Académique Documents
Professionnel Documents
Culture Documents
Capturing and Analyzing Live Network Traffic in A Virtual Environment Using Open Source IDS Snort & Logging Alerts in MYSQL
Transféré par
Editor IJRITCCTitre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Capturing and Analyzing Live Network Traffic in A Virtual Environment Using Open Source IDS Snort & Logging Alerts in MYSQL
Transféré par
Editor IJRITCCDroits d'auteur :
Formats disponibles
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1450 1456
________________________________________________________________________________________________________________________________
Capturing and Analyzing Live Network Traffic in a Virtual Environment using
Open Source IDS: Snort & Logging Alerts in MYSQL
1
Sumiti Bansal, 2Saurabh Mittal, 3Mandeep Singh
1,2
GGITC, Ambala, 3SJP polytechnic, Yamunanagar
Abstract--Network intrusion detection along with firewall provides an important layer of security for computer system or network. This paper
describes a virtual network created using virtualization tool implemented with snort IDS to monitor traffic crossing the network. Snort is a
freeware and open source NIDS tool which is basically a rule-driven system. The uniqueness of this hands-on learning is that it also allows new
developer to learn snort rule writing by testing and debugging their rules against the live traffic. The main aim of this research paper is to
provide a brief overview of snort and configure it in a virtual network to log or alert intrusions in a network. We have made our own set of
signatures in the snort and have implemented it in a specified virtual network so that our created network will remain congestion and hasle free.
Keywords: Networks, Virtualization, snort, MySQL, Barnyard2.
_________________________________________________*****_________________________________________________
1.
Introduction
As load on the network expands, it is apparent that more and
more possibilities of attacks or intrusion to occur between
networks. There are many complexities that have created a
demand for a sophisticated means to analyze the traffic and
security level of networks such as analyzing packets of
information overloading the system, check unidentified user in
gaining access to the database files,
identified
misconfiguration of devices, network slowdown and many
more. Network-based IDSs can monitor an entire, large
network or devices and impose little overhead on a network.
Network-based IDS [10] are mostly passive devices that
monitor ongoing network activity without adding significant
overhead or interfering with network operation. They are easy
to secure against attack and may even be undetectable to
attacker. They require little effort to install and use on existing
networks. Currently the problems of network traffic, they are
exposed to suspicious packets. This suspicious network packet
will make the traffic of system congested. In our virtual
network we have implemented snort in such a way that the
network packets creating congestion can either be blocked or
an alert can be generated. Depending upon the alert count we
can block the suspicious packet and network can be made
congestion free.
2.
Problem Overview
To analyze and discuss the implementation of snort as a type
of open source intrusion detection tool, a deep
understanding of the snort process needs to be explained
before it can be implemented further in the network. After this
general introduction, there will be a detailed experiment
launching snort over a virtual network and how the ids will be
configured to attempt to log or alert the suspicious packet. A
virtual network has been developed and new rules have been
created furthermore the created rules are analyzed in a live
network traffic and comparison of alerts is considered for
further actions.
3. Snort
Snort is a lightweight intrusion detection system that can log
packets coming across your network. This program is used on
smaller networks but on larger ones, with Gigabit Ethernet, it
may become unreliable. Snort doesn't require that you
recompile your kernel or add any software or hardware to
your existing distribution but it does require that you have root
privileges. Snort is an open source Signature based IDS.
There are predefined rules for finding attacks. Snort rules are
provided by Sourcefire and can be downloaded by registered
users for their use. To include rules one has to change the
configuration file. When a packet comes, rules are matched
with the packet. If matching occurs with any of the rules,
actions specified in the rule will be performed. The actions
can be of four types.
(a) It can be to alert the nodes.
(b) Log the incoming matched packet.
(c) Pass the packet without any action.
(d) Drop the packet.
Snort works in three different modes.
Sniffer mode
Packet logger mode
Network intrusion detection mode.
In Sniffer mode snort detects the incoming packets and
displays them in console.
In packet logger mode, Snort collects the packets and logs
them to disk.
1450
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_____________________________________________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1450 1456
________________________________________________________________________________________________________________________________
In network intrusion detection system (NIDS) mode alerts
will be generated. Alerts can be generated in different ways. It
can be logged or can be displayed to console. Alerts can also
be generated in such a way that it will display only useful
information or will display the entire header information.
