Académique Documents
Professionnel Documents
Culture Documents
Hiding Sensitive Association Rule Using Heuristic Approach
Transféré par
Lewis TorresCopyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Hiding Sensitive Association Rule Using Heuristic Approach
Transféré par
Lewis TorresDroits d'auteur :
Formats disponibles
International Journal of Data Mining & Knowledge Management Process (IJDKP) Vol.3, No.
1, January 2013
HIDING SENSITIVE ASSOCIATION RULE USING HEURISTIC APPROACH
Kasthuri S1 and Meyyappan T2
1
Research Scholar, Alagappa University, Karaikudi.
Kasthu.s@gmail.com
2
Professor, Alagappa University, Karaikudi.
Meyslotus@yahoo.com
ABSTRACT
Data mining is the process of identifying patterns from large amount of data. Association rule mining aims to discover dependency relationships across attributes. It may also disclose sensitive information. With extensive application of data mining techniques to various domains, privacy preservation becomes mandatory. Association rule hiding is one of the techniques of privacy preserving data mining to protect the sensitive association rules generated by association rule mining. This paper adopts heuristic approach for hiding sensitive association rules. The proposed technique makes the representative rules and hides the sensitive rules.
KEYWORDS
Association Rule Hiding, Data Mining, Privacy Preserving Data Mining, Distortion, Representative Rule.
1. INTRODUCTION
Data mining is a knowledge extracting process of analyzing data from different point of views. This knowledge is expressed in decision trees, clusters or association rules. Association rule mining is a common task in data mining. By discovering interesting association rules in datasets, an organization can identify underlying patterns useful in strategic decision making. This technique has been successfully applied to many application domains such as the analysis of market baskets, website linkages etc. The knowledge discovered can be beneficial to cooperating organizations. In order to preserve their competitive edge some partners may hesitate to disclose sensitive information. Privacy preserving data mining is a major research area for protecting sensitive data or knowledge. Association rule hiding is one of the privacy preserving techniques to hide sensitive association rules. The main aim of all association rule hiding algorithm is to minimally modify the original database and see that no sensitive association rule is derived from it. Next section describes the association rule mining. Section 3 explains approaches of association rule hiding algorithms. Section 4 presents the statement of the problem. Section 5 analyses the related work on heuristic approaches based on data distortion technique. Section 6 presents the proposed algorithm for sensitive rule hiding. Section 7 shows the examples demonstrating the algorithm. Concluding remarks and future works are described in section 8.
DOI : 10.5121/ijdkp.2013.3105
57
International Journal of Data Mining & Knowledge Management Process (IJDKP) Vol.3, No.1, January 2013
2. ASSOCIATION RULE MINING
Let I = {i1,., in} be a set of items. Let D be a database which contains set of transactions. Each transaction t D is an item set such that t is a proper subset of I. As transaction t supports X, a set of items in I, if X is a proper subset of t. Assume that the items in a transaction or an item set are sorted in lexicographic order. An association rule is an implication of the form X Y, where X and Y are subsets of I and XY= . The support of rule X Y can be calculated by the following equation: Support(X Y) = |X Y| / |D|, where |X Y| denotes the number of transactions ceontaining the itemset XY in the database, |D| denotes the number of the transactions in the database D. The confidence of rule is computed by Confidence(X Y) = |X Y|/|X|, where |X| is number of transactions in database D that contains itemset X. A rule X Y is strong if support(X Y) min_support and confidence(X Y) min_confidence, where min_support and min_confidence are two given minimum thresholds. Association rule mining algorithms calculate the support and confidence of the rules. The rules having support and confidence higher than the user specified minimum support and confidence are retrieved. Association rule hiding algorithms prevents the sensitive rules from being revealed out. The problem can be declared as follows Database D, minimum confidence, minimum support are given and a set R of rules are mined from database D. A subset SR of R is denoted as set of sensitive association rules.SR is to be hidden. The objective is to modify D into a database D from which no association rule in SR will be mined and all non sensitive rules in R could still be mined from D.
3. APPROACHES OF ASSOCIATION RULE HIDING ALGORITHMS
Association rule hiding algorithms can be divided into three distinct approaches. They are heuristic approaches, border-revision approaches and exact approaches.
3.1 Heuristic Approach Heuristic approaches can be further categorized into distortion based schemes and blocking based
schemes. To hide sensitive item sets, distortion based scheme changes certain items in selected transactions from 1s to 0s and vice versa. Blocking based scheme replaces certain items in selected transactions with unknowns. These approaches have been getting focus of attention for majority of the researchers due to their efficiency, scalability and quick responses.
