Académique Documents
Professionnel Documents
Culture Documents
Network Scanning With Vulnerability Assessment and Report Generation
Transféré par
Nikita Yogendrasinh Jhala0 évaluation0% ont trouvé ce document utile (0 vote)
264 vues33 pagesNetwork Scanning with vulnerability assessment and report generation
Titre original
Network Scanning with vulnerability assessment and report generation
Copyright
© © All Rights Reserved
Formats disponibles
PDF, TXT ou lisez en ligne sur Scribd
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentNetwork Scanning with vulnerability assessment and report generation
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme PDF, TXT ou lisez en ligne sur Scribd
0 évaluation0% ont trouvé ce document utile (0 vote)
264 vues33 pagesNetwork Scanning With Vulnerability Assessment and Report Generation
Transféré par
Nikita Yogendrasinh JhalaNetwork Scanning with vulnerability assessment and report generation
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme PDF, TXT ou lisez en ligne sur Scribd
Vous êtes sur la page 1sur 33
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Network Scanning and Vulnerability Assessment
with Report Generation
NIKITA JHALA(12MCE12)
CSE-INS,
IT,Nirma University
May 13, 2014
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Project Prole
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Problem Statement
To scan the network and nd internal as well as external
threats in IPR.
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
1 Topics Covered in previous Reviews
Key points
2 Literature Survey
3 Existing Tools
4 Implementation
Implementation Method
Generic Architecture
Overview of OpenVAS
Overview of NMAP
Tool Developed:Network Scanner
5 Conclusion & Future Work
6 References
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Topics Covered in previous Reviews
1 Topics Covered in Review 1
Project Objectives
Literature Survey
Scope Of Project
Testing Method
Project Plan
2 Topics Covered in Review 2
Working Technology Behind NMAP (Scanning Techniques,
Ping Options, Fingerprinting)
Proposed Architecture for integrated Scanner
Issues in integration
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Key points
Outline
1 Topics Covered in previous Reviews
Key points
2 Literature Survey
3 Existing Tools
4 Implementation
Implementation Method
Generic Architecture
Overview of OpenVAS
Overview of NMAP
Tool Developed:Network Scanner
5 Conclusion & Future Work
6 References
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Key points
Introduction
What is Network Scanner?
What is vulnerability assessment and penetration testing
Why Vulnerability Assessment is needed?
Purpose of Project
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Tools Used
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Conclusion of Literature Survey
Recommended approach to vulnerability scanning is to:
Tune the vulnerability scan proles to suit your requirements
Perform detailed analysis of the results
Run secondary tools (nmap, a secondary vulnerability
scanning solution and / or specialised tools). The use of
multiple tools will provide a greater level of coverage and
assist in conrming discovered vulnerabilities.
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Implementation Method
Outline
1 Topics Covered in previous Reviews
Key points
2 Literature Survey
3 Existing Tools
4 Implementation
Implementation Method
Generic Architecture
Overview of OpenVAS
Overview of NMAP
Tool Developed:Network Scanner
5 Conclusion & Future Work
6 References
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Implementation Method
Implementation Method
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Generic Architecture
Outline
1 Topics Covered in previous Reviews
Key points
2 Literature Survey
3 Existing Tools
4 Implementation
Implementation Method
Generic Architecture
Overview of OpenVAS
Overview of NMAP
Tool Developed:Network Scanner
5 Conclusion & Future Work
6 References
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Generic Architecture
Generic Architecture
Figure : Generic Architecture of Network Scanner
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Overview of OpenVAS
Outline
1 Topics Covered in previous Reviews
Key points
2 Literature Survey
3 Existing Tools
4 Implementation
Implementation Method
Generic Architecture
Overview of OpenVAS
Overview of NMAP
Tool Developed:Network Scanner
5 Conclusion & Future Work
6 References
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Overview of OpenVAS
OpenVAS
The Open Vulnerability Assessment System (OpenVAS) is a framework of
several services and tools.
Services:
1 Core:OpenVAS Scanner executes the actual Network Vulnerability
Tests (NVTs) which are served with daily updates via the OpenVAS
NVT Feed or via a commercial feed service.
2 Central Service:OpenVAS Manager consolidates plain
vulnerability scanning into a full vulnerability management solution.
3 OpenVAS Administrator acts as a command line tool or as a full
service daemon oering the OpenVAS Administration Protocol
(OAP). The most important tasks are the user management.
