Académique Documents
Professionnel Documents
Culture Documents
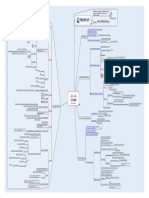
Certified Ethical Hacking Module 5 Map
Transféré par
Rismal Ray VaughanCopyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Certified Ethical Hacking Module 5 Map
Transféré par
Rismal Ray VaughanDroits d'auteur :
Formats disponibles
Use Attrib +h [file/directory] Attrib.
exe
Allows data to be stored in hidden files
that are linked to a normal visible file Two ways of hiding files in NT/2000
Hides hidden.txt within test.txt NTFS Alternate Data Streaming
notepad test.txt:hidden.txt
test.txt has to already exist
The process of hiding data within images
Windows App
Simple encrypt/decrypt of data Image Hide
No increase in image size
Hides information within an .mp3 file
Mp3stego
Hidden in the mp3 bit stream
Whitespace steganography program
Snow.exe Tools
Hides data in ASCII text by appending
whitespace to the end of lines Steganography
Windows App
Easy to use
Hides data in GIF images Camera/Shy Hiding Files
To view the messages live on the web Comes with its own browser app
Automated tool for detecting
steganographic content in images Stegdetect Countermeasures
Moves the contents of a file to ids data
strem makestrm.exe
Tools
Packetstorm utility to write files to the NTFS ADS
ads_cat
Contains utilities to add, extract and remove ADS
Displays NTFS files that have ADS streams
Lists files with ADS List ADS
Countermeasures
One manual way to remove a stream is to
copy the file to a FAT partition, then back.
FAT Copy
This removes the stream
Spyware can install remote Motivation and Study Techniques to help Cisco
Also known as rootkits control and backdoors you learn, remember, and pass your
CISSP
technical exams!
Screen capture CEH
Keystroke logging Usually these tools offer multiple different More coming soon...
ways of interacting with a filesystem
Microphone enable
Log file analysis Visit us www.mindcert.com
Spector
eBlaster
Software that interacts with the OS Remote Control and Subscribe via RSS
Replaces core functions within the OS Tools Backdoors
Good at hiding its existence RootKit
Windows
Available for NetBIOS Port
Unix
Most effective method o breaking into Windows is Password guessing
Detects and removes Spector from your system Anti-Spector
Assuming TCP Port 139 is open
Tools IPC$
Detects and removes spy software Countermeasures
Spyguard Connect to an enumerated share C$
Default Admin shares
Admin$
Once intruders have gained access they administrator same as root under UNIX
The default admin account is
will need to cover their tracks Administrator Password
Intruders will normally install Sometimes has a blank password
Backdoors so they can always
Create or use a username/password file
come back to the machine using
a covert channel FOR /F "token=1, 2*" %1 in
Can use a simple DOS Shell script
Automated password guessing (credentials.txt)
These normally include looking at logs Build a script using the FOR command
do net use \\target\IPC$ %i /u: %j
Therefore, logs are always sanitized or To cover tracks you have to look
cleared down totally. at general sys admin activities
Windows application
Sometimes, the intruder actually
disables logging totally Automates password guessing for
Legion NetBIOS sessions
Comes with NT/2000 Resource Kit Remote Password Guessing Scans multiple Class C addresses
Command line util to find out audit
Manual dictionary attack tool
status of a target machine Auditpol.exe Tools
c:\>auditpol \\<ip address of target> Windows tool
Can be run over the network
Now Cerberus Internet Scanner
Comes with NT/2000 Resource Kit Covering Tracks NTInfoscan (now CIS)
Vulnerability Scanner designed for NT4
Dumps and event log for a local or Will check NetBIOS shares
Produces a tab delimited CSV file remote system Dumpel.exe
Block access to TCP and UDP Ports 135 to 139
Lets the intruder know what is in the logs
Tools Disable WINS client on all adapters
Simple tool for clearing the event logs
on Windows/2000 Use strong passwords Or two factor authentication
eslave.exe
Correct privileges are required on the remote system
Countermeasures Security Log
Selectively erases records from the
Win 2000 security log Event 529 or 539
Command line application WinZapper Log failed logon attempts
From Foundstone
Needs admin rights VisualLast
Look at a logging application Visual Log manager
GUI commercial system for Windows
Evidence Eliminator
Counters all privacy issues
Eavesdropping is sniffing the
passwords from the network segment Subtopic
Find a valid user
Create a list of possible passwords Switch ports by default only see your
To eavesdrop you have to be traffic and broadcasts Have to use a tool to get around this
Ken in each password
Manual Password Cracking able to sniff all VLAN traffic
Success Hubs forward all frames out of all ports
If the system allows you in
Telnet
Try again Else Some passwords are unencrypted POP3
etc..
