Académique Documents
Professionnel Documents
Culture Documents
Extrusion Detection in Mobile Ad-hoc Networks
Transféré par
mansoor.ahmed1000 évaluation0% ont trouvé ce document utile (0 vote)
35 vues8 pagesdoc
Titre original
Extrusion Detection
Copyright
© © All Rights Reserved
Formats disponibles
DOC, PDF, TXT ou lisez en ligne sur Scribd
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentdoc
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme DOC, PDF, TXT ou lisez en ligne sur Scribd
0 évaluation0% ont trouvé ce document utile (0 vote)
35 vues8 pagesExtrusion Detection in Mobile Ad-hoc Networks
Transféré par
mansoor.ahmed100doc
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme DOC, PDF, TXT ou lisez en ligne sur Scribd
Vous êtes sur la page 1sur 8
Extrusion Detection
Deployment analysis in Mobile Ad-hoc Networks
Muhammad Ahmed Noor (Author)
Usman Institute of Technology
Karachi, Pakistan
e-mail id : manoorkhihotmail!com
AbstractIn this research paper we will research how the
extrusion detection will prevent the outgoing confidential
information from Manet Networks. This techniques detects
outgoing confidential information at the Gateway andor the
client! although the confidential information may "e encrypted!
compressed or o"fuscated "efore transmitted such as emails or
other porta"le storage media e.g. memory stick.
"! INT#$%&'TI$N (N% )('*G#$&% $+ IN,-NTI$N
Extrusion Detection is the technolo#y that detects the
accidental or$and intentional data leaka#e %orm the network!
&here are two approaches'!one is the extrusion detection at
the #ateway le(el by usin# the so%tware) Extrusion detection
so%tware *ED+, that scans out#oin# web, email, and "M tra%%ic
%or con%idential in%ormation that is send outside the network!
-ne o% the disad(anta#es o% the ED+ is that they do not
encrypted or compressed %iles or contents!
&here%ore i% the attacker compresses or encrypts a %ile or
%ile contents be%ore attachin# it to an email, ED+ will be unable
to detect such sensiti(e data and in this way this sensiti(e data
will be leaked! "n the same way i% a user encrypts a %ile be%ore
copyin# it to .+/ stick, 0D-1-M or other such media, so the
con(entional Desktop ED+ systems will be unable to detect
such trans%er o% such sensiti(e data!
-ne way to sol(e this problem is to simply block all
encrypted$compressed %iles %rom lea(in# the #ateway! &his
solution makes another problem! As it incures a hi#h %alse
positi(e rate and deny access le#itimate out#oin#
encrypted$compressed %iles$contents!
II. .&MM(#/ $+ T0- IN,-NTI$N
Ad(anta#e o% the present in(ention is to pro(ide a computer
implemented methodolo#y %or extrusion detection o%
ob%uscated content! &his method di%%erentiates %iles accessible
%iles either sensiti(e or not sensiti(e by computer the si#nature
to pre(ent extrusion o% ob%uscated contents! &his method also
includes monitorin# e(ents on the local computer *includes the
use o% ob%uscation tools to create such ob%uscated %iles,, and
determine that i% the %ile bein# opened by an ob%uscation tool,
this is classi%ied as sensiti(e! -ne case is, only sensiti(e %iles
output by ob%uscation tools are scan throu#h si#nature
computin# step! "n another case, usin# the si#nature to pre(ent
extrusion o% ob%uscated content includes sendin# the si#nature
to a data leaka#e detection en#ine %or use in extrusion detection
system!
&he extrusion detection can be carried out, %or example, on
the computer and$or #ateway le(el with which the computer is
communicati(ely coupled! "n another case the method may
include monitorin# %or out#oin# data that include one or more
attachments! "n one case the attachment was ob%uscated by
more than one ob%uscation *%or example compressed, encrypted
and then multiple compressions or encryptions! "n this case the
analysis includes computin# a si#nature o% the extracted
attachments and comparin# that si#nature to the si#nature o%
known sensiti(e in%ormation!
Another embodiment o% this in(ention pro(ides a system
%or extrusion detection o% ob%uscated contents! &his
%unctionality can be implemented in di%%erent ways such as
so%tware*e!#! codin#,, 2ardware *%or example #ateway le(el,,
%irmware *%orm example one or more microcontrollers,, or
some combination o% so%tware, hardware, %irmware!
