Académique Documents
Professionnel Documents
Culture Documents
TBLDAPEnviron 1370 PDF
Transféré par
Hermes GuerreroDescription originale:
Titre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
TBLDAPEnviron 1370 PDF
Transféré par
Hermes GuerreroDroits d'auteur :
Formats disponibles
Extreme Networks Technical Brief
Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) Environment
Configuration Requirements
The following components are required to install the access control solution: Linux server with Linux Red Hat 4.0 FreeRADIUS 1.1.x OpenLDAP 2.3.x Extreme Networks Summit X450e switches Windows XP clients Authentication is typically accomplished using a Remote Authentication Dial-In User Service (RADIUS) protocol which holds the authentication database. The solution to providing secure edge provisioning requires the addition of an authenticating element to the network configuration that can work with directory services. In other words, to integrate the Universal Port in an LDAP environment, a RADIUS server must be added to use the LDAP database. The following is a configuration example that enables an IP phone or PC to use the Universal Port technology to authenticate to an LDAP environment.
Overview
Customers with a directory services authentication solution such as Lightweight Directory Access Protocol (LDAP) require cost-effective, secure edge access devices. For added security, customers need a dynamic policy enforcement edge solution that does not depend on open, unsecured edge ports. Customers also want to use existing directory services infrastructures to reduce administrative overhead as well as reduce time and effort to configure edge switches. Extreme Networks Universal Port framework can establish and enforce policies based on an authenticated user or device. Each port is secured because it is not part of any subnet until access is granted by an authentication authority.
Configuration Instructions
Basic Configuration Steps
1. Install and configure RADIUS Server on existing Linux server 2. Install and configure OpenLDAP 3. Add vendor specific attributes to RADIUS server and LDAP server 4. Configure edge switches 5. Configure supplicant
Internet
Avaya HQ callserver
Current Domain Authentication
Avaya G250
802.1x PC
EAPS PrimaryPort 21 EAPS SecondaryPort 24
Transit 1
EAPS SecondaryPort 22
FreeRadius
Directory Services OpenLDAP
Transit 2
EAPS RING (RFC 3619)
EAPS PrimaryPort 23
EAPS Master
EAPS PrimaryPort 23
EAPS SecondaryPort 24
802.1x phone
802.1x phone
5070-01
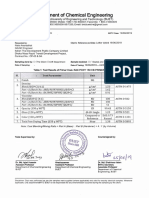
Figure 1: Completed Authentication Design
2007 Extreme Networks, Inc. All rights reserved.
Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) EnvironmentPage 1
Extreme Networks Technical Brief
Install and Test the RADIUS Server
RADIUS protocol is defined in IETF RFC 2865. RADIUS protocol allows a Network Access Server (NAS) to perform authentication, authorization, and accounting for users. RADIUS is a client/server protocol based on UDP. The RADIUS client, the network access server, is typically a router, switch, or wireless access point. In this configuration, the RADIUS server is a daemon process running on a UNIX server. RADIUS server software can be obtained from several sources. This solution uses FreeRADIUS available on the following URLs: http://www.freeradius.org or www.redhat. com. FreeRADIUS fits well in a distributed, heterogeneous computing environment.
Configuring the Server
FreeRADIUS configuration files are usually stored in the /etc/raddb folder. 1. Enter the following commands to modify the radiusd. conf file global settings.
log_auth = yes (log authentication requests to the log file) log_auth_badpass = no (dont log passwords if request rejected) log_auth_goodpass = no (dont log passwords if request accepted)
2. Enter the following commands to modify LDAP Settings.
modules { ldap { server = ldaptest.extremenetworks.com basedn = o=ldaptestdemo,dc=extremenetworks,dc=com filter = (cn=%{Stripped-User-Name:-%{User-Name}}) base_filter = (objectclass=radiusprofile) start_tls = no dictionary_mapping = ${raddbdir}/ldap.attrmap authtype = ldap ldap_connections_number = 5 timeout = 4 timelimit = 3 net_timeout = 1 } }
Enter the Following Commands to Install and Test FreeRADIUS
tar -zxvf freeradius-1.0.2.tar.gz (extract with gunzip and tar) ./configure make make install (run this command as root) radiusd or (start RADIUS server) radiusd -X (start RADIUS server in debug mode) radtest test test localhost 0 testing123 (test RADIUS server)
If radtest receives a response, the FreeRADIUS server is up and running. Note: Another free tool, NTRadPing, can be used to test authentication and authorization requests from Windows clients. NTRadPing displays detailed responses such as attribute values sent back from the RADIUS server.
