Académique Documents
Professionnel Documents
Culture Documents
CloudByte ElastiStor Guide
Transféré par
MohaideenCopyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
CloudByte ElastiStor Guide
Transféré par
MohaideenDroits d'auteur :
Formats disponibles
CloudByte ElastiStor Patch 5
Installation and
Administration Guide
Build: 1.4.0.790
Copyright 2016 CloudByte Inc.. All rights reserved.
Information in this document is subject to change without notice. The software described in this document is furnished under a
license agreement or nondisclosure agreement. The software may be used or copied only in accordance with the terms of those
agreements. No part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form or any means
electronic or mechanical, including photocopying and recording for any purpose other than the purchaser's personal use without the
written permission of CloudByte Inc..
CloudByte Inc.
4675 Stevens Creek Blvd, Suite 122
Santa Clara, CA 95051
USA
+1-(408)-663-6900
info@cloudbyte.com
www.cloudbyte.com
CONTENTS
CHAPTER I Getting started with CloudByte ElastiStor
8
8
Introduction
CloudByte ElastiStor feature highlights
11
Physical storage infrastructure
14
Installation overview
17
Hardware Compatibility List
18
Host interoperability matrix
19
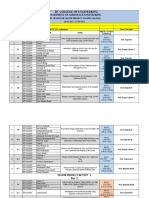
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
20
What's new in ElastiStor 1.4.0 Patch 4
20
What's new in ElastiStor 1.4.0 Patch 3
25
What's new in ElastiStor 1.4.0 Patch 2
27
What's new in ElastiStor 1.4.0 Patch 1
32
What's new in CloudByte ElastiStor 1.4
40
CHAPTER III Installing CloudByte ElastiStor
44
Planning your installation
44
System requirements
45
Network configuration details
45
Installation options
46
Installing ElastiCenter
46
Installing ElastiCenter HA
54
Installing Node
55
Upgrading to CloudByte ElastiStor 1.4.0 Patch 5
64
release Moving your CloudByte ElastiStor setup to a new network environment
70
CHAPTER IV CloudByte ElastiStor Appliance
Installing ElastiCenter and ElastiStor
75
Moving your CloudByte ElastiStor Appliance (ESA) to a new network environment
84
Upgrading to CloudByte ElastiStor 1.4.0 Patch 5
88
CHAPTER V ElastiCenter, ElastiStor's management console
97
Introduction
97
ElastiCenter User Interface
98
Launching CloudByte ElastiCenter
102
Authentication
102
Reset password and configure auto-alert options
103
Replacing default SSL Certificate
104
Customizing the CloudByte ElastiCenter theme
105
CHAPTER VI Configuring CloudByte ElastiStor
75
108
Setting up your storage
108
Creating a Site
112
Creating an HA Group
112
Adding a Node
114
Configuring Disk Array enclosure
115
Creating a Pool
120
Configuring Spare
123
Migrating a Pool
123
Pool encryption
123
Creating an Account
125
Delete account user
126
Provisioning a VSM
126
Configuring VSM migration
131
Migrant VSM activation
134
Provisioning storage
138
Choosing a Pool to provision VSM
142
SASmultipathing
144
Modifying QoS after provisioning VSM
147
Modifying QoS after provisioning Storage Volume
148
Modifying storage capacity
149
Configuring High Availability
150
Configuring local backup
156
Configuring remote disaster recovery
160
Upgrading a High Availability DR setup
163
Assuring Quality of Service
164
Monitoring QoS
167
QoStips
167
CHAPTER VII Setting up data access protocols
169
Data access using iSCSI
169
Installing MPIO on Windows Server
180
Configuring Multipath on ElastiCenter
183
Configuring MPIO on Windows Server for a LUN in ElastiStor
185
Data access using CIFS
193
Data access using FC
198
Data access using NFS
201
Restore snapshots while mapping iSCSI LUNs
203
Restore snapshots while mapping CIFS share
210
Restore snapshots while mapping FC LUNs
214
Restore snapshots while mapping NFS Share
220
CHAPTER VIII Managing CloudByte ElastiStor
Delegated administration
225
Monitoring
230
Drill-down feature
234
CloudByte ElastiStor reporting
235
Global Settings
238
CHAPTER IX Licensing
How do I access license details?
CHAPTER X CloudByte ElastiStor REST APIs
CloudByte ElastiStor API references
CHAPTER XI Connecting to ElastiStor
242
242
245
245
251
Mapping FC LUN to the clients
251
Mapping iSCSI LUN
262
Resizing iSCSI LUN
266
Mapping CIFS share to the clients
274
Mapping NFS share to clients
277
CHAPTER XII Frequently asked questions
225
281
Product FAQs
281
Installation FAQs
284
Pool FAQs
287
Access Protocol FAQs
289
Storage Volume FAQs
293
QoSFAQs
294
High Availability FAQs
297
NIC FAQs
298
Global Settings
298
CloudByte ElastiStor best practices
301
Promoting secondary ElastiCenter and backing up configurations
302
IOPS conversion matrix
307
CHAPTER XIII Glossary
311
CHAPTER I Getting started with CloudByte ElastiStor
CHAPTER I Getting started with CloudByte ElastiStor
The following topics help you get started with CloudByte ElastiStor:
l
"Introduction"
"CloudByte ElastiStor feature highlights"
"Physical storage infrastructure"
"Simple hardware setup"
"Installation overview"
Introduction
What is CloudByte ElastiStor
CloudByte ElastiStor is a full-featured software-defined storage QoS solution, purpose-built for the cloud and virtualized environments. Software-only ElastiStor makes storage predictable, affordable and easy, even as you scale to thousands of applications.
Installable on a wide range of industry-standard servers, ElastiStor frees enterprises and service providers from vendor lock-ins.
ElastiStor lets you custom-build storage infrastructure based on your requirements, with support for SATA, SAS, and SSD hardware
as well as NFS, CIFS, FC, and iSCSI protocols.
Cloud-scale Performance
The allocation of application-specific storage silos to deliver performance does not scale well in todays cloud and virtualized environments. ElastiStor enables you to guarantee performance (IOPS, throughput, and latency) for every application right from a common storage platform. This fully shared storage optimizes your infrastructure, minimizes your CAPEX, and enables more
performance applications to move to the cloud.
No Vendor Lock-in
In addition to being software-defined, ElastiStor eliminates the need for you to lock into specific vendors or overspend on proprietary
hardware. The benefits of commodity, industry-standard resources are first reflected in minimized CAPEX, and later make shifting
vendors easy with no proprietary hardware lock-in.
Hardware Flexibility
Restricting storage media choice is not an ideal scenario when you have a wide variety of performance needs, from archival to big
data applications, and it is definitely not practical to fit every performance-sensitive application on an all-SSD array. ElastiStor is
software-only so you continue to work with the storage media of your choice SSD, SAS, SATA, or any mix optimized for your performance needs.
Simple Management
Managing storage for a large number of applications and their constantly changing performance demands is not for the faint hearted.
Manual tuning of spindles or other hardware is no longer an option. Being software-defined, ElastiStor allows you to instantly provision fully-elastic storage volumes for any workload from the shared storage pool to enable fast deployment and reconfiguration
options. Now it is a simple matter to schedule backups, migrate sites, and empower customers with comprehensive management
rights for their dedicated storage. Additionally, datacenter admins will be able to provision and manage QoS-aware storage volumes
for VMs right from VMWare vCenter, Citrix XenCenter, OpenStack Horizon, or CloudStack.
CHAPTER I Getting started with CloudByte ElastiStor
Affordable
With CloudByte ElastiStor you can now replace hundreds of legacy storage silos in your datacenters with a single, extensible storage platform. By fully sharing your infrastructure, deploying industry-standard hardware and optimally choosing your storage media,
ElastiStor can significantly reduce your datacenter footprint, leading to 80-90% cost savings over 3-5 years. Add simplified management that brings down your operational costs, and you get the lowest cost storage QoS solution.
Features at a glance
Along with the standard storage features, CloudByte ElastiStor provides certain product-specific features of which some are unique.
CloudByte ElastiStor features
Guaranteed Storage QoS within Shared Storage
Share your storage and deliver predictable performance to every application. For the first time ever, ElastiStor allows storage endpoints to be defined beyond capacity, in terms of IOPS, throughput and latency. This allows applications with diverse workloads to
be guaranteed QoS from a shared storage platform. Together with linear scaling, a single extensible shared storage platform from
ElastiStor can now replace legacy solutions dedicated storage silos. By fully sharing storage and optimally utilizing resources,
ElastiStor steeply cuts down your storage footprint, leading to 80-90% cost savings over 3-5 years.
On-Demand Performance Provisioning
Do you still manually configure hardware to provision performance for any new application? Break the need for hardwiring storage
with ElastiStors on-demand provisioning. Just enter the required SLA/QoS parameters and let ElastiStor automate node selection
and resource allocation for you. ElastiStor includes an intelligent heuristics daemon which continuously learns the quantity of various controller resources needed to deliver the required QoS.
vCenter-like Administration Console
ElastiStor makes managing storage as easy as managing VMs, even as you scale to hundreds of applications. Storage admins can
now comprehensively manage the entire storage cluster, spanning across multiple sites, from a single web-based console. Further,
ElastiStor gives you unprecedented access and control over resource usage within shared storage, right down to the applicationlevel granularity.
REST APIs and Plugins for Easy Integration
Every action performed at ElastiStor admin console translates into a REST based API call in the backend. Using these REST APIs,
admins can comprehensively provision and manage ElastiStor volumes from VMware vCenter, Citrix XenCenter, OpenStack Horizon, or any other admin portal. Our plugin for VMware vCenter allows admins to create and manage QoS-aware VMs right from
vCenter console.
N-way High Availability
ElastiStor enables N-way High Availability, exponentially increasing reliability (mean time to failure), compared to the standard 2way HA provided by existing solutions. CloudBytes storage un-fragmentation and its patented VSM architecture make N-way HA
affordable and feasible.
Delegated Administration
A much requested feature from the cloud service providers, delegated administration empowers both CSPs and its customers to
monitor and control storage volumes. Management privileges vary based on the admin functionality for example, a super admin can
manage the entire storage cluster, whereas a customer admin can manage just the storage resources allotted to that particular customer.
Standard storage features
The following Storage features are available in CloudByte ElastiStor:
CHAPTER I Getting started with CloudByte ElastiStor
Feature
Scalability
Description
l
128-bit file system
Zettabyte storage capacity
Unlimited file size
NFSv3
NFSv4
CIFS
ISCSI
FC
Storage Connectivity
SAS JBODs
Storage Resilience
RAID Z1
RAID Z2
De-duplication
Compression
Thin Provisioning
Unlimited Clones
Unlimited Snapshots
N-way high availability (N-way HA)
Partial failure transfer to the available node
Active-Active mode
HA with/without storage redundancy
Tenant level disaster recovery
High availability across primary and DR sites
Block level replication
Synchronous mirroring,
Asynchronous mirroring
RPOLast minute
RTOFew minutes
Protection against silent data corruption
Fixes corrupt block without having to take the file system offline
Access Protocols
Storage Efficiency
Back up
Availability
Disaster Recovery
Data Integrity
Note: The supported capacity of ElastiStor depends on the hardware. With adequate hardware support, ElastiStor can scale
up to any extents.
10
CHAPTER I Getting started with CloudByte ElastiStor
How CloudByte ElastiStor is different from legacy storage solutions
The following table explains the major differences:
Feature
Legacy solutions
CloudByte ElastiStor
Storage Architecture
Monolithic
"Patented VSM Architecture"
Tenant Solution
Only at access layers
At all Storage Stack layers
Full featured tenants
No guaranteed QoS, delegated
administration, or complete security
Provides guaranteed QoS, delegated administration rights, and complete security
Access to tenant-level
resource usage
No
Yes
Security
Limited
Fully secure (complete isolation, access with encrypted key)
Patented VSM Architecture
In a CloudByte Controller, each tenant is completely isolated at storage stack levels and unified as a VirtualStorage Machine (VSM).
With complete isolation, VSMs can be treated as if they are allotted dedicated storage controller enabling:
l
Shared storage tenants with guaranteed QoS (IOPS, Throughput, and latency), delegated administration rights, and complete
security.
Easy shared storage management with access to and control over tenant-level resource usage (disk, cache, network, and
CPU).
Together with its rich customizability and scalability, CloudByte ElastiStor offers a powerful storage virtualization solution for service providers and enterprises.
CloudByte ElastiStor feature highlights
Quality of Service (QoS) within shared storage
CloudByte ElastiStor assures highly predictable performance using its unique QoS-centric approach to provisioning. The feature
highlights include:
n
Guaranteed throughput, latency, and IOPS: Easily commission storage with guaranteed throughput, latency, and
IOPS (Input/Output Operations Per Second) at various levels. You can decide to configure QoS at a Pool level, VSM level, or
Storage Volume level.
Multi-dimensionality: Configure IOPS, throughput, latency, and capacity.
Grid-like service: Utilize available unused storage resources efficiently.
On-demand modification: Edit settings at a later point of time without restart.
See Also:"Assuring Quality of Service"
Multi-protocol support
CloudByte ElastiStor provides LUN access using the following protocols:
11
CHAPTER I Getting started with CloudByte ElastiStor
Fiber Channel (FC)
iSCSI
CIFS
NFS
See Also: "Setting up data access protocols"
Simplified storage provisioning
Assume that you require 20 GB storage and 10000 IOPS. With too many pools and VSMs, manually verifying the apt Pool is a cumbersome task. Instead, use the auto-provisioning feature in ElastiStor to handle this situation.
ElastiStor provides a simplified storage provisioning where it intelligently provides a list of best-fit pools.
Server disk space is divided into storage spaces based on the number of applications, individualistic requirements, and expected
performance from each application. With ElastiStor, you can enter the required SLA/QoS parameters and automate the host selection and resource allocation.
See Also: "Provisioning storage"
Delegated administration
Delegated administration lets you determine the actions various administrators take using administrative tools on different
resources.
The administration roles are mapped to functions using security policies. You can create and maintain separate administration capabilities depending on your needs.
See Also: "Delegated administration"
Multi-way High Availability
CloudByte ElastiStor provides N-way High Availability.
See Also: "Configuring High Availability"
Disaster Recovery
CloudByte ElastiStor equips you to effectively recover data in the case of adversities.
Use the Mirror feature for remote disaster recovery. When you mirror data, a remote snapshot, a read-only copy of the data on the
primary setup, is created in the secondary storage setup. In the case of disaster, you can activate the mirror to take care of the services handled by the primary setup.
See Also: "Configuring remote disaster recovery"
12
CHAPTER I Getting started with CloudByte ElastiStor
REST APIs for easy integration
CloudByte ElastiStor REST APIs provide a bundle of functions that encompasses all the features in the CloudByte ElastiStor
Administrator Console (CloudByte ElastiCenter). That is, you need not have ElastiCenter to configure and manage CloudByte
ElastiStor. Rather you can use your own portal.
The feature highlights include:
n
APIs for all the features in ElastiCenter. The APIs function as an end-to-end translation of the Administrative Console.
APIs are pluggable with delegated administration preset.
CloudByte provides off-the-shelf plug-ins which you can install and start using.
Intuitive administration console CloudByte ElastiCenter
CloudByte ElastiStors centralized management console CloudByte ElastiCenter makes configuration and management of storage
simple even when you have thousands of applications.
Comprehensively manage your entire storage cluster from a single Web-based console. Monitor, control, and audit storage resource
usage down to application-level granularity.
The ElastiCenter features include:
n
Wizards that walk you through the entire setup
Interactive graphical representations that help you monitor data
13
CHAPTER I Getting started with CloudByte ElastiStor
Highly usable action pods that let you manage tasks, with easy access and minimal navigation
See Also:"ElastiCenter User Interface"
Physical storage infrastructure
The following illustration briefs the components of CloudByte ElastiStor:
14
CHAPTER I Getting started with CloudByte ElastiStor
Building your storage infrastructure starts with the creation of a Site, the fundamental infrastructure building block where your Node
and storage and network infrastructure reside.
The following illustration shows the composition of a Site:
15
CHAPTER I Getting started with CloudByte ElastiStor
See also "Setting up your storage" on page 108
See also " ElastiCenter, ElastiStor's management console" on page 97
Simple hardware setup
The following figure illustrates a simple hardware setup, to form a HAGroup, that you can use to get started:
16
CHAPTER I Getting started with CloudByte ElastiStor
Connect the SAS cable between the SAS Port of the Node and Disk Array's INPort . To form a daisy chain, connect SAS cable
between OUTPort of one Disk Array and INPort of another Disk array.
This sets up a group of Nodes.
An HAGroup can have a maximum of four Nodes.
Installation overview
The installation of CloudByte ElastiStor involves installing
l
ElastiCenter. See the procedures in "Installing ElastiCenter"
Node. See the procedures in "Installing Node"
17
CHAPTER I Getting started with CloudByte ElastiStor
You can install the components separately or together.
Note:Installing ElastiCenter and Node together is not recommended for production environments.
Hardware Compatibility List
As a convenience to our customers and partners, CloudByte comprehensively evaluates a variety of hardware components that can
be used in storage solutions.
The CloudByte Support website summarizes information on hardware components that have undergone complete certification testing. As drivers change frequently, please contact CloudByte sales or support teams should you have questions about specific hardware or hardware driver versions.
Access the latest Hardware Compatibility List at the following URL: http://www.cloudbyte.com/support/hardware-compatibility-list/
18
CHAPTER I Getting started with CloudByte ElastiStor
Host interoperability matrix
This section is an overview of compatibility of CloudByte ElastiStor with various OS platforms and environments.
Access the host interoperability matrix at the following URL: http://www.cloudbyte.com/support/host-interoperability-matrix/
19
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
CloudByte ElastiStor 1.4.0 Patch 5 is a stability release including major performance enhancements and various bug fixes. Following are the high points of this release:
l
Better iSCSI I/O handling
Usability and supportability improvements
Performance and QoS improvements
Improvements in bad disk detection and handling logic
QoS functionality enhancements for cloned volumes
Two new monitoring services are added:
l
cbc_monitor_pools_ioerror to check the status of Pool I/Os. If the I/Os are suspended, ElastiCenter generates the Alert es.pool.io.suspended.
CB-Log Monitoring Service to detect disk I/O errors.
What's new in ElastiStor 1.4.0 Patch 4
CloudByte ElastiStor 1.4.0 Patch 4 release includes the following new features:
l
"Assigning real IP spaces"
"Backing up your interfaces"
Assigning real IP spaces
Multiple client virtual machines can access ElastiStor VSMs on same IP addresses. The feature helps in scenarios where multiple
customers need the same network range.
You are not mandated to specify IP address while creating a VSM. Later, you can let the delegated administrator (say, your client
administrator) specify the IP address. Even if different client administrators specify the same IP address, it will not result in a conflict.
Scenario
Two customers need the same network range. You can provide the same VSM IP address for both. The feature takes away the
need of IP address conversion.
20
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
Illustration
Workflow
Assign VLAN to Account
1. Create an Account in ElastiCenter.
2. Add VLAN Interface. For details, see VLAN interface.
3. Assign the VLANinterface to Account (created in step 1).
1. In the Account dashboard, select the Account.
2. In the Actions pane, select Manage Shared NICs.
3. From the list, select the VLAN interfaces that you want to assign to the Account.
4. Click Apply.
Provision VSM
1. Create VSM on the VLAN.
2. When you provision a VSM, in the networking details section of the Provision VSM Wizard, specify the VLAN interface you
created. The list contains VLANs both assigned and unassigned VLANs .
When provisioning a VSM on ElastiCenter, you can choose not to specify an IP address for the VSM.
21
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
When you have provisioned a VSM without assigning an IP address, the following page appears:
22
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
Assign IP address after creating a VSM
1. In the VSMs page, click Advanced Settings.
2. In the Primary IP Address tab, specify an IP address for the VSM.
3. Click Save.
Proceed to provisioning Storage Volumes.
Limitations
l
You cannot assign real IP spaces if you have configured VLAN on a LAGG.
VSM migration fails if the VSMs are assigned same IP address.
There might be a delay in the deletion of VSMs.
Backing up your interfaces
Back up NIC
For the NICthat you have chosen during the installation, you can set up a backup using ElastiCenter. The redundancy prevents interruption of management network access and connection among the Nodes or between Node and ElastiCenter.
Configuring redundant NIC
Prerequsite
The NIC and the backup NICshould be on the same network.
23
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
Procedures
1. In the Nodes page, click Network Interface Cards (Actions pane > Network Interface Cards)
2. Click Configure Backup Interface.
3. In the dialog, select a NIC as the backup from the drop-down list.
4. Click OK.
Back up LAGG
For the LAGG that you have added (Add LAGG ) you can set up a back up. The following sections explain the procedures. Backing up
your lagg assures that the VSMs are always accessible.
Assumptions
All the NICs in the primary LAGG and backup LAGG should be on the same network.
24
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
Procedures
1. In the HAGroups page, click Manage LAGG interface (Actions pane > Manage LAGG interfaces).
2. In the Actions pane, click Configure Backup Interface.
3. Specify the following details:
l
For LAGG interface 1, select the LAGG for which you want to configure back up.
In the LAGG interface 2 field, select the LAGG for back up.
4. Click OK.
What's new in ElastiStor 1.4.0 Patch 3
CloudByte ElastiStor 1.4.0 Patch 3 release includes the following new features:
l
"Hardware-based disk encryption/ Support for self-encrypting drives (SED)"
"Space reclamation"
Hardware-based disk encryption/ Support for self-encrypting drives (SED)
The current release of ElastiStor introduces a hardware-level disk encryption by supporting the self-encrypting drives.
25
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
This is a hardware-based data encryption technique
Encryption workload is moved to the drive instead of the processor. This improves system performance.
This is a full disk encryption, which means the entire disk data is encrypted (metadata included)
The data on the disk is encrypted at all times
The feature enables drive locking mechanism using the passphrase specified by the Administrator.
Restricts data access only to the authorized hosts with the specified passphrase.
Enabling Encryption
l
Hardware based encryption can be enabled only on SEDs.
SEDs can be used to create GELI (software) encrypted Pools as well.
You cannot create an encrypted Pool with a combination of SED and other data disks.
Using ElastiCenter
1. In the Add Pool page, select Enable Encryption.
2. Select Hardware as the Encryption type.
3. Specify a Passphrase.
4. Click Next.
Changing the passphrase
You can change the passphrase used to encrypt Pool by doing the following:
1. Go to the Encrypted Pool page.
2. In the Actions pane, select Change passkey.
3. In the Change Passkey dialog box, specify the new passkey and confirm.
26
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
Schedule passphrase change
1. Go to the Encrypted Pool page.
2. In the Actions pane, select Schedule change passkey.
3. In the following dialog box, specify the scheduling interval.
4. Click OK.
Note: CloudByte recommends you to perform a Refresh Hardware after deleting the encrypted Pool.
Space reclamation
On deletion of files on the Client filesystems (ext4/NTFS), you can reclaim space on the thin provisioned iSCSI LUNs. This is
achieved by supporting the SCSI UNMAP CDB.
Enabling the space reclamation feature using ElastiCenter
1. In the Storage Volumes page, click the iSCSI Volume for which you want to enable the space reclamation feature.
2. In the Actions pane, click Manage iSCSI configuration.
3. Click Edit.
4. Enable UNMAP by selecting Enable from the drop-down list.
5. Click Save.
Note: CloudByte recommends you to select the option Optimize drives in the disk defragmenter utility on Windows 2012 Clients, to reclaim dead space on the thin-provisioned Volumes.
What's new in ElastiStor 1.4.0 Patch 2
CloudByte ElastiStor 1.4 Patch 2 release includes the following new features:
27
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
"Geli Encryption"
"NFS home directory"
"QoS Alerts"
" GUI changes to distinguish your ElastiStor"
Geli Encryption
In the latest release, CloudByte ElastiStor has introduced a software-level disk encryption mechanism using the block device-layer
disk encryption system GELI.
The following graphic illustrates the encryption architecture:
This is a software encryption technique inherited from GELI
The encryption algorithm used is AES-XTS
This is a full disk encryption, which means the entire disk data is encrypted (metadata included)
The encryption key used is encrypted using the passphrase specified by the Administrator
Both the encryption key and passphrase are required to unlock the disks
Enabling Encryption on ElastiCenter
1. In the Add Pool page, select Enable Encryption.
2. Specify a Passphrase.
3. Click Next.
28
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
NFS home directory
The latest release of CloudByte ElastiStor lets you use a NFSshare like a home directory. The users on the common NFS share do
not have access to delete the other user files.
To use the NFS Share on ElastiStor like a home directory, perform the procedures in File system NFS options.
Note: Set Map as Root Users to No.
29
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
QoS Alerts
You are alerted when there is a variation in the quality of service (QoS) you have opted for.
Currently, only throttling alerts are available. The alerts are dependent on the following "Global Settings":
l
alert.qos.throttling.percentage: Sends an alert if the throttled IOPS percentage exceeds the specified value
(default is 20) and if alert.qos.throttle.count is encountered for the specified number of times.
alert.qos.throttle.count: Sends an alert if the number of consistent throttling exceeds the specified value (default is
10) and alert.qos.throttling.percentage exceeds the specified value.
GUI changes to distinguish your ElastiStor
ElastiCenter uses different color schemes for the Community Edition and Enterprise Edition. That difference is visible in log in
screen and the top portion of the page which houses the notification menu.
30
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
31
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
For details, see Community Edition and Enterprise Edition.
What's new in ElastiStor 1.4.0 Patch 1
CloudByte ElastiStor 1.4 Patch 1 release includes the following new features:
l
"Support for LDAP authentication"
"Global Settings to provision without specifying IOPS"
"VSM Webshell terminal on ElastiCenter"
"Option to check if the Disks are Write Cache Enabled"
Support for LDAP authentication
You can use an external LDAP server such as Microsoft Active Directory to authenticate ElastiCenter users.To do this, map the
ElastiCenter administrator types with the groups created in the directory service, for example Active Directory Server groups using
CloudByte ElastiStor global settings.
The following illustration explains how the authentication works:
32
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
Setting up LDAP authentication involves procedures on both ElastiCenter and the Active Directory Server.
On Active Directory Sever
Create Active Directory user
1. On your Active Directory Server, select Server Manager (Start > Administrative Tools).
2. In the Server Manager, click Tools.
3. In the right pane, click Active Directory Users and Groups.
4. In the Active Directory Users and Groups wizard, right-click your Domain name.
5. Select New and then select User.
33
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
6. In the User page, specify the relevant information of the user and then click Next.
7. In the following page, specify and confirm password for the user.
8. Click Finish.
Create Active Directory Group
Note: Create an individual group for each administrator type in ElastiCenter. For details, see http://www.docs.cloudbyte.com/delegated-administration/
1. On your Active Directory Server, select Server Manager (Start > Administrative Tools).
2. In the Server Manager, click Tools.
3. In the right pane, click Active Directory Users and Groups.
4. In the Active Directory Users and Groups wizard, right-click your Domain name.
5. Select New and then select Group.
6. Specify a name for the group to be created.
7. Click OK.
Adding Users to the Groups
Add users to the group that you want to map with the users in the various administrator type groups in ElastiCenter.
34
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
1. On your Active Directory Server, select Server Manager (Start > Administrative Tools).
2. In the Server Manager, click Tools.
3. In the right pane, click Active Directory Users and Groups.
4. In the Active Directory Users and Groups wizard, click your Domain name.
5. From the list of Groups and users, right-click the User you want to add to the Group.
6. Click Add to a Group.
7. In the dialog box, specify the name of the Group to which you want to add the user.
8. At the prompt, click OK.
On ElastiCenter
1. In the admin section of ElastiCenter, click LDAP Configuration.
35
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
2. In the Actions pane, click configure LDAP.
36
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
3. In the Configure LDAP page, specify the configuration details:
Option
Description
Host Name
The fully qualified domain name or the IP address of the LDAP Server. For example, my.ladap.com or 10.10.10.10
Port
The port on which the LDAP Server is listening. The default port is 389.
Bind DN
The distinguished name of the user on the LDAP Server. For example, test\Administrator.
Bind Password
Password for the name specified in the Bind DN field.
Search Base
Distinguished name of the Directory tree level, where the query should start the search. For
example, CN=Users,DC=CBQA,DC=com.
4. Click OK.
Set Group names for administrators on ElastiCenter
1. In the admin section of ElastiCenter, click Global Settings.
37
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
2. In the Global Settings page, search for LDAP.
3. To define the user roles, click Edit and then specify the Group name for the administrators.
4. Repeat step 3 for all types of administrators on ElastiCenter.
Log in to ElastiCenter using the LDAP user credentials
Once you have configured LDAP authentication for CloudByte ElastiStor, you must add users to the administrator roles in
ElastiStor. For details of administrator types, see http://www.docs.cloudbyte.com/delegated-administration/ .
1. Launch ElastiCenter using the URL in the following format: https://ElastiCenter_Management_IP_Address.
2. Specify the following login credentials of an AD user: username and password.
3. Re-log in to ElastiCenter as super administrator.
38
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
4. As a super administrator, map the administrator roles to the newly added users.
1. In ElastiCenter, select the Account to which the user belongs to.
2. In the Actions pane, select Manage Administrator.
3. Select Assign Administrator.
Note: If you want to map the administrator roles for Site-Admin or the View-Admin, follow the procedures in the section Create Site administrators or view administrators
Global Settings to provision without specifying IOPS
The new global settings option provisioning.uncontrolled.iops lets you enable/disable provisioning with uncontrolled
IOPS.
VSM Webshell terminal on ElastiCenter
An option for advanced troubleshooting, where you might have to access the VSM terminal, for example, to check if your iSCSI service is running. This option lets you monitor various processes and services, snapshot list, volume list, etc .
To access the terminal,
1. In ElastiCenter, click Virtual Storage Machines and then select the VSM.
2. In the Actions Pane , click Terminal.
Option to check if the Disks are Write Cache Enabled
The feature lets you see if the disks are write cache enabled.
39
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
When you Add Pool or Disk group to the Pool, the list of disks displayed shows Yes if disks are Write Cache Enabled.
What's new in CloudByte ElastiStor 1.4
CloudByte ElastiStor 1.4 release includes the following new/enhanced features:
s
l
"Faster and resilient HA"
"Improved QoS Control"
"8Gbps FC target support"
"Detecting faulty disks"
"Replacing faulty disks"
Faster and resilient HA
Significant improvement in HA takeover and giveback time while ensuring data continuity.
Improved QoS Control
Offers tighter control over QoS. Also, you can define throughput for a Storage Volume.
8Gbps FC target support
Now, you can configure 8Gbps FC targets (QLogic).
Detecting faulty disks
When a disk in a Pool goes bad, ElastiCenter displays the bad disk in Alerts as shown in the following screen:
40
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
The ElastiCenter displays bad disks as seen in the following screen:
You cannot create Pool on a bad disk.
You cannot label a bad disk.
Replacing faulty disks
You can now replace a faulty disk from the ElastiCenter.
41
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
Procedures
1. In the Pools page, select a Pool.
2. In the Actions pane, click Manage RAIDConfiguration.
3. In the Disk Groups page, select a Disk Group in which you want to replace a disk.
4. For the disk you want to replace, click the disk offline icon.
5. At the confirmation prompt click Yes. The red icon in the status indicates the disk is offline.
6. For the offline disk, click the replace icon.
42
CHAPTER II What's new in ElastiStor 1.4.0 Patch 5
7. Select a disk from the drop-down list and then click OK.
Note: A disk can also be replaced without bringing it to offline. But it is recommended to make the disk offline and then
replace it.
43
CHAPTER III Installing CloudByte ElastiStor
CHAPTER III Installing CloudByte ElastiStor
The following topics provide steps to install CloudByte ElastiStor:
n
"Planning your installation"
"System requirements"
"Network configuration details"
"Installation options"
"Installing ElastiCenter"
"Installing Node"
The following illustration is a quick-start representation of ElastiStor installation:
Planning your installation
CloudByte ElastiStor installation comprises the following:
n
Installing ElastiCenter: Install the administrative infrastructure used to manage the Nodes.
Installing Node: Node is the storage infrastructure that is managed by ElastiCenter. You can install only one Node per
machine. An HA Group can have up to four Nodes.
Installing on production environments
CloudByte recommends you to install ElastiCenter and Nodes on separately.
Installing on development environments
You can install both ElastiCenter and Nodes together on the same machine. This is the typical installation used for development and
test setups. Here you play around with test data for evaluation, rather than production where you have business critical data.
