Académique Documents
Professionnel Documents
Culture Documents
Dual Encryption Schema With Cheating Text and NTRU
Transféré par
seventhsensegroupCopyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Dual Encryption Schema With Cheating Text and NTRU
Transféré par
seventhsensegroupDroits d'auteur :
Formats disponibles
International Journal of Computer Trends and Technology- volume4Issue2- 2013
Dual Encryption Schema With Cheating Text and NTRU
Jagadeeshbabu.G#1, Rakesh Nayak#2,
#1 Student, Sri Vasavi Engineering College, TaddepalliGudem, Andhra Pradesh, #2 Assoc. Professor, Department of IT, Sri Vasavi Engineering College, TaddepalliGudem, Andhra Pradesh , Abstract: Shared data systems have grown in numbers and hence they are susceptible to many security challenges. The sender embeds a plain message in another plain text called Cheating Text. The positions of the characters of the plain text in the cheating text are stored in a Real Message Index File (RIF).This file is encrypted using Nth degree truncated polynomial ring (NTRU) scheme and sent along with the cheating text. The receiver once received, proceeds to decrypt the RIF table and gets back the original message from the received cheating text. Authentication to decrypt is achieved by NTRU key exchanges prior to session initiation at both senders and receivers side along with the MD5 hash of the RIF. An NTRU 263-bit encryption key, has cryptographic strength equivalent to renowned powerful 1024-bit RSA key. We propose to replace any secure Scheme with a more robust NTRU crypto system.
Keywords NTRU,MD5,RIF,CPT.
is the implementation of three layered content protection procedures involving steganography using cheating text, RIF hashing using MD5 and finally entire content ciphering using NTRU suggests that finally obtained ciphered content is so robust and secure that it has potential to be compared with any 1024-bit ciphers such as RSA or ECC(Elliptic Curve). The main theme of the cryptography is to transform a message such that it is incomprehensive to an unauthorized reader. This is an overt secret writing; that is, the transformed result is obviously recognizable as a secret message[1]. On the other hand, steganography is one kind of covert secret message or hidden writing. Its aim is to conceal the very existence of a message-to send a secret message without incurring suspicion. In this paper, A hash value of the positional indexes(RIF) of characters pertaining to cheating text containing the plain text is hashed using MD5 and then cheating text and RIF combo is ciphered using the NTRU Algorithm in order to provide authentication at both the ends based on key exchanges of both the sender and reciever. The NTRU is a public-key algorithm competes with RSA and elliptic curve. The encrypted file is sent to the receiver along with the cheating text and the hash value of the plain text. The receiver decrypts the RIF file and obtains the original message using the cheating text. The hash value is re-calculated at the receivers end to verify the message and hence authentication is achieved. II RELATED WORK In public key cryptography each user or the device taking part in the communication generally have a pair of keys, a public key and a private key, and a set of operations associated with the keys to do the cryptographic operations.
I INTRODUCTION Message Encryption schemes currently being used encrypt the total message that needs to be transmitted. This paper encrypts that part of the message which is confidential rather than the total message using the concept of cheating text. Cheating text is any kind of meaningful text which is a metamorphosis of hidden writing. The concept of cheating text comes from Steganography, in particular data hiding[1]. Plain text message is inserted into another text called the cheating text and the positions of the characters of the plain text are stored in another file called real message index table(RIF). Now the RIF table is hashed using MD5 which serves as the primary cipher coating. The entire contents(cheating text + hashed RIF table) are then encrypted using an Nth token polynomial cipher which acts as the second coating thus justifying dual encryption schema. One interesting feature of this kind of an approach
ISSN: 2231-2803
http://www.internationaljournalssrg.org
Page 169
International Journal of Computer Trends and Technology- volume4Issue2- 2013
Only the particular user knows the private key whereas the public key is distributed to all users taking part in the communication. Some public key algorithm may require a set of predefined constants to be known by all the devices taking part in the communication. NTRU and RSA are an example of such public key crypto systems. Unlike private key cryptos, that does not require any sharing of secret key between the communicating parties, the public key cryptos are much slower than the private key cryptos. Normally hash functions suffer from various types of collisions. MD5[2] is a hash algorithm to prepare a message digest for a given plaintext. However, this suffers from Wangs collision attack. MD5 algorithm is modified to sustain the Wangs collision attack. The idea is to use 64-bit chaining variables instead of 32-bit chaining variables. In this following algorithm Padding bits means message is "padded" (extended) so that its length (in bits) is congruent to 448 modulo 512[3]. RSA is a Public key algorithm invented in 1977 by Rivest, Shamir, and Adelman. RSA[4] supports Encryption and