Académique Documents
Professionnel Documents
Culture Documents
BlueCoat SB SSL Visibility en v1c
Transféré par
zhogueTitre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
BlueCoat SB SSL Visibility en v1c
Transféré par
zhogueDroits d'auteur :
Formats disponibles
Security
Empowers
Business
The use of SSL encryption for all enterprise Internet traffic is growing steadily. Applications that make use of SSL
such as SharePoint, Exchange, WebEx, Salesforce.com and Google Apps are commonplace. Even email
applications like Gmail, Yahoo, and Zimbra are being used in workplace environments as hosted email or BYOD apps.
Its clear that organizations now need complete visibility into the SSL traffic coming across the WAN. They need
the ability to preserve complete network and web histories from encrypted network and web traffic for compliance,
regulatory and logging requirements. Blue Coat has solutions today to address the SSL dilemma.
Risks Associated With SSL
For end users, SSL has long been a means to secure web-based
transactions that enable e-commerce and online banking. Over time,
the simplicity of SSL has made it the perfect vehicle for migrating new
online services to web-based models, including applications for viewing
medical records, ordering prescriptions, and filing tax returns.
Surveys show that over 50 percent of enterprise applications now use
SSL SharePoint, Exchange, WebEx, Salesforce.com and Google Apps
are examples. Many social networking and consumer applications such
as Facebook and Gmail already default to full-time use of SSL by their
end users. The use of SSL in enterprise traffic and across the Internet
has grown steadily, with a 52 percent CAGR in SSL-based WAN traffic.
Its clear that there are legitimate needs for encrypted data within, to
and from the enterprise. But as many IT managers are aware, its privacy
benefits can be overshadowed by its risks.
While encrypting web sessions protects end-user data from being
viewed in transit over the Internet, it creates a blind spot for IT
administrators: they typically have no visibility into SSL-encrypted traffic.
For that reason, SSL has quickly become one of the most popular ways
to mask malicious code such as Trojan horses and viruses. Incoming
threats can hide in SSL to bypass security architectures, and the same
threats are now a growing problem for outbound enterprise traffic. This
is becoming a hot button for security applications that tackle data loss
prevention (DLP), compliance reporting and lawful intercept solutions
that could, at one time, see what was outgoing, but are suddenly in the
dark because of the growth of SSL traffic.
This lack of visibility into SSL can make it difficult or impossible for
network administrators to enforce corporate acceptable use policies
and to ensure that threats like viruses, spam and malware are stopped
before they reach individual users. The inability to examine the contents
of SSL communications also makes it possible for information to be
accidentally leaked out of the enterprise or worse, stolen.
Regulatory compliance requirements, including the identification of
accidental or intentional leakage of confidential information, are also
virtually impossible to meet because of SSL encryption. In many
instances, enterprises face conflicting requirements to encrypt and
examine data. In typical installations, these seemingly incompatible
requirements cannot be met with acceptable performance. This SSL
conundrum has wreaked havoc on organizations subject to industry
and government compliance mandates, such as HIPAA and SarbanesOxley (SOX), which require that only authorized individuals have access
to hardware and software resources within the network infrastructure.
Other compliance mandates require organizations with publicly
accessible networks to be able to provide law enforcement agencies
with documentation of network activity which requires that all traffic be
unencrypted.
SSL Control Approaches
Network operators already deploy an array of network and security
appliances to protect their enterprises, enforce internal acceptable-use
policies and satisfy government regulations. These devices provide
solutions for detecting rogue applications, controlling unrestricted
SOLUTION BRIEF
BLUE COAT SSL VISIBILITY
SOLUTION BRIEF
Security
Empowers
Business
web surfing, firewalling traffic, providing VPNs, and providing network
access control (NAC), intrusion detection (IDS), intrusion prevention
(IPS), unified threat management (UTM), regulatory compliance,
virus protection, spam control, and other security measures. These
appliances work almost entirely by providing deep packet inspection
and flow analysis, looking for known patterns of mischievous activity
and blocking or recording it. Unfortunately, these network and security
appliances, in many instances, can only inspect plaintext traffic and are
unable to inspect SSL-encrypted communications for attack signatures.
They are therefore becoming less and less effective as the volume of
encrypted SSL traffic continues to grow.
