Académique Documents
Professionnel Documents
Culture Documents
A Survey of Software Vulnerability and Auditing Tools
Transféré par
IJAFRC0 évaluation0% ont trouvé ce document utile (0 vote)
17 vues8 pagesVulnerability has defined as “A flaw or weakness in a system's design, implementation, operation,
or management that could be exploited to violate the system's security policy.” In this paper, we
have discussed different types of software vulnerabilities and software auditing tool model. Also,
a comparative analysis of different auditing tools is provided on the basis of subject of detection,
detection techniques and detection time.
Copyright
© © All Rights Reserved
Formats disponibles
PDF, TXT ou lisez en ligne sur Scribd
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentVulnerability has defined as “A flaw or weakness in a system's design, implementation, operation,
or management that could be exploited to violate the system's security policy.” In this paper, we
have discussed different types of software vulnerabilities and software auditing tool model. Also,
a comparative analysis of different auditing tools is provided on the basis of subject of detection,
detection techniques and detection time.
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme PDF, TXT ou lisez en ligne sur Scribd
0 évaluation0% ont trouvé ce document utile (0 vote)
17 vues8 pagesA Survey of Software Vulnerability and Auditing Tools
Transféré par
IJAFRCVulnerability has defined as “A flaw or weakness in a system's design, implementation, operation,
or management that could be exploited to violate the system's security policy.” In this paper, we
have discussed different types of software vulnerabilities and software auditing tool model. Also,
a comparative analysis of different auditing tools is provided on the basis of subject of detection,
detection techniques and detection time.
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme PDF, TXT ou lisez en ligne sur Scribd
Vous êtes sur la page 1sur 8
International Journal of Advance Foundation and Research in Computer (IJAFRC)
Volume 1, Issue 4, April 214! I""# 2$4% & 4%'$
(% ) * 214, IJAFRC All Ri+hts Reserved ,,,!i-afrc!or+
A "urve. of "oft,are Vulnera/ilit. and Auditin+ 0ools
Rajender Kumar*, Manish Kumar.
NIT Kurukshetra, Haryana
rajenderk18@gmail.com , itsmanishsidhu@gmail.com
A 1 " 0 R A C 0
Vulnera/ilit. has defined as 2A fla, or ,ea3ness in a s.stem4s desi+n, implementation, operation,
or mana+ement that could /e e5ploited to violate the s.stem4s securit. polic.!6 In this paper, ,e
have discussed different t.pes of soft,are vulnera/ilities and soft,are auditin+ tool model! Also,
a comparative anal.sis of different auditin+ tools is provided on the /asis of su/-ect of detection,
detection techni7ues and detection time!
Inde5 0erms8 ".stem "ecurit., Relia/ilit., 9erformance, soft,are auditin+ tools, race condition,
/uffer overflo,, ,indo, of vulnera/ilit., spoofin+, cross&site scriptin+!
I! I#0R:;<C0I:#
In today!s li"e, Internet #ecomes essential $art o" li"e. %e use it "or #anking, message trans"er, sho$$ing,
#usiness etc. %ith the increased use o" internet, danger o" in"ormation the"t and attack are also increased.
Most targeted attacks, &iruses, and 'orms ha&e #een made $ossi#le #y &ulnera#ilities in so"t'are that
read un(trusted data "rom the net'ork. In com$uter security, &ulnera#ility is a 'eakness 'hich allo's an
attacker to reduce a system)s in"ormation assurance. *s sho'n in "ig. 1, +ulnera#ility is the joint or
com#ination o" three di""erent elements, a system 'eakness or "la', attacker access to the 'eakness, and
attacker ca$a#ility to e-$loit the 'eakness. *ttacker uses some so"t'are tools or some $attern analysis
techni.ue to e-$loit &ulnera#ility.
Fi+ure 1! /o"t'are &ulnera#ility
International Journal of Advance Foundation and Research in Computer (IJAFRC)
Volume 1, Issue 4, April 214! I""# 2$4% & 4%'$
(= ) * 214, IJAFRC All Ri+hts Reserved ,,,!i-afrc!or+
* security risk may #e classi"ied as &ulnera#ility. The usage o" &ulnera#ility 'ith the same meaning o"
risk can lead to con"usion. The risk is tied to the $otential o" a signi"icant loss. Then there are
&ulnera#ilities 'ithout risk, "or e-am$le, 'hen the a""ected asset has no &alue. The 'indo' 011 o"
&ulnera#ility is the time "rom 'hen the security hole 'as introduced or mani"ested in de$loyed
so"t'are, to 'hen access 'as remo&ed, a security "i- 'as a&aila#le 2 de$loyed, or the attacker 'as
disa#led. It can #e classi"ied in the "ollo'ing stages,
1irth, The #irth stage denotes the creation o" the &ulnera#ility during the de&elo$ment $rocess.
