Académique Documents
Professionnel Documents
Culture Documents
Efficient Data Hiding System Using LZW Cryptography and Gif Image Steganography
Titre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Efficient Data Hiding System Using LZW Cryptography and Gif Image Steganography
Droits d'auteur :
Formats disponibles
International Journal of Technical Research and Applications e-ISSN: 2320-8163,
www.ijtra.com Volume 3, Issue 2 (Mar-Apr 2015), PP. 28-32
EFFICIENT DATA HIDING SYSTEM USING LZW
CRYPTOGRAPHY AND GIF IMAGE
STEGANOGRAPHY
Intisar Majeed Saleh, Hanaa Hameed Merzah
AL. Rafidain University College
Baghdad, Iraq
Intisar_alyssiri@yahoo.com, Hanamerza2007@gmail.com
Abstract The combination of steganography and
cryptography is considered as one of the best security methods
used for message protection, due to this reason, in this paper, a
data hiding system that is based on image steganography and
cryptography is proposed to secure data transfer between the
source and destination. Animated GIF image is chosen as a
carrier file format for the steganography due to a wide use in web
pages and a LSB (Least Significant Bits) algorithm is employed to
hide the message inside the colors of the pixels of an animated
GIF image frames. To increase the security of hiding, each frame
of GIF image is converted to 256 color BMP image and the
palette of them is sorted and reassign each pixels to its new index,
furthermore, the message is encrypted by LZW ( Lempel _
Ziv_Welch) compression algorithm before being hidden in the
image frames. The proposed system was evaluated for
effectiveness and the result shows that, the encryption and
decryption methods used for developing the system make the
security of the proposed system more efficient in securing data
from unauthorized users. The system is therefore, recommended
to be used by the Internet users for establishing a more secure
communication.
Keywords:- Steganography, LSB, Animated GIF, LZW.
I. INTRODUCTION
The cryptography and steganography techniques occupies a
distinctive place in the area of security as they help to solve
the problem of transmission of confidential information over
the network in the form of a more secure against violations of
unauthorized persons . Cryptography is the art and science of
creating nonreadable data or cipher so that only intended
person is only able to read the data[1], Unfortunately it is
sometimes not enough to keep the contents of a message
secret, it may also be necessary to keep the existence of the
message secret. The technique used to implement this, is
called steganography.Steganography comes from the Greek
words Stegans (Covered) and Graptos (Writing), it usually
refers to information or a file that has been concealed inside a
digital Picture, Video, Text or Audio file[2,3]. For this reason,
in this paper, we focus on the combination of steganography
and cryptography to protect the private information within the
digital image ,and more specifically on the GIF image which
being used widely on the Internet. When information is hidden
inside a carrier file, the data is encrypted with LZW
compression method.
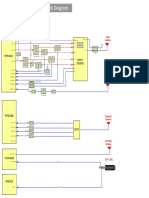
The general scheme for embedding data is depicted in
Figure 1. A message is embedded in a file by the stegosystem
encoder, which has as inputs the original cover, the secret
message and a key. The resulting stego object is then
transmitted over a communication channel to the recipient
where the stegosystem decoder using the same key processes it
and the message can be read.
Fig. 1.
A General Steganographic Model
The steganographic process can be represented using
formulas. The stego object is given by:
I' = f( I,m,k )
where: I is the stego object, I is the original object, m is the
message and k is the key that the two parties share. The stego
object may be subject to many distortions, which can be
represented as a noise process n:
I'' = I'+n(I')
At the decoder we wish to extract the signal m, so we can
consider the unwanted signal to be I. The embedded signal
should resist common signal distortions as those depicted in
Figure 2. Two kinds of compression exist: lossy and lossless.
Both methods save storage space but have different results.
Lossless compression permits exact reconstruction of the
original message; therefore it is preferred when the original
information must remain intact. Such compression schemes
are the images saved as GIF (Graphic Interchange Format).
