Académique Documents
Professionnel Documents
Culture Documents
Atm Work
Transféré par
Sozo Net WorkTitre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Atm Work
Transféré par
Sozo Net WorkDroits d'auteur :
Formats disponibles
1
ABSTRACT
Security measures at banks can play a critical, contributory role in preventing attacks on
customers. These measures are of paramount importance when considering vulnerabilities and
causation in civil litigation. Banks must meet certain standards in order to ensure a safe and
secure banking environment for their customers. This paper focuses on vulnerabilities and the
increasing wave of criminal activities occurring at Automated Teller Machines (ATMs) where
quick cash is the prime target for criminals rather than at banks themselves. A biometric and
GSM measure as a means of enhancing the security has emerged from the discourse.
CHAPTERONE
INTRODUCTION
1.1
BACKGROUND OF THE STUDY
Automated teller machine is a mechanical device that has its roots embedded in the accounts and
records of a banking institution. It is a machine that allows the banks customers carry out
banking
transactions
like,
deposits,
transfers,
balance
enquiries,
and
withdrawal.
Notwithstanding, we lived in a world where people no longer want to encounter long queues for
any reason, they dont not want to wait on queue for too long a time before they are attended to
and this has led to the increasing services being rendered by banks to further improve the
convenience of banking through the means of electronic banking. On this note the advent of
ATM is imperative, although with its own flaws. Crime at ATMs has become a nationwide issue
that faces not only customers, but also bank operators. Security measures at banks can play a
critical, contributory role in preventing attacks on customers. These measures are of paramount
importance when considering vulnerabilities and causation in civil litigation and banks must
meet certain standards in order to ensure a safe and secure banking environment for their
customers. Basically, the ATM scam involves thieves putting a thin, clear, rigid plastic sleeve
into the ATM card slot. When you insert your card, the machine can't read the strip, so it keeps
asking you to re-enter your PIN number. Meanwhile, someone behind you watches as you tap in
your number. Eventually you give up, thinking the machine has swallowed your card and you
walk away. The thieves then remove the plastic sleeve complete with card, and empty your
account. The way to avoid this is to run your finger along the card slot before you put your card
in. The sleeve has a couple of tiny prongs that the thieves need to get the sleeve out of the slot,
and you'll be able to feel them. The primary focus of this work is on developing a biometric
strategy (Fingerprint) and GSM to enhance the security features of the ATM for effective
banking transaction.
1.2
STATEMENT OF THE PROBLEM
In recent years, in line with global trends, the banking sector has faced rising levels of cash card
fraud resulting in the subsequent illegal withdrawal of funds from customer accounts. The
account-holder is normally held responsible for the loss of funds from their accounts and, as
such, the impact of this fraud could be potentially far-reaching. As a result of this, the banking
sector has to embrace biometrics as the solution to the growing problem of counterfeit ATM
cards and ID theft. Among others include
1. Fraudulent card readers, called skimmers are placed over the authentic reader to transfer
numbers and codes to nearby thieves.
2. Spy cameras are also used by password voyeurs to collect access codes.
3. In cases of card lost, if the loss is not noticed immediately, consumers may loose all
funds in an account.
4. If you forget your pin number, you cannot use the card.
5. The machine can retain your card when the machine malfunctions, when you forget your
secret number or if the card is damaged.
1.3
AIM AND OBJECTIVES
The aim of this project work is to simulate an embedded fingerprint authentication system, which
is used for ATM security applications. The specific objectives include:
I.
II.
To design a module that will collect customers finger print.
To design a module that will collect customers phone number and store them in a
III.
centralized database.
To design a module that will forward 4-digit number to their mobile when the finger print
IV.
reading matches.
To design a module that allows the customer to run his transaction after the system
V.
accepts the code generated.
To create a platform that will be able to analyze biometric data in the global image
analysis.
1.4
SCOPE OF THE STUDY
This study is on development of a secured ATM System for Nigeria Banks which will be
implemented using the finger print and GSM for securing the ATM System.There is a centralized
database to take care of customers personal and biometric data. The system is designed to query
the database by inputting a user finger print and if it matches with the one in a system it will
generate a 4-digit number that will enable the user to continue with his transactions.
1.5
SIGNIFICANCE OF THE STUDY
The current system of passwords and pin numbers needed to access financial services has drawn
a lot of criticism of late due to the increasing incidents of hacking. The system is at the mercy of
hackers, who use the hacked data to draw funds from the victims account. This is where
Biometrics with its foolproof system comes in. some of the reasons for building this system
include:
* Increase security - Provide a convenient and low-cost additional tier of security.
* Reduce fraud by employing hard-to-forge technologies and materials. For e.g. Minimize the
opportunity for ATM fraud.
* Eliminate problems caused by lost ATMs or forgotten passwords by using physiological
attributes. For e.g. prevent unauthorized use of lost, stolen or "borrowed" ATM cards.
* Replace hard-to-remember secret digits which may be shared or observed.
* Integrate a wide range of biometric solutions and technologies, customer applications and
databases into a robust and scalable control solution for facility and network access
* Make it possible, automatically, to know WHO did WHAT, WHERE and WHEN!
CHAPTER TWO
LITERATURE REVIEW
2.1
THE EVOLUTION OF THE COMPUTERISED BANKING SYSTEM
During the 1990s researchers at the Stanford Institute invented ERMA according to Molina
(1990) the Electronic Recording Method of Accounting is a computer processing system. ERMA
began as a project for the bank of America in an effort to computerize the banking industry.
ERMA computerized the manual processing of checks and account management and
automatically updated and posted checking accounts. Because of the historical evolution and
peculiarities, engendered taking into account the model of the European structure of a banking
system, a banking system n two levels has been created; the National Bank of Romania, as the
Central Bank, and the Commercial Banks(Vossen,1991). Considering the role and importance
held by the banks as regards the good operation of the economic agents and the requirements of
all the categories of economic agents in the market economy, as well as of the physical persons
beneficiaries of credits, depositors etc.. The computers security system should be sound enough
to maintain privacy of personal information. But still, we can that computerized banking is really
a boom to the customers in accessing and managing their account effectively, anytime and almost
anywhere. (Lewis, 2001). Recent media attention to information privacy issues has shown that
citizens are increasingly concerned about information privacy and their right to it. Governmental
and other organizations have been collecting data about individuals t an increasing and to many,
alarming rate. The ability to gather so much information on individuals is largely because of
advances in information technology (Renon, 1997).