Network operators have had to choose between two extremes in
confronting these issues. They can take a draconian approach by
blocking SSL communications entirely, or allow SSL communications
transparently, without inspection, by leaving port 443 open on their
security infrastructure. This approach greatly reduces the effectiveness
of networks and of security appliances, which cant examine encrypted
flows. Neither choice is a viable option for enterprise networks.
Other approaches have been used. They all provide plaintext inspection
of SSL-encrypted flows, enabling the dropping of content that doesnt
meet acceptable-use policies, or the logging of suspected attacks to a
management station. Just as importantly, they identify and permit SSL in
legitimate use cases. In many instances, these methods are successful
at examining encrypted SSL, but they typically suffer other major
problems that limit their effectiveness.
For more information on the technical aspects of SSL, download
the Blue Coat SSL Technical Primer here.
Blue Coat SSL Visibility Solutions
Blue Coat can give enterprises visibility into encrypted traffic with the
SSL Visibility Appliance and Encrypted TAP for ProxySG. The SSL
Visibility Appliance provides high performance and multiple streams
of decrypted content for use in IDS, IPS, compliance, logging, threat
analysis and other measures across all network ports. For organizations
considering the use of SSL proxy and interception in their ProxySG
deployment, Encrypted TAP offers complete visibility of encrypted web
traffic for use in logging, forensics, and analysis. Its available as an addon option to ProxySG Secure Web Gateway appliances.
Blue Coat SSL Visibility Appliance
The Blue Coat SSL Visibility Appliance
The Blue Coat SSL Visibility Appliance provides decrypted content of
SSL flows to existing security appliances used for intrusion detection
and prevention, forensics, compliance and data loss. This enables them
to provide their security applications with visibility into both SSL and
non-SSL network traffic. End users can add SSL inspection capabilities
to their network security architectures immediately to close the security
loophole that SSL creates.
Features and Benefits
The unique capabilities of the Blue Coat SSL Visibility Appliance help
organizations to remove risks arising from lack of visibility into SSL
traffic while increasing the performance of security and network
appliances. It offers line-rate high-performance throughput, and allows
for non-SSL flows to be sent directly to attached security appliances in
less than 40 microseconds, minimizing delay for applications such as
VoIP. The Appliance is available in three performance-level models. The
high-end system, the SV3800, supports decryption of up to 4Gbps of
SSL traffic in a WAN link of up to 40Gbps (20 Gbps in each direction) for
a variety of SSL versions and cipher suites.
The SSL Visibility Appliance can support the simultaneous analysis of
up to 6,000,000 TCP flows for SSL content. It handles up to 400,000
concurrently active SSL sessions that are being inspected. The setup
and teardown rate of up to 11,500 SSL sessions per second is more
than 10 times higher than other solutions.
Deploying the SSL Visibility Appliance is transparent to end systems
and to intermediate network elements. It doesnt require network
reconfiguration, IP addressing or topology changes, or modification to
client and web browser configurations. The Appliance can be deployed
inline or through the use of SPAN/TAP or a mirror port to handle inbound
and outbound SSL traffic. Deployments that provide decrypted data to
active security appliances enable policy and enforcement actions on
SOLUTION BRIEF
SSL traffic; deployments that feed passive security appliances are better
suited for logging and visibility requirements.
Security
Empowers
Business
The decrypted content from the SSL Visibility Appliance is designed for
application preservation. Intercepted plaintext is delivered to security
appliances as a generated TCP stream that contains the packet headers
as they were received. This allows applications and appliances used for
IDS, IPS, forensics, data loss prevention, and other measures to expand
their scope to SSL-encrypted traffic.
The SSL Visibility Appliance also supports input aggregation and output
mirroring. Input aggregation allows aggregation of traffic from multiple
network taps onto a single passive-tap segment for inspection. Output
mirroring allows the Appliance to feed traffic to one or two attached
passive security appliances in addition to the primary active security
appliance.
SSL Visibility Appliances are designed for high availability with
integrated fail-to-open hardware and configurable link state monitoring
and mirroring for guaranteed network availability and network security.
For those deployments where security certification is a requirement,
Blue Coats SSL Visibility Appliances are in the process of receiving
FIPS 140-2 Level 2 certification.
ProxyAV, DLP, etc.
