Académique Documents
Professionnel Documents
Culture Documents
Security Protection Mechanism For Social Networking Websites Based On Real-Time Proxy
Transféré par
seventhsensegroup0 évaluation0% ont trouvé ce document utile (0 vote)
11 vues5 pagesDuring the last two decades Information
technology has grown tremendously and became the
main source of knowledge. In past few years the
world getting closer and closer this is only because of
Social networking websites such as Facebook,
Twitter etc. Yet with usefulness and the popularity,
the misuse and cybercrime are more evident. So
prevention and detection of these threats is become a
major challenge
To minimize this risk of accessing
social networking applications we proposed
anapplication. The idea is to integrate many
commercial software and online security services into
a security module, simultaneously execute webpage
security threat scan, then scanthe information sent by
the web server with security module before sending
to the client. If security threats were found in the web
page, the system will add this web page to the
blacklist and issue a warning to the client side to
prevent attack. Later on, as long as the client is to
receive the webpage in the blacklist, a warning will
be issued to the client side. Through this mechanism,
we can lower the security risk of the clients using
social networking websites.
Titre original
Security Protection Mechanism for Social Networking Websites
Based on Real-Time Proxy
Copyright
© © All Rights Reserved
Formats disponibles
PDF, TXT ou lisez en ligne sur Scribd
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDuring the last two decades Information
technology has grown tremendously and became the
main source of knowledge. In past few years the
world getting closer and closer this is only because of
Social networking websites such as Facebook,
Twitter etc. Yet with usefulness and the popularity,
the misuse and cybercrime are more evident. So
prevention and detection of these threats is become a
major challenge
To minimize this risk of accessing
social networking applications we proposed
anapplication. The idea is to integrate many
commercial software and online security services into
a security module, simultaneously execute webpage
security threat scan, then scanthe information sent by
the web server with security module before sending
to the client. If security threats were found in the web
page, the system will add this web page to the
blacklist and issue a warning to the client side to
prevent attack. Later on, as long as the client is to
receive the webpage in the blacklist, a warning will
be issued to the client side. Through this mechanism,
we can lower the security risk of the clients using
social networking websites.
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme PDF, TXT ou lisez en ligne sur Scribd
0 évaluation0% ont trouvé ce document utile (0 vote)
11 vues5 pagesSecurity Protection Mechanism For Social Networking Websites Based On Real-Time Proxy
Transféré par
seventhsensegroupDuring the last two decades Information
technology has grown tremendously and became the
main source of knowledge. In past few years the
world getting closer and closer this is only because of
Social networking websites such as Facebook,
Twitter etc. Yet with usefulness and the popularity,
the misuse and cybercrime are more evident. So
prevention and detection of these threats is become a
major challenge
To minimize this risk of accessing
social networking applications we proposed
anapplication. The idea is to integrate many
commercial software and online security services into
a security module, simultaneously execute webpage
security threat scan, then scanthe information sent by
the web server with security module before sending
to the client. If security threats were found in the web
page, the system will add this web page to the
blacklist and issue a warning to the client side to
prevent attack. Later on, as long as the client is to
receive the webpage in the blacklist, a warning will
be issued to the client side. Through this mechanism,
we can lower the security risk of the clients using
social networking websites.
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme PDF, TXT ou lisez en ligne sur Scribd
Vous êtes sur la page 1sur 5
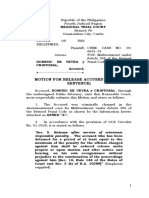
International Journal of Computer Trends and Technology (IJCTT) volume 10 number 3 Apr 2014
ISSN: 2231-2803 http://www.ijcttjournal.org Page148
Security Protection Mechanism for Social Networking Websites
Based on Real-Time Proxy
Komal Navale
1
, Rajendra Pisal
2
, Vishal Suravase
3
, Santosh Reddy
4
1
(CSE, JCEM/ Shivaji University, India)
2
(CSE, JCEM/ Shivaji University, India)
3
(CSE, JCEM/ Shivaji University, India)
4
(CSE, JCEM/ Shivaji University, India)
ABSTRACT
During the last two decades Information
technology has grown tremendously and became the
main source of knowledge. In past few years the
world getting closer and closer this is only because of
Social networking websites such as Facebook,
Twitter etc. Yet with usefulness and the popularity,
the misuse and cybercrime are more evident. So
prevention and detection of these threats is become a
major challenge
To minimize this risk of accessing
social networking applications we proposed
anapplication. The idea is to integrate many
commercial software and online security services into
a security module, simultaneously execute webpage
security threat scan, then scanthe information sent by
the web server with security module before sending
to the client. If security threats were found in the web
page, the system will add this web page to the
blacklist and issue a warning to the client side to
prevent attack. Later on, as long as the client is to
receive the webpage in the blacklist, a warning will
be issued to the client side. Through this mechanism,
we can lower the security risk of the clients using
social networking websites.