I" the &ulnera#ility is created intentionally then the #irth stage and the disco&ery stage occur
simultaneously. +ulnera#ilities that are detected and corrected #e"ore de$loyment are not
considered.
;iscover., 3isco&ery stage is that stage o" li"e cycle in 'hich some indi&iduals ha&e kno'ledge
a#out the 'eakness o" the system.
;isclosure, The disclosure stage occurs once the disco&erer re&eals the &ulnera#ility to someone
else. This can #e any disclosure, "ull and $u#lic &ia $osting to 4ugtra. or a secret traded among
#lack hats.
Correction, The correction stage $ersists 'hile the &endor analy5es the &ulnera#ility, de&elo$s a
"i-, and releases it to the $u#lic.
9u/licit., In the $u#licity stage the method o" achie&ing $u#licity is not $aramount #ut
kno'ledge o" &ulnera#ility is s$read to a much larger audience.
"criptin+, 6nce the &ulnera#ility is scri$ted or a tool is created that automates the e-$loitation o"
the &ulnera#ility, the scri$ting stage has #een set in motion.
;eath, %hen the num#er o" systems &ulnera#le to an e-$loit is reduced to an insigni"icant
amount then the death stage has occurred. This can ha$$en #y $atching &ulnera#le systems,
retiring old systems, or a lack o" interest in the e-$loit #y hackers.
Fi+ure 2! %indo' o" &ulnera#ility 011
International Journal of Advance Foundation and Research in Computer (IJAFRC)
Volume 1, Issue 4, April 214! I""# 2$4% & 4%'$
> ) * 214, IJAFRC All Ri+hts Reserved ,,,!i-afrc!or+
II! ":F0?AR@ V<A#@RA1IAI0I@" CA0@B:RI@"
7ollo'ing is a list o" &ulnera#ly categories 081 along 'ith #rie" descri$tions,
1. Calformed data8 This category is .uite #road, encom$assing any instance o" data "lo'ing into a
$rogram that causes it to o$erate outside o" its original s$eci"ication. /ome o" the $ro#lems
o#ser&ed include sending "ragmented net'ork $ackets, sending long streams that the $rogram is
not $re$ared to handle and including s$ecial characters in data 'ithout $ro$erly esca$ing them.
This mal"ormed in$ut can come directly "rom a user 9'ho might #e #reaking the a$$lication
either intentionally or #y mistake:, remote de&ices that share a net'ork 'ith the target com$uter
9com$uters, ;3*s, net'ork e.ui$ment, etc.:, or e&en other $rocesses on the same com$uter.
8. Race Condition8 In a race condition 0<1, t'o or more clients try to access a resource that
su$$orts only serial access. I" the timing is right, the clients may o#tain access simultaneously,
#e"ore the su#system in charge o" seriali5ation can deny access. *lso, since &alidation and
granting access are t'o se$arate ste$s 9non(atomic:, a malicious $rogram can e-ecute #et'een
them and alter the $arameters o" the transaction 9e-., user is &alidated as ha&ing access to a
certain "ile, a $rogram changes the "ile name #e"ore access is $ro&ided= the user might #e gi&en
non(&alidated access to a "ile:.
<. Format "trin+ Vulnera/ilit. D4E8 This &ulnera#ility in&ol&es using "ormatted in$ut2out$ut 9e-.
;rint"9: and scan"9: in >2>??: 'here user(s$eci"ied data is treated as a "ormatting string. This
allo's access to the $rogram stack 'here the arguments o" "ormatting "unction are, 'hich can
lead to stack o&er"lo's and denials o" ser&ice.
@. Cemor. Aea38 Memory leaks occur 'hen the $rogrammer allocates memory dynamically 9e-.
Asing malloc9: in >: and ne&er "rees it. Modern languages like >B and Ca&a $ro&ide gar#age
collection, #ut memory management in >2>?? is di""icult to im$lement. *n attacker can use
mal"ormed data to e-$loit a memory leak and cause a denial o" ser&ice #y using all a&aila#le hea$
s$ace.
D. 1uffer overflo,8 4u""er o&er"lo's 0D1 occur 'hen a $rogrammer allocates a #u""er that is not
large enough to handle an incoming data stream. 3e$ending on the location o" the #u""er 9stack or
hea$:, data 'ill o&er'rite user(allocated &aria#les, "unction arguments or return addresses.
E. Code in-ections D(E8 This attack relies on inserting code in an already running $rogram. 7or
e-am$le, i" a $rogrammer does not $ro$erly esca$e .uotes in ;FRG, a user might #e a#le to
a$$end custom /HG code to .ueries generated #y the ;FRG scri$t. >ode can also #e injected using
a stack o&er"lo' 'ith a string that contains the e-ecuta#le code.
