Académique Documents
Professionnel Documents
Culture Documents
Casabac Info SSL
Transféré par
Rodrigo Románovich FiodorovichTitre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Casabac Info SSL
Transféré par
Rodrigo Románovich FiodorovichDroits d'auteur :
Formats disponibles
Casabac
Security Aspects using Casabac GUI Server
Technologies
SSL communication with Java and
Tomcat
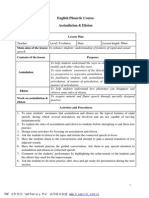
This document describes briefly how to enable Tomcats SSL capabilities and shows how to make use of it
out of a Java application. We review some issues and provide example code, demonstrating basic things
to be done to get a working environment. Make sure you have Java Version 1.4 installed on your system
since JSSE (Java Secure Socket Extension) is already included. If you are using an older version you need
to install the JSSE package, which is separately available from Sun. JSSE contains the SSL (Secure
Socket Layer) that provides all functionality to make use of secure Internet communication paths.
This document is independent from Casabac GUI Server - but is a summary of experiences we made
when connecting our Casabac SWT Client (written in Java) to a server using http-ssl.
Configuring Tomcat
SSL Support
To enable SSL support, open the servers configuration file
$CATALINA_HOME/conf/server.xml
and just uncomment the element:
<!-- Define a SSL Coyote HTTP/1.1 Connector on port 8443 -->
All settings may be left on the defaults. Tomcat will listen on port 8443 for HTTPS requests.
Java Keytool
Java provides a command line tool to create an SSL certificate, which is requested by Tomcat when it
tries to initialise. If you already got an officially signed certificate, you dont need this step. More below
we describe how you can import it into the servers keystore. However, for testing purpose, or during
development its sufficient to use a private and unsigned one.
With the following command you create a new certificate in your OS default keystore:
%JAVA_HOME%\bin\keytool -genkey -alias tomcat -keypass changeit -keyalg RSA
If your OS default keystore (it contains the certificates) doesnt exist, a new one is created in your home
folder and the new certificate becomes added. The keystore file is named .keystore. Tomcat will
automatically find it next time the server gets started (as long as Tomcat runs under your user name).
You can rename/copy the keystore file to any location. Then, you have to adjust the server configuration
file to let Tomcat know where to look up:
Add a new attribute the new location to the "SSL HTTP/1.1 Connector" entry in server.xml:
KeystoreFile=C:\dir\myKeystoreFile
If the password is different from changeit, add the password attribute as well:
1/4
Casabac
Security Aspects using Casabac GUI Server
Technologies
KeystorePass=changed
Signed Certificates
If you purchased a signed certificate from one of the global certificate authorities (i.e. VeriSign Inc.) you
may not need to create your own. Simply import it into your server side keystore file:
%JAVA_HOME%\bin\keytool -import -file <certificate> -keypass changeit -keystore <keystore>
More detailed information on Tomcat can be found on http://jakarta.apache.org/tomcat/.
SSL With Internet Explorer
After restarting Tomcat you should try first if you can access your pages either via HTTP or HTTPS, i.e.:
https://localhost:8443/MyApplication/index.html
http://localhost:8080/MyApplication/index.html
SSL With Java
Now try to access the same page from your Java code. A primitive example on how that could be done is
given below. If your server has a signed certificate installed in its keystore, it should work from scratch
and you should see the source code of your web page on the OS console. However, if the certificate is not
signed and hence unknown by the underlying Java SSL framework, some other steps need to be done to
make it work (see next sections).