44
CHAPTER III Installing CloudByte ElastiStor
System requirements
The following topics explain the system requirements for installing CloudByte ElastiStor.
l
CloudByte Nnode is built on commodity servers.
The connectivity between Controller and Storage is either on Ethernet (iSCSI) or on SFF-8088 SAS cables.
ElastiStor OS is built using FreeBSD as the base platform and therefore CloudByte ElastiStor's Hardware Supported List is
similar to that of FreeBSD Release version.
Minimum hardware requirements to build CloudByte ElastiStor
n
Supported AMD64, Intel 64 (x86-64), or i386 Processor and System Board (with Dual Core Processor and 8GB of RAM)
Four 1 Gigabit Ethernet Controller Cards
One or more SAS HBAs, depending on the number of disk arrays connected
OS boot disk drive size of 20 GB. However, the recommended size is 2.4 * RAM size + 33GB
Minimum hardware requirements for CloudByte ElastiCenter
n
Supported AMD64, Intel 64 (x86-64), or i386 Processor and System Board (with Dual Core Processor and 8GB of RAM)
OS boot disk drive size of 20 GB. However, the recommended size is 2.4 * RAM size + 33GB
1 Gigabit Ethernet Controller Cards
For supported list of
n
AMD64 Processors, see FreeBSD 9.0 supported list of AMD64 processors
i386 Processors and System Boards of CloudByte ElastiStor, see FreeBSD 9.0 supported list of i386 Processors
Disk Controllers of CloudByte ElastiStor, see FreeBSD 9.0 supported list of Disk Controllers
Ethernet Interfaces of CloudByte ElastiStor, see FreeBSD 9.0 supported list of Ethernet Interfaces
Hardware Compatibility List
For the complete list of compatible hardware, see Hardware Compatibility List .
Network configuration details
You need the following network configuration details to proceed. All the options are mandatory.
Option
Description
Hostname
Name of the host, for example CloudByte.
Root Password
The password assigned to the root account.
IP address
The IPv4 addresses that you want to access.
Net Mask
The IPv4 subnet mask, for example 255.255.255.0.
Gateway
The IPv4 gateway IP address, for example 10.0.0.1.
DNS
The IPv4 address of the DNS server, for example 8.8.8.8.
Search
Domain search, for example lab.engineering.cloudbyte.com.
45
CHAPTER III Installing CloudByte ElastiStor
Installation options
The installation wizard provides the following installation options.
n
ElastiCenter: Installs only ElastiCenter, which is the central administrative console to manage your Node. Choose if you
prefer to install Node later. For procedures, see "Installing ElastiCenter"
Node: Installs only the Node, which is managed using ElastiCenter. Choose if you prefer to install ElastiCenter later. For procedures, see "Installing Node"
Both ElastiCenter and Node: Installs both ElastiCenter and Node. This installation is not recommended for production
deployments. For procedures, see "Installing ElastiCenter"
Installing ElastiCenter
Note: The steps to install ElastiCenter or ElastiCenter and Node together are similar. The only difference has been detailed
in step 4.
The following figure illustrates the ElastiCenter installation workflow:
1. Insert the CloudByte ElastiStor installation disk into your computer's DVD or CD drive and boot up your Node (ensure that
the disk drive is set as your system's primary boot device). The installation starts up and the following screen with the boot
46
CHAPTER III Installing CloudByte ElastiStor
options appear:
By default, the boot option Boot CloudByte ElastiStor is selected. So you need not interfere. To select a different boot option, see
"Boot options".
The Welcome screen appears:
47
CHAPTER III Installing CloudByte ElastiStor
2. In the following screen, accept the license agreement.
3. Select the Only ElastiCenter option. For details, see "Installation options".
4. (Applies only if you are installing Both ElastiCenter and Node) Select "Installing ElastiCenter HA".
48
CHAPTER III Installing CloudByte ElastiStor
5. (If you have multiple disks) At prompt, select the disk where you want to install CloudByte ElastiStor and then click OK.
6. (If you have multiple Ethernet Interfaces) At prompt, select the Ethernet Interface and then click OK.
49
CHAPTER III Installing CloudByte ElastiStor
The following screen appears:
7. Specify the "Network configuration details".
8. Click OK. The following screen appears:
9. Select Continue to confirm the settings so that the installation can start up. To modify any of the values, select Back. Installation starts and the wizard shows the progress.
50
CHAPTER III Installing CloudByte ElastiStor
10. In the following screen, specify the region you belong to:
11. Confirm the country and then confirm the time zone.
51
CHAPTER III Installing CloudByte ElastiStor
The installation completes and the following screen appears:
After installing the packages, CloudByte ElastiStor reboots (indicated by the following screen).
Wait till the system automatically reboots. The following screen welcomes you after the reboot:
52
CHAPTER III Installing CloudByte ElastiStor
The following screen with a login prompt indicates that installation is successful. You can proceed to configure CloudByte
ElastiStor.
53
CHAPTER III Installing CloudByte ElastiStor
Installing ElastiCenter HA
1. Follow the procedures in the section "Installing ElastiCenter" till step 3.
2. Select ElastiCenter HA.
3. Do either of the following:
1. Select primary ElastiCenter and then in the following screen, specify the ElastiCenter Management IP address.
54
CHAPTER III Installing CloudByte ElastiStor
2. Select Secondary ElastiCenter and then in the following screen, specify the primary ElastiCenter IP address.
4. Click OK.
5. Follow the procedures from step 4 in the section "Installing ElastiCenter" and complete the ElastiCenter installation process.
You can now
1. Launch ElastiCenter in Mozilla Firefox Web browser (by specifying the URL, provided in the "Network configuration details",
in the format https://ipaddress).
2. Log in.
3. Perform the configuration procedures. For details, see "Configuring CloudByte ElastiStor".
Boot options
Option
Description
Boot CloudByte
The default option. Select to start the installation with all standard options enabled.
Escape to loader prompt
Lets you perform advanced configuration in a CLI environment.
Reboot
Select to reboot.
Boot CloudByte with ACPI
Select to boot with advanced configuration and power interface. Helpful for power management.
Boot CloudByte with Safe Mode
Diagnostic mode with reduced functionality.
Boot CloudByte with Single User Mode
Lets only a single user to login. That is the root user.
Boot CloudByte with Verbose
To view behind the scene activities that occur during the installation. Particularly useful
for troubleshooting .
Installing Node
1. Insert the CloudByte ElastiStor installation disk into your computer's DVD or CD drive and boot up your Node Server (ensure
that the disk drive is set as your system's primary boot device). The installation starts up and the following screen with the
55
CHAPTER III Installing CloudByte ElastiStor
boot options appear:
By default, the boot option Boot CloudByte ElastiStor is selected. So you need not interfere. To select a different boot
option, see "Installing Node".
The Welcome screen appears.
2. In the following screen, accept the license information.
56
CHAPTER III Installing CloudByte ElastiStor
3. Select the installation option. For details, see "Installation options".
57
CHAPTER III Installing CloudByte ElastiStor
4. At prompt, Specify the ElastiCenter IP address and then click OK.
5. (If you have multiple disks) At prompt, select the disk where you want to install CloudByte ElastiStor.
58
CHAPTER III Installing CloudByte ElastiStor
6. (If you have multiple Ethernet Interfaces) At prompt, select the Ethernet Interface.
The following screen appears:
7. Specify the "Network configuration details".
8. Click Done. The following screen appears:
59
CHAPTER III Installing CloudByte ElastiStor
9. Select Continue to confirm the settings so that the installation can start up. To modify any of the values, select Back. Installation starts and the wizard shows the progress.
60
CHAPTER III Installing CloudByte ElastiStor
10. In the following screen, specify the region you belong to:
11. Confirm the country and then confirm the time zone.
61
CHAPTER III Installing CloudByte ElastiStor
The installation completes and the following screen appears:
After installing the packages, CloudByte ElastiStor reboots (indicated by the following screen).
62
CHAPTER III Installing CloudByte ElastiStor
Wait till the system automatically reboots. The following screen welcomes you after the reboot:
The following screen with a login prompt indicates that installation is successful. You can proceed to configure
CloudByte ElastiStor.
Note:When you deploy ElastiStor on production environments, ensure that all disks are SCSIreservationenabled.
To enable SCSI reservation:
1. Make an SSH connection to the Node.
2. Run the following command: rm /etc/disablescsi.
63
CHAPTER III Installing CloudByte ElastiStor
Upgrading to CloudByte ElastiStor 1.4.0 Patch 5
Versions from which you can upgrade
If you are using the following versions of ElastiStor, you can upgrade to ElastiStor 1.4.0 Patch 5.
l
1.4.0.272
1.4.0.340
1.4.0.528
1.4.0.6019
1.4.0.7004
Installation options
You have the following two installation options:
l
Upgrade: Upgrades from any of the versions mentioned in "Versions from which you can upgrade" to ElastiStor 1.4.0 Patch
5.
New Installation: Replaces the current version of ElastiStor with ElastiStor 1.4.0 Patch 5.
When you upgrade, ensure that you upgrade ElastiCenter first, and then proceed to upgrade the Node.
The workflow is as follows:
1. Back up ElastiCenter. For details see the section "Backing up configurations".
2. Upgrade ElastiCenter using the steps in the following section Upgrade procedures.
3. Log in to the Node as root and then run the following command to download the Volume configuration script: fetch
http://cloudbyte.com/downloads/updateVolSize.py
4. Run the following command: python updateVolSize.py
5. Move the Node to Maintenance Mode. For details see the section Bringing Node to maintenance mode in "Configuring High
Availability".
6. Upgrade the Node using the procedures in the following section Upgrade procedures.
7. Move the Node to Available mode. For details, see the section Making a Node available in "Configuring High Availability".
8. Refresh hardware for the upgraded Node.
9. Ensure that the Pools on the Node are online.
10. Repeat the procedures (from step 3 to step 7) for the other Node.
Upgrade procedures
1. Boot up your server and insert the CloudByte ElastiStor installation disk into your computer's DVD or CD drive. The installation starts up and the following screen with the boot options appear:
64
CHAPTER III Installing CloudByte ElastiStor
By default, the boot option Boot CloudByte ElastiStor is selected. Do not interfere.
The Welcome screen appears.
65
CHAPTER III Installing CloudByte ElastiStor
2. In the following screen, accept the license information.
3. Select Upgrade in the following screen:
The upgrade progresses as shown in the following screen:.
66
CHAPTER III Installing CloudByte ElastiStor
The upgrade completes and the following screen appears:
After installing the packages, CloudByte ElastiStor reboots (indicated by the following screen).
67
CHAPTER III Installing CloudByte ElastiStor
Wait till the system automatically reboots. The following screen welcomes you after the reboot:
68
CHAPTER III Installing CloudByte ElastiStor
The following screen with a login prompt indicates that upgrade is successful. You can proceed to configure
CloudByte ElastiStor.
69
CHAPTER III Installing CloudByte ElastiStor
You can now
1. Launch ElastiCenter in Mozilla Firefox Web browser (by specifying the URL, provided in the "Network configuration details",
in the format https://ipaddress).
2. Log in.
3. Perform the configuration procedures. For details, see "Configuring CloudByte ElastiStor".
release Moving your CloudByte ElastiStor setup to a new network environment
Assume that you have to move your existing ElastiStor setup to a different location or network. For example, you have created a
setup on staging environment and have performed all the tests. Now your setup is ready for production.
In this case, you can move your Storage setup to the production site using the procedures explained in this section.
70
CHAPTER III Installing CloudByte ElastiStor
Procedures
1. Move all Nodes to Maintenance mode. For details, see "Configuring High Availability"
2. On ElastiCenter server, change the network configurations of ElastiCenter. For details, see "release Moving your CloudByte
ElastiStor setup to a new network environment ""release Moving your CloudByte ElastiStor setup to a new network environment "
3. Change the network configurations of Node. For details, see "Change the network configuration details of Node"
71
CHAPTER III Installing CloudByte ElastiStor
4. In the ElastiCenter database, update the network configurations of Nodes. For details, see "release Moving your CloudByte
ElastiStor setup to a new network environment "
5. In ElastiCenter, change the IPaddress of the HAgroup. For details, see "Creating an HA Group ".
6. Restart the Nodes.
7. Bring all the Nodes back to Available mode. For details, see "Configuring High Availability"
8. (Optional) Change the network configuration setup for VSM. For details, see "Provisioning a VSM".
Change the network configurations of ElastiCenter
1. Log in to ElastiCenter as root.
2. In the /usr/local/cb/bin/, run the following command: python Change_network_config.py
3. Perform the steps as shown in the following sample command line :
Choose an option
1)Change the network configuration details of ElastiCenter
2)Update the network configuration details of Node
1
Here, you have to select 1 as highlighted
You are going to change some or all of the network configuration details that you specified at the
time of installation.
Specify the New IP address for ElastiCenter
20.10.83.57
To change the Netmask, specify the details in the dotted decimal format. To bypass this step, specify
No
255.0.0.0
To change the Gateway, specify the details. To bypass this step, specify No
20.10.83.1
To change the DNS, specify the details. To bypass this step, specify No
8.8.8.8
To change the Network Interface card, specify the details. To bypass this step, specify No
em0
To change the Domain name, specify the details. To bypass this step, specify No
cloudbyte.com
The new network details of ElastiCenter are as follows:
IP address: 20.10.60.50
Netmask : 255.0.0.0
Gateway: 20.10.1.1
DNS: 8.8.8.8
Network Interface Card: re0
Domain Name: cloudbyte.com
Review the details and confirm by specifying Yes. Specify No to exit and cancel the changes. To
change the details later, rerun the Change_network_config script.
Yes
Network details have been changed. Update the same in the associated Nodes.
Reboot ElastiCenter
4. Reboot ElastiCenter using the following command: reboot
Note: Unless you update the ElastiCenter's new IP address on the Nodes, ElastiCenter displays the Node status as offline
(though the Node is up and accessible).
Change the network configuration details of Node
1. Log in to Node as root.
2. In the /usr/local/cb/bin/, run the following command: python Change_network_config.py
72
CHAPTER III Installing CloudByte ElastiStor
3. Perform the steps as shown in the following sample command line :
You are going to change some or all of the network configuration details that you specified at the
time of installation.
To change the
20.10.83.57
To change the
No
255.0.0.0
To change the
20.10.83.1
To change the
8.8.8.8
To change the
em0
To change the
cloudbyte.com
To update the
IP address, specify the details. To bypass this step, specify No
Netmask, specify the details in the dotted decimal format. To bypass this step, specify
Gateway, specify the details. To bypass this step, specify No
DNS, specify the details. To bypass this step, specify No
Network Interface card, specify the details. To bypass this step, specify No
Domain name, specify the details. To bypass this step, specify No
Elasticenter IP address, specify the details. To bypass this step, enter No
Here, you have to specify the new IP address of ElastiCenter if changed,else specify No.
The new network details of ElastiCenter are as follows:
IP address: 20.10.83.57
Netmask : 255.0.0.0
Gateway: 20.10.83.1
DNS: 8.8.8.8
Network Interface Card: em0
Domain Name: cloudbyte.com
Review the details and confirm by specifying Yes. Specify No to exit and cancel the changes. To
change the details later, rerun the Change_network_config script.
Yes
Network details have been changed.
Reboot the Node
4. Reboot the Node using the following command: reboot
Update the network configurations of Node in the associated ElastiCenter
1. Log in to ElastiCenter as root.
2. In the /usr/local/cb/bin/, run the following command: python Change_network_config.py
3. Perform the steps as shown in the following sample command line :
Choose an option
1)Change the network configuration details of ElastiCenter
2)Update the network configuration details of Node
2
Here, you have to select 2 as highlighted
You are going to update ElastiCenter with the network configuration details of one of the following
Nodes:
+-------+--------------+
| Node | Old IP address|
+-------+--------------+
| Node1 | 20.10.83.60 |
+-------+--------------+
73
CHAPTER III Installing CloudByte ElastiStor
| Node2 | 20.10.83.6
|
+-------+--------------+
Specify the old IP address of the Node
20.10.83.60
Specify the New IP address of the Node
20.10.83.57
To change the Netmask, specify the details in the dotted decimal format. To bypass this step, specify
No
255.0.0.0
To change the Gateway, specify the details. To bypass this step, specify No
20.10.83.1
To change the DNS, specify the details. To bypass this step, specify No
8.8.8.8
To change the Network Interface card, specify the details. To bypass this step, specify No
em0
To change the Domain name, specify the details. To bypass this step, specify No
cloudbyte.com
The new network details of ElastiCenter are as follows:
Old IP address: 20.10.83.60
New IP address: 20.10.60.57
Netmask : 255.0.0.0
Gateway: 20.10.1.1
DNS: 8.8.8.8
Network Interface Card: re0
Domain Name: cloudbyte.com
Review the details and confirm by specifying Yes. Specify No to exit. To update the details later,
rerun the Change_network_config script.
Yes
Network details have been updated in ElastiCenter.
Reboot ElastiCenter
4. Reboot ElastiCenter using the following command: reboot
After completing the network configuration modifications, go back to the section "Procedures" and complete the procedures.
Tips
Ensure the following:
l
A physical connectivity between the Nodes and ElastiCenter exists using the command ping.
The IP address and Subnet are configured correctly using the command ifconfig -a .
The Gateway is configured correctly using the command netstat -rn.
74
CHAPTER IV CloudByte ElastiStor Appliance
CHAPTER IV CloudByte ElastiStor Appliance
This chapter applies to only the ElastiStor Appliance users.Skip this chapter if you are
l
Using only the CloudByte ElastiStor OS
Evaluating ElastiStor with the trial version downloaded from the CloudByte website
The following topics help you get started with CloudByte ElastiStor Appliance:
l
"Installing ElastiCenter and ElastiStor"
"Moving your CloudByte ElastiStor Appliance (ESA) to a new network environment "
Installing ElastiCenter and ElastiStor
The following figure illustrates the CloudByte ElastiStor installation workflow for ESA:
Prerequisites
l
The following details are required before you start the installation:
IP address for
Management
Primary ElastiCenter
Secondary ElastiCenter
Description
The IP address used for accessing the ElastiCenter.
Host IP address of the Node where primary ElastiCenter has to be installed.
Host IP address of the Node where secondary ElastiCenter has to be installed.
75
CHAPTER IV CloudByte ElastiStor Appliance
Note:ElastiCenter Management IP address and ElastiCenter Host IP address cannot be the same.
Installing primary ElastiCenter
1. Insert the CloudByte ElastiStor installation disk into your computer's DVD or CD drive and boot up your Node.
Note: Ensure that the disk drive is set as your system's primary boot device.
The installation starts up and the following screen with the boot options appears:
By default, the boot option Boot CloudByte ElastiStor is selected. So you need not interfere. To select a different boot option,
see "Installing ElastiCenter and ElastiStor".
The Welcome screen appears:
76
CHAPTER IV CloudByte ElastiStor Appliance
2. In the following screen, accept the license agreement.
77
CHAPTER IV CloudByte ElastiStor Appliance
3. Select the option Both ElastiCenter and Node.
The following screen appears:
78
CHAPTER IV CloudByte ElastiStor Appliance
4. Select ElastiCenter HA. The following screen appears:
5. Select primary ElastiCenter and then in the following screen, specify the ElastiCenter Management IP address (IP address
used to access the ElastiCenter).
6. Click OK.
79
CHAPTER IV CloudByte ElastiStor Appliance
7. (If you have multiple disks) At prompt, select the disk where you want to install CloudByte ElastiStor and then click OK.
8. (If you have multiple Ethernet Interfaces) At prompt, select the Ethernet Interface and then click OK.
80
CHAPTER IV CloudByte ElastiStor Appliance
The following screen appears:
9. Specify the "Network configuration details".
10. Click OK. The following screen appears:
11. Select Continue to confirm the settings so that the installation can start up. To modify any of the values, select Back. Installation starts and the wizard shows the progress.
81
CHAPTER IV CloudByte ElastiStor Appliance
12.
1. In the following screen, specify the region you belong to:
13. Confirm the country and then confirm the time zone.
82
CHAPTER IV CloudByte ElastiStor Appliance
14. The installation completes and the following screen appears:
Installing secondary ElastiCenter
1. Perform the steps 1 to 4 in the section "Installing primary ElastiCenter".
2. In the following screen, select secondary ElastiCenter.
3. Specify the primary ElastiCenter's Host IP address.
83
CHAPTER IV CloudByte ElastiStor Appliance
4. Perform the steps 6 to 14 in the section "Installing primary ElastiCenter" to complete the secondary ElastiCenter installation
procedures.
Note:After the installation, ensure that the primary ElastiCenter is active prior to working with the Secondary ElastiCenter. If
secondary ElastiCenter is active before the primary ElastiCenter, you will have to reboot secondary ElastiCenter.
Moving your CloudByte ElastiStor Appliance (ESA) to a new network environment
When you get started with ElastiStor Appliance, the initial step is to configure the network settings. You have to modify some or all
of the default network configuration settings depending on your environment.
All CloudByte ElastiStor Appliance models have the following default network configurations. Go through the following default network settings so that you can change the required values.
For example, if your scenario might require only changing the IPaddresses. In that case, you have to replace only the values
10.11.12.3 (Management IP address), 10.11.12.1 (Primary Node), and 10.11.12.2 (Secondary Node). You can leave all other values
intact.
Network detail
Description
Default
Management IP address
The IP address used for accessing the ElastiCenter.
10.11.12.3
Primary Node IP address
Host IP address of the Node where primary ElastiCenter is installed.
10.11.12.1
Host IP address of the Node where secondary ElastiCenter is
installed.
10.11.12.2
Netmask
The standard IPv4 subnet mask.
255.0.0.0
Gateway
The IPv4 gateway IP address.
10.11.12.254
The standard IPv4 address of the DNS Server.
8.8.8.8
Secondary Node IP address
DNS
84
CHAPTER IV CloudByte ElastiStor Appliance
Domain name
Health check IP range
IPMI address of primary Node
IPMI address of secondary
Node
Domain search, for example lab.engineering.cloudbyte.com.
cloudbyte.com
Health check IP range of the HA Group.
10.11.12.1110.11.12.12
You can remotely log in to primary Node.
10.11.12.101
You can remotely log in to secondary Node.
10.11.12.102
Default log in credentials:
Component
User name
Password
ElastiCenter
admin
password
IPMI
ADMIN
ADMIN
SSH
root
test
Procedures
1. Bring the Nodes in the appliance (ESA-A50 and ESA-A100) to maintenance mode. For details, see "Configuring High Availability"
2. (On the secondary Node) In the /usr/local/cb/bin/, run the following command: python Change_network_config.py
3. Perform the steps as shown in the following sample command line :
You have logged into the secondary Node and the associated ElastiCenter.
You are going to change some or all of the network configuration details that you specified at the
time of installation.
Specify the new IP address for the secondary Node
20.10.60.50
To change the Netmask, specify the details in the dotted decimal format. To bypass this step, specify
No. No
To change the Gateway, specify the details. To bypass this step, specify No. No
To change the DNS, specify the details. To bypass this step, specify No. No
To change the Network Interface card, specify the details. To bypass this step, specify No. No
To change the Domain name, specify the details. To bypass this step, specify No. No
Specify the management IP address used to access ElastiCenter
20.10.39.71
Specify the primary Node IP address
20.10.60.40
The new network details of the secondary Node are as follows:
IP address: 20.10.60.50
Netmask : 255.0.0.0
Gateway: 20.10.1.1
DNS: 8.8.8.8
Network Interface Card: re0
Domain Name: cloudbyte.com
Management IP address: 20.10.39.71
Primary node IP address:20.10.60.40
Review the details and confirm by specifying Yes. Specify No to exit and cancel the changes. To
change the details later, rerun the Change_network_config script.
85
CHAPTER IV CloudByte ElastiStor Appliance
Network configuration details changed successfully.
Reboot the Node.
4. Reboot the secondary Node using the following command:reboot.
5. (On the primary Node) In the /usr/local/cb/bin/, run the following command: python Change_network_config.py
6. Perform the steps as shown in the following command line :
You have logged into the primary Node and the associated ElastiCenter.
You are going to change some or all of the network configuration details that you specified at the
time of installation.
Specify the new IP address for the secondary Node
20.10.60.50
To change the Netmask, specify the details in the dotted decimal format. To bypass this step, specify
No. No
To change the Gateway, specify the details. To bypass this step, specify No. No
To change the DNS, specify the details. To bypass this step, specify No. No
To change the Network Interface card, specify the details. To bypass this step, specify No. No
To change the Domain name, specify the details. To bypass this step, specify No. No
Specify the management IP address used to access ElastiCenter
20.10.39.71
The new network details of the primary Node are as follows:
IP address: 20.10.60.50
Netmask : 255.0.0.0
Gateway: 20.10.1.1
DNS: 8.8.8.8
Network Interface Card: re0
Domain Name: cloudbyte.com
Management IP address: 20.10.39.71
Review the details and confirm by specifying Yes. Specify No to exit and cancel the changes. To
change the details later, rerun the Change_network_config script.
Specify the following network configuration details of the secondary Node:
IP address: 20.10.60.50
Netmask: 255.0.0.0
Gateway : 20.10.1.1
DNS: 8.8.8.8
Network Interface Card: re0Domain name: cloudbyte.com
The network details of the secondary Node are as follows:
IP address: 20.10.60.50
Netmask: 255.0.0.0Gateway: 20.10.1.1DNS: 8.8.8.8
Network Interface Card: re0
Domain Name: cloudbyte.com
IP address used to access the Management Console: 20.10.39.71
Review the details and confirm by specifying Yes.Specify No to exit and cancel the changes.
To change the details later, rerun the Change_network_config script.
Network configuration details changed successfully.
Reboot the Node.
7. Reboot the primary Node using the following command:reboot.
86
CHAPTER IV CloudByte ElastiStor Appliance
8. After the system is rebooted,launch ElastiCenter using the following steps:
1. Launch a Web browser and specify URL in the following format:
https://New IP Address to access the management console
2. Specify the following default credentials:
Credentials
Value
User name
admin
Password
password
9. In ElastiCenter, change the IPaddress of the HAgroup. For details, see "Creating an HA Group "
10. Bring the secondary Node to Available mode. for details, see "Configuring High Availability"
11. Bring the primary Node to Available mode. for details, see "Configuring High Availability"
12. In the ElastiCenter admin pane, select ElastiCenter HA.
87
CHAPTER IV CloudByte ElastiStor Appliance
Ensure that both the Nodes are in sync with each other as shown in the following screen:
Upgrading to CloudByte ElastiStor 1.4.0 Patch 5
Versions from which you can upgrade
If you are using the following versions of ElastiStor, you can upgrade to ElastiStor 1.4.0 Patch 5.
l
1.4.0.272
1.4.0.340
1.4.0.528
1.4.0.6019
1.4.0.7004
Installation options
You have the following two installation options:
88
CHAPTER IV CloudByte ElastiStor Appliance
Upgrade: Upgrades from any of the versions mentioned in "Versions from which you can upgrade" to ElastiStor 1.4.0 Patch
5.
New Installation: Replaces the current version of ElastiStor with ElastiStor 1.4.0 Patch 5.
Prerequisites
l
Either have IPMI access or physical access to ESA.
Both the Nodes in ESA are in sync with each other (see step 12 in the following section Workflow).
Back up ElastiCenter and Node configurations. For details, see Back up configurations.
Assumptions
The document assumes the following:
l
Node 1 is the primary Node and hosts Pool 1.
Node 2 is the secondary Node and hosts Pool 2.
Workflow
1
Node 1(Primary)
Node 2(Secondary)
a. Bring the Node to Maintenance mode
b. Power off the Node.
2
3
Becomes Primary, all configurations from Node 1 are
taken over.
a. Ensure that the configurations are taken over
b. Insert the product CD and boot as DVD.
Perform the procedures in "Upgrade procedures" . On successful upgrade, the Node comes online as secondary Node .
Move the Node to Available Mode.
a. Bring the Node to Maintenance mode
b. Power off the Node.
Becomes Primary, all configurations from Node 2 are taken
over
a. Ensure that the configurations are taken over
b. Insert the product CD and boot as DVD.
Perform the procedures in "Upgrade procedures" .
On successful upgrade, the Node comes online as secondary Node
10
Move the Node to Available Mode.
11
In the ElastiCenter admin pane, select ElastiCenter HA.
12
Ensure that both the Nodes are in sync with each other as shown in the following screen (screen 1).
13
Confirm that the version number (provided in the release notes) matches the one provided in the following screen
(screen 2).
89
CHAPTER IV CloudByte ElastiStor Appliance
Screen 1:
Screen 2:
Upgrade procedures
1. Boot up your server and insert the CloudByte ElastiStor installation disk into your computer's DVD or CD drive. The installation starts up and the following screen with the boot options appear:
90
CHAPTER IV CloudByte ElastiStor Appliance
By default, the boot option Boot CloudByte ElastiStor is selected. Do not interfere.
The Welcome screen appears.
91
CHAPTER IV CloudByte ElastiStor Appliance
2. In the following screen, accept the license information.
3. Select Upgrade in the following screen:
The upgrade progresses as shown in the following screen:.
92
CHAPTER IV CloudByte ElastiStor Appliance
The upgrade completes and the following screen appears:
After installing the packages, CloudByte ElastiStor reboots (indicated by the following screen).
93
CHAPTER IV CloudByte ElastiStor Appliance
Wait till the system automatically reboots. The following screen welcomes you after the reboot:
94
CHAPTER IV CloudByte ElastiStor Appliance
The following screen with a login prompt indicates that upgrade is successful. You can proceed to configure
CloudByte ElastiStor.
95
CHAPTER IV CloudByte ElastiStor Appliance
You can now
1. Launch ElastiCenter in Mozilla Firefox Web browser (by specifying the URL, provided in the "Network configuration details",
in the format https://ipaddress).
2. Log in.
3. Perform the configuration procedures. For details, see "Configuring CloudByte ElastiStor".
96
CHAPTER V ElastiCenter, ElastiStor's management console
CHAPTER V
ElastiCenter, ElastiStor's management con-
sole
Introduction
ElastiCenter is the centralized management tool that you use to configure, monitor, manage, and deploy the services provided by
CloudByte ElastiStor.
ElastiCenter lets you
n
Use the Graphical User Interface to manage the storage environment
Generate statistical and configuration reports to help troubleshoot
Delegate administration tasks
Track events
Globally control various settings
Using ElastiCenter, the entire ElastiStor deployment, consisting of multiple geographical sites spanning clusters and servers, can
be managed from a single browser session. Storage management tasks such as High Availability and disaster recovery can be done
from the same session.
To illustrate, let us examine the processing of a file recovery request for a particular storage tenant using a legacy solution and
CloudByte ElastiStor:
Legacy solution
The administrator has to
1. Manually recover the file from the DR storage system
CloudByte ElastiStor
In CloudByte ElastiStor, using ElastiCenter, the administrators can perform
actions remotely from the management portal. The administrator can, from
the same browser session,
1. Log in to the primary site.
2. Manually transfer to the primary site
2. Identify the storage file system that needs to be recovered.
3. Merge with the primary site.
3. Browse for the corresponding backup copies on the remote DR site.
4. Recover data with a single click.
The following illustration shows the workflow to setup a storage environment using CloudByte ElastiCenter:
97
CHAPTER V ElastiCenter, ElastiStor's management console
ElastiCenter User Interface
The following topics orient you with the ElastiCenter User Interface.
Navigation pane
The navigation pane in the left-hand side of ElastiCenter provides a list of options.
When you select an option, you are taken to a specific component page. Use the component pages to perform various configuration
and management tasks.
98
CHAPTER V ElastiCenter, ElastiStor's management console
Note:The options displayed in the navigation pane depend on the administrative privileges you have. If you are a super
administrator, you have all the options. For further details, see "Managing CloudByte ElastiStor".
Content pane
The content pane displays the component pages that provide options and data to configure CloudByte ElastiStor. For example, if
you select Sites in the navigation pane, the Sites page appears.
99
CHAPTER V ElastiCenter, ElastiStor's management console
Summary pane
Summary pane sums up the number of storage components, such as Sites or Pools, in the storage infrastructure.
Actions pane
Action pane, in the right-hand side of the content pane, provides a list of configuration options. For example, in the HA Groups page,
go the Actions pane and add Node.
100
CHAPTER V ElastiCenter, ElastiStor's management console
Notification menu
The information menu in the top right-hand side of ElastiCenter lets you access Alerts, Events, Reports, and Administrator data.
You also have the option to go back to the Home page.