I. Inte+er errors8 Integer o&er"lo' and under"lo' occur 'hen a &alue assigned to a &aria#le goes
#eyond the #ounds "or the integer ty$e 9e-. a E@#it integer is assigned to a <8#it &aria#le, or a
loo$ e-ecutes more than <8IEI times using an Junsigned short intK &aria#le:.
8. ! (;ot dot) attac38 %ith this attack, a user can access locations outside o" their restricted s$ace
#y sending mal"ormed data 9in&ol&ing su#strings like J..2K: to a $rogram 'ith the desired
$ri&ilege 9e-. 7T; ser&er:. This is $ossi#le i" the a$$lication does not &alidate user(s$eci"ied
"ilenames.
L. Cross&site scriptin+8 *$$lications that are &ulnera#le to a M//8 attack allo' a malicious user to
insert a link to their code in the original a$$lication 9e-. instant messaging 'indo's, 'e# $ages,
etc.:. I" a regular user "ollo's that link 9#y accident or #y #eing tricked to click on it:, the
International Journal of Advance Foundation and Research in Computer (IJAFRC)
Volume 1, Issue 4, April 214! I""# 2$4% & 4%'$
>1 ) * 214, IJAFRC All Ri+hts Reserved ,,,!i-afrc!or+
a$$lication 'ill e-ecute code "rom the e-ternal source. In com#ination 'ith 6/ &ulnera#ilities,
this may lead to the installation o" malicious $rograms 9e-. 4ackdoors, s$y('are, etc.:.
1N. "poofin+8 /$oo"ing 0I1 is the $rocess o" arti"icially changing the source o" data. 3i""erent "la&ors
include ARG s$oo"ing 9changing the $ercei&ed ARG o" a ser&er to gain a user!s con"idence:, I;
s$oo"ing 9changing the I; sender address in net'ork $ackets:. I" an a$$lication grants access to
remote machines #ased on I; only, an attacker can s$oo" the identity o" an authori5ed machine
and gain access. /$oo"ing is also a social engineering issue 9tricking users to o#tain their trust:
'ith some so"t'are #eing more &ulnera#le than others 9e-. 'e# #ro'sers and ARG s$oo"ing:.
11. ?ea3 @ncr.ption8 In some cases, sensiti&e data are transmitted 'ith a $oorly designed
encry$tion or no encry$tion at all. This category in&ol&es issues 'ith storing
unencry$ted2sensiti&e data in user(accessi#le locations 9log "iles, registry, etc.:, transmitting data
o&er a net'ork and user authentication.
18. "tora+e 9rotection8 This category com#ines issues 'ith data storage such as creating "iles 'ith
'rong $ermissions or in a shared location. Many attacks ha&e #een $ossi#le #ecause o" $oorly
$rotected tem$orary "iles, 'hich may contain sensiti&e and2or unencry$ted in"ormation.
1<. 0rustin+ the @nvironment8 This &ulnera#ility mainly in&ol&es using en&ironment &aria#les
'ithout &alidation, such as $ath strings or storing data in en&ironment &aria#les.
1@. ".mlin3 attac38 /ymlink attacks in&ol&e gi&ing a $rogram a $ointer to a "ile instead o" the "ile
itsel". *n attacker can redirect the in$ut or out$ut o" a $rogram #y creating a symlink 'ith the
same name as that o" a "ile the $rogram uses.
1D. ;efaultFIncorrect confi+urations8 This category co&ers &ulnera#ilities that arise "rom im$ro$er
con"iguration or installation o" so"t'are. Most issues in&ol&e installation o" a ser&er a$$lication
'ith a de"ault username and2or $ass'ord that can allo' unauthori5ed users to gain access to the
system.
III! ":F0?AR@ A<;I0I#B 0::A"
The Oi&en auditing tool 081 detects malicious codes 9+irus, Trojan: in source code and so"t'are
&ulnera#ilities 9#u""er o&er"lo', "ormat string #ug, race condition:./ome o" the main auditing tools can #e
gi&en as,
1. RA0"8 R*T/ stands "or Rough *uditing Tool "or /ecurity. /ecure so"t'are security engineers
de&elo$ R*T/ "or scanning ;ython, ;erl, >, >?? and ;H; code. It scans the source code "iles "or
security(related issues. Major $ro#lem detected #y R*T/ are #u""er o&er"lo's and race conditions
9Time 6" >heck, Time 6" Ase:, dangerous "unction calls. R*T/ $er"orm only rough analysis o"
source code and it is not a#le to "ind e&ery #ugs and errors in the code. Manual checking is
necessary a"ter R*T/!s scan.