3. Use the following commands to Uncomment LDAP from the authorize section.
authorize { preprocess chap mschap suffix ldap eap files }
Configure the FreeRADIUS Server
Configuring the RADIUS server involves configuring the server, the client, and the user (both for authentication and authorization). LDAP is an open standard that defines a method for accessing and updating information in an X.500-like directory. LDAP can be used to keep user information in a central location to avoid having to store identical user information on each system. LDAP is also used to maintain and access information in a consistent and controlled manner. LDAP simplifies user administration tasks by managing users in a central directory. Because LDAP lacks interoperability with a RADIUS client, a RADIUS server is configured to authenticate users against LDAP.
4. Use the following commands to Uncomment LDAP from the authenticate section.
authenticate { Auth-Type PAP { pap } Auth-Type CHAP { chap } Auth-Type MS-CHAP { mschap } unix ldap eap
2007 Extreme Networks, Inc. All rights reserved.
Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) EnvironmentPage 2
Extreme Networks Technical Brief
Configuring the Attribute Mappings
Attributes are configured in /etc/freeradius/ladp.attrmap. This file maps the RADIUS Attribute to an LDAP Attribute. Because Samba has NT/LM password hashes, the default mapping for LM-Password and NT-Password must be changed. Use the following commands to configure attribute mappings.
checkItem checkItem checkItem replyItem replyItem replyItem User-Password LMPassword NTPassword Tunnel-Type Tunnel-Medium-Type Tunnel-Private-Group-Id userPassword sambaLMPassword sambaNTPassword radiusTunnelType radiusTunnelMediumType radiusTunnelPrivateGroupId
Configuring the Client
Clients are configured in /etc/raddb/clients.conf. There are two ways to configure RADIUS clients. Either group the NAS by IP subnet or list the NAS by hostname or IP address. Use the following commands to configure the client using the second method.
client 192.168.1.1 { secret = extreme1 shortname = ldap-demo }
Configuring the Authentication Method
The authentication method is configured in /etc/raddb/eap.conf. The authentication method used by FreeRADIUS is the Protected EAP (PEAP) method. To activate PEAP, a TLS tunnel is required to encrypt communication between supplicant and RADIUS server. This means that server certificates are required. Use the following commands to configure the authentication method.
peap { default_eap_type = mschapv2 } tls { private_key_password = whatever private_key_file = ${raddbdir}/certs/cert-srv.pem certificate_file = ${raddbdir}/certs/cert-srv.pem CA_file = ${raddbdir}/certs/demoCA/cacert.pem dh_file = ${raddbdir}/certs/dh random_file = ${raddbdir}/certs/random fragment_size = 1024 include_length = yes }
Start the RADIUS Service
Use the following command to start radiusd in foreground with debugging enabled ( useful for troubleshooting).
radiusd X f
2007 Extreme Networks, Inc. All rights reserved.
Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) EnvironmentPage 3
Extreme Networks Technical Brief
Install OpenLDAP
OpenLDAP software is an open source implementation of LDAP and can be obtained at http://www.openldap.org. Use the following procedure to install OpenLDAP packages. 1. Verify the Red Hat Linux installed releases. The release number is stored in the /etc/redhat-release file. 2. Verify the version of OpenLDAP currently installed by entering the rpm -qa | grep openldap command at the Linux prompt.
# rpm -qa |grep openldap openldap-2.3.xx-x openldap-clients-2.3.xx-x openldap-servers-2.3.xx-x
3. If a default Red Hat Linux installation was used, there is at least one OpenLDAP Red Hat Package Manager (RPM) installed. The LDAP RPMs can either be found on the Red Hat CD or download from one of the following RPM download sources. www.rpmfind.net www.redhat.com Search on openldap and select the RPM based on the distribution Select Download, and then search on openldap
4. After downloading the RPMs to the Linux server, change to the download directory and start the installation using the rpm command.