A. Brief Discription of the Drawings
3"4!5 is a block dia#ram o% the Extrusion Detection
+ystem!
3"4!6 is the client system o(er(iew
3"4!7 +ecurity 0lient Module block dia#ram
3"4!8a and 3"4!8b illustrate a method %or extrusion
detection o% ob%uscated contents,
+E0.1"&9 +E1:E1
DA&A ;EAKA4E
DE&E0&"-N EN4"NE
NE&<-1K
0;"EN& 0;"EN& 0;"EN&
+E0."1&9 0;"EN&
M-D.;E
+E0."1&9 0;"EN&
M-D.;E
+E0."1&9 0;"EN&
M-D.;E
III. %-T(I1-% %-.'#I2TI$N $+ T0- IN,-N.I$N
+ystem Architecture
3"4!5 is the block dia#ram o% extrusion detection system!
As we can see that security ser(er is connected to a network!
&he security ser(ers ha(e data leaka#e detection en#ine and
ser(er is connected with the one or more client=s computers
throu#h the network usin# a wide (ariety o% communication
protocols such as &0P$"P, 2&&P, 3&P, +M&P etc! %ormats such
as 2&M; or >M; and protected by :PN, secure 2&&P etc!
&he client computer is a de(ice that can ha(e number o%
applications, -peratin# systems! &he -peratin# +ystem could
Microso%t <indows, Apple -peratin# +ystem or ;inux
Distribution! "n other embodiment, the client computer may be
machine with ha(in# computer %unctionality, such as a Personal
di#ital assistant *PDA,, smartphone, (ideo #ame or cellular
telephone etc! +uch computin# de(ices can send messa#es with
one or more %iles attached to the external networks or
destinations and such de(ice can also recei(e messa#es or
attachment %orm others networks! "n 3"4!5 there are three
clients but likewise there may ha(e thousands or millions o%
such clients!
&he security client module executes on the computer
client ! in one case the security client module is pro#rammed or
con%i#ured %or di%%erentiate %iles as sensiti(e or not sensiti(e,
this module monitors all reads and write to %iles on the system
and which detect any possible data leaka#e! -ne o% the
%unctionality o% our in(ention is to detect when as ob%uscation
tools such as P4P, pk?ip , crypt, etc! is launched on the client
computer! "% such kinds o% ob%uscation tools has been used or
accessed a %ile that is known to contain con%idential contents,
then the resultin# ob%uscated %ile created can be tracked! &his
can be achie(ed by computin# an ob%uscated data hash %or
example MD@ o% the ob%uscated %ile! &his hash or other
si#nature is then %orwarded to ser(er=s data leaka#e detection
en#ine! &he security module can be incorporated into -+ o% the
computer or part o% separate packa#e! &he security client
module may be %urther set to communicate with the security
ser(er (ia network such as wireless! &he security client module
can also report in%ormation re#ardin# a potential in%ormation
leak, and send this in%ormation to the ser(er! &he ser(er can
then pro(ide the recommendation to the client module!
+ecurity product may be pro(ided by a (endor to the security
ser(er! 3or example so%tware, appliances or ser(ices etc! &he
security ser(er may be used as an email ser(er, 2&&P ser(er,
"M ser(er or other such ser(ers like #ateway proxy and may
include on e or more computer systems con%i#ured to
communicate with client computer throu#h wireless network!
"n this case data leaka#e detection en#ine resides on the
security ser(er! +uch a client side data leaka#e detection en#ine
can be used alternati(e to ser(er side data leaka#e detection
en#ine!
3or each extracted %ile, the data leaka#e detection en#ine
computes a si#nature o% that %ile with the help o% e!#! MD@,
1abin %in#erprints or other so%tware and compares this
si#nature a#ainst si#natures computed %or ob%uscated %iles on
the client computers! "% the si#natures match then the data
leaka#e detection system simply blocks that %ile
&he security ser(er may be used or con%i#ured with some other
%unctionalities %or example ser(er may pro(ide si#nature and
code to the client computers %or detectin# malicious so%tware
%or other harm%ul %iles!
