Académique Documents
Professionnel Documents
Culture Documents
3G Motorolla
Transféré par
Subrata SenCopyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
3G Motorolla
Transféré par
Subrata SenDroits d'auteur :
Formats disponibles
CP13: Introduction to UMTS USR6
CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Copyrights
The Motorola products described in this document may include copyrighted Motorola computer programs stored in semiconductor memories
or other media. Laws in the United States and other countries preserve for Motorola certain exclusive rights for copyright computer programs,
including the exclusive right to copy or reproduce in any form the copyright computer program. Accordingly, any copyright Motorola computer
programs contained in the Motorola products described in this document may not be copied or reproduced in any manner without the express
written permission of Motorola. Furthermore, the purchase of Motorola products shall not be deemed to grant either directly or by implication,
estoppel or otherwise, any license under the copyrights, patents or patent applications of Motorola, except for the rights that arise by operation
of law in the sale of a product.
Restrictions
The software described in this document is the property of Motorola. It is furnished under a license agreement and may be used and/or
disclosed only in accordance with the terms of the agreement. Software and documentation are copyright materials. Making unauthorized
copies is prohibited by law. No part of the software or documentation may be reproduced, transmitted, transcribed, stored in a retrieval
system, or translated into any language or computer language, in any form or by any means, without prior written permission of Motorola.
Accuracy
While reasonable efforts have been made to assure the accuracy of this document, Motorola assumes no liability resulting from any
inaccuracies or omissions in this document, or from the use of the information obtained herein. Motorola reserves the right to make changes
to any products described herein to improve reliability, function, or design, and reserves the right to revise this document and to make
changes from time to time in content hereof with no obligation to notify any person of revisions or changes. Motorola does not assume
any liability arising out of the application or use of any product or circuit described herein; neither does it convey license under its patent
rights of others.
Trademarks
Motorola and the Motorola logo are registered trademarks of Motorola Inc.
M-Cell™, Taskfinder™ and Intelligence Everywhere™ are trademarks of Motorola Inc.
All other brands and corporate names are trademarks of their respective owners.
CE Compliance
The CE mark confirms Motorola Ltd’s statement of compliance with
EU directives applicable to this product. Copies of the Declaration
of Compliance and installation information in accordance with the
requirements of EN50385 can be obtained from the local Motorola
representative or the CNRC help desk, contact details below:
Email: csc.emea@motorola.com
Tel: +44 (0) 1793 565 444
© 2005-2006 CP13: Introduction to UMTS USR6
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Contents
■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■
CP13: Introduction to UMTS USR6
Chapter 1: Introduction
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1- 3
WCDMA Technology and Deployment Status . . . . . . . . . . . . . . . . . . . . . . . . . . . 1- 4
HSPA Standardization and Deployment Schedule. . . . . . . . . . . . . . . . . . . . . . . . . 1- 6
Radio Capability Evolution with HSPA . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1- 8
Higher Cell Capacity and Higher Spectral Efficiency . . . . . . . . . . . . . . . . . . . . . 1-10
WCDMA/HSPA Standardization and Background . . . . . . . . . . . . . . . . . . . . . . . . . 1-12
3rd Generation Partnership Project (3GPP) . . . . . . . . . . . . . . . . . . . . . . . . . . 1-12
Long Term Evolution (LTE) of the 3GPP Radio Technology . . . . . . . . . . . . . . . . . . . . 1-14
LTE Detailed Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-14
Chapter 2: Network Architecture
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 3
UMTS Domains . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 4
Domain split . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 4
User equipment Domain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 4
Mobile equipment Domain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 4
USIM Domain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 4
Infrastructure Domain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 4
Access Network Domain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 6
Core Network Domain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 6
Serving Network Domain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 6
Home Network Domain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 6
Transit Network Domain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 6
UMTS Architecture - Release 1999 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 8
The Core Network (CN) Entities . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2- 8
The Access Network (AN) Entities . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-10
The Mobile Station (MS) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-10
UMTS Network - Release 1999 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-12
Entities of the CN-CS Domain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-12
Entities Common to the CS and PS Domains . . . . . . . . . . . . . . . . . . . . . . . . . 2-14
UMTS Network R4 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-16
Media Gateways (MGWs) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-16
MSC Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-16
UMTS Network Release 5 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-18
IP MULTIMEDIA SUBSYSTEM (IMS) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-18
UMTS Terrestrial Radio Access Network (UTRAN) . . . . . . . . . . . . . . . . . . . . . . . . 2-20
UTRAN Functions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-20
Radio network Controller (RNC) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-22
Controlling Radio Network Controller (CRNC). . . . . . . . . . . . . . . . . . . . . . . . . 2-22
Serving Radio Network Controller (SRNC) . . . . . . . . . . . . . . . . . . . . . . . . . . 2-24
Drift Radio Network Controller (DRNC) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-26
Horizon 3G-n macro . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-28
Transport subsystem . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-28
Baseband subsystem. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-28
RF subsystem . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-30
Control subsystem . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-30
Antenna and Feeder Subsystem . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-30
© 2005-2006 CP13: Introduction to UMTS USR6 i
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Contents CP13: Introduction to UMTS USR6
User Equipment (UE) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-32
Introduction to User Equipment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-32
UE Architecture . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-34
Integrated Circuit (IC) Card . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-34
Terminal Equipment (TE) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-36
Mobile Equipment (ME). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-36
Chapter 3: Network Services
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3- 3
Services in the UMTS Environment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3- 4
Quality of Service (QoS) Architecture . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3- 6
Quality of Service Classes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3- 8
Conversational Class . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3- 8
Streaming Class . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3- 8
Interactive class . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3- 8
Background Task . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3- 8
Supported Service Rates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-10
Description of Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-10
The Security Architecture . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-12
Security and Privacy . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-14
User authentication: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-14
Network authentication: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-14
Confidentiality . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-14
Data integrity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-14
Mobile equipment identification . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-14
Authentication and Key Agreement . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-16
Distribution of authentication data from HE to SN . . . . . . . . . . . . . . . . . . . . . . . 3-16
Authentication and Key Agreement . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-16
Ciphering Algorithms . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-18
F8 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-18
F9 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-18
Generation of Authentication Vectors/Tokens . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-20
SQN and RAND . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-20
Authentication Key Management Field . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-20
Algorithms f1 -f5 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-20
AUTN and AV . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-20
USIM Authentication Function . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-22
Retrieval of SQN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-22
Computation of X-MAC . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-22
Verification of SQN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-22
Computation of CK and IK . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-22
User Authentication Response . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-22
Access Link Data Integrity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-24
Data integrity protection method . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-24
Input parameters to the integrity algorithm . . . . . . . . . . . . . . . . . . . . . . . . . . 3-24
Ciphering of User/Signalling Data . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-26
Input parameters to the cipher algorithm . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-26
Chapter 4: W-CDMA Theory
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4- 3
Multiple Access Schemes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4- 4
Frequency Division Multiple Access (FDMA) . . . . . . . . . . . . . . . . . . . . . . . . . 4- 4
Time Division Multiple Access (TDMA) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4- 4
Code Division Multiple Access (CDMA) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4- 4
W-CDMA Characteristics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4- 6
Re-Use of Frequency . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4- 8
Re-Use of Codes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-10
Spectral Efficiency (GSM and UMTS) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-12
ii CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
CP13: Introduction to UMTS USR6 Contents
Direct Spread (DS)-CDMA Implementation . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-14
Transmitter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-14
Receiver . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-14
Spreading . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-16
De-spreading . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-18
Orthogonal Codes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-20
Channelisation Code Tree . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-20
De-spreading Other Users Signals . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-22
Processing Gain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-24
Exercise 1 - Spreading . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-26
NOTES . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-26
Exercise 2 - Spreading/Despreading . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-28
Exercise 3 - Spreading/Despreading . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-30
Scrambling . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-32
Scrambling Codes vs Channelisaton Codes . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-34
Scrambling and Summation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-36
De-Scrambling and Data Recovery . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-38
Multi-path Radio Channels . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-40
Inter-symbol Interference . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-40
Signal Fade . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-40
Matched Filter Operation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-42
The Rake Receiver . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-44
Chapter 5: The Physical Layer
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5- 3
Physical Layer Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5- 4
QPSK . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5- 6
Structure of Transmission. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5- 8
Downlink Transmission . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5- 8
Uplink Transmission . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5- 8
Channel Locations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-10
Channels on the Air Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-12
Logical Channels . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-14
Control Channels. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-14
Traffic Channels . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-14
Transport Channels . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-16
Random Access Channel (RACH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-16
Forward Access Channel (FACH). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-16
Broadcast Channel (BCH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-16
Paging Channel (PCH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-16
Dedicated Channel (DCH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-16
Physical Channels . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-18
Common Physical Channels (CPCHs) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-18
Channel Mapping. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-20
Physical signals . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-20
Generic Frame Structure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-22
Radio Frame . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-22
System Frame . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-22
Timeslot . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-22
Synchronisation Channel (SCH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-24
The Primary SCH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-24
The Secondary SCH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-24
Modulation Symbol "a" . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-24
Synchronisation (Cell Search) Procedure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-26
Step 1: Slot synchronisation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-26
Step 2: Frame synchronisation and code-group identification . . . . . . . . . . . . . . . . . 5-26
Step 3: Scrambling-code identification . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-26
Synchronisation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-27
Common Pilot Channel (CPICH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-30
© 2005-2006 CP13: Introduction to UMTS USR6 iii
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Contents CP13: Introduction to UMTS USR6
Primary Common Pilot Channel (P-CPICH) . . . . . . . . . . . . . . . . . . . . . . . . . . 5-30
Secondary Common Pilot Channel (S-CPICH) . . . . . . . . . . . . . . . . . . . . . . . . 5-30
P-CCPCH Frame Structure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-32
SCH and P-CCPCH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-34
Paging Indicator Channel (PICH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-36
PICH Channel Structure. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-36
Discontinuous Reception (DRX) on the PICH . . . . . . . . . . . . . . . . . . . . . . . . . 5-38
Secondary Common Control Physical Channel (S-CCPCH) . . . . . . . . . . . . . . . . . . . . 5-40
Secondary CCPCH Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-41
Physical Random Access Channel (PRACH) . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-42
Structure of the PRACH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-42
Random Access Transmission . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-42
PRACH Pre-amble . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-42
Structure of the random-access transmission . . . . . . . . . . . . . . . . . . . . . . . . . 5-43
Structure of PRACH Message Part . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-44
Acquisition Indicator Channel (AICH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-46
Relationship Between PRACH and AICH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-48
Downlink Dedicated Physical Channels (DL-DPCH). . . . . . . . . . . . . . . . . . . . . . . . 5-50
DL-DPCH Structure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-50
Downlink Slot Formation in Case of Multi-Code Transmission . . . . . . . . . . . . . . . . . 5-52
Uplink Dedicated Physical channels (UL-DPCH) . . . . . . . . . . . . . . . . . . . . . . . . . 5-54
Downlink Flow Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-56
Uplink Flow Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-58
Radio Frame Equalisation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-58
Rate Matching . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-58
DTX . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-58
Chapter 6: MAC, RLC, BMC, PDCP and RRC Protocols and Procedures
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6- 3
Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6- 4
Layer 2 Protocols. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6- 4
Layer 3 Protocols. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6- 4
Medium Access Control (MAC) Protocol . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6- 6
Transport Formats . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6- 8
Radio Link Control (RLC) Protocol . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-10
Transparent Mode (TM) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-10
Unacknowledged Mode (UM) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-10
Acknowledged Mode (AM) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-10
Packet Data Convergence Protocol (PDCP) . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-12
Broadcast/Multicast Control (BMC) Protocol . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-14
Radio Resource Control (RRC) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-16
RRC Procedures . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-18
Broadcast of System Information.. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-18
Cell Selection/Re-selection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-20
UE State Transition Algorithm . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-22
RRC connection establishment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-24
Establishment of signalling connections between the UE and the Core Network and direct
transfer of signalling messages. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-24
Radio bearer establishment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-26
Measurement Procedures . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-28
Chapter 7: Radio Resource Management Functions
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7- 3
Radio Resource Management Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7- 4
Introduction to Radio Resource Management . . . . . . . . . . . . . . . . . . . . . . . . . 7- 4
Handover Control. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7- 6
Measurement Control. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7- 8
Monitored List Determination . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7- 8
iv CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
CP13: Introduction to UMTS USR6 Contents
Intra-frequency Handover. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-10
Algorithm Description. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-10
Intra-frequency Hard Handover . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-12
Inter-frequency Hard Handover . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-14
Overview of Inter-Frequency Hard Handover . . . . . . . . . . . . . . . . . . . . . . . . . 7-14
Handover Procedure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-16
Inter-RAT Hard Handover. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-18
Algorithm Overview. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-18
Preconditions for UMTS to GSM Handover . . . . . . . . . . . . . . . . . . . . . . . . . . 7-20
Handover Procedures for UMTS to GSM . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-24
UMTS to GSM Handover Measurement . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-26
Hierarchical Cell Structure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-28
HCS Handover Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-30
Compressed Mode Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-32
Algorithm Overview. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-32
Macro Diversity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-34
SRNS Relocation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-36
SRNS Relocation Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-36
Static Relocation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-36
Relocation Due to Hard Handover . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-38
Relocation Due to Cell or URA Update . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-38
Power Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-40
Open Loop Power Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-42
Closed Loop Power Control (Inner Loop) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-44
Directed Retry . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-46
Dynamic Channel Configuration Control (DCCC) . . . . . . . . . . . . . . . . . . . . . . . . . 7-48
Rate Re-allocation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-48
UE State Transition. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-48
Measurements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-48
Purpose . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-48
Load Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-50
Overview of Load Control. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-52
Chapter 8: HSDPA Overview
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 3
HSDPA (High Speed Downlink Packet Access) for WCDMA . . . . . . . . . . . . . . . . . . . 8- 4
Feature Study . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 4
Compatibility with Release ‘99 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 4
Demand for Packet Switched Traffic . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 4
HSDPA Targets. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 6
Higher Data Rates for Streaming-, Interactive- and Background Services . . . . . . . . . . . 8- 6
Consideration of UE Processing Time and Memory Requirements . . . . . . . . . . . . . . 8- 6
Higher Spectrum Efficiency . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 6
Small Changes to existing Techniques and Architectures . . . . . . . . . . . . . . . . . . . 8- 6
Efficient Resource Sharing in Downlink among Users . . . . . . . . . . . . . . . . . . . . 8- 6
HSDPA Characteristics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 8
Modulation Types . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 8
Higher Throughput Rates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 8
AMC (Adaptive Modulation and Coding) . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 8
Hybrid ARQ . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8- 8
Transmission and Retransmission Scheduling in NodeB . . . . . . . . . . . . . . . . . . . 8- 8
QPSK versus 16-QAM Modulation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-10
QPSK . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-10
16–QAM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-10
Maximum Throughput Rates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-12
UMTS Rel’. 99 / Rel. 4 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-12
HSDPA – Rel. 5 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-12
Important Changes for HSDPA . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-14
New 2 ms Subframe for HSDPA . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-14
© 2005-2006 CP13: Introduction to UMTS USR6 v
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Contents CP13: Introduction to UMTS USR6
New Physical Channels and Transport Channel with HSDPA . . . . . . . . . . . . . . . . . 8-14
No Fast Power Control and variable Spreading Factor . . . . . . . . . . . . . . . . . . . . 8-14
New UE Capabilities / Categories. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-14
New MAC-hs in NodeB and UE. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-14
Impact on NBAP and Frame Protocol Procedure . . . . . . . . . . . . . . . . . . . . . . . 8-14
New Channels with HSDPA. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-16
Transport Channel: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-16
Physical Channels . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-16
Future Enhancements of HSDPA . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-18
Beamforming . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-18
Transmit Diversity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-18
MIMO . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-18
Chapter 9: HSUPA Overview
Chapter Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9- 3
Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9- 4
HSUPA vs R99 DCH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9- 4
Key Technologies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9- 4
Impact on Radio Access Network Architecture . . . . . . . . . . . . . . . . . . . . . . . . . . 9- 6
HSUPA Protocol Architecture . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9- 6
HSUPA Channels . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9- 8
E-DCH Transport Channel Processing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-10
E-DCH Dedicated Physical Data Channel (E-DPDCH) . . . . . . . . . . . . . . . . . . . . . . 9-12
E-DCH Dedicated Physical Control Channel (E-DPCCH) . . . . . . . . . . . . . . . . . . . . . 9-14
E-DCH HARQ Indicator Channel (E-HICH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-16
E-DCH Absolute Grant Channel (E-AGCH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-18
Reason for having 2 ms amd 10 ms TTIs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-20
Chapter 10: UMTS Terrestrial Interface Protocols
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10- 3
Introduction to UMTS Terrestrial Interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10- 4
Introduction to UMTS Protocols . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10- 6
Access Stratum . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10- 6
Non-Access Stratum . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10- 6
General Protocol Model . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10- 8
Horizontal Layers. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10- 8
Vertical Planes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10- 8
IU-CS Interface Protocols Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-10
IU-PS Interface Protocols Overview. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-12
Iub Interface (ATM) Protocols Overview. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-14
Iub Interface (IP) Protocols Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-16
ATM/IP Dual Protocol Stack . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-18
Iur Interface Protocols Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-20
Chapter 11: UMTS Terrestrial Physical and Data Link Layer
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11- 3
Terrestrial Physical/Data Link Layer Overview. . . . . . . . . . . . . . . . . . . . . . . . . . . 11- 4
ATM Principles . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11- 6
Concepts of ATM Protocol . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11- 8
ATM Layer . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-10
Structure of an ATM Cell . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-10
Virtual Channels and Paths . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-12
Use of Virtual Channels and Paths . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-12
Virtual Path and Virtual Connection Switching. . . . . . . . . . . . . . . . . . . . . . . . . . . 11-14
ATM Adaptation Layer (AAL) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-16
Functions of the ATM Adaptation Layer . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-16
Types of Services at the ATM Adaptation Layer . . . . . . . . . . . . . . . . . . . . . . . . 11-16
vi CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
CP13: Introduction to UMTS USR6 Contents
ATM Service Characteristics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-18
ATM QoS. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-20
E1/T1 Architecture . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-22
Logical Links . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-22
E1 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-22
T1 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-22
ATM Cell to E1 Cell Mapping . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-24
E1 Link Multiplexing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-26
Inverse Multiplexing for ATM (IMA) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-28
Synchronous Digital Hierarchy (SDH) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-30
SDH Drop and Insert . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-32
Network Simplification . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-32
Survivability . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-32
Software Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-32
Bandwidth on Demand . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-32
Principles of SDH. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-34
Typical UMTS ATM Transport Network . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-36
Daisy Chaining . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-36
Circuit Emulation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-36
ATM Protection Switch . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-36
Introduction to IP RAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-38
TDM Network . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-38
Data Network. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-40
Hybrid Transport Network . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-42
IP Transport Protocols on the Iub Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-44
Concepts of Data Link Layer Protocols . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-44
Internet Protocol (IP) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-46
SCTP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11-48
Virtual Local Area Networks (VLANs) and Layer 2/3 Switching . . . . . . . . . . . . . . . . 11-50
Chapter 12: Annexe A
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12- 3
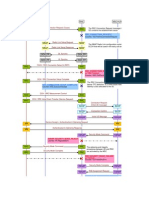
Paging for a UE in Idle Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12- 4
Paging for the UE in RRC Connected Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . 12- 6
RRC Connection Establishment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12- 8
RRC DCH Release . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12-10
RA Update . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12-12
SRNC Relocation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12-14
Chapter 13: Glossary
Glossary of technical terms . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13- 3
A Interface - AUTO . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13- 3
B Interface - Byte. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13- 7
C - CW . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-11
D Interface - DYNET . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-19
E - EXEC. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-24
F Interface - Full Rate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-27
G Interface - GWY . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-30
H Interface - Hyperframe . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-33
I - IWU . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-34
k - KW . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-39
L1 - LV . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-40
M - MUX . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-42
NACK - nW. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-48
O - Overlap. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-51
PA - PXPDN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-53
QA- Quiesent mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-60
R - RXU . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-61
© 2005-2006 CP13: Introduction to UMTS USR6 vii
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Contents CP13: Introduction to UMTS USR6
S7- SYSGEN. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-66
T -TxBPF. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-75
U - UUS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-81
V - VTX host . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-83
W - WWW . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-84
X - X Window. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-85
ZC . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13-86
viii CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
About This Manual Version 1 Rev 0
CP13: Introduction to UMTS USR6
■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■ ■
© 2005-2006 CP13: Introduction to UMTS USR6 1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0
This page intentionally left blank.
2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Introduction Version 1 Rev 0
Chapter 1
Introduction
© 2005-2006 CP13: Introduction to UMTS USR6 1-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Introduction
This page intentionally left blank.
1-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
On completion of this chapter the student should be able to:
• State the WCDMA Technology and Deployment Status
• State the HSxPA Standardization and Deployment Schedule
• Describe the Radio Capability Evolution with HSPA
• Describe the WCDMA/HSxPA Standardization and Background
• State how the HSxPA standard migrates towards LTE
© 2005-2006 CP13: Introduction to UMTS USR6 1-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 WCDMA Technology and Deployment Status
WCDMA Technology and Deployment Status
The first Third Generation Partnership Project (3GPP) Wideband Code Division Multiple
Access (WCDMA) networks were launched during 2002. By the end of 2005 there were
100 open WCDMA networks and a total of over 150 operators having frequency licenses
for WCDMA operation. Currently, the WCDMA networks are deployed in Universal Mobile
Telecommunications System (UMTS) band around 2GHz in Europe and Asia including Japan
and Korea.WCDMA in America is deployed in the existing 850 and 1900 spectrum allocations
with a total of 9 bands being supported at Release 7 of the 3GPP specifications.
As of 2006 there are signs that 3G take-up is increasing. 70 operators are now offering 3G on a
commercial basis and 3G services are now available in all European Union member states. While
Japan retains the highest penetration of 3G services, Europe now has the highest number of
subscribers. It is estimated that there are around 45 million 3G subscribers in the EU, indicating
that Europe has overtaken Japan as leader in terms of subscriptions. In June 2007 the number
of WCDMA 3G subscribers went over the 70 million mark worldwide.
The number of available WCDMA 3G handsets continues to grow with handsets that support
High Speed Packet Access (HSPA) with rates up to 7.2 mbps downlink and 1.8 mbps uplink.
Applications include MP3 file players, mobile TV, as well of course voice.
As WCDMA mobile penetration increases, it allows WCDMA networks to carry a larger share of voice
and data traffic.WCDMA technology provides a few advantages for the operator in that it enables data
but also improves basic voice. The offered voice capacity is very high because of interference control
mechanisms including frequency reuse of 1, fast power control and soft handover. WCDMA makes it
possible to offer substantially more voice minutes to customers. At the same time WCDMA can also
enhance the voice service with wideband AMR codec, which provides clearly better voice quality than
the fixed land line telephone. In short, WCDMA can offer more voice minutes with better quality.
In addition to the high spectral efficiency, 3G WCDMA provides even more dramatic evolution in
terms of base station capacity and hardware efficiency. The high integration level in WCDMA is
achieved because of the wideband carrier: a large number of users are supported per carrier, and
fewer radio frequency carriers are required to provide the same capacity. With fewer RF parts and
more digital baseband processing, WCDMA can take benefit of the fast evolution in digital signal
processing capacity. The high base station integration level allows efficient building of high-capacity
sites since the complexity of RF combiners, extra antennas or feeder cables can be avoided.
WCDMA operators are able to provide interesting data services including browsing, person-to-person
video calls, sports and news video clips and mobile-TV. WCDMA enables simultaneous voice and data
which allows, for example, browsing or emailing during voice conferencing, or real time video sharing
during voice calls. The operators also offer laptop connectivity to the Internet and corporate intranet
with the maximum bit rate of 384 kbps both in downlink and in uplink. The initial terminals and networks
were limited to 64–128 kbps in uplink while the latest products provide 384-kbps uplink.
1-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
WCDMA Technology and Deployment Status Version 1 Rev 0
WCDMA Technology and Deployment Status
• 9 Frequency bands supported R7
• More voice minutes with better quality
• Base station capacity and hardware efficiency
• Data services offered
© 2005-2006 CP13: Introduction to UMTS USR6 1-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 HSPA Standardization and Deployment Schedule
HSPA Standardization and Deployment Schedule
High-speed downlink packet access (HSDPA) was standardized as part of 3GPP Release 5 with the
first specification version in March 2002. High-speed uplink packet access (HSUPA) was part of 3GPP
Release 6 with the first specification version in December 2004. HSDPA and HSUPA together are
called ‘high-speed packet access’ (HSPA). The first commercial HSDPA networks were available at
the end of 2005 and the commercial HSUPA networks are expected to be available by 2007.
The HSDPA peak data rate available in the terminals is initially 1.8Mbps and will increase to 3.6 and 7.2
Mbps during 2006 and 2007, and potentially beyond 10Mbps. The HSUPA peak data rate in the initial
phase is expected to be 1–2 Mbps with the second phase pushing the data rate to 3–4Mbps.
HSPA is deployed on top of the WCDMA network either on the same carrier or – for a high-capacity
and high bit rate solution – using another carrier. In both cases, HSPA and WCDMA can share
all the network elements in the core network and in the radio network including base stations,
Radio Network Controller (RNC), Serving GPRS Support Node (SGSN) and Gateway GPRS
Support Node (GGSN). WCDMA and HSPA are also sharing the base station sites, antennas and
antenna lines. The upgrade from WCDMA to HSPA requires new software package and, potentially,
some new pieces of hardware in the base station and in RNC to support the higher data rates and
capacity. Because of the shared infrastructure between WCDMA and HSPA, the cost of upgrading
from WCDMA to HSPA is very low compared with building a new standalone data network.
1-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
HSPA Standardization and Deployment Schedule Version 1 Rev 0
HSPA Standardization and Deployment Schedule
© 2005-2006 CP13: Introduction to UMTS USR6 1-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Radio Capability Evolution with HSPA
Radio Capability Evolution with HSPA
The performance of the radio system defines how smoothly applications can be used over the
radio network. The key parameters defining application performance include data rate and network
latency. There are applications that are happy with low bit rates of a few tens of kbps but require
very low delay, like Voice-Over-IP (VoIP) and real time action games. On the other hand, the
download time of a large file is only defined by the maximum data rate, and latency does not
play any role. GPRS Release 99 typically provides 30–40 kbps with latency of 600 ms. EGPRS
Release 4 pushes the bit rates 3–4 times higher and also reduces latency below 300 ms. The
EGPRS data rate and latency allow smooth application performance for several mobile-based
applications including Wireless Application Protocol (WAP) browsing and push-to-talk.
WCDMA enables peak data rates of 384 kbps with latency 100–200 ms, which makes Internet
access close to low-end digital subscriber line (DSL) connections and provides good performance
for most low-delay Internet Protocol (IP) applications as well.
HSPA pushes the data rates up to 1–2Mbps in practice and even beyond 3Mbps in good
conditions. Since HSPA also reduces network latency to below 100 ms, the end user
experienced performance is similar to the fixed line DSL connections. No or only little effort
is required to adapt Internet applications to the mobile environment. Essentially, HSPA is a
broadband access with seamless mobility and extensive coverage.
HSPA was initially designed to support high bit rate non-real time services. The simulation results show,
however, that HSPA can provide attractive capacity also for low bit rate low-latency applications like VoIP.
3GPP Releases 6 and 7 further improve the efficiency of HSPA for VoIP and other similar applications.
1-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Radio Capability Evolution with HSPA Version 1 Rev 0
Radio Capability Evolution with HSPA
© 2005-2006 CP13: Introduction to UMTS USR6 1-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Radio Capability Evolution with HSPA
Radio Capability Evolution with HSPA
Higher Cell Capacity and Higher Spectral Efficiency
Higher cell capacity and higher spectral efficiency are required to provide higher data rates and
new services with the current base station sites. The diagram opposite illustrates the estimated
cell capacity per sector per 5MHz with WCDMA, with basic HSPA and with enhanced HSPA in the
macro-cell environment. Basic HSPA includes a one-antenna Rake receiver in the terminals and
two-branch antenna diversity in the base stations. Enhanced HSPA includes two-antenna equalizer
mobiles and interference cancellation in the base station. The simulation results show that HSPA
can provide substantial capacity benefit. Basic HSDPA offers up to three times WCDMA downlink
capacity, and enhanced HSDPA up to six times WCDMA. The spectral efficiency of enhanced
HSDPA is close to 1 bit/s/Hz/cell. The uplink capacity improvement with HSUPA is estimated
between 30% and 70%. HSPA capacity is naturally suited for supporting not only symmetric
services but also asymmetric services with higher data rates and volumes in downlink.
1-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Radio Capability Evolution with HSPA Version 1 Rev 0
Radio Capability Evolution with HSPA
© 2005-2006 CP13: Introduction to UMTS USR6 1-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 WCDMA/HSPA Standardization and Background
WCDMA/HSPA Standardization and Background
This section introduces the standardization framework around WCDMA, HSDPA
and HSUPA and presents the standardization schedule and future development for
Long Term Evolution (LTE), currently ongoing.
3rd Generation Partnership Project (3GPP)
The 3GPP is the forum where standardization is handled for GSM, EDGE, HSDPA, HSUPA and LTE.
The background of 3GPP is in the days when WCDMA technology was being standardized
following technology selections in different regions during 1997. Following that, WCDMA was
chosen in several places as the basis for third-generation mobile communication systems and
there was regional activity in several places around the same technological principles. It became
evident, however, that this would not lead to a single global standard aligned down to bit level
details. Thus, at the end of 1998 the US, Europe, Korea and Japan joined forces and created
3GPP. China followed a bit later. Note also that the related standardization organization, although
marked as regional, usually had members from other countries/ regions as well.
The first major milestone was reached at the end of 1999 when Release 99 specifications were
published, containing the first full series of WCDMA specifications. Release 4 specifications followed in
early 2001. The working method had been moved between Release 99 and Release 4 away from the
yearly ‘release’ principle. The release cycle was made longer than just 1 year, which enabled making
bigger releases with less frequent intervals. This also allowed having more consideration of what is the
necessary release content rather than when are release publication data needed. Release 5 followed
in 2002 and Release 6 in 2004. and Release 7 specifications were ready in the second half of 2006.
3GPP originally had four different Technical Specification Groups (TSGs), and later five following the
move of GSM/EDGE activities to 3GPP, returning to four again after two of the groups amalgamated:
• TSG Radio Access Network (RAN) focuses on the radio interface and internal interfaces between
Base Transceiver Stations (BTSs)/ Radio Network Controllers (RNCs) as well as the interface
from RNC to the core network. HSDPA and HSUPA standards were under TSG RAN responsibility.
• TSG Core and Terminals (CT) focuses on the core network issues as well as covering,
for example, signalling between the core network and terminals.
• TSG Services and System Architecture (SA). focuses on the services
and overall system architecture.
• TSG GSM/EDGE RAN (GERAN) covers similar issues like TSG RAN but for
the GSM/GPRS/EDGE-based radio interface.
Under each TSG there are further working groups where the actual technical work is done.
1-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
WCDMA/HSPA Standardization and Background Version 1 Rev 0
WCDMA/HSPA Standardization and Background
3GPP
• TSG Radio Access Network (RAN)
• TSG Core and Terminals (CT)
• TSG Services and System Architecture (SA)
• TSG GSM/EDGE RAN (GERAN)
© 2005-2006 CP13: Introduction to UMTS USR6 1-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Long Term Evolution (LTE) of the 3GPP Radio Technology
Long Term Evolution (LTE) of the 3GPP Radio Technology
3GPP work on the Evolution of the 3G Mobile System started with the RAN Evolution Work
Shop, 2 - 3 November 2004 in Toronto, Canada. The Work Shop was open to all interested
organizations, members and non members of 3GPP. Operators, manufacturers and research
institutes presented more than 40 contributions with views and proposals on the evolution
of the Universal Terrestrial Radio Access Network (UTRAN).
A set of high level requirements was identified in the Work Shop:
• Reduced cost per bit
• Increased service provisioning – more services at lower cost with better user experience
• Flexibility of use of existing and new frequency bands
• Simplified architecture, Open interfaces
• Allow for reasonable terminal power consumption
LTE Detailed Requirements
A number of detailed requirements were established in technical report 25.913 summarised here:
• Peak data rate — Instantaneous downlink peak data rate of 100 Mb/s within a 20 MHz
downlink spectrum allocation (5 bps/Hz) Instantaneous uplink peak data rate of 50 Mb/s
(2.5 bps/Hz) within a 20MHz uplink spectrum allocation);
• Control-plane latency — Transition time of less than 100 ms from a camped state, such
as Release 6 Idle Mode, to an active state such as Release 6 CELL_DCH Transition
time of less than 50 ms between a dormant state such as Release 6 CELL_PCH
and an active state such as Release 6 CELL_DCH;
• Control-plane capacity — At least 200 users per cell should be supported in the
active state for spectrum allocations up to 5 MHz;
• User-plane latency — Less than 5 ms in unload condition (ie single user with
single data stream) for small IP packet;
• User throughput — Downlink: average user throughput per MHz, 3 to 4 times Release 6 HSDPA
Uplink: average user throughput per MHz, 2 to 3 times Release 6 Enhanced Uplink;
• Spectrum efficiency — Downlink: In a loaded network, target for spectrum efficiency
(bits/sec/Hz/site), 3 to 4 times Release 6 HSDPA ) Uplink: In a loaded network, target for
spectrum efficiency (bits/sec/Hz/site), 2 to 3 times Release 6 Enhanced Uplink;
• Mobility — E-UTRAN should be optimized for low mobile speed from 0 to 15 km/h. Higher
mobile speed between 15 and 120 km/h should be supported with high performance.
Mobility across the cellular network shall be maintained at speeds from 120 km/h to 350
km/h (or even up to 500 km/h depending on the frequency band);
•
1-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Long Term Evolution (LTE) of the 3GPP Radio Technology Version 1 Rev 0
Long Term Evolution (LTE) of the 3GPP Radio Technology
LTE Introduction
MME/UPE MME/UPE
Evolved Packet Core (EPC)
S1
X2 E-UTRAN
eNB eNB
X2
X2
eNB
Note: K ey P oints:
MME = Mobility Management E ntity • 100mbps DL 50mbps UL
UP E = User P lane E ntity
• S hort control and us er plane latenc y
• G reater s pec tral efficiency
• UT R AN and G E R AN compatible
© 2005-2006 CP13: Introduction to UMTS USR6 1-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Long Term Evolution (LTE) of the 3GPP Radio Technology
Long Term Evolution (LTE) of the 3GPP Radio Technology
• Coverage — Throughput, spectrum efficiency and mobility targets above should be met for 5 km
cells, and with a slight degradation for 30 km cells. Cells range up to 100 km should not be precluded;
• Further Enhanced Multimedia Broadcast Multicast Service (MBMS) — While reducing
terminal complexity: same modulation, coding, multiple access approaches and UE bandwidth
than for unicast operation. Provision of simultaneous dedicated voice and MBMS services
to the user. Available for paired and unpaired spectrum arrangements
• Spectrum flexibility — E-UTRA shall operate in spectrum allocations of different sizes, including
1.25 MHz, 1.6 MHz, 2.5 MHz, 5 MHz, 10 MHz, 15 MHz and 20 MHz in both the uplink and
downlink. Operation in paired and unpaired spectrum shall be supported The system shall
be able to support content delivery over an aggregation of resources including Radio Band
Resources (as well as power, adaptive scheduling, etc) in the same and different bands, in
both uplink and downlink and in both adjacent and non-adjacent channel arrangements. A
“Radio Band Resource” is defined as all spectrum available to an operator;
• Co-existence and Inter-working with 3GPP Radio Access Technology (RAT) —
Co-existence in the same geographical area and co-location with GERAN/UTRAN on
adjacent channels. E-UTRAN terminals supporting also UTRAN and/or GERAN operation
should be able to support measurement of, and handover from and to, both 3GPP UTRAN
and 3GPP GERAN. The interruption time during a handover of real-time services between
E-UTRAN and UTRAN (or GERAN) should be less than 300 ms;
• Architecture and migration —Single E-UTRAN architecture. The E-UTRAN architecture
shall be packet based, although provision should be made to support systems supporting
real-time and conversational class traffic E-UTRAN architecture shall minimize the
presence of "single points of failure" E-UTRAN architecture shall support an end-to-end
QoS Backhaul communication protocols should be optimised;
• Radio Resource Management Requirements — Enhanced support for end to end
QoS. Efficient support for transmission of higher layers. Support of load sharing and
policy management across different Radio Access Technologies.
1-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Long Term Evolution (LTE) of the 3GPP Radio Technology Version 1 Rev 0
Long Term Evolution (LTE) of the 3GPP Radio Technology
LTE Introduction
MME/UPE MME/UPE
Evolved Packet Core (EPC)
S1
X2 E-UTRAN
eNB eNB
X2
X2
eNB
Note: K ey P oints:
MME = Mobility Management E ntity • 100mbps DL 50mbps UL
UP E = User P lane E ntity
• S hort control and us er plane latenc y
• G reater s pec tral efficiency
• UT R AN and G E R AN compatible
© 2005-2006 CP13: Introduction to UMTS USR6 1-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Long Term Evolution (LTE) of the 3GPP Radio Technology
This page intentionally left blank.
1-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Network Architecture Version 1 Rev 0
Chapter 2
Network Architecture
© 2005-2006 CP13: Introduction to UMTS USR6 2-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Network Architecture
This page intentionally left blank.
2-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
On completion of this chapter the student should be able to:
• Name and state the purpose of the UMTS Domains
• Describe the architecture of a UMTS network.
• Describe the purpose of the major network components.
• Describe the options for evolution to future releases.
© 2005-2006 CP13: Introduction to UMTS USR6 2-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Domains
UMTS Domains
Domain split
A basic architectural split is between the user equipment (terminals) and the infrastructure. This results
in two domains: the User Equipment Domain and the Infrastructure domain. User equipment is the
equipment used by the user to access UMTS services. User equipment has a radio interface to the
infrastructure. The infrastructure consists of the physical nodes which perform the various functions
required to terminate the radio interface and to support the telecommunication services requirements
of the users. The infrastructure is a shared resource that provides services to all authorised end
users within its coverage area. The reference point between the user equipment domain and the
infrastructure domain is termed the "Uu" reference point (UMTS radio interface).
User equipment Domain
This domain encompasses a variety of equipment types with different levels of functionality.
These equipment types are referred to as user equipment (terminals), and they may also be
compatible with one or more existing access (fixed or radio) interfaces e.g. dual mode UMTS-GSM
user equipment. The user equipment may include a removable smart card that may be used
in different user equipment types. The user equipment is further sub-divided in to the Mobile
Equipment Domain (ME) and the User Services Identity Module Domain (USIM). The reference
point between the ME and the USIM is termed the "Cu" reference point.
Mobile equipment Domain
The Mobile Equipment performs radio transmission and contains applications. The mobile equipment
may be further sub-divided into several entities, e.g. the one which performs the radio transmission
and related functions, Mobile Termination, (MT), and the one which contains the end-to-end
application or (e.g. laptop connected to a mobile phone), Terminal Equipment, (TE).
USIM Domain
The USIM contains data and procedures which unambiguously and securely identify itself. These
functions are typically embedded in a standalone smart card. This device is associated to a given
user, and as such allows to identify this user regardless of the ME he uses.
Infrastructure Domain
The Infrastructure domain is further split into the Access Network Domain, which is characterized by
being in direct contact with the User Equipment and the Core Network Domain. This split is intended
to simplify/assist the process of de-coupling access related functionality from non-access related
functionality and is in line with the modular principle adopted for the UMTS. The Access Network
Domain comprises roughly the functions specific to the access technique, while the functions in the Core
network domain may potentially be used with information flows using any access technique. This split
allows for different approaches for the Core Network Domain, each approach specifying distinct types
of Core Networks which can be connected to the Access Network Domain, as well as different access
techniques, each type of Access Network connected to th Core Network Domain. The reference point
between the access network domain and the core network domain is termed the "lu" reference point.
2-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Domains Version 1 Rev 0
UMTS Domains
Home
Network
Domain
[Zu]
Cu Uu Iu [Yu]
SIM
CARD
Serving Transit
Network Network
Domain Domain
USIM Mobile Access Core
Domain Equipment Network Network
Domain Domain Domain
User Equipment Infrastructure
Domain Domain
© 2005-2006 CP13: Introduction to UMTS USR6 2-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Domains
UMTS Domains
Access Network Domain
The Access Network Domain consists of the physical entities which manage the resources of the
access network and provides the user with a mechanism to access the core network domain.
Core Network Domain
The Core Network Domain consists of the physical entities which provide support for the network
features and telecommunication services. The support provided includes functionality such as the
management of user location information, control of network features and services, the transfer
(switching and transmission) mechanisms for signalling and for user generated information.
The core network domain is sub-divided into the Serving Network Domain, the Home Network
Domain and the Transit Network Domain. The reference point between the serving network domain
and the home network domain is termed the [Zu] reference point. The reference point between the
serving network domain and the transit network domain is termed the [Yu] reference point.
Serving Network Domain
The serving network domain is the part of the core network domain to which the access network
domain that provides the user’s access is connected. It represents the core network functions that
are local to the user’s access point and thus their location changes when the user moves. The
serving network domain is responsible for routing calls and transport user data/information from
source to destination. It has the ability to interact with the home domain to cater for user specific
data/services and with the transit domain for non-user specific data/services purposes.
Home Network Domain
The home network domain represents the core network functions that are conducted at a permanent
location regardless of the location of the user’s access point. The USIM is related by subscription
to the home network domain. The home network domain therefore contains at least permanently
user specific data and is responsible for management of subscription information. It may also
handle home specific services, potentially not offered by the serving network domain.
Transit Network Domain
The transit network domain is the core network part located on the communication path between the
serving network domain and the remote party. If, for a given call, the remote party is located inside the
same network as the originating UE, then no particular instance of the transit domain is activated.
2-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Domains Version 1 Rev 0
UMTS Domains
Home
Network
Domain
[Zu]
Cu Uu Iu [Yu]
SIM
CARD
Serving Transit
Network Network
Domain Domain
USIM Mobile Access Core
Domain Equipment Network Network
Domain Domain Domain
User Equipment Infrastructure
Domain Domain
© 2005-2006 CP13: Introduction to UMTS USR6 2-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Architecture - Release 1999
UMTS Architecture - Release 1999
The diagram opposite illustrates the basic configuration of a Public Land Mobile Network
(PLMN) supporting UMTS and GSM/GPRS. This architecture is as defined in Release
1999 of the 3GPP (Dec 02) specifications (TS23.002)
The Core Network (CN) Entities
The CN is constituted of a Circuit Switched (CS) domain and a Packet Switched (PS)
domain. These two domains differ by the way they support user traffic, as explained
below. These two domains are overlapping, i.e. they contain some common entities. A
PLMN can implement only one domain or both domains.
CS Domain
The CS domain refers to the set of all the CN entities offering "CS type of connection" for user
traffic as well as all the entities supporting the related signalling. A "CS type of connection" is a
connection for which dedicated network resources are allocated at the connection establishment
and released at the connection release. The entities specific to the CS domain are:
• MSC - The Mobile-services Switching Centre
• GMSC - Gateway Mobile Service Switching Centre
• VLR - Visitor Location Register
PS Domain
The PS domain refers to the set of all the CN entities offering "PS type of connection"
for user traffic as well as all the entities supporting the related signalling. A "PS type of
connection" transports the user information using autonomous concatenation of bits called
packets: each packet can be routed independently from the previous one. The entities
specific to the PS domain are the GPRS specific entities, i.e.
• SGSN - Serving GPRS Support Node
• GGSN - Gateway GPRS Support Node
Entities Common to the CS and PS domains
The following entities are common provide common functions to the CS and PS Domains:
• HLR - The Home Location Register
• AUC - Authentication Centre
• EIR - Equipment Identity Register
2-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Architecture - Release 1999 Version 1 Rev 0
UMTS Architecture - Release 1999
Gi
GMSC AuC GGSN
Gp
C H Gc
HLR
PSTN PSTN Gr
D Gn
EIR
VLR G
F Gf
VLR
MSC E SGSN
Gs
MSC CN
IuCS IuPS Gb
A
BSS RNS IuPS IuCS RNS BSS
BSC RNC Iur RNC BSC
Abis lub lub Abis
BTS BTS Node B Node B Node B Node B BTS BTS
Um MS Um
Uu
ME
SIM-ME I/f
Cu
SIM or USIM
© 2005-2006 CP13: Introduction to UMTS USR6 2-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Architecture - Release 1999
UMTS Architecture - Release 1999
The Access Network (AN) Entities
Two different types of access network are used by the CN: the Base Station System (BSS) and
the Radio Network System (RNS). The BSS offers a Time Division Multiple Access (TDMA)
based technology to access the Mobile Station whereas the RNS offers a Wideband-Code
Division Multiple Access (W-CDMA) based technology. The MSC (resp. SGSN) can
connect to one of these Access Network type or to both of them.
The Base Station System (BSS)
The Base Station System (BSS) is the system of base station equipments (transceivers,
controllers, etc...) which is viewed by the MSC through a single A-interface as being the entity
responsible for communicating with Mobile Stations in a certain area. Similarly, in PLMNs supporting
GPRS, the BSS is viewed by the SGSN through a single Gb interface. The functionality for
the A interface is described in GSM 08.02 and for the Gb interface in TS 23.060. The radio
equipment of a BSS may support one or more cells. A BSS may consist of one or more base
stations. Where an Abis-interface is implemented, the BSS consists of one Base Station
Controller (BSC) and one or more Base Transceiver Station (BTS).
The Radio Network System (RNS)
The Radio Network System (RNS) is the system of base station equipments (transceivers, controllers,
etc...) which is viewed by the MSC through a single Iu-interface as being the entity responsible
for communicating with Mobile Stations in a certain area. Similarly, in PLMNs supporting GPRS,
the RNS is viewed by the SGSN through a single Iu-PS interface. The functionality for the Iu-CS
interface is described in TS 25.410 and for the Iu-PS interface in TS 23.060. The radio equipment
of a RNS may support one or more cells. A RNS may consist of one or more base stations. The
RNS consists of one Radio Network Controller (RNC) and one or more Node B.
The Mobile Station (MS)
The mobile station consists of the physical equipment used by a PLMN subscriber; it comprises
the Mobile Equipment (ME) and the Subscriber Identity Module (SIM), called User Services
Identity Module (USIM) for Release 99 and following releases. The ME comprises the
Mobile Termination (MT) which, depending on the application and services, may support
various combinations of Terminal Adapter (TA) and Terminal Equipment (TE) functional
groups. These functional groups are described in GSM 04.02.
2-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Architecture - Release 1999 Version 1 Rev 0
UMTS Architecture - Release 1999
Gi
GMSC AuC GGSN
Gp
C H Gc
HLR
PSTN PSTN Gr
D Gn
EIR
VLR G
F Gf
VLR
MSC E SGSN
Gs
MSC CN
IuCS IuPS Gb
A
BSS RNS IuPS IuCS RNS BSS
BSC RNC Iur RNC BSC
Abis lub lub Abis
BTS BTS Node B Node B Node B Node B BTS BTS
Um MS Um
Uu
ME
SIM-ME I/f
Cu
SIM or USIM
© 2005-2006 CP13: Introduction to UMTS USR6 2-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Network - Release 1999
UMTS Network - Release 1999
The diagram opposite shows a simplified schematic of a Release 1999 UMTS Network.
It illustrates only those entities associated with providing a UMTS service (i.e. excludes
any entities specifically associated with GSM/GPRS)
Entities of the CN-CS Domain
The Mobile Services Switching Centre (MSC)
The Mobile-services Switching Centre (MSC) constitutes the interface between the radio system
and the fixed networks. The MSC performs all necessary functions in order to handle the circuit
switched services to and from the mobile stations. In order to obtain radio coverage of a given
geographical area, a number of base stations are normally required; i.e. each MSC would thus
have to interface several base stations. In addition several MSCs may be required to cover a
country. The Mobile-services Switching Centre is an exchange which performs all the switching
and signalling functions for mobile stations located in a geographical area designated as the
MSC area. The main difference between a MSC and an exchange in a fixed network is that
the MSC has to take into account the impact of the allocation of radio resources and the mobile
nature of the subscribers and has to perform procedures required for the location registration
(see TS 23.012) and procedures required for handovers (see TS 23.009).
The Gateway MSC (GMSC)
If a network delivering a call to the PLMN cannot interrogate the HLR, the call is routed to
an MSC. This MSC will interrogate the appropriate HLR and then route the call to the MSC
where the mobile station is located. The MSC which performs the routing function to the actual
location of the MS is called the Gateway MSC (GMSC). The acceptance of an interrogation to
an HLR is the decision of the operator. The choice of which MSCs can act as Gateway MSCs
is for the operator to decide (i.e. all MSCs or some designated MSCs).
The Visitor Location Register (VLR)
A mobile station roaming in an MSC area is controlled by the Visitor Location Register (VLR) in
charge of this area. When a Mobile Station (MS) enters a new location area it starts a registration
procedure. The MSC in charge of that area notices this registration and transfers to the VLR the
identity of the location area where the MS is situated. If this MS is not yet registered, the VLR and the
HLR exchange information to allow the proper handling of calls involving the MS. A VLR may be in
charge of one or several MSC areas. The VLR contains also the information needed to handle the calls
set-up or received by the MSs registered in its database. The following elements are included:
• The International Mobile Subscriber Identity (IMSI);
• The Mobile Station International ISDN number (MSISDN);
• The Mobile Station Roaming Number (MSRN), see TS 23.003 for allocation principles;
• The Temporary Mobile Station Identity (TMSI), if applicable;
• The Local Mobile Station Identity (LMSI), if used;
• The location area where the mobile station has been registered;
• The last known location and the initial location of the MS.
2-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Network - Release 1999 Version 1 Rev 0
UMTS Network - Release 1999
PSTN PDN
CN-CS CN-PS
CN Domain
GMSC GGSN
HLR
VLR
AuC
MSC SGSN
OMC-T Iu-CS Iu-PS
(Transport)
OMC-U UTRAN
(UTRAN)
RNS RNS
RNC RNC
Iur
Iub Iub Iub Iub
Node B Node B Node B Node B
Uu
User Equipment
© 2005-2006 CP13: Introduction to UMTS USR6 2-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Network - Release 1999
UMTS Network - Release 1999
Entities Common to the CS and PS Domains
The Home Location Register (HLR)
This functional entity is a database in charge of the management of mobile subscribers. A PLMN may
contain one or several HLRs: it depends on the number of mobile subscribers, on the capacity of the
equipment and on the organisation of the network. The following kinds of information are stored there:
• Subscription information.
• Location information enabling the charging and routing of calls towards the
MSC where the MS is registered (e.g. the MS Roaming Number, the VLR
Number, the MSC Number, the Local MS Identity).
• If GPRS is supported, location information enabling the charging and routing of messages in
the SGSN where the MS is currently registered (e.g. the SGSN Number).
• The types of identity are attached to each mobile (e.g. International Mobile Station Identity
(IMSI), one or more Mobile Station International ISDN Number(s) (MSISDN), if GPRS
is supported zero or more Packet Data Protocol (PDP) address(es)).
The Authentication Centre (AuC)
The Authentication Centre (AuC) is an entity which stores data for each mobile subscriber
to allow the International Mobile Subscriber Identity (IMSI) to be authenticated and to
allow communication over the radio path between the mobile station and the network to be
ciphered. The AuC transmits the data needed for authentication and ciphering via the HLR to
the VLR, MSC and SGSN which needs to authenticate a mobile station. The Authentication
Centre (AuC) is associated with an HLR, and stores an identity key for each mobile subscriber
registered with the associated HLR. This key is used to generate:
• Data which are used to authenticate the International Mobile Subscriber Identity (IMSI).
• A key used to cipher communication over the radio path between the mobile station and the network.
The Equipment Identity Register (EIR)
The Equipment Identity Register (EIR) in the GSM system is the logical entity which is
responsible for storing in the network the International Mobile Equipment Identities (IMEIs),
used in the GSM system. The equipment is classified as "white listed", "grey listed", "black
listed" or it may be unknown as specified in TS 22.016 and TS 29.002.
This functional entity contains one or several databases which store(s) the IMEIs used
in the GSM system. An EIR shall as a minimum contain a "white list" (Equipment
classified as "white listed"). See also TS 22.016 on IMEI.
2-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Network - Release 1999 Version 1 Rev 0
UMTS Network - Release 1999
PSTN PDN
CN-CS CN-PS
CN Domain
GMSC GGSN
HLR
VLR
AuC
MSC SGSN
OMC-T Iu-CS Iu-PS
(Transport)
OMC-U UTRAN
(UTRAN)
RNS RNS
RNC RNC
Iur
Iub Iub Iub Iub
Node B Node B Node B Node B
Uu
User Equipment
© 2005-2006 CP13: Introduction to UMTS USR6 2-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Network R4
UMTS Network R4
In R4 the separation of the switching and call control functions within the core network is commonly
referred to as a softswitch architecture. The call control component, i.e. the MSC server, is the
softswitch in this case. This separation of functions makes it easier to scale the network as
the traffic demand increases. If the network planners require more switching capacity they can
add MGWs; if they require more call control capacity they then add more MSC servers. This is
a clear distinction from the UMTS Release 99 and GSM networks, in which the call control and
switching functions are all carried out within the MSC and gateway MSC (GMSC).
Media Gateways (MGWs)
This translates media traffic between different types of network. Functionality
carried out by the MGW includes:
• Termination of bearer channels from the circuit switched and packet switched networks;
• Echo cancellation for circuit switched circuits;
• Translation of media from one CODEC form to another,
Each MGW is controlled by one or more MSC servers.
MSC Server
This performs functions such as call control for mobile-originated and mobile-terminated calls, and
mobility management in terms of maintenance of the registry of mobiles within its area of control.
The MSC server integrates with the Visitor Location Register (VLR) component, which holds
location information as well as CAMEL (customized applications for mobile network enhanced
logic) data for subscribers. Functions carried out by the MSC server include:
• Controlling the registration of mobiles to provide mobility management;
• Providing authentication functions;
• Routing mobile-originated calls to their destination;
• Routing mobile-terminated calls by using paging to individual mobiles.
The MSC server terminates signalling from the mobile network over the Iu interface to the RNC. It also
controls the establishment of bearers across its core by the use of MGWs under its control.
2-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Network R4 Version 1 Rev 0
UMTS Network R4
Network Management (NMS)
CN CS Domain
Um MSC Server
GERAN
BTS BSC MGW MGW PSTN/ISDN
HLR/VLR/EIR
Uu
UTRAN CN PS Domain
NODEB RNC SGSN GGSN Data Network
© 2005-2006 CP13: Introduction to UMTS USR6 2-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Network Release 5
UMTS Network Release 5
Release 5 (R5) builds on the partial implementation of IP packet switching within the core network,
to move to an all-IP architecture. In this release, packets can be moved end-to-end using IP
transport with an enhanced GPRS network connected to an IP multimedia subsystem (IMS). The
GPRS backbone for R5 must be able to provide similar levels and classifications of QoS usually
associated with ATM networks. This is to allow for the delivery of time-sensitive traffic such as
voice and multimedia. As well as enhancements to the core network, the RAN also migrates
from ATM to IP. Even though the vision for R5 is for a total IP solution, the operator may well
still use ATM as a transport solution for some parts of the network. This is possible because all
UMTS releases must provide backward compatibility with earlier releases.
Notice that in the R5 network, the CS domain can be dispensed with since the services
associated with it, such as transfer of voice traffic, can be carried over the GPRS and IMS
networks using IP QoS mechanisms. That given, many operators may still be using the R4
CS domain as well as the R5 IMS architecture. This allows for a gradual migration to an all-IP
architecture with the minimal disruption to service. Some voice calls may be handled using
the CS domain and some, for example video call services, via the IMS.
IP MULTIMEDIA SUBSYSTEM (IMS)
R5 introduces a new network domain called the IP Multimedia Subsystem (IMS). This is an IP
network domain designed to provide appropriate support for real-time multimedia services.
The UE communicates with the IMS using GPRS, with the IMS being directly connected to
the GGSN. The IMS provides services to mobile users such as:
• Real-time communication using voice, video or multimedia messaging
(i.e. voice and video telephony);
• Audioconferencing and videoconferencing;
• Content delivery services such as video, audio or multimedia download;
• Content streaming services such as video, audio or multimedia streaming
(e.g. using video on demand server);
• Multimedia Messaging Service (MMS).
Each operator’s IMS can be connected to other operators’ IMSs, allowing multimedia services
between users on different networks. Connections to the public Internet allow MMS messaging
as well as voice over IP (VoIP) and video telephony between mobile and fixed-line users. Finally,
the interface to the ISDN (or other circuit switched networks) allows VoIP calls to be connected
through to conventional fixed-line and mobile users, e.g. GSM. Connections between the IMS and
other IP networks are controlled by firewalls to protect against hacking. The interface between the
IMS and the CS network is controlled by the softswitch and MGW components. Within the operator’s
network the IMS is connected to the Home Subscriber Server (HSS) to allow for subscriber
authentication, authorization and mobility management. For R5 and beyond, the IMS can be used
to provide transport for all of the operator’s services, including conventional voice calls.
2-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Network Release 5 Version 1 Rev 0
UMTS Network Release 5
Network Management (NMS)
Um
PSTN/ISDN
GERAN
BTS BSC
CN PS Domain
SGSN GGSN
Uu ATM/IP IMS
UTRAN
HSS
NODEB RNC
IP Multimedia
© 2005-2006 CP13: Introduction to UMTS USR6 2-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Terrestrial Radio Access Network (UTRAN)
UMTS Terrestrial Radio Access Network (UTRAN)
The UTRAN consists of a set of Radio Network Subsystems (RNSs) connected to the Core
Network through the IuCS and IuPS. A RNS consists of a Radio Network Controller (RNC) and
one or more Node Bs. A Node B is connected to the RNC through the Iub interface. A Node
B can support FDD mode, TDD mode or dual-mode operation. The RNC is responsible for the
Handover decisions that require signalling to the UE. An RNC may include a combining/splitting
function to support combination/splitting of information streams.
Inside the UTRAN, the RNCs of the Radio Network Subsystems can be interconnected together
through the Iur. Iu(s) and Iur are logical interfaces. Iur can be conveyed over direct physical
connection between RNCs or virtual networks using any suitable transport network.
UTRAN Functions
The following is a list of the functions performed by the UTRAN sub-systems. These
functions will be discussed in further detail in later chapters.
Functions related to overall system access control
• Admission Control
• Congestion Control
• System information broadcasting
Radio channel ciphering and deciphering
Functions related to mobility
• Handover
• SRNS Relocation
Functions related to radio resource management and control
• Radio resource configuration and operation
• Radio environment survey
• combining/splitting control
• Radio bearer connection set-up and release (Radio Bearer Control)
• Allocation and deallocation of Radio Bearers
• Radio protocols function
• RF power control
• RF power setting
• Radio channel coding/decoding
• Channel coding control
• Initial (random) access detection and handling
• CN Distribution function for Non Access Stratum messages
Functions related to broadcast and multicast services
NOTE: Only Broadcast is applicable for Release 1999.
• Broadcast/Multicast Information Distribution
• Broadcast/Multicast Flow Control
• CBS Status Reporting
2-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Terrestrial Radio Access Network (UTRAN) Version 1 Rev 0
UMTS Terrestrial Radio Access Network (UTRAN)
Core Network
Iu Iu
RNS RNS
Iur
RNC RNC
Iub Iub Iub Iub
Node B Node B Node B Node B
© 2005-2006 CP13: Introduction to UMTS USR6 2-21
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Radio network Controller (RNC)
Radio network Controller (RNC)
A Radio Network Controller (RNC) is a network component within the PLMN with the
functions to support one or more Node B, Cell and/or User Equipment.
Typically one RNC can support up to 300 Node Bs, which in turn can provide resources for up
to 6 cells. However, it should be noted that the ultimate limiting factor in planning the number of
RNCs required within a PLMN will be the traffic capacity that the RNC can support. Typical values
will start at around 1000 Erlang, rising to 10,000 Erlang as networks mature.
A Radio Network Controller (RNC) can be considered to operate in one or more of the following roles:
• Controlling Radio Network Controller (CRNC)
• Serving Radio Network Controller (SRNC)
• Drift Radio Network Controller (DRNC)
Controlling Radio Network Controller (CRNC)
Controlling RNC is a role an RNC can take with respect to a specific set of Node
B’s. There is only one Controlling RNC for any Node B. The Controlling RNC has the
overall control of the logical resources of its node B’s.
The main functions of a CRNC are:
• Control of the Radio Resources for the Node-B it controls.
• Provision of Services to the Node-B that it controls.
• Load and Congestion Control
• Admission Control
• Code allocation for new radio links
2-22 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Radio network Controller (RNC) Version 1 Rev 0
Radio network Controller (RNC)
UTRAN CRNC Functions
· Controlling of the Radio Resources
· Provision of Services to the Node-B
· Load and Congestion Control
· Admission Control
· Code Allocation for new Radio Links
C-RNC Iu Iu C-RNC
lur
© 2005-2006 CP13: Introduction to UMTS USR6 2-23
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Radio network Controller (RNC)
Radio network Controller (RNC)
Serving Radio Network Controller (SRNC)
A Serving RNC is the RNC located within a Serving RNS (SRNS). SRNS is a role an RNS
can take with respect to a specific connection between an UE and UTRAN.
There is one Serving RNS for each UE that has a connection to UTRAN.
The Serving RNS is in charge of the radio connection between a UE and the UTRAN.
The Serving RNS terminates the Iu for this UE.
The main functions of an SRNC are:
• Termination of the Radio Resource Control Signalling between the RNC and the UE.
• L2 Processing (PDCP, RLC, MAC).
• Radio Resource Control operations.
• Mapping of Iu Bearer Parameters onto Transport Channels Parameters.
• Hand-over decisions.
• Outer loop power control.
• Macro-Diversity combining and splitting.
2-24 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Radio network Controller (RNC) Version 1 Rev 0
Radio network Controller (RNC)
UTRAN SRNC Functions
· Termination of the Radio Resource Control Signalling
between the RNC and the UE
· L2 Processing (PDCP, RLC, MAC)
· Radio Resource Control Operations
· Mapping of Bearer Parameters onto Transport Channel Parameters
· Hand-Over Decisions
· Outer Loop Power Control
· Macro-diversity Combining and Splitting
S-RNC
© 2005-2006 CP13: Introduction to UMTS USR6 2-25
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Radio network Controller (RNC)
Radio network Controller (RNC)
Drift Radio Network Controller (DRNC)
A Drift RNC is located within a Drift RNS. DRNS is role that an RNS can take with
respect to a specific connection between a UE and UTRAN.
A DRNS is any RNS that supports the Serving RNS by providing radio resources via the cell(s) it
controls, to provide additional radio bearer services for a specific connection between a UE and UTRAN.
There may be zero, one or more DRNSs associated with a specific
connection between a UE and UTRAN.
The main functions of a DRNC are:
• Macro-diversity combining and splitting.
• No L2 processing, i.e. no re-transmissions, acknowledgements or negative acknowledgements.
• Transparent routing of data on the Iub and Iur Interfaces, except when Common
or shared channels are used.
2-26 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Radio network Controller (RNC) Version 1 Rev 0
Radio network Controller (RNC)
UTRAN DRNC Functions
· Macro-diversity Combining and Splitting
· No L2 Processing
· Transparent Routing except for Common/Shared Channels
S-RNC D-RNC
© 2005-2006 CP13: Introduction to UMTS USR6 2-27
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Horizon 3G-n macro
Horizon 3G-n macro
The Horizon 3G-n macro logical structure is divided in four subsystems responsible for all
processing needed for radio transmission and reception in one or more cells.
The Horizon 3G-n macro Subsystems are:
• Transport subsystem.
• Baseband subsystem.
• Control subsystem
• Antenna and feeder subsystem
Transport subsystem
It’s responsible for the termination of the IuB interface connecting the Horizon 3G-n to
RNC to exchange information and performs ATM switching
It is formed by two boards: NDTI (NodeB Digital Trunk Interface) and NAOI
(NodeB ATM Optical Interface)
Baseband subsystem
The baseband subsystem processes uplink and downlink signals at the physical
layer, and includes the following functions:
• Forwarding and controlling baseband signals and RF signals
• Processing uplink and downlink baseband signals
• Supporting the HSDPA
• Supporting the resource pool
• Supporting RRU connection
• Search over UL access channels
• Demodulation over dedicated channels
• Uplink channel encoding
• Channel estimation
• RAKE receiving
• Softer combination
• Decoding
HULP (NodeB HSUPA Up-link Processing Unit), HDLP (NodeB HSDPA Down-link Processing
Unit), HBBI (HSDPA Baseband Processing and Interface Unit) (or NBBI (NodeB Baseband
Processing and Interface Unit) ), and HBOI (HSDPA Baseband Processing and Optical
Interface Unit) boards are part of the baseband subsystem .
2-28 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Horizon 3G-n macro Version 1 Rev 0
Horizon 3G-n macro
Logical structure of the Horizon 3G-n macro
Figure 2-1
Transport Baseband RF
Subsystem Subsystem Subsystem
RNC Antenna
Control Subsystem
H3G-n macro
© 2005-2006 CP13: Introduction to UMTS USR6 2-29
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Horizon 3G-n macro
Horizon 3G-n macro
RF subsystem
All RF signals and it conversion to digital signals are processed by the RF subsystem.
This subsystem include the following functions:
• • Modulate and demodulate RF signals.
• • Amplifying the received signals
• • Analog-to-digital conversion and viceversa.
• • Digital down and up conversion.
• • Matched filtering.
• • Digital Automatic Gain Control (DAGC).
• • Shaping and filtering downlink spread signals.
• • converting RF signals to the transmit frequency band.
• • Power amplification.
The MTRU (Multi-carrier Transceiver Unit) and MAFU (Multi-carrier Antenna Filter
Unit) boards are installed in this subsystem.
Control subsystem
The control subsystem provides the control of the entire Horizon 3G-n macro Indoor, provides the
system synchronization clock, alarm management, IuB signal termination, resource and configuration
management environment monitoring, and control the RET antennas system.
The control subsystem is formed by two boards: NMON (NodeB Monitor Unit) and
NMPT (NodeB Main Processing and Timing Unit).
Antenna and Feeder Subsystem
This subsystem transmits and receives signals over the air interface. With the help of the
(optional) TMA, amplifies weak signals from the antennas, improves the receiver sensitivity
and enhances the uplink coverage of the Horizon 3G-n macro BTS.
The Antenna and Feeder subsystem is formed by the following components:
• Antenna.
• Feeder.
• TMA ( Optional)
2-30 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Horizon 3G-n macro Version 1 Rev 0
Horizon 3G-n macro
logical structure of the Horizon 3G-n macro Indoor
Figure 2-2
Transport Baseband subsystem RF subsystem Antenna
subsystem
MTRU MAFU
HULP Rx0 Rx0 TMA
NDTI/
RNC NAOI HBBI
Rx1 Antenna
Duplexer
HDLP Rx1
TMA
Tx PA Tx
NMPT
NMON
Control
subsystem
© 2005-2006 CP13: Introduction to UMTS USR6 2-31
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 User Equipment (UE)
User Equipment (UE)
Introduction to User Equipment
UMTS aims to offer service capabilities that enable a wide variety of services to be implemented.
Such services range from simple services like speech, to complex multimedia services containing
several simultaneous media components that place totally different requirements on the system and
on the terminal equipment. By standardising service capabilities rather than actual services, more
flexibility is available for service providers/network operators to create unique services. The same
principle also applies for UMTS terminals, i.e. the types of terminals are not standardised and are
therefore not limited in any way. A wide range of terminal types is likely in the UMTS environment,
e.g. speech only terminals, videophones, data terminals, wideband data terminals, fax terminals,
multi-band/multi-mode terminals and any combination of the aforementioned.