3.2 Border Revision Approach
Border revision approach modifies borders in the lattice of the frequent and infrequent item sets to hide sensitive association rules. This approach tracks the border of the non sensitive frequent item sets and greedily applies data modification that may have minimal impact on the quality to accommodate the hiding sensitive rules. Researchers proposed many border revision approach algorithms such as BBA (Border Based Approach), Max Min1 and Max-Min2 to hide sensitive association rules. The algorithms uses different techniques such as deleting specific sensitive items and also attempt to minimize the number of non sensitive item sets that may be lost while sanitization is performed over the original database in order to protect sensitive rules.
3.3 Exact Approach
Third class of approach is non heuristic algorithm called exact, which conceive hiding process as constraint satisfaction problem. These problems are solved by integer programming. This approach can be concerned as descendant of border based methodology.
58
International Journal of Data Mining & Knowledge Management Process (IJDKP) Vol.3, No.1, January 2013
4. PROBLEM STATEMENT
Data mining represents a wide range of tools and techniques to extract useful information which can contain sensitive information from a large collection of data. Data should be manipulated or distorted in such a way that sensitive information cannot be discovered through data mining techniques. Sensitive information has to be protected against unauthorized access. The major challenge faced is better balancing the confidentiality of the disclosed with the legitimate needs of the data user. The proposed approach is based on modification of database transactions.
5. ANALYSIS OF EXISTING TECHNIQUES
In Distortion Based Technique (Proposed By Veryki- os Et Al, Etc.) [1], authors propose strategies and a suite of algorithms for hiding sensitive knowledge. In order to achieve this, transactions are modified by removing few items, or inserting new items depending on the hiding strategy. The distortion based Technique (Proposed by shyue-liang wang et al.) [2] hides certain specific items that are sensitive. In this technique, two algorithms are proposed to modify data in the Dataset. If the sensitive item is on the LHS of the rule then the first algorithm increases its support. If the sensitive item is on the right of the rule then the second algorithm decreases its support. In [1], author tries to hide every rule without checking if rules can be pruned after some transactions have been changed. In [2] the author hides all the rules which contain sensitive items either in the left or in the right. Two different algorithms are applied over the data. The first algorithm hides association rules with sensitive items on the LHS and the second one for sensitive items on the RHS. It takes more number of passes to prune all the rules containing sensitive items.
6. PROPOSED APPROACH
The proposed approach selects all the association rules containing sensitive items either in the left or in the right from the set of all association rules generated from a dataset. These rules are represented in representative rules (RR) format with sensitive item on the left hand side or right hand side of the rules. Select a rule from the set of RRs which contains sensitive item. Select a transaction which completely supports RR i.e. it contains all the sensitive items in the RR. The proposed approach hides the sensitive item by modifying the database without changing the support of the sensitive item.
6.1 Representative Association Rule
The number of association rules discovered in a given database is very large. A considerable percentage of these rules are redundant and useless. A user should be presented with original, novel, and interesting. To address this problem, [6] introduced a representation of association rules, called representative rules (RR). RR is a set of rules that allow deducing all association rules without accessing a database. The cover operator was introduced for driving a set of association rules from a given association rule. The cover of the rule A=>B, A, is defined as follows: C(A => B) = {AB=>V , V B and Z V = and V } Each rule in C (AB ) consists of a subset of items occurring in the rule A B. The number of different rules in the cover of the association A B is equal to 3m 2m , m = |B|.