+IG.3
Display
Memory 4raphics
Adapter
Network
Adapter
+tora#e
.ser
"nter%ace
+ecurity Module
+ecurity Module
Processor
3"4!6 illustrate a %unctional (iew o% a client computer! A client
computer includes a processor operati(ely coupled (ia a bus to
memory, a stora#e de(ice, #raphics adapter, and connected
throu#h network adapter! A display is operati(ely coupled to
#raphic adapter!
&he processor could be any 0P. that is capable o%
executin# the operatin# system, applications and other
executable %iles! Memory may be 1AM, 1-M or some other
%lash memory! &he memory has the security module that is
connected throu#h the security module o% in the stora#e!
Modules described in this dia#ram represent one embodiment
o% the present in(ention! +ome other embodiments may include
other or di%%erent modules and %unctionality! &he method are
stored on the stora#e de(ice as executable %iles loaded in to the
memory and executed by the processor as one or more
processes!
3"4!7 illustrates the block dia#ram that shows the security
client module con%i#ured in accordance with in the present
in(entions! "t includes the ser(er inter%ace module, %orwardin#
module, reportin# module, si#nature module, classi%ication and
%ile monitorin# module!
Each o% the abo(e modules can be implemented on the
so%tware that can be run on the client computer! 2owe(er some
module reAuires the hardware lo#ic or combination o% so%tware
and hardware!
&he ser(er communication module enable the
communication between the client and security ser(er! &he
si#nature database stores si#natures o% exclusions! &hese
exclusions are the %iles or pro#rams that are trusted pro#ram,
routines, and applications!
+i#nature scannin# module scans the si#nature check in its
database o% exclusions! Exclusions are trusted$allowed
pro#rams, routines, applications etc! that are known identi%yin#
malicious so%tware on the client so%tware %or example (iruses,
malware and other security threats! 3or example si#nature
contains a (alue that is %ound in malicious so%tware! +o its
blocked! &he si#nature are desi#ned to deal with windows exe
%ormat and other known %ormats that mi#ht contain malicious
so%tware or (irus!
&he reportin# module is con%i#ured to pro(ide a user
inter%ace to report any unusual acti(ity or some particular
security e(ents, such as the detection o% (iruses, intrusions and
action taken! "n one particular case the reportin# module
reports presents noti%ication to the user that an extrusion
attempt was detected and stopped! "t has also be con%i#ured to
collect in%ormation and send it an analysis a#ent, such as a
remote security response center!
&he classi%ication module is con%i#ured to (eri%y that
weather the %iles on the client computer is sensiti(e or not
sensiti(e! &his classi%ication can be done in the back#round or
in real time when the %iles are modi%ied, added, created etc!
+IG.4
+i#natures
*E!#!
exclusions$known
attacks,
+er(er "nter%ace
Module
+i#nature
+cannin#
Module
1eportin#
Module
3ile Monitorin#
Module
0lassi%ication
Module
3orwardin#
Module
+IG. 5
&he %ile monitorin# module is pro#rammed to con%i#ure to
monitor all the chan#es to %iles on the system! 3or examples
this module can detects when application / is attemptin# to
open a %ile 3, or Application A/0 is a ob%uscation tool, such as
compression or encryption al#o! And %ile 3 can be con%idential
%ile or %ile 4 is the sa(e as copy o% %ile 3 etc!
&he %orwardin# module is pro#rammed to %orward in%ormation
obtained as a result pro(ided by the monitorin# module to the
data leaka#e detection en#ine! &he %orwardin# module could be
part to the ser(er inter%ace module! &he %unction o% %orwardin#
module will be discussed in more detailed way with re%erence
to 3"4+! 8a-b!
3"4! 8a and 3"4!8b illustrate a process %or extrusion detection
o% the ob%uscated contents!
/y the method shown in 3"4!8 classi%yin# %iles stored on the
client computer as either sensiti(e or not sensiti(e! &he
process o% classi%ication is carried out in the back#round or in
the real time as the %ile makes chan#es or created, added,
copied etc! &he method continues its work by %indin# weather
the client use ob%uscation tools to create ob%uscated %iles! &his
is achie(ed by comparin# the si#nature o% ob%uscated %iles and
the data base o% such si#natures! &hen it determines the names
o% known executable! +uch as win?ip!exe is a known
executable o% compression application! "t can be pro#ramed
that the ob%uscation tools a(ailable to the user can be
pro#rammed or con%i#ured to issue an e(ent or some indicator
to in%orm the method! 3urthermore all the unknown pro#rams
that operates on the client has been classi%ied as sensiti(e and
i% that pro#ram produces some sort o% %ile then it is considered
as a ob%uscation pro#rams!