Terminal development trends for today’s terminals are mainly towards higher integration levels resulting
in smaller size. The goal of "four 100’s" has been a rule of thumb target for handsets, i.e., 100 hour
standby, 100 cc size, 100 gram weight and also 100 MIPS performance. The size targets have
already been achieved and any requirement for smaller terminals is questionable from the usability
and physical size limitations perspective. The other target parameters have no maximum limitations.
On the other hand, we can see the following further trends for near future terminals:
• Application specific terminals (smart traffic, vending machine radio, etc.);
• Increased number of value adding features (graphics, smart messaging, PC connectivity
and compatibility, memory databases, speech recognition, messaging features, display
functions, and different source coding methods (e.g., JPEG));
• Support for higher number of source codecs (several speech codecs);
• Multiband terminals (e.g., GSM in 900MHz and DCS1800);
• Multimode terminals (e.g., UMTS/GSM dualmode terminal);
• Dynamic SW configurability;
These trends are more than likely to continue in the future. Multiband and multimode terminals
with high integration levels would be preferred by the users. Technological development of these
terminals relies on new packaging and interconnection technologies, as well as technological
steps like SW-radio. The concept trends of mobile handheld terminals is likely to diverge from
simple speech terminals towards a variety of different types, e.g., communicators, wearable
phones, data terminals, etc. The dominant role of speech terminals will be challenged in
the future by these new data- and multimedia-oriented terminals.
2-32 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
User Equipment (UE) Version 1 Rev 0
User Equipment (UE)
· Speech Only
· Videophones
· Data Terminals
· Wideband Data Terminals
· Fax Terminals
· Application Specific Terminals
· Multiband/Multimode Terminals
· Dynamic Software Configurability
· Value Adding Features
© 2005-2006 CP13: Introduction to UMTS USR6 2-33
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 User Equipment (UE)
User Equipment (UE)
UE Architecture
The UMTS UE will consists of a number of logical software and hardware modules. Although
these modules may be delivered by a single vendor as single physical and indivisable package,
it is also possible that they will be independent physical units.
The reference architecture showing the modules of the UE, along with their corresponding network
functions are illustrated opposite and described in the following paragraphs.
Integrated Circuit (IC) Card
The IC card is the module on which are implemented the user and subscription dependent functions of
the UE. The primary component of the IC card is the User Service Identity Module (USIM)
The mandatory requirements for IC Cards used for holding USIM application, are related to
the need to have one USIM application on the IC card, as well as to the security issues. The
following functionality is required from the IC card holding a USIM application:
• Physical characteristics same as used for GSM SIM
• The support of one USIM application
• The support of one or more user profile on the USIM
• Possibility to update USIM specific information over the air, (e.g. such information as service
profile information, algorithms, etc.) in a secure and controlled manner.
• Security mechanisms to prevent USIM application specific information from
unauthorised access or alteration.
• User authentication.
In addition to the mandatory functions, the IC Card may support the following
additional, optional functionality
• The support for more than one simultaneous application (Multiple USIM, Ecash
and/or some other applications).
• Possibility to have shared applications/files between multiple subscriptions, including
ADNs, other user/SP controlled files and data.
• Possibility for some applications/files to be restricted to one or some of the
subscriptions, under user/SP control.
• Inclusion of a payment method (electronic money and/or prepaid and/or subscription details)
• An interface allowing highly secure downloading and configuration of new functionality,
new algorithms and new applications into the IC card as well as updating the
existing applications, algorithms and data.
• Support for storing and possibly executing encryption related information,
such as keys and algorithms.
• In multi application cards a functionality to prevent the unauthorised access and alteration
of USIM specific information by other applications residing on the card.
• The ability to accept popular value-adding IC card applications, such as digital signature
applications, EMV credit/debit card, electronic purses such as Mondex and Visacash, etc.
• Possibility for one UMTS SP to block multiple subscription on the card the SP has issued.
Shared applications could include databases (e.g. telephone books), service profiles (e.g.
controlling divert information), users preferences (e.g. short dialling codes) and SP-specific
parameters inside a USIM application (e.g. call barring tables).
2-34 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
User Equipment (UE) Version 1 Rev 0
User Equipment (UE)
UE Architecture
USER USER
APPLICATION APPLICATION
USER
EQUIPMENT TERMINAL TERMINAL
(UE) EQUIPMENT EQUIPMENT
TAF
USIM NT CORE
NETWORK
Tu
IC CARD Iu
RT UTRAN
MT
MOBILE
EQUIPMENT
© 2005-2006 CP13: Introduction to UMTS USR6 2-35
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 User Equipment (UE)
User Equipment (UE)
Terminal Equipment (TE)
The TE is the part of the UE on which the users end-to-end application functions execute,
terminating the services transported via the UMTS bearers. The TE is regarded as a service
dependent component, interacting with a peer TE in the external network.
Mobile Equipment (ME)
The ME is the users subscription independent, but mobile system dependent component
of the UE. It will terminate all control plane functions and the user plane UMTS
bearer. The ME consists of the following modules:
• Terminal Adaptation Function (TAF)
• Mobile Termination (MT)
TAF
The TAF provided the interaction between the TE and MT, via the R interface/reference
point. This may include the ability of the TE to control the MT by, for example, the use
of commands sets ( e.g. Modem AT control commands).
MT
The MT is the telecom service independent, but UMTS dependent portion of the UE which terminates
the radio transmissions to and from the network. Within the MT two further modules are defined.
The Radio Termination (RT) which is dependent upon the the radio access network. A
single RT will provide common functions for all services using the same radio access
technology. For UMTS the RT terminates the UTRAN physical layer (Uu interface) and also
encompasses the Access-Stratum layer 2 and layer three protocols.
The RT interfaces to the Network Termination (NT), at the Tu reference points. While the RT
is RAN dependent, the NT is CN dependent, and thus terminates, at the serving network, the
Non-access Stratum layer 3 protocols, for functions such as mobility management, call control, session
management, etc. To fulfil many of these functions, the NT must have access to information stored on
the USIM (e.g. security information), this is accessed via the interface at the Cu reference points.
2-36 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
User Equipment (UE) Version 1 Rev 0
User Equipment (UE)
UE Architecture
USER USER
APPLICATION APPLICATION
USER
EQUIPMENT TERMINAL TERMINAL
(UE) EQUIPMENT EQUIPMENT
TAF
USIM NT CORE
NETWORK
Tu
IC CARD Iu
RT UTRAN
MT
MOBILE
EQUIPMENT
© 2005-2006 CP13: Introduction to UMTS USR6 2-37
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 User Equipment (UE)
This page intentionally left blank.
2-38 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 User Equipment (UE)
This page intentionally left blank.
2-38 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 User Equipment (UE)
This page intentionally left blank.
2-38 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Network Services Version 1 Rev 0
User Equipment (UE)
Chapter 3
Network Services
© 2005-2006 CP13: Introduction to UMTS USR6 3-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Network Services
This page intentionally left blank.
3-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
On completion of this chapter the student should be able to:
• Describe the UMTS service classifications
• Describe Quality of Service Architecture
• Describe the UMTS Security Architecture
© 2005-2006 CP13: Introduction to UMTS USR6 3-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Services in the UMTS Environment
Services in the UMTS Environment
Back in the days of 1G networks there was only one available service, speech. When 2G was released
the idea of having third parties providing services or service content was open to development.
The diagram opposite illustrates how services, their creation and content provision are located in UMTS.
The system must be able to handle end-to-end service requirements in all levels and the high
investment required is mainly there to provide the necessary QoS for those services. The lower
layers (Physical and Network) have more hardware requirements so therefore more cost.
The service creation layer is provided by such things as HTML and WAP and the Content Provider
Layer provides the end user services, for instance a banks internet service.
The commercial nature of the UMTS services means that sensitive information will be transferred
and the security mechanisms used must be robust enough to cope.
3-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Services in the UMTS Environment Version 1 Rev 0
Services in the UMTS Environment
Content Provider Layer
Network Management
End-to-end QoS
Security Functions
Service Creation Layer
Network Element Layer
Physical Transmission Layer
© 2005-2006 CP13: Introduction to UMTS USR6 3-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Quality of Service (QoS) Architecture
Quality of Service (QoS) Architecture
From the end user point of view, the UMTS network is a network for services. In this respect
the technology itself is not the most important aspect but it is an enabler providing QoS so
that the end-users can be satisfied with the end-to-end services they use.
The end-to-end services in the UMTS network are carried by bearers and a bearer is a service
providing QoS between two defined points. The UMTS network contains many system levels
having their own QoS properties. For example the air interface and the Iub. The QoS that has
to be provided by the different bearers is illustrated by the diagram opposite.
The end-to-end service sets the requirement for QoS. These requirements are then mapped to
the next level which in turn maps the QoS to the next level and so on. As a result the UMTS
network forms a connection through itself fulfilling the original QoS requirements. To make
this possible the QoS requirements are classified by traffic classes.
The leading principles that are applied to UMTS QoS classes are:
• The QoS classes must allow for efficient use of the UMTS UTRA service (radio capacity);
• The CN and UTRAN must be allowed to evolve independently;
• The UMTS network can evolve independently but must be backwards compatible
with its surrounding networks;
• The operator must be allowed to utilise existing technology within the UMTS system i.e. ATM and IP.
3-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Quality of Service (QoS) Architecture Version 1 Rev 0
Quality of Service (QoS) Architecture
UE
MSC/VLR GMSC
TE MT NodeB RNC SGSN GGSN
End-to-end Services
Local Bearer External Bearer
Services UMTS Bearer Services Services
CN Bearer
Radio Access Bearer Services Services
Iu Bearer Backbone Bearer
Radio Bearer Services Services Services
UTRA Bearer Physical Bearer
Services Physical Bearer Services Services
© 2005-2006 CP13: Introduction to UMTS USR6 3-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Quality of Service Classes
Quality of Service Classes
Network Services are considered end-to-end, this means from a Terminal Equipment (TE)
to another TE. An End-to-End Service may have a certain Quality of Service (QoS) which is
provided for the user of a network service. It is the user that decides whether he is satisfied
with the provided QoS or not. To realise a certain network QoS a Bearer Service with clearly
defined characteristics and functionality is to be set up from the source to the destination of
a service. The diagram opposite illustrates the QoS classes for UMTS.
The main distinguishing factor between these QoS classes is how delay sensitive the
traffic is: Conversational class is meant for traffic which is very delay sensitive while
Background class is the most delay insensitive traffic class.
Conversational and Streaming classes are mainly intended to be used to carry real-time traffic flows.
Interactive class and Background are mainly meant to be used by traditional Internet applications like
WWW, Email, Telnet, FTP and News. Due to looser delay requirements, compared to conversational
and streaming classes, both provide better error rate by means of channel coding and retransmission.
Conversational Class
The most well known use of this scheme is telephony speech (e.g. GSM). But with Internet and
multimedia a number of new applications will require this scheme, for example voice over IP and video
conferencing tools. Real time conversation is always performed between peers (or groups) of live
(human) end-users. This is the only scheme where the required characteristics are strictly given by
human perception. (e.g. The real time data flow is always aiming at a live (human) destination).
Streaming Class
This scheme is one of the newcomers in data communication, raising a number of new requirements in
both telecommunication and data communication systems. It is characterised by the fact that the time
relations (variation) between information entities (i.e. samples, packets) within a flow shall be preserved,
although it does not have any requirements on low transfer delay. The delay variation of the end-to-end
flow shall be limited, to preserve the time relation (variation) between information entities of the stream.
When the user is looking at (listening to) real time video (audio) the scheme of real time streams applies.
Interactive class
Interactive traffic is the other classical data communication scheme that on an overall level is
characterised by the request response pattern of the end-user. At the message destination there is an
entity expecting the message (response) within a certain time. Round trip delay time is therefore one
of the key attributes. Another characteristic is that the content of the packets shall be transparently
transferred (with low bit error rate). Examples are: web browsing, data base retrieval, server access.
Background Task
Background traffic is one of the classical data communication schemes that on an overall level
is characterised by that the destination is not expecting the data within a certain time. The
scheme is thus more or less delivery time insensitive. Another characteristic is that the content
of the packets shall be transparently transferred (with low bit error rate).
Examples are background delivery of E-mail notification, SMS, download of databases
and reception of measurement records.
3-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Quality of Service Classes Version 1 Rev 0
Quality of Service Classes
QoS C las s R equirement for R equirement for S ervic e
realtime data
performanc e trans mis s ion
C onvers ational V ery high E rrors are S peech s ervice and
permitted to a videophone
certain degree
S treaming High Data needs to be Multimedia s ervice
trans ferred s teadily
and continuously
Interactive F airly high Data needs to be W eb brows er and
integral and correct location-bas ed
s ervices
B ackground No requirement Data needs to be E -mail
integral and correct
© 2005-2006 CP13: Introduction to UMTS USR6 3-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Supported Service Rates
Supported Service Rates
The supported bit rates supported used in UMTS range somewhere between 0 to 7.2 mbit/s per
user. However the actual bit rates are meaningless without defining the QoS offered together
with the bit rates. The slides opposite illustrate typical data rates together with the types of
service offered. Different combinations of the supported bit rates maybe put together in one
call, for example you may have Sig 3.4 kbit/s + CS service + PS Service.
Description of Terminology
In the sub sections below the terminology used in the slides is explained.
Connection Oriented and Connectionless Oriented Services
Connection-oriented — Requires a session connection (analogous to a phone call) be
established before any data can be sent. This method is often called a "reliable" network
service. It can guarantee that data will arrive in the same order. Connection-oriented services
set up virtual links between end systems through a network.
Connectionless — Does not require a session connection between sender and receiver.
The sender simply starts sending packets (called datagrams) to the destination. This service
does not have the reliability of the connection-oriented method, but it is useful for periodic
burst transfers. A connectionless network provides minimal services.
Traffic Type
The bearer requirements are that the following is provided:
• Guaranteed/constant bit rate;
• Non-guaranteed/dynamically variable bit rate;
• Real time dynamically variable bit rate with a minimum guaranteed bit rate.
• Real time and non real time services
Traffic Characteristics
Point-to-point services to be provided:
• Uni-directional — Service offered in one direction;
• Bi-directional — Service offered in both directions;
• Symmetric — The data rate is roughly the same uplink and downlink;
• Asymmetric — The data rate is more heavily weighted in one direction.
Uni-directional Point-to-Multipoint:
• Multicast — Thie end user is specified before the connection is established. Multicast
Broadcast Multimedia Service (MBMS) is an example of this:
• Broadcast — The messages are broadcast to to all UE”s and the end user is not
known before. Cell Broadcast is an example of this.
3-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Supported Service Rates Version 1 Rev 0
Supported Service Rates
S R B S ervic e Data R ate
B idirectional S ignalling 3.4 kbit/s , 13.6 kbit/s
T R B C S S ervic e Data R ate
AMR S peech S ervice 12.2 kbit/s ,
T rans parent Data S ervice 64 kbit/s , 56 kbit/s , 32 kbit/s , and 28.8 kbit/s
Non-trans parent Data S ervice 57.6 kbit/s , 28.8 kbit/s , and 14.4 kbit/s
T R B P S S ervic e Data R ate
B idirectional s ymmetric V oIP s peech 64 kbit/s , 32 kbit/s , 16 kbit/s , 8 kbit/s
s ervice
B idirectional s ymmetric or as ymmetric 256 kbit/s , 144 kbit/s , 128 kbit/s , 64
s treaming s ervice kbit/s , 32 kbit/s and 8 kbit/s
144 kbit/s , 128 kbit/s , 64 kbit/s , 32
Unidirectional as ymmetric s treaming s ervice kbit/s and 8 kbit/s
B idirectional s ymmetric or as ymmetric 384 kbit/s , 256 kbit/s , 144 kbit/s , 128
interactive s ervice kbit/s , 64 kbit/s , 32 kbit/s , 16 kbit/s and
8 kbit/s
B idirectional s ymmetric or as ymmetric 384 kbit/s , 256 kbit/s , 144 kbit/s , 128
background s ervice kbit/s , 64 kbit/s , 32 kbit/s , 16 kbit/s and
8 kbit/s
3648 kbit/s , 2048 kbit/s , 1536 kbit/s ,
High-s peed data s ervice interactive and 1024 kbit/s , 768 kbit/s
background unidirectional
© 2005-2006 CP13: Introduction to UMTS USR6 3-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 The Security Architecture
The Security Architecture
Five security feature groups are defined. Each of these feature groups meets certain
threats, accomplishes certain security objectives:
Network access security (I): the set of security features that provide users with secure access to
3G services, and which in particular protect against attacks on the (radio) access link.
Network domain security (II): the set of security features that enable nodes in the provider domain to
securely exchange signalling data, and protect against attacks on the wireline network.
User domain security (III): the set of security features that secure access to mobile stations.
Application domain security (IV): the set of security features that enable applications in the
user and in the provider domain to securely exchange messages.
Visibility and configurability of security (V): the set of features that enables the user to
inform himself whether a security feature is in operation or not and whether the use and
provision of services should depend on the security feature.
3-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
The Security Architecture Version 1 Rev 0
The Security Architecture
Application
Stratum
(IV)
User Application Provider Application
Home
(V) (III) (I) Stratum/
(I)
TE USIM HE Serving
Stratum
(II)
(I) (I)
SN
Transport
(I) Stratum
MT AN
© 2005-2006 CP13: Introduction to UMTS USR6 3-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Security and Privacy
Security and Privacy
User authentication:
The property that the Serving Network (SN) corroborates the identity of the user;
Network authentication:
The property that the user corroborates that he is connected to a serving network that is authorised by
the users HE to provide him services; this includes the guarantee that this authorisation is recent.
Confidentiality
Cipher algorithm agreement: the property that the MS and the SN can securely
negotiate the algorithm that they shall use subsequently;
Cipher key agreement: the property that the MS and the SN agree on a cipher
key that they may use subsequently;
Confidentiality of user data: the property that user data cannot be
overheard on the radio access interface;
Confidentiality of signalling data: the property that signalling data cannot be
overheard on the radio access interface.
Data integrity
Integrity algorithm agreement: the property that the MS and the SN can securely negotiate
the integrity algorithm that they shall use subsequently;
Integrity key agreement: the property that the MS and the SN agree on an
integrity key that they may use subsequently;
Data integrity and origin authentication of signalling data: the property that the
receiving entity (MS or SN) is able to verify that signalling data has not been modified in
an unauthorised way since it was sent by the sending entity (SN or MS) and that the data
origin of the signalling data received is indeed the one claimed.
Mobile equipment identification
In certain cases, SN may request the MS to send it the mobile equipment identity of the terminal. The
mobile equipment identity shall only be sent after authentication of SN with exception of emergency
calls. The IMEI should be securely stored in the terminal. However, the presentation of this identity to
the network is not a security feature and the transmission of the IMEI is not protected. Although it is not
a security feature, it should not be deleted from UMTS however, as it is useful for other purposes.
3-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Security and Privacy Version 1 Rev 0
Security and Privacy
User Authentication
Network Authentication
Confidentiality
Data integrity
Mobile equipment identification
© 2005-2006 CP13: Introduction to UMTS USR6 3-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Authentication and Key Agreement
Authentication and Key Agreement
Authentication and Key Agreement (AKA) achieves mutual authentication by the user and the
network showing knowledge of a secret key K which is shared between and available only to the USIM
and the AuC in the user’s HE. In addition the USIM and the HE keep track of counters SEQMS and
SEQHE respectively to support network authentication. The method was chosen in such a way as to
achieve maximum compatibility with the current GSM security architecture and facilitate migration from
GSM to UMTS. The method is composed of a challenge/response protocol identical to the GSM
subscriber authentication and key establishment protocol combined with a sequence number-based
one-pass protocol for network authentication derived from the ISO standard ISO/IEC 9798-4
Distribution of authentication data from HE to SN
Upon receipt of a request from the VLR/SGSN, the HE/AuC sends an ordered array of n authentication
vectors (the equivalent of a GSM "triplet") to the VLR/SGSN. Each authentication vector consists of
the following components: a random number RAND, an expected response XRES, a cipher key
CK, an integrity key IK and an authentication token AUTN. Each authentication vector is good
for one authentication and key agreement between the VLR/SGSN and the USIM.
Authentication and Key Agreement
When the VLR/SGSN initiates an authentication and key agreement, it selects the next
authentication vector from the array and sends the parameters RAND and AUTN to the user.
The USIM checks whether AUTN can be accepted and, if so, produces a response RES which
is sent back to the VLR/SGSN. The USIM also computes CK and IK.
The VLR/SGSN compares the received RES with XRES. If they match the VLR/SGSN
considers the authentication and key agreement exchange to be successfully completed.
The established keys CK and IK will then be transferred by the USIM and the VLR/SGSN
to the entities which perform ciphering and integrity functions.
3-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Authentication and Key Agreement Version 1 Rev 0
Authentication and Key Agreement
MS SN/VLR HE/HLR
Authentication request
Distribution Generate
authentication vectors vectors AV (1 . . . n)
from HE to SN Authentication data respons e
AV (1 . . . n)
Store authentication vectors
Select authentication vectors
User authentication request
RAND(i) || U
A TN(i)
Verify AUTN(i)
compute User authentication Authentication Key
RES(i)
Compare RES(i) and XRES(i)
Compute CK(i) and IK(i) Select CK(i) and IK(i)
© 2005-2006 CP13: Introduction to UMTS USR6 3-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Ciphering Algorithms
Ciphering Algorithms
The ciphering algorithms used in UMTS are shown on the slide opposite. As can be seen a
lot of different algorithms are active in the UMTS system. Algorithms f1 to f5 are of the type
that are used to compute numbers for use in authentication procedures.
Two very important algorithms, f8 and f9 are also shown, they have the following functions.
F8
This algorithm will perform the ciphering function. The ciphering function is performed either in
the RLC sub-layer or in the MAC sub-layer according to the following rules:
• If a radio bearer is using a non-transparent RLC mode (AM or UM), ciphering
is performed in the RLC sub-layer.
• If a radio bearer is using the transparent RLC mode, ciphering is performed
in the MAC sub-layer (MAC-d entity).
Ciphering when applied is performed in the S-RNC and the ME and the context needed for
ciphering (CK, Count-C, etc.) is only known in S-RNC and the ME.
F9
Most of the control signalling information elements that are sent between the MS and the network
are considered sensitive and must be integrity protected. Therefore a message authentication
function has been developed to solve this problem. The MS will still go through the initial
RRC connection establishment sequence and perform the set-up security functions. After this
however some signalling messages will be encoded using the f9 algorithm. This will be the
case for all RRC, MM, CC, GMM and SM Messages. The MM procedure in the MS will be
the process responsible for starting the integrity protection procedure.
AK Anonymity Key
AKA Authentication and key agreement
AUTN Authentication Token
MAC The message authentication code included in AUTN, computed using f1
XRES Expected Response
3-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Ciphering Algorithms Version 1 Rev 0
Ciphering Algorithms
· F1 - Message authentication function used to compute MAC
· F1* - Message authentication function used to compute MAC-S
· F2 - Message authentication function used to compute RES and XRES
· F3 - Key generating function used to compute CK
· F4 - Key generating function used to compute IK
· F5 - Key generating function used to compute AK in normal procedures
· F5* - Key generating function used to compute AK in re-synchronisation procedures
· K-Long-term secret key shared between the USIM and the AuC
· F8 - Data transfer between the UE and RNC
· F9 - Signalling elements between the UE and RNC
© 2005-2006 CP13: Introduction to UMTS USR6 3-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Generation of Authentication Vectors/Tokens
Generation of Authentication Vectors/Tokens
Upon the receipt of the authentication data request from the VLR/SGSN, the HE may have
pre-computed the required number of authentication vectors and retrieve them from the HLR
database or may compute them on demand. The HE/AuC sends an authentication response back to
the VLR/SGSN that contains an ordered array of n authentication vectors AV(1..n). The diagram
opposite shows the generation of an authentication vector AV by the HE/AuC.
SQN and RAND
The HE/AuC starts with generating a fresh sequence number SQN and an unpredictable
challenge RAND. SQNs are unique to each user (the HE/AuC keeps a counter: SQNHe
for each user) and are generated in batches, with a "time stamp" derived from a clock
giving universal time. RAND is a randomly generated number.
Authentication Key Management Field
An authentication and key management field AMF is used as a third input variable to the algorithms and
is also included in the authentication token of each authentication vector. AMF may be used by the
operator to "switch" functions in the USIM (e.g to indicate the algorithm and key used to generate a
particular authentication vector, or set the number of entries in a Sequence list (the list size)
Algorithms f1 -f5
Subsequently the following values are computed using the various algorithms (f1 - f5):
A message authentication code MAC = f1K(SQN || RAND || AMF) where f1 is
a message authentication function.
An expected response XRES = f2K (RAND) where f2 is a (possibly truncated)
message authentication function.
A cipher key CK = f3K (RAND) where f3 is a key generating function.
An integrity key IK = f4K (RAND) where f4 is a key generating function.
An anonymity key AK = f5K (RAND) where f5 is a key generating function.
AUTN and AV
Finally the authentication token (AUTN = SQN ⊕ AK || AMF || MAC) and the authentication Vector
(AV:=RAND||XRES||CK||IK||MAC) are constructed from the products of the algorithms.
Here, AK is an anonymity key used to conceal the sequence number as the latter may expose
the identity and location of the user. The concealment of the sequence number is to protect
against passive attacks only. If no concealment is needed then f5 ≡ 0 (AK = 0).
3-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Generation of Authentication Vectors/Tokens Version 1 Rev 0
Generation of Authentication Vectors/Tokens
Generate SQN
Generate RAND
SQN RAND
AMF
K
f1 f2 f3 f4 f5
MAC XRES CK IK AK
AUTN := SQN ⊕ AK || AMF || MAC
AV := RAND || XRES || CK || IK || AUTN
© 2005-2006 CP13: Introduction to UMTS USR6 3-21
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 USIM Authentication Function
USIM Authentication Function
The VLR/SGSN invokes the procedure by selecting the next unused authentication vector
from the ordered array of authentication vectors in the VLR/SGSN database. The VLR/SGSN
sends to the USIM the random challenge RAND and an Authentication Token AUTN for
network authentication from the selected authentication vector.
Upon receipt the user proceeds as shown in the diagram opposite.
Retrieval of SQN
Upon receipt of RAND and AUTN the USIM first computes the anonymity key AK = f5K (RAND)
and retrieves the sequence number SQN = (SQN ⊕ AK) ⊕ AK.
Computation of X-MAC
Next the USIM computes XMAC = f1K (SQN || RAND || AMF) and compares this with MAC which is
included in AUTN. If they are different, the user sends user authentication reject back to the VLR/SGSN
with an indication of the cause and the user abandons the procedure. In this case, VLR/SGSN
shall initiate an Authentication Failure Report procedure towards the HLR. VLR/SGSN may also
decide to initiate a new identification and authentication procedure towards the user.
Verification of SQN
Next the USIM verifies that the received sequence number SQN is in the correct range.
If the USIM considers the sequence number to be not in the correct range, it sends synchronisation
failure back to the VLR/SGSN including an appropriate parameter, and abandons the procedure.
If the sequence number is considered to be in the correct range however, the USIM computes RES =
f2K (RAND) and includes this parameter in a user authentication response back to the VLR/SGSN.
Computation of CK and IK
Finally the USIM computes the cipher key CK = f3K (RAND) and the integrity key IK = f4K (RAND).
USIM shall store original CK, IK until the next successful execution of AKA.
User Authentication Response
Upon receipt of user authentication response the VLR/SGSN compares RES with the expected
response XRES from the selected authentication vector. If XRES equals RES then the
authentication of the user has passed. The VLR/SGSN also selects the appropriate cipher
key CK and integrity key IK from the selected authentication vector.
If XRES and RES are different, VLR/SGSN shall initiate an Authentication Failure Report
procedure towards the. VLR/SGSN may also decide to initiate a new identification
and authentication procedure towards the user.
3-22 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
USIM Authentication Function Version 1 Rev 0
USIM Authentication Function
RAND AUTN
f5 SQN AK AMF MAC
AK
SQN
K
(USIM)
f1 f2 f3 f4
XMAC RES CK IK
Verify MAC = XMAC
Verify that SQN is in the correct range
© 2005-2006 CP13: Introduction to UMTS USR6 3-23
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Access Link Data Integrity
Access Link Data Integrity
Most control signalling information elements that are sent between the UEand the network are
considered sensitive and must be integrity protected. A message authentication function shall be
applied on these signalling information elements transmitted between the UE and the RNC.
Data integrity protection method
The diagram opposite illustrates the use of the integrity algorithm f9 to authenticate the data
integrity of a signalling message. Based on the input parameters the user computes message
authentication code for data integrity MAC-I using the integrity algorithm f9. The MAC-I is then
appended to the message when sent over the radio access link. The receiver computes XMAC-I
on the message received in the same way as the sender computed MAC-I on the message sent
and verifies the data integrity of the message by comparing it to the received MAC-I.
Input parameters to the integrity algorithm
COUNT-I
The integrity sequence number COUNT-I is 32 bits long. There is one COUNT-I value per logical
signalling channel. COUNT-I is derived from a count of the number of RRC SDUs send/received.
IK
The integrity key IK is 128 bits long. There may be one IK for CS connections (IKCS)
and one IK for PS connections (IKPS). IK is established during UMTS AKA as the
output of the integrity key derivation function f4.
FRESH
The network-side generated FRESH message is 32 bits long. There is one FRESH parameter
value per user. The input parameter FRESH protects the network against replay of signalling
messages by the user. At connection set-up the RNC generates a random value FRESH and
sends it to the user in the (RRC) security mode command. The value FRESH is subsequently
used by both the network and the user throughout the duration of a single connection. This
mechanism assures the network that the user is not replaying any old MAC-Is.
DIRECTION
The direction identifier DIRECTION is 1 bit long. The direction identifier is input to avoid the
use of identical set of input parameter values up-link and down-link messages. The value of the
DIRECTION is 0 for messages from UE to RNC and 1 for messages from RNC to UE.
MESSAGE
The signalling message itself with the radio bearer identity. The latter is appended in front
of the message. Note that the radio bearer identity is not transmitted with the message
but it is needed to avoid the circumstance where for different instances of message
authentication codes the same set of input parameters is used.
3-24 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Access Link Data Integrity Version 1 Rev 0
Access Link Data Integrity
COUNT-I DIRECT
ION COUNT-I DIREC
TION
MESSAGE FRESH MESSAGE FRESH
IK f9 IK f9
MAC-I XMAC-I
Sender Receiver
UE or RNC RNCor UE
© 2005-2006 CP13: Introduction to UMTS USR6 3-25
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Ciphering of User/Signalling Data
Ciphering of User/Signalling Data
User data and some signalling information elements are considered sensitive and must be confidentiality
protected. To ensure identity confidentiality the temporary user identity (P-)TMSI must be transferred in
a protected mode at allocation time and at other times when the signalling procedures permit it.
These needs for a protected mode of transmission are fulfilled by a confidentiality function
which is applied on dedicated channels between the UE and the RNC.
The diagram opposite illustrates the use of the ciphering algorithm f8 to encrypt plaintext by
applying a keystream using a bit per bit binary addition of the plaintext and the ciphertext.
The plaintext may be recovered by generating the same keystream using the same input
parameters and applying a bit per bit binary addition with the ciphertext.
Input parameters to the cipher algorithm
COUNT-C
The integrity sequence number COUNT-C is 32 bits long. There is one COUNT-C value per logical
signalling channel. COUNT-C is derived from a count of the number of RLC/MAC SDUs send/received.
CK
The Cipher key CK is 128 bits long. There may be one CK for CS connections (CKCS)
and one CK for PS connections (CKPS). CK is established during UMTS AKA as the
output of the integrity key derivation function f3.
BEARER
The radio bearer identifier BEARER is 5 bits long.
There is one BEARER parameter per radio bearer associated with the same user and multiplexed
on a single 10ms physical layer frame. The radio bearer identifier is input to avoid the condition
where for different keystream an identical set of input parameter values is used.
DIRECTION
The direction identifier DIRECTION is 1 bit long. The direction identifier is input to avoid the
use of identical set of input parameter values up-link and down-link messages. The value of the
DIRECTION is 0 for messages from UE to RNC and 1 for messages from RNC to UE.
LENGTH
The length indicator LENGTH is 16 bits long. The length indicator determines the
length of the required keystream block. LENGTH shall affect only the length of the
KEYSTREAM BLOCK, not the actual bits in it.
3-26 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Ciphering of User/Signalling Data Version 1 Rev 0
Ciphering of User/Signalling Data
COUNT-C DIRECTION COUNT-C DIRECTION
BEARER LENGTH BEARER LENGTH
CK f8 CK f8
KEYSTREAM KEYSTREAM
BLOCK BLOCK
PLAINTEXT CYPHERTE
XT
BLOCK BLOCK
Sender Receiver
UE or RNC RNCor UE
© 2005-2006 CP13: Introduction to UMTS USR6 3-27
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Ciphering of User/Signalling Data
This page intentionally left blank.
3-28 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
W-CDMA Theory Version 1 Rev 0
Chapter 4
W-CDMA Theory
© 2005-2006 CP13: Introduction to UMTS USR6 4-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 W-CDMA Theory
This page intentionally left blank.
4-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
On completion of this chapter the student should be able to:
• Describe various options for multiple access schemes.
• State the Characteristics of UMTS W-CDMA.
• State why W-CDMA has been chosen for the UMTS multiple access scheme.
• Describe W-CDMA spreading and despreading procedures.
• Describe the use of orthagonal codes and the channelisation code tree.
• Describe the scrambling and summation process.
• Describe the effects of multi-path radio channels and the purpose of the RAKE receiver.
© 2005-2006 CP13: Introduction to UMTS USR6 4-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Multiple Access Schemes
Multiple Access Schemes
There are 3 forms of multiple access schemes, frequency, time and code. The major issue
with the first two is the requirement to have guard bands.
Frequency Division Multiple Access (FDMA)
FDMA divides radio channels into a range of radio frequencies and is used in the traditional analogue
system. With FDMA, only one subscriber is assigned to a channel at one time. Other subscribers
cannot access this channel until the original call is terminated or handed off to a different channel.
Time Division Multiple Access (TDMA)
TDMA is a common multiple access technique employed in digital cellular systems. It divides
radio channels into time slots to obtain higher capacity. As with FDMA, no other conversations
can access an occupied channel until that channel is vacated.
Code Division Multiple Access (CDMA)
CDMA assigns each subscriber a unique code to put multiple users on the same channel
at the same time. CDMA users can share the same frequency channel because their
conversations are distinguished only by digital code.
4-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Multiple Access Schemes Version 1 Rev 0
Multiple Access Schemes
Power Time
FDMA
Power Frequency
Time
TDMA
Frequency
Codes Time
CDMA
Frequency
© 2005-2006 CP13: Introduction to UMTS USR6 4-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 W-CDMA Characteristics
W-CDMA Characteristics
The vital statistics for our W-CDMA UMTS system is shown opposite. Don’t be confused
by the slots and frames, this is not a TDMA system, every user does share the same band.
The frames and slots are used for interleaving, power control.
The major points are:
FDD requires paired frequencies for up and down channels.
The chip rate of 3.84 Mcps provides a bandwidth of 5 MHz. A chip is the original
signal split or chipped by the spreading code.
The carrier spacing of 200 kHz is used to allow re-farming of GSM frequencies
which have been set at 200 kHz spacing.
The frame length is set at 10 ms. Each frame is split into 15 timeslots, each timeslot
contains user data, power control and signalling data.
The UMTS system does not require synchronisation due to the framing structure and
use of matched filters for the framing alignment.
The spreading factor is the ratio between the user data and the chip rate. As the user
data increases this factor will vary between 4 and 512. The spreading factor is a rough
indication of the number of users in the system.
The user data rates available in the FDD system is up to 384 Kbps.
4-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
W-CDMA Characteristics Version 1 Rev 0
W-CDMA Characteristics
Multiple Access Scheme CDMA
Duplexing Method FDD
Chip Rate 3.84 Mcps
Bandwidth 5 MHz
Carrier Spacing 200 kHz Raster
Frame Length 10 ms
Slots per Frame 15
Inter-cell Synchronization None
Spreading Factor Variable (4-512)
User Data Rate 3-384 Kbps
© 2005-2006 CP13: Introduction to UMTS USR6 4-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Re-Use of Frequency
Re-Use of Frequency
Mobile telephones and cell broadcast networks use cellular radio, a technique developed in
recent years to enable the use of mobile telephones. It would be impossible to provide each
phone with an individual radio frequency, so the idea of cellular radio evolved.
A region is divided into geographical areas called cells, varying in size depending on the number of
users in the area. In cities cells are small whereas in rural areas cells are much larger.
In GSM cells use a set of frequencies that are different from any neighbouring cell, but can
be the same as another cell as long as it is far enough away.
For UMTS, a frequency re-use of one, may be employed. This means that all cells within a given
geographical area, or even an entire network may use the same carrier frequency.
An alternate method of discriminating between neighbouring cells must therefore be found.
4-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Re-Use of Frequency Version 1 Rev 0
Re-Use of Frequency
2 5
4 7
2
1 6 4
6
5 3 1
7 2 5 3
4 7 2 5
6 4 7 2
1
3 1 6 4
5 3 1 6
7 2 5 33
4 7 2
1 6 4
3 1
© 2005-2006 CP13: Introduction to UMTS USR6 4-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Re-Use of Codes
Re-Use of Codes
Codes are used to uniquely identify a cell in the network. Frequency planning is more or less a thing of the
past but code planning will have to be implemented. Code planning will be much easier then frequency
planning since we have 512 Codes to play with, the code re-use pattern will thus be extremely large.
Codes can be reused when the separation between cells containing the same channel set is far
enough apart so that co-channel interference can be kept below acceptable levels. The number of
cells in a cluster is 512, which provides greater separation between co-channel cells than GSM.
4-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Re-Use of Codes Version 1 Rev 0
Re-Use of Codes
1 10
5 2 11
7 4 4
30 6 17 19
31 28 15 12
29 7 16 18
1 27 4 22 20
26 14 6 21
25 13 23 39
32 2 5 38
34 33 24
36 37 40
35 41
© 2005-2006 CP13: Introduction to UMTS USR6 4-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Spectral Efficiency (GSM and UMTS)
Spectral Efficiency (GSM and UMTS)
The Slide opposite shows how spectrally efficient UMTS and GSM is in comparison to
each other when employed in a multi-cellular structure.
The capacity, which Shannon derived in 1947, provided a Law, which we now call Shannons Law.
This details the digital capacity of the link given the transmit power and the bandwidth.
If we are using, FDMA, TDMA or CDMA, the capacity is still controlled by this law. However,
some gains are made by technology and coding methods.
4-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Spectral Efficiency (GSM and UMTS) Version 1 Rev 0
Spectral Efficiency (GSM and UMTS)
GSM UMTS
8 Calls = 200 kHz Carrier 256 Calls = 5 MHz Carrier
1 Call = 25 kHz 1 Call = 19.4 kHz
7 x 200 kHz = 1.4 MHz 7 Cells, 5 MHz
1 Call = 25 kHz 1 Call = 2.8 kHz
© 2005-2006 CP13: Introduction to UMTS USR6 4-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Direct Spread (DS)-CDMA Implementation
Direct Spread (DS)-CDMA Implementation
Transmitter
The digital modulator will take digital speech/data and multiply it with the spreading code.
The radio modulator moves the baseline signal from the digital modulator onto
a 2GHz carrier to produce the W-CDMA output.
Receiver
The modulated carrier is moved by the radio demodulator to the digital demodulator which
can be very complicated due to the large number of users.
Here the input is multiplied by the de-spreading codes to produce digital speech.
4-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Direct Spread (DS)-CDMA Implementation Version 1 Rev 0
Direct Spread (DS)-CDMA Implementation
Single User Channel Multiple User Channel Multiple User Channel Output
5 MHz 5 MHz 5 MHz 0
W-CDMA
Digital Radio Modulated Carrier
Digital Radio Digital Digital
C S
Signal Modulator Modulator Demodulator Demodulator
o p Signal
m l
b i
Spreading Radio Spreading
i t
Tx Code Carrier t
Radio Code Rx
n Carrier
Generator Generator
e e
r r
Digital Digital Radio Radio Digital Digital
Signal Modulator Modulator Demodulator Demodulator Signal
Input
External Interference
0 t0
© 2005-2006 CP13: Introduction to UMTS USR6 4-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Spreading
Spreading
The spreading operation is the multiplication of each user data bit with a "Spreading Code" , which
is a pre-defined bit pattern. To discriminate between User data "bits" and spreading code "bits", the
symbols in the spreading code are referred to as "Chips". The chip rate for UMTS is fixed at 3.84 Mcps.
After the spreading operation each "Bit" of the data signal is represented by a number of "chips".
The number of chips representing each bit is referred to as the Spreading Factor (SF) and is
given by dividing the chip rate by the source signal bit rate; in this example:
3.84
Mcs / 480 kbps = (SF=8)
The spreading operation has resulted in an increase of the "signalling rate of the user data, in this case
by a factor of 8, and corresponds to a widening of the "spectrum" occupied by the user data signal.
Due to this, CDMA systems are more generically referred to as "Spread Spectrum" systems.
The SF is also referred to as the Processing Gain (PG), which is expressed as a Decibel ratio and
describes the gain or amplitude increase that will be applied to the signal at the receiving station as a
result of the de-spreading operation. This concept is described in more detail later in this chapter
4-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Spreading Version 1 Rev 0
Spreading
Data 1
480 kB/s –1
Spreading
Code 1
3.84 Mcs –1
Spread 1
Data –1
© 2005-2006 CP13: Introduction to UMTS USR6 4-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 De-spreading
De-spreading
De-spreading is performed at the receiving station (UE or Node B) by multiplying the chip rate,
spread user data signal by a chip rate spreading code. By using the same spreading code
as used at the transmitting station for the spreading operation, the multiplication of the two
chip rate signals will reproduce the original bit rate user data signal.
To aid accurate recovery of the user data, a Correlation Receiver is employed in most CDMA
systems. The correlation receiver integrates the product of the de-spreading process on a
chip-by-chip basis. In the upper diagram opposite, the example shown illustrated that for a perfectly
received de-spread signal, the correlation receiver output has effectively "Lifted" the amplitude
of the received signal by a factor of 8, a function of the processing gain.
4-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
De-spreading Version 1 Rev 0
De-spreading
Spread 1
Data –1
Spreading 1
Code –1
Correlation
RX
Integrator
O/P
Recovered 1
Data –1
© 2005-2006 CP13: Introduction to UMTS USR6 4-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Orthogonal Codes
Orthogonal Codes
Transmissions from a single source are separated by channelisation codes. The channelisation codes
of UTRA are based upon the Orthogonal Variable Spreading Factor (OVSF) technique.
There are a finite number of OVSF codes available, and some restrictions in their use.
OVSF codes are, as their name implies, orthogonal codes. Orthogonal codes possess good
cross correlation properties allowing easy discrimination between signals produced using correctly
selected codes. For OVSF the cross correlation between codes is zero, meaning interferer
signals between different codes is effectively "zero" after correlation.
Channelisation Code Tree
For separating channels from the same source, channelisation codes called Orthogonal
Variable Spreading Factors are used.
The lines in the diagram represent codes, these are Orthogonal Variable Spreading Factor (OVSF)
codes, allowing to mix in the same timeslot channels with different spreading factors while preserving
the orthogonality. The OVSF codes can be defined using the code tree shown opposite.
Each level in the code tree defines a Spreading Factor (SF) indicated in the figure. All codes within
the code tree cannot be used simultaneously in a given timeslot. A code can be used in a timeslot
if and only no other code on the path from the specific code to the root of the tree or in the sub-tree
opposite the specific code is used in this timeslot. This means that the number of available codes in a
slot is not fixed but depends on the rate and spreading factor of each physical channel.
The spreading codes can be used to identify individual channels, but a mobile usually has to identify
the base station that it is currently parented on. A long code is usually used for that.
4-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Orthogonal Codes Version 1 Rev 0
Orthogonal Codes
Channelisation Code Tree
Cch, 8, 0
Cch, 4, 0 (1, 1, 1, 1, 1, 1, 1, 1)
(1, 1, 1,1) Cch, 8,1
Cch, 2, 0
(1, 1, 1, 1, -1, -1, -1, -1)
(1, 1) Cch, 8,2
Cch, 4, 1 (1, 1, -1, -1, 1, 1, -1, -1)
(1, 1, -1, -1) Cch, 8,3
Cch, 1, 0
(1, 1, -1, -1,- 1, -1, 1, 1)
(1) Cch, 8,4
Cch, 4, 2 (1, -1, 1,- 1, 1,-1, 1, -1)
Cch, 8,5
(1, -1, 1, -1)
Cch, 2, 1 (1, -1, 1, -1, -1, 1, -1, 1)
(1, -1) Cch, 8,6
Cch, 4, 3 (1, -1, -1, 1, 1, -1, -1, 1)
(1, -1, -1, 1) Cch, 8,7
(1, -1, -1, 1, -1, 1, 1, -1)
SF = 1 SF = 2 SF = 4 SF= 8
© 2005-2006 CP13: Introduction to UMTS USR6 4-21
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 De-spreading Other Users Signals
De-spreading Other Users Signals
It must be remembered that in a CDMA system, all users are potentially transmitting
on the same frequency. This means that at any given receiver station, in addition to
the desired signal, multiple interferer signals will also be received. It is the task of the
correlation receiver to reject these interferer signals.
The diagram opposite shows the effect of de-spreading and correlation at a given receiving
station (e.g UE "A"), on an interferer signal, (e.g a signal transmitted on the same carrier for
reception by UE "B"). The de-spreading/correlation of the interferer signal will result in a cross
correlation of zero (i.e. the output of the integration process will be zero). This process is only
true when correctly selected orthogonal spreading codes are employed.
4-22 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
De-spreading Other Users Signals Version 1 Rev 0
De-spreading Other Users Signals
Data for UE B 1
-1
Spreading Code 1
for UE B -1
Spread Data 1
for UE B -1
Spread Code 1
for UE A -1
Correlation RX
Integrator O/P
at UE A
Recovered Data 1
at UE A -1
© 2005-2006 CP13: Introduction to UMTS USR6 4-23
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Processing Gain
Processing Gain
Processing Gain can be defined as the Chip Rate divided by the bit rate. This gives a ratio
that can be converted to decibels by using the following formula.
PG = 10 x log SF
The gain that we get from the Processing Gain is an extremely important part of CDMA. It is in fact
because of this relationship that CDMA is so effective and is used even in space transmissions.
Processing gain will determine how much the received signal can be lifted out of the noise floor.
There is one simple rule to follow, the higher the SF the higher the processing gain will be, the
lower the SF the lower the processing gain. As we know, the SF is also inversely proportional to
the speed of the transmission. This means that the higher the speed of transmission the lower
the processing gain will be. Due to this relationship the power output must be increased for any
transmitter if the transmission rate is increased due to the loss in Processing Gain.
This will also mean that if the Frame Erasure Rate (FER) is increased on the
receiver side the power must be increased or the transmission rate must drop on
the transmitter side to meet the FER requirement.
4-24 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Processing Gain Version 1 Rev 0
Processing Gain
PG = 10 x log (Chip Rate/Bit Rate)
or
PG = 10 x log (SF)
© 2005-2006 CP13: Introduction to UMTS USR6 4-25
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Exercise 1 - Spreading
Exercise 1 - Spreading
This Exercise demonstrates the Modulo-2 Addition, Spreading Factor usage, Code Lengths
and in general will give the student a feel for the Spreading Principle.
NOTES
____________________________________________________________________________________________
____________________________________________________________________________________________
____________________________________________________________________________________________
4-26 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Exercise 1 - Spreading Version 1 Rev 0
Exercise 1 - Spreading
Spreading
Data 1
-1
Spreading Code 1
-1
Spread Data 1
-1
De-spreading
Spreading Code 1
-1
De-spread Data 1
-1
Calculation Box
SF = 4 S/N = 5dB
PG = 4 (ratio) C/I = 5 dB - 6 dB
PG = 6 dB = -1 dB
© 2005-2006 CP13: Introduction to UMTS USR6 4-27
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Exercise 2 - Spreading/Despreading
Exercise 2 - Spreading/Despreading
To gain some experience in Spreading the student can complete the following exercise.
The student can complete the despreading part of the exercise and then calculate the
SF and PG. See if it matches with the answers provided.
Note the irregular structure in the answer.
NOTES
____________________________________________________________________________________________
____________________________________________________________________________________________
____________________________________________________________________________________________
4-28 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Exercise 2 - Spreading/Despreading Version 1 Rev 0
Exercise 2 - Spreading/Despreading
Spreading
Data 1
-1
Spreading Code 1
-1
Spread Data 1
-1
De-spreading
Spreading Code 1
-1
De-spread Data 1
-1
Wrong 1
Spreading Code -1
De-spread Data 1
Wrong Code -1
Calculation Box
SF = 4 S/N = 5dB
PG = 4 (ratio) C/I = 5 dB - 6 dB
PG = 6 dB = -1 dB
© 2005-2006 CP13: Introduction to UMTS USR6 4-29
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Exercise 3 - Spreading/Despreading
Exercise 3 - Spreading/Despreading
In this exercise the student must complete the following:
1. Determine the SF used?
2. Do the spreading part of the exercise?
3. Do the despreading part of the exercise using the right code?
4. Do the despreading part of the exercise using the wrong code?
5. Complete the calculation?
NOTES
____________________________________________________________________________________________
____________________________________________________________________________________________
____________________________________________________________________________________________
4-30 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Exercise 3 - Spreading/Despreading Version 1 Rev 0
Exercise 3 - Spreading/Despreading
Spreading
Data 1
-1
Spreading Code 1
-1
Spread Data 1
-1
De-spreading
Spreading Code 1
-1
De-spread Data 1
-1
Wrong 1
Spreading Code -1
De-spread Data 1
Wrong Code -1
Calculation Box
SF = S/N = 5dB
PG = C/I =
PG = = -1 dB
© 2005-2006 CP13: Introduction to UMTS USR6 4-31
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Scrambling
Scrambling
As previously described, OVSF spreading codes can be used to separate individual users on a
common RF carrier freq. However, because of the need to maintain orthogonality of codes, the number
of codes available is very limited (512 Downlink, 256 Uplink). These 512 code must be reused in every
cell, as such they do not become unique to a cell and users located at the boundaries of cells, would
receive transmissions using the same OVSF code, from more than one cell. For UMTS therefore,
OVSF codes are used only as channelisation codes, used identify individual physical channels. A
further coding, process, known as a "Scrambling" is performed, in order to discriminate between
the transmissions between different cells on the downlink and different UEs on the uplink.
Each physical channel is first individually spread to chip rate using a channelisation code (Cch sf,k) taken
from the OVSF code tree, resulting in an increase in bandwidth of the signal form "Bit Rate" to "Chip Rate"
The Sequence of chips produced by the channelisation process is then "Scrambled", using
a chip-to-chip multiplication with a complex-valued scrambling code (Csc). The code
chosen is used to identify the source of the signal. As scrambling is performed on top of
spreading, it has no further effect on the bandwidth of the signal.
Although the primary purpose of using a scrambling code is to identify all channels from a single
source, that single source may use more than scrambling code. For example, in the downlink, a cell
may transmit using one of 16 possible scrambling codes. After scrambling, all physical channels are
then combined, using complex addition, before being forwarded to the RF Modulator for transmission.
4-32 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Scrambling Version 1 Rev 0
Scrambling
Channel x
Data
Cch SF,x Csc,x
Channel y
Data
Σ
Cch SF,x Csc, x
Channel z
Data
Cch SF,x Csc,x
© 2005-2006 CP13: Introduction to UMTS USR6 4-33
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Scrambling Codes vs Channelisaton Codes
Scrambling Codes vs Channelisaton Codes
The Slide shows the major differences between Scrambling Codes (SC) and Channelisation Codes (CC).
4-34 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Scrambling Codes vs Channelisaton Codes Version 1 Rev 0
Scrambling Codes vs Channelisaton Codes
CC SC
Separation of Data & Control Channels
Usage Uplink Separation of UEs
(from the same UE)
Usage Downlink Separation of channels to different UEs Separation of Cells
LC - 10ms=38400 Chips or
Length Uplink 4 - 256 Chips
SC = 66.7us = 256 Chips
Length Downlink 4 - 512 Chips LC =38400 Chips
24
Number of Codes Uplink = 2 – 1 = 16,777,215
512 Uplink and Downlink 18
available Downlink = 2 – 1 = 262,143
(truncated to 8,192)
LC=10ms = Gold Code
Code Family OVSF
SC = Extended S2 Family
Spreading Increases Tx Bandwidth No effect on Bandwidth
© 2005-2006 CP13: Introduction to UMTS USR6 4-35
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Scrambling and Summation
Scrambling and Summation
The diagram opposite illustrates the process of scrambling and summation of multiple channels,
prior to modulation onto the RF carrier and transmission over the UMTS air interface (Uu).
For the purposes of this example, three separate data streams (Channels X, Y and Z),
each carrying a user bit sequence of "1,0,0,1", have been spread using channelisation
codes of Cch 8,1 , Cch 8,2 and Cch 8,3 respectively.
The spread signals are then independently scrambled using a single scrambling code. The
resultant chip sequences are then combined using complex addition, to produce the multi level
digital baseband signal, that will be used to modulate the RF carrier.
4-36 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Scrambling and Summation Version 1 Rev 0
Scrambling and Summation
Spread Data 1
Channel X Cch 8,1 -1
Spread Data 1
Channel Y Cch 8,2 -1
Spread Data 1
Channel Z Cch 8,3 -1
Scrambling 1
code -1
Channel X after 1
scrambling -1
Channel Y after 1
scrambling -1
Channel Z after 1
scrambling -1
+3
Complex added +2
scrambled codes +1
-1
-2
-3
© 2005-2006 CP13: Introduction to UMTS USR6 4-37
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 De-Scrambling and Data Recovery
De-Scrambling and Data Recovery
The diagram opposite illustrates the processes of de-scrambling of a complex scrambled
signal and the recovery of user data from one channel.
The input signal, (derived from the example on the preceding page) is first de-scrambled
by multiplication with the specified scrambling code. The result is a combined version of
all received channels, represented by a complex chip sequence.
The dispreading process must now be performed to recover the user data. The example
illustrates the recovery of the data for Channel "X" from the preceding page. By performing
a direct multiplication of the complex signal with the appropriate channelisation code, the
illustrated correlation receiver output will be obtained. As can be seen, the integrated output
indicates bit values of “1,0,0,1", the expected result for this example.
4-38 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
De-Scrambling and Data Recovery Version 1 Rev 0
De-Scrambling and Data Recovery
+3
+2
Received +1
Scrambled -1
-2
-3
Scrambling 1
Code -1
+3
+2
De-scrambled +1
Signal -1
-2
-3
Chan Code for
Chan Y (Cch8,2)
Correlation
Output
© 2005-2006 CP13: Introduction to UMTS USR6 4-39
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Multi-path Radio Channels
Multi-path Radio Channels
Radio propagation for mobile communications suffers greatly from the effects of mulipath reflections,
diffractions and attenuation of the signal energy. These effects are causes by objects such as buildings,
hills, etc, resulting in "Multipath Propagation", which has two main effects upon the signal.
Inter-symbol Interference
Inter-symbol interference occurs when the signal energy from more than one radio path, pertaining to a
single symbol (or chip in the case of W-CDMA), such that the energy from the various paths overlaps.
This results in the smearing of the signal, such that is hard to define where one chip starts and one chip
ends and the true value of the chips may be distorted. This problem can be resolved, providing the delay
between the two paths is greater than one chip period (0.26µs at 3.84 Mcs). This equates to a path
length difference of 78 m). Delays of 1 or 2 µs are typical in urban areas, with 20µs possible in hilly areas.
Signal Fade
In multi-path situations where path lengths are multiples of half a wavelength of the received frequency
(7cm at 2GHz), the signals on two (or more) paths will arrive in anti-phase to each other. This results
in cancellation of the signals, causing fast or Rayleigh fading. Such fading can result in signal level
drops in the order of 20 to 30dB, making the reception of error free data bits very difficult.
4-40 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Multi-path Radio Channels Version 1 Rev 0
Multi-path Radio Channels
© 2005-2006 CP13: Introduction to UMTS USR6 4-41
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Matched Filter Operation
Matched Filter Operation
The main task of the matched filter is to determine the timing reference of the
information as it arrives at the receiver.
The filter will perform a chip-by-chip comparison of the received signal against a known
"Pilot" reference, to identify multiple copies of the same chip pattern.
After several iterations of the multiple paths have been accumulated, the time dispersion between
the two paths can be calculated and tracked, allowing the paths to be separated.
4-42 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Matched Filter Operation Version 1 Rev 0
Matched Filter Operation
RF
Front End Matched Slot Wise
Circuitry Filter Accumulation
© 2005-2006 CP13: Introduction to UMTS USR6 4-43
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 The Rake Receiver
The Rake Receiver
The Rake receiver performs a similar (but not identical) function to the equaliser in GSM.
Instead of training bits, the pilot signals (all zeros) are used as a basis for the search for the
best path. The rake receiver then constructs its fingers to track the other multi-path rays by
stepping through delays one chip at a time until it finds another, lower level pilot. It can then
use the weightings to bring the rays into phase and constructive addition. Note that the different
rays are uncorrelated if the delay difference is greater than one chip.
The effect of the propagation environment on spread spectrum modulated signals is to produce
a series of signal components that have traversed differing paths. This is known as multipath
interference and, depending on whether or not there is a significant specula multipath component,
the envelope of the multipath signal may be Rician or Rayleigh distributed.
Multipath results in two signal perturbations, known as Inter-Symbol Interference (ISI) and fading.
Both introduce severe degradation in the system performance. ISI creates signal components that
are delayed into the next signal period, making these signals overlap and therefore interfere with
one another. Fading is caused by signals of opposite phase cancelling in the receiver. To combat
this, a RAKE receiver may be used. This is the type of receiver shown in the figure and contains
many signal paths, each with an individual delay. These delays are changed so that the total delay
from the transmitter for all paths is the same and thus when combined they are in-phase.
4-44 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
The Rake Receiver Version 1 Rev 0
The Rake Receiver
D0
t1 Cch sf,k
D1
t2
Cch sf,k
D2
t3
Cch sf,k
D3
Cch sf,k
© 2005-2006 CP13: Introduction to UMTS USR6 4-45
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 The Rake Receiver
This page intentionally left blank.
4-46 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
The Physical Layer Version 1 Rev 0
Chapter 5
The Physical Layer
© 2005-2006 CP13: Introduction to UMTS USR6 5-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 The Physical Layer
This page intentionally left blank.
5-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
On completion of this chapter the student should be able to:
• Describe the procedures performed by the Air Interface Physical Layer
• Describe the UMTS Channel Structure.
◦ Logical Channels
◦ Transport Channels
◦ Physical Channels
• Describe the Downlink and Uplink Flow Processes.
© 2005-2006 CP13: Introduction to UMTS USR6 5-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Physical Layer Services
Physical Layer Services
The Physical Layer (L1) will be the main discussion in this section since this is
where most of the air interface tasks are performed.
The physical layer offers data transport services to higher layers. The access to these services
is through the use of transport channels via the MAC sub-layer. The physical layer is expected
to perform the following functions in order to provide the data transport service.
• Macrodiversity distribution, combining and soft handover execution.
• Error detection on transport channels and indication to higher layers.
• FEC encoding/decoding of transport channels.
• Multiplexing of transport channels and demultiplexing of coded composite
transport channels (CCTrCHs).
• Rate matching of coded transport channels to physical channels.
• Mapping of coded composite transport channels on physical channels.
• Power weighting and combining of physical channels.
• Modulation and spreading/demodulation and despreading of physical channels.
• Frequency and time (chip, bit, slot, frame) synchronisation.
• Radio characteristics measurements including FER, SIR, Interference Power,
etc., and indication to higher layers.
• Inner - loop power control.
• RF processing.
When network elements (UEs and network) provide compatible service bearers (for example
support a speech bearer) they should be assured of successful interworking. Moreover,
different implementation options of the same (optional) feature would lead to incompatibility
between UE and network. Therefore, this shall be avoided.
5-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Physical Layer Services Version 1 Rev 0
Physical Layer Services
Macrodiversity distribution, combining and soft handover execution.
Error detection on transport channels.
FEC encoding & decoding of transport channels.
Mux & Demux of transport channels and CCTrCHs.
Rate matching of coded transport channels to physical channels.
Mapping of coded composite transport channels on physical channels.
Power weighting and combining of physical channels.
Modulation demodulation and spreading of physical channels.
Frequency and time synchronisation.
Radio characteristics measurements.
Inner - loop power control.
RF processing.
© 2005-2006 CP13: Introduction to UMTS USR6 5-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 QPSK
QPSK
The modulation scheme used in W-CDMA is quadrature phase shift keying (PSK) which
allows 2 bits to be sent per symbol (I and Q). The reason for using QPSK is that it is
fairly resilient to amplitude variations. The major problem with CDMA is that all users are
on the same frequency and thus interfering with each other.
5-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
QPSK Version 1 Rev 0
QPSK
QPSK
Q
(0,1) (0,0)
(1,1) (1,0)
2 bits per symbol
© 2005-2006 CP13: Introduction to UMTS USR6 5-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Structure of Transmission
Structure of Transmission
The physical layer receives information, on a transport channel, as Transport Blocks (or Transport
Block sets) from Layer 2. This information will consist of User Plane or Control Plane streams.
In addition the physical layer will generate Layer 1 control information, used to maintain the radio
bearer between the UE and the UTRAN. This layer 1 control information must be transmitted
on the physical channel along with the transport channel information.
As previously discussed, even when FDD mode is in use, a radio frame/timeslot structure is
observed. (A 10 ms radio frame is divided into 15 timeslots). Though it is important to note
that any given radio bearer is able to use all timeslots in every radio frame.
Downlink Transmission
On the downlink each timeslot will contain transport channel information and Layer 1 control
information in time-multiplex. Each timeslot will contain fields supporting transport block information,
interspersed with Layer 1 control fields. The exact structure of the fields is dependent upon the
type of physical channel in use, and is described in detail later in this chapter.
Uplink Transmission
On the Uplink a time-multiplex structure is not practical as Discontinuous Transmission (DTX)
is frequently employed. The combination of DTX and Time-multiplex would result in a "Bursty"
transmission, which would generate audio band noise perceptible to the other party in a voice call.
To overcome this problem, the transport channel information and Layer 1 control information
are I/Q code multiplexed within each timeslot, allowing them to be transmitted in parallel.
This make the transmission of Layer 1 control information continuous and hence prevents
bursty transmission, even when DTX is applied.
5-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Structure of Transmission Version 1 Rev 0
Structure of Transmission
© 2005-2006 CP13: Introduction to UMTS USR6 5-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Channel Locations
Channel Locations
The radio interface is the section of the network between the UE and the Network. This section of
the network is where the biggest limitation lies at the moment, it is the most vulnerable section and
therefore very complex methods have to be invented in order to transmit the required data at the high
speeds that is demanded of today’s networks. The radio interface is composed of Layers 1, 2 and 3.
The slide opposite shows the UTRA radio interface protocol architecture around the physical
layer (Layer 1). The physical layer interfaces with the Medium Access Control (MAC) sub-layer
of Layer 2 and the Radio Resource Control (RRC) Layer of Layer 3.
The physical layer offers different Transport channels to MAC. A transport channel is characterized
by how the information is transferred over the radio interface.
MAC offers different Logical channels to the Radio Link Control (RLC) sub-layer of Layer
2. The type of information transferred characterizes a logical channel.
Physical channels are defined in the physical layer. In FDD mode, physical channels are defined by a
specific carrier frequency, scrambling code, channelization code (optional), time start and stop (giving
duration) and, on the uplink, relative phase (0 or π/[Symbol_ps2]). In the TDD mode the physical
channels is also characterized by the timeslot. The physical layer is controlled by RRC.
5-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Channel Locations Version 1 Rev 0
Channel Locations
Layer 2 RLC
Logical Channels
Layer 2 MAC
Transport Channels
Layer 1 Physical Layer
Physical Channels
UE
© 2005-2006 CP13: Introduction to UMTS USR6 5-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Channels on the Air Interface
Channels on the Air Interface
The diagram opposite shows the most common channels used on the air interface. The
channels are divided horizontally into the Physical Channels (PCHs), the Transport Channels
(TCHs) and the Logical Channels (LCHs). Vertically they are divided into 2 channel types,
the Dedicated Channels and the Common Channels. Dedicated Channels are dedicated to
one UE only and Common Channels can be shared by multiple UEs.
5-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Channels on the Air Interface Version 1 Rev 0
Channels on the Air Interface
DCCH DTCH BCCH PCCH CCCH CTCH
Logical
Channels
PTM
CCH
DCH
Transport
BCH PCH FACH RACH Channels
PDCH PCCH
P-CCPCH S-CCPCH PICH PRACH SCH CPICH AICH
DPDCH DPCCH
Physical
Channels
P-SCH S-SCH Primary Secondary
© 2005-2006 CP13: Introduction to UMTS USR6 5-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Logical Channels
Logical Channels
The MAC layer provides data transfer services on logical channels. A set of logical channel
types is defined for different kinds of data transfer services as offered by MAC. Each logical
channel type is defined by what type of information is transferred.
A general classification of logical channels is into two groups:
• Control Channels (for the transfer of control plane information).
• Traffic Channels (for the transfer of user plane information).
Control Channels
Broadcast Control Channel (BCCH)
A downlink channel for broadcasting system control information.
Paging Control Channel (PCCH)
A downlink channel that transfers paging information. This channel is used when
the network does not know the location cell of the UE, or, the UE is in the cell
connected state (utilising UE sleep mode procedures).
Common Control Channel (CCCH)
Bi-directional channel for transmitting control information between network and UEs. This channel
is commonly used by the UEs having no RRC connection with the network and by the UEs using
common transport channels when accessing a new cell after cell reselection.
Dedicated Control Channel (DCCH)
A point-to-point bi-directional channel that transmits dedicated control information between a UE
and the network. This channel is established through RRC connection set-up procedure.
Traffic Channels
Dedicated Traffic Channel (DTCH)
A Dedicated Traffic Channel (DTCH) is a point-to-point channel, dedicated to one UE, for the
transfer of user information. A DTCH can exist in both uplink and downlink.
Common Traffic Channel (CTCH)
A point-to-multipoint unidirectional channel for transfer of dedicated user information
for all or a group of specified UEs.
5-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Logical Channels Version 1 Rev 0
Logical Channels
Between MAC and RLC
DCCH DTCH BCCH PCCH CCCH CTCH
U-RNTI PTM
© 2005-2006 CP13: Introduction to UMTS USR6 5-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Transport Channels
Transport Channels
The physical layer offers information transfer services to MAC and higher layers. The
physical layer transport services are described by how and with what characteristics data
is transferred over the radio interface. An adequate term for this is ’Transport Channel’. A
general classification of transport channels is into two groups:
• Common transport channels (where there is a need for inband identification of
the UEs when particular UEs are addressed.
• Dedicated transport channels (where the UEs are identified by the physical channel, i.e. code
and frequency for FDD and code, time slot and frequency for TDD).
Random Access Channel (RACH)
A contention based uplink channel used for transmission of relatively small amounts of data,
e.g. for initial access or non-real-time dedicated control or traffic data.
Forward Access Channel (FACH)
Common downlink channel without closed-loop power control used for transmission
of relatively small amount of data.
Broadcast Channel (BCH)
A downlink channel used for broadcast of system information into an entire cell.
Paging Channel (PCH)
A downlink channel used for broadcast of control information into an entire cell allowing efficient
UE sleep mode procedures. Currently identified information types are paging and notification.
Another use could be UTRAN notification of change of BCCH information.
