Académique Documents
Professionnel Documents
Culture Documents
Security On The Abusive Social Network Sites - A Survey
Transféré par
Editor IJRITCCTitre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Security On The Abusive Social Network Sites - A Survey
Transféré par
Editor IJRITCCDroits d'auteur :
Formats disponibles
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 9
ISSN: 2321-8169
5663 - 5665
______________________________________________________________________________________________
Security on the Abusive Social Network Sites- A Survey
J.Adamkani
Dr.K.Nirmala
Research Scholar,
Quaid-E-Millath,
Govt College for Women,
University of Madras
Research Supervisor,
Dept. of Computer Science,
Quaid-E-Millath,
Govt College for Women
Abstract-To share business interests, the internet social network have become the common platform where users communicate through which
My Space, Second Life and similar web2.0 sites can pose malicious security hazards. The social networking sites are viewed as a kind of online
cocktail party in business view as a friendly comfortable place to establish contacts, associate buyers or sellers and raise personal or corporate
file. To the maxim, cocktail party metaphor is not pure, obviously in the content of a load glass house for social network serves, the users are
served in with care and endless visibility through a highly amplified bullhorn. The social network sites are accessed from the comfort and
privacy by maximum users, there is a possibility of false sense of anonymity where the users natural defences can too devasted due to the lack of
physical contact on social network site by which there is an endanger of disclosing the information of individuals which would never think of
revealing to another at a cocktail partys.
Keywords Social Networks, MySpace, Web 2.0, Cocktail party
_________________________________________________*****_________________________________________________
I.
INTRODUCTION
In the materialistic world of nuisance, social networks have
become part of the business and personal fabric. To conduct
business and personal relationships there are about a billion
users using social networks around the globe by which the
risks of attackers targeting the users as well as user concern
has grown to personal privacy.
proprietary information
organisations.
II.
to
inviting
law
suits
for
MOBILE APPLICATIONS
In mobile application developments the rise of social media
has inextricably linked with the revolting spanning the
industry. The employees in industry typically download
huge application but not concerning about using their own
company issued mobile devices. To the extent they
download more than they bargained for hence malware is
designed to reveal the users private information to a third
party replicate itself on other devices, destroy user data or
even impersonate the device owner.
2.1 Social Engineering
1.1 Security Threats
Business enterprises the communicating with customers,
build their brands and reveal information favour social
media platforms viz Facebook, twitter and LinkedIn are
increasing at large to the rest of the world. Does not mean
social media are exclusively for linking, friending, up-voting
or digging. The mere fact emphasis on risks to use social
media ranging from damming the brand to exposing
Social Engineering has been the choice of smooth talking
scammers before computer networks. But the potential
victim who have the soft spot in hearts were forced for
grifters and flimflam artists due to the rise of the internet
this has taken to a new level by social media through face
book, twitter, foursquare and my space where users share
personal information about themselves than ever in which
assumed trust of dangerous level is encouraged by social
media platforms.
2.2 social networking sites
Through third party apps by way of advertisement there
found malicious code into the social networking site which
5663
IJRITCC | September 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 9
ISSN: 2321-8169
5663 - 5665
______________________________________________________________________________________________
go right to the source in the form of hackers .In a work
computer by visiting malicious sites can extract personal
information where shortened URLs are used to trick users
by twitter it is easy to retweet a post by twitter which is
especially vulnerable so that eventually could be seen by
hundreds of thousands of people.
2.3 Our employees
There can be lapses in judgment even by the most
responsible employees by making mistakes or behaving
emotionally. All the occasions could not be perfect by
everybody. If the comment is made on a work related social
media account in the office then it is out there and cannot be
retrieved by a high level communication executive by whom
the brand is damaged and endangered an account which was
not tuned is to the corporate mission in contrast imagine
what a disgruntled low-level employee wish out as much
invested in job might be able to do with social media tools
and a chip on the shoulder.
addresses, contact numbers, job title, date of birth, schedule
details, daily routines and business or family information,
unscrupulous individuals may use against us, its far better
to communicate in generalities than to reveal information.