8. Fla,Finder8 7la'7inder is a static source(code security scanner "or > and >?? $rograms that
looks "or commonly misused "unctions, ranks their risk, and re$orts a list o" $otential
&ulnera#ilities ranked #y risk le&el. It analy5es the $rogram source code and detects all $ossi#le
security "la's and $roduces them according to their risk le&el. It is &ery use"ul tool to remo&e
some "la' "rom the $rogram #e"ore release them to $u#lic.
<. 9"CA#8 ;/>*N detects the $ro#lematic use o" "unctions like $rint"9: and scan"9: in the source
code o" > $rogram. It also "inds the mishandling o" "unctions used to dis$lay 'arning and error
message. It is not a#le to identi"y #u""er o&er"lo's in the source code.
International Journal of Advance Foundation and Research in Computer (IJAFRC)
Volume 1, Issue 4, April 214! I""# 2$4% & 4%'$
>2 ) * 214, IJAFRC All Ri+hts Reserved ,,,!i-afrc!or+
@. I0"48 >igital de&elo$s the IT/@ in 1LLL. It is de&elo$ed to automatically $er"orm source code
re&ie' "or security. It statically scans > and >?? source code "or detecting &ulnera#ility and
security "la's. It scans all the source code o" a > language $rogram to determine dangerous
"unction calls. *"ter detecting &ulnera#ilities, it determines the risk le&el and $roduces a $ro#lem
re$ort 'hich includes the descri$tion o" $ro#lem and suggestion ho' to "i- the code.
D. 1::#8 466N is a tool that automates the $rocess o" scanning "or #u""er o&errun &ulnera#ilities in
> source code using dee$ semantic analysis. It detects $ossi#le #u""er o&er"lo' &ulnera#ilities #y
in"erring &alues to #e $art o" an im$licit ty$e 'ith a $articular #u""er si5e. 466N is #ased on the
conce$t that #u""er o&er"lo' detection is an integer range analysis $ro#lem. The algorithm #uilds
a &alue $air #y taking the allocated si5e and the actual length o" each character string. This
a$$roach is also taken 'ith the $arameters o" the standard > li#rary "unctions that handle
character strings.
E. 1AA"08 4last stands "or 4erkeley Ga5y *#straction /o"t'are +eri"ication Tool. It is so"t'are tool
'hich act as a &eri"ication system or checker "or > $rograms. 4last checks the #eha&ioral
$ro$erty o" inter"ace and sa"ety $ro$erty o" $rogram in a so"t'are system. It checks reach( a#ility
o" a s$eci"ied la#el in the $rogram. I" there is no $ath to the s$eci"ied error la#el, 4last re$orts
that the system is in sa"e condition. 6ther'ise, it checks i" the $ath is "easi#le using sym#olic
e-ecution o" the $rogram. I" the $ath is "easi#le, 4last out$uts the $ath as an error trace.
I. "tac3Buard8 /tackOuard 0L1 is a com$iler techni.ue "or $ro&iding code $ointer integrity
checking to the return address in "unction acti&ation records. It is im$lemented as a small $atch
to gcc that enhances the code generator "or emitting code to set u$ and tear do'n "unctions 0L1.
The enhanced setu$ code $laces a JcanaryK 'ord ne-t to the return address on the stack. The
enhanced "unction tear do'n code "irst checks to see that the canary 'ord is intact #e"ore
jum$ing to the address $ointed to #y the return address 'ord. >ritical to the /tackOuard JcanaryK
a$$roach is that the attacker is $re&ented "rom "orging a canary #y em#edding the canary 'ord
in the o&er"lo' string 01N1.
8. 9ointBuard8 It generali5es the /tackOuard de"ense to $lace JcanariesK ne-t to all code $ointers
9"unction $ointers and longjm$ #u""ers: and to check "or the &alidity o" these canaries 'hene&er a
code $ointer is dere"erenced. I" the canary has #een tram$led, then the code $ointer is corru$t
and the $rogram should issue an intrusion alert and e-it, as it does under /tackOuard $rotection.
L. RaceBuard8 RaceOuard 01N1 detects attem$ts to e-$loit race condition &ulnera#ilities at run time
#y detecting a change in the en&ironment #et'een the times the $rogram $ro#es "or the
e-istence o" a "ile, and the time it tries to create it. RaceOuard achie&es this #y caching the "ile
names that are $ro#ed, and 'hen creation attem$ts occur that hit e-isting "iles= the names are
com$ared to the cache. It seeks to detect $ertinent changes in the "ile system #et'een the time an
a$$lication $ro#es "or a nominated tem$orary "ile name, and the time the "ile is actually created
01N1.