3.
Implementation
4.1 Setting up the Network
We have developed a virtual network where snort can be
implemented. The design of our network is shown below in fig
4.1. The snort is installed on ubuntu which act as IDS and all
the other nodes are connected to virtual network using this
node and automatically assigned IPs via the DHCP protocol
running on the router.
Tools used to Create the Network:
Virtualization software
Ubuntu 12.04 iso file
Machine 1
virtual
network
Virtual
network
Machine
with Snort
sensor
installed
Machine 3
Machine 2
Virtual
network
Fig 4.1: Virtual Network Structure
Virtualization software virtual box:
Users of VirtualBox [9] can load multiple guest OSs under a
single host operating-system (host OS). Each guest OS can be
start paused and stopped independently within its own virtual
machine (VM). The user can independently configure each
VM and run it under a choice of software-based
virtualization or hardware assisted virtualization if the
underlying host hardware supports this. The host OS and guest
OS applications can communicate with each other through a
number of mechanisms including a common clipboard and a
virtualized network facility and he have configured these
Guest VMs to directly communicate with each other.
Steps in Creating the Network:
1.
We have virtual box in the system and it can be
downloaded from the following address
http://www.oracle.com/technetwork/serverstorage/virtualbox/downloads/index.html?ssSourceSiteId=otnj
p#vbox
2. ubuntu 12.04 has been as the virtual operating system
with 2 Network adapter attached to bridged adapter, from
which one is running in Promiscuous mode
3. Another ubuntu 12.04 has been installed as the second
virtual operating system acting as target with 1 network
adapter attached to bridged adapter.
4.2 Deployment
Sensor location is crucial for analysis of all traffic coming in
and going out of the virtual network. Typically, a good entry
point is at the border between the virtual network and the
internet. We have used Snort on an interface where no IP
address is assigned i.e. a network interface card to be in
promiscuous mode [7] so as to protect IDS itself from
intrusions. For example, on a Linux machine, we have bring
up interface eth0 using command ifconfig eth0 up without
assigning an actual IP address. The advantage is that when the
Snort host doesnt have an IP address itself, nobody can
access it. We have configured an IP address on eth1 that was
used to access the sensor itself.
4.3 Snort Installation
Snort [1] [10] was installed with integration to a database
which has a logging facility of data that can be viewed and
analyzed later on. Different types of database servers like
MySQL, PostgresSQL, Oracle, Microsoft SQL server and
other ODBC-compliant databases can be used with Snort.
Snort was installed from its source code, and for this we were
in need to build it first. Download the required version of
Snort from its web site (http://www.snort.org/) and follow the
steps below
Making the snort environment [6]
Before installing Snort we have to check the number of
software packages installed,
1.
Ubuntu installation can be upgraded by:
Sudo apt-get update
Sudo apt-get upgrade
2.
Prerequisite packages from the Ubuntu repositories can
be installed as:
Sudo apt-get install mysql-server nmap nbtscan apache2 php5
php5-mysql php5-gd libpcap0.8-dev libpcre3- dev g++ bison
flex libpcap-ruby
1451
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_____________________________________________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1450 1456
________________________________________________________________________________________________________________________________
make zlib1g-dev libmysqld-dev libdnet libdnet-dev libpcre3
libpcre3- dev gcc make flex byacc bison linux-headers-generic
libxml2-dev libdumbnet-dev zlib1g zlib1g-dev
Basic requirements:
Snort rule:
Creating Database
Installing Barnyard2
3. Download and Install Data Acquisition API from:
Wget http://www.snort.org/dl/snort-current/daq-0.6.2.tar.gz
Once downloaded, extract using command:
Sudo tar -xvzf daq-0.6.2.tar.gz
cd daq-0.6.2
./configure
Sudo make
Sudo make install
4. Download and install snort using command
wget http://www.snort.org/dl/snort-current/snort-2.9.2.3.tar.gz
Once downloaded, extract it:
Sudo tar -xvzf snort-2.9.2.3.tar.gz
cd snort-2.9.2.3
. /configure --prefix /usr/local/snort && make && make
install
Now we are ready with a dedicated machine installed with
snort IDS.
4.4 Making snort to work as network intrusion detection
system
Snort is a popular network intrusion detection system.