Digital Signatures ,most widely used public key algorithm and gets its security from integer factorization problem. Relatively easy to understand and implement, RSA gets its security from factorization problem. Difficulty of factoring large numbers is the basis of security of RSA. Over 1000 bits long numbers are used. In this paper, NTRU performance is compared with that of RSA. III ABOUT NTRU Unlike RSA, NTRU[6] is not widely used, and in fact the NTRU cryptosystem needed changes early on to improve its security by addressing weaknesses and performance. But today NTRU is recognized as faster than the widely used RSA algorithm. Comparing NTRU to other cryptosystems like RSA and ECC shows that NTRU, at a high security level, is much faster than RSA (around five orders of magnitude) and ECC (around three orders of magnitude). NTRU may be more resistant over time to attack than RSA because NTRU is constructed in what crypto researchers call a "lattice" framework. NTRU[8] consists of two algorithms: NTRU Encrypt for public-key encryption and NTRU Sign for digital signatures. NTRU is lattice-based and not known to be breakable even with quantum computers. Commonly used cryptosystems like RSA or ECC, on the other hand, will be broken if and when quantum computers become available. In addition, NTRU is significantly faster than other public-key cryptosystems. III PROPOSED SCHEME In the proposed crypto System the message is embedded into another text called cheating text. The position of the each character of the cheating text is told in a table called character position table. Another table called the RIF is generated from character positions table (CPT) for the characters of the original message. The RIF is encrypted with any public key crypto system, we propose to use NTRU for better performance. The cheating text along with the encrypted RIF and the hash value of the original message are sent. The receiver will decrypt the RIF and gets back the original message from the cheating text using RIF. This received original message is again hashed and compared with the received hash value. If they are equal the original text is authenticated. The algorithm for encryption and decryption of the process is explained below. Algorithm: Step 1: Take the input value as Plain text. Step 2: Take the meaning full cheating text. Step 3: Verify the cheating text, all the plaintext was existed in the cheating text or not. If existed got to Step 4 otherwise go to Step 2. Step 4: Generate the CPT to the cheating text. Step 5: Generate the RIF (real message Index File) Step 6: Encrypt the RIF with the any secure Scheme. Step 7: Generate the hash value to the RIF using MD5. Step 8:Encrypt the cheating text and RIF hashes using NTRU. Step 9: Send the compressed results data to the receiver.
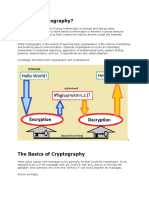
FIG1: Protection Scheme with NTRU
ISSN: 2231-2803
http://www.internationaljournalssrg.org
Page 170
International Journal of Computer Trends and Technology- volume4Issue2- 2013
The original message is embedded in a meaningful cheating text. The positions of the characters of the plain text in the cheating text are stored as Real Message Index File (RIF). This file is encrypted and sent along with the cheating text and hash value of the original message in the zipped format like pretty good policy as shown in Fig 1. In the following we show the decrypting process of the Improved Document Protection Scheme. We just reverse the direction of the encrypting process and generate the CPT again and then use the data in the RIF to find out the corresponding character. Algorithm: Step 1: Decrypt using NTRU using session key exchanges and then decompress the hash value and the real message index file. Step 2: Generate the Hash value of the plain text for finding the correct text. If hash value matched with the received hash value go to S3. Otherwise select one more cheating text. Step 3: Generate the CPT with the help of Cheating text. Step 4: If the correct cheating text found decrypt the RIF. Step 5: According to the position record in the RIF, we find out the corresponding characters in the CPT. Finally, we will get the real message. message and hence authentication is achieved. This scheme can be applied for authentication like security in data bases. VI REFERENCES
[1] H. J. Highland, Data encryption: a non-mathematical approach-Part 5, Journal of computer and Security, pp.93-97, 1995. [2] Ch. Rupa and P. S. Avadhani, An Improved Method to Reduce the Occurrence of Collision Attack on Hash Function, Int. J. computing mathematical applications, vol2, No1-2, pp.121-131, 2008. [3] H. Dobbertin, Cryptanalysis of MD5 Compress, proc. of Eurocrypt 96, 1996. [4] Aamer Nadeem et al, "A Performance Comparison of Data Encryption Algorithms", IEEE information and communication, pp .84-89, 2005. [5] Priya Dhawan.,"Performance Comparison: Security Design Choices, Microsoft Developer NetworkOctober2002.http://msdn2.microsoft.com/en us/ library/ms978415 .aspx [6]http://features.techworld.com/security/3275990/ntruencrypt-the-fastestpublic-key-algorithm-youve-never-heard-of/ [7] R Weis and S Lucks, Cryptographic Hash Functions-Recent Results on Cryptanalysis and their Implications on System Security, 5th System Administration and Network Engineering Conference, pp 15-19, 2006. [8] Carlos Cid,Recent developments in Cryptographic hash Functions: Security implications and future directions, Information Security Technical Report ,vol.26, pp.100-107, 2006.
