Académique Documents
Professionnel Documents
Culture Documents
Huawei FusionCloud Desktop Solution Security White Paper
Transféré par
Gabriel DarkCopyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Huawei FusionCloud Desktop Solution Security White Paper
Transféré par
Gabriel DarkDroits d'auteur :
Formats disponibles
Huawei FusionCloud Desktop Solution
Security Technical White Paper
Issue 01
Date 2014-12-01
HUAWEI TECHNOLOGIES CO., LTD.
Copyright Huawei Technologies Co., Ltd. 2014. All rights reserved.
No part of this document may be reproduced or transmitted in any form or by any means without
prior written consent of Huawei Technologies Co., Ltd.
Trademarks and Permissions
and other Huawei trademarks are trademarks of Huawei Technologies Co., Ltd.
All other trademarks and trade names mentioned in this document are the property of their respective
holders.
Notice
The purchased products, services and features are stipulated by the contract made between Huawei and
the customer. All or part of the products, services and features described in this document may not
be within the purchase scope or the usage scope. Unless otherwise specified in the contract, all
statements, information, and recommendations in this document are provided "AS IS" without warranties,
guarantees or representations of any kind, either express or implied.
The information in this document is subject to change without notice. Every effort has been made in the
preparation of this document to ensure accuracy of the contents, but all statements, information, and
recommendations in this document do not constitute a warranty of any kind, express or implied.
Huawei Technologies Co., Ltd.
Address: Huawei Industrial Base
Bantian, Longgang
Shenzhen 518129
People's Republic of China
Website: http://enterprise.huawei.com
Issue 01 (2014-12-01) Huawei Proprietary and Confidential i
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper Contents
Contents
1 Security Problem and Development Trend of Traditional Office Desktops .................... 1
1.1 Security Problem of Traditional Desktops .................................................................................................................... 1
1.1.1 Vulnerability to Data Leakage due to Scattered Terminals ........................................................................................ 1
1.1.2 Management Difficulty due to Multiple Networks and Diversified Terminals .......................................................... 1
1.1.3 Excessive Terminal Security Software....................................................................................................................... 1
1.2 Development Trend of Office Desktops ....................................................................................................................... 1
2 Security Threats and Security Framework of Desktop Cloud ............................................. 3
2.1 Overview ...................................................................................................................................................................... 3
2.2 Security Threats of Desktop Cloud ............................................................................................................................... 3
2.3 Security Framework of Desktop Cloud ........................................................................................................................ 5
3 Terminal Security .......................................................................................................................... 7
3.1 TC Security ................................................................................................................................................................... 7
3.1.1 Overview of TC Security ........................................................................................................................................... 7
3.1.2 Hardware Security ..................................................................................................................................................... 7
3.1.3 BIOS Security ............................................................................................................................................................ 7
3.1.4 OS Security ................................................................................................................................................................ 8
3.2 802.1X Authentication Supported for TC to Access Networks..................................................................................... 8
3.3 Restricted TC access ..................................................................................................................................................... 8
4 Identity Authentication and Access Management Security ............................................... 10
4.1 Access and Authentication .......................................................................................................................................... 10
4.2 AD Domain Authentication ........................................................................................................................................ 10
4.2.1 AD Domain Authentication ..................................................................................................................................... 10
4.2.2 Single Sign-on ......................................................................................................................................................... 11
4.3 Fingerprint Authentication .......................................................................................................................................... 12
4.4 AD Smartcard Authentication ..................................................................................................................................... 13
4.5 Third-Party Digital Certificate Authentication............................................................................................................ 15
4.6 Dynamic Password Two-factor Authentication .......................................................................................................... 15
5 Network Security ........................................................................................................................ 17
5.1 Transmission Security ................................................................................................................................................. 17
5.2 Network Isolation ....................................................................................................................................................... 17
5.2.1 DHCP Quarantine .................................................................................................................................................... 17
Issue 01 (2014-12-01) Huawei Proprietary and Confidential ii
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper Contents
5.2.2 DHCP Snooping ...................................................................................................................................................... 18
5.2.3 Plane Isolation ......................................................................................................................................................... 18
5.3 Security Area Isolation................................................................................................................................................ 19
5.4 Anti-Counterfeit of IPs and MAC ............................................................................................................................... 20
5.5 Fixed IP Addresses Supported for VMs ...................................................................................................................... 21
5.6 Security Group ............................................................................................................................................................ 21
6 Virtualization Isolation .............................................................................................................. 22
7 Data Storage Security ................................................................................................................. 24
7.1 User Data Isolation ..................................................................................................................................................... 24
7.2 Data Access Control ................................................................................................................................................... 24
7.3 Residual Information Protection ................................................................................................................................. 24