See Also:"Monitoring" and "CloudByte ElastiStor reporting"
Admin options
The Admin options help you with various administrative tasks.
101
CHAPTER V ElastiCenter, ElastiStor's management console
See Also:CloudByte ElastiStor API Reference, "Licensing", and "Delegated administration"
Launching CloudByte ElastiCenter
CloudByte ElastiCenter is a browser based console which you can launch using one of the popular browsers such as Mozilla Firefox
or Google Chrome.
Note:Ensure that you have updated Adobe Flash Player to the most recent version.
To access ElastiCenter,
1. Launch Mozilla Firefox Web browser.
2. Specify the URL in the following format: https://IP Address
Note:The IP Address you specify is the one that you configured in the installation screen. See "Installing ElastiCenter" for
details.
Authentication
You need credentials (username and password) to log in to CloudByte ElastiCenter.
1. After installation is completed, launch ElastiCenter using the URL in the following format: https://IP Address.
102
CHAPTER V ElastiCenter, ElastiStor's management console
2. Specify the following default credentials :
Credentials
Value
Username
admin
Password
password
After you log in, you can change the password.
Reset password and configure auto-alert options
After you log in, you are prompted to:
l
Change your password
Update your profile. CloudByte Technical Support might use this information to contact you when your storage infrastructure
encounters any issues.
Review the auto-alert details that CloudByte Technical Support collects automatically. Technical Support might use the
information to resolve potential problems that your storage infrastructure encounters. You have the option not to share particular information.
To reset password and configure auto-alert options,
103
CHAPTER V ElastiCenter, ElastiStor's management console
1. Login to ElastiCenter using the default credentials (admin|password). The following screen appears:
2. Specify a new password and then confirm.
3. Update your profile.
4. Review the auto-alert information, and uncheck the options that you do not want to share.
5. Click Update.
Replacing default SSL Certificate
The connection between ElastiCenter and browser is secured using SSL. If required, you can replace the default certificate using
the following procedures.
Note:The utility used to perform the following tasks is keytool. You can use a utility of your preference.
104
CHAPTER V ElastiCenter, ElastiStor's management console
1. In the ElastiCenter console, run the command as shown in the following example: keytool -genkey -alias
primarycb -keyalg RSA -keystore mysprimary.keystore -keysize 2048. At prompt, provide password
and the domain details.
2. In the ElastiCenter console, generate Certificate Signing Request (CSR) by executing the command as shown in the following example:keytool -certreq -keyalg RSA -alias primarycb -file mycertreq.csr -keystore
myprimary.keystore. You are then prompted to specify a password for keystore.
3. Get the CSR signed by the trusted CA. (for example, VeriSign or Thawte).
4. (Optional) Append the certificate with intermediate CA and trusted root CA.
5. Import the CA's certificate into your keystore as a trusted certificate using the following command:
keytool -importcert -file verisign.cer -keystore myprimary.keystore -alias primarycb
6. Copy the keystore to the directory /usr/local/apache-tomcat-6.0.33/conf.
7. Edit the following lines in the file server.xml in the directory /usr/local/apache-tomcat-6.0.33/conf/
keystoreFile="conf/myprimary.keystore"
keystorePass="cloudbyte"
8. Run the following command to shut down Tomcat:/usr/local/apache-tomcat-6.0.33/bin/shutdown.sh
9. Kill Java processes using the following command: pkill java
10. Execute the following command to ensure that no Java process is running:pgrep java
11. Start Tomcat using the command /usr/local/apache-tomcat-6.0.33/bin/startup.sh
Customizing the CloudByte ElastiCenter theme
This section will help you customize CloudByte ElastiCenter with minimal modifications in CSS files.
Edit the theme.css file to make customizations
1. The company logo above the navigation pane (left pane) can be changed by replacing the image in the folder images/cloudbyte. Name your image as company-logo. To avoid distortion in the image, ensure that the image does not exceed the following dimensions: 215 px width, 67 px length.
2. The company logo on the left corner of the notification menu can be changed by replacing the image in the folder
images/cloudbyte. Name your image as edit-logo. Ensure that your image is in PNG format. To avoid distortion in the
image, also ensure that the image does not exceed the following dimensions: 166 px width, 24 px length.
3. To change the header border in ElastiCenter, edit the highlighted line in the following section:
#dashboard-header_wrap{
background: #E7E8E7;
position:relative;
z-index:3;
border-top:4px, solid #ed1652;
}
4. To change icons on the notification menu, replace the following images (referred to in the screenshot) in theimages folder.
Ensure that all your images are in PNG format.
Image to be replaced
Name the image as
home
alert
105
CHAPTER V ElastiCenter, ElastiStor's management console
events
reports
5. To change the active tab top border, edit the highlighted line in the following section:
.nav ul li:hover,.active-nav{
background:#fff;
border-top:4px solid #bcdf5a!important;
}
6. To change the widget top border, edit the highlighted line in the following section:
.tcl-graph{
margin:0 12px 15px 3px;
border-top:4px solid #BCDF5A;
}
106
CHAPTER V ElastiCenter, ElastiStor's management console
Modify the index.jsp file to include theme.css file
For the CSS changes to take effect, include the theme.css file in index.jsp file located in the following path: /usr/local/apache-tomcat-6.0.33/webapps/client/.
Add the highlighted section as shown in the following sample snippet:
<head>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8" />
<title>CloudByte ElastiCenter 1.3</title>
<link type="text/css" rel="stylesheet" href="css/theme.css" />
<link type="text/css" rel="stylesheet" href="css/<filename>.css" />
<script src="lib/jquery.js" type="text/javascript">
</script>
<script src="lib/jquery-ui/js/jquery-ui.js" type="text/javascript">
</script>
</head>
107
CHAPTER VI Configuring CloudByte ElastiStor
CHAPTER VI Configuring CloudByte ElastiStor
CloudByte ElastiStor is configured and managed using the administrator console named CloudByte ElastiCenter. The following topics explain the configuration and management tasks that you can perform.
n
"Setting up your storage"
"Creating a Site "
"Creating an HA Group "
"Adding a Node"
"Configuring Disk Array enclosure"
"Creating a Pool"
"Creating an Account"
"Setting up data access protocols"
"Provisioning a VSM"
"Configuring VSM migration"
"Provisioning storage"
"Choosing a Pool to provision VSM"
"Modifying QoS after provisioning VSM"
"Configuring High Availability"
"Configuring local backup"
"Configuring remote disaster recovery"
"Assuring Quality of Service"
Setting up your storage
In CloudByte ElastiStor, the set of configurations that you perform can be divided in to tasks related to
n
Infrastructure, the base structure of your storage service
Accounts, that you create for storage specific needs
The following illustration shows how your infrastructure and account are organized in CloudByte ElastiStor:
108
CHAPTER VI Configuring CloudByte ElastiStor
The following sections explain the concepts in detail:
Site
Building your storage infrastructure starts with the creation of a Site, the fundamental infrastructure unit where your Node and storage and network infrastructure reside.
The following figure depicts the structure of a Site:
The following figure explains each component of the Site:
109
CHAPTER VI Configuring CloudByte ElastiStor
Accounts
After you set up the storage infrastructure, build the account infrastructure. That is, you set up the client/customer for using your storage infrastructure.
The following figure explains how an account is constituted in CloudByte ElastiStor:
110
CHAPTER VI Configuring CloudByte ElastiStor
The following figure explains each component associated with an account:
111
CHAPTER VI Configuring CloudByte ElastiStor
Creating a Site
Use the Sites page (ElastiCenter > Sites) to create a Site.
The Sites page provides a graphical representation of the Sites that you have created. It provides the Site details such as HA
Groups, Pools, Provisioned Storage, and VSMs that you have set up.
Click any of the Site details link for specific review and configuration. For example, click HA Groups to access details of the HA
Groups associated with the Site.
To create a Site
1. In the Sites page, click Add Site in the actions pane.
The Add Site page appears.
2. Specify the following details:
Field
Description
Name
Unique name for the site.
Location
Where the site is located.
Description
A meaningful description for the Site.
3. Click Add.
Creating an HA Group
Use the HA Groups page (ElastiCenter > HA Groups) to create an HA Group.
All Nodes in the HA group you create must be on the same
112
CHAPTER VI Configuring CloudByte ElastiStor
Public network: used for management of Nodes.
Private network: used with VSMs for data transfer.
Creation of HA Groups leads to the formation of High availability Clusters. For details, see "Configuring High Availability"
1. In the HA Groups page, click Add HA Group.
The Add HA Group page appears.
2. Specify the following options and then click Add.
Field
Site
Name
Description
IP Address Range
Description
The Site to which you add the HA Group.
Unique name for the HA Group.
Meaningful description for the HA Group.
Provide a range of dedicated IP addresses in the management network. For instance, ensure
that you do not specify the IP address used for Node, ElastiCenter, VSM, or client. Provide the
first and last IP address in the range, for example 1.1.1.100 and 1.1.1.104. The IP addresses
you specify are used to check the heartbeat between nodes.
Changing CARP IP address range
1. Bring Node1 to maintenance mode.
2. Bring Node2 to maintenance mode.
3. In the HA Groups page, select the HA Group for which you want to change the CARP IP range.
4. Click Settings in the actions pane.
113
CHAPTER VI Configuring CloudByte ElastiStor
5. In the following page, click edit and then change the details.
6. Click Save.
Adding a Node
1. In the ElastiCenter navigation pane, click Nodes.
2. In the actions pane, Click Add Node.
3. In the Add Node page, specify the following details:
Field
Site
Description
Select a Site.
114
CHAPTER VI Configuring CloudByte ElastiStor
HA Group
Name
IP Address
Select the HA Group to which the Node has to be added.
Unique name for the Node.
IP address of the Node.
4. Click Add Node.
Deleting a Node from an HAGroup
Follow the procedures to delete a Node from a single Node HA Group:
1. Delete all the Storage Volumes on the Node.
2. Delete all the VSMs on the Node.
3. Delete all the Pools on the Node.
4. Bring down the Node to maintenance mode.
5. Click the delete icon to remove the Node from HA Group.
Follow the procedures to delete a Node from an HA Group with more than one Node:
1. Bring down the Node to maintenance mode.
2. Click the delete icon to remove the node from HA Group.
Configuring Disk Array enclosure
After you add Node, you are redirected to the Node page.
When there is no Disk Array attached to the Node, the following page appears. Ensure that you attach a Disk Array to the Node and
then click Refresh Hardware.
Note: When you attach a new Disk Array to a Node, click Refresh Storage/Refresh Hardware to make the Disk Array visible
on the ElastiCenter.
115
CHAPTER VI Configuring CloudByte ElastiStor
To configure a newly attached Disk Array enclosure, follow the procedures:
1. In the Node page, click the image in the section Shared Storage.
The following screen appears:
116
CHAPTER VI Configuring CloudByte ElastiStor
2. Click Configure A New Disk Array. The Disk Array Configuration page appears:
3. Specify the Name, Bay Alignment, Number of columns and Number of Rows. For details, see the "Configuration details".
4. Click Next and then do the following:
117
Click the option under the column Blink. For details, see "SCSI Enclosure Service".
Specify the bay location for the disks from the drop down list under the column Bay.
CHAPTER VI Configuring CloudByte ElastiStor
5. Click Apply. On successful configuration, the Node page appears with a representation of the shared storage:
Note:You can also partially configure a Disk Array Enclosure. Suppose you have 12 disks, you can initially configure around
8 disks and other 4 disks can be configured as per the requirement.
Configuration details
Horizontal and vertical alignments
The Disk Arrays can be idealized either in terms of horizontal or vertical alignments.
The following figure represents a vertical alignment:
118
CHAPTER VI Configuring CloudByte ElastiStor
The following figure represents a horizontal alignment:
Slots per row
Slots per row is the number of disks each row can accommodate. For example, three slots per row implies that a single row can
accommodate three disks.
SCSI Enclosure Service
SCSI Enclosure Service (SES) helps monitor the status of each device in a disk array enclosure such as disk slots, fans, heat
sinks, or power supplies.
The service helps you
119
CHAPTER VI Configuring CloudByte ElastiStor
Identify a disk or verify the slot in which the disk is located.
Locate and disable a faulty disk.
With specific and general alerts on enclosure components.
Blink identification
Blink identification LED on the disk slot of a disk array. When you click Blink, at the physical location of the disks, the identification
LED in the specified disk slot blinks. If the disk is not in the SCSI enclosure, the LED blink does not occur.
If the disk is in the SCSI enclosure and still if the blink does not occur, verify the health of the disk.
Enclosure component alerts
CloudByte ElastiStor provides common and specific alerts for the enclosure components such as disk slots, power supplies,
voltage sensors, current sensors, temperature sensors, fans, and audible alarm.
The common alerts which apply to all components include the ones related to
l
Removal and installation of the component
State in which the component is, such as critical, non-critical, OK, or unrecoverable
Specific alerts are generated for the following enclosure components: power supply, voltage sensor, current sensor, and temperature sensor.
By default, CloudByte sends alerts over mail to the email you specified when you updated your profile the first time you logged in to
CloudByte ElastiCenter. To expand the mailing list, add the IDs separated by comma in the Global settings (Information Pane >
Admin > Global Settings > alert.email.addresses).
To view alerts in CloudByte ElastiCenter, click Alerts in the information pane.
Deleting a Disk Array
1. Delete all Pools in the Disk Array.
2. In the HA Groups page, select the HA group from which Disk Array has to be deleted.
3. For the Disk Array to be deleted, click Manage Disk Array and then click the delete icon.
Creating a Pool
1. Go to the Node page (ElastiCenter > Nodes).
2. From the list of Nodes, select the one for which you create the storage Pool.
3. In the actions pane, go to the section Tasks and then click Add Pool.
120
CHAPTER VI Configuring CloudByte ElastiStor
The Add Pool page appears.
4. Select the Site, HAGroup, and CBNode to which the Pool belongs.
5. Specify a name for the Pool and then click Next.
6. In the following screen, specify the RAID storage type and then choose one or more of the available disks.
7. (Optional) Enable Sector Size.
Note: For optimal performance, ensure that the disks in the same Pool belong to the same disk array.
121
CHAPTER VI Configuring CloudByte ElastiStor
8. Click Next. The QoS settings page appears.
9. Specify the following details:
Field
Description
122
CHAPTER VI Configuring CloudByte ElastiStor
Total IOPS
The maximum per second I/O limit for a Pool.
Average
Latency
The desired average latency in milliseconds per I/O. Latency is the round-trip time per I/O request-response as measured
by the client.
10. Click Add Pool.
Note:The number of disks required to create a Pool depends on the RAID type and protection/performance you look for. For
example, for a high performance application, you can create RAID 10 Pool. Similarly, for a high capacity application, you can
set up RAID z1 with 8 disks.
Configuring Spare
1. Go to the Pools page (Navigation pane > Pools).
2. In the Actions pane, click Manage RAIDConfiguration. The Disk Group page appears.
3. In the Actions pane, select Add Spare.
4. In the Add Spare page, select a disk from the drop-down list.
5. Click Add.
Migrating a Pool
You cannot migrate a pool. Only a VSM can be migrated.
Pool encryption
GELI encryption
This is a software-level disk encryption mechanism using the block device-layer disk encryption system GELI.
The following graphic illustrates the encryption architecture:
123
CHAPTER VI Configuring CloudByte ElastiStor
This is a software encryption technique inherited from GELI
The encryption algorithm used is AES-XTS
This is a full disk encryption, which means the entire disk data is encrypted (metadata included)
The encryption key used is encrypted using the passphrase specified by the Administrator
Both the encryption key and passphrase are required to unlock the disks
Enabling GELI encryption on ElastiCenter
1. In the Add Pool page, select Enable Encryption.
2. Specify a Passphrase.
3. Click Next.
Hardware-based disk encryption/ Support for self-encrypting drives (SED)
This is a hardware-level disk encryption mechanism using the self-encrypting drives.
l
This is a hardware-based data encryption technique
Encryption workload is moved to the drive instead of the processor. This improves system performance.
This is a full disk encryption, which means the entire disk data is encrypted (metadata included)
The data on the disk is encrypted at all times
The feature enables drive locking mechanism using the passphrase specified by the Administrator.
Restricts data access only to the authorized hosts with the specified passphrase.
SED-based encryption conditions
l
Hardware based encryption can be enabled only on SEDs.
SEDs can be used to create GELI (software) encrypted Pools as well.
124
CHAPTER VI Configuring CloudByte ElastiStor
You cannot create an encrypted Pool with a combination of SED and other data disks.
Enabling SED-based encryption on Elasticenter
1. In the Add Pool page, select Enable Encryption.
2. Select Hardware as the Encryption type.
3. Specify a Passphrase.
4. Click Next.
Changing the passphrase
You can change the passphrase used to encrypt Pool by doing the following:
1. Go to the Encrypted Pool page.
2. In the Actions pane, select Change passkey.
3. In the Change Passkey dialog box, specify the new passkey and confirm.
Schedule passphrase change
1. Go to the Encrypted Pool page.
2. In the Actions pane, select Schedule change passkey.
3. In the following dialog box, specify the scheduling interval.
4. Click OK.
Note: CloudByte recommends you to perform a Refresh Hardware after deleting the encrypted Pool.
Creating an Account
Use the Account page (ElastiCenter > Accounts) to create an Account.
125
CHAPTER VI Configuring CloudByte ElastiStor
1. Click Add Account. The Add Account page appears.
2. Specify the following details:
Field
Description
Name
Unique name for the account.
Description
Meaningful description of the account.
Assign Admin
Select the type of administrator that you want to create. When you select an administrator
type, the username and password fields appear. For details, see "Delegated administration" .
3. Click Add Account. The Account is created. The wizard prompts you to continue and provision VSM.
4. Click Provision VSM to continue.
Delete account user
1. In ElastiCenter, select Accounts in the navigation pane.
2. From the list of Accounts, select the Account from which you want to delete a user.
3. Go to the Tasks section of the actions pane and then select Account Users.
4. Click the delete icon for the account user that you want to delete.
5. At prompt, click Yes.
Provisioning a VSM
Use either the Create Account wizard or Virtual Storage Machines page (ElastiCenter > Virtual Storage Machines) to provision
VSM.
1. Click Provision VSM.
126
CHAPTER VI Configuring CloudByte ElastiStor
The Provision VSM page appears.
2. Specify the following details:
Field
Description
Account
The Account for which you create the VSM.
Name
A unique name for the VSM.
Capacity
The amount of disk space to be allotted for the VSM.
127
CHAPTER VI Configuring CloudByte ElastiStor
Total IOPS
The maximum per second I/O limit for the VSM.
Total
Throughput
When you specify the Total IOPS, CloudByte calculates the Total Throughput and is automatically added. You cannot edit
this field.
3. Click Next and then specify the provisioning details by selecting a Pool from the list.
4. Click Next.
5. Select the network interface details. For details, see "VLAN interface".
6. Specify the tenant IP address and default gateway.
128
CHAPTER VI Configuring CloudByte ElastiStor
7. Click Provision.
Multipathing
Multipathing is the ability to configure a server with multiple paths to the storage for take over on network failure. CloudByte
ElastiStor supports multipathing for iSCSI. When network failure occurs, redundant network takes over and ensures that the iSCSI
LUN is available.
Note: SATA disks or any disk with SATA interface is not supported for HA and multipathing configuration.
The details of the supported Maximum Multiple Connections (MCS) per LUN are as follows:
n
8 connections per LUN
16 sessions per LUN
To enable multipathing,
1. In ElastiCenter, select Virtual Storage Machine.
2. In the VSM page, select the VSM for which you want to enable multipathing.
3. In the action pane, select Advanced Settings.
4. Click Edit.
129
CHAPTER VI Configuring CloudByte ElastiStor
5. Specify the required details.
130
CHAPTER VI Configuring CloudByte ElastiStor
Field
Description
Secondary IP address
Provide secondary IP address to enable multipathing.
Secondary Interface
Select an interface from the list.
6. If partial failover of Pool is enabled (which is enabled by default), click yes at the prompt to disable it.
Configuring VSM migration
The objective of VSM migration is to optimize QoS. VSM migration helps to control the QoS parameters within a Pool and to move
data.
You can migrate a VSM
l
From a Pool to another within the same Node or to a different Node.
Across Sites.
Note: When you migrate a VSM across Nodes, ensure that the Node to which the migrating VSMbelongs to is not down.
1. In the VSM page, select a VSM from the list.
2. In the Actions pane, go to Migrate and then click Schedule.
3. In the following page, specify the required details:
131
CHAPTER VI Configuring CloudByte ElastiStor
Field
Description
Site
Select a Site to migrate the VSM.
IOPS
The IOPS of the primary VSM is populated by default. You can modify
the value to provision IOPS required for migration.
Throughput
The throughput of the primary VSM is populated by default. You cannot
modify this value as it is depends on the values of IOPS and Block SIze.
4. Click Next.
5. Select the Pool to migrate VSM and then click Next.
132
CHAPTER VI Configuring CloudByte ElastiStor
6. Select the Backup interface, IP Address, and schedule of migration (in the format minutes/hours/days/month/year).
7. Click Add to create migrant VSM.
133
CHAPTER VI Configuring CloudByte ElastiStor
Migrant VSM activation
Activation consideration
l
The Migrant VSM can be activated only after the base snapshot is successfully transferred from the primary VSM. You can
check the status of data transfer by clicking View Transfer Status (Actions > Tasks).
The backup interface and IP address range of the native and the migrant VSMs must be same.
Note: After activation, this backup IP address will not be active and therefore need to be removed at the Pool level.
1. In the migrant VSM page, click Settings in the Actions pane.
2. In the Settings page, click Edit and then select an interface from the drop-down list.
3. Click Save.
134
CHAPTER VI Configuring CloudByte ElastiStor
4. Click the VSM, the Migrant VSM, and then click Activate.
5. At prompt, click Yes.
After the VSM migration is active, the re-mount prompt appears. Ensure that you re-mount the Storage Volumes before you proceed.
VLAN interface
VLAN interface can be created on a NIC whenever there is a need for the interface to subscribe to a separate broadcast domain (usually needed for high traffic data networks).
Additionally, multiple VLAN interfaces can be created on a single physical NIC, thereby allowing access to multiple networks at the
same time. The VLANs act as virtual individual NICs, each belonging to a separate broadcast domain.
135
CHAPTER VI Configuring CloudByte ElastiStor
Adding VLAN interface
1. In the HA Groups page (ElastiCenter > HA Groups), go to the actions pane and then click Tasks > Manage VLANInterfaces.
2. In the VLANInterfaces page, go to the actions pane and then click Tasks > Add VLANInterface.
3. In the Add VLANInterface dialog box, specify the VLANtag (which must be a numeric value) and then select the parent NIC.
4. Click OK.
Defining the VLAN Interface for the VSM
When you provision a VSM, in the networking details section of the Provision VSMWizard, specify the VLANinterface you created
(in the Interface field).
136
CHAPTER VI Configuring CloudByte ElastiStor
LAGG interface
LAGG interface allows aggregation of multiple network interfaces into a single virtual LAGG interface, providing fault-tolerance and
high-speed multi-link throughput. The aggregation protocols supported by LAGG determines which ports are used for outgoing traffic
and whether a specific port accepts incoming traffic.
Adding LAGG interface
1. In the HA Groups page (ElastiCenter > HA Groups), go to the actions pane and then click Tasks > Manage LAGG Interfaces.
2. In the LAGGInterfaces page, go to the actions pane and then click Tasks > Add LAGG Interface.
3. In the Add LAGGInterface dialog box, specify the following details:
137
LAGG ID:Unique id (numeric value) for the LAGGinterface.
Protocol Type:
l
Failover: Select Failover to send traffic only through the active port. If the master port becomes unavailable,
the next active port is used. The first interface added is the master port. Any interfaces added after that are
used as failover devices. By default, received traffic is only accepted when received through the active port.
Load Balance: Balances outgoing traffic across the active ports based on hashed protocol header information and accepts incoming traffic from any active port. This is a static setup and does not negotiate aggregation with the peer or exchange frames to monitor the link
LACP:LACP negotiates a set of aggregable links with the peer in to one or more Link Aggregated Groups.
Each LAGG is composed of ports of the same speed, set to full-duplex operation. The traffic will be balanced
across the ports in the LAGG with the greatest total speed, in most cases there will only be one LAGG which
contains all ports.
CHAPTER VI Configuring CloudByte ElastiStor
4. Click Next.
5. From the list of available NICs, drag and drop the ones you want to assign to a LAGG.
6. Click Add.
Provisioning storage
l
Before you provision a Storage Volume, you must create a VSM.
The maximum supported size of the Storage Volume depends on the available capacity of VSM.
There is no limit to the number of Storage Volumes that you can create. But the composite capacity of the created Storage
Volumes must be less than or equal to the capacity of the VSM they belong to. For example, if the total capacity of the VSM
is 1 TB, then you can create a Storage Volume with the capacity of 1 TB or multiple storage volumes where the total capacity
of all volumes is less than or equal to 1 TB.
You can enable both compression and deduplication on the same Storage Volume.
File system storage (NFS and CIFS) works together on the same Storage Volume, but block level storage (iSCSI) does not.
You can back up Storage Volume by creating snapshots and then rolling back when required. For details, see "Configuring
local backup".
Note:By default, ElastiStor Storage Volume is thin provisioned. You can expand the Storage Volume up to the size of the
Pool, provided the Pool has available storage.
Use the Storage Volumes page (ElastiCenter > Storage Volumes) to provision storage.
138
CHAPTER VI Configuring CloudByte ElastiStor
1. Click Provision Storage.
2. The Add Storage Volume page appears.
3. Specify the following details:
Field
Description
Account
Account for which you provision the storage.
Name
Unique name for the storage.
Capacity
Amount of disk space to be allocated.
139
CHAPTER VI Configuring CloudByte ElastiStor
Provision Mode Shared or Dedicated. For details, see the section Difference between Shared and Dedicated in "QoSFAQs" .
Block Size
Block size of the volume.
Average
Latency
Desired average latency in milliseconds per I/O. Latency is the round trip time per I/O request-response.
Control IOPS
Select the required IOPS using the slider. Qos can be enforced either throughonly IOPS or only Throughput.
Control
Throughput
Select the required throughput using the slider. Qos can be enforced either throughonly IOPS or only Throughput.
4. Click Next and then select the VSM on which you want to provision the Storage Volume.
140
CHAPTER VI Configuring CloudByte ElastiStor
5. Click Next. The screen to specify the advanced settings appears.
6. Specify the following details:
Field
Description
Volume Hierarchy
The VSM on which the Storage Volume is mounted.
Record Size
The block size to which data has to be divided.
Synchronization
Leave the default settings as it is.
Deduplication
If ON, new data is deduplicated.
Compression
If ON, new data is compressed.
Mount Point
(Applies only for NFS and CIFS) Specify the Storage Volume mount point for the client to use the storage.
Enable NFS
Select to access the Storage Volume using NFS protocol.
Enable CIFS
Select to access the Storage Volume using CIFS protocol.
Enable iSCSI
Select to access the Storage Volume using iSCSI protocol.
7. Click Provision.
Note:Disconnect all associated clients before you delete an iSCSI Storage Volume.
141
CHAPTER VI Configuring CloudByte ElastiStor
Choosing a Pool to provision VSM
CloudByte ElastiStor follows a QOS-centric approach to provisioning. When you provision a VSM, your choice of the Pool depends
on the availability of Pools that satisfy the required throughput and IOPS.
Selecting the Pool
1. In the ElastiCenter navigation pane, click Virtual Storage Machine.
2. Click Provision VSM.
3. After you specify the VSM details such as Name and the QoS details, click Next.
4. In the following screen, select the Pool after evaluating the IOPS.
5. Click Next to specify the Network details.
Choosing a VSM to provision Storage Volume
When you provision storage, your choice depends on the availability of VSMs that satisfy the required throughput and IOPS.
To provision storage,
1. In ElastiCenter, click Storage Volumes in the navigation pane.
2. Click Provision Storage.
3. In the following screen, specify the basic storage details and then click Next.
142
CHAPTER VI Configuring CloudByte ElastiStor
4. Select a VSM that satisfies the QoS requirements. The graphical representation helps you with the IOPS data.
5. Click Next and then proceed to complete the provisioning.
Auto-Provisioning
ElastiStor can automate Node selection and resource allocation if you provide the required SLA/QoS parameters. Sensing the level
of storage performance and capacity the application requires, ElastiStor automatically allots the right Pool.
Auto-provisioning is particularly helpful when you have innumerable Pools/VSMs. CloudByte ElastiStor chooses the appropriate
Pool/VSM for provisioning automatically.
How to auto-provision
1. In ElastiCenter, select Global Settings.
2. Click the Edit icon for provisioning.sb.auto and provisioning.tsm.auto.
3. In the Value column, specify yes (instead of the default nowhich implies provisioning is manual) as shown in the following
screen:
143
CHAPTER VI Configuring CloudByte ElastiStor
Example
Assume that auto-provisioning is enabled and there are three Pools (pool1with 500 IOPS, pool2with 400 IOPS, and pool3with
300 IOPS respectively). If the administrator wants to create a VSM with 100 IOPS, pool1(the Pool with the highest IOPS value) is
automatically selected for VSM creation.
SASmultipathing
CloudByte ElastiStor supports SASmultipathing. Having multiple physical paths to the disk array enclosure assures effective path
failover by providing redundant paths for data access.
l
By default, SAS multipathing is enabled.
SAS multipathing is an active/passive setup
At any point in time, there is only one active path for I/O
If a failure occurs, instead of the active path, the one that was redundant (so far) takes over avoiding any interruption to data
access
144
CHAPTER VI Configuring CloudByte ElastiStor
Prerequisites
l
Two LSI SAS616X switches
LSI SAS2008 HBA (at the Node side)
l
Firmware: 07.15.08.00
Driver: 15.00.00.00
SAS cables
Disk array enclosure with multiple IN ports (for example Dell MD1220)
Controllers (for example Dell R720)
In the Node page, clear all existing pools to avoid Pool name conflicts. To do this, first configure the Disk Array in the Node
page. Then select the Node and then at the bottom of the page, click Clear for the Pools to be deleted.
Sample setup
The following figure shows a simple SASmultipath setup:
145
CHAPTER VI Configuring CloudByte ElastiStor
Verifying the setup in ElastiCenter
When you have the multipath set up, the paths are visible in the related Node page.
1. In CloudByte ElastiCenter, click Nodes.
2. In the Nodes page, select the Node and then click the Disk Array in Shared Storage. The Disk Table provides the details as
highlighted in the following figure:
In the case of a failure, as shown in the following instance the path disappears from the table:
146
CHAPTER VI Configuring CloudByte ElastiStor
The figure implies that there is only a single SAS path available.
Modifying QoS after provisioning VSM
Assume that you have provisioned storage for a VSM and now you want to change the QoS settings. For example, your pool has an
IOPS limit of 100. You have provisioned VSM with 50 IOPS. You can modify the values.
Note: In the example, you can increase the value up to 100 (which means, the entire IOPS is consumed).
To modify the QoS settings,
1. In ElastiCenter, select Virtual Storage Machines.
2. Select the VSM for which you want to modify the QoS settings.
3. In the QoS settings section of the actions pane, click Basic Settings. The highlighted section displays the QoS-related settings.
147
CHAPTER VI Configuring CloudByte ElastiStor
4. Click the Edit icon and then modify the editable fields.
5. Click Apply.
Modifying QoS after provisioning Storage Volume
1. In ElastiCenter, select Storage Volumes.
2. Select the Storage Volume for which you want to modify the QoS settings.
3. In the Storage Volume page, click Settings.
148
CHAPTER VI Configuring CloudByte ElastiStor
4. Click the edit icon and then modify the QoS details.
5. Click Save.
Modifying storage capacity
1. In ElastiCenter, select Storage Volumes.
2. Select the Storage Volume for which you want to modify the storage capacity.
149
CHAPTER VI Configuring CloudByte ElastiStor
3. In the following page, click Settings.
4. In the following page, click Edit and then modify the quota.
5. Click Save.
Note:The quota of the Storage Volume cannot exceed the VSM size.
Configuring High Availability
CloudByte ElastiStor supports High Availability in two-way, three-way, and four-way configurations.
Note: SATA disks or any disk with SATA interface is not supported for HA and multipathing configuration.