Dedicated Channel (DCH)
A channel dedicated to one UE used in uplink or downlink.
5-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Transport Channels Version 1 Rev 0
Transport Channels
Between the Physical Layer and MAC
CCH
BCH PCH FACH RACH
DCH
© 2005-2006 CP13: Introduction to UMTS USR6 5-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Physical Channels
Physical Channels
Common Physical Channels (CPCHs)
P-SCH ; Primary Synchronisation Channel; Secondary Synchronisation
S-SCH Channel
Synchronisation to the network
P-CCPCH Primary Common Control Physical Channel
Cell Information and Frequency info
S-CCPCH Secondary Common Control Physical Channel
Paging Information and Transfer of small amounts of user data. Downlink
only.
PRACH Physical Random Access Channel
Initial message when UE wants to gain access to the network; Transfer of
small amounts of data; Uplink only
PICH Paging Indicator Channel
Provides UEs with efficient sleep mode operation
AICH Acquisition Indicator Channel
Acknowledges an effective request for access after preamble has been
send up
P-CPICH; Primary Common Pilot Indicator Channel; Secondary Pilot Indicator
S-CPICH Channel
Helps with channel estimation and shows the attractiveness of the cell
DPDCH/DPCCH Dedicated Physical Channels
Uplink and downlink control and data information; Dedicated to a single
user
5-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Physical Channels Version 1 Rev 0
Physical Channels
PDCH PCCH
P-CCPCH S-CCPCH PICH PRACH SCH CPICH AICH
DPDCH DPCCH
P-SCH S-SCH Primary Secondary
© 2005-2006 CP13: Introduction to UMTS USR6 5-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Channel Mapping
Channel Mapping
The diagram opposite summarises the mapping of logical channels onto transport
channels, and transport channels onto physical channels.
The DCHs are coded and multiplexed, as described later in this chapter, and the resulting data
stream is mapped sequentially (first-in-first-mapped) directly to the physical channel(s).
The mapping of BCH and FACH/PCH is equally straightforward, where the data stream after coding
and interleaving is mapped sequentially to the Primary and Secondary CCPCH respectively. Note
that the BCCH logical channel can be mapped to both BCH and FACH, so as to be available to idle
mode and connected mode UEs respectively. Also for the RACH, the coded and interleaved bits are
sequentially mapped to the physical channel, in this case the message part of the PRACH.
Physical signals
Physical signals are entities with the same basic on-air attributes as physical channels but do not
have transport channels or indicators mapped to them. Physical signals may be associated with
physical channels in order to support the function of physical channels. SCH, CPICH, and AICH
are classified as physical signals and hence are not shown on the diagram opposite.
5-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Channel Mapping Version 1 Rev 0
Channel Mapping
Uplink Downlink
DCCH DCCH
CCCH PCCH BCCH CCCH CTCH
DTCH DTCH
Common Common
Paging Dedicated
Broadcast Control Traffic
Control Control Channel
Contro Channel Channel
Channel Dedicated
Channel
Traffic Channel
RACH DCH PCH BCH FACH DCH
Primary
CCPCH
DPDCH
DPCCH
DPDCH
PRACH
DPCCH
Sec
CCPCH
© 2005-2006 CP13: Introduction to UMTS USR6 5-21
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Generic Frame Structure
Generic Frame Structure
The diagram opposite illustrates the generic frame structure, use to delimit the transfer
of units of information on the UMTS air interface.
Radio Frame
As previously outlined the basic unit of the air interface is the radio frame. A radio frame is defined as ’a
processing duration which consists of 15 timeslots’. The length of a radio frame corresponds to 38,400
chips." With a system chip rate of 3.84 Mcps being employed, a radio frame thus has a duration of 10 ms.
System Frame
Several physical layer procedures (e.g. Paging and Random Access) span more than a single
frame. To accommodate these procedures, a system frame is defined. The frame within the
system frame structure is identified by a System Frame Number (SFN), which is a 12 bit
binary number, thus a System Frame can consist of 4096 frames.
Timeslot
Each radio frame consists of 15 timeslots. A slot duration consists of fields containing bits.
The length of the slot always corresponds to 2560 chips. The time duration of a timeslot is
approximately 666 µs. The number of fields within each timeslot is dependent upon the physical
channel in use. Similarly the number of bits which can be accommodate by a timeslot is
dependent upon the spreading factor in use for that physical channel.
5-22 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Generic Frame Structure Version 1 Rev 0
Generic Frame Structure
666μs
SLOT
Time Slot = 2560 chips
FRAME
TS0 TS1 TSn TS13 TS14
SYSTEM FRAME
Frame Frame Frame Frame
1 n 4094 4095
10ms
40.96 secs
© 2005-2006 CP13: Introduction to UMTS USR6 5-23
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Synchronisation Channel (SCH)
Synchronisation Channel (SCH)
The Synchronisation Channel (SCH) is a downlink signal used for cell search. The SCH
consists of two sub channels, the Primary and Secondary SCH. The 10 ms radio frames of
the Primary and Secondary SCH are divided into 15 slots, each of length 2560 chips. The
diagram opposite illustrates the structure of the SCH radio frame.
The Primary SCH
The Primary SCH consists of a modulated code of length 256 chips, the Primary
Synchronisation Code (PSC) denoted cp in the diagram, transmitted once every slot.
The PSC is the same for every cell in the system.
The Secondary SCH
The Secondary SCH consists of repeatedly transmitting a length 15 sequence of modulated codes
of length 256 chips, the Secondary Synchronisation Codes (SSC), transmitted in parallel with
the Primary SCH. The SSC is denoted csi,k in the diagram, where i = 0, 1, …, 63 is the number
of the scrambling code group, and k = 0, 1, …, 14 is the slot number. Each SSC is chosen
from a set of 16 different codes of length 256. This sequence on the Secondary SCH indicates
which of the code groups the cell’s downlink scrambling code belongs to.
Modulation Symbol "a"
The primary and secondary synchronization codes are modulated by the symbol a shown
in the diagram, which indicates the presence/ absence of Space Time Transmit Diversity
(STTD) encoding on the P-CCPCH and is given by the following table:
P-CCPCH STTD encoded a = +1
P-CCPCH not STTD encoded a = -1
5-24 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Synchronisation Channel (SCH) Version 1 Rev 0
Synchronisation Channel (SCH)
Tslot = 2560 chips
256 chips
Primary
SCH acp acp acp acp acp
Secondary
SCH acsi,0 acsi,1 acsi,2 acsi,3 acsi,14
One 10ms SCH radio frame
© 2005-2006 CP13: Introduction to UMTS USR6 5-25
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Synchronisation (Cell Search) Procedure
Synchronisation (Cell Search) Procedure
During the cell search, the UE searches for a cell and determines the downlink scrambling code and
frame synchronisation of that cell. The cell search is typically carried out in three steps:
Step 1: Slot synchronisation
During the first step of the cell search procedure the UE uses the SCH’s primary synchronisation
code to acquire slot synchronisation to a cell. This is typically done with a single matched filter (or
any similar device) matched to the primary synchronisation code which is common to all cells. The
slot timing of the cell can be obtained by detecting peaks in the matched filter output.
Step 2: Frame synchronisation and code-group identification
During the second step of the cell search procedure, the UE uses the SCH’s secondary synchronisation
code to find frame synchronisation and identify the code group of the cell found in the first step.
This is done by correlating the received signal with all possible secondary synchronisation code
sequences, and identifying the maximum correlation value. Since the cyclic shifts of the sequences
are unique the code group as well as the frame synchronisation is determined.
Step 3: Scrambling-code identification
During the third and last step of the cell search procedure, the UE determines the exact primary
scrambling code used by the found cell. The primary scrambling code is typically identified through
symbol-by-symbol correlation over the CPICH with all codes within the code group identified in
the second step. After the primary scrambling code has been identified, the Primary CCPCH
can be detected, and the system and cell specific BCH information can be read.
If the UE has received information about which scrambling codes to search for,
steps 2 and 3 above can be simplified.
5-26 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Synchronisation (Cell Search) Procedure Version 1 Rev 0
Synchronisation (Cell Search) Procedure
Synchronisation
ScramblingCode slot number
Group
#0 #1 #2 #3 #4 #5 #6 #7 #8 #9 #10 #11 #12 #13 #14
Group 0 1 1 2 8 9 10 15 8 10 16 2 7 15 7 16
Group 1 1 1 5 16 7 3 14 16 3 10 5 12 14 12 10
Group 2 1 2 1 15 5 5 12 16 6 11 2 16 11 15 12
Group 3 1 2 3 1 8 6 5 2 5 8 4 4 6 3 7
Group 4 1 2 16 6 6 11 15 5 12 1 15 12 16 11 2
Group 5 1 3 4 7 4 1 5 5 3 6 2 8 7 6 8
Group 6 1 4 11 3 4 10 9 2 11 2 10 12 12 9 3
Group 7 1 5 6 6 14 9 10 2 13 9 2 5 14 1 13
Group 8 1 6 10 10 4 11 7 13 16 11 13 6 4 1 16
Group 9 1 6 13 2 14 2 6 5 5 13 10 9 1 14 10
Group 10 1 7 8 5 7 2 4 3 8 3 2 6 6 4 5
Group 11 1 7 10 9 16 7 9 15 1 8 16 8 15 2 2
Group 12 1 8 12 9 9 4 13 16 5 1 13 5 12 4 8
Group 13 1 8 14 10 14 1 15 15 8 5 11 4 10 5 4
Group 14 1 9 2 15 15 16 10 7 8 1 10 8 2 16 9
Group 15 1 9 15 6 16 2 13 14 10 11 7 4 5 12 3
Group 16 1 10 9 11 15 7 6 4 16 5 2 12 13 3 14
Group 17 1 11 14 4 13 2 9 10 12 16 8 5 3 15 6
Group 18 1 12 12 13 14 7 2 8 14 2 1 13 11 8 11
Group 19 1 12 15 5 4 14 3 16 7 8 6 2 10 11 13
Group 20 1 15 4 3 7 6 10 13 12 5 14 16 8 2 11
Group 21 1 16 3 12 11 9 13 5 8 2 14 7 4 10 15
Group 22 2 2 5 10 16 11 3 10 11 8 5 13 3 13 8
Group 23 2 2 12 3 15 5 8 3 5 14 12 9 8 9 14
Group 24 2 3 6 16 12 16 3 13 13 6 7 9 2 12 7
Group 25 2 3 8 2 9 15 14 3 14 9 5 5 15 8 12
Group 26 2 4 7 9 5 4 9 11 2 14 5 14 11 16 16
Group 27 2 4 13 12 12 7 15 10 5 2 15 5 13 7 4
Group 28 2 5 9 9 3 12 8 14 15 12 14 5 3 2 15
Group 29 2 5 11 7 2 11 9 4 16 7 16 9 14 14 4
Group 30 2 6 2 13 3 3 12 9 7 16 6 9 16 13 12
Group 31 2 6 9 7 7 16 13 3 12 2 13 12 9 16 6
Group 32 2 7 12 15 2 12 4 10 13 15 13 4 5 5 10
© 2005-2006 CP13: Introduction to UMTS USR6 5-27
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Synchronisation (Cell Search) Procedure
Synchronisation (Cell Search) Procedure
ScramblingCode slot number
Group
#0 #1 #2 #3 #4 #5 #6 #7 #8 #9 #10 #11 #12 #13 #14
Group 33 2 7 14 16 5 9 2 9 16 11 11 5 7 4 14
Group 34 2 8 5 12 5 2 14 14 8 15 3 9 12 15 9
Group 35 2 9 13 4 2 13 8 11 6 4 6 8 15 15 11
Group 36 2 10 3 2 13 16 8 10 8 13 11 11 16 3 5
Group 37 2 11 15 3 11 6 14 10 15 10 6 7 7 14 3
Group 38 2 16 4 5 16 14 7 11 4 11 14 9 9 7 5
Group 39 3 3 4 6 11 12 13 6 12 14 4 5 13 5 14
Group 40 3 3 6 5 16 9 15 5 9 10 6 4 15 4 10
Group 41 3 4 5 14 4 6 12 13 5 13 6 11 11 12 14
Group 42 3 4 9 16 10 4 16 15 3 5 10 5 15 6 6
Group 43 3 4 16 10 5 10 4 9 9 16 15 6 3 5 15
Group 44 3 5 12 11 14 5 11 13 3 6 14 6 13 4 4
Group 45 3 6 4 10 6 5 9 15 4 15 5 16 16 9 10
Group 46 3 7 8 8 16 11 12 4 15 11 4 7 16 3 15
Group 47 3 7 16 11 4 15 3 15 11 12 12 4 7 8 16
Group 48 3 8 7 15 4 8 15 12 3 16 4 16 12 11 11
Group 49 3 8 15 4 16 4 8 7 7 15 12 11 3 16 12
Group 50 3 10 10 15 16 5 4 6 16 4 3 15 9 6 9
Group 51 3 13 11 5 4 12 4 11 6 6 5 3 14 13 12
Group 52 3 14 7 9 14 10 13 8 7 8 10 4 4 13 9
Group 53 5 5 8 14 16 13 6 14 13 7 8 15 6 15 7
Group 54 5 6 11 7 10 8 5 8 7 12 12 10 6 9 11
Group 55 5 6 13 8 13 5 7 7 6 16 14 15 8 16 15
Group 56 5 7 9 10 7 11 6 12 9 12 11 8 8 6 10
Group 57 5 9 6 8 10 9 8 12 5 11 10 11 12 7 7
Group 58 5 10 10 12 8 11 9 7 8 9 5 12 6 7 6
Group 59 5 10 12 6 5 12 8 9 7 6 7 8 11 11 9
Group 60 5 13 15 15 14 8 6 7 16 8 7 13 14 5 16
Group 61 9 10 13 10 11 15 15 9 16 12 14 13 16 14 11
Group 62 9 11 12 15 12 9 13 13 11 14 10 16 15 14 16
Group 63 9 12 10 15 13 14 9 14 15 11 11 13 12 16 10
5-28 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Synchronisation (Cell Search) Procedure
This page intentionally left blank.
© 2005-2006 CP13: Introduction to UMTS USR6 5-29
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Common Pilot Channel (CPICH)
Common Pilot Channel (CPICH)
The CPICH is a fixed rate (30 kbps, SF=256) downlink physical channel that carries a pre-defined
bit/symbol sequence. The diagram opposite shows the frame structure of the CPICH.
In case transmit diversity (open or closed loop) is used on any downlink channel in the
cell, the CPICH shall be transmitted from both antennas using the same channelization and
scrambling code. In this case, the pre-defined symbol sequence of the CPICH is different for
Antenna 1 and Antenna 2, see lower diagram opposite. In case of no transmit diversity, the
symbol sequence of Antenna 1 in the lower diagram opposite is used.
There are two types of Common pilot channels, the Primary and Secondary CPICH. They
differ in their use and the limitations placed on their physical features.
Primary Common Pilot Channel (P-CPICH)
The Primary Common Pilot Channel (P-CPICH) has the following characteristics:
• The same channelization code is always used for the P-CPICH (SF=256,0).
• The P-CPICH is scrambled by the primary scrambling code.
• There is one and only one P-CPICH per cell.
• The P-CPICH is broadcast over the entire cell.
The Primary CPICH is the phase reference for the following downlink channels:
SCH, Primary CCPCH, AICH, PICH. The Primary CPICH is also the default phase
reference for all other downlink physical channels.
Secondary Common Pilot Channel (S-CPICH)
A Secondary Common Pilot Channel (S-CPICH) has the following characteristics:
An arbitrary channelization code of SF=256 is used for the S-CPICH.
A S-CPICH is scrambled by either the primary or a secondary scrambling code.
There may be zero, one, or several S-CPICH per cell.
A S-CPICH may be transmitted over the entire cell or only over a part of the cell.
A Secondary CPICH may be the reference for the Secondary CCPCH and the downlink DPCH.
If this is the case, the UE is informed about this by higher-layer signalling.
5-30 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Common Pilot Channel (CPICH) Version 1 Rev 0
Common Pilot Channel (CPICH)
Frame Structure
Pre-dened symbol sequence
Tslot = 2560 chips, 20bits = 10 symbols
Slot #0 Slot #1 Slot #i Slot #14
1 radio frame: Tf = 10ms
Modulation Pattern for Common Pilot Channel
Antenna 1 A AA A A A A A A A A A A A A A A A A A A A
Antenna 2 -A -A A A -A -A A A -A -A A A -A -A A A -A -A A A -A -A
slot #14 slot #0 slot #1
Frame#i Frame#i+1
Frame Boundary
© 2005-2006 CP13: Introduction to UMTS USR6 5-31
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 P-CCPCH Frame Structure
P-CCPCH Frame Structure
The Primary CCPCH is a fixed rate (30 kbps, SF=256) downlink physical channels used to carry the BCH.
The frame structure of the Primary CCPCH is illustrated opposite.
The frame structure differs from the downlink DPCH in that no Transmit Power Control
(TPC) commands, no Transport Format Combination Indicator (TFCI) and no pilot bits are
transmitted The Primary CCPCH is not transmitted during the first 256 chips of each slot.
Instead, Primary SCH and Secondary SCH are transmitted during this period.
5-32 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
P-CCPCH Frame Structure Version 1 Rev 0
P-CCPCH Frame Structure
256 chips
Data
(Tx OFF)
18 bits
Tslot = 2560 chips, 20 bits
Slot #0 Slot #1 Slot #i Slot #14
Tf = 10ms
© 2005-2006 CP13: Introduction to UMTS USR6 5-33
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 SCH and P-CCPCH
SCH and P-CCPCH
The diagram opposite shows the construction of the SCH and the P-CCPCH. It is thus clear
that different channels can be multiplexed onto one link. The structure of these 2 Physical
Channels are very important to the synchronization process.
5-34 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
SCH and P-CCPCH Version 1 Rev 0
SCH and P-CCPCH
SCH SCH SCH
Frame 0 Frame 1 Frame 2
Data on P-CCPCH Data on P-CCPCH Data on P-CCPCH
© 2005-2006 CP13: Introduction to UMTS USR6 5-35
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Paging Indicator Channel (PICH)
Paging Indicator Channel (PICH)
PICH Channel Structure.
The Paging Indicator Channel (PICH) is a fixed rate (SF=256) physical channel
used to carry the Paging Indicators (PI). The PICH is always associated with a
S-CCPCH to which a PCH transport channel is mapped.
5-36 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Paging Indicator Channel (PICH) Version 1 Rev 0
Paging Indicator Channel (PICH)
12 bits
288 bits for paging indication (transmission off)
b 0 b1 b287 b288 b299
One radio frame (10ms)
© 2005-2006 CP13: Introduction to UMTS USR6 5-37
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Paging Indicator Channel (PICH)
Paging Indicator Channel (PICH)
Discontinuous Reception (DRX) on the PICH
The PICH Channel is used to alert the mobile that a possible paging message will be broadcast to
it on the PCH channel. Each mobile will calculate a paging occasion, which it listens to for such
an alert. In order to save on UE battery life the time between monitoring the paging occasions can
be altered, also the number of paging indicators per frame that carry the alerts may be configured.
These settings are all broadcast in the cell system information messages.
The main parameters that determine the time between the UE monitoring
its paging indicator are as follows:
DRX Cycle length.
The DRX Cycle Length is made up of a number of system Frames (each 10ms duration). It is this
period that determines how long the mobile is actually in DRX mode thus conserving battery power.
The cycle is repeated continuously and the UE must only become active once during each cycle.
The duration of the cycle is variable and maybe altered to suit network conditions.
Paging Occasion.
The Paging Occasion determines the frame number the UE becomes active in, during the DRX Cycle.
Paging Indicator.
The Paging Indicator is repeated multiple times per system frame. The UE calculates which
paging indicator to listen to using network-determined parameters.
The mobile listens to the system information messages to obtain the parameters required for receiving
paging indicators in the selected cell. It then performs a standard calculation using the cell parameters
and its IMSI. The result of this calculation is a single paging indicator during the DRX cycle time. In
other words the mobile must power up and listen to the calculated paging indicator (now know as
its paging occasion) between a repetition period of 80ms to 5.12s (DRX Cycle Period).
The diagram opposite illustrates the frame structure of the PICH.
5-38 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Paging Indicator Channel (PICH) Version 1 Rev 0
Paging Indicator Channel (PICH)
DRX Cycle, 80s to 5.12s
Paging Indicators 18,36,72 or 144 per 10msecs PICH Frame.
Frame. 10s
Calculated Paging Occasion
UE is in DRX until this Paging Indicator
© 2005-2006 CP13: Introduction to UMTS USR6 5-39
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Secondary Common Control Physical Channel (S-CCPCH)
Secondary Common Control Physical Channel (S-CCPCH)
The Secondary CCPCH is used to carry the FACH and PCH. There are two types of Secondary
CCPCH: those that include TFCI and those that do not include TFCI. It is the UTRAN that
determines if a TFCI should be transmitted, hence making it mandatory for all UEs to support the
use of TFCI. The set of possible rates for the Secondary CCPCH is the same as for the downlink
DPCH. The frame structure of the Secondary CCPCH is shown opposite.
The parameter k in the diagram determines the total number of bits per downlink Secondary CCPCH
slot. It is related to the spreading factor SF of the physical channel as SF = 256/2k. The spreading factor
range is from 256 down to 4. The values for the number of bits per field are given in the table opposite.
The channel bit and symbol rates given in the table are the rates immediately before spreading.
The FACH and PCH can be mapped to the same or to separate Secondary CCPCHs. If FACH and
PCH are mapped to the same Secondary CCPCH, they can be mapped to the same frame.
The main difference between a CCPCH and a downlink dedicated physical channel
is that a CCPCH is not inner-loop power controlled.
The main difference between the Primary and Secondary CCPCH is that the transport channel
mapped to the Primary CCPCH (BCH) can only have a fixed predefined transport format
combination, while the Secondary CCPCH support multiple transport format combinations using
TFCI. Furthermore, a Primary CCPCH is transmitted over the entire cell while a Secondary
CCPCH may be transmitted in a narrow lobe in the same way as a dedicated physical
channel (only valid for a Secondary CCPCH carrying the FACH).
For slot formats using TFCI, the TFCI value in each radio frame corresponds to a certain
transport format combination of the FACHs and/or PCHs currently in use. This correspondence
is (re-)negotiated at each FACH/PCH addition/removal.
5-40 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Secondary Common Control Physical Channel (S-CCPCH) Version 1 Rev 0
Secondary Common Control Physical Channel (S-CCPCH)
TFCI Data Pilot
NTFCIbits Ndatabits Npilotbits
Tslot = 2560 chips, 20*2kbits (k = 0..6)
Slot #0 Slot #1 Slot #i Slot #14
1 radio frame: Tf = 10ms
Secondary CCPCH Fields
Slot Channel Channel SF Bits/ Bits/ Ndata Npilot NTFCI
Format Bit Rate Symbol Rate Frame Slot
#i (kbps) (ksps)
0 30 15 256 300 20 20 0 0
1 30 15 256 300 20 12 8 0
2 30 15 256 300 20 18 0 2
3 30 15 256 300 20 10 8 2
4 60 30 128 600 40 40 0 0
5 60 30 128 600 40 32 8 0
6 60 30 128 600 40 38 0 2
7 60 30 128 600 40 30 8 2
8 120 60 64 1200 80 72 0 8*
9 120 60 64 1200 80 64 8 8*
10 240 120 32 2400 160 152 0 8*
11 240 120 32 2400 160 144 8 8*
12 480 240 16 4800 320 312 0 8*
13 480 240 16 4800 320 296 16 8*
14 960 480 8 9600 640 632 0 8*
15 960 480 8 9600 640 616 16 8*
16 1920 960 4 19200 1280 1272 0 8*
17 1920 960 4 19200 1280 1256 16 8*
* If TFCI bits are not used, then DTX shall be used in TFCI field.
© 2005-2006 CP13: Introduction to UMTS USR6 5-41
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Physical Random Access Channel (PRACH)
Physical Random Access Channel (PRACH)
Structure of the PRACH
The random-access transmission is based on a Slotted ALOHA approach with fast acquisition indication.
The UE can start the random-access transmission at the beginning of a number of well-defined time
intervals, denoted access slots. There are 15 access slots per two frames and they are spaced 5120
chips apart, see diagram opposite. Information on what access slots are available for random-access
transmission is given by higher layers and is based upon the Access Service Class (ASC) of the UE
Random Access Transmission
The structure of the random-access transmission is also shown opposite. The
random-access transmission consists of one or several preambles of length 4096
chips and a message of length 10ms or 20ms.
PRACH Pre-amble
Each preamble is of length 4096 chips and consists of 256 repetitions of a signature of
length 16 chips. There are a maximum of 16 available signatures
5-42 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Physical Random Access Channel (PRACH) Version 1 Rev 0
Physical Random Access Channel (PRACH)
RACH access slot numbers and their spacing
radio frame: 10ms radio frame: 10ms
5120
chips
#0 #1 #2 #3 #4 #5 #6 #7 #8 #9 #10 #11 #12 #13 #14
Access slot
Random Access Transmission
Random Access Transmission
Random Access Transmission
Random Access Transmission
Structure of the random-access transmission
Preamble Preamble Preamble Message part
4096 chips 10ms (one radio frame)
Preamble Preamble Preamble Message part
4096 chips 20ms (two radio frames)
© 2005-2006 CP13: Introduction to UMTS USR6 5-43
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Physical Random Access Channel (PRACH)
Physical Random Access Channel (PRACH)
Structure of PRACH Message Part
The structure of the Random-access message part is shown opposite. The 10ms message
is split into 15 slots, each of length Tslot = 2560 chips. Each slot consists of two parts,
a data part that carries Layer 2 information and a control part that carries Layer 1 control
information. The data and control parts are transmitted in parallel.
The data part consists of 10*2k bits, where k=0,1,2,4. This corresponds to a spreading
factor of 256, 128, 64, and 32 respectively for the message data part. The value for the
number of bits in the data field are given in the table opposite.
The control part consists of 8 known pilot bits to support channel estimation for coherent detection
and 2 TFCI bits. This corresponds to a spreading factor of 256 for the message control part.
The total number of TFCI bits in the random-access message is 15*2 = 30. The TFCI value
corresponds to a certain transport format of the current Random-access message.
The Random Access Channel(s) (RACH) is characterised by:
• Existence in uplink only
• Limited data field
• Collision risk
• Open loop power control
5-44 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Physical Random Access Channel (PRACH) Version 1 Rev 0
Physical Random Access Channel (PRACH)
Data
Data
Ndatabits
Pilot TFCI
Control
Npilotbits NTFCIbits
Tslot = 2560 chips, 10*2kbits (k = 0..3)
Slot #0 Slot #1 Slot #i Slot #14
Message part radio frame TRACH = 10ms
Random-access message data fields
Slot Format #i Channel Bit Channel Bits/ Bits/Slot Ndata
SF
Rate (kbps) Symbol Rate Frame
(ksps)
0 15 15 256 150 10 10
1 30 30 128 300 20 20
2 60 60 64 600 40 40
3 120 120 32 1200 80 80
© 2005-2006 CP13: Introduction to UMTS USR6 5-45
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Acquisition Indicator Channel (AICH)
Acquisition Indicator Channel (AICH)
The Acquisition Indicator Channel (AICH) is a fixed rate (SF=256) physical channel used to carry
Acquisition Indicators (AI). Acquisition Indicator AIs corresponds to signature s on the PRACH.
The diagram opposite illustrates the structure of the AICH.
The AICH consists of a repeated sequence of 15 consecutive access slots (AS), each of length
5120 chips. Each access slot consists of two parts, an Acquisition-Indicator (AI) part consisting
of 32 real-valued symbols a0, …, a31 and a part of duration 1024 chips with no transmission
that is not formally part of the AICH. The part of the slot with no transmission is reserved for
possible use by CSICH or possible future use by other physical channels.
The spreading factor (SF) used for channelization of the AICH is 256.
The phase reference for the AICH is the Primary CPICH.
5-46 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Acquisition Indicator Channel (AICH) Version 1 Rev 0
Acquisition Indicator Channel (AICH)
Al part = 4096 chips, 32 real-valued symbols 1024 chips
a0 a1 a 2 a30 a31 Transmission Off
AS # 14 AS # 0 AS # 1 AS # i AS # 14 AS # 0
20ms
© 2005-2006 CP13: Introduction to UMTS USR6 5-47
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Relationship Between PRACH and AICH
Relationship Between PRACH and AICH
The PRACH contains two sets of access slots as shown below. Access slot set 1 contains
PRACH slots 0 - 7 and starts τp-a chips before the downlink P-CCPCH frame for which SFN
mod 2 = 0. Access slot set 2 contains PRACH slots 8 - 14 and starts (τp-a -2560) chips
before the downlink P-CCPCH frame for which SFN mod 2 = 1.
5-48 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Relationship Between PRACH and AICH Version 1 Rev 0
Relationship Between PRACH and AICH
AICH access
slots SFN mod 2 = 0 SFN mod 2 = 1
Tp-a #0 #1 #2 #3 #4 #5 #6 #7 #8 #9 #10 #11 #12 #13 #14
#0 #1 #2 #3 #4 #5 #6 #7 #8 #9 #10 #11 #12 #13 #14
PRACH
access slots Access slot set 1 Access slot set 2
10ms 10ms
© 2005-2006 CP13: Introduction to UMTS USR6 5-49
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Downlink Dedicated Physical Channels (DL-DPCH)
Downlink Dedicated Physical Channels (DL-DPCH)
DL-DPCH Structure
There is only one type of downlink dedicated physical channel, the Downlink
Dedicated Physical Channel (Downlink DPCH).
Within one Downlink DPCH, dedicated data generated at Layer 2 and above, i.e. the Dedicated
Transport Channel (DCH), is transmitted in time-multiplex with control information generated at
Layer 1 (known pilot bits, TPC commands, and an optional TFCI). The downlink DPCH can thus
be seen as a time multiplex of a downlink DPDCH and a downlink DPCCH.
The diagram opposite shows the frame structure of the downlink DPCH. Each frame of length
10ms is split into 15 slots, each of length Tslot = 2560 chips, corresponding to one power-control
period. The parameter k in the diagram determines the total number of bits per downlink DPCH
slot. It is related to the spreading factor SF of the physical channel as SF = 512/2k. The spreading
factor may thus range from 512 down to 4. The exact number of bits of the different downlink
DPCH fields (Npilot, NTPC, NTFCI, Ndata1 and Ndata2) is dependent upon the SF. What slot format to
use is configured by higher layers and can also be reconfigured by higher layers.
There are basically two types of downlink Dedicated Physical Channels; those that include
TFCI (e.g. for several simultaneous services) and those that do not include TFCI (e.g. for
fixed-rate services). It is the UTRAN that determines if a TFCI should be transmitted and it
is mandatory for all UEs to support the use of TFCI in the downlink.
The Pilot bits are provided to permit frame synchronisation and channel estimation at the receiving node.
TPC symbol will indicate a step increase or decrease of transmitter power by the receiving node.
TPC Bit Pattern Transmitter power
control command
NTPC = 2 NTPC = 4 NTPC = 8
11 1111 1111 1111 1
00 0000 00000000 0
5-50 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Downlink Dedicated Physical Channels (DL-DPCH) Version 1 Rev 0
Downlink Dedicated Physical Channels (DL-DPCH)
DPDCH DPCCH DPDCH DPCCH
Data 1 TPC TFCI Data 2 Pilot
Npilot bits
Tslot = 2560 chips
Slot #0 Slot #1 Slot #i Slot #14
One radio frame = 10ms
K = 0.........7
© 2005-2006 CP13: Introduction to UMTS USR6 5-51
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Downlink Dedicated Physical Channels (DL-DPCH)
Downlink Dedicated Physical Channels (DL-DPCH)
Downlink Slot Formation in Case of Multi-Code Transmission
For slot formats using TFCI, the TFCI value in each radio frame corresponds to a
certain combination of bit rates of the DCHs currently in use. This correspondence
is re-negotiated at each DCH addition/removal.
When the total bit rate to be transmitted on one downlink CCTrCH exceeds the maximum bit rate
for a downlink physical channel, multicode transmission is employed, i.e. several parallel downlink
DPCHs are transmitted for one CCTrCH using the same spreading factor. In this case, the Layer 1
control information is put on only the first downlink DPCH. The additional downlink DPCHs belonging
to the CCTrCH do not transmit any data during the corresponding time period.
TFCI Transport Formation Combination Indicator
DCH Dedicated Channel
CCTrCH Coded Composite Transport Channel
DPCH Dedicated Physical Channel
TPC Transmit Power Control
5-52 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Downlink Dedicated Physical Channels (DL-DPCH) Version 1 Rev 0
Downlink Dedicated Physical Channels (DL-DPCH)
DPDCH
DPDCH
TPC TFCI Pilot
Transmission
Power Physical Channel 1
Transmission
Power Physical Channel 2
Transmission
Power Physical Channel L
One Slot (2560 chips)
© 2005-2006 CP13: Introduction to UMTS USR6 5-53
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Uplink Dedicated Physical channels (UL-DPCH)
Uplink Dedicated Physical channels (UL-DPCH)
There are two types of uplink dedicated physical channels, the Uplink Dedicated Physical Data
Channel (Uplink DPDCH) and the Uplink Dedicated Physical Control Channel (uplink DPCCH).
The DPDCH and the DPCCH are I/Q code multiplexed within each radio frame.
The uplink DPDCH is used to carry the DCH transport channel. There may be zero,
one, or several uplink DPDCHs on each radio link.
The uplink DPCCH is used to carry control information generated at Layer 1. The Layer 1 control
information consists of known pilot bits to support channel estimation for coherent detection,
Transmit Power Control (TPC) commands, Feedback Information (FBI), and an optional
Transport Format Combination Indicator (TFCI). The transport-format combination indicator
informs the receiver about the instantaneous transport format combination of the transport
channels mapped to the simultaneously transmitted Uplink DPDCH radio frame.
There is one and only one Uplink DPCCH on each radio link.
The diagram opposite shows the frame structure of the Uplink dedicated physical
channels. Each radio frame of length 10ms is split into 15 slots, each of length Tslot
= 2560 chips, corresponding to one TPC period.
The parameter k in the diagram determines the number of bits per uplink DPDCH slot. It is related
to the spreading factor SF of the DPDCH as SF = 256/2k. The DPDCH spreading factor may range
from 256 down to 4, giving data rates between 15kbs and 960kbs The spreading factor of the uplink
DPCCH is always equal to 256, i.e. there are 10 bits per uplink DPCCH slot. What slot format
to use is configured by higher layers and can also be reconfigured by higher layers.
The FBI bits are used to support techniques requiring feedback from the UE to the UTRAN Access Point,
including closed loop mode transmit diversity and Site Selection Diversity Transmission (SSDT).
There are two types of Uplink Dedicated Physical Channels; those that include TFCI (e.g.
for several simultaneous services) and those that do not include TFCI (e.g. for fixed-rate
services). It is the UTRAN that determines if a TFCI should be transmitted and it is
mandatory for all UEs to support the use of TFCI in the uplink.
Multi-code operation is possible for the uplink Dedicated Physical Channels. When multi-code
transmission is used, several parallel DPDCH are transmitted using different channelization
codes. However, there is only one DPCCH per radio link.
5-54 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Uplink Dedicated Physical channels (UL-DPCH) Version 1 Rev 0
Uplink Dedicated Physical channels (UL-DPCH)
Data
DPDCH
Ndatabits
Pilot TFCI FBI TPC
DPCCH Npilotbits NTFCIbits NFBIbits NTPCbits
Tslot = 2560 chips, 10*2kbits (k = 0..6)
Slot #0 Slot #1 Slot #i Slot #14
Tf = 10ms
K = 0........7
© 2005-2006 CP13: Introduction to UMTS USR6 5-55
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Downlink Flow Process
Downlink Flow Process
The downlink flow process consists of the following physical layer functions.
Data arrives to the coding/multiplexing unit in the form of transport block sets once
every transmission time interval. The transmission time interval is transport-channel
specific from the set {10ms, 20ms, 40ms and 80ms}.
The following coding/multiplexing steps can be identified for downlink:
• Add CRC to each transport block
• Transport block concatenation and code block segmentation
• Channel coding
• Rate matching
• First insertion of discontinuous transmission (DTX) indication bits
• First interleaving
• Radio frame segmentation
• Multiplexing of transport channels
• Second insertion of DTX indication bits
• Physical channel segmentation
• Second interleaving
• Mapping to physical channels
It should be noted that not every step is applicable to every data type.
5-56 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Downlink Flow Process Version 1 Rev 0
Downlink Flow Process
CRC attachment
TrBk concatenation /
Code block segmentation
Channel coding
Rate matching Rate matching
1st insertion of DTX
indication
1st interleaving
Radio frame segmentation
TrCH Multiplexing
2nd insertion of DTX
indication
CCTrCH
Physical channel
segmentation
2nd interleaving
Physical channel mapping
PhCH#2
PhCH#1
© 2005-2006 CP13: Introduction to UMTS USR6 5-57
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Uplink Flow Process
Uplink Flow Process
The uplink flow process is largely the same as that for the downlink, and is illustrated in the
diagram opposite. The differences in the individual process steps are as follows.
Radio Frame Equalisation
Radio frame size equalisation is padding the input bit sequence in order to ensure that the output can
be segmented in data segments of equal size. Radio frame size equalisation is only performed in the
UL (DL rate matching output block length is always an integer multiple of the frame length).
Rate Matching
The rate matching operation in the uplink, is a much more dynamic process that may vary on a
frame-by-frame basis. The rate matching operation needs to take into account the the number of bits
coming from all transport channels. When the data rate of one service, the dynamic rate matching
adjusts the rates of the remaining service as well so that all symbols in the radio frame will be used.
For example if with two transport channels, one has a momentary zero rate, rate matching used repetition
to increase the symbol rate for the other service sufficiently so that all uplink channel symbols are used.
DTX
Because Uplink rate matching ensures that all unused transport channel bits are filled, there
is no requirement for DTX indication bits to be inserted in the uplink flow
5-58 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Uplink Flow Process Version 1 Rev 0
Uplink Flow Process
CRC attachment
TrBk concatenation /
Code block segmentation
Channel coding
Radio Frame equalisation
1st interleaving
Radio frame segmentation
Rate matching Rate matching
TrCH Multiplexing
CCTrCH
Physical channel
segmentation
2nd interleaving
Physical channel mapping
PhCH#1
PhCH#2
© 2005-2006 CP13: Introduction to UMTS USR6 5-59
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Uplink Flow Process
This page intentionally left blank.
5-60 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
MAC, RLC, BMC, PDCP and RRC Protocols and Procedures Version 1 Rev 0
Chapter 6
MAC, RLC, BMC, PDCP and RRC
Protocols and Procedures
© 2005-2006 CP13: Introduction to UMTS USR6 6-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 MAC, RLC, BMC, PDCP and RRC Protocols and Procedures
This page intentionally left blank.
6-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
• Describe the Radio Protocol Stack
• Describe the MAC layer
• Describe the RLC layer
• Describe the PDCP protocol
• Describe the BMC protocol
• Describe the RRC protocol and its common procedures
© 2005-2006 CP13: Introduction to UMTS USR6 6-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Introduction
Introduction
In this chapter we are going to look at the layer 2 protocols in more detail after being introduced
to them in previous chapter in the shape of the MAC and RLC layers. The layer 3 protocols
are also going to be discussed and some of the more common procedures explored to
gain a better understanding of the essential functions of UMTS.
Layer 2 Protocols
Layer 2 offers services of information transmission to layer 3 in the form of Radio Bearers (RB) for
data services and Signalling Radio Bearers (SRB) for control information originated either in the
Radio Resource Control (RRC) protocol or in the Non Access Stratum (NAS). With respect to
the flow of control information, it goes through the RLC and MAC layers, while in the case of data
information, depending on the specific service, there exist two additional sub-layers, namely the Packet
Data Convergence Protocol (PDCP) and the Broadcast Multicast Control (BMC).
Layer 3 Protocols
With respect to layer 3, only the lowest sub-layer, denoted as Radio Resource Control
(RRC) terminates in the UTRAN control plane.
Each layer communicates with the same layer at the peer entity (e.g. the RRC layer at the UE
communicates with the RRC at the RNC), and this communication is defined by the specific protocol of
each layer. At the UTRAN side, the RLC and above radio protocols are located in the RNC. In turn,
with respect to the MAC protocol, some of its functionalities are located in the Node B and others
in the RNC. The layered structure is constructed upon the assumption that each layer provides
message transfer services to the upper layers. At one extreme network entity (e.g. UE or RNC),
a given layer receives Service Data Units (SDUs) containing the messages from its upper layer,
processes them adding the required headers and control elements and eventually delivers them in
the form of Protocol Data Units (PDUs) to its lower layer. Note that the PDU delivered by a given
layer corresponds to the SDU seen by its lower layer. At the lowest layer, the information is finally
transferred through the channels existing in the physical layer (i.e. the specific code sequences, time
slots and frequency bands). At the other extreme network entity (e.g. RNC or UE), the information
is received at the physical layer and delivered to the upper layers until reaching the destination
layer. Note that this transfer of information requires the definition of adequate interfaces between
adjacent layers specifying the path that information follows depending on its nature.
Layer 2 offers to the upper layers the service of information transmission between the UE and the
UTRAN by means of the Radio Bearers (RBs) and Signalling Radio Bearers (SRBs). The former
provide the transmission of user data while the latter are intended to transfer control information that
can be originated either in the RRC protocol or in upper layers. Whenever a service is provided to
a given UE (e.g. a voice service, a videoconference service, an interactive web browsing service,
etc.) it should be associated to a specific RB that specifies the configuration and the parameters
of the sub-layers in layer 2 and the physical layer depending on the characteristics of the service
being provided. The information flow associated to a RB or a SRB is mapped into different types
of channels depending on the position in the layered protocol architecture.
6-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Introduction Version 1 Rev 0
Introduction
© 2005-2006 CP13: Introduction to UMTS USR6 6-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Medium Access Control (MAC) Protocol
Medium Access Control (MAC) Protocol
The MAC protocol exists in the lowest sub-layer of layer 2 protocol architecture of the radio interface. It
exists in the UE, the node B and the RNC entities. The MAC provides data transfer services to the
logical channels and it is serviced by the physical layer by means of the transport channels, so one
of the main functionalities of the MAC is the mapping between logical and transport channels.
The MAC layer at either the UTRAN or the UE receives MAC SDUs from the RLC and it is
responsible for transferring them to the corresponding peer MAC entity at the other side. A MAC
SDU is the minimum amount of information that can be transferred between the two sub-layers
in a logical channel. This transfer service is done in unacknowledged mode, which means that
the delivery to the other side is not guaranteed, so the RLC layer must have mechanisms to
detect errors and losses of SDUs as well as perform retransmissions. Furthermore, the MAC
protocol does not execute any type of segmentation of the MAC SDUs.
For each MAC SDU, a MAC header is added, whose length and contents depend on the specific
transport channels. The MAC header includes the C/T field that identifies the specific logical
channel when several logical channels are multiplexed onto the same transport channel, as well
as fields to identify the specific UE in the case of common transport channels like RACH or
FACH. It is also possible that the MAC header is empty. Typically, this would be the case of the
transfer of user information through a DCH transport channel that is not multiplexed with any
other channel at the MAC layer, and in which no UE identification is required.
The MAC layer functions (as well as the tasks discussed above and on the next page) also include:
• Priority handling of data flows
• Priority handling between UEs by dynamic scheduling
• Identity of UEs on common channels
• Traffic volume monitoring
• Dynamic transport channel switching
• Ciphering for transport RLC mode
• Access service class selection.
6-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Medium Access Control (MAC) Protocol Version 1 Rev 0
Medium Access Control (MAC) Protocol
MAC MAC MAC MAC MAC MAC
BCCH Control Control Control Control Control BCCH PCCH CCCH CTCH DCCH DTCH Control
MAC-b MAC- hs MAC- e MAC- es MAC- c/sh MAC-d
(NodeB) (NodeB) (NodeB) (RNC) (RNC) (RNC)
BCH HS-DSCH HS-DSCH E-DCH BCH PCH FACH RACH RACH DCH DCH
© 2005-2006 CP13: Introduction to UMTS USR6 6-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Transport Formats
Transport Formats
The combination of a MAC SDU and a MAC header is a MAC PDU, which corresponds to a TB
transferred to the physical layer through the corresponding transport channel. In each Transmission
Time Interval (TTI) the MAC layer selects a suitable Transport Format (TF) or a Transport Format
Combination (TFC), depending on the instantaneous source rate, the service characteristics and
the Transport Format Combination Set (TFCS). Each TF is related to a given instantaneous
bit rate. Once the selection is done, the MAC layer delivers a set of TBs to the physical layer,
denoted as the Transport Block Set (TBS). The transport blocks must be delivered in the same
order in which the corresponding MAC SDUs were delivered by the RLC layer.
Transport Block (TB):Transport Block (TB) is the basic unit MAC transfers to L1 for L1 processing. A
TB is equivalent to a MAC Protocol Data Unit (PDU). TB size indicates the number of bits in a TB
Transport Block Set (TBS):Transport Block Set (TBS) is a set of TBs MAC transfers
on a transport channel at one time to L1. A TBS is equivalent to a MAC PDU Set.
TBS size indicates the number of bits in a TBS.
Transport Format (TF):Transport Format (TF) is a format L1 applies for transferring a TBS
to MAC on a transport channel at a Transmission Time Interval (TTI). The TF consists
of two parts — a dynamic part and a semi-static part.
Transport Format Set (TFS):Transport Format Set (TFS) is a set of TFs. A TF represents a bit
rate. A TFS consisting of multiple TFs may have multi rates. For example, a fixed-rate DCH has
only a single TF. A variable-rate DCH has a TFS, with one TF for each rate.
Transport Format Combination (TFC):Transport Format Combination (TFC) is the combination of
currently valid TFs on all transport channels of a UE. It contains the TF from each transport channel.
Transport Format Combination Set (TFCS)Transport Format Combination Set
(TFCS) is a set of TFCs of a UE.
Transport Format Combination Indicator (TFCI):Transport Format Combination Indicator
(TFCI) is a label for a specific TFC within a TFCS.
Transport Format Identification (TFI)Transport Format Identification (TFI) is a label for a
specific TF within a TFS. is a label for a specific TF within a TFS.
0101010011110101001 (MAC PDU)
Transport Channel (TrCH)
Transport Block Set Size (Size in bits)
10ms, 20ms, 40ms or 2ms for HSDPA
Transmission Time Interval (TTI)
Transport Block (TB)
Transport Block Set (TBS)
Basic unit of the transport
format – generated every
10ms or multiple of 10ms
Transport Transport Block Size (TBS)
Format
Size of the Transport Block
Indicator
in bits
(TFI)
Physical Layer
6-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Transport Formats Version 1 Rev 0
Transport Formats
0101010011110101001 (MAC PDU)
Transport Channel (TrCH)
Transmission Time Interval (TTI) = 10ms
Transport Block Set Size is 336 bits
168 bits
Transport Block Set (TBS)
Transport 168 bits
Format
Indicator
(TFI)
Example Transport Format:
Dynamic part – 168 bit TB, 336 bit TBS
Semi- static – TTI 10ms, turbo coding, 1/3 rate conv coding, 16 crc
Transport Transport
Channel (TrCH1) Channel (TrCH2)
168 bits 168 bits
TBS size is 336 bits
TBS size is 336 bits
(TBS)
(TBS)
(TTI) = 10ms
(TTI) = 10ms
(TFI) 168 bits (TFI) 168 bits
Transport Format Combination
Indicator (TFCI) Coded Composite Transport Channel (CCTrCH)
DPCCH DPDCH
© 2005-2006 CP13: Introduction to UMTS USR6 6-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Radio Link Control (RLC) Protocol
Radio Link Control (RLC) Protocol
The RLC sub-layer is located in both the UE and the RNC immediately above the MAC sub-layer
according to the radio interface protocol architecture. In the control plane, it provides services
directly to layer 3, while in the user plane it may also provide services to the PDCP and BMC
sub-layers. In turn, it receives information transfer services from the MAC layer by means of the
logical channels.The RLC protocol receives from the upper layer RLC SDUs
The RLC protocol receives from the upper layer RLC SDUs and transmits RLC PDUs to the
MAC layer (note that the RLC PDUs are the same as the MAC SDUs).
Essentially, the RLC provides three types of data transfer services corresponding to the three modes
of operation: Transparent Mode (TM); Unacknowledged Mode (UM); and Acknowledged Mode
(AM). Each mode is associated with a different Service Access Point (SAP) for upper layers,
denoted as TM-SAP, UM-SAP and AM-SAP, respectively, and with different RLC entities,
Transparent Mode (TM)
The features of TM are defined by a no delay, no overhead and no assured delivery of data.
The transparent mode can be used by any of the logical channels except the CTCH, and
it is the only mode that can be used by the BCCH and PCCH for the transfer of broadcast
and paging messages. It is the mode typically used by the streaming service class in
the case of dedicated channels and CS voice services.
Unacknowledged Mode (UM)
The features of UM are defined by low delay, lower transmission efficiency caused by having a
UM header and no assured delivery of data. Unlike TM the segmentation of RLC PDUs is allowed
and is taken care of by the UM header when re-segmentation takes place.
UM can be used by CCCH, CTCH, DTCH and DCCH logical channels, and it is normally used by some
RRC control procedures, in which there exist specific RRC acknowledgement messages, so that
acknowledgement at the RLC layer is not necessary. Voice over IP services may also use this mode.
Acknowledged Mode (AM)
The features of AM are defined by high delay caused by having assured delivery of data,
low transmission efficiency caused by having a large AM header.
Services (web browsing, FTP download) with the following features:
• Not insensitive to delay
• High or very high requirement for transmission quality
6-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Radio Link Control (RLC) Protocol Version 1 Rev 0
Radio Link Control (RLC) Protocol
© 2005-2006 CP13: Introduction to UMTS USR6 6-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Packet Data Convergence Protocol (PDCP)
Packet Data Convergence Protocol (PDCP)
The PDCP only exists in the user plane and is specifically for PS services. Its main functionality
is to improve the efficiency in the radio transmission by means of executing header compression
of the IP data packets coming from upper layers. It receives PDCP SDUs from upper layers and
delivers to the RLC sub-layer different PDCP PDUs. The types of PDCP PDUs:
• PDCP Data PDU, which contains a PDCP SDU, either compressed or uncompressed,
or header compression related control signalling. The type of information
contained is indicated in a one-byte header;
• PDCP-No-Header PDU, which contains an uncompressed PDCP SDU
without adding any type of header;
• PDCP SeqNum PDU, which, apart from containing a compressed or uncompressed
PDCP SDU, also includes a PDCP SDU sequence number.
The specific header compression protocol depends on the particular upper layer protocols that form the
incoming PDCP SDU and on the configuration of the PDCP sub-layer by upper layers. For TCP/IP
packets, the IP header compression mechanism described in IETF RFC 2507 is used, which is
essentially based on providing a variable length TCP/IP header whose contents are specified by the
bits of the first byte. The amount of information in the header is reduced by sending only the changes
from one packet to the next. In this way, it is possible to reduce the TCP/IP header from the usual value
of 40 bytes down to 4 or 5 bytes. Note that when such a TCP/IP compressed packet is lost due to
errors in the lower layers, the incremental condition of the header compression mechanism makes it no
longer possible to decode the headers of the subsequent packets. Consequently, in such cases it is
necessary to send sporadic uncompressed TCP/IP segments. Different types of compressed headers
are accepted by the protocol. The type of compression is indicated in the PDCP Data PDU header.
For RTP/UDP/IP packets, in which certain time constraints must be met, the Robust Header
Compression (ROHC) method defined in IETF RFC 3095 is used. This protocol supports
segmentation of packets and can transmit information packets from several contexts, distinguished
by the Context Identifier (CID), which is included either in the PDCP header or in the upper layer
packet. The ROHC protocol involves some signalling parameters that must be exchanged between
the compressor and the decompressor entities at the transmitter and the receiver sides.
The PDCP protocol may operate with any of the three RLC modes (i.e. transparent,
unacknowledged and acknowledged), and the selection will depend on the specific service
characteristics. When operating with acknowledged RLC mode configured with in-sequence
delivery, the PDCP with ROHC protocol also provides support for a lossless SRNS
relocation procedure by means of PDCP sequence numbering.
6-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Packet Data Convergence Protocol (PDCP) Version 1 Rev 0
Packet Data Convergence Protocol (PDCP)
Applications
Data
protocols IP PPP FTP etc
• Header
de/compres s ion
P DC P • T rans fer of us er data
• F orwarding of P DC P
S DUs and as s ociated
s equence numbers
R LC
MAC
P HY S
© 2005-2006 CP13: Introduction to UMTS USR6 6-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Broadcast/Multicast Control (BMC) Protocol
Broadcast/Multicast Control (BMC) Protocol
Like the PDCP, the BMC protocol only exists in the user plane, and provides a broadcast/multicast
transmission service operating in RLC unacknowledged mode.
The BMC entity at the UTRAN side is located in the RNC and its functions include the storage of
Cell Broadcast Messages, which are transmitted in a given cell to certain UEs that support the
SMS Cell Broadcast Service. These messages, which carry information that depends on the
geographical area, are transmitted by means of the CTCH logical channel and the mobile should
be able to receive them in idle mode as well as in the rest of RRC states. The stored messages
are scheduled by the BMC in order to decide the appropriate instant for their transmission. The
specific scheduling algorithm is implementation dependent. At the UE side, the BMC entity
delivers the received cell broadcast messages to the upper layers.
Traffic volume monitoring is done by the BMC – by making predictions on the expected amount
of capacity in terms of bit rate that is needed for the transmission of cell broadcast messages
– and indicates it to the RRC entity, so that it can act accordingly.
6-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Broadcast/Multicast Control (BMC) Protocol Version 1 Rev 0
Broadcast/Multicast Control (BMC) Protocol
Applications
• S torage of cell
broadcas t mes s ages
• Traffic volume -
Data monitoring and radio
protocols IP PPP FTP etc res ource reques ts for
CBS
• S cheduling of cell
B MC broadcas t ms gs
P DC P
• Trans mis s ion of cell
broadcas t ms gs
R LC • S toring of ms g IDs and
s erial numbers of rx’d
C B S ms gs in UE s
• Delivery of cell
MAC
broadcas t mes s ages
to upper layers (NAS )
P HYS
© 2005-2006 CP13: Introduction to UMTS USR6 6-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Radio Resource Control (RRC)
Radio Resource Control (RRC)
According to the radio interface protocol architecture that was shown in the first slide of this chapter,
the RRC protocol only exists in the control plane and occupies the lowest sub-layer of layer 3
while, at the same time, being the highest layer of the Radio Access Network (i.e. the UTRAN
part) protocol stack. Although layer 3 is partitioned in other sub-layers above RRC, they belong
to the Non Access Stratum (NAS) and are specified between the UE and the Core Network
parts of the UMTS architecture. Some examples of control protocols above the RRC include
Session Management (SM), Connection Management (CM), Mobility Management (MM) or
GPRS Mobility Management (GMM). Supplementary Services (SS), Short Message Services
or GPRS Short Message Services (GSMS) and Connection Control (CC)
The RRC protocol provides the service of transferring signalling information to the NAS upper
layer entities. Besides, RRC handles the control plane signalling between the UE and the UTRAN
through Signalling Radio Bearers. This includes procedures specific of the Access Stratum
(AS) that allow the appropriate configuration of the lower layers in both control and user planes
taking into account the network status. Therefore, these signalling procedures provide the support
for the execution of the Radio Resource Management (RRM) strategies.
The RRC functions include:
• Broadcast of information related to the non-access stratum (Core Network)
• Broadcast of information related to the access stratum
• Establishment, maintenance and release of an RRC connection between the UE and UTRAN
• Establishment, reconfiguration and release of Radio Bearers
• Assignment, reconfiguration and release of radio resources for the RRC connection
• RRC connection mobility functions
• Control of requested QoS
• UE measurement reporting and control of the reporting
• Outer loop power control
• Control of ciphering
• Paging.
• Initial cell selection and cell re-selection;
• Arbitration of radio resources on uplink DCH;
• RRC message integrity protection;
• CBS control
6-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Radio Resource Control (RRC) Version 1 Rev 0
Radio Resource Control (RRC)
© 2005-2006 CP13: Introduction to UMTS USR6 6-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 RRC Procedures
RRC Procedures
In this part of the course some of the more important RRC procedures will be discussed to allow
understanding of the signalling that must take place to allow UMTS to operate.
Broadcast of System Information.
This procedure allows the broadcasting of system information messages from the UTRAN to
the terminals of a given cell. These messages are organised into System Information Blocks
(SIBs), ranging from 1 to 18, which are sent periodically on the BCCH. A System Block (SB)
is a block of SIBs. There exists a Master Information Block (MIB) that includes the reference
information to decode the rest of the SIBs and which is the first block that the mobile should read
when it selects a new cell. Additionally, it contains a tag that allows the detection of changes in
certain SIBs whose information does not change frequently, so that the terminals do not need to
decode continuously all the broadcast messages. In the case of important changes in the SIBs,
the network may notify these to the mobiles in Cell_PCH and URA_PCH states through a Paging
Type 1 message in the PCH channel, while the mobiles in Cell_FACH are informed through the
FACH channel by means of the System Information Change Indication message.
Supported System Information Block Types
The list below shows the SIBs that are currently supported. The missing ones
are for UMTS TDD mode of working.
A normally running RNC cell broadcasts SIB1/3/5/7/11 and optionally SIB2/18. Configuration
of system information blocks (SIBs) are shown in the table opposite.
• SIB 1 — Contains NAS system information as well as UE timers and counters to
be used in idle mode and in connected mode.
• SIB 2 — Contains the URA identification.
• SIB 3 — Contains parameters for cell selection and reselection.
• SIB 5— Contains parameters for the configuration of the common physical channels in a cell
e.g., power offset of AICH and PICH, SCCPCH information and PRACH information.
• SIB 7— Contains the fast changing parameters e.g., UL interference and dynamic persistence level.
• SIB 11 — Contains measurement control information to be used in a cell e.g.,
FACH measurement occasion information, measurement control system information
and neighbouring cell measurement information.
• SIB 18 — Contains PLMN identities of neighbouring cells to be considered
in idle mode as well as in connected mode.
6-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
RRC Procedures Version 1 Rev 0
RRC Procedures
Non acces s
C ore Network S IB 1 s tratum s ys info +
UE timers and
counter
Iu
SB
C ell s ys tem info
i.e cell s election
S IB 3 and res election
R NC MIB
Iub E xample only info
BCH
S C C P C H and
NodeB S IB 5 P R AC H
information
© 2005-2006 CP13: Introduction to UMTS USR6 6-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 RRC Procedures
RRC Procedures
Cell Selection/Re-selection
The goal of the cell selection procedures is to fast find a cell to camp on. To speed up
this process, at "power up" or when returning from "out of coverage", the UE shall start
with the stored information from previous network contacts. If the UE is unable to find
any of those cells the initial cell search will be initiated.
If it is not possible to find a cell from a valid PLMN the UE will choose a cell in a forbidden PLMN
and enter a "limited service state". In this state the UE regularly attempt to find a suitable cell
on a valid PLMN. If a better cell is found the UE has to read the system information for that cell.
The cell to camp on is chosen by the UE on link quality basis. However, the network can set cell
re-selection thresholds in order to take other criteria into account, such as, for example:
• available services;
• cell load;
• UE speed.
In CDMA, it is important to minimise the UE output power, and also to minimise the power consumption
in the UE. In order to achieve that, an ’Immediate Cell Evaluation Procedure’ at call set up can
ensure that the UE transmits with the best cell, while keeping the power consumption low.
Cell Re-selection
The cell reselection procedure is a procedure to check the best cell to camp on. The evaluation of
the measurements for this procedure is always active, in idle mode, after the cell selection procedure
has been completed and the first cell has been chosen. The goal of the procedure is to always
camp on a cell with good enough quality even if it is not the optimal cell all the time.
It is also possible to have a "time to trigger" and hysteresis criteria in the cell reselection to control the
number of cell reselections. The parameters needed for the cell reselection procedure (e.g., the
offset value and the hysteresis) are unique on a cell to neighbour cell relation basis. These have
therefore to be distributed, together with time to trigger value, in system information in the serving
cell. This implies that the UE does not need to read the system information in the neighbouring
cells before the cell reselection procedure finds a neighbouring cell with better quality.
6-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
RRC Procedures Version 1 Rev 0
RRC Procedures
go here whenever
a new PLMN
is selected
cell information no cell information
1
stored for the PLMN stored for the PLMN
Stored
Initial
Information no suitable cell found
Cell Selection
Cell Selection
no suitable
cell found
suitable cell found suitable cell found
no
suitable
Cell Selection cell
suitable NAS found
when leaving cell found Camped
registration
connected normally
rejected
mode
leave suitable
return to idle mode cell selected
idle mode trigger
Connected Cell no suitable
Mode Reselection cell found
go here when no USIM in the UE Any Cell
1 USIM inserted Selection
no acceptable cell found
an acceptable cell found
Cell Selection acceptable
when leaving cell found Camped on suitable
1
connected Any Cell cell found
mode
leave acceptable
return to idle mode cell selected
idle mode trigger
Connected
Mode Any Cell
(Emergency no acceptable cell found
Reselection
calls only)
© 2005-2006 CP13: Introduction to UMTS USR6 6-21
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 RRC Procedures
RRC Procedures
UE State Transition Algorithm
After the RRC connection is set up, the RNC observes UE activity and uses the UE
state transition algorithm to transit the UE state.
UE State Transition Algorithm
The figure opposite shows the RRC states in UTRA RRC Connected Mode, including transitions
between UTRA RRC connected mode and GSM connected mode for CS domain services,
and between UTRA RRC connected mode and GSM/GPRS packet modes for PS domain
services. It also shows the transitions between Idle Mode and UTRA RRC Connected Mode
and furthermore the transitions within UTRA RRC connected mode. In our algorithm, we
only care for the state transition in the UTRAN connected mode.
The principle of UE state transition is that:
• The state of the UE transits from CELL_DCH to CELL_FACH or from CELL_FACH
to CELL_PCH/URA_PCH if the activity of UE decreases.
• The state of the UE transits from CELL_PCH/URA_PCH to CELL_FACH or from
CELL_FACH to CELL_DCH if the activity of UE increases.
Paging
This procedure is used to transmit paging information to selected UEs that are in idle mode or in
Cell_PCH and URA_PCH states. It makes use of the Paging Type 1 message. The reasons for a
paging message can be the establishment of a network originated call or session set-up, the request
to trigger a cell update procedure, the change to Cell_FACH state because of downlink packet data
activity, the request to start the release of an RRC connection and the request to read updated system
information in the broadcast channel. A similar procedure exists for paging mobiles in Cell_DCH and
Cell_FACH states, but in this case a Paging Type 2 message is sent through the DCCH.
6-22 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
RRC Procedures Version 1 Rev 0
RRC Procedures
UE State Transition and Status of the RRC Connection
UTRAN Connected Mode UTRAN Inter-RAT
Handover
GSM
URA_PCH Connected
Mode
CELL_PCH GSM Handover
Release RR
CELL_DCH Connection
(with HS-
DSCH) GPRS Packet
CELL_FACH Transfer Establish RR
Mode Connection
Cell
CELL_DCH Reselection
Release RRC Establish RRC Release of Initiation of
connection connection temporary temporary
Release RRC block flow block flow
Establish RRC
connection connection
Camped on a UTRAN Cell Camped on a GSM/GPRS Cell
Idle Mode
© 2005-2006 CP13: Introduction to UMTS USR6 6-23
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 RRC Procedures
RRC Procedures
RRC connection establishment
UEs in idle mode that require the initiation of a signalling connection make use of the RRC connection
establishment procedure. The procedure starts with a RRC Connection Request message mapped
to the CCCH logical channel and transmitted through the RACH. The mobile identifies itself by
means of NAS identifiers like the IMSI or the TMSI and it includes the establishment cause. There
exist several causes including the registration, the establishment of originating calls for each of the
four possible service classes (conversational, streaming, interactive and background) or the transfer
of higher layer signalling. Upon receipt of this message, the network may either accept or reject the
request by means of a RRC Connection Setup or a RRC Connection Reject message, respectively,
which is mapped to the CCCH logical channel and the FACH transport channel. In the case of
acceptance, the RRC Connection Setup message includes the Radio Network Terminal Identifier
(RNTI) for the mobile and the indication about whether to pass to Cell_DCH or to Cell_FACH. It also
includes the characterisation of the allocated dedicated radio channel in terms of code sequence
and TFCS in both the uplink and downlink direction, when the user is moved to the Cell_DCH. In
any case, the mobile terminal is now in connected mode and there is a DCCH logical channel
allocated to it that includes SRB#1, SRB#2, SRB#3 and optionally SRB#4. The procedure completes
when the mobile sends the RRC Connection Setup Complete message through DCCH and either
DCH or RACH transport channel, thus acknowledging the correct reception and configuration
of the allocated channel. Only one RRC connection may exist for a given mobile.
Establishment of signalling connections between the UE and the Core Network and
direct transfer of signalling messages.
These procedures are intended to establish and release NAS signalling connections between the
terminal and the different core network domains (i.e. CS and PS domains). This allows the direct
transfer of signalling messages between the upper layer entities of mobiles that have previously
established a RRC connection. The term ‘direct transfer’ refers to the transmission of signalling NAS
messages through the RRC layer either in the uplink or in the downlink direction.
The establishment of the signalling connection is done by means of the Initial Direct Transfer
procedure, which is initiated by the NAS of the UE. In this case, the RRC layer of the UE sends an
Initial Direct Transfer message to the peer entity at the SRNC that includes the message denoted as
Initial UE Message (which belongs to the RANAP protocol defined between RNC and CN and that
contains a NAS message) and some information about the core network domain (i.e. CS or PS) to
which the NAS message should be delivered. Once the signalling connection has been established
with the Initial Direct Transfer message, subsequent NAS messages corresponding to this connection
are transmitted with the Uplink Direct Transfer and Downlink Direct Transfer messages between
RRC entities. Some examples of NAS messages that can be exchanged could be, for example,
a CM Service Request in order to start a call, a MM Location Updating Request, etc.
6-24 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
RRC Procedures Version 1 Rev 0
RRC Procedures
UE S R NC CN
RRC Message (Logical Channel) RANAP Message
RRC Connection Request (CCCH)
Establish radio resource at the
Node B for SRB (NBAP Signalling)
RRC
connection RRC Connection Setup (CCCH)
establishment
(UE-UTRAN) Establish resources at the Iu
RRC Connection Complete (DCCH) interface
Signalling
Initial Direct Transfer (DCCH) Initial UE Message
connection
establishment
(UE-CN)
UL/DL Direct Transfer Messages
RAB Assignment Request Message
Service
establishment
(UE-CN) Radio Bearer Setup (DCCH)
Establish radio resource at the
Node B for RB (NBAP Signalling)
Radio Bearer Setup Complete (DCCH)
© 2005-2006 CP13: Introduction to UMTS USR6 6-25
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 RRC Procedures
RRC Procedures
Radio bearer establishment
The radio bearer establishment is a procedure initiated by the upper layers of the network side in
order to request the allocation of radio resources to a mobile terminal that previously has established
a RRC connection. The establishment of a RRC connection involves the establishment of different
SRBs by means of the allocation of the required radio resources to allow the transfer of signalling
messages between the UE and the network. At a given instant during the RRC connection, the
upper layer signalling messages exchanged by the UE and the Core Network may request the
initiation of a user service belonging to a certain service class and with different requirements (e.g.
a circuit switched call by means of a CC Setup message or a packet transfer by means of a SM
Activate PDP Context Request). This user service requires the extension of the radio resource
allocation to the corresponding user taking into consideration the service requirements. Then, after
the acceptance of the new service by the admission control, the RRC of the SRNC will receive from
the core network (i.e. from the MSC for CS services or from the SGSN for PS services) the order to
allocate the corresponding radio resources to the terminal. This will initiate the establishment of a radio
bearer through the corresponding RRC procedure, which starts with the transmission of a Radio
Bearer Setup message from the RRC at the SRNC to the peer entity at the UE side. This message
includes all the parameters to configure the RLC/MAC/PHY layers according to the transport and
physical channels that are being assigned for both the uplink and downlink direction (e.g. transport
channel type, code sequence, TFCS, RLC mode, etc.). Note that depending on the service nature
(i.e. CS or PS) and the specific service requirements, this procedure may or may not involve the
establishment of a dedicated channel. Similarly, and in the case when previous physical dedicated
channels are already allocated to the user, the procedure may involve the modification of the physical
channel characteristics. When the transport and physical channels allocated in the radio bearer
are successfully established, the RRC at the UE side will issue a Radio Bearer Setup Complete
message. In the case of failure, it will issue a Radio Bearer Setup Failure message.
