Académique Documents
Professionnel Documents
Culture Documents
Thesis Final Ch. 1-3
Transféré par
Gjenerrick Carlo MateoDescription originale:
Titre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Thesis Final Ch. 1-3
Transféré par
Gjenerrick Carlo MateoDroits d'auteur :
Formats disponibles
EMILIO AGUINALDO COLLEGE
THE USE OF MODERN TECHNOLOGIES IN THE
SUPPRESSION OF CRIMES IN SELECTED
BARANGAYS IN TONDO MANILA
A Thesis Presented to the Faculty of
The School of Criminology
Emilio Aguinaldo College
Ermita, Manila
In
Partial Fulfillment
of the Requirements for the Degree of
Bachelor of Science in Criminology
By:
GJENERRICK CARLO R. MATEO
JOHN MAHATMAL.BARLAM
JOHN CLARKS.NAYRE
ALYSSA CAMILLE R. BAUTISTA
KIMBERLY MARIAH JACQUELINE C. DOMINGO
October, 2014
EMILIO AGUINALDO COLLEGE
Chapter 1
THE PROBLEM AND ITS BACKGROUND
Introduction
According to Walsh, the term criminal can and has been applied to many types of
behavior, some of which nearly all of us have been guilty of at some time in our lives. We
call think of acts that we feel ought to be criminal but are not, or acts that should not be
criminal but are. Paul Tappan in 1947 defined crime as an international act in violation
of the criminal law committed without defense or excuse, and penalized by the state.
A crime is thus an act or omission in violation of law for which punishment is prescribed;
the person committing it must have intended to do so and must have done so without
legally acceptable defense or justification.
Many studies have already been conducted since 18th century just to determine
the causes of criminality and criminal behavior. Because of this, many theories have
arisen from the minds of different scalars across the globe, they have different ideas, but
they share only one purpose, and that is to provide an answer.
EMILIO AGUINALDO COLLEGE
Some say that there are factors to be considered as reasons, like when some of
them explains that the non-existence of norms in a society encourages a person to
commit unlawful acts, some claimed that the body type of the person has something to
do with regards to his criminal behavior, others put emphasis on a persons set of needs
required for his survival and according to them, failure of a person to attain this needs
will result in criminality, others blamed the bad spirits, others said it is inherited, but there
is one theory that was appreciated by the majority and also accepted to stand as basis
for the explanation of the causes of criminality and criminal behavior. The differential
associational theory of Edwin Sutherland who is considered as the Dean of Modern
Criminology by stating that Criminal Behavior is Learned and NOT Inherited
Crime is learned through socialization of communication with other people. The
techniques of committing crimes are also learned by participation with other people or
group of people through verbal and non-verbal means Sutherland
Crime happens in the environment, and just like a contagious disease it affects
the members of society and just easily spread all throughout the world.Because of
Sutherlands brilliant explanation about crimes and criminality, it was universally
accepted even up until now. And since crime happens in the environment agencies all
over the world utilized Police visibility as means of crime prevention. A Proactive Law
Enforcement strategy that lessens the possibility of the occurrence of crimes by instilling
fear or deterrence in the minds of possible criminal offenders.
EMILIO AGUINALDO COLLEGE
Deterrence is the main key in the effectiveness of this method. However, there
are still some places in the Philippines wherein the utilization of Police Omnipresence is
nearly impossible, especially in rural areas or provinces, and even in the dark streets of
Metro Manila. The absence of deterrence might raise the possibility for criminality to
occur. Criminals might just evade the punishment provided for the crime which they have
committed especially when there is no witness.
So, what might be the possible measures to take to provide solution to a crime
that was committed because of the absence of deterrence on the part of the offenders?
What would be the possible steps to be considered as recourse by someone who was
victimized by a robber in one of the darkest allies in tondo? By the parents of a high
school student who was raped in the backyard of the school in which shes enrolled? Or
even by an Actor who was illegally detained, tied up and got beaten up by a group of
men in one of the most fancy condominiums in Taguig?
As we all know, on January 22, 2014 (Wednesday), Its Showtime host Vhong Navarro
was allegedly tied up and attacked by a group of men inside a condominium unit in Fort
Bonifacio, Taguig.
EMILIO AGUINALDO COLLEGE
His suspect is a businessman named Cedrick Lee together with its companion.
Lee admitted that he and his companions are the ones responsible for beating up
Navarro but just for purposes of defending his friend DenieceCornejo who according to
Lee is about to be raped by Navarro. Contrary to the statement of Navarro who denied
being a rapist, claiming that the incident was a setup.
However, Lee has his witnessed and on the other hand Navarro has no evidence
to prove his version of story. But on January 29, 2014 the National Bureau of
Investigation released video footages from Forbeswood Condominium that became a
turning point to the case providing what really happened. Because of this, it is evident
that utilizing modern technologies is an important method in elucidating the truth for the
proper administration of justice and to effectively suppress criminality.
The main objective of this study is to provide the public in general, the citizens, or
members of the community, law enforcement agencies, barangay officials, security
agencies, the different branches of the government, the local government of Manila, and
others nationwide, the knowledge regarding the benefits of utilizing modern technologies
in the suppression of crimes, to furnish them information that was scientifically acquired
through research with regards to its effectiveness, to propose the use of modern
technologies as security measures in both public and private establishments by stating
its importance and most of all to make our contributions by exerting our efforts as
responsible members or the society in the pursuit of total absence of criminality and to
support the continuous improvement of public safety.
EMILIO AGUINALDO COLLEGE
Theoretical Framework.
The continuous increase in crime rate and in improper administration of justice
became a major problem not only for law enforcement officers but also for every
responsible members of the community as well as for all the participants in the criminal
justice system. The utilization of modern technologies became a necessity for everyone
who is in pursuit for the total absence of criminality and criminal behavior as well as for
those who are trying to attain a safe place to live, invests and do business with.
The dissemination of information regarding the effectiveness of modern
technologies in the suppression of crimes and its contribution in the proper
administration of justice is the purpose of conducting this study. Various studies have
been conducted for assessing the effectiveness of modern technologies in the
suppression of crimes.
The theory underlying the effectiveness of public surveillance technology as a
crime control tool is based on the belief that, if potential offenders know they are being
watched, they will refrain from criminal activity. This belief is consistent with rational
choice theory, which posits that potential offenders make purposeful, rational (albeit
bounded) decisions to commit crimes after weighing the potential costs and benefits of
the crime in question. Also, Video footagedocumenting crimes that transpired and
EMILIO AGUINALDO COLLEGE
identifying perpetrators and witnesses may aid in investigations and prosecutions,
increasing police and prosecutorial efficiency, benefiting victims of crimes whose cases
are able to be closed through the use of video evidence, and incapacitating a greater
number
of
offenders
from
committing
future
crimes.
(http://www.cops.usdoj.gov/Publications/e071112381_EvalPublicSurveillance.pdf p4,5)
Millions of closed-circuit television (CCTV) cameras are installed in streets and
businesses throughout the world with the stated goal of reducing crime and increasing
public safety. The United Kingdom is one of the most enthusiastic proponents, with an
estimated 1.9 million cameras in 2011 one for every 32 U.K. residents and the
number continues to rise. Chicago reportedly has at least 15,000 cameras installed in
one of the largest U.S. networks which has prompted civil liberties groups to express
strong concerns while in New York, cameras are increasingly found both on public
transit as well as in businesses and even high-end residences. The 9/11 attacks led
many
municipalities
to
start
installing
CCTV
systems.
See
more
at:
http://journalistsresource.org/studies/government/criminal-justice/surveillance-camerasand-crime#sthash.feM704Zs.dpuf
EMILIO AGUINALDO COLLEGE
Here in the Philippines, several barangays and business establishments started
the utilization of modern technologies in the prevention of crimes by instilling fear of
apprehension in the mind of the would be criminal offender as well as to suppress crime
once it was committed by determining the perpetrator with the use of Closed-Circuit
Television (CCTV).
This study will determine the effectiveness of modern technologies in combatting
crime in the city of Manila and to disseminate the information to its benefactors by
collecting all the data and information from different barangays, law enforcement
agencies and business establishments and making an assessment after thorough
evaluation and scientific analysis.