Marketed as the de facto standard in intrusion detection by
its developer SourceFire, it is a lightweight and open source
tool for the monitoring and real-time analysis of computer
networks. By itself Snort does not actually prevent network
intrusions and attacks. It is primarily designed to monitor and
report the network status and traffic based on rules defined by
the user [3]. An example of a simple rule in snort would be as
follows
Alert tcp any any -> any
Packet;sid:11011)
any (msg: Incoming TCP
This rule is designed to raise an alert if an external TCP
packet enters the internal network [8]. In industry practicing
this rule would not exist since it would log every single packet
entering the network, and this would be extremely excessive.
In reality, the IDS would be configured using selected rules
along with custom rules defined by the network security
administrator that could be unique to the specific network that
is being monitored.
The purpose of snort IDS here is to actively alert and monitor
the target computer that is the victim of any kind of intrusion.
The methods outlined will not be able to prevent the intrusion,
but the goal will be to provide alerts through Snort to inform
the user that a possible intrusion is taking place.
4.4.1
Snort rule:
Rules in snort follow a specific standard and are defined
within plaintext *.rule file. They can be downloaded from
snort official website or can be created by own according to
our requirements i.e. user defined rules
Snort rules can be downloaded from:
Wget-Osnortrules-snapshot-2923.tar.gz
http://www.snort.org/reg-rules/snortrules-snapshot2923.tar.gz/
User defined rules:
These rules are created and maintained locally, according to
the specific needs of the network.
For example if we want to generate an alert when someone is
pinging with ttl 225.The following snort rule can generate the
same.
Alert icmp any any --> any any (msg:ICMP pinging; ttl:
225; Sid: 1100 ;)
4.4.2
Creating database
Databases are used with Snort to store log and alert data
generated during analysis of packets. We can use multiple
types of databases with Snort such as MySQL. Before snort
starts logging to MySQL database, we need to create a
database on the database server for Snort. We have created a
database name snortdb. After creating the database, tables
were created as shown in fig. 4.4.2.1 where Snort data is
logged. However, we need not to create tables manually
because Snort comes with a script that will do the entire job.
Steps in creating database :
Step1: Creating MySQL User and Granting Permissions to
User and Setting Password
# mysql -h localhost -u root -p
Mysql>create database snortdb;
Step2: Creating MySQL User and Granting Permissions to
User and Setting Password
mysql> grant CREATE, INSERT, DELETE, UPDATE,
SELECT on snortdb.* to user@localhost;
mysql> set password for rr = password('password');
Step3:Creating Tables in the Snort Database
# mysql -h localhost -u user -p snort < contrib/create_mysql
1452
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_____________________________________________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1450 1456
________________________________________________________________________________________________________________________________
Where create_mysql is a script present in the contrib
directory that will create all of the necessary tables. Tables
generated were verified using following command
Mysql > show tables;
Result is shown below; all alerts will be logged and
retrieved in these tables.
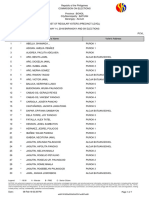
Fig 4.4.2.1 snort tables
4.4.3
Installing barnyard:
Barnyard2 is an output system for Snort. Snort creates a
special binary output format called unified. It reads this file,
and then resends the data to a database back-end. Unlike the
database output plug-in, Barnyard2 manages the sending of
events to the database and stores them when the database
temporarily cannot accept connections.
Type the following commands on command prompt to install
barnyard2
Cd /usr/local/snort
Wget www.findthatzip-file.com/search-68149119-fzip/winrarwinzip-download-barnyard2-2.10.tar.gz.htm
tar -xvzf barnyard2-2.10.tar.gz
cd barnyard2-2.10
cd firnsy-barnyard2*
sudo autoreconf -fvi -I ./m4
sudo
./configure
--with-mysql
--with-mysqllibraries=/usr/lib/i386-linux-gnu
sudo make
sudo make install
sudo cp etc/barnyard2.conf /usr/local/snort/etc
sudo mkdir /var/log/barnyard2
sudo chmod 666 /var/log/barnyard2
sudo touch /var/log/snort/barnyard2.waldo
By using barnyard2 we can send the output to multiple
interfaces like syslog, a local file or database. Snort
performance also increases after barnyard2 handles the
database.
