Académique Documents
Professionnel Documents
Culture Documents
312 38
Transféré par
Sumazly SulaimanDescription originale:
Titre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
312 38
Transféré par
Sumazly SulaimanDroits d'auteur :
Formats disponibles
PassGuide 312-38
EC-Council 312-38
EC-Council Network Security Administrator
Q&A Demo
(C) Copyright 2006-2011 CertBible Tech LTD,All Rights Reserved.
Build Your Dreams
PassGuide 312-38
Important Note
Please Read Carefully
Study Tips
This product will provide you questions and answers carefully compiled and written by our
experts. Try to understand the concepts behind the questions instead of cramming the
questions.
Go through the entire document at least twice so that you make sure that you are not missing
anything.
Latest Version
We are constantly reviewing our products. New material is added and old material is revised.
Free updates are available for 120 days after the purchase. You should check your member
zone at PassGuide an update 3-4 days before the scheduled exam date.
Feedback
If you spot a possible improvement then please let us know. We always interested in
improving product quality.
Feedback should be send to feedback@passguide.com. You should include the following:
Exam number, version, page number, question number, and your login ID.
Our experts will answer your mail promptly.
Be Prepared. Be Confident. Get Certified.
-------------------------------------------------------------------------------------------------------------------------
Sales and Support Manager
Sales Team. sales@passguide.com Support Team. support@passguide.com
---------------------------------------------------------------------------------------------------------------------
Copyright
Each pdf file contains a unique serial number associated with your particular name and
contact information for security purposes. So if we find out that a particular pdf file is being
distributed by you, CertBible reserves the right to take legal action against you according to
the International Copyright Laws.
Build Your Dreams
PassGuide 312-38
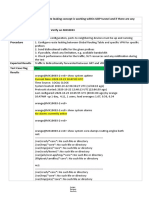
Question: 1
Fill in the blank with the appropriate term.
______________is typically carried out by a remote attacker attempting to gain information or
access to a network on which it is not authorized or allowed.
A. Network reconnaissance
Answer: A
Question: 2
A __________is a term in computer terminology used for a trap that is set to detect, deflect,
or in some manner counteract attempts at unauthorized use of information systems.
A. honeypot
Answer: A
Question: 3
You have just set up a wireless network for customers at a coffee shop. Which of the
following are good security measures to implement?
Each correct answer represents a complete solution. Choose two.
A. Using WPA encryption
B. Using WEP encryption
C. Not broadcasting SSID
D. MAC filtering the router
Answer: A, B
Question: 4
Which of the following is a non-profit organization that oversees the allocation of IP addresses,
management of the DNS infrastructure, protocol parameter assignment, and root server
system management?
A. ITU
B. ICANN
C. IEEE
D. ANSI
Answer: B
Question: 5
Which of the following is a network maintenance protocol of the TCP/IP protocol suite that is
responsible for the resolution of IP addresses to media access control (MAC) addresses of a
Build Your Dreams
PassGuide 312-38
network interface card (NIC)?
A. ARP
B. RARP
C. DHCP
D. PIM
Answer: A
Question: 6
Which of the following tools is an open source network intrusion prevention and detection
system that operates as a network sniffer and logs activities of the network that is matched
with the predefined signatures?
A. Kismet
B. Snort
C. Dsniff
D. KisMAC
Answer: B
Question: 7
The __________is used for routing voice conversations over the Internet. It is also known by
other names such as IP Telephony, Broadband Telephony, etc.
A. VoIP
Answer: A
Question: 8
Which of the following fields in the IPv6 header is decremented by 1 for each router that
forwards the packet?
A. Next header
B. Traffic class
C. Hop limit
D. Flow label
Answer: C
Question: 9
Which of the following IP class addresses are not allotted to hosts?
Each correct answer represents a complete solution. Choose all that apply.
Build Your Dreams
PassGuide 312-38
A. Class E
B. Class C
C. Class D
D. Class A
E. Class B
Answer: A, C
Question: 10
Mark works as a Network Administrator for Infonet Inc. The company has a Windows 2000
Active Directory domain-based network. The domain contains one hundred Windows XP
Professional client computers. Mark is deploying an 802.11 wireless LAN on the network. The
wireless LAN will use Wired Equivalent Privacy (WEP) for all the connections. According to
the company's security policy, the client computers must be able to automatically connect to
the wireless LAN. However, the unauthorized computers must not be allowed to connect to
the wireless LAN and view the wireless network. Mark wants to configure all the wireless
access points and client computers to act in accordance with the company's security policy.