Security Solution
CERTIFICATE
CERTIFICATE
CERTIFICATE
CN: Gmail
CA: ProxySG Cert
CN: Gmail
CA: ProxySG Cert
CN: Gmail
CA: Verisign
SSL interception and filtering is not a new feature for the Blue Coat
ProxySG. SSL Proxy has been an integral part of it for well over five
years. It includes the ability to selectively inspect attachments for
malware, and content for data leakage prevention, through the use of
policy. It also enables third-party integration of anti-malware and DLP
offerings over ICAP (Internet Content Adaptation Protocol). SSL Proxy
terminates and re-establishes SSL connections and allows the ProxySG
to securely send attachments and content for inspection services.
Encrypted Tap builds on the SSL Proxy and allows all or selected SSLencrypted web traffic to be decrypted and its content streamed to a
third-party system for additional analysis, archiving, and forensics.
Encrypted Tap is available for the SG600, SG900 and SG9000 series
Blue Coat ProxySG appliances. These appliances already include SSL
hardware assist and SSL licenses, and would need only the additional
Encrypted TAP license to deliver SSL visibility.
The ProxySG with SSL Proxy and Encrypted Tap allows organizations
to eliminate the SSL blind spot with visibility and control over SSLencrypted traffic. They can stop rogue applications from using SSL to
subvert enterprise controls and security measures, and they can scan
SSL-encrypted traffic for viruses, worms, and Trojans, and stop them at
the gateway.
The solution can also help prevent spyware from installing or
communicating over SSL; halt secured phishing and pharming attacks
that use SSL to hide from IT controls or to increase the appearance of
authenticity; and accelerate approved and safe SSL-encrypted traffic.
ProxySG
SSL Visibility
Appliance
Features and Benefits
Encrypted Traffic
Decrypted Traffic
Encrypted Tap
Blue Coat Encrypted Tap is a new optional feature for ProxySG
appliances that works with the SSL proxy to provide complete visibility
into SSL traffic. Encrypted Tap sends a stream of decrypted traffic
to third-party logging systems for analysis, archiving, and forensics.
By providing this SSL visibility and control, Blue Coat now offers a
complete SSL web security solution with its ProxySG family of secure
proxy appliances.
ProxySG also allows administrators to take a granular approach to
proxying SSL for applications of different trust levels and privacy
concerns pass-through, check/verify then pass-through, or proxy with
full visibility and control.
The policy capabilities of the ProxySG allow for the display of splash
screens reminding users of acceptable use, and warning them that
monitoring extends to SSL.
Encrypted Tap on the ProxySG allows for visibility of both internal
and external SSL traffic. It does more than enhance security it also
provides a better user experience. The Blue Coat solution actually
improves overall session performance up to 1,000 percent by leveraging
the ProxySGs MACH5 acceleration technologies (caching, compression,
and bandwidth prioritization policies).
SOLUTION BRIEF
Security
Empowers
Business
All ProxySG appliances are powered by a purpose-built operating
system, and can be centrally managed as part of an enterprise-wide
solution deployment.
Requirements for Encrypted Tap
ProxySG (SG600/SG900/SG9000)
Collection system (system configured to receive tapped data)
For complete security, a dedicated ProxySG interface on a private
network with the collection system
Minimum SGOS release: 6.5
SSL License on the ProxySG
Encrypted TAP License
Choosing the right solution
SSL VISIBILITY APPLIANCES
ENCRYPTED TAP FOR PROXYSG
Multiple streams (up to three attached security
devices with decrypted traffic)
Single stream output
Copy of decrypted traffic can be sent to:
Inline deployment with policy enforcement
options for active appliances
Inline with passive appliances
SPAN/Tap/Mirror deployment with passive
appliances
Copy of decrypted traffic only
High Performance (multi-gigabit/sec SSL visibility
throughput
Performance based on ProxySG performance
Policy capability based on IP addresses, and
other network parameters
Full policy (CPL) integration
Detection of all SSL flows, irrespective of
destination port value, using DPI techniques
SSL Visibility of web traffic
All ProxySG deployment methodologies supported
(see SWG Deployment Methodologies white paper)
Provides the clear text of any SSL flow including
HTTPS, POP3, SMTP and other protocols that
use TLS.
Standalone appliance
Requires existing or new ProxySG
About Blue Coat
Security technology can focus on prevention and prohibition and
instill a culture of fear or it can center on possibilities, and help you
unleash your full business potential.