Before you proceed
Ensure the following on all Nodes in the HA Group:
l
Same NIC (for example, if em0 is the interface used on one Node, the same should apply for all Nodes) and same capacity
Disks are shared (across the Nodes)
Same system hardware configuration
Identical SAS HBA (identical firmware and driver)
Identical FCHBA (identical firmware and driver)
Procedures
The following procedures explain how to configure a two-way High Availability setup:
1. Set up your hardware. For details see "Hardware setup diagram for High Availability"
2. Create a Site. For details, see "Creating a Site ".
3. Create an HA Group. For details, see "Creating an HA Group ".
When you specify the IP address range while adding the HAGroup, ensure that you specify a range that matches the number
of nodes you add.
4. Add a Node (Node1). For details, see "Adding a Node".
5. Label shared disks. For details, see "Configuring Disk Array enclosure"
Note: You can perform this step later, after you add all other Nodes. In that case, you have to refresh the hardware
(Nodes > select specific Node > select Refresh Hardware in the Tasks section of the action pane) for labeling to take
effect.
6. Add Node 2. For details, see "Adding a Node".
Now you have established a two-way HA. The following screen provides a visual representation of the configuration.
150
CHAPTER VI Configuring CloudByte ElastiStor
Proceed to create Pools, VSMs, and Storage Volumes.
151
CHAPTER VI Configuring CloudByte ElastiStor
Hardware setup diagram for High Availability
Bringing Node to maintenance mode
When you want to service your Node, change its status to maintenance mode. In this mode, the Node is up and controlled by the
administrator, but is not an active part of the High Availability Group.
To bring a Node to maintenance mode,
152
CHAPTER VI Configuring CloudByte ElastiStor
1. Select the Node that you want to bring to maintenance mode (ElastiCenter > Nodes).
2. In the Node Page, go to the actions pane and then click Move to maintenance icon.
The Change State of Node dialog box appears.
3. Select Maintenance as the state.
4. Optionally specify a reason for changing the state and then click OK.
Take Over
When Node failure occurs, takeover happens as illustrated in the following screens:
n
153
The following screen depicts the Node Page that lists a two-way HA. Here, Node2 is in maintenance mode.
CHAPTER VI Configuring CloudByte ElastiStor
In the following screen, Node1 has taken over.
Note: In ElastiStor, every Node has a designated partner. If the Node goes down, the resources of that Node are failed over
to the partner Node.
Making a Node available
After a downtime, when you bring up the Node, you have to manually change the status to Available.
1. Select the Node that you want to bring up (ElastiCenter > Node).
2. In the Node page, go to the actions pane and then click Move to available icon.
154
CHAPTER VI Configuring CloudByte ElastiStor
3. Select Available as the state.
4. Optionally specify a reason for changing the state and then click OK.
HA Jobs
To view the details of the past High Availability events, perform the following procedures;
1. (In ElastiCenter)In the HA Groups page, select an HA Group for which you want to view event details.
2. In the Actions pane, click View Jobs.
You can view the details of the past HA events and the time taken to perform these events as shown in the following screen:
155
CHAPTER VI Configuring CloudByte ElastiStor
Configuring local backup
Backup refers to copying and archiving of data. In the event of data loss, you can use the backup to restore the original data.
You can create a
n
Snapshot, which is a read-only virtual copy of your Storage Volume and VSM.
Clone, which is a real copy of your Storage Volume
In CloudByte ElastiStor, backup operates as follows:
n
The first backup is a full backup.
The first backup is followed by incremental backups based on snapshot technology.
ElastiStor supports continuous production during snapshot recovery of a Storage Volume.
Backing up VSM
1. In ElastiCenter, select Virtual Storage Machines in the navigation pane.
2. From the list, select the VSM to create local backup.
3. In the following page, go to the Local Backup section of the Actions pane and then select either of the following options:
n
Schedule: Schedule your backup by choosing a frequency.
Snapshot: Manually create a snapshot on demand.
Add snapshot
1. In the Local Backup section, click Create Snapshot.
2. In the Create Snapshot dialog box, specify a unique name.
3. Click OK.
156
CHAPTER VI Configuring CloudByte ElastiStor
Add schedule
1. In the Local Backup section, click Add Snapshot Schedule. The Add Snapshot Schedule page appears.
2. Specify the following details and then click Add.
Field
Description
Name
A unique name for the backup schedule.
Retention Copies
Schedule
Specify the number of backup copies that you want to create.
Select the frequency.
Backup best practice
As a best practice, CloudByte recommends a multiple backup schedule.
For example, you can configure a multiple backup schedule comprising
Frequency
Retentioncopies
Every 15 minutes
Every hour
24
Every day
30
Manage snapshots and schedules
To view the snapshots and schedules that you have created, click Manage Snapshots/Manage Snapshot Schedules in the local
backup section. You have options to rollback and disable the schedules/snapshots.
Backing up Storage Volume
1. In ElastiCenter, select Storage Volume in the Navigation pane.
2. From the list, select the Storage Volume to create snapshot.
3. In the following page, go to the Local Backup section of the actions pane and then click Create Snapshot.
157
CHAPTER VI Configuring CloudByte ElastiStor
4. In the Create Snapshot dialog box, specify a unique name for the snapshot and then click OK.
Restoring Snapshots
1. In ElastiCenter, select Storage Volumes in the Navigation pane.
2. From the list, select the Storage Volume to restore data.
3. In the following page, go to the Local Backup section of the actions pane and then click Manage Snapshots.
4. From the list of snapshots, select the one that you want to restore, click the restore icon, and then confirm at prompt.
158
CHAPTER VI Configuring CloudByte ElastiStor
Add schedule
1. In the Local Backup section, click Add Snapshot Schedule. The Add Snapshot Schedule page appears.
2. Specify the following details and then click Add.
Field
Description
Name
A unique name for the backup schedule.
Retention Copies
Schedule
Specify the number of backup copies that you want to create.
Select the frequency.
Manage snapshots and schedules
To view the snapshots and schedules that you have created, click Manage Snapshots/Manage Snapshot Schedules in the local
backup section. You have options to rollback and disable the schedules/snapshots.
Cloning the Storage Volume
You can create a READ/WRITE copy of your Storage Volume using the clone option. Unlike Snapshot which is a read-only virtual
copy, clone is a real copy of your Storage Volume. It consumes the same disk space as the parent Storage Volume.
ElastiStor uses snapshot as the point of reference for your clone. The workflow is as follows:
1. Create a Storage Volume.
2. Create a snapshot.
3. Create a Clone of the Storage Volume using Snapshot as the point of reference.
Creating a clone
1. In ElastiCenter, select Storage Volume in the navigation pane.
2. From the list, select the Storage Volume to create a clone.
3. In the following page, go to the actions pane and then select Local Backup > Create Snapshot.
4. In the Create Snapshot dialog box, specify a name and then click OK.
159
CHAPTER VI Configuring CloudByte ElastiStor
5. Click Manage Snapshot (actions pane > Local Backup).
6. From the list of snapshots, go to the one which you want to use as reference for creating the snapshot and then click the
Clone icon (highlighted in the circle).
7. Specify a unique clone name, where to mount the clone, and then click OK.
Configuring remote disaster recovery
The disaster recovery mechanism in CloudByte ElastiStor helps you effectively retrieve data in disaster situations.
Currently, ElastiStor supports disaster recovery for a single Site. You can rebuild a primary Site using the disaster recovery copy.
ElastiStor provides disaster recovery across Sites over WANs.
Setting up remote disaster recovery
1. In the ElastiCenter navigation pane, click Virtual Storage Machines.
2. From the list of VSMs, select the one for which remote disaster recovery has to be configured.
3. In the actions pane, click Create DR VSM in Remote Backup.
Note: You have this option only if you have not created a DRVSM. If a DRVSM is created, you can modify the settings.
160
CHAPTER VI Configuring CloudByte ElastiStor
4. In the Add DRVSM page,
1. Select the Site on which you want to configure the DR VSM.
2. Specify a name for the DR VSM.
3. Click Next.
5. In the following page, select a Pool and then click Next.
6. Select the Backup interface, IP Address, and specify a schedule for the DR VSM (in the format minutes/hours/days/month/year).
7. Click Add.
A message appears to confirm that the DR VSM has been added.
Managing remote disaster recovery
For a specific VSM, use the Remote Backup section in the actions pane to configure remote disaster recovery.
1. In the ElastiCenter navigation pane, click Virtual Storage Machines.
2. From the list, select the VSM to manage remote disaster recovery.
3. In the actions pane, use the options in the section Remote Backup.
161
CHAPTER VI Configuring CloudByte ElastiStor
Disaster recovery options
n
Name: Provides details of DRVSM and displays the transfer details.
Disable Transfer: Select and confirm to disable disaster recovery.
Edit Schedule: Edit the disaster recovery schedule.
Delete DR VSM: Remove a disaster recovery setup that you have configured.
Recovering data
Note: The DR VSM can be activated only after the base snapshot is successfully transferred from the primary VSM. You
can check the status of data transfer by clicking View Transfer Status (Actions > Tasks).
1. In the ElastiCenter navigation pane, click Virtual Storage Machines.
2. From the list of VSMs, select the DR VSM that is associated with the Primary VSM where the disaster occurred.
3. In the DR VSM page, go to actions pane and then click Tasks > Activate.
162
CHAPTER VI Configuring CloudByte ElastiStor
4. In the following page, specify the network settings of the DR VSM and then click OK.
5. At confirmation prompt, click Yes.
After you activate the DR VSM, the re-mount prompt appears. Ensure that you re-mount the Storage Volumes before you proceed.
For details, see "Connecting to ElastiStor".
Upgrading a High Availability DR setup
Follow the procedures to seamlessly upgrade a High Availability disaster recovery environment. Node 1 and Node 2 imply the nodes
on primary cluster. Similarly, DR Node 1 and DR Node 2 imply the nodes on the secondary cluster:
1. Upgrade ElastiCenter. For details, see "Upgrading to CloudByte ElastiStor 1.4.0 Patch 5"
2. Move the Node 1 to maintenance mode. For details, see "Configuring High Availability".
3. Upgrade Node 1. For details, see "Upgrading to CloudByte ElastiStor 1.4.0 Patch 5"
4. Bring the Node 1 to Available mode. For details, see "Configuring High Availability".
5. Move the Node 2 to Maintenance mode.
6. Upgrade Node 2.
7. Bring the Node 2 to Available mode.
8. Move the DR Node 1 to Maintenance mode.
9. Upgrade DR Node 1.
10. Bring the DR Node 1 to Available mode.
11. Move the DR Node 2 to Maintenance mode.
163
CHAPTER VI Configuring CloudByte ElastiStor
12. Upgrade DR Node 2.
13. Bring the DR Node 2 to Available mode.
Confirm if the DR Transfer occurs after the upgrade as scheduled. In the case of any exceptions, contact CloudByte Technical Support.
Assuring Quality of Service
Introduction
Assuring quality of service makes your storage performance predictable. CloudByte ElastiStor is unique in its QoS offering as it lets
you
n
Easily commission storage with guaranteed IOPS at various levels. You can decide to configure QoS at a Pool level, VSM
level, or Storage Volume level.
Configure multidimensional QoS involving IOPS, throughput, latency, and capacity.
Utilize untapped system resources. For example, assume that you have three VSMs but only one is active. In this case, the
active VSM can use the entire systems capability.
On-demand modification of settings without system restarts.
Choosing your QoS
The following points help you choose an appropriate QoS:
Endpoint: Decide at what level you want to implement QoS.
Select a capable pool: Based on VSMs requirements, you provision it on a capable Pool that can meet the requirements.
Define the pool level QoS, based on Pool configuration and the controller level. QoS is determined based on the Pool capacity,
which is the underlying storage capability.
QoS provisioning: Understand your VSMs QoS requirements across the data access and data protection needs. Based on the
requirement of the VSM, you can either choose QoS automatically or manually. Ensure that you are aware of the Pool settings and
how effectively you want to use it at the VSM level.
Sub-divide QoS: Within a VSM, based on varying needs, further sub-divide QoS across Storage Volume, based on the guarantee
that the administrator wants to set. For example, when a VSM is used to store logs in the database, since logs need higher IOPS
and lower throughput and latency, set it accordingly. Whereas a database requires low IOPS, high throughput, and high latency.
Configuration
Use ElastiCenter to configure QoS settings. The configuration can be at the following levels:
n
Pool: For details, see "Creating a Pool".
Account: For details, see "Creating an Account".
VSM: For details, see "Provisioning a VSM".
164
CHAPTER VI Configuring CloudByte ElastiStor
Configuring Grace
What is Grace
Grace is the provisioning of unused IOPS/throughput of Pools to Storage Volumes based on the performance requirements. You can
configure Grace at Pool level and Storage Volume level.
For example, assume that you have a Pool with the capacity of 100 IOPS and Grace enabled. Two VSMs named VSM A and VSM
B, with a capacity of 30 IOPS and 60 IOPS respectively are created under the Pool.
Under VSM A (with 30 IOPS capacity), Storage Volumes named E and F are created, and assigned 10 IOPS and 15 IOPS
respectively.
Under VSM B (with 60 IOPS capacity), Storage Volume G is created and assigned 35 IOPS.
The grace available in this scenario is 40 IOPS.
Configuring Grace at the Pool level
Grace is enabled by default at the Pool level. You can edit Grace after creating the Pool.
To edit,
1. Go to the Pool page and then in the actions pane, click Settings.
2. Click Edit and then choose to enable/disable Grace.
165
CHAPTER VI Configuring CloudByte ElastiStor
Configuring Grace at the Storage Volume level
To enable Grace at the Storage Volume level, ensure that Grace is enabled at the respective Pool level.
To edit,
1. Go to the Storage Volume page and then in the actions pane, click Settings.
2. Click Edit and then choose to enable/disable Grace.
166
CHAPTER VI Configuring CloudByte ElastiStor
3. Click Save.
Monitoring QoS
In the Storage Volume page, select the Volume for which you want to monitor QoS. The page that appears displays the monitoring
data.
QoStips
Storage capacity
Discs, storage connectivity, and type
Capability: Ensure that you are well aware of the capabilities of your storage subsystem. For example, the right interconnection
between the controller and storage, the type of disks on the disk array, and the ability to expand the capacity.
Limitations: Ensure that you have assessed the limitations. For example, increasing storage capacity does not make any sense
if the network does not support.
167
CHAPTER VI Configuring CloudByte ElastiStor
Controller characteristics
RAM, CPU, and network:
CPU: If the storage is more I/O bound than CPU bound, it is more effective. CPU load should not be more than 60-70 percent, or
you add more cores.
RAM: RAM determines the ability to cache. Larger RAM means more filesystem caches. In a READ-centric scenario, larger RAM
helps generate better QOS. That is, more I/O and throughput but lesser latency.
Network: Network capacity decides data access and data protection. Assure adequate network bandwidth to export performance
to clients. Network should do justice to the storage system.
Segregation: Segregate data access and data protection so that protection workloads do not interfere with data access workloads.
Pool creation
Storage group tips
As a best practice, create storage with 8 to 10 disks.
When you add storage groups, keep them identical. For example, do not add disparate groups to the same Pool. For example, if one
group has SATA disks and another group has SAS disks, then do not assign both to the same Pool. That is, do not create hybrid
Pools.
Multiple Pools within a Controller
Tips to avoid contention points: Be judicious when you add multiple Pools to a controller. For example, it does not make
sense if network bandwidth is already utilized to the maximum with the existing Pools, or CPUs are already busy serving the existing Pools. QoS also suffers because of over provisioning.
When to combine multiple pools: When no conflict pertaining to bandwidth, CPU, or Memory exist, you can combine Pools.
Optimizing QoS
Disk characteristics: Better the disk characteristics, better the QOS. For example, the IOPS, throughput, and latency of SATA
disks are not as good as that of SS disks.
Disk layout: Better the disk layout, better the QoS. For example, keep the disk layout to 8 to 10 disks.
Improving WRITE performance: If the application requires synchronous WRITES, associate high performing disk to the
Pool to speed up the WRITEs. This guarantees better QOS.
Improving READ performance: To improve the READ performance or increase the filesystem cache hit rate, add high performing disks as cache devices to the Pool.
168
CHAPTER VII Setting up data access protocols
CHAPTER VII Setting up data access protocols
CloudByte ElastiStor provides LUN access using the following protocols:
l
Fiber Channel
iSCSI
CIFS
NFS
When you create a Storage Volume, you are provided with an option to select the access protocols that you want to enable.
Deleting a Storage Volume disables the protocol access services automatically.
The following sections help you configure data access protocols supported by CloudByte ElastiStor:
n
"Data access using iSCSI"
"Data access using CIFS"
"Data access using FC "
"Data access using NFS"
Data access using iSCSI
iSCSI is Internet SCSI (Small Computer System Interface), an Internet Protocol (IP)-based storage networking standard for linking
data storage connections. By offering SCSI commands over IP networks, iSCSI is used to transmit data over intranets. For further
details, see http://en.wikipedia.org/wiki/ISCSI.
iSCSI concepts
Authentication Group: A grouping of multiple iSCSI users.
Use this option if you use CHAP or mutual CHAP. You can configure Authentication group at both VSM and Storage Volume levels.
CHAP: An authentication method which uses a user/secret or IQNs for outgoing authentication. The Storage Volumes on
CloudByte ElastiStor authenticate the initiator.
Mutual CHAP: A super set of CHAP which uses peer user/peer secret for outgoing/incoming authentication between Storage
Volumes and initiator.
Initiator group: Defines who can initiate the LUN.
It is a combination of multiple IQNs. By default, CloudByte ElastiStor creates two initiator groups (all where everyone can initiate the
LUN and none where no one can). After you create the Storage Volume, when you manage the iSCSI options, you are prompted to
choose an initiator group. You can either select the default one or the ones that you create. You configure initiator group in the Storage Volume.
169
CHAPTER VII Setting up data access protocols
iSCSI configuration workflow
You configure iSCSI at the following levels:
n
Account
VSM
Storage Volume
The following figure illustrates the work flow for configuring the iSCSI protocol options:
170
CHAPTER VII Setting up data access protocols
Account iSCSI options
Configuring iSCSI at account level involves the following tasks:
1. In ElastiCenter, select Accounts.
2. In the Accounts page, select the account for which you want to specify the protocol options.
3. In the action pane, select the protocol option and then specify the details.
171
CHAPTER VII Setting up data access protocols
The following options are available:
Manage iSCSI Authentication Groups
In the Add Authentication Group dialog box, specify the following details:
Field
Description
Name
A unique name for the authentication group.
Description
A meaningful description for the authentication group.
CHAP Username
Username for CHAP authentication. For uniqueness, specify the initiator IQN name as username.
CHAP Secret
Password for CHAP authentication in alpha-numeric format. The password must have 12 to 16 characters.
Mutual CHAP Username Username for mutual CHAP authentication. For uniqueness, specify the initiator IQN name as username. The
value must be same as that of the CHAP user.
Mutual CHAP Secret
Password for mutual CHAP authentication (should be different from CHAP secret). The password must have
12 to 16 characters.
Initiator Groups
In the Add Intiator Group dialog box, specify the following details:
Field
Description
Name
Unique name of the initiator group.
Allowed Intiator
List of allowed initiators, separated by comma.
Authorized Networks
List of allowed networks followed by subnet mask in the format 10.0.0.0/8, separated by comma.
VSM iSCSI Options
This is the set of iSCSI options specific to a VSM. By default, CloudByte ElastiStor creates a default VSM iSCSI options group
defaultwhich contains industry standard options.
After you create the VSM, when you manage the iSCSI options, you are prompted to choose the VSM iSCSI options group. You can
either select the default one or the ones that you create.
Field
Description
IQN Name
Specify a unique IQN.
Number of
worker threads
Select the number of worker threads.
Discovery Auth
Method
Specify the authentication method.
Discovery Auth
Group
Specify the authentication group.
Timeout
Sets the limit on how long an I/O can be outstanding before an error occurs. Values range from 0 to 300. The
default value is 30.
NOPIN Interval
The frequency of sending a NOP-IN packet in seconds. The values range from 0 to 300. The default value is 20.
172
CHAPTER VII Setting up data access protocols
MAX R2T
Specify a value between 1 and 255. The default value is 32.
Max Sessions
Specify a value between 1 and 64. The default value is 8.
Max Connections
Specify a value between 1 and 64. The default value is 16.
First Burst
Length
Maximum data in bytes that an iSCSI initiator may send to the target during the execution of a single iSCSI command
unsolicited. Values range from 1 to 2^32 with a default of 65,536.
Max Burst
Length
Maximum WRITE size in bytes the target is willing to receive between R2Ts. Values range from 1-2^32. The default
value is 262,144.
Max Receive
Data Segment
length
In bytes. Values range from 1 to 2^32. The default value is 262,144.
Max Outstanding R2T
Maximum number of ready to receive packets (R2Ts) the target can have as outstanding. This is for a single iSCSI
command,where larger values should yield performance increases until MaxOutstandingR2T exceeds the size of the
largest Write I/O divided by MaxBurstLength. Values range from 1 to 255. The default value is 16.
Default time to
wait
Minimum time in seconds to wait before attempting a logout or an active task reassignment after an unexpected
connection termination/reset. Values range from 1 to 300. The default value is 2.
Default time to
retain
Maximum time in seconds after Time2Wait before which an active task reassignment is still possible after an unexpected connection termination/reset. Values range from 1 to 300. The default value is 60.
Volume iSCSI Options
This is the set of iSCSI options specific to a Storage Volume. By default, CloudByte ElastiStor creates a default Volume iSCSI
options group default which contains industry standard options. After you create the VSM, when you manage the iSCSI options,
you are prompted to choose the Volume iSCSI options group. You can either select the default one or the ones that you create.
Field
Description
Status
Select either Enabled or Disabled.
IQN Name
Specify the unique IQN.
Authentication
Method
Specify the authentication method.
Authentication
Group
Specify the authentication group.
Initiator Group
Specify the initiator group.
Initial Digest
Select one of the advanced data integrity options.
iSCSI Block Length
Select the block length.
Queue Depth
Pending I/O requests for the Volume. The values range from 0-255. 0 implies that the status disabled. The
default value is 32.
Configuration scenarios
The following scenarios explain iSCSI configuration in detail:
173
CHAPTER VII Setting up data access protocols
Scenario 1: Assigning the same iSCSI initiator groups to two Storage Volumes under a VSM
iSCSI initiator groups can be configured for only Storage Volumes based on initiator groups in the account. For example, Storage
Volumes under the VSM can have different iSCSI initiator groups.
For procedures, see "Configuring initiator group and restricting access"
Scenario 2: Assigning different authentication groups to multiple Storage Volumes under a VSM
You can have different authentication groups for VSMs and Storage Volumes.
For procedures, see "iSCSI authentication workflow"
iSCSI access control workflow
An initiator groupdefines who can initiate the LUN. After you create the Storage Volume, when you manage the iSCSI options, you
are prompted to choose an initiator group.
174
CHAPTER VII Setting up data access protocols
Data access to the iSCSI Storage Volume can be restricted to either a single machine or to multiple machines in a Subnet.
Configuring initiator group and restricting access
1. In the ElastiCenter, select Accounts.
2. In the Accounts page, select the account for which you want to specify the protocol options.
3. Select Manage iSCSI Initiator Groups in the Actions pane.
4. Select Add Initiator Group in the Tasks menu.
5. Provide the required details.
Field
Name
Description
Unique name of the initiator group.
175
CHAPTER VII Setting up data access protocols
Allowed Intiator
List of IQNs, separated by comma for restricting the access to iSCSI Storage Volume from multiple machines
in a Subnet.
Authorized Networks
List of allowed networks, followed by subnet mask in the format 10.0.0.0/8, separated by comma.
6. Click OK.
7. In the Storage Volumes page, select the Storage Volume to which you want to assign the initiator.
8. Select Manage iSCSI Configuration (Actions pane > Tasks).
9. Click Edit, enter the required details, and then save the changes.
10. In the Confirmation dialog box, click Modify.
iSCSI authentication workflow
An iSCSI Authentication Group is a grouping of multiple iSCSI users. You can select the users who can access the iSCSI target.
After you create users, you can group them as iSCSI users for authentication.
1. In the ElastiCenter, select Accounts.
2. In the Accounts page, select the account for which you want to specify the protocol options.
176
CHAPTER VII Setting up data access protocols
3. Select Manage iSCSI Authentication Groups in the Actions pane.
4. Click Add Authentication Group in the following page:
177
CHAPTER VII Setting up data access protocols
5. Enter the required details and then click OK.
Field
Name
Description
Description
A unique name for the authentication group.
A meaningful description for the authentication group.
CHAP Username
Username for CHAP authentication. For uniqueness, specify the initiator IQN name as username. CHAPis
an authentication method which uses a user/secret or IQNs for outgoing authentication. The Storage
Volumes on CloudByte ElastiStor authenticate the initiator.
CHAP Secret
Password for CHAP authentication in alpha-numeric format.The password must have 12 to 16 characters.
Mutual CHAP User- Username for mutual CHAP authentication. For uniqueness, specify the initiator IQN name as username.
name
The value must be same as that of the CHAP user. Mutual CHAP is a super set of CHAP which uses peer
user/peer secret for outgoing/incoming authentication between Storage Volumes and initiator.
Mutual CHAP
Secret
Password for mutual CHAP authentication (should be different from CHAP secret).
Description
The password must have 12 to 16 characters.
6. In the Storage Volumes page, select the Storage Volume for which you want to assign the authentication group.
178
CHAPTER VII Setting up data access protocols
7. Select Manage iSCSI Configuration (Actions pane > Tasks).
8. Click Edit, enter the required details, and then click Save. In the following screen, you have selected CHAPas the authentication method.
9. In the Confirmation dialog box, click Modify.
179
CHAPTER VII Setting up data access protocols
Restricting access to iSCSI VSM by managing Authentication Groups
The procedures are same as in the section Restricting access to iSCSI Storage Volume by managing Authentication Groupsexcept
that, instead of Storage Volume, you have to select VSM from step 7 onward.
Installing MPIO on Windows Server
Multipath I/O (MPIO) is a Microsoft-provided framework that allows storage providers to develop Multipath solutions that contain
hardware-specific information required to optimize connectivity with storage arrays.
MPIO provides an alternate data path between storage devices and Windows operating system. MPIO is protocol-independent and
can be used with Fibre Channel (FC), Internet SCSI (iSCSI) and Serial Attached SCSI (SAS) interfaces.
Installing MPIO functionality involves the following procedures:
Note: The following documentation is for Windows Server 2008. The procedures are similar for other versions of Windows
Server. However, there might be minor variations owing to the differences in UI strings and navigation.
1. On Windows Server, select Multipath I/O and then click Install (Server Manager Console > Add Features Wizard).
Note: This step can be skipped if Multipath I/O is already installed.
180
CHAPTER VII Setting up data access protocols
2. Restart the Windows Server after you complete the installation.
3. After reboot, configure Multipath as follows:
1. Open MPIO application (Start > Administrative Tools > MPIO).
2. Click Discover Multi-paths tab.
3. Enable Add support for iSCSI devices.
181
CHAPTER VII Setting up data access protocols
4. Click Add.
4. In the Reboot required dialog box click Yes.
After reboot, a new device called "MSFT2005IBusType 0x9" (or similar ID) appears in the MPIO Properties.
182
CHAPTER VII Setting up data access protocols
Configuring Multipath on ElastiCenter
Prerequisites:
l
In the Network Interface Cards page (Nodes> Network Interface Cards), configure static IP addresses for each interface to configure multipath as shown in the following screen:
183
CHAPTER VII Setting up data access protocols
Procedures
1. In the VSMs page, click Provision VSM and then complete the procedures to create a VSM.
2. Select the provisioned VSM and then in the VSM page select Advanced Settings.
3. In the Advanced Settings page, click Edit.
4. In the following screen, provide the required details and then click Save.
Field
Secondary IP Address
184
Description
Alternate IP Address to configure multipath for a single LUN.
CHAPTER VII Setting up data access protocols
Secondary Subnet
Subnet address for multipath configuration.
Secondary Interface
Alternate Interface to configure multipath.
5. Provision a Storage Volume in the VSM on which Multipath I/O is configured.
6. (In the following page) Enter the required details and complete the procedures.
Configuring MPIO on Windows Server for a LUN in ElastiStor
Adding the first path to the iSCSI target
1. Add two target portal IP addresses of the Disk Station (iSCSI Initiator Properties > Discovery).
2. Select a target that uses MPIO and then click Log On (iSCSI Initiator Properties page > Target).
1. Select the option Automatically restore this connection when the computer starts.
2. Select the option Enable multi-path.
3. Click Advanced.
185
CHAPTER VII Setting up data access protocols
3. In the Advanced Settings page, check the following options:
l
Microsoft iSCSI Initiator.
First Subnet of the Initiator Computer
First Subnet of the DiskStation (both the IP addresses of the initiator and the target are within the same Subnet)
4. Click OK and ensure that the target has been connected.
186
CHAPTER VII Setting up data access protocols
5. Close the iSCSI Initiator Application.
Adding the second path to the iSCSI target
1. In the iSCSI initiator properties page:
1. Select the Target to use MPIO (ensure that it is connected).
2. Click Log on.
187
CHAPTER VII Setting up data access protocols
2. In the Advanced Settings page, check the following and then click OK.
188
Microsoft iSCSIinititator
Second Subnet of the Initiator Computer
Second Subnet of the DiskStation (both the IP addresses of the Initiator and the Target are within the same Subnet)
CHAPTER VII Setting up data access protocols
3. Select Details in the iSCSI Initiator Properties page.
189
CHAPTER VII Setting up data access protocols
4. In the Target Properties page, click Devices tab.
190
CHAPTER VII Setting up data access protocols
5. Select a device name and then click Advanced
191
CHAPTER VII Setting up data access protocols
6. Select a load balance policy and then click OK. The following screenshot shows Round Robin with Subset as the Load balance policy.
192
CHAPTER VII Setting up data access protocols
Data access using CIFS
The Common Internet File System (CIFS), is a network protocol whose most common use is sharing files on a Local Area Network
(LAN).
The following workflow explains how to configure CIFS options:
193
CHAPTER VII Setting up data access protocols
Configure VSM CIFS options at the VSM level. File system CIFS options can be configured at the Storage Volume level (if you have
enabled the protocol option).
VSM CIFS options
By default, CloudByte ElastiStor creates a default VSM CIFS options group with industry standard options.
After you create the VSM, Manage CIFS Configuration option can be used to manage CIFS options at VSM level. You can either
select the default one or select options from the drop down menu.
Field
Description
Authentication
Model
By default the Authentication Model is user.
NetBios Name
A unique name for the VSM CIFS options template.
Server Description
A meaningful description of the VSM CIFS options template.
Workgroup
The workgroup that the server will appear to be in.
DOS Charset
The character set that is used while communicating with the Windows clients. The default is CP437
UNIX Charset
The character set that is internally used. The default is UTF-8.
Log Level
Sets the amount of log/debug messages that are sent to the log file. Default is Minimum. Keep it
this way for best performance unless more information is needed for troubleshooting.
Time Server
Determines whether or not ElastiStor advertises itself as a time server to Windows clients.
File system CIFS options
By default, CloudByte ElastiStor creates a default file system CIFS options group with industry standard options. After you create
the Storage Volume, Manage CIFS Configuration option can be used to manage CIFS options at Storage Volume level.
194
CHAPTER VII Setting up data access protocols
Option
Description
Status
If Enabled, CIFS Share can be accessed. If NFS is enabled on a Storage Volume, you can access CIFS share by setting
Status to enable.
Name
A unique name for the file system CIFS options template.
Description
A meaningful description of the CIFS options template.
Read Only
If checked, prohibits write access to the share.
If selected, clients when they browse the shared directory using Windows Explorer can see the list of shares. If unse-
Browseable lected, client has to explicitly specify the full server path in Windows Explorer.
Inherit Permissions
If selected, permissions on new files and directories are inherited from parent directory.This option is (particularly) helpful in scenarios where there are large systems with many users involved. Inheriting permissions let a single home share
to be used flexibly by each user. Leave this unselected if Type of ACL is set to Windows in the Volume's permissions.
Recycle Bin
If selected, instead of purging the files, they are moved to recycle bin of CIFS share on deletion.
Hide Dot
Files
Dot files (unlike on UNIX) appear on Windows. Select the option to hide the Dot files.
Hosts Allow
Host-based protection feature. Comma-separated or space separated list of IP addresses that are allowed to access the
shares. If nothing is specified, the default value ALL applies.
Hosts Deny
Host-based protection feature. Comma-separated or space separated list of IP addresses that are denied access to the
file system. If you specify ALL, IP Addresses that are not listed in the Host Allow field are denied permission.