Skeptical: with a high degree of scepticism viz, stock tips,
advance news, personal gossip and so on, social network
sites are full of useful business information as well as to
substantial amount of useless disinformation. Where users
will lie in order to boost their own agenda while others spout
unsubstantiated rubbish out of stupidly of ignorance.
Thoughtful: Though the release of personal inhibitions the
internet has a curious way like a loudmouth is not favoured
by many. It is advisablenot to be a victim of byte by typing
anything online which include outrageous, claims, sender,
obscenity and so. Thus through thought one can be cool and
professional by thinking twice before typing.
To be Professional: To present a video or picture to a social
network site, one must make sure it presents in the best
possible light by dressing professional and avoiding to wear
a funny hat.
Wary: Mostly users always are not the same what they are
on the internet, the 14 year old kid in Milwaukee or prisoner
in Romania may be a CEO to chat with others in Denver
until they are identified independently. Sometimes may turn
to screen a new hire or confirming a prospective business
partner by using the same business tools to ascertain the
business or financial information.
2.4 Lack of the social media policy
The organization just turn employee loose on social
networking platform and are to represent without a social
media policy for a enterprise by inviting disaster the goals
and parameter of the enterprises social media initiative are
to be spell out contrary one will get exactly what they are
inviting will be problems.
III.
BUSINESS PROTECTION
The business protection can be enhance by the extend
threats.
Discrect: The unwanted visitors can be protected through
the identity theft or malicious threats. It is advisable to
refrain by typing anything into a profile page, bulletin board,
instant message or other type of online electronic form
which can includes personal and business names and
Ensuring of privacy policies:Privacy guidelines are
ensured by major social network services published on their
websites which include the type of information to sell to
other parties where due care should taken to read and
understand by spending an amount of time .Presumably if
the terms are not liked ,the better not to use the service.
IV.
SECURE SCOCIAL NETWORK
IDENTIFICATION.
The services incorporated through secure social network
include the websites Myspace, Facebook, twitter and
windows live spaces where informations are exchanged but
the users viz photos videos personal messages and so on
.The more the usage ,the more risk occur in using them
where the traffic is enrooted by hackers ,spammers, various
writers, identity thieves and other criminals. It is advisable
to protect through the tips.
4.1 Links through caution
Avoidance of treat links in the received mails should be
strictly flowed.
5664
IJRITCC | September 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 9
ISSN: 2321-8169
5663 - 5665
______________________________________________________________________________________________
4.2 Posting of self pass word
The click forgot your pass word on the account log in
page is what the hackers break into financial or other
accounts where the security questions viz your birthday,
hometown, high school class, mother middle name etc
search for the answers by breaking into account It is
advisable to use own password questions by hot drawing
from anyone materialistically.
4.3 Negligence of users in trust of messages from whom it
is from
Oftenly messages code like they are from known ones break
into accounts through hackers but the case is not so. By this
anonymous method is to be used to track the known ones
where it is suspected whether a message is fraudulent. New
social networks are inhibited in the process.
4.4 Protection of giving ones email address
Synonymously it is advisable to safeguard the scan of ones
email address book from social networking services.
Commonly if ones contacts are on the network an offer to
enter the email address and password is encountered when
one joins a new social network. This will function when a
user has sent an email message with a social network and
the site may use information except a few social network
sites. Many sites are bound to explain what they does.
4.5 Use of social network site directly into user browser
There is high risk of losing ones personal information when
the user click to their site through email or another website
when entering ones account name and password into a fake
site.
internet. Due attention is to be rendered when excess
information is installed on ones site. It is a general
phenomena of allowing users to download third party
applications on dues personal page where high possibility of
stolen of personal information occurs by sedatives. Ensuring
of safety precautions is to be taken with any other program
or file while extracting from the web through the third party
applications. Thus ascertain and favour of social networking
sit e is predominantly to be think many times before use.