6-26 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
RRC Procedures Version 1 Rev 0
RRC Procedures
UE S R NC CN
RRC Message (Logical Channel) RANAP Message
RRC Connection Request (CCCH)
Establish radio resource at the
Node B for SRB (NBAP Signalling)
RRC
connection RRC Connection Setup (CCCH)
establishment
(UE-UTRAN) Establish resources at the Iu
RRC Connection Complete (DCCH) interface
Signalling
Initial Direct Transfer (DCCH) Initial UE Message
connection
establishment
(UE-CN)
UL/DL Direct Transfer Messages
RAB Assignment Request Message
Service
establishment
(UE-CN) Radio Bearer Setup (DCCH)
Establish radio resource at the
Node B for RB (NBAP Signalling)
Radio Bearer Setup Complete (DCCH)
© 2005-2006 CP13: Introduction to UMTS USR6 6-27
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 RRC Procedures
RRC Procedures
Measurement Procedures
These procedures allow the mobile terminals to provide the network with different measurement
reports that will be used by the radio resource management strategies to take the appropriate
decisions that maintain the required QoS for the accepted mobiles.
The network configures the measurements that should be provided by the mobile terminal by indicating
the objects to be measured (i.e. the cells, the transport channels and the physical channels), the
criteria to be used (i.e. periodic reporting or event-triggered reporting when certain events are
detected at the UE) and the RLC mode to be used (i.e. acknowledged or unacknowledged). This
configuration is done by means of the Measurement Control message. Measurements are required
only by terminals in Cell_DCH and Cell_FACH states, although in some cases such as traffic
volume monitoring, terminals in Cell_PCH may also send measurement reports.
The Measurement Reports provided by the terminals include several types of measurements,
which are classified into the following groups:
• Intra-frequency measurements - These correspond to downlink physical channels in the cells with
the same frequency as the cells from the Active Set. The measured cells belong to the Monitored
Set, which is broadcast in the cell where the mobile is allocated. These measurements include:
◦ Ec/No of the primary CPICH channel, which is equivalent to the ratio between the power
of the pilot channel and the total received power at the antenna connector.
◦ Downlink path loss — which can be measured as the difference between the transmitted
and the received CPICH power. The transmitted CPICH power is broadcast by the network.
◦ Downlink Received Signal Code Power (RSCP) for the primary CPICH, corresponding
to the power measured at the code of the primary CPICH.
◦ Measured time difference between P-CCPCH frames of the different cells.
• Inter-frequency measurements — These are done over downlink physical channels of cells
with a different frequency to that of the cells in the active set. The measurements included in
this group are essentially the same as in the intra-frequency measurements.
• Inter-RAT measurements — These are done over cells from other RATs, like GSM/GPRS, and will
be required to decide the execution of inter-RAT handovers. The measured quantities for GSM cells
include the GSM carrier RSSI, BSIC and the observed time difference with respect to the GSM cell.
• Traffic volume measurements — These include uplink measurements of the RLC buffer
occupancy, providing instantaneous and average values as well as the measured variance.
• Quality measurements — These report downlink quality parameters, such as the
transport block error rate for specific transport channels.
• UE internal measurements — These measurements include the UE transmission power,
the UE received RSSI and the observed difference between reception and transmission
times (i.e. the difference between the start of the uplink DPCCH/DPDCH transmission
and the reception of the first path of the downlink DPCH).
6-28 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
RRC Procedures Version 1 Rev 0
RRC Procedures
Neighbour Cells
Intra-frequency measurements Inter-RAT measurements
• Ec/No of the primary CPICH channel • GSM RSSI
C ore Network • Downlink path loss • BSIC
• RSCP for the primary CPICH
Iu Inter-frequency measurements
• Ec/No of the primary CPICH channel
• Downlink path loss
R NC • RSCP for the primary CPICH
Iub
UE internal measurements
• UE transmission power
• UE received RSSI
NodeB
Traffic volume measurements
• RLC buffer occupancy
Quality measurements
• transport block error rate
© 2005-2006 CP13: Introduction to UMTS USR6 6-29
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 RRC Procedures
This page intentionally left blank.
6-30 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Radio Resource Management Functions Version 1 Rev 0
Chapter 7
Radio Resource Management
Functions
© 2005-2006 CP13: Introduction to UMTS USR6 7-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Radio Resource Management Functions
This page intentionally left blank.
7-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
On completion of this chapter the student should be able to:
• Describe basic Radio Resource and Mobility Management functions.
• Describe handover control
• Describe compressed mode
• Describe macro diversity
• Describe SRNS relocation
• Describe power control
• Describe DCCC
• Describe load control
© 2005-2006 CP13: Introduction to UMTS USR6 7-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Radio Resource Management Overview
Radio Resource Management Overview
Introduction to Radio Resource Management
Radio Resource Management (RRM) consists of a series of procedures designed to achieve the
most efficient utilisation of the air interface (Uu). The purpose of RRM is to:
• Guarantee Quality of Service
• Maintain planned coverage
• Offer high capacity
To achieve this end, the objectives of RRM can be summarises as:
• Power Control - Minimise User/Network transmission power, whilst maintaining requested Quality
of Service, to reduce interference on the system, thus increasing capacity and coverage.
• Admission and Load Control - To maintain the load of the entire system at a steady, manageable level
• Handover Control - maintain QoS, even when the UE moves to other cells or systems
7-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Radio Resource Management Overview Version 1 Rev 0
Radio Resource Management Overview
)
oS
(Q
Co
ice
ve
Power Control
rv
ra
Se
g
e
of
ty
Handover Control
ali
Qu
Admission and Load Control
Capacity
© 2005-2006 CP13: Introduction to UMTS USR6 7-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Handover Control
Handover Control
The handover function in UTRAN manages the mobility of the UE and the radio interface. It is based on
radio measurements and cell topology and it is used to maintain the Quality of Service requested by
the Core Network regardless of UE mobility. The RNC supports the following handover types:
• Intra-frequency soft, softer and hard handover,
• Inter-frequency hard handover
• Inter-RAT hard handover in both CS and PS domains.
In addition, the procedures may be intra-RNC or inter-RNC and may require
the performance of SRNS relocation.
The decision on what handover type needs to be performed depends on a number of conditions
and parameters that are presented in the following sections. In general, soft/softer handover has
higher priority than intra-frequency hard handover and inter-frequency and inter-RAT HHO only occurs
in border cells that have inter-frequency or inter-RAT neighbouring cells set accordingly.
Three different handover causes are supported in the RNC:
• Handover due to poor radio link quality
• Handover due to radio interface overload
• Operator forced handover.
7-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Handover Control Version 1 Rev 0
Handover Control
© 2005-2006 CP13: Introduction to UMTS USR6 7-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Measurement Control
Measurement Control
The handover algorithm also controls the measurement reporting performed by the UE
in CELL_DCH state for handover purposes. The MEASUREMENT CONTROL message
is used to set up and modify the way measurements are taken by the UE. The contents
and frequency of the MEASUREMENT REPORT messages from the UE depends on the
measurement type, the UE state and its measurement capability.
The list of cells that the UE must monitor is divided into three different categories.
• Active Set: Group of UTRAN cells which the UE has a radio link established to, i.e. it
is in soft/softer handover with. The Active Set contains only UTRAN cells that operate
on the same UMTS frequency. In USR3.0 the maximum number of cells in the Active
Set is fixed to 3. This is a hard coded parameter in USR3.0.
• Monitored Set: Cells that are not currently in the Active Set, but the UE is monitoring for
handover according to a neighbour list assigned by UTRAN (stored as CELL_INFO_LIST
in the UE). The Monitored Set may contain UTRAN and GSM cells and the UTRAN cells
may be under different UMTS frequencies. The maximum number of cells to measure in
USR3.0 is: 32 intra-frequency, 32 inter-frequency and 32 inter-RAT cells.
• Detected Set: Cells that are not included in the neighbour list to monitor but are detected by the
UE on its own. The UE only reports detected UTRAN cells that are under the same frequency
as the active cells and only when in CELL_DCH state. The purpose is to provide information
to the network operator for manually updating the neighbour cell list of cells.
Monitored List Determination
The best cell in the active set to control the monitored list. The strategy is as follows:
• If there is only one cell in the active set, use its neighbour list to build the monitored set list.
• If there is more than one cell in the active set use the neighbour list of the
best cell to build the monitored set list.
• If a 1D event is received, indicating a new best cell, use the neighbour list of the
new best cell to build the monitored set list.
• If the best cell is removed, use the neighbour list of the best cell amongst those left in
the active set at that time in order to build the new monitored list.
7-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Measurement Control Version 1 Rev 0
Measurement Control
Monitored
Set
Monitored Monitored
Set Set
Monitored Active Detected
Set Set Set
Active Monitored
Set Set
Monitored Active Detected
Set Set Set
Monitored Monitored
Set Set
Detected Monitored Detected
Set Set Set
© 2005-2006 CP13: Introduction to UMTS USR6 7-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Intra-frequency Handover
Intra-frequency Handover
Algorithm Description
The figure opposite shows the scenario where a mobile moves from one cell to another. It can be
seen that in CDMA there is blur zone where the mobile can be connected to both cells, maximizing
the quality of service. This is often referred to as Soft or Softer Handover.
The handover control function for soft handover is responsible of the following tasks.
• Determining whether a soft handover is necessary.
• Receiving intra-frequency measurement reports from UEs (intra-frequency measurement
results and information about intra-frequency events that triggered the measurement report),
which may refer to Node Bs under the same or different RNCs.
• Deciding whether to add any of these reported cells to the active set or drop any of the
cells from the active set (adding or deleting the radio links)
• When radio links are added, splitting/combining or splitting/selection functions in the appropriate
network elements are also instructed to begin diversity processing with the new radio link.
Intra-frequency Event Driven Reporting
Event Event Description
Event 1a A Primary CPICH enters the Reporting Range.
Event 1b A Primary CPICH leaves the Reporting Range.
Event 1c A Non-active Primary CPICH becomes better than an active Primary CPICH
Event 1d Change of best cell
Event 1f Absolute value of a Primary CPICH becomes worse than a threshold
(Used to trigger interFreq Ho)
7-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Intra-frequency Handover Version 1 Rev 0
Intra-frequency Handover
• The UE has a radio connection with cell A
• When the UE established an additional radio
connection with Cell B this is called a softer
handover
• When the UE establishes an additional radio
connection with Cell C this is a soft handover
even when Cell C is located under a different
RNC
Cell A Cell C
Cell B
© 2005-2006 CP13: Introduction to UMTS USR6 7-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Intra-frequency Handover
Intra-frequency Handover
Intra-frequency Hard Handover
Although soft/softer handover is the preferred procedure to handle RRC connection mobility,
there are times when only a hard handover can be performed. The hard handover procedure
removes all the RL(s) in the active set and establishes new RL(s). An intra-frequency hard
handover is only performed when one of the following conditions apply.
• There is no Iur interface between the source and target RNC.
• The UE is using a PS RAB at a bit rate above a preset threshold.
7-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Intra-frequency Handover Version 1 Rev 0
Intra-frequency Handover
Cell A
Cell B
• A hard handover occurs when the UE has to release the old radio
links before it establishes a radio connection with a new cell
Occurs on 1D (change of best cell) event when:
1. There is no Iur interface between the source and target RNC
2. The UE is using a BE PS RAB at a bit rate above a preset threshold
© 2005-2006 CP13: Introduction to UMTS USR6 7-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Inter-frequency Hard Handover
Inter-frequency Hard Handover
Overview of Inter-Frequency Hard Handover
Based on handover triggering causes, inter-frequency handover includes the following types:
• Inter-frequency handover based on coverage The UE might leave the coverage of the
current frequency during the movement of the UE. In this case, the RNC needs to trigger
an inter-frequency handover based on coverage to avoid call drop.
• Inter-frequency handover based on load To balance the loads between inter-frequency
concentric cells, the RNC would choose some UEs to do inter-frequency handover
according to user and service priorities.
• Inter-frequency handover based on speed When the Hierarchical Cell Structure (HCS) is
used, cells are divided into different layers according to their coverage. Marco cell corresponds
to large coverage and low priority and Micro cell corresponds to small coverage and high
priority. Inter-frequency handover can be triggered by UE speed estimation algorithm of
the HCS. The UE with high speed is handed over to a cell with larger coverage to reduce
the frequency of handover, while the UE with low speed is handed over to a cell with
smaller coverage and larger capacity to improve the system capacity.
Handover Triggering Conditions
The inter-frequency handover triggering conditions are as follows:
Inter-frequency Handover Type Triggering Conditions
Handover based on coverage UE Reporting of event 2D or
periodically measurement reporting.
When receiving event 1F, the RNC will decide
to try a blind handover to inter-frequency cell if
a blind handover neighboring cell is available.
Note: Blind handovers only used in specific
strategic areas.
Handover based on load Load could be shared by inter-frequency cells.
Estimation decision from Load Reshuffling
(LDR) Algorithm Module.
Handover based on estimation decision of the Estimation decision of the UE speed in HCS
UE speed in HCS
7-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Inter-frequency Hard Handover Version 1 Rev 0
Inter-frequency Hard Handover
f1 f2
• Handover based on coverage
• Handover based on load
• Handover based on speed
© 2005-2006 CP13: Introduction to UMTS USR6 7-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Inter-frequency Hard Handover
Inter-frequency Hard Handover
Handover Procedure
Inter-frequency handover procedure includes the following three phases:
1. Handover measurement
2. Handover decision
3. Handover execution
Phase Inter-Frequency Inter-Frequency Inter-Frequency
Handover Based on Handover Based on Handover Based on
Coverage Load Speed
Handover The UE reports The HCS speed
measurement event 2D. Then the estimation algorithm
RNC enables the initiates a handover
compressed mode and procedure. If the
starts inter-frequency handover is from
measurement. a micro cell to
Periodical reporting another macro cell,
mode or event reporting and blind handover
mode can be used. condition is fulfilled,
When receiving event the RNC performs
1F, the RNC will decide blind handover to the
to try a blind handover. target cell. Otherwise,
the RNC enables the
compressed mode and
starts inter-frequency
measurement.
Handover decision After UE reports The RNC performs load The UE reports event
event 2B, the RNC reshuffling algorithm 2C. Then the RNC
performs handover and then performs blind performs handover
decision. Or the UE handover decision. decision.
periodically reports
the inter-frequency
measurement report,
and the RNC decides
the handover after
evaluation.
Handover execution The RNC initiates a The RNC initiates a The RNC initiates a
handover procedure. blind handover to the handover procedure.
target cell.
7-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Inter-frequency Hard Handover Version 1 Rev 0
Inter-frequency Hard Handover
© 2005-2006 CP13: Introduction to UMTS USR6 7-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Inter-RAT Hard Handover
Inter-RAT Hard Handover
The purpose of the inter-RAT handover procedure is to, under the control of the network, transfer a UE
connection from one radio access technology (e.g. UTRAN) to another (e.g. GSM). The RNC supports
both, handover from GSM to UTRAN and, handover from UTRAN to GSM on CS and PS domains (Cell
Change Order), but not simultaneously. This section covers only handover from UTRAN to GSM.
Algorithm Overview
In order to offer worldwide coverage, the handover from UTRAN to GSM is a key feature, especially
during early deployment stages where islands of UMTS coverage are envisaged. The procedure
is initiated from UTRAN with a RRC message HANDOVER FROM UTRAN COMMAND. Then the
UE must establish the connection to GSM and release all UMTS radio resources.
When the UE works in CELL_DCH state, the UMTS GSM handover is the procedure during which the
WCDMA RAN initiates handover (for CS services) or cell reselection (for PS services) to the GSM.
Based on triggering causes, UMTS to GSM handover includes:
• UMTS to GSM coverage-based handover. The coverage of UMTS s usually discontinuous
at the very beginning of the network rollout. On the border, if the signal quality of
UMTS rather than GSM is poor and if all services of the UE are supported by GSM,
UMTS to GSM coverage-based handover is triggered.
• UMTS to GSM load-based handover. If the load of UMTS rather than GSM is heavy and all
services of the UE are supported by GSM, UMTS GSM load-based handover is triggered.
• UMTS GSM service-based handover. Based on layered services, traffic of different classes
is handed over to different systems. For example, when an Adaptive Multi Rate (AMR)
speech service is requested, this call could be handed over to GSM.
UMTS to GSM Handover Triggering Conditions
• UMTS to GSM coverage-based handover. The CPICH Ec/N0 or CPICH RSCP of the UMTS
cell to which the UE connects is lower than the corresponding threshold. In addition, there is
a GSM cell whose GSM carrier RSSI is higher than the preset threshold.
• UMTS to GSM load-based handover. The load of the UMTS cell to which
the UE connects is higher than the threshold.
• UMTS to GSM service-based handover. When a service is established, the Core
Network (CN) requests a handover of the service to GSM.
7-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Inter-RAT Hard Handover Version 1 Rev 0
Inter-RAT Hard Handover
UMTS GSM
• UMTS to GSM coverage-based handover
• UMTS to GSM Load-based handover
• UMTS to GSM Service-based handover
© 2005-2006 CP13: Introduction to UMTS USR6 7-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Inter-RAT Hard Handover
Inter-RAT Hard Handover
Preconditions for UMTS to GSM Handover
Overview of Preconditions
Before the UMTS GSM handover is performed, the following preconditions must be taken into account:
• Service handover indicators. The indicators are configured by CN and indicate
CN policy for service handover to GSM.
• GSM cell capability. The capability, Inter-RAT cell type, of each GSM cell must be
configured at the RNC. The parameter indicates whether the cell supports GSM, GPRS, or
EDGE. It also indicates that the cell may not be supported by 2G.
• Service capability. The required 2G Capability, of each service must be configured at
the RNC. The parameter indicates whether the service is supported by GSM, GPRS, or
EDGE. It also indicates that the service may not be supported by 2G.
• UE capability. The RNC obtains the capability information of a UE according to the UE
CAPABILITY INFORMATION reported by the UE. The information indicates whether the UE
supports GSM, GPRS, or EDGE. It also indicates that the UE may not be supported by 2G.
Service Handover Indicators
Among the four preconditions, service handover indicators are taken into account firstly. An
indicator is contained in the RAB assignment signalling that is delivered by the CN. Based on the
indicators, the other three preconditions, and the handover types (UMTS to GSM handover based
on coverage/load/service), the RNC decides whether to perform inter-RAT handover.
There are the following service handover indicators:
• Handover to GSM should be performed
• Handover to GSM should not be performed
• Handover to GSM shall not be performed
By default, the RNC does the following:
• For a UE with a single signalling RAB, the handover to GSM is not allowed.
• For the UE accessing combined services (with CS services), the RNC sets the service
handover indicator of the UE to that of the CS service because the CS service
has the highest Quality of Service (QoS) priority.
• For the UE accessing combined services (with only PS services), the RNC sets the service
handover indicator of the UE to that of the PS service who has the highest QoS priority.
7-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Inter-RAT Hard Handover Version 1 Rev 0
Inter-RAT Hard Handover
© 2005-2006 CP13: Introduction to UMTS USR6 7-21
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Inter-RAT Hard Handover
Inter-RAT Hard Handover
GSM Cell Capability
With the Inter-RAT cell type capability, the RNC decides whether to start inter-RAT measurement.
Service Capability
For combined services, the RNC selects the Required 2G Capability parameter
required by the RAB that has the highest priority.
UE Capability
With the UE CAPABILITY INFORMATION, the RNC decides whether to start inter-RAT measurement.
7-22 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Inter-RAT Hard Handover Version 1 Rev 0
Inter-RAT Hard Handover
Service Capabilities
configured at the RNC
Iub
Iu
CN RNC
UE Capabilities
RAB ASSIGNMENT REQUEST
• Handover indicators (last slide)
GSM Cell
capabilities
i.e. supports
GPRS/EDGE?
© 2005-2006 CP13: Introduction to UMTS USR6 7-23
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Inter-RAT Hard Handover
Inter-RAT Hard Handover
Handover Procedures for UMTS to GSM
The UMTS to GSM handover includes the following four phases:
• Handover triggering
• Handover measurement
• Handover decision
• Handover execution
Non coverage-based handover has two cases:
• UMTS to GSM handover based on load
• UMTS to GSM handover based on service
When the UE works in CELL_FACH or CELL_PCH/URA_PCH state, the inter-RAT handover is
initiated by the UE. In this situation, the handover is the procedure for inter-RAT cell reselection.
During cell reselection, the UE evaluates the quality of the existing cell on which it is camped,
starts inter-RAT measurement, selects a best cell in another system according to the cell
reselection criteria, and then initiates the access to GSM/GPRS/EDGE.
7-24 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Inter-RAT Hard Handover Version 1 Rev 0
Inter-RAT Hard Handover
© 2005-2006 CP13: Introduction to UMTS USR6 7-25
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Inter-RAT Hard Handover
Inter-RAT Hard Handover
UMTS to GSM Handover Measurement
UMTS GSM handover based on coverage
After receiving a 2D event report message, the RNC performs the following:
1) Decides an inter-RAT handover measurement based on coverage.
2) Starts periodic controlling or 3A event triggered measurement reporting.
The Inter-RAT report mode can be set to Periodic reporting or Event trigger.
3) Decides to initiate an inter-RAT handover based on measurement reports from the UE. If a
2F event is received, the RNC will stop inter-RAT handover measurement.
UMTS GSM handover based on load
After receiving a 3C event report message, the RNC decides to initiate an inter-RAT handover.
7-26 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Inter-RAT Hard Handover Version 1 Rev 0
Inter-RAT Hard Handover
© 2005-2006 CP13: Introduction to UMTS USR6 7-27
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Hierarchical Cell Structure
Hierarchical Cell Structure
In a 3G network, the so-called hot spots in radio communications may appear with an increase of
subscribers and traffic. This requires more cells to increase the network capacity. More cells and
smaller cell radius indicate that more frequent handovers of UEs take place. For a UE in fast speed,
frequent handovers reduce call quality, increase uplink interference, and increase signaling load.
In this situation, Hierarchical Cell Structure (HCS) is required to divide cells into
different hierarchies. The RNC supports the HCS with eight hierarches, typically there
are three Macro Cells, Micro Cells and Pico Cells.
The features of different cells are as follows:
Macro Cell:
• Large coverage
• Continuous coverage networking
• Low requirement on capacity
• Fast-moving environment
Micro cell:
• Densely populated areas
• High requirement on capacity
• Slow-moving environment
Pico cell:
• Indoor coverage
• Outdoor dead-area coverage.
Where, the pico cell has the highest priority and the macro cell has the lowest priority.
7-28 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Hierarchical Cell Structure Version 1 Rev 0
Hierarchical Cell Structure
Large coverage
Macro Cell Low capacity
Fast moving
Densely populated areas
Micro Cell High capacity
S low moving
Indoor Coverage
Pico Cell
Outdoor dead area coverage
© 2005-2006 CP13: Introduction to UMTS USR6 7-29
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Hierarchical Cell Structure
Hierarchical Cell Structure
HCS Handover Overview
The HCS handover is divided into the following two phases.
Speed Estimation
The speed estimation on each hierarchy of an HCS cell falls into one of the following types:
• Fast speed
• Normal speed
• Slow speed
According to the number of changes of the best cell within a given time unit, the speed estimation
algorithm estimates the moving speed of the UEs. See details as follows:
• If the number of changes of best cell for a UE is above the fast-speed threshold,
this UE is calculated to be in fast speed;
• If the number of changes of best cell for a UE is below the slow-speed threshold,
this UE is calculated to be in slow speed;
• If the number of changes of best cell for a UE is between fast-speed threshold and
slow-speed threshold, this UE is calculated to be in normal speed.
HCS Handover Based on Speed Estimation
After the moving speed of the UE is estimated, inter-hierarchy handover algorithm initiates
the corresponding handover based on this speed decision.
According to the results of speed estimation:
• The UE in fast speed is handed over to the cell of lower priority;
• The UE in slow speed is handed over to the cell of higher priority;
• The UE in normal speed is not required to be handed over to any cell.
7-30 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Hierarchical Cell Structure Version 1 Rev 0
Hierarchical Cell Structure
T he change of best cell (E vent
1D) is monitored for a time
period and if there has been no
change of best cell with that
time then handover to micro
cell and vice versa.
© 2005-2006 CP13: Introduction to UMTS USR6 7-31
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Compressed Mode Control
Compressed Mode Control
Algorithm Overview
Compressed mode is used to allow UEs to perform inter-frequency and inter-RAT measurements.
The prerequisite is that the UE supports the functionality. The RNC supports compressed mode
in uplink, downlink and combined uplink + downlink, according to UE capabilities.
Compressed Mode (CM) operation is used when a dual mode UE (UMTS + GSM and/or DCS1800) or
a dual band UE (UMTS + UMTS) nears the limit of coverage in a UMTS system that borders a GSM,
DCS1800, or another UMTS system on a different frequency. The CM algorithm creates a “hole"
or gap in the transmitted DL and/or UL radio frame, allowing the UE receiver to change frequency
and monitor the adjacent GSM or DCS1800 system (for inter-RAT handover) or UMTS system (for
inter-frequency handover). Even though there is a gap in the transmitted frame no data is lost. All of
the data that would normally have been sent in the frame is compressed to fit into fewer slots.
The process for compressing the data to fit into fewer than the normal 15 slots is called “time
compression". Several time compression methods are available: spreading factor reduction by
2 (SF/2), puncturing (rate matching), and higher layer scheduling. Puncturing refers to applying
rate matching techniques for creating a transmission gap in a radio frame. SF/2 consists of
reducing the spreading factor by 2 during one compressed radio frame to enable transmission of the
information bits in half of the radio frame (7.5 slots). And in the higher layer scheduling method,
only a subset of the allowed TFCs are used in the compressed mode frame.
The UE can be configured with a single compressed mode pattern sequence for each
measurement purpose. These settings are currently established using Motorola Internal
MML commands and, include the following patterns:
• For inter-frequency measurements
◦ FDD measurement
• For inter-RAT measurements
◦ GSM carrier RSSI measurement
◦ Initial BSIC identification
◦ BSIC confirmation
Depending on whether the UE needs to perform FDD measurements only, GSM measurements only
or both, the RNC activates the appropriate gap patterns. For FDD operation only, a single “FDD
measurement” gap is activated. For GSM operation only, three simultaneous gap patterns are activated
(RSSI, BSIC_ID, and BSIC_confirmation). For combined FDD and GSM operation, three simultaneous
gap patterns are used (RSSI, BSIC_ID and FDD measurement). The BSIC re-confirmation gap pattern
is not used when the UE needs to measure simultaneously inter-frequency and inter-RAT neighbours
in order to decrease the impact of compressed mode operation on quality and performance.
The compressed mode procedure is initiated by the CRNC by sending a RADIO LINK
RECONFIGURATION PREPARE message to the Node B with a modification of the
Transmission Gap Pattern Sequence Code Information radio link parameters. On the other
hand, deactivation is achieved via the COMPRESS MODE COMMAND.
7-32 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Compressed Mode Control Version 1 Rev 0
Compressed Mode Control
FDD
Measurement
Gap activated
UMTS
UMTS Source Combined
Interfreq Cell
Cell
RSSI
BSIC_ID
FDD Measurement
RSSI
BSIC_ID
BSIC_re-confirm
10ms
GSM Cell
Transmission gap available for
inter-frequency measurements
© 2005-2006 CP13: Introduction to UMTS USR6 7-33
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Macro Diversity
Macro Diversity
Macrodiversity provides an improved error correction capability through the use of combining/splitting
at the RNC and Node B. Communications will be sent via the Iur interface from the RNC in the
D-RNS to the RNC in the S-RNS and on to the Iu to the core network.
This function controls the duplication/ replication of information streams to receive/ transmit the same
information through multiple physical channels from/ towards a single mobile terminal.
This function also controls the combining of information streams generated by a single source (diversity
link), but conveyed via several parallel physical channels (diversity sub-links). Macrodiversity control
should interact with channel coding control in order to reduce the BER when combining the different
information streams. In some cases, depending on physical network configuration, there may be
several entities that combine the different information streams, i.e. there may be combining/splitting
at the S-RNC, D-RNC or Node B level. This function is located in the UTRAN.
7-34 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Macro Diversity Version 1 Rev 0
Macro Diversity
UTRAN
lu
D-RNS D-RNS S-RNS
Iur Iur
RNC RNC RNC
© 2005-2006 CP13: Introduction to UMTS USR6 7-35
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 SRNS Relocation
SRNS Relocation
SRNS Relocation Overview
The Serving RNS (SRNS) manages the connection between the UE and the UTRAN and
can be relocated. The SRNS relocation is of three types:
• Static relocation (UE not involved)
• Relocation due to hard handover (UE involved)
• Relocation due to cell or URA update (UE involved)
If no Iur interface exists, the relocation can be triggered only by the hard handover or cell/URA update.
Purposes
The main benefits of SRNS relocation are as follows:
When the Iur interface is involved
Relocating the SRNC to the DRNC can avoid data forwarding on the Iur interface. Thus it can reduce
the bandwidth occupied by the Iur interface and the transmission delay of user plane. When the
SRNC and the DRNC become independent of each other, the data of cell radio resource management
algorithms cannot be transmitted over the Iur interface. Thus the algorithms cannot be optimized. This
problem can be solved by initiating the static relocation to relocate the SRNC to the CRNC.
When the Iur interface is not involved
SRNS relocation can ensure communications not interrupted when the UE moves
to the coverage area of another RNC.
Static Relocation
When the Iur interface exists, the UE may use the radio resources of one RNC
and connects to the CN through another RNC.
After SRNS relocation, the Iur resources for the UE are released. The target RNC not only
provides radio resources for the UE but also connects the UE to the CN.
The purposes of the static SRNS relocation are as follows:
• To reduce the bandwidth occupied by the Iur interface
• To reduce the transmission delay of user plane
• To get the parameters of cell-level algorithms to optimize the performance
7-36 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
SRNS Relocation Version 1 Rev 0
SRNS Relocation
© 2005-2006 CP13: Introduction to UMTS USR6 7-37
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 SRNS Relocation
SRNS Relocation
Relocation Due to Hard Handover
The relocation happens when the UE is in CELL_DCH state and moves from one RNC to
another RNC with no Iur interface connecting the two RNCs.
Relocation Due to Cell or URA Update
The relocation happens when the UE reselects a cell that belongs to another RNC.
7-38 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
SRNS Relocation Version 1 Rev 0
SRNS Relocation
© 2005-2006 CP13: Introduction to UMTS USR6 7-39
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Power Control
Power Control
The power control mechanism is an essential part of cellular systems using the spread spectrum
technique of medium access. There are important functions of power control.
First, is to support high system capacity, which is basically achieved in CDMA-based systems
by reducing the level of adverse interference. The major contribution to system interference
level, in uplink and downlink direction respectively, comes from simultaneous RF signal
transmissions by many UEs and adjacent Node Bs on the same frequency.
The second function of power control procedures is to preserve required radio communication
quality regardless of dynamic changes in the propagation environment resulting from the
mobility of UEs, the changing number of active users in the system, and the ever propagation
characteristics of and radio channel. The quality may be defined here as low delay and
error-free transmission of digitised user data through radio channel.
One of the ways to obtain, at the same time, large system capacity and high service quality is
to keep UE and Node B RF signals transmission power at the lowest possible level and adjust
it dynamically upon variations of propagation conditions. The more accurate are UE and Node
B power control mechanisms to follow real dynamic structure of RF environment, the higher
system capacity and service quality performance may be achieved.
The goal of power control in WCDMA system is thus dynamic interference control,
rather than wide coverage area support.
The UE and UTRAN power control procedures use different sources of feedback information on temporal
propagation channel condition in the process of adjusting their transmitted signals power levels.
7-40 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Power Control Version 1 Rev 0
Power Control
Power Control Concept
• To Support High System Capacity by reducing the level of Interference.
• To Preserve The Required Radio Communication Quality Resulting From:
◦ Changes to the Propagating Environment due to UE Mobility
◦ Changes to the number of active users
◦ Changes to the Propagating Characteristics of the Radio Channel
Three Types of Power Control
• Open Loop Power Control
• Inner Closed Loop Power Control
• Outer Closed Loop Power Control
© 2005-2006 CP13: Introduction to UMTS USR6 7-41
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Open Loop Power Control
Open Loop Power Control
In UTRAN, open loop power control is applied only immediately prior to
initiating a transmission on the PRACH.
The UE determines an estimation of the downlink pathloss between the base station and the
UE by measuring the UTRA carrier received signal strength at the mobile. Through the medium
of the System Information messages on the P-CCPCH, the UE will also have access to certain
cell parameters, such as Cell ERP, Cell size, receiver sensitivity, etc.
Form this information the UE will calculate the required mean output power level required to
achieve the access requirements of the cell it wishes to connect to. The UE will now send its
first RACH Pre-amble at this calculated value. If no positive or negative acquisition indicator
is detected, the UE will increase its power by the required power-ramping factor, (cell defined
parameter), and send a second RACH Pre-amble. This process will be repeated until an
acknowledgement is received, or the max retries value is exceeded.
If a positive Ack is received, the UE will again adjust its output power, according to an offset value
notified by the cell, and transmit the RACH message part. On receipt of the RACH Message part, the
UTRAN can accurately calculate the uplink path loss and initiate the use of closed loop power control.
7-42 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Open Loop Power Control Version 1 Rev 0
Open Loop Power Control
UE monitors Common Pilot
and Broadcast information,
and calculates DL path Loss
Using DL path loss as
"perceived" UL path
loss, UE calculates TX
power O/P required
access network
Only used prior to initial transmission on PRACH
© 2005-2006 CP13: Introduction to UMTS USR6 7-43
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Closed Loop Power Control (Inner Loop)
Closed Loop Power Control (Inner Loop)
The objective of Closed loop power control is to maintain the the received signal strength, at the
base station, for all UEs at the same average level. As all UEs in a cell transmit on the same
frequency, a single overpowered mobile could block a whole cell to other users.
The uplink inner-loop power control adjusts the UE transmit power in order to keep the received
uplink Signal-to-Interference Ratio (SIR) at a given SIR Target (SIRtarget). The serving cells
(cells in the active set) should Estimate Signal-to-Interference Ratio (SIRest) of the uplink,
using the received pilot symbols in each uplink uplink timeslot.
The serving cells should then generate TPC commands and transmit the commands once per
slot, using the TPC symbols in each time slot, according to the following rule: if SIRest > SIRtarget
then the TPC command to transmit is "0", while if SIRest < SIRtarget then the TPC command
to transmit is "1". The UE uses this information to derive TPC_cmd.
After deriving of the TPC_cmd, the UE shall adjust the transmit power of the uplink
with a step Δ (in dB) which is given by:
D = DTPC × TPC_cmd.
The step size ΔTPC is a layer 1 parameter which is derived from the UE-specific higher-layer
parameter "TPC-StepSize" which is under the control of the UTRAN. If "TPC-StepSize" has the
value "dB1", then the layer 1 parameter ΔTPC shall take the value 1dB and if "TPC-StepSize"
has the value "dB2", then ΔTPC shall take the value 2dB.
A similar process is used in the downlink, to control the relative power weighting to
be applied to each downlink dedicated channel.
7-44 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Closed Loop Power Control (Inner Loop) Version 1 Rev 0
Closed Loop Power Control (Inner Loop)
UE monitors DL Signal to
Interference Ratio (SIR)
And compares against
Target SIR level
UE sends Transmit Power Control (TPC)
information to Node B, adjusting Node B
transmit power output in an attempt to
acheive target SIR
Inner Loop Power Control command rate is 1500Hz
© 2005-2006 CP13: Introduction to UMTS USR6 7-45
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Directed Retry
Directed Retry
The Directed Retry Decision (DRD) algorithm includes three components:
• RRC Retry Decision algorithm
• Redirection algorithm
• RAB Retry Decision algorithm
Within the UTRAN, a UE can take on one of two connection modes: namely, RRC connected
mode and idle mode. When a UE wants to establish an RRC connection it must first send an RRC
CONNECTION SETUP REQUEST message to the UTRAN (RNC). At this stage of the call set-up
process, the objective of the RRC CONNECTION REQUEST is to establish an SRB on a DCH. To
invoke the DRD algorithm, the UE should include a RACH measurement report (containing the CPICH
EcNo measurements of several neighbour/candidate cells). This list of candidate cells is then ranked in
descending order, based on the EcNo measurements. If the UE cannot establish an RRC connection
with its preferred cell, the candidate list is then sequentially examined in a top-down manner until a
suitable cell is obtained. If none of the cells in the list satisfy the criteria of the RRC Retry Decision
algorithm, the UE fails in its attempt to establish an RRC connection and the Redirection algorithm
is invoked. If on the other hand the UE is successful in its attempt to establish the requested RRC
connection, the CN then initiates the RAB assignment procedure. If the assignment procedure is
not successful, the RAB Retry Decision algorithm is invoked. The DRD algorithm can be triggered
by both UE originating and terminating calls. The Figure opposite illustrates the RRC and RAB
establishment procedures incorporating the three components of the DRD algorithm.
7-46 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Directed Retry Version 1 Rev 0
Directed Retry
UE RNC CN
RRC CONNECTION REQUEST
(Containing RACH Measurement Report)
RRC Retry
RRC CONNECTION SETUP Decision Algorithm
(Containing (New) Cell Information)
RRC CONNECTION SETUP COMPLETE
Redirection Algorithm
RRC DIRECT TRANSFER
RANAP DIRECT TRANSFER
RANAP RAB ASSIGNMENT REQUEST
RAB Retry
Decision Algorithm
RANAP RAB ASSIGNMENT RESPONSE
© 2005-2006 CP13: Introduction to UMTS USR6 7-47
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Dynamic Channel Configuration Control (DCCC)
Dynamic Channel Configuration Control (DCCC)
Dynamic Channel Configuration Control (DCCC) includes the following two parts.
Rate Re-allocation
Upsize and downsize the data rate of the Best Effort (BE) services, (i.e. interactive
and background) in the CELL_DCH RRC state.
Dynamically adjust the uplink and downlink bandwidth of the Dedicated Channel (DCH)
according to the traffic volume which reflects the state of data transmission.
Dynamically adjust the bandwidth of the Dedicated Channel (DCH) according to
the quality of radio link due to coverage.
Dynamically adjust the bandwidth of the Dedicated Channel (DCH) according to the load congestion.
This part of the algorithm works in conjunction with the load control mechanism.
UE State Transition
Switch the UE state to the CELL_FACH and CELL_PCH/URA_PCH state when the
UE inactivity is detected, and back to CELL_DCH state when the UE activity is
detected because there is data to be transmitted.
Measurements
The traffic volume measurement executed by UEs are used in the uplink bandwidth re-allocation
process and the UE state transition to improve the resource utilization.
The downlink Transmitted Code Power (TCP) measurements executed by NodeBs are
used in the downlink rate re-allocation to keep the link stability.
The Traffic Volume Measurements (TVMs) executed by RNC are used in the downlink bandwidth
re-allocation process and the UE state transition to improve the resource utilization.
Purpose
The DCCC is to improve the performance of the network resource utilization and to keep
the link stability. This is done in three keys ways as listed below:
• In the downlink and uplink, the DCCC re-allocates the bandwidth based on the traffic
volume measurement. In this way, the DCCC algorithm makes efficient use of the resource
such as the OVSF code resources, the Channel Element (CE) resources of the NodeB
and the transmission resources on the Iub and the Iur interfaces.
• In the downlink, the DCCC downgrades the data rate if the link quality deteriorates,
in order to prevent the call drop.
• The state of the UE can transit from CELL_DCH to CELL_FACH, or from CELL_FACH
to CELL_PCH/URA_PCH. In the state of CELL_FACH or the CELL_PCH/URA_PCH,
the resources of the network and the UE battery can be saved.
7-48 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Dynamic Channel Configuration Control (DCCC) Version 1 Rev 0
Dynamic Channel Configuration Control (DCCC)
Rate Re-allocation
• Control of BE services
• Adjust DCH rate based on
data throughput
RNC
• Adjust DCH rate based on
UL TVM link quality
taken in
• Adjust DCH rate based on
UE
congestion
NodeB
UE State Transition
Switch the UE state based on
DL TVM DL TCP Taken activity
taken in the in NodeB
RNC
© 2005-2006 CP13: Introduction to UMTS USR6 7-49
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Load Control
Load Control
The WCDMA system is a self interference system. With the load of the system increasing,
the interference rises. If the interference is high enough, it affects the coverage and QoS
of established services. Therefore, capacity, coverage and Quality of Service (QoS) of
the WCDMA system are mutually affected. The purpose of load control is to maximize
system capacity while ensuring the coverage and QoS.
In different phases of UE access as shown in the diagram below, different load
control algorithms are used as follows:
• Before UE access: Potential User Control (PUC) and Cell Breathing
• During UE access: Call Admission Control (CAC) and Intelligent Access Control (IAC)
• After UE access: Load Reshuffling (LDR), and Overload Control (OLC).
In addition, functional load control algorithms vary according to the load levels of
the cell, as shown in the slide opposite.
7-50 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Load Control Version 1 Rev 0
Load Control
PUC CAC LDR
CELL BREATHING IAC OLC
1. Before UE access 2. During UE access 3. After UE access
time
© 2005-2006 CP13: Introduction to UMTS USR6 7-51
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Overview of Load Control
Overview of Load Control
The load control algorithm is built into the RNC. The input of load control comes from
the measurement information taken from the NodeB.
Load control has the following sub-features:
• PUC — The function of PUC is to balance traffic load among inter-frequency cells. By
modifying cell selection and reselection parameters and broadcasting them through
system information, PUC leads UEs to cells with light load. The UEs may be in idle
mode, CELL_FACH state, CELL_PCH state, or URA_PCH state.
• Cell Breathing — This feature is also know as intra-frequency load balancing. The
technique alters the power level of the CPICH to either capture more traffic is the
loading is light or push traffic away if the loading is high.
• CAC — The function of CAC is to decide on resource requests from UEs, such as access,
reconfiguration, and handover requests, according to the resource status of the cell.
• IAC — The purpose of IAC is to increase the access success rate with the current QoS
assured through rate negotiation, queuing, pre-emption, and DRD.
• LDR — The function of LDR is to reduce the load of a cell when the available
resource of the cell reaches the specified alarm threshold. The purpose of LDR is to
increase the access success rate in the following ways:
◦ Inter-frequency load handover
◦ BE service rate reduction
◦ AMR voice service rate reduction
◦ Uncontrolled realtime traffic QoS renegotiation
◦ CS inter-system load handover
◦ PS inter-system load handover
• OLC — The function of OLC is to reduce the cell load rapidly by restricting the Transport
Format (TF) of the BE service or releasing UEs when the cell is overloaded. The purpose
of OLC is to ensure the stability of the system and the QoS of most UEs.
7-52 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Overview of Load Control Version 1 Rev 0
Overview of Load Control
NodeB transmit
power (noise)
Cell Load (number of subscribers)
OLC starts: to reduce the TFs of BE
subscribers, and release some UEs forcibly
CAC: to prevent new calls into cells with heavy load
DRD starts: to enable rejected UEs to
retry neighbouring cells or GSM cells
Load control is PUC starts: to enable UEs in idle mode to camp on cells with light load
unneeded Cell breathing starts: to switch loads of hot spot cells to othe r cells
LDR starts: to check and release initial congestion in cells
© 2005-2006 CP13: Introduction to UMTS USR6 7-53
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Overview of Load Control
This page intentionally left blank.
7-54 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
HSDPA Overview Version 1 Rev 0
Chapter 8
HSDPA Overview
© 2005-2006 CP13: Introduction to UMTS USR6 8-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 HSDPA Overview
This page intentionally left blank.
8-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
On completion of this chapter the Student will be able to:
• Describe the important changes and characteristics of HSDPA
• State the new channels of HSDPA and how they operate in principle
• Describe the extended UTRAN protocol stack with HSDPA
• State the advantages and disadvantages of HSDPA and future enhancements
© 2005-2006 CP13: Introduction to UMTS USR6 8-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 HSDPA (High Speed Downlink Packet Access) for WCDMA
HSDPA (High Speed Downlink Packet Access) for WCDMA
HSDPA considers the trend that the volume of IP-based traffic has already exceeded that for
circuit-switched traffic in most fixed networks. The same change can be anticipated in mobile networks
because of new IP-based mobile services becoming available and are used by increasing number of
people in their daily communication. Current estimates show that in advanced mobile communication
markets, packet-switched traffic will overtake circuit-switched traffic in the near future. Delivery
of digital content over mobile networks will generate additional traffic and revenue.
Feature Study
The HSDPA feature in 3GPP Release 5 is the result of a study carried out in the Release 4
time frame. This study considered a number of techniques in order to provide instantaneous
high speed data in the downlink. Some of the considerations and goals taken into
account in the evaluation of the different techniques were:
• To focus on the streaming, interactive and background services: services which
require a constant and/high throughput or low error rate.
• To prioritise urban environments and then indoor deployments (but not limited to
these environments and supporting full mobility).
• To enable compatibility with advanced antenna and receiver techniques: transmit and
receive diversity methods are used and might be enhanced
• To take into account User Equipment processing time and memory requirements:
UE’s limitations are taken into account by the network
• To minimize changes on existing techniques and architecture: modest changes
to NodeB hardware and UTRAN software
Compatibility with Release ‘99
HSDPA is designed to co-exist on the same carrier as the current Release ’99 WCDMA services,
enabling a smooth and cost-efficient introduction of HSDPA into existing WCDMA networks.
Demand for Packet Switched Traffic
The increasing demand for capacity in order to provide high data rate multimedia services in
wireless environments necessitates enhanced radio transmission techniques and network protocol
functionality. Such techniques have to be added to already existing mobile cellular networks. For
3rd generation UMTS networks based on WCDMA, the HSDPA is being introduced to meet this
demand and improve spectral efficiency by higher order modulation using 16-QAM.
Note: HSDPA achieves gross data rates in downlink up to 14 Mbit/s under ideal
conditions. The reverse link (uplink) may remain on 64 kbit/s unless the operator decides
to use High Speed Uplink Packet Access (HSUPA).
8-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
HSDPA (High Speed Downlink Packet Access) for WCDMA Version 1 Rev 0
HSDPA (High Speed Downlink Packet Access) for WCDMA
© 2005-2006 CP13: Introduction to UMTS USR6 8-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 HSDPA Targets
HSDPA Targets
Higher Data Rates for Streaming-, Interactive- and Background Services
HSDPA is a feature based on a downlink shared channel that allows user net-data rates of up to
10 Mbit/s. It is designed to support services that require instantaneous high rates in the downlink
and lower rates on the uplink. This feature also decreases the level of retransmissions (at the
radio link and hence higher layers), in turn allowing the reduction of delivery time. Examples of
end-user services targeted by HSDPA are internet browsing and video on demand.
Consideration of UE Processing Time and Memory Requirements
HSDPA takes UE limitations like available physical memory for transmission and especially for
retransmission into account. Also the physical channel processing capability is considered.
(Examples: Minimum inter-TTI interval, transport channel bits per TTI)
Higher Spectrum Efficiency
With 16-QAM applied in downlink, throughput rates can be doubled compared to QPSK which
is used for Rel. ’99 and Rel. 4 physical channels. The amount of bits/Hz is increased with
16-QAM as one modulation symbol corresponds to 4 chips whereas in QPSK one modulation
symbol represents 2 chips. Even when HSDPA is using QPSK modulation the spectrum efficiency
increases as HSDPA exploits good C/I conditions. This is achieved by reducing the protection
(increasing the code rate) and thus having more capacity for the application data.
Small Changes to existing Techniques and Architectures
HSDPA minimizes the necessary upgrades and changes in UTRAN and UE.
Nevertheless some protocol additions are necessary in NodeB and UE as well some
enhancements of existing procedures and protocols.
Efficient Resource Sharing in Downlink among Users
HSDPA introduces a new transport channel type that makes efficient use of valuable radio frequency
resources. Beside this, it takes into account the bursty nature of packet switched data by sharing
the channelization codes, transmission power and infrastructure hardware among users.
8-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
HSDPA Targets Version 1 Rev 0
HSDPA Targets
© 2005-2006 CP13: Introduction to UMTS USR6 8-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 HSDPA Characteristics
HSDPA Characteristics
High Speed Downlink Packet Access comes with certain characteristics which
distinguishes it clearly from Rel. ’99 UTRAN.
Modulation Types
QPSK is already known from Rel. ’99 UTRAN. Besides QPSK, HSDPA incorporates the
16-QAM modulation to increase the peak data rates for users served under favorable radio
conditions. Support for QPSK is mandatory, though the support for 16-QAM is optional for the
network and UE. 16-QAM (Quadrature Amplitude Modulation) was newly introduced in Rel .5
with HSDPA. It is a so called higher order modulation which basically doubles the data rate in
good radio conditions. Thus it increases the spectrum efficiency of WCDMA.
Higher Throughput Rates
HDSPA supports peak throughput rates far beyond 2 Mbit/s when radio conditions are suitable and
therefore it satisfies the demand for instantaneous high throughput of packet switched services e.g.
streaming or interactive traffic class. Theoretically, under optimum condition (Code Rate of 1:1) the
following maximum throughput can be achieved: (with 16-QAM (Quadrature Amplitude Modulation)
and 15 channelization codes simultaneously used) 960kbit/s x 15 = 14.4 Mbit/s
AMC (Adaptive Modulation and Coding)
AMC is a key feature of HSDPA allowing adjustment of modulation between QPSK and 16-QAM
according to radio conditions and retransmission ratio. In addition a variable code rate is used to
flexibly adapt the data rate to the physical channel capacity depending on the UE’s downlink C/I..
Hybrid ARQ
HARQ functionality combines retransmission with the original transmissions. There a two
different ways for HARQ to operate. Either identical retransmission of the data block are sent
or retransmission are not identical and differ in data and parity bits compared to the original
transmission. The first method is known as chase combining and, the latter as incremental
redundancy . HARQ operates on an N-channel Stop and Wait principle.
Transmission and Retransmission Scheduling in NodeB
All Rel. ’99 transport channels are terminated at the RNC, except BCH; hence the retransmission
procedure for packet data is located in the serving RNC. In order to maximize throughput and reduce
delays when retransmitting, additional intelligence is put into the NodeB. In this way, retransmission
is controlled by the NodeB, leading to faster retransmission and therefore shorter delay for packet
data services. A scheduler in NodeB evaluates for different users what the radio channel conditions
are, how much data is pending for each user, how much time has passed since a particular user
was last served, for which user retransmission are pending etc. From this input data the scheduler
in NodeB may derive a decision how to assign resources to certain users.
8-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
HSDPA Characteristics Version 1 Rev 0
HSDPA Characteristics
© 2005-2006 CP13: Introduction to UMTS USR6 8-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 QPSK versus 16-QAM Modulation
QPSK versus 16-QAM Modulation
The figure illustrates the I/Q Plane for QPSK and 16-QAM modulation technique.
QPSK
Each symbol corresponds to 2 consecutive input bits. The four symbols are represented
by different phase shifts in the I/Q plane.
16–QAM
Each symbol corresponds to four consecutive input bits. Thus the data rate can be doubled with
16-QAM compared to QPSK. The 16 symbols are represented in the I/Q plane by different phase
shifts and amplitudes. In 16-QAM modulation the symbol value is determined by phase and
amplitude. Compared to that, in QPSK the phase is only modulated and variation in amplitude
have only minor influence on the decision space in the I/Q diagram. However with 16-QAM the
decision space is heavily influenced by amplitude variations, thus higher constraints are put on
the transmitter linearity. Note, a more accurate phase estimate is necessary with 16-QAM since
constellation points have smaller differences in phase domain compared to QPSK.
Note: The number of constellation points in the I/Q-diagram can be calculated with 2m,
where m represents the number of bits or chips per modulation symbol. QPSK modulation
has four constellation points in the I/Q-diagram: 2^m = 4 ⇔ m = 2. 16-QAM modulation
has 16 constellation points in the I/Q-diagram: 2^m = 16 ⇔ m = 4
8-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
QPSK versus 16-QAM Modulation Version 1 Rev 0
QPSK versus 16-QAM Modulation
© 2005-2006 CP13: Introduction to UMTS USR6 8-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Maximum Throughput Rates
Maximum Throughput Rates
The formulas opposite consider the physical maximum throughput rates available in FDD mode
of WCDMA according to releases and modulation. In Rel. ’99 and Rel. 4 only QPSK is used
whereas Rel. 5 allows also to user higher order modulation scheme 16-QAM. The standard chip
rate is 3.84 Mchips/s across all releases. The slot duration is in all releases 0.67ms corresponding
to 2560 chips. Note that the physical maximum chip rate achievable with 3.84 Mchips/s and
QPSK modulation is: 2 chips/symbol x 3.84 Mchips/s = 7.68 Mchips/s
UMTS Rel’. 99 / Rel. 4
Downlink:
⇒ In the downlink, the DPDCH and DPCCH are time multiplexed onto I and Q plane so the
DPDCH data rate also depends on the DPCCH data rate. The physical maximum bit rate
(ignoring losses due to DPCCH) using spreading factor ‘4’ is 5.76 Mbit/s.
⇒ The downlink slot format # 16 allows for 1248 DPDCH bits/slot and per physical channel.
⇒ The maximum DPDCH data rate considering 3 spreading codes @ sf4 is: 1248
bits/slot x 15 slots x (3 OVSF’s) = 5.616 Mbit/s
Uplink:
⇒ In the uplink each channel DPDCH and DPCCH is assigned an orthogonal channelization
code. As both physical channels are I/Q multiplexed, (i.e. separated onto I and Q phases),
the maximum physical data rate has to be calculated with 1 bit/symbol.
⇒ The uplink slot format # 6 allows for 640 bits/slot.
⇒ The maximum DPDCH data rate considering 6 spreading codes @ sf4 is therefore: 5.76 Mbit/s.
HSDPA – Rel. 5
In HSDPA the spreading factor for the user plane is fixed to ‘16’. Thus up to 15 physical
channels can be allocated at maximum per UE.
⇒ QPSK:
⇒ The downlink slot format # 0 allows for 320 bits/slot and per physical channel.
This results in 960 bits/ 2 ms subframe.
⇒ The maximum physical data rate considering 15 spreading codes @ sf16 is: 7.2 Mbit/s.
16-QAM
⇒ The downlink slot format #1 allows for 640 bits/slot and per physical channel.
This results in 1920 bits/ 2 ms subframe.
⇒ The maximum physical data rate considering 15 spreading codes @ sf16 is: 14.4 Mbit/s.
8-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Maximum Throughput Rates Version 1 Rev 0
Maximum Throughput Rates
UMTS Rel. 99 / Rel 4
Downlink
2 bits/symbol x [3.84 Mcps / (4 chips/symbol)] x (3 OVSF's) = 5.76 Mbits/S
Uplink
1 bits/symbol x [3.84 Mcps / (4 chips/symbol)] x (6 OVSF's) = 5.76 Mbits/S
HSDPA Rel. 5
QPSK
2 bits/symbol x [3.84 Mcps / (16 chips/symbol)] x (15 OVSF's) = 7.2 Mbits/S
16-QAM
4 bits/symbol x [3.84 Mcps / (16 chips/symbol)] x (15 OVSF's) = 14.4 Mbits/S
© 2005-2006 CP13: Introduction to UMTS USR6 8-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Important Changes for HSDPA
Important Changes for HSDPA
HSDPA involves significant changes in the UTRAN providing a high flexibility to react
to changing air-interface conditions or variable user QoS.
New 2 ms Subframe for HSDPA
The TTI (Transmission Time Interval) in HSDPA has been reduced to 2 ms in order to be faster
in retransmitting erroneous data blocks compared to the minimum TTI of 10 ms in UTRA-FDD.
Another advantage of the shorter TTI in HSDPA is that NodeB can adapt literally every data
block to fast changing radio conditions by the means of AMC. Thus it is possible to counteract
fading on the air-interface by adjusting modulation and coding every 2 ms.
New Physical Channels and Transport Channel with HSDPA
New channels are introduced for HSDPA: HS-PDSCH, HS-SCCH, HS-DPCCH and HS-DSCH.
No Fast Power Control and variable Spreading Factor
With HSDPA, two of the most fundamental features of WCDMA, fast power control and variable
spreading factor are disabled and replaced by AMC (Adaptive Modulation and Coding). Note:
AMC uses multicode operation (the UE can use more than one channelization code in parallel)
in order to increase the data rate for a certain user and adapts the code rate to the air-interface
quality. By these means AMC is able to improve the user throughput or at least keep it constant
even the downlink channel quality deteriorates between subsequent transmissions.
New UE Capabilities / Categories
The HSDPA feature is optional for both UE and network in Rel. 5. The UE indicates its
HSDPA support and its HS-DSCH physical layer category within the radio access capability
parameter.. The physical layer category defines among other parameters the maximum
number of channelization codes the UE supports in parallel for multicode operation. A UE
may support up to 5, 10 or 15 channelization codes in parallel.
New MAC-hs in NodeB and UE
The implementation of Medium Access Control (MAC-hs) in NodeB and UE is a pre-requisite
for allowing the NodeB to schedule transmissions and retransmission, to maintain the HSDPA
specific channels and to operate with AMC and Hybrid ARQ.
Impact on NBAP and Frame Protocol Procedure
NBAP procedures need to support HSDPA capability and HSDPA related parameters. The increased
bandwidth needs to be supported by the frame protocol. Among other parameters the frame protocol
needs to cater for HSDPA flow control information, priority queue handling and UE capability information.
8-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Important Changes for HSDPA Version 1 Rev 0
Important Changes for HSDPA
© 2005-2006 CP13: Introduction to UMTS USR6 8-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 New Channels with HSDPA
New Channels with HSDPA
The support of HSDPA is based on several new physical channels and one new transport channel.
Transport Channel:
HS-DSCH (High Speed Downlink Shared Channel)
The HS-DSCH is the actual transport resource carrying the packet data of the user applications.
As it also follows the shortened TTI of 2 ms, it allows for short round trip delay in the
operation between NodeB and UE. The 2 ms TTI is short when compared to 10, 20, 40 or
80 ms TTI’s supported by Rel. ’99 and Rel. 4 transport channels. HS-DSCH describes the
physical layer processing by MAC-hs of a HSDPA transport block.
⇒ Dynamic part: TB size = TBS size {1 to 200 000 bits with 8 bit granularity}; modulation
scheme {QPSK, 16-QAM}; redundancy / constellation version {1 … 8}.
⇒ Static part: TTI {2 ms for FDD}; type of channel coding {turbo coding}; mother
code rate {1/3}, CRC size {24 bits}
⇒ No semi-static attributes are defined for HS-DSCH.
Physical Channels
High Speed Shared Control Channel (HS-SCCH)
The HS-SCCH has a fixed spreading factor of value ‘128’ and is configured only in the downlink
direction. It also adopts the shortened TTI of 2 ms. In theory, up to 127 HS-SCCH’s can be configured
in a cell. However, the UE is required only to be able to listen to up to four HS-SCCH in parallel.
The HS-SCCH allows the efficient sharing of one or more HS-PDSCH’s among different users.
Nevertheless every UE needs to be informed on the DCCH via RRC messages about the specific
HS-SCCH-set that it shall monitor in order to receive data via the HS-PDSCH’s.
High Speed Physical Downlink Shared Channel (HS-PDSCH)
The HS-PDSCH has a fixed spreading factor of value ‘16’. Thus, it provides for multicode operation
using up to 15 channelization codes in parallel. Of course the UE must support the use of up to 15
channelization codes which depends on its category. The HS-PDSCH adopts the shortened TTI of 2 ms.
Uplink Dedicated Control Channel Associated with HS-DSCH Transmission (Uplink HS-DPCCH).
The HS-DPCCH has a fixed spreading factor of value ‘256’ and is only configured in uplink direction.
The HS-DPCCH also follows the shortened TTI of 2 ms. Its purpose is to provide feedback
information about the downlink receive quality and whether the packet data received by the UE
are error-free or need to be retransmitted. Thus the NodeB is quickly notified of unsuccessful
transmissions and/or changing radio conditions in downlink direction.
8-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
New Channels with HSDPA Version 1 Rev 0
New Channels with HSDPA
Transport
Channels
Physical
Channels
© 2005-2006 CP13: Introduction to UMTS USR6 8-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Future Enhancements of HSDPA
Future Enhancements of HSDPA
UMTS UTRA FDD aims to support a variety of multiple antenna transmission techniques in
order to enhance coverage, system throughput and spectral efficiency of HSDPA. A major
aim of using multiple antenna transmission in macro-cellular environments is to increase the
coverage ratio at medium and higher data rates, let’s say 2 Mbit/s and beyond. In a typical
deployment, two to four or more transmit antennas might be used per sector.
Beamforming
Beamforming makes use of adaptive antennas and can therefore provide a better C/I to UEs in
the downlink. At the same time beamforming allows re-use of scarce downlink channelization
codes as the individual UEs are separated in space and possibly through different downlink
scrambling codes, thus making use of secondary scrambling codes. The signals toward different
UEs from the same cell are typically transmitted under the same primary scrambling code and
separated by means of orthogonal channelization codes. However, some of the beams may be
transmitted under a secondary scrambling code with its associated channelization code tree, thereby
increasing the resources in the cell. Note that the loss of the reduced orthogonality between
primary and secondary scrambling code can be partly mitigated in the case of beamforming by
splitting the cell into multiple scrambling code regions, so the spatial isolation between beams
using different scrambling codes helps to compensate the lack of orthogonality.
Transmit Diversity
The downlink capacity could be improved by using receive antenna diversity in the UE. However for
small and cheap mobiles it is not feasible to use two antennas and receiver chains. Therefore, the
WCDMA standard already supports the use of base station transmit diversity in Rel. ’99. There are
two modes: open loop (TSTD and STTD) and closed loop mode (mode1 with phase adjustment only
and mode 2 with phase and amplitude adjustment). The open loop mode simply transmits the coded
information from two antennas, but on the diversity antenna the bits are time reversed and complex
conjugated. The STTD method provides two kinds of diversity. The physical separation of the antennas
provides space diversity and the time difference derived from a bit-reversing process provides for time
diversity, thus the decoding in the receiver becomes more reliable. The closed loop mode can only be
applied to the downlink channel, if there is an associated uplink channel. Thus this mode can only be
used with dedicated channels (DPCH, PDSCH or HS-PDSCH with an associated uplink DPCCH).
MIMO
With MIMO (Multiple Input Multiple Output) at the transmitter, x independent data streams are transmitted
out of the x antennas on the same frequency band. At the receiver, each antenna receives all of the
transmitted sub-streams superimposed, not separately. If multipath scattering is sufficient, these x data
streams have different spatial signatures to each of the e.g. p receive antennas and they are separable,
the signals arrive with different phases. When a transmitter has x antennas and the receiver has p
antennas, the link speed increases linearly with min (x,p) given the same power and bandwidth budget.
8-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Future Enhancements of HSDPA Version 1 Rev 0
Future Enhancements of HSDPA
© 2005-2006 CP13: Introduction to UMTS USR6 8-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Future Enhancements of HSDPA
This page intentionally left blank.
8-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
HSUPA Overview Version 1 Rev 0
Chapter 9
HSUPA Overview
© 2005-2006 CP13: Introduction to UMTS USR6 9-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 HSUPA Overview
This page intentionally left blank.
9-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Chapter Objectives Version 1 Rev 0
Chapter Objectives
• Describe the key technologies used in HSUPA
• Describe the RAN architecture impacts
• Describe the HSUPA transport and physical channels
• Describe the different TTIs available for HSUPA
© 2005-2006 CP13: Introduction to UMTS USR6 9-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Introduction
Introduction
After the first release of HSDPA in 3GPP R5 in mid 2002 work started on the High Speed
Uplink Packet Access (HSUPA) and over the course of the next 3 years the concept
materialized into the specifications and was realized in 3GPP R6.
HSUPA vs R99 DCH
HSUPA is not a standalone feature, but uses the basic features of R99 to operate. Cell selection,
randon access and basic mobility features etc are used and remain unchanged with HSUPA operation.
The change occurs in the way the user data is delivered from the UE to the NodeB on the uplink.
HSUPA provides a flexible path beyond the 384 kbps uplink which is the realistic maximum before
HSUPA. A similar technology to that of HSDPA is being used by introducing fast uplink HARQ,
NodeB based uplink scheduling and easier multicode transmission than that of R99.
Key Technologies
The new uplink transport channel Enhanced DCH (E-DCH) brings some of the same features to the
uplink as the HSDPA with its new transport channel HS-DSCH to the downlink. The E-DCH supports
fast NodeB based scheduling,fast physical layer HARQ with incremental redundancy and at USR7
a shorter 2ms TTI. E-DCH is not a shared channel like HSDPA, but it is in fact a dedicated channel
and can therefore support technologies like fast power control, variable SFand soft handovers.
Uplink Scheduling
The uplink scheduling mechanism is of central importance for HSUPA. The uplink scheduler is
located in the Node B close to the air interface in a similar way as HSDPA.
Task of the uplink scheduler is to control the uplink resources the UEs in the cell are using. The
scheduler therefore grants maximum allowed transmit power ratios to each UE. This effectively
limits the transport block size the UE can select and thus the uplink data rate.
The scheduling mechanism is based on absolute and relative grants. The absolute grants are used to
initialize the scheduling process and provide absolute transmit power ratios to the UE, whereas the
relative grants are used for incremental up- or downgrades of the allowed transmit power.
Note that one UE has to evaluate scheduling commands possibly from different radio links.
This is due to the fact that uplink macro diversity is used in HSUPA.
Hybrid Automatic Repeat Request (HARQ)
The HARQ protocol is a retransmission protocol improving robustness against link adaptation
errors. The Node B can request retransmissions of erroneously received data packets and will
send for each packet either an Acknowledgement (ACK) or a Negative Acknowledgement
(NACK) to the UE. Furthermore, the Node B can do soft combining, i.e. combine the
retransmissions with the original transmissions in the receiver.
Due to uplink macro diversity, one UE has to evaluate ACK/NACK information for the
same packet possibly from different radio links.
Reduction of Transmission Time Interval
To accelerate packet scheduling and reduce latency, HSUPA allows for a reduced TTI of 2 ms
corresponding to 3 timeslots. A WCDMA radio frame of 10 ms therefore consists of 5 subframes.
Unlike HSDPA, however, the support of this 2 ms TTI in the UE is not mandatory.
Instead, it is a UE capability. It is configured at call setup whether 2 ms TTI or 10
ms TTI is to be used for HSUPA transmission.
9-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Introduction Version 1 Rev 0
Introduction
20 Users Per Cell 60 Users Per Cell
USR 6 USR 7
1.44 Mbps Per User 5.76 Mbps Per User
Iub
Iu
CN RNC
NodeB
• Variable SF
• HARQ
• BTS Based Scheduling
• Fast Power Control
• Soft Handover
• TTI Length of 2 (USR7) and 10ms
© 2005-2006 CP13: Introduction to UMTS USR6 9-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Impact on Radio Access Network Architecture
Impact on Radio Access Network Architecture
Both the uplink scheduling and the HARQ protocol are located in the Node B, in order to move
processing closer to air interface and be able to react faster on the radio link situation.