4.5 Configuring snort
To simplify the initial set up and configuration of Snort on the
target machine, we first download the source code file and
install snort from there. We have used Linux box running
ubuntu operating system to detect intrusion into our system
placed inside our virtual network. Whenever any intrusion will
be detected by Snort, it will generate an alert. And if system
successfully generates an alert then that means network will
have been well configured and traffic monitoring is taking
place [4]. All the alerts generated are stored and logged in the
MYSQL database created during installation of sql.
We have confirmed snort installation by running it in packet
sniffing mode by running the following command
Snort -i eth1 l /var/log/snort
-i <interface> tells snort which interface to watch.
-l <logging directory>tells snort in which directory to log the
packets.
The result is shown in fig 4.5.1. Where we got a message
commencing packet processing verifying that snort has
started capturing packets.
Fig.4.5.1 Packet Logging Mode Verifying Snort
Installation
The captured packets in this mode are logged in a local file
that can be analyzed later by typing the following command:
Snort r /varlog/snort.log.timestamp
Where:
Timestamp is the time when file was creates.
r <filename> takes the name of the file generated.
The output is shown in fig.4.5.2 where a total of 5 packets are
logged in the file. Logged packets provide much information
1453
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_____________________________________________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1450 1456
________________________________________________________________________________________________________________________________
about the data in the network such as source ip address, the
content of one such packet is explained in table 1 below.
Load.rule : such rules will generate an alert whenever a
download occur on the network such as torrent download etc.
Table 5.2 contains rules defined in this category
Social.rule : This rule will generate an alert whenever there is
an access to social networking sites.for eq facebook.com. The
rules are contained in table 5.3
Table 5.1:Local.rule
1. alert tcp any any <> any 21(msg:ftp login;sid:10000;)
2.alert tcp any any <> any 22(msg:telnet login;sid:10004;)
3. alert icmp any any <> any !80(msg:icmp ping
Packet;ttl:24;sid:10018
Fig. 4.5.2 Snort Packet logged in the directory
Table 4.5.1: Contents of packet logged
04/3018:41:27.624176
192.168.1.1
Timestamps
1900
Source Port
->
Direction indicator
192.168.1.5
Destination IP address
50649
Destination Port
UDP
Port host
TTL:64
Time to live
TOS:0*0
Type of service
ID:922
Identification number
Iplen:20
Length of packet
Dgmlen:359
Length of datagram
Source IP address
Table 5.2:Load.rules
1 Alert tcp any any -> any any (msg:mp3 download;
uricontent:.mp3;nocase;flow:established,to_server;
sid:10011;rev:1;)
2. Alert tcp any any -> any any (msg:pdf download;
uricontent:.pdf;nocase;flow:established,to_server;
sid:10011;rev:1;)
Table5.3:Social.rules
1.
alert tcp any any -> any any (msg:"facebook
access";content:www.facebook.com;
sid:10004;rev:1;)
2.
alert tcp any any -> any any (msg:"youtube
access";content:www.youtube.com; sid:10008;rev:1;)
6.
5. Creating Rules in Snort
Our next step was to create rules in the Snort. This is the most
important part of the IDS configuration because it determines
which packets are going to raise alerts. However, there are
different sources for finding and deploying rules, and we have
developed user defined rules which are created and
maintained locally, according to the specific needs of the
network. Three alert files were created these are:
Local.rule : rules contained in these file will generate an alert
when protocol such as ftp or telnet is used. Table 5.1 contains
rules defined in this category
Detecting and analyzing packets against user defined
Snort Rules
Since rules have now been defined to alert and log the
network suspicious packets. These rules are now analyzed
with live data entering in the network. For this we have started
snort to run in NIDS mode several times a day and of the run
output is shown below in figure 6.1 where a total of 450916
packets were being received analyzed by snort, the alerts thus
generated are shown on console as shown in figure 6.2 below
and are logged in database file as well as will be seen later.
Snort was configured to include the user defined rule files
which we have created above and all other default rules that
come along with snort were uncommented.