EMILIO AGUINALDO COLLEGE
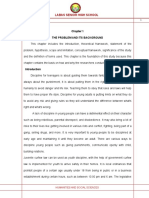
Process
INPUT
Study basis
Theory
Effectiveness
of modern
technologies
in the
suppression
of crimes
OUTPUT
Data and
Information
Gathering
Evaluation of
collected datas
and information
Interpretation of
collected datas
and information
Conduct
surveys in
barangays
w/in the city
of Manila as
well as to ask
for datas
and
information
from Law
Enforcement
Agencies.
Record and
Organize all useful
collected datas
and information.
Make a thorough
Interpretation of
collected datas
and information
by means of
statistics and
scientific analysis.
Outcome
-Assessment of
the Effectiveness
of utilizing
modern
technologies in
the suppression
of crimes
-Effects in crime
control because
of its utilization
-Information
regarding its
effectiveness
-Proposal of its
use by stating its
importance
through
presentation
Figure 1.
Conceptual Paradigm
9
EMILIO AGUINALDO COLLEGE
Statement of Problem
This study determines the use of Modern Technologies in the Suppression of
Crimes in the Selected Barangays in Tondo Manila.Specifically the following problem will
be answered in this study:
Specifically the following problem will be answered in this study:
1. The Personal Profile of the Respondents in terms of:
1.1.1. Age
1.2.
Sex
1.3.
Civil status
1.4.
Educational Attainment
1.5.
Length of stay in the locality
2. What are the common crimes committed within the community according to the
record of the police station?
3. What are the advantages of utilizing modern technologies relative crime prevention
and suppression?
4. What are the respondents recommended modern technologies necessary for the
enhancement of security in selected Barangays in Tondo Manila?
10
EMILIO AGUINALDO COLLEGE
Assumptions
1. the utilization of modern technologies will help the people in their pursuit for the total
absence of criminality.
2. The utilization of modern technologies will be an effective way to assist the state in
the proper administration of justice.
3. The utilization of modern technologies will not only prevent the occurrence of crimes
but also an effective method of suppressing it.
4. The utilization of modern technologies will also be an effective way to assure ones
feeling of safety and security.
5. The utilization of modern technologies was used to monitor and record images of
what takes place in specific locations in real time.
Significance of the Study
The ultimate benefactors of this study are:
The community the citizenswho lives in the City of Manila particularly in Tondo. will
be educated or be provided with knowledge regarding easy and efficient methods of
pursuing justice with the help of modern technologies.
Law Enforcement Agencies to inform them of the necessity of utilizing modern
technologies as a helpful method in fulfilling their duty particularly in criminal
investigation.
11
EMILIO AGUINALDO COLLEGE
Barangay Officials To propose the installations of cctv and other gadgets that can
increase the safety and security within their community.
Security Agencies To provide them information regarding modern technologies that
will enhance their capacity in providing security within the establishment they are
employed.
Branches of GovernmentTo inform them all the help that can be provided of modern
technologies particularly in security, crime prevention, crime suppression and even in the
effective, efficient and appropriate means of administering justice.
Scope of Limitation
The study will determine the effectiveness of Modern Technologies utilized in the
suppression of crimes in Tondo Manila. Covering Selected Barangays in Tondo Manila
and Police Stations 1 and 7. It encompasses all strategies in determining crimes inside
the City of Manila particularly in Tondo. However, in several places they have their own
techniques and different ways in detecting crimes which is not subject for furtherance of
study. It focuses on the strict and active monitoring of the conditions of the community so
as to suppress all the kinds of evil motive which result to wrongful acts. But it does not
help all the time to suppress the crime because the funds of local government of Manila
for public security is not sufficient, which the government should take proper action in
promulgating the safety of every person who lives in the City of Manila.
12
EMILIO AGUINALDO COLLEGE
Definition of Terms
For the purpose of better understanding, the following terms were defined
operationally:
Crime- An act or omission that is punishable by the law. (Criminology Memory Aid)
Criminality- The quality, state or fact about being criminal. (Websters New World
Dictionary)
Criminal Offender- A person that violates a law. (Criminology Memory Aid)
Deterrence- To keep of discourage from doing something by instilling fear, anxiety or
doubt. (Websters New World Dictionary)
Modern- Having to do with the latest styles, methods or ideas. (Websters New World
Dictionary)
Modern Technology- Characterized by using the most up-to-date machinery and
equipment developed from the application at scientific knowledge.
Police Omnipresence- The civil force of a national or local government (by instilling)
that ispresent in a place.
Suppression- An action suppressing something such as an activity. (Websters New
World Dictionary)
Technology- The science or study of the practical or industrial arts and applied science
(Websters New World Dictionary)
Utilize- Make practical and effective use of. (Websters New World Dictionary)
13
EMILIO AGUINALDO COLLEGE
CHAPTER 2
REVIEW OF RELATED STUDIES AND LITERATURES
In this chapter, the researchers will bring additional information and ideas related
to the topic which were taken from literatures and studies. The researcher also believes
that this would help to make this study more understandable and accurate.
Foreign Literature.
Modern Technology (sample-essay-modern-technology-paragraphs.pdf)
Accessibility to a wide range of options has been expanded through modern
technology. Never before could people cross a continent or an ocean in an afternoon.
Travel is not the only way technology has created accessibility. Software which types
from voice commands has made using computers more accessible for school or work.
People with special needs have many new options thanks to modern technology such
as special chairs or text readers. Actually, those people who need hearing aids as a
result of normal aging have access to continued communication and enjoyment of
entertainment they did not previously have. There are many ways technology has
improved lives through increased accessibility.
14
EMILIO AGUINALDO COLLEGE
Foreign Studies.
Data And Information Security In Modern Day Businesses
(Festus Olubukunmi Ajibuwa)
All organizations require information for planning, controlling, recording
transactions, performance measurement and decision-making. And such Information
whether internal or external must be kept properly and well protected from intruders,
hackers and unauthorized individuals.
Organizations across the globe in every industry sector are under increasing pressure
and scrutiny to maintain the security and integrity of their data. Companies are faced
with an enormous liability if sensitive, business critical, or confidential information gets
into the wrong hands.
The field of information security has grown and evolved significantly in recent years. As
a career choice there are many ways of gaining entry into the field. It offers many areas
for specialization including Information Systems Auditing, Business Continuity Planning
and Digital Forensics Science, to name a few. Although information security has
traditionally been the responsibility of IT departments, some companies have made it a
business issue as well as a technological one. Companies are now adding strategic,
operational, and organizational safeguards to the technological measures they currently
employ to protect corporate information. But most companies continue to view
15
EMILIO AGUINALDO COLLEGE
information security as a technological problem calling for technological solutions even
though technology managers concede that today`s networks cannot be made
impenetrable and that new security technologies have a short life span as hackers
quickly devise ways around them. Delegating security to technologists also ignores
fundamental questions that only business managers can answer. Not all of a company`s
varied information assets have equal value, for instance; some require more attention
than others. One on-line retailer, Egghead.com, lost 25 percent of its stock market value
in December 2000, when hackers struck its customer information systems and gained
access to 3.7 million credit card numbers. Egghead, of course, had security systems in
place and claimed that no data were actually stolen, but it lacked the kind of coordinated
organizational response necessary to convince customers and shareholders that their
sensitive data were actually secure. Information security means the appropriate
protection of information, systems, services and data communications by administrative,
technical and other measures both in ordinary and exceptional circumstances. The
confidentiality, integrity and availability of information is protected against threats
and damage caused by faults in hardware and software, natural events and willful,
negligent or accidental events.
The central concepts of information security have the following meanings:
Confidentiality: information and systems are accessible only to those authorized to use
them. Third parties are not given a possibility to alter or destroy information nor to
16
EMILIO AGUINALDO COLLEGE
process it otherwise.
Integrity: information and systems are reliable, correct and up-to-date and they have not
been altered nor can they be altered in an uncontrolled way as a result of hardware or
software faults, natural events or human activities.
SECURITY ASPECTS IN MODERN WEB APPLICATIONS
(Jarkko Miettinen )
Ten years is a long time on software industry, especially in the field of web applications.
During that ten years, web technologies have advanced immensely and many
applications that simply were impossible in 1999 are now used every day by millions of
users. Unfortunately, new technologies have bought new attacks with them. Many of the
attacks that were effective against Effect were not even invented when development of
Effect started. During those then years of Effect development, the development process
at Effect has changed from unstructured development to structured Scrum-process with
proper code reviews, testing and education. Effects of this change were visible also in
this work as many of the vulnerabilities found were old and could not get to the code
base nowadays. Until this thesis work, however, security issues were not substantially
brought up.