Keywords- Information security, personal data,
social networking website, Facebook, proxy
I. INTRODUCTION
A social networking service[1] is a platform
to build social networksor social relationsamong
people, for example, share interests, activities,
backgrounds or real-life connections. Social
networking is web-based services that allow
individuals to create a public profile, to create a list
of users with whom to share connection, and view
and cross the connections within the system.
Although young generation is fond of these
applications, social networking websites also
encounter a number of privacy threats. These threats
reveal the information security risk of social
networking websites such as internet fraud, identity
theft, virus and phishing.
This means social networking is a very
popular internet community service. Social
International Journal of Computer Trends and Technology (IJCTT) volume 10 number 3 Apr 2014
ISSN: 2231-2803 http://www.ijcttjournal.org Page149
networkingwebsites gather a large amount of user
data including name,Picture, birthday, contact
information, gender, politicalorientation, religion,
personal interests and educationalbackground. These
data are open to the public by default;hence increase
the risk of personal privacy leakage.
Popularinteractive application services such as
games, psychologicaltests and fan communities can
also be used to conduct Trojan, virus and web linked
code attacks, or even money transferscams. For this
reason, the security threats of socialnetworking
websites, such as Facebook, needs to be investigated
and ameliorated.
This paper declares that proposed
application is divided into four modules namely
Social networking application, SecurityModule,
Sample Attacks,Proxy. Social networking application
is a sample social networking application which
includes the some basic functionality such as
addfriends, remove friends, search friends
etc.Security module uses the some security
softwares and online security services to prevent and
detect security threats. The module proxy is from
where client side requests are diverted to the web
server of requested website. Proxy server downloads
the data of the requested website and analyses that
data against the threats. And if the website was found
as threaten then the warning message is sent to the
client side. The next time whenever the client side
request for the same website then the proxy send
warning message to the client side directly instead of
analyzing that website.
II. METHODOLOGIES
Fig. Represents the process of the entire service.
It consists of five steps:
1. Client uses a browser to request for particular
social networking website.
2. Instead of crawling the requested webpage, the
browser redirects the request to the proxy.
3. Proxy sends the URL to online webpage
analysisservice [6-10] which will then download the
webcontent for security scan.
4. Relate online webpage service and local
scanningresult. Store the comparative analysis result
into the database. And if the requested website were
found threaten the proxy then add the URL to
International Journal of Computer Trends and Technology (IJCTT) volume 10 number 3 Apr 2014
ISSN: 2231-2803 http://www.ijcttjournal.org Page150
blacklist and respondwarning message to the user, if
it potential threatexists.
5. When any user request to browse the same
webpagelater on, proxy will send warning message to
the userdirectly according the black list.
III. SCOPE
The system uses proxy to collect many
online anti-virus and online webpage security
scanning services. Inaddition it combines webpage
scanning software to simultaneously scan the
webpage security of which user is about to browse. If
the requesting webpage threatening the warning
message is sent to the client and scanning result is
stored in the black list.
Whenever the next time user wants to
browse the same webpage in the list the blacklist
used to raise warning.
IV. LITERATURE SURVEY
IV.1 THREAT
A threat to a computer system is defined as
any potential occurrence,either accidental or
malicious, that can have an undesirable effecton the
assets and resources of the organization. The most
commonthreats to an individual or organization
involving the Internet orWeb include the following:
Virus
Trojan Horse
Worm
Scams
Malware
IV.2 WEB THREAT
Web threat is any threat that uses the
internet to facilitate cybercrime. Web threats use
multiple types of malware and fraud, all of
whichutilize HTTP or HTTPS protocols, but may
also employ otherprotocols and components, such as
links in email or IM, or malwareattachments or on
servers that access the Web.