Find a valid user
Algorithms Certified Ethical Hacker Collect these passwords and hashes and
Find encryption algorithms used
Module 5 - System Hacking Some passwords are encrypted then run attacks against them offline
Obtain encrypted passwords
Create list of possible passwords
Automatic Password Cracking Eavesdropping Windows Application
Encrypt each word
Password auditing and recovery tool
Success See if it works LOphtcrack Captures individual login sessions
SMB Packet capture listens to the local
network segment Uses either Dictionary
Try again Else Attacks the 24 byte hashed password
Or Brute Force attacks
Easiest to crack Tools
Only letters Windows command line application
Only numbers Listens on the network and captures
KerbCrack kerbsniff 2000/XP kerberos logins
Only special characters
Conists of two programs
Harder to crack Letters and numbers Uses dictionary or brute force to crack the password
Password Types kerbcrack
Letters and special characters
Numbers and special characters Sending a NetBIOS name release to the
Most secure passwords NetBIOS name service (UDP 137)
Letters, numbers, and special characters places the name in conflict No longer able to use it
Using a dictionary of words Blocks the client from participating in
Dictionary attack nbname
Tools the NetBIOS network
Or a wordlist
Denial of Service Carries out a NetBIOS DoS attack
Going through all possible combinations
Brute force attack Crashes computers running Windows 2000/XP/NT
Eventually Will always work SMBDie
Sends a specially crafted SMB request
A mixture of dictionary and brute force attacks Hybrid attack Password Attacks
It is important to gain root or
Ask the user for there password Social engineering administrative level access
Once hacker has access to a system May have gained access with a non
Look over there shoulder Shoulder surfing admin account
Try to find password evidence in trash Small .exe that adds a user to the local admin
Dumpster diving
group
NT/2000/XP Windows clients by default send LM Privilege Escalation Need to logon to the server console
GetAdmin
and NTLM password hashes Run from the command line
Win9x Clients only send LM hashes Tools
Only works on NT4.0 SP3
123ANDREW First converted to Uppercase
Exposes a LPC Flaw in NT
hk.exe
Password is padded with null characters to Escalates a non admin user to an admin user
123ANDREW_____ make it a 14 character length
Your password is 123andrew Lan Manager Hashes
123ANDR Example Log all keyboard activity
The 14 character string is split in two halves
EW_____ Physical devices that are connected to
Hardware the keyboard port
Each string is encrypted and the Password Cracking
results concatenated Types
Applications that have to be installed
Subtopic Software on a users machine
SAM file in NT/2000 contains the Hardware Keystroke logger
usernames and encrypted passwords Keystroke Loggers Keyghost
USB or PS2
C:\windows\system32\config
Bootable Linux distribution Windows software
Such as Backtrack Tools
Boot to an alternate OS Invisible to the user
IKS Software Keylogger
Mount the drive Then dumps this to a configurable
NT/2000 Passwords Buffer of 100 keystrokes text file on the machine
In the repair directory Called SAM._
Backup the SAM from the Repair directory File is locked when OS running
Cracking Passwords
use c:\expand same._sam Expand the file
Use L0phtcrack Extract the hashes from the files
Send an email with a link Trick the user into trying SMB
authentication against the attacker
Embed code etc..
