) u dkjy e fMu n fhv dku fy g/ ' Du k' fa w G[ m data section & JUw p fp dw fw p fa ' o u dk encrypt
jy e fv ky fw mjz p fy gw , f/ ' Dencryption routine u a e F8 u dkE Sdy fv dku f& i fa w mhy Hk( 5 2 ) t w dki f; jr i f& y gr , f/
y Hk( 5 2 )
y Hk( 5 2 ) r Smjr i f& w mu a w mh a e mu fx y f CALL w p fc kjz p fy gw , f/ F7 u dkE Sdy fjy D; CALL x Ju dk 0 i fMu n fh
v dku fMu & a t mi f/ y Hk( 5 3 ) /
y Hk( 5 3 )
y Hk( 5 3 ) u dka w mh& Si f; jy p & mr v dka w mhb l; v dkUx i fy gw , f/
t u sOf; c sKy fjy e f& Si f; jy & r , fq dk& i fa w mh ' Dy & dk* & r fa v ; [ m u Re fa w mfw dkUu dk t m& Hkv TJw Jhu k' fu dk y x r q Hk; jy y g
w , f/ ' Dha e mu fr Sma w mh code section u dk decrypt v ky fy gw , f/ Nag u dkz e fw D; z dkU self-modifying u k' f
t c sdKUu dk t v ky fv ky fa p y gw , f/ Nag t w Gu fv dkt y fw Jh data section u dk decrypt v ky fy gw , f/ jy D; & i f nag u dk
run jy D; main y & dk* & r fu dkz e fw D; z dkU self-modifying u k' ft c sdKUu dk t v ky fv ky fa p y gw , f/ ' Dha e mu fr Sma w mhy & dk* & r f
u dk run jy D; y & dk* & r f& JUv ky fa q mi fc su f jy D; q Hk; v dkU r x Gu fc i fr Sm t jc m; enxor w p fc ke JU encryption jy e fv ky fjc i f; jz i fh
data section u dk z su fq D; v dku fy gw , f/
' ga w Gu dk ' Da e & mr Smy J e d* Hk; c sKy fv dku fjy D; nag u dk z su fz dkUjy i fy gr , f/ y & dk* & r fu dk Olly r Smjy e fz Gi fhv dku fy g/
( Ctrl+F2) / y Hk( 5 4 ) /
y Hk( 5 4 )
VA 401016 e JU VA 401017 Mu m; r Sm PUSH 0; u dk z e fw D; w mjz p fw Jht w Gu f ' Da e & mr Sm JMP
40106A; v dkUjy i fy gr , f/ ' ga y r , fhr Sw fx m; & r Smu ' Dt c sde fr Sma w mh ' Dbyte a w Gu dk encrypt v ky fx m; w ke f; & Sdy g
a o ; w , f/ y x r q Hk; VA 401016 e JU VA 401017 r Sm b ma w G& Sda e o v Jq dkw m t & i fMu n fhMu y gr , f/ t a y : u dk
scroll e n f; e n f; q GJv dku fy g/ y Hk( 5 5 ) /
,., Polymorphic - ...- . .` .
y Hk( 5 5 )
a jy mi f; & r Smu a w mh y Hk( 5 5 ) r Smjr i f& w Jht w dki f; 305A a e & mr Smy g/ ' gu dk & dk; & Si f; v Sw Jh enxor o Hk; jy D; a jz & Si f;
v dkU& y gw , f/ Code section decryption r Sm XOR v ky fw m[ m 5A e JUq dkw m r Sw fr dy go v m; / Crackers'
Tools u dkz Gi fhv dku fy g/ y Hk( 5 6 ) /
y Hk( 5 6 )
INFO: :
XOR A, B; // C
XOR A, C; // B
XOR B, C; // A
' ga Mu mi fhJMP 40106A (EB57) t w Gu f EB u dk XOR v ky fy gr , f/ y Hk( 5 7 ) /
y Hk( 5 7 )
B1 q dkw mu a w mhVA 401016 r Sm& dS& r , fhbyte jz p fy gw , f/ 57 u dk XOR v ky fy gr , f/ y Hk( 5 8 ) /
y Hk( 5 8 )
0D q dkw mu a w mhVA 401017 r Sm& dS& r , fhbyte jz p fy gw , f/
Decrypt v ky fr Smjz p fw Jht w Gu f y Hk( 5 5 ) u 305A a e & mr Sm EB57 v dkU u Re fa w mfw dkUu assemble
r v ky fw my g/ ' ga y r , fh 305A a e & mr Sm B10D v dkUjy i f& r Smjz p fy gw , f/ VA 401016 a e & mr Sm right-click
E Sdy fjy D; Binary edit u dka & G; y g/ y Hk( 5 9 ) /
y Hk( 5 9 )
,., Polymorphic - ...- . .` .
,
y Hk( 5 9 ) t w dki f; jy i fv dku f& i fa w mhy Hk( 6 0 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 6 0 )
' Djy i fv dku fw Jhz dki fu dk Patch.exe t r n fe JUo dr f; v dku fjy D; Patch.exe z dki fu dk Olly r Smz Gi fhv dku fy g/ y Hk( 6 1 ) /
y Hk( 6 1 )
y Hk( 6 1 ) u VA 401299 u CALL 40130F u a w mhdecryption routine u dka c : o Hk; w my g/ Encrypt
v ky fx m; w Jhu k' fa w Gu dk y x r q Hk; Mu n fhv dku fMu & a t mi f/ y Hk( 6 2 ) /
y Hk( 6 2 )
y Hk( 6 2 ) r Sm u Re fa w mfw dkU patch v ky fx m; w Jhu k' fu dk a w GU& y gw , f/ F8 u dkE Sdy fjy D; ' Da e & mr Sm b mq u fjz p f
r v Jq dkw mMu n fhv dku fMu & a t mi f/ y Hk( 6 3 ) /
y Hk( 6 3 )
y Hk( 6 1 ) u VA 401299 u dkv ky fa q mi fjy D; c sde fr Sm jr i f& w mu a w mh y Hk( 6 3 ) r Smjr i f& w Jht w dki f; jz p fy gw , f/
Self-modifying u k' f[ m 57EB w e fz dk; u dk VA 401016/401017 r Smo Gm; x m; a w mhr Smjz p fy gw , f/ u Re fa w mf
w dkUt a e e JU decryption call u dk execute v ky fjy D; o Gm; y gjy D/ Decryption call (VA 401299) u dkv ky fa q mi fjy D;
c sde fr Sm ' Du k' fa w Gu dk a c : o Hk; w Jhcall 401011 (VA 40129E) x Ju dk F7 E Sdy fjy D; 0 i fMu n fhv dku fMu & a t mi f/
y Hk( 6 4 )
y Hk( 6 3 ) r Smjr i f& w Jht w dki f; VA 401013 u dk execute v ky fjy D; c sde fr Sma w mh VA 401011 a e & mr Sm JMP
40106A; v dkUa y : v mw ma w GU& y gw , f/ u se fw Jht y dki f; u dka w mh & Si f; jy p & mr v dka w mhb l; x i fy gw , f/ y & dk* & r fu
nag t w Gu fv dkt y fw Jhu k' fa w Gu dk decrypt v ky fjy D; w Jha e mu fr Sm VA 401011 a e & mu dk x y fa & mu fv mr Sm jz p fy g
w , f/
' Dw p fc gr Sma w mhVA 40106A & Sd& mq Djump jz p fo Gm; jy D; nag window u dka u smfo Gm; r Smjz p fy gw , f/
INFO: : u Re fa w mfht a e e JU 1 byte x Jo Hk; & r , fha jz & Si f; e n f; u dkv J a jy mc Jhy gw , f/ Messagebox u PUSH 0;
u dk PUSH 1; t jz p fa jy mi f; z dkUy g/ w u , fv dkU o i fht a e e JU ' gu dkMu dK; p m; Mu n fhc si fw , fq dk& i fa w mh VA 401039
u 5A a e & mr Sm 5B v dkU assemble v ky f& y gr , f/ b my Jjz p fjz p f ' De n f; u a w mh t a u mi f; q Hk; e JU t v G, fq Hk;
a jz & Si f; w Jhe n f; jz p fy gw , f/
,.,, Registration number - ,.- .....`... .....`.
tcef;(24) - Registr ation number udk tGefvdkif;wGif ppfaq;jcif;tm; z,f&Sm;jcif;
.-...--. registration number - .-.-_.,-,.. ..`... .,.- . .. ,_ ._..-
- ..`.--. Registration number - .-..-. .-..- - ......--
-.,- --. - -. ..-.- - . , .. , - .. .. ` . .-. .`, -. . -..
-.-. . , -, . . register ..` . . .. .. ...-. ' Software Protection' ,..,
-. . ..-. registration - ,........--- .-...-- crack -_ . .`..
-. ........`..-. .-...--. -.,- , . - ... . .- `.. --....-.
.-. . . - - -.,- .-...... ..`.-. Crack .......-
....-.-. Download Accelerator PLUS (DAP) `.. -. DAP -. -.,--..--
`.,.,.`. speed , download ... - ... . `.. ` . download ... ..-. .-. .. .,
`., . .... . -. `.. -. `.. download accelerator ....-.`..- FlashGet
-.-. link .- .`....- ..-- resume .,, download ...- ....-
.-. .-., DAP - www.speedbit.com -., download .`. install - -.
version -.-. .....`....... -,.-.,.,. crack `..-.-. Version 8.0.4.1 `..
-. -. version `.. `.. ..-.-... .-.-. - -
Crack . -, .-. - .. ..... .-.-. .-..- -.,.......-.- ,
,
.-..- SVK Protector , protect ..-.`.. -. ..., ..`. .-. -, .-. .,,
pack ..-.- unpack `. -., .. - . -..-. . .-. unpack ,_.- Packer
(Protector) ...' , .. . .. ... .` .`.. ... -, .-. .,, , .. . SVKP , pack
..-.- -. unpack .. . -.- --_ .. .`. .`.. -. SVKP - .......
-.-. Pavol Cerven ,.._ - .,.- -. .- .`, ` SVKP , - .- - unpacker
.--..-.-.--.-.. SVKP , - .- - unpacking . , ... -. .`.. -.-
-.-. .. . .,, unpack .-.-`........--- unpack ,_.- --_.
. .`.` .`.. -. AHTeam -........- Quick Unpack 2.1 -. packer .-..-.......-
unpack ... ... SVKP , protect ..-..--- `.,. ,_ .. . .,-. ,
SVKP -. . - protect . - - .- _ - ,_ .. .,.- . .`-. .- -.-. , RSA
algorithm - ..``. , API function ...-_....`..`. , anti-debug _ ....
..._....`. ,, .-.. tracer .-. dump . . .. -.- . ..` . - `.. -.
, SVKP `. pr otect ...... .. unpack ` .
. , ...- ` .,.._ .. -, .-. .,, ..- - . .,. `.........
`.. -.
, OEP - . .` .
, Stolen byte ...- ..`.
, .- dump ` .
,, IAT - ` ` .
, .-``.
,.,, Registration number - ,.- .....`... .....`.
, OEP - ..`.
OEP - . ..-.-.-. stolen code .-. -..-...-. -,.-.-.,, stole
..- . code section . ... instruction ...- OEP ,... . OEP .. .---., break
.. .. .-. .` DAP.exe . - Olly . ... Olly _..-.-.- `.. Alt + O
-.`. Debugging options . SFX tab -...- ,
,
,.. `..--. Trace real entry blockwise radio button - .. .. ` Pass
exceptions to SFX extractor checkbox - check - .-- -..-. ......
.-..-. ..`.-... .---. -..-...-. Olly . Help ... ....- ..`..
Trace real entry blockwise (inaccurate)
OllyDbg uses 4-K blocks to step through the packed code. This method may cause detection of false real
entry.
Pass exceptions to SFX extractor
This option tells OllyDbg to pass some kinds of software exceptions that occur while tracing for real SFX
entry (memory access violation, INT3 breakpoint, division by 0, privileged or illegal instruction) directly to self-
extractor.
.-..` DAP.exe . - Olly ...-_--... ,
,
,.. `..--. VA 0053F432 .. Olly -. . . ... . . . -, .-. - -. stolen
byte .- .,.- - code section - .. . instruction ......-.,` - -,.-.- -.
. . . -. . . .. VA 0053F432 . ..- - scroll ,_.,_...-.`. -_...
,,
,,
,.,, Registration number - ,.- .....`... .....`.
,
--. .-. ,,- -, .-. - `. .- NOP instruction .,...- . . - .- . .. . .-. .`
,- VA 0053F432 .,..- ... - - -. . - . . . - ..- `...-. ,- Trace real
entry blockwise radio button ... Stop at entry of self-extractor -`,...-
, Stolen bytes - . .` .
-.-. unpack ... . - . ., -.. .`.. -. ..-.- , . ...- .-.
.. - . .. . Ctrl + F2 -.`. .-..- `,.- ,- . ... . ..
,
,- No button - ...- Entry point - ...- - Alt+O -.`. ,-.
Exception tab -`-
,
,.. Memory access violation , Ignore aslo following - `.---.
`...-. ,,-. entry point ...- `,...-
,,
,,.. F7 - -..`. CALL function ... VA 00731001 -... CALL function
. ..- ...- ` . . Registers window - -_- .,
.,
.,--_-. ESP register .,.... ,.,-.- .-... -..-...-. ESP
-,...`..... .,.... right-click .`. Follow in Dump -...- .,-.
.- ...
,.,, Registration number - ,.- .....`... .....`.
.
.,
.,- 38 07 91 70 .,.... right-click .`. hardware, on access - Dword -...-
` .. F9 (Run) - .-
,
,-. exception -`..- Shift+F9 -. Exception error ---. Shift+F9
-. ,-.-... SVKP version ..-_`. Shift+F9 - . - ..- - -. ,- . . ,
,- . - . ..
,
,-..-- Alt + M -.`. memory map window - . ,
,
,- highlight `...,-.,.... right-click .`. set memory breakpoint on access -
.. .. ` .. Shift+F9 -. ,- . `. ...
,
,.,, Registration number - ,.- .....`... .....`.
.
,-.-. SVKP . decompression code `..-. Alt+M -...`. PE header
... right-click . `.. Remove memory breakpoint -.... memory breakpoint
-.....`...-. Shift+F9 -. .,.- PUSHAD instruction ..... .-,...
,,
,,
,,-.`..- -,.-.... .- ... - - -. . - . . . - ...- OEP (VA
0053F432) .-.... `.. Ctrl+G -.`. OEP -,..-.-_ ,
,
,- OK button -...-. ,-. `....
,
VA 0053F432 .,... . ..., breakpoint -. .- . - - . ,- .`. .. .
.-. .` , . . hardware breakpoint .--..-.--- Debug menu - Hadrware
breakpoints -...`. breakpoint .--.-- `...-. trace -.. Ctrl+F11 (Trace into)
- .. . - -, .-. - ..., breakpoint .-.--- OEP .,..- ...-,-.
...-.-. .,.-...-. -,.-.- stolen bytes -... trace --.,...-- `,-_.
.` Olly . View menu - Run trace -...- ,,
,,
,,-.-. Olly - PUSHAD -., CALL 0042B5E4 trace ...-.- `-.
Highlight `...,-.,..-.-. -,.-.-...,- stolen bytes
INFO: : Stolen bytes . -.-.-. . exe . -., . . - . exe .-.,.-..-
,.,, Registration number - ,.- .....`... .....`.
,
.. ..- `.. ` . packer . - . . ...-. .. ..- -. OEP . .. - . - . -., dump
`.-.,.-...-. dump ..` .... exe ....-. ...-.-. . .. ... ..-
.,... ..-. .. .-. - ., .-. . . -.. .- -. crash `.. --. . -.-.-. -.
.-..- crack . . .. -.- . . -. . -.. .- - pack ..- , . ..-. crash
.`.. - . -..-. . .-. stolen bytes .--. OEP ....--... protector run
.,-
, .- dump ` .
-. . ..-. OEP - .- ` `.. - - - process (Task Manager...,- DAP.exe)
- dump -.. Olly . . right-click .`. make dump of process -...- .,-.
.- ...
.,
.,- Get MAP button -...- .,
.,
,,- , .- -, .-. - . stolen byte .- . ..- . - . ..... .,..,.....- -
scroll .`.-_-.... .,-. `.... 00E60000 .,..-...`. Add button -.
,-. `....
,
,.,, Registration number - ,.- .....`... .....`.
,
,- Name . - - - . . . . . .- ..._-. .-_-`. Apply button
-...- ,-..-...
,
.,.- .. .-.-. .,- 00E90000 .,..- .. .` . Add button -.
,
-. . . ,- Name . - - - . . . . . .- ..._-. .-_-`. Apply
button -...- `...-. .,- Close button -...- ,-. `....
,
,.,, Registration number - ,.- .....`... .....`.
,
,- , ... , `..- .,...- - . `.. .. ` .. Dump button -.` .
dumped.exe .-._,.- ... ...-. dump -.` .. .`
,, IAT (Impor t Addr ess Table) - ` ` .
-. . ..-. IAT - ` . ..
,,
,,-. OEP .,... . 0013F432 -.-_`. AutoSearch button -.... Found
something! .- MessagBox ..... Get Import button -.`. import function
.-- -_ ,,.. function .-..-.......- import .... ......,-. .-.-.
....-.... Show Invalid button -....
,
` .. .-. ,- . invalid `...,- address .- . right-click .`. Trace Level1
(Disasm) - .... ,-. `....
,
,.,, Registration number - ,.- .....`... .....`.
,
. ..-. dumped.exe . - ` . .-. .. ,,- Fix Dump button - .. . -
` .. dumped.exe -.....- ,,-. `....
,,
,,-.`..`...-. ImpREC - IAT ` ` ..... - dumped_.exe ._ ,
..- . . .._ ...-.
, . - ` ` .
dumped_.exe ..... .-_.. .,
.,
-, .-. - - ..-. .- . Windows - -, .-. - . -. PE ..---. .`..,
-. -, .-. - OEP -`-_.. dumped_.exe - PE Editor 1.7 .. .-`. OEP -
A805B3 .`..- .,
.,
.,... . .- .. -.-.-. OEP -`.... LordPE , .` , LordPE ,`- .-..
.--. ......-. OEP .,.... A805B3 . - ..- .-. .. .-.-. ,,-
-, .-. - . stolen bytes ... virtual address -. OEP [E805B3-400000 = A805B3h] ...,
`..-., ``.. .-...- ... .-.-. .,- . `.,- , .
,
--. .-. dumped_.exe . . PE header `.,..., .-. CFF explorer .. PE
header -`,``. .-...- . -.`.,.. .. .-. - SVKP , protect ..-
DAP.exe . - .. `. . . unpack ` .. ..` `.. -.
,.,, Registration number - ,.- .....`... .....`.
,,
, Registr ation number - ,.- .....` ... .. . ..` .
u Re faw mfw dkU unpack v ky fx m; w Jh dump_.exe z dki fu dk PEiD e JU p p faq ; Mu n fhw Jht c gr Smaw mh y Hk( 3 1 )
t w dki f; jr i f&y gw , f/
y Hk( 3 1 )
u Re faw mf b maMu mi fh section t o p faw Gu dk x y fx n fh&o v Jq dkw m o i fht ae e JU &Si f; av mu fjy Dx i fy g
w , f/ OEP [ m t o p fx y fay gi f; x m; w Jh section x Jr Sm&Sdae w mr dkUv dkUy g/ dump_.exe u dk Visual C++ 6.0
e JUa&; o m; x m; w m ao c smjy Dr dkUy &dk* &r f&J Ut v ky fv ky fy Hku dkao c smMu n fh&at mi f/ dump_.exe u dky Hkr Se ft w dki f; z Gi fh
v dku fy g/ y Hk( 3 2) /
y Hk( 3 2)
y Hk( 3 2) u dkt i fw me u ft q u ft o G, f&Sdw Jhu Ge fy sLw mr SmMu n fhr , fq dk&i faw mhaMu mfji maw Gu dkaw GU&r Smjz p f
y gw , f/ Help menu u About u dkMu n fhy gr , f/ y Hk( 3 3 ) /
y Hk( 3 3 )
,.,, Registration number - ,.- .....`... .....`.
,
y Hk( 3 3 ) r Smjr i f&w mu aw mhaq mhz f0 Jv f[ m register r v ky fx m; aMu mi f; e JU0 , fo Hk; z dkUjz p fy gw , f/
y Hk( 3 4 )
Help menu u dka&G; v dku f&i faw mh y Hk( 3 4 ) t w dki f; jr i f&r Smy g/ Enter Registration Info button u dk
ESdy fjy D; register v ky fMu n fhMu v dku f&at mi f/ y Hk( 3 5 ) /
y Hk( 3 5 )
y Hk( 3 5 ) r Sm OK u dka&G; ay ; &i faw mhy Hk( 3 6 ) t w dki f; jr i f&r Smjz p fy gw , f/
y Hk( 3 6 )
u Re faw mfhu Ge fy sLw m[ m t i fw me u fe JUc sdw fq u fx m; jc i f; r &Sdw Jht w Gu f ' Dv dkay : ae w my g/ ' Dav mu f
q dk&i f crack v ky fz dkU t c su ft v u faw Gaw mfaw mfav ; v Hkav mu fjy Dv dkUx i fy gw , f/ ' gaMu mi fh dump_.exe u dk
Olly r Smz Gi fhjy D; p p fMu n fh&at mi f/ y Hk( 3 7 ) /
y Hk( 3 7 )
,.,, Registration number - ,.- .....`... .....`.
,
y Hk( 3 7 ) u aw mhOEP &Sd&mu dkjy y gw , f/ DB 2A? DB 84? DB 3F? DB AD p w maw Gu dkMu n fhv dku f&i f
aw mh' gaw G[ m u k' faw Gjz p faMu mi f; e m; v n fr Smy g/ ( VB r Smq dk&i faw mh' gaw G[ m p-code aw Gjz p fy gw , f/ ) F9
ESdy fjy D; y &dk* &r fu dkrun v dku fy g/
y Hk( 3 8 )
y Hk( 3 8 ) u exception u dkShift+F9 ESdy fjy D; au smfv dku fy g/ ae mu fx y f exception w p fc kx y faw GUy gr , f/
y Hk( 3 9 )
' Dexception u dkv JShift+F9 ESdy fjy D; au smfv dku fy g/ ' gq dk&i faw mhOlly r Sm dump_.exe y &dk* &r f run
ae y gv dr fhr , f/ ' Dt c g register v ky fMu n fhMu y gr , f/ y Hk( 4 0 ) /
y Hk( 4 0 )
y Hk( 4 0 ) r Sm OK u dka&G; v dku f&i faw mhy Hk( 4 1 ) t w dki f; jr i f&r Smy g/
y Hk( 4 1 )
y Hk( 4 1 ) u MessageBox u dkaw mh o i fjr i fz l; r Smy g/ ' D MessageBox u dkb , fae &mu ac : o Hk; w mv J
o d&at mi fv dkUOlly u dkPause execution (F12) v ky fv dku fy g/
y Hk( 4 2)
Pause ay ; v dku fw Jht c g y Hk( 4 2) t w dki f; jr i f&y gw , f/ ' Dt c g u dka&G; jy D; Call Stack (Ctrl+K) u dk
Mu n fhv dku fy g/
y Hk( 4 3 )
,.,, Registration number - ,.- .....`... .....`.
,,
y Hk( 4 3 ) r Sm jr i f&w Jht w dki f; ' DMessageBox u dk mfc42.#4224 u ac : o Hk; w mjz p fy gw , f/ ' gaMu mi fh' D
CALL &Sd&mu dkMu n fhy gr , f/ y Hk( 4 4 ) /
y Hk( 4 4 )
y Hk( 4 4 ) u BadBoy u dkac : r o Hk; c i fr Sm conditional jump (JE, JNZ) aw Gu dk aw GU&y gw , f/ ' Dt c g
Resource Hacker aq mhz f0 Jv fu dko Hk; jy D; BadBoy message t c sdKUu dkMu n fhy gr , f/ MessageBox w p fc kay : z dkU
q dkw m MessageBox r Smjy r , fh p mo m; aw Gu dk stack ay : t &i fu l; w i f&w , fv dkU ajy mc Jhz l; w m jy e ft r Sw f&y g/
' gaMu mi fhBadBoy message t c sdKUu dkMu n fhv dku fMu &at mi f/
PUSH 0F2BF = 62143,
"Your registration could not be completed due to unknown result from the activation server. \n\n Please try
again in a few minutes, or email sales@speedbit.com for more help.\n"
PUSH 0F2C0 = 62144,
"Your registration could not be completed due to submission of incorrect request to the Activation Server
\n\nPlease re-check the details you have entered or contact sales@speedbit.com \n"
PUSH 0F2BE = 62142,
"Your registration could not be completed due to lack of Internet connection with SpeedBit activation
server.\n\nPlease try again in a few minutes, or email sales@speedbit.com for more help.\n"
PUSH 0F2BD = 62141,
"Your registration could not be completed due to lack of Internet connection.\n\nPlease make sure you are
connected to the Internet.\n"
Message aw Gt m; v Hk; u aw mhau mi f; w mw p fc kr Sr &Sdy gb l; / ' gaMu mi fhv Jy kH( 4 5 ) u MessageBoxA u dk
t v ky fv ky fap w m jz p fy gw , f/
y Hk( 4 5 )
au mi f; jy D/ y &dk* &r f&JUOEP &Sd&mq Djy e fMu n fhMu &at mi f/ y Hk( 4 6 ) /
y Hk( 4 6 )
y Hk( 4 6 ) u JMP u dka&G; jy D; Enter key ESdy fv dku f&i f y Hk( 4 7 ) t w dki f; jr i f&y gw , f/
y Hk( 4 7 )
y Hk( 4 7 ) u JMP u dka&G; jy D; Enter key ESdy fv dku f&i f y Hk( 4 8 ) t w dki f; jr i f&y gw , f/
y Hk( 4 8 )
,.,, Registration number - ,.- .....`... .....`.
,.
c kc sde fx daw mhb mu k' fr Sr , fr , f&& a&; x m; w m r aw GU&y gb l; / ' Du k' faw G[ m cracker aw Gu dk t m&Hkv TJ
z dkUv ky fx m; w Jhdiversion u k' faw Gq dkw m ao c smy gw , f/ c ke u register v ky fw ke f; u u Re faw mfw dkU a&mu f&Sdae c Jh
w Jh address aw G[ m 4xx,xxx 0 e f; u si fr Smy g/ v u f&Sd u Re faw mfw dkU jr i fae &w Jh address aw G[ m 4,xxx,xxx
0 e f; u si fjz p fy gw , f/ ' gaMu mi fhSear ch for u ae string p mo m; aw Gu dk&Smaw mhv Jy Hk( 4 9 ) t w dki f; jr i f&w my g/
y Hk( 4 9 )
' gq dk&i f string aw Gu dk&Smz dkU4xx,xxx aw Gq Do Gm; Mu n fhy gr , f/ Ctrl+G u dkESdy fjy D; 401000 v dkU&dku fx n fh
v dku fy g/ jy D; &i f Sear ch for u ae All r efer enced text str ings u dka&G; v dku f&i f y Hk( 5 0 ) t w dki f; jr i f&y gr , f/
y Hk( 5 0 )
' Dav mu fq dk u Re faw mfw dkUt w Gu f aw mfaw mft q i fajy y gjy D/ ' Dw p fc g Help menu u About r Smjr i fc Jh&
w JhDAP Unregistered q dkw Jhp mo m; u dk&SmMu n fhy gr , f/ y Hk( 5 1 ) / ( y Hk( 3 3 ) u dkjy e fMu n fhy g/ )
y Hk( 5 1 )
y Hk( 5 1 ) r Sm OK ESdy fjy D; &Smaw mhu Re faw mfw dkUv dkc si fw Jhp mo m; u dkr aw GUy gb l; /
Resource Hacker u dkt o Hk; jy Kjy D; ' Dp mo m; aw Gu dk&SmMu n fhy gr , f/
y Hk( 5 2)
b maMu mi fh "DAP Unregistered" p mo m; u dk &Smr aw GUw mv Jq dkw m o i fht ae e JU e m; v n fav mu fjy D
x i fy gw , f/ w u , faw mh ' Dp mo m; aw Gu dk code section/ data section a&; x m; w mr [ kw fb J resource
section r Sm o dr f; x m; w mr dkUv dkUy g/ ' Dstring aw Gu dkv dkt y fr So m stack ay : u l; w i fjy D; t o Hk; jy Kw mjz p fy gw , f/
10003 = 2713 = DAP Premium
10008 = 2718 = DAP Unregistered
' gaMu mi fh code section r Sm PUSH 2718 v dkU&dku fx n fhjy D; ajy mi f; &SmMu n fhv dku f&at mi f/
Disassembler window r Sm right-click ESdy fjy D; Sear ch for u Command u dka&G; v dku fy g/ y Hk( 5 3 ) /
,.,, Registration number - ,.- .....`... .....`.
,.
y Hk( 5 3 )
y Hk( 5 3 ) u Find button u dka&G; jy D; &Smv dku fw Jht c gr Sm y Hk( 5 4 ) t w dki f; aw GU&y gw , f/
y Hk( 5 4 )
Help menu u About u dka&G; w Jht c gr Sm "DAP Unregistered" v dkUjy &w Jht aMu mi f; &i f; u aw mhJNZ
u jump r jz p fv dkUjz p fy gw , f/ Jump jz p fEdki f^ r jz p fEdki fu dk VA 004DAF53 u CMP DWORD PTR DS:
[5DCEA0], EBX r Smp p faq ; w mjz p fy gw , f/ ' gaMu mi fhdump window &JU 5DCEA0 ae &mr Sm breakpoint
o w fr Sw fjy D; b maw Gq u fjz p fr v Jq dkw m ap mi fhMu n fhMu &at mi f/
y Hk( 5 5 )
' gaMu mi fh5DCEA0 ae &mr Sm right-click ESdy fjy D; Br eakpoint u Har dwar e, on access Byte
u dka&G; y g/ jy D; &i f F9 u dkESdy fjy D; y &dk* &r fu dkrun Mu n fhy g/
y Hk( 5 6 )
' gq dk y Hk( 5 6 ) r Smjr i f&w Jht w kdi f; MOV DWORD PTR DS:[ESI+F8], EDI u dk execute
v ky fjy D; c sde fr Sm u Re faw mfw dkUo w fr Sw fx m; w Jhbreakpoint ae &mr Sm &y fo Gm; w maw GU&y gw , f/ F9 u dkx y fEdSy fy g/
y Hk( 5 7 )
,.,, Registration number - ,.- .....`... .....`.
.
y Hk( 5 7 ) r Smjr i f&w Jht w kdi f; MOV DWORD PTR SS:[EBP-277C], EAX u dk execute v ky fjy D; c sde fr Sm
hardware breakpoint &Sd&mr Sm x y f&y fjy e fy gw , f/ ' Dae &mr Sm o w dx m; ap v dkw mu aw mhw u , fv dkU5DCEA0
u byte w e fz dk; e JUo kn w dkUn Dc Jhc sde fr Sm polymorphic u k' faw Gu dkau smfv Tm; r Smjz p fy gw , f/ F9 u dkq u fESdy fy g/
y Hk( 5 8 )
y Hk( 5 8 ) r Smjr i f&w Jht w kdi f; MOV EAX, DWORD PTR DS:[5DCEA0] u dk execute v ky fjy D; c sde fr Sm
hardware breakpoint &Sd&mr Sm x y f&y fjy e fy gw , f/ F9 u dkq u fESdy fy g/ Hardware breakpoint &Sd&ma&mu fw Jh
t c gr Sm &y fy gv dr fhr , f/ DAP y &dk* &r f run w Jht x d F9 u dkESdy fv mc Jhy g/ DAP y &dk* &r fu dkjr i fw Jht c gr Smaw mh
Help menu u About u dka&G; v dku fy g/
y Hk( 5 9 )
' Dt c sde fr Smaw mh Help menu u dk a&G; v dku fc sde fr Smy J y Hk( 5 9 ) r Smjr i f&w Jh hardware breakpoint r Smy J
y &dk* &r f[ m &y fw e fUae w maw GU&y gw , f/ About submenu u dkaw mi f a&G; v dkUr &aw mhy gb l; / ' gaMu mi fh HW
BP u dkjz Kw fv dku fy gr , f/ y Hk( 6 0 ) /
y Hk( 6 0 )
jy D; &i f Help menu u About u dka&G; v dku fy g/
y Hk( 6 1 )
' Dt c gr Smaw mh u Re faw mfw dkU aq mhz f0 Jv f brekpoint o w fr Sw fx m; w Jhae &mu dk a&mu fv my gjy D/ Dump
window u 5DCEA0 r Smaw mhbyte w e fz dk; u o kn jz p fae y gw , f/ ' Dt c sde fr Sm EBX &JUw e fz dk; u v J o kn jz p f
ae y gw , f/ o kn w e fz dk; ESp fc ku dkEdIi f; , SOfw Jht c gr Smaw mhJNZ (Jump if not zero) [ m jump r jz p fEdki fw Jht w Gu f
PUSH 2718 (DAP Unregistered) q Da&mu fv mr Smy g/ y &dk* &r f[ m register v ky fx m; jc i f; &Sd^ r &Sdu dk dump
window u 5DCEA0 r Sm&Sdw Jhbyte w e fz dk; u dkz w fjy D; q Hk; jz w fae y Hky g/ ' gaMu mi fh5DCEA0 r Sm o kn t p m; 1
v dkUjy i fv dku fy gr , f/
' gaMu mi fh 5DCEA0 u byte (00) ae &mr Sm right-click ESdy fjy D; Binary Edit u dka&G; v dku fy g/
y Hk( 6 2) / y Hk( 6 2) t w dki f; jr i f&w Jht c gr Sm 01 v dkUjy i fjy D; OK u dka&G; v dku fy g/ ' Dae mu fr Smaw mhjy i fx m; w Jhbyte (01)
u dko dr f; q n f; z dkU 01 ae &mr Sm right-click ESdy fjy D; Copy to executable file u dka&G; jy D; patch.exe q dkw Jht r n fe JU
z dki fu dko dr f; v dku fy g/
,.,, Registration number - ,.- .....`... .....`.
.
y Hk( 6 2)
o dr f; v dku fw Jhz dki f t v ky fr v ky fo d&at mi f ( patch.exe) z dki fu dk jy e fz Gi fhv dku fy g/ jy D; &i f Help menu u
About u dka&G; v dku f&i f y Hk( 6 3 ) t w dki f; jr i f&y gw , f/
y Hk( 6 3 )
w p fc kc kaw mhr Sm; ae y gjy D/ patch.exe z dki fu dkOlly r Smz Gi fhjy D; jy e fp p fMu n fhy gr , f/ y Hk( 6 4 ) /
y Hk( 6 4 )
y Hk( 6 4 ) r Smjr i f&w Jht w dki f; entry point &Sd&mae &mr Smaw mh dump window u 5DCEA0 &JU byte
w e fz dk; [ m 01 jz p fy gw , f/ F9 ESdy fjy D; y &dk* &r fu dk run Mu n fhy g/ jy D; &i faw mh Help menu u About u dka&G;
v dku fy g/ y Hk( 6 5 ) /
y Hk( 6 5 )
y Hk( 6 5 ) u dump window u dkMu n fhv dku f&i faw mh5DCEA0 u byte w e fz dk; [ m o kn jz p fae w m aw GU&
r Smy g/ ' gaMu mi fhv J y Hk( 6 3 ) r Smjr i f&w Jht w dki f; DAP Unregistered v dkUjy ae w mjz p fy gw , f/ b , fae &mr Sm
5DCEA0 &JU byte w e fz dk; [ m 1 t p m; 0 ajy mi f; o Gm; o v Jq dkw mMu n fh&at mi f/ ' gaMu mi fh5DCEA0 u byte
(01) ae &mr Sm hardware breakpoint o w fr Sw fEdki fz dkU Br eakpoint u Har dwar e, on wr ite byte
u dka&G; v dku fy g/ ' Dw p fc gr Smaw mh access t p m; write u dka&G; v dku fw m o w djy Ky g/ Breakpoint o w fr Sw fjy D;
o Gm; &i faw mhF9 u dkESdy fv dku fy g/ y Hk( 6 6 ) /
y Hk( 6 6 )
,.,, Registration number - ,.- .....`... .....`.
.
y Hk( 6 6 ) r Smjr i f&w Jht w dki f; MOV DWORD PTR DS:[ESI+F8], EDI u dk execute v ky fjy D; c sde fr Sm
5DCEA0 &JU byte (01) w e fz dk; ajy mi f; o Gm; w mjz p fy gw , f/ ' gaMu mi fh ' Dae &mr Sm y Hk( 6 7 ) t w dki f; jy i fv dku fjy D;
y &dk* &r fu dkq u f run (F9) Mu n fhy g/
y Hk( 6 7 )
F9 u dkESdy fjy D; q u f run Mu n fh&mr Smaw mhy Hk( 6 8 ) t w dki f; jr i f&y gw , f/
y Hk( 6 8 )
y Hk( 6 8 ) r Sm OK button u dka&G; ay ; v dku f&i faw mhq u ft v ky fr v ky faw mhb Jy &dk* &r f[ m jy D; q Hk; o Gm; w maw GU
&y gw , f/ ' gq dk&i faw mh01 ajy mi f; w dki f; t v ky fr jz p fw maw mhao c smy gjy D/ u Re faw mfht x i fajy m&r , fq dk&i faw mh
y &dk* &r f[ m 1 jz p f^ r jz p fu dk main window p w i fr ay : v mc i fr Sm p p fw mjz p fEdki fy gw , f/ ' gaMu mi fh hardware
breakpoint ESp fc k o w fr Sw fjy D; 5DCEA0 u byte w e fz dk; u dk ap mi fhMu n fhMu &at mi f/ HW BP w p fc ku aw mh
on access jz p fjy D; ae mu fw p fc ku aw mhon write jz p fy gw , f/ y Hk( 6 9 ) /
y Hk( 6 9 )
Breakpoint aw Go w fr Sw fjy D; o Gm; &i faw mhF9 key u dkESdy fv mc Jhy g/ u Re faw mfw dkU o w fr Sw fx m; w JhBP
w dki f; r Sm Olly u &y fy gv dr fhr , f/ F9 ESdy fjy D; q u fo Gm; y g/ y Hk( 7 0 ) t w dk i f; jr i f&&i faw mhc P &y fv dku fy g/
y Hk( 7 0 )
,.,, Registration number - ,.- .....`... .....`.
.
' Dae &mr Sm u Re faw mf b maMu mi fh&y fc dki f; &o v Jq dkw m o i fht ae e JU &Si f; v my gv dr fhr , f/ w u , faw mh
polymorphic u k' faw Gu dk aw GUv dku fv dkU &y fc dki f; v dku f&w my g/ 0045E6F5 u JNZ [ m jump r jz p fw Jht w Gu f
polymorphic u k' faw Gq Da&mu fv mr Smy g/ 0045E71B u PUSHAD u dk o w dx m; r dy go v m; / PUSHAD
q dkw mu aw mh"PUSH all Double" u dk q dkv dkw mjz p fjy D; CPU u dk stack ay : r Sm&Sdw JhEAX u ae t p c sDjy D; EDI
r Smt q Hk; o w fw Jh 32bit (DOWRD) register t m; v Hk; x Jr Smy gw Jht &m t m; v Hk; u dk o dr f; x m; ay ; z dkU n Te fMu m; y g
w , f/ PUSHAD u dko Hk; &i f ESP w e fz dk; u dkap mi fhMu n fh&y gw , f/ y Hk( 7 1 ) /
y Hk( 7 1 )
' Dt c sde fr Smaw mhF9 u dkr ESdy fb Jy Hk( 7 2) r Smjr i f&w Jht x dF8 u dko m ESdy fv mc Jhy g/
y Hk( 7 2)
y Hk( 7 2) u JMP ECX ae &mr Sm F8 u dkESdy f&i faw mh y Hk( 7 3 ) t w dki f; jr i f&y gr , f/ b maMu mi fhv Jq dkaw mh
ECX &JUw e fz dk; [ m 0012E774 jz p fae v dkUy g/
y Hk( 7 3 )
PUSHAD u dk POPAD e JUw GJo Hk; &y gw , f/ POPAD [ m stack u ae register x Jr Sm&Sdw Jht &m
t m; v Hk; u dku l; y gw , f/ ' gaMu mi fhPOPAD &Sdw Jhae &mr Sm breakpoint o w fr Sw fjy D; F9 (run) u dkESdy fv dku fy g/
y Hk( 7 4 )
' Dt c gr Sm y Hk( 7 3 ) [ m ( 7 4 ) t w dki f; u k' faw Gajy mi f; o Gm; r Smjz p fy gw , f/ PUSH + RETN u aw mh JMP
e JUn Dw mjz p fw Jht w Gu f F8 u dkESdy fr , fq dk&i f VA 0045E81D q Djump v ky fo Gm; r Smjz p fy gw , f/ VA 0045E81D
u aw mht a&; r Mu D; v Sw Jht w Gu f ae mu fx y f HW BP w p fc k&Sd&mq Da&mu fat mi f F9 u dkESdy fv kdu fy g/ y Hk( 7 5 ) /
y Hk( 7 5 )
,.,, Registration number - ,.- .....`... .....`.
.,
y Hk( 7 5 ) r Smaw GU&w Jh JE u aw mh polymorphic u k' faw Gu dk au smfv Tm; o Gm; w m aw GU&y gw , f/ ' Dae &mu dk
r Sw fo m; x m; y g/ w u , fv dkU u Re faw mfw dkU register v ky fw mr at mi fjr i f&i f ' Dae &mu dk patch v ky f&r Smr dkUv dkUy g/
F9 u dkx y fESdy fy g/ y Hk( 7 6 ) /
y Hk( 7 6 )
y Hk( 7 6 ) u dk Mu n fhr , fq dk&i f polymorphic u k' faw Gu kdx y faw GUy gw , f/ w u , fv dkUo m o i fht ae e JU
polymorphic u k' faw Gt aMu mi f; u dko m a&SUo i fc e f; p mw ke f; u r av hv mx m; c Jhb l; q dk&i f c kq dk&i f OD; aESmu fajc mu f
ae av mu fy gjy D/ ' Dw p fc gr Smv J JNZ [ m jump r jz p fw Jht w Gu f polymorphic u k' faw G[ m b maw Gv ky fo v J
q dkw m x y fav hv mMu n fhy gr , f/ y Hk( 7 7 ) /
y Hk( 7 7 )
y Hk( 7 7 ) u JMP ECX ae &mx da&mu fat mi f F8 u dkESdy f&i faw mhy Hk( 7 8 ) t w dki f; jr i f&y gr , f/
y Hk( 7 8 )
y Hk( 7 8 ) u 0012DEE5 ae &mx da&mu fat mi f F8 u dkESdy fv mc Jh&i faw mhy Hk( 7 9 ) t w dki f; jr i f&y gw , f/
y Hk( 7 9 )
,.,, Registration number - ,.- .....`... .....`.
.
PUSH + RETN u aw mhJMP e JUn Dw mjz p fw Jht w Gu f F8 u dkESdy fr , fq dk&i f VA 004AED97 q Djump
v ky fo Gm; r Smjz p fy gw , f/ ' D VA 004AED97 u v Jx l; jc m; r Ir &Sdy gb l; / ' gaMu mi fh F9 u dkq u fEdSy fy g/ ' Dv dke JU
491C56? 49201F? 491ABB? 4918E8? 4ADF16? 4AEB94? 4AE4F8? 49444A? 469148? 4DA1C3?
4DF802 p w Jh hardware breakpoint aw Gu dk jz w fo e f; jy D; o Gm; w Jhae mu fr Smaw mh DAP &JU main window
ay : v mr Smjz p fy gw , f/ Main window r ay : c i fr Sm dump window u 5DCEA0 &JU byte w e fz dk; [ m 1 jz p f^
r jz p f p p fw mjz p fEdki fw , fv dkU c ke u u Re faw mfht jr i fu dkajy mc Jhy gw , f/ [ kw f?r [ kw f o dEdki fat mi fv dkU 4DA1C3 u dk
a&mu fc sde fr Sm 5DCEA0 &JUbyte w e fz dk; u dk1 v dkUjy i fMu n fhMu &at mi f/ y Hk( 8 0 ) /
y Hk( 8 0 )
y Hk( 8 0 ) t w dki f; jy i fjy D; c sde fr Smaw mh hardware breakpoint aw Gt m; v Hk; u dk jz Kw fv dku fjy D; y &dk* &r fu dk run
(F9) Mu n fhy g/ y Hk( 8 1 ) /
y Hk( 8 1 )
y Hk( 8 1 ) t &q dk&i faw mh t ajc t ae au mi f; y Hk&y gw , f/ Buy DAP q dkw Jht &ky fu av ; u t o u fr Jhae y g
w , f/ q dkv dkc si fw mu aw mh0 , fp &mr v dkaw mhy gb l; / Help menu u dkMu n fhy gr , f/ y Hk( 8 2) /
y Hk( 8 2)
y Hk( 8 2) u dk jr i f&w mu aw mh t m; &p &my gy J/ 4DA1C3 r Sm jy i fz dkUq Hk; jz w fv dku fw m r Se fo Gm; y gw , f/
' gaMu mi fh' Dae &mu dkpatch v ky fz dkU Mu dK; p m; Mu n hfy gr , f/ 4DA1C3 r Sm breakpoint (F2) o w fr Sw fjy D; y &dk* &r fu dk
jy e fp v dku fy g/ ( Ctrl+F2) / jy D; &i f F9 u dkESdy fv dku f&i faw mhy Hk( 8 3 ) t w dki f; jr i f&y gr , f/
,.,, Registration number - ,.- .....`... .....`.
.
y Hk( 8 3 )
y Hk( 8 3 ) t w dki f; jr i f&w Jht c gr Smaw mhy Hk( 8 4 ) t w dki f; jy i f&y gr , f/
y Hk( 8 4 )
y Hk( 8 4 ) t w dki f; jy i fjy D; &i faw mhz dki fu dkESp fo u f&mt r n fe JUo dr f; v dku fy g/ y &dk* &r fau mi f; au mi f; t v ky fv ky f
y gv dr fhr , f/
p u m; r p y fajy m&r , fq kd&i faw mhBetaMaster u aw mh004ADF16 r Sm breakpoint &y fo Gm; jy D; ae mu fr Sm
dump window u 5DCEA0 &JU byte w e fz dk; u dk 01 v dkUjy i fc Jhy gw , f/ ' gq dk b mjz p fr v Jq dkw m Mu n fhv dku fMu &
at mi f/
y Hk( 8 5 )
y Hk( 8 5 ) r Smjr i f&w Jht w kdi f; ? e JU
w dkUay smu fo Gm; w m aw GU&y gw , f/ u se fw mu aw mht w lw ly Jjz p fy gw , f/ w u , fv dkU ' Dv dkjr i fc si f&i faw mhy Hk( 8 6 )
t w dki f; u k' fu dkjy i f&r Smjz p fy gw , f/
y Hk( 8 6 )
t ESp fc sKy fajy mjy &r , fq dk&i faw mhu Re faw mfw dkUt ae e JU DAP y &dk* &r fu dkv si fjr e fp Gm patch v ky fEdki fw m[ m
Resource Hacker &JU au s; Z l; aMu mi fhjz p fy gw , f/ PUSH 2718 ("DAP Unregistered") u dk &Smaz Gaw GU&Sdjc i f; u
DAP y &dk* &r fu dkpatch v ky fEdki fz dkUt q i fajy ap c Jhw mjz p fy gw , f/ DAP &JUy Hkr Se fv ky faq mi fc su fu aw mhPremium
version jz p fap z dkUt i fw me u fu dkt q u ft o G, fv ky fy gw , f/ o i f&dku fx n fhv dku fw Jhu k' fe JUt D; ar ; v f[ m r Se fu e fc Jh
r , fq dk&i f ' Du k' fe JU t D; ar ; v fw dkUu dk registry e JU dapreg8.key z dki fx Jr Smo dr f; q n f; r Smjz p fjy D; ae mu fw p fMu dr f y &dk
* &r fu dkjy e ft z Gi fhr Sm ' gaw Gu dk p p faq ; r Smjz p fy gw , f/ u Re faw mfw dkUu aw mh DAP y &dk* &r fu dk registry e JU
dapreg8.key z dki fw dkUu dk r p p faq ; ap aw mhb J v Sn fhp m; Edki fc Jhv dkU Premium version t jz p fo Hk; p GJEdki fw mjz p fy gw , f/
BetaMaster &JU dap-8.0.4.1-patch.exe z dki fu v J crack v ky f&mr Sm r sm; p Gmt ax mu ft u ljy Kc Jhy gaMu mi f; ajy m
Mu m; v dky gw , f/
ae mu fq Hk; t ae e JU o w day ; v dkw mu aw mhDAP 9.2 u dkArmadillo 5.40 e JU protect v ky fx m; w mjz p fjy D;
registration scheme [ mv J y dkjy D; t q i fhjr i fhv mw m aw GU&y gw , f/ DAP 9.2 u dk 20 0 9 ? Mo * kw fv ? 3 &u fr Sm
download v ky fx m; w mjz p fy gw , f/
,.,, Registration number - ,.- .....`... .....`.
.,
u Re faw mfht ae e JU Armadillo e JU protect v ky fx m; w mu dk unpack r v ky fc si faw mht w Gu f DAP 9.2
t w Gu f loader z dki fy Ja&; y gaw mhr , f/
Premium user jz p fz dkUb , fae &mr Sm jy i f&r v Jq dkw mu dkw e f; a&; r Sm jz p fy gw , f/
y Hk( 8 7 )
y Hk( 8 7 ) u u k' fu dky Hk( 8 8 ) t w dki f; jy i fy gr , f/
y Hk( 8 8 )
y Hk( 8 8 ) r Smjy i fw mu e r le mjy i fjy w my g/ w u , fjy i f&r Smu aw mhABEL loader r Smy g/
y Hk( 8 9 )
ABEL loader r Sm y Hk( 8 9 ) t w dki f; jy i fjy D; &i f loader z dki fu dkESp fo u f&mt r n fe JUo dr f; jy D; z Gi fhv dku fy g/ DAP
&JUHelp menu u About submenu u dka&G; v dku f&i faw mhy Hk( 9 0 ) t w dki f; jr i f&r Smjz p fy gw , f/
y Hk( 9 0 )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 388 -
tcef;(25) - Themida tm;avhvmjcif;
a & SUo i fc e f; p ma w Gr Sm u Re fa w mfht a e e JU packer/protector a w G b , fv dkt v ky fv ky fo v Jq dkw mu dk
t Mu r f; z si f; a q G; a E G; c Jho v dk pack v ky fx m; w Jh z dki ft c sdKUu kdv J unpack v ky fjy c Jhy gw , f/ ' Dw p fc gr Sma w mh cracker
a w Gu dk ' ku t a y ; q Hk; ? cracker a w Gt w Gu f p dw ft a E Smi fht , Su fjz p f& q Hk; protector w p fc kjz p fw Jh Themida
t a Mu mi f; u dk a v hv mMu n fhy gr , f/ Themida & JU t v ky fv ky fy Hku dk o djc i f; t m; jz i fhThemida u dk b , fv dk unpack
v ky f& r , fq dkw mu dk o i fht a e e JU e m; v n fE dki fr Smjz p fw Jht w Gu f y x r q Hk; Themida t a Mu mi f; u dk t e n f; i , f
a q G; a E G; v dky gw , f/
( 1 ) Themida q dko n fr Sm . . .
Themida q dkw mu a w mh a q mhz f0 Jv fa w Gu dk crack v ky fjc i f; & e fu u mu G, fE dki fa t mi fv dkU Secure
Engine protection p e p fu dk o Hk; x m; w Jh protection p e p fw p fc kjz p fy gw , f/ Cracker a w Gt jr i ft & q dk& i fa w mh
Themida [ m o Hk; p GJa e u s a q mhz f0 Jv f protector a w Ge JU v Hk; 0 r w lb J u GJjy m; jc m; e m; a e y gw , f/ Developer
a w Gt w Gu fu a w mh Themida [ m v G, fu lp Gm t o Hk; jy KE dki fjy D; o lw dkUjz p fa p c si fw Jh t q i fhjr i fhw Jh protection
a w Gu dkv G, fu lp Gme JU a & G; c s, fE dki fy gw , f/ y Hk( 1 ) /
y Hk( 1 )
Advanced Anti-Debugger ' Doption u a w mh o i fh& JU application u dk debugger a w G& e fu u mu G, f
a y ; r Smjz p fy gw , f/ SecureEngine [ m debugger a w mfa w mfr sm; r sm; u dk ( user-mode e JU kernel-mode
debugger a w Gt y gt 0 i f) p Hkp r f; o d& SdE dki fy gw , f/
Anti Dumpers Protect v ky fx m; w Jha q mhz f0 Jv fa w Gt w Gu f t E & m, ft & Sdq Hk; tool a w Gx Ju w p fc ku a w mh
memory dumper a w Gjz p fy gw , f/ ' D tool a w Gu dk cracker a w Gu decrypt v ky fx m; w Jhu k' f ( o dkU) a ' w m
a w Gu dk r Sw fOmP fx Ju a e disk a y : r Smo dr f; q n f; z dkU t o Hk; jy KMu w mjz p fy gw , f/ ' Dha e mu f protect r v ky fc i fr Sm
& Sda e w Jht w dki f; r lv y & dk* & r f& JU w du sw Jh image u dkjy e fv n f& , lE dki fy gw , f/ ' D option u dka & G; c s, fjc i f; t m; jz i fh
Secure Engine u Memor yGuard e n f; y n mu dko Hk; jy D; r Sw fOmP fu a e disk a y : u dk dump v ky fjc i f; r S
u mu G, fa y ; y gw , f/
Entrypoint Obfuscation o lUu dka & G; c s, fx m; r , fq dk& i fa w mhSecureEngine u o i fhapplication & JU entry
point u dka & ma x G; o Gm; a p y gw , f/ Application x Jr Sm& Sdw Jhy x r q Hk; t v ky fv ky fw Jhinstruction a w G[ m Secure
Engine & JU u k' fa w Gjz p fy gv dr fhr , f/ ' Dv dk SecureEntr yPoint e n f; y n mu dk t o Hk; jy Kx m; w Jht w Gu f cracker
a w Gu o i fh application & JU r Se fu e fw Jh entry point u dkr & & SdE dki fw Jht w Gu f crack v ky fz dkU& m c u fc Jo Gm; a p y gv dr fh
r , f/
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 389 -
Resources Encryption ' Doption u dka & G; c s, fx m; r , fq dk& i fa w mho i fhapplication u t o Hk; jy Kw Jhresource
a w Gu dk encrypt v ky fy gv dr fhr , f/ ' ga Mu mi fh cracker a w G[ m o i fh application & JU z GJUp n f; w n fa q mu fy Hku dk
a p mi fhr Mu n fhE dki fa w mhy gb l; / SecureEngine u resourece a w Gu dk v Hkjc HKp dw fc sa p z dkU v dkt y fr So m v dkt y fw Jh
resource a w Gu dkdecrypt v ky fr Smjz p fy gw , f/
VMWare/ Virtual PC ' D option u a w mh protect v ky fx m; w Jh o i fh application u dk VMWare e JU
Virtual PC w dkUv dkvirtual OS w p fc ka t mu fr Sm t v ky fv ky fE dki fa p z dkUjz p fy gw , f/
Advance API-Wrapping ' Doption u a w mh protect v ky fx m; w Jh o i fh application u t o Hk; jy Kw Jh API
t r sdK; r sdK; u dkc GJjc r f; p dp p fE dki fjc i f; r & SdE dki fa t mi f SecureAPIWr apper e n f; y n mu dk t o Hk; jy Kx m; y gw , f/
Anti-Patching ' D option u dk a & G; c s, fr , fq dk& i fa w mh protect v ky fx m; w Jh application u dk A dki f; & y fp f^
cracker^ t jc m; application a w Gu jy Kjy i fx m; jc i f; & Sd^ r & Sdp p fy gw , f/ w u , fv dkU t jc m; protector w p fc kc ku dk
x y fr Ht o Hk; jy Kz dkU & n f& G, fx m; & i fy Jjz p fjz p f? exe z dki f& JUu k' ft c sdKUu dk x y fr Hjy Kjy i fv dkw m& Sd& i fy Jjz p fjz p f Themida u
u k' fa w Gjy i fx m; jc i f; & Sd^ r & Sd t v dkt a v smu fp p fa q ; jc i f; u u mu G, fE dki fz dkU ' D option u dk None v kdUa & G; c s, fa y ;
x m; & y gr , f/ ' Dv dkr Sr [ kw f& i fa w mh Themida u error message u dkjy jy D; y & dk* & r fu dk c su fc si f; & y fq dki f; a p
y gr , f/
Metamorph Security ' De n f; y n mu a w mhapplication q Dprotect v ky fx m; w Jhu k' fa w Gu dk a y gi f; x n fhE dki fz dkU
SecureEngine u dkc Gi fhjy Ky gw , f/ ' D SmartMetamor ph e n f; y n m[ m r l& i f; a w Gu dk a w Ga v hv mjc i f; & e fu
u mu G, fE dki fz dkU q i fw lu k' fa w Gt a e e JU a jy mi f; v Ja y ; jy D; a w Gu dkv Sn fhp m; y gw , f/
Advanced Debugger Monitors ' Doption u dka & G; c s, fv dku fr , fq dk& i fa w mh SecureEngine u t q i fhjr i fh
w Jh anti-debugging e n f; y n ma w Gu dk o i fh& JU application a w Gx J x n fho Gi f; r Smjz p fy gw , f/ ' gr So m cracker
a w G[ m o i fh& JUu k' fu dk a v hv mE dki fz dkU debugger a w Gu dk t o Hk; r jy KE dki fr Smy g/ SecureEngine & JU Debugger
Guard e n f; y n m[ m r Sw fOmP fr Sm t v ky fv ky fa e Mu w Jh debugger a w Gt m; v Hk; u dk p Hkp r f; o d& SdE dki fy gw , f/ t q Hk;
p Ge fa jy m& & i f kernel r Sm t v ky fv ky fa e Mu w Jhring 0 debugger a w Gu dka w mi f p Hkp r f; o d& SdE dki fy gw , f/
Compression SecureEngine u application w p fc ku dk protect v ky fc sde fr Sm t v Ge fMu D; r m; r sm; jy m; v Sw Jh
u k' fa w Gu dk application q Da y gi f; x n hfw mjz p fw Jht w Gu f o i fh& JU application u kd t & G, ft p m; Mu D; r m; a p r Sm
jz p fy gw , f/ Protect v ky fc sde fr Sm o i fh application & JU t & G, ft p m; Mu D; r m; jc i f; u u mu G, fE dki fz dkU ' Doption u dk
a & G; c s, fr , fq dk& i fa w mh application u k' f? resource a w Ge JU protection u k' fa w Gu dk compress v ky fa y ; r Sm
jz p fy gw , f/ SecureEngine [ m SmartCompr ession e n f; y n mu dk t o Hk; jy Kx m; w mjz p fw Jht w Gu f o lU& JU
decompression algorithm [ m o i hf application u dk r Sw fOmP fa y : u l; w i fw Jht c sde fr Sm application & JU
p Gr f; a q mi f& n fE Ie f; u dkx dc dku fa p r Smr [ kw fy gb l; /
Monitor Blockers o i fh application u z dki ft a jr mu ft r sm; ( o dkU) registry key a w Gu dk & , lo Hk; p GJc sde fr Sm
cracker a w G& e fu u mu G, fE dki fz dkU SecureEngine u Monitor Blocker e n f; y n mu dk t o Hk; jy Ky gw , f/
Cracker a w Gu registry key ( o dkU) z dki ft o Gi f; t x kw fa w Gu dk a p mi hfMu n fhw Jh ' Dtool a w Gu dk t o Hk; r jy KE dki fb l;
q dk& i fa w mh crack v ky fw Jht c gr Sm r Se fu e fw Jhq Hk; jz w fc su fu dk c sE dki fz dkU c J, Of; a p r Smjz p fy gw , f/ ( o i hft a e e JU trial
version a w Gt w Gu f trial o u fw r f; w p fc ku dk o w fr Sw fz dkUt w Gu f z dki fw p fc kr Sma & ; jc i f; ( o dkU) registry key
w p fc kt a e e JU o w fr Sw fjc i f; w dkUu dkjy Kv ky f& w mjz p fy gw , f/ )
Delphi/BCB form protection o i fht a e e JU o i fh& JU application u dk Delphi ( o dkU) Borland C++ builder
w dkUe JU a & ; o m; x m; w Jht c g o i fh application & JU form a w Gu dk u mu G, fz dkU t o Hk; jy Kw my g/ ' ga Mu mi fhr dkUv J o i fh
application t v ky fv ky fa e c sde fr Sm Delphi/BCB form a w Gu dk extract v ky fMu w Jh cracking tool a w Gu dk
SecureEngine u u s& IH; a p w my g/
( 2 ) Secur eEngine q dko n fr Sm . . .
