Académique Documents
Professionnel Documents
Culture Documents
Imanager U2000 Unified NMS Product Description - (V100R002C01 - 05) PDF
Transféré par
Wandeto AnthonyDescription originale:
Titre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Imanager U2000 Unified NMS Product Description - (V100R002C01 - 05) PDF
Transféré par
Wandeto AnthonyDroits d'auteur :
Formats disponibles
iManager U2000 Unified Network Management
System
V100R002C01
Product Description
Issue
05
Date
2010-11-19
HUAWEI TECHNOLOGIES CO., LTD.
Copyright Huawei Technologies Co., Ltd. 2010. All rights reserved.
No part of this document may be reproduced or transmitted in any form or by any means without prior written
consent of Huawei Technologies Co., Ltd.
Trademarks and Permissions
and other Huawei trademarks are trademarks of Huawei Technologies Co., Ltd.
All other trademarks and trade names mentioned in this document are the property of their respective holders.
Notice
The purchased products, services and features are stipulated by the contract made between Huawei and the
customer. All or part of the products, services and features described in this document may not be within the
purchase scope or the usage scope. Unless otherwise specified in the contract, all statements, information,
and recommendations in this document are provided "AS IS" without warranties, guarantees or representations
of any kind, either express or implied.
The information in this document is subject to change without notice. Every effort has been made in the
preparation of this document to ensure accuracy of the contents, but all statements, information, and
recommendations in this document do not constitute the warranty of any kind, express or implied.
Huawei Technologies Co., Ltd.
Address:
Huawei Industrial Base
Bantian, Longgang
Shenzhen 518129
People's Republic of China
Website:
http://www.huawei.com
Email:
support@huawei.com
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
iManager U2000 Unified Network Management System
Product Description
About This Document
About This Document
Intended Audience
The iManager U2000 Product Description describes the position, functional characteristics,
system architecture and networking mode of the U2000, appended with standards that the
U2000 complies with, and performance indexes.
This document provides guides for getting the features and functionalities of the U2000.
The intended audiences of this document are:
l
Network Planning Engineer
Data Configuration Engineer
System Maintenance Engineer
Change History
Updates between document issues are cumulative. Therefore, the latest document issue contains
all updates made in previous issues.
Changes in Issue 05 (2010-11-19)
The fifth release. The fifth release has the following changes:
17.3.19 Manageable OP-Bypass Equipment is added..
Changes in Issue 04 (2010-09-24)
The fourth release. The third release has the following changes:
This chapter is optimized: 5.2 Security Management.
Changes in Issue 03 (2010-08-16)
The third release. The second release has the following changes:
3 Configuration Requirements
This chapter is added to describes the software and hardware configuration requirements of the
U2000.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
iii
iManager U2000 Unified Network Management System
Product Description
About This Document
Changes in Issue 02 (2010-07-30)
The second release. Optimize all of this document.
Changes in Issue 01 (2010-03-30)
Initial release.
iv
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Contents
Contents
About This Document...................................................................................................................iii
1 Positioning and Benefits...........................................................................................................1-1
1.1 Network Position.............................................................................................................................................1-2
1.1.1 Network Management Trend.................................................................................................................1-2
1.1.2 Product Orientation................................................................................................................................1-2
1.2 Product Characteristics....................................................................................................................................1-3
1.3 Manageable Equipment...................................................................................................................................1-6
2 System Architecture...................................................................................................................2-1
2.1 Software Structure...........................................................................................................................................2-2
2.1.1 Software Structure of the U2000 Single-Server System........................................................................2-2
2.1.2 Software Structure of the U2000 HA System (Veritas Hot Standby)....................................................2-3
2.2 External Interfaces...........................................................................................................................................2-4
2.2.1 NBI.........................................................................................................................................................2-5
2.2.2 SBI........................................................................................................................................................2-13
3 Configuration Requirements...................................................................................................3-1
3.1 Hardware Configuration of the U2000 Server................................................................................................3-2
3.2 Software Configuration of the U2000 Server.................................................................................................3-3
3.3 Configuration of the U2000 Client..................................................................................................................3-5
4 Networking and Application................................................................................................... 4-1
4.1 Deployment Mode...........................................................................................................................................4-2
4.1.1 Centralized Deployment of a Single-Server System..............................................................................4-3
4.1.2 Centralized Deployment of an HA System............................................................................................4-3
4.2 Networking Mode Between the U2000 and NEs............................................................................................4-4
4.2.1 Inband Networking Mode......................................................................................................................4-4
4.2.2 Outband Networking Mode....................................................................................................................4-5
4.3 Application Scenarios of U2000 Management...............................................................................................4-6
4.3.1 Unified Management of Network Products...........................................................................................4-7
4.3.2 Single Metro Solution............................................................................................................................4-9
4.3.3 Single Backhaul Solution.....................................................................................................................4-12
4.3.4 Single Backbone Solution....................................................................................................................4-16
4.3.5 Single FAN Solution............................................................................................................................4-18
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Contents
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions...........................................................................................................................5-1
5.1 Overview of Functions and Features...............................................................................................................5-3
5.2 Security Management......................................................................................................................................5-4
5.3 Topology Management................................................................................................................................... 5-9
5.4 Alarm Management.......................................................................................................................................5-15
5.5 Performance Management.............................................................................................................................5-29
5.6 Inventory Management.................................................................................................................................5-34
5.7 Log Management...........................................................................................................................................5-36
5.8 Database Management..................................................................................................................................5-39
5.9 NE Communication Parameter Management................................................................................................5-41
5.10 DCN Management.......................................................................................................................................5-42
5.11 NE Software Management..........................................................................................................................5-42
5.12 Report Management....................................................................................................................................5-43
5.13 System Monitoring......................................................................................................................................5-46
6 MSTP Network Feature Management...................................................................................6-1
6.1 MSTP NE Management..................................................................................................................................6-2
6.2 MSTP Protection Subnet Management.........................................................................................................6-10
6.3 E2E MSTP Management...............................................................................................................................6-11
6.4 SDH ASON Management.............................................................................................................................6-16
7 WDM Network Feature Management....................................................................................7-1
7.1 WDM NE Management.................................................................................................................................. 7-2
7.2 WDM NA NE Management..........................................................................................................................7-11
7.3 WDM Protection Subnet Management.........................................................................................................7-20
7.4 End-to-End WDM Management...................................................................................................................7-21
7.5 WDM ASON Management...........................................................................................................................7-24
8 RTN Network Feature Management......................................................................................8-1
8.1 RTN NE Management.....................................................................................................................................8-2
8.2 RTN Protection Subnet Management...........................................................................................................8-10
8.3 End-to-End RTN Management.....................................................................................................................8-11
9 PTN Network Feature Management.......................................................................................9-1
9.1 PTN NE Management.....................................................................................................................................9-2
9.2 E2E PTN Management..................................................................................................................................9-19
10 Router Feature and Switch Feature Management............................................................10-1
10.1 Router Management....................................................................................................................................10-3
10.2 Router V8 Management..............................................................................................................................10-6
10.3 Automatic NE Configuration Management................................................................................................10-7
10.4 Switch Management....................................................................................................................................10-8
10.5 Template Management..............................................................................................................................10-13
10.6 Diagnosis Management.............................................................................................................................10-14
10.7 Cluster Management.................................................................................................................................10-16
vi
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Contents
10.8 Node Redounded Management.................................................................................................................10-17
10.9 Report Subsystem Management................................................................................................................10-18
10.10 VPN Service Management......................................................................................................................10-18
10.11 Tunnel Service Management...................................................................................................................10-20
11 Feature Management for Security Devices ......................................................................11-1
11.1 Security Device Management.....................................................................................................................11-2
11.2 Single-Point Web Configuration for Security Devices...............................................................................11-2
11.3 Centralized Security Policy Configuration.................................................................................................11-3
11.3.1 Policy Package Management.............................................................................................................11-4
11.3.2 Security Policy Configuration............................................................................................................11-4
11.3.3 Attack Defense Configuration............................................................................................................11-5
11.3.4 Policy Resource Configuration..........................................................................................................11-5
11.3.5 Mapping Service................................................................................................................................11-6
11.4 Report Subsystem Management..................................................................................................................11-6
11.5 VPN Service Management..........................................................................................................................11-6
11.5.1 IPSec End-to-End Service..................................................................................................................11-7
11.5.2 Remote Access Service......................................................................................................................11-7
12 FTTx Network Feature Management.................................................................................12-1
12.1 OLT Management.......................................................................................................................................12-2
12.2 ONU Management....................................................................................................................................12-12
13 MSAN Network Feature Management..............................................................................13-1
13.1 MSAN Management...................................................................................................................................13-2
14 DSLAM Network Feature Management............................................................................14-1
14.1 DSLAM Management.................................................................................................................................14-2
15 Reliability................................................................................................................................15-1
15.1 Reliability Design........................................................................................................................................15-2
15.2 Reliability Indicator.....................................................................................................................................15-3
15.3 HA System..................................................................................................................................................15-3
15.4 DCN Protection...........................................................................................................................................15-4
15.5 Disk Mirroring.............................................................................................................................................15-5
15.6 Data Backup................................................................................................................................................15-5
16 Performance Indicators.........................................................................................................16-1
17 Management Capability.......................................................................................................17-1
17.1 NE Equivalent Coefficient..........................................................................................................................17-2
17.1.1 Equivalent NEs in the Transport Domain..........................................................................................17-3
17.1.2 Equivalent NEs in the IP Domain......................................................................................................17-6
17.1.3 Equivalent NEs in the Access Domain..............................................................................................17-9
17.2 Management Capabilities of the U2000 on Different Hardware Platforms..............................................17-10
17.3 Manageable Equipment.............................................................................................................................17-14
17.3.1 Manageable MSTP Series Equipment..............................................................................................17-15
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
vii
Contents
iManager U2000 Unified Network Management System
Product Description
17.3.2 Manageable WDM Series Equipment..............................................................................................17-16
17.3.3 Manageable NA WDM Series Equipment.......................................................................................17-18
17.3.4 Manageable Submarine Line Equipment.........................................................................................17-19
17.3.5 Manageable RTN Series Equipment................................................................................................17-19
17.3.6 Manageable PTN Series Equipment................................................................................................17-19
17.3.7 Manageable FTTx Series Equipment...............................................................................................17-20
17.3.8 Manageable MSAN Series Equipment............................................................................................17-22
17.3.9 Manageable DSLAM Series Equipment..........................................................................................17-23
17.3.10 Manageable Router Series Equipment...........................................................................................17-23
17.3.11 Manageable Switch Series Equipment...........................................................................................17-24
17.3.12 Manageable Metro Service Platform Equipment...........................................................................17-26
17.3.13 Manageable Broadband Access Series Equipment........................................................................17-26
17.3.14 Manageable VoIP Gateway Equipment.........................................................................................17-26
17.3.15 Manageable WLAN Series equipment...........................................................................................17-27
17.3.16 Manageable Firewall Series Equipment.........................................................................................17-27
17.3.17 Manageable DPI Equipment..........................................................................................................17-31
17.3.18 Manageable SVN Series Equipment..............................................................................................17-32
17.3.19 Manageable OP-Bypass Equipment...............................................................................................17-32
18 Standards Compliance..........................................................................................................18-1
A Glossary and Abbreviations..................................................................................................A-1
viii
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Figures
Figures
Figure 1-1 Position of the U2000 in the TMN hierarchy.....................................................................................1-3
Figure 1-2 Centralized network management...................................................................................................... 1-4
Figure 2-1 U2000 software structure....................................................................................................................2-2
Figure 2-2 Veritas hot standby HA system (Solaris) software structure..............................................................2-3
Figure 2-3 Veritas hot standby HA system (Windows) software structure..........................................................2-4
Figure 2-4 Functions of external interfaces..........................................................................................................2-5
Figure 4-1 Centralized deployment of the single-server system..........................................................................4-3
Figure 4-2 Centralized deployment of the HA system.........................................................................................4-4
Figure 4-3 Example network in inband networking mode...................................................................................4-5
Figure 4-4 Example network in outband networking mode.................................................................................4-6
Figure 4-5 Unified management of network products......................................................................................... 4-8
Figure 4-6 Network management solution for a single metro network..............................................................4-10
Figure 4-7 SingleBackhaul solution...................................................................................................................4-13
Figure 4-8 Network management solution for a single backbone network........................................................4-17
Figure 4-9 Networking application of the FTTx access network management.................................................4-19
Figure 4-10 FTTx predeployment flow..............................................................................................................4-20
Figure 4-11 FTTx fault diagnosis (1).................................................................................................................4-22
Figure 4-12 FTTx fault diagnosis (2).................................................................................................................4-22
Figure 4-13 PnP function of the MDU after replacement..................................................................................4-24
Figure 4-14 Implementation of the dual homing protection..............................................................................4-24
Figure 4-15 Implementation of the fast service cutover.....................................................................................4-25
Figure 5-1 Basic functions of the U2000............................................................................................................. 5-1
Figure 5-2 Security management overview..........................................................................................................5-4
Figure 5-3 Right................................................................................................................................................... 5-5
Figure 5-4 RADIUS-based user authentication....................................................................................................5-8
Figure 5-5 LDAP user authentication.................................................................................................................. 5-9
Figure 5-6 Topology view and its functions......................................................................................................5-10
Figure 5-7 Alarm display in the topology view.................................................................................................5-12
Figure 5-8 Illustration of automatic topology discovery....................................................................................5-13
Figure 5-9 Clock view and its functions............................................................................................................5-14
Figure 5-10 Relationships between alarm states................................................................................................5-17
Figure 5-11 Alarm reporting and handling flowchart........................................................................................5-17
Figure 5-12 Alarm panel....................................................................................................................................5-18
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ix
iManager U2000 Unified Network Management System
Product Description
Figures
Figure 5-13 Alarm bar chart...............................................................................................................................5-19
Figure 5-14 Viewing alarms...............................................................................................................................5-20
Figure 5-15 Alarm correlation analysis..............................................................................................................5-23
Figure 5-16 Relationships between a root alarm and its correlative alarms.......................................................5-24
Figure 5-17 Alarm synchronization...................................................................................................................5-26
Figure 5-18 Difference between alarm masking and alarm suppression...........................................................5-27
Figure 5-19 Various alarm notification means...................................................................................................5-27
Figure 5-20 Alarm association...........................................................................................................................5-28
Figure 5-21 Alarm maintenance experience base..............................................................................................5-29
Figure 5-22 Performance management process.................................................................................................5-31
Figure 5-23 Relationships between a template, an instance, and a task.............................................................5-32
Figure 5-24 Inventory management window and its functions..........................................................................5-35
Figure 5-25 Log management window and functions........................................................................................5-37
Figure 5-26 Window and functions of dumping and exporting logs.................................................................5-38
Figure 5-27 NMS database management...........................................................................................................5-40
Figure 5-28 Diagram of the NE resource report.................................................................................................5-45
Figure 5-29 Diagram of the network resource report.........................................................................................5-46
Figure 5-30 System monitoring processes.........................................................................................................5-47
Figure 5-31 System monitoring information......................................................................................................5-48
Figure 9-1 Unicast MPLS tunnel .......................................................................................................................9-11
Figure 9-2 CES service application model.........................................................................................................9-13
Figure 9-3 ATM service application model.......................................................................................................9-14
Figure 9-4 E-Line Service..................................................................................................................................9-15
Figure 9-5 E-AGGR service scenario 1..............................................................................................................9-16
Figure 9-6 E-AGGR service scenario 2..............................................................................................................9-16
Figure 9-7 E-LAN service .................................................................................................................................9-17
Figure 10-1 Cluster topology...........................................................................................................................10-16
Figure 10-2 Navigation path to cluster functions.............................................................................................10-17
Figure 15-1 Switchover between active and standby sites in HA system..........................................................15-4
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Tables
Tables
Table 2-1 NBI functions supported by transport equipment................................................................................2-6
Table 2-2 NBI functions supported by access equipment....................................................................................2-6
Table 2-3 NBI functions supported by IP equipment...........................................................................................2-7
Table 3-1 Configuration requirements of the U2000 servers that manage networks of different scales ............ 3-2
Table 3-2 Recommended configurations of the disk array...................................................................................3-2
Table 3-3 System software of the U2000.............................................................................................................3-3
Table 3-4 High availability software....................................................................................................................3-4
Table 3-5 Software Configurations of the U2000................................................................................................3-5
Table 3-6 Hardware and software configuration requirements of the U2000 client............................................3-5
Table 4-1 Deployment modes of the U2000........................................................................................................ 4-2
Table 4-2 Relationships between faults and their causes that are identified by means of the alarm-based root cause
identification........................................................................................................................................................4-23
Table 5-1 Overview of functions and features of the U2000............................................................................... 5-3
Table 5-2 Alarm severity....................................................................................................................................5-15
Table 5-3 Alarm display functions.....................................................................................................................5-19
Table 5-4 Alarm function...................................................................................................................................5-20
Table 5-5 Performance monitoring templates....................................................................................................5-31
Table 5-6 Statistical items for resource inventory management........................................................................5-35
Table 5-7 Resource Report.................................................................................................................................5-44
Table 9-1 Types of PTN service interfaces..........................................................................................................9-3
Table 15-1 Reliability indicators of the U2000..................................................................................................15-3
Table 15-2 Data backup......................................................................................................................................15-5
Table 16-1 Performance indicators.....................................................................................................................16-1
Table 16-2 DCN bandwidth requirements..........................................................................................................16-2
Table 17-1 Management capabilities of the U2000 on different OptiX NE Equivalents...................................17-3
Table 17-2 Management capabilities of the U2000 on different IP NE Equivalents.........................................17-6
Table 17-3 Management capabilities of the U2000 on different access NE Equivalents................................17-10
Table 17-4 Management capabilities of the U2000 on different hardware platforms......................................17-11
Table 17-5 Manageable MSTP series equipment.............................................................................................17-15
Table 17-6 Manageable WDM equipment.......................................................................................................17-17
Table 17-7 Manageable NA WDM equipment................................................................................................17-18
Table 17-8 Manageable submarine line equipment..........................................................................................17-19
Table 17-9 Manageable RTN equipment.........................................................................................................17-19
Table 17-10 Manageable PTN series equipment..............................................................................................17-20
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
xi
Tables
iManager U2000 Unified Network Management System
Product Description
Table 17-11 Manageable FTTx series equipment............................................................................................17-20
Table 17-12 Manageable MSAN series equipment..........................................................................................17-22
Table 17-13 Manageable DSLAM series equipment.......................................................................................17-23
Table 17-14 Manageable router series equipment............................................................................................17-24
Table 17-15 Manageable switch series equipment...........................................................................................17-24
Table 17-16 Manageable Metro service platform equipment...........................................................................17-26
Table 17-17 Manageable broadband access series equipment.........................................................................17-26
Table 17-18 Manageable VoIP gateway equipment.........................................................................................17-27
Table 17-19 Manageable WLAN series equipment.........................................................................................17-27
Table 17-20 Manageable firewall series equipment.........................................................................................17-27
Table 17-21 Manageable DPI equipment.........................................................................................................17-32
Table 17-22 Manageable SVN series equipment.............................................................................................17-32
Table 17-23 Manageable OP-Bypass equipment.............................................................................................17-32
Table 18-1 Details of the Standards and Protocols.............................................................................................18-2
xii
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
1 Positioning and Benefits
Positioning and Benefits
About This Chapter
This topic describes the position of the iManager U2000 unified network management system
(hereinafter referred to as U2000) in the telecommunications management network (TMN), the
product characteristics, and the equipment that the U2000 can manage.
1.1 Network Position
This topic provides information about the development trend of network management and the
position of the U2000 in the TMN hierarchy.
1.2 Product Characteristics
The U2000 improves the capability of managing converged networks, scalability, and ease of
use to construct a customer-centered and future-oriented NMS of a new generation.
1.3 Manageable Equipment
This topic provides information about the equipment that the U2000 V100R002C01SPC003 can
manage.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
1-1
iManager U2000 Unified Network Management System
Product Description
1 Positioning and Benefits
1.1 Network Position
This topic provides information about the development trend of network management and the
position of the U2000 in the TMN hierarchy.
1.1.1 Network Management Trend
With the development of IT and IP technologies and the convergence of telecommunications,
IT, media, and consumer electronic industries, the telecommunications industry has witnessed
tremendous changes. Broadband services and mobile services have become the mainstream
services on telecommunications networks and convergence of networks is being implemented
widely, which bring changes in the market orientation and business modes of carriers.
1.1.2 Product Orientation
The U2000 is the equipment management system developed by Huawei and is also the major
and future-oriented network management product and solution.
1.1.1 Network Management Trend
With the development of IT and IP technologies and the convergence of telecommunications,
IT, media, and consumer electronic industries, the telecommunications industry has witnessed
tremendous changes. Broadband services and mobile services have become the mainstream
services on telecommunications networks and convergence of networks is being implemented
widely, which bring changes in the market orientation and business modes of carriers.
l
The development of the all-IP architecture is a leading factor in the transition from the
existing vertical network that is divided by technology and service to the flattened
horizontal network.
Improving user experience, lowering operation expenditure (OPEX), and improving
efficiency are the driving forces for fixed-mobile convergence (FMC).
Network convergence requires network management to be consolidated.
To be oriented to the future network development trend, the U2000 combines all-IP and FMC
and manages bearer and access equipment in a centralized manner.
l
The U2000 can perform not only integrated management of multi-domain equipment but
also integrated management at the element and network management layers. The U2000
has revolutionized the layer-based management mode to meet the management
requirements in the transition from the existing vertical network to the flattened horizontal
network.
The U2000 is a unified network management system (NMS) of multiple domains and it
aims to minimize operation and maintenance (O&M) costs for customers and to bring more
network benefits.
1.1.2 Product Orientation
The U2000 is the equipment management system developed by Huawei and is also the major
and future-oriented network management product and solution.
In the TMN hierarchy, the U2000 is located at the element management layer and network
management layer, and supports all functions of the element and network management layers.
Figure 1-1 shows the position of the U2000 in the TMN hierarchy.
1-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
1 Positioning and Benefits
Figure 1-1 Position of the U2000 in the TMN hierarchy
1.2 Product Characteristics
The U2000 improves the capability of managing converged networks, scalability, and ease of
use to construct a customer-centered and future-oriented NMS of a new generation.
Centralized Network Management
The U2000 manages transport equipment, access equipment, and IP equipment in a centralized
manner. Specifically, it manages Huawei products and services of the products. The products
include MSTP, WDM, OTN, microwave, and PTN equipment, routers, switches, MSANs,
DSLAMs; the services include FTTx, firewall services.
In addition, the U2000 manages end-to-end (E2E) services across domains in access and bearer
networks, as shown in Figure 1-2. The services include SDH, WDM, microwave, packet, PTN,
CX, and switch services.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
1-3
iManager U2000 Unified Network Management System
Product Description
1 Positioning and Benefits
Figure 1-2 Centralized network management
Multiple Operating Systems
The U2000 is developed based on the integrated management application platform (iMAP) of
Huawei. It supports Sun workstations, PC servers, Sybase databases, SQL Server databases, and
Solaris, Windowsoperating systems (OSs).
The U2000 is a stand-alone application that can be installed on different OSs and databases.
Hence, it is compatible with multiple OSs. The U2000 provides high-end solutions for largescale networks and low-cost solutions for small- and medium-scale networks.
Leading Scalable NMS Architecture
By adopting the mature and widely-used client/server (C/S) architecture, the U2000 supports
distributed and hierarchical database system, service processing system, and client application
system and it also supports concurrent operations of multiple clients. Modularized architecture
is scalable so that the U2000 meets the management requirements of complex and large-scale
networks.
1-4
The U2000 uses an object-oriented, multiprocessing, modularized, and componentized
architecture design, thereby decreasing the degree of the coupling of NE management
components. In this way, the U2000 supports smooth online increase in management
capability from a single domain to multiple domains.
The U2000 has the capability of flexibly integrating NBIs.
The loose coupling framework supports the independent upgrade and maintenance of
subsystems.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
1 Positioning and Benefits
Visualized Management
l
Service supervision:
Supports service-centered visualized supervision and the function of querying affected
services by alarm.
Provides abundant detection and diagnosis methods based on services to quickly check
service connectivity and locate faults.
Supports service-based performance query, threshold pre-warning, and trend analysis
in the GUI.
Service deployment:
Provides templates to set service-related parameters once instead of setting parameters
repeatedly.
Supports bulk deployment of services, increasing the configuration efficiency.
Calculates static routes and allocates labels automatically, without manual intervention.
Object relationship:
Associates services with tunnels and tunnels with routes. Hierarchical object
relationships represent the bearer relationships explicitly.
Provides bearer relationships to quickly locate and rectify faults.
Network-wide clock:
Supports the automatic discovery of clocks (1588 clock, synchronous Ethernet clock,
and SDH clock) and addition of the clocks to the clock topology view.
Provides the unified topology view of network-wide clocks and refreshes the tracking
relationships and synchronization status of the clocks when faults occur in networks.
Monitors clock status and displays clock alarms, tracking relationships, and protection
status in real time.
Cross-Domain E2E Service Provisioning
l
Supports E2E TDM service provisioning and management across traditional microwave
and MSTP networks, which speeds up network deployment and service provisioning of a
large number of microwave services.
Supports E2E packet service provisioning and management across IP microwave and PTN/
Hybrid MSTP networks, which accelerates service provisioning in an IP network.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
1-5
iManager U2000 Unified Network Management System
Product Description
1 Positioning and Benefits
Supports Ethernet, CES, and ATM service management for PTN, MSTP, RTN, SW, and
NE40 devices, and supports E2E management of MPLS tunnels and PWs, which push the
fixed market towards fixed-mobile convergence (FMC).
Supports E2E service (Ethernet, CES, and ATM) provisioning across PTN and CX
networks, and supports E2E management of MPLS tunnels and PWs, which push the
mobile market towards FMC.
1.3 Manageable Equipment
This topic provides information about the equipment that the U2000 V100R002C01SPC003 can
manage.
For information about the equipment of specific types that the U2000 V100R002C01SPC003
can manage, see the following topics:
1-6
Manageable MSTP Series Equipment
Manageable WDM Equipment
Manageable NA WDM Equipment
Manageable Submarine Line Equipment
Manageable RTN Equipment
Manageable PTN Equipment
Manageable FTTx Access Series Devices
Manageable MSAN Series Devices
Manageable DSLAM Series Devices
Manageable Router Series Devices
Manageable Switch Series Devices
Manageable Metro Service Platform Devices
Manageable Broadband Access Series Devices
Manageable VoIP Gateway Devices
Manageable WLAN Series Devices
Manageable Firewall Series Devices
Manageable DPI Equipment
Manageable SVN Series Devices
Manageable OP-Bypass Equipment
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
System Architecture
About This Chapter
The U2000 provides solutions to single-layer management for small- and medium-scale
networks. In addition, the U2000 provides standard external interfaces, through which the
U2000 is interconnected with an upper layer management system to form a hierarchical
management network. The U2000 assists the system at the network management layer and the
system at the service management layer to manage large-scale networks.
2.1 Software Structure
This topic describes the software structure of the U2000 single-server system and U2000 HA
system.
2.2 External Interfaces
The U2000 offers abundant northbound interfaces (NBIs) that help to achieve unified
management of transport, IP, and access equipment, fast integration between OSS and the
U2000, and better quality of customer service. Currently, NBIs jointly developed by Huawei
and mainstream OSS vendors are widely used by 72% of the top 50 carriers worldwide.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
2-1
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
2.1 Software Structure
This topic describes the software structure of the U2000 single-server system and U2000 HA
system.
2.1.1 Software Structure of the U2000 Single-Server System
This topic describes the software structure of the U2000 single-server system.
2.1.2 Software Structure of the U2000 HA System (Veritas Hot Standby)
This topic describes the software structure of the U2000 HA system (Veritas Hot Standby).
2.1.1 Software Structure of the U2000 Single-Server System
This topic describes the software structure of the U2000 single-server system.
In the U2000 single-server system, there is only one U2000 server but multiple U2000 clients.
The clients can gain access to the server at the same time.
Figure 2-1 shows the structural relationships between main modules of the U2000 single-server
system.
Figure 2-1 U2000 software structure
2-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
2.1.2 Software Structure of the U2000 HA System (Veritas Hot
Standby)
This topic describes the software structure of the U2000 HA system (Veritas Hot Standby).
The U2000 HA system (Veritas Hot Standby) applies to geographic redundancy of an HA
system.
The U2000 HA system (Veritas Hot Standby) supports the Solaris and Windows. Figure 2-2
and Figure 2-3 show the software structure.
Figure 2-2 Veritas hot standby HA system (Solaris) software structure
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
2-3
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
Figure 2-3 Veritas hot standby HA system (Windows) software structure
The Veritas volume replicator (VVR) is used to duplicate the U2000 data on the primary
site to the secondary site so that data is synchronized between the primary and secondary
sites in real time.
The Veritas cluster server (VCS) is used to monitor the system and application service in
real time. When a fault occurs in hardware or software, the VCS restarts or stops the
application service.
The Veritas volume manager (VxVM) is used to manage the disks and data volumes of
servers.
2.2 External Interfaces
The U2000 offers abundant northbound interfaces (NBIs) that help to achieve unified
management of transport, IP, and access equipment, fast integration between OSS and the
U2000, and better quality of customer service. Currently, NBIs jointly developed by Huawei
and mainstream OSS vendors are widely used by 72% of the top 50 carriers worldwide.
In addition to conventional NBIs such as SNMP, CORBA, and TL1 NBIs, the U2000 offers the
XML NBI that is based on the MTOSI 2.0 standards. The XML NBI provides multiple extensible
functions, including alarm management, inventory management, performance management,
service provisioning, and diagnosis test. By using these interfaces, the U2000 can integrate with
the OSS in a fast and holistic manner. Figure 2-4 shows the functions of external interfaces.
2-4
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
Figure 2-4 Functions of external interfaces
2.2.1 NBI
The U2000 offers extensive network monitoring information, such as alarms, performance
statistics, and inventory information, for OSSs through northbound interfaces (NBIs). The NBIs
support network management functions, such as service provisioning and diagnosis test.
Through the NBIs, the U2000 can integrate with different OSSs flexibly.
2.2.2 SBI
Using the southbound interface (SBI), the U2000 can connect to NEs and manage them. The
U2000 supports the following SBIs: SNMP, CLI, Qx, SSH, and Telnet SBIs.
2.2.1 NBI
The U2000 offers extensive network monitoring information, such as alarms, performance
statistics, and inventory information, for OSSs through northbound interfaces (NBIs). The NBIs
support network management functions, such as service provisioning and diagnosis test.
Through the NBIs, the U2000 can integrate with different OSSs flexibly.
NOTE
Supported
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
2-5
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
Not supported
The equipment of each product domain supports different NBI functions. For details, see the
following tables.
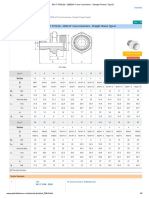
Table 2-1 NBI functions supported by transport equipment
Interfa
ce
Feature
MSTP
Hybir
d
MSTP
WDM
OTN
TDM
RTN
Packet
RTN
Marin
e
XML
Alarm
Performa
nce
Inventory
Service
provisioni
ng
Alarm
Performa
nce
Inventory
Service
provisioni
ng
SNMP
Alarm
FTP
Performa
nce
TL1
Inventory
Service
provisioni
ng
Diagnosis
test
CORB
A
Custom
er OSS
Test
Table 2-2 NBI functions supported by access equipment
2-6
Interface
Feature
DSLAM
GPON/FTTx
XML
Alarm
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Interface
2 System Architecture
Feature
DSLAM
GPON/FTTx
Performance
Inventory
Service provisioning
Alarm
Performance
Inventory
Service provisioning
SNMP
Alarm
FTP
Performance
TL1
Inventory
Service provisioning
Diagnosis test
CORBA
Customer OSS Test
Table 2-3 NBI functions supported by IP equipment
Interface
Feature
NE
CX
Switch
PTN
XML
Alarm
Performance
Inventory
Service
provisioning
Alarm
Performance
Inventory
Service
provisioning
SNMP
Alarm
FTP
Performance
TL1
Inventory
Service
provisioning
CORBA
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
2-7
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
Interface
Feature
NE
CX
Switch
PTN
Customer
OSS Test
Diagnosis
test
XML NBI (Transport)
Complying with the TMF MTOSI 2.0 series standards, the XML NBI enables the U2000 to
provide unified alarm, performance, inventory, and service provisioning management on
transport equipment for OSSs.
The XML NBI supports the following functions:
l
Alarm management
Alarm reporting
Synchronization of active alarms
Alarm acknowledgment
Alarm unacknowledgment
Collection of alarm statistics
Performance management
Query of history performance data
Query of current performance data
Reporting of performance threshold-crossing events
Query of performance threshold-crossing events
Inventory management
Query of physical inventory, such as NEs, shelves, slots, boards, and physical ports
Query of logical inventory, such as logical ports, fibers or cables, tunnels, and services
Export of inventory data and reporting of changes in inventory
XML NBI (Access)
Complying with the TMF MTOSI 2.0 series standards, the XML NBI enables the U2000 to
provide unified alarm, performance, inventory, and service provisioning management on access
equipment for OSSs.
The XML NBI supports the following functions:
l
Alarm management
Alarm reporting
Synchronization of active alarms
Alarm acknowledgment
Alarm unacknowledgment
Collection of alarm statistics
Inventory management
Query of IP DSLAM inventory (ADSL ports, SHDSL ports, and templates)
2-8
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
Service provisioning management
Provisioning of FTTH services (GPON)
XML NBI (IP)
Complying with the TMF MTOSI 2.0 series standards, the XML NBI enables the U2000 to
provide unified alarm, performance, inventory, and service provisioning management on IP
equipment for OSSs.
The XML NBI supports the following functions:
l
Alarm management
Alarm reporting
Synchronization of active alarms
Alarm acknowledgment
Alarm unacknowledgment
Collection of alarm statistics
Performance management
Query of history performance data
Query of current performance data
Reporting of performance threshold-crossing events
Query of performance threshold-crossing events
Inventory management
Query of physical inventory, such as NEs, shelves, slots, boards, and physical ports
Query of logical inventory, such as logical ports, fibers or cables, tunnels, and services
Export of inventory data and reporting of changes in inventory
QoS management
Service provisioning management
Provisioning of route and MAN tunnel resources (MPLS tunnels and IP tunnels)
Provisioning of route and MAN service resources (ATM PWE3, CES PWE3, Ethernet
PWE3, VPLS, and L3VPN)
ANCP service management
CORBA NBI (Transport)
Complying with the TMF MTNM V3.5 series standards, the CORBA NBI enables the U2000
to provide unified alarm management and inventory management. The CORBA NBI also
enables the U2000 to provide service provisioning, performance, and diagnosis test management
for transport equipment.
The CORBA NBI supports the following functions:
l
Alarm management
Alarm reporting
Synchronization of active alarms
Alarm acknowledgment
Alarm unacknowledgment
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
2-9
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
Collection of alarm statistics
l
Performance management
Query of history performance data
Query of current performance data
Reporting of performance threshold-crossing events
Query of performance threshold-crossing events
Inventory management
Query of physical inventory, such as NEs, shelves, slots, boards, and physical ports
Query of logical inventory, such as logical ports, fibers or cables, and trails
Service provisioning management
Provisioning of end-to-end (E2E) services (SDH, WDM, OTN, MSTP, ASON, and
RTN) in the transport domain
Provisioning of per-NE services (SDH, WDM, OTN, and MSTP) in the transport
domain
Diagnosis test management
Port loopback and alarm insertion
Ethernet CC, LB, and LT tests
2M pseudo random binary sequence (PRBS) tests
OAM management on MPLS LSP, PW, PWE3 and VPLS services
CORBA NBI (Access)
Complying with the TMF MTNM V3.5 series standards, the CORBA NBI enables the U2000
to provide unified alarm management.
The CORBA NBI supports the following functions:
l
Alarm management
Alarm reporting
Synchronization of active alarms
Alarm acknowledgment
Alarm unacknowledgment
Collection of alarm statistics
CORBA NBI (IP)
Complying with the TMF MTNM V3.5 series standards, the CORBA NBI enables the U2000
to provide unified alarm management. In addition, the CORBA NBI enables the U2000 to
provide service provisioning and performance management for metropolitan area network
(MAN) equipment.
The CORBA NBI supports the following functions:
l
Alarm management
Alarm reporting
Synchronization of active alarms
Alarm acknowledgment
2-10
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
Alarm unacknowledgment
Collection of alarm statistics
l
Performance management for MAN equipment
Query of history performance data
Query of current performance data
Reporting of performance threshold-crossing events
Query of performance threshold-crossing events
Inventory management for MAN equipment
Query of physical inventory, such as NEs, shelves, slots, boards, and physical ports
Query of logical inventory, such as logical ports, fibers or cables, and trails
QoS management and protection management
Service provisioning management for MAN equipment
Provisioning of services for MAN tunnels (MPLS tunnels and IP tunnels)
Provisioning of MAN services (ATM PWE3, CES PWE3, Ethernet PWE3, and VPLS)
SNMP NBI
Complying with the SNMP v1/v2c/v3 standard, the SNMP NBI enables the U2000 to provide
unified alarm management for OSSs.
The SNMP NBI supports the following functions:
l
Alarm reporting
Synchronization of active alarms
Alarm acknowledgment
Alarm unacknowledgment
Heartbeat alarm reporting
Setting of alarm filter criteria
TL1 NBI
Complying with the GR 831 standard, the TL1 NBI enables the U2000 to provide service
provisioning (xDSL, xPON, broadband, and narrowband services), inventory query, and
inventory provisioning in the access domain for OSSs.
The TL1 NBI supports the following functions:
l
Service provisioning management for access equipment
Provisioning of xDSL (ADSL, SHDSL, and VDSL2) services
Provisioning of xPON (GPON and EPON) services
Provisioning of multicast services
Provisioning of voice services
Provisioning of services for the BRAS
Management of service virtual ports and PVCs
Management of VLANs
Management of Ethernet ports
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
2-11
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
Management of ACL and QoS
l
Inventory management for access equipment
Query of resources, such as equipment, shelves, boards, daughter boards, ports, and
service ports
Notification of resource changes
Management and maintenance of resources
FTP Performance NBI
The FTP performance NBI enables the U2000 to provide performance statistics export for OSSs.
The U2000 exports performance statistics to a specified FTP server for analysis purposes.
The FTP performance NBI supports the following functions:
l
Setting of the following conditions for exporting performance statistics:
Monitoring period of performance events
Monitoring indicator of performance events
Export period of performance statistics
Export of performance statistics to a specified FTP server
Customer OSS Test NBI
The customer OSS test NBI includes two types of NBI: narrowband line test NBI and ADSL
line test NBI. Narrowband line test NBI tests narrowband access devices (lines and terminals).
ADSL line test NBI queries ADSL ports, and captures and releases ADSL lines.
The customer OSS test NBI supports the following functions:
l
Narrowband line test NBI:
Dial tone test for POTS users
Feed voltage test for POTS users
Loop current test for POTS users
Line test for POTS users
Ringing test for POTS users
DTMF or pulse test for POTS users
Howler tone test for POTS users
Circuit test for ISDN user
Line test for ISDN users
NT1 terminal test for ISDN users
Narrowband line capture test
Narrowband line release test
Ringing current voltage test
Stopping a test
ADSL line test NBI:
Query of the information about an ADSL user port
Controlling of the DSLAM test bus
2-12
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
Loopback diagnosis test performed at the central office end on the user port
OAM test
2.2.2 SBI
Using the southbound interface (SBI), the U2000 can connect to NEs and manage them. The
U2000 supports the following SBIs: SNMP, CLI, Qx, SSH, and Telnet SBIs.
Qx Interface
Qx interfaces are simplified interfaces based on the Q3 interfaces defined in ITU-T
recommendations. They are used for private communications. Qx interfaces use a protocol based
on standard TCP/IP packets. Qx interfaces support data transmission over media such as in-band
DCCs or ECCs and out-of-band channels, featuring low overheads, standard structures, and high
efficiency. Qx interfaces are classified into Qx4 interfaces and Qx5 interfaces (Qx4 is the earlier
version). Qx4 interfaces are used for managing the OptiX 2500+ and earlier transport equipment;
Qx5 interfaces are used for managing transport equipment later than the OptiX 2500+. The
U2000 can adapt to various protocols.
The U2000 uses Qx interfaces to connect and manage transport equipment, such as MSTP,
WDM, RTN, PTN, and OTN equipment.
SNMP SBI
The SNMP SBI is used to connect and manage SNMP equipment.
The U2000 supports the SNMP SBI that complies with the SNMP v1/v2c/v3 standard. Through
the SNMP SBI, the U2000 can be connected to Huawei routers, switches, and security access
equipment.
SNMP is a TCP/IP-based network management protocol at the application layer. SNMP uses
the UDP protocol at the transmission layer. Through the SNMP SBI, the U2000 can manage the
network equipment that supports proxy processes.
Telnet/SSH Telnet (STelnet) SBI
The Telnet and STelnet SBIs are a basic type of interface used for remote login to and
management of NEs. The Telnet and STelnet SBIs compensate the disadvantages of the SNMP
SBI and allow the U2000 to perform more management functions. Through the Telnet and
STelnet SBIs, the U2000 can be connected to Huawei routers, switches, and security equipment.
l
Telnet is a TCP/IP-based network management protocol at the application layer. Through
the Telnet SBI, you can log in to an NE in the CLI and run commands directly in the CLI
to maintain and configure the NE. Using the TCP protocol at the transmission layer, the
Telnet protocol provides services for network communication. The Telnet protocol
transmits communication data in plain text, which is not secure.
Similar to Telnet, Secure Shell (SSH) is also a TCP/IP-based network management protocol
at the application layer. The SSH protocol, however, transmits encrypted data. Using the
TCP protocol at the transmission layer, the SSH protocol encrypts data at the application
layer. The SSH protocol ensures the security of network communications by means of
authentication, encryption, and authorization. The SSH protocol supports authentication
by password and RSA. In addition, the SSH protocol transmits compressed data, which
speeds up the transmission.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
2-13
iManager U2000 Unified Network Management System
Product Description
2 System Architecture
TFTP/FTP/SFTP SBI
The TFTP, FTP, and SFTP SBIs are used for backing up NE data, upgrading NE software, and
loading patches. TFTP, FTP, and SFTP are TCP/IP-based network management protocols at the
application layer and are dependent on the UDP protocol.
l
Trivial File Transfer Protocol (TFTP) is a basic and standard protocol that requires least
extra overheads, as compared with FTP and SFTP, to upload and download files. The TFTP
protocol does not support password configuration and transfers file contents in plain text.
File Transfer Protocol (FTP) is a set of standard protocols used for transferring files on
networks. The FTP protocol transfers passwords and file contents in plain text.
SSH FTP (SFTP) uses the SSH protocol to provide secure file transfer and processing. For
data backup using the SFTP protocol, passwords and data are encrypted during
transmission.
Syslog SBI
The Syslog SBI serves as an interface for the U2000 to receive system logs from NEs. With the
Syslog SBI, the U2000 can manage NE logs.
2-14
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
3 Configuration Requirements
Configuration Requirements
About This Chapter
This topic describes the software and hardware configuration requirements of the U2000 server
and client.
3.1 Hardware Configuration of the U2000 Server
This topic describes the hardware configuration requirement of the U2000 server.
3.2 Software Configuration of the U2000 Server
This topic describes the software that can be configured for the NMS server, including system
software and NMS software.
3.3 Configuration of the U2000 Client
This topic describes the requirements on software and hardware configuration when the
U2000 client runs on the Windows and Solaris OSs.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
3-1
iManager U2000 Unified Network Management System
Product Description
3 Configuration Requirements
3.1 Hardware Configuration of the U2000 Server
This topic describes the hardware configuration requirement of the U2000 server.
Configuration Principles
l
Select proper hardware configurations according to the network scale.
If multiple configuration schemes can meet the requirements of the current network scale,
determine the specific hardware configurations according to the requirements of customers.
Configuration Requirements
Table 3-1 Configuration requirements of the U2000 servers that manage networks of different
scales
Network Scale
Small-scale
network: less than
2000 equivalent
NEs
Medium-scale
network:
2000-6000
equivalent NEs
Large-scale
network:
6000-15000
equivalent NEs
PC Server
(Windows)
HP DL380G6 (CPU:
2 x Xeon quatri-core
2.0 GHz or later;
memory: 8 GB; hard
disk: 5 x 146 GB)
HP DL580G5 (CPU:
4 x Xeon quatri-core
2.13 GHz or later;
memory: 16 GB;
hard disk: 4 x 146
GB)
Server (Solaris)
Sun T5220 (CPU: 4C
x 1.2 GHz; memory:
16 GB; hard disk: 6 x
146 GB)
Sun T5220 (CPU: 8C
x 1.4 GHz; memory:
32 GB; hard disk: 6 x
146 GB)
Sun M4000 (CPU: 4
CPU x 2.53 GHz
(quatri-core);
memory: 32 GB;
hard disk: 2 x 146
GB) + disk array
Server Type
Table 3-2 Recommended configurations of the disk array
Hardware Configuration Item
Capacity
OceanStor S2600
6 x 300 GB
You need to determine hardware configurations according to the network scales and the
management capacities of the NMSs based on different hardware platforms.
3-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
3 Configuration Requirements
NOTE
If the HA system is applied, you need to multiply the hardware quantity by 2. For example, if the current
large-scale network applies the HA system, the following hardware requirements need to be met:
l
Two M4000s and two OceanStor S2600s.
3.2 Software Configuration of the U2000 Server
This topic describes the software that can be configured for the NMS server, including system
software and NMS software.
Configuration Principles
The software for the U2000 server is as follows:
l
System software: It includes the operating system software and database software. To select
the required system software, see 3.1 Hardware Configuration of the U2000 Server.
High availability software: It refers to the Veritas software that is applicable to only the
high availability system.
NMS software: It refers to the software developed by Huawei. The NMS software in this
document refers to the U2000 software.
Configuration Requirements
The U2000 can run on multiple OSs, including Windows, Solaris. Table 3-3 lists the
configuration standards of the system software.
Table 3-3 System software of the U2000
Item
Software
Platform
Software
Type
Version
Supported OS
Language
Delivered
software
platform
x86 (Windows
32 bit)
OS
Windows
Server 2003 R2
Enterprise +SP2
Chinese
SPARC (Solaris
64 bit)
Compatible
software
platform
Issue 05 (2010-11-19)
x86 Windows
(32 bit)
Database
SQL Server
2000 Standard +
SP4
OS
Solaris 10
(10/08) +
Huawei Patch
9.0.1
Database
Sybase 15.0.3
with EBF16476
+ EBF16548
OS
Windows
Server 2003
Standard
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
English
3-3
iManager U2000 Unified Network Management System
Product Description
3 Configuration Requirements
Item
Software
Platform
Software
platform no
longer
supported
Software
Type
Version
Database
SQL Server
2000 Standard
SPARC (Solaris
64 bit)
OS
Solaris 10
Database
Sybase 12.5
x86 Windows
(32 bit)
OS
Windows 2000
Server
Database
MS SQL Server
7.0 or SQL
Server 2000
OS
Solaris 8
Database
Sybase 12.0
SPARC (Solaris
32 bit)
Supported OS
Language
High Availability Software
The high availability system of the U2000 can be deployed on the Windows, Solaris OSs with
the high availability software being Veritas. Table 3-4 shows the Veritas software versions in
each platform.
Table 3-4 High availability software
Platform
High Availability Software
Solaris
l Delivered configurations: Veritas 5.1
l Compatible configurations: Veritas 5.0MP3+RP2 and Veritas 4.1
l Configurations no longer supported: Veritas 4.0 and earlier versions +
Watchman scheme
Windows
Delivered configurations: Veritas 5.1
Software Configurations of the U2000
The NMS software, namely, the U2000 server software, can be installed through the installation
DVD or the installation package.
3-4
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
3 Configuration Requirements
Table 3-5 Software Configurations of the U2000
Configurat
ion Item
Typical Configuration
U2000
software
Installation DVD or installation software package
NOTE
If you install the server software through the software package, prepare a proper software
package according to the components to be installed.
3.3 Configuration of the U2000 Client
This topic describes the requirements on software and hardware configuration when the
U2000 client runs on the Windows and Solaris OSs.
The U2000 client can be installed on both Windows and Solaris. Currently, it cannot be installed
on SUSE Linux.
It is recommended that the U2000 client is installed on Windows.
Table 3-6 shows the hardware configuration and software configuration.
Table 3-6 Hardware and software configuration requirements of the U2000 client
Platform
Hardware Configuration
Software Configuration
Windows
l Recommended
configuration: Intel E5200
(dual-core) (2.5 GHz or
greater); memory (2 GB or
greater)
Recommended OS:
l Lowest configuration: Intel
E2140 (dual-core) (1.6 GHz
or greater); memory (2 GB
or greater)
l Windows Vista Business with SP1
Sun T5220
Solaris 10 (10/08) with Huawei Patch
9.0.1
Solaris
Issue 05 (2010-11-19)
l Windows XP Professional SP3
Compatible OS:
l Windows XP Professional SP3
l Windows 7 Ultimate (64-bit version)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
3-5
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Networking and Application
About This Chapter
The U2000 provides a centralized network-wide management solution to transport, access, and
IP networks. In addition, the U2000 provides standard external interfaces to integrate with the
operations support system (OSS), thereby meeting the management requirements of large-scale
networks.
4.1 Deployment Mode
You can select a proper deployment mode according to the network scale and deployment
requirements.
4.2 Networking Mode Between the U2000 and NEs
The U2000 adopts the widely used C/S architecture. In such architecture, the client and the server
communicate through the LAN or wide area network (WAN). The U2000 server communicates
with its managed NEs in inband or outband networking mode.
4.3 Application Scenarios of U2000 Management
This topic describes typical application scenarios of U2000 management.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-1
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
4.1 Deployment Mode
You can select a proper deployment mode according to the network scale and deployment
requirements.
The U2000 supports the HA system (Veritas hot standby) to ensure the high availability (HA)
of the system.
Table 4-1 provides information about the deployment modes of the U2000.
Table 4-1 Deployment modes of the U2000
NMS
Deployment
Solution
Supporte
d
Platform
Requirem
ent on
Disaster
Recovery
Networki
ng
Complexi
ty
Maximum Network Scale
Centralized
deployment
scheme for a
single-server
system
l Windo
ws
Low
Simple
l The Windows-based
system supports a
medium-scale network
(2,000 to 6,000 equivalent
NEs).
l Solaris
l The Solaris-based system
supports an ultra-largescale network (15,000 to
20,000 equivalent NEs).
Centralized
deployment
scheme for an
HA system
l Windo
ws
High
Simple
l Solaris
l The Windows-based
system supports a
medium-scale network
(2000 to 6000 equivalent
NEs).
l The Solaris-based system
supports an ultra-largescale network (15,000 to
20,000 equivalent NEs).
4.1.1 Centralized Deployment of a Single-Server System
In the centralized deployment mode of a single-server system, there is only one U2000 server
on which all processes run. The U2000 server supports communication with and operations on
multiple clients. Centralized deployment is applicable to small- and medium-scale networks
because the deployment scheme is simple and requires low costs.
4.1.2 Centralized Deployment of an HA System
In the centralized deployment mode of an HA system, the servers at the primary and secondary
sites form an HA system and the data is synchronized in real time between the servers. When
the server at the primary site is faulty, applications are switched to the server at the secondary
site automatically to continue monitoring networks and ensure system running without
interruption.
4-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
4.1.1 Centralized Deployment of a Single-Server System
In the centralized deployment mode of a single-server system, there is only one U2000 server
on which all processes run. The U2000 server supports communication with and operations on
multiple clients. Centralized deployment is applicable to small- and medium-scale networks
because the deployment scheme is simple and requires low costs.
The single-server system is deployed on Windows or Solaris, and supports the networking
scheme of a single server and multiple clients, the clients and the server are connected through
LAN or WAN, as shown in Figure 4-1.
Figure 4-1 Centralized deployment of the single-server system
NMS Client n
NMS Client
......
......
NMS Server
4.1.2 Centralized Deployment of an HA System
In the centralized deployment mode of an HA system, the servers at the primary and secondary
sites form an HA system and the data is synchronized in real time between the servers. When
the server at the primary site is faulty, applications are switched to the server at the secondary
site automatically to continue monitoring networks and ensure system running without
interruption.
The centralized HA system can be deployed on the Windows or Solaris platform. There is only
one server at each of the primary and secondary sites. Figure 4-2 shows an example network.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-3
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Figure 4-2 Centralized deployment of the HA system
Primary Site
Ethernet Port
Secondary Site
Diskarray (Optional)
Diskarray (Optional)
Router
Router
Switch
Ethernet Port
Switch
DCN
GNE
NMS Client
4.2 Networking Mode Between the U2000 and NEs
The U2000 adopts the widely used C/S architecture. In such architecture, the client and the server
communicate through the LAN or wide area network (WAN). The U2000 server communicates
with its managed NEs in inband or outband networking mode.
4.2.1 Inband Networking Mode
In inband networking mode, the U2000 uses the service channels that are provided by the
managed equipment to transmit messages for network management and manage the network.
The messages are transmitted between the U2000 and the equipment through the service
channels of the managed equipment.
4.2.2 Outband Networking Mode
In outband networking mode, the U2000 uses the communication channels that are provided by
the equipment other than the managed equipment to transmit messages for network management
and manage the network. Generally, the management interface on the control card of the
managed equipment functions as the access interface.
4.2.1 Inband Networking Mode
In inband networking mode, the U2000 uses the service channels that are provided by the
managed equipment to transmit messages for network management and manage the network.
The messages are transmitted between the U2000 and the equipment through the service
channels of the managed equipment.
Figure 4-3 shows an example network in inband networking mode.
4-4
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Figure 4-3 Example network in inband networking mode
Networking Description
The equipment managed by the U2000 is all connected to the managed network. The U2000
needs to be connected to only the nearby equipment on the managed network. After configuring
the related routes, you can manage all the equipment on the network.
The way of connecting the U2000 with the managed network depends on the distance between
the U2000 and its nearby equipment. If the U2000 and its nearby equipment are in the same
telecommunications room, you can connect them in LAN mode. If the U2000 and its nearby
equipment are far from each other, you can connect them in private line mode. In this case, the
private line mode is similar to the outband networking mode.
l
Networking advantages: The inband networking mode is flexible and cost-effective. It does
not need extra equipment.
Networking disadvantages: When a fault occurs in the network, the communication channel
between the U2000 and its managed network is broken. As a result, you cannot maintain
the managed network on the U2000.
4.2.2 Outband Networking Mode
In outband networking mode, the U2000 uses the communication channels that are provided by
the equipment other than the managed equipment to transmit messages for network management
and manage the network. Generally, the management interface on the control card of the
managed equipment functions as the access interface.
In outband networking mode, the U2000 can be connected to the managed equipment in multiple
ways. For example, the U2000 can be connected to the managed equipment through the data
communication network (DCN), E1 lines, or routers. This topic considers the DCN as an example
to describe how the U2000 manages equipment. Figure 4-4 shows an example network in
outband networking mode.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-5
4 Networking and Application
iManager U2000 Unified Network Management System
Product Description
Figure 4-4 Example network in outband networking mode
Networking description
The equipment managed by the U2000 is all connected to the managed network. The U2000
connects with the equipment on the managed network through the DCN that is made up of other
equipment. In this manner, the U2000 manages the network and equipment.
l
Networking advantages: In outband networking mode, the U2000 is not connected to its
managed equipment directly but is connected to its managed equipment through other
equipment. Compared with the inband networking mode, this mode provides more reliable
equipment management channels. When managed equipment is faulty, the U2000 locates
information about the faulty equipment in a timely manner and monitors the equipment in
real time.
Networking disadvantages: In outband networking mode, the U2000 manages equipment
through a maintenance channel that is independent of the service channel. To provide such
a maintenance channel, you need to construct a network that is made up of extra equipment.
Thus, the cost of constructing the network is high.
4.3 Application Scenarios of U2000 Management
This topic describes typical application scenarios of U2000 management.
4.3.1 Unified Management of Network Products
This topic describes the application of the U2000 for unified management of network products,
that is, typical solutions provided by the U2000.
4.3.2 Single Metro Solution
The U2000 provides perfect solutions for single metro networks in terms of network deployment,
service deployment, and service assurance.
4-6
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
4.3.3 Single Backhaul Solution
All-IP networks become a trend in telecommunications and various mobile data services sprout
out everywhere. With the development of all-IP networks and mobile data services, networks
become complex to maintain because devices are in a huge number and of various types and are
widely used. Therefore, the operation, administration, and maintenance (OAM) system must be
improved with proper OPEX to support the configuration of more complex, flexible and various
services and to provide fault monitoring means.
4.3.4 Single Backbone Solution
The U2000 provides perfect solutions for single backbone networks in terms of network
deployment, service deployment, and service assurance.
4.3.5 Single FAN Solution
The single FAN Solution is the optical access solution that supports a large capacity of
subscribers and long-distance transmission and provides high bandwidth. The U2000 provides
a comprehensive solution for FTTx access devices to manage and maintain the OLT, ONU,
SBU, CBU, and ONT in a centralized manner.
4.3.1 Unified Management of Network Products
This topic describes the application of the U2000 for unified management of network products,
that is, typical solutions provided by the U2000.
l
The U2000 is the platform for managing access, transport, and datacom equipment. It
supports unified management of equipment across domains and also revolutionizes the
vertical management mode to support unified management at the element and network
management layers. In addition, the U2000 supports right- and domain-based management.
This feature enables the U2000 to manage the equipment in each domain respectively to
meet the requirements for managing different networks and departments without
interference.
The U2000 follows the network convergence trend and provides management solutions for
various networking scenarios. The U2000 has a uniform GUI style, which is simple and
convenient for service provisioning. Highly effective service monitoring and service
assurance ensure good user experience and cut the network O&M cost effectively.
The U2000 provides unified northbound interfaces (NBIs), thereby reducing the workload
of OSS integration.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-7
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Figure 4-5 Unified management of network products
Network Deployment
l
Centralized deployment and right- and domain-based management
By controlling the rights of NMS users, the U2000 assigns different management rights to
different users and specifies the objects that can be managed by the users, which ensures
system security.
High availability solution
The U2000 supports the high availability (HA) feature. In this manner, the HA system
monitors the U2000 and automatically implements data protection in real time.
Service Provisioning
The U2000 automatically creates a service after you click the source and sink. This function
ensures that new services can be provisioned quickly. Specifically, the time required for
provisioning services decreases from minutes to seconds and the efficiency of the configuration
on a per-NE basis is improved by 90%.
l
Automatic discovery of end-to-end services.
Provisioning of end-to-end services across domains.
Supports E2E TDM service provisioning and management across traditional microwave
and MSTP networks, which speeds up network deployment and service provisioning
of a large number of microwave services.
Supports E2E packet service provisioning and management across IP microwave and
PTN/Hybrid MSTP networks, which accelerates service provisioning in an IP network.
Supports Ethernet, CES, and ATM service management for PTN, MSTP, RTN, SW,
and NE40 devices, and supports E2E management of MPLS tunnels and PWs, which
push the fixed market towards fixed-mobile convergence (FMC).
4-8
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Supports E2E service (Ethernet, CES, and ATM) provisioning across PTN and CX
networks, and supports E2E management of MPLS tunnels and PWs, which push the
mobile market towards FMC.
Service Assurance
The U2000 supports cross-domain fault location, which greatly improves the efficiency of
rectifying faults and ensures normal running of services.
l
Network-wide equipment is monitored in a centralized manner and the number of alarms
decreases greatly.
Multiple network management systems (NMSs) and teams are combined into one NMS
and one team, thereby greatly improving the efficiency of rectifying faults.
Alarm correlation and intelligent analysis help to accurately locate faults.
Service-oriented alarm management helps to directly locate the base station that is affected
by an alarm and thus the efficiency of rectifying faults is improved by 50%.
Unified fiber management enables the U2000 to clearly display the fiber connections of
network-wide equipment. You can directly locate the equipment that a fiber is connected
to according to an alarm generated on the fiber.
4.3.2 Single Metro Solution
The U2000 provides perfect solutions for single metro networks in terms of network deployment,
service deployment, and service assurance.
Networking Diagram
Under the trend of all-service and super-broadband, the integration of mobile broadband and
fixed broadband speeds up, and operators tend to act as all-service operators. An integrated
super-broadband bearer network helps to quickly and flexibly deploy all services and greatly
reduce the TCO of the network. The construction of such a bearer network becomes a challenge
for operators.
Carrying multiple services is one of the most distinctive features of the Metro Ethernet. Services
such as the high-speed internet (HSI), IPTV, and voice over IP (VoIP) services must be
established on logical channels, as shown in Figure 4-6.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-9
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Figure 4-6 Network management solution for a single metro network
The U2000 provides perfect solutions for single metro networks in terms of network deployment,
service deployment, and service assurance.
Network Deployment
The U2000 must meet the following requirements in the network deployment stage:
l
Automatic discovery of network-wide equipment
The U2000 supports the ability to automatically discover network topologies and links.
Automatic discovery of existing services
The U2000 provides the function of automatically discovering services. With this function,
existing services on the network side can be restored to the U2000 through only two steps.
Visualized service deployment
One-stop configuration: The U2000 provides the tunnel template, L2/L3VPN/VPLS/
PWE3 service template, and QoS policy template for you to perform one-stop service
configuration. These templates predefine 80% parameters, thus reducing the
configuration workload.
Batch deployment: The U2000 supports the ability to deploy services in batches and
the deployment efficiency is increased two to three times.
Automatic computation: The U2000 automatically computes static routes and assigns
labels without any manual intervention.
Service Deployment
The Metro Ethernet often carries heavy service traffic. To adapt to this feature, the U2000
provides the functions of deploying services in batches and quickly creating end-to-end services
to accelerate the deployment process.
4-10
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
End-to-end service management and deployment
The U2000 allows you to quickly establish specific logical channels on physical networks
through GUIs. You can verify the validity of services before deployment and modify
services after the logical channels are established.
Creation of an end-to-end tunnel: After you select the ingress, egress, and transit nodes,
an end-to-end tunnel can be automatically created. After tunnel configuration,
parameter settings can be instantly deployed and both the primary and bypass hop-byhop tunnels can be displayed in the topology view. The U2000 supports the ability to
create forward and backward tunnels at the same time, which facilitates tunnel
management. In addition, the U2000 supports automatic assignment of LSP labels, thus
freeing you from manually assigning labels.
Creation of an end-to-end service: After you select the ingress node, the egress node,
and the tunnel that is used to carry an end-to-end service, the service can be
automatically created. The U2000 can automatically check service configurations and
service connectivity, ensuring that services can be successfully deployed at a time.
Batch management of multicast parameters
The U2000 supports the ability to set, adjust, and verify multicast parameters in batches,
which helps operators to improve the efficiency of IPTV service deployment and helps
users to know the running status of multicast services in real time.
Service Assurance
The U2000 monitors the running status of the network 24 hours a day and 7 days a week in
multiple ways. It can detect network faults or degradation in a timely manner and report end-toend SLA data of the network.