Lossy compression, on the other hand, does not maintain the
originals integrity. Such compression scheme is an image
saved as JPEG (Joint Photographic Experts Group). The JPEG
formats provide close approximations to high-quality digital
photos but not an exact duplicate.
Fig. 2: common signal distortions over the transmission
channel
28 | P a g e
International Journal of Technical Research and Applications e-ISSN: 2320-8163,
www.ijtra.com Volume 3, Issue 2 (Mar-Apr 2015), PP. 28-32
Geometric distortions are specific to images and video and
in the case of 8-bit characters). As the compressor characterinclude operations such as: rotation, translation, scaling.
serially examines the text, it stores every unique two-character
Cropping is another type of geometric distortion that leads to
string into the table as a code/character concatenation, with the
irretrievable loss of data. The signal can be processed in many
code mapping to the corresponding first character. As each
ways, including resampling, analog-to-digital and digital-totwo-character string is stored, the first character is sent to the
analog conversions, requantization, recompression, printing,
output. Whenever a previously-encountered string is read from
rescanning, copying, filtering and so on. All those processes
the input, the longest such previously-encountered string is
introduce additional degradation into the object that a
determined, and then the code for this string concatenated with
steganographic scheme must withstand.[4 ]
the extension character (the next character in the input) is
stored in the table. The code for this longest previouslyII. LEST SIGNIFICANT BIT (LSB)
encountered string is output and the extension character is
Least significant bit (LSB) insertion is a common, simple
used as the beginning of the next word.
approach to embedding information in a cover image [5]. In
The decompressor algorithm only requires the compressed
this method, we can take the binary representation of the
text as an input, since it can build an identical string table from
hidden_data and overwrite the LSB of each byte within the
the compressed text as it is recreating the original text.
cover_image. If we are using 24-bit color, the amount of
However, an abnormal case shows up whenever the sequence
change will be minimal and indiscernible to the human eye. As
character/string/character/string/character (with the same
an example, suppose that we have three adjacent pixels (nine
character for each character and string for each string) is
bytes) with the following RGB encoding:
10010101 00001101 11001001
10010110 00001111 11001010
10011111 00010000 11001011
Now suppose we want to "hide" the following 9 bits of data
(the hidden data is usually compressed prior to being hidden):
101101101. If we overlay thes 9 bits over the LSB of the 9
bytes above, we get the following (where bits in bold have
been changed):
10010101 00001100 11001001
10010111 00001110 11001011
10011111 00010000 11001011
Note that we have successfully hidden 9 bits but at a cost of
only changing 4, or roughly 50%, of the LSBs. Similar
methods can be applied to 8-bit palette based images (like GIF
images) but the changes, as the reader might imagine, are
more dramatic[6]. This is alleviated in this paper by sorting the
palette and reassigns each pixel to the index of its color in the
new palette before the embedding process.
III. LEMPEL-ZIV-WELCH (LZW)
LZW is a universal lossless data compression algorithm
created by Abraham Lempel, Jacob Ziv, and Terry Welch. It
was published by Welch in 1984 as an improved
implementation of the LZ78 algorithm published by Lempel
and Ziv in 1978. The algorithm is designed to be fast to
implement but is not usually optimal because it performs only
limited analysis of the data.
The compressor algorithm builds a string translation table
from the text being compressed. The string translation table
maps fixed-length codes (usually 12-bit) to strings. The string
table is initialized with all single-character strings (256 entries
+-----------------------+
| +-------------------+ |
| |
GIF Signature
| |
| +-------------------+ |
| +-------------------+ |
| | Screen Descriptor | |
| +-------------------+ |
| +-------------------+ |
| | Global Color Map | |
| +-------------------+ |
. . .
. . .
| +-------------------+ | ---+
| | Image Descriptor | |
|
| +-------------------+ |
|
| +-------------------+ |
|
| | Local Color Map
| |
|-Repeated 1 ton
times
| +-------------------+ |
|
| +-------------------+ |
|
| |
Raster Data
| |
|
| +-------------------+ | ---+
. . .