Blue Coat ProxySG Appliance
Conclusion
Blue Coat Systems Inc.
www.bluecoat.com
Corporate Headquarters
Sunnyvale, CA
+1.408.220.2200
EMEA Headquarters
Hampshire, UK
+44.1252.554600
APAC Headquarters
Singapore
+65.6826.7000
Forecasts point to continued growth in SSL-encrypted traffic. IT
network operators are looking for new solutions that satisfy the need
for information security for the enterprise and for individual users, as
well as requirements for corporate compliance, acceptable-use policies
and government regulations for security and privacy. The solution must
not impact network performance, because compliance at the expense
of throughput is no more acceptable than meeting user and application
bandwidth requirements while ignoring security. It has been difficult, if
not impossible, to satisfy these competing requirements for security,
performance and control. Blue Coat offers a choice of solutions that give
any organization visibility into SSL encrypted traffic.
Blue Coat offers more than the industrys most advanced and
sophisticated security technology. We offer a whole new outlook
on how security technology provides business value. Its called
Business Assurance Technology. And its delivered by our Centers,
a comprehensive array of technologies, products, services, and
capabilities that give you total protection and help you see
and exploit new opportunities. With the products, services, and
technologies within Resolution Center, you get the intelligence
you need to understand all of the traffic on your network even
encrypted SSL traffic so you can make informed decisions. Blue
Coat offers two options for SSL Visibility, a key component in our
Resolution Center.
Learn more about our Centers at
www.bluecoat.com/business-assurance-technology
2013 Blue Coat Systems, Inc. All rights reserved. Blue Coat, the Blue Coat logos, ProxySG, PacketShaper, CacheFlow, IntelligenceCenter, CacheEOS, CachePulse, Crossbeam, K9, the K9 logo, DRTR, Mach5, Packetwise, Policycenter, ProxyAV, ProxyClient,
SGOs, WebPulse, Solera Networks, the Solera Networks logos, DeepSee, See Everything. Know Everything., Security Empowers Business, and BlueTouch are registered trademarks or trademarks of Blue Coat Systems, Inc. or its affiliates in the U.S. and certain
other countries. This list may not be complete, and the absence of a trademark from this list does not mean it is not a trademark of Blue Coat or that Blue Coat has stopped using the trademark. All other trademarks mentioned in this document owned by third parties
are the property of their respective owners. This document is for informational purposes only. Blue Coat makes no warranties, express, implied, or statutory, as to the information in this document. Blue Coat products, technical services, and any other technical data
referenced in this document are subject to U.S. export control and sanctions laws, regulations and requirements, and may be subject to export or import regulations in other countries. You agree to comply strictly with these laws, regulations and requirements, and
acknowledge that you have the responsibility to obtain any licenses, permits or other approvals that may be required in order to export, re-export, transfer in country or import after delivery to you. v.SB-SSL-VISIBILITY-EN-v1c-0813
Vous aimerez peut-être aussi
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (119)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (587)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2219)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (894)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- Crypt of Cthulhu 49 1987 Cosmic-JukeboxDocument71 pagesCrypt of Cthulhu 49 1987 Cosmic-JukeboxNushTheEternal100% (3)
- A Business Development PlanDocument90 pagesA Business Development PlanRishabh Sarawagi100% (1)
- Boeing 7E7 - UV6426-XLS-ENGDocument85 pagesBoeing 7E7 - UV6426-XLS-ENGjk kumarPas encore d'évaluation
- Car Loan ProposalDocument6 pagesCar Loan ProposalRolly Acuna100% (3)