CONCLUSION
With much attention and precaution by users, social network
sites are potentially more useful and worth full business
tools with excepted behaviours, personal and company
impacts there arise a powerful persuasive communication
plan to educate the user communicating about social media
risks with an adequate amount of caution and common sense
in business. More advice is pertained to organisations to
support the communicating plan with targeted protection in
order to mitigate risks of social networking as the
phenomena which exists to gain momentum.
REFERENCES
Dr. Paul Judge, 2011, Social Networking Security and Privacy
Study. [2] http://www.networkworld.com/news/2011/053111socialmedia-security.html?page=2
[3]
http://www.microsoft.com/security/onlineprivacy/socialnetworking.aspx
[4]
http://www.networkworld.com/news/2011/053111-socialmediasecurity.html?page=1 [5] Gary Loveland, , May 2009,Secure
Enterprise 2.0 Forum, Q1 2009 Web 2.0 Hacking Security Report.
4.6 Ascertain of who the user accept as a friend on a
social network
There is high possibility of creation of fake profiles from
unknown users in order to access information.
4.7 Ascertain and preference of social network carefully
It is advised to know the privacy policy by evaluating the
site what the user plan to use and monitors the content that
people post on the site. The same criteria is to be maintained
when using the credit card to a site where the users personal
information is provided.
4.8 Ascertain of information revealed on the social
network site is permanent
There is a provision of evacuation of print photos or text or
images and videos when users remove account on the
5665
IJRITCC | September 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
Vous aimerez peut-être aussi
- Assessment Task 6Document4 pagesAssessment Task 6Emelyn Laraga Mejasco IPas encore d'évaluation
- Information Security For Young Adults: HCM Information Security, #1D'EverandInformation Security For Young Adults: HCM Information Security, #1Pas encore d'évaluation
- Security For Social NetworkingDocument16 pagesSecurity For Social NetworkingSanni KumarPas encore d'évaluation
- Social Media SecurityDocument5 pagesSocial Media SecurityDia SinhaPas encore d'évaluation
- Social Networks Are HazourdousDocument28 pagesSocial Networks Are HazourdousTripti negiPas encore d'évaluation
- Social Media SecurityDocument4 pagesSocial Media SecurityMoon 701Pas encore d'évaluation
- EDUC16b Module 9Document13 pagesEDUC16b Module 9Shiela Marie Visaya RiveraPas encore d'évaluation
- Social Networking & SecurityDocument3 pagesSocial Networking & Securityahmadvand58Pas encore d'évaluation
- Data Privacy On Social MediaDocument8 pagesData Privacy On Social MediaNicole SorianoPas encore d'évaluation
- 2011 12SocialNetworkingSites MSISACDocument2 pages2011 12SocialNetworkingSites MSISACGreg BeloroPas encore d'évaluation
- ELECTIVE 2 HandoutsDocument10 pagesELECTIVE 2 HandoutsLoy GuardPas encore d'évaluation
- SpywareThreats #AdwareAlerts3. #PhishingPrevention #MalwareMenaceDocument11 pagesSpywareThreats #AdwareAlerts3. #PhishingPrevention #MalwareMenaceJared Panes SiaPas encore d'évaluation
- Chapter 1 Solutions Quick Quiz 1: Script Kiddies Cybercriminals Probe For Information LayeringDocument4 pagesChapter 1 Solutions Quick Quiz 1: Script Kiddies Cybercriminals Probe For Information LayeringOmJood Al HosaniPas encore d'évaluation
- Module 9Document25 pagesModule 9Kayce Bernel AdecerPas encore d'évaluation
- Case StudyDocument3 pagesCase Studyummi syafiqahPas encore d'évaluation