FIG2:Decryption
.V CONCLUSION A message encryption scheme based on cheating text is proposed. For message encryption NTRU is proposed. The scheme is cost effective because only a index table called RIF file is hashed and sent to the receiver along with the cheating text in which the original message is embedded. The size of data being passed to hashing algorithms, as well to cryptography techniques, is also significant. The original message can be retrieved from the RIF file table and the cheating text. The hash value is recalculated at the receivers end to verify the
ISSN: 2231-2803
http://www.internationaljournalssrg.org
Page 171
Vous aimerez peut-être aussi
- Non-Linear Static Analysis of Multi-Storied BuildingDocument5 pagesNon-Linear Static Analysis of Multi-Storied Buildingseventhsensegroup100% (1)
- Efficient Cryptographic Protocols Preventing "Man-in-the-Middle" Attacks, PHD Thesis, Jonathan KatzDocument167 pagesEfficient Cryptographic Protocols Preventing "Man-in-the-Middle" Attacks, PHD Thesis, Jonathan KatzTa Thanh Dinh100% (1)
- Customer Letter State FarmDocument2 pagesCustomer Letter State FarmCatalin Cimpanu [ZDNet]Pas encore d'évaluation
- Chapter 1 - Introduction To Network SecurityDocument47 pagesChapter 1 - Introduction To Network SecurityXendra AqeylaaPas encore d'évaluation
- Network Design and Security ManagementDocument52 pagesNetwork Design and Security ManagementmehraDpaPas encore d'évaluation
- Introduction To FirewallsDocument76 pagesIntroduction To FirewallsLalmohan KsPas encore d'évaluation
- Siblu Khan 1101216058 CSE: Presented byDocument26 pagesSiblu Khan 1101216058 CSE: Presented byBGIIT COMPUTER EDUCATIONPas encore d'évaluation
- Cryptography and Network Security Lecture NotesDocument171 pagesCryptography and Network Security Lecture NoteskomalPas encore d'évaluation
- 01-Introduction To CryptographyDocument107 pages01-Introduction To CryptographyHggPas encore d'évaluation
- Cryptography Course WorkDocument27 pagesCryptography Course WorkSovan PalPas encore d'évaluation
- Mini Project ReportDocument11 pagesMini Project ReportKiran BogamPas encore d'évaluation
- CryptographyDocument20 pagesCryptographyArfath PashaPas encore d'évaluation
- Chapter 3 Encryption Principles and AlgorithmsDocument25 pagesChapter 3 Encryption Principles and AlgorithmsHiziki TarePas encore d'évaluation
- Pentest ReportDocument11 pagesPentest ReportTimotheeCPas encore d'évaluation
- Technologies Impact On PrivacyDocument29 pagesTechnologies Impact On PrivacyjhonaPas encore d'évaluation
- 02 - Chapter 2 - Conventional Encryption and Message ConfidentialityDocument16 pages02 - Chapter 2 - Conventional Encryption and Message ConfidentialityShreesha N RodriguesPas encore d'évaluation
- Chapter8 OverviewDocument10 pagesChapter8 OverviewEuber ChaiaPas encore d'évaluation
- 06 Chapter1Document27 pages06 Chapter1Sravya ReddyPas encore d'évaluation
- Cryptography and Network Security - Test - 1 - R177219023Document4 pagesCryptography and Network Security - Test - 1 - R177219023singhal9549akashPas encore d'évaluation
- Report PDFDocument35 pagesReport PDFPramod KumarPas encore d'évaluation
- 598 3156 1 PBDocument8 pages598 3156 1 PBstephenlim7986Pas encore d'évaluation
- Cryptography inDocument97 pagesCryptography inDhanraj DSPas encore d'évaluation
- Chapter 3 FinalDocument80 pagesChapter 3 FinalMihretu BekelePas encore d'évaluation
- Secret MessagingDocument45 pagesSecret MessagingAsha SumithaPas encore d'évaluation
- CryptographyDocument7 pagesCryptographyZonia NillPas encore d'évaluation
- Unit 8Document42 pagesUnit 8Tin SiocoPas encore d'évaluation