It is important for managers and professionals to understand the issues surrounding personal
information privacy in order to protect the rights of those from and about whom they collect
data. The speed employed by the computerized banking for executing and confirming the
transactions is faster than the traditional speed of the ATM processing. (Bergstrom, 1994).
2.2
OVERVIEW OF ATM
According to Renon, (1997), an automated teller machine or automatic teller machine, also
known as an automated banking machine (ABM), cash machine, cashpoint, cashline, or
colloquially hole in the wall, is an electronic telecommunications device that enables the
customers of a financial institution to perform financial transactions without the need for a
human cashier, clerk or bank teller.
On most modern ATMs, the customer is identified by inserting a plastic ATM card with a
magnetic stripe or a plastic smart card with a chip that contains a unique card number and some
security information such as an expiration date, name and serial number. Authentication is
provided by the customer entering a personal identification number (PIN).Using an ATM,
customers can access their bank deposit or credit accounts in order to make a variety of
transactions such as cash withdrawals, check balances, transfer money, pay bills or credit mobile
phones. If the currency being withdrawn from the ATM is different from that in which the bank
account is denominated the money will be converted at an official exchange rate. Thus, ATMs
often provide the best possible exchange rates for foreign travelers, and are widely used for this
purpose(Renon, 1997). ATMs may be found in stores and shopping malls. Sometimes, they can
be found in bars or restaurants. Other times, at special events, people may set one up so the
guests can use the machine, like at a fundraiser. People need a debit card or credit card in order
to use an ATM. They will also need to have a Personal Identification Number (PIN), which is a
code that lets them get into their account.There are a number of scams with ATMs. In one scam,
con artists look over the victim's shoulder and find their PIN; this is known as shoulder surfing.
In another, they may install a video camera and get PIN numbers from that way. They then make
cards using the PIN number and account number to be able to use that person's account(Renon,
1997)
2.3
OVERVIEW OF BIOMETRICS
Biometric recognition, or biometrics, refers to the automatic identification of a person based on
his/her anatomical (e.g., fingerprint, iris) or behavioral (e.g., signature) characteristics or traits.
Renon, (1997), this method of identification offers several advantages over traditional methods
involving ID cards (tokens) or PIN numbers (passwords) for various reasons: (i) the person to be
identified is required to be physically present at the point-of-identification; (ii) identification
based on biometric techniques obviates the need to remember a password or carry a token. With
the increased integration of computers and Internet into our everyday lives, it is necessary to
protect sensitive and personal data. By replacing PINs (or using biometrics in addition to PINs),
biometric techniques can potentially prevent unauthorized access to ATMs, cellular phones,
laptops, and computer networks. Unlike biometric traits, PINs or passwords may be forgotten,
and credentials like passports and driver's licenses may be forged, stolen, or lost. As a result,
biometric systems are being deployed to enhance security and reduce financial fraud. Various
biometric traits are being used for real-time recognition, the most popular being face, iris and
fingerprint. However, there are biometric systems that are based on retinal scan, voice, signature
and hand geometry. In some applications, more than one biometric trait is used to attain higher
security and to handle failure to enroll situations for some users. Such systems are called
multimodal biometric systems.
According to Bergstrom, (1994). A biometric system is essentially a pattern recognition system
which recognizes a user by determining the authenticity of a specific anatomical or behavioral
characteristic possessed by the user. Several important issues must be considered in designing a
practical biometric system. First, a user must be enrolled in the system so that his biometric
template or reference can be captured. This template is securely stored in a central database or a
smart card issued to the user. The template is used for matching when an individual needs to be
identified. Depending on the context, a biometric system can operate either in a verification
(authentication) or an identification mode.
2.4
MODELS OF BIOMETRICS
There are different models of biometric systems. The models include
Iris Recognition
Charp, S.
(1994), With the integration of digital cameras that could acquire images at
increasingly high resolution and the increase of cell phone computing power, mobile phones
have evolved into networked personal image capture devices, which can perform image
processing tasks on the phone itself and use the result as an additional means of user input and a
source of context data (Charp, S. 1994). this image acquisition and processing capability of
mobile phones could be ideally utilized for mobile iris biometric. Recently, iris recognition
technology has been utilized for the security of mobile phones. As a biometric of high reliability
and accuracy, iris recognition provides high level of security for cellular phone based services for
example bank transaction service via mobile phone. One major challenge of the implementation
10
of iris biometric on mobile phone is the iris image quality, since bad image quality will affect the
entire iris recognition process. Previously, the high quality of iris images was achieved through
special hardware design. For example, the Iris Recognition Technology for Mobile Terminals
software once used existing cameras and target handheld devices with dedicated infrared
cameras (Fluaghter, R. 1990)). To provide more convenient mobile iris recognition, an iris
recognition system in cellular phone only by using built-in mega-pixel camera and software
without additional hardware component was developed (Glass, H. 2000)). Considering the
relatively small CPU processing power of cellular phone, in this system, a new pupil and iris
localization algorithm apt for cellular phone platform was proposed based on detecting dark
pupil and corneal specular reflection by changing brightness & contrast value. Results show that
this algorithm can be used for real-time iris localization for iris recognition in cellular phone.