Redirecting SMB to the Attacker
But the attacker has the encrypted credentials The SMB authentication will fail
SMB server to capture usernames and
passwords from incoming SMB traffic
Man in the Middle attacks (MITM)
Can relay the traffic to another server
to provide a MITM attack SMBRelay
Receives a connection on port 139
These are then extracted with L0phtcrack Collects NTLM password hashes to a text file
Increases speed of L0phtcrack
Removes duplication SMBGrind
Provides facility to target specific users Tools
Registers a NetBIOS name on the network
Helps resolve IP address from NetBIOS name NBTDeputy
Works well with SMBRelay
Windows and Unix Command line tools
Cracks both Unix and Windows passwords
John the Ripper
Extremely fast
May not reflect correct password Resulting Passwords are Case Insensitive
Enforce 7-12 character alpha-numeric
passwords
Set the password expiration policy to 30 days
Physically isolate and protect the server Countermeasures
Syskey initiates 128 bit encryption for the SAM Use the "syskey" utility
Monitor all server logs for password attacks
Vous aimerez peut-être aussi
- Cyber-Attacks and Cybersecurity The Pressing Need For The LatterDocument4 pagesCyber-Attacks and Cybersecurity The Pressing Need For The LatterInternational Journal of Innovative Science and Research TechnologyPas encore d'évaluation
- CA Module 1Document23 pagesCA Module 1Zahir MuhammedPas encore d'évaluation
- Cyber Security in AfricaDocument5 pagesCyber Security in AfricaBlack Hat HackerPas encore d'évaluation
- Paper Information SecurityDocument12 pagesPaper Information SecurityKaleb SiahaanPas encore d'évaluation
- Master cyber risks with an IBM-powered cybersecurity degreeDocument4 pagesMaster cyber risks with an IBM-powered cybersecurity degreehemant mohitePas encore d'évaluation
- Cyber SecurityDocument22 pagesCyber SecurityCarey HallPas encore d'évaluation
- Defensive Cyber Operations Technical Advisor A Complete Guide - 2021 EditionD'EverandDefensive Cyber Operations Technical Advisor A Complete Guide - 2021 EditionPas encore d'évaluation
- Mobile Security Risks: Who's ListeningDocument37 pagesMobile Security Risks: Who's ListeningvinodkunmarPas encore d'évaluation
- Excellent Presentation On Cyber SecurityDocument61 pagesExcellent Presentation On Cyber SecurityDr Dheeraj Mehrotra80% (5)
- Malware Protection EbookDocument20 pagesMalware Protection Ebookmarcelo santiniPas encore d'évaluation
- CYBERSECURITYDocument22 pagesCYBERSECURITYmichellebulgar0Pas encore d'évaluation
- Data Network Threats and Penetration TestingDocument5 pagesData Network Threats and Penetration TestingJournal of Telecommunications100% (1)
- CyberSecurityDocument48 pagesCyberSecuritySuraj DasPas encore d'évaluation
- Cyber Security AwarenessDocument40 pagesCyber Security AwarenessAbhsihekPas encore d'évaluation
- The Threat Environment: Attackers and Their AttacksDocument8 pagesThe Threat Environment: Attackers and Their AttacksbseosPas encore d'évaluation
- ATTACK Design and Philosophy 2020Document46 pagesATTACK Design and Philosophy 2020Free FoxPas encore d'évaluation
- Cybersecurity Course Quiz With AnswersDocument2 pagesCybersecurity Course Quiz With AnswersTarik AmezianePas encore d'évaluation
- Computer Security Vulnerabilities A Complete Guide - 2020 EditionD'EverandComputer Security Vulnerabilities A Complete Guide - 2020 EditionPas encore d'évaluation
- Information Security Architecture Standard RequirementsD'EverandInformation Security Architecture Standard RequirementsPas encore d'évaluation
- Infysec TrainingDocument2 pagesInfysec Trainingvivekgandhi7k7Pas encore d'évaluation
- Cybersecuritypedia - Ethical Hacking Questions and AnswersDocument33 pagesCybersecuritypedia - Ethical Hacking Questions and Answersmayurigupta007Pas encore d'évaluation