- IT1352 Cryptography and Network SecurityDocument29 pagesIT1352 Cryptography and Network SecurityVishnupriya OmprakashPas encore d'évaluation
- Assignment 2 - Part 2 - CryptographyDocument11 pagesAssignment 2 - Part 2 - CryptographyPJ1988Pas encore d'évaluation
- Ijettcs 2014 08 25 137Document6 pagesIjettcs 2014 08 25 137International Journal of Application or Innovation in Engineering & ManagementPas encore d'évaluation
- U21CS601 CT Unit 123 Part B QADocument13 pagesU21CS601 CT Unit 123 Part B QASanthosh kannaPas encore d'évaluation
- 7 Data Encryption and Decryption Data Encryption Standard AlgorithmDocument6 pages7 Data Encryption and Decryption Data Encryption Standard Algorithmaswanth0015Pas encore d'évaluation
- NSC Word All Unit QBDocument45 pagesNSC Word All Unit QByuvaraaj aletiPas encore d'évaluation
- What Is Cryptography?: Cryptography Is The Science of Using Mathematics To Encrypt and Decrypt DataDocument10 pagesWhat Is Cryptography?: Cryptography Is The Science of Using Mathematics To Encrypt and Decrypt Datadivya6990Pas encore d'évaluation
- CNS MID AnswersDocument7 pagesCNS MID AnswershafeezaPas encore d'évaluation
- Encrption: Keywords: Encryption, DES, Blowfish, RSA, AESDocument10 pagesEncrption: Keywords: Encryption, DES, Blowfish, RSA, AESabdul hadiPas encore d'évaluation
- 9 - Data-Privacy PDFDocument20 pages9 - Data-Privacy PDFGonPas encore d'évaluation
- Unit 1Document21 pagesUnit 1Vansh ChaudharyPas encore d'évaluation
- Chapter 2 & 3Document20 pagesChapter 2 & 3Yakubu AliuPas encore d'évaluation
- CryptographyDocument12 pagesCryptographyMuhammad AnsPas encore d'évaluation
- RSA and ECC Thesis PDFDocument21 pagesRSA and ECC Thesis PDFHarpreet SinghPas encore d'évaluation
- CryptographyDocument27 pagesCryptographyganesh_ecb123Pas encore d'évaluation
- A Comprehensive Review of Cryptographic AlgorithmsDocument9 pagesA Comprehensive Review of Cryptographic AlgorithmsIJRASETPublicationsPas encore d'évaluation
- Methods Toward Enhancing Rsa Algorithm: A SurveyDocument18 pagesMethods Toward Enhancing Rsa Algorithm: A SurveyAIRCC - IJNSAPas encore d'évaluation
- Real-Time Segregation of Encrypted Data Using EntropyDocument10 pagesReal-Time Segregation of Encrypted Data Using EntropyammuvijuPas encore d'évaluation
- Unit - Ii: Traditional Symmetric-Key CiphersDocument124 pagesUnit - Ii: Traditional Symmetric-Key Cipherssanthosh RPas encore d'évaluation
- Computer Security: Computer Threats and EncryptionDocument21 pagesComputer Security: Computer Threats and EncryptionPro NebyuPas encore d'évaluation
- Chapter - 1Document35 pagesChapter - 1Manish AeronPas encore d'évaluation
- Unit 3 Public Key CryptographyDocument8 pagesUnit 3 Public Key Cryptographygr8797131Pas encore d'évaluation
- 2 Marks CryptographyDocument13 pages2 Marks Cryptography219 DibyanshuKumarPas encore d'évaluation
- Lecture 2 CryptographyDocument10 pagesLecture 2 Cryptographyxtviper33Pas encore d'évaluation
- Cryptography AnswersDocument21 pagesCryptography Answers219 DibyanshuKumarPas encore d'évaluation
- CryptographyDocument7 pagesCryptographyDhananjay KumarPas encore d'évaluation
- Introduction Graphic in PCDocument43 pagesIntroduction Graphic in PChahajsPas encore d'évaluation
- Answer - Model - CS409 - Cryptography and Network Security - Nov 2018Document16 pagesAnswer - Model - CS409 - Cryptography and Network Security - Nov 2018Harshit SrivastavaPas encore d'évaluation
- Digital SignatureDocument10 pagesDigital Signaturerahulsaini031Pas encore d'évaluation