What will he do to accomplish this?
Each correct answer represents a part of the solution. Choose three.
A. Configure the authentication type for the wireless LAN to Open system.
B. Disable SSID Broadcast and enable MAC address filtering on all wireless access points.
C. On each client computer, add the SSID for the wireless LAN as the preferred network.
D. Broadcast SSID to connect to the access point (AP).
E. Configure the authentication type for the wireless LAN to Shared Key.
F. Install a firewall software on each wireless access point.
Answer: B, C, E
Question: 11
Which of the following is a digital telephone/telecommunication network that carries voice,
data, and video over an existing telephone network infrastructure?
A. X.25
B. Frame relay
C. PPP
D. ISDN
Answer: D
Question: 12
Peter, a malicious hacker, obtains e-mail addresses by harvesting them from postings, blogs,
DNS listings, and Web pages. He then sends large number of unsolicited commercial e-
mail (UCE) messages on these addresses. Which of the following e-mail crimes is Peter
Build Your Dreams
PassGuide 312-38
committing?
A. E-mail Storm
B. E-mail bombing
C. E-mail Spam
D. E-mail spoofing
Answer: C
Question: 13
John works as a C programmer. He develops the following C program:
#include <stdlib.h>
#include <stdio.h>
#include <string.h>
int buffer(char *str) {
char buffer1[10];
strcpy(buffer1, str);
return 1;
}
int main(int argc, char *argv[]) {
buffer (argv[1]);
printf("Executed\n");
return 1;
}
His program is vulnerable to a __________ attack.
A. SQL injection
B. Denial-of-Service
C. Buffer overflow
D. Cross site scripting
Answer: C
Question: 14
John works as a professional Ethical Hacker. He has been assigned the project of testing the
security of www.we-are-secure.com. He is using a tool to crack the wireless encryption keys.
The description of the tool is as follows:
It is a Linux-based WLAN WEP cracking tool that recovers encryption keys. It operates by
passively monitoring transmissions. It uses
Ciphertext Only Attack and captures approximately 5 to 10 million packets to decrypt the
WEP keys.
Which of the following tools is John using to crack the wireless encryption keys?
A. Kismet
Build Your Dreams
PassGuide 312-38
B. PsPasswd
C. Cain
D. AirSnort
Answer: D
Question: 15
Which of the following attacks are computer threats that try to exploit computer application
vulnerabilities that are unknown to others or undisclosed to the software developer?
Each correct answer represents a complete solution. Choose all that apply.
A. Zero-hour
B. Buffer overflow
C. Zero-day
D. Spoofing
Answer: A, C
Build Your Dreams
Vous aimerez peut-être aussi
- CCTv1 Exam BlueprintDocument5 pagesCCTv1 Exam BlueprintFirdamdam SasmitaPas encore d'évaluation
- CND Exam (Answer)Document23 pagesCND Exam (Answer)Foodbank JatibeningPas encore d'évaluation
- T8-Itc560 Internet of Things - Packet Tracer and Iot Development Tasks - Assignment 2Document31 pagesT8-Itc560 Internet of Things - Packet Tracer and Iot Development Tasks - Assignment 2vatsal jainPas encore d'évaluation
- ADSelfService Plus OverviewDocument22 pagesADSelfService Plus OverviewTruong Nguyen XuanPas encore d'évaluation
- ENSA 312-38 QuestionDocument90 pagesENSA 312-38 QuestionPhoneit PoloPas encore d'évaluation
- Cpte 2018Document10 pagesCpte 2018Ankit BinjolaPas encore d'évaluation
- BeEF XSS FrameworkDocument3 pagesBeEF XSS Frameworkmario_soares_94Pas encore d'évaluation
- Sample Report - InternshipDocument74 pagesSample Report - InternshipDzitalinfo DzitalinfoPas encore d'évaluation
- How To Set Up Stream Media Server Via iVMS-4200Document12 pagesHow To Set Up Stream Media Server Via iVMS-4200miferePas encore d'évaluation