SecureEngine q dkw mu a w mh r su fa r Smu fa c w f cracking & e fr S Windows application a w Gu dk
u mu G, fE dki fz dkUt w Gu f t o Hk; jy Kw Jh q e f; o p fw Jhe n f; y n mw p fc kjz p fy gw , f/ t jc m; protector a w G[ m o mr e f
application a w G& & Sdw Jht c Gi fht mP m? ' gr Sr [ kw f OS u u e fUo w fx m; w Jh? c Gi fhjy Kx m; w Jh t c Gi fht mP ma v mu fu dk
o mt o Hk; jy KMu w mjz p fy gw , f/ ' ga Mu mi fhv J kernel-level r Smt v ky fv ky fa e Mu w Jh cracking tool a w mfa w mfr sm;
r sm; u application-level a v mu fr Sm t v ky fv ky fa e Mu w Jh o lw dkUu dk t v G, fw u la v hv mE dki fMu w mjz p fjy D; o lw dkU
& JU protection routine a w Gu dk crack v ky fE kdi fMu w mjz p fy gw , f/ SecureEngine u dk ' Dv dkt jz p fr sdK; u a & Smi f& Sm;
E dki fz dkU ' DZ dki f; jy Kx m; y gw , f/ o lU& JUu k' fa w G[ m OS e JU t c Gi fht a & ; w ln Dp Gm t v ky fv ky fa e Mu w mjz p fy gw , f/
' ga Mu mi fhv J b , f protection e n f; y n mu dkr q dk OS & JU u e fUo w fr Ir & Sdb J v Gw fv y fp Gm v ky fa q mi fE dki fw my g/
w p fz u fu Mu n fhjy e f& i fv J cracking tool a w G[ m Secure Engine u kernel e JU t q i fhw ln Dp Gm t v ky fv ky f
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 390 -
a e w mjz p fw Jht w Gu f protection routine a w Gu dk crack v ky fE dki fjc i f; ? a v hv mE dki fjc i f; ? p Hkp r f; a w GU& Sdjc i f; r & Sdy gb l; /
Themida e JU WinLicense w dkU[ m SecureEngine e n f; y n mu dkt o Hk; jy KMu w mjz p fy gw , f/
SecureEngine u t o Hk; jy Kw Jhe n f; y n ma w Gu a w mha t mu fy gt w dki f; jz p fy gw , f
AntiAPISpyer r Mu mc P q dko v dky J cracker a w G[ m application w p fc ku a c : o Hk; w Jh API a w Gb , fv dk
t v ky fv ky fo v Jq dkw ma v hv mMu jy D; protection a w Gu dka u smfv Tm; z dkU Mu dK; p m; Mu y gw , f/ SecureEngine u ' Dv dk
crack v ky fw mu dk w m; jr p fz dkUt w Gu f AntiAPISpyer e n f; y n mu dk t o Hk; jy Kw mjz p fjy D; protect v ky fx m; w Jh
application u a c : o Hk; w JhAPI a w Gu dkr jr i fE dki fa t mi fjy Kv ky fy gw , f/
AntiBr eakpoints o mr e ft m; jz i fha w mh cracker a w Gu debugger a w Gu dk o Hk; Mu w mu application
w p fc ku dk u dk, fMu dKu fw Jha e & mr Sm & y fa p c si fv dkYjz p fy gw , f/ Breakpoint a w Gu application w p fc kt v ky fv ky fw m
u dk & y fw e fUa p E dki fjy D; ' D& y fw e fUc sde fr Sm application u b ma w Gv ky fa q mi fa e o v Jq dkw m cracker a w Gu dk o d& Sd
a p E dki fy gw , f/ SecureEngine u a w mh breakpoint r sdK; p Hku dkp Hkp r f; z dkU t q i fhjr i fhw Jhe n f; y n ma w Gy g& Sdjy D;
breakpoint u dka w GUw me JU o lw dkUa w Gu dka u smfv Tm; jy D; y & dk* & r ft v ky fv ky fw mu dkjy D; q Hk; a p r Smjz p fy gw , f/
v u f& Sda q mhz f0 Jv f protector a w mfa w mfr sm; r sm; u a w mh protect v ky fx m; w Jh application a w Gx Ju
brekpoint a w Gu dk & Sma z G& mr Sm t m; e n f; c su f & Sda e w ke f; y gb J/ Oy r mjy & & i f o lw dkUa w G[ m API routine & JU y x r
q Hk; instruction a w Gu dko m breakpoint o w fr Sw fx m; jc i f; & Sd^ r & Sd p p fa q ; Mu v dkUy g/ ' gu dk a u smfv Tm; E dki fz dkU
t w Gu f cracker a w Gu API & JUp Hkp r f; v dkUr & E dki fw Jh routine t v , fr Smo m breakpoint u dko w fr Sw fMu y gw , f/
y Hkr Se f crcking tool a w Gu dkt o Hk; jy Kjy D; OS breakpoint p Hkp r f; w Jh routine a w Gu dk v G, fu lp Gma u smfv Tm; E dki f
y gw , f/
AntiCr ackTools SecureEngine & JU AntiCrackTools e n f; y n mu a w mh t E & m, f& Sdw Jh cracking tool
a w G r Sw fOmP fx Jr Sm t v ky fv ky fa e a Mu mi f; o d& Sdc Jh& i f protect v ky fx m; w Jh application u dk& y fw e fUa p w my g/
' gr Sr [ kw f ' Dtool a w Gx Ju w p fc ku dk p Hkp r f; o d& Sdc sde fr Sm o w fr Sw fx m; w Jh protection routine u dk t v ky fv ky fa p
y gw , f/ AntiCr ackTools e n f; y n mu & Iy fa x G; v Sw Jhe n f; v r f; a w Go Hk; jy D; r Sw fOmP fx Ju cracking tool
a w Gu dkp Hkp r f; jy D; kernel-mode r Smt v ky fv ky fy gw , f/
AntiDumper Pro a q mhz f0 Jv f protector a w Gt m; v Hk; u o lw dkUt v ky fr v ky fc i fr Sm protect v ky fx m; w Jhz dki fu dk
encrypt v ky fx m; Mu w mjz p fy gw , f/ Protect v ky fx m; w Jh application u dkz Gi fhw Jht c sde fr Sma w mh CPU u
e m; v n ft v ky fv ky fa p E dki fz dkU application u dk decrypt v ky f& y gw , f/ Cracker a w mfa w mfr sm; r sm; u
application t v ky fv ky fa e c sde fr Sm r Sw fOmP fx Ju a e disk a y : dump v ky fE dki fz dkU tool a w Gu dkt o Hk; jy KMu y gw , f/
SecureEngine u a w mh dump v ky fw Jh tool r Se fo r Qu dk dump r v ky fE dki fa t mi f w m; q D; y gw , f/ Device
driver t a e e JU t v ky fv ky fw Jhdumper a w Ga w mi f y gy ga o ; w , f/
v u f& Sd protector a w mfa w mfr sm; r sm; u a w mh run a e c sde fr Sm executable header u dkz su fjc i f; w dkUv dk
memory dumper & e fu u mu G, fw Jhe n f; y n m& y fa w Gr Sm t m; e n f; c su f& Sdy gw , f/ ' ga Mu mi fhv Ja e mu fy dki f; x Gu f& Sd
w Jh dumping tool a w Gu ' De n f; a w Gu dk v G, fu lp Gma u smfv Tm; E dki fw my g/ y Hk( 2 ) e JU y Hk( 3 ) r Smjy x m; w mu a w mh
r Sw fOmP fu a e dump v ky fx m; w Jh r l& i f; y & dk* & r fe JU AntiDumperPro e n f; y n me JUu mu G, fx m; w Jh y & dk* & r fu dk
jy o jc i f; jz p fy gw , f/
y Hk( 2 ) r Sw fOmP fr Sdump v ky fx m; a o m r l& i f; y & dk* & r f
y Hk( 3 ) AntiDumper Pr o e n f; y n mjz i fhu mu G, fx m; o n fhy & dk* & r f
ClearCode ClearCode e n f; y n mu a w mh u k' fa w Gu dk t v ky fv ky fjy D; w Jha e mu f z , f& Sm; y p fw mjz p fy gw , f/
Application w p fc k[ m r Sw fOmP fx J t v ky fv ky fa e c sde fr Sm r Sw fOmP fx Jr Sm& Sdw Jht & ma w Gu dk disk a y : r Smo dr f; q n f;
z dkU cracker a w Gu dumping tool a w Gu dk t o Hk; jy KMu w mjz p fw Jht w Gu f execute v ky fjy D; jy D; c si f; u k' f block
a w Gu dkr Sw fOmP fx Ju a e c su fc si f; z , f& Sm; jc i f; t m; jz i fhcrakcer a w Gdump v ky fw Jh& e fu u mu G, fE dki fy gw , f/
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 391 -
CodeEncrypt CodeEncrypt e n f; y n mu a w mh u k' fa w Gu dk t v ky fr v ky fc sde fr Sm encrypt v ky fx m; a y ; y g
w , f/ Execute v ky fjy D; jy D; c si f; u k' fa w Gu dk encrypt jy e fv ky fw mjz p fw Jht w Gu f crakcer a w Gr Sw fOmP fx Ju a e
dump v ky fjc i f; r Su mu G, fE dki fy gw , f/ y Hk( 4 ^ 5 ) /
y Hk( 4 ) Pr otect r v ky fx m; c sde f
y Hk( 5 ) Pr otect v ky fx m; c sde f
CodeReplace CodeReplace u a w mh e n f; y n m& y ft o p fw p fc kjz p fjy D; application u k' f& JU t p dw ft y dki f;
t c sdKUr Sm r v dkt y fw Jhu k' fa w Ge JU u sy e f; t p m; x dk; w mjz p fy gw , f/ SecureEngine u w u , fhu k' fu dk v Hkjc HK& w Jh
a e & mw p fc kr Sm encrypt v ky fjy D; o dr f; q n f; v dku fy gw , f/ w u , fhu k' fu a w mh protection scheme [ mr Se fu e f
a Mu mi f; e JU & Sda Mu mi f; a o c smr So m decrypt jy e fv ky fjy D; t v ky fv ky fw mjz p fy gw , f/ w u , fv dkUo m cracker
w p fa , mu f[ m r l& i f; y & dk* & r ft jz p f jy e fw n fa q mu fr , fq dk& i f r l& i f; u k' ft p m; r q dki fw Jhu k' fa w Gu dko m & & Sdr Sm
jz p fy gw , f/ Cracker [ m protection scheme u dkv Hk; 0 z , f& Sm; r , fq dkjy e f& i fv J SecureEngine & JUt p dw f
t y dki f; jz p fv mr , fhr l& i f; u k' fu dkz , f& Sm; o v dkjz p fa e y gw , f/
' De n f; y n mu dk t jc m; protector a w Gr Sm p r f; o y ft o Hk; jy Kjc i f; r & Sda o ; y gb l; / t e n f; i , fa o m protector
t c sdKUu o m w ln Dw Jhe n f; y n mu dkt o Hk; jy Kz dkU Mu dK; p m; Mu a y r , fh SecureEngine u jy Kv ky fo v dk u k' f block
w p fc kv Hk; u dkjy Kv ky fE dki fjc i f; r & Sdb Jinstruction w p fc kw n f; o mz , f& Sm; jc i f; u dkjy Kv ky fy gw , f/
DebuggerGuard ' De n f; y n mu a w mh r Sw fOmP fx Jr Sm& Sdw Jh debugger u dk p Hkp r f; z dkUjz p fy gw , f/ x Gu f& Sdjy D; o m;
cracking tool a w Gu a w mh ' De n f; y n mu dk a u smfv Tm; E dki fjc i f; r & Sdy gb l; / w u , fv dkU cracker w p fa , mu fu
o lw dkUb , fv dkt v ky fv ky fo v Jq dkw m o d& i fa w mi f a u smfv Tm; z dkUq dkw m r jz p fE dki fo a v mu fy gb J/ ' ga Mu mi fh
' De n f; y n mu protect v ky fx m; w Jh application a w Gu dk debugger a w Gu i f; a 0 ; w Jh y w f0 e f; u si fr Sm a u mi f; p Gm
t v ky fv ky fa p E dki fy gw , f/
a q mhz f0 Jv f protector a w G[ m r Sw fOmP fx Jr Sm debugger a w G& Sd^ r & Sdu dk o d& SdE dki fz dkU t v Ge fx i f& Sm; w Jh
v Sn fhu Gu fa w Gu dk t o Hk; jy KMu y gw , f/ ' De n f; v r f; a w Gu dk p ma p mi fa w G? p mt ky fa w Ge JU t Ge fv dki f; w dkUr Sm a z mfjy jy D; jz p f
w ma Mu mi fh' De n f; v r f; a w Gu debugger a w Gu dko d& SdE dki fz dkU r jz p fE dki fw my g/
DynamicEncryption SecureEngine u application w p fc ku dk protect v ky fc sde fr Sm r w ln Dw Jh algorithm
a w Ge JU key a w Gu dk t o Hk; jy Kx m; w mjz p fw Jht w Gu f cracker a w Gu ' D protect v ky fx m; w Jh application
a w Gt m; v Hk; u dkdecrypt v ky fz dkU e n f; v r f; u dk& Sma z Ga w GU& SdE dki fr Sm r [ kw fy gb l; /
GarbageCode GarbageCode u a w mh w u , fhu k' fa w Gu dk r q dki fw Jhu k' fa w Ge JU a & mx m; jc i f; jz p fy gw , f/
' Dv dkjy Kv ky fx m; jc i f; t m; jz i fhcracker a w Gu routine w p fc kc ku dk a v hv mw Jht c gr Sm r q dki fw Jhu k' fa w Gu dk jr i fa e & r Sm
jz p fy gw , f/ GarbageCode e n f; y n mr Sm t q i fhjr i fhw Jh algorithm a w Gy g& Sdw Jht w Gu f x kw fa y ; v dku fw Jh r q dki f
w Jhu k' fa w G[ m w u , fhu k' fa w Ge JU q i fa e r Smjz p fjy D; cracker a w Gt w Gu f b , fu k' f[ m u k' ft p p ft r Se fv J q dkw m
a 0 c GJz dkUc u fa e r Smjz p fy gw , f/ Oy r mjy & & i f cracker w p fa , mu f[ m disassemble v ky fx m; w Jh application
w p fc ku dkMu n fhr , fq dk& i f r lv instruction t a & t w Gu f 1000 & Sd& r , fht p m; 8000 a v mu fu dka w GU& r Smjz p fy g
w , f/
t c sdKU protector a w Gu a w mh w u , fhu k' fa w Gu dk r q dki fw Jhu k' fa w Gu dk a & ma E Sm& mr Sm t u e fUt o w fe JUo m
t o Hk; jy Kw mjz p fw Jht w Gu f cracker a w Gu b , fu k' f[ mt p p f? b , fu k' f[ mt w kv Jq dkw m v G, fu lp Gmc GJx kw fE dki fy g
w , f/ r sm; a o mt m; jz i fha w mhroutine t c sdKUu dko m r q dki fw Jhu k' fa w Ge JU a & ma E SmMu w mjz p fy gw , f/
y Hk( 6 ) e JU y Hk( 7 ) r Sma z mfjy x m; w mu a w mh r l& i f; u k' f block e JU GarbageCode e n f; y n mu dkt o Hk; jy Kx m; w Jh
u k' f block w dkUjz p fy gw , f/
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 392 -
xor [esi], bh
sub [esi+1], bl
xor [esi+2], ah
xor [esi+3], al
add esi, 4
loop EncodeData
y Hk( 6 ) Encode v ky fx m; a o ma ' w m
xor [esi], bh
push ebx
sub ebx, eax
xor edi, ebx
pop ebx
sub [esi+1], bl
dec edi
xor edi, eax
xor [esi+2], ah
jmp short $+2
pusha
mov ecx, eax
xor ebx, edx
rdtsc
popa
xor [esi+3], al
rol edx, cl
sub edi, edx
push eax
xor eax, edi
mov edi, eax
pop eax
add esi, 4
dec edx
imul edx, eax, 3
loop EncodeData
y Hk( 7 ) Gar bageCode e n f; y n mu dkt o Hk; jy Kx m; y Hk
intDebugShield x86 architecture u a q mhz f0 Jv f debugger a w Gu t o Hk; jy Kw Jh debugging p Gr f; a q mi f
& n fu dk jz p fa p y gw , f/ ' Dp Gr f; a q mi f& n fo mr & Sdc Jh& i f a q mhz f0 Jv f debugger a w G[ m r Se fu e fp Gm t v ky fv ky fE dki fr Sm
r [ kw fy gb l; / SecureEngine u protect v ky fx m; w Jh application w p fc kt v ky fv ky fa e c sde fr Sm debugger
a w Gv Hk; 0 r & Sda p z dkU x86 debugging p Gr f; a q mi f& n fu dk t jy n fht 0 x de f; c sKy fy gw , f/ o mr e f protector a w Gr Sma w mh
' De n f; u dko Hk; p GJE dki fjc i f; r & Sdy gb l; / b ma Mu mi fhv Jq dka w mho lw dkU[ m kernel-mode r Sm t v ky fr v ky fE dki fMu v dkUy g/
InteractiveEngine InteractiveEngine u a w mh SecureEngine e JU protect v ky fx m; w Jh application
w dkUMu m; q u fo G, fa y ; w JhE Sp fr sdK; o Hk; e n f; y n mw p fc kjz p fy gw , f/ Protect v ky fx m; w Jhapplication [ m r Sw fOmP f
x Jr Sm o l& Sd^ r & Sde JU crack v ky fz dkUMu dK; p m; a e jc i f; & Sd^ r & Sdu dk p p fa q ; a y ; z dkU SecureEngine u dk Mu dKu fw Jht c sde fr Sm a jy m
q dkE dki fy gw , f/ InteractiveEngine e JUt w l SecureEngine e JU protect v ky fx m; w Jh application w dkU[ m
w p fa y gi f; w p fp n f; w n f; t v ky fv ky fMu y gw , f/
w u , fv dkUo m cracker w p fa , mu f[ m protection scheme u dkz , f& Sm; c Jhr , fq dk& i f ' gu dk protect
v ky fx m; w Jhapplication x Ht o da y ; r Smjz p fjy D; r Sw fOmP fx Jr Sm t v ky fv ky fa e jc i f; u dk& y fq dki f; r Smjz p fy gw , f/
MemoryGuard t c sdKUt a jc t a e a w Gr Sma w mh cracker w p fa , mu f[ m protect v ky fx m; w Jh application
w p fc ku dk r l& i f; u k' ft jz p f jy e fv n fw n fa q mu fr Sm r [ kw fy gb l; / ' Dv dkv ky fr , fht p m; y & kd* & r f& JU t jy Kt r lu dk
a jy mi f; v Ja p z dkU r Sw fOmP fx Jr Sm a ' w m ( o dkU) u k' ft c sdKUu dk a jy mi f; v Jr Smjz p fy gw , f/ ' Dv kdt jz p fr sKd; u dk * dr f; a w Gr Sm
Mu HK& a v h& Sdjy D; t y dkq ka w G& & Sdc si fw Jht w Gu f ' Dv dkv ky fMu w mjz p fy gw , f/ ( Oy r m Red Alert 2 * dr f; w Gi f num
lock r S* key E Si fh\ key w dkUu dkE Sdy f y dku fq HE Si fhsatellite c dk; jc i f; / )
SecureEngine u a w mh protect v ky fx m; w Jh application w p fc k r Sw fOmP fx J t v ky fv ky fa e c sde fr Sm
u k' fa w G? a ' w ma w Gu dk t p m; x dk; 0 i fa & ; jc i f; r S a & Smi f& Sm; E dki fz dkU & Iy fa x G; v Sw Jh e n f; y n mu dk t o Hk; jy Kx m; y gw , f/
MonitorBlocker Cracker a w mfa w mfr sm; r sm; u a w mh application w p fc ku b , fz dki fa w G? b , f registry
key a w Gu dk , lo Hk; a e o v Jq dkw m o d& a t mi f z dki f^ registry monitor a w Gu dk t o Hk; jy KMu y gw , f/ Application
a w mfa w mfr sm; r sm; [ m o lw dkU& JU trial o u fw r f; e JUy w fo u fw Jht c su ft v u fa w Gu dkz dki f ( o dkU) registry key t a e
e JU o Hk; Mu w mjz p fy gw , f/ Cracker a w G[ m ' ga w Gu dka v hv mjy D; application w p fc k& JU trial o u fw r f; u dk b , f
v dkv Sn fhp m; & r v Jq dkw m q Hk; jz w fMu w mjz p fy gw , f/
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 393 -
v u f& Sd protector t r sm; p k[ m OS p e p fx Jr Sm register v ky fx m; w Jh window & JU class t r n fa w Gu dk
& Smjc i f; ? r Sw fOmP fx Ju executable u dkp Hkp r f; jc i f; a w Gjy Kv ky fjy D; z dki f^ registry monitor a w Gu dkp Hkp r f; w Jhe n f; y n m
a w Gu dkt o Hk; jy KMu w mjz p fy gw , f/
SecureEngine u a w mh t v Ge ft q i fhjr i fhv Sw Jh e n f; y n mu dkt o Hk; jy Kw mjz p fjy D; protector a w Gx Jr Sm
' De n f; u dkt o Hk; jy Kz l; jc i f; r & Sda o ; y gb l; /
MutatorEngine ' De n f; y n mu a w mh protect v ky fr , fh application x Ju instruction a w Gu dk w ln Dw Jh
t jc m; instruction a w Ge JUt p m; x dk; r Smjz p fy gw , f/ ' De n f; u dk t o Hk; jy Kjc i f; t m; jz i fhapplication w p fc kr Sm w ln Dw Jh
u k' fa w G& Sda e jc i f; u a & Smi f& Sm; E dki fjy D; cracker a w Gu u k' fa w Gu dka jc & mc H& mr Sm y dkr dkc u fc Ja p y gw , f/
PasswordProtect SecureEngine r Sm o i fh appication u dk t c Gi fhr & b J t o Hk; r jy KE dki fa t mi f password
a y ; x m; v dkU& y gw , f/
PolymorphicLayers Protect v ky fx m; w Jh application ( o dkU) protection scheme u dk disassemble
v ky fjc i f; r S a & Smi f& Sm; E dki fz dkU SecureEngine u encryption layer a w Gu dkt o Hk; jy Ky gw , f/ Encryption layer
a w Gr Sm u k' fa w Gu dkv Hk; 0 encrypt v ky fx m; w mjz p fjy D; v dkt y fw Jht c sde fr So m decrypt v ky fw mjz p fy gw , f/
Encryption u dk y dkr dkt m; jz n fhw Jht a e e JU SecureEngine u polymorphic encryption layer a w Gu dk
t o Hk; jy Ky gw , f/ Polymorphic layer w dki f; r Sm r w ln Dw Jh algorithm a w Ge JU encryption key a w G& Sdjy D;
encryption layer & JUt p e JUt q Hk; u dka w mi f o d& SdE dki fz dkU c u fc Jy gv dr fhr , f/ y Hk( 8 ) /
y Hk( 8 ) Polymor phic layer r sm; jz i fhpr otect v ky fx m; a o m application
RealTimeSpy RealTimeSpy u a w mhapplication w p fc k[ m v Hkjc HKp dw fc s& w Jhy w f0 e f; u si fw p fc kr Sm t v ky f
v ky fa e jc i f; & Sd^ r & Sdu dk p p fa q ; z dkU ThreadEngine & JUp Gr f; t m; u dk t o Hk; jy Kw mjz p fw Jht w Gu f protect v ky fx m; w Jh
application u dkcrack v ky fE dki fr Sm r [ kw fy gb l; /
Protector a w mfa w mfr sm; r sm; u a w mh application u dk decrypt v ky fjy D; c sde fr Sm r Sw fOmP fx Jr Sm y p fx m;
a v h& Sdy gw , f/ ' ga Mu mi fhv J cracker a w Gu decrypt v ky fx m; w Jhapplication u dk jy e fv n f& , ljy D; r l& i f; t w dki f;
jz p fa t mi f v ky fMu w mjz p fy gw , f/
SecureAPIWrapper Cracker w p fa , mu f[ m protection scheme u dkz , f& Sm; z dkU Mu dK; p m; r , fq dk& i f
application u a c : , lo Hk; w Jh API a w Gu dk o dz dkUv dky gw , f/ SecureAPIWrapper [ m application u a c : o Hk;
w Jh API t m; v Hk; u dk u mu G, fa y ; x m; w mjz p fw Jht w Gu f y & dk* & r fu dk disk a y : dump v ky fr , fq dk& i f cracker
a w Gt a e e JU b , f API a w Gu dka c : o Hk; o v Jq dkw mu dk o dr Smr [ kw fy gb l; /
SecureEntryPoint Application w p fc ku dk protect v ky fc sde fr Sm SecureEngine u application & JU
entrypoint u dkz , f& Sm; v dku fjy D; ' Dy x r q Hk; u k' fa w Ga e & mr Sm r q dki fw Jhu k' fa w Ge JU t p m; x dk; v dku fy gw , f/ EP a e & m
u r lv instruction a w Gu dka w mh SecureEngine u k' ft jz p f a jy mi f; v Jv dku fw mjz p fy gw , f/ w u , fv dkU
cracker a w Gu entrypoint u dk& Smr , fq dk& i f o lw dkUt a e e JU r q dki fw Jhu k' fa w Gu dko m & & Sdr Smjz p fy gw , f/ y Hk( 9 ) /
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 394 -
y Hk( 9 )
SmartMorph SecureEngine [ m application a w Gu dk protect v ky fz dkUt w Gu f t v Ge fr sm; jy m; v Sw Jhu k' f
a w Gu dk a y gi f; x n fhy gw , f/ Application x Jr Sm& Sdw Jh u k' fa w Gr w ln Da p a & ; t w Gu f SmartMorph e n f; y n mu
r lv u k' fa w Gu dk w p fc ke JUw p fc k r w la t mi f t o Gi fa jy mi f; a y ; y gw , f/ u k' fa w Gr w ln Da y r , fhv ky fa q mi fc su fu a w mh
w ln Dy gw , f/ ' ga Mu mi fh cracker a w Gu ' Du k' fa w G[ m r w ln Db l; x i fjy D; x y fr Ha v hv m& w Jht w Gu f crack v ky f
c sde fy dkv mr Sm jz p fy gw , f/ y Hk( 1 0 ) /
y Hk( 1 0 ) w ln Da o mu k' fu dkr w ln Dp Gmv ky fa q mi fMu y Hk
u Re fa w mfht a e e JU SecureEngine & JU t v ky fv ky fy Hku dk & Si f; jy & w Jh t a Mu mi f; & i f; u Themida & JUt v ky f
v ky fy Hkt a o ; p dw fu dk & Si f; jy c si f& Hko u fo u fw i f r [ kw fy gb l; / ' De n f; y n ma w Gu dk o dx m; jc i f; t m; jz i fh t r n fr o d
protector a w Ge JU a w GUMu HK& w Jht c g protector a w G& JU t v ky fv ky fy Hku dk o dx m; a p c si fv dkUy g/
( 3 ) Themida (Anti-Debugger ) z dki ft m; unpack v ky fjc i f;
' Dw p fc gr Sma w mhThemida e JU protect v ky fx m; w Jhz dki fa w Gu dk unpack v ky fMu n fhMu y gr , f/ t o Hk; jy Kx m;
w Jh Themida version u a w mh 1.9.1 jz p fy gw , f/ Themida e JU protect v ky fx m; w Jh Unpackme_lvl1.exe
z dki fu dk http://hvaonline.net r Sm download v ky f, lE dki fy gw , f/ Unpackme_lvl1.exe z dki fu dk PEiD e JU
p p fa q ; w Jht c g y Hk( 1 1 ) t w dki f; a w GU& y gw , f/
mov edi,eax
add eax,7FC97Eh
mov ebx,eax
shl ebx,2
push eax
pop edi
add eax,0E35F09h
sub eax,63958Bh
mov ecx, eax
xchg ebx,ecx
imul ebx,4
mov ecx,eax
schg edi,ecx
mov ebx,84A8473h
xor ebx,8354D0Dh
add eax,ebx
xor ebx,ebx
or ebx,eax
shl ebx,1
shl eax,1
Smar t Metamor ph
Technology
Copyright White Cracker (Myanmar Cracking Team)
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 395 -
y Hk( 1 1 )
y Hk( 1 1 ) r Smjr i f& w Jht w dki f; PEiD u Themida version t w dt u su dk p p fr a y ; E dki fa y r , fh t e D; p y fq Hk;
c e fUr Se f; a y ; E dki fc Jhy gw , f/ Unpackme_lvl1.exe z dki fu dkOlly r Smz Gi fhjy D; run (F9) Mu n fhy gr , f/
y Hk( 1 2 )
Olly r Sm F9 E Sdy fjy D; Mu n fhw Jht c gr Sm y Hk( 1 2 ) t w dki f; jr i f& y gw , f/ w u , fa w mh u Re fa w mfh& JU Olly u dk
debugger a w Gp Hkp r f; jc i f; r Su mu G, fE dki fz dkU Hide Caption? HideOD e JU IsDebugPresent plug-in DLL a w G
t o Hk; jy Kx m; y gw , f/ HideOD plug-in u dkv Jy Hk( 1 3 ) t w dki f; a & G; c s, fx m; y ga o ; w , f/
y Hk( 1 3 )
b ma Mu mi fh y Hk( 1 2 ) t w dki f; jr i f& o v Jq kdw m o d& a t mi f Unpackme_lvl1.exe u dk protect v ky fx m; w Jh
Themida option u dkMu n fhMu & a t mi f/ y Hk( 1 4 ) /
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 396 -
Protection Options for Unpackme_lvl1.exe
-----------------------------------
Macros Information
-----------------------------------
VM Macros: 0
CodeReplace Macros: 0
ENCRYPT Macros: 0
CLEAR Macros: 0
XBundler files
-----------------------------------
No files to bundle
Protection Options
-----------------------------------
Anti-Debugger : ENABLED
Anti-Dumpers: DISABLED
API-Wrapping Level: 0
Virtual Machine: ENABLED
Entry Point Ofuscation: DISABLED
Memory Guard: DISABLED
Anti-File Monitor: DISABLED
Anti-Registry Monitor: DISABLED
Resource Encryption: DISABLED
VMWare compatible: DISABLED
Delphi/BCB form protection: DISABLED
Advanced Protection Options
-----------------------------------
Encrypt Application: DISABLED
.NET assemblies: DISABLED
DLL plugin: DISABLED
Active Context: DISABLED
Last Section Name: hacnho
Compression
-----------------------------------
Application compression: DISABLED
Resources compression: DISABLED
SecureEngine compression: DISABLED
Virtual Machine Settings
-----------------------------------
Number of Virtual APIs wrapped: 0
Entry Point Virtualization: 0 instructions
Virtual Machine Processor: Mutable CISC
processor
Number of CPUs: 1
Opcode Type: Static opcodes
Dynamic Opcode: DISABLED
y Hk( 1 4 )
w u , fa w mh Themida u dk protect v ky fv dku fc sde fr Sm Anti-Debugger option u dka & G; c s, fc Jhv dkU jz p fy g
w , f/ ( o mr e f protector a w mfa w mfr sm; r sm; [ m anti-debug v Sn fhp m; r Ia w Gu dk x n fho Gi f; x m; a y r , fh Hide
Caption? HideOD e JU IsDebugPresent plug-in DLL a w Gu kda u smfv Tm; E dki fjc i f; r & Sdy gb l; / )
Themida & JU Anti-Debugger option u dk a u smfv Tm; E dki fz dkUt w Gu f o i fht a e e JU fly & JU The0DBG +
hideToolz ( o dkU) CodeRipper & JU RAMODBG u dk download v ky f, l& y gr , f/ u Re fa w mft o Hk; jy Kr Smu a w mh
RAMODBG jz p fy gw , f/ RAMODBG [ m Olly debugger u dk Themida y & dk* & r fa w Gu r p Hkp r f; r o d& Sd
E dki fa t mi f jy Kjy i fx m; w JhOlly y & dk* & r fo mjz p fjy D; o lUr Sm t x l; p Dr Hx m; w Jhplugin a w Gjz p fw JhAPI break? Strong
OD? Poison e JU Phant0m w dkUy g0 i fw Jht w Gu f Themida & JU Version 1.9.5/2.0.1.0/2.0.3.0 a w Gr Sm
a u mi f; a u mi f; debug v ky fE dki fy gw , f/
a u mi f; jy D/ Unpackme_lvl1.exe y & dk* & r fu dkRAMODBG r Smz Gi fhMu n fh& i f y Hk( 1 5 ) t w dki f; jr i f& y gr , f/
y Hk( 1 5 )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 397 -
Ctrl+G (Go to address in disassembler) u dkE Sdy fjy D; u Re fa w mfw dkU o Gm; c si fw Jh^ & Smc si fw Jha e & mu dk
w e f; o Gm; Mu y gr , f/ y Hk( 1 6 ) /
y Hk( 1 6 )
y Hk( 1 6 ) r Smjr i f& w Jh native API w p fc kjz p fw Jh ZwFreeVirtualMemory() API function & Sd& mq Do Gm;
y gr , f/ y Hk( 1 7 ) /
y Hk( 1 7 )
y Hk( 1 7 ) t w dki f; ZwFreeVirtualMemory q Da & mu fw Jht c g RETN 10; a e & mr Sm breakpoint o w fr Sw f
y gr , f/ o w fr Sw fjy D; & i fa w mhF9 (run) u dkE Sdy fv dku fy g/
y Hk( 1 8 )
' gq dky Hk( 1 7 ) r Smjr i f& w Jht w dki f; breakpoint & Sd& mu dkw e f; a & mu fv my gr , f/
jy D; & i fa w mh F9 (run) u dk 1 8 Mu dr fE Sdy fy g/ y Hk( 1 9 ) t w dki f; jr i f& y gr , f/ ( r Sw fc su f/ / Debug v ky fo n fh
y & dk* & r fa y : r lw n fjy D; t Mu dr ft a & t w Gu f a jy mi f; v Jr n fjz p fy go n f/ F9 (run) u dk 1 8 Mu dr fE Sdy fjc i f; o n f Unpack
me_lvl1.exe t w Gu fo mjz p fy go n f/ F9 u dkE Sdy f& mw Gi f e m; e m; jy D; r SE Sdy fy g/ q u fw dku f 1 8 c gr E Sdy fy gE Si fh/ )
y Hk( 1 9 )
F9 (run) u dk 1 7 Mu dr fE Sdy fw Jht x dr Sma w mh y Hk( 1 8 ) u breakpoint & Sd& mr Smy J& y fy gw , f/ 1 8 Mu dr fa jr mu f
E Sdy fw Jht c gr Sma w mh code section x Ja & mu fjy D; y & dk* & r f run w ma w GU& y gr , f/ ' gq dk b mv ky f& r , fq dkw m o i fo d
a v mu fy gjy D/
Ctrl+F2 (Restart) u dkE Sdy fjy D; y & dk* & r fu dk jy e fp y g/ ZwFreeVirtualMemory r Sm breakpoint o w f
r Sw fjy D; ' Dbreakpoint & Sd& mq DF9 (Alt+F9) E Sdy fjy D; a & mu fa t mi fv mc Jhy g/ y Hk( 1 8 ) t w dki f; breakpoint q Da & mu f
v mw Jht c g F9 (run) 1 7 c gE Sdy fy g/ 1 7 Mu dr fE Sdy fjy D; & i fa w mh ZwFreeVirtualMemory r Smo w fr Sw fx m; w Jh
breakpoint u dkjz Kw fy g/
Alt+M u dkE Sdy fjy D; memory window u dka c : y g/ y Hk( 2 0 ) /
y Hk( 2 0 )
y Hk( 2 0 ) u code section r Sm right-click E Sdy fjy D; Set memory breakpoint on access u dka & G; v dku fy g/
jy D; & i f F9 u dkjy e fE Sdy fy g/ Code section & JU entry point & Sd& ma e & mr Sm y & dk* & r fu v m& y fy gv dr fhr , f/
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 398 -
y Hk( 2 1 )
' Dt c gr Sma w mh Unpackme_lvl1.exe y & dk* & r fu dk dump v ky fz dkUjy i fy gr , f/ Olly & JU disassembler
window r Sm right-click E Sdy fjy D; Make dump process u dka & G; y g/ y Hk( 2 2 ) /
y Hk( 2 2 )
Dump v ky fx m; w Jh y & dk* & r fu dk dumped.exe t r n fe JUo dr f; v dku fjy D; ImpREC 1.7 e JU IAT a w Gu dk
jy i fy gr , f/ y Hk( 2 3 ) /
y Hk( 2 3 )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 399 -
y Hk( 2 3 ) r Sm DDE1 u dko Hk; jy D; IAT Autosear ch e JU& Smw m RVA (28000) u dkr & & Sdw Jht w Gu f Olly
Dump plugin u RVA u dk, lo Hk; x m; w mjz p fy gw , f/ Get Impor ts u dkt o Hk; jy Kjy D; API a w Gu dk import
v ky fy g/ Show Invalid u dko Hk; jy D; invalid API a w Gu dk& Smy g/ Invalid API address w p fc ka y : right-click
E Sdy fjy D; Cut Thunk(s) u dka & G; y g/ jy D; & i fa w mh Fix Dump button u dkE Sdy fjy D; u Re fa w mfw dkU o dr f; q n f; v dku fw Jh
dumped.exe u dkjy i fy g/ ImpREC u jy i fv dku fw Jhz dki fu dk dumped_.exe t r n fe JU o dr f; a y ; y gv dr fhr , f/ ' Dz dki fu dk
z Gi fhMu n fhv dku f& i f a u mi f; a u mi f; t v ky fv ky fw m a w GU& y gr , f/ ' ga y r , fhz dki ft & G, ft p m; u e n f; e n f; Mu D; a e w mr dkU
r v dkw ma w Gz , fx kw fMu y gr , f/ dumped_.exe u dkCFF explorer e JUz Gi fhv dku fy g/ y Hk( 2 4 ) /
y Hk( 2 4 )
y Hk( 2 4 ) r Smjr i f& w Jh hacnho section a y : right-click E Sdy fjy D; Delete Section (Header and Data)
u dka & G; v dku fy g/ jy D; & i f z dki fu dk dumped_fixed.exe t r n fe JUo dr f; v dku fy g/ y Hk( 2 5 ) t w dki f; jr i f& y gr , f/
y Hk( 2 5 )
' gq dk& i fa w mh Anti-Debugger option u dka & G; jy D; protect v ky fx m; w Jh Themida z dki ft w Gu f unpack
v ky fjc i f; jy D; p D; o Gm; y gjy D/
( 4 ) Themida (Anti-Debugger ? Anti-File/Registr y Monitor ) z dki ft m; unpack v ky fjc i f;
' Dw p fc gr Sma w mh w p fq i fhw u fjy D; a v hv mMu n fhMu & a t mi f/ Unpack v ky fz dkU a & G; c s, fx m; w Jh y & dk* & r fu
a w mh Unpackm_lvl2.exe jz p fy gw , f/ Unpackm_lvl2.exe u dk protect v ky fx m; w Jh Themida option u dk
Mu n fhMu & a t mi f/ y Hk( 2 6 ) /
Protection Options for Unpackm_lvl2.exe
---------------------------------
Macros Information
---------------------------------
VM Macros: 0
CodeReplace Macros: 0
ENCRYPT Macros: 0
CLEAR Macros: 0
XBundler files
---------------------------------
No files to bundle
Protection Options
---------------------------------
Anti-Debugger : ENABLED
Anti-Dumpers: DISABLED
API-Wrapping Level: 0
Virtual Machine: ENABLED
Entry Point Ofuscation: DISABLED
Memory Guard: DISABLED
Anti-File Monitor : ENABLED
Anti-Registr y Monitor : ENABLED
Resource Encryption: DISABLED
VMWare compatible: DISABLED
Delphi/BCB form protection: DISABLED
Advanced Protection Options
---------------------------------
Encrypt Application: DISABLED
.NET assemblies: DISABLED
DLL plugin: DISABLED
Active Context: DISABLED
Last Section Name: hacnho
Compression
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 400 -
---------------------------------
Application compression: ENABLED
Resources compression: ENABLED
SecureEngine compression: ENABLED
Virtual Machine Settings
---------------------------------
Number of Virtual APIs wrapped: 0
Entry Point Virtualization: 0 instructions
Virtual Machine Processor: Mutable CISC processor
Number of CPUs: 1
Opcode Type: Static opcodes
Dynamic Opcode: DISABLED
y Hk( 2 6 )
Unpackm_lvl2.exe u dkOlly r Smz Gi fhMu n fh& i fa w mhy Hk( 2 7 ) t w kdi f; jr i f& y gw , f/
y Hk( 2 7 )
Ctrl+G E Sdy fjy D; ZwFreeVirtualMemory & Sd& mu dko Gm; y g/ y Hk( 2 8 ) t w dki f; RETN 10; r Sm breakpoint
o w fr Sw fy g/
y Hk( 2 8 )
jy D; & i f F9^ Shift+F9 u dkE Sdy fjy D; breakpoint & Sd& mq Da & mu fa t mi fv my g/ y Hk( 2 9 ) /
y Hk( 2 9 )
y Hk( 2 9 ) t w dki f; jr i f& w Jht c gr Sma w mh F9 key u dkb , fE Sp fMu dr fE Sdy fw Jht c g y & dk* & r f& JU main window u dk
jr i f& o v Jq dkw m a p mi hfMu n fha & w Gu fy g/ F9 (run) u dk 2 6 Mu dr fE Sdy fw Jht c gr Sm main window u dk jr i f& y gw , f/
' gq dk y & dk* & r fu dk Ctrl+F2 (Restart) e JU jy e fp v dku fjy D; y Hk( 2 9 ) & Sd& mq Dt a & mu fv mc Jhy g/ F9 u dk 2 5 Mu dr fE Sdy fy g/
2 5 Mu dr fjy n fhw Jht c sde fr Sma w mh RETN 10; r Smo w fr Sw fx m; w Jh breakpoint u dkjz Kw fv dku fy g/ Alt+M u dkE Sdy fjy D;
memory window u dka c : y g/ code section r Sm right-click E Sdy fjy D; Set memor y br eakpoint on access
u dka & G; y g/ t m; v Hk; jy D; & i fa w mh F9 u dkE Sdy fjy D; y & dk* & r fu dk run y g/ code section & JU entry point (OEP) & Sd& mu dk
a & mu fv my gr , f/ y Hk( 3 0 ) /
y Hk( 3 0 )
y & dk* & r fu dk dump v ky fz dkUt w Gu f disassembly window r Sm right-click E Sdy fjy D; Make dump of
pr ocess u dka & G; y g/ jy D; & i f dumped.exe t r n fe JU z dki fu dkdump v ky fy g/
Dump v ky fx m; w Jhz dki fu dk IAT jy i fz dkUt w Gu f ImpREC u dkz Gi fhy g/ y Hk( 2 3 ) r Sm v ky fc Jhw Jht w dki f; v ky fjy D;
dump v ky fx m; w Jhz dki fu dkjy i fy g/ dumped_.exe q dkw Jhz dki f& v my gr , f/ RVA w e fz dk; r Sm 28000 x n fh& w Jh
t a Mu mi f; & i f; u a w mhy Hk( 3 1 ) a Mu mi fhjz p fy gw , f/
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 401 -
y Hk( 3 1 )
dumped_.exe u dk CFF explorer r Smz Gi fhjy D; hacnho section u dkz su fy g/ ' Dha e mu f PE header u dkjy e f
rebuild v ky fjy D; jy i fx m; w Jhz dki fu dk dumped_.exe t r n fe JUy J o dr f; v dku fr , fq dk& i f y Hk( 3 2 ) t w dki f; jr i f& r Smjz p fy g
w , f/
y Hk( 3 2 )
y Hk( 3 2 ) u dk t a o t c smMu n fhr , fq dk& i f v u f& Sd dumped.exe (1,259KB) z dki f[ m a & SUt c e f; r Sm dump
v ky fc Jhw Jhdumped.exe (791KB) z dki fe JU t & G, ft p m; c si f; u Gma e w m a w GU& y gw , f/
( 5 ) Themida (Anti-Debugger ? Anti-Dumper s ...) z dki ft m; unpack v ky fjc i f;
a e mu fw p fq i fhu dk x y fjy D; a v hv mMu n fhy gr , f/ ' Dw p fc g unpack v ky fz dkU a & G; c s, fx m; w Jh y & dk* & r fu a w mh
Unpackme_lvl3.exe jz p fy gw , f/ Unpackme_lvl3.exe u dk protect v ky fx m; w Jh Themida option u dk
Mu n fhMu & a t mi f/ y Hk( 3 3 ) /
Protection Options for Unpackme_lvl3.exe
---------------------------------
Macros Information
---------------------------------
VM Macros: 0
CodeReplace Macros: 0
ENCRYPT Macros: 0
CLEAR Macros: 0
XBundler files
---------------------------------
No files to bundle
Protection Options
---------------------------------
Anti-Debugger : ENABLED
Anti-Dumper s: ENABLED
API-Wrapping Level: 0
Virtual Machine: ENABLED
Entry Point Ofuscation: DISABLED
Memory Guard: DISABLED
Anti-File Monitor : ENABLED
Anti-Registr y Monitor : ENABLED
Resource Encryption: DISABLED
VMWare compatible: DISABLED
Delphi/BCB form protection: DISABLED
Advanced Protection Options
---------------------------------
Encrypt Application: DISABLED
.NET assemblies: DISABLED
DLL plugin: DISABLED
Active Context: DISABLED
Last Section Name: hacnho
Compression
---------------------------------
Application compression: ENABLED
Resources compression: ENABLED
SecureEngine compression: ENABLED
Virtual Machine Settings
---------------------------------
Number of Virtual APIs wrapped: 0
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 402 -
Entry Point Virtualization: 0 instructions
Virtual Machine Processor: Mutable CISC processor
Number of CPUs: 1
Opcode Type: Static opcodes
Dynamic Opcode: DISABLED
y Hk( 3 3 )
Unpackme_lvl3.exe u dkOlly r Smz Gi fhMu n fh& i fa w mhy Hk( 3 4 ) t w kdi f; jr i f& y gw , f/
y Hk( 3 4 )
Ctrl+G E Sdy fjy D; ZwFreeVirtualMemory & Sd& mu dko Gm; y g/ y Hk( 3 5 ) t w dki f; RETN 10; r Sm breakpoint
o w fr Sw fy g/
y Hk( 3 5 )
jy D; & i f F9^ Shift+F9 u dkE Sdy fjy D; breakpoint & Sd& mq Da & mu fa t mi fv my g/ y Hk( 3 6 ) /
y Hk( 3 6 )
y Hk( 3 6 ) t w dki f; jr i f& w Jht c gr Sma w mh F9 key u dkb , fE Sp fMu dr fE Sdy fw Jht c g y & dk* & r f& JU main window u dk
jr i f& o v Jq dkw m a p mi hfMu n fha & w Gu fy g/ F9 (run) u dk 2 7 Mu dr fE Sdy fw Jht c gr Sm main window u dk jr i f& y gw , f/
' gq dk y & dk* & r fu dk Ctrl+F2 (Restart) e JU jy e fp v dku fjy D; y Hk( 3 6 ) & Sd& mq Dt a & mu fv mc Jhy g/ F9 u dk 2 6 Mu dr fE Sdy fy g/
2 6 Mu dr fjy n fhw Jht c sde fr Sma w mh RETN 10; r Smo w fr Sw fx m; w Jh breakpoint u dkjz Kw fv dku fy g/ Alt+M u dkE Sdy fjy D;
memory window u dka c : y g/ code section r Sm right-click E Sdy fjy D; Set memor y br eakpoint on access
u dka & G; y g/ t m; v Hk; jy D; & i fa w mh F9 u dkE Sdy fjy D; y & dk* & r fu dk run y g/ code section & JU entry point (OEP) & Sd& mu dk
a & mu fv my gr , f/ y Hk( 3 7 ) /
y Hk( 3 7 )
y & dk* & r fu dk dump v ky fz dkUt w Gu f disassembly window r Sm right-click E Sdy fjy D; Make dump of
pr ocess u dka & G; y g/ jy D; & i f dumped.exe t r n fe JU z dki fu dkdump v ky fy g/
Dump v ky fx m; w Jhz dki fu dk IAT jy i fz dkUt w Gu f ImpREC u dkz Gi fhy g/ y Hk( 2 3 ) r Sm v ky fc Jhw Jht w dki f; v ky fjy D;
dump v ky fx m; w Jhz dki fu dkjy i fy g/
dumped_.exe u dk CFF explorer r Smz Gi fhjy D; hacnho section u dkz su fy g/ ' Dha e mu f PE header u dkjy e f
rebuild v ky fjy D; jy i fx m; w Jhz dki fu dk dumped_.exe t r n fe JUy J o dr f; v dku fr , fq dk& i f y Hk( 3 8 ) t w dki f; jr i f& r Smjz p fy g
w , f/
y Hk( 3 8 )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 403 -
Anti-Dumpers option a & G; x m; w Jht w Gu f dump v ky fw m b mr Sx l; jc m; r Ir & Sdv dkU o i fht a e e JU x i fy g
v dr fhr , f/ w u , fa w mh' Dv kdr [ kw fy gb l; / Unpackme_lvl3.exe u dkLordPE r Sm dump v ky fMu n fhy g/ y Hk( 3 9 ) /
y Hk( 3 9 )
LordPE e JU dump v ky fMu n fhw Jht c g o i fht a e e JU dump v ky fv dkU& r Sm r [ kw fy gb l; /
( 6 ) Themida (Anti-Dumper s? Memor y Guar d ...) z dki ft m; unpack v ky fjc i f;
a e mu fw p fq i fhu dk x y fjy D; a v hv mMu n fhy gr , f/ ' Dw p fc g unpack v ky fz dkU a & G; c s, fx m; w Jh y & dk* & r fu a w mh
Unpackm_lvl4.exe jz p fy gw , f/ Unpackm_lvl4.exe u dk protect v ky fx m; w Jh Themida option u dk Mu n fh
Mu & a t mi f/ y Hk( 4 0 ) /
Protection Options for Unpackm_lvl4.exe
---------------------------------
Macros Information
---------------------------------
VM Macros: 0
CodeReplace Macros: 0
ENCRYPT Macros: 0
CLEAR Macros: 0
XBundler files
---------------------------------
No files to bundle
Protection Options
---------------------------------
Anti-Debugger : ENABLED
Anti-Dumper s: ENABLED
API-Wr apping Level: 1
Virtual Machine: ENABLED
Entry Point Ofuscation: DISABLED
Memor y Guar d: ENABLED
Anti-File Monitor : ENABLED
Anti-Registr y Monitor : ENABLED
Resour ce Encr yption: ENABLED
VMWare compatible: DISABLED
Delphi/BCB form protection: DISABLED
Advanced Protection Options
---------------------------------
Encrypt Application: DISABLED
.NET assemblies: DISABLED
DLL plugin: DISABLED
Active Context: DISABLED
Last Section Name: hacnho
Compression
---------------------------------
Application compression: ENABLED
Resources compression: ENABLED
SecureEngine compression: ENABLED
Virtual Machine Settings
---------------------------------
Number of Virtual APIs wrapped: 0
Entry Point Virtualization: 0 instructions
Virtual Machine Processor: Mutable CISC processor
Number of CPUs: 1
Opcode Type: Static opcodes
Dynamic Opcode: DISABLED
y Hk( 4 0 )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 404 -
y Hk( 4 1 )
Unpackm_lvl4.exe u dkOlly r Smz Gi fhMu n fh& i fa w mhy Hk( 4 1 ) t w kdi f; jr i f& y gw , f/
y Hk( 4 2 )
t & i f o i fc e f; p m( 3 ) c kr Sma w mhAPI-Wrapping u dkr a & G; c s, fc Jhw Jht w Gu f magic jump u dkjy i fp & mr v dky g
b l; / ' Dw p fc gr Sma w mhmagic jump u dk& Sm& y ga w mhr , f/
Alt+M u dkE Sdy fjy D; memory window u dka c : y g/ y Hk( 4 3 ) /
y Hk( 4 3 )
y Hk( 4 3 ) u code section r Sm right-click E Sdy fjy D; Set memory breakpoint on write u dka & G; y g/ jy D; & i f
F9 (Run) u dkE Sdy fy g/
y Hk( 4 4 )
y Hk( 4 4 ) t w dki f; jr i f& w Jht c g F8 (Step Over) u dkw p fc gE Sdy fjy D; F9 (Run) u dkx y fE Sdy fy g/
y Hk( 4 5 )
y Hk( 4 5 ) t w dki f; jr i f& w Jht c g y Hk( 4 6 ) u VA 005276FF u dkjr i f& w Jht x dF9 (Run) u dkq u fE Sdy fy g/
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 405 -
y Hk( 4 6 )
y Hk( 4 6 ) t w dki f; jr i f& w Jht c g F9 (Run) u dkx y fE Sdy fy g/
y Hk( 4 7 )
' Dha e mu fr Sma w mhy Hk( 4 8 ) u JMP 0052764C; q Da & mu fw Jht x dF8 (Step over) u dkE Sdy fy g/
y Hk( 4 8 )
JMP 0052764C; u dk execute v ky fjy D; c sde fr Sma w mh y Hk( 4 8 ) t w dki f; VA 0052764C & Sd& mq Da & mu fv m
y gw , f/ JMP 00526C27; & Sd& mr Sm o w fr Sw fjy D; JMP 00526C27; q Da & mu fw Jht x d F9 u dkE Sdy fv mc Jhy g/ JMP
00526C27; u dkexecute v ky fjy D; c sde fr Sma w mhy Hk( 4 9 ) t w dki f; VA 00526C27 & Sd& mq Da & mu fv my gw , f/
y Hk( 4 9 )
y Hk( 4 8 ) r Sma w GU& w Jh JE 00526CD4; [ m u Re fa w mfw dkU & Sma e w Jh magic jump y g/ ' Da e & mr Sm JE
00526CD4; t p m; JMP 00526CD4; v dkUjy i fy gr , f/ y Hk( 5 0 ) /
y Hk( 5 0 )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 406 -
y Hk( 5 1 ) r Smjr i f& w JhJE a w Gu dk NOP v dkUjy i fa y ; & y gr , f/
y Hk( 5 1 )
JE a w Gu dkNOP v dkUjy i fjy D; c sde fr Sma w mhy Hk( 5 2 ) r Smjr i f& w Jht w dki f; a w GU& y gw , f/
y Hk( 5 2 )
' Dw p fc g v ky f& r Smu a w mh Alt+M u dkE Sdy fjy D; memory window r Smo w fr Sw fx m; w Jh memory
breakpoint u dkz , f& Sm; z dkUy g/ jy D; & i fa w mh Ctrl+G u dkE Sdy fjy D; ZwFreeVirtualMemory & Sd& mr Sm breakpoint
o w fr Sw fy gr , f/ y Hk( 5 3 ) /
y Hk( 5 3 )
y Hk( 5 3 ) t w dki f; breakpoint o w fr Sw fjy D; & i fa w mh F9 u dkE Sdy fy g/ Breakpoint & Sd& mq Da & mu fv my gr , f/
y Hk( 5 4 ) /
y Hk( 5 4 )
VA 7C90DA54 q Da & mu fw Jht c g code section & JU entry point (OEP) & Sd& mq Da & mu fa t mi f F9 u dk
1 5 Mu dr fE Sdy fy g/ jy D; & i f VA 7C90DA54 r Sm o w fr Sw fx m; w Jh breakpoint u dkjz Kw fjy D; memory window
(Alt+M) r Sm Set memory breakpoint on access u dka & G; a y ; y g/ ' gq dk y Hk( 5 5 ) r Smjr i f& w Jht w dki f; OEP & Sd& mq D
a & mu fv my gr , f/ ( r Sw fc su f/ / o i ft o Hk; jy Kw Jh Windows version a y : r lw n fjy D; F9 E Sdy f& r , fh t Mu dr f t a &
t w Gu f a jy mi f; v JE dki fy gw , f/ )
y Hk( 5 5 )
' gq dk dump v ky fjy D; dumped.exe t r n fe JU z dki fu dko dr f; v dku fy g/ ( o i fc e f; p m & Sn fv sm; r Smp dk; w Jht w Gu f
r & Si f; jy a w mhy gb l; / a & SUy dki f; t c e f; r sm; u dkjy e fMu n fhy g/ )
Dump v ky fjy D; o m; z dki fu dk ImpREC o Hk; jy D; IAT u dkjy i fy g/ jy i fjy D; o m; z dki fu dk dumped_.exe t r n fe JU
o dr f; y g/ ( a & SUy dki f; t c e f; r sm; u dkjy e fMu n fhy g/ )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 407 -
dumped_.exe z dki fu dk CFF explorer r Smz Gi fhjy D; hacnho section u dkz su fy g/ jy i fjy D; o m; z dki fu dk
dumped_fix.exe t r n fe JUo dr f; y g/ ( a & SUy dki f; t c e f; r sm; u dkjy e fMu n fhy g/ )
jy D; & i f PEiD u KDK & JU Rebuild PE plug-in u dkt o Hk; jy Kjy D; PE header u dkjy i fy g/ y Hk( 5 6 ) /
y Hk( 5 6 )
y Hk( 5 6 ) t w dki f; jy i fjy D; & i fa w mhz dki fa w G& JUt & G, ft p m; u dky Hk( 5 7 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 5 7 )
' Da e & mr Sm o w da y ; v dkw mu a w mh Themida e JU protect r v ky fx m; c i f Unpackme.exe z dki f& JU r lv
t & G, ft p m; [ m 251KB y J& Sdy gw , f/
' Da v mu fq dk& i f Themida e JU protect v ky fx m; w Jh z dki fa w Gu dk o i fht a e e JU unpack v ky fE kdi fa v mu fjy D
x i fy gw , f/
( 7 ) Default option a & G; c s, fjy D; pack v ky fx m; a o m Themida z dki ft m; unpack v ky fjc i f;
' Dw p fc g unpack v ky fMu n fhr , fhz dki fu a w mh Themida & JU option t m; v Hk; u dka & G; c s, fjy D; protect
v ky fx m; w Jh UnPackMe_Themida 1.9.1.0.c.exe z dki fy Jjz p fy gw , f/ y x r q Hk; ' Dz dki fu dk SND Team & JU
download section r Sm download v ky f, ly g/ ' Dw p fc g unpack v ky fjy r Smu a w mh a & SUo i fc e f; p ma w Ge JU w lr Sm
r [ kw fo v dk v ky fw Jhe n f; v r f; u v Jy dkr dkv G, fu lw mv Ja w GU& r Smy g/
Unpack v ky f& mr Sm a t mu fy gt q i fh( 3 ) c ku dkv ky fa q mi f& y gr , f/
( u ) OEP u dk& Sma z Gjc i f;
( c ) IAT u dkw n fa q mu fjc i f;
( * ) Dump v ky fjc i f;
( u ) OEP u dk& Sma z Gjc i f;
y x r q Hk; UnPackMe_xxx.exe z dki f& JU OEP u dk& Sma z Gy gr , f/
1 / y Hk( 5 8 ) t w dki f; command bar r Sm ZwFreeVirtualMemory u dkbreakpoint o w fr Sw fy gr , f/
y Hk( 5 8 )
2 / Breakpoint o w fr Sw fjy D; w Jht c g Shift+F9 u dkE Sdy fjy D; EDI register u dka p mi fhMu n fhy g/
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 408 -
y Hk( 5 9 )
Olly u a w mh ZwFreeVirtualMemory & Sd& ma e & mw dki f; r Sm y Hk( 5 9 ) t w dki f; & y fa e r Smjz p fy gw , f/ Shift+
F9 u dkE Sdy fjy D; EDI register u dka p mi fhMu n fhy g/ Shift+F9 E Sdy fv dkU EDI w e fz dk; [ m w la e r , fq dk& i f breakpoint
u dkjy e fjz Kw fv dku fy g/
y Hk( 6 0 )
y Hk( 6 0 ) r Smjr i f& w Jht w dki f; EDI w e fz dk; 0041C029 a & mu fw Jht c g Shift+F9 E Sdy fv Jw e fz dk; a jy mi f; v Jjc i f;
r & Sda w mhw Jht w Gu f 7C90DA48 (ZwFreeVirtualMemory) r Smo w fr Sw fx m; w Jh breakpoint u dkjz Kw fv dkU& jy D
jz p fy gw , f/ Breakpoint jz Kw fjy D; a e mu fr Sma w mh memory window (Alt+M) u dko Gm; jy D; UnpackMe & JU
.code section a y : right-click E Sdy fjy D; Set memor y br eakpoint on access u dka & G; v dku fy g/ jy D; & i f
Shift+F9 u dkE Sdy fy g/ y Hk( 6 1 ) r Smjr i f& w Jht w dki f; OEP & Sd& mq Da & mu fv my gr , f/
y Hk( 6 1 )
w u , fa w mhy Hk( 6 1 ) r Smjr i f& w mu a w mhOEP t p p fr [ kw fa o ; y gb l; /
y Hk( 6 2 )
OEP t p p fu y Hk( 6 2 ) u NOP instruction t jy D; r Smr Sp w my g/
y Hk( 6 3 )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 409 -
' ga Mu mi fh' Da e & m ( 004271B0-004271DBx d) u dk jy i f& y gr , f/ OEP [ m 004271B0 jz p fw mu dka w mh
r Sw fo m; x m; y g/
( c ) IAT u dkw n fa q mu fjc i f;
' Dw p fc gr Sma w mhIAT u dkjy i fz dkUv ky fy gr , f/
1 / y & dk* & r fu dkjy e fp v dku fy g/ ( Ctrl+F2)
2 / Memory window (ALt+M) u dkz Gi fhjy D; .code section a y : right-click E Sdy fjy D; Set memor y
br eakpoint on wr ite u dka & G; v dku fy g/ jy D; & i f Shift+F9 u dkE Sdy fy g/ y Hk( 6 4 ) t w dki f; jr i f& y gr , f/
y Hk( 6 4 )
F8 u dkE Sdy fy g/ VA 006F5E02 q Du dka & mu fv my gr , f/ ' Da e mu f y Hk( 6 5 ) t w dki f; jr i f& a t mi f Shift+F9
u dkE Sdy fv mc Jhy g/
y Hk( 6 5 )
3 / ' Dw p fc gr Sma w mhmagic string u dk& Smy gr , f/ y Hk( 6 5 ) r Sm right-click E Sdy fjy D; Sear ch for u Binar y str ing
u dka & G; y g/ jy D; & i f y Hk( 6 6 ) t w dki f; 3D00000100 u dk& dku fx n fhjy D; & Smy g/
y Hk( 6 6 )
w u , fv dkU ' De n f; e JU& Smv dkU b mr Sr a w GUb l; q dk& i fa w mh y Hk( 6 5 ) r Sm right-click E Sdy fjy D; Sear ch for u
Command u dka & G; y g/ jy D; & i f y Hk( 6 7 ) t w dki f; cmp eax, 10000 u dk& dku fx n fhjy D; & Smy g/
y Hk( 6 7 )
' gq dky Hk( 6 8 ) r Smjr i f& w Jht w dki f; magic string ("ALLUSERPROFILE...") & Sd& mu dka & mu fv my gr , f/
y Hk( 6 8 )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 410 -
4 / ' Dha e mu f CRC u dkp p fa q ; w Jh jump instruction (JE) u dk& Smy gr , f/ Disassemble window r Sm right-
click E Sdy fjy D; Sear ch for u Binar y str ing u dka & G; y g/ jy D; & i f y Hk( 6 9 ) t w dki f; 3985????????0F84 u dk
& dku fx n fhjy D; & Smy g/
y Hk( 6 9 )
' gq dk& i fa w mhy Hk( 7 0 ) t w dki f; magic jump u kda w GU& r Smjz p fy gw , f/
y Hk( 7 0 )
VA 0070667F (JE 0070673A) r Sm right-click E Sdy fjy D; Br eakpoint u Har dwar e, on
execution u dka & G; y g/
5 / a e mu fx y fv ky f& r Smu a w mh API redirection u dkv ky fa q mi fw Jh jump a w Gu dk & Sma z Gz dkUy g/ ' Djump a w Gu
t jr Jw r f; ( 4 ) c k& Sdjy D; jump v ky fw Jh address u v J t w lw ly Jjz p fy gw , f/ Oy r m - ( JE 04xxxxx) / ' D JE
instruction ( 4 ) c k[ m magic string ("ALLUSERPROFILE...") a t mu fr Smy J& Sdy gw , f/
' ga Mu mi fh disassemble window r Sm right-click E Sdy fjy D; Sear ch for u Binar y str ing u dka & G; y g/
jy D; & i f 0F84???????? u dk& dku fx n fhjy D; & Smy g/
y Hk( 7 1 ) t w dki f; a w GU& i fa w mh& y fv kdu fy g/
y Hk( 7 1 )
y Hk( 7 1 ) r Smjr i f& w mu a w mh virtual address w l jump (JE) 3 c ky g/ a e mu fw p fc ku a w mh highlight
jz p fa e w Jh address (00706E10-00706E12) a e & mr Smy g/ ' D jump (JE) u dkjr i fc si f& i fa w mh Ctrl+G E Sdy fjy D;
00706E11 v dkU& dku fx n fhv dku fy g/ y Hk( 7 2 ) t w dki f; a e mu f jump (JE) w p fc ka y : v my gv dr fhr , f/
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 411 -
y Hk( 7 2 )
' ga Mu mi fh0F84???????? v dkU& Smr , fht p m; 0F84??000000 v dkU& Sm& i f jump (JE) u dk& Sma w GUw m y dkjr e f
r Smjz p fy gw , f/ VA 00706E11 (JE 00706EE7) r Sm right-click E Sdy fjy D; Br eakpoint u Har dwar e, on
execution u dka & G; y g/
Ctrl+F2 E Sdy fjy D; y & dk* & r fu dkjy e fp v dku fy g/
6 / ' gq dkCRC u dkp p fa q ; w Jhjump q Dw e f; a & mu fv my gr , f/ y Hk( 7 3 ) /
y Hk( 7 3 )
JE a e & mr Sm JMP v dkUa jy mi f; jy D; Shift+F9 u dkE Sdy fy g/
7 / ' Dt c gr Sma w mhAPI u dkp p fw Jha e & m ( VA 00706E11) a & mu fv mw ma w GU& y gr , f/ y Hk( 7 4 ) /
y Hk( 7 4 )
y Hk( 7 4 ) r Smjr i f& w Jht w dki f; JE 00706EE7 a e & mw dki f; r Sm NOP instruction e JUt p m; x dk; v dku fy g/ jy D; & i f
hardware breakpoint a w Gt m; v Hk; u dkjz Kw fv dku fy g/
8 / ' Dt c g OEP(004271DC) & Sd& ma e & mr Sm breakpoint o w fr Sw fjy D; breakpoint q Da & mu fa t mi f F9
u dkE Sdy fy g/ y Hk( 7 5 ) /
y Hk( 7 5 )
r Sw f& e f/ / w u , fa w mhOEP t p p f& JU virtual address [ m 004271B0 o mjz p fy gw , f/
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 412 -
y Hk( 7 6 )
UnpackMe_xxx.exe u dk Visual C++ 6.0 e JUa & ; o m; x m; jc i f; jz p fy gw , f/ ' ga Mu mi fh y Hk( 7 6 ) r Sm
jy x m; w Jhu k' fa w Gt p m; Visual C++ 6.0 signature u dka jy mi f; a y ; & y gr , f/ Visual C++ u k' ft p [ m PUSH
EBP e JUp a v h& Sdjy D; GetVersion API u dka c : o Hk; y gw , f/ o lU& JU signature u a w mh a t mu fy gt w dki f; jz p fy g
w , f/
55 8B EC 6A FF 68 60 0E 45 00 68 C8 92 42 00 64 A1 00 00 00 00 50 64 89 25 00 00 00 00 83
C4 A8 53 56 57 89 65 E8 FF 15 DC 0A 46 00
' Dhex w e fz dk; a w Gu dky Hk( 7 6 ) r Smt p m; x dk; v dku f& i f y Hk( 7 7 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 7 7 )
VA 004271D6 a e & mr Sm CALL kernel32.GetVersion v dkUjy i fy gr , f/ ( r jy i fv J& y gw , f/ )
y Hk( 7 8 )
jy D; & i f 004271B0 r Sm right-click E Sdy fjy D; New or igin her e u dka & G; y gr , f/ ' gu a w mh OEP
a e & mt o p fu dko w fr Sw fw mjz p fy gw , f/
9 / ' Dt c gr Sma w mhIAT u dkjy i fz dkU UIF (Universal Import Fixer) u dkz Gi fhy g/
Task Manager u a e process id w e fz dk; u dkz w fjy D; a w mhProcess ID a e & mr Sm & dku fx n fhy g/
Olly & JU memor y window u a e v dkt y fw Jhw e fz dk; a w Gu dkz w fjy D; a t mu fy gt w dki f; jz n fhp Gu fy g/ y Hk( 7 9 ) /
Code Start: 401000? Code End: 463000? New IAT VA: 469000/
y Hk( 7 9 )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 413 -
y Hk( 7 9 ) t w dki f; w e fz dk; a w Gjz n fhjy D; & i fa w mh Fix Dir ectly Impor ts e JU Fast Speed w dkUu dk a & G; c s, fjy D;
Start button u dkE Sdy fy g/ y Hk( 8 0 ) t w dki f; a w GU& y gr , f/
y Hk( 8 0 )
( * ) Dump v ky fjc i f;
' Dt c gr Sma w mhUIF e JUjy i fx m; w JhUnpackMe_xxx.exe z dki fu dkdump v ky fy gr , f/
y Hk( 8 1 )
Disassemble window r Sm right-click E Sdy fjy D; y Hk( 8 0 ) t w dki f; a & G; c s, fy g/ jy D; & i f dump.exe t r n fe JU
z dki fu dko dr f; q n f; y g/ ' Dha e mu fr Sma w mhdump v ky fx m; w Jhz dki fu dkjy i fw Jht y dki f; jz p fy gw , f/ y Hk( 8 2 ) /
y Hk( 8 2 )
t c e f; ( 2 5 ) - Themida t m; a v hv mjc i f;
- 414 -
OEP u a w mh 00271B0 jz p fy gw , f/ OEP a e & mr Sm 00271B0 v dkU& dku fx n fhjy D; IAT autosearch
u dkE Sdy fjy D; & Sm& i fa w mhimport a w Gw p fc kr Sa w GUr Smr [ kw fy gb l; / b ma Mu mi fhv Jq dka w mhIAT & JU RVA r Sm; a e v dkUy g/
' ga Mu mi fh y Hk( 8 2 ) r Sma w GU& w Jh RVA e JU Size a e & mr Sm y Hk( 8 0 ) r Sma w GU& w Jh RVA e JU Size w e fz dk; a w Gu dk
x n fha y ; y g/ jy D; & i f Get Imports u dka & G; jy D; dump.exe z dki fu dkjy i fy g/ a e mu fq Hk; r Sm dump_.exe z dki fx Gu fv m
y gv dr fhr , f/
dump_.exe z dki fu a e r v dkt y fw Jh Tuts4You section u dk CFF Explorer o Hk; jy D; z su fy g/ ' Dha e mu f
PEiD & JU plug-in w p fc kjz p fw Jh Rebuild PE o Hk; jy D; PE header u dkjy i fv dku fc sde fr Sma w mh y Hk( 8 3 ) t w dki f;
z dki ft & G, ft p m; a o ; i , fo Gm; w m jr i f& y gw , f/
y Hk( 8 3 )
dump_(fix).exe z dki fu dkPEiD e JUp p fMu n fh& i fa w mhy Hk( 8 4 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 8 4 )
e d* Hk; c sKy ft a e e JU a jy mMu m; v dkw mu a w mh Themida [ m version t o p fa w Ga jy mi f; v Jo Gm; w dki f; patch
v ky f& r , fha e & ma w Gu w la w mhr Sm r [ kw fy gb l; / Themida 1.9.1 a e mu fy dki f; version a w Gr Sm w ln Dw Jh address
e JU JE 4 c k y gr v ma w mhy gb l; / Themida developer a w G[ m cracking z dk& r fa w Gu dk a p mi hfMu n fha e w mjz p fw Jh
t w Gu f cracker a w Ga z mfjy a e w Jh unpacking e n f; v r f; a w Gu dk v kdu fv Hz ma x ; v Qu f& Sdy gw , f/ ' ga Mu mi fh t c sdKU
cracker a w Gu Themida & JUt m; e n f; c su ft c sdKUu dk a w GU& SdMu a y r , fh z dk& r fa w Gr Sm a z mfjy a v hr & SdMu y gb l; / o i fh
t a e e JU Themida z dki fa w Gu dk unpack v ky fc si fw , fq dk& i fa w mh cracker a w Ga z mfjy a e w Jh o i fc e f; p ma w Gu dk
t jr Jw a p a v hv ma e & r , fht jy i f u dk, fy dki f[ e fe JU unpack v ky fE dki fz dkU Mu dK; p m; a e & r Smjz p fy ga Mu mi f; . . .
tcef ;(26) - CRC qd k onf rS m
- 415 -
tcef;(26) - CRC qdkonfrSm
r Mu mr Dv mr n f/
tcef ;(27) - Thread rsm;pGm&Sdaom application rsm;ud k crack vkyfjcif;
- 416 -
tcef;(27) - Thr ead rsm;pGm&Sdaom application rsm;udk cr ack vkyfjcif;
r Mu mr Dv mr n f/
tcef ;(28) - CD-ROM Protection taMumif; odaumif;p&mrsm;
- 417 -
tcef;(28) - CD-ROM Pr otection taMumif; odaumif;p&mrsm;
r Mu mr Dv mr n f/
tcef ;(29) - Flashy x&dk*sefESifh Windows Registry
- 418 -
tcef;(29) - Flashy x&dk*sefESifh Windows Registr y
u Re fa w mfw dkUt a e e JU a & SUt c e f; a w Gr Sm a v hv mc Jhw ma w Gu a q mhz f0 Jv fa w Gu dk b , fv dk crack v ky fr , f
q dkw Jh t q dk; jr i f o i fc e f; p ma w Gjz p fy gw , f/ ' Dw p fc gr Sma w mh reversing u dkt o Hk; c sjy D; x & dk* se f^ A dki f; & y fp fa w G& JU
t v ky fv ky fy Hku dk a v hv mMu n fhy gr , f/ a v hv mMu n fhr Smu a w mh Flashy x & dk* se fu dky g/ v dkt y fw Jh a q mhz f0 Jv fa w G
u a w mh-
( u ) Fast Scanner 3?
( c ) Olly Debugger 1.10?
( * ) UnFSG 2.0?
( C ) RegCleaner 4.3 by Jouni Vuorio?
( i ) Proactive System Password Recovery 4.1.3.455E Si fht x u f/
u Re fa w mfw dkU ' Dy & dk* & r fu dk r a v hv mc i f t x l; o w dx m; & r Smu antivirus a q mhz f0 Ja w Gu dk c P y dw fx m;
a y ; z dkU jz p fy gw , f/ b mv dkUv Jq dka w mh y Hk( 1 ) r Sm jy x m; w Jht w dki f; antivirus y & dk* & r fa w Gu Flashy.exe z dki fu dk
x & dk* se ft a e e JU o dx m; jy D; z dki fu dkz su fy p fv dkYy g/
y Hk( 1 )
a u mi f; y gjy D/ u Re fa w mfw dkUt a e e JU Flashy u dk b , fv dka & ; o m; x m; o v Jq dkw m Olly r Sm p p fa q ; Mu n fh
Mu & a t mi f/
y Hk( 2 )
u Re fa w mfw dkUt a e e JU Flashy u dk p p fv dku fw Jht c gr Sm y Hk( 2 ) r Smt w dki f; message w p fc ku dk jr i f& r Smy g/
b mv dkUv Jq dka w mh entry point u 00400000 jz p fa e v dkUy g/ y Hk( 3 ) / ( r Sw fc su f/ PE header w Gi f entry point
o n f t jr Jw r f; 00401000 r So m p w i fa v h& Sdy go n f/ x dkt a Mu mi f; u dk PE Header t c e f; w Gi f t a o ; p dw f
a q G; a E G; x m; y go n f/ )
y Hk( 3 )
y Hk( 4 ) w Gi f jy x m; o n fht w dki f; context menu r S Sear ch for | All r efer enced text str ings u dk
t o Hk; jy Kjy D; stringr sm; u dk& Sma o mfv n f; y Hk( 4 ) w Gi f jy x m; o n fht w dki f; r n fo n fhstringu dkr Qr a w GY& y g/
tcef ;(29) - Flashy x&dk*sefESifh Windows Registry
- 419 -
y Hk( 4 )
' gb ma Mu mi fhv Jq dkw m t a o t c sm Mu n fhv dku fMu & a t mi f/ y Hk( 2 ) u message r Sm self extracting
z dki fjz p fE dki fy gw , fv dkU Olly u t Mu Hjy Kx m; w mu dk a w GU& r Smy g/ ' gq dk ' Dz dki fu dk compress v ky fx m; w m a o c sm
y gjy D/
y dkjy D; a o c sma t mi f b , fa q mhz f0 Jv fe JU compress (protect) v ky fx m; w , fq dkw m Mu n fhv dku fMu & a t mi f/
y Hk( 5 ) /
y Hk( 5 )
y Hk( 5 ) t w dki f; Fast Scanner 3 e JU Mu n fhv dku fw Jht c gr Sm Flashy.exe z dki fu dk FSG 2.0 t o Hk; jy Kjy D;
compressv ky fx m; w m a w GU& y gr , f/ ' ga Mu mi fhr dkU u Re fa w mfw dkUt a e e JYy & dk* & r fu k' fu kdp p fa q ; v dkU r & w my g/
y Hk( 6 )
Fast Scanner 3 u a w mh FSG u dk unpack v ky fz dkU VMUnpacker ( o dkU) Quick Unpack u dk
o Hk; c dki f; y gw , f/ ' ga y r , fhu Re fa w mfw dkUt a e e JU UnFSG 2.0 u dko m t o Hk; jy Ky gr , f/
y Hk( 7 )
y Hk( 7 ) t w dki f; unpackv ky fjy D; & i f u Re fa w mfw dkUt a e e JU & & Sdv mw Jhz dki fu dkFlashy-Unpacked.exet r n fe JU
o dr f; q n f; jy D; Fast Scannere JYjy e fp p fa q ; Mu n fhy gr , f/ y Hk( 8 ) /
tcef ;(29) - Flashy x&dk*sefESifh Windows Registry
- 420 -
y Hk( 8 )
w u , fa w mh Flashyy & dk* & r fu dk Microsoft Visual C++ 6.0b mo mp u m; e JU a & ; x m; w my g/ u k' fu dk
a jc & mr c HE dki fa t mi fv dkU FSG2.0u dkt o Hk; jy Kjy D; u mu G, fx m; w my g/
a u mi f; y gjy D/ ' Dw p fc g Flashy-Unpacked.exe u dk Olly e JY z Gi fhjy D; text string a w Gu dk& Smjy D; a v hv m
Mu n fhMu y gr , f/ y Hk( 9 ) /
y Hk( 9 )
' Do i fc e f; p mr Sm y & dk* & r fw p fc kv Hk; & JU t v ky fv ky fy Hku dk a q G; a E G; r Sm r [ kw fb J Windows registry u dk
t o Hk; jy Kjy D; y & dk* & r f b , fv dkt v ky fv ky fo Gm; o v J q dkw mu dko m a q G; a E G; r Sm jz p fy gw , f/ y Hk( 8 ) r Sm jr i f& w Jht w dki f;
p p c si f; "user administrator hacked" q dkw Jh shell script u dk t v ky fv ky fr Sm jz p fy gw , f/ t u sdK; q u fu a u m
b mjz p fE dki fy go v J/ t c sdKU u Ge fy sLw ma w Gr Sm o Hk; p GJo lt c sdKU[ m logon user name u dk Administrator account
w p fc kw n f; t a e e JU o Hk; p GJMu y gw , f/ t c sdKUu a w mh admin privilege e JU t jc m; account x y fv ky fjy D;
o Hk; p GJMu y gw , f/ Administrator account t jy i f t jc m; account u dk jy Kv ky fjy D; o Hk; p GJw Jho la w Gu a w mh
Safemode t a e e JY 0 i fw Jht c sde fu v GJjy D; jy e m o dy fr & Sdy gb l; / b mv dkUv Jq dka w mh Flashy u Administrator
account& JYlogonpasswordu dk a jy mi f; v dku fv dkUy g/ t & i fu b m passwordy Ja y ; x m; a y ; x m; passwordu dk
hacked"v dkU a jy mi f; v Jv dku fy gw , f/ y Hk( 1 0 ) /
y Hk( 1 0 )
tcef ;(29) - Flashy x&dk*sefESifh Windows Registry
- 421 -
Flashy u y Hk( 9 ) r Sm jy x m; w Jht w dki f; Administrator account & JY logon password u dk " hacked"
v dkU a jy mi f; x m; y gw , f/ ' gu dk Proactive System Password Recovery 4.1.3.455 u dk t o Hk; jy Kjy D;
Mu n fh& IE dki fy gw , f/ ' ga Mu mi fhr dkU r Sw fx m; & r Smu Falshy x & dk* se f x dx m; w Jh Windows u dk logon v ky fw Jht c g
Administrator account t a e e JU 0 i f& r , fq dk& i f password a e & mr Sm "hacked" q dkw Jhp mv Hk; u dk & dku fx n fh
& y gr , f/
jy D; & i f Falshy u GetDr iveType function u dk t o Hk; jy Kjy D; D? E? F? G? H? I e JU J drive w dkUu dk
p p fa q ; jy D; t J' Ddrive a w G[ m Falsh drive a w G[ kw f^ r [ kw f p p fy gw , f/ Falsh drive o m jz p fc Jhr , fq dk& i f
CopyFileA functionu dkt o Hk; jy Kjy D; foldert r n fe JUw lw Jhexez dki fa w Gu dkz e fw D; v dku fy gw , f/
y Hk( 1 1 )
y Hk( 1 1 ) r Sm jy x m; w Jht w dki f; Falshy u RegOpenKeyExA function u dkt o Hk; jy Kjy D; HKEY_
CURRENT_USER u "Software\Microsoft\Windows\Current\Explorer" u dk z Gi fhy gw , f/ jy D; & i f
v u f& Sdlogonv ky fx m; w Jho Hk; p GJo lt r n fu dkp Hkp r f; y gw , f/ y Hk( 1 2 ) /
y Hk( 1 2 )
Falshy u b ma Mu mi fh Logon User Name u dk p Hkp r f; o v Jq dkw m u Re fa w mfw dkU Mu n fhMu y gr , f/
y Hk( 1 3 ) /
y Hk( 1 3 )
w u , fa w mh Falshy [ m "%"%s\Documents and Settings\%s\Start Menu\Programs\
Startup\systemID.pif" u ' kw d, %s a e & mr Sm Logon User Name u dk t p m; x dk; jy D; y Hk( 1 3 ) r Sm
jy x m; w Jht w dki f; systemID.pifu dko Gm; x m; c si fv dkU jz p fy gw , f/
jy D; & i f system32 folder x Ju dk Falshy.exe u dk u l; w i fv dku fjy D; z dki f& JU attribute u dk hidden t a e e JU
o w fr Sw fv dku fy gw , f/ jy D; & i f Registry x Ju HKEY_LM & JU Run x Jr Sm a e mu fw p fMu dr f Windows
jy e fw u fv m& i f Falshy u dk t v ky fv ky fz dkU0 i fa & ; v dku fy gw , f/ ' gu dk Registry editor r Sm Mu n fh& IE dki fy gw , f/
y Hk( 1 4 ) /
y Hk( 1 4 )
' Dha e mu f Flashy [ m HKEY_CU & JU "Software\Microsoft\Windows\CurrentVersion\
Policies\System"" x Jr Sm DisableRegistryTools e JU DisableTaskMgr w dkUu dk y Hk( 1 5 ) r Sm jy x m; w Jht w dki f;
0 i fa & ; y gw , f/
tcef ;(29) - Flashy x&dk*sefESifh Windows Registry
- 422 -
y Hk( 1 5 )
' Dv dk0 i fa & ; w Jht u sdK; q u fu a w mhy Hk( 1 6 ) e JU y Hk( 1 7 ) r Sm jy x m; w Jht w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 1 6 )
y Hk( 1 7 )
y Hk( 1 6 ) r Sm jy x m; w Jht w dki f; Registry editor u dk o Hk; v dkUr & a t mi f disable v ky fx m; y gw , f/
y Hk( 1 7 ) u a w mh Task Manager u dk disable v ky fx m; w my g/ ' gu b mv dkUv Jq dka w mh Flashy y & dk* & r fu dk
y dw fv dkUr & a t mi f? z su fv dkUr & a t mi f v ky fx m; w my g/ ' gw i fr u a o ; y gb l; / Flashy [ m HKEY_CU & JU
"Software\Microsoft\Windows\CurrentVersion\Policies\Explorer" x Jr Sm NoFolderOptions e JU
"Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced" x Jr Sm HideFileExt w dkUu dk
y Hk( 1 5 ) r Sm jy x m; w Jht w dki f; 0 i fa & ; y gw , f/ b mv dkU HideFileExtu dk o w fr Sw fo v Jq dka w mhFlashy[ m folder
a w Gu dk r jr i fE dki fa t mi f z Gu fv dku fjy D; t J' D folder t r n fa w Gu dk t o Hk; jy Kjy D; application(.exe)) z dki fa w Gu dk
z e fw D; v dku fy gw , f/ ' ga Mu mi fhr dkU z dki fa w G& JUa e mu fr Sm z dki f extension a w G y gv mc Jhr , fq dk& i f o Hk; p GJo la w G[ m
z dki fr Se f; o da e w ma Mu mi fh click & Jr Sm r [ kw fw Jht w Gu f z dki f extension u dk a z smu f& jc i f; jz p fy gw , f/ NoFolder
Optionsu dko Hk; p GJjc i f; & JU t u sdK; q u fu a w mhy Hk( 1 8 ) r Sm jr i f& w Jht w dki f; jz p fy gw , f/
y Hk( 1 8 )
y Hk( 1 8 ) u dk o w dx m; jy D; Mu n fhr , fq dk& i f c gw dki f; jr i fa e Mu Folder Options q dkw Jh submenu a v ;
a y smu fa e w m o w dx m; r dr Smy g/ Registry editor u dk u Rr f; u si fp Gm t o Hk; r jy KE dki fa o ; w Jho la w Gt w Gu f w p fp Hk
w p fa , mu fu z Gu fx m; w Jhz dki fu dk Mu n fhc si fw , fq dk& i f Folder Options u dk t o Hk; jy Kjy D; Mu n fh& I& r Sm jz p fy gw , f/
y Hk( 1 9 ) /
tcef ;(29) - Flashy x&dk*sefESifh Windows Registry
- 423 -
y Hk( 1 9 )
u Re fa w mfw dkU Flashy & JUt v ky fv ky fy Hku dk a v hv mc Jhjy D; y gjy D/ ' Da w mh ' Dy & dk* & r fu dk b , fv dkE Sdr fE Si f; r v Jq dkw m
Mu n fhMu & a t mi f/ y x r q Hk; Task Manager r Sm t v ky fv ky fa e w Jh Flashy y & dk* & r fu dk y dw f& y gr , f/ ' ga y r , fh
Task Manager u dk u Re fa w mfw dkUu a c : , lo Hk; v dkUr & w Jht w Gu f u Re fa w mfw dkUt a e e JU command prompt u dk
t o Hk; jy KMu y gr , f/ Command prompt r Sm tasklist v dkU & dku fx n fhv dku fw Jht c g Task Manager r Sm
v u f& Sdt v ky fv ky fa e w Jh y & dk* & r fa w Gu dk jr i f& r Sm jz p fy gw , f/ u Re fa w mfw dkU& JU Flashy [ m Process ID(PID)
1224e JU t v ky fv ky fa e w m jr i f& r Smy g/ y Hk( 2 0 ) /
y Hk( 2 0 )
Flashyu dky dw fz dkU u Re fa w mfw dkU taskkillcommandu dkt o Hk; jy KMu y gr , f/ y Hk( 2 1 ) /
y Hk( 2 1 )
' Dha e mu f u Re fa w mfw dkUt a e e JU Registryeditoru dk t o Hk; jy Kv dkU& a t mi f v ky f& y gr , f/ Startu Runr Sm
REG ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /V DisableRegistryTools
/T REG_SZ /D "0" /F v dkU & dku fx n fhv dku fy g/ ' gq dk Registry editor u dk u Re fa w mfw dkU t o Hk; jy Kv dkU& y gjy D/
y Hk( 2 2 ) /
y Hk( 2 2 )
jy D; & i f system32 folderq Do Gm; jy D; Flashyu dkz su fy gr , f/ y Hk( 2 3 ) /
y Hk( 2 3 )
tcef ;(29) - Flashy x&dk*sefESifh Windows Registry
- 424 -
' Da e mu f RegCleaner 4.3u dko Hk; jy D; registryx Jr Sm a & ; x m; w mu dkz su fy gr , f/ y Hk( 2 3 ) /
y Hk( 2 4 )
Start menu u Run r Sm gpedit.msc v dkU & dku fx n fhjy D; Group Policy u dk a c : , ly gr , f/ jy D; & i f
y Hk( 2 5 ) r Sm jy x m; w Jht w dki f; FolderOptionsu dkjy e fjr i f& a t mi f jy i fy gr , f/
y Hk( 2 5 )
' ght jy i f HKEY_CU"Software\Microsoft\Windows\CurrentVersion\Policies\System"x Jr Sm
DisableTaskMgr & JUw e fz dk; u dk o kn v dkU jy i fv dku fy gr , f/ ' gr So m Task Manager u dk a c : , lt o Hk; jy Kv dkU & y g
r , f/ a e mu fq Hk; u a w mhy Hk( 2 6 ) r Sm jy x m; w JhsystemIDu dkz su fy p fz dkUy g/
y Hk( 2 6 )
t c e f; ( 3 0 ) - Olly Debug Script
- 425 -
tcef;(30) - Olly Debug Scr ipt
' Dt c e f; r Sm a v hv mMu r Smu a w mh Olly debug script t a Mu mi f; y g/ w c gw & Hr Sm t c sdKU unpacker
a w G[ m script a w Ge JUv mw mu w a Mu mi f; ? r dr du dk, fw dki f script a w Gu dk a & ; o m; E dki fa p z dkUt w Gu fw a Mu mi f; Olly
script plugin u dk & Si f; jy & jc i f; jz p fy gw , f/ Olly script t w Gu f v dkt y fw Jh DLL z dki fu a w mh ODbgScript
1.78.3.dll ( o dkU) OllyScript 0.92.dll y g/ ' ght jy i f Arjun Sapkota a & ; o m; w Jh Olly Script Editor
& Sd& i fa w mho i fht w Gu f script a & ; o m; w m t a x mu ft u ljy Ky gv dr fhr , f/
( 1 ) UPX jz i fhpack v ky fx m; a o m z dki ft w Gu f OEP u dk& Smjc i f;
notepad.exe u dk UPX e JU pack v ky fy gr , f/ CFF explorer r Sm UPX plugin w c gw n f; y gv m
jy D; o m; jz p fy gw , f/ y Hk( 1 ) u pack button u dkE Sdy fjy D; pack v ky fv dku fy g/
y Hk( 1 )
Notepad x Jr Sm y Hk( 2 ) r Sm jr i f& w Jh script a w Gu dka & ; o m; jy D; UPXOepFinder.osc t r n fe JU o dr f; q n f;
v dku fy g/
// UPX OEP Finder
// Copyright Myo Myint Htike, July 16 2010
findop eip, #61#
bphws $RESULT, "x"
run
bphwc $RESULT
findop eip, #E9#
bphws $RESULT, "x"
run
bphwc $RESULT
sto
ret
y Hk( 2 )
y Hk( 2 ) u script u dk& Si f; & r , fq dk& i fa w mh-
( 1 ) findop eip, #61# = v u f& Sdaddress (EIP) u p jy D; a w mh61 (POPAD) q dkw Jhopcode w e fz dk; u dk & Sma z Gy g
w , f/ w u , fv dkU & Smr a w GUc Jhb l; q dk& i f $RESULT w e fz dk; [ m o kn jz p fy gr , f/ w u , fv dkU POPAD
instruction u dka w GUc Jh& i f ' Dinstruction & Sd& m virtual address u dk$RESULT w e fz dk; t a e e JU r Sw fy gw , f/
( 2 ) bphws $RESULT, "x" = bphws u a w mh"Set hardware breakpoint" u dkq dkv dky gw , f/ "x" u a w mh
' D hardware breakpoint u dk execute v ky fc sde fr Smy J o Hk; r , fv dkU a Mu n mw my g/ w u , fv dkU u k' fu dkz w fw Jh
t c sde fr Sm breakpoint o w fr Sw fv dk& i f "r"? u k' fu dk jy i fc sde fr Sm breakpoint o w fr Sw fv dk& i f "w" u dk t o Hk; jy KE dki f
y gw , f/ e r le mt a e e JU jy & & i f - bphws 401000, "x"/
( 3 ) run = o lu a w mhOlly & JU run (F9) e JU w ly gw , f/ u Re fa w mfw dkU o w fr Sw fv dku fw Jhhardware breakpoint
& Sd& mx drun r Smjz p fy gw , f/
( 4 ) bphwc $RESULT = u Re fa w mfw dkU o w fr Sw fx m; w Jhbreakpoint u dkjy e fjz Kw fy gw , f/
( 5 ) findop eip, #E9# = v u f& Sdaddress (EIP) u p jy D; a w mhE9 (JMP xxxxxxxx) q dkw Jhopcode w e fz dk; u dk
& Sma z Gy gw , f/
( 6 ) bphws $RESULT, "x" = JMP insturction & Sd& m virtual address r Sm breakpoint o w fr Sw fy gw , f/
t c e f; ( 3 0 ) - Olly Debug Script
- 426 -
( 7 ) ' Dha e mu f breakpoint & Sd& mx drun y gr , f/
( 8 ) JMP instruction r Sm o w fr Sw fc Jhw Jhbreakpoint u dkjy e fjz Kw fy gw , f/
( 9 ) sto = Olly u Step over (F8) e JU w ly gw , f/ v u f& Sdu k' fu dk execute v ky fjy D; a e mu fw p fa Mu mi f; q D
o Gm; y gw , f/ Step into (F7) jz p fw Jhsti u dkv Jt o Hk; jy KE dki fy gw , f/
( 1 0 ) ret = Script v ky fa q mi fc su f jy D; q Hk; y gw , f/
' Dw c gr Sma w mhu Re fa w mfw dkU pack v ky fc Jhw Jhnotepad.exe z dki fu dkOlly r Sm z Gi fhy gr , f/ y Hk( 3 ) /
y Hk( 3 )
Plugins menu OdbgScript Script(S) u Load... u dka & G; y g/
y Hk( 4 )
y Hk( 4 ) & JU Load u a e UPXOepFinder.osc u dka & G; y g/ y Hk( 5 ) t w dki f; jr i f& y gr , f/
y Hk( 5 )
y Hk( 5 ) t w dki f; jr i f& w Jht c gr Sma w mh u Re fa w mfw dkU& Sma e w Jh OEP u dk & Sma w GUjy D jz p fy gw , f/ ' Dt c gr Sm
dump v ky fjy D; z dki fu dk o dr f; q n f; y g/ jy D; & i f IAT u dkjy i fq i fy g/ ( ' Dt w Gu f ]t c e f; ( 1 3 ) Packer (Protector)
r sm; } t c e f; u dkjy e fMu n fhy g/ )
( 2 ) SLVc0dePr otector jz i fhpack v ky fx m; a o mz dki fu dk unpack jy Kv ky fjc i f;
' Dw p fc gr Sma w mh SLVc0deProtector e JU pack v ky fx m; w Jh SLVc0deProtector (SCP-0.61.exe)
a q mhz f0 Jv fz dki fu dk unpack v ky fMu n fhy gr , f/ SCP-0.61.exe z dki f[ m SLVc0deProtector 0.61 e JU protect
v ky fx m; w Jhz dki f jz p fy gw , f/ ' Dz dki fu dk unpack v ky fz dkU Mu dK; p m; Mu n fhy gr , f/ SCP-0.61.exe u dk Olly r Sm
z Gi fhMu n fhy g/ y Hk( 6 ) /
y Hk( 6 )
t c e f; ( 3 0 ) - Olly Debug Script
- 427 -
y Hk( 6 ) t w dki f; jr i f& w Jht c g a t mu fy g script u dkrun Mu n fhy gr , f/
/*
SLVc0deProtector 0.61 OEP Finder
Made by: GaBoR RES
*/
gpa "OutputDebugStringA", "kernel32.dll"
bphws $RESULT, "x"
run
bphwc $RESULT
rtu
sto
rtu
find eip, #4F6C6C79#
find $RESULT, #4F6C6C79#
fill $RESULT, 4, 47
findop eip, #F3A4#
bphws $RESULT, "x"
run
bphwc $RESULT
find eip, #5858FFE0#
bphws $RESULT, "x"
run
bphwc $RESULT
sto
sto
sto
cmt eip, "OEP found by GaBoR RES"
msg "Dump the process with Imprec, fix the IAT & fix header!"
ret
y Hk( 7 )
' Dw p fc gr Sma w mh Plugins menu OdbgScript Script(S) u a e Load u dk r a & G; a w mhy gb l; /
Disassemble window r Sm right-click E Sdy fjy D; y Hk( 8 ) u Script Window (W) u dka & G; y gr , f/
y Hk( 8 )
' Dha e mu fr Sma w mhLoad Script u Open u dka & G; y gr , f/ y Hk( 9 ) /
y Hk( 9 )
jy D; & i f y Hk( 7 ) u script u dkz Gi fhc sde fr Sma w mhy Hk( 1 0 ) t w dki f; jr i f& y gv dr fhr , f/
t c e f; ( 3 0 ) - Olly Debug Script
- 428 -
y Hk( 1 0 )
y Hk( 1 0 ) u script a w Gu dk w p fq i fhc si f; a v hv mMu n fhy gr , f/ y Hk( 1 0 ) r Sm right-click E Sdy fjy D; Step (tab)
u dka & G; c s, fy g/
y Hk( 1 1 )
y Hk( 1 0 ) u p ma Mu mi f; - 1 u dkt v ky fv ky fjy D; c sde fr Sm y Hk( 1 1 ) t w dki f; jr i f& y gw , f/
( 1 ) gpa "OutputDebugStringA", "kernel32.dll" = o w fr Sw fx m; w Jh library z dki fx Ju o w fr Sw fx m; w Jh
procedure & JU address u dk& , ly gw , f/ ' Da e & mr Sma w mh kernel32.dll z dki fx Ju OutputDebugStringA
function & JU address jz p fw Jh7C85AD4C u dk& , ly gw , f/
( 2 ) bphws $RESULT,"x" = 7C85AD4C r Sm hardware breakpoint o w fr Sw fy gw , f/
( 3 ) run = 7C85AD4C x drun (F9) y gw , f/
( 4 ) bphwc $RESULT = 7C85AD4C r Sm o w fr Sw fc Jhw Jhbreakpoint u dkjy e fjz Kw fy gw , f/
( 5 ) rtu = Olly r Sma w mh "Run to user code" (Alt + F9) e JUw ly gw , f/ y Hk( 1 2 ) t w dki f; VA 00157703
q Da & mu fv my gw , f/
y Hk( 1 2 )
( 6 ) sto = Step over (F8) u dka & G; v dku fc sde fr Sm JMP 0015770B q Da & mu fv my gw , f/
( 7 ) rtu = "Run to user code" (Alt + F9) u dkx y fv ky fc sde fr Sma w mhy Hk( 1 3 ) t w dki f; jr i f& y gw , f/
y Hk( 1 3 )
( 8 ) find eip,#4F6C6C79# = v u f& Sd EIP (0015570B) u a e 4F6C6C79 u dk& Smy gw , f/ 00157D87 r Sm
4F6C6C79 u dka w GUy gw , f/ ' ga Mu mi fh$RESULT w e fz dk; [ m 00157D87 jz p fy gw , f/ y Hk( 1 4 ) / 4F6C6C79
q dkw m w u , fa w mhOlly q dkw Jhstring jz p fy gw , f/
t c e f; ( 3 0 ) - Olly Debug Script
- 429 -
y Hk( 1 4 )
( 9 ) find $RESULT, #4F6C6C79# = $RESULT w e fz dk; jz p fw Jh 00157D87 u a e 4F6C6C79 u dk
x y f& Smy gw , f/ b ma Mu mi fhv Jq dka w mhy x r w p fc k[ m Ollydbg.exe jz p fv dkUy g/
( 1 0 ) fill $RESULT, 4, 47 = 00157D87 r Sma w GUc Jhw JhOlly q dkw Jhp mv Hk; a w Gu dk GGGG e JU t p m; x dk; y gw , f/
w u , fa w mh' g[ m debugger u dkr p Hkp r f; a p E dki fz dkU jz p fy gw , f/
( 1 1 ) findop eip, #F3A4# = v u f& Sd EIP (00157D87) u a e F3A4 (REP MOVS BYTE PTR
ES:[EDI], BYTE PTR DS:[ESI]) opcode u dk& Sma z Gy gw , f/ 00157845 r Sm a w GUy gw , f/
( 1 2 ) bphws $RESULT, "x" = 00157845 r Sm hardware breakpoint o w fr Sw fy gw , f/ y Hk( 1 5 ) /
y Hk( 1 5 )
' Dbreakpoint u a w mhprotector u dku dk, fw dki f decompress jy e fv ky fa p r , fhbreakpoint jz p fy gw , f/
( 1 3 ) run = 00157845 x drun (F9) y gw , f/
( 1 4 ) bphwc $RESULT = 00157845 r Sm o w fr Sw fc Jhw Jhbreakpoint u dkjy e fjz Kw fy gw , f/
( 1 5 ) find eip, #5858FFE0# = v u f& Sd EIP (00157845) u a e 5858FFE0 (POP EAX, POP EAX,
JMP EAX) p w Jh hex code a w Gu dk & Sma z Gy gw , f/ o lw dkUu OEP & Sd& mq D jump v ky fr Sm jz p fy gw , f/
0015798C r Sm 5858FFE0 u dka w GUy gw , f/
( 1 6 ) bphws $RESULT, "x" = 0015798C r Sm hardware breakpoint o w fr Sw fy gw , f/
( 1 7 ) run = 0015798C x drun (F9) y gw , f/ ' Dt c g y Hk( 1 6 ) t w dki f; jr i f& y gw , f/
y Hk( 1 6 )
( 1 8 ) bphwc $RESULT = 00157845 r Sm o w fr Sw fc Jhw Jhbreakpoint u dkjy e fjz Kw fy gw , f/
( 1 9 ^ 2 0 ^ 2 1 ) sto = y Hk( 1 6 ) u u k' fu dk Step over (F8) 3 c g v ky fa q mi fjy D; o Gm; w Jht c g y Hk( 1 7 ) t w dki f; 004042B0
q Da & mu fv mw m a w GU& r Smy g/
y Hk( 1 7 )
t c e f; ( 3 0 ) - Olly Debug Script
- 430 -
( 2 2 ) cmt eip, "OEP found by GaBoR RES" = v u f& SdEIP (004042B0) & JU comment a e & mr Sm "OEP
found by GaBoR RES" v dkU jr i f& y gr , f/ y Hk( 1 7 ) /
( 2 3 ) msg "Dump the process with Imprec, fix the IAT & fix header!" = Dump v ky fv dkU
& jy Djz p fw Jht a Mu mi f; t o da y ; w my g/ y Hk( 1 8 ) /
y Hk( 1 8 )
( 2 4 ) ret = Script v ky fa q mi fc su f jy D; q Hk; y gw , f/
Script v ky fa q mi fc su f jy D; q Hk; c sde fr Sma w mhy Hk( 1 9 ) t w dki f; v ky fMu y gr , f/
y Hk( 1 9 )
y Hk( 1 9 ) u a e Dump button u dka & G; jy D; E Sp fo u f& mt r n fe JU z dki fu dk o dr f; q n f; v dku fy g/ w u , fv dkU
z dki ft & G, ft p m; u dka o ; i , fa p c si f& i f ::ICU:: section u dkz su fy p fy g/
( 3 ) Yoda' s Pr otector 1.03.3 jz i fhpack v ky fx m; a o mz dki fu dk unpack jy Kv ky fjc i f;
' Dw p fc gr Sma w mh Yoda's Protector 1.03.3 e JU protect v ky fx m; w Jh calc.exe (calculator) z dki fu dk
unpack v ky fMu n fhy gr , f/ calc.exe z dki fu dk Windows & JU System32 folder a t mu fr Sm& Smjy D; Yoda Protector
e JU protector v ky fv dku fy g/ w u , fa w mh Yoda's Protector [ m Danilo Bzdok & JU Yoda's Cryptor u dk
Ashkbiz Danehkar u jy e fjy i fq i fx m; w Jh protector w p fc ko mjz p fjy D; version 1.03.3 r Sm q u fr a & ; a w mhb J
& y fc Jhy gw , f/ Yoda's Cryptor r Smy gw Jhv Sn hfp m; r Ia w Gu a w mh
( 1 ) PE header u dkz su fjc i f; ?