. . .
|GIF Terminator
-|
+-----------------------+
encountered in the input and character/string is already stored
in the string table. When the decompressor reads the code for
character/string/character in the input, it cannot resolve it
because it has not yet stored this code in its table. This special
case can be dealt with because the decompressor knows that
the extension character is the previously-encountered
character.
A. Compressor Algorithm
Build a table and store all possible strings in it
STRING = get input character
WHILE there are still input characters DO
CHARACTER = get input character
IF STRING+CHARACTER is in the string table then
STRING = STRING+character
ELSE
output the code for STRING
add STRING+CHARACTER to the string table
STRING = CHARACTER
END of IF
END of WHILE
output the code for STRING
29 | P a g e
International Journal of Technical Research and Applications e-ISSN: 2320-8163,
www.ijtra.com Volume 3, Issue 2 (Mar-Apr 2015), PP. 28-32
B. Decompressor Algorithm
of color map entries following a Screen Descriptor is
Build a table and store all possible strings in it
equal to 2**(# bits per pixel), where each entry
Read OLD_CODE
consists of three byte values representing the relative
OLD_CODE = get translation of OLD_CODE
intensities of red, green and blue respectively. The
output OLD_CODE
structure of the Color Map block is:
CHARACTER = OLD_CODE
bits
WHILE there are still input characters DO
7 6 5 4 3 2 1 0 Byte #
Read NEW_CODE
+---------------+
| red intensity | 1 Red value for color index 0
IF NEW_CODE is not in the string table THEN
+---------------+
STRING = OLD_CODE
|green intensity| 2 Green value for color index 0
STRING = STRING+CHARACTER
+---------------+
ELSE
| blue intensity| 3 Blue value for color index 0
+---------------+
STRING = get translation of NEW_CODE
| red intensity | 4 Red value for color index 1
END of IF
+---------------+
output STRING
|green intensity| 5 Green value for color index 1
CHARACTER = first character in STRING
+---------------+
| blue intensity| 6 Blue value for color index 1
add OLD_CODE + CHARACTER to the string table
+---------------+
OLD_CODE = get translation of NEW_CODE
:
:
(Continues for remaining colors)
END of WHILE
IV. GRAPHIC INTERCHANGE FORMAT (GIF)
The Graphics Interchange Format (GIF) is a bitmap
image format that was introduced by CompuServe in 1987 and
has since come into widespread usage on the World Wide
Web due to its wide support and portability. The format
supports up to 8 bits per pixel, allowing a single image to
reference a palette of up to 256 distinct colors chosen from the
24-bit RGB color space. It also supports animations and
allows a separate palette of 256 colors for each frame. GIF
images are compressed using the Lempel-Ziv-Welch (LZW)
lossless data compression technique to reduce the file size
without degrading the visual quality.
A. General File Format
The GIF Signature identifies the data following as a
valid GIF image stream. It consists of the following
six characters. The first three characters are G I F and
the last three characters are a version number for this
particular GIF definition.
The Screen Descriptor describes the overall
parameters for all GIF images following. This
information is stored in a series of 8-bit bytes as
described below.
bits
7 6 5 4 3 2 1 0 Byte #
+------------------+
|
| 1
+-Screen Width -+ Raster width in pixels (LSB first)
|
| 2
+-----------------+
|
| 3
+-Screen Height-+ Raster height in pixels (LSB first)
|
| 4
+-+------+-+------+
M = 1, Global color map follows Descriptor
|M| cr |0|pixe l | 5 cr+1 = # bits of color resolution
+-+-----+-+-----+
pixel+1 = # bits/pixel in image
| background
| 6 background=Color index of screen background
+-----------------+
(color is defined from the Global color
|0 0 0 0 0 0 0 0 | 7 map or default map if none specified)
+-----------------+
The Global Color Map is optional but recommended
for images where accurate color rendition is desired.