- Report FirewallDocument27 pagesReport FirewallAbas WaniPas encore d'évaluation
- In Cybersecurity, Best Practices Are The WorstDocument4 pagesIn Cybersecurity, Best Practices Are The WorstKelvin LamPas encore d'évaluation
- Smokescreen Illusion Black: Benefits of Using Deception TechnologyDocument6 pagesSmokescreen Illusion Black: Benefits of Using Deception TechnologyPrasad KshirsagarPas encore d'évaluation
- Microsoft Digital Defense Report 2022Document114 pagesMicrosoft Digital Defense Report 2022selenePas encore d'évaluation
- MCE Cybersecurity ForensicDocument105 pagesMCE Cybersecurity Forensicgowdanischith03Pas encore d'évaluation
- Indonesia Cyber Security Strategy 2020Document37 pagesIndonesia Cyber Security Strategy 2020Kelabang Hero100% (1)
- The Pocket Guide To Cyber SecurityDocument61 pagesThe Pocket Guide To Cyber Securityguacharo20045585100% (2)
- Cyber Crime and LawDocument47 pagesCyber Crime and LawMtPas encore d'évaluation
- Threat ModellingDocument3 pagesThreat ModellingayeshashafeeqPas encore d'évaluation
- Inmarsat BGAN Terminal Comparison PDFDocument2 pagesInmarsat BGAN Terminal Comparison PDFJoel BarbaraPas encore d'évaluation
- Course VIII Advanced Cyber Security TechniquesDocument288 pagesCourse VIII Advanced Cyber Security Techniquesسلام امانPas encore d'évaluation
- Cloud Computing Security IssuesDocument23 pagesCloud Computing Security IssuesAdarsh Varma100% (1)
- XMPP Presentation 160108105545 PDFDocument17 pagesXMPP Presentation 160108105545 PDFRiska AAPas encore d'évaluation
- Cyber SecurityDocument4 pagesCyber SecurityAPas encore d'évaluation
- Identifying and Mitigating Cyber Threats To Financial Systems - The MITRE CorporationDocument3 pagesIdentifying and Mitigating Cyber Threats To Financial Systems - The MITRE CorporationSgt2Pas encore d'évaluation
- The Future of Cyber SecurityDocument51 pagesThe Future of Cyber SecurityStephen LahanasPas encore d'évaluation
- Cyber Security Term Paper 2018-Odd: Hardware Attacks Allow Greater AccessDocument13 pagesCyber Security Term Paper 2018-Odd: Hardware Attacks Allow Greater AccessVinay BharwaniPas encore d'évaluation
- Cybersecurity ReportDocument100 pagesCybersecurity ReportAnonymous QlJjisdlLIPas encore d'évaluation
- CISEv2-Learn Ethical HackingDocument6 pagesCISEv2-Learn Ethical HackingDinesh Chauhan100% (1)
- Social Engineering and Its ImportanceDocument12 pagesSocial Engineering and Its ImportanceSean AndyPas encore d'évaluation
- Unit-5 Cybersecurity: Organizational Implications: IV-II SEM CSE, Cyber Security Unit - VDocument13 pagesUnit-5 Cybersecurity: Organizational Implications: IV-II SEM CSE, Cyber Security Unit - VLakshmi Narayana ReddyPas encore d'évaluation
- CompTIA ActualTests CAS-002 v2017-03-07 by Cyrenity-Windsword 465q PDFDocument239 pagesCompTIA ActualTests CAS-002 v2017-03-07 by Cyrenity-Windsword 465q PDFAleksandarOrdanoskiPas encore d'évaluation
- An Overview of Cybercrime in India: February 2012Document11 pagesAn Overview of Cybercrime in India: February 2012qwerty12345678909876Pas encore d'évaluation
- Learn Cyber SecurityDocument1 pageLearn Cyber SecurityPHẠM MINH TRÍPas encore d'évaluation
- Cloud Security Strategy A Complete Guide - 2021 EditionD'EverandCloud Security Strategy A Complete Guide - 2021 EditionPas encore d'évaluation
- Windows XP Privilege Escalation ExploitDocument3 pagesWindows XP Privilege Escalation Exploitgauth92Pas encore d'évaluation
- Securing Linux Servers For Service Providers: December 21, 2001Document55 pagesSecuring Linux Servers For Service Providers: December 21, 2001mustang431Pas encore d'évaluation
- Cloud Security Compliance A Complete Guide - 2021 EditionD'EverandCloud Security Compliance A Complete Guide - 2021 EditionPas encore d'évaluation