( 2 ) CRC u dkp p fa q ; jc i f; ( u k' fE Si fhz dki f) ?
( 3 ) IsDebuggerPresent p p fa q ; r I?
( 4 ) API r sm; u dkredirect v ky fjc i f; E Si fhimport t c su ft v u fr sm; u dk z su fq D; jc i f; /
Yoda's Protector r Smy gv mw Jh v Sn fhp m; r It o p fa w Gu a w mh GetCurrentProcessId()? CreateTool
help32Snapshot() w dkUu dkt o Hk; jy Kjy D; PID u dkw dku fq dki fp p fa q ; u m PID c si f; r w ln Dc Jh& i f Olly u dky dw fa p jc i f; e JU
BlockInput() API u dkt o Hk; jy Kjy D; mouse? keyboard w dkU& JU v ky fa q mi fc su fa w Gu dk & y fw e fUa p jc i f; w dkU jz p fy g
w , f/
calc.exe u dky Hk( 2 0 ) r Sm jr i f& w Jht w dki f; a & G; c s, fjy D; protect v ky fv dku fy g/
t c e f; ( 3 0 ) - Olly Debug Script
- 431 -
y Hk( 2 0 )
u Re fa w mfw dkU protect v ky fx m; w Jhcalc.exe z dki fu dkunpack jy e fv ky fz dkU script a & ; Mu n fhy gr , f/ y Hk( 2 1 ) /
#log // Copyright Myo Myint Htike, Aug 10 2010
var BaseOfCode
var SizeOfCode
var BlockI
var DLLName
var handle
gmi eip, CODEBASE
mov BaseOfCode, $RESULT
gmi eip, CODESIZE
mov SizeOfCode, $RESULT
gpa "LoadLibraryA", "kernel32.dll"
mov handle, $RESULT
mov DLLName, "USER32.DLL"
CheckDLL:
go handle
scmpi DLLName, [[esp+4]]
je DLLFound
jmp CheckDLL
DLLFound:
mov handle, [esp]
bphws handle, "x"
esto
bphwc handle
gpa "BlockInput", "user32.dll"
fill $RESULT, 0C, 90
add $RESULT, 0C
mov BlockI, $RESULT
gpa "GetCurrentProcessId", "kernel32.dll"
mov [$RESULT], 00000xxxB8 // mov eax, CurrentProcessID
/* xxx o n f Olly t v ky fv ky fa e a o m v u f& Sd PID e Hy gw fjz p fo n f/ x dkUa Mu mi fh task manager r SOlly \ PID u dk
z w fjy D; PID e Hy gw fa jy mi f; a y ; & e fv dko n f/ */
fill $RESULT+5, 4, 90
gpa "IsDebuggerPresent", "kernel32.dll"
mov [$RESULT], 000000B8
mov [$RESULT+4], 90909000
mov [$RESULT+8], C3
bphws BlockI, "x"
esto
esto
bphwc BlockI
bprm BaseOfCode, SizeOfCode
esto
bpmc
an eip
cmt eip, "This is OEP - Found by rhythm (Myanmar Cracking Team)"
msg "Dump and fix IAT now - Good day"
ret
y Hk( 2 1 )
t c e f; ( 3 0 ) - Olly Debug Script
- 432 -
y Hk( 2 1 ) u u k' fa w Gu dk& Si f; jy & r , fq dk& i fa w mh
( 1 ) var BaseOfCode - Code section \ address t p u dkvariable t jz p f a Mu n mo n f/
( 2 ) var SizeOfCode - Code section \ size u dkvariable t jz p f a Mu n mo n f/
( 3 ) var BlockI - BlockInput function \ return a e & mw Gi f breakpoint o w fr Sw fr n fhvariable jz p fo n f/
( 4 ) var DLLName - calc.exe u a c : , lo Hk; p GJa o m DLL t r n fr sm; u dkz w f& I& e fjz p fo n f/
( 5 ) var handle - DLL z dki f\ address t p jz p fo n f/
( 6 ) gmi eip, CODEBASE EIP a & mu f& Sda e a o m module E Si fhy w fo u fa o m t c su ft v u fr sm; u dk p Hkp r f;
o n f/ CODEBASE o n f code section \ address u dk q dkv dkjc i f; jz p fo n f/ y Hk( 2 2 ) / CODEBASE
w e fz dk; o n f 01001000 jz p fo n f/
y Hk( 2 2 )
( 7 ) mov BaseOfCode, $RESULT CODEBASE w e fz dk; jz p fa o m 01001000 u dk BaseOfCode x Jw Gi f
v mx m; o n f/
( 8 ) gmi eip, CODESIZE code section \ size u dk p Hkp r f; o n f/ y Hk( 2 2 ) / CODESIZE w e fz dk; o n f
00013000 jz p fo n f/
( 9 ) mov SizeOfCode, $RESULT CODESIZE w e fz dk; jz p fa o m 00013000 u dk SizeOfCode x Jw Gi f
v mx m; o n f/
( 1 0 ) gpa "LoadLibraryA", "kernel32.dll" kernel32.dll \ LoadLibraryA API & Sd& m address u dk
p Hkp r f; o n f/
( 1 1 ) mov handle, $RESULT LoadLibraryA API \ address jz p fa o m 7C801D7B u dk handle
x Jw Gi f o dr f; o n f/ API address r sm; o n f Windows OS E Si fhDLL version w dkUt a y : r lw n fjy D; u GJjy m; E dki fy g
o n f/ y Hk( 2 3 ) /
y Hk( 2 3 )
( 1 2 ) mov DLLName, "USER32.DLL" user32.dll u dk& Sm& e ft w Gu f DLLName w Gi f v mo dr f; y go n f/
t b , fa Mu mi fhq dka o mf y x r q Hk; t Mu dr ft jz p f calc.exe u dk Olly w Gi fz Gi fha o mt c g y Hk( 2 4 ) w Gi f jr i f& o n fht w dki f;
user32.dll u dkr Sw fOmP fa y : o dkU u l; w i fjc i f; r & Sda o ; a o ma Mu mi fhjz p fo n f/
y Hk( 2 4 )
( 1 3 ) go handle handle w e fz dk; 7C801D7B q Do dkUo Gm; o n f/ x dkUa Mu mi fhv u f& SdEIP o n f 7C801D7B
jz p fv mo n f/ y Hk( 2 5 ) r SESP w e fz dk; u dkright-click E Sdy fjy D; Follow in Stack u dka & G; y g/
t c e f; ( 3 0 ) - Olly Debug Script
- 433 -
y Hk( 2 5 )
( 1 4 ) scmpi DLLName, [[esp+4]] ESP+4 (0006EC04) w Gi f& Sda o m DLL string E Si fh USER32.DLL
w dkUn D^ r n Dp p fo n f/ p mv Hk; t Mu D; ^ t a o ; u dkv sp fv sL& Io n f/
y Hk( 2 6 )
( 1 5 ) je DLLFound [[ESP+4] o n f USER32.DLL jz p fv Qi f DLLFound q Do dkU a & mu fo Gm; r n f/
( 1 6 ) jmp CheckDLL [[ESP+4] o n f USER32.DLL r jz p fv Qi f CheckDLL q Do dkU jy e fa & mu fo Gm; jy D;
user32.dll z dki fu dkq u f& Smr n f/
( 1 7 ) mov handle, [esp] "user32.dll" u dka w GUc sde fw Gi f user32.dll u dk v u f& Sdt v ky fv ky fa e o n fh process
\ a e & mv Gw fw Gi f u l; w i fa e & mc sx m; a y ; o n f/ 10294CA o n f i f; z dki f\ handle jz p fo n f/
y Hk( 2 7 )
( 1 8 ) bphws handle, "x" 10294CE w Gi f hardware breakpoint (execution) o w fr Sw fo n f/
( 1 9 ) esto Shift+F9 u dk E Sdy fo n f/
( 2 0 ) bphwc handle Hardware breakpoint u dkjy e fjz Kw fo n f/
( 2 1 ) gpa "BlockInput", "user32.dll" user32.dll r S BlockInput API & Sd& m address u dk z w fo n f/
7E46CA7E jz p fo n f/ y Hk( 2 8 ) /
y Hk( 2 8 )
( 2 2 ) fill $RESULT, 0C, 90 y Hk( 2 8 ) \ 7E46CA7E r Sp jy D; NOP (90) 1 2 c kjz i fht p m; x dk; o n f/ NOP jz i fh
t p m; x dk; & jc i f; r Sm BlockInput API o n f keyboard E Si fh mouse w dkU\ event r sm; u dk v sp fv sL& Ia o ma Mu mi fh
jz p fo n f/
y Hk( 2 9 )
( 2 3 ) add $RESULT, 0C 7E46CA7E u dk0C
16
a y gi f; o n f/
( 2 4 ) mov BlockI, $RESULT a y gi f; v ' fjz p fa o m 7E46CA8A u dkBlockI w Gi f o dr f; o n f/
( 2 5 ) gpa "GetCurrentProcessId", "kernel32.dll" kernel32.dll r SGetCurrentProcessId API & Sd& m
address u dkz w fo n f/ 7C8099C0 jz p fo n f/ y Hk( 3 0 ) /
t c e f; ( 3 0 ) - Olly Debug Script
- 434 -
y Hk( 3 0 )
( 2 6 ) mov [$RESULT], 00000xxxB8 Task manager w Gi f a w GY& a o m Olly \ PID u dku l; jy D; xxx
a e & mw Gi f t p m; x dk; y g/ y Hk( 3 1 ) /
y Hk( 3 1 )
OllyDbg.exe \ PID r Sm ACC
16
(2764
10
) jz p fa o ma Mu mi fh mov [$RESULT], 00000xxxB8
o n f mov [$RESULT], 00000ACCB8 jz p fv mo n f/ 7C8099C0 w Gi f MOV EAX, ACC jz i fht p m;
x dk; o n f/ y Hk( 3 2 ) /
( 2 7 ) fill $RESULT+5, 4, 90 7C8099C5 w Gi f NOP 4 c kjz i fh t p m; x kd; o n f/ y Hk( 3 2 ) / Yoda protector
o n f OllyDbg.exe \ PID u dk GetProcessId API jz i fhp p fjy D; OllyDbg.exe \ child process jz p fa o m
calc.exe \ PID u dk CreateToolhelp32Snapshot API jz i fh p p fa q ; o n f/ CreateToolhelp32Snapshot
o n f PID u dk p p fa q ; a o mt c g GetProcessId u dk jy e fa c : o Hk; o jz i fh PID u dk ACC [ k t a o o w fr Sw fx m;
jc i f; jz p fo n f/ PID c si f; r w lv Qi f y & dk* & r fv ky fa q mi fc su f jy D; p D; o Gm; y gv dr fhr n f/
y Hk( 3 2 )
( 2 8 ) gpa "IsDebuggerPresent", "kernel32.dll" kernel32.dll r S IsDebuggerPresent API & Sd& m
address u dkz w fo n f/ 7C813133 jz p fo n f/ y Hk( 3 3 ) /
y Hk( 3 3 )
( 2 9 ) mov [$RESULT], 000000B8 7C813133 w Gi f MOV EAX, 0 jz i fh t p m; x dk; o n f/ y Hk( 3 4 ) /
MOV EAX, 0 o n f debugger r & Sda Mu mi f; v Sn fhp m; jc i f; jz p fo n f/
( 3 0 ) mov [$RESULT+4], 90909000 7C813138 w Gi f NOP (90) 4 c kjz i fht p m; x dk; o n f/ y Hk( 3 4 ) /
( 3 1 ) mov [$RESULT+8], C3 7C81313B w Gi f RETN (C3) jz i fht p m; x dk; o n f/ y Hk( 3 4 ) /
y Hk( 3 4 )
( 3 2 ) bphws BlockI, "x" BlockI(7E46CA8A) w Gi f hardware breakpoint o w fr Sw fo n f/
t c e f; ( 3 0 ) - Olly Debug Script
- 435 -
( 3 3 ) esto Shift +F9 E Sdy fo n f/ ( run u dkr o Hk; b J esto u dk o Hk; & jc i f; r Sm exception r sm; & Sdc Jhv Qi f a u smfv Tm; E dki f
& e fjz p fo n f/ ODbgScript 1.74 a e mu fy dki f; w Gi fr l esto command u dk t o Hk; r jy Ka w mhb J erun [ kt p m; x dk; c Jh
o n f/ ) esto command u dk v ky fa q mi fjy D; o Gm; a o mt c g 7E46CA8A (HW BP) q Do dkU a & mu fv mr n f/
y Hk( 3 5 )
( 3 4 ) esto esto command u dkv ky fa q mi fjy D; o Gm; a o mt c g 7E46CA8A (HW BP) q Do dkU a & mu fv mr n f/
( 3 5 ) bphwc BlockI HW BP u dkjy e fjz Kw fo n f/
( 3 6 ) bprm BaseOfCode, SizeOfCode exe module \ code section w Gi f memory breakpoint
o w fr Sw fo n f/
( 3 7 ) esto esto command u dkv ky fa q mi fjy D; o Gm; a o mt c g 7E46CA8A (HW BP) q Do dkU a & mu fv mr n f/
( 3 8 ) bpmc memory breakpoint u dkjy e fjz Kw fo n f/
( 3 9 ) an eip Analyze v ky fo n f/ r v ky fv Qi fv n f; & y go n f/
( 4 0 ) cmt eip, "This is OEP - Found by rhythm (Myanmar Cracking Team)" & Si f; jy & e f v dkt y fr n f
r x i fy g/
( 4 1 ) msg "Dump and fix IAT now - Good day" & Si f; jy & e f v dkt y fr n f r x i fy g/
( 4 2 ) ret & Si f; jy & e f v dkt y fr n f r x i fy g/
y Hk( 3 6 )
y Hk( 3 6 ) t w dki f; jr i f& w Jht c gr Sma w mh dump v ky fv dkU& y gjy D/ Dump v ky fw Jht y dki f; u a w mh o djy D; o m; r dkU
r & Si f; jy a w mhy gb l; /
gpa "GetCurrentProcessId", "kernel32.dll"
mov [$RESULT], 00000xxxB8 // mov eax, CurrentProcessID
fill $RESULT+5, 4, 90
gpa "IsDebuggerPresent", "kernel32.dll"
mov [$RESULT], 000000B8
mov [$RESULT+4], 90909000
mov [$RESULT+8], C3
y Hk( 3 7 )
w u , fv dkU RAMODbg u dko m t o Hk; jy Kc Jhr , fq dk& i f y Hk( 3 7 ) u u k' fa w Gu dk c se fv Sy fx m; c Jhv dkU & y gw , f/
b ma Mu mi fhv Jq dka w mh RAMODbg u dko Hk; c sde fr Sm debugger u dk task manager r Sm process t jz p fr a w GU& w Jh
t w Gu fy g/ ' Dht jy i f anti-debugger a w Gu RAMODbg u dk & SmE dki fjc i f; r & Sdw Jht w Gu f IsDebuggerPresent
API u dk jy i fp & mr v dky gb l; / t Mu Ha y ; v dkw mu y & dk* & r fa w Gu dk debug v ky fa w mhr , fq dk& i f PhantOm plugin u dk
t o Hk; jy Kz dkUy g/ ODbgScript 1.78.3 command a w Gu a w mha t mu fy gt w dki f; jz p fy gw , f/
General Purpose
BACKUP CLOSE EVAL GSL REFRESH VAR
Assembly
ASM ASMTXT EXEC/ENDE? OPCODE? PREOP?
Automation
AN CMT DBH DBS KEY LBL LC LCLR OPENDUMP OPENTRACE TC
t c e f; ( 3 0 ) - Olly Debug Script
- 436 -
Breakpoints
BC BD BP BPCND BPD BPGOTO BPHWC BPHWS BPL BPLCND BPMC BPRM BPWM
BPX COB COE EOB EOE GBPM GBPR SBP RBP
Mathematic, Binary Operands
ADD AND DEC DIV INC MOV MUL NEG NOT OR REV ROL ROR SHL SHR SUB TEST
XOR XCHG
Jump, Call, Conditional Jumps
CALL CMP JA JAE JB JBE JE JG JGE JMP JNE JNZ JZ RET?
Log Commands
LOG LOGBUF WRT WRTA
Strings
ATOI BUF GLBL GSTR GSTRW ITOA LEN READSTR SCMP SCMPI STR
Stepping
AI AO ERUN ESTEP ESTI ESTO GO RTR RTU RUN STEP STI STO TI TICND TO TOCND
Information
GAPI GCI GCMT GMA GMEMI GMEXP GMI GMIMP GN GPA GPI GRO REF TICK
Memory
ALLOC DM DMA DPE FILL FREE GFO LM MEMCPY POP PUSH
Search
FIND FINDCALLS FINDCMD FINDOP FINDOPREV FINDMEM GREF REPL
User Interface
ASK MSG MSGYN PAUSE SETOPTION
Script Parameters
HISTORY UNICODE
ODbgScript r Sm t o Hk; jy KE dki fw Jhflag a w Gu a w mhy Hk( 3 8 ) t w dki f; jz p fy gw , f/
!CF Carry
!PF Parity
!AF Auxiliary carry
!ZF Zero flag
!SF Sign
!TF Trap
!IF Interrupt
!DF Direction
!OF Overflow
y Hk( 3 8 )
t o Hk; jy Ky Hku a w mhy Hk( 3 9 ) t w dki f; jz p fy gw , f/
var counter
star t:
cmp !ZF,0
je end
inc counter
sti
jmp start
end:
msg "Zeroflag is 0"
y Hk( 3 9 )
,., Wrapper ..`..._ .......- crack ` .
,,
...':-) Wr apper .e:._ =:e--e:. cr ack -e.-.
r Mu mr Dv mr n f/
,., Armadillo ... .` .
,.
tcef;(32) - Ar madillo tm;avhvmjcif;
Armadillo q dkw m u r ma y : r Sm t a u mi f; q Hk; protector q dkw m cracker w dki f; o dMu y gw , f/
v u f& Sdr Sm Armadillo & JU Level 10 key p e p f[ m cracker a w Gkeygen r a & ; E dki fMu a o ; b l; v dkY a jy mE dki fo v dk
]Armadillo developer r sm; E Si fh t i fw mA sL; } v ky fc Jh& mr Smv n f; Armadillo & JU t a u mi f; q Hk; protection
function a w Gjz p fw Jh Strategic Code Splicing e JY Nanomites p e p fw dkYu dk c sD; r Gr f; x m; w m a w GY& y gw , f/
' Da e Ya c w f * dr f; a w mfa w mfr sm; r sm; e JY a q mhz f0 Jv f a w mfa w mfr sm; r sm; u dkv n f; Armadillo e JY protect v ky fx m; w m
a w GY& y gw , f/ ' ga Mu mi fh Armadillo t a Mu mi f; t a o ; p dw f o dE dki fa t mi fv dkY Armadillo & JU protection
function r sm; u dk r dw fq u fo Gm; y gr , f/
' Do i fc e f; p mr Sm o Hk; x m; w Jh Armadillo version a w Gu a c w fa e mu fu sa u mi f; a e mu fu sa e r Sm
jz p fa y r , fh u Re fa w mfht a e e JY o lU& JU t o Hk; t E Ie f; ? t v ky fv ky fy Hka w Gu dk e m; v n fa p c si fw ma Mu mi fh ' Du sLw dk& D& , fu dk
a & ; o m; & jc i f; jz p fy gw , f/
Armadillo & JU public build version r Sm t o Hk; jy KE dki fw Jhfunction a w Gu a w mh-
( 1 ) CopyMemII + Debug-Blocker (Best Protection)
( 2 ) Standard Protection + Debug-Blocker
( 3 ) Standard Protection only
( 4 ) Minimum Protection
o D; o e fYr Sm, lo Hk; & w Jhcustom build version r Sma w mha t mu fy g function a w Gu dk t o Hk; jy KE dki fy gw , f-
( 1 ) Nanomites Processing
( 2 ) Import Table Elimination
( 3 ) Strategic Code Splicing
( 4 ) Memory-Patching Protections
( 5 ) Random PE Section Names
p w ma w Gjz p fy gw , f/
, Standar d Pr otection + Debug Blocker - .-. ..` .
y x r q Hk; t a e e JY t a jc c Ht u sq Hk; protection jz p fw Jh Debug-Blocker t a Mu mi f; u dk a q G; a E G; r Sm
jz p fy gw , f/
INFO: : Debug-blocker q dkw mu a w mh r dr dy & dk* & r fu dk debug v ky fa e o v m; q dkw mu dk p p fa q ; w Jh
v ky fa q mi fc su fw p fc kjz p fNy D; y & dk* & r fu dk debug v ky fr c H& a t mi f w m; q D; y gw , f/ Armadillo e JY protect
v ky fx m; w Jhy & dk* & r fa w Gt v ky fv ky f& i f parent process/child process q dkNy D; process E Sp fc k t v ky fv ky fy gw , f/
' Dprocess E Sp fc k[ m t c si f; c si f; debug v ky fc Ha e & o v m; q dkw m t jr J p p fa q ; a e y gw , f/
' ga Mu mi fh' Djz p f& y fu dk b , fv dk a u smfv Tm; Mu r , fq dkw m t a o ; p dw f a v hv mMu n fh& a t mi f/
' Do i fc e f; p mr Sm t o Hk; jy Kr , fh Armadillo e JY protect v ky fx m; w Jh e r le mz dki fu a w mh UnpackMe_
Armadillo 4.44.b jz p fy gw , f/ http://myanmarcrackingteam.blog.com r Sm download v ky f, lE dki fy g
w , f/
UnpackMe_ Armadillo 4.44.b.exe z dki fu dk Olly e JYz Gi fhv dku f& i f y Hk( 1 ) t w dki f; jr i f& y gr , f/ ( ' Dz dki fu dk
Armadillo 4.44 e JY protect v ky fx m; w m o dx m; Ny D; o m; r dkY u Re fa w mfht a e e JY PEiD/ProtectionID w dkYe JY
r p p fa q ; v dka w mhy gb l; / )
y Hk( 1 )
,., Armadillo ... .` .
,.
Armadillo z dki fa w Gu dk unpack v ky f& mr Sm StrongOD plugin u dk t o Hk; jy Kx m; r , fq dk& i fa w mh
t a u mi f; q Hk; jz p fy gw , f/
y Hk( 1 ) t w dki f; jr i f& w Jht c sde fr Sm Ctrl+N u dkE Sdy fNy D; b , f API a w Gu dk a c : o Hk; x m; o v Jq dkw m Mu n fhy g
r , f/ y Hk( 2 ) /
y Hk( 2 )
y Hk( 2 ) r Sma w mh u Re fa w mfw dkY& JU target z dki fu a c : o Hk; x m; w Jh API CALL a w Gu dk jr i f& y gw , f/ Ny D; & i f
WriteProcessMemory a y : r Sm right-click E Sdy fNy D; Follow import in Disassembler u dka & G; y g/ y Hk( 3 ) /
y Hk( 3 )
y Hk( 3 ) u VA 7C802216 a e & mr Sm breakpoint o w fr Sw fy g/ VA 7C802213 r Sm software
beakpoint o w fr Sw fv dkY r & y gb l; / b ma Mu mi fhv Jq dka w mh Armadillo u t c sdKU API a w G& JU y x r q Hk; BYTE
5 c ku dk p p fa q ; v dkYy g/ w u , fv dkYINT3 u dko ma w GYc Jh& i f ' g[ m software breakpoint o w fr Sw fx m; w , fq dkw m
o d& Sdo Gm; Ny D; y & dk* & r fu dk Ny D; q Hk; a p v dkYy g/ w u , fv dkYVA 7C802213 r Sm breakpoint o w fr Sw fc si f& i f hardware
breakpoint a w mho w fr Sw fv dkY& y gw , f/
Breakpoint o w fr Sw fNy D; & i fa w mh F9 u dkE Sdy fv dku fy g/ ' gq dk u Re fa w mfw dkY breakpoint o w fr Sw fx m; w Jh
q Dr Sm & y fw e fYo Gm; y gv dr fhr , f/ ' Dt c g Alt+F9 u dkE Sdy fNy D; user code & Sd& mq Du dk o Gm; y gr , f/ y Hk( 4 ) /
y Hk( 4 )
u Re fa w mfw dkYt a e e JY y Hk( 4 ) r Smjr i f& w Jht w dki f; user code & Sd& ma e & ma & mu fw Jht c g a e mu fx y f
WriteProcessMemory u dk a w GY& jy e fy gw , f/ WriteProcessMemory & JU v ky fa q mi fc su fu dkMu n fhy gr , f/
The Wr itePr ocessMemor y function writes memory in a specified process. The entire area to be written to must be
accessible, or the operation fails.
BOOL Wr itePr ocessMemor y(
HANDLE hProcess, // handle to process whose memory is written to
LPVOID lpBaseAddress, // address to start writing to
LPVOID lpBuffer, // pointer to buffer to write data to
DWORD nSize, // number of bytes to write
LPDWORD lpNumberOfBytesWritten // actual number of bytes written
);
WriteProcessMemory API [ m process w p fc k& JU r Sw fOmP fx Jr Sm u dk, fa & ; c si fw Jh? u dk, fjy i fc si fw Jh
u k' fa w G ( byte a w G) u dk jy i fw mjz p fy gw , f/ y Hk( 4 ) u dkMu n fhy g/ VA 4CA34C r Sm u Re fa w mfw dkYjy i fc si fw Jh
p mv Hk; a w Gu dk o Gm; x m; r Sm jz p fNy D; ? u Re fa w mfw dkY a & ; r Smu a w mh 2 Bytes o mjz p fy gw , f/ ' ga Mu mi fh y Hk( 4 ) u
UnPackMe.004CA34C a e & mr Sm right-click E Sdy fNy D; Follow in dump - Immediate constant u dka & G; y g/
y Hk( 5 ) t w dki f; jr i f& y gr , f/
,., Armadillo ... .` .
,,
y Hk( 5 )
y Hk( 5 ) u 60 E8 (PUSHAD) a e & mr Sm EB FE (JMP) v dkYjy i fy gr , f/ ' Dv dka jy mi f; Ny D; F9 u dkE Sdy fy g/
u Re fa w mfw dkY breakpoint o w fr Sw fx m; w Jh VA 7C802216 a e & mr Sm x y f& y fo Gm; y gv dr fhr , f/ ' Dt c g y Hk( 3 ) r Sm
o w fr Sw fx m; w Jhbreakpoint u dk r v dkt y fa w mhw Jht w Gu f jy e fjz Kw fv dku fy g/
' Dw p fc gr Sma w mh Olly & JU plugin w p fc kjz p fw Jh Command line r Sm WaitForDebugEvent API
t w Gu f breakpoint o w fr Sw fy gr , f/ y Hk( 6 ) /
y Hk( 6 )
y Hk( 6 ) t w dki f; o w fr Sw fNy D; o Gm; & i f F9 u dkE Sdy fy g/ u Re fa w mfw dkY breakpoint o w fr Sw fx m; w Jh
WaitForDebugEvent a e & mu dk a & mu fv my gr , f/ y Hk( 7 ) /
y Hk( 7 )
y Hk( 7 ) t w dki f; jr i f& w Jht c g Alt + F9 u dkE Sdy fNy D; user code & Sd& ma e & mu dk o Gm; y g/ y Hk( 8 ) t w dki f;
jr i f& y gr , f/ ( WaitForDebugEvent r Sm o w fr Sw fx m; w Jhbreakpoint u kda w mhv Hk; 0 r jz Kw fy ge JY/ )
y Hk( 8 )
y Hk( 8 ) r Smjr i f& w Jht x d u Re fa w mfw dkY v ky fa q mi fc Jhw m? a v hv mc Jhw mu a w mh y & dk* & r f& JU parent process
u dky g/ w u , fa w mh u Re fa w mfw dkY dump v ky f& r Smu child process u dko m jz p fy gw , f/ ' ga Mu mi fh child
process t a Mu mi f; u dk a v hv mMu n fhMu & a t mi f/
Olly & JU File menu u Attach u dka & G; v dku fy g/ y Hk( 9 ) /
y Hk( 9 )
y Hk( 9 ) r Sm t e Da & mi ft a e e JY jr i f& w mu v u f& Sd debug v ky fc Ha e & w Jh parent process y g/ Child
process u a w mh PID E04 e JY t v ky fv ky fa e y gw , f/ Child process & JU process ID (PID) u dk o d& Sdo Gm; Ny D
jz p fw Jht w Gu f y Hk( 8 ) u dk jy e fo Gm; y gr , f/ t J' Da e & mr Sm u Re fa w mfw dkYy Hk( 1 0 ) t w dki f; jy i fy gr , f/
y Hk( 1 0 )
,., Armadillo ... .` .
,,
u Re fa w mfw dkY b ma Mu mi fh DebugActiveProcessStop API u dko Hk; & w mv Jq dka w mh child process u dk
parent process u a e c GJx kw fc si fv dkYy g/ ' gr So m u Re fa w mfw dkYt a e e JY v Gw fv Gw fv y fv y f debug v ky fE dki fr Sm
jz p fy gw , f/
INFO: : DebugActiveProcessStop u dk Windows XP r Smo m t o Hk; jy KE kdi fy gw , f/ Windows 2000 e JY
t a p my dki f; OS a w Gr Sm ' Dfunction u dk t o Hk; r jy KE dki fy gb l; /
Ny D; & i fa w mh VA 0048F7E7 a & mu fw Jht x d F8 u dkE Sdy fv mc Jhy g/ ' gq dk child process u dk parent
process u debug r v ky fE dki fa t mi f c GJx kw fv dku fE dki fy gNy D/
' Dw p fc gr Sma w mh child process u dk dump v ky fy ga w mhr , f/ Olly t o p fw p fc ku dk z Gi fhv dku fy g/ Ny D; & i f
Olly & JU File menu u Attach u dka & G; v dku fy g/ y Hk( 1 1 ) /
y Hk( 1 1 )
y Hk( 1 1 ) r Smjr i f& w Jhchild process u dka & G; jy D; Attach button u dkE Sdy fv dku f& i f y Hk( 1 2 ) t w dki f; jr i f& y gr , f/
y Hk( 1 2 )
y Hk( 1 2 ) t w dki f; jr i f& w Jht c g F9 (Run) u dkE Sdy fNy D; F12 (Pause) u dkE Sdy fv dku fy g/ y Hk( 1 3 ) t w dki f;
jr i f& y gr , f/
y Hk( 1 3 )
y Hk( 1 3 ) r Smjr i f& w mu a w mh child process & JU OEP a e & my g/ EB FE q dkw m u Re fa w mfw dkY jy i fx m; w Jh
[ ma w Gy g/ ' Da e & mu dk r lv u k' fa w Gjz p fw Jh60 E8 e JYt p m; jy e fx dk; y gr , f/ y Hk( 1 4 ) /
y Hk( 1 4 )
y Hk( 1 4 ) t w dki f; t p m; x dk; Ny D; & i fa w mhy Hk( 1 5 ) t w dki f; a jy mi f; v Jo Gm; r Sm jz p fy gw , f/
,., Armadillo ... .` .
,,
y Hk( 1 5 )
y Hk( 1 5 ) t w dki f; jy i fNy D; & i f Command line plugin u dko Hk; jy D; CreateThread e JY VirtualProtect API
w dkYu dk breakpoint o w fr Sw fy gr , f/ y Hk( 1 6 ) /
y Hk( 1 6 )
Ny D; & i f Alt + B u dkE Sdy fNy D; breakpoint a w G& Sd& ma e & mu dk o Gm; y gr , f/ y Hk( 1 7 ) /
y Hk( 1 7 )
y Hk( 1 7 ) r Smjr i f& w mu CALL t p jz p fw Jh mov edi, edi a e & ma w Gr Sm breakpoint o w fr Sw fx m; w m
a w Gy g/ u Re fa w mfw dkY CALL t q Hk; r Sm breakpoint u dk a jy mi f; o w fr Sw fy gr , f/ ' ga Mu mi fh v u f& Sd breakpoint
a e & ma w Gr Sm Enter E Sdy fNy D; CALL t q Hk; a w Gr Sm breakpoint a jy mi f; o w fr Sw fv dku fy g/ y Hk( 1 8 ) /
y Hk( 1 8 )
y Hk( 1 8 ) t w dki f; jr i f& w Jht c gr Sma w mhF9 u dkE Sdy fy g/ ' Dt c sde fr Sm y Hk( 1 0 ) w ke f; u u Re fa w mfw dkYc P & y fx m; c Jhw Jh
parent process u dkv n f; F9 E Sdy fa y ; & r Sm jz p fy gw , f/ ' Dt c g VirtualProtect API r Sm u Re fa w mfw dkY
o w fr Sw fv dku fw Jhbreakpoint q Da & mu fv mr Sm jz p fy gw , f/
y Hk( 1 9 )
y Hk( 2 0 ) t w dki f; jr i f& w Jht x dF8 u dkE Sdy fv mc Jhy g/
y Hk( 2 0 )
y Hk( 2 0 ) t w dki f; jr i f& w Jht c g F8 u dkE Sdy fy g/
y Hk( 2 1 )
y Hk( 2 1 ) t w dki f; jr i f& w Jht c gr Sm code windows r Sm right-click E Sdy fNy D; Search for u a e All
commands u dka & G; Ny D; PUSH 100 u dk& dku fx n fhy g/ Ny D; & i f Find button u dkE Sdy fy g/ ( w u , fa w mh PUSH 100
[ m Armadillo u Encrypt/Decrypt function t w Gu f t o Hk; jy Kw Jhbuffer jz p fy gw , f/ )
,., Armadillo ... .` .
,,
y Hk( 2 2 )
y Hk( 2 2 ) u t a y : q Hk; PUSH 100 a e & mu dk E Sdy fv dku fy g/ y Hk( 2 3 ) t w dki f; a w GY& y gr , f/
y Hk( 2 3 )
y Hk( 2 3 ) r Smjr i f& w Jh PUSH EBP a e & mr Sm RETN e JYt p m; x kd; v dku fy g/ VirtualProtect r Smo w fr Sw f
x m; w Jhbreakpoint u dk jz Kw fv dku fy g/ jy D; & i f F9 u dkE Sdy fy g/ y Hk( 2 4 ) /
y Hk( 2 4 )
y Hk( 2 4 ) t w dki f; jr i f& w Jha e mu fr Sma w mhF8 u dkE Sdy fy g/ y Hk( 2 5 ) t w dki f; jr i f& y gr , f/
y Hk( 2 5 )
y Hk( 2 5 ) u a e y Hk( 2 6 ) r Smjr i f& w Jht x dF8 u dkE Sdy fv mc Jhy g/
y Hk( 2 6 )
y Hk( 2 6 ) t w dki f; jr i f& w Jht c g a t mu fu dk scroll e n f; e n f; q GJNy D; CALL ECX & Sd& mu dk & Smy g/
y Hk( 2 7 )
CALL ECX & Sd& mu dk o w fr Sw fy g/ Ny D; & i f F9 u dkE Sdy fNy D; ' D CALL a e & mu dk v my g/ ' D CALL [ m
u Re fa w mfw dkY& Sma e w JhOEP a e & mjz p fy gw , f/ CALL ECX u dka & mu fw Jht c g F7 u dkE Sdy fy g/ y Hk( 2 8 ) t w dki f; OEP
& Sd& ma e & mu dk a w GY& r Sm jz p fy gw , f/
,., Armadillo ... .` .
,,,
y Hk( 2 8 )
y Hk( 2 8 ) t w dki f; a w GY& w Jht c gr Sma w mh ' Dz dki fu dk dump v ky f& r Smjz p fy gw , f/ Dump v ky fx m; w Jhz dki fu dk
ImpREC e JYjy i fv dku f& i f Armadillo 4.44 & JU Debug Blocker u dkz , f& Sm; E dki fc JhNy D; r dr dp dw fMu dKu f debug
v ky fE dki fNy Djz p fy gw , f/
, Minimum Pr otection - .-. ..`.
' Dw p fc gr Sma w mh Minimum Protection e JY protect v ky fx m; w Jh Armadillo 4.4 z dki fu dk unpack
v ky fMu n fhy gr , f/ t v G, fu lq Hk; t & mu dk b ma Mu mi hf y x r q Hk; r & Si f; jy o v Jv dkY o i fht a e e JY o Ho , & Sda u mi f;
& Sdy gv dr hfr , f/ u Re fa w mfht a e e JY Armadillo & JU t a jc c Ht v ky fv ky fy Hku dk a o ; p dw fa q G; a E G; c si fv dkY t c kr S& Si f; jy w m
jz p fy gw , f/
' Do i fc e f; p mt w Gu f a & G; x m; w mu a w mh Armadillo 4.4 e JY protect v ky fx m; w Jh calc.exe z dki fjz p fy g
w , f/ http://myanmarcrackingteam.blog.com r Sm download v ky f, lE dki fy gw , f/ Minimum Protection
r Sm o i fht a e e JYa t mu fy gt c su f( 3 ) c ku dk a jz & Si f; & y gv dr fhr , f/
( 1 ) OutputDebugStringA Exploit
( 2 ) PE Header a jy mi f; v Jr I
( 3 ) Import Redirection
, OutputDebugStr ingA Exploit
OutputDebugStringA API o Hk; Ny D; Olly u dk exploit jz p fa p w Jh v Sn fhp m; c su fu a w mh c ka e mu fy dki f; r Sm
Olly & JU plugin a w Gu t v G, fw u l a u smfv Tm; E dki fw Jht w Gu f r & Si f; jy v dka w mhy gb l; / y Hk( 2 9 ) /
y Hk( 2 9 )
' De n f; u dk a u smfv Tm; z dkYu v G, fy gw , f/ OutputDebugStringA t v ky fr v ky fE dki fa t mi f PUSH 234
a e & mr Sm RETN e JYt p m; x dk; v dku f& Hky gy J/
, OEP - . .` .
PE Header b , fv dka jy mi f; v Jo Gm; w mu dk a v hv mE dki fz dkY u Re fa w mfw dkYt a e e JY unpack v ky fz kdY Mu dK; p m;
Mu n fhy gr , f/ Armadillo 4.4 e JYprotect v ky fx m; w Jhcalc.exe z dki fu dk Olly e JYz Gi fhv dku fy g/ y Hk( 3 0 ) /
y Hk( 3 0 )
y Hk( 3 0 ) r Smjr i f& w Jh entry point u a w mh Standard Protection + Debug-Blocker e JY protect
v ky fx m; w Jhz dki f& JU entry point e JY r w lw m o w djy Kr dr Smy g/ PUSHAD t p m; PUSH EBP v dkY jr i f& y gw , f/
u Re fa w mfw dkYt a e e JY unpack v ky fE dki fz dkYt w Gu f OEP u dk t & i fa w GYa t mi f & Sm& r Smjz p fy gw , f/ b ma Mu mi fhv J
q dka w mhOEP u dko dr Sdump v ky fE dki fr Smr dkYv dkYy g/
,., Armadillo ... .` .
,,
a u mi f; Ny D/ Minimum Protection u dk a u smfv Tm; E dki fz dkYt w Gu f VirtualProtect API r Sm breakpoint
o w fr Sw fy gr , f/ Ctrl + G (Goto address in disassembler) u dkE Sdy fNy D; VirtualProtect u dk& dku fx n fhy g/
y Hk( 3 1 ) /
y Hk( 3 1 )
y Hk( 3 1 ) u OK u dkE Sdy fv dku f& i f VirtualProtect API & Sd& mq Dw e f; a & mu fo Gm; y gr , f/
y Hk( 3 2 )
y Hk( 3 2 ) t w dki f; breakpoint o w fr Sw fv dku fy g/ jy D; & i f Stack windows r Sm y Hk( 3 3 ) t w dki f; jr i f& w Jht x d
F9 u dkE Sdy fy g/
y Hk( 3 3 )
y Hk( 3 3 ) t w dki f; jr i f& w Jht c g y Hk( 3 2 ) r Sm o w fr Sw fc Jhw Jh breakpoint u dkjz Kw fv dku fy g/ Ny D; & i f Ctrl+G u dk
E Sdy fNy D; CreateThread API & Sd& mq Do Gm; Ny D; y Hk( 3 4 ) t w dki f; CreateThread API r Sm breakpoint o w fr Sw fy g/
y Hk( 3 4 )
y Hk( 3 4 ) t w dki f; breakpoint o w fr Sw fjy D; w Jht c g F9 u dkE Sdy fy g/ Breakpoint q Dr Sm & y fo Gm; y gv dr fhr , f/
' Dt c g F8 u dkE Sdy fy g/ y Hk( 3 5 ) t w dki f; jr i f& y gr , f/
y Hk( 3 5 )
y Hk( 3 5 ) u RETN x d F8 u dkE Sdy fv mc Jhy g/ Ny D; & i f a e mu fw p fc g F8 u dkx y fE Sdy f& i f y Hk( 3 6 ) t w dki f; jr i f& y g
r , f/
y Hk( 3 6 )
,., Armadillo ... .` .
,,
y Hk( 3 6 ) t w dki f; jr i f& w Jht c gr Sm a t mu fe m; u dk e n f; e n f; scroll q GJNy D; Mu n fhv dku fy g/ y Hk( 3 7 ) /
y Hk( 3 7 )
y Hk( 3 7 ) u CALL ECX r Sm breakpoint o w fr Sw fy g/ Armadillo 3.x w ke f; u a w mh CALL ECX
t p m; CALl EDI jz p fy gw , f/ ' gu a w mh generic unpacker a w Gu a e unpack v ky fw mu dk u mu G, fE dki fz dkY
t w Gu f e n f; v r f; a jy mi f; v dku fw m jz p fy gw , f/ Ny D; & i f F9 u dkE Sdy fy g/ u Re fa w mfw dkY& Sma e w JhOEP & Sd& mu dk a c : , lw Jh
CALL jz p fy gw , f/ VA 8E8D96 a & mu fw Jht c g F7 u dkE Sdy fy g/ u Re fa w mfw dkY & Sma e w Jh OEP & Sd& mq D
a & mu fo Gm; r Smjz p fy gw , f/ y Hk( 3 8 ) /
y Hk( 3 8 )
y Hk( 3 8 ) r Smjr i f& w Jh VA 1012475 u a w mh u Re fa w mfw dkY & Sma e w Jh OEP jz p fy gw , f/ OEP u dko d& Ny Dr dkY
dump v ky fy g/ Dump v ky fw mu dk a & SUo i fc e f; p ma w Gr Sm & Si f; jy Ny D; o m; r dkY o i fc e f; p m & Sn fr Smp dk; w Jht w Gu f x y fr H
r & Si f; v i f; a w mhy gb l; / Dump v ky fx m; w Jhz dki fu dk ImpREC e JYjy i fy gr , f/
y Hk( 3 9 )
ImpREC e JYjy i fw Jht q i fha w Gu a w mha t mu fy gt w dki f; jz p fy gw , f-
,., Armadillo ... .` .
,,,
( 1 ) IAT jy i fr , fhprocess (calc.exe) u dka & G; c s, fy g/
( 2 ) OEP w e fz dk; u dk & dku fx n fhy g/ Ny D; v Qi f IAT AutoSearch button u dka & G; y g/
( 3 ) Get Imports u dk a & G; y g/ Ny D; v Qi f Show Invalid u dkE Sdy fNy D; invalid jz p fa e a o m API r sm; u dk & Smy g/
( 4 ) Invalid API r sm; a y : w Gi f right-click E Sdy fNy D; Cut thunk(s) u dka & G; c s, fy g/ Ny D; v Qi f Fix Dump u dkE Sdy fNy D;
u Re fa w mfw dkYdump v ky fx m; a o mz dki fu dk jy i fq i fy g/
Dump v ky fx m; a o mz dki fu dk dumped.exe [ kt r n fa y ; y g/ dumped.exe z dki fu dk jy i fq i fx m; a o mz dki fu dk
dumped_.exe [ ke mr n fa y ; y g/
Dump v ky fjc i f; t y dki f; Ny D; p D; w Jht c gr Sma w mh u Re fa w mfw dkY& JU a e mu fq Hk; & & Sdv mw Jh dumped_.exe u dk
z Gi fhMu n fhy g/ z Gi fhMu n fhv dku fw Jht c gr Sm u Re fa w mfw dkY& JU unpacked v ky fx m; w Jhz dki f[ m t v ky fr v ky fy gb l; /
, PE Header .`. . .
dumped_.exe b ma Mu mi fh t v ky fr v ky fo v Jq dkw mu dk a jc & ma u mu fMu n fhMu & a t mi f/ y Hk( 3 8 ) u dk jy e f
Mu n fhv dku fy g/ u Re fa w mfw dkYt a e e JY dump r v ky fa o ; c i f t a e t x m; r Sm Memory Map Windows (Alt+M)
u dka c : Ny D; PE header u dk Mu n fhv dku fMu & a t mi f/ y Hk( 4 0 ) /
y Hk( 4 0 )
y Hk( 4 0 ) r Sma w GY& w Jht w dki f; PE header [ m y su fp D; a e Ny D; Olly u o lUu dk r r Sw fr da w mhy gb l; /
w e fz dk; ( 3 ) c k[ m t z su fc Hx m; & y gw , f/ ' gu b ma w Gv n f; q dka w mh DOS header x Ju PE header & JU offset?
PE header x Ju number of section w e fz dk; e JY exe & JU EntryPoint w dkYjz p fy gw , f/ ' gu dk jy i fE dki fz dkY calc.exe
u dk a e mu fx y f Olly w p fc ke JYz Gi fhNy D; PE header e JYy w fo u fw Jh t c su ft v u fa w Gu dk binary copy t a e e JYu l; Ny D;
binary paste v mc sx m; w Jhe n f; e JY a jz & Si f; E dki fy gw , f/ jy D; & i f LordPE e JY dump v ky fa y gh/ ' ga y r , fhv n f;
' De n f; o Hk; & i fv n f; y Hk( 3 9 ) r Sm u Re fa w mfw dkY jr i fc Jhw Jh ImpREC u unresolved thunks a w Gu a w mh & Sda e OD; r Sm
y gy J/ Thunks a w Ga y : right-click E Sdy fNy D; Trace Level 1 u dko Hk; & i fv n f; import t r Sm; a w Gu dk a y ; a e OD; r Smy J
jz p fy gw , f/
,, IAT `.,.
.text section [ m import thunk a w G x m; & Sd& ma e & m jz p fy gw , f/ y Hk( 3 8 ) t w dki f; OEP a e & mu dk
a & mu f& Sdt jy D; r Sm y Hk( 4 0 ) u .text section u dk E Sp fc su fE Sdy fv dku fy g/ y Hk( 4 1 ) /
y Hk( 4 1 )
y Hk( 4 1 ) r Smjr i f& w Jht w dki f; t c sdKUw e fz dk; a w G[ m r Se fu e fjc i f; r & Sdy gb l; / t a y : o Hk; c kjz p fw Jh RegOpenKey
ExA? RegQueryValueExA e JY RegCloseKey p w Jh API a w Gu a w mh advapi32.dll z dki fx Ju import
a w Gu dk n Te f; y gw , f/ p w kw a jr mu fu a w mh r Sw fOmP fx Ju ArmDll z dki fx Ju dk import a w Gu dk n Te f; y gw , f/
u Re fa w mfw dkYt a e e JY b , fa e & mr Sm IAT a w Gu dk redirect v ky fw , fq dkw mu dk& SmNy D; redirect r v ky fa t mi f
u mu G, f& r Smjz p fy gw , f/ y Hk( 4 1 ) u dk HEX/ASCII (16 bytes) view e JYMu n fhv dku fy g/ y Hk( 4 2 ) /
y Hk( 4 2 )
,., Armadillo ... .` .
,,.
y Hk( 4 2 ) t w dki f; r Sm; , Gi f; w Jh import w e fz dk; w p fc ka y : right-click E Sdy fNy D; Br eakpointHar dwar e,
on wr iteDwor d u dka & G; y gr , f/
Olly u dk restart (Ctrl+F2) v ky fv dku fy g/ Ny D; & i f F9 u dkE Sdy fv dku fy g/ y Hk( 4 3 ) r Sm v m& y fy gv dr fhr , f/
y Hk( 4 3 )
y Hk( 4 3 ) u a w mhy x r t q i fhy J & Sdy ga o ; w , f/ t a & ; r Mu D; a o ; y gb l; / F9 u dk q u fE Sdy fy g/ y Hk( 4 4 ) /
y Hk( 4 4 )
y Hk( 4 4 ) u a w mht a & ; t Mu D; q Hk; t y dki f; jz p fy gw , f/
( 1 ) VA A06347 r Sm Armadillo [ m o lU& JU p m& i f; x Ju API e mr n fa w Gu ke fr u ke f w dku fp p fy gw , f/
( 2 ) VA A06373 r Sma w mhAPI a w Gu dk stricmp o Hk; Ny D; w dku fp p fy gw , f/
( 3 ) VA A0637D u a w mh t a & ; Mu D; q Hk; jz p fy gw , f/ w u , fv dkY w dku fp p fw Jh API a w G[ m Armadillo
& JUp m& i f; x Jr Smo m & Sda e r , fq dk& i f jump v ky fE dki fr Sm r [ kw fy gb l; / q dkv dkw mu ' DAPI u dk a c : o Hk; w dki f; ArmDll
z dki fx Ju API u dka c : o Hk; a e r Sm? emulate v ky fa e r Sm jz p fy gw , f/
( 4 ) VA A063C2 r Sma w mhAPI & JUw e fz dk; u dk a & ; y gw , f/
( 5 ) VA A063C4 u a w mhu Re fa w mfw dkYv u f& Sda & mu fa e w Jha e & m jz p fy gw , f/
VA A06347 u a w mh p m& i f; x Ju API e mr n fa w Gu dk w dku fp p fw Jht v ky fo mv ky fNy D; redirection a w G
v ky fw mu dk w m; q D; z dkYu u Re fa w mfw dkYt a e e JY JNZ A06390 u dk JMP A06390 v dkYjy i fr S& y gr , f/ ' ga y r , fh
' Dt c sde fr Sma w mhredirection a w Gv ky fNy D; o m; Ny Dr dkYa e mu fu so Gm; y gNy D/
' ga Mu mi fh VA A0637D a e & mr Sm hardware breakpoint o w fr Sw fy g/ OEP u dkv n f; o dNy D; o m;
jz p fw mr dkY VirtualProtect/CreateThread e n f; a w Gu dkv n f; r o Hk; c si fa w mhy gb l; / OEP a e & mjz p fw Jh VA
1012475 r Sm hardware breakpoint o w fr Sw fv dku fNy D; Olly u dk jy e fp v dku fy g/ ' gq dk y Hk( 4 5 ) q Dw e f; a & mu fv m
y gr , f/
y Hk( 4 5 )
,., Armadillo ... .` .
,,.
y Hk( 4 5 ) u JNZ A06390 a e & mr Sm JMP A06390 v dkYjy i fv dku fy g/ Ny D; & i f VA A0637D r Sm
o w fr Sw fx m; w Jhhardware breakpoint u dkjz Kw fNy D; F9 u dkE Sdy fy g/ OEP & Sd& mq Da & mu fo Gm; y gr , f/ y Hk( 4 6 ) /
y Hk( 4 6 )
' Dt c gr Sm Alt+M u dkE Sdy fNy D; memory windows u .text section u dkE Sp fc su fE Sdy fv dku fy g/ jy D; & i f
LongAddr ess e JYMu n fhv dku fy g/ y Hk( 4 7 ) /
y Hk( 4 7 )
y Hk( 4 1 ) e JY y Hk( 4 7 ) w dkYu dk E dIi f; , SOfMu n fhy g/ t p dr f; e JY0 dki f; jy x m; w ma w G[ m t & i fu emulated api a w Gy g/
Emulated api a w Gjz p fw ma Mu mi fh dump v ky fNy D; import u dkjy i fw Jht c g ImpREC u r o dE dki fw ma Mu mi fh
y & dk* & r fu a u mi f; a u mi f; t v ky fr v ky fE kdi fw m jz p fy gw , f/
c kw p fc gr Sm import a w Gu dk jy i fNy D; Ny Dr dkY y Hk( 3 9 ) u t q i fha w Gt w dki f; calc.exe z dki fu dk dump v ky fNy D;
import a w Gu dk jy i fv dku fy g/ ' gq dk& i f a t mi fjr i fp Gm t v ky fv ky fw Jh Minimum Protection u dk z , f& Sm; Ny D; o m;
unpacked z dki fu dk & & Sdr Smjz p fy gw , f/
t r Se fu a w mh o i fc e f; p mu Ny D; o Gm; y gNy D/ ' ga y r , fh u Re fa w mhft a e e JY t e n f; i , f a q G; a E G; c si fy g
a o ; w , f/ y Hk( 4 8 ) u dkMu n fhy g/
y Hk( 4 8 )
w u , fa w mh u Re fa w mfw dkY& JU calc.exe u dk pack r v ky fc i fr Sm r l& i f; z dki ft & G, ft p m; u 112KB
y J& Sdy gw , f/ Pack v ky fv dku fc sde fr Sm 740KB jz p fv my gw , f/ Unpack jy e fv ky fc sde fr Sma w mh 1,024KB
x da w mi fjz p fo Gm; y gw , f/ ' gu calc.exe v dk z dki ft a o ; a v ; a w Gr Sm jy e mr & Sda y r , fh professional
a q mhz f0 Jv fa w Gv dk z dki ft & G, ft p m; t & r f; Mu D; w Jht c gr Sma w mh jy e m& Sdy gw , f/ ' ga Mu mi fh u Re fa w mfw dkYt a e e JY
t w w fE dki fq Hk; z dki ft & G, ft p m; a o ; a t mi f v ky fMu n fhMu y gr , f/
dumped_.exe u dk LordPE e JYz Gi fhy g/
y Hk( 4 9 )
,., Armadillo ... .` .
,
BaseofCode u dk 1000 v dkYjy i fy g/ BaseofData u dk 14000 v dkYjy i fy g/ Ny D; & i f u dkE Sdy fNy D; u
a y gi f; x n fhv dku fw Jh a w Gjz p fw Jh .text1? .adata? .data1 e JY .pdata w dkYu dka & G; Ny D; wipe section header
u dka & G; c s, fy g/ Ny D; & i f save v ky fy g/
Ny D; & i f LordPE & JU Options u Dumpfix e JY Realign filehar dcor e w dkYu dka & G; c s, fv dku fNy D;
Rebuild PE button u dkE Sdy fNy D; dumped_.exe u dk rebuild jy e fv ky fy g/
y Hk( 5 0 )
' gq dk z dki ft & G, ft p m; [ m y Hk( 5 0 ) r Smjr i f& w Jht w dki f; 1 1 % t x du sHKUo Gm; r Sm a w GY& y gr , f/
y Hk( 5 1 )
y Hk( 5 1 ) u dkMu n fhw Jht c gr Smv n f; r l& i f; z dki fe JY2KB a v mu fo m u Gmjc m; a w mhw m a w GY& r Smy g/
, Standar d Pr otection - .-. ..`.
' Dw p fc gr Sma w mh Standard Protection e JY protect v ky fx m; w Jh Armadillo 4.4 z dki fu dk unpack
v ky fMu n fhy gr , f/ ' Dw p fc go i fc e f; p mr Sma w mh u Re fa w mfht a e e JY & Si f; jy Ny D; o m; t y dki f; a w Gu dk y Hke JY t a o ; p dw f & Si f; jy
a w mhr Sm r [ kw fw Jht w Gu f o i fht a e e JYt a y : u t y dki f; a w Gu dk a u sn u fa t mi f a v hv mx m; & r Sm jz p fy gw , f/
' Do i fc e f; p mt w Gu f a & G; x m; w mu a w mh Armadillo 4.4 e JY protect v ky fx m; w Jh Notepad2.exe
z dki fjz p fy gw , f/ http://myanmarcrackingteam.blog.com r Sm download v ky f, lE dki fy gw , f/ Standard
Protection e JYy w fo u fw Jho dr Sw fz G, f& mr sm; u a w mha t mu fy gt w dki f; jz p fy gw , f-
( 1 ) Minimum protection r Smo Hk; w Jhv Sn fhp m; c su ft c sdKUu kdjy e fo Hk; x m; y gw , f/
( 2 ) Loader & JUu k' fu dk encrypt v ky fx m; w ma Mu mi fhredirection a e & mu dk & Sma z Gz dkYy dkc u fv my gw , f/
( 3 ) Decrypt/Encrypt v ky fi e f; p Ofa w G[ m CRC w Gu fc su fr It a y : r lw n fNy D; ? u Re fa w mfw dkY& JU u k' fa w G jy Kjy i f
a jy mi f; v Jr Iu target z dki ft a y : t u sdK; o u fa & mu fr I & Sdy gw , f/
, OEP - . .` .
OEP u dk& Smz dkYt w Gu f Notepad2.exe u dk Olly r Smz Gi fhy gr , f/ y Hk( 5 2 ) /
y Hk( 5 2 )
y Hk( 5 2 ) t w dki f; jr i f& w Jha e mu fr Sma w mh Ctrl + G u dkE Sdy fNy D; VirtualProtect e JY CreateThread w dkYr Sm
breakpoint o w fr Sw fy gr , f/
y Hk( 5 3 )
,., Armadillo ... .` .
,
y Hk( 5 3 ) t w dki f; VirtualProtect e JY CreateThread w dkY& JU function t q Hk; r Sm breakpoint o w fr Sw fv dkY
t jy D; r Sm y Hk( 5 4 ) u dkjr i f& w Jht x dF9 u dkE Sdy fy g/
y Hk( 5 4 )
y Hk( 5 4 ) t w dki f; jr i f& w Jht c gr Sm VirtualProtect r Smo w fr Sw fx m; w Jh breakpoint u dkjz Kw fNy D; F9 u dk
q u fE Sdy fy g/ y Hk( 5 5 ) r Sm & y fo Gm; y gv dr fhr , f/
y Hk( 5 5 )
y Hk( 5 5 ) t w dki f; jr i f& w Jht c gr Sma w mh CreateThread r Smo w fr Sw fx m; w Jh breakpoint u dkjz Kw fNy D; F8 u dk
q u fE Sdy fy g/
y Hk( 5 6 )
y Hk( 5 6 ) t w dki f; jr i f& w Jht c g y Hk( 5 7 ) q Da & mu fw Jht x dF8 u dkq u fE Sdy fv my g/
y Hk( 5 7 )
y Hk( 5 7 ) & JU a t mu fe m; a v mu fu dk e n f; e n f; a v mu f scroll q GJNy D; Mu n fhv dku fy g/ y Hk( 5 8 ) t w dki f; jr i f& y gr , f/
y Hk( 5 8 )
y Hk( 5 8 ) r Smjr i f& w Jh CALL ECX r Sm breakpoint o w fr Sw fv dku fy g/ Ny D; & i f F9 u dkE Sdy fv dku f& i f VA
B7F9EA q Dw e f; a & mu fv my gv dr fhr , f/ ' Dha e mu fr Sma w mh F7 u dkE Sdy fv dku fr , fq dk& i f u Re fa w mfw dkY& Sma e w Jh OEP
q Da & mu fy gNy D/ y Hk( 5 9 ) /
r Sw fc su f/ / o i fht a e e JY t x l; o w djy Ko i fhw mu ' Do i fc e f; p mw p fc kv Hk; r Sm a w GY& w Jh virtual address a w G[ m
w p fa , mu fe JYw p fa , mu f w lr Sm r [ kw fw mu dky g/
y Hk( 5 9 )
VA 447508 [ m u Re fa w mfw dkY & Sma e w Jh OEP jz p fy gw , f/ ' Da e & mu dk hardware breakpoint
o w fr Sw fy gr , f/ ' gr So m a e mu fy dki f; y & dk* & r fu dk dump v ky fw Jht c g v G, fu l t q i fa jy r Sm jz p fy gw , f/
,., Armadillo ... .` .
,
, IAT - ` ` .
IAT u dkjy i fz dkYt w Gu f u Re fa w mfw dkYt a e e JY y Hk( 5 9 ) t w dki f; jr i f& c sde fr Sm Alt+M u dkE Sdy fNy D; memory
windows u dka c : y gr , f/ y Hk( 6 0 ) /
y Hk( 6 0 )
t y dki f; ( 2 ) w ke f; u a jy mc Jho v dky J Armadillo u PE header x Ju t c su ft v u ft c sdKUu dk jy i fq i fv dku fw Jh
t w Gu f PE header e JYy w fo u fw Jh t c su ft v u fa w Gu dk Mu n fhv dkYr & a w mhy gb l; / ' ga y r , fh t c kt a e t x m; r Sm
p dw f0 i fp m; w mu a w mh .rdata section o mjz p fy gw , f/ t J' Dr Sm u Re fa w mfw dkY& JU import a w Gu dk o dr f; x m; v dkY
jz p fy gw , f/ y Hk( 6 0 ) u .rdata a e & mu dk E Sp fc su fE Sdy fv dku fy g/
y Hk( 6 1 )
y Hk( 6 1 ) r Sma w GY& w Jht w dki f; u Re fa w mfw dkY& JU import a w Gu dk jy i fE dki fw m r a w GY& y gb l; / ' ga Mu mi fh VA
45101C r Sm right-click E Sdy fNy D; Br eakpointHar dwar e, on wr iteDwor d u dka & G; y gr , f/ jy D; & i f
Ctrl+F2 E Sdy fNy D; Olly u dk jy e fp y g/ Olly u dkjy e fp Ny D; w Jha e mu f F9 u dkE Sdy fy g/ y Hk( 6 2 ) r Sm & y fo Gm; y gv dr fhr , f/
y Hk( 6 2 )
y Hk( 6 2 ) & JU t a y : e m; a v ; u dk Mu n fhMu n fhy g/ y Hk( 6 3 ) t w dki f; a w GY& y gr , f/
y Hk( 6 3 )
y Hk( 6 3 ) & JU VA B7C50A u JNZ u dk JMP v kdYjy i fv dku f& i f u Re fa w mfw dkY& JU emulated API a w G
r Se fu e fo Gm; r Sm jz p fy gw , f/ ' Dt c gr Sm VA 45101C r Smo w fr Sw fc Jhw Jh hardware breakpoint u dk
jy e fjz Kw fv dku fy g/ VA B7C50A r Sm hardware breakpoint o w fr Sw fy g/ OEP jz p fw Jh VA 447508
r Smv n f; hardware breakpoint o w fr Sw fy g/ Ny D; & i f F2 u dkE Sdy fNy D; Olly u dkjy e fp v dku fy g/ y Hk( 6 4 ) u VA
B7C50A q Dw e f; a & mu fv my gv dr fhr , f/
y Hk( 6 4 )
,., Armadillo ... .` .
,
y Hk( 6 4 ) u JNZ a e & mr Sm JMP v dkYjy i fy g/ VA B7C50A r Smo w fr Sw fc Jhw Jh hardware breakpoint u dk
jy e fjz Kw fv dku fNy D; F9 u dkE Sdy fv dku fy g/ y Hk( 6 5 ) t w dki f; jr i f& y gr , f/
y Hk( 6 5 )
y Hk( 6 5 ) t w dki f; jr i f& v kdY Olly u dk r y dw fv dku fy ge JY/ jy e fr p v dku fy ge JY/ Exception t c sdKUa Mu mi fh
y & dk* & r f[ m crash jz p fNy D; terminate jz p fo Gm; w my g/ b ma Mu mi fhv Jq dka w mh u Re fa w mfw dkYu byte t c sdKUu dk
jy i fq i fv dku fw ma Mu mi fh encrypt/decrypt process u t v ky fr v ky fE dki fa w mhb J OEP q Da & mu fr v ma w mhw m
jz p fy gw , f/ ' ga y r , fh u Ha u mi f; w mu a w mh valid thunk a w Gy gw Jh .rdata u a w mh t a u mi f; t w dki f;
& Sdy ga o ; w , f/
Notepad2.exe u dk a e mu fx y f Olly w p fc ke JY x y fz Gi fhy g/ VA B7C50A r Smo w fr Sw fx m; w Jh
hardware breakpoint u dkjz Kw fy g/ Ny D; & i f F9 u dkE Sdy fy g/ u Re fa w mfw dkYhardware breakpoint o w fr Sw fx m; w Jh
OEP q Dw e f; a & mu fv my gv dr fhr , f/
y Hk( 6 6 )
y Hk( 6 6 ) t w dki f; jr i f& c sde fr Sm Alt+M u dkE Sdy fNy D; memory windows u dka c : y gr , f/ y Hk( 6 5 ) b u fu Olly
r Smv n f; memory windows u dka c : y gr , f/ y Hk( 6 7 ) /
y Hk( 6 7 )
y Hk( 6 7 ) t w dki f; jr i f& w Jht c g y x r Olly u .rdata u dkE Sdy fNy D; t J' Dx Jr Sm& Sdw Jhbinary a w Gt m; v Hk; u dk copy
(Binar yBinar y copy) u l; Ny D; ' kw d, Olly u .rdata x Jr Sm paste (Binar yBinar y paste)
v mv ky fy gr , f/ Ny D; & i f LongAddr ess view e JYMu n fhv dku fy g/ y Hk( 6 8 ) /
y Hk( 6 8 )
y Hk( 6 8 ) [ m y Hk( 6 1 ) e JY r w la w mhw m o w djy Kr dr Smy g/ ' Dt c g y x r Olly u dky dw fv dkY& y gjy D/ Ny D; & i fa w mh
LordPE e JY y & dk* & r fu dk dump v ky fy g/ ImpREC e JY import a w Gu dkjy i fy g/ t y dki f; ( 2 ) r Sm a jy mc Jho v dk z dki ft & G, f
t p m; u dk a o ; a t mi fv ky fy g/ ' gq dk a t mi fjr i fp Gme JY unpack v ky fv dkY jy D; p D; o Gm; y gNy D/ & Si f; jy Ny D; o m; jz p fw Jht w Gu f
o i fc e f; p m & Sn fr Smp dk; w Jht w Gu f u Re fa w mfht a e e JYx y fr Hr & Si f; jy a w mhy gb l; /
,, CopyMemII + Debug-Blocker - .-. ..` .