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Overview of OpenVAS
Architecture Overview: OpenVAS Services
Figure : OpenVAS Architecture
The OpenVAS Scanner oers the communication protocol OTP (OpenVAS
Transfer Protocol) which allows to control the scan execution. Traditionally,
the desktop- and cli-tool OpenVAS Client acts as a direct OTP client.
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Overview of OpenVAS
Architecture Overview: OpenVAS Services
Figure : OpenVAS Architecture
The Manager controls the Scanner via OTP (OpenVAS Transfer Protocol) and
itself oers the XML-based, stateless OpenVAS Management Protocol (OMP).
All intelligence is implemented in the Manager so that it is possible to
implement various lean clients that will behave consistently e.g. with regard to
ltering or sorting scan results.
The Manager also controls a SQL database (sqlite-based) where all
conguration and scan result data is centrally stored.
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Overview of OpenVAS
Architecture Overview: OpenVAS Services
Figure : OpenVAS Architecture
The OpenVAS Administrator oers the OpenVAS Administration Protocol
(OAP) which oers tasks are the user management and feed management.
OpenVAS CLI contains the command line tool omp which allows to create
batch processes to drive OpenVAS Manager.
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Overview of NMAP
Outline
1 Topics Covered in previous Reviews
Key points
2 Literature Survey
3 Existing Tools
4 Implementation
Implementation Method
Generic Architecture
Overview of OpenVAS
Overview of NMAP
Tool Developed:Network Scanner
5 Conclusion & Future Work
6 References
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Overview of NMAP
NMAP
Figure : NMAP Overview
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Overview of NMAP
NMAP Vulnerability assessment
Nmap NSE Vulscan 2.0: script written for nmap that adds vulnerability
scanning.
Working:
1 The nmap option -sV enables version detection per service
which is used to determine potential aws according to the
identied product.
2 The data is looked up in an oine version of dierent
vulnerability databases.
Usage:nmap -sV script =
vulscan www.example.com [script-args vulscandb =
your own database]
Databases used: cve,exploitdb,openvas,ovsdb, scipvuldb, securityfocus,
securitytracker, xforce
Disadvantage: Large no. of false positive
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Tool Developed:Network Scanner
Outline
1 Topics Covered in previous Reviews
Key points
2 Literature Survey
3 Existing Tools
4 Implementation
Implementation Method
Generic Architecture
Overview of OpenVAS
Overview of NMAP
Tool Developed:Network Scanner
5 Conclusion & Future Work
6 References
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Tool Developed:Network Scanner
Network Scanner: Architecture
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Tool Developed:Network Scanner
Network Scanner: Features Overview
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Tool Developed:Network Scanner
Network Scanner: Features Overview
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Tool Developed:Network Scanner
Issues Targeted & Solutions
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Tool Developed:Network Scanner
How Scan duration can be reduced?
Perform Nmap Scan
Upload or Load Nmap output to OpenVAS Module
Create Scan Conguration with this Nmap
Run Task
Results
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Tool Developed:Network Scanner
Network Scanner:Limitations
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Tool Developed:Network Scanner
Network Scanner: Demo Overview
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Conclusion & Future Work
Conclusion: Network Scanner uses best of both tools.Also user do
not require to do any installation or conguration to
use this tool.
Its report generation is much better than both
tools.This report generated are meant for higher
authorities and non-technical people who want to
have knowledge of their organizations network.