The U2000 provides the following service assurance measures for the broadband bearer network:
l
Reduction of IP alarms
On the U2000, four technologies are used to reduce the great number of IP alarms, and the
number of alarms in typical scenarios is reduced by 85%.
Fault location
The U2000 can display network-wide routes and allows you to accurately diagnose service
faults layer by layer and hop by hop. Service faults can be located to specific NEs and
protocols, and the location duration is reduced from several hours to only several minutes.
Visualized service monitoring
Supports service-oriented visualized service monitoring so that you can directly query
services affected by a specific alarm.
Provides abundant service-based test and diagnosis methods that can be used to quickly
check service connectivity and rectify faults.
Provides service-based functions of displaying performance through GUIs, generating
alerts when performance thresholds are exceeded, and analyzing the performance trend.
Supports layered management so that you can query the network bearing relation in real
time.
Visualized object relation
On the U2000, services are associated with tunnels and tunnels are associated with
routes so that the network bearing relation can be easily identified.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-11
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
When a fault occurs, you can quickly locate and rectify the fault according to the bearing
relation.
l
Fast check of network-wide links
The network scanning tool can automatically compute IP links between equipment,
which improves the network check efficiency.
The status of network-wide links can be monitored through only two clicking
operations.
Different network quality is shown in different colors: red, yellow, and green. This helps
you to easily find network problems and rectify the problems accordingly.
Independent Web-based performance report system (iWeb)
You can log in to the iWeb report system anytime, any place.
You can use the Internet Explorer to log in to the iWeb report system, without upgrading
any client.
The iWeb report system provides various reports, including resource reports,
performance reports, and fault reports.
Real-time alarm monitoring and notification
The U2000 can monitor network faults and the status of equipment and interfaces in real
time. By notifying the related personnel of network faults through SMSs or emails, the
U2000 effectively ensures the normal running of the network.
Performance monitoring 24 hours a day and 7 days a week
The U2000 regularly collects the traffic data of all the links or some key links on the entire
network to provide effective support for network monitoring.
End-to-end SLA monitoring on network nodes
The U2000 regularly collects the SLA data between PEs, between the local CE and PE,
and between the PE and remote CE. With these data, you can discover network degradation,
predict the trend of network running, and optimize the network accordingly.
NOTE
l PE: Provider Edge
l CE: Customer Edge
4.3.3 Single Backhaul Solution
All-IP networks become a trend in telecommunications and various mobile data services sprout
out everywhere. With the development of all-IP networks and mobile data services, networks
become complex to maintain because devices are in a huge number and of various types and are
widely used. Therefore, the operation, administration, and maintenance (OAM) system must be
improved with proper OPEX to support the configuration of more complex, flexible and various
services and to provide fault monitoring means.
All-IP implementation in the mobile bearer network presents the following challenges to the
OAM:
4-12
Unified management of many types of devices: Fibers, microwaves, copper cables, and
Ethernet may function as media to carry services of mobile bearer networks. The
maintenance and management of various types of media challenge carriers.
End-to-end (E2E) service provisioning and QoS assurance: The OAM experience of
traditional SDH and MSTP networks must be inherited for the OAM of all-IP bearer
networks. In addition, all-IP networks need to be merged with connectionless bearer
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
networks. Therefore, carriers need to improve their capabilities in E2E service management
and QoS monitoring.
l
As shown in Figure 4-7, in mobile bearer networks, 2G and 3G services on the base station
(BS) side are transmitted through TDM-E1, IMA-E1, or FE ports and then carried over
E2E PWs. In addition, fixed networks and mobile networks are merged. Specifically, the
CX series equipment carries broadband services and the PTN equipment functions as the
mobile access service gateways at the two ends.
Figure 4-7 SingleBackhaul solution
The U2000 provides solutions to the Network Deployment, Service Provisioning, and Service
Assurance of mobile bearer networks.
Network Deployment
One visit to site without field software commissioning
l
Issue 05 (2010-11-19)
The data communication network (DCN) becomes available automatically and the
U2000 searches for devices remotely. In this case, software commissioning engineers or
customer engineers do not need to visit sites and only hardware installation engineers need
to visit sites to install devices. That is, the devices do not require field software
commissioning.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-13
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Software commissioning is implemented in the network management center (NMC) in a
centralized manner. Hence, customer engineers do not need to visit sites for cooperation
and the duration of software commissioning is reduced by 50%.
Auto-discovery of NEs and links
l
The U2000 automatically searches for all NEs in a specified range and creates the NEs in
the Main Topology.
NEs that are searched out are displayed in a list, which helps you modify and maintain NE
properties in a unified manner.
The U2000 automatically searches for fibers in a specified range and creates the fibers in
the Main Topology.
Fast fiber search and creation. Automatic fiber search helps you create fibers quickly and
correctly and facilitates network construction.
Automatic network-side IP address assignment
l
Automatic IP address assignment on the NE network side: Network-side IP addresses of
NEs can be automatically assigned when fibers are created, which simplifies network
deployment.
Centralized management of IP addresses of NEs: A report is provided to collect the IP
addresses of all NEs on the entire network.
Plug-and-play (PnP) function of devices. After a device is connected to a microwave network,
all devices on the network are searched out and are displayed in a list. The U2000 supports onetouch device creation.
PnP function of cards. A physical card is automatically displayed when the NE Panel is
displayed. The U2000 supports one-touch card creation.
Packet service cutover of PTN equipment. Six steps complete the cutover of packet services. In
the daytime, cutover tasks are created in batches and service data to be cut over are verified. At
night, services are automatically cut over. Automatic cutover reduces the workload and increases
the efficiency.
l
With an increase in services, packet service cutover can quickly balance the service traffic
load between the RNC and base station controllers (BSCs).
To meet the requirements of frequent network adjustment, packet service cutover can
efficiently and correctly adjust services to reduce errors and service interruption.
Automatic WDM optical power commissioning. Automatic WDM optical power
commissioning lowers the skill requirements for deployment engineers and increases the overall
deployment efficiency to a great extent.
l
WDM optical power is automatically adjusted.
Multiple types of fibers are supported, such as G.652, G.653, G.655, and the combination
of G.652 and G.655.
Mainstream WDM equipment from Huawei and many networking modes are supported.
For example, the chains, rings, intersecting rings, and mesh networks are supported.
Wizard-based network adjustment. Wizard-based network adjustment simplifies network
adjustment.
4-14
Nodes can be added to a ring or link and the link capacity can be expanded.
Wizard-based and step-by-step operations increase the efficiency in network adjustment
and lower the skill requirements of OAM engineers.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
The entire process of network expansion can be assured. Specifically, network resources
are checked before network expansion, an automatic service rollback is triggered upon an
expansion failure, and a comparison report is generated after a successful network
expansion. This ensures a high reliability in network expansion and facilitates management.
Service Provisioning
E2E management and service provisioning
l
The E2E packet service provisioning and management of the IP microwave and PTN/MSTP
devices speeds up service provisioning on the IP network.
The E2E TDM service provisioning and management of the traditional microwave and
MSTP devices increases the efficiency in the network deployment and service provisioning
of a huge number of microwave devices.
E2E service provisioning on the network of the PTN equipment and CX equipment is
supported.
E2E packet service provisioning on the network of the PTN equipment and MSTP
equipment is supported.
The network of the OptiX RTN 910/950 and PTN equipment is supported and E2E CES
service provisioning can be performed on the mixed network.
The network of the PTN equipment and CX equipment is supported.
Visualized E2E service provisioning
l
Visualized tunnels.
Visualized protection relationships between tunnels.
Visualized service topologies that can be previewed.
Bulk deployment: The U2000 supports the bulk deployment of Metro Ethernet services to better
meet the requirements of deploying these services in a large number. Bulk deployment speeds
up service deployment.
Fast service provisioning: Configuration is applied to NEs quickly after you specify the source,
sink, and TE constraints. In addition, hops of working and protection trails are displayed in the
topology view.
Quick, accurate, and automatic service restoration. The U2000 provides an automatic service
restoration function that is easy to use. By using this function, only two steps are required to
restore network-side services to the E2E service configuration on the U2000. As a result, services
are quickly provisioned.
l
Services are automatically created after you specify the source and sink and select a routing
policy. In this case, service provisioning is efficient and errors are reduced.
Services can be created in batches, which achieves the fast provisioning of a large number
of services.
The creation and management of E2E services that traverse both microwave and MSTP
equipment are supported, which is unique in the industry.
Service Assurance
Service-based E2E OAM
l
Issue 05 (2010-11-19)
All OAM data are configured based on E2E services and you do not need to configure
OAM data for each node on an E2E trail separately.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-15
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Default parameters are provided and one-touch tunnel configuration is supported. Wizardbased Ethernet OAM is supported and a remote maintenance endpoint point (MEP) is
automatically generated.
Service-based fault diagnosis and fast fault locating
l
E2E service diagnosis is supported and the diagnosis is not required on each node. This
helps to locate a fault quickly.
Fault information is collected during a diagnosis. The fault information helps analyze fault
causes quickly.
Visualized network-wide clock
l
Clocks such as IEEE 1588v2 clocks, synchronous Ethernet clocks, and SDH clocks can be
auto-discovered in the topology view. In addition, network-wide clocks are displayed in a
unified topology view. In the topology view, the clock tracing status and clock
synchronization status are refreshed in real time when a network fault occurs.
The clock status is monitored in real time and the clock alarm, clock tracing status, and
clock protection are displayed in real time.
Server-centered alarm monitoring
l
Relevant alarms are displayed in the E2E service management window when the network
is faulty and affects service provisioning.
Services affected by alarms can be located by a one-touch operation in the alarm
management window.
You can view network-wide alarms on the U2000 client or Web browser after alarms are
generated.
4.3.4 Single Backbone Solution
The U2000 provides perfect solutions for single backbone networks in terms of network
deployment, service deployment, and service assurance.
With the development of carrier-class IP technologies such as MPLS, VPN, and OAM
technologies, carrier-class network technologies based on the IP backbone network become
increasingly mature. The single backbone solution is provided for multi-service core bear
networks, Internet backbone networks, and international gateways. Carrier-class maintenance
must be performed strictly on the IP core network because of its core position on a
telecommunications network. As shown in Figure 4-8, the single backbone network has the
following networking features:
4-16
The core layer uses the dual-plane structure and fully meshed connections are set up
between Ps.
Dual-homing connections are set up between convergence-layer equipment (PEs) and Ps.
Two sets of equipment are deployed on important nodes for backup.
The MPLS VPN is planned in a unified manner to perform isolation between users or
services.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Figure 4-8 Network management solution for a single backbone network
Network Deployment
The U2000 meets the following requirements in the network deployment stage:
l
Automatic discovery of topologies and services
The U2000 supports the ability to automatically discover network topologies, links, and IP
services.
End-to-end reliability
The U2000 supports the abilities to manage mainstream routing protocols such as OSPF,
IS-IS, and BGP, configure IGP (OSPF and IS-IS) fast convergence, and configure BFD,
VRRP, IP FRR, VPN FRR, and MPLS OAM to ensure service reliability.
End-to-end QoS deployment
The U2000 supports QoS deployment in common Diff-Serv mode so that traffic can be
classified according to the service priorities of users. On a PE, complex traffic classification
is performed according to the source IP address, destination IP address, interface, and
VLAN; on a P, only simple traffic classification is performed. In addition, the U2000
supports VPN HQoS deployment to schedule multiple services on a VPN and different
VPN traffic on public TE tunnels.
Service Deployment
The U2000 provides the following functions to effectively and accurately deploy services:
l
Issue 05 (2010-11-19)
Supports the setup of MPLS tunnels.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-17
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Supports the deployment of mainstream services (for example, L2VPN, L3VPN, and
PWE3 services) that are carried over tunnels, provides multiple service configuration
templates and batch configuration templates, and supports the automatic verification of
parameter settings.
Provides simple and user-friendly GUIs to effectively improve service deployment
efficiency.
After a service is created in the topology view, the U2000 immediately displays the creation
and deployment results. All parameters can be set in only one GUI, which quadruples the
configuration efficiency.
Service Assurance
The U2000 provides the following service assurance measures for the single backbone network:
l
Protection switchover in less than 50 ms in case of local faults
You can configure MPLS TE FRR to implement fast route convergence. This ensures that
traffic can be switched in 50 ms after a fault occurs on a node or link on the network. On
an MPLS TE network, after the primary LSP is configured with FRR, traffic is quickly
switched to the bypass LSP if a link or a set of equipment becomes faulty. MPLS TE FRR
is a temporary local protection mechanism. With this mechanism, when the primary LSP
recovers, traffic is switched back to the primary LSP or a new LSP.
Protection switchover in less than 200 ms in case of end-to-end faults
With VPN FRR deployed, when a fault occurs on a remote PE, the local PE can quickly
switch traffic to the remote backup PE in 200 ms. The switching duration is irrelevant to
the number of routes on the private network.
Real-time alarm monitoring and notification
The U2000 can monitor network faults and the status of equipment and interfaces in real
time. On the U2000, the status and severities of equipment alarms are identified by colors
of nodes in the topology view. Maintenance engineers can quickly locate alarm-affected
services from specific equipment alarms. By notifying remote users of network faults
through SMSs or emails, the U2000 ensures the timely processing of network faults.
Performance monitoring 24 hours a day and 7 days a week
The U2000 periodically collects the key performance indicators of networkwide links or
specified links and dynamically displays the network running status, providing important
references for locating network faults. The U2000 provides support for network monitoring
by regularly collecting the traffic data on network-wide links or important links.
End-to-end SLA monitoring on network nodes
The U2000 regularly collects the SLA data between PEs, between the local CE and PE,
and between the PE and remote CE. With these data, you can discover network degradation,
predict the trend of network running, and optimize the network accordingly.
Layered fault diagnosis and location
After a fault occurs, the U2000 analyzes the tunnel associated with the specific service and
the route associated with the tunnel, and then diagnoses the service according to different
network layers to accurately locate the faulty point (equipment, port, or service) and the
causes of the fault for the purpose of troubleshooting.
4.3.5 Single FAN Solution
The single FAN Solution is the optical access solution that supports a large capacity of
subscribers and long-distance transmission and provides high bandwidth. The U2000 provides
4-18
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
a comprehensive solution for FTTx access devices to manage and maintain the OLT, ONU,
SBU, CBU, and ONT in a centralized manner.
In the FTTx access solution, a single fiber is used to provide voice, data, and video services. The
FTTx access solution meets the networking requirements for the fiber to the curb (FTTC), fiber
to the building (FTTB), fiber to the home (FTTH), base station transmission, IP private line
interconnection, and wholesale services. Figure 4-9 shows the networking application of the
FTTx access network management.
Figure 4-9 Networking application of the FTTx access network management
Network Deployment
In an FTTx network, the U2000 provides the ONU predeployment and remote acceptance
functions. By using the functions, you can improve the ONU deployment efficiency and reduce
the operational expenditure (OPEX).
l
The U2000 provides the ONU predeployment function. Before powering on an ONU, create
a corresponding virtual NE and configure service data on the U2000. After you power on
the ONU, the U2000 automatically applies the preset configuration to the ONU to complete
the service deployment. Therefore, the network predeployment and device installation can
be started at the same time. In this way, the time required for network construction is
reduced by half.
The U2000 provides the function of predeploying NEs by means of a sheet. By using this
function, you can import data of NEs to the U2000 in batches, thus installing the devices
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-19
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
without software commissioning and performing remote acceptance. Engineers only need
to visit a site once. The plug and display (PnP) feature of the ONU is implemented.
Therefore, the deployment efficiency is greatly improved, and the network construction
cost is reduced.
l
The U2000 provides flexible authentication that works together with the preconfiguration
function to implement the PnP of the ONU. In this way, the installation cost is greatly
reduced. After you replace an ONU with a new one upon a fault, you only need to enter
the authentication information. Then, the U2000 automatically applies the configuration
data of the faulty ONU to the new ONU. You do not need to re-configure the new ONU.
The U2000 provides the remote acceptance function for the ONU. Specifically, the
U2000 automatically applies the preconfiguration data after the ONU goes online and
implement the remote service acceptance, if you create an acceptance task for the ONU
when it is offline.
The U2000 provides a solution to quick ONU deployment. With the solution, engineers only
need to visit a site once and complete the ONU deployment in five steps as follows:
1.
Plan data: With the Excel-based plan tool, you can easily copy and paste data. This function
is applicable to the configuration of a large amount of data.
2.
Perform offline deployment: Import Excel sheets that contain planned data to the U2000
and complete the offline pre-provisioning of services.
3.
Install ONUs on site: Install ONUs without software commissioning on site.
4.
Activate services: Power on ONUs. The PnP features of the ONUs take effect.
5.
Perform remote acceptance: Engineers do not need to visit the site. Instead, NEs
automatically report acceptance results without manual intervention.
Figure 4-10 shows the FTTx predeployment flow.
Figure 4-10 FTTx predeployment flow
4-20
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Service Provisioning
The U2000 provides the following three convenient and fast service provisioning means. With
these means, you can fast provision the configuration data of FTTx NEs regardless of whether
the OSS is interconnected with the EMS.
l
Automatic provisioning upon interconnection with the OSS:
The U2000 provides standard and open northbound interfaces (NBIs) that implement fast
interconnection with the OSS for the FTTx solution.
Sheet-based service provisioning:
The U2000 provides the convenient and fast predeployment for ONUs and preconfiguration
for services in the FTTx solution. With this function, the U2000 automatically provisions
services and thus reduces costs in labor.
FTTx service provisioning template:
The U2000 provides templates for provisioning FTTx services. You can customize service
provisioning templates for different subscribers. With such a template, you can implement
the one-touch service provisioning. In this way, the efficiency and correctness of service
provisioning are greatly improved.
Service Assurance
l
FTTx fault diagnosis:
By using the traditional method, you need to locate a subscriber fault part by part. In
addition, you need to locate faults of different types in different user interfaces for function
modules. Those user interfaces are not integrated and thus you need to frequently switch
between the user interfaces. As the FTTx is used more widely, access fault diagnosis
becomes more important. The U2000 provides the FTTx fault diagnosis function. With this
function, you only need to enter the object to be diagnosed and then perform one-touch
fault diagnosis. Figure 4-11 and Figure 4-12 show the fault diagnosis of FTTx services.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-21
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Figure 4-11 FTTx fault diagnosis (1)
Figure 4-12 FTTx fault diagnosis (2)
Root cause identification upon an FTTx alarm:
With this function, you can quickly and correctly identify the cause why an ONU is
unreachable. The cause can be identified as a backbone fiber fault, a branch fiber fault, or
4-22
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
power-off of an ONU. In this way, the orders for useless field jobs are reduced.Table 4-2
shows how to identify the cause of a fault by means of the alarm-based root cause
identification.
Table 4-2 Relationships between faults and their causes that are identified by means of the
alarm-based root cause identification
Cause
Alarm Reported
From the OLT
Alarm Reported
From the ONU
U2000 Alarm
Backbone fiber cut
LOS alarm without
the ONU ID
None
When the OLT
reports the LOS
alarm for the PON
port, the U2000
determines that the
backbone fiber
connected to the
PON port is faulty.
Branch fiber cut
LOSi alarm with the
ONU ID
None
When the OLT
reports the LOSi
alarm with the ONU
ID, the U2000
determines that the
branch fiber
connected to the
ONU is faulty.
ONU power-off
Power-off alarm
with the ONU ID
Dying gasp alarm
When the OLT
reports the poweroff alarm with the
ONU ID, the
U2000 determines
that the ONU is
powered off.
PnP (plug and play) of the MDU after replacement:
When an MDU is faulty, you need to locate the fault and recover services quickly. It is time
consuming to locate and troubleshoot an internal fault in the MDU. Therefore, it is
recommended that you directly replace the faulty MDU and save and repair faulty MDUs
in a centralized manner. The U2000 provides the PnP function of the MDU. With this
function, you only need to rebind the MAC address or SN of the MDU on the U2000 and
then the U2000 automatically applies the configuration and NE software version to the
MDU. You need configure the MDU neither on site nor on the OSS.Figure 4-13 shows
the implementation of the PnP function after replacement.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-23
4 Networking and Application
iManager U2000 Unified Network Management System
Product Description
Figure 4-13 PnP function of the MDU after replacement
Dual homing protection at the PON port:
As the split ratio increases, the number of subscribers connected to a PON port increases.
The dual homing protection at the PON port is provided to fast recover services when the
backbone fiber between the PON port and the splitter is faulty. The U2000 supports the
dual homing protection of type B at the PON port. When the active fiber connected to the
OLT is faulty, the U2000 automatically switches the services to the standby fiber. This
solution improves the disaster tolerance capability of the OLT. Figure 4-14 shows the
implementation of the dual homing protection at the PON port.
Figure 4-14 Implementation of the dual homing protection
4-24
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
4 Networking and Application
Fast service cutover at the PON port:
The PON port on a live network is not pluggable. When an PON port or card is faulty or
the network is adjusted, you can delete the faulty PON port, create an EPON port or card,
and then add all MDU data to the new port or card to implement batch data migration. In
this case, the data configuration is complex and relevant services will be interrupted for a
long period of time. The U2000 provides the service cutover function. When a PON port
of an OLT is faulty, disconnect the fiber from the faulty PON port and connect the fiber to
an idle PON port of the same OLT. Then, duplicate the configuration data of the faulty
PON port to the idle PON port. That is, you migrate the configuration of the MDUs
connected to the PON port to the idle PON port. In this manner, relevant services fast
recover.Figure 4-15 shows the implementation of the dual homing protection.
Figure 4-15 Implementation of the fast service cutover
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
4-25
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Basic Functions
About This Chapter
The U2000 provides all management functions at element management layer and network
management layer.
Figure 5-1 shows the basic functions of the U2000.
Figure 5-1 Basic functions of the U2000
Security
management
Security
management policy
Right- and domainbased management
NE user
management
Security of NE
access
NE license
management
Topology
management
Subnet
management
NE management
Card
management
Link
management
Fault
management
Performance
management
Network
management
Alarm severity
and status
Performance
handling process
MSTP network
management
Network-wide
alarm monitoring
Monitoring template
management
WDM network
management
Alarm
statistics
Monitored instance
management
RTN network
management
Alarm handling
Performance
data viewing
PTN network
management
Remote alarm
notification
Data lifecycle
management
Router and switch
network management
Network performance
monitoring
Security network
management
Alarm correlation
analysis
Access network
management
5.1 Overview of Functions and Features
This topic presents an overview of functions and features of the U2000.
5.2 Security Management
This topic describes how to implement security management by managing users, login, and the
authorization of right- and domain-based operations, ensuring the security of the U2000.
Meanwhile, the security management supports the log management in terms of the login,
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-1
5 Basic Functions
iManager U2000 Unified Network Management System
Product Description
operations, and running, and supports the HA scheme and data backup to achieve an excellent
security solution.
5.3 Topology Management
In topology management, the managed NEs and their connections are displayed in a topology
view. You can learn the network structure and monitor the operating status of the entire network
in real time by browsing the topology view.
5.4 Alarm Management
When an exception occurs on a network, the U2000 needs to notify maintenance engineers of
the exception in a timely manner, so that the maintenance engineers will recover the network
efficiently.
5.5 Performance Management
The performance of a network may deteriorate because of internal or external problems and
faults may occur. The performance management function enables you to detect the deteriorating
tendency in advance and solve the potential threats so that faults can be prevented.
5.6 Inventory Management
The U2000 supports unified inventory management of physical resources and service resources
on the entire network. On the U2000, you can quickly and clearly view information about various
resources network-wide. The inventory information serves as a reference for service planning
and expansion planning.
5.7 Log Management
Logs record the information about operations performed on the U2000 and important events that
occur in the U2000. The U2000 allows administrators to query and save logs and collect statistics
on logs periodically. This facilitates detection of unauthorized logins and operations and fault
analysis. Specifically, by browsing and collecting statistics on logs, you can query the client
from which a U2000 user logs in to the U2000 server and query the operations performed by
the user after login. You can also dump and print logs. Logs also can record operations that the
OSS performs on NEs through NBIs.
5.8 Database Management
Database management involves the management of NE databases and U2000 databases, and
maintenance of data consistency between the U2000 and NEs.
5.9 NE Communication Parameter Management
The U2000 communicates with managed NEs successfully only after you correctly set the
connection parameters of the U2000 and the managed NEs.
5.10 DCN Management
DCN management is applicable to MSTP, WDM, microwave, submarine cable NEs.
5.11 NE Software Management
The NE software management module (called DC) is an independent subsystem of the U2000
and it is used to manage software and data on NEs. The DC enables you to back up NE data and
upgrade or downgrade NE software.
5.12 Report Management
The U2000 provides reports about alarms, logs, and resources. You can print the required data
or save the data as a file when viewing it. The reports in tabular format can be filtered by
equipment type and saved in XLS, TXT, HTML, or CSV files.
5.13 System Monitoring
The U2000 provides a GUI-based system monitoring tool, which is used to manage the
U2000 and query the system information.
5-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
5.1 Overview of Functions and Features
This topic presents an overview of functions and features of the U2000.
Table 5-1 Overview of functions and features of the U2000
Issue 05 (2010-11-19)
Function
or
Feature
Description
Unified
network
managem
ent
The U2000 provides the unified GUI-based management of Huawei NEs in the
transport, IP, and access domains. It is a unified network management system
(NMS) that offers comprehensive functions in managing NE alarms, network
alarms, security, performance, topology, logs, inventories, reports, and
databases. This function meets the requirements of network convergence and
rapid development of customer services.
Centraliz
ed task
managem
ent
Centralized task management is an NMS task management mechanism that
manages and coordinates all scheduled tasks in a unified management GUI. Two
types of tasks are managed in the centralized task management: system scheduled
tasks (periodic) and custom scheduled tasks (one-off). The two types of tasks
can run automatically at a scheduled time and users can set parameters and
browse the task status, progress, and results.
NE
template
managem
ent
NE template management allows users to bulk configure NEs by means of
duplication, which makes NE configuration faster and easier. After a template is
referenced in NE configuration management, NE resources are assigned
automatically with parameter values in that template. This avoids tedious and
labor-intensive configuration.
NE data
configura
tion and
managem
ent
In NE data configuration, the U2000 supports bulk configuration of NE services
by using configuration templates, importing data sheets, and loading
configuration files. In data management, the U2000 supports the backup,
restoration, and synchronization of NMS data and NE data. With this function,
services can be provisioned quickly in the GUI.
License
managem
ent
NE license management allows users to query, apply for, install, and adjust NE
licenses (in case of capacity change and server change). By setting NE licenses,
users can perform functions as required. NE licenses also controls the validity
periods of and functions available to NEs. Users can view the status of NEs and
make adjustment accordingly in license management.
Client
auto
update
(CAU)
The CAU function enables the U2000 client to upgrade automatically through
the Internet provided that the U2000 server functions properly and communicates
successfully with the U2000 client.
Check
after the
upgrade
The U2000 can be upgraded smoothly without service interruption. After the
upgrade, the NE status, basic services, and routing relationships are checked and
a check report is generated. This helps to ensure the normal running of major
services immediately after the upgrade and achieve timely detection of issues
such as data loss.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-3
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Function
or
Feature
Description
Online
Help
The Online Help is displayed if users press F1 when using the U2000. It provides
comprehensive help information and supports fast searches for information. The
help information is also available in offline mode.
5.2 Security Management
This topic describes how to implement security management by managing users, login, and the
authorization of right- and domain-based operations, ensuring the security of the U2000.
Meanwhile, the security management supports the log management in terms of the login,
operations, and running, and supports the HA scheme and data backup to achieve an excellent
security solution.
Figure 5-2 shows the overview of security management.
Figure 5-2 Security management overview
5-4
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
NOTE
This section mainly describes the NMS user security.
l For the security solution to the log management, see Log Management.
l For the U2000 HA scheme, see Deployment Mode.
l For the backup and restoration of the database, see 5.8 Database Management.
l For details about the firewall security policy, system enhancement policy, OS and database security
policy, and data transmission security policy, see chapter "Security Planning" in the iManager U2000
Planning Guide
User Management
This feature is to assign NMS users the appropriate rights for management and maintenance
functions according to the O&M requirements when NMS users are planned.
l
User management: The U2000 uniquely identifies the login, operation, and management
rights of NMS users according to user names and passwords. Only one default user, user
admin, is provided after the U2000 is installed. User admin is a superuser and has all
operation and management rights. Other users are directly or indirectly created by user
admin.
The U2000 supports the creation, modification, and deletion of users.
The creation of users involves setting detailed information about users, the user group
to which a user belongs, the management domains, the operation rights, and the ACL.
User group management: The U2000 supports the creation, modification, and deletion of
user groups. The U2000 supports the function of creating a user group to manage users that
have the same rights and to bulk manage rights of NMS users, which reduces management
costs. After the management attributes of a user group are set and a user is added to the
user group, the user has all rights of the user group. A user can be added to multiple user
groups. In this case, the user has all the rights of the user groups as well as the rights that
are assigned to the user. The U2000 provides five default user groups: security management
group, operator group, administrator group, monitor group, and maintainer group.
Right Management
A right defines the operations that can be performed on managed objects. Different users have
different operation rights over different managed objects. The right elements include managed
objects and operation rights, as shown in Figure 5-3.
Figure 5-3 Right
Right management
Managed
objects
Operation rights(login,
operation, querying)
After NMS users are planned, the users can perform operations on NEs only after rights are
assigned to them.
l
Issue 05 (2010-11-19)
Management domain rights define the objects that can be managed by users or user groups,
and the range of the configuration data. For example, if user A is not authorized to manage
equipment C and object set D, equipment C and object set D are invisible to user A in the
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-5
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
topology view. An object set is a collection of multiple pieces of equipment. The U2000
supports the creation, modification, and deletion of object sets.
l
Operation rights define the operations that a user can perform. When multiple users manage
the same device or object set, they have different operation rights over the device if different
operation rights are assigned to them. An operation set is a collection of multiple rights.
Operation right management is implemented by managing the operation sets or specific
rights. If operation sets are assigned to users or user groups, they have rights that the
operation sets include. The U2000 supports the creation, modification, and deletion of
operation sets.
The U2000 also supports right- and domain-based management. Only the operations within
the rights of a user in a certain domain can be performed on NEs of this domain. Only
system administrator and members of the security management group can assign rights and
domains to other users.
Domain-based management refers to dividing equipment nodes, services, or data to
different domains. The administrators of different domains manage different objects
with the domain rights that are assigned to them. Meanwhile, certain NEs can be
assigned directly to a certain user.
Right-based management refers to domain-based authentication. Users and user groups
have different operation rights if they are assigned these rights. After dividing domains
and then dividing rights, the personnel with different duties or positions in the same
domain have different operation rights over different objects in the domain.
User Authentication Management
U2000 provides three types of user authentication management: local authentication, RADIUS
authentication, and LDAP authentication.
l
Local authentication: NMS user management, login authentication, and the security
strategy are all implemented by the U2000 server. Local authentication is the management
method of the login authentication by default. For the details, see Local Authentication.
RADIUS authentication: When a user logs into the U2000, the RADIUS server verifies
and authenticates the login request, and the U2000 assign rights to login users according
the rights that their user group has. For the details, see RADIUS-based Authentication.
LDAP authentication: When a user logs into the U2000, the LADP server verifies and
authenticates the login request, and the U2000 assign rights to login users according the
rights that their user group has. The LADP-based authentication is similar to the RADIUSbased authentication, but the authentication protocols are different. For details, see LDAPBased Authentication.
Local Authentication
In the local authentication mode, user security management ensures the secure running of the
U2000 in multiple aspects, including local user management, right management, password
policy, account policy, and login control.
l
Setting of the password policy
Setting the minimum password length and maximum password length.
Setting the correlation policy between the current password and history passwords,
including the maximum times for password repetition, the number of characters of
history passwords that the current password cannot contain, and whether the password
can be similar to history passwords.
5-6
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Setting the validity period of the password, including the maximum and minimum
period validity of the password, the number of days warning given before the password
expiry.
Setting the rules for the forms of passwords.
l
The account policy involves the account validity period, minimum length of a user name,
automatic unlocking time, maximum number of login attempts, timeout period for a login
or unlocking failure, and user policy of no login within a period.
Login control involves the login mode, the login period control, and the IP address control.
User login mode specifies whether multiple users are allowed to log into the U2000 at
the same time. Usually, multiuser mode is adopted. If you need to perform special
operations on the U2000 server, you can set the user login mode to single-user mode,
avoiding interferences from the operations of other users.
Users can log in to the U2000 only in the specified login period.
The ACL controls the login IP addresses of clients. Users can log in to the U2000 server
only from certain IP addresses. Therefore, even if the user account and the password
are obtained by unauthorized users, these users cannot log in to the U2000 server, and
thus the U2000 security is improved.
RADIUS-Based Authentication
When the RADIUS authentication is adopted, the administrator does not need to create a user
account on the NMS in advance. The user account for logging in to the U2000 is an existing
account that can pass the authentication of the RADIUS server.
When a user enters the user name and password, the security process of the U2000 server sends
the user name and password to the RADIUS server. If the user passes the RADIUS
authentication, the security process learns the user group to which this user belongs, and then
the security process assigns rights to the user according to the operation set policy of the user
group.
NOTE
Before adopting the RADIUS authentication mode, make sure that the name of the user group defined on
the U2000 is the same as that defined in the account database of carriers. In addition, make sure that the
account to be authorized for logging in to the U2000 is added to the corresponding user group.
For the RADIUS-based authentication process, see Figure 5-4.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-7
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Figure 5-4 RADIUS-based user authentication
OSS
Authentication
GUI
Security
NBI
User group
privilege
AAA agent
Security
server
RADIUS
server
User and
user group datebase
U2000 server
U2000 user
LDAP-Based Authentication
As a distributed client/server system protocol, LDAP is adopted in the VPN and WAN to control
the users' access to the network and prevent unauthorized users from accessing the networks.
The LDAP-based authentication mode is similar to the RADIUS-based authentication mode
except for different authentication protocols. Compared with the RADIUS authentication, the
LDAP authentication supports the following features:
l
Supporting common mode (encryption-free), SSL mode, and TLS mode for the
communication between the U2000 and the LDAP server.
Supporting multiple LDAP authentication servers and being compatible with the HA
scheme of the U2000.
For the LDAP-based authentication process, see Figure 5-5.
5-8
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Figure 5-5 LDAP user authentication
OSS
Securiyt
NBI
User group
database
AAA agent
Security
server
LDAP server
User and
user group
database
U2000 server
U2000 user
Session Management
l
If a user does not perform operations on the client temporarily, the user can lock the client
manually or set the time for the U2000 to automatically lock the client to prevent
unauthorized operations. To unlock the client, the user must enter the password of the
current login user or use the account of the administrator.
The members of the administrator group can monitor sessions and operations of common
U2000 users, forcibly log out U2000 users, and unlock U2000 users.
The U2000 can automatically detect and clear invalid sessions.
Client lockout: If a user does not perform operations on the client temporarily, the user can
lock out the client or set the time to automatically lock the U2000 client to prevent
unauthorized operations. To unlock the client, the user must enter the password of the
current login user or use the account of the administrator.
5.3 Topology Management
In topology management, the managed NEs and their connections are displayed in a topology
view. You can learn the network structure and monitor the operating status of the entire network
in real time by browsing the topology view.
The U2000 has the Physical Root, Clock View, Tunnel View, and Custom View. Required
information can be easily learned in different views, which enables you to learn and monitor the
operating status of the entire network conveniently.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-9
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
The U2000 offers service topology management for various end-to-end services, for example,
VPLS services, PWE3 services, L3VPN services, E-AGGR services, and tunnel services. By
means of the service topology, users can view and configure services easily.
Topology View and Its Functions
The topology view of the U2000 consists of a navigation tree on the left side and a view on the
right side. The navigation tree shows the network hierarchy. The view displays the objects at
different coordinates on the background map, which helps to identify the locations of deployed
objects.
Figure 5-6 shows the topology view of the U2000 and its functions.
Figure 5-6 Topology view and its functions
1
13
5-10
12
11
10
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
1: Name of the network
management system
You can change the name of
the network management
system (NMS) as required.
5 Basic Functions
2: Menu bar
3 and 4: Toolbar buttons
With submenus, you can
perform operations on the NMS
and NEs, such as configuring
and managing tasks.
l 3: You can click a
button to perform a
simple task quickly.
For example, exiting an
NMS, locking a
terminal, logging out of
an NMS, launching the
NE Explorer, viewing
alarms, and viewing
performance data.
l 4: You can click a
button to perform a
simple task quickly on
the Main Topology. For
example, zooming in,
zooming out,
refreshing, saving,
locking, or unlocking
views, showing or
hiding navigation trees,
and searching for
objects.
5: Alarm button bar
6: Filter tree and legend
Alarms of different severities
are displayed in different
colors.
In this area, you can set the
display types of the objects in a
view and view the descriptions
of legends in the view. The
filter tree and legends help you
to locate an object quickly.
The number displayed on an
alarm button indicates the
number of the alarms of the
corresponding severity. You
can click a button to view the
alarms of the corresponding
severity on the current
U2000. For example,
viewing current alarms and
displaying the alarm panel.
7: Current client time
When an abnormal event
occurs in the U2000, the
color of Abnormal event
indicator is changed from
green to red. You can click
the indicator to view the
current abnormal event on
the U2000.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-11
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
8: Name of the current login
user of the U2000.
11: Coordinates of the
pointer in the Main
Topology.
9: Name and the IP address of
the U2000 server that the
U2000 client currently logs in
to.
10: Physical map
The name of the U2000 server
is the name that you set on the
U2000 client.
In the Main Topology, you
can launch the NE
Explorer, view
performance data, create
NEs, configure NE data,
create connections, view
fibers/cables, delete
topological objects, and
view current alarms.
12: Topology navigation tree
13: Network-wide NE
statistics
In this area, all NEs managed by
the U2000 are displayed. Using
this tree, you can locate the
required NE quickly.
In this area, all NEs
managed by the U2000 are
displayed.
You can collect statistics
on the NE types and the
number of NEs of each
type on the entire network.
Alarm Display in the Topology View
In the topology view, alarms are displayed in different colors or icons to indicate different status
of the subnets and NEs. The alarms are displayed with two methods: color-coded display and
small icon display. The default method is the small icon display, as shown in Figure 5-7.
You can choose nodes of different levels from the Physical Root navigation tree, for example,
a subnet, a node, or an NE to browse current alarms.
Figure 5-7 Alarm display in the topology view
The alarm display in the topology view has the following features:
5-12
The color of a topological node indicates the operating status (such as normal, unknown,
or offline) and alarm status of the monitored NE.
When an NE generates multiple alarms of different severities, the color or icon that indicates
the highest alarm severity of these alarms is displayed in the topology view.
When multiple nodes in a subnet generate alarms, the subnet is displayed in the color or
icon that indicates the highest alarm severity of these alarms.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
You can switch to the current alarm window of an NE using the shortcut menu of the NE
node. In addition, you can query the details of current alarms in the NE Panel.
Automatic Topology Discovery
The U2000 provides an automatic topology discovery function to automatically add NEs to the
topology view. Therefore, the operational expenditure (OPEX) is reduced.
The U2000 supports the automatic topology discovery as follows:
l
Bulk creation of NEs
Bulk creation of SNMP/ICMP-based NEs: SNMP/ICMP-based NEs involve the router,
switch, security access NEs. When the U2000 communicates with the preceding NEs
successfully, it can search out the required NEs by IP address or by network segment
and then bulk create these NEs.
Bulk creation of transport/ PTN NEs: Based on the IP address, network segment, or
network service access point (NSAP) address of a GNE, the U2000 automatically
searches out all the NEs that communicate with the GNE and bulk creates the NEs.
Bulk import of NEs: Security GNEs, service monitoring GNEs, and security virtual
network (SVN) series security NEs periodically sends proactive registry messages that
contain the IP addresses of NEs to the U2000 server. With the proactive registry
management, the U2000 bulk creates the NEs after receiving the messages.
Configuring NEs automatically: The U2000 provides the function of configuring autodiscovered NEs (such as PTN NEs) automatically.
Searching for NEs at a scheduled interval: The U2000 searches for NEs of a specified type
in a specified network segment according to the preset conditions at a scheduled interval.
It automatically adds the new NEs to the topology view. NE types are as follows: the
access router, switch, and security NEs.
Creating fibers/cables or links automatically: The U2000 supports the function of bulk
creating fibers/cables and links. It supports the function of bulk searching and adding new
fibers/cables and links to the topology view automatically after a search.
Figure 5-8 Illustration of automatic topology discovery
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-13
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
1.
The automatic topology discovery is implemented step by step through a wizard. The
wizard instructs you to set the parameters required for the automatic discovery, such as NE
type, SNMP parameters, and the IP address range.
2.
After you set the parameters, the U2000 searches for the required NEs in the specified
network segments according to the preset conditions. All NEs from Huawei and other
vendors that meet the conditions are displayed in the topology view. Meanwhile, the basic
configuration data of the NEs is uploaded, which simplifies the configuration of these NEs.
3.
You can stop the automatic topology discovery at any time. If the discovery fails, the cause
is displayed.
Clock View and Its Functions
In the clock view, you can set the NE clocks, query network-wide clock synchronization status,
search for clocks, and traces clocks. The U2000 supports the passive optical network (PON)
clocks synchronous Ethernet clocks, IEEE 1588 v2 clocks, and SDH clocks. In the clock view,
NEs of various types can be displayed, such as the PTN, router, access, MSTP, RTN, and NG
WDM NEs.
Figure 5-9 shows the clock view of the U2000 and its functions.
Figure 5-9 Clock view and its functions
5-14
Discovering the clock topology automatically: The U2000 searches for clock links between
all NEs in the entire network to obtain the clock tracing relationships of all NEs. You can
search for clock links by NE or by clock link type. When the clock source of an NE is
changed, the U2000 performs a search again to renew the clock tracing relationships.
Viewing the clock topology: After the U2000 automatically discovers the clock topology,
you can view the clock tracing relationships in the entire network. To adjust the clock
topology, you can manually create and delete topological nodes and links.
Configuring clocks: In the clock configuration window of the NE Explorer, you can
configure the clocks of the NE. You can configure the following clocks: PON clocks
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
synchronous Ethernet clocks, IEEE 1588 v2 clocks, and SDH clocks. The clock
configuration function varies with NE types.
l
Monitoring the change of clocks: When an NE or a link fails or a switching of clock sources
occurs in a network, the U2000 automatically updates the clock tracing relationships and
the clock synchronization status in the topology view. According to the clock alarms of the
NE whose clock is changed, you can identify the fault.
Switching clocks manually: You can select a clock link and set its clock tracing relationship
as the current clock tracing relationships of the NE.
5.4 Alarm Management
When an exception occurs on a network, the U2000 needs to notify maintenance engineers of
the exception in a timely manner, so that the maintenance engineers will recover the network
efficiently.
Alarm management consists of the following functions:
l
Network-wide alarm monitoring and remote alarm notification enable the U2000 to notify
maintenance engineers of network exceptions in time so that the engineers will rectify faults
quickly and effectively.
Alarm correlation analysis, alarm association (with NEs, ports, or services), alarm masking,
alarm suppression, and maintenance experience base improve the accuracy and efficiency
of alarm processing.
Alarm synchronization ensures the reliability of alarms.
Custom functions such as alarm filtering, alarm redefinition, and time localization meet
individualized requirements in different scenarios.
Alarm Severity
Table 5-2 shows different alarm severities and the handling methods.
Table 5-2 Alarm severity
Issue 05 (2010-11-19)
Alarm Severity
Definition
Handling Method
Critical
A critical alarm indicates a
fault or an event that may
seriously affect an NE or the
entire network, such as a
board failure or a clock board
failure.
Handle a critical alarm
immediately to avoid a
system breakdown.
Major
A major alarm indicates a
fault or an event that may
affect part of a network, such
as a board failure or line
failure.
Handle a major alarm in a
timely manner to avoid loss
of important functions.
Minor
A minor alarm indicates a
general fault or an event
about the functioning of a
board or line.
Minor alarms remind
maintenance engineers of
identifying alarm causes and
rectifying possible faults.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-15
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Alarm Severity
Definition
Handling Method
Warning
A warning alarm indicates a
fault or an event that does not
affect the system
performance and services but
may potentially affect the
service quality of the NE or
resources. Some warning
alarms indicate status
change. For example, when
an NE recovers, a switching
alarm is generated.
Maintenance engineers can
learn the information about
the operating status of the
network and NEs according
to warning alarms and handle
the alarms depending on
actual situations.
Handle different severities of alarms by using different methods. The U2000 supports the
function of redefining the alarm severity so that you can change the severity of a specific alarm
as required. The severity of an alarm needs to be adjusted when the impact of the alarm becomes
larger or smaller.
Alarm Status
l
Alarm acknowledgment and alarm clearance
Alarm acknowledgment: An acknowledged alarm indicates that this alarm has been
handled by a user. An alarm can be acknowledged in the following two ways:
Manual acknowledgment: You can select an alarm from the current alarm window
to acknowledge it.
Automatic acknowledgment: If you enable the automatic alarm acknowledgment,
the U2000 acknowledges an alarm immediately after it is cleared or automatically
acknowledges the alarms that are cleared within the specified time at 01:00 every
day.
Alarm clearance: When you delete an alarm, the alarm is cleared from the NE and the
current alarm library of the U2000. After that, the alarm is moved to the history alarm
library.
Alarm status classification
Based on the acknowledgment and clearance status, alarm status can be classified into the
following types:
Unacknowledged and uncleared
Acknowledged and uncleared
Unacknowledged and cleared
Acknowledged and cleared
NOTE
Acknowledged and cleared alarms become history alarms after a preset period elapses. All nonhistory alarms are current alarms.
Changing alarm states
Changing the clearance status
5-16
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
When the condition triggering an alarm disappears, the NE or the U2000 server recovers.
In this case, the NE or the U2000 server reports a clearance alarm. The alarm state
changes from uncleared to cleared. You can also manually clear an alarm.
Changing the acknowledgment status
If an alarm is acknowledged, it indicates that the alarm will be handled or has been
handled. After the alarm is acknowledged, the alarm state changes from
unacknowledged to acknowledged.
You can unacknowledge an acknowledged alarm if necessary. After the alarm is
unacknowledged, the alarm state changes from acknowledged to unacknowledged.
l
Relationships between alarm states
Figure 5-10 shows the relationships between alarm states and how an alarm changes from
one state to another.
Figure 5-10 Relationships between alarm states
Alarm Reporting and Handling Flowchart
Figure 5-11 shows the alarm reporting and handling flowchart of the U2000.
Figure 5-11 Alarm reporting and handling flowchart
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-17
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Network-Wide Alarm Monitoring
Traditionally, a network is maintained separately by domain. Faults across domains need to be
located manually, which lowers the locating efficiency. The U2000 provides unified means of
alarm monitoring, such as the alarm panel and alarm browsing, which helps users to understand
the operating status of the network in real time. It also provides alarm query templates that are
a collection of common query criteria. You can create different alarm query templates according
to the region, type, and network layer of the device on which an alarm is generated. The alarm
query templates facilitate the query and monitoring of alarms.
The alarm display function is implemented in three different ways: alarm panel display, alarm
bar chart, and alarm query and browsing. Figure 5-12 shows the alarm panel, and Figure
5-13 shows the alarm bar chart.
Figure 5-12 Alarm panel
5-18
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Figure 5-13 Alarm bar chart
Table 5-3 Alarm display functions
Function
Description
Alarm panel
The alarm panel collects statistics on the alarms of managed objects
by severity and displays the number of the alarms of each severity.
The alarm panel provides a summary of system faults and can be
used as a monitoring panel.
Alarm bar chart
The alarm bar chart shows the real-time alarm statistics. The alarm
bar chart displays the alarm statistics collected by the alarm panel.
Querying and viewing
alarms
l Viewing current alarms: Query the fault alarms that are not
handled, that is, unacknowledged or uncleared alarms.
l Viewing history alarms: Query the fault alarms that are handled,
that is, acknowledged and cleared alarms.
l Viewing alarm logs: Query all fault alarms that are reported by
NEs.
l Viewing event logs: Query current abnormal events.
l Setting an alarm query template: Save common query conditions
as an alarm query template. You can directly use the template to
query alarms based on the same query conditions. This function
helps you to view and monitor the required alarms.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-19
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Alarm browsing consists of operations of viewing current alarms, history alarms, alarm logs,
and event logs, and supports multiple custom functions, as shown in Figure 5-14 and Table
5-4.
Figure 5-14 Viewing alarms
Alarm browsing
Dynamic alarm template
Alarm sorting
Alarm details
Alarm color display
Alarm filtering
Alarm cause and handling suggestion
Alarm handling means
Table 5-4 Alarm function
5-20
Function
Description
Dynamic alarm panel
The alarm panel shows the number of the alarms of different
severities of the U2000 client. Pop-ups of the alarm panel or the
blinks of alarm indicators show current alarms. Click the alarm
panel to display the window for viewing alarms.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Function
Description
Alarm filtering
When a large number of alarms exist, you can filter alarms by alarm
name, alarm severity, status, type, last occurrence time segment
and clearance time segment. The alarm filtering function improves
the efficiency of viewing alarms.
You can filter alarms by attributes of alarm sources, such as the
objects of NEs, object groups, and maintenance areas, and create
the required alarm filter templates by customizing the filter criteria.
In this manner, you can select the required alarm filter template to
filter alarms.
Alarm template
The alarm template can be customized. Therefore, you can sort
alarms flexibly as required and locate the required alarms quickly.
Alarm viewing
You can view the alarms relevant to NEs and services on the
U2000 to learn the operating status of the NEs and networks.
l Viewing current alarms: View current alarms of all severities
on the entire network.
l Viewing all current alarms of a specific severity: You can
quickly learn the critical, major, or minor alarms of the entire
network from the alarm icons on the toolbar.
l Viewing the alarms of a specified NE or U2000: You can select
an NE or a U2000 in the Main Topology and quickly learn the
current alarms of the selected object.
l Viewing the current alarms of a trail: In the trail management
window, you can quickly learn the alarms and events of the
managed trails. This function facilitates trail maintenance.
l Viewing history alarms: By viewing all history alarms of the
U2000, you can learn the faults that occurred on the U2000 and
NEs. The history alarm data can be used for long-term
performance analysis.
Alarm query
You can query alarms by object where the alarms are generated,
function type, alarm status, or alarm severity. The query results
can be saved and printed.
Alarm display in color
Alarms of different severities are displayed in different colors in
the alarm list. The colors can be customized.
Alarm display in the
topology view
When an NE reports an alarm, the icon in the upper left corner of
the NE or the color of the NE in the topology view varies with the
alarm severity. You can right-click the NE to query current alarms
of the NE.
Alarm locating
You can select an alarm and locate the topological object where
this alarm is generated. For a physical alarm, you can locate the
board where the alarm is generated in the NE panel.
Alarm sort
You can sort alarms by field and customize the columns displayed
in the alarm list. Alarms can be saved to a file (.txt, .html, .xls,
or .csv) and can be printed.
Customized display
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-21
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Function
Description
Details
You can obtain the details of an alarm, such as the alarm name and
identification information.
Handling suggestion
The handling suggestion provides information, such as the alarm
cause, recovery suggestion, alarm description, maintenance
experience, and cause type.
In the Handling Suggestion area, a link to the corresponding alarm
reference topic in the Online Help is provided. You can click on
Click here to show detail information to display the
corresponding alarm reference topic in the Online Help.
You can view the information about an alarm in the alarm browsing window, including the
severity, name, alarm source, location information, occurrence time, first occurrence time, last
occurrence time, clearance time, acknowledgment time, clearance user, acknowledgment user,
clearance status, acknowledgment status, location, direction, trail domain, alarm reversion,
protection subnet name, alarm plane, trail name, ASON object name, and affected services.
Alarm Statistics
You can quickly learn alarm information by collecting statistics on alarms and analyzing them.
The U2000 can collect statistics on alarms based on the preset conditions. The conditions can
be the name, severity, function type, generation time, alarm status, source of an alarm, or a
combination of the preceding items.
Alarm Masking and Correlation Analysis
l
By using the alarm masking function, you can set the alarm/event masking conditions to
avoid display of a large number of redundant alarms.
While an NE is being repaired, tested, or deployed, the NE may report a large number of
alarms which can be ignored. In this case, you need to mask these alarms so that the
U2000 does not display and save them.
The U2000 provides the following correlation analysis means: alarm/event correlation analysis,
transient alarm analysis, repeated event analysis, alarm/event frequency analysis, and analysis
on duration of acknowledged but uncleared alarms. Figure 5-15 shows the implementation of
alarm correlation analysis.
5-22
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Figure 5-15 Alarm correlation analysis
Correlation Analysis
The Default Correlation and Correlation Analysis windows are provided for a
correlation analysis. In the Default Correlation window, the predefined rules for the
alarm correlation analysis are displayed. These rules can be enabled if required. In the
Correlation Analysis window, the rules for the alarm correlation analysis can be
customized.
Correlative alarms are the alarms whose causes are relevant to each other. One of the
alarms is the root cause.
Various alarms are generated when a certain fault occurs. If non-root alarms are
reported, the fault locating and analysis are affected. You can set the rules for the
correlation analysis on the U2000 according to certain features of correlative alarms,
such as generation time and physical locations where the alarms are generated. In this
manner, the U2000 directly discards non-root alarms that meet the preset conditions,
labels them as correlative alarms, and saves them to a suppressed alarm database, or
downgrades their severities.
Figure 5-16 shows the relationships between a root alarm and its correlative alarms.
The alarm for high memory usage of a service causes the alarm for high memory usage
and the alarm for high CPU usage. The alarm for high CPU usage causes the alarm for
abnormal exit of the U2000 service. Therefore, the alarm for high memory usage of a
service is the root alarm and the rest are the correlative alarms.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-23
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Figure 5-16 Relationships between a root alarm and its correlative alarms
Transient alarm analysis/Repeated event analysis
Transient alarms are the alarms that are cleared twice within the preset period.
If transient alarms are reported continuously within a short period, the NE or services
may be repeatedly switched between the normal state and the abnormal state. To
resolve the problem in time, enable the transient alarm analysis to raise the alarm
severity so that maintenance engineers will pay attention to the alarms. For example,
if an alarm is reported and cleared repeatedly for five times within ten seconds, the
U2000 changes the severity of the alarm to major.
If the repeated alarms generated due to certain faults or under certain circumstances
are redundant to maintenance engineers, lower the alarm severity, sort the repeated
alarms, or directly mask these alarms.
Repeated events are the events that are reported repeatedly within the preset interval.
Alarms or events that are reported repeatedly within a short period due to certain faults
may be redundant to maintenance engineers. For these alarms or events, you can set
analysis rules for transient alarm and repeated events on the U2000. Then, the U2000
displays only the first repeated event or cleared transient alarm and discards the rest.
Alarm/Event frequency analysis
Alarms of the same type that are generated within a period may be relevant to each
other. After you enable the alarm/event frequency analysis, if the number of the same
alarms generated within a period reaches a certain number, it can be concluded that
those alarms are relevant to each other.
After you set rules for the event/alarm frequency analysis, if the number of specified
alarms generated within a specified period exceeds the preset threshold, it can be
concluded that these alarms are relevant to each other. Then, the U2000 handles these
alarms according to the preset method.
Analysis on duration of acknowledged but uncleared alarms
Major alarms are normally cleared within 30 minutes after they are handled. If a major
alarm is not cleared in 30 minutes after it is processed, further actions are required. To
ensure that major alarms are handled in time, enable the analysis on duration of
5-24
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
acknowledged but uncleared alarms. If a major alarm is not cleared in 30 minutes after
it is handled, the U2000 changes the severity of the alarm to critical.
Enable this analysis function for the acknowledged alarms that are not cleared for a long
time. The U2000 changes severities of the alarms to a higher level to remind
maintenance engineers of handling the alarms in a timely manner.
l
Alarm Correlation on NEs
Alarm correlation rules on NEs are an inherent alarm performance monitoring
mechanism of a logical function block of an NE. These rules cannot be modified.
Understanding the monitoring mechanism helps you to correctly analyze and identify
faults, thus improving the maintenance efficiency.
A root alarm is directly caused by an abnormal event or a fault on the network. A root
alarm generally causes correlative alarms whose severities are lower. For example,
when a fiber is cut, the SDH physical interface (SPI) functional module of an optical
board detects the R_LOS alarm (root alarm). Then, the regenerator section termination
(RST) function module of the regeneration section generates correlative alarms, such
as the R_LOF, R_OOF, B1_SD, and B1_EXC. To prevent the generation of correlative
alarms, you can set the preceding alarm correlation analysis rules and enable the alarm
correlation analysis on the NE to suppress correlative alarms. In this manner, the NE
reports only the root alarm R_LOS to the U2000.
Alarm Correlation on the NMS
After you set alarm correlation analysis rules on the U2000 and enable the alarm correlation
analysis, correlative alarms are masked.
CAUTION
l Alarm correlation analysis depends on alarm correlation rules. The rules will affect the
analysis result. Exercise caution when setting the rules.
l The default correlation analysis rules on the U2000 are recommended.
l By default, the alarm correlation analysis is disabled. Manually enable this function if
necessary.
Alarm Dumping and Acknowledgment
Alarm acknowledgment enables you to check whether alarms are handled according to the
acknowledgment status of the alarms. Then, you can handle alarms in a timely manner.
l
Alarm dumping: Automatic dumping and manual dumping of alarms are supported.
Automatic dumping is classified into overflow dumping and periodic dumping.
Alarm acknowledgment: Alarms can be acknowledged manually or automatically.
NOTE
Alarm logs can be saved in various formats, such as TXT, HTML, PDF, CVS, and XLS.
Alarm Synchronization
After communication between the U2000 and an NE recovers from an interruption, or the
U2000 is restarted, some alarms on the NE are not reported to the U2000. The NE alarms on the
U2000 are different from the actual alarms on the NE. In the case, you need to synchronize
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-25
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
alarms. Manual synchronization of alarms ensures that the U2000 displays the current operating
status of the NE correctly.
The U2000 supports the function of synchronizing NE alarms manually or automatically. You
can set the policy for automatic alarm synchronization. After you enable automatic alarm
synchronization, the U2000 automatically synchronizes alarms to ensure alarm consistency
between the U2000 and NEs after the communication between the U2000 and NEs recovers or
the U2000 is restarted. Figure 5-17 shows the implementation of alarm synchronization.
Alarms are synchronized according to the following rules:
l
If an alarm is cleared from an NE but uncleared on the U2000, the alarm will be cleared
from the U2000.
If an alarm is present on an NE but absent on the U2000, the alarm will be added to the
U2000.
Figure 5-17 Alarm synchronization
Alarm Redefinition
The U2000 allows you to redefine the severities of alarms on NEs according to the requirements.
This function changes the alarm severity displayed on the U2000, highlighting only the required
alarms.
Alarm Suppression
The U2000 supports the function of suppressing NE alarms. If you set the status of an alarm to
Suppressed, the NE does not report the alarm.
The difference between alarm suppression and alarm masking is as follows: If you enable alarm
masking, an NE still reports the masked alarm but the U2000 does not receive the alarm. If you
enable alarm suppression, the NE does not report the suppressed alarm. For details, see Figure
5-18.
5-26
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Figure 5-18 Difference between alarm masking and alarm suppression
Various Alarm Notification Means
The U2000 provides various alarm notification means. It can notify maintenance engineers of
alarms at any time from anywhere. Therefore, the maintenance engineers will locate and rectify
faults quickly and effectively.
The U2000 also supports two remote notification means: email and short message service (SMS).
When a fault occurs in a network, the U2000 notifies non-onsite maintenance engineers of the
fault. Then, the maintenance engineers will locate and rectify the fault promptly.
l
Different filter criteria can be set to enable the U2000 to notify maintenance engineers of
only the required alarms.
For the alarms that are cleared within a period (a customized delay), the U2000 does not
notify maintenance engineers of these alarms because they do not affect services any more.
Figure 5-19 shows the alarm notification means.
Figure 5-19 Various alarm notification means
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-27
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Alarm Association
The U2000 supports the function of locating alarms, that is, associating alarms with the
topological object (NE or NE panel) where the alarms are generated. This function improves
fault locating efficiency. Figure 5-20 shows the alarm association function.
Figure 5-20 Alarm association
Alarm association
Alarm source: NE, board,
or port etc
Alarm Maintenance Experience Base
You can obtain the alarm handling information from the alarm maintenance experience base.
This base is a database that stores alarm details. For details, see Figure 5-21.
5-28
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Alarm maintenance experience is summarized and recorded on the U2000 by users during
maintenance. If a similar fault occurs, relevant alarm handling information is available in the
base for reference to achieve quick and efficient alarm handling.
By using the function of importing alarm/event maintenance experience, you can import the
previously exported alarm/event maintenance experience to the U2000.
By using the function of exporting alarm/event maintenance experience, you can export alarm/
event maintenance experience on the U2000 to a file. This makes it easier to view alarm/event
maintenance experience in the file.
Figure 5-21 Alarm maintenance experience base
Alarm Time Localization
The NE that reports an alarm and the U2000 may be in different time zones. For the correct
alarm generation time, the U2000 automatically converts the alarm generation time (expressed
in the NE time) into the local time of the U2000.
The U2000 can display the time when an alarm is generated, acknowledged, cleared, or received
as the local time of the U2000 client or server.
5.5 Performance Management
The performance of a network may deteriorate because of internal or external problems and
faults may occur. The performance management function enables you to detect the deteriorating
tendency in advance and solve the potential threats so that faults can be prevented.
Benefit
NMS provides performance monitoring functions to support performance management at both
the NE level and the network level. By creating a performance instance, you can enable the NMS
to collect performance data from network devices according to a specified period.
l
Monitoring NE performance. This function supports the monitoring of performance
indicators at the NE level, including:
CPU usage
Memory usage
Hard disk usage
Total of online accesses
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-29
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Number of PPPoE online accesses
Number of packets received or forwarded by devices
l
Monitoring network traffic. This function is used to collect the traffic statistics of network
ports and is implemented by collecting the statistics of the following performance
indicators:
Inbound traffic
Outbound traffic.
Inbound bandwidth utilization
Outbound bandwidth utilization
Error Packet Rate
Monitoring SLA data. This function supports multiple types of SLA data monitoring and
is implemented by monitoring the following performance indicators:
Delay and loss ratio of ICMP, TCP, UDP, and SNMP packets between network nodes
Delay, jitter, and loss ratio of packets between network devices
Connection delay and download speed of Internet services such as the HTTP and FTP
services
Collecting interface-based traffic and performance indicators. This function supports
the collection of interface-based traffic in BGP/MPLSVPN, VPLS, and PWE3 services,
and the collection of performance indicators such as delay, packet loss ratio, and jitter in
the BGP/MPLS VPN SLA service.
Setting performance thresholds. This function allows you to set the thresholds for specific
performance indicators. The NMS also provides default global settings to facilitate batch
configuration. You can set the following parameters:
Upper and lower thresholds
Trend thresholds
Non-burst peak thresholds
The NMS reports alarms when the values of some indicators are out of the set ranges
Maintaining data. With this function, you can perform the following operations:
Storing performance statistics
Dumping performance statistics
Regularly compressing performance statistics
Process
The U2000 provides a graphical user interface (GUI) to monitor the key indicators of a network
and provide statistics on the collected performance data. This facilitates network performance
management.