' Dw p fc gr Sma w mh CopyMemII + Debug-Blocker e JY protect v ky fx m; w Jh Armadillo 4.4 z dki fu dk
unpack v ky fMu n fhy gr , f/
INFO: : CopyMemII u dk child process u dk debug v ky fz dkYt w Gu f t o Hk; jy KE dki fNy D; code section r Sm parent
process u PAGE_GUARD u dko w fr Sw fNy D; target u v kdt y fw Jh u k' ft p dw ft y dki f; t c sdKUu dk decrypt
,., Armadillo ... .` .
,,
v ky fy gw , f/ CopyMemII q dkw m parent process & JU t * Fg& y fw p fc kjz p fNy D; 1000h bytes p m& Sdw Jh child
process & JU code section block u dk decrypt v ky fy gw , f/ ' Du k' fu dk t v ky fv ky fNy D; a e mu fr Sma w mh jy e fNy D;
encrypt v ky fy gw , f/ q dkv dkw mu parent process [ m page r Sm t r Sm; t , Gi f; w p fp Hkw p f& m & Sd?r & Sd
a p mi fhMu n fha e Ny D; a y smu fq Hk; a e w Jh block u dk decrypt v ky fr dc Jh& i f o lUa e & mr Sm t p m; x dk; y p fv dku fy gw , f/
' ga Mu mi fh u Re fa w mfw dkY& JUt v ky fu y & dk* & r fw p fc kv Hk; u dk decrypt v ky fE dki f& r Smjz p fNy D; b , fv dke n f; e JYr S encrypt
jy e fjz p fa p v dkY r & y gb l; / DLL E Si fh OCX z dki fa w Gu dk protect v ky fw Jht c gr Sma w mh CopyMem2 protection u dk
t o Hk; jy Kv dkY r & y gb l; / z dki ft & G, ft p m; Mu D; r m; w Jh y & dk* & r fa w Gu dk protect v ky f& mr Smv n f; CopyMem2 u dk
t o Hk; r jy Ko i fhy gb l; / w u , fv dkY Visual Basic y & dk* & r fa w Gr Sm CopyMem2 u dk t o Hk; jy Kc Jh& i f Windows
Vista E Si fht x u f Windows a w Gr Smo m t v ky fv ky fy gv dr fhr , f/
CopyMemII [ mv n f; Debug-Blocker v dky J process E Sp fc ku dk z e fw D; y gw , f/ ' ga Mu mi fh
w p fc gw p f& Hr Sm process w p fc k[ m Debug-Blocker y Jy go v m; ? CopyMemII y Jy go v m; ? E Sp fc kv Hk; y J
y go v m; q dkw m a jy m& c u fy gw , f/ CopyMemII [ m code section u dk protect v ky fy gw , f/
t x l; o w da y ; v dkw mu CopyMemII e JY protect v ky fx m; w Jh y & dk* & r fa w Gu dk unpack v ky fw Jht c gr Sm
memory u dka p mi fhMu n fhw JhAnti-virus a q mhz f0 Jv fa w Ge JYFirewall a q mhz f0 Jv fa w Gu dk y dw fx m; a y ; z dkYy g/
' Do i fc e f; p mr Sm t o Hk; jy Kr , fh Armadillo e JY protect v ky fx m; w Jh e r le mz dki fu a w mh UnpackMe_
Armadillo 4.4.exe jz p fy gw , f/ http://myanmarcrackingteam.blog.com r Sm download v ky f, lE dki fy g
w , f/ Armadillo version t e dr fha w Ge JYjy v dkY p dw fr y su fy ge JY/ ' De n f; v r f; u dko Hk; Ny D; Armadillo 6.x e JY protect
v ky fx m; w Jhz dki fa w Gu dkv n f; unpack v ky fE dki fy gw , f/
' Do i fc e f; p mt w Gu f v dkt y fw Jh tool u a w mh ArmaDetach 1.31 jz p fy gw , f/ u Re fa w mfw dkYt a e e JY
a & SUt y dki f; a w Gr Sm Armadillo & JUo a b mu dk a u sn u fa t mi fv dkY b m tool r Sr o Hk; b J u dk, fw dki fb , fv dk unpack
v ky f& r , fq dkw m w p fq i fhc si f; jy c Jhy gw , f/ w u , fa w mht q i fhjr i hfe n f; v r f; a w Ge JYprotect v ky fx m; w Jhz dki fa w Gu dk
unpack v ky fw Jht c gr Sma w mh tool r o Hk; b J unpack v ky fw m[ m t q i fha w G t & r f; & Iy fa x G; Ny D; t q i fhw p fq i fh
a v mu fr Sm; c Jh& i f t p u a e jy e fp & w Jht w Gu f t c sde ft v Ge ft r i f; u ke fa p y gw , f/ ' ga Mu mi fhr dkY unpack v ky fw m
jr e fq e fa t mi fv dkY u Re fa w mfw dkYt a e e JY t y kdi f; ( 1 ) u detach v ky fw Jht q i fhu dk a u smfc si fw Jht w Gu f ArmaDetach
1.31 u dko Hk; jc i f; jz p fy gw , f/ w u , fv dkYo i fht a e e JYt a Mu mi f; u dk t a o ; p dw fo dc si f& i fa w mh WaSt3d_ByTes
a & ; w Jh ]Armadillo 4.42 (Debug-Blocker + CopyMem2)} e JY cr assy b mo mjy e fw Jh ]Armadillo &
CopyMem2 Decryption} w dkYu dk z w fy gv dkYn Te f; c si fy gw , f/
a u mi f; Ny D? p v dku fMu & a t mi f/ ArmaDetach 1.31 u dk z Gi fhv dku fy g/ Ny D; & i f u Re fa w mfw dkY unpack
v ky fc si fw JhUnpackMe_ Armadillo 4.4.exe z dki fu dk ArmaDetach x Ju dk drag q GJNy D; o Gi f; v dku fy g/ y Hk( 6 9 ) /
y Hk( 6 9 )
y Hk( 6 9 ) t w dki f; jr i f& w Jha e mu f Olly u dk o D; o e fYz Gi fhy g/ Ny D; & i f File menu u Attach u dka & G; y g/ y Hk( 7 0 ) /
,., Armadillo ... .` .
,
y Hk( 7 0 )
y Hk( 7 0 ) u child process ID jz p fw Jh0A54 u dka & G; Ny D; attach v ky fy g/ y Hk( 7 1 ) t w dki f; jr i f& y gv dr fhr , f/
y Hk( 7 1 )
y Hk( 7 1 ) t w dki f; a w GY& w Jht c gr Sm Run (F9) u dkE Sdy fNy D; Pause (F12) u dka & G; y g/ OEP q Da & mu fv my gr , f/
y Hk( 7 2 )
y Hk( 7 2 ) u JMP a e & mr Sm y Hk( 6 9 ) r Sma w GYw Jh r lv bytes a w Ge JY t p m; x dk; v dku fy g/ ' gq dk y Hk( 7 3 ) t w dki f;
a w GY& y gr , f/
y Hk( 7 3 )
a u mi f; Ny D/ ImpREC u dkz Gi fhy g/ Ny D; & i f y Hk( 7 4 ) t w dki f; v dkt y fw ma v ; a w G& dku fx n fha y ; y g/
y Hk( 7 4 )
,., Armadillo ... .` .
,
y Hk( 7 4 ) u dkMu n fhy g/ w u , fa w mh ' Dy Hkt w dki f; jy i fjy D; dump v ky fr , fq dk& i f y & dk* & r f[ m t v ky fv ky fr Sm
r [ kw fy gb l; / b ma Mu mi fhv n f; q dka w mh u Re fa w mfw dkYt a e e JY import a w Gu dk r jy i f& a o ; v dkYy g/ y Hk( 7 4 ) t w dki f;
ImpREC u dkz Gi fhNy D; import a w Gu dk o Gi f; & w mu import a w G& JU address t p u dk o dc si fv dkYy g/ RVA 60818 u dk
r Sw fx m; y g/ ' gu dk Olly r Sm& SmMu n fhy gr , f/ Olly & JU Dump Windows r Sm Ctrl+G E Sdy fNy D; VA 460818
a e & mu dkMu n fhv dku fy g/ y Hk( 7 5 ) /
y Hk( 7 5 )
y Hk( 7 5 ) r Smjr i f& w Jht w dki f; import a w G[ m r Sm; a e y gw , f/ ' ga Mu mi fh u Re fa w mfw dkYt a e e JY r Se fu e fw Jh
import a w Gu dk o Gi f; Ny D; dump v ky f& y gr , f/
ArmaDetach a e mu fw p fc ku dk x y fz Gi fhv dku fy g/ Ny D; & i f UnpackMe_ Armadillo 4.4.exe z dki fu dk
ArmaDetach x Ju dk drag q GJNy D; o Gi f; v dku fy g/ y Hk( 7 6 ) /
y Hk( 7 6 )
Ny D; & i fa w mhy Hk( 7 0 ? 7 1 ? 7 2 ) w dkYr Sm v ky fa q mi fc Jhw Jht w dki f; v ky fa q mi fy g/
y Hk( 7 2 ) u JMP a e & mr Sm y Hk( 7 6 ) r Sma w GYw Jh r lv bytes a w Ge JY t p m; x dk; v dku fy g/ ' gq dk y Hk( 7 7 ) t w dki f;
a w GY& y gr , f/
y Hk( 7 7 )
' Dha e mu fr Sma w mh import a w Gjy i fz dkYt w Gu f magic jump u dk& Smy gr , f/ y Hk( 7 5 ) r Smv ky fc Jho v dk Olly & JU
Dump Windows r Sm Ctrl+G E Sdy fNy D; VA 460818 a e & mu dkMu n fhv dku fy g/ y Hk( 7 8 ) /
y Hk( 7 8 )
y Hk( 7 5 ) e JY r w lw mu a w mh y Hk( 7 8 ) r Sm 00 00 00 00 a w Go m & Sdy gw , f/ VA 460818 r Sm
Br eakpointHar dwar e, on wr iteByte o w fr Sw fy gr , f/ Ny D; & i f u dkE Sdy fy gr , f/ y x r q Hk; y Hk( 7 9 ) r Sm
& y fo Gm; y gr , f/
y Hk( 7 9 )
,., Armadillo ... .` .
,,
F9 u dk q u fE Sdy fy g/ y Hk( 8 0 ) r Sm & y fo Gm; y gr , f/
y Hk( 8 0 )
y Hk( 8 0 ) & JU t a y : e m; a v ; u dk Mu n fhy g/ u Re fa w mfw dkY& Smc si fw Jhmagic jump u dka w GYy gv dr fhr , f/
y Hk( 8 1 )
y Hk( 8 1 ) u VA CCC1BC [ m u Re fa w mfw dkY & Sma e w Jh import a w Gu dk t r Se fjy i fa y ; r , fh jump
jz p fy gw , f/ VA 460818 r Smo w fr Sw fc Jhw Jh hardware breakpoint u dkjz Kw fNy D; y Hk( 8 1 ) u VA CCC1BC
a e & mr Sm hardware breakpoint o w fr Sw fy g/ ( t x l; o w djy K& r Smu VA CCC1BC a e & m[ m t c sde fe JYt r Q
a jy mi f; v Ja e w w fw my g/ Magic jump a e & m[ m ' Da e Yr Sm VA CCC1BC jz p fa y r , fh a e mu f& u fMu & i f t jc m;
a e & m jz p fa e w w fy gw , f/ )
VA CCC1BC r Sm breakpoint o w fr Sw fNy D; & i f ' kw d, Olly e JY ArmaDetach u dky dw fv dkY& y gNy D/
Ny D; & i fa w mhy Hk( 7 6 ? 7 7 ) t w dki f; t o p fjy e fv ky fy g/ y Hk( 7 7 ) t w dki f; jy i fNy D; & i fa w mhF9 u dkE Sdy fy g/ y Hk( 8 2 ) u hardware
breakpoint & Sd& mq Dw e f; a & mu fv my gr , f/
y Hk( 8 2 )
y Hk( 8 2 ) u JNZ a e & mr Sm JMP v dkYjy i fy g/ VA CCC1BC r Smo w fr Sw fx m; w Jh hardware breakpoint
u dkjy e fjz Kw fy g/
Ny D; & i f CopyMem2 t a e e JY detach v ky fx m; w Jh y x r Olly r Smz Gi fhx m; w Jh dump windows u
import & JUt q Hk; u dk scroll e n f; e n f; q GJNy D; Mu n fhy g/ ( y Hk- 7 5 & JUa t mu fe m; a v ; r Sm jz p fy gw , f/ ) y Hk( 8 3 ) t w dki f;
jr i f& y gr , f/
y Hk( 8 3 )
y Hk( 8 3 ) r Smjr i f& w Jh import & JU t q Hk; address jz p fw Jh 460F1C u dkr Sw fo m; y g/ Ny D; & i f Debug-Blocker
t a e e JY detach v ky fx m; w Jh ' kw d, Olly r Smz Gi fhx m; w Jh dump windows u VA 460F1C r Sm hardware
breakpoint o w fr Sw fy g/ y Hk( 8 4 ) /
y Hk( 8 4 )
y Hk( 8 4 ) u VA 460F1C r Sm Br eakpointHar dwar e, on wr iteDwor d o w fr Sw fNy D; & i f F9
u dkE Sdy fy g/ y Hk( 8 5 ) t w dki f; jy i fx m; w Jhimport a w Ga & mu f& Sdv my gr , f/ y Hk( 8 5 ) /
,., Armadillo ... .` .
,.
y Hk( 8 5 )
y Hk( 8 5 ) t w dki f; jr i f& w Jht c gr Sma w mh y Hk( 8 5 ) & JU VA 460818 u a e VA 460F1C x du dk Binar y
Binar y copy v ky fNy D; y Hk( 7 5 ) r Sm Binar yBinar y paste v ky fy g/ y Hk( 8 6 ) /
y Hk( 8 6 )
y Hk( 8 6 ) r Sma w GY& w mu a w mh Debug-Blocker e JY detach v ky fx m; w Jh Olly r Sm jy i fx m; c Jhw Jh import
a w Gu dk CopyMem2 e JY detach v ky fx m; w Jh Olly r Sm import a w G v mx m; t Ny D; t a e t x m; jz p fy gw , f/
t e Da & mi fa w Ge JYjr i f& w mu a w mh r lv t a e t x m; e JY a jy mi f; v Jo Gm; w Jh import a w Gjz p fy gw , f/ ' gq dk ' kw d, Olly
e JYArmaDetach u dky dw fv dkY& y gNy D/
Import a w Gv Jjy i fNy D; Ny Djz p fw Jht w Gu f y & dk* & r fu dk dump v ky fy gr , f/ LordPE ( o dkY) dumper
a q mhz f0 Jv fw p fc kc ke JYdump v ky fv dku fy g/ y Hk( 8 7 ) /
y Hk( 8 7 )
Ny D; & i fa w mhdump v ky fx m; w Jhz dki fu dk import a w Gjy i fq i fy gr , f/ y Hk( 8 8 ) /
y Hk( 8 8 )
y Hk( 8 8 ) u dkMu n fhy g/ IAT AutoSear ch button u dkE Sdy fv dku fw me JYRVA w e fz dk; e JYSize w dkYu dk ImpREC
u o lUt v dkv dk x n fho Gm; y gw , f/ ' Dw e fz dk; a w Gu dk jy i fa y ; & a t mi fv dkYy Hk( 8 9 ) u dkMu n fhy g/
,., Armadillo ... .` .
,.
y Hk( 8 9 )
u Re fa w mfw dkYo dx m; w mu RVA w e fz dk; u 60818 u p y gw , f/ 60F1F r Smq Hk; y gw , f/ ' ga Mu mi fho lU& JU
size [ m 708 jz p fy gw , f/ ' ga Mu mi fh y Hk( 8 8 ) u RVA a e & mr Sm 60818 v dkYjy i fNy D; Size a e & mr Sm 708 v dkYjy i fNy D;
Get Impor ts button u dkE Sdy fy g/ Ny D; & i f Show Invalid button u dkE Sdy fy g/ Invalid jz p fa e w Jh thunk a w G
u se fy ga o ; w , f/ ' Dthunk a w Gu dk Cut thunk(s) e JY & Si f; x kw fv dku fy g/ Ny D; & i f Fix Dump button u dkE Sdy fNy D;
c ke u dump v ky fx m; w Jhz dki fu dk fix v ky fy gr , f/ Fix v ky fx m; w Jhz dki fu dk z Gi fhv dku f& i fa w mh y Hk( 9 0 ) t w dki f; jr i f& y g
r , f/
y Hk( 9 0 )
' gq dk& i fa w mh Armadillo 4.40 (Debug-Blocker+CopyMem2) e JY protect v ky fx m; w Jhz dki fu dk
a t mi fjr i fp Gm unpack v ky fE dki fNy Djz p fy gw , f/
u Re fa w mfw dkYt a e e JY Armadillo & JU t a jc c Ht u sq Hk; protection a w Gu dk Armadillo 4.4 e JY e r le m
unpack v ky fjy c Jhy gw , f/ o i fr Sw fx m; z dkYu a w mh Armadillo version a jy mi f; c Jh& i f t a jc c Hv Sn fhp m; c su ft c sdKU
v n f; a jy mi f; v n f; w w fw mu dky g/
' Dw p fc gr Sma w mh Armadillo & JU custom build r Smy g& Sdw Jh t q i fhjr i fh protection a w Gu dk a v hv m
Mu n fhMu & a t mi f/
, Standar d Pr otection + Str ategic Code Splicing - .-. ..` .
' Dw p fc gr Sma w mh Standard Protection + Strategic Code Splicing e JY protect v ky fx m; w Jh
Armadillo 4.4 z dki fu dk unpack v ky fMu n fhy gr , f/
INFO: : Strategic Code Splicing q dkw mu a w mh dump r v ky fE dki fa t mi f w m; q D; w Jh e n f; v r f; w p fc kjz p fNy D;
Strategic Code Splicing u o i fh& JUu k' fa w Gu dk r Sw fOmP f& JU a e & mt E SHYt jy m; r Sm o Gm; x m; v dku fy gw , f/
u k' fa w Gu dkv n f; a jy mi f; v Jy p fv dku fw Jht w Gu f t v ky fv ky fy Hku a w mh w ln Dr Smjz p fa y r , fhv n f; u k' fa w Gu a w mh
a jy mi f; v Jo Gm; r Smjz p fy gw , f/
t x l; o w da y ; v dkw mu CopyMemII e JY protect v ky fx m; w Jh y & dk* & r fa w Gu dk unpack v ky fw Jht c gr Sm
memory u dka p mi fhMu n fhw JhAnti-virus a q mhz f0 Jv fa w Ge JYFirewall a q mhz f0 Jv fa w Gu dk y dw fx m; a y ; z dkYy g/
' Do i fc e f; p mr Sm t o Hk; jy Kr , fh Armadillo e JY protect v ky fx m; w Jh e r le mz dki fu a w mh UnpackMe_
Armadillo 4.4.exe jz p fy gw , f/ http://myanmarcrackingteam.blog.com r Sm download v ky f, lE dki fy g
w , f/ ' Do i fc e f; p mt w Gu f v dkt y fw Jhtool u a w mhArmInline 0.96f jz p fy gw , f/
, IAT - ` ` .
a u mi f; Ny D/ UnpackMe_ Armadillo 4.4.exe u dk Olly e JYz Gi fhv dku fy g/ y Hk( 9 1 ) /
y Hk( 9 1 )
,., Armadillo ... .` .
,
y Hk( 9 1 ) t w dki f; jr i f& w Jht c gr Sm OEP u dk& Smz dkY Mu dK; p m; y gr , f/ a & SUt y dki f; a w Gw ke f; u VirtualProtect e JY
CreateThread w dkYu dk breakpoint o w fr Sw fc Jha y r , fh c kc sde fr Sma w mh CreateThread u dko m breakpoint
o w fr Sw fy ga w mhr , f/ b ma Mu mi fhv n f; q dka w mh VirtualProtect u dk breakpoint o w fr Sw fc Jhw mu IAT
u dkjy i fz dkYmagic jump u dk& Smc si fv dkYy g/ F9 u dkE Sdy fy g/ y Hk( 9 2 ) q Da & mu fv my gr , f/
y Hk( 9 2 )
y Hk( 9 2 ) t w dki f; jr i f& w Jht c gr Sm y Hk( 9 3 ) t w dki f; jr i f& o n ft x dF8 u dkE Sdy fv mc Jhy g/
y Hk( 9 3 )
y Hk( 9 3 ) u CALL ECX u dka & mu fw Jht c g F7 u kdE Sdy fy g/ ' g[ m u Re fa w mfw dkY& Sma e w Jh OEP jz p fy gw , f/
( a & SUy dki f; o i fc e f; p ma w Gr Smv n f; a q G; a E G; Ny D; jz p fy gw , f/ )
y Hk( 9 4 )
c kt a e t x m; [ m Standard Protection t w Gu f OEP & Smc Jhw Jh t a e t x m; y J & Sdy ga o ; w , f/ IAT
u dkjy i fz dkYe JYStrategic Code Splicing u dkjy i fz dkYu se fa o ; w m t r Sw f& y g/
y Hk( 9 4 ) & JU a t mu fe m; a v mu fu dk scroll q GJNy D; Mu n fhv dku fy g/ y Hk( 9 5 ) /
y Hk( 9 5 )
y Hk( 9 5 ) r Smjr i f& w mu a w mh Strategic Code Splicing q dkw my gy J/ u k' fa w Gu dk r Sw fOmP f& JU a e & m
t E SHYt jy m; r Sm o Gm; x m; x m; y gw , f/ Ny D; & i f u Re fa w mfw dkY& JUu k' fa w Gu dkv n f; t jc m; u k' fa w Ge JY t p m; x dk; x m;
y gw , f/ y dkNy D; t a o ; p dw fo dE dki fa t mi fv dkYMemory Map (Alt+M) u dka c : Mu n fhy gr , f/ y Hk( 9 6 ) /
y Hk( 9 6 )
,., Armadillo ... .` .
,
y Hk( 9 5 ) u n Te f; x m; w Jh jump address a w G[ m UnpackMe z dki fx Jr Sm r & Sdy gb l; / y Hk( 9 6 ) r Sm jr i f& w Jh
t w dki f; t jc m; w p fa e & mr Sm& Sda e y gw , f/ w u , fa w mh y Hk( 9 6 ) r Smjr i f& w Jh 18E0000 y gw Jh section u dk dump
v ky fNy D; UnpackMe z dki fx Jr Sm v mx n fhNy D; v dkt y fw Jh t c su ft v u fa v ; a w Gjy i fq i fv dku f& i f Strategic Code
Splicing u dka u smfv Tm; E dki fy gw , f/ ' ga y r , fhu Re fa w mfht a e e JY' Dx u fy dkv G, fw mu dk jy c si fy gw , f/
, IAT -``.
' Dv dkr jy c i fr Sm IAT u dk jy i fz dkYv ky fy gr , f/ a e mu fx y f Olly w p fc ke JY UnpackMe z dki fu dkz Gi fhv dku fy g/
Dump windows u VA 460818 a e & mr Sm Br eakpointHar dwar e, on wr iteByte e JYbreakpoint
o w fr Sw fy g/ y Hk( 9 7 ) /
y Hk( 9 7 )
b ma Mu mi fh ' Da e & mr Sm breakpoint o w fr Sw f& o v Jq dkw m a & SUt c e f; a w Gr Sm & Si f; jy Ny D; jz p fy gw , f/ Ny D; & i f
F9 E Sp fc gE Sdy fy g/ y Hk( 9 8 ) t w dki f; a w GY& y gr , f/
y Hk( 9 8 )
y Hk( 9 8 ) u dka & mu fw Jht c g t a y : e m; a v mu fu dk Mu n fhy g/ y Hk( 9 9 ) /
y Hk( 9 9 )
y Hk( 9 9 ) u VA CDC1BC a e & m[ m u Re fa w mfw dkYjy i f& r , fh magic jump y g/ VA 460818 r Sm
o w fr Sw fx m; w Jh hardware breakpoint u dkjz Kw fNy D; VA CDC1BC r Sm hardware breakpoint o w fr Sw fy g/
Ctrl+2 (Restart) u dkE Sdy fNy D; Olly u dkjy e fp y g/ Ny D; & i f F9 u dkE Sdy fy g/ VA CDC1BC q Dw e f; a & mu fv my gr , f/
y Hk( 1 0 0 ) /
y Hk( 1 0 0 )
y Hk( 1 0 0 ) u JNZ a e & mr Sm JMP v dkYjy i fNy D; VA CDC1BC r Sm o w fr Sw fx m; w Jhhardware breakpoint
u dkjz Kw fy g/
y Hk( 1 0 1 )
y Hk( 1 0 1 ) u VA 460F1C r Sm Br eakpointHar dwar e, on wr iteDwor d o w fr Sw fy g/ Ny D; & i f
F9 u dkE Sdy fy g/ ' gq dky Hk( 1 0 2 ) t w dki f; import a w Gu dk jy i fq i fNy D; o Gm; y gNy D/
y Hk( 1 0 2 )
,., Armadillo ... .` .
,
' kw d, Olly & JU dump windows u import a w Gu dk 460818 u a e 460F1C x d binary u l; y g/
y x r Olly u dump windows r Sm paste v ky fNy D; t p m; x dk; y g/
y Hk( 1 0 3 )
y Hk( 1 0 3 ) r Smjr i f& w Jht w dki f; import a w Gu dk jy i fq i fNy D; w m a w GY& y gr , f/
, Str ategic Code Splicing - ` ` .
Import a w Gjy i fNy D; w Jha e mu fr Sma w mh w p fp p D u GJa e w Jhu k' fa w Gu dk jy i fy gr , f/ ' kw d, Olly u dky dw fNy D;
ArmInline u dkz Gi fhy g/
y Hk( 1 0 4 )
ArmInline u dkz Gi fhNy D; u Re fa w mfw dkY jy i fc si fw Jh process u dka & G; y gr , f/ ' Dt c g y Hk( 1 0 4 ) t w dki f;
ArmInline u v dkt y fw Jh t c su ft v u fa w Gu dk o lU[ mo mo l & SmNy D; x n fho Gm; y gw , f/ y Hk( 9 6 ) u dkMu n fhy g/
y Hk( 1 0 4 ) u Length of Spliced Code a e & mr Sm 10000 t p m; 20000 v dkYjy i fa y ; y g/ Ny D; & i f Remove Splices
u dkE Sdy fy g/
y Hk( 1 0 5 )
y Hk( 1 0 5 ) r Sma w GY& w Jht w dki f; u k' fa w Gu dk a e & m 2057 a e & mx d c GJx kw fx m; w mu dk ArmInline u
jy i fa y ; v dku fy gw , f/
a u mi f; Ny D/ y Hk( 9 5 ) u VA 427480 a e & mu dk Olly r Smo Gm; Mu n fhv dku fy g/ y Hk( 9 5 ) e JY r w la w mhw m
a w GY& y gr , f/
y Hk( 1 0 6 )
y Hk( 1 0 6 ) t w dki f; a w GYw Jht c gr Sma w mh u Re fa w mfw dkY& JU y & dk* & r fu dk dump v ky fv dkY& Ny Djz p fy gw , f/ Dump
v ky fz dkYt w Gu f LordPE e JYdump v ky fv dku fy g/ ( y Hk- 8 7 r Sm & Si f; jy Ny D; jz p fy gw , f/ )
Dump z dki fu dk b , fv dkjy i f& r v Jq dkw mu a w mhy Hk( 8 8 ? 8 9 ) r Sm t a o ; p dw f & Si f; jy x m; y gw , f/ o i fc e f; p m
& Sn fr Smp dk; w Jht w Gu f r & Si f; jy a w mhy gb l; /
' Dt q i fha w Gt m; v Hk; v ky fa q mi fNy D; w Jht c sde fr Sma w mhy Hk( 1 0 7 ) t w dki f; jr i f& r Smjz p fy gw , f/
,., Armadillo ... .` .
,
y Hk( 1 0 7 )
CopyMem2 + Debug-Blocker + Strategic Code Splicing u dka w mh u Re fa w mfht a e e JY r & Si f; jy
v dka w mhy gb l; / Standard Protection a e & mr Sm CopyMem2 + Debug-Blocker o i fc e f; p me JY t p m; x dk;
E dki fv dkYy g/ r q dkp a v mu fy J u GJv GJr I& Sdy gr , f/ o i fht a e e JYu dk, fw dki f unpack v ky fE dki fr , fv dkYa r Qmfv i fhy gw , f/
, CopyMem2 + Debug-Blocker + Impor t Table Elimination - .-. ..` .
' Dw p fc gr Sma w mh CopyMem2 + Debug-Blocker + Import Table Elimination a w Ge JY protect
v ky fx m; w JhArmadillo 4.4 z dki fu dk unpack v ky fMu n fhy gr , f/
INFO: : Import Table Elimination q dkw mu a w mh dump r v ky fE dki fa t mi f w m; q D; w Jh e n f; v r f; w p fc kjz p fNy D;
y & dk* & r f& JU import table u dk z , f& Sm; z su fq D; v dku fw Jht w Gu f import a w Gu dk jy e fv n fw n fa q mu f& mr Sm
t c u fa w GYa p r Sm jz p fy gw , f/
t x l; o w da y ; v dkw mu CopyMemII e JY protect v ky fx m; w Jh y & dk* & r fa w Gu dk unpack v ky fw Jht c gr Sm
memory u dka p mi fhMu n fhw JhAnti-virus a q mhz f0 Jv fa w Ge JYFirewall a q mhz f0 Jv fa w Gu dk y dw fx m; a y ; z dkYy g/
' Do i fc e f; p mr Sm t o Hk; jy Kr , fh Armadillo e JY protect v ky fx m; w Jh e r le mz dki fu a w mh UnpackMe_
Armadillo 4.4.exe jz p fy gw , f/ http://myanmarcrackingteam.blog.com r Sm download v ky f, lE dki fy g
w , f/ ' Do i fc e f; p mt w Gu f v dkt y fw Jhtool u a w mhArmaDetach 1.31 e JYArmInline 0.96f w dkYjz p fy gw , f/
ArmaDetach u dkz Gi fhNy D; unpack v ky fr , fhUnpackMe z dki fu dk drag v ky fy g/ y Hk( 1 0 8 ) /
y Hk( 1 0 8 )
y Hk( 1 0 8 ) r Sma w GY& w Jht w dki f; unpackme z dki fu dk import table elimination e JYprotect v ky fx m; y gw , f/
' ga Mu mi fh a & SUo i fc e f; p ma w Gr Sm import a w Gu dk jy i fq i f& mr Sm u Re fa w mfw dkYt o Hk; jy Kc Jhw Jh magic jump e n f; v r f;
( o dkY) PUSH 100 e n f; v r f; w p fc kw n f; u dk ' Da e & mr Sm t o Hk; jy Kv dkYr & a w mhy gb l; /
Olly e JY UnpackMe z dki fu dk attach v ky fy g/ jy D; & i f OEP a e & mr Sm y Hk( 1 0 9 ) t w dki f; jy i fy g/ a & SUt y dki f;
a w Gr Sm & Si f; jy Ny D; jz p fv dkYt a o ; p dw f r & Si f; a w mhy gb l; /
y Hk( 1 0 9 )
,., Armadillo ... .` .
,,
y Hk( 1 0 9 ) & JUa t mu fe m; u dk e n f; e n f; scroll q GJMu n fhy g/ y Hk( 1 1 0 ) /
y Hk( 1 1 0 )
y Hk( 1 1 0 ) u D73C98 [ m imagebase & JUw e fz dk; x u f t r sm; Mu D; Mu D; a e y gw , f/ ' g[ m import table
u dkz su fNy D; Armadillo & JU DLL z dki fx Jr Sm import a w Gu dk o dr f; x m; v dkYjz p fy gw , f/ CALL DWORD PTR
DS:[D73C98] a y : right-click E Sdy fNy D; Follow in Dump Memor y addr ess u dka & G; y g/ y Hk( 1 1 1 ) t w kdi f;
jr i f& y gr , f/
y Hk( 1 1 1 )
y Hk( 1 1 1 ) u dk o w dx m; Mu n fhy g/ a & SUo i fc e f; p ma w Gw ke f; u v dk import a w G[ m VA 460818 u a e p w m
r [ kw fw m o w djy Kr dr Smy g/ Ny D; & i f import a w G[ m DLL t p Ofv dku fr [ kw fb J random jz p fa e w m o w djy Kr d
r Smy g/ Import Table Elimination u dko Hk; v dkY ' Dv dkjz p fo Gm; w my g/ y Hk( 1 1 1 ) u Dump windows r Sm import
a w G& JUt p e JY t q Hk; u dk & SmNy D; r Sw fo m; y g/ VA 0DB3B00 u gdi32.GetViewportExtEx (77F17CF1) e JU
VA 00DB4408 u user32.RemovePropA w dkYjz p fy gw , f/ ' ga Mu mi fhlength [ m 90C jz p fy gw , f/
' Dw p fc gr Sma w mh a e mu fx y f ArmaDetach u dkz Gi fhNy D; unpack v ky fr , fh UnpackMe z dki fu dk drag
v ky fy g/ y Hk( 1 1 2 ) /
y Hk( 1 1 2 )
Olly e JY UnpackMe z dki fu dk attach v ky fy g/ jy D; & i f entry point a e & mr Sm y Hk( 1 1 3 ) t w dki f; jy i fy g/
a & SUt y dki f; a w Gr Sm & Si f; jy Ny D; jz p fv dkYt a o ; p dw f r & Si f; a w mhy gb l; /
y Hk( 1 1 3 )
VirtualProtect e JY CreateThread w dkYr Sm breakpoint o w fr Sw fy g/ Ny D; & i f y Hk( 1 1 4 ) t w dki f; Stack
Windows r Smjr i f& o n ft x dF9 u dkE Sdy fy g/
y Hk( 1 1 4 )
,., Armadillo ... .` .
,
, IAT - ` ` .
y Hk( 1 1 4 ) t w dki f; jr i f& w Jht c gr Sm VirtualProtect r Smo w fr Sw fx m; w Jh breakpoint u dkjz Kw fNy D; F8 u dk
E Sdy fy g/ y Hk( 1 1 5 ) /
y Hk( 1 1 5 )
y Hk( 1 1 5 ) t w dki f; jr i f& w Jht c gr Sma w mh PUSH 100 e n f; e JY IAT u dkjy i fy gr , f/ Code Windows r Sm
Ctrl + F5 E Sdy fNy D; PUSH 100 u dk& dku fx n fhNy D; & Smy g/
y Hk( 1 1 6 )
y Hk( 1 1 5 ) t w dki f; a w GY& w Jht c gr Sma w mhVA CA2310 u PUSH EBP a e & mr Sm RETN v dkYjy i fv dku fy g/
Ny D; & i f F9 u dkE Sdy fy g/ y Hk( 1 1 6 ) q Dr Sm & y fo Gm; y gr , f/
y Hk( 1 1 7 )
Ny D; & i fa w mh a & SUo i fc e f; p ma w Gr Sm v ky fc Jho v dk CreateThread breakpoint u dkjz Kw fNy D; CALL ECX
& Sd& mx dF8 u dkE Sdy fv my g/ CALL ECX & Sd& ma & mu fw Jht c g F7 u dkE Sdy fy g/ y Hk( 1 1 8 ) t w dki f; a w GY& y gr , f/
y Hk( 1 1 8 )
, Impor t Table Elimination - ` ` .
y Hk( 1 1 8 ) u dkMu n fhy g/ y Hk( 1 0 9 ) e JY u k' fc si f; r w lw m a w GY& r Smy g/ CopyMem2 u dko Hk; x m; w Jht w Gu f
u k' fa w Gu dk encrypt v ky fx m; w ma Mu mi fh OEP e m; u u k' fa w G r w lw mjz p fy gw , f/ t o Hk; jy Kz dkY v dkt y fr So m
decrypt v ky fNy D; u se fw Jht c sde fr Sm encrypt jy e fv ky fy gw , f/
a u mi f; Ny D/ y Hk( 1 1 8 ) t w dki f; jr i f& w Jht c gr Sm Alt + M u dkE Sdy fNy D; memory windows r Sm F1 7C F1 77
u dk& Smy gr , f/ ' g[ m GetViewportExtEx & JU import address jz p fy gw , f/
y Hk( 1 1 9 )
' gq dk y Hk( 1 2 0 ) t w dki f; a w GY& y gr , f/
,., Armadillo ... .` .
,
y Hk( 1 2 0 )
y Hk( 1 1 6 ) r Sm right-click E Sdy fNy D; LongAddr ess u dka & G; v dku fy g/ y Hk( 1 2 1 ) /
y Hk( 1 2 1 )
y Hk( 1 2 1 ) & JU import a w Gu dk VA 00DD3B00 u a e VA 00DD4408 x d Binar yBinar y copy
v ky fNy D; y Hk( 1 1 1 ) r Sm Binar yBinar y paste v ky fy g/ y Hk( 1 2 2 ) /
y Hk( 1 2 2 )
y Hk( 1 2 2 ) u dkMu n fhw Jht c g y Hk( 1 1 0 ) e JYr w la w mhb J kernel32.GetVersion v dkYa y : v mw m a w GY& r Smy g/
Import a w Gu dka w mh jy i fNy D; o Gm; y gNy D/ ' ga y r , fh import a w Gu dko dr f; q n f; & m data segment & JU virtual
address [ m imagebase (400000) y w f0 e f; u si fe m; r [ kw fb J t & r f; Mu D; a e y gw , f/ q dkv dkw mu Armadillo
u o lt v ky fv ky fa e c sde fr Sm import a w Gu dk memory x Ju DLL z dki fw p fc kc ku a e a c : o Hk; a e v dkYy g/ w u , fv dkY
' Dt a e t x m; t w dki f; dump v ky fc Jhr , fq dk& i f ' D DLL z dki fu dk dump r v ky fE dki fw Jht w Gu f u Re fa w mfw dkY& JU
y & dk* & r f[ m t v ky fv ky fr Sm r [ kw fy gb l; / ' ga Mu mi fh ' gu dk jy i f& y gr , f/ ArmaInline u dkz Gi fhy g/ ( Debug-
Blocker t a e e JYdateach v ky fx m; c Jhw JhOlly e JYArmaDetach w dkYu dk y dw fv dkY& y gNy D/ )
y Hk( 1 2 3 )
y Hk( 1 2 2 ) u dkMu n fhy g/ ArmaInline u IAT & JU base u dk r Sm; x n fhx m; y gw , f/ Length [ mv n f;
r Sm; a e y gw , f/ ' ga Mu mi fh DB3AFC a e & mr Sm DB3B00? 324 a e & mr Sm 90C v dkYjy i fv dku fNy D; Rebase IAT
button u dkE Sdy fv dku fy g/ y Hk( 1 2 4 ) t w dki f; jr i f& y gr , f/
,., Armadillo ... .` .
,,
y Hk( 1 2 4 )
' Dha e mu fr Sma w mhy Hk( 1 2 5 ) u dkMu n fhy gr , f/
y Hk( 1 2 5 )
y Hk( 1 2 5 ) u dkMu n fhv dku fw Jht c g t & i f DBxxxx e JYp w Jh import a w G[ m 46xxxx e JYp w ma w GY& y gw , f/
' gq dk& i fa w mh u Re fa w mfw dkYt a e e JY Import Table Elimination u dk a u smfv Tm; E kdi fNy D jz p fy gw , f/ y & dk* & r fu dk
LordPE e JY dump v ky fNy D; ImpREC e JYjy i fv dku f& Hky gy J/ ImpREC r Smv n f; b m* P e f; r Sjy i fp & m r v dka w mhy g
b l; / ImpREC e JYjy i fx m; w Jhz dki fu dk z Gi hfv dku f& i f y Hk( 1 2 6 ) t w dki f; jr i f& r Smjz p fy gw , f/
y Hk( 1 2 6 )
,, CopyMem2 + Debug-Blocker + Memor y Patching Pr otection - .-. ..` .
' Do i fc e f; p mu a w mh CopyMem2 + Debug-Blocker e JY unpack v ky fw Jhe n f; t w lw ly Jjz p fw mr dkY
r a q G; a E G; a w mhy gb l; /
., Debug-Blocker + Impor t Table Elimination + Memor y Patching Pr otection + Str ategic
Code Splicing + Random PE Names + Nanomites - .-. ..`.
' Dw p fc g a q G; a E G; v dkw mu a w mh Nanomites protection jz p fa y r , fh Nanomites o D; o e fYe JY protect
v ky fx m; w Jh Armadillo z dki fu dk & Sma z G& w m t q i fr a jy w ma Mu mi fh u se fw Jh protection a w Ge JYa & mx m; w Jh Easy
CD-DA Extractor 2010.6 a q mhz f0 Jv fu dky J a & G; c s, fv dku fy gw , f/ ' Da q mhz f0 Jv fu dk Armadillo 8.0 e JYprotect
v ky fx m; w m jz p fy gw , f/ a & SUy dki f; o i fc e f; p ma w Gr Sm t o Hk; jy Kc Jhw Jhz dki fa w Gu dk Armadillo 4.x e JY protect v ky fx m;
w mjz p fNy D; ArmaGeddon w dkYv dk? DilloDie w dkYv dk generic unpacker a w Gt r sm; Mu D; a y : x Gu fv mc Jhw ma Mu mi fh
c kc sde fr Sma w mh Armadillo 4.x u dk o dy ft o Hk; r jy KMu a w mhy gb l; / u Re fa w mfht a e e JY 2 0 1 1 ? ' DZ i fb mr Sm x Gu f& Sdw Jh
Armadillo 8.6 e JY protect v ky fx m; w Jh Easy CD-DA Extractor 15.3.2 z dki fu dk unpack v ky fjy c si fy gw , f/
' ga y r , fho lu Nanomites u dk t o Hk; r jy Kx m; w Jht w Gu f ' Do i fc e f; p mr Sm t o Hk; jy Kz dkYt q i fr a jy y gb l; / ' ga Mu mi fh
o i fht a e e JY o dx m; & r Smu 8.0 u a e 8.6 t x d Armadillo e JY protect v ky fx m; w Jhz dki fa w Gu dk unpack
v ky fw Jhe n f; u t w lw ly J q dkw mu dky g/ Armadillo 8.x r Smt o Hk; jy Kw Jhe n f; a w G[ m Armadillo 4.x e JY
t a jc c Ht m; jz i fha w mh w ln Dy gw , f/ r o dr o ma v ; y J u GJv GJr I& Sda y r , fh a & SUt y dki f; a w Gr Sm & Si f; jy z dkY u se fc Jhw Jh
t a Mu mi f; t & mt c sdKUu dk x y fr Hx n fho Gi f; & Si f; jy x m; w Jht w Gu f o i fc e f; p mu dk * & kw p dku f z w f& Ia p v dky gw , f/
' Do i fc e f; p mu dko m e m; v n fc Jhr , fq dk& i f Armadillo e JYprotect v ky fx m; w Jhb , fz dki fu dkr q dk o i fht a e e JYunpack
v ky fE dki fr Sm jz p fy gw , f/
a u mi f; Ny D/ Unpack p v ky fMu & a t mi f/ ArmaDetach u Armadillo 8.x e JYprotect v ky fx m; w Jhz dki fu dk
detach r v ky fE dki fy gb l; / ImpREC [ m Armadillo 8.x e JY protect v ky fx m; w Jhz kdi fu dk import jy i f& mr Sm
jy e mt c sdKU& Sdw Jht w Gu f o lUu dkv n f; t o Hk; r jy KE dki fy gb l; / ' Do i fc e f; p mr Sm t o Hk; jy Kr , fh tool a w Gu a w mh
Import Fixer 1.6? ArmInline 0.96f? LordPE e JYArmadillo Nanomites Fixer 1.3 w dkYjz p fy gw , f/
a u mi f; Ny D/ ezcddax.exe z dki fu dk Olly e JYz Gi fhy g/ y Hk( 1 2 7 ) /
,., Armadillo ... .` .
,.
y Hk( 1 2 7 )
y Hk( 1 2 7 ) r Smjr i f& w mu a w mhentry point jz p fy gw , f/
., Debug-Blocker -.-. ..`.. OEP -..`.
Debug-Blocker u dk Armadillo r Sm t o Hk; jy K& w Jh t a Mu mi f; & i f; u a w mh pack v ky fx m; w Jhz kdi fu dk
y dkNy D; x de f; c sKy fr I & , lc si fv dkY jz p fy gw , f/ t a jc c Ht m; jz i fh Debug-Blocker [ m child process u dk debug
v ky fr , fh parent process u dkz e fw D; y gw , f/ w u , fv dkY u Re fa w mfw dkYt a e e JY u Re fa w mfw dkY& JU target z dki fu dk Olly
r Sm debug v ky fNy D; protector u dk r v Sn hfp m; c Jhb l; q dk& i f u Re fa w mfw dkY a & SUa v Qmu fjr i fa e & r Smu debugger
(parent process) & JUu k' fa w Gy J jz p fa e r Smy g/ Pack v ky fx m; w Jh w u , fh application & JUu k' fu dka w mh jr i f& r Sm
r [ kw fy gb l; / ' ga Mu mi fh Debug-Blocker e JY protect v ky fx m; w Jhu k' fa w Gu dk u Re fa w mfw dkYt a e e JY unpack
v ky fc si fw , fq dk& i f parent process u dk access v ky f& r Sm r [ kw fb J child process u dk access v ky fy dki fc Gi fh
& & Sd& r Smjz p fy gw , f/
y Hk( 1 2 7 ) u dkMu n fhy g/ y Hkr Se ft m; jz i fhparent process & JU entry point [ m .adata section r Sm& Sdy gw , f/ ' D
section [ m ' kw d, exe z dki f& JU data section jz p fy gw , f/ ' ga Mu mi fh y Hk( 1 2 7 ) r Smjr i f& w Jh u k' fa w G[ m .text1
section x Jr Sm& Sdw Jh ' kw d, exe z dki fu dk t v ky fv ky fa p E dki fz dkY t Mu dKjy i fa y ; & w Jh loader v dkY , lq E dki fy gw , f/ .text
section r Sm& Sdw Jh y x r exe z dki fu a w mh w u , fh application jz p fy gw , f/ ' ga Mu mi fh u Re fa w mfw dkY unpack
v ky fr , fh ezcddax.exe z dki fr Sma w mh b , f section a w G[ m b mjz p fw , fq dkw m r o dE dki fa t mi f Random PE
Names protection u dko Hk; Ny D; section e mr n fa w Gu dk random e mr n fa w Ga y ; x m; w m jz p fy gw , f/ y Hk( 1 2 8 ) /
y Hk( 1 2 8 )
Armadillo 8.x & JU Debug-Blocker u dk a u smfv Tm; E dki fz dkYt w Gu f u Re fa w mfw dkYt a e e JY OpenMutexA
API u dk t o Hk; jy K& y gr , f/
The OpenMutex function returns a handle of an existing named mutex object.
HANDLE OpenMutex(
DWORD dwDesiredAccess, // access flag
BOOL bInheritHandle, // inherit flag
LPCTSTR lpName // pointer to mutex-object name
);
w u , fv dkY OpenMutex function [ m a t mi fjr i fp Gm v ky fa q mi fE dki fc Jhr , fq dk& i f return jy e fy dkYr , fh
w e fz dk; [ m mutex object & JU handle w e fz dk; jz p fNy D; v ky fa q mi fc su f[ m FAIL jz p fc Jhr , fq dk& i f NULL w e fz dk; u dk
y dkYr Smjz p fNy D; error jz p f& w Jht a Mu mi f; u dk GetLastEr r or function o Hk; Ny D; p Hkp r f; r Smjz p fy gw , f/
OpenMutex [ m w ln Dw Jh mutex object a w G& JU handle a w Gu dk z Gi fhz dkY t r sm; Mu D; u dk c Gi fhjy Ky gw , f/
& S, f, mv ky fx m; w Jh resource w p fc ku dk thread ( o dkY) process t r sm; Mu D; u w jy dKi fe u fw n f; & , ljc i f; u
u mu G, fz dkY mutex object a w Gu dk t o Hk; jy Ky gw , f/ MutexName r Sm process ID e JY DANumber w p fc k
y g0 i fy gw , f/ ( Oy r m - FF4::DAAF4DE502) / Armadillo u Cr eateMutex e JY z e fw D; x m; jc i f; r & Sdw Jh
mutex w p fc ku dk b ma Mu mi fh z Gi fhz dkY Mu dK; p m; a e & w my go v J/ & dk; & dk; a v ; y gy J? ' Dmutex u dk child process x Jr Sm
v n f; y J p p fa q ; y gv dr fhr , f/ ' ga Mu mi fhr dkY v u f& Sd process [ m parent mode r Sm t v ky fv ky fa e w mv m; ? child
mode r Sm t v ky fv ky fa e w mv m; q dkw mu dk process u o da e y gw , f/ w u , fv dkY mutex [ m r & Sdc Jhb l; q dk& i f
process [ m parent jz p fy gv dr fhr , f/ & Sda e c Jh& i fa w mh child jz p fy gw , f/ u Re fa w mfw dkYt a e e JY parent process
[ m run a e o n fhw dki f child process u t v ky fv ky fa e w , fv dkY protector u , HkMu n fa t mi f
v Sn hfp m; & y gv dr fhr , f/ ' ga Mu mi fh OpenMutexA & JU a e mu fq Hk; byte a w Gr Sm breakpoint o w fr Sw fy gr , f/
o i fht a e e JY a e mu fq Hk; byte a w Gr Sm breakpoint o w fr Sw fz dkY t a & ; Mu D; y gw , f/ b ma Mu mi fhv n f; q dka w mh
Armadillo u API t c sdKU& JU y x r q Hk; 5 bytes r Sm INT3 (CC) a w G& Sd? r & Sdp p fa q ; v dkYjz p fNy D; a w GY& Sdc Jh& i f error
w u fNy D; process u dkNy D; q Hk; a p r Sm jz p fy gw , f/
,., Armadillo ... .` .
,.
y Hk( 1 2 9 )
Breakpoint o w fr Sw fNy D; F9 u dkE Sdy f& i f y Hk( 1 2 9 ) t w dki f; jr i f& y gr , f/ a e mu fw p fMu dr f F9 u dk x y fE Sdy fy g/
y Hk( 1 3 0 ) /
y Hk( 1 3 0 )
y Hk( 1 3 0 ) t w dki f; jr i f& w Jht c gr Sma w mh EAX w e fz dk; u dk 0 u a e 1 v kdY a jy mi f; y gr , f/ Ny D; & i f RETN 0C
r Smo w fr Sw fx m; w Jhbreakpoint u dkjz Kw fv dku fy g/ ' gq dk Debug-Blocker u dk a u smfv Tm; E dki fNy Djz p fy gw , f/
c kc sde fr Sma w mhOEP u dk & Smy gr , f/ OEP u dk& Smz dkYCr eateThr ead r Sm breakpoint o w fr Sw fy gr , f/
The Cr eateThr ead function creates a thread to execute within the address space of the calling process.
HANDLE Cr eateThr ead(
LPSECURITY_ATTRIBUTES lpThreadAttributes, // pointer to thread security attributes
DWORD dwStackSize, // initial thread stack size, in bytes
LPTHREAD_START_ROUTINE lpStartAddress, // pointer to thread function
LPVOID lpParameter, // argument for new thread
DWORD dwCreationFlags, // creation flags
LPDWORD lpThreadId // pointer to returned thread identifier
);
y Hk( 1 3 1 )
Cr eateThr ead [ m u dk, fa c : o Hk; a e w Jh process & JU a e & mv Gw fw p fc kr Sm t v ky fv ky fa p r , fh thread
w p fc ku dk z e fw D; w m jz p fy gw , f/ Cr eateThr ead r Sm breakpoint o w fr Sw fNy D; & i f F9 u dkE Sdy fy g/
y Hk( 1 3 2 )
F9 u dkE Sdy fw Jht c g y Hk( 1 3 2 ) t w dki f; jr i f& y gr , f/ F9 u dk y Hk( 1 3 3 ) t w dki f; jr i f& w Jht x d q u fE Sdy fy g/
rpct4.dll? ole32.dll p w JhDLL a w Gr Sm breakpoint & y fNy D; a e mu f y Hk( 1 3 3 ) u dk a & mu f& Sdv mr Smjz p fy gw , f/
y Hk( 1 3 3 )
y Hk( 1 3 3 ) t w dki f; jr i fa w GYNy D; w Jha e mu fr Sma w mh a & SUo i fc e f; p mw ke f; u OEP & Smc Jho v dk y Hk( 1 3 4 ) t w dki f;
jr i f& w Jht x dF8 u dkE Sdy fv mc Jhy g/
,., Armadillo ... .` .
,,
y Hk( 1 3 4 )
y Hk( 1 3 4 ) & JU CALL EDX a e & ma & mu f& i f F7 u dkE Sdy fy g/ u Re fa w mfw dkY& Sma e w Jh OEP u dka w GYy gv dr fhr , f/
Armadillo 4.x w ke f; u CALL ECX & Sd& ma e & m[ m OEP jz p fw mu dk o i fht a e e JY jy e ft r Sw f& y g/ Armadillo
6.x r Sma w mhCALL EAX jz p fy gw , f/ F7 u dkE Sdy fv dku f& i f y Hk( 1 3 5 ) t w dki f; OEP u dka w GYy gv dr fhr , f/
y Hk( 1 3 5 )
y Hk( 1 3 5 ) u OEP a e & mr Sm hardware breakpoint o w fr Sw fy g/ ' gq dk& i fa w mh u Re fa w mfw dkYt a e e JY
OEP u dk& Smw m Ny D; q Hk; o Gm; Ny Djz p fy gw , f/
., Impor t Table Elimination - .-. ..` .
' Dw p fc gr Sma w mhImport Table Elimination u dk a u smfv Tm; z dkYMu dK; p m; y gr , f/
y Hk( 1 3 6 )
y Hk( 1 3 6 ) u dkMu n fhy g/ JMP 031100FF u a w mh Strategic Code Splicing v ky fx m; w Jhu k' fjz p fy gw , f/
' gu dka w mh a e mu ft y dki f; r Sm & Si f; jy y gr , f/ VA 401B7E u CALL 0073F902 a e & mr Sm Enter key
E Sdy fv dku fy g/ y Hk( 1 3 7 ) t w dki f; jr i f& y gr , f/
y Hk( 1 3 7 )
y Hk( 1 3 7 ) & JU GetCommandLineW a t mu fe m; u dkMu n fhv dku fy g/ GetModuleHandleA v dk
r jz p fr a e o Hk; & r , fh API a e & mr Sm u Gu fv y fjz p fa e w m a w GY& y gr , f/ Armadillo [ m t c sdKU API a w Gu dk
encrypt v ky fx m; y gw , f/ v dkt y fv dkY a c : o Hk; r So m decrypt jy e fv ky fy gw , f/ Ny D; & i f import a w Go dr f; x m; w Jh
data segment a e & m[ m imagebase (40xxxx) w e fz dk; x u f a u smfv Ge fa e y gw , f/ q dkv dkw mu memory x Ju
DLL z dki fw p fc kx Jr Sm ' D import a w Gu dk Armadillo u o dr f; x m; v dkY jz p fy gw , f/ ' ga Mu mi fh dump
v ky fw Jht c gr Sm import a w Gy gr v mw m jz p fy gw , f/ ' gu dk u Re fa w mfw dkYt a e e JYjy i f& y gr , f/
VA 73F9B0 a y : right-click E Sdy fNy D; Follow in DumpMemor y addr ess u dka & G; y g/ y Hk( 1 3 8 ) /
y Hk( 1 3 8 )
,., Armadillo ... .` .
,,
y Hk( 1 3 8 ) u VA 11B6E3C r Sm Br eakpointHar dwar e, on wr iteDwor d o w fr Sw fy g/
Ny D; & i f Ctrl + F2 u dkE Sdy fNy D; Olly u dk jy e fp y g/ ( r Sw fx m; & r Smu ' Daddress a w G[ m t jr Jw r f; a jy mi f; v Ja e r Sm
jz p fy gw , f/ )
Debug-Blocker u dka u smfv Tm; z dkY OpenMutexA r Sm breakpoint o w fr Sw fNy D; F9 u dkE Sdy fy g/
' kw d, t Mu dr f breakpoint r Sma w mh EAX & JUw e fz dk; u dk 1 v dkYa jy mi f; y g/ ( Debug-Blocker t y dki f; u dka w mh
& Si f; jy Ny D; jz p fv dkYa u smfv dku fy gr , f/ )
EAX & JUw e fz dk; u dk 1 v dkYa jy mi f; ? Ny D; & i f OpenMutexA r Smo w fr Sw fx m; w Jh breakpoint u dkjy e fjz Kw fNy D;
F9 u dkE Sdy fv dku f& i fa w mhu Re fa w mfw dkYo w fr Sw fx m; w Jhhardware breakpoint a e & mu dk a & mu fv my gr , f/
y Hk( 1 3 9 )
y Hk( 1 3 9 ) u VA 011B6E3C a e & mu dk a o c smMu n fhx m; y g/ Ny D; & i f y Hk( 1 4 0 ) u dk jr i fa w GY& o n ft x d F9
u dkE Sdy fa e y g/
y Hk( 1 4 0 )
y Hk( 1 4 0 ) u dk a o c smMu n fhy g/ c ke u u Re fa w mfw dkYjr i fc Jhw Jh GetModuleHandleA t w Gu fa e & mr Sm
Cr eateFontIndir ectW u dkv mx m; y gw , f/ ' gu v n f; t jr Jr a o c smy gb l; / a e mu fw p fc g x y fp r , fq dk& i f
a e mu f API w p fc kjz p fr Smy g/ b , f API y Jv mx m; x m; u Re fa w mfw dkY p dw fr 0 i fp m; y gb l; / u Re fa w mfw dkY
p dw f0 i fp m; w mu y Hk( 1 4 0 ) r Sm jr i f& w Jh GetTickCount o mjz p fy gw , f/ b ma Mu mi fhv n f; q dka w mh Armadillo
[ m t c sdKU API a w Gu dk security.dll z dki fx Ju dk redirect v ky fy p fy gw , f/ security.dll u API wrapper t jz p f
v ky fa q mi fNy D; API a w Gu dk emulate v ky fa y ; y gw , f/ ' ga Mu mi fh Armadillo u dk security.dll q D API a w G
redirect r v ky fE dki fa p z dkYw m; q D; & y gr , f/
The GetTickCount function retrieves the number of milliseconds that have elapsed since Windows was started.
DWORD GetTickCount(VOID)
Retur n Values
If the function succeeds, the return value is the number of milliseconds that have elapsed since Windows was
started.
Remar ks
The elapsed time is stored as a DWORD value. Therefore, the time will wrap around to zero if Windows is run
continuously for 49.7 days.
y Hk( 1 4 1 )
t v G, fu lq Hk; & Si f; jy & r , fq dk& i fa w mh GetTickCount API u dka c : o Hk; y gw , f/ & v ' fu dk SS:[EBP-
2C58] r Smo dr f; q n f; y gw , f/ y Hk( 1 4 0 ) & JUt q Hk; e m; r Sm a w GY& w Jh JE 13327C8 u a w mh VA 1332324 u
,., Armadillo ... .` .
,,
a e mu fx y f GetTickCount API q Do Gm; w m jz p fy gw , f/ Ny D; & i f & v mw Jhw e fz dk; (EAX) u dk SS:[EBP-2C58]
x Ju w e fz dk; e JY E Iw fy gw , f/ ' Da v mu fq dk& i f & Si f; a v mu fNy Dv dkYx i fy gw , f/ q dkv dkw mu ' D CALL a w Gu
GetTickCount CALL E Sp fc kMu m; r Sm Mu ma e w Jht c sde fa w Gu dk w Gu fc su fw mjz p fy gw , f/ w u , fv dkYo i fht a e e JY
' D CALL a w GMu m; r Sm breakpoint a w Go w fr Sw fv dku f& i f t c sde fu a E Smi fha E S; o Gm; r Smjz p fy gw , f/ ' Dt c g
Armadillo u ' DCALL E Sp fc kMu m; r Sm o i fa & mu fa e w mu dk & dy fr do Gm; r Sm jz p fy gw , f/ ' ga Mu mi fh Armadillo u dk
v Sn fhp m; z dkY u Re fa w mfw dkY Mu dK; p m; & r Smjz p fy gw , f/ a e mu fx y f& Sm& r Smu a w mh Armadillo u API a w Gu dk
redirect v ky fw Jha e & mu dky g/
y Hk( 1 4 2 )
y Hk( 1 4 2 ) u VA 013325BA r Sm a e mu f API e mr n fu dk o dr f; y gw , f/ CALL 01311340 u a w mh
API a w G& JU address u dkw Gu fc su fy gw , f/ w u , fv dkY VA 133261D r Sm& Sdw Jh a e mu fq Hk; execute v ky fw Jh
CALL 01311340 u dk execute r v ky fb l; q dk& i f Armadillo [ m API a w G& JU w u , fh address a w Gu dk
r Sw fOmP fa y : u l; w i fr Sm r [ kw fy gb l; / ' ga Mu mi fh VA 13325D0 u CALL 01311340 u dk a u smfv Tm; E dki fr , fh
conditional jump u dk& Smy gr , f/ y Hk( 1 4 2 ) r Smjr i f& w Jht w dki f; VA 1332598 u JNZ 013325DE jz p fy gw , f/
a u mi f; Ny D/ VA 011B6E3C a e & mr Sm o w fr Sw fx m; w Jh hardware breakpoint u dk jy e fjz Kw fv dkY& Ny D
jz p fy gw , f/ GetTickCount CALL a w G& Sdw Jh VA 1332324 e JY VA 1332703? IAT redirect v ky fw Jh
conditional jump & Sdw Jh VA 1332598 w dkYr Sm hardware breakpoint a w Go w fr Sw fy g/ ' gq dk HD BP ( 4 ) c k
& Sdo Gm; Ny Djz p fy gw , f/ a e mu fw p fc ku a w mh a & SUr Smo w fr Sw fx m; c Jhw Jh OEP & Sdw Jha e & my g/ Ny D; & i fa w mh Ctrl + F2
u dkE Sdy fNy D; Olly u dkjy e fp v dku fy g/
Debug-Blocker u dka u smfv Tm; z dkY OpenMutexA r Sm breakpoint o w fr Sw fNy D; F9 u dkE Sdy fy g/ ' kw d,
a jr mu f breakpoint r Sma w mh EAX & JUw e fz dk; u dk 1 v dkYa jy mi f; y g/ EAX & JUw e fz dk; u dk 1 v dkYa jy mi f; ? Ny D; & i f
OpenMutexA r Smo w fr Sw fx m; w Jh breakpoint u dkjy e fjz Kw fNy D; F9 u dkE Sdy fv dku f& i fa w mh u Re fa w mfw dkY o w fr Sw f
x m; w JhGetTickCount breakpoint a e & mu dk a & mu fv my gr , f/ y Hk( 1 4 3 ) /
y Hk( 1 4 3 )
VA 1332324 u CALL DWORD PTR DS:[13C9388] a e & mr Sm MOV EAX, 10 v dkYa jy mi f; y g/
VA 1332703 u CALL DWORD PTR DS:[13C9388] a e & mr Sm MOV EAX, 12 v dkYa jy mi f; y g/ ' gq dk
t c sde fo dy fu Gma w mhr Sm r [ kw fa w mhy gb l; / Ny D; & i f IAT redirect v ky fw Jh conditional jump & Sdw Jh VA 1332598
r Sm NOP v dkYjy i fy gr , f/
' Dv dkjy i fNy D; o Gm; & i f t a & ; Mu D; w Jh t c su fw p fc k a jy m& y gOD; r , f/ Armadillo developer a w Gu
u Re fa w mfw dkY ' Dv dkjy i fr , fq dkw m o dx m; y gw , f/ b ma Mu mi fhv Jq dka w mh a & SUo i fc e f; p ma w Gw ke f; u v n f; magic
jump u dk& SmNy D; JNZ a e & mr Sm JMP v dkYjy i fv dku f& Hke JY IAT redirection u dk a u smfv Tm; E dki fc Jhw , f r [ kw fv m; /
Armadillo u jy Kjy i fx m; w Jhu k' fa w Gu dk p p fa q ; Ny D; ' Dv dk jy i fx m; c Jh& i f error w e fz dk; w p fc ku dk jy e fy dkYr Smjz p fy gw , f/
' ga Mu mi fh u Re fa w mfw dkYjy i fx m; w Jh a e & mo Hk; a e & mu u k' fa w Gu dk v ky fa q mi fNy D; Ny D; c si f; r Sm t J' Du k' fa w Gu dk
r l& i f; u k' ft w dki f; jy e fjy i fx m; c Jhz dkY v dkt y fy gw , f/ u Re fa w mfw dkYt a e e JY u Re fa w mfw dkY jy i fc Jhw Jh u k' fa w Gu dk
v ky fa q mi fNy D; Ny D; c si f; r Sm a & mu f& Sdr , fh virtual address u a e breakpoint o w fr Sw fNy D; a p mi fha e & r Smjz p fy gw , f/
y Hk( 1 4 4 ) /
,., Armadillo ... .` .
,,
y Hk( 1 4 4 )
y Hk( 1 4 4 ) u VA 13327CD r Sm breakpoint o w fr Sw fy gr , f/ u Re fa w mfw dkY u k' fa w Gjy i fx m; w Jh
hardware breakpoint ( 3 ) a e & mr Sm breakpoint a w Gu dk jy e fjz Kw fy gr , f/ jy D; & i f F9 u dkE Sdy fy g/
y Hk( 1 4 5 )
y Hk( 1 4 5 ) r Smjr i f& w Jht w dki f; breakpoint & Sd& mq Da & mu fv mw Jht c g u k' fa w Gjy i fx m; w Jh ( 3 ) a e & mr Sm r l& i f;
u k' fa w G jy e ft p m; x dk; y gr , f/ u k' fjy i fx m; w Jha e & mr Sm right-click E Sdy fNy D; Undo selection u dka & G; v dku f& i f
r l& i f; u k' fa w Gjy e fa & mu fv my gr , f/ VA 13327CD r Smo w fr Sw fx m; w Jhbreakpoint u dkv n f; jy e fjz Kw fv dku fy g/
t m; v Hk; v ky fa q mi fNy D; & i fa w mhF9 u dkE Sdy fv dku fy g/ OEP & Sd& ma e & mu dk a & mu fv my gv dr fhr , f/
y Hk( 1 4 6 )
' gq dk& i fa w mh y Hk( 1 3 5 ) w ke f; u r jr i fc Jh& w Jh GetModuleHandleA API u dkjr i f& Ny Djz p fy gw , f/ ' DAPI
[ m OEP e JYe D; w Jht w Gu f? t a & ; Mu D; w Jht w Gu f Armadillo u ' DAPI u dk t & i fu encypt v ky fx m; y gw , f/
' gq dk& i fa w mhImport Table Elimination u dkjy i fw Jht y dki f; Ny D; o Gm; Ny Djz p fy gw , f/
., Str ategic Code Splicing - .-. ..` .
Import Table Elimination u dk jy i fNy D; & Hke JYa w mhr Ny D; a o ; y gb l; / y Hk( 1 4 7 ) u dkMu n fhy g/
y Hk( 1 4 7 )
y Hk( 1 4 7 ) u dkMu n fhw Jht c gr Sm t c sdKU jump a w G[ m imagebase w e fz dk; x u fa u smfNy D; a & mu fa e w m
a w GY& y gw , f/ ' g[ m Strategic Code Splicing u dko Hk; x m; v dkYjz p fy gw , f/ c kc sde fr Sm dump v ky fr , fq dk& i fa w mh
' D{ & d, mx J a & mu fa e w Jhu k' fa w Gy gv mr Sm r [ kw fy gb l; /
' ga Mu mi fh a & SUo i fc e f; p ma w Gv dky J ArmaInline u dko Hk; jy D; splice jz p fa e w Jhu k' fa w Gu dk jy i fy gr , f/
ArmaInline u dkz Gi fhy g/ y Hk( 1 4 8 ) /
,., Armadillo ... .` .
,,,
y Hk( 1 4 8 )
y Hk( 1 4 8 ) u Length of Spliced Code a e & mr Sm 10000 t p m; 20000 v dkYjy i fNy D; Remove Splices
u dka & G; v dku fy g/ Splice jz p fa e w Jha e & m 2293 a e & mu dk jy i fa y ; v dku fE kdi fw m a w GY& y gw , f/ y Hk( 1 4 9 ) /
y Hk( 1 4 9 )
w u , f jy i fa y ; v m; ? r jy i fa y ; b l; v m; o dE dki fa t mi fv dkYu dko Gm; Mu n fhv dku fy g/ y Hk( 1 5 0 ) /
y Hk( 1 5 0 )
y Hk( 1 4 7 ) e JY y Hk( 1 5 0 ) w dkY u k' fa w G r w la w mhw mu dk a w GY& y gr , f/ ' gq dk& i fa w mh u Re fa w mfw dkY& JU splice
u k' fjy i fw Jht y dki f; Ny D; q Hk; o Gm; y gNy D/ ArmaInline u dky dw fv dkY& y gNy D/
.,, Dump ` .. IAT - ` ` .
' Dw p fc gr Sma w mhu Re fa w mfw dkYjy i fx m; w Jhz dki fu dk dump v ky fy gr , f/ y Hk( 1 5 1 ) /
y Hk( 1 5 1 )
y Hk( 1 5 1 ) t w dki f; dump v ky fNy D; w Jha e mu fr Sm import a w Gu dk jy i fy gr , f/ Import a w Gu dk r jy i fc i fr Sm IAT
b , fu a e p o v J? o lU& JU length b , fa v mu f& Sdo v Jq dkw mu dk p Hkp r f; y gr , f/ y Hk( 1 4 6 ) u CALL 0073F9B0
a e & mr Sm Enter key E Sdy fy g/
y Hk( 1 5 2 )
y Hk( 1 5 2 ) r Sm right-click E Sdy fNy D; Follow in dumpMemor y addr ess u dka & G; y g/ y Hk( 1 5 3 ) t w dki f;
jr i f& y gr , f/
,., Armadillo ... .` .
,,
y Hk( 1 5 3 )
y Hk( 1 5 3 ) t w dki f; jr i f& w Jht c g t a y : b u fu dk scroll q GJNy D; IAT t p u dk& Smy gr , f/
y Hk( 1 5 4 )
y Hk( 1 5 4 ) u VA 11B6388 [ m IAT t p jz p fy gw , f/
y Hk( 1 5 5 )
y Hk( 1 5 5 ) t w dki f; IAT t q Hk; x dscroll q GJv mNy D; a e mu fr Sma w mhIAT length u 17B4 v dkYjy o y gw , f/
a u mi f; Ny D/ IAT t p e JY o lU& JU length u dko dNy Djz p fw Jht w Gu f Import Fixer u dkz Gi fhNy D; IAT jy i fz dkY
Mu dK; p m; y gr , f/ y Hk( 1 5 6 ) /
y Hk( 1 5 6 )
Import Fixer u dkz Gi fhNy D; w Jha e mu fr Sma w mh-
,., Armadillo ... .` .
,,
( 1 ) Processes & Modules u u dk, fjy i fc si fw Jh ezcddax.exe u dka & G; y gr , f/ Tools menu & JU Pr efer ences
r Sm Create a new IAT u dka & G; x m; a y ; y g/
( 2 ) Ny D; & i f IT & IAT u dkE Sdy fy g/ Code section & Sd& mu dk a & G; c s, fa y ; y g/ r sm; a o mt m; jz i fh Armadillo & Sd& m
code section u dk t v dkt a v smu f a & G; c s, fa y ; x m; w w fy go n f/ OEP w e fz dk; u dk & dku fx n fhy g/
( 3 ) IAT & JUt p w e fz dk; jz p fw Jh11B6388 u dk& dku fx n fhy g/ o lU& JU length w e fz dk; jz p fw Jh17B4 u dk& dku fx n fhy g/
( 4 ) w e fz dk; a w Gt m; v Hk; & dku fx n fhNy D; w Jht c g Show invalid thunks u dka & G; y g/
( 5 ) Invalid jz p fa e w Jh thunk a w Gu dk cut v ky fNy D; Fix dump button u dka & G; y g/ Ny D; & i f LordPE e JY dump
v ky fx m; w Jhz dki fu dk jy i fy g/
' gq dk& i fa w mhdump v ky fjc i f; e JYIAT u dkjy i fq i fjc i f; t y dki f; Ny D; o Gm; Ny Djz p fy gw , f/ u Re fa w mfw dkYLordPE
e JY dump v ky fx m; w Jhz dki fu dk dump.exe v dkYt r n fa y ; v dku fy g/ ' gq dk Import Fixer e JY jy i fx m; w Jhz dki fu dk
dumped_IF.exe e mr n fe JY t v dkt a v smu f o dr f; q n f; o Gm; r Sm jz p fy gw , f/ ' Dha e mu fr Sma w mh Import Fixer u dk
y dw fv dkY& y gNy D/
., Nanomite - ` . ` .
dumped_IF.exe z dki fu dk z Gi fhMu n fhv dku fy g/ y & dk* & r f[ m y Gi fhv mr Sm r [ kw fy gb l; / b ma Mu mi fhv Jq dka w mh
u Re fa w mfw dkYt a e e JYNanomites u dkjy i fz dkYu se fa o ; v dkYjz p fy gw , f/
INFO: : Nanomites q dkw mu a w mh child e JY parent process w dkY& JU q u fE G, fr Iu dk p p fa q ; w Jh a e mu fx y f
v Sn hfp m; c su fw p fc k jz p fy gw , f/ ' ga Mu mi fh ' D protection u dko Hk; a w mhr , fq dk& i f Debug-Blocker ( o dkY)
CopyMem2 e JY protect v ky fx m; z dkY v kdy gw , f/ Armadillo [ m y & dk* & r f& JU r l& i f; u k' fx Ju jump t c sdKUu dk
INT3 instruction e JYt p m; x kd; y p fv dku fy gw , f/ ' ga Mu mi fh y & dk* & r fu ' D instruction a w Gu dk execute
v ky fw dki f; r Sm child process [ m b , fa e & mu dk jump v ky f& r v Jq dkw m parent process u dk q Hk; jz w fa p y gw , f/
w u , fv dkY u Re fa w mfw dkYr Sm child process u dk x de f; c sKy fa e w Jh parent process Mu D; o m r & Sdc Jhb l; q dk& i f
y & dk* & r f[ m INT3 instruction a Mu mi fh b , fa e & mu dk o Gm; & r v Jq dkw m r o dE dki fjz p fNy D; crash jz p fo Gm; r Smy g/
b ma Mu mi fhv Jq dka w mhINT3 instruction w p fc ku dk execute v ky fw dki f; exception w p fc k x Gu fv mv dkYy g/
Nanomites t a Mu mi f; u dk ' Dx u fe n f; e n f; y dkNy D; a v hv mMu n fhMu & a t mi f/
Armadillo r Sm parent process [ m child process & JU EIP address u dko dx m; z dkYv dkw , fq dkw m
t Mu r f; z si f; o dx m; & y gr , f/ ' DEIP r Sm exception a w Gu dk x kw fy gw , f/ Ny D; a w mht jc m; register w e fz kd; ? flag
w e fz dk; a w Gv n f; x m; y gw , f/ ' Dt c su ft v u fa w Ge JU table a w Gu dko Hk; Ny D; o u fq dki f& m jump a w G jump
jz p fw , f? r jz p fb l; q kdw mu dk v ky fa q mi fz dkYt w Gu f child & JU EIP u dk jy Kjy i fy gw , f/
' Dt w Gu f Armadillo [ m nano_addr? nano_type? nano_dest e JY nano_size q dkw Jh table
a v ; c ku dk t o Hk; jy Ky gw , f/
( 1 ) nano_addr table [ m INT3 a e & m[ m child & JU EIP [ kw f? r [ kw fe JYnano w p fc ku dk y dki fq dki fx m; jc i f; & Sd?
r & Sd p p fy gw , f/ r Se fu e fc Jh& i f Armadillo [ m a e mu f table u dk & , lE dki fz dkY reference w p fc ku dk r Sw fw r f; w i f
y gw , f/
( 2 ) nano_type table u a w mh Jump t r sdK; t p m; a w Ge JYo u fq dki fNy D; child & JU register w e fz dk; e JY o lU& JU flag
a w G& JUt jc t a e u dk o dr f; q n f; y gw , f/ ' Dw e fz dk; a w Gu dk o dx m; r , fq dk& i f jump w p fc ku dk a q mi f& Gu fE dki fjc i f; & Sd?
r & Sdo d& SdE dki fy gw , f/
( 3 ) Jump jz p fNy D; o Gm; & i fa w mhArmadillo u nano_dest table u dko Hk; y gw , f/ t J' Dr Sm child & JU EIP t o p fu dk
x kw fa y ; y gw , f/
( 4 ) Jump r jz p fa o ; b l; q dk& i fa w mh Armadillo u nano_size table u dk t o Hk; jy Ky gw , f/ ' Dtable r Sm jump
opcode & JU size y g& Sdy gw , f/ Child & JU EIP e JY jump & JU size w dkYu dka y gi f; Ny D; child & JU EIP t o p fw e fz dk; u dk
w Gu fc su fy gw , f/
' ga w Gu a w mh o Dt dk& Do u fo u fo m jz p fy gw , f/ v u fa w GYe m; v n fE dki fz kdYt w Gu f Olly r Sm nanomite
a w Gu dk v u fa w GY& Sma z Gp p fa q ; Mu n fhMu & a t mi f/ Olly e JYezcddax.exe z dki fu dkz Gi fhy g/ GetThr eadContext r Sm
hardware breakpoint o w fr Sw fy g/ GetThr eadContext [ m Armadillo u child & JU flag a w Ge JY
register e JYy w fo u fw Jh t c su ft v u fa w Gu dk & , lz dkY t o Hk; jy Kw Jh API jz p fy gw , f/ F9 u dkE Sp fMu dr fE Sdy fv dku fNy D;
y Hk( 1 5 7 ) r Smjr i f& w Jht w dki f; F8 u dkE Sdy fv mc Jhy g/
,., Armadillo ... .` .
