Académique Documents
Professionnel Documents
Culture Documents
Outline Ways by Which Information Can Be Misused
Transféré par
api-247871582Titre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Outline Ways by Which Information Can Be Misused
Transféré par
api-247871582Droits d'auteur :
Formats disponibles
Outline ways by which information can be misused
Ways in which information can be misused The Internet is not only used by innocent members of the public, but also by fraudulent traders, software pirates, hackers and con-artists, to name but a few. Here are a few ways in which information can be misused:
Violation of privacy Users have passwords to keep their data private and secure it from being stolen or modified. Some computer users such as hackers use software to decipher codes and passwords to gain unauthorised access to computer systems for their own illegal purposes. This violation of privacy resulted in the creation of the Computer Misuse Act of 1990, where users if found guilty were punishable by fines or imprisonment.
There are three levels of hacking:
Viewing another user's information without permission o
this includes accessing someone's files or email or accessing their personal information without their knowledge or permission.
Using accessed information for illegal purposes
o
the information that the user has, is accessed by the hacker and used as blackmail or for unfair advantage
Altering accessed information for fraudulent purposes
o
the hacker alters the accessed information, such as changing figures on bank accounts or deleting files
Propaganda This is a form of communication through email, online articles, websites and other electronic methods, to bias users' attitudes toward supporting a cause. The information shared is usually partially true. This information is bombarded using many electronic methods to create the chosen result in users' attitudes.
Computer Fraud This is a criminal activity where someone uses a computer to defraud an individual or organisation of money or goods. Computer fraud can be difficult to detect because the user committing the crime is very skilled, discreet and difficult to locate since they are accessing the computer through the Internet from another user's computer.
Electronic eavesdropping This is a method of using a computer system to record the keystrokes such as passwords and websites that a user accesses. These details are then transferred over the internet to the illegal user for fraudulent use.
Surveillance
This is where users' activity on the computer is monitored and observed secretly to detect illegal activity. That is, a user can be illegally monitored to see when they perform an illegal activity! Many times this is authorized by governments, huge corporations, or influential individuals. These surveillance programs are used widely and almost anything on the Internet could potentially be monitored for proof of illegal activity.
Identity Theft / Credit card fraud This is when a user pretends to be another user by assuming that person's identity, usually to access credit card information in order to use the funds on the credit card without permission.
Vous aimerez peut-être aussi
- Jamaica Driver's Education Handbook: A Comprehensive Driver Training GuideD'EverandJamaica Driver's Education Handbook: A Comprehensive Driver Training GuidePas encore d'évaluation
- F5 T1 Human Social Biology P2 2010-2011Document12 pagesF5 T1 Human Social Biology P2 2010-2011asjawolverinePas encore d'évaluation