5-30
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Figure 5-22 Performance management process
Function Description
The following is a function description of performance module.
Performance Monitoring Template Management
Performance monitoring template: a collection of performance indicators. The indicators are
included in various indicator groups. By setting a performance monitoring template, you can
manage a performance monitoring task easily.
The following table describes different types of performance monitoring templates.
Table 5-5 Performance monitoring templates
Issue 05 (2010-11-19)
Template
Description
Data monitoring template
A data monitoring template is a collection of
indicators for collecting performance data. It
may contain indicators and indicator groups
for collecting performance data of network
resources. In the case of network quality
analysis (NQA) indicators, set certain service
level agreement (SLA) parameters in the
template and apply the parameters to data
monitoring instances.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-31
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Template
Description
TCA monitoring template
A threshold crossing alert (TCA) monitoring
template is a collection of indicators with
specified thresholds. It may monitor TCAs of
the specified resources. TCAs are classified
into upper threshold alarms and lower
threshold alarms. Thresholds include the
upper and lower thresholds for triggering and
clearing alarms and the upper and lower
alarm severities. In the case of NQA
indicators, set certain SLA parameters in the
template and apply the parameters to TCA
monitoring instances.
Template-Based SLA Parameters
This function collects most SLA parameters into data templates and TCA templates. In this
manner, you need not create SLA parameters when creating an instance, which improves
operation efficiency.
Monitoring Instance Management
Instance: An instance consists of a resource and a template. By means of an instance, you can
collect data of certain performance indicators of a resource. An instance is considered as one or
more performance collection tasks.
Task: A task is the minimum unit for performance collection. A task consists of a resource and
an indicator group. The management of a task is implemented by management of an instance.
Figure 5-23 shows the relationships between a template, an instance, and a task.
Figure 5-23 Relationships between a template, an instance, and a task
Monitoring instances enable you to collect performance statistics on resources of specified
equipment according to a preset monitoring template and schedule policy. One monitoring
instance collects statistics on only one resource. A monitoring instance can be either a data
monitoring instance or a TCA monitoring instance. You can perform the following operations
on the U2000:
l
5-32
Create monitoring instances for resources, such as NEs, boards, ports, and links, and
monitor the IP SLA of the PTN and third-party equipment.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Modify monitoring instances.
Query monitoring instances.
Suspend monitoring instances.
Resume monitoring instances.
Synchronize resources corresponding to monitoring instances.
Query TCAs.
Query the VPN SLA test result by means of a matrix.
Control the management capability, that is, control the number of created monitoring
instances by a license.
Schedule Policy Management
The schedule policy enables you to set the time segments and periods at which the data is
collected. The schedule policy can be applied to resources when a monitoring instance is created
or modified.
Viewing History Performance Data
You can collect the network performance data in a specified period to learn the network
performance. History performance data provides reference data for predicting a performance
change of the network.
You can view the history performance data of a network in a graph, bar chart, or table, and save
the performance data in different file formats.
NOTE
l The information displayed in a graph or bar chart can be saved in HTML, CSV, TXT, or PDF format.
l The information displayed in a table can be saved in TXT, CSV, or HTML format.
In addition, you can compare the performance data in different periods in a graph or bar chart
or compare the indicators of different resources in the same diagram.
Viewing Real-Time Performance Data
You can view real-time performance data in a table, graph, or bar chart, and save the performance
data in different file formats.
NOTE
l The information displayed in a graph or bar chart can be saved in HTML, CSV, TXT, or PDF format.
l The information displayed in a table can be saved in TXT, CSV, or HTML format.
Sorting Resources with Top N Performance
You can view resources with top N performance sorted by indicators, and the result will be
refreshed in real time.
Sorting Resources with Top N Deteriorated Performance
You can sort resources with top N deteriorated performance by alarms of the resources.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-33
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Query of Top N Deteriorated Resources
This function sorts resources by TCA duration according to the preset conditions, enabling you
to locate the current deteriorated resources quickly. In addition, this function enables you to
learn the health status of the entire network and solve problems accordingly.
Data Lifecycle Management
You can back up performance data to a specified storage medium manually or automatically
when excessive performance data is saved in the database of the U2000.
Data can be dumped in the following two ways:
l
Automatic Dumping: Performance data is dumped automatically based on the preset
parameters, such as different periods and the database usage.
Manual Dumping: Performance data is dumped based on the user-defined conditions
according to the dump type before the end date.
Monitoring Network Performance
You can view the performance data of NEs, interfaces, IP links, L2 links, static, tunnels, dynamic
tunnels, and test cases on the same network through network grouping. In addition, you can
perform various tests on a network, such as the tests of UDP jitter and FTP ping, to evaluate the
quality of networks and services and analyze correlation between the quality of networks and
services.
l
Creating a network group
Associate the monitoring instances of resources of different types within the same network
according to the customized grouping rules, such as an area-based rule or service-based
rule. Then, you can browse and compare data easily.
Analyzing the interface performance trend
After the network interface indicators are set, a performance trend analysis graph for either
the current time, or 12 hours before and after the current time can be generated. The
performance trend analysis graph helps you understand the general change trend of the
interface performance in a timely manner.
Viewing the results of network monitoring test cases in a matrix
You can view the results of network monitoring test cases in a matrix. In this manner, you
can understand the information about network-related indicators, evaluate network
performance, and analyze correlation between the indicators and network performance.
5.6 Inventory Management
The U2000 supports unified inventory management of physical resources and service resources
on the entire network. On the U2000, you can quickly and clearly view information about various
resources network-wide. The inventory information serves as a reference for service planning
and expansion planning.
l
You can perform the following operations on the U2000:
Maintain inventory information
Query inventory information
Collect statistics on resource inventories according to the preset statistical items
5-34
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Save inventory information to XLS, TXT, HTML, or CSV files
Print inventory information
l
The U2000 supports auto-discovery of a new asset (such as a new device, board, etc). If an
existing asset is updated, an NE icon would remind you of that the data on the U2000 is
asynchronous with the data on the NE. With the U2000, you can quickly identify the causes
of the data asynchronization.
Figure 5-24 shows the inventory management window of the U2000.
Figure 5-24 Inventory management window and its functions
View inventory resources by type
Collect statistics on inventory resources
Perform operations on inventory records
Table 5-6 Statistical items for resource inventory management
Issue 05 (2010-11-19)
Resource
Statistical Item
Telecommunic
ations Room
Telecommunications Room Name, Relevant Station, Country, Province,
City, Location, Room Number, Cabling Mode, Antistatic Floor or Not,
Thickness of the Antistatic Floor (mm).
Rack
Rack Name, Relevant Telecommunications Room, Rack Type, Height
(mm), Width (mm), Depth (mm), Power Box Type, Voltage, Number of
Batteries, Internal Battery or Not, Internal Power Supply or Not, Internal
MDF or Not, Internal Transmission or Not, Number of Shelves .
Shelf
Shelf Name, Shelf Type, Relevant NE, Shelf ID, Software Version, Alias,
Relevant Telecommunications Room, Relevant Rack, Shelf No.,
Equipment No..
NE
NE Name, NE Type, NE IP Address, NE MAC Address, NE ID, Software
Version, Physical Location, Create Time, Fiber/Cable Count, Run Status,
Relevant Subnet, Relevant Subnet Path, Alias, Patch Version List.
Board
Board Name, Board Type, Relevant NE, NE Type, Shelf ID, Slot ID,
Hardware Version, Software Version, Serial Number, Alias.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-35
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Resource
Statistical Item
Subboard
Subboard Name, Subboard Type, Slot Number, Sub-Slot Number,
Relevant NE, Hardware Version, Software Version, Serial Number, Alias,
Subboard Description, .
Port
Port Type, NE Type, Device Name, Frame, Slot, Port, Name.
Optical Module
Port, Logical Card, Physical Card, Serial Number, CLEI Code, Part
Number, Date of Manufacture, User Label.
Slot Used
Statistics
NE Type, Total Slot Number, Used Slot Number.
ONU
Terminal Type, ONU Version, Amount.
Fiber/Cable
Name, Level/Capacity, Direction, Source NE, Source Port, Sink NE, Sink
Port, Length, Attenuation, Fiber/Cable Type, Medium Type, Created on,
Creator, Maintainer, Alarm Severity, Disabled Status.
Link
Alarm Severity, Link Name, Type of Borne Network Protocol, Source NE,
Source Port, Source IP, Sink NE, Sink Port, Sink IP, Link Level, Link Rate,
Up Band Width, Down Band Width, User Label.
Router/Switch
Interface
Name, NE Name, Description, IPv4 Address, IPv6 Address, MAC
Address, Type, Rate, Administrative Status, IPv4 Operating Status, IPv6
Enable Status, IPv6 Operating Status.
PON Port
Splitting Status
OLT Device Name, Name, Optical Split, Used Optical Split, Idle Optical
Split, Remaining Bandwidth.
5.7 Log Management
Logs record the information about operations performed on the U2000 and important events that
occur in the U2000. The U2000 allows administrators to query and save logs and collect statistics
on logs periodically. This facilitates detection of unauthorized logins and operations and fault
analysis. Specifically, by browsing and collecting statistics on logs, you can query the client
from which a U2000 user logs in to the U2000 server and query the operations performed by
the user after login. You can also dump and print logs. Logs also can record operations that the
OSS performs on NEs through NBIs.
Figure 5-25 shows the log management window and functions of the U2000.
5-36
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Figure 5-25 Log management window and functions
Log Classification
The logs of the U2000 are classified into operation logs, system logs, security logs, and NE logs.
The logs can be saved to TXT, HTML, CSV, PDF, and XLS files.
l
Operation logs record the non-security-related operations that users perform, such as
creating a subnet and enabling or disabling the alarm sound.
System logs record the operations that the U2000 automatically performs, such as scheduled
tasks and system tasks.
Security logs record the security-related operations that users perform, such as login, logout,
lockout, and unlocking.
NE Syslog operation logs record operation results of managed NEs. You can learn the
operation logs of NEs on the U2000 client instead of from each NE.
NE Syslog running logs record the operating information of NEs managed by the U2000.
The U2000 obtains from NEs all Syslog running logs of NEs. You can browse the Syslog
running logs of the managed NEs on the U2000 instead of from each NE.
Querying and Collecting Statistics on Logs
U2000 administrators can set query conditions to query logs by operation user, operation
terminal, operation result, risk level, operation time, operation name, operation object, or a
combination of all of the preceding items according to the requirements. The administrators can
learn about the operations performed on the U2000 by the current user.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-37
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Forwarding Logs
l
U2000 log forwarding: The U2000 can forward its operation logs to the Syslog server to
save the operation information, which releases storage space on the U2000 server. The logs
serve as a reference for maintenance.
NE log forwarding: The U2000 can forward the information about various NEs in the format
that complies with the system log protocol to the Syslog server. Then, U2000 administrators
and maintenance engineers can view the status of NEs according to the importance of the
NE information.
Dumping and Exporting Logs
The log dumping function enables you to delete the logs that are not required, automatically at
a scheduled time or manually. This function prevents logs from occupying too much space. The
log exporting function enables you to export logs to a file for logs viewing or fault locating.
Figure 5-26 shows the window and functions of the U2000 for dumping and exporting logs.
Figure 5-26 Window and functions of dumping and exporting logs
Dumping logs
Operation logs, system logs, and security logs can be dumped periodically and
automatically or dumped manually. The logs can also be dumped upon an overflow
when the size of the logs exceeds the preset threshold.
The U2000 provides only one default system task for each type of logs. You cannot
delete the system tasks or create new dumping tasks. You can only modify the
parameters of the system tasks.
Dumped logs are saved to CSV or XML files. You can compress the files into a ZIP
file. By default, logs are dumped to the $IMAP_ROOT/dump/ThresholdExport/
Log (Solaris/Linux) or %IMAP_ROOT%\dump\ThresholdExport\Log (Windows)
path.
5-38
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
After the logs are dumped, they are deleted from the database to release the database
space.
l
Exporting logs
The U2000 provides only one default system task for each type of logs. You cannot
delete the system tasks or create new exporting tasks. You can only modify the
parameters of the system tasks.
Exported logs are saved to CSV or XML files. You can compress the files into a ZIP
file. By default, logs are exported to the $IMAP_ROOT/dump/fileint/syslogs (Solaris/
Linux) or %IMAP_ROOT%\dump\fileint\syslogs (Windows) path.
After the logs are exported, they are not deleted from the database.
5.8 Database Management
Database management involves the management of NE databases and U2000 databases, and
maintenance of data consistency between the U2000 and NEs.
NE Database Management
To ensure NE data security, the U2000 provides the functions of backing up and restoring NE
data.
In NE software management, you can back up and restore NE data on a server.
l
Back up the NE database to a local or remote server in a manual or scheduled manner.
Restore the NE database from a local or remote server.
You can use the system control and communication unit (SCC) or CF board on the NE to back
up and restore the NE database for the transport access NEs.
l
Back up the NE database to the SCC board manually.
Back up the NE database to the CF board manually or automatically.
Restore the NE configuration data from the SCC board or CF board.
NMS Database Management
The database of the U2000 supports two types of storage files. One type is used to store data
and the other type is used to store the logs that record the operating information of the database.
To ensure data security, periodically back up the database. See Figure 5-27.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-39
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Figure 5-27 NMS database management
NMS Database
Storage Device
Automatically Back Up
Manually Back Up
All important system data are
stored in the NMS database.
Alarm
Configuration
Performance
Log
Security
The U2000 provides a database backup and restoration tool. The tool facilitates database
maintenance and ensures the stability and security of the U2000. It provides the following NMS
database management functions:
l
Back up the U2000 database to a local or remote server in the following ways:
Immediate backup
Scheduled backup through task scheduling
Restore the U2000 database from a local or remote server.
Dump data in the U2000 database, including logs (such as operation logs, system logs,
security logs, and alarm/event logs) and other data (such as performance data).
Manual dump
Periodic dump
Import or export script files: Export the configuration data in the U2000 to script files, or
import the configuration data to the U2000 from script files. The configuration upgrade
wizard instructs users to restore the U2000 database by using the configuration data script
that has been backed up. The functions of importing and exporting script files are applicable
to only the PTN MSTP, WDM, and microwave NEs.
Script files can be exported in a scheduled manner through task scheduling.
The U2000 information about the MSTP and WDM NEs can be exported to a TXT file so
that the information can be used by the MDS 6600. In addition, the U2000 can import a
TXT file that contains the MDS 6600 data.
Initialize the U2000 database: Clear and initialize the U2000 database before restoring the
database in the case where the database data is in disorder or damaged.
Keeping Data Consistency Between the U2000 and NEs
If the configuration data is not synchronous between the U2000 and the NE, the NE icon has a
sign. The U2000 provides rich functions to ensure the security and consistency of the NE
5-40
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
configuration data, such as the uploading, downloading, consistency check, synchronization,
duplication, preconfiguration, and the initialization of the NE data on the U2000.
l
Uploading: Data on NEs is reported to the U2000 to overwrite the NE data on the U2000.
The data that is present on the U2000 but absent on NEs is not deleted.
Downloading: The NE data on the U2000 is applied to the NEs to overwrite the data on
the NEs.
Consistency check: Check whether the NE data on the U2000 is consistent with the data
on NEs. If it is inconsistent, synchronize or upload the NE configuration data.
Synchronization: Upload the inconsistent data (including the conflicting data, and the data
that is present on NEs but absent on the U2000) to the NE layer on the U2000. The data
that is present both on the U2000 and NEs is not uploaded, and the data that is present on
the U2000 but absent on NEs is not deleted.
Duplication: When NEs are of the same type and of the same software version, if the
configuration data of an NE to be configured is the same as that of a configured NE, you
can configure the new NE by duplicating the data of the configured NE. Duplicating the
NE data only changes the data on the U2000 and does not affect the data on the NE. To
make the duplicated data take effect on the NE, you need to apply the configuration.
Preconfiguration: The configuration data of an NE is saved only at the NE layer on the
U2000 and does not affect the actual configuration data on the NE. The preconfiguration
function is generally used for the large-scale service adjustment or expansion.
Initialization of the NE data on the U2000: The NE data on the U2000 is deleted and the
NE becomes unconfigured after the initialization.
NOTE
The PTN RTN, NA WDM, and NG WDM product series do not support preconfiguration and the
downloading of configuration data. The U2000 provides more reliable functions, that is, the database
package backup and restoration, to resolve the data restoration problem. This is because:
l
The configuration data does not contain complete NE data. The complete data can be obtained by
using the database package restoration function.
During the downloading of configuration data, the U2000 converts the configuration data to the Qx
interface information. Then, the data can be exchanged between the U2000 and the NE, but the
efficiency is relatively low. In the database package restoration mode, databases are directly
downloaded to the NE, which ensures a high efficiency.
On the U2000, only one set of configuration data can be saved, but the database package can have
many backup copies. Select the backup package as required.
5.9 NE Communication Parameter Management
The U2000 communicates with managed NEs successfully only after you correctly set the
connection parameters of the U2000 and the managed NEs.
You can query or set the following parameters on the U2000:
l
Query and set the NE access protocol parameters.
Manage the default access protocol parameters.
Query and set the NE Telnet or STelnet parameters.
Manage the Telnet or STelnet parameter template.
DCN management is applicable to PTN NEs. The U2000 communicates with NEs, and manages
and maintains network nodes through a DCN network. In the DCN network, the U2000 and NEs
are considered as nodes. These nodes are connected through Ethernet or data communications
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-41
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
channel (DCC). In an actual network, the U2000 and NEs may be located at different floors of
the same building or in different buildings or cities. Hence, the U2000 and NEs are usually
connected through an external DCN network that consists of equipment such as switches and
routers. Relatively, the DCN network between NEs is referred to as an internal DCN network.
DCN management involves the following operations:
l
Modify gateway NE (GNE) parameters.
Change the GNE of a non-GNE.
Set the secondary GNE of a non-GNE.
Convert a GNE to a non-GNE.
Convert a non-GNE to a GNE.
Check the GNE switching status.
Test the communication between the U2000 and a GNE.
Check the network communication status.
5.10 DCN Management
DCN management is applicable to MSTP, WDM, microwave, submarine cable NEs.
The U2000 communicates with NEs, and manages and maintains network nodes through a DCN
network. In the DCN network, the U2000 and NEs are considered as nodes. These nodes are
connected through Ethernet or data communications channel (DCC). In an actual network, the
U2000 and NEs may be located at different floors of the same building or in different buildings
or cities. Hence, the U2000 and NEs are usually connected through an external DCN network
that consists of equipment such as switches and routers. Relatively, the DCN network between
NEs is referred to as an internal DCN network.
DCN management involves the following operations:
l
Modify gateway NE (GNE) parameters.
Change the GNE of a non-GNE.
Set the secondary GNE of a non-GNE.
Convert a GNE to a non-GNE.
Convert a non-GNE to a GNE.
Check the GNE switching status.
Test the communication between the U2000 and a GNE.
Check the network communication status.
5.11 NE Software Management
The NE software management module (called DC) is an independent subsystem of the U2000
and it is used to manage software and data on NEs. The DC enables you to back up NE data and
upgrade or downgrade NE software.
5-42
The DC implements the upgrade and downgrade of NEs in the following ways:
Saving: After the system is configured, the data is saved in the memory of NEs. This feature
saves the system configuration to the flash memory or hard disk of NEs. This prevents the
loss of the configuration file in case of system restart. The DC saves data through:
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Saving operation (manual)
Saving task (manual)
Saving policy (automatic)
l
Backup: Backs up the configuration to storage devices other than NEs. The backup data is
used for restoring the NE configuration. If the DC has the rights to manage the NE and no
loading, backup, or restoration operation is being performed on the NE, the NE accepts the
request for backup. The DC then transmits the contents for backup to the specified backup
directory on the FTP/TFTP/SFTP server through FTP/TFTP/SFTP. The DC backs up data
through:
Backup operation (manual)
Backup task (manual)
Backup policy (automatic)
Loading: Loads software for the upgrade to an NE. If the DC has the rights to manage the
NE and no loading, backup, or restoration operation is being performed on the NE, the NE
accepts the request for loading. The DC then transmits the contents for loading to the NE
through FTP/TFTP/SFTP. The DC loads data through:
Loading operation (manual)
Loading task (manual)
Upgrading task (automatic)
Restoration: Restores NE data from the backup to an NE. If the DC has the rights to manage
the NE and no loading, backup, or restoration operation is being performed on the NE, the
NE accepts the request for restoration. The DC then transmits the contents for restoration
to the NE through FTP/TFTP/SFTP. The DC restores data through the manual restoration
operation.
Policy and Task: The DC provides different methods for implementing features. For
example, you can save and back up data through a policy or a task.
A policy is periodic. It is mainly used for the operations that are performed frequently,
such as data saving and data backup.
A task is not periodic. It is mainly used for the operations that are not performed
frequently, such as data upgrading and data loading.
Users can select a method according to the actual situation.
5.12 Report Management
The U2000 provides reports about alarms, logs, and resources. You can print the required data
or save the data as a file when viewing it. The reports in tabular format can be filtered by
equipment type and saved in XLS, TXT, HTML, or CSV files.
You can view reports on the U2000 in the following ways:
l
Viewing resource reports on the U2000 client
Viewing iWeb reports through the IE browser, including alarm reports, log reports,
performance reports, and resource reports of equipment in the IP domain
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-43
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Table 5-7 Resource Report
Type
Report
SDH statistics report
Port statistics report
Statistics report of SDH tributary port resources
Statistics report of lower order cross-connections
SDH fiber/cable or radio link resource usage report
Statistics report of trails between SDH NEs
Statistics report of SDH protection subnet resources
Statistics report of SDH trail resources
Microwave report
Radio link report
Microwave license capacity report
MSTP Ethernet report
Statistics report of Ethernet port resources
Statistics report of services resources between Ethernet
NEs
WDM statistics report
Report on WDM protection group switching status
WDM NE master/slave shelf info report
Statistics report of WDM client-side port resources
Statistics report of WDM link resources
Statistics report of inter-station wavelength resources
Statistics report of WDM bandwidth resources
WDM channel resource report
Wavelength resource usage report
xPON statistics report
Report on PON port splitting status
PTN statistics report
Interface resource report
Project document
Board manufacturer information
Export electronic labels
Clock tracing diagram
Networking diagram
Timeslot allocation diagram
5-44
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Resource Report Diagram
Figure 5-28 and Figure 5-29 show the diagrams of the NE-level resource report and the networklevel resource report.
Figure 5-28 Diagram of the NE resource report
Display the NEs on NMS
The resource report shows the
statistical value of each parameter
The buttons for querying and setting parameters
and the print and save buttons are displayed
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-45
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Figure 5-29 Diagram of the network resource report
Display the NEs on NMS
The resource report shows the
statistical value of each parameter
The buttons for querying and setting parameters
and the print and save buttons are displayed
iWeb Report
The iWeb report system provides a complete set of flexible and convenient services. It allows
you to generate, distribute, and manage reports based on the Web. The powerful report system
helps you to monitor, analyze, and improve network performance, and make decisions
accordingly.
The iWeb report system supports the following alarm and log reports:
l
Details report on equipment alarm severity distribution
Report on equipment alarm severity distribution
Equipment connectivity statistics report
General alarm information report
History change record report
For information on the functions of the iWeb report system, see 10.9 Report Subsystem
Management.
5.13 System Monitoring
The U2000 provides a GUI-based system monitoring tool, which is used to manage the
U2000 and query the system information.
The function of managing system processes enables you to perform the following operations as
shown in Figure 5-30.
5-46
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
5 Basic Functions
Monitor the processes, databases and server information about the U2000 in real time. For
the running status of the U2000 server, see System Information Monitoring.
Start and stop processes automatically or manually.
When the U2000 is started, all the processes start automatically.
The U2000 restarts a process automatically if this process stops abnormally.
Processes can be started or stopped manually as required.
Set the security communication mode.
Figure 5-30 System monitoring processes
System Information Monitoring
The U2000 provides a GUI-based system monitoring function. Users can view the service
process status and resource usage (such as the CPU, memory, hard disks, and database) of the
U2000 in real time, and the running status of all the components installed on the U2000 server.
When items monitored by the U2000 are abnormal, the corresponding status icons turn red. By
default, the U2000 sets thresholds for certain monitored items such as the CPU usage and
database usage. When a value of the monitored item reaches the corresponding threshold, the
system sends an alarm and the corresponding status icon turns red. Users can modify the
thresholds if necessary.
The system monitoring tool of the U2000 also provides the function of querying system
information, as shown in the following figure.
l
Query process information.
Query hard disk information.
Query database information.
Monitor the server.
Query component information.
Query operation logs.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
5-47
5 Basic Functions
iManager U2000 Unified Network Management System
Product Description
Figure 5-31 System monitoring information
5-48
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
MSTP Network Feature Management
About This Chapter
This topic describes the functional features of MSTP NE management and network management.
6.1 MSTP NE Management
NE management refers to the management of configurations of an NE in terms of attributes,
communication, services, protection, and clocks. The configuration data is saved to the database
of the U2000 and to the database of the NE.
6.2 MSTP Protection Subnet Management
A protection subnet is a network structure with the comprehensive self-protection function. In
the U2000, the protection subnet is a generalized concept that includes not only the network
structure with the comprehensive self-protection function, such as an MSP ring and a path
protection (PP) ring, but also the network structure without the self-protection function, such as
an unprotected ring and an unprotected chain.
6.3 E2E MSTP Management
E2E network management is also referred to as trail management. You can construct the
configuration data of E2E network management by searching for the data at the NE layer of the
U2000, or directly configure the data at the network layer of the U2000, and apply the data to
all the related NEs. Compared with configuring NE data on a per-NE basis, configuring NE data
by using the trail management function is faster and more convenient.
6.4 SDH ASON Management
The automatically switched optical network (ASON) is a new generation of optical network that
integrates the exchange and transport functions. After a user initiates a service request, the ASON
selects a route automatically, establishes and removes connections through the signaling control,
and performs network connections automatically and dynamically. An ASON NE refers to the
equipment that is equipped with both SDH and ASON features. An ASON is managed by the
U2000 that combines ASON and SDH features.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-1
6 MSTP Network Feature Management
iManager U2000 Unified Network Management System
Product Description
6.1 MSTP NE Management
NE management refers to the management of configurations of an NE in terms of attributes,
communication, services, protection, and clocks. The configuration data is saved to the database
of the U2000 and to the database of the NE.
Basic NE Configuration
You can perform the following operations on the U2000:
l
Modify NE attributes such as:
NE name
NE ID
Extended NE ID
Remarks
NE pre-configuration
NOTE
For the NE whose ID needs to be set through the DIP switch, modify the NE ID on the U2000.
Synchronize NE time: Align all NEs with the system time of the U2000 server
automatically.
Query physical resources in the following lists:
NE list
Board manufacturer information
Board list
Cabinet list
Subrack list
Equipment room list
Use the board plug and play function: After a board is inserted into the slot, the NE Panel
automatically displays the board icon and board information.
Replace a board. You can replace a board with a board of another type on the U2000.
Query the actual physical board type of a board that is used as a board of another type.
The user can replace board A with board B whose rate and number of ports is the same
or less as of board A.
Enable the function of automatically disabling the NE: periodically disable some NE
functions that may affect services, such as loopback and automatic laser shutdown (ALS).
When the time expires, these operations will stop automatically.
Environment monitoring information. The following items can be set:
PMU interface
EMU interface
CAU interface
NE fan speed
Virtual NE management
Create a virtual NE.
6-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
Add a board.
Create fibers between the virtual NE and other NEs.
Create SDH services.
Create protection subnets.
Search for and create trails on the virtual NE.
l
Support the replacement of the boards.
Supports the management of inband DCN.
Support graphical display of performance events relevant to the optical power.
Create a board with adjustable bandwidth for a preconfigured NE.
Orderwire Configuration
You can perform the following operations on the U2000:
l
Set and query the orderwire phone numbers, call waiting time, and orderwire phone port
availability.
Set and query the network-wide conference call number.
Set and query the length of the subnet ID and the related subnet of the optical interface.
Configure and query the SDH network node interface (NNI) connection for orderwire.
Configure and query the F1 data port.
Configure and query the broadcast data port.
Board Protection Configuration
You can perform the following operations on the U2000:
l
Configure board 1+1 protection.
Configure 1:N tributary protection switching (TPS) protection for a tributary board.
Configure board level protection.
Configure port protection.
Query the data backup status between the active and standby SCC boards.
SDH Interface Configuration
You can perform the following operations on the U2000:
l
Interface board management: query and set the SDH interface boards installed on NEs.
Set the parameters of SDH interfaces.
Set the parameters of CES interfaces.
Set the parameters of PDH interfaces.
Modify the optical/electrical attributes of the port.
Set overhead interfaces, including:
Orderwire
Hotline number
Special line number
Conference call number
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-3
6 MSTP Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Subnet number length
F1 data port
Broadcast data port
Communication port
Data port
Out-ring route
l
Set the optical amplifier board interface.
Manage the optical power of a board.
Set tone and data access (TDA) interfaces, including:
TDA clock source
TDA power feeding
Query and set the overhead including:
Regenerator section overhead (J0)
Lower order path overhead (V5, J2)
VC4 higher order path overhead (J1, C2) and its pass-through or termination
VC3 higher order path overhead (J1, C2)
Enable the PRBS function.
Enable the function of pre-alerts for the port optical power.
Set and query the TUG structure in the transmit and receive directions.
Perform lower order loopbacks.
Query the in service (IS) port status and the out of service (OOS) port status of a line board
or a data board.
Manage the power consumption.
Set and query the optical power threshold of a line board.
Configuration for SDH Services and Protection
You can perform the following operations on the U2000:
6-4
Configure VC12, VC3, or VC4 services and select protection groups for them. In the
platform 4.0 equipment, select protection groups of these services.
Manage Transmux services, including M13/E13 Transmux and M13/E13 Transmux Server
services.
Configure VC4-4C, VC4-8C, VC4-16C, or VC4-64C concatenated service; bind or unbind
services, and select protection groups for them.
Configure other services: enterprise system connection (ESCON) services, 64 kbit/s
services (including TDA board services, Nx64 kbit/s services), and DSL services.
Manage subnetwork connection multiple protection (SNCMP) services.
Activate or deactivate services.
Manage subnetwork connection protection (SNCP) services.
Manage subnetwork connection tunnel protection (SNCTP) services.
Convert an SNCP service to a normal service or convert a normal service to an SNCP
service.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
Configure multiple multiplex section protection (MSP) rings at a single optical port.
Configure multiple MSP rings by VC4 at an optical port to increase the usage of network
resources.
Configure REG. After the line board is set as REG, each pair of optical interfaces of the
line board provides a special receive or transmit function. Through the internal switch, the
SDH signals from the receiving optical interface are sent out directly to the corresponding
transmitting optical interface after passing through the regenerator section layer and being
amplified. The REG function is completely implemented by the board without the
cooperation of the SCC board and a cross-connect board.
Query the capacity of higher order and lower order cross-connections on an NE.
Configuration for ATM Interfaces, Services, and Protection
You can perform the following operations on the U2000:
l
Query and configure the ATM interface board on an NE.
Query the bandwidth of ATM board.
Set the parameters for an ATM interface.
Configure ATM traffic.
Configure ATM cross-connections.
Create a network to network interface (NNI) on the ATM processing board.
Configure ATM cross-connections.
Configure ATM protection groups.
Configure ATM protection pairs.
Configure ATM services from ATM board to SDH line.
Activate or deactivate ATM cross-connections.
Configure ATM bound path.
Perform ATM operation, administration and maintenance (OAM).
Set or query the section-end attribute of a connection point.
Set or query the continuity check (CC) activation status of the connection point.
Perform a remote loopback test.
Set or query the NE loopback location identifier (LLID).
Upload, download, duplicate the OAM data of the NE or perform the related consistency
check.
Configure an inverse multiplexing over ATM (IMA) group.
Configuration for Ethernet Interfaces and Services
You can perform the following operations on the U2000:
l
Query and configure the Ethernet interface board on an NE.
Configure fast Ethernet transparent transmission board.
Set the parameters of the Ethernet internal interfaces, including:
Basic attributes
TAG attributes
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-5
6 MSTP Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Network attributes
Encapsulation/mapping
Link capacity adjustment scheme (LCAS)
Bound path
Advanced attributes
l
Configure the parameters of the external ports of Ethernet interface, including:
Basic attributes
Flow control
TAG attributes
Network attributes
Advanced attributes
Configure point-to-point LPT and point-to-multipoint LPT.
Configure E-Line services, including Ethernet private line (EPL) and Ethernet virtual
private line (EVPL). Create a new service and configure a bound path.
Configure Ethernet private LAN (EPLAN) services. Create a new virtual bridge (VB) and
configure the following parameters: service mount, VLAN filtering table, VLAN unicast,
MAC address disabling, bound path, self-learning MAC address, VB port MAC address
table capacity, and VLAN MAC address table capacity.
Configure the parameters of Ethernet Layer-2 switching, including:
Aging time
Spanning Tree Protocol
Multiple Spanning Tree Protocol
IGMP snooping protocol
Configure QinQ service: QinQ is an embedded technology in VLAN, and tags users with
multi-layer VLAN ID, so that VLAN can be extended. Perform operations such as adding,
stripping and exchanging of tags in different scenarios.
Configure Ethernet link aggregation group (LAG), which contains intra-board LAG and
inter-board LAG.
Create or delete an LAG.
Add or delete LAG ports.
Query LAG ports and aggregation state.
Configure the parameters of quality of service (QoS), including:
Flow configuration
CAR configuration
CoS configuration
Flow shaping management
Port shaping management
Differentiated service (DiffServ) domains
CAR policy
Port WRED Policy
V-UNI ingress policy
V-UNI egress policy
6-6
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
PW policy
Weighted random early detection (WRED) congestion and discarding policy of services
QinQ policy
Weighted fair queuing (WFQ) schedule policy
CoS queue scheduling priority mapping
l
Test frame receiving and transmitting on Ethernet boards, including the EGT, EFT, EGS,
EFS and EMS boards.
Query the opposite NE of the data services on these boards.
Use QoS template to simplify the QoS configuration for Ethernet services.
Enable the automatic reporting function of RMON performance of Ethernet boards.
Support the dumping of history RMON performance of Ethernet boards.
Support the protocol diagnosis function.
Support the alarm function in the case of no traffic at Ethernet ports.
Support the Ethernet port mirroring.
Set and query the MAC address of a data board.
Support the traffic statistics function at a port.
Support traffic monitoring and report for an Ethernet port.
Allow the board to respond to the ping command.
Create flows in batches.
Support the ability to manage multi-protocol label switching (MPLS). The MSTP
equipment builds a label switched path (LSP) with a PE router, identifies LSP labels and
service priorities, and encapsulates LSPs into virtual concatenation groups (VCGs) for
transmission.
Configure the static routes and address resolution.
Configure E-Line services, E-LAN services, E-AGGR services, and clock services.
RPR Management
You can perform the following operations on the U2000:
l
Modify resilient packet ring (RPR) node information.
Set and query the node information of an NE in the RPR.
Set the RPR link information of an NE.
Query the topology of the RPR that the NE belongs to.
Query the protection status, switching status, and switching position of the RPR that an NE
belongs to.
Configure forced switching, manual switching, or clear switching in the RPR that an NE
belongs to.
Clock Configuration
You can perform the following operations on the U2000:
l
Query the clock synchronization status.
Set the clock source priority tables, including:
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-7
6 MSTP Network Feature Management
iManager U2000 Unified Network Management System
Product Description
System clock source priority list
Priority table for phase-locked sources of 1st external clock output
Priority table for phase-locked sources of 2nd external clock output
l
Set clock source switching, including:
Clock source restoration parameters
Clock source switching condition
Clock source switching
Configure clock subnets, including:
Clock subnet
Clock quality
Synchronization status message (SSM) output control
Clock ID status
Set phase-locked sources output by external clock, including:
External clock output phase-locked source
2 Mbit/s phase-locked source external clock attributes
IEEE 1588 Packet Clock
You can perform the following operations on the U2000:
l
Configure the selection mode of a frequency source.
Set the PTP clock source port.
Set the quality level of the clock source.
Set the PTP clock source priority.
Configure a PTP clock service.
Set the clock interface configuration.
Set the external clock interface configuration.
Ethernet OAM Management
You can perform the following operations on the U2000 for configuring the 802.1ag Ethernet
OAM:
l
Create and configure maintenance nodes.
Perform a continuity check (CC) check.
Perform a loopback (LB) check.
Perform a link trace (LT) check.
Perform a ping test.
Perform performance detection.
You can perform the following operations on the U2000 for configuring the 802.3ah Ethernet
OAM:
6-8
Query remote OAM parameters.
Set link monitoring parameters. This function helps to detect the events of frame error,
frame error period, and frame error seconds.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
Perform a remote loopback test.
Enable the reporting of Ethernet OAM loopback events.
Peform OAM management for MPLS tunnels.
MPLS Tunnel Protection Group Configuration
You can perform the following operations on the U2000 for configuring an MPLS tunnel
protection group:
l
Create an MPLS tunnel 1+1 protection group and an MPLS tunnel 1:1 protection group,
including the switching mode, return mode, wait-to-restore (WTR) time, and hold-off time.
Perform MPLS tunnel protection switching.
Query the protection switching status of an MPLS tunnel.
MS PW Configuration
By creating a multi-segment pseudowire (MS-PW) to transmit services, tunnel resources and
transmit services over different networks can be saved.
CES Service Configuration
CES is mainly used for service transparent transmission of TDM trail switching data in the PTN
network.
You can perform the following operations on the U2000 for configuring CES services:
l
Create the corresponding PW when creating a CES service.
Create UNI-UNI and UNI-NNI CES services.
Create CES services of structure-aware TDM circuit emulation service over packet
switched network (CESoPSN) and of structure-agnostic TDM over packet (SAToP).
Configure QoS of the CES service.
Configure CES service alarm transparent transmission.
Select the tunnel where a PW is carried online.
MSTP Configuration
The MSTP can be used to clear loops in a network. The MSTP uses a specific algorithm to block
some redundant trails and change a loop network to a non-loop tree network. This function
prevents packet increase in a loop network and generation of broadcast storms in an endless
cycle. Different from the STP and RSTP, the MSTP can forward data according to VLAN packets
and achieve load balance of VLAN data.
You can perform the following operations on the U2000 for configuring the following MSTP
attributes:
l
Configure parameters of port groups and bridges.
Configure CIST and MSTI parameters.
Query CIST status and MSTI status.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-9
6 MSTP Network Feature Management
iManager U2000 Unified Network Management System
Product Description
OSPF Protocol Configuration
You can perform the following operations on the U2000 by using OSPF protocol as the network
protocol:
l
Manage the OSPF routes and set relevant parameters.
Enable or disable port-level OSPF and LSA.
Import static routes.
CES ACR Clock
CES ACR (Adaptive Clock Recover) is based on CES services and recovers the clock of the
source at the sink in adaptive mode. The sink equipment can recover the TDM clock (in FIFO
mode) according to the change in the buffer for receiving CES services (the change is caused
by the packets received on the NNI side).
Packet Function
Implement the packet functions, such as the PW OAM, PW APS, MCSP, MC LAG, MS PW,
CES, and bidirectional tunnel.
6.2 MSTP Protection Subnet Management
A protection subnet is a network structure with the comprehensive self-protection function. In
the U2000, the protection subnet is a generalized concept that includes not only the network
structure with the comprehensive self-protection function, such as an MSP ring and a path
protection (PP) ring, but also the network structure without the self-protection function, such as
an unprotected ring and an unprotected chain.
To perform protection subnet management, the relevant license is required.
You can perform the following operations on the U2000:
l
Create protection subnets of different types.
Linear MSP: 1+1 and M:N.
MSP ring: two-fiber bidirectional MS shared protection ring, two-fiber unidirectional
MS dedicated protection ring, and four-fiber bidirectional MS shared protection ring.
PP ring: two-fiber unidirectional PP ring and two-fiber bidirectional PP ring.
Dual node connection (DNI) protection.
Non-protection (NP) ring and NP chain.
6-10
Search for a protection subnet according to the information of NEs and fibers or cables, to
form a complete protection subnet.
Transfer an NP chain to a 1+1 linear MSP without interrupting services.
Start or stop the MSP protocol of the MSP subnet, such as enabling or disabling the MSP
protocols network-wide or the MSP protocol for a single node.
Support the automatic generation of the services on the protection channel according to the
services on the working channel.
Adjust the bandwidth dynamically. To be specific, you can dynamically adjust the MSP
bandwidth according to the service demands and how the network bandwidth is used
currently to improve the utilization of network bandwidth. For example, for an STM-16
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
MSP of an 8 x VC4 bandwidth, if the 6 x VC4 bandwidth is enough, then change the
protection bandwidth from 8 x VC4 to 6 x VC4 bandwidth and save 4 x VC4 for the use
of non-MSP-protected services.
l
Expand the capacity of an MSP ring and a linear MSP chain. To be specific, you can expand
the link capacity by replacing the line boards on both sides of the link without interrupting
active services. For example, upgrade an STM-16 MSP ring to STM-64 smoothly.
Change the revertive mode of linear MSP protection without restarting the protocol.
Expand and add nodes to multiple types of protection subnets, including MSP, SNCP, PP,
NP ring, NP chain and their combinations.
Query the names, types and status of all protection subnets.
Query and set the switching status, wait-to-restore (WTR) time, and the trigger condition
of the protection subnet.
Query all the isolated nodes and delete useless nodes.
Set and view SDH NNIs.
Query the relevant trail by protection subnet.
Manage the entire RPR ring network. To be specific, you can create, delete, and search for
an RPR ring; you can manage the RPR ring protection parameters and link parameters.
RPR ring topology can be displayed through a view.
Generate the MSTP protection subnet report to facilitate the statistics and maintenance of
the protection subnets.
6.3 E2E MSTP Management
E2E network management is also referred to as trail management. You can construct the
configuration data of E2E network management by searching for the data at the NE layer of the
U2000, or directly configure the data at the network layer of the U2000, and apply the data to
all the related NEs. Compared with configuring NE data on a per-NE basis, configuring NE data
by using the trail management function is faster and more convenient.
To perform E2E network management, the relevant licenses is required.
MSTP Trail Management
You can perform the following operations on the U2000:
l
Create and maintain an SDH trail.
Create an SDH trail, designate a timeslot, and select the protection priority strategy and
the resource usage strategy. The service levels include VC12, VC3, VC4, VC4 server
trail, VC4-4C, VC4-8C, VC4-16C and VC4-64C.
Activate or deactivate, and lock or unlock an SDH trail.
Join or split, and enable or disable a VC4 server trail.
During search of SDH trails, the U2000 retains the attributes of the existing ones as they
are.
Upgrade an SDH trail to an ASON trail.
Downgrade an ASON trail to an SDH trail.
Query the service status on a per-NE basis according to SDH trails.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-11
6 MSTP Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Manage optical power: Query the input power, output power, and power thresholds for
SDH boards.
Set and query the overhead bytes of all NEs on the trail, such as the trace byte.
The U2000 prompts users to configure trace bytes when timeslot out-of-sequence occurs
to the MS.
Query the status of a lower order service.
Set overhead pass-through or termination for all NEs on the trail.
Insert alarms such as AIS and remote defect indication (RDI) into the trails at the VC4
level.
Set loopback on any nodes on a trail, including VC4 loopback, tributary loopback,
optical interface loopback and cross-connection loopback.
Perform a PRBS test on a trail.
Modify the add/drop ports on a trail and the timeslots occupied by the trail without
interrupting services.
Adjust the original route partially by changing the NE, board or timeslot that the trail
passes through.
Modify the route for concatenated services without interrupting services.
Set SNCP switching on a trail.
Implement the function of automatically generating dually-fed SDH services for 1+1
linear MSP.
Duplicate an SDH trail so that SDH trails can be created in batches.
Duplicate an SDH trail that is configured with DNI protection, so that SDH trails can
be created in batches.
Manage discrete SDH services, such as querying or analyzing discrete services.
Analyze the connectivity of an SDH trail and locate a fault of an SDH trail.
View the usage of VC12 or VC3 trails related to a VC4 server trail in graphical format,
and the information about the VC12 or VC3 trails.
Convert SDH discrete cross-connections to a mono nodal trail.
Manage SDH trails based on permissions and domains.
Search for fibers on an SDH trail.
l
Manage the alarms and performance events related to an SDH trail.
Configure alarm suppression or alarm reversion for a trail.
Query current and history alarms, current and history performance data, unavailable
time (UAT) and performance threshold-crossing records of an SDH trail.
Set performance parameters for an SDH trail.
Query the SDH trails and customer information affected by an alarm.
Display R_LOS alarms in the Transmission Media Layer Route view.
Search for trails. Based on the NE configuration data at the NE layer, and the fiber
connection data and protection subnet information at the network layer, the U2000
generates the network layer information about E2E trails.
Name trails automatically.
Filter trails in three ways.
Filter all: Filter all trails and display only the qualified trails.
6-12
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
Secondary filter: Filter those trails that are already displayed according to the filter
criteria.
Incremental filter: Filter all trails and display the newly qualified trails together with
the currently displayed ones.
Ethernet Trail Management
You can perform the following operations on the U2000:
l
Create and maintain an Ethernet trail.
Create trunk links at VC12, VC3, VC4, VC4-4C, VC4-8C and VC4-16C levels.
Create an unterminated trunk link.
Create an Ethernet trail. The service includes EPL, EVPL, unterminated EPL, EPLAN,
EVPL based on QinQ, EVPL based on RPR and EVPLAN based on RPR.
Create a protection Ethernet trail that has one source and dual sinks.
Create an Ethernet trail that belongs to multiple VLANs.
NOTE
For release 4.0 NEs (version 4.bb.cc.dd), the SDH NNI needs to be created on Ethernet line boards.
Activate or deactivate an Ethernet trail.
During search of Ethernet trails, the U2000 retains the attributes of the existing ones as
they are.
Manage discrete Ethernet services, such as querying or analyzing discrete services.
Search for an Ethernet trail.
Filter trails in three ways.
Filter all: Filter all trails and display only the qualified trails.
Secondary filter: Filter those trails that are already displayed according to the filter
criteria.
Incremental filter: Filter all trails and display the newly qualified trails together with
the currently displayed ones.
Manage the alarms and performance events related to an Ethernet trail.
Query the Ethernet trails and customer information affected by an alarm.
Query current and history alarms related to an Ethernet trail.
Implement the RMON performance function for an Ethernet trail.
ATM Trail Management
You can perform the following operations on the U2000:
l
Create and maintain an asynchronous transfer mode (ATM) trail.
Create an ATM trunk link.
Create an ATM trail.
Activate or deactivate an ATM trail.
Manage ATM discrete services, such as querying or analyzing discrete services.
Search for an ATM trail.
l
Issue 05 (2010-11-19)
Manage the alarms and performance events related to an ATM trail.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-13
6 MSTP Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Query the ATM trails and customer information affected by an alarm.
Query the current and history alarms related to an ATM trail.
l
Filter trails in three ways.
Filter all: Filter all trails and display only the qualified trails.
Secondary filter: Filter those trails that are already displayed according to the filter
criteria.
Incremental filter: Filter all trails and display the newly qualified trails together with
the currently displayed ones.
Management of Packet Services
You can perform the following operations on the U2000:
l
Manage PWE3 services.
Create an ETH PWE3 service or a CES PWE3 service.
Predeploy a PWE3 service.
Implement the function of automatically discovering PWE3 services.
Modify and delete PWE3 services, and filter PWE3 services to view the desired services.
Manage multi-hop PWE3 services.
Manage the protection of PWE3 services.
View the topology of PWE3 services.
View the alarms of a PWE3 service.
View the performance of a PWE3 service.
Manage discrete PWE3 services.
Manage PWE3 services based on permissions and domains.
Create PWE3 services by using the duplication function.
Manage PWE3 service templates.
Implement the function of automatically generating Ethernet OAM for PWE3 services.
Set loopback and view the loopback status.
Manage tunnels.
Create a tunnel based on the static CR protocol.
Predeploy a tunnel.
Implement the function of automatically discovering tunnels.
Modify and delete tunnels, and filter tunnels to view the desired tunnels.
View the topology of tunnels, including working routes and protection routes.
View the alarms of a tunnel.
View the performance of a tunnel.
View the results of testing and checking a tunnel.
Manage discrete tunnels.
Create, modify, and delete 1+1 or 1:1 tunnel protection groups, and implement the
function of automatically discovering 1+1 or 1:1 tunnel protection groups.
Manually switch 1+1 or 1:1 tunnel protection groups.
6-14
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
View the topology of a 1+1 or 1:1 tunnel protection group.
Configure OAM.
View the tunnel names in the global LSP view.
Manage bidirectional tunnels.
l
Manage VPLS services.
Create a VPLS service.
Predeploy a VPLS service.
Implement the function of automatically discovering VPLS services.
Modify and delete VPLS services, and filter VPLS services to view the desired services.
Manage VPLS services.
View the topology of VPLS services.
View the alarms of a VPLS service.
View the performance of a VPLS service.
Manage discrete VPLS services.
Manage VPLS services based on permissions and domains.
Manage VPLS service templates.
Implement the function of automatically generating Ethernet OAM for VPLS services.
Set loopback and view the loopback status.
Manage E-AGGR service.
Create an E-AGGR service.
Predeploy an E-AGGR service.
Implement the function of automatically discovering E-AGGR services.
Modify and delete E-AGGR services, and filter E-AGGR services to view the desired
services.
View the topology of an E-AGGR service.
View the alarms of an E-AGGR service.
View the performance of an E-AGGR service.
Manage discrete E-AGGR services.
Manage E-AGGR services based on permissions and domains.
Manage E-AGGR service templates.
Configure OAM.
Set loopback and view the loopback status.
Manage composite services.
Manage composite services in the scenarios where an EPL service accesses a PWE3
service, a PWE3 service accesses another PWE3 service, and a PWE3 service accesses
an E-AGGR service.
Modify and delete composite services, and filter composite services to view the desired
services.
Implement the function of automatically discovering composite services.
View the topologies of composite services and the internal connections between
composite services.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-15
6 MSTP Network Feature Management
iManager U2000 Unified Network Management System
Product Description
View the status of composite services.
Network Expansion and Service Handover Management
You can perform the following operations on the U2000:
l
Expand a PTN by adding nodes, deleting nodes, and upgrading or adjusting link capacities.
Implement the handover of PWE3 trails at present.
Prepare a manual or automatic service handover plan.
Prepare a service handover plan by using either the rollback handover policy or the besteffort handover policy.
Hand over, restore, and verify the trails of handover groups in batches.
Create and modify handover groups and handover plans, and delete handover groups and
handover plans in batches.
Create and delete active and preconfigured services in handover groups.
Clock Topology Management
The U2000 provides the following functions:
l
Supporting the IEEE 1588 V2, SDH, and synchronous Ethernet clocks
Displaying the clock trace relationship
Displaying the clock alarm status
6.4 SDH ASON Management
The automatically switched optical network (ASON) is a new generation of optical network that
integrates the exchange and transport functions. After a user initiates a service request, the ASON
selects a route automatically, establishes and removes connections through the signaling control,
and performs network connections automatically and dynamically. An ASON NE refers to the
equipment that is equipped with both SDH and ASON features. An ASON is managed by the
U2000 that combines ASON and SDH features.
ASON Topology Management
You can perform the following operations on the U2000:
6-16
Discover ASON topologies and resources automatically.
Synchronize NEs in a domain: The U2000 can obtain the topology of the network through
the active NE.
Set an account and a password for NE management, and implement the function of
automatically uploading the configuration data of NEs that are already created.
Set the active and standby NEs.
Synchronize cross-connections for NEs.
Manage domains, including creating and deleting domains, and changing the domain name.
Query the ASON NE software version.
Search for ASON discrete signaling.
Manage the node IDs of ASON NEs.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
Enable or disable the optical virtual private network (OVPN) status of the NE.
Query SRGs relevant to an NE.
Control Link Management
You can perform the following operations on the U2000:
l
Synchronize network-wide control links.
Filter links by domain or source/sink information.
View control links.
Query the current alarm and history alarm about a control link.
Set alarm suppression for a control link.
Customize whether to display the color of alarms in the SDH Control Link
Management window.
Print or save the report list about control links information.
Component Link Management
You can perform the following operations on the U2000:
l
Synchronize network-wide component links.
Filter component links by domain or source/sink information.
View component link information.
Create component links.
Delete component links.
Set resources reservation.
Query VC4 timeslot usage status.
Query link timeslot segmentation.
Print or save the report list about component links information.
TE Link Management
You can perform the following operations on the U2000:
l
Synchronize network-wide traffic engineering (TE) links by domain.
Filter TE links by domain, source/sink information or OVPN customer.
View TE links.
Create virtual TE links.
Delete virtual TE links.
Create fibers.
Set the distance for a TE link.
Set the risk link group number.
Create a link resource report.
View bandwidth usage.
Allocate TE links to an OVPN customer.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-17
6 MSTP Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Query the alarms of a TE link.
Set alarm suppression for a TE link.
Query the performance of a TE link.
View the interrupted TE links.
Query SRGs relevant to a TE link.
Customize the cost for a TE link.
Query the affected TE links according to control plane alarms.
ASON Trail Management
You can perform the following operations on the U2000:
6-18
Filter ASON services by actual route, original route or shared mesh restoration trail.
Synchronize ASON trails by domain or basic attributes.
View ASON trails.
View the details of an ASON trail.
Create an ASON server trail of the diamond, gold, silver, or copper class.
Create an ASON trail of the diamond, gold, silver, copper or iron class.
Set the OVPN customer of an ASON trail.
Activate or deactivate ASON trails or SDH ASON server trails.
Delete inactive SDH ASON trails or inactive SDH ASON server trails.
Delete SDH ASON trails or SDH ASON server trails on the NMS side.
Duplicate ASON trails.
Optimize ASON trails.
Pre-calculate and optimize service trails.
Set routing attributes of ASON trails, including rerouting lockout status, revertive lockout
status, rerouting priority, rerouting revertive mode, WTR time, schedule revertive time,
rerouting policy, trigger condition, crankback and rerouting triggered by B3 bit error.
Query the rerouting reversion status of a revertive ASON trail.
Create the associated trails with a same initial node or different initial nodes.
Set association for ASON trails.
Remove association for ASON trails.
Set the association source for ASON trails.
Query the related SDH trails for ASON trails.
Set a preset restoration trail for an ASON trail.
Downgrade an ASON trail to an SDH trail.
Migrate a trail without interrupting services.
View the actual route, original route or associated route of an ASON trail.
View the preset restoration trail or shared mesh restoration trail of an ASON trail.
Revert ASON trails manually.
Switch the working or protection trail of a diamond trail manually.
View the alarms of an ASON trail.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
Set alarm suppression for the selected ASON trail.
View the control plane performance of an ASON trail.
View the performance events of an ASON trail.
Create the ASON trail report.
Refresh the original route, actual route or associated route of an ASON trail.
Refresh the preset restoration trail or shared MESH restoration trail for an ASON trail.
Set an actual route as an original route.
Restore to the original route in batches.
Set names for ASON trails in batches according to the naming rules.
Query the service level agreement (SLA) conformity of ASON trails.
View actual routes of gold services after MSP switching.
Save the attributes of the service after you create an ASON service successfully.
Restore the default attributes of an ASON service when you create the ASON service.
Set SNCP access to an ASON trail.
Manage creators of SDH ASON trails.
Reroute the preset SDH ASON restoration trail in case of a fault.
Implement the function of automatically refreshing routes after a diamond trail protection
switching.
Set the associated route attribute of the associated ASON trails.
UNI Trail Management
You can perform the following operations on the U2000:
l
Synchronize UNI services by domain.
View the information about a UNI service.
Filter UNI services by domain or source/sink information.
Deactivate a UNI service.
Delete a UNI service.
ASON Clock Subnet Management
You can perform the following operations on the U2000:
l
Create an ASON clock subnet.
Create a preconfigured ASON clock subnet.
Convert a preconfigured ASON clock subnet into an ASON clock subnet.
Convert a traditional clock subnet into an ASON clock subnet.
Manage a hybrid network composed of an ASON clock subnet and a traditional clock
subnet.
Manage the startup time for the SDH ASON clock recovery.
SRG Management
You can perform the following operations on the U2000:
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-19
6 MSTP Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Create, delete and modify an SRG.
Manage SRGs of the pipe type, fiber type, NE type, site type, and customized type.
One-End Terminated ASON Server Trail Management
You can perform the following operations on the U2000:
l
Create and delete a one-end terminated ASON server trail.
Activate and deactivate a one-end terminated ASON server trail.
Associate one-end terminated ASON server trails.
Create and delete an ASON-SDH trail that contains one-end terminated ASON server trails.
Activate and deactivate an ASON-SDH trail that contains one-end terminated ASON server
trails.
Search for an ASON-SDH trail that contains one-end terminated ASON server trails.
Set association relationships between the ASON trails that have different sources and sinks.
Integration of SDH and ASON Trails
You can perform the following operations on the U2000:
l
Specify the explicit route for ASON services when creating an ASON-SDH trail. That is,
an ASON-SDH trail includes an SDH trail and an ASON trail.
View SDH and ASON trails at the same time in the SDH Trail Management window.
Manage overhead bytes, alarms and performance of an ASON-SDH trail in a unified
manner.
Query the related ASON trails by an SDH trail.
Query the related SDH trails by an ASON trail.
Downgrade an ASON trail to an SDH trail.
Upgrade an SDH trail to an ASON trail.
Set the revertive attributes when an SDH trail is being migrated to an ASON trail.
Create dually fed and selectively received VC4 ASON server trails.
Calculate working and protection routes using the SPC first policy.
The alarm in the ASON section of an ASON-SDH trail supports the alarm statistics
function.
Script Export and Import for Simulated Network Planning Information
You can perform the following operations on the U2000:
l
Export the scripts of the simulated network planning information, including the networkwide configuration file, NE configuration file, network layer information file, ASON
information file, TE link information, associated ASON service information, route
calculation policy, component link information, ASON resource reservation information,
WTR time information, preset restoration trails and route calculation policy for nodes.
Import the scripts of the simulated network planning information.
ASON NE Catastrophe Restoration
The U2000 supports an ASON NE catastrophe restoration scheme.
6-20
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
6 MSTP Network Feature Management
SDH ASON Management on a Per-NE Basis
You can perform the following operations on the U2000:
l
Manage the ASON features of NEs.
Manage IDs of ASON NEs.
Manage the ASON feature of boards.
Manage control plane parameters, including the bandwidth occupancy (%), bandwidth
weight, distance weight, hop weight, and customized cost weight. In addition, the route
selection policy is supported.
Manage control channels.
Query LMP component links.
Query LMP TE links.
Set the LMP auto discovery mode.
Manage fiber resource thresholds.
Query OSPF control links.
Query OSPF SDH TE links.
Query OSPF component links.
Manage OSPF IP addresses.
Manage OSPF TE link flood thresholds.
Manage OSPF protocol authentication.
Manage ASON trail groups.
Query ASON trails.
Maintain SDH ASON signaling.
Maintain SDH ASON switch controllers.
Maintain ASON shared mesh switch controllers.
Manage the auto-reporting status of control plane alarms.
Manage the levels and suppression status of control plane alarms.
Manage control plane performance parameters.
Query the performance of the control plane.
Manage resource reservation.
Manage the VC4 timeslot occupation status.
Manage the virtual interfaces of ASON links.
Manage the inactive PPPoE interfaces.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
6-21
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
WDM Network Feature Management
About This Chapter
This topic describes the functions and features of WDM NE management and network
management.
7.1 WDM NE Management
NE management refers to management of the configurations of an NE in terms of attributes,
services, protection, and clocks. The configuration object is a single NE. The data is saved to
the NE database on the U2000 and the NE database on the NE.
7.2 WDM NA NE Management
NE management includes setting of attributes and configuration of communication, services,
protection, and clocks on a per-NE basis. The configuration data is saved at the NE layer on the
U2000 and in the database of the NE.
7.3 WDM Protection Subnet Management
A protection subnet is a network with holistic self-protection. On the U2000, the protection
subnet is a general concept that refers to not only a network with holistic self-protection, such
as a multiplex section protection (MSP) ring or a path protection (PP) ring, but also a network
without self-protection, such as an unprotected ring or an unprotected chain.
7.4 End-to-End WDM Management
End-to-end network management is also referred to as trail management. You can construct the
configuration data about end-to-end network management by searching for the data at the NE
layer of the U2000, or directly configure the data at the network layer of the U2000, and apply
the data to all related NEs. Compared with configuring NE data on a per-NE basis, configuring
NE data by using the trail management function is quicker and more convenient.
7.5 WDM ASON Management
The automatically switched optical network (ASON) is a new generation of optical network that
integrates switch and transport functions. After a user initiates a service request, the ASON
selects a route automatically, establishes and disconnects connections by using signaling control,
and establishes network connections automatically and dynamically. An ASON NE refers to the
equipment that is enabled with both WDM and ASON features. An ASON network is managed
by the U2000 that combines ASON and WDM features.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-1
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
7.1 WDM NE Management
NE management refers to management of the configurations of an NE in terms of attributes,
services, protection, and clocks. The configuration object is a single NE. The data is saved to
the NE database on the U2000 and the NE database on the NE.
Basic NE Configuration
You can perform the following operations on the U2000:
l
Synchronize NE time: Send the computer system time, NTP server time, or standard NTP
server time at the U2000 server to all NEs for synchronizing the NE time. You can set the
U2000 to automatically synchronize the NE time by specifying the automatic
synchronization period.
Query the physical inventory information, including information about the
telecommunications rooms, racks, NEs, shelves, boards, and ports.
Implement the board plug and play feature: After a board is inserted into a slot, the NE
Panel automatically displays the board and the board information.
Disable NE functions automatically: You can set the time when the U2000 automatically
disables certain NE functions that may affect services. At the time specified, these functions
are automatically disabled.
Modify the following NE attributes:
NE name
NE ID
Extended NE ID
Remarks
NE pre-configuration
Modify the following attributes of an optical NE:
Name
Remarks
Resources assigned
Manage environment monitoring information: You can set the PMU interface, NE fan
speed, temperature monitoring, and voltage monitoring.
Manage network operator information: You can set the information about the network
operator, including the international identifier, domestic identifier, and user-defined
identifier.
Search for and create NEs by discovering NE IP addresses automatically.
Orderwire Configuration
You can perform the following operations on the U2000:
7-2
Set a board as an orderwire board and query the orderwire board information.
Set and query the orderwire phone numbers, call waiting time, dialing mode, and orderwire
phone port availability.
Set and query network-wide conference call numbers.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Set and query the subnet number length and the related subnet of an optical interface.
Set and query an NNI orderwire phone.
Set and query an F1 data port.
Set and query a broadcast data port.
Set E1 cross-connections.
Configuration for Ethernet Interfaces and Services
By using the U2000, you can perform the following operations:
l
Configure Ethernet port mirroring. You can monitor packets, perform routine maintenance
and in-service commissioning through a mirrored port in a flexible manner.