,,,
y Hk( 1 5 7 )
GetThr eadContext [ m context structure e JYc sdw fq u fw Jh pointer w p fc ku dk parameter t a e e JY
t o Hk; jy Ky gw , f/ ' Dstructure u dk [EBP-714] {VA 12ED18} x Jr Sm o dr f; y gw , f/ y Hk( 1 5 8 ) /
y Hk( 1 5 8 )
y Hk( 1 5 8 ) & JU y x r q Hk; DWORD u a w mh context structure t r sdK; t p m; u dka z mfjy y gw , f/ t e Da & mi fe JY
0 dki f; jy x m; w mu a w mhexception a w Gx kw fa y ; r , fhson & JU EIP jz p fy gw , f/ t jy me JY0 dki f; x m; w mu a w mhEFlag
register jz p fy gw , f/
' ga w G[ kw f? r [ kw f p p fa q ; E dki fz dkYt w Gu f u Re fa w mfw dkY import jy i fx m; w Jh dumped_IF.exe z dki fu dk
a e mu f Olly w p fc ke JYz Gi fhNy D; VA 4358C6 a e & mu dk o Gm; v dku fy g/ y Hk( 1 5 9 ) /
y Hk( 1 5 9 )
y Hk( 1 5 9 ) r Smjr i f& w Jh INT3 u a w mh nanomite jz p fy gw , f/ q dkv dkw mu context structure x Jr Sm
o dr f; x m; w Jh address [ m exception x kw fa y ; r , fh instruction jz p fNy D; a e & mw p fa e & mx u f t jr Jw r f;
y dk& Sdw , fq dkw my g/
Parent process e JY w GJv ky fr , fh dumped_IF.exe u dky dw fv dku fy g/ GetThr eadContext r Sm
o w fr Sw fx m; w Jh hardware breakpoint u dkv n f; z , fv dku fy g/ VA 832663 u dkv n f; p m& Gu fw p fc kr Sm
r Sw fx m; v dku fy g/ Ny D; & i f y Hk( 1 6 0 ) t w dki f; jr i f& o n ft x dF8 u dkE Sdy fv mc Jhy g/
y Hk( 1 6 0 )
y Hk( 1 6 0 ) r Sm 0 dki f; jy x m; w mu a w mh Armadillo u y x r q Hk; t Mu dr f nano_addr table u dk & , lw Jha e & m
jz p fy gw , f/ ' Do i fc e f; p mr Sma w mh' Da e & m[ m VA 9003B8 jz p fy gw , f/ y Hk( 1 6 1 ) /
,., Armadillo ... .` .
,,.
y Hk( 1 6 1 )
y Hk( 1 6 1 ) u dkMu n fhv dku fw Jht c g Armadillo u table a v ; a w G t c k ( 3 0 ) a v mu f c GJy p fv dku fw m a w GY&
y gw , f/ y Hk( 1 6 2 ) t w dki f; jr i f& w Jht x dF8 u dkE Sdy fv mc Jhy g/
y Hk( 1 6 2 )
y Hk( 1 6 2 ) r Sma w mhArmadillo u child & JU EIP [ m nano w p fc ku dk y dki fq dki fx m; jc i f; & Sd? r & Sdp p fy gw , f/
Armadillo [ m o u fq dki f& m nano_addr table i , fa v ; a w Gq Du a e t c su ft v u fa w G & , ly gw , f/
w u , fv dkY nano [ m t p p fjz p fc Jh& i f JNZ 00832A56 [ m jump jz p fr Sm r [ kw fy gb l; / w u , fv dkY nano [ m
t w kt a , mi f jz p fc Jhr , fq dk& i f JNZ 00832A56 [ m jump jz p fo Gm; y gr , f/ VA 8327C5 u dk p m& Gu fv Gw f
w p fc kr Sm x y fr Hr Sw fo m; y gr , f/
u Re fa w mfw dkY& JU v u f& Sdo i fc e f; p mr Sma w mh nano [ m w u , fh nano jz p fw Jht w Gu f jump jz p fr Sm
r [ kw fy gb l; / y Hk( 1 6 3 ) t w dki f; jr i f& w Jht x dF8 u dkq u fE Sdy fv my g/
y Hk( 1 6 3 )
y Hk( 1 6 3 ) r Smjr i f& w mu a w mh nano_type table u dka c : , lw mjz p fy gw , f/ VA 832828 u dk p m& Gu fv Gw f
w p fc kr Sm x y fr Hr Sw fo m; y gr , f/ VA 832835 r Sm w e fz dk; u dk & & Sdy gw , f/ ' Do i fc e f; p mr Sma w mhnano_type & JU es
[ m DWORD (B3B4FFEE) jz p fy gw , f/ t jc m; Armadillo r Sma w mh nano_type [ m BYTE
jz p fE dki fy gw , f/ nano_type? register a w Ge JY FLAG u dkMu n fhNy D; b , fv dk jump t r sdK; t p m; v Jq dkw m o dE dki f?
w Gu fc si fhE dki fy gw , f/ y Hk( 1 6 4 ) t w dki f; jr i f& o n ft x dF8 u dkE Sdy fv my g/
y Hk( 1 6 4 )
y Hk( 1 6 4 ) r Smjr i f& w Jh 206 q dkw mu a w mh flag jz p fy gw , f/ VA 832898 u CALL EDX u dk
v ky fa q mi fNy D; EAX w e fz dk; u dk Mu n fhv dku f& i f jump jz p fr v m; ? r jz p fb l; v m; q dkw m q Hk; jz w fv dkY& y gNy D/ y Hk( 1 6 5 ) /
y Hk( 1 6 5 )
,., Armadillo ... .` .
,,.
EAX = 1 Jump jz p fy gw , f/ Jump jz p f& i f Armadillo u nano_dest table u dko Hk; y gw , f/
EAX = 0 Jump r jz p fy gb l; / Jump r jz p f& i f Armadillo u nano_size table u dko Hk; y gw , f/
VA 83289D u dk p m& Gu fv Gw f w p fc kr Sm x y fr Hr Sw fo m; y gr , f/ y Hk( 1 6 4 ) u JE 0083295E [ m jump
jz p fc Jhr , fq dk& i f y Hk( 1 1 6 ) q Da & mu fo Gm; r Sm jz p fy gw , f/
y Hk( 1 6 6 )
y Hk( 1 6 6 ) r Sm 0 dki f; jy x m; w Jhu k' fu a w mhArmadillo u nano_dest table t a e e JYz w fw Jha e & mjz p fy gw , f/
VA 832986 r Sma w mh register EDX r Sm child & JU EIP w e fz dk; o p f a & mu f& Sdv mr Smjz p fy gw , f/ VA 832986
u dk p m& Gu fv Gw f w p fc kr Sm x y fr Hr Sw fo m; y gr , f/
c kc sde fr Sma w mh u Re fa w mfw dkYt a e e JY v Sn hfp m; r I v ky f& y ga w mhr , f/ Nano jump a w G r jz p fa t mi fv dkY
u Re fa w mfw dkYt a e e JY t w i f; t Mu y fv ky f& y ga w mhr , f/ ' ga Mu mi fh u Re fa w mfw dkYv u f& Sda & mu fa e w Jh VA 83289A
a e & mu a e Ctrl + G E Sdy fNy D; 832915 u dk& dku fx n fhy g/ y Hk( 1 6 7 ) /
y Hk( 1 6 7 )
VA 832915 r Sm right-click E Sdy fNy D; New or igin her e o w fr Sw fy g/ ' Dha e mu fr Sma w mh F8 u dk
E Sdy fv mc Jhr , fq dk& i fa w mh SetThr eadContext u dka w GY& y gr , f/ SetThr eadContext u a w mh child & JU EIP
t o p fu dk jy i fa y ; w JhAPI jz p fy gw , f/ u Re fa w mfw dkYt a e e JYtrace v ky fw mu dk ' Da e & mr Sm & y fv dku fMu & a t mi f/
a u mi f; Ny D/ c kc sde fr Sma w mh nanomite process b , fv dkt v ky fv ky fo v Jq dkw m o i fht a e e JY a u mi f; a u mi f;
e m; v n fa v mu fy gNy D/ ' Dt y dki f; r Sma w mh u k' f protect r & Sdw Jht w Gu f u Re fa w mfw dkYt a e e JY Mu dKu fw Jha e & mr Sm
Mu dKu fw Jhbreakpoint u dko w fr Sw fv dkY& y gw , f/
w u , fw r f; a w mh nanomite a w Gu dk u dk, fw dki fjy i fr , fq dk& i fa w mh t v Ge fv u f0 i fr Sm jz p fy gw , f/
u Re fa w mfht a e e JY t a o ; p dw f& Si f; jy & w mu Nanomite Fixer tool a w Gu nanomite a w Gjy i fw Jht c g error
w u fc Jh& i f ' Dnanomite a w Gu dk u dk, fw dki fjy i fq i fE dki fa t mi fv dkY& Si f; jy w mjz p fy gw , f/
u Re fa w mfw dkYt a e e JY Import Fixer tool e JYjy i fx m; w Jh dumped_IF.exe z dki fu dkz Gi fhw Jht c g nanomite
a w G& Sda e a o ; w Jht w Gu f error w u fc Jhy gw , f/ ' ga Mu mi fh nanomite a w Gu dk z , f& Sm; z dkY Mu dK; p m; Mu y gr , f/
' Da e & mr Sm u Re fa w mfo Hk; r , fh tool u a w mh Armadillo Nanomite Fixer 1.3 jz p fy gw , f/ ' D tool u dka w mh
Google u a e y Jjz p fjz p f? Myanmar Cracking Team b a v mhr Smy Jjz p fjz p f download v ky f, lE dki fy gw , f/
c kc sde fr Sma w mh y Gi fha e w Jh y & dk* & r ft m; v Hk; u dk y dw fv dkY& y gNy D/ Ny D; & i fa w mh y Hk( 1 6 8 ) t w dki f; Armadillo
Nanomite Fixer 1.3 tool u dk z Gi fhv dku fy g/
,., Armadillo ... .` .
,.
y Hk( 1 6 8 )
y Hk( 1 6 8 ) t w dki f; jr i f& w Jht c g Please Select Ar madillo Dupmed File. u dka & G; Ny D; u Re fa w mfw dkY
dump v ky fx m; w Jh dumped_IF.exe z dki fu dk a & G; a y ; y g/ Ny D; & i f Please Select Or iginal/Ar madillo
Pr otected File. u dka & G; Ny D; r l& i f; ezcddax.exe z dki fu dka & G; a y ; y g/ Ny D; & i f Sear ch Nano button u dka & G; y g/
Nanomite a w Gu dk & Smy gv dr fhr , f/ y Hk( 1 6 9 ) /
y Hk( 1 6 9 )
y Hk( 1 6 9 ) r Sma w mh nanomite p kp ka y gi f; 6658 a w GYy gw , f/ ' ga y r , fh o i fht a e e JY o dx m; & r Smu INT3
(CC) w dki f; nanomite r [ kw fy gb l; / w u , fh nanomite t p p fu 545 c ko mjz p fy gw , f/ ' Dnanomite a w Gu dk
jy i fz dkYt w Gu f Patch Nano button u dkE Sdy fy g/ ' gq dk& i f nanomite jy i fw Jht y dki f; a t mi fjr i fp Gm Ny D; q Hk; o Gm; Ny D
jz p fy gw , f/ Nanomite jy i fq i fx m; w Jhz dki fu dk tool u dumped_IF_ArmNF.exe e mr n fe JY o dr f; q n f; a y ; r Sm
jz p fy gw , f/ a e mu fq Hk; & & Sdv mw Jh dumped_IF_ArmNF.exe z dki fu dkz Gi fh& i f y & dk* & r f a u mi f; a u mi f; t v ky f
v ky fw m a w GY& y gr , f/
Nanomite a w Gw u , fjy i f? r jy i f u Re fa w mfw dkYy x r q Hk; a w GYc Jhw JhVA 4358C6 a e & mu dk o Gm; Mu n hfE dki f
y gw , f/ ( y Hk- 1 5 9 e JYE Idi f; , SOfMu n fhy g/ )
y Hk( 1 7 0 ? 1 5 9 )
y Hk( 1 7 0 ) u dkMu n fhv dku f& i f y Hk( 1 5 9 ) r Sma w GY& w Jh INT3 a e & mr Sm JE 4358CE e JY t p m; x kd; v dku fw m
a w GY& y gw , f/ ' ga Mu mi fh w u , fv dkY nanomite fixer tool a w Gnanomite jy i fw mt q i fr a jy c Jh& i f o i fht a e e JY
' Derror w u fo Gm; w Jha e & mr Sm u dk, fw dki fjy i fq i fE dki fNy Djz p fy gw , f/
' Da v mu fq dk& i fa w mh Armadillo & JU protection t m; v Hk; e JY y w fo u fw ma w Gu dk a q G; a E G; Ny D; o Gm; Ny D
jz p fy gw , f/ ' Do i fc e f; p mu dk a Mu n u fp Gm e m; v n fx m; r , fq dk& i f a e mu fy dki f; x Gu f& Sdr , fh Armadillo e JY protect
v ky fx m; w Jhz dki fa w Gu dkv n f; a t mi fjr i fp Gm unpack v ky fE dki fr , fv dkYa r Qmfv i fh& y ga Mu mi f; /
,., Armadillo ... .` .
,.
., Ar madillo . .. .. . ..` .
' Do i fc e f; p mr Sma w mh Armadillo & JUv dki fp i fu dk z , f& Sm; w Jh e n f; v r f; u dk a jy mjy r Smjz p fy gw , f/ ' Da e Ya c w f
t Ge fv dki f; u a ' gi f; v ky fv ky fw Jh* dr f; a w Gr Smy Jjz p fjz p f? t c sdKUa q mhz f0 Jv fa w Gr Smy Jjz p fjz p f t c sde f? t Mu dr fu e fYo w fc su fu dk
Armadillo e JY protect v ky fx m; w ma w GY& y gw , f/ o mr e ft m; jz i fha w mh ' Dt c sde f? t Mu dr fu e fYo w fc su fu dk Trial
Reset 4.x tool a v ; e JY z , f& Sm; E dki fa y r , fh w p fc gw a v r Sm ' D tool e JY z , f& Sm; v dkY r & w Jht c ga w G & Sdy gw , f/
' ga Mu mi fh b , fv dky Jy Jjz p fjz p f Armadillo v dki fp i fu dk u dk, fw dki fz , f& Sm; E dki fa t mi fv dkY ' Do i fc e f; p mr Sm & Si f; jy r Sm
jz p fy gw , f/
' Dw p fc go i fc e f; p mt w Gu f a & G; x m; w mu a w mh Armadillo 8.6 & JU Standard Protection e JY protect
v ky fx m; w JhNotepad.exe z dki fjz p fy gw , f/ Myanmar Cracking Team r Sm download v ky f, lE dki fy gw , f/
Notepad.exe u dk i g; Mu dr fa v mu f z Gi fhv dku f? y dw fv dku f v ky fMu n fhy g/ a jc mu fMu dr fa jr mu fw Jht c g y Hk( 1 7 1 )
t w dki f; a w GY& y gr , f/
y Hk( 1 7 1 )
y Hk( 1 7 1 ) t w dki f; jr i f& w mu a w mh a q mhz f0 Jv fu dk 5 Mu dr fo ma y ; o Hk; c Gi fhjy Kv dkYy g/ t c sdKU* dr f; a w Gr Smv n f; r de p f
a jc mu fq , fo m a y ; u p m; w m jr i fz l; r Smy g/ u Re fa w mfw dkYt a e e JY expired jz p fo Gm; & i f a q mhz f0 Jv fu dk q u fo Hk; v dkY
r & a w mhw Jht w Gu f a e mu fx y f 5 Mu dr f q u fo Hk; v dkY& a t mi f Mu dK; p m; Mu n fhy gr , f/ ' gq dk u Re fa w mfw dkYt a e e JY
a q mhz f0 Jv fu dk crack v ky fp & mr v kda w mhb J a e mu fx y f q u fo Hk; v dkY& r Sm jz p fy gw , f/
Notepad.exe u dk Olly r Smz Gi fhy g/ y Hk( 1 7 2 ) /
y Hk( 1 7 2 )
Notepad.exe u dk Olly r Smz Gi fhv dku fNy D; w Jha e mu fr Sma w mh u Re fa w mfw dkY p dw ft 0 i fp m; q Hk; u a w mh
OpenMutexA API jz p fy gw , f/ Armadillo [ m application & JU o u fw r f; u ke f? r u ke f p p fa q ; z dkY
OpenMutexA u dk t o Hk; jy Ky gw , f/ Ny D; & i f ]%08X:SIMULATEEXPIRED} y Hkp H& Sdw Jh string w p fc ky gw Jh
mutex u dk& Smy gw , f/ ' ghjy i f Armadillo [ m Debug-Blocker & JU parent/childe t a jc t a e u dk q Hk; jz w fz dkY
v n f; mutex a w Gu dk t o Hk; jy Ky ga o ; w , f/ w u , fv dkYo m OpenMutexA u o kn w e fz dk; r [ kw fw Jh
w e fz dk; w p fc ku dk y dkYr , fq dk& i f Armadillo [ m child t jz p f a y smfa y smfMu D; v ky fa q mi fy gw , f/
Ctrl + G u dkE Sdy fNy D; OpenMutexA u dk & dku fx n fhy g/ Ny D; & i f MOV EDI, EDI r Sm hardware
breakpoint o w fr Sw fy g/
y Hk( 1 7 3 )
y Hk( 1 7 3 ) r Sm hardware breakpoint u dko w fr Sw fNy D; F9 u dkE Sdy fy g/ y Hk( 1 7 4 ) /
y Hk( 1 7 4 )
,., Armadillo ... .` .
,.
' Do i fc e f; p mr Sma w mh Notepad.exe u dk Debug-Blocker e JY protect r v ky fx m; w Jht w Gu f ' Dw e fz dk; u dk
w p fc go m a w GU& r Smjz p fy gw , f/ ' Dmutex u dk u Re fa w mfw dkYt a e e JYp dw fr 0 i fp m; y gb l; / y Hk( 1 7 5 ) t w dki f; jr i f& o n f
t x dF9 u dk q u fE Sdy fy g/
y Hk( 1 7 5 )
y Hk( 1 7 5 ) r Smjr i f& w Jh "CAF8F981:SIMULATEEXPIRED" u o m u Re fa w mfw dkYp dw f0 i fw Jh mutex
jz p fy gw , f/ ' g[ m Armadillo & JU v dki fp i fv ky fi e f; p Of p Ny Dq dkw m t c su fa y ; y gw , f/ u Re fa w mfw dkYt a e e JY
' Dt q i fhr Sm Armadillo & JUv dki fp i f key u dk b , fa e & mr Smo dr f; o v Jq dkw m a v hv mMu y gr , f/ a t mu fr Sm
a z mfjy x m; w Jha e & ma w Gu dk o w dx m; Ny D; a p mi fhMu n fhy g/
( 1 ) Registry x Ju CLSID key?
( 2 ) Registry x Ju License key w e fz dk; ?
( 3 ) Temp folder x Ju .tmp z dki f/
' ga Mu mi fh c kc sde fr Sm u Re fa w mfw dkYv ky f& r Smu t & i fo w fr Sw fx m; w Jh breakpoint a w Gu dkjz Kw fNy D;
Cr eateFileA? RegOpenKeyExA e JY RegQuer yValueExA w dkYr Sm hardware breakpoint a w G
o w fr Sw fz dkY jz p fy gw , f/ Ctrl + G E Sdy fNy D; API e mr n fa w Gu dk& dku fx n fhNy D; hardware breakpoint o w fr Sw fy g/
Ny D; & i f F9 u dkE Sdy fy g/ y Hk( 1 7 6 ) /
y Hk( 1 7 6 )
y Hk( 1 7 6 ) r Smjr i f& w Jht w dki f; Armadillo [ m Registry & JU HKEY_LOCAL_MACHINE a t mu fu
Software\Licenses u dk z w fz dkY Mu dK; p m; a e y gw , f/ b , fw e fz dk; a w Gu dk z w fz dkY Mu dK; p m; a e w , fq dkw m q u fMu n fh
Mu & a t mi f/ F9 u dkq u fE Sdy fy g/ y Hk( 1 7 7 ) /
y Hk( 1 7 7 )
y Hk( 1 7 7 ) r Smjr i f& w Jht w dki f; Software\Licenses a t mu fu {0ACA77C8D62757C9D} w e fz dk; u dk
z w fz dkYMu dK; p m; a e y gw , f/ Registry Editor u dkz Gi fhNy D; ' Dw e fz dk; & Sd? r & Sdv n f; Mu n fh& IE dki fy gw , f/ y Hk( 1 7 8 ) /
y Hk( 1 7 8 )
y Hk( 1 7 8 ) r Smjr i f& w Jh {0ACA77C8D62757C9D} u dk notepad r Sm u l; x m; v dku fy g/ Ny D; & i f F9 u dk
q u fE Sdy fy g/ y Hk( 1 7 6 ) t w dki f; HKEY_LOCAL_MACHINE a t mu fu Software\Licenses u dk z w fz dkY
Mu dK; p m; y gw , f/
F9 u dkq u fE Sdy fy g/ y Hk( 1 7 9 ) t w dki f; jr i f& y gr , f/
,., Armadillo ... .` .
,.
y Hk( 1 7 9 )
y Hk( 1 7 9 ) r Smjr i f& w Jht w dki f; Software\Licenses a t mu fu {IACA77C8D62757C9D} w e fz dk; u dk
z w fz dkY Mu dK; p m; y gw , f/ y Hkr Smjr i f& w Jh {IACA77C8D62757C9D} u dk notepad r Sm u l; x m; v dku fy g/ F9 u dk
q u fE Sdy fy g/ y Hk( 1 8 0 ) /
y Hk( 1 8 0 )
y Hk( 1 7 9 ) r Smjr i f& w Jht w dki f; Armadillo [ m Registry & JU HKEY_CLASSES_ROOT a t mu fu
CLSID u dk z w fz dkYMu dK; p m; a e y gw , f/ F9 u dkq u fE Sdy fy g/ y Hk( 1 8 1 ) /
y Hk( 1 8 1 )
y Hk( 1 8 0 ) r Smjr i f& w Jht w dki f; CLSID a t mu fu {01E04581-4EEE-11d0-BFE9-00AA005B4383}
w e fz dk; u dk z w fz dkYMu dK; p m; a e y gw , f/ t c sdKU application a w Gr Sma w mhCLSID a t mu fr Sm subkey a w Gt r sm; Mu D;
& SdE dki fa y r , fht c sdKU application a w Gr Sma w mhsubkey w p fc ko m& Sdy gw , f/
' Dw e fz dk; u a w mh t a & ; r Mu D; y gb l; / Ny D; & i f F9 u dkq u fE Sdy fy g/ y Hk( 1 8 0 ) t w dki f; CLSID u dkz w fy gw , f/
F9 u dkq u fE Sdy fy g/ y Hk( 1 8 2 ) /
y Hk( 1 8 2 )
y Hk( 1 8 1 ) r Smjr i f& w Jht w dki f; CLSID a t mu fu {03022430-ABC4-11D0-BDE2-00AA001A1953}
w e fz dk; u dk z w fz dkYMu dK; p m; a e y gw , f/ ' Dw e fz dk; v n f; t a & ; r Mu D; y gb l; / Ny D; & i f F9 u dkq u fE Sdy fy g/ y Hk( 1 8 3 ) /
y Hk( 1 8 3 )
y Hk( 1 8 3 ) r Smjr i f& w Jh {F4C6B247-2FD7-6BC5-51B1-CC9DD8EE32E1} u dk notepad r Sm u l; x m;
v dku fy g/ ' Dw e fz dk; [ m u Re fa w mfw dkY& Sma e w Jhw e fz dk; jz p fy gw , f/ Ny D; & i f F9 u dkq u fE Sdy fy g/ y Hk( 1 8 4 ) /
y Hk( 1 8 4 )
a e mu fx y f F9 x y fE Sdy fr , fq dk& i fa w mh Armadillo u y Hk( 1 8 4 ) r Smjr i f& w Jh encrypt v ky fx m; w Jh string
a w Gu dkz w fy gv dr fhr , f/ ' ga Mu mi fh& Si f; r jy v dka w mhy gb l; / y Hk( 1 8 5 ) u dkMu n fhy g/
,., Armadillo ... .` .
,.,
y Hk( 1 8 5 )
y Hk( 1 8 5 ) t w dki f; jr i f& & i fa w mh RegOpenKeyExA e JY RegQuer yValueExA r Sm o w fr Sw fx m; w Jh
hardware breakpoint a w Gu dk jz Kw fv dkY& Ny Djz p fy gw , f/ Ny D; & i f F9 u dkE Sdy fy g/ y Hk( 1 8 6 ) /
y Hk( 1 8 6 )
y Hk( 1 8 6 ) r Smjr i f& w Jht w dki f; Armadillo u v u f& Sd current user & JU Temp folder x Ju
C173B989.TMP z dki fu dkz w fy gw , f/ F9 u dkq u fE Sdy fy g/
y Hk( 1 8 7 )
y Hk( 1 8 7 ) r Smjr i f& w Jht w dki f; Armadillo u ALL users & JU Temp folder x Ju C173B989.TMP
z dki fu dkz w fy gw , f/
y Hk( 1 8 6 ? 1 8 7 ) r Smjr i f& w Jh C173B989.TMP u dk notepad r Sm u l; x m; v dku fy g/ F9 u dkq u fE Sdy fy g/
a e mu fq Hk; r Sma w mhy Hk( 1 8 8 ) r Smjr i f& w Jht w dki f; Key Expired dialog u dkjr i f& r Smjz p fy gw , f/
y Hk( 1 8 8 )
a e mu fq Hk; t a e e JY r Sw fc su fjy Kv dkw mu a w mh Armadillo & JU v dki fp i f expire jz p fw mu dk z , f& Sm; z dkYt w Gu f
u Re fa w mfw dkYt a e e JYa t mu fy g t c su f( 3 ) c su fu dk v ky fa q mi f& y gr , f-
( 1 ) HKEY_LOCAL_MACHINE|Software\Licenses a t mu fu {0ACA77C8D62757C9D}?
{IACA77C8D62757C9D}? t jc m; w e fz dk; a w Gt m; v Hk; u dk z , f& Sm; & y gr , f/ ( w p fc gw a v r Sma w mh
HKEY_LOCAL_MACHINE\SOFTWARE\The Silicon Realms Toolworks\Armadillo a t mu fr Sm
{0ACA77C8D62757C9D} w e fz dk; & Sdc Jh& i fv n f; z , f& Sm; & y gr , f/ )
( 2 ) HKEY_CLASSES_ROOT\CLSID a t mu fu {F4C6B247-2FD7-6BC5-51B1-CC9DD8EE32E1}
u dk z , f& Sm; & y gr , f/
( 3 ) v u f& Sdcurrent user e JU ALL users w dkY& JU Temp folder x Ju C173B989.TMP z dki fu dkz su fy p f& y gr , f/
( r & Sd& i fa w mhz su fp & mr v dky gb l; )
' D( 3 ) c ku dk u dk, fw dki fz , f& Sm; r , fq dk& i fa w mh E Sp fr de p fa v mu fMu mE dki fy gw , f/ y & dk* & r fa & ; o m; r , fq dk& i f
a w mh y dkNy D; t q i fa jy y gv dr hfr , f/ y & dk* & r fu k' fa w Gu dka w mh r a z mfjy a w mhy gb l; / b ma Mu mi fhv n f; q dka w mh
w p fa , mu fe JYw p fa , mu f a & ; o m; a e Mu w Jh y & dk* & r fb mo mp u m; a w Gr w ln DMu v dkY jz p fy gw , f/ b , fv dky Jjz p fjz p f
u Re fa w mfw dkYt a e e JYArmadillo & JU v dki fp i fo u fw r f; u ke fw mu dka w mha t mi fjr i fp Gm z , f& Sm; v dku fE dki fNy Djz p fy gw , f/
,., Armadillo ... .` .
,.
, Ar madillo . Envir onment Var iables
Armadillo u dk developer t c sdKUu o lw dkY& JUa q mhz f0 Jv fa w Gu dk cracker a w Gunpack v ky fjc i f; & e fu
u mu G, fz dkYt w Gu f t o Hk; jy KMu Ny D; t c sdKUu t c sde f? t Mu dr f u e fYo w fc su fx m; & Sdz dkY t o Hk; jy KMu y gw , f/ t c sdKU
u a w mha q mhz f0 Jv fa w Gr Sm registration e n f; v r f; t jz p f x n fho Gi f; Mu y gw , f/
Armadillo & JU protection a w Gt u ke fo Hk; x m; w Jhz dki fu dk b , fv dk a u smfv Tm; & r v Jq dkw mu dk a & SUy dki f;
o i fc e f; p ma w Gr Sm & Si f; jy c JhNy D; y gNy D/ t c sde f? t Mu dr f u e fYo w fc su fa w G o dr f; q n f; x m; w Jh v dki fp i fz dki f? u D; a w Gu dk
v n f; b , fv dkz , f& Sm; & r v Jq dkw m & Si f; jy c JhNy D; y gNy D/ ' Dw p fc gr Sma w mh registration e n f; v r f; t jz p f o Hk; x m; w Jh
environment variable t a Mu mi f; u dk a q G; a E G; r Sm jz p fy gw , f/ b ma Mu mi fhv n f; q dka w mh environment
variable u dk registration e n f; v r f; t jz p f t o Hk; jy Kx m; w Jh t c sdKUa q mhz f0 Jv fa w Gu dk o mr e fe n f; t w dki f; crack
v ky fr , fq dk& i f t c sde fu ke fNy D; crack v ky f& w Jht q i fha w Gt & r f; r sm; v dkYjz p fy gw , f/
INFO: : Environment Variable (EV) q dkw mb mv J/ Process w dki f; r Sm environment block w p fc kp D& SdNy D;
t J' Dx Jr Sm environment variable a w Ge JYo lw dkY& JUw e fz dk; a w Gy g0 i fy gw , f/ Command processor (cmd.exe)
r Sm o lU& JU environmet block u dkjy z dkY ( o dkY) EV t o p fa w Gu dkz e fw D; z dkY SET q dkw Jh command & Sdy gw , f/
Command processor u a e a c : o Hk; w Jh? command processor u p w i fv dku fw Jh y & dk* & r fa w G[ m command
processor & JU EV a w Gu dk , lo Hk; c Gi fh& Sdy gw , f/ a jy m& & i fa w mh child process [ m parent process & JU EV
a w Gu dk , lo Hk; E dki fy gw , f/ b my Jjz p fjz p f o i fht a e e JY child process t w Gu f r w ln Dw Jh environment w p fc ku dk
z e fw D; v dkw , fq dk& i f environment block t o p fw p fc kz e fw D; Ny D; o lUt x J pointer w p fc ku dk Cr eatePr ocess
function & JU parameter t a e e JYx n fho Gi f; jc i f; jz i fho w fr Sw fE dki fy gw , f/
t w dkc sKy fa jy m& & i fa w mh EV q dkw m child process x Ju dk variable a w Gx n fho Gi f; jz w fo e f; a p w Jh
e n f; v r f; w p fc kjz p fy gw , f/
Armadillo [ mv n f; key e JYy w fo u fw Jh t c su ft v u fa w Gu dk o Gw fo Gi f; z dkY ' D variable a w Gu dk
t o Hk; jy Ky gw , f/ y & dk* & r fa & ; w Jho la w G[ m protect v ky fx m; w Jh y & dk* & r fa w Gq D registration t a jc t a e u dk
p Hkp r f; z dkY ' Dv dk variable a w G& Sd? r & Sd r Mu mc P p p fa q ; a v h& Sdy gw , f/ ' ga Mu mi fhr kdY o i fht a e e JY variable a w Gu dk
o dx m; c Jhr , fq dk& i f b , f Armadillo e JY protect v ky fx m; w Jh y & dk* & r fu dkr q dk t v G, fw u l crack v ky fE dki fr Sm
jz p fy ga w mhw , f/
' Do i fc e f; p mr Sm e r le mjy r , fh z dki fa w Gu a w mh Armadillo 8.6 e JY protect v ky fx m; w Jh Notepad.exe e JY
GetData Recover MyFiles 4.9.4.1343 w dkYjz p fy gw , f/ Myanmar Cracking Team r Sm download
v ky f, lE dki fy gw , f/
Notepad.exe u dk a & SUo i fc e f; p ma w Gr Sm & Si f; jy c Jhw Jhe n f; a w Go Hk; Ny D; dump v ky fv dku fy g/
Notepad.exe z dki fu dk dump v ky fz dkYt w Gu f a t mu fy gt w dki f; v ky fa q mi fy g/
( 1 ) Cr eateThr ead r Sm breakpoint o w fr Sw fy g/ Debug-Blocker r o Hk; w Jht w Gu f OpenMutexA r Sm
breakpoint o w fr Sw fp & mr v dka w mhy gb l; / 100739D [ m OEP jz p fy gw , f/
( 2 ) OEP u dko dNy D; w Jha e mu f IAT u dkjy i fy gr , f/ VA 1001000 r Sm BreakpointHardware, on
writeDword o w fr Sw fy g/ Ny D; & i f Olly u dkjy e fp y g/
( 3 ) GetTickCount e n f; u dko Hk; Ny D; IAT u dkjy i fy g/ Ny D; & i f dumper a q mhz f0 Jv fw p fc kc ke JY dump v ky fy g/
Import Fixer e JYdump z dki fu dkjy i fy g/
Dump v ky fx m; w Jhz dki fu dk z Gi fhv dku fy g/ ' Dt c g c ke u t Mu dr ft a & t w Gu fu dk p p fa q ; w Jh u e fYo w fc su f
r & Sda w mhw m a w GY& r Smy g/ r de p fu e fYo w fc su fu dkv n f; o mr e f v ky f& Hke JYz , f& Sm; E dki fw m a w GY& y gw , f/
' Dw p fc gr Sma w mhRecover MyFiles a q mhz f0 Jv fu dk crack v ky fMu n fhMu y gr , f/ RecoverMyFiles.exe
z dki fu dke JYOlly e JYz Gi fhv dku fy g/ y Hk( 1 8 9 ) /
y Hk( 1 8 9 )
,., Armadillo ... .` .
,.
y Hk( 1 8 9 ) u a w mh entry point & Sd& ma e & mjz p fy gw , f/ RecoverMyFiles.exe [ m Standard
Protection + Debug-Blocker protection u dkt o Hk; jy Kx m; w Jht w Gu f OpenMutexA r Sm breakpoint
o w fr Sw f& y gr , f/
Ctrl + G u dkE Sdy fNy D; OpenMutexA API & JUt q Hk; r Sm breakpoint o w fr Sw fy g/ y Hk( 1 9 0 ) /
y Hk( 1 9 0 )
y Hk( 1 9 0 ) t w dki f; breakpoint o w fr Sw fNy D; w Jht c g F9 u dk E Sp fMu dr fE Sdy fy g/ ' kw d, t Mu dr fa jr mu f F9 E Sdy fv dkY
RETN 0C r Sm& y fw Jht c g a & SUo i fc e f; p ma w Gr Sm v ky fc Jho v dk EAX w e fz dk; 0 u dk 1 v dkYa jy mi f; Ny D; RETN 0C
r Smo w fr Sw fx m; w Jhbreakpoint u dk jy e fjz Kw fv dku fy g/ ' gq dk Debug-Blocker u dka u smfv Tm; E kdi fNy Djz p fy gw , f/
' Dt c gr Sma w mhCtrl + G E Sdy fNy D; Cr eateThr ead API r Sm breakpoint o w fr Sw fy g/ y Hk( 1 9 1 ) /
y Hk( 1 9 1 )
y Hk( 1 9 1 ) t w dki f; breakpoint o w fr Sw fNy D; w Jht c g stack windows r Sma w GY& r , fh y Hk( 1 9 2 ) t w dki f;
jr i f& o n ft x dF9 u dkE Sdy fy g/
y Hk( 1 9 2 )
y Hk( 1 9 2 ) t w dki f; a w GY& w Jht c g Cr eateThr ead r Smo w fr Sw fx m; w Jh breakpoint u dkjz Kw fNy D; y Hk( 1 9 3 )
t w dki f; jr i f& w Jht x dF8 u dkE Sdy fv mc Jhy g/
y Hk( 1 9 3 )
y Hk( 1 9 3 ) t w dki f; a & mu f& Sdv mw Jht c g F7 u dkE Sdy fy g/ ' g[ m u Re fa w mfw dkY& Sma e w JhOEP y Jjz p fy gw , f/
y Hk( 1 9 4 )
y Hk( 1 9 4 ) u OEP a e & mjz p fw JhVA 105A3DC r Sm hardware breakpoint o w fr Sw fy g/
y Hk( 1 9 5 )
,., Armadillo ... .` .
,.,
y Hk( 1 9 5 ) u VA 105A359 a e & mr Sm Enter key E Sdy fy g/ y Hk( 1 9 6 ) t w dki f; jr i f& y gr , f/
y Hk( 1 9 6 )
y Hk( 1 9 5 ) u VA 41034C a e & mr Sm right-click E Sdy fNy D; Follow in DumpMemory address u dk
a & G; y g/ y Hk( 1 9 7 ) t w dki f; jr i f& y gr , f/
y Hk( 1 9 7 )
y Hk( 1 9 7 ) u VA 130282C a e & mr Sm right-click E Sdy fNy D; BreakpointHardware, on write
Dword o w fr Sw fy g/
Ctrl + F2 E Sdy fNy D; Olly u dkjy e fp y g/ OpenMutexA r Sm breakpoint o w fr Sw fy g/ Ny D; & i f F9
u dkE Sp fMu dr fE Sdy fy g/ ' kw d, t Mu dr fa jr mu f OpenMutexA r Smv m& y fw Jht c g EAX w e fz dk; 0 u dk 1 t jz p fa jy mi f; Ny D;
breakpoint u dk z , f& Sm; y g/ Ny D; & i f F9 u dkE Sdy fy g/
y Hk( 1 9 8 )
' Dt c g IAT redirection u dka u smfv Tm; z dkY u Re fa w mfw dkY o w fr Sw fx m; w Jh hardware breakpoint (on
write) a e & mr Sm v m& y fy gr , f/ F9 u dk q u fE Sdy fy g/
y Hk( 1 9 9 )
y Hk( 1 9 9 ) u a w mh u Re fa w mfw dkY IAT redirection u dka u smfv Tm; z dkY jy i fq i f& r , fha e & ma w Gy g/ VA
130282C r Smo w fr Sw fx m; w Jh hardware breakpoint u dkz , fNy D; a t mu fy ga e & ma w Gr Sm hardware
breakpoint o w fr Sw fy g/
02889BD6 CALL DWORD PTR DS:[292B338] ; kernel32.GetTickCount
02889FB5 CALL DWORD PTR DS:[292B338] ; kernel32.GetTickCount
02889E4A JNZ SHORT 02889E90
Ny D; & i f Ctrl + F2 E Sdy fjy D; Olly u dkjy e fp y g/
OpenMutexA r Sm breakpoint o w fr Sw fy g/ F9 u dkE Sp fMu dr fE Sdy fy g/ ' kw d, t Mu dr fa jr mu f
OpenMutexA r Smv m& y fw Jht c g EAX w e fz dk; 0 u dk 1 t jz p fa jy mi f; Ny D; OpenMutexA r Sm o w fr Sw fx m; w Jh
software breakpoint (F2) u dk z , f& Sm; y g/ Ny D; & i f F9 u dkE Sdy fy g/
y Hk( 2 0 0 )
y Hk( 2 0 0 ) t w dki f; jr i f& w Jht c gr Sm VA 02889BD6 a e & mr Sm MOV EAX, 10? VA 02889FB5
a e & mr Sm EAX, 12 e JY VA 02889E4A a e & mr Sm NOP t jz p fjy i fy g/ ( b ma Mu mi fhjy i f& w , fq dkw m
,., Armadillo ... .` .
,..
a & SUo i fc e f; p ma w Gr Sm & Si f; jy Ny D; jz p fy gw , f/ ) jy i fNy D; w Jht c g ' Da e & m ( 3 ) c kr Sm o w fr Sw fx m; w Jh hardware
breakpoint a w Gu dk jz Kw fy g/
y Hk( 2 0 1 )
Hardware breakpoint a w Gu dk jz Kw fNy D; w Jht c g y Hk( 2 0 1 ) r Smjr i f& w Jh VA 288A07F a e & mr Sm
breakpoint (F2) o w fr Sw fy g/ Ny D; & i fa w mh F9 u dkE Sdy fy g/ VA 288A07F r Sm& y fy gv dr fhr , f/ ' Dt c g VA
02889BD6? VA 02889FB5 e JY VA 02889E4A w dkYr Sm jy i fx m; w Jhu k' fa w Gu dk Undo Selection v ky fNy D;
r lv t w dki f; jy e fx m; y g/ VA 288A07F r Smo w fr Sw fx m; w Jh breakpoint u dkv n f; jz Kw fy p fv dku fy g/ Ny D; & i fa w mh
u dkE Sdy fv dku fy g/ y Hk( 2 0 2 ) t w dki f; OEP & Sd& ma e & mu dk a & mu fv my gr , f/
y Hk( 2 0 2 )
' Dt c g dump v ky fz dkYjy i fy gr , f/ y Hk( 2 0 2 ) u code windows a y : right-click E Sdy fNy D; Make dump of
process u dka & G; y g/
y Hk( 2 0 3 )
y Hk( 2 0 3 ) u Dump button u dka & G; Ny D; dumped.exe e mr n fe JYo dr f; v dku fy g/ Ny D; & i fa w mh dumped.exe
z dki fu dk jy i fy gr , f/ Import Fixer 1.6 u dkz Gi fhy g/
y Hk( 2 0 4 )
y Hk( 2 0 4 ) t w dki f; OEP? IAT & JUt p e JY IAT & JU length (size) w e fz dk; a w Gu dk & dku fx n fha y ; y g/
t x l; o w dx m; & r Smu o i fhu Ge fy sLw mr Sm IAT & JUt p w e fz dk; [ m t jc m; w p fc k jz p fE dki fy gw , f/ ( ' Dw e fz dk; u dk
b ma Mu mi fhx n fh& o v Jq dkw mu dk a & SUo i fc e f; p ma w Gr Sm & Si f; jy Ny D; jz p fy gw , f/ ) Show ivalid thunks button
,., Armadillo ... .` .
,..
u dka & G; Ny D; invalid jz p fa e w Jh thunks a w Gu dk cut v ky fv dku fy g/ Ny D; & i f Fix dump button u dkE Sdy fNy D; y Hk( 2 0 3 ) r Sm
dump v ky fx m; w Jhdumped.exe z kdi fu dk fix v ky fy g/ dumped_IF.exe e mr n fe JYz dki fu dk o dr f; q n f; y g/
' gq dk& i fa w mh a u mi f; r Ge fp Gm t v ky fv ky fw Jh unpack v ky fx m; w Jh dumped_IF.exe z dki fu dk & Ny D
jz p fy gw , f/ Dump v ky fx m; w Jhz dki f[ m z dki ft & G, ft p m; t e n f; i , fMu D; a e y ga o ; w , f/ ' Dz dki ft & G, ft p m; u dk
a o ; a t mi f v ky fw mu a w mhv u f& Sdo i fc e f; p me JYr o u fq dki fv dkYa u smfv dku fy gr , f/
Armadillo e JY protect v ky fx m; w Jhz kdi fa w Gu dk crack v ky fw Jht c g p dw f0 i fp m; z dkY a u mi f; w mu
Armaaccess.dll z dki fy g/ ' Dz dki fu dk protect v ky fx m; w Jhz dki fx J x n fho Gi f; Ny D; jz p fa p ? o D; o e fYjz p fa p x m; & SdNy D;
environment variable a w Gjz p fw Jh USERNAME e JY USERKEY w dkYu dk w dku fq dki fp p fa q ; w Jht c g ' Dz dki fu dk
z w fy gw , f/ y & dk* & r fa w G[ m Armaaccess.dll z dki fu dkz w fz dkYGetProcAddressA API e JYLoadLibraryA API
w dkYu dk o Hk; w mr sm; y gw , f/
Recovery My Files r Sma w mh' De n f; t p m; string a w Gu dk 0 Su fv dku fy gw , f/ y Hk( 2 0 5 ) /
y Hk( 2 0 5 )
String a w Gu dk 0 Su f& mr Sm r o do ma t mi fv dkY ArmacCesS.DLl t a e e JY 0 Su fw m o w djy Kr dr Smy g/
p mv Hk; c si f; r w lw Jht w Gu f cracker a w Gu dk armaccess.dll z dki fr Se f; a 0 c GJ& c u fa p r Smjz p fy gw , f/ A = A4, r = 97,
m = 88, a = 84 p o jz i fh0 Su fNy D; y Hk( 2 0 6 ) u u k' fa w Ge JYencrypt v ky fx m; w ma w Gu dk decrypt jy e fv ky fy gw , f/
y Hk( 2 0 6 )
y Hk( 2 0 5 ) u CALL 0053120C x Jr Sm string a w Gu dk decrypt v ky fNy D; CALL 004187CC x Jr Sm
ArmacCesS.DLl z dki fu dk & Sma z Gp p fa q ; y gw , f/ r & Sdw Jht c gr Sm y Hk( 2 0 7 ) t w dki f; p p fa q ; r Smjz p fy gw , f/
y Hk( 2 0 7 )
y Hk( 2 0 7 ) t w dki f; VA 0081992F u dka & mu fw Jht c g Ctrl + G E Sdy fNy D; GetEnvir onmentVar iableW
r Sm hardware breakpoint o w fr Sw fy g/ CALL 004069F8 [ m badboy CALL a w Gjz p fNy D; JMP
00819A9D a w G[ mv n f; badboy jump a w Gjz p fw , fq dkw m o dx m; & y gr , f/ ' ga Mu mi fh Ctrl + A u dkE Sdy fNy D;
Analyze v ky fy g/ Ny D; & i f CALL 004069F8 a y : right-click E Sdy fNy D; Find references toCall
destination u dka & G; v dku fy g/ y Hk( 2 0 7 ) r Smjr i f& w Jht w dki f; CALL 004069F8 & Sdw Jh a e & mw dki f; r Sm breakpoint
o w fr Sw fy g/ Ny D; & i f LCB plugin u dko Hk; Ny D; breakpoint a w Gu dk export v ky fx m; y g/ LCB plugin [ m Label
,., Armadillo ... .` .
,.
a w G? Comment a w G? Breakpoint a w Gu dk r Sw fx m; a y ; & mr Sm t a u mi f; q Hk; jz p fy gw , f/ o i fht a e e JYr Sw fx m; z dkYu
u Re fa w mfw dkY[ m ' DCALL 004069F8 a w G& Sdw Jh a e & mt c sdKUu dk a u smfE dki f& y gr , f/ ' ga Mu mi fh VA 81994B u
JNZ SHORT 00819960 a e & mr Sm JMP v dkYa jy mi f; Mu n fhy gr , f/ Ny D; & i f F9 u dkE Sdy fy g/ y Hk( 2 0 8 ) /
y Hk( 2 0 8 )
' Dt c g u Re fa w mfw dkY hardware breakpoint o w fr Sw fx m; w Jh GetEnvir onmentVar iableW
a e & mq Da & mu fv mNy Djz p fy gw , f/ Stack windows r Smv n f; Mu n fhv dku fy g/ y Hk( 2 0 9 ) /
y Hk( 2 0 9 )
Stack windows r SmMu n fhv dku fw Jht c g u Re fa w mfw dkY & Sma e w Jh EV w p fc ka & mu fa e w m a w GY& y gw , f/
Ny D; & i f Alt + F9 E Sdy fNy D; user code & Sd& mq Dx Gu fv dku fy g/ y Hk( 2 1 0 ) /
y Hk( 2 1 0 )
o mr e ft m; jz i fh u Re fa w mfw dkYt a e e JY y Hk( 2 1 0 ) & Sd& ma e & mu dk b , fa w mhr S a & mu fr v mE dki fy gb l; / c kv dk
a & mu fv m& w m[ m JNZ u dk JMP a jy mi f; v dku fv dkYjz p fy gw , f/
a u mi f; Ny D/ Olly u dk jy e fp v dku fy g/ GetEnvir onmentVar iableW r Smo w fr Sw fx m; w Jh hardware
breakpoint u dkjz Kw fv dku fy g/ Ny D; & i f LCB plugin e JY export v ky fx m; w Jh breakpoint 7 7 3 c ku dk import
jy e fv ky fy g/ Ny D; & i f y Hk( 2 1 1 ) r Smjr i f& w Jht x d F9 u dkE Sdy fy g/ Olly [ m VA 443981 e JY VA 815CE8 w dkYr Sm
& y fy gv dr fhr , f/ ( ' Da e & ma w Gu t a & ; r Mu D; w Jht w Gu f F9 u dk q u fE Sdy fv mc Jhy g)
y Hk( 2 1 1 )
y Hk( 2 1 1 ) u VA 819951 u CALL 004069F8 a e & mr Sm Olly [ m v m& y fy gv dr fhr , f/
u Re fa w mfw dkYt a e e JY ' D CALL E Sp fc kq u fw dku f& Sdw Jha e & mr Sm Olly u dk & y fa p v dkYr & y gb l; / ' ga Mu mi fh JNZ
SHORT 00819960 a e & mr Sm right-click E Sdy fNy D; New or igin her e u dka & G; y g/ JNZ u dk JMP v dkYa jy mi f; y g/
Ny D; & i f GetEnvir onmentVar iableW r Sm hardware breakpoint o w fr Sw fy g/ F9 u dkE Sdy fy g/ y Hk( 2 1 2 ) /
,., Armadillo ... .` .
,.
y Hk( 2 1 2 )
y Hk( 2 1 2 ) r Sma w mh u Re fa w mfw dkYv dkc si fw Jh EV w p fc ku dk & y gNy D/ USERNAME u dk Notepad r Sm
r Sw fo m; x m; y g/ F9 u dk y Hk( 2 1 3 ) t w dki f; jr i f& w Jht x dx y fE Sdy fy g/
y Hk( 2 1 3 )
y Hk( 2 1 3 ) r Smjr i f& w Jht w dki f; badboy CALL q Da & mu fv my gw , f/ JNZ SHORT 00817EA3 a e & mr Sm
right-click E Sdy fNy D; New or igin her e u dka & G; y g/ JNZ u dk JMP v dkYa jy mi f; y g/ F9 u dkE Sdy fy g/ y Hk( 2 1 4 ) /
y Hk( 2 1 4 )
y Hk( 2 1 4 ) r Sma w mh u Re fa w mfw dkYv dkc si fw Jh EV a e mu fw p fc ku dk a w GYy gw , f/ TYPE u dk Notepad r Sm
r Sw fo m; x m; y g/ F9 u dk x y fE Sdy f& i fa w mha t mu fy gt w dki f; jr i f& y gr , f/
y Hk( 2 1 5 )
y Hk( 2 1 5 ) r Smv n f; u Re fa w mfw dkYv dkc si fw Jh EV a e mu fw p fc ku dk a w GYy gw , f/ DESC u dk Notepad r Sm
r Sw fo m; x m; y g/ F9 u dkE Sdy fy g/ y Hk( 2 1 6 ) /
y Hk( 2 1 6 )
JNZ SHORT 00817F17 a e & mr Sm right-click E Sdy fNy D; New or igin her e u dka & G; y g/ JNZ u dk JMP
v dkYa jy mi f; y g/ F9 u dkE Sdy fy g/ y Hk( 2 1 7 ) /
y Hk( 2 1 7 )
y Hk( 2 1 7 ) r Smv n f; u Re fa w mfw dkYv dkc si fw Jh EV a e mu fw p fc ku dk a w GYy gw , f/ KEYCREATED u dk
Notepad r Sm r Sw fo m; x m; y g/ F9 u dkE Sdy fy g/ y Hk( 2 1 8 ) /
y Hk( 2 1 8 )
JNZ SHORT 00817F43 a e & mr Sm right-click E Sdy fNy D; New or igin her e u dka & G; y g/ JNZ u dk JMP
v dkYa jy mi f; y g/ F9 u dkE Sdy fy g/ y Hk( 2 1 9 ) /
y Hk( 2 1 9 )
y Hk( 2 1 8 ) w ke f; u F9 E Sdy fc sde fr Sm GetEnvir onmentVar iableW q Da & mu fr v mw Jht w Gu f y Hk( 2 1 8 ) u
JNZ u dk JMP v dkYr jy i fv n f; & y gw , f/ y Hk( 2 1 9 ) u JNZ SHORT 00817F92 a e & mr Sm right-click E Sdy fNy D;
New or igin her e u dka & G; y g/ JNZ u dk JMP v dkYa jy mi f; y g/ F9 u dkE Sdy fy g/ y Hk( 2 2 0 ) /
y Hk( 2 2 0 )
,., Armadillo ... .` .
,.
y Hk( 2 1 7 ) r Smv n f; u Re fa w mfw dkYv dkc si fw Jh EV a e mu fw p fc ku dk a w GYy gw , f/ KEYSTRING u dk Notepad
r Sm r Sw fo m; x m; y g/ F9 u dkE Sdy fy g/ y Hk( 2 2 1 ) /
y Hk( 2 2 1 )
y Hk( 2 2 1 ) u JNZ SHORT 0081802D [ m CALL 004069F8 u dk a u smfE dki fjc i f; r & Sdw Jht w Gu f JMP
v dkYa jy mi f; p & m r v dky gb l; / F9 u dkE Sdy fy g/ y Hk( 2 2 2 ) /
y Hk( 2 2 2 )
y Hk( 2 2 2 ) u JE SHORT 0081997F a e & mr Sm right-click E Sdy fNy D; New or igin her e u dka & G; y g/ JE u dk
JMP v dkYa jy mi f; y g/ F9 u dkE Sdy fy g/ y Hk( 2 2 0 ) /
y Hk( 2 2 3 )
y Hk( 2 2 3 ) r Sm u Re fa w mfw dkYv dkc si fw Jh EV a e mu fw p fc ku dk a w GYy gw , f/ EXTRAINFO u dk Notepad r Sm
r Sw fo m; x m; y g/ F9 u dkE Sdy fy g/ y Hk( 2 2 4 ) /
y Hk( 2 2 4 )
y Hk( 2 2 4 ) u JNZ SHORT 00443988 a e & mr Sm right-click E Sdy fNy D; New or igin her e u dka & G; y g/ JNZ
u dk JMP v dkYa jy mi f; y g/ F9 u dkE Sdy fy g/ ' Dt c g y & dk* & r f crash jz p fo Gm; w ma w GY& y gr , f/ ' ga Mu mi fh ' Da e & mr Sm JNZ
u dk JMP v dkYjy i fv dkYr & y gb l; /
a u mi f; Ny D/ u Re fa w mfw dkY GetEnvir onmentVar iableW breakpoint r Sm r Sw fo m; c Jhw Jh
environment variable a w Gu dk w p kw p n f; w n f; jy e fa & ; Mu n fhr , fq dk& i fa w mh USERNAME? TYPE?
DESC? KEYSTRING e JYEXTRAINFO w dkYjz p fy gw , f/
' D environment variable a w Gu dk& z dkY conditional jump a w Ga e & mr Sm unconditional jump
a w Gt jz p fjy i fc Jh& w Jha e & ma w Gu a w mha t mu fy gt w dki f; jz p fy gw , f-
( 1 ) VA 81994B JNZ 819960
( 2 ) VA 817E68 JNZ 817EA3
( 3 ) VA 817F07 JNZ 817F17
( 4 ) VA 817F86 JNZ 817F92
t a y : JNZ a e & ma w Gr Sm JMP v dkYjy i fNy D; y & dk* & r fu dk save v dku fy g/ Ny D; & i f dumped_IF.exe z dki fu dk
o D; o e fYz Gi fhMu n fhv dku fy g/ y Hk( 2 2 5 ) /
y Hk( 2 2 5 )
,., Armadillo ... .` .
,.
u Re fa w mfw dkYt a e e JY 4 a e & mr Sm u k' fa w Gu dk jy i fc Jha y r , fh registered version r jz p fa o ; y gb l; /
y Hk( 2 2 5 ) r Smjr i f& w Jht w dki f; badboy a w Gu se fa e w ke f; y g/ b ma Mu mi fhv n f; q dka w mh u Re fa w mfw dkYu a w Gu dk y & kd* & r f
r p w i fc i fa o ; w Jht y kdi f; r Smy J jy i fc Jhv dkYjz p fy gw , f/ About menu u dka c : o Hk; c sde f? z dki fa w Gu dk recovery
v ky fNy D; w Jha e mu f save v ky fr , fht c sde f p w ma w Gr Sm environment variable a w Gp p fa q ; w mu dk r jy i fq i f
& a o ; y gb l; / ' Dv kdo m jy i fr , fq dk& i f t c sde fu ke f v u f0 i fr Sm jz p fw Jht w Gu f u Re fa w mfw dkYt a e e JY & Sma z GNy D;
r jy i fq i fa w mhy gb l; /
a u mi f; Ny D/ Environment variable a w G& JU w e fz dk; a w Gu dk o w fr Sw fMu & a t mi f/ ' Dv dko w fr Sw fz dkY
t o Hk; jy Kr , fh tool u a w mh Armadillo Reducer 1.7.1 jz p fNy D; Myanmar Cracking Team r Sm download
v ky f, lE dki fy gw , f/
y Hk( 2 2 6 )
y Hk( 2 2 6 ) r Smjr i f& w Jht w dki f; Select your Ar madillo Fixed Dump button u dkE Sdy fNy D; u Re fa w mfw dkY
u k' fjy i fx m; w Jh dumped_IF.exe z dki fu dka & G; y g/ Envir onment Patcher button u dkE Sdy fy g/ Ny D; & i f y Hk( 2 2 7 )
t w dki f; jy i fq i fy g/
y Hk( 2 2 7 )
y Hk( 2 2 8 ) t w dki f; jy i fq i fNy D; & i fa w mh Patch it button u dkE Sdy fy g/ Ny D; & i f patch v ky fx m; w Jh z dki fu dk
z Gi fhv dku fy g/ y Hk( 2 2 8 ) t w dki f; a w GY& r Smjz p fy gw , f/
y Hk( 2 2 8 )
' gq dk& i fa w mh u Re fa w mfw dkY& JU crack v ky fjc i f; a t mi fjr i fp GmNy D; q Hk; o Gm; Ny D jz p fy gw , f/ Armadillo
Reducer tool r o Hk; b J u dk, fw dki f patch v ky fc si fw , fq dk& i fa w mh SetEnvir onmentVar iableW u dko Hk; Ny D;
patch v ky fE dki fy gw , f/
,., Armadillo ... .` .
,.,
, Ar madillo . Envir onment Var iables
tcef;(33) - POPCAP? BigFish? TryMedia? Oberon *drf;rsm;udk crack vkyfjcif;
- 494 -
tcef;(33) - POPCAP? BigFish? Tr yMeida? Ober on *drf;rsm;udk cr ack vkyfjcif;
r Mu mr Dv mr n f/
tcef;(34) - Virtualization rd wf quf
- 495 -
tcef;(34) - Vir tualization rdwfquf
r Mu mr Dv mr n f/
tcef;(35) - WinLicense zdkifrsm;udk crack vk yf jcif ;
- 496 -
tcef;(35) - WinLicense zdkifrsm;udk cr ack vkyfjcif;
r Mu mr Dv mr n f/
tcef;(36) - Kernel mode wGif tvkyfvkyfonfh y&dk*&rfrsm;udk crack vk yf jcif ;
- 497 -
tcef;(36) - Ker nel mode wGif tvkyfvkyfonfh y&dk*&rfrsm;udk cr ack vkyfjcif;
r Mu mr Dv mr n f/
tcef;(37) - Serial fisher udk b,fvdk zefwD;rvJ
- 498 -
tcef;(37) - Ser ial fisher udk b,fvdk zefwD;rvJ
r Mu mr Dv mr n f/
tcef;(38) - udk,fydkif loader a&;Mu&atmif
- 499 -
tcef;(38) - udk,fydkif loader a&;Mu&atmif
r Mu mr Dv mr n f/
tcef;(39) - Obfuscation ES if h Deobfuscation
- 500 -
tcef;(39) - Obfuscation ESifh Deobfuscation
r Mu mr Dv mr n f/
,.,, Inline-patch ` .
tcef;(40) - Inline-patch vkyfjcif;
' Dw p fc gr Sma w mh inline-patch v ky fw mu kd a v hv mMu n fhy gr , f/ Inline-patch -..-.-.-.
loader - decompression stub - ....-`.,.. .-.- -.--``. .,.-.....-.
application - .- - . ... OEP . .- . ....` .`.. -. ,_ .- -. , . .
. .`. . . .-. patch . . . . . ...- ,_ ... - . . Pack ..- . .- - -
crack .- -,.-.-.,, ...,..`. File Drop ,_., ..-. -..-...-.
pack ..-.- . unpack . . crack .-..-. `.. -. . . . pack
..-., unpack --.-. ... .... .-.-.--- Offset Patch ,_.,
patch ...-. - . Pack ..-., unpack ..-.-. -.-. .-.-.-
-- Search & Replace Pattern ,_.-_. ..` ...-.- . -, .-. - .,, File
Drop ,_ .. .- .`.. .., . ...-. . . `.. -. File Drop -. .........- crack
. - - . - . .. - . ... ..-.....-..... upload .-. . .`. .
.- - - . .-. . - . . . . ... .- ....... - - -, .-. - .,, inline-patch
,_ .- . .`.-.`.. -.
, UPX `. pr otect ........ inline-patch ` .
UPX r Sm inline-patch v ky fw mu dk ]t c e f; ( 1 4 ) - Packer (Protector) r sm; } t c e f; r Sm & Si f; jy Ny D;
jz p fy gw , f/ ' ga y r , fh & Si f; jy c Jhw mu o mr e f MessageBox a v ; w p fc k x n fho Gi f; y Hka v ; o m jz p fy gw , f/
Professional a q mhz f0 Jv fa w Gu dk inline-patch v ky fe n f; e JY crack v ky fw mu dka w mh ' Do i fc e f; p mr Sm a q G; a E G;
o Gm; y gr , f/ ' Do i fc e f; p mt w Gu f a & G; c s, fx m; w mu a w mh PDF Password Cracker Enterprise 3.2 jz p fNy D;
http://www.crackpdf.com r Sm download v ky f, lE dki fy gw , f/
a q mhz f0 Jv fu dk crack r v ky fc i f y x r q Hk; a q mhz f0 Jv f& JU o a b mo b m0 u dk a v hv mMu n fhy gr , f/
a q mhz f0 Jv f& JU u e fYo w fc su fa w Go dE dki fa t mi fv dkYcrackpdf.exe u dkz Gi fhv dku fy g/ y Hk( 1 ) /
y Hk( 1 )
Registration key [ m Machine ID a y : r lw n fNy D; a jy mi f; v JE dki fr , fv dkY x i fy gw , f/ E Sp fo u f& m
key w p fc ku dk& dku fx n fhNy D; OK button u dkE Sdy fv dku f& i f y Hk( 2 ) t w dki f; jr i f& y gv dr fhr , f/
y Hk( 2 )
Key r x n fha w mhb JTry button u dkE Sdy fv dku f& i fa w mhy Hk( 3 ) t w dki f; jr i f& r Smy g/
y Hk( 3 )
,.,, Inline-patch ` .
u se fw Jh u e fYo w fc su fa w Gu dka w mh r a z mfjy a w mhy gb l; / u e fYo w fc su fa w G p p fNy D; o Gm; Ny Djz p fw Jht w Gu f
crackpdf.exe z dki fu dk b , fb mo mp u m; e JY a & ; x m; w , f? b , f packer/protect w Jh pack/protect
v ky fx m; w , fq dkw mu dkp p fMu n fhy gr , f/ y Hk( 4 ) /
y Hk( 4 )
UPX 3.05 e JY pack v ky fx m; y gw , f/ Crack v ky f& w m t q i fa jy a t mi fv dkY crackpdf.exe u dk CFF
Explorer o Hk; Ny D; unpack v ky fv dku fy g/ Unpack v ky fx m; w Jhz dki fu dk Resource Hacker e JYz Gi fhy g/ y Hk( 5 ) /
y Hk( 5 )
' Da q mhz f0 Jv fu dk crack v ky fz dkYt w Gu f e n f; v r f; r sdK; p Hk & Sda y r , fh u Re fa w mfu a w mh Visual C++
e JYa & ; x m; w Jh a q mhz f0 Jv fa w Gu dk crack v ky f& mr Sm Resource Hacker u dkt o Hk; jy Kw m r sm; y gw , f/ y Hk( 5 ) r Sm
u Re fa w mfw dkY p dw f0 i fp m; w mu 1045 q dkw Jh DialogID jz p fy gw , f/ b ma Mu mi fhv Jq dka w mh a q mhz f0 Jv fr p c i f ' D
dialog a v ; a y : v dkYjz p fy gw , f/ w u , fv dkYregistered version o Hk; c Jhr , fq dk& i f ' Ddialog a y : r Sm r [ kw fv dkYy g/
u Re fa w mfw dkYt a e e JY' Ddialog u dka u smfE dki fz dkYMu dK; p m; & r Smjz p fy gw , f/
a u mi f; Ny D/ crackpdf.exe u dkOlly e JYz Gi fhy gr , f/
y Hk( 6 )
y Hk( 6 ) u a w mh OEP & Sd& ma e & mjz p fy gw , f/ u Re fa w mfw dkY& Smc si fw Jh dialog & Sd& ma e & mu dk & SmMu n fhy gr , f/
Disassembler windows a y : r Sm right-click E Sdy fNy D; Search for All constants u dka & G; v dku fy g/ y Hk( 7 ) /
,.,, Inline-patch ` .
y Hk( 7 )
y Hk( 7 ) u OK button u dkE Sdy fv dku f& i fa w mhy Hk( 8 ) t w dki f; jr i f& r Smy g/
y Hk( 8 )
y Hk( 8 ) u PUSH 415 a e & mu dkE Sp fc su fE Sdy fv dku fy g/ y Hk( 9 ) /
y Hk( 9 )
y Hk( 9 ) r Sm u Re fa w mfw dkY& JU Registration dialog (1045) u dk DialogBoxParamA API e JYa c : o Hk; w m
jr i f& r Smy g/ ' D dialog u dk VA 404730 u a e a c : o Hk; w mv J a w GY& y gw , f/ ' ga Mu mi fh y Hk( 1 0 ) t w dki f; VA
404730 u dko Gm; y gr , f/
y Hk( 1 0 )
y Hk( 1 0 ) [ m ' Do i fc e f; p m& JU t a & ; Mu D; q Hk; t y dki f; y J jz p fy gw , f/ VA 404716 r Sm EAX & JUw e fz dk; [ m 0
jz p f^ r jz p fu dk p p fy gw , f/ w u , fv dkY0 r jz p fc Jh& i f data segment & JU VA 54B3D4 r Sm 0 w e fz dk; u dk o Gm; o dr f; Ny D;
VA 404730 r Sm registration dialog (1045) a c : o Hk; w Jh CALL u dkv ky fa q mi fa p y gw , f/ w u , fv dkY EAX
w e fz dk; 0 jz p fc Jh& i fa w mh BadBoy u dka u smfv Tm; E dki fr Sm jz p fy gw , f/ ' ga Mu mi fh EAX w e fz dk; u dk 0 jz p fa p z dkY EAX
w e fz dk; u dko w fr Sw fa y ; w JhVA 40470F u CALL 00409E98 q DEAX w e fz dk; 0 jz p fa t mi f0 i fjy i fy gr , f/
,.,, Inline-patch ` .