- Application Permutation in CryptographyDocument3 pagesApplication Permutation in CryptographyBasyirah Mohd ZawawiPas encore d'évaluation
- Cs1028 Network SecurityDocument120 pagesCs1028 Network SecurityAnusha ManiPas encore d'évaluation
- Ijert Ijert: Improvement Over Public Key Encryption Algorithm For Security in Network CommunicationsDocument4 pagesIjert Ijert: Improvement Over Public Key Encryption Algorithm For Security in Network CommunicationsNandha KumarPas encore d'évaluation
- (1-5) Cryptography Symmetric VS Asymmetric Encryption (2) - FormatDocument5 pages(1-5) Cryptography Symmetric VS Asymmetric Encryption (2) - Formatahasanova627Pas encore d'évaluation
- Encryption StandardsDocument76 pagesEncryption Standardsbhasker7100% (1)
- CS1028 Network Security PDFDocument120 pagesCS1028 Network Security PDFSelva RajPas encore d'évaluation
- Bca505 NotesDocument55 pagesBca505 NotesShubhamPas encore d'évaluation
- Cryptography and Network Security Two Marks Unit-1 Network Security 1. Specify The Four Categories of Security Threads?Document11 pagesCryptography and Network Security Two Marks Unit-1 Network Security 1. Specify The Four Categories of Security Threads?PiriyangaPas encore d'évaluation
- No Network Is 100Document7 pagesNo Network Is 100AngelDayanaPas encore d'évaluation
- Pro Cryptography and Cryptanalysis: Creating Advanced Algorithms with C# and .NETD'EverandPro Cryptography and Cryptanalysis: Creating Advanced Algorithms with C# and .NETPas encore d'évaluation
- Hacking Network Protocols: Unlocking the Secrets of Network Protocol AnalysisD'EverandHacking Network Protocols: Unlocking the Secrets of Network Protocol AnalysisPas encore d'évaluation
- An Efficient Model of Detection and Filtering Technique Over Malicious and Spam E-MailsDocument4 pagesAn Efficient Model of Detection and Filtering Technique Over Malicious and Spam E-MailsseventhsensegroupPas encore d'évaluation
- Comparison of The Effects of Monochloramine and Glutaraldehyde (Biocides) Against Biofilm Microorganisms in Produced WaterDocument8 pagesComparison of The Effects of Monochloramine and Glutaraldehyde (Biocides) Against Biofilm Microorganisms in Produced WaterseventhsensegroupPas encore d'évaluation
- Fabrication of High Speed Indication and Automatic Pneumatic Braking SystemDocument7 pagesFabrication of High Speed Indication and Automatic Pneumatic Braking Systemseventhsensegroup0% (1)
- Optimal Search Results Over Cloud With A Novel Ranking ApproachDocument5 pagesOptimal Search Results Over Cloud With A Novel Ranking ApproachseventhsensegroupPas encore d'évaluation
- Extended Kalman Filter Based State Estimation of Wind TurbineDocument5 pagesExtended Kalman Filter Based State Estimation of Wind TurbineseventhsensegroupPas encore d'évaluation
- Experimental Investigation On Performance, Combustion Characteristics of Diesel Engine by Using Cotton Seed OilDocument7 pagesExperimental Investigation On Performance, Combustion Characteristics of Diesel Engine by Using Cotton Seed OilseventhsensegroupPas encore d'évaluation
- Ijett V5N1P103Document4 pagesIjett V5N1P103Yosy NanaPas encore d'évaluation
- Design, Development and Performance Evaluation of Solar Dryer With Mirror Booster For Red Chilli (Capsicum Annum)Document7 pagesDesign, Development and Performance Evaluation of Solar Dryer With Mirror Booster For Red Chilli (Capsicum Annum)seventhsensegroupPas encore d'évaluation
- Comparison of The Regression Equations in Different Places Using Total StationDocument4 pagesComparison of The Regression Equations in Different Places Using Total StationseventhsensegroupPas encore d'évaluation