IV! "@C<RI0G A<;I0I#B 0::A C:;@A
Malicious #eha&ior can #e caused "rom de"ect o" $rogram or e-ecution o" code that is inserted in the
$rogram "or malicious $ur$ose. I" malicious $rogram 'ill #e e-ecuted, the com$uter is occurred any
damage. Hence, 'e need a measure to $re&ent the damage. The method o" auditing tool 081 com$iles
source code and analy5es e-ecution "lo' o" $rogram 'ith the result and com$ares 'ith e-ecution "lo' o"
e-isting malicious code. 4ecause the method com$ares 'ith in"ormation a#out e-ecution "lo' o"
International Journal of Advance Foundation and Research in Computer (IJAFRC)
Volume 1, Issue 4, April 214! I""# 2$4% & 4%'$
>$ ) * 214, IJAFRC All Ri+hts Reserved ,,,!i-afrc!or+
malicious code, analysis o" malicious code should #e achie&ed in the ad&ance. *nd it re.uires a techni.ue
that analy5es the e-ecution "lo' in com$iled source code.
Fi+ure $! Architecture of securit. auditin+ tool D%E
To detect malicious code and so"t'are &ulnera#ility, analysis in"ormation and automata theory o"
malicious code are used. *lso, there are methods that can e-amine &ulnera#ility o" $rogram &ia e-ecution
"lo' o" $rogram. In so"t'are auditing tool consists o" analysis module, rule $rocess, detection module,
and re$orter. *nalysis module analy5es target code. Rule $rocess analy5es malicious code and so"t'are
&ulnera#ilities and creates rule. *lso, detection module e-amines using analy5ed intermediate codes and
rule. 3etection module consists o" malicious code detector and &ulnera#ility detector. It se$arates and
e-amines malicious codes and so"t'are &ulnera#ilities that are included on source code inside. It
e&aluates security o" so"t'are through t'o e-aminations. Re$orter dis$lays results that detection
module e-amined. *rchitecture o" so"t'are auditing tool descri#es in "igure <.
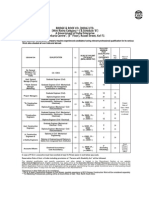
V! C:C9ARA0IV@ A#AAG"I"
Oi&en security, auditing tool can &eri"y security o" so"t'are that use in u#i.uitous com$uting
en&ironment com#ining e-istent &ulnera#ility audit tool and malicious code detection tool. IT/@, M6;/,
and 4G*/T are a tool that is used in s$eci"ication area. Ho'e&er, gi&en security auditing tool can &eri"y
security o" so"t'are e""ecti&ely than other tool. ;ro$osed tool can e&aluate e-actly so"t'are security,
#ecause it can detect #oth malicious codes and so"t'are &ulnera#ilities simultaneously. Moreo&er, it
di""ers "rom sim$ly $attern matching tool in many res$ects, and detection o" ne' malicious codes is easy
#ecause it is #ased on rule. Ta#le 1 is results that com$are 081 e-istent detection tools 'ith $ro$osed
security auditing tool.
International Journal of Advance Foundation and Research in Computer (IJAFRC)
Volume 1, Issue 4, April 214! I""# 2$4% & 4%'$
>4 ) * 214, IJAFRC All Ri+hts Reserved ,,,!i-afrc!or+
0a/le 1! Compare proposed securit. auditin+ tool ,ith e5istent auditin+ tool D%E
VI! C:#CA<"I:#
The Internet 'ill continue to gro' and change the role that so"t'are $lays in our li&es. *s our li&es
de$end more and more on the Internet and so"t'are, security #ecomes essential. %hen so"t'are
&ulnera#ilities are disco&ered, it is in the $u#lic interest that e-isting systems 'ith &ulnera#ilities are
#eing "i-ed in a timely "ashion. The .uestion is that 'hen &ulnera#ilities are disco&ered, ho' disco&erers
should disclose them. 3i""erent ty$e o" &ulnera#ility ha&e di""erent e""ect on so"t'are or 'e# a$$lication.
3i""erent tools and techni.ues are used according to the demand o" en&ironment. %e ha&e discussed
se&eral ty$es o" &ulnera#ilities and their detection and $re&ention measures. 4ut continuous e&olution o"
&ulnera#ilities $arallel to e&olution o" so"t'are is a challenge that needs to #e addressed #y making ne'
techni.ues to enconunter the &ulnera#ilities. %e ha&e discussed a security auditing tool to detect
so"t'are &ulnera#ilities and malicious code $atterns. +ulnera#ility $re&ention is easier than curing it, so
the so"t'ares should #e so designed that they address e-isting &ulnera#ilities.