,
y Hk( 1 1 )
y Hk( 1 1 ) u dk a o a o c smc smMu n fhy g/ EAX w e fz dk; o kn jz p fz dkY[LOCAL.6] (DWORD PTR SS:[EBP-
18]) & JUw e fz dk; [ m o kn jz p fz dkY v dky gr , f/ [LOCAL.6] & JUw e fz dk; o kn jz p fa p z dkYt w Gu f JNZ 00409EF6 [ m
VA 409EF6 q D jump jz p f& y gr , f/ ' ga Mu mi fh JNZ 00409EF6 a e & mr Sm JE 00409EF6 ( o dkY) JMP
00409EF6 v dkYjy i f& y gr , f/ u Re fa w mfw dkYJE 00409EF6 v dkYjy i fv dku fy gr , f/
y Hk( 1 2 )
y Hk( 1 2 ) t w dki f; jy i fv dku fw Jht c g HEX w e fz dk; [ m 75 1B u a e 74 1B v dkYa jy mi f; o Gm; y gw , f/ jy D; & i fa w mh
u k' fjy i fx m; w mu dksave v ky fNy D; run Mu n fhv dku fy g/
y Hk( 1 3 )
' Dt c gr Sma w mh y Hk( 1 3 ) r Smjr i f& w Jh Purchase q dkw Jh button a v ; a y smu fo Gm; Ny D; HomePage q dkw Jh
button a v ; a & mu fv my gr , f/ Registration dialog v n f; a y : v ma w mhr Sm r [ kw fa w mhy gb l; /
w u , fa w mh u Re fa w mfht a e e JY ' Do i fc e f; p mr Sm b , fv dk crack v ky f& r v Jq dkw mu dk t " du jy c si fw m
r [ kw fy gb l; / a q mhz f0 Jv fw p fc ku dk unpack r v ky fb J? File Drop e n f; u dk r o Hk; b J b , fv dk crack/patch
& r v Jq dkw mu dko m jy o c si fw m jz p fy gw , f/ ' ga Mu mi hf inline-patch v ky fe n f; t a Mu mi f; u dk q u fv u f a v hv m
Mu y gr , f/
Inline-patch v ky fe n f; [ m unpacking & JU o a b mw & m; u dk e m; v n fo a b ma y gu fr So m t o Hk; jy KE dki fy g
w , f/ ' ga Mu mi fh o i fht a e e JY UPX u dk u dk, fw dki f b , fv dk unpack v ky f& r , fq dkw mu dk o dx m; & y gr , f/
t x l; o jz i fhdecompression stub b , ft c sde fr Smjy D; r v Jq dkw m o dx m; & y gr , f/ y & dk* & r f& JU OEP b , fr Sm& Sdw , f
q dkw mu dk o dx m; & y gr , f/ ( UPX u dk b , fv dk unpack v ky f& r , fq dkw mu dk ]t c e f; ( 1 4 ) - Packer (Protector)
r sm; }r Sm & Si f; jy Ny D; jz p fy gw , f/ )
a u mi f; Ny D/ u Re fa w mfw dkYt a e e JYunpack r v ky fx m; w Jhr l& i f; z dki fu dkjy e fMu n fhv dku fMu & a t mi f/ y Hk( 1 4 ) /
,.,, Inline-patch ` .
y Hk( 1 4 )
y Hk( 1 4 ) r Smjr i f& w mu a w mh UPX e JY pack v ky fx m; w Jh crackpdf.exe z dki f& JU entry point (EP)
& Sd& mjz p fy gw , f/
a u mi f; Ny D/ u k' fa w G& JU a t mu fq Hk; e m; jz p fw Jh00 00 00 byte a w Gp ka e & m a e & mq Do Gm; v dku fMu & a t mi f/
y Hk( 1 5 )
UPX e JY pack v ky fx m; w Jh z dki fw dki f; r Sm 00 00 00 a w G& JU t x u fe m; u JMP xxx [ m OEP q Du dk
n Te f; w m jz p fy gw , f/ q dkv dkw mu VA 55A2CC q Da & mu fw Jht c gr Sm UPX [ m u k' fa w Gu dk r l& i f; t w dki f;
jy e fv n f decompress v ky fNy D; o Gm; Ny Djz p fy gw , f/ ' ga Mu mi fh JMP 4AD3D3 a e & mr Sm u Re fa w mfw dkY inline-
patch v ky fc si fw Jh u k' fu dk v mx m; y gr , f/ ' Da e & mr Sma w mh u Re fa w mfw dkYjy i fc si fw m w p fc kw n f; & Sdy gw , f/
' gu a w mh y Hk( 1 2 ) & JU VA 409ED9 u JNZ 00409EF6 (75 1B) a e & mr Sm JE 00409EF6 (74 1B) v dkY
jy i fc si fw my g/ ' ga Mu mi fhy Hk( 1 6 ) t w dki f; jy i fv dku fy gr , f/
y Hk( 1 6 )
y Hk( 1 6 ) u dk a o a o c smc smMu n fhy g/ u Re fa w mfw dkYjy i fc si fw Jha e & mu VA 409ED9 jz p fy gw , f/ jy i fc si fw m
u 75 1B u dk 74 1B e JY t p m; x kd; c si fw my g/ 1B c si f; u w la e w Jht w Gu f t p m; x dk; p & m r v dka w mhy gb l; /
' ga Mu mi fhMOV BYTE PTR DS:[409ED9] v dkYy J a & ; v dku fw my g/ ' Da e mu fr Sma w mhVA 55A2D3 r Sm JMP
4AD3D3 u dk a & ; y g/ Ny D; & i f jy i fx m; w Jhu k' fa w Gu dk crackpdf(inline-patch).exe e mr n fe JYo dr f; v dku fy g/
o dr f; x m; w Jhz dki fu dkz Gi fhr , fq dk& i f registered version jz p fw Jhy & dk* & r fy Gi fhv my gv dr fhr , f/
' Da e mu fr Sma w mh uPPP u dkz Gi fhNy D; Offset Patch u dka & G; y g/ crackpdf.exe e JY crackpdf(inline-
patch).exe z dki fw dkYu dk E dIi f; , SOfy g/ ' gq dk y Hk( 1 7 ) t w dki f; jr i f& y gr , f/ Ny D; & i fa w mh Save u dka & G; Ny D; Create patch
button u dkE Sdy fr , fq dk& i f u Re fa w mfw dkYv dkc si fw Jhz dki ft & G, ft p m; a o ; a o ; e JYpatch z dki fa v ; u dk& r Smjz p fy gw , f/
y Hk( 1 6 )
tcef;(41) - tqifhjrifh keygen rsm;ud k zef wD ;jcif ;
- 506 -
tcef;(41) - tqifhjrifh keygen rsm;udk zefwD;jcif;
r Mu mr Dv mr n f/
tcef;(42) - 64-bit y&dk*&rfrsm;udk crack vk yf jcif ;
- 507 -
tcef;(42) - 64-bit y&dk*&rfrsm;udk cr ack vkyfjcif;
r Mu mr Dv mr n f/
tcef;(43) - Developer rsm;\ anti-cracking vQd KU0S uf csuf
- 508 -
tcef;(43) - Developer rsm;\ anti-cr acking vQdKU0Sufcsuf
r Mu mr Dv mr n f/
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 509 -
tcef;(44) - Anti Unpacking enf;vrf;rsm;
' Do i fc e f; p mr Sm a q mhz f0 Jv fa w Gu dk crack r v ky fE dki fa t mi f developer a w Gu b , fv dkv Sn fhp m; a v h& Sdo v J
q dkw mu dk t u s, fw 0 i fh& Si f; jy r Sm jz p fw Jht w Gu f developer a w Gt w Gu fa & m? cracker a w Gt w Gu fy g t a x mu f
t u ljy Ka p r Sm jz p fy gw , f/ a q mhz f0 Jv fa w Gu dk crack r v ky fE dki fa p z dkU developer a w mfa w mfr sm; r sm; u packer/
protector a w G& JU t u lt n Du dk, ljy D; pack/protect v ky fMu y gw , f/ Cracker a w Gu a w mh pack v ky fx m; w Jh
z dki fa w Gu dk unpack v ky fjy D; crack v ky fMu & w mjz p fw Jht w Gu f cracker a w Gt c u fa w GUa p E dki fr , fh anti-
unpacking e n f; v r f; r sm; u dka z mfjy v dku fy gw , f/
Unpack v ky f& mr Sm t c u fa w GUa p E dki fr , fhe n f; v r f; ( 4 ) c ku a w mh-
( 1 ) Anti-Dumping
( 2 ) Anti-Debugging
( 3 ) Anti-Emulating
( 4 ) Anti-Intercepting
( 1 ) Anti-Dumping
Dump v ky fw , fq dkw mu a w mh r Sw fOmP fr Sm v u f& Sdt v ky fv ky fa e w Jh y & dk* & r f (process) & JU u k' fa w Gu dk
disk a y : o dr f; q n f; jc i f; u kd q dkv dkw my g/ Anti-dumping t w Gu f v Sn fhp m; r Ia w Gu a w mh a t mu fy gt w dki f;
jz p fy gw , f/
( 1 . 1 ) SizeOfImage
Dump v ky fjc i f; u dk w m; q D; z dkU t a u mi f; q Hk; e n f; v r f; u a w mh Process Environment Block (PEB)
x Ju SizeOfImage w e fz dk; u dk a jy mi f; z dkUjz p fy gw , f/ y Hk( 5 ) / ' Dv dka jy mi f; v dku f& i f debugger u process u dk
attach v ky fjc i f; r Su mu G, fE dki fo v dk process u dk access v ky fw m t [ e fUt w m; jz p fa p y gw , f/ ' ghjy i f dump
v ky fr , fh page t a & t w Gu fu dkv J r r Se fr u e f jz p fa p y gw , f/ ' De n f; [ m default mode r Sm t v ky fv ky fw Jh
LordPE v dktool r sdK; u dkdump r v ky fE dki fa t mi f w m; q D; E dki fy gw , f/
e r le mu k' fu a w mha t mu fy gt w dki f; jz p fy gw , f/
mov eax, fs:[30h] ; PEB (ProcessEnvironmentBlock)
mov eax, [eax+0ch] ; LdrData
; get InLoadOrderModuleList
mov eax, [eax+0ch]
; New SizeOfImage
mov dword ptr [eax+20h], 1000h
' De n f; v r f; u dk v u f& Sdr Sm packer a w mfa w mfr sm; r sm; u t o Hk; jy Kv su f& Sdy gw , f/ b my Jjz p fjz p f? user-
mode r Smq dk& i fa w mh ' De n f; v r f; u dk t v G, fw u l a c sz su fE dki fy gw , f/ u Re fa w mfw dkUt a e e JU SizeOfImage
w e fz dk; u dk v sp fv sL& Ijy D; o lUt p m; VirtualQuery() function u dk a c : o Hk; E dki fy gw , f/ VirtualQuery() [ m
attribute c si f; w ln Djy D; t p Dt p Ofw u sjz p fa e w Jh page t a & t w Gu fu dk return jy e fy dkUy gw , f/ r Sw fOmP fx Ju
section a w GMu m; r Sm a e & mv Gw fr jz p fE dki fw ma Mu mi fh jy D; c Jhw Jh page e , fy , f& JU t q Hk; a e mu fu y x r page u dk
query v ky fjy D; page e , fy , fa w Gu dk a & w Gu fE dki fy gw , f/ a & w Gu fr Iu dk ImageBase u a e p w mq dk& i fa w mh
MEM_IMAGE t r sdK; t p m; u dk return jy e fy dkUw Jht x d q u fv u fv ky fa q mi fa e y gv dr hfr , f/ Page w p fc k[ m
MEM_IMAGE t r sdK; t p m; r [ kw fb l; q dk& i fa w mho l[ m z dki fq Du v mw mr [ kw fy gb l; /
( 1 . 2 ) Header u dkz su fjc i f;
t c sdKU unpacker a w G[ m image e JUo u fq dki fw Jht c su ft v u fa w Gu dk & & Sdz dkU section table u dk p p fa q ;
Mu y gw , f/ PE header x Ju section table u dk z su fy p fw my Jjz p fjz p f? a jy mi f; v Jw my Jjz p fjz p f t c su ft v u fa w G
& & Sdz dkU t a E Smi fht , Su fjz p fa p y gw , f/ ' gu a w mh ProcDump v dk image w p fc ku dk dump v ky fz dkU section table
u dkr SDc dka e w Jhtool a w Gu dkt c u fa w GUa p z dkU t o Hk; jy KE dki fy gw , f/
e r le mu k' fu a w mha t mu fy gt w dki f; jz p fy gw , f/
// This function will erase the current images
// PE header from memory preventing a successful image
// if dumped
inline void Er asePEHeader Fr omMemor y()
{
DWORD OldProtect = 0;
// Get base address of module
char *pBaseAddr = (char*)GetModuleHandle(NULL);
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 510 -
// Change memory protection
VirtualProtect(pBaseAddr, 4096, // Assume x86 page size
PAGE_READWRITE, &OldProtect);
// Erase the header
ZeroMemory(pBaseAddr, 4096);
}
' De n f; v r f; u dk t o Hk; jy Kw mu a w mh Yoda's Crypter jz p fy gw , f/ t a y : r Sm q dkc Jho v dky gy J Virtual
Query() function u dk image & JUt & G, ft p m; w e fz dk; jy e fv n f& & SdE dki fz dkUe JU page a w G[ m executable v m; ?
writable v m; p w ma w Gu dk o d& SdE dki fz dkU t o Hk; jy KE dki fy gw , f/ ' ga y r , fh z su fy p fv dku fw Jh section table u dk
jy e fv n fo d& SdE dki fz dkUt w Gu fa w mhe n f; v r f; r & Sda o ; y gb l; /
( 1 . 3 ) Nanomites
Nanomite a w Gu a w mh dump v ky fjc i f; r S u mu G, fz dkUt w Gu f y dkjy D; t q i fhjr i fhw Jh e n f; v r f; w p fc kjz p fjy D;
Armadillo r Sm p w i ft o Hk; jy Kc Jhw mjz p fy gw , f/ o lw dkUa w G[ m branch instruction (Jxx instruction) a w Gu dk
INT3 function e JUt p m; x dk; jy D; z , f& Sm; c H& w Jh jump instruction a w Ge JUy w fo u fw Jht c su ft v u fa w Gu dk
a o a o c smc sm encrypt v ky fx m; w Jh table x Jr Smo dr f; q n f; y gw , f/ ' Dt c su ft v u fa w Gr Sm jump & JU
destination? v dkt y fw Jh CPU flag a w Ge JU jump a w G& JUt & G, ft p m; ( o mr e ft m; jz i fha w mh 2 bytes ( o dkU) 5
bytes) a w Gy g0 i fy gw , f/
Nanomite e JU protect v ky fx m; w Jhprocess w p fc k[ m self-debugging jz p fz dkUv dky gw , f/ Armadillo
r Sma w mh debug blocker v dkU o dx m; Mu y gw , f/ Debug blocker [ m w ln Dw Jh process y Hkw lu dk t o Hk; jy Kjy D;
breakpoint w p fc k[ m nanomite w p fc k ( o dkU) w u , fh debug breakpoint w p fc kv m; q dkw mp p fa q ; jy D; jump
t jz p f , l^ r , lu dk q Hk; jz w fy gw , f/ ' ga Mu mi fh nanomite u dka w GUc sde fr Sm debugge u exception w p fc ku dk
x kw fa y ; jy D; debugger u exception a w Gu dk z r f; r da p w mjz p fy gw , f/ Debugge x Jr Sm exception u dka w GU
c sde fr Sm debugger u exception address u dk revover jy e fv ky fjy D; ' gu dk address table w p fc kt x Jr Sm
& Smy gw , f/ w u , fv dkU & Smw m u dku fn Dc Jh& i f nanomite t r sdK; t p m; u dk type table x Ju a e & , ly gw , f/ CPU
flag a w G[ m t r sdK; t p m; u dku fn Dc Jhr , fq dk& i f branch t jz p f, ly gv dr fhr , f/ ' Dv dkjz p fc sde fr Sm destination address
u dk destination table u a e & jy D; ' D address u a e execution u dkq u fjz p fa p y gw , f/ ' Dv kdr Sr [ kw f& i fa w mh
instruction u kda u smfv Tm; E dki fz dkU jump & JU t & G, ft p m; u dk size table u a e & , ly gw , f/ Armadillo [ m
cracker a w Gu dk x i fa , mi fx i fr Sm; jz p fa p z dkUt w Gu f INT3 a w Gu dk debugger a w Gr p p fa q ; E dki fw Jhu k' fa w GMu m; r Sm
a e & mt E SHU jz e fUc sx m; y gw , f/
( 1 . 4 ) Stolen bytes
Stolen bytes q dkw mu a w mh r l& i f; y & dk* & r fu jz w fx kw f& , lv mc Jhw Jh opcode a w Gjz p fjy D; o lw dkU[ m
r Sw fOmP f& JUw p fa e & mu a e o D; jc m; p D run y gw , f/ jz p fE dki fa jc t r sm; q Hk; u a w mh stolen byte a w G[ m OEP
t e m; u jz w fx kw fx m; w Jhu k' fa w Gjz p fjy D; o lw dkUu dk t jc m; r q dki fw Jh junk code a w Ge JUa & mx m; jy D; OEP e m;
r a & mu fc i f r Sw fOmP fx Jr Sm t v ky fv ky fMu y gw , f/ ' ga Mu mi fh OEP u a e dump v ky fw Jht c g r l& i f; u k' fa w G
y gr v mw Jht w Gu f y & dk* & r f[ m a u mi f; r Ge fp Gm t v ky fr v ky fE dki fa w mhy gb l; / jz w fx kw f, lv mw Jhu k' fa w Gu dk junk
code a w Ge JU a & mx m; w mjz p fw Jht w Gu f b , ft & m[ m r l& i f; u k' fv m; ? r q dki fw Jhu k' fv m; q dkw mu dk cracker a w G
t w Gu f x i fa , mi fx i fr Sm; jz p fa p y gw , f/ ' ga Mu mi fhv J dump v ky fx m; w Jhz dki fr Sm r lv u k' fa w Gu dk jy e fx m; z dkU
q dkw m t & n ft c si f; & Sdw Jh^ t a w GUt Mu HK& Sdw Jh cracker a w Gt w Gu fy J t q i fa jy E dki fy gv dr fhr , f/ Stolen byte a w G& JU
t p e JU t q Hk; r Sm jump instruction a w Gu dk x m; a v h& SdMu y gw , f/ Stolen byte a w Gu dk p w i fr dw fq u fc Jhw m
u a w mhASProtect r Smjz p fy gw , f/
push ebp
mov ebp, esp
mov ecx, 7
push 0
dec ecx
jnz short 0048E9D0
y Hk( 1 ) r l& i f; u k' fr Sjz w fx kw fv mc Jha o m Stolen bytes r sm; u dkjy e fv n fa e & mc sx m; y Hk
db 00
db 00
db 00
db 00
db 00
db 00
db 00
db 00
push 0
push 0
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 511 -
dec ecx
jnz short 0048E9D0
y Hk( 2 ) Stolen bytes r sm; u dkjz w fx kw fjy D; a e mu f jr i f& y Hk
( 1 . 5 ) Guar d Pages
Guard page a w Gu dk v dkt y fw Jht c sde f decrypt v ky fz dkUe JU decompress v ky fz dkU t o Hk; jy KMu y gw , f/
Armadillo u decrypt v ky fz dkU t o Hk; jy Kjy D; Shrinker u a w mhdecompress v ky fz dkUt w Gu f t o Hk; jy KMu y gw , f/
b , ft a Mu mi f; a Mu mi f; a Mu mi fhy Jjz p fjz p f guard page w p fc ku dk y x r q Hk; t Mu dr f access v ky fc sde fr Sm EXCEP
TION_GUARD_PAGE (0x80000001) q dkw Jh exception w p fc k a y : v my gv dr fhr , f/ ' gu dk t r sdK; r sdK; t z Hkz Hk
t o Hk; jy KE dki fa y r , fhv J t Mu r f; z si f; t m; jz i fha w mh o l[ m ring 3 u k' ft w Gu f demand-paging p e p ft jz p f v ky f
a q mi fy gw , f/ Page w p fc k[ m o w fr Sw fx m; w Jhe , fy , fw p fc kt w Gi f; & Sd^ r & Sdp p fa q ; jy D; EXCEPTION_GU
ARD_PAGE exception u dkz r f; jc i f; jz i fh' De n f; u dk& & Sdy gw , f/
' De n f; u dk Shrinker u v dkt y fw Jht c sde f decompress v ky fz dkUt w Gu f t o Hk; jy Ky gw , f/ Access v ky fc Jhw Jh
page a w Gu dko m decompress v ky fjc i f; jz i fhy & dk* & r fp w i fc sde fu dko do do mo m a v smhu sa p y gw , f/ Page w dki f; u dk
access v ky fw m r [ kw fw ma Mu mi fh r Sw fOmP fu dk w u , fw r f; o Hk; p GJr Iu dkv J a v smhu sa p y gw , f/ Application
w p fc kv Hk; u dk decompress v ky f& w Jh t jc m; packer a w Gx u fp m& i f application & JUv ky fa q mi fc su fu dkv J
w kd; w u fa p y gw , f/ Shrinker u ntdll & JU KiUserExceptionDispatcher() function u dk hook v ky fjc i f; jz i fh
t v ky fv ky fw mjz p fjy D; EXCEPTION_GUARD)PAGE (0x80000001) u dka p mi fhMu n fhy gw , f/ w u , fv dkU
process & JU image a e & mx Jr Sm exception u dka w GUc Jh& i fa w mh Shrinker u o D; jc m; page w p fc ku dk disk a y :
u a e u l; w i fr Smjz p fjy D; ' gu dkdecompress v ky fjy D; execution q u fv ky fa p r Smjz p fy gw , f/
' De n f; & JU a e mu fr lu GJw p fc ku dka w mh Armadillo u t o Hk; jy Kw mjz p fjy D; v dkt y fr S decrypt v ky fz dkUjz p fy g
w , f/ CopyMem2 v dkU a c : y gw , f/ b my Jjz p fjz p f? nanomite a w Ge JUjz p fw ma Mu mi fh self-debugging u dk
t o Hk; jy Kz dkUv dky gw , f/ ' gu a w mhShrinker e JUr w lw Jht c su fy gy J/ Armadillo [ m access v ky fc sde fr Sdisk u a e
u l; w i fw mx u f? r Sw fOmP fr Sm page t m; v Hk; u dk c su fc si f; y J decompress v ky fy gw , f/ Armadillo [ m
debugge x Ju exception a w Gu dkz r f; z dkU debugger u dk t o Hk; jy Kjy D; EXCEPTION_GUARD)PAGE
(0x80000001) exception u dk a p mi fhMu n fha e y gw , f/ w u , fv dkU process & JU image a e & mx Jr Sm exception
u dka w GUc Jh& i fa w mh Armadillo u access v ky f, la e w Jh o D; jc m; page w p fc ku dk decrypt v ky fjy D; execution
q u fv ky fa p r Smjz p fy gw , f/ w u , fv dkU page E Sp fc ku dk access v ky fw mq dk& i fa w mh resume v ky fw Jht c g a e mu f
page w p fc kr Sm exception w p fc ka y : v mjy D; Armadillo u ' Dpage t w Gu fv Jdecrypt v ky fr Smjz p fy gw , f/
Guard page e n f; y n mr Sm guard page w p fc ku dk page w p fc kc si f; decrypt v ky fz dkUt w Gu f t o Hk; jy Ky g
w , f/ w p fc sde fr Sm page w p fc kc si f; u dk disk a y : a & ; jc i f; jz i fh ' De n f; v r f; u dk a u smfv Tm; E dki fy gw , f/ Page a w Gu dk
o lw dkU& JUa e & mr Sm jy e fr x m; E dki fa t mi fv ky fw Jh page redirection e n f; u a w mh ' Dt m; e n f; c su fu dk a & Smi f& Sm; E dki fy g
v dr fhr , f/ Page a w Gu dk access v ky f, lr It m; v Hk; [ m v u f& Sdpage a w G& Sda e w Jhr Sw fOmP fx Ju t jc m; a e & ma w Gq D
n Te f; a e Mu y gw , f/ t u sdK; q u fu a w mh kernel32.ReadProcessMemory() function u dko Hk; jy D; r Sw fOmP fu dk
dump v ky fv dkUr & E dki fa p w my g/ kernel32.WriteFile() function u v J r lv address a w Gu dk t o Hk; jy Kjy D;
r Sw fOmP fu dk dump v ky fv dkUr & a p y gb l; / b ma Mu mi fhv Jq dka w mh redirection u dk a w GU& r Smr [ kw fa w mhv dkUy g/
b , fv dky Ja jy ma jy m r Sw fOmP fu dk dump v ky fz dkU e n f; E Sp fe n f; a w mh & Sdy gw , f/ y x r e n f; u a w mh a e & mv TJx m; w Jh
page a w G& JU address u dk& Smz dkUy g/ ' kw d, e n f; u a w mh r lv address a w Gu dkt o Hk; jy Kjy D; a ' w ma w Gu dk user-
mode copy v ky fz dkUy g/ jy D; & i f ' ga w Gu dk r Sw fOmP fr Sma e & mc sx m; w Jhblock w p fc kq Du l; & y gr , f/ ' Dha e mu fr Sma w mh
' Dr Sw fOmP f& JU block u a e a ' w ma w Gu dkw dku f& dku fa & ; & r Smjz p fy gw , f/
( 1 . 6 ) Impor ts
Import v ky fx m; w Jh funtion a w Gu dko m o dr , fq dk& i f y & kd* & r fw p fc k[ m b , fv dkt v ky fv ky fo v J?
b , fv dka & ; x m; o v Jq dkw Jht Mu Hu dk c e fUr Se f; o d& SdE dki fw Jht w Gu f import a w Gt a Mu mi f; [ m t v Ge ft a & ; Mu D; y gw , f/
' Dv dkv ky fjc i f; r S u mu G, fE dki fz dkUt w Gu f packer t c sdKU[ m import v ky fx m; w Jh function a w Gt w Gu f address
e Hy gw fa w Gu dka jz & Si f; jy D; p D; jy D; w Jht c sde fr Sm import table u dka jy mi f; y p fv dku fy gw , f/ a jy mi f; v Jy p fv dku fw , fv dkU q dk
& mr Sm import table u dk v Hk; 0 z su fq D; y p fw mr sdK; & Sdo v dk import v ky fx m; w Jhaddress a w Gu dk b mr Sr & Sdw Jhbuffer
a w Gq D n Te f; v dku fw mr sdK; v J jz p fE dki fy gw , f/ ' gu dk API redirection v dkUa c : y gw , f/ Buffer a w Gx Jr Smv J
w u , fh function a w G& JU address a w Gq Do Gm; w Jh jump w p fc ka w mh& Sdy gw , f/ y Hkr Se fq dk& i fa w mh ' D buffer u dk
dump v ky fv dkUr & y gb l; / ' ga Mu mi fhv J w u , fh function a w G& JU address a w G[ m a y smu fq Hk; a e jy D; y & dk* & r f[ m
crash jz p f& w my g/ ( API redirection t a Mu mi f; u dk ]t c e f; ( 1 4 ) IAT E Si fh API Redirection} t c e f; w Gi f
t a o ; p dw f a q G; a E G; jy D; jz p fy go n f/ )
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 512 -
( 1 . 7 ) Vir tual Machine
Virtual machine u a w mh anti-dumping e n f; y n ma w Gr Sm t jr i fhq Hk; jz p fy gw , f/ b ma Mu mi fhv J
q dka w mh r Sw fOmP fr Sm jr i fa w GUa e Mu u k' fa w Gu dk w dku f& dku fn Te fjy E dki fjc i f; r & Sdv dkUy g/ Import table r Smv J
w u , fhu dkv dkt y fw Jh function a w G ( LoadLibrary() E Si fh GetProcAddress()) a v mu fy Jy gE dki fjy D; y & dk* & r f
b , fv dkt v ky fv ky fo v Jq dkw Jh o Jv Ge fp u dk c se fx m; a v hr & Sdy gb l; / ' Dhx u fy dka jy m& r , fq dk& i f p-code a w Gu dka w mi fr S
encode v ky fE dki fy gw , f/ o a b mc si f; w lw Jh y & dk* & r fE Sp fc ku dka w mi fr S r w ln Dp Gm encode v ky fa y ; E dki fy gw , f/
' De n f; v r f; u dkt o Hk; jy Kw mu a w mhVMProtect jz p fy gw , f/
P-code u dk, fw dki fu dku polymorphic u k' fjz p fE dki fjy D; b mr Sr [ kw fw Jhu k' fa w Gu dk u k' ft p p fa w GMu m;
x n fhjy D; native u k' fa w Gt w Gu fv J ' Dv dky J jy Kv ky fMu w mjz p fy gw , f/ ' De n f; u dk t o Hk; jy Kw mu a w mh Themida
jz p fy gw , f/
P-code r Sm o w fr Sw fx m; w Jhw e fz dk; u dk o w fr Sw fx m; w Jh r Sw fOmP fa e & ma w Gr Sm p p fa q ; w Jh anti-debug
ging routine a w Gy gv mE dki fy gw , f/ ' De n f; u dkt o Hk; jy Kw mu a w mhHyperUnpackMe2 jz p fy gw , f/
P-code interpreter u dkv J obfuscate v ky fE dki fy gw , f/ Interpret v ky fz dkUe n f; v r f; u dka w mhc su fc si f; Mu D;
o d& Sdr Smr [ kw fy gb l; / ' De n f; u dkt o Hk; jy Kw mu a w mhThemida e JU Virtual CPU jz p fy gw , f/
( 2 ) Anti-Debugging
Debugger u a w mh process u dk attach v ky fjy D; u k' fa w Gu dk w p fq i fhc si f; p p fa q ; jc i f; ( o dkU) o w fr Sw f
x m; w Jha e & mr Sm & y fw e fUE dki fa t mi f breakpoint r sm; x m; jc i f; w dkUu dk jy Kv ky fy gw , f/ Process u dkv J memory-
dumper a w Gx u fp m& i f y dkr dkw du sp Gm dump v ky fa y ; E dki fy gw , f/ Anti-debugging e n f; v r f; 6 c ku a w mh
a t mu fy gt w dki f; jz p fy gw , f/
( 1 ) API u dkt a jc c Ha o m anti-debugging?
( 2 ) Exception u dkt a jc c Ha o m anti-debugging?
( 3 ) Process E Si fhthread w dkUu dkw dku f& dku fp Hkp r f; jc i f; ?
( 4 ) u k' fr sm; jy Kjy i fx m; jc i f; & Sd^ r & Sdp Hkp r f; jc i f; ?
( 5 ) Hardware E Si fhregiser w dkUu dkp Hkp r f; jc i f; ?
( 6 ) t c sde fu dkt a jc c Ha o m anti-debugging/
( 2 . 1 ) API u dkt a jc c Ha o m anti-debugging
API t a jc jy K anti-debugging u a w mh t & dk; & Si f; q Hk; jz p fjy D; Microsoft u w & m; 0 i fx kw fjy e fx m; w Jh?
x kw fjy e fjc i f; r & Sdw Jh API function a w Gu dkt o Hk; jy Kjy D; debugger a w G& Sd^ r & Sde JU o lw dkU& JUv ky fa q mi fc su fa w Gu dk
p Hkp r f; w mjz p fy gw , f/ ' Do i fc e f; p mr Sm IsDebuggerPresent() e JU CheckRemoteDebugger() w dkUv dk p mw p f
a Mu mi f; w n f; e JUa c : o Hk; w JhAPI a w Gu dka v hv mr Smjz p fo v dk CloseHandle() e JU debugger a w Gdetach v ky fx m;
jc i f; & Sd^ r & Sdp p fa q ; w Jht e n f; i , f& Iy fa x G; w Jhe n f; v r f; a w Gu dkv Ja v hv mr Smjz p fy gw , f/
( 2 . 1 . 1 ) IsDebugger Pr esent (ker nel32.dll)
y x r q Hk; anti-debugging e n f; v r f; u a w mhMicrosoft API call w p fc kjz p fw JhIsDebuggerPresent
jz p fy gw , f/ ' Dfunction [ m v u f& Sdt v ky fv ky fa e w Jh PEB (Process Environment Block) u dk analyze
v ky fjy D; DebuggerPresent flag u dkMu n fhy gw , f/ Function u return jy e fw Jhw e fz dk; u dk ' Dflag r Sm x m; & Sdw m
jz p fy gw , f/ w u , fv dkU return jy e fw Jhw e fz dk; [ m o kn jz p fc Jh& i fa w mh r & Sdb l; v dkU developer a w Gu q Hk; jz w fMu
y gw , f/ PEB u dkt o Hk; jy Kx m; w JhIsDebuggerPresent & JUv ky fa q mi fc su fu a w mhy Hk( 3 ) t w dki f; jz p fy gw , f/
if(IsDebuggerPresent()) // Win 32
{
MessageBoxA(NULL, "Please close your debugger and restart the program", "Debugger Detected!",0);
ExitProcess(0);
}
y Hk( 3 )
t c sdKU packer a w Gu a w mhIsDebuggerPresent u dka & Smi f& Sm; Mu jy D; PEB u dkw dku f& dku fMu n fh& Iy gw , f/
mov eax, fs:[30h] ;PEB
;check BeingDebugged
cmp byte [eax+2], 0
jne being_debugged
y Hk( 4 )
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 513 -
' gu dk a u smfv Tm; z dkUt w Gu f PEB & JU BeingDebugged flag u kd FALSE (0) jz p fa t mi f v ky f& y gr , f/
PEB structure u a w mhy Hk( 5 ) r Sm jr i f& w Jht w dki f; jz p fy gw , f/
typedef str uct _PEB
{
BOOLEAN InheritedAddressSpace; // 00
BOOLEAN ReadImageFileExecOptions; // 01
BOOLEAN BeingDebugged; // 02
BOOLEAN SpareBool; // 03
HANDLE Mutant; // 04
PVOID ImageBaseAddress; // 08
PPEB_LDR_DATA LdrData; // 0C
PRTL_USER_PROCESS_PARAMETERS ProcessParameters; // 10
PVOID SubSystemData; // 14
PVOID ProcessHeap; // 18
PVOID FastPebLock; // 1c
PPEBLOCKROUTINE FastPebLockRoutine; // 20
PPEBLOCKROUTINE FastPebUnlockRoutine; // 24
ULONG EnvironmentUpdateCount; // 28
PPVOID KernelCallbackTable; // 2c
PVOID EventLogSection; // 30
PVOID EventLog; // 34
PPEB_FREE_BLOCK FreeList; // 38
ULONG TlsExpansionCounter; // 3c
PVOID TlsBitmap; // 40
ULONG TlsBitmapBits[0x2]; // 44
PVOID ReadOnlySharedMemoryBase; // 4c
PVOID ReadOnlySharedMemoryHeap; // 50
PPVOID ReadOnlyStaticServerData; // 54
PVOID AnsiCodePageData; // 58
PVOID OemCodePageData; // 5c
PVOID UnicodeCaseTableData; // 60
ULONG NumberOfProcessors; // 64
ULONG NtGlobalFlag; // 68
BYTE Spare2[0x4]; // 6c
LARGE_INTEGER CriticalSectionTimeout; // 70
ULONG HeapSegmentReserve; // 78
ULONG HeapSegmentCommit; // 7c
ULONG HeapDeCommitTotalFreeThreshold; // 80
ULONG HeapDeCommitFreeBlockThreshold; // 84
ULONG NumberOfHeaps; // 88
ULONG MaximumNumberOfHeaps; // 8c
PPVOID *ProcessHeaps; // 90
PVOID GdiSharedHandleTable; // 94
PVOID ProcessStarterHelper; // 98
PVOID GdiDCAttributeList; // 9c
PVOID LoaderLock; // a0
ULONG OSMajorVersion; // a4
ULONG OSMinorVersion; // a8
ULONG OSBuildNumber; // ac
ULONG OSPlatformId; // b0
ULONG ImageSubSystem; // b4
ULONG ImageSubSystemMajorVersion; // b8
ULONG ImageSubSystemMinorVersion; // bc
ULONG ImageProcessInitRoutine; // c0
ULONG GdiHandleBuffer[0x22]; // c4
ULONG PostProcessInitRoutine; // 14c
ULONG TlsExpansionBitmap; // 150
BYTE TlsExpansionBitmapBits[0x80]; // 154
ULONG SessionId; // 1d4
} PEB, *PPEB;
y Hk( 5 ) PEB Str uctur e
Debugging v ky f& mr Sm t o Hk; r sm; Mu w mu a w mh IsDebuggerPresent & JU y x r q Hk; instruction r Sm
breakpoint o w fr Sw fMu w my g/ t c sdKU unpacker a w Gu ' D breakpoint t w Gu f t a o t c smp p fa q ; Mu y g
w , f/
Oy r mu k' fu a w mhy Hk( 6 ) t w dki f; jz p fy gw , f/
push offset l1
call GetModuleHandleA
push offset l2
push eax
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 514 -
call GetProcAddress
cmp b [eax], 0cch
je being_debugged
...
l1: db "kernel32", 0
l2: db "IsDebuggerPresent", 0
y Hk( 6 )
t c sdKU unpacker a w Gu a w mh function x Ju y x r q Hk; byte jz p fw Jh 64 ("FS:") q dkw Jh opcode u dk
p p fa q ; y gw , f/ e r le mu k' fu a w mhy Hk( 7 ) t w dki f; jz p fy gw , f/
push offset l1
call GetModuleHandleA
push offset l2
push eax
call GetProcAddress
cmp b [eax], 64h
jne being_debugged
...
l1: db "kernel32", 0
l2: db "IsDebuggerPresent", 0
y Hk( 7 )
( 2 . 1 . 2 ) CheckRemoteDebugger Pr esent (ker nel32.dll)
IsDebuggerPresent e JUw la y r , fh BeingDebugged flag t w Gu f v u f& Sd process & JU PEB block
u dkp p fa q ; y gw , f/ ' DAPI [ m t jc m; process a w Gdebug v ky fc H& jc i f; & Sd^ r & Sd p p fa q ; z dkUt w Gu fjz p fjy D; r dr d
process u dkv J debug v ky fc H& jc i f; & Sd^ r & Sd p p fa q ; E dki fy gw , f/ CheckRemoteDebuggerPresent [ m
ntdll.dll & JU NtQueryInformationProcess u dk ProcessInformationClass w e fz dk; 7 (ProcessDebug
Port) e JU a c : o Hk; w mjz p fy gw , f/ ' DAPI r Sm parameter E Sp fc ky g0 i fjy D; w p fc ku a w mh v u f& Sd process e JUq dki fw Jh
handle jz p fjy D; ? a e mu fw p fc ku a w mh process [ m debugger e JUc sdw fq u fx m; jc i f; & Sd^ r & Sd return jy e fr , fh
w e fz dk; jz p fy gw , f/ ' DAPI u dko Hk; z dkU Windows XP SP1 t e n f; q Hk; jz p f& y gr , f/ e r le mu k' fu a w mhy Hk( 8 ) t w dki f;
jz p fy gw , f/
.386
.model flat, stdcall
option casemap :none ; case sensitive
include \masm32\include\windows.inc
include \masm32\include\user32.inc
include \masm32\include\kernel32.inc
includelib \masm32\lib\user32.lib
includelib \masm32\lib\kernel32.lib
.data
DbgNotFoundTitle db "Debugger status:",0h
DbgFoundTitle db "Debugger status:",0h
DbgNotFoundText db "Debugger not found!",0h
DbgFoundText db "Debugger found!",0h
krnl db "kernel32.dll",0h
chkrdbg db "CheckRemoteDebuggerPresent",0h
.data?
IsItPresent dd ?
.code
star t:
PUSH offset krnl ;kernel32.dll
CALL LoadLibrary
PUSH offset chkrdbg ;CheckRemoteDebuggerPresent
PUSH EAX
CALL GetProcAddress
; IsItPresent variable will store the result
PUSH offset IsItPresent
PUSH -1
CALL EAX
MOV EAX, DWORD PTR[IsItPresent]
TEST EAX, EAX
JNE @DebuggerDetected
PUSH 40h
PUSH offset DbgNotFoundTitle
PUSH offset DbgNotFoundText
PUSH 0
CALL MessageBox
JMP @exit
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 515 -
@DebuggerDetected:
PUSH 30h
PUSH offset DbgFoundTitle
PUSH offset DbgFoundText
PUSH 0
CALL MessageBox
@exit:
PUSH 0
CALL ExitProcess
end start
y Hk( 8 )
t c sdKU packer a w Gu a w mh kernel32.CheckRemoteDebuggerPresent() function u dkt o Hk; r jy Kb J
ntdll.NtQueryInformationProcess() function u dko m w dku f& dku ft o Hk; jy KMu y gw , f/
( 2 . 1 . 3 ) NtQuer yInfor mationPr ocess (ntdll.dll)
Microsoft [ m Ntxxx API a w Gu dk b , fv dkt o Hk; jy K& r v Jq dkw m jy n fhp Hkp Gm a z mfjy a y ; a v h r & Sdy gb l; /
NtQueryInformationProcess()u dka e mu fy dki f; x Gu f& Sdr , fhWindows a w Gr Sm t o Hk; r jy KE dki fa w mhw mjz p fE dki fo v dk
function & JUv ky fa q mi fc su fa w Gv J a jy mi f; v Ja u mi f; a jy mi f; v Jy gv dr fhr , fv dkU MSDN 2008 r Smr Sw fc su fa y ; x m;
y gw , f/ ' Dfunction [ m process w p fc ke JUy w fo u fw Jht c su ft v u fa w Gu dk p Hkp r f; y gw , f/ o lU& JU prototype
u a w mhy Hk( 9 ) t w dki f; jz p fy gw , f/
NTSTATUS WINAPI NtQuer yInfor mationPr ocess(
__in HANDLE ProcessHandle,
__in PROCESSINFOCLASS ProcessInformationClass,
__out PVOID ProcessInformation,
__in ULONG ProcessInformationLength,
__out_opt PULONG ReturnLength
);
y Hk( 9 )
' Dfunction r Sma w mh parameter 5 c ky g0 i fa y r , fh u Re fa w mfw dkUu a w mh y x r E Sp fc ku dko m p dw f0 i fp m; y g
w , f/ y x r parameter u a w mhprocess & JU handle u dkp Hkp r f; z dkUjz p fjy D; o lUw e fz dk; [ m -1 jz p fc Jh& i f v u f& Sdt v ky f
v ky fa e w Jh process u dkt o Hk; jy Kz dkU function u dka jy mw mjz p fy gw , f/ ' kw d, parameter u a w mh Process
InformationClass e JUy w fo u fy gw , f/ MSDN u ProcessInformationClass e JUy w fo u fjy D; 4 c ko m a z mfjy
a y ; y gw , f/ ' D4 c ku a w mh ProcessBasicInformation (0)? ProcessDebugPort (7)? ProcessWow64
Information(26) e JU ProcessImageFileName (27) w dkUjz p fy gw , f/ w u , fa w mhWindows XP r Sm class
3 8 c k& Sdjy D; Windows Vista r Sma w mhclass 4 5 c k& Sdy gw , f/
NtQueryInformationProcess() [ m ntdll.dll x Jr Sm& Sda y r , fh export v ky fv dkU& w Jh function r [ kw f
y gb l; / ' ga Mu mi fhmodule (.exe) w p fc ku dk r Sw fOmP fa y : u l; w i fc sde fr Sm ' Dfunction u dko Hk; v dkUr & y gb l; / y & dk* & r f
t v ky fv ky fa e p Ofr Smy J ' Dfunction u dk t o Hk; jy Kv dkU& r Smjz p fy gw , f/ ' gu dk run-time dynamic link v ky fw , fv dkU
a c : y gw , f/ q dkv dkw mu dll z dki fx Ju function a w Gu dk function pointer a w Gt jz p ft & i fa e & mc sx m; jy D; r S
a c : o Hk; w mjz p fy gw , f/ NtQueryInformationProcess() u dkt o Hk; jy Kz dkU y x r q Hk; t a e e JU LoadLibrary() u dk
o Hk; jy D; ntdll.dll z dki fu dk u l; w i f& y gr , f/ jy D; a w mh u Re fa w mfw dkUo Hk; r , fh function & JU pointer u dk GetProc
Address() o Hk; jy D; & , l& y gr , f/
w u , fv dkU ProcessInformationClass r Sm ProcessDebugPort (7) u dkx n fhjy D; t o Hk; jy Kr , fq dk& i f
debug v ky f& mr Smt o Hk; jy Kx m; w Jh port e Hy gw fu dk return jy e fy dkUr Smjz p fy gw , f/ Debugger u dkt o Hk; r jy Kx m;
& i fa w mho kn t a e e JU return jy e fr Smjz p fy gw , f/ y Hk( 1 0 ) /
HMODULE hmod;
FARPROC _NtQueryInformationProcess;
hmod = LoadLibrary("ntdll.dll");
_NtQueryInformationProcess = GetProcAddress(hmod, "NtQueryInformationProcess");
status = (_NtQueryInformationProcess) (-1, 0x07, &retVal, 4, NULL);
if (retVal != 0)
{
MessageBoxA(NULL, "Debugger Detected Via NtQueryInformationProcess ProcessDebugPort",
"Debugger Detected", MB_OK);
}
else
{
MessageBoxA(NULL, "No Debugger Detected", "No Debugger Detected", MB_OK);
}
y Hk( 1 0 )
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 516 -
a e mu fw p fc ku a w mh Microsoft u w & m; 0 i fx kw fa 0 x m; jc i f; r & Sdw Jh NtQueryProcessInformation()
& JU ProcessDebugFlags (0x1F) flag y g/ NtQueryProcessInformation() u dk ProcessDebugFlags
e JUa c : o Hk; c sde fr Sm return jy e fr Smu a w mh NoDebugInherit jz p fjy D; EPROCESS & JUq e fUu si fz u fw e fz dk; jz p fy g
w , f/ q dkv dkw mu debugger u dka w GU& Sdc Jhr , fq dk& i f function u FALSE (0) u dkreturn jy e fy dkUr Smjz p fy gw , f/
e r le mu k' fu a w mhy Hk( 1 1 ) t w dki f; jz p fy gw , f/
inline bool CheckPr ocessDebugFlags()
{
#define NTSTATUS ULONG
typedef NTSTATUS (WINAPI *pNtQueryInformationProcess)
(HANDLE ,UINT ,PVOID ,ULONG , PULONG);
DWORD NoDebugInherit = 0;
NTSTATUS Status;
// Get NtQueryInformationProcess
pNtQueryInformationProcess NtQIP = (pNtQueryInformationProcess)
GetProcAddress( GetModuleHandle( _TEXT("ntdll.dll") ), "NtQueryInformationProcess" );
Status = NtQIP(GetCurrentProcess(), 0x1f, // ProcessDebugFlags
&NoDebugInherit, 4, NULL);
if (Status != 0x00000000)
return false;
if(NoDebugInherit == FALSE)
return true;
else
return false;
}
y Hk( 1 1 )
a e mu fw p fc ku dkv J Microsoft u w & m; 0 i fx kw fa 0 x m; jc i f; r & Sdy gb l; / ProcessDebugObjectHandle
class y g/ Windows XP r Smp w i fr dw fq u fc Jhw Jh debug object w p fc kjz p fy gw , f/ Process session w p fc k
p w i fc sde fr Sm debug object w p fc ku dkz e fw D; v dku fjy D; o le JUt w l handle w p fc kw GJy gv my gw , f/ ProcessDebug
ObjectHandle class u dko Hk; jy D; ' Dhandle & JU w e fz dk; u dk query v ky f, lE dki fy gw , f/ e r le mu k' fu a w mh y Hk( 1 2 )
t w dki f; jz p fy gw , f/
inline bool DebugObjectCheck()
{
#define NTSTATUS ULONG
typedef NTSTATUS (WINAPI *pNtQueryInformationProcess)
(HANDLE ,UINT ,PVOID ,ULONG , PULONG);
HANDLE hDebugObject = NULL;
NTSTATUS Status;
// Get NtQueryInformationProcess
pNtQueryInformationProcess NtQIP = (pNtQueryInformationProcess)
GetProcAddress( GetModuleHandle( _TEXT("ntdll.dll") ), "NtQueryInformationProcess" );
Status = NtQIP(GetCurrentProcess(), 0x1e, // ProcessDebugObjectHandle
&hDebugObject, 4, NULL);
if (Status != 0x00000000)
return false;
if(NoDebugInherit == FALSE)
return true;
else
return false;
}
y Hk( 1 2 )
ProcessDebugPort u dk t o Hk; jy K& mr Sm t x i f& Sm; q Hk; u a w mh MSLRH jz p fy gw , f/ ProcessDebug
Flags u dk t o Hk; jy Kw mu a w mh HyperUnpackMe2 jz p fy gw , f/ ProcessDebugObjectHandle u dk t o Hk; jy K
w mu a w mhHyperUnpackMe2 jz p fy gw , f/
' De n f; v r f; a w Gu a w mh w u , fa u mi f; w Jh anti-debugging e n f; v r f; a w Gjz p fy gw , f/ Cracker a w G
[ m ' De n f; a w Gu dk v G, fv G, fe JUa w mha u smfv dkU& r Sm r [ kw fy gb l; / b my Jjz p fjz p f y & dk* & r fu dk trace v kdu fc sde fr Sma w mh
ZwNtQueryInformationProcess() u return jy e fc sde fr Sm Process Information u dkjy i fE dki fy gw , f/ a e mu f
w p fe n f; u a w mh ZwNtQueryInformationProcess() u dk hook v ky fr , fh system driver u dkt o Hk; jy Kz dkU
jz p fy gw , f/ NtQueryInformationProcess() u dk cracker a w Gu a u smfv Tm; E dki fc Jhr , fq dk& i f t jc m; anti-
debugging e n f; v r f; a w mfa w mfr sm; r sm; [ mv n f; a u smfv Tm; c H& r Smjz p fy gw , f/ ( Oy r m Check
RemoteDebuggerPresent()? UnhandledExceptionFilter())
( 2 . 1 . 4 ) NtQuer ySystemInfor mation (ntdll.dll)
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 517 -
NtQuerySystemInformation() e JUy w fo u fw Jht c su ft v u f t jy n fht p Hku dkv n f; Microsoft u
a z mfjy a y ; x m; jc i f; r & Sdy gb l; / NtQuerySystemInformation() & JU prototype u a w mh y Hk( 1 3 ) t w dki f; jz p fy g
w , f/
NTSTATUS WINAPI NtQuer ySystemInfor mation(
__in SYSTEM_INFORMATION_CLASS SystemInformationClass,
__in_out PVOID SystemInformation,
__in ULONG SystemInformationLength,
__out_opt PULONG ReturnLength
);
y Hk( 1 3 )
' Da e & mr Sm u Re fa w mfw dkU p dw f0 i fp m; w mu a w mh SystemInformationClass class y g/ Windows XP
r Sma w mhclass 7 2 c k& Sdjy D; Windows Vista r Sma w mhclass 1 0 6 c k& Sdy gw , f/ ' ga y r , fhMicrosoft u a w mhclass
9 c ko ma z mfjy jy D; Windows NT r Smu w n f; u y gv mw Jh SystemKernelDebuggerInformation class u dk
a w mi f a z mfjy jc i f; r & Sdy gb l; /
SystemKernelDebuggerInformation class [ m flag E Sp fc k& JUw e fz dk; u dk return jy e fy dkUy gw , f/
w p fc ku a w mhAL x Jr Sm& Sdw JhKdDebuggerEnabled jz p fjy D; a e mu fw p fc ku a w mhAH x Jr Sm& Sdw JhKdDebugger
NotPresent y g/ ' ga Mu mi fhdebugger o m& Sdc Jhr , fq dk& i f AH x Ju return jy e fy dkUr , fhw e fz dk; [ m FALSE jz p fy g
r , f/ e r le mu k' fu a w mhy Hk( 1 4 ) t w dki f; jz p fy gw , f/
push eax
mov eax, esp
push 0
push 2 ; SystemInformationLength
push eax
; SystemKernelDebuggerInformation
push 23h
call NtQuerySystemInformation
pop eax
test ah, ah
je being_debugged
y Hk( 1 4 )
' De n f; u dkt o Hk; jy Kw mu a w mhSafeDisc jz p fy gw , f/
( 2 . 1 . 5 ) NtQuer yObject (ntdll.dll)
NtQueryObject() function u dka w mh MSDN 2008 r Sm v Hk; 0 a z mfjy x m; jc i f; r & Sdy gb l; / o lU& JU
prototype u a w mhy Hk( 1 5 ) r Smjr i f& w Jht w dki f; jz p fy gw , f/
NtQuer yObject(
__in HANDLE ObjectHandle,
__in OBJECT_INFORMATION_CLASS ObjectInformationClass,
__out PVOID ObjectInformation,
__in ULONG Length,
__out PULONG ResultLength
);
y Hk( 1 5 )
' Da e & mr Sm u Re fa w mfw dkUt a e e JU o dz dkUv dkw mu a w mh ObjectInformationClass & JU ObjectTypeInfor-
mation structure y g/ y Hk( 1 6 ) /
typedef str uct _OBJECT_TYPE_INFORMATION
{
UNICODE_STRING TypeName;
ULONG TotalNumberOfHandles;
ULONG TotalNumberOfObjects;
WCHAR Unused1[8];
ULONG HighWaterNumberOfHandles;
ULONG HighWaterNumberOfObjects;
WCHAR Unused2[8];
ACCESS_MASK InvalidAttributes;
GENERIC_MAPPING GenericMapping;
ACCESS_MASK ValidAttributes;
BOOLEAN SecurityRequired;
BOOLEAN MaintainHandleCount;
USHORT MaintainTypeList;
POOL_TYPE PoolType;
ULONG DefaultPagedPoolCharge;
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 518 -
ULONG DefaultNonPagedPoolCharge;
}
OBJECT_TYPE_INFORMATION, *POBJECT_TYPE_INFORMATION;
y Hk( 1 6 ) OBJECT_TYPE_INFORMATION str uctur e ( Windows NT t w Gu fo m )
t a y : r Sma jy mc Jho v dky gy J? Windows XP r Sm debugging session w p fc kp w i fc sde fr Sm debug object
w p fc ky gw Jhhandle w p fc ku dkz e fw D; y gw , f/ ' ga Mu mi fh& Sdjy D; o m; object a w G& JUp m& i f; u dk query v ky fz dkU jz p fE dki fjy D;
& Sda e w Jh debug object a w G& JUt a & t w Gu fu dk p p fE dki fy gw , f/ ' D API u dk Windows NT platform a w Gr Sm
t o Hk; jy Kjy D; Windows XP e JUa e mu fy dki f; Windows a w Gr Sma w mh p m& i f; x Jr Sm& Sdw Jh debug object w p fc ku dk
return jy e fy dkUw Jh v ky fa q mi fc su fw dk; v my gw , f/ Debugger o m& Sdc Jhr , fq dk& i f return w e fz dk; [ m o kn r [ kw fw Jh
w e fz dk; w p fc kjz p fy gv dr fhr , f/ e r le mu k' fu a w mhy Hk( 1 7 ) r Sm jr i f& w Jht w dki f; jz p fy gw , f/
typedef struct _OBJECT_TYPE_INFORMATION {
UNICODE_STRING TypeName;
ULONG TotalNumberOfHandles;
ULONG TotalNumberOfObjects;
} OBJECT_TYPE_INFORMATION, *POBJECT_TYPE_INFORMATION;
inline bool ObjectListCheck()
{
#define NTSTATUS ULONG
typedef NTSTATUS(NTAPI *pNtQueryObject) (HANDLE, UINT, PVOID, ULONG, PULONG);
POBJECT_ALL_INFORMATION pObjectAllInfo = NULL;
void *pMemory = NULL;
NTSTATUS Status;
unsigned long Size = 0;
// Get NtQueryObject
pNtQueryObject NtQO = (pNtQueryObject)GetProcAddress(GetModuleHandle( _TEXT("ntdll.dll") ),
"NtQueryObject" );
// Get the size of the list
Status = NtQO(NULL, 3, //ObjectAllTypesInformation
&Size, 4, &Size);
// Allocate room for the list
pMemory = VirtualAlloc(NULL, Size, MEM_RESERVE | MEM_COMMIT, PAGE_READWRITE);
if(pMemory == NULL)
return false;
// Now we can actually retrieve the list
Status = NtQO((HANDLE)-1, 3, pMemory, Size, NULL);
if (Status != 0x00000000) // Status != STATUS_SUCCESS
{
VirtualFree(pMemory, 0, MEM_RELEASE);
return false;
}
// We have the information we need
pObjectAllInfo = (POBJECT_ALL_INFORMATION)pMemory;
unsigned char *pObjInfoLocation = (unsigned char*)pObjectAllInfo->ObjectTypeInformation;
ULONG NumObjects = pObjectAllInfo->NumberOfObjects;
for(UINT i = 0; i < NumObjects; i++)
{
POBJECT_TYPE_INFORMATION pObjectTypeInfo = (POBJECT_TYPE_INFORMATION)pObjInfoLocation;
// The debug object will always be present
if (wcscmp("DebugObject", pObjectTypeInfo->TypeName.Buffer) == 0)
{
// Are there any objects?
if (pObjectTypeInfo->TotalNumberOfObjects > 0)
{
VirtualFree(pMemory, 0, MEM_RELEASE);
return true;
}
else
{
VirtualFree(pMemory, 0, MEM_RELEASE);
return false;
}
}
// Get the address of the current entries
// string so we can find the end
pObjInfoLocation = (unsigned char*)pObjectTypeInfo->TypeName.Buffer;
// Add the size
pObjInfoLocation += pObjectTypeInfo->TypeName.Length;
// Skip the trailing null and alignment bytes
ULONG tmp = ((ULONG)pObjInfoLocation) & -4;
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 519 -
// Not pretty but it works
pObjInfoLocation = ((unsigned char*)tmp) + sizeof(unsigned long);
} // end of for loop
VirtualFree(pMemory, 0, MEM_RELEASE);
return true;
}
y Hk( 1 7 )
( 2 . 1 . 6 ) NtSetInfor mationThr ead (ntdll.dll)
Windows 2000 r Sm p w i fr dw fq u fc Jhjy D; ZwQuertInformationProcess() & JU wrapper jz p fy gw , f/
Function & JU prototype u a w mhy Hk( 1 8 ) r Smjr i f& w Jht w dki f; jz p fy gw , f/
NtSetInfor mationThr ead
(
IN HANDLE ThreadHandle,
IN THREAD_INFORMATION_CLASS ThreadInformationClass,
IN PVOID ThreadInformation,
IN ULONG ThreadInformationLength
);
y Hk( 1 8 )
' Da e & mr Sm u Re fa w mfw dkU p dw f0 i fp m; w mu a w mh thread handle e JU ThreadInformationClass w dkU
y g0 i fw Jhy x r e JU ' kw d, parameter a w Gjz p fy gw , f/ ThreadInformationClass u dka w mhy Hk( 1 9 ) r Sm t u s, fc sJU
& Si f; jy x m; y gw , f/
typedef enum _THREAD_INFORMATION_CLASS
{
ThreadBasicInformation,
ThreadTimes,
ThreadPriority,
ThreadBasePriority,
ThreadAffinityMask,
ThreadImpersonationToken,
ThreadDescriptorTableEntry,
ThreadEnableAlignmentFaultFixup,
ThreadEventPair,
ThreadQuerySetWin32StartAddress,
ThreadZeroTlsCell,
ThreadPerformanceCount,
ThreadAmILastThread,
ThreadIdealProcessor,
ThreadPriorityBoost,
ThreadSetTlsArrayAddress,
ThreadIsIoPending,
ThreadHideFromDebugger
}
THREAD_INFORMATION_CLASS, *PTHREAD_INFORMATION_CLASS;
y Hk( 1 9 )
w u , fv dkU o i fht a e e JU ThreadInformationClass w e fz dk; u dk 0x11 (ThreadHideFromDebugger)
v dkUo w fr Sw fc Jh& i f debugger u thread e JUo u fq dki fw Jhevent a w Gt m; v Hk; u dk v u fc Hr & & Sda w mhw Jht w Gu f v u f& Sd
t v ky fv ky fa e w Jhprocess u dk q u fjy D; Debug v ky fE kdi fjc i f; r & Sda w mhy gb l; / e r le mu k' fu a w mh y Hk( 2 0 ) t w dki f; jz p fy g
w , f/
inline bool HideThr ead(HANDLE hThread)
{
#define NTSTATUS ULONG
typedef NTSTATUS (NTAPI *pNtSetInformationThread) (HANDLE, UINT, PVOID, ULONG);
NTSTATUS Status;
// Get NtSetInformationThread
pNtSetInformationThread NtSIT = (pNtSetInformationThread)
GetProcAddress(GetModuleHandle( _TEXT("ntdll.dll") ), "NtSetInformationThread");
// Shouldn't fail
if (NtSIT == NULL)
return false;
// Set the thread info
if (hThread == NULL)
Status = NtSIT(GetCurrentThread(), 0x11, // HideThreadFromDebugger
0, 0);
else
Status = NtSIT(hThread, 0x11, 0, 0);
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 520 -
if (Status !=0x00000000)
return false;
else
return true;
}
y Hk( 2 0 )
Function u dka c : o Hk; & i fa w mh hThread a e & mr Sm NULL e JUt p m; x dk; a y ; & y gr , f/ ' De n f; v r f; u dk t o Hk;
jy K& mr Sm t x i f& Sm; q Hk; u a w mhHyperUnpackMe2 jz p fy gw , f/
( 2 . 1 . 7 ) OpenPr ocess (ker nel32.dll)
Debugger u dkp Hkp r f; w Jh' De n f; u a w mhprocess w p fc k[ m debugger w p fc ka t mu fr Sm t v ky fv ky fjc i f; & Sd^
r & Sdu dk p Hkp r f; o d& SdE dki fz dkUt w Gu f process privilege u dkt o Hk; c sw mjz p fy gw , f/ ' De n f; u t v ky fjz p fy gw , f/ b m
a Mu mi fhv Jq dka w mh process w p fc k[ m debugger e JUw GJx m; c sde f ( o dkU) debugger a t mu fr Smt v ky fv ky fa e c sde fr Sm
debugger u process privilege u dk r Se fu e fp Gmo w fr Sw fE dki fjc i f; r & Sdc Jh& i f b , f process w dki f; r q dke JUq dki fw Jh
handle u dkz Gi fhz dkU process u dkt c Gi fha y ; E dki fw Jh SeDebugPrivilege u dk process u v u fc H& & Sdv dkUjz p fy gw , f/
' Du dp r Sm u Re fa w mfw dkUt a e e JU y Hkr Se f& , lt o Hk; jy KE dki fjc i f; r & Sdw Jh csrss.exe (Client/Server Runtime Sub-
system) v dkr sdK; t a & ; Mu D; w Jh system process w p fc ka w mi fy g0 i fy gw , f/ o le JUy w fo u fw Jh e r le mu k' fu a w mh
y Hk( 2 1 ) r Smjr i f& w Jht w dki f; jz p fy gw , f/
// The function will attempt to open csrss.exe with PROCESS_ALL_ACCESS rights.
// If it fails we're not being debugged however, if its successful we probably are
inline bool CanOpenCsr ss()
{
HANDLE Csrss = 0;
bool InheritHandle = FALSE;
// If we're being debugged and the process has SeDebugPrivileges privileges
// then this call will be successful, note that this only works with PROCESS_ALL_ACCESS.
Csrss = OpenProcess(0x1F0FFF, InheritHandle, CsrGetProcessId()); // 0x1F0FFF = PROCESS_ALL_ACCESS
// If the function fails, the return value is NULL.
if (Csrss != NULL)
{
CloseHandle(Csrss);
return true;
}
else
return false;
}
y Hk( 2 1 )
Process w p fc k[ m SeDebugPrivilege u dkt o Hk; jy Kc sde fr Sm csrss.exe [ m system process w p fc kjz p f
a e w ma w mi f csrss.exe u dk v Hk; 0 x de f; c sKy fE dki fw Jh t c Gi fht a & ; u dk & & Sdy gw , f/ ' ga Mu mi fh SeDebugPrivilege u
' D process e JUy w fo u fw Jh u e fUo w fc su fa w Gu dk z , f& Sm; y gw , f/ ' Dhjy i f privilege u debugger u z e fw D;
v dku fw Jh child process a w Gx da w mi f t u sHK; 0 i fy ga o ; w , f/ t u sdK; q u fu a w mh debug v ky fc Hx m; & w Jh
application w p fc k[ m csrss.exe & JU PID u dko m & & SdE dki fr , fq dk& i f o l[ m OpenProcess() function u w q i fh
process a w Gu dk x de f; c sKy fE dki fr Smjz p fy gw , f/ PID u dka w mh CreateToolhelp32Snapshot() function e JU
Process32Next() u dko Hk; jy D; ( o dkU) NtQuerySystemInformation(SystemProcessInormation(5)) u dk
o Hk; jy D; & & SdE dki fy gw , f/ Windows XP u a w mh ' Dt w Gu f CsrGetProcessId() function u dkr dw fq u fc Jhjy D;
t o Hk; jy K& w m y dkr dkv G, fu la p y gw , f/ Process w p fc k[ m debug v ky fc Hx m; & w , fq dk& i f SeDebugPrivilege u
y Hk( 2 2 ) r Sm jr i f& w Jht w dki f; enable jz p fa e r Smy g/
y Hk( 2 2 ) Pr ocess u dkdebug v ky fx m; & jc i f; & Sd^ r & SdPr ocess Explor er jz i fhMu n fhx m; y Hk
' De n f; v r f; u csrss.exe u dk r Sm; , Gi f; w Jhv ky fa q mi fc su fa w Gv ky fa q mi fc dki f; jy D; denial-of-service u dk
jy Kv ky fz dkU v r f; y Gi fha p y gw , f/ e n f; v r f; w p fc ku a w mh r jz p fE dki fw Jh r Sw fOmP f address w p fc kr Sm thread w p fc ku dk
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 521 -
z e fw D; z dkUjz p fjy D; a e mu fw p fc ku a w mh r jy D; q Hk; E dki fw Jh loop u dk v ky fa q mi fw Jh thread w p fc ku dkz e fw D; z dkUjz p fy gw , f/
OllyDbg e JU Windbg u a w mh process u dk debug v ky fz dkU debug privilege & & Sdz dkUv dkt y fa y r , fh Turbo
Debug u a w mhr v dkt y fy gb l; / 0 r f; e n f; p & mw p fc ku a w mh Olly & JU phantom plugin u dkt o Hk; jy Kc Jhr , fq dk& i f
SeDebugPrivilege flag [ m disabled jz p fa e w Jht c su fy g/ ( Cracker a w Gt w Gu fa w mh 0 r f; o mp & mo w i f;
w p fc ka y gh/ )
( 2 . 1 . 8 ) OutputDebugStr ing (ker nel32.dll)
OutputDebugString() u dkp w i fr dw fq u fc Jhw mu a w mh Windows 2000 r Smjz p fjy D; u se fw Jh anti-
debug function a w Ge JUt e n f; i , f u GJjy m; a e y gw , f/ ReCrypt e JU pack v ky fx m; w Jhz dki fa w Gr Sm a w GUE dki fjy D;
u Re fa w mfw dkU& JU process [ m debugger a t mu fr Sm t v ky fv ky fa e w mr [ kw f& i f error u k' fu dk return jy e fy dkU
w mjz p fy gw , f/ b ma Mu mi fh error w u f& w mv Jq dka w mh process t w Gu f string u dkv u fc H& & Sdz dkU debugger
u dkv dkt y fv dkUy g/ y Hk( 2 3 ) /
DWORD Val = 666;
SetLastError(Val);
OutputDebugString("String");
if (GetLastError() == Val) // Is Value equal to 0?
{
MessageBox(NULL, "Debugger Detected Via OutputDebugString", "Debugger Detected", MB_OK);
}
else {
MessageBox(NULL, "No Debugger Detected", "No Debugger Detected", MB_OK);
}
y Hk( 2 3 )
Debugger u dka w GUc Jhr , fq dk& i f GetLastError() u return jy e fr , fhw e fz dk; [ m 0 jz p fy gw , f/
( 2 . 1 . 9 ) FindWindow
FindWindow u dkt o Hk; jy Kjy D; p Hkp r f; w Jhe n f; u a w mh process [ m debugger e JU attach v ky fx m; jc i f;
& Sd^ r & Sdu dk p Hkp r f; w mr [ kw fb J o w fr Sw fx m; w Jh string e JUu dku fn Dw Jh class t r n f& Sd& m t a y : q Hk; window & JU
handle u dk& , lw mjz p fy gw , f/ Debugger a w mfa w mfr sm; r sm; & JU class a w Gu dk FindWindow t o Hk; jy Kjy D;
p p fa q ; E dki fy gw , f/ WinDbg u dkp Hkp r f; c si f& i fa w mh FindWindow e JUt w l WinDbgFrameClass class u dk
a c : o Hk; & r Smjz p fy gw , f/ w u , fv dkUo m return w e fz dk; [ m NULL jz p fc Jhr , fq dk& i f ' D window u dk & Smr a w GU
y gb l; / y Hk( 2 4 ) /
// Determine if a window with the class name exists...
HANDLE Hnd;
Hnd = FindWindow("OLLYDBG", 0);
if (hnd == NULL)
{
MessageBoxA(NULL, "OllyDbg Not Detected", "Not Detected", MB_OK);
}
else {
MessageBoxA(NULL, "Ollydbg Detected Via OllyDbg FindWindow()", "OllyDbg Detected", MB_OK);
}
y Hk( 2 4 )
( 2 . 1 . 1 0 ) Registr y Key
Registry u a e w q i fh debugger & Sd^ r & Sdp Hkp r f; w Jh ' De n f; u a w mh debugger e JU process w GJx m; jc i f;
& Sd^ r & Sd ( o dkU) debugger t v ky fv ky fa e jc i f; & Sd^ r & Sdu dk p Hkp r f; w mr sdK; r [ kw fy gb l; / ' De n f; v r f; a w Gt p m; o lu
debugger u dk install v ky fx m; jc i f; & Sd^ r & Sd p Hkp r f; w my g/ q dkv dkc si fw mu o i fh& JU OS r Sm a q mhz f0 Jv fa w Gu dk
debug v ky fz dkU Olly u dk shell extension t a e e JU o w fr Sw fx m; c Jhr , fq dk& i f registry r Sm y Hk( 2 5 ) t w dki f;
jr i f& r Smjz p fjy D; o i fht a e e JU RegQueryValue() o Hk; jy D; ' Dstring a w Gu dk& Sm& r Smjz p fy gw , f/
HKEY_CLASSES_ROOT\dllfile\shell\Open with Olly&Dbg\command
HKEY_CLASSES_ROOT\exefile\shell\Open with Olly&Dbg\command
y Hk( 2 5 )
' ght jy i f Registry r Sm vsjitdebugger.exe ( o dkU) ollydbg.exe p w Jh string a w Gu dk& Smjy D; debugger
& Sd^ r & Sdp Hkp r f; E dki fy ga o ; w , f/
( 2 . 1 . 1 1 ) DebugActivePr ocess jz i fhu dk, fw dki f debug v ky fjc i f; (ker nel32.dll)
' De n f; v r f; a v ; [ m process w p fc k[ m w c sde fr Sm debugger w p fc kw n f; a t mu fr Smo m t v ky fv ky fE dki f
w , fq dkw Jh t m; e n f; c su fu dk t c Gi fha u mi f; , lx m; w my g/ q kdv dkw mu debugger w p fc ku process w p fc ku dk
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 522 -
z Gi fhx m; c sde fr Sm a e mu f debugger w p fc ku ' Dprocess u dk attach v ky fv dkUr & a w mhy gb l; / ' De n f; v r f; a t mi fjr i fz dkU
t w Gu f process u child process w p fc ku dk y x r q Hk; z e fw D; & y gr , f/ Child process u r dc i f( r db )
process & JU PID u dk ( b , fe n f; e JUy J jz p fy ga p ) v Sr f; z w fjy D; DebugActiveProcess() o Hk; u m Debug v ky f& r Sm
jz p fy gw , f/ Child process u dkz e fw D; z dkUt w Gu f CreateProcess() u dko Hk; & r Smjz p fy gw , f/ Child process u
r dc i f process a y : r Sm DebugActiveProcess() e JU debug v ky fv dkU& ^ r & p r f; o y fjy D; debug v ky fv dkUr & c Jh& i f
r dc i f process u dkdebugger w p fc kc ke JU z Gi hfx m; a Mu mi f; o d& Sdjy D; y & dk* & r fu dkjy D; q Hk; a p r Smy g/ y Hk( 2 6 ) /
pid = GetCurrentProcessId();
_itow_s((int)pid, (wchar_t*)&pid_str, 8, 10); // Converts an integer to a string.
wcsncat_s((wchar_t*)&szCmdline, 64, (wchar_t*)pid_str, 4);
STARTUPINFOA si;
PROCESS_INFORMATION pi;
success = CreateProcess(path, szCmdline, NULL, NULL, FALSE, 0, NULL, NULL, &si, &pi);
success = DebugActiveProcess(pid);
if (success == 0)
{
printf("Error Code: %d\n", GetLastError());
MessageBoxA(NULL, "Debugger Detected - Unable to Attach", "Debugger Detected", MB_OK);
}
if (success == 1)
MessageBoxA(NULL, "No Debugger Detected", "No Debugger", MB_OK);
y Hk( 2 6 )
( 2 . 1 . 1 2 ) NtYieldExecution (ntdll.dll)
NtYieldExecution u a w mh v u f& Sdt v ky fv ky fa e w Jh thread u dk o lU& JU u se fa e a o ; w Jh execution
a w Gu dkq u fr v ky fa p b J schedule q GJx m; w Jh t jc m; thread a w Gu dk execute v ky fa p y gw , f/ w u , fv dkU
execute v ky fz dkU schedule o w fr Sw fx m; w Jh thread a w Gr & Sdc Jhb l; q dk& i f function u error w p fc ku dk jy e fy dkUr Sm
jz p fy gw , f/ Application w p fc k[ m debug v ky fc Hx m; & c sde fr Sm u k' fa w Gu dkw p fa Mu mi f; c si f; p p fa q ; w Jht jy Kt r l
[ m debug event a w Gu dkjz p fa p y gw , f/ t u sdK; q u fu a w mh debugger thread [ m execution t jr Jw r f;
q u fv ky fz dkU schedule q GJc Ha e & y gw , f/ ' Dt c su fu high priority e JY t v ky fv ky fa e w Jh thread & Sd^ r & Sd
a u mu fc su fc sz dkU t o Hk; jy KE dki fa y r , fhv J debugger & Sd^ r & Sd a u mu fc su fc sz dkUt w Gu fv J t o Hk; jy KE dki fy gw , f/ e r le m
u k' fu a w mhy Hk( 2 7 ) t w dki f; jz p fy gw , f/
push 20h
pop ebp
l1: push 0fh
call Sleep
call NtYieldExecution
cmp al, 1
adc ebx, ebx
dec ebp
jne l1
inc ebx
je being_debugged
y Hk( 2 7 )
' De n f; v r f; u dkt o Hk; jy Kw mu a w mhExtreme Debugger Detector jz p fy gw , f/
( 2 . 1 . 1 3 ) NtSetLdtEntr ies (ntdll.dll)
LDT(local descriptor table) u dk Windows u t o Hk; r jy Kw mjz p fw ma Mu mi fh debugger a w Gt w Gu f
v J v Hk; 0 t o Hk; jy Kv dkU& r Sm r [ kw fy gb l; / ' ga Mu mi fh ' gu dk & dk; & Si f; v Sw Jh anti-debugger e n f; v r f; t jz p f t o Hk;
jy KE dki fy gw , f/ t x l; o jz i fh t c sdKUu k' fa w Gu dk a e & mc sa y ; r , fh LDT entry t o p fw p fc ku dk z e fw D; E dki fy gw , f/
' Dha e mu f LDT entry t o p fq Do Gm; r , fh call ( o dkU) jump w p fc ku dk z e fw D; jc i f; jz i fh debugger [ m ' Da e & ma w G
q Do Gm; z dkU t c u fa w GUa e r Smjz p fy gw , f/ e r le mu k' fu a w mhy Hk( 2 8 ) t w dki f; jz p fy gw , f/
;base must be <= PE->ImageBase
;but no need for 64kb align
base equ 12345678h
;sel must have bit 2 set
;CPU will set bits 0 and 1
;even if we dont do it
sel equ 777h
xor eax, eax
push eax
push eax
push eax
;4k granular, 32-bit
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 523 -
;present, DPL3, exec-only code
;limit must not touch kernel mem
;calculate carefully to use APIs
push (base and 0ff000000h) \
+ 0c1f800h \
+ ((base shr 10h) and 0ffh)
push (base shl 10h) + 0ffffh
push sel
call NtSetLdtEntries
;jmp far sel:l1
db 0eah
dd offset l1 base
dw sel
l1: ;execution continues here
;but using LDT selector
...
y Hk( 2 8 )
Turbo Debug32 u a w mh LDT e , fy , fx Ju u k' fa w Gu dk disassemble v ky fE dki fr Sm r [ kw fy gb l; /
' ga y r , fh execution u a w mh a u mi f; a u mi f; t v ky fv ky fa e r Smjz p fy gw , f/ OllyDbg u v J LDT e , fy , fx Jr Sm
execution q u fv ky fz kdU ji i f; q e fr Smjz p fy gw , f/ WinDbg u o m LDT x Ju u k' fa w Gu dk r Se fu e fp Gm dis-
assemble v ky fE dki fr Smjz p fy gw , f/ ' De n f; v r f; u dk malware t c sdKUu t o Hk; jy KMu y gw , f/ ' De n f; v r f; [ m system
bit a w Gu dka e & mr Smx m; jy D; Type field r Sm a w Gt r sm; Mu D; y g0 i fa e w Jh ReactOS (http://www.reactos.org/)u
r w du sw Jhp mw r f; t c sdKUu dkt a jc c Hw m jz p fa u mi f; jz p fE dki fy gw , f/
( 2 . 1 . 1 4 ) CloseHandle (ker nel32.dll)
w u , fv dkU r Sm; , Gi f; a e w Jh handle w p fc ku dk kernel32.dll & JU CloseHandle() function x Jjz w fo e f;
a p r , fq dk& i f ( o dkUr [ kw f ntdll.dll & JU NtClose() function x Jw dku f& dku f) ? debugger o m & Sdr a e b l; q dk& i f error
u k' fw p fc ku dk jy e fy dkUr Smjz p fy gw , f/ Debugger u dko m& Sda e c Jhr , fq dk& i fa w mh EXCEPTION_INVALID_
HANDLE(0xC0000008) ( o dkU) EXCEPTION_HANDLE_NOT_CLOSABLE(0xC0000235) u dk
a w GU& r Smjz p fy gw , f/ ' Dexception u dk exception handler e JU z r f; , lE dki fjy D; ' g[ m debugger w p fc k t v ky f
v ky fa e w mu dkn Te fjy a e y gw , f/ e r le mu k' fu a w mhy Hk( 2 9 ) t w dki f; jz p fy gw , f/
xor eax, eax
push offset being_debugged
push d fs:[eax]
mov fs:[eax], esp
push eax
push eax
push 3 ; OPEN_EXISTING
push eax
push eax
push 80000000h ; GENERIC_READ
push offset l1
call CreateFileA
push eax
; HANDLE_FLAG_PROTECT_FROM_CLOSE
push 2
push -1
xchg ebx, eax
call SetHandleInformation
push ebx
call CloseHandle
...
l1: db myfile, 0
y Hk( 2 9 )
' Djy e mu dk a jz & Si f; z dkUu a w mh Windows XP r Sm v G, fu lv Ge f; v Sy gw , f/ Exception u dka z smu fz dkU
t w Gu f debugger u FirstHandler Vectored Exception Handler u dk register v ky f& r Smjz p fy gw , f/
w u , fa w mh kernel32.dll & JU AddVectoredExceptionHandler() function u dk hook v ky fz dkUt w Gu f
jy e m& Sdy gw , f/ ' gu a w mh t jc m; handler w p fc ku dk y x r q Hk; handler t jz p f register v ky fjc i f; u a e w m;
q D; & mr Smjz p fy gw , f/ b my Ja jy ma jy m exception u dka z smu fz dkU SEH u dk register v ky f& w Jh NtClose() function
u dkhook v ky f& w mx u fp m& i fa w mhv G, fu la e w ke f; y Jjz p fy gw , f/
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 524 -
( 2 . 1 . 1 5 ) NtSystemDebugContr ol (ntdll.dll)
NtSystemDebugControl() function [ m debugger a w Gu dk p Hkp r f; & mr Sm a w mfa w mfa v ; a u mi f; w Jh
function w p fc kjz p fy gw , f/ o lUu dk Windows NT r Smr dw fq u fc Jhjy D; o lU& JUp Gr f; a q mi f& n f[ m Windows
a e mu fy dki f; version a w Gr Sm a w mfa w mfa v ; w dk; w u fv my gw , f/ o lUr Sm NtQuerySystemInformation()
function & JU SystemProcessInformation class e JUr w lw Jh SysDbgQueryModuleInformation
command y g& Sdy gw , f/ WindowsXP r Sm SysDbgReadVirtual command u dk r dw fq u fc Jhjy D; system
x Ju b , fa e & mu r q dk r Sw fOmP fw ku dkz w f& IE dki fy gw , f/ w u , fhr Sw fOmP fe JU MSR w dkUu dk a & ; E dki fz w fE dki fw Jh?
r Sw fOmP fw kx Ju dk a & ; o m; E dki fw Jh t jc m; command a w Gv J& Sdy gw , f/ Windows 2003 SP1 e JU a e mu fy dki f; a w G
r Sma w mh' Dfunction a w Gt m; v Hk; u dky dw fy i fx m; y gw , f/
( 2 . 1 . 1 6 ) ReadFile (ker nel32.dll)
kernel32.dll & JU ReadFile() function u dka w mh u k' f stream e JUy w fo u fw Jh z dki f content a w Gu dk
z w fjc i f; jz i fh self-modification t w Gu fe n f; v r f; w p fc kt jz p f t o Hk; jy KE dki fy gw , f/ ' De n f; [ m debugger a w Gc s
x m; r , fh a q mhz f0 Jv f breakpoint a w Gu dkz , f& Sm; & mr Sm x da & mu fw Jhe n f; v r f; w p fc kjz p fy gw , f/ ' De n f; v r f; u dk
1 9 9 9 c kE Sp fr Sm Peter Ferrie u y x r q Hk; a q G; a E G; c Jhz l; jy D; 2 0 0 7 r Sma w mh Protr Bania u v lo d& Si fMu m; x kw fa z mfc Jh
y gw , f/ e r le mu k' fu a w mhy Hk( 3 0 ) t w dki f; jz p fy gw , f/
xor ebx, ebx
mov ebp, offset l2
push 104h ; MAX_PATH
push ebp
push ebx ; self filename
call GetModuleFileNameA
push ebx
push ebx
push 3 ; OPEN_EXISTING
push ebx
push 1 ; FILE_SHARE_READ
push 80000000h ; GENERIC_READ
push ebp
call CreateFileA
push ebx
push esp
; more bytes might be more useful
push 1
push offset l1
push eax
call ReadFile
; replaced by "M"
; from the MZ header
l1: int 3
...
l2: db 104h dup (?) ;MAX_PATH
y Hk( 3 0 )
' Djy e mu dk a jz & Si f; z dkUu a w mh API call a w Ga e mu fr Sm a q mhz f0 Jv f breakpoint a w Gu dkr o Hk; b J
hardware breakpoint a w Gu dko Hk; z dkUjz p fy gw , f/
( 2 . 1 . 1 7 ) Wr itePr ocessMemor y (ker nel32.dll)
' De n f; v r f; u v J ReadFile() function e n f; v r f; u dk t e n f; i , fa jy mi f; v Jx m; w my g/ ' ga y r , fh
process & JU r Sw fOmP fa e & mr Sm a & ; & r , fha ' w ma w G& Sdx m; jy D; o m; jz p f& y gr , f/ e r le mu k' fu a w mh y Hk( 3 1 ) t w dki f;
jz p fy gw , f/
push 1
push offset l1
push offset l2
push -1 ;GetCurrentProcess()
call WriteProcessMemory
l1: nop
l2: int 3
y Hk( 3 1 )
' De n f; v r f; u dk NsAnti u t o Hk; jy Ky gw , f/ ' Djy e mu dk a jz & Si f; z dkUu a w mh API call a w Ga e mu fr Sm
a q mhz f0 Jv f breakpoint a w Gu dkr o Hk; b Jhardware breakpoint a w Gu dko Hk; z dkUjz p fy gw , f/
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 525 -
( 2 . 1 . 1 8 ) UnhandledExceptionFilter (ker nel32.dll)
Exception w p fc ku dka w GUc sde fr Sm register v ky fx m; w Jh SEH ( o dkU) VEH a w Gr & Sd& i f? register
v ky fx m; w Jh handler a w Gu exception u dk u dki fw G, fE kdi fjc i f; r & Sdb l; q dk& i f a e mu fq Hk; t m; x m; & mt jz p f
UnhandledExceptionFilter() function u dka c : , l& y gv dr fhr , f/ q dkv dkw mu exception w p fc k[ m
unhandled exception filter q Da & mu fv m& i f process [ m debug v ky fc Hx m; & w mjz p fjy D; register v ky fx m; w Jh
top level exception filter u dka c : , lo Hk; v dkUr & a w mhy gb l; / SetUnhandledExceptionFilter() function u
top level exception filter u dko w fr Sw fy gw , f/ t c sdKU packer a w Gu a w mh _BasepCurrentTopLevel
Filter() function e JU exception filter u dku dk, fw dki fo w fr Sw fy gw , f/ UnhandledExceptionFilter() [ m
debugger & Sd^ r & Sdu kdq Hk; jz w fz dkU NtQueryInformationProcess(ProcessDebugPort class) function u dk
a c : o Hk; y gw , f/ e r le mu k' fu a w mhy Hk( 3 2 ) t w dki f; jz p fy gw , f/
push @not_debugged
call SetUnhandledExceptionFilter
xor eax, eax
mov eax, dword [eax] ; trigger exception
; program terminated if debugged
; ...