Set the following attributes of an internal Ethernet interface:
Basic attributes
Flow control
Tag attributes
Network attributes
Bound path
Advanced attributes
Set the following attributes of an external Ethernet interface:
Basic attributes
Flow control
Tag attributes
Network attributes
Advanced attributes
Configure E-Line services such as Ethernet private line (EPL), Ethernet virtual private line
(EVPL) (QinQ), and VLAN subnetwork connection protection (SNCP) services.
NOTE
l QinQ is a VLAN embedding technique that employs multi-layer VLAN IDs to identify different users.
In this manner, VLAN resources are expanded. The U2000 supports the function of adding labels.
l A VLAN SNCP service is a VLAN-based E-Line service that is configured with SNCP protection.
You can create VLAN SNCP and QinQ VLAN SNCP services, and perform conversion between a
VLAN SNCP service and a common Ethernet service.
Configure Ethernet private LAN (EPLAN) services: You can create a virtual bridge (VB)
and set parameters including service mounting, VLAN filtering, VLAN unicast, MAC
address disablement, bound path, and MAC address automatic learning.
Set the following parameters for QoS:
Flow
CAR
CoS
Flow shaping
Port shaping
Issue 05 (2010-11-19)
Configure link capacity adjustment scheme (LCAS): LCAS can dynamically adjust the
number of virtual containers for mapping desired services, so as to satisfy different
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-3
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
bandwidth requirements of services. In this manner, bandwidth utilization and robustness
of virtual connections are improved.
l
Configure OAM for Ethernet services.
Configure OAM for Ethernet ports.
Configure the intra-board LAG function.
Configure the inter-board LAG function.
Configure the VLAN group function.
Configure port MAC address filtering.
Test frames received and transmitted on Ethernet boards.
Configure the protocol diagnosis function.
Configure the QinQ type area.
Configure the following attributes for Ethernet Layer 2 switching:
Aging time
Spanning tree
IGMP snooping protocol
Configure the multiple spanning tree protocol (MSTP): MSTP is compatible with STP and
RSTP, and it also addresses the defects of STP and RSTP. MSTP supports fast convergence.
In addition, MSTP provides multiple redundancy trails for data forwarding, implementing
load balancing of VLAN data during data forwarding.
Configure MPLS tunnels: On a PSN network, an MPLS tunnel carries pseudo wires (PWs)
where various services are encapsulated. In this manner, data packets can be transparently
transmitted among NEs. You can dynamically adjust the required number of virtual
containers for service mapping so as to adapt to the requirements for different service
bandwidths, at the same time improving bandwidth utilization and robustness of virtual
concatenations.
Configure link-state pass through (LPT): LPT is used to return the remote-end link status
to the near end. The near-end equipment performs operations depending on the remote-end
link status. The Ethernet board periodically monitors the network to learn the Ethernet
status. When the connection status of Ethernet ports changes due to a link fault, you can
use the LPT function to quickly switch services from the working route to the protection
route between the two ends. The LPT feature protects transmission of important data.
Configure Ethernet ring protection switching (ERPS): Based on the traditional Ethernet
mechanism, ERPS uses the ETH OAM function and the ring automatic protection switching
(R-APS) protocol to achieve fast protection switching on the Ethernet ring network.
Configure automatic reporting of RMON performance of Ethernet boards.
Dump history RMON performance data of Ethernet boards.
WDM Board Configuration
You can perform the following operations on the U2000:
7-4
Configure optical transponder boards.
Configure service multiplexing and de-multiplexing boards.
Configure tributary and line boards.
Configure protection boards.
Configure optical amplifier boards.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Configure spectrum analysis boards.
Configure optical supervisory channel boards.
Configure optical add/drop multiplexing boards.
Configure variable optical attenuator boards.
Configure optical equalization boards.
Configure automatic optical fiber monitoring boards.
Configure dispersion compensation boards.
Configure wavelength management boards.
Dynamically manage ports.
Query the line rate of an optical transport network (OTN).
Overhead Configuration
You can configure OTN overheads as follows on the U2000:
l
Configure and query section monitoring (SM) overheads.
Configure and query optical transmission section (OTS) overheads.
Configure and query path monitoring (PM) overheads.
Configure and query tandem connection monitoring (TCM) overheads.
Query optical channel payload unit (OPU) overheads.
Configure and query fault type and fault location reporting channel (FTFL) overheads.
You can configure WDM overheads as follows on the U2000:
l
Configure optical channel (OCh) overheads at SDH interfaces.
Configure optical transponder unit (OTU) overheads at OTN interfaces.
Configure optical demultiplexer unit (ODU) overheads at OTN interfaces.
Query OPU overheads at OTN interfaces.
Configure OTS overheads at OTN interfaces.
You can configure SDH overheads for the OptiX OSN 8800 T32 and OptiX OSN 8800 T64 as
follows on the U2000:
l
Configure regenerator section overheads (J0).
Configure lower order path overheads (V5 and J2).
Configure VC4 higher order path overheads (J1 and C2) and pass-through or termination.
Configure VC3 higher order path overheads (J1 and C2).
WDM Service Configuration
At an optical add/drop multiplexer (OADM) station, you can perform ADM configurations for
Gigabit Ethernet (GE)/fiber channel (FC) services by using the OTU board as follows:
l
Configure several WDM service boards in specified slots to form a cross-connect unit
group.
Perform the add/drop, pass-through, and loopback operation on GE/FC services in each
cross-connect unit group.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-5
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Implement wavelength cross-connection protection (WXCP), with working and protection
cross-connections configured on the sink NE.
Configure electrical cross-connections:
l
The U2000 allows you to configure electrical cross-connections to control the service flow
at the electrical layer, and to dynamically groom, converge, and split sub-wavelength
services. In this manner, the network structure and network survivability are enhanced.
The U2000 supports integrated grooming of GE, ODU0, ODU1, ODU2, and ODU3
services implemented by the XCS.
The U2000 supports distributed grooming of GE, ODU0, ODU1, and ODU2 services and
Any services.
The U2000 supports unidirectional and bidirectional SNCP at the ODU3, ODU2, ODU1,
or ODU0 level.
Configure optical cross-connections:
l
Create optical cross-connections dynamically, and manage optical cross-connections by
board or NE, including creation, activation, deactivation, deletion and query.
Create, query, and delete edge ports.
Configure optical broadcast cross-connection services on a per-NE basis.
Perform service management operations:
l
Lock WDM trails and view the lock status of the corresponding trails in the Service
Management window of the NE Explorer.
View the name of the trail that a service belongs to.
Query the trail that a service belongs to.
Perform service package management on the OptiX OSN 1800. The service package module
helps you perform typical service configurations. In this manner, you need not perform onsite
commissioning. This reduces costs in deployment commissioning and product maintenance. In
addition, the equipment can be configured in a one-key manner.
Manage licenses for service types and cross-connect capacities of the OptiX OSN 8800 T32 and
OptiX OSN 8800 T64.
ROADM Configuration
By using the reconfigurable optical add/drop multiplexer (ROADM) function on the U2000,
you can perform add/drop and pass-through configuration for optical channels. The WDM
equipment uses the DWC and wave selective switch (WSS) to implement the ROADM function.
7-6
Configure ROADM boards based on DWC boards: Wavelength grooming is implemented
by using the DWC boards. This configuration method is often used for common nodes on
a chain or ring network.
Configure ROADM boards based on WSS boards: There are two types of network
structures, WSSD+WSSM and WSS+RMU/ROAM. This configuration method is often
used for cross-connect nodes on a ring network.
Configure ROADM boards based on multiplexing and demultiplexing boards:
Wavelengths cannot be groomed dynamically. This configuration method is often used for
common nodes on a chain network.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Clock Configuration
You can perform the following operations on the U2000:
l
Configure a clock source for a board.
Configure transparent transmission for an external clock.
Configure a clock for the SCC board.
Configure a clock for the optical supervisory channel unit.
Specify the clock source traced by the SCC board.
Define clock source priorities.
PTP Clock (1588V2 Clock) Configuration
You can perform the following operations on the U2000:
l
Configure the frequency source mode.
Configure PTP clock synchronization attributes.
Query the clock source received at a port.
Configure the PTP clock subnet.
Configure PTP packet attributes.
Configure an external time interface.
Physical Clock Configuration
You can perform the following operations on the U2000:
l
Configure input attributes of external clocks.
Configure the system clock source priority table.
Configure clock source protection and clock source switching.
Configure phase-locked source output of external clocks.
Configure the quality of clock sources.
WDM Protection Configuration
You can perform the following operations on the U2000:
l
Configure optical line protection.
Configure an optical wavelength protection group.
Configure port protection.
Configure 1:N (N 8) optical channel protection.
Configure 1+N (N 48) optical channel protection.
Configure protection for clock transparent transmission.
Configure optical wavelength share protection (OWSP) with the Metro WDM equipment
and the NG WDM equipment.
Configure WXCP protection for GE/FC services.
Configure a WXCP protection group for the sink NE.
Configure and query WXCP protection parameters.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-7
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Query the status of WXCP protection switching.
Query services with WXCP protection.
Perform WXCP protection switching.
l
Configure a TPS protection group.
Configure a DPPS protection group.
Configure 1+1 protection for boards.
Configure 1+1 protection for SCC boards.
Configure 1+1 protection for cross-connect and synchronous timing (XCS) boards.
Perform working/protection switching.
Query the switching status.
Configure SNCP protection.
Configure sub-wavelength (SW) SNCP for GE services or Any services on an OTU
board.
Configure SNCP for optical channel data unit (ODUk) services.
Configure MS SNCP.
Configure VLAN SNCP for an Ethernet board.
Perform protection switching.
Query the switching status.
Configure board protection switching (BPS).
Configure distribute board protect system (DBPS). DBPS protects 10GE and GE ports on
a TBE board. The cross-connection granularity is the GE service.
Configure ODUk SPRings at the ODU1 and ODU2 levels.
In 1+1 protection for SCC boards, you can query the data backup status between the active
and standby SCC boards.
Optical Power Adjustment
You can perform the following operations on the U2000:
l
Manage the optical power. For example, query the input power, output power, and power
threshold of each WDM board.
Perform intelligent power adjustment (IPA). When a fiber is cut, the optical amplifier board
detects signal loss at the local station. The local station reports an exception event to the
U2000. After the user confirms the event, the optical amplifier boards at the upstream and
downstream stations reduce their output power to a safe value to prevent a fiber maintainer
from being injured by the laser emitted from the cut fiber. After the fiber is reconnected,
the optical signals recover to normal and the optical power of each optical amplifier board
automatically returns to a normal value.
Perform automatic level control (ALC). The U2000 supports adjustment modes including
wavelength count detection, power detection, and link attenuation (gain mode). In
wavelength count detection mode and power detection mode, you can manually control
whether to enable the ALC function.
The wavelength count detection mode applies to a transmission link where no service
is added or dropped or where the number of wavelengths added and dropped are the
same at an OADM station. When the spectrum analyzer unit detects that the total optical
power of the wavelengths greatly differs from the standard power corresponding to the
7-8
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
wavelength count, an exception event is reported to the U2000. After the user confirms
the event, the user needs to manually issue a command to adjust the attenuation of each
station on the link.
The power detection mode applies to a transmission link where the number of add
wavelengths differs from the number of drop wavelengths at an OADM station. When
the optical amplifier board detects that the output power is abnormal, the station
automatically issues a command to adjust the attenuation of each station on the link.
This mode does not involve a spectrum analyzer unit and is therefore cost-effective.
The link attenuation adjustment mode also applies to a transmission link where the
number of add wavelengths differs from the number of drop wavelengths at an OADM
station. When the optical power is attenuated to the detection threshold, a command is
automatically issued to adjust the attenuation of each station on the link.
NOTE
The link attenuation adjustment mode is also referred to as the gain mode, which compares line attenuation
with amplifier gain, and then compares the difference between line attenuation and amplifier gain with
node gain compensation offset. After the nominal gain of the optical amplifier unit and the attenuation of
the attenuation adjustment unit are adjusted, the attenuation is equal to the gain, ensuring the power budget
of the entire link.
Perform automatic power equilibrium (APE). If the MCA board at the receive end detects
that the optical power of certain channels is abnormal, the station reports an exception event
to the U2000. After the user confirms the event, the U2000 issues a command to the optical
attenuation adjustment board of the upstream station. This board adjusts the optical power
of the abnormal channel so that the optical signal noise ratio (OSNR) of each channel at
the receive end is equalized.
Perform ROADM optical power equalization. After ROADM is enabled for dynamically
configuring wavelength services, the WDM equipment outputs multiplexed wavelengths.
The optical power between each channel, however, may be greatly different, especially for
new add wavelengths. To avoid negative impact on transmission performance, the ROADM
optical power equalization mechanism is provided. The ROADM first distinguishes
between pass-through wavelengths and the add wavelengths. Then the DWC/WSS adjusts
the optical power of the pass-through wavelengths, and the optical attenuation adjustment
board adjusts the add wavelengths based on wavelength flags.
Configure pre-alerts for optical power at ports.
Dispersion Compensation
You can perform the following operations on the U2000:
l
Perform dispersion compensation (with the help of the DCM board) at each band to
implement dispersion equalization.
Use tunable dispersion compensators (TDCs) to adjust dispersion precisely.
In the submarine system, use a separate dispersion compensation board, such as the TDC1
or TDC2 board, to perform dispersion compensation for signals on the line side of an OTU
board.
Wavelength Monitoring
By using the U2000, you can perform wavelength monitoring management for the OptiX BWS
1600G, OptiX OSN 6800, OptiX OSN 8800 T32, and OptiX OSN 8800 T64.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-9
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
WDM PRBS
By using the U2000, you can perform a pseudo-random binary sequence (PRBS) test on a board
to check the path quality. You can also check whether a WDM link functions properly before a
service is provisioned.
SDH Board Configuration
By using the U2000, you can configure SDH line boards for the OptiX OSN 8800 T32 and OptiX
OSN 8800 T64. You can perform the following operations:
l
Configure dynamic SDH ports.
Adjust the rates of optical ports on SDH boards.
Query the status of a port.
Configuration for SDH Services and Protection
You can perform the following operations on the U2000:
l
Configure SDH line boards, SDH services, and SDH service protection for the OptiX OSN
8800 T32 and OptiX OSN 8800 T64.
Configure VC12, VC3, or VC4 services and select protection groups for them.
Activate or deactivate services.
Configure SNCP services.
Switch between an SNCP service and a common service.
Query the capacities of higher order and lower order cross-connections on an NE.
Configure subnetwork connection tunnel protection (SNCTP). SNCTP provides protection
channels at the VC4 level. When the working channel is faulty, all its services are switched
to the protection channel.
Configure linear multiplex section protection (MSP). In the MSP protection, bytes K1 and
K2 in the SDH multiplex section overhead (MSOH) are used to transmit protocol
information to control the transmit and receive routes of services on a chain network.
Configure MSP rings, including two-fiber and four-fiber MSP rings.
Configure transoceanic MSP rings. A transoceanic multiplex section (MS) is an MS based
on the transoceanic MSP protocol and used to provide path protection for higher-order
services on a transoceanic ring network.
Power Consumption Management
You can perform the following operations on the U2000:
7-10
Manage NE power consumption to achieve energy conservation and environment
protection when the NE runs in the normal state.
Query power consumption of a board or an NE.
Configure energy conservation for an NE. You can dynamically adjust NE power
consumption to achieve environment protection and energy conservation.
View network-wide NE power consumption reports.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Submarine Line Management
You need to create a line group for actual submarine lines on the U2000. Hence, you can measure
and analyze line data, and monitor the working status of lines. By using the U2000, you can
perform submarine line management as follows:
l
Create a submarine line.
Modify a submarine line.
Activate a submarine line.
Delete a submarine line.
Submarine Line Monitoring
You can monitor and test the status of fibers and repeaters and analyze test data to monitor the
working status of a submarine system and identify faults. By using the U2000, you can perform
submarine line monitoring as follows:
l
Managing submarine line thresholds.
Monitor submarine lines and the status of a repeater in in-service mode.
Use the fast fault identification function.
Identify a fault on a submarine line in off-service mode.
Perform tests of multiple types: manual test, comparison test in single-test mode, and
comparison test in periodic mode.
Synchronize, query, and analyze the test data.
Refresh monitoring information in real time.
Query the gain report and performance report.
PFE Management
By using the U2000, you can manage the PFE 1670. The PFE 1670 is the power supply
equipment for the submarine transmission system.
FC Service Test
The FC service test uses the 12LOM board to replace the FC test equipment (such as the
SmartBits) for running the test. The FC service test verifies whether the FC service line and the
equipment under test are in the normal state. By using the U2000, you can perform FC service
tests.
7.2 WDM NA NE Management
NE management includes setting of attributes and configuration of communication, services,
protection, and clocks on a per-NE basis. The configuration data is saved at the NE layer on the
U2000 and in the database of the NE.
Basic NE Configuration
By using the U2000, you can perform the following operations:
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-11
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Synchronize the NE time: Send the computer system time and NTP server time at the
U2000 server to all NEs for synchronizing the NE time. You can configure the U2000 to
automatically synchronize the NE time by specifying the automatic synchronization period.
Query physical resources in the following items:
NE list
Bard manufacturer information
board list
Shelf list
Telecommunications room list
Implement the board plug and play feature: After a board is inserted into a slot, the NE
Panel automatically displays the board and the board information.
Disable the NE functions automatically: You can set the time when the U2000
automatically disables certain NE functions that may affect services, such as the loopback
and automatic laser shutdown (ALS) functions. At the time specified, these functions are
disabled automatically.
Configure or modify the NE attributes:
Modify the NE name.
Modify the NE remarks.
Enable or disable automatic board installation.
Enable or disable LAN port access control.
Set start time for 24-hour performance monitoring.
Enable or disable daylight saving time (DST).
Modify the IP address and subnet mask of an NE.
Enable or disable ARP proxy.
Enable or disable the OSI protocol.
Modify a shelf name.
Modify shelf remarks.
Set the time zone and DST.
Perform a cold reset or warm reset on an NE.
Reset the NE in DBERASE mode, with the NE database erased.
Reset the NE in SWDL mode after the NE software is downloaded.
Enable or disable performance reporting.
Enable or disable alarm reporting.
Enable or disable database change (DBCHG) reporting.
Clear audible and visual alarm indication of an NE in a cabinet.
Set the NE alarm delay time, including the delay time for alarm start and the delay time
for alarm end.
Set the longitude and latitude of an NE.
Set the affiliated gateway IP address.
Set the affiliated gateway port.
Set the state model of an NE.
7-12
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Set the country code and national segment code of an NE.
Enable or disable the buzzer of an NE.
l
Modify the following attributes of an optical NE:
Type
Name
Remarks
Vendor
Resources assigned
Query and modify the parameters in the Card Attribute window.
Set the primary and secondary states.
Query logical boards and physical boards on an NE.
Query the PCB version, software version, FPGA version, and BIOS version of a board.
Query the CLEI code, vendor ID, part number, serial number, date of manufacture, and
board description.
Query the backup power and rated power voltage.
Set the upper temperature threshold and lower temperature threshold.
Set the fan speed, working mode, and LED state.
Perform a cold reset on a board.
Perform a warm reset on a board.
Manage environment monitoring information: You can set the fan speed mode and speed
level on an NE.
Manage fibers and cables as follows:
View fiber cable information.
Create or delete a fiber cable.
Create a fiber cable report.
Dynamically add a port: SFP/XFP client-side colored ports support the new functions of
dynamically add, delete, and modify.
Search and create NEs by discovering NE IP addresses automatically.
Orderwire Configuration
By using the U2000, you can perform the following operations:
l
Set and query orderwire phone numbers and call waiting time.
Set and query network-wide conference call numbers.
Set and query the subnet number length.
Configuration for Ethernet Interfaces and Services
By using the U2000, you can perform the following operations:
l
Configure Ethernet port mirroring. You can monitor packets, perform routine maintenance,
and in-service commissioning through a mirrored port in a flexible manner.
Set the following attributes for an internal Ethernet interface:
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-13
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Basic attributes
Tag attributes
Network attributes
Advanced attributes
Flow control
l
Set the following attributes for an external Ethernet interface:
Basic attributes
Flow control
Tag attributes
Network attributes
Advanced attributes
Configure Ethernet private line (EPL), Ethernet virtual private line (EVPL) (QinQ), and
VLAN subnetwork connection protection (SNCP) services.
NOTE
l QinQ is a VLAN embedding technique that employs multi-layer VLAN IDs to identify different users.
In this manner, VLAN resources are expanded. The U2000 supports the function of adding labels.
l A VLAN SNCP service is a VLAN-based E-Line service with SNCP protection. You can create VLAN
SNCP and QinQ VLAN SNCP services, and perform conversion between a VLAN SNCP service and
a common Ethernet service.
Configure Ethernet private LAN (EPLAN) services: You can create a virtual bridge (VB)
and set parameters including service mounting, VLAN filtering, VLAN unicast, MAC
address disablement, bound path, and MAC address automatic learning.
Set the following parameters for QoS:
Flow
CAR
CoS
Port shaping
Configure OAM for Ethernet services.
Configure OAM for Ethernet ports.
Configure the intra-board LAG function.
Configure the DLAG function.
Configure the VLAN group function.
Configure port MAC address filtering.
Test frames received and transmitted on Ethernet boards.
Configure the protocol diagnosis function.
Configure the QinQ type area.
Set the following parameters for Ethernet Layer 2 switching:
Aging time
Spanning tree
IGMP snooping protocol
7-14
Configure automatic reporting of RMON performance of Ethernet boards.
Dump history RMON performance data of Ethernet boards.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
WDM Board Configuration
By using the U2000, you can perform the following operations:
l
Configure optical transponder boards.
Configure service multiplexing and de-multiplexing boards.
Configure tributary and line boards.
Configure protection boards.
Configure optical amplifier boards.
Configure spectrum analysis boards.
Configure optical supervisory channel boards.
Configure optical add/drop multiplexing boards.
Configure variable optical attenuator boards.
Configure wavelength monitoring.
Configure optical equalization boards.
Overhead Configuration
By using the U2000, you can configure OTN overheads as follows:
l
Configure and query section monitoring (SM) overheads.
Configure and query path monitoring (PM) overheads.
Configure and query tandem connection monitoring (TCM) overheads.
Query optical channel payload unit (OPU) overheads.
Configure and query fault type and fault location reporting channel (FTFL) overheads.
By using the U2000, you can configure WDM overheads as follows:
l
Configure an optical channel (OCh) overhead management-SONET interface.
Configure OTU overheads at the OCh overhead management-OTN interface.
Configure ODU overheads at the OCh overhead management-OTN interface.
Configure OPU overheads at the OCh overhead management-OTN interface.
Configure TCM overheads at the OCh overhead management-OTN interface.
Configure OTS overheads at the OCh overhead management-OTN interface.
WDM Service Configuration
At an optical add/drop multiplexer (OADM) station, you can configure ADM for GE/Any
services by using the LQG, LOG, and other boards as follows:
l
Configure several WDM service boards in specified slots to form a cross-connect unit
group.
Perform the add/drop, pass-through, and loopback operation on GE services in each crossconnect unit group.
Implement unidirectional and bidirectional WXCP protection with working and protection
cross-connections configured on the sink node.
Configure electrical cross-connections: The U2000 allows you to configure electrical crossconnections to control service flows at the electrical layer. In this manner, the network structure
and network survivability are improved. The following two features are supported:
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-15
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Integrated grooming of GE, ODU1, ODU2, and ODU3 services implemented by XCS.
Distributed grooming of GE, ODU1, ODU2, and Any services.
Configure ODU3, ODU2, ODU1, ODU0, GE/Any, and OTU1 cross-connections, and
unidirectional and bidirectional SNCP at the ODU0, ODU1, ODU2, and ODU3 levels.
l
Create OCh cross-connections dynamically, and manage optical cross-connections by
board or NE, including creation, activation, deactivation, deletion and query.
Create edge ports.
Perform the following service management operations:
l
Lock WDM trails and view the lock status of the trails in the Service Management window
of the NE Explorer.
View the names of the trails that a service traverses.
Query the trails that a service traverses.
ROADM Configuration
By using the ROADM function on the U2000, you can perform add/drop and pass-through
configurations on optical channels. The WDM equipment uses DWC and WSS to implement
the re-configuring of optical add/drop multiplexing.
l
DWC type of ROADM: DWC is applicable to common nodes on a chain or ring network.
WSS type of ROADM: WSS is applicable to cross-connect nodes on a ring. This feature
is applicable to grooming of multi-dimensional optical cross-connections. A maximum of
eight dimensions are supported.
The U2000 supports optical broadcast cross-connection services on a per-NE basis.
Clock Configuration
By using the U2000, you can perform the following operations:
Configure the master clock.
l
Add a clock source.
Delete a clock source.
Query a clock source.
Configure a clock for the OTC board.
l
Set the input attributes of a clock for the OTC board.
Set the output attributes of a clock for the OTC board.
Set the working route of a clock for the OTC board.
Set the synchronization clock source.
WDM Protection Configuration
By using the U2000, you can perform the following operations:
7-16
Configure 1+1 optical channel protection.
Configure 1:N optical channel protection.
Configure inter-shelf protection.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Configure port protection.
Configure optical line protection.
Configure intra-board 1+1 protection: This function includes intra-board 1+1 protection
implemented by dual-fed OTU boards and intra-board 1+1 protection implemented with
the help of the DCP or OLP board.
Configure client-side 1+1 protection.
Configure protection for clock transparent transmission.
Configure OWSP protection.
Configure WXCP protection for GE/OTU1 services.
Configure a WXCP protection group for the board in the sink slot.
Configure and query WXCP protection parameters.
Query the status of WXCP protection switching.
Query services with WXCP protection.
Perform WXCP protection switching.
Configure board 1+1 protection.
Configure SCC board 1+1 protection.
Configure XCS board 1+1 protection.
Configure AUX board 1+1 protection.
Perform switching between working and protection boards.
Query the switching status.
Configure SNCP protection.
Configure subwavelength (SW) SNCP for GE or Any services on an OTU board.
Configure SNCP for optical channel data unit (ODUk) services.
Configure VLAN SNCP for an Ethernet board.
Perform protection switching.
Query the switching status.
Configure board protection switching (BPS). The BPS protection uses two boards: the
working and protection boards. BPS protection protects any single port on the two boards
by board-level switching.
In 1+1 protection for SCC boards, you can query the status of data backup between the
active and standby SCC boards.
Optical Power Adjustment
By using the U2000, you can perform the following operations:
l
Manage the optical power. For example, query the input power, output power, and power
threshold of each WDM board.
Perform intelligent power adjustment (IPA). When a fiber is cut, the optical amplifier board
detects signal loss at a station. The station reports an exception event to the U2000. After
the user confirms the event, the optical amplifier boards at the upstream and downstream
stations reduce their output power to a safe value to prevent the fiber maintenance personnel
from being injured by the laser emitted from the cut fiber. After the fiber is reconnected,
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-17
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
the optical signals recover to normal and the optical power of each optical amplifier board
automatically returns to a normal value.
l
Perform automatic level control (ALC). Link attenuation (gain mode) can be used as the
adjustment mode. The link attenuation adjustment mode applies to a transmission link
where the number of add wavelengths differs from the number of drop wavelengths at an
OADM. When the optical power is attenuated to the detection threshold, a command is
automatically issued to adjust the attenuation of each station on the link.
NOTE
The link attenuation adjustment mode is also referred to as the gain mode, which compares line attenuation
with amplifier gain, and also compares node gain with compensation offset. After the nominal gain of an
optical amplifier unit and the attenuation value of an attenuation adjustment unit are adjusted, the
attenuation value is equal to the gain value, ensuring the power budget of the entire link.
Perform automatic power equilibrium (APE). If an MCA board at the receive end detects
that the optical power of certain channels is abnormal, the station reports an exception event
to the U2000. After the user confirms the event, the U2000 issues a command to the optical
attenuation adjustment board at the upstream station. This board adjusts the optical power
of the abnormal channel so that the optical signal-to-noise ratio (OSNR) of each channel
at the receive end is equalized.
Perform ROADM optical power equalization. After ROADM is enabled for dynamically
configuring wavelength services, the WDM equipment outputs multiplexed wavelengths.
The optical power, however, may deviate greatly on channels, especially on new
wavelength channels. To avoid negative impact on transmission performance, the ROADM
optical power equalization mechanism is provided. The ROADM first distinguishes
between pass-through wavelengths and add wavelengths. Then the DWC/WSS adjusts the
optical power of the pass-through wavelengths, and the optical attenuation adjustment
board adjusts the add wavelengths based on wavelength flags.
Configure pre-alerts for the optical power at a port.
Dispersion Compensation
l
The G.652 and G.655 fibers have positive dispersion coefficient and positive dispersion
slope at the 1550 nm window. After an optical signal is transmitted over a certain distance,
accumulation of positive dispersion broadens the optical signal pulse and seriously affects
system transmission performance. To minimize this impact, a negative DCM is used on
the network. The negative DCM uses negative dispersion to compensate the positive
dispersion of the transmission fiber, so as to maintain the original shape of the signal pulse.
An OEQ NE can apply dispersion compensation at each band to achieve dispersion
equalization.
The U2000 supports 40G dispersion compensation, which uses the TDC to adjust dispersion
precisely.
Wavelength Monitoring
Wavelength monitoring uses a wavelength supervisory unit to monitor the wavelengths that are
transmitted from a WDM-side optical interface on the OTU board (including the service
convergence unit) and to control wavelength shift. By using the U2000, you can perform
wavelength monitoring. This function ensures wavelength stability.
7-18
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
WDM PRBS
By using the U2000, you can perform pseudo-random binary sequence (PRBS) on a board to
check the path quality. You can also check whether a WDM link functions properly before a
service is provisioned.
Housekeeping Configuration
By using the U2000, you can perform the following operations:
l
Set and query the environmental alarm property.
Create environmental alarm attributes.
Set the normal state of the environmental alarm property.
Query environmental alarm attributes.
Modify environmental alarm attributes.
Delete environmental alarm attributes.
Set and query the external control property.
Create external control attributes.
Query external control attributes.
Modify external control attributes.
Delete external control attributes.
Set the control time of the external control relay.
Query of AO Buffer Records
By using the U2000, you can perform the following operations:
l
Query the records in the automatic output (AO) buffer. The record information includes:
Time at which the record is generated
Autonomously generated correlation tag (ATAG) of the record
Type of the record
Description of the record
Filter the records in the AO buffer.
Save the records in the AO buffer to a file.
Export the AO buffer information to the browser of the operating system for printing.
EAPE Management
Enhanced automatic power equalization (EAPE) management can reduce the bit error rate (BER)
of a service. By using the U2000, you can query the EAPE function of an OCh trail.
Power Consumption Management
By using the U2000, you can perform the following operations:
l
Manage NE power consumption to achieve energy conservation and environment
protection when the NE runs in the normal state.
Query the power consumption of a board or an NE.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-19
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Configure energy conservation for an NE. You can dynamically adjust NE power
consumption to achieve environment protection and energy conservation.
View network-wide NE power consumption reports.
ASON Management
Topology Management
By using the U2000, you can perform the following operations:
l
Discover ASON topologies and resources automatically.
Synchronize NEs in a domain: On the U2000, you can obtain the topology of a network
from the active NE.
Set the active and standby NEs.
Manage domains, including creating and deleting domains, and changing domain names.
Query the ASON NE software version.
Manage IDs of ASON NEs.
Query the status (enabled/disabled) of the ASON NE software.
Enable or disable the ASON feature of an ASON NE.
TE Link Management
By using the U2000, you can perform the following operations:
l
Synchronize network-wide links by domain or payload type.
Filter links by domain, link signal type, payload type, or source/sink information.
View TE links.
Create fibers.
Manage TE links whose payload type is OCh.
Set the length of a TE link.
Create a link resource report.
7.3 WDM Protection Subnet Management
A protection subnet is a network with holistic self-protection. On the U2000, the protection
subnet is a general concept that refers to not only a network with holistic self-protection, such
as a multiplex section protection (MSP) ring or a path protection (PP) ring, but also a network
without self-protection, such as an unprotected ring or an unprotected chain.
To perform protection subnet management on the U2000, the relevant license is required.
You can perform the following operations on the U2000:
l
Search for a wavelength protection subnet.
Create a 1:N wavelength protection subnet by using the search function.
Create ODUk SPRings at ODU1 and ODU2 levels by using the search function.
Manage a wavelength protection subnet.
Set parameters of a 1:N wavelength protection subnet.
Perform and verify 1:N wavelength protection switching.
7-20
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Set parameters of an ODUk SPRing protection subnet.
Perform and verify the ODUk Wavelength Protection Switching
Query and delete a protection subnet.
Query and delete an isolated node.
Query protection subnet resources.
7.4 End-to-End WDM Management
End-to-end network management is also referred to as trail management. You can construct the
configuration data about end-to-end network management by searching for the data at the NE
layer of the U2000, or directly configure the data at the network layer of the U2000, and apply
the data to all related NEs. Compared with configuring NE data on a per-NE basis, configuring
NE data by using the trail management function is quicker and more convenient.
To perform end-to-end network management on the U2000, the relevant license is required.
You can perform the following operations on the U2000:
l
Search for a trail.
Based on the NE configuration data and fiber connection data at the NE layer, the U2000
generates the network-layer information about end-to-end trails, including OTS trails, OCh
client trails, OCh trails, optical multiplex section (OMS) trails, optical supervisory channel
(OSC) trails, ODUk trails and optical channel transport unit (OTUk) trails.
Manage conflicts trails generated during the search process.
Joint trails automatically during the trail search process.
Reserve user-defined information about trails during WDM trail search.
Search for inverse multiplexing trails for 40G and 10G services.
Optimize OMS trails search.
Create a trail.
The U2000 automatically generates an OTS trail after fibers are correctly connected
between specified boards.
Select an NE in the topology and view relevant alarms when creating a trail.
Analyze failure causes when a route fails to be computed at the optical or electrical layer
during trail creation.
Create and manage third-party WDM wavelength trails (OCh trails).
Create ODU0, ODU1, ODU2 or ODU3 trails, and create ODU0, ODU1, ODU2 or
ODU3 cross-connections by using the trail management function.
Search for and manage ODU3 trails.
View detailed information about a route during WDM trail creation.
Create a client trail, and create GE, FC, and FE services based on OCh or ODUk trails
by using the trail management function.
Create SNCP or WXCP by using the trail management function.
Create a WDM trail by double-clicking an NE and select the source and sink nodes.
Select the explicit route for protection when creating a WDM trail.
Use the end-to-end management function for ASON-WDM trails.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-21
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Create multi-layer WDM trails, and create client and ODUk cross-connections by using
the trail management function.
Create trails by means of duplication. That is, create multiple trails by duplicating a
trail. In addition, generate client and ODUk cross-connections in batches by using the
trail management function.
Create WDM trails where fiber jumpers are connected inside a station.
Set port attributes.
View new cross-connections.
l
Manage customers that trails belong.
Create a customer and customer group.
View and modify customer information.
View the trails related to a customer.
View current and history alarms for a customer.
Delete a customer.
View trails.
Join trails of the same level.
Split a trail into trails of the same level.
Query the route information about a trail.
Display the signal flow diagram of a trail.
Query the transmission media layer for a trail.
Query the client trail for a trail.
Query the server trail for a trail.
Query detailed information about a trail, including its attributes and channel allocation.
Query the optical power of a trail. That is, query the optical power of a WDM trail, and
the input and output optical power of the source and sink nodes of the trail.
Query DPPS protection for a trail.
Query valid routes for protected WDM trails.
Query the associated working and protection trails for OCh trails.
Display intra-site fibers in solid lines and inter-site fibers in dotted lines in the signal
flow diagram of a trail.
Display working and protection routes in different colors in the signal flow diagram of
a trail.
Switch from the signal flow diagram of a trail to another window to query alarms.
Query the detailed information about a trail group. The information includes the
direction, name, trail status, source and sink nodes, source and sink wavelengths, bearer
rate, rate, and service type.
Enable or disable service alarms.
Switch between the window for viewing WDM trails and the window for viewing
associated SDH trails.
Support lockout of WDM trails.
Manage the alarms and performance events related to a trail.
Query current alarms of a trail.
7-22
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Query history alarms of a trail.
Query current performance data of a trail.
Query history performance data of a trail.
Query UAT of a trail.
Query performance threshold-crossing records of a trail.
Set the performance parameters and performance threshold of a WDM trail.
Query Ethernet performance of an OCh client trail with services.
Manage in real time network-wide WDM trails with alarms.
View alarms in case of a fiber cut in the signal flow diagram. That is, when alarms occur
in case of a fiber cut, a fiber is displayed in red in the signal flow diagram.
Set the alarm threshold of a trail.
Manage service alarms.
l
Query reports on resource statistics.
Collect the statistics on WDM client-side port resources.
Collect the statistics on WDM inter-site wavelength resources.
Collect the statistics on WDM link resources.
Collect the statistics on WDM wavelength resources.
Generate a statistics report on WDM wavelength resources utilization.
Generate a statistics report on WDM bandwidth resources.
Manage trails.
Query 1+1 protection of optical-layer trails and perform 1+1 protection switching for
the optical-layer trails.
Query trails with WXCP and SNCP protection, and perform protection switching for
the trails.
Use the TTI byte to check fiber connection relationships over an OCh trail.
Apply the automatic naming rule for WDM trails.
Modify the source and sink of ODUk (k = 0, 1, 2, 3) trails and client trails.
Support ODU trail end-to-end management.
Search for and end-to-end manage GE trails based on ODUk.
Manage optical-layer alarms and configure optical-layer overheads on a trail.
Analyze connectivity of a WDM trail and identify a fault on a WDM trail.
Enable and disable WXCP or SNCP protection for an ODUk trail or a client trail.
Set the end-to-end optical power mode.
Implement the "save as" and "print" functions for channel allocation of a WDM trail.
Save the signal flow diagram of a WDM trail.
Manage WDM trails base on rights and domains.
Manage WDM discrete services.
Manage WDM platinum trails.
Create WDM trails by using eight clients at the same time.
View relevant fibers based on trails.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-23
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
View directly the timeslots and wavelengths that are used by a configured client service
trail in the signal flow diagram.
Add a column in the WDM Trail Management window to indicate whether protection
is configured.
Identify whether an OCh trail is used by a client trail.
l
Delete a trail. You can delete a WDM trail (except an OTS trail) from the NE layer and
network layer of the U2000.
Implement enhanced automatic power equilibrium (EAPE) based on OCh trails. The EAPE
function automatically adjusts the transmitted optical power of each channel according to
the signal quality of each channel monitored by the OTU board at the receive end, to ensure
that the quality of signals in each channel at the receive end satisfies the preset requirements.
In this way, service availability is ensured.
Filter trails in the following ways:
Filter all: Filter all trails and display only the qualified trails on a network.
Secondary filter: According to filter criteria, filter trails from those that are already
displayed.
Incremental filter: Filter the newly added trails and display the qualified trails, which
should also be the trails included in the currently displayed trails.
7.5 WDM ASON Management
The automatically switched optical network (ASON) is a new generation of optical network that
integrates switch and transport functions. After a user initiates a service request, the ASON
selects a route automatically, establishes and disconnects connections by using signaling control,
and establishes network connections automatically and dynamically. An ASON NE refers to the
equipment that is enabled with both WDM and ASON features. An ASON network is managed
by the U2000 that combines ASON and WDM features.
Topology Management
You can perform the following operations on the U2000:
l
Discover ASON topologies and resources automatically.
Synchronize NEs in a domain: The U2000 can obtain the topology of an ASON domain
from the active NE.
Set the active and standby NEs.
Manage domains, including creating and deleting domains, and changing domain names.
Query the ASON NE software version.
Manage IDs of ASON NEs.
Query the version of the ASON software.
Manage the OVPN status of ASON NEs.
Disable the ASON feature at the electrical layer.
Control Link Management
You can perform the following operations on the U2000:
7-24
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Synchronize network-wide control links.
Filter control links by domain or source/sink information.
View control links.
Query the information about current or history alarms on a control link.
Set alarm suppression for a control link.
User-define whether to display the color of alarms in the Control Link Management
window.
TE Link Management
You can perform the following operations on the U2000:
l
Synchronize network-wide TE links by domain or payload type.
Filter TE links by domain, link signal type, payload type (optical layer or electrical layer),
OVPN customer, or source/sink information.
View TE links.
Query relevant ASON trails for a TE link.
Create fibers according to the TE link whose payload type is OCh.
Create a virtual TE link.
Delete a virtual TE link.
Manage TE links whose payload type is OCh, ODUk, ODU1_ODU2, or client (GE/Any).
Set the length of a TE link.
Set the risk link group number.
Create a link resource report.
View resource usage.
Query the information about current or history alarms on a link.
Set alarm suppression for control-plane alarms.
Query the status of a TE link.
Delete an interrupted TE link.
Query relevant TE links according to control-plane alarms.
Customize the cost for a TE link.
Allocate optical-layer TE links to OVPN customers.
ASON Trail Management
You can perform the following operations on the U2000:
l
Filter relevant WDM ASON trails by domain, name, actual route, original route, creation
time, planning time, activation status, protection type, service level, alarm level,
management status, whether the original route is active, and whether inverse multiplexing
is available.
Synchronize network-wide WDM ASON trails by domain, service level, or attributes.
View WDM ASON trails.
Query detailed information about WDM ASON trails.
Create WDM ASON trails of the diamond, gold, silver, or copper class.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-25
7 WDM Network Feature Management
7-26
iManager U2000 Unified Network Management System
Product Description
Create WDM ASON trails of the OCh, ODU0, ODU1, ODU2, ODU3, or client level.
Create an inverse multiplexing WDM ASON trail.
Create associated WDM ASON trails with the same source node or different source nodes.
Duplicate WDM ASON trails.
Pre-compute routes when creating or optimizing WDM ASON trails.
Activate or deactivate WDM ASON trails.
Apply planning data to an ASON trail.
Delete inactive WDM ASON trails.
Delete a WDM ASON trail from the NMS.
Set routing attributes, including rerouting lockout status, reversion lockout status, rerouting
priorities, revertive mode, WTR time, scheduled revertive time, rerouting policy, trigger
condition, crankback times, rerouting triggered by SD, and rerouting hold-off time.
Set association source for WDM ASON trails.
Set association for WDM ASON trails.
Cancel association for WDM ASON trails.
Downgrade a WDM ASON trail to a traditional trail.
Query relevant server-layer trails for WDM ASON trails.
Query relevant client-layer trails for WDM ASON trails.
Query relevant trails for ASON trails.
Migrate an electrical-layer ASON trail in-service.
Enable or disable optical parameters verify of WDM ASON OCh trails, including OSNR,
PMD, and dispersion.
Revert a WDM ASON trail to the original route.
Optimize WDM ASON trails.
Switch services in the working or protection diamond trail manually.
Revert WDM ASON trails manually.
Refresh the actual route, original route, associated routes, or signal flow diagram of a WDM
ASON trail.
Set the current route as the original route.
Refresh the preset restoration trail for a WDM ASON trail.
Set one or two preset restoration trails for a WDM ASON trail.
Delete the preset restoration trail for a WDM ASON trail.
View the actual route, original route, or associated routes of a WDM ASON trail.
View the preset restoration trail for a WDM ASON trail.
View alarms of a WDM ASON trail.
View the control-plane alarm suppression information about WDM ASON trails.
Set control-plane alarm suppression for WDM ASON trails.
View performance events of WDM ASON trails.
View control-plane performance of WDM ASON trails.
View the control-plane performance parameters of WDM ASON trails.
Create WDM ASON trail reports.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Revert to original routes in batches.
Set names for WDM ASON trails in batches according to the naming rules.
Save the attributes of a service after creating a WDM ASON service successfully.
Restore the default attributes of a service when creating a WDM ASON service.
Manage creators of WDM ASON trails.
Refresh routes automatically after diamond trail protection switching.
Set the OVPN customer when creating an ASON OCh trail.
Set the OVPN customer of a WDM ASON OCh trail.
Implement sharing of wavelengths in the working and protection diamond ASON trails at
the optical layer.
Implement sharing of wavelengths in associated trails at the optical layer.
Set the route attributes of associated ASON trails, including trigger condition for rerouting
associated routes and shared policy of associated services.
Query the optical power of ASON trails.
Refresh wavelengths at the notification of wavelength changes on an OCh ASON trail.
SRG Management
You can perform the following operations on the U2000:
l
Create, delete, and modify an SRG.
Manage SRGs of the channel type or customized type.
Combination of ASON Trails and Traditional Trails
You can perform the following operations on the U2000:
l
Create an ASON-WDM trail at the OCh, ODU2, ODU1, or client level.
Simplify the layers where multi-layer services are provisioned. To be specific, when you
create a client trail, its server-layer ASON-WDM trail is automatically created.
Implement the OVPN with colored routes in the WDM.
View both WDM trails and managed ASON trails in the WDM Trail Management
window.
Manage overhead bytes, alarms, and performance events of an ASON-WDM trail in a
centralized manner.
Query the ASON trails relevant to a WDM trail.
Query the WDM trails relevant to an ASON trail.
Downgrade an ASON trail to a traditional trail.
Upgrade a traditional WDM trail to a WDM ASON trail.
Collect the alarm statistics of the ASON section, which is added to the alarm statistics of
the ASON-WDM trail.
Manage, search for, upgrade, and downgrade ODU3 ASON-WDM trails.
Exchange of Scripts
You can perform the following operations on the U2000:
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-27
7 WDM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Import and export scripts of WDM ASON nodes.
Import and export scripts of WDM TE links
Import and export scripts of WDM ASON trails.
ASON Management on a Per-NE Basis
You can perform the following operations on the U2000:
l
Manage the ASON features of NEs.
Manage IDs of ASON NEs.
Manage control-plane parameters, including the bandwidth occupancy (%), bandwidth
weight, distance weight, hop weight, and customized cost weight.
Manage LMP control channels.
Manage LMP TE links.
Implement LMP automatic discovery.
Manage OSPF control links.
Manage OSPF TE links.
Manage OSPF IP addresses.
Authenticate the OSPF protocol.
Authenticate the RSVP protocol.
Manage the WDM fiber resource threshold.
Manage WDM ASON trails.
Maintain ASON signaling.
Maintain the ASON switching controller.
Manage the LMP status.
Manage the OSPF protocol status.
Manage the automatic reporting status of control-plane alarms.
Manage levels and suppression status of control-plane alarms.
Query SCN control routes.
Manage control-plane performance parameters.
Query control-plane performance.
Manage resource reservation.
Manage the resource occupation status.
By using the U2000, you can configure SDH ASON feature for the OptiX OSN 8800 I and OptiX
OSN 8800 II as follows:
7-28
Query OSPF SDH TE links.
Query OSPF member links.
Manage the flood threshold of OSPF TE links.
Manage ASON trail groups.
Query SDH ASON trails.
Manage the fiber resource threshold.
Maintain SDH ASON signaling.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
7 WDM Network Feature Management
Maintain the SDH ASON switch controller.
Maintain the ASON-shared MESH switch controller.
Manage control-plane performance of SDH ASON trails.
Manage control-plane alarms of SDH ASON trails.
Manage resource reservation.
Manage VC4 timeslot occupation status.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
7-29
iManager U2000 Unified Network Management System
Product Description
8 RTN Network Feature Management
RTN Network Feature Management
About This Chapter
This topic describes the functional features of RTN NE management and network management.
8.1 RTN NE Management
NE management refers to the management of configurations of an NE in terms of attributes,
communication, services, protection, and clocks. The configuration object is a single NE. The
data is saved to the NE layer of the U2000 and to the database on the NE.
8.2 RTN Protection Subnet Management
A protection subnet is a network structure providing comprehensive self-protection functions.
8.3 End-to-End RTN Management
End-to-end network management is also referred to as trail management. You can construct the
configuration data of the end-to-end network management by searching for the data at the NE
layer of the U2000, or directly configure the data at the network layer of the U2000, and apply
the data to all the related NEs. Compared with configuring NE data on a per-NE basis,
configuring NE data by using the trail management function is faster and more convenient.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
8-1
8 RTN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
8.1 RTN NE Management
NE management refers to the management of configurations of an NE in terms of attributes,
communication, services, protection, and clocks. The configuration object is a single NE. The
data is saved to the NE layer of the U2000 and to the database on the NE.
Basic NE Configuration
You can perform the following operations on the U2000:
l
Support the ability to manage the connections between back-to-back RTN NEs. On the
Main Topology of the U2000, the connections between back-to-back RTN NEs indicate
the relationships between the RTN NEs on the same station that are connected in a backto-back manner through network interfaces.
Modify NE attributes such as:
NE name
NE ID
Extended NE ID
Remarks
Synchronize NE time: Align all NEs with the system time of the U2000 server. The user
can configure the U2000 to automatically synchronize the NE time by specifying the
automatic synchronization period.
Query physical resources in the following lists:
NE list
Board manufacturer information
Board list
Cabinet list
Subrack list
Equipment room list
Support the plug and play feature for boards: After a board is inserted into a slot, the NE
Panel automatically displays the board and board information.
Automatically disable the NE functions: Some NE functions that may affect services, such
as loopback and automatic laser shutdown (ALS), can be periodically disabled. When the
time expires, these operations automatically stop.
Environment monitoring information. You can set the interfaces of environment
monitoring.
Support the license management function for equipment.
Support the press-to-install function for logical boards.
Support the hop management function.
Orderwire Configuration
You can perform the following operations on the U2000:
8-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
8 RTN Network Feature Management
Set and query the orderwire phone numbers, call waiting time, and orderwire phone port
availability.
Set and query the orderwire occupied bytes.
Set and query the F1 data port.
Set and query the broadcast data port.
Equipment Protection Configuration
You can perform the following operations on the U2000:
l
Configure 1+1 board protection.
Configure 1+1 IF protection.
Interface Configuration
You can perform the following operations on the U2000:
l
Set the parameters for an SDH interface.
Set automatic laser shutdown.
Set the parameters for a PDH interface.
Set the parameters for an IF interface.
Set the parameters for a digital interface.
Set the parameters for an outdoor unit (ODU) interface.
Set overhead interfaces, including:
Orderwire
Broadcast data port
Query and set the overhead including:
Regenerator section overhead (J0).
Lower order path overhead (V5, J2)
VC-4 higher order path overhead (J1, C2) and its pass-through or termination.
VC-3 higher order path overhead (J1, C2).
Enable IEEE 1588 overhead bytes.
Support PRBS.
Support the features of packet radio. You can configure a microwave interface in terms of
basic and advanced attributes, IF attributes, and Layer-2 and Layer-3 attributes.
Support the ability to configure the long and short serial numbers for an MP group.
Configuration for RTN Service and Protection
You can perform the following operations on the U2000:
l
Configure VC-12, VC-3, or VC-4 services.
Convert between an SNCP service and a normal service.
Modify attributes of SNCP services.
Perform SNCP protection switching.
Support 1+1 linear MSP, 1:N (N 3) linear MSP.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
8-3
8 RTN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Support the N+1 protection.
Support IF 1+1 protection.
Support the REG configuration.
Support MSP rings.
Support the XPIC feature.
Support Hybrid radio and the AM feature, carrying hybrid E1 and Ethernet services and
enhancing the availability of radio links.
Configuration for Ethernet Interfaces and Services
You can perform the following operations on the U2000:
l
Configure Ethernet internal interfaces, including:
TAG attributes
Encapsulation/mapping
Network attributes
Link capacity adjustment scheme (LCAS)
Bound path
Configure external Ethernet ports, including:
Basic attributes
Flow control
TAG attributes
Network attributes
Advanced attributes.
Configure jumbo frames.
Configure QinQ types.
Configure Ethernet private line (EPL) services.
Configure EVPL (QinQ) services.
Configure Ethernet private LAN (EPLAN) services. You can create a new virtual bridge
(VB) and configure the following: service mount, VLAN filtering, VLAN unicast, disable
MAC address, bound path, self-learning MAC address, and VLAN MAC address table
capacity.
Test frame receiving and transmitting on Ethernet boards.
Configure quality of service (QoS), including:
Flow setting
CAR
CoS
Port shaping
Board shaping
Configure Ethernet Layer-2 switching, including:
Aging time
Spanning tree
IGMP snooping protocol.
8-4
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
8 RTN Network Feature Management
Support the ability to diagnose protocol faults and to restore protocols.
Configure point-to-point LPT management and point-to-multipoint LPT management.
Configure intra-board Ethernet LAGs.
Configure Ethernet ring protection.
Configure the RMON performance functions such as browsing history groups of Ethernet
ports, collecting performance statistics of a group, setting an alarm group of Ethernet ports,
and setting a history control group.
Clock Configuration
You can perform the following operations on the U2000:
l
Query the clock synchronization status.
Set clock source priority list, including:
System clock source priority list
Priority table for phase-locked sources of the first external clock output
Priority table for phase-locked sources of the second external clock output
Set clock source switching, including:
Clock source restoration parameters
Clock source switching condition
Clock source switching
Configure clock subnets, including:
Clock subnet
Clock quality
Synchronization status message (SSM) output control
Clock ID status
Set the external clock output phase-locked source, including:
External clock output phase-locked source
2M phase-locked source external clock attributes
Ethernet OAM Management
You can configure the 802.1ag Ethernet OAM as follows on the U2000:
l
Support maintenance domain (MD), maintenance association (MA), maintenance end point
(MEP), and maintenance intermediate point (MIP).
Perform CC check.
Perform LB check.
Perform LT check.
Perform Ping tests.
Perform performance detect.
You can configure the 802.3ah Ethernet OAM as follows on the U2000:
l
Support OAM self-loop detection.
Enable OAM automatic discovery.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
8-5
8 RTN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Support link event notification and the adjustment of the OAM error frame monitoring
threshold.
Perform remote loopback.
IS-IS Protocol Configuration
The U2000 uses the intermediate system-to-intermediate system (IS-IS) protocol as the protocol
of the network control plane, and provides the following configuration functions:
l
Configure an IS-IS protocol instance.
Enable the IS-IS protocol for a port.
Import routes.
Configure link TE information.
OSPF Protocol Configuration
The U2000 uses the open shortest path first (OSPF) protocol as the protocol of the network
control plane, and provides the following configuration functions:
l
Configure an OSPF protocol instance.
Enable the OSPF protocol for a port.
Import routes.
Configure the TE information about a link.
MPLS Signaling Protocol Configuration
The U2000 supports the configuration of the following signaling protocols:
l
RSVP-TE protocol: Resource reservation protocol-traffic engineering (RSVP-TE) is
derived from the RSVP protocol. The RSVP protocol is a type of QoS protocol. The RSVP
protocol reserves resources for specific services in a network to ensure the service quality.
As the TE is generated, RSVP is extended accordingly to support LSP creation and to realize
TE.
LDP protocol: Label distribution protocol (LDP) is a control and signaling protocol of
multi-protocol label switching (MPLS).
RTN equipment supports using the RSVP-TE protocol to create dynamic LSP connection and
using the LDP protocol to create PW connection.
Static Route Management Configuration
The U2000 supports the configuration of static route management.
Address Resolution Configuration
The U2000 supports the configuration of address resolution.
IEEE 1588 Packet Clock Configuration
You can perform the following operations on the U2000:
8-6
Configure the selection mode of a frequency source.
Set the PTP system time.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Configure a PTP clock subnet.
Configure a PTP clock service.
Set the WTR time for a PTP clock source.
Set the PTP clock source priority.
8 RTN Network Feature Management
ACR Clock Configuration
Configure CES ACR or 1588 ACR clock.
LAG Configuration
Link aggregation group (LAG) aggregates multiple Ethernet physical links to form a logical link
of faster rate for transmitting data. This function improves the link availability and increases
link capacity.
The U2000 supports the configuration of the following LAG attributes:
l
Configure the load sharing type, including sharing and non-sharing.
Configure the LAG type, including manual and static.
Configure the service distribution algorithm of the LAG.
Configure the port priority and system priority of the LAG.
BFD Configuration
Bidirectional forwarding detection (BFD) can be used to check the Ethernet link status.
BFD is a simple Hello protocol. It is similar to the neighbor detection of those famous protocols
in many aspects. A pair of systems periodically sends detection packets on the channel on which
session between the two systems was created. If a system does not receive any detection packet
from the opposite end within a specific time, the system assumes that a failure occurred in some
part of the bidirectional channel of the adjacent system.
QoS Configuration
Quality of service (QoS) indicates the performance of the data flow that travels through a
network. The QoS is used to ensure end-to-end service quality. The QoS cannot increase the
bandwidth, but it can minimize the delay and jitter in the network by reasonably allocating and
monitoring network resources. In this way, the quality of important services is ensured.
The DiffServ (DS) domain consists of a group of network nodes that enable the DiffServ
function, that is, DS nodes. In a DS domain, all DS nodes use the same service provision policy
to realize the same per-hop behavior (PHB). The DS nodes are classified into edge DS nodes
and internal DS nodes. The edge DS nodes usually perform complex flow classification on the
traffic that enters the DS domain. Traffic of different types is marked with different PHB service
types. For internal DS nodes, you need to perform only simple flow classification based on PHB
service type.
The U2000 supports the following QoS operations:
l
Configure Diffsever domains.
Configure ATM CoS mapping.
Configure simple flow classification and complex flow classification.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
8-7
8 RTN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Configure CAR and Shaping.
Configure the color blindness mode.
Configure the WFQ schedule policy.
Configure the port WREQ schedule policy.
To simplify the operation and share some common QoS configuration parameters, the
U2000 supports creating QoS function point policy. The function point policies are as
follows: port policy, ATM policy, and V-UNI ingress policy. Use these function point
policies to bind the CAR configuration attribute, shaping configuration attribute, flow
classification configuration attributes, WFQ schedule policy and WRED policy attributes.
MPLS Tunnel Configuration
The MPLS tunnel is defined in the MPLS protocol. Independent from the service, the MPLS
tunnel realizes end-to-end transmission, and carries the PWs related to the service.
The U2000 supports the following functions for configuring an MPLS tunnel on a per-NE basis:
l
Configure basic attributes of the MPLS.
Configure static unicast MPLS tunnels.
Create forward and backward MPLS tunnels at the same time.
Create the E-LSP.
Manage PWs.
Manage tunnel labels and PW labels.
MPLS Tunnel Protection Group Configuration
The U2000 supports the following functions for configuring an MPLS tunnel protection group:
l
Create a 1+1 MPLS tunnel protection group and a 1:1 MPLS tunnel protection group,
containing the switching mode, revertive mode, wait-to-restore (WTR) time, and hold-off
time.
Perform MPLS tunnel protection switching.
Query the protection switching status of an MPLS tunnel.
PWs with UDP Encapsulation
The U2000 supports the PWs with UDP encapsulation that are carried in IP tunnels.
IP Tunnel and GRE Tunnel Configuration
If the equipment at both ends of an IP network does not support MPLS tunnel, PWE3 services
can pass through the IP network by using an IP tunnel or GRE tunnel.
An IP tunnel and GRE tunnel mainly applies to the Offload scenarios of mobile communication.
The U2000 supports the configuration of bidirectional IP tunnels and GRE tunnels on a per-NE
basis.
The U2000 supports the Offload protection between MPLS and GRE tunnels.
8-8
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
8 RTN Network Feature Management
CES Service Configuration
CES is used for transparent transmission of switching data on TDM circuits in the packet
transport network.
The U2000 supports the following functions for configuring CES services:
l
Create the corresponding PW when creating a CES service.
Create UNI-UNI and UNI-NNI CES services.
Create CES services of structure-aware TDM circuit emulation service over packet
switched network (CESoPSN) and of a structure-agnostic TDM over packet (SAToP).
Configure QoS of the CES service.
Configure the recovery value of idle timeslots.
Carry CES services over IP/GRE tunnels.
ATM Service Configuration
ATM emulation service is mainly used to transparently transmit ATM services in the packet
transport network..
The U2000 supports the following functions for creating ATM services:
l
Create an ATM service that contains multiple ATM connections.
Create UNI-UNI and UNIs-NNI ATM services.
Create PVP and PVC ATM services.
Create the corresponding PW when creating an ATM service.
Configure the IMA group.
Configure QoS of the ATM service.
Configure CoS mapping.
E-Line Service Configuration
The E-line service is a point-to-point Ethernet service. The equipment transmits user packets
from the user side to the network side based on Port or Port+VLAN. User data can be
transparently transmitted in a point-to-point manner.
The U2000 supports the following functions for configuring E-line services on a per-NE basis:
l
Create UNI-UNI E-Line services.
Create UNI-NNI E-Line services that are carried on ports.
Create UNI-NNI E-Line services that are carried on PWs.
Create UNI-NNI E-Line services that are carried on QinQ links.
Configure the service and the QoS of the corresponding PW when creating an L2VPN
service.
Configure the V-UNI group.
E-AGGR Service Configuration
The E-AGGR service is a multipoint-to-point Ethernet service. The equipment uses several ports
to access services from the V-UNI side, and converges the services into one PW at the network
side for transmission. User data from multiple points can be converged into one point.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
8-9
8 RTN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
The U2000 supports the following functions for configuring E-AGGR services on a per-NE
basis:
l
Configure the VLAN forwarding table items of an E-AGGR service.
Configure the service and the QoS of the corresponding PW when creating an E-AGGR
service.
Configure the V-UNI group.
MPLS OAM Configuration
MPLS OAM is an OAM function of the MPLS network. This function can check the quality of
LSPs in an MPLS network. The MPLS OAM scheme can effectively check, acknowledge, and
locate a defect inside the network at the MPLS layer. It can report and handle a defect. When a
fault occurs, the MPLS OAM provides a trigger scheme of protection switching.
The U2000 provides the following functions for configuring MPLS OAM:
l
Configure MPLS OAM parameters of a tunnel.
Perform CV/FFD checks.
Perform LSP ping checks.
Perform PW ping checks.
Perform LSP traceroute checks.
ATM OAM Configuration
ATM OAM is an end-to-end OAM function for ATM services. This function can check the
quality of ATM links that pass through multiple NEs. The ATM OAM function checks an ATM
link by inserting some OAM cells of the standard cell structure to the user cell flow.
The U2000 provides the following functions for configuring ATM OAM:
l
Set segment end attributes.
Perform CC activation test.
Perform remote loopback.
Set the LLID.
8.2 RTN Protection Subnet Management
A protection subnet is a network structure providing comprehensive self-protection functions.
To perform protection subnet management, you need to have the related license.
You can perform the following operations on the U2000:
8-10
Create an RTN protection subnet.
Create an IF 1+1 protection subnet.
Create an IF N+1 protection subnet.
Manage RTN protection subnets.
Set the parameters for a protection subnet.
Query the switching status of a protection subnet.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Query and delete a protection subnet.
Query protection subnet resources.
8 RTN Network Feature Management
8.3 End-to-End RTN Management
End-to-end network management is also referred to as trail management. You can construct the
configuration data of the end-to-end network management by searching for the data at the NE
layer of the U2000, or directly configure the data at the network layer of the U2000, and apply
the data to all the related NEs. Compared with configuring NE data on a per-NE basis,
configuring NE data by using the trail management function is faster and more convenient.
To perform end-to-end network management, the relevant license is required.
You can perform the following operations on the U2000:
l
Create and maintain an RTN trail
Create a PDH microwave trail
Create an SDH microwave trail.
Activate or deactivate an RTN trail.
Manage the alarms and performance events related to an RTN trail.
Query current and history alarms, current and history performance data, UAT, and
performance threshold-crossing records of an RTN trail.