VII! R@F@R@#C@"
011 %. *. *r#augh , %. G. 7ithen , C. McHugh , J%indo's o" &ulnera#ility, * case study analysisK, in
journal o" com$uter, *>M, &ol. <<, issue 18, $$. D8(DL, 8NNN.
081 K. ;etko&, J6&ercoming $rogramming "la's, inde-ing o" common so"t'are &ulnera#ilities,K In
$roceedings o" the 8nd annual con"erence on in"ormation security curriculum de&elo$ment, $$.
18I(1<D, 8NND.
0<1 C. Phang, /. /u, 7. Qang,R3etecting race conditions in 'e# ser&ices,R In International con"erence on
internet and 'e# a$$lications and ser&ices, $$. 18@, 7e# 8NNE.
International Journal of Advance Foundation and Research in Computer (IJAFRC)
Volume 1, Issue 4, April 214! I""# 2$4% & 4%'$
>' ) * 214, IJAFRC All Ri+hts Reserved ,,,!i-afrc!or+
0@1 %. Han, M. Ren, /. Tian, G. 3ing, Q. He, R/tatic *nalysis o" 7ormat /tring +ulnera#ilities,R In 7irst
*>I/ International /ym$osium on /o"t'are and Net'ork Fngineering 9//NF:, $$. 188(18I, 3ec.
8N11.
0D1 3. 7u , 7. /hi ,K4u""er o&er"lo' e-$loit and de"ensi&e techni.uesK, in 7ourth IFFF International
>on"erence on Multimedia In"ormation Net'orking and /ecurity , $$. 88(LN, 8N18.
0E1 ;. Kumar , R.K. ;ateriya ,K* /ur&ey on /HG Injection *ttacks, 3etection and ;re&ention
Techni.uesK, in Third IFFF International >on"erence on >om$uting >ommunication S
Net'orking Technologies 9I>>>NT:,$$. 1(D, 8N18.
0I1 H. Peng, RResearch on 3e&elo$ing a Ga# Fn&ironment "or >ookie /$oo"ing *ttack and 3e"ense
Fducation,R In 7i"th International >on"erence on >om$utational and In"ormation /ciences
9I>>I/:,$$. 1LIL(1L88, 8N1<.
081 M. Gee, /. >ho, >. Cang, H. ;ark, F. >hoi, J* Rule(#ased /ecurity *uditing Tool "or /o"t'are
+ulnera#ility 3etection,K in International >on"erence on Hy#rid In"ormation Technology, IFFF ,
$$. @ID(@8<, 8NNE.
0L1 >. >o'an, ;. %agle, >. ;u, R4u""er 6&er"lo's, *ttacks and 3e"enses "or the +ulnera#ility o" the
3ecade,R In ;roceedings 3*R;* In"ormation /ur&i&a#ility >on"erence and F-$osition, &ol. 8, $$.
11L(18L, 8NNN.
01N1 >. >o'an, /. 4eattie, >. %right and O. K. Hartman, RRaceOuard, Kernel ;rotection 7rom
Tem$orary 7ile Race +ulnera#ilities,R In ;roceedings o" the 1Nth A/FNIM /ecurity /ym$osium,
*ug. 8NN1.
Vous aimerez peut-être aussi
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- Daily Accomplishment Report - JANRICKDocument3 pagesDaily Accomplishment Report - JANRICKJudy Anne BautistaPas encore d'évaluation
- Effects of Social Media On The Psychology of PeopleDocument6 pagesEffects of Social Media On The Psychology of PeopleIJAFRCPas encore d'évaluation
- NCP MCI 6.5 - DumpsbaseDocument61 pagesNCP MCI 6.5 - Dumpsbasemahmoudkerdieh1100% (1)
- Tiktok Clone ScriptDocument10 pagesTiktok Clone ScriptWebsenor infotechPas encore d'évaluation
- Data Security and Anonymization For Collaborative Data PublishingDocument7 pagesData Security and Anonymization For Collaborative Data PublishingIJAFRCPas encore d'évaluation
- Performance Analysis and Lifetime Maximization of Wireless Sensor Network Using Efficient Clustering AlgorithmDocument5 pagesPerformance Analysis and Lifetime Maximization of Wireless Sensor Network Using Efficient Clustering AlgorithmIJAFRCPas encore d'évaluation
- CFS Based Feature Subset Selection For Software Maintainance PredictionDocument11 pagesCFS Based Feature Subset Selection For Software Maintainance PredictionIJAFRCPas encore d'évaluation
- Detecting User Relevant ApplicationsDocument7 pagesDetecting User Relevant ApplicationsIJAFRCPas encore d'évaluation
- Efficient Algorithm Comparison To Solve Sudoku PuzzleDocument5 pagesEfficient Algorithm Comparison To Solve Sudoku PuzzleIJAFRCPas encore d'évaluation
- Monitoring Applications in Wireless Sensor NetworksDocument4 pagesMonitoring Applications in Wireless Sensor NetworksIJAFRCPas encore d'évaluation