@not_debugged:
; process the exception
; continue the execution
y Hk( 3 2 )
' Djy e mu dka jz & Si f; z dkU NtQueryInformationProcess() & JU return w e fz dk; u dkjy i fa y ; & y gr , f/
( 2 . 1 . 1 9 ) BlockInput (user 32.dll)
Cracker a w G debugger u dkt o Hk; jy Kjc i f; r S w m; q D; w Jh function w p fc kjz p fy gw , f/ Mouse e JU
keyboard event a w Gu dkapplication a w Gq Dr a & mu fa t mi f block v ky fE dki fjy D; ' Dfunction u o m event a w Gu dk
unblock jy e fv ky fE dki fy gw , f/ ' De n f; v r f; u dk t o Hk; jy Kw mu a w mh Yoda's protector jz p fy gw , f/ ( Yoda's
protector t a Mu mi f; u dk]Olly Debug Script} t c e f; w Gi f t a o ; p dw fa q G; a E G; jy D; jz p fy go n f/ )
BlockInput(TRUE);
' Djy e mt w Gu f BlockInput() & Sd& mu dk RETN o w fr Sw fa y ; v dku f& i f & y gjy D/ ' gr Sr [ kw f Ctrl + Alt
+ Del E Sdy f& i f unblock jz p fy gw , f/
( 2 . 1 . 2 0 ) SuspendThr ead (ker nel32.dll)
SuspendThread() function u a w mh OllyDng e JU Turbo Debug w dkUv dk user-mode debugger
a w Gu dk disable v ky f& mr Sm t v Ge fx da & mu fw Jhe n f; v r f; w p fc kjz p fy gw , f/ ' De n f; u dka w mh process a w G p dp p f
a & w Gu fjc i f; jz i fh& & SdE dki fjy D; w u , fv dkU ]explorer.exe} e JUu dku fn Dr Ir & Sdc Jhb l; q dk& i f r dc i f process & JU t " du thread
u dkq dki f; i Hhx m; y gw , f/ ' De n f; u dkt o Hk; jy Kw mu a w mhYoda's Protector r Smjz p fy gw , f/
( 2 . 1 . 2 1 ) Guar d Pages
Guard page a w Gu dkt o Hk; jy Kjy D; debugger u dkp Hkp r f; E dki fy gw , f/ ' De n f; [ m Olly & JU on-access/write
memory breakpoint e JUy w fo u fy gw , f/ Olly & JU memory breakpoint a w G[ m guard page
a w Gu dkt o Hk; jy Kx m; w mjz p fy gw , f/ r Sw fOmP fw p fc ku dk access v ky fc sde fr Sm guard page a w Gu o w da y ; E dki fy g
w , f/ Exception handler w p fc ku dk register v ky fc sde fr Sm execute v ky fE kdi fw Jh^ a & ; E dki fw Jh page w p fc ku dka e & m
c sx m; v dku fjy D; C3(RET instruction) q dkw Jhopcode u dk a & ; v dku fy gw , f/ ' Da e mu fr Sma w mhpage protection
[ m PAGE_GUARD t jz p fa jy mi f; o Gm; y gw , f/ ' Dha e mu f instruction u dk execute v ky fz dkUMu dK; y r f; y gw , f/
Access v ky fc Ha e & w Jhaddress [ m guard page w p fc k& JUt p dw ft y dki f; w p fc kjz p fc Jhr , fq dk& i f exception handler
u EXCEPTION_GUARD_ PAGE (0x80000001) exception w p fc ku dk& & Sdy gw , f/ Process w p fc k[ m
debugger a t mu fr Sm debug v ky fc Hx m; & jy D; guard page u dk t o Hk; jy Ka e c Jh& i f exception u x Gu fr v m
E dki fa w mhy gb l; / ' gq dk access v ky fr Iu dk memory breakpoint t jz p fr Sw f, ly gw , f/ Packer a w Gu ' De n f; u dk
t o Hk; jy KMu w mjz p fy gw , f/ e r le mu k' fu a w mhy Hk( 3 3 ) t w dki f; jz p fy gw , f/
; set up exception handler
push .exception_handler
push dword [fs:0]
mov [fs:0], esp
; allocate memory
push PAGE_READWRITE
push MEM_COMMIT
push 0x1000
push NULL
t c e f; ( 4 4 ) Anti Unpacking e n f; v r f; r sm;
- 526 -
call [VirtualAlloc]
test eax,eax
jz .failed
mov [.pAllocatedMem],eax
; store a RETN on the allocated memory
mov byte [eax],0xC3
; then set the PAGE_GUARD attribute of the allocated memory
lea eax,[.dwOldProtect]
push eax
push PAGE_EXECUTE_READ | PAGE_GUARD
push 0x1000
push dword [.pAllocatedMem]
call [VirtualProtect]
; set marker (EAX) as 0
xor eax,eax
; trigger a STATUS_GUARD_PAGE_VIOLATION exception
call [.pAllocatedMem]
; check if marker had not been changed (exception handler not called)
test eax,eax
je .debugger_found
:::
.exception_handler
; EAX = CONTEXT record
mov eax,[esp+0xc]
; set marker (CONTEXT.EAX) to 0xffffffff
; to signal that the exception handler was called
mov dword [eax+0xb0],0xffffffff
xor eax,eax
retn
y Hk( 3 3 )
y Hk( 3 3 ) u u k' fu dk& Si f; & r , fq dk& i f y x r q Hk; r Sw fOmP fw p fc ku dk a e & mc sx m; y gw , f/ a e & mc sx m; w Jhr Sw f
OmP fr Sm u k' fa w Gu dko dr f; q n f; y gw , f/ ' Dha e mu f PAGE_GUARD atribute u dk enable v ky fy gw , f/ ' Dha e mu f
EAX u dk 0 v dkU initialize v ky fjy D; page-guard v ky fx m; w Jha e & mc sx m; w JJhr Sw fOmP fx Jr Sm u k' fa w Gu dk execute
v ky fjc i f; jz i fh STATUS_GUARD_PAGE_VIOLATION u dkt p y sdK; a y ; v dku fy gw , f/ w u , fv dkU u k' fa w G
[ m OllyDbg r Sm debug v ky fc Ha e & r , fq dk& i f exception handler u dka c : v dkUr & a w mhw ma Mu mi fh EAX & JU
w e fz dk; [ m r a jy mi f; v JE dki fa w mhy gb l; /
' De n f; u dkt o Hk; jy Kw mu a w mh PC Guard jz p fy gw , f/ Guard page a w G[ m exception w p fc ku dk
t p y sdK; w ma Mu mi fh cracker a w G[ m exception handler u dka c : , lE dki fz dkU exception w p fc ku dk w r i fz e fw D; jc i f;
jz i fh ' De n f; u dk a u smfv Tm; E dki fy gw , f/ ' ga Mu mi fh y Hk( 3 3 ) u u k' fa e & mr Sm RETN instruction u dk INT3 e JU
t p m; x dk; & y gr , f/ jy D; r So m RETN v dku fy gr , f/ INT3 u dk execute v ky fc sde fr Sm Shift+F9 u a e w p fq i fh
exception handler u dka c : z dkU debugger u dkz dt m; a y ; & y gr , f/ Exception handler u dka c : jy D; c sde fr Sma w mh
EAX w e fz dk; u dk o i fha w mfw Jhw e fz dk; w p fc k o w fr Sw fr Smjz p fjy D; ' Dha e mu fr Sma w mh RETN instruction u dk execute
v ky fy gv dr fhr , f/
w u , fv dkU exception handler u exception [ m STATUS_GUARD_PAGE_VIOLATION
[ kw f^ r [ kw f p p fa q ; c Jhr , fq dk& i f exception handler x Jr Sm breakpoint w p fc ku dko w fr Sw fjy D; Exception
Record parameter u dkjy i f& r Smjz p fy gw , f/ ExceptionCode u dka w mh STATUS_GUARD_PAGE_
VIOLATION v dkUu dk, fw dki fjy i f& r Smjz p fy gw , f/
q u fv u fa z mfjy y gr n f/
t c e f; ( 4 5 ) Armadillo developer r sm; E Si fht i fw mA sL;
- 527 -
tcef;(45) - Ar madillo developer rsm;ESifh tifwmAsL;
t i fw mA sL; a r ; jr e f; o l\ r Sw fc su f/ , c kt i fw mA sL; o n f t q i fhjr i fhw e f; u sr f; jy Kt w Gu f & n f& G, fjc i f; jz p fy go n f/
r lv a w mhy p fa c gi f; p Ofo n f t v Ge fu s, fjy e fYa o ma Mu mi fh t a Mu mi f; t & mu dk jc HKi Hkr da p & e ft w Gu f a c gi f; p Of
a jy mi f; v dku fo n f/ x dkYt w Gu fa Mu mi fh t i fw mA sL; r y Do a w mha y / t i fw mA sL; u dk v Ge fc Jha o m w p fE Sp fu w n f; u
jy Kv ky fc Jha o mfv n f; v Hkjc HKa & ; E Si fh reversing t z GJUt p n f; r sm; t w Gu fr l p dw f0 i fp m; p & m jz p fq J[ k x i fy go n f/
t i fw mA sL; a jz Mu m; o l E Sp fOD; r Sm Armadillo Team r S r e fb mE Sp fOD; jz p fa o ma Mu mi fh t c sdKUa e & mr sm; w Gi f
t a jz E Sp fc k jz p fa e o n fu dk a w GYMu & r n f jz p fy go n f/ t c sde fa y ; Ny D; a jz Mu m; c JhMu a o m x dko lE Sp fa , mu fu dk t v Ge f
a u s; Z l; w i fr do v dk & & Sdo r Q o w i f; t c su ft v u fr sm; u dk u sr f; w Gi f x n fho Gi f; a & ; o m; jc i f; r jy KE dki fo n fht w Gu fr l
p dw fr a u mi f; jz p fr do n f/ x dkYjy i f o lw dkYE Sp fOD; a jz Mu m; a o m t a jz r sm; o n f reversing t z GJYt p n f; r sm; t w Gu f
a q G; a E G; c su f w p fp Hkw p f& m j z p fa y : a p z dkYa r Qmfv i fhy go n f/
( 1 ) v Hkjc HKa & ; p e p fw p fc ku dk u dk, fw dki f w n fa q mu fw me JY third party u dk v dki fp i fc sa y ; v dku fw m b , f[ m
y dka u mi f; v J/
a jz / v Hkjc HKa & ; p e p fa u mi f; w p fc ku dk u dk, fha q mhz f0 Jv f team u w n fa q mu fw mu t r sm; Mu D; A [ ko kw & Sdz dkY
v dko v dk cracker a w G& JU a e mu fq Hk; a y : e n f; p e p fa w Gu dkv n f; t jr Ja v hv ma e z dkY v dky gw , f/ a u mi f; w Jh
t c su fu a w mh u Re fa w mfw dkYu t c sde fjy n fh t m; x kw fv dkY jy D; jy n hfp Hkw Jh p e p fw p fc ku dk w n fa q mu fE dki fNy D; ?
t o Hk; jy Kc Gi fhv dki fp i f c sa y ; v dku fr , fq dk& i f v u f& Sd third party u dk t o Hk; jy Ka e w Jho la w Gt a e e JY w p f0 u fw p fy su f
v Hkjc HKa & ; e p fa w Gu dk w n fa q mu fa e r , fht p m; o lw dkY& JU t c sde fa w Gu dk o lw dkYv ky fc si fw Jh t y dki f; a w Gr Sm jr SKy fE SH
E dki fy gw , f/
a jz / a q mhz f0 Jv fv Hkjc HKa & ; q dkw m w p f& u fE Sp f& u fe JY a v hv mv dkY& w Jht & m r [ kw fy gb l; / c dki fc dki fr mr m w n fa q mu f
E dki fz dkYq dkw m[ m ' De , fy , fr Sm E Sp fa y gi f; r sm; p Gm t a w GYt Mu HK& Sdr S jz p fw my g/ c i fA sm; t a e e JY t c sde ft r sm; Mu D;
a y ; z dkYv dko v dk a e mu fq Hk; a y : cracking e n f; y n ma w G? tool a w G o Hk; w w fz dkYv n f; v dky gw , f/ c i fA sm; u
c i fA sm; & JU product t o p ft w Gu f t m; x kw fv Hk; y e f; a e & w , fq dk& i fa w mh ' Db u fu dk v Sn fhMu n fhE dki fr Sm
r [ kw fb l; a v / ' ga Mu mi fh o lw dkYt a e e JY v Hkjc HKa & ; p e p fa w Gt w Gu f t c sde fu ke fc Hp & m r v dka w mho v dk o lw dkY
u Rr f; u si f& m e , fy , fr [ kw fw Jht w Gu f o lw dkYu dk, fw dki fa & ; a e & i f crack c H& z dkYu a w mht e n f; e JYt r sm; y J/
( 2 ) c i fA sm; w dkY a q mhz f0 Jv fu dk v Hkjc HKa & ; p e p ft w Gu f o Hk; p GJr , fho lw dki f; & JU v dkt y fc su fjz p fv mz dkY b , fv dk w dk; w u f
a t mi f v ky fr v J/ ' gr Sr [ kw f cripple ware w dkY? online key validation w dkYv dky J a q mhz f0 Jv fv Hkjc HKr Ip e p f
a v mu x Ju t q i fhw p fq i fht a e e JYq u fv u f& y fw n fNy D; t J' Dt q i fhu dky J y dka u mi f; a t mi f v ky fr v m; /
a jz / t r Se fa w mh u Re fa w mfw dkY , HkMu n fw mu o Hk; p GJo la w Gu dk a y ; w Jh v u f& Sda q mhz f0 Jv fe JY u k' ft Mu Ha y ; c su fa w Gu
v Hkjc HKr Ib u fu w p fc kw n f; y g/ w u , fv dkYo lw dkYu website w p fc ka y : u dk o lw dkYproduct u dk o Gm; w i fr , fq dk& i f
u Re fa w mfw dkYb u fu key validation a q mhz f0 Jv fa y ; E kdi fo v dk q dki ft a o ; a v ; a w Gt w Gu f q dk& i fa w mh
Armadillo r Sm built in v ky fa y ; x m; y gw , f/
a jz / v Hkjc HKa & ; p e p fq dkw m a q mhz f0 Jv fw n fa q mu fy Hk c dki fr mo a v mu f c dki fr mw , f/ u Re fa w mfw dkYu a q mhz f0 Jv fu dk
t w dku ft c dku f r c H& a t mi f u mu G, fw Jh Ny D; jy n fhp Hkw Jh e n f; p e p fe JY v ky fa q mi fc su fa w Gu dk y Hhy dk; a y ; x m; w , f/
' ga y r , fh v Hk; 0 t w dku ft c dku f r c H& b l; v dkYa w mh r q dkv dky gb l; / t c sde fa w mfa w mfr sm; r sm; r Sm w n fa q mu fw Jhy Hkp H
r Sm; , Gi f; r Ia Mu mi fh a q mhz f0 Jv f[ m jz p fo i fhw mx u f t m; e n f; o Gm; w mr sdK; & Sdw w fw , f/ u Re fa w mfx i fw mu a w mh
y & dk* & r fr ma w Gu u Re fa w mfw dkY y p n f; u dk o Hk; w Jht jy i f hidden/subtle check a w Gu dk x n fha y ; o i fhw , fv dkY
x i fw , f/ a o a o c smc sm v ky fr , fq dk& i fa w mha u mi f; a u mi f; p de fa c : E dki fr Smy J/
a jz / t a u mi f; q Hk; v Hkjc HKa & ; p e p fq dkw mu a q mhz f0 Jv f& JU demo version y Ja y gh/ u k' ft c sdKU application r Sm
w u , fu dk c se fv Sy fx m; c H& w m/ a e mu fNy D; a z smu fx m; w Jh t y dki f; a w Gu v n f; jr i fo mx i fo m r jz p f& b l; / Oy r m
File save v ky fw Jh function w dkY? b mw dkYa v / y dkNy D; c u fc J& Iy fa x G; w Jh t y dki f; a w Gu dk a z smu fx m; w mu y dkNy D;
o i fha w mfw , f/
( 3 ) c i fA sm; w dkY SafeDisc w dkYv dk u kr P Da w Gu SDK x kw fv dku fa w mh developer a w Gu a q mhz f0 Jv fa & ; o m; w Jh
t q i fhr Sm v Hkjc HKr Ip e p fu dk w p fc gw n f; x n fha & ; o Gm; v dkY& w , f/ ' g[ m c i fA sm; w dkYt w Gu f a u mi f; w Jht c su fv m; /
a jz / a u mi f; w Jht c su fu a w mh a q mhz f0 Jv fz e fw D; o la w Gu dk i gw dkY u mu G, fz dkY v dkt y fw , fq dkw Jh t o da v ;
x n fha y ; v dku fo v dky J/ a o a o c smc sm t a o ; p dw f v ky fjc i f; t m; jz i fhv Hkjc HKa & ; t w Gu f y dka u mi f; v mo v dk a q mhz f0 Jv f
v dki fp i fu dky g u mu G, fNy D; o m; jz p fo Gm; w , f/ x y fx y fw kd; v dkY& w Jh v dki fp i ft r sdK; t p m; jz p fw Jh variable licensing
scheme r Smq dk& i f y & kd* & r fr mu exe z dki fw p fc ku dk & r Smjz p fNy D; o lU& JU user 0 , fx m; w Jh v dki fp i fa y : r Sm r lw n fv dkY
license key u v dki fp i f0 , fx m; w Jht y dki f; a w Gu dk unlock v ky fo Gm; r Sm jz p fy gw , f/
( 3 . 1 ) a q mhz f0 Jv f security u dk a e mu fq Hk; t q i fhu sr Sx n fho Gi f; w m y dkr sm; v G, fo v m; /
t c e f; ( 4 5 ) Armadillo developer r sm; E Si fht i fw mA sL;
- 528 -
a jz / ' ga y gh/ a e mu fq Hk; t q i fhq dk& i fa w mh y dkv G, fw ma y gh/ ' ga y r , fh a y : jy Lv mjz p fa e w Jh y & kd* & r fa w Gt w Gu f
u a w mht a u mi f; q Hk; t a jz jz p fr Sm r [ kw fb l; / ' ga Mu mi fhu Re fa w mfw dkYu developer a w Gu dk a q mhz f0 Jv fz e fw D; w Jh
t q i fhr Smu w n f; u x n fho Gi f; E dki fz dkYNanomite w dkY? Secured Section w dkYv dk SDK a w Gx kw fv ky fa y ; x m; w m/
a jz / a u mi f; u sdK; u a w mh o Hk; p GJo lu b , fa e & mr Sma w mhjz i fh special protection x n fhv dku fr , f? special check
a w Gx n fhv dku fr , f p o n fjz i fh a & G; E dki fo v dk v Hkjc HKa & ; p e p fu dk t a u mi f; q Hk; jz p fa t mi f o Hk; p GJE dki fo Gm; v dr fhr , f/
w c sdKUv ky fa q mi fc su fa w Gu a w mh application u dk a E S; o Gm; a p w ma y gh/ ' ga Mu mi fh y & kd* & r fr mu application & JU
p Gr f; a q mi f& n fu dk r x dc dku fa p b J o Hk; p GJE dki f& i fa w mhy dkjy D; a u mi f; v dr fhr , f x i fw , f/
a jz / SDK a w Gu & n f& G, fc su ft w dki f; u mu G, fr Ia y ; E dki fo v dk a q mhz f0 Jv fe JY v Hkjc HKa & ; p e p fu dk t c sdK; n Dn D
a y gi f; p y fa y ; y gw , f/ v Hkjc HKa & ; p e p fu dk w dku f& dku fMu D; r SDc dka e & jc i f; u i f; a v a v y dka u mi f; a v a v y J/
( 4 ) v Hkjc HKa & ; & Ia x mi fht jy i f c i fA sm; t a e e JYz dki ft & G, ft p m; ? w Gu fc su fr IMu mc sde f? t jc m; a q mhz f0 Jv fa w Ge JYo [ Z mw
jz p fr I? t v G, fw u l t o Hk; jy KE dki fr Ip w Jht c su fa w Gu dk a w G; y l& r Sma y gh/ t J' ga w Gu dk c i fA sm; b , fv dk u dki fw G, fo v J/
t J' Dt c su fa w Gu c i fA sm; & JU z e fw D; r It a y : t w m; t q D; jz p fo v m; /
z dki ft & G, ft p m;
a jz / t c ka c w fr Sm u Ge fy sLw mw dki f; storage r sm; w Jh hard drive a w G & SdMu w mc sn f; y J/ ' ga Mu mi fh z dki ft & G, f
t p m; u a w mh [ dk; t & i fa c w fw ke f; u v dk y lp & m r v dky gb l; / ' ga y r , fh t w w fE dki fq Hk; a w mh t & G, ft p m; a o ; i , f
u sp fv sp fa t mi f Mu dK; p m; x m; y gw , f/
w Gu fc su fr I t jr e fE Ie f;
a jz / Microprocessor a w Gu jr e fo x u f jr e fjr e fv ma w mh ' gu v n f; jy e m r [ kw fa w mhy gb l; / u Re fa w mf
u a w mh u Re fa w mfw dkY ASM u k' fa w Gu dk t & G, ft p m; a o ; i , fjr e fq e fa t mi f t jr J Mu dK; p m; c Jhw my gy J/ Memory
w dkY? disk space w dkYu v n f; t & i fu w e fz dk; Mu D; c Jha y r , fht c k t & r f; o u fo ma e y gNy D/
a jz / t c ka c w fr Sm u Ge fy sLw ma w Gu t & r f; jr e fv mMu Ny D/ CPU u v n f; jr e fo x u fu dk jr e fv mw , f/ ' ga y r , fh
u Re fa w mfw dkYu a w mh c i fA sm; q Dr Sm a c w fr Du Ge fy sLw m r & Sda w mi f system t a [ mi f; a w Gr Sm o Hk; v dkY& a t mi f Mu dK; p m;
x m; y gw , f/ t jr e fE Ie f; q dkw m t a & ; y gw Jht c su fy g/ ' ga Mu mi fh u Re fa w mfw dkYb u fu a w mh t w w fE dki fq Hk;
jr e fa t mi f v ky fa y ; x m; w my J/ w p fc gw a v a w mhv n f; Assembly u dko Hk; Ny D; t jr e fq Hk; jz p fa t mi f v ky f& w ma y gh/
o [ Z mw jz p fr I
a jz / u Re fa w mfw dkYq Dr Sm Windows OS t m; v Hk; & Sdw , f/ Version t a [ mi f; a w Gr Sm 1 0 0 % o [ Z mw jz p fa p z dkY
u Re fa w mfw dkYproduct a w Gu dk OS t m; v Hk; r Sm p r f; o y fy gw , f/
t o Hk; jy K& v G, fu lr I
a jz / z e fw D; r I t [ e fYt w m; q dkv dkY. . . c i fA sm; t a e e JYw jc m; e n f; v r f; a w Gu a e z e fw D; & r Sma y gh/
a jz / jy e m t jz p fq Hk; u a w mh o [ Z mw jz p fz dkYy J/ u Re fa w mfw dkYw p fc gw a v q dk t a w mfa u mi f; w Jh u mu G, fa & ;
e n f; v r f; u dk a w GYw , f/ ' ga y r , fh t J' gu OS t m; v Hk; e JY r u dku fjy e fb l; ? ' gr Sr [ kw f virtual machine a y : r Sm
t v ky fr v ky fjy e fb l; / a e mu fq Hk; Mu a w mh ' gu dk r o Hk; b J a e v dku f& a & m/ ' ghjy i f r p r f; o y fc i f OS version u dk
t & i fMu n fha e & w , f/ t J' ga w Gu v Hkjc HKa & ; p e p fu dk t m; e n f; a p w ma w Gy J/ ' ga y r , fh u Re fa w mfw dkYu a w mh 1 0 0 %
o [ Z mw jz p fr Iu dky J x de f; o dr f; x m; y gw , f/
( 5 ) t i fw me u ft o Hk; jy Kw m w dk; y Gm; v mw me JYt r Q online key validation u y dkNy D; a y : jy Lv m jz p fv mw , f/
' ga Mu mi fhsecurtiy trend u t J' Db u fu dk o Gm; r , fv dkYx i fv m; / ' gr Sr [ kw f b m& Sda o ; v J/
a jz / c i fA sm; a r ; c Ge f; u dk u Re fa w mf e m; v n fo a v mu f a jz & & i f v Hkjc HKa & ; p e p fu & SdNy D; o m; / u Re fa w mfw dkY
r dc i fu kr P Djz p fw Jh Digital River u a e v Hkjc HKr Ip e p f x n fho Gi f; Ny D; o m; a q mhz f0 Jv fa w Gu dk t i fw me u fu a e y J
a & mi f; a e w m/ Protection u a w mh e n f; y n mu dk t jr J x y fc sy fr u Gm v dku fa e & r Smy J/ e n f; y n mu dk, fw dki f
o lUu dk, fo l u mu G, fE dki fw Jhp Gr f; t m; & Sdw Jht a jc t a e a & mu fw Jht c sde fx da y gh/
a jz / u Re fa w mfu a w mh a o a o c smc sm w n fa q mu fx m; w Jh q mA mt a jc c Hw Jh p p fa q ; r Ia w Gu t e m* w fr Sm
jz p fv mE kdi fw , f/ jy e mw p f& y fu a w mh t i fw me u fA dki f; & y fp fa w G? spyware a w G? malware a w G y Gx a e w Jh
t c sde fr Sm application u t dr fu dk z ke f; q u fNy D; v dki fp i fu dk p p fa q ; w mr sdK; b , fo Hk; p GJo lu r S ' gu dk v u fc HE dki fr Sm
r [ kw fb l; / Online key validation u a w mh a o c sm w n fa q mu fx m; z dkY v dkw , f/ a e mu fNy D; validation
o u fo u f r jz p fo i hfb l; / t i fw me u fq mA ma w Gu dk token w p fc kt a e e JY t o Hk; jy KNy D; v dkt y fw Jht c sde fr Sm
u k' ft p dw ft y dki f; a w Gu dk decrypt v ky fo i fho v dk v dkt y fw Jht c sde fr Sm encrypt v ky fE dki fp Gr f; t m; & Sdo i fhw , f/
t e m* w fr Sma w mh e n f; p e p ft r sdK; r sdK; a y gi f; p y fv ky fMu r , fv dkY x i fw my J/ e n f; y n mu a e & mw dki f;
r w Gi fu s, fa o ; a w mh a v ma v mq , fr Sm t r sm; jy n fo lu v u fr c HE dki fa o ; b l; / Oy r m v dki fp i fu dk p p fa q ; z dkY
t i fw me u fv dkw , f/ ' ga y r , fht J' Da c w fw ke f; u v lw dki f; r Sm t i fw me u f r & Sdb l; /
t c e f; ( 4 5 ) Armadillo developer r sm; E Si fht i fw mA sL;
- 529 -
( 6 ) v le JY v lUt z GJUt p n f; r Sm v la w mfa w mfr sm; r sm; o dy fx l; c Re fMu w , f/ t y i fy e f; c HNy D; c i fA sm; w dkY protection
a w Gu dk a z mu fz dkY Mu dK; p m; Mu w , f/ ' ga y r , fh , x mb lw u su s a jy mr , fq dk& i f o lw dkYr & Sd& i f c i fA sm; w dkYy p n f; u dk
b , fo lr S o Hk; r Sm r [ kw fb l; / ' ga Mu mi fh reverse engineering t z GJUt p n f; t a y : c i fA sm; & JU t jr i fu dk o dv dky g
w , f/
a jz / o lw dkYr S r & Sd& i f u Re fa w mfw dkYy p n f; v n f; r v dky gb l; / & dk; o m; jr J & dk; o m; w Jho la w G t w Gu fq dk key w p fc k
a v mu fy J v dkv dr fhr , f/ o lw dkY w & m; Oy a ' a b mi fjy i fy u t v ky fv ky fw Jht jy i f Oy a ' c sdK; a z mu fw Jho lq dkw m a v ; p m;
c H& z dkYc u fc Jo n fhw dki fa t mi f u Re fa w mfu a w mhy dka w mfw Jhcracker a w G& JU t o dOmP fy n mu dk a v ; p m; y gw , f/
a jz / u Re fa w mfhb u fu a w mh reverse engineering u t a & ; Mu D; w , fv dkY x i fw , f/ Reverse engineering
q dkw m a q mhz f0 Jv fa w Gu dk crack z dkYw p fc kw n f; r [ kw fb l; / ' ga y r , fh v la w Gu a w mh ' Dv dky J jr i fa e Mu w , f/ RE
u dk anti-virus u kr P Da w Gu virus a w G? malware a w Gu dk a v hv mz dkY o Hk; w , f/ RE u a e tool a w G?
technique a w Gt r sm; Mu D; x Gu fv mE dki fNy D; a u mi f; w Jhb u fr Sm t o Hk; c sE dki fw , f/ a e mu fNy D; source code r a y ; w Jh
a q mhz f0 Jv fa w G& JU , kda y gu fa w Gu dk & SmE dki fw , f/ ' gr Sy dkNy D; v Hkjc HKw Jha q mhz f0 Jv fa w Gjz p fv mr , f/
a jz / u Re fa w mfht jr i fu a w mh RE u dk cracking e JY c GJjc m; a p c si fw my J/ RE t o dki f; t 0 dki f; u v la w Gu a y smf& Ti fr I
t w Gu f& , f? a v hv mz dkYt w Gu f& , fy J v ky fw mjz p fNy D; b , fo lUu dkr S ' ku r a y ; Mu b l; / o lw dkY t a w GYt Mu HKa w Gu dk
z dk& r fa w Gr Sma w mh r Qa 0 Mu w ma y gha v / u Re fa w mfx i fw mu a q mhz f0 Jv fu mu G, fa & ; o r m; a w Gu underground
research r sm; r sm; v ky fz dkYv dkNy D; o lw dkYu dkv n f; o lc dk; a w Gv dkYx i fr a e a p c si fb l; / ( t c sde f t a w mfr sm; r sm; r Sma y gh)
( 7 ) c i fA sm; [ m c i fA sm; & JU v Hkjc HKa & ; p e p fu dk c sdK; a z mu fc Hv dku f& w m a w GYNy Dq dky ga w mh/ b , fv dkjy e fNy D; w HkYjy e fjz p fr v J/
w & m; 0 i f e n f; v r f; a b mi f t jy i fu jz p fjz p fa y gh/ ' gr Sr [ kw f o lw dkYu dk a v ; p m; r da e r v m; /
a jz / [ kw fw , f/ u Re fa w mfu a w mh t a w mf a v ; p m; r dr Smy J/ u Re fa w mhf v ky fa z mfu dki fz u fa w Gu a w mh o a b mw lr Sm
r [ kw fy gb l; / ' ga y r , fh e n f; v r f; a w G c dk; x m; w Jh key a w Gu dk a v Qmu fjz e fYa 0 jc i f; r jy K& i fa w mh y dkNy D; a w mh
a v ; p m; z dkYa u mi f; r Sma y ghA sm/ ' ga y r , fha o c smw mu o lw dkYu ' gr sdK; r v ky fb J a e r Smr [ kw fb l; /
a jz / u Re fa w mfu a w mh p r w fu sNy D; credit card a w Gu dkc dk; Ny D; a q mhz f0 Jv fa w G0 , f, lw mr sdK; v dk o lc dk; u si fho lc kd; Mu H
r v ky fo a & GU u Re fa w mfw dkY v Hkjc HKa & ; p e p fu dk c sdK; a z mu fE dki fw Jho la w Gu dk a v ; p m; w , f/ c u fc u fc Jc Je JY u Re fa w mfw dkY
u k' fa w Gu dk c sdK; a z mu fz dkY disassembling e JY debugging v ky fw Jho la w Gu dka w mh a v ; p m; r dw m t r Se fy J/ ' ga y r , fh
o lw dkY b mv ky fE dki fw , fq dkw mu dk Mu Gm; 0 gNy D; u Re fa w mfw dkYu dk r c e fYa v ; p m; v ky fw w fw Jh a q mi fhMu Gm; Mu Gm; i e Ja v ;
a w Gu dka w mh r a v ; p m; E dki fb l; / o lw dkYa r ha e w mu o lw dkY u Ge fy sLw m p u dki fw w fp t c sde fr Smw i f ' gr sdK; t v ky fa w Gu
u Re fa w mfw dkY v ky fc Jhw ma w G q dkw my J/ a e mu fNy D; p e p fw p fc ku dk u mu G, fa p mi fha & Smu f& w m[ m p e p fw p fc ku dk
c sdK; a z mu f& w mx u f t r sm; Mu D; v u f0 i fw , f/
( 8 ) c i fA sm; t w Gu f t a u mi f; q Hk; v Hkjc HKa & ; e n f; v r f; u b mv J/ Oy r m - Address table z su fy p fw mw dkY? Anti-
debug v ky fw Jhe n f; w dkY? child process w dkYv dka y gh/
a jz / u Re fa w mfw dkY& JU level t jr i fhq Hk; key p e p fy g/ a e mu fNy D; u Re fa w mfw dkY& JU Strategic Code Splicing e JY
Memory patching protection a w Ga y gh/
a jz / u Re fa w mfu a w mh Nanomites u t a u mi f; q Hk; y JA s/ o lUr Sm t m; e n f; c su fa w G & Sda e a y r , fh cracker
t r sm; p ku dk u mu G, fa y ; E dki fv dr fhr , f/ Import Table Elimination v J a u mi f; w my gy J/
a jz / v dki fp i ft a e e JYu a w mh u Re fa w mfw dkY key p e p f& JU level 10 u dko Hk; & i f c i fA sm; application a w Gu dk keygen
v ky fc H& jc i f; u u mu G, fa y ; v dr fhr , f/
( 9 ) a e mi ft e m* w fr Sm v Hkjc HKa & ; t q i fhw dk; jr Si fha t mi f b , fv dk jy Kjy i fa jy mi f; v Jr Ia w Gv ky fr v J/
a jz / u Re fa w mfw dkYu a w mh u Re fa w mfw dkY security e n f; v r f; a w Ge JY key a w G& JU Mu Hhc dki fr Iu dk t jr Jw dk; w u fa t mi f
v ky fa e w my J/ a e mu fx y fx Gu fa y : v mp & m& Sdw mu 64-bit window application a w Gt w Gu f v Hkjc HKa & ; p e p fy g/
a jz / u Re fa w mfw dkYu a w mh u Re fa w mfw dkY v Hkjc HKa & ; v ky fa q mi fc su fa w Gu dk t jr Jw dk; w u fa t mi f v ky fa e w my J/
a e mu fNy D; cracking z dk& r fa w Gu dkv n f; v dku fMu n fh& w , f/ u Re fa w mfw dkYu dk w dku fc dku fE dki fr , fh w p fc kc k a w GYw me JY
t jr e fjy i fq i f& w , f/ t jr Jw r f; a w mh v Hkjc HKa & ; p e p fa w Gu dk c sdK; a z mu f& c u fc Ja t mi f Mu dK; p m; a e w my gy J/ ' gu
t c u fc Jq Hk; p de fa c : r Iw p f& y fy J/
( 1 0 ) Reversing t o dki f; t 0 dki f; u dk b mr sm; a jy mc si fa o ; v J/
a jz / w c sdKU cracker v u fo p fu a v ; a w Gu o dy fi , fw , f/ o lw dkYv ky fa e o r Qa w G[ m jy n fa x mi fp kt p dk; & & JU
Oy a ' u dk c sdK; a z mu fa e w mjz p fa Mu mi f; o w da w mi f r lr d& JUv m; r o db l; / o lw dkY * & kr p dku fo v dk u dk, fhu dk, fu dk
[ kw fv SNy D x i fa e w Jh o la w Gu v n f; e m; r v n fMu b l; / ' ga Mu mi fh b , fo lv ky fa e w , fq dkw m a x mu fjy z dkY
o dy fv G, fo Gm; w , f/ ( o dy fa y : jy Lv mjz p fc si fw Jha & m* ga v )
a jz / t a x Gt x l; a w mh r & Sdy gb l; / w c sdKUa o my k* dKv fa w G a v ; p m; r Iq dkw mu dk y dkNy D; e m; v n fz dkYe JY b m& n f& G, fc su fr S
r & Sdb J v Hkjc HKa & ; p e p f a & ; o m; o la w Gu dk w kdu fc dku fw mr sdK; u dka w mh & y fw e fYa p c si fw , f/ u Re fa w mfw dkYu o lw dkY
t c e f; ( 4 5 ) Armadillo developer r sm; E Si fht i fw mA sL;
- 530 -
p dw fu l; a w Gu dk c dk; w , f? o lw dkYq Du o do Gm; w m p o jz i fh z dk& r fa w Ga y : r Sm Mu Gm; 0 ga e Mu w mu dk z w f& w m
o dy f& , fc si fw , f/ u Re fa w mfw dkYu o lw dkYx u ft & i f ' gr sdK; a w Gv ky fc Jhw m Mu mMu mv Sa y gh/
( 1 1 ) c i fA sm; w dkY product a w Gt jy i f b , fe n f; v r f; a w Gu a q mhz f0 Jv fv Hkjc HKa & ; t w Gu f t a u mi f; q Hk; jz p fr v J/
Oy r m personal build a w G? watermarking a w G? a q mhz f0 Jv f update a w Ge JY techincal support a w Gu dk
ji i f; y , fw mr sdK; a y gh/
a jz / t J' ga w Gt m; v Hk; u Oy r ma u mi f; a w Gy J/ t a u mi f; q Hk; e n f; v r f; u a w mh u mu G, fz dkYq dkw Jh p dw fw p fc ku dk
t jr Jo Gi f; x m; z dkYy gy J/ t a & SUu u k' fa w G& JU checksum r Se fu e fr S a e mu fy dki f; u k' fa w G q u ft v ky fv ky fa t mi f
jy Kv ky fw mr sdK; v dka y gh/ y & dk* & r ft r sm; p ku y & dk* & r f run E dki fz dkYp D' D& Sdz dkYv dkw , f/ p D' Du dk drive x J w p fc ga v mu f x n fh
run v dku fr S application u dk t v ky fv ky fc Gi fha y ; w m/ t J' g[ m u mu G, fa & ; p e p fa w Gu dk c sdK; a z mu fy p fz dkY
t v G, fq Hk; y J/ w u , fv dkY u kr P Da w Gu p D' Du dk a e & mt E SHYr Sm x y fc gx y fc g access v ky fjc i f; u a e u mu G, fz dkY
v ky fx m; & i fa w mi f Z GJa u mi f; w Jhcracker a w G& e fu r u mu G, fE kdi fb l; /
a jz / Virtual machine a w Gu a q mhz f0 Jv f security t w Gu f t & r f; a u mi f; w Jh e n f; v r f; jz p fy gw , f/ P-code
a w Gu dk c GJjc r f; p dw fjz mz dkYu Assembly u k' fa w Gx u f y dkc u fw , f/ Virtual machine a w Gu dk u mu G, fa & ;
& n f& G, fc su fe JYo Hk; w m[ m t c kt a jc t a e r Sma w mhw dk; w u fv mw Jhe n f; v r f; t o p fy J/
a jz / Hidden/Delayed check a w Gv n f; a u mi f; w my J/ c i fA sm; t i fw me u fr Sm w p fy dki f; w p fp crack x m; w Jh
a q mhz f0 Jv fa w Gu dk a w GYz l; r , f x i fw , f/ t J' D a q mhz f0 Jv fa w Gu t v ky fa u mi f; a u mi f; v n f; r v ky fb l; a v /
Hidden/Delay check a w Gu v dku fz dkYo dy fc u fw , f/ Check a w Gu dk a u mi f; a u mi f; r u dki fw G, fE dki fw Jhcracker
a w Gu o lw dkYt o dki f; t 0 dki f; r Sma w mha o mu fa y gy J/
a jz / Watermark a w Gu security jz p fz dkY r a o c smb l; / ' ga y r , fh , dka y gu f[ ma y gu fa w Ge JY c dk; , lw Jho lu dk
a jc & mc Hv dkY& w , f/ w u , fv dkY c i fA sm; customer u w p fa , mu fa , mu fu dk o lUa q mhz f0 Jv fv dki fp i f a y ; v dku fw , f
q dky ga w mh/ Watermark & Sdw m t J' Da e & mMu a w mha u mi f; o Gm; a & m/
( 1 2 ) Physical security? Oy r ma jy m& & i f dongle a w Ga y gh/ a p s; u Gu fr Sm o dy fa c w fr p m; a o ; b l; a e mf/ o Hk; p GJo lu dk
p dw ft a E Smi fht , Su fa y ; w Jh v Hkjc HKa & ; p e p fa w Gu r w Gi fu s, fb l; v dkY x i fw , f/ v Hkjc HKa & ; p e p fa w Gu p dw ft a E Smi fh
t , Su f jz p fc si fp & ma u mi f; a e z dkY v dkv dkYv m; / Oy r m driver a w G install v ky fc dki f; w mr sdK; ? register v ky fz dkY
v dkt y fc su fa w G a w mi f; w me JY dongle a w Ga y gh/ v Hkjc HKa & ; p e p fa w Gu y dkNy D; jr i fo mx i fo m & Sdo i fhw , fr v m; /
Oy r m - Fingerprint v dk? online key validation v dkr sdK; /
a jz / [ kw fu Jh/ Dongle a w Gu a y : jy Lv ma w mhr jz p fa o ; y gb l; / Dongle a w Gu dk p u fr Sm w y fNy D; o Hk; a e & w m[ m
w p fc sdKU user a w Gt w Gu fa w mh z dt m; jz p fa p w , f/ t c ka w mh e n f; e n f; a v ; w dk; w u fv my gNy D/ USB port r Sm
o Hk; v dkY & a e Ny Da v / t & i fu parallel port a w Gw ke f; u a w mh w u , f t v ky f& Iy fc Jhw my J/ y & dk* & r f w p fc kc si f; p D
t w Gu f w p fc kp Dw y fa e & a o ; w , f/ ' ga Mu mi fha e & m v dkt y fc su fu p de fa c : r Iw p f& y f jz p fv mw , f/
a jz / u Re fa w mfv n f; v Hkjc HKa & ; p e p fa w Gu p dw ft a E Smi fht , Su fa y ; w m r Mu dKu fy gb l; / u Re fa w mfw dkY Armadillo
u a e registration r Sm key u dk t v dkt a v smu f x n fha y ; E kdi fw Jh y a & m* su fr sdK; v ky fa y ; E kdi fw , f/ End user
a w Gt w Gu f o u fo ma p w ma y gh/ ' gu v lt r sm; p kt w Gu f t q i fa jy w , f/
a jz / Online key validation u t v ky f& Iy fa p w , f/ t i fw me u f o Hk; z dkYv dkw Jht jy i f o Hk; p GJo la w Gu v n f;
& Iy fw , fv dkY jr i fMu w , f/ Web server u dk b , fa e Y a e Yp GJe JY 0 i fo Gm; w , fq dkw m b , fo lo dE dki fr Smv J/ v lr sm; p k
u v n f; t J' gu dk spyware v dkv dk x i fMu a o ; w , f/
a jz / v Hkjc HKa & ; p e p fu t v ky f& Iy fa p w m r a u mi f; b l; / ' ga y r , fh t v ky f& Iy fa p w Jh p e p fa w Gu y dkNy D; a u mi f; w , fv dkY
x i fw , f/ t c sde fu p u m; a jy my gv dr fhr , f/ o Hk; p GJo la w G' gu dkv u fc Hz dkYt q i fo i fhjz p fw Jht c sde fu s& i fa y gh/
( 1 3 ) u kr P Da w Gu a q mhz f0 Jv f security a w Ge JYy w fo u fv dkYt o dy n my dki f; t m; e n f; a e a o ; w , fv dkYx i fo v m; /
' gu a e mu fy dki f; r Sp Ofp m; & r Smy gq dkw Jht a w G; u dk u dki fp GJx m; Ny D; a w mha v /
a jz / t r Se fy J/ Microsoft v dk e n f; y n mb Dv l; Mu D; u dky JMu n fh/ c i fA sm; jr i fz l; w Jh a jr mu fr sm; p Gma o m OS install
p D' Dy Gm; a w Gu dky J p Of; p m; a w mh/ u Re fa w mfh t jr i fa w mh o lw dkY security r n Hhb l; / u kr P DMu D; a w GMu a w mh t J' gu dk
b , fa w mhr S r p Of; p m; c Jhw m? a e mu fNy D; u ke fu sp & dw f w p fc kv dk o a b mx m; w m/ Shareware o r m; a w GMu a w mh
' gu dk w u , fu dk w Ge f; t m; a y ; w m/ o lw dkY t o u fa o G; a Mu mu t Ge fv dki f; a y : u a e p u m; a jy m a & mi f; & w ma v /
w u , fv dkY r a & mi f; & a w mhb l; q dk& i f p D; y Gm; y su fr Smy J/ u kr P DMu D; a w Gu v n f; t c ka w mh o a b ma y gu fv my gNy D/
u Re fa w mfht v ky f& Si f Digital River u kr P Dq dk& i f t c k Digital Rights Management p e p fu dk y & dkr dk; & Si f;
v ky fa w mhsecurity u t " du a e & mu y g0 i fa e Ny D/
( 1 4 ) Developer a w G[ m a q mhz f0 Jv fz e fw D; r Ie JY v Hkjc HKa & ; p e p fw dkY t c sdK; n Da y gi f; p y fE dki fz dkY o lw dkYa q mhz f0 Jv fu dk
b , fv dk t u mt u G, fa w Gv ky f& r v Jq dkw m o dx m; z dkYv dko v m; / o lw dkY& JU resource a w Gb ma w Gjz p fw , f? API
call a w Gu b , fu kdredirect v ky fw , f? child process b ma Mu mi fhz e fw D; & w , fq dkw mr sdK; u dk o dz dkYv dko v m; /
t c e f; ( 4 5 ) Armadillo developer r sm; E Si fht i fw mA sL;
- 531 -
a jz / v dko v m; a r ; & i f r v dka v mu fy gb l; / ' ga y r , fh developer w p fa , mu ft a e e JY b ma w Gjz p fa e w , fq dkw mu dk
e m; v n fE dki fo a v mu ft x de m; v n fc si fw , f/ ' ga y r , fht J' gu bug a w Gjy i fz dkYa v mu fy J t o Hk; 0 i fw my g/
( 1 5 ) c i fA sm; t Mu dKu fq Hk; y & dk* & r fb mo mp u m; w p fc ku dk a jy mjy y gv m; / v Hkjc HKr I& Sdw Jhu k' fa w G z e fw D; E dki fr , fv dkYa & m
x i fo v m; /
a jz / u Re fa w mfo a b mu sw mu a w mh C y J/ ' gu v n f; u Re fa w mf E Sp fa y gi f; r sm; p Gm o Hk; v mv dkYy g/ v Hkjc HKr I
& Sdo v m; q dka w mh r & Sdy gb l; / a p s; u Gu fx Jr Sm C u dk disassemble v ky fE kdi fw Jh tool a w Gu w jc m; [ ma w G
x u fa w mi f r sm; a o ; w , f/ Assembly u w c sdKUv Sn fhu Gu fu a v ; a w G& , f? lower level u k' fa w Gu a w mh
cracker a w Gu dk y dkNy D; v G, fv G, fu lu l v Sn hfp m; E kdi fy gw , f/ ' ga Mu mi fh ' ga w Gu dky J t v Hkjc HKq Hk; v dkY a jy m& r , f/
a e mu fNy D; a w mhy & dk* & r fr mu v Hkjc HKr Iu dk r p Of; p m; b J a & ; o m; & i f b mo mp u m; u b mr Sr x l; b l; /
a jz / w p fu dk, fa & q Hk; jz w fc su fe JY o a b mu sw mu a w mh Assembly y J/ u Re fa w mfu a & ; v dku fo r Q t m; v Hk; u dk
x de f; c sKy fc si fw , f/ a e mu fNy D; fancy code flow a w Gu dk o Hk; Ny D; p e p fw u sjz p fa t mi f c u fc u fc Jc J a & ; E dki fw , f/
' gq dk v Hkjc HKw Jhu k' fq dkw m b mv J/ y & dk* & r fr m& JU t & n ft c si f; a y : r Sm r lw n fw , f/ b , fb mo mp u m; r q dk a o a o
c smc sm p e p fw u sa & ; x m; & i f v Hkjc HKw my J/
( 1 6 ) a y : jy Lv mjz p fw Jh a q mhz f0 Jv fa w Gu dk u mu G, fr I x y fa y gi f; x n fha y ; jc i f; [ m t u sdK; & Sdw , fv dkY x i fv m; /
' gr Sr [ kw f o lw dkY& JU a y : jy Lv mjz p fr Iu t u mt u G, fa w Gu dk c sdK; a z mu fc si fp & m a u mi f; a e r v m; / ' ga Mu mi fh
v Hkjc HKa & ; p e p fa w Gu u kr P Dt a o ; a v ; a w Gr Smy J y dkt a & ; Mu D; a e o v m; /
a jz / t u sdK; & Sdw , fv dkY x i fy gw , f/ w p fc gr St q i fhjr Si fhw i fjc i f; r v ky fc Jhw Jh y & dk* & r fw p fc k t w dku ft c dku fc H& w , f
q dkw Jh t jz p ft y su f[ m q dk; 0 g; y gw , f/ ' ga y r , fh jz p fE dki fa jc & Sm; w , f/ Version 1.0 r Sm t w dku ft c dku f c H& & i f
a e mu f version 2.0 Mu & i f v Hkjc HKa & ; p e p f a q mhz f0 Jv fa & m? r lv y & dk* & r fu dky g jy e fv n f jy i fq i fMu r Smy g/
a jz / Cracker u t c sde fu ke fc HNy D; w dku fc dku fz dkY Mu dK; p m; w , fq dk& i f c i fA sm; y & dk* & r f a y : jy Lv mjz p fw , fq dkw Jh
o a b ma y ghA sm/
a jz / a e mu fNy D; u kr P Dt a o ; a v ; a w Gr Smv n f; u s, fu s, fjy e fYjy e fY jz e fYjz L; a & mi f; c sa e w Jh y & dk* & r fa w G& Sd& i f
v Hkjc HKa & ; t w Gu f t p Dt r Ha w G& Sdo i fhw , f/ 0 i fa i Gq Hk; & HI; w m& , f e n f; y n m t c dk; c H& w ma w Gu q dki fa o ; a o ; a v ;
a w Gu dk jz Kw fy p fE dki fw , f/
( 1 7 ) a e mu fx y f b mr sm; x y fjz n hfc si fa o ; o v J/
a jz / u Re fa w mf p Of; p m; v dkY& o r Qu dk a jy mr , fa v /
Cracking q dki f& ma 0 g[ m& r sm;
- 532 -
Cr acking qdkif&ma0g[m&rsm;
ActiveMARK Trymedia o n f RealNetworks \ t p dw ft y dki f; w p fc kjz p fjy D; ActiveMark r Sm
Trymedia \ pack/protect v ky fo n fhe n f; y n mw p f& y fjz p fo n f/ Trygames r Sm Trymedia \ w p fp dw f
w p fy dki f; jz p fjy D; Trymedia \ * dr f; r sm; u dk download v ky fjc i f; u dp ? trial q dki f& mu dp E Si fh a & mi f; c sjc i f; u dp w dkUu dk
jy Kv ky fo n f/
alphanumer ic code Alphanumeric u k' fq dko n fr Sm p mv Hk; r sm; ? * P e f; r sm; a y gi f; p y fx m; jc i f; jz p fjy D;
i f; w dkUu dk u Ge fy sLw mu o m process v ky fE kdi fo n fh e m; r v n fE dki fa o my Hkp Hw p fc kt o Gi fjz i fh a & ; x m; jc i f; jz p fo n f/
e r le m alphanumeric u k' fw p fc kr Sm ASCII jz p fo n f/ x dkx u fy dkjy D; a jy m& v Qi f alphanumeric u k' fq dko n fr Sm
machine u k' fjz p fjy D; i f; w dkUu dk v Hk; 0 z w fr & E dki fa o m ASCII p mv Hk; t jz p f assemble v ky fjy D; a & ; x m; jc i f; jz p f
o n f/
API API [ lo n f OS u jz n fhp Gr f; a y ; E dki fa o m function r sm; t m; p kp n f; x m; jc i f; o mjz p fo n f/ Windows
y & dk* & r ft m; v Hk; o n f API unction r sm; u dk t o Hk; jy KMu o n f/ x dk function r sm; o n f Windows p e p f\ dll
z dki fr sm; jz p fa o m kernel? user? gdi? shell? advapi p o n fhz dki fr sm; x Jw Gi f & Sdo n f/ API u dk native API E Si fh
Win32 API [ l E Sp fr sdK; c GJx m; o n f/
API r edir ection API redirection [ lo n f packer^ protector t r sm; p ku IAT ( o kdUr [ kw f import
table) t m; ( w p fp dw fw p fa ' o o dkUr [ kw f v Hk; 0 ) z su fq D; y p fv dku fa o m v ky fa q mi fc su fw p fc kjz p fa o mfv n f; IAT
x Jw Gi f redirect t v ky fc H& a o m API t o D; o D; \ o u fq dki f& mu k' fE Si fhq dki fa o m pointer w p fc ku dk a & ; v dku fo n f/
q dkv dko n fr Sm packer o n f pack^ protect v ky fx m; a o my & dk* & r ft w Gu f system \ DLL r sm; x Jr S API \
address u dka y ; E dki f& e f o w dx m; & r n fjz p fo n f/ API redirection v ky fx m; o n fh y & dk* & r fa w mfa w mfr sm; r sm; o n f
anti-virus a q mhz f0 Jv fr sm; E Si fhjy e mw u fa v h& Sdo n f/
ar r ay y & dk* & r fa & ; o m; jc i f; w Gi f array o n f w ln Da o m a ' w mt r sdK; t p m; u dk p kp n f; a y ; jy D; array x Jw Gi f
y g0 i fo n fht & mr sm; u dk a c : , lo Hk; p GJv dkv Qi f index ( o dkU) element jz i fh a c : , lo Hk; p GJ& o n f/ Array r sm; o n f
y & dk* & r fa & ; o m; jc i f; w Gi f t c & mu sv So n f/
ASCII American Standard Code for Information Interchange \ t w dka u mu fjz p fjy D; p mv Hk; r sm; ?
* P e f; r sm; ? o a u Fw r sm; y g0 i fa o m t u & m 2 5 6 v Hk; & Sdo n f/ ASCII u dk 1 9 6 8 c kE Sp fw Gi f hardware E Si fh a q mhz f
0 Jv fr sm; Mu m; a ' w mr sm; t m; y dkUa q mi f& e ft w Gu f & n f& G, fjc i f; jz p fo n f/ ASCII u dk p H ASCII E Si fh x y fjz n fh
ASCII [ l t p kE Sp fc kc GJx m; o n f/
assembler Assembly b mo mp u m; jz i fh a & ; o m; x m; o n fhy & dk* & r fr sm; t m; exe y & dk* & r fz dki ft jz p f a jy mi f; v J
a y ; a o m y & dk* & r fjz p fo n f/
Assembly language Low-level y & kd* & r fb mo mp u m; w p fc kjz p fjy D; mnemonic u k' fr sm; u dk t o Hk; jy Ko n f/
Assembler u dkt o Hk; jy K machine b mo mp u m; t jz p f a jy mi f; E dki fo n f/ t o Hk; jy Ko n fh y & dkq u fq ma y : r lw n f
jy D; instruction r sm; u GJjy m; r I& Sdo n f/ Assembly b mo mp u m; u dk t o Hk; jy Kjc i f; \ t u sdK; a u s; Z l; u m; t v ky f
v ky fo n fhE Ie f; jr e fq e fv mjc i f; ? hardware E Si fhy & dk* & r fr mMu m; w dku f& dku fq u fo G, fE dki fjc i f; w dkUjz p fo n f/
BadBoy Trial version a q mhz f0 Jv fw p fc kw Gi f o Hk; p GJo lt m; 0 , f, l& e fz dt m; a y ; a o m message r sm; ? a Mu mfji m
r sm; / ( o dkU) Disassemble v ky fx m; a o m y & dk* & r fw p fc kw Gi f i f; w dkU& Sd& ma e & m/
base addr ess t y dki f; E Sp fc k& Sda o m r Sw fOmP f address w p fc k\ w p fp dw fw p fa ' o / i f; o n f r a jy mi f; v Jb J
& Sda e jy D; w Gu fc su fr n fh a ' w m byte w p fc k\ a e & mn Te f; r Sw fw p fc ku dk jz n fhp Gr f; a y ; o n f/ Base address w p fc k\
a e mu fw Gi f offset w e fz dk; w p fc ku y fv dku fjy D; t c su ft v u fr sm; \ w du sa o ma e & mu dk & SmE dki f& e ft w Gu f base w Gi f
i f; w e fz dk; u dk v ma y gi f; & o n f/ t a p my dki f; OS r sm; w Gi f t o Hk; jy Ko n f/
base r elocation .reloc section r Sm& Sda o m entry r sm; u dk base relocation [ ka c : o n f/ t b , fha Mu mi fh
q dka o mf i f; w dkUu dk t o Hk; jy Kr Io n f loaded image \ base address a y : r lw n f jz p fo n f/ Base relocation
o n f image x Jr Sw n fa e & mr sm; u dk p kp n f; x m; jc i f; jz p fjy D; i f; w dkUx J a y gi f; x n fh& e f w e fz dk; w p fc k v dky gv dr fhr n f/
Base relocation entry r sm; t m; chunk w GJr sm; t a e jz i fh package v ky fx m; jc i f; jz p fo n f/ Chunk t o D; o D;
o n f image x Jr S4KB page w p fc kt w Gu f relocation [ k a z mfjy jc i f; jz p fo n f/
binar y u de f; * P e f; p e p fr sm; r S 0 E Si fh 1 u dko m a z mfjy E dki fa o m E Sp fv Dp e p f/ x dk* P e f; r sm; u dk logical w e fz dk;
jz p fa o m TRUE ( o kdU) FALSE t a e jz i fh a z mfjy E dki fo n f/ E Sp fv D* P e f; r sm; o n f v lo m; r sm; e m; v n fE dki f& e f
c u fc Ja o ma Mu mi fh8 v Dp e p fE Si fh1 6 v Dp e p fu dk t o Hk; r sm; Mu o n f/
bind
bit Binary digit \ t w dka u mu f/ u Ge fy sLw mu u dki fw G, fa o mt c su ft v u fr sm; w Gi f t a o ; q Hk; , le p f/
Bitw p fc ko n f E Sp fv D* P e f; w p fc kr S 1 ( o dkU) 0 u dko m a z mfjy E dki fo n f/ 8 bits o n f p mv Hk; w p fv Hk; E Si fhn Da o m
a Mu mi fht u & m? q , fv D* P e f; E Si fht jc m; p mv Hk; r sm; u dk a z mfjy E dki fa y o n f/
br eakpoint y & kd* & r ft v ky fv ky fjc i f; u dk & kw fw & u f & y fw e fUE dki f& e fE Si fh x dkt c sde fw Gi f y & dk* & r fr n fo dkUv ky fa q mi f
a e o n fu dk Mu n fh& Ip p fa q ; E dki f& e f y & dk* & r fw Gi f; o w fr Sw fx m; o n hf a e & mw p fc k/ Breakpoint r sm; u dk debugger
Cracking q dki f& ma 0 g[ m& r sm;
- 533 -
r sm; t w Gi f; o w fr Sw fMu jy D; r sm; a o mt m; jz i fh jump r sm; ? call r sm; w Gi f t o Hk; jy KMu o n f/ Breakpoint u dk
a q mhz f0 Jv f breakpoint? hardware breakpoint E Si fhmemory breakpoint [ l 3 r sdK; c GJjc m; E dki fo n f/
buffer over flow t c su ft v u fr sm; u dk a jy mi f; a & TY& e ft w Gu f , m, Dz , fx m; a o m r Sw fOmP fa e & mr sm; w Gi f
r v dkv m; t y fa o mt jz p fa Mu mi fh r Sw fOmP fw p fc kv Hk; jy n fhv QHo Gm; jc i f; / y & dk* & r fr mr sm; y & dk* & r fa & ; & mw Gi f r Sm; , Gi f;
p Gm a & ; o m; r Ia Mu mi fha o mfv n f; a u mi f; ? [ u fu mr sm; u OS \ p Gr f; a q mi f& n fu dk u sq i f; a p v dka o ma Mu mi fh w dku f
c dku fa o mt c gw Gi fv n f; a u mi f; Mu HKa w GU& o n f/
bypass Crack v ky f& mw Gi f r v dkv m; t y fa o m routine r sm; ? messagebox r sm; u dk a u smfv Tm; jc i f; ? v Sn fhp m;
jc i f; /
cave y & dk* & r fw p fc kw Gi f u k' f^ a ' w mt jz p f t o Hk; r jy Kb J v Gw fa e a o ma e & mr sm; / i f; w dkUu dk u k' fr sm; x n fho Gi f;
& e ft w Gu f t o Hk; jy Ko n f/
cell t c su ft v u fu dk o dr f; q n f; x m; o n fh unit w p fc k/ Oy r m binary cell w p fc k\ unit w p fc ko n f 1 bit
E Si fhy w fo u fa o mt c su ft v u fr sm; u dk o dr f; q n f; E dki fo n f/
cell addr ess t c su ft v u fu dk o dr f; q n f; x m; o n fhcell & Sd& m address /
char acter p mv Hk; w p fv Hk; a o mfv n f; a u mi f; ? * P e f; w p fc ka o mfv n f; a u mi f; ? t jc m; o a u Fw w p fc kc ka o mfv n f;
a u mi f; t u & mw p fc ku dk u dk, fp m; jy Ko n f/ y & dk* & r fb mo mp u m; w Gi fr l character w p fc k ( o dkU) w p fc kx u fy dka o m
identifier w p fc ku dk string [ ka c : o n f/
checksum Image \ w Gu fc su fx m; a o mw e fz dk; / ( a ' w mr sm; u dk o dr f; q n f; & mw Gi f t r Sm; r sm; a w GUMu HKjc i f; & Sd
^ r & Sd p p fa q ; & e f t o Hk; jy Ka o m w Gu fc su fx m; o n fhw e fz dk; / a ' w mr sm; u dk o dr f; q n f; jy D; a o mf i f; e n f; v r f; u dky i f
t o Hk; jy K checksum u dkw Gu fc su fy go n f/ checksum E Sp fc k r w ln Dc Jha o mf error u dkjy a ' w mu dk a e mu f
w p fMu dr f jy e fv n fo dr f; q n f; y go n f/ Checksum r sm; o n f error w dki f; u dk r p p fa q ; E dki fy g/ Checksum
w dkUo n f error jz p fa e a o ma ' w mr sm; u dk r jy i fq i fa y ; E dki fy g/ ) Checksum r sm; o n f kernel- mode driver
r sm; E Si fh t c sdKUa o m system DLL r sm; t w Gu f v dkt y fo n f/ Checksum w e fz dk; r sm; u dk exe/dll z dki fx Jw Gi fy i f
o dr f; q n f; o n f/ exe/dll z dki fu dk patch v ky fc Jhv Qi f HEX w e fz dk; r sm; a jy mi f; o Gm; jy D; checksum w e fz dk; v n f;
a jy mi f; o Gm; w w fo n f/
child pr ocess Process w p fc ka t mu fw Gi f t v ky fv ky fa o m a e mu f process w p fc k/ t u , f parent
process u dk y dw fc Jhv Qi f child process o n fv n f; t v dkt a v smu f y dw fo Gm; r n fjz p fo n f/ Armadillo w Gi f
child process o n f r dc i f process t m; debug v ky fc Hx m; & jc i f; & Sd? r & Sdu dk t jr Jp p fa q ; a v h& Sdo n f/
class OOP b mo mp u m; w dki f; \ t a jc c H, le p f/ Class r sm; o n f object r sm; u dkz e fw D; & mw Gi f t o Hk; jy Ko n fh
template r sm; jz p fMu o n f/ Class r sm; u dk a ' w mt r sdK; t p m; t o p fz e fw D; & e f t o Hk; jy KE dki fo n f/ y & dk* & r fa & ; o m;
jc i f; t m; v Hk; u dk class w p fc kt w Gi f; w Gi f a & ; o m; E dki fo n f/ Class r sm; w Gi f member varialble r sm; E Si fh member
method r sm; y g0 i fo n f/
CLR Common Language Runtime \ t w dka u mu f/ .net y & dk* & r fr sm; t v ky fv ky f& e ft w Gu f v dkt y fa o m
virtual machine/
code segment y & dk* & r f instruction r sm; y g& Sda o m memory segment w p fc k/ y & dk* & r f t v ky fv ky fa o mt c g
code segment u dk memory segment t jz p f r Sw fOmP fa y : u l; w i fo n f/ y i fr y & dk* & r f segment u kd
r Sw fOmP fw Gi fx m; & Sdjy D; auxiliary segment r sm; u dkr l v dkt y fr So m u l; w i fo n f/
comment y & dk* & r fE Si fh o u fq dki fa o m t c su ft v u fr sm; u dk r Sw fc su fa y ; jc i f; / Compiler u x dkr Sw fc su fr sm;
u dk compile v ky fjc i f; r & Sdy g/
compiler Syntactic E Si fh semantic p n f; r sOf; r sm; u dk v dku fe mjy D; high-level b mo mp u m; r sm; jz i fha & ; o m;
x m; a o m source u k' fr sm; u dk y & dk* & r f execution r v ky fr Dobject u k' ft x da jy mi f; v Ja y ; E dki fa o m y & dk* & r f/
conditional br eakpoint o w fr Sw fx m; a o m t a jc t a e E Si fh u dku fn Dv Qi f y & dk* & r fu dk & y fw e fUa p E dki fo n fh
t q i fhjr i fha o m breakpoint/
conditional jump Low-level y & dk* & r fb mo mp u m; r sm; w Gi f o w fr Sw fx m; a o ma e & mo dkUa & mu f& e f t a jc
t a e w p f& y fu dk E dIi f; , SOfjy D; n D^ r n Dq Hk; jz w fa o m jump instruction/ Oy r m JE? JNZ/
constant y & dk* & r ft v ky fv ky fa e p Of w e fz dk; r a jy mi f; v Ja o m identifier/
CopyMem2 Armadillo \ anti-dumping e n f; v r f; w p fc kjz p fNy D; cracker r sm; t m; memory r S
y & dk* & r fu dk dump r v ky fE dki fa t mi f w m; q D; a y ; o n f/ CopyMemII u dk child process t m; debug v ky f& e f
t w Gu f t o Hk; jy KE dki fNy D; code section w Gi f father process u PAGE_GUARD u dko w fr Sw fNy D; target
u v kdt y fa o m u k' ft p dw ft y dki f; t c sdKUu dk decrypt v ky fo n f/ CopyMemII o n f father process \ t * Fg& y f
w p fc kjz p fNy D; 1000h bytes p m& Sda o m child process \ code section block t m; decrypt v ky fo n f/
x dku k' fr sm; t m; t v ky fv ky fNy D; a e mu f jy e f encrypt v ky fo n f/ q dkv dko n fr Sm father process o n f page t m;
t r Sm; t , Gi f; w p fp Hkw p f& m & Sd?r & Sd a p mi fhMu n fha e Ny D; a y smu fq Hk; a e o n fh block t m; decrypt v ky fr dc Jhv Qi f
o lUa e & mw Gi f t p m; x dk; y p fv dku fo n f/ DLL E Si fh OCX z dki fr sm; u dk protect v ky f& mw Gi fr l CopyMem2
protection u dk t o Hk; jy K r & y g/ z dki ft & G, ft p m; Mu D; r m; a o m y & dk* & r fr sm; u dk protect v ky f& mw Gi fv n f;
Cracking q dki f& ma 0 g[ m& r sm;
- 534 -
CopyMem2 u dk t o Hk; r jy Ko i fhy g/ t u , f Visual Basic y & dk* & r fr sm; w Gi f CopyMem2 u dk t o Hk; jy Kc Jha o mf
Windows Vista E Si fht x u f Windows r sm; w Gi fo m t v ky fv ky fy gv dr fhr n f/
cr ack Trial version a q mhz f0 Jv fr Su e fUo w fc su fr sm; u dk z , f& Sm; jc i f; ? u k' fr sm; x n fho Gi f; jc i f; /
cr acker a q mhz f0 Jv fr sm; \ v dki fp i fo u fw r f; u dk z , f& Sm; o l/
cr acking Crack v ky fjc i f; ? ( o dkU) crack v ky fjc i f; y n m/
Cr ackMe v lo p fw e f; cracker r sm; t w Gu f cracking y n mu dk o i fMu m; y dkUc s& e f& n f& G, f a & ; o m; x m; a o m
e r le my & dk* & r f/ ( o dkU) t q i fhjr i fh cracker r sm; \ t & n ft a o G; u dk p r f; o y f& e f c u fc Je u fe Jp Gm a & ; o m; x m; a o m^
pack v ky fx m; a o m y & dk* & r f/
CRC Cyclic Redundancy Check \ t w dka u mu f/ u k' fr sm; jy Kjy i fx m; jc i f; & Sd^ r & Sd? a q mhz f0 Jv f
breakpoint r sm; o w fr Sw fx m; jc i f; & Sd^ r & Sdu kdp p fa q ; a o me n f; v r f; / Cracker r sm; u u k' fr sm; u dkjy Kjy i fo n fht c g
CRC w e fz dk; a jy mi f; v Jo Gm; o n fht w Gu f anti-debugging e n f; v r f; r sm; w Gi f w Gi fu s, fp Gmt o Hk; jy Kv su f& Sdo n f/
cr ypto t c su ft v u fr sm; u dk a jy mi f; v J& e f u k' fr sm; u dk t o Hk; jy Kjc i f; / z w f& Io lu i f; w dkUu dk z w f& IE dki f& e ft w Gu f
key w p fc ku dk t o Hk; jy K& r n fjz p fo n f/ Oy r m Adobe Acrobat \ File-open password/
CS u k' fr sm; u dk o dr f; q n f; x m; a o m r Sw fOmP ft u e fU/ Code segment \ t w dka u mu f/
data segment y & dk* & r fu v dkt y fa o mt c g a c : o Hk; a o m t c su ft v u fr sm; u dk o dr f; q n f; x m; a o m r Sw fOmP f
t u e fU/
debug y & dk* & r fw Gi f; t r Sm; r sm; & Sd^ r & Sd p Hkp r f; o n f/ Cracker r sm; u r l u k' fr sm; u dk jy i fq i f& e ft w Gu f? crack
v ky f& e ft w Gu f debug v ky fMu jc i f; jz p fo n f/
debug blocker r dr dy & dk* & r fu dk debug v ky fa e o v m; q dko n fu dk p p fa q ; a o m v ky fa q mi fc su fw p fc kjz p fNy D;
y & dk* & r fu dk debug v ky fr c H& a t mi f w m; q D; a y ; o n f/ Armadillo jz i fh protect v ky fx m; o n fhh y & dk* & r fr sm;
t v ky fv ky fv Qi f parent process/child process [ l process E Sp fc k t v ky fv ky fo n f/ x dk process E Sp fc ko n f
t c si f; c si f; debug v ky fc Ha e & jc i f; & Sd? r & Sdu dk t jr J p p fa q ; v Qu f& Sdo n f/
debugge Parent process (debugger) \ debug v ky fjc i f; u dkc H& a o m child process /
debugger a ' w mr sm; u dk p p fa q ; E dki f& e ft w Gu f? variable w e fz dk; r sm; a jy mi f; v Jo Gm; jc i f; u dk a p mi fhMu n fhp p fa q ;
E dki f& e ft w Gu f y & dk* & r fr mt m; y & dk* & r ft w Gi f; w p fq i fhc si f; Mu n fh& IE dki f& e f ' DZ dki f; jy Kx m; a o m y & dk* & r f/ Cracker
r sm; t w Gu f r & Sdr jz p fv dkt y fa o m tool/
debug object
decimal q , fv Do Hk; * P e f; p e p f/
decompiler Assembly u k' f ( o dkU) machine u k' fr Shigh-level source u k' ft jz p f a jy mi f; v Ja y ; E dki fa o m
y & dk* & r f/ jy e mu m; t c sdKU Assembly b mo mp u m; r sm; w Gi f high-level source u k' fE Si fh o u fq dki fa o mu k' f
r & Sdjc i f; jz p fo n f/
decompr ession stub Pack v ky fx m; a o m y & dk* & r fr sm; w Gi f pack v ky fx m; a o m^ compress v ky fx m; a o m
u k' fu dk r l& i f; u k' ft jz p f jy e fa jy mi f; a y ; a o mjz p fp Of ( o dkU) routine/
decr yption Encrypt v ky fx m; a o m a ' w mr sm; u kdr lv u k' ft o Gi fo dkU jy e fa jy mi f; jc i f; /
delay impor t table Visual C++ u DELAYIMP.H w Gi f t e u fz Gi fhx m; o n fh ClmgDelayDescr
z GJUp n f; y Hk\ array w p fc kjz p a o m Delayload information u dk n Te fjy o n f/ i f; w dkUx Jw Gi fa w GU& a o m API u dk
y x r t Mu dr f a c : , lr o Hk; r c si f; Delayloaded DLL r sm; t m; u l; w i fjc i f; r & Sdy g/ Windows w Gi f delay loading
DLL E Si fhy w fo u fjy D; v Hk; v Hk; v sm; v sm; , HkMu n f& jc i f; r & Sdy g/
destination z dki fw p fc ku dk ( o dkU) w e fz dk; w p fc ku dk u l; r n fh? a & TUr n fha e & m/
disassembler Machine u k' fu dk Assembly source u k' ft jz p fa jy mi f; v Ja y ; a o m y & dk* & r f/ t c sdKU
debugger r sm; w Gi f built-in disassembler y gv ma v h& Sdjy D; exe y & dk* & r fu dk v lo m; w dkU z w f& IE dki fa o m
Assembly b mo mp u m; t jz p f Mu n fh & a p o n f/
diver sion code Cracker r sm; u dk v Sn fhp m; & e ft w Gu f x n hfo Gi f; x m; a o m y & dk* & r fE Si fhr q dki fo n fhu k' f/
DLL Dynamic Link Library \ t w dka u mu f/ Function r sm; E Si fh a ' w mr sm; y g0 i fa o m module/ DLL
w p fc ku dk exe z dki fr Sa o mfv n f; a u mi f; ? t jc m; DLL z dki fw p fc kr Sa o mfv n f; a u mi f; a c : , lo Hk; p GJo n f/ DLL
w p fc ku dk r Sw fOmP fa y : u l; w i fc sde fw Gi f a c : , lo Hk; o n fh process \ address a e & mt jz p f a e & mc sx m; jc i f; c H&
o n f/ DLL z dki fr sm; u dk v dkt y fr So m a c : , lo Hk; p GJo n fht w Gu f r Sw fOmP fw Gi f a e & mv Gw f y dkr dk& & Sda p o n f/ DLL
z dki fw p fc ku dk t jc m; y & dk* & r fr sm; u v n f; t o Hk; jy KE dki fy go n f/
dongle Hardware key w Gi fMu n fhy g/
DOS header PE z dki fr sm; o n f DOS header E Si fhp a v h& Sdjy D; z dki f\ y x r q Hk; 64 bytes t jz p fa w GU& o n f/
y & dk* & r fo n f DOS r Sp w i ft v ky fv ky fo n f/ x dkUa Mu mi fh DOS u r Se fu e fa o m executable z dki fjz p fa Mu mi f;
t o dt r Sw fjy Kr So m header a e mu w Gi f o dr f; q n f; x m; a o m DOS stub u dk t v ky fv ky fr n fjz p fo n f/ DOS
header o n f structure w p fc kjz p fjy D; windows.inc ( o dkU) winnt.h z dki fr sm; w Gi f i f; u dk t " dy m, fz Gi fhq dkx m;
o n f/ DOS header structure w Gi f member t a & t w Gu f 19 c k& Sdo n f/
Cracking q dki f& ma 0 g[ m& r sm;
- 535 -
DOS stub DOS stub o n f y Hkr Se ft m; jz i fh 'This program must be run under Microsoft Windows'
q dka o mp mo m; u dk x kw fa y ; a v h& Sdjy D; i f; u dk, fw dki fy i f DOS y & dk* & r fjz p fE dki fo n f/ Windows application r sm; u dk
build v ky fc sde fw Gi f linker u exe z dki fx Jo dkU winstub.exe [ ka c : a o m stub y & dk* & r fu dk link c sdw fa y ; v dku fjc i f;
jz p fo n f/
dotNet Reactor .net y & dk* & r fr sm; u dk crack v ky fjc i f; r Su mu G, fE dki f& e f protect v ky fa y ; a o m protector/
double ' r u de f; r sm; u dk a Mu n m& e ft w Gu f t o Hk; jy Ka o m keyword/ 1.7 x 10
-308
Pr S 1.1 x 10P
+4932
Px d
w e fz dk; r sm; u dk u dki fw G, fE dki fo n f/
dr iver a q mz hf0 Jv f? hardware r sm; u dk OS E Si fhc sdw fq u f& mw Gi f r & Sdr jz p fv dkt y fa o m PE z dki fr sm; /
DS t c su ft v u fr sm; u dk o dr f; q n f; x m; a o m r Sw fOmP ft u e fU/ Data segment \ t w dka u mu f/
dump r Sw fOmP fx Jr Sdecompress v ky fx m; a o mz dki fu dk disk a y : o dkU o dr f; q n f; jc i f; /
EAX o c sFmq dki f& mu dp r sm; E Si fhstring r sm; u dk o dr f; q n f; & e fo Hk; a o m register/
EBP Stack u dp r sm; a q mi f& Gu f& e f stack pointer E Si fhw GJo kH; o n f/ Base pointer \ t w dka u mu f/
EBX Stack r sm; E Si fhc sdw fq u f& mw Gi f o Hk; o n fhregister /
ECX * P e f; r sm; a y gi f; & mE Si fhlooping r sm; w Gi f o Hk; o n fhregister/
EDI String/array \ destination u dk o w fr Sw f& mw Gi ft o Hk; jy Ko n fh register/ Destination index \
t w dka u mu f/
EDX r sm; a o mt m; jz i fho c sFmp m; v ' fr St <u i f; u dk o dr f; q n f; o n fhregister/
EIP a e mu f instruction \ address u dk o dr f; x m; a y ; o n fhregister/ EIP w e fz dk; u dk a jy mi f; v J r & y g/
emulator
encode Cracker r sm; \ debug v ky fjc i f; r Su mu G, fE dki f& e f r l& i f; u k' fu dk t o Gi fa jy mi f; v Jo n f/ ( o dkU)
z dki ft & G, ft p m; u dk a o ; i , fa p & e f u k' fu dkc sHKUo n f/
endian r Sw fOmP fx Jw Gi f hex w e fz dk; r sm; u dk a jy mi f; jy e fp Djc i f; / n mz u ft u sq Hk; p mv Hk; o n f significant t jz p f
q Hk; p mv Hk; jz p fo n f/ Oy r m 72 5E 7A 25 w e fz dk; u dk r Sw fOmP fw Gi f; w Gi f 25 7A 5E 72 t jz p f a w GU& y go n f/
entr y point y & dk* & r fw Gi f; & Sd execution p w i fr n fha e & mw p fc k/ y & dk* & r fp w i fz w f& I t v ky fv ky fr n fh y x r q Hk;
instruction & Sd& m virtual address/
entr ypoint Method .net application p w i fc sde fr Sm a c : , lo Hk; o n fh y x r q Hk; Method jz p fjy D; ? Method
\ t a & ; y gy Hkr Sm y & dk* & r f\ v ky fa q mi fc su fr sm; u dk y & dk* & r fp w i fo n fht c sde fr Sp jy D; register v ky fo n fh routine
& Sd& ma & mu fo n ft x da jc & mc HE dki fjc i f; jz p fo n f/
enxor XOR instruction u dkt o Hk; jy K encrypt v ky fjc i f; /
ES A GD' D, dku dp & y fr sm; t w Gu f t o Hk; r sm; o n f/ Extra segment \ t w dka u mu f/
ESI String/array \ source u dk o w fr Sw f& mw Gi fo Hk; o n f/ Source index \ t w dka u mu f/
ESP Stack r Sw du sa o m a e & mw p fc ku dk n Te fjy o n f/ Stack pointer \ t w dka u mu f/
exception
exception handler
exe r n fo n fhz dki ft u lt n Dr Sr v dkb J o D; o e fU& y fw n fE dki fa o m y & dk* & r f/
EXE Passwor d 2004 Salfeld computer r Sx kw fv ky fjy D; exe z dki fr sm; u dk o lw y g; r z Gi fha p v dka o mt c g
password t o Hk; jy K u mu G, fE dki fa o my & dk* & r f/ Password u dk exe t w Gi f; w Gi fy i f o dr f; q n f; jy D; v dkt y fr So m
decrypt jy e fv ky fy go n f/
executable t v ky fv ky fE dki fa o m y & dk* & r f/ Oy r m - file0.bat? file1.exe? or file2.com/
exploit OS ( o dkU) a q mhz f0 Jv fw p fc kc k\ v Hkjc HKa & ; q dki f& mt m; e n f; c su fu dk & Sma z Gjy D; t c Gi fha u mi f; , lo n f/
file alignment z dki fx Jw Gi f section r sm; u dk alignment c sx m; r I/ field x Jr Sw e fz dk; o n f 512 (200h)
jz p fv Qi f section w dki f; o n f 512bytes \ a jr Smu fa z mfu de f; * P e f; r sm; jz i fh p w i f& r n f/ t u , f y x r q Hk;
section o n f offset 200h & Sdjy D; i f; \ t & G, ft p m; o n f 10bytes o m& Sdc Jhv Qi fy i f a e mu f section o n f
400h w Gi fp w i fr n fjz p fo n f/ 512 e JU 1024 Mu m; r Sv Gw fa e a o m offset a e & mr sm; u dkr l t o Hk; jy Kr n f r [ kw fa y /
Finger Pr int CPU ID? BIOS ID? Hard disk? Motherboard ID p o n fw dkYu dk z w f& Ijy D; hardware ID
t jz p f jy e fv n fw Gu fc su fa y ; o n fhregistration e n f; v r f; /
Fish Packer UPX? UPack u Jho dkU z dki f\ t & G, ft p m; u dk t a o ; i , fq Hk; jz p fa t mi f compress v ky fa y ; a o m
packer jz p fjy D; unpack v ky f& mw Gi f t e n f; i , fc u fc Jr I& Sdy go n f/
flag t a jc t a e E Sp fc kt e u fr Sw p fc ku dk o w fr Sw fo n fhregister/ Zero flag o n f w e fz dk; E Sp fc ku dk E dIi f; , SOfa o m
t c g n Dc Jhv Qi f flag w e fz dk; u dk 1 [ ko w fr Sw fy go n f/ Carry flag? parity flag? auxiliary flag? zero flag?