59
International Journal of Data Mining & Knowledge Management Process (IJDKP) Vol.3, No.1, January 2013
The process of generating representative rules is decomposed in to two sub processes: frequent item-sets generations and generation of RR from frequent item-sets. Let be a frequent itemset and B . The association rule A /B is representative rule if there is no association rule (A / A) where Z , and there is no association rule (A / A) such that AA . Formally, a set of representative rules (RR) for a given association rules (AR) can be defined as follows: RR= { rR rAR, r r and r C(r)} Each rule in RR is called representative association rule. No representative rule may belong in the cover of another association rule [8], [9]. The proposed algorithm gives a modified dataset after distorting the database. A Database, value of min_support, min_confidence, and a set of sensitive items are given as input this algorithm. Association rules are generated using association rule mining algorithm. Select the rules containing sensitive item from the association rules. The selected rules are represented in the representative rules format. The sensitive item is deleted from a transaction, which fully supports the selected RR and added to a transaction, which partially supports RR. The algorithm is given below Algorithm: Hiding Of Sensitive Association Rules Input: (1) D: A source database (2) min_supp : A min_support. (3) min_conf : A min_confidence. (4) H: A set of sensitive items. Output: A transformed database D where rules containing H on LHS/RHS will be hidden 1. Find item sets from D; 2. For each sensitive item h H { 3. If h is a small item set then H=H- {h}; 4. If H is null then EXIT; 5. Select all the rules with min_supp containing h and store in SR//h can either be on LHS or RHS 6. Repeat { 7. Select rule from SR with same LHS 8. Combine RHS of selected rule and store in R; // representative rules 9. } Until (U is empty); 10. Sort R in descending order by supported items; 11. Select a rule r from SR 12. Compute confidence of rule r; 13. If conf>min_conf then {//change the position of sensitive item h. 14. Find Ti = {t in D |t completely supports R; 15. If t contains x and h then 16. Remove h from t 17. Find Ti = {t in D|t does not support and partially supports x; 18. Add h to t 19. Repeat 20. { 21. Choose the first rule from U;
60
International Journal of Data Mining & Knowledge Management Process (IJDKP) Vol.3, No.1, January 2013
22. Compute confidence of r; 23. } Until(SR is empty); 24. }//end of if conf>min_conf 25. Else 26. Go to step 11; 27. Update D with new transaction t; 28. Remove h from H; 29. Go to step 2; 30.}//end of for each h H 1. 2. 3. 4. All the rules containing sensitive item(s) either in the left or in the right are selected. Rules are converted in representative rules (RRs) format. A rule from the set of RRs, which has sensitive item on the left of the RR is selected. The sensitive item(s) from the transaction that completely supports the RR is removed and add the same sensitive item to a transaction which partially supports RR. 5. The confidence of the rules in U is recomputed. The framework of the proposed approach is shown in figure 1. Figure 1 Framework of the proposed Approach
Original Database
Association Rules
Sensitive Association Rules based on Sensitive item
Modified Database
Rule Hiding
Representative Association rules
7. IMPLEMENTATION OF THE PROPOSED ALGORITHM
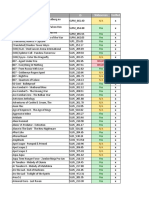
The proposed algorithm can be illustrated with the following example for a given set of transactional data in Table -1 Table -1: Transactional Dataset1 TID ITEMS T1 bread, butter, milk T2 bread, butter, milk, cheese T3 butter, milk, fruits T4 bread, milk, cheese, fruits T5 cheese, fruits T6 bread, butter For the Dataset given in Table - 1 at a min_supp of 33% and a min_conf of 70 % and sensitive item H= {milk} we choose all the rules containing butter either in RHS or LHS and represent them in representative rule format. Out of the 8 association rules the rules containing sensitive items are 6 as shown in Table 2
61
International Journal of Data Mining & Knowledge Management Process (IJDKP) Vol.3, No.1, January 2013
Table - 2: Sensitive association rules (w.r.t sensitive item milk) AR bread => milk milk => bread bread, cheese => butter milk, cheese => bread butter => milk milk => butter SUPP 50 50 33.333 33.333 50 50 CONF 75 75 100 100 75 75
From this rules set select the rules that can be represented in the form of representative rules Like milk=> butter and milk=>bread can be represented as milk=> bread, butter Now delete milk from a transaction where bread, butter, milk all the three are present and add milk to a transaction where bread and butter both are absent or only one of them is present. For this we change transaction T2 to bread, butter, cheese and transaction T5 to milk, cheese, and fruits. This results in changing the position of the sensitive item without changing its support. This is shown in Table 3. Table-3: Modified Dataset1 for the proposed Approach (Sensitive Item milk) TID T1 T2 T3 T4 T5 T6 ITEMS bread, butter, milk bread, butter, cheese butter, milk, fruits bread, milk, cheese, fruits milk, cheese, fruits bread, butter
The new set of association rules generated from this modified dataset is shown in Table-4. Table-4: Association rules remaining unhidden after modifying the Dataset1 AR SUPP CONF butter=> bread 50 75 bread=>butter 50 75 i.e. all the rules of the original association rules set containing sensitive items on the LHS or on the RHS are hidden.