- Hidemyacc - How to Hide Your Online Accounts A Step-by-Step Guide to Protecting Your Digital IdentityD'EverandHidemyacc - How to Hide Your Online Accounts A Step-by-Step Guide to Protecting Your Digital IdentityPas encore d'évaluation
- Guide: Security in Social NetworksDocument16 pagesGuide: Security in Social NetworksEver Medina UnchupaicoPas encore d'évaluation
- Discuss Security Issues of Social NetworkingDocument3 pagesDiscuss Security Issues of Social Networkingdohn98813Pas encore d'évaluation
- Empowerment TechnologyDocument17 pagesEmpowerment Technologywewe.trillanesPas encore d'évaluation
- Week 1 PPT 1Document19 pagesWeek 1 PPT 1CHARLS JAYBEE ATILLOPas encore d'évaluation
- Social Networking and Internet Safety TipsDocument15 pagesSocial Networking and Internet Safety TipsEmilija SabPas encore d'évaluation
- Cyber SafetyDocument8 pagesCyber Safetyask ygmPas encore d'évaluation
- Cybersafe For Humans: A Simple Guide to Keep You and Your Family Safe OnlineD'EverandCybersafe For Humans: A Simple Guide to Keep You and Your Family Safe OnlinePas encore d'évaluation
- Social Networking at WorkDocument6 pagesSocial Networking at WorkGFI SoftwarePas encore d'évaluation
- Cyber Safety 12thDocument22 pagesCyber Safety 12thShrishty RaoPas encore d'évaluation
- Chaudhary UmarDocument6 pagesChaudhary Umarm saPas encore d'évaluation
- Social Media Account Hacking Using Kali Linux Based Tool BeEFDocument11 pagesSocial Media Account Hacking Using Kali Linux Based Tool BeEFsai KiranPas encore d'évaluation
- Cyber AttackDocument11 pagesCyber AttackRiya goelPas encore d'évaluation
- Facebook Security Breach Exposes Accounts of 50 Million Users A Google Bug Exposed The Information of Up To 500,000 UsersDocument5 pagesFacebook Security Breach Exposes Accounts of 50 Million Users A Google Bug Exposed The Information of Up To 500,000 UsersDaksh PandyaPas encore d'évaluation
- Cyber Security: Fatma DEMİR FD 28.01.2023Document6 pagesCyber Security: Fatma DEMİR FD 28.01.2023Fatma DemirPas encore d'évaluation
- Cybersecurity for the Modern Adult: Protecting Yourself OnlineD'EverandCybersecurity for the Modern Adult: Protecting Yourself OnlinePas encore d'évaluation
- Empowerment-Tech12 Q1 - Mod1Document12 pagesEmpowerment-Tech12 Q1 - Mod1joleza12Pas encore d'évaluation
- Social Networks Have Become An Integral Part of Modern SocietyDocument2 pagesSocial Networks Have Become An Integral Part of Modern SocietyAnant NaikPas encore d'évaluation
- Digital Dangers: Navigating the Perils of Online Safety and Piracy. Protecting Yourself and Your Content in the Digital AgeD'EverandDigital Dangers: Navigating the Perils of Online Safety and Piracy. Protecting Yourself and Your Content in the Digital AgePas encore d'évaluation
- Social NetworkingDocument3 pagesSocial NetworkingJohn DoePas encore d'évaluation
- Individual Assessment 3: Professional Computing PracticeDocument6 pagesIndividual Assessment 3: Professional Computing PracticePhương Trúc VănPas encore d'évaluation
- Concept PaperDocument8 pagesConcept PaperGenesisPas encore d'évaluation
- Cybersafe for Business: The Anti-Hack Handbook for SMEsD'EverandCybersafe for Business: The Anti-Hack Handbook for SMEsPas encore d'évaluation
- E Safety M.dawood - AwanDocument7 pagesE Safety M.dawood - AwanDawood AwanPas encore d'évaluation
- FOC Unit-5 Part-IIDocument7 pagesFOC Unit-5 Part-IINarendra SahuPas encore d'évaluation
- A Case Study On The Benefit of RA 10844 DICTDocument7 pagesA Case Study On The Benefit of RA 10844 DICTjolebeb castanaresPas encore d'évaluation