The existence of this color map is indicated in the 'M'
field of byte 5 of the Screen Descriptor. The number
The Image Descriptor defines the actual placement
and extents of the following image within the space
defined in the Screen Descriptor. Also defined are
flags to indicate the presence of a local color lookup
map, and to define the pixel display sequence. The
information stored in image descriptor is:
bits
7 6 5 4 3 2 1 0 Byte #
+---------------+
|0 0 1 0 1 1 0 0| 1 ',' - Image separator character
+---------------+
|
| 2 Start of image in pixels from the
+- Image Left -+ left side of the screen (LSB first)
|
| 3
+---------------+
|
| 4
+- Image Top -+ Start of image in pixels from the
|
| 5 top of the screen (LSB first)
+---------------+
|
| 6
+- Image Width -+ Width of the image in pixels (LSB first)
|
| 7
+---------------+
|
| 8
+- Image Height-+
Height of the image in pixels (LSB first)
|
| 9
+-+-+-+-+-+-----+ M=0 - Use global color map, ignore 'pixel'
|M|I|0|0|0|pixel| 10 M=1 - Local color map follows, use 'pixel'
+-+-+-+-+-+-----+ I=0 - Image formatted in Sequential order
I=1 - Image formatted in Interlaced order
pixel+1 - # bits per pixel for this image
A Local Color Map is optional. If the 'M' bit of byte
10 of the Image Descriptor is set, then a color map
follows the Image Descriptor that applies only to the
following image. At the end of the image, the color
map will revert to that defined after the Screen
Descriptor. Note that the 'pixel' field of byte 10 of the
Image Descriptor is used only if a Local Color Map is
indicated. This defines the parameters not only for the
image pixel size, but determines the number of color
map entries that follow. The bits per pixel value will
also revert to the value specified in the Screen
Descriptor when processing of the image is complete.
Raster Data: The format of the actual image is
defined as the series of pixel color index values that
30 | P a g e
International Journal of Technical Research and Applications e-ISSN: 2320-8163,
www.ijtra.com Volume 3, Issue 2 (Mar-Apr 2015), PP. 28-32
make up the image. The image pixel values are
processed as a series of color indices which map into
the existing color map. The resulting color value from
the map is what is actually displayed. This series of
pixel indices, the number of which is equal to imagewidth*image-height pixels, are passed to the GIF
Frame5
Frame6
image data stream one value per pixel, compressed
and packaged according to a version of the LZW
compression algorithm.
V. THE WORKING SYSTEM ALGORITHMS
a) The Hiding Algorithm
Frame7
b) The Text Message
You give but little when you give of your possessions. It is
when you give of yourself that you truly give. For what are
your possessions but things you keep and guard for fear you
may need them tomorrow? And tomorrow, what shall
tomorrow bring to the over prudent dog burying bones in the
trackless sand as he follows the pilgrims to the holy city? And
what is fear of need but need itself? Is not dread of thirst when
your well is full, the thirst that is unquenchable?
There are those who give little of the much which they
have--and they give it for recognition and their hidden desire
makes their gifts unwholesome. And there are those who have
little and give it all. These are the believers in life and the
bounty of life, and their coffer is never empty. There are those
who give with joy, and that joy is their reward. And there are
those who give with pain, and that pain is their baptism.
And there are those who give and know not pain in giving,
nor do they seek joy, nor give with mindfulness of virtue;
They give as in yonder valley the myrtle breathes its fragrance
into space. Through the hands of such as these God speaks,
and from behind their eyes He smiles upon the earth.