Set the performance parameters for an RTN trail.
Query the RTN trails and customer information affected by an alarm.
Filter trails in three ways
Filter all: Filter all trails and display only the qualified trails on a network
Secondary filter: Filter the trails that are displayed, according to the filter criteria.
Incremental filter: Filter all trails and display the newly qualified trails together with
the currently displayed ones
Management of Packet Services
l
PWE3 service management
Create PWE3 services of multiple types, such as ATM, CES, and Ethernet.
Predeploy a PWE3 service.
Implement the function of automatically discovering PWE3 services.
Modify and delete PWE3 services, and filter PWE3 services to view the desired services.
Manage multi-segment PWE3 services.
Implement the protection management of PWE3 services.
View the topology of PWE3 services.
View the alarms of a PWE3 service.
View the performance of a PWE3 service.
Manage discrete PWE3 services.
Manage PWE3 services based on rights and domains.
Clone a PWE3 service.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
8-11
8 RTN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Manage PWE3 service templates.
Implement the function of automatically generating Ethernet OAM for PWE3 services.
l
Tunnel Management
Create static CR, RSVP, LDP, and IP tunnels.
Create RSVP and LDP tunnels in batches.
Predeploy a tunnel.
Implement the function of automatically discovering tunnels.
Modify and delete a tunnel, and filter tunnels to view the desired tunnels.
View the topology of tunnels, including the working and protection routes.
View the alarm of a tunnel.
View the performance of a tunnel.
Manage discrete tunnels.
Create, modify, and delete 1+1 or 1:1 tunnel protection groups, and implement the
function of automatically discovering 1+1 or 1:1 tunnel protection groups.
Switch services in a 1+1 or 1:1 tunnel protection group manually.
Implement the function of displaying the topology of 1+1 or 1:1 tunnel protection
groups.
Network-Wide Clock Topology Management
8-12
Support the IEEE 1588 V2, SDH, and synchronous Ethernet clocks.
Display clock trace relationship.
Display clock alarm status.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
PTN Network Feature Management
About This Chapter
This topic describes the functions and features of PTN NE management and network
management.
9.1 PTN NE Management
NE configuration includes the configuration of attributes, communications, services, protection
schemes, and clocks on an NE.
9.2 E2E PTN Management
E2E network management is also referred to as trail management, which means the trail-based
configuration of network management data. The trail-based configuration can be performed by
searching for the NE-layer data on the U2000 or by configuring the network-layer data on the
U2000. Then, the configuration is delivered to all associated NEs. Compared with the NE-based
configuration, the trail-based configuration is easier.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-1
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
9.1 PTN NE Management
NE configuration includes the configuration of attributes, communications, services, protection
schemes, and clocks on an NE.
Basic NE Configuration
l
Modifying NE attributes such as:
NE name
NE ID
Extended NE ID
Remarks
NE pre-configuration
Synchronizing NE time: NE time can be synchronized by delivering the system time of the
U2000 server to all NEs. In addition, you can specify automatic synchronization time and
automatic synchronization period on the U2000.
Plug and play feature of boards: After a board is inserted into a correct slot, the NE Panel
displays the board and board information.
Disabling functions automatically: Service-affecting functions, such as loopback and
automatic laser shutdown (ALX), can be disabled automatically by specifying an automatic
disabling time. When the time arrives, these functions are disabled automatically.
Environment monitoring
Board replacement
Fan management
Service Interface Types Configuration
The working mode and application scenarios of an interface are determined by the general
attributes, Layer 2 attributes, and Layer 3 attributes of the interface.
Basic attributes are the physical attributes of an interface. Layer 2 attributes are the data link
layer attributes of an interface, such as ATM, VLAN, and QinQ. Layer 3 attributes are the
network layer attributes of an interface, such as IP attribute.
Table 9-1 lists the types of PTN service interfaces supported by the U2000.
9-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Table 9-1 Types of PTN service interfaces
Service
Interface
Supported
Port Mode/
Encapsulation
Type
Port Type
MP Group
Supported or
Not
Function
SDH interface
General
attributes
Physical port
Not supported
The general
attributes of an
SDH interface
can be
configured
according to its
Layer 3
attributes or be
set to a
channelized
STM service
interface.
Layer 2
attributes
Physical port
Not supported
Carrying ATM
services
Layer 3
attributes
Physical port
Not supported
Carrying
tunnels after the
PPP protocol is
enabled
General
attributes
Physical port
Not supported
Carrying TDM
services
Layer 2
attributes
Physical port
Not supported
Carrying IMA
signals
Layer 3
attributes
Physical port
Supported
Added to a
multi-link PPP
(MP) group
after the PPP
protocol is
enabled
General
attributes
N/A
The general
attributes of an
Ethernet
interface can be
configured
according to the
Layer 2
attributes and
Layer 3
attributes of the
interface.
PDH interface
Ethernet
interface
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-3
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Service
Interface
Ethernet virtual
interface
Supported
Port Mode/
Encapsulation
Type
Port Type
MP Group
Supported or
Not
Function
Layer 2
attributes
Physical port
Not supported
Carrying userside or networkside Ethernet
services
Layer 3
attributes
Physical port
Not supported
Carrying
tunnels
General
attributes
Logical port
Not supported
The general
attributes of an
Ethernet
interface can be
configured
according to
Layer 2
attributes and
Layer 3
attributes.
Layer 2
attributes
Logical port
Not supported
VLAN Sub
Interface:
carrying
Ethernet
services
Layer 3
attributes
Logical port
Not supported
l EOA
Virtual
Interface:
carrying IP
tunnels or
GRE tunnels
l VLAN Sub
Interface:
used for
BFD,
L3VPN or
carrying
tunnels
l L3 Virtual
Interface:
carrying IPLINE
services
9-4
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Service
Interface
ADSL interface
G.SHDSL
interface
Serial interface
Issue 05 (2010-11-19)
9 PTN Network Feature Management
Supported
Port Mode/
Encapsulation
Type
Port Type
MP Group
Supported or
Not
Function
Advanced
attributes
Logical port
Not supported
The advanced
attributes of an
Ethernet virtual
interface can be
configured
according to
attributes of an
ADLS2+
interface.
General
attributes
Physical port
Carrying ADSL
signals
DSLTRUNK
attributes
Logical port
Carrying ADSL
signals
General
attributes
Physical port
Carrying
G.SHDSL
signals
Bound mode
N/A
Carrying
G.SHDSL
signals
EFM bound
group
Logical port
Set according to
the bound mode
ATM bound
group
Logical port
Set according to
the bound mode
IMA bound
group
Logical port
Carrying
G.SHDSL
signals
General
attributes
The general
attributes of a
serial interface
can be
configured
according to the
Layer 3
attributes of the
interface.
Layer 3
attributes
Logical port
Supported
A serial
interface can be
added to an MP
group after the
PPP protocol is
enabled.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-5
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Service
Interface
Supported
Port Mode/
Encapsulation
Type
Port Type
MP Group
Supported or
Not
Function
MP Group
General
attributes
The general
attributes of an
MP group can
be configured
according to the
IP attributes of
the group.
IP attributes
Logical port
Carrying
tunnels
Microwave Interface Configuration
You can perform the following operations on the U2000:
l
Configure a microwave interface, including general attributes, IF attributes, Layer 2
attributes, Layer 3 attributes, and advanced attributes.
Configure a radio link, including IF 1+1 protection, IF boards, and ODU boards.
Configure HOP management.
IS-IS Protocol Configuration
The U2000 uses the intermediate system-to-intermediate system (IS-IS) protocol as the protocol
of the network control plane, and provides the following configuration functions:
l
Configure node attributes
Configure port attributes
Import routes
Configure the TE information of a link
Configure GR sessions
Configure route aggregation
View route forwarding tables
OSPF Protocol Configuration
The U2000 uses the open shortest path first (OSPF) protocol as the protocol of the network
control plane, and provides the following configuration functions:
9-6
Configure node attributes
Configure port attributes
Configure peer attributes
Import routes
Configure the TE information of a link
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Configure route aggregation
Query peer information
View route forwarding tables
9 PTN Network Feature Management
MP-BGP Protocol Configuration
The U2000 uses the internal border gateway protocol (IBGP) to implement L3VPN functions,
and provides the following configuration functions:
l
Configure MP-BGP instances
Configure MP-BGP peers
Configure route filtering policies
LDP Protocol Configuration
The U2000 uses the label distribution protocol (LDP) to create LSP connections and PW
connections, and provides the following configuration functions:
l
Configure MPLS-LDP peer entities
Configure node attributes
Configure port attributes
Configure IP address filtering tables
Configure routing policies
Configure label policies
RSVP Protocol Configuration
The U2000 uses the resource reserved protocol (RSVP) to create LSP connections, and provides
the following configuration functions:
l
Configure node attributes
Configure port attributes
Static Route Management Configuration
The U2000 supports the configuration of static route management.
Address Resolution Configuration
The U2000 supports the configuration of address resolution.
Clock Configuration
The U2000 supports the configuration of various clock modes, and provides the following
functions:
l
Configure the clock domain
Query the status of clock synchronization
Configure the IEEE 1588 Packet Clock
Configure clock services
Configure clock synchronization attributes
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-7
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Configure the clock source priority table
Configure clock subnets
Configure external time interfaces
l
Configure ACR clocks
Configure CES ACR and 1588 ACR clocks
Configure physical-layer clocks
Query the status of clock synchronization
Set clock source priority tables, including
System clock source priority list
Priority table for phase-locked sources of 1st external clock output
Priority table for phase-locked sources of 2nd external clock output
Setting clock source switching parameters, including
Clock source reversion parameters
Clock source switching condition
Clock source switching
Configure clock subnets, including
Clock subnets
Clock quality
SSM output control
Clock ID status
Setting phase-locked sources output by external clock, including
External clock output phase-locked source
2 Mbit/s phase-locked source external clock attributes
Board-Level Protection Configuration
You can perform the following operations on the U2000:
l
Configure TPS protection of a subboard.
Configure board 1+1 protection for the SCC and cross-connect boards.
Check the switching status.
Perform protection switching.
Synchronization Protocol Configuration
In the application scenario of dual-homing, the status of the peer equipment needs to be obtained
either for the MC LAG or for the cross-MC LMSP. Meanwhile, the actions on both sides need
to be negotiated based on different fault cases. With the method of adding information of the
peer end, a channel is established for control status synchronization with the peer end. In this
manner, the control packets can be transmitted and received through the channel and link fault
detection can be performed.
9-8
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
LAG/MC LAG Configuration
A link aggregation group (LAG) aggregates multiple Ethernet physical links to form a logical
link with a higher transmission rate. This function improves link availability and increases link
capacity.
A multi-chassis (MC) LAG achieves load sharing between NEs.
The U2000 supports the configuration of the following LAG/MC LAG attributes:
l
Load sharing type (sharing or non-sharing)
LAG types (manual or static)
Load sharing hash algorithm
Port priority and system priority
LMSP/MC LMSP Configuration
Linear MSP (LMSP) includes 1+1 linear MSP and 1:N linear MSP. The protection scheme uses
the protection channel to protect services that are transmitted on the working channel. When the
working channel fails, services are switched to the protection channel. Linear MSP applies to
the POS interface and structured STM interface.
The multi-chassis (MC) LMSP can implement the LMSP between NEs.
The U2000 supports the following LMSP/MC LMSP functions:
l
Create LMSP groups
Check the status of LMSP groups
Perform a linear MSP switching
MSTP Configuration
The multiple spanning tree protocol (MSTP) can be used to clear loops in a network. The MSTP
uses a specific algorithm to block some redundant trails and change a loop network to a nonloop tree network. This function prevents packet increase in a loop network and generation of
broadcast storms in an endless cycle. Different from the STP and RSTP, the MSTP can forward
data according to VLAN packets, achieving load balance of VLAN data.
The U2000 provides the following functions:
l
Configure parameters of port groups and bridges
Configure CIST and MSTI parameters
Query CIST status and MSTI status
IGMP Snooping Configuration
The Internet group management protocol snooping (IGMP Snooping) is the multicast constraint
scheme that runs on Layer 2 equipment, and is used to manage and control multicast groups.
The U2000 supports the configuration of IGMP snooping for E-LAN services, and provides the
following functions:
l
Configure IGMP Snooping protocol parameters
Configure fast leave ports
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-9
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Manage routes
Configure route member ports
Query statistics of IGMP protocol packets.
BFD Configuration
The bidirectional forwarding detection (BFD) protocol can be used to check the Ethernet link
status.
BFD is a simple Hello protocol. It is similar to the neighbor detection of those famous protocols
in many aspects. A pair of systems periodically send detection packets on the bidirectional
channel where a session between the two systems is created. If a system does not receive any
detection packet from the opposite end in a specific time, the system regards that a failure occurs
on the channel.
The U2000 supports the BFD detection on IP/GRE tunnels and the interior gateway protocol
(IGP).
LPT Configuration
The link state pass through (LPT) protocol is used to return the remote-end link status to the
near end. The near-end equipment performs operations according to the remote-end link status.
When the intermediate transmission network is faulty, the LPT immediately informs the access
equipment at both ends of the transmission network to activate the backup network. In this
manner, the normal transmission of important data is ensured.
QoS Configuration
The quality of service (QoS) indicates the performance of the data flow that travels through a
network. The QoS is used to ensure end-to-end service quality. The QoS cannot increase the
bandwidth, but it can minimize the delay and jitter in the network by properly allocating and
monitoring network resources. In this manner, the quality of important services is ensured.
The DiffServ (DS) domain consists of a group of network nodes that enable the DiffServ
function, that is, DS nodes. In a DS domain, all DS nodes use the same service provision policy
to achieve the same per-hop behavior (PHB). DS nodes are classified into edge DS nodes and
internal DS nodes. Edge DS nodes usually perform complex flow classification on the traffic
that enters the DS domain. Different types of traffic are marked with different PHB service types.
Internal DS nodes only need to perform simple flow classification based on PHB service types.
The U2000 supports the following QoS functions:
9-10
Configure QoS profile
Configure DiffServ domains
Configure ATM CoS mapping
Configure SVLAN DEI used flag
Configure simple flow classification and complex flow classification
Configure CAR and shaping
Configure the color blindness mode
Configure the WFQ schedule policy
Configure the port WRED policy
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Configure the service WRED policy
To simplify operations and share common QoS configuration parameters, the U2000
supports the creation of QoS function point policies, including port policy, ATM policy,
V-UNI ingress policy, V-UNI egress policy, PW policy, and QinQ policy. By using these
function point policies, you can bind CAR configuration, shaping configuration, flow
classification configuration, WFQ schedule policy, WRED policy, and color blindness
mode.
Configure CoS queue mapping
Configure the QoS profile for applying the same QoS policies to multiple NEs.
MPLS Tunnel Configuration
The multi-protocol label switch (MPLS) protocol achieves transparent transmission of data
services. MPLS tunnels are the tunnels defined in the MPLS protocol. Independent from the
service, the MPLS tunnel achieves end-to-end transmission and carries the PWs related to the
service.
See Figure 9-1. Unicast MPLS tunnel is mainly used to transparently transmit point-to-point
PWE3 services.
Figure 9-1 Unicast MPLS tunnel
The U2000 provides the following functions associated with MPLS tunnels on a per-NE basis:
l
Configure MPLS basic attributes
Configure static unicast MPLS tunnels
Create forward and backward MPLS tunnels at the same time
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-11
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Create static and bidirectional MPLS tunnels
Create the E-LSP
Manage PWs
Manage tunnel labels and PW labels
MPLS Tunnel Protection Group Configuration
The U2000 provides the following functions associated with MPLS tunnel protection groups:
l
Create MPLS tunnel 1+1 protection groups and MPLS tunnel 1:1 protection groups and
configuring switching mode, revertive mode, wait-to-restore (WTR) time, and hold-off
time for the groups
Perform MPLS tunnel protection switching
Query the status of an MPLS tunnel protection group
MS PW Configuration
By creating multi-segment pseudowire (MS-PW) to transmit services, you can save tunnel
resources and transmit services over different networks.
PW APS/MC PW APS Configuration
As a network protection mechanism, PW automatic protection switching (APS) is intended to
protect the services on the working PW with a protection PW. That is, when the working PW is
faulty, the services on the working PW are switched to the protection PW. In this manner, the
services on the working PW are protected.
The MC PW APS can be used to implement inter-NE PW APS protection.
The following PW APS/MC PW APS functions can be performed on a per-NE basis:
l
Create protection groups
Bind the master and slave protection pairs
IP Tunnel and GRE Tunnel Configuration
If the equipment at the two ends of an IP network does not support MPLS tunnels, PWE3 services
can pass through the IP network by using IP tunnels or GRE tunnels.
IP tunnels and GRE tunnels mainly apply to the Offload scenarios of mobile communication.
The U2000 supports the configuration of bidirectional IP tunnels and GRE tunnels on a per-NE
basis.
Dual-Homing Protection Configuration
In the case of dual-homing protection, two PE nodes (dual-homing nodes) are connected to one
CE node through attachment circuit (AC) links so that the services received by the PE nodes at
both ends of the bearer network can be protected.
The following types of dual-homing protection can be configured for ATM and CES services:
9-12
1:1 MC-PW APS and 1:1 MC-LMSP
1:1 MC-PW APS and 1+1 MC-LMSP
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
1:1 PW redundancy and 1:1 MC-LMSP
1+1 PW redundancy and 1+1 MC-LMSP
9 PTN Network Feature Management
The following types of dual-homing protection can be configured for E-line services.
l
1:1 MC-PW APS and MC-LAG
1:1 PW redundancy and MC-LAG
CES Service Configuration
Circuit emulation services (CES services) achieve transparent transmission of TDM circuit
switching data on the PSN.
See Figure 9-2. The 2G/3G stations or Intranet line accesses the PTN equipment by using the
E1/ channelized STM-1 line. The equipment divides the E1 signals into pieces, encapsulates the
pieces into the Ethernet, and transmits the E1 signals to the opposite end by using the PW.
Figure 9-2 CES service application model
The U2000 provides the following functions associated with CES services:
l
Create CES services and corresponding PWs at the same time
Create UNI-UNI and UNI-NNI CES services
Create CES services of structure-aware TDM circuit emulation service over packet
switched network (CESoPSN) and CES services of structure-agnostic TDM over packet
(SAToP)
Configure QoS policies of CES services
Configure idle timeslot recovery value
Configure CES service alarm transparent transmission
Select the tunnel where a PW is carried online
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-13
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
ATM Service Configuration
ATM emulation services achieve transparent transmission of ATM services on the PSN.
See Figure 9-3. The 3G station accesses the PTN equipment by using the ATM IMA group.
The equipment encapsulates the ATM cells into the Ethernet, and transmits the ATM cells to
the opposite end by using the PW.
Figure 9-3 ATM service application model
The U2000 provides the following functions associated with ATM services:
l
Create ATM services that contain multiple ATM connections
Create UNI-UNI and UNI-NNI ATM services
Create PVP and PVC ATM services
Create ATM services and corresponding PWs at the same time
Configure the IMA group
Configure QoS policies of ATM services
Configure the CoS mapping table.
Select the tunnel where a PW is carried online
E-Line Service Configuration
E-line services achieve point-to-point transparent transmission of user data. The equipment
transmits user packets from the user side to the network side based on Port or Port+VLAN.
See Figure 9-4. Company A has branches in City 1 and City 3. Company C has branches in City
1 and City 2. Branches of Company A or Company C that are in different cities need data
communication. The PTN equipment can provide E-line services for Company A and Company
C, to meet their communication requirements. In addition, the service data can be completely
isolated.
9-14
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Figure 9-4 E-Line Service
The U2000 supports the following functions associated with E-line services on a per-NE basis:
l
Create UNI-UNI E-Line services
Create UNI-NNI E-Line services that are carried on ports
Create UNI-NNI E-Line services that are carried on PWs
Create UNI-NNI E-Line services that are carried on QinQ links
Configure QoS policies for L2VPN services and corresponding PWs during the creation
of L2VPN services
Configure the V-UNI group
Select the tunnel where a PW is carried online
E-AGGR Service Configuration
E-AGGR services achieve multipoint-to-point aggregation of user data. The equipment uses
several ports to access services from the V-UNI side, and converges the services into one PW
at the network side for transmission.
See Figure 9-5 and Figure 9-6. A carrier wants to construct a 3G network. Services of each
Node B are converged and transported to the RNC. The data between each Node B and RNC is
regarded as one service. At the convergence point, the QoS parameters such as the overall
bandwidth are specified.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-15
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Figure 9-5 E-AGGR service scenario 1
Figure 9-6 E-AGGR service scenario 2
The U2000 supports the following functions associated with E-AGGR services on a per-NE
basis:
9-16
Configure the VLAN forwarding table items of an E-AGGR service
Configure QoS policies for L2VPN services and corresponding PWs during the creation
of L2VPN services
Configure the V-UNI group
Select the tunnel where a PW is carried online
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
E-LAN Service Configuration
Based on the self-learning of MAC addresses, E-LAN services achieve packet forwarding
between multiple V-UNI and NNI interfaces.
See Figure 9-7. The HQ of Company A is in City 3. Company A has Branch A in City 1, City
2, and City 3, and has Branch B in City 1 and City 2. Branch A and Branch B do not have business
with each other. Hence, the data should be isolated between the two branches. The HQ has
requirements of communicating with each branch and accessing the Internet.
Figure 9-7 E-LAN service
E-LAN services use different VLAN IDs to identify service data of different branches. In this
way, data is shared within a branch and is isolated from the data for other branches. The Internet
data of the HQ is also isolated from the internal service data by using the VLAN.
The U2000 supports the following functions associated with E-LAN services on a per-NE basis:
l
Create E-LAN services that are carried on port
Create E-LAN services that are carried on PWs
Create E-LAN services that are carried on QinQ links
Configure QoS policies for L2VPN services and corresponding PWs during the creation
of L2VPN services
Configure the V-UNI and NNI interfaces of an E-LAN service
Configure the split horizon group of an E-LAN service
Configure the V-UNI group
Configure the MAC address learning parameters
Configure the unknown frame processing mode
Configure the static MAC address
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-17
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Disable an MAC address
Configure the self-learning of MAC addresses
Select the tunnel where a PW is carried online
Service Mirroring Configuration
In service mirroring, all packets that enter a certain port are duplicated and then duplicated
packets are transmitted through an observation port. In this manner, the normal service is scarcely
affected when packets of the mirrored service are captured and analyzed.
You can configure the service mirroring as follows:
l
Local service mirroring
Remote service mirroring
MPLS OAM Configuration
MPLS OAM is an OAM function of the MPLS network. This function can check the quality of
LSPs in an MPLS network. The MPLS OAM scheme can effectively detect a defect inside the
network at the MPLS layer, and then report and handle the defect. When a fault occurs, the
MPLS OAM triggers a protection switching.
The U2000 provides the following MPLS OAM functions:
l
Configure MPLS OAM parameters of a tunnel
Perform CV/FFD check
Perform LSP ping check
Perform PW ping check
Perform LSP traceroute check
Perform PW traceroute check
Enable and disable FDI
Ethernet Service OAM Configuration
Ethernet service OAM is an end-to-end OAM function for services. This function can check the
quality of Ethernet links that pass through multiple NEs. The Ethernet service OAM checks an
Ethernet link by sending OAM packets. The OAM packet is handled only at the MAC layer. As
a low rate protocol, the OAM protocol occupies very low network bandwidth. Hence, this
function does not affect services carried by the link.
The U2000 provides the following Ethernet service OAM functions:
9-18
Create maintenance domains (MDs), maintenance associations (MAs), maintenance end
points (MEPs), and maintenance intermediate points (MIPs)
Perform a CC check
Perform an LB check
Perform an LT check
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Ethernet Port OAM Configuration
The Ethernet port OAM is mainly used to automatically check the connectivity and performance
and locate the faults of the physical links. It is applicable when the physical Ethernet ports are
directly connected.
The U2000 provides the following Ethernet port OAM functions:
l
Configure OAM parameters
Configure the OAM error frame monitoring
Query the remote OAM parameters
ATM OAM Configuration
ATM OAM is an end-to-end OAM function for ATM services. This function can check the
quality of ATM links that pass through multiple NEs. The ATM OAM function checks an ATM
link by inserting some OAM cells of the standard cell structure into the user cell flow.
The U2000 provides the following ATM OAM functions:
l
Set segment end attributes
Perform CC activation tests
Perform remote loopbacks
Settin the LLID
Configure ATM alarm transmission
NMS Server Configuration
After the IP address of the NMS is configured on the gateway NE, all the managed non-gateway
NEs can automatically go online after being powered on.
9.2 E2E PTN Management
E2E network management is also referred to as trail management, which means the trail-based
configuration of network management data. The trail-based configuration can be performed by
searching for the NE-layer data on the U2000 or by configuring the network-layer data on the
U2000. Then, the configuration is delivered to all associated NEs. Compared with the NE-based
configuration, the trail-based configuration is easier.
To perform E2E network management on the U2000, the relevant license is required.
PWE3 Service Management
You can perform the following operations on the U2000:
l
Create PWE3 services of multiple types, such as ATM, CES, and Ethernet services.
Predeploys PWE3 services.
Implement the function of automatically discovering PWE3 services.
Modify and delete PWE3 services, and view PWE3 services by using the filtering function.
Manage PWE3 services.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-19
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Implement the protection management of PWE3 services.
View the topology of PWE3 services.
View the alarms of PWE3 services.
View the performance events of PWE3 services.
Create a monitoring instance for a PWE3 service.
Test and check PWE3 services.
Manage discrete PWE3 services.
Manage PWE3 services based on authority.
Clone PWE3 services.
Manage PWE3 service templates.
Implement the function of automatically generating Ethernet OAM for PWE3 services.
Set and view the status of port loopback at the node of PWE3 services.
VPLS Service Management
You can perform the following operations on the U2000:
l
Create VPLS services.
Predeploy VPLS services.
Implement the function of automatically discovering VPLS services.
Modify and delete VPLS services, and view VPLS services by using the filtering function.
Manage VPLS services.
View the topology of VPLS services.
View the alarms of VPLS services.
View the performance events of VPLS services.
Create a monitoring instance for a VPLS service.
Test and check VPLS services.
Manage discrete VPLS services.
Manage VPLS services based on authority.
Manage VPLS service templates.
Implement the function of automatically generating Ethernet OAM for VPLS services.
Set and view the status of port loopback at the node of VPLS services.
L3VPN Service Management
You can perform the following operations on the U2000:
9-20
Create an L3VPN service that supports the BGP/MPLS protocol.
Predeploy an L3VPN service.
Implement the function of automatically discovering L3VPN services.
Modify and delete L3VPN services, and view L3VPN services by using the filtering
function.
View the topology of L3VPN services.
View the alarms of an L3VPN service.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
View the performance events of an L3VPN service.
Create a monitoring instance for a L3VPN service.
Test and check L3VPN services.
Manage discrete L3VPN services.
Manage L3VPN services based on authority.
Manage L3VPN service templates.
Configure the VRRP.
Set and view the status of port loopback at the node of L3VPN services.
Configure OAM.
Tunnel Management
You can perform the following operations on the U2000:
l
Create static CR, RSVP, LDP, and IP tunnels.
Create RSVP and LDP tunnels in batches.
Predeploy a tunnel.
Implement the function of automatically discovering tunnels.
Modify and delete a tunnel, and view tunnels by using the filtering function.
View the topology of tunnels, including the working and protection routes.
View the alarms of a tunnel.
View the performance events of a tunnel.
Create a monitoring instance for a tunnel.
Test and check a tunnel.
Manage discrete tunnels.
Manage static CR, RSVP, LDP, and IP tunnels.
Create, modify, and delete 1+1 or 1:1 tunnel protection groups, and implement the function
of automatically discovering 1+1 or 1:1 tunnel protection groups.
Switch services in a 1+1 or 1:1 tunnel protection group manually.
Implement the function of displaying the topology of 1+1 or 1:1 tunnel protection groups.
Create a tunnel and its protection tunnel at the same time.
Display the name of a tunnel in the global LSP view.
Manage the bidirectional static CR tunnels.
Set and view the status of port loopback at the node of tunnel.
Configure OAM.
IP Line Service Management
You can perform the following operations on the U2000:
l
Create an IP line service.
Predeploy an IP line service.
Implement the function of automatically discovering IP line services.
Implement the protection management of IP line service.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
9-21
iManager U2000 Unified Network Management System
Product Description
9 PTN Network Feature Management
Modify and delete IP line services, and view IP line services by using the filtering function.
View the topology of IP line services.
View the alarms of an IP line service.
View the performance events of an IP line service.
Test and check an IP line service.
Manage IP line services based on rights and domains.
Set and view the status of port loopback at the node of IP line services.
Composite Service Management
You can perform the following operations on the U2000:
l
Manage PWE3 access into PWE3 and PWE3 access into E-AGGR services.
Modify and delete composite services, and view composite services by using the filtering
function.
Implement the function of automatically discovering composite services.
View the topology of composite services, including the internal connections between the
services.
Display the status of composite services.
PTN Network Expansion and Service Cutover Management
You can perform the following operations on the U2000:
9-22
Expand a PTN by adding nodes, deleting nodes, and upgrading or adjusting link capacities.
Implement the cutover of PWE3 trails.
Prepare a manual or scheduled service cutover plan.
Prepare a service cutover plan by using either the rollback cutover policy or the best-effort
cutover policy.
Hand over, restore, and verify the trails of cutover groups in batches.
Create and modify cutover groups and cutover plans, and delete cutover groups and cutover
plans in batches.
Create and delete active and pre-configured services in cutover groups.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
10
10 Router Feature and Switch Feature Management
Router Feature and Switch Feature
Management
About This Chapter
This topic describes router features and switch features.
10.1 Router Management
Router management allows you to configure and maintain routers by means of the GUI.
10.2 Router V8 Management
Router V8 management allows you to view NE configurations by means of GUIs.
10.3 Automatic NE Configuration Management
Automatic NE configuration management is implemented by means of DHCP on the U2000.
Automatic NE configuration management allows you to deploy and remotely debug case-shaped
routers, reducing the costs in device deployment and increasing the efficiency of device
deployment.
10.4 Switch Management
Switch management allows you to configure and maintain switches by means of the GUI.
10.5 Template Management
In NE configuration management, many operations need to be performed repeatedly. The
template management function is introduced to solve this problem. This function allows you to
rapidly configure NEs in batches.
10.6 Diagnosis Management
Diagnosis management provides easy-to-use diagnostic functions for you to test network and
service connectivity. Diagnostic cases can be run manually or run automatically at scheduled
times.
10.7 Cluster Management
The Huawei Group Management Protocol (HGMP) is mainly used to solve the problems of
automatic management operations and centralized management for multiple dispersed low-end
and mid-range switches.
10.8 Node Redounded Management
Enhanced-Trunk (E-Trunk), developed on the basis of Link Aggregation Control Protocol
(LACP), is a protocol that controls and implements link aggregation among multiple sets of
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10-1
10 Router Feature and Switch Feature Management
iManager U2000 Unified Network Management System
Product Description
equipment. E-Trunk is mainly applied to a scenario where a CE is dual homed to a VPLS, VLL,
or PWE3 network. In the scenario, E-Trunk can be used to protect the PEs and the links between
the CE and PEs.
10.9 Report Subsystem Management
The report subsystem allows you to generate, distribute, and manage reports based on the Web
and helps you to monitor, analyze, and optimize network performance.
10.10 VPN Service Management
The U2000 provides centralized and unified management, including service deployment, service
monitoring, and service diagnosis, on VPN services, namely, BGP/MPLS VPN service, VPLS
service, and PWE3 service.
10.11 Tunnel Service Management
Tunnel service management is used to plan and deploy services on the entire MPLS network.
Carriers can plan, deploy, audit, and monitor end-to-end LSPs through tunnel service
management, thus reducing the costs of operating and maintaining MPLS networks.
10-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
10 Router Feature and Switch Feature Management
10.1 Router Management
Router management allows you to configure and maintain routers by means of the GUI.
Device Management
Device types and software versions can be automatically identified and differentiated
management can be performed accordingly.
Component Management
l
Information about components, including frames, boards, power supplies, fans, and ports
can be automatically obtained.
Information about components can be refreshed and component status can be monitored.
Panel Management
Information about components on panels, including frames, boards, power supplies, fans, and
ports, can be displayed.
Clock Management
Physical clocks and PTP clocks can be configured and managed.
Interface Management
The following interfaces can be configured:
l
Ethernet interfaces
POS interfaces
Virtual interfaces such as subinterfaces, trunk interfaces, loopback interfaces, and virtual
template (VT) interfaces
LLDP Management
LLDP can be globally configured or on interfaces.
Ethernet Features Management
l
VLAN functions, including global VLAN, port VLAN, VLAN stacking, and VLAN
mapping, can be configured.
MAC address forwarding can be managed by configuring static MAC addresses, MAC
address learning rules, and MAC address aging.
The VLAN switch feature is supported.
Ethernet OAM Management
OAM is implemented on the basis of two standards: IEEE 802.1ag and IEEE 802.3ah. The
U2000 can continuously monitor user services, and identify and locate faults by means of IEEE
802.1ag; the U2000 can monitor user services of the last mile and report faults by means of IEEE
802.3ah.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10-3
10 Router Feature and Switch Feature Management
iManager U2000 Unified Network Management System
Product Description
Ethernet OAM management supports the following functions:
l
Manages global information.
Supports IEEE 802.1ag-related functions, such as the configurations of the MD, MA, local
MEP, remote MEP, and MIP, and diagnostic operations (including loopback, link trace,
MAC ping, and MAC trace).
Supports IEEE 802.3ah-related functions, such as Ethernet OAM configurations, querying
ports, and loopback detection.
Channel Management
The following channels can be configured and managed:
l
VTYs
Telnet and FTP services
Syslog parameters
Alarms
SSH services
NAP services
QoS Management
The following QoS functions are supported:
l
Traffic classifications, traffic behaviors, and traffic policies
Interface QoS and system QoS
DS domain policies
Traffic mirroring and port mirroring
HQoS, including the discard policy, HQoS flow queue policy, HQoS flow queue mapping,
HQoS scheduler, and HQoS user scheduling
Route Management
Static routes, routing information, routing policies, OSPF routes, and BGP/IS-IS public network
and private network routes can be configured.
MPLS Management
The following NE-level MPLS configurations are supported:
l
MPLS-related protocols
MPLS TE tunnel
MPLS interface parameters
Static LSPs
MPLS OAM detection and protection groups
ACL Management
ACLs-based access control is supported.
10-4
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
10 Router Feature and Switch Feature Management
BRAS Management
The following broadband remote access service (BRAS) features of multi-service gateways are
supported:
l
Address pool management
Authorization, authentication and accounting (AAA) management
Domain and Point-to-Point Protocol (PPP) management
Built-in Web server management
Layer 3 Internet Service Provider (ISP) configuration management
Portal server management
VLAN management
User management
Real-time statistics collection on domains, IP address segments, and device IP addresses
VPDN Management
The Layer-2 Tunneling Protocol (L2TP) can be configured on multi-service gateways and L2TP
tunnels can be managed.
BFD Management
The following BFD functions are supported:
l
BFD attributes
BFD sessions
BFD alarms
BFD for VRF/PW/MPLS TE/VSI/physical links
VRRP/VGMP Management
l
Virtual Router Redundancy Protocol (VRRP) configurations, including global VRRP
attributes, interface attributes, and interface VR, and VRRP alarms, are supported.
VRRP Group Management Protocol (VGMP) configurations, including global VGMP
attributes, VGMP members, and VGMP alarms, are supported.
VPN Management
The following VPN management functions are supported:
l
Tunnel policies
PWs
PW templates
VSIs
VRFs
MSE Management
MSE functions, including global MSE, AAA, user management, and interface services, are
supported.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10-5
10 Router Feature and Switch Feature Management
iManager U2000 Unified Network Management System
Product Description
Layer 3 Multicast Management
The following Layer 3 multicast functions are supported:
l
Manage routers
Manage IGMP
Manage PIM
Manage MSDP
Manage L3VPN RP
Layer 2 Multicast Management
The following VSI-based Layer 2 multicast functions are supported for routers:
l
IGMP snooping
SSM mapping
Multicast CAC
Multicast groups
E-Trunk Management
The E-trunk search and discovery, E-trunk configuration, E-trunk member management, and
trunk member monitoring are supported.
Smart Configuration Tool
The Smart Configuration Tool (SCT) can import the routers managed by the U2000. CLI
grammar check, template configuration, navigation paths are supported. The SCT can issue
configurations in batches and can be integrated with the U2000.
ANCP Management
The following ANCP features are supported for routers:
l
ANCP management
ANCP global configuration
Line management
Neighbor management
10.2 Router V8 Management
Router V8 management allows you to view NE configurations by means of GUIs.
Device Management
NE software versions can be automatically identified.
10-6
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
10 Router Feature and Switch Feature Management
Panel Management
l
Information about components such as frames, boards, power supplies, fans, subboards,
and ports on the NE panel can be displayed.
Showing alarms using alarm indicators on the NE panel.
Information about alarms can be displayed.
Real-time performance data and historical performance data can be displayed.
NE Management
The following functions can be configured and information about these functions can be
displayed:
l
Routing protocols, including BGP, OSPF, and IS-IS
Security, including AAA and attack defense
MPLS
VPN, including L2VPN and L3VPN
QoS
Interfaces, including Ethernet and trunk interfaces
Channels, including SNMP, Telnet, and NETCONF channels
10.3 Automatic NE Configuration Management
Automatic NE configuration management is implemented by means of DHCP on the U2000.
Automatic NE configuration management allows you to deploy and remotely debug case-shaped
routers, reducing the costs in device deployment and increasing the efficiency of device
deployment.
Automatic NE configuration management supports the following functions:
l
Starts or stops the DHCP server.
Manages configuration data.
Assigns NE IP addresses automatically.
Upgrades NE versions.
Modifies and applies NE scripts.
Views script application results.
Changes management IP addresses.
Automatic NE configuration management uses the C/S model, in which the NEs serve as the
DHCP clients and the U2000 serves as the DHCP server to remotely deploy and commission
NEs.
Function
The detailed functions are as follows:
l
Manages planned records
The functions of managing configuration data, creating a data record and importing data
records in batches are provided.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10-7
10 Router Feature and Switch Feature Management
iManager U2000 Unified Network Management System
Product Description
Manages DHCP servers
The function of automatically assigning IP addresses to NEs is supported when the DHCP
server function is enabled.
Manages scripts
The function of managing device scripts on the U2000 is provided for automatically
deploying device configurations.
Upgrades system versions remotely
The function of remotely upgrading device versions is provided. Both automatic and
manual upgrade modes are available.
Deploys device scripts remotely
The function of remotely deploying device scripts is provided. Both automatic and manual
deployment modes are available.
Monitors task status during automatic device deployment
The function of monitoring task status during automatic device deployment is provided.
10.4 Switch Management
Switch management allows you to configure and maintain switches by means of the GUI.
Device Management
Device types and software versions can be automatically identified and differentiated
management can be performed accordingly.
Component Management
l
Information about components, including frames, boards, power supplies, fans, and ports
can be automatically obtained.
Information about components can be refreshed and component status can be monitored.
Panel Management
Information about components on panels, including frames, boards, power supplies, fans, and
ports, can be displayed.
LLDP Management
LLDP can be globally configured or on interfaces.
Interface Management
The following interfaces can be configured:
10-8
Ethernet interfaces
POS interfaces
Virtual interfaces such as subinterfaces, trunk interfaces, loopback interfaces, and Tunnel
interfaces
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
10 Router Feature and Switch Feature Management
Ethernet Features Management
The VLAN, VCT, and VLAN switch features are supported.
OAM Management
OAM is implemented on the basis of two standards: IEEE 802.1ag and IEEE 802.3ah. The
U2000 can continuously monitor user services, and identify and locate faults by means of IEEE
802.1ag; the U2000 can monitor user services of the last mile and report faults by means of IEEE
802.3ah.
Ethernet OAM management supports the following functions:
l
Manages global information.
Supports IEEE 802.1ag-related functions, such as the configurations of the MD, MA, local
MEP, remote MEP, and MIP, and diagnostic operations (including loopback, link trace,
MAC ping, and MAC trace).
Supports IEEE 802.3ah-related functions, such as Ethernet OAM configurations, querying
ports, and loopback detection.
Route Management
Static routes, routing policies, OSPF routes, IS-IS routes, and BGP routes can be configured.
MPLS Management
The following NE-level MPLS configurations are supported:
l
MPLS-related protocols
MPLS TE tunnel
MPLS interface parameters
Static LSPs
MPLS OAM detection and protection groups
BFD Management
The following BFD functions are supported:
l
BFD attributes
BFD sessions
BFD alarms
BFD for VRF/PW/MPLS TE/VSI/physical links
VRRP/VGMP Management
l
Virtual Router Redundancy Protocol (VRRP) configurations, including global VRRP
attributes, interface attributes, and interface VR, and VRRP alarms, are supported.
VRRP Group Management Protocol (VGMP) configurations, including global VGMP
attributes, VGMP members, and VGMP alarms, are supported.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10-9
10 Router Feature and Switch Feature Management
iManager U2000 Unified Network Management System
Product Description
VPN Management
The following VPN functions are supported:
l
Tunnel policies
PWs
PW templates
VSIs
VRFs
EPON Management
PON interface management and ONU management are supported.
Channel Management
The following channels can be configured and managed:
l
VTYs
FTP services
Local users
Syslog parameters
Alarm services
SSH services
SNMP parameters
DLDP Management
The Device Link Detection Protocol (DLDP), packet authentication mode, and statistics
collection are supported.
MSTP Management
MSTP domains, MSTP protection, and statistics collection are supported.
DHCP Management
DHCP servers, DHCP relay, client addresses, and DHCP statistics are supported.
Web Authentication Management
The Web authentication server is supported.
Controllable Multicast Management
Multicast group, multicast template, and interface filtering are supported.
Mirroring Management
Local/remote interface mirroring, VLAN mirroring, MAC address mirroring, flow mirroring,
CPU mirroring, and CPU buffer statistics are supported.
10-10
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
10 Router Feature and Switch Feature Management
IP Source Guard Management
Static user binding table, dynamic check, and clearance of dynamic configurations are supported.
Interface Security Management
Ethernet interface security management is supported.
MAC Address Authentication Management
MAC address authentication is supported.
PPPoE+ Management
PPPoE+ functions are supported.
AAA and User Management
AAA and user management are supported.
MFF Management
Static gateways, MFF servers, and MFF network-side interfaces are supported.
ARP Management
Proxy ARP and ARP Ping-IP are supported.
DHCP Snooping Management
Alarms on spoofing attacks, DoS attacks, lease-extending packet attacks, packet sending rate,
and packet discarding are supported.
Firewall Management
Firewall functions are supported.
NAT
Network address translation (NAT) is supported.
Traffic Suppression Management
Traffic suppression is supported on Ethernet interfaces.
Anti-attack Management
Whitelists, blacklists, user-defined flow, and CAR are supported.
IP Source Trail Management
Attack source search and URPF are supported.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10-11
10 Router Feature and Switch Feature Management
iManager U2000 Unified Network Management System
Product Description
MBGP Management
Route advertisement policies, route exchange policies, and route attributes are supported.
RRPP Management
RRPP, RRPP instances, RRPP rings, and working mode are supported.
Smart Link Management
Smart Link groups, data flow policies for Smart Link groups, and Monitor Link groups are
supported.
IGMP Proxy Management
Static router interfaces, multicast policies, prompt leave, and IGMP proxy are supported.
IGMP Snooping Management
Static router interfaces, multicast policies, and IGMP snooping are supported.
MSDP Management
MSDP peers and SA messages are supported.
PIM-DM Management
Multicast sources, multicast neighbors, multicast forwarding, and assertion management are
supported.
PIM-SM Management
Multicast sources, multicast neighbors, dynamic RP, and SPT switching are supported.
IGMP Management
IGMP groups, IGMP group policies, and IGMP features are supported.
Multicast Route Management
Static multicast routes, multicast route policies, and multicast forwarding are supported.
Layer 2 Multicast Management
Layer 2 multicast and multicast VLAN replication are supported.
802.1x Management
802.1x management is supported.
Batch VLAN Management
Managing VLANs in batches is supported.
10-12
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
10 Router Feature and Switch Feature Management
Port Isolation Configuration
Port isolation is supported.
PoE Configuration
PoE is supported.
Stack Configuration
Stack functions are supported.
QoS Management
The following QoS functions are supported:
l
Traffic classifications, traffic behaviors, and traffic policies
Interface QoS and system QoS
DS domain policies
Traffic mirroring and port mirroring
VLANIF Configuration
VLAN interfaces are supported.
Ethernet Configuration
LDT, MAC tables, BPDU tunnels, and SEP are supported.
Security Configuration
The ACL, firewall, NAT, and ARP features are supported.
Basic Configuration
NAP remote deployment is supported.
10.5 Template Management
In NE configuration management, many operations need to be performed repeatedly. The
template management function is introduced to solve this problem. This function allows you to
rapidly configure NEs in batches.
Template Features
Default templates are available. When a template is referenced, the attribute settings on the
template automatically apply to the configured resource.
A template has the following features:
l
Issue 05 (2010-11-19)
Offline configuration
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10-13
10 Router Feature and Switch Feature Management
iManager U2000 Unified Network Management System
Product Description
Global templates are created in advance and saved on the U2000. They are not created on
devices. The creation of global templates is irrelevant to the equipment status.
l
Global validity
A global template can be referenced by all the devices managed by the U2000.
Minimal duplicate data
After a global template is applied, the U2000 keeps only one record on the devices that
reference this template.
When a device references a global template, the U2000 does not add a record of template
data. The U2000 only records the reference relationship between the device and the
template.
A global template can be referenced by a large number of devices of the same type. The
number of global templates, therefore, is small. Consequently, global templates are easy to
manage.
Main Templates
The main templates are as follows:
l
ACL template
An ACL template allows you to configure ACLs on multiple interfaces of different routers
at the same time, simplifying attack defense configurations on the network access side.
QoS template
Routers support the following QoS templates, which can be applied to NE interfaces in
batches:
CBQoS templates
DS domain templates
HQoS templates
PQ templates
Interface CAR templates
IP multicast template
Routers support the following IP multicast templates:
Layer 2 CAC templates, which can be applied to VSIs, PWs, and NE interfaces to adjust
and configure multicast CAC configurations in batches
Layer 2 static multicast group templates, which can be applied to PWs and NE interfaces
to adjust and configure static multicast groups in batches
VPN service template
Used to configure VPN services in batches.
Switch EPON template
Used to configure ONU services in batches.
10.6 Diagnosis Management
Diagnosis management provides easy-to-use diagnostic functions for you to test network and
service connectivity. Diagnostic cases can be run manually or run automatically at scheduled
times.
10-14
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
10 Router Feature and Switch Feature Management
Test Diagnosis Functions
l
The U2000 provides test cases, such as VPLS MAC ping/traceroute, ICMP ping/traceroute,
PWE3 ping/traceroute, LSP ping/traceroute, and ICMP VRF ping/traceroute, which can
help you to test network connectivity at each protocol layer.
The U2000 allows you to combine several test cases into a test suite, so that you can perform
test cases in batches. By diagnosing services layer by layer, the U2000 can rapidly locate
the network layer where a fault occurs.
Application layer
DNS, DHCP, FTP, HTTP, SNMP, and VoIP
Transport layer
TCP and UDP
Network layer
ICMP ping/traceroute, ICMP VRF ping/traceroute, ICMP jitter, multicast ping/trace,
multicast VRF trace, and MTU ping
Data link layer
8021.ag MAC ping and CE ping
MPLS service
PWE3 ping, PWE3 trace, LSP ping, LSP trace, VPLS MAC ping, VPLS MAC trace,
MAC study, MFIB ping, and service ping
The U2000 supports intelligent diagnostic result analysis. A result analysis template can
be customized to include diagnostic indicators such as delay, jitter, and packet loss ratio
and a result analysis policy based on service levels. Diagnostic result analysis can help you
rapidly determine network status.
Test Diagnosis Management
Test diagnosis management allows you to test network connectivity and QoS and rapidly
pinpoint a fault location.
A test diagnostic tool consists of the following parts:
l
Test suite
A test suite consists of multiple test cases. Test cases are implemented on different
layers: the application layer, transport layer, network layer, and data link layer. Test
cases for MPLS services can also be created.
You can choose to perform all test cases or only some cases in a test suite at the same
time. QoS can be determined based on the parameters shown in the test results, such as
delay, jitter, and packet loss ratio.
Diagnostic policy
Test suites can be performed at a specified interval, such as daily, weekly, or monthly.
Network scanning
Network information is collected and virtual link connectivity and side-by-side link
connectivity are tested. The U2000 displays scanning progress in real time and allows you
to stop the scanning. It also provides the traceroute function to locate faults.
l
Issue 05 (2010-11-19)
Historical data
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10-15
10 Router Feature and Switch Feature Management
iManager U2000 Unified Network Management System
Product Description
The U2000 records historical data of test suite operations. It supports filtering and querying
historical data based on test suite names, test results, or test time.
l
Diagnostic result analysis
The U2000 supports intelligent diagnostic result analysis. A result analysis template can
be customized to include diagnostic indicators such as delay, jitter, and packet loss ratio
and a result analysis policy based on service levels. Diagnostic result analysis can help you
rapidly determine network status.
10.7 Cluster Management
The Huawei Group Management Protocol (HGMP) is mainly used to solve the problems of
automatic management operations and centralized management for multiple dispersed low-end
and mid-range switches.
Cluster network management involves the following functions:
l
Managing cluster views
Configuring clusters
Managing cluster configuration files
Managing image programs
Locating cluster faults
The U2000 provides cluster management for the CX200/CX200D/CX300/CX380/CX600/
S2300/S3300/S5300. This function allows you to manage network equipment in a more
convenient and efficient manner. With this function, you can monitor the network status through
the physical topology of cluster networks and reduce improper operations on single equipment
during management. Therefore, the U2000 meets the ever-increasing service requests.
Figure 10-1 and Figure 10-2 show the cluster topology management window and functions
provided by theU2000.
Figure 10-1 Cluster topology
10-16
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
10 Router Feature and Switch Feature Management
Figure 10-2 Navigation path to cluster functions
The U2000 provides the following functions:
l
Automatically discovering and dynamically refreshing cluster equipment nodes
Automatically discovering and dynamically refreshing the physical topology of cluster
networks and links
Managing the configurations of cluster equipment in batches and in a unified and
centralized manner
Maintaining the equipment of a cluster in a centralized manner and supporting fault
detection and recovery
Facilitating the backup and recovery of configuration data
Setting the parameters, such as the management VLAN, IP address pool, and multicast
MAC address, for the switches of a cluster
Supporting the plug-and-play feature of protocols such as NDP, NTDP, and HGMP
Supporting the access to command or member switches through Telnet based on the nodes
in the cluster view
10.8 Node Redounded Management
Enhanced-Trunk (E-Trunk), developed on the basis of Link Aggregation Control Protocol
(LACP), is a protocol that controls and implements link aggregation among multiple sets of
equipment. E-Trunk is mainly applied to a scenario where a CE is dual homed to a VPLS, VLL,
or PWE3 network. In the scenario, E-Trunk can be used to protect the PEs and the links between
the CE and PEs.
This function allows you to perform the following operations:
l
Creat an E-Trunk, bind Eth-Trunks, and configure the attributes of the E-Trunk and the
Eth-Trunks.
Display the automatically discovered E-Trunk information in the database of the NMS to
the interface of the NMS.
Automatically discover the E-Trunk by user specify the equipment range, the configuration
of the equipment and the E-Trunk group can be automatically discovered.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10-17
10 Router Feature and Switch Feature Management
iManager U2000 Unified Network Management System
Product Description
10.9 Report Subsystem Management
The report subsystem allows you to generate, distribute, and manage reports based on the Web
and helps you to monitor, analyze, and optimize network performance.
The report subsystem can generate reports in both manual and automatic modes. It can be easily
integrated with the security management module of the U2000.
For more information, refer to the iManager U2000 (RPT)V100R002C01 Release Notes.
10.10 VPN Service Management
The U2000 provides centralized and unified management, including service deployment, service
monitoring, and service diagnosis, on VPN services, namely, BGP/MPLS VPN service, VPLS
service, and PWE3 service.
Service Deployment
The U2000 provides a user-friendly service configuration GUI on which you can complete all
configuration operations. The parameters of multiple sets of equipment can be automatically
generated through related service templates. User configuration results can be previewed through
the topology before being delivered.
l
Customer management
The U2000 supports the operations of adding, deleting, and modifying customers, and
binding customers to VPN services.
BGP/MPLS VPN service management
Configuring L3VPNs in networking modes such as Full-Mesh, Hub-Spoke, and
Extranet
Configuring VPN FRR and IP FRR for L3VPNs and binding L3VPNs to TE tunnels
Configuring static, OSPF, and BGP private routes
Configuring VPN services in inter-AS OptionA or inter-AS OptionB mode
Configuring the service wholesale feature of BGP/MPLS VPNs based on the ME60
In service wholesale mode, the ME60 forwards all the user service packets of a certain ISP
to the access server of the ISP through VPNs.
In this mode, the ME60 does not forward packets according to the destination IP
addresses of the packets as it usually does. Instead, the ME60 forwards packets
according to the ISP information of the users and forwards all the packets from the users
to the access server of the ISP. The access server of the ISP then implements the related
services or performs service accounting.
With the service wholesale feature, the U2000 can support the multi-ISP service. The
multi-ISP service is also called the virtual ISP service. For a multi-ISP service, multiple
ISPs exist on a physical network. These ISPs lease the physical network of the physical
network provider to operate services. Generally, the providers who construct physical
networks are called network service providers (NSPs) and the providers who lease
physical networks to operate services are called ISPs.
10-18
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
10 Router Feature and Switch Feature Management
The ME60 supports the multi-ISP service by wholesaling the user service packets of
different ISPs to related ISPs.
l
VPLS service management
Supporting the VPLS services in LDP signaling (Martini) mode
Supporting the interworking of different VSIs
Supporting VLL/VPLS services
PWE3 service management
Configuring static and dynamic PWE3 services
Supporting PWE3 services in CES, ATM, Ethernet, IWF, and heterogeneous
interworking mode
Backing up PW configurations
Configuring PW FRR
Composite service management
The U2000 supports the management on composite services, such as the access of a VLL
to another VLL, the access of a VLL to a VPLS network, the access of a VLL to an L3VPN,
L3VPN multi-VRF, and inter-AS OptionA.
Automatic Service Discovery
The U2000 provides the function of automatically discovering BGP/MPLS VPN, VPLS, and
PWE3 services that are running on the managed network. In addition, the U2000 can quickly
load services on the current network to itself for unified management and monitoring, without
requiring much user participation.
Service Monitoring
l
The U2000 provides the visual topology display function for MPLS VPN, VPLS, and
PWE3 services. The running status of the resources used by the current service, such as an
interface, a VRF, or a VSI, can be displayed in the related topology view, thus helping you
to quickly locate faults. Moreover, the U2000 also allows you to customize topology views.
For example, you can place the services of key customers in one topology view for
monitoring.
You can quickly locate a faulty service based on the alarm generated by the related NE.
Service Diagnosis
l
The diagnosis tools are used to detect the connectivity of networks and locate faults.
Through the service diagnosis function, you can generate diagnosis tasks according to the
selected services and directly operate equipment nodes in topology views. The diagnosis
results can be directly displayed.
Service Check and Test
l
Configuration check: checking the consistency of VPN service configurations on different
sites and showing the positions of configuration errors
Service connectivity test: testing the service connectivity through the ping and tracert tests,
and locating the fault equipment
Protocol status test: checking the service protocol status and the forwarding table, and
displaying the error information, thereby helping you to locate faults
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10-19
10 Router Feature and Switch Feature Management
iManager U2000 Unified Network Management System
Product Description
10.11 Tunnel Service Management
Tunnel service management is used to plan and deploy services on the entire MPLS network.
Carriers can plan, deploy, audit, and monitor end-to-end LSPs through tunnel service
management, thus reducing the costs of operating and maintaining MPLS networks.
Tunnel Deployment
l
Enabling MPLS, LDP, and MPLS TE on the network equipment and interfaces in batches
Implement the planning of traffic on MPLS core networks by supporting the deployment
of end-to-end MPLS TE tunnel services
Facilitating the implementation of the MPLS access scheme by supporting the deployment
of static LSP services
Implementing the end-to-end MPLS OAM protection by supporting the configuration of
end-to-end MPLS TE protection groups, configuration of MPLS OAM detection, and
monitoring of related alarms
Automatic Tunnel Discovery
With the help of a network administrator, the LSPs and related protection groups that are
previously deployed on the network can be restored to the U2000. This satisfies the requirement
in the special case where the LSP deployment is prior to the U2000 installation. Moreover, less
time of the network administrator is required and the impact of incorrect operations on original
services is prevented.
Tunnel Monitoring
l
Supporting the networkwide tunnel view and displaying multiple types of tunnels, such as
static, RSVP, LDP, and IP tunnels, and their alarms in the topology view
Collecting and displaying the performance data of tunnels
Switching to the related tunnel from an alarm
Tunnel Diagnosis
The U2000 supports LSP ping and LSP tracert functions through which you can diagnose
deployed MPLS TE tunnels and static tunnel services.
10-20
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
11
11 Feature Management for Security Devices
Feature Management for Security
Devices
About This Chapter
This topic describes the features supported by security devices.
11.1 Security Device Management
Security device management allows you to configure and maintain security devices by means
of the GUI.
11.2 Single-Point Web Configuration for Security Devices
Single-point Web configuration integrates the existing Web functions on the device by
embedding browser controls in the Client/Server interfaces. Single-point configuration applies
to all the configurations of security devices. In collaboration with centralized security policy
configuration, it provides an integrated and comprehensive network security management
solution.
11.3 Centralized Security Policy Configuration
Deploying a set of security devices with comprehensive security technologies on a network does
not mean that the network is well secured.
11.4 Report Subsystem Management
The report subsystem provides a complete set of convenient services. It allows you to generate,
distribute, and manage reports based on the Web. The powerful report subsystem can help you
to monitor, analyze, improve, and plan network performance.
11.5 VPN Service Management
The VPN service management module is an important part to implement the IPSec VPN/L2TP
VPN solution. It is used to configure and monitor IPSec and L2TP VPN service.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
11-1
11 Feature Management for Security Devices
iManager U2000 Unified Network Management System
Product Description
11.1 Security Device Management
Security device management allows you to configure and maintain security devices by means
of the GUI.
Security device management supports the following functions:
l
Device management
Identifies software versions and adapt to different types of devices automatically.
Supports channel management, including local users using Telnet and STelnet, SNMP
parameters, and trap parameters.
Component management
Information about device components, including frames, boards, power supplies, fans,
and ports can be automatically obtained.
Information about device components can be refreshed and device component status
can be monitored.
Panel management
Information about components on the panel, including frames, boards, power supplies, fans,
and ports, can be displayed.
Interface management
General interface information and Ethernet interfaces can be configured.
GTP management
Security devices can filter GTP packets according to GTP policies to protect GPRS
networks from attacks such as GTP overbilling attacks.
Automatic registration
The U2000 can automatically update the IP address of a receiving device based on
registration messages sent by the receiving device.
11.2 Single-Point Web Configuration for Security Devices
Single-point Web configuration integrates the existing Web functions on the device by
embedding browser controls in the Client/Server interfaces. Single-point configuration applies
to all the configurations of security devices. In collaboration with centralized security policy
configuration, it provides an integrated and comprehensive network security management
solution.
The Web features of security devices provide easy-to-use Web configuration windows through
which users can operate and maintain devices.
The single-point Web configuration is a proxy-based Web access mode. It can be implemented
without affecting local browsers such as Internet Explorer and Firefox. The single-point Web
configuration includes two parts: Web proxy and Web browser. The functions of single-point
Web configuration are as follows:
11-2
Users can open the Web management window of a device on a U2000 client.
Users can log in to the Web window automatically.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
11 Feature Management for Security Devices
Users can access security devices by means of the Hyper Text Transfer Protocol (HTTP)
or the Hyper Text Transfer Protocol Secure (HTTPS) protocol.
Multiple Web protocols, such as Java script, Hyper Text Marked Language (HTML), CSS,
and Applet, and technologies related to Web 2.0 are supported.
11.3 Centralized Security Policy Configuration
Deploying a set of security devices with comprehensive security technologies on a network does
not mean that the network is well secured.
During network security maintenance, deploying a satisfied security scheme for a small-sized
local network is a complicated task. Designing and deploying a reliable security scheme for a
large-scale network is a more difficult and challenging task.
Centralized security policy configuration provides a reliable and stable protection system for a
network. It is implemented on security devices deployed on the network.
Centralized security policy configuration has the following features:
l
Policy package management
A policy package can manage all security devices on a network. A policy package
consists of security policy, attack defense, and service port mapping.
Users can create their own policy packages. A policy package can include all security
configurations such as creating, deploying, removing, and verifying configurations.
Configuration and management scope
Security policy
Attack defense
Service port mapping
Policy resource
Policy recovery
During network security management and maintenance, the data consistency between
the U2000 and devices must be ensured so that the actual network configurations can
be accurately displayed on the U2000.
Policy recovery can restore the security policies and attack defense configurations
deployed on devices and the used resources of devices to the U2000, achieving the data
consistency between the NMS and devices.
Policy audit
Auditing the configuration data difference between the U2000 and devices helps to ensure
data consistency between the NEs and the U2000.
l
Issue 05 (2010-11-19)
Security policy configuration and management in two dimensions
1.
Service-dimension configuration: manages services that are deployed on multiple or
all devices on a network. This allows users to manage and audit services in a unified
manner. Users do not need to configure and check services on devices separately,
reducing the cost and improving the efficiency.
2.
Single NE-dimension configuration: manages the configurations of a single NE. Users
can check security configurations, create, modify, deploy, and remove configurations
on a single NE, and import the configurations of other NEs to this NE.
Policy deployment status display
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
11-3
11 Feature Management for Security Devices
iManager U2000 Unified Network Management System
Product Description
Whether a policy is deployed, whether the deployment is successful, and whether the
deployment status is the same as that on the device can be displayed. This helps to prevent
duplicate deployment of a policy.
l
History record query
The detailed procedures for configuring and maintaining policy packages are recorded. The
historical operations that users performed on policy packages can be checked.
11.3.1 Policy Package Management
This topic describes the fuction of policy package management.
11.3.2 Security Policy Configuration
The U2000 allows you to manually create and modify security device rules.
11.3.3 Attack Defense Configuration
The U2000 provides attack defense functions.
11.3.4 Policy Resource Configuration
The configuration of policy resources includes the configuration of service,addess sets,period
and ports sets.
11.3.5 Mapping Service
The U2000 It provides the configuration function that re-maps the most common service ports
to other ones.
11.3.1 Policy Package Management
This topic describes the fuction of policy package management.
This feature allows you to create, modify, delete, verify, deploy, undeploy, discover, and audit
policy packages, view the deployment and audit result of policy packages.
By changing operations based on single policies and single devices to centralized operations
based on batch policies and multiple devices, this feature increases operation efficiency and
reduces maintenance cost.