"% the user has used ob%uscation tool, then the %low continues
with monitorin# %or ob%uscation o% protected content!
-therwise the %ile opened by the ob%uscation tool is
considered as sensiti(e! "% not the method continues to
compute the si#nature e!#! MD@ o% suspect %ile output by the
ob%uscation tools and send that si#nature to a data leaka#e
detection en#ine!
&his method continues to classi%yin#, detectin# ob%uscation o%
protected content and report the contents i% ob%uscation occurs!
3"4! 8b illustrate the method o% detectin# transmission o%
ob%uscation content and blockin# that content %orm lea(in# the
secure area! &he method include i% an out#oin# messa#es,
emails, text messa#es etc! includes attachments , the
attachments could be o% any type! &hen the method includes
extractin# that particular attachment %or analysis! &he process
%urther continues by takin# si#nature o% the attachment and
compares the si#nature to si#natures o% known sensiti(e
in%ormation!
+tart
-ut#oin#
Attachm
ent
Extract Attachment
0ompute si#nature o% extracted
%ile
0ompare si#nature to si#natures
o% known sensiti(e in%ormation
MatchB
/lock extrusion attempt
+top
No
No
+tart
Monitor e(ents on the client
0lassi%y %iles stored on the client as
either sensiti(e or not sensiti(e
2as user
launched an
ob%uscation tool
B
"s tar#et %ile
classi%ied
sensiti(eB
0omputer si#nature o% suspect %iles
output by the ob%uscation tool
+end si#nature o% suspect %ile to
data leaka#e detection en#ine
+top
No
No
+IG.6a
+IG.6"
"% the si#nature matches the si#nature o% the suspect %ile then
the %ile is considered as ob%uscated %ile and system will block
the %ile and mark as sensiti(e! "% not, then the method
continues to monitorin# %or out#oin# communications
includin# protected contents!
-n the other hand, i% the si#nature does match a si#nature o%
known sensiti(e in%ormation, then the method continues with
blockin# the extrusion attempt!
I,. #-.-(#'0 '0(11-NG-.
Problems in deployin# Extrusion Detection in MANE&+
&here are many problems in deployin# 0lient-+er(er based
Extrusion Detection in Mobile Ad-hoc Networks! &he reasons
are as %ollows'!!
1) Deployment of Extrusion Detection Server
"t is (ery di%%icult to deploy Extrusion Detection +er(er
because o% ad-hoc network! &he clients connected throu#h the
network temporarily!
2) lients have limite! processing power
"n Mobile Ad-hoc Networks, the nodes are mostly mobiles,
which ha(e less processin# power and less computin# space!
+o it is (ery di%%icult to deploy security clinet module in
mobile de(ices!
") #ess power Bac$up (Battery life)
Mostly mobile de(ice ha(e less battery backup! +o i% the
mobile de(ices will scan si#natures monitor e(ents on the
cleint*mobile de(ice, then it will reAuire more battery
backup!
,. #-+-#-N'-.