It is well to give when asked, but it is better to give unasked,
through understanding;
b) The Extracting Algorithm
VI. PRACTICAL IMPLEMENTATION
We have completed a project using this technique using
Visual Basic 6.0. Various animated GIF images are used as
source image and the results are noted. Let us see one of the
results here:
a) Cover Image Frames
Frame1
Frame3
Frame8
Frame1
Frame2
Frame3
Frame4
Frame5
Frame6
Frame7
Frame8
Frame2
Frame4
nd to the open-handed the search for one who shall
receive is joy greater than giving. And is there aught you
31 | P a g e
International Journal of Technical Research and Applications e-ISSN: 2320-8163,
www.ijtra.com Volume 3, Issue 2 (Mar-Apr 2015), PP. 28-32
would withhold? All you have shall some day be given;
3- The maximum size of the embedded text message could be
therefore give now, that the season of giving may be yours and
very huge depend on the LZW code of the text and number of
not your inheritors'
frames in the image.
c) Stego-Image Frames
4- The lossless compression method used in the image and in
d) The Palette
the embedded text result to extract the text without any
changes in the message.
[1]
[2]
[3]
Before Sorting
After Sorting
VII. CONCLUSIONS
1- The processing of compressed a text message by using
LZW compression method considered as an encryption
method, therefore the detection of the hidden message become
more complex.
2- Hide the text in all frames of the animated image and the
animation property of the image make the observation of the
hidden text very difficult.
[4]
[5]
[6]
[7]
REFERENCES
Atul Kahate (2009), Cryptography and Network Security,
2nd edition, McGraw-Hill.
Mohamed Elsading Eltahir, Laiha Mat, B. B Zaidan and A.
A. Zaidan," High Rate Video Streaming Steganography"
,International Conference on Information Management and
Engineering(ICIME09)
Session
10,P.P
550553,2009.(Conference proceding).
Fazida Othman, Miss Laiha. Maktom, A.Y.TAQA, B. B
Zaidan, A. A Zaidan,"An Extensive Empirical Study for the
impact of Increasing Data Hidden on the Images
Texture",Internatioal Conference on future Computer and
Communication(ICFCC
09),Session
7,P.P
477481,2009(Confernce proceding).
Richard Popa "An Analysis of Steganographic
Techniques".
Johnson, N.F. & Jajodia, S., "Exploring Steganography:
Seeing the Unseen",Computer Journal,February 1998.
Murshed, Md. M. "Steganography using LSB hiding
"Upper lowa University Fayette, lowa, USA.
"Graphics Interchange format, Version 87a". 15 June
1987.Retrieved13 October 2012.
32 | P a g e
Vous aimerez peut-être aussi
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- Energy Gap Investigation and Characterization of Kesterite Cu2znsns4 Thin Film For Solar Cell ApplicationsDocument4 pagesEnergy Gap Investigation and Characterization of Kesterite Cu2znsns4 Thin Film For Solar Cell ApplicationsInternational Jpurnal Of Technical Research And Applications100% (1)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- Sumita PDFDocument5 pagesSumita PDFInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Exponential Smoothing of Postponement Rates in Operation Theatres of Advanced Pediatric Centre - Time Series Forecasting With Regression AnalysisDocument7 pagesExponential Smoothing of Postponement Rates in Operation Theatres of Advanced Pediatric Centre - Time Series Forecasting With Regression AnalysisInternational Jpurnal Of Technical Research And Applications100% (2)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- Postponement of Scheduled General Surgeries in A Tertiary Care Hospital - A Time Series Forecasting and Regression AnalysisDocument6 pagesPostponement of Scheduled General Surgeries in A Tertiary Care Hospital - A Time Series Forecasting and Regression AnalysisInternational Jpurnal Of Technical Research And Applications100% (2)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (895)