17
EMILIO AGUINALDO COLLEGE
This thesis represented efforts of a security push at Effect similar to what Microsoft went
through in 2002 [HL03], except in smaller scale. Work on the thesis started with selfeducation on the fundamentals of computer and information security. Fundamentals
were followed by small parts from the field of computer security that seemed to make
sense in the direction the thesis was going to although not all the knowledge found
direct application in the empirical part.
What found direct use in the empirical part was all the research into web technologies,
as knowing the problem domain is the first requirement for any successful analysis.
Thus, different web technologies used to build web applications and common
vulnerabilities in such applications were discussed and provided a good starting point to
later analyses. In the empirical part of this thesis, application of the security assessment
methods suffered some reversals, partly for lack of proper tools, partly for lack of
experience. Lack of tools made editing attack tree models cumbersome and proper
attack surface analysis well nigh impossible. Still the result were, if not the best, at least
good in the sense that new vulnerable areas in Effect were uncovered. Most of the
earlier work of Effect security had been, rightly so, focused on common web application
vulnerabilities and this thesis work demonstrated that an application is not made secure
just by fixing the most common vulnerabilities. In a way, the security push is still
ongoing. The knowledge gained in this thesis theoretical and experimental part has yet
to diffuse to other developers and not all devised enhancements for security are
implemented nor will they all ever be because of the trade off that need to made.
18
EMILIO AGUINALDO COLLEGE
In this thesis, two possibly very useful methods, attack trees and attack surface analysis
could not be applied in full because lack of tools and knowledge. Should there be
another security push, revisiting those analysis methods and tools should be a starting
point. Two large stones that were left completely unturned were use of static analysis
tools and of other programming languages.
Static analysis tools, such as CodeSecure based on WebSSARI [HYH+ 04], analyze the
code of the application without actually running it, hoping to find signs of vulnerabilities
such as insecure flow of data or unchecked memory accesses. If such tool could be
integrated seamlessly into development environment, benefits would be great. Warning
of security errors as modern development environments warn of syntax errors is one
thing but more importantly, such tool could most certainly analyze security issues in
third party libraries used.
Different programming languages could offer at least two benefits: better specification of
levels of trust for the data and a possibility to separate security concerns from other
concerns, making parts of a program easier to understand and use.
Ultimately, none of these methods and tools will be a silver bullet for the slaying beast of
security problems. Still, sometimes even grazing it will be worthwhile.
19
EMILIO AGUINALDO COLLEGE
Security Control Room Studies
Gill et al. (2005) evaluated 13 CCTV projects which were set-up under the Home Office
Crime Reduction Programme (comprising of 14 separate CCTV systems). At six control
rooms, surveillance video was recorded on the more traditional analogue S-VHS tapes,
six recorded video digitally on a computer hard drive, and one recorded video on digital
tape. Various aspects of the control room operations were examined such as:
ownership, design, management, work practices, communication, operator pay and
training, as well as the processing of CCTV evidence. The study did not examine the
impact of specific technologies on operator performance when carrying out tasks.
Despite this, a number of findings which related to the technical aspects of a control
room system which could have affected operator performance were identified:
1. At a majority of the control rooms, digital tools (e.g., intelligent CCTV, digital radio,
user interfaces etc.) were not used to support operators in their tasks.
2. In comparison to analogue CCTV systems, digital systems could be searched more
quickly, which saved police time when looking for evidence. The average search time
required to search digital CCTV was 18 minutes and 40 minutes to search analogue
CCTV video.
20
EMILIO AGUINALDO COLLEGE
3. At seven control rooms, CCTV cameras were unable to fully adapt to the levels of
light. In addition to low light levels, some CCTV cameras were positioned too close to
lights, which over-exposed camera lenses and created strobing and glare in the images.
In fact, four out of the seven residential cameras suffered from inappropriate lighting
levels at night, two of which were so dark the images were virtually useless (Gill et al.,
2005, p 27). The problems with camera lighting at night affected operators when
carrying a monitoring task in real-time and also affected the police when analysing postevent recordings.
4. A number of control rooms were found operating a high camera-to-operator and
camera-to- monitor ratio, which meant that too few eyes were looking at too many
cameras and monitors.
This reduced the ...probability of spotting an incident or providing usable recordings
(Gill et al., 2005, p 14).
5. In the control rooms which recorded analogue CCTV (n = 6), video was recorded at
low- quality as a result of tapes were being re-used far too often.
6. In the control rooms which recorded video digitally, the video quality was also poor.
The problems with video quality were apparent at eight of the control rooms (both
analogue and digital systems). Six control rooms recorded video at 1-2 fps and two
21
EMILIO AGUINALDO COLLEGE
control rooms recorded at 1 frame every 3-5 seconds. At vast majority of the control
rooms, Gill et al. found that the video quality was too low to aid the police in their
investigations or even be used as evidence in court.
7. Operators and management had limited knowledge of digital technology (recording
settings) in the case of two systems which consequently compromised the effectiveness
of the system.
Non-Security Control Room Studies
Luff and Heath (2001) carried out naturalistic observations within in one particular type
of control room: station control rooms in the London Underground. In-depth field work
which involved making audio-visual recordings were carried out in the major stations of
the London Underground. The study specifically examined how operators maintained
situation awareness: how they monitored their surrounding domain and the activities of
their colleagues. The results showed that operators made use of a wide range of
communication and information technologies: radios, passenger announcement
systems, train information, emergency control, and alarm systems. The technology most
used was the banks of video monitors that displayed CCTV video in real-time (4-12
monitors per bank with up to 80 CCTV cameras in total). These monitors displayed
video of various public areas within the London
22
EMILIO AGUINALDO COLLEGE
Underground such as train platforms, corridors, passageways etc. Control room
operators (station supervisor as described by the authors) were responsible for utilising
technology to monitor suspicious and troublesome behaviour within the station and
track targets smoothly from one camera to another.
The observations revealed that operators were not able to monitor platform scenes
effectively, and this was because the images were not always clear due to a number of
technical observational difficulties.
Operators struggled with their tasks due to the low-quality CCTV images observed onscreen, and this was due to the following problems:
1. Limited lighting provided near to the CCTV cameras.
2. Dirty CCTV camera lenses from train break dust.
3. Dirty video monitors within the control room due to a lack of cleaning.
4. Monitors kept on the same view for long periods of time which caused a burnt-out
effect.
As a result of poor maintenance of the CCTV systems, operators struggled to monitor
scenes. For example, they were unable to distinguish whether a crowd was stationary
or moving. Furthermore, operators were unable to follow targets smoothly from one
camera to another due to camera blind spots created as a result of hundreds of years of
gradual station development. Luff and Heath believed that the problems operators faced
23
EMILIO AGUINALDO COLLEGE
when dealing with fragmented images was inevitable in the video coverage of a large
and complex station (p 158).
Operators reported that they found it difficult to visualize scenes at the end of train
platforms. In fact, certain individuals such as beggars and buskers discovered some of
the camera blind spots, and frequently placed themselves outside of the CCTV camera
views. The analysis of these tasks revealed that operators used various technologies to
monitor fragmented and difficult to see station scenes.
Given these problems with surveying scenes, it is not surprising that operators
struggled.
Following 12-months of field work, Luff and Heath made a number of general design
suggestions to improve operator task performance specifically when working on within a
London Underground control room:
1. Extend the existing London Underground systems so that they are more integrated.
This
was
proposed
to
reduce
the
need
for:
maintenance,
need
different
controls/connections, and information handling.
2. Configure the technology appropriately to: allow for a selection of a sequence of
images so that incidents can be easily tracked, monitored, and to support the invocation
of appropriate next actions.
3. Introduce automated surveillance technology to detect events such as crowding.
4. Make relevant information about the station accessible to operators in different
locations of the control room to improve the efficiency in locating scenes on CCTV.
24
EMILIO AGUINALDO COLLEGE
5. Implement a touch-screen interface allowing operators to quickly select camera views
on their video monitors without delaying the situation assessment and response.
Although these design recommendations can be applied to the design of all types of
CCTV control rooms, Luff and Heath fail to discuss an important aspect of carrying out
tasks within such a complex work environment: context and its impact on the design of
systems. CCTV owners and managers therefore could benefit with additional
recommendations which take into account the various contextual factors surrounding
the operators work system (see Chapter 3, Section 3.3.2.2, Table 3.1).