The policy packages verifying function ensures the correctness of policy package configurations
and correlations among the policies within the same policy package. With the policy verifying
function, you can correctly deploy policy packages on devices and avoid repeated modifications
due to configuration errors during policy deployment.
Policy auditing is to audit the policy configuration differences between the NMS and device, so
as to determine whether the policy needs to be deployed or discovered.
Policy discovery is to recover the data synchronized to the database to the NMS for management.
The rights to perform various operations on policy packages are under control. Operations on
policy packages are recorded in logs for the policy maintenance personnel to monitor and manage
policies.
11.3.2 Security Policy Configuration
The U2000 allows you to manually create and modify security device rules.
The U2000 allows you to manually create the device rule, including:
11-4
Specify the name of a new rule
Select the source security zone
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Add the source address manually
Select the destination security zone
Add the destination address
Select the service
Select the action
Add the device
Add the time range
Choose whether to generate logs
Configure functions such as ASPF
Configure functions such as DDoS
Configure functions such as package filtering
11 Feature Management for Security Devices
After a rule is created and deployed to a device, the device filters device information according
to this rule.
The U2000 allows you to modify the device rule, including:
l
Change the name of a rule
Change the source security zone
Change the source address
Change the destination security zone
Change the destination address
Change the service
Change the action
Change the device
Change the time range
Change whether to generate logs
Modify functions such as ASPF
Modify functions such as DDoS
Modify functions such as package filtering
The U2000 also allows you to delete a rule, or the value of a certain configuration item of a rule.
11.3.3 Attack Defense Configuration
The U2000 provides attack defense functions.
This feature provides attack defense functions against SYN flood, UDP flood, ICMP flood,
HTTP get flood, DNS request flood, connection flood, scanning, malformed packet, special
packet control, and blacklist for security devices.
11.3.4 Policy Resource Configuration
The configuration of policy resources includes the configuration of service,addess sets,period
and ports sets.
l
Configuring services, address set, time range, and port set
Services
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
11-5
11 Feature Management for Security Devices
iManager U2000 Unified Network Management System
Product Description
As flexible support for the IP protocol, security services can be classified into TCP
services, UDP services, ICMP services, and other services. The U2000 provides some
basic services by default. You can create different services by adding different
parameter settings to the same protocol. Different types of services can form a service
group. A rule corresponds to one or multiple services. In the case where a rule
corresponds to multiple services, these services can be in a service group or map to these
services. When you log in to the U2000 for the first time, the U2000 provides some
services by default.
Address set
When setting source and destination addresses on the U2000, you can either set single
IP addresses or set address sets.
Time range
Time ranges are classified into two types: continuous time ranges and periodic time
ranges. A continuous time range starts from one time point and ends at another time
point. Rules are valid only within the time range. A period time range is on a weekly
cycle. You need to set the start time and end time of a day and specify on which days
of a week the rules are valid. Then the rules will take effect on a weekly cycle.
Port set
A port set is a collection of single, continuous, or discontinuous port numbers, specifying
the ports through which the server can provide services. The value of a port set ranges
from 0 to 65535.
l
Configuration log server
Binary flow logs of devices can be sent to binary servers via configuration of log server.
11.3.5 Mapping Service
The U2000 It provides the configuration function that re-maps the most common service ports
to other ones.
Mapping Service means security devices map the service ports of networking program to outof-ordered ports when forwarding network data packets.It implies the most common ports to
prevent the outer attack to programs.
11.4 Report Subsystem Management
The report subsystem provides a complete set of convenient services. It allows you to generate,
distribute, and manage reports based on the Web. The powerful report subsystem can help you
to monitor, analyze, improve, and plan network performance.
10.9 Report Subsystem Management lists the details of the report subsystem management.
11.5 VPN Service Management
The VPN service management module is an important part to implement the IPSec VPN/L2TP
VPN solution. It is used to configure and monitor IPSec and L2TP VPN service.
11.5.1 IPSec End-to-End Service
The IPSec end-to-end service is to securely connect two intranets trustable to each other through
Internet. It is applied when secure communication connections need to be established. This
application mode can be used to protect the sensitive data transmitted on the Internet.
11-6
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
11 Feature Management for Security Devices
11.5.2 Remote Access Service
The U2000 supports the implementation of remote VPN access through L2TP, IPSec (IKEv2)
and L2TP over IPSec technologies. The remote access service is applicable to employees
accessing the enterprise intranet in remote dial-up mode over the Internet.
11.5.1 IPSec End-to-End Service
The IPSec end-to-end service is to securely connect two intranets trustable to each other through
Internet. It is applied when secure communication connections need to be established. This
application mode can be used to protect the sensitive data transmitted on the Internet.
l
Service deployment
This feature provides both the single service deployment function and the service batch
deployment function. Service deployment is used to make services take effect on devices.
You can view the deployment results through the auditing function.
Service discovery
This feature supports the function of automatically discovering services. With this function,
you can discover running IPSec VPN services on the network and then restore the
discovered services to the U2000 for unified management and monitoring.
Service monitoring
By monitoring the status of managed services in real time, the performance management
module allows you to view the service status in the topology view. The performance
management module monitors the service status and performance indicators and displays
collected performance data in graphs or reports.
Display of the service topology
This feature provides the function of visualizing the service topology. In the topology view,
you can view service alarms, service statuses, and service-related device alarms.
Service audit
This feature supports to audit the differences of service configuration between the NMS
and device.
11.5.2 Remote Access Service
The U2000 supports the implementation of remote VPN access through L2TP, IPSec (IKEv2)
and L2TP over IPSec technologies. The remote access service is applicable to employees
accessing the enterprise intranet in remote dial-up mode over the Internet.
l
Service deployment
The remote access service management supports the deployment of a single service and
the deployment of services in batches. In addition, you can view deployment results in the
service topology view. Remote access services include L2TP service, L2TP over IPSec
service and IPSec (IKEv2) service three types.
Service monitoring
The L2TP service, L2TP over IPSec service and IPSec (IKEv2) service management can
manage and monitor the online users of remote access services. It also provides the
functions of displaying the statuses of online users in real time, restricting the number of
online users, and forcing users to log out.
l
Issue 05 (2010-11-19)
Display of the service topology
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
11-7
11 Feature Management for Security Devices
iManager U2000 Unified Network Management System
Product Description
The remote access service management provides the function of visualizing the service
topology. In the topology view, you can view service alarms, service statuses, and servicerelated device alarms.
l
Service audit
The remote access service management supports to audit the differences of service
configuration between the NMS and device.
Service resource management
The remote access service management provides the function of radius template
management and user domain management.
11-8
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12
12 FTTx Network Feature Management
FTTx Network Feature Management
About This Chapter
This topic describes the functions and features of FTTx NE management and network
management.
12.1 OLT Management
For NE configuration management, the U2000 provides graphical user interfaces (GUIs) for
configuring NEs and maintaining NE configurations. You can configure services for equipment
in the GUIs.
12.2 ONU Management
For NE configuration management, the U2000 provides graphical user interfaces (GUIs) for
configuring NEs and maintaining NE configurations. You can configure services for equipment
in the GUIs.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-1
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
12.1 OLT Management
For NE configuration management, the U2000 provides graphical user interfaces (GUIs) for
configuring NEs and maintaining NE configurations. You can configure services for equipment
in the GUIs.
Device Management
Device management includes the management of NE panels, basic and common device
attributes, clock sources, security, protocols, and device templates.
NE Panel Management
You can perform the following operations on the U2000:
l
Display the NE panel by double-clicking an NE.
Query the details of equipment.
Collect statistics on device resources.
Query the information about shelves.
Collect the statistics on shelf resources.
Query inter-shelf links.
Add, delete, start, disable, reset, and confirm a board.
Query the CPU usage and memory usage of boards in real time.
Display the port view by double-clicking a board.
Perform an active/standby switchover on the control boards.
Configure traffic management and rate limitation for GPON boards.
Configure rate limitation for EPON boards.
Management of Basic and Common Device Attributes
The management of basic and common device attributes includes the query of the global
information about devices and the configuration of the global policies of devices.
You can perform the following operations on the U2000:
l
Query the system information about devices.
Query the statistics on the resources and status of devices.
Query the license information about the functions and resources of devices.
Configure the system time, IP address of a device, and the binding between a Layer 3
interface and an IP address.
Configure the SNMP protocol port.
Set device handshake parameters.
Configure the policy for automatically backing up device data.
Enable and disable the energy-conservation function of a device.
Configure and manage license files.
Clock Source Management
Clock source management includes the management and configuration of equipment-level clock
source information, such as information about the line clock, 1588 clock, and clock priorities.
12-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12 FTTx Network Feature Management
Security Management
You can perform the following operations on the U2000:
l
Enable and disable anti-ICMP attack, anti-IP attack, anti-IP spoofing, anti-MAC spoofing,
and anti-DoS attack.
Set the aging time of an MAC address.
Enable and disable MAC address learning.
Configure the security attributes for user login in the CLI.
Protocol Management
You can perform the following operations on the U2000:
l
Manage the Link Aggregation Control Protocol (LACP), Spanning Tree Protocol (STP)/
Rapid Spanning Tree Protocol (RSTP)/Multiple Spanning Tree Protocol (MSTP),
Bidirectional Forwarding Detection (BFD), and Internet Group Management Protocol
(IGMP).
Control the Address Resolution Protocol (ARP) proxy.
Configure the Policy Information Transfer Protocol (PITP) mode/Relay Agent Info Option
(RAIO) customized format.
Control the Dynamic Host Configuration Protocol (DHCP) option 82 function.
Control the DHCP proxy and DHCP relay forwarding functions.
Configure 802.1ag attributes of the Ethernet packet.
Global Configuration of Services
The global configuration of services includes the configuration of the VLAN, QoS, xDSL,
GPON, EPON, and multicast services.
Device Template Management
Device template management includes the display of different types of device templates on the
U2000. Templates include the GPON template, EPON template, MDU SNMP template, IGMP
template, traffic template, VLAN service template, optical transceiver alarm template, and PW
template. Currently, the U2000 supports only query and generation of global templates.
Network Interface Management
Network interface management includes the management and maintenance of E1/T1 ports and
the Ethernet port.
Management and Maintenance of E1/T1 Ports
E1/T1 ports are classified into TDM E1/T1 ports, CES E1/T1 ports, and IMA E1/T1 ports.
TDM E1/T1 ports can be used as access ports or upstream ports, depending on the function of
a board.
On E1 ports for upstream transmission, you can perform only the loopback operation.
On E1 ports for PRA access, you can perform the following operations: configure or delete port
attributes, set the alarm threshold of L2 signaling bit errors, query timeslots, and enable or disable
services.
On CES E1/T1 ports, you can collect real-time performance statistics of the ports, configure port
attributes, set a port alias, and perform loopback.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-3
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
On IMA E1/T1 ports, you can query real-time performance statistics of the ports, and manage
IMA groups and IMA links, such as adding, deleting, modifying, resetting, blocking, and
unblocking an IMA group or link.
Management of Ethernet Ports
Ethernet port management includes the management of ports and aggregation groups. You can
perform the following operations on the U2000:
l
Configure port attributes.
Create, delete, query, and modify an aggregation group.
Activate and deactivate an Ethernet port.
Collect real-time performance statistics and clear the performance statistics.
Configure the PPPoE, DHCP option 82, 802.3ah ETH OAM loopback, and port rate limit
functions.
Query the attributes of optical transceivers on Ethernet optical ports.
Connection Management
Connection management includes the management of service virtual ports and E1 connections.
Service Virtual Port Management
A service virtual port enables user equipment to access the OLT. The service virtual port provides
service streams between the user equipment and the OLT for carrying user services. You can
perform the following operations on the U2000:
12-4
Query, add, delete, modify, activate, and deactivate a service virtual port.
Collect the real-time performance statistics and clear the performance statistics.
Perform ATM ping tests.
Configure the extended attributes of a service virtual port. Extended attributes allow for
greater flexibility of addressing customer requirements. Extended attributes include the
maximum number of learnable MAC addresses, the PPPoE session, the encapsulation type,
and the maximum number of MAC addresses that can be bound.
Configure the connection attributes of a service virtual port, including the alias, VPI/VCI,
transmit traffic profile, and receive traffic profile.
Shift the VLAN ID of a service virtual port to change the VLAN ID of the service virtual
port. After successful shifting, the service port assumes the new VLAN ID.
Bind IP addresses to a service virtual port and query the bound IP addresses. To specify
that only the users with certain IP addresses can access the service virtual port, perform the
binding operation. After successful binding, the service forwarding module checks the
source IP address of user packets. If the source IP address does not match any of the IP
addresses bound to the service virtual port, the user packets are dropped. Otherwise, the
user packets are forwarded. This ensures the security of user access.
Bind static MAC addresses to a service virtual port. To specify that only the users with
certain static MAC addresses can access the service virtual port, perform this operation.
After successful binding, the service forwarding module checks the source MAC address
of user packets. If the source MAC address does not match any of the MAC addresses
bound to the service virtual port, the user packets are dropped. Otherwise, the user packets
are forwarded. This ensures the security of user access.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12 FTTx Network Feature Management
Configure service bundles. If several service virtual ports carry the same service, a service
bundle can be configured to bundle the service streams over the service virtual ports.
E1 Connection Management
In the FTTx scenario, an E1 connection is used for transmitting the TDM service over the GPON
network by encapsulating the TDM packets directly into a GPON GEM frame. In E1 connection
management, you can query, add, modify, and delete an E1 connection on the U2000.
Layer 2 Management
Layer 2 management includes the management of the VLAN, the Rapid Spanning Tree Protocol
(RSTP), Multiple Spanning Tree Protocol (MSTP), Access Node Control Protocol (ANCP), and
Rapid Ring Protection Protocol (RRPP).
VLAN Service Management
VLAN service management includes the management of the standard VLAN, MUX VLAN,
smart VLAN, and super VLAN. You can perform the following operations on the U2000:
l
Query, add, delete, and modify a VLAN.
Collect the real-time performance statistics of a VLAN.
Clear the real-time performance statistics of a VLAN.
Manage a Layer 3 interface and its subinterfaces.
RSTP Management
You can perform the following operations on the U2000:
l
Modify and restore the default value of the trail overheads of a port.
Collect the RSTP statistics of a port.
Clear the RSTP statistics of a port.
MSTP Management
MSTP management includes the management of domains, instances, and ports. You can perform
the following operations on the U2000:
l
Modify and restore the default setting of a domain.
Add, delete, and modify an instance.
Modify a port.
Query the statistics of a port.
ANCP Management
You can perform the following operations on the U2000:
l
Add, delete, modify, enable, and disable an ANCP session.
Query the real-time status of an ANCP session.
RRPP Management
For RRPP management, you can perform the query, add, delete, and modify operations.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-5
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Layer 3 Management
Layer 3 management includes the management of the Dynamic Host Configuration Protocol
(DHCP), Multi-protocol Label Switching (MPLS)/pseudo wire emulation edge-to-edge
(PWE3), and Layer 3 routes.
DHCP Management
DHCP management includes the management of the DHCP server group, MAC address
segment, standard mode, DHCP domain, and VLAN L3 interface. You can perform the
following operations on the U2000:
l
Query, add, delete, and modify a DHCP server group.
Query, add, delete, and modify a MAC address segment.
Query, enable, disable, and modify a standard mode.
Query, add, delete, and modify a DHCP domain.
Modify a VLAN Layer 3 interface.
MPLS/PWE3 Management
The MPLS is a transmission technology. It implements transparent transmission of data packets
between users. The MPLS tunnel is defined in the MPLS protocol. Independent of a service, an
MPLS tunnel implements end-to-end transmission and carries service-related PWs.
You can perform the following operations on the MPLS tunnel on a per-NE basis on the U2000:
l
Configure the basic attributes of the MPLS.
Configure the MPLS tunnel of the static unicast type.
Create forward MPLS tunnels.
Create an E-LSP.
Manage PWs.
Manage tunnel tags and PW labels.
ACL and QoS Management
ACL and QoS management includes the management of the access control list (ACL), quality
of service (QoS), time segments, and hierarchical QoS (HQoS).
In a traditional packet-based network, all packets are treated in the same way. Every router adopts
the first-in first-out (FIFO) policy to process packets, and makes its best effort to transmit packets
to the destination. The router, however, does not make any commitment to packet transmission
performance, such as the delay, delay variation (jitter), packet loss rate, and reliability. With the
rapid development of the computer network, more and more networks are connected to the
Internet. In addition, new services are emerging and raise new requirements on the service
capability of the IP network. Therefore, network-wide end-to-end QoS solutions are called into
attention, which necessitates QoS assurance for services. To achieve so, devices must be able
to apply QoS techniques and provide hierarchical QoS guarantee for different types of service
streams (especially for those highly sensitive to delay and jitter). For ACL management, you
can perform the following operations on the U2000:
12-6
Configure one or more time segments, and associate a time segment with an ACL by
specifying the name of the time segment in the ACL.
Query, modify, create, and delete the ACL of the standard, extended, Layer 2, and userdefined types.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12 FTTx Network Feature Management
QoS management includes filtering packets based on ACL, tagging priorities, limiting traffic
and port rate, collecting statistics on traffic, redirecting, and mirroring. On the U2000, you can
query, add, modify, and delete a QoS policy.
HQoS stands for the hierarchical QoS. It not only controls user traffic but also schedules packets
according to the priorities of user services. On the U2000, you can query, add, modify, and delete
an HQoS policy.
BFD Management
The BFD can quickly check the link status between two devices.
To mitigate the impact of device faults on services and to improve the network availability, a
network device needs to quickly detect any fault occurring between the device and its adjacent
devices. Actions can then be taken to ensure service continuity. The BFD enables the device to
check the connectivity of a type of data protocol of the same trail between two systems. The trail
can be a physical or a logical link, including a tunnel. The BFD mechanism is a remedy for the
weakness of the existing detection mechanism.
User Security and System Security Management
You can perform the following operations on the U2000:
l
Configure user access in PITP mode.
Configure user access in DHCP option 82 mode.
Configure user access control.
Configure system secure access.
Ethernet Connectivity Fault Management
As the Ethernet technology extends from carrier networks to metropolitan area networks
(MANs) and wide area networks (WANs), carriers are increasingly concerned about the
maintainability of equipment, especially the Ethernet equipment. An imperative demand for the
operation, administration and maintenance (OAM) of transport equipment hence arises. The
802.1ag connectivity fault management (CFM) provides a method for detecting faults end-toend. The Ethernet OAM mechanisms supported by 802.1ag CFM include connectivity check
(CC), loopback (LB), link trace (LT), and forward AIS alarms. You can perform the following
operations on the U2000:
l
Manage maintenance domains (MDs). Ethernet CFM divides a network into up to eight
levels. A bridge can span multiple levels to manage different MDs. A CFM MD is
constituted by bridges. An MD is the combination of bridges and maintenance levels. MDs
can be classified into three layers: user domain (levels 7-5), service provider domain (levels
4-3), and carrier domain (levels 2-0). Different MDs are maintained by different
management entities.
Manage maintenance associations (MAs). An MD can be divided into multiple MAs. Each
MA maps a service instance (SI) that belongs to an MD and is identified by a VLAN. An
MA can be regarded as a combination of an MD and a VLAN. According to the standards,
multiple VLANs can map one SI, and one SI maps one MA.
Manage maintenance points (MPs). An MA consists of MPs defined on the ports of bridges.
An MP is a combination of a bridge port, a VLAN, and a maintenance level. MPs are
classified into maintenance association end points (MEPs) and maintenance association
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-7
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
intermediate points (MIPs). MEPs initiate and respond to CFM messages; MIPs
transparently transmit or respond to CFM messages but do not initiate the messages.
Protection Group Management
Protection group management involves the protection switchover and protection group.
Protection switchover: Important board resources and port resources are generally backed up to
enhance system reliability. If a fault occurs on a working member, protection switchover will
be triggered to transfer services to the protection member that will continue to handle the
services.
Protection group: You can manage the working member and the protection member in the
protection group. In a protection group, you can manage the relationship between the members
involved in the protection switchover, record the status of members, and manage the
configuration data and status that are involved by the protection relationship between the
members.
With the protection group feature, you can protect the following objects on the U2000:
l
Active and standby control boards
Aggregation groups on active control board and standby control board
Ports on active and standby control boards
Upstream Ethernet ports
Upstream aggregation links of Ethernet ports
Objects configured with GPON/EPON type B protection
Objects configured with GPON type C protection
Objects configured with EPON type D protection
Objects configured with GPON/EPON type B dual-homing
GPON Service Management
Gigabit passive optical network (GPON) uses the passive optical transmission technology. It
supports a downstream transmission rate of 2.448 Gbit/s and an upstream transmission rate of
1.244 Gbit/s.
GPON service management supports two modes: distributed mode and profile mode. The
equipment and the U2000 support both modes. In the distributed mode, GPON service
management includes the management of the UNI ports, GEM ports, and ONUs. In the profile
mode, GPON service management includes the management of the UNI ports and ONUs; in this
mode, the GEM port is encapsulated in the line template of the UNI port.
For GPON UNI port management, you can perform the following operations on the U2000:
12-8
Modify the port attributes, such as the minimum reach, maximum reach, configuration
status of the ONU auto-discovery function, configuration status of the downstream FEC
function, status of the laser switch, and update cycle of the encryption key of the GPON
UNI port.
Enable and disable the ONU auto-discovery function for a GPON UNI port. After the ONU
auto-discovery function is enabled, the OLT regularly checks whether any ONUs newly
connected to the GPON UNI port are online.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12 FTTx Network Feature Management
Cut over services to implement GPON port backup on the OLT. If the active GPON port
on the OLT is faulty, you can switch over the ONU services from the faulty GPON port to
the specified standby GPON port on the OLT.
Query the alarms of GPON UNI ports. This function allows you to maintain and manage
GPON UNI ports according to the details about and suggested solutions for active alarms.
Enable and disable the laser of a GPON UNI port. By default, the laser of a GPON UNI
port is enabled so that the ONUs connected to the GPON UNI port can go online.
Detect and isolate rogue ONU on a GPON UNI port.
Query the real-time performance statistics and clear the performance statistics.
A GEM port identifies the virtual service channel that carries service streams between the
MA5600T or MA5603T and an ONU. An ONU can provision services only after the mapping
between the GEM port, T-CONT, and service stream is configured on the ONU. For GEM port
management, you can perform the following operations on the U2000:
l
Enable and disable the encryption function. When the encryption function is enabled, the
device encrypts the service stream carried on the GEM port. This feature enhances the
security of user data.
Bind a GEM port to an ONU to establish the mapping between the GEM port on the OLT
and the T-CONT on the ONU.
Limit the rate of packets of a specified priority on a GEM port according to the specified
traffic profile.
Query the real-time performance statistics and clear the performance statistics of a GEM
port.
An ONU provides user interfaces. A GPON UNI port can be connected to a maximum of 128
ONUs. For GPON ONU management, you can perform the following operations on the U2000:
l
Add, delete, and modify an ONU.
Generate topological nodes. Perform this operation to generate topological nodes for ONT
management in the topology view.
Locate directly an ONU in the topology view through the topological node.
Activate and deactivate an ONU.
Re-register an ONU. After an online ONU is reset by force, the ONU re-registers with the
OLT to update the registration information about the ONU.
Re-discover an ONU. ONU re-discovery is applicable only to the ONU that adopts the
once-on authentication mode.
Configure the parameters of value-added service (VAS). The VAS feature of the GPON
ONU is used for provisioning VAS, such as the VoIP service.
Upgrade ONUs.
Query the real-time performance statistics of ONUs and clear the performance statistics.
EPON Service Management
The Ethernet passive optical network (EPON) is an Ethernet-based passive optical network
(PON). It is a new generation broadband access technology, using the point to multi-point
(P2MP) structure and the passive optical fiber transmission mode. As a new technology of fiber
broadband access for the "last mile", the PON does not require node devices but only a simple
optical splitter at the optical branching point. The PON has the following features:
l
Issue 05 (2010-11-19)
Fewer optical fibers.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-9
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Shared bandwidth between branches.
Less investment in telecommunications rooms.
Higher equipment security.
Faster network deployment.
Lower overall costs for network construction.
The EPON uses the wavelength division multiplexing (WDM) technology for concurrent
bidirectional signal transmission. Upstream and downstream signals are transmitted over
different wavelengths: upstream uses a 1310 nm wavelength and downstream uses a 1490 nm
wavelength. The EPON provisions the voice, data, and video services for users over a single
optical fiber.
Currently, the EPON supports a maximum symmetric transmission rate of 1.25 Gbit/s in
upstream and downstream, and a maximum transmission reach of 20 km. In downstream
direction, the EPON broadcasts encrypted data to different users; in upstream direction, the
EPON employs the time division multiplexing (TDM) technology. In this way, the EPON
implements bandwidth sharing in upstream and downstream directions and accommodates the
bandwidth requirements of access users.
EPON service management includes the management of EPON UNI ports and ONUs.
The EPON UNI port is the downstream port for the EPON access. The OLT is connected to
various types of ONUs, including MDUs, through the UNI port to provision high-speed Internet
service for users. For EPON UNI port management, you can perform the following operations
on the U2000:
l
Modify the attributes of an EPON UNI port, including the alias, ONU auto-discovery
function, the maximum distance between an ONU and the OLT, and the tag attribute of
packets.
Display the topology of the optical distribution node (ODN). The EPON UNI port, as an
ODN, is connected to a remote MDU. With this feature, you can enter the ODN+MDU
Layer 2 topology view, and view the ODN-centered star topology. In addition, you can
add, delete, and modify the MDU, and configure relevant services.
Enable and disable an EPON UNI port. The laser of an EPON UNI port is enabled by default
so that the ONUs connected to the EPON UNI port can go online.
Enable and disable the ONU auto-discovery function for an EPON UNI port. After the
ONU auto-discovery function is enabled, the OLT regularly checks whether any ONUs
newly connected to the EPON UNI port go online.
Cut over services to implement EPON port backup on the OLT. If the active EPON port
on the OLT is faulty, you can switch over the ONU services from the faulty EPON port to
a specified standby EPON port on the OLT.
Query the alarms of EPON UNI ports. This function allows you to maintain and manage
EPON UNI ports according to the details about and suggested solutions for active alarms.
Query the real-time performance statistics and clear the performance statistics.
An ONU provides user interfaces. For EPON ONU management, you can perform the following
operations on the U2000:
12-10
Add, delete, and modify an ONU.
Generate topological nodes. Perform this operation to generate topological nodes for ONT
management in the topology view.
Locate directly an ONU in the topology view through the topological node.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12 FTTx Network Feature Management
Activate and deactivate an ONU.
Re-register an ONU. After an online ONU is reset by force, the ONU re-registers with the
OLT to update the registration information about the ONU.
Re-discover an ONU. ONU re-discovery is applicable only to the ONU that adopts the
once-on authentication mode.
Configure the parameters of value-added service (VAS). The VAS feature of the EPON
ONU is used for provisioning VAS, such as the VoIP service.
Upgrade ONUs.
Query the real-time performance statistics of ONUs and clear the performance statistics.
Multicast Service Management
Multicast is a point-to-multipoint (P2MP) communication mode in which the source sends
information to a specified subset of objects under a network node. Multicast services are
applicable to the streaming media, distance learning, video conferencing, video on demand
(VOD), network gaming, data replication, and other P2MP transmission.
Multicast communication uses a class D IP address (224.0.0.0 to 239.255.255.255) as the
destination IP address. A source host sends out a packet that uses a class D IP address as the
destination. If other hosts in the network are interested in the multicast packet, these hosts can
send a request to join the multicast group and receive the packet. The hosts outside of the group
cannot receive the packets sent by the source host.
In controllable multicast, network equipment determines whether a user has the rights to watch
programs by identifying the join or request packets of the user. Then, the access device controls
and forwards the multicast services accordingly.
There are two multicast modes:
l
IGMP snooping: IGMP snooping is a multicast control mechanism at the data link layer.
It is used to manage and control multicast services.
IGMP proxy: In a tree topology, the OLT does not set up routes for forwarding multicast
packets; the OLT only relays and forwards multicast protocol packets. To multicast users,
the OLT is a multicast router that implements the router functions defined in the IGMP
protocol. To multicast routers, the OLT is a multicast user.
You can perform the following operations on the U2000 to manage multicast services:
l
Manage multicast users.
Manage multicast VLANs.
Manage the virtual upstream ports of multicast services.
Manage multicast subtending ports.
Service Provisioning Template
The OLT supports the E2E service template to improve the service provisioning efficiency.
Alarm Responsibility Division
The alarm responsibility division function helps quickly and accurately identify the possible
cause of an out-of-management alarm of an ONU, such as whether the backbone optical fiber
or branch optical fiber is faulty, or the terminal is experiencing a power outage. In this manner,
physical visits to the sites of fault can be reduced.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-11
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
12.2 ONU Management
For NE configuration management, the U2000 provides graphical user interfaces (GUIs) for
configuring NEs and maintaining NE configurations. You can configure services for equipment
in the GUIs.
Device Management
Device management includes the management of NE panels, basic and common device
attributes, clock sources, security, protocols, global configuration of services, and device
templates.
NE Panel Management
You can perform the following operations on the U2000:
l
Display the NE panel by double-clicking an NE.
Query the details of equipment.
Collect statistics on device resources.
Query the information about shelves.
Collect the statistics on shelf resources.
Query inter-shelf links.
Add, delete, start, disable, reset, and confirm a board.
Query the real-time performance statistics on the CPU usage and memory of boards.
Display the port view by double-clicking a board.
Perform an active/standby switchover on the control boards.
Management of Basic and Common Device Attributes
The management of basic and common device attributes includes the query of the global
information about devices and the configuration of the global policies of devices.
You can perform the following operations on the U2000:
l
Query the system information about devices.
Query the statistics on the resources and status of devices.
Query the license information about the functions and resources of devices.
Configure the system time, IP address of a device, and the binding between a Layer 3
interface and an IP address.
Configure the SNMP protocol port.
Set device handshake parameters.
Configure the policy for automatically backing up device data.
Enable and disable the energy-conservation function of a device.
Configure and manage license files.
Clock Source Management
Clock source management includes the management and configuration of equipment-level clock
source information, such as information about the line clock, 1588 clock, and clock priorities.
12-12
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12 FTTx Network Feature Management
Security Management
You can perform the following operations on the U2000:
l
Enable and disable anti-ICMP attack, anti-IP attack, anti-IP spoofing, anti-MAC spoofing,
and anti-DoS attack.
Set the aging time of an MAC address.
Enable and disable MAC address learning.
Configure the security attributes for user login in the CLI.
Protocol Management
You can perform the following operations on the U2000:
l
Manage the Link Aggregation Control Protocol (LACP), Spanning Tree Protocol (STP)/
Rapid Spanning Tree Protocol (RSTP)/Multiple Spanning Tree Protocol (MSTP),
Bidirectional Forwarding Detection (BFD), and Internet Group Management Protocol
(IGMP).
Control the Address Resolution Protocol (ARP) proxy.
Configure the Policy Information Transfer Protocol (PITP) mode/Relay Agent Info Option
(RAIO) custom format.
Control the Dynamic Host Configuration Protocol (DHCP) option 82 function.
Control the DHCP proxy and DHCP relay forwarding functions.
Configure 802.1ag attributes of the Ethernet packet.
Global Configuration of Services
The global configuration of services includes the configuration of the VLAN, QoS, xDSL, and
multicast services.
Device Template Management
Device template management includes the display of different types of device templates on the
U2000. Templates include the GPON template, EPON template, MDU SNMP template, IGMP
template, traffic template, VLAN service template, optical transceiver alarm template, and PW
template. Currently, the U2000 supports only query and generation of global templates.
Network Interface Management
Network interface management includes the management of GPON ports, EPON ports, Ethernet
ports, and xDSL bonding groups.
Management of GPON NNI Ports
The GPON network to network interface (NNI) is the upstream port provided by the control
board. You can perform the following operations on the U2000:
l
Configure the suppression level of the broadcast, multicast, and unknown unicast packet
traffic.
Configure and query the alarm thresholds of an optical transceiver.
Collect the real-time performance statistics on the number of discarded Ethernet frames,
transmitted Ethernet frames, received Ethernet frames, transmitted GEM frames, received
GEM frames, transmitted PLOAM messages, received PLOAM messages, transmitted
OMC messages, and received OMC messages.
Management of EPON NNI Ports
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-13
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
EPON NNI is the upstream port provided by the ONU. You can perform the following operations
on the U2000:
l
Configure and query the alarm thresholds of an optical transceiver.
Collect the real-time performance statistics on the number of transmitted frames,
transmitted bytes, received frames, received bytes, received OAMPDU frames, and
received MPCP frames.
Management of Ethernet Ports
Ethernet port management includes the management of ports and aggregation groups. You can
perform the following operations on the U2000:
l
Configure port attributes.
Create, delete, query, and modify an aggregation group.
Activate and deactivate an Ethernet port.
Collect real-time performance statistics and clear the performance statistics.
Configure the PPPoE, DHCP option 82, 802.3ah ETH OAM loopback, and port rate limit
functions.
Query the attributes of optical transceivers on Ethernet optical ports.
Management of xDSL Bonding Groups
You can perform the following operations on the U2000:
l
Create, delete, and modify an xDSL bonding group.
Set the upstream PVC value for an xDSL bonding group.
Connection Management
ONU connection management includes the management of service virtual ports.
Service Virtual Port Management
A service virtual port enables user equipment to access the ONU. The service virtual port
provides service streams between the user equipment and the ONU for carrying user services.
You can perform the following operations on the U2000:
12-14
Query, add, delete, modify, activate, and deactivate a service virtual port.
Collect the real-time performance statistics and clear the performance statistics.
Perform ATM ping tests.
Configure the extended attributes of a service virtual port. Extended attributes allow for
greater flexibility of addressing customer requirements. Extended attributes include the
maximum number of learnable MAC addresses, the PPPoE session, the encapsulation type,
and the maximum number of MAC addresses that can be bound.
Configure the connection attributes of a service virtual port, including the alias, VPI/VCI,
transmit traffic profile, and receive traffic profile.
Shift the VLAN ID of a service virtual port to change the VLAN ID of the service virtual
port. After successful shifting, the service port assumes the new VLAN ID.
Bind IP addresses to a service virtual port and query the bound IP addresses. To specify
that only the users with certain IP addresses can access the service virtual port, perform the
binding operation. After successful binding, the service forwarding module checks the
source IP address of user packets. If the source IP address does not match any of the IP
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12 FTTx Network Feature Management
addresses bound to the service virtual port, the user packets are dropped. Otherwise, the
user packets are forwarded. This ensures the security of user access.
l
Bind static MAC addresses to a service virtual port. To specify that only the users with
certain static MAC addresses can access the service virtual port, perform the binding
operation. After successful binding, the service forwarding module checks the source MAC
address of user packets. If the source MAC address does not match any of the MAC
addresses bound to the service virtual port, the user packets are dropped. Otherwise, the
user packets are forwarded. This ensures the security of user access.
Configure service bundles. If several service virtual ports carry the same service, a service
bundle can be configured to bundle the service streams over the service virtual ports.
Layer 2 Management
Layer 2 management includes the management of the VLAN, the Rapid Spanning Tree Protocol
(RSTP), the Multiple Spanning Tree Protocol (MSTP), and the Access Node Control Protocol
(ANCP).
VLAN Service Management
VLAN service management includes the management of the standard VLAN, MUX VLAN,
smart VLAN, and super VLAN. You can perform the following operations on the U2000:
l
Query, add, delete, and modify a VLAN.
Collect the real-time performance statistics of a VLAN.
Clear the real-time performance statistics of a VLAN.
Manage a Layer 3 interface and its subinterfaces.
RSTP Management
You can perform the following operations on the U2000:
l
Modify and restore the default value of the trail overheads of a port.
Collect the RSTP statistics of a port.
Clear the RSTP statistics of a port.
MSTP Management
MSTP management includes the management of domains, instances, and ports. You can perform
the following operations on the U2000:
l
Modify and restore the default setting of a domain.
Add, delete, and modify an instance.
Modify a port.
Query the statistics of a port.
ANCP Management
You can perform the following operations on the U2000:
l
Add, delete, modify, enable, and disable an ANCP session.
Query the real-time status of an ANCP session.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-15
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Layer 3 Management
Layer 3 management includes the management of the Dynamic Host Configuration Protocol
(DHCP), Multi-protocol Label Switching (MPLS)/pseudo wire emulation edge-to-edge
(PWE3), and Layer 3 routes.
DHCP Management
DHCP management includes the management of the DHCP server group, MAC address
segment, standard mode, DHCP domain, and VLAN L3 interface. You can perform the
following operations on the U2000:
l
Query, add, delete, and modify a DHCP server group.
Query, add, delete, and modify a MAC address segment.
Query, enable, disable, and modify a standard mode.
Query, add, delete, and modify a DHCP domain.
Modify a VLAN Layer 3 interface.
MPLS/PWE3 Management
The MPLS is a transmission technology. It implements transparent transmission of data packets
between users. The MPLS tunnel is defined in the MPLS protocol. Independent of a service, an
MPLS tunnel implements end-to-end transmission and carries service-related PWs.
You can perform the following operations on the MPLS tunnel on a per-NE basis on the U2000:
l
Configure the basic attributes of the MPLS.
Configure the MPLS tunnel of the static unicast type.
Create forward MPLS tunnels.
Create an E-LSP.
Manage PWs.
Manage tunnel tags and PW label.
ACL and QoS Management
ACL and QoS management includes the management of the access control list (ACL), quality
of service (QoS), and time segments.
In a traditional packet-based network, all packets are treated in the same way. Every router adopts
the first-in first-out (FIFO) policy to process packets, and makes its best effort to transmit packets
to the destination. The router, however, does not make any commitment to packet transmission
performance, such as the delay, delay variation (jitter), packet loss rate, and reliability. With the
rapid development of the computer network, more and more networks are connected to the
Internet. In addition, new services are emerging and raise new requirements on the service
capability of the IP network. Therefore, network-wide end-to-end QoS solutions are called into
attention, which necessitates QoS assurance for services. To achieve so, devices must be able
to apply QoS techniques and provide hierarchical QoS guarantee for different types of service
streams (especially for those highly sensitive to delay and jitter). For ACL management, you
can perform the following operations on the U2000:
12-16
Configure one or more time segments, and associate a time segment with an ACL by
specifying the name of the time segment in the ACL.
Query, modify, create, and delete the ACL of the standard, extended, Layer 2, and userdefined types.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12 FTTx Network Feature Management
QoS management includes filtering packets based on ACL, tagging priorities, limiting traffic
and port rate, collecting statistics on traffic, redirecting, and mirroring. On the U2000, you can
query, add, modify, and delete a QoS policy.
User Security and System Security Management
You can perform the following operations on the U2000:
l
Configure user access in PITP mode.
Configure user access in DHCP option 82 mode.
Configure user access control.
Configure system secure access.
Manage BFD sessions.
BFD Management
The BFD mechanism can quickly check the link status between two devices.
To mitigate the impact of device faults on services and to improve the network availability, a
network device needs to quickly detect any fault occurring between the device and its adjacent
devices. Actions can then be taken to ensure service continuity. The BFD enables the device to
check the connectivity of a type of data protocol of the same trail between two systems. The trail
can be a physical or a logical link, including a tunnel. The BFD mechanism is a remedy for the
weakness of the existing detection mechanism.
Ethernet Connectivity Fault Management
As the Ethernet technology extends from carrier networks to metropolitan area networks
(MANs) and wide area networks (WANs), carriers are increasingly concerned about the
maintainability of equipment, especially the Ethernet equipment. An imperative demand for the
operation, administration and maintenance (OAM) of transport equipment hence arises. Within
Ethernet technology, the 802.1ag connectivity fault management (CFM) provides a method for
detecting faults end-to-end. The Ethernet OAM mechanisms supported by 802.1ag CFM include
connectivity check (CC), loopback (LB), link trace (LT), and forward AIS alarms. You can
perform the following operations on the U2000:
l
Manage maintenance domains (MDs). Ethernet CFM divides a network into up to eight
levels. A bridge can span multiple levels to manage different MDs. A CFM MD is
constituted by bridges. An MD is the combination of bridges and maintenance levels. MDs
can be classified into three layers: user domain (levels 7-5), service provider domain (levels
4-3), and carrier domain (levels 2-0). Different MDs are maintained by different
management entities.
Manage maintenance associations (MAs). An MD can be divided into multiple MAs. Each
MA maps a service instance (SI) that belongs to an MD and is identified by a VLAN. An
MA can be regarded as a combination of an MD and a VLAN. According to the standards,
multiple VLANs can map one SI, and one SI maps one MA.
Manage maintenance points (MPs). An MA consists of MPs defined on the ports of bridges.
An MP is a combination of a bridge port, a VLAN, and a maintenance level. MPs are
classified into maintenance association end points (MEPs) and maintenance association
intermediate points (MIPs). MEPs initiate and respond to CFM messages; MIPs
transparently transmit or respond to CFM messages but do not initiate the messages.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-17
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
xDSL Service Management
xDSL service management includes the management of the asymmetrical digital subscriber loop
(ADSL), ADSL2+, ATM global single-pair high-speed digital subscriber line (G.SHDSL), and
very high speed digital subscriber lines 2 (VDSL2) services. The features of these services are
as follows:
ADSL Service Management
ADSL is a technology for providing the asymmetric and high-speed private line access service
over common twisted pairs. The ADSL supports the asymmetrical transmission in the upstream
and downstream directions, which is suitable for the user data access service and can provide
high-speed data transmission channels for users. The ADSL2+ is an extension of the ADSL
technology. It supports a maximum transmission rate of 24 Mbit/s and 2.5 Mbit/s in the
downstream and upstream respectively and a maximum transmission distance of 6.5 km. You
can perform the following operations on the U2000:
l
Activate and deactivate a port.
Perform and cancel a loopback.
Deactivate a port and then activate it again to initialize the port.
Reconfigure port attributes.
Configure the port attributes, such as the associated line template, alarm template, extended
template, and monitoring thresholds. These attributes are used to activate the ADSL port.
Query the real-time and history performance statistics.
G.SHDSL Service Management
G.SHDSL is a technology for providing a high-rate symmetrical data service over one or two
twisted pairs. The 2-wire, 4-wire, 6-wire, and 8-wire G.SHDSL access services are supported
to allow for a transmission distance ranging from 3 km to 6 km. The rates of the 2-wire, 4-wire,
6-wire, and 8-wire G.SHDSL lines range from 192 kbit/s to 5696 kbit/s, 384 kbit/s to 4608 kbit/
s, 576 kbit/s to 17088 kbit/s, and 768 kbit/s to 22784 kbit/s respectively. You can perform the
following operations on the U2000:
l
Activate and deactivate a port.
Maintain a port.
Bind and unbind a port. You can bind multiple ATM G.SHDSL ports. This increases the
bandwidth at the physical layer and improves the rate of the ATM G.SHDSL port.
Configure port attributes, such as the associated line profile and alarm profile. These
attributes are used to activate the ATM G.SHDSL port.
Query the real-time performance statistics.
VDSL2 Service Management
VDSL2 is an extension of the VDSL technology. It provides high-speed private line access in
the symmetrical or asymmetrical mode over common twisted pairs. VDSL2 supports a high
bandwidth with symmetric rates of up to 100 Mbit/s and multiple spectrum template and
encapsulation modes. Based on these features, it provides short-distance and high-speed access
solutions to the next generation broadband access scenarios. You can perform the following
operations on the U2000:
12-18
Activate and deactivate a port.
Perform and cancel a loopback.
Deactivate a port and then activate it again to initialize a port.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12 FTTx Network Feature Management
Reconfigure port attributes.
Configure the port attributes, such as the associated line profile, alarm profile, extended
profile, and monitoring thresholds of a VDSL2 port. These attributes are used to activate
the VDSL2 port.
Query the real-time and history performance statistics.
Ethernet Access Management
Ethernet access management includes the management of ports and aggregation groups. You
can perform the following operations on the U2000:
l
Configure port attributes.
Create, delete, query, and modify an aggregation group.
Activate and deactivate an Ethernet port.
Collect real-time performance statistics and clear the performance statistics.
Control the PPPoE, DHCP Option 82, 802.3ah ETH OAM loopback, and port rate limit
functions.
Query the attributes of optical transceivers for Ethernet optical ports.
Multicast Service Management
Multicast is a point-to-multipoint (P2MP) communication mode in which the source sends
information to a specified subset of objects under a network node. Multicast services are
applicable to the streaming media, distance learning, video conferencing, video on demand
(VOD), network gaming, data replication, and other P2MP transmission.
Multicast communication uses a class D IP address (224.0.0.0 to 239.255.255.255) as the
destination IP address. A source host sends out a packet that uses a class D IP address as the
destination. If other hosts in the network are interested in the multicast packet, these hosts can
send a request to join the multicast group and receive the packet. The hosts outside of the group
cannot receive the packets sent by the source host.
In controllable multicast, network equipment determines whether a user has the rights to watch
programs by identifying the join or request packets of the user. Then, the access device controls
and forwards the multicast services accordingly.
There are two multicast modes:
l
IGMP snooping: IGMP snooping is a multicast control mechanism at the data link layer.
It is used to manage and control multicast services.
IGMP proxy: In a tree topology, the OLT does not set up routes for forwarding multicast
packets; the OLT only relays and forwards multicast protocol packets. To multicast users,
the OLT is a multicast router that implements the router functions defined in the IGMP
protocol. To multicast routers, the OLT is a multicast user.
You can perform the following operations on the U2000 to manage multicast services:
l
Manage multicast users.
Manage multicast VLANs.
Manage the virtual upstream ports of multicast services.
Manage multicast subtending ports.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-19
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Narrowband Service Management
Narrowband service management includes the management of the media gateway (MG),
signaling gateway (SG), POTS ports, and IP ports.
MG Management
In the next generation network (NGN), the media gateway (MG) and the media gateway
controller (MGC) are separated. That is, the functions of the user plane are separated from the
functions of the control plane. The messages of the user plane interact with each other by using
the MG and the messages of the control plane interact with each other by using the MGC. An
MG device consists of the MG, MGC, digital signal processor (DSP) management, and ringing
mapping. You can perform the following operations on the U2000:
l
Manage MGs
Manage MGCs
Manage ringing mapping
Manage DSP channels
SG Management
Signaling gateway (SG) management includes the management of signaling gateways and
associations. An SG is a part for signaling interaction. An SG is a signaling proxy for receiving
and transmitting signaling messages between the No.7 signaling network and the IP network.
An SCTP association provides data transmission for the transfer of the protocol data unit of one
or more ports.
VoIP PSTN Port Management
The public switched telephone network (PSTN) is a communication network that provides
telephone services for public users over analog subscriber lines. It is also called plain old
telephone service (POTS).
Voice over IP (VoIP) is a communication mode for delivery of voice and data over Internet
Protocol (IP) networks. In the VoIP technology, voice information is transmitted in digital form
in discrete packets rather than through the traditional circuit-oriented protocols of PSTN.
The VoIP PSTN service is provided through the VoIP PSTN ports on the voice service board
of an ONU. A gateway is established on the ONU between the PSTN network and the IP network.
You can perform the following operations on the U2000:
l
Configure and modify port attributes.
Enable and disable services.
Perform and cancel a loopback.
Reset a port.
Collect the real-time performance statistics.
VoIP ISDN BRA Port Management
ISDN basic rate access (BRA) is the basic rate interface (BRI) and user-network interface
provided by the ONU. The BRI supports a transmission rate of 44 kbit/s and provides 2 B
channels for carrying services and 1 D channel for transmitting the call control signaling and
maintaining the management signaling. The rate of B channels is 64 kbit/s and the rate of D
channel is 16 kbit/s. In the upstream direction, the ONU transmits the ISDN service to the NGN
network in IP networking mode. The ISDN service is called the VoIP ISDN BRA service. You
can perform the following operations on the U2000:
12-20
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
12 FTTx Network Feature Management
Configure and modify port attributes.
Enable and disable services.
Perform and cancel a loopback.
Activate and deactivate a port.
Reset a port.
Query the statistics on the usage of MG ports and collect the number of VoIP ISDN BRA
ports by port status.
Configure the alarm threshold of Layer 2 signaling errors.
Collect the real-time performance statistics.
VoIP ISDN PRA Port Management
ISDN primary rate access (PRA) is the primary rate interface (PRI) and user-network interface
provided by the ONU. The PRI supports a transmission rate of 2.048 Mbit/s and provides 30 B
channels and 1 D channel. The rates of the B channel and D channel are 64 kbit/s. In the upstream
direction, the ONU transmits the ISDN service to the NGN network in IP networking mode. The
ISDN service is called the VoIP ISDN PRA service. You can perform the following operations
on the U2000:
l
Configure and modify port attributes.
Enable and disable services.
Perform and cancel a loopback.
Query the statistics on the usage of MG ports and collect the number of VoIP ISDN PRA
ports by port status.
Configure the alarm threshold of Layer 2 signaling errors.
Query the timeslots that are occupied by a specified VoIP ISDN PRA port.
Sheet-based Predeployment Management
The U2000 provides the sheet-based predeployment solution which enables you to import device
data to the U2000 in batches. This solution provides for plug-and-play (PnP) of equipment,
implements software-commissioning-free and requires only one site visit. Therefore, this
solution improves deployment efficiency and reduces network construction cost, and at the same
time allows for concurrent offline configuration and on-site construction. Sheet-based
predeployment has the following features:
l
Offline deployment by importing a predeployed sheet
Automatic upgrade of NE software
Automatic issuing of configuration data
Plug-and-Play Feature Management
When an MDU is faulty, it is essential to locate the fault and recover services quickly. It is,
however, time-consuming to locate and troubleshoot an internal fault of the MDU. Therefore,
faulty MDUs are directly replaced, and are stored and repaired later in a centralized manner.
Solution limitations:
l
The versions of the MDUs of the same type in the entire network must be the same.
The configuration data of the MDUs must be backed up periodically to safeguard the data.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12-21
12 FTTx Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Only one MDU can go offline and one MDU be automatically discovered during automatic
replacement.
Solution implementation procedure:
l
1. Back up the configuration data as required by using the DC component.
2. Replace the MDU that encounters a severe hardware fault.
3. The hardware installation engineer replaces the faulty MDU with a new MDU and
furnishes the maintenance engineer with the identification information about the new
MDU.
4. The maintenance engineer modifies the authentication information about the MDU on
the U2000, starts the automatic upgrade of the NE software by using the DC component,
and loads the configuration file to the MDU.
Solution benefit:
l
The MDU implements PnP and is replaced quickly.
The configuration data is restored quickly.
MDU replacement methods:
l
Manual replacement based on a MAC address (EPON) or SN (GPON)
Automatic replacement based on the key or password
Automatic one-to-one replacement based on the MAC address
Remote Acceptance
To achieve one site visit and reduce the O&M cost in FTTx network construction, the deployed
ONUs must support remote acceptance. With the FTTx PnP solution, you can perform the
following acceptance operations:
l
Narrowband emulation acceptance, to check whether the voice links are in the normal state
by using the call emulation test.
PPPoE dialup emulation acceptance, to check whether the links for Internet access are in
the normal state.
ONT Automatic Bulk Upgrade
An FTTH network is deployed with a large number of ONTs. When the ONTs are upgraded,
the following problems may occur:
l
The range of ONTs to be upgraded cannot be determined when ONTs are added to the
network during service provisioning.
l
l
The online status of ONTs in user premises cannot be confirmed.
The U2000 provides the automatic offline bulk upgrade solution for ONTs. You can perform
the following operations on the U2000:
12-22
Upgrade ONTs in batches.
Upgrade ONTs automatically by creating a periodic upgrade task.
Upgrade offline ONTs automatically when the ONTs go online.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
13
13 MSAN Network Feature Management
MSAN Network Feature Management
About This Chapter
This topic describes the functions and features of MSAN NE management and network
management.
13.1 MSAN Management
For NE configuration management, the U2000 provides graphical user interfaces (GUIs) for
configuring NEs and maintaining NE configurations. You can configure services for equipment
in the GUIs.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
13-1
13 MSAN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
13.1 MSAN Management
For NE configuration management, the U2000 provides graphical user interfaces (GUIs) for
configuring NEs and maintaining NE configurations. You can configure services for equipment
in the GUIs.
Device Management
Device management includes the management of NE panels, basic and common device
attributes, clock sources, security, protocols, global configuration of services, and device
templates.
NE Panel Management
You can perform the following operations on the U2000:
l
Display the NE panel by double-clicking an NE.
Query the details of equipment.
Collect statistics on device resources.
Query the information about shelves.
Collect the statistics on shelf resources.
Query inter-shelf links.
Add, delete, start, disable, reset, and confirm a board.
Query the real-time performance statistics on the CPU usage and memory of boards.
Display the port view by double-clicking a board.
Perform an active/standby switchover on the control boards.
Management of Basic and Common Device Attributes
The management of basic and common device attributes includes the query of the global
information about devices and the configuration of the global policies of devices.
You can perform the following operations on the U2000:
l
Query the system information about devices.
Query the statistics on the resources and status of devices.
Query the license information about the functions and resources of devices.
Configure the system time, IP address of a device, and the binding between a Layer 3
interface and an IP address.
Configure the SNMP protocol port.
Set device handshake parameters.
Configure the policy for automatically backing up device data.
Enable and disable the energy-conservation function of a device.
Configure and manage license files.
Clock Source Management
Clock source management includes the management and configuration of equipment-level clock
source information, such as information about the line clock, 1588 clock, and clock priorities.
13-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
13 MSAN Network Feature Management
Security Management
You can perform the following operations on the U2000:
l
Enable and disable anti-ICMP attack, anti-IP attack, anti-IP spoofing, anti-MAC spoofing,
and anti-DoS attack.
Set the aging time of a MAC address.
Enable and disable MAC address learning.
Configure the security attributes for user login in the CLI.
Protocol Management
You can perform the following operations on the U2000:
l
Manage the Link Aggregation Control Protocol (LACP), Spanning Tree Protocol (STP)/
Rapid Spanning Tree Protocol (RSTP)/Multiple Spanning Tree Protocol (MSTP),
Bidirectional Forwarding Detection (BFD), and Internet Group Management Protocol
(IGMP).
Control the Address Resolution Protocol (ARP) proxy.
Configure the Policy Information Transfer Protocol (PITP) mode/Relay Agent Info Option
(RAIO) custom format.
Control the Dynamic Host Configuration Protocol (DHCP) option 82 function.
Control the DHCP proxy and DHCP relay forwarding functions.
Configure 802.1ag attributes of the Ethernet packet.
Global Configuration of Services
The global configuration of services includes the configuration of the VLAN, QoS, xDSL, and
multicast services.
Device Template Management
Device template management includes the display of different types of device templates on the
U2000. Templates include the IGMP template, traffic template, VLAN service template, and
PW template. Currently, the U2000 supports only query and generation of global templates.
Network Interface Management
Network interface management includes the management and maintenance of E1/T1 ports and
the Ethernet port.
Management and Maintenance of E1/T1 Ports
E1/T1 ports are classified into TDM E1/T1 ports, CES E1/T1 ports, and IMA E1/T1 ports.
TDM E1/T1 ports can be used as access ports or upstream ports, depending on the functions of
the boards.
On E1 ports for upstream transmission, you can perform only the loopback operation.
On E1 ports for PRA access, you can perform the following operations: configure or delete port
attributes, set the alarm threshold of L2 signaling bit errors, query timeslots, and enable or disable
services.
On CES E1/T1 ports, you can collect real-time performance statistics of ports, configure the port
attributes, set port alias, and perform loopback.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
13-3
13 MSAN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
On IMA E1/T1 ports, you can query real-time performance statistics of the ports, and manage
IMA groups and IMA links, including adding, deleting, modifying, resetting, blocking, and
unblocking an IMA group or link.
Management of Ethernet Ports
Ethernet port management includes the management of ports and aggregation groups. You can
perform the following operations on the U2000:
l
Configure port attributes.
Create, delete, query, and modify an aggregation group.
Activate and deactivate an Ethernet port.
Collect real-time performance statistics and clear the performance statistics.
Configure the PPPoE, DHCP option 82, 802.3ah ETH OAM loopback, and port rate limit
functions.
Query the attributes of optical transceivers for Ethernet optical ports.
Connection Management
Connection management includes the management of service virtual ports and CESoP
connections.
Service Virtual Port Management
A service virtual port enables user equipment to access the OLT. The service virtual port provides
service streams between the user equipment and the OLT for carrying user services. You can
perform the following operations on the U2000:
13-4
Query, add, delete, modify, activate, and deactivate a service virtual port.
Collect the real-time performance statistics and clear the performance statistics.
Perform ATM ping tests.
Configure the extended attributes of a service virtual port. Extended attributes allow for
greater flexibility of addressing customer requirements. Extended attributes include the
maximum number of learnable MAC addresses, the PPPoE session, the encapsulation type,
and the maximum number of MAC addresses that can be bound.
Configure the connection attributes of a service virtual port, including the alias, VPI/VCI,
transmit traffic profile, and receive traffic profile.
Shift the VLAN ID of a service virtual port to change the VLAN ID of the service virtual
port. After successful shifting, the service port assumes the new VLAN ID.
Bind IP addresses to a service virtual port and query the bound IP addresses. To specify
that only the users with certain IP addresses can access the service virtual port, perform the
binding operation. After successful binding, the service forwarding module checks the
source IP address of user packets. If the source IP address does not match any of the IP
addresses bound to the service virtual port, the user packets are dropped. Otherwise, the
user packets are forwarded. This ensures the security of user access.
Bind static MAC addresses to a service virtual port. To specify that only the users with
certain static MAC addresses can access the service virtual port, perform the binding
operation. After successful binding, the service forwarding module checks the source MAC
address of user packets. If the source MAC address does not match any of the MAC
addresses bound to the service virtual port, the user packets are dropped. Otherwise, the
user packets are forwarded. This ensures the security of user access.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
13 MSAN Network Feature Management
Configure service bundles. If several service virtual ports carry the same service, a service
bundle can be configured to bundle the service streams over the service virtual ports.
Management of CESoP Connection Management
The circuit emulation service over packet (CESoP) simulates circuit emulation services over
packets. After the CESoP connection is set up and the required service stream is created, the
communication over the CESoP E1 line is successful.
Layer 2 Management
Layer 2 management includes the management of the VLAN, the Rapid Spanning Tree Protocol
(RSTP), Multiple Spanning Tree Protocol (MSTP), Access Node Control Protocol (ANCP), and
Rapid Ring Protection Protocol (RRPP).
VLAN Service Management
VLAN service management includes the management of the standard VLAN, MUX VLAN,
smart VLAN, and super VLAN. You can perform the following operations on the U2000:
l
Query, add, delete, and modify a VLAN.
Collect the real-time performance statistics of a VLAN.
Clear the real-time performance statistics of a VLAN.
Manage a Layer 3 interface and its subinterfaces.
RSTP Management
You can perform the following operations on the U2000:
l
Modify and restore the default value of the trail overheads of a port.
Collect the RSTP statistics of a port.
Clear the RSTP statistics of a port.
MSTP Management
MSTP management includes the management of domains, instances, and ports. You can perform
the following operations on the U2000:
l
Modify and restore the default setting of a domain.
Add, delete, and modify an instance.
Modify a port.
Query the statistics of a port.
ANCP Management
You can perform the following operations on the U2000:
l
Add, delete, modify, enable, and disable an ANCP session.
Query the real-time status of an ANCP session.
RRPP Management
For RRPP management, you can perform the query, add, delete, and modify operations.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
13-5
13 MSAN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Layer 3 Management
Layer 3 management includes the management of the Dynamic Host Configuration Protocol
(DHCP), Multi-protocol Label Switching (MPLS)/pseudo wire emulation edge-to-edge
(PWE3), and Layer 3 routes.
DHCP Management
DHCP management includes the management of the DHCP server group, MAC address
segment, standard mode, DHCP domain, and VLAN L3 interface. You can perform the
following operations on the U2000:
l
Query, add, delete, and modify a DHCP server group.
Query, add, delete, and modify a MAC address segment.
Query, enable, disable, and modify a standard mode.
Query, add, delete, and modify a DHCP domain.
Modify a VLAN Layer 3 interface.
MPLS PWE3 Management
The MPLS is a transmission technology. It implements transparent transmission of data packets
between users. The MPLS tunnel is defined in the MPLS protocol. Independent of a service, an
MPLS tunnel implements end-to-end transmission and carries service-related PWs.
You can perform the following operations on the MPLS tunnel on a per-NE basis on the U2000:
l
Configure the basic attributes of the MPLS.
Configure the MPLS tunnel of the static unicast type.
Create forward MPLS tunnels.
Create an E-LSP.
Manage PWs.
Manage tunnel tags and PW labels.
ACL and QoS Management
ACL and QoS management includes the management of the access control list (ACL), quality
of service (QoS), time segments, and hierarchical QoS (HQoS).
In a traditional packet-based network, all packets are treated in the same way. Every router adopts
the first-in first-out (FIFO) policy to process packets, and makes its best effort to transmit packets
to the destination. The router, however, does not make any commitment to packet transmission
performance, such as the delay, delay variation (jitter), packet loss rate, and reliability. With the
rapid development of the computer network, more and more networks are connected to the
Internet. In addition, new services are emerging and raise new requirements on the service
capability of the IP network. Therefore, network-wide end-to-end QoS solutions are called into
attention, which necessitates QoS assurance for services. To achieve so, devices must be able
to apply QoS techniques and provide hierarchical QoS guarantee for different types of service
streams (especially for those highly sensitive to delay and jitter). For ACL management, you
can perform the following operations on the U2000:
13-6
Configure one or more time segments, and associate a time segment with an ACL by
specifying the name of the time segment in the ACL.
Query, modify, create, and delete the ACL of the standard, extended, Layer 2, and userdefined types.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
13 MSAN Network Feature Management
QoS management includes filtering packets based on ACL, tagging priorities, limiting traffic
and port rate, collecting statistics on traffic, redirecting, and mirroring. On the U2000, you can
query, add, modify, and delete a QoS policy.
HQoS stands for the hierarchical QoS. It not only controls user traffic but also schedules packets
according to the priorities of user services. On the U2000, you can query, add, modify, and delete
an HQoS policy.
User Security and System Security
You can perform the following operations on the U2000:
l
Configure user access in PITP mode.
Configure user access in DHCP option 82 mode.
Configure user access control.
Configure system secure access.
Manage BFD sessions.
Ethernet Connectivity Fault Management
As the Ethernet technology extends from carrier networks to metropolitan area networks
(MANs) and wide area networks (WANs), carriers are increasingly concerned about the
maintainability of equipment, especially the Ethernet equipment. An imperative demand for the
operation, administration and maintenance (OAM) of transport equipment hence arises. Within
Ethernet technology, the 802.1ag connectivity fault management (CFM) provides a method for
detecting faults end-to-end. The Ethernet OAM mechanisms supported by 802.1ag CFM include
connectivity check (CC), loopback (LB), link trace (LT), and forward AIS alarms. You can
perform the following operations on the U2000:
l
Manage maintenance domains (MDs). Ethernet CFM divides a network into up to eight
levels. A bridge can span multiple levels to manage different MDs. A CFM MD is
constituted by bridges. An MD is the combination of bridges and maintenance levels. MDs
can be classified into three layers: user domain (levels 7-5), service provider domain (levels
4-3), and carrier domain (levels 2-0). Different MDs are maintained by different
management entities.