- Study of Nano-Systems For Computer SimulationsDocument6 pagesStudy of Nano-Systems For Computer SimulationsInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Sumita PDFDocument5 pagesSumita PDFInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- Qualitative Risk Assessment and Mitigation Measures For Real Estate Projects in MaharashtraDocument9 pagesQualitative Risk Assessment and Mitigation Measures For Real Estate Projects in MaharashtraInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (588)
- Digital Compressing of A BPCM Signal According To Barker Code Using FpgaDocument7 pagesDigital Compressing of A BPCM Signal According To Barker Code Using FpgaInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- Aesthetics of The Triumphant Tone of The Black Woman in Alice Walker's The Color PurpleDocument30 pagesAesthetics of The Triumphant Tone of The Black Woman in Alice Walker's The Color PurpleInternational Jpurnal Of Technical Research And Applications100% (2)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (266)
- An Experimental Study On Separation of Water From The Atmospheric AirDocument5 pagesAn Experimental Study On Separation of Water From The Atmospheric AirInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Modelling The Impact of Flooding Using Geographic Information System and Remote SensingDocument6 pagesModelling The Impact of Flooding Using Geographic Information System and Remote SensingInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- Overview of TCP Performance in Satellite Communication NetworksDocument5 pagesOverview of TCP Performance in Satellite Communication NetworksInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Pod-Pwm Based Capacitor Clamped Multilevel InverterDocument3 pagesPod-Pwm Based Capacitor Clamped Multilevel InverterInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- Li-Ion Battery Testing From Manufacturing To Operation ProcessDocument4 pagesLi-Ion Battery Testing From Manufacturing To Operation ProcessInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- An Inside Look in The Electrical Structure of The Battery Management System Topic Number: Renewable Power Sources, Power Systems and Energy ConversionDocument5 pagesAn Inside Look in The Electrical Structure of The Battery Management System Topic Number: Renewable Power Sources, Power Systems and Energy ConversionInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- Implementation of Methods For Transaction in Secure Online BankingDocument3 pagesImplementation of Methods For Transaction in Secure Online BankingInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2259)
- Scope of Replacing Fine Aggregate With Copper Slag in Concrete - A ReviewDocument5 pagesScope of Replacing Fine Aggregate With Copper Slag in Concrete - A ReviewInternational Jpurnal Of Technical Research And Applications100% (1)
- Time Efficient Baylis-Hillman Reaction On Steroidal Nucleus of Withaferin-A To Synthesize Anticancer AgentsDocument5 pagesTime Efficient Baylis-Hillman Reaction On Steroidal Nucleus of Withaferin-A To Synthesize Anticancer AgentsInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- The Construction Procedure and Advantage of The Rail Cable-Lifting Construction Method and The Cable-Hoisting MethodDocument3 pagesThe Construction Procedure and Advantage of The Rail Cable-Lifting Construction Method and The Cable-Hoisting MethodInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Evaluation of Drainage Water Quality For Irrigation by Integration Between Irrigation Water Quality Index and GisDocument9 pagesEvaluation of Drainage Water Quality For Irrigation by Integration Between Irrigation Water Quality Index and GisInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Open Loop Analysis of Cascaded Hbridge Multilevel Inverter Using