http:$$en!wikipedia!or#$wiki$MobileCadChocCnetwork
http:$$w7!antd!nist!#o($wahnCmahn!shtml
http:$$en!wikipedia!or#$wiki$ExtrusionCdetection
https:$$secdiary!com$article$extrusion-detection$
http:$$www!cl!cam!ac!uk$Drnc5$extrusion!pd%
http:$$www!#oo#le!com$patents$.+E5E5F7G
Vous aimerez peut-être aussi
- Remote Access Tools PolicyDocument2 pagesRemote Access Tools Policythanhtam3819100% (1)
- Basics of TCP/IP, Switching, Routing and Firewalling.: WWW - Google.deDocument17 pagesBasics of TCP/IP, Switching, Routing and Firewalling.: WWW - Google.deeva sharmaPas encore d'évaluation
- Java Application ProjectsDocument39 pagesJava Application ProjectsIraniya PandiyanPas encore d'évaluation
- Wireless Body Area Networks (WBAN) : Viswavardhanreddy KDocument87 pagesWireless Body Area Networks (WBAN) : Viswavardhanreddy KaditvasPas encore d'évaluation
- Embedded Systems Security: Practical Methods for Safe and Secure Software and Systems DevelopmentD'EverandEmbedded Systems Security: Practical Methods for Safe and Secure Software and Systems DevelopmentÉvaluation : 4.5 sur 5 étoiles4.5/5 (2)
- Tool Review e Remote Forensic Preservation and Examination ToolsDocument14 pagesTool Review e Remote Forensic Preservation and Examination Toolsselar89100% (1)
- What Is A MicroprocessorDocument21 pagesWhat Is A MicroprocessorArghya SantraPas encore d'évaluation
- Redhat Linux System Administration Rh133Document284 pagesRedhat Linux System Administration Rh133Adrian Bravo100% (1)
- Storyboard Data Warehouse Planning GuestDocument15 pagesStoryboard Data Warehouse Planning GuestHani SalemmPas encore d'évaluation
- Veeam ExamDocument5 pagesVeeam Examcrisandy3150% (2)
- Secure MANET ProposalDocument6 pagesSecure MANET Proposalsolo_gauravPas encore d'évaluation
- Cost of Product Development: Cloud vs On-PremiseDocument7 pagesCost of Product Development: Cloud vs On-PremiseYakubuPas encore d'évaluation
- SAE J1939 Canopen GatewayDocument54 pagesSAE J1939 Canopen Gatewaysreekanthmk100% (1)
- OSSTMMDocument213 pagesOSSTMMorion57854375Pas encore d'évaluation
- Access Control Systems Typically Use Keypads, Magnetic Card Readers, or Proximity Readers To Secure A Facility From Unauthorized AccessDocument4 pagesAccess Control Systems Typically Use Keypads, Magnetic Card Readers, or Proximity Readers To Secure A Facility From Unauthorized AccessguhanmPas encore d'évaluation
- Title Page No: 2. Objective 3. System AnalysisDocument28 pagesTitle Page No: 2. Objective 3. System AnalysispradeepyadavmuPas encore d'évaluation
- Extrusion Detection System: Problem StatementDocument3 pagesExtrusion Detection System: Problem Statementmansoor.ahmed100Pas encore d'évaluation
- Mcabcamsc ProjectDocument23 pagesMcabcamsc ProjectdivyashreebollamwarPas encore d'évaluation
- CryptoSystems Using RSA and DES Encryption (Synopsis)Document11 pagesCryptoSystems Using RSA and DES Encryption (Synopsis)sanjaykumarguptaaPas encore d'évaluation
- Hacker HighSchool-Security Awareness For TeensDocument192 pagesHacker HighSchool-Security Awareness For TeensMuhammad IchsanPas encore d'évaluation
- Rsa DocumentationDocument61 pagesRsa DocumentationPrasad NamaPas encore d'évaluation
- Literature: SurveyDocument10 pagesLiterature: SurveySobhan DasariPas encore d'évaluation
- Loadrunner Frequently Asked QuestionsDocument4 pagesLoadrunner Frequently Asked Questionsn2bhukyaPas encore d'évaluation
- Airline Reservation System Project Report inDocument76 pagesAirline Reservation System Project Report inSharma Nishant50% (2)
- Personal Computers Hardware and SoftwareDocument9 pagesPersonal Computers Hardware and SoftwareAldin AljusevicPas encore d'évaluation