1454
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_____________________________________________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1450 1456
________________________________________________________________________________________________________________________________
alerts were generated. Out of these 4070 alert, YouTube
access have generated the maximum number of alert (i.e.
around 58%) and we can say that YouTube has been used
maximum number of times in our virtual network, This
comparison is given in graph 7.1
Fig. 6.1: Snort Post run Output
Fig7.1: Alerts Count in Mysql
Fig. 6.2: Snort alert on Console
Fig. 7.2: Total Alerts Logged by Snort
Fig. 6.2 above clearly states the alert generated by snort
whenever a packet matches a defined signaturies. Various
fields are shown here such as signature Id i.e. 100012 for a
signature named mp3 download that is triggerd whenever
someone tries to download a mp3 file
7.
Results
We analyzed our virtual network for all the incoming packets
against the defined rules [5] and generated a count on for how
much time a particular rule was fired, as shown in fig.7.2
where an alert is generated on the console as shown in figure
6.2 above and an entry is made into the database each time a
signature matches the incoming packet, figure 7.2 clearly
shows the signature detected by the snort. The total number of
alerts generated is logged as count in the database shown
below.
Snort was run several times in our virtual network we
have created capturing the live traffic and a total of 4070
Fig.7.1: Comparison of Alert
1455
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_____________________________________________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1450 1456
________________________________________________________________________________________________________________________________
8. Conclusion
This paper describes the implementation of ids in a virtual
environment so as to test the traffic for any kind of intrusion
or anomaly in the network. Based upon the alert count we
concluded that a particular packet can also make a network
congested In Snort we can either block or drop that particular
packet from the network so as to make network free from any
kind of congestion. All the logs or alerts generated in Snort
during live analysis of data packets can be stored in a database
that can be retrieved later on using simple SQL querying.
Barnyard2 can also be a useful tool as it can log that details
which are miss by MYSQL. We have successfully
implemented and analyze snort in a virtual environment using
virtual box and MYSQL. Now days there are many dynamic
websites which automatically updates after few seconds and
sends packets after regular intervals so in that case the alerts
generated will be very high, as in the case of you tube. The
future work is to introduce a threshold parameter to limit the
occurrence of alerts based on the number of times that rule is
triggered in a given time period.
9.
[1]
[2]
[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
References
O.B. Lawal, A. Ibitola, O.B. Longe, Analysis and
Evaluation of Network-Based Intrusion Detection and
Prevention System in an Enterprise Network Using Snort
Freeware, African Journal of Computing & IC ,Volume 6
, 2013
Vindo kumar Signature Based Intrusion Detection System
Using Snort ,International Journal of Computer
Applications & Information Technology Volume 1, 2012.
Jinsheng xu,jinghua zhang,triveni gadipalli,xiaohong yuan
, Learning Snort Rules by Capturing Intrusions in Live
Network Traffic Replay, proceedings of the 15th
colloquium for information systems security education
Fairborn, ohio, 2011
Raihana Md Saidi, Abd. Hamid Othman, Asnita Hashim,
Normal Signature Based IDS for Ecafe, Faculty of
Computer and Mathematical Sciences, University
Teknologi MARA
Matthew Ruston, Wired TCP SYN Flooding and Snort
IDS School of Computer Science, University of Windsor
Jason Weir Building a Debian\Snort based IDS, 2012
Rafeeq Ur Rehman, Intrusion Detection Systems with
Snort Advanced IDS Techniques Using Snort, Apache,
MySQL, PHP, and ACID, Prentice Hall PTR
Kurundkar G.D, Naik N.A, Dr.Khamitkar S.D Network
Intrusion Detection using Snort, International Journal of
Engineering Research and Applications, Volume 2, Issue
2,2012.
Oracle VM
VirtualBox, en.wikipedia.org/wiki/
VirtualBox
Snort [http://www.snort.org].
Engage Security IDSCentre
[http://www.engagesecurity.com/products/idscenter/].