Macro diversity is exploited for HSUPA, i.e. the uplink data packets can be received by more than 1
cell. There is one serving cell controlling the serving radio link assigned to the UE. The serving cell is
having full control of the scheduling process and is providing the absolute grant to the UE. The serving
radio link set is a set of cells contains at least the serving cell and possibly additional radio links from
the same Node B. The UE can receive and combine one relative grant from the serving radio link set.
There can also be additional non-serving radio links at other Node Bs. The UE can have zero, one
or several non-serving radio links and receive one relative grant from each of them.
Different Node Bs will deliver correctly received data packets to the RNC. Therefore some
selective combining functionality is needed in the RNC to sort out duplicates.
CN
Radio Network Controller (RNC)
UTRAN
• Selective Combining
Node B (of serving radio link set): Node B (of non-serving radio link set):
• Scheduling: absolute/relative grants; • Scheduling: absolute/relative grants;
• HARQ: Soft-combining, generation of • HARQ: Soft-combining, generation of
ACK/NACK ACK/NACK
HSUPA Protocol Architecture
The HSUPA related functionalities in Node B and RNC are also reflected in the protocol
architecture as shown in the slide opposite (Serving and Controlling RNC are the same).
New protocol entities are highlighted by shading).
Node B contains a new MAC entity called MAC-e, and the RNC contains a new MAC entity called
MAC-es. Both MAC-e and MAC-es entities terminate within the MAC layer of the UE.
9-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Impact on Radio Access Network Architecture Version 1 Rev 0
Impact on Radio Access Network Architecture
© 2005-2006 CP13: Introduction to UMTS USR6 9-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 HSUPA Channels
HSUPA Channels
As said before, HSUPA is a new uplink transport channel, E-DCH, which supports enhanced
features to those of the uplink transport channels of R99. Uplink transport channel processing
for E-DCH is similar to the processing of the uplink DCH with two exceptions. There can be only
one E-DCH transport channel in the UE, unlike DCHs that are multiplexed together to a Single
Coded Composite Transport Channel (CCTrCH) of DCH type. Nevertheless, the MAC layer can
multiplex multiple parallel services to the single E-DCH. The other significant difference is HARQ
support for the E-DCH which is provided in the transport channel processing chain.
After transport channel processing, the E-DCH maps to one or multiple parallel new dedicated physical
data channels – E-DPDCHs – for physical layer transmission. This is completely parallel to uplink DCH
processing chain and physical channels, so both E-DCH and DCH can coexist in the same UE with the
restriction that the maximum DCH data rate is 64 kbps when the E-DCH is configured.
Using E-DPDCH transmissions a simultaneous and parallel control channel is sent a separate
code channel – E-DPCCH. This E-DPCCH transmits all the necessary information about the
E-DPDCH that is needed in order to know how to receive the data channel.
In the downlink, 3 new channels are introduced for control purposes:
• E-AGCH: E-DCH Absolute Grant Channel carrying absolute grants;
• E-RGCH: E-DCH Relative Grant Channel carrying relative grants;
• E-HICH: E-DCH Hybrid ARQ Indicator Channel carrying ACK/NACK.
E-AGCH is only transmitted from the serving cell. E-RGCH and E-HICH are transmitted from radio
links that are part of the serving radio link set and from non-serving radio links.
Note that HSUPA channels are added on top of uplink / downlink dedicated channels. Each
UE therefore additionally carries an uplink and downlink Dedicated Physical Channel (DPCH).
In the downlink, a Fractional Dedicated Channel (F-DPCH) can be used alternatively. The
F-DPCH has been introduced in 3GPP release 6 in order to optimize the downlink channelization
code usage. With this concept, several UEs can share one downlink channelization code of SF
256. For this purpose, the F-DPCH uses a new slot format only containing the Transmit Power
Control (TPC) bits. Unlike the regular downlink DPCH slot formats, no pilot or data fields are
present. By assigning a UE specific timing offset, it is possible to multiplex up to 10 UEs onto
one channelization code for FDPCH. The F-DPCH is available in USR7.
9-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
HSUPA Channels Version 1 Rev 0
HSUPA Channels
E-DCH Absolute Grant
Channel – Absolute grants
E-DCH Relative Grant E-DCH Relative Grant
Channel – Relative grants Channel – Relative grants
E-DCH Hybrid ARQ Indicator E-DCH Hybrid ARQ Indicator
Channel – ACK/NACK Channel – ACK/NACK
Node B with
Node B with
serving E-
non-serving
DCH radio
E-DCH radio
link set
link E-DCH Dedicated Physical E-DCH Dedicated Physical
Data Channel – Uplink data Data Channel – Uplink data
E-DCH Dedicated Physical E-DCH Dedicated Physical
Control Channel – Uplink Control Channel – Uplink
RSN, E-TFCI, Happy Bit RSN, E-TFCI, Happy Bit
© 2005-2006 CP13: Introduction to UMTS USR6 9-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 E-DCH Transport Channel Processing
E-DCH Transport Channel Processing
Transport channel processing is the functionality that transforms the transport blocks delivered by the
MAC layer to bits transmitted on physical channels. The diagram below shows the overview of DCH
and E-DCH transport channel processing from the MAC layer to the physical channels.
A single E-DCH transport channel processing chain always gets one transport block to process for
transmission in one TTI, because – for the DCH – a set of transport blocks for each configured
DCH will be delivered to the processing chain. In the slide opposite the differences between the
elements of transport channel processing chains for the E-DCH and DCH are illustrated:
• CRC attachment for the E-DCH always attaches a 24-bit CRC to the transport
block received fromthe MAC layer. In comparison, the CRC length for the DCH is
configurable and can be 0, 8, 12, 16, or 24 bits.
• Code block segmentation for the E-DCH splits its input into equal size code blocks so that the
length of the block does not exceed 5114 bits. For the DCH the same block first concatenates the
transport block set to a single block of data before splitting. Also the size of the maximum code block
with the DCH depends on the coding in use (5114 for turbo-coding and 504 for convolutional coding).
• Channel coding for the E-DCH is always turbo-coding with a code rate of 1/3. DCH channel coding
may be either convolutional coding with code rates 1/2 or 1/3 or turbocoding with a code rate of 1/3.
• Physical layer HARQ funtionality/rate matching for the E-DCH matches the channel
codes output bits to the available physical channel bits and produces the different
redundancy versions needed for incremental redundancy HARQ.
• Physical channel segmentation for the E-DCH distributes the channel bits among the
multiple E-DPDCHs if more than one E-DPDCH is needed. The functionality is also the
same in the corresponding block in the DCH processing chain.
• Interleaving and physical channel mapping for the E-DCH, as well as for the
DCH, interleaves the bits in the radio frame and maps the bits to be transmitted
to their final positions in the physical channel.
9-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
E-DCH Transport Channel Processing Version 1 Rev 0
E-DCH Transport Channel Processing
© 2005-2006 CP13: Introduction to UMTS USR6 9-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 E-DCH Dedicated Physical Data Channel (E-DPDCH)
E-DCH Dedicated Physical Data Channel (E-DPDCH)
The E-DPDCH has a very similar structure to the DPDCH of R99 with a few exceptions.
They both support OVSFs to adjust the number of channel bits to the amount of data
actually being transmitted. They both could go beyond the data rate that one physical
data channel can support by transmitting multiple channels in parallel. They both use
BPSK modulation and follow the same fast power control loop.
The main difference are; the E-DPDCH supports fast physical layer level HARQ and fast Node B based
scheduling. However, these are not really properties of the physical data channel as such, but the
HARQ is visible in the transport channel processing chain and the scheduling is visible in the MAC layer.
The biggest difference for E-DPDCH is the support of a SF of 2, which allows delivering
twice as many channel bits per code than the minimum spreading factor of 4 that the DPDCH
supports. The maximum possible data rate of 5.76 Mbps is achieved by allocating 2*SF2 and
2*SF4. The same result could be achieved by using 6 SF4 codes with DPDCH, but the power
efficiency of the UE would be reduced in comparison to using SF2.
An E-DCH transport block with user data is mapped onto one sub-frame of 2 ms in case a TTI of 2 ms
has been configured, or onto one radio frame of 10 ms in case a TTI of 10 ms has been configured.
The amount of data bits that can be carried within one timeslot depends on the selected slot
format. The slot format determines the Spreading Factor (SF) and therefore the amount
of bits per slot. The slot format is shown in the table below.
The E-DPDCH is time aligned with the uplink Dedicated Physical Control Channel (DPCCH).
9-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
E-DCH Dedicated Physical Data Channel (E-DPDCH) Version 1 Rev 0
E-DCH Dedicated Physical Data Channel (E-DPDCH)
© 2005-2006 CP13: Introduction to UMTS USR6 9-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 E-DCH Dedicated Physical Control Channel (E-DPCCH)
E-DCH Dedicated Physical Control Channel (E-DPCCH)
The E-DPCCH is a new uplink physical channel used for transmitting out-of-band information
about E-DPDCH transmission from the mobile to the base station.
The E-DPCCH has only one possible slot format, which uses a spreading factor of 256 with a
channelization code of 1 and is capable of delivering 30 channel bits in a 2-ms sub-frame. It is
designed to deliver 10 bits of information for each E-DPDCH TTI transmitted. The E-DPCCH uses
the same (30, 10) second-order Reed–Muller coding as used for TFCI coding in the DPCCH. This
means that the 10 information bits result in 30 bits to be transmitted in the physical channel. This
number of bits can be carried by the E-DPCCH in 2 ms sub frames. If the TTI length of the E-DPDCH
is 10 ms, then the 30-bit E-DPCCH sub-frame is repeated five times allowing reduced power level.
With this procedure the same E-DPCCH structure can be employed regardless of the TTI used
for E-DPDCH transmission. The E-DPCCH frame structure is illustrated opposite.
The 10 information bits on the E-DPCCH consist of three different segments::
• The Retransmission Sequence Number (RSN) the retransmission sequence number of 2 bits
informing the HARQ sequence number of the transport block currently being sent on E-DPDCHs.
The initial transmission of a transport block is sent with RSN = 0, the first retransmission with RSN
= 1, the second retransmission with RSN = 2, and all subsequent transmissions with RSN = 3.;
• An E-DCH Transport Format Combination Indicator (E-TFCI) 7 bits indicating the transport
format being transmitted simultaneously on E-DPDCHs. In essence, the E-TFCI tells the receiver
the transport block size coded on the E-DPDCH. From this information the receiver can derive
how many E-DPDCHs are transmitted in parallel and what spreading factor is used;
• Happy bit – as inferred from the name – is 1 bit only. It indicates whether the UE is
content with the current data rate (or relative power allowed to be used for E-DPDCHs)
or whether it could use higher power allocation.
The E-DPCCH is time aligned with the uplink DPCCH.
All channels transmitted in uplink (E-DPDCH, E-DPCCH, HS-DPCCH, DPCCH,
possibly DPDCH) are IQ multiplexed.
9-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
E-DCH Dedicated Physical Control Channel (E-DPCCH) Version 1 Rev 0
E-DCH Dedicated Physical Control Channel (E-DPCCH)
• Retransmission Sequence Number (RSN) – 2 bits
• E-DCH Transport Format Indicator (E-TFCI) – 7 bits
• Happy Bit - 1 bit
© 2005-2006 CP13: Introduction to UMTS USR6 9-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 E-DCH HARQ Indicator Channel (E-HICH)
E-DCH HARQ Indicator Channel (E-HICH)
The E-HICH is a new downlink physical channel used for transmitting positive and negative
acknowledgements for uplink packet transmission. If the Node B received the transmitted E-DPDCH
TTI correctly it will respond with a positive Acknowledgement (ACK) and if it received the TTI
incorrectly it will respond with a Negative Acknowledgement (NACK).
E-HICH information is BPSK-modulated with on/off keying and the modulation depends on which cell is
transmitting the E-HICH. If the E-HICH is coming from the radio link set contained in the serving E-DCH
radio link (transmitted from the base station that has the serving E-DCH cell), then both ACKs and
NACKs are transmitted. The E-HICHs transmitted by Node Bs that do not contain the serving E-DCH
cell only transmit ACKs. If such a cell does not receive the E-DPDCH TTI correctly, then it does
nothing. The UE will continue retransmitting until at least one cell responds with an ACK.
The purpose of this arrangement is to save downlink transmission power. The assumption behind
the different modulations is that those Node Bs that do not have the serving E-DCH cell are
typically the ones that do not have the best connection to the UE and are more likely not to receive
the E-DPDCH TTI correctly and have a significantly larger portion of NACKs than ACKs to be
transmitted. In this way only the ACKs actually consume downlink capacity. As for the serving
E-DCH radio link set the assumption is that typically more ACKs than NACKs are transmitted. When
both ACK and NACK actually result in BPSK bit transmission (+1 and –1, respectively) the peak
power required to transmit a reliable ACK is smaller when the receiver needs to separate +1 from
–1 than would be the case if it needed to separate +1 from 0 (as no transmission).
All the cells in the same Node B are assumed to receive uplink E-DPDCH transmission in cooperation
and, thus, even if there are multiple cells in the Node B participating in a softer handover the TTI
reception either succeeds or fails only once, not separately in all the cells. Due to this all E-HICHs
transmitted from the Node B containing the serving E-DCH cell transmit both ACKs and NACKs,
effectively enabling the UE to combine the radio links for more reliable ACK/NACK detection.
E-HICH and E-RGCH channel structures are exactly the same and are shown opposite. Each delivers
1 bit of information in three slots. In the case of a 10-ms TTI the three slots are repeated four
times resulting in an 8-ms-long message. The exception is the E-RGCH transmitted from cells not
belonging to the serving E-DCH radio link set. That channel always – regardless of the E-DCH TTI
– transmits a 10-ms-long message (i.e., the three slots are always repeated five times).
The E-HICH/E-RGCH basic building block is a 40-bit-long orthogonal sequence which allows the
orthogonal multiplexing of 40 bits in one slot on a single spreading factor 128-code channel. The same
E-HICH/E-RGCH bit is repeated three times over three slots, but uses a different signature in each of
the three slots following a deterministic code hopping pattern. This is because different signature pairs
have different isolations in a real radio environment and, thus, the effect is averaged this way.
E-HICHs and E-RGCHs utilize 40-bit-long orthogonal sequences for multiplexing multiple E-HICHs
and E-RGCHs (40 in total) to a single downlink code channel of spreading factor 128.
One cell can use multiple channelization codes to exceed the limit of 40 signatures (e.g., 20
E-HICHs and 20 E-RGCHs in a code) with the constraint that the E-HICH and E-RGCH intended
for the same UE must be transmitted with the same channelization code.
9-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
E-DCH HARQ Indicator Channel (E-HICH) Version 1 Rev 0
E-DCH HARQ Indicator Channel (E-HICH)
© 2005-2006 CP13: Introduction to UMTS USR6 9-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 E-DCH Absolute Grant Channel (E-AGCH)
E-DCH Absolute Grant Channel (E-AGCH)
The E-AGCH is a downlink physical channel used for transmitting an absolute value of
the Node B scheduler’s decision that lets the UE know the relative transmission power
it is allowed to use for data channel transmission (E-DPDCH), thus effectively telling
the UE the maximum transmission data rate it may use.
The E-AGCH delivers 5 bits to the UE for the absolute grant value, indicating the exact power
level the E-DPDCH may use in relation to the DPCCH. In addition, the E-AGCH carries a 1-bit
indication for the absolute grant scope. With this bit the Node B scheduler can allow/disallow
UE transmission in a particular HARQ process. This bit is only applicable for 2-ms TTI E-DCH
operation. In addition to this the E-AGCH uses a primary and a secondary UE-id for identifying
the intended receiver and delivering one additional bit of information.
The E-AGCH uses a fixed spreading factor of 256 and QPSK modulation.
The absolute grant consists of a 5 bit grant value according to the table below and 1 bit indicating
the scope of the grant. The scope of the absolute grant tells the UE whether the absolute
grant is valid for a specific HARQ process or for all HARQ processes.
The absolute grant is channel coded with convolutional coding of code rate 1/3. The resulting 60 bits are
transmitted in a 2 ms sub-frame in case of 2 ms TTI, or repeated in all 5 sub-frames in case of 10 ms TTI.
Absolute grant value — is a 5-bit integer number ranging from 0 to 31 that has a specific mapping
(as shown below) to the E-DPDCH/DPCCH power ratio the UE may use.
Absolute grant scope — can be used to activate/de-activate a particular HARQ
process (identified by the E-AGCH timing) or all HARQ processes. The absolute grant
scope can only be used with a 2-ms E-DCH TTI.
Primary/Secondary UE-id or primary/secondary E-RNTI — is used to mask the CRC of the E-AGCH.
Each UE may have up to two UE-ids which it checks from each E-AGCH and if it detects one or the
other as matching the transmission it knows that the E-AGCH transmission was destined for it.
The structure of an E-AGCH is very similar to an HS-SCCH for HSDPA. A 16-bit CRC is calculated
over the 6 information bits and masked with either a primary or a secondary UE-id.With these ids
the UE knows whether the E-AGCH transmission was meant for it or not. The package is then
coded and rate-matched to fit the three-slot-long (2-ms) SF 256 channel. If a 10-ms E-DCH TTI
is used the three slots are repeated five times to fill the whole radio frame.
For both 2 ms and 10 ms TTI, the E-AGCH timing is 5120 chips offset from P-CCPCH frame timing.
9-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
E-DCH Absolute Grant Channel (E-AGCH) Version 1 Rev 0
E-DCH Absolute Grant Channel (E-AGCH)
© 2005-2006 CP13: Introduction to UMTS USR6 9-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Reason for having 2 ms amd 10 ms TTIs
Reason for having 2 ms amd 10 ms TTIs
While HSDPA only supports a single TTI (2 ms), with HSUPA there are two TTI lengths – 2 and
10 ms – that can be chosen. The motivation for the 2-ms length was the potential delay benefit
while 10 ms was needed for range purposes to ensure cell edge operation.
A potential delay benefit could be obtained if there are not too many retransmissions using a 2-ms
TTI, as the delay between retransmissions is shorter compared with the 10- ms case. A problem
occurs when approaching the cell edge where signalling using a 2-ms period starts to consume a lot of
transmission power, especially at the Node B. The difference from HSDPA is that now potentially a
much larger number of users are expected to be active simultaneously and, thus, aiming to also provide
downlink signalling to such a large number of users using a 2-ms period would become impossible.
With data rates below 2Mbps there are no major differences from the capacity point of view regardless
of the TTI used. When going above 2 Mbps per user, then the block size using 10 ms would get too
big and, thus, data rates above 2 Mbps are only provided using a 2-ms TTI. As with macro-cells,
practical data rates in the uplink have limitations due to transmission power limitations. This means
the 10-ms TTI is expected as the starting value for system deployment; this has also been reflected
in terminal capabilities (where a 2-ms TTI is optional for most categories).
9-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Reason for having 2 ms amd 10 ms TTIs Version 1 Rev 0
Reason for having 2 ms amd 10 ms TTIs
Area where only a 10ms
TTI is acceptable E-DCH/HSDPA Serving Cell
l
ntro
H Co
C
E-D A
DP
H/HS NodeB
DC
H
/DC
- DCH
E
Area where both a 2ms and a
10ms TTI is acceptable
© 2005-2006 CP13: Introduction to UMTS USR6 9-21
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Reason for having 2 ms amd 10 ms TTIs
This page intentionally left blank.
9-22 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Terrestrial Interface Protocols Version 1 Rev 0
Chapter 10
UMTS Terrestrial Interface Protocols
© 2005-2006 CP13: Introduction to UMTS USR6 10-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Terrestrial Interface Protocols
This page intentionally left blank.
10-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
On completion of this chapter the student should be able to:
• Describe the General Protocol Model for UMTS.
• Describe the Interface specific protocol structure for the following interfaces:
◦ luCS
◦ luPS
◦ lub
◦ lu r
© 2005-2006 CP13: Introduction to UMTS USR6 10-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Introduction to UMTS Terrestrial Interfaces
Introduction to UMTS Terrestrial Interfaces
Within the UTRAN there are a number of four terrestrial interfaces that are implemented by existing
transmission techniques. The four, namely IuCS, IuPS, Iub and Iur are discussed in this chapter. The
different transmission techniques that can be employed for each interface defines the protocol stack that
is used. The slide opposite shows the different options for each interface currently. However it should be
noted that the complete IP RAN will be available in the near future to give all the interfaces the IP option.
The air interface and its protocol stack is covered in other parts of the manual.
10-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Introduction to UMTS Terrestrial Interfaces Version 1 Rev 0
Introduction to UMTS Terrestrial Interfaces
Uu
IuCS
Iub
NodeB MSCu
E1 ATM SDH
ATM
SDH ATM
IP
E1 IP
RAN
Uu FE IP
RNC
Iub
NodeB IuPS
SGSN
© 2005-2006 CP13: Introduction to UMTS USR6 10-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Introduction to UMTS Protocols
Introduction to UMTS Protocols
As has been outlined in previous chapters, one of the underlying principles in the design and
development of UMTS is to prepare a universal infrastructure able to carry both existing and future
services. All design work should be such that technological and evolution changes in one part of the
network should have no (or at least minimal impact) on other network components or services.
From a protocol perspective, this is acheived by confining , as far as is reasonably practicable,
protocol functions and services within one or several physical domains. To this end, the
3G protocol architecture can be divided into two strata.
• Access Stratum
• Non-Access Stratum
Access Stratum
The Access Stratum (AS) is a functional entity that encompasses radio protocols between
the UE and the UTRAN and, terrestrial interface (Iu) protocols between the UTRAN and the
Core Network (CN). These protocols all terminate within the UTRAN.
Non-Access Stratum
The Non-access Stratum (NAS) includes CN protocols that form a direct connection
between the UE and the CN itself. The NAS is transparent to the UTRAN and thus
these protocols do not terminate in the UTRAN.
The NAS protocols encompass functions such as; Mobility Management (MM), Call Control
(CC), Short Message Services (SMS) and Suplementary Services (SS) associated with
the circuit switched CN and, GPRS Mobility Management (GMM), Session Managment
(SM) and GPRS SMS assocoiated with the packet switched CN.
The NAS tries to remain independent of the underlying radio technology. Thus the NAS protocols can
remain unchanged regardless of the Radio Access Network (RAN) that carries them.
10-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Introduction to UMTS Protocols Version 1 Rev 0
Introduction to UMTS Protocols
UMTS Protocol Architecture
UE UTRAN Core Network
Core Non-Access Stratum Core
Network Network
Protocols Protocols
Access Stratum
Radio Radio Iu Iu
Protocols Protocols Protocols Protocols
Uu-Interface Iu-Interface
© 2005-2006 CP13: Introduction to UMTS USR6 10-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 General Protocol Model
General Protocol Model
The protocols in the UTRAN are designed according to a set protocol model. The structure
consists of Layers (Horizontal) and Planes (Vertical). All these entities are independent of each
other and can be changed at any time. It is also important to note that these protocol stacks are
not developed for specific entities e.g. RNC or Node-B etc, but rather for the interfaces between
these different entities. Let’s have a closer look at the Layers and Planes.
Horizontal Layers
The General protocol stack only consists of two layers, the Transport Network Layer and the Radio
Network Layer. From the bottom, the Physical layer (Part of the Transport Network Layer) will provide
the physical medium for transmission. Above the Physical layer is the Transport layer (Part of the
Transport Network Layer) which contains the transport protocols. These protocols are not defined
within the UMTS specifications. The Transport Network Protocol proposed for UMTS is ATM. The top
layer is called the Radio Network layer, this is the layer responsible for all UTRAN related tasks.
The tasks performed on Radio Network Layer are transparent to Transport Network Layer.
Vertical Planes
Control Plane
The Control plane only exists on L3 of the Horizontal planes and is responsible for all UMTS specific
signalling. The protocols used for the control plane are the RANAP protocol for the Iu interface, the
RNSAP protocol for the Iur interface and the NBAP protocol for the Iub interface. These are all
termed Application protocols and will be used for tasks like setting up bearers to the UE. Operation
& Maintenance actions will always set up the signalling Bearers for the Application protocol.
User Plane
This plane is being used for transfer of all kinds of information e.g. multimedia, e-mail, speech
etc. The User Plane consists of the Data Stream that will be transported on the Data Bearer.
Each data stream is identified and characterised by one or more frame protocols.
Transport Network Control Plane
This plane is used for all signalling that must be transferred in the Transport Layer and does not
include any Radio Network Layer information. The protocol used for the Control Plane is called
Access Link Control Application Protocol (ALCAP). This protocol will handle the setting up of
Data Bearers for the User Plane of the Transport layer. The introduction of the ALCAP protocol
made it possible for the Application Protocols to run with complete independence of the data
bearing technology. It should be noted that we shall not use the ALCAP protocol in the setting
up of the Signalling Bearers for the Application Protocols or for ALCAP.
Transport Network User Plane
Both the Signalling Bearer (for Application Protocol) in the Control Plane and the Data Bearer in the User
Plane belong to the Transport Network Layer. The Data bearers in the Transport Network User Plane
are directly controlled by the Transport Network Control Plane during real time operations. The control of
the Signalling Bearer(s) for Application Protocol are considered Operations and Maintenance functions.
10-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
General Protocol Model Version 1 Rev 0
General Protocol Model
Control Plane User Plane
Radio
Network
Application Data
Layer Protocol Stream(s)
Transport Network Transport Network Transport Network
User Plane Control Plane User Plane
Transport
ALCAP(S)
Network
Layer
Signalling Signalling Data
Bearer(s) Bearer(s) Bearer(s)
Physical Layer
© 2005-2006 CP13: Introduction to UMTS USR6 10-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 IU-CS Interface Protocols Overview
IU-CS Interface Protocols Overview
The Iu—CS interface is the logical interface between the RNC and the Circuit Switched Core Network.
The diagram opposite shows the Iu—CS protocol stack, which consists of the following planes:
• Transport Network Layer User Plane (section A)
• Transport Network Layer Control plane (section B)
• Transport Network Layer User Plane (section C)
As the upper layer protocol are the applications of the lower layer protocol, the bottom-up
configuration principle should be followed for the configuration of section A, section B and section
C. Therefore, the Iu—CS interface should be considered in the following sequence:
• All their planes share the physical layer (recommended to be provided using STM-1
bearers) and the ATM layer, which have common characteristics.
• In the radio network and transport network control planes, an SAAL NNI layer
is used to provide signalling bearers.
• An SS7 MTP-3 layer provides the signalling transport for section A and section B.
• An SS7 SCCP layer provides the connection oriented signalling mechanism for section A
• The signalling application in section A is RANAP.
• The signalling application in section B, is Q.AAL2.
• The user plane bearer of section C, is provided by an AAL2 path.
NOTE On the Iu-CS, a single SAAL NNI link can share the transport of
both RANAP and ALCAP signalling.
10-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
IU-CS Interface Protocols Overview Version 1 Rev 0
IU-CS Interface Protocols Overview
Radio Control Plane User plane
Network
RANAP Iu UP
Layer
Transport User Plane Control Plane User Plane
Network
Layer Q.AAL2
Q.2630.1
A Q.2150.1
SCCP
MTP3-B B MTP3-B C
SAAL NNI SAAL NNI
AAL2 PATH
ATM
Physical Layer
© 2005-2006 CP13: Introduction to UMTS USR6 10-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 IU-PS Interface Protocols Overview
IU-PS Interface Protocols Overview
The Iu—PS interface is the logical interface between the RNC and the Packet Switched Core Network.
The diagram opposite shows the Iu—PS protocol stack, which consists of the following planes:
• Transport Network Layer User Plane (section A)
• Transport Network Layer Control plane (section B)
• Transport Network Layer User Plane (section C)
As the upper layer protocol are the applications of the lower layer protocol, the bottom-up
configuration principle should be followed for the configuration of section A, section B and section
C. Therefore, the Iu—CS interface should be considered in the following sequence:
• All their planes share the physical layer (recommended to be provided using STM-1
bearers) and the ATM layer, which have common characteristics.
• In the radio network and transport network control planes, an SAAL NNI layer
is used to provide signalling bearers.
• An SS7 MTP-3 layer provides the signalling transport for section A and section B.
• An SS7 SCCP layer provides the connection oriented signalling mechanism for section A
• The signalling application in section A is RANAP.
• Tthe user plane bearer in section C, is provided by an IPoA path leading to SGSN.
10-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
IU-PS Interface Protocols Overview Version 1 Rev 0
IU-PS Interface Protocols Overview
Radio Control Plane User plane
Network
RANAP Iu UP
Layer
Transport
User Plane Control Plane User Plane
Network
Layer
A B C
SCCP GTP-U
MTP3-B UDP
IP
SAAL NNI
AAL Type 5
ATM ATM
Physical Layer Physical Layer
© 2005-2006 CP13: Introduction to UMTS USR6 10-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Iub Interface (ATM) Protocols Overview
Iub Interface (ATM) Protocols Overview
The Iub (ATM) interface is the logical interface between the RNC and Node B. The diagram
opposite shows the Iub protocol stack, which consists of the following planes:
• Transport Network Layer User Plane (section A)
• Transport Network Layer Control plane (section B)
• Transport Network Layer User Plane (section C)
As the upper layer protocol are the applications of the lower layer protocol, the bottom-up
configuration principle should be followed for the configuration of section A, section B and section
C. Therefore, the Iub interface should be considered in the following sequence:
• All their planes share the physical layer (recommended to be provided using E1 links)
and the ATM layer, which have common characteristics.
• In the radio network and Transport network control planes, an SAAL UNI layer
is used to provide signalling bearers.
• The signalling application in section A is NBAP, which in turn comprises two different signalling port
types, namely, Iub ports Node B Control Port (NCP) and Communication Control Port(s) (CCP)).
• The signalling application in section B is Q.AAL2.
• Add the user plane data bearer in section C is provided by an AAL2 path.
10-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Iub Interface (ATM) Protocols Overview Version 1 Rev 0
Iub Interface (ATM) Protocols Overview
© 2005-2006 CP13: Introduction to UMTS USR6 10-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Iub Interface (IP) Protocols Overview
Iub Interface (IP) Protocols Overview
The Iub (IP) interface is the logical interface between the RNC and Node B. The diagram
opposite shows the Iub protocol stack, which consists of the following planes:
• Transport Network Layer User Plane (section A) carrying Radio Network Layer Control Plane.
• Transport Network Layer User Plane (section C) carrying Radio Network Layer User Plane.
The concepts of the IP transport protocols on the Iub interface are described below.
Data Link Layer — The data link layer protocols related to IP transport. The protocols consist
of Point-to-Point Protocol (PPP) and Multipoint Protocol (MP).
Internet Protocol (IP) — The IP provides a connectionless service between networks. It defines the rules
and details for data communication. It is used along with the TCP to provide guaranteed data transfer.
Stream Control Transmission Protocol (SCTP) — The SCTP is mainly used for reliably
transmitting datagrams through an unreliable network.
User Datagram Protocol (UDP) — UDP does not guarantee reliability or ordering. Datagrams
may arrive out of order, appear duplicated, or go missing without notice. Avoiding the
overhead of checking whether every packet actually arrived makes UDP faster and more
efficient for applications that do not need guaranteed delivery.
10-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Iub Interface (IP) Protocols Overview Version 1 Rev 0
Iub Interface (IP) Protocols Overview
© 2005-2006 CP13: Introduction to UMTS USR6 10-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 ATM/IP Dual Protocol Stack
ATM/IP Dual Protocol Stack
The development of data services and the introduction of HSDPA and HSUPA are posing higher
and higher requirements for Iub bandwidth. The transmission of ATM over E1 is quite expensive
and the efficiency of data services per bit is getting lower. In this situation, operators need low-cost
Iub transmission solutions. A good solution to Iub transmission is IP transport because of its lower
cost and multiple access modes. Operators who have existing ATM-based networks hope to protect
their current investment and reduce the impact of IP transport on the existing services.
In hybrid ATM&IP transport mode, data streams over two different paths reach the same NodeB: one
over ATM (for realtime data streams) and the other over IP (for non-realtime data streams).
10-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
ATM/IP Dual Protocol Stack Version 1 Rev 0
ATM/IP Dual Protocol Stack
Control Plane User Plane
Radio
RACH FP
HSDSCH FP
FACH FP
PCH FP
DCH FP
Network
Layer NBAP
Transport
Transport Network Transport
Network User Control Plane Network User
Plane Plane
ALCAP
Transport
Network SAAL SCTP SAAL UDP
Layer
AAL5 IP AAL5 AAL2 IP
Data Link Data Link
ATM Layer ATM ATM Layer
Physical Layer
© 2005-2006 CP13: Introduction to UMTS USR6 10-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Iur Interface Protocols Overview
Iur Interface Protocols Overview
The Iur interface is the logical interface between two RNC's. The diagram opposite shows
the Iur protocol stack, which consists of the following planes:
• Transport Network Layer User Plane (section A)
• Transport Network Layer Control plane (section B)
• Transport Network Layer User Plane (section C)
As the upper layer protocol are the applications of the lower layer protocol, the bottom-up
configuration principle should be followed for the configuration of section A, section B and section
C. Therefore, the Iu—CS interface should be considered in the following sequence:
• All their planes share the physical layer (recommended to be provided using STM-1
bearers) and the ATM layer, which have common characteristics.
• In the radio network and transport network control planes, an SAAL NNI layer
is used to provide signalling bearers.
• An SS7 MTP-3 layer provides the signalling transport for section A and section B.
• An SS7 SCCP layer provides the connection oriented signalling mechanism for section A
• The signalling application in section A is RNSAP.
• The signalling application in section B, is Q.AAL2.
• The user plane bearer of section C, is provided by an AAL2 path.
10-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Iur Interface Protocols Overview Version 1 Rev 0
Iur Interface Protocols Overview
Radio Control Plane User plane
Network
RNSAP Iu UP
Layer
Transport User Plane Control Plane User Plane
Network
Layer Q.AAL2
Q.2630.1
A Q.2150.1
SCCP
MTP3-B B MTP3-B C
SAAL NNI SAAL NNI
AAL2 PATH
ATM
Physical Layer
© 2005-2006 CP13: Introduction to UMTS USR6 10-21
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Iur Interface Protocols Overview
This page intentionally left blank.
10-22 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
UMTS Terrestrial Physical and Data Link Layer Version 1 Rev 0
Chapter 11
UMTS Terrestrial Physical and Data
Link Layer
© 2005-2006 CP13: Introduction to UMTS USR6 11-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 UMTS Terrestrial Physical and Data Link Layer
This page intentionally left blank.
11-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
On completion of this chapter the student should be able to:
• State the transport mechanisms used for the UMTS transport network.
• Describe the basic principles of ATM.
• Describe the use of PDH and SDH bearers for UMTS.
© 2005-2006 CP13: Introduction to UMTS USR6 11-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Terrestrial Physical/Data Link Layer Overview
Terrestrial Physical/Data Link Layer Overview
One very important aspect that is sometimes overlooked is the transport medium required
between the different entities. In the case of UMTS the Network Operator will run into problems
if the wrong links are utilised. Speed of transfer and cost will be two of the major determining
factors when planning the UMTS network. Other issues that need to be addressed are the
types of converting equipment used between the different types of terrestrial interfaces. In
the following pages a closer look will be taken at these aspects.
It should also be mentioned that as data rates increase the use of E1/T1 systems become more
difficult. ATM was preferred transport mechanism on the CN. Voice and IP over ATM is conducted
using ATM adaptation layers. Recently there has been a move towards using IP as the main
transport mechanism, firstly on the Iub and then in later releases on the Iu.
11-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Terrestrial Physical/Data Link Layer Overview Version 1 Rev 0
Terrestrial Physical/Data Link Layer Overview
Uu
IuCS
Iub
NodeB MSCu
E1 ATM SDH
ATM
SDH ATM
IP
E1 IP
RAN
Uu FE IP
RNC
Iub
NodeB IuPS
SGSN
© 2005-2006 CP13: Introduction to UMTS USR6 11-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 ATM Principles
ATM Principles
ATM is used to transfer different types of information with different rates over one or more
common links with a high bit rate. This properties makes ATM an extremely useful system
when it comes to wideband or broadband data transfer.
ATM is a cell-switching and multiplexing technology that combines the benefits of circuit
switching (guaranteed capacity and constant transmission delay) with those of packet switching
(flexibility and efficiency for intermittent traffic). It provides scalable bandwidth from a few
Mbps to many Gbps. Because of its asynchronous nature, ATM is more efficient than
synchronous technologies, such as Time-Division Multiplexing (TDM).
With TDM, each user is assigned to a time slot, and no other station can send in that time slot. If a
station has much data to send, it can send only when its time slot comes up, even if all other time slots
are empty. However, if a station has nothing to transmit when its time slot comes up, the time slot is
sent empty and is wasted. Because ATM is asynchronous, time slots are available on demand with
information identifying the source of the transmission contained in the header of each ATM cell.
11-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
ATM Principles Version 1 Rev 0
ATM Principles
Fixed Bit Stream
Variable Bit Stream
Discontinues
Bit Stream
© 2005-2006 CP13: Introduction to UMTS USR6 11-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Concepts of ATM Protocol
Concepts of ATM Protocol
ATM protocol reference model consists of three planes: control plane, user plane, and management
plane, and three function layers: physical layer, ATM layer, and ATM Adaptation Layer (AAL).
Plane Function
User plane Transfers user data such as protocol data and voice data
Control plane Transfers signaling control data such as connection setup signaling
and connection release signaling
Management plane Transfers the OM data of the network. The management plane
is divided into layer management part and plane management
part that manage the data at each layer and the inter-layer data
respectively.
The physical layer is provided by E1 or optical SDH.
The ATM physical layer has four functions: Cells are converted into a bitstream, the transmission
and receipt of bits on the physical medium are controlled, ATM cell boundaries are tracked, and
cells are packaged into the appropriate types of frames for the physical medium. For example,
cells are packaged differently for SONET than for other media types.
11-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Concepts of ATM Protocol Version 1 Rev 0
Concepts of ATM Protocol
Management Plane
Control Plane User Plane
Plane Management
Layer Management
Higher Layer
ATM Adaptation Layer
ATM Layer
Physical Layer
© 2005-2006 CP13: Introduction to UMTS USR6 11-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 ATM Layer
ATM Layer
ATM switching is a fast packet switching technology. In ATM switching, each packet
that consists of 53 bytes is called a cell. Based on the physical layer, the ATM layer
communicates with the peer layer through ATM cells.
Structure of an ATM Cell
One ATM cell consists of 48-byte payload and 5-byte header. This part
describes the structure of the cell header.
Type of ATM Cell Header
Cell headers are categorized into User to Network Interface (UNI) cell header and
Network to Network Interface (NNI) cell header:
• UNI cell headers apply to communications between ATM users and ATM network
nodes, for example, between a NodeB and an RNC.
• NNI cell headers apply to communications between two ATM network nodes,
for example, between an RNC and a CN.
Format of an ATM Cell
As shown in the slide opposite, an ATM cell header consists of Generic Flow Control (GFC),
Virtual Channel Identifier (VCI), Virtual Path Identifier (VPI), Payload Type (PT), Cell Loss
Priority (CLP), and Header Error Control (HEC). This is expanded below:
• The GFC field is occasionally used only by UNI cells. It is there to provide local
functions, such as identifying multiple stations that share a single ATM interface. The
GFC field is typically not used and is set to a default value.
• VPI and VCI: One VCI occupies 16 bits, one VPI of a UNI cell 8 bits, and one VPI of
an NNI cell 12 bits. VPI and VCI are valid only on the link level.
• The PT field occupies 3 bits. The first bit indicates whether the cell contains user data or control
data. If the cell contains user data, the second bit indicates congestion, and the third bit indicates
whether the cell is the last in a series of cells that represent a single AAL5 frame.
• CLP: When the traffic is heavy, CLP determines the cells to be discarded (CLP =
1) and the cells not to be discarded (CLP = 0).
• The HEC field protects the information of the cell header and delimits cells.
11-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
ATM Layer Version 1 Rev 0
ATM Layer
© 2005-2006 CP13: Introduction to UMTS USR6 11-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Virtual Channels and Paths
Virtual Channels and Paths
On a physical level ATM connects via the specification of Virtual Paths (VPs) and Virtual Channels
(VCs). A Virtual Channel will be located inside a Virtual Path. A Virtual Channel Identifier (VCI) will
identify the Virtual Channel and the Virtual Path Identifier (VPI) will identify the Virtual Path (VP).
In total we could have up to 256 addresses for a VP User to Network Interface
(UNI) and 4096 for a VP Network to Network Interface (NNI). When VCIs are used,
up to 216 channels per path can be addressed.
Use of Virtual Channels and Paths
A virtual channel provides an end-to-end connection, referred to as a Virtual Channel
Connection. This connection in turn may consist of a number of VC and VP components.
These components are illustrated opposite and are defined as follows:
Virtual Channel Link
A virtual channel link is a unidirectional facility transporting ATM cells between two consecutive
ATM entities where a VCI value is assigned, remapped or removed. For example, between
an ATM endpoint and a VC Switch, or between two VC switches.
Virtual Channel Connection
A virtual channel connection is a concatenation of virtual channel connections.
Virtual Path Link
A virtual path link is a unidirectional facility transporting ATM cells between two consecutive
ATM entities where a VPI value is assigned, remapped or removed. For example, between
an ATM endpoint and a VC Switch, or between two VC switches.
Virtual Path Connection
A virtual path connection is a concatenation of virtual path connections.
11-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Virtual Channels and Paths Version 1 Rev 0
Virtual Channels and Paths
Virtual Path (VP)
ATM Path
Virtual Channel (VC)
Each VP within the physical layer has a different VPI value
Each VC within a VP has a different VCI value
Use of Virtual Channels and Paths
Virtual Channel Connection Endpoints
Virtual Channel Connection
Virtual Channel Link Virtual Channel Link
ATM ATM
END VP Switch VC Switch END
SYSTEM SYSTEM
VC Switch - VCI and VPI
Virtual Path Link Virtual Path Link values change
Virtual Path Connection
Virtual Path Connection Endpoints
© 2005-2006 CP13: Introduction to UMTS USR6 11-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Virtual Path and Virtual Connection Switching
Virtual Path and Virtual Connection Switching
When addressing is carried out on VP level only a VP address would be needed since all the VCs are
inside the VP. Therefore we would only switch on VP level like illustrated in the diagram. If however
VCs need to be switched a VP Switch combined with a VC Switch would be needed.
The switching in ATM could get complicated at times therefore special tools have
been developed to help with this aspect.
11-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Virtual Path and Virtual Connection Switching Version 1 Rev 0
Virtual Path and Virtual Connection Switching
VC Switch
Endpoint
of VPC
VP Switch VP Switch
Representation of VP Switching Representation of VC and VP Switching
© 2005-2006 CP13: Introduction to UMTS USR6 11-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 ATM Adaptation Layer (AAL)
ATM Adaptation Layer (AAL)
This part describes the functions and services of ATM adaptation layer, and the
service functions of the SAAL and Q.AAL2.
Functions of the ATM Adaptation Layer
The ATM Adaptation Layer (AAL) is right above the ATM layer. The AAL adapts
higher layer applications to the ATM layer.
For various types of service, the AAL performs the adaptation in different ways. It segments data from
the upper layer into Service Date Units SDUs. Each SDU has 48 bytes. The AAL reassembles
and restores the SDUs from the ATM layer, and then transfers them to the upper layer.
To increase the ATM switching rate, the AAL performs all QoS related functions such
as cell loss handling, misdelivery, delay, and variation.
Types of Services at the ATM Adaptation Layer
Different services have different requirements for the timing of, the bit rates of, and the connection
mode for the source and the sink. According to these requirements, ITU-T classifies services into four
categories: A, B, C, and D and defines them as AAL1, AAL2, AAL3/4, and AAL5 respectively.
AAL1
AAL1, a connection-oriented service, is suitable for handling Constant Bit Rate (CBR) sources ,
such as voice and videoconferencing. ATM transports CBR traffic using circuit-emulation services.
AAL1 requires timing synchronization between the source and the destination. For this reason,
AAL1 depends on a medium, such as SONET, that supports clocking.
AAL2
Another traffic type has timing requirements like CBR but tends to be bursty in nature. This is called
Variable Bit Rate (VBR) traffic. This typically includes services characterized as packetized voice or
video that do not have a constant data transmission speed but that do have requirements similar to
constant bit rate services. AAL2 is suitable for VBR traffic. The AAL2 process uses 44 bytes of the
cell payload for user data and reserves 4 bytes of the payload to support the AAL2 processes.
VBR traffic is characterized as either real-time (VBR-RT) or as non-real-time (VBR-NRT).
AAL2 supports both types of VBR traffic.
AAL3/4
AAL3/4 supports both connection-oriented and connectionless data. It was designed for network
service providers and is closely aligned with Switched Multimegabit Data Service (SMDS).
AAL3/4 is used to transmit SMDS packets over an ATM network.
AAL5
AAL5 is the primary AAL for data and supports both connection-oriented and connectionless data.
It is used to transfer most non-SMDS data, such as classical IP over ATM and LAN Emulation
(LANE). AAL5 also is known as the Simple and Efficient Adaptation Layer (SEAL).
11-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
ATM Adaptation Layer (AAL) Version 1 Rev 0
ATM Adaptation Layer (AAL)
Class A Class B Class C Class D
Timing Relation Required Not Required
Bit Rate Constant Variable Available Unspecified
Connection Connection
Connection Rate
Orientated Less
Emulation Connection Connection
Variable Bit
Examples of Circuits Orientated Data Less Data
Rate Video
CPCM Transmission Transmission
Service Type AAL 3/4 or
AAL 1 AAL 2
to be used AAL 5
© 2005-2006 CP13: Introduction to UMTS USR6 11-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 ATM Service Characteristics
ATM Service Characteristics
Below is the description of ATM services, which are used for configuration of the ATM
layer, including CBR, RTVBR, NRTVBR and UBR.
• Constant Bit Rate (CBR): A service that does not implement error check,
flow control or other processing.
• Variable Bit Rate (VBR): This service is sub-classified into realtime transmission (RT-VBR)
and non-realtime transmission (NRT-VBR). RT-VBR is used to describe a service featuring
variable data streams and strict realtime requirement, (e.g. interactive compressed
video such as video conference). NRT-VBR is used on the communication occasions
requiring timing transmission. In such cases, some delays and variations, e.g., those
in E-mail transmission, can be accepted by the application.
• Unspecified Bit Rate (UBR): This is a service that does not make any commitment or
feedback to congestion. It is suitable for transmitting IP datagrams. In case of congestion,
UBR cells will be discarded. However, neither relevant feedback nor the request for
slowing down the transmission speed will be returned to the sender. The RNC5000 also
supports UBR+, which guarantees a the minimum cell rate.
11-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
ATM Service Characteristics Version 1 Rev 0
ATM Service Characteristics
Service characteristic CBR RT-VBR NRT-VBR UBR
Guaranteed bandwidth Y Y Y N
Applicable to realtime
Y Y N N
communication
Applicable to burst
N N Y Y
communication
Feedback on congestion N N N N
© 2005-2006 CP13: Introduction to UMTS USR6 11-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 ATM QoS
ATM QoS
ATM supports QoS guarantees comprising traffic contract, traffic shaping, and traffic policing.
A traffic contract specifies an envelope that describes the intended data flow. This envelope specifies
values for peak bandwidth, average sustained bandwidth, and burst size, among others. When an ATM
end system connects to an ATM network, it enters a contract with the network, based on QoS parameters.
Traffic shaping is the use of queues to constrain data bursts, limit peak data rate, and smooth jitters
so that traffic will fit within the promised envelope. ATM devices are responsible for adhering to the
contract by means of traffic shaping. ATM switches can use traffic policing to enforce the contract. The
switch can measure the actual traffic flow and compare it against the agreed-upon traffic envelope. If
the switch finds that traffic is outside of the agreed-upon parameters, it can set the Cell Loss Priority
(CLP) bit of the offending cells. Setting the CLP bit makes the cell discard eligible, which means
that any switch handling the cell is allowed to drop the cell during periods of congestion.
11-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
ATM QoS Version 1 Rev 0
ATM QoS
Parameter Abbreviations Meaning
Peak cell rate PCR Max. cell transmission rate (cell/s)
Sustainable cell rate SCR Long-term average cell transmission rate (cell/s)
Minimum cell rate MCR Minimum cell transmission rate
Cell delay variation
CDVT Max. tolerable cell jitter (0.1µs)
tolerance
Indicating which cells can be discarded (CLP=1),
Cell loss priority CLP and which cells had better not be discarded
(CLP=0) when congestion occurs to the network
Tag TAGGING Tagging the cells with CLP=0
© 2005-2006 CP13: Introduction to UMTS USR6 11-21
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 E1/T1 Architecture
E1/T1 Architecture
Logical Links
We have seen some of the mediums over which the data is transmitted, now let us consider
the format of the data that is carried over these mediums.
In GSM all the data is in digital form, and the path that the data takes is called a logical link. The format of
the data is dependent on where in the system the data is and what sort of data needs to be transferred.
E1
In the European GSM system the basic building block of data that gets carried around the
network is based around the multiplexed 2.048 Mbit/s frame.
This frame contains 32 channels of 64 Kbit/s. 30 are used for user information. Channel 0 is
reserved for timing and synchronisation and channel 16 is used for signalling.
E1 also specifies the sampling rate, frequency bandwidth, bits per sample, time slots per frame,
output bit rate, encoding law and the dedicated signalling and synchronisation channels.
T1
T1 is the American version of E1.
There are significant differences in the make up of the TDM frame.
T1 uses 24 time slots per frame, with 24 PCM channels per frame. The output bit rate is 1.544 Mbit/s
and the signalling used in the frame is only used once every 6th frame, instead of every frame in E1.
11-22 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
E1/T1 Architecture Version 1 Rev 0
E1/T1 Architecture
E1
Frequency Range 300 - 3400Hz
Sample Rate 8000Hz
Bits per Sample 8
Time Slots per Frame 32
Output Bit Rate 2.048 Mbps
Encoding Law A LAW
Signalling Capabilities TS0 Sync
TS16 Signalling
T1/DS1
Frequency 300 - 3400Hz
Sampling Rate 8000Hz
Bits per Sample 8
Bits per Frame 193
PCM Channels per Frame 24
Output Bit Rate 1.544 Mbps
Encoding Law μ Law
Signalling Capabilities 1st bit in frame - Sync
1 bit in timeslots 6 and 12
© 2005-2006 CP13: Introduction to UMTS USR6 11-23
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 ATM Cell to E1 Cell Mapping
ATM Cell to E1 Cell Mapping
The ATM cell is mapped into bits 9 to 128 and bits 137 to 256 (i.e. time slots 1 to 15 and time slots 17
to 31) of the 2048 kbit/s frame as specified in ITU-T Recommendation G.704[2] and as shown in the
Figure opposite. The ATM cell octet structure shall be aligned with the octet structure of the frame.
There shall be no relationship between the beginning of an ATM cell and the beginning of an
2048 kbit/s transmission frame. Since the frame payload capacity (30 octets) is not an integer
multiple of cell length (53 octets), ATM cells will cross the E1 frame boundary.
11-24 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
ATM Cell to E1 Cell Mapping Version 1 Rev 0
ATM Cell to E1 Cell Mapping
TS0 ATM Mapping Field TS16 ATM Mapping Field
Synch 15 Octets Sig 15 Octets
125 µs E1 frames - 256 bits per frame
© 2005-2006 CP13: Introduction to UMTS USR6 11-25
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 E1 Link Multiplexing
E1 Link Multiplexing
The standard E1 and T1 streams can be further multiplexed to put more
channels over one transmission path.
11-26 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
E1 Link Multiplexing Version 1 Rev 0
E1 Link Multiplexing
E1 Series Hierarchies
E1 E2 E3 E4 E5
2.048 Mb/s 8.448 Mb/s 34.368 Mb/s 139.264 Mb/s 564.992 Mb/s
30 TCH
x4
120 TCH
x4
480 TCH
x4 1,920 TCH
7,680 TCH
x4
© 2005-2006 CP13: Introduction to UMTS USR6 11-27
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Inverse Multiplexing for ATM (IMA)
Inverse Multiplexing for ATM (IMA)
Inverse Multiplexing for ATM (IMA) is a methodology which provides a modular bandwidth,
for user access to ATM networks and for connection between ATM network elements, at rates
between the traditional order multiplex level. An example is to achieve rates between the
DS1/E1 and DS3/E3 levels in the asynchronous digital hierarchies. DS2/E2 physical links are
not necessarily readily available throughout a given network. Therefore the introduction of ATM
Inverse Multiplexers provides an effective method of combining the transport bandwidths of multiple
links (e.g., DS1/E1 links) grouped to collectively provide higher intermediate rates.
The ATM Inverse Multiplexing technique involves inverse multiplexing and de-multiplexing of
ATM cells in a cyclical fashion among links grouped to form a higher bandwidth logical link
whose rate is approximately the sum of the link rates. This is referred to as an IMA group.
The figure opposite provides a simple illustration of the ATM Inverse Multiplexing technique in
one direction. The same technique applies in the opposite direction.
IMA groups terminate at each end of the IMA virtual link. In the transmit direction, the ATM cell stream
received from the ATM layer is distributed on a cell by cell basis, across the multiple links within the IMA
group. At the far-end, the receiving IMA unit recombines the cells from each link, on a cell by cell basis,
recreating the original ATM cell stream. The aggregate cell stream is then passed to the ATM layer.
The IMA interface periodically transmits special cells that contain information that permit
reconstruction of the ATM cell stream at the receiving end of the IMA virtual link. The receiver
end reconstructs the ATM cell stream after accounting for the link differential delays, smoothing
CDV introduced by the control cells, etc. These cells, defined as IMA Control Protocol (ICP)
cells, provide the definition of an IMA frame. The transmitter must align the transmission of
IMA frames on all links. This allows the receiver to adjust for differential link delays among the
constituent physical links. Based on this required behavior, the receiver can detect the differential
delays by measuring the arrival times of the IMA frames on each link.
At the transmitting end, the cells are transmitted continuously. If there are no ATM layer cells to be
sent between ICP cells within an IMA frame, then the IMA transmitter sends filler cells to maintain
a continuous stream of cells at the physical layer. The insertion of Filler cells provides cell rate
decoupling at the IMA sublayer. The Filler cells should be discarded by the IMA receiver.
11-28 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Inverse Multiplexing for ATM (IMA) Version 1 Rev 0
Inverse Multiplexing for ATM (IMA)
Inverse Multiplexing and De-multiplexing of ATM cells
IMA Group IMA Group
Physical Link #0
PHY PHY
Physical Link #1
PHY PHY
Single ATM CellStream Original ATM Cell
from ATM Layer Stream to ATM Layer
Physical Link #2
PHY PHY
Tx direction: cells distributed across links in round robin sequence
Rx direction: cells recombined into single ATM stream
IMA Frames
IMA Frame 2 IMA Frame 1 IMA Frame 0
ATM ATM ATM F ICP2 F F ATM F ICP1 ATM F ATM F ICP0 Link 0
M-1 3 2 1 0 M-1 3 2 1 0 M-1 3 2 1 0
F ICP2 ATM F F ATM ICP1 ATM ATM ATM ATM ICP0 ATM F F Link 1
F ATM ATM ICP2 F ATM F ATM ICP1 ATM ATM F ATM ICP0 ATM Link 2
Time
ICP1 ICP Cell in Frame # 1 F Filler Cell ATM ATM Layer Cell
© 2005-2006 CP13: Introduction to UMTS USR6 11-29
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Synchronous Digital Hierarchy (SDH)
Synchronous Digital Hierarchy (SDH)
With the advent of fully digital and synchronous networks the CCITT defined a new
multiplexing hierarchy called Synchronous Digital Hierarchy (SDH). In the USA is called
Synchronous Optical Network (SONET) with the two major differences being terminology
and the basic line rates used (SONET - 51.84 Mbps).
SDH uses a basic transmission rate of 155.52 Mbps (abbreviated to 155 Mbps) and multiples of 4n.
This basic rate is known as a Synchronous Transport Module level 1 (STM-1),
higher rates are STM-4 and STM-16.
As with PDH, the signal is repetitive frames with a repeat period of 125µs. Any of
the PDH rates can be multiplexed into the STM-1.
The main advantages of SDH are:
• It allows direct access to tributary signals without demultiplexing the composite signal.
• It supports advance operations, administration and maintenance by dedicating channels for this
purpose. The network can therefore be reconfigured under software control from remote terminals.
• Overhead bytes have been preserved for growth to support services and technologies of the future.
11-30 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Synchronous Digital Hierarchy (SDH) Version 1 Rev 0
Synchronous Digital Hierarchy (SDH)
SDH Bit Rates
Synchronous Transport Transmission
Module Rate
STM - 1 155.52 Mbps
STM - 4 622.08 Mbps
STM - 16 2,488.32 Mbps
STM - N N x 155.52 Mbps
© 2005-2006 CP13: Introduction to UMTS USR6 11-31
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 SDH Drop and Insert
SDH Drop and Insert
SDH overcomes the limitations of plesiochronous networks, and will allow transmission networks
to evolve to meet the demands of emerging broadband services.
Network Simplification
Synchronous transmission equipment eliminates the multiplexer mountain, leading to lower equipment
and maintenance costs, and improved service provisioning. The diagram shows how 2Mbps channels
can be dropped and inserted from a Synchronous Transfer Module, Type 1 (STM-1) by means
of remote commands at a network management station. The flexibility of SDH transmission is
attractive to carriers because it offers the potential of generating new revenues.
Survivability
SDH includes overheads for end-to-end monitoring and maintenance of transmission equipment;
the network management station can immediately identify the failure of links and equipment.
Furthermore, as shown in the diagram, an SDH network can be constructed with a self-healing
ring architecture that automatically reroutes traffic until the faulty segment is repaired; there will be
no disruption of service to the end user, allowing carriers to guarantee service levels.
Software Control
SDH also includes overheads for management channels; these are used for performance
monitoring, equipment configuration, resource management, network security, inventory
management, network planning and network design. Since all of these management
operations can be performed remotely, SDH offers the possibility of centralised network
management and provisioning, with associated cost savings.
Bandwidth on Demand
The flexibility of SDH allows carriers to allocate network capacity dynamically in that users will be able to
subscribe at very short notice to large bandwidth services e.g. video-conferencing. This feature opens
up the possibility of providing new services e.g. high-speed LAN interconnection and High Definition TV.
11-32 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
SDH Drop and Insert Version 1 Rev 0
SDH Drop and Insert
SDH Drop and Insert
155Mbps alternate routing
using ring topology
SDH Mux Management of SDH Mux
2Mbps traffic
2Mbps interface 2Mbps interface
12 63 155Mbps 155Mb/s
SDH Mux 155Mbps SDH Mux
2Mbps interface 2Mbps interface
© 2005-2006 CP13: Introduction to UMTS USR6 11-33
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Principles of SDH
Principles of SDH
Although a full description of SDH is beyond the scope of this course, this
section will cover the main principles.
The diagram shows the SDH multiplex structure, indicating how an STM is formed from various PDH
traffic rates. The following terms are used in the diagram, and further explained below:
• C - Container
• VC - Virtual Container
• TU - Tributary Units
• TUG - Tributary Unit Group
• AU - Administrative Unit
• AUG - Administrative Unit Group
• STM - Synchronous Transfer Module
The following table lists the container size suffices used when referring to equivalent
PDH traffic rates within SDH signals:
Container Suffix Bit rate kbps
0 64
11 1,554
12 2,048
21 6,312
22 8,448
31 34,368
32 44,736
4 139,264
11-34 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Principles of SDH Version 1 Rev 0
Principles of SDH
SDH Multiplex Structure
x1
STM-N AUG AU-4 VC-4 C-4 140 Mbit/s
x3
x1
x3 TUG-3 TU-3 VC-3
x7
AU-3 VC-3 C-3 45 Mbit/ s
34 Mbit/ s
x7 x1
TUG-2 TU-2 VC-2 C-2 6 Mbit/ s
x3
TU-12 VC-12 C-12 2 Mbit/ s
x4
TU-11 VC-11 C-11 1.5 Mbit/s
© 2005-2006 CP13: Introduction to UMTS USR6 11-35
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Typical UMTS ATM Transport Network
Typical UMTS ATM Transport Network
The diagram opposite shows a typical implementation of an ATM transport network to
support the UMTS interfaces. The UMTS nodes as shown are connected to a single SDH
ring, whereas there may actually be several rings involved depending on the network
providers configuration and may include PDH interfaces as well.
Node Bs use E1 physical interfaces and in the case where multiple E1’s are used IMA is utilised by
the Node B. The ATM Mux shown in the figure is expected to provide E1 (VC-12) to STM-1 (VC-4)
mapping and vice versa in addition to providing IMA and reverse IMA capability. For a large number
of Node B’s, the transport network will have to provide a significant number of E1 interfaces.
The ATM switch will be utilised for VP and VC switching and will be expected to provide aggregation of
logical interfaces to physical interfaces via VP and VC switching. The ATM network is also expected to
be configurable to limit the throughput of a given physical interface. For example, the RNC STM-1
physical interfaces need to be limited to a bandwidth of 100Mbps due to the hardware limitations.
Daisy Chaining
From USR 2.0 it will be possible to configure Node B’s in a daisy chain. All types
of daisy chain are supported with the exception of closed loop. Up to 3 Node B’s
(4 including hub node B) can be daisy chained.
Circuit Emulation
From USR 2.0 the node B has the ability to terminate an ATM AAL1 connection and generate
a circuit data stream for use by another piece of network equipment connected to the Node
B. Using circuit emulation, the E1 connections are routed first through the UMTS base station
where it uses its ATM data, and converts the ATM AAL1 data to circuit data. The resulting
circuit data is sent out another E1 connection to the attached network equipment. This is
likely to be a BTS as operators move from GSM to UMTS.
ATM Protection Switch
From USR 2.0 this feature provides higher availability radio network system, especially improved
availability, when it is used in addition to a lower layer protection (e.g. SDH). This is done
by providing 1:1 redundancy for important Permanent Virtual Circuits(PVCs), these are
NCP PVC, ALCAP PVC, NodeB OM PVC, it is set by configuration.
The system switches from the primary PVCs to the secondary ones automatically
under the following conditions:
• Detection of signal failure of the primary PVCs
• Detection of signal degradation of the primary PVCs
• OAM command from operator
• Others scenarios specified in I.630 not covered in this course.
To determine that a PVC is not functioning properly, the equipment collects PM statistics
on quality of the PVC (lost packets, buffer overflow, etc), in order to indicate to the
OAM that a switch to the secondary PVC is needed.
11-36 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Typical UMTS ATM Transport Network Version 1 Rev 0
Typical UMTS ATM Transport Network
Ethernet
(Option under
STM-1 RNC
investigation)
OMC
STM-1 ATM Switch
Ethernet
MSCu
RNC
STM-1
SDH Ring
(STM-1/STM-4/STM-16)
Node B
Node B
E1, IMA
ATM Switch
E1, IMA
ATM Mux
STM-1 SGSN
E1, IMA STM-1
E1, IMA
Node B RNC
Node B BTS
Circuit Emulation
Node B
© 2005-2006 CP13: Introduction to UMTS USR6 11-37
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Introduction to IP RAN
Introduction to IP RAN
With the IP transport technology, the IP RAN feature enables IP transport on the Iub interface.
The IP RAN feature is implemented to:
• Provide enough transmission bandwidth for high speed data services such as HSDPA
• Greatly reduce OPEX for transport and operation and maintenance
• Provide more flexible networking for the operator to reduce network deployment costs
The IP RAN feature yields the following benefits:
• Fully utilizing rich IP network resources.
Mainstream data communication networks are based on IP transport. They have multiple
access modes and large-scale deployment. The IP RAN feature enables the operator to
fully utilize the existing IP network resources for Iub networking.
• Economical IP network construction.
While facing the competition from the ATM network, the more economical IP
network is preferred by a number of vendors.
• Following the trend in network migration to protect the operator’s investment.
The IP transport technology is taking the lead in the data communication field,
and will dominate this field in the future.
The IP RAN can be configured in three different ways:
• TDM network
• Data network
• Hybrid transport network
TDM Network
In TDM networking mode, the RNC and NodeBs support IP over PPP over E1, which can be
based on PDH/SDH or Multiple Spanning Tree Protocol (MSTP).
Benefits: ensures security and QoS. Line clock signals can be extracted.
Restrictions: relatively high costs of E1 leasing
11-38 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Introduction to IP RAN Version 1 Rev 0
Introduction to IP RAN
NodeB
RNC
TDM Networking
NodeB IP over PPP over E1
© 2005-2006 CP13: Introduction to UMTS USR6 11-39
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Introduction to IP RAN
Introduction to IP RAN
Data Network
The data network can be any of the following three types:
• Layer 2 network, for example, metropolitan area Ethernet
• Layer 3 network
• MSTP network
The data network can be accessed through FE or E1.
A common IP network has the following benefits and restrictions:
• Benefits: good availability and relatively low costs of leasing
• Restrictions: low security without QoS assurance. The requirements for
realtime services cannot be satisfied.
An IP network with assured QoS or a private network has the following benefits and restrictions:
• Benefits: high security and assured QoS
• Restrictions: relatively high costs.
11-40 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Introduction to IP RAN Version 1 Rev 0
Introduction to IP RAN
NodeB
Router Router
Router Router
RNC
Data Networking
NodeB IP accessed via FE
or E1
© 2005-2006 CP13: Introduction to UMTS USR6 11-41
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Introduction to IP RAN
Introduction to IP RAN
Hybrid Transport Network
Hybrid transport enables services of different QoSs to be transported in different paths:
• The speech service with high QoS requirements is carried on the private
network such as PDH and SDH
• Data services with low QoS requirements are carried on the data network such as Ethernet.
The hybrid transport network has the following benefits and restrictions:
• Benefits: flexible to meet different requirements
• Restrictions: complicated management.
The relation between the transmission on the Iub interface and the
transmission technologies is as follows:
• Control plane on the Iub interface:
◦ To reduce signaling delay and connection time, data on the control plane for
the Iub interface is carried on the private network.
• User plane on the Iub interface:
◦ Realtime services are carried by private networks whereas non-realtime
services are carried by Ethernet.
The IP hybrid transport technology for the Iub interface has the following characteristics:
• The two paths from the RNC to the NodeB can connect to two transport networks
with different QoS requirements either:
◦ Through different ports, or
◦ Through the same port that connects to the external data equipment according
to Differentiated Services Code Point (DSCP)
• When the bandwidth of the low QoS network is restricted, low QoS services can be carried on the
high QoS network. When the bandwidth of the high QoS network is limited, the RNC reduces
the rate of the low QoS services that are carried on high QoS network, or the RNC rejects the
access of high QoS services if no low QoS services are carried on the high QoS network.
• The mapping between types of services and transmission modes is configurable.
The default mapping is as follows:
◦ The interactive service and the background service in the PS domain has low QoS
requirements. The two types of services are carried on the high QoS network only
when the bandwidth of the low QoS network is restricted.
◦ Other services have high QoS requirements such as Iub data on the
control plane, RRC signaling, CS services, common channel data of cells, PS
conversational service, and PS streaming service.
11-42 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Introduction to IP RAN Version 1 Rev 0
Introduction to IP RAN
TDM Networking
High QoS
NodeB
Router Router
Router Router
RNC
Data Networking
NodeB Low QoS
© 2005-2006 CP13: Introduction to UMTS USR6 11-43
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 IP Transport Protocols on the Iub Interface
IP Transport Protocols on the Iub Interface
This part describes concepts of IP transport protocols on the Iub interface and includes:
• Concepts of Data Link Layer Protocols
• Internet Protocol (IP)
• Stream Control Transmission Protocol (SCTP)
• Point-tp-Point Protocol (PPP)
• Multilink Protocol (MP)
Concepts of Data Link Layer Protocols
This part describes the data link layer protocols related to IP transport. The
protocols consists of PPP and MP.