- SBA 2020-2021 v2.1Document12 pagesSBA 2020-2021 v2.1Anthonya KnightPas encore d'évaluation
- Csec Agricultural Science Syllabus With Specimen PapersDocument138 pagesCsec Agricultural Science Syllabus With Specimen Papersapi-508592459Pas encore d'évaluation
- Edpm 2019 S.B.ADocument13 pagesEdpm 2019 S.B.Aalexcharles433Pas encore d'évaluation
- RequiredDocuments For SLBDocument2 pagesRequiredDocuments For SLBRenesha AtkinsonPas encore d'évaluation
- Caribbean Examinations Council Caribbean Secondary Certificate of Education Guidelines For On-Site Moderation SciencesDocument9 pagesCaribbean Examinations Council Caribbean Secondary Certificate of Education Guidelines For On-Site Moderation SciencesjokerPas encore d'évaluation
- HSB Unit Test 2Document11 pagesHSB Unit Test 2Jessica Kinney0% (1)
- Cape IT Unit 1 Mod 1 Christmas Exam 2012 Paper 1b ANSWERSDocument9 pagesCape IT Unit 1 Mod 1 Christmas Exam 2012 Paper 1b ANSWERSaflayersPas encore d'évaluation
- CXC It May - June 2012Document12 pagesCXC It May - June 2012jason deruloPas encore d'évaluation
- July 8 CXC BiologyDocument66 pagesJuly 8 CXC BiologyShantay BurtonPas encore d'évaluation
- CSEC Information Technology January 2018 P2Document21 pagesCSEC Information Technology January 2018 P2Tyrese SmithPas encore d'évaluation
- Computer Fundamentals and Information ProcessingDocument132 pagesComputer Fundamentals and Information ProcessingRicardo EdwardsPas encore d'évaluation
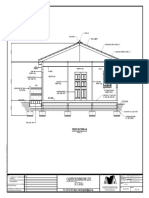
- Cadtech Designs Ltd. (C.T.D.L) : Cross Section A-ADocument2 pagesCadtech Designs Ltd. (C.T.D.L) : Cross Section A-Aceon sampsonPas encore d'évaluation
- Csec Integrated Science - Radiation NotesDocument12 pagesCsec Integrated Science - Radiation NotesSelina SookhansinghPas encore d'évaluation
- It Syllabus CapeDocument162 pagesIt Syllabus CapeGrace JohnPas encore d'évaluation
- HSB Sba.: Wednesday, October 27, 2021 10:44 AMDocument1 pageHSB Sba.: Wednesday, October 27, 2021 10:44 AMdamian pierre0% (1)
- CSEC Bio Notes 2Document14 pagesCSEC Bio Notes 2MiaPas encore d'évaluation
- MSG 10 MeasurementsDocument13 pagesMSG 10 MeasurementsKaira PaulPas encore d'évaluation
- CAPE - Agricultural Science - UNIT 1 - Animal ProductionDocument28 pagesCAPE - Agricultural Science - UNIT 1 - Animal Productionkeith Da SilvaPas encore d'évaluation
- Cape+2016 It MockDocument7 pagesCape+2016 It MockannmariePas encore d'évaluation
- CSEC IT Study GuideDocument7 pagesCSEC IT Study Guideasww adsdPas encore d'évaluation
- Mark Scheme End of Year Exam: EDPM Paper 2 Question 1 (Copy Test) Total 10 Marks AccuracyDocument6 pagesMark Scheme End of Year Exam: EDPM Paper 2 Question 1 (Copy Test) Total 10 Marks AccuracyJanicSmithPas encore d'évaluation
- Cape It Unit 2 Notes Mod 2 So 13 HTML PDFDocument26 pagesCape It Unit 2 Notes Mod 2 So 13 HTML PDFSadeGreenePas encore d'évaluation
- Cape It IaDocument25 pagesCape It Iaannmarie100% (1)
- Csec Industrial Technology: Building and Furniture TechnologyDocument267 pagesCsec Industrial Technology: Building and Furniture TechnologyEldon LiburdPas encore d'évaluation
- UNIT 8 Number Sequences CSEC Revision TestDocument5 pagesUNIT 8 Number Sequences CSEC Revision TestAmaziah GedaliahPas encore d'évaluation
- FORM TP 2014044: 1 Hour 15 MinutesDocument11 pagesFORM TP 2014044: 1 Hour 15 MinutesIsraelPas encore d'évaluation
- SBA Treatment Handbook For LRs - V02Document52 pagesSBA Treatment Handbook For LRs - V02Joy NapierPas encore d'évaluation
- Information Systems Development Methodologies in PDFDocument6 pagesInformation Systems Development Methodologies in PDFsuyatno sstPas encore d'évaluation
