Académique Documents
Professionnel Documents
Culture Documents
Final Com Viva
Transféré par
Pallavi ElgondaDescription originale:
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Final Com Viva
Transféré par
Pallavi ElgondaDroits d'auteur :
Formats disponibles
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
SUBJECT: OPERATING SYSTEM
1. Because of virtual memory, the memory can be shared among
a) processes
b) threads
c) instructions
d) none of the mentioned
Ans:A
2. _____ is the concept in which a process is copied into main memory from the secondary
memory according to the requirement.
a) Paging
b) Demand paging
c) Segmentation
d) Swapping
Ans:B
3. The pager concerns with the
a) individual page of a process
c) entire thread
Ans:A
4. Swap space exists in
a) primary memory
c) CPU
Ans:B
b) entire process
d) first page of a process
b) secondary memory
d) none of the mentioned
5. When a program tries to access a page that is mapped in address space but not loaded in
physical memory, then
a) segmentation fault occurs
b) fatal error occurs
c) page fault occurs
d) no error occurs
Ans:C
6. Effective access time is directly proportional to
a) page-fault rate
b) hit ratio
c) memory access time
d) none of the mentioned
Ans:A
7. In FIFO page replacement algorithm, when a page must be replaced
a) oldest page is chosen
b) newest page is chosen
c) random page is chosen
d) none of the mentioned
Ans:A
8. Which algorithm chooses the page that has not been used for the longest period of time
whenever the page required to be replaced?
a) first in first out algorithm
b) additional reference bit algorithm
c) least recently used algorithm
d) counting based page replacement algorithm
Ans:C
Department of CSE/IT
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
9. A process is thrashing if
a) it is spending more time paging than executing b) it is spending less time paging than executing
c) page fault occurs
d) swapping can not take place
Ans:A
10. Working set model for page replacement is based on the assumption of
a) modularity
b) locality
c) globalization
d) random access
Ans:B
11) Which of the following page replacement algorithms suffers from Beladys Anomaly ?
a) Optimal replacement
b) LRU
c) FIFO
d) Both optimal replacement and FIFO
Ans:C
12) A process refers to 5 pages, A, B, C, D, E in the order : A, B, C, D, A, B, E, A, B, C, D, E. If
the page replacement algorithm is FIFO, the number of page transfers with an empty internal
store of 3 frames is :
a) 8
b) 10
c) 9
d) 7
Ans: C
13) In question 2, if the number of page frames is increased to 4, then the number of page
transfers :
a) decreases
b) increases
c) remains the same
d) None of these
Ans: B
14) A memory page containing a heavily used variable that was initialized very early and is in
constant use is removed, then the page replacement algorithm used is :
a) LRU
b) LFU
c) FIFO
d) None of these
Ans: C
15) A virtual memory system uses First In First Out (FIFO) page replacement policy and
allocates a fixed number of frames to a process. Consider the following statements
P : Increasing the number of page frames allocated to a process sometimes increases the page fault
rateQ : Some programs do not exhibit locality of reference
Which of the following is TRUE?
a) Both P and Q are true, and Q is the reason for P
b) Both P and Q are true, but Q is not the reason for P
c) P is false but Q is true
d) Both P and Q are false
Ans: C
Department of CSE/IT
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
16) Users _______ that their processes are running on a paged system.
a) are aware
b) are unaware
c) None of these
Ans: B
17) If no frames are free, _____ page transfer(s) is/are required.
a) one
b) two
c) three
d) four
Ans: B
18) When a page is selected for replacement, and its modify bit is set :
a) the page is clean
b) the page has been modified since it was read in from the disk
c) the page is dirty
d) a and b
Ans: B and C
19) The aim of creating page replacement algorithms is to :
a) replace pages faster
b) increase the page fault rate
c) decrease the page fault rate
d) to allocate multiple pages to processes
Ans: C
20) A FIFO replacement algorithm associates with each page the _______
a) time it was brought into memory
b) size of the page in memory
c) page after and before it
d) All of these
Ans: A
21) Optimal page replacement algorithm is :
a) Replace the page that has not been used for a long time
b) Replace the page that has been used for a long time
c) Replace the page that will not be used for a long time
d) None of these
Ans: C
22) Optimal page replacement algorithm is difficult to implement, because :
a) it requires a lot of information b) it requires future knowledge of the reference string
c) it is too complex
d) it is extremely expensive
Ans: B
23) LRU page replacement algorithm associates with each page the ______
a) time it was brought into memory
b) the time of that pages last use
c) page after and before it
d) All of these
Ans: B
24) For 3 page frames, the following is the reference string :
70120304230321201701
i) How many page faults does the LRU page replacement algorithm produce ?
a) 10
b) 15
c) 11
d) 12
Department of CSE/IT
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
Ans: D
ii) How many page faults does the FIFO page replacement algorithm produce ?
a) 10
b) 15
c) 11
d) 12
Ans: B
25) The two methods how LRU page replacement policy can be implemented in hardware
are : (choose two)
a) Counters
b) RAM
c) Stack
d) Registers
Ans: A and C
26) Round robin scheduling falls under the category of :
a) Non preemptive scheduling
b) Preemptive scheduling
c) None of these
Ans: B
27) With round robin scheduling algorithm in a time shared system,
a) using very large time slices converts it into First come First served scheduling algorithm
b) using very small time slices converts it into First come First served scheduling algorithm
c) using extremely small time slices increases performance
d) using very small time slices converts it into Shortest Job First algorithm
Ans: A
28) The portion of the process scheduler in an operating system that dispatches processes is
concerned with :
a) assigning ready processes to CPU
b) assigning ready processes to waiting queue
c) assigning running processes to blocked queue
d) All of these
Ans: A
29) Complex scheduling algorithms :
a) are very appropriate for very large computers
c) use many resources
Ans: A
b) use minimal resources
d) All of these
30) The FIFO algorithm :
a) first executes the job that came in last in the queue
b) first executes the job that came in first in the queue
c) first executes the job that needs minimal processor
d) first executes the job that has maximum processor needs
Ans: B
31) The strategy of making processes that are logically runnable to be temporarily suspended
is called :
a) Non preemptive scheduling
b) Preemptive scheduling
c) Shortest job first
d) First come First served
Ans: B
Department of CSE/IT
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
32) Scheduling is :
a) allowing a job to use the processor
c) Both a and b
Ans: C
b) making proper use of processor
d) None of these
33) There are 10 different processes running on a workstation. Idle processes are waiting for
an input event in the input queue. Busy processes are scheduled with the Round-Robin
timesharing method. Which out of the following quantum times is the best value for small
response times, if the processes have a short runtime, e.g. less than 10ms ?
a) tQ = 15ms
b) tQ = 40ms
c) tQ = 45ms
d) tQ = 50ms
Ans: A
34) Orders are processed in the sequence they arrive if _______ rule sequences the jobs.
a) earliest due date
b) slack time remaining
c) first come, first served
d) critical ratio
Ans: C
35) Which of the following algorithms tends to minimize the process flow time ?
a) First come First served
b) Shortest Job First
c) Earliest Deadline First
d) Longest Job First
Ans: B
36) Under multiprogramming, turnaround time for short jobs is usually ________ and that
for long jobs is slightly ___________.
a) Lengthened; Shortened
b) Shortened; Lengthened
c) Shortened; Shortened
d) Shortened; Unchanged
Ans: B
37) Which of the following statements are true ?
I. Shortest remaining time first scheduling may cause starvation
II. Preemptive scheduling may cause starvation
III. Round robin is better than FCFS in terms of response time
a) I only
b) I and III only
c) II and III only
d) I, II and III
Ans: D
38) An un-interruptible unit is known as :
a) single
b) atomic
c) static
d) None of these
Ans: B
39) The TestAndSet instruction is executed :
a) after a particular process
b) periodically
c) atomically
d) None of these
Department of CSE/IT
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
Ans: C
40) Semaphore is a/an _______ to solve the critical section problem.
a) hardware for a system
b) special program for a system
c) integer variable
d) None of these
Ans: C
41) The two atomic operations permissible on semaphores are : (choose two)
a) wait
b) stop
c) hold
d) signal
Ans: A and D
42) Spinlocks are :
a) CPU cycles wasting locks over critical sections of programs
b) locks that avoid time wastage in context switches
c) locks that work better on multiprocessor systems
d) All of these
Ans: D
43) The main disadvantage of spinlocks is that :
a) they are not sufficient for many process
b) they require busy waiting
c) they are unreliable sometimes
d) they are too complex for programmers
Ans: B
44) The wait operation of the semaphore basically works on the basic _______ system call.
a) stop()
b) block()
c) hold()
d) wait()
Ans: B
45) The signal operation of the semaphore basically works on the basic _______ system call.
a) continue()
b) wakeup()
c) getup()
d) start()
Ans: B
46) If the semaphore value is negative :
a) its magnitude is the number of processes waiting on that semaphore
b) it is invalid
c) no operation can be further performed on it until the signal operation is performed on it
d) None of these
Ans: A
Department of CSE/IT
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
47) The code that changes the value of the semaphore is :
a) remainder section code
b) non critical section code
c) critical section code
d) None of these
Ans: C
48) The following program consists of 3 concurrent processes and 3 binary semaphores.