1456
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_____________________________________________________________________________________________________________________
Vous aimerez peut-être aussi
- A Review of Wearable Antenna For Body Area Network ApplicationDocument4 pagesA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCPas encore d'évaluation
- Regression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeDocument7 pagesRegression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeEditor IJRITCCPas encore d'évaluation
- Channel Estimation Techniques Over MIMO-OFDM SystemDocument4 pagesChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCPas encore d'évaluation
- Channel Estimation Techniques Over MIMO-OFDM SystemDocument4 pagesChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCPas encore d'évaluation
- IJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Document3 pagesIJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Editor IJRITCCPas encore d'évaluation
- A Review of Wearable Antenna For Body Area Network ApplicationDocument4 pagesA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCPas encore d'évaluation
- Importance of Similarity Measures in Effective Web Information RetrievalDocument5 pagesImportance of Similarity Measures in Effective Web Information RetrievalEditor IJRITCCPas encore d'évaluation
- A Review of 2D &3D Image Steganography TechniquesDocument5 pagesA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCPas encore d'évaluation
- Diagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmDocument5 pagesDiagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmEditor IJRITCCPas encore d'évaluation
- Performance Analysis of Image Restoration Techniques at Different NoisesDocument4 pagesPerformance Analysis of Image Restoration Techniques at Different NoisesEditor IJRITCCPas encore d'évaluation
- A Review of 2D &3D Image Steganography TechniquesDocument5 pagesA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCPas encore d'évaluation
- Hybrid Algorithm For Enhanced Watermark Security With Robust DetectionDocument5 pagesHybrid Algorithm For Enhanced Watermark Security With Robust Detectionrahul sharmaPas encore d'évaluation
- Modeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleDocument4 pagesModeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleEditor IJRITCCPas encore d'évaluation
- Comparative Analysis of Hybrid Algorithms in Information HidingDocument5 pagesComparative Analysis of Hybrid Algorithms in Information HidingEditor IJRITCCPas encore d'évaluation
- Network Approach Based Hindi Numeral RecognitionDocument4 pagesNetwork Approach Based Hindi Numeral RecognitionEditor IJRITCCPas encore d'évaluation
- Efficient Techniques For Image CompressionDocument4 pagesEfficient Techniques For Image CompressionEditor IJRITCCPas encore d'évaluation
- Fuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewDocument4 pagesFuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewEditor IJRITCCPas encore d'évaluation
- Itimer: Count On Your TimeDocument4 pagesItimer: Count On Your Timerahul sharmaPas encore d'évaluation
- Predictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth KotianDocument3 pagesPredictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth Kotianrahul sharmaPas encore d'évaluation
- Prediction of Crop Yield Using LS-SVMDocument3 pagesPrediction of Crop Yield Using LS-SVMEditor IJRITCCPas encore d'évaluation
- A Clustering and Associativity Analysis Based Probabilistic Method For Web Page PredictionDocument5 pagesA Clustering and Associativity Analysis Based Probabilistic Method For Web Page Predictionrahul sharmaPas encore d'évaluation
- 44 1530697679 - 04-07-2018 PDFDocument3 pages44 1530697679 - 04-07-2018 PDFrahul sharmaPas encore d'évaluation
- 45 1530697786 - 04-07-2018 PDFDocument5 pages45 1530697786 - 04-07-2018 PDFrahul sharmaPas encore d'évaluation
- A Study of Focused Web Crawling TechniquesDocument4 pagesA Study of Focused Web Crawling TechniquesEditor IJRITCCPas encore d'évaluation
- Vehicular Ad-Hoc Network, Its Security and Issues: A ReviewDocument4 pagesVehicular Ad-Hoc Network, Its Security and Issues: A Reviewrahul sharmaPas encore d'évaluation
- 41 1530347319 - 30-06-2018 PDFDocument9 pages41 1530347319 - 30-06-2018 PDFrahul sharmaPas encore d'évaluation
- Space Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud DataDocument12 pagesSpace Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud Datarahul sharmaPas encore d'évaluation