PDPWM For Photovoltaic SystemsDocument3 pagesOpen Loop Analysis of Cascaded Hbridge Multilevel Inverter Using PDPWM For Photovoltaic SystemsInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- Physico-Chemical and Bacteriological Assessment of River Mudzira Water in Mubi, Adamawa State.Document4 pagesPhysico-Chemical and Bacteriological Assessment of River Mudzira Water in Mubi, Adamawa State.International Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Performance Analysis of Microstrip Patch Antenna Using Coaxial Probe Feed TechniqueDocument3 pagesPerformance Analysis of Microstrip Patch Antenna Using Coaxial Probe Feed TechniqueInternational Jpurnal Of Technical Research And Applications100% (1)
- Effect of Trans-Septal Suture Technique Versus Nasal Packing After SeptoplastyDocument8 pagesEffect of Trans-Septal Suture Technique Versus Nasal Packing After SeptoplastyInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- A Study On The Fresh Properties of SCC With Fly AshDocument3 pagesA Study On The Fresh Properties of SCC With Fly AshInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Investigation of Coverage Level and The Availability of GSM Signal in Ekpoma, NigeriaDocument6 pagesInvestigation of Coverage Level and The Availability of GSM Signal in Ekpoma, NigeriaInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Parametric Modeling of Voltage Drop in Power Distribution NetworksDocument4 pagesParametric Modeling of Voltage Drop in Power Distribution NetworksInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Study of Carbohydrate Metabolism in Severe Acute Malnutrition and Correlations of Weight and Height With Pp-Sugar and BmiDocument9 pagesStudy of Carbohydrate Metabolism in Severe Acute Malnutrition and Correlations of Weight and Height With Pp-Sugar and BmiInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (120)
- Production of Starch From Mango (Mangifera Indica.l) Seed Kernel and Its CharacterizationDocument4 pagesProduction of Starch From Mango (Mangifera Indica.l) Seed Kernel and Its CharacterizationInternational Jpurnal Of Technical Research And Applications100% (1)
- Structural and Dielectric Studies of Terbium Substituted Nickel Ferrite NanoparticlesDocument3 pagesStructural and Dielectric Studies of Terbium Substituted Nickel Ferrite NanoparticlesInternational Jpurnal Of Technical Research And ApplicationsPas encore d'évaluation
- Ascii Table - ASCII Character Codes and HTML, Octal, Hex and Decimal Chart ConversionDocument1 pageAscii Table - ASCII Character Codes and HTML, Octal, Hex and Decimal Chart ConversionYash RajputPas encore d'évaluation
- 8MP Starlight Motorized IR Bullet Camera: TC-C38TS Spec: I8/A/E/Y/M/H/2.7-13.5mm/V5.0Document4 pages8MP Starlight Motorized IR Bullet Camera: TC-C38TS Spec: I8/A/E/Y/M/H/2.7-13.5mm/V5.0Wael Gab AllahPas encore d'évaluation
- Lk720 Manual (Lkgps2)Document8 pagesLk720 Manual (Lkgps2)Oscar Caguana43% (7)
- FinalDocument178 pagesFinalBiki JhaPas encore d'évaluation
- File Handling in CLDocument12 pagesFile Handling in CLNaresh KuppiliPas encore d'évaluation
- SMSC Emi Ucp Interface 4.5Document89 pagesSMSC Emi Ucp Interface 4.5mircammPas encore d'évaluation
- AL - PCS - WINE Software Manual July 2002Document116 pagesAL - PCS - WINE Software Manual July 2002Yip YipPas encore d'évaluation
- CDDIDocument1 pageCDDIDonika MarkandePas encore d'évaluation
- Week 01 Systems Development in An Organizational ContextDocument43 pagesWeek 01 Systems Development in An Organizational ContextMuhd FarisPas encore d'évaluation
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- SAP SuccessFactors Foundation PDFDocument466 pagesSAP SuccessFactors Foundation PDFDiogo Palermo ToblerPas encore d'évaluation
- ProctorU Test-Taker Detailed Service DescriptionDocument8 pagesProctorU Test-Taker Detailed Service DescriptionGLPas encore d'évaluation