- A Multi-Level Storage Tank Gauging and Monitoring System Using A Nanosecond PulseDocument8 pagesA Multi-Level Storage Tank Gauging and Monitoring System Using A Nanosecond PulseseventhsensegroupPas encore d'évaluation
- Application of Sparse Matrix Converter For Microturbine-Permanent Magnet Synchronous Generator Output Voltage Quality EnhancementDocument8 pagesApplication of Sparse Matrix Converter For Microturbine-Permanent Magnet Synchronous Generator Output Voltage Quality EnhancementseventhsensegroupPas encore d'évaluation
- Key Drivers For Building Quality in Design PhaseDocument6 pagesKey Drivers For Building Quality in Design PhaseseventhsensegroupPas encore d'évaluation
- Color Constancy For Light SourcesDocument6 pagesColor Constancy For Light SourcesseventhsensegroupPas encore d'évaluation
- Implementation of Single Stage Three Level Power Factor Correction AC-DC Converter With Phase Shift ModulationDocument6 pagesImplementation of Single Stage Three Level Power Factor Correction AC-DC Converter With Phase Shift ModulationseventhsensegroupPas encore d'évaluation
- Design and Implementation of Height Adjustable Sine (Has) Window-Based Fir Filter For Removing Powerline Noise in ECG SignalDocument5 pagesDesign and Implementation of Height Adjustable Sine (Has) Window-Based Fir Filter For Removing Powerline Noise in ECG SignalseventhsensegroupPas encore d'évaluation
- FPGA Based Design and Implementation of Image Edge Detection Using Xilinx System GeneratorDocument4 pagesFPGA Based Design and Implementation of Image Edge Detection Using Xilinx System GeneratorseventhsensegroupPas encore d'évaluation
- The Utilization of Underbalanced Drilling Technology May Minimize Tight Gas Reservoir Formation Damage: A Review StudyDocument3 pagesThe Utilization of Underbalanced Drilling Technology May Minimize Tight Gas Reservoir Formation Damage: A Review StudyseventhsensegroupPas encore d'évaluation
- An Efficient Expert System For Diabetes by Naïve Bayesian ClassifierDocument6 pagesAn Efficient Expert System For Diabetes by Naïve Bayesian ClassifierseventhsensegroupPas encore d'évaluation
- An Efficient Encrypted Data Searching Over Out Sourced DataDocument5 pagesAn Efficient Encrypted Data Searching Over Out Sourced DataseventhsensegroupPas encore d'évaluation
- An Efficient and Empirical Model of Distributed ClusteringDocument5 pagesAn Efficient and Empirical Model of Distributed ClusteringseventhsensegroupPas encore d'évaluation
- Separation Of, , & Activities in EEG To Measure The Depth of Sleep and Mental StatusDocument6 pagesSeparation Of, , & Activities in EEG To Measure The Depth of Sleep and Mental StatusseventhsensegroupPas encore d'évaluation
- Study On Fly Ash Based Geo-Polymer Concrete Using AdmixturesDocument4 pagesStudy On Fly Ash Based Geo-Polymer Concrete Using AdmixturesseventhsensegroupPas encore d'évaluation
- Review On Different Types of Router Architecture and Flow ControlDocument4 pagesReview On Different Types of Router Architecture and Flow ControlseventhsensegroupPas encore d'évaluation
- High Speed Architecture Design of Viterbi Decoder Using Verilog HDLDocument7 pagesHigh Speed Architecture Design of Viterbi Decoder Using Verilog HDLseventhsensegroupPas encore d'évaluation
- Free Vibration Characteristics of Edge Cracked Functionally Graded Beams by Using Finite Element MethodDocument8 pagesFree Vibration Characteristics of Edge Cracked Functionally Graded Beams by Using Finite Element MethodseventhsensegroupPas encore d'évaluation
- Ijett V4i10p158Document6 pagesIjett V4i10p158pradeepjoshi007Pas encore d'évaluation
