Académique Documents
Professionnel Documents
Culture Documents
Synopsis: TITLE-Cryptography What Is Cryptography: Cryptography Is The Practice and
Transféré par
manish240519880 évaluation0% ont trouvé ce document utile (0 vote)
45 vues3 pagesPublic-key cryptography was invented in 1976 by Whitfield Diffie and Martin Hellman. In this system, each person gets a pair of keys, called the public key and the private key. RSA encryption is widely used and is a 'de-facto' encryption standard.
Description originale:
Titre original
crypto1
Copyright
© Attribution Non-Commercial (BY-NC)
Formats disponibles
DOC, PDF, TXT ou lisez en ligne sur Scribd
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentPublic-key cryptography was invented in 1976 by Whitfield Diffie and Martin Hellman. In this system, each person gets a pair of keys, called the public key and the private key. RSA encryption is widely used and is a 'de-facto' encryption standard.
Droits d'auteur :
Attribution Non-Commercial (BY-NC)
Formats disponibles
Téléchargez comme DOC, PDF, TXT ou lisez en ligne sur Scribd
0 évaluation0% ont trouvé ce document utile (0 vote)
45 vues3 pagesSynopsis: TITLE-Cryptography What Is Cryptography: Cryptography Is The Practice and
Transféré par
manish24051988Public-key cryptography was invented in 1976 by Whitfield Diffie and Martin Hellman. In this system, each person gets a pair of keys, called the public key and the private key. RSA encryption is widely used and is a 'de-facto' encryption standard.
Droits d'auteur :
Attribution Non-Commercial (BY-NC)
Formats disponibles
Téléchargez comme DOC, PDF, TXT ou lisez en ligne sur Scribd
Vous êtes sur la page 1sur 3
SYNOPSIS
TITLE- Cryptography
What is Cryptography: cryptography is the practice and
hiding information. It is to be noted that encryption is no
longer an exemptible option when conducting ecommerce.
Given the importance it bears on ecommerce, it id one area
that will have its share of security concerns as well.
Encryption on its own cannot guarantee foolproof security so
cryptography is to be needed.
Public-key cryptography:
• Public-key cryptography was invented in 1976 by
Whitfield Diffie and Martin Hellman.
• In this system, each person gets a pair of keys, called
the public key and the private key.
• Each person’s public key is published while the private
key is kept secret.
• Anyone can send a confidential message just using
public information, but it can only be decrypted with a
private key that is in the sole possession of the
intended recipient.
Cryptography can be classified as the study of
techniques and applications that depend on the existence of
difficult problems. A cryptanalyst attempts to compromise
cryptographic mechanisms and cryptology (from the Greek
kryptos logos, meaning “hidden word”) is the discipline of
cryptography and cryptanalysis combined.
The concept of public key cryptography is to solve the key
management problem. In their concept, each person gets a
pair of keys one called public key and other is called private
key. This eliminates the need for the sender and receiver to
share secret information, as all communication involve only
public keys, and no private key is ever transmitted or
shared. This option also secured the communication against
eavesdropping or betrayal.
The only requirement is that public keys must be associated
with their users in a trusted manner. With PKI, anyone can
send a confidential message by using public key, which is in
the possession of the intended recipient. Furthermore,
public-key cryptography meets the need for privacy and
authentication.
Important points:
• Using public key infrastructure (PKI), anyone can send a
confidential message using public information, which
can be decrypted with a private key in the sole
possession of the intended recipient.
• RSA encryption is widely used and is a ‘de-facto’
encryption standard.
• The MD5 algorithm is intended for digital signature
applications, where large file must be compressed
securely before being encrypted.