- A Content Based Region Separation and Analysis Approach For Sar Image ClassificationDocument7 pagesA Content Based Region Separation and Analysis Approach For Sar Image Classificationrahul sharmaPas encore d'évaluation
- Safeguarding Data Privacy by Placing Multi-Level Access RestrictionsDocument3 pagesSafeguarding Data Privacy by Placing Multi-Level Access Restrictionsrahul sharmaPas encore d'évaluation
- Image Restoration Techniques Using Fusion To Remove Motion BlurDocument5 pagesImage Restoration Techniques Using Fusion To Remove Motion Blurrahul sharmaPas encore d'évaluation
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (266)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (120)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- E-Commerce and The EntrepreneurDocument30 pagesE-Commerce and The EntrepreneurAlex MucheruPas encore d'évaluation
- Media and Information Literacy - G12 - Learning Competencies 5 & 6Document41 pagesMedia and Information Literacy - G12 - Learning Competencies 5 & 6Clark Jhayson PapilerasPas encore d'évaluation
- NTP SiemensDocument347 pagesNTP Siemensbeerman81Pas encore d'évaluation
- Adding Spring Security To CRM Rest Api PDFDocument8 pagesAdding Spring Security To CRM Rest Api PDFGastonCuestaPas encore d'évaluation
- Windows Username and Password: Weight: 1Document12 pagesWindows Username and Password: Weight: 1Aamir ShaikhPas encore d'évaluation
- Software Engineering Part 1 50 MCQ CEXAMINDIA (1) - UnlockedDocument7 pagesSoftware Engineering Part 1 50 MCQ CEXAMINDIA (1) - UnlockedAditya SharmaPas encore d'évaluation
- Project Report Employee Management SystemDocument23 pagesProject Report Employee Management SystemSonu KumarPas encore d'évaluation
- Securing Windows PDFDocument136 pagesSecuring Windows PDFBobPas encore d'évaluation
- GCP Infra GuideDocument78 pagesGCP Infra GuideSatya PPas encore d'évaluation
- PCVL Brgy 1207001Document14 pagesPCVL Brgy 1207001Yes Tirol DumaganPas encore d'évaluation
- Car Sale ManagementDocument17 pagesCar Sale ManagementsundarrajPas encore d'évaluation
- Object-Oriented Programming ProjectDocument10 pagesObject-Oriented Programming ProjectĐức TuânPas encore d'évaluation
- A Security Overview in Google's Android PhoneDocument12 pagesA Security Overview in Google's Android PhonesunithaanilPas encore d'évaluation
- Fundamentals of Computer - 100 MCQ Questions MCQ SetsDocument26 pagesFundamentals of Computer - 100 MCQ Questions MCQ SetsSanket ChikshePas encore d'évaluation
- 4tronix Bit:bot Makecode Starter GuideDocument5 pages4tronix Bit:bot Makecode Starter GuideBobbyPas encore d'évaluation
- Index of Visual Basic programsDocument47 pagesIndex of Visual Basic programssridharanPas encore d'évaluation
- The Java Throw, Try and Catch Statements: ExampleDocument8 pagesThe Java Throw, Try and Catch Statements: Example26 MADHANPRASANNAPas encore d'évaluation
- Triple Des Encryption For Ipsec: Feature SummaryDocument8 pagesTriple Des Encryption For Ipsec: Feature SummaryRamakrishna ReddyPas encore d'évaluation
- Microsoft: Exam Questions DP-900Document21 pagesMicrosoft: Exam Questions DP-900Srinivas GorantlaPas encore d'évaluation
- DoccccDocument43 pagesDoccccnogag61Pas encore d'évaluation
- 1815 and 1859 Inheritance in C++Document10 pages1815 and 1859 Inheritance in C++Vinay GuptaPas encore d'évaluation
- DevSecOps - WhitepaperDocument20 pagesDevSecOps - WhitepaperTanat Tonguthaisri100% (1)
- Esteem 10 Installation GuideDocument7 pagesEsteem 10 Installation GuideSusi MulyaniPas encore d'évaluation
- Brochure Rapidresponse Overview KinaxisDocument4 pagesBrochure Rapidresponse Overview KinaxisKrish BanothuPas encore d'évaluation
- PreferencesDocument3 pagesPreferencesohsweet jeremyPas encore d'évaluation
- Introducing The Security FabricDocument158 pagesIntroducing The Security FabricPepePas encore d'évaluation
- Blockchain Based Proxy Re-EncryptionDocument8 pagesBlockchain Based Proxy Re-EncryptionBhanu RoyalPas encore d'évaluation
- Blockchain-Enabled Security and Operation of Cyber - PhysicalSystemDocument6 pagesBlockchain-Enabled Security and Operation of Cyber - PhysicalSystemSanjayPas encore d'évaluation
- ONF Certified SDN EngineerDocument13 pagesONF Certified SDN EngineerRicardo OrtizuPas encore d'évaluation
- Conversion de Bits A Bytes, MB, GBDocument4 pagesConversion de Bits A Bytes, MB, GBMartel AlvarezPas encore d'évaluation