- Number: 220-1001 Passing Score: 800 Time Limit: 120 Min: Website: VCE To PDF Converter: Facebook: TwitterDocument40 pagesNumber: 220-1001 Passing Score: 800 Time Limit: 120 Min: Website: VCE To PDF Converter: Facebook: TwitterJavier Jesús ParionaPas encore d'évaluation
- Mastering Binary Math and SubnettingDocument110 pagesMastering Binary Math and SubnettingSaleem Pasha100% (2)
- Course Setup Guide - Official Comptia Content Network 2019 UpdateDocument16 pagesCourse Setup Guide - Official Comptia Content Network 2019 UpdateNguyen LePas encore d'évaluation
- Fireware Essentials Exam QuestionsDocument32 pagesFireware Essentials Exam QuestionsMarceloeKeila TrindadePas encore d'évaluation
- SD-WAN Network As Secure As My MPLS Network - V3 PDFDocument2 pagesSD-WAN Network As Secure As My MPLS Network - V3 PDFITUMELENGPas encore d'évaluation
- Ms 98-367Document38 pagesMs 98-367Toka Barisovi BarisoviPas encore d'évaluation
- CORGIBUCKS Statement of WorkDocument7 pagesCORGIBUCKS Statement of Worksexyflanders123Pas encore d'évaluation
- MagicINFO Server InstallationDocument35 pagesMagicINFO Server InstallationNolberto AmadorPas encore d'évaluation
- IPASOLINK VR10 SpecificationsDocument32 pagesIPASOLINK VR10 SpecificationsWisam Hassan100% (1)
- ECCouncil PracticeTest 312-38 v2020-04-17 by Kelly 187qDocument111 pagesECCouncil PracticeTest 312-38 v2020-04-17 by Kelly 187qCATHERINE AURELLIAPas encore d'évaluation
- Eccouncil: Ec-Council Certified Network DefenderDocument9 pagesEccouncil: Ec-Council Certified Network DefenderNitish KumarPas encore d'évaluation
- CompTIA PenTest+ Certification Exam Questions PT0-001Document6 pagesCompTIA PenTest+ Certification Exam Questions PT0-001john miloPas encore d'évaluation
- Server Side Web Applications AttacksDocument25 pagesServer Side Web Applications AttacksBasharat AliPas encore d'évaluation
- SDLC Security Penetration Testing MethodologiesDocument36 pagesSDLC Security Penetration Testing Methodologieszaoui dantePas encore d'évaluation
- CWNA Chapter 9 Lab DirectionsDocument4 pagesCWNA Chapter 9 Lab DirectionsAbdelkebir LabyadPas encore d'évaluation
- ET 115 ch1-ch6 QuizDocument18 pagesET 115 ch1-ch6 QuizhyperphackPas encore d'évaluation
- 5 Ways I Bypassed Your Web Application Firewall (WAF)Document18 pages5 Ways I Bypassed Your Web Application Firewall (WAF)JOSÉ IGNACIO PARRA VALENZUELA100% (1)
- Zimbra Vs Other Email PlatformsDocument10 pagesZimbra Vs Other Email PlatformsriazdollarPas encore d'évaluation
- CS435: Introduction To Software Engineering: Dr. M. ZhuDocument56 pagesCS435: Introduction To Software Engineering: Dr. M. Zhurohan pandyaPas encore d'évaluation
- Exam Question DumpDocument28 pagesExam Question DumpnikeshPas encore d'évaluation
- Braindump2go 312-50v11 Exam DumpsDocument4 pagesBraindump2go 312-50v11 Exam DumpsLê Huyền MyPas encore d'évaluation
- Guide To Successful Data Loss Prevention Risk Reduction: Part 1Document16 pagesGuide To Successful Data Loss Prevention Risk Reduction: Part 1arunchockanPas encore d'évaluation
- Wireless Hacking and Penetratin TestingDocument81 pagesWireless Hacking and Penetratin TestingbabuPas encore d'évaluation
- CNDDocument4 pagesCNDDandy GonzálezPas encore d'évaluation
- A Complex Polyalphabetic Cipher TechniqueDocument9 pagesA Complex Polyalphabetic Cipher Techniqueirfan123456Pas encore d'évaluation
- Checkpoint VPN-1 FireWall-1 NG Management II Instructors SlidesDocument357 pagesCheckpoint VPN-1 FireWall-1 NG Management II Instructors Slidescameo001Pas encore d'évaluation
- CCNA SecurityDocument14 pagesCCNA SecurityEric NapholzPas encore d'évaluation
- Security+ Last Dump 21 Dec CorrectedDocument356 pagesSecurity+ Last Dump 21 Dec Correctedrovobo3542Pas encore d'évaluation