# rpm -ivh openldap*
5. Verify that the OpenLDAP RPMs have been installed with the rpm -qa | grep openldap command at the Linux prompt.
# rpm -qa | grep openldap openldap-2.3.xx-x openldap-clients-2.3.xx-x openldap-servers-2.3.xx-x
Configure OpenLDAP
Once the build is complete, the slapd and slurpd daemons are located in /usr/local/libexec. The config files are in /etc/openldap and ready to start the main server daemon, slapd.
Configuring Slapd for Startup
Before slapd can be started, /etc/openldap/slapd.conf must be edited to indicate where to store data and who is allowed access to the data. Use the following commands to configure slapd for startup.
Change Suffix - Change rootDN - Used slappasswd to generate rootpw - Added rootpw entry. database (use default) suffix dc=xxxxxx,dc=org rootdn cn=xxxx,dc=xxxxxx,dc=org rootpw {SSHA}c5PemO1KWqz0254r4rnFVmxKA/evs4Hu directory /var/lib/ldap allow bind_v2 pidfile /var/run/slapd.pid
2007 Extreme Networks, Inc. All rights reserved.
Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) EnvironmentPage 4
Extreme Networks Technical Brief
Adding New Schemas
The radius schema and samba schema for PEAP authentication must be included into the slapd.conf file. After modifying the file, the LDAP server must be restarted to load the new schemas. Use the following commands to add new schemas.
cp /usr/share/doc/freeradius-1.0.1/RADIUS-LDAPv3.schema /etc/openldap/schema/ cp /usr/share/doc/samba-3.0.10/LDAP/samba.schema /etc/openldap/schema
Use the following commands to modify slapd.conf
include/etc/openldap/schema/RADIUS-LDAPv3.schema include/etc/openldap/schema/samba.schema
Populating LDAP Database with Organization and User Entries
Use the following commands to make the user entry in the LDAP directory (slapd.conf).
dn: objectClass: objectClass: objectClass: objectClass: sn: uid: cn: radiusTunnelMediumType: radiusTunnelType: radiusTunnelPrivateGroupId: sambaNTPassword: sambaLMPassword: userPassword:: sambaSID: uid=newperson3,o=ldaptestdemo,dc=extremenetworks,dc=com top person radiusprofile (Defined in the RADIUS-LDAPv3 schema) sambaSamAccount ldaptestdemo newperson3 (This username given in the Odyssey client) newperson3 IEEE-802 VLAN 2 (Value of the VLAN tag) A3A685F89364D4A5182B028FBE79AC38 C23413A8A1E7665FC2265B23734E0DAC e1NIQX00MXZzNXNYbTRPaHNwUjBFUU9raWdxbldySW89 S-1-0-0-28976
The samba-related attributes may already be populated in the LDAP server if there is an LDAP-enabled samba infrastructure in place. Note: If the samba related entries are not present, then the values for sambaNTPassword and sambaNMPPassword can be created by running the mkntpwd command.
cd /usr/share/doc/samba-3.0.10/LDAP/smbldap-tools/mkntpwd make ./mkntpwd L <password> (provides value for sambaLMPassword attribute) ./mkntpwd N <password> (provides value for sambaNTPassword attribute)
2007 Extreme Networks, Inc. All rights reserved.
Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) EnvironmentPage 5
Extreme Networks Technical Brief
Add Vendor-Specific Attributes to RADIUS and LDAP Server
Configuring the RADIUS Dictionary
To add Extreme Networks VSAs, enter the following commands to modify the dictionary file in /etc/raddb.