- ACS Cybersecurity Guide PDFDocument72 pagesACS Cybersecurity Guide PDFAkshrayKcPas encore d'évaluation
- MindCert Cisco IPsec MindMap PDFDocument1 pageMindCert Cisco IPsec MindMap PDFzinzinPas encore d'évaluation
- Security awareness training essentialsDocument12 pagesSecurity awareness training essentialsNenad Bulatović100% (1)
- Ultra-Low Latency Market DataDocument4 pagesUltra-Low Latency Market DataQuanthousePas encore d'évaluation
- Ccna Security NotesDocument8 pagesCcna Security NotesluyandaPas encore d'évaluation
- Week 7 - The Dark Web and Its Impact On SecurityDocument20 pagesWeek 7 - The Dark Web and Its Impact On SecurityGo YarPas encore d'évaluation
- Developing A National Strategy For CybersecurityDocument24 pagesDeveloping A National Strategy For CybersecurityMSFTSIRPas encore d'évaluation
- Towards Resilient Machine Learning For Ransomware Detection - 1812.09400Document10 pagesTowards Resilient Machine Learning For Ransomware Detection - 1812.09400somnath_iiiPas encore d'évaluation
- Human Based vs Computer Based Social Engineering MethodsDocument9 pagesHuman Based vs Computer Based Social Engineering MethodsPrerna BhajbhujePas encore d'évaluation
- The Changing Threat: PlenaDocument52 pagesThe Changing Threat: Plenajo1327Pas encore d'évaluation
- ACLDocument69 pagesACLr00t32Pas encore d'évaluation
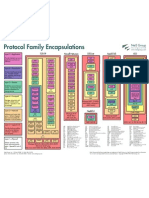
- Protocol EncapsulationDocument1 pageProtocol Encapsulationmrots100% (1)
- Changing Role of Network AdministratorDocument12 pagesChanging Role of Network AdministratorBlind Acre MediaPas encore d'évaluation
- Broadband Gets Personal Broadband Gets Personal Broadband Gets PersonalDocument20 pagesBroadband Gets Personal Broadband Gets Personal Broadband Gets Personaloss279100% (7)
- Rosetta Stone For UnixDocument4 pagesRosetta Stone For UnixRismal Ray VaughanPas encore d'évaluation
- Baseline Process Best Practices White Paper PDFDocument25 pagesBaseline Process Best Practices White Paper PDFRismal Ray VaughanPas encore d'évaluation
- Fedora 12 Cheat SheetDocument1 pageFedora 12 Cheat SheetRismal Ray VaughanPas encore d'évaluation
- ITU-R Recommendations and Reports ListDocument78 pagesITU-R Recommendations and Reports ListRismal Ray VaughanPas encore d'évaluation
- Install and Configure Active Directory, DNS and DHCP On Windows Server 2008Document31 pagesInstall and Configure Active Directory, DNS and DHCP On Windows Server 2008Nguyen Quoc Huy92% (77)
- Forensics Analysis of Hacking Cases From Doctor of Security SystemDocument26 pagesForensics Analysis of Hacking Cases From Doctor of Security SystemRismal Ray VaughanPas encore d'évaluation
- Security Issues in E-Home Network and Software InfrastructuresDocument7 pagesSecurity Issues in E-Home Network and Software InfrastructuresRismal Ray VaughanPas encore d'évaluation
- Albert Eintein: Gentle GeniusDocument19 pagesAlbert Eintein: Gentle GeniusRismal Ray Vaughan100% (2)
- Implementing Best Practices in CNAPDocument36 pagesImplementing Best Practices in CNAPRismal Ray VaughanPas encore d'évaluation
- Configure NAT On Cable ModemDocument7 pagesConfigure NAT On Cable ModemRismal Ray VaughanPas encore d'évaluation
- How To Subnet in Your HeadDocument2 pagesHow To Subnet in Your HeadRismal Ray Vaughan100% (1)
- Troubleshooting Hardware and Booting Problems Cisco ProductDocument72 pagesTroubleshooting Hardware and Booting Problems Cisco ProductRismal Ray VaughanPas encore d'évaluation
- How To Calculate A TCP-IP Subnet Mask: Melanie Gross Network Tutorials 8Document2 pagesHow To Calculate A TCP-IP Subnet Mask: Melanie Gross Network Tutorials 8silviustan0% (1)
- Aishwarya Reddy - Resume OHDocument8 pagesAishwarya Reddy - Resume OHHARSHAPas encore d'évaluation