Phishing
Web browser exploit
Third party add-ons
Download
Hybrid Attack
IV.3 MECHANISMS IN MALICIOUS WEBSITES
The victims who visit the malicious websites
will be redirectedand exploited by the Web-based
Trojans, implemented in scriptinglanguages including
JavaScript.
IV3.1 STRATEGIES FOR REDIRECTING
VISITORS TO WEB-BASED
Trojans
To redirect the visitors to the actual Web-
based Trojan, attackersare typically using one of the
following three categories ofstrategies.
V. EMBEDDED HTML TAGS
Embedded HTML tags such as iframe,
frame, and others, areused to embed the Web-based
International Journal of Computer Trends and Technology (IJCTT) volume 10 number 3 Apr 2014
ISSN: 2231-2803 http://www.ijcttjournal.org Page151
Trojan into the source code of thewebsite. The aim of
this HTML element is to create an inline framethat
displays another document. When that page is
opened, theincluded document is displayed in the
inline frame. Thus attackerstake advantage of this to
include the Web-based Trojan directly,setting the
iframe to be invisible by setting the height or width
ofthe iframe to zero or a very small value, for
example:
<iframe src=URL to Trojan width=0 height=0
frameborder=0></iframe>
V.1 TROJAN HORSE
Trojan horse attacks are accomplished by
inserting maliciouscode into other peoples programs.
When the user executes theirprogram, they
unintentionally execute the Trojan horse program.
Many current web sites insert a small piece of code
like a cookieinto your browser file, which may
contain a Trojan horse.
V.2 MALICIOUS SCRIPTS
The second category uses the script tag to
include Web-basedTrojan scripting or redirector
scripting, which are often XSS(Cross-Site Scripting)
vulnerabilities.
V.3 EMBEDDED OBJECTS
The third category of strategies is based on
the embedded objecttag for activating third-party
applications like Flash or Baofengmedia player or
Browser Helper Objects to display the embedded
object. When vulnerabilities in these applications and
BHOs arefound, attackers then use this strategy to
inject the objects to thevulnerable applications, which
exploit them in order to remotelyexecute code on the
victims machine.
V.4 ARP SPOOFING
This is another advanced strategy to build
malicious websitewhen the attackers cannot gain
control of the target website. Theattacker uses ARP
spoofing in order to act as a Man-in-the-Middle, and
hijacks all of the traffic from and to the victims in the
sameEthernet subnet. The attacker then injects
malicious code into theHTML responses from the
target website, or all of the web traffic,to achieve
virtual malicious websites.
VI. MODULES
VI.1 SOCIAL NETWORKING APPLICATION
Now-a-days social networking website has
become a popular networking culture. It has been
proven that peoples can keep in touch and share
feelings, as well ascollaborating research and
network marketing through social networking
website. We design a simple sample social
networking application which is used to set profile ,
add and ignore friends requests , send messages to
friends, search etc.
VI.2 SECURITY MODULE
The idea is tointegrate many commercial
protection software and online securityscanning
services into a security module, simultaneously
executewebpage security threat scan, then scan the
information sent by theweb server with the security
module before sending to the client. Ifsecurity threats
were found in the web page, the system will addthis
International Journal of Computer Trends and Technology (IJCTT) volume 10 number 3 Apr 2014
ISSN: 2231-2803 http://www.ijcttjournal.org Page152
web page to the blacklist and issue a warning to the
client sideto prevent attack.
VI.3 PROXY
The functionality of proxy is to segregate
theclient and the networking threat. Using
simultaneous scan of manyprotection software and
online services can increase therecognition rate of
security threats. Later one, as long as the clientis to
receive the webpage in the blacklist, a warning will
be issueddirectly to the client side. Through this
mechanism, we can lowerthe security risk of the
clients using social networking websites.