ATTRIBUTE ATTRIBUTE ATTRIBUTE ATTRIBUTE ATTRIBUTE ATTRIBUTE ATTRIBUTE ATTRIBUTE ATTRIBUTE ATTRIBUTE VALUE VALUE VALUE VALUE Extreme-CLI-Authorization Extreme-Shell-Command Extreme-Netlogin-Vlan Extreme-Netlogin-Url Extreme-Netlogin-Url-Desc Extreme-Netlogin-Only Extreme-User-Location Extreme-Netlogin-Vlan-Tag Extreme-Netlogin-Extended-Vlan Extreme-Security-Profile Extreme-CLI-Authorization Extreme-CLI-Authorization Extreme-Netlogin-Only Extreme-Netlogin-Only 201 202 203 204 205 206 208 209 211 212 integer string string string string integer string integer string string 0 1 0 1 Extreme Extreme Extreme Extreme Extreme Extreme Extreme Extreme Extreme Extreme
Disabled Enabled Disabled Enabled
Configuring Additional Attributes Mappings
Attributes are configured in /etc/freeradius/ladp.attrmap.
## Attributes for Extreme Networks Vendor-Specific RADIUS replyItem Extreme-Security-Profile radiusExtremeSecurityProfile replyItem Extreme-Netlogin-Vlan-Tag radiusExtremeNetloginVlanTag replyItem Extreme-Netlogin-Extended-Vlan radiusExtremeNetloginExtendedVlan
Modifying RADIUS Schema
Additional attributes for RADIUS must be configured to extend the RADIUS-LDAP-V3.schema under the /etc/openldap directory. Use the following commands to modify the RADIUS schema.
attributetype ( 1.3.6.1.4.1.3317.4.3.1.61 NAME radiusExtremeSecurityProfile DESC EQUALITY caseIgnoreIA5Match SYNTAX 1.3.6.1.4.1.1466.115.121.1.26 ) attributetype ( 1.3.6.1.4.1.3317.4.3.1.62 NAME radiusExtremeNetloginVlanTag DESC EQUALITY caseIgnoreIA5Match SYNTAX 1.3.6.1.4.1.1466.115.121.1.26 ) attributetype ( 1.3.6.1.4.1.3317.4.3.1.63 NAME radiusExtremeNetloginExtendedVlan DESC EQUALITY caseIgnoreIA5Match SYNTAX 1.3.6.1.4.1.1466.115.121.1.26 )
2007 Extreme Networks, Inc. All rights reserved.
Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) EnvironmentPage 6
Extreme Networks Technical Brief
Restarting the LDAP Server
Use the following syntax to use to stop and start LDAP services.
service ldap restart
For phone authentication (which uses EAP-based md5 authentication) the password is stored in cleartext in the UserPassword field for the phone entries in LDAP.
Configure the Switch
This configuration applies to Summit X450e switches but can also be used for other Extreme Networks switches that support 802.1x. Refer to the software configuration guide of the switch for details. Use the following commands to activate the switch for 802.1X port-based authentication.
create vlan voice create vlan data create vlan ldap configure voice tag 10 configure data tag 20 configure ldap ipaddress 192.168.1.1/24 enable ipforwarding create vlan nvlan en netlogin dot1x en netlogin port 13-24 dot1x configure radius netlogin primary server 192.168.1.2 1812 client-ip 192.168.1.1 vr VR-Default configure radius netlogin primary shared-secret extreme1 enable radius netlogin enable netlogin dot1x
To make the port able to run the scripts, when told to do so by RADIUS/LDAP:
configure upm event user-authenticate profile a-avaya ports 1-23
LDAP UID entries: In the ldap phone uid details, use the following to execute a script:
Extreme-Security-Profile
To make the port to be added tagged in the voice vlan:
Extreme-Netlogin-Extended-Vlan = TVoice (use UData for a PC)
NOTE: The fields required for authentication depend on the end-station; XP uses EAP-PEAP and must have encrypted fields for the UID password. Avaya phones authenticate with MD-5 and must have an unencrypted field in LDAP. Scripts: This a-avaya script tells the phone to configure itself in the voice VLAN, and to send tagged frames. The script also informs the phone of the fileserver and callserver.