- Topic - 7 Security, System Control, and AuditDocument14 pagesTopic - 7 Security, System Control, and AuditKhizer SikanderPas encore d'évaluation
- Bluetooth SecurityDocument42 pagesBluetooth Securitysandeepsharma707Pas encore d'évaluation
- Nexus Service Marketing System DocumentationDocument26 pagesNexus Service Marketing System DocumentationĐức Thành Ngọc BíchPas encore d'évaluation
- Safety Workspace Reference Guide - External Users: How To Navigate Through IntralinksDocument15 pagesSafety Workspace Reference Guide - External Users: How To Navigate Through IntralinksAngela Lucía NúñezPas encore d'évaluation
- (Software Design Specification) : CS 4500, University of Utah Spring 2006Document14 pages(Software Design Specification) : CS 4500, University of Utah Spring 2006Najmul HasanPas encore d'évaluation
- Virtual Private NetworkDocument16 pagesVirtual Private NetworkArthur FisherPas encore d'évaluation
- Malware Removal Starter Kit: How To Combat Malware Using Windows PEDocument18 pagesMalware Removal Starter Kit: How To Combat Malware Using Windows PEodairismePas encore d'évaluation
- Cholantechnology 4@Document32 pagesCholantechnology 4@ஸ்ரீ கண்ணன்Pas encore d'évaluation
- Shortcut Remover From ExternalDocument2 pagesShortcut Remover From ExternalvijaymfsPas encore d'évaluation
- What Is A Firewall?: The WordDocument5 pagesWhat Is A Firewall?: The WordKrishna ForuPas encore d'évaluation
- ONLINE VOTING SYSTEMDocument47 pagesONLINE VOTING SYSTEMspatade7Pas encore d'évaluation
- NT2580Week 2 ProjectDocument12 pagesNT2580Week 2 ProjectMahlikBrownPas encore d'évaluation
- Unit I Overview & Instructions: Cs6303-Computer ArchitectureDocument16 pagesUnit I Overview & Instructions: Cs6303-Computer Architecturetamizhanps100% (1)
- Jones x433 01 FinalDocument16 pagesJones x433 01 Finalapi-254756020Pas encore d'évaluation
- GSM Based Vehicle TrackingDocument4 pagesGSM Based Vehicle TrackingNagavijay ReddyPas encore d'évaluation
- Literature SurveyDocument5 pagesLiterature SurveySiva KumarPas encore d'évaluation
- Term Paper: Security of Cisco RoutersDocument11 pagesTerm Paper: Security of Cisco RoutersKaran GabaPas encore d'évaluation
- Colegiul Tehnic"Gheorghe Asachi"-Onesti: An Scolar 2013 - 2014Document19 pagesColegiul Tehnic"Gheorghe Asachi"-Onesti: An Scolar 2013 - 2014Răzvan AlexandruPas encore d'évaluation
- Jobseekers.com - A website to organize job data for seekers and companiesDocument9 pagesJobseekers.com - A website to organize job data for seekers and companiesvikaskumar615Pas encore d'évaluation
- Basic Security: A Brief Overview About Networking SecurityDocument11 pagesBasic Security: A Brief Overview About Networking SecurityPhanitAminoVichianratPas encore d'évaluation
- CDC0019 SynopsisDocument2 pagesCDC0019 Synopsistariq76Pas encore d'évaluation
- AcknowledgementDocument12 pagesAcknowledgementJaydip PatelPas encore d'évaluation
- CIMA P3 Notes - Performance Strategy - Chapter 8Document6 pagesCIMA P3 Notes - Performance Strategy - Chapter 8Mark Horance Hawking100% (1)
- IPC AND SYNCHRONIZATION TECHNIQUESDocument9 pagesIPC AND SYNCHRONIZATION TECHNIQUESShubhashreeBhattacharyaPandaPas encore d'évaluation
- HMS Project ProposalDocument17 pagesHMS Project ProposalKCyuPunPas encore d'évaluation
- Saprouter-Sap Security In-Depth Vol 06Document23 pagesSaprouter-Sap Security In-Depth Vol 06Nadeeja Wijesundara100% (1)
- OWASP Guia de Referencia RápidaDocument20 pagesOWASP Guia de Referencia Rápidamarco20142014Pas encore d'évaluation
- SY0-301 CardsDocument8 pagesSY0-301 Cardsbpb2468Pas encore d'évaluation
- Data SecurityDocument12 pagesData SecurityLynette Ballad BalangatanPas encore d'évaluation