Submitted To:
Submitted by:
Amit Mishra Manish Tanwar
Astt. Professor IV Year, A2
Computer
Science
Vous aimerez peut-être aussi
- Cse CryptographyDocument19 pagesCse Cryptographytejas it do d he got f foods manchiPas encore d'évaluation
- Computer Cryptography: Code - A Set of Information That Will Allow Words To Be Changed To Other WordsDocument5 pagesComputer Cryptography: Code - A Set of Information That Will Allow Words To Be Changed To Other WordsTemitayo OyinPas encore d'évaluation
- Term PaperDocument5 pagesTerm PaperSai Teja UppuluriPas encore d'évaluation
- Cryptography: Presented byDocument11 pagesCryptography: Presented byapi-19799369Pas encore d'évaluation
- CryptographyDocument14 pagesCryptographyPankaj AggarwalPas encore d'évaluation
- Cryptography ReportDocument16 pagesCryptography ReportGRACEPas encore d'évaluation
- LESSON 6 - CryptographyDocument12 pagesLESSON 6 - CryptographyKIBEPas encore d'évaluation
- ON Cryptography: BY: Deepak Krishna 08/ ME/08 Mechanical Fiem, KolkataDocument14 pagesON Cryptography: BY: Deepak Krishna 08/ ME/08 Mechanical Fiem, KolkataEmanuel MaričićPas encore d'évaluation
- Topic 7 - Cryptography & PKIDocument33 pagesTopic 7 - Cryptography & PKIs.l.mills86Pas encore d'évaluation
- Cryptography: P.Nikhila N.Vishnu PriyaDocument13 pagesCryptography: P.Nikhila N.Vishnu PriyaNIkhila ReddyPas encore d'évaluation
- Cryptography: Latika Arora, IT/06/321Document5 pagesCryptography: Latika Arora, IT/06/321Yatish TagraPas encore d'évaluation
- CrytographyDocument21 pagesCrytographySonia AgrawalPas encore d'évaluation
- IS AssignmentDocument24 pagesIS Assignmentyuvanpgr-wm20Pas encore d'évaluation
- Types of CryptographyDocument11 pagesTypes of CryptographyBridget Smith92% (12)
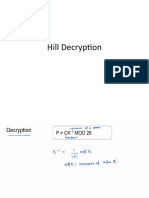
- Hill DecryptionDocument49 pagesHill DecryptionDhamodaran SrinivasanPas encore d'évaluation
- CryptographywordDocument3 pagesCryptographywordRUBENPas encore d'évaluation
- Data Comm Presentation - IVDocument7 pagesData Comm Presentation - IVNeha PankiPas encore d'évaluation
- Cryptography: Encryption Is The Process of Transforming Information (Referred To As Plaintext)Document16 pagesCryptography: Encryption Is The Process of Transforming Information (Referred To As Plaintext)Gaurav KumarPas encore d'évaluation
- Cse CryptographyDocument15 pagesCse CryptographyPrasannaPas encore d'évaluation
- Cse CryptographyDocument18 pagesCse Cryptographyholyshit453Pas encore d'évaluation
- SohaiDocument16 pagesSohaiJHON ANDREI SEMAPas encore d'évaluation
- Cryptography: Hiding The WordDocument18 pagesCryptography: Hiding The WordNiharika BundelaPas encore d'évaluation
- Easychair Preprint: Esha Rawat, Anuska Singh, Alap Mahar and Amit AgarwalDocument7 pagesEasychair Preprint: Esha Rawat, Anuska Singh, Alap Mahar and Amit AgarwalStubborn BloodPas encore d'évaluation
- Paper Presentation On Network Security & Cryptography: Aditya Engineering CollegeDocument6 pagesPaper Presentation On Network Security & Cryptography: Aditya Engineering CollegeSujit SeelaPas encore d'évaluation
- Cryptography Full ReportDocument9 pagesCryptography Full ReportSushant SharmaPas encore d'évaluation
- Information SecurityDocument11 pagesInformation Securityapi-3798998Pas encore d'évaluation
- Assymetric CryptographyDocument2 pagesAssymetric CryptographyMisa PerisicPas encore d'évaluation
- CSE Cryptography ReportDocument21 pagesCSE Cryptography ReportOtunuya Chukwudi Henry EngrPas encore d'évaluation
- Presentation On Cryptograph Y: Submitted byDocument13 pagesPresentation On Cryptograph Y: Submitted byBidya dhar pandeyPas encore d'évaluation