- Math May-June 2015Document32 pagesMath May-June 2015shaniahPas encore d'évaluation
- CSEC Biology January 2005 P3Document4 pagesCSEC Biology January 2005 P3Makayla AlexanderPas encore d'évaluation
- July 2020 p2 AnswersDocument18 pagesJuly 2020 p2 AnswersMs. ButePas encore d'évaluation
- Not Geography Past Papers IgnoreDocument3 pagesNot Geography Past Papers IgnoreJay JustPas encore d'évaluation
- OUP - Just Click For The CaribbeanDocument292 pagesOUP - Just Click For The CaribbeanDemetre ford100% (1)
- CSEC Biology June 2002 P1 Specimen PaperDocument13 pagesCSEC Biology June 2002 P1 Specimen PaperJoy BoehmerPas encore d'évaluation
- CSEC Study Guide - February 22, 2011Document11 pagesCSEC Study Guide - February 22, 2011ChantelleMorrisonPas encore d'évaluation
- CAPE IT UNIT 1 Past Paper QuestionsDocument23 pagesCAPE IT UNIT 1 Past Paper QuestionsSieana ClarkePas encore d'évaluation
- Grade 10 Human BioDocument6 pagesGrade 10 Human BioJohn ThomasPas encore d'évaluation
- Chemistry SBA P3 Jan 2015Document8 pagesChemistry SBA P3 Jan 2015ValPas encore d'évaluation
- CXC Mock Exam 2010 IT Paper 2 Questions and AnswersDocument14 pagesCXC Mock Exam 2010 IT Paper 2 Questions and AnswersAkini SamuelsPas encore d'évaluation
- CXC Jan 2000 p2Document7 pagesCXC Jan 2000 p2omar_oj_40% (1)
- CXC Accounts - SBA Mark Scheme - 2 - 0Document2 pagesCXC Accounts - SBA Mark Scheme - 2 - 0Fada FrassPas encore d'évaluation
- POB WorksheetDocument11 pagesPOB WorksheetGavin LeePas encore d'évaluation
- CSEC Principles of AccountsDocument38 pagesCSEC Principles of AccountsSydney BaboolalPas encore d'évaluation
- CSEC Geography Specimen Paper 01Document13 pagesCSEC Geography Specimen Paper 01Ashleigh JarrettPas encore d'évaluation
- HSB - Lesson A1Document31 pagesHSB - Lesson A1Osmany MadrigalPas encore d'évaluation
- CSEC Integrated Science June 2014 P032Document12 pagesCSEC Integrated Science June 2014 P032Courtney mcintoshPas encore d'évaluation
- CSEC Physics - Definitions and FormulaeDocument39 pagesCSEC Physics - Definitions and FormulaeA.BensonPas encore d'évaluation
- Maths MCDocument5 pagesMaths MCADrian ZeeGreatPas encore d'évaluation
- Agriculture TestDocument10 pagesAgriculture TestAlijan DamaniPas encore d'évaluation
- Living Organisms and Cells MCQDocument3 pagesLiving Organisms and Cells MCQOsmany Madrigal100% (1)
- Sexual Reproduction in PlantsDocument2 pagesSexual Reproduction in PlantsMichael TimsonPas encore d'évaluation
- HSB - Inheritance and GenesDocument16 pagesHSB - Inheritance and GenesJalisaPas encore d'évaluation
- CXC CSEC Math Exam Pass Rates - CaribExamsDocument1 pageCXC CSEC Math Exam Pass Rates - CaribExamsS.L.L.C100% (1)
- Csec It Mock ExamDocument10 pagesCsec It Mock Examvidur_talreja100% (1)
- Form 3 t1 Scheme of Work Re Pob SyllabusDocument3 pagesForm 3 t1 Scheme of Work Re Pob Syllabusapi-298964589Pas encore d'évaluation
- June 2018 p1Document10 pagesJune 2018 p1SalomePas encore d'évaluation
- Misuse of Information in Data IntegrityDocument2 pagesMisuse of Information in Data IntegrityMildred C. WaltersPas encore d'évaluation
- Cyber SecurityDocument17 pagesCyber SecurityDhrumil DancerPas encore d'évaluation
- Powerpoint TutorialDocument38 pagesPowerpoint TutorialRenzkhurt bautistaPas encore d'évaluation
- GR 11 It Mte 2018 Final 1Document7 pagesGR 11 It Mte 2018 Final 1api-247871582Pas encore d'évaluation
- Tournament Excel NewDocument4 pagesTournament Excel Newapi-247871582Pas encore d'évaluation