In another transport control room study (Chen, Choi, Ruiz, Shi and Taib, 2005), in-situ
observations, interviews and questionnaires were carried out within a traffic control
room to gain insights into how operators performed their work. The focus of the field
work was to understand how operators utilize multiple hardware equipment and
software applications when managing mobility and public safety related incidents within
a control room. The results were used to formulate use scenarios1 and then implement
a mock-up application to improve operator performance when dealing with traffic
incidents. The main limitation with this study is the lack of background given on the
research methodology and data analyses (this is discussed in more detail in Chapter 3,
Section 3.5). Furthermore, in review of the study findings, it is unclear what tasks
operators performed in the control room and what their work environment was like, as
no discussion is given on the field study observations. Chen et al. instead placed more
focus on the subjective findings gathered from the interviews and questionnaires and
25
EMILIO AGUINALDO COLLEGE
used this data to inform the design of a new mock-up system. Interviews with 14 control
room operators revealed a number of the subjective preferences with the regards to the
current information system they used to manage traffic incidents and specifically to
locate scenes:
75% of operators were happy with their working environment (p 2), but several said
that there should be a better way to integrate applications to allow critical data to be
retrieved more easily.
70% of operators would have liked a map-based search tool for accessing geographical
information.
33% of operators preferred a personalised way to filter information.
70% expected simpler procedures to login and log out of their systems.
60% thought a speech interface would be beneficial and 21% thought a multimodal
(speech, gesture, touch, and others) would be beneficial.
These findings were then examined with 11 control room operators using a
questionnaire. The two main issues reported in the questionnaire related to the
26
EMILIO AGUINALDO COLLEGE
problems with the contact pages (database), as the data was: 1) out-of-date and 2)
inconsistent. The third biggest issue was the slow search speed at which the system
operated; and this slow speed was potentially due to an indirect result of ineffective
navigation tools
Once the field research was complete, a mock-up user interface (web based) was
created to validate the findings. The aim of the mock-up system was to examine
whether operators could be better supported when handling incidents.
The design involved integrating a number of company policies into the flow of
information within the user interface. This integration was included in the design to
reduce operators cognitive load when performing tasks with the system. A browsing
navigation was proposed rather than a stand-alone search function so that entry point
information can be found using an advanced search function. Other features included
the use of: 1) expansion of fields when completing information (this reduced the need to
scroll excessively); 2) completion markers (in the form of checkboxes) to allow
operators to visualise completed actions; and 3) error handling (the checkboxes trigger
warnings when actions are incomplete).
The mock-up user interface was evaluated with six operators using a real-life traffic
incident scenario.
27
EMILIO AGUINALDO COLLEGE
Operators were timed in their tasks which required the retrieval and handling of contact
information with both the existing contact system and the mock-up system. In addition to
task performance, operators were asked to rate the system under several criteria using
a 5-point Likert scale. The results of the evaluation were described by the authors as
preliminary. The overall findings from the evaluation revealed that the mock-up system
was more efficient (37% overall improvement in task time completion), despite
operators receiving no training with the new system. Chen et al. believed this finding
was a result of introducing the process flow and progress markers within the user
interface. The subjective results were in line with the task performance data. Operators
preferred the mock-up system as they were able to enter specific geographical locations
and perform searches by entering specific criteria into the database system. There was
a strong preference for the new proposed system in terms of: easy to learn, ease of
use, intuitiveness, speed and accuracy of retrieval, helpfulness, level of comfort, and
overall its effectiveness. The integration of information sources was considered
important for improving operator performance in the London Underground control rooms
(Luff and Heath, 2001).
The study by Chen et al. (2005) examined task performance issues within a real-world
context, and like the study London Underground study by Luff and Heath (2001), both
studies examine one specific task: locating a scene. As both these studies examines
one specific task within one specific control room setting, the findings are limited and
28
EMILIO AGUINALDO COLLEGE
therefore do not provide a broader understanding of the task performance issues within
control rooms where CCTV and other related technology is heavily used.
For example, the interaction between different control room stakeholders was not
examined, nor was there a discussion of the interplay between users when using
communication devices such as radio and telephone.
In contrast to the study by Chen et al. (2005), McCarthy et al. (1997) carried out a 12month ethnographic study to compare two different systems currently being used by
operators within two ambulance controls rooms. The field research involved field
observations and open-ended interviews with operators at two different ambulance
control rooms. The main objectives of the field study were to: 1) understand how
operators performed a specific task (locating a scene of emergency in order to dispatch
an ambulance); 2) compare the effectiveness of tasks performed by operators at each
control room; and 3) use these findings to assess the potential usefulness of the
technology used at one control room if it was to be used at another control room (where
technology is not heavily used). The control rooms which were evaluated included:
29
EMILIO AGUINALDO COLLEGE
Ambulance Control Room 1 (ACC1):
o Located within an urban environment.
o Operators were supported by a high technology system.
o Tasks involved: receiving calls, entering jobs electronically into a system, locating
scenes using a database system, passing the information to a gazetteer (a reference
tool for information about places and place names), which identifies the possible
location, confirms the location to the caller, and then passes to the dispatch team
electronically.
Ambulance Control Room 1 (ACC2):
o Located within a rural environment.
o Operators were supported by a low technology system (a manual system to
locate a scene).
o Operators are given access to a database of telephone numbers of public
telephone boxes, local general practitioners, and other important landmarks and
locations.
o Tasks involved: receiving calls, locating a scene of emergency using a paper
map of the area, and then writing the job details down on note paper.
30
EMILIO AGUINALDO COLLEGE
The analysis of the field research revealed that the most critical activity operators
performed was identifying a scene of emergency. This task was described as highly
complex since postal addresses were difficult to identify (for e.g., some houses were not
numbered, some street names clashed etc).
McCarthy et al. described the nature and context of this scene locating task at each of
the ambulance control rooms in detail.
Similar to the study conducted by Chen et al. (2005), field research was carried out to
identify the problems operators experienced when locating a scene within a control
room environment. McCarthy et al. found that task performance was severely affected
as a result of ineffective communication between public callers (those requesting an
ambulance) and control room operators (those receiving calls from public callers to
dispatch an ambulance). Communication was ineffective for a number of reasons: 1)
pubic callers had strong regional accents; 2) public callers provided operators with
insufficient location descriptions; and 3) operators lacked experience in locating scenes
of emergency.
McCarthy et al. suggested that some technologies, such as the gazetteer and an
electronic map could compensate for operators lack of direct access to the knowledge
on the local geographical areas. This particular control room provided detailed insights
31
EMILIO AGUINALDO COLLEGE
into the nature of ambulance control room work; however the study findings are largely
task descriptive, and does not provide a detailed discussion on the implication of these
problems on operator performance and system effectiveness.
To conclude, there have been a number of field studies within control rooms which
examine the nature and context of operator tasks. These studies were carried out with
the aim of improving system design, apart from the security control room study by Gill et
al. (2005) which examined the overall effectiveness in terms of crime reduction. In
review of these studies, there is a common theme: all involved operators performing
what would be widely known (by operators and other researchers) a reactive task
whereby the operator is involved in locating a scene using CCTV cameras, video
technology, and maps based artefacts.
Reactive tasks are time critical tasks and the ability to perform these tasks effectively
and efficiently depends on two factors: 1) how well an operators work-system is set-up
and configured and 2) the effectiveness of communication (verbal and technical)
between operators and other users. The transport control room studies (Chen et al.,
2005 and Luff and Heath, 2001) did not examine the role and effectiveness of
technology in much detail across a wide range of control rooms. Instead, field research
was limited to 1-2 control rooms to examine a specific task with the aim of improving
system design. Furthermore, secondary tasks such as administrative paper work and
32
EMILIO AGUINALDO COLLEGE
making copies of CCTV evidence were not mentioned in these studies. Based on the
previous control room studies, a number of important research questions were identified
for further investigation in Study 1
1. What tasks are performed by CCTV operators where CCTV and other associated
technologies are used within a control room environment?
2. Do CCTV operators have a good understanding, knowledge, and experience in their
tasks and the surveillance areas?
3. What factors do CCTV operators use to aid their situational awareness?
4. How do CCTV operators communicate and collaborate with other CCTV control room
stakeholders, and is it effective?
5. Are operators provided with integrated (e.g., a geographical information system
linked to CCTV cameras) or segregated tools?