CIFSauthentication workflow
A CIFS Authentication Group is a grouping of multiple CIFS users. You can select the users who can access the CIFS share.
1. In the ElastiCenter, select Accounts.
2. In the Accounts page, select the account for which you want to specify the protocol options.
3. Select Manage CIFS Authentication Groups in the Actions pane.
4. Click Add Authentication Group in the following page:
195
CHAPTER VII Setting up data access protocols
5. Specify the required details and then click OK.
196
Field
Description
Name
A unique name for the authentication group.
CHAPTER VII Setting up data access protocols
Description
A meaningful description for the authentication group.
User name
Specify a name for the user.
Password
Specify a password for the user.
Full name
Specify the full name of the user.
6. In the VSM page, select the VSM for which you want to assign the authentication group.
7. Select Manage CIFS Configuration (Actions pane > Tasks).
8. Click Edit, select a Discovery Authentication Group from the drop-down list and then click Save.
197
CHAPTER VII Setting up data access protocols
9. In the confirmation prompt, click Modify.
Data access using FC
Fiber Channel (FC) Protocol is the standard transport protocol for delivering serial SCSI commands over Fiber Channel interconnects. Fiber Channel Protocol is designed to operate in a highly-efficient manner using hardware for protocol offload engines
(POEs). Fiber Channel is fast, reliable, and scalable data transport system. For further details, see http://en.wikipedia.org/wiki/Fibre_Channel.
Supported Hardware for Fibre Channel
l
QLogic HBA is used by CloudByte as FC targets.
The client can use any available HBAs in the market (such as Emulex or Brocade).
For more information, see the Hardware Compatibility List .
FC in CloudByte ElastiStor
The following figure illustrates how you configure the FC setup in CloudByte ElastiStor:
Access over FC protocol involves an initiator group and a target group. Initiator represents the FC client, for example a Windows client and target is the CloudByte Node.
198
CHAPTER VII Setting up data access protocols
The Storage Volumes can be accessed by both the initiator group and the target group.
FC Initiator group
An initiator group is the list of initiators who are authorized to access the FC LUN. By default, CloudByte creates a default initiator
group named none that does not allow access to any initiator.
The initiator group is a list of WWPNs. You can create the initiator group, add initiators and ports, and then mask the LUNs to the
added initiator.
You create the initiator group at the account level and assign it at the Storage Volume level.
FC Target group
You group the FC target ports to form a target group. This means, all the FC target ports which you have grouped are used for this
particular group. The Nodes WWPNs uniquely identify each target port on the system. By default, CloudByte creates a default target group named ALL that allows access to all targets. If required, you can create a new target group and replace the default one,
though CloudByte recommends using the default target group ALL.
You create the target group at the account level and assign it at the Storage Volume level.
Creating an initiator group
1. In ElastiCenter, select Accounts.
2. In the Accounts page, select the account for which you want to specify the protocol options.
3. In the Action Pane, select Access Protocol Options > Manage FC Initiator Group.
4. Refresh Hardware (Nodes > select the specific Node> click Refresh Hardware in the Tasks section).
Note: Step 4 applies only if you have added FCports to the Node after adding the Node to the HA Groups.
5. In the following page, click Add Initiator Group.
199
CHAPTER VII Setting up data access protocols
6. Specify a unique name and select the appropriate WWPNs of the FCinitiators to form the group.
7. Click Add.
Creating a target group
1. In ElastiCenter, select Accounts.
2. In the Accounts page, select the account for which you want to specify the protocol options.
3. In the Action Pane, select Access Protocol Options > Manage FC Target Group.
4. Refresh Hardware (Nodes > select the specific Node> select Refresh Hardware in the Tasks section of the task list).
Note: Step 4 applies only if you have added FCports to the Node after adding the Node to the HA Groups.
5. In the following page, click Add Target Group.
6. Specify a unique name and WWPNs to form the group.
7. Click Add.
Assigning Storage Volume to initiator group and target group
1. In the Storage Volumes page, select the Storage Volume for which you want to assign the initiator/target group.
2. In the Action Pane, select Tasks > Manage FC Configuration.
200
CHAPTER VII Setting up data access protocols
3. In the FC Configuration page, click Edit and then replace the default initiator group/target group.
4. Click Save.
Note:You can also perform the same task at the Account level (Accounts > select Account > Manage FC Initiator Group/Target Group).
Data access using NFS
Network File System (NFS) allows a server to share directories and files with clients over a network
Note: This release does not support access control when using NFS.
The following section details the setup:
VSM NFS options
1. In the VSM Page, click Manage NFS Configuration (Actions > Tasks).
2. (In the following page) Click Edit, change the Number of NFS Worker Threads, and then save the settings.
File system NFS options
1. In the navigation pane, select Storage Volumes.
2. In the Storage Volume page, select the Storage Volume for which you want to specify the NFS options.
201
CHAPTER VII Setting up data access protocols
3. In the following page, select Manage NFS Configuration in the Tasks section of the actions pane.
4. In the Authorized NFS clients page, click Add NFS Clients.
5. Specify the following NFS details:
Option
Description
Network/IP
addresses
Single Network ID with subnet mask (for example,10.10.1.100/8). You can also provide a comma-separated
list of IP addresses for which access has to be provided (for example,10.20.10.120, 10.20.10.121) instead.
All Directories
Yes the client can mount any sub directory within the Path.
Map as Root
Users
l
l
Read-only
6. Click Add.
202
Yesrestricts all users to root.
No restricts write or delete accesses to other users' files.
Yes prohibits writing to the share.
CHAPTER VII Setting up data access protocols
Restore snapshots while mapping iSCSI LUNs
On ESX Server
1. In ElastiCenter, create a Storage Volume.
2. Mount the Storage Volume on ESX client:
1. (In the following screen) Click on ESX Server and then select the configuration option.
2. In the iSCSI initiator properties window (Storage Adapters > Properties), select Dynamic Discovery.
3. Select Add (Add Send Target Server window appears).
4. In the iSCSI tab, specify the tenant IP Address and then click OK.
3. Add Storage.
1. Click Storage in the left pane.
2. Select Add Storage.
3. Mark the storage type as Disk/LUN and then click Next.
203
CHAPTER VII Setting up data access protocols
4. (In the following screen) Select the listed LUN and then click Next.
5. Mark the File System Version as VMFS-5.
6. Specify a name for the DataStore and then click Next.
7. (In the following page) Mark Maximum available space option and then click next.
8. Click Finish.
4. Copy data to the new Volume.
204
CHAPTER VII Setting up data access protocols
1. Right Click on the Datastore name and then select Browse Data.
2. Click on the upload icon to copy data as seen in the following page:
5. Create a snapshot on the Storage Volume using the following procedures:
1. In the Storage Volumes page, select the Storage Volume for which you want to create a local backup.
2. In the following page, select Create Snapshot in the Actions pane.
3. Specify a name for the snapshot to be created and then click OK.
6. Delete data from the DataStore on the ESX Client.
205
CHAPTER VII Setting up data access protocols
7. In ElastiCenter, click Manage Snapshots (Actions pane > Local Backup) to view the list of previously captured snapshots.
8. From the list of snapshots, select the snapshot you want to restore and then click Restore icon to roll back the Storage
Volume content to previous state.
9. On the ESX client, refresh the Storage Volume and then view the required data.
On Windows XP, Windows 7, Windows 8, Windows Server 2008, and Windows Server 2012
1. In ElastiCenter, create an iSCSI Storage Volume.
2. Mount the Storage Volume on the Windows Client.
1. On Windows machine, launch iSCSI Initiator (Programs > Administrative Tools > ISCSI Initiator).
2. In the Target tab, specify the target (tenant IP address).
206
CHAPTER VII Setting up data access protocols
3. Click Quick Connect. The Quick Connect screen appears, displaying the target name.
4. Select the Target name and then click on Connect.
5. Click OK.
3. Create Storage Drive to use the iSCSI target.
1. Launch Server Manager and then select Disk Management in the left pane.
2. Right-click the unallocated space (New Simple Volume wizard appears).
3. Select New Simple Volume.
207
CHAPTER VII Setting up data access protocols
4. Ensure that the new Storage Volume appears as shown in the following page.
5. Copy data to the new Volume.
208
CHAPTER VII Setting up data access protocols
6. Create a snapshot on the Storage Volume using the following procedures:
1. In the Storage Volumes page, select the Storage Volume for which you want to create a local backup.
2. In the following page, select Create Snapshot in the Actions pane.
3. Specify a name for the snapshot and then click OK.
7. Delete the data on the mounted Storage Volume from the Windows Client.
8. In ElastiCenter, click Manage Snapshots (Actions pane > Local Backup) to view the list of previously captured snapshots.
209
CHAPTER VII Setting up data access protocols
9. Before restoring the snapshot, make the volume offline on the Windows Client (Disk Management > Right-Click Disk).
10. From the list of snapshots, select the snapshot you want to restore and then click Restore icon to roll back the Storage
Volume content to previous state.
11. On the Windows Client, bring the Storage Volume online.
Restore snapshots while mapping CIFS share
On Windows
1. In ElastiCenter, create a Storage Volume and name it, say, testvol1.
When you create the first CIFS Storage Volume, the Create User page appears.
2. Create user credentials to map CIFS share on Windows Client as follows:
210
CHAPTER VII Setting up data access protocols
1. In the Accounts page, select the Account associated with the Storage Volume.
2. Select Manage CIFSAuthentication Groups in the Actions pane.
3. Select Add Authentication Group in the Tasks section.
4. In the following page, provide the relevant credentials and then click OK.
211
CHAPTER VII Setting up data access protocols
3. Mount the Storage Volume on Windows Client as follows:
1. Open your Windows Client and then select Computer > Map Network Drive.
2. Write some data.
4. Ensure that you have enabled CIFS as follows:
1. On Windows Client, launch Map Network Drive dialog box (Computer > Map Network Drive).
2. Specify the drive and the tenant IP address (with CIFS share name) in a format as shown in the following screen:
3. Provide the CIFS share access path and then click Finish.
4. Ensure that the option Connect using different credentials is checked.
5. Provide the CIFS username and password and then click OK.
6. Ensure that CIFS share is connected (highlighted), as shown in the following page:
212
CHAPTER VII Setting up data access protocols
7. Copy some data.
8. Create a snapshot on the Storage Volume using the following procedures:
1. In the Storage Volumes page, select the Storage Volume for which you want to create a local backup.
2. In the following page, select Create Snapshot in the Actions pane.
3. Specify a name for the snapshot to be created and then click OK.
9. Go to Windows Client and then delete the data from the mounted Storage Volume.
10. In ElastiCenter, click Manage Snapshots (Actions pane > Local Backup) to view the list of previously captured snapshots.
11. For the snapshot you want to restore, click Restore icon to roll back the Storage Volume content to previous state.
213
CHAPTER VII Setting up data access protocols
12. On Windows Client, refresh the Storage Volume and then check the data.
Restore snapshots while mapping FC LUNs
On ESX Server
1. In ElastiCenter, create an FC Storage Volume.
2. In ElastiCenter assign an ESX Server as initiator to the FC Storage Volume.
3. (In the following screen) Click on ESX Server and then select the configuration option.
214
CHAPTER VII Setting up data access protocols
4. Add Storage:
1. Click Storage in the left pane.
2. Mark the storage type as Disk/LUN and then click Next.
3. (In the following screen) Select the listed LUN and then click Next.
4. Mark the File System Version as VMFS-5.
5. Specify a name for the DataStore and then click Next.
6. (In the following page) Mark Maximum available space option and then click next.
7. Click Finish.
5. Copy data.
215
CHAPTER VII Setting up data access protocols
1. Right Click on the Datastore name and then select Browse Data.
2. Click on the upload icon to copy data as seen in the following page:
6. Create a snapshot on the Storage Volume using the following procedures:
1. In the Storage Volumes page, select the Storage Volume for which you want to create a local backup.
2. In the following page, select Create Snapshot in the Actions pane.
3. Specify a name for the snapshot to be created and then click OK.
7. Delete data from the DataStore on the ESX Client.
216
CHAPTER VII Setting up data access protocols
8. In ElastiCenter, click Manage Snapshots (Actions pane > Local Backup) to view the list of previously captured snapshots.
9. From the list of snapshots, select the snapshot you want to restore and then click Restore icon to roll back the Storage
Volume content to previous state.
10. On the ESX client, refresh the Storage Volume and then view the required data.
On Windows Server 2008
1. In ElastiCenter, create an FC Storage Volume.
2. In ElastiCenter, assign a Windows client as an initiator to the FC Storage Volume.
3. Create Storage Drive to use the FC LUN.
1. Launch Server Manager and then select Disk Management in the left pane.
2. Right-click the unallocated space (New Simple Volume wizard appears).
217
CHAPTER VII Setting up data access protocols
3. Select New Simple Volume.
4. Ensure that the new Storage Volume appears as shown in the following screen:
5. Copy some data to the Volume.
218
CHAPTER VII Setting up data access protocols
6. Create a snapshot on the Storage Volume using the following procedures:
1. In the Storage Volumes page, select the Storage Volume for which you want to create a local backup.
2. In the following page, select Create Snapshot in the Actions pane.
3. Specify a name for the snapshot and then click OK.
7. Delete the data on the mounted Storage Volume from the Windows Client.
8. In ElastiCenter, click Manage Snapshots (Actions pane > Local Backup) to view the list of previously captured snapshots.
219
CHAPTER VII Setting up data access protocols
9. Before restoring the snapshot, make the volume offline on the Windows Client (Disk Management > Right-Click Disk).
10. From the list of snapshots, select the snapshot you want to restore and then click Restore icon to roll back the Storage
Volume content to previous state.
11. On the Windows Client, bring the Storage Volume online.
Restore snapshots while mapping NFS Share
On ESX Server
1. In ElastiCenter, create a Storage Volume.
2. Mount the Storage Volume on ESX Client.
1. In the following page, Click on ESX Server.
2. Click Storage in the left pane under the Hardware section.
220
CHAPTER VII Setting up data access protocols
3. Select Add Storage option.
4. Mark the storage type as Network File System and then click next.
3. Add Storage.
1. In the Server tab, specify NFS Server IP Address.
2. In the Folder tab, specify the access path of NFS share.
3. Specify a name for DataStore and then click Next.
4. Copy some data.
221
CHAPTER VII Setting up data access protocols
1. Right Click on the Datastore name (Browse Datastore wizard appears).
2. Select Browse Datastore.
3. Click on upload icon to copy data as seen in the following page:
5. Create a snapshot on the Storage Volume using the following procedures:
1. In the Storage Volumes page, select the Storage Volume for which you want to create a local backup.
2. In the following page, select Create Snapshot in the Actions pane.
3. Specify a name for the snapshot to be created and then click OK.
6. Delete the data from the DataStore on the ESX Client.
222
CHAPTER VII Setting up data access protocols
7. In ElastiCenter, click Manage Snapshots (Actions pane > Local Backup) to view the list of previously captured snapshots.
8. From the list of snapshots, select the snapshot you want to restore and then click Restore icon to roll back the Storage
Volume content to previous state.
9. On ESX Client, refresh the Storage Volume and then view the required data.
On Linux Client
1. In ElastiCenter, create an NFS Storage Volume.
2. Mount the volume on Linux client and then write some data.
Use the following command to mount the volume: mount Tenant IP Address : Access Path Directory Path
l
Directory Path: Local Directory Path where the NFS volume is to be mounted.
Example: mount 20.10.17.117:/Acctestvol3 /mnt/vol1
To copy data to the volume, use the following command:
cp /Source Filename Destination Filename
Example: cp /root/Desktop/test2 /mnt/vol1
cp /root/Desktop/test1 /mnt/vol1
223
CHAPTER VII Setting up data access protocols
3. Create a snapshot on the Storage Volume using the following procedures:
1. In the Storage Volumes page, select the Storage Volume for which you want to create a local backup.
2. In the following page, select Create Snapshot in the Actions pane.
3. Specify a name for the snapshot to be created and then click OK.
4. Delete the data from the mounted Storage volume using the following command:
rm -r Filename Filename
Example: rm r test test2
5. In ElastiCenter, click Manage Snapshots (Actions pane > Local Backup) to view the list of previously captured snapshots.
6. From the list of snapshots, click on Restore icon to roll back the Storage Volume content to previous state.
7. On the Linux Client, check data. Use the ls command to view the list of files.
224
CHAPTER VIII Managing CloudByte ElastiStor
CHAPTER VIII Managing CloudByte ElastiStor
The following sections explain the management features in CloudByte ElastiStor:
n
"Delegated administration"
"Monitoring""Monitoring"
"Drill-down feature"
"CloudByte ElastiStor reporting"
Delegated administration
Administration in CloudByte can be categorized based on services. You can have administration at the Site level or at the Account
level. Your Site can have multiple Site administrators.
Note: Currently, CloudByte ElastiStor supports only role-based administration. Future releases will have delegated administration fully implemented.
As the root administrator, you can distribute the tasks to administrators. Delegated administration is an act of providing and restricting privileges by establishing access control based on the responsibility of each individual administrator.
n
Delegated administration lets you determine the actions that each administrator can take using administrative tools on different resources.
Delegated administration roles are mapped to administrative functions using security policies. You can create and maintain
separate administration capabilities, depending on your needs.
You establish delegated administration by creating role hierarchy.
Role hierarchy enables you to keep a tight control on how delegation happens and who can delegate what to whom. One
administrator can create sub-roles for other administrators with limited administrative privileges.
Role hierarchy
The following is a pictorial representation of how role-hierarchy functions in CloudByte ElastiStor administration:
225
CHAPTER VIII Managing CloudByte ElastiStor
Administrator
Super administrator
Site administrator
Account super
dministrator
Account administrator
226
Can
Perform all possible actions across Sites, Accounts, and VSMs
Cannot
Not applicable
Delete/Modify/Create another Site administrator
Manage permissible actions within the permitted Sites
Manage more than one Site
Have only read-only access
Create/Delete/Modify Accounts (if permitted by super
administrator)
Manage only that Account
Manage anything outside the Account
Do everything permissible for an Account administrator
Manage anything with respect to the
infrastructure
Manage what is permitted within the Account
Manage other account admins within the
Account.
CHAPTER VIII Managing CloudByte ElastiStor
View administrator
View all the permitted Sites and underlying infrastructure
Delete/Modify/Create another View
administrator
Have only read-only access
View Site administrators
View all the permitted Accounts
View Cluster administrators and Account administrators
Generate reports
Note: You can only have one super administrator. Only the super administrator can change his/her password. Administrators can change their password and passwords of administrators under them.
Adding delegated administrators
Create Site administrators or view administrators
Note: You can create Site administrators or view administrators only if you are a super administrator.
1. Log in as a super administrator.
2. In the navigation pane, select Delegated Administrator. The Delegated Administrators page appears.
3. Click Add Delegated Admin.
4. In the Add Delegated Admin Details page, specify the following details:
227
CHAPTER VIII Managing CloudByte ElastiStor
Email: Specify a unique email address for the Site administrator or View administrator
Password: Administrator password
Delegated Admin Type:Select the type of Delegated Administrator from the drop-down menu
5. Click Next and then drag and drop one or more Sites for which you want to delegate administration as seen in the following
screen:
6. Click Add.
228
CHAPTER VIII Managing CloudByte ElastiStor
Create Account administrators
You can create Account administrators for either existing or new accounts.
Create Account administrators for a new account
Note: The type of administrator that you can assign tasks to depends on the privileges you have.
1. In ElastiCenter, select Accounts in the navigation pane.
2. In the Accounts page, click Add Account.
3. In the Account Details page, when you specify the account details, choose the type of administrator that you want to create
(Account Super Admin or Account Admin).
4. Specify the credentials for the administrator and then click Add Account.
Create Account administrators for an existing account
Note:The type of administrator that you can assign task to depends on the privileges you have.
1. In ElastiCenter, select Accounts in the navigation pane.
2. In the Accounts page, select the account for which you want to add new administrators.
3. In the following page, click Add Administrator in the Delegated Administration section of the tasks pane.
229
CHAPTER VIII Managing CloudByte ElastiStor
4. In the Add Account dialog box, specify the details and then click OK.
Monitoring
Monitoring provides an intuitive visualization of storage statistics.
Monitoring foregrounds relevant backend activities in an easy user interface for administrators. It provides a generic outlook of the
components such as storage, input/output, throughput, latest data, status, alerts, and system configuration.
Various dashboards dynamically represent disk utilization, storage utilization, throughput, input/output, and status of network interface cards attached to the system.
Alerts and Events feature keeps a regular check on what is happening with the product. All events - even adding an additional IP
address or modifying an existing one - get registered and monitored.
The feature also provides a notification system where the administrator is informed through email/text messages when an alert is
generated in the system.
Continuous monitoring of your network
n
Helps you discover problems long before they become critical
Enables you to take proactive measures
Ensures that performance is always at expected levels
Ensures that resources are effectively utilized
Monitoring in CloudByte ElastiStor
Monitoring in CloudByte ElastiStor can be classified as follows:
n
Node level alerts: The alert information specific to the Node.
Dashboard alerts: Graphical representation of monitoring statistics at granular levels.
230
CHAPTER VIII Managing CloudByte ElastiStor
Events: A snapshot of all ElastiCenter-specific events.
Node level alerts
Node level alerts provide a list of alerts specific to the Nodes.
1. In ElastiCenter, click Alerts. All alerts associated with the Node are displayed.
2. Click the Acknowledge icon to acknowledge the alert and it disappears from the list. To acknowledge all the alerts, click Bulk
Acknowledge in the Actions pane.
Emailing alerts
The following settings in Global Settings let you email alerts:
l
By default , alerts are not emailed. To receive alerts over email, set alert.email.enable to true . The alerts are mailed
to the email that you specified when you updated your profile. For details, see "Reset password and configure auto-alert
options". To add multiple users, add the email IDs separated by comma in alert.email.addresses.
You can set a filter to the alerts mailed based on severity using the option alert.email.severity. By default, all alerts
are mailed (as the value set is 4).
To specify the sender email ID, use the option alert.email.sender. If you do not specify an ID, the ElastiCenter domain
name is displayed along with IP address of ElastiCenter.
Events
To get a list of ElastiCenter events,
1. In ElastiCenter, click Events.
2. Select Events in the Select View. All events are listed.
To get a list of specific events, go to the component page and then click Events. For example, for events related to only Storage
Volumes:
1. In the Storage Volumes page, select a Storage Volume for which you want to generate events.
2. In the following page, click Events in the actions pane.
231
CHAPTER VIII Managing CloudByte ElastiStor
Dashboard Alerts
Dashboard provides a visual representation of monitoring statistics such as performance, usage, capacity, and availability.
To see the details, select the component and then make a specific selection.
The following figure is a dashboard representation of the alerts
Advanced debugging options
The Troubleshooting option provided in the Node page, Pool page, and VSM page provides a set of information that help you with
advanced debugging. The options provide information such as the following:
l
For Pools: Pool I/O Status and Pool Properties
For VSMs: NIC and Netstat information
For Nodes: I/O Status of various disks, GMultipath status, and Camcontrol device list for all available disks
When you select an option, details are provided in a tabular format. To access the Troubleshooting option,
1. In the Node/Pool/VSM page, click a specific Node/Pool/VSM.
2. In the Actions pane, click Troubleshooting under Tasks.
232
CHAPTER VIII Managing CloudByte ElastiStor
3. Select the action and then click Update.
233
CHAPTER VIII Managing CloudByte ElastiStor
Drill-down feature
A monitoring feature in Pools, Storage Volumes, and VSMs that lets you monitor
n
IOPS
Throughput
Latency
Average block size (applicable only to Storage Volume)
READ vs WRITE (applicable only to Storage Volume)
Select a time interval option such as start time and end time, last 24 hours, or last week to plot a graph.
Using the drill-down feature
To use the drill down feature, select the component and then select a specific feature.
Drill-down procedure for Site
1. From the list, select a Pool for which you want to monitor IOPS.
2. Click Compare Volumes.
3. In the following page, set the desired parameters.
234
CHAPTER VIII Managing CloudByte ElastiStor
4. Click Update.
Comparing IOPS
1. From thelist, select the Pool for which you want to monitor Storage Volume IOPS.
2. Click Compare Volumes.
3. In the following page, set the desired parameters.
4. Click Update.
Note: IOPS comparison is applicable only for Storage Volumes in the same Pool.
CloudByte ElastiStor reporting
CloudByte ElastiStor provides detailed reports that you can save or print. The reports can be generated in the formats PDF, HTML,
and CSV. You can schedule reports and email the generated reports.
You can generate reports at granular levels, for instance at Account level or Pool level. Reports help you with various statistics such
as QoS data.
CloudByte provides the following reports, which you can generate, print, and circulate:
l
Account IOPS Provisioning
Pool IOPS Provisioning
Account Storage Provisioning
Pool Storage Provisioning
Account QoS
Pool QoS
235
CHAPTER VIII Managing CloudByte ElastiStor
Account Storage
Pool Storage
Volume Usage
HA Group Info
Global Accounts IOPS Storage Provisioning
Note: In future releases, you can define your own reports and add new report types.
Accessing the reports
1. In ElastiCenter, select Reports.
2. Click the respective icon to generate or schedule a report.
3. In the dialog box that appears, specify the relevant details and then click OK.
Configuring email for reports
To send the generated reports over mail, Click Generate new Report icon in the Actions pane and then specify the address to which
the report has to be mailed.
236
CHAPTER VIII Managing CloudByte ElastiStor
To change the default settings for configuring email for reports, select Global Settings and then specify the details for the highlighted
options:
237
CHAPTER VIII Managing CloudByte ElastiStor
Global Settings
Global settings let the administrator configure various options used to control CloudByte ElastiStor. For example, email configuration. To configure global settings,
1. In ElastiCenter, select Global Settings.
2. Select a target category. A list of settings is provided by default.
3. Edit the relevant settings.
Note: You cannot add new settings.
This section lists the global settings options available on the ElastiCenter.
Option
alert.email.addresses
238
Description
Comma separated list of email addresses used
for sending alerts.
Default Value
Email ID you specified in the Update
Profile section in ElastiCenter.
CHAPTER VIII Managing CloudByte ElastiStor
Option
Description
alert.email.enable
If true, emails are sent to the specified email
addresses.
alert.email.sender
Sender of the alert email.
alert.email.severity
Set the email severity level to one of the following:
l
1 - ERROR
2 - CRITICAL
3 - WARNING
4 - INFO
Default Value
TRUE
alert.smtp.host
SMTP hostname to send alert emails.
localhost
alert.smtp.password
Password for SMTP authentication (applies only
if alert.smtp.useAuth is true).
alert.smtp.port
The port of the SMTP server.
alert.smtp.useAuth
If true, SMTP authentication is enabled to send
emails.
alert.smtp.username
Username for SMTP authentication (applies only
if alert.smtp.useAuth is true).
autoSupport.config.details
Send configuration details to CloudByte as part
of an auto support email.
autosupport.httpnotify.apikey
API key of CloudByte auto support server.
autosupport.httpnotify.enable
Send HTTP post request to CloudByte auto support server.
autosupport.httpnotify.ipaddress
The IP address of CloudByte auto support server.
autoSupport.infastructure.statistics
Send infrastructure statistics to CloudByte as
part of an auto support email.
Yes
autoSupport.product.alerts
Send product related alerts to CloudByte as part
of an auto support email.
Yes
autoSupport.reg.details
Send registration details to CloudByte as part of
an auto support email.
autoSupport.tenant.statistics
Send tenant statistics to CloudByte as part of an
auto support email.
Yes
bad.disk.threshold
The number of defects grown on disk that will
declare it as a bad disk
512
cache.multiplication.factor
The number of Cache READs which equal a disk
READ. The default value is 3 which means 1 disk
READ equals 3 cache READs. Only a value
between 2 and 6 is supported.
devman.backup.files.retain
The number of backup files to be retained.
devman.backup.path
The path of ElastiCenter backup directory.
/var/devman/backups
587
False
Yes
False
Yes
239
CHAPTER VIII Managing CloudByte ElastiStor
Option
Description
devman.backup.scheduling.interval The interval time for ElastiCenter backup.
Default Value
1
devman.build.number
The build version of ElastiStor.
Available in /cbdir/buildversion
monitor.purge.retain.days
The number of days that the data has to be
retained for.
60
monitor.qos.stats.interval
The time interval (in seconds) taken for QoS stat- 300
istics to be retrieved from Nodes.
monitor.refresh.interval
The time interval (in seconds) required to
refresh the Storage Volumes page.
300
monitor.storage.stats.interval
The time interval (in seconds) taken for storage
statistics to be retrieved from Nodes.
300
monitor.system.purge.retain.days
The number of days that the data has to be
retained for.
no.of.nodes.per.hagroup
Limiting number of Nodes in an HA Group.
project.invite.required
Specify if invitation confirmation is required
when add account to project.
False
provisioning.sb.algo
Algorithm used for auto-provisioning Storage
Volume.
Best Fit
provisioning.sb.auto
Enable/Disable auto-provisioning of Storage
Volumes.
No
provisioning.tsm.algo
Algorithm used for auto-provisioning VSM.
Best Fit
provisioning.tsm.auto
Enable/Disable auto-provisioning of VSMs.
No
qos.penalty.allowed.delta
Percentage (as a value between 1 and 100) up to 10
which penalty will be not be considered
qos.penality.blocksize
Standard blocksize (in KB) per IOPS, used in provisioning and penality enforcement.
qos.penalty.blocksize.factor
Considers block size for penalty calculations. Spe- No
cify yes to Enable and No to Disable.
qos.penalty.cachehit.factor
Considers cache hit for penalty caclulations. Specify yes to Enable and No to Disable.
No
qos.penalty.enforcement.timeinterval
The time interval (in seconds) for which penalty
has to be applied on QoS values.
300
qos.penalty.readwrite.factor
Considers READs vs WRITEs for penalty caclulations. Specify yes to Enable and No to Disable.
No
read.multiplication.factor
Specify how many READs equal a WRITE. The
default value is 4 which means 1 WRITE equals 4
READs. Only a value between 3 and 6 is supported.
report.email.sender
Sender of report email.
report.smtp.host
SMTP hostname used for sending out report
emails.
report.smtp.password
Password for SMTP authentication (applies only
if report.smtp.useAuth is true).
240
localhost
CHAPTER VIII Managing CloudByte ElastiStor
Option
Description
Default Value
report.smtp.port
The port of the SMTP server.
587
report.smtp.useAuth
If true, SMTP authentication is enabled to send
emails.
False
report.smtp.username
Username for SMTP authentication (applies only
if report.smtp.useAuth is true).
ui.protocol.enablefc
Enable/Disable all FC protocol related options
from ElastiCenter.
ui.protocol.enablehaadmincreation Enable/Disable haAdmin creation options from
ElastiCenter.
True
False
ui.protocol.enablezilmirroring
Enable/Disable ZIL mirroring creation options
from ElastiCenter.
False
provisioning.uncontrolled.iops
Enable/Disable provisioning with uncontrolled
(zero) IOPS. Specify TRUE to enable.
False
alert.qos.throttling.percentage
Sends an alert if the throttled IOPS percentage
exceeds the specified value and if alert.qos.throttle.count is encountered for the
specified number of times.
20
alert.qos.throttle.count
Sends an alert if the number of consistent throttling exceeds the specified value and alert.qos.throttling.percentage exceeds the
specified value.
10
devman.enable.ipspaces
Enable/Disable the Assigning real IP
spaces feature.
False
241
CHAPTER IX Licensing
CHAPTER IX Licensing
When you install the Community Edition of CloudByte ElastiStor, a free perpetual license file is already uploaded to ElastiCenter.
You can use the license for up to 25TB usage of storage on CloudByte ElastiStor.
The license file has relevant details that implement license to use various features that you have purchased. CloudByte provides
license file in the format L4J.
The following FAQs help you with licensing.
How do I access license details?
1. Click Admin (at the top-right corner of the page).
2. Select License from the drop-down list.
3. The License page appears.
I want to evaluate CloudByte ElastiStor. How will the trial license be enforced?
When you install a the Community Edition of CloudByte ElastiStor, the free perpetual license file is, by default, uploaded. You need
not do any licensing tasks.
I received the license file from CloudByte. How will I proceed?
1. Place the license file (with the extension .l4j) on the machine from which you access CloudByte ElastiCenter.
2. Log in to CloudByte ElastiCenter.
3. In the Actions pane, click Upload New License and then Upload License.
242
CHAPTER IX Licensing
The Add License wizard appears.
4. Choose the license file that you have received and then click Upload.
The Check screen confirms the validity of the license and the Finish screen provides the license details. When you get back
to the License page, all license details are listed.