8. CONCLUSIONS
In this paper, the database privacy problems are addressed and a new technique for privacy preservation is proposed. Association rule hiding techniques are used to hide sensitive association rules. A new heuristic method to hide the sensitive association rules is proposed. Data distortion technique is applied so that sensitive information cannot be discovered through data mining techniques. Confidence of the rules is represented as representative rules. Confidence of the rule is recomputed and compared with threshold level. The confidence of the sensitive rules might be reduced while maintaining the support. From the experimental results, it is observed that all the rules containing sensitive items are hidden. The algorithm is implemented and numerical example is shown. Further research is in progress to evolve a method which can avoid the computational overhead associated with confidence of the rules.
62
International Journal of Data Mining & Knowledge Management Process (IJDKP) Vol.3, No.1, January 2013
REFERENCES
Vassilios S. Verykios,, Ahmed K. Elmagarmid , Elina Bertino, Yucel Saygin, Elena Dasseni. Association Rule Hiding, IEEE Transactions on knowledge and data engineering, Vol.6, NO.4, April 2004 [2] Shyue-Liang Wang, Yu-Huei Lee, Billis S., Jafari, A. Hiding sensitive items in privacy preserving association rule mining, IEEE International Conference on Systems, Man and Cybernetics, Volume 4, 10-13 Oct. 2004 Page(s): 3239 - 3244 . [3] E. Dasseni, V. Verykios, A. Elmagarmid and E. Bertino. Hiding Association Rules by Using Confidence and Support, in Proceedings of 4th Information Hiding Workshop, 369-383, Pittsburgh, PA, 2001. [4] JIAWEI HAN and MICHALINE KAMBER, Data Mining Conceptsd And Techniques, Morgon Kaufman Publishers 2002 [5] Wang. S.L., Jafari, A. Using unknowns for hiding sensitive predictive association rules, Information Reuse and Integration, Conf, 2005. IRI -2005 IEEE International Conference on. 15-17 Aug. 2005 Page(s): 223 - 228. [6] Marzena Kryszkiewicz. Representative Association Rules, In proceedings of PAKDD98, Melbourne,Australia(Lecture notes in artificialIntelligence,LANI 1394, Springer-Verleg,1998,pp 198209. [7] Yucel Saygin, Vassilios S. Verykios, Chris Clifton. Using unknowns to prevent discovery of association rules, ACM SIGMOD Record Volume 30 Issue 4, pp. 45 - 54 , (2001) [8] Yiqun Huang, Zhengding Lu, Heping Hu, A method of security improvement for privacy preserving association rule mining over vertically partitioned data, 9th International Database Engineering and Application Symposium, pp. 339 343, (2005) [9] Saygin Y., Verykios V.S. and Elmagarmid A.K., Privacy preserving association rule mining, IEEE Proceedings of the 12th Intl Workshop on Research Issues in Data Engineering, pp. 151 158, (2002) [10] Aris GkoulalasDivanis;Vassilios S. Verykios Asssociation Rule Hiding For Data Mining Springer, DOI 10.1007/978-1-4419-6569-1, Springer Science + Business Media, LLC 2010 [1]
63
Vous aimerez peut-être aussi
- An Effective Heuristic Approach For Hiding Sensitive Patterns in DatabasesDocument6 pagesAn Effective Heuristic Approach For Hiding Sensitive Patterns in DatabasesInternational Organization of Scientific Research (IOSR)Pas encore d'évaluation
- Maintaining Privacy and Data Quality To Hide Sensitive Items From DatabaseDocument4 pagesMaintaining Privacy and Data Quality To Hide Sensitive Items From DatabaseInternational Journal of Application or Innovation in Engineering & ManagementPas encore d'évaluation
- Hiding Sensitive Predictive Association Rules: Shyue-Liang Wang, Ayat JafariDocument6 pagesHiding Sensitive Predictive Association Rules: Shyue-Liang Wang, Ayat Jafarigayathri pingiliPas encore d'évaluation
- Improved Association Rule Hiding Algorithm For Privacy Preserving Data MiningDocument6 pagesImproved Association Rule Hiding Algorithm For Privacy Preserving Data MiningIOSRJEN : hard copy, certificates, Call for Papers 2013, publishing of journalPas encore d'évaluation