It is clear that, a better understanding is needed on the nature and context of CCTV,
what tasks are performed by operators and what problems they encounter, and it affect
on other stakeholders and the technical parts of the system thus the socio-technical
33
EMILIO AGUINALDO COLLEGE
impact. This understanding is important so that it can then be used to improve the
effectiveness of CCTV system design, configuration, and use.
Effective, Design, Configuration, and Use of Digital CCTV (Hina Uttam Keval )
The research carried out in this thesis was motivated by the need to understand how
CCTV is used in the management of security tasks, and the factors that reduce its
effectiveness. The overarching goals for this research were: 1) theoretical and 2)
practical. Firstly, an understanding of security observation tasks was needed as this
research does not currently exist. Secondly, by building an understanding of the context
and use of CCTV and other technologies used for security observation tasks, a practical
framework can be developed to support CCTV practitioners and owners. The purpose
of such a framework is to improve the design, configuration, and set-up of CCTV
systems to ensure they are fit for purpose. The field study in this thesis (presented in
Chapter 4) demonstrated the importance of taking into account and correctly configuring
the: CCTV system environment, CCTV users workstation set-up, task requirements
(number of video monitor displays, display type, video quality etc.), and stakeholder
communication (see Chapter 4, Section 4.4.2.5). The empirical studies (presentedin
Chapters 8 and 9) investigated the effect of using low-quality CCTV video for a face
identification and event detection task performed by human observers. The results from
these experiments provide minimum recommendations on video quality required for
34
EMILIO AGUINALDO COLLEGE
achieving effective task performance when using digital CCTV systems (in real-time via
a network or when in play-back mode).
This research was extremely timely as there is a lot of investment in CCTV deployments
and a large interest in using it for a growing range of security purposes. One of the key
reasons for the high interest in CCTV is because of events such as the terrorist attacks
in London (July 2005). In addition to terrorism, a number of changes led to people
investing more and more in CCTV deployments. Firstly, there was a change in the way
in which society perceived and utilized security systems (particularly CCTV). There
were also changes in peoples attitudes towards security in response to crime of all
types. The number of CCTV deployments and the overall interest in using CCTV for
security purposes was further encouraged by the rapid developments in the CCTV
technology market. Furthermore, there have been technical developments in video and
networking that transformed the way in which CCTV is being used. As a result, CCTV is
being applied to new application areas and there are a large number of CCTV owners
and a more heterogeneous group of users interacting with CCTV systems.
It has been a topic of debate for many years whether CCTV is effective or not. Several
studies in the field of criminology have examined the effectiveness of CCTV from a
sociological and political perspective - assessing whether CCTV has reduced, deterred
and/or displaced crime. Research has also been conducted to establish whether CCTV
35
EMILIO AGUINALDO COLLEGE
has made society feel safer and whether the technology works well enough to support
police activities (see the control room study by Gill et al., 2005: Chapter
2, Section 2.2). These studies are important, as they provide policy-makers (such as
Home Office and local authorities) with an understanding of CCTV and the key issues
which reduce the effectiveness of public surveillance systems. These studies do not
provide CCTV owners and consultants with meaningful guidance on how CCTV
systems can be improved in terms of effectiveness. Therefore, further research was
needed to examine both the social and technical factors surrounding CCTV design and
usage to develop objective and therefore quantifiable guidance.
A review of the research in HCI and security revealed that very few studies examine the
effectiveness of CCTV security from the CCTV users perspective and how their task
performance is affected by people and technology. The only study which looked at
performance to some extent was the CCTV effectiveness study by Gill et al., 2005. This
study identified a number of operator factors which reduced the effectiveness of CCTV:
low-quality equipment, too few operators, low operator to monitor/video display ratio,
insufficient operator training (these findings are discussed in more detail in
Chapter 2, Section 2.2).
Field studies at non-security control rooms which examine operator tasks, found that
operator performance is reduced as a result of poor configuration and maintenance of
equipment within the control room and the CCTV camera environment (see Chapter 2,
Section 2.3). In addition, operator performance was reduced as a result of ineffective
36
EMILIO AGUINALDO COLLEGE
peer-to-peer communication (McCarthy et al., 1997; Luff et al., 2000). The implications
of these findings were not discussed in much detail and the research was not taken
further to improve the way in which CCTV and other technologies are used by operators
within control rooms and other security work environments. Consequently, subsequent
CCTV system deployments are being ignored, the various problems within CCTV
control rooms and their designs still exist, and stakeholders are not paying attention to
these problems simply because they are not aware of the problems or solutions. The
field study carried out in this thesis identified a number of issues which were discovered
in the previous control room studies (see Chapter 4, Section 4.5.2), such as: 1)
operators being overloaded with too many CCTV cameras (Gill et al., 2005); 2) CCTV
video being recorded at low-quality (Gill et al., 2005); 3) an ineffective CCTV camera
environment (Luff and Heath, 2001); and 4) poor radio communication (McCarthy et al.,
1997). In addition to these findings, the field study presented in this thesis identified a
wider number of operator performance issues: operators being overloaded with audio
communication and other audio alerts; ineffective equipment set-up and layout;
ineffective camera and mapping systems; and various technical issues were identified
with CCTV cameras and operator radios. These findings are detailed in Chapter 4,
Section
4.4.2.5.
Prior to this field research (Chapter 4), there was a limited awareness and
understanding of what CCTV technology was being used for, and what security
37
EMILIO AGUINALDO COLLEGE
observation tasks were being performed by operators and other CCTV stakeholders.
The BS EN ISO 11064 standard (ISO, 2004) is the only guidance that considers the
human element of control room design. The standard is based on ergonomic principles
and provides guidance on the physical aspects of control rooms such as: workstation
arrangements, control room layout, use of displays and controls, and maintenance.
Additional guidance is needed which details human-centred guidance on the set-up of
digital CCTV and other technology used by human operators. Furthermore, greater
emphasis is required on the configuration of CCTV systems as a whole.
There has been little empirical research on the effectiveness of digital CCTV video for
security observation tasks performed by human observers. The guidance which does
exist (UK Home Office Operational Requirements: Aldridge, 1994; Cohen et al., 2007)
offers very limited guidance on digital and networked CCTV systems. A number of
empirical research studies have been conducted by human centered multimedia
researchers to assess the impact of video quality on human task performance with a
number of video applications. These studies were carried out to identify the minimum
video quality requirements for networked multimedia applications. In both Internet and
mobile applications and services, it is desirable to reduce the amount of bandwidth
needed without affecting the users perception and performance with the interface. This
type of evaluation has not been conducted for CCTV applications.
This thesis provides field and empirical research on the problems associated with CCTV
system design and specifically the performance limitations of digital CCTV video when
38
EMILIO AGUINALDO COLLEGE
used by human observers for security observation tasks. This research involved an
investigation which required reviewing a number of interdisciplinary areas related to
CCTV (HCI, psychology, computer science, sociology, human factors, as well as
legislation and guidelines). From the research findings, a number of substantive and
methodological contributions were made by applying HCI knowledge and methods to
improve CCTV practice, in particular the design and deployment of CCTV security
systems and their context of use.
These contributions have led to the development of a best-practice framework for CCTV
deployment (TEC-VIS), which provides guidance for a new CCTV deployment or a
redesign. Specific guidance isalso provided to CCTV owners on the configuration of
CCTV security systems (e.g., the users tasks, work environment and the technology
used to support their tasks).
Local Studies.
The maintenance of Peace and Order in Brgy 212 zone 19 Manila
(Jerome M. Mingo)
Base on the findings, the ff. conclusions were drawn
1.) The socio-demographic profile of the respondents which are the residents of
Brgy. 212 zone 19 Manila was good enough to obsereved the maintenance of
39
EMILIO AGUINALDO COLLEGE
peace and order to their barangay relatively with effective maintenance of peace
and order in the research locale of the study
2.) The maintenance of peac e and order in Brgy. 212 zone 19 Manila was effective
3.) The maintenance of the peace and order in Brgy. 212 zone 19 Manila was
meeting serious problem with regards to the implementation of the ordinances,
programs and campaigns.
4.) The is ni significant difference on the assessment of the respondents on the
extent of maintenance of peace and order of Brgy. 212 zone 19 Manila.
Recommendations
In the light of the above findings and conclusions, the ff. recommendations were
made:
1.) In the implementation of programs and campaigns the authorities should be more
responsible and serious so that the residents of the brgy should observe the
effort expert by the authorities.