Future Work: Phase 4
Figure : Project Plan
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
TIMELINE
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
References
VeriSign White Paper, An Introduction to Network Vulnerability Testing
Gordon Fyodor Lyon, Nmap Network Scanning:Ocial Nmap Project Guide
to Network Discovery and Security Scanning, Insecure Press , ISBN-10:
0979958717
James Messer,Secrets of Network Cartography: A comprehensive guide to
Nmap, A NetworkUptime.com Publication
Feng Cheng, Sebastian Roschke, Christoph Meinel, An Integrated Network
Scanning Tool for Attack Graph Construction,6th International Conference on
Advances in Grid and Pervasive Computing (GPC 2011), Oulu, Finland, May
2011
VrmlMap:3D mapping of computer networks , Available at:
http://www-moncube.cea.fr/doku.php/en:vrml:vrml
Hagen Hopfner,Visualizing your network with RadialNet,Linux Magazine,
September 2008, Issue 94
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Topics Covered in previous Reviews Literature Survey Existing Tools Implementation Conclusion & Future Work References
Thank You
CSE Department CSE-INS,IT,Nirma University
Network Scanning and Vulnerability Assessment with Report Generation
Vous aimerez peut-être aussi
- Effective Pandas. Patterns For Data Manipulation (Treading On Python) - Matt Harrison - Independently Published (2021)Document392 pagesEffective Pandas. Patterns For Data Manipulation (Treading On Python) - Matt Harrison - Independently Published (2021)Anonymous dTrW1iA100% (4)
- SCCM Security ChecklistDocument4 pagesSCCM Security Checklistnia17Pas encore d'évaluation
- Vulnerability Assessment GuideDocument23 pagesVulnerability Assessment Guideengrk04100% (2)
- CND PDFDocument1 pageCND PDFShivPas encore d'évaluation
- Emphasis On Cloud: This Photo CC By-SaDocument33 pagesEmphasis On Cloud: This Photo CC By-SaDavid CowenPas encore d'évaluation
- Vulnerability Management ProcessDocument4 pagesVulnerability Management ProcessHiren Dhaduk0% (1)
- GIAC Certified Intrusion Analyst A Complete Guide - 2021 EditionD'EverandGIAC Certified Intrusion Analyst A Complete Guide - 2021 EditionPas encore d'évaluation
- Malware Report TemplateDocument3 pagesMalware Report TemplateLa Tonya IbekilliNem Williams100% (1)
- Network Performance and Security: Testing and Analyzing Using Open Source and Low-Cost ToolsD'EverandNetwork Performance and Security: Testing and Analyzing Using Open Source and Low-Cost ToolsPas encore d'évaluation
- Addressing SIEMDocument69 pagesAddressing SIEMalexioPas encore d'évaluation
- Azure Commercial - Pen Test Report 2018 PDFDocument78 pagesAzure Commercial - Pen Test Report 2018 PDFjunk emailPas encore d'évaluation
- Intrusion Detection Systems A Complete Guide - 2021 EditionD'EverandIntrusion Detection Systems A Complete Guide - 2021 EditionPas encore d'évaluation
- Windows Forensic Analysis Toolkit: Advanced Analysis Techniques for Windows 8D'EverandWindows Forensic Analysis Toolkit: Advanced Analysis Techniques for Windows 8Évaluation : 3.5 sur 5 étoiles3.5/5 (2)
- Do407 Exam 1 4Document20 pagesDo407 Exam 1 4phyo nyi aungPas encore d'évaluation
- A Multi-Granularity FPGA With Hierarchical Interconnects For Efficient and Flexible Mobile Computing PDFDocument13 pagesA Multi-Granularity FPGA With Hierarchical Interconnects For Efficient and Flexible Mobile Computing PDFBoppidiSrikanthPas encore d'évaluation
- Principles of Secure Network DesignDocument10 pagesPrinciples of Secure Network DesignSalai PengPas encore d'évaluation
- Sample Penetration Testing Report TemplateDocument37 pagesSample Penetration Testing Report TemplateMarcos GomezPas encore d'évaluation
- Security Information and Event ManagementDocument39 pagesSecurity Information and Event ManagementeddiePas encore d'évaluation
- Ransomware Guide From CISA - September 2020Document16 pagesRansomware Guide From CISA - September 2020dracknerPas encore d'évaluation
- Best Practices DecryptionDocument5 pagesBest Practices DecryptionPartha DashPas encore d'évaluation
- Cloud Security Compliance A Complete Guide - 2021 EditionD'EverandCloud Security Compliance A Complete Guide - 2021 EditionPas encore d'évaluation
- Open VasDocument32 pagesOpen VasArpit PatelPas encore d'évaluation