- Cse CryptographyDocument18 pagesCse CryptographysavisuPas encore d'évaluation
- Key DistributionDocument1 pageKey DistributionAndo JoshuaPas encore d'évaluation
- UntitledDocument154 pagesUntitledJuanca100% (1)
- Cse CryptographyDocument18 pagesCse CryptographyHari HaranPas encore d'évaluation
- Cryptography and Network SecurityDocument11 pagesCryptography and Network Securityapi-26830587100% (2)
- Cryptography and Network SecurityDocument11 pagesCryptography and Network SecuritypreetiPas encore d'évaluation
- Cryptography and Network Security PDFDocument11 pagesCryptography and Network Security PDFpreetiPas encore d'évaluation
- Cryptography and Its TypesDocument2 pagesCryptography and Its TypesSaloni ChaudharyPas encore d'évaluation
- Khairunnisa Binti MD ZahirDocument8 pagesKhairunnisa Binti MD ZahirMichałPas encore d'évaluation
- Qdoc - Tips - Cryptography and Network SecurityDocument11 pagesQdoc - Tips - Cryptography and Network SecurityTic tokPas encore d'évaluation
- Cryptography and Network SecurityDocument11 pagesCryptography and Network SecurityRaymondPas encore d'évaluation
- Public Key Infrastructure by Muhedin Abdullahi MohammedDocument123 pagesPublic Key Infrastructure by Muhedin Abdullahi Mohammedshabir AhmadPas encore d'évaluation
- CSModule2 Part2Document21 pagesCSModule2 Part2OK BYEPas encore d'évaluation
- CryptographyDocument20 pagesCryptographySrilekha RajakumaranPas encore d'évaluation
- Unit 307Document25 pagesUnit 307n9166254105Pas encore d'évaluation
- Topic: Cryptology: History of CryptographyDocument24 pagesTopic: Cryptology: History of CryptographyAziz Ur RehmanPas encore d'évaluation
- Chapter 3Document120 pagesChapter 3Azmeraw ZenawPas encore d'évaluation
- CryptographyDocument19 pagesCryptographySrilekha RajakumaranPas encore d'évaluation
- Information Systems Security LAB: Asymmetric CryptographyDocument11 pagesInformation Systems Security LAB: Asymmetric CryptographyAbdullah Al-HallakPas encore d'évaluation
- CNS Lect 6.0Document17 pagesCNS Lect 6.0Sameer KhanPas encore d'évaluation
- Cryptography: Joemari Saysay Sabao, MitDocument17 pagesCryptography: Joemari Saysay Sabao, Mitpia espanilloPas encore d'évaluation
- Principes of CryptologyDocument15 pagesPrincipes of CryptologyAbdul Rehman AhmadPas encore d'évaluation
- What Is Cryptography - Definition FromDocument2 pagesWhat Is Cryptography - Definition FromGirgio Moratti CullenPas encore d'évaluation
- Major Doc Fine1Document75 pagesMajor Doc Fine1Anil SagarPas encore d'évaluation
- EncryptionDocument4 pagesEncryptionNadeem MahmoodPas encore d'évaluation
- Chapter Four Security Techniques Origin of CryptographyDocument33 pagesChapter Four Security Techniques Origin of CryptographyGetnete degemuPas encore d'évaluation
- CryptographyDocument27 pagesCryptographyganesh_ecb123Pas encore d'évaluation
- Explain Basic Objectives of CryptographyDocument62 pagesExplain Basic Objectives of Cryptographyrojemav574Pas encore d'évaluation
- Encryption Demystified The Key to Securing Your Digital LifeD'EverandEncryption Demystified The Key to Securing Your Digital LifePas encore d'évaluation
- Cryptology for Beginners #1 Guide for Security, Encryption, Crypto, Algorithms and PythonD'EverandCryptology for Beginners #1 Guide for Security, Encryption, Crypto, Algorithms and PythonPas encore d'évaluation
- CC Certified in Cybersecurity The Complete ISC2 Certification Study GuideD'EverandCC Certified in Cybersecurity The Complete ISC2 Certification Study GuidePas encore d'évaluation
- Units 7 and 8 - Computer Etiquette and Computer & CyberSecuritiesDocument20 pagesUnits 7 and 8 - Computer Etiquette and Computer & CyberSecuritiesmarsan walangPas encore d'évaluation