2.) That those ordinances enacted and made the authorities are worth and for the
benefits or good of the members of the members of brgy. It should be effective to
maintain peace and order.
3.) The authorities in charge should be pro-active in for all violation and anticipation
of the elicit acts that would break and destroy the peace and order situation.
40
EMILIO AGUINALDO COLLEGE
4.) That those programs, campaigns and ordinances made by the authorities should
be versatile in making ordinances for the deterence to all offenders that the
desire is to break and destroy the peace and order situation.
5.) The authorities in charge should aware and observe if the ordinances are
productive and effective to maintain peace and order.
Crime prevention strategies in Roxas city: Impact to public safety
(Sebastian C. Caduco Jr.) 2005
Conclusion:
Based on the above findings, the following conclusions are drawn:
1.) Socio-demographic profile of police personnel
1.1)
Functional assignment
The police personnel assigned in concerned police agency have not
distributed according to the 85 percent and 15 percent and office
distribution ratio as prescribed by the police organization to enhance
police visibility.
1.2)
Police eligibility
All police personnel assigned at the concerned police agency were having
their appropriate eligibility, commensurate to their present ranks.
1.3)
Educational Qualification
41
EMILIO AGUINALDO COLLEGE
Majority of the police personnel assigned in concerned police agency were
college graduates, and some from them are not yet completing the four
year baccalauretate course as required by the police profession.
1.4)
Years in Police Service
Most of the police personnel assigned the concerned police station were
already acquired enough experience in policing activities, and very few the
considered novices in the police service.
1.5)
Highest Training Completed
All the police personnel assigned in the concerned police station have
already completed the highest training prescribed by their ranks, and as
required for promotion and permanency in the said ranks
2.1) Community Counseling
The concerned police agency was responsive in this particular
category, which this requires use of discretion in attending non-criminal conduct,
disposing of minor complaints.
2.2) Indefference of the public
The concerned police agency was meeting slightly serious problems in relation with this
particular category, especially the traditional apathy and negative attitude of the public
with the things that the police are doing.
2.3) Inter-Relationship with Society
42
EMILIO AGUINALDO COLLEGE
The concerned police agency was meeting slightly serious problems in relation with this
particular, more commonly the conflict arising out in the strict enforcement of the laws.
Recommendations
In the light the above finding and conclusions, the following recommendations are
made:
1. Strictly observe 85 percent and 15 percent distributions of police personnel
assigned in field and office duties to ensure a more decentralized concept of
policing activities for more reponsive crime prevention strategies, and encourage
undergraduate police personnel to complete repective formal degrees.
2. Develop linkages with other concerned local government agencies, and the local
government unit as well, and to forestall participation in the police decision
making process.
3. Activation of more police community precinct(PCP), and community action
centers(COMPACT), and continiously advocate the concept and philosophy of
community oriented policing system(COPS)
4. Similar study be conducted in another time and setting which will focus on the
extent of responsiveness of the crime prevention strategies, purposely to confirm
or negate the findings of the present study.
43
EMILIO AGUINALDO COLLEGE
Research Synthesis.
Above enumerated studies and literature were focused more on law enforcement, crime
prevention and elimination of factors that contribute in criminality, which also are the
similar characteristics of this study, that makes it related to studies enumerated above.
This study (The use of Modern Technologies in the Suppression of Crimes in Selected
Barangays in Tondo Manila) focused more on the methods utilized in the total
abolishment of criminality, effect of modernity in the investigation of crimes by utilizing
new materials and other techniques in crime suppression which were not tackled or
discussed in those related studies mentioned above that were all conducted by scalars
in the same field of study and profession.
44
EMILIO AGUINALDO COLLEGE
Chapter 3
RESEARCH METHODOLOGY
Research Design
In this research, the researcher will use a descriptive type of research in gathering data and
information. This type of research can effectively and accurately acquire information needed to
support the current study which can also give suggestions to answer the problems and
questions stated before. This is a collective type of data gathering to ensure that every opinion
of respondents was clearly and completely gathered.
The subject of the study
Setting:
Tondo is one of the sixteen areas of Manila, Philippines. The locale has existed
prior to the arrival of the Spaniards, referred to as "Tundun" on the Laguna Copperplate
Inscription. One of the most densely populated areas of land in the world. Tondo is
located in the northwest portion of the city and is primarily residential-industrial in
nature. Many of the city's slums are found in this area.
45
EMILIO AGUINALDO COLLEGE
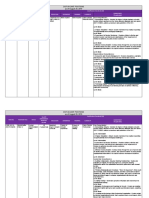
Figure 2
Research Locale
46
EMILIO AGUINALDO COLLEGE
Respondents
This study aims to determine the advantages of utilizing modern technologies in
Tondo, Manila. The respondents will be composed of active members of community
(preferably of legal age) residing and constantly aware of events and happenings in the
locality, Personnel of Police Stations 1 and 7 involve in the investigation, prosecution,
and suppression of crimes within the area of Tondo, Barangay Officials in different
Barangay community in Tondo preferably those who are utilizing modern technologies
in their fight against criminality.
Sampling Technique.
Purposive sampling will be utilized in this research. Within the population
sample there would be sample representative, depending on his opinion or purpose,
thus being the representation subjective.
Sampling size
1.
2.
3.
SAMPLES
A (Residents)
B (Law Enforcers)
C (Brgy Officials)
TOTAL =
47
QUANTITY
60
20
20
100
EMILIO AGUINALDO COLLEGE
Research Instrument
This study will be utilizing a survey questionnaire made by the researcher and will be
validated by the experts. This is composed of four parts. The first part includes items
that will determine the Profile of the respondents in terms of age, gender, civil status,
educational attainment and length of stay in the community. The second part involves
the Respondents assessment regarding the Common Crimes committed in the
community. The next part aims to determine the perception of the respondents relative
to the advantages of utilizing modern technologies relative to crime prevention and
suppression, and finally the last part will aim to determine the Modern Technologies as
recommended by the respondents which for them are necessary for the enhancement
of security in selected Barangays in Tondo Manila
48
EMILIO AGUINALDO COLLEGE
Data Collection Procedures
The researchers will conduct study in selected barangays in Tondo Manila to
obtain all details regarding crimes which are usually committed in the area of study, all
pertinent data of the respondents and also the respondents recommended modern
technologies necessary for the enhancement of security in selected Barangays in
Tondo Manila.
The questionnaires were the main instruments for data gathering which were
personally distributed by the researcher himself. They contained a covering letter
describing the study and indicating the confidentiality of the information that may be
given out by the respondents.
49
EMILIO AGUINALDO COLLEGE
STATISTICAL DESIGN
In the computation of the responses, percentage formula and weighted
percentage mean will be used in the tabulation of data.