VI.4 SAMPLE ATTACKS
We are using some sample attacks such as
Fragmentation Attack, size Of Attack etc. application
to make attack over sample social networking.
VII. CONCLUSION
We have designed architecture for
mitigating the privacy risks of using a social
networking site. Our design strikes a balance between
protecting the users' privacy and maintaining
Facebooks usability. We argue that, although some
privacy and security risks remain, the threat of
privacy compromise is greatly reduced because our
architecture raises the cost of technical privacy
attacks and shifts the communication medium to one
in which a user may hold a reasonable expectation of
privacy and thereby enjoy an accompanying legal
framework for privacy protection.
VIII. REFERENCES
Books:
[1] Wanying Luo , Qi Xie, Hengartner, FaceCloak: An
Architecture for User Privacy on Social Networking Sites in
Computational Science and Engineering, August 2009, pp. 26-33.
[2] Wikipedia Facebook,
http://en.wikipedia.org/wiki/Facebook.
Vous aimerez peut-être aussi
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (895)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- DDAL-ELW02 - Boromar Ball PDFDocument22 pagesDDAL-ELW02 - Boromar Ball PDFGuilherme Büttenbender WalterPas encore d'évaluation
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- Legal English ReviewerDocument3 pagesLegal English ReviewerNadine OsorioPas encore d'évaluation
- Jonathan Grayson vs. Aurora Police Department LawsuitDocument17 pagesJonathan Grayson vs. Aurora Police Department LawsuitopenlineblogPas encore d'évaluation
- Judgement in The Case Pilferage of Narcotics by IPS OfficerDocument99 pagesJudgement in The Case Pilferage of Narcotics by IPS OfficerSampath Bulusu100% (1)
- Sex Offender Resident in Flossmoor, Il Received Bail Keep Them OutDocument6 pagesSex Offender Resident in Flossmoor, Il Received Bail Keep Them OutKIDZ KORNAPas encore d'évaluation
- Experimental Investigation On Performance, Combustion Characteristics of Diesel Engine by Using Cotton Seed OilDocument7 pagesExperimental Investigation On Performance, Combustion Characteristics of Diesel Engine by Using Cotton Seed OilseventhsensegroupPas encore d'évaluation
- Fabrication of High Speed Indication and Automatic Pneumatic Braking SystemDocument7 pagesFabrication of High Speed Indication and Automatic Pneumatic Braking Systemseventhsensegroup0% (1)
- Comparison of The Regression Equations in Different Places Using Total StationDocument4 pagesComparison of The Regression Equations in Different Places Using Total StationseventhsensegroupPas encore d'évaluation
- Extended Kalman Filter Based State Estimation of Wind TurbineDocument5 pagesExtended Kalman Filter Based State Estimation of Wind TurbineseventhsensegroupPas encore d'évaluation
- An Efficient Model of Detection and Filtering Technique Over Malicious and Spam E-MailsDocument4 pagesAn Efficient Model of Detection and Filtering Technique Over Malicious and Spam E-MailsseventhsensegroupPas encore d'évaluation
- Optimal Search Results Over Cloud With A Novel Ranking ApproachDocument5 pagesOptimal Search Results Over Cloud With A Novel Ranking ApproachseventhsensegroupPas encore d'évaluation
- Comparison of The Effects of Monochloramine and Glutaraldehyde (Biocides) Against Biofilm Microorganisms in Produced WaterDocument8 pagesComparison of The Effects of Monochloramine and Glutaraldehyde (Biocides) Against Biofilm Microorganisms in Produced WaterseventhsensegroupPas encore d'évaluation
- Color Constancy For Light SourcesDocument6 pagesColor Constancy For Light SourcesseventhsensegroupPas encore d'évaluation