- CXC It Practice Questions 2022Document2 pagesCXC It Practice Questions 2022api-247871582Pas encore d'évaluation
- Msword PresentationDocument8 pagesMsword Presentationapi-247871582Pas encore d'évaluation
- Yousef Almulla: This Is A Complete Research On Effective Communication With More Emphasis On WorkplaceDocument109 pagesYousef Almulla: This Is A Complete Research On Effective Communication With More Emphasis On WorkplaceArshad NazarPas encore d'évaluation
- SoftwareDocument46 pagesSoftwareapi-247871582Pas encore d'évaluation
- ExcelnotesDocument34 pagesExcelnotesapi-247871582Pas encore d'évaluation
- Wordprocessing Presentation 2Document35 pagesWordprocessing Presentation 2api-247871582Pas encore d'évaluation
- Communication in The Workplace Class AssignmentDocument2 pagesCommunication in The Workplace Class Assignmentapi-247871582Pas encore d'évaluation
- Excel: A Brief OverviewDocument31 pagesExcel: A Brief Overviewprakash1010100% (1)
- Msword PresentationDocument8 pagesMsword Presentationapi-247871582Pas encore d'évaluation
- Excel Practical ActivityDocument2 pagesExcel Practical Activityapi-247871582Pas encore d'évaluation
- 6 MGMT PPT 1Document37 pages6 MGMT PPT 1api-247871582Pas encore d'évaluation
- Communicate in The WorkplaceDocument36 pagesCommunicate in The Workplaceapi-247871582100% (2)
- Grade 11 Mock ExamDocument1 pageGrade 11 Mock Examapi-247871582Pas encore d'évaluation
- Apply Occupational Health and Safety Procedures 1Document16 pagesApply Occupational Health and Safety Procedures 1api-247871582100% (2)
- GR 11 It Mte 2018 Final 1Document7 pagesGR 11 It Mte 2018 Final 1api-247871582Pas encore d'évaluation
- Itimed1092a - Operate A Presentation Package AdvanceDocument6 pagesItimed1092a - Operate A Presentation Package Advanceapi-247871582Pas encore d'évaluation
- bsbmkp0054b - Design and Deliver PresentationDocument5 pagesbsbmkp0054b - Design and Deliver Presentationapi-247871582Pas encore d'évaluation
- Health and Safety NotesDocument3 pagesHealth and Safety Notesapi-247871582100% (1)
- Msword PresentationDocument8 pagesMsword Presentationapi-247871582Pas encore d'évaluation
- Types of Fire ExtinguishersDocument20 pagesTypes of Fire Extinguishersapi-247871582Pas encore d'évaluation
- Hcit Excel Final TaskDocument2 pagesHcit Excel Final Taskapi-247871582100% (1)
- Input DevicesDocument5 pagesInput Devicesapi-247871582Pas encore d'évaluation
- Itidat1072a Operate Spreadsheet Application AdvanceDocument5 pagesItidat1072a Operate Spreadsheet Application Advanceapi-247871582Pas encore d'évaluation
- Parent Mentor Training Manual - 21st Century Parenting ModuleDocument31 pagesParent Mentor Training Manual - 21st Century Parenting Moduleapi-247871582Pas encore d'évaluation
- Parenting Digital Age Slideshare 100626122454 Phpapp02Document67 pagesParenting Digital Age Slideshare 100626122454 Phpapp02api-247871582Pas encore d'évaluation
- Parent Mentor Training Manual - 21st Century Parenting ModuleDocument31 pagesParent Mentor Training Manual - 21st Century Parenting Moduleapi-247871582Pas encore d'évaluation
- Sandra ScottDocument7 pagesSandra Scottapi-247871582Pas encore d'évaluation
- Haines Man Sentenced To 20 Years in Prison For Sexually Exploiting MinorsDocument2 pagesHaines Man Sentenced To 20 Years in Prison For Sexually Exploiting MinorsAlaska's News SourcePas encore d'évaluation
- Various Cases in ConflictsDocument221 pagesVarious Cases in ConflictsHollyhock MmgrzhfmPas encore d'évaluation