- Face Granulation Using Difference of Gaussian (DOG) Method For Face RecognitionDocument7 pagesFace Granulation Using Difference of Gaussian (DOG) Method For Face RecognitionIJAFRCPas encore d'évaluation
- Detection and Defense of DDoS AttacksDocument11 pagesDetection and Defense of DDoS AttacksIJAFRCPas encore d'évaluation
- To Design and Algorithm Using Zero Watermarking With Stegnography For Text DocumentDocument10 pagesTo Design and Algorithm Using Zero Watermarking With Stegnography For Text DocumentIJAFRCPas encore d'évaluation
- A Review of BFOA Application To WSNDocument7 pagesA Review of BFOA Application To WSNIJAFRCPas encore d'évaluation
- DDos System: A Disparagement System With Cache Based and Question Generation in Client-Server ApplicationDocument13 pagesDDos System: A Disparagement System With Cache Based and Question Generation in Client-Server ApplicationIJAFRCPas encore d'évaluation
- Pocket Barcode Application-Data Transmission Between PDA & PC Using Wireless NetworkDocument5 pagesPocket Barcode Application-Data Transmission Between PDA & PC Using Wireless NetworkIJAFRCPas encore d'évaluation
- A Survey On Designing of Turbo Encoder & Turbo DecoderDocument8 pagesA Survey On Designing of Turbo Encoder & Turbo DecoderIJAFRCPas encore d'évaluation
- Perceptions On Data Aggregation in Wireless Sensor NetworkDocument5 pagesPerceptions On Data Aggregation in Wireless Sensor NetworkIJAFRCPas encore d'évaluation
- The Various Ways of Programming and Embedding Firmware Into An ARM Cortex-M3 Microcontroller Based HardwareDocument6 pagesThe Various Ways of Programming and Embedding Firmware Into An ARM Cortex-M3 Microcontroller Based HardwareIJAFRCPas encore d'évaluation
- A Short Study On Effective Predictors of Academic Performance Based On Course EvaluationDocument6 pagesA Short Study On Effective Predictors of Academic Performance Based On Course EvaluationIJAFRCPas encore d'évaluation
- A Review of Compact Asymmetric Coplanar Strip Fed Monopole Antenna For Multiband ApplicationsDocument5 pagesA Review of Compact Asymmetric Coplanar Strip Fed Monopole Antenna For Multiband ApplicationsIJAFRCPas encore d'évaluation
- Automated Leukemia Detection by Using Contour Signature MethodDocument8 pagesAutomated Leukemia Detection by Using Contour Signature MethodIJAFRCPas encore d'évaluation
- Analytical Evolution of WIMAX Coded OFDM in Various Fading EnvironmentDocument8 pagesAnalytical Evolution of WIMAX Coded OFDM in Various Fading EnvironmentIJAFRCPas encore d'évaluation
- Face Verification With Age Progression Using Discriminative Method and Gradient Orientation PyramidDocument10 pagesFace Verification With Age Progression Using Discriminative Method and Gradient Orientation PyramidIJAFRCPas encore d'évaluation
- Application of Malicious URL Detection in Data MiningDocument6 pagesApplication of Malicious URL Detection in Data MiningIJAFRCPas encore d'évaluation
- Metamaterial Based Fractal Body Worn Antenna - A ReviewDocument6 pagesMetamaterial Based Fractal Body Worn Antenna - A ReviewIJAFRCPas encore d'évaluation
- Energy Efficient Reconfigurable Fixed Width Baugh-Wooley MultiplierDocument9 pagesEnergy Efficient Reconfigurable Fixed Width Baugh-Wooley MultiplierIJAFRCPas encore d'évaluation
- A Comparative Study On Classification and Clustering Techniques Using Assorted Data Mining ToolsDocument8 pagesA Comparative Study On Classification and Clustering Techniques Using Assorted Data Mining ToolsIJAFRCPas encore d'évaluation
- Designing of Efficient FPGA Based Random Number Generators Using VHDL.Document8 pagesDesigning of Efficient FPGA Based Random Number Generators Using VHDL.IJAFRCPas encore d'évaluation
- A Study On Denial-Of-Service Attacks and Their Countermeasure ApproachesDocument11 pagesA Study On Denial-Of-Service Attacks and Their Countermeasure ApproachesIJAFRCPas encore d'évaluation