sign flag p o n fjz i fhflag r sm; p Gm& Sdy go n f/
flat memor y Windows OS r sm; w Gi f t o Hk; jy Ko n f/ Memory segment \ t & G, ft p m; o n f 4GB & Sd
o n f/
float ' r u de f; r sm; u dk a Mu n m& e ft w Gu f t o Hk; jy Ka o m keyword/ 3.4 x 10P
-38
P r S1.7 x 10P
+38
P x d w e fz dk;
r sm; u dk u dki fw G, fE dki fo n f/
Cracking q dki f& ma 0 g[ m& r sm;
- 536 -
fr eewar e t i fw me u fw Gi f t c r Jha y ; a o m y & dk* & r f/ Freeware a q mhz f0 Jv fr sm; w Gi f register v ky fp & mr v dky g/
FS t a x Ga x Go Hk; segment/ 80286 E Si fht x u f y & dkq u fq mr sm; w Gi f t o Hk; jy Ko n f/
FSG Fast Small Good \ t w dka u mu f/ exe z dki fr sm; u dk compress v ky fa y ; a o m packer y & dk* & r f/
full ver sion r n fo n fhu e fUo w fc su fr Sr & Sda o m? a q mhz f0 Jv f\ p Gr f; a q mi fE dki fr It m; v Hk; u dk t o Hk; jy KE dki fa o m
version/
function o w fr Sw fx m; a o mt v ky fu dk v ky fa q mi fE dki f& e f instruction r sm; u dkp kp n f; x m; a o m? statement
r sm; u dkp kp n f; x m; a o m y & dk* & r f\ routine w p fc k/ u dk E Si fh [ kE Sp fr sdK; c GJE dki fo n f/ API? routine? subroutine?
call r sm; [ kv n f; a c : o n f/
GoodBoy 0 , f, lo n fht w Gu fa u s; Z l; w i fa Mu mi f; ? register v ky fjc i f; a t mi fjr i fa Mu mi f; p o n fh messagebox?
dialogbox r sm; E Si fh i f; w dkUu dka c : o Hk; o n fhroutine r sm; ? API r sm; /
GS t a x Ga x Go Hk; segment/ 80386 E Si fht x u f y & dkq u fq mr sm; w Gi f t o Hk; jy Ko n f/
guar d page
handle Pointer w p fc k\ pointer/ q dkv dko n fr Sm t jc m; variable w p fc k\ address y g0 i fa o m variable
w p fc k/ i f; w Gi f v dkc si fa o m object \ address y g0 i fo n f/ OS w p fc kw Gi f pointer r sm; u a jy mi f; v G, fa o m
block w p fc ku dk n Te f; a e p Ofw Gi f handle u r Sw fOmP f\ r a jy mi f; v JE dki fa o ma e & mw Gi f o dr f; x m; o n fh pointer
w p fc ku dk n Te f; o n f/ t u , f y & dk* & r fr sm; o n f handle r So mp w i fc Jhv Qi f i f; w dkUu block u dk& , lc sde fw dki f; w Gi f
OS r Sy & dk* & r fr sm; t m; x dc dku fr I r & Sda p b J r Sw fOmP fp Dr Hc e fUc GJr Ir sm; u dk a q mi f& Gu fE dki fr n fjz p fo n f/
har dwar e br eakpoint o mr e f breakpoint r sm; o n f u k' fr sm; a jy mi f; v Jo Gm; a o mt c g breakpoint
y su fo Gm; a v h& Sdy go n f/ o w fr Sw fx m; o n hfa e & m& Sd u k' fu dk a c : , lo Hk; jc i f; & Sd^ r & Sd a p mi fhMu n fhv dka o mt c gw Gi fv n f;
a u mi f; ? dump window (data window) r Sa ' w mr sm; u dk a & ; jc i f; ? z w fjc i f; & Sd^ r & Sdu dk a p mi fhMu n fhv dka o mt c g
w Gi fv n f; a u mi f; hardware breakpoint u dkt o Hk; jy Ky go n f/
har dwar e key a q mhz f0 Jv f( o dkU) u Ge fy sLw mu dk w & m; r 0 i fo Hk; p GJjc i f; r Su mu G, f& e f t o Hk; jy Ka o m printer port
connector u Jho kdUa o m device/ Dongle [ kv n f; a c : o n f/
HASP key Aladdin Knowledge Systems r Sx kw fv ky fo n fhdongle key/
heap flag
hexadecimal * P e f; r sm; u dk a z mfjy & e ft w Gu f t o Hk; jy Ko n fh 1 6 v Dp e p f/ p e p fw Gi f q , fv Dp e p f* P e f; r sm;
jz p fa o m 0-15 u dka z mfjy & e ft w Gu f 0-9? A-F w dkUy g0 i fo n f/ 1 6 v Dp e p f * P e f; w p fv Hk; o n f 4 bits E Si fh n Dr Q
o n f/ Oy r m E Sp fv Dp e p f* P e f; jz p fa o m 0101 0011 o n f 1 6 v Dp e p fw Gi f 53 E Si hfw ln Do n f/ E Sp fv Dp e p fjz i fh
a z mfjy jc i f; o n f z w f& I& c u fc Jo n fht w Gu f 1 6 v Dp e p fjz p fa o m hexadecimal p e p fu dk x Gi fMu jc i f; jz p fo n f/ Intel
x kw f CPU a w G\ mnemonic r Smy ga o m opcode r sm; E Si fh shellcode r sm; u dk HEX u k' fr sm; E Si fh a z mfjy Mu
o n f/
hook y & dk* & r fr mr S debug v ky f& mw Gi f^ v ky fa q mi fc su fr sm; u dkt q i fhjr Si fh& mw Gi f t jc m; routine r sm; E Si fhc sdw f
q u f& e f? routine r sm; x n fho Gi f; & e f routine^ y & dk* & r fw p fc kw Gi f; & Sda e & mw p fc k/
IAT Import Address Table \ t w dka u mu f/ Win32 exe z dki fjz p fo n fh application w dki f; w Gi f IAT & Sdjy D;
application w p fc ku Windows \ API function w p fc ku dka c : o Hk; o n fht c gw Gi f IAT t m; lookup table
t jz p ft o Hk; jy Ko n f/ x dkUa Mu mi fhy & dk* & r ft v ky fr v ky fc i f y & dk* & r fu a c : o Hk; & e ft w Gu f? IAT w p fc ku dk w n fa q mu f
& e ft w Gu f Windows loader o n f API t o D; o D; \ address t o D; o D; u dk& Sm& r n fjz p fo n f/ y & dk* & r ft v ky f
v ky fa e o n fht c sde fw Gi f API w p fc ku dk a c : o Hk; v dkv Qi f IAT x Jw Gi fMu n fhjy D; DLL x Jo Gm; & e fv dka o m address u dk
c su fc si f; & Sma z Ga y o n f/ Unpack v ky fx mo n fhz dki fr sm; w Gi f packer/protector r sm; u IAT u dk z su fx m; o n fh
t w Gu f IAT u dk jy e fv n fw n fa q mu f& e fv dko n f/
IDA Interactive DisAssembler \ t w dka u mu fjz p fjy D; DOS^ Windows^ Unix^ Macintosh^ Java^
.Net^ Console y & dk* & r fr sm; t jy i f t jc m; OS r sm; w Gi fa & ; o m; x m; w Jh y & dk* & r fr sm; u kdy g debug v ky fa y ; E dki fa o m
t a u mi f; q Hk; a o m disassembler w p fc kjz p fo n f/
IL .net y & dk* & r fr sm; u kd compile v ky f& mw Gi f machine u k' ft jz p f w dku f& dku f compile v ky fjc i f; r [ kw fb J IL
[ ka c : a o m Intemediate Language t jz p f compile v ky fv dku fjc i f; jz p fo n f/ IL & JUt " du t m; o mc su fr Sm
compile v ky fx m; o n fhy & dk* & r fr sm; w Gi f identifier (class name? function name? variable name) r sm;
r y su fr , Gi f; y Jw n f& Sda e jc i f; jz p fo n f/
imagebase PE z dki fr sm; t w Gu f preferred load address jz p fo n f/ Imagebase w e fz dk; o n f 400000h
jz p fv Qi f PE loader u 400000h r Sp w i fa o m virtual address a e & mw Gi f z dki fu dk u l; w i f& e f Mu dK; p m; a y
v dr fhr n f/ exe y & dk* & r fr sm; w Gi f imagebase w e fz dk; o n f 400000h jz p fjy D; ( Visual C++ DLL method jz i fh
compile v ky fx m; a o m Windows OS \ y & dk* & r fz dki fr sm; r St y ) dll z dki fr sm; w Gi fr l 1000000h jz p fo n f/
immediate value Assembly b mo mp u m; instruction w p fc k v ky fa q mi fc sde fw Gi f t o Hk; jy Ka o m u de f; a o
w e fz dk; / Instruction x J& Sdaddress w p fc ku point v ky fjc i f; x u f instruction x Jw Gi f u dk, fw dki fy g0 i fo n f/
Cracking q dki f& ma 0 g[ m& r sm;
- 537 -
Impor t Table Elimination Dump r v ky fE dki fa t mi f w m; q D; o n fh a e mu fx y f e n f; v r f; w p fc k/ y & dk* & r f\
import table u dk z , f& Sm; z su fq D; v dku fo n fht w Gu f import r sm; u dk jy e fv n fw n fa q mu f& mw Gi f t c u fa w GYa p
r n f jz p fy go n f/
index r egister Index register r sm; u dk i f; w dkU\ r lv w e fz dk; r a jy mi f; v Jo a & GU t a x Ga x Go Hk; register r sm;
t jz p f ( EIP r Sw y g; ) t o Hk; jy KE dki fo n f/ Index register [ ka c : a 0 : o n fht a Mu mi f; r Sm i f; w dkUo n f r Mu mc P
q dko v dk r Sw fOmP f\ address u dk o dr f; q n f; a v h& Sd jz p fo n f/ t c sdKU opcode ( movb, scasb,..) r sm; o n f
i f; w dkUu dk t o Hk; jy KMu o n f/
inline patching t x l; o jz i fhpack/protect v ky fx m; a o mz dki fr sm; w Gi f z dki fu dk unpack r v ky fa w mhb J u k' fjy i f
jc i f; ? u k' ft o p fx n fho Gi f; jc i f; /
instr uction Assembly b mo mp u m; w Gi f mnemonics u dka c : a 0 : a o m t o Hk; t E Ie f; /
inter ceptor
inter pr et y & dk* & r fu k' fr sm; u dk machine u k' ft jz p fo dkU w p fa Mu mi f; c si f; b mo mjy e fo n f/
inter pr eter Basic/ CNC b mo mp u m; r sm; u dk a & ; o m; E dki fa o m? machine u k' ft jz p f interpret v ky fa y ; E dki f
a o m y & dk* & r fi , f/
inter r upt & kw fjc n f; & y fw e fUa p jc i f; / ( o dkU) DOS p e p fw Gi f t o Hk; jy Ka o m INT function/
jump o w fr Sw fx m; a o m a e & mo dkU a u smfv Tm; jc i f; /
junk code
ker nel OS \ y i fr a u sm& dk; jz p fjy D; r Sw fOmP f? z dki fr sm; E Si fh hardware r sm; u dk p Dr Hc e fUc GJo n f/ i f; t jy i f t c sde f
E Si fh& u fp GJw dkUu dkx de f; o dr f; jc i f; ? application r sm; u dkz Gi fhjc i f; E Si fhresource r sm; u dka e & mc sx m; jc i f; w dkU jy Kv ky fo n f/
keygen o u fq dki f& m user t r n fE Si fhq dki fa o m key u dkx kw fa y ; E dki fa o m cracker r sm; u z e fw D; x m; a o mz dki f/
KeygenMe v lo p fw e f; cracker r sm; t w Gu f cracking y n mu dk o i fMu m; y dkUc s& e f& n f& G, fjy D; a & ; o m; x m;
a o m e r le my & dk* & r f/ ( o dkU) t q i fhjr i fh cracker r sm; \ t & n ft a o G; u dk p r f; o y f& e f c u fc Je u fe Jp Gm a & ; o m; x m;
a o my & dk* & r f/
link exe z dki ft jz p fo dkU r a jy mi f; r DDLL ( o dkU) OBJ z dki fr sm; E Si fhc sdw fq u fjc i f; /
linker exe z dki ft jz p fo dkUa & mu f& Sd& e f DLL ( o dkU) OBJ z dki fr sm; E Si fhc sdw fq u f& mw Gi f t o Hk; jy Ko n fhy & dk* & r f/
loader Process w p fc ku dkp w i fo n fh t a o ; p m; application w p fc kjz p fjy D; unpack v ky fa e o n fh^ protect
v ky fx m; jc i f; u dk jy e fa jz a e o n fh process ( a q mhz f0 Jv f) u dk a p mi fhq dki f; o n f/ x dkUa e mu f y & dk* & r fx Jr S y & dk* & r fa & ;
o m; o l c se f& p fc Jha o mt r Sm; r sm; ^ t m; e n f; c su fr sm; t m; t c Gi fha u mi f; , ljy D; r Sw fOmP fx Jr S process u dk patch
v ky fo n f/ ( o dkU) a & SYa jy ; y & dk* & r f/
machine code u Ge fy sLw m\ CPU u w dku f& dku fe m; v n fE dki fa o m instruction r sm; E Si fha ' w mr sm; y g0 i fa o m
p e p fw p fc k/ CPU model w dki f; w Gi f i f; w dkU\ u dk, fy dki f machine u k' f ( o dkU) instruction set & Sdjy D;
w p fx y fw n f; u sc si fr Su sE dki fa y v dr fhr n f/
malicious code t z su ft a r Smi fhv ky fi e f; r sm; v ky fa q mi f& e f? v Hkjc HKa & ; t c su ft v u fr sm; c dk; , l& e f y & dk* & r fr sm;
w Gi f x n fho Gi f; v dku f^ x m; a o m y & dk* & r fE Si fh v Hk; 0 r o u fq dki fa o mu k' f/ Malicious u k' fr sm; o n f y & dk* & r fz dki f
t c si f; c si f; u l; p u fE dki fo n f/
malwar e Malicious u k' fr sm; y g0 i fa o m a q mhz f0 Jv f/
MD5 MIT Lab E Si fh RSA Data Security Inc. w dkUr S x kw fv ky fv dku fa o m 128-bit encryption p e p f/
e r le mt m; jz i fhphpBB z dk& r fr sm; w Gi f login password u dk encrypt v ky f& mw Gi f t o Hk; jy Ko n f/
memor y br eakpoint Section w p fc kt w Gi f; ? o w fr Sw fx m; o n fh address e , fy , ft w Gi f; y & dk* & r fr S
t c su ft v u fr sm; u dk a & ; o m; a o mt c g? t c su ft v u fr sm; & , la o mt c g o d& SdE dki f& e fE Si fh y & dk* & r fu dk& y fw e fUE dki f& e f
o w fr Sw fa o m breakpoint/
Memor y-patching pr otection Cracker r sm; u loader a & ; jy D; r Sw fOmP fx Jr S u k' fr sm; u dk v ky fjc i f; r S
u mu G, fw m; q D; o n fhe n f; v r f; /
metadata .net y & dk* & r fr sm; w Gi f y g0 i fa o m a ' w mt r sdK; t p m; r sm; E Si fhy w fo u fo n fh t a o ; p dw ft c su ft v u f
r sm; / .net reflector u Jho dkUa o ma q mhz f0 Jv fr sm; o n f exe z dki fx Jr Smetadata r sm; u dkz w fjy D; r l& i f; source u k' fu dk
jy e fv n fa z mfx kw fa y ; jc i f; jz p fo n fht w Gu f cracker r sm; t v G, fw u l crack r v ky fE dki fa p & e f metadata r sm; u dk
obfuscation v ky fx m; & e fv dkt y fo n f/
metamor phic code u dk, fw dki fjy e fjy D; y & dk* & r fjy e fa & ; E dki fo n fhu k' f/ t c sdKUA dki f; & y fp fr sm; u z dki ft o p fr sm; u dk
u l; p u fa p v dka o mt c gw Gi f t o Hk; jy Ko n f/ x dkUa Mu mi fh A dki f; & y fp fx dx m; a o my & dk* & r fr sm; o n f r l& i f; y & dk* & r fE Si fh
r n fo n fht c gr Sw ln Da w mhr n f r [ kw fa y / u Ge fy sLw mA dki f; & y fp fr sm; u e n f; u dk t o Hk; jy K& o n fht a Mu mi f; & i f; r Sm
anti-virus a q mhz f0 Jv fr sm; u i f; w dkU\ signature r sm; u dkr Sw fr djc i f; r Sa & Smi f& Sm; E dki f& e fjz p fo n f/
mnemonics Assembly b mo mp u m; w Gi f a y gi f; jc i f; ? E Iw fjc i f; p a o m v ky fa q mi fc su fw p fc ku dk v ky fa q mi f
E dki fa o mu k' f/
module Cracking w Gi f exe z dki fE Si fh i f; exe z dki fu a c : , lt o Hk; jy Kx m; a o m DLL z dki fr sm; /
MoleBox y & dk* & r fw p fc krun a e c sde fw Gi f v dkt y fa o mz dki ft m; v Hk; u dk exe z dki fw p fc kw n f; t jz p f pack v ky fa y ; E dki f
Cracking q dki f& ma 0 g[ m& r sm;
- 538 -
a o m t q i fhjr i fh packer/ t u , f o m DLL t w Gi f; w Gi f registration routine a & ; x m; y gu cracker t z dkU
crack v ky f& e fc u fc Ja p r n fjz p fo n f/
nag scr een y & dk* & r fw p fc ku dk z Gi fh^ y dw fa o mt c gw Gi f a w GU& a o m p dw ft a E Smi fht , Su fjz p fa p o n fh message
screen E Si fha Mu mfji mr sm; / Trial version a q mhz f0 Jv fr sm; w Gi fo m a w GU& a v h& Sdo n f/
nanomite Dump v ky fjc i f; u dk w m; q D; & mw Gi f t o Hk; jy Ka o m t q i fhjr i fhe n f; v r f; jz p fjy D; Armadillo w Gi f
p w i ft o Hk; jy Kc Jho n f/ Jump t c sdKUu dk INT3 function jz i fht p m; x dk; o n fhe n f; v r f; jz p fo n f/
z , f& Sm; c Hv dku f& o n fh jump instruction r sm; E Si fh y w fo u fo n fh t c su ft v u fr sm; u dk a o a o c smc sm encrypt
v ky fx m; o n fhtable x Jw Gi f o dr f; q n f; y go n f/
neutr alize Anti-virus a q mhz f0 Jv fr sm; u A dki f; & y fp f( o dkU) x & dk* se fu dk p Hkp r f; o d& Sda o mt c g A dki f; & y fp ft w Gi f; & Sd
u k' fu dkz , f& Sm; jc i f; ( o dkU) A dki f; & y fz dki fu dkz su fjc i f; p o n fw dkUu dk jy Kv ky fjc i f; /
NFO Crack v ky fx m; a o mz dki fE Si hf o u fq dki fa o mt c su ft v u fr sm; ? cracking team r sm; E Si fh y w fo u fa o m
t c su ft v u fz dki f/
NSPack exe? dll? ocx p o n fhz dki ft r sdK; t p m; r sm; t jy i f .net z dki fr sm; u kdy g compress v ky fa y ; E dki fa o m
packer y & dk* & r f/ Pack v ky fx m; a o mz dki ft & G, ft p m; r Sm UPX z dki fr sm; a v mu fy i f& Sdjy D; pack v ky fx m; a o mz dki f
o n f Windows 98 w Gi fy i f a u mi f; p Gmt v ky fv ky fE dki fo n f/
obfuscation Method E Si fhclass t r n fr sm; u dk & Sm r & E dki fa t mi f z w f r & E dki fa o m p mv Hk; r sm; t jz p f a jy mi f; v J
a y ; a o mjz p fp Of/
octal 8 v D* P e f; p e p f/
ocx PE z dki ft r sdK; t p m; w p fc kjz p fjy D; .dll z dki fu Jho kdUy i f imagebase o n f 1,000,000 r Sp w i fo n f/
OEP r lv entry point/ Pack v ky fx m; a o m z dki fr sm; w Gi f y x r q Hk; a w GU& a o m address u dk entry point
[ ka c : jy D; decompression stub v ky fa q mi fc su ft jy D; w Gi f a w GU& a o m address u dk OEP [ ka c : o n f/ OEP
u dko dr So m dump p w i f v ky fa q mi fE dki fjy D; OEP u dk & Sma z Ga y ; o n fh a q mhz f0 Jv fr sm; o n fv n f; cracker r sm; u dk
t a x mu ft y Hhr sm; p Gm jz p fa p y go n f/
offset w du sa o mu k' fw p fc k& Sd& m address p r Sw fE Si fh i f; t r Sw fE Si fht u Gmt a 0 ; /
Olly Cracker r sm; t w Gu f t a u mi f; q Hk; a o m ring-3 debugger/
opcode y & dkq u fq mu e m; v n fE dki fa o m instruction w p fc k/ Opcode t r sm; p kw Gi f operand r sm; y g& Sdo n f/
optional header File header \ a e mu fw Gi f u y fv su f& Sda o m a e mu fx y f 224bytes jz p fjy D; PE
z dki ft w Gi f; & Sd logical layout E Si fhy w fo u fa o mt a Mu mi f; t & mr sm; y g0 i fo n f/ ( Oy r m- AddressOfEntry
Point) /
or dinar y br eakpoint u k' fr sm; w Gi f o w fr Sw fo n fho mr e f breakpoint/
over flow flag w e fz dk; w p fc ku dk o dr f; q n f; E dki fp Gr f; y r mP x u fa u smfv Ge fa o mt c g 1 w e fz dk; u dk o w fr Sw fo n fh
flag/ t w Gu ft c su fr sm; w Gi f t r sm; q Hk; t o Hk; jy Ko n f/
over lay exe z dki fx Jw Gi f a e mu fq u fw GJt a e jz i fhx n fho Gi f; x m; a o m a ' w m ( o dkU) z dki f/
p-code
pack exe z dki fu dk compress v ky fjc i f; ? execute v ky fE dki fz dkU decompress jy e fv ky fjc i f; E Si fh execution
p w i fjc i f; w dkUu dk v ky fa q mi fa y ; & o n fh decompression stub u dk x n fho Gi f; p Of; p m; & a o mv ky fi e f; p Of/ Pack
v ky fjc i f; jz i fhz dki ft & G, ft p m; u dk u so Gm; a p jy D; a e & mv Gw fy dkr dk& v my go n f/
packer r lv z dki f\ t & G, ft p m; u dk t e n f; q Hk; 3 0 % a v mu f a v Qmhc sE dki fjy D; cracker r sm; t w Gu f u k' fu dk
a jc & mc HE dki f& e f c u fc Ja p a o m y & dk* & r f/
patch u dk, fw kdi fa o mfv n f; a u mi f; ? y & dk* & r f\ t u lt n D, l a o mfv n f; a u mi f; y & dk* & r fu k' fu dk jy i fq i fo n f/
PE file Windows OS r sm; w Gi fo m t v ky fv ky fa o m y & dk* & r fr sm; ? z dki fr sm; /
PE header IMAGE_NT_HEADERS [ ka c : a o m structure w p fc kjz p fjy D; structure w Gi f
Windows loader u r & Sdr jz p fv dkt y fa o m t c su ft v u fr sm; y g0 i fo n f/
PE signatur e y & dk* & r fu dk r n fo n fh compiler jz i fh compile v ky fx m; o n f? r n fo n fh packer jz i fh pack
v ky fx m; o n fu dk o d& SdE dki f& e f w dku fq dki fp p fa q ; a o m hex u k' fr sm; /
PEB - - - - Process Environment Block
PhantOm Anti-debugging v ky fa q mi fc su f a jr mu fjr m; p Gmy g0 i fo n fh Olly \ t a u mi f; q Hk; a o m plugin
w p fc k/
pir ate ver sion Crack v ky fx m; a o m? o lw y g; \ u k' fu dk w & m; r 0 i f & , lo Hk; p GJx m; a o m a q mhz f0 Jv f/
pointer to r aw data z dki f\ t p r S section \ a ' w mr sm; x d& Sda o m offset/ i f; o n f module header r S
FileAlignment \ q w dk; u de f; jz p f& a y r n f/
pointer Variable w p fc k& JU address u dko dr f; x m; a o m variable w p fc k/
polymor phic code r lv algorithm u dk y u w dt w dki f; & Sda e a p a t mi fv ky fa e p Oft w Gi f; t o Gi fa jy mi f; v J
o Gm; a o mu k' f/ e n f; y n mt m; u Ge fy sLw mA dki f; & y fp fr sm; ? shell u k' fr sm; E Si fh u Ge fy sLw m worm r sm; u i f; w dkU
& Sda e jc i f; u dk z Hk; u G, fE dki f& e ft w Gu f t o Hk; jy Ko n f/
Cracking q dki f& ma 0 g[ m& r sm;
- 539 -
pr efetch
pr ocess Windows w Gi f t a jc c Ht u sq Hk; a o m block w p fc k/ y & dk* & r fr sm; t v ky fv ky f& mw Gi f t o Hk; jy Ka o m a e
& mv Gw fr sm; jz p fjy D; Windows u u k' f module r sm; u dk process \ a e & mv Gw fo dkU u l; w i fE dki fjy D; y & dk* & r fw p fc k
t v ky fv ky fE dki f& e ft w Gu f t e n f; q Hk; thread w p fc k t v ky fv ky fa e & y gr n f/
pr otector Packer w p fc ko mjz p fjy D; & dk; & Si f; a o m packer r sm; x u fp mv Qi f u k' fr sm; t m; y dkjy D; p dp p fc GJjc m; o n f/
Protector r sm; \ t " du t m; e n f; c su fr Sm protect v ky fx m; a o mz dki f\ t & G, ft p m; jz p fo n f/ Packer r sm; u
pack v ky fx m; a o m z dki f\ t & G, ft p m; r sm; u dk a o ; i , fa t mi fv ky fa e c sde fw Gi f protector r sm; u cracker & e fu
u mu G, fE dki f& e ft w Gu f u k' fr sm; t v Ge ft r i f; x n fho Gi f; Mu o n fht w Gu f protect v ky fx m; a o m t c sdKUz dki fr sm; o n f
( a o ; i , fa o mz dki fr sm; ) r lv z dki fx u f 6 0 0 % Mu D; o Gm; a Mu mi f; a w GU& o n f/
r ecur sion Function w p fc ku dk t Mu dr fMu dr f v ky fa q mi fjc i f; /
Reflector .net y & dk* & r fr sm; u dk decompile v ky f& e ft w Gu f t o Hk; jy Ka o m a q mhz f0 Jv f/ Decompile v ky fx m;
a o mu k' fr sm; u dk C#? VB? Delphi? IL? Chrome E Si fhVisual C++ b mo mp u m; r sm; jz i fhMu n fh& IE dki fo n f/
r egistr ation a q mhz f0 Jv fu dk trial version r S full version jz p fa p & e ft w Gu f v dkt y fa o m t c su ft v u f
r sm; u dk & dku fx n hfjc i f; ( o dkU) x dko dkUjy Kv ky fE dki f& e f a & ; o m; x m; a o mu k' fr sm; /
r egistr y Cracking w Gi f registration E Si fhy w fo u fa o mt c su ft v u fr sm; x m; & Sd& m database/
r elocation table Base relocation information u dk n Te fjy o n f/
r esour ce y & dk* & r fw p fc kt w Gi f; w Gi f y g0 i fa o m icon r sm; ? bitmap r sm; ? dialog r sm; E Si fhstring r sm; /
r ever sing OS ( o dkU) y & dk* & r fw p fc k\ o a b mo b m0 u dk debugging tool r sm; t o Hk; jy K a v hv mjc i f; /
r ever se engineer Reversing u dk t x l; jy K a v hv mo l/
r ip v dkt y fa o mu k' fu dk , lo n f? jz w fx kw fo n f/
RSA Encryption e , fy , fw Gi f w Gi fu s, fp Gmt o Hk; jy Kv Qu f& Sda e o m public/private key algorithm/
Microsoft Windows w Gi f cryptographic service provider (CSP) t jz p ft o Hk; jy Ko n f/
RVA Relative Virtual Address \ t w dka u mu f/
section y & dk* & r fw p fc kt w Gi f; & Sdu k' f? a ' w mE Si fhresource r sm; o dr f; q n f; & ma e & m/
section alignment PE header r Smr w ln Dw Jh Alignment field E Sp fc k& Sdy gw , f/ o lw dkUa w Gu a w mh section
alignment e JU file alignment y g/ Section alignment q dkw m u a w mh t a y : r Smq dkx m; w Jht w dki f;
r Sw fOmP fx Jr Sm section a w Gu dk b , fv dkn Sd, lr v Jq dkw m jz p fy gw , f/ Section r sm; \ Alignment u dk r Sw fOmP f
w Gi f; u l; w i fo n f/ Byte jz i fhjy o n f/ w e fz dk; o n f File Alignment E Si fh n D& r n f ( o dkU) Mu D; & r n f/ y Hka o
w e fz dk; o n f system \ page t & G, ft p m; jz p fo n f/
segment r egister r Sw fOmP f\ segment u dk t o Hk; jy Ko n f/ 16- bit OS r sm; w Gi f t o Hk; jy Ko n f/ DOS w Gi f
r Sw fOmP fu dk 64KB & Sda o m segment r sm; t jz p f y dki f; v dku o n fht w Gu f r Sw fOmP f\ address u dk o w fr Sw fv dk
v Qi f segment E Si fh offset u dk a t mu fy gt w dki f; ( 0172:0500 ( segment:offset) ) o w fr Sw f& o n f/ Segment
register r sm; o n f 16- bit register r sm; jz p fo n f/
SEH Structured Exception Handler \ t w dka u mu f/
Sentinel Rainbow Technology (www.rainbow.com ) r Sx kw fv ky fo n fhdongle key/
ser ial fishing Debug v ky f& mw Gi f y & dk* & r fu w Gu fc su fv dku fa o m serial u dk& Sma z Gjc i f; / Serial fishing u dk
y & dk* & r fw dki f; w Gi f v ky f r & a y /
session
shar ewar e r 0 , fc i f t c r Jho Hk; p GJE dki fa o m r ly dki fc Gi fhv ky fx m; o n fha q mhz f0 Jv f/
shellcode a q mhz f0 Jv f bug r sm; r Sw q i fh t c Gi fha u mi f; , ljy D; payload t jz p ft o Hk; jy Ka o m machine u k' f\
w p fp dw fw p fa ' o / Machine w Gi ft v ky fv ky fa e a o m a q mhz f0 Jv f\ t m; e n f; c su fu dk t c Gi fha u mi f; , ljy D; t c Gi fhr & Sd
a o mo Hk; p GJo lr sm; t m; OS \ command-line r Sw q i fh u Ge fy sLw me JU c sdw fq u fE dki fa t mi fc Gi fhjy Ky gw , f/ y Hkr Se f
t m; jz i fhnull-terminated (\0) string t a e E Si fho dr f; q n f; jc i f; jz p fjy D; null character r sm; r y g0 i fE dki fy g/
sign flag t a y gi f; ^ t E Iw fo a u Fw jz p f^ r jz p f o w fr Sw fa o m flag/
size of r aw data Disk a y : & Sd z dki fx Jr Sm& dSa o m section \ a ' w mt & G, ft p m; / Module header r S
FileAlignment \ q w dk; u de f; jz p fjy D; ? t u , f i f; w e fz dk; o n f virtual size x u fi , fv Qi f section \
u se fa o mt y dki f; r sm; o n f o kn E Si fh jy n fha e r n fjz p fo n f/ Section uninitialized a ' w mo u fo u fo m
& Sdc sde fw Gi f a e & m o kn jz p f& a y r n f/
SLVc0dePr otector TeamICU r S SLV u a & ; o m; jy D; ( 1 ) Anti-debugging? ( 2 ) Anti-API break
point? ( 3 ) DOS header u dkz su fjc i f; ? ( 4 ) r lv z dki ft r n fu dk p p fa q ; jc i f; p o n fhv Sn fhp m; r Ir sm; y g0 i fo n f/
Smar tCheck VB y & dk* & r fr sm; u dk serial z r f; & mw Gi f t a u mi f; q Hk; a o m debugger/ SmartCheck jz i fhVB
u k' fr sm; t v ky fv ky fy Hku dk event r sm; r Sw q i fh t a o ; p dw fMu n fh& IE dki fo n f/ SmartCheck o n f p-code r sm; u dk
debug v ky fE dki fjc i f; r & Sdy g/
sour ce a & TUa jy mi f; r n fh^ u l; , lr n fha ' w mr sm; & Sd& ma e & m?
sour ce code y & dk* & r fb mo mp u m; r sm; jz i fhy & dk* & r fr mr sm; a & ; o m; x m; a o mu k' f/
Cracking q dki f& ma 0 g[ m& r sm;
- 540 -
SS Routine r sm; r Sa y ; y dkUa o m address r sm; u dk o dr f; q n f; & e f t o Hk; jy Ka o m register/ Stack segment \
t w dka u mu f/
stack o D; o e fUz , fx m; a o m r Sw fOmP fa e & mjz p fjy D; i f; w Gi f y & dk* & r fu procedure? function call address?
parameter E Si fhlocal variable w dkUE Si fhy w fo u fa o m t c su ft v u fw dkUu dk o dr f; q n f; o n f/ Last in First Out
(LIFO) e n f; y n mu dk t o Hk; jy Ko n f/
stolen bytes r lv exe z dki fr S , lv mc Jha o m? r lv exe z dki fr Sz su f, lv mc hJa o m p mv Hk; r sm; jz p fjy D; packer \
u k' fx Jw Gi f i f; w dkUu dk v mx m; o n f/ OEP a & mu fc sde fw Gi f y & dk* & r fu dk r Sw fOmP fr S dump v ky f, la o mt c g
dump v ky fv dku fa o m exe z dki fx Jw Gi f x dkp mv Hk; r sm; y g& Sda w mhr n fr [ kw fa y / x dkp mv Hk; r sm; r & Sda w mhv Qi f y & dk* & r f
r sm; a u mi f; p Gmt v ky fv ky fE dki fr n fr [ kw fa y / e n f; v r f; o n f y & dk* & r fu dk crack r v ky fE dki f& e f u mu G, fr Iw p fc k
jz p fo n f/
Str ategic Code Splicing Dump r v ky fE dki fa t mi f w m; q D; o n fh e n f; v r f; w p fc k/ ( Dump v ky fjc i f;
q dko n fr Sm a q mhz f0 Jv fw p fc kc k\ t u lt n Djz i fhr Sw fOmP fx Jw Gi f decrypt/unpack v ky fx m; a o m u k' fr sm; u dkexe
z dki f t a e jz i fh o dr f; q n f; jc i f; jz p fo n f/ ) Strategic Code Splicing u o i f\ u k' fr sm; u dk z , fx kw fv dku fjy D;
r Sw fOmP f\ a e & mt E SHYt jy m; w Gi f o Gm; x m; v dku fo n f/ u k' fr sm; u dkv n f; a jy mi f; v Jy p fv dku fo n fht w Gu f t v ky f
v ky fy Hkr Sm w ln Dr n fjz p fa o mfv n f; u k' fr sm; r Smr l a jy mi f; v Jo Gm; r n fjz p fo n f/
str ing w p fv Hk; ( o dkU) w p fv Hk; x u fy dka o m p u m; v Hk; r sm; y g0 i fa o mp mo m; /
Str ongName StrongName w p fc kw Gi f y & dk* & r fE Si fhy w fo u fa o m assembly \ identity r sm; y g0 i fjy D;
i f; w dkUr Sm & dk; & Si f; v Sa o mp mo m; r sm; E Si fhjz p fjy D; t r n f? version t r Sw f? culture w dkUt jy i f public key w p fc kE Si fh
digital signature w p fc kw dkU y g0 i fE dki fo n f/ i f; w dkUu dk assembly z dki fw p fc kr S o u fq dki f& m private key u dk
t o Hk; jy Kjy D; x kw fa y ; jc i f; jz p fo n f/ Microsoft Visual Studio e JU .NET framework u dkt o Hk; jy KMu a o m
t jc m; tool r sm; u StrongName r sm; u dkassembly w p fc kt a e jz i fho w fr Sw fE dki fo n f/
SVKP SVKP o n f exe z dki fr sm; t m; protect v ky fa y ; o n fh protector w p fc kjz p fjy D; protect v ky f& e ft w Gu f
r w ln Da o m e n f; v r f; 4 & y fu dk t o Hk; jy Ko n f/ i f; w dkUr Sm ( 1 ) RSA algorithm u dk t o Hk; jy Kjc i f; ? ( 2 ) API
function r sm; u dk v Sn fhp m; r Ijy Kv ky fx m; jc i f; ? ( 3 ) anti-debug v Sn fhp m; r Ir sm; x n fho Gi f; x m; jc i f; ? ( 4 ) r Sw fOmP f
E Si fhtracer r sm; r Sdump r v ky fE dki fa t mi fu mu G, fx m; jc i f; w dkUjz p fo n f/
tamper
Themida a q mhz f0 Jv fr sm; u dk crack v ky fjc i f; & e fr S u mu G, fE dki f& e f SecureEngine protection p e p fu dk
o Hk; x m; o n fhprotection p e p fw p fc k/ Cracker r sm; t jr i ft & Themida o n f o Hk; p GJa e u sa q mhz f0 Jv f protector
r sm; E Si fh v Hk; 0 r w lb J u GJjy m; jc m; e m; v su f& Sdo n f/ Developer r sm; t w Gu fr l Themida o n f v G, fu lp Gm t o Hk; jy K
E dki fjy D; i f; w dkUjz p fa p c si fa o m t q i fhjr i fho n fhprotection r sm; u dk v G, fu lp Gma & G; c s, fE dki fo n f/
thr ead Mu D; r m; a o m process w p fc k ( o dkU) y & kd* & r fw p fc k\ w p fp dw fw p fa ' o jz p fa o m process w p fc kjz p fjy D;
u k' fr sm; u dk execute v ky f& a o m , le p fw p fc kjz p fo n f/ Thread u dk virtual processor w p fc kt jz p fr Sw f, lE dki fjy D;
i f; w Gi f u dk, fy dki f context E Si fhstack & Sdo n f/ Windows o n f t v ky fv ky fa e a o m thread w p fc ku dk E Sp fo u f& m
t c sde fw Gi f & y fw e fUE dki fo n f/
TimeDateStamp TimeDateStamp o n fz dki fu dk z e fw D; c Jha o mt c sde fu dk & n fn Te f; o n f/ Olly w Gi f i f; u dk
hex * P e f; jz i fhjy o n f/ t c sdKU PE Viewer r sm; w Gi fr l hex E Si fhr jy b J & dk; & dk; y Hkp HE Si fho mjy o n f/
TLS table Thread Local Storage \ initialization section u dkn Te fjy o n f/ TLS section w Gi f
declspec (thread) jz i fha Mu n mx m; a o m thread \ local variables r sm; y g0 i fo n f/ i f; variable r sm; t o Hk;
jy Kc sde fw Gi f compiler u o lw dkUt m; .tls [ kt r n f& a o m section w Gi fo Gm; x m; o n f/
tr acer o w fr Sw fx m; a o m breakpoint a & mu fo n ft x d y & dk* & r f\ u k' fr sm; u dk w p fa Mu mi f; c si f;
a jc & mc Ha y ; E dki fa o m y & dk* & r f ( o dkU) function/
tr ial ver sion t c sde f^ t Mu dr f t u e fUt o w fjz i fho Hk; p GJ& a o ma q mhz f0 Jv f/
uncondition jump r n fo n fht a Mu mi f; jy c su fjz p fy ga p o w fr Sw fx m; a o m address o dkUa u smfv Tm; a o m
jump/
UNICODE Unicode Consortium u 1 9 8 8 E Si fh 1 9 9 1 u mv t w Gi f; develope v ky fc Jha o m 16-bit o Hk;
p mv Hk; / p mv Hk; w p fv Hk; u dk a z mfjy w dki f; 2 bytes t o Hk; jy Ko n f/ jz p fE dki fa o m Unicode p mv Hk; 65,536 x Jr S39,000
u dkt o Hk; jy Kv Qu f& Sdjy D; i f; w dkUx Jr S21,000 u dk w & kw fp mv Hk; r sm; t w Gu f t o Hk; jy Ko n f/ u se f& Sda e a o mp mv Hk; r sm; u dk
r l t v Gw fx m; & Sdx m; o n f/
unpack Pack v ky fx m; a o ma ' w mr sm; u dk r lv u k' fo dkU jy e fa jy mi f; jc i f; /
unpacker Pack v ky fx m; a o m z dki fr sm; u dk unpack jy e fv ky fa y ; E dki fa o my & dk* & r f/
unr egister ed 0 , f, lo Hk; p GJjc i f; r & Sda o m t a jc t a e /
UPX exe z dki fr sm; u dk t & G, ft p m; a o ; i , fa t mi f v ky f& mw Gi f e mr n fMu D; v Sjy D; t q i fhjr i fh protection
e n f; v r f; r sm; o Hk; x m; jc i f; r & Sda o m packer/ Ultimate Packer for eXecutables \ t w dka u mu f/
vir tual addr ess r Sw fOmP fx Jw Gi f application u t o Hk; jy Ka o m address /
vir us y & dk* & r fz dki fu dk u dk, fw dki fy Gm; E dki fa o m? u l; p u fa p E dki fa o m r a u mi f; a o m & n f& G, fc su fjz i fhu Ge fy sLw mo Hk; p GJ
Cracking q dki f& ma 0 g[ m& r sm;
- 541 -
o lu dk t a E Smi fht , Su fjz p fa p a o m y & dk* & r fz dki f/ A dki f; & y fp fr sm; o n f r a w mfw q a o mfv n f; a u mi f; ? w r i f& n f& G, fjy D;
a o mfv n f; a u mi f; q dk; u sdK; r sm; jz p fa p o n f/
Water mar k x i fo mjr i fo m& Sda o m watermark E Si fh a z smu fx m; a o m watermark [ l E Sp fr sdK; & Sdo n f/
a q mhz f0 Jv fr sm; u dk c dk; o Hk; jc i f; r S u mu G, f& e f t o Hk; jy Ko n f/ Armadillo \ hidden watermark o n f
encrypted string t a e jz i fhw n f& Sda e jy D; y & dk* & r fu dk unpack v ky f& mw Gi f i f; u dk z , f& Sm; E dki f& e f t a & ; Mu D; o n f/
r z , f& Sm; E kdi fy gu watermark t v ky fv ky fo n fht w Gu f Anti-virus r sm; u x dkz dki fu dk A dki f; & y fp ft a e jz i fh
jr i fw w fo n f/ t c sdKU watermark r sm; o n f user E Si fhy w fo u fa o m t c su ft v u fr sm; u dk w dw fw q dw f
x n fho Gi f; x m; o n fht w Gu f r dr da q mhz f0 Jv fo n f t i fw me u fw Gi f y sHUE SHYc Jhy gu r dr dq Dr S jy e fYo Gm; a Mu mi f;
c su fc si f; o d& SdE dki fo n f/
wor m u Ge fy sLw mt o D; o D; \ r Sw fOmP fw Gi f u dk, fy Gm; r sm; x kw fa y ; a e a o m? u Ge fy sLw mr sm; Mu m; y sHUE SHUv Qu f& Sd
a o m y & dk* & r f/
Yoda' s Cr yptor Danilo Bzdok u a & ; o m; jc i f; jz p fjy D; ( 1 ) PE header u dkz su fjc i f; ? ( 2 ) CRC u dk
p p fa q ; jc i f; ( u k' fE Si fhz dki f) ? ( 3 ) IsDebuggerPresent p p fa q ; r I? ( 4 ) API r sm; u dk redirect v ky fjc i f; E Si fh import
t c su ft v u fr sm; u dk z su fq D; jc i f; p o n fhv Sn hfp m; r Ir sm; y g0 i fo n f/ Open source u k' fjz p fo n f/
Yoda' s Pr otector Yoda's Cryptor u dk jy e fjy i fq i fx m; o n fhprotector w p fc ko mjz p fjy D; version 1.03.3
w Gi f q u fr a & ; a w mhb J & y fc Jho n f/ Yoda's Cryptor \ v ky fa q mi fc su fr sm; t jy i f PID r sm; p p fa q ; o n fh Get
CurrentProcessId API? mouse E Si fh keyboard w dkU\ v ky fa q mi fc su fr sm; u dk & y fw e fUa p o n fh BlockInput
API w dkUu dk x y fr Hx n fho Gi f; x m; o n f/
zer o flag w e fz dk; E Sp fc k E dIi f; , SOf& mw Gi f( E Iw f& mw Gi f) o kn jz p f^ r jz p fq Hk; jz w fa o m flag/
Cracking qd k if &m tif wmeuf 0uf bf qd k uf rsm;
- 542 -
C
C
C
r
r
r
a
a
a
c
c
c
k
k
k
i
i
i
n
n
n
g
g
g
q
q
q
d
d
d
k
k
k
i
i
i
f
f
f
&
&
&
m
m
m
t
t
t
i
i
i
f
f
f
w
w
w
m
m
m
e
e
e
u
u
u
f
f
f
0
0
0
u
u
u
f
f
f
b
b
b
f
f
f
q
q
q
d
d
d
k
k
k
u
u
u
f
f
f
r
r
r
s
s
s
m
m
m
;
;
;
( Link r sm; u dk20 11? ar 1 &u fw Gi f p p faq ; x m; jc i f; jz p fy go n f/ t c sdKUlink r sm; r &SdEdki faw mhy g/ )
( 1) Cr acking q kdi f&m0 u fb fq dku fr sm;
http://www.accessroot.com
http://www.tuts4you.com
http://unpack.cn
http://www.cin1team.biz
http://www.aoreteam.com
http://www.reversing.be
http://www.at4re.com
http://www.reaonline.net/
http://www.ahteam.org
http://www.reteam.org
http://quequero.org/
http://www.cracktool.com
http://www.teamicu.org
http://reversengineering.wordpress.com
http://reversingtools.blogspot.com
http://portal.b-at-s.info/news.php
http://exelab.ru
http://www.pediy.com
http://www.wasm.ru
http://ricardonarvaja.info
http://appznet.ws
http://www.ica-zone.com
http://lndl.c0mhost.net
http://www.lastepidemic.net/
http://astatalk.com
http://forum.reverse4you.org
http://www.ica-zone.com/forum/index.php
http://board.anticrack.de
http://www.tpodt.com/
http://www.secretashell.com/PEid/
http://www.alame.com/vb/
http://www.woodmann.com
http://reng.ru/board/
http://www.absolutelock.de
http://www.ibsensoftware.com
http://pro-hack.ru
http://azmoaore.reversedcode.com
http://www.securitylab.ru/tools/
http://ap0x.jezgra.net/
http://www.openrce.org/
http://www.encryptpe.com/
http://www.chinadfcg.com/
http://www.cracking.com.cn/
http://www.debugman.com/
http://club.myarc.cn/
http://www.ccgcn.com/
http://forum.exetools.com/
http://crackmes.de/
http://petools.org.ru/
http://www.pearmor.com/
http://www.chinadcm.com/
http://bbs.wmzhe.com/
http://ocn.e5v.com/bbs/index.php
http://bbs.chinapyg.com/
http://bbs.vxer.cn/
http://bbs.thulu.com/
http://bbs.crsky.com/
http://bbs.cniso.org/
Cracking qd k if &m tif wmeuf 0uf bf qd k uf rsm;
- 543 -
http://www.cracktool.com/
http://bbs.crkcn.com/
http://bbs.hanzify.org/index.php
( 2) Cr acked Ver sion jz e fUc sDae ao m0 u fb fq dku fr sm;
http://www.appzworld.com
http://www.dl4everything.com/
http://bookviet4a.org/
http://macedonianwarez.com/
http://www.albania-warez.com
http://www.thehotzone.org
http://knockdownload.com/
http://techcognize.com
http://www.fileserve-warez.com/
http://filescorner.com/
http://www.warezvilla.net
http://www.xdowns.com/
http://soft-best.net
http://www.directdl.com
http://www.warezraid.com
http://www.lugarus.com
http://www.megauploaded.com
http://katz.cd
http://avaxhome.ws
http://www.rapidshared.org
http://www.9iv.com
http://www.ddlcentral.com
http://www.inethouse.com
http://www.freeserials.com
http://www.phazeddl.com
http://www.appzplanet.com
http://warezall.com
http://wowebook.net/
http://movie4all.org/
http://www.downloadzunlimited.com/
http://wowwarez.net/
http://www.fullrelease.net/
http://www.free4vn.org/
( 3) Cr acked Ver sion jz e fUc sDae ao mz dk&r fr sm;
http://www.projectw.org
http://www.projectws.org
http://forumw.org
http://forum.ru
http://warezforum.info
http://www.cyberwarez.info
http://sharecentral.net
http://tehparadox.com/
( 4) y &dk* &r fa&; o m; jc i f; q dki f&m0 u fb fq dku fr sm;
http://www.codeproject.com
http://www.functionx.com
http://www.ucancode.com
http://www.dreamincode.net
http://www.codeguru.com
http://www.csharpkey.com/
http://www.hackchina.com
http://www.programmersheaven.com
http://stackoverflow.com/
http://blogs.technet.com/
http://www.flounder.com/
( 5 ) Cr acks? Ser ials ESi fhKeygens jz e fUc sDae ao m0 u fb fq dku fr sm;
Cracking qd k if &m tif wmeuf 0uf bf qd k uf rsm;
- 544 -
http://www.crackteam.ws
https://www.prs-distro.com/
http://keygens.nl
http://crackstorage.net/
http://www.crack.ms/
http://www.astalavista.ms
http://www.cracksfm.com
http://crackzplanet.com
http://www.allseek.info
http://www.anycracks.com
http://www.bestserials.com
http://www.crack-cd.com
http://www.crackspider.net
http://www.cracksportal.com
http://www.freeserials.com
http://www.icracks.net
http://www.mscracks.com
http://www.thebugs.ws
http://download-crack-serial.com/
References - 545 -
References
(01) Basic Rules of Cracking ParaBytes
(02) Cracker Definition Invoker
(03) A Little Guide for Wannabe Reverser Zephyrous
(04) The C Programming Language Brian W. Kernighan & Dennis M. Ritchie
(05) PC Assembly Language Paul A. Carter
(06) Win32asm Tutorial Thomax Bleeker
(07) Assembly for Beginners The Cyborg
(08) Assembly Tutorials Ralph
(09) Win32 Assembler Coding for Crackers 1.1 Goppit
(10) Assembler : The Basics in Reversing Lena151
(11) The Wikibook of Reverse Engineering
(12) CrackProof Your Software Pavol Cerven
(13) Disassembling Code: IDA Pro and SoftICE Vlad Pirogov
(14) RCE Emphasizing On Breaking Software Protection tHE mUTABLE
(15) Portable Executable File Format Goppit
(16) Basic Nag Removal + Header Problems Lena151
(17) Indept Unpacking & Anti-Anti-Debugging, A Combination Packer & Protector Lena151
(18) Serial Fishing Teleport Pro nick123b
(19) Serial Fishing CD to MP3 Maker 1.15 ThunderPwr
(20) KeygenMe Tutorial 1 Ziggy
(21) Basic + Aesthetic Patching Lena151
(22) Intermediate Level Patching, Kanal in PEiD Lena151
(23) tElock + Advanced Patching Lena151
(24) Win32 Programmer Reference Microsoft
(25) Often Used APIs in Registration Schemes and Other Lena151
(26) Reversing - Secrets of Reverse Engineering Eldad Eilam
(27) Reversing Using the Program's Resources Lena151
(28) ActiveMARK 5.xx (Dumping and Rebuilding) SSIEvIN
(29) Unpacking Protections Lena151
(30) Unpacking Advanced Packers Lena151
(31) API Redirection Lena151
(32) VB - Introduction to SmartCheck and Configuration Lena151
(33) VB - Use of Decompilers and a Basic Anti-Anti-Trick Lena151
(34) Info About P-code Mahai
(35) P-code Instruction Meaning of Quick Fact Nisy
(36) VB P-code Information Mr Silver
(37) Delphi in Olly & DeDe Lena151
(38) Insights and Practice in Basic (self) Keygenning Lena151
(39) Java Target ThunderPwr
(40) Cracking Java Programs CodeRipper
(41) Reversing .Net Kwazy Webbit
(42) .Net Reversing Tips tKC
(43) Manul Unpacking .NET Applications Newbie_Cracker
(44) Serial Fishing in .NET (Live Debugging) zyzygy
(45) Removing StrongName Signature in .NET Applications Newbie_Cracker
(46) Symbian Exploitation and Shellcode Development Collin Mulliner
(47) Symbian Executable File Format Antony Pranata
(48) Primer in Reversing Engineering Symbian 3rd Applications argv
(49) Reversing Symbian S60 Applications 1.4 Shub-Nigurrath
(50) Patching Packed Executables at Runtime Using Loaders Lena151
(51) Basic Crypto Techniques detten
(52) Keygenning MD5 Nieylana
(53) Encryption Decryption Polymorphic Code Lena151
References - 546 -
(54) SVKP1.4x (Finding-The-OEP-Dumping) Teddy Rogers
(55) Bypassing & Killing Server Checks Lena151
(56) Themida 1.9.1.0 UnpackMe hacnho
(57) Themida Unpacking Joker_Italy
(58) Unpacking Themida 1.x SubZero
(59) Themida 1.9.1.0 Help Themida Team
(60) Manual Unpacking Yoda's Protector 1.03.3 NhatPhuongLe
(61) Writing OllyDbg Scripts Buzifier
(62) Anti-Unpacking Techniques Peter Ferrie
(63) Anti-Debugging A Developers View Tyler Shields
(64) Anti-Debugging Series Tyler Shields
(65) Windows Anti-Debug Reference Nicolas Falliere
(66) Anti-Debugging & Software Protection Advice CrackZ
(67) An Anti-Reverse Engineering Guide Josh_Jackson
(68) Anti Reverse Engineering Uncovered Nicolas Brulez
(69) CheckRemoteDebuggerPresent() Windows API ap0x
(70) Playing with RTDSC Piotr Bania
(71) Thwarting Virtual Machine Detection Tom Liston & Ed Skoudis
(72) The Art of Unpacking Mark Vincent Yason
(73) Windows Internals Mark E. Russinovich & David A. Solomon
(74) Armadillo developer r sm;ESi fht i fwmAsL; wannar
(75) Manually unpacking for Armadillo 4.44 (Debug Blocker) NoLimit
(76) Armadillo 4.30a (Minimum Protection) haggar
(77) Armadillo 4.30a (Standard Protection) haggar
(78) Armadillo 4.42 (Debug Blocker+CopyMemII) WaSt3d_ByTes
(79) Armadillo 6.40 (Debug Blocker+CopyMemII + Memory Patching Protection) Unknown
(80) Armadillo 4.xx (Code Splicing) MaDMAn_H3rCul3s
(81) Armadillo 4.40 (CopyMem2+Debug Blocker+Import Table Elimination) Ahmadmansoor
(82) Armadillo 4.40 (CopyMem2+Debug Blocker+Import Table Elimination) +NCR/CRC
(83) Armadillo 4.40 (Custom Unpacking+All Protections) DappA
(84) Armadillo 8.00 (Debug-Blocker+Imports Elimination+Code Splicing+Nanomites) perceptron
(85) Reversing Armadillo 4.2 AndreaGeddon
(86) Armadillo License Removal Ghandi
(87) Armadillo 8.xx (Environmental Variables Patching) Mr. eXoDia
(88) Armadillo 7.40 (Security.dll Patching) Mr. eXoDia
(89) Microsoft Computer Dictionary Microsoft
Vous aimerez peut-être aussi
- Readings in Contemporary Chinese Cinema: A Textbook of Advanced Modern ChineseD'EverandReadings in Contemporary Chinese Cinema: A Textbook of Advanced Modern ChineseÉvaluation : 3 sur 5 étoiles3/5 (1)
- Crackerလမ္းညႊန္Document419 pagesCrackerလမ္းညႊန္ဘုန္းျပည့္ စံုေက်ာ္Pas encore d'évaluation
- THE LTSPICE XVII SIMULATOR: Commands and ApplicationsD'EverandTHE LTSPICE XVII SIMULATOR: Commands and ApplicationsÉvaluation : 5 sur 5 étoiles5/5 (1)
- Monetine 999 CrackerguideebookDocument419 pagesMonetine 999 Crackerguideebookbyuuhar100% (1)
- Divided States: Strategic Divisions in EU-Russia RelationsD'EverandDivided States: Strategic Divisions in EU-Russia RelationsPas encore d'évaluation
- C9400-LC-24S ZPCBST Pass Uut Spirent LogDocument6 pagesC9400-LC-24S ZPCBST Pass Uut Spirent LogJP MaxxPas encore d'évaluation
- Programming FPGAs: Getting Started with VerilogD'EverandProgramming FPGAs: Getting Started with VerilogÉvaluation : 3.5 sur 5 étoiles3.5/5 (2)
- BacktrackDocument91 pagesBacktrackFaustino Manuel50% (2)
- الحاكمات المنطقية المبرمجة PLCDocument56 pagesالحاكمات المنطقية المبرمجة PLCwaseem masoudPas encore d'évaluation
- GT4 Strategy GuideDocument120 pagesGT4 Strategy GuideGiovanni BassiPas encore d'évaluation
- C9400-LC-24XS ZPCBST Pass Uut Spirent LogDocument6 pagesC9400-LC-24XS ZPCBST Pass Uut Spirent LogJP MaxxPas encore d'évaluation
- Polar Orbiter Ingester PDFDocument58 pagesPolar Orbiter Ingester PDFEduardo Luisenrique Sanchez CarrionPas encore d'évaluation
- AnonSec OpNASAdronesDocument102 pagesAnonSec OpNASAdronesCasandra Edwards100% (2)
- Leer Importante!Document3 pagesLeer Importante!Francisco AgüeroPas encore d'évaluation
- Aconex MaterialDocument142 pagesAconex MaterialSajid PatelPas encore d'évaluation
- Overview:: © Dukestar Technologies Pvt. Ltd. 1/16Document16 pagesOverview:: © Dukestar Technologies Pvt. Ltd. 1/16Vijay DasPas encore d'évaluation
- This Is Ducksay! / / / / - : But Which Version?Document47 pagesThis Is Ducksay! / / / / - : But Which Version?fu shrdPas encore d'évaluation
- #TheGame23 Presents - #HIVEMIND23 - The TechnoMeritocrazyDocument14 pages#TheGame23 Presents - #HIVEMIND23 - The TechnoMeritocrazydiPas encore d'évaluation
- 4444Document30 pages4444macedo0584359Pas encore d'évaluation
- Johanes AgusDocument41 pagesJohanes AgusGerry Dwi PutraPas encore d'évaluation
- Ilide - Info Zxa10 c300 v125 Version Upgrade Guide PRDocument15 pagesIlide - Info Zxa10 c300 v125 Version Upgrade Guide PRstream sysPas encore d'évaluation
- Reamonn - Tonight - .By - MerlinDocument4 pagesReamonn - Tonight - .By - MerlinAnn ParaskPas encore d'évaluation
- TM 11-459Document157 pagesTM 11-459Barry FollandPas encore d'évaluation
- 1991 - SuperStor User's ManualDocument41 pages1991 - SuperStor User's ManualradutariPas encore d'évaluation
- Igi 2Document31 pagesIgi 2sanchit-abrol-3458Pas encore d'évaluation
- Guide 3Document39 pagesGuide 3bonaji5766Pas encore d'évaluation
- Cdma Bts 3606eDocument73 pagesCdma Bts 3606ehendpraz88Pas encore d'évaluation
- Hdclone 3.7: User'S ManualDocument59 pagesHdclone 3.7: User'S ManualBlaze CopierPas encore d'évaluation
- Original Instruction Manual: Parts ListDocument26 pagesOriginal Instruction Manual: Parts ListÖzten Elektrik Abdullah ÖztenPas encore d'évaluation
- To 1-1-8 2Document170 pagesTo 1-1-8 2Abhinandan JainPas encore d'évaluation
- Sony SCD-1 Technical White PaperDocument20 pagesSony SCD-1 Technical White PaperbenjaminblackPas encore d'évaluation
- Final Fantasy Ix (PS) Faqs & Guides: Shotgunnova View/Download Original File GamefaqsDocument284 pagesFinal Fantasy Ix (PS) Faqs & Guides: Shotgunnova View/Download Original File Gamefaqsbilly_zunigaPas encore d'évaluation
- GameFAQs Fallout New Vegas (X360) FAQ - Walkthrough by Absolute SteveDocument140 pagesGameFAQs Fallout New Vegas (X360) FAQ - Walkthrough by Absolute SteveFrancisco Julián IñiguezPas encore d'évaluation
- Greer CompanyDocument22 pagesGreer CompanyEduardoMiullerPas encore d'évaluation
- Code128 Barcode User ManualDocument9 pagesCode128 Barcode User ManualJeniffer Navarro VillablancaPas encore d'évaluation
- Mitsubishi Manuals 59Document91 pagesMitsubishi Manuals 59Jose Concepción HernándezPas encore d'évaluation
- A245 04pa Programming Manual PDFDocument120 pagesA245 04pa Programming Manual PDFcarlos dos santosPas encore d'évaluation
- HKS EVC Easy Writer ManualDocument21 pagesHKS EVC Easy Writer ManualMike Is RadPas encore d'évaluation
- Megaman ZX AdventDocument69 pagesMegaman ZX AdventBryan CarriónPas encore d'évaluation
- JEDI Course Notes Intro1 MasterDocumentDocument244 pagesJEDI Course Notes Intro1 MasterDocumentMarkQuindozaPas encore d'évaluation
- A HeartsDocument69 pagesA Heartsapi-3703916Pas encore d'évaluation
- Izotope - Ozone Advanced 7.0.1.1362, Insight 1.05.481Document7 pagesIzotope - Ozone Advanced 7.0.1.1362, Insight 1.05.481thepsalmistPas encore d'évaluation
- How To Install CubaseDocument2 pagesHow To Install CubaseAlex MihailPas encore d'évaluation
- Lightwave DPSS PDFDocument174 pagesLightwave DPSS PDFeduardoquijadaPas encore d'évaluation
- Wellbore Cementing Model: DEA 67 LLDocument50 pagesWellbore Cementing Model: DEA 67 LLsergeyalejandroPas encore d'évaluation
- Red Hat Enterprise Linux-6-6.5 Technical Notes-En-USDocument398 pagesRed Hat Enterprise Linux-6-6.5 Technical Notes-En-USWaldek ZiębińskiPas encore d'évaluation
- Montaje Sirocco 14 (Ing) 150717Document100 pagesMontaje Sirocco 14 (Ing) 150717John BuonoPas encore d'évaluation
- Stellaris PSGDocument21 pagesStellaris PSGdjstojicPas encore d'évaluation
- Prueba de Fuga Hidrostática y Neumática Niveles I y IIDocument135 pagesPrueba de Fuga Hidrostática y Neumática Niveles I y IIFrancisco javierPas encore d'évaluation
- Ti99 Extended Basic ManualDocument130 pagesTi99 Extended Basic Manualjunkit99Pas encore d'évaluation
- Tetris Tutorial in C++ Platform Independent Focused in Game Logic For Beginners - JavilopDocument44 pagesTetris Tutorial in C++ Platform Independent Focused in Game Logic For Beginners - Javilopziedus100% (2)
- RobotrekDocument47 pagesRobotrekapi-19737643Pas encore d'évaluation
- GgbioDocument266 pagesGgbioajaybioinfoPas encore d'évaluation
- Arboles DecisionDocument30 pagesArboles DecisionIsi RomeroPas encore d'évaluation
- Faqs Fallout New VegasDocument140 pagesFaqs Fallout New VegasHaris MuhamadPas encore d'évaluation
- ModelingAndSimulation PDFDocument744 pagesModelingAndSimulation PDFShaza AltreifiPas encore d'évaluation
- To 1-1-691 Actualizada 2016Document396 pagesTo 1-1-691 Actualizada 2016maury69Pas encore d'évaluation
- NetworkingDocument207 pagesNetworkingarchankumarturagaPas encore d'évaluation
- CNC YASNAC J50M Instruction ManualDocument298 pagesCNC YASNAC J50M Instruction Manualramon navaPas encore d'évaluation
- Process Costing FIFO CRDocument21 pagesProcess Costing FIFO CRMiyangPas encore d'évaluation
- ManualDocument480 pagesManualMgKAGPas encore d'évaluation
- EP Tax Calculation For Online PaymentDocument3 pagesEP Tax Calculation For Online PaymentMgKAGPas encore d'évaluation
- Finance Department: Position Forecasting The Meets Times RemarkDocument1 pageFinance Department: Position Forecasting The Meets Times RemarkMgKAGPas encore d'évaluation
- Aung Kyaw Myint CVDocument3 pagesAung Kyaw Myint CVMgKAG100% (2)
- Cover Letter2Document5 pagesCover Letter2MgKAGPas encore d'évaluation
- Sa June11 Process2Document8 pagesSa June11 Process2LeoEdeOmoregiePas encore d'évaluation
- Sa June11 Process2Document8 pagesSa June11 Process2LeoEdeOmoregiePas encore d'évaluation
- ProcesscostingDocument37 pagesProcesscostingFlorence LapinigPas encore d'évaluation
- Cover LetterDocument5 pagesCover LetterMgKAGPas encore d'évaluation
- Cover Letter2Document5 pagesCover Letter2MgKAGPas encore d'évaluation
- Bank Reconciled KBZ MMKDocument2 pagesBank Reconciled KBZ MMKMgKAGPas encore d'évaluation
- Process Costing FIFO CRDocument21 pagesProcess Costing FIFO CRMiyangPas encore d'évaluation
- Application Form For WCMDocument6 pagesApplication Form For WCMMgKAG67% (3)
- Ma Shet Ma Phyit MoeDocument151 pagesMa Shet Ma Phyit MoeKhwankhaw SnPas encore d'évaluation
- Quote # QU1029 Summit ParkviewDocument1 pageQuote # QU1029 Summit ParkviewMgKAGPas encore d'évaluation
- (今日英语.-多媒体教程全集 (26张dvd) ) .English Today 01Document4 pages(今日英语.-多媒体教程全集 (26张dvd) ) .English Today 01MgKAGPas encore d'évaluation
- FO Cash Sale Summary FileDocument66 pagesFO Cash Sale Summary FileMgKAGPas encore d'évaluation
- Novotel Inle Lake Daily Cash Drop SummaryDocument1 pageNovotel Inle Lake Daily Cash Drop SummaryMgKAGPas encore d'évaluation
- Alar Card Menu (New)Document5 pagesAlar Card Menu (New)MgKAGPas encore d'évaluation
- Resident Manager Job DescriptionDocument5 pagesResident Manager Job DescriptionMgKAGPas encore d'évaluation
- FO Cash Sale Summary FileDocument1 pageFO Cash Sale Summary FileMgKAGPas encore d'évaluation
- 11th Crm-Food ProductionDocument34 pages11th Crm-Food ProductionMgKAGPas encore d'évaluation
- Food Production Operations TutorialDocument109 pagesFood Production Operations TutorialMgKAG100% (1)
- Pa System GFDocument1 pagePa System GFMgKAGPas encore d'évaluation
- Staff Male$ Female ToiletDocument1 pageStaff Male$ Female ToiletMgKAGPas encore d'évaluation
- The Regency Hotel Room Rates in BaganDocument2 pagesThe Regency Hotel Room Rates in BaganMgKAGPas encore d'évaluation
- Human Resource ManagementDocument60 pagesHuman Resource ManagementvibgorPas encore d'évaluation
- Electric Charges Calculation For Myanmar EPCDocument1 pageElectric Charges Calculation For Myanmar EPCMgKAGPas encore d'évaluation
- SQL DBA Mod 1 IntroDocument27 pagesSQL DBA Mod 1 IntroDivyaPas encore d'évaluation
- Railway Reservation System Er DiagramDocument4 pagesRailway Reservation System Er DiagramPenki Sarath67% (3)
- Investigations in Environmental Science: A Case-Based Approach To The Study of Environmental Systems (Cases)Document16 pagesInvestigations in Environmental Science: A Case-Based Approach To The Study of Environmental Systems (Cases)geodePas encore d'évaluation
- Papi AdbDocument50 pagesPapi AdbSilvio Figueiredo0% (1)
- Approvals Management Responsibilities and Setups in AME.BDocument20 pagesApprovals Management Responsibilities and Setups in AME.BAli LoganPas encore d'évaluation
- The Little Book of Deep Learning: An Introduction to Neural Networks, Architectures, and ApplicationsDocument142 pagesThe Little Book of Deep Learning: An Introduction to Neural Networks, Architectures, and Applicationszardu layakPas encore d'évaluation
- Example Italy ItenararyDocument35 pagesExample Italy ItenararyHafshary D. ThanialPas encore d'évaluation
- Aegis SGR BrochureDocument2 pagesAegis SGR BrochureAmazonas ManutençãoPas encore d'évaluation
- Rubrics For Lab Report For PC1 Lab, PC2 Lab, CIC LabDocument4 pagesRubrics For Lab Report For PC1 Lab, PC2 Lab, CIC LabHunie PopPas encore d'évaluation
- Contract of Lease-Water Refilling StationDocument4 pagesContract of Lease-Water Refilling StationEkeena Lim100% (1)
- 2021 Edelman Trust Barometer Press ReleaseDocument3 pages2021 Edelman Trust Barometer Press ReleaseMuhammad IkhsanPas encore d'évaluation
- Group Assignment: Consumer Buying Behaviour Towards ChipsDocument3 pagesGroup Assignment: Consumer Buying Behaviour Towards ChipsvikasPas encore d'évaluation
- Pic32mx1xx2xx283644-Pin Datasheet Ds60001168lDocument350 pagesPic32mx1xx2xx283644-Pin Datasheet Ds60001168lR khanPas encore d'évaluation
- SISU Datenblatt 7-ZylDocument2 pagesSISU Datenblatt 7-ZylMuhammad rizkiPas encore d'évaluation
- Modicon Quantum - 140DDI85300Document5 pagesModicon Quantum - 140DDI85300Samdan NamhaisurenPas encore d'évaluation
- Model 200-30A200P-31-21A Solenoid ValveDocument4 pagesModel 200-30A200P-31-21A Solenoid Valveemuno008Pas encore d'évaluation
- Agro Chems MrRGAgarwalDocument17 pagesAgro Chems MrRGAgarwalapi-3833893Pas encore d'évaluation
- A Study of Factors Influencing The Consumer Behavior Towards Direct Selling Companies With Special Reference To RCM Products1Document79 pagesA Study of Factors Influencing The Consumer Behavior Towards Direct Selling Companies With Special Reference To RCM Products1Chandan SrivastavaPas encore d'évaluation
- Steam Turbine and Governor (SimPowerSystems)Document5 pagesSteam Turbine and Governor (SimPowerSystems)hitmancuteadPas encore d'évaluation
- UE Capability Information (UL-DCCH) - Part2Document51 pagesUE Capability Information (UL-DCCH) - Part2AhmedPas encore d'évaluation
- Portfolio Corporate Communication AuditDocument8 pagesPortfolio Corporate Communication Auditapi-580088958Pas encore d'évaluation
- Jurisdiction of The Supreme CourtDocument1 pageJurisdiction of The Supreme CourtAnshul Yadav100% (1)
- Matching a Vendor's HRSG in THERMOFLEXDocument30 pagesMatching a Vendor's HRSG in THERMOFLEXRafraf EzdinePas encore d'évaluation
- A400 PDFDocument4 pagesA400 PDFsnarmePas encore d'évaluation
- GFRDDocument9 pagesGFRDLalit NagarPas encore d'évaluation
- Soal Pat Inggris 11Document56 pagesSoal Pat Inggris 11dodol garutPas encore d'évaluation
- Private Car Package Policy - Zone B Motor Insurance Certificate Cum Policy ScheduleDocument3 pagesPrivate Car Package Policy - Zone B Motor Insurance Certificate Cum Policy ScheduleijustyadavPas encore d'évaluation
- Kinds of ObligationDocument50 pagesKinds of ObligationKIM GABRIEL PAMITTANPas encore d'évaluation
- 60 Years of Cannes Lions Infographics: The 50sDocument9 pages60 Years of Cannes Lions Infographics: The 50sSapientNitroPas encore d'évaluation
- An-7004 IGBT Driver Calculation Rev00Document8 pagesAn-7004 IGBT Driver Calculation Rev00Raghuram YaramatiPas encore d'évaluation