Voice Recognition
Kingsbury, A. (2000), the speaker-specific characteristics of speech are due to difference in
physiological and behavioral aspects of the speech production system in humans. The main
physiological aspect of the human speech production system is the vocal tract shape. The vocal
tract modifies the spectral content of an acoustic wave as it passes through it, thereby producing
speech. Therefore, it is common in speaker verification systems to make use of features derived
only from the vocal tract. The microphone in the mobile phone captures the speech. Then, using
spectral analysis, an utterance may be represented as a sequence of feature vectors. Utterances,
spoken by the same person but at different times, result in similar yet a different sequence of
features vectors. So, the irrespective of the mood of the consumer, his transaction is accepted or
rejected. A voice signal conveys a persons physiological characteristics such as the vocal chords,
glottis, and vocal tract dimensions. Automatic speaker recognition (ASR) is a biometric method
11
that encompasses verification and identification through voice signal processing. The speech
features encompass high-level and low level parts. While the high-level features are related to
dialect, speaker style and emotion state that are not always adopted due to difficulty of
extraction, the low-level features are related to spectrum, which are easy to be extracted and are
always applied to ASR
Face Recognition
Klausmeier, J. (1984), Facial recognition is considered to be one of the most tedious among all
scans. Further, difficulty in acquisition of face and cost of equipments make it more complex.
However, some WAP enabled phones like CX 400K and LG-SD1000 manufactured by LG
electronics, have built in camera that can acquire images and can be transmitted over internet.
This it is sent to the credit card company to verify the face received matches with the face in
their database. If it matches, the goods are sent, else the order is rejected. We in our IMAGE
PROCCESSING LAB took two faces with small differences (you see a small dot in the forehead
of second face) and programmed MATLAB to find the difference between the two.
2.5
FINGER PRINT IDENTIFICATION ON MOBILE PHONE
Fingerprint biometric has been adopted widely for access control in places requiring high level of
security such as laboratories and military bases. By attaching a fingerprint scanner to the mobile
phone, this biometric could also be utilized for phone related security issues.
2.6
E-COMMERCE AND SECURITY ISSUES
Molina, J.K. (1997), whilst Australian businesses and consumers have embraced electronic
technology, there remains a substantial degree of mistrust in the confidentiality of electronically
12
filed and transferred information and the general security of e-commerce systems. These
businesses and consumers remain reticent in committing financial and private information to
electronic systems because of security issues. The issue of security, however, overlays all the
other issues of structure of commercial computer transactions and associated data transfer,
whether the transfer of funds is involved or not. Security must be of paramount importance in
any transactional based computer system. The dichotomy however, is that due to the very nature
of computers and their programming, it must be accepted that total security is not possible. The
best that can be expected is to approach the issues of security procedures, disaster recovery and
crisis management as part of a commercial risk management program in which the amount you
spend on security follows an assessment of the exposure you have to fraud. The best that can be
done is to try and keep up to date and ahead of the threats.
2.7
IMAGE MATCHING
Olea, J. and Prieto, G. (1999), image matching is a fundamental aspect of many problems in
computer vision, including object or scene recognition, solving for 3D structure from multiple
images, stereo correspondence, and motion tracking. This method describes image features that
have many properties that make them suitable for matching differing images of an object or
scene. The features are invariant to image scaling and rotation, and partially invariant to change
in illumination and 3D camera viewpoint. They are well localized in both the spatial and
frequency domains, reducing the probability of disruption by occlusion, clutter, or noise. Large
numbers of features can be extracted from typical images with efficient algorithms. In addition,
the features are highly distinctive, which allows a single feature to be correctly matched with
high probability against a large database of features, providing a basis for object and scene
recognition. The cost of extracting these features is minimized by taking a cascade filtering
13
approach, in which the more expensive operations are applied only at locations that pass an
initial test.
2.8
NEED FOR BIOMETRICS IN MOBILE PHONES:
Nowadays, shopping through the internet has become very popular and surely, a WAP enabled
mobile phone provides the facilities to consumers to shop online. Credit cards continue to be an
efficient tool for online money transactions. But, on the other hand, credit card's number can be
stolen on its way to its destination and can be misused by hackers. Thus, e-Business through a
mobile phone becomes insecure. Also anti-fraud Software, like those provided by Artic Soft and
ISC, created a back door entry and were largely involved in data spoofing. In addition to this,
many user and companies were prone to the attack of many viruses and Trojan horses. With so
much of problems faced, the service provide turned their attention towards biometrics to prevent
data spoofing and to provide secure e-Transactions
2.9
ONLINE AND OFF-LINE IRIS RECOGNITION SYSTEM
Sands, W. (1997), there are mainly two kinds of iris recognition attendance management system
on the market. One is on-line iris recognition attendance management sys-tem and the other is
off-line iris recognition attendance management system. On-line system always needs to connect
with a PC or workstation and all the iris recognition templates of people to be verified must be
stored in a database in the PC or workstation. Thereby, matching iris recognition needs the
support of the background PC. This kind of attendance management system is easy to paralyze in
case of malfunctions of iris recognition attendance machines, trans-mission line or PC. Once
several systems connect to form a network, burden of PC and the response time of the system
will be added.
14
By contraries, an off-line iris recognition attendance management system can finish all the
process including capturing the image of iris recognition, extracting minutiae, storing and
matching. All the operating of matching iris recognition needs no sup-port of PC and the burden
of PC is lightened. The same systems can connect to form a 485 network and finally connect to
the center PC of management sys-tem. So off-line systems are widely used in many occasions.
The shortcomings of this system are that there must be a managing PC nearly and it is difficult to
lay the transmission lines where topography is bad. With the development of wireless techniques
such as RFID, GPS, Wi-Fi, Bluetooth etc, many companies manufacture wireless modules. So
we can adopt the wireless techniques to solve the above-mentioned questions. There are mainly
two kinds of iris recognition attendance management system on the market. One is on-line iris
recognition attendance management sys-tem and the other is off-line iris recognition attendance
management system. On-line system always needs to connect with a PC or workstation and all
the iris recognition templates of people to be verified must be stored in a database in the PC or
workstation. Thereby, matching iris recognition needs the support of the background PC. This
kind of attendance management system is easy to paralyze in case of malfunctions of iris
recognition attendance machines, trans-mission line or PC. Once several systems connect to form
a network, burden of PC and the response time of the system will be added.
2.10
OVERVIEW OF THE FINGER PRINT BIOMETRICS
Fingerprint recognition or fingerprint authentication refers to the automated method of verifying
a match between two human fingerprints. Fingerprints are one of many forms of biometrics used
to identify individuals and verify their identity. The analysis of fingerprints for matching
purposes generally requires the comparison of several features of the print pattern. These include
patterns, which are aggregate characteristics of ridges, and minutia points, which are unique
15
features found within the patterns. It is also necessary to know the structure and properties of
human skin in order to successfully employ some of the imaging technologies.The three basic
patterns of fingerprint ridges are the arch, loop, and whorl:
Arch: The ridges enter from one side of the finger, rise in the center forming an arc, and
then exit the other side of the finger.