- 312-50v11 Dumps Certified Ethical Hacker Exam (CEH v11)Document23 pages312-50v11 Dumps Certified Ethical Hacker Exam (CEH v11)Lê Huyền MyPas encore d'évaluation
- Sales Interview Questions and AnswersDocument4 pagesSales Interview Questions and AnswersSubham SinghPas encore d'évaluation
- VMware 1V0-621 VCA PDF QuestionsDocument6 pagesVMware 1V0-621 VCA PDF QuestionsPass4 LeadsPas encore d'évaluation
- Itil Dumps Practice PaperDocument13 pagesItil Dumps Practice Paperdevdas2020Pas encore d'évaluation
- Case StudyDocument4 pagesCase StudyariaPas encore d'évaluation
- Pentesting BibleDocument56 pagesPentesting BibleRajeev GhoshPas encore d'évaluation
- SRS for Skype P2P Video Broadcasting PlatformDocument24 pagesSRS for Skype P2P Video Broadcasting PlatformDinesh Wasalwar67% (3)
- CMDBuildReady2Use OverviewManual ENG V100Document41 pagesCMDBuildReady2Use OverviewManual ENG V100Manuel VegaPas encore d'évaluation
- CPTE: Certified Penetration Testing Engineer v3.5 Course IntroductionDocument11 pagesCPTE: Certified Penetration Testing Engineer v3.5 Course IntroductionGudden GuptaPas encore d'évaluation
- Hermans K. SSCP Certification Guide. A Comprehensive Guide... 2023Document310 pagesHermans K. SSCP Certification Guide. A Comprehensive Guide... 2023Jeffrey GrantPas encore d'évaluation
- INE Cyber Security Pass - User GuideDocument22 pagesINE Cyber Security Pass - User GuideJ SanctisPas encore d'évaluation
- How To Secure Your WebsiteDocument5 pagesHow To Secure Your WebsiteRotimi AkinyelePas encore d'évaluation
- CCTV Security CamerasDocument22 pagesCCTV Security Cameras2mcctv.comPas encore d'évaluation
- Cara Menanak Nasi AmanDocument99 pagesCara Menanak Nasi AmanBudhi HartaPas encore d'évaluation
- Internet of Things Landscape // Matt Turck of FirstMark CapitalDocument1 pageInternet of Things Landscape // Matt Turck of FirstMark CapitalFirstMark CapitalPas encore d'évaluation
- ISC2 Exam Action PlanDocument11 pagesISC2 Exam Action PlanMuhammad AbdullahPas encore d'évaluation
- Braindump2go JN0-230 Exam DumpsDocument4 pagesBraindump2go JN0-230 Exam DumpsMaruf AhmedPas encore d'évaluation
- Cyberark Defender: Cyberark Cau201 Version DemoDocument7 pagesCyberark Defender: Cyberark Cau201 Version DemoHakanPas encore d'évaluation
- CNA 430 - Firewall and Penetration Testing Final Project: Submitted byDocument24 pagesCNA 430 - Firewall and Penetration Testing Final Project: Submitted byfsamu2001Pas encore d'évaluation
- Thorteaches Study Guide CISM Domain 1Document30 pagesThorteaches Study Guide CISM Domain 1Toni BioksicPas encore d'évaluation
- Ethical Hacking PDFDocument2 pagesEthical Hacking PDFBrandon0% (1)
- Cisco Certified Network Professional CyberOps A Complete Guide - 2019 EditionD'EverandCisco Certified Network Professional CyberOps A Complete Guide - 2019 EditionPas encore d'évaluation
- GIAC Certified Perimeter Protection Analyst Complete Self-Assessment GuideD'EverandGIAC Certified Perimeter Protection Analyst Complete Self-Assessment GuidePas encore d'évaluation
- An Extensible Technology Framework For Cyber Security EducationDocument136 pagesAn Extensible Technology Framework For Cyber Security EducationSumazly SulaimanPas encore d'évaluation
- SP2010 QsDocument47 pagesSP2010 QsvinorpatilPas encore d'évaluation
- SP2010 QsDocument47 pagesSP2010 QsvinorpatilPas encore d'évaluation
- Certified Ethical Hacking: Ron Woerner, CISSP, CEHDocument35 pagesCertified Ethical Hacking: Ron Woerner, CISSP, CEHranjithc24Pas encore d'évaluation
- Security Evaluation of SCTP: Bachelor ThesisDocument61 pagesSecurity Evaluation of SCTP: Bachelor ThesisGábor NémethPas encore d'évaluation
- m800 Pri E1 Audiocodec Plantilla A CargarDocument7 pagesm800 Pri E1 Audiocodec Plantilla A CargarDong-YulHeiPas encore d'évaluation