- System Information SummaryDocument12 pagesSystem Information SummaryMubashir AliPas encore d'évaluation
- 2nd Level Operations MPBN Engineer Job Description2Document2 pages2nd Level Operations MPBN Engineer Job Description2javedPas encore d'évaluation
- Grade 1 ComputerDocument72 pagesGrade 1 Computerkem erlinaPas encore d'évaluation
- Ccna Training Ccnav3 - New Questions 4Document31 pagesCcna Training Ccnav3 - New Questions 4Remi PaternackPas encore d'évaluation
- IntelDocument20 pagesIntelkamalsyal100% (2)
- OceanStor 5300 V3&5500 V3&5600 V3&5800 V3&6800 V3&6900 V3 Storage System V300R001 Maintenance Guide 06Document359 pagesOceanStor 5300 V3&5500 V3&5600 V3&5800 V3&6800 V3&6900 V3 Storage System V300R001 Maintenance Guide 06Jeerahnon ThanumaiweerakunPas encore d'évaluation
- Fico Fico Xpress Optimization Xpress Optimization: Installation GuideDocument40 pagesFico Fico Xpress Optimization Xpress Optimization: Installation GuideYeimmy Julieth Cardenas MillanPas encore d'évaluation
- 8085 Microprocessor Architecture, Registers, Buses and Pin DescriptionDocument43 pages8085 Microprocessor Architecture, Registers, Buses and Pin DescriptionElisha NdhlovuPas encore d'évaluation
- Es ZG626 Course HandoutDocument4 pagesEs ZG626 Course Handout2023ht01598Pas encore d'évaluation
- EM-IGS-Series (IGS-10020MT - IGS-10080MFT - IGS-12040MT - IGS-20040MT) - v3.0Document401 pagesEM-IGS-Series (IGS-10020MT - IGS-10080MFT - IGS-12040MT - IGS-20040MT) - v3.0jkrreeoonPas encore d'évaluation
- Dept. of Electrical and Electronics Engineering Motihari College of Engineering, MotihariDocument15 pagesDept. of Electrical and Electronics Engineering Motihari College of Engineering, MotihariGanesh KumarPas encore d'évaluation
- h14377 Emc Vnxe1600 Block Storage System SsDocument7 pagesh14377 Emc Vnxe1600 Block Storage System Sscanche_xPas encore d'évaluation
- Siemens Compact Errors C Arm VB01CDocument134 pagesSiemens Compact Errors C Arm VB01CHabib100% (4)
- E1 PTAct 9 9 1 HandoutDocument3 pagesE1 PTAct 9 9 1 HandoutzableyherePas encore d'évaluation
- Cisco Catalyst 9300 Switch DatasheetDocument14 pagesCisco Catalyst 9300 Switch Datasheetbonsai todayPas encore d'évaluation
- Faculty of Engineering: ECE 4240 - Microprocessor InterfacingDocument3 pagesFaculty of Engineering: ECE 4240 - Microprocessor InterfacingDheereshPas encore d'évaluation
- BRKSPG-2904 Miami PDFDocument165 pagesBRKSPG-2904 Miami PDFAnonymous cRxoHJ32QvPas encore d'évaluation
- System Center Configuration Manager - Administration Ebook v2Document197 pagesSystem Center Configuration Manager - Administration Ebook v2RaphaelPas encore d'évaluation
- ExamDocument114 pagesExamVishnu KrishnaPas encore d'évaluation
- College Document SharingDocument2 pagesCollege Document SharingsamuelPas encore d'évaluation
- Red Hat Enterprise Linux 6 Installation Guide FR FRDocument617 pagesRed Hat Enterprise Linux 6 Installation Guide FR FRYoussef AddiPas encore d'évaluation
- Semiconductor MemoriesDocument63 pagesSemiconductor MemoriesNayanjyot SinghPas encore d'évaluation
- Narasimha RaoDocument3 pagesNarasimha RaoMahesh MahiPas encore d'évaluation
- Is LBA Mandatory For SCAN Listener in Oracle RAC?Document8 pagesIs LBA Mandatory For SCAN Listener in Oracle RAC?OrSklAcademyPas encore d'évaluation
- Manual OmniDrive USB2 CF V1-21EDocument2 pagesManual OmniDrive USB2 CF V1-21EJuan RiosPas encore d'évaluation
- Manage Oracle Social Network objectsDocument8 pagesManage Oracle Social Network objectsFernanda Gerevini PereiraPas encore d'évaluation
- Studio 5000 Logix Designer - 35.00.01 (Released 2 - 2023)Document17 pagesStudio 5000 Logix Designer - 35.00.01 (Released 2 - 2023)Everton PodencianoPas encore d'évaluation
- Vsphere Esxi 67 Upgrade GuideDocument89 pagesVsphere Esxi 67 Upgrade GuideGus VahyaPas encore d'évaluation