- RSA and ECC Thesis PDFDocument21 pagesRSA and ECC Thesis PDFHarpreet SinghPas encore d'évaluation
- Utica-CYBERCERTGRAD Currguide HiresDocument3 pagesUtica-CYBERCERTGRAD Currguide HiresCas NascimentoPas encore d'évaluation
- A.1 Cross-Site ScriptingDocument7 pagesA.1 Cross-Site ScriptingJastine AnnePas encore d'évaluation
- C235 - IT Security and Management: Modern Symmetric CiphersDocument33 pagesC235 - IT Security and Management: Modern Symmetric CiphersSundeel Bin HaleemPas encore d'évaluation
- White Paper Template 27Document44 pagesWhite Paper Template 27mPas encore d'évaluation
- 05 - Anonymous CommunicationDocument52 pages05 - Anonymous CommunicationDaudet Polycarpe TiomelaPas encore d'évaluation
- Attacktive Dierctory ReportDocument5 pagesAttacktive Dierctory ReportAjay KulkarniPas encore d'évaluation
- Cyber Arms - Security in CyberspaceDocument395 pagesCyber Arms - Security in CyberspaceEvandro SantosPas encore d'évaluation
- Lab Experiment #04 - Live Vulnerability On Internet DevicesDocument4 pagesLab Experiment #04 - Live Vulnerability On Internet DevicesKatherine PiercePas encore d'évaluation
- Hands-On Ethical Hacking and Network Defense: Linux Operating System VulnerabilitiesDocument40 pagesHands-On Ethical Hacking and Network Defense: Linux Operating System VulnerabilitiespreethaPas encore d'évaluation
- How To Hack WifiDocument10 pagesHow To Hack WifiJakyy100% (1)
- Cyber Security Fundamental To India S SovereigntyDocument19 pagesCyber Security Fundamental To India S SovereigntyAkshayPas encore d'évaluation
- Detecting Ransomware With Alienvault UsmDocument6 pagesDetecting Ransomware With Alienvault UsmKhoa Nguyen Hong NguyenPas encore d'évaluation
- Outbound Mail Returned by MAILER-DAEMON@Document1 pageOutbound Mail Returned by MAILER-DAEMON@Yuran NevesPas encore d'évaluation
- Topic 1A: Identify Security Control TypesDocument525 pagesTopic 1A: Identify Security Control TypesANGEL SAYANIPas encore d'évaluation
- SLM - Unit 01Document22 pagesSLM - Unit 01SureshPas encore d'évaluation
- Danielle Keats Citron, Hate Crimes in Cyberspace (2014)Document352 pagesDanielle Keats Citron, Hate Crimes in Cyberspace (2014)Tzu MinminPas encore d'évaluation
- FBI Letter To Senator WydenDocument6 pagesFBI Letter To Senator WydenSoftpediaPas encore d'évaluation
- Revision Questions Class:VIII Topics:Virus & Anti Virus, Frames in HTML Multiple Choice QuestionsDocument6 pagesRevision Questions Class:VIII Topics:Virus & Anti Virus, Frames in HTML Multiple Choice QuestionsAbottPas encore d'évaluation
- Xstream 3-2-2022Document16 pagesXstream 3-2-2022Hichem Ghouti0% (1)
- Iso27002 2022Document1 pageIso27002 2022bona utamaPas encore d'évaluation
- Attributes Impacting Cybersecurity Policy DevelopmentDocument23 pagesAttributes Impacting Cybersecurity Policy Developmentjuly aniñirPas encore d'évaluation
- Hydra PDFDocument23 pagesHydra PDFPentest PentestPas encore d'évaluation
- 7 Email Red FlagsDocument1 page7 Email Red FlagsalbertopaezPas encore d'évaluation
- Nana D 5 DR CVDocument2 pagesNana D 5 DR CVChakri ChaturvedPas encore d'évaluation
- Screenshot 2023-02-25 at 09.35.32Document1 pageScreenshot 2023-02-25 at 09.35.32EesaPas encore d'évaluation
- Cisco ESA Admin Guide 14-0Document1 416 pagesCisco ESA Admin Guide 14-0Samir AliyevPas encore d'évaluation
- Certified Network Security Specialist CNSS QuestionsDocument14 pagesCertified Network Security Specialist CNSS QuestionsKaroPas encore d'évaluation
- WSC2019 TP54 ModuleA ActualDocument10 pagesWSC2019 TP54 ModuleA ActualDũng Dương ĐìnhPas encore d'évaluation