- Linux 033Document40 pagesLinux 033Narender GudaPas encore d'évaluation
- How A Company Handles Its Data CenterDocument3 pagesHow A Company Handles Its Data CenterjoshmalikPas encore d'évaluation
- Part 2Document6 pagesPart 2LewisPas encore d'évaluation
- s3 99510 3GPP IMEI SecurityDocument7 pagess3 99510 3GPP IMEI SecuritySultan Muhammad Rifqi El-MuammaryPas encore d'évaluation
- Ns 2 RecallDocument6 pagesNs 2 RecallarunsmilePas encore d'évaluation
- Audit Checklist For POSDocument3 pagesAudit Checklist For POSErin SmithPas encore d'évaluation
- K.L.N College of EngineeringDocument11 pagesK.L.N College of Engineeringsuganya004Pas encore d'évaluation
- Chapter 9Document14 pagesChapter 9shashankniecPas encore d'évaluation
- CAM Cloud-Assisted Privacy Preserving Mobile Health MonitoringDocument4 pagesCAM Cloud-Assisted Privacy Preserving Mobile Health MonitoringRavi RathodPas encore d'évaluation
- 1.1 Project Description: Modules Involved in The Project: Students ModuleDocument51 pages1.1 Project Description: Modules Involved in The Project: Students ModulemanikmathiPas encore d'évaluation
- System-on-Chip Security: Validation and VerificationD'EverandSystem-on-Chip Security: Validation and VerificationPas encore d'évaluation
- AtenolDocument6 pagesAtenolmansoor.ahmed100Pas encore d'évaluation
- Electrical Machines I: Week 13: Ward Leonard Speed Control and DC Motor BrakingDocument15 pagesElectrical Machines I: Week 13: Ward Leonard Speed Control and DC Motor Brakingmansoor.ahmed100Pas encore d'évaluation
- 1Document18 pages1Mansoor AhmedPas encore d'évaluation
- T=K ϕ I E E I R N= E K ϕ T=K I: Separately Excited DC Motor Series DC MotorDocument2 pagesT=K ϕ I E E I R N= E K ϕ T=K I: Separately Excited DC Motor Series DC Motormansoor.ahmed100Pas encore d'évaluation
- Notice: All The Images in This VTP LAB Are Used For Demonstration Only, You Will See Slightly Different Images in The Real CCNA ExamDocument14 pagesNotice: All The Images in This VTP LAB Are Used For Demonstration Only, You Will See Slightly Different Images in The Real CCNA Exammansoor.ahmed100Pas encore d'évaluation
- Lotus Notes Client Version 8.5Document4 pagesLotus Notes Client Version 8.5mansoor.ahmed100Pas encore d'évaluation
- SUSE Linux 11 Administration WorkbookDocument153 pagesSUSE Linux 11 Administration Workbookmansoor.ahmed100Pas encore d'évaluation
- Lab 3Document5 pagesLab 3mansoor.ahmed100Pas encore d'évaluation
- LogitechDocument11 pagesLogitechmansoor.ahmed100Pas encore d'évaluation
- MS Electrical Engineering at DHA Suffa UniversityDocument34 pagesMS Electrical Engineering at DHA Suffa Universitymansoor.ahmed100Pas encore d'évaluation
- PDC PmphandbookDocument0 pagePDC PmphandbookAhmed FoudaPas encore d'évaluation
- 3103 WorkbookDocument91 pages3103 Workbookmansoor.ahmed100Pas encore d'évaluation
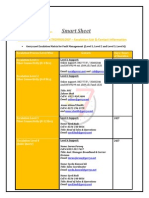
- Smart Sheet: GERRYS INFORMATION TECHNOLOGY - Escalation List & Contact InformationDocument1 pageSmart Sheet: GERRYS INFORMATION TECHNOLOGY - Escalation List & Contact Informationmansoor.ahmed100Pas encore d'évaluation
- H.M RashidDocument10 pagesH.M Rashidmansoor.ahmed100Pas encore d'évaluation
- Practice Problem 2 - SolutionDocument14 pagesPractice Problem 2 - Solutionmansoor.ahmed100Pas encore d'évaluation
- Anomaly in Manet2Document14 pagesAnomaly in Manet2mansoor.ahmed100Pas encore d'évaluation
- FIOS: A Fair, Efficient Flash I/O Scheduler: Stan Park Kai Shen University of RochesterDocument22 pagesFIOS: A Fair, Efficient Flash I/O Scheduler: Stan Park Kai Shen University of Rochestermansoor.ahmed100Pas encore d'évaluation
- Practice Problem 2Document2 pagesPractice Problem 2mansoor.ahmed100Pas encore d'évaluation