Can I check the past licensing activities?
In the License page, click View History. The details of the license are listed.
243
CHAPTER IX Licensing
Can I get support from CloudByte for the trial version of the product?
Yes. Contact CloudByte technical support at support@cloudbyte.com
244
CHAPTER X CloudByte ElastiStor REST APIs
CHAPTER X CloudByte ElastiStor REST APIs
CloudByte ElastiStor REST APIs provide a bundle of functions that encompasses all the features in the CloudByte ElastiStor
Administrator Console (CloudByte ElastiCenter). You do not need ElastiCenter to configure and manage CloudByte ElastiStor.
Rather you can use your own portal.
The CloudByte ElastiStor REST APIs provide powerful, convenient, and simple REST-based APIs which can interact with
CloudByte ElastiStor.
Click one of the following links to get a complete list of CloudByte ElastiStor REST APIs and documentation relevant to your administrative privileges:
l
Super administrator APIs
Site administrator APIs
Account super administrator APIs
CloudByte ElastiStor API references
The following sections explain the implementation.
How to use CloudByte ElastiStor REST APIs
1. Install CloudByte ElastiCenter. For details, see "Installing CloudByte ElastiStor".
2. Authenticate as Administrator. For details, see "Launching CloudByte ElastiCenter"
3. Obtain the CloudByte REST API authorization token. This token is passed in each request using the API Key request parameter. For details, see "Obtaining the REST API key".
4. Form the request URL. For details, see "Forming the API request".
Obtaining the REST API key
1. Log in to ElastiCenter as Super Admin.
2. In the navigation pane, select Delegated Administrator. The list of administrators appears.
3. From the list of Accounts, click the specific account for which you want to generate the API key.
4. In the following page, click Generate Keys.
245
CHAPTER X CloudByte ElastiStor REST APIs
5. Click Yes to confirm. The API key is generated and displayed as shown in the following screen:
Forming the API request
The following is a sample GET request:
https://<ElastiCenterIPaddress>/client/apicommand=listSite&apiKey=Xxj48vo357IsQ5H5KOPQksMzFBGYgTJNqgItBAulgu5YeOkwT4L8DAWUb_
p43Nlv23e4eBeuN3Ts8_0-m3AyQA&response=json
Interpreting the URL
URL Component
246
Description
CHAPTER X CloudByte ElastiStor REST APIs
https://<ElastiCenter IP address>/client/api?
Base URL which includes the IP address to access
CloudByte ElastiCenter; the web service API entry point.
command=listSite
The web service command you execute. For the complete list of commands, see ElastiStor APIs.
apiKey=UjGmN7gGwzMhFsSese3TNNOWiXHGn53eon_7sHx3aL-9_
t3sHAOV_rNqVzwTnrJyCaTAg9FucSBvMp49nbnfEQ
The API key that you generated.
response=json
Response format. This can be XML or JSON. To get an
XML response, replace json with xml in the URL.
Apart from these, the URL also has the additional parameters (required or optional) for the command.
Sample response in JSON
{ listSiteResponse : { count:2 ,site : [
id: 66291daa-4c40-4462-8747-926ebc488963,
name: Bangalore,
location: India,
managedstate: Available,
revisionnumber: 0,
currentUsedSpace: 29,
currentAvailableSpace: 9943,
currentTotalSpace: 9972,
currentThroughput: 605,
currentIOPS: 151,
currentLatency: 163,
currentThrottle: 20,
controllers: [
{
nodePools: 4,
id: 4c6e2246-52c1-3227-b51a-9928cf3b675a,
clusterid: 88bf812b-5142-4780-8ad3-13178bbf30a1,
name: host1,
hostname: Both,
nodeTsms: 4,
ipaddress: 10.36.36.50
}
],
haclusters: [
{
id: 88bf812b-5142-4780-8ad3-13178bbf30a1,
haClusterPools: 4,
haClusterNodes: 1,
name: Cluster1,
247
CHAPTER X CloudByte ElastiStor REST APIs
haClusterTsms: 4
}
],
hapools: [
{
controllerId: 4c6e2246-52c1-3227-b51a-9928cf3b675a,
id: 38e66579-bb91-3de3-815a-48c35e2c5943,
availiops: 50,
totalthroughput: 102400,
name: Pool1,
poolTsms: 1,
availthroughput: 51200,
totaliops: 100
},
{
controllerId: 4c6e2246-52c1-3227-b51a-9928cf3b675a,
id: 226e2e02-a3e5-3609-b70d-aea8ef655f74,
availiops: 75,
totalthroughput: 153600,
name: Pool2,
poolTsms: 1,
availthroughput: 76800,
totaliops: 150
},
{
controllerId: 4c6e2246-52c1-3227-b51a-9928cf3b675a,
id: 810f428d-9c26-3d91-8675-62cc3ca56da0,
availiops: 100,
totalthroughput: 153600,
name: pool3,
poolTsms: 1,
availthroughput: 102400,
totaliops: 150
},
{
controllerId: 4c6e2246-52c1-3227-b51a-9928cf3b675a,
id: 11d6fd85-5782-39fe-b85d-079d73742757,
availiops: 175,
totalthroughput: 384000,
name: P4,
poolTsms: 1,
availthroughput: 179200,
totaliops: 375
}
248
CHAPTER X CloudByte ElastiStor REST APIs
],
tsms: [
{
controllerId: 4c6e2246-52c1-3227-b51a-9928cf3b675a,
id: 1cb805fe-dd22-357e-b198-121fa08d0971,
availiops: 25,
totalthroughput: 51200,
name: T1,
ipaddress: 10.37.37.51,
availthroughput: 25600,
totaliops: 50
},
{
controllerId: 4c6e2246-52c1-3227-b51a-9928cf3b675a,
id: 90a4e6f8-cb3c-317f-8cdf-3986e8759747,
availiops: 50,
totalthroughput: 76800,
name: T2,
ipaddress: 10.37.37.52,
availthroughput: 51200,
totaliops: 75
},
{
controllerId: 4c6e2246-52c1-3227-b51a-9928cf3b675a,
id: cab14af0-84b6-3761-900b-9675b32b6ba5,
availiops: 25,
totalthroughput: 51200,
name: T3,
ipaddress: 10.37.37.53,
availthroughput: 25600,
totaliops: 50
},
{
controllerId: 4c6e2246-52c1-3227-b51a-9928cf3b675a,
id: 17b17719-137d-3f95-9f4f-468a17a45957,
availiops: 100,
totalthroughput: 204800,
name: T4,
ipaddress: 10.37.37.54,
availthroughput: 102400,
totaliops: 200
}
]
}, {
249
CHAPTER X CloudByte ElastiStor REST APIs
id: 74692191-75a9-4294-9b1e-402127c9e327,
name: test,
managedstate: Available,
revisionnumber: 0,
currentUsedSpace: 0,
currentAvailableSpace: 0,
currentTotalSpace: 0,
currentThroughput: 0,
currentIOPS: 0,
currentLatency: 0,
currentThrottle: 0
} ] } }
Sample response in XML
<listSiteResponse cloud-stack-version=1.1.0.4.2013-02-06T10:19:20Z>
<count>1</count>
<site>
<id>ad63d28a-9de9-443f-8260-4309337f40c3</id>
<name>site</name>
<managedstate>Available</managedstate>
<revisionnumber>0</revisionnumber>
<currentUsedSpace>0</currentUsedSpace>
<currentAvailableSpace>1996</currentAvailableSpace>
<currentTotalSpace>1996</currentTotalSpace>
<currentThroughput>0</currentThroughput>
<currentIOPS>0</currentIOPS>
<currentLatency>0</currentLatency>
<currentThrottle>0</currentThrottle>
</site>
</listSiteResponse>
250
CHAPTER XI Connecting to ElastiStor
CHAPTER XI Connecting to ElastiStor
The following sections explain how you map volumes to various clients:
l
"Mapping iSCSI LUN"
"Mapping CIFS share to the clients"
"Mapping FC LUN to the clients"
"Mapping NFS share to clients"
Mapping FC LUN to the clients
On VMware vSphere client
1. Ensure that you have enabled FC for the particular Storage Volume. For details, see "Data access using FC ".
2. In the vSphere Client, go to Configuration > Storage.
3. Click Devices and then select Rescan All.
4. In the Rescan dialog box, click OK. The refreshed list of devices appears.
251
CHAPTER XI Connecting to ElastiStor
5. Click Datastore.
6. In the datastore list, select the datastore and then click Add Storage.
The Add Storage wizard appears.
252
CHAPTER XI Connecting to ElastiStor
7. Follow the instructions on the Wizard and then complete the procedures to add storage.
Mapping FC LUN on Windows Server 2008
Discovering the FC target
Note: The mapping procedures are similar for other versions of Windows Server. However, there might be minor variations
owing to the differences in UI strings and navigation.
Note: Microsoft Multipath I/O (MPIO) takes care of presenting a pseudo device.
1. Ensure that you have enabled FC for the particular Storage Volume. For details, see "Data access using FC ".
2. On Windows Server 2008, select Server Manager > Disk Management > Rescan Disks.
253
CHAPTER XI Connecting to ElastiStor
After rescan, the Volumes that you have created for FC are discovered.
254
CHAPTER XI Connecting to ElastiStor
3. Right-click the unallocated space and then click Online.
4. Once online, right-click and then select Initialize Disk.
255
CHAPTER XI Connecting to ElastiStor
The Initialize Disk dialog box appears.
5. Click OK.
6. Right-click the unallocated space and then select New Simple Volume as shown in the following screen:
256
CHAPTER XI Connecting to ElastiStor
The New Simple Volume Wizard appears.
257
CHAPTER XI Connecting to ElastiStor
7. Follow the instructions and complete the wizard to create the partition.
8. Ensure that the created disk is added to the Disk management console (indicated by the blue ribbon).
258
CHAPTER XI Connecting to ElastiStor
9. Ensure that the drive created out of FC LUN is shown (as in) the following screen:
259
CHAPTER XI Connecting to ElastiStor
Mapping FC LUN as a raw disk
1. On the Windows Virtual Machine, right-click and then select Edit Settings.
2. In the Virtual Machine Properties page, click Add.
260
CHAPTER XI Connecting to ElastiStor
3. Select Hard Disk as the device type and then click Next.
4. Select Raw device mappings and then click Next.
5. From the list of LUNs, select a LUN which has to be mapped as a raw device.
6. Follow the wizard and complete the procedures.
7. When the Raw mapped LUN message appears, click OK.
On Kernel-based Virtual Machine
1. Do either of the following:
l
As root, make an SSH connection to the KVM client.
On the KVM client, log in as root.
2. At command prompt, do the following to map FC LUN to KVM.
3. Run the following command to verify the number of FC Hosts: ls /sys/class/fc_host/
The following is a sample output:
host0 host1 host2 ..........hostX
Note: The number that follows host(1, 2, or X) is the HBA number of the FC Host.
4. Run the following command to discover the FC LUNs:
echo "1" >/sys/class/fc_host/hostHBA number/issue_lip
For example,
echo "1" >/sys/class/fc_host/host7/issue_lip
5. Repeat the step 4 for all the FC Hosts.
6. Run the following command to fetch the WWPN of the FC Host:
cat /sys/class/fc_host/host<HBA number>/port_name
For example,
261
CHAPTER XI Connecting to ElastiStor
cat /sys/class/fc_host/host7/port_name
7. Run the following command to add each FC LUN as a device to the KVM client:
echo "scsi add-single-device h c t l" > /proc/scsi/scsi
Parameter
Description
HBA number of the Host.
Channel ID on the HBA.
SCSI target ID.
FC LUN ID.
8. Run the following command to to list the disks: fdisk -l
Mapping iSCSI LUN
Note: Do not present the same LUN to multiple clients/initiators until an OS Clustering (for example, Red Hat Cluster Suite
(RHCS) or Microsoft Cluster Server (MSCS)) uses the shared LUN.
On Linux
The following procedures might work on most of the Linux setups. However the certified versions are
l
OpenSUSE-11.4-x86 -64 bit and 12.1 version
Red Hat Enterprise Linux Server release 6.0
CentOS-6.4-x86
Without CHAP authentication
1. At command prompt, run the following command, to discover the iSCSI target: iscsiadm -m discovery -t st -p
<VSM_IP_address:port>.
The iSCSI target (iqn) is displayed as shown in the following example: 10.10.8.201:3260,1 iqn.2012-09.CertStorage:isci-on-iscsiSet
2. Connect to the target in either of the following ways:
l
To connect to all targets, run the following command: iscsiadm m node l
To connect to an individual target, run the command as shown in the sample command: iscsiadm m node T
<target_name_displayed_when_you_run_discover_command> p <VSM_IP_address:port> l
A success message is displayed.
2. To create multiple partitions from the LUN, run the following command: fdisk -l.
All available disks and partitions are listed.
3. Use the following command to create the partition: fdisk <disk(Discovered LUN)>
4. (Optional) Enter the command m to list the commandline help.
5. Create a partition using the command n (primary or extended).
6. Specify the cylinder size and value.
262
CHAPTER XI Connecting to ElastiStor
7. Specify the size of the partitions and enter w for WRITE changes.
8. Create a file system on the created partitions using the following command: mkfs.<ext2,ext3,ext4,ntfs,vfat>
<partition>
9. Create an empty directory using the following command: mkdir <directoryname>
10. Mount the partitions to the empty directory using the following command: mount <partition name> <directoryname>
11. Perform READ and WRITE operations on mount point.
Sample CLI snapshot
<codedoc code>[root@qaprod ~]# iscsiadm -m discovery -t sendtargets -p 10.10.8.201
10.10.8.201:3260,1 iqn.2012-09.CertStorage:isci-on-iscsiSet
[root@qaprod ~]# iscsiadm -m node -T
iqn.2012-09.CertStorage:iscion-iscsiSet --portal 10.10.8.201:3260 --login
Logging in to [iface: default, target: iqn.2012-09.CertStorage:iscion-iscsiSet,
portal: 10.10.8.201,3260]
Login to [iface: default, target: iqn.2012-09.CertStorage:isci-on-iscsiSet,
portal: 10.10.8.201,3260] successful.
[root@qaprod ~]# fdisk -l
Disk /dev/sda: 500.1 GB, 500107862016 bytes
255 heads, 63 sectors/track, 60801 cylinders
Units = cylinders of 16065 * 512 = 8225280 bytes
Sector size (logical/physical): 512 bytes / 512 bytes
I/O size (minimum/optimal): 512 bytes / 512 bytes
Disk identifier: 0x00018542
Device Boot
/dev/sda1
Start
*
End
1
Blocks
64
Id
512000
System
83
Linux
8e
Linux LVM
Partition 1 does not end on cylinder boundary.
/dev/sda2
64
60802
487873536
Disk /dev/dm-0: 53.7 GB, 53687091200 bytes
255 heads, 63 sectors/track, 6527 cylinders
Units = cylinders of 16065 * 512 = 8225280 bytes
Sector size (logical/physical): 512 bytes / 512 bytes
I/O size (minimum/optimal): 512 bytes / 512 bytes
Disk identifier: 0x00000000
Disk /dev/dm-0 doesn't contain a valid partition table
Disk /dev/dm-1: 10.3 GB, 10284433408 bytes
255 heads, 63 sectors/track, 1250 cylinders
Units = cylinders of 16065 * 512 = 8225280 bytes
Sector size (logical/physical): 512 bytes / 512 bytes
I/O size (minimum/optimal): 512 bytes / 512 bytes
Disk identifier: 0x00000000
263
CHAPTER XI Connecting to ElastiStor
Disk /dev/dm-1 doesn't contain a valid partition table
Disk /dev/dm-2: 435.6 GB, 435607830528 bytes
255 heads, 63 sectors/track, 52959 cylinders
Units = cylinders of 16065 * 512 = 8225280 bytes
Sector size (logical/physical): 512 bytes / 512 bytes
I/O size (minimum/optimal): 512 bytes / 512 bytes
Disk identifier: 0x00000000
Disk /dev/dm-2 doesn't contain a valid partition table
Disk /dev/sdb: 1073 MB, 1073741824 bytes
255 heads, 63 sectors/track, 130 cylinders
Units = cylinders of 16065 * 512 = 8225280 bytes
Sector size (logical/physical): 512 bytes / 512 bytes
I/O size (minimum/optimal): 4096 bytes / 1048576 bytes
Disk identifier: 0x4408a443
Device Boot
Start
/dev/sdb1
End
1
Blocks
131
Id
1045504
System
7
HPFS/NTFS
Partition 1 has different physical/logical endings:
phys=(129, 254, 63) logical=(130, 42, 40)
[root@qaprod ~]# fdisk /dev/sdb1
WARNING: DOS-compatible mode is deprecated. It's strongly recommended to
switch off the mode (command 'c') and change display units to
sectors (command 'u').
Command (m for help): m
Command action
a
toggle a bootable flag
edit bsd disklabel
toggle the dos compatibility flag
delete a partition
list known partition types
print this menu
add a new partition
create a new empty DOS partition table
print the partition table
quit without saving changes
create a new empty Sun disklabel
change a partition's system id
change display/entry units
verify the partition table
write table to disk and exit
extra functionality (experts only)
Command (m for help): n
Command action
e
extended
primary partition (1-4)
264
CHAPTER XI Connecting to ElastiStor
p
Selected partition 1
First cylinder (1-1008, default 1):
Using default value 1
Last cylinder, +cylinders or +size{K,M,G} (1-1008, default 1008):
Using default value 1008
Command (m for help): w
The partition table has been altered!
Calling ioctl() to re-read partition table.
</codedoc>
With CHAP authentication
For all targets
1. Open /etc/iscsi/iscsid.conf using an editor and then specify the details for the following section:
<codedoc code node.session.auth.authmethod = CHAP
node.session.auth.username = <CHAP username>
node.session.auth.password = <CHAP secret>
node.session.auth.username_in= <Mutual CHAP username> (give only when you are doing mutual CHAP)
node.session.auth.password_in = <Mutual CHAP secret>
(give only when you are doing mutual CHAP)
discovery.sendtargets.auth.authmethod = CHAP
discovery.sendtargets.auth.username = <CHAP username>
discovery.sendtargets.auth.password = <CHAP secret>
discovery.sendtargets.auth.username = <Mutual CHAP username>
discovery.sendtargets.auth.password_in = <Mutual CHAP secret>
(give only when you are doing mutual CHAP)
(give only when you are doing mutual CHAP)
</codedoc>
2. Restart the iSCSI daemon using the following command: /etc/init.d/iscsi restart.
3. Follow the procedures in the section "Without CHAP authentication".
For as specific target
Specify the details as follows at command prompt:
iscsiadm -m node -T "<Target_Name>" -p <VSM_IP_address>:<port> -op=update --name node.session.auth.authmethod --value=CHAP
iscsiadm -m node -T "< Target_Name > -p < VSM_IP_address >:<port> -op=update --name node.session.auth.username --value=<CHAP_username>
iscsiadm -m node -T "< Target_Name > -p < VSM_IP_address >:<port> --op=update
--name node.session.auth.password --value=<password>
iscsiadm -m node T "<Target_ Name>" -p < VSM_IP_address >:<port> -l
265
CHAPTER XI Connecting to ElastiStor
Resizing iSCSI LUN
The following sections explain how to expand your iSCSI storage volume on CentOS:
l
"Mapping iSCSI LUN"
"Editing Quota Size (in ElastiCenter)"
"LUN expansion and resizing file system (on CentOS Console)"
Exporting the iSCSI LUN (On CentOS Console)
In the CentOS console, run the commands provided in the table in sequence to export the iSCSI LUN:
Step
Task
Command
Example
Discover the iSCSI targets.
Log in to the iSCSI target. iscsiadm -m node -T <Complete Target Name> -l
Display the current partitions on the hard disk.
fdisk l
Create a file system on
the hard disk drive.
mkfs.ext3 <Partition name>
mkfs.ext3 /dev/sdc
Create a directory.
mkdir <Directory name>
mkdir /mnt/cbdata
Mount the partition into
your directory.
mount <Partition name>
<Directory name>
mount /dev/sdc /mnt/cbdata
-o sync
df kh
(Optional) Retrieve the
current size of the mounted LUN.
Copy some data to the
directory /mnt/cbdata.
cp
Unmount directory from
the disk.
umount <Directory name>
umount /mnt/cbdata
10
Log out of iSCSI target.
iscsiadm -m node -u -T
<Complete target name> -p
<Target IP Address>
iscsiadm -m node -u -T
iqn.2014-02.Acc1.TSM3:TSM3TSM3ISCSI11 -p
11.11.11.11
iscsiadm -m discovery -t
st -p <Target IP Address>
Editing Quota Size (in ElastiCenter)
1. In the ElastiCenter, select Storage Volumes.
2. In the Storage Volumes page, click Settings > Edit.
266
iscsiadm -m discovery -t st
-p 11.11.11.11
Details
Outputs the complete
target name.
iscsiadm -m node -T
iqn.2014-02.FCAcc.Test:FCAcciscsivol1 -l
The partition is displayed in the output.
At prompt, confirm by
typing y as shown in the
following example:
/dev/sdc is entire
device, not just one partition! Proceed anyway?
(y,n) y
CHAPTER XI Connecting to ElastiStor
3. Increase the Quota size of the LUN and then click Save.
LUN expansion and resizing file system (on CentOS Console)
In the CentOS console, run the commands provided in the table in sequence to expand the LUN and resize the file system:
Step
Task
Command
Example
Log in to iSCSI target.
iscsiadm -m node -T <Complete target name> -p
<Target IP Address> l
Display current partitions on
the hard disk.
fdisk l
Mount the partition into the
directory.
mount partition name <Dir- mount /dev/sdb /mnt/cbdata/
ectory name> -o sync
-o sync
Resize the expanded volume.
resize2fs /dev/sdb/ total
space of volume
Retrieve the current size of
the resized LUN.
df kh
Details
iscsiadm -m node -T
iqn.2014-02.Acc1.TSM3:TSM3TSM3ISCSI11 -p
16.10.10.3 l
Check the output
to see if the disk
size has
increased.
resize2fs /dev/sdb/ 5G
In this example,
5G is the total
space on the resized Volume.
On Windows Server 2008
Discovering the iSCSI target
Note: The mapping procedures are similar for other versions of Windows Server. However, there might be minor variations
owing to the differences in UI strings and navigation.
267
CHAPTER XI Connecting to ElastiStor
1. Ensure that you have enabled iSCSI. For details, see "Data access using iSCSI".
2. On Windows Server 2008, launch iSCSI Initiator (Programs > Administrative Tools > ISCSI Initiator).
3. In the Target tab, specify the target (tenant IP address).
4. Click Quick Connect. The Quick Connect screen appears, displaying the target name.
5. Click Done.
Create storage drive to use the iSCSI target
1. Launch Server Manager and then select Disk Management in the left pane.
268
CHAPTER XI Connecting to ElastiStor
2. Right-click the unallocated space (the highlighted section) and then select Initialize Disk. The Initialize Disk dialog box
appears.
269
CHAPTER XI Connecting to ElastiStor
3. Click OK.
4. Right-click in the space and then select New Simple Volume as shown in the following screen:
270
CHAPTER XI Connecting to ElastiStor
The New Simple Volume wizard appears.
5. Follow the instructions to complete the wizard, to create the partition.
6. Ensure that the created disk is added to the Disk management console.
On Kernel-based Virtual Machine
Note:The following section provides procedures performed on RHEL 6.3. The procedures might be similar on other flavors of
Linux.
1. On your Linux desktop, select Applications > System Tools > Virtual Machine Manager.
2. Select a host machine.
3. Click Edit > Connection Details.
271
CHAPTER XI Connecting to ElastiStor
4. Click Storage tab.
5. Click the Add Storage Pool + icon at the bottom left side of the dialog box. The Add a New Storage Pool wizard appears.
6. Specify a name for the Pool, select iSCSI as the type, and then click Forward.
272
CHAPTER XI Connecting to ElastiStor
7. In the following screen, specify the required details.
Field
Target Path
Description
Path of the target directory (to use for the Storage Pool).
273
CHAPTER XI Connecting to ElastiStor
Host Name
Host name or IP address of the iSCSI target.
Source Path
iSCSI target IQN.
IQN
Select the check box and then enter the IQN for the initiator.
8. Click Finish.
Mapping CIFS share to the clients
On Windows Server 2008/Windows Server 2012
The following procedures explain how to map CIFS share from CloudByte ElastiStor on Windows Server 2008/Windows Server
2012.
On Windows Server 2008
Note: The mapping procedures are similar for other versions of Windows Server. However, there might be minor variations
owing to the differences in UI strings and navigation.
1. Ensure that you have enabled CIFS. For details, see "Data access using CIFS".
2. On Windows Server, launch Map Network Drive dialog box (Computer > Map Network Drive).
3. Specify IP address of VSM and its access path in the following format:\\<VSM IP Address>\<Access Path>.
4. Click Finish.
5. (If you are using the VSM for the first time) At prompt, specify the credentials in the Enter Network Password dialog box. This
is the username and password that you have created for the account user in ElastiCenter.
274
CHAPTER XI Connecting to ElastiStor
6. Click OK.
7. (If again prompted) Specify the credentials in the Enter Network Password dialog box.
8. Ensure that CIFS share is connected, as shown in the following screen:
On Windows Server 2012
The following procedures explain how to map CIFS share from CloudByte ElastiStor on Windows Server 2012.
Discovering the CIFS share
Note: The mapping procedures are similar for other versions of Windows Server. However, there might be minor variations
owing to the differences in UI strings and navigation.
275
CHAPTER XI Connecting to ElastiStor
1. Ensure that you have enabled CIFS. For details, see "Data access using CIFS".
2. On Windows Server 2012, launch Map Network Drive dialog box (Computer/Shortcut on Desktop to Computer > Map Network Drive).
The Map Network dialog box appears.
3. (If you are using the VSM for the first time) At prompt, specify the credentials in the Enter Network Password dialog box. This
is the username and password that you have created for the account user in ElastiCenter.
276
CHAPTER XI Connecting to ElastiStor
4. Click Finish.
5. (If again prompted) Specify the credentials in the Enter Network Password dialog box.
6. Ensure that CIFS share is connected, as shown in the following screen:
Mapping NFS share to clients
On Red Hat Enterprise Linux
Note:The mapping procedures are similar for other flavors of Linux.
1. Ensure that you have enabled the NFS. For details, see "Data access using NFS".
2. On your RedHat Enterprise Linux server, at command prompt, specify the following command to verify the NFS export:
showmount -e <tenant IP address>
277
CHAPTER XI Connecting to ElastiStor
If correctly exported, the path to the filesystem along with the authorized network is displayed.
3. Create a directory to mount the NFS using the following command: mkdir <directoryname>
4. Mount the NFS on this directory using the following command: mount -o mountproto=tcp <tenant IP
address:>/<exported path><directoryname>
5. Enter the following command: mount
6. If successfully mounted, the following is displayed in the mount list: <tenant IP address>:<exportpath> on <directoryname> type nfs (rw,addr=<tenant IP address>)
Sample CLI snapshot
[root@localhost ~]# showmount -e 20.10.26.199
Export list for 20.10.26.199:
/acctsample (everyone)
#Here everyone implies that the exported path is shared to all (as configured in NFS page).
If you specify a specific client IP, that IP is displayed.
[root@qaprod ~]# mkdir /mnt/nfslocal
[root@qaprod ~]# mount -t nfs -o vers=3,proto=tcp,nolock,sync 20.10.26.199:/acctsample /mnt/nfslocal/
[root@qaprod ~]# mount
/dev/mapper/VolGroup-lv_root on / type ext4 (rw)
proc on /proc type proc (rw)
sysfs on /sys type sysfs (rw)
devpts on /dev/pts type devpts (rw,gid=5,mode=620)
tmpfs on /dev/shm type tmpfs (rw,rootcontext="system_u:object_r:tmpfs_t:s0")
/dev/sda1 on /boot type ext4 (rw)
none on /proc/sys/fs/binfmt_misc type binfmt_misc (rw)
sunrpc on /var/lib/nfs/rpc_pipefs type rpc_pipefs (rw)
gvfs-fuse-daemon on /root/.gvfs type fuse.gvfs-fuse-daemon (rw,nosuid,nodev)
20.10.26.199:/acctsample on /mnt/nfslocal type nfs
(rw,sync,vers=3,mountproto=tcp,addr=20.10.26.199,mountaddr=20.10.26.199)
On Kernel-based Virtual Machine
Note:The following section provides procedures performed on RHEL 6.3. The procedures might be similar on other flavors of
Linux.
1. On your Linux desktop, select Applications > System Tools > Virtual Machine Manager.
2. Select a host machine.
3. Click Edit > Connection Details.
278
CHAPTER XI Connecting to ElastiStor
4. Click Storage tab.
5. Click the Add Storage Pool + icon at the bottom left side of the dialog box. The Add a New Storage Pool wizard appears.
6. Specify a name for the Pool, select Network Exported Directory as the type, and then click Forward.
279
CHAPTER XI Connecting to ElastiStor
7. In the following page, specify the required details.
Field
Target Path
Format
Path of the target directory (to use for the Storage Pool).
Set the Format option to NFS.
Host Name
Host name or IP address of the NFS Server.
Source Path
Enter the NFS path (path on the Host that is being shared).
8. Click Finish.
280
Description
CHAPTER XII Frequently asked questions
CHAPTER XII Frequently asked questions
Product FAQs
Is it possible to scale-out using CloudByte ElastiStor?
Each CloudByte ElastiStor node can be scaled to 1 PB of raw storage capacity. You can linearly increase capacity and performance
by adding additional ElastiStor nodes.
Can I use ElastiStor to improve the performance of storage solutions such as EMC Symmetrix or
Hitachi Unified Storage?
Like other storage systems, CloudByte ElastiStor is an independent storage system with distinct architecture.
ElastiStor does not improve performance but shares the performance between competing applications granularly in a desired way.
However, CloudByte recommends you to use raw disk for storage media rather than storage from other vendors.
Note: In ElastiStor 1.4, support is limited to SAS connected disk arrays (and not any other storage product beneath).
How many flavors and versions of CloudByte ElastiStor are available in the market?
CloudByte ElastiStor 1.0 was the pioneering release of the product. The ongoing release is CloudByte ElastiStor 1.3.2.
Which RAID levels are supported by CloudByte ElastiStor?
RAID5, RAID6, RAID10, RAID50, RAID60.
Are there any CloudByte ElastiStor management plug-ins available?
Yes. The plugins for VMWare vCenter and OpenStack Cinder are available off-the-shelf.
Can I use the same IP address for multiple tenants?
Each tenant is identified by unique IP address.
Does ElastiStor support iPV6?
Current version of CloudByte ElastiStor does not have built in support for iPV6.
What is the skill set required to manage and configure ElastiStor?
Basic storage administration (SAN and NAS) and networking skills.
Provide ElastiStor specifications in terms of the supported number of logical table entries, for
example, the maximum number of simultaneous tenant networks, maximum number of storage
clients, maximum number of LUNs, maximum number of NFS mount points, etc.
ElastiStor does not have theoretical limitations on the number of Storage Volumes, VLANs and VSMs per Node as revealed in the
tests done with 12000 Volumes. Also, ElastiStor supports unlimited snapshots and clones. For details, see ElastiStor Scalability
281
CHAPTER XII Frequently asked questions
The CloudByte documentation ( http://www.docs.cl oudby te.com/ena bl ing-out-of-ba nd-communica tionbetween-nodes-in-a n-ha -group/ ) refers to configuring IPMI between Nodes in an HA Group. Is such a
configuration required for ElastiCenter HA also?
No. IPMI based out of band communication between peer Nodes is used during Node HA process when necessary. This configuration is not mandatory for ElastiCenter HA. However, it is helpful to have the IPMI configured for the regular remote access and
troubleshooting.
Is SNMP monitoring support available on ElastiStor?
Yes.
Is SNMP based IOPS and capacity monitoring support available on ElastiStor?
SNMP support for volume statistics such as IOPS will be available in the future releases.
How to configure a spare disk?
Follow the procedures at the URL http://www.docs.cloudbyte.com/disk-replacement-scenarios/ .
In pages where Graphs ought to appear, I see a message invalid data throughout ElastiCenter.
Why?
Try using a different browser.
Adobe Flash is required to see the charts. For details, see http://www.docs.cloudbyte.com/wp-content/uploads/CloudByte_troubeshooting_invalid-data_graphs.pdf . Future releases will provide HTML5 support.
How to set up a secondary ElastiCenter manually?