2007 Extreme Networks, Inc. All rights reserved.
Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) EnvironmentPage 7
Extreme Networks Technical Brief
create upm profile a-avaya create log entry Starting_UPM_Script_AUTH-AVAYA set var callServer 10.147.12.12 set var fileServer 10.147.10.3 set var voiceVlan voice set var CleanupProfile CleanPort set var sendTraps false # create log entry Starting_UPM_AUTH-AVAYA_Port_$EVENT.USER_PORT #********************************************************* # adds the detected port to the device unauthenticated profile port list #********************************************************* create log entry Updating_Unauthenticated_Port_List_Port_$EVENT.USER_PORT #configure upm event user-unauthenticated profile CleanupProfile ports $EVENT.USER_PORT #********************************************************* # Configure the LLDP options that the phone needs #********************************************************* configure lldp port $EVENT.USER_PORT advertise vendor-specific dot1 vlan-name vlan $voiceVlan configure lldp port $EVENT.USER_PORT advertise vendor-specific avaya-extreme call-server $callServer configure lldp port $EVENT.USER_PORT advertise vendor-specific avaya-extreme file-server $fileServer configure lldp port $EVENT.USER_PORT advertise vendor-specific avaya-extreme dot1q-framing tagged configure lldp port $EVENT.USER_PORT advertise vendor-specific med capabilities #*************************************************************** # Configure the POE limits for the port based on the phone requirement #*************************************************************** # If port is PoE capable, uncomment the following line configure lldp port $EVENT.USER_PORT advertise vendor-specific med power-via-mdi #configure inline-power operator-limit $EVENT.DEVICE_POWER ports $EVENT.USER_PORT create log entry UPM_Script_A-AVAYA_Finished_Port_$EVENT.USER_PORT
NOTE: This script refers specifically to Avaya but it should be applicable to any LLDP-enabled phone.
Configure the Supplicant
Figure 2 illustrates the configuration of a Windows XP supplicant. No additional installation is required. For enhanced security, install the FreeRADIUS server CA certificate (the CA that signed the certinstalled in eap.conf). Use the following procedure to configure the Supplicant. 1. Open the network configuration panel and select the network card and enter the properties.
Figure 2: Configuration for a Windows XP Supplicant
2007 Extreme Networks, Inc. All rights reserved. Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) EnvironmentPage 8
Extreme Networks Technical Brief
2. Select the Authentication tab. See Figure 3.
Figure 3: Authentication Tab
3. Enable 802.1x and disable authenticate as computer. Choose EAP type of PEAP and click on Properties. See Figure 4.
Figure 4: Protected EAP Properties Window
2007 Extreme Networks, Inc. All rights reserved.
Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) EnvironmentPage 9
Extreme Networks Technical Brief
4. Unselect the Validate server certificate and select Secured password (EAP-MSCHAP v2) as the authentication method. Click Configure. See Figure 5.
Figure 5: EAP MSCHAPv2 Window
5. Unselect the checkbox.
www.extremenetworks.com
Corporate and North America
Extreme Networks, Inc. 3585 Monroe Street Santa Clara, CA 95051 USA Phone +1 408 579 2800
email: info@extremenetworks.com
Europe, Middle East, Africa and South America
Phone +31 30 800 5100
Asia Pacific
Phone +852 2517 1123
Japan
Phone +81 3 5842 4011
2007 Extreme Networks, Inc. All rights reserved. Extreme Networks, the Extreme Networks Logo and Summit are either registered trademarks or trademarks of Extreme Networks, Inc. in the United States and/or other countries. All other names and marks are the property of their respective owners. Specifications are subject to change without notice. 1370_01 10/07 Using the Universal Port in a Lightweight Directory Access Protocol (LDAP) Environment Technical Brief
Vous aimerez peut-être aussi