public void loadMyPage()
{
try
{
java.net.URLConnection urlc = new java.net.URL(https://localhost:8443/index.html).openConnection();
java.io.InputStreamReader isr = new java.io.InputStreamReader(urlc.getInputStream(), "UTF-8");
java.io.BufferedReader br = new java.io.BufferedReader(isr);
StringBuffer sb = new StringBuffer();
while (true)
{
String s = br.readLine();
if (s == null) break;
sb.append(s + "\n");
}
br.close();
System.out.print(sb.toSting());
}
catch (Exception e)
{
e.printStackTrace();
}
Dealing With Client Side Authentication Issues
Trying to connect to Tomcat via Java and HTTPS may result in the following exception:
javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: No trusted
certificate found
When Tomcat does not respond with a signed certificate the client side SSL layer does not accept it. This
means, the JRE could not authenticate the servers certificate by means of its local keystore and
therefore the server might not be the one it claims to be. Each JRE contains a pre configured standard
keystore (or truststore) for authenticating signed certificates. If you are interested in, have a look at:
2/4
Casabac
Security Aspects using Casabac GUI Server
Technologies
%JAVA_HOME%\jre\lib\security\cacerts
Replacing The Trust Manager
One way to overcome the SSL handshake exception is to provide and register a custom-made trust
manager in your Java application. What the code below does, it accepts all kinds of server provided SSL
certificates regardless whether signed or unsigned. Just run it once before you attempt to initiate the URL
connection:
private void registerMyTrustManager()
{
TrustManager[] trustAll = new javax.net.ssl.TrustManager[]
{
new javax.net.ssl.X509TrustManager()
{
public java.security.cert.X509Certificate[] getAcceptedIssuers(){ return null; }
public void checkClientTrusted(java.security.cert.X509Certificate[] certs,String authType){}
public void checkServerTrusted(java.security.cert.X509Certificate[] certs,String authType){}
}
};
try
{
javax.net.ssl.SSLContext sc = javax.net.ssl.SSLContext.getInstance("SSL");
sc.init(null, trustAll, new java.security.SecureRandom());
javax.net.ssl.HttpsURLConnection.setDefaultSSLSocketFactory(sc.getSocketFactory());
}
catch (Exception e)
{
e.printStackTrace();
}
Now all certificates (signed and unsigned) become accepted and the exception disappears. Of course this
is not advisable for a production system but quite useful for testing.
Providing a Custom Key Store
A more laborious but recommended procedure to avoid the SSL handshake exception is done by letting
the JRE address a keystore containing servers real certificate. For testing purpose you could simply use
the one you have created during Tomcat configuration. Just pass the keystore location and password as
JVM parameters when you start your application. Inside your Java code, it would be the same to set the
two parameters as system properties.
-Djavax.net.ssl.trustStore=C:/myFolder/myKeyStoreFile
-Djavax.net.ssl.trustStorePassword=changeit
One step ahead its maybe required to move an unsigned Tomcat certificate from Tomcats keystore into
your own, or even the JRE keystore. Thereby all required certificates could accumulate in one repository.
a) Export:
%JAVA_HOME%\bin\keytool -export -alias tomcat -keypass changeit -file C:\myCerti
b) Import:
%JAVA_HOME%\bin\keytool -import -file C:\myCerti -keypass changeit -keystore JAVA_HOME%/jre/lib/security/cacerts
Patching Hostname Verification
If you did one of the previously described approaches and re-run your code you will immediately notice
the story is not over now, because your client throws an IOException:
3/4
Casabac
Security Aspects using Casabac GUI Server
Technologies
java.io.IOException: HTTPS hostname wrong:
should be <localhost>
This error message is quite misleading; it means your URL doesnt match the name/IP of your server,
which is an important security check but unfounded in our arbitrary environment. However, in real life its
considerably important to ensure that the URL hostname and the server's identification hostname match.
To circumvent that misbehaviour you need to do one last step. The following code snippet figures out
how to set a special hostname verifier that is called to confirm the host name; it always confirms any:
private void registerMyHostnameVerifier()
{
javax.net.ssl.HostnameVerifier myHv = new javax.net.ssl.HostnameVerifier()
{
public boolean verify(String hostName,javax.net.ssl.SSLSession session)
{
return true;
}
}
javax.net.ssl.HttpsURLConnection.setDefaultHostnameVerifier(myHv);
}
Summary
Now youre done and the initially provided example should work. A summarized cooking recipe would
look like this:
Create a keystore for Tomcat: use Java key tool
Configure Tomcat: uncomment the HTTPS section, restart, make a smoke test with Internet Explorer
Call the methods to install trust manager and hostname verifier
Create a HTTPS URL connection and load your data
4/4
Vous aimerez peut-être aussi
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (894)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (587)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (119)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2219)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (265)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- What Is A Political SubjectDocument7 pagesWhat Is A Political SubjectlukaPas encore d'évaluation
- USAF Electronic Warfare (1945-5)Document295 pagesUSAF Electronic Warfare (1945-5)CAP History LibraryPas encore d'évaluation
- K-12 Grade 9 Science Roll Roll AwayDocument20 pagesK-12 Grade 9 Science Roll Roll AwayMeya Jhana Navidad75% (8)
- Scribd: Get Unlimited Downloads With A 30 Day Free TrialDocument3 pagesScribd: Get Unlimited Downloads With A 30 Day Free TrialMrdonPas encore d'évaluation
- Node - Js 8 The Right Way: Extracted FromDocument11 pagesNode - Js 8 The Right Way: Extracted FromRodrigo Románovich FiodorovichPas encore d'évaluation
- Texto BasuraDocument169 pagesTexto BasuraRodrigo Románovich FiodorovichPas encore d'évaluation
- Fisica Hoja CalculoDocument1 pageFisica Hoja CalculoRodrigo Románovich FiodorovichPas encore d'évaluation
- Texto BasuraDocument1 pageTexto BasuraRodrigo Románovich FiodorovichPas encore d'évaluation
- Texto BasuraDocument1 pageTexto BasuraRodrigo Románovich FiodorovichPas encore d'évaluation
- Scribd: Get Unlimited Downloads With A 30 Day Free TrialDocument3 pagesScribd: Get Unlimited Downloads With A 30 Day Free TrialMrdonPas encore d'évaluation
- Scribd: Get Unlimited Downloads With A 30 Day Free TrialDocument3 pagesScribd: Get Unlimited Downloads With A 30 Day Free TrialMrdonPas encore d'évaluation
- Scribd: Get Unlimited Downloads With A 30 Day Free TrialDocument3 pagesScribd: Get Unlimited Downloads With A 30 Day Free TrialMrdonPas encore d'évaluation
- MWS SSL ArticleDocument11 pagesMWS SSL ArticleRodrigo Románovich FiodorovichPas encore d'évaluation
- Texto BasuraDocument1 pageTexto BasuraRodrigo Románovich FiodorovichPas encore d'évaluation
- Texto BasuraDocument1 pageTexto BasuraRodrigo Románovich FiodorovichPas encore d'évaluation
- Texto BasuraDocument1 pageTexto BasuraRodrigo Románovich FiodorovichPas encore d'évaluation
- ReadmeDocument2 pagesReadmeRodrigo Románovich FiodorovichPas encore d'évaluation
- Git Compactar CommitsDocument3 pagesGit Compactar CommitsRodrigo Románovich FiodorovichPas encore d'évaluation
- 544355534.assimlation & ElisionDocument7 pages544355534.assimlation & ElisionAlejandro SanhuezaPas encore d'évaluation
- Execute QueryDocument1 pageExecute QueryRodrigo Románovich FiodorovichPas encore d'évaluation
- RFC 6749Document76 pagesRFC 6749Krishna KoneruPas encore d'évaluation
- HTTP/2 Proxies and End-to-End SecurityDocument12 pagesHTTP/2 Proxies and End-to-End SecurityRodrigo Románovich FiodorovichPas encore d'évaluation
- IntelliJ IDEA Mac OS X Keymap ReferenceDocument1 pageIntelliJ IDEA Mac OS X Keymap ReferencealeshivanPas encore d'évaluation
- Diagram PDFDocument1 pageDiagram PDFRodrigo Románovich FiodorovichPas encore d'évaluation
- GoogleComputeEngine PDFDocument2 pagesGoogleComputeEngine PDFkrishy19sPas encore d'évaluation
- JbossDocument12 pagesJbossAdnan AlicicPas encore d'évaluation
- Atalhos Teclado Android StudioDocument1 pageAtalhos Teclado Android StudioDiogo CardosoPas encore d'évaluation
- Git Fetch: Public BranchDocument1 pageGit Fetch: Public BranchRodrigo Románovich FiodorovichPas encore d'évaluation
- Using Google Compute Engine: 1 Getting An Account and Setting Up PaymentDocument11 pagesUsing Google Compute Engine: 1 Getting An Account and Setting Up PaymentRodrigo Románovich FiodorovichPas encore d'évaluation