Point-to-Point Protocol (PPP)
The PPP is used on the data link layer. The PPP provides standard methods for
encapsulating the multi-protocol datagrams on point-to-point links. These datagrams include
IP, Internetwork Packet Exchange (IPX), and Apple Talk.
As shown in the diagram opposite, the PPP consists of the following three parts:
• Link Control Protocol (LCP): used to configure, test, suspend, or remove a data link.
• Network Control Protocol (NCP): used to configure parameters at the network layer for
communications between the equipment. The NCP in this part refers to Network control
Protocol, which is different from NodeB Control Port (NCP).
• Extended protocols, such as MP: used to combine multiple physical links into a logical link to
provide a relatively high bandwidth and to enable quick data transfer. Motorola RNC uses
the MP protocol through the addition of Multi Link PPP (MLPPP) data.
Multilayer Protocol (MP)
With the wide application of PPP, MP comes into being as the extended protocol of the PPP.
The MP provides relatively large bandwidth to efficiently transport the data. In addition, the MP
dynamically allocates the link resources to effectively save the valuable resources.
The MP protocol can flexibly arrange multiple independent physical links between point-to-point
systems. It provides a virtual link for the whole system, and the bandwidth of the virtual
link is the sum of bandwidths of the N (N ≥ 1) physical links.
Along the development of network technologies, bandwidth is significantly increased.
In this sense, MP is less applied in practice.
11-44 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
IP Transport Protocols on the Iub Interface Version 1 Rev 0
IP Transport Protocols on the Iub Interface
Other
IP IPX Protocols Network Layer
IPCP IPXCP Other Control
Protocols
Network Control Protocol
PPP Data Link
Layer
Authentication and other options
Link Control Protocol
Synchronous or Asynchronous Physical Media Physical
Layer
© 2005-2006 CP13: Introduction to UMTS USR6 11-45
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 IP Transport Protocols on the Iub Interface
IP Transport Protocols on the Iub Interface
Internet Protocol (IP)
The IP provides a connectionless service between networks. It defines the rules and details for
data communication. It is used along with the TCP to provide guaranteed data transfer.
IPv4 and IPv6
The current and most popular network layer protocol of the TCP/IP is IPv4 that was launched
in 1981. IPv4 will be gradually replaced by IPv6 that was launched in 1995.
Principles for IP Address Planning
When using TCP/IP to communicate, each communication entity needs an IP address. In the
application of the RAN, adhere to the following principles when planning the IP addresses:
• IP addresses and subnet masks must be valid. Ensure that the network number cannot
be all-zeros and that the host number cannot be all-zeros or all-ones.
• The IP addresses of classes A, B, and C are valid, but those of classes D and E are invalid.
• Do not set the IP address to a loopback address of 127.X.X.X.
IP Address Structure
In the IP network, the IP address should be assigned to the hosts. If you connect a computer to the
Internet, you need to apply for an IP address from the Internet Service Provider (ISP).
The length of the IP address is 32 bits. The IP address consists of the following two parts:
• Network number (net-id): The first bits are called class segments (class bits) that
is used to identify the class of an IP address.
• Host number (host-id): identifies different hosts in the same network.
IP addresses are categorized into five classes, as shown in the diagram opposite. You
can identify an IP address class by its first bits.
The IP addresses of classes A, B, and C are most commonly used. IP addresses of class
D are used for multicasting. IP addresses of class E are reserved.
11-46 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
IP Transport Protocols on the Iub Interface Version 1 Rev 0
IP Transport Protocols on the Iub Interface
IP Address Range
Note that some IP addresses are reserved for special purposes. The table below
describes the classified IP addressing.
Network Available
Address Range Description
Type Range
A 0.0.0.0 1.0.0.0
127.255.255.255 126.0.0.0 • An all-zero host number means that the IP
address is the network address for network
routing.
• An all-one host number means that the IP
address is used to broadcast messages to all
the hosts on the network.
• When the DHCP is used, the local host can
take 0.0.0.0 as the temporary IP address but
never as the valid destination address.
• The IP address with network number of 0
represents the current network that can be
referenced by other computers without knowing
its network number.
• All the IP addresses in the 127.X.X.X format
are reserved for loopback testing. The packets
sent to this address are not sent to lines. The
packets are handled internally as input packets.
B 128.0.0.0 128.0.0.0
191.255.255.255 191.254.0.0 • An all-zero host number means that the IP
address is the network address for network
routing.
• An all-one host number means that the IP
address is used to broadcast messages to all
the hosts on the network.
C 192.0.0.0 192.0.0.0
223.255.255.255 223.255.254 .0 • An all-zero host number means that the IP
address is the network address for network
routing.
• An all-one host number means that the IP
address is used to broadcast messages to all
the hosts on the network.
D 224.0.0.0 None IP addresses of class D is used for multicasting.
239.255.255.255
E 240.0.0.0 None Reserved. The IP address of 255.255.255.255 is
255.255.2 used for broadcasting in the LAN.
55.255
© 2005-2006 CP13: Introduction to UMTS USR6 11-47
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 IP Transport Protocols on the Iub Interface
IP Transport Protocols on the Iub Interface
SCTP
The Stream Control Transmission Protocol (SCTP) is mainly used for reliably
transmitting datagrams through unreliable network.
Compared with the Transmission Control Protocol (TCP), the SCTP has the following advantages:
• Supporting the transmission of datagrams that are not delimitated by the upper layer
• Having better real-time performance
• Having higher security
• Avoiding the blocking of line headers
• Supporting the multi-homing function
The SCTP is more suitable than the TCP for the signaling transmission of higher requirements for
real-time performance, security and reliability. Therefore, it has a promising prospect for applications.
SCTP Endpoint
The SCTP endpoint is the logical transmitter or receiver of SCTP packets.
The SCTP endpoint on a multi-homing host can be either a group of valid destination
transport addresses for data transmission to the peer host, or a group of valid originating
transport addresses for transmitting SCTP packets.
All the transport addresses used by an SCTP endpoint must use the same port number but can use
multiple IP addresses. The transport address used by an SCTP endpoint at a time must be unique.
A transport address is defined by the network layer address, transport layer protocols, and port number.
When the SCTP protocol works on the IP transport layer, the transport address is defined by the IP
address and SCTP port number. Then, the SCTP protocol acts as the transport layer protocol.
SCTP Association
SCTP association is the mapping between two SCTP endpoints. It involves two SCTP endpoints and
protocol status data. The protocol status data includes verification tag and transport sequence number.
SCTP association is uniquely identified by the transport address of the SCTP endpoint that uses the
SCTP association. There is a maximum of one SCTP association between two SCTP endpoints.
The SCTP message consists of the common header and the chunks the diagram on
the next page shows the SCTP message structure. Multiple chunks can be bundled
and transmitted in one datagrams to save bandwidth.
11-48 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
IP Transport Protocols on the Iub Interface Version 1 Rev 0
IP Transport Protocols on the Iub Interface
© 2005-2006 CP13: Introduction to UMTS USR6 11-49
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 IP Transport Protocols on the Iub Interface
IP Transport Protocols on the Iub Interface
Virtual Local Area Networks (VLANs) and Layer 2/3 Switching
This allows packet forwarding decisions to be made using the data link layer (Ethernet etc).
Layer 2 Switching
Fundamentally a layer 2 device is a switch with physical ports. The main benefit of Layer 2
switching is to make efficient use of network bandwidth. The first switches in fact sent traffic
arriving on all input ports to all the output ports without any processing. As the networks become
more complex it can be that, two or more ports on the same switch are connected to the same
LAN. This means that packets arriving at the switch leave on multiple ports onto the same LAN,
hence duplicate packets are created which will lead to congestion in the network.
Layer 2 switching eliminates looping traffic by defining a Spanning Tree and uses a Spanning Tree
Protocol to configure the spanning tree. The Spanning Tree Protocol identifies ports that are connected
to the same LAN and configures the switch to send any given packet out only on one port that is
connected to a given LAN. However the Spanning Tree Protocol keeps a track of these secondary
ports and allows traffic to be passed if the primary port goes OOS for any reason.
Layer 3 Switching
A layer 2 device is a switch that communicates using frames at layer 1 over physical ports. Whereas a
Layer 3 device is a router that communicates with packets. and a packet is encapsulated inside of
a frame. A router has interfaces for connection into the network medium i.e. Ethernet.
The Ethernet frame contains a source layer 2 MAC address and a destination layer 2 MAC address.
The IP packet contains a source layer 3 IP address and a destination layer 3 IP address. The router
maintains a routing table of network paths it has discovered. The router will examine the layer 3 IP
destination address of the packet. It will examine the routing table and determine if a path exists.
VLANs
VLAN processing is an extension to the concept of Layer 2 switching. The VLAN adds a four byte
tag field between the data link layer header (i.e. Ethernet) and the network layer (i.e. IP). This tag
contains among other things a VLAN Identifier (VID) and associated user priority field.
VLAN switches look for this tag and make a switching decision based on the tag
information that determines which port(s) to send the incoming packet out on. The
VLAN protocol defines three types of traffic:
• Untagged
• Priority Tagged
• VLAN Tagged.
Untagged packets are packets without any VLAN tag. Priority tagged packets are packets
with a VLAN tag, but a VID of zero (the NULL VID) and a valid priority field within the VLAN
tag. VLAN tagged packets contain a VLAN tag with a valid VID field (non-zero). VLAN-aware
switches must be able to classify and forward packets of all three types in order to work
with legacy equipment as well as other VLAN-aware equipment.
Incoming packets may be untagged, priority tagged, or VLAN tagged. Depending on how the
switch is configured, an untagged packet may leave priority-or- VLAN-tagged. Incoming VLAN
tagged packets may leave untagged or even tagged with a different VID.
There are also multiple ways of configuring what constitutes a VLAN. The VLAN specifications define a
port-based approach where each port is a member of a particular VLAN. All traffic coming or going on
this port would be a member of the configured VLAN. There is also a MAC-based approach to VLAN
processing where membership on a VLAN is defined by the source MAC address of a remote host.
11-50 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
IP Transport Protocols on the Iub Interface Version 1 Rev 0
IP Transport Protocols on the Iub Interface
Ethernet VPN Ethernet
VLAN V18 VLAN V18
R R
NodeB
RNC
© 2005-2006 CP13: Introduction to UMTS USR6 11-51
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 IP Transport Protocols on the Iub Interface
This page intentionally left blank.
11-52 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Annexe A Version 1 Rev 0
Chapter 12
Annexe A
© 2005-2006 CP13: Introduction to UMTS USR6 12-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Annexe A
This page intentionally left blank.
12-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Objectives Version 1 Rev 0
Objectives
On completion of this chapter the student should be able to:
• Describe selected UMTS Signalling Flow procedures.
© 2005-2006 CP13: Introduction to UMTS USR6 12-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Paging for a UE in Idle Mode
Paging for a UE in Idle Mode
This example shows how paging is performed for a UE in RRC Idle Mode. The UE may be paged
for a CS or PS service. Since the UE is in RRC Idle Mode, the location is only known at CN level
and therefore paging is distributed over a defined geographical area (e.g. LA).
NOTE:
The example below illustrates scenario where LA spans across 2 RNCs.
1. The CN initiates the paging of a UE over a LA spanning two RNCs (i.e. RNC1 and
RNC2) via a RANAP message called the Paging message.
Parameters Sent:
CN Domain Indicator, Permanent NAS UE Identity, Temporary UE Identity, Paging Cause.
2. Paging of UE performed by cell1 using Paging Type 1 message.
3. Paging of UE performed by cell2 using Paging Type 1 message.
The UE detects page message from RNC1 (as example) and the procedure for NAS signalling
connection establishment follows. NAS message transfer can now be performed.
This procedure described for RRC idle mode, applies also to the RRC connected
mode in the case of CELL_PCH and URA_PCH states.
12-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Paging for a UE in Idle Mode Version 1 Rev 0
Paging for a UE in Idle Mode
Node B Node B RNC RNC
UE CN
1.1 2.1 1 2
1. Paging
RANAP RANAP
1. Paging
RANAP RANAP
2.PCCH: Paging Type 1
3.PCCH: Paging Type 1
© 2005-2006 CP13: Introduction to UMTS USR6 12-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Paging for the UE in RRC Connected Mode
Paging for the UE in RRC Connected Mode
This will occur in case the position of the UE is already known; a mobility management
session will be active at this stage. Two possible solutions exists:
• The UTRAN co-ordinates the paging request with the existing RRC connection.
• The UE co-ordinates the paging request with the existing RRC connection.
The following example shows how paging is performed for a UE in RRC Connected
Mode (CELL_DCH and CELL_FACH states) when the UTRAN co-ordinates the paging
request with the existing RRC connection using DCCH.
1. CN initiates the paging of a UE via RANAP message Paging Request Message.
Parameters used: CN Domain Indicator, Permanent NAS UE Identity,
Temporary UE Identity, Paging Cause.
2. SRNC sends RRC message Paging Type 2.
12-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Paging for the UE in RRC Connected Mode Version 1 Rev 0
Paging for the UE in RRC Connected Mode
Serving
UE CN
RNC
1. Paging
RANAP RANAP
2. DCCH Paging Type 2
RRC RRC
© 2005-2006 CP13: Introduction to UMTS USR6 12-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 RRC Connection Establishment
RRC Connection Establishment
The following example shows establishment of a RRC connection in Dedicated
Transport Channel (DCH) state.
The following sequence are identified:
1. The UE initiates set-up of an RRC connection by sending RRC message
Connection Request on CCCH.
Parameters used: Initial UE Identity, Establishment cause, Initial UE Capability.
2. The SRNC decides to use a DCH for this RRC connection, allocates RNTI and
radio resources for the RRC connection. When a DCH is to be set-up, NBAP message
Radio Link Setup Request is sent to Node B.
Parameters used: Cell id, Transport Format Set, Transport Format Combination Set, frequency, UL
scrambling code(FDD only), Time Slots (TDD only), User Codes (TDD only), Power control information.
3. Node B allocates resources, starts PHY reception, and responses with NBAP message, Radio
Link Setup Response. Parameters used: Signalling link termination, Transport layer addressing
information (AAL2 address, AAL2 Binding Identity) for the Iub Data Transport Bearer.
4. SRNC initiates set-up of Iub Data Transport bearer using ALCAP protocol. This request
contains the AAL2 Binding Identity to bind the Iub Data Transport Bearer to the DCH. The
request for set-up of Iub Data Transport bearer is acknowledged by Node B.
5./6. The Node B and SRNC establish synchronism for the Iub and Iur Data Transport Bearer by
means of exchange of the appropriate DCH Frame Protocol frames Downlink Synchronisation
and Uplink Synchronisation. Then Node B starts DL transmission.
7. Message RRC Connection Setup is sent on CCCH from SRNC to UE.
Parameters: Initial UE Identity, RNTI, Capability update Requirement, Transport Format Set,
Transport Format Combination Set, frequency, DL scrambling code (FDD only), Time Slots
(TDD only), User Codes (TDD only), Power control information.
8. Message RRC Connection Setup Complete is sent on DCCH from UE to SRNC.
Parameters: Integrity information, ciphering information.
12-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
RRC Connection Establishment Version 1 Rev 0
RRC Connection Establishment
Node B Serving
UE
Serving RNS RNC
1. CCCH: RRC Connection Request
RRC RRC
Allocate RNTI
Select L1 and L2
parameters
2. Radio Link Setup Request
NBAP NBAP
Start Rx
3. Radio Link Setup Response
NBAP NBAP
4. ALCAP Iub Data Transport Bearer Setup
5. Downlink Synchronisation
DCH DCH
6. Uplink Synchronisation
DCH DCH
Start Rx
7. CCCH: RRC Connection Setup
RRC RRC
8. DCCH: RRC Connection Setup Complete
RRC RRC
© 2005-2006 CP13: Introduction to UMTS USR6 12-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 RRC DCH Release
RRC DCH Release
This example shows RRC Connection release of a dedicated channel, in the case of macrodiversity on
two Nodes B’s; the first one connected to the Serving RNC, the second one to the Drift RNC.
1. The CN initiates the release of a dedicated Channel by sending the message Iu
Release Command to the SRNC. Parameters used: Cause.
2. The SRNC confirms the release by sending an Iu Release Complete message to the CN.
Parameters used: Data volume Report (if data volume reporting to PS is required).
3. The SRNC initiates release of Iu Data Transport bearer using ALCAP protocol.
4. Message RRC Connection Release from SRNC to UE to initiate the RRC connection release.
Parameters: Cause.
5. Message RRC Connection Release Complete from UE to SRNC to confirm
the RRC connection release.
6. The SRNC initiates the release of the link by sending the Radio Link
Deletion to the Node B (SRNC).
7. The SRNC initiates the release of the link by sending the Radio Link Deletion to the Drift RNC.
8. The Drift RNC initiates the release of the link by sending the Radio Link
Deletion to the Node B (Drift RNC).
9. The Node B (SRNC) confirms the release of the link by sending the Radio
Link Deletion Response to the SRNC.
10. The Node B (Drift RNC) confirms the release of the link by sending the Radio
Link Deletion Response to the Drift RNC.
11. The Drift RNC confirms the release of the link by sending the Radio Link
Deletion Response to the SRNC.
12. The Node B (SRNC) initiates release of Iub Data Transport bearer using ALCAP protocol.
13. The Node B (Drift RNC) initiates release of Iub Data Transport bearer using ALCAP protocol.
14. The Drift RNC initiates release of Iur Data Transport bearer using ALCAP protocol.
12-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
RRC DCH Release Version 1 Rev 0
RRC DCH Release
Node B Node B Drift Serving
UE CN
Drift RNS Serving RNS RNC RNC
1. Iu Release
RANAP RANAP
Complete
2. Iu Release
RANAP RANAP
Complete
3. ALCAP Iu Bearer Release
4. RRC connection Release
RRC RRC
5. RRC Connection Release Complete
RRC RRC
6. Radio Link Deletion
NBAP NBAP
7. Radio Link
RNSAP RNSAP
Deletion
8. Radio Link Deletion
NBAP NBAP
9. Radio Link Deletion Response
NBAP NBAP
10. Radio Link Deletion
NBAP NBAP
Response
11. Radio Link
Deletion
RNSAP RNSAP
Response
12. ALCAP Iub Bearer Release
13. ALCAP Iub Bearer Release ALCAP Iur Bearer Release
© 2005-2006 CP13: Introduction to UMTS USR6 12-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 RA Update
RA Update
This example shows location registration when changing Routing Area including change of
3G SGSN when the UE is in MM idle state towards the 3G SGSN.
The illustrated transfer of MM signalling to/from the UE uses an established RRC connection. This
RRC connection can have been established beforehand due to ongoing inter-working between UE and
3G-MSC/VLR or be established only for this location registration procedure towards the 3G-SGSN. For
each indicated MM message sent in this case to/from UE, the CN discriminator indicates 3G-SGSN.
The following procedure will take place to perform the RA update:
1. The RRC connection is established, if not already done. The UE sends the initial message
Routing Area Update Request (old P-TMSI, old RAI, etc.) to the new 3G-SGSN. The old P-TMSI
and the old RAI are assigned data in UMTS. The SRNS transfers the message to the 3G-SGSN.
The sending of this message to 3G-SGSN will also imply establishment of a signalling connection
between SRNS and 3G-SGSN for the concerned UE. The UTRAN shall add the RAC and the
LAC of the cell where the message was received before passing the message to the SGSN.
2. The new 3G-SGSN send an SGSN Context Request (old P-TMSI, old RAI) to the old
3G-SGSN to get the IMSI for the UE. (The old RAI received from UE is used to derive
the old 3G-SGSN identity/address.) The old 3G-SGSN responds with SGSN Context
Response (e.g. IMSI, PDP context information and Authentication triplets).
3. Security functions may be executed.
4. The new 3G-SGSN informs the HLR of the change of 3G-SGSN by sending Update
GPRS Location (IMSI, SGSN number, SGSN address) to the HLR.
5. The HLR cancels the context in the old 3G-SGSN by sending Cancel Location (IMSI). The
old 3G-SGSN removes the context and acknowledges with Cancel Location Ack.
6. The HLR sends Insert Subscriber Data (IMSI, subscription data) to the new 3G-SGSN.
The new 3G-SGSN acknowledges with Insert Subscriber Data Ack.
7. The HLR acknowledges the Update GPRS Location by sending Update GPRS
Location Acknowledge to the new 3G-SGSN.
8. The new 3G-SGSN validates the UE’s presence in the new RA. If due to regional, national
or international restrictions the UE is not allowed to attach in the RA or if subscription
checking fails, then the new 3G-SGSN rejects the Routing Area Update Request with
an appropriate cause. If all checks are successful, then the new 3G-SGSN responds to
the UE with Routing Area Update Accept (new P-TMSI, new RAI, etc.).
9. The UE acknowledges the new P-TMSI with Routing Area Update Complete.
10. When the location registration procedure is finished, the 3G-SGSN may release the signalling
connection towards the SRNS for the concerned UE. The SRNS will then release the RRC
connection if there is no signalling connection between 3G-MSC/VLR and SRNS for the UE.
12-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
RA Update Version 1 Rev 0
RA Update
New Old
UE SRNS HLR
3G_SGSN 3G_SGSN
1. RRC connection
establishment
1. RRC update required (old RAI, old P-TMSI)
2. SGSN Context Required (old P-TMSI, old RAI)
2. SGSN Context Resp. (IMSI, Auth.triplets)
3. Security Functions
4. Update GPRS Location
5. Cancel Location
5. Cancel Location Ack
6. Insert Subscriber Data
6. Insert Subscriber Data Ack
7. Update GPRS Location Ack
8. RA upd Accept (new RAI, new P-TMSI
9. RA update complete
10. Release
10. RRC connection release
© 2005-2006 CP13: Introduction to UMTS USR6 12-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 SRNC Relocation
SRNC Relocation
This example shows SRNS relocation when the source RNC and target RNC
are connected to different 3G-MSC.
The procedure is as follows:
1. The UTRAN makes the decision to perform the Serving RNC relocation procedure,
including the decision of onto which RNC (Target RNC) the Serving RNC functionality
is to be relocated. The source SRNC sends SRNC Relocation required messages
to the MSC. This message includes parameters such as target RNC identifier and an
information field that shall be passed transparently to the target RNC.
2. Upon reception of SRNC Relocation required message the Anchor MSC prepares itself for the
switch and determines from the received information that the SRNC relocation will (in this case)
involve another MSC. The Anchor MSC will then send a Prepare SRNC Relocation Request to
the applicable non-anchor MSC, including the information received from the Source RNC.
3. The non-anchor MSC will send a SRNC Relocation Request message to the target RNC.
This message includes information for building up the SRNC context, transparently sent
from Source RNC (UE ID, No of connected CN nodes, UE capability information), and
directives for setting up Iu user plane transport bearers. When Iu user plane transport
bearers have been established, and target RNC has completed its preparation phase,
SRNC Relocation Proceeding 1 message is sent to the non-anchor MSC.
4. The Prepare SRNC Relocation Response that is sent from non-anchor MSC to Anchor MSC will
contain the "SRNC Relocation Proceeding 1 received" command from the target RNC.
5. When the "SRNC Relocation Proceeding 1" command has been received in the Anchor
MSC, the user plane transport bearers has been allocated between the target RNC and
Anchor MSC and the Anchor MSC is ready for the SRNC move. Then the Anchor MSC
indicates the completion of preparation phase at the CN side for the SRNC relocation by
sending the SRNC relocation proceeding 2 message to the Source RNC.
6. When the source RNC has received the "SRNC Relocation Proceeding 2" message, the
source RNC sends a SRNC Relocation Commit message to the target RNC. The target
RNC executes switch for all bearers at the earliest suitable time instance.
7. Immediately after a successful switch at RNC, the target RNC (=SRNC) sends "SRNC Relocation
Complete" message to the non-anchor MSC. This message is included by the non-anchor MSC
in the "Complete SRNC relocation message" that is sent to the anchor MSC. Upon reception of
this message, the Anchor-MSC switches from the old Iu transport bearers to the new ones.
8. After a successful switch at the Anchor MSC, a release indication is sent towards the Source
RNC. This will imply release of all UTRAN resources that were related to this UE.
9. When the target RNC is acting as SRNC, it will send New MM System Information
to the UE indicating e.g. relevant Routing Area and Location Area. Additional RRC
information may then also be sent to the UE, e.g. new RNTI identity.
12-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
SRNC Relocation Version 1 Rev 0
SRNC Relocation
Source Target Anchor Non-anchor
UE HLR
RNC RNC MSC MSC
1. SRNC Relocation Required
2. Prepare SRNC Relocation
3. SRNC Relocation Request
3. SRNC Relocation Proceeding
4. Prepare SRNC response
5. SRNC Reloc Proceed 2
(a) 6. SRNC Reloc
Commit
7. SRNC Reloc Complete
9. New MM System Info
(b) 7. Complete SRNC Reloc
8. Release
10. Routing Area Update
© 2005-2006 CP13: Introduction to UMTS USR6 12-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 SRNC Relocation
This page intentionally left blank.
12-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 SRNC Relocation
This page intentionally left blank.
12-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 SRNC Relocation
This page intentionally left blank.
12-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary Version 1 Rev 0
Chapter 13
Glossary
© 2005-2006 CP13: Introduction to UMTS USR6 13-1
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary
This page intentionally left blank.
13-2 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
This Glossary of technical terms contains standard Motorola acronyms, abbreviations
and numbers used throughout the documentation set.
A Interface - AUTO
3GPP Third Generation Partnership Project
8-PSK 8 Symbol Phase Shift Keying
A Interface Interface between MSC and BSS. The interface is based on the
use of one or more E1/T1 digital links. The channels on these
links can be used for traffic or signalling.
A3 Authentication algorithm that produces SRES, using RAND and
Ki.
A38 A single algorithm performing the function of A3 and A8.
A5 Stream cipher algorithm, residing on an MS, that produces
ciphertext out of plaintext, using Kc.
A8 Ciphering key generating algorithm that produces Kc using
RAND and Ki.
AA Anonymous Access
AAL-2 ATM Adaptation Layer 2 (for real-time services) ( ITU-T I.363.2)
AAL-5 ATM-Adaptation Layer 5 (non-real time) ( ITU-T I.363.5)
A-Bit Acknowledgement Request Bit ( used in LLC-protocol 
Logical Link Control)
AB See Access Burst.
Abis interface Interface between a remote BSC and BTS. Motorola offers
a GSM standard and a unique Motorola Abis interface. The
Motorola interface reduces the amount of message traffic and
thus the number of 2 Mbit/s lines required between BSC and BTS.
ABM Asynchronous Balanced Mode
ABR Answer Bid Ratio. The ABR is the ratio of successful calls to total
number of calls. As a measure of effective calls, it reflects the
performance of the total network
ac-dc PSM AC-DC Power Supply module.
ac Alternating Current. In electricity, AC occurs when charge
carriers in a conductor or semiconductor periodically reverse their
direction of movement. Household utility current in most countries
is AC with a frequency of either 50 or 60 hertz (complete cycles
per second). The RF current in antennas and transmission lines
is another example of AC. An AC waveform can be sinusoidal,
square, or sawtooth-shaped. Some AC waveforms are irregular
or complicated. Square or sawtooth waves are produced by
certain types of electronic oscillators, and by a low-end UPS
when it is operating from its battery.
AC Access Class (C0 to C15).
AC Application Context.
ACC Automatic Congestion Control. A method by which congested
switches automatically communicate their congestion level to
other switches. (3GTS 22.011)
© 2005-2006 CP13: Introduction to UMTS USR6 13-3
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
Access Burst The Access Burst is used by the MS to access the BTS. It carries
RACH uplink from the MS to the BTS to start a call.
ACCH Associated Control CHannel. Control information associated with
TCH or DCCH.
ACK, Ack ACKnowledgement.
ACM Accumulated Call meter. The ACM is a function contained within
the SIM. It accumulates the total units (in the home currency) for
both the current call and all preceding calls. For security reasons,
the SIM only allows the value of the ACM to be incremented,
not decremented. Resetting of the ACM is only possible after
entering PIN2.
ACM Address Complete Message.
ACPIM AC Power Interface Module. Used in M-Cell6 indoor ac BTS
equipment.
AC PSM AC Power Supply Module. Used in M-Cell6 BTS equipment.
ACSE Association Control Service Element. The ACSE is one of the
three Application Service Elements (ASE) which reside in the
application layer of the OSI protocol and act as an interface to the
lower layer protocols. It is used by applications to create a title
for identification. See also ASI and ROSE.
ACU Antenna Combining Unit.
A/D Analogue to Digital (converter). See ADC.
ADC ADministration Centre.
ADC Analogue to Digital Converter. A device that converts a signal
that is a function of a continuous variable into a representative
number sequence carrying equivalent information.
ADCCP Advanced Data Communications Control Protocol. A bit-oriented
data-link-layer (DL) protocol used to provide point-to-point and
point-to-multipoint transmission of data frames that contain
error-control information. Note: ADCCP closely resembles
high-level data link control (HDLC).
ADM Asynchronous Disconnected Mode
ADM ADMinistration processor.
ADMIN ADMINistration.
ADN Abbreviated Dialling Number. Abbreviated dialling is a telephone
service feature that (a) permits the user to dial fewer digits to
access a network than are required under the nominal numbering
plan, and (b) is limited to a subscriber-selected set of frequently
dialled numbers.
ADPCM Adaptive Differential Pulse Code Modulation. Differential
pulse-code modulation (DPCM) in which the prediction algorithm
is adjusted in accordance with specific characteristics of the input
signal.
AE Application Entity. The system-independent application activities
that are made available as application services to the application
agent.
13-4 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
AEC Acoustic Echo Control. In a system, the reduction of the power
level of an echo or the elimination of an echo.
AEF Additional Elementary Functions.
AET Active Events Table. Alarms and events are sent to the Events
Log in the GUI. Different operators will have different subscription
lists. All alarms and events are sent to the AET before they are
re-routed to different subscription lists.
AFC Automatic Frequency Control. A device or circuit that maintains
the frequency of an oscillator within the specified limits with
respect to a reference frequency.
AFN Absolute Frame Number.
AGC Automatic Gain Control. A process or means by which gain is
automatically adjusted in a specified manner as a function of a
specified parameter, such as received signal level.
AGCH Access Grant CHannel. A GSM common control channel used to
assign MS to a SDCCH or a TCH.
AH Authentication Header ( RFC 2402)
Ai Action indicator.
AI Acquisition Indicator
AI Artificial Intelligence. A branch of computer science whose goal
is to develop electronic devices that can operate with some of the
characteristics of human intelligence. Among these properties
are logical deduction and inference, creativity, the ability to make
decisions based on past experience or insufficient or conflicting
information, and the ability to understand natural language.
AIB Alarm Interface Board.
AICH Acquisition Indicator Channel (UMTS Physical Channel)
AIO A class of processor.
Air interface The radio link between the BTS and the MS.
AL See Application Layer.
ALCAP Access Link Control Application Part ( ITU-T Q.2630.1 /
Q.2630.2)
AM Acknowledged Mode operation ( UMTS-RLC)
AM Amplitude Modulation. Modulation in which the amplitude of a
carrier wave is varied in accordance with some characteristic
of the modulating signal.
AMA Automatic Message Accounting (processor). A service feature
that automatically records data regarding user-dialled calls.
AMD Acknowledged Mode Data (UMTS RLC PDU-type)
AMR Adaptive Multi-Rate. The capability of operating at gross bit-rates
of 11.4 kbit/s (half-rate) and 22.8 kbit/s (full-rate) over the air
interface.
AM/MP Cell broadcast mobile terminated message. A message
broadcast to all MSs in a cell.
© 2005-2006 CP13: Introduction to UMTS USR6 13-5
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
ANSI American National Standards Institute. ANSI is the primary
organisation for fostering the development of technology
standards in the United States. ANSI works with industry groups
and is the U.S. member of ISO and the IEC. Long established
computer standards from ANSI include ASCII and SCSI.
Antenna A transmitter/receiver which converts electrical currents into RF
and vice versa. In GSM systems, transmits and receives RF
signals between the BTS and MS.
AoC Advice of Charge.
AoCC Advice of Charge Charging supplementary service.
AoCI Advice of Charge Information supplementary service.
AOC Automatic Output Control.
AP Application Process.
AP-AICH CPCH Access Preamble Acquisition Indicator Channel (UMTS
Physical Channel)
API Access Preamble Acquisition Indicator
APN Access Point Name ( Reference to a GGSN)
Application Layer See OSI RM. The Application Layer is the highest of seven
hierarchical layers. It interfaces directly to, and performs common
application services for, the application processes. It also issues
requests to the Presentation Layer. The common application
services provide semantic conversion between associated
application processes.
ARFCN Absolute Radio Frequency Channel Number. The GSM available
frequency is divided in two bands. Each band is divided into
200kHz slots called ARFCN. Each ARFCN is shared between
8 mobiles, each using it in turn. Each mobile uses the ARFCN
for one TS (Timeslot) and then waits for its turn to come around
again. A mobile has use of the ARFCN once per the TDMA
frame. The combination of a TS number and ARFCN is called a
physical channel.
ARQ Automatic Repeat-reQuest. Error control for data transmission in
which the receiver detects transmission errors in a message and
automatically requests a retransmission from the transmitter.
ARP Address Resolution Protocol. A Transmission Control Protocol
/ Internet Protocol (TCP/IP) protocol that dynamically binds a
Network Layer (NL) IP address to a Data Link Layer (DL) physical
hardware address, e.g., Ethernet address.(RFC 826)
AS Application Server
AS Access Stratum ( UMTS)
ASC Access Service Class
ASCE Association Control Service Element. An ASE which provides
an AP with the means to establish and control an association
with an AP in a remote NE. Maps directly onto the Presentation
layer (OMC).
13-6 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
ASCII American Standard Code for Information Interchange. ASCII is
a standard developed by ANSI to define how computers write
and read characters. It is the most common format for text files
in computers and on the Internet. In an ASCII file, alphabetic,
numeric, and special characters are represented with a 7-binary
digit binary number. 128 possible characters are defined. UNIX
and DOS-based operating systems (except for Windows NT) use
ASCII for text files. Windows NT uses a newer code, Unicode.
IBM’s System 390 servers use a proprietary 8-bit code called
extended binary-coded decimal interchange code. Conversion
programs allow different operating systems to change a file from
one code to another.
ASE Application Service Element (OMC). A coherent set of integrated
functions to help accomplish application communication, e.g.,
within an application entity (AE).
ASE Application Specific Entity (TCAP).
AS-ILCM Application Server - Incoming Leg Control Model
ASN.1 Abstract Syntax Notation One. A formal notation used
for describing data transmitted by telecommunications
protocols, regardless of language implementation and physical
representation of these data, whatever the application, whether
complex or very simple.( ITU-T X.680 / X.681)
AS-OLCM Application Server - Outgoing Leg Control Model
ASP Alarm and Status Panel.
ASR Answer Seizure Ratio. The percentage of calls that are
completed successfully.
ATB All Trunks Busy. An equipment condition in which all trunks
(paths) in a given trunk group are busy.
AT-Command Attention-Command
Ater The interface between XCDR and BSC.
ATI Antenna Transceiver Interface.
ATM Asynchronous Transfer Mode. A high-speed multiplexing and
switching method utilising fixed-length cells of 53 octets to
support multiple types of traffic. ( ITU-T I.361)
ATT (flag) ATTach.
ATTS Automatic Trunk Testing Subsystem. Ensures the quality of
telephone lines by means of a series of tests. ATTS can be
initiated by either an operator command or by a command file,
which can be activated at a predetermined time.
AU Access Unit.
AUC Authentication Centre. A GSM network entity which provides the
functionality for verifying the identity of an MS when requested by
the system. Often a part of the HLR.
AUT(H) AUThentication.
AUTO AUTOmatic mode.
© 2005-2006 CP13: Introduction to UMTS USR6 13-7
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
B Interface - Byte
B Interface Interface between MSC and VLR.
BA BCCH Allocation. The radio frequency channels allocated in a
cell for BCCH transmission.
BAIC Barring of All Incoming Calls supplementary service.
BAOC Barring of All Outgoing Calls supplementary service.
Baud The unit in which the information carrying capacity or signalling
rate of a communication channel is measured. One baud is one
symbol (state transition or level-transition) per second. This
coincides with bits per second only for two-level modulation with
no framing or stop bits
BBBX Battery Backup Board.
BBH Base Band Hopping. Method of frequency hopping in which each
transceiver at the base station is tuned to a different frequency,
and the signal is switched to a different transceiver for each burst.
BCC Base station Colour Code. The BCC and the NCC are part of the
BSIC. The BCC comprises three bits in the range 000 to 111.
See also NCC and BSIC.
BCCH Broadcast Control CHannel. A GSM control channel used to
broadcast general information about a BTS site on a per cell or
sector basis.
BCD Binary Coded Decimal. The representation of a decimal digit by a
unique arrangement of no fewer than four binary digits.
BCF Base station Control Function. The GSM term for the digital
control circuitry which controls the BTS. In Motorola cell sites this
is a normally a BCU which includes DRI modules and is located
in the BTS cabinet.
B channel Bearer channel. Used in ISDN services to carry 64kbit/s of data,
when used at full capacity.
BCH Broadcast Channel (UMTS Transport Channel)
BCIE Bearer Capability Information Element. Specific GSM parameters
in the Setup message are mapped into a BCIE for signalling to
the network and within the PLMN. The BCIE is used to request a
bearer service (BS) from the network.
BCTP Bearer Control Tunneling Protocol ( ITU-T Q.1990)
BCU Base station Control Unit. A functional entity of the BSS which
provides the base control function at a BTS site. The term no
longer applies to a type of shelf (see BSC and BSU).
BCUP Base Controller Unit Power.
BEC Backward Error Correction
BEG BEGin Message ( TCAP)
BEP Bit Error Probability.
13-8 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
BER Bit Error Rate. The number of erroneous bits divided by the total
number of bits transmitted, received, or processed over some
stipulated period. The BER is usually expressed as a coefficient
and a power of 10; for example, 25 erroneous bits out of 100,000
bits transmitted would be 25 out of 105 or 25 x 10-5.
BES Business Exchange Services.
BFI Bad Frame Indication. An indication of unsuccessfully decoded
speech frames. See FER.
BG Border Gateway
BGCF Breakout Gateway Control Function
BH Busy Hour. In a communications system, the sliding 60-minute
period during which occurs the maximum total traffic load in a
given 24-hour period.
BHCA Busy Hour Call Attempt. A statistic based on call attempts that a
switch processes during a BH. See also BH.
BI Barring of all Incoming call supplementary service.
BIB Backward Indicator Bit
BIB Balanced-line Interconnect Board. Provides interface to 12
balanced (6-pair) 120 ohm (37-pin D-type connector) lines for 2
Mbit/s circuits. See also T43.
BICC Bearer Independent Call Control ( ITU-T Q.1902.1 – Q.1902.6)
BIC-Roam Barring of all Incoming Calls when Roaming outside the Home
PLMN Country supplementary service.
Bi-directional neighbour See Reciprocal neighbour..
BIM Balanced-line Interconnect Module.
Bin From BINary. An area in a data array used to store information.
Also, a name for a directory that contain files stored in binary
format.
BL BootLoad. Also known as download. For example, databases
and software can be downloaded to the NEs from the BSS.
BLER Block Error Rate
BLLNG BiLLiNG.
bit Binary digit. A character used to represent one of the two states
or digits (0 or 1) in the numeration system with a radix of two.
Also, a unit of storage capacity.
bit/s Bits per second (bps). A measure of data transmission speed.
The number of binary characters (1s or 0s) transmitted in one
second. For example, an eight-bit parallel transmission link which
transfers one character (eight bits) per second is operating at
8 bps.
block A group of bits (binary digits) transmitted as a unit, over which a
parity check procedure is applied for error control purposes.
Bm Full rate traffic channel. See also Full Rate.
BMC Broadcast / Multicast Control ( 3GTS 25.324)
© 2005-2006 CP13: Introduction to UMTS USR6 13-9
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
BN Bit Number. Number which identifies the position of a particular
bit period within a timeslot.
BPF Bandpass Filter. A filter that ideally passes all frequencies
between two non-zero finite limits and bars all frequencies not
within the limits.
BPSM µBCU Power Supply Module.
BRI Basic Rate Interface. An ISDN multipurpose user interface
allowing simultaneous voice and data services provided over
two clear 64 kb/s channels (B channels) and one clear 16 kb/s
channel (D channel). The interface is also referred to as 2B+D.
BS Base Station. See BSS.
BS Basic Service (group).
BS Bearer Service. A type of telecommunication service that
provides the capability for the transmission of signals between
user-network interfaces. The PLMN connection type used to
support a bearer service may be identical to that used to support
other types of telecommunication service.
BSC Base Station Controller. A network component in the GSM PLMN
which has the digital control function of controlling all BTSs. The
BSC can be located within a single BTS cabinet (forming a BSS)
but is more often located remotely and controls several BTSs
(see BCF, BCU, and BSU).
BS_CV_MAX Maximum Countdown Value to be used by the mobile station (
Countdown Procedure)
BSG Basic Service Group.
BSIC Base Transceiver Station Identity Code. Each cell has a BSIC. It
is a local colour code that allows a mobile station to distinguish
between different neighbouring base stations. The BSIC is an
octet, consisting of three bits for the Network Colour Code (NCC)
and three bits for the Base station Colour Code (BCC). The
remaining two bits are unused. See also NCC and BCC.
BSIC-NCELL BSIC of an adjacent cell.
BSP Base Site control Processor (at BSC).
BSN Backward Sequence Number. A field in a signal unit (SU) that
contains the forward sequence number (FSN) of a correctly
received signal unit being acknowledged in the signal unit that is
being returned to the sender. See also FSN and SU.
BSS Base Station System. The system of base station equipment
(Transceivers, controllers and so on) which is viewed by the
MSC through a single interface as defined by the GSM 08
series of recommendations, as being the entity responsible for
communicating with MSs in a certain area. The radio equipment
of a BSS may cover one or more cells. A BSS may consist of one
or more base stations. If an internal interface is implemented
according to the GSM 08.5x series of recommendations, then the
BSS consists of one BSC and several BTSs.
13-10 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
BSSAP BSS Application Part (part of SS7) . Protocol for LAPD or
LAPB signalling links on the A-interface. Comprises DTAP
and BSSMAP messages. Supports message communication
between the MSC and BSS.
BSSGP Base Station System GPRS Protocol
BSSC Base Station System Control cabinet. The cabinet which houses
one or two BSU shelves at a BSC or one or two RXU shelves at a
remote transcoder (RXCDR).
BSSMAP Base Station System Management Application Part (part of SS7).
Call processing protocol for A-interface messages exchanged
between the MSC and BSS. The BSS interprets these messages.
BSSOMAP BSS Operation and Maintenance Application Part (part of SS7).
BSU Base Station Unit shelf. The shelf which houses the digital
control modules for the BTS (part of BTS cabinet) or BSC (part
of BSSC cabinet).
BT British Telecom.
BT Bus Terminator. In order to avoid signal reflections on the bus,
each bus segment has to be terminated at its physical beginning
and at its end with the characteristic impedance.
BTC Bus Terminator Card.
BTF Base Transceiver Function.
BTP Base Transceiver Processor (at BTS). One of the six basic task
groups within the GPROC.
BTS Base Transceiver Station. A network component in the GSM
PLMN which serves one cell, and is controlled by a BSC. The
BTS contains one or more Transceivers (TRXs).
Burst A period of modulated carrier less than one timeslot. The physical
content of a timeslot.
BVCI BSSGP Virtual Connection Identifier
Byte A sequence of adjacent binary digits operated upon as a unit.
Generally consists of eight bits, usually presented in parallel. A
byte is usually the smallest addressable unit of information in a
data store or memory.
C - CW
C/R-Bit Command / Response Bit
C/T-Field logical Channel / Transport channel identification Field
C Conditional.
C Interface Interface between MSC and HLR/AUC.
C7 See SS7.
CA Cell Allocation. The radio frequency channels allocated to a
particular cell.
CA Central Authority. Software process that controls the BSS.
CAB Cabinet.
© 2005-2006 CP13: Introduction to UMTS USR6 13-11
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
CADM Country ADMinistration. The Motorola procedure used within
DataGen to create new country and network files in the DataGen
database.
CAI Channel Assignment Indicator
CAI Charge Advice Information.
CAT Cell Analysis Tool. The CAT is part of the Motorola Cell
Optimization product. It is intended for engineering staff and
OMC administrators. CAT provides information about GSM
network cell performance.
CB Cell Balancer. The CB process balances the cells configured for
GPRS across PRPs. In the event of a PRP outage, this process
sends message(s) indicating that GPRS service is unavailable to
the appropriate CRM(s) for the cells that could not be moved to
an INS (IN Service) PRP.
CB Cell Broadcast. See CBSMS.
CB Circuit Breaker.
CBA Cell Broadcast Agent.
CBC Cell Broadcast Centre. The call processing centre for CBSMS
messages.
CBCH Cell Broadcast CHannel. The channel which is used to broadcast
messages to all MSs in a specific cell.
CBF Combining Bandpass Filter.
CBL Cell Broadcast Link. A bi-directional data link which allows
communications between the BSS and the CBC.
CBM Circuit Breaker Module.
CBMI Cell Broadcast Message Identifier.
CBS Cell Broadcast Service. See CBSMS.
CBSMS Cell Broadcast Short Message Service. CBSMS allows a number
of unacknowledged general messages to be broadcast to all MSs
within a particular region. The content may include information
such as local traffic conditions, the weather, the phone number of
the local taxi company, etc. The messages are sent from a CBC
via a BSC to a BTS and from there on a special cell broadcast
channel to the MSs. The CBC is considered as a node outside
the PLMN and can be connected to several BSCs. However, a
BSC is only connected to one CBC.
CBUS Clock Bus.
CC Connection Confirm. Part of SCCP network connectivity.
CC Country Code. A one to three digit number which specifically
identifies a country of the world that an international call is being
routed to (e.g., 1 = North America, 44 = United Kingdom).
CC Call Control. CC functions, such as number translations and
routeing, matrix path control, and allocation of outgoing trunks
are performed by the MSC.
13-12 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
CCB Cavity Combining Block, a three way RF combiner. There are
two types of CCB, CCB (Output) and CCB (Extension). These,
with up to two CCB Control cards, may comprise the TATI. The
second card may be used for redundancy.
CCBS Completion of Calls to Busy Subscriber supplementary service.
CCCH Common Control CHannels. A class of GSM control channels
used to control paging and grant access. Includes AGCH, PCH,
and RACH.
CCCH_GROUP Group of MSs in idle mode.
CCPCH Common Control Physical Channel (see also P-CCPCH and
S-CCPCH)
CCD Common Channel Distributor.
CCDSP Channel Coding Digital Signal Processor.
CCF Conditional Call Forwarding. See CFC.
CCH Control CHannel. Control channels are channels which carry
system management messages.
CCH Council for Communications Harmonization (referred to in GSM
Recommendations).
CCITT Comité Consultatif International Télégraphique et Téléphonique.
This term has been superseded. See ITU-TSS.
CCM Current Call Meter.
CCP Capability/Configuration Parameter.
CCPE Control Channel Protocol Entity.
CCS Hundred call-seconds. A single call lasting one hundred seconds
is one CCS. Also, a measure of traffic load obtained by multiplying
the number of calls per hour by the average holding time per call
expressed in seconds, and dividing by 100. Often used in practice
to mean hundred call seconds per hour with “per hour" implied;
as such, it is a measure of traffic intensity. See also erlang.
CCTrCH Coded Composite Transport Channel (UMTS)
CCU Channel Codec Unit. The CCU performs the following functions:
Channel coding functions, including FEC and interleaving, Radio
channel measurement functions, including received quality level,
received signal level, and information related to timing advance
measurements.
Cct Circuit.
CD/CA-ICH Collision Detection / Channel Assignment Indicator Channel
(UMTS Physical Channel)
CDB Control Driver Board.
CDE Common Desktop Environment. Part of the SUN software
(crontab - cron job file).
CDI Collision Detection Indicator
© 2005-2006 CP13: Introduction to UMTS USR6 13-13
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
CDMA Code-Division Multiple Access. CDMA is a digital cellular
technology that uses spread-spectrum techniques. Unlike
competing systems, such as GSM, that use TDM, CDMA does
not assign a specific frequency to each user. Instead, every
channel uses the full available spectrum. Individual conversations
are encoded with a pseudo-random digital sequence.
CDR Call Detail Record. A record of voice or data SVCs, which
includes calling and called numbers, local and remote node
names, data and timestamp, elapsed time, and call failure class
fields. This is the information needed to bill the customer for calls
and facility usage data for calls.
CD-ROM Compact Disk-Read Only Memory.
CDUR Chargeable DURation.
CEB Control Equalizer Board (BTS).
CED Called station identifier.
CEIR Central Equipment Identity Register.
Cell By GSM definition, a cell is an RF coverage area. At an
omni-site, cell is synonymous with site; at a sectored site, cell is
synonymous with sector. This differs from analogue systems
where cell is taken to mean the same thing as site. (See below)
CEND End of charge point. The time at which the calling, or called, party
stops charging by the termination of the call or by an equivalent
procedure invoked by the network or by failure of the radio path.
CEPT Conférence des administrations Européennes des Postes et
Telecommunications.
CERM Circuit Error Rate Monitor. Identifies when discontinuity is
detected in a circuit. An alarm is generated and sent to the
OMC-R when the error count exceeds an operator specified
threshold. The alarm identifies the RCI or CIC and the path
where the error is detected.
CF Conversion Facility.
CF Call Forwarding. A feature available to the mobile telephone
user whereby, after initiation of the feature by an authorised
subscriber, calls dialled to the mobile telephone of an authorised
subscriber will automatically be routed to the desired number.
See also CFC and CFU.
CF Control Function. CF performs the SGSN mobility management
functions and OA&M functions for the GSN module.
CFB Call Forwarding on mobile subscriber Busy supplementary
service. Service automatically redirects incoming calls for phone
busy situations.
CFC Call Forwarding Conditional supplementary service. Service
automatically redirects incoming calls for busy, no reply, or not
reachable situations. See also CFB, CFNRc, and CFNRy.
CFM Configuration Fault Management RSS process.
13-14 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
CFNRc Call Forwarding on mobile subscriber Not Reachable
supplementary service. Service automatically redirects incoming
calls for not reachable situations.
CFNRy Call Forwarding on No Reply supplementary service. Service
automatically redirects incoming calls for no reply situations.
CFU Call Forwarding Unconditional supplementary service. Service
automatically redirects all incoming calls.
CG Charging Gateway.
CGF Charging Gateway Function.
Channel A means of one-way transmission. A defined sequence of
periods (for example, timeslots) in a TDMA system; a defined
frequency band in an FDMA system; a defined sequence of
periods and frequency bands in a frequency hopped system.
CHAP Challenge Handshake Authentication Protocol ( RFC 1334)
CIM Coaxial Interconnect Module.
Channel Mode See Full Rate and Half Rate. These are the channel modes
that are currently used.
CHP CHarging Point.
CHV Card Holder Verification information.
CKSN Ciphering Key Sequence Number. The CKSN is a number which
is associated with the ciphering key, Kc. It is used to ensure
authentication consistency between the MS and the VLR.
CI Cell Identity. A block of code which identifies a cell within a
location area.
CI CUG Index.
C/I Carrier to Interference ratio.
CIC Circuit Identity Code. The unique identifier of the terrestrial
portion of a circuit path. A CIC is either a 64 kbit/s or 16 kbit/s
connection depending on whether a site has local or remote
transcoding. A CIC with local transcoding occupies a complete
E1/T1 timeslot. A 16 kbit/s CIC, at a site with remote transcoding,
occupies a sub-channel of an E1/T1 timeslot.
CIC Call Instance Code ( BICC)
CID Channel Identity ( ATM)
CIDR Classless Inter-Domain Routing ( RFC 1519)
CIO Cell Individual Offset ( 3GTS 25.331)
CIR, C/I Carrier to Interference Ratio. Indicates the received signal power
level relative to the interference power level.
Ciphertext Unintelligible data produced through the use of encipherment.
CKSN Ciphering Key Sequence Number.
CLI Calling Line Identity. The identity of the caller. See also CLIP
and CLIR.
CLIP Calling Line Identification Presentation supplementary service.
Allows the called party to identify the caller. See also CLIR.
© 2005-2006 CP13: Introduction to UMTS USR6 13-15
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
CLIR Calling Line Identification Restriction supplementary service.
Allows the caller to withhold their identity from the called party.
See also CLIP.
CLK Clock.
CLKX Clock Extender half size board. The fibre optic link that distributes
GCLK to boards in system (part of the BSS, etc).
CLM ConnectionLess Manager. Coordinates global control over
the BSS by handling of all connectionless messages (that is,
messages that are not directly concerned with a connected call).
This includes such messages as global resets, load limiting and
circuit blocking.
CLR CLeaR.
CM Configuration Management. Configuration management allows
the operator to perform network configuration tasks, and to
maintain all details of the network configuration at the OMC.
CM Connection Management. See CLM.
CM Connectionless Manager. See CLM.
CMD CoMmanD.
CMM Channel Mode Modify. Message sent to an MS to request a
channel mode change. When it has received the CMM message,
the MS changes the mode to the indicated channel and replies
with a Channel Mode Modify Acknowledge message indicating
the new channel mode.
CMIP Common Management Information Protocol. Protocol used for
communication over the OML.
CMISE Common Management Information Service Element. An ASE
which provides a means to transfer management information via
CMIP messages with another NE over an association established
by ASCE using ROSE (OMC).
CMR Cellular Manual Revision. Documentation updates.
CNG CalliNg tone.
Codec Coder/Decoder. A speech coding unit that converts speech into a
digital format for radio broadcast, and vice versa.
CODEX Manufacturer’s name for a type of multiplexer and packet switch
commonly installed at the Motorola OMC-R.
Coincident Cell A cell whose cell boundary follows the boundary of a co-located
neighbour cell. The coincident cell has a different frequency type,
but the same BSIC, as that of the neighbour cell.
COLI COnnected Line Identity. Identity of the connected line. See also
COLP and COLR.
Collocated Placed together; two or more items together in the same place.
Colour Code An 8-bit code assigned to a BTS to distinguish interfering signals
from another cell.
COLP COnnected Line Identification Presentation supplementary
service. Allows the calling party to identify the line identity of the
connected party. See also COLR.
13-16 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
COLR COnnected Line Identification Restriction supplementary service.
Allows the connected party to withhold its line identity from the
calling party. See also COLP.
COM Code Object Manager (software).
COM COMplete.
COMB Combiner. The purpose of a combiner in the BSS is to combine
transmitter outputs from the RCUs onto an antenna.
COMM, Comms COMMunications.
CommHub Communications Hub. Provides Ethernet switching and IP
routeing for the GSN complex local networking and GSN complex
E1 interfaces to the public data network.
CommsLink Communications Link. See also 2 Mbit/s link.
Compact PCI See cPCI.
CON CONtinue Message ( TCAP)
CONF CONFerence circuit. Circuit used for multi-party conference calls.
CONFIG CONFIGuration Control Program.
Congestion Situation occurring when an element cannot receive all the
service it is requesting.
CONNACK CONNect ACKnowledgement. Part of the synchronization
process. After a connection has been established, the CONNACK
message indicates that traffic channels are available.
CP Call Processing. The CP process in the BTS controls the MS to
BSS to MS signalling link, MS originated and terminated calls
and inter-BSS and inter-BTS handovers.
CPCH Common Packet Channel (UMTS Transport Channel) FDD
only
cPCI Compact Peripheral Component Interconnect. A set of standards
that define a common card cage, power supplies, and processor
boards.
CPCS Common Part Convergence Sublayer
CPGM CCCH Paging Manager. The CPGM processes the paging
messages sent from the SGSN to the BSC/BTS.
CPICH Common Pilot Channel (UMTS Physical Channel / see also
P-CPICH and S-CPICH)
CPS Code and Puncturing Scheme.
CPU Central Processing Unit. The portion of a computer that controls
the interpretation and execution of instructions. Also, the portion
of a digital communications switch that executes programmed
instructions, performs arithmetic and logical operations on
signals, and controls input/output functions.
C/R Command/Response field bit.
CR Carriage Return (RETURN).
© 2005-2006 CP13: Introduction to UMTS USR6 13-17
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
CR Connection Request (Part of SCCP network connectivity). An
SCCP Connection Request message is sent from the BSS to the
MSC to establish a connection. See also CREF.
CRC Cyclic Redundancy Check (3 bit). An error-detection scheme that
(a) uses parity bits generated by polynomial encoding of digital
signals, (b) appends those parity bits to the digital signal, and
(c) uses decoding algorithms that detect errors in the received
digital signal.
CRE Call RE-establishment procedure. Procedure for re-establishing
a call in the event of a radio link failure.
CREF Connection REFused (Part of SCCP network connectivity). In
a number of operating circumstances, a CREF message may
be sent from the MSC to the BSS in response to a Connection
Request (CR).
CRM Cell Resource Manager. The CRM allocates and activates
timeslots and subchannels on the available carriers.
CRM Cell Resource Machine.
CRM-LS/HS Cellular Radio Modem-Low Speed/High Speed. Low speed
modem used to interwork 300 to 2400 bit/s data services under
V.22bis, V.23, or V.21 standards. High speed modem used to
interwork 1200 to 9600 bit/s data services under V.22bis, V.32,
or V.29/V.27ter/V.21 standards.
CNRC Controlling RNC
CRO Motorola Controlled Roll Out Group. A CRO consists of a
customer site implementation of a new product, software release,
or combination of products/releases.
CRT Cathode Ray Tube (video display terminal).
CS Coding Scheme
CS Circuit Switched.
CS-1 GPRS Coding Scheme-1 (9.05 kbit/s per TCH).
CS-2 GPRS Coding Scheme-2 (13.4 kbit/s per TCH).
CS-3 GPRS Coding Scheme-3 (15.6 kbit/s per TCH).
CS-4 GPRS Coding Scheme-4 (21.4 kbit/s per TCH).
CSCF Call Session Control Function ( SIP)
CSD Circuit Switched Data
CSFP Code Storage Facility Processor (at BSC and BTS). A GPROC
device which facilitates the propagating of new software instances
with reduced system down time. See also IP.
CSICH CPCH Status Indicator Channel (UMTS Physical Channel)
CSP Central Statistics Process. The statistics process in the BSC.
CSPDN Circuit Switched Public Data Network. A publicly available
communications network using circuit switched digital data
circuits.
CT Call Transfer supplementary service.
CT Channel Tester.
13-18 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
CT Channel Type.
CTCH Common Traffic Channel (Logical)  PTM
CTP Call Trace Product (Tool). The CTP is designed to help operators
of GSM900 and DCS1800 communication networks tune and
optimize their systems. CTP allows Call Trace data to be
analysed and decoded.
CTP Control Terminal Port.
CTR Common Technical Regulation.
CTS Clear to Send. A handshake signal used with communication
links, especially RS232 or CCITT Rec. V.24, to indicate (to a
transmitter from a receiver) that transmission may proceed.
Generated in response to a request to send signal. See also RTS.
CTU Compact Transceiver Unit (M-Cellhorizon radio).
CUG Closed User Group supplementary service. A CUG is used
to control who can receive and/or place calls, by creating a
unique group. When a CUG is configured for an interface, only
those subscribers that are members of the same CUG can
receive/place calls.
Cumulative value The total value for an entire statistical interval.
CV Countdown Value
CW Code Word
CW Call Waiting supplementary service. A subscriber feature which
allows an individual mobile telephone user currently engaged in a
call to be alerted that another caller is trying to reach him. The
user has a predetermined period of time in which to terminate the
existing conversation and respond to the second call.
cwnd Congestion window
D Interface - DYNET
D Interface Interface between VLR and HLR.
D/A Digital to Analogue (converter). See DAC.
DAB Distribution Alarm Board (in BTS6 cabinet).
DAC Digital to Analogue Converter. A device that converts an input
number sequence into a function of a continuous variable.
DACS Digital Access Cross-connect System. A data concentrator and
organizer for Tl / El based systems.
DAK Downlink Acknowledgement
DAN Digital ANnouncer (for recorded announcements on MSC).
DAS Data Acquisition System.
DAT Digital Audio Tape. Audio-recording and playback medium/format
that maintains a signal quality equal to that of the CD-ROM
medium/format.
DataGen Sysgen Builder System. A Motorola offline BSS binary object
configuration tool.
© 2005-2006 CP13: Introduction to UMTS USR6 13-19
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
Data Link Layer See OSI RM. This layer responds to service requests from the
Network Layer and issues service requests to the Physical Layer.
It provides the functional and procedural means to transfer data
between network entities and to detect and possibly correct
errors that may occur in the Physical Layer.
dB Decibel. A unit stating the logarithmic ratio between two numeric
quantities. See also dBm.
DB DataBase.
DB Dummy Burst (see Dummy burst).
DBA DataBase Administration/Database Administrator.
dBm A dB referenced to 1 milliwatt; 0 dBm equals one milliwatt.
DBMS DataBase Management System.
dc Direct Current. DC is the unidirectional flow or movement of
electric charge carriers, usually electrons. The intensity of the
current can vary with time, but the general direction of movement
stays the same at all times. As an adjective, the term DC is used
in reference to voltage whose polarity never reverses.
DCB Diversity Control Board (part of DRCU).
DCCH Dedicated Control CHannel. A class of GSM control channels
used to set up calls and report measurements. Includes SDCCH,
FACCH, and SACCH.
DCD Data Carrier Detect signal. Hardware signal defined by the
RS-232-C specification that indicates that a device such as a
modem is on-line and ready for transmission.
DCE Data Circuit terminating Equipment. The DCE performs
functions such as signal conversion and coding, at the
network end of the line between the DTE and the line.
Also, The RS232 configuration designated for computers. DCE
equipment can be connected to DTE equipment with a straight
cable, but to other DCE equipment only with a null modem cable.
DCF Data Communications Function.
DCF Duplexed Combining bandpass Filter. (Used in Horizonmacro).
DCH Dedicated CHannel (Transport)
D channel Data channel. Used in ISDN to perform call signalling and
connection setup functions. In some circumstances, the channel
can also be used to carry user data.
DCN Data Communications Network. A DCN connects Network
Elements with internal mediation functions or mediation devices
to the Operations Systems.
DC PSM DC Power Supply Module.
DCS1800 Digital Cellular System at 1800 MHz. A cellular phone network
using digital techniques similar to those used in GSM 900, but
operating on frequencies of 1710 - 1785 MHz (receive) and
1805 - 1880 MHz (transmit).
DDF Dual-stage Duplexed combining Filter. (Used in Horizonmacro).
The DDF is an integrated combiner, filter and duplexer.
13-20 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
DDS DataGen Data Store. Store area for DataGen input and output
files.
DDS Data Drive Storage.
DDS Direct Digital Synthesis. A technology for generating highly
accurate and frequency-agile (rapidly changeable frequency over
a wide range), low-distortion output waveforms.
DEQB Diversity Equalizer Board.
DES Data Encryption Standard
DET DETach.
DFE Decision Feedback Equalizer. A receiver component/function.
The DFE results in a very sharp Bit Error Rate (BER) threshold
by using error feedback.
DGT Data Gathering Tool. The DGT collects all the relevant data
relating to a specified problem and copies it to tape or file,
together with a problem description. The file or tape is then sent
to Motorola for analysis.
DHCP Dynamic Host Configuration Protocol ( RFC 2131)
DHP Digital Host Processor. A hard GPROC based device located
at Horizonmicro2 BTS sites. It represents the MCU of a slave
Horizonmicro2 FRU. The MCU that the DHP represents is
responsible for providing DRI and carrier support.
DIA Drum Intercept Announcer.
Digit 4 Bit
DINO E1/HDSL Line termination module (part of Horizonmicro).
DINO T1 Line termination module (part of Horizonmicro).
DISC DISConnect.
Discon Discontinuous.
DIQ Diversity In phase and Quadrature phase.
DIR Device Interface Routine. Software routine used in the BSS.
DL Data Link (layer). See Data Link Layer.
DL See Downlink.
DLCI Data Link Connection Identifier. In frame-relay transmission
systems, 13-bit field that defines the destination address of a
packet. The address is local on a link-by-link basis.
DLD Data Link Discriminator.
DLNB Diversity Low Noise Block.
DLR Destination Local Reference
DLS DownLink Segmentator. The DLS segments LLC frames into
RLC data blocks to be transmitted over the air interface.
DLSP Data Link Service Process. Handles messages for an OMP and
a shelf GPROC.
DLSP Digital Link Signalling Processor.
Dm Control channel (ISDN terminology applied to mobile service).
© 2005-2006 CP13: Introduction to UMTS USR6 13-21
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
DMA Deferred Maintenance Alarm. An alarm report level; an
immediate or deferred response is required (see also PMA).
DMA Direct Memory Access. Transfer of data from a peripheral device,
such as a hard disk drive, into memory without that data passing
through the microprocessor. DMA transfers data into memory at
high speeds with no processor overhead.
DMR Digital Mobile Radio.
DMX Distributed Electronic Mobile Exchange (Motorola’s networked
EMX family).
DN Directory Number.
DNIC Data Network Identifier Code. In the CCITT International X.121
format, the first four digits indicate the international data number,
the next three digits are the data country code, and the final digit
is the network code.
DNS Domain Name Service. A service that translates from logical
domain or equipment names to IP addresses.
Downlink Physical link from the BTS towards the MS (BTS transmits, MS
receives).
DP Dial/Dialled Pulse. A dc pulse produced by an end instrument that
interrupts a steady current at a sequence and rate determined
by the selected digit and the operating characteristics of the
instrument.
DPC Destination Point Code. A part of the label in a signalling
message that uniquely identifies, in a signalling network, the
(signalling) destination point of the message.
DPC Digital Processing and Control board.
DPCCH Dedicated Physical Control Channel (UMTS Physical Channel)
DPCH Dedicated Physical Channel (UMTS / Term to combine DPDCH
and DPCCH)
DPDCH Dedicated Physical Data Channel (UMTS Physical Channel)
DPCM Pulse-code modulation (PCM) in which an analog signal is
sampled and the difference between the actual value of each
sample and its predicted value, derived from the previous sample
or samples, is quantified and converted, by encoding, to a
digital signal. Note: There are several variations of differential
pulse-code modulation.
DPNSS Digital Private Network Signalling System (BT standard for PABX
interface).
DPP Dual Path Preselector. BTS module.
DPR, DPRAM Dual Port Random Access Memory.
DPROC Data PROCessor.
DPSM Digital Power Supply Module.
DRAM Dynamic Random Access Memory. A type of semiconductor
memory in which the information is stored in capacitors on a
integrated circuit.
13-22 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
DRC Data Rate Converter board. Provides data and protocol
conversion between PLMN and destination network for 8 circuits.
Part of IWF.
DRCU Diversity Radio Channel Unit. Contains transceiver, digital control
circuits, and power supply. Part of the BSS.
DRI Digital Radio Interface. Provides encoding/decoding and
encryption/decryption for radio channels. Part of BSS.
DRIM Digital Radio Interface extended Memory. A DRI with extra
memory.
DRIX DRI Extender half size board. Fibre optic link from DRI to BCU.
Part of the BSS.
DRNC Drift Radio Network Controller
DRX, DRx Discontinuous reception (mechanism). A means of saving battery
power (for example in hand-portable units) by periodically and
automatically switching the MS receiver on and off.
DS-1 Digital transmission System 1 (or Digital Signal level 1). Term
used to refer to the 1.44 Mbit/s (U.S.) or 2.108 Mbit/s (Europe)
digital signal carried on a T1 facility.
DS-2 German term for 2 Mbit/s line (PCM interface).