- A Comparative Study of K-Means, K-Medoid and Enhanced K-Medoid AlgorithmsDocument4 pagesA Comparative Study of K-Means, K-Medoid and Enhanced K-Medoid AlgorithmsIJAFRCPas encore d'évaluation
- Predictive Model For Blood-Brain BarrierDocument12 pagesPredictive Model For Blood-Brain BarrierIJAFRCPas encore d'évaluation
- SEVO Systems Pocket BrochureDocument8 pagesSEVO Systems Pocket BrochureNikhil RajanPas encore d'évaluation
- CCMTA Canadá PDFDocument18 pagesCCMTA Canadá PDFANPACTPas encore d'évaluation
- Test ScriptDocument2 pagesTest Scriptkunalkm59Pas encore d'évaluation
- EBM D400R4 Catalog SheetDocument2 pagesEBM D400R4 Catalog SheetRenan Verolli Dal'AvaPas encore d'évaluation
- SUP-01-Document ControlDocument2 pagesSUP-01-Document ControlSALAH HELLARAPas encore d'évaluation
- Designing For Payload Modularity: Richard Drake Mr. Jeff OwenDocument7 pagesDesigning For Payload Modularity: Richard Drake Mr. Jeff Owensalman GtrPas encore d'évaluation
- B&R Construction Company Job OpeningsDocument9 pagesB&R Construction Company Job OpeningsroopavijaykumarPas encore d'évaluation
- Chenchu Ramaiah Neti: Phone: +91-8970888117Document3 pagesChenchu Ramaiah Neti: Phone: +91-8970888117chaitumdsPas encore d'évaluation
- Securing SC Series Storage Best Practices Dell 2016 (BP1082)Document17 pagesSecuring SC Series Storage Best Practices Dell 2016 (BP1082)Le Ngoc ThanhPas encore d'évaluation
- FMEA - Review - List - 916 PBDocument5 pagesFMEA - Review - List - 916 PBajeyan879Pas encore d'évaluation
- CSE 460/598 Software Analysis and Design Class ScheduleDocument4 pagesCSE 460/598 Software Analysis and Design Class SchedulevenkatPas encore d'évaluation
- B15-Content - Analysis - in - Social - Media (1) - BbhavaniDocument59 pagesB15-Content - Analysis - in - Social - Media (1) - Bbhavanigandhambhavani2003Pas encore d'évaluation
- Seismic ApplicationsDocument12 pagesSeismic ApplicationsAnonim AnonimPas encore d'évaluation
- Sick EncoderDocument6 pagesSick EncoderUsman KhanPas encore d'évaluation
- Noise Figure and Modulation Techniques AnalysisDocument16 pagesNoise Figure and Modulation Techniques Analysisgdd ddPas encore d'évaluation
- Adverbs of Frequency in Computing SupportDocument2 pagesAdverbs of Frequency in Computing SupportAntonio Ticona GómezPas encore d'évaluation
- JWT Service ImplDocument2 pagesJWT Service ImplscribdPas encore d'évaluation
- OpticalDocument3 pagesOpticalAshok Pradhan100% (1)
- What Are The Classes of Amplifiers? Basic Concepts On Class A, B & C AmplifiersDocument4 pagesWhat Are The Classes of Amplifiers? Basic Concepts On Class A, B & C AmplifiersLello FloPas encore d'évaluation
- A Miniaturized Dielectric-Resonator - Ieee - ConfDocument4 pagesA Miniaturized Dielectric-Resonator - Ieee - ConfSaikat Ch BakshiPas encore d'évaluation
- Tricks With Forward Proxy, HAProxy, Squid and A Bit More. - by Alexey Nizhegolenko - FAUN - DevelopeDocument1 pageTricks With Forward Proxy, HAProxy, Squid and A Bit More. - by Alexey Nizhegolenko - FAUN - DevelopeNha DoPas encore d'évaluation
- Project Management With Pert & CPMDocument26 pagesProject Management With Pert & CPML'HOMME Business PlanPas encore d'évaluation
- FM Global Property Loss Prevention Data Sheets: List of FiguresDocument25 pagesFM Global Property Loss Prevention Data Sheets: List of Figureskw teoPas encore d'évaluation
- Manually Configure Devices by Using Device Manager: Windows XPDocument4 pagesManually Configure Devices by Using Device Manager: Windows XPlucky_4u15Pas encore d'évaluation
- SA02-16 - General Requirement RTUDocument60 pagesSA02-16 - General Requirement RTUhiryanizamPas encore d'évaluation
- Barbees Dett620 A4scriptDocument2 pagesBarbees Dett620 A4scriptapi-238146938Pas encore d'évaluation
- Microsoft GP 10 (VSTDGPProgrammersGuide)Document120 pagesMicrosoft GP 10 (VSTDGPProgrammersGuide)Atif RehmanPas encore d'évaluation