7.4 Data Backup ............................................................................................................................................................... 24
8 Management Security................................................................................................................. 26
8.1 Log Management ........................................................................................................................................................ 26
8.1.1 Log Type .................................................................................................................................................................. 26
8.1.2 Log Backup .............................................................................................................................................................. 26
8.1.3 Log Format .............................................................................................................................................................. 26
8.2 Account and Password Security .................................................................................................................................. 27
8.2.1 Account and Default Password ................................................................................................................................ 27
8.2.2 Password Encryption and Changing Principles ....................................................................................................... 27
8.3 Rights- and Domain-Based Management ................................................................................................................... 27
8.4 Role-Based Management ............................................................................................................................................ 29
8.5 Certificate Snap-ins .................................................................................................................................................... 29
8.5.1 Communication Certificate Snap-ins Between Components ................................................................................... 29
8.5.2 Unified O&M and Auditing ..................................................................................................................................... 29
9 Infrastructure Security ............................................................................................................... 31
9.1 Web Security ............................................................................................................................................................... 31
9.2 OS Security ................................................................................................................................................................. 32
9.2.1 Windows 2008 OS Security Hardening ................................................................................................................... 32
9.2.2 SUSE Linux OS Security Hardening ....................................................................................................................... 32
9.3 Security Patch ............................................................................................................................................................. 33
9.4 Antivirus ..................................................................................................................................................................... 33
9.4.1 Antivirus Software for Cloud Computing Platform Components ............................................................................ 33
9.4.2 User VM Antivirus Software ................................................................................................................................... 33
9.5 Database Security ....................................................................................................................................................... 34
9.5.1 Database Security Configuration ............................................................................................................................. 34
9.5.2 Data Backup............................................................................................................................................................. 34
9.6 Physical Security ........................................................................................................................................................ 34
10 User VM Security ...................................................................................................................... 35
10.1 Terminal Security Management ................................................................................................................................ 35
Issue 01 (2014-12-01) Huawei Proprietary and Confidential iii
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper Contents
10.1.1 Virtual Desktop Compliance Management ............................................................................................................ 35
10.1.2 Network Access Control ........................................................................................................................................ 35
10.1.3 Staff Activity Monitoring ....................................................................................................................................... 36
10.1.4 Patch Management ................................................................................................................................................. 36
10.1.5 Software Distribution ............................................................................................................................................. 36
10.1.6 USB Flash Drive Management .............................................................................................................................. 36
10.2 Document Security Management .............................................................................................................................. 36
11 Summary of Huawei's Desktop Cloud Solution ................................................................ 37
11.1.1 For Unauthenticated Users ..................................................................................................................................... 38
11.1.2 For Malicious Administrator .................................................................................................................................. 39
Issue 01 (2014-12-01) Huawei Proprietary and Confidential iv
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2 1 Security Problem and Development Trend of Traditional
Security Technical White Paper Office Desktops
1 Security Problem and Development Trend
of Traditional Office Desktops
1.1 Security Problem of Traditional Desktops
1.1.1 Vulnerability to Data Leakage due to Scattered Terminals
Traditional personal computers (PCs) for office desktop are scattered; therefore, any PC is
vulnerable to data leakage. To prevent data leakage, security chassis and anti-data leakage
software must be installed on PCs. In addition, security personnel are required to check
storage devices at office building gates. These measures require a large number of workforce
and high costs.
1.1.2 Management Difficulty due to Multiple Networks
and Diversified Terminals
Different types of networks are physically isolated and access terminals vary with private
networks. Therefore, the management is difficult and passwords are hard to remember. In
some industries having high security requirements, multiple types of computers or access
terminals are used, for example, a computer for Internet access, a computer for industry
private network access, and a computer for office network access. Therefore, the
informatization construction mode is complicated.
1.1.3 Excessive Terminal Security Software
To ensure terminal security, a PC runs various software including antivirus software,
anti-Trojan horse software, personal firewall, progress protection software, terminal
monitoring software, USB key, terminal encryption software, and software preventing
unauthorized network connection. These applications may affect PCs' running efficiency.
Moreover, if a PC is down, the system restoration and reinstallation take a long time.
1.2 Development Trend of Office Desktops
There are a variety of solutions to office desktop security in the industry. For example, a
diskless workstation is used to prevent data leakage from terminal hard disks, and a PC uses
two main boards for the access to multiple types of networks. However, these solutions have
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 1
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2 1 Security Problem and Development Trend of Traditional
Security Technical White Paper Office Desktops
poor usability and expansibility and cannot fundamentally resolve the security problems.