Percentage Formula
P=F/N x 100
Where:
P = percentage
F = frequency
N = number of respondents
Weighted Mean Formula
WM = TWV/TF
Where:
WM = weighted mean
TWV = total weighted value
TF
= total frequency/number of respondents
50
Vous aimerez peut-être aussi
- G1 Research Chapter 1 4Document112 pagesG1 Research Chapter 1 4Shannen Roz UrbiztondoPas encore d'évaluation
- Group6 Chapters1234&5Document75 pagesGroup6 Chapters1234&5Desh ElzenPas encore d'évaluation
- Crim 2016 003 PDFDocument14 pagesCrim 2016 003 PDFMharisol BalaisPas encore d'évaluation
- Naga City Crime Prevention Strategies, Implementation and ImpactDocument3 pagesNaga City Crime Prevention Strategies, Implementation and ImpactFrederick EboñaPas encore d'évaluation
- Problems Encountered by Police Personnel in Conducting DrugsDocument4 pagesProblems Encountered by Police Personnel in Conducting DrugsGeran Rhey Pector RamosoPas encore d'évaluation
- List of 2010-2011 CriminologyDocument4 pagesList of 2010-2011 CriminologyArman Domingo75% (4)
- Thesis FinalistDocument42 pagesThesis FinalistAngelica Pilapil100% (1)
- CRIME-RATE-VICTORIA EditedDocument11 pagesCRIME-RATE-VICTORIA Editedroneldayo62Pas encore d'évaluation
- Front Page ThesisDocument46 pagesFront Page ThesisStephanie Torres Academia100% (1)
- Title FinalDocument5 pagesTitle FinalJusiah Mae Janolino Tabangan IIPas encore d'évaluation
- Assessment of Crime Prevention Programs of Selected Barangays in Cabanatuan CityDocument5 pagesAssessment of Crime Prevention Programs of Selected Barangays in Cabanatuan CityInternational Journal of Innovative Science and Research Technology100% (1)
- Criminological Research: Laguna State Polytechnic UniversityDocument80 pagesCriminological Research: Laguna State Polytechnic UniversityEuneel Escala100% (2)
- 1 The Problem and Its SettingDocument47 pages1 The Problem and Its SettingHaha HohoPas encore d'évaluation
- Problems Encountered by Police PersonnelDocument34 pagesProblems Encountered by Police PersonnelAG1LE100% (1)
- The Impact of Community Policing On Crime Prevention in Barangay WesternDocument7 pagesThe Impact of Community Policing On Crime Prevention in Barangay WesternAbdul majeed SaripadaPas encore d'évaluation
- Community Policing...Document146 pagesCommunity Policing...Nell100% (1)
- Lived Experiences of Licensed Criminologist Graduates of Jose Rizal Memorial State University-Tampilisan CampusDocument2 pagesLived Experiences of Licensed Criminologist Graduates of Jose Rizal Memorial State University-Tampilisan CampusRinna Rain100% (1)
- RRLDocument2 pagesRRLEzra gambican100% (1)
- Effectiveness of Mandatory Reserve OfficerDocument3 pagesEffectiveness of Mandatory Reserve OfficerMichael James AnanayoPas encore d'évaluation
- Level of Effectivity of CCTV Systems in Crime PreventionDocument17 pagesLevel of Effectivity of CCTV Systems in Crime PreventionJaeann Clarke Agan100% (1)
- TUCDM-Chapter-1-5 (복구됨) gandaDocument46 pagesTUCDM-Chapter-1-5 (복구됨) gandaDayson Angela100% (1)
- University of Cagayan Valley Senior High SchoolDocument21 pagesUniversity of Cagayan Valley Senior High SchoolELMA MALAGIONAPas encore d'évaluation
- Final Chapter 1-5 PatrollingDocument61 pagesFinal Chapter 1-5 Patrollingchristine dela cruz50% (2)
- RRLDocument12 pagesRRLDaylene DelebiosPas encore d'évaluation
- Thesis Group 2Document6 pagesThesis Group 2Michael Dimayuga100% (8)
- Thesis - Garcia, OropesaDocument11 pagesThesis - Garcia, OropesaJ Navarro100% (1)
- Local LiteratureDocument12 pagesLocal LiteratureKen Mitchell Morales100% (1)
- Thesis EditedDocument16 pagesThesis EditedCarol Jane Abalos DechosPas encore d'évaluation
- Jose Rizal University College of Liberal Arts, Criminology & EducationDocument39 pagesJose Rizal University College of Liberal Arts, Criminology & EducationRanier Factor Aguilar100% (1)
- Chapter 1Document13 pagesChapter 1Zuriel Docallas100% (1)
- Group 3 Chapter 1 5Document70 pagesGroup 3 Chapter 1 5A plus Educational CenterPas encore d'évaluation
- Eng-10 RRLDocument12 pagesEng-10 RRLMary MaePas encore d'évaluation
- Peacekeeping Action Team in Crime Prevention of Selected Villages in Cebu City PhilippinesDocument9 pagesPeacekeeping Action Team in Crime Prevention of Selected Villages in Cebu City PhilippinesIJARP Publications100% (1)
- Final Case StudyDocument25 pagesFinal Case StudyShannen Roz UrbiztondoPas encore d'évaluation
- The Assessment of Performance of PolicemDocument37 pagesThe Assessment of Performance of Policemlargil taojo100% (2)
- Thesis Final DawDocument44 pagesThesis Final DawGabriel Casiple83% (6)
- Final ManuscriptDocument73 pagesFinal ManuscriptLeu Gim Habana PanuganPas encore d'évaluation
- List of Criminology Thesis PDFDocument5 pagesList of Criminology Thesis PDFMichael V ValientePas encore d'évaluation
- Thesis Criminology 2Document47 pagesThesis Criminology 2Maria fe PerezPas encore d'évaluation
- Implementation and Effectiveness of Police Checkpoint in Cotabato CityDocument7 pagesImplementation and Effectiveness of Police Checkpoint in Cotabato CityPsychology and Education: A Multidisciplinary JournalPas encore d'évaluation
- Police Visibility in The Prevention of Crime PreventionDocument4 pagesPolice Visibility in The Prevention of Crime PreventionDarcknyPusodPas encore d'évaluation
- Lowering of MACR Thesis - Modified 20191206Document30 pagesLowering of MACR Thesis - Modified 20191206Jerry EspinosaPas encore d'évaluation
- PNP Dumalinao Community Relation Programs: Its Impact To Effective Crime PreventionDocument16 pagesPNP Dumalinao Community Relation Programs: Its Impact To Effective Crime PreventionElla BanlasanPas encore d'évaluation
- KBPATcaseDocument19 pagesKBPATcaseCristyl Vismanos GastaPas encore d'évaluation
- Attitude and Perception of CriminologyDocument13 pagesAttitude and Perception of CriminologyGADOR JEEZYL100% (1)
- Thesis Final DependDocument14 pagesThesis Final DependLeia Grace Elaine100% (6)
- Index Crime Analysis in Metro Angeles - Mabalacat A Comparative StudyDocument34 pagesIndex Crime Analysis in Metro Angeles - Mabalacat A Comparative StudyronaldPas encore d'évaluation
- FINAL CHAPTER 1-5.editedDocument58 pagesFINAL CHAPTER 1-5.editedchristine dela cruzPas encore d'évaluation
- Factors That Influenced and Problems Encountered in The Criminologist Licensure ExaminationDocument12 pagesFactors That Influenced and Problems Encountered in The Criminologist Licensure ExaminationInternational Journal of Innovative Science and Research TechnologyPas encore d'évaluation
- Republic Act Number 11131: The Criminology Profession Act of 2018Document18 pagesRepublic Act Number 11131: The Criminology Profession Act of 2018Shrwn Go ChocoPas encore d'évaluation
- The Impact of Height Qualification On The Self-Esteem of NEMCO's Criminology StudentDocument12 pagesThe Impact of Height Qualification On The Self-Esteem of NEMCO's Criminology StudentBenmark Jabay100% (1)
- Chapter 5 TheftDocument4 pagesChapter 5 TheftjmarPas encore d'évaluation
- Crime Prevention and Community Safety Among Residents in Tagum CityDocument22 pagesCrime Prevention and Community Safety Among Residents in Tagum CityAnthony NugasPas encore d'évaluation
- Cagayan de Oro College.2Document10 pagesCagayan de Oro College.2Jenevie DecenillaPas encore d'évaluation
- Best Practices of Tarlac State University College of Criminal Justice Education in Maintaing The Status of Top Performing SchoolDocument14 pagesBest Practices of Tarlac State University College of Criminal Justice Education in Maintaing The Status of Top Performing SchoolChabelita Gomez Feliciano100% (1)
- The Problem and Its Background Rationale: Pangasinan State UniversityDocument64 pagesThe Problem and Its Background Rationale: Pangasinan State UniversitySweet jenesie MirandaPas encore d'évaluation
- Index Crime Paradigm Abstract AcknowledgmentDocument7 pagesIndex Crime Paradigm Abstract AcknowledgmentronaldPas encore d'évaluation