- A Multi-Level Storage Tank Gauging and Monitoring System Using A Nanosecond PulseDocument8 pagesA Multi-Level Storage Tank Gauging and Monitoring System Using A Nanosecond PulseseventhsensegroupPas encore d'évaluation
- Ijett V5N1P103Document4 pagesIjett V5N1P103Yosy NanaPas encore d'évaluation
- Design, Development and Performance Evaluation of Solar Dryer With Mirror Booster For Red Chilli (Capsicum Annum)Document7 pagesDesign, Development and Performance Evaluation of Solar Dryer With Mirror Booster For Red Chilli (Capsicum Annum)seventhsensegroupPas encore d'évaluation
- Implementation of Single Stage Three Level Power Factor Correction AC-DC Converter With Phase Shift ModulationDocument6 pagesImplementation of Single Stage Three Level Power Factor Correction AC-DC Converter With Phase Shift ModulationseventhsensegroupPas encore d'évaluation
- Application of Sparse Matrix Converter For Microturbine-Permanent Magnet Synchronous Generator Output Voltage Quality EnhancementDocument8 pagesApplication of Sparse Matrix Converter For Microturbine-Permanent Magnet Synchronous Generator Output Voltage Quality EnhancementseventhsensegroupPas encore d'évaluation
- FPGA Based Design and Implementation of Image Edge Detection Using Xilinx System GeneratorDocument4 pagesFPGA Based Design and Implementation of Image Edge Detection Using Xilinx System GeneratorseventhsensegroupPas encore d'évaluation
- Design and Implementation of Height Adjustable Sine (Has) Window-Based Fir Filter For Removing Powerline Noise in ECG SignalDocument5 pagesDesign and Implementation of Height Adjustable Sine (Has) Window-Based Fir Filter For Removing Powerline Noise in ECG SignalseventhsensegroupPas encore d'évaluation
- The Utilization of Underbalanced Drilling Technology May Minimize Tight Gas Reservoir Formation Damage: A Review StudyDocument3 pagesThe Utilization of Underbalanced Drilling Technology May Minimize Tight Gas Reservoir Formation Damage: A Review StudyseventhsensegroupPas encore d'évaluation
- An Efficient and Empirical Model of Distributed ClusteringDocument5 pagesAn Efficient and Empirical Model of Distributed ClusteringseventhsensegroupPas encore d'évaluation
- An Efficient Encrypted Data Searching Over Out Sourced DataDocument5 pagesAn Efficient Encrypted Data Searching Over Out Sourced DataseventhsensegroupPas encore d'évaluation
- Review On Different Types of Router Architecture and Flow ControlDocument4 pagesReview On Different Types of Router Architecture and Flow ControlseventhsensegroupPas encore d'évaluation
- High Speed Architecture Design of Viterbi Decoder Using Verilog HDLDocument7 pagesHigh Speed Architecture Design of Viterbi Decoder Using Verilog HDLseventhsensegroupPas encore d'évaluation
- An Efficient Expert System For Diabetes by Naïve Bayesian ClassifierDocument6 pagesAn Efficient Expert System For Diabetes by Naïve Bayesian ClassifierseventhsensegroupPas encore d'évaluation
- Separation Of, , & Activities in EEG To Measure The Depth of Sleep and Mental StatusDocument6 pagesSeparation Of, , & Activities in EEG To Measure The Depth of Sleep and Mental StatusseventhsensegroupPas encore d'évaluation
- Non-Linear Static Analysis of Multi-Storied BuildingDocument5 pagesNon-Linear Static Analysis of Multi-Storied Buildingseventhsensegroup100% (1)
- Study On Fly Ash Based Geo-Polymer Concrete Using AdmixturesDocument4 pagesStudy On Fly Ash Based Geo-Polymer Concrete Using AdmixturesseventhsensegroupPas encore d'évaluation
- Free Vibration Characteristics of Edge Cracked Functionally Graded Beams by Using Finite Element MethodDocument8 pagesFree Vibration Characteristics of Edge Cracked Functionally Graded Beams by Using Finite Element MethodseventhsensegroupPas encore d'évaluation