This scenario applies if you haven't configured ElastiCenter HA during installation. If ElastiCenter fails, you can promote the secondary ElastiCenter to primary ElastiCenter. For procedures, see Setting up secondary ElastiCenter
I am unable to access ElastiCenter on the browser Chrome (version 45). Is there a workaround
to access ElastiCenter?
Yes. Do the following to access ElastiCenter on Google Chrome version 45:
1. SSH to ElastiCenter as root.
2. Download the server.xml file from the following URL: http://cloudbyte.com/downloads/server.xml
3. Backup the existing xml file in the location /usr/local/apache-tomcat-6.0.33/conf/server.xml
4. Run the following command to replace the existing server.xml file with the new xml (that you downloaded): cp new_
server.xml /usr/local/apache-tomcat-6.0.33/conf/server.xml
5. Run the commands to restart Tomcat service:
1. /usr/local/apache-tomcat-6.0.33/bin/shutdown.sh
2. pgrep java
3. (Optional, if the java service is running) pkill java
4. /usr/local/apache-tomcat-6.0.33/bin/startup.sh
6. Open a new tab in the browser.
7. Launch ElastiCenter.
282
CHAPTER XII Frequently asked questions
I encountered the error weak ephemeral Diffie-Hellman key while trying to access ElastiCenter. I
am using Mozilla Firefox version 39 browser. Is there a workaround to access ElastiCenter?
Yes. Do the following to access ElastiCenter on Mozilla Firefox version 39:
1. Launch Mozilla Firefox browser.
2. In the Address bar, type the following:
about:config
.
3. In the Search bar, search for the following parameter:
security.ssl3.dhe_rsa_aes_128_sha
4. Set the parameter to
false (security.ssl3.dhe_rsa_aes_128_sha = false)
by doing either of the following:
l
Right click the parameter and then select Toggle.
Double click the parameter.
5. Repeat step 3 and step 4 for the parameter
security.ssl3.dhe_rsa_aes_256_sha
6. Open a new tab in the browser.
7. Launch ElastiCenter.
I cannot access the configuration file config.xml from ElastiCenter. How can I access it otherwise?
The following procedures let you manually restore a earlier file version to its original location:
1. Move the Node to Maintenance mode. For details, see "Configuring High Availability"
2. Run the following command to copy the latest config.xml file from the backup location: cp /var/backups/node/config.xml YYYY-MM-DD-HH-00-00 /cf/conf/config.xml.
YYYY-MM-DD-HH-00-00 is the date and time when the file was backed up .
3. Move the Node to available mode. For details, see "Configuring High Availability"
283
CHAPTER XII Frequently asked questions
Does ElastiStor support NPIV?
No
What is API key?
The API Key is used to authenticate the CloudByte REST API token requests. See, "CloudByte ElastiStor API references" to
obtain a Rest API Key.
Installation FAQs
I cannot access CloudByte ElastiCenter after successful installation. Why?
This might be because of one of the following reasons:
l
Java Service is not running
Database is not up and running
To resolve this issue, do either or both of the following:
1. In the ElastiCenter server, at command prompt, run the following command: pgrep mysql.
If you do not get the MySql process ID, run the following command to bring up the database service: service mysqlserver onerestart
2. In the ElastiCenter server, at command prompt, run the following: pgrep java.
If you don't get the Java process ID, run the following command to bring up the Java service: service cbdevman onerestart
3. Try accessing ElastiCenter.
Can you explain the memory requirements for installing CloudByte ElastiStor?
The following table provides the details. The values are same for installing both Node and ElastiCenter. Also, the same values apply
if you install both Node and ElastiCenter on the same machine:
Memory
Minimum
Recommended
RAM
1 GB
8 GB or higher
Hard Disk
20 GB
(2.4 X RAM size + 32 GB) or higher. For example, if the RAM is 8 GB, for better performance, 52 GB or
higher is recommended
If you do not comply with the recommended hard disk memory, you might encounter a message that prompts correction (for better
performance). However, if you meet the minimum memory requirements, even if you ignore the message, installation will be successful.
284
CHAPTER XII Frequently asked questions
I get the message 'Installation cannot proceed as no NIC is present'. What will I do?
You encounter this issue because the NIC that you use is not supported. For a list of supported NICs and other hardware, see the
Hardware Compatibility List .
I get the message 'Installation cannot proceed as no disk is present'. What will I do?
This is because the internal RAID/SAS card in the server is not supported. For a list of supported disks and other hardware, see the
Hardware Compatibility List .
What if I get a mountroot during installation?
Retry installing by reinserting the CD. Also ensure that there are no network issues.
If the issue persists, use the following command to proceed: mountroot > cd9669:/dev/cd0 ro
Why am I not able to access the system after the first reboot post installation?
Verify the following:
n
ElastiStor has correctly rebooted. This is indicated by the root login prompt when the installation concludes.
Network port connectivity
Network details are correctly added
Will the installation rollback on failure?
Yes
Explain the upgrade options for ElastiStor?
You can upgrade based on the option that you have selected in the existing installation. That is, if you have opted to install both
Node and ElastiCenter, then you have the option to upgrade both.
What happens to the installation when there is a hard disk failure?
Installation may or may not be successful, but the product is unlikely to function.
What happens if the CD ROM gets disconnected while installing?
Reconnect and start the installation from the beginning.
Do I need an internet connection for installing CloudByte?
No. But it is recommended because it facilitates time synchronization with NTP.
What happens if the network connection is lost and system boots after installing?
It waits for the connectivity to be restored and then boots up.
What happens to the installation during a power loss?
You have to reinstall.
285
CHAPTER XII Frequently asked questions
Can I install ElastiStor on my laptop?
Yes. If you meet the minimum hardware requirements, the installation is not device dependent.
Can I install ElastiCenter on a virtual machine?
Yes. CloudByte recommends that you have a minimum RAM of 8 GB on your VM.
Is ElastiStor installation possible over SAN boot?
Yes
Can I downgrade my ElastiStor installation?
Not currently supported
Can I do a network installation of CloudByte ElastiStor?
To perform a network installation of CloudByte ElastiStor, you have to set up a PXEserver and then perform a network boot.
After I installed ElastiCenter on ESX 5.0, my virtual machine stopped responding. Why?
If your virtual machine on ESX 5.0 hangs, do the following:
1. (In the ElastiCenter command prompt) Run the following command: sysctl kern.timecounter.hardware=ACPIfast
2. Run the following command to edit the loader.conf file: vi /boot/loader.conf
3. Append the loader.conf with the following line: kern.timecounter.hardware=ACPI-fast
I did not come across the ElastiCenter HA option while installing ElastiCenter. Why?
The option to configure ElastiCenter HA is available only when you choose the installation option Both ElastiCenter and Node i.e.,
installing both ElastiCenter and Node on a single machine. For details, see http://www.docs.cloudbyte.com/installing-both-elasticenter-and-node/
Can I back up ElastiCenter even if I havent configured ElastiCenter HA?
Yes. You can setup a secondary ElastiCenter (secondary setup) to ensure backup in the case your primary ElastiCenter (primary
setup) fails. If a failure occurs, you can promote your secondary setup. For details, see http://www.docs.cloudbyte.com/cloudbyteelastistor-product-faqs/promoting-secondary-elasticenter-and-backing-up-configurations/
Does installing ElastiCenter in HA mode involve any manual procedures?
No. During installation, one ElastiCenter is installed as primary and the second one as secondary.
Is it mandatory to have ElastiCenters and ElastiStor Nodes on the same subnet?
Not necessary for them to be on the same Subnet as long as the IP address is reachable.
286
CHAPTER XII Frequently asked questions
Pool FAQs
What is the recommended storage pool RAID configuration?
If you need high performance, mirroring is recommended. For larger SATA drives (for example 4TB), CloudByte recommends
RAIDz2.
How can I expand the tpool size?
1. SSH to the Node.
2. Run the following command: cd /usr/local/cb/bin.
3. Run the following to expand the tpool size: ./expandtpool OS_disk_name. For example, ./expandtpool ada0
The size of the tpool increases by 10G.
Can I create a mixed disk pool, for example with SATA and SSD disks?
Yes. But CloudByte does not recommend this because you get only the performance of the lowest disk; in this case SATA.
How many log devices can I attach to a Pool?
Depends on the workload. For instance, in a WRITE intense scenario, a higher ZIL improves your WRITE performance.
How much L2ARC should I add to the Pool?
Depends on the workload. For instance, in a READ intense scenario, a higher L2R improves READ performance.
How to improve the performance of L2ARC and the log device?
L2ARC and log device are intended to improve the READ and WRITE respectively. Therefore, high performance SSD storage is
recommended for an L2ARC or ZIL
What Pool do you recommend for a data protection use case?
A large RAIDz Group with high performance data disks and one or two parity disks are ideal.
What is the recommended RAID-Z configuration?
For RAID-Z1, RAID-Z2, and RAID-Z3 CloudByte recommends a 2^n + p configuration.
Parameter
Description
RAID-Z 1, RAID-Z 2, and RAID-Z 3.
Parity: p=1 for RAID-Z1, p=2 for RAID-Z2 and p=3 for RAID-Z3 where RAID-Z1 = 3, 5, 9, 17, , RAID-Z2 = 4, 6, 10,
18, , RAID-Z3 = 5, 7, 11, 19,
Is single parity RAID equivalent to well known RAID 5?
Almost similar. Also it eliminates the WRITE HOLE problem in RAID 5.
Is double parity RAID equivalent to well known RAID 6?
Almost similar. Also, it eliminates the WRITE HOLE problem in RAID 5.
287
CHAPTER XII Frequently asked questions
What is RAID triple parity and when should I use it?
RAID triple parity tolerates failure of three disks in a RAID group. Use it when you handle critical data and want to evade chances of
disk failure.
Do you recommend NFS/CIFS/ISCSI/FC setup on the same Pool or should I have the access protocols set up on different Pools?
It doesn't matter. Configure based on the usage and requirement.
Can a VSM span multiple Pools?
Not in the current release.
Is Pool IOPS derived from the disk?
Disk plays a role in deriving IOPS, but is also based on RAM and L2ARC.
Can I extend the Pool IOPS by extending the Pool?
Yes
Can I delete a Pool with active Storage Volume?
No
Can I identify the failed disks in a Pool?
ElastiCenter Alerts provides you with the details.
What happens if you pull a disk from a Pool that has a spare disk?
Spare disk is attached to the Pool.
What happens if you pull a disk from a Pool that does not have a spare disk?
Leaves the Pool in a degraded list.
How do I disable SCSI reservation on disks?
Warning: Do not disable SCSI reservation on production environments. The following procedures are recommended only for
troubleshooting on development and testing setups.
1. Make an SSH connection to the Node.
2. Run the following command touch /etc/disablescsi.
When you move your setup from test to production environment, ensure that all disks are SCSIreservation-enabled.
Do the following to enable SCSI reservation:
1. Make an SSH connection to the Node.
2. Run the following command rm /etc/disablescsi.
288
CHAPTER XII Frequently asked questions
How will I clear the pools created in an older setup?
If you add a new Pool on the disks being consumed by existing Pool, it will be deleted automatically. However, to manually clear the
Pools from an older setup, do either of the following (depending on the scenario):
l
Reinstalled ElastiStor without removing the Pools: In the Nodes page, go to the section Existing Pools (at the
bottom of the page) and then click the Clear link under the column Clear.
Connected disk arrays (with Pools) to a different Node: Apply Refresh Hardware after connecting to the new
Node. All existing Pools are displayed in the Nodes page. Go to the section Existing Pools (at the bottom of the page) and
then click the Clear link under column Clear.
How do I configure partial failover?
CloudByte ElastiStor supports selective failover of Pools. If partial failover is enabled, in the case of network failure, the secondary
node in the cluster takes over.
By default, partial failover is enabled. If not enabled, go to the Pool settings and enable.
1. In ElastiCenter, select Pools in the left pane.
2. In the Pools page, select the Pool for which you want to enable partial failover.
3. In the Actions pane, select Settings.
4. Click Edit and then enable partial failover.
Access Protocol FAQs
Can I use the same secret key for mutual authentication in the case of LUN export?
No. The key must be unique.
What is the maximum number of NFS or iSCSI LUNs that you can have on ElastiStor?
You can create N number of NFS or iSCSI LUNs, based on your requirement.
289
CHAPTER XII Frequently asked questions
Can I send an I/O of 1MB size in a single request on NFS?
Yes. NFS volumes are currently allowed to be mounted with an rsize/wsize of 1M.
Can I disable the configuration options related to the protocols I do not use, in ElastiCenter?
Yes. The current release supports disabling of FC-specific options.
1. In the ElastiCenter, click admin > Global Settings.
2. Go to ui.protocol.enablefc, click the Edit icon, and then specify false.
3. For the changes to take effect, either relogin to ElastiCenter or refresh the browser.
All FC-specific options disappear from ElastiCenter UI.
When I use FC I see a LUN with the ID 0 and size 1MB displayed though i did not create it. Why?
This is a system LUN and is not for use.
Deleting data on my CIFS share doesnt increase the free space. Why?
This is because the data is not permanently deleted. Instead, data is moved to the CIFS share recycle bin. To delete data permanently, do the following:
On ElastiCenter
1. In the Storage Volumes page, select a CIFS Storage Volume.
2. Click Manage CIFS configuration in the actions pane.
3. Click Edit and then disable the CIFS share Recycle bin option.
290
CHAPTER XII Frequently asked questions
4. Click Save.
On Windows client
If you have not disabled this option (earlier) and then data is already moved to the CIFS share Recycle Bin, to clear the data, you
must do the following:
291
CHAPTER XII Frequently asked questions
(If Show hidden files and folders option is enabled) Go to the folder .recycle and then clear the data.
(If Show hidden files and folders option is disabled) Do the following:
1. Go to Control Panel > Folder Options > View tab.
2. Enable hidden files, folders, and drives. Now you can view the .recycle folder.
3. Clear the data.
I am on a common NFS Share. Is there a way to restrict an other user on this share from deleting
my files?
Yes. If you want a home directory kind of nfs share, when configuring the NFS Storage Volume (see the following screen), set the
option Map as Root Users to No.
I changed the primary IP address of the VSM. Now I cannot access the iSCSI Storage Volumes.
What should I do?
1. Log out of all the iSCSI Volumes on the clients.
2. Delete the login entries of the VSM on the clients.
3. Relogin to the clients with the new IP address.
292
CHAPTER XII Frequently asked questions
Storage Volume FAQs
Can I migrate a Storage Volume?
No. You can migrate only VSMs.
Can I mirror a Storage Volume?
You can do a DR of your storage volume.
Can I keep Storage Volume in a sleep state?
No.
Can a Storage Volume span multiple pools?
No.
Will enabling compression and deduplication impact performance?
Yes, they can significantly impact. Compression and deduplication are CPU and memory intensive processes.
What is the right latency for Storage Volume?
Depends on the disk from which the Pool is created. For example, SSDs are of lower latency when compared to SATA.
293
CHAPTER XII Frequently asked questions
I enabled READ-only property for iSCSI Volume mounted on a Windows client, and observe that
the property hasn't taken effect. How can I make the Volume READ only?
For the READ-only property to take effect, disconnect the iSCSI Volume and then remount it on the Client.
Can I have Storage Volumes with same names under different accounts?
Yes.
Can the storage capacity be changed after configuring a Storage Volume?
Yes.
QoSFAQs
What is QoS?
Assuring your client/application the promised IOPS, throughput, and latency.
Is QoS applicable only to Cloud Service Providers?
No. QoS is applicable to enterprise scenarios as well.
What is the maximum IOPS I can set?
The maximum IOPS directly depends on the underlying storage. SSD is the best choice followed by SAS and SATA.
Is QoS disk dependent?
Yes
Is QoS a licensed option?
No
What is the difference between dedicated and shared options?
Dedicated: If the Storage Volume needs exclusive QoS configuration.
Shared: If the Storage Volume can share the QoS configuration with another Storage Volume.
The following figure explains the concepts:
294
CHAPTER XII Frequently asked questions
For example, if both Storage Volume 1 and Storage Volume 2 are committed to busy service round the clock, Dedicated would be
your choice. Whereas, if Storage Volume 1 and Storage Volume 2 represent services in a cross-geographical setup where activities
related to Storage Volume 1 end toward the time activities related to Storage Volume 2 start, Shared would be your choice.
Do I have to set all the QoS parameters (IOPS, Latency, and Throughput)?
No. IOPS is a must. Depending on requirement, you can choose to configure Latency and Throughput.
What is the difference between IOPS, Latency, and Throughput?
IOPS: The READ/WRITE capability.
Latency: Time that ElastiStor takes to acknowledge a READ/WRITE back to the client.
Throughput: Data that can be transferred as part of READ/WRITE operations.
Is it a must to set QoS?
Yes
Can I increase/decrease QoS on-the-fly?
Yes
Is QoS guaranteed in an HA environment?
Yes
What are the recommended QoS settings in an HA environment?
In multiway HA, for example in a two-way HA, each Node should be provisioned a maximum of up to 50 percent of the capacity
295
CHAPTER XII Frequently asked questions
Can I set QoS for my backups?
Yes
Can I set QoS for my DR operations?
Yes
Can I get the same QoS on the secondary Node in the case of a disaster?
Yes, provided you have the same or better infrastructure quality.
What is the upper limit for setting FC LUNS?
255 per target
How do you calculate IOPS, latency, and throughput?
Throughput = IOPS * Block Size.
Latency depends on the following factors:
l
Workload characteristics such as L2ARC Size and ZIL size.
Seek time on the disk
Workload access patterns such as sequential, random, read only, read write, write only.
Speed of the underlying disks, that is, if spinning disks such as SAS or SATA or faster ones such as SSDs
Dataset cached in the L1ARC caches and L2ARC caches.
Presence of Intent log ZIL to log the writes and respond quickly.
How the ZIL is configured, that is if it is on spinning disks or SSD disks.
Underlying RAID configuration, for example striped or mirrored.
System load in terms of CPU cycles available.
Can I set QoS for my backups?
Not for the current release.
Can I set QoS for my DR operations?
Not for the current release.
Can I get the same QoS on the secondary Node in the case of a disaster?
Yes, provided the secondary node has same system configuration as the primary.
When do I use Grace?
Particularly useful when you check if the IOPS and throughput set for a particular Storage Volume are correct. If a particular Storage
Volume is continuously eating up grace, it is an indication that it is over-provisioned and deserves more IOPS/throughput.
296
CHAPTER XII Frequently asked questions
How can I compare the QoS values of selected Volumes?
1. In CloudByte ElastiCenter, click Pools in the left pane.
2. In the Pools page, select the Pool for which you want to compare the QoS values of the selected Storage Volumes.
3. Select the Storage Volumes.
4. Select the QoSparameter (IOPS, throughput, or latency) that you want to compare.
5. Click Update.
The chart on top of the page displays the comparison with time stamp as the reference.
High Availability FAQs
The Node fails to move back to available mode. Why?
In the case of failure, verify the storage connectivity and check for any error messages in the View Jobs (HAGroup > select the specific HAGroup > actions pane > Tasks). If you cannot resolve, contact Technical Support.
How do I configure redundant management NIC?
You can establish a highly available network connection with a redundant (backup) network interface. The redundant network interface protects against network failures. If the active management network interface becomes unavailable, the system automatically
switches to the redundant interface to maintain availability.
Assumptions
l
Management interface is named em0
Backup interface is named em1
Node has been added on ElastiCenter.For details, see Adding a Node.
Procedures
Do the following to set up em1 as the redundant network interface:
1. Log in to ElastiStor Node as root.
2. Run the following command to edit the config.xml: vi /cf/conf/config.xml
3. In the config.xml, search for the tag <type>webgui</type> and specify the following as the next line: backupif>Management_Interface/backupif>
For example,
<if>em0</if>
<type>webgui</type>
<backupif>em0</backupif>
4. In the config.xml, search for <if>Backup_interface</if> and specify the following as the next line:<backupif>Backup_interface</backupif>
For example,
<if>em1</if>
<backupif>em0</backupif>
Sample Snippet
<lan>
<uuid>fbfaf211-fd6d-4a70-984a-9642720b9d61</uuid>
<if>em0</if>
<backupif>em1</backupif>
<ipaddr>192.168.16.23</ipaddr>
<subnet>24</subnet>
297
CHAPTER XII Frequently asked questions
<type>webgui</type>
<gateway>192.168.16.1</gateway>
<status>active</status>
<mtu>1500</mtu>
</lan>
<lan>
<status>active</status>
<subnet>none</subnet>
<uuid>5b0fa24e-463c-4933-817b-94b94129445c</uuid>
<ipaddr>none</ipaddr>
<mtu>1500</mtu>
<type>none</type>
<gateway>none</gateway>
<if>em1</if>
<backupif>em0</backupif>
</lan>
How will I protect my setup against network failures?
See the FAQ How do I configure redundant management NIC?
What should I do if my primary ElastiCenter (in ElastiCenter HA setup) goes down?
For troubleshooting this issue, see Troubleshooting ElastiCenter HA.
ElastiCenter displays the message HA ring broken. What does the message refer to?
The HA ring broken message is displayed when the management network fails. You may have to analyze the logs to find out
the reason for the network failure.
NIC FAQs
What do the terms degraded, active, and inactive imply?
Term
Degraded
Active
Inactive
Description
The interface is active on one Node but inactive on another in the same HA Group.
The interface is connected to the network on all Nodes in the HA Group.
Either the interface is not connected to the network or it is connected but not active (possibly
because the interface status could not be fetched while adding the Node to the HA Group. In
this case, in the Node page, click Network Interface Cards and then click Refresh).
Global Settings
Global settings let the administrator configure various options used to control CloudByte ElastiStor. For example, email configuration. To configure global settings,
1. In ElastiCenter, select Global Settings.
2. Select a target category. A list of settings is provided by default.
3. Edit the relevant settings.
Note: You cannot add new settings.
298
CHAPTER XII Frequently asked questions
This section lists the global settings options available on the ElastiCenter.
Option
Description
Default Value
alert.email.addresses
Comma separated list of email addresses used
for sending alerts.
Email ID you specified in the Update
Profile section in ElastiCenter.
alert.email.enable
If true, emails are sent to the specified email
addresses.
TRUE
alert.email.sender
Sender of the alert email.
alert.email.severity
Set the email severity level to one of the following:
l
1 - ERROR
2 - CRITICAL
3 - WARNING
4 - INFO
alert.smtp.host
SMTP hostname to send alert emails.
localhost
alert.smtp.password
Password for SMTP authentication (applies only
if alert.smtp.useAuth is true).
alert.smtp.port
The port of the SMTP server.
alert.smtp.useAuth
If true, SMTP authentication is enabled to send
emails.
alert.smtp.username
Username for SMTP authentication (applies only
if alert.smtp.useAuth is true).
autoSupport.config.details
Send configuration details to CloudByte as part
of an auto support email.
autosupport.httpnotify.apikey
API key of CloudByte auto support server.
autosupport.httpnotify.enable
Send HTTP post request to CloudByte auto support server.
autosupport.httpnotify.ipaddress
The IP address of CloudByte auto support server.
autoSupport.infastructure.statistics
Send infrastructure statistics to CloudByte as
part of an auto support email.
Yes
autoSupport.product.alerts
Send product related alerts to CloudByte as part
of an auto support email.
Yes
autoSupport.reg.details
Send registration details to CloudByte as part of
an auto support email.
autoSupport.tenant.statistics
Send tenant statistics to CloudByte as part of an
auto support email.
Yes
bad.disk.threshold
The number of defects grown on disk that will
declare it as a bad disk
512
587
False
Yes
False
Yes
299
CHAPTER XII Frequently asked questions
Option
Description
Default Value
cache.multiplication.factor
The number of Cache READs which equal a disk
READ. The default value is 3 which means 1 disk
READ equals 3 cache READs. Only a value
between 2 and 6 is supported.
devman.backup.files.retain
The number of backup files to be retained.
devman.backup.path
The path of ElastiCenter backup directory.
/var/devman/backups
devman.backup.scheduling.interval The interval time for ElastiCenter backup.
devman.build.number
The build version of ElastiStor.
Available in /cbdir/buildversion
monitor.purge.retain.days
The number of days that the data has to be
retained for.
60
monitor.qos.stats.interval
The time interval (in seconds) taken for QoS stat- 300
istics to be retrieved from Nodes.
monitor.refresh.interval
The time interval (in seconds) required to
refresh the Storage Volumes page.
300
monitor.storage.stats.interval
The time interval (in seconds) taken for storage
statistics to be retrieved from Nodes.
300
monitor.system.purge.retain.days
The number of days that the data has to be
retained for.
no.of.nodes.per.hagroup
Limiting number of Nodes in an HA Group.
project.invite.required
Specify if invitation confirmation is required
when add account to project.
False
provisioning.sb.algo
Algorithm used for auto-provisioning Storage
Volume.
Best Fit
provisioning.sb.auto
Enable/Disable auto-provisioning of Storage
Volumes.
No
provisioning.tsm.algo
Algorithm used for auto-provisioning VSM.
Best Fit
provisioning.tsm.auto
Enable/Disable auto-provisioning of VSMs.
No
qos.penalty.allowed.delta
Percentage (as a value between 1 and 100) up to 10
which penalty will be not be considered
qos.penality.blocksize
Standard blocksize (in KB) per IOPS, used in provisioning and penality enforcement.
qos.penalty.blocksize.factor
Considers block size for penalty calculations. Spe- No
cify yes to Enable and No to Disable.
qos.penalty.cachehit.factor
Considers cache hit for penalty caclulations. Specify yes to Enable and No to Disable.
No
qos.penalty.enforcement.timeinterval
The time interval (in seconds) for which penalty
has to be applied on QoS values.
300
qos.penalty.readwrite.factor
Considers READs vs WRITEs for penalty caclulations. Specify yes to Enable and No to Disable.
No
300
CHAPTER XII Frequently asked questions
Option
Description
Default Value
read.multiplication.factor
Specify how many READs equal a WRITE. The
default value is 4 which means 1 WRITE equals 4
READs. Only a value between 3 and 6 is supported.
report.email.sender
Sender of report email.
report.smtp.host
SMTP hostname used for sending out report
emails.
report.smtp.password
Password for SMTP authentication (applies only
if report.smtp.useAuth is true).
report.smtp.port
The port of the SMTP server.
587
report.smtp.useAuth
If true, SMTP authentication is enabled to send
emails.
False
report.smtp.username
Username for SMTP authentication (applies only
if report.smtp.useAuth is true).
ui.protocol.enablefc
Enable/Disable all FC protocol related options
from ElastiCenter.
ui.protocol.enablehaadmincreation Enable/Disable haAdmin creation options from
ElastiCenter.
localhost
True
False
ui.protocol.enablezilmirroring
Enable/Disable ZIL mirroring creation options
from ElastiCenter.
False
provisioning.uncontrolled.iops
Enable/Disable provisioning with uncontrolled
(zero) IOPS. Specify TRUE to enable.
False
alert.qos.throttling.percentage
Sends an alert if the throttled IOPS percentage
exceeds the specified value and if alert.qos.throttle.count is encountered for the
specified number of times.
20
alert.qos.throttle.count
Sends an alert if the number of consistent throttling exceeds the specified value and alert.qos.throttling.percentage exceeds the
specified value.
10
devman.enable.ipspaces
Enable/Disable the Assigning real IP
spaces feature.
False
CloudByte ElastiStor best practices
CloudByte recommends the following best practices to make CloudByte ElastiStor work effectively:
Best practice
Description
Reference
Create Pools with same vendor/RPMs/sectors/cylinders
Pool FAQs
On client-side, ensure multipath-enabled ISCSI/FC LUN
MPIO
Device mapper
LAGG
To avail HA, set up network LAGG on the Node
Configuring interfaces
Network switch stacking
Stack network switch to handle network failure
Creating Pools
Client Multipathing
301
CHAPTER XII Frequently asked questions
SAS Multipathing
Performance and redundancy
Set up SAS multipath for effective path failover
Configure ZIL, cache, and hot spare drives for Pools for better
performance and redundancy
Network MTUs
Configure Network MTUs based on client application recommendation
MTU revision
Revise MTU prior to starting I/O on client. Changing the MTU
later might disrupt I/O
Secondary ElastiCenter
Separate ZIL and Cache device
Block Length for iSCSI LUNs
Reducing Dell R720 boot time
SAS multipathing
Set up secondary ElastiCenter for management HA.
Promoting secondary
ElastiCenter
Configure separate ZIL and cache device for each Pool.
Ensure that the iSCSI LUNs consumed by ESX clients have
blockLength=512
How to reduce the boot time?
Backing up ElastiCenter and
Node configurations
How to backup and restore ElastiCenter and Node configurations
Storage naming conventions
Rules for naming storage components
Optimizing the boot time for
Dell PowerEdge R720/Dell
PowerEdge R820
Backing up configurations
Storage naming conventions
Promoting secondary ElastiCenter and backing up configurations
Setting up and promoting secondary ElastiCenter
The following sections explain how to setup a secondary ElastiCenter (secondary setup) to ensure backup in the case your primary
ElastiCenter (primary setup) fails. If a failure occurs, you can promote your secondary setup.
As shown in diagram 1, the primary ElastiCenter manages and monitors multiple Storage Nodes spread across datacenters. All configurations on primary ElastiCenter are replicated on the secondary. In case the primary ElastiCenter fails, the secondary can be promoted as shown in diagram 2.
302
CHAPTER XII Frequently asked questions
Diagram 1:
Diagram 2:
Important:The primary and secondary setups cannot be used at the same time. Ensure that only the database service is
operational on the secondary setup. Promote the secondary setup only when the primary setup is down.
Prerequisites
l
The primary and secondary setups are on same subnet
ElastiCenter and Node are installed separately
303
CHAPTER XII Frequently asked questions
Setting up the secondary ElastiCenter
The procedures involve action at both the primary and secondary setups.
Note: If you copy and paste the commands in the section, ensure that they appear correctly on the CLI.
1. (On both the setups) Log in as root and access (over SSH or directly) the command prompt on the machine where the
ElastiCenters are installed.
2. (On the secondary setup) Run the following command: service rabbitmq onestop
3. (On the secondary setup) Run the following command to ensure that the RabbitMQ service is stopped: service rabbitmq onestatus
4. (On secondary setup) Run the following command to ensure that no Java process is running:
ps auxwww | grep java
5. If any of the Java processes or RabbitMQ service is running, kill it using the following command: kill -9 PID_of_process
6. Else, ensure the following:
l
Size of/tpoolfolder is same on both primary ElastiCenter and secondary ElastiCenter using the following command:
zpool list
/folder in secondary ElastiCenter database has enough space for backup. This means the available space in / directory on the secondary ElastiCenter must be greater than the used space in /tpool directory on the primary
ElastiCenter.
7. (Optional) On the secondary setup, start the mysql service using the command: service mysql -server onestart .
8. (On the secondary setup) Run the script /usr/local/cb/bin/cb_config_slave.sh .
9. Perform the steps as shown in the following command line :
Select your choice:
1) Configure secondary ElastiCenter.
2) Promote secondary to primary ElastiCenter.
3) Exit
1
Here, you have to select 1 as highlighted.
You have selected to configure secondary ElastiCenter.
Do you want to continue? (Yes/No) Yes
Here, you have to select Yes as highlighted.
Specify primary ElastiCenter's IP address:
20.10.97.1
Wait for the script to execute.
Stopping Tomcat and RabbitMQ services...
Tomcat and RabbitMQ services stopped.
Restarting MySql service...
MySql service started.
Starting backup of primary ElastiCenter...
Primary Elasticenter backup completed.
Starting the setting up of secondary ElastiCenter...
Setting up the secondary ElastiCenter completed.
Syncing reports...
Promoting the secondary setup
Before you proceed
If the primary setup is down, try the following before promoting the secondary setup:
304
CHAPTER XII Frequently asked questions
Verify the error logs in java/Rabbitmq/Mysql or the service status. For example, service mysql-server
onestatus.
Restart the service that is not running.
If downtime prevails despite the service restart, promote the secondary setup.
Procedures
Note: If you copy and paste the commands in the section, ensure that they appear correctly on the CLI.
1. Power off the primary ElastiCenter.
2. (On the secondary ElastiCenter console) Run the script /usr/local/cb/bin/cb_config_slave.sh .
3. Perform the steps as shown in the following command line :
Select your choice:
1) Configure secondary ElastiCenter.
2) Promote secondary to primary Elasticenter.
3) Exit
2
Here, you have to select 2 as highlighted.