- Efficient Graph-Based Algorithms For Discovering and Maintaining Association Rules in Large DatabasesDocument24 pagesEfficient Graph-Based Algorithms For Discovering and Maintaining Association Rules in Large DatabasesAkhil Jabbar MeerjaPas encore d'évaluation
- EclatDocument24 pagesEclatMade TokePas encore d'évaluation
- Main Focus: Sanitization Problem Is NP-hard. Towards The SolutionDocument1 pageMain Focus: Sanitization Problem Is NP-hard. Towards The SolutionSrinivasPas encore d'évaluation
- An Efficient Technique For Protecting Sensitive Information: AbstractDocument4 pagesAn Efficient Technique For Protecting Sensitive Information: AbstractIjact EditorPas encore d'évaluation
- Application of Particle Swarm Optimization To Association Rule MiningDocument11 pagesApplication of Particle Swarm Optimization To Association Rule MiningAnonymous TxPyX8cPas encore d'évaluation
- Data Mining ReportDocument15 pagesData Mining ReportKrishna KiranPas encore d'évaluation
- Knowledge HidingDocument37 pagesKnowledge Hidingfac fasjesPas encore d'évaluation
- Mining Association Rules From Infrequent Itemsets: A SurveyDocument8 pagesMining Association Rules From Infrequent Itemsets: A SurveyKurumeti Naga Surya Lakshmana KumarPas encore d'évaluation
- Fast Algorithms For Mining Association RulesDocument32 pagesFast Algorithms For Mining Association RulesDeepa LakshmiPas encore d'évaluation
- Fast Algorithms For Mining Association RulesDocument32 pagesFast Algorithms For Mining Association Rulesrudra_saktiPas encore d'évaluation
- Fast Algorithms For Mining Association RulesDocument32 pagesFast Algorithms For Mining Association Rulesk.s insandjiPas encore d'évaluation
- Fast - Algorithms - For - Mining Association Rules - R Agrawal - R Srikant-IBMDocument32 pagesFast - Algorithms - For - Mining Association Rules - R Agrawal - R Srikant-IBMulfadiyah kumalasariPas encore d'évaluation
- Data Mining: A Database PerspectiveDocument19 pagesData Mining: A Database PerspectiveSijo JohnPas encore d'évaluation
- 4.Eng-Association Rule Mining For Different MinimumDocument8 pages4.Eng-Association Rule Mining For Different MinimumImpact JournalsPas encore d'évaluation
- A Framework To Discover Association Rules Using Frequent Pattern MiningDocument5 pagesA Framework To Discover Association Rules Using Frequent Pattern MiningIIR indiaPas encore d'évaluation
- Parallel Data Mining of Association RulesDocument10 pagesParallel Data Mining of Association RulesAvinash MudunuriPas encore d'évaluation
- Base Knowledge BasedDocument14 pagesBase Knowledge BasednagaidlPas encore d'évaluation
- A TestDocument7 pagesA TestJimmy HuynhPas encore d'évaluation
- Image Content With Double Hashing Techniques: ISSN No. 2278-3091Document4 pagesImage Content With Double Hashing Techniques: ISSN No. 2278-3091WARSE JournalsPas encore d'évaluation
- Fast Algorithms For Mining Association RulesDocument13 pagesFast Algorithms For Mining Association RulesVíctor Cáceres monsalvePas encore d'évaluation
- Data MinningDocument8 pagesData MinningNithi RamPas encore d'évaluation
- Generalized Association Rule Mining Using Genetic AlgorithmsDocument11 pagesGeneralized Association Rule Mining Using Genetic AlgorithmsAnonymous TxPyX8cPas encore d'évaluation
- A Study On Post Mining of Association Rules Targeting User InterestDocument7 pagesA Study On Post Mining of Association Rules Targeting User Interestsurendiran123Pas encore d'évaluation
- Ijet V4i3p8 PDFDocument12 pagesIjet V4i3p8 PDFInternational Journal of Engineering and TechniquesPas encore d'évaluation
- DARM: Decremental Association Rules Mining: Mohamed Taha, Tarek F. Gharib, Hamed NassarDocument9 pagesDARM: Decremental Association Rules Mining: Mohamed Taha, Tarek F. Gharib, Hamed NassarKurumeti Naga Surya Lakshmana KumarPas encore d'évaluation
- Expert Systems With Applications: Hamid Reza Qodmanan, Mahdi Nasiri, Behrouz Minaei-BidgoliDocument11 pagesExpert Systems With Applications: Hamid Reza Qodmanan, Mahdi Nasiri, Behrouz Minaei-BidgoliAtik FebrianiPas encore d'évaluation
- MiningAssoc AgrawalAS VLDB94 PDFDocument13 pagesMiningAssoc AgrawalAS VLDB94 PDFPraveen ChoudharyPas encore d'évaluation