Loop: The ridges enter from one side of a finger, form a curve, and then exit on that same
side.
Whorl: Ridges form circularly around a central point on the finger.
Scientists have found that family members often share the same general fingerprint patterns,
leading to the belief that these patterns are inherited.
2.11
BENEFITS OF USING FINGERPRINT BIOMETRIC
Biometrics is a unique approach to identity management that offers userconvenience, increased
security, cost-effective provisioning and a non-repudiated,compliant audit trail for the system
operator. Traditional credentials or specialized knowledge tokens or passwords cannot guarantee
that the person using thesystem is the authorized individual. In addition, these forms of
identification can befrustrating for users and expensive for system operators.Given the benefits
of biometrics, why is it not pervasive or preferred? Simply put,the knowledge required to design
and deploy a successful biometric system is notwidely available. And, until recently, the
technology was not reliable enough toprovide the expected return on investment (ROI).This
paper encapsulates the best practices associated with the design and deploymentof fingerprint
16
biometric systems. The reader will learn how to avoid common pitfalls,ensure the system meets
user and operator expectations, and deliver the required ROI.Frost & Sullivan intends this paper
to be approachable, informative, andunderstandable to senior executives that want to know more
about what it takesto deploy biometrics in their organizations and reap the benefits of
theirinvestment. It is not a technical cookbook, but rather is a basis for asking questionsand
evaluating design choices to ensure that each fingerprint biometric deploymentproduces the
expected returns from the first day of deployment.
2.12
FINGERPRINT
BIOMETRICS
AS
SOLUTION
TO
IDENTITY
MMANAGEMENT CHALLENGES
In his own rendering Wise, S. and Kingsbury, G. (2000)stated that, fingerprint biometrics
identifies a user in a non-repudiated way. It can enhanceuser convenience, reduce (or even
eliminate) credential management costsand provide user-specific provisioning. Biometric
transactions are auditable andnon-repudiated. As a result of these benefits, many organizations
are adoptingfingerprint biometrics for identity management.A fingerprint is uniqueand copies
can be detected and prevented. This is in sharpcontrast to user IDs and passwords, which can be
easily replicated and usedinstantaneously by sophisticated electronic programs to gain access to
valuableenterprise assets. Combining a credential (i.e., a badge or other token) with apassword is
much more secure. The credential can be perfectly identified with someelectronic means to
detect presence and authenticity.
17
SECTION THREE
METHODOLOGY AND SYSTEM ANALYSIS
3.1
METHODOLOGY
The project methodology can be simply defined as the set of procedure that is followed from the
beginning to the completion of the software development process. The nature of the
methodology is dependent on a number of factors, including the software development
environment, the organizations practices, the nature or type of the software being developed, the
requirements of the users, the qualification and training of the software development team, the
available hardware software resources, the availability of existing design modules, and even the
budget and the time schedule. There are two broad categories of design methodologies used the
systematic and the formal types. As the name imply, the formal type makes extensive use of
mathematical notations for the object transformations and for checking consistencies. The
systematic type is less mathematical and it consists of the procedural component, which
prescribes what action or task to perform and the representation component, which prescribes
how the software structure should be represented.The research methodology is an orderly
manner or steps in which a close and careful study is carried out to find out what type of data is
maintained, its organization, storage and retrieval. The methods adopted for this software
engineering design are;
a. The structured systems analysis and design methodology (SSADM)
18
b. The object oriented analysis and design methodology (OOADM)
c. Prototyping
3.1.1
Structured Systems Analysis and Design Method
Structured Systems Analysis and Design Method (SSADM) is a systems approach to the analysis
and design of information systems. SSADM is a model by which an Information system design
can be arrived at. SSADM is one particular implementation which builds on the work of different
schools of structured analysis and development methods. The three most important techniques
that are used in SSADM are:
Stages of SSADM
SSADM involves the application of a sequence of analysis, documentation and design tasks
(Goodland &Riha, 1999). It has the following steps.
a.
Feasibility Study
This is a form of investigation into the goals and implications of state management company in
order to determine whether or not the given project is feasible or not, if the project is technically
possible, financially and socially justifiable, and acceptable to the organization. The project of
this stage is a formal feasibility study document. .
b.
Investigation of the Current Environment
This involves investigation and fact recording to understand the existing system i.e. the
operations of the ATM system and to identify the basic information requirements. This involves
19
knowing how the system operates, problems of the system and volumes of work done by the
system and operating cost. This involves interviewing employees, circulating questionnaires,
observations and reviewing existing documentation about the system under review.
c.
Business System Option (BSOs)
This is done using the outputs of the previous stage to develop a set of business system options.
This stage describes possible new systems in terms of functionality and implementation issues.
This involves developing alternative new system solutions.
d.
Requirements specification
Detailed functional and non-functional requirements are identified and new techniques are
introduced to define the required processing and data structure.
e.
Technical System Options
This describes the costs, benefits, and constraints of implementing the specification.
f.
Logical design
This defines how data is processed by theATM System and describes user dialogs. The logical
design specifies the main methods of interaction in terms of menu structures and command
structures. These are the main interfaces with which the user will interact with the system.
g.
Physical design
20
This involves developing user interface structures and implementing logical processes. This is
the final state where all the logical specifications of the system are converted to descriptions of
the system in terms of real hardware and software. The logical data structure is converted into a
physical architecture in terms of database structures.
3.1.2
Object-Oriented Analysis and Design Method (OOADM)
Object-oriented Analysis and Design (OOAD) software engineering approach models the ATM
System as a group of interacting objects. Each object represents some entity of interest in the
system being modeled, and is characterized by its class, its state (data elements), and its
behavior. The steps to undergo are;
Object-oriented Analysis
Object-oriented analysis (OOA) looks at the problem domain, with the aim of producing a
conceptual model of the information that exists in the area being analyzed. The sources for the
analysis can be a written requirements statement, a formal vision document, and interviews with
stakeholders or other interested parties.
a. Object-oriented Design
The result of object-oriented analysis is used in object-oriented design. This involves a
description of what the system is functionally required to do, in the form of a conceptual model.