The semaphores are initialized as S0 = 1, S1 = 0, S2 = 0.
Process P0
while(true)
{
wait(S0);
print 0;
release(S1);
release(S2);
}
Process P1
wait(S1);
release(S0);
Process P2
wait(S2);
release(S0);
How many times will P0 print 0 ?
a) At least twice
b) Exactly twice
c) Exactly thrice
d) Exactly once
Ans: A
49) Each process Pi, i = 0,1,2,3,,9 is coded as follows :
repeat
P(mutex)
{Critical Section}
V(mutex)
forever
The code for P10 is identical except that it uses V(mutex) instead of P(mutex). What is the largest
number of processes that can be inside the critical section at any moment (the mutex being
initialized to 1)?
a) 1
b) 2
Department of CSE/IT
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
c) 3
Ans: C
d) None of these
50) Two processes, P1 and P2, need to access a critical section of code. Consider the following
synchronization construct used by the processes :
Process P1 :
while(true)
{
w1 = true;
while(w2 == true);
Critical section
w1 = false;
}
Remainder Section
Process P2 :
while(true)
{
w2 = true;
while(w1 == true);
Critical section
w2 = false;
}
Remainder Section Here, w1 and w2 are shared variables, which are initialized to false. Which one
of the following statements is TRUE about the above construct?
a) It does not ensure mutual exclusion
b) It does not ensure bounded waiting
c) It requires that processes enter the critical section in strict alternation
d) It does not prevent deadlocks, but ensures mutual exclusion
Ans: D
51) Each request requires that the system consider the __________, _____________,
____________ to decide whether the current request can be satisfied or must wait to avoid a
future possible deadlock. (choose three)
a) resources currently available
b) processes that have previously been in the system
c) resources currently allocated to each process
d) future requests and releases of each process
Ans: A, C and D
52) Given a priori information about the ________ number of resources of each type that
maybe requested for each process, it is possible to construct an algorithm that ensures that the
system will never enter a deadlock state.
a) minimum
b) average
c) maximum
d) approximate
Ans: C
Department of CSE/IT
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
53) A deadlock avoidance algorithm dynamically examines the __________, to ensure that a
circular wait condition can never exist.
a) resource allocation state
b) system storage state
c) operating system
d) resources
Ans: A
54) A state is safe, if :
a) the system does not crash due to deadlock occurrence
b) the system can allocate resources to each process in some order and still avoid a deadlock
c) the state keeps the system protected and safe
d) All of these
Ans: B
55) A system is in a safe state only if there exists a :
a) safe allocation
b) safe resource
c) safe sequence
d) All of these
Ans: C
56) All unsafe states are :
a) deadlocks
b) not deadlocks
c) fatal
d) None of these
Ans: b
57) A system has 12 magnetic tape drives and 3 processes : P0, P1, and P2. Process P0 requires
10 tape drives, P1 requires 4 and P2 requires 9 tape drives.
Process
P0
P1
P2
Maximum needs (process-wise : P0 through P2 top to bottom)
10
4
9
Currently allocated (process-wise)
5
2
2
Which of the following sequence is a safe sequence ?
a) P0, P1, P2
b) P1, P2, P0
c) P2, P0, P1
d) P1, P0, P2
Ans: D
58) If no cycle exists in the resource allocation graph :
a) then the system will not be in a safe state
b) then the system will be in a safe state
Department of CSE/IT
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
c) either a or b
Ans: B
d) None of these
59) The resource allocation graph is not applicable to a resource allocation system :
a) with multiple instances of each resource type b) with a single instance of each resource type
c) Both a and b
Ans: A
60) The Bankers algorithm is _____________ than the resource allocation graph algorithm.
a) less efficient
b) more efficient
c) None of these
Ans: A
SUBJECT:C++
1) 3.4E - 38 is equivalent to ?
A.3.4 x 10 x 38
B.3.4 x 38
C.3.4 x 10-38
D. None of these
Ans : C
2) Which statement is most appropriate for C++ language ?
A.Type Less language
B.Statically types Language
C.Dynamically typed language
D.Both B and C
Ans: B
Department of CSE/IT
10
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
3) Which of the following operator can not be overloaded ?
A.Scope resolution operator
B.Arrow operator
C.Equality operator
D.Assignment operator
Ans: A
4) A floating point number contains......?
A.Both integral and fractional part
C.Integral part only
B.Fractional part only
D.None of these
Ans: A
5) Keyword used for Dynamic method resolution ?
A.abstract
C.virtual
B.dynamic
D.typeid
Ans: C
6) Which of the following is not a feature of C++ ?
A.Operator overloading
C.Inheritance
B.Namespaces
D.Reflection
Ans: D
7) What is the right way to declare a copy constructor of a class if the name of class is X ?
A.X(const X* arg)
B.X( const X& arg)
C.X(X arg)
D.X(X* arg)
Ans: B
8) What is the implicit pointer that is passed as the first argument for nonstatic member
functions ?
A.self pointer
B.std::auto_ptr pointer
C.myself pointer
D.this pointer
Ans: D
9) Which classes allow primitive types to be accessed as objects?
A.Storage
B.Virtual
C.Friend
D.Wrapper
Ans: D
10)Which looping process checks the test condition at the end of the loop?
A. for
B. while
D.no looping process checks the test condition at the end
Ans:C
11)Statement scanf(%d,80);
A. Assign an integer to variable i
C.Print the value of I
Ans: A
C.do-while
B. Give an error message
D.Assign an float to variable i
Department of CSE/IT
11
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
12)Which looping process is best used when the number of iterations is known?
A.for
B. while
C.do-while
D.all looping processes require that the iterations be known
Ans: A
13)*ptr++ is equivalent to:
A. ptr++
Ans: D
B.*ptr
C.++*ptr
D.None of the above
14) Which of the following relationship is known as inheritance relationship?
A. has-a relationship
C. association relationship
Ans: B
B. is-a relationship
D. none of the above
15)A continue statement causes execution to skip to
A. the return 0; statement
C. the statement following the continue statement
Ans: D
B. the first statement after the loop
D. the next iteration of the loop
SUBJECT:JAVA
1) Which is a valid keyword in java?
A. interface B. string
C. Float
D. unsigned
Ans: A
2)What is the numerical range of a char?
A. -128 to 127
B. -(215) to (215) 1
C. 0 to 32767
D. 0 to 65535
Ans: D
3) Which is a reserved word in the Java programming language?
A. method
B. native
C. subclasses
D. reference
Department of CSE/IT
12
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
Ans: B
4) Which one of the following will declare an array and initialize it with five numbers?
A. Array a = new Array(5);
C. int a [] = new int[5];
B. int [] a={23,22,21,20,19};
D int [5] array;
Ans: B
5) Which is the valid declarations within an interface definition?
A. public double methoda();
C. static void methoda(double d1);
B. public final double methoda();
D. protected void methoda(double d1);
Ans: A
6) Which is a valid declarations of a String?
A. String s1 = null;
C. String s3 = (String) 'abc';
B. String s2 = 'null';
D. String s4 = (String) '\ufeed';
Ans: A
7) What is the name of the method used to start a thread execution?
A. init();
B. start();
C. run();
D. resume();
Ans: B
8) Which of the following will directly stop the execution of a Thread?
A. wait()
code
B. notify()
C. notifyall()
D. exits synchronized
Ans: A
9) What method must be defined by a class implementing the java.io.Runnable interface?
A. void run()
B. public void run()
C. public void start()
D. void run(int priority)
Ans: B
10) Which will contain the body of the thread?
A. run();
B. start();
C. stop();
D. main();
Ans: A
Department of CSE/IT
13
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
11) Which method registers a thread in a thread scheduler?
A. run();
B. construct(); C. start();
D. register();
Ans: D
12) Which of the following will not directly cause a thread to stop?
A. notify()
B. wait()
C. InputStream access D. sleep()
Ans: A
13) What allows the programmer to destroy an object x?