- Biochemical Aspect of DiarrheaDocument17 pagesBiochemical Aspect of DiarrheaLiz Espinosa0% (1)
- Preterite vs Imperfect in SpanishDocument16 pagesPreterite vs Imperfect in SpanishOsa NilefunPas encore d'évaluation
- AMA Manual 10th Edition PDFDocument1 014 pagesAMA Manual 10th Edition PDFKannan Fangs S100% (2)
- Metabolic Pathway of Carbohydrate and GlycolysisDocument22 pagesMetabolic Pathway of Carbohydrate and GlycolysisDarshansinh MahidaPas encore d'évaluation
- Equifax Credit ReportDocument1 pageEquifax Credit ReportzhoguePas encore d'évaluation
- Fund Accounting QuizDocument5 pagesFund Accounting QuizzhoguePas encore d'évaluation
- Security Everywhere WhitepaperDocument4 pagesSecurity Everywhere WhitepaperzhoguePas encore d'évaluation
- Fall Brook Membership FlyerDocument4 pagesFall Brook Membership FlyerzhoguePas encore d'évaluation
- ExampleDocument1 pageExamplezhoguePas encore d'évaluation
- Orbit BioscientificDocument2 pagesOrbit BioscientificSales Nandi PrintsPas encore d'évaluation
- FeistGorman - 1998-Psychology of Science-Integration of A Nascent Discipline - 2Document45 pagesFeistGorman - 1998-Psychology of Science-Integration of A Nascent Discipline - 2Josué SalvadorPas encore d'évaluation
- Pilar College of Zamboanga City, IncDocument14 pagesPilar College of Zamboanga City, IncIvy VillalobosPas encore d'évaluation
- GVP College of Engineering (A) 2015Document3 pagesGVP College of Engineering (A) 2015Abhishek SunilPas encore d'évaluation
- 150 Most Common Regular VerbsDocument4 pages150 Most Common Regular VerbsyairherreraPas encore d'évaluation
- Flotect Vane Operated Flow Switch: Magnetic Linkage, UL ApprovedDocument1 pageFlotect Vane Operated Flow Switch: Magnetic Linkage, UL ApprovedLuis GonzálezPas encore d'évaluation
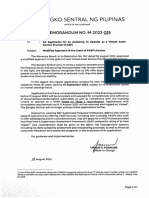
- BSP Memorandum No. M-2022-035Document1 pageBSP Memorandum No. M-2022-035Gleim Brean EranPas encore d'évaluation
- The Rescue FindingsDocument8 pagesThe Rescue FindingsBini Tugma Bini Tugma100% (1)
- TIA Portal v11 - HMI ConnectionDocument4 pagesTIA Portal v11 - HMI ConnectionasdasdasdasdasdasdasadaPas encore d'évaluation
- Dislocating The Sign: Toward A Translocal Feminist Politics of TranslationDocument8 pagesDislocating The Sign: Toward A Translocal Feminist Politics of TranslationArlene RicoldiPas encore d'évaluation
- Unit-2 Fourier Series & Integral: 2130002 - Advanced Engineering MathematicsDocument143 pagesUnit-2 Fourier Series & Integral: 2130002 - Advanced Engineering MathematicsDarji DhrutiPas encore d'évaluation
- Dalit LiteratureDocument16 pagesDalit LiteratureVeena R NPas encore d'évaluation
- Lauritzen 1964Document10 pagesLauritzen 1964Priyanka GandhiPas encore d'évaluation
- PSE Inc. V CA G.R. No. 125469, Oct 27, 1997Document7 pagesPSE Inc. V CA G.R. No. 125469, Oct 27, 1997mae ann rodolfoPas encore d'évaluation
- Lecture Notes - Sedimentation TankDocument45 pagesLecture Notes - Sedimentation TankJomer Levi PortuguezPas encore d'évaluation
- January: DiplomaDocument24 pagesJanuary: DiplomagwzglPas encore d'évaluation
- Alberta AwdNomineeDocs Case Circle BestMagazine NewTrailSpring2016Document35 pagesAlberta AwdNomineeDocs Case Circle BestMagazine NewTrailSpring2016LucasPas encore d'évaluation
- Evoe Spring Spa Targeting Climbers with Affordable WellnessDocument7 pagesEvoe Spring Spa Targeting Climbers with Affordable WellnessKenny AlphaPas encore d'évaluation
- Service Manual Pioneer CDJ 2000-2 (RRV4163) (2010)Document28 pagesService Manual Pioneer CDJ 2000-2 (RRV4163) (2010)GiancaPas encore d'évaluation
- Chrome Settings For CameraDocument6 pagesChrome Settings For CameraDeep BhanushaliPas encore d'évaluation
- Reviewer in Intermediate Accounting IDocument9 pagesReviewer in Intermediate Accounting ICzarhiena SantiagoPas encore d'évaluation
- Text Detection and Recognition in Raw Image Dataset of Seven Segment Digital Energy Meter DisplayDocument11 pagesText Detection and Recognition in Raw Image Dataset of Seven Segment Digital Energy Meter DisplaykkarthiksPas encore d'évaluation