Manage maintenance associations (MAs). An MD can be divided into multiple MAs. Each
MA maps a service instance (SI) that belongs to an MD and is identified by a VLAN. An
MA can be regarded as a combination of an MD and a VLAN. According to the standards,
multiple VLANs can map one SI, and one SI maps one MA.
Manage maintenance points (MPs). An MA consists of MPs defined on the ports of bridges.
An MP is a combination of a bridge port, a VLAN, and a maintenance level. MPs are
classified into maintenance association end points (MEPs) and maintenance association
intermediate points (MIPs). MEPs initiate and respond to CFM messages; MIPs
transparently transmit or respond to CFM messages but do not initiate the messages.
Protection Group Management
Protection group management involves the protection switchover and protection group.
Protection switchover: Important board resources and port resources are generally backed up to
enhance system reliability. If a fault occurs on a working member, protection switchover will
be triggered to transfer services to the protection member that will continue to handle the
services.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
13-7
13 MSAN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Protection group: You can manage the working member and the protection member in the
protection group. In a protection group, you can manage the relationship between the members
involved in the protection switchover, record the status of members, and manage the
configuration data and status that are involved by the protection relationship between the
members.
With the protection group feature, you can protect the following objects on the U2000:
l
Active and standby control boards
Aggregation groups on active control board and standby control board
Ports on active and standby control boards
Upstream Ethernet ports
Upstream aggregation links of Ethernet ports
xDSL Service Management
xDSL service management includes the management of the asymmetrical digital subscriber loop
(ADSL), ADSL2+, ATM global single-pair high-speed digital subscriber line (G.SHDSL), and
very high speed digital subscriber lines 2 (VDSL2) services. The features of these services are
as follows:
ADSL Service Management
ADSL is a technology for providing the asymmetric and high-speed private line access service
over common twisted pairs. ADSL supports the asymmetrical transmission in the upstream and
downstream directions, which is suitable for the user data access service and can provide highspeed data transmission channels for users. ADSL2+ is an extension of the ADSL technology.
It supports a maximum transmission rate of 24 Mbit/s and 2.5 Mbit/s in the downstream and
upstream respectively and a maximum transmission distance of 6.5 km. You can perform the
following operations on the U2000:
l
Activate and deactivate a port.
Perform and cancel a loopback.
Deactivate a port and then activate it again to initialize the port.
Reconfigure port attributes.
Configure the port attributes, such as the associated line template, alarm template, extended
template, and monitoring thresholds. These attributes are used to activate the ADSL port.
Query the real-time and history performance statistics.
G.SHDSL Service Management
G.SHDSL is a technology for providing a high-rate symmetrical data service over one or two
twisted pairs. The 2-wire, 4-wire, 6-wire, and 8-wire G.SHDSL access services are supported
to allow for a transmission distance ranging from 3 km to 6 km. The rates of the 2-wire, 4-wire,
6-wire, and 8-wire G.SHDSL lines range from 192 kbit/s to 5696 kbit/s, 384 kbit/s to 4608 kbit/
s, 576 kbit/s to 17088 kbit/s, and 768 kbit/s to 22784 kbit/s respectively. You can perform the
following operations on the U2000:
13-8
Activate and deactivate a port.
Perform and cancel a loopback.
Bind and unbind a port. You can bind multiple ATM G.SHDSL ports. This increases the
bandwidth at the physical layer and improves the rate of the ATM G.SHDSL port.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
13 MSAN Network Feature Management
Configure port attributes, such as the associated line profile and alarm profile. These
attributes are used to activate the ATM G.SHDSL port.
Query the real-time performance statistics.
VDSL2 service Management
VDSL2 is an extension of the VDSL technology. It provides high-speed private line access in
the symmetrical or asymmetrical mode over common twisted pairs. VDSL2 supports a high
bandwidth with symmetric rates of up to 100 Mbit/s and multiple spectrum template and
encapsulation modes. Based on these features, it provides short-distance and high-speed access
solutions to the next generation broadband access scenarios. You can perform the following
operations on the U2000:
l
Activate and deactivate a port.
Perform and cancel a loopback.
Deactivate a port and then activate it again to initialize a port.
Reconfigure port attributes.
Configure the port attributes, such as the associated line profile, alarm profile, extended
profile, and monitoring thresholds of a VDSL2 port. These attributes are used to activate
the VDSL2 port.
Query the real-time and history performance statistics.
Multicast Service Management
Multicast is a point-to-multipoint (P2MP) communication mode in which the source sends
information to a specified subset of objects under a network node. Multicast services are
applicable to the streaming media, distance learning, video conferencing, video on demand
(VOD), network gaming, data replication, and other P2MP transmission.
Multicast communication uses a class D IP address (224.0.0.0 to 239.255.255.255) as the
destination IP address. A source host sends out a packet that uses a class D IP address as the
destination. If other hosts in the network are interested in the multicast packet, these hosts can
send a request to join the multicast group and receive the packet. The hosts outside of the group
cannot receive the packets sent by the source host.
In controllable multicast, network equipment determines whether a user has the rights to watch
programs by identifying the join or request packets of the user. Then, the access device controls
and forwards the multicast services accordingly.
There are two multicast modes:
l
IGMP snooping: IGMP snooping is a multicast control mechanism at the data link layer.
It is used to manage and control multicast services.
IGMP proxy: In a tree topology, the OLT does not set up routes for forwarding multicast
packets; the OLT only relays and forwards multicast protocol packets. To multicast users,
the OLT is a multicast router that implements the router functions defined in the IGMP
protocol. To multicast routers, the OLT is a multicast user.
You can perform the following operations on the U2000 to manage multicast services:
l
Manage multicast users.
Manage multicast VLANs.
Manage the virtual upstream ports of multicast services.
Manage multicast subtending ports.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
13-9
13 MSAN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
MG Management
In the next generation network (NGN), the media gateway (MG) and the media gateway
controller (MGC) are separated. That is, the functions of the user plane are separated from the
functions of the control plane. The messages of the user plane interact with each other by using
the MG and the messages of the control plane interact with each other by using the MGC. An
MG device consists of the MG, MGC, digital signal processor (DSP) management, and ringing
mapping. You can perform the following operations on the U2000:
l
Manage MGs.
Manage MGCs.
Manage ringing mapping.
Manage DSP channels.
SG Management
Signaling gateway (SG) management includes the management of signaling gateways and
associations. An SG is a part for signaling interaction. AN SG is a signaling proxy for receiving
and transmitting signaling messages between the No.7 signaling network and the IP network.
An SCTP association provides data transmission for the transfer of the protocol data unit of one
or more ports.
Narrowband VoIP Service Management
Narrowband VoIP service management includes the management of the MG, SG, POTS ports,
and IP ports.
VoIP PSTN Port Management
The public switched telephone network (PSTN) is a communication network that provides
telephone services for public users over analog subscriber lines. It is also called plain old
telephone service (POTS).
Voice over IP (VoIP) is a communication mode for delivery of voice and data over Internet
Protocol (IP) networks. In the VoIP technology, voice information is transmitted in digital form
in discrete packets rather than through the traditional circuit-oriented protocols of PSTN.
The VoIP PSTN service is provided through the VoIP PSTN ports on the voice service board
of an ONU. A gateway is established on the ONU between the PSTN network and the IP network.
You can perform the following operations on the U2000:
l
Configure and modify port attributes.
Enable and disable services.
Perform and cancel a loopback.
Reset a port.
Collect the real-time performance statistics.
VoIP ISDN BRA Port Management
ISDN basic rate access (BRA) is the basic rate interface (BRI) and user-network interface
provided by the ONU. The BRI supports a transmission rate of 44 kbit/s and provides 2 B
channels for carrying services and 1 D channel for transmitting the call control signaling and
maintaining the management signaling. The rate of B channels is 64 kbit/s and the rate of D
channel is 16 kbit/s. In the upstream direction, the ONU transmits the ISDN service to the NGN
13-10
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
13 MSAN Network Feature Management
network in IP networking mode. The ISDN service is called the VoIP ISDN BRA service. You
can perform the following operations on the U2000:
l
Configure and modify port attributes.
Enable and disable services.
Perform and cancel a loopback.
Activate and deactivate a port.
Reset a port.
Query the statistics on the usage of MG ports and collect the number of VoIP ISDN BRA
ports by port status.
Configure the alarm threshold of Layer 2 signaling errors.
Collect the real-time performance statistics.
VoIP ISDN PRA Port Management
ISDN primary rate access (PRA) is the primary rate interface (PRI) and user-network interface
provided by the ONU. The PRI supports a transmission rate of 2.048 Mbit/s and provides 30 B
channels and 1 D channel. The rates of the B channel and D channel are 64 kbit/s. In the upstream
direction, the ONU transmits the ISDN service to the NGN network in IP networking mode. The
ISDN service is called the VoIP ISDN PRA service. You can perform the following operations
on the U2000:
l
Configure and modify port attributes.
Enable and disable services.
Perform and cancel a loopback.
Query the statistics on the usage of MG ports and collect the number of VoIP ISDN PRA
ports by port status.
Configure the alarm threshold of Layer 2 signaling errors.
Query the timeslots that are occupied by a specified VoIP ISDN PRA port.
V5 Voice Service Management
V5 voice service management includes the management of V5 interfaces, service ports, semipermanent connections (SPCs), VFB boards, ATI boards, and CDI boards.
V5 Interface Management
The V5 interface is a standard digital interface between the access network (AN) and the local
exchange (LE). The V5 interface supports the access of abundant integrated services. In addition,
it separates accesses and services to optimize the network organization. You can perform the
following operations on the U2000:
l
Manage the attributes of V5 interfaces.
Restart the PSTN protocol on the V5 interface.
Switch over the logical communication channels of a specified V5 interface for protection.
Manage 2M links.
Manage communication channels.
Manage ISDN communication channels.
Configure the ringing mode for users.
Service Port Management
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
13-11
13 MSAN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Service ports are classified into V5 PSTN ports, V5 ISDN BRA ports, and V5 ISDN PRA ports.
You can perform the following operations to manage V5 PSTN ports on the U2000:
l
Configure and modify port attributes.
Enable and disable services.
Perform and cancel a loopback.
Reset a port.
Collect real-time performance statistics.
You can perform the following operations to manage V5 ISDN BRA ports on the U2000:
l
Configure and modify port attributes.
Enable and disable services.
Perform and cancel a loopback.
Activate and deactivate a port.
Reset a port.
Query the statistics on the usage of MG ports and collect the number of V5 ISDN BRA
ports by port status.
Configure the alarm threshold of Layer 2 signaling errors.
Collect real-time performance statistics.
You can perform the following operations to manage V5 ISDN PRA ports on the U2000:
l
Configure and modify port attributes.
Enable or disable services.
Perform and cancel a loopback.
Query the statistics on the usage of MG ports and collect the number of V5 ISDN PRA
ports by port status.
Configure the alarm threshold of Layer 2 signaling errors.
Query the timeslots occupied by a specified V5 ISDN PRA port.
SPC Management
SPC can connect, release, check, and protect one or more 64 kbit/s channels of different ports
of the same board or different boards. SPCs occupy dedicated and fixed voice channels to meet
the communication requirements of special and VIP access subscribers and ensure the
communication quality. You can perform the following operations on the U2000:
l
Set up common SPCs between narrowband service ports.
Set up VoIP-based IP SPCs.
Set up internal SPCs.
Configure private lines.
Set up V5 SPCs.
Set up V5 pre-SPCs.
VFB Board Management
The UA5000(PVMV1) provides point-to-point voice frequency (VF) channels to transmit voice
or data in dedicated networks. You can connect VF telephones or modems (connecting user
terminals) to the VF channels at the two sides so that the voice or data is interconnected over
dedicated lines. The VFB board of the UA5000(PVMV1) is a 2/4-wire VF dedicated line
13-12
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
13 MSAN Network Feature Management
interface board and supports the VF dedicated line services. The VFB board provides the function
of adjusting the 2/4-wire port through software. It provides sixteen 2-wire port or eight 4-wire
ports. You can perform the following operations on the U2000:
l
Configure the attributes of ports provided by the VFB board.
Add SPCs.
Certain dedicated networks access LEs or interwork with remote dedicated networks over the
access network. In dedicated networks, many users adopt the E&M trunk ports. To access these
users over the access network, ONUs must provide the E&M trunk ports.
ATI Board Management
The ATI board, inserted in a service shelf, transparently transmits E/M signaling and 2-wire/4wire VF signals by using SPCs. This helps the HONET system access certain dedicated
networks. The ATI board provides six 2-wire/4-wire E&M trunk ports. Each port provides the
2-wire/4-wire VF line and the 1E1M signaling line. If the 1E1M signaling line is not in use, the
2-wire/4-wire VF line can be used independently to transmit VF signals. You can perform the
following operations on the U2000:
l
Configure the 2-wire/4-wire VF and E&M trunk service.
Configure the hotline service of E&M trunk ports.
CDI Board Management
The CDI board is a 16-channel direct-dialing-in subscriber interface board of the HONET access
system, which implements the transparent transmission through analog subscriber ports. The
CDI board implements the transparent extension inside the HONET system for the analog
subscriber ports of external exchanges by means of digital-to-analog conversion between CDI
ports and ASL ports, transparent transmission, and signaling processing of hosts. In addition, as
a foreign exchange office (FXO) port, the CDI port works with the foreign exchange subscriber
(FXS) port provided by the ASL board to implement the analog access of the POTS users to the
LE. You can perform the following operations on the U2000:
l
Configure the Z interface extension service.
Configure the PBX bidirectional service.
Configure the DDI service.
Narrowband Data Service Management
Narrowband data service management includes the management of multifunctional terminal
adapters (MTAs), HSL boards, and TDM G.SHDSL ports.
MTA Management
The MTA of the UA5000(PVMV1) provides the synchronous port with the rate of 64/128 kbit/
s and the synchronous or asynchronous port with the sub-rate of 2.4/4.8/9.6/19.2 kbit/s. The
MTA also provides physical communication channels between terminal users and the DDN
network or other digital terminal users. You can perform the following operations on the U2000:
l
Configure the attributes of MTA ports.
Add SPCs.
HSL Management
The HSL board of the UA5000 (PVMV1) provides two V.35 ports and two FE1 ports to access
N x 64k (n ranges from 1 to 31) data services. You can perform the following operations on the
U2000:
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
13-13
13 MSAN Network Feature Management
iManager U2000 Unified Network Management System
Product Description
Configure the attributes of V.35 ports provided by the HSL board.
Add SPCs.
TDM G.SHDSL ports
The UA5000(PVMV1) uses the SDL board to carry G.SHDSL services. The SDL board accesses
the G.SHDSL service of data dedicated line subscribers in TDM mode. You can perform the
following operations on the U2000:
13-14
Configure the TDM G.SHDSL service.
Configure the subtend service of the TDM G.SHDSL port.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
14
14 DSLAM Network Feature Management
DSLAM Network Feature Management
About This Chapter
This topic describes the functions and features of DSLAM NE management and network
management.
14.1 DSLAM Management
For NE configuration management, the U2000 provides graphical user interfaces (GUIs) for
configuring NEs and maintaining NE configurations. You can configure services for equipment
in the GUIs.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
14-1
14 DSLAM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
14.1 DSLAM Management
For NE configuration management, the U2000 provides graphical user interfaces (GUIs) for
configuring NEs and maintaining NE configurations. You can configure services for equipment
in the GUIs.
Device Management
Device management includes the management of NE panels, basic and common device
attributes, clock sources, security, protocols, global configuration of services, and device
templates.
NE Panel Management
You can perform the following operations on the U2000:
l
Display the NE panel by double-clicking an NE.
Query the details of equipment.
Collect statistics on device resources.
Query the information about shelves.
Collect the statistics on shelf resources.
Query inter-shelf links.
Add, delete, start, disable, reset, and confirm a board.
Query the real-time performance statistics on the CPU usage and memory of boards.
Display the port view by double-clicking a board.
Perform an active/standby switchover on the control boards.
Management of Basic and Common Device Attributes
The management of basic and common device attributes includes the query of the global
information about devices and the configuration of the global policies of devices.
You can perform the following operations on the U2000:
l
Query the system information about devices.
Query the statistics on the resources and status of devices.
Query the license information about the functions and resources of devices.
Configure the system time, IP address of a device, and the binding between a Layer 3
interface and an IP address.
Configure the SNMP protocol port.
Set device handshake parameters.
Configure the policy for automatically backing up device data.
Enable and disable the energy-conservation function of a device.
Configure and manage license files.
Clock Source Management
Clock source management includes the management and configuration of equipment-level clock
source information, such as information about the line clock, 1588 clock, and clock priorities.
14-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
14 DSLAM Network Feature Management
Security Management
You can perform the following operations on the U2000:
l
Enable and disable anti-ICMP attack, anti-IP attack, anti-IP spoofing, anti-MAC spoofing,
and anti-DoS attack.
Set the aging time of a MAC address.
Enable and disable MAC address learning.
Configure the security attributes for user login in the CLI.
Protocol Management
You can perform the following operations on the U2000:
l
Manage the Link Aggregation Control Protocol (LACP), Spanning Tree Protocol (STP)/
Rapid Spanning Tree Protocol (RSTP)/Multiple Spanning Tree Protocol (MSTP),
Bidirectional Forwarding Detection (BFD), and Internet Group Management Protocol
(IGMP).
Control the Address Resolution Protocol (ARP) proxy.
Configure the Policy Information Transfer Protocol (PITP) mode/Relay Agent Info Option
(RAIO) custom format.
Control the Dynamic Host Configuration Protocol (DHCP) option 82 function.
Control the DHCP proxy and DHCP relay forwarding functions.
Configure 802.1ag attributes of the Ethernet packet.
Global Configuration of Services
The global configuration of services includes the configuration of the VLAN, QoS, xDSL, and
multicast services.
Device Template Management
Device template management includes the display of different types of device templates on the
U2000. Templates include the IGMP template, traffic template, VLAN service template, and
PW template. Currently, the U2000 supports only query and generation of global templates.
Network Interface Management
Network interface management includes the management and maintenance of E1/T1 ports and
the Ethernet port.
Management and Maintenance of E1/T1 Ports
E1/T1 ports are classified into TDM E1/T1 ports, CES E1/T1 ports, and IMA E1/T1 ports.
TDM E1/T1 ports can be used as access ports or upstream ports, depending on the functions of
boards.
On E1 ports for upstream transmission, you can perform only the loopback operation.
On E1 ports for PRA access, you can perform the following operations: configure or delete port
attributes, set the alarm threshold of L2 signaling bit errors, query timeslots, and enable or disable
services.
On CES E1/T1 ports, you can collect real-time performance statistics of ports, configure the port
attributes, set port alias, and perform loopback.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
14-3
14 DSLAM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
On IMA E1/T1 ports, you can query real-time performance statistics of the ports, and manage
IMA groups and IMA links, including adding, deleting, modifying, resetting, blocking, and
unblocking an IMA group or link.
Management of Ethernet Ports
Ethernet port management includes the management of ports and aggregation groups. You can
perform the following operations on the U2000:
l
Configure port attributes.
Create, delete, query, and modify an aggregation group.
Activate and deactivate an Ethernet port.
Collect real-time performance statistics and clear the performance statistics.
Configure the PPPoE, DHCP option 82, 802.3ah ETH OAM loopback, and port rate limit
functions.
Query the attributes of optical transceivers for Ethernet optical ports.
Connection Management
ONU connection management includes the management of service virtual ports.
Service Virtual Port Management
A service virtual port enables user equipment to access the ONU. The service virtual port
provides service streams between the user equipment and the ONU for carrying user services.
You can perform the following operations on the U2000:
14-4
Query, add, delete, modify, activate, and deactivate a service virtual port.
Collect the real-time performance statistics and clear the performance statistics.
Perform ATM ping tests.
Configure the extended attributes of a service virtual port. Extended attributes allow for
greater flexibility of addressing customer requirements. Extended attributes include the
maximum number of learnable MAC addresses, the PPPoE session, the encapsulation type,
and the maximum number of MAC addresses that can be bound.
Configure the connection attributes of a service virtual port, including the alias, VPI/VCI,
transmit traffic profile, and receive traffic profile.
Shift the VLAN ID of a service virtual port to change the VLAN ID of the service virtual
port. After successful shifting, the service port assumes the new VLAN ID.
Bind IP addresses to a service virtual port and query the bound IP addresses. To specify
that only the users with certain IP addresses can access the service virtual port, perform the
binding operation. After successful binding, the service forwarding module checks the
source IP address of user packets. If the source IP address does not match any of the IP
addresses bound to the service virtual port, the user packets are dropped. Otherwise, the
user packets are forwarded. This ensures the security of user access.
Bind static MAC addresses to a service virtual port. To specify that only the users with
certain static MAC addresses can access the service virtual port, perform the binding
operation. After successful binding, the service forwarding module checks the source MAC
address of user packets. If the source MAC address does not match any of the MAC
addresses bound to the service virtual port, the user packets are dropped. Otherwise, the
user packets are forwarded. This ensures the security of user access.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
14 DSLAM Network Feature Management
Configure service bundles. If several service virtual ports carry the same service, a service
bundle can be configured to bundle the service streams over the service virtual ports.
Layer 2 Management
Layer 2 management includes the management of the VLAN, the Rapid Spanning Tree Protocol
(RSTP), Multiple Spanning Tree Protocol (MSTP), Access Node Control Protocol (ANCP), and
Rapid Ring Protection Protocol (RRPP).
VLAN Service Management
VLAN management includes the management of the standard VLAN, MUX VLAN, smart
VLAN, and super VLAN. You can perform the following operations on the U2000:
l
Query, add, delete, and modify a VLAN.
Collect the real-time performance statistics of a VLAN.
Clear the real-time performance statistics on VLANs.
Manage a Layer 3 interface and its subinterfaces.
RSTP Management
You can perform the following operations on the U2000:
l
Modify and restore the default value of the trail overheads of a port.
Collect the RSTP statistics of a port.
Clear the RSTP statistics of a port.
MSTP Management
MSTP management includes the management of domains, instances, and ports. You can perform
the following operations on the U2000:
l
Modify and restore the default setting of a domain.
Add, delete, and modify an instance.
Modify a port.
Query the statistics of a port.
ANCP Management
You can perform the following operations on the U2000:
l
Add, delete, modify, enable, and disable an ANCP session.
Query the real-time status of an ANCP session.
RRPP Management
For RRPP management, you can perform the query, add, delete, and modify operations.
Layer 3 Management
Layer 3 management includes the management of the Dynamic Host Configuration Protocol
(DHCP), Multi-protocol Label Switching (MPLS)/pseudo wire emulation edge-to-edge
(PWE3), and Layer 3 routes.
DHCP Management
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
14-5
14 DSLAM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
DHCP management includes the management of the DHCP server group, MAC address
segment, standard mode, DHCP domain, and VLAN L3 interface. You can perform the
following operations on the U2000:
l
Query, add, delete, and modify a DHCP server group.
Query, add, delete, and modify a MAC address segment.
Query, enable, disable, and modify a standard mode.
Query, add, delete, and modify a DHCP domain.
Modify a VLAN Layer 3 interface.
MPLS PWE3 Management
The MPLS is a transmission technology. It implements transparent transmission of data packets
between users. The MPLS tunnel is defined in the MPLS protocol. Independent of a service, an
MPLS tunnel implements end-to-end transmission and carries service-related PWs.
You can perform the following operations on the MPLS tunnel on a per-NE basis on the U2000:
l
Configure the basic attributes of the MPLS.
Configure the MPLS tunnel of the static unicast type.
Create forward MPLS tunnels.
Create an E-LSP.
Manage PWs.
Manage tunnel tags and PW labels.
ACL and QoS Management
ACL and QoS management includes the management of the access control list (ACL), quality
of service (QoS), time segments, and hierarchical QoS (HQoS).
In a traditional packet-based network, all packets are treated in the same way. Every router adopts
the first-in first-out (FIFO) policy to process packets, and makes its best effort to transmit packets
to the destination. The router, however, does not make any commitment to packet transmission
performance, such as the delay, delay variation (jitter), packet loss rate, and reliability. With the
rapid development of the computer network, more and more networks are connected to the
Internet. In addition, new services are emerging and raise new requirements on the service
capability of the IP network. Therefore, network-wide end-to-end QoS solutions are called into
attention, which necessitates QoS assurance for services. To achieve so, devices must be able
to apply QoS techniques and provide hierarchical QoS guarantee for different types of service
streams (especially for those highly sensitive to delay and jitter). For ACL management, you
can perform the following operations on the U2000:
l
Configure one or more time segments, and associate a time segment with an ACL by
specifying the name of the time segment in the ACL.
Query, modify, create, and delete the ACL of the standard, extended, Layer 2, and userdefined types.
QoS management includes filtering packets based on ACL, tagging priorities, limiting traffic
and port rate, collecting statistics on traffic, redirecting, and mirroring. On the U2000, you can
query, add, modify, and delete a QoS policy.
HQoS stands for the hierarchical QoS. It not only controls user traffic but also schedules packets
according to the priorities of user services. On the U2000, you can query, add, modify, and delete
an HQoS policy.
14-6
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
14 DSLAM Network Feature Management
User Security and System Security
You can perform the following operations on the U2000:
l
Configure user access in PITP mode.
Configure user access in DHCP option 82 mode.
Configure user access control.
Configure system secure access.
BFD Management
The BFD mechanism is used for quickly checking the link status between two devices.
To mitigate the impact of device faults on services and to improve the network availability, a
network device needs to quickly detect any fault occurring between the device and its adjacent
devices. Actions can then be taken to ensure service continuity. The BFD enables the device to
check the connectivity of a type of data protocol of the same trail between two systems. The trail
can be a physical or a logical link, including a tunnel. The BFD mechanism is a remedy for the
weakness of the existing detection mechanism.
Ethernet Connectivity Fault Management
As the Ethernet technology extends from carrier networks to metropolitan area networks
(MANs) and wide area networks (WANs), carriers are increasingly concerned about the
maintainability of equipment, especially the Ethernet equipment. An imperative demand for the
operation, administration and maintenance (OAM) of transport equipment hence arises. Within
Ethernet technology, the 802.1ag connectivity fault management (CFM) provides a method for
detecting faults end-to-end. The Ethernet OAM mechanisms supported by 802.1ag CFM include
connectivity check (CC), loopback (LB), link trace (LT), and forward AIS alarms. You can
perform the following operations on the U2000:
l
Manage maintenance domains (MDs). Ethernet CFM divides a network into up to eight
levels. A bridge can span multiple levels to manage different MDs. A CFM MD is
constituted by bridges. An MD is the combination of bridges and maintenance levels. MDs
can be classified into three layers: user domain (levels 7-5), service provider domain (levels
4-3), and carrier domain (levels 2-0). Different MDs are maintained by different
management entities.
Manage maintenance associations (MAs). An MD can be divided into multiple MAs. Each
MA maps a service instance (SI) that belongs to an MD and is identified by a VLAN. An
MA can be regarded as a combination of an MD and a VLAN. According to the standards,
multiple VLANs can map one SI, and one SI maps one MA.
Manage maintenance points (MPs). An MA consists of MPs defined on the ports of bridges.
An MP is a combination of a bridge port, a VLAN, and a maintenance level. MPs are
classified into maintenance association end points (MEPs) and maintenance association
intermediate points (MIPs). MEPs initiate and respond to CFM messages; MIPs
transparently transmit or respond to CFM messages but do not initiate the messages.
Protection Group Management
Protection group management involves the protection switchover and protection group.
Protection switchover: Important board recourses and port recourses are generally backed up to
enhance system reliability. If a fault occurs on a working member, protection switchover will
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
14-7
14 DSLAM Network Feature Management
iManager U2000 Unified Network Management System
Product Description
be triggered to transfer services to the protection member that will continue to handle the
services.
Protection group: You can manage the working member and the protection member in the
protection group. In a protection group, you can manage the relationship between the members
involved in the protection switchover, record the status of members, and manage the
configuration data and status that are involved by the protection relationship between the
members.
With the protection group feature, you can protect the following objects on the U2000:
l
Active and standby control boards
Aggregation groups on active control board and standby control board
Ports on active and standby control boards
Upstream Ethernet ports
Upstream aggregation links of Ethernet ports
xDSL Service Management
xDSL service management includes the management of the asymmetrical digital subscriber loop
(ADSL), ADSL2+, ATM global single-pair high-speed digital subscriber line (G.SHDSL), and
very high speed digital subscriber lines 2 (VDSL2) services. The features of these services are
as follows:
ADSL Service Management
ADSL is a technology for providing the asymmetric and high-speed private line access service
over common twisted pairs. ADSL supports the asymmetrical transmission in the upstream and
downstream directions, which is suitable for the user data access service and can provide highspeed data transmission channels for users. ADSL2+ is an extension of the ADSL technology.
It supports a maximum transmission rate of 24 Mbit/s and 2.5 Mbit/s in the downstream and
upstream respectively and a maximum transmission distance of 6.5 km. You can perform the
following operations on the U2000:
l
Activate and deactivate a port.
Perform and cancel a loopback.
Deactivate a port and then activate it again to initialize the port.
Reconfigure port attributes.
Configure the port attributes, such as the associated line template, alarm template, extended
template, and monitoring thresholds. These attributes are used to activate the ADSL port.
Query the real-time and history performance statistics.
G.SHDSL Service Management
G.SHDSL is a technology for providing a high-rate symmetrical data service over one or two
twisted pairs. The 2-wire, 4-wire, 6-wire, and 8-wire G.SHDSL access services are supported
to allow for a transmission distance ranging from 3 km to 6 km. The rates of the 2-wire, 4-wire,
6-wire, and 8-wire G.SHDSL lines range from 192 kbit/s to 5696 kbit/s, 384 kbit/s to 4608 kbit/
s, 576 kbit/s to 17088 kbit/s, and 768 kbit/s to 22784 kbit/s respectively. You can perform the
following operations on the U2000:
14-8
Activate and deactivate a port.
Perform and cancel a loopback.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
14 DSLAM Network Feature Management
Bind and unbind a port. You can bind multiple ATM G.SHDSL ports. This increases the
bandwidth at the physical layer and improves the rate of the ATM G.SHDSL port.
Configure port attributes, such as the associated line profile and alarm profile. These
attributes are used to activate the ATM G.SHDSL port.
Query the real-time performance statistics.
VDSL2 Service Management
VDSL2 is an extension of the VDSL technology. It provides high-speed private line access in
the symmetrical or asymmetrical mode over common twisted pairs. VDSL2 supports a high
bandwidth with symmetric rates of up to 100 Mbit/s and multiple spectrum template and
encapsulation modes. Based on these features, it provides short-distance and high-speed access
solutions to the next generation broadband access scenarios. You can perform the following
operations on the U2000:
l
Activate and deactivate a port.
Perform and cancel a loopback.
Deactivate a port and then activate it again to initialize a port.
Reconfigure port attributes.
Configure the port attributes, such as the associated line profile, alarm profile, extended
profile, and monitoring thresholds of a VDSL2 port. These attributes are used to activate
the VDSL2 port.
Query the real-time and history performance statistics.
Multicast Service Management
Multicast is a point-to-multipoint (P2MP) communication mode in which the source sends
information to a specified subset of objects under a network node. Multicast services are
applicable to the streaming media, distance learning, video conferencing, video on demand
(VOD), network gaming, data replication, and other P2MP transmission.
Multicast communication uses a class D IP address (224.0.0.0 to 239.255.255.255) as the
destination IP address. A source host sends out a packet that uses a class D IP address as the
destination. If other hosts in the network are interested in the multicast packet, these hosts can
send a request to join the multicast group and receive the packet. The hosts outside of the group
cannot receive the packets sent by the source host.
In controllable multicast, network equipment determines whether a user has the rights to watch
programs by identifying the join or request packets of the user. Then, the access device controls
and forwards the multicast services accordingly.
There are two multicast modes:
l
IGMP snooping: IGMP snooping is a multicast control mechanism at the data link layer.
It is used to manage and control multicast services.
IGMP proxy: In a tree topology, the OLT does not set up routes for forwarding multicast
packets; the OLT only relays and forwards multicast protocol packets. To multicast users,
the OLT is a multicast router that implements the router functions defined in the IGMP
protocol. To multicast routers, the OLT is a multicast user.
You can perform the following operations on the U2000 to manage multicast services:
l
Manage multicast users.
Manage multicast VLANs.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
14-9
14 DSLAM Network Feature Management
14-10
iManager U2000 Unified Network Management System
Product Description
Manage the virtual upstream ports of multicast services.
Manage multicast subtending ports.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
15 Reliability
15
Reliability
About This Chapter
Reliability design assures that measures are taken to prevent potential risks so that the product
can work in a safer manner.
15.1 Reliability Design
This topic describes the reliability design of the U2000. The reliability design of the U2000
ensures hardware reliability, software reliability, and system security and reliability.
15.2 Reliability Indicator
This topic describes the indicators of the reliability design.
15.3 HA System
The high availability (HA) system helps you improve the running reliability of the U2000 server.
15.4 DCN Protection
You can use a data communication network (DCN) to connect the U2000 to a standby gateway
NE (GNE). This improves the reliability of the communication connection between the
U2000 and equipment.
15.5 Disk Mirroring
The disk mirroring function helps to improve the reliability of disk data on the U2000 server.
15.6 Data Backup
The data backup function helps to improve the reliability of important U2000 data.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
15-1
iManager U2000 Unified Network Management System
Product Description
15 Reliability
15.1 Reliability Design
This topic describes the reliability design of the U2000. The reliability design of the U2000
ensures hardware reliability, software reliability, and system security and reliability.
Hardware Reliability
U2000Hardware reliability is improved by disk redundancy, equipment redundancy, and HA
system.
l
Disk redundancy: The U2000 supports disk redundancy. For example, RAID1, RAID10,
hot standby, or disk array can be used for different hardware platforms.
Equipment redundancy: During network deployment, the U2000 improves reliability by
means of redundant equipment such as switches and NICs.
HA system: For details, see 15.3 HA System.
Software Reliability
Software reliability mechanism of the U2000 enables the U2000 to withstand software failures
such as software application failure or database damage.
The U2000 supports the automatic protection mechanism so that it can monitor and check the
running status of its processes. When the U2000 detects that a process stops abnormally or is
faulty, it records system logs. Then, the system restarts the process automatically and ensures
that the process runs in the normal state. The system can also generate an alarm that urges a user
to manually resolve the problem.
In the case of an HA system, when the active server is faulty (for example, software applications
fail or the database quits unexpectedly), switchover is performed between the active server and
the standby server and the standby server starts to monitor networks.
Periodic and effective backup of the U2000 data ensures that the system runs stably and recovers
promptly from faults. The U2000 provides various data backup methods. For details, see 15.6
Data Backup.
System Security and Reliability
System security and reliability involve the following aspects:
15-2
OS enhancement: The U2000 provides the SetSolaris to enhance the security of Solaris OS.
Antivirus scheme: The U2000 uses the OfficeScan of Trend Micro as the antivirus software
on Windows OS.
Operation security: The U2000 supports user management, right management, user security
management, ACL, AAA, and a series of security policies to ensure the security of
operations that are performed on the U2000.
Communication security and reliability: The U2000 client and server communicate with
each other in SSH mode, which ensures security of communication between them. In
addition, DCN protection ensures the reliability of communication connections between
the U2000 and NEs.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
15 Reliability
15.2 Reliability Indicator
This topic describes the indicators of the reliability design.
Table 15-1 lists the reliability indicators of the U2000.
Table 15-1 Reliability indicators of the U2000
Item
Indicator
Remarks
MTBF
The average fault interval is
larger than 6 months.
HA system
The fault is defined as database
crash.
MTTR
The average fault recovery time
is no more than 15 minutes.
HA system
The fault is defined as database
crash.
HA switching time
15 minutes
70% of the management
capacity
NMS start time
10 minutes
70% of the management
capacity
NMS shutdown time
10 minutes
70% of the management
capacity
15.3 HA System
The high availability (HA) system helps you improve the running reliability of the U2000 server.
The non-distributed U2000 server works in 1+1 backup mode. If the active site is faulty,
applications on the U2000 are automatically switched to the standby site so that the U2000
application is not interrupted. See Figure 15-1.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
15-3
iManager U2000 Unified Network Management System
Product Description
15 Reliability
Figure 15-1 Switchover between active and standby sites in HA system
Normal Status
Real time data replication
Application
When a fault occurs, the NMS application is switched to the standby site.
Applicaton
The protection mechanism of an HA system has two aspects:
l
Database synchronization and backup between the active and standby sites
Automatic application switchover between the active and standby sites
The U2000 provides the following HA schemes:
l
HA system (Veritas 1+1 hot standby): Applicable to remote hot standby of the nondistributed system, featuring automatic switching.
15.4 DCN Protection
You can use a data communication network (DCN) to connect the U2000 to a standby gateway
NE (GNE). This improves the reliability of the communication connection between the
U2000 and equipment.
The communication between non-GNEs and the U2000 is forwarded by the GNE. In the
U2000, you can set the active GNE and standby GNE for NEs in advance. When the
communication between the active GNE and the U2000 is interrupted, the U2000 automatically
switches to the standby GNE for communication, so that the communication between the
U2000 and NEs is not interrupted. When the communication between the U2000 and the active
GNE recovers, the U2000 determines whether to use the active GNE again according to the
preset revertive mode.
NOTE
The recommended number of non-gateway NEs (including non-gateway NEs that connects to the GNE by using
the extended ECC) that connect to each GNE is fewer than 50. Once the limit is exceeded, the number of GNEs
should be increased.
15-4
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
15 Reliability
15.5 Disk Mirroring
The disk mirroring function helps to improve the reliability of disk data on the U2000 server.
If the server has two or more than two hard disks, you can create disk mirroring (RAID 1) when
installing the U2000. After you create disk mirroring, if the active disk is damaged, run a
command to switch the data to the standby disk, thereby restoring the working data and parameter
settings before the active disk is damaged.
The RAID 5 and hot spare disk are recommended for the disk array where six hard disks are
configured. Specifically, configure RAID 5 by using any four hard disks and use the remaining
one as a hot spare disk.
15.6 Data Backup
The data backup function helps to improve the reliability of important U2000 data.
The security of network data is a concern of users. Table 15-2 lists the data backup solutions
provided by the U2000.
Table 15-2 Data backup
Issue 05 (2010-11-19)
Data to Be Backed Up
Solution
Operation
Alarm log, abnormal event
log, performance log,
security log, and operation
log
Dump logs.
Perform operations on the
U2000 client. For details, see
the U2000 Online Help.
Configuration data
Export the configuration data
to script files in the MML
command format. The script
files neglect the structural
differences among databases
of the U2000 of different
versions, and are suitable for
data backup in case of
version upgrade. The script
files supported by the
U2000 include network-wide
configuration files, U2000
naming file, NE
configuration file, NE list
files, U2000 computer
information files, service
implementation
configuration files, networklayer information files, and
network simulation and
planning information files.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
15-5
iManager U2000 Unified Network Management System
Product Description
15 Reliability
Data to Be Backed Up
Solution
Database
Back up all data in the
U2000 database.
Operation
In general, restoring all data
on the database takes less
than three hours. The
restoration duration is
determined by the network
size and the bandwidth
between the U2000 server
and the remote server.
Supported backup scenarios
are as follows:
l OS: Windows, SUSE
Linux, or Solaris.
l Database: Oracle,
Sybase, or SQL Server.
l Data backup path:
immediate backup to the
local, immediate backup
to the remote. and
scheduled backup to the
remote. If the scheduled
backup fails, the U2000
reports an alarm.
l Source of data to be
restored: local restoration
or remote restoration.
NE database
15-6
Back up the NE data.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
16
16 Performance Indicators
Performance Indicators
This topic describes the performance indicators of the U2000.
Table 16-1 Performance indicators
Issue 05 (2010-11-19)
Item
Subitem
Indicator
Storage capacity
Capacity of current alarms
Maximum: 100,000 pieces
Capacity of history alarms
Maximum: 2,000,000 pieces
Capacity of logs, including
operation logs and system
logs
Maximum: 1,000,000 pieces
Resources occupied
CPU usage
The CPU usage is normally
not greater than 10%.
Processing capability
Response speed of handling
an alarm
The interval from the time at
which an alarm is generated
on the equipment to the time
at which the alarm is
displayed on the U2000 is
normally not longer than 10
seconds.
Response speed of handling
performance data
In the case of 1,000 pieces of
performance data, the
interval from the time at
which they are reported to the
U2000 to the time at which
they are stored in the
database is normally 10
seconds.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
16-1
iManager U2000 Unified Network Management System
Product Description
16 Performance Indicators
Item
Subitem
Indicator
Alarm handling capability
In a normal circumstance,
100 (400 at maximum) pieces
of alarms can be handled per
second by a full-domain
U2000. When managing only
access equipment, the U2000
can handle 50 pieces of
alarms per second.
User
Maximum: 500
User group
Maximum: 50
Object set
Maximum: 100
Operation Set
Maximum: 255
HA switchover time
Switchover between remote
active and standby servers
Less than 15 minutes
Stability
Mean time between failures
(MTBF)
The MTBF is longer than six
months. A failure is the
situation where the database
quits unexpectedly.
Mean time to recovery
(MTTR)
The MTTR is not longer than
15 minutes. A failure is the
situation where the database
quits unexpectedly.
Number of managed physical
nodes
Maximum: 15,000
Number of managed
equivalent NEs
Maximum: 20,000
VPN access interface
Maximum: 5,000,000
Number of tunnels
Maximum: 100,000
Number of manageable
GNEs
Not more than 3000
Number of manageable NEs
for a GNE
Not more than 50
U2000 user management
capability
Management capability
Service capability
HWECC/IP over DCC
networking capacity
Table 16-2 DCN bandwidth requirements
16-2
Item
Bandwidth
Bandwidth required for the communication
between a U2000 client and the U2000 server
2 Mbit/s
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
16 Performance Indicators
Item
Bandwidth
Bandwidth required for the communication
between N Equivalent NEs and the U2000
server
A bandwidth of 2 Mbit/s may not meet the
bandwidth requirements in different
networks. In this case, you can set the CIR or
PIR by using the following formula:
CIR:
l N > 56: 2048 kbit/s + (N - 56) x 0.5 kbit/
s
l N <= 56: 2 Mbit/s
PIR:
l N > 56: 10240 kbit/s + (N - 56) x 5 kbit/s
l N <= 56: 10 Mbit/s
Issue 05 (2010-11-19)
Bandwidth required for the communication
between an OSS and the U2000 server
2 Mbit/s
Bandwidth required for the communication
between the primary and secondary sites in an
HA system (Veritas hot standby)
2 Mbit/s
NOTE
A minimum of 2 Mbit/s is required.
NOTE
A minimum of 2 Mbit/s is required. A bandwidth
of 2 Mbit/s is enough if you do not synchronize all
performance data by using PMS. If you want to
synchronize the performance data, more
bandwidth is required.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
16-3
iManager U2000 Unified Network Management System
Product Description
17
17 Management Capability
Management Capability
About This Chapter
Management capability refers to the capability of the NMS to manage network resources, which
are expressed in the number of equivalent NEs.
The key technical specifications include the number of equivalent NEs, number of clients, and
number of physical NEs.The management capability of the U2000 in a network that consists of
different types of NEs is affected by the following factors:
l
The management capability refers to the maximum number of equivalent NEs that can be
managed by the U2000 on certain hardware configuration conditions. The management
capability depends on the hardware and varies with the hardware configuration.
If a client also runs on the computer where the server is running, the management capability
is reduced by 50%. Hence, it is recommended that you run the client and server on different
computers.
The system limits the number of physical nodes. Hence, the number of physical nodes is a
restriction for the management capability.
Virtual NEs are not included in the management capability. A pre-configured NE is equal
to a real NE. One third-party NE is equal to one equivalent NE. The equivalent coefficient
of the OEM equipment is calculated in the way similar to Huawei equipment.
17.1 NE Equivalent Coefficient
The NE equivalent coefficient is the ratio of the resources used by physical NEs or ports to the
resources used by equivalent NEs.
17.2 Management Capabilities of the U2000 on Different Hardware Platforms
This topic describes the management capabilities of the U2000 on different hardware platforms.
17.3 Manageable Equipment
This topic describes the equipment that can be managed by the U2000.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-1
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
17.1 NE Equivalent Coefficient
The NE equivalent coefficient is the ratio of the resources used by physical NEs or ports to the
resources used by equivalent NEs.
Equivalent NE and Equivalent Coefficient
l
Equivalent NE: The functional features, cross-connect capacity, and number of cards, ports,
or channels are specific to NEs of different types. As these NEs require different resources
of the NMS, the number of NEs that can be managed by the NMS depends on the NE types.
For easy description and calculation of the management capability, the concept of
equivalent NE is defined so that NEs of different types or a number of ports can be converted
to equivalent NEs by a uniform criteria according to the system resources required by
them. The system resources required by an equivalent NE is equal to the resources for
managing an STM-1 transport NE.
Equivalent coefficient: Equivalent coefficient = (Resources used by physical NEs or ports)/
(Resources used by equivalent NEs)
Currently, a set of U2000 can manage a maximum of 15,000 physical NEs, 15,000 equivalent
NEs, and 100 clients. This conclusion is drawn after the tests under a certain environment and
objectively reflects the actual management capability of the U2000.
The management scales of the U2000 are defined as follows:
l
Small-scale network: 2,000 equivalent NEs of the U2000
Medium-scale network: 6,000 equivalent NEs of the U2000
Large-scale network: 15,000 equivalent NEs of the U2000
NOTE
It is recommended that you enable no more than 100,000 performance collection instances at the same time to
ensure the running efficiency of the U2000.
Calculating the Number of Equivalent NEs
Generally, the number of equivalent NEs that the U2000 can manage is calculated according to
the following rules:
l
The basic unit of an equivalent NE of the U2000 is OptiX Metro 1000.
Number of equivalent NEs = <Number of equivalent NEs in the transport domain> +
<Number of equivalent NEs in the IP domain> + <Number of equivalent NEs in the access
domain>
The comparison coefficient of an equivalent NE of the U2000 to the equivalent NE in each
domain is as follows:
1 equivalent NE in the transport domain = 1 equivalent NE of the U2000
4 equivalent nodes in the IP domain = 1 equivalent NE of the U2000
3.3 equivalent nodes in the access domain = 1 equivalent NE of the U2000
NOTE
The preceding rules are not fixed. For more details, see the Management Capability Instructions.
17.1.1 Equivalent NEs in the Transport Domain
<Number of equivalent NEs in the transport domain> = (Number of transport NEs of type_I x
Equivalent coefficient + ... + (Number of transport NEs of type_n x Equivalent coefficient)
17-2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
17.1.2 Equivalent NEs in the IP Domain
<Number of equivalent NEs in the IP domain> = (Number of IP NEs of type_I x Equivalent
coefficient) + ... + (Number of IP NEs of type_n x Equivalent coefficient)
17.1.3 Equivalent NEs in the Access Domain
<Number of equivalent NEs in the access domain> = Number of FTTx OLT equivalent NEs +
Number of FTTx MDU equivalent NEs + Number of MSAN equivalent NEs + Number of
DSLAM equivalent NEs + Number of equivalent NEs of other access equipment
17.1.1 Equivalent NEs in the Transport Domain
<Number of equivalent NEs in the transport domain> = (Number of transport NEs of type_I x
Equivalent coefficient + ... + (Number of transport NEs of type_n x Equivalent coefficient)
NOTE
For example, there are 5 OptiX OSN 9500 (equivalent coefficient: 10), 10 OptiX OSN 7500 (equivalent
coefficient: 6.5), and 100 OptiX OSN 3500 (equivalent coefficient: 4.5). Then, you can calculate the number
of equivalent NEs in the transport domain as follows:
Number of equivalent NEs in the transport domain = 5 x 10 + 10 x 6.5 + 100 x 4.5 = 565
The management capability of the U2000 varies with OptiX NE Equivalents, as shown in Table
17-1.
Table 17-1 Management capabilities of the U2000 on different OptiX NE Equivalents
NE Series
NE Type
Equivalent Coefficient for
the U2000
OSN series
OptiX OSN 500
OptiX OSN 1500
3.5 (With ASON)
2.5 (Without ASON)
OptiX OSN 2000
OptiX OSN 2500
4.5 (With ASON)
3.5 (Without ASON)
OptiX OSN 2500 REG
3.5 (Without ASON)
OptiX OSN 3500
6.5 (With ASON)
4.5 (Without ASON)
OptiX OSN 7500
10 (With ASON)
6.5 (Without ASON)
OptiX OSN 9500
15 (With ASON)
10 (Without ASON)
MSTP series
Issue 05 (2010-11-19)
OptiX Metro 100
0.5
OptiX Metro 200
0.5
OptiX Metro 500
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-3
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
NE Series
SDH series
Metro WDM series
LH WDM series
Marine series
17-4
NE Type
Equivalent Coefficient for
the U2000
OptiX 155/622H (Metro 1000)
OptiX Metro 1000V3
OptiX Metro 1050
1.5
OptiX Metro 1100
1.5
OptiX 155/622 (Metro 2050)
OptiX 2500+(Metro 3000)
OptiX Metro 3100
OptiX 10G (Metro 5000)
OptiX 155C
OptiX 155S
OptiX 155/622B_I
OptiX 155/622B_II
OptiX 2500
OptiX 2500 REG
1.5
OptiX Metro 6020
OptiX Metro 6040
OptiX Metro 6040V2
OptiX Metro 6100
1.5
OptiX Metro 6100V1
1.5
OptiX Metro 6100V1E
1.5
OptiX OSN 900A
OptiX BWS OAS, OptiX BWS
OCS, OptiX BWS OIS
1.5
OptiX BWS 320GV3
1.5
OptiX BWS 1600G, OptiX BWS
1600G OLA
1.5 +1.5 *N (N refers to the
number of slave shelves)
OptiX OTU40000
OptiX BWS 1600S
1.5
OptiX PFE 1670
OptiX SLM 1630
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
NE Series
NE Type
Equivalent Coefficient for
the U2000
NG WDM series
OptiX OSN 1800
OptiX OSN 3800
3.5 (With ASON)
1.5 (Without ASON)
OptiX OSN 6800
4+4*N (With ASON)
2+2*N (Without ASON)
N refers to the number of slave
shelves
OptiX OSN 8800 T32
10+10*N (With ASON)
6+6*N (Without ASON)
N refers to the number of slave
shelves
OptiX OSN 8800 T64
16+16*N (With ASON)
12+12*N (Without ASON)
N refers to the number of slave
shelves
NA WDM series
OptiX BWS 1600A
1.5
OptiX BWS 1600(NA)
1.5
OptiX OSN 1800(NA)
OptiX OSN 3800A
3.5 (With ASON)
1.5 (Without ASON)
OptiX OSN 6800A
4+4*N (With ASON)
2+2*N (Without ASON)
N refers to the number of slave
shelves
OptiX OSN 8800 T32(NA)
10+10*N (With ASON)
6+6*N (Without ASON)
N refers to the number of slave
shelves
OptiX OSN 8800 T64(NA)
16+16*N (With ASON)
12+12*N (Without ASON)
N refers to the number of slave
shelves
RTN series
Issue 05 (2010-11-19)
OptiX RTN 605
0.4
OptiX RTN 610
0.4
OptiX RTN 620
0.5
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-5
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
NE Series
NE Type
Equivalent Coefficient for
the U2000
OptiX RTN 910
0.5
OptiX RTN 950
OptiX RTN 5000S
17.1.2 Equivalent NEs in the IP Domain
<Number of equivalent NEs in the IP domain> = (Number of IP NEs of type_I x Equivalent
coefficient) + ... + (Number of IP NEs of type_n x Equivalent coefficient)
NOTE
For example, there are 5 NE5000E (equivalent coefficient: 10), 200 S5300 (equivalent coefficient: 1.25),
and 1000 CX200 (equivalent coefficient: 0.625). Then, you can calculate the number of equivalent NEs in
the IP domain as follows:
Number of equivalent NEs in the IP domain = 5 x 10 + 200 x 1.25 + 1000 x 0.625 = 925
The management capability of the U2000 varies with IP NE Equivalents, as shown in Table
17-2.
Table 17-2 Management capabilities of the U2000 on different IP NE Equivalents
NE Series
NE Type
Equivalent Coefficient for
the U2000
Router
NE05/NE08(E)/NE16(E)
0.75
NE20/NE20E
1.25
NE40/NE80
NE40E-X3
1.25
NE40E-4
1.25
NE40E-X8
2.5
NE40E-8
2.5
NE40E-X16
NE40E-16
NE5000E
10*N (N: number of chassis)
R-series router
AR-series router
0.25
SSP
10
NSE
10
Security equipment for
load balancing and
blocking
17-6
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
NE Series
NE Type
Equivalent Coefficient for
the U2000
Switch
S2000 series
0.125
S2300 series
0.625
S2700 series
0.625
S3000 series
0.125
S3300 series
0.75
S3700 series
0.75
S5000 series
0.25
S5300 series
1.25
S5700 series
1.25
S6500 series
0.75
S7800 series
1.25
S8016 series
1.25
S8500 series
1.25
S9303 series
2.0
S9306 series
3.5
S9312 series
6.0
OptiX PTN 1900
2.5
OptiX PTN 3900
4.5
OptiX PTN3900-8
4.0
OptiX PTN 912
0.5
OptiX PTN 910
0.5
OptiX PTN 950
CX200 series
0.625
CX300 series
1.25
CX600-X1
0.5
CX600-X2
CX600-X3
1.25
CX600-4
1.25
CX600-X8
2.5
PTN series
MAN service platform
Issue 05 (2010-11-19)
17 Management Capability
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-7
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
NE Series
Firewall
USG
SRG
17-8
NE Type
Equivalent Coefficient for
the U2000
CX600-8
2.5
CX600-X16
CX600-16
Eudomen 300/500/1000
0.5
Eudomen 200E series
0.25
Eudomen 1000E series
0.75
Eudomen 8040
Eudomen 8080
Eudomen 8080E
Eudomen 8160E
USG9110
USG9120
USG9210
USG9220
USG9310
USG9320
USG5000 series
0.75
USG3030
0.25
USG3040
0.25
USG2100 series
0.25
USG2200 series
0.25
USG50
0.25
SRG1200
0.25
SRG20-10
0.25
SRG20-11
0.25
SRG20-12
0.25
SRG20-15
0.25
SRG20-20
0.25
SRG20-21
0.25
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
NE Series
17 Management Capability
NE Type
Equivalent Coefficient for
the U2000
SRG20-30
0.25
SRG20-31
0.25
SRG20-31-D
0.25
SIG9810
SIG9820
SIG9800 Server
SVN
SVN3000
0.25
Broadband access
MA5200E/F series
1.5
MA5200G series
10
ME60 series
10
Voice gateway
VG1040/1041 series
0.25
WLAN AP
AP
0.25
SIG
17.1.3 Equivalent NEs in the Access Domain
<Number of equivalent NEs in the access domain> = Number of FTTx OLT equivalent NEs +
Number of FTTx MDU equivalent NEs + Number of MSAN equivalent NEs + Number of
DSLAM equivalent NEs + Number of equivalent NEs of other access equipment
NOTE
l Number of FTTx OLT equivalent NEs = (Number of ONTs x Equivalent coefficient) + (Number of
MDUs x Equivalent coefficient) + (Number of P2P ports x Equivalent coefficient)
l Number of FTTx MDU equivalent NEs = (Number of ports of type_I x Equivalent coefficient) + ... +
(Number of ports of type n x Equivalent coefficient)
l Number of MSAN equivalent NEs = (Number of ports of type_I x Equivalent coefficient) + ... +
(Number of ports of type n x Equivalent coefficient)
l Number of DSLAM equivalent NEs = (Number of ports of type_I x Equivalent coefficient) + ... +
(Number of ports of type_n x Equivalent coefficient)
l Number of equivalent NEs of other access equipment = (Number of NEs of type_I x Equivalent
coefficient) + ... + (Number of NEs of type_n x Equivalent coefficient)
The management capability of the U2000 varies with access NE Equivalents, as shown in Table
17-3.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-9
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Table 17-3 Management capabilities of the U2000 on different access NE Equivalents
Class
Type
Equivalent Coefficient for
the U2000
FTTx OLT
(calculation based on
the managed ONT,
MDU, and P2P
resources in the case
of OLT)
ONT
1/64
MDU
1/32
P2P port
1/64
FTTx MDU
(calculation based on
the managed user
ports in the case of
MDU)
xDSL port
1/128
E1 port
1/128
ETH port
1/128
PSTN/ISDN/HSL port
1/160
xDSL port
1/128
E1 port
1/128
ETH port
1/128
PSTN/ISDN/HSL port
1/160
MSAN (calculation
based on the number
of managed ports)
DSLAM (calculation xDSL port
based on the number
E1 port
of managed ports)
Other NEs
(calculation based on
the NE types)
1/128
1/128
ETH port
1/128
MD5500
1.5
8850
18
8825
18
8750
18
MA5200V1R2/R9
17.2 Management Capabilities of the U2000 on Different
Hardware Platforms
This topic describes the management capabilities of the U2000 on different hardware platforms.
Table 17-4 lists the management capabilities of the Table 17-4 on different hardware platforms.
17-10
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Table 17-4 Management capabilities of the U2000 on different hardware platforms
Server
Short Name
of Computer
Managem
ent
Capability
Number of
Clients
Support
Unified
Network
Manageme
nt
Number of
Physical
NEs
Mainstream Server to Be Delivered with the U2000 V100R002C01
Sun Server
T5220-4C*1.2
G-16G
2000
32
No
T5220-8C*1.4
G-32G
6000
64
Yes
M4000-4P*2.
53G-32G
15000
100
Yes
HP
DL380G6-2P
*2.0G-8G
2000
32
Yes
HP
DL580G5-4P
*2.13G-16G
6000
64
Yes
Array:
6*300G Array
PC Server
Compatible Server (Reuse)
SUN Server
Fujitsu
Server
Issue 05 (2010-11-19)
M4000-2P*2.
15G-16G
6000
64
No
SUN
V890-4P*1.5
G-16G
3000
48
No
SUN
V890-2P*1.5
G-8G
1500
32
No
SUN
V445-4P*1.6
GHz-8G
1500
32
No
SUN
E2900-8P*1.5
GHz-32G
5000
80
Yes
SUN
E2900-12P*1.
5GHz-48G
5000
100
Yes
PW650-4P*1.
8GHz-16G
2000
48
No
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Maximum
number of
physical
NEs: 15000
Maximum
number of
SDH paths:
300000
Maximum
number of
WDM paths:
50000
17-11
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Server
PC Server
Short Name
of Computer
Managem
ent
Capability
Number of
Clients
Support
Unified
Network
Manageme
nt
PW650-2P*1.
8GHz-8G
1500
32
No
IBM
X3650-2P*2.0
G-8G
2000
32
No
IBM
X3850M2-4P
*2.13G-16G
6000
64
No
Number of
Physical
NEs
Compatible Server for the Single-Domain Upgrade
The servers are applicable to only the single-domain upgrade instead of the
cross-domain management in centralized manner. For example, if the T2000
is installed on SUN V490, the T2000 can be directly upgraded to the U2000,
but the U2000 cannot have the management functions of the IP and access
domains in this case.
SUN Server
17-12
SUN
Netra240-2P*
1.5GHz-2G
600
16
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
No
SUN
Netra240
does not
support the
management
of PTN
devices. If
T2000 is
installed on
Netra240,
after
upgraded to
the U2000,
the U2000
cannot have
the
management
functions of
the PTN
devices. If
must to
manage the
PTN
devices, the
Netra240
must be
changed.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Server
PC Server
Issue 05 (2010-11-19)
17 Management Capability
Short Name
of Computer
Managem
ent
Capability
Number of
Clients
Support
Unified
Network
Manageme
nt
SUN
V490-2P*1.6
GHz-4G
800
24
No
SUN
V440-2P*1.6
GHz-4G
800
24
No
SUN
V240-2P*1.5
GHz-4G
600
16
No
SUN
V245-2P*1.5
GHz-4G
600
16
No
IBM
X3500-2P*2.0
G-4G
2000
64
No
IBM
X3200-1P*2.4
G-2G
600
14
No
HP
ML350-2P*2.
0G-4G
2000
64
No
HP
ML110-1P*2.
4G-2G
600
24
No
HP
ML570-4P*2.
0G-4G
2000
48
No
DELL
R900-4P*2.13
G-4G
2000
48
No
DELL
PE6800-4P*2.
0G-4G
2000
48
No
DELL
PE2900-2P*2.
0G-4G
1500
32
No
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Number of
Physical
NEs
17-13
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Server
Short Name
of Computer
Managem
ent
Capability
Number of
Clients
Support
Unified
Network
Manageme
nt
DELL
PE840-1P*2.4
G-2G
600
24
No
HP
DL380G5-2P
*2.0G-8G
6000
64
No
HP
DL580G5-4P
*2.13G-16G
10000
100
No
IBM
X3650-2P*2.0
G-8G
6000
64
No
IBM
X3850M2-4P
*2.13G-16G
10000
100
No
Number of
Physical
NEs
17.3 Manageable Equipment
This topic describes the equipment that can be managed by the U2000.