These models are as a set of use cases, one or more UML class diagrams, and a number of
interaction diagrams.
b. Object-oriented Implementation
21
This step is involved with defining classes, creating objects, calling operations, implanting
inheritance and association.
3.1.3
Prototyping
A prototype is an original type, form, or instance of something serving as a typical example,
basis, or standard for other things of the same category. Software prototyping, an activity during
certain software development, is the creation of prototypes, i.e., incomplete versions of the
software program being developed.
Prototyping Stages
The process of prototyping involves the following steps
a.
Identify Basic Requirements
Determine basic requirements including the input and output information desired. Details, such
as security, can typically be ignored.
b.
Develop Initial Prototype
The initial prototype is developed that includes only user interfaces.
c.
Review
The customers, including end-users, examine the prototype and provide feedback on additions or
changes.
d.
Revise and Enhance the Prototype
22
Using the feedback both the specifications and the prototype can be improved. Negotiation about
what is within the scope of the contract/product may be necessary. If changes are introduces,
then, repeating developing initial prototype and review may be needed
3.2
INFORMATIONGATHERING
The methods used in data collection in this research are:
Observation: I observed how people go about their business while conducting ATM
transaction and notes were taken, I used this method with the view of setting an insight
of ways in which activities in the ATM system is actually carried out.
Internet: I obtained information relating to Finger print biometric with the help of the
internet. This method is one of my important sources of information gathering.
PersonalInterview: I interviewedsome of the staffs in the banking sector and some
customers that conduct some transactions using ATM. This helped to gather necessary
information.
3.3
ANALYSIS OF THE EXISTING SYSTEM
The existing system as I gathered operates as stated below:
A bank customer comes to an ATM machine, inserts the ATM card and selects a language. The
customer will enter his/her four digit secret number and press enter. Select the type of transaction
the customer wants to perform, withdraw or deposit money, then the customer will choose
23
whether to perform another transaction, if no the customer will choose whether to collect receipt
for the transaction. When the machine beeps at you, take your card, cash and receipt (if
applicable). You can use the receipt to record the transaction in your check register or passbook.
3.4
LIMITATIONS OF THE EXISTING SYSTEM
With the current upsurge and nefarious activities of Automated Teller Machine (ATM) ranging
from ATM card theft, skimming, pin theft, card reader techniques, pin pad techniques, force
withdrawals and lot more, fraudster is threatening electronic payment system in the nations
banking sector, users are threatening massive dumping of the cards if the unwholesome act is not
checked. In summary:
They are not safe since they are located outside the bankhall.
If one forgets the pin number he or she will not be able to withdraw money from their
accounts.
If one makes mistakes three times in entering the pin number the card will be swallowed
down the machine and it takes time to retrieve it.
3.7
OVERVIEW OF THE PROPOSED SYSTEM
A biometric system is essentially a pattern recognition system that operates by
acquiringbiometric data from an individual, extracting a feature vector from the acquired data,
comparingthis feature vector from the database feature vector. Person authentication has always
been anattractive goal in computer vision. Authentication systems based on human
characteristics suchas face, finger, iris and voice are known Biometrics systems. The basis of
every biometric systemis to get the input image and generate prominent feature vectors like
color, texture, etc.
3.8
JUSTIFICATION OF THE PROPOSED SYSTEM
24
Password and PINs have been the most frequently used authentication method. Their use
involves controlling access to a building or a room, securing access to computers, network, the
applications on the personal computers and many more. In some higher security applications,
handheld tokens such as key fobs and smart cards have been deployed. Due to some problems
related to these methods, the suitability and reliability of these authentication technologies have
been questioned especially in this modern world with modern applications. Biometrics offer
some benefits compare to these authentication technologies.
Increased Security
Biometric technology can provide a higher degree of security compared to traditional
authentication methods. Biometrics is preferred over traditional methods for many reasons which
include the fact that the physical presence of the authorized person is required at the point of
identification. This means that only the authorized person has access to the resources.Effort by
people to manage several passwords has left many choosing easy or general words, with
considerable number writing them in conspicuous places. This vulnerability leads to passwords
easily guessed and compromised. Also, tokens can be easily stolen as it is something you have.
By contrast, it is almost impossible for biometrics data to be guessed or even stolen in the same
manner as token or passwords. Some biometric systems can be broken under certain conditions,
today's biometric systems are highly unlikely to be fooled by a picture of a face.
Increased Convenience
One major reason passwords are sometimes kept simple is because they can be easily forgotten.
To increase security, many computer users are mandated to manage several passwords and this
25
increases the tendency to forget them. Card and tokens can be stolen and forgotten as well even
though attaching them to keyholders or chains can reduce the risk. Because biometric
technologies are based on something you are, it makes them almost impossible to forgot or
manage. This characteristic allows biometrics to offer much convenience than other systems
which are based on having to keep possession of cards or remembering several passwords.
Biometrics can greatly simplify the whole process involved in authentication which reduces the
burden on user as well as the system administrator (For PC applications where biometrics
replaces multiple passwords).Biometric authentication also allows for the association of higher
levels of rights and privileges with a successful authentication. Information of high sensitivity
can be made more readily available on a network which is biometrically protected than one
which is password protected. This can increase convenience as a user can access otherwise
protected data without any need of human intervention.
Increased Accountability
Traditional authentication methods such as tokens, passwords and PINs can be shared thereby
increasing the possibility of unaccountable access, even though it might be authorized. Many
organizations share common passwords among administrators for the purpose of facilitating
system administration. Unluckily, because there is uncertainty as to who at a particular point in
time is using the shared password or token, accountability of any action is greatly reduced. Also,
the user of a shared password or token may not be authorized and sharing makes it even hard to
verify, the security (especially confidentiality and integrity) of the system is also
reduced.Increase in security awareness in organizations and the applications being used has led
to the need for strong and reliable auditing and reporting. Deploying biometrics to secure access
26
to computers and other facilities eliminates occurrence such as buddy-punching and therefore
provides a great level of certainty as to who accessed what computer at what point in time.