A. x.delete()
C. Runtime.getRuntime().gc()
object
B. x.finalize()
D. Only the garbage collection system can destroy an
Ans: D
14) Which class or interface defines the wait(),notify(),notifyAll() methods?
A. Object
B. Thread
C. Runnable
D. Class
Ans: A
SUBJECT:OOAD
1. Which diagram is NOT commonly used for illustrating use cases?
(a) system sequence diagram
(b) activity diagram
(c) use case diagram
(d) Collaboration diagram
Ans:d
2. What can UML interfaces be used for?
(a) to provide concrete classes with the stereotype <<interface>>
Department of CSE/IT
14
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
(b) to program in Java and C++, but not in C#
(c) to define executable logic that can be reused in several classes
(d) to specify required services for types of objects
Ans:d
3) Which diagram determines logical view of the system?
a.
b.
c.
d.
Use Case
Activity
Interaction diagrams
Component
Ans:c
4) Number of diagrams fall under static view of the system
a.
b.
c.
d.
3
5
4
6
Ans:c
5) Finite state machines and interactions come under which things?
a.
b.
c.
d.
Structural
Behavioral
Grouping
Annotational
Ans:b
6) Collection of operations that specify a service to a class is
a.
b.
c.
d.
Inheritance
Collaboration
Use Case
Interface
Ans:d
7) Elements that works together and provides a co-operative behavior is in case of
a.
b.
c.
d.
Class
Object
Collaboration
Composition
Ans:c
Department of CSE/IT
15
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
8) Generalization is also called as
a.
b.
c.
d.
Is a kind
Has a kind
Have a
None
Ans:a
9) Dependency stereotype
a.
b.
c.
d.
Visibility
Navigation
Friend
Composition
Ans:c
10) Semantic relationship between two classifiers is
a.
b.
c.
d.
Realization
Association
Generalization
Dependency
Ans:A
SUBJECT:ACD
1) Which of the following string has length 0?
A. a
B.
C.abc
D.s
Ans: B
2) A grammar is a _____________ device
A. generative
B. cognitive
C. acceptor
D. cant say
Ans: A
3) Let NFA has a finite number n of states ,the DFA will have at most ________states.
A. 2n
B. n/2
C. n*n
D. 2*n
Ans: A
4) Which of the following is not a prefix of abc ?
Department of CSE/IT
16
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
A.
B. a
C. ab
D. bc
Ans: D
5) Let maximum number of states in a DFA =128 .Then its equivalent NFA
has_______________ states.
A.3
B.5
C.7
D.9
Ans:C
6) Let r and s are regular expressions denoting the languages R and S.Then ( r + s) denotes
A.R U S
B.R S
C.both A & B
D.None
Ans: A
7) A variable that derives is called ___________ variable
A.Mutable
B.Callable
C.Nullable
D.Both A & C
Ans: C
8) Context sensitive grammar are described by type ____________ grammar
A. 3
B. 8
C.6
D. 1
Ans:d
9) A PDA behaves like as FA when the number of auxiliary memory it has is
A. 0
B. 1
C. 2
D. None
Ans: A
10) If PCP is decidable then MPCP is
A. Decidable
B. Un decidable
C. Cannot say
D. None
Ans: A
11) The intersection of a CFL and a regular language is__________
A.PDA
B.CFL
C.Both A & B
D.None
Ans: B
12) Let r and s are regular expressions denoting the languages R and S.Then ( rs) denotes
A.PDA
B.RS
C.Both A & B
D.None
Ans: B
13) ______________ grammar is also known as Type 3 grammar.
Department of CSE/IT
17
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
A.Active
B.Passive
C.Regular
D.None
Ans: C
14) An automation is a _____________ device
A.PDA B.Language recognizing
C.Both A & B
D.None
Ans: B
15) If A={ 0 ,1 } then the number of possible strings of length n is ________
B. n2
A. n
C. nn
D. 2n
Ans: D.
SUBJECT: COMPUTER NETWORKS
1) Which of the following is a congestion control algorithm?
a. The leaky bucket
b. Token bucket
c. Resource Respondezsilvous plait protocol
d. All of above
Ans:d
2) Demodulation is the process of ?
a.
b.
c.
d.
e.
converting digital signals to analog signals
converting analog signals to digital signals
dividing the high-speed signals into frequency bands
combining many low speed signals into one high speed channel
None of above
3) In OSI network architecture, the dialogue control and token management are
responsibilities of ?
a.
b.
session layer
network layer
Department of CSE/IT
18
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
c. transport layer
d. data link layer
Ans:a
4) What is the main function of transport layer ?
a. node to node delivery
b. process to process message delivery
c. synchronization
d. updating and maintenance of routing tables
Ans:b
5) To deliver a message to the correct application program running on a host, the .... address
must be consulted ?
a. port
b. physical
c. IP
d. None
Ans:c
6) How many hosts are attached to each of the local area networks at your site?
a. 128
b. 254
c. 256
d. 64
Ans:b
7) The physical layer is concerned with the movement of _______ over the physical medium.
a.
b.
c.
d.
programs
dialogs
protocols
bits
Ans:d
8) A packet whose destination is outside the local TCP/IP network segment is sent to the
Department of CSE/IT
19
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
a.
b.
c.
d.
File server
Default gateway
DNS server
DHCP server
Ans:b
9) An IP address contains________ bits ?
a.
b.
c.
d.
8
16
32
64
Ans:c
10) Which application below uses the UDP protocol?
a.
b.
c.
d.
DNS
TFTP
RIP
All of the above
Ans:d
11) Which of the IP headers decides when the packet should be discarded?
a.
b.
c.
d.
Fragment control
TTL
Checksum
Header length
Ans:b
12) Which of the following is used for modulation and demodulation?
a.
b.
c.
d.
modem
protocols
gateway
multiplexer
ans:a
Department of CSE/IT
20
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
13) Which one of the following is not a connectionless protocol?
a.
b.
c.
d.
UDP
Ethernet
IPX
All
Ans:b
14) Which port is reserved for use of the SMTP protocol?
a.
b.
c.
d.
21
23
25
53
Ans:c
15) IPv6 has _______ -bit addresses.
a.
b.
c.
d.
32
64
128
Variable
Ans:c
16) Topology not used in LANS
a.
b.
c.
d.
Mesh
Bus
Ring
Star
Ans:
17) The process-to-process delivery of the entire message is the responsibility of the _______
layer.
A) Network
B) Transport
C) Application
D)
Physical
Department of CSE/IT
21
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
Ans:b
18) The _______ layer is the layer closest to the transmission medium.
a. Physical
b. Data link
c. Transport
d. Network
Ans:a
19) As the data packet moves from the upper to the lower layers, headers are _______.
a.
b.
c.
d.
Added
Removed
Rearranged
Rearranged
Ans:a
20) The _______ layer lies between the network layer and the application layer.
a. Network
b. Data link
c. Transport
d. None
Ans:c
21) The _______ layer changes bits into electromagnetic signals.
a) Physical
b) Data link
c) Transport
d) None
Ans:a
22) Which of the following is an application layer service?
a. Remote log-in
b. File transfer and access
c. Mail service
Department of CSE/IT
22
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
All the above
Ans:d
23) Why was the OSI model developed?
a. Manufacturers disliked the TCP/IP protocol suite.
b. The rate of data transfer was increasing exponentially
c. Standards were needed to allow any two systems to communicate
d. None of the above
Ans:c
24) The_____ address identifies a process on a host.
a. physical
b. IP
c. port
d. specific
ans:c
25) The ____ address uniquely defines a host on the Internet.
a. physical
b. IP
c. port
d. specific
ans:b
SUBJECT: DBMS
1.
A.
What does SQL stand for?
A. Structured Question Language
B. Structured Query Language
C. Strong Question Language
Ans:a
Department of CSE/IT
23
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
2.
Which SQL statement is used to update data in a database?
A.
B.
C.
D.
SAVE AS
SAVE
UPDATE
MODIFY
Ans:c
3. Which SQL statement is used to delete data from a database?
A. COLLAPSE
B. DELETE
C. REMOVE
Ans:b
4. Which SQL statement is used to insert new data in a database?
A.
B.
C.
D.
INSERT NEW
INSERT INTO
ADD NEW
ADD RECORD
Ans:b
5. With SQL, how do you select a column named "FirstName" from a table named
"Persons"?
A. SELECT FirstName FROM Persons
B. SELECT Persons. FirstName
C. EXTRACT FirstName FROM Persons
Ans:a
Department of CSE/IT
24
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
6. With SQL, how do you select all the records from a table named "Persons" where the
value of the column "FirstName" is "Peter"?