- Install Linux TarDocument1 pageInstall Linux TarRodrigo Románovich FiodorovichPas encore d'évaluation
- Oauthservicewhitepaper 2110557Document14 pagesOauthservicewhitepaper 2110557Rodrigo Románovich FiodorovichPas encore d'évaluation
- Oauth Ebook 2012 02Document19 pagesOauth Ebook 2012 02Pankaj SainiPas encore d'évaluation
- Concurrent Programming in ErlangDocument205 pagesConcurrent Programming in Erlanganoop.jo.scariaPas encore d'évaluation
- Cost-effective laboratory thermostats from -25 to 100°CDocument6 pagesCost-effective laboratory thermostats from -25 to 100°CCynthia MahlPas encore d'évaluation
- Natural ApproachDocument3 pagesNatural ApproachNovita SariPas encore d'évaluation
- Standard Calibration Procedure Thermocouple Doc. No. Call/SCP/024 Rev. 00 May 01, 2015Document4 pagesStandard Calibration Procedure Thermocouple Doc. No. Call/SCP/024 Rev. 00 May 01, 2015Ajlan KhanPas encore d'évaluation
- International Studies: JIIT University, NoidaDocument3 pagesInternational Studies: JIIT University, NoidavaibhavPas encore d'évaluation
- Test Bank For Environmental Science For A Changing World Canadian 1St Edition by Branfireun Karr Interlandi Houtman Full Chapter PDFDocument36 pagesTest Bank For Environmental Science For A Changing World Canadian 1St Edition by Branfireun Karr Interlandi Houtman Full Chapter PDFelizabeth.martin408100% (16)
- Signal Sampling, Quantization, Binary Encoding: Oleh Albert SagalaDocument46 pagesSignal Sampling, Quantization, Binary Encoding: Oleh Albert SagalaRamos D HutabalianPas encore d'évaluation
- Impact of K-Pop Music On The Academic PDocument29 pagesImpact of K-Pop Music On The Academic Pdave tayron paggao100% (1)
- Fox Hunting - The Art of Dating and SeductionDocument93 pagesFox Hunting - The Art of Dating and SeductionEdward Ashley Latimore100% (1)
- Audit of Organizational Communication NetworksDocument17 pagesAudit of Organizational Communication NetworksLissette ObleaPas encore d'évaluation
- Struts HTML Checkbox enDocument4 pagesStruts HTML Checkbox enjudesahayarajPas encore d'évaluation
- IBM's Corporate Service Corps: The Shift To A Globally Integrated EnterpriseDocument2 pagesIBM's Corporate Service Corps: The Shift To A Globally Integrated EnterprisePYXERA GlobalPas encore d'évaluation
- Cricket Bat Thesis - 2006 SymesDocument297 pagesCricket Bat Thesis - 2006 SymesAnonymous unj3NHW82vPas encore d'évaluation
- Curriculum VitaeDocument4 pagesCurriculum Vitaebtk_20Pas encore d'évaluation
- Thinking Maps in Writing Project in English For Taiwanese Elementary School StudentsDocument22 pagesThinking Maps in Writing Project in English For Taiwanese Elementary School StudentsThilagam MohanPas encore d'évaluation
- Material Safety Data Sheet: Section I - Chemical Product and Company IdentificationDocument2 pagesMaterial Safety Data Sheet: Section I - Chemical Product and Company IdentificationMu ClasPas encore d'évaluation
- Affine CipherDocument3 pagesAffine CipheramitpandaPas encore d'évaluation
- 11 - Chapter 5 PDFDocument35 pages11 - Chapter 5 PDFlouisPas encore d'évaluation
- AufEx4 02 02Document28 pagesAufEx4 02 02BSED SCIENCE 1APas encore d'évaluation
- QTouch LibraryDocument21 pagesQTouch LibraryLenin RuizPas encore d'évaluation
- 373 07 2Document143 pages373 07 2fpttmmPas encore d'évaluation
- Methods of Data Collection: Primary, Secondary, Observation, Interview & QuestionnaireDocument19 pagesMethods of Data Collection: Primary, Secondary, Observation, Interview & QuestionnairePraveen Nair100% (2)
- SINGLE OPTION CORRECT ACCELERATIONDocument5 pagesSINGLE OPTION CORRECT ACCELERATIONShiva Ram Prasad PulagamPas encore d'évaluation
- Soft Start - Altistart 48 - VX4G481Document2 pagesSoft Start - Altistart 48 - VX4G481the hawakPas encore d'évaluation
- ScifiDocument156 pagesScifiSynergymag0% (1)
- Professional Training Academy: Professional Level IV - Preparation & Final TestDocument2 pagesProfessional Training Academy: Professional Level IV - Preparation & Final TestJayant SinhaPas encore d'évaluation
- HA200Document4 pagesHA200Adam OngPas encore d'évaluation
- Components of GMP - Pharma UptodayDocument3 pagesComponents of GMP - Pharma UptodaySathish VemulaPas encore d'évaluation