START
3.9
FLOWCHART
OFATM
THECARD
EXISTING SYSTEM
INSERT
ENTER YOUR PIN
NO
IS PIN CORRECT
?
YES
SELECT TRANSACTION
WITHDRAW OR DEPOSIT MONEY
ANOTHER TRANSACTION
?
?
YES
NO
TAKE YOUR CASH, CARD AND RECEIPT
END
27
3.10
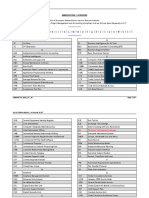
A HIGH LEVEL MODEL OF THE PROPOSED SYSTEM
FINGERPRINT ATM SYSTEM
HOME
ATM
NEW PIN
BANKER LOGIN
ENTER ACCOUNT NUMBER
USERNAME
FINGERPRINT SCAN
PASSWORD
ADD NEW ACCOUNT
DEPOSIT
SMS PORT
28
CHAPTER FOUR
SYSTEM DESIGN
4.1
GENERAL SYSTEM FUNCTION
The system will generally perform the following function:
There is a module that enables the banker/system administrator to take customers details
including their fingerprint scan and open account for them.
There is a module that enables the users to make deposits.
The system enables the customer to have access to their account when they produce their
account number and fingerprint scan.
When customers enter their account number, the system displays a prompt for finger print
reading, upon which a 4-digit number is forwarded to the customers phone.
There is a module that allows the customer to run his transaction after accepting the 4-
digit that was sent to the mobile phone.
The system generates a 4-digit random number for user authentication each time the
scanned finger print matches with the account number.
4.2
SYSTEM SPECIFICATION
This section shows the requirement of the system and what it is supposed to contain for effective
design.
29
4.2.1
Home Page Specification
Banker login: to login an administrative staff or the CEO admin to perform an
administrative functions like adding new account and deposits.
Home: to display the default page of the system.
Deposit: this enables the administrator to enter new deposits to the system.
Sms port: responsible for the forwarding of messages to customers mobile phone.
Atm: enables the customers to conduct their transactions after the correct authentication.
Add new account: enables the system administrator to open/add new customer account.
4.2.2
User Interface Specification
It is the specification for the user interface which is also path of the software that the user
interacts with, whether it is for input or output purposes.
4.2.2.1
Input Form Specification
The input form and their specification are shown below
A. Banker login form: this form enables the system administrator to login into the
system. The fields here are;
Username
Password
B. Add new account form: this form enables the administrator to collect and add new
customers data into the system. The fields here are:
Account name
Address
Phone number
Account number
Account type
Amount
30
Register
Exit
Place your finger print
C. Account deposit form: this form enables one to deposit money to the system. The
fields here are:
Account number
Amount
Deposit
Exit
D. Banker login form: this form enables the administrator/banker to login to the system.
The fields here are:
Username
Password
Login
Exit
E. Form port: this form handles the Sms sending information in the system. The fields
here are:
Enter your port number
Update
Close
4.2.2.2 Output Form specification
The output form here is the form that shows the details of the input processed by the biometric
atm authentication system. The output form is the transaction page that displays after the system
authentication. The fields here are:
4.2.3
Withdrawal
Balance enquiry
Mtn top up
Ministatement
Cancel
Database Specification
31
There is a database named atm to handle all the details of the finger print ATMsystem. The
database is designed with Microsoft access and incorporated into visual basic 6.0 platform. It has
four tables, we are going to look at the four tables. They includes:
a.
Admin: this table has the information needed for any admin staff to login. The fields
b.
in it includes:
Id
int(11)
Username
varchar(20) null
Password
varchar(20) null
Account: this table contains all the information about all the registered account. the
c.
fields here are:
Id
int(11)
Accountno
varchar(50)
Account_name varchar(200)
Amount
varchar(20)
Address
varchar(200)
Phoneno
varchar(20)
Passport
varchar(200)
Date_Of_Opened varchar(200)
Account_type
varchar(200)
Fingerprint_Id
varchar(6)
Sms
varchar(7)
Smsport
varchar(8)
Transaction: this table contains all the information about customers transaction and
d.
the type of transaction carried out. The fields here are:
Id
int(11)
Accountno
varchar(50)
Amount
varchar(11)
Purpose
varchar(200)
Date_no
varchar(20)
Enroll: this table contains the data of all the enrolled customers. The fields here are:
Id
int(11)
Template
blob
32
4.2.4
Program Module Specification
The program module specification describes the specification of what the program would do to
enhance good design guide during the process. As it concerns this particulars application
package, it describes different activities involved in the program modules. The classifications of
the modules are vividly described under the subsections below.
There are total of seven modules in this system specified according to their functions. They
include:
i.
ii.
Home:this module displays the default page of the system anytime a user click on it.
Add new account: this module allows the system administrator/banker to register/add
iii.
iv.
v.
new customers to the system.
Deposit: this module enables a deposit to be made in the system.
New pin: this module allows customers to obtain new pin to run their transactions.
Banker login: this module allow banker/system administrator to have access to the
vi.
administrator restricted area.
Atm: this module enables bank customers to run their transactions after the accurate
vii.
authentication.
Sms port: this module is responsible for forwarding messages (4-digit secret number) to
the customers after putting their account number and fingerprint scanning.
4.3
MAIN MENU DESIGN
4.3.1
Home Page Design
33
This subsection is responsible for contents in the main menu interface. Based on the fulfillment
of this project application package software, the main menu was designed to have a link to all the
form interfaces within the application. The figure below has a descriptive explanatory diagram of
the sketch of the main menu design. Different information that will enable the user, understand
the procedure as well as a guide for the software.
FINGERPRINT ATM SYSTEM
HOME
Input Data
ATM
NEW PIN
BANKER LOGIN
ENTER ACCOUNT NUMBER
USERNAME
Input From the Keyboard
FINGERPRINT SCAN
PASSWORD
DISPLAY REPORT
CPU
ADD NEW ACCOUNT
DEPOSIT
SMS PORT
Fig 2 user interface design
4.3.2
Program Module Design
4.3.2.1 System Flowchart
DATABASE
Output
34
START
DISPLAY BANKER LOGIN FORM
ENTER USERNAME AND PASSWORD
NO
IS USERNAME AND PASSWOR CORRECT ?