A.
B.
C.
D.
7.
SELECT [all] FROM Persons WHERE FirstName='Peter'
SELECT [all] FROM Persons WHERE FirstName LIKE 'Peter'
SELECT * FROM Persons WHERE FirstName<>'Peter'
SELECT * FROM Persons WHERE FirstName='Peter'
Ans:d
With SQL, how do you select all the records from a table named "Persons" where the
value of the column "FirstName" starts with an "a"?
A.
B.
C.
D.
8.
SELECT * FROM Persons WHERE FirstName='%a%'
SELECT * FROM Persons WHERE FirstName='a'
SELECT * FROM Persons WHERE FirstName LIKE 'a%'
SELECT * FROM Persons WHERE FirstName LIKE '%a'
Ans:c
Which SQL statement is used to return only different values?
A. SELECT DISTINCT
B. SELECT UNIQUE
C. SELECT DIFFERENT
Ans:a
Department of CSE/IT
25
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
9. Which SQL keyword is used to sort the result-set?
A.
B.
C.
D.
ORDER BY
SORT
ORDER
SORT BY
Ans:a
10. With SQL, how can you return all the records from a table named "Persons" sorted
descending by "FirstName"?
A.
B.
C.
D.
SELECT * FROM Persons SORT BY 'FirstName' DESC
SELECT * FROM Persons ORDER BY FirstName DESC
SELECT * FROM Persons SORT 'FirstName' DESC
SELECT * FROM Persons ORDER FirstName DESC
Ans:
11. With SQL, how can you insert a new record into the "Persons" table?
A. INSERT ('Jimmy', 'Jackson') INTO Persons
B. INSERT VALUES ('Jimmy', 'Jackson') INTO Persons
C. INSERT INTO Persons VALUES ('Jimmy', 'Jackson')
Ans:c
12. With SQL, how can you insert "Olsen" as the "LastName" in the "Persons" table?
A. INSERT INTO Persons (LastName) VALUES ('Olsen')
B. INSERT INTO Persons ('Olsen') INTO LastName
C. INSERT ('Olsen') INTO Persons (LastName)
Ans:a
13. How can you change "Hansen" into "Nilsen" in the "LastName" column in the Persons
table?
A.
B.
C.
D.
MODIFY Persons SET LastName='Hansen' INTO LastName='Nilsen
UPDATE Persons SET LastName='Hansen' INTO LastName='Nilsen'
UPDATE Persons SET LastName='Nilsen' WHERE LastName='Hansen'
MODIFY Persons SET LastName='Nilsen' WHERE LastName='Hansen'
Ans:c
Department of CSE/IT
26
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
14. With SQL, how can you delete the records where the "FirstName" is "Peter" in the
Persons Table?
A. DELETE ROW FirstName='Peter' FROM Persons
B. DELETE FirstName='Peter' FROM Persons
C. DELETE FROM Persons WHERE FirstName = 'Peter'
Ans:c
15. With SQL, how can you return the number of records in the "Persons" table?
A.
B.
C.
D.
Ans:
SELECT COUNT(*) FROM Persons
SELECT COLUMNS(*) FROM Persons
SELECT COUNT() FROM Persons
SELECT COLUMNS() FROM Persons
16. A trigger is?
A.
B.
C.
D.
A statement that enables to start any DBMS
A statement that is executed by the user when debugging an application program
A condition the system tests for the validity of the database user
A statement that is executed automatically by the system as a side effect of modification
to the database
Ans:d
17. Related fields in a database are grouped to form ?
A. Data Fields
B. Data Record
C. Menu
D. Bank
Ans:b
18. Entities having primary key are called ?
A. Primary Entities
B. Strong Entities
Department of CSE/IT
27
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
C. Weak Entities
D. Primary Key
Ans:b
19. In the E-R diagrams, the term cardinality is a synonym for the term ?
A. Attribute
B. Degree
C. Entities
D. Cartesian
Ans:d
20. TRUNCATE statement in SQL is a ?
A. DML statement
B. DDL statement
C. DCL statement
D. None of above
Ans:b
21. The default date format in SQL is ?
A. DD-MON-YY
B. DD-MM-YY
C. DD-MM-YYY
D. MM-DD-YY
Ans:a
22. The master list of an indexed file ?
A. Is sorted in ascending order
B. contains only a list of keys and record numbers
Department of CSE/IT
28
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
C. has a number assigned to each record
D. Both B and C
Ans:c
23. An un normalized relation contains values ?
A. Atomic
B. Non-Atomic
C. Classified
D. None of these
Ans:c
24. A relation scheme is said to be in form if the values in the domain of each attribute of
the relation are atomic ?
A. Un normalized
B. First Normal
C. Boyce CODD
D. None of these
Ans:b
25. A second Normal form does not permit dependency between a non prime attribute
and the relation key ?
A. Partial
B. Multi
C. Functional
D. Valued
Ans:a
26. In a Third Normal Form relation, every attribute is non transitively and fully
dependent on the every candidate key ?
A. Prime
B. Non Prime
C. Unique
Department of CSE/IT
29
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
D. None of these
Ans:c
27. A generalization of the Boyce Codd Normal form to relation schemes which includes the
multi valued dependencies is called?
A. Second Normal Form
B. Third Normal Form
C. Fourth Normal Form
D. Fifth Normal Form
Ans:d
28. In relational schema, each tuple is divided into fields called ?
A. Relations
B. Domains
C. Queries
D. All of above
Ans:b
29. A logical schema?
A. is the entire database
B. is a standard way of organizing information into accessible parts
C. describes how data is actually stored on disk
D. All of above
Ans:b
30. Periodically adding, changing and deleting file records is called file?
A. updating
B. upgrading
C. restructuring
D. renewing
Department of CSE/IT
30
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
ans:a
SUBJECT:SOFTWARE ENGINERING
1.The user interface analysis and design process is an iterative process and it can be
Represented as a ________________. [ A]
A. Spiral model
B. Increment model
C. Waterfall model
D. None
2. ______________Failure Costs are incurred when we detect a defect in our product. [A ]
A. Internal
B. External
C. Both A&B
D. None
Department of CSE/IT
31
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
3. One of the important phases of software development______________ [ B]
A. Design
B. Testing
C. Analysis
D. None
4. _______________ focuses on the functional requirements of the software. [B ]
A. White Box Testing
B. Black Box Testing
C. A&B
D. None
5. ____________ Also called glass box testing. [A ]
A. White Box Testing
B. Black Box Testing
C. A&B
D. None
6. The essential purpose of testing is _________________. [ C]
A. Design
B. Analysis
C. Correctness
D. None
7. _______________risk monitors the projects likely risk and resources are set aside. [A ]
A. Reactive Risk
B. Proactive Risk
C. Project Risk
D. None
8. ______________ also called risk estimation. [ B]
A. Risk Refinement
B. Risk Projection
C. Risk Avoidance
D. None
9. ______________focuses on the identification and assessment of potential hazards
That may affect software negatively and cause an entire system to fail. [A ]
A. Software Safety
B. Performance
C. Software Reliability
D. None
10. _____________involves the series of inspections, reviews, and tests used throughout the
Software process to ensure each work product meets the requirements. [C ]
A.Quality of Conformance B. Quality assurance
C. Quality Control
D. None
11. Softwaremeans [D ]
a) Programs
c) Data
b) Documents
d) All
12. Software engineering is required for _________projects [ B]
a) Small single developer
b) Large
c) Both a & b
d) None
13. When compared with traditional engineering disciplines the software engineering is [A ]
a) Young
b) Old
c) Contemporary
d) None
14. Below software engineering phase requires less skilled manpower [C ]
a) Analysis
b) Design
Department of CSE/IT
32
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
c) Coding
d) All
15. The software playing the roles of [ C]
a) Product
b) Service
c) Both a & b
d) None
16. Waterfall model is a [ A]
a) Software process
c) Both a&b
b) Software product
d) None
17. The unified process is a ______________process [C ]
a) Iterative
b) Incremental
c) Both a & b
d) None
18. Below is not a non-functional requirement [D ]
a) Reliability
b) Quality
c) Performance
d) None
19. The software requirements specification document consists of [D ]
a) Functional requirements b) Non- functional requirements
c) Analysis models
d) All
20. Below is the activity performed in software design phase [D ]
a) Data design
b) Architectural design
c) Procedural design
d)All
21. ________software is a collection of programs written to service other programs [D ]
(A)Embedded
(B) Engineering
(C) Application
(D) System
22. The_________model is a realistic approach to the development of large scale systems and
software [A ]
(A) Spiral
(B) incremental
(C) waterfall model
(D) RAD
23. RAD is [ C]
(A) Rapid Artificial Development
(C) Rapid Application Development
(B) Rapid Application Developer
(D) None
24. _____________activity combines code generation and testing that is required to uncover
errors in the code [ B]
(A) Planning
(B)Construction
(C)Modeling
(D)None
25. ___________models describes how a system responds to internal or external events [A ]
(A)State machine
(B)Data
(C)Behavioural
(D) None
26. _________viewpoints provide detailed system requirements covering the system features
and interfaces [ B]
(A)Indirect
(B)Interactor
Department of CSE/IT
33
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
(C)Domain
(D)None of these
27. __________means that all services required by the user should be defined [C ]
(A) consistency
(B) contradictory
(C)completeness
(D)None of these
28. _________abstraction refers to a sequence of instructions that have a specific limited
function. [B]
(A)Data
(B)Procedural
(C)Object
(D)None of these
29. _______Model focus on the design of the business or technical process that the system must
accommodate [ C]
(A)Structural
(B) Framework
(C)Process
(D)Dynamic
30. _______is an indication of the relative interdependence among modules [A ]
(A) Coupling
(B) Cohesion
(C)Refinement
(D) None of the Above
SUBJECT:DAA
1.