- Pursue Lesson 3 - Module 2Document12 pagesPursue Lesson 3 - Module 2Cherry Rose J. DeniegaPas encore d'évaluation
- Lesson 1: The Current State of Ict Technologies: What Is It?Document6 pagesLesson 1: The Current State of Ict Technologies: What Is It?LC MoldezPas encore d'évaluation
- Social Media AwarenessDocument25 pagesSocial Media AwarenessAhrlynne Cuadrante Mendez RodaPas encore d'évaluation
- A Case Study On The Issues of Social Media As A Platform For DefamationDocument7 pagesA Case Study On The Issues of Social Media As A Platform For Defamationjolebeb castanaresPas encore d'évaluation
- Privileged Attack Vectors: Building Effective Cyber-Defense Strategies to Protect OrganizationsD'EverandPrivileged Attack Vectors: Building Effective Cyber-Defense Strategies to Protect OrganizationsPas encore d'évaluation
- Lesson 7 - Policing The InternetDocument11 pagesLesson 7 - Policing The InternetEnola HolmesPas encore d'évaluation
- Keeping Safe On Social MediaDocument7 pagesKeeping Safe On Social MediaCarla GonçalvesPas encore d'évaluation
- EmTech Q3 M1Document9 pagesEmTech Q3 M1Duncan OsoteoPas encore d'évaluation
- MKT533- Customer JourneysDocument3 pagesMKT533- Customer JourneysGrace KittyamunkongPas encore d'évaluation
- Social networking and digital safetyDocument1 pageSocial networking and digital safetyPriyanshu RajPas encore d'évaluation
- TVL-ICT-CS11 - w7-8Document6 pagesTVL-ICT-CS11 - w7-8Nixon BarcellanoPas encore d'évaluation
- CYBER SAFETY (1)Document14 pagesCYBER SAFETY (1)ARJUN AGGARWALPas encore d'évaluation
- Traditional Group Based Policy Management Approach For Online Social NetworksDocument6 pagesTraditional Group Based Policy Management Approach For Online Social NetworksIOSRJEN : hard copy, certificates, Call for Papers 2013, publishing of journalPas encore d'évaluation
- Empowerment Tech NotesDocument7 pagesEmpowerment Tech NotesGelian Mae PadaPas encore d'évaluation
- Cyber-Enabled Crimes vs. Cyber-Dependent CrimesDocument8 pagesCyber-Enabled Crimes vs. Cyber-Dependent CrimesAntonioCerdeiraPas encore d'évaluation
- Activity 1Document3 pagesActivity 1Jimson B. CasalmePas encore d'évaluation
- Regression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeDocument7 pagesRegression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeEditor IJRITCCPas encore d'évaluation
- Channel Estimation Techniques Over MIMO-OFDM SystemDocument4 pagesChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCPas encore d'évaluation
- Importance of Similarity Measures in Effective Web Information RetrievalDocument5 pagesImportance of Similarity Measures in Effective Web Information RetrievalEditor IJRITCCPas encore d'évaluation
- A Review of Wearable Antenna For Body Area Network ApplicationDocument4 pagesA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCPas encore d'évaluation
- IJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Document3 pagesIJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Editor IJRITCCPas encore d'évaluation
- Modeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleDocument4 pagesModeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleEditor IJRITCCPas encore d'évaluation
- Performance Analysis of Image Restoration Techniques at Different NoisesDocument4 pagesPerformance Analysis of Image Restoration Techniques at Different NoisesEditor IJRITCCPas encore d'évaluation
- A Review of Wearable Antenna For Body Area Network ApplicationDocument4 pagesA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCPas encore d'évaluation