17.3.1 Manageable MSTP Series Equipment
17.3.2 Manageable WDM Series Equipment
17.3.3 Manageable NA WDM Series Equipment
17.3.4 Manageable Submarine Line Equipment
17.3.5 Manageable RTN Series Equipment
17.3.6 Manageable PTN Series Equipment
17.3.7 Manageable FTTx Series Equipment
17.3.8 Manageable MSAN Series Equipment
17.3.9 Manageable DSLAM Series Equipment
17.3.10 Manageable Router Series Equipment
17.3.11 Manageable Switch Series Equipment
17.3.12 Manageable Metro Service Platform Equipment
17.3.13 Manageable Broadband Access Series Equipment
17.3.14 Manageable VoIP Gateway Equipment
17-14
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
17.3.15 Manageable WLAN Series equipment
17.3.16 Manageable Firewall Series Equipment
17.3.17 Manageable DPI Equipment
17.3.18 Manageable SVN Series Equipment
Manageable SVN series equipment are listed as follows:
17.3.19 Manageable OP-Bypass Equipment
Manageable OP-Bypass equipment are listed as follows:
17.3.1 Manageable MSTP Series Equipment
Manageable MSTP series equipment is listed as follows:
Table 17-5 Manageable MSTP series equipment
Category
Equipment
Description
SDH series
OptiX 155C
OptiX 155C SDH transmission unit for
the access network
OptiX 155S
OptiX 155S simplified STM-1 optical
transmission system
OptiX 1556/622B_I
OptiX 155/622B STM-1/STM-4
compatible optical transmission system
(19-inch rack)
OptiX 1556/622B_II
MSTP series
Issue 05 (2010-11-19)
OptiX 2500
OptiX 2500 STM-4/STM-16
compatible optical transmission system
OptiX 2500 REG
OptiX 2500 REG STM-16 regenerator
OptiX Metro 100
OptiX Metro 100 terminal STM-1
optical transmission system
OptiX Metro 200
OptiX Metro 200 ultra compact STM-1
optical transmission system
OptiX Metro 500
OptiX Metro 500 ultra compact STM-1
multi-service transmission system
OptiX 155/622H (Metro
1000)
OptiX 155/622H(Metro1000) STM-1/
STM-4 MSTP
OptiX Metro 1000
OptiX 155/622H(Metro1000) STM-1/
STM-4 MSTP optical transmission
system V3 series
OptiX Metro 1050
OptiX Metro 1050 compact STM-1/
STM-4 multi-service optical
transmission system
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-15
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Category
OSN series
Equipment
Description
OptiX Metro 1100
OptiX Metro 1100 compact container
STM-16 multi-service transmission
system
OptiX 155/622 (Metro
2050)
OptiX 155/622(Metro2050) STM-1/
STM-4 compatible optical transmission
system
OptiX 2500+ (Metro
3000)
OptiX 2500+(Metro3000) STM-16
MADM/MSTP optical transmission
system
OptiX Metro 3100
OptiX Metro 3100 STM-16 multiservice transmission system
OptiX 10G (Metro 5000)
OptiX 10G(Metro5000)STM-64
MADM optical transmission system
OptiX OSN 500
OptiX OSN 500 STM-1/STM-4 multiservice CPE optical transmission system
OptiX OSN 1500
OptiX OSN 1500 intelligent optical
transmission system
OptiX OSN 2000
OptiX OSN 2000 enhanced STM-1/
STM-4 multi-service optical
transmission system
OptiX OSN 2500
OptiX OSN 2500 intelligent optical
transmission system
OptiX OSN 2500 REG
OptiX OSN 2500 REG STM-16
regenerator
OptiX OSN 3500
OptiX OSN 3500 intelligent optical
transmission system
OptiX OSN 3500 II
OptiX OSN 7500
OptiX OSN 7500 intelligent optical
switching system
OptiX OSN 9500
OptiX OSN 9500 intelligent optical
switching system
17.3.2 Manageable WDM Series Equipment
Manageable WDM series equipment is listed as follows:
17-16
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Table 17-6 Manageable WDM equipment
Category
Equipment
Description
Metro WDM series
OptiX Metro 6020
OptiX Metro 6020 compact
container CWDM system
V100R001
OptiX Metro 6040
OptiX Metro 6040 compact
container WDM system
V100R001
OptiX Metro 6040 V2
OptiX Metro 6040 compact
container DWDM system
V200R001 or higher
OptiX Metro 6100
OptiX Metro 6100 DWDM
multi-service transmission
system V100R002
OptiX Metro 6100V1
OptiX Metro 6100 DWDM
multi-service transmission
system V100R003
OptiX Metro 6100 V1E
OptiX Metro 6100 WDM
multi-service transmission
system V100R004 or higher
OptiX OSN 900A
OptiX OSN 900A compact
WDM system (A Type)
OptiX BWS 320G
OptiX BWS 320G backbone
DWDM optical transmission
system V300R002
OptiX BWS 320G V3
OptiX BWS 320G backbone
DWDM optical transmission
system V300R004
OptiX BWS 1600G, OptiX
BWS 1600G OLA
OptiX BWS 1600G
backbone DWDM optical
transmission system
V100R003 or higher
OptiX BWS 1600S
OptiX BWS 1600S
submarine line terminal
equipment
OptiX OTU40000
OptiX OTU 40000 backbone
DWDM optical transmission
system
OptiX OSN 1800
OptiX OSN 1800 compact
multi-service edge optical
transport platform
LH WDM series
NG WDM series
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-17
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Category
Equipment
Description
OptiX OSN 3800
OptiX OSN 3800 compact
intelligent optical transport
platform
OptiX OSN 6800
OptiX OSN 6800 intelligent
optical transport platform
OptiX OSN 8800 T32
OptiX OSN 8800 T32
intelligent optical transport
platform
OptiX OSN 8800 T64
OptiX OSN 8800 T64
intelligent optical transport
platform
NOTE
The OptiX BWS 1600G OLA is an independent power supply subrack. It is supported by the OptiX BWS
1600G backbone DWDM optical transmission system V100R004 and higher versions.
17.3.3 Manageable NA WDM Series Equipment
Manageable NA WDM series equipment is listed as follows:
Table 17-7 Manageable NA WDM equipment
Category
Equipment
Description
LH WDM series
OptiX BWS 1600A
OptiX BWS 1600A WDM
Optical Transmission
System
OptiX BWS 1600G(NA)
OptiX BWS 1600G(NA)
Backbone DWDM Optical
Transmission System
OptiX OSN 1800(NA)
compact intelligent optical
transport platform
OptiX OSN 1800(NA)
OptiX OSN 3800A compact
intelligent optical transport
platform
OptiX OSN 3800A
OptiX OSN 6800A
intelligent optical transport
platform
OptiX OSN 6800A
OptiX OSN 8800 I/II(NA)
intelligent optical transport
platform
OptiX OSN 8800 I/II(NA)
NG WDM series
17-18
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
17.3.4 Manageable Submarine Line Equipment
Manageable submarine line equipment is listed as follows:
Table 17-8 Manageable submarine line equipment
Category
Equipment
Description
Submarine line series
OptiX SLM 1630
OptiX SLM 1630 submarine
line monitor
OptiX PFE 1670
OptiX PFE 1670 Power
Feeding Equipment
OptiX BWS 1600S
OptiX BWS 1600S
submarine line terminal
equipment
17.3.5 Manageable RTN Series Equipment
Manageable RTN series equipment is listed as follows:
Table 17-9 Manageable RTN equipment
Category
Equipment
Description
RTN series
OptiX RTN 605
OptiX RTN 605 radio
transmission system
OptiX RTN 610
OptiX RTN 610 radio
transmission system
OptiX RTN 620
OptiX RTN 620 radio
transmission system
OptiX RTN 910
OptiX RTN 910 radio
transmission system
OptiX RTN 950
OptiX RTN 950 radio
transmission system
OptiX RTN 5000S
OptiX RTN 5000S radio
transmission system
17.3.6 Manageable PTN Series Equipment
Manageable PTN series equipment is listed as follows:
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-19
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Table 17-10 Manageable PTN series equipment
Category
Equipment
Description
PTN series
OptiX PTN 1900
OptiX PTN 1900 multiservice packet transmission
platform
OptiX PTN 3900
OptiX PTN 3900 multiservice packet transmission
platform
OptiX PTN 3900-8
OptiX PTN 3900-8 multiservice packet transmission
platform
OptiX PTN 912
OptiX PTN 912 multiservice packet transmission
platform
OptiX PTN 910
OptiX PTN 910 multiservice packet transmission
platform
OptiX PTN 950
OptiX PTN 950 multiservice packet transmission
platform
17.3.7 Manageable FTTx Series Equipment
Manageable FTTx series equipment are listed as follows:
Table 17-11 Manageable FTTx series equipment
Category
OLT series
17-20
Equipment
Description
MA5600T
SmartAX MA5600T Multi-service Access
Module
MA5603T
SmartAX MA5603T Optical Access
Equipment
MA5680T
SmartAX MA5680T Optical Access
Equipment
MA5683T
SmartAX MA5683T Optical Access
Equipment
MA5606T
SmartAX MA5606T Optical Access
Equipment, Only the version of V800R105
support.
MA5603U
SmartAX MA5603U Multi-service
Access Module
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Category
MDU series
ONT series
Issue 05 (2010-11-19)
17 Management Capability
Equipment
Description
MA5606T
SmartAX MA5606T Optical Access
Equipment
MA5620
SmartAX MA5620 Multiple Dwelling
Unit
MA5626
SmartAX MA5626 Multiple Dwelling
Unit
MA5628
SmartAX MA5628 Multiple Dwelling
Unit
MA5620E
SmartAX MA5620E EPON Multiple
Dwelling Unit
MA5626E
SmartAX MA5626E EPON Multiple
Dwelling Unit
MA5620G
SmartAX MA5620G GPON Multiple
Dwelling Unit
MA5626G
SmartAX MA5626G GPON Multiple
Dwelling Unit
MA5610
SmartAX MA5610 Multi-service Access
Module
MA5612
SmartAX MA5612 Multi-service Access
Module
MA5616
SmartAX MA5616 Multi-service Access
Module
MA5651
SmartAX MA5651 Multiple Dwelling
Unit
MA5651G
SmartAX MA5651G Multiple Dwelling
Unit
MA5652G
SmartAX MA5652G GPON Multiple
Dwelling Unit
MA5635
SmartAX MA5635 Multi-service Access
Module
MA5662
SmartAX MA5662 Multi-Service Access
Module
SRG2220
SRG2220 Service Router Gateway
EchoLife:OT550
EchoLife:HG850
EchoLife:HG850a
EchoLife:HG851
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-21
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Category
Equipment
Description
EchoLife:HG852
EchoLife:HG853
EchoLife OT925
SmartAX OT928
EchoLife:HG810
EchoLife:HG811
EchoLife:HG813
EchoLife:HG860
EchoLife:HG861
EchoLife:HG863
EchoLife:HG865
EchoLife:HG810a
EchoLife:HG866
EchoLife:HG866e
U5KG
810e
813e
850e
925e
U5KE
HG8240
HG8245
HG8247
17.3.8 Manageable MSAN Series Equipment
Manageable MSAN series equipment are listed as follows:
Table 17-12 Manageable MSAN series equipment
17-22
Category
Equipment
Description
UA5000 series
UA5000
UA5000 Universal Access Unit
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Category
MD5500 series
17 Management Capability
Equipment
Description
UA5000(PVU)
UA5000 Universal Access Unit
UA5000(IPMB)
UA5000 Universal Access Unit
UA5000(PVMV1)
UA5000 Universal Access Unit
MD5500
MD5500 Multi-service
Distribution Module
17.3.9 Manageable DSLAM Series Equipment
Manageable DSLAM series equipment are listed as follows:
Table 17-13 Manageable DSLAM series equipment
Category
MA5100 series
MA5300 series
MA5600 series
MA5600V8 series
Equipment
Description
MA5100V2
SmartAX MA5100 Multi-service
Access Module
MA5105
SmartAX MA5105 Multi-service
Access Module
MA5300
SmartAX MA5300 Broadband
Access System
MA5600V3
SmartAX MA5600 Multi-service
Access Module
MA5605
SmartAX MA5605 Multi-service
Access Module
MA5615
SmartAX MA5615 Broadband
Access System
MA5600T
SmartAX MA5600T Multiservice Access Module
MA5603T
SmartAX MA5603T Multiservice Access Module
MA5606T
SmartAX MA5606T Multiservice Access Module
17.3.10 Manageable Router Series Equipment
Manageable router series equipment are listed as follows:
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-23
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Table 17-14 Manageable router series equipment
Category
Device
Description
NE series routers
NE05
Net engine 05 router
NE08
Net engine 08 router
NE16
Net engine 16 router
NE08E
Net engine 08E router
NE16E
Net engine 16E router
NE20
Net engine 20 router
NE20E
Net engine 20E router
NE40
Net engine 40 universal switching router
NE80
Net engine 80 universal switching router
NE40E/NE80E
Net engine 40E/80E core router
NE5000E
Net engine 5000E core router
R series routers
R series routers
AR18
Advanced router 18 serials router
AR28
Advanced router 28 serials router
AR46
Advanced router 46 serials router
AR19
Advanced router 19 serials router
AR29
Advanced router 29 serials router
AR49
Advanced router 49 serials router
R/AR series routers
17.3.11 Manageable Switch Series Equipment
Manageable switch series equipment are listed as follows:
Table 17-15 Manageable switch series equipment
17-24
Category
Device
Description
S8500 series switches
S8505
Quidway S8505 Series Routing
Switches
S8505E
Quidway S8505E Series Routing
Switches
S8508
Quidway S8508 Series Routing
Switches
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Category
Device
Description
S8512
Quidway S8512 Series Routing
Switches
S7800 series switches
S7800
Quidway S7800 Series Ethernet
Switches
S6500 series switches
S6502
Quidway S6502 Series Ethernet
Switches
S6503
Quidway S6502 Series Ethernet
Switches
S6506R
Quidway S6506R Series Ethernet
Switches
S6506
Quidway S6506 Series Ethernet
Switches
S50 series switches
Quidway S5000 Series Ethernet
Switches
S55 series switches
Quidway S5500 Series Ethernet
Switches
S56 series switches
Quidway S5600 Series Ethernet
Switches
S30 series switches
Quidway S3000 Series Ethernet
Switches
S35 series switches
Quidway S3500 Series Ethernet
Switches
S39 series switches
Quidway S3900 Series Ethernet
Switches
S20 series switches
Quidway S2000 Series Ethernet
Switches
S24 series switches
Quidway S2400 Series Ethernet
Switches
S2300
Quidway S2300 Series Ethernet
Switches
S2700
Quidway S2700 Series Ethernet
Switches
S3300
Quidway S3300 Series Ethernet
Switches
S3700
Quidway S3700 Series Ethernet
Switches
S5300
Quidway S5300 Series Ethernet
Switches
S5000 series switches
S3000 series switches
S2000 series switches
box series switches
Issue 05 (2010-11-19)
17 Management Capability
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-25
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Category
frame series switches
Device
Description
S5700
Quidway S5700 Series Ethernet
Switches
S9300
Quidway S9300 Terabit Routing
Switch
17.3.12 Manageable Metro Service Platform Equipment
Manageable Metro service platform equipment are listed as follows:
Table 17-16 Manageable Metro service platform equipment
Category
Device
Description
CX series devices
CX200
CX200 Metro Services Platform
CX200C
CX200C Metro Services Platform
CX200D
CX200D Metro Services Platform
CX300
CX300 Metro Services Platform
CX380
CX380 Metro Services Platform
CX600
CX600 Metro Services Platform
17.3.13 Manageable Broadband Access Series Equipment
Manageable broadband access series equipment are listed as follows:
Table 17-17 Manageable broadband access series equipment
Category
Device
Description
Multi-service
gateways
MA5200E
Multiservice access 5200E service gateway
MA5200F
Multiservice access 5200F service gateway
MA5200G
Multiservice access 5200G service gateway
ME60 series
Multiservice engine 60 serials service gateway
17.3.14 Manageable VoIP Gateway Equipment
Manageable VoIP gateway equipment are listed as follows:
17-26
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Table 17-18 Manageable VoIP gateway equipment
Category
Device
Description
VoIP Gateway
VG10
VoIP gateways 10
VG20
VoIP gateways 20
VG80
VoIP gateways 80
XE series
17.3.15 Manageable WLAN Series equipment
Manageable WLAN Series equipment are listed as follows:
Table 17-19 Manageable WLAN series equipment
Category
Device
Description
WLAN
WA10 AP
WLAN 10
WA12 AP
WLAN 12
17.3.16 Manageable Firewall Series Equipment
Manageable firewall series equipment are listed as follows:
Table 17-20 Manageable firewall series equipment
Issue 05 (2010-11-19)
Category
Device
Description
Eudemon
E8080E
Eudemon 8000E series Firewall
E8160E
Eudemon 8000E series Firewall
NE40E-FW
Eudemon 8000E series Firewall
NE80E-FW
Eudemon 8000E series Firewall
E8040
Eudemon 8000 series Firewall
E8080
Eudemon 8000 series Firewall
E1000E U2
Eudemon 1000E series Firewall
E1000E U3
Eudemon 1000E series Firewall
E1000E U5
Eudemon 1000E series Firewall
E1000E U6
Eudemon 1000E series Firewall
Eudemon1000E-D
Eudemon 1000E series Firewall
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-27
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Category
USG
17-28
Device
Description
Eudemon1000E-I
Eudemon 1000E series Firewall
E300
Eudemon 300 series Firewall
E500
Eudemon 500 series Firewall
E1000
Eudemon 1000 series Firewall
E200
Eudemon 200 series Firewall
E100E
Eudemon E100E series Firewall
E200S
Eudemon E200S series Firewall
USG9310
USG9300 Unified Security Gateway
USG9320
USG9300 Unified Security Gateway
USG9210
USG9200 Unified Security Gateway
USG9220
USG9200 Unified Security Gateway
USG5320
USG5000 Unified Security Gateway
USG5330
USG5000 Unified Security Gateway
USG5350
USG5000 Unified Security Gateway
USG5360
USG5000 Unified Security Gateway
USG5310
USG5000 Unified Security Gateway
USG5300ADD
USG5000 Unified Security Gateway
USG5300ADI
USG5000 Unified Security Gateway
USG2130
USG2100 Unified Security Gateway
USG2130W
USG2100 Unified Security Gateway
USG2160
USG2100 Unified Security Gateway
USG2160W
USG2100 Unified Security Gateway
E200E-B
E200E Unified Security Gateway
USG2160
USG2100 Unified Security Gateway
USG2160W
USG2100 Unified Security Gateway
USG2160BSR
USG2100 Unified Security Gateway
USG2160BSR-W
USG2100 Unified Security Gateway
USG2130BSR
USG2100 Unified Security Gateway
USG2130BSR-W
USG2100 Unified Security Gateway
USG2120BSR
USG2100 Unified Security Gateway
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Category
Issue 05 (2010-11-19)
17 Management Capability
Device
Description
USG2160HSR
USG2100 Unified Security Gateway
USG2160HSR-W
USG2100 Unified Security Gateway
USG2130HSR
USG2100 Unified Security Gateway
USG2130HSR-W
USG2100 Unified Security Gateway
Eudemon200E-B
E200E Unified Security Gateway
Eudemon200E-BW
E200E Unified Security Gateway
USG2130HSR-P
USG2100 Unified Security Gateway
USG2130HSR-WP
USG2100 Unified Security Gateway
USG2160HSR-P
USG2100 Unified Security Gateway
USG2160HSR-WP
USG2100 Unified Security Gateway
USG2110-F
USG2100 Unified Security Gateway
USG2110-F-W
USG2100 Unified Security Gateway
USG2110-A-W
USG2100 Unified Security Gateway
USG2110-A-GW-W
USG2100 Unified Security Gateway
USG2110-A-GW-C
USG2100 Unified Security Gateway
USG2110-A-GW-T
USG2100 Unified Security Gateway
USG50
USG50 Unified Security Gateway
USG2110
USG2100 Unified Security Gateway
USG2210
USG2100 Unified Security Gateway
USG2220
USG2100 Unified Security Gateway
USG2230
USG2100 Unified Security Gateway
USG2250
USG2100 Unified Security Gateway
USG2250-D
USG2100 Unified Security Gateway
USG2205BSR
USG2200 Unified Security Gateway
USG2220BSR
USG2200 Unified Security Gateway
USG2220BSR-D
USG2200 Unified Security Gateway
E200E_C
E200E Unified Security Gateway
E200E_F
E200E Unified Security Gateway
E200E-F-D
E200E Unified Security Gateway
USG2220BSR
USG2200 Unified Security Gateway
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-29
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Category
SRG
17-30
Device
Description
USG2205BSR
USG2200 Unified Security Gateway
USG2220HSR
USG2200 Unified Security Gateway
USG2205HSR
USG2200 Unified Security Gateway
USG5150
USG5100 Unified Security Gateway
USG5120
USG5100 Unified Security Gateway
USG5150BSR
USG5100 Unified Security Gateway
USG5120BSR
USG5100 Unified Security Gateway
USG5150HSR
USG5100 Unified Security Gateway
USG5120HSR
USG5100 Unified Security Gateway
USG2205HSR
USG2200 Unified Security Gateway
USG2220HSR-D
USG2200 Unified Security Gateway
USG2220TSM
USG2200 Unified Security Gateway
USG2250TSM
USG2200 Unified Security Gateway
USG5120-D
USG5100 Unified Security Gateway
USG5120BSR-D
USG5100 Unified Security Gateway
USG3040
USG3040 Unified Security Gateway
USG3030
USG3030 Unified Security Gateway
SRG2220
SRG2200 Secure Routing Gateway
SRG2220-D
SRG2200 Secure Routing Gateway
SRG2210
SRG2200 Secure Routing Gateway
SRG3230
SRG3200 Secure Routing Gateway
SRG3240
SRG3200 Secure Routing Gateway
SRG3240-D
SRG3200 Secure Routing Gateway
SRG3250
SRG3200 Secure Routing Gateway
SRG3260
SRG3200 Secure Routing Gateway
SRG20-20
SRG20 Secure Routing Gateway
SRG20-21
SRG20 Secure Routing Gateway
SRG20-30
SRG20 Secure Routing Gateway
SRG20-31
SRG20 Secure Routing Gateway
SRG20-31-D
SRG20 Secure Routing Gateway
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Category
EGW
17 Management Capability
Device
Description
SRG2220
SRG2200 Secure Routing Gateway
SRG2220-D
SRG2200 Secure Routing Gateway
SRG20-10
SRG20 Secure Routing Gateway
SRG1210
SRG1200 Secure Routing Gateway
SRG1210W
SRG1200 Secure Routing Gateway
SRG1220
SRG1200 Secure Routing Gateway
SRG1220W
SRG1200 Secure Routing Gateway
SRG1210-S
SRG1200 Secure Routing Gateway
SRG1210-S
SRG1200 Secure Routing Gateway
SRG20-11
SRG20 Secure Routing Gateway
SRG20-12
SRG20 Secure Routing Gateway
SRG20-15
SRG20 Secure Routing Gateway
SRG20-15W
SRG20 Secure Routing Gateway
SRG20-12W
SRG20 Secure Routing Gateway
EGW2160
EGW2100 series Enterprise Gateway
EGW2160W
EGW2100 series Enterprise Gateway
EGW2130
EGW2100 series Enterprise Gateway
EGW2130W
EGW2100 series Enterprise Gateway
EGW2220
EGW2200 series Enterprise Gateway
EGW2220-D
EGW2200 series Enterprise Gateway
EGW2210
EGW2200 series Enterprise Gateway
EGW3260
EGW3200 series Enterprise Gateway
EGW3250
EGW3200 series Enterprise Gateway
EGW3240
EGW3200 series Enterprise Gateway
EGW3240-D
EGW3200 series Enterprise Gateway
EGW3230
EGW3200 series Enterprise Gateway
EGW2112GW
EGW2100 series Enterprise Gateway
17.3.17 Manageable DPI Equipment
Manageable DPI equipment are listed as follows:
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17-31
iManager U2000 Unified Network Management System
Product Description
17 Management Capability
Table 17-21 Manageable DPI equipment
Category
Device
Description
SIG
SIG9810
SIG9810 DPI Equipment
SIG9820
SIG9820 DPI Equipment
NE40E-DPI
NE40E-DPI DPI Equipment
NE80E-DPI
NE80E-DPI DPI Equipment
SIG Server
SIG DPI Equipment
DPI Server
DPI DPI Equipment
RADIUS Server
RADIUS DPI Equipment
URL Classify Server
URL Classify DPI
Equipment
17.3.18 Manageable SVN Series Equipment
Manageable SVN series equipment are listed as follows:
Table 17-22 Manageable SVN series equipment
Category
Device
Description
SVN
SVN3000
SVN3000
17.3.19 Manageable OP-Bypass Equipment
Manageable OP-Bypass equipment are listed as follows:
Table 17-23 Manageable OP-Bypass equipment
17-32
Category
Device
Description
OP-Bypass
OP-Bypass
OP-Bypass
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
18
18 Standards Compliance
Standards Compliance
This topic describes the standards that the U2000 is compliant with.
The U2000 is developed according to the network management system model that the ITU-T
TMN series standards define. The information model is constructed based on the object-oriented
concept. Complying with multiple standards, the U2000 has good expandability and reusability.
The U2000 complies with the following international standards and protocols:
l
RFC 793 Telnet/TCP/IP standards
RFC 1155, RFC 1157, RFC 1212, RFC 1213 and RFC 1215 SNMP V1 series standards
RFC 1905, RFC 1906, RFC 1907, RFC 1908, RFC 2011, RFC 2012, RFC 2013, RFC 2571,
RFC 2572, RFC 2573, RFC 2574, RFC 2576, RFC 2578, RFC 2579, and RFC 2580 SNMP
V2 series standards
RFC 3411, RFC 3412, RFC 3413, RFC 3414, RFC 3415, RFC 3416, RFC 3417, and RFC
3418 SNMP V3 series standards
RFC 3164 Syslog standards
ISO 8824 and ISO 8825 ASN.1 standards
ITU-T standards for managing the telecommunications management network: M.3000, M.
3010, M.3020, M.3100, and M.3400 (without accounting)
HTTP and JAVA interface protocols and standards
W3C SOAP 1.1/WSDL
TL1 (Telcordia GR-811, GR-831, etc.)
The XML service delivery and inventory query are based on the MTOSI standards as
follows: TMF 518, TMF 612, and TMF 864
CORBA 2.5 protocol
ISO 8824 and ISO 8825 ASN.1 standards
The CORBA alarm northbound interface complies with the MTNM standards as follows:
TMF 513, TMF 608, and TMF 814
Table 18-1 lists the details of the standards and protocols.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
18-1
iManager U2000 Unified Network Management System
Product Description
18 Standards Compliance
Table 18-1 Details of the Standards and Protocols
Standards
and
Protocols
18-2
Description
RFC 793
Transmission Control Protocol (Darpa Internet Program Protocol
Specification)
RFC 1155
Structure and Identification of Management Information for TCP/IP-based
Internets
RFC 1212
Concise MIB Definitions
RFC 1213
Management Information Base for Network Management of TCP/IP-based
Internets: MIB-II
RFC 1215
A Convention for Defining Traps for use with the SNMP
RFC 1905
Protocol Operations for Version 2 of the Simple Network Management
Protocol
RFC 1906
Transport Mappings for Version 2 of the Simple Network Management
Protocol
RFC 1907
Management Information Base for Version 2 of the Simple Network
Management Protocol
RFC 1908
Coexistence between Version 1 and Version 2 of the Internet-standard
Network Management Framework
RFC 2011
SNMPv2 Management Information Base for the Internet Protocol using
SMIv2
RFC 2012
SNMPv2 Management Information Base for the Transmission Control
Protocol using SMIv2
RFC 2013
SNMPv2 Management Information Base for the User Datagram Protocol
using SMIv2
RFC 2571
An Architecture for Describing SNMP Management Frameworks
RFC 2572
Message Processing and Dispatching for the Simple Network Management
Protocol
RFC 2573
SNMP Applications
RFC 2574
User-based Security Model (USM) for version 3 of the Simple Network
Management Protocol
RFC 2576
Coexistence between Version 1, Version 2, and Version 3 of the Internetstandard Network Management Framework
RFC 2578
Structure of Management Information Version 2 (SMIv2)
RFC 2579
Textual Conventions for SMIv2
RFC 2580
Conformance Statements for SMIv2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Standards
and
Protocols
Issue 05 (2010-11-19)
18 Standards Compliance
Description
RFC 3411
An Architecture for Describing Simple Network Management Protocol
(SNMP) Management Frameworks
RFC 3412
Message Processing and Dispatching for the Simple Network Management
Protocol (SNMP)
RFC 3413
Simple Network Management Protocol (SNMP) Applications
RFC 3414
User-based Security Model (USM) for version 3 of the Simple Network
Management Protocol (SNMPv3)
RFC 3415
View-based Access Control Model (VACM) for the Simple Network
Management Protocol (SNMP)
RFC 3416
Version 2 of the Protocol Operations for the Simple Network Management
Protocol (SNMP)
RFC 3417
Transport Mappings for the Simple Network Management Protocol (SNMP)
RFC 3418
Management Information Base (MIB) for the Simple Network Management
Protocol (SNMP)
RFC 3164
BSD syslog Protocol
ISO
8824-4-200
0
Information Technology - Abstract Syntax Notation One (ASN.1):
Parameterization of ASN.1 Specifications Amendment 1: ASN.1 semantic
model
ISO
8825-2-199
8
Information Technology - ASN.1 Encoding Rules: Specification of Packed
Encoding Rules (PER) Second Edition; Technical Corrigendum 1:
12/15/1999; Amendment 1: 12/01/2000
ITU-T M.
3000
Overview of TMN recommendations
ITU-T M.
3010
Principles for a telecommunications management network
ITU-T M.
3013
Considerations for a telecommunications management network
ITU-T M.
3017
Framework for the integrated management of hybrid circuit/packet networks
ITU-T M.
3020
TMN interface specification methodology
ITU-T M.
3100
Generic network information model
ITU-T M.
3101
Managed Object Conformance statements for the generic network information
model
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
18-3
iManager U2000 Unified Network Management System
Product Description
18 Standards Compliance
Standards
and
Protocols
18-4
Description
ITU-T M.
3180
Catalogue of TMN management information
ITU-T M.
3200
TMN management services and telecommunications managed areas:
overview
ITU-T M.
3300
TMN F interface requirements
ITU-T M.
3400
TMN management functions
ITU-T X.
720
Management information model
ITU-T X.
721
Definition of management information
ITU-T X.
722
Guidelines for the definition of managed objects
ITU-T X.
733
Information technology - Open Systems Interconnection - Systems
Management: alarm reporting function
ITU-T X.
903
Information technology - Open distributed processing - Reference Model:
architecture
ITU-T G.
707
Network node interface for the synchronous digital hierarchy (SDH)
ITU-T G.
773
Protocol suites for Q-interfaces for management of transmission systems
ITU-T G.
774 (01, 02,
03, 04)
Synchronous digital hierarchy (SDH) - Management information model for
the network element view
ITU-T G.
783
Characteristics of synchronous digital hierarchy (SDH) equipment functional
blocks
ITU-T G.
784
Synchronous digital hierarchy (SDH) management
ITU-T G.
803
Architecture of transport networks based on the synchronous digital hierarchy
(SDH)
ITU-T G.
831
Management capabilities of transport networks based on the synchronous
digital hierarchy (SDH)
ITU-T G.
851.1
Management of the transport network - Application of the RM-ODP
framework
ITU-T G.
852.1
Enterprise viewpoint for simple subnetwork connection management
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
Standards
and
Protocols
Issue 05 (2010-11-19)
18 Standards Compliance
Description
ITU-T G.
852.2
Enterprise viewpoint description of transport network resource model
ITU-T G.
852.3
Enterprise viewpoint for topology management
ITU-T G.
852.6
Enterprise viewpoint for trail management
ITU-T G.
853.1
Common elements of the information viewpoint for the management of a
transport network
ITU-T G.
853.2
Subnetwork connection management information viewpoint
ITU-T G.
853.3
Information viewpoint for topology management
ITU-T G.
853.6
Information viewpoint for trail management
ITU-T G.
854.1
Computational interfaces for basic transport network model
ITU-T G.
854.3
Computational viewpoint for topology management
ITU-T G.
854.6
Computational viewpoint for trail management
Rational
Unified
Process 5.5
Rational Unified Process
Sif99025
EML-NML interface models
TMF513
V2.0
Multi-Technology Network Management Business Agreement NML-EML
Interface Version 2.0
TMF608
V2.0
Multi-Technology Network Management Information Agreement NML-EML
Interface Version 2.0
TMF814
V2.0
Multi Technology Network Management Solution Set Conformance
Document Version 2.0
TMF814
V2.0
Multi Technology Network Management Solution Set Conformance
Document Version 2.0
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
18-5
iManager U2000 Unified Network Management System
Product Description
A Glossary and Abbreviations
Glossary and Abbreviations
A
Abnormal Resource
When the NMS carries out the operation of device resource polling on the device
management module or the module is refreshed manually, the physical resources of some
devices, such as the card, sub-card and port, cannot be accessed because they have been
deleted or have some faults. So, after the NMS carries out the operation of device resource
polling on the device management module or the module is refreshed manually again,
the result of polling the physical resources differ from the first time. The physical
resources that cannot be polled in the second time are called the abnormal resource.
AIS insertion
If there are excessive errors in a channel, AIS can be inserted in this channel to indicate
it is unavailable. For a line board, you can set whether to insert AIS when there are
excessive errors in the B1, B2 and B3 bytes. For a tributary board at the E1 or T1 level,
you can set whether to insert AIS when there are excessive errors in BIP-2. For a tributary
board at the E3 level or higher, you can set whether to insert AIS when there are excessive
errors in the B3 byte.
AIS
Alarm Indication Signal. A signal sent downstream in a digital network if an upstream
failure has been detected and persists for a certain time.
Alarm correlation
analysis
In the case alarm2 is raised within five seconds after alarm1 is raised, and alarm2
complies with the conditions defined in the alarm correlation analysis rule, you can either
suppress the alarm2 or raise its severity level according to the behavior defined in the
alarm correlation rule. Such a process is called alarm correlation analysis.
Alarm Level
Alarm level is to identify the severity of an alarm or event. It is divided up into four
levels: critical, major, minor, warning alarm.
Alarm Status
Device reports the trap information to NMS. NMS displays the received information on
the alarm start on the topological view.
The alarm state contains four types: urgent alarm, important alarm, subordinate alarm
and prompt alarm.
Auto Discovery
Issue 05 (2010-11-19)
NMS tests the remote device by using PING or the SNMP parameter module configured
in advanced to discover the IP device or the device that supports SNMP and to add the
discovered devices automatically.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
A-1
iManager U2000 Unified Network Management System
Product Description
A Glossary and Abbreviations
Alarm reversion
For the port that has already been configured but not actually loaded with services, this
function can be used to avoid generating relevant alarm information, thus preventing
alarm interference.
Alarm severity
According to ITU-T recommendations, the alarm is classified into four severities:
Critical, Major, Minor, and Warning.
Alarm suppression
The suppressed alarm of a specific object is not reported. The object here may be the
networkwide equipment, a specific NE, a specific board and even a specific function
module of a specific board.
Alarm
A visible or an audible indication to notify the person concerned that a failure or an
emergency has occurred. See also Event.
ATM protection group An ATM protection group refers to the logically bound ATM VP network or subnetwork
connections that share the same physical transmission channel. In the VP group (VPG),
a pair of VP connections (working connection and its protection connection) is used for
monitoring the automatic protection switching, called monitoring connections (APS
VPCs). If the monitoring connections switch over, the whole VPG will switch over to
quicken the ATM protection switching (as quick as the protection switching of the SDH
layer.
ALS
Automatic Laser Shutdown. ALS is turned on when the optical interface board does not
carry services or the optical fibre is faulty. Its service life can be prolonged by decreasing
the duration during which laser is on.
Attribute
Property of an object.
Automatic switching
When the active board or path fails, the standby one can automatically take over the job
of the active one.
B
Band Width
In the data communication area, bandwidth specifies the maximum value of the rate
when the data passes through some data channel.
Baseline
Select the test result when the line is in good condition as the line test baseline, to provide
a basis of comparison and analysis for the following line test result.
Baseline collection test One of the test types for submarine line. In the case of deployment or fault restoration,
or when updating the baseline is required, you need to collect the baseline, to provide
reference for comparison tests, and alerts or alarms.
Binding
In virtual concatenated payload configuration, designating one binding number to
identify the VC4s of the same virtual concatenated payload is called "bind". If a fault
occurs to one of the bound services, all bound services will switch as a whole.
Bit error alarm
threshold
When the bit error reaches a specific limit, the equipment will report an alarm. This limit
is the bit error alarm threshold. The threshold can be divided into crossing threshold and
defect threshold.
C
Comparison test in
periodic mode
A-2
One of the test types for submarine line. Carry out polling tests for multiple lines on the
same LMU board periodically, compare the test result with the baseline data in in-service
mode, and provide alerts or alarms for the line.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
A Glossary and Abbreviations
Comparison test in
single-test mode
One of the test types for submarine line. Test a line by using test parameters of the
baseline collection test in in-service mode, compare the test result with the baseline data,
and provide alerts or alarms for the line.
Check alarms
The check feature compares one (or more) uncleared alarm on the NMS with that on the
NE. If an alarm is included in the current alarms on the NE, it is kept on the NMS. If
not, it will be removed from the NMS.
Client
A kind of terminal (PC or workstation) connected to a network that can send instructions
to a server and get results through a user interface. See also server.
Clock View
The Clock View provides a visible platform to enable:1. NE clock settings2.
Networkwide clock synchronisation status query3. Clock tracing and search functions
Configuration data
The data that configures the NE hardware for coordination between this NE and other
NEs in the entire network and operation of specified services. Configuration data is the
instruction file of NEs, and it is the key for efficient network running. The typical
configuration data includes board configuration, clock configuration and protection
relationship.
Configuration
management
Configuration management enables inventory query of network configuration resources,
including relevant configuration of NMS or SNMS, NE, subnet, links, SNC, route, TP,
edge point, equipment, and so on. Real-time inventory change report can also be provided
through this resource, it will be timely reported to the upper NMS to notify the carrier
of the current network operation status and ensure data consistency of the upper NMS
or SNMS.
Configure
To set the basic parameters of an operation object.
Connection point
A reference point where the output of a trail termination source or a connection is bound
to the input of another connection, or where the output of a connection is bound to the
input of a trail termination sink or another connection. The connection point is
characterized by the information which passes across it. A bidirectional connection point
is formed by the association of a contradirectional pair.
Connection
A "transport entity" which consists of an associated pair of "unidirectional connections"
capable of simultaneously transferring information in opposite directions between their
respective inputs and outputs.
Current alarms
Alarms that do not clear, or has cleared but is not acknowledged.
Current performance
data
The performance data stored in the current register is called current performance data.
The current 15-minute or 24-hour register (only one for each) is applied to collect the
performance data in the current monitoring period. It changed within the monitor period.
Change Audit Service
Change Audit Service is developed to record the change on the network device, including
the changes on the information about the device, the configuration and the mapping. It
provides one integrated database. Every application program records these changes in
the database and ensures that these changes in the database are reflected on other
applications.
Cluster
The cluster is an administrative domain composed of a set of switches. It consists of a
command switch and multiple member switches. The management over all the switches
within the cluster is realized through a public IP address.
Configuration File
Text file, including various configuration on the device.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
A-3
A Glossary and Abbreviations
iManager U2000 Unified Network Management System
Product Description
D
DCC
Within an STM-N signal there are two DCC channels, one is the 192 kbit/s DCC-R
channel composed of bytes D1-D3, and the other is the 576 kbit/s DCC- channel
composed of bytes D4-D12. All NEs can communicate with one another through the
DCC-R. The DCC-M is not the regenerator section overhead and does not support
communications among regenerators, and it is used to support communication channels
of more universal purpose.
DNI
Dual Node Interconnection. The protection mode defined in G. 842 Recommendation
for the inter-ring service . By using the recommended protection modes, the protection
of the interconnecting service between two ring networks composed of the devices from
different manufacturers and in different protection modes can be realised. Moreover, in
case of fibre failure or node failure, services can also be protected.
Domain
The domain of the NMS specifies the scope of address or functions which are available
to a certain user.
Dump
Dump is a process of exporting alarm data from the database to the customized file and
meanwhile the exported data is cleared in the database.
E
ECC
Embedded Control Channel. An ECC provides a logical operations channel between
SDH NEs, utilising a data communications channel (DCC) as its physical layer.
EMU
Environment Monitoring Unit. As one type of power and environment monitoring unit,
EMU is installed on the top of the OptiX 155/622H equipment cabinet to monitor the
environment variables, such as the power supply and temperature. With external signal
input through the relay, fire alarm, smoke alarm, burglary alarm, and so on can be
monitored as well. Displayed on the NMS, the change of environment can be monitored
timely and accurately.
Equipment set
An aggregate of multiple managed equipment. Equipment set facilitates the user
authority management on equipment in the management domain of the NMS. If some
operation authorities over one equipment set are assigned to a user (user group), these
operation authorities over all equipment of the equipment set are assigned to the user
(user group).
F
Failure
The fault cause persisted long enough to consider the ability of an item to perform a
required function to be terminated. The item may be considered as failed; a fault has now
been detected.
Fault
A fault is the inability of a function to perform a required action. This does not include
an inability due to preventive maintenance, lack of external resources, or planned actions.
Filter
The filter is used to filter the matched logs and have the unmatched one left.
Forced switch
This command performs the ring switch from working channels to the protection
channels. This switch occurs regardless of the state of the protection channels, unless
the protection channels are satisfying a higher priority bridge request.
A-4
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
A Glossary and Abbreviations
H
History alarms
Alarms that have cleared and been acknowledged.
History performance
data
The performance data stored in the history register and the auto-report performance data
stored on the NMS are called history performance data in a unified way.
I
Intermediate office
It refers to the equipment used for optical fibre management and dispatch in the
metropolitan area. It has multiple pairs of interfaces for the optical fibre connection.
Every two interfaces in a pair are connected with each other to form a longer physical
optical fibre path. The physical optical fibre path connecting the transmission equipment
can comprise two or more sections of optical fibre cascaded via the intermediate office.
There is an intermediate office information list for some fibre & cable connections, which
shows the section information about the fibre & cable.
In-Service Mode
One of the test modes for submarine line. By using the in-service test mode , you can
test submarine cables and repeaters without damaging the existing services of the
submarine system.
Image (OS)
Binary file, equivalent to the OS of the device and a part of the device version.
IP address
In the TCP/IP protocol, it is used to uniquely identify the address of the communication
port, which consists of four bytes in decimal digits, for example, 129.9.161.55.
J
Jitter
This index shows the delay stability of many Ping operations with the unit of ms.
L
Label
A mark on a cable, a subrack, or a cabinet for identification.
Layer
A concept used to allow the transport network functionality to be described hierarchically
as successive levels; each layer being solely concerned with the generation and transfer
of its characteristic information.
LCT
Local Craft Terminal. The LCT provides the user with single-layer management network
solutions to the transmission network of up to five NEs to realise integrated management
of multi-service transmission network. Usually it uses the cross-over cable or serial port
cable to connect one NE, so as to configure and maintain a single NE. See also U2000
LCT.
Licence
A permission provided by a vendor to authorise the use of specific functions of a product.
Usually the licence consists of encrypted codes, and the operation authority varies with
different level of licence.
Link
The link is responsible to transmit the data from one station to next neighbour station
correctly.
Lock NE login
This function prohibits the users at lower levels from logging in NE and forces logged
NE users with lower level to log out.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
A-5
A Glossary and Abbreviations
iManager U2000 Unified Network Management System
Product Description
M
Main Topology
The default NMS client interface and all topology management functions are accessed
here.
Management
information
The signal passing across an access point.
Manual switch
When the protection channel is efficient and there is no higher-level switching request,
this mode switches the service from the working channel to the protection channel, thus
testing whether network still has the protection capability.
Manual test
One of the test types for submarine line. You need to set test parameters manually, start
the test, and save the test result as the baseline of the in-service mode.
MO
Managed Object. The management view of a resource within the telecommunication
environment that may be managed via the agent. Examples of SDH managed objects
are: equipment, receive port, transmit port, power supply, plug-in card, virtual container,
multiplex section, and regenerator section.
MS
Multiplex Section. A multiplex section is the trail between and including two multiplex
section trail termination functions.
MSP
Multiplex section protection. The nodes online achieve protection switching through the
K1 and K2 bytes in the multiplex section, including linear 1+1 MS protection switching
link, linear 1:n MS protection switching link, dedicated MS protection ring and shared
MS protection ring.
N
NE database
There are three types of database on NE SCC board as following: (1) DRDB: a dynamic
database in a dynamic RAM, powered by battery; (2) SDB: a static database in a powerdown RAM; (3) FDB0, FDB0: permanently saved databases in a Flash ROM. In efficient
operation, the NE configuration data is saved in DRDB and SDB at the same time.
Backing up an NE database means backing up the NE configuration data from SDB to
FDB0 and FDB1.
NE Explorer
NE Explorer is the main operation interface of the NMS. For easy navigation, the NE
Explorer window presents an expandable directory tree (Function Tree) in the lower left
pane. The configuration, management and maintenance of the equipment are accessed
here.
NE
Network Element. NE includes the hardware unit and the software running on it. Usually,
one NE has at least an SCC (system control and communication) board which responsible
for the management and monitoring of the NE. The NE software runs on the SCC board.
NM
Network Management. In the telecommunication management network structure, the
NMS is located between the NE level and network level, which can supports all functions
at NE level and part of the network level management functions. See also U2000.
NNI
Network Node Interface. NNI identifies the interface between the ATM network nodes.
See also SDH NNI.
Node
Node is one of the topology objects and the minimum unit that represents the device
displayed on the topological view. The device is displayed with the node icon on the
topological view. The type of the node includes the router, the switch and the 3rd-party
device and the virtual node.
A-6
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
A Glossary and Abbreviations
O
Online help
An indexed collection of information on all aspects of the NMS. They can be accessed
at any time from the Help menu or by pressing the F1 key.
Optical time domain
reflectormeter
OTDR is an optical fault locator and analysis tool for optical fiber networks. The OTDR
features a light, compact, hand-held design with an intelligent user interface that is easy
and quick to use. The color LCD display and backlight design makes testing work more
comfortable and convenient, whether during daylight or at night.
Out-of-Service Mode
One of the test modes for submarine line. By transmitting detection light with high power,
the out-of-service test can detect the fiber status and repeater status, to realize the status
detection and fault point location after fiber cut. In general, when detecting that a line is
abnormal during a test in in-service mode, you can carry out a test in out-of-service mode
to locate the fault.
OWSP
Optical Wavelength Shared Protection. OWSP is a bidirectional ring, where each node
is equipped with an OWSP. There are two channels (1 and 2) in the main optical path
on the internal and external rings in each span on a ring. The fibre and the OWSP on the
main optical path are connected with the optical ports inputting 1 and 2 on the mux/
demux board (unnecessary to be connected with the OTU), and thus 1 and 2 can be
added and dropped at every node.
P
Path protection
The working principle of path protection: When the system works in path protection
mode, the PDH path uses the dual-fed and signal selection mode. Through the tributary
unit and cross-connect unit, the tributary signal is sent simultaneously to the east and
west lines. Meanwhile, the cross-connect matrix sends the signal dually sent from the
opposite end to the tributary board through the active and standby buses, and the
hardware of the tributary board will selectively receive the signal from the two groups
of buses automatically according to the AIS number of the lower order path.
Path
A trail in a path layer.
Performance register
Performance register is the memory space for performance event counts, including 15min current performance register, 24-hour current performance register, 15-min history
performance register, 24-hour history performance register, UAT register and CSES
register.
Performance threshold Performance events usually have upper and lower thresholds. When the performance
event count value exceeds the upper threshold, a performance threshold-crossing event
is generated; when the performance event count value is below the upper threshold for
a period of time, the performance threshold-crossing event is ended. In this way,
performance jitter caused by some sudden events can be shielded.
PMU
One type of power and environment monitoring unit.
Private line
Both communication parties are connected permanently.
Procedure
A generic term for an action.
Process
A generic term for a collection of actions.
Protection path
A specific path that is part of a protection group and is labeled protection.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
A-7
A Glossary and Abbreviations
iManager U2000 Unified Network Management System
Product Description
Protection strategy
In case the service route provides multiple service protections, different protection
strategies can be selected as required. Protection strategy refers to the protection mode
given the priority in use for the trail: protection, no protection, and extra traffic. Of the
above, the protection preference is divided into trail protection and sub-network
connection protection.
Protection subnet
The resources that form a protection subnetwork include NEs and fiber cables. The
creation of the protection subnetwork actually means that corresponding logical system
is configured for each NE by means of creating the protection subnetwork, the optical
interfaces (or VC4) of each board are mapped into the logical system, and then these
independent logical systems are connected with one another to form a complete network
structure.
Packets Loss Ratio
This index shows the packet loss ratio after many Ping operations with the unit of %.
Poll Status
The NMS polls the device status and other configuration data periodically and displays
the polling results on the topology view.
The polling status contains normal, unknown, off-line, light fault, subordinate fault,
important fault and urgent fault.
R
ROADM
Reconfiguration Optical Add/Drop Multiplexing. ROADM helps you to terminate or
pass through any one wavelength at every node without affecting the existing services.
At the same time, ROADM can change wavelengths through the NMS remotely, to adjust
wavelengths added or dropped in a quick and convenient manner. In addition, ROADM
enables power equalization at path level through a built-in power equalization function,
and thus adjusts power for pass-through paths in a better way than a band-based dynamic
gain equalizer (DGE) does.
Route
The IP route selection is in table driving mode. In each host and each router of the Internet,
there is a routing table that contains information about how the service is transmitted
from the source to the sink, providing a basis for route selection. Ethernet static routing
in ET1 refers to the mapping relationship between the Ethernet port and the bound path.
Its routing type includes port routing and VLAN routing. Port routing: It means
configuring a route between the Ethernet port and the bound path port, which is usually
used for point-to-point networking communication; VLAN routing: It means configuring
a route between the Ethernet port and the bound path port based on the VLAN service.
It can be used flexibly in point-to-point, point-to-multipoint or multipoint-to-multipoint
communication. The implementation is to divide and converge the data stream according
to the VLAN flag of the packet. As a VLAN flag can be added to the Ethernet port, the
equipment can be applied more flexibly.
Report
The report that is generated manually in a real-time fashion.
RTT
RTT is the round trip time, which is the time delay of the ping task.
S
Script file
A-8
It is the text file describing the physical information and configuration information of
the entire network, including the NE configuration file, port naming file, end-to-end
configuration file, NE physical view script file, NM information file and service
implementation data script file.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
A Glossary and Abbreviations
Schedule Task
The report on schedule task that is generated at a interval along with the periodical
running of the schedule tasks.
Script
A list of instructions for performing a specific task or action, written in a scripting
language.
SDH NNI
SDH Network Node Interface. It is applied to build communications connection with
the equipment beyond the NMS management area. Usually, the NM creates an SDH NNI
by creating a logical system on the port of an idle line board, and the NE must be a TM
without protection and fibre connection.
Section
A trail in a section layer.
Settings
Parameters of an operation that can be selected by the user.
Severity
See Alarm Severity.
Subnet mask
Also referred to as the network mask off code, it is used to define network segments, so
that only the computers in the same network segment can communicate with one another,
thus suppressing broadcast storm between different network segments.
Subnet number
Subnetwork number is used to differentiate the different network sections in the subnetwork conference. Actually it is the first several digits (one or two) of the user phone
number. An orderwire phone number is composed of the sub-network number and the
user number.
Subnet
Sub-network is the logical entity in the transmission network and comprises a group of
network management objects. A sub-network can contain NEs and other sub-networks.
A sub-network planning can better the organisation of a network view.
Support
The frame on the bottom of a cabinet, when installing the cabinet on the antistatic floor.
Synchronise NE time
Send the system time of the NMS server to NEs so as to synchronise all NEs with the
server.
T
T2000
The T2000 is a subnetwork management system (SNMS). In the TMN architecture, the
T2000 is located between the NE level and network level, which can supports all function
of NE-level and part of the network-level management functions. See also NM.
T2100
The T2100 is a network level management system for the optical transmission network,
and is located in the network management layer (NML) in the telecommunication
management network (TMN) architecture.
TDA clock source
TDA is short for Tone Data Access. For the 2500+ NE equipment, it can be installed
with the external TDA board for which the clock source must be set so that the TDA
board can switch according to the set clock source sequence when clock source switching
occurs.
TMN
Telecommunications Management Network. The entity which provides the means used
to transport and process information related to management functions for the
telecommunications network.
Topology
The NMS topology is a basic component of the man-machine interactive interface. The
topology clearly shows the structure of the network, the alarms of different NEs, subnetworks in the network, the communication status as well as the basic network operation
status.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
A-9
A Glossary and Abbreviations
iManager U2000 Unified Network Management System
Product Description
Trail management
function
A network level management function of the NMS. Through trail management, you can
configure end-to-end services, view graphic interface and visual routes of a trail, query
detailed information of a trail, filter, search and locate a trail quickly, manage and
maintain trails in a centralised manner, manage alarms and performance data by trail,
and print a trail report.
Trail
A trail is a kind of transport entity, mainly engaged in transferring signal from the input
of the trail source to the output of the trail sink, and monitoring the integrality of the
transferred signal. According to the different levels of the trail, the trail includes various
types (OTS, OCH, OMS, SPI, RS, MS, VC4 server trail, VC4, VC3 and VC12). Among
them, OTS, OCH and OMS represent the trails in a DWDM layer network. For the ADM
and TM equipment in the SDH network, each optical fibre connection corresponds to an
SPI, RS or MS trail, and a trail is the general name for service carriers, including SDH
and PDH services.
Tributary loopback
A fault can be located for each service path by performing loopback to each path of the
tributary board. There are three kinds of loopback modes: No loopback, Outloop and
Inloop.
Threshold
The alarm range will be defined after the performance data is collected. The threshold
contains the upper and lower one, related with the unit and index.
U
U2000
To be oriented to the future network trend, the iManager U2000 that is the unifed network
management system (NMS) combines all-IP and FMC, and manages carrier equipment
and access equipment in a centralized manner.
UAT
Unavailable Time. A UAT event is reported when the monitored object generates 10
consecutive severely errored seconds (SES) and the SESs begin to be included in the
unavailable time. The event will end when the bit error ratio per second is better than
10-3 within 10 consecutive seconds.
UNI
UNI is the abbreviation for User Network Interface. It identifies the interface between
the user and the ATM network node.
Unprotected
Services transmitted through an ordinary way, once a failure or interruption occurs, the
data cannot be restored for lack of protection mechanism.
Upload
Report all or part of the configuration data of the NE to the NM and overwrite the
configuration data saved in the NE layer on the NM side.
User group
User set refers to the set of NMS users with the same management authorities. The default
user group includes: system administrator, system maintainer, system operator and
system supervisor. The attributes of user set include name and detailed description.
User
The user of the NMS client, and the user and his/her password define the corresponding
authority of operation and management of the NMS.
V
VC4 loopback
A-10
The fault of each VC4 path on the optical fibre can be located by setting loopback for
each VC4 path of the line. There are three kinds of loopback modes: No loopback,
Outloop, Inloop.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
iManager U2000 Unified Network Management System
Product Description
A Glossary and Abbreviations
VC4 server trail
The path rate of the VC4 server trail is 150.336Mbit/s. The VC4 server trail provides
transparent channels (that is, circuit group) for circuit-layer network nodes (for example,
a switch) in a path-layer network, and acts as the basic unit of inter-office communication
path. When the VC4 server trail is configured, only the higher order cross-connection of
VC4 is generated in the intermediate NE, but no cross-connection is generated at the two
ends, that is, no service is added/dropped. Therefore, the VC4 server trail is not a
traditional service. It is only the basis for VC3 and VC12 trail creation.
VCI
The VCI, shorted for Virtual Channel Identifier, occupies 16 bits in both NNI cell or
UNI cell. It indicates the virtual channel in the path. The VPI and VCI together indicate
a virtual connection.
View
Organize and display rules and filter conditions of the topology data. Customize the view
according to requirements of every product and organize the data in the view displayed
by the topology module, such as the layer 2 view, VPN view and IP view. By default,
the platform provides the physical view. The topology view can be planned according
to the domain, maintenance relationship and so on.
Edits and displays the rule of the topology data or the filter conditions. It can be tailored
according to the requirements
Virtual fibre
A virtual fibre is created between SDH equipment that has WDM equipment in between.
From SDH equipment perspective, creation of virtual fibres disassociates its fibre
connection with WDM equipment and prevents impact on the auto fibre search function,
ensuring independence of SDH trail management.From WDM equipment perspective,
its service bearer layer is a virtual fibre instead of a true one after the virtual fibre is
created. Deletion of the true fibre does not affect trail management.
Virtual NE
Like a common NE, a virtual NE is also displayed with an icon on a view, but it is only
an NE simulated according to the practical situation, which does not represents an actual
NE. Therefore, the actual status of this NE cannot be queried and its alarm status cannot
be displayed with colours. Usually, when the trail management function is used for the
NEs or sub-networks the NMS cannot manage, or the equipment is interconnected with
other vendors NEs for service configuration, the end-to-end service configuration
method and the trail management capability are provided.
VLAN ID
Namely, it is the virtual LAN identifier. One Ethernet port can support 4K VLAN routes,
and one NE can support up to 8K VLAN routes.
VPI
The VPI, shorted for Virtual Path Identifier, occupies 12 bits in the NNI cell, and 8 bits
in the UNI cell.
W
Wavelength protection The wavelength protection group is important to describe the wavelength protection
group
structure. Its function is similar to that of the protection sub-network in the SDH NE.
The wavelength path protection can only work with the correct configuration of the
wavelength protection group.
WDM service
The WDM service is accessed at the client side of the OTU board that can access SAN
services.
Web LCT
In the TMN architecture, the Web LCT is located in the NE management level, which
can manage the RTN series and NG WDM series equipment.
Working path
A specific path that is part of a protection group and is labelled working.
Issue 05 (2010-11-19)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
A-11
A Glossary and Abbreviations
iManager U2000 Unified Network Management System
Product Description
WTR time
A period of time that must elapse before a - from a fault recovered - trail/connection can
be used again to transport the normal traffic signal and/or to select the normal traffic
signal from.
WTR
Wait to Restore. This command is issued when working channels meet the restoral
threshold after an SD or SF condition. It is used to maintain the state during the WTR
period unless it is pre-empted by a higher priority bridge request.
WXCP
Wavelength Cross-Connection Protection. It is a path protection type for ring networks.
In this protection mode, services are switched between the primacy and secondary rings
through cross-connection based on the dual fed signal selection principle.
A-12
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Issue 05 (2010-11-19)
Vous aimerez peut-être aussi
- NEC PASOLINK TrainingDocument108 pagesNEC PASOLINK Trainingpurgedsoul100% (13)
- Hardening Tips For The Red Hat Enterprise Linux 5Document2 pagesHardening Tips For The Red Hat Enterprise Linux 5Capital City GoofballPas encore d'évaluation
- CISCO Prime Network OSS Integration Guide For MTOSI 3GPPDocument148 pagesCISCO Prime Network OSS Integration Guide For MTOSI 3GPPWandeto AnthonyPas encore d'évaluation
- Cisco Prime Central 1.2 NBI GuideDocument181 pagesCisco Prime Central 1.2 NBI GuideWandeto AnthonyPas encore d'évaluation
- MWTM 6.1.7 PDFDocument1 448 pagesMWTM 6.1.7 PDFWandeto AnthonyPas encore d'évaluation
- Cisco Prime Central 1.2 NBI GuideDocument181 pagesCisco Prime Central 1.2 NBI GuideWandeto AnthonyPas encore d'évaluation
- CISCO Prime Network OSS Integration Guide For MTOSI 3GPPDocument148 pagesCISCO Prime Network OSS Integration Guide For MTOSI 3GPPWandeto AnthonyPas encore d'évaluation
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (266)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (588)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (121)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- SF6 Analyser 973 3-035-R GBDocument3 pagesSF6 Analyser 973 3-035-R GBSivakumar NatarajanPas encore d'évaluation
- Datasheet: SE-B1, B2, B3, B4Document4 pagesDatasheet: SE-B1, B2, B3, B4Juan GuzmanPas encore d'évaluation
- Motion - Kinetix Selection GuideDocument170 pagesMotion - Kinetix Selection GuideNicolás A. SelvaggioPas encore d'évaluation
- Kioxia Thgjfat0t44bail Bics4 128gb Ufs Ver 3 1 e Rev2 00Document50 pagesKioxia Thgjfat0t44bail Bics4 128gb Ufs Ver 3 1 e Rev2 00Kiran NimbalkarPas encore d'évaluation
- 40CCF Zen CassetteDocument2 pages40CCF Zen CassetteErwin MaldoPas encore d'évaluation
- Gekko DSDocument2 pagesGekko DSAnte NekicPas encore d'évaluation
- Whelen InstallGuide UPS690Document4 pagesWhelen InstallGuide UPS690Anonymous S9LuwmPas encore d'évaluation
- Sounder PDFDocument2 pagesSounder PDFPercy GoitsemangPas encore d'évaluation
- Service KlimaDocument50 pagesService Klimaspirittotti100% (1)
- Installation & Operating Manual X300 Series DC Power Power SystemDocument58 pagesInstallation & Operating Manual X300 Series DC Power Power SystemEdwin RTPas encore d'évaluation
- ProductSheet HeadEnd HttvStream HBBTVDocument2 pagesProductSheet HeadEnd HttvStream HBBTVlikebossPas encore d'évaluation
- At Command ManualDocument38 pagesAt Command ManualOpulens KeyPas encore d'évaluation
- M100700D - MME For Fanuc 6 - 11 - 12 ManualDocument38 pagesM100700D - MME For Fanuc 6 - 11 - 12 ManualTony AntonyPas encore d'évaluation
- The Fabulous Four September 2013Document14 pagesThe Fabulous Four September 2013Julián Castro-CifuentesPas encore d'évaluation
- Circuito Integrado TA8207KDocument11 pagesCircuito Integrado TA8207KIberê CamposPas encore d'évaluation
- NE100, NE101 Spectra Theodolite Data SheetDocument2 pagesNE100, NE101 Spectra Theodolite Data Sheetbbutros_317684077Pas encore d'évaluation
- Open Core Protocol Specification: Release 2.1 OCP-IP ConfidentialDocument240 pagesOpen Core Protocol Specification: Release 2.1 OCP-IP ConfidentialBalaramkishore GangireddyPas encore d'évaluation
- Canafusion - CA-2000 Specification - 1Document1 pageCanafusion - CA-2000 Specification - 1Anggaran RSUD.M.Natsir SolokPas encore d'évaluation
- 通訊原理Document303 pages通訊原理ZenPhiPas encore d'évaluation
- Motorola's STARLINE Cable Simulator Are Used in Place of Fixed Forward Equalizer in Systems Where The Amplifiers Are Located Close TogetherDocument2 pagesMotorola's STARLINE Cable Simulator Are Used in Place of Fixed Forward Equalizer in Systems Where The Amplifiers Are Located Close TogetherRodrigo AlonzoPas encore d'évaluation
- Abb Pricelist 2016 16.03.2016 PDFDocument216 pagesAbb Pricelist 2016 16.03.2016 PDFhiralalnhpcPas encore d'évaluation
- Microwave Imaging Using Arrays of Vivaldi Antenna For Breast Cancer ApplicationsDocument6 pagesMicrowave Imaging Using Arrays of Vivaldi Antenna For Breast Cancer ApplicationsWARSE JournalsPas encore d'évaluation
- Military HandbookDocument80 pagesMilitary HandbookLuthfyatma HardyPas encore d'évaluation
- Pressure Controller Application Guide: ModelDocument2 pagesPressure Controller Application Guide: ModelSIVAM81Pas encore d'évaluation
- DMR-UBT1GL-K Operating InstructionsDocument96 pagesDMR-UBT1GL-K Operating InstructionsZakaria ZebbichePas encore d'évaluation
- 623 2320 1 PBDocument4 pages623 2320 1 PBbatuhanPas encore d'évaluation
- New Microsoft Word DocumentDocument18 pagesNew Microsoft Word DocumentSreekanth PagadapalliPas encore d'évaluation
- GB - T 3733 (B) - 200824° Cone Connectors - Straight Thread, Type BDocument3 pagesGB - T 3733 (B) - 200824° Cone Connectors - Straight Thread, Type BEr.Amritpal SinghPas encore d'évaluation
- Infinium OMNI Express Patient Monitor ManualDocument41 pagesInfinium OMNI Express Patient Monitor ManualCarl AzzopardiPas encore d'évaluation
- A Review On Surface Treatment For Concrete - Part 2 - Performance OkeDocument11 pagesA Review On Surface Treatment For Concrete - Part 2 - Performance Okealdi sophianPas encore d'évaluation