- Mining Rare Association Rules From E-Learning DataDocument10 pagesMining Rare Association Rules From E-Learning Datasuchi87Pas encore d'évaluation
- CBAR: An Efficient Method For Mining Association Rules: Yuh-Jiuan Tsay, Jiunn-Yann ChiangDocument7 pagesCBAR: An Efficient Method For Mining Association Rules: Yuh-Jiuan Tsay, Jiunn-Yann Chiangmahapreethi2125Pas encore d'évaluation
- A Multi-Tier Architecture For High-Performance Data Mining: Rantzau, Schwarz @informatik - Uni-Stuttgart - deDocument13 pagesA Multi-Tier Architecture For High-Performance Data Mining: Rantzau, Schwarz @informatik - Uni-Stuttgart - deNitin DograPas encore d'évaluation
- Data Mining: Prof Jyotiranjan HotaDocument17 pagesData Mining: Prof Jyotiranjan HotaBikash BeheraPas encore d'évaluation
- IV-cse DM Viva QuestionsDocument10 pagesIV-cse DM Viva QuestionsImtiyaz AliPas encore d'évaluation
- Informative Pattern Discovery Using Combined MiningDocument5 pagesInformative Pattern Discovery Using Combined MiningInternational Journal of Application or Innovation in Engineering & ManagementPas encore d'évaluation
- Assignment ON Data Mining: Submitted by Name: Manjula.TDocument11 pagesAssignment ON Data Mining: Submitted by Name: Manjula.TLõvey Dôvey ÃnanthPas encore d'évaluation
- Data Warehousing and Data MiningDocument18 pagesData Warehousing and Data Mininglskannan47Pas encore d'évaluation
- Discovering Stock Price Prediction Rules Using Rough SetsDocument19 pagesDiscovering Stock Price Prediction Rules Using Rough Setss_murugan02Pas encore d'évaluation
- Ijcs 2016 0303008 PDFDocument16 pagesIjcs 2016 0303008 PDFeditorinchiefijcsPas encore d'évaluation
- V1i6 Ijertv1is6251 PDFDocument6 pagesV1i6 Ijertv1is6251 PDFBudi Man TaroPas encore d'évaluation
- Evaluating The Performance of Apriori and Predictive Apriori Algorithm To Find New Association Rules Based On The Statistical Measures of DatasetsDocument6 pagesEvaluating The Performance of Apriori and Predictive Apriori Algorithm To Find New Association Rules Based On The Statistical Measures of DatasetsBudi Man TaroPas encore d'évaluation
- Apriori Based Novel Frequent Itemset Mining Mechanism: Issn NoDocument8 pagesApriori Based Novel Frequent Itemset Mining Mechanism: Issn NoWARSE JournalsPas encore d'évaluation
- Data Mining For Biological Data Analysis: Glover Eric Leo Cimi Smith CalvinDocument8 pagesData Mining For Biological Data Analysis: Glover Eric Leo Cimi Smith CalvinEric GloverPas encore d'évaluation
- Sophistication in Order To PerformDocument1 pageSophistication in Order To PerformSrinivasPas encore d'évaluation
- Introducing Parallelism in Privacy Preserving Data Mining AlgorithmsDocument4 pagesIntroducing Parallelism in Privacy Preserving Data Mining AlgorithmsInternational Journal of computational Engineering research (IJCER)Pas encore d'évaluation
- p132 ClosetDocument11 pagesp132 Closetjnanesh582Pas encore d'évaluation
- DWM Unit 2Document4 pagesDWM Unit 2Vijay KrishPas encore d'évaluation
- Design and Implementation of Efficient APRIORI AlgorithmDocument4 pagesDesign and Implementation of Efficient APRIORI Algorithmsigma70egPas encore d'évaluation
- A New Efficient Matrix Based Frequent Itemset Mining Algorithm With TagsDocument4 pagesA New Efficient Matrix Based Frequent Itemset Mining Algorithm With Tagshnoor6Pas encore d'évaluation
- International Journal of Computational Engineering Research (IJCER)Document8 pagesInternational Journal of Computational Engineering Research (IJCER)International Journal of computational Engineering research (IJCER)Pas encore d'évaluation
- Literature Survey of Association Rule Based Techniques For Preserving PrivacyDocument6 pagesLiterature Survey of Association Rule Based Techniques For Preserving PrivacyIjact EditorPas encore d'évaluation
- Visualizing Association Rules: Introduction To The R-Extension Package ArulesvizDocument24 pagesVisualizing Association Rules: Introduction To The R-Extension Package ArulesvizDevendraReddyPoreddyPas encore d'évaluation
- Visualizing Association Rules: Introduction To The R-Extension Package ArulesvizDocument24 pagesVisualizing Association Rules: Introduction To The R-Extension Package ArulesvizDevendraReddyPoreddyPas encore d'évaluation