DSCH Downlink Shared Channel (UMTS Transport Channel)
DSE Data Switching Exchange.
DSI Digital Speech Interpolation. A compression technique that relies
on the pauses between speech bursts to provide additional
compression. DSI enables users to gain an additional 2:1
compression on the average on their line.
DSN Digital Switching Network
DSO 64 kbit/s timeslot on an E1/T1.
DSP Digital Signal Processor. A specialized, programmable computer
processing unit that is able to perform high-speed mathematical
processing.
DSS1 Digital Subscriber Signalling No 1. N-ISDN user network interface
signalling.
DSSI Diversity Signal Strength Indication.
DTAP Direct Transfer Application Part (Part of SS7). Call processing
protocol for A-Interface messages exchanged directly between
the MSC and the mobile unit without interpretation by the BSS.
DTCH Dedicated Traffic Channel (UMTS Logical Channel)
DTE Data Terminal Equipment. An end instrument that
converts user information into signals for transmission
or reconverts the received signals into user information.
Also, the RS232 configuration designated for terminals. DTE
equipment can be connected to DCE with a straight cable, but to
other DTE equipment only with a null modem.
DTF Digital Trunk Frame. A frame or electronic rack of digital trunk
interface equipment.
DT1 DaTa form 1 (Part of SCCP network connectivity).
© 2005-2006 CP13: Introduction to UMTS USR6 13-23
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
DTI Digital Trunk Interface.
DTM Dual Transer Mode.
DTMF Dual Tone Multi-Frequency. Multifrequency signalling in which
specified combinations of two voice band frequencies, one from a
group of four low frequencies and the other from a group of four
higher frequencies, are used. The sounds a push button tone
telephone makes when it dials a number.
DTR Data Terminal Ready signal. Method of flow control (RS232
Interface). A modem interface control signal sent from the DTE
to the modem, usually to indicate to the modem that the DTE is
ready to transmit data.
DTRX Dual Transceiver Module. (Radio used in Horizonmicro
(M-Cellarena) and Horizonmacro (M-Cellarenamacro)).
DTX, DTx Discontinuous Transmission (mechanism). A means of saving
battery power (for example in hand-portable units) and reducing
interference by automatically switching the transmitter off when
no speech or data are to be sent.
Dummy burst A period of carrier less than one timeslot whose modulation is a
defined sequence that carries no useful information. A dummy
burst fills a timeslot with an RF signal when no information is
to be delivered to a channel.
DYNET DYnamic NETwork. Used to specify BTSs sharing dynamic
resources.
E - EXEC
E See Erlang.
E1 Also known as CEPT1. The 2.048 Mbit/s rate used by European
CEPT carrier to transmit 30 64 kbit/s digital channels for voice
or data calls, plus a 64 kbit/s signalling channel and a 64 kbit/s
channel for framing and maintenance.
E Interface Interface between MSC and MSC.
EA External Alarm. See EAS. Typical external alarms are: Door
open, High humidity, Low humidity, Fire, Intruder.
EAS External Alarm System. The EAS is responsible for the monitoring
of all customer-defined environmental alarms at a site. The
customer defines the alarm string and the severity of the alarms
based on the individual requirements of the site. Indications are
provided when the alarms are set or cleared.
Eb/No Energy per Bit/Noise floor, where Eb is the signal energy per bit
and No is the noise energy per hertz of noise bandwidth.
EBCG Elementary Basic Service Group.
EC Echo Canceller. Performs echo suppression for all voice circuits.
If cancellation does not take place, the PLMN subscriber hears
the voice signal as an echo, due to the total round-trip delay
introduced by the GSM system (typically 180 ms).
ECB Provides echo cancelling for telephone trunks for 30 channels
(EC).
13-24 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
ECID The Motorola European Cellular Infrastructure Division.
ECM Error Correction Mode. A facsimile mode, in which the sending
machine will attempt to send a partial page up to four times.
Ec/No Ratio of energy per modulating bit to the noise spectral density.
ECSD Enhanced Circuit Switched Data ( HSCSD + EDGE)
ECT Event Counting Tool. The ECT provides information about the
number and type of events and alarms generated throughout the
network. It extracts data from the event log files for specified
dates, allowing the user to generate reports on individual network
elements, groups of elements, or the whole network.
ECT Explicit Call Transfer supplementary service. ECT enables a
user to connect two other parties with which he is engaged in a
telephone call and leave the connection himself.
EDGE Enhanced Data-rates for Global Evolution.
EEL Electric Echo Loss.
EEPROM Electrically Erasable Programmable Read Only Memory. An
EEPROM is a special type of PROM that can be erased by
exposing it to an electrical charge. Like other types of PROM,
EEPROM retains its contents even when the power is turned off.
EGPRS Enhanced GPRS.
EGSM900 Extended GSM900. EGSM900 provides the BSS with a further
range of frequencies for MS and BSS transmit. EGSM MSs can
use the extended frequency band as well as the primary band,
while non-EGSM MSs cannot use the extended frequency band.
A GSM900 cell can contain both GSM900 and EGSM900 carrier
hardware. EGSM operates on the frequency range, 880 - 915
MHz (receive) and 925 - 960 MHz (transmit).
EI Events Interface. Part of the OMC-R GUI.
EIA Electronic Industries Alliance.
EIR Equipment Identity Register. The EIR contains a centralized
database for validating the IMEI. The register consists of lists of
IMEIs organised as follows: White List - IMEIs which are known
to have been assigned to valid MS equipment. Black List - IMEIs
which have been reported stolen or which are to be denied service
for some other reason. Grey List - IMEIs which have problems
(for example, faulty software). These are not, however, sufficiently
significant to warrant a black listing.
EIRP Effective Isotropically Radiated Power. The arithmetic product of
the power supplied to an antenna and its gain.
EIRP Equipment Identity Register Procedure.
EL Echo Loss.
EM Event Management. An OMC-R application. It provides a
centralised facility for reporting network-wide generated events
and alarms, and for monitoring the status of the Network.
© 2005-2006 CP13: Introduction to UMTS USR6 13-25
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
EMC ElectroMagnetic Compatibility. The ability of systems, equipment,
and devices that utilize the electromagnetic spectrum to operate
in their intended operational environments without suffering
unacceptable degradation or causing unintentional degradation
because of electromagnetic radiation or response.
EMF Electro Motive Force. The rate at which energy is drawn from a
source that produces a flow of electricity in a circuit; expressed
in volts.
EMI Electro Magnetic Interference. Any electromagnetic disturbance
that interrupts, obstructs, or otherwise degrades or limits the
effective performance of electronics/electrical equipment.
eMLPP enhanced Multi-Level Precedence and Pre-emption service. This
service has two parts: precedence and pre-emption. Precedence
involves assigning a priority level to a call in combination with
fast call set-up. Pre-emption involves the seizing of resources,
which are in use by a call of a lower precedence, by a higher level
precedence call in the absence of idle resources. Pre-emption
can also involve the disconnection of an on-going call of lower
precedence to accept an incoming call of higher precedence.
EMMI Electrical Man Machine Interface.
EMX Electronic Mobile Exchange (Motorola’s MSC family).
en bloc Fr. - all at once (a CCITT #7 Digital Transmission scheme);
En bloc sending means that digits are sent from one system to
another ~ (that is, all the digits for a given call are sent at the same
time as a group). ~ sending is the opposite of overlap sending.
A system using ~ sending will wait until it has collected all the
digits for a given call before it attempts to send digits to the next
system. All the digits are then sent as a group.
END END Message ( TCAP)
EOP Enhanced One-Phase
EOT End of Tape.
EPCR EGPRS Packet Channel Request.
EPROM Erasable Programmable Read Only Memory. EPROM is a type of
memory that retains its contents until it is exposed to ultraviolet
light. The ultraviolet light clears its contents, making it possible to
re-program the memory.
EPSM Enhanced Power Supply Module. Used in +27 V positive earth
cabinets.
EQ50 Static model against which the performance of the equalizer is
tested to extremes. See also TU3, TU50, HT100 and RA250.
EQB Equalizer Board. Control circuit for equalization for 8 time slots
each with equalizing circuitry and a DSP.
EQCP Equalizer Control Processor.
EQDSP Equalizer Digitizer Signal Processor.
Equalization The process by which attenuation and/or phase shift is rendered
essentially constant over a band of frequencies, even though the
transmission medium or the equipment has losses that vary with
frequency.
13-26 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
Equalizer An electrical network in which attenuation (or gain) and/or
phase shift varies as a function of frequency. Used to provide
equalization.
Erlang International (dimensionless) unit of traffic intensity defined as
the ratio of time a facility is occupied to the time it is available
for occupancy. One erlang is equal to 36 CCS. In the US this is
also known as a traffic unit (TU).
ERP Ear Reference Point. Facility for assessing handset and headset
acoustic responses.
ERP Effective Radiated Power. The power supplied to an antenna
multiplied by the antenna gain in a given direction.
ERR ERRor.
ESN Electronic Serial Number (North American Market)
ESP Encapsulating Security Payload ( RFC 2406)
ESP Electro-static Point. Connection point on the equipment for an
anti-static wrist strap.
ESQL Embedded SQL (Structured Query Language). An RDBMS
programming interface language.
E-TACS Extended TACS (analogue cellular system, extended).
Ethernet A standard protocol (IEEE 802.3) for a 10 Mbit/s baseband local
area network (LAN) bus using carrier-sense multiple access
with collision detection (CSMA/CD) as the access method,
implemented at the Physical Layer in the OSI RM, establishing
the physical characteristics of a CSMA/CD network.
ETR ETSI Technical Report.
ETS European Telecommunication Standard.
ETSI European Telecommunications Standards Institute.
ETX End of Transmission.
EXEC Executive Process.
F Interface - Full Rate
F Interface Interface between MSC and EIR.
FA Fax Adaptor. Device which complements Group 3 facsimile
apparatus in order to be able to communicate over a GSM
PLMN.
FA Full Allocation.
FA Functional Area.
FAC Final Assembly Code.
FACCH Fast Associated Control Channel. A GSM dedicated control
channel which temporarily uses the TCH to perform high speed
transmissions, and carries control information after a call is set
up. See also SDCCH.
FACCH/F Fast Associated Control Channel/Full rate. See also Full Rate.
© 2005-2006 CP13: Introduction to UMTS USR6 13-27
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
FACCH/H Fast Associated Control Channel/Half rate. See also Half Rate.
FACH Forward Access Channel (UMTS Transport Channel)
FB See Frequency correction burst.
FBI Feedback Information  UMTS
FBI Final Block Indicator
FBM Flow control Buffer Management. FBM is a functional unit
residing on the PRP. It controls buffer capacity for each cell
and each mobile so that the incoming data from the SGSN
matches the air throughput.
FC-AL Fibre Channel Arbitrated Loop. A serial data transfer
architecture. FC-AL is designed for mass storage devices and
other peripheral devices that require very high bandwidth.
Using optical fibre to connect devices, FC-AL supports
full-duplex data transfer rates of 100MBps.
FCCH Frequency Correction CHannel. A GSM broadcast control
channel which carries information for frequency correction of
the MS.
FCP Fault Collection Process. Part of the fault management process
in the BTS.
FCS Frame Check Sequence. The extra characters added to a
frame for error detection and correction.
FDD Frequency Division Duplex
FDDI Fiber Distributed Data Interconnect (optical Layer 2)
FDM Frequency Division Multiplex. A multiplexing technique that
uses different frequencies to combine multiple streams of data
for transmission over a communications medium. FDM assigns
a discrete carrier frequency to each data stream and then
combines many modulated carrier frequencies for transmission.
FDMA Frequency Division Multiple Access. The use of frequency
division to provide multiple and simultaneous transmissions
to a single transponder.
FDN Fixed Dialling Number. The fixed dialling feature limits dialling
from the MS to a pre-determined list maintained on the SIM
card. It can be used to limit calling to certain areas, exchanges
or full phone numbers.
FDP Fault Diagnostic Procedure.
FEC Forward Error Correction. Correction of transmission errors by
transmitting additional information with the original bit stream.
If an error is detected, the additional information is used to
recreate the original information.
13-28 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
FEP Front End Processor. An OMC-R device. The FEP is a driver
that stores data in its own database about all of the sites in the
system. All bursts from the sites are directed to the FEP. It can
also interrogate the sites and collect its data either manually or
automatically at pre-defined times.
FER Frame Erasure Ratio. The ratio of successfully decoded good
speech frames against unsuccessfully decoded bad frames.
FFS, FS For Further Study.
FH See Frequency Hopping.
FHI Frequency Hopping Indicator.
FIB Forward Indicator Bit. Used in SS7 - Message Transfer Part.
The forward indicator bit and backward indicator bit together
with the forward sequence number and backward sequence
number are used in the basic error control method to perform
the signal unit sequence control and acknowledgement
functions.
FIFO Memory logic device in which the information placed in the
memory in a given order is retrieved in that order.
FIR Finite Impulse Response (filter type).
FISU Fill In Signal Unit
FK Foreign Key. A database column attribute; the foreign key
indicates an index into another table.
FM Fault Management (at OMC).
FM Frequency Modulation. Modulation in which the instantaneous
frequency of a sine wave carrier is caused to depart from
the centre frequency by an amount proportional to the
instantaneous value of the modulating signal.
FMC Fixed Mobile Convergence
FMIC Fault Management Initiated Clear. An alarm type. If an FMIC
alarm is received, the fault management software for the
network item clears the alarm when the problem is solved. See
also Intermittent and OIC.
FMUX Fibre optic MUltipleXer module.
FN Frame Number. Identifies the position of a particular TDMA
frame within a hyperframe.
FOA First Office Application. A full functional verification of new
product(s) on a commercial system using accepted technology
and approved test plans.
FOX Fibre Optic eXtender board.
FPB First Partial Bitmap
FR See Full Rate.
FR Frame Relay. An interface protocol for statistically
multiplexed packet-switched data communications in which
(a) variable-sized packets (frames) are used that completely
enclose the user packets they transport, and (b) transmission
rates are usually between 56 kb/s and 1.544 Mb/s (the T-1 rate).
© 2005-2006 CP13: Introduction to UMTS USR6 13-29
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
Frame A set of consecutive Pulse Code Modulation (PCM) time slots
containing samples from all channels of a group, where the
position of each sample is identified by reference to a frame
alignment signal. Also, an information or signal structure which
allows a receiver to identify uniquely an information channel.
Frame Alignment The state in which the frame of the receiving equipment is
synchronized with respect to that of the received signal to
accomplish accurate data extraction.
FRMR Frame Reject
FRU Field Replaceable Unit. A board, module, etc. which can be
easily replaced in the field with a few simple tools.
Frequency Correction Period of RF carrier less than one timeslot whose modulation
bit stream allows frequency correction to be performed easily
within an MS burst.
Frequency Hopping The repeated switching of frequencies during radio transmission
according to a specified algorithm. Frequency hopping
improves capacity and quality in a highly loaded GSM network.
Multipath fading immunity can be increased by using different
frequencies and interference coming from neighbour cells
transmitting the same or adjacent frequencies can be reduced.
FS Frequency Synchronization. All BSS frequencies and timing
signals are synchronized to a high stability reference oscillator
in the BSS. This oscillator can free run or be synchronized to
the recovered clock signal from a selected E1/T1 serial link.
MSs lock to a reference contained in a synchronization burst
transmitted from the BTS site.
FSL Free Space Loss. The decrease in the strength of a radio
signal as it travels between a transmitter and receiver. The
FSL is a function of the frequency of the radio signal and the
distance the radio signal has travelled from the point source.
FSN Forward Sequence Number. See FIB.
FTAM File Transfer, Access, and Management. An ASE which
provides a means to transfer information from file to file. (OMC).
ftn forwarded-to number.
FTP Fault Translation Process (in BTS).
FTP File Transfer Protocol. A client-server protocol which allows
a user on one computer to transfer files to and from another
computer over a TCP/IP network. Also the client program the
user executes to transfer files (RFC 959).
Full Rate Refers to the current capacity of a data channel on the GSM
air interface, that is, 8 simultaneous calls per carrier. See also
HR - Half Rate.
13-30 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
G Interface - GWY
G Interface Interface between VLR and VLR.
Gateway MSC An MSC that provides an entry point into the GSM PLMN
from another network or service. A gateway MSC is also an
interrogating node for incoming PLMN calls.
GB, Gbyte Gigabyte. 230 bytes = 1,073,741,824 bytes = 1024 megabytes.
GBIC Gigabit Interface Converter Converter for connection to the
Gigabit Ethernet.
GBL Gb Link.
GBM Gb Manager.
GCC Generic Call Control
GCLK Generic Clock board. System clock source, one per site (part
of BSS, BTS, BSC, IWF, RXCDR).
GCR Group Call Register. The register which holds information
about VGCS or VBS calls.
GDP Generic DSP Processor board. Interchangeable with the
XCDR board.
GDP E1 GDP board configured for E1 link usage.
GDP T1 GDP board configured for T1 link usage.
GDS GPRS Data Stream.
GEA GPRS Encryption Algorithm
GERAN GSM EDGE Radio Access Network
GGSN Gateway GPRS Support Node. The GGSN provides internet
working with external packet-switched networks.
GHz Giga-Hertz (109).
GID Group ID. A unique number used by the system to identify a
user’s primary group.
GIP GPRS Initialization Process
GMB GSM Multiplexer Board (part of the BSC).
GMM GPRS Mobility Management.
GMR General Manual Revision.
GMSC Gateway Mobile-services Switching Centre. See Gateway
MSC.
GMSC-S Gateway MSC Server
GMSK Gaussian Minimum Shift Keying. The modulation technique
used in GSM.
GND GrouND.
GOS Grade of Service. A traffic statistic defined as the percentage
of calls which have a Probability of Busy or Queueing Delay.
An alternative criterion is a maximum time for a percentage
of calls to wait in the busy queue before they are assigned a
voice channel.
© 2005-2006 CP13: Introduction to UMTS USR6 13-31
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
GPA GSM PLMN Area.
GPC General Protocol Converter.
G-PDU T-PDU + GTP-Header
GPROC Generic Processor board. GSM generic processor board: a
68030 with 4 to 16 Mb RAM (part of BSS, BTS, BSC, IWF,
RXCDR).
GPROC2 Generic Processor board. GSM generic processor board: a
68040 with 32 Mb RAM (part of BSS, BTS, BSC, IWF, RXCDR).
{4354} GPROC3 Generic Processor board. GSM generic processor board:
a 68060 with 128 Mb RAM (part of BSS, BTS, BSC, IWF,
RXCDR).
GPRS General Packet Radio Service. A GSM data transmission
technique that does not set up a continuous channel from a
portable terminal for the transmission and reception of data, but
transmits and receives data in packets. It makes very efficient
use of available radio spectrum, and users pay only for the
volume of data sent and received.
GPS Global Positioning by Satellite. A system for determining
position on the Earth’s surface by comparing radio signals from
several satellites.
GR Gb Router.
GSA GSM Service Area. The area in which an MS can be reached
by a fixed subscriber, without the subscriber’s knowledge of the
location of the MS. A GSA may include the areas served by
several GSM PLMNs.
GSA GSM System Area. The group of GSM PLMN areas accessible
by GSM MSs.
GSD GSM Systems Division.
GSL GPRS Signalling Link.
GSM Groupe Spécial Mobile (the committee).
GSM Global System for Mobile communications (the system).
GSM900 See PGSM.
GSM MS GSM Mobile Station.
GSM PLMN GSM Public Land Mobile Network.
GSM RF GSM Radio Frequency.
GSN GPRS Support Node. The combined functions provided by
the SGSN and GGSN.
GSN Complex A GSN Complex consists of an ISS Cluster, GGSN and SGSNs
connected to a single CommHub.
GSR GSM Software Release.
GT Global Title. A logical or virtual address used for routing SS7
messages using SCCP capabilities. To complete message
routing, a GT must be translated to a SS7 point code and
subsystem number.
13-32 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
GTE Generic Table Editor. The Motorola procedure which allows
users to display and edit MCDF input files.
GTM Gb Transmit Manager.
GTP GPRS Tunneling Protocol
GTS GBRS TBF Scheduler
Guard period Period at the beginning and end of timeslot during which MS
transmission is attenuated.
GUI Graphical User Interface. A computer environment or program
that displays, or facilitates the display of, on-screen options.
These options are usually in the form of icons (pictorial
symbols) or menus (lists of alphanumeric characters) by means
of which users may enter commands.
GUI client A computer used to display a GUI from an OMC-R GUI
application which is being run on a GUI server.
GUI server A computer used to serve the OMC-R GUI application process
running locally (on its processor) to other computers (GUI
clients or other MMI processors).
GWM GateWay Manager.
GWY GateWaY (MSC/LR) interface to PSTN.
H Interface - Hyperframe
H Interface Interface between HLR and AUC.
H-M Human-Machine Terminals.
HAD, HAP HLR Authentication Distributor.
Half Rate Refers to a type of data channel that will double the current
GSM air interface capacity to 16 simultaneous calls per carrier
(see also FR - Full Rate).
HANDO, Handover HANDOver. The action of switching a call in progress from
one radio channel to another radio channel. Handover allows
established calls to continue by switching them to another
radio resource, as when an MS moves from one BTS area to
another. Handovers may take place between the following
GSM entities: timeslot, RF carrier, cell, BTS, BSS and MSC.
HCS Hierarchical Cell Structure
HCU Hybrid Combining Unit. (Used in Horizonmacro). Part of
the DDF, the HDU allows the outputs of three radios to be
combined into a single antenna.
HDLC High level Data Link Control. A link-level protocol used to
facilitate reliable point-to-point transmission of a data packet.
Note: A subset of HDLC, LAP-B, is the layer-two protocol for
CCITT Recommendation X.25.
HDSL High bit-rate Digital Subscriber Line. HDSL is a data
transmission mechanism which supports duplex high speed
digital communication (at E1 rates) on one or more unshielded
twisted pair lines.
© 2005-2006 CP13: Introduction to UMTS USR6 13-33
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
HLC High Layer Compatibility. The HLC can carry information
defining the higher layer characteristics of a teleservice active
on the terminal.
HLR Home Location Register. The LR where the current location
and all subscriber parameters of an MS are permanently stored.
HMAC Keyed Hashing for Message Authentication ( RFC 2104)
HMS Heat Management System. The system that provides
environmental control of the components inside the ExCell,
TopCell and M-Cell cabinets.
HO HandOver. See HANDO.
HPU Hand Portable Unit. A handset.
HOLD Call hold supplementary service. Call hold allows the
subscriber to place a call on hold in order to make another call.
When the second call is completed, the subscriber can return
to the first call.
HPLMN Home PLMN.
HR See Half Rate.
HS HandSet.
HSCSD High Speed Circuit Switched Data
HSI/S High Speed Interface card.
HSM HLR Subscriber Management.
HSN Hopping Sequence Number. HSN is a index indicating the
specific hopping sequence (pattern) used in a given cell. It
ranges from 0 to 63.
HT100 Hilly Terrain with the MS travelling at 100 kph. Dynamic model
against which the performance of a GSM receiver can be
measured. See also TU3, TU50, RA250 and EQ50.
HTTP HyperText Transfer Protocol ( RFC 2616)
HU Home Units. The basic telecommunication unit as set by the
HPLMN. This value is expressed in the currency of the home
country.
HW Hardware.
Hybrid Combiner A combiner device which requires no software control and is
sufficiently broadband to be able to cover the GSM transmitter
frequency band. See also COMB.
Hybrid Transformer A circuit used in telephony to convert 2-wire operation to
4-wire operation and vice versa. For example, every land-line
telephone contains a hybrid to separate earpiece and
mouthpiece audio and couple both into a 2-wire circuit that
connects the phone to the exchange.
Hyperframe 2048 superframes. The longest recurrent time period of the
frame structure.
13-34 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
I - IWU
I Information frames. Part of RLP.
I+S Information + Supervisory
IA Incoming Access supplementary service. An arrangement
which allows a member of a CUG to receive calls from outside
the CUG.
IA5 International Alphanumeric 5 character set.
IADU Integrated Antenna Distribution Unit. The IADU is the
equivalent of the Receive Matrix used on BTSs that pre-date
the M-Cell range.
IANA Internet Assigned Numbers Authority
IAM Initial Address Message. A message sent in the forward
direction that contains (a) address information, (b) the signaling
information required to route and connect a call to the called
line, (c) service-class information, (d) information relating to
user and network facilities, and (e) call-originator identity or
call-receiver identity.
IAS Internal Alarm System. The IAS is responsible for monitoring
all cabinet alarms at a BSS.
IC Integrated Circuit. An electronic circuit that consists of
many individual circuit elements, such as transistors,
diodes, resistors, capacitors, inductors, and other active and
passive semiconductor devices, formed on a single chip of
semiconducting material and mounted on a single piece of
substrate material.
IC Interlock Code. A code which uniquely identifies a CUG within
a network.
IC(pref) Interlock Code of the preferential CUG.
ICANN Internet Corporation for Assigned Names and Numbers
ICB Incoming Calls Barred. An access restriction that prevents a
CUG member from receiving calls from other members of that
group.
ICC Integrated Circuit(s) Card.
ICH Indicator Channel (UMTS Physical Channel / see also PICH,
AICH, CD/CA-ICH)
ICM In-Call Modification. Function which allows the service mode
(speech, facsimile, data) to be changed during a call.
ICMP Internet Control Message Protocol. An extension to the Internet
Protocol (IP) that allows for the generation of error messages,
test packets, and informational messages related to IP. The
PING command, for example, uses ICMP to test an Internet
connection( RFC 792).
I-CSCF Interrogating Call Session Control Function ( SIP)
ID, Id IDentification/IDentity/IDentifier.
IDN Integrated Digital Network. A network that uses both digital
transmission and digital switching.
© 2005-2006 CP13: Introduction to UMTS USR6 13-35
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
IDS Interface Design Specification.
IDS Informix Dynamic Server. The OMC-R relational database
management system.
IE Information Element. The part of a message that contains
configuration or signalling information.
IEC International Electrotechnical Commission. An international
standards and conformity assessment body for electrical,
electronic and related technologies.
IEEE Institute of Electrical and Electronic Engineers. A non-profit,
technical professional association.
IEI Information Element Identifier. The identifier field of the IE.
IETF Internet Engineering Task Force (www.ietf.org)
I-ETS Interim European Telecommunication Standard.
IF Intermediate Frequency. A frequency to which a carrier
frequency is shifted as an intermediate step in transmission
or reception.
IFAM Initial and Final Address Message.
IHOSS Internet Hosted Octet Stream Service
IKE Internet Key Exchange ( RFC 2409)
IKMP Internet Key Management Protocol
ILCM Incoming Leg Control Model
IM InterModulation. The production, in a nonlinear element of a
system, of frequencies corresponding to the sum and difference
frequencies of the fundamentals and harmonics thereof that
are transmitted through the element.
IMACS Intelligent Monitor And Control System.
IMEI International Mobile station Equipment Identity. Electronic
serial number that uniquely identifies the MS as a piece or
assembly of equipment. The IMEI is sent by the MS along with
request for service. See also IMEISV.
IMEISV International Mobile station Equipment Identity and Software
Version number. The IMEISV is a 16 digit decimal number
composed of four elements:- a 6 digit Type Approval
Code; - a 2 digit Final Assembly Code; - a 6 digit Serial
Number; and - a 2 digit Software Version Number (SVN).
The first three elements comprise the IMEI. When the network
requests the IMEI from the MS, the SVN (if present) is also sent
towards the network. See also IMEI and SVN.
IMM IMMediate assignment message. IMMs are sent from the
network to the MS to indicate that the MS must immediately
start monitoring a specified channel.
IMPI IP Multimedia Private Identity
IMPU IP Multimedia Public Identity
IMS Internet Protocol Multimedia Core Network Subsystem (
Rel. 5 onwards)
13-36 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
IMSI International Mobile Subscriber Identity. Published mobile
number (prior to ISDN) that uniquely identifies the subscription.
It can serve as a key to derive subscriber information such as
directory number(s) from the HLR. See also MSISDN.
IMT-2000 International Mobile Telecommunications for the year 2000
IN Intelligent Network. A network that allows functionality to
be distributed flexibly at a variety of nodes on and off the
network and allows the architecture to be modified to control
the services.
IN Interrogating Node. A switching node that interrogates an HLR,
to route a call for an MS to the visited MSC.
INS IN Service.
INS Intelligent Network Service. A service provided using the
capabilities of an intelligent network. See also IN.
InterAlg Interference Algorithm.
Intermittent Intermittent alarms are transient and not usually associated
with a serious fault condition. After the intermittent alarms are
displayed in the Alarm window, the operator must handle and
clear the alarm. The system will report every occurrence of an
intermittent alarm unless it is throttled. See also FMIC and OIC.
Interworking The general term used to describe the inter-operation of
networks, services, supplementary services and so on. See
also IWF.
Interval A recording period of time in which a statistic is pegged.
Interval expiry The end of an interval.
I/O Input/Output.
IOS Intelligent Optimization Service. Tool for improving the network
quality. The IOS generates reports based on performance data
from the BTS and OMC-R.
IOV-I / IOV-UI Input Offset Variable for I+S and UI-Frames ( for ciphering
in GPRS)
IP Initialisation Process. The IP is primarily responsible for
bringing up the site from a reset, including code loading
the site from a suitable code source. IP also provides the
CSFP functionality, allowing two BSS code load version to be
swapped very quickly, allowing the site to return to service as
soon as possible.
IP Internet Protocol. A standard protocol designed for use
in interconnected systems of packet-switched computer
communication networks. IP provides for transmitting blocks
of data called datagrams from sources to destinations,
where sources and destinations are hosts identified by
fixed-length addresses. The internet protocol also provides for
fragmentation and reassembly of long datagrams, if necessary,
for transmission through small-packet networks ( RFC 791).
See also TCP and TCP/IP.
IPBCP IP Bearer Control Protocol ( ITU-T Q.1970)
© 2005-2006 CP13: Introduction to UMTS USR6 13-37
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
IPC Inter-Process Communication. Exchange of data between one
process and another, either within the same computer or over
a network.
IPCP Internet Protocol Control Protocol ( RFC 1332)
IP, INP INtermodulation Products. Distortion. A type of spurious
emission.
IPR Intellectual PRoperty.
IPSM Integrated Power Supply Module (-48 V).
IPX Internetwork Packet EXchange A networking protocol used by
the Novell NetWare operating systems. Like UDP/IP, IPX is a
datagram protocol used for connectionless communications.
Higher-level protocols are used for additional error recovery
services.
IR Incremental Redundancy (Hybrid Type II ARQ)
Iridium A communications system comprising a constellation of 66
low-earth-orbiting (LEO) satellites forming a mobile wireless
system allowing subscribers to place and receive calls from any
location in the world. The satellite constellation is connected
to existing terrestrial telephone systems through a number of
gateway ground-stations.
ISAKMP Internet Security Association and Key Management Protocol
ISAM Indexed Sequential Access Method. A method for managing
the way a computer accesses records and files stored on a
hard disk. While storing data sequentially, ISAM provides direct
access to specific records through an index. This combination
results in quick data access regardless of whether records are
being accessed sequentially or randomly.
ISC International Switching Centre. The ISC routes calls to/from
other countries.
ISCP Interference Signal Code Power ( 3GTS 25.215 / 3GTS
25.102)
ISDN Integrated Services Digital Network. A digital network using
common switches and digital transmission paths to establish
connections for various services such as telephony, data telex,
and facsimile. See also B channel and D channel.
ISG Motorola Information Systems group (formerly CODEX).
ISO International Organisation for Standardization. ISO is a
world-wide federation of national standards bodies from some
130 countries, one from each country.
ISP Internet Service Provider
ISQL An Interactive Structured Query Language client application for
the database server. See also IDS.
ISS Integrated Support Server. The ISS resides on a Sun Netra
t 1125 and performs the CGF, DNS, NTP, and NFS functions
for the GSN.
IST Integrated System Test.
13-38 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
ISUP ISDN User Part. An upper-layer application supported by
signalling system No. 7 for connection set up and tear down
( ITU-T Q.761 – Q.765).
IT Inactivity Test (Part of SCCP network connectivity).
ITC Information Transfer Capability. A GSM Bearer Capability
Element which is provided on the Dm channel to support
Terminal adaptation function to Interworking control procedures.
ITU International Telecommunication Union. An intergovernmental
organization through which public and private organizations
develop telecommunications. It is responsible for adopting
international treaties, regulations and standards governing
telecommunications.
ITU-T International Telecommunication Union - Telecommunications
Standardization Sector. The standardization functions were
formerly performed by CCITT, a group within the ITU.
Iub-FP Iub-Frame Protocol ( 3GTS 25.427 / 25.435)
Iu-FP Iu-Frame Protocol ( 3GTS 25.415)
Iur-FP Iur-Frame Protocol ( 3GTS 25.424, 3GTS 25.425, 25.426,
25.435)
IWF InterWorking Function. A network functional entity which
provides network interworking, service interworking,
supplementary service interworking or signalling interworking.
It may be a part of one or more logical or physical entities in a
GSM PLMN.
IWMSC InterWorking MSC. MSC that is used to deliver data to/from
SGSN.
IWU InterWorking Unit. Unit where the digital to analogue (and visa
versa) conversion takes place within the digital GSM network.
k - KW
k kilo (103).
k Windows size.
K Constraint length of the convolutional code.
KAIO Kernel Asynchronous Input/Output. Part of the OMC-R
relational database management system.
kb, kbit kilo-bit.
kbit/s, kbps kilo-bits per second.
kbyte kilobyte. 210 bytes = 1024 bytes
Kc Ciphering key. A sequence of symbols that controls the
operation of encipherment and decipherment.
kHz kilo-Hertz.
Ki Individual subscriber authentication Key. Part of the
authentication process of the AUC.
© 2005-2006 CP13: Introduction to UMTS USR6 13-39
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
KIO A class of processor.
KPI Key Performance Indicator.
KSW Kiloport SWitch board. TDM timeslot interchanger to connect
calls. Part of the BSS.
KSWX KSW Expander half size board. Fibre optic distribution of TDM
bus. Part of the BSS.
kW kilo-Watt.
L1 - LV
L1 Layer 1 (of a communications protocol).
L2 Layer 2 (of a communications protocol).
L2ML Layer 2 Management Link. L2ML is used for transferring layer
2 management messages to TRX or BCF. One link per TRX
and BCF.
L2R Layer 2 Relay function. A function of an MS and IWF that
adapts a user’s known layer 2 protocol LAPB onto RLP for
transmission between the MT and IWF.
L2R BOP L2R Bit Orientated Protocol.
L2R COP L2R Character Orientated Protocol.
L2TP Layer 2 Tunneling Protocol ( RFC 2661)
L3 Layer 3 (of a communications protocol).
LA Link Adaptation.
LA Location Area. An area in which an MS may move freely
without updating the location register. An LA may comprise one
or several base station areas.
LAC Location Area Code. The LAC is part of the LAI. It is an
operator defined code identifying the location area.
LAI Location Area Identity. The information indicating the location
area in which a cell is located. The LAI data on the SIM is
continuously updated to reflect the current location of the
subscriber.
LAN Local Area Network. A data communications system that (a)
lies within a limited spatial area, (b) has a specific user group,
(c) has a specific topology, and (d) is not a public switched
telecommunications network, but may be connected to one.
LANX LAN Extender half size board. Fibre optic distribution of LAN
to/from other cabinets. Part of BSS, etc.
LAPB Link Access Protocol Balanced. The balanced-mode, enhanced
version of HDLC. Used in X.25 packet-switching networks.
LAPD Link Access Protocol D-channel (Data). A protocol that
operates at the data link layer (layer 2) of the OSI architecture.
LAPD is used to convey information between layer 3 entities
across the frame relay network. The D-channel carries
signalling information for circuit switching.
13-40 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
LAPDm Link Access Protocol on the Dm channel. A link access
procedure (layer 2) on the CCH for the digital mobile
communications system.
Layer 1 See OSI-RM and Physical Layer.
Layer 2 See OSI-RM and Data Link Layer.
Layer 3 See OSI-RM and Network Layer.
Layer 4 See OSI-RM and Transport Layer.
Layer 5 See OSI-RM and Session Layer.
Layer 6 See OSI-RM and Presentation Layer.
Layer 7 See OSI-RM and Application Layer.
LC Inductor Capacitor. A type of filter.
LCF Link Control Function. LCF GPROC controls various links in
and out of the BSC. Such links include MTL, XBL, OMF and
RSL. See also LCP.
LCN Local Communications Network. A communication network
within a TMN that supports data communication functions
(DCFs) normally at specified reference points q1 and q2. LCNs
range from the simple to the complex. LCN examples include
point-to-point connections and networks based on star and
bus topologies.
LCP Link Control Processor. An LCP is a GPROC or PCMCIA
board device which supplies the LCF. Once the LCF has been
equipped, and assuming GPROCs have been equipped,
processors are allocated by the software.
LCS Location Services
LE Local Exchange.
LED Light Emitting Diode. A type of diode that emits light when
current passes through it. Depending on the material used the
colour can be visible or infrared.
LF Line Feed. A code that moves the cursor on a display screen
down one line. In the ASCII character set, a line feed has a
decimal value of 10. On printers, a line feed advances the
paper one line.
LI Length Indicator. Delimits LLC PDUs within the RLC data
block, when an LLC PDU boundary occurs in the block.
LI Line Identity. The LI is made up of a number of information
units: the subscriber’s national ISDN/MSISDN number; the
country code; optionally, subaddress information. In a full
ISDN environment, the line identity includes all of the address
information necessary to unambiguously identify a subscriber.
The calling line identity is the line identity of the calling party.
The connected line identity is the line identity of the connected
party.
LLC Logical Link Control.
LLC Lower Layer Compatibility. The LLC can carry information
defining the lower layer characteristics of the terminal.
Lm Traffic channel with capacity lower than a Bm.
© 2005-2006 CP13: Introduction to UMTS USR6 13-41
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
LMP LAN Monitor Process. Each GPROC which is connected to a
LAN has an LMP, which detects faults on the LAN. LAN alarms
are generated by the GPROC.
LMS Least Mean Squares. Parameters determined by minimizing
the sum of squares of the deviations.
LMSI Local Mobile Station Identity. A unique identity temporarily
allocated to visiting mobile subscribers in order to speed up
the search for subscriber data in the VLR, when the MSRN
allocation is done on a per cell basis.
LMT Local Maintenance Terminal. Diagnostic tool, typically an IBM
compatible PC.
LNA Low Noise Amplifier. An amplifier with low noise characteristics.
LND Last Number Dialled.
Location area An area in which a mobile station may move freely without
updating the location register. A location area may comprise
one or several base station areas.
LPC Linear Predictive Coding. A method of digitally encoding analog
signals. It uses a single-level or multi-level sampling system in
which the value of the signal at each sample time is predicted
to be a linear function of the past values of the quantified signal.
LPD Link Protocol Discriminator
LPLMN Local PLMN.
LQC Link Quality Control.
LR Location Register. The GSM functional unit where MS location
information is stored. The HLR and VLR are location registers.
LSB Least Significant Bit
LSSU Link Stations Signalling Unit (Part of MTP transport system).
LSTR Listener Side Tone Rating. A rating, expressed in dB, based
on how a listener will perceive the background noise picked
up by the microphone.
LTA Long Term Average. The value required in a BTS’s GCLK
frequency register to produce a 16.384 MHz clock.
LTE Local Terminal Emulator.
LTP Long Term Predictive.
LTU Line Terminating Unit.
LU Local Units.
LU Location Update. A location update is initiated by the MS when
it detects that it has entered a new location area.
LV Length and Value.
13-42 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
M - MUX
M Mandatory.
M Mega (106).
M3UA MTP-3 User Adaptation Layer ( RFC 3332 / 3GPP 29.202
(Annex A))
M-Cell Motorola Cell.
M&TS Maintenance and TroubleShooting. Functional area of Network
Management software which (1) collects and displays alarms,
(2) collects and displays Software/Hardware errors, and (3)
activates test diagnostics at the NEs (OMC).
MA Mobile Allocation. The radio frequency channels allocated to
an MS for use in its frequency hopping sequence.
MAC Medium Access Control. MAC includes the functions related
to the management of the common transmission resources.
These include the packet data physical channels and their
radio link connections. Two Medium Access Control modes are
supported in GSR5, dynamic allocation and fixed allocation.
(UMTS  3GTS 25.321) (E)GPRS  3GTS 04.60 / 3GTS
44.060)
MACN Mobile Allocation Channel Number. See also MA.
Macrocell A cell in which the base station antenna is generally mounted
away from buildings or above rooftop level.
MAF Mobile Additional Function.
MAH Mobile Access Hunting supplementary service. An automatic
service which searches for the first available mobile user out of
a defined group.
MAI Mobile Allocation Index.
MAIDT Mean Accumulated Intrinsic Down Time.
MAINT MAINTenance.
MAIO Mobile Allocation Index Offset. The offset of the mobile hopping
sequence from the reference hopping sequence of the cell.
MAP Mobile Application Part (part of SS7 standard). The
inter-networking signalling between MSCs and LRs and EIRs.
MAPP Mobile Application Part Processor.
MASF Minimum Available Spreading Factor
Max [X, Y] The value shall be the maximum of X or Y, which ever is bigger
MB, Mbyte Megabyte. 220 bytes = 1,048,576 bytes = 1024 kilobytes.
Mbit/s Megabits per second.
MBZ Must Be Zero
MCAP Motorola Cellular Advanced Processor. The MCAP Bus is the
inter-GPROC communications channel in a BSC. Each card
cage in a BSC needs at least one GPROC designated as an
MCAP Server.
© 2005-2006 CP13: Introduction to UMTS USR6 13-43
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
MCC Mobile Country Code. The first three digits of the IMSI, used
to identify the country.
MCDF Motorola Customer Data Format used by DataGen for simple
data entry and retrieval.
MCI Malicious Call Identification supplementary service. This
feature is supported by a malicious call trace function by
printing the report at the terminating MSC when the mobile
subscriber initiates a malicious call trace request.
MCS Modulation and Coding Scheme.
MCSC Motorola Customer Support Centre.
MCU Main Control Unit for M-Cell2/6. Also referred to as the Micro
Control Unit in software.
MCUF Main Control Unit, with dual FMUX. (Used in M-Cellhorizon).
MCU-m Main Control Unit for M-Cellmicro sites (M-Cellm). Also referred
to as the Micro Control Unit in software.
MCUm The software subtype representation of the Field Replaceable
Unit (FRU) for the MCU-m.
MD Mediation Device. The MD (which handles the Q3 interface)
allows the OSI Processor to communicate between the
Network Management Centre (NMC) and OMC-R for network
configuration, events and alarms.
MDL mobile Management entity - Data Link layer.
MD-X Message Digest Algorithm (MD-2, 4, 5 are defined) (MD-5 
RFC 1321)
ME Maintenance Entity (GSM Rec. 12.00).
ME Mobile Equipment. Equipment intended to access a set of GSM
PLMN and/or DCS telecommunication services, but which does
not contain subscriber related information. Services may be
accessed while the equipment, capable of surface movement
within the GSM system area, is in motion or during halts at
unspecified points.
MEF Maintenance Entity Function (GSM Rec. 12.00). A function
which possesses the capability to detect elementary anomalies
and convey them to the supervision process.
MF MultiFrame. In PCM systems, a set of consecutive frames in
which the position of each frame can be identified by reference
to a multiframe alignment signal.
MF Multi-Frequency (tone signalling type). See DTMF.
MF MultiFunction block.
MEGACO Media Gateway Control Protocol ( ITU-T H.248 incl. Annex
F – H and IETF RFC 3015)
MGCF Media Gateway Control Function
MGCP Media Gateway Control Protocol ( RFC 2705)
MGMT, mgmt Management.
MGR Manager.
13-44 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
MGW Media Gateway
MHS Message Handling System. The family of services and
protocols that provides the functions for global electronic-mail
transfer among local mail systems.
MHS Mobile Handling Service.
MHz Mega-Hertz (106).
MI Maintenance Information.
MIB Management Information Base. A Motorola OMC-R database.
There is a CM MIB and an EM MIB.
MIC Mobile Interface Controller.
Microcell A cell in which the base station antenna is generally mounted
below rooftop level. Radio wave propagation is by diffraction
and scattering around buildings, the main propagation is within
street canyons.
min minute(s).
MIN Mobile Identity Number (North American Market)
Min [X, Y] The value shall be the minimum of X or Y, which ever is smaller
µs micro-second (10-6).
µBCU Micro Base Control Unit. The µBCU is the Macro/Microcell
implementation of a BTS site controller.
MIT Management Information Tree. A file on the Motorola OMC-R.
The MIT file effectively monitors data on every device and
every parameter of each device that is in the current versions
of software on the OMC-R. The data is stored as a text file
on the OMC-R. The MIT file also contains the hierarchical
relationships between the network devices.
MLP MAC Logical Channel Priority
MM Man Machine. See MMI.
MM Mobility Management. MM functions include authorization,
location updating, IMSI attach/detach, periodic registration, ID
confidentiality, paging, handover, etc.
MMCC Multimedia Call Control
MME Mobile Management Entity.
MMF Middle Man Funnel process.
MMI Man Machine Interface. The method by which the user
interfaces with the software to request a function or change
parameters. The MMI may run on a terminal at the OMC, or
an LMT. The MMI is used to display alarm reports, retrieve
device status, take modules out of service and put modules
into service.
MMI client A machine configured to use the OMC-R software from an MMI
server.
MMI processor MMI client/MMI server.
© 2005-2006 CP13: Introduction to UMTS USR6 13-45
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
MMI server A computer which has its own local copy of the OMC-R
software. It can run the OMC-R software for MMI clients to
mount.
MML Man Machine Language. The tool of MMI.
MMS Multiple Serial Interface Link. (see also 2Mbit/s link)
MNC Mobile Network Code. The fourth, fifth and optionally sixth
digits of the IMSI, used to identify the network.
MNRG Mobile Not Reachable for GPRS flag
MNT MaiNTenance.
Mobis Motorola Signalling Link between the BSC and BTS.
MO Mobile Originated.
MOC Mobile Originating Call
MO/PP Mobile Originated Point-to-Point messages. Transmission of
a SMS from a mobile to a message handling system. The
maximum length of the message is 160 characters. The
message can be sent whether or not the MS is engaged in
a call.
MOMAP Motorola OMAP.
MoU Memorandum of Understanding. Commercial term. An MoU
usually sets out the broad parameters of an understanding as
well as the general responsibilities and obligations of each
party in a proposed venture. It has little legal significance
except to indicate the parties’ commitments and acts as an aid
to interpreting the parties’ intentions. There are various types
of MOUs: compliance MOUs help ensure that all Motorola
units comply with applicable laws and regulations; intellectual
property MOUs deal with copyright, trademark, and patent
rights; and business arrangement MOUs relate to the terms
and conditions of a product or service transfer.
MPC Multi Personal Computer (was part of the OMC).
MPCC Multiparty Call Control
MPH (mobile) Management (entity) - PHysical (layer) [primitive].
MPROC Master Processor
MPTY MultiParTY (Multi ParTY) supplementary service. MPTY
provides a mobile subscriber with the ability to have a
multi-connection call, i.e. a simultaneous communication with
more than one party.
MPX MultiPleXed.
MRC Micro Radio Control Unit.
MRFC Multimedia Resource Function Controller
MRFP Multimedia Resource Function Processor
MRN Mobile Roaming Number.
MRP Mouth Reference Point. Facility for assessing handset and
headset acoustic responses.
MRU Maximum Receive Unit ( PPP)
13-46 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
MRW Move Receiving Window
MS Mobile Station. The GSM subscriber unit. A subscriber
handset, either mobile or portable, or other subscriber
equipment, such as facsimile machines, etc.
MSB Most Significant Bit
MSC Mobile-services Switching Centre, Mobile Switching Centre.
The MSC handles the call set up procedures and controls the
location registration and handover procedures for all except
inter-BTS, inter-cell and intra-cell handovers. MSC controlled
inter-BTS handovers can be set as an option at the switch.
MSCM Mobile Station Class Mark.
MSC-S MSC-Server
MSCU Mobile Station Control Unit.
msec millisecond (.001 second).
MSI Multiple Serial Interface board. Intelligent interface to two 2
Mbit/s digital links. See 2 Mbit/s link and DS-2. Part of BSS.
MSIN Mobile Station Identification Number. The part of the IMSI
identifying the mobile station within its home network.
MSISDN Mobile Station International ISDN Number. Published mobile
number (see also IMSI). Uniquely defines the mobile station as
an ISDN terminal. It consists of three parts: the Country Code
(CC), the National Destination Code (NDC) and the Subscriber
Number (SN).
MSS Maximum Segment Size ( TCP)
MSRN Mobile Station Roaming Number. A number assigned by the
MSC to service and track a visiting subscriber.
MSU Message Signal Unit (Part of MTP transport system). A signal
unit containing a service information octet and a signalling
information field which is retransmitted by the signalling link
control, if it is received in error.
MT Mobile Terminated. Describes a call or short message destined
for an MS.
MT (0, 1, 2) Mobile Termination. The part of the MS which terminates the
radio transmission to and from the network and adapts terminal
equipment (TE) capabilities to those of the radio transmission.
MT0 is mobile termination with no support for terminal, MT1
is mobile termination with support for an S-type interface and
MT2 is mobile termination with support for an R-type interface.
MTBE Mean Time Between Exceptions.
MTBF Mean Time Between Failures. An indicator of expected system
reliability calculated on a statistical basis from the known failure
rates of various components of the system. MTBF is usually
expressed in hours.
MTC Mobile Terminating Call
MTL Message Transfer Link. The MTL is the 64 kbit/s PCM timeslot
that is used to convey the SS7 signalling information on the A
interface between the MSC and the BSC.
© 2005-2006 CP13: Introduction to UMTS USR6 13-47
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
MTM Mobile-To-Mobile (call).
MTP Message Transfer Part. The part of a common-channel
signaling system that transfers signal messages and performs
associated functions, such as error control and signaling link
security ( ITU-T Q.701 – Q.703).
MTP-3b Message Transfer Part level 3 / broadband ( ITU-T Q.2210)
MT/PP Mobile Terminated Point-to-Point messages. Transmission of a
short message from a message handling system to a mobile.
The maximum length of the message is 160 characters. The
message can be received whether or not the MS is engaged in
a call.
MTTR Mean Time To Repair. The total corrective maintenance time
divided by the total number of corrective maintenance actions
during a given period of time.
MTU Maximum Transmit Unit ( IP)
Multiframe Two types of multiframe are defined in the system: a 26-frame
multiframe with a period of 120 ms and a 51-frame multiframe
with a period of 3060/13 ms.
MU Mark Up.
MUMS Multi User Mobile Station.
MUX Multiplexer. A device that combines multiple inputs into an
aggregate signal to be transported via a single transmission
channel.
NACK - nW
NACK, Nack No Acknowledgement
NAS Non-Access-Stratum ( UMTS)
NAT Network Address Translation ( RFC 1631)
N/W Network.
NB Normal Burst (see Normal burst).
NBAP NodeB Application Part ( 3GTS 25.433)
NBIN A parameter in the frequency hopping sequence generation
algorithm.
NBNS NetBios Name Service
NC Neighbour Cell
NCC Network Colour Code. The NCC and the BCC are part of the
BSIC. The NCC comprises three bits in the range 000 to 111.
It is the same as the PLMN Colour Code. See also NCC and
BSIC.
NCELL Neighbouring (of current serving) Cell.
NCH Notification CHannel. Part of the downlink element of the
CCCH reserved for voice group and/or voice broad-cast calls
and notification messages.
NCP Network Control Protocol ( PPP)
13-48 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
NCRM Network Cell Reselection Manager.
ND No Duplicates. A database column attribute meaning the
column contains unique values (used only with indexed
columns).
NDC National Destination Code. Part of the MSISDN. An NDC is
allocated to each GSM PLMN.
NDUB Network Determined User Busy. An NDUB condition occurs
when a call is about to be offered and the maximum number of
total calls for the channel has been reached. In practice, the
total number of calls could be three: one for the basic call, one
for a held call and one for call waiting.
NE Network Element (Network Entity). A piece of
telecommunications equipment that provides support or
services to the user.
NEF Network Element Function block. A functional block that
communicates with a TMN for the purpose of being monitored,
or controlled, or both.
NET Norme Européennes de Telecommunications.
NetPlan An RF planning tool, NetPlan can import data from the OMC
and use it to carry out a network frequency replan.
Network Layer See OSI RM. The Network Layer responds to service requests
from the Transport Layer and issues service requests to the
Data Link Layer. It provides the functional and procedural
means of transferring variable length data sequences from
a source to a destination via one or more networks while
maintaining the quality of service requested by the Transport
Layer. The Network Layer performs network routing, flow
control, segmentation/desegmentation, and error control
functions.
NF Network Function.
NFS Network File System. A file system that is distributed over a
computer network. Also, a file system, on a single computer,
that contains the low-level networking files for an entire network.
NHA Network Health Analyst. The NHA is an optional feature. It
detects problems by monitoring network statistics and events
via the OMC-R. The NHA analyses the event history, statistics
and network configuration data to try to determine the cause of
the detected problems.
NI Network Indicator
NIB Network Interface Board.
NIC Network Interface Card. A network interface device in the form
of a circuit card that provides network access.
NIC Network Independent Clocking.
NIS Network Information Service. It allows centralised control of
network information for example hostnames, IP addresses and
passwords.
© 2005-2006 CP13: Introduction to UMTS USR6 13-49
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
N-ISDN Narrowband Integrated Services Digital Network: Services
include basic rate interface (2B+D or BRI) and primary rate
interface (30B+D - Europe and 23B+D - North America or PRI).
Supports narrowband speeds at/or below 1.5 Mbps.
NIU Network Interface Unit. A device that performs interface
functions, such as code conversion, protocol conversion, and
buffering, required for communications to and from a network.
NIU-m Network Interface Unit, micro. M-Cellmicro MSI.
NL See Network Layer.
NLK Network LinK processor(s).
Nm Newton metres.
NM Network Management (manager). NM is all activities which
control, monitor and record the use and the performance of
resources of a telecommunications network in order to provide
telecommunication services to customers/users at a certain
level of quality.
NMASE Network Management Application Service Element.
NMC Network Management Centre. The NMC node of the GSM
TMN provides global and centralised GSM PLMN monitoring
and control, by being at the top of the TMN hierarchy and linked
to subordinate OMC nodes.
NMSI National Mobile Station Identification number, or, National
Mobile Subscriber Identity. The NMSI consists of the MNC and
the MSIN.
NMT Nordic Mobile Telephone system. NMT produced the world’s
first automatic international mobile telephone system.
NN No Nulls. A database column attribute meaning the column
must contain a value in all rows.
Normal burst A period of modulated carrier less than a timeslot.
NPB Next Partial Bitmap
NPI Number Plan Identifier.
N-PDU Network-Protocol Data Unit ( IP-Packet, X.25-Frame)
NRZ Non Return to Zero. A code in which ones are represented by
one significant condition and zeros are represented by another,
with no neutral or rest condition.
NS Network Service
NSAP Network Service Access Point. An NSAP is a registration made
by an application which specifies its desired listening criteria.
The registration is limited to a particular CPU and port number.
Criteria can include: DNICs, national numbers, subaddress
ranges, protocol-ids, and extended addresses.
NSAPI Network Service Access Point Identifier
NSE Network Service Entity
NSP Network Service Provider. A national or regional company
that owns or maintains a portion of the network and resells
connectivity.
13-50 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
NSS Network Status Summary. A feature of the OMC-R MMI,
which provides different network maps giving visual indication
of the network configuration and performance, and how the
different network management functions are implemented by
the OMC-R.
NST Network Service Test(er). A PCU process that periodically tests
all alive NS-VCs on a PICP board.
NS-VC Network Service - Virtual Circuit.
NS-VCG Network Service – Virtual Connection Group
NS-VL Network Service – Virtual Link
NT Network Termination. Network equipment that provides
functions necessary for network operation of ISDN access
protocols.
NT Non Transparent.
NTAAB NTRAC Type Approvals Advisory Board. Committee engaged
in harmonisation type approval of telecom terminals in Europe.
NTP Network Time Protocol. A protocol built on top of TCP/IP that
assures accurate local timekeeping with reference to radio,
atomic or other clocks located on the Internet. This protocol is
capable of synchronizing distributed clocks within milliseconds
over long time periods.
Numbers # - The symbol used for number.2 Mbit/s link - As used in
this manual set, the term applies to the European 4-wire
2.048 Mbit/s digital line or link which can carry 30 A-law PCM
channels or 120 16 kbit/s GSM channels.4GL - 4th Generation
Language. Closer to human languages than typical high-level
programming languages. most 4GLs are used to access
databases.
NUA Network User Access.
NUI Network User Identification.
NUP National User Part. (part of SS7).
NV NonVolatile.
NVRAM Non-Volatile Random Access Memory. Static random access
memory which is made into non-volatile storage either by
having a battery permanently connected, or, by saving its
contents to EEPROM before turning the power off and
reloading it when power is restored.
nW Nano-Watt (10-9).
O - Overlap
O Optional.
OA Outgoing Access supplementary service. An arrangement
which allows a member of a CUG to place calls outside the
CUG.
OA&M Operation, Administration, & Management.
© 2005-2006 CP13: Introduction to UMTS USR6 13-51
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
OAMP Operation, Administration, Maintenance, and Provisioning.
O&M Operations and Maintenance.
OASCU Off-Air-Call-Set-Up. The procedure in which a
telecommunication connection is being established whilst the
RF link between the MS and the BTS is not occupied.
OCB Outgoing Calls Barred within the CUG supplementary service.
An access restriction that prevents a CUG member from
placing calls to other members of that group.
Octet 8 bit
OCXO Oven Controlled Crystal Oscillator. High stability clock source
used for frequency synchronization.
OD Optional for operators to implement for their aim.
OFL % OverFlow.
offline IDS shutdown state.
online IDS normal operating state.
OIC Operator Initiated Clear. An alarm type. OIC alarms must be
cleared by the OMC-R operator after the fault condition that
caused the alarm is resolved. See also FMIC and Intermittent.
OLCM Outgoing Leg Control Model
OLM Off_Line MIB. A Motorola DataGen database, used to modify
and carry out Radio Frequency planning on multiple BSS
binary files.
OLR Overall Loudness Rating.
OMAP Operations and Maintenance Application Part (part of SS7
standard) (was OAMP).
OMC Operations and Maintenance Centre. The OMC node of the
GSM TMN provides dynamic O&M monitoring and control of
the PLMN nodes operating in the geographical area controlled
by the specific OMC.
OMC-G Operations and Maintenance Centre - Gateway Part. (Iridium)
OMC-G Operations and Maintenance Centre - GPRS Part.
OMC-R Operations and Maintenance Centre - Radio Part.
OMC-S Operations and Maintenance Centre - Switch Part.
OMF Operations and Maintenance Function (at BSC).
OML Operations and Maintenance Link. The OML provides
communication between an OMC-R and a BSC or RXCDR for
transferring network management (O&M) data.
OMP Operation and Maintenance Processor. Part of the BSC.
OMS Operation and Maintenance System (BSC-OMC).
OMSS Operation and Maintenance SubSystem.
13-52 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
OOS Out Of Service. Identifies a physical state. The OOS state
indicates the physical device is out of service. This state is
reserved for physical communication links. Also, identifies a
telephony state. The OOS state is used by the BTS device
software to indicate that the BTS is completely out of service.
OPC Originating Point Code. A part of the label in a signalling
message that uniquely identifies, in a signalling network, the
(signalling) origination point of the message.
OPWA One Pass With Advertising ( Term in RSVP)
ORAC Olympus Radio Architecture Chipset.
OS Operating System. The fundamental program running on a
computer which controls all operations.
OSA Open Service Access
OSI Open Systems Interconnection. The logical structure for
communications networks standardized by the ISO. The
standard enables any OSI-compliant system to communicate
and exchange information with any other OSI-compliant
system.
OSI RM OSI Reference Model. An abstract description of the digital
communications between application processes running in
distinct systems. The model employs a hierarchical structure of
seven layers. Each layer performs value-added service at the
request of the adjacent higher layer and, in turn, requests more
basic services from the adjacent lower layer:Layer 1 - Physical
Layer, Layer 2 - Data Link Layer, Layer 3 - Network Layer,
Layer 4 - Transport Layer, Layer 5 - Session Layer, Layer 6 -
Presentation Layer, Layer 7 - Application Layer.
OSF Operation Systems Function block.
OSF/MOTIF Open Software Foundation Motif. The basis of the GUI used
for the Motorola OMC-R MMI.
OSP Octet Stream Protocol
OSS Operator Services System.
OTDOA Observed Time Difference Of Arrival
Overlap Overlap sending means that digits are sent from one system to
another as soon as they are received by the sending system. A
system using ~ will not wait until it has received all digits of a
call before it starts to send the digits to the next system. This
is the opposite of en bloc sending where all digits for a given
call are sent at one time. See en bloc.
OVSF Orthogonal Variable Spreading Factor
PA - PXPDN
P1, P2, P3 Puncturing Schemes 1, 2, and 3.
P/F Bit Polling/Final - Bit
PA Power Amplifier.
PAB Power Alarm Board. Part of the BSS.
© 2005-2006 CP13: Introduction to UMTS USR6 13-53
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
PABX Private Automatic Branch eXchange. A private automatic
telephone exchange that allows calls within the exchange and
also calls to and from the public telephone network.
PACCH Packet Associated Control Channel.
Packet A sequence of binary digits, including data and control signals,
that is transmitted and switched as a composite whole.
Packet Switching The process of routing and transferring data by means of
addressed packets so that a channel is occupied during the
transmission of the packet only, and upon completion of the
transmission the channel is made available for the transfer of
other traffic.
PAD Packet Assembler/Disassembler facility. A hardware device
that allows a data terminal that is not set up for packet switching
to use a packet switching network. It assembles data into
packets for transmission, and disassembles the packets on
arrival.
PAGCH Packet Access Grant Channel ((E)GPRS)
Paging The procedure by which a GSM PLMN fixed infrastructure
attempts to reach an MS within its location area, before any
other network-initiated procedure can take place.
PAP Password Authentication Protocol ( RFC 1334)
PATH CEPT 2 Mbit/s route through the BSS network.
PBCCH Packet Broadcast Control Channel ((E)GPRS)
PBUS Processor Bus.
PBX Private Branch eXchange. In the general use of the term, PBX
is a synonym for PABX. However, a PBX operates with only a
manual switchboard; a private automatic exchange (PAX) does
not have a switchboard, a private automatic branch exchange
(PABX) may or may not have a switchboard.
PC Personal Computer. A general-purpose single-user
microcomputer designed to be operated by one person at a
time.
pCA PCU Central Authority. One pCA software process is located at
every PCU. The CA is in control of the PCU. It is resident on
the master DPROC (MPROC) only, and maintains a list of the
status of every device and every software process at the site.
PCCH Paging Control Channel (UMTS Logical Channel)
PCCCH Packet Common Control Channel.
P-CCPCH Primary Common Control Physical Channel (UMTS / used as
bearer for the BCH TrCH)
PCH Paging CHannel. A common access RF channel providing
point-to-multipoint unidirectional signaling downlink. Provides
simultaneous transmission to all MSs over a wide paging area.
PCHN Paging Channel Network.
13-54 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
PCHN Physical Channel. The physical channel is the medium over
which the information is carried. In the case of GSM radio
communications this would be the Air Interface. Each RF
carrier consists of eight physical channels (or timeslots) used
for MS communications. In the case of a terrestrial interface
the physical channel would be cable. See also Physical Layer.
PCI Packet Control Interface.
PCI Peripheral Component Interconnect. A standard for connecting
peripherals to a personal computer, PCI is a 64-bit bus, though
it is usually implemented as a 32-bit bus.
PCM Pulse Code Modulation. Modulation in which a signal is
sampled, and the magnitude (with respect to a fixed reference)
of each sample is quantized and converted by coding to a
digital signal. Provides undistorted transmission, even in the
presence of noise. See also 2 Mbit/s link, which is the physical
bearer of PCM.
pCM PCU Configuration Management. pCM is a GWM process. It
distributes all database changes performed at the BSC to the
PCU boards.
PCN Personal Communications Network. Any network supporting
PCS, but in particular DCS1800.
PCPCH Physical Common Packet Channel (UMTS Physical Channel)
P-CPICH Primary Common Pilot Channel (UMTS Physical Channel)
PCR Preventative Cyclic Retransmission. A form of error correction
suitable for use on links with long transmission delays, such
as satellite links.
PCS The U.S. Federal Communications Commission (FCC) term
used to describe a set of digital cellular technologies being
deployed in the U.S. PCS works over GSM, CDMA (also called
IS-95), and North American TDMA (also called IS-136) air
interfaces.
PCS System Personal Communications Services System. In PCS, a
collection of facilities that provides some combination of
personal mobility, terminal mobility, and service profile
management. Note: As used here, "facilities" includes
hardware, software, and network components such as
transmission facilities, switching facilities, signalling facilities,
and databases.
PCS1900 A cellular phone network using the higher frequency
range allocated in countries such as the USA. It operates
on the frequency range, 1850 - 1910 MHz (receive) and
1930 - 1990 MHz (transmit).
P-CSCF Proxy Call Session Control Function ( SIP)
PCU Packet Control Unit. A BSS component that provides GPRS
with packet scheduling over the air interface with the MS, and
packet segmentization and packetization across the Frame
Relay link with the SGSN.
PCU Picocell Control unit. Part of M-Cellaccess.
pd Potential difference. Voltage.
© 2005-2006 CP13: Introduction to UMTS USR6 13-55
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
PD Protocol Discriminator field. The first octet of the packet header
that identifies the protocol used to transport the frame.
PD Public Data. See PDN.
PDB Power Distribution Board.
PDCH Packet Data Channel. PDCH carries a combination of PBCCH
and PDTCH logical channels.
PDCP Packet Data Convergence Protocol ( 3GTS 25.323)
PDF Policy Decision Function
PDF Power Distribution Frame (MSC/LR).
PDN Public Data Network. A network established and operated by
a telecommunications administration, or a recognized private
operating agency, for the specific purpose of providing data
transmission services for the public.
PDP Packet Data Protocol.
PDSCH Physical Downlink Shared Channel (UMTS Physical Channel)
PDTCH Packet Data Traffic Channel ((E)GPRS)
PDU Power Distribution Unit. The PDU consists consisting of the
Alarm Interface Board (AIB) and the Power Distribution Board
(PDB).
PDU Protected Data Unit.
PDU Protocol Data Unit. A term used in TCP/IP to refer to a unit of
data, headers, and trailers at any layer in a network.
PEDC Pan-European Digital Cellular network. The GSM network in
Europe.
Peg A single incremental action modifying the value of a statistic.
Also, A number indicating the use of a device or resource.
Each time the device or resource is used the peg count is
incremented.
PER Packed Encoding Rules ( ITU-T X.691)
Pegging Modifying a statistical value.
PFC Packet Flow Context
pFCP PCU Fault Collection Process. See pFTP.
pFTP PCU Fault Transaction Process. The pFTP resides on the PSP
as part of the GWM Functional Unit process. All alarms at the
PCU are reported to pFTP. All DPROCs and the MPROC have
a local pFCP to handle Software Fault Management indications
(SWFMs). The pFTP forwards alarms to the Agent at the BSC
and generates messages to pCA for device transitions as
needed, based on faults reported.
PFI Packet Flow Identifier
PGSM Primary GSM. PGSM operates on the standard GSM frequency
range, 890 - 915 MHz (receive) and 935 - 960 MHz (transmit).
PH Packet Handler. A packet handler assembles and disassembles
packets.
PH PHysical (layer). See Physical Layer.
13-56 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
PHI Packet Handler Interface.
Physical Layer See OSI-RM. The Physical Layer is the lowest of seven
hierarchical layers. It performs services requested by the Data
Link Layer. The major functions and services of the layer
are: (a) establishment and termination of a connection to a
communications medium; (b) participation in the process of
sharing communication resources among multiple users; and,
(c) conversion between the representation of digital data in
user equipment and the corresponding signals transmitted over
a communications channel.