- Network Security MonitoringDocument0 pageNetwork Security MonitoringUmakanth V SherkhanePas encore d'évaluation
- NessusDocument23 pagesNessusShivaprakash TimmapurPas encore d'évaluation
- Vulnerability Scanning With NessusDocument6 pagesVulnerability Scanning With NessusSpyDr ByTePas encore d'évaluation
- Enbedded Devices Security Firmware Reverse EngineeringDocument104 pagesEnbedded Devices Security Firmware Reverse EngineeringMijondanoCarburaPas encore d'évaluation
- 2016 Cybersecurity Playbook PDFDocument26 pages2016 Cybersecurity Playbook PDFfptstopPas encore d'évaluation
- Pentesting ReportDocument3 pagesPentesting ReportLovepreetSidhu100% (1)
- Building Next Gen SOC-20pDocument20 pagesBuilding Next Gen SOC-20psasuke Chibi100% (2)
- Cyber Handbook EnterpriseDocument38 pagesCyber Handbook EnterprisehackerPas encore d'évaluation
- Identifying and Blocking DNS TunnelsDocument10 pagesIdentifying and Blocking DNS TunnelsAbhiPas encore d'évaluation
- Certified Cyber Forensics Professional The Ultimate Step-By-Step GuideD'EverandCertified Cyber Forensics Professional The Ultimate Step-By-Step GuidePas encore d'évaluation
- Nessus Guide TutorialDocument31 pagesNessus Guide TutorialHarini PriyaPas encore d'évaluation
- SIEM Pro ConsDocument58 pagesSIEM Pro Conssagar gautam0% (1)
- Hardening Process ChecklistDocument1 pageHardening Process ChecklistHiren DhadukPas encore d'évaluation
- Guide To Computer and Network Data Analysis Applying Forensic Techniques To Incident ResponseDocument107 pagesGuide To Computer and Network Data Analysis Applying Forensic Techniques To Incident ResponsecatalinolopezPas encore d'évaluation
- Pen Testing SyllabusDocument12 pagesPen Testing SyllabusavinashbaadshahPas encore d'évaluation
- Tutorial 6 Kali Linux SleuthkitDocument8 pagesTutorial 6 Kali Linux Sleuthkithuynhphuc112Pas encore d'évaluation
- Network Security AuditDocument17 pagesNetwork Security AuditHagi Shahid0% (2)
- Computer Hacking Forensic Investigator Chfi v9Document5 pagesComputer Hacking Forensic Investigator Chfi v9harshadspatil0% (2)
- ICSI - CNSS Certified Network Security SpecialistDocument262 pagesICSI - CNSS Certified Network Security Specialistnahid01Pas encore d'évaluation
- EDRM Security Questionnaire 1.1Document39 pagesEDRM Security Questionnaire 1.1olufunso akinsanya100% (1)
- What Is Mitre Att&Ck?: Presented byDocument27 pagesWhat Is Mitre Att&Ck?: Presented byzoumPas encore d'évaluation
- BSI CyberSecurity ReportDocument11 pagesBSI CyberSecurity ReportJeya Shree Arunjunai RajPas encore d'évaluation
- Windows 10 ForensicsDocument24 pagesWindows 10 Forensicsmanticon01100% (1)
- Thor's Microsoft Security Bible: A Collection of Practical Security TechniquesD'EverandThor's Microsoft Security Bible: A Collection of Practical Security TechniquesPas encore d'évaluation
- Philip Sow SplunkDocument29 pagesPhilip Sow SplunkbobwillmorePas encore d'évaluation
- Cyber Risk Management FrameworkDocument9 pagesCyber Risk Management Frameworkleo58800% (1)
- Enterprise IT Security: The Ultimate GuideDocument44 pagesEnterprise IT Security: The Ultimate GuideVlad VikernesPas encore d'évaluation
- Nist SP 1800-2 PDFDocument497 pagesNist SP 1800-2 PDFricardo ruben rochaPas encore d'évaluation
- A GISPP Guide For Information Security Career Path V1.1Document23 pagesA GISPP Guide For Information Security Career Path V1.1Muhammad Nauman Javed AzharPas encore d'évaluation
- © 2018 Caendra, Inc. - Hera For PTP - NessusDocument17 pages© 2018 Caendra, Inc. - Hera For PTP - NessusSaw GyiPas encore d'évaluation
- Information Security Policy TemplatesDocument7 pagesInformation Security Policy Templatescavoi1980Pas encore d'évaluation
- The Definitive Guide To Managed Detection and Response (MDR)Document56 pagesThe Definitive Guide To Managed Detection and Response (MDR)Alfredo Alejandro Márquez100% (1)
- Best Practices For Securing Computer NetworksDocument2 pagesBest Practices For Securing Computer NetworksswvylPas encore d'évaluation
- Checklist Web Application SecurityDocument2 pagesChecklist Web Application SecurityZoltán BalázsPas encore d'évaluation
- Cyber Wardog Lab - Basic Malware Analysis Lab SetupDocument16 pagesCyber Wardog Lab - Basic Malware Analysis Lab SetupPeter Punky100% (2)