If all c(i, j )s and r(i, j)s are calculated, then OBST algorithm in worst case takes one
of the following time.
(a) O(n log n)
(b) O(n3)
(c) O(n2)
(d) O(log n)
(e) O(n4).
Ans:b
2.
The following is a weighted binary tree, then what is the weighted array for the TVS
Department of CSE/IT
34
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
problem?
(a)
(b)
(c)
(d)
(e)
[9, 2, 7, 0, 0, 0, 0, 0, 0, 0, 0, 0, 6, 4]
[9, 2, 0, 0, 0, 0, 0, 0, 0, 0, 0, 7, 4, 6]
[9, 0, 0, 0, 0, 0, 0, 0, 0, 0, 2, 6, 7, 4]
[9, 2, 0, 0, 0, 7, 0, 0, 0, 0, 0, 0, 6, 4]
[9, 2, 0, 0, 0, 7, 0, 0, 0, 0, 6, 4, 0, 0].
Ans:d
3.
What are the entries of the array TREE[ ] for the above weighted binary tree for the
TVS problem.
(a) [1, 2, 3, 4, 5, 6, 0, 0]
(b) [1, 2, 0, 0, 0, 3, 0, 0, 0, 0, 0, 0, 4, 5, 6]
(c) [1, 2, 3, 0, 0, 0, 0, 4, 5, 6]
(d) [1, 2, 3, 0, 0, 0, 0, 0, 4, 5, 6]
(e) [1, 2, 3, 0, 0, 0, 4, 0, 0, 0, 0, 0, 0, 5, 6].
Ans: e
4.
For a 15-puzzle problem let the initial arrangement be the following one, then answer
the questions 4 7 with the following arrangement.
10
9
12
11
13
1
2
15
4
8
5
7
14
6
3
What is the value of x used to find the reachability of the solution?
(a) 1
(b) 0
Department of CSE/IT
35
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
(c) 8
(d) 10
(e) 13.
Ans:a
5.
The values for the position(i), position(j) where i = 14 and j =11, are
(a) 2, 8
(b) 8, 2
(c) 8, 13
(d) 2, 13
(e) 13, 8.
Ans:c
6.
The values for less(i), less(j) where i =5, j =7 are
(a) 0, 6
(b) 6, 0
(c) 2, 4
(d) 2, 6
(e) 1, 6.
Ans:e
7.
What is the value to find the reachability of the problem with which you can say the
solution is reachable or not?
(a) 71
(b) 72
(c) 73
(d) 69
(e) 68.
Ans:b
8.
The upper bound on the time complexity of the nondeterministic sorting algorithm is
(a) O(n)
(b) O(n log n)
(c) O(1)
(d) O( log n)
(e) O(n2).
Ans:a
9.
The worst case time complexity of the nondeterministic dynamic knapsack algorithm
is
(a) O(n log n)
Department of CSE/IT
36
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
(b)
(c)
(d)
(e)
O( log n)
O(n2)
O(n)
O(1).
Ans:d
10. For the LCBB solution of knapsack problem with the data (p1p4) = (10,10,12,18) and
(w1w4) = (2, 4, 6, 9) and m = 18, then the values of u(1) and (1) respectively are
(a) -38, -44
(b) -44, -38
(c) -44, -32
(d) -32, -44
(e) -32, -38.
Ans:d
11.
If for the above problem, the tree is created following the FIFOBB, then the values for
(5) and u(5) respectively are
(a) -40, -40
(b) -40, -38
(c) -40, -32
(d) -22, -32
(e) -32, -22.
Ans:a
12.
There is a chain of 20 stores; each of the store having 5 departments. Then, which of
the following is a correct representation of array size?
(a) 5 * 20
(b) 6 * 21
(c) 20 * 5
(d) 21 * 6
(e) 19 * 4
Ans:c
13.
From the following, select the valid data structure which reflects hierarchical
relationship between the elements.
(a) Graph
(b) Queue
(c) Linked list
(d) Stack
(e) Tree.
Ans:e
14.
Which of the following matrix does have high proportions of zero entries as the
elements?
(a) Inverse Matrix
(b) Sparse Matrix
(c) Determinant
Matrix
(d) Square Matrix
(e) Transpose Matrix.
Ans:b
15.
Let there is a queue whose initial values for Front and Rear are 0 and 1 respectively.
Later queue found to be having the elements 3, 2, 1, 5. If a new element is inserted in
the queue, then which of the following statements is correct?
(a) Front = 0 and Rear = 5
(b) Front = 0 and Rear = 4
(c) Front = 1 and Rear = 4
(d) Front = 1 and Rear = 5
(e) Insertion is not possible as there is no space in the queue.
Ans:a
Department of CSE/IT
37
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
16.
One from the following is also known as Pre-Order traversal. What that one is?
(a) LNR
(b) LRN
(c) RLN
(d) RNL
(e) NLR.
Ans:e
17.
Which of the following data structure is the best example for the multitasking
systems?
(a) Tree
(b) Queue
(c) Stack
(d) Linked List
(e) Graph.
Ans:b
18.
The initial configuration of the queue is having the elements x, y, z, a forming a
queue. To get the new configuration a, z, y, x one needs a minimum of
(a) 3 additions and 4 deletion
(b) 3 deletions and 4 additions
(c) 3 deletions and 2 additions
(d) 3 deletions and 3 additions
(e) 4 deletions and 4 additions.
Ans:d
19.
To form the new configuration in the above problem, what best data structure is seems
to be used?
(a) Tree
(b) Queue
(c) Linked List
(d) Circular Queue (e)
Stack.
Ans:e
20.
Recursive algorithms are based on
(a) Divide and conquer approach
(c) Bottom-up approach
(e) Heuristic approach.
Ans:b
(b) Top-down approach
(d) Hierarchical approach
21. What do you call the selected keys in the quick sort method?
(a) Outer key (b) Inner Key
(c) Partition key
(d) Pivot key (e) Recombine key.
Ans:d
22. Primary clustering occurs in
(a) Linear probing
(b) Quadratic probing
(c) Mid-square method (d) Order probing
Ans:a
(e) Chaining.
23. How many nodes do a full binary tree with N leaves contain?
(a) 2N nodes
(b) N nodes (c) 2N-1 nodes
(d) N-1 nodes
(e) 2(N-1) nodes.
Ans:c
24. How many nodes does a complete binary tree of level 5 have?
(a) 16 (b) 15 (c) 32
(d) 31 (e) 64.
Ans:d
25. How do you determine the cost of a spanning tree?
(a) By the sum of the costs of the edges of the tree
Department of CSE/IT
38
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
(b) By the sum of the costs of the edges and vertices of the tree
(c) By the sum of the costs of the vertices of the tree
(d) By the sum of the costs of the edges of the graph
(e) By the sum of the costs of the edges and vertices of the graph.
Ans:a
26. What would be the depth of tree whose level is 9?
(a) 10 (b) 8
(c) 9
(d) 11 (e) 7.
Ans:c
27. A node of a directed graph G having no out-degree and a positive in-degree is called
(a) Source node (b) Sink node
(c) Sibling node
(d) Null node (e) In-node.