- Online Stalking and Online Activities: An evaluation of risks and their perceptionD'EverandOnline Stalking and Online Activities: An evaluation of risks and their perceptionPas encore d'évaluation
- Abihays GroupsDocument25 pagesAbihays GroupsWeng Ching KapalunganPas encore d'évaluation
- Case Digest (Free Telephone Workers Union Vs Honorable Minister of LaborDocument2 pagesCase Digest (Free Telephone Workers Union Vs Honorable Minister of LaborGjenerrick Carlo MateoPas encore d'évaluation
- Testamentary Succession CasesDocument69 pagesTestamentary Succession CasesGjenerrick Carlo MateoPas encore d'évaluation
- Oblicon Last Part 1Document85 pagesOblicon Last Part 1Gjenerrick Carlo MateoPas encore d'évaluation
- Mateo - VICTORIANO Vs ELIZALDE ROPE WORKERS UNION Case DigestDocument2 pagesMateo - VICTORIANO Vs ELIZALDE ROPE WORKERS UNION Case DigestGjenerrick Carlo MateoPas encore d'évaluation
- Case Digests Treaties To JurisdictionDocument6 pagesCase Digests Treaties To JurisdictionGjenerrick Carlo MateoPas encore d'évaluation
- Legal Ethics REVIEWERDocument41 pagesLegal Ethics REVIEWERGjenerrick Carlo MateoPas encore d'évaluation
- First Optima Realty CorporationDocument10 pagesFirst Optima Realty CorporationGjenerrick Carlo MateoPas encore d'évaluation
- Case Digest For Crim 2 Ocotber 4 2019Document12 pagesCase Digest For Crim 2 Ocotber 4 2019Gjenerrick Carlo MateoPas encore d'évaluation
- Pci Leasing and FinanceDocument6 pagesPci Leasing and FinanceGjenerrick Carlo MateoPas encore d'évaluation
- G.R. NO. 192105 December 9, 2013 ANTONIO LOCSIN, II, Petitioner, Mekeni Food Corporation, RespondentDocument5 pagesG.R. NO. 192105 December 9, 2013 ANTONIO LOCSIN, II, Petitioner, Mekeni Food Corporation, RespondentGjenerrick Carlo MateoPas encore d'évaluation
- PnocDocument8 pagesPnocGjenerrick Carlo MateoPas encore d'évaluation
- Case AssignmentsDocument27 pagesCase AssignmentsGjenerrick Carlo MateoPas encore d'évaluation
- In The Matter of Save The Supreme Court Judicial Independence UK 15143Document2 pagesIn The Matter of Save The Supreme Court Judicial Independence UK 15143Gjenerrick Carlo MateoPas encore d'évaluation
- Obli Assigned CasesDocument89 pagesObli Assigned CasesGjenerrick Carlo MateoPas encore d'évaluation
- Training Critical Thinking For Tactical Command: April 2004Document12 pagesTraining Critical Thinking For Tactical Command: April 2004Gjenerrick Carlo MateoPas encore d'évaluation
- Dof Vacant Positions As of August 20, 2019: Salary Grade/Basic Monthly Salary Qualification Standards (QS)Document34 pagesDof Vacant Positions As of August 20, 2019: Salary Grade/Basic Monthly Salary Qualification Standards (QS)Gjenerrick Carlo MateoPas encore d'évaluation
- Resident Marine Mammals of The Protected Seascape of Tañon Strait v. Secretary Angelo ReyesDocument2 pagesResident Marine Mammals of The Protected Seascape of Tañon Strait v. Secretary Angelo ReyesAlicia BanhagPas encore d'évaluation
- Professional Regulation CommissionDocument1 pageProfessional Regulation CommissionGjenerrick Carlo MateoPas encore d'évaluation
- Computational FormulasDocument2 pagesComputational FormulasGjenerrick Carlo MateoPas encore d'évaluation
- MdteuDocument3 pagesMdteuGjenerrick Carlo MateoPas encore d'évaluation
- National Headquarters, Philippine National Police Directorate For Investigation and Detective ManagementDocument3 pagesNational Headquarters, Philippine National Police Directorate For Investigation and Detective ManagementGjenerrick Carlo MateoPas encore d'évaluation
- Criminological Theories (Socio View)Document26 pagesCriminological Theories (Socio View)Gjenerrick Carlo MateoPas encore d'évaluation
- Robert Garigue CISO BriefingDocument63 pagesRobert Garigue CISO Briefingadityagour2394Pas encore d'évaluation
- Group 3 (Data Security and Privacy in Nursing Informatics)Document14 pagesGroup 3 (Data Security and Privacy in Nursing Informatics)sameer.hamdanPas encore d'évaluation
- Executive Risk Description ListDocument16 pagesExecutive Risk Description ListRemyaPas encore d'évaluation
- Running Head: Ethical Hacking Paper 1Document11 pagesRunning Head: Ethical Hacking Paper 1Aayush GargPas encore d'évaluation
- EY - Protecting Your Data PDFDocument8 pagesEY - Protecting Your Data PDFlateshv2728Pas encore d'évaluation
- Computer Security Strength & Risk: A Quantitative ApproachDocument156 pagesComputer Security Strength & Risk: A Quantitative Approachshamsu_qPas encore d'évaluation
- M04 - Providing Network Systems AdministrationDocument75 pagesM04 - Providing Network Systems Administrationabenezer abitiPas encore d'évaluation
- What Is A Hacker, Really?: Types of Hacking/HackersDocument3 pagesWhat Is A Hacker, Really?: Types of Hacking/HackersEba GobenaPas encore d'évaluation
- Acc400 Chapter 8 Quiz Note FileDocument6 pagesAcc400 Chapter 8 Quiz Note Filemad_hatter_Pas encore d'évaluation
- Research PaperDocument29 pagesResearch PaperDiana CortezPas encore d'évaluation
- 29 GIS SeismicDocument6 pages29 GIS SeismicKhader Abu-daggaPas encore d'évaluation
- Policy Template Guide: NIST Cybersecurity FrameworkDocument17 pagesPolicy Template Guide: NIST Cybersecurity FrameworkHesham Elsayed100% (1)
- Vulnerability Assessment and Critical Control Points For Food FraudDocument2 pagesVulnerability Assessment and Critical Control Points For Food FraudYann RouchonPas encore d'évaluation
- Policy Information-Best Practice Controls For Malware Ransomware PreventionDocument406 pagesPolicy Information-Best Practice Controls For Malware Ransomware PreventionPauloPas encore d'évaluation
- iOT Security GuidelineDocument53 pagesiOT Security Guidelinediffusi0nPas encore d'évaluation
- Analisis Active DirectoryDocument1 137 pagesAnalisis Active DirectoryNelson TorresPas encore d'évaluation
- CMMI CP Model Development ApproachDocument15 pagesCMMI CP Model Development ApproachMarco Antonio AgnesePas encore d'évaluation
- Cyber Security - I.ravi KumarDocument38 pagesCyber Security - I.ravi KumarMr. RAVI KUMAR IPas encore d'évaluation
- CNIL PIA 1 MethodologyDocument19 pagesCNIL PIA 1 MethodologyMarko PetricPas encore d'évaluation
- POC RAPIDPoint500eSecurity WhitePaper SNG 1800000006868047Document16 pagesPOC RAPIDPoint500eSecurity WhitePaper SNG 1800000006868047MostafaMahmoudAhmedPas encore d'évaluation
- AIN1501 Study ContentDocument211 pagesAIN1501 Study ContentNaadhirah LoonatPas encore d'évaluation
- Splunk and The SANS Top 20 Critical Security ControlsDocument65 pagesSplunk and The SANS Top 20 Critical Security ControlsAnonymous Vo0jGODNQ5Pas encore d'évaluation
- Welcome To The User Awareness Training of Isms ISO/IEC 27001:2005Document64 pagesWelcome To The User Awareness Training of Isms ISO/IEC 27001:2005Rajendra ThuvarakanPas encore d'évaluation
- Infosecurity Professional Magazine Issue 20Document27 pagesInfosecurity Professional Magazine Issue 20oddfeverPas encore d'évaluation
- 06 Risk Assessment and Treatment Process 1667748676Document20 pages06 Risk Assessment and Treatment Process 1667748676Raj Thakur100% (1)
- Ashutosh Jain (CISA-Qualified, CEH, M.SC IT)Document2 pagesAshutosh Jain (CISA-Qualified, CEH, M.SC IT)Amit KumarPas encore d'évaluation
- A Systematic Review of Cybersecurity Risks in HighDocument40 pagesA Systematic Review of Cybersecurity Risks in HighTugas SekolahPas encore d'évaluation
- Sast, Dast and Vulnerability Assessments, 1+1+1 4: Gordon MackayDocument30 pagesSast, Dast and Vulnerability Assessments, 1+1+1 4: Gordon MackayFillipe AlvesPas encore d'évaluation
- CIS CAS ControlsDocument191 pagesCIS CAS Controlsgamal abdelazizPas encore d'évaluation
- Cisco Lead2pass 200-201 Sample Question 2022-Dec-26 by Barton 88q VceDocument12 pagesCisco Lead2pass 200-201 Sample Question 2022-Dec-26 by Barton 88q VcepjaironPas encore d'évaluation