Therefore, the solutions are not widely used.
To address security problems of traditional office desktops, the IT architecture transformation
is crucial. Desktop cloud is the best method currently. Desktop cloud separates terminals and
information, and stores data on the background data center (centralized computing, storage,
and network), instead of on various thin clients (TCs). Only the encrypted screen images are
sent to terminals. This greatly reduces the risks of data leakage from PCs.
Figure 1-1 Evolution from the traditional desktop to desktop cloud
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 2
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2 2 Security Threats and Security Framework of Desktop
Security Technical White Paper Cloud
2 Security Threats and Security Framework
of Desktop Cloud
2.1 Overview
As a new method of providing computing resources, desktop cloud features high security,
convenience, and cost effectiveness. However, users also have doubts about the security of the
cloud computing system. Therefore, cloud computing must ensure the confidentiality,
integrity, and usability of user data and resources. This document analyzes the security risks
and threats of cloud computing and introduces the countermeasures of Huawei's secure and
reliable desktop cloud solution.
2.2 Security Threats of Desktop Cloud
Besides the security threats of traditional data centers, desktop cloud must face the following
security threats and challenges of cloud computing infrastructure:
Cloud terminal security threats
In clouds, user data is not stored in the cloud terminals (such as TCs). However,
threats exist when malicious software, such as Trojan horse malware that intercepts
keyboard operations, is installed on the clients, and login passwords may be stolen.
The mobile access of users also brings security threats while bringing convenience. If
a user password is disclosed, malicious users can access the desktop on any cloud
terminal through the Internet while for PCs local login is required. Therefore, an
identity authentication mechanism more enhanced than passwords should be
supported.
As in clouds, data is not stored in the cloud terminals and hence management on the
access terminals is loose, for example, the access office is not under strict supervision
of the gate sentry. When data is copied from VMs to terminals through non-standard
or malicious network access on the terminals, information disclosure is likely to
occur.
Network access security threats
All operations and interface interactions for data processing are based on a network
that can be accessed anytime anywhere. In addition, the distributed deployment of
cloud computing resources complicates route and domain name configuration and
therefore makes the cloud computing system more vulnerable to network attacks,
such as domain name server (DNS) and distributed denial-of-service (DDoS) attacks.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 3
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2 2 Security Threats and Security Framework of Desktop
Security Technical White Paper Cloud
Data in the terminals and the data centers is faced with threats in confidentiality and
integrity. Some sensitive information, such as passwords, can be stolen. Screen
display packets can be intercepted and resolved to get critical information.
Traditional network security still faces challenges.
Threats and challenges brought by virtual technologies
Security threats are posed to the Hypervisor, which is a core component of
virtualization.
The Hypervisor works as follows:
Receives commands from the central processing unit (CPU) and transfers them
to hardware controllers and peripherals.
Coordinates the allocation of all resources.
Works as the core of virtualization and runs at the highest privilege level (even
higher than that at which the operating system runs).
Once the Hypervisor is hacked, all virtual machines (VMs) running on the
Hypervisor are completely under attack.
Resource sharing poses security risks.
Resource sharing among many users poses the following security risks:
User data may leak out because of inappropriate isolation.
Users may be attacked by other users within the same physical environment.
The virtualization capability of network firewalls or Intrusion Prevention
Systems (IPSs) may be insufficient. As a result, the static network partitions and
the isolation model cannot meet the requirements for dynamic resource sharing.
The change of network isolation mode causes a security loophole.
Logical isolation replaces physical isolation, causing a security loophole on the
enterprise network. Generally, an enterprise network uses high-security measures
such as physical isolation to ensure the information security between organizations or
departments at different security levels. Cloud computing logically isolates
enterprises, and organizations or departments inside an enterprise.
Malicious network traffic between VMs can run away from audits.
If in one VLAN, the communication between VMs that belong to one PC can be
directly conducted in the PC without traffic going through external networks. Hence,
the existing network supervision and audit system cannot monitor this part of traffic.
Data security threats
Residual data security threats
After VMs or disks are deleted, the released storage space is allocated to other users.
If no security measure is taken on the data, other users can obtain the original data by
some data recovery methods.
Reuse of memory or residual memory cause data security threats.
Data is collected in the data center, which is easy for administrator to spy on the data
by certain methods.
Migration of physical disks may also cause data leakage.
VM terminal security threats
Traditional security threats still exist.
Virus and Trojan horse malware are still traditional threats to data security. Antivirus
system and OS security patches should be updated in real time.