Ans:a
28. The time complexity of the normal quick sort, randomized quick sort algorithms in the
worst case is
(a) O(n2), O(n log n)
(b) O(n2), O(n2)
2
(c) O(n log n), O(n )
(d) O(n log n), O(n log n)
(e) O(n log n), O(n2 log n).
Ans:b
29. Let there be an array of length N, and the selection sort algorithm is used to sort it,
how many times a swap function is called to complete the execution?
(a) N log N times
(b) log N times (c) N2 times
(d) N-1 times
(e) N times.
Ans: d
30. The Sorting method which is used for external sort is
(a) Bubble sort (b) Quick sort
(c) Merge sort
(d) Radix sort
(e) Selection sort.
Ans:c
31. In analysis of algorithm, approximate relationship between the size of the job and the
amount of work required to do is expressed by using _________
(a) Central tendency
(b) Differential equation
(c) Order of execution
(d) Order of magnitude
(e) Order of Storage.
Ans:d
32. Pick the correct prefix form to the given infix expression
{a*[b/(c-d)*f]/g}/[e+h]
(a) //*a/b*-cdfg+ch (b) abcd-f*/g/*eh+/
(c) //*a*/b-cdfg+eh (d) //*ab*/-cdfg+eh
(e) -//*a*/bcdfg+eh.
Ans:c
33. For recursive MinMax algorithm, the average, worst cases are __________
Department of CSE/IT
39
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
(a)
(c)
(e)
Ans: a
(b)
(d)
34. P, Q and R are pointer variables. The statements below are intended to swap the contents of
the nodes pointed to by P and rewrite it so that it will work as intended.
P = Q; R = Q; Q = R;
(a) R=Q; P=R; Q=R;
(b) R=P; P=P; Q=Q;
(c) P=P; P=Q; R=Q;
(d) R=P; P=Q; Q=R;
(e) P=R; R=Q; Q=R;
Ans:d
35. For defining the best time complexity, let f (n) = log n and g (n) = n, _________
(a) f (n) (g(n)), but g(n) (f(n))
(b) f (n) (g(n)), but g(n) (f(n))
(c) f (n) (g(n)), and g(n) (f(n))
(d) f (n) (g(n)), and g(n) (f(n))
(e) Cant be defined for best case.
Ans:b
36. If f, r are the front, rear pointers respectively in a circular queue then the condition
+ size) % size == 1) && ( (f != 0) || (r != -1) ) represents
(a) Queue has only one element
(b) Two Elements
(c) More than 2 elements but not full
(d) Impossible values
(e) Queue is full.
Ans:e
(( f r
37. For the following two statements, choose the correct answer.
I. n2O(n3).
II. n = ((n+1)!).
(a) (I) and (II) are TRUE
(b) (I), (II) are FALSE
(c) (I) is FALSE, but (II) is TRUE
(d) (I) is TRUE and (II) is FALSE
(e) (I) is TRUE but (II) cant be defined.
Ans:d
38. The statement head->Link->Link->Link = NULL terminates a linked list after its
__________ node.
(a) 2nd
(b) 4th
(c) 5th
(d) 3rd
(e) first.
Ans:d
39. For analyzing an algorithm, which is better computing time?
(a) O (100 Log N)
(b) O (N)
(c) O (2N)
(d) O (N log N)
(e) O (N2).
Ans:a
Department of CSE/IT
40
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
40. To implement the Round Robin algorithm, which of the following data structure is used?
(a) Stack
(b) Linear Queue
(c) Circular Queue
(d) Priority Queue
(e) Double Stack.
Ans:c
41. Let f, t: NR 0, and t (n) O (f (n)) iff t(n) c.f (n) where c is positive real constant
and
n no, then no is ___________
(a) Upper bound
(b) Lower bound
(c) Duality value
(d) Threshold value
(e) Maximum value.
Ans:d
42. In a circular queue, we can disambiguate empty from full queue by
(a) Using a gap in the array
(b) Incrementing queue positions by 2 instead of 1
(c) Keeping a count of the number of elements
(d) (a) and (c) above
(e) (a), (b), and (c) above.
Ans:d
43. In a graph, a vertex with degree one is known as ___________
(a) Pendant vertex (b) Leaf
(c) Root
(d) End vertex
Ans:a
(e) Internal.
44. Consider the usual algorithm for determining whether a sequence of parentheses is
balanced. What is the maximum number of parentheses that will appear on the stack AT
ANY ONE TIME when the algorithm analyzes: (()(())(()))
(a) 1
(b) 2
(c) 3
(d) 4
(e) 5 or more.
Ans:c
45. If a graph G = (N, E), where E= {}, then the corresponding adjacency matrix is _____
(a) Unit Matrix
(b) Identity Matrix
(c) Having Diagonal elements Zero
(d) Matrix with all 1s
(e) Zero Matrix.
Ans:e
46. Suppose we have an array implementation of the stack class, with ten items in the stack
stored at data[0] through data[9]. The SIZE is 42. Where does the push method place the
new entry in the array?
(a) data[0]
(b) data[1]
(c) data[9]
(d) data[10]
(e) data[11].
Ans:d
47. Breadth first search __________
(a) Scans each incident node along with its children.
(b) Scans all incident edges before moving to other node.
(c) Is same as backtracking
(d) Scans all the nodes in random order.
Department of CSE/IT
41
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
(e) Scans all the nodes in pre-order manner.
Ans:b
48. Provided the space is available, then to insert an element in the queue, we can use for the
following structure
struct queue
{
int Q[20];
int f, r;
}Q;
(a) ++Q[r] = x;
x;
(d) Syntax error
Ans:b
(b) Q[++r] = x;
(c) Q[r]++ =
(e) Q[r++] = x;
49. Which method of traversal does not use stack to hold nodes that are waiting to be
processed?
(a) Dept First
(b) D-search
(c) Breadth first
(d) Back-tracking
(e) Bounding.
Ans:c
50. If the characters 'D', 'C', 'B', 'A' are placed in a queue (in that order), and then removed
one at a time, in what order will they be removed?
(a) ABCD
(b) ABDC
(c) DCAB
(d) DCBA
(e) ACDB.
Ans:d
SUBJECT:COMPUTER ORGANIZATION
1) In Reverse Polish notation, expression A*B+C*D is written as
(A) AB*CD*+ (B) A*BCD*+
(C) AB*CD+* (D) A*B*CD+
[ A
2) What characteristic of RAM memory makes it not suitable for permanent storage?
(A) too slow
(B) unreliable
(C) it is volatile
(D) too bulky
[ C
3)Computers use addressing mode techniques for _____________________.
(A) giving programming versatility to the user by providing facilities as pointers to
memory counters for loop control
(B) to reduce no. of bits in the field of instruction
(C) specifying rules for modifying or interpreting address field of the instruction
(D) All the above
[ D
4) (2FAOC)16 is equivalent to
(A) (195 084)10
(C) Both (A) and (B)
(B) (001011111010 0000 1100)2
(D) None of these
5)_________ register keeps track of the instructions stored in program stored in
memory.
(A) AR (Address Register)
(B) XR (Index Register)
(C) PC (Program Counter)
(D) AC (Accumulator)
[ C
Department of CSE/IT
42
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
6) Generally Dynamic RAM is used as main memory in a computer system as it
(A) Consumes less power (B) has higher speed
(C) has lower cell density (D) needs refreshing circuitary
7 )In signed-magnitude binary division, if the dividend is (11100)2 and divisor is
(10011)2 then the result is
(A) (00100)2
(B) (10100)2 (C) (11001)2
(D) (01100)2
8 )Logic X-OR operation of (4ACO)H & (B53F)H results
(A) AACB
(B) 0000
(C) FFFF
(D) ABCD
9) If (97)16 is converted into binary what is the relation between the no.of zeros
and no.of ones
(A)No.of zeros 2 more than no.of ones
(B) No.of zeros 3 more than no.of ones
(C) No.of zeros 4 more than no.of ones
(D)none
[ A
10 )In computers, subtraction is carried out generally by
(A) 1's complement method
(B) 2's complement method
(C) signed magnitude method (D) BCD subtraction method
[ B
11) _________ register keeps tracks of the instructions stored in program stored in
memory.
(A) AR (Address Register)
(B) XR (Index Register)
(C) PC (Program Counter)
(D) AC (Accumulator)
[ C
12) The multiplicand register & multiplier register of a hardware circuit implementing
booth's algorithm have (11101) & (1100). The result shall be
(A) (812)10
(B) (-12)10
(C) (12)10
(D) (-812)10
[ A ]
13) A floating point number that has a 0 in the MSB of mantissa is said to have
(A) Overflow
(B) Underflow (C) Important number (D) Undefined[ B
14) In the expression (43)9=(x4)y how manyvalues are possible for x
(A) 1
(B) 2
(C) 5
(D7
[ B
15) A microprogram sequencer
(A) generates the address of next micro instruction to be executed.