- Performance and Emissions Characteristics of Diesel Engine Fuelled With Rice Bran OilDocument5 pagesPerformance and Emissions Characteristics of Diesel Engine Fuelled With Rice Bran OilseventhsensegroupPas encore d'évaluation
- A Comparative Study of Impulse Noise Reduction in Digital Images For Classical and Fuzzy FiltersDocument6 pagesA Comparative Study of Impulse Noise Reduction in Digital Images For Classical and Fuzzy FiltersseventhsensegroupPas encore d'évaluation
- A Review On Energy Efficient Secure Routing For Data Aggregation in Wireless Sensor NetworksDocument5 pagesA Review On Energy Efficient Secure Routing For Data Aggregation in Wireless Sensor NetworksseventhsensegroupPas encore d'évaluation
- DSST Cybersecurity Practice Test 2Document7 pagesDSST Cybersecurity Practice Test 2putegrainPas encore d'évaluation
- Information Security: ACC 444 - Enterprise Process AnalysisDocument64 pagesInformation Security: ACC 444 - Enterprise Process AnalysisBear CooporPas encore d'évaluation
- Prevention of Buffer Overflow Attack Blocker Using IDSDocument5 pagesPrevention of Buffer Overflow Attack Blocker Using IDSijcsn100% (1)
- MONA:secure Multi Owner Data Sharing For Dynamic Groups On CloudDocument3 pagesMONA:secure Multi Owner Data Sharing For Dynamic Groups On Cloudgvitha50Pas encore d'évaluation
- Innerfrench - Learn To Think in FrenchDocument2 pagesInnerfrench - Learn To Think in FrenchLolo lolePas encore d'évaluation
- Guion de Ingles IIIDocument5 pagesGuion de Ingles IIIAndreaPas encore d'évaluation
- CEHDocument6 pagesCEHmela4ever125Pas encore d'évaluation
- PAN-OS Release Notes Upto 8.0.4Document94 pagesPAN-OS Release Notes Upto 8.0.4JAVITH ALI.RPas encore d'évaluation
- PasswordDocument13 pagesPasswordsharathjatti7Pas encore d'évaluation
- Syssec 01Document95 pagesSyssec 01clu5t3r100% (1)
- Rsa & Juniper Networks: Securing Remote Access With SSL Vpns and Strong AuthenticationDocument8 pagesRsa & Juniper Networks: Securing Remote Access With SSL Vpns and Strong AuthenticationAbeer AbborahPas encore d'évaluation
- Introduction and History of CryptographyDocument9 pagesIntroduction and History of CryptographynikhilPas encore d'évaluation
- Acknowledgement: IES IPS Academy Staff Members and The Institute, in General, For Extending ADocument4 pagesAcknowledgement: IES IPS Academy Staff Members and The Institute, in General, For Extending AShivam BarsainyaPas encore d'évaluation
- Cisa Mock Exam PDFDocument61 pagesCisa Mock Exam PDFmanishPas encore d'évaluation
- Upe CFX Config CommonDocument105 pagesUpe CFX Config Commonthatipamula sudhakarPas encore d'évaluation
- Network Security Assignment No 4 RSA Implementation Group MembersDocument4 pagesNetwork Security Assignment No 4 RSA Implementation Group MembersMuhammad Junaid AliPas encore d'évaluation
- Cryptography Full ReportDocument9 pagesCryptography Full ReportSushant SharmaPas encore d'évaluation
- A Penetration TestDocument7 pagesA Penetration TestSALMANRIZPas encore d'évaluation
- 1.2.4.12 Lab - Social EngineeringDocument2 pages1.2.4.12 Lab - Social EngineeringAgustinus Kurniawan0% (1)
- Symantec Trust Network (STN) Certification Practice StatementDocument188 pagesSymantec Trust Network (STN) Certification Practice StatementAnastasia KoytsoykoyPas encore d'évaluation
- Entry of Malicious Software in To PC From InternetDocument5 pagesEntry of Malicious Software in To PC From InternetParmeshwar Nath TripathiPas encore d'évaluation
- TimestampDocument5 pagesTimestampHafedh TrimechePas encore d'évaluation
- User Oms GroupDocument27 pagesUser Oms GroupharyantojogjaboyPas encore d'évaluation