Data leakage on VMs
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 4
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2 2 Security Threats and Security Framework of Desktop
Security Technical White Paper Cloud
Measures should be taken to prevent user or enterprise information from leaking on
the cloud terminals or networks.
Management security
The security conduct code of an administrator is crucial to the data security in a data
center. Identity authentication, right management, and audit of an administrator are
faced with great challenges.
Cloud infrastructure security risks
API security risks
The infrastructure and the application software may be provided by different
providers and the application software may run on different VMs in a distributed
mode. If application software does not adapt to an infrastructure, many security
loopholes will be generated.
Traditional basic security is still faced with threats.
OS bugs, application component bugs, web attacks, and password cracking are still
great threats to data security.
2.3 Security Framework of Desktop Cloud
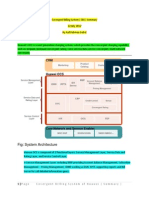
Figure 1-2 shows the security framework of Huawei desktop cloud security solution that is
provided to address the threats and challenges of cloud computing.
Figure 1-2 Security framework of Huawei's desktop cloud solution
Each layer of the security structure is described as follows:
TC security
Terminal security and legality verification is required when the TC is accessing the
cloud.
Access and authentication management
Active Directory (AD) domain authentication, finger prints, universal serial bus (USB)
keys, and dynamic tokens are used to authenticate users who attempt to access the cloud
computing system.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 5
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2 2 Security Threats and Security Framework of Desktop
Security Technical White Paper Cloud
Network security
Network plane isolation, firewalls, security access gateway, and data transfer encryption
are used to ensure the security of service operation and maintenance.
Virtualization security
Virtual machines (VMs) are isolated from each other based on the virtualization
mechanism.
Data security
The integrity and confidentiality of user data are ensured by user authentication, data
access control, and data encryption.
Management security
The management security is ensured using user accounts, passwords, administrator and
user permissions, and logs.
Infrastructure security
The infrastructures security is ensured by hardening the system and database and
installing patches.
User VM security
The VM security is ensured by functions such as network access control, staff activity
monitoring, patch management, and software distribution.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 6
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 3 Terminal Security
3 Terminal Security
3.1 TC Security
3.1.1 Overview of TC Security
The TC hardware and software designs use various security mechanisms to prevent virus
attacks. TCs provide the following security mechanisms:
Hardware security
BIOS security
OS security
3.1.2 Hardware Security
The internal storage device of a TC is encrypted with unique hardware information. The
encryption algorithm and the unique hardware information are bound together so that the
encrypted internal can only be used for booting and reading the located TC. This can prevent
TC data from being modified.
3.1.3 BIOS Security
BIOS security of TCs is enhanced as follows:
The BIOS can boot a TC only from the internal memory.
The BIOS can boot a TC only from the internal memory instead of the universal serial
bus (USB) or Pre-boot Execution Environment (PXE).
The BIOS can boot TCs only from the encrypted internal memory.
When the BIOS of a TC runs, it attempts to decrypt the internal memory according to the
unique hardware information before booting the TC. If the internal memory does not
support encryption, is not encrypted, or is encrypted with the information different from
the unique hardware information of this TC, the BIOS cannot boot the TC from the
internal memory. In this manner, the internal memory and the TC are bound together
exclusively so that the TC will not boot the system of a third party and third parties
cannot access the internal memory of the TC. This ensures the security of desktop cloud
terminals in hardware level.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 7
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 3 Terminal Security
3.1.4 OS Security
TCs run a simplified and offline Linux, WES7, XPe OS that implements the following
security mechanisms:
Prohibits use of USB storage devices.
The TC OS prohibits use of USB storage devices such as USB disks and USB flash
drives from the driver layer
Prohibits direct access to internal memory.
Users can only indirectly access the internal memory using programs provided by a TC
but cannot directly access internal memory using an interface. This effectively prevents
system files from being damaged.
Prohibits unauthorized software installation.
Software cannot be installed on a TC locally. To install a software package to a TC, users
must send the software package to the Thin Client Management (TCM) system first. To
ensure that only authorized software can be installed on a TC, the following security
requirements must be met:
Only TCM administrators can install software on a TC.
The TCM recognizes only software package in a customized proprietary format.
After a TC receives a software package from the TCM, it verifies the integrity of the
package locally. If the software package is modified or has not been authenticated,
the TC will not install the software.
Restricts use of ports.
To prevent attacks, TCs only provide the required local ports to communicate with the
TCM, and other ports are not used.
Blocks viruses.
Viruses spread through storage devices and networks. A TC does not have virus running
environment and spreading channels.