- Hunting On The Endpoint PDFDocument30 pagesHunting On The Endpoint PDFMondher SmiiPas encore d'évaluation
- Firewall Policy: Prepared byDocument8 pagesFirewall Policy: Prepared byChristine MbinyaPas encore d'évaluation
- Ddos AttacksDocument29 pagesDdos AttackssportythievePas encore d'évaluation
- TILE-Gx8072 ProcessorDocument2 pagesTILE-Gx8072 Processorraees74Pas encore d'évaluation
- ATT Flexware Devices Virtualized Industry Standard Network Hardware Means Deployment Speed and Flexibility Companion Report 2018 Rev ADocument2 pagesATT Flexware Devices Virtualized Industry Standard Network Hardware Means Deployment Speed and Flexibility Companion Report 2018 Rev ADian Agung NugrohoPas encore d'évaluation
- Mobile Python - Rapid Pro To Typing of Applications On The Mobile PlatformDocument349 pagesMobile Python - Rapid Pro To Typing of Applications On The Mobile PlatformMohit Garg100% (2)
- WAP To Find The Sum of The Series S 1 + (3/2!) + (5/3!) + (7/4!) + ....... To NDocument8 pagesWAP To Find The Sum of The Series S 1 + (3/2!) + (5/3!) + (7/4!) + ....... To NSOUMYA MAHAPATRAPas encore d'évaluation
- A P J Abdul Kalam Technological University 2020Document396 pagesA P J Abdul Kalam Technological University 2020Shashank PriyadarshiPas encore d'évaluation
- Pardot SpecialistDocument7 pagesPardot SpecialistrajPas encore d'évaluation
- Computer Science, 9618 Home Assignment (35 Marks)Document5 pagesComputer Science, 9618 Home Assignment (35 Marks)Saurya PandeyPas encore d'évaluation
- Finding A Suitable Site For A New School Using Model Builder2Document23 pagesFinding A Suitable Site For A New School Using Model Builder2lahiyaPas encore d'évaluation
- Unit 1 Cs 191cse046jDocument21 pagesUnit 1 Cs 191cse046jTRB hubPas encore d'évaluation
- Sequence DetectorDocument25 pagesSequence DetectorYudish Nandraj KistoPas encore d'évaluation
- FANUC Series 30: i/31i/32i-MODEL ADocument11 pagesFANUC Series 30: i/31i/32i-MODEL AŞener GÜNEYLİPas encore d'évaluation
- Security Device Installation PDFDocument6 pagesSecurity Device Installation PDFErwink I MPas encore d'évaluation
- Cloud Security and Its InfrastructureDocument22 pagesCloud Security and Its InfrastructureRahul saini100% (1)
- 2018 Snote 2581369 - Vat Ksa and Uae Imports Process Ksa April 2018Document27 pages2018 Snote 2581369 - Vat Ksa and Uae Imports Process Ksa April 2018prasad kkavPas encore d'évaluation
- SERDIA2010 - How To Install / Uninstall: 1. InstallationDocument12 pagesSERDIA2010 - How To Install / Uninstall: 1. InstallationJorge Luis Condori ZevallosPas encore d'évaluation
- Installation GuideDocument38 pagesInstallation GuideDeepak Poornachandran100% (1)
- Acer Back To School PromoDocument9 pagesAcer Back To School PromoAubrey CaballeroPas encore d'évaluation
- Muhammad Hamza EjazDocument3 pagesMuhammad Hamza EjazMuhammad Hamza EjazPas encore d'évaluation
- Date Field FunctionsDocument21 pagesDate Field FunctionsChavala SatishPas encore d'évaluation
- Harris VDCP SpecificationDocument58 pagesHarris VDCP SpecificationsadfsdfsdafPas encore d'évaluation
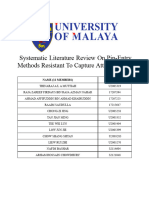
- Systematic Literature Review On PIN-Entry Methods Resistant To Capture AttacksDocument21 pagesSystematic Literature Review On PIN-Entry Methods Resistant To Capture Attacks17207394Pas encore d'évaluation
- Unit 3: Combinational Circuit DesignDocument30 pagesUnit 3: Combinational Circuit DesignKarn AroraPas encore d'évaluation
- WeldQ Test Centre Examiner Manual v1.3Document63 pagesWeldQ Test Centre Examiner Manual v1.3mammad EhsaniPas encore d'évaluation
- 5 Trends in Nursing InformaticsDocument2 pages5 Trends in Nursing Informaticscamile buhanginPas encore d'évaluation
- IAB - Proj Dimas: Integrated Architecture BuilderDocument114 pagesIAB - Proj Dimas: Integrated Architecture BuilderDimas CaceresPas encore d'évaluation
- Health IT Security Risk Assessment ToolDocument57 pagesHealth IT Security Risk Assessment ToolTUP BOXPas encore d'évaluation
- Speed Control of Three Phase Induction Motor Using PLC Under Open and Closed Loop ConditionDocument6 pagesSpeed Control of Three Phase Induction Motor Using PLC Under Open and Closed Loop ConditionTana AzeezPas encore d'évaluation