- Bitraser Cloud User Guide: Legal Notices About Stellar Contact UsDocument81 pagesBitraser Cloud User Guide: Legal Notices About Stellar Contact Usjitesh waghmarePas encore d'évaluation
- Perc6 ConfigurationDocument27 pagesPerc6 ConfigurationCarlos Ml Perez BautistaPas encore d'évaluation
- AP WebFeeds DeveloperGuide v2!5!061510Document48 pagesAP WebFeeds DeveloperGuide v2!5!061510mayurvandraPas encore d'évaluation
- NetBackup AdminGuide MSSQL WinDocument256 pagesNetBackup AdminGuide MSSQL WinAshok YarlagaddaPas encore d'évaluation
- ANR - Application Not Responding: Strict ModeDocument2 pagesANR - Application Not Responding: Strict ModePRAKHAR SRIVASTAVAPas encore d'évaluation
- HwontlogDocument5 pagesHwontlogJairo RamosPas encore d'évaluation
- ES2402 16P 2C User Manual PDFDocument97 pagesES2402 16P 2C User Manual PDFPaul Ramos CarcaustoPas encore d'évaluation
- Installation Guide SC90Document50 pagesInstallation Guide SC90aPas encore d'évaluation
- Laboratory Exercise 1: Switches, Lights, and MultiplexersDocument9 pagesLaboratory Exercise 1: Switches, Lights, and MultiplexersRyan ReasPas encore d'évaluation
- Cisco Catalyst 9000 1.1Document7 pagesCisco Catalyst 9000 1.1jamesPas encore d'évaluation
- Django 1.2 ManualDocument1 077 pagesDjango 1.2 ManualNathaniel SimPas encore d'évaluation
- 98 375 html5Document276 pages98 375 html5Luis Gerardo AlonsoPas encore d'évaluation
- RAN16.0 Troubleshooting Guide (02) (PDF) - EN PDFDocument258 pagesRAN16.0 Troubleshooting Guide (02) (PDF) - EN PDFSyedmuslimshahPas encore d'évaluation
- IP Spoofing and Web SpoofingDocument11 pagesIP Spoofing and Web SpoofingDevendra ShamkuwarPas encore d'évaluation
- Digitalcrafts Immersive Bootcamp Course Packet V4.originalDocument11 pagesDigitalcrafts Immersive Bootcamp Course Packet V4.originalDe VoPas encore d'évaluation
- Migration From Sybase Installation InstructionsDocument5 pagesMigration From Sybase Installation InstructionsUjjal RegmiPas encore d'évaluation
- SJ-20100908091007-005-ZXC10 BSCB (V8.0.3.002) Controller Technical Manual PDFDocument124 pagesSJ-20100908091007-005-ZXC10 BSCB (V8.0.3.002) Controller Technical Manual PDFengrSadiquePas encore d'évaluation
- LIC Integrity PactDocument2 pagesLIC Integrity PactRKPas encore d'évaluation
- L3 Block Diagram XT1063-XT1064-XT1068-XT1069 V1.0Document4 pagesL3 Block Diagram XT1063-XT1064-XT1068-XT1069 V1.0Renato AlmeidaPas encore d'évaluation
- Hacking With Linux 2020:A Complete Beginners Guide to the World of Hacking Using Linux - Explore the Methods and Tools of Ethical Hacking with LinuxD'EverandHacking With Linux 2020:A Complete Beginners Guide to the World of Hacking Using Linux - Explore the Methods and Tools of Ethical Hacking with LinuxPas encore d'évaluation
- Chip War: The Quest to Dominate the World's Most Critical TechnologyD'EverandChip War: The Quest to Dominate the World's Most Critical TechnologyÉvaluation : 4.5 sur 5 étoiles4.5/5 (227)
- Computer Science: A Concise IntroductionD'EverandComputer Science: A Concise IntroductionÉvaluation : 4.5 sur 5 étoiles4.5/5 (14)
- Unlock Any Roku Device: Watch Shows, TV, & Download AppsD'EverandUnlock Any Roku Device: Watch Shows, TV, & Download AppsPas encore d'évaluation
- CompTIA Security+ All-in-One Exam Guide, Sixth Edition (Exam SY0-601)D'EverandCompTIA Security+ All-in-One Exam Guide, Sixth Edition (Exam SY0-601)Évaluation : 5 sur 5 étoiles5/5 (1)
- iPhone X Hacks, Tips and Tricks: Discover 101 Awesome Tips and Tricks for iPhone XS, XS Max and iPhone XD'EverandiPhone X Hacks, Tips and Tricks: Discover 101 Awesome Tips and Tricks for iPhone XS, XS Max and iPhone XÉvaluation : 3 sur 5 étoiles3/5 (2)
- Chip War: The Fight for the World's Most Critical TechnologyD'EverandChip War: The Fight for the World's Most Critical TechnologyÉvaluation : 4.5 sur 5 étoiles4.5/5 (82)