- A Review On Energy Efficient Secure Routing For Data Aggregation in Wireless Sensor NetworksDocument5 pagesA Review On Energy Efficient Secure Routing For Data Aggregation in Wireless Sensor NetworksseventhsensegroupPas encore d'évaluation
- Ijett V4i10p158Document6 pagesIjett V4i10p158pradeepjoshi007Pas encore d'évaluation
- Key Drivers For Building Quality in Design PhaseDocument6 pagesKey Drivers For Building Quality in Design PhaseseventhsensegroupPas encore d'évaluation
- A Comparative Study of Impulse Noise Reduction in Digital Images For Classical and Fuzzy FiltersDocument6 pagesA Comparative Study of Impulse Noise Reduction in Digital Images For Classical and Fuzzy FiltersseventhsensegroupPas encore d'évaluation
- Performance and Emissions Characteristics of Diesel Engine Fuelled With Rice Bran OilDocument5 pagesPerformance and Emissions Characteristics of Diesel Engine Fuelled With Rice Bran OilseventhsensegroupPas encore d'évaluation
- National Plan of ActionDocument45 pagesNational Plan of ActionAtiq Rahman PappuPas encore d'évaluation
- DA1 - Graft and CorruptionDocument8 pagesDA1 - Graft and CorruptionShaneBattierPas encore d'évaluation
- Motion To Release (Served Sentence) - SampleDocument4 pagesMotion To Release (Served Sentence) - SampleKim MedranoPas encore d'évaluation
- Almonte v. BienDocument7 pagesAlmonte v. Bienida_chua8023Pas encore d'évaluation
- Trespass To PersonDocument5 pagesTrespass To PersonAnukritiPas encore d'évaluation
- Final NotesDocument71 pagesFinal NotesMohamedFadhil100% (3)
- Chapter One 1.1 Background of The StudyDocument18 pagesChapter One 1.1 Background of The StudypeterPas encore d'évaluation
- Irish NaturalizationDocument14 pagesIrish NaturalizationФенамин НорадреналиновичPas encore d'évaluation
- K - Crim - SB-10-CRM-0238-0239 - People Vs Lloren, Et Al - 11 - 17 - 2017 PDFDocument51 pagesK - Crim - SB-10-CRM-0238-0239 - People Vs Lloren, Et Al - 11 - 17 - 2017 PDFSiak Ni Namnama100% (1)
- CFPA - E - Guideline - No - 25 - 2010 - F Plano de EmergênciaDocument21 pagesCFPA - E - Guideline - No - 25 - 2010 - F Plano de EmergênciaFernandoFerreiraPas encore d'évaluation
- 315 Estafa DefenseDocument10 pages315 Estafa DefenseAnonymous gAkmNz100% (1)
- State JurisdictionDocument14 pagesState JurisdictionHadait Ullah Baqri100% (1)
- Robation Re-Parole Re-Executive Clemency ArdonDocument10 pagesRobation Re-Parole Re-Executive Clemency ArdonppadojPas encore d'évaluation
- Hard Wired Island - Retrofuture Cyberpunk (HQ)Document400 pagesHard Wired Island - Retrofuture Cyberpunk (HQ)fishbait42Pas encore d'évaluation
- Palestinian-Israeli Conflict Position Paper - 2016Document9 pagesPalestinian-Israeli Conflict Position Paper - 2016api-97531232Pas encore d'évaluation
- Planning The Modern Public Library BuildingDocument16 pagesPlanning The Modern Public Library BuildingLakshya AroraPas encore d'évaluation
- Case DigestDocument12 pagesCase DigestPhi SalvadorPas encore d'évaluation
- Criminal Law BAR Questions 1990 2016Document81 pagesCriminal Law BAR Questions 1990 2016Mere JayPas encore d'évaluation
- ILLEGAL RECRUITMENT Under RA 8042 As AmendedDocument5 pagesILLEGAL RECRUITMENT Under RA 8042 As AmendedJhomel Delos ReyesPas encore d'évaluation
- ADocument3 pagesAEleni ZiagalouPas encore d'évaluation
- Adultery and FornicationDocument5 pagesAdultery and FornicationSonofManPas encore d'évaluation
- Belo The Belt: Limitations On Lawyers' Language On Social MediaDocument18 pagesBelo The Belt: Limitations On Lawyers' Language On Social MediaImmediateFalcoPas encore d'évaluation
- Cyber Security MCQ Set-3 ExamRadarDocument3 pagesCyber Security MCQ Set-3 ExamRadarSuprit PradhanPas encore d'évaluation
- Body Modification EssayDocument2 pagesBody Modification EssaySelma YılmazPas encore d'évaluation