(B) generates the control signals to execute a microinstruction.
(C) sequentially averages all microinstructions in the control memory.
(D) enables the efficient handling of a micro program subroutine.
[ A
16) can be represented in a signed magnitude format and in a 1s complement
Department of CSE/IT
43
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
format as
(A) 111011 & 100100 (B) 100100 & 111011
(C) 011011 & 100100 (D) 100100 & 011011
[ A
17) The instructions which copy information from one location to another either in the
processors internal register set or in the external main memory are called
(A) Data transfer instructions.
(B) Program control instructions.
(C) Input-output instructions.
(D) Logical instructions.
[ A ]
18 )Content of the program counter is added to the address part of the instruction in order to
obtain the effective address is called.
(A) relative address mode.
(B) index addressing mode.
(C) register mode.
(D) implied mode.
[ A ]
19) The 2s compliment form (Use 6 bit word) of the number 1010 is
(A) 111100.
(B) 110110.
(C) 110111.
(D) 1011.
20) In Assembly language programming, minimum number of operands required for an
instruction is/are
(A) Zero. (B) One.
(C) Two.
(D) Both (B) & (C).
[ A
21 )The maximum addressing capacity of a micro processor which uses 16 bit database & 32
bit address base is
(A) 64 K.
(B) 4 GB.
(C) both (A) & (B).
(D) None of these.
[ B ]
22) The gray code equivalent of (1011)2 is
(A) 1101.
(B) 1010.
(C) 1110.
(D) 1111.
[ D
23) Which of the following number will have same value in both sign magnitude
notation and 2s complement notation
(A) 1000 0000 (B) 1100 0000
(C) 1110 0000 (D) 1111 0000
[ B
24 )A stack organized computer has
(A) Three-address Instruction. (B) Two-address Instruction.
(C) One-address Instruction.
(D) Zero-address Instruction.
25) A Program Counter contains a number 825 and address part of the instruction contains
the number 24. The effective address in the relative address mode, when an instruction is read
from the memory is
(A) 849.
(B) 850.
(C) 801.
(D) 802.
[ B ]
26) A system program that translates and executes an instruction simultaneously is
(A) Compiler. (B) Interpreter. (C) Assembler. (D) Operating system. [ C ]
27) Indicate which of the following is not true about an interpreter
(A)Interpreter generates an object program from the source program
(B) Interpreter is a kind of translator
(C) Interpreter analyses each source statement every time it is to be executed
(D) None of the above
[ B
Department of CSE/IT
44
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
28)The term baud is a measure of the:
(A)speed at which data travels over the communication line
(B) memory capacity
(C)c) instruction execution time
(D) all of the above
[ A
29)A bootstrap is:
(A) a memory device (B) a device to support the computer
(C) a small initialisation program to start up a computer
(D) an error correction technique
[ C
[ B
[ C
30)Subtract ( 1010)2 from ( 1101 )2 using 1s complement..
(A)(1100)2
(B)b)(0011)2
(C)(1001)2
(D)(0101)2
31)Using 2s Complement, subtraction, of (1010)2 from (0011)2 is
(A) (0111)2
(B) (1001)2
(C) (0111)2
(D) (1001)2
32) Karnaugh map (K-map) technique provides a systematic method for simplifying ----------(A) multiplexers (B) lgic gates (C) Boolean expressions d) none of these .
[ C ]
33) K-map technique generally used up to --------Variables
(A)2
(B) 8
(C) 7
(D) 6
[ D
34)In a array multiplier circuit with J multiplier bits & K multiplicand bits, the number of
AND gates required are ____________
(A)J*K
(B)J+K (C)J-I
(D)K-1
[ B
]
35)Which of the following is also called the next address generator for a control memory?
(A)Program counter
(B) control address register
(C)Microprogram sequencer (D) none of the above
[ B ]
36 )A computer must at least consist of _______
(A)Data bus
(B) Address bus
(C) Control bus
(D)All of the above
[ D
37)The _________ micro operation can be used to Selectively Complement bits
of a register
(A)OR
(B) AND
(C) Exclusive-OR
(D) None of the above
[ C
38 )1KB,2KB,4KB memory chips have 10 bit address data. Bus size in each case is
(A)8,16,24
(B)8,16,32
(C)8,16,64
(D)8,16,128
[ B
39) Microprogram is provided by manufacturer.These microprograms are termed as
(A)Software
(B)Netware
(C)Firmware
(D)Hardware [ C
40) Programmable Peripheral Interface is
(A) 8255
(B)8251
(C)8257
(D)8259
[ A ]
Department of CSE/IT
45
DRK COLLEGE OF ENGINEERING &TECHNOLOGY
Department of CSE/IT
46
Vous aimerez peut-être aussi
- Student Sumit Networking Assignment (9!17!2430 - 17)Document4 pagesStudent Sumit Networking Assignment (9!17!2430 - 17)VehinPas encore d'évaluation
- CBLM CG CleanlivingroomDocument18 pagesCBLM CG CleanlivingroomEm Boquiren Carreon80% (5)
- CompTIA A+ Certification All-in-One Exam Questions Prep (220-701 & 220-702)D'EverandCompTIA A+ Certification All-in-One Exam Questions Prep (220-701 & 220-702)Évaluation : 2.5 sur 5 étoiles2.5/5 (6)
- ETP48600 V100R001C02 Embedded Power User ManualDocument70 pagesETP48600 V100R001C02 Embedded Power User ManualLFFstarPas encore d'évaluation
- MERP AdventuresDocument118 pagesMERP AdventuresMarcos Melgar100% (3)
- Virtual Memory: A) Processes A) Oldest Page Is ChosenDocument6 pagesVirtual Memory: A) Processes A) Oldest Page Is ChosenYellaturi Siva Kishore ReddyPas encore d'évaluation
- PPSC Computer Lecturer MCQDocument143 pagesPPSC Computer Lecturer MCQRana afaqPas encore d'évaluation
- Computer Science MCQsDocument14 pagesComputer Science MCQsMuhammad Sikandar DarPas encore d'évaluation
- MCQ On Operating System-All UnitDocument15 pagesMCQ On Operating System-All Unitprashant kumarPas encore d'évaluation
- Quizz - BDocument6 pagesQuizz - BsunnyPas encore d'évaluation
- PPSC Lecturer Computer Science Past Paper 2017Document33 pagesPPSC Lecturer Computer Science Past Paper 2017Faisal KhanPas encore d'évaluation
- 10066Document13 pages10066visitmajeedPas encore d'évaluation
- 03-04 SoluionsDocument2 pages03-04 SoluionsAditya MittalPas encore d'évaluation
- Question Bank - Unit3Document10 pagesQuestion Bank - Unit3Pratham WakdePas encore d'évaluation
- Bca502: Core - 19: Operating Systems Multiple Choice QuestionsDocument29 pagesBca502: Core - 19: Operating Systems Multiple Choice QuestionsUrvishPas encore d'évaluation
- CS C372/IS C362 - Operating System: Birla Institute of Technology & Science, Pilani QUIZ 2 - Closed BookDocument2 pagesCS C372/IS C362 - Operating System: Birla Institute of Technology & Science, Pilani QUIZ 2 - Closed BookVishal MittalPas encore d'évaluation
- C3 Memory Managment - NokeyDocument22 pagesC3 Memory Managment - NokeyshinkiriloveforeverPas encore d'évaluation
- Os Mcq's - 100Document32 pagesOs Mcq's - 100Srinath Gm G MPas encore d'évaluation
- Unit 5 OsDocument5 pagesUnit 5 OsPrashant JainPas encore d'évaluation
- Technical Questions: C) 31 Voice Channels & 1 Signalling ChannelDocument17 pagesTechnical Questions: C) 31 Voice Channels & 1 Signalling Channelapi-3843022Pas encore d'évaluation