- ATM LayersDocument14 pagesATM LayersSatyabrata NayakPas encore d'évaluation
- Qos Indirecto (CALIDAD DE SERVICIO)Document3 pagesQos Indirecto (CALIDAD DE SERVICIO)Jonny LassoPas encore d'évaluation
- Teltonika LTE Outdoor Router RUT750Document3 pagesTeltonika LTE Outdoor Router RUT750bogdy00733054Pas encore d'évaluation
- Communications Networks: By:-Deltiin India Tech Private LimitedDocument32 pagesCommunications Networks: By:-Deltiin India Tech Private LimitedarunpatokarPas encore d'évaluation
- Bittorrent: A Bittorrent File Distribution Consists of These EntitiesDocument6 pagesBittorrent: A Bittorrent File Distribution Consists of These Entitiespittviper313Pas encore d'évaluation
- ZebOS Network PlatformDocument6 pagesZebOS Network PlatformgschatzPas encore d'évaluation
- CCNA4 Practice Final Exam PDFDocument13 pagesCCNA4 Practice Final Exam PDFYummyUnliPas encore d'évaluation
- SP WIFI Solution CiscoDocument64 pagesSP WIFI Solution CiscoRalph NassifPas encore d'évaluation
- VMware NSX T Data Center - 5Document41 pagesVMware NSX T Data Center - 5Yohan De SilvaPas encore d'évaluation
- Netbiter Easyconnect User ManualDocument46 pagesNetbiter Easyconnect User Manualoperaciones1 sesaPas encore d'évaluation
- Configure VLANs and Assign Ports in Packet TracerDocument6 pagesConfigure VLANs and Assign Ports in Packet TracerArmel Bacdayan LacanariaPas encore d'évaluation
- Specification of STGI-7100I S IP Gateway ServerDocument4 pagesSpecification of STGI-7100I S IP Gateway Serverwilliam morenoPas encore d'évaluation
- User Manual: AC1200 Wi-Fi RouterDocument164 pagesUser Manual: AC1200 Wi-Fi RouterDeepakPas encore d'évaluation
- Assignment 2Document3 pagesAssignment 2NidhulPas encore d'évaluation
- Synchronous Optical Network: Sonet Standard For Synchronous Data Transmission On Optical MediaDocument19 pagesSynchronous Optical Network: Sonet Standard For Synchronous Data Transmission On Optical Mediamohammed draeyPas encore d'évaluation
- Lab - Configuring Vlans and Trunking TopologyDocument2 pagesLab - Configuring Vlans and Trunking TopologyHarman HayerPas encore d'évaluation
- Riot Lol Results PCDocument3 pagesRiot Lol Results PCDusko StanisicPas encore d'évaluation
- Networking Server System: Pulkit Tiwari - 21180118 - Netcamp Summer TrainingDocument42 pagesNetworking Server System: Pulkit Tiwari - 21180118 - Netcamp Summer TrainingShubham SrivastavaPas encore d'évaluation
- AWS Certified Solutions Architect Associate Sample QuestionsDocument5 pagesAWS Certified Solutions Architect Associate Sample QuestionsSanaanKhanPas encore d'évaluation
- HF2421&HF2421G User ManualV1.2 (20190116)Document79 pagesHF2421&HF2421G User ManualV1.2 (20190116)ztodorovicsezampro.rsPas encore d'évaluation
- Apc NMC 6-5-0Document12 pagesApc NMC 6-5-0ElvinPas encore d'évaluation
- Microservices for Beginners Crash Course: Monolithic vs Microservices ArchitectureDocument9 pagesMicroservices for Beginners Crash Course: Monolithic vs Microservices ArchitectureJimmy KumarPas encore d'évaluation
- Sim7020 Series: Simcom Nb-Iot ModuleDocument3 pagesSim7020 Series: Simcom Nb-Iot ModuleAlejandro DemitiPas encore d'évaluation
- ECE 512 Assignment 01Document3 pagesECE 512 Assignment 01Igeh AyietuomaPas encore d'évaluation
- Module 7: Dhcpv4: Switching, Routing and Wireless Essentials V7.0 (Srwe)Document31 pagesModule 7: Dhcpv4: Switching, Routing and Wireless Essentials V7.0 (Srwe)Priscille Elvie Cérese MIENEPas encore d'évaluation
- Route leaking concept UDP tunnelDocument11 pagesRoute leaking concept UDP tunnelmhmdmhmdPas encore d'évaluation
- File Transfer ProtocolDocument17 pagesFile Transfer Protocolraj293Pas encore d'évaluation