- A Review of 2D &3D Image Steganography TechniquesDocument5 pagesA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCPas encore d'évaluation
- Comparative Analysis of Hybrid Algorithms in Information HidingDocument5 pagesComparative Analysis of Hybrid Algorithms in Information HidingEditor IJRITCCPas encore d'évaluation
- A Review of 2D &3D Image Steganography TechniquesDocument5 pagesA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCPas encore d'évaluation
- Channel Estimation Techniques Over MIMO-OFDM SystemDocument4 pagesChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCPas encore d'évaluation
- Fuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewDocument4 pagesFuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewEditor IJRITCCPas encore d'évaluation
- Diagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmDocument5 pagesDiagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmEditor IJRITCCPas encore d'évaluation
- A Study of Focused Web Crawling TechniquesDocument4 pagesA Study of Focused Web Crawling TechniquesEditor IJRITCCPas encore d'évaluation
- Efficient Techniques For Image CompressionDocument4 pagesEfficient Techniques For Image CompressionEditor IJRITCCPas encore d'évaluation
- Prediction of Crop Yield Using LS-SVMDocument3 pagesPrediction of Crop Yield Using LS-SVMEditor IJRITCCPas encore d'évaluation
- Network Approach Based Hindi Numeral RecognitionDocument4 pagesNetwork Approach Based Hindi Numeral RecognitionEditor IJRITCCPas encore d'évaluation
- Predictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth KotianDocument3 pagesPredictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth Kotianrahul sharmaPas encore d'évaluation
- 45 1530697786 - 04-07-2018 PDFDocument5 pages45 1530697786 - 04-07-2018 PDFrahul sharmaPas encore d'évaluation
- 44 1530697679 - 04-07-2018 PDFDocument3 pages44 1530697679 - 04-07-2018 PDFrahul sharmaPas encore d'évaluation
- Itimer: Count On Your TimeDocument4 pagesItimer: Count On Your Timerahul sharmaPas encore d'évaluation
- A Clustering and Associativity Analysis Based Probabilistic Method For Web Page PredictionDocument5 pagesA Clustering and Associativity Analysis Based Probabilistic Method For Web Page Predictionrahul sharmaPas encore d'évaluation
- Hybrid Algorithm For Enhanced Watermark Security With Robust DetectionDocument5 pagesHybrid Algorithm For Enhanced Watermark Security With Robust Detectionrahul sharmaPas encore d'évaluation
- Safeguarding Data Privacy by Placing Multi-Level Access RestrictionsDocument3 pagesSafeguarding Data Privacy by Placing Multi-Level Access Restrictionsrahul sharmaPas encore d'évaluation
- A Content Based Region Separation and Analysis Approach For Sar Image ClassificationDocument7 pagesA Content Based Region Separation and Analysis Approach For Sar Image Classificationrahul sharmaPas encore d'évaluation
- Vehicular Ad-Hoc Network, Its Security and Issues: A ReviewDocument4 pagesVehicular Ad-Hoc Network, Its Security and Issues: A Reviewrahul sharmaPas encore d'évaluation
- 41 1530347319 - 30-06-2018 PDFDocument9 pages41 1530347319 - 30-06-2018 PDFrahul sharmaPas encore d'évaluation
- Image Restoration Techniques Using Fusion To Remove Motion BlurDocument5 pagesImage Restoration Techniques Using Fusion To Remove Motion Blurrahul sharmaPas encore d'évaluation
- Space Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud DataDocument12 pagesSpace Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud Datarahul sharmaPas encore d'évaluation