PI Presentation Indicator. The PI forms part of the calling name
information. Depending on database settings, the PI may
prevent the called party from seeing the identity of the calling
party.
PIA Packet Immediate Assignment.
Picocell A cell site where the base station antenna is mounted within
a building.
PICH Page Indicator Channel (UMTS Physical Channel)
PICP Packet Interface Control Processor. A PCU hardware
component, the PICP is a DPROC board used for network
interfacing functions such as SGSN and BSC.
PICS Protocol Implementation Conformance Statement. A statement
made by the supplier of an implementation or system claimed
to conform to a given specification, stating which capabilities
have been implemented.
PID Process IDentifier/Process ID.
PIM PCM Interface Module (MSC).
PIN Personal Identification Number. A password, typically four
digits entered through a telephone keypad.
PIN Problem Identification Number.
PIX Parallel Interface Extender half size board. Customer alarm
interface, part of the BSS. The PIX board provides a means of
wiring alarms external to the BSS, BSC, or BTS into the base
equipment.
PIXT or PIXIT Protocol Implementation eXtra information for Testing.
A statement made by a supplier or implementor of an
implementation under test (IUT) which contains information
about the IUT and its testing environment which will enable a
test laboratory to run an appropriate test suite against the IUT.
PK Primary Key. A database column attribute, the primary key is a
not-null, non-duplicate index.
PL See Presentation Layer.
Plaintext Unciphered data.
PlaNET Frequency planning tool.
© 2005-2006 CP13: Introduction to UMTS USR6 13-57
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
PLL Phase Lock Loop (refers to phase locking the GCLK in the
BTS). PLL is a mechanism whereby timing information is
transferred within a data stream and the receiver derives the
signal element timing by locking its local clock source to the
received timing information.
PLMN Public Land Mobile Network. The mobile communications
network.
PM Performance Management. An OMC application. PM enables
the user to produce reports specific to the performance of the
network.
PMA Prompt Maintenance Alarm. An alarm report level; immediate
action is necessary. See also DMA.
PMC PCI Mezzanine Card.
PMR Packet Management Report.
PMS Pseudo MMS.
PM-UI Performance Management User Interface.
PMUX PCM MUltipleXer.
PN Permanent Nucleus group of the GSM committee.
PNCH Packet Notification Channel ((E)GPRS)
PNE Présentation des Normes Européennes. Presentation rules
of European Standards.
POI Point of Interconnection. A point at which the cellular network
is connected to the PSTN. A cellular system may have multiple
POIs.
POP Post Office Protocol ( RFC 1939)
POTS Plain Old Telephone Service. Basic telephone service without
special features such as call waiting, call forwarding, etc.
pp, p-p Peak-to-peak.
PP Point-to-Point.
ppb Parts per billion.
PPB PCI (Peripheral Component Interconnect) to PCI Bridge board.
The PPB allows an MPROC to be linked to a separate bus.
The PPB and MPROC are paired boards.
PPCH Packet Paging Channel ((E)GPRS)
PPE Primitive Procedure Entity.
ppm Parts per million (x 10-6).
PPP Point-to-Point Protocol ( RFC 1661)
PRA PCPCH Resource Availability
PRACH Physical Random Access Channel  UMTS Packet Random
Access Channel ((E)GPRS)
Pref CUG Preferential CUG. A Pref CUG, which can be specified for each
basic service group, is the nominated default CUG to be used
when no explicit CUG index is received by the network.
13-58 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
Presentation Layer See OSI RM. The Presentation Layer responds to service
requests from the Application Layer and issues service
requests to the Session Layer. It relieves the Application
Layer of concern regarding syntactical differences in data
representation within the end-user systems.
Primary Cell A cell which is already optimized in the network and has a
co-located neighbour whose cell boundary follows the boundary
of the said cell. The primary cell has a preferred band equal to
the frequency type of the coincident cell.
PRM Packet Resource Manager. The PRM is a PRP process. It
performs all RLC/MAC functions and realises UL/DL power
control and timing advance.
PROM Programmable Read Only Memory. A storage device that, after
being written to once, becomes a read-only memory.
PRP Packet Resource Process(or). A PCU hardware component,
the PRP is a DPROC board which manages the packet
resources at the PCU and is the processor where all of the
radio related processing occurs. GPRS channels are routed to
PRPs which perform the RLC/MAC processing, air interface
scheduling, and frame synchronization of the channels.
Ps Location probability. Location probability is a quality criterion
for cell coverage. Due to shadowing and fading a cell edge is
defined by adding margins so that the minimum service quality
is fulfilled with a certain probability.
PS Puncturing Scheme.
PSA Periodic Supervision of Accessibility. PSA is a fault
management function. It periodically sends messages to
BSSs requesting information on their current state. This
verifies whether the BSSs are operational or not. If a BSS fails
to respond to a PSA request for its status, the OMC-R will
generate an alarm for that BSS.
PSC Primary Synchronization Code
P-SCH Primary Synchronization Channel (physical)
PSD Power Spectral Density ( 3GTS 25.215 / 3GTS 25.102)
PSK Phase Shift Keying
PSI Packet System Information.
PSAP Presentation Services Access Point.
pSAP PCU System Audit Process. pSAP is a GWM process. It
periodically monitors the soft devices to maintain the reliability
of the system.
PSM Power Supply Module.
pSM PCU Switch Manager. The pSM resides on the PSP as part of
the GWM Functional Unit process. The pSM maintains data
paths within the PCU and communicates with the BSC.
PSP PCU System Processor board. Part of GPRS.
PSPDN Packet Switched Public Data Network. See Packet Switching
and PDN.
© 2005-2006 CP13: Introduction to UMTS USR6 13-59
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
PSTN Public Switched Telephone Network. The domestic land
line telecommunications network. It is usually accessed by
telephones, key telephone systems, private branch exchange
trunks, and data arrangements.
PSU Power Supply Unit.
PSW Pure Sine Wave.
PT Protocol Type ( GTP or GTP’)
PTACH Packet Timing Advance Control Channel
PTCCH Packet Timing Advance Control Channel ((E)GPRS)
PTCCH/D Packet Timing Advance Control Channel / Downlink Direction
((E)GPRS)
PTCCH/U Packet Timing Advance Control Channel / Uplink Direction
((E)GPRS)
PTM Point to Multipoint
P-TMSI Packet TMSI
PTO Public Telecommunications Operator.
PTP Point to Point
PTR Packet Timeslot Reconfiguration.
PUA Packet Uplink Assignment.
PUCT Price per Unit Currency Table. The PUCT is the value of the
Home unit in a currency chosen by the subscriber. The PUCT
is stored in the SIM. The value of the PUCT can be set by
the subscriber and may exceed the value published by the
HPLMN. The PUCT value does not have any impact on the
charges raised by the HPLMN.
PVC Permanent Virtual Circuit. Also, in ATM terminology,
Permanent Virtual Connection. A virtual circuit that is
permanently established, saving the time associated with circuit
establishment and tear-down. See also SVC.
PW Pass Word.
PWR Power.
PXPDN Private eXchange Public Data Network. See also PDN.
QA- Quiesent mode
QA Q (Interface) - Adapter. TMN interface adapter used to
communicate with non-TMN compatible devices and objects.
Used to connect MEs and SEs to TMN (GSM Rec. 12.00).
Q3 Interface between NMC and GSM network.
Q-adapter See QA.
QAF Q-Adapter Function.
QE Quality Estimate
QEI Quad European Interface. Interfaces four 2 Mbit/s circuits to
TDM switch highway. See MSI.
13-60 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
QIC Quarter Inch Cartridge (Data storage format).
QoS Quality Of Service. An alarm category which indicates that a
failure is degrading service.
Queue Data structure in which data or messages are temporarily
stored until they are retrieved by a software process. Also a
series of calls waiting for service. See also FIFO.
Quiescent mode IDS intermediate state before shutdown.
R - RXU
R Value of reduction of the MS transmitted RF power relative
to the maximum allowed output power of the highest power
class of MS (A).
RA RAndom mode request information field.
RA Radio Access.
RA Routing Area.
RA250 Rural Area with the MS travelling at 250 kph. Dynamic model
against which the performance of a GSM receiver can be
measured. See also TU3, TU50, HT100 and EQ50.
RAB Random Access Burst. Data sent on the RACH.
RAB Radio Access Bearer
RAC Routing Area Code
RACCH Random Access Control CHannel. A GSM common control
channel used to originate a call or respond to a page.
RACH Random Access CHannel. The RACH is used by the mobile
station to request access to the network. See also RAB.
RADIUS Remote Authentication Dial In User Service ( RFC 2865)
RAI Routing Area Identification
Radio Frequency A term applied to the transmission of electromagnetically
radiated information from one point to another, usually using air
or vacuum as the transmission medium. An electromagnetic
wave frequency intermediate between audio frequencies and
infrared frequencies used in radio and television transmission.
RAM Random Access Memory. A read/write, nonsequential-access
memory in which information can be stored, retrieved and
modified. This type of memory is generally volatile (i.e., its
contents are lost if power is removed).
RANAP Radio Access Network Application Part ( 3GTS 25.413)
RAND RANDom number (used for authentication). The RAND is sent
by the SGSN to the MS as part of the authentication process.
RAT Radio Access Technology
RATI Receive Antenna Transceiver Interface.
RAx Rate Adaptation.
RB Receive Block Bitmap ( EGPRS)
© 2005-2006 CP13: Introduction to UMTS USR6 13-61
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
RBB Receive Block Bitmap ( GPRS)
RBDS Remote BSS Diagnostic System (a discontinued Motorola
diagnostic facility).
RBER Residual Bit Error Ratio. RBER is a ratio of the number of
bits in error to the total number of bits received, within error
detected speech frames defined as good. The measurement
period over which the calculation is made is 480 ms. During this
period, 24 speech frames are decoded and a ratio calculated.
By referring to a lookup table, the ratio is then converted to an
RBER Quality number between 0 and 7.
RBTS Remote Base Transceiver Station. A BTS that is not co-located
with the BSC that controls it.
RCB Radio Control Board. Part of the DRCU.
RCI Radio Channel Identifier. The unique identifier of the radio
channel portion of the circuit path.
RCI Radio Channel Interface. The RCI changes the MS address
used in the RSS (channel number) to the address used in
Layer 3 in the BSC CP.
RCP Radio Control Processor.
RCU Radio Channel Unit. Part of the BSS. Contains transceiver,
digital control circuits, and power supply. Note: The RCU is
now obsolete, see DRCU.
RCVR Receiver.
RDB Requirements Database.
RDBMS Relational DataBase Management System (INFORMIX). The
database management system for the OMC-R database.
RDI Restricted Digital Information.
RDIS Radio Digital Interface System.
RDM Reference Distribution Module. The RDM provides a stable
3MHz reference signal to all transceivers. It is used for carrier
and injection frequency synthesis.
RDN Relative Distinguished Name. A series of RDNs form a unique
identifier, the distinguished name, for a particular network
element.
REC, Rec RECommendation.
Reciprocal neighbour Used to describe adjacent cells; each being designated as
a neighbour of the other. Also known as bi-directional and
two-way neighbour.
Registration The process of a MS registering its location with the MSC in
order to make or receive calls. This occurs whenever the MS
first activates or moves into a new service area.
REJ REJect(ion).
REL RELease.
RELP Residual Excited Linear Predictive. A form of speech coding.
RELP coders are usually used to give good quality speech at
bit rates in the region of 9.6 kbit/s.
13-62 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
RELP-LTP RELP Long Term Prediction. A name for GSM full rate. See
Full Rate.
Remotely Tuned Combiner A combiner device which houses two processors (for
paired-redundancy) and several tuneable cavities. See also
COMB
resync Resynchronize/resynchronization.
REQ REQuest.
Reuse Pattern The minimum number of cells required in a pattern before
channel frequencies are reused, to prevent interference.
Varies between cell configuration type and channel type. The
pattern shows assignments of adjacent channels to minimize
interference between cells and sectors within the pattern area.
Revgen A Motorola DataGen utility for producing an MMI script from a
binary object database.
RF See Radio Frequency.
RFC, RFCH Radio Frequency Channel. A partition of the system RF
spectrum allocation with a defined bandwidth and centre
frequency.
RFE Radio Front End (module).
RFE Receiver Front End (shelf).
RFEB Receiver Front End Board. Part of DRCU II.
RFI Radio Frequency Interference.
RFM Radio Frequency Module.
RFN Reduced TDMA Frame Number.
RFU Reserved for Future Use.
R-GSM Railways-GSM
RJ45 Registered Jack 45. An eight-wire connector used commonly
to connect computers onto a local-area networks (LAN),
especially Ethernets.
RISC Reduced Instruction Set Computer. A type of microprocessor
that recognizes a relatively limited number of instruction types,
allowing it to operate at relatively higher speeds.
RL Remote login. RL is a means by which the operator performs
configuration management, fault management, and some
performance management procedures at the NEs. The RL
software manages the X.25 connection for remote login. The
circuit is made by the OMC-R calling the NE.
RLC Release Complete. An SCCP message type used with RLSD
to release a connection.
RLC Radio Link Control. Air interface transmission layer. The RLC
function processes the transfer of PDUs from the LLC layer.
(UMTS  3GTS 25.322) ((E)GPRS / 3GTS 04.60 / 3GTS
44.060)
RLM RF Link Manager.
© 2005-2006 CP13: Introduction to UMTS USR6 13-63
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
RLP Radio Link Protocol. An ARQ protocol used to transfer user
data between an MT and IWF. See GSM 04.22. ( 3GTS
24.022)
RLR Receive Loudness Rating. See SLR.
RLSD ReLeaSeD. An SCCP message type used with RLC to release
a connection.
RMS Root Mean Square (value). The most common mathematical
method of defining the effective voltage or current of an AC
wave. For a sine wave, the rms value is 0.707 times the peak
value.
RMSU Remote Mobile Switching Unit. An RMSU is a line concentrator.
It may be inserted between the MSC and some of the BSS
sites served by the MSC to reduce the number of terrestrial
signalling and traffic circuits required.
RNC Radio Network Controller
RNR Receive Not Ready
RNS Radio Network Subsystem
RNTABLE Table of 128 integers in the hopping sequence.
RNSAP Radio Network Subsystem Application Part ( 3GTS 25.423)
RNTI Radio Network Temporary Identifier
ROAM Reliability, Operability, Availability, Maintainability.
Roaming Situation where mobile station operates in a cellular system
other than the one from which service is subscribed.
ROM Read Only Memory. Computer memory that allows fast
access to permanently stored data but prevents addition to or
modification of the data. ROM is inherently non-volatile storage
- it retains its contents even when the power is switched off.
ROSE Remote Operations Service Element. An ASE which carries a
message between devices over an association established by
ASCE (a CCITT specification for O & M) (OMC).
Roundtrip Time period between transmit and receive instant of a timeslot
in the BTS, propagation determined by the response behaviour
of the MS and the MS to BTS delay distance.
RPE Regular Pulse Excited (codec). See RPE-LTP.
RPE-LTP Regular Pulse Excitation - Long Term Prediction. The GSM
digital speech coding scheme. GSM uses a simplified RPE
codec, with long-term prediction, operating at 13 kbits/s to
provide toll quality speech.
RPLMN Registered PLMN
RPOA Recognised Private Operating Agency. Private
telecommunications operator recognised by the appropriate
telecommunications authority.
RPR Read Privilege Required. Part of the table structure of the
OMC database schema. Access to the column is allowed only
for privileged accounts.
13-64 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
RR Radio Resource management. Part of the GSM management
layer. The functions provided by RR include paging, cipher
mode set, frequency redefinition, assignments, handover and
measurement reports.
RR Receive Ready.
RRBP Relative Reserved Block Period
RRC Radio Resource Control ( 3GTS 25.331)
RRSM Radio Resource State Machine. Translates messages through
Call Processing (CP). Activates and deactivates radio channels
as controlled by the CRM.
RRSM Radio Resource Switch Manager.
RS232 Recommended Standard 232. The interface between a
terminal (DTE) and a modem (DCE) for the transfer of serial
data. Standard serial interface.
RSCP Received Signal Code Power ( 3GTS 25.215)
RSE Radio System Entity.
RSL Radio Signalling Link. RSL is used for signalling between the
BSC and BTSs. The interface uses a 64 kbit/s timeslot with
a LAPD protocol.
RSLF Radio System Link Function.
RSLP Radio System Link Processor.
RSS Radio SubSystem (replaced by BSS).
RSSI Received Signal Strength Indicator. A parameter returned from
a transceiver that gives a measure of the RF signal strength
between the MS and BTS, either uplink or downlink.
RSVP Resource Reservation Protocol ( RFC 2205)
RSZI Regional Subscription Zone Identity. The RSZI defines the
regions in which roaming is allowed. The elements of the RSZI
are:The Country Code (CC) which identifies the country in
which the GSM PLMN is located,The National Destination Code
(NDC) which identifies the GSM PLMN in that country,The
Zone Code (ZC) which identifies a regional subscription zone
as a pattern of allowed and not allowed location areas uniquely
within that PLMN.
RTC Remotely Tuneable Channel Combiner. RTCs are used to
fine-tune the cavities to the right frequency. A poorly tuned
cavity can cause power destined for the antenna to be reversed.
RTE Remote Terminal Emulator.
RTF Radio Transceiver Function. RTF is the function that supports
the air interface channel and the DRI/Transceiver pair. When
equipping a DRI at a remote BTS, one or more RTFs must
be equipped.
RTF Receive Transmit Functions.
RTO Retransmission Time Out
RTP Real Timer Protocol ( RFC 1889)
© 2005-2006 CP13: Introduction to UMTS USR6 13-65
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
RTS Request to Send. A handshaking signal used with
communication links, especially RS232 or CCITT Rec. V.24 to
indicate (from a transmitter to a receiver) that data is ready for
transmission. See also CTS.
RTT RoundTrip Time ( RFC 793)
RU Rack Unit.
Run level System processor operating mode.
Rx Receive(r).
RX Receive window buffer.
RXCDR Remote Transcoder. An RXCDR is used when the transcoding
is performed at a site away from the BSC. This site would be
at or near the MSC. This enables 4:1 multiplexing in which the
transcoded data for four logical channels is combined onto one
64 kbit/s link, thus reducing the number of links required for
interconnection to the BSCs. See also XCDR.
RXF Receive Function (of the RTF).
RXLEV Received signal level. An indication of received signal level
based on the RSSI. RXLEV is one of the two criteria for
evaluating the reception quality (the basis for handover and
power control). See also RXQUAL. The MS reports RXLEV
values related to the apparent received RF signal strength. It is
necessary for these levels to attain sufficient accuracy for the
correct functioning of the system.
RXLEV-D Received signal level downlink.
RXLEV-U Received signal level uplink.
RXQUAL Received signal quality. An indication of the received signal
quality based on the BER. RXQUAL is one of the two criteria
for evaluating the reception quality (the basis for handover
and power control). See also RXLEV. The MS measures the
received signal quality, which is specified in terms of BER
before channel decoding averaged over the reporting period of
length of one SACCH multiframe.
RXQUAL-D Received signal quality downlink.
RXQUAL-U Received signal quality uplink.
RXU Remote Transcoder Unit. The shelf which houses the remote
transcoder modules in a BSSC cabinet at a remote transcoder
site.
S7- SYSGEN
S7 See SS7.
S/W SoftWare.
SABM Set Asynchronous Balanced Mode. A message which
establishes the signalling link over the air interface.
SABME SABM Extended.
SABP Service Area Broadcast Protocol ( 3GTS 25.419)
13-66 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
SACCH Slow Associated Control CHannel. A GSM control channel
used by the MS for conveying power control and timing
advance information in the downlink direction, and RSSI and
link quality reports in the uplink direction.
SACCH/C4 Slow Associated Control CHannel/SDCCH/4.
SACCH/C8 Slow Associated Control CHannel/SDCCH/8.
SACCH/T Slow Associated Control CHannel/Traffic channel.
SACCH/TF Slow Associated Control CHannel/Traffic channel Full rate.
SACCH/TH Slow Associated Control CHannel/Traffic channel Half rate.
SAGE A brand of trunk test equipment.
SAP Service Access Point. In the reference model for OSI, SAPs of
a layer are defined as gates through which services are offered
to an adjacent higher layer.
SAP System Audits Process. SAP is on each GPROC in the BSS. It
monitors the status of the BSS on a periodic (scheduled) and
on-demand basis during normal mode. SAP detects faulty or
degrading hardware and software (through the use of audit
tests) and notifies the Alarms handling software of the condition.
SAPI Service Access Point Indicator (identifier). The OSI term for the
component of a network address which identifies the individual
application on a host which is sending or receiving a packet.
SAR Segmentation And Reassembly (ATM-sublayer)
SAW Surface Acoustic Wave. SAW devices basically consist of an
input transducer to convert electrical signals to tiny acoustic
waves, which then travel through the solid propagation medium
to the output transducer where they are reconverted to
electrical signals. SAW band pass filters are used for sorting
signals by frequency.
SB Synchronization Burst (see Synchronization burst).
SBUS Serial Bus. An SBUS is a logical device made up of the
communication path between the GPROCs and LANX cards
in a cage.
SC Service Centre (used for Short Message Service).
SC Service Code.
SCCA System Change Control Administration. Software module
which allows full or partial software download to the NE (OMC).
SCCP Signalling Connection Control Part (part of SS7).
S-CCPCH Secondary Common Control Physical Channel (used as bearer
for the FACH and PCH TrCH’s / UMTS Physical Channel)
SCEG Speech Coding Experts Group (of GSM).
SCH Synchronization CHannel. A GSM broadcast control channel
used to carry information for frame synchronization of MSs and
identification of base stations.
SCI Status Control Interface. A slave to the Status Control Manager.
SCIP Serial Communication Interface Processor.
© 2005-2006 CP13: Introduction to UMTS USR6 13-67
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
SCM Status Control Manager. Accepts messages from other
processors within the switch requesting status displays in the
form of one or more lights on a hardware panel. The SCM maps
the status display requests into specific commands to the status
control interface processor to turn on and/or turn off lights.
SCN Sub-Channel Number. One of the parameters defining a
particular physical channel in a BS.
SCP Service Control Point (an intelligent network entity).
S-CPICH Secondary Common Pilot Channel (UMTS Physical Channel)
S-CSCF Serving Call Session Control Function ( SIP)
SCSI Small Computer Systems Interface. A processor-independent
standard for system-level interfacing between a computer and
intelligent devices including hard disks, floppy disks, CD-ROM,
printers, scanners, and many more. SCSI-1 can connect up to
seven devices to a single SCSI adaptor (or host adaptor) on
the computer’s bus.
SCTP Stream Control Transmission Protocol ( RFC 2960)
SCU Slim Channel Unit.
SCU900 Slim Channel Unit for GSM900.
SDCCH Stand-alone Dedicated Control CHannel. A GSM control
channel where the majority of call setup occurs. Used for MS to
BTS communications before MS assigned to TCH. A SDCCH
is used by a single MS for call setup, authentication, location
updating and SMS point to point.
SDL Specification Description Language. A method for visually
depicting the functionality of call processing, operations and
maintenance software.
SDM Sub-rate Data Multiplexor
SDMA Space Division Multiple Access
SDT SDL Development Tool. A software tool to model and validate
real-time, state-based product software designs.
SDU Service Data Unit. In layered systems, a set of data that is sent
by a user of the services of a given layer, and is transmitted to
a peer service user semantically unchanged.
SDR Special Drawing Rights. The SDR is the International Monetary
Fund unit of account. It also serves as a basis for the unit of
account for a number of other international organizations and
as a basis for private financial instruments. The SDR is based
on the values of the euro, U.S. dollar, Japanese yen and pound
sterling.
SE Support Entity. See SEF.
Secondary Cell A cell which is not optimized in the network and has a
co-located neighbour whose cell boundary follows the boundary
of the said cell. The secondary cell has a preferred band the
same as that of its own frequency type.
SEF Support Entity Function. SEFs are functions not directly
involved in the telecommunication process. They include fault
localisation, protection switching, etc. (GSM Rec.12.00).
13-68 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
Session Layer See OSI RM. The Session Layer responds to service requests
from the Presentation Layer and issues service requests to
the Transport Layer. It provides the mechanism for managing
the dialogue between end-user application processes. It
provides for either duplex or half-duplex operation and
establishes checkpointing, adjournment, termination, and
restart procedures.
SF Spreading Factor
SFH Synthesizer Frequency Hopping. The principle of SFH is that
every mobile transmits its time slots according to a sequence of
frequencies that it derives from an algorithm. The frequency
hopping occurs between time slots and, therefore, a mobile
station transmits (or receives) on a fixed frequency during one
time slot. It must then hop before the time slot on the next
TDMA frame. Due to the time needed for monitoring other
base stations the time allowed for hopping is approximately 1
ms, according to the receiver implementation. The receive and
transmit frequencies are always duplex frequencies.
SFN System Frame Number
SG Security Gateway (IPsec /  RFC 2401)
SGSN Serving GPRS Support Node. The SGSN provides the control,
transmission, OAMP, and charging functions. It keeps track of
the individual MS locations, and performs security functions
and access control. The SGSN is connected to the BSS via a
Frame Relay network.
SGW Signaling Gateway (SS7  IP)
SHA Secure Hash Algorithm
SHCCH Shared Channel Control Channel (UMTS Logical Channel /
 TDD only)
SI Screening Indicator. The supplementary service (SS) screening
indicator is sent by the MS at the beginning of the radio
connection to allow the network to assess the capabilities of the
MS and hence determine either whether a particular network
initiated SS operation may be invoked or which version of a
network initiated SS operation should be invoked. The SS
screening indicator is only relevant to network initiated SS
operation and is valid for the duration of a radio connection.
SI Service Interworking. Part of the IWF.
SI Supplementary Information.
SI System Information.
SIA Supplementary Information A.
SIB System Information Block
© 2005-2006 CP13: Introduction to UMTS USR6 13-69
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
SID Silence Descriptor. The transmission of comfort noise
information to the RX side is achieved by means of a SID
frame. A SID frame is transmitted at the end of speech bursts
and serves as an end of speech marker for the RX side. In
order to update the comfort noise characteristics at the RX
side, SID frames are transmitted at regular intervals also during
speech pauses. This also serves the purpose of improving the
measurement of the radio link quality by the radio subsystem
(RSS).
SIF Signal Information Field. The bits of a message signal unit that
carry information for a certain user transaction; the SIF always
contains a label.
Signalling System No.7 See SS7.
SIM Subscriber Identity Module. Removable module which is
inserted into a mobile equipment; it is considered as part of
the MS. It contains security related information (IMSI, Ki, PIN),
other subscriber related information and the algorithms A3 and
A8.
SIMM Single Inline Memory module.
SIMM System Integrated Memory Module. A small plug-in circuit
board providing additional RAM for a computer.
SIO Service Information Octet. Eight bits contained in a message
signal unit, comprising the service indicator and sub-service
field. A value in the SIF of an SS7 signalling message
specifying the User Part type.
SIP Session Initiation Protocol ( RFC 3261)
SIR Signal to Interference Ratio
SITE BSC, BTS or collocated BSC-BTS site.
SIX Serial Interface eXtender. Converts interface levels to TTL
levels. Used to extend 2 serial ports from GPROC to external
devices (RS232, RS422, and fibre optics).
SK Secondary Key. A database column attribute, the secondary
key indicates an additional index and/or usage as a composite
key.
SL See Session Layer.
SL Signalling Link. The signalling links between the various
network elements are: Remote BTS to BSC - Radio Signalling
Link (RSL), BSC to MSC - Message Transfer Link (MTL),
OMC(R) to BSS - Operations and Maintenance Link (OML),
Remote XCDR to BSC - XCDR signalling Link (XBL), CBC to
BSC - Cell Broadcast Link (CBL).
SLC Signaling Link Code
SLF Subscriber Locator Function
SLNK Serial Link. One of four communications paths between SCIP
and peripheral equipment. The information on the link is sent
serially in a bit-synchronous format.
13-70 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
SLR Send Loudness Rating. The SLR, in the mobile to land
direction, and the Receive Loudness Rating (RLR) in the land
to mobile direction, determine the audio signal levels for the
customers speech. The loudness ratings are calculated from
the send and receive sensitivity masks or frequency responses.
SLR Source Local Reference (SS7)
SLS Signaling Link Selection
SLTA Signalling Link Test Acknowledge. Message sent from the
MSC to the BSC in response to an SLTM.
SLTM Signalling Link Test Message. During the process of bringing
an MTL link into service, the BSC sends an SLTM message to
the MSC. The MSC responds with an SLTA message.
SM Switch Manager. The function of the SM is to connect a MS
terrestrial trunk from the MSC (designated by the MSC), to the
radio channel given to a MS by the cell resource manager in
the BSS software.
SM Summing Manager.
SM Session Management
SMAE System Management Application Entity (CCITT Q795, ISO
9596). OSI terminology for a software Management Information
Server that manages a network.
SMASE System Management Application Service Element.
SMCB Short Message Cell Broadcast.
SME Short Message Entity. An entity that may send or receive Short
Messages. The SME may be located in a fixed network, an
MS, or a SC. See also SMS.
SMG Special Mobile Group. To avoid confusion between the GSM
system and the GSM committee with its wider responsibilities,
the committee was renamed SMG in 1992.
SMP Motorola Software Maintenance Program. A Motorola program
designed to ensure the highest quality of software with the
highest level of support.
SMS Short Message Service. SMS is a globally accepted wireless
service that enables the transmission of alphanumeric
messages between mobile subscribers and external systems
such as electronic mail, paging, and voice-mail systems. It
transfers the short messages, up to 160 characters, between
Smts and MSs via an SMS-SC. See also SMS-SC, SMS/PP
and Smt.
SMSCB Short Message Service Cell Broadcast. SMSCB is a service in
which short messages may be broadcast from a PLMN to MSs.
SMSCB messages come from different sources (e.g. traffic
reports, weather reports). Messages are not acknowledged by
the MS. Reception of SMSCB messages by the MS is only
possible in idle mode. The geographical area over which each
message is transmitted is selected by the PLMN operator, by
agreement with the provider of the information.
SMS-G-MSC SMS Gateway MSC (for Short Messages destined to Mobile
Station)
© 2005-2006 CP13: Introduction to UMTS USR6 13-71
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
SMS-IW-MSC SMS Interworking MSC (for Short Messages coming from
Mobile Station)
SMS-SC Short Message Service - Service Centre. SMS-SC is an
interworking unit between stationary networks and the GSM
Network. It acts as a store and forward centre for short
messages. See also SMS, SMS/PP and Smt.
SMS/PP Short Message Service/Point-to-Point. Two different
point-to-point services have been defined: Mobile Originated
(MO) and Mobile Terminated (MT). A short message always
originates or terminates in the GSM network. This means that
short messages can never be sent between two users both
located in stationary networks. See also SMS, SMS-SC and
Smt.
Smt Short message terminal. See also SMS, SMS-SC and
SMS/PP. There are different types of Smt interfaces, one being
the Computer Access Interface which provides services for
external computers communicating with SMS-SCs through the
Computer Access Protocol.
SMTP Simple Mail Transfer Protocol ( RFC 2821)
SN Subscriber Number.
SND Sequence Number Downlink ( GTP)
SND SeND.
SNDCP Subnetwork Dependent Convergence Protocol
SNDR SeNDeR.
SNMP Simple Network Management Protocol
SNN SNDCP N-PDU Number Flag
SN-PDU Segmented N-PDU (SN-PDU is the payload of SNDCP)
SNR Signal to Noise Ratio
SNR Serial NumbeR.
SNU Sequence Number Uplink ( GTP)
SOA Suppress Outgoing Access (CUG SS). An arrangement which
prevents a member of a CUG placing calls outside the CUG.
SOAP Simple Object Access Protocol (
http://www.w3.org/TR/2000/NOTE-SOAP-20000508)
Software Instance A complete set of software and firmware objects including the
database object.
SP Service Provider. The organisation through which the
subscriber obtains GSM telecommunications services. This
may be a network operator or possibly a separate body.
SP Signalling Point. A signalling point is a node within a SS7
network.
SP Special Product.
SP SPare.
13-72 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
SPARC Scalable Processor ArChitecture. a 32- and 64-bit
microprocessor architecture from Sun Microsystems that is
based on the Reduced Instruction Set Computer (RISC).
SPARC has become a widely-used architecture for hardware
used with UNIX-based operating systems.
SPC Signalling Point Code.
SPC Suppress Preferential CUG. Prohibits the use of the preferential
CUG, on a per call basis.
SPI Security Parameter Index ( RFC 2401)
SPI Signalling Point Inaccessible.
SPP Single Path Preselector.
SQE Signal Quality Error.
SQL Structured Query Language. The standard language for
relational database management systems as adopted by the
American National Standards Institute (ANSI X3.135-1989) and
the International Standards Organization (ISO 9075-1989).
SRB Signaling Radio Bearer
SRD Service Request Distributor.
SRES Signed RESponse (authentication). The SRES is calculated by
the MS, using the RAND, and sent to the SGSN to authenticate
the MS.
SRNC Serving RNC
SRTT Smoothed RoundTrip Time ( RFC 793)
SS Supplementary Service. A modification of, or a supplement to,
a basic telecommunication service.
SS System Simulator.
SS7 ITU-TSS Common Channel Signalling System No. 7. Also
known as C7, S7 or SS#7. The standard defines the procedures
and protocol by which network elements in the PSTN exchange
information over a digital signalling network to effect wireless
(cellular) and wireline call setup, routing and control.
SSA SubSystem-Allowed. SSA is used for SCCP subsystem
management. An SSA message is sent to concerned
destinations to inform those destinations that a subsystem
which was formerly prohibited is now allowed. (see ITU-T
Recommendation Q.712 para 1.15).
SSAP Site System Audits Processor.
SSC Supplementary Service Control string. When a subscriber
selects a supplementary service control from the menu in a
GSM network, the mobile station invokes the SSC by sending
the network the appropriate functional signalling message.
SSCF/NNI Service Specific Coordination Function – Network Node
Interface Protocol ( ITU-T Q.2140)
SSCF/UNI Service Specific Coordination Function – User Network
Interface Protocol ( ITU-T Q.2130)
S-SCH Secondary Synchronization Channel (physical)
© 2005-2006 CP13: Introduction to UMTS USR6 13-73
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
SSCOP Service Specific Connection Oriented Protocol ( ITU-T
Q.2110)
SSCOPMCE Service Specific Connection Oriented Protocol in a Multi-link or
Connectionless Environment ( ITU T Q.2111)
SSCS Service Specific Convergence Sublayer
SSDT Site Selection Diversity Transmission
SSF Subservice Field. The level 3 field containing the network
indicator and two spare bits.
SSM SCCP Switch Manager.
SSM Signalling State Machine.
SSN Start Sequence Number ( related to ARQ-Bitmap in GPRS
/ EGPRS)
SSN Send Sequence Number ( GSM MM and CC-Protocols)
SSN SubSystem Number. In SS7, each signalling point (SP) may
contain a number of subsystems. Each subsystem has a
unique ID, the SSN (e.g. 149 for SGSN and 6 for HLR).
SSP Service Switching Point. Intelligent Network Term for the Class
4/5 Switch. The SSP has an open interface to the IN for
switching signalling, control and handoff.
SSP Subsystem-prohibited. SSP is used for SCCP subsystem
management. An SSP message is sent to concerned
destinations to inform SCCP Management at those destinations
of the failure of a subsystem.
SSS Switching SubSystem. The SSC comprises the MSC and the
LRs.
SSSAR Service Specific Segmentation And Reassembly ( ITU-T
I.366.1)
ssthresh Slow start threshold
STAN Statistical ANalysis (processor).
STAT STATistics.
stats Statistics.
STC Signaling Transport Converter on MTP-3 and MTP-3b (
ITU-T Q.2150.1) / Signaling Transport Converter on SSCOP
and SSCOPMCE ( ITU-T Q.2150.2)
STC System Timing Controller. The STC provides the timing
functions for the GPROC.
STMR Side Tone Masking rating. A rating, expressed in dB, based on
how a speaker will perceive his own voice when speaking.
STTD Space Time block coding based Transmission Diversity
SUERM Signal Unit Error Rate Monitor. A link error rate monitor.
STP Signalling Transfer Point. A node in the SS7 telephone network
that routes messages between exchanges and between
exchanges and databases that hold subscriber and routing
information.
13-74 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
SU Signal Unit. A group of bits forming a separately transferable
entity used to convey information on a signalling link.
SUFI Super Field (RLC-Protocol)
SunOS Sun Microsystems UNIX Operating System. SunOS was
renamed Solaris.
Superframe 51 traffic/associated control multiframes or 26
broadcast/common control multiframes (period 6.12s).
Super user User account that can access all files, regardless of protection
settings, and control all user accounts.
SURF Sectorized Universal Receiver Front-end (Used in
Horizonmacro).
SVC Switch Virtual Circuit. A temporary virtual circuit that is set up
and used only as long as data is being transmitted. Once the
communication between the two hosts is complete, the SVC
disappears. See also PVC.
SVM SerVice Manager. The SVM provides overall management
authority for all in-service service circuits.
SVN Software Version Number. The SVN allows the ME
manufacturer to identify different software versions of a given
type approved mobile. See also IMEI and IMEISV.
SW Software.
SWFM SoftWare Fault Management. Software faults are handled
through a SWFM facility which routes those events to the OMC
independently through the FCP.
SYM SYstem information Manager. The SYM builds and sends
GPRS system information messages over the BCCH.
sync synchronize/synchronization.
Synchronization burst Period of RF carrier less than one timeslot whose modulation
bit stream carries information for the MS to synchronize its
frame to that of the received signal.
Synthesizer hopping Synthesizer hopping is a method of frequency hopping in
which the RCUs are re-tuned in real-time, from frequency to
frequency.
SYS SYStem.
SYSGEN SYStem GENeration. The Motorola procedure for loading a
configuration database into a BTS.
T -TxBPF
T Timer.
T Transparent.
T Type only.
© 2005-2006 CP13: Introduction to UMTS USR6 13-75
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
T1 Digital WAN carrier facility that transmits DS-1-formatted
data at 1544 kbp/s through the telephone-switching network.
companies. T1 lines are widely used for private networks as
well as interconnections between an organization’s PBX or
LAN and the telco.
T43 Type 43 Interconnect Board. Provides interface to 12
unbalanced (6-pair) 75 ohm (T43 coax connectors) lines for 2
Mbit/s circuits (See BIB).
TA Terminal Adaptor. A physical entity in the MS providing terminal
adaptation functions (see GSM 04.02).
TA See Timing Advance.
TAC Type Approval Code. Part of the IMEISV.
TACS Total Access Communication System. European analogue
cellular system.
TAF Terminal Adaptation Function.( 3GTS 27.001)
TAI Timing Advance Index
TATI Transmit Antenna Transceiver Interface. The TATI consists of
RF combining equipments, either Hybrid or Cavity Combining.
See CCB.
TAXI Transparent Asynchronous Transmitter/Receiver Interface
(physical layer). A 100 Mbps ATM transmission standard
defined by the ATM Forum.
TB Transport Block
TBD To Be Determined.
TBF Temporary Block Flow. MAC modes support the provision of
TBFs allowing the point-to-point transfer of signalling and user
data between the network and an MS.
TBR Technical Basis for Regulation. An ETSI document containing
technical requirements and procedures.
TBS Transport Block Set
TBUS TDM Bus. A TBUS is a logical device made up of the TDM
backplane of a cage, the KSW devices managing the TDM
highway of the cage, and local and remote KSWX devices (if
they exist).
TC Transaction Capabilities. TC refers to a protocol structure
above the network layer interface (i.e., the SCCP service
interface) up to the application layer including common
application service elements but not the specific application
service elements using them. TC is structured as a Component
sub-layer above a Transaction sub-layer.
TCAP Transaction Capabilities Application Part. The layer of the
SS7 protocol that is used to obtain Routing data for certain
services.( Q.771 – Q.773)
TCB TATI Control Board.
TCH Traffic CHannel. GSM logical channels which carry either
encoded speech or user data.
TCH/F A full rate TCH. See also Full Rate.
13-76 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
TCH/F2.4 A full rate TCH at ? 2.4 kbit/s.
TCH/F4.8 A full rate TCH at 4.8 kbit/s.
TCH/F9.6 A full rate TCH at 9.6 kbit/s.
TCH/FD Traffic Channel / Fullrate Downlink
TCH/FS A full rate Speech TCH.
TCH/H A half rate TCH. See also Half Rate.
TCH/H2.4 A half rate TCH at ? 2.4 kbit/s.
TCH/H4.8 A half rate TCH at 4.8 kbit/s.
TCH/HS A half rate Speech TCH.
TCI Transceiver Control Interface.
TCP Transmission Control Protocol. TCP is one of the main
protocols in TCP/IP networks. Whereas the IP protocol deals
only with packets, TCP enables two hosts to establish a
connection and exchange streams of data. TCP guarantees
delivery of data and also guarantees that packets will be
delivered in the same order in which they were sent. See also
IP and TCP/IP.
TCP/IP Transmission Control Protocol/Internet Protocol. Two
interrelated protocols that are part of the Internet protocol suite.
TCP operates on the OSI Transport Layer and IP operates on
the OSI Network Layer. See also IP and TCP.
TCTF Target Channel Type Field
TC-TR Technical Commitee Technical Report.
TCTV Transport Channel Traffic Volume
TCU Transceiver Control Unit.
TDD Time Division Duplex
TDF Twin Duplexed Filter. Used in M-Cellhorizon.
TDM Time Division Multiplexing. A type of multiplexing that combines
data streams by assigning each stream a different time slot in a
set. TDM repeatedly transmits a fixed sequence of time slots
over a single transmission channel. Within T-Carrier systems,
such as T-1 and T-3, TDM combines PCM streams created for
each conversation or data stream.
TDMA Time Division Multiple Access. A technology for delivering
digital wireless service using TDM. TDMA works by dividing
a radio frequency into time slots and then allocating slots to
multiple calls. In this way, a single frequency can support
multiple, simultaneous data channels.
TDU TopCell Digital Unit. Part of the TopCell BTS hardware. A TDU
is capable of supporting 6 TRUs for supporting up to 6 sectors.
TE Terminal Equipment. Equipment that provides the functions
necessary for the operation of the access protocols by the user.
Tei Terminal endpoint identifier. A number that identifies a specific
connection endpoint within a service access point.
TEI Terminal Equipment Identity.
© 2005-2006 CP13: Introduction to UMTS USR6 13-77
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
TEID Tunnel Endpoint Identifier ( GTP / 3GTS 29.060)
TEMP TEMPorary.
TEST TEST control processor.
TF Transport Format
TF Transmission Function. The TF provides layered protocol
software for handling payload information transfer and for
providing signalling communications between the control
function and external systems.
TFA TransFer Allowed. An SPC route management message used
to notify adjacent signalling points of an accessible route.
TFC Transport Format Combination
TFCI Transport Format Combination Identifier
TFCS Transport Format Combination Set
TFI Transport Format Indication (UMTS). Temporary Flow Identity
((E)GPRS)
TFP TransFer Prohibited. An SPC route management message
used to notify adjacent signalling points of an inaccessible
route.
TFS Transport Format Set
TFTP Trivial File Transfer Protocol. TFTP is a simple form of FTP. It
uses UDP and provides no security features. It is often used by
servers to boot diskless workstations, X-terminals, and routers.
TGD Transmission Gap start Distance ( 3GTS 25.215)
TGL Transmission Gap Length ( 3GTS 25.215)
TGPRC Transmission Gap Pattern Repetition Count ( 3GTS 25.215)
TGSN Transmission Gap Starting Slot Number ( 3GTS 25.215)
THIG Topology Hiding Inter Network Gateway
TI Transaction Identifier.
TID Tunnel Identifier
Timeslot The multiplex subdivision in which voice and signalling bits are
sent over the air. Each RF carrier is divided into 8 timeslots.
See also ARFCN.
Timing advance A signal sent by the BTS to the MS. It enables the MS to
advance the timing of its transmission to the BTS so as to
compensate for propagation delay.
TL See Transport Layer.
TLLI Temporary Logical Link Identifier.
TLS Transport Layer Security ( RFC 2246 / RFC 3546 / formerly
known as SSL or Secure Socket Layer)
TLV Type, Length and Value. An encoding element composed of
three fields: a type identifier, a length indicator, and content
octets.
TM Transparent Mode operation ( UMTS-RLC)
13-78 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
TM Transmission Modules
TM Traffic Manager.
TMD Transparent Mode Data (UMTS RLC PDU-type)
TMI TDM Modem Interface board. Provides analogue interface
from IWF to modems for 16 circuits. Part of IWF.
TMM Traffic Metering and Measuring. TMM provides system tools
to be used by traffic engineering and switch maintenance
personnel to determine if the system is operating correctly.
TMM reports are provided for trunk circuits, trunk groups,
service circuits, call routing and miscellaneous system data.
TMN Telecommunications Management Network. The
physical entities required to implement the
Network Management functionality for the PLMN.
Also, TMN was originated formally in 1988 under the ITU-TS
as a strategic goal to create or identify standard interfaces
that would allow a network to be managed consistently across
all network element suppliers. The concept has led to a
series of interrelated efforts at developing standard ways to
define and address network elements. TMN uses the OSI
Management Standards as its framework. TMN applies to
wireless communications and cable TV as well as to private
and public wired networks.
TMSI Temporary Mobile Subscriber Identity. A unique identity
temporarily allocated by the MSC to a visiting mobile subscriber
to process a call. May be changed between calls and even
during a call, to preserve subscriber confidentiality.
TN Timeslot Number.
TOM Tunneling of Messages.
TON Type Of Number.
TPC Transmit Power Command
T-PDU Payload of a G-PDU which can be user data, i.e. possibly
segmented IP-frames, or GTP signaling information ( GTP)
TQI Temporary Queuing Identifier
Traffic channels Channels which carry user’s speech or data. See also TCH.
Traffic unit Equivalent to an erlang.
Training sequence Sequence of modulating bits employed to facilitate timing
recovery and channel equalization in the receiver.
Transport Layer See OSI RM. The Transport Layer responds to service requests
from the Session Layer and issues service requests to the
Network Layer. Its purpose is to provide transparent transfer
of data between end users, thus relieving the upper layers
from any concern with providing reliable and cost-effective
data transfer.
TRAU Transcoding Rate and Adaption Unit
TRS Timeslot Resource Shifter. The TRS determines which
timeslots are active in a PRP board to perform a control of the
GPRS traffic.
© 2005-2006 CP13: Introduction to UMTS USR6 13-79
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
TRAU Transcoder Rate Adaption Unit. TRAU converts the encoded
voice and rate adapted data into 64 kbps data for the PSTN.
TrCH Transport Channel (UMTS)
TrGW Transition Gateway (IPv4  IPv6)
TRM Terrestrial Resource Management.
TRU TopCell Radio unit.
TRX Transceiver(s). A network component which can serve full
duplex communication on 8 full-rate traffic channels according
to specification GSM 05.02. If Slow Frequency Hopping (SFH)
is not used, then the TRX serves the communication on one
RF carrier.
TS Technical Specification.
TS TeleService. Any service provided by a telecommunication
provider.
TS TimeSlot (see Timeslot).
TS1 Training Sequence 1.
TS2 Training Sequence 2.
TSA TimeSlot Acquisition.
TSA TimeSlot Assignment.
TSDA Transceiver Speech & Data Interface.
TSC Training Sequence Code. A training sequence is sent at the
centre of a burst to help the receiver identify and synchronize
to the burst. The training sequence is a set sequence of bits
which is known by both the transmitter and receiver. There are
eight different TSCs numbered 0 to 7. Nearby cells operating
with the same RF carrier frequency use different TSCs to allow
the receiver to identify the correct signal.
TSI TimeSlot Interchange. The interchange of timeslots within a
TDM stream.
TSDI Transceiver Speech and Data Interface.
TSM Transceiver Station Manager.
TSN TRAU SyNc.
TSTD Time Switched Transmit Diversity
TSW Timeslot SWitch.
TTCN Tree and Tabular Combined Notation. TTCN is a programming
language endorsed by ISO that is used to write test suites for
telecommunications systems.
TTL Transistor to Transistor Logic. A common semiconductor
technology for building discrete digital logic integrated circuits.
TTL Time To Live ( IP-Header / RFC 791)
TTY TeleTYpe (refers to any terminal).
TU Traffic Unit.
13-80 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
TU3 Typical Urban with the MS travelling at 3 kph. Dynamic model
against which the performance of a GSM receiver can be
measured. See also TU50, HT100, RA250 and EQ50.
TU50 Typical Urban with the MS travelling at 50 kph. Dynamic model
against which the performance of a GSM receiver can be
measured. See also TU3, HT100, RA250 and EQ50.
TUP Telephone User Part. TUP was an earlier implementation of
SS7 and generally does not allow for data type applications.
TV Type and Value.
Two-way neighbour See Reciprocal neighbour.
Tx Transmit(ter).
TX Transmit window buffer.
TXF Transmit Function. See RTF.
TXPWR Transmit PoWeR. Tx power level in the
MS_TXPWR_REQUEST and MS_TXPWR_CONF
parameters.
TxBPF Transmit Bandpass Filter. See BPF.
U - UUS
UA Unnumbered Acknowledgment. A message sent from the MS
to the BSS to acknowledge release of radio resources when a
call is being cleared.(LAPD/LLC/RLP-Frame Type)
UA User Agent
UAC User Agent Client
UARFCN UMTS Absolute Radio Frequency Channel Number
UAS User Agent Server
UCS2 Universal Coded Character Set 2. A codeset containing all of
the characters commonly used in computer applications.
UDI Unrestricted Digital Information.
UDP User Datagram Protocol. UDP is a connectionless protocol
that, like TCP, runs on top of IP networks. Unlike TCP/IP,
UDP/IP provides very few error recovery services, offering
instead a direct way to send and receive datagrams over an IP
network. It is used primarily for broadcasting messages over a
network.( RFC 768)
UDUB User Determined User Busy.
UE User Equipment
UFE Uplink Frame Error.
UHF Ultra High Frequency. The UHF range of the radio spectrum is
the band extending from 300 MHz to 3 GHz.
UI Unnumbered Information (Frame) ( LAPD) / Unconfirmed
Information ( LLC) / Frame Type
© 2005-2006 CP13: Introduction to UMTS USR6 13-81
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
UIC Union International des Chemins de Fer. The UIC is the
worldwide organisation for cooperation among railway
companies. Its activities encompass all fields related to the
development of rail transport.
UICC Universal Integrated Circuit Card ( 3GTS 22.101 / Bearer
card of SIM / USIM)
UID User ID. Unique number used by the system to identify the user.
UL Upload (of software or database from an NE to a BSS).
UL UpLink.
ULC UpLink Concatenator. The ULC concatenates RLC data blocks
into LLC frames.
Um Air interface.
UM Unacknowledged Mode operation ( UMTS-RLC)
UMD Unacknowledged Mode Data (UMTS RLC PDU-type)
UMTS Universal Mobile Telecommunication System. The European
implementation of the 3G wireless phone system. UMTS, which
is part of IMT-2000, provides service in the 2GHz band and
offers global roaming and personalized features. Designed as
an evolutionary system for GSM network operators, multimedia
data rates up to 2 Mbps are expected.
UNIX A multiuser, multitasking operating system that is widely used
as the master control program in workstations and especially
servers. UNIX was developed by AT&T and freely distributed to
government and academic institutions, causing it to be ported
to a wider variety of machine families than any other operating
system. As a result, UNIX became synonymous with open
systems.
UPCMI Uniform PCM Interface (13 bit). The UPCMI is introduced for
design purposes in order to separate the speech transcoder
impairments from the basic audio impairments of the MS.
UPD Up to Date.
Uplink Physical link from the MS towards the BTS (MS transmits, BTS
receives).
UPS Uninterruptable Power Supply. A device that is inserted
between a primary power source, such as a commercial utility,
and the primary power input of equipment to be protected,
e.g., a computer system, for the purpose of eliminating the
effects of transient anomalies or temporary outages. Backup
power is used when the electrical power fails or drops to an
unacceptable voltage level.
UPU User Part Unavailable.
URA UTRAN Registration Area
URI Uniform Resource Identifier
URL Uniform Resource Locators ( RFC 1738)
USAT USIM Application Toolkit
USCH Uplink Shared Channel (UMTS Transport Channel  TDD only
13-82 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
Useful part of burst That part of the burst used by the demodulator; differs from
the full burst because of the bit shift of the I and Q parts of the
GMSK signal.
USF Uplink State Flag.
USIM Universal Subscriber Identity Module [3GTS 31.102]
USSD Unstructured Supplementary Service Data. The USSD
mechanism allows the MS user and a PLMN operator defined
application to communicate in a way which is transparent to
the MS and to intermediate network entities. The mechanism
allows development of PLMN specific supplementary services.
UTRAN UMTS Radio Access Network
UUS User-to-User Signalling supplementary service. The UUS
supplementary service allows a mobile subscriber to
send/receive a limited amount of information to/from another
PLMN or ISDN subscriber over the signalling channel in
association with a call to the other subscriber.
UWC Universal Wireless Convergence (Merge IS-136 with GSM)
V - VTX host
V Value only.
VA Viterbi Algorithm (used in channel equalizers). An algorithm to
compute the optimal (most likely) state sequence in a model
given a sequence of observed outputs.
VAD Voice Activity Detection. A process used to identify presence or
absence of speech data bits. VAD is used with DTX.
VAP Videotex Access Point.
VBS Voice Broadcast Service. VBS allows the distribution of speech
(or other signals which can be transmitted via the speech
codec), generated by a service subscriber, into a predefined
geographical area to all or a group of service subscribers
located in this area.
VC See Virtual Circuit.
VCI Virtual Circuit Identifier ( ATM)
VCO Voltage Controlled Oscillator. An oscillator whose clock
frequency is determined by the magnitude of the voltage
presented at its input. The frequency changes when the
voltage changes.
VCXO Voltage Controlled Crystal Oscillator.
VDU Visual Display Unit. A device used for the real-time temporary
display of computer output data. Monitor.
VGCS Voice Group Call Service.
VHE Virtual Home Environment ( 3GTS 22.121, 3GTS 23.127)
© 2005-2006 CP13: Introduction to UMTS USR6 13-83
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
Videotex The Videotex service is an interactive service, that by means of
proper access points and standardized procedures, provides
the access to data base information stored in host computers
external to the PLMN, via public telecommunication networks.
Virtual Circuit A connection between two devices, that functions as though
it is a direct connection, even though it may physically be
circuitous. The term is used most frequently to describe
connections between two hosts in a packet-switching network.
VLR Visitor Location Register. A GSM network element which
provides a temporary register for subscriber information for a
visiting subscriber. Often a part of the MSC.
VLSI Very Large Scale Integration (in ICs). The process of placing
between 100,000 and one million electronic components on
a single chip.
VMSC Visited MSC. (Recommendation not to be used).
vocoder Abbreviation for voice-coder. A device that usually consists of
a speech analyzer, which converts analog speech waveforms
into narrowband digital signals, and a speech synthesizer,
which converts the digital signals into artificial speech sounds.
VOX Voice Operated Transmission. An acoustoelectric transducer
and a keying relay connected so that the keying relay is
actuated when sound, or voice energy above a certain
threshold is sensed by the transducer. A vox is used to
eliminate the need for push-to-talk operation of a transmitter by
using voice energy to turn on the transmitter
VPI Virtual Path Identifier ( ATM)
VPLMN Visited PLMN.
VSC Videotex Service Centre.
V(SD) Send state variable.
VSP Vehicular Speaker Phone.
VSWR Voltage Standing Wave Ratio. In a transmission line, the ratio
of maximum to minimum voltage in a standing wave pattern.
Note: The VSWR is a measure of impedance mismatch
between the transmission line and its load. The higher the
VSWR, the greater the mismatch. The minimum VSWR, i.e.,
that which corresponds to a perfect impedance match, is unity.
VTX host The components dedicated to Videotex service.
W - WWW
WAN Wide Area Network. A physical or logical network that provides
data communications to a larger number of independent users
than are usually served by a LAN and is usually spread over a
larger geographic area than that of a LAN. WANs may include
physical networks, such as ISDN networks, X.25 networks,
and T1 networks.
WAP Wireless Application Protocol
WINS Windows Internet Name Service
13-84 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Glossary of technical terms Version 1 Rev 0
Glossary of technical terms
W-LAN Wireless Local Area Network ( IEEE 802.11)
WPA Wrong Password Attempts (counter). Some supplementary
services have the option of the subscriber using a password.
If a password check is done with an incorrect password, the
WPA is incremented by one. If a password check is passed,
the WPA is set to zero. If the WPA exceeds the value three,
the subscriber will have to register a new password with the
service provider.
WS Work Station. The remote device via which O&M personnel
execute input and output transactions for network management
purposes.
WSF Work Station Function block.
WSN Window Size Number
WWW World Wide Web. An international, virtual-network-based
information service composed of Internet host computers that
provide on-line information in a specific hypertext format. WWW
servers provide hypertext metalanguage (HTML) formatted
documents using the hypertext transfer protocol, HTTP.
Information on the WWW is accessed with a hypertext browser.
X - X Window
X.25 X.25, adopted as a standard by the CCITT, is a commonly used
protocol for public packet-switched networks (PSPDNS). The
X.25 protocol allows computers on different public networks to
communicate through an intermediary computer at the network
layer level. The protocol corresponds closely to the data-link
and physical-layer protocols defined in the OSI communication
model.
X.25 link A communications link which conforms to X.25 specifications
and uses X.25 protocol (NE to OMC links).
XBL Transcoder to BSS Link. The carrier communications link
between the Transcoder (XCDR) and the BSS.
XCB Transceiver Control Board. Part of the Transceiver.
XCDR Full-rate Transcoder. The XCDR is the digital signal processing
equipment required to perform GSM-defined speech encoding
and decoding. In terms of data transmission, the speech
transcoder interfaces the 64 kbit/s PCM in the land network to
the 13 kbit/s vocoder format used on the Air Interface. See
also RXCDR.
XCDR board The circuit board required to perform speech transcoding at
the BSS or (R)XCDR). Also known as the MSI (XCDR) board.
Interchangeable with the GDP board.
© 2005-2006 CP13: Introduction to UMTS USR6 13-85
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
Glossary of technical terms
XFER Transfer.
XID eXchange IDentifier.
xterm X terminal window. A terminal emulator program for the X
Window System. A user can have many different invocations
of xterm running at once on the same display, each of which
provides independent input and output for the process running
in it (normally a shell).
X Window A specification for device-independent windowing operations
on bitmap display devices.
ZC
ZC Zone Code. Part of the RSZI. The ZC identifies a regional
subscription zone as a pattern of allowed and not allowed
location areas uniquely within a PLMN.
13-86 CP13: Introduction to UMTS USR6 © 2005-2006 Motorola, Inc.
FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Version 1 Rev 0 Glossary of technical terms
This page intentionally left blank.
© 2005-2006 CP13: Introduction to UMTS USR6 13-87
Motorola, Inc. FOR TRAINING PURPOSES ONLY - THIS MANUAL WILL NOT BE UPDATED
Pub-Date
Vous aimerez peut-être aussi
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- Hack Wifi Password Using CMD: Wi-Fi Hacking MethodDocument22 pagesHack Wifi Password Using CMD: Wi-Fi Hacking MethodDele AdigunPas encore d'évaluation
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- Document On RBS6000 LTE CommissioningDocument75 pagesDocument On RBS6000 LTE CommissioningRomar Oropeza100% (7)
- VoIP - Telephony 2.0 Course Book (Cisco)Document567 pagesVoIP - Telephony 2.0 Course Book (Cisco)Milli YeshiwasPas encore d'évaluation
- Alcatel Lucent 7670 Routing Switch Platform General Information Release 7.1Document230 pagesAlcatel Lucent 7670 Routing Switch Platform General Information Release 7.1Mojo CratPas encore d'évaluation
- How To Extend LTE Coverage With Limited RRU Capacity-Read OnlyDocument14 pagesHow To Extend LTE Coverage With Limited RRU Capacity-Read OnlyArtty Numatti67% (3)
- GUL StrategyDocument53 pagesGUL Strategykammola201175% (8)
- Node B Traffic FactorsDocument6 pagesNode B Traffic FactorsVikas DwivediPas encore d'évaluation
- 3G Call Establishment and Handover ProceduresDocument16 pages3G Call Establishment and Handover ProceduresSubrata Sen100% (2)
- 3G Call Establishment and Handover ProceduresDocument16 pages3G Call Establishment and Handover ProceduresSubrata Sen100% (2)
- WCDMA RNO RF Optimisation Guidance-20040719-A-1.0 PDFDocument27 pagesWCDMA RNO RF Optimisation Guidance-20040719-A-1.0 PDFTô Tuấn AnhPas encore d'évaluation
- WCDMA RNO Single Site Verification Guidance-20040716-A-1.1Document21 pagesWCDMA RNO Single Site Verification Guidance-20040716-A-1.1Subrata SenPas encore d'évaluation
- 3G MotorollaDocument509 pages3G MotorollaSubrata SenPas encore d'évaluation
- Wcdma AluDocument170 pagesWcdma AluSubrata SenPas encore d'évaluation
- 3G MotorollaDocument509 pages3G MotorollaSubrata SenPas encore d'évaluation
- Informacion 3GDocument26 pagesInformacion 3GStyp Canto Rondón100% (3)
- Multi-Carrier Deployment StrategiesDocument15 pagesMulti-Carrier Deployment StrategiesSubrata SenPas encore d'évaluation
- UMTS OptimizationDocument116 pagesUMTS OptimizationSubrata SenPas encore d'évaluation
- GSM Timer and Flow SequencesDocument26 pagesGSM Timer and Flow SequencesKuu KiiPas encore d'évaluation
- Informacion 3GDocument26 pagesInformacion 3GStyp Canto Rondón100% (3)
- R3 3G2G Parameters Tuning Ed1Document68 pagesR3 3G2G Parameters Tuning Ed1Subrata SenPas encore d'évaluation
- WCDMA RNO RF Optimisation Guidance-20040719-A-1.0 PDFDocument27 pagesWCDMA RNO RF Optimisation Guidance-20040719-A-1.0 PDFTô Tuấn AnhPas encore d'évaluation
- ALCATEL UTRAN ServicesDocument26 pagesALCATEL UTRAN ServicesSubrata SenPas encore d'évaluation
- 3 GDocument51 pages3 GSubrata SenPas encore d'évaluation
- Gprs Measurements Temsproducts 2Document33 pagesGprs Measurements Temsproducts 2Subrata SenPas encore d'évaluation
- WCDMA RNO Single Site Verification Guidance-20040716-A-1.1Document21 pagesWCDMA RNO Single Site Verification Guidance-20040716-A-1.1Subrata SenPas encore d'évaluation
- WCDMA RNP Paging Area Planning GuidanceDocument27 pagesWCDMA RNP Paging Area Planning GuidanceSubrata SenPas encore d'évaluation
- W RNO Single Site Verification GuideDocument30 pagesW RNO Single Site Verification GuideSubrata SenPas encore d'évaluation
- Gprs Measurements Temsproducts 2Document33 pagesGprs Measurements Temsproducts 2Subrata SenPas encore d'évaluation
- IELTS SpeakingDocument15 pagesIELTS SpeakingSubrata SenPas encore d'évaluation
- WCDMA RNP Paging Area Planning GuidanceDocument27 pagesWCDMA RNP Paging Area Planning GuidanceSubrata SenPas encore d'évaluation
- WCDMA RNP Neighboring Cell Planning GuidanceDocument20 pagesWCDMA RNP Neighboring Cell Planning GuidanceSubrata SenPas encore d'évaluation
- WCDMA RNP Cell Primary Scrambling Code Planning GuidanceDocument31 pagesWCDMA RNP Cell Primary Scrambling Code Planning GuidanceSubrata Sen100% (1)
- Fundamentalsofwimax 110419014205 Phpapp01Document103 pagesFundamentalsofwimax 110419014205 Phpapp01Andi Abdul AzisPas encore d'évaluation
- Bluetooth TechnologyDocument13 pagesBluetooth TechnologyParthasarathi AnbalaganPas encore d'évaluation
- Icnd120cg PDFDocument74 pagesIcnd120cg PDFHetfield Martinez BurtonPas encore d'évaluation
- Gujarat Technological University: Prime Institute of Engineering and TechnologyDocument49 pagesGujarat Technological University: Prime Institute of Engineering and Technologymunshi samihaPas encore d'évaluation
- Connect gateway networkDocument3 pagesConnect gateway networkSyafei SyafeiiPas encore d'évaluation
- AACC - UC Knowledge TransferDocument38 pagesAACC - UC Knowledge TransferJin ZoongPas encore d'évaluation
- 01 Msan Ua5000 Description Issue1 0Document37 pages01 Msan Ua5000 Description Issue1 0papadong2000Pas encore d'évaluation
- Allama Iqbal Open University, Islamabad (Department of Computer Science) WarningDocument2 pagesAllama Iqbal Open University, Islamabad (Department of Computer Science) WarningziabuttPas encore d'évaluation
- NSV Series On Vmware Getting Started GuideDocument59 pagesNSV Series On Vmware Getting Started GuideMani MaranPas encore d'évaluation
- 390 1523438714303Document196 pages390 1523438714303Nilupul BasnayakePas encore d'évaluation
- Nokia BSC2i OverviewDocument16 pagesNokia BSC2i OverviewealforaPas encore d'évaluation
- GPON Sevice Board Comparison PDFDocument3 pagesGPON Sevice Board Comparison PDFSebastian MontesPas encore d'évaluation
- FCC Report On Wireless MarketDocument308 pagesFCC Report On Wireless MarketMSH_JD_CPAPas encore d'évaluation
- Networking Basics MCQsDocument9 pagesNetworking Basics MCQsHarinisanthoshPas encore d'évaluation
- 10.2.4.8 Worksheet - Research Firewalls: IT Essentials 5.0Document2 pages10.2.4.8 Worksheet - Research Firewalls: IT Essentials 5.0John Thiery FedericoPas encore d'évaluation
- Mimo Part IIDocument34 pagesMimo Part IIQPas encore d'évaluation
- Trust Models For Efficient Communication in Mobile Cloud ComputingDocument8 pagesTrust Models For Efficient Communication in Mobile Cloud ComputingDragomir DanPas encore d'évaluation
- Call Set-Up in A GSM Network: Msisdn CC + NDC + SNDocument7 pagesCall Set-Up in A GSM Network: Msisdn CC + NDC + SNgoutam4321Pas encore d'évaluation
- Mapping VPN Traffic Onto Lsps Using Route Policies: Test CaseDocument21 pagesMapping VPN Traffic Onto Lsps Using Route Policies: Test CaseghostreamPas encore d'évaluation
- Thompson ST536v6 ManualDocument2 pagesThompson ST536v6 ManualcarnuscaedesPas encore d'évaluation
- ICT Module BTEC National Health & Social Care: Workbook 11Document6 pagesICT Module BTEC National Health & Social Care: Workbook 11desbestPas encore d'évaluation
- Astellia Boosting NGTAFRDocument2 pagesAstellia Boosting NGTAFRPhuong NguyenPas encore d'évaluation
- ISCOM2924GF-4GE - 4C Configuration Guide (A - 01) PDFDocument337 pagesISCOM2924GF-4GE - 4C Configuration Guide (A - 01) PDFGilson NascimentoPas encore d'évaluation
- WiFi Troubleshooting Using Wireshark - Network Computing PDFDocument13 pagesWiFi Troubleshooting Using Wireshark - Network Computing PDFAnonymous JM2vjHPas encore d'évaluation
- HC-05-Bluetooth To Serial Port ModuleDocument6 pagesHC-05-Bluetooth To Serial Port ModuleHhhhPas encore d'évaluation