- 8.research Plan-N.M MISHRADocument3 pages8.research Plan-N.M MISHRAnmmishra77Pas encore d'évaluation
- Association Rule Mining On Distributed Data: Pallavi DubeyDocument6 pagesAssociation Rule Mining On Distributed Data: Pallavi Dubeyjkl316Pas encore d'évaluation
- Python Machine Learning for Beginners: Unsupervised Learning, Clustering, and Dimensionality Reduction. Part 1D'EverandPython Machine Learning for Beginners: Unsupervised Learning, Clustering, and Dimensionality Reduction. Part 1Pas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- Demand Forecasting of A Perishable Dairy Drink: An ARIMA ApproachDocument15 pagesDemand Forecasting of A Perishable Dairy Drink: An ARIMA ApproachLewis TorresPas encore d'évaluation
- MR - Random Forest Algorithm For Distributed Action Rules DiscoveryDocument16 pagesMR - Random Forest Algorithm For Distributed Action Rules DiscoveryLewis TorresPas encore d'évaluation
- The Stock Market Volatility Between China and Asean Countries Association Studies Based On Complex NetworksDocument16 pagesThe Stock Market Volatility Between China and Asean Countries Association Studies Based On Complex NetworksLewis TorresPas encore d'évaluation
- Linking Early Detection/treatment of Parkinson's Disease Using Deep Learning TechniquesDocument16 pagesLinking Early Detection/treatment of Parkinson's Disease Using Deep Learning TechniquesLewis TorresPas encore d'évaluation
- Class Imbalance Handling Techniques Used in Depression Prediction and DetectionDocument17 pagesClass Imbalance Handling Techniques Used in Depression Prediction and DetectionLewis TorresPas encore d'évaluation
- Identifying Similar Web Pages Based On Automated and User Preference Value Using Scoring MethodsDocument13 pagesIdentifying Similar Web Pages Based On Automated and User Preference Value Using Scoring MethodsLewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- Linking Early Detection/treatment of Parkinson's Disease Using Deep Learning TechniquesDocument16 pagesLinking Early Detection/treatment of Parkinson's Disease Using Deep Learning TechniquesLewis TorresPas encore d'évaluation
- An Experimental Evaluation of Similarity-Based and Embedding-Based Link Prediction Methods On GraphsDocument18 pagesAn Experimental Evaluation of Similarity-Based and Embedding-Based Link Prediction Methods On GraphsLewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- Understanding Customers' EvaluationsDocument11 pagesUnderstanding Customers' EvaluationsLewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- Call For Papers - International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesCall For Papers - International Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- Access and Connection Via Tech Data As An Enabler Af A Thin or Nonexistent MarketDocument8 pagesAccess and Connection Via Tech Data As An Enabler Af A Thin or Nonexistent MarketLewis TorresPas encore d'évaluation
- Categorization of Factors Affecting Classification Algorithms SelectionDocument19 pagesCategorization of Factors Affecting Classification Algorithms SelectionLewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- Distortion Based Algorithms For Privacy Preserving Frequent Item Set MiningDocument13 pagesDistortion Based Algorithms For Privacy Preserving Frequent Item Set MiningLewis TorresPas encore d'évaluation
- International Journal of Distributed and Parallel SystemsDocument2 pagesInternational Journal of Distributed and Parallel SystemsijdpsPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- Access and Connection Via Tech Data As An Enabler Af A Thin or Nonexistent MarketDocument8 pagesAccess and Connection Via Tech Data As An Enabler Af A Thin or Nonexistent MarketLewis TorresPas encore d'évaluation
- Call For Papers: ISSN:2230-9608 (Online) 2231-007X (Print)Document2 pagesCall For Papers: ISSN:2230-9608 (Online) 2231-007X (Print)Lewis TorresPas encore d'évaluation