- Woolridge V SumnerDocument30 pagesWoolridge V SumnerBernice Purugganan AresPas encore d'évaluation
- PNB vs. Nepumuceno ProductionsDocument2 pagesPNB vs. Nepumuceno Productionsjune bay100% (1)
- Waiving of Right Must Be Consented To by All Due Process RightsDocument17 pagesWaiving of Right Must Be Consented To by All Due Process RightsTitle IV-D Man with a plan100% (2)
- CasesDocument130 pagesCasesHuehuehuePas encore d'évaluation
- J Butler - Revisiting Bodies and PleasuresDocument10 pagesJ Butler - Revisiting Bodies and PleasuresDiego Madias100% (1)
- Klasa - 7 - Placement - Test - Answer KeyDocument2 pagesKlasa - 7 - Placement - Test - Answer KeyKarolina PawlakPas encore d'évaluation
- Freedom of SpeechDocument7 pagesFreedom of Speechلبنیٰ افتخارPas encore d'évaluation
- Legal Issues in Psychiatric NursingDocument24 pagesLegal Issues in Psychiatric NursingRic TinPas encore d'évaluation
- Members of The Propaganda MovementDocument2 pagesMembers of The Propaganda MovementjhomalynPas encore d'évaluation
- Reading Passage - Worksheet 3Document2 pagesReading Passage - Worksheet 3Aishath AfzaPas encore d'évaluation
- Jewish TravelerDocument60 pagesJewish TravelerAna HiršlPas encore d'évaluation
- 2008 Precinct Tally ALABAMA To MICHIGANDocument117 pages2008 Precinct Tally ALABAMA To MICHIGANJohn MPas encore d'évaluation
- Diana Novak's ResumeDocument1 pageDiana Novak's Resumedhnovak5Pas encore d'évaluation
- DH 1129Document12 pagesDH 1129The Delphos HeraldPas encore d'évaluation
- Juvenile Delinquency Prevention Program FinalDocument11 pagesJuvenile Delinquency Prevention Program FinaleliasPas encore d'évaluation
- The Impact of Bullying in School On The Adolescent's Sense of SelfDocument175 pagesThe Impact of Bullying in School On The Adolescent's Sense of Selfgina dunggonPas encore d'évaluation
- Petition for Nullity Ruling on Psychological IncapacityDocument4 pagesPetition for Nullity Ruling on Psychological IncapacitykeziahcorporalPas encore d'évaluation
- Export Processing Zone Authority vs. Hon. Ceferino E. DulayDocument3 pagesExport Processing Zone Authority vs. Hon. Ceferino E. DulayDei GonzagaPas encore d'évaluation
- Peak Ebpp DescriptionDocument4 pagesPeak Ebpp Descriptionapi-259241412Pas encore d'évaluation
- Legal Aspects of Business: Indian Institute of Management, Rohtak Post Graduate ProgrammeDocument5 pagesLegal Aspects of Business: Indian Institute of Management, Rohtak Post Graduate ProgrammeAKANKSHA SINGHPas encore d'évaluation
- Supreme Court Rules LRTA Has Standing to Appeal Civil Service RulingDocument18 pagesSupreme Court Rules LRTA Has Standing to Appeal Civil Service RulingKristela AdraincemPas encore d'évaluation
- Notice of Loss RequirementsDocument5 pagesNotice of Loss RequirementsRodel Cadorniga Jr.Pas encore d'évaluation
- JISSCOR Union estopped from protesting electionDocument2 pagesJISSCOR Union estopped from protesting electionAngelo TiglaoPas encore d'évaluation
- C 55 N O F C'E OF H or 1 55 N Sieci'Te A RIDocument1 pageC 55 N O F C'E OF H or 1 55 N Sieci'Te A RIRonna FererPas encore d'évaluation
- TAC Syllabus for 02A/OV-10 Pilot TrainingDocument39 pagesTAC Syllabus for 02A/OV-10 Pilot TrainingSesquipedaliacPas encore d'évaluation
- How To Handle Cargo ClaimsDocument3 pagesHow To Handle Cargo Claimspinko11Pas encore d'évaluation
- 25 CONVOCAca ODocument2 pages25 CONVOCAca OPr walcyr JuniorPas encore d'évaluation
- Civil procedure; Prescription of claims in intestate proceedingsDocument11 pagesCivil procedure; Prescription of claims in intestate proceedingsFrance De LunaPas encore d'évaluation