- About TractorDocument28 pagesAbout TractorCristy DaylagPas encore d'évaluation
- Work at HeightDocument10 pagesWork at HeightShoaib RazzaqPas encore d'évaluation
- PEI Trucking Sector - 2010: DefinitionDocument3 pagesPEI Trucking Sector - 2010: Definitionn3xtnetworkPas encore d'évaluation
- Practice-1 defining calendarsDocument5 pagesPractice-1 defining calendarspramod nagmotiPas encore d'évaluation
- September 10, 2014Document22 pagesSeptember 10, 2014The Standard NewspaperPas encore d'évaluation
- April 2014 1396445255 131fa 88 PDFDocument2 pagesApril 2014 1396445255 131fa 88 PDFkavithaPas encore d'évaluation
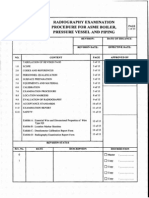
- Radiography Examination Procedure For Asme Boiler, Pressure Vessel and PipingDocument15 pagesRadiography Examination Procedure For Asme Boiler, Pressure Vessel and PipingEko Kurniawan100% (1)
- Construction Claims DelaysDocument23 pagesConstruction Claims Delaysgerx11xregPas encore d'évaluation
- Process Validation ProtocolDocument10 pagesProcess Validation ProtocolDivya SekarPas encore d'évaluation
- Aluprofilsystem en 0Document481 pagesAluprofilsystem en 0Vasile TomoiagaPas encore d'évaluation
- JBT GreenDocument3 pagesJBT GreenRagu VenkatPas encore d'évaluation
- Guide To Stability Design Criteria For Metal Structures-6ed Zeiman 2010 1117pDocument1 117 pagesGuide To Stability Design Criteria For Metal Structures-6ed Zeiman 2010 1117pcgingenieros94% (31)
- Hexagon Head Screw ISO 4017 - M8 X 20 - 5.6Document1 pageHexagon Head Screw ISO 4017 - M8 X 20 - 5.6Cbh FastenersPas encore d'évaluation
- E97847 PDFDocument94 pagesE97847 PDFraghu12421Pas encore d'évaluation
- Curriculum Vitae New 2017 MD Sajid AlamDocument6 pagesCurriculum Vitae New 2017 MD Sajid AlamAlam MD SazidPas encore d'évaluation
- Final Weld Strength CalnsDocument3 pagesFinal Weld Strength CalnsSajal KulshresthaPas encore d'évaluation
- Adobe Case Study - DTI Intelligent DocumentsDocument3 pagesAdobe Case Study - DTI Intelligent DocumentsrpcooperPas encore d'évaluation
- 1-M Vib Meas Hwp-A MotorDocument3 pages1-M Vib Meas Hwp-A MotorNovindra PutraPas encore d'évaluation
- Clearing Pending TransactionsDocument10 pagesClearing Pending TransactionsVinay ChughPas encore d'évaluation
- November 2016Document20 pagesNovember 2016Deepak JainPas encore d'évaluation
- Mechanical and Tribological Performance of Aluminium Metal Matrix CompositesDocument27 pagesMechanical and Tribological Performance of Aluminium Metal Matrix CompositesPradeepkumar SamanthulaPas encore d'évaluation
- Mass Marketing EmptyDocument4 pagesMass Marketing EmptyvalenciaPas encore d'évaluation
- The Military Simulation, Modelling, and Virtual Training Market 2013-2023Document28 pagesThe Military Simulation, Modelling, and Virtual Training Market 2013-2023VisiongainGlobal100% (1)
- Air CompressorDocument21 pagesAir CompressorAjayPas encore d'évaluation
- Austin Hardware Catalog PDFDocument284 pagesAustin Hardware Catalog PDFMarc Lee Blumenstine0% (1)
- OM - Session 24 Quality Control Lean MFGDocument70 pagesOM - Session 24 Quality Control Lean MFGSiddhant Singh100% (1)
- Inplant Trainging ReportDocument8 pagesInplant Trainging ReportanbudeviaishuyaPas encore d'évaluation
- Fluid Flow Mean Velocity and Pipe Diameter For Known Flow RateDocument10 pagesFluid Flow Mean Velocity and Pipe Diameter For Known Flow Ratefaisal mahmood azamPas encore d'évaluation
- Catalog General Kaysun - 2016 Eng SPDocument376 pagesCatalog General Kaysun - 2016 Eng SPAnca JianuPas encore d'évaluation