- Research Assignment - DetailsDocument2 pagesResearch Assignment - Detailsmansoor.ahmed100Pas encore d'évaluation
- Mobile Ad-Hoc and Sensor NetworksDocument27 pagesMobile Ad-Hoc and Sensor Networksmansoor.ahmed100Pas encore d'évaluation
- VrableDocument28 pagesVrablemansoor.ahmed100Pas encore d'évaluation
- A Study of Linux File System EvolutionDocument14 pagesA Study of Linux File System EvolutionVictor LyapunovPas encore d'évaluation
- Paper Title (Use Style: Paper Title) : Subtitle As Needed (Paper Subtitle)Document3 pagesPaper Title (Use Style: Paper Title) : Subtitle As Needed (Paper Subtitle)mansoor.ahmed100Pas encore d'évaluation
- BlueSky Cloud File System Optimizes Enterprise Storage CostsDocument14 pagesBlueSky Cloud File System Optimizes Enterprise Storage Costsmansoor.ahmed100Pas encore d'évaluation
- Paper Title (Use Style: Paper Title) : Subtitle As Needed (Paper Subtitle)Document3 pagesPaper Title (Use Style: Paper Title) : Subtitle As Needed (Paper Subtitle)mansoor.ahmed100Pas encore d'évaluation
- CMOS Digital Logic Circuits Chapter SummaryDocument56 pagesCMOS Digital Logic Circuits Chapter Summarymansoor.ahmed100Pas encore d'évaluation
- HP Z240 Workstation Technical SpecsDocument4 pagesHP Z240 Workstation Technical SpecsMartand Pratap SinghPas encore d'évaluation
- Mdce InstallDocument67 pagesMdce Installrmehta26Pas encore d'évaluation
- Advanced Use of C Language: ContentDocument23 pagesAdvanced Use of C Language: ContentsybaritzPas encore d'évaluation
- HDWriterAE (5 3L019) - ManualDocument173 pagesHDWriterAE (5 3L019) - ManualzeljavalybiPas encore d'évaluation
- Bareos Manual Main ReferenceDocument491 pagesBareos Manual Main ReferenceAlejandro GonzalezPas encore d'évaluation
- New DC ManualDocument79 pagesNew DC ManualPavan PakkiPas encore d'évaluation
- Sip and h323 ComunicationDocument14 pagesSip and h323 ComunicationMoises ReznikPas encore d'évaluation
- Software: ConversionsDocument6 pagesSoftware: ConversionsRoger SepulvedaPas encore d'évaluation
- Idrive OverviewDocument7 pagesIdrive OverviewLetsogile BaloiPas encore d'évaluation
- SnomONE Online BookDocument588 pagesSnomONE Online Bookgdurante5Pas encore d'évaluation
- OpenSolaris DTrace - Harry J Foxwell PDFDocument181 pagesOpenSolaris DTrace - Harry J Foxwell PDFÉcio FerreiraPas encore d'évaluation
- MVI56 104S DatasheetDocument2 pagesMVI56 104S DatasheetDeysi PeñaPas encore d'évaluation
- Octave Print PdflatexDocument2 pagesOctave Print PdflatexMatthewPas encore d'évaluation
- Meridian 1 Basic System AdminDocument159 pagesMeridian 1 Basic System AdminBill HoffmanPas encore d'évaluation
- Zyxel NBG-460N 3.60 Ed4Document370 pagesZyxel NBG-460N 3.60 Ed4truleacristian4642Pas encore d'évaluation
- Chapter 16 - Multimedia Network Communications and ApplicationsDocument68 pagesChapter 16 - Multimedia Network Communications and ApplicationsFarzaan Pardiwala100% (2)
- 04 Chapter 1 - PLCDocument36 pages04 Chapter 1 - PLCsaliana binti sanusi100% (3)
- File Tracking SystemDocument5 pagesFile Tracking SystemAlad Manoj Peter100% (1)
- CP R70 ClusterXL AdminGuideDocument242 pagesCP R70 ClusterXL AdminGuideoorhan41Pas encore d'évaluation
- Mayavi Making 3D Data Visualization ReusableDocument6 pagesMayavi Making 3D Data Visualization Reusable2e7ahPas encore d'évaluation
- QuantizationDocument89 pagesQuantizationannanndhiii100% (1)
- Max+Plus II Getting StartedDocument380 pagesMax+Plus II Getting StartedCarlos E. ArrietaPas encore d'évaluation
- PC I DevicesDocument1 pagePC I Devicesnono heryanaPas encore d'évaluation
- Mis Planning and Development BY Ankur MittalDocument30 pagesMis Planning and Development BY Ankur Mittalankurmittal2112Pas encore d'évaluation