Fig. 7 system flowchart
YES
DISPLAY ADMINISTRATOR AREA
4.3.2.2 PROGRAM FLOWCHART
BANKER MODULE
ADD NEW ACCOUNT
ENTER DEPOSIT
SMS PORT
END
35
Fig. 8 banker module
ATM USER MODULE
36
37
38
CHAPTER FIVE
SUMMARY, CONCLUSION AND RECOMMENDATION
5.1
SUMMARY OF ACHIEVEMENTS
Rapid development of banking technology has changed the way banking activities are dealt with.
One banking technology that has impacted positively and negatively to banking activities and
transactions is the advent of automated teller machine (ATM). With an ATM, a customer is able
to conduct several banking activities such as cash withdrawal, money transfer, paying phone and
electricity bills beyond official hours and physical interaction with bank staff. In a nutshell, ATM
provides customers a quick and convenient way to access their bank accounts and to conduct
financial transactions.
The system will generally perform the following function:
There is a module that enables the banker/system administrator to take customers details
including their fingerprint scan and open account for them.
There is a module that enables the users to make deposits.
The system enables the customer to have access to their account when they produce their
account number and fingerprint scan.
When customers enter their account number, the system displays a prompt for finger print
reading, upon which a 4-digit number is forwarded to the customers phone.
There is a module that allows the customer to run his transaction after accepting the 4-
digit that was sent to the mobile phone.
The system generates a 4-digit random number for user authentication each time the
scanned finger print matches with the account number.
5.2
PROBLEMS ENCOUNTERED
39
There was some constraints encountered during collection of data, poor data collection becomes
apparent due to interviewing of banking organizations and their customers. Many of them were
reluctant to disclose important information and statistical data which otherwise would have been
relevant to this research, due to some banking secrets which breeds some indifferent attitudes
towards that effect.It takes a long time and large commitment of resources to get a good result,
unavailability of text and materials on this topic, made gathering of facts very difficult, some of
the facts were gathered from the internet, which is quite expensive.
5.3
CONCLUSSION AND RECOMMENDATION
The growth in electronic transactions has resulted in a greater demand for fast and accurate user
identification and authentication. Access codes for buildings, banks accounts and computer
systems often use PIN's for identification and security clearances. Conventional method of
identification based on possession of ID cards or exclusive knowledge like a social security
number or a password are not all together reliable. ID cards can be lost, forged or misplaced;
passwords can be forgotten or compromised, but ones biometric is undeniably connected to its
owner. It cannot be borrowed, stolen or easily forged. Using the proper PIN gains access, but the
user of the PIN is not verified. When credit and ATM cards are lost or stolen, an unauthorized
user can often come up with the correct personal codes. Despite warning, many people continue
to choose easily guessed PIN's and passwords - birthdays, phone numbers and social security
numbers. Recent cases of identity theft have heightened the need for methods to prove that
someone is truly who he/she claims to be. Biometric authentication technology using fingerprint
identifier may solve this problem since a persons biometric data is undeniably connected to its
owner, is nontransferable and unique for every individual. Biometrics is not only a fascinating
pattern recognition research problem but, if carefully used, could also be an enabling technology
40
with the potential to make our society safer, reduce fraud and lead to user convenience by
broadly providing the following three functionalities (a) positive identification (b) large scale
identification and (c) screening.
REFERENCES
Bergstrom, R. (1994), ATM attached importance and techniques, London: Pitman
publication ltd.
41
Charp, S.(1994), Networking and Telecommunications. Technical Horizons in Education, New
York: John Publishing.
Fluaghter, R. (1990), Computerized Adaptive Testing, Hillsdale, New York: ACM press.
Glass, H. (2000), Interpretation of international banking system, New Jersey: Vintage
publication.
Kingsbury, A. (2000), Mobilebanking services and operations, Birmingham: Morgan Kaufmann
Publishers.
Klausmeier, J. (1984), Networking and Microcomputers Eric Digest NY, Clearing House on
Information Resources, New York: Academic press.
Lewis, I. (2001), Computerization of banking systems, New York: Pearson Publication.
Molina, J.K. (1997), Item Banks Information Storage and Management; Analysis of a Computer
System,Megrowhill, New York: Vintage books.
Olea, J. and Prieto, G. (1999), Tests Information: Fundamental Application. Educational
Research, Washington DC: DP Publication ltd.
Renom, J. (1997), Perspective Tests Adaptive Information, New York: Yarchi Press.
Sands, W. (1997), Computerized Adaptive Testing, American Psychological association,
Washington DC: McGraw Hill.
Vossen, G. (1991), Data models, Database Languages. And Database Management Systems
Adison-Wesley Publishing, New Orleans: Pitman Publication.
Wise, S. and Kingsbury, G. (2000), Practical Issues in Developing and Maintaining a
Computerized Adaptive Test: Fundamental Application, New York: ACM Press.