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- Complete Hemi Sync Gateway Experience ManualDocument43 pagesComplete Hemi Sync Gateway Experience Manualapi-385433292% (92)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (894)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (587)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (119)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2219)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (265)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- Android Attendance Management SystemDocument54 pagesAndroid Attendance Management Systemskpetks75% (12)
- Addition and Subtraction of PolynomialsDocument8 pagesAddition and Subtraction of PolynomialsPearl AdamosPas encore d'évaluation
- About Version ControlDocument6 pagesAbout Version ControlMaria Kristina Cassandra HeukshorstPas encore d'évaluation
- 256267a1Document5 083 pages256267a1Елизавета ШепелеваPas encore d'évaluation
- 9 - NCP Computer Science PGDocument19 pages9 - NCP Computer Science PGM AmbreenPas encore d'évaluation
- Homo Sapiens ActivityDocument8 pagesHomo Sapiens ActivityJhon Leamarch BaliguatPas encore d'évaluation
- Manual Bombas CHWDocument16 pagesManual Bombas CHWFred GarciaPas encore d'évaluation
- Rakpoxy 150 HB PrimerDocument1 pageRakpoxy 150 HB Primernate anantathatPas encore d'évaluation
- Brooks Instrument FlowmeterDocument8 pagesBrooks Instrument FlowmeterRicardo VillalongaPas encore d'évaluation
- 2.0 - SITHKOP002 - Plan and Cost Basic Menus Student GuideDocument92 pages2.0 - SITHKOP002 - Plan and Cost Basic Menus Student Guidebash qwertPas encore d'évaluation
- WA Beretta M92FS Parts ListDocument2 pagesWA Beretta M92FS Parts ListDenis Deki NehezPas encore d'évaluation
- HP 5973 Quick ReferenceDocument28 pagesHP 5973 Quick ReferenceDavid ruizPas encore d'évaluation
- LLoyd's Register Marine - Global Marine Safety TrendsDocument23 pagesLLoyd's Register Marine - Global Marine Safety Trendssuvabrata_das01100% (1)
- Youth, Time and Social Movements ExploredDocument10 pagesYouth, Time and Social Movements Exploredviva_bourdieu100% (1)
- Fundamental Managerial Accounting Concepts 9th Edition Edmonds Solutions ManualDocument35 pagesFundamental Managerial Accounting Concepts 9th Edition Edmonds Solutions ManualDrMichelleHutchinsonegniq100% (15)
- Pfrs 16 LeasesDocument4 pagesPfrs 16 LeasesR.A.Pas encore d'évaluation
- EE-434 Power Electronics: Engr. Dr. Hadeed Ahmed SherDocument23 pagesEE-434 Power Electronics: Engr. Dr. Hadeed Ahmed SherMirza Azhar HaseebPas encore d'évaluation
- Fiery Training 1Document346 pagesFiery Training 1shamilbasayevPas encore d'évaluation
- Merchandise Floor Ready Standards - Supplier InformationDocument46 pagesMerchandise Floor Ready Standards - Supplier InformationGarmentLearner100% (1)
- Lec 10 - MQueues and Shared Memory PDFDocument57 pagesLec 10 - MQueues and Shared Memory PDFUchiha ItachiPas encore d'évaluation
- Wika Type 111.11Document2 pagesWika Type 111.11warehouse cikalongPas encore d'évaluation
- Solr 3000: Special Operations Long Range Oxygen Supply 3,000 PsigDocument2 pagesSolr 3000: Special Operations Long Range Oxygen Supply 3,000 Psigмар'ян коб'ялковськийPas encore d'évaluation
- Manual - Sentron Pac Profibus Do Modul - 2009 02 - en PDFDocument106 pagesManual - Sentron Pac Profibus Do Modul - 2009 02 - en PDFDante Renee Mendoza DelgadoPas encore d'évaluation
- Call SANROCCO 11 HappybirthdayBramanteDocument8 pagesCall SANROCCO 11 HappybirthdayBramanterod57Pas encore d'évaluation
- Front Cover Short Report BDA27501Document1 pageFront Cover Short Report BDA27501saperuddinPas encore d'évaluation
- Models of Health BehaviorDocument81 pagesModels of Health BehaviorFrench Pastolero-ManaloPas encore d'évaluation
- Bethany Getz ResumeDocument2 pagesBethany Getz Resumeapi-256325830Pas encore d'évaluation
- Marijuana Grow Basics - Jorge CervantesDocument389 pagesMarijuana Grow Basics - Jorge CervantesHugo Herrera100% (1)
- BSC6900 UMTS V900R011C00SPC700 Parameter ReferenceDocument1 010 pagesBSC6900 UMTS V900R011C00SPC700 Parameter Referenceronnie_smgPas encore d'évaluation