- International Journal of Data Mining & Knowledge Management Process (IJDKP)Document2 pagesInternational Journal of Data Mining & Knowledge Management Process (IJDKP)Lewis TorresPas encore d'évaluation
- Cusps: Ramesh 04-Jun-1976 12:30:00 PM Krishnagiri 78:14:0 E, 12:32:0 N Tzone: 5.5 KP (Original) Ayanamsha 23:26:2Document1 pageCusps: Ramesh 04-Jun-1976 12:30:00 PM Krishnagiri 78:14:0 E, 12:32:0 N Tzone: 5.5 KP (Original) Ayanamsha 23:26:2Suresh NatarajanPas encore d'évaluation
- Travel Advertisement RubricDocument2 pagesTravel Advertisement Rubricapi-316353024Pas encore d'évaluation
- Enterpreneurship Assignment 2Document8 pagesEnterpreneurship Assignment 2Khusbu JaiswalPas encore d'évaluation
- Conquering College The Most Fun You Can Have Learning The Things You Need To Know NodrmDocument144 pagesConquering College The Most Fun You Can Have Learning The Things You Need To Know NodrmVithorPas encore d'évaluation
- History of Computer ReviewerDocument10 pagesHistory of Computer ReviewerNeil Andrew Aliazas78% (9)
- PP in Ii 001Document15 pagesPP in Ii 001Dav EipPas encore d'évaluation
- Passmore Et Al (2019) Workplace CoachingDocument47 pagesPassmore Et Al (2019) Workplace CoachingMalarvilie KrishnasamyPas encore d'évaluation
- Digital Signal Processing Lab ManualDocument61 pagesDigital Signal Processing Lab ManualOmer Sheikh100% (6)
- Individual Performance Commitment and Review Form (Ipcrf) : Annex EDocument8 pagesIndividual Performance Commitment and Review Form (Ipcrf) : Annex Emenzi magnoPas encore d'évaluation
- Rivers and Their Origin (Top MCQ)Document24 pagesRivers and Their Origin (Top MCQ)Anil Yadav100% (1)
- Module 3: Literature Review and CitationDocument3 pagesModule 3: Literature Review and CitationLysss EpssssPas encore d'évaluation
- Ficha Tecnica Reflector 2000W Led Lluminacion de Campos de Futbol Estadios Goled Philips Osram Opalux LedDocument5 pagesFicha Tecnica Reflector 2000W Led Lluminacion de Campos de Futbol Estadios Goled Philips Osram Opalux Ledluis perdigonPas encore d'évaluation
- Introduction To Rhetorical Analysis: Week 1Document16 pagesIntroduction To Rhetorical Analysis: Week 1Will KurlinkusPas encore d'évaluation
- Generic StructureDocument6 pagesGeneric StructureAndre AlvarezPas encore d'évaluation
- Module 6 - Using and Evaluating Instructional MaterialsDocument5 pagesModule 6 - Using and Evaluating Instructional MaterialsMaria Victoria Padro100% (4)
- Vocology For The Singing Voice PDFDocument120 pagesVocology For The Singing Voice PDFNathalia Parra Garza100% (2)
- 9A02505 Electrical Machines-IIIDocument4 pages9A02505 Electrical Machines-IIIsivabharathamurthyPas encore d'évaluation
- Research 9: Activity 4: Background of The StudyDocument7 pagesResearch 9: Activity 4: Background of The StudyPhilip AmelingPas encore d'évaluation
- Exposure: The PhotoreactionDocument16 pagesExposure: The PhotoreactionGeetha ThiruvengadamPas encore d'évaluation
- An Introduction To EFTDocument24 pagesAn Introduction To EFTkunjammuPas encore d'évaluation
- Union Metal SemiconductorDocument4 pagesUnion Metal SemiconductorskinhugoPas encore d'évaluation
- Spying From Space - Constructing America's Satellite Command and Control Systems (PDFDrive)Document230 pagesSpying From Space - Constructing America's Satellite Command and Control Systems (PDFDrive)MohammadPas encore d'évaluation
- 20160323110112-Sae 1215Document1 page20160323110112-Sae 1215awesome_600Pas encore d'évaluation
- WideScreen Code For PS2 GamesDocument78 pagesWideScreen Code For PS2 Gamesmarcus viniciusPas encore d'évaluation
- SAP Group Reporting 1909Document28 pagesSAP Group Reporting 1909SUDIPTADATTARAY86% (7)
- Ground Vehicle Operations ICAODocument31 pagesGround Vehicle Operations ICAOMohran HakimPas encore d'évaluation
- Motorola Talkabout T82 PDFDocument184 pagesMotorola Talkabout T82 PDFAlex TamayoPas encore d'évaluation
- Inglês - Degrees of ComparisonDocument4 pagesInglês - Degrees of ComparisonVersehgi IIPas encore d'évaluation
- MLAB 3 - BoilerDocument3 pagesMLAB 3 - BoilerReden LopezPas encore d'évaluation
- Critique of Violence - Walter BenjaminDocument14 pagesCritique of Violence - Walter BenjaminKazım AteşPas encore d'évaluation