You have selected to promote secondary Elasticenter to primary Elasticenter.
Do you want to continue ? (Yes/No)Yes
Here, you have to select Yes as highlighted.
Dropped secondary ElastiCenter.
Starting RabbitMQ and Tomcat services..
Promoted secondary Elasticenter to primary Elasticenter. Check catalina logs for errors(if any).
4. (On all the ElastiStor consoles) Modify the /usr/local/agent/listener/cbc.conf file by changing the IP address of
ElastiCenter. Specify the IP address of secondary ElastiCenter.
5. (On the ElastiStor console) Run the following command to restart all the python/cbc services on the Node: service -l
| grep cbc | grep -v cbc_ec | xargs -I {} service {} onerestart
Also, ensure that the ElastiCenter is accessible to the Nodes with same status as prior to the promotion.
Note: During the promotion process, if a Node is offline or is powered down, then manually start the cbc_monitor_
hajobs service and point it to the promoted ElastiCenter.
Backing up configurations
How to backup and restore ElastiCenter configuration
By default, CloudByte schedules a backup everyday. You can modify the settings using the following options in Global Settings:
l
devman.backup.files.retain
devman.backup.path
devman.backup.scheduling.interval.
But, in the case you need to do a manual backup, follow the steps:
305
CHAPTER XII Frequently asked questions
Backing up
1. In the ElastiCenter server, at command prompt, run the following: cd /usr/local/cb/bin/
2. Run the following command to create backup file: ./backup.sh. The backup file is created in the /var/devman/backups
(unless you modify the path). The following is a sample file name: backup_Jul26_1374815679.tar.bz2.
3. Copy the file and store it elsewhere.
Restoring
1. Copy the backed up TAR file to a location on ElastiCenter, for example /var.
2. Go to the directory /usr/local/cb/bin and then run the following command: ./restore.sh <path of backedup file>.
For example ./restore.sh /var/backup_Jul26_1374815679.tar.bz2.
The configuration is restored.
How to collect logs
Do the following to collect the logs of the datacenter (both Nodes and ElastiCenter):
1. Log in as root.
2. In the ElastiCenter server, at command prompt, run the following command: cd /usr/local/cb/bin/.
3. Run the following command: python logCollector.py
4. At prompt, specify the root password for all Nodes from which you want to gather the logs.
How to backup and restore Node configuration
Backing up
By default, CloudByte schedules a daily backup in the location /cf/conf. CloudByte recommends you to move this backup daily
to a safe location. Either schedule a cron job or manually copy the files from the conf directory.
You can backup configurations manually by doing the following:
1. cp /usr/local/agent/cb* .
2. cp -r /cf/conf .
Restoring
1. Reinstall the Node with the same configurations (for example, same IP address, Hostname, and ElastiCenter details) as in
the previous installation.
2. Copy the following backed up files to the reinstalled Node:
l
config.xml file to the location /cf/conf/config.xml
haconfig.xml file to the location /cf/conf/haconfig.xml
ipmi.conf file to the location /usr/local/agent/listener/ipmi.conf
cbc_node_id file to the location /usr/local/agent/cbc_node_id
cbd_node_id file to the location /usr/local/agent/cbd_node_id
3. After copying all the files, reboot the Node.
306
CHAPTER XII Frequently asked questions
IOPS conversion matrix
The following sections provide details of the IOPS conversion matrix as implemented in CloudByte ElastiStor. The conversion matrix helps you understand the penalty enforcement factors associated with the QoS.
Assume that, as a service provider, you have assigned a client a specific number of IOPS. Depending on the work load pattern, to
maintain guaranteed QoS, you might have to increase or decrease the IOPS. Based on the standard QoScharacteristics CloudByte
automatically calculates the equivalent of your load.
For example, in a 100 % READ scenario, there is a surplus IOPS owing to the 0% WRITE. Similarly in a 100 percent
WRITEscenario, there is a deficit of IOPS. This demands a check and balance in the IOPSprovisioning which is taken care of by
CloudByte.
Since it is imperative that IOPS provisioning conform to a specific matrix, you are provided with a set of Global Settings options
which you can tweak to maintain and optimize the performance. Note that you can also optimize the performance at per Pool level
also.
Measuring storage performance
Prior to reading the following sections, CloudByte recommends you to read the following white paper that provides an introduction to
Measuring Storage Performance.
Concepts
IOPS
Description
Standard IOPS
This is the benchmarked IOPS. The details are as follows: 80 READ/20 WRITE, and 4K block size. This acts as
the frame of reference for QoS in CloudByte ElastiStor.
Operating IOPS
IOPS under a given workload that can be measured against the standard IOPS.
Pool IOPS
The standard IOPS that can be delivered by a given pool.
Provisioned IOPS
. The standard IOPS provisioned to a volume
Illustration
Consider a Pool assigned with 1300 Standard IOPS. There are three Storage Volumes with the following conditions:
Storage Volume
Provisioned IOPS
Block Size
Workload (READ/WRITE)
Operational IOPS
Volume 1
500
4K
80% /20%
500
Volume 2
200
4K
100% /0%
170
Volume 3
400
4K
0% /100%
600
In the case of VSM 3 where WRITEs are more, operational IOPS exceeds the standard IOPS which demands the implementation of
penalty enforcement.
Penalty enforcement options in Global Settings
The following options in the Global Settings are used to enforce IOPS penalty:
307
CHAPTER XII Frequently asked questions
Settings
Description
qos.penalty.factor
If Yes, penalty is applied based on the criteria explained above.
qos.penalty.enforcement.timeinterval
Seconds after which penalty enforcement should refresh.
read.multiplication.factor
For details, see the following sections
cache.multiplication.factor
For details, see the following sections.
Enabling penalty enforcement factors at the Pool level
1. In the Pools page, select the Pool for which you want to enforce IOPS penalty.
2. In the actions pane, click Settings and then click Edit.
3. Select Enable for the option Penalty Enforcement Factor.
4. Click Save.
Deciding the penalty
The following workflow helps you understand the penalty factors:
308
CHAPTER XII Frequently asked questions
Calculating the operating IOPS
Standard IOPS
1000 @80%Read, 80% Write, 4K block size
Read/write variation
CloudByte equates one WRITE to four READS. You can tune this on per pool basis if required.
Calculation
If standard IOPS are 100 at 80 READS/20 WRITES, the following is the formula to convert the operating IOPS into standard IOPS:
Operating
IOPS
At
READ/WRITE
Equivalent Standard IOPS
Throttle at
(IOPS)
100
100/0
80 READS +20 READS (as READs occur in place of WRITEs). Here you convert 20 WRITEs to
READS. That is, 20x4=80 READs. The total standard IOPS that can be consumed is 80 + 80 =
160 IOPS.
160
100
80/20
80 READS + 20 READS
100
100
60/40
60 READs + 40 READs (as WRITES occur in place of READs). Here you convert 20 READs to
WRITEs. 20 READs are equal to 20/4=5 WRITEs. The total standard IOPS that can be consumed is 80+5 = 85 IOPS.
85
309
CHAPTER XII Frequently asked questions
100
40/20
40 READs + 60WRITEs (as WRITEs occur in place of READs). Here you convert 40 READs to
WRITES. 40 READs are equal to 40/4=10 WRITEs. The total standard IOPS that can be consumed is 40+10 = 50 IOPS.
50
100
20/80
20 READs + 80 WRITEs (as WRITEs occur in place of READs). Here you convert 60 READs to
WRITEs. 60 READs are equal to 60/4=15 WRITEs. The total standard IOPS that can be consumed is 20+15 = 35 IOPS.
35
100
0/100
0 READs + 100 WRITEs (as WRITEs occur in place of READs). Here you convert 80 READs to
WRITEs. 80 READs are equal to 80/4=20 WRITEs. The total standard IOPS that can be consumed is 0+20 = 20 IOPS.
20
READ/WRITEvariation and block size variation
The calculation considers the following assumptions:
l
X operating IOPS are converted to X1 after considering the block size variation
X1 IOPS are converted to X2 after considering READ/WRITEvariation
Throttling happens at X2 IOPS
310
CHAPTER XIII Glossary
CHAPTER XIII Glossary
Terms
Description
Account
An entity with specific storage needs. Account represents a department of an Enterprise or a customer of a
Cloud Service Provider.
Alerts
Notifications that demand action. Alerts can be on a range of issues such as network cable pullout or degradation
of a Pool.
Asynchronous rep- The process of writing data to local storage and then queuing it up for replication on remote storage at assigned
lication
intervals. If the local storage fails before the data is written in remote storage, then replication fails.
Auto-Provisioning
ElastiStor can automate Node selection and resource allocation if you provide the required SLA/QoS parameters.
Sensing the level of storage performance and capacity the application requires, ElastiStor automatically allots the
right Pool.
Block Size
The size of a block in data storage and file systems. Block is a sequence of bytes or bits, having a nominal size.
CIFS
For details, see http://technet.microsoft.com/en-us/library/cc939973.aspx
HA Group
Houses a group of Nodes. HA Group enables takeover during failures. Workload of a failed Node is assigned to
another Node in the same HA Group based on availability and performance requirements.
Dashboard
A graphical representation of the key performance indicators. It presents an overview of all the Sites in
ElastiCenter in an organized manner. You can update information instantaneously.
Delegated Administration
The process of distributing administrative tasks and content in the portal to dedicated administrators. Using
access control lists, you determine the actions administrators take on various resources. Delegated administration roles are mapped to administrative functions using security policies. You can create and maintain separate administration capabilities depending on your needs.
Disaster Recovery
Disaster implies unplanned outage. Your storage system must be capable of effective backup and recovery so
that there is no damage to the data that is handled in the case of any adversity.
Disk Array
Popularly called JBODs, disk array is a set of disks clubbed to single disk shelf.
Disk Type
The type of disk supported by CloudByte ElastiStor. The supported disk types are SAS, SATA, and SSD.
Domain Search
Searching the DNS to which you want to add a controller.
Event
Any storage activity. ElastiStor notifies events based on the configuration.
FC (Fibre Channel)
A high-speed interconnect between controllers and back-end disk enclosures. FC components include HBAs,
hubs, and switches. The term also refers to a high-speed, fully duplex serial communication protocol permitting
data transfer up to 10GB per second.
FTP (File Transfer
Protocol)
An application layer protocol used to transfer bulk-volumes of files between machines or hosts.
Global Settings
Lets the administrator configure options that control ElastiStor.
Grace
Provisioning of Pool's unused IOPS/Throughput to Storage Volumes based on their performance requirements.
High-Availability
High Availability minimizes/prevents the consequences of downtime in the storage setup. A typical High Availability environment comprises two setups: one active while the partner remains dormant. In a downtime, the passive setup takes over the storage tasks that the active setup was performing. This effects a reversal of states each
setup was in. When the downtime is over, all events are given back to the original active setup.
Host
Physical machines on which you configure ElastiStor.
311
CHAPTER XIII Glossary
Terms
Initiator Group
Description
When an initiator group is associated with a LUN, only initiators from that group can access the LUN. Initiators are
identified by unique addressing methods.
IOPS (Input/OutThe number of READs or WRITEs per second. It is used to measure the performance of storage solution. Total
put operations per IOPS is the average input/output operations per second, Read IOPS is the average READ operations per
second)
second, and Write IOPS is the average WRITEoperations per second.
iSCSI
Internet Small Computer Systems Interface is a client-server protocol used to enable the transfer of SCSI packets
over a TCP/IP (Ethernet) network.
Lagg Interface
Allows integration of multiple network interfaces with a single virtual interface. This helps in fault-tolerance and
high-speed multi-link throughput.
LUN (Logical Unit
Number)
Unique address to identify a logical unit. Logical unit is the conceptual subunit of a storage disk or set of disks.
Mirrored Disks
A High Availability setup where you have a different set of disks on each node. Active disks are replicated/mirrored on the partnering node.
Mirroring
Storing duplicate copies of data on one or more sets of additional Storage Volumes, apart from the set of Storage Volume that stores the original data.
Monitoring
Provides an intuitive visualization of storage statistics. Monitoring foregrounds relevant back end activities in an
easy user interface for the administrator.
Network Failure
Indicates that the system is unable to reach the network. For example, due to physical port failure.
NFS
A distributed file system protocol that lets clients access files over a network in the same way they access local
storage.
Physical Infrastructure
Real entities pertaining to the hardware.
Pool
Physical storage devices on which you store data.
Provisioning
A set of steps to allocate storage to Hosts and applications. For example, creating Storage Volumes in Pools.
QoS (Quality of
Service)
Lets you easily commission storage with guaranteed IOPS at various levels. You can decide to configure QoS at a
Pool level, VSM level, or Storage Volume level.
Report
Detailed information related to configuration. Use Configuration Reports for component configuration details.
Dynamic Reports provide QoS statistics.
Rest APIs
Every action performed at ElastiStor admin console translates into a REST based API call in the back end. This
enables administrators to fully manage ElastiStor from their portals. CloudByte plugin for VMware vCenter (also
based on REST API) enables storage management from vCenter.
Shared Disks
A High Availability setup where you have a common set of disks shared between primary and secondary nodes.
The disks can be either hard disks or iSCSI disks.
Shared Storage
Storage devices that are connected to and used by two or more systems.
Site
Represents a data center or part of a data center. Building storage infrastructure starts with the creation of Site.
It is the fundamental infrastructure unit where your controller, storage, and network infrastructure reside.
Snapshot
Copy of a Storage Volume created at specific intervals.
Storage Capacity
The overall disk space (and not the free disk space).
Striping
Writes data across two or more disks in an array but utilizes only a part of the space on each disk. The amount of
space used by stripe on each disk is always the same. A virtual disk may write several stripes on the same set of
disks in the array.
312
CHAPTER XIII Glossary
Terms
Description
Synchronous Replication
The process of writing the same data to two separate volumes, stored on different physical hardware, before the
application receives an I/O complete message. This results in both the volumes being always in sync.
Takeover
The process of taking over the storage control activity from a node. Typically, when there is a downtime on the
primary node, the secondary node takes over the control of storage.
Thin Provisioning
The process of optimizing efficiency of using the available storage space. It is the allocation of disk storage space
flexibly among multiple users, based on the minimum space each user requires at any given time.
Throughput
Amount of work a system can perform at specific intervals. It is also the amount of data moved successfully from
one place to another in a given time period.
Virtual Storage
Machine(VSM )
Virtual storage controller capable of hosting Storage Volumes and LUNs.
VSM Architecture
Unique to CloudByte ElastiStor, this is a patented architecture. In a Storage Controller, each application is fully
isolated across all storage stack levels and unified under a Virtual Storage Machine (VSM). VSM isolation allows
controller resources allotted to applications to be easily monitored, controlled, and provisioned.
VMware vSphere
client
A Microsoft Windows desktop application that enables you to access VMware ESXi and VMware vCenter.
ZFS (Zettabyte File ZFS is a 128-bit file system that provides features such as data integrity verification, disk management, snapshots,
System)
and transactional operations.
313
Vous aimerez peut-être aussi
- (123doc) - Toefl-Reading-Comprehension-Test-41Document8 pages(123doc) - Toefl-Reading-Comprehension-Test-41Steve XPas encore d'évaluation
- Brocade San Switch TroubleshootingDocument7 pagesBrocade San Switch TroubleshootingMohaideenPas encore d'évaluation
- Oracle Database Shutdown BasicsDocument2 pagesOracle Database Shutdown BasicsMohaideenPas encore d'évaluation
- Clearing The Faults and Understanding Led Status On Sun Sparc Enterprise Mx000 ServersDocument10 pagesClearing The Faults and Understanding Led Status On Sun Sparc Enterprise Mx000 ServersMohaideenPas encore d'évaluation
- Configure Probe Based IPMP in Solaris 11Document5 pagesConfigure Probe Based IPMP in Solaris 11MohaideenPas encore d'évaluation
- Veritas Cluster CommandsDocument8 pagesVeritas Cluster CommandsMohaideenPas encore d'évaluation
- Azure Stack HciDocument1 600 pagesAzure Stack HciPt BuddhakirdPas encore d'évaluation
- WP Nutanix Complete Cluster Technical WhitepaperDocument15 pagesWP Nutanix Complete Cluster Technical WhitepaperShukur SharifPas encore d'évaluation
- Shostack ModSec08 Experiences Threat Modeling at MicrosoftDocument11 pagesShostack ModSec08 Experiences Threat Modeling at MicrosoftwolfenicPas encore d'évaluation
- An Overview of Vmware Vcloud SuiteDocument46 pagesAn Overview of Vmware Vcloud SuitemzcronierPas encore d'évaluation
- Exam AZ 900: Azure Fundamental Study Guide-1: Explore Azure Fundamental guide and Get certified AZ 900 examD'EverandExam AZ 900: Azure Fundamental Study Guide-1: Explore Azure Fundamental guide and Get certified AZ 900 examPas encore d'évaluation
- Huawei FusionSphere 5.1 Brochure (Server Virtualization)Document2 pagesHuawei FusionSphere 5.1 Brochure (Server Virtualization)Anthony ThomasPas encore d'évaluation
- EMC XtremIO LUN ProvisioningDocument27 pagesEMC XtremIO LUN ProvisioningMohaideenPas encore d'évaluation
- Log Building News - Issue No. 76Document32 pagesLog Building News - Issue No. 76ursindPas encore d'évaluation
- GA WP ArchitectingResilientPrivateClouds 0511Document16 pagesGA WP ArchitectingResilientPrivateClouds 0511onlyforaccountsPas encore d'évaluation
- Human EpigenomicsDocument234 pagesHuman EpigenomicsHeron HilárioPas encore d'évaluation
- TSO00364USEN - Ibm System Storage Product GuideDocument20 pagesTSO00364USEN - Ibm System Storage Product Guidetschok53Pas encore d'évaluation
- VMware VSAN 6.5 Technical OverviewDocument43 pagesVMware VSAN 6.5 Technical OverviewAlonso BPas encore d'évaluation
- Plaza 66 Tower 2 Structural Design ChallengesDocument13 pagesPlaza 66 Tower 2 Structural Design ChallengessrvshPas encore d'évaluation
- Why Nutanix Acropolis HypervisorDocument21 pagesWhy Nutanix Acropolis HypervisorRishab SachdevaPas encore d'évaluation
- Cisco HyperFlex Systems Technical DeckDocument81 pagesCisco HyperFlex Systems Technical Deckkinan_kazuki104Pas encore d'évaluation
- Carriage RequirementsDocument63 pagesCarriage RequirementsFred GrosfilerPas encore d'évaluation
- Lefthandhyper VbriefDocument2 pagesLefthandhyper Vbriefapi-107213063Pas encore d'évaluation
- Hitachi Nas Platform 3080 and 3090 Vmware SBDocument4 pagesHitachi Nas Platform 3080 and 3090 Vmware SBRyan GlasgowPas encore d'évaluation
- SVC DatasheetDocument8 pagesSVC DatasheetAman Kumar AroraPas encore d'évaluation
- Deploying Piston OpenStack On Quanta QCT HardwareDocument4 pagesDeploying Piston OpenStack On Quanta QCT HardwareJohnson Ebenezer DPas encore d'évaluation
- CDP Enterprise Data SheetDocument4 pagesCDP Enterprise Data SheetGeorgePas encore d'évaluation
- Flex Pod Solution BriefDocument4 pagesFlex Pod Solution Briefazcomp99Pas encore d'évaluation
- Dell Compellent SC8000 Storage Center ControllerDocument2 pagesDell Compellent SC8000 Storage Center Controllerhamdymedo100% (1)
- The Intelligent, Automated IT InfrastructureDocument24 pagesThe Intelligent, Automated IT InfrastructureGreen PeacePas encore d'évaluation
- Netapp V-Series For Heterogeneous Storage Environments: SystemsDocument4 pagesNetapp V-Series For Heterogeneous Storage Environments: SystemsdebajyotiguhaPas encore d'évaluation
- VMware Virtual SAN DatasheetDocument2 pagesVMware Virtual SAN DatasheetmizakPas encore d'évaluation
- Cds Release Notes 603Document16 pagesCds Release Notes 603newbeonePas encore d'évaluation
- Metaswitch Clearwater CoreDocument5 pagesMetaswitch Clearwater CoreblitoPas encore d'évaluation
- VMware Virtual SAN DatasheetDocument2 pagesVMware Virtual SAN DatasheetFoo BarringtonPas encore d'évaluation
- Huawei OceanStor 5000 V5 Mid-Range Storage Systems Data SheetDocument6 pagesHuawei OceanStor 5000 V5 Mid-Range Storage Systems Data SheetCCIE DetectPas encore d'évaluation
- Equallogic Ps6500e SpecsheetDocument2 pagesEquallogic Ps6500e SpecsheetVaidas BikulčiusPas encore d'évaluation
- IaaS Solution BrochureDocument6 pagesIaaS Solution BrochureblussierttPas encore d'évaluation
- EV 10 Best Practice - Implementing Enterprise Vault On VMware (January 2012)Document31 pagesEV 10 Best Practice - Implementing Enterprise Vault On VMware (January 2012)TekkiePas encore d'évaluation
- Unit 2Document16 pagesUnit 2Parth SuruPas encore d'évaluation
- Architecture & ConsiderationDocument7 pagesArchitecture & Consideration18941Pas encore d'évaluation
- Infoscale Integration Vmware Vsphere EsxiDocument23 pagesInfoscale Integration Vmware Vsphere EsxiMontero WilmerPas encore d'évaluation
- Storage System 5500 V5Document6 pagesStorage System 5500 V5Bisrat AwayePas encore d'évaluation
- Open Source Cloud Computing Platform Apache Cloudstack 2018Document7 pagesOpen Source Cloud Computing Platform Apache Cloudstack 2018Amit VekariaPas encore d'évaluation
- Netapp Storage Solutions For Vmware: Virtualize 100% of Your Data Center With ConfidenceDocument4 pagesNetapp Storage Solutions For Vmware: Virtualize 100% of Your Data Center With ConfidenceEmmanuel ZamaPas encore d'évaluation
- Dell Ps5000xv SpecsheetDocument2 pagesDell Ps5000xv SpecsheetEhtesham OpelPas encore d'évaluation
- Cisco Server Virtualization DatacenterDocument12 pagesCisco Server Virtualization DatacenterQuang ChiếnPas encore d'évaluation
- WP 8 Strategies For Building A Modern DatacenterDocument11 pagesWP 8 Strategies For Building A Modern DatacenterMohammad Waqas Moin SheikhPas encore d'évaluation
- The Challenge: Enterprise-Class Software-Defined Storage FoundationDocument2 pagesThe Challenge: Enterprise-Class Software-Defined Storage FoundationHienLeMinhPas encore d'évaluation
- How To Build A SAN: The Essential Guide For Turning Your Windows Server Into Shared Storage On Your IP NetworkDocument9 pagesHow To Build A SAN: The Essential Guide For Turning Your Windows Server Into Shared Storage On Your IP NetworkVo Van SinhPas encore d'évaluation
- Server Virtualization DissertationDocument4 pagesServer Virtualization DissertationEssayWritingWebsiteReviewsManchester100% (1)
- Cisco Cache Engine 500 2Document6 pagesCisco Cache Engine 500 2Asco TheraPas encore d'évaluation
- Introduction of iSCSI Target in Windows Server 2012Document72 pagesIntroduction of iSCSI Target in Windows Server 2012Boppana Kishore ChowdaryPas encore d'évaluation
- Starwind Iscsi San & Nas: What'S New inDocument2 pagesStarwind Iscsi San & Nas: What'S New injama99Pas encore d'évaluation
- Red Hat Gluster Storage: Open, Software-Defined Storage For Physical, Virtual, Cloud, and Container EnvironmentsDocument6 pagesRed Hat Gluster Storage: Open, Software-Defined Storage For Physical, Virtual, Cloud, and Container EnvironmentssergiutPas encore d'évaluation
- HP 3PAR Storeserv StorageDocument16 pagesHP 3PAR Storeserv StoragejcrlimaPas encore d'évaluation
- Scaleout Sessionserver™: Fast, Scalable In-Memory StorageDocument5 pagesScaleout Sessionserver™: Fast, Scalable In-Memory StoragesyellaneniPas encore d'évaluation
- Configure Cisco Imm For Flashstack and Deploy Red Hat Enterprise LinuxDocument125 pagesConfigure Cisco Imm For Flashstack and Deploy Red Hat Enterprise Linuxsalist3kPas encore d'évaluation
- The Benefits of Serial Attached SCSI (SAS) For External SubsystemsDocument3 pagesThe Benefits of Serial Attached SCSI (SAS) For External SubsystemsminhzeroPas encore d'évaluation
- Hyper-V Datacenter Virtualization Module 1Document62 pagesHyper-V Datacenter Virtualization Module 1JeFawkPas encore d'évaluation
- Highly Available Virtual Machines With IBM Storwize V7000 and Microsoft Hyper-VDocument27 pagesHighly Available Virtual Machines With IBM Storwize V7000 and Microsoft Hyper-Vcm2wongPas encore d'évaluation
- Ibm TSM For Sharepoint 6.1 Vss Backup and Restore Solution GuideDocument38 pagesIbm TSM For Sharepoint 6.1 Vss Backup and Restore Solution GuideShine SivadasanPas encore d'évaluation
- IBM Storwize V7000: Maximising Storage Efficiency To Transform The Economics of Data StorageDocument8 pagesIBM Storwize V7000: Maximising Storage Efficiency To Transform The Economics of Data StorageSaqib AzizPas encore d'évaluation
- CloudSigma Detailed Service DescriptionDocument23 pagesCloudSigma Detailed Service DescriptionVamshiPas encore d'évaluation
- VMware VSphere 5 What You Need To Know PresentationDocument42 pagesVMware VSphere 5 What You Need To Know PresentationktgeorgePas encore d'évaluation
- Dell Storage sc7020 SpecDocument5 pagesDell Storage sc7020 Speckalila rifdaPas encore d'évaluation
- Cloudstack ThesisDocument8 pagesCloudstack Thesissuzannehornbillings100% (2)
- Azure Stack HCIDocument17 pagesAzure Stack HCIalogeno_Pas encore d'évaluation
- Virtual Storage Platform 5000 Series DatasheetDocument2 pagesVirtual Storage Platform 5000 Series DatasheetkunternethPas encore d'évaluation
- h18144 Dell Emc Powerstore Family Top ReasonsDocument2 pagesh18144 Dell Emc Powerstore Family Top ReasonsSathvik JPas encore d'évaluation
- Cloud Enabling TechnologiesDocument3 pagesCloud Enabling TechnologiesmonighosPas encore d'évaluation
- MICROSOFT AZURE ADMINISTRATOR EXAM PREP(AZ-104) Part-3: AZ 104 EXAM STUDY GUIDED'EverandMICROSOFT AZURE ADMINISTRATOR EXAM PREP(AZ-104) Part-3: AZ 104 EXAM STUDY GUIDEPas encore d'évaluation
- System Panic PCIe FabricDocument6 pagesSystem Panic PCIe FabricMohaideenPas encore d'évaluation
- Cisco NX-OS Software CLI Command Injection Vulnerability (CVE-2019-1609)Document3 pagesCisco NX-OS Software CLI Command Injection Vulnerability (CVE-2019-1609)MohaideenPas encore d'évaluation
- Getting Started With ZFSDocument43 pagesGetting Started With ZFSMohaideenPas encore d'évaluation
- LDOMS ConceptDocument3 pagesLDOMS ConceptMohaideen100% (1)
- What Is SUID GUID and Sticky BitDocument2 pagesWhat Is SUID GUID and Sticky BitMohaideenPas encore d'évaluation
- Solaris 10 Boot Process x86Document3 pagesSolaris 10 Boot Process x86MohaideenPas encore d'évaluation
- MDS 9000 Chassis BackupDocument7 pagesMDS 9000 Chassis BackupMohaideenPas encore d'évaluation
- Solaris 10 Boot Process SparcDocument3 pagesSolaris 10 Boot Process SparcMohaideen100% (1)
- Oracle Database Startup BasicsDocument3 pagesOracle Database Startup BasicsMohaideenPas encore d'évaluation
- Introducing UnisphereDocument22 pagesIntroducing UnisphereMohaideenPas encore d'évaluation
- Commands For Basic FOS TroubleshootingDocument2 pagesCommands For Basic FOS TroubleshootingMohaideenPas encore d'évaluation
- Truecopy Hur Support Matrix Hitachi VSP g1000 g800 g600 g400 g200 and Hus VMDocument5 pagesTruecopy Hur Support Matrix Hitachi VSP g1000 g800 g600 g400 g200 and Hus VMMohaideenPas encore d'évaluation
- Configuring Link Based IPMP Configuration Active ActiveDocument1 pageConfiguring Link Based IPMP Configuration Active ActiveMohaideenPas encore d'évaluation
- Ufs Filesystem Greater Than 1TBDocument1 pageUfs Filesystem Greater Than 1TBMohaideenPas encore d'évaluation
- VXVM Creating Volume and File SystemDocument6 pagesVXVM Creating Volume and File SystemMohaideenPas encore d'évaluation
- BMOM5203 Full Version Study GuideDocument57 pagesBMOM5203 Full Version Study GuideZaid ChelseaPas encore d'évaluation
- Assignment#10 Global Strategy and The Multinational CorporationDocument1 pageAssignment#10 Global Strategy and The Multinational CorporationAnjaneth A. VillegasPas encore d'évaluation
- OZO Player SDK User Guide 1.2.1Document16 pagesOZO Player SDK User Guide 1.2.1aryan9411Pas encore d'évaluation
- DPSD ProjectDocument30 pagesDPSD ProjectSri NidhiPas encore d'évaluation
- CEE Annual Report 2018Document100 pagesCEE Annual Report 2018BusinessTech100% (1)
- Existential ThreatsDocument6 pagesExistential Threatslolab_4Pas encore d'évaluation
- Dynamics of Machinery PDFDocument18 pagesDynamics of Machinery PDFThomas VictorPas encore d'évaluation
- Electives - ArchitDocument36 pagesElectives - Architkshitiz singhPas encore d'évaluation
- Proceeding of Rasce 2015Document245 pagesProceeding of Rasce 2015Alex ChristopherPas encore d'évaluation
- MASONRYDocument8 pagesMASONRYJowelyn MaderalPas encore d'évaluation
- A Case Study of Coustomer Satisfaction in Demat Account At: A Summer Training ReportDocument110 pagesA Case Study of Coustomer Satisfaction in Demat Account At: A Summer Training ReportDeepak SinghalPas encore d'évaluation
- Pe 03 - Course ModuleDocument42 pagesPe 03 - Course ModuleMARIEL ASIPas encore d'évaluation
- Solved Simplex Problems PDFDocument5 pagesSolved Simplex Problems PDFTejasa MishraPas encore d'évaluation
- Review1 ScheduleDocument3 pagesReview1 Schedulejayasuryam.ae18Pas encore d'évaluation
- Opc PPT FinalDocument22 pagesOpc PPT FinalnischalaPas encore d'évaluation
- 13 Adsorption of Congo Red A Basic Dye by ZnFe-CO3Document10 pages13 Adsorption of Congo Red A Basic Dye by ZnFe-CO3Jorellie PetalverPas encore d'évaluation
- Application of Graph Theory in Operations ResearchDocument3 pagesApplication of Graph Theory in Operations ResearchInternational Journal of Innovative Science and Research Technology100% (2)
- Chapter3 Elasticity and ForecastingDocument25 pagesChapter3 Elasticity and ForecastingGee JoePas encore d'évaluation
- Harper Independent Distributor Tri FoldDocument2 pagesHarper Independent Distributor Tri FoldYipper ShnipperPas encore d'évaluation
- Countries EXCESS DEATHS All Ages - 15nov2021Document21 pagesCountries EXCESS DEATHS All Ages - 15nov2021robaksPas encore d'évaluation
- Soft Ground Improvement Using Electro-Osmosis.Document6 pagesSoft Ground Improvement Using Electro-Osmosis.Vincent Ling M SPas encore d'évaluation
- HirePro Video Proctored Online-Instruction Sheet - Bain IndiaDocument1 pageHirePro Video Proctored Online-Instruction Sheet - Bain Indiaapoorv sharmaPas encore d'évaluation
- Carob-Tree As CO2 Sink in The Carbon MarketDocument5 pagesCarob-Tree As CO2 Sink in The Carbon MarketFayssal KartobiPas encore d'évaluation
- Movie Piracy in Ethiopian CinemaDocument22 pagesMovie Piracy in Ethiopian CinemaBehailu Shiferaw MihiretePas encore d'évaluation