Vous aimerez peut-être aussi
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (895)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- E PostOffice SRSDocument12 pagesE PostOffice SRSSozo Net WorkPas encore d'évaluation
- PCB Reverse EngineeringDocument2 pagesPCB Reverse Engineeringbill1022Pas encore d'évaluation
- Web Based Research InfoDocument44 pagesWeb Based Research InfoSozo Net WorkPas encore d'évaluation
- Crime Diary Yyy YyyDocument41 pagesCrime Diary Yyy YyySozo Net WorkPas encore d'évaluation
- Integrated Database Management System For A Multilocation Enterprise FullDocument51 pagesIntegrated Database Management System For A Multilocation Enterprise FullSozo Net WorkPas encore d'évaluation
- Online NewsDocument77 pagesOnline NewsSozo Net WorkPas encore d'évaluation
- E PaymentDocument56 pagesE PaymentSozo Net Work0% (1)
- 3D Internet and Network MediaDocument24 pages3D Internet and Network MediaSozo Net Work100% (1)
- Sales Forecasting FullDocument43 pagesSales Forecasting FullSozo Net WorkPas encore d'évaluation
- Socket LayerDocument23 pagesSocket LayerSozo Net Work100% (1)
- Credit CardDocument28 pagesCredit CardSozo Net WorkPas encore d'évaluation
- Digital PreservationDocument26 pagesDigital PreservationSozo Net WorkPas encore d'évaluation
- Youth Service Primary Assignment Deployment SystemDocument7 pagesYouth Service Primary Assignment Deployment SystemSozo Net WorkPas encore d'évaluation
- DescriptionDocument3 pagesDescriptionSozo Net WorkPas encore d'évaluation
- Registration Full Name Username Password EmailDocument4 pagesRegistration Full Name Username Password EmailSozo Net WorkPas encore d'évaluation
- UntitledDocument1 pageUntitledSozo Net WorkPas encore d'évaluation
- Inventory ManagementDocument7 pagesInventory ManagementSozo Net WorkPas encore d'évaluation
- Chapter One: Each Time The Employee Attempts To Check in or Out, If There Is A Match, The Attendance Is RecordedDocument5 pagesChapter One: Each Time The Employee Attempts To Check in or Out, If There Is A Match, The Attendance Is RecordedSozo Net WorkPas encore d'évaluation
- STA309A: Multi-Channel Digital Audio Processor With DDX®Document71 pagesSTA309A: Multi-Channel Digital Audio Processor With DDX®Uday KrishnaPas encore d'évaluation
- Implementation of Serial Port Communication Based On Modbus-RTU Communication Protocol in C#Document4 pagesImplementation of Serial Port Communication Based On Modbus-RTU Communication Protocol in C#SEP-Publisher100% (2)
- An-715 Ibis ModelDocument8 pagesAn-715 Ibis ModelDDragos GeorgePas encore d'évaluation
- Abbreviations Used in ICTDocument7 pagesAbbreviations Used in ICTរ័ត្នវិសាល (Rathvisal)Pas encore d'évaluation
- DM9368 PDFDocument8 pagesDM9368 PDFEnrique MirazoPas encore d'évaluation
- Cognos Developer Resume Bayshore Ny PDFDocument6 pagesCognos Developer Resume Bayshore Ny PDFuser659nPas encore d'évaluation
- ThinkCentre M72e DatasheetDocument4 pagesThinkCentre M72e DatasheetrogromPas encore d'évaluation
- Motorola SEMV12 SmartStream, Encryptor ModulatorDocument2 pagesMotorola SEMV12 SmartStream, Encryptor Modulatorjuanlasserre9444Pas encore d'évaluation
- (REFERENCE) MIKE11 Short Introduction - TutorialDocument94 pages(REFERENCE) MIKE11 Short Introduction - Tutorialafiqah_507Pas encore d'évaluation
- WiMAX Modeling Techniques and Applications PDFDocument133 pagesWiMAX Modeling Techniques and Applications PDFคนชายแดน ฝั่งตะวันตกPas encore d'évaluation
- MOTOBRIDGE Brochure FinalDocument4 pagesMOTOBRIDGE Brochure Finalpy5rcbPas encore d'évaluation
- Lecture05 - 8086 AssemblyDocument43 pagesLecture05 - 8086 Assemblytesfu zewduPas encore d'évaluation
- 3gwireless Secured Itlab - Com.vnDocument5 pages3gwireless Secured Itlab - Com.vnTelekom FilesPas encore d'évaluation
- List of 7400 Series Integrated CircuitsDocument15 pagesList of 7400 Series Integrated CircuitssansurePas encore d'évaluation
- DX DiagDocument13 pagesDX DiagAdrian AnghelPas encore d'évaluation
- System Bus in Computer Architecture: Goran Wnis Hama AliDocument34 pagesSystem Bus in Computer Architecture: Goran Wnis Hama AliGoran WnisPas encore d'évaluation
- RoIP Gateways Brochure For Web 2016Document8 pagesRoIP Gateways Brochure For Web 2016Jorge Casali100% (1)
- Edt GDDocument364 pagesEdt GDAre VijayPas encore d'évaluation
- Tilak Maharashtra Vidyapeeth, Pune: How To Begin A Project WorkDocument6 pagesTilak Maharashtra Vidyapeeth, Pune: How To Begin A Project WorkAdnan AnsariPas encore d'évaluation
- System Compatibility ReportDocument3 pagesSystem Compatibility ReportGendis manjaPas encore d'évaluation
- 6236 Implementing and Maintaining Microsoft SQL Server 2008 Reporting ServicesDocument444 pages6236 Implementing and Maintaining Microsoft SQL Server 2008 Reporting Servicessportiefke84Pas encore d'évaluation
- 25W - 15960 - 5 Poster Conosci HDDocument2 pages25W - 15960 - 5 Poster Conosci HDRenzo SattiPas encore d'évaluation
- Andriod Operating SystemDocument12 pagesAndriod Operating SystemHari HaranathPas encore d'évaluation
- ISO Stands For International - This Is Called A Model For Open Is Commonly Known As OSI Model. - The ISO-OSI Model Is A Seven Layer ArchitectureDocument11 pagesISO Stands For International - This Is Called A Model For Open Is Commonly Known As OSI Model. - The ISO-OSI Model Is A Seven Layer ArchitectureAmmu MolePas encore d'évaluation
- Mastering Citrix® XenDesktop® - Sample ChapterDocument63 pagesMastering Citrix® XenDesktop® - Sample ChapterPackt PublishingPas encore d'évaluation
- Database ProgrammingDocument441 pagesDatabase ProgrammingWahyu Koerniawan100% (1)
- Assignment 1Document7 pagesAssignment 1Altaf KondakamaralaPas encore d'évaluation
- How To Play HEVC (THIS FILE)Document2 pagesHow To Play HEVC (THIS FILE)BonedusterPas encore d'évaluation
- IoT Based Water Level Monitoring System With An Android ApplicationDocument4 pagesIoT Based Water Level Monitoring System With An Android ApplicationEditor IJRITCCPas encore d'évaluation