- Free Flashcards About Stack #2087230Document3 pagesFree Flashcards About Stack #2087230Tonde PhiriPas encore d'évaluation
- OS Sheet (4)Document4 pagesOS Sheet (4)alcinialbob1234Pas encore d'évaluation
- Tutorial: Operating System MCQS (PART-1)Document115 pagesTutorial: Operating System MCQS (PART-1)Noor ThamerPas encore d'évaluation
- OS Multiple Choice QuestionsDocument6 pagesOS Multiple Choice QuestionsSheena MohammedPas encore d'évaluation
- ÔN TẬP CUỐI MÔN OSDocument16 pagesÔN TẬP CUỐI MÔN OSNguyễn Bảo HưngPas encore d'évaluation
- MCQ 1Document41 pagesMCQ 1jaijohnkPas encore d'évaluation
- Objective Type QuestionsDocument115 pagesObjective Type QuestionsRama Kasturi100% (3)
- Ec8791 MCQ For ModelDocument7 pagesEc8791 MCQ For ModelVijayanand SPas encore d'évaluation
- MCQ's For Operating SystemsDocument11 pagesMCQ's For Operating SystemsYussif AliPas encore d'évaluation
- OS Sheet (3)Document9 pagesOS Sheet (3)alcinialbob1234Pas encore d'évaluation
- MCQ 1Document22 pagesMCQ 1gogochor5Pas encore d'évaluation
- Operating System Questions MCQDocument13 pagesOperating System Questions MCQSwetha D75% (4)
- Assignment Unit 4Document18 pagesAssignment Unit 4Sachin KumarPas encore d'évaluation
- Sunbeam OS Day4 MCQ'sDocument13 pagesSunbeam OS Day4 MCQ'sYash KuncolienkerPas encore d'évaluation
- SPPU All Course MCQ: All MCQ PDF Format Mba / Be /ba /engieenaring / BSC /MSC /bca/ BcomDocument8 pagesSPPU All Course MCQ: All MCQ PDF Format Mba / Be /ba /engieenaring / BSC /MSC /bca/ BcomQueency FernandesPas encore d'évaluation
- Technical Questions: Ans: (C)Document17 pagesTechnical Questions: Ans: (C)api-3774860Pas encore d'évaluation
- OS Sheet1Document5 pagesOS Sheet1Yash JoshiPas encore d'évaluation
- COA MergeDocument426 pagesCOA MergeParth chaudhariPas encore d'évaluation
- 作業系統HW2Document7 pages作業系統HW2Chia ChenPas encore d'évaluation
- Course:Operatingsystem Course Code: - 22516 Semester:V MCQ Question BankDocument10 pagesCourse:Operatingsystem Course Code: - 22516 Semester:V MCQ Question Banksudarshan sonawanePas encore d'évaluation
- QB OsDocument19 pagesQB OsArijit SinghPas encore d'évaluation
- Rtos - MCQDocument20 pagesRtos - MCQpavanPas encore d'évaluation
- Operating System MCQS (GATE)Document40 pagesOperating System MCQS (GATE)Jitender Sharma75% (4)
- MCQS On Real Time Systems (6 Sem, CSE) : Prepared By: Sandigdha Acharya, Asst - Prof (CSE)Document12 pagesMCQS On Real Time Systems (6 Sem, CSE) : Prepared By: Sandigdha Acharya, Asst - Prof (CSE)Rajeev BansalPas encore d'évaluation
- Wipro Selection ProcedureDocument164 pagesWipro Selection Proceduresiva507Pas encore d'évaluation
- OS ToughDocument7 pagesOS ToughReoPas encore d'évaluation
- Group 3 McqsDocument3 pagesGroup 3 McqsKomal TariqPas encore d'évaluation
- MCQ 4 & 5Document4 pagesMCQ 4 & 5nithyasaviPas encore d'évaluation
- Os + DsDocument12 pagesOs + DsAniket AggarwalPas encore d'évaluation
- Operating System (OSY) MCQ 5iDocument10 pagesOperating System (OSY) MCQ 5iomkar Jadhav169Pas encore d'évaluation
- QusDocument4 pagesQusdeepaPas encore d'évaluation
- Typical Questions & AnswersDocument82 pagesTypical Questions & AnswersSudip PaulPas encore d'évaluation
- GATE QuestionsDocument90 pagesGATE Questionsas14jnPas encore d'évaluation
- Computer Science Past Papers MCQS SolvedDocument24 pagesComputer Science Past Papers MCQS SolvedLEGAL AFFAIRS DIVISION100% (1)
- OS Sheet (4) SolutionDocument5 pagesOS Sheet (4) Solutionhussienboss99Pas encore d'évaluation
- Practice Set Questions of Unit-5 & Unit-6 QuestionsDocument12 pagesPractice Set Questions of Unit-5 & Unit-6 Questionsmanikanta.reddy329Pas encore d'évaluation
- Rtos MCQDocument48 pagesRtos MCQshruti patilPas encore d'évaluation
- Mathematical and Computational Modeling: With Applications in Natural and Social Sciences, Engineering, and the ArtsD'EverandMathematical and Computational Modeling: With Applications in Natural and Social Sciences, Engineering, and the ArtsRoderick MelnikPas encore d'évaluation
- C Programming for the Pc the Mac and the Arduino Microcontroller SystemD'EverandC Programming for the Pc the Mac and the Arduino Microcontroller SystemPas encore d'évaluation
- Computer Knowledge Bit Bank for All Competitive ExamsD'EverandComputer Knowledge Bit Bank for All Competitive ExamsÉvaluation : 4 sur 5 étoiles4/5 (4)
- MidasDocument14 pagesMidasBawantha sandarathPas encore d'évaluation
- Renderoc TgxtraDocument2 pagesRenderoc TgxtratalatzahoorPas encore d'évaluation
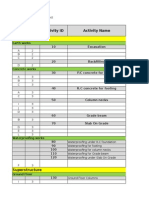
- WBS Activity List FullDocument216 pagesWBS Activity List FullAhmed SakrPas encore d'évaluation
- TwainDocument2 pagesTwainZuber HashmiPas encore d'évaluation
- Winstar XpressDocument12 pagesWinstar XpressseraphimusePas encore d'évaluation
- Maximo7 5 v4Document73 pagesMaximo7 5 v4Chinna BhupalPas encore d'évaluation
- XDM-100 GD A02 03 enDocument98 pagesXDM-100 GD A02 03 enrahulPas encore d'évaluation
- Introduction To Unified Modelling Language UmlDocument23 pagesIntroduction To Unified Modelling Language UmlhughbertzPas encore d'évaluation
- Default - Config Stepp II Keep30Document2 pagesDefault - Config Stepp II Keep30egar38Pas encore d'évaluation
- Nancy Katrak-Wonders of The WorldDocument39 pagesNancy Katrak-Wonders of The WorldSomnath BanerjeePas encore d'évaluation
- SDN TutorialDocument31 pagesSDN TutorialSaravanaRaajaa100% (1)
- Authorising Corporate or Qualifed SignaturesDocument2 pagesAuthorising Corporate or Qualifed SignaturesannastacyPas encore d'évaluation
- BRG-S-T-D-RD 85+835-1X30Document19 pagesBRG-S-T-D-RD 85+835-1X30Aziz ul HakeemPas encore d'évaluation
- Installation - Insomnia PDFDocument2 pagesInstallation - Insomnia PDFIna HadjiPas encore d'évaluation
- Sea OcDocument296 pagesSea OcJunaid Shah100% (1)
- Hmi DVP PDFDocument160 pagesHmi DVP PDFAdayroi AtuPas encore d'évaluation
- Monuments and Sites 16 What Is OUVDocument110 pagesMonuments and Sites 16 What Is OUVBernd PaulowitzPas encore d'évaluation
- Oracle EPM 11-1-2 3 Tuning Guide v2Document110 pagesOracle EPM 11-1-2 3 Tuning Guide v2chanLng100% (2)
- The Republic of The Union of Myanmar: U Han ZawDocument16 pagesThe Republic of The Union of Myanmar: U Han ZawZin Ko LinnPas encore d'évaluation
- Django by Example GoingLiveDocument22 pagesDjango by Example GoingLivebacklever95Pas encore d'évaluation
- Product Description Directions For Use: Surface PreparationDocument1 pageProduct Description Directions For Use: Surface Preparationrajeshji_000Pas encore d'évaluation
- Red Telephone BoxDocument3 pagesRed Telephone BoxPaulo CondePas encore d'évaluation
- 20 1703YSeriesElevatorManualDocument27 pages20 1703YSeriesElevatorManualnjava1978Pas encore d'évaluation
- Compatibility ChartsDocument101 pagesCompatibility ChartsArunMuraliPas encore d'évaluation
- Hassan Fathy - Architecture and EnvironmentDocument4 pagesHassan Fathy - Architecture and EnvironmentHäuser TrigoPas encore d'évaluation
- Can in Automation Brochure PDFDocument10 pagesCan in Automation Brochure PDFravichandran0506Pas encore d'évaluation