3.2 802.1X Authentication Supported for TC to Access
Networks
A TC can access to networks only after it passes the 802.1X authentication to prevent the
access of an illegal terminal. EAP-MD5 mode that uses user name and password and
EAP-TLS mode that uses digital certificate are supported.
3.3 Restricted TC access
In scenarios where higher requirements are posed for information security, only
specified users can log in to the virtual desktops that contain sensitive information from
specified TCs.
By binding the TC MAC address/MAC address group to the domain users/domain user
group, domain users or user groups can be specified to access to specified TCs or TC
groups. To access a fixed TC, any authentication methods of the WI can be used.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 8
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 3 Terminal Security
The desktop cloud
administrator enables the TC Login Experience
binding function over the ITA UI
and record the bound TC that is bound to the user
Desktop user
relationship between TC MAC
and users. +
There are two import modes:
TC that has not been bound for the user
Desktop user
X
+
Method One: Recorded manually
1. When users log in to the WI, 2. If the information matches 3. Users log in to
the TC sends the user name, the binding information saved the VM
domain name, and MAC in the ITA, the system continue successfully.
address to the desktop cloud with the AD authentication and
system to check whether the login process. Otherwise, the
user has been bound to the TC. login is banned.
Method Two: Imported in batches
Users that are bound to a fixed TC can log in to the VM only over the bound TC.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 9
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 4 Identity Authentication and Access Management Security
4 Identity Authentication and Access
Management Security
4.1 Access and Authentication
4.1.1.1 System Administrator Access Authentication
The cloud computing system has the following administrators:
FusionCompute O&M system administrator
FusionAccess desktop business maintenance system administrator
Both of the administrators access the management systems by the authentication mode of
"user account + password + verification code".
4.1.1.2 User Access Authentication
In desktop cloud scenarios, to connect to a desktop cloud, users can be authenticated using the
following methods:
AD domain authentication
Fingerprint authentication
USB key authentication (supporting the integration of AD intelligent cards and the
third-party digital certificate identity authentication)
Dynamic password Two-factor authentication
4.2 AD Domain Authentication
4.2.1 AD Domain Authentication
Desktop cloud users must be authenticated by the AD server before accessing VMs. The AD
has the following function in the desktop cloud system:
Authenticates domain accounts and VMs.
All VMs in a desktop cloud system are managed in a domain, and domain authentication is
required for VMs to access each other. All VMs must be accessed using domain accounts.
Figure 1-3 shows the domain account and VM authentication processes.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 10
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 4 Identity Authentication and Access Management Security
Figure 1-3 Domain account and VM authentication process
User logs in
VM joins the domain
1.Username and
password
3.Query the VM list
4. Return the VM list
HDC
TC WI
2.Domain account
authentication
Joins the domain and passes
the authentication
VM AD
The AD domain account authentication process is as follows:
1 A user types the username and password on the Web Interface (WI) to log in to the VM.
2. After the WI receives the login request from the user, it sends a domain account
authentication request to the AD.
3. After the AD has authenticated the domain account, the AD sends the authentication
result to the WI. Then the WI obtains the VM list from the HDC and sends the VM list to
the user.
4.2.2 Single Sign-on
With the single sign-one function, a user can access a VM by entering the domain account and
password only once, which makes the login convenient and fast. Figure 1-4 shows the login
process.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 11
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 4 Identity Authentication and Access Management Security
Figure 1-4 Login process
4.3 Fingerprint Authentication
Huawei's desktop cloud solution supports the following user authentication measures for
system access.
Fingerprint authentication
Using an optical-electric conversion device and the computer image processing
technology, the fingerprint authentication system analyzes and compares fingerprints to
quickly and accurately verify the identities of individuals. Because biometric fingerprints
are difficult to forge, fingerprint authentication is reliable. In addition, it is convenient to
use.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 12
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 4 Identity Authentication and Access Management Security
Figure 1-5 Fingerprint authentication
The process is as follows:
1 The fingerprint reader connects to the cloud terminal, the user enters its fingerprint on
the cloud terminal, the cloud terminal converts the fingerprint into a corresponding user
name and password and then transfers the information to WI over Hypertext Transfer
Protocol Secure (HTTPS).
2. The WI requests the AD server to authenticate the user information.
3. If the user is authenticated, the WI sends to the user a list of the VMs owned by the user.
4. The user clicks the desired VM, and the WI sends the authentication information to the
selected VM and the user's terminal.
5. The cloud terminal uses the authentication information to log in to the VM.
6. After login, the VM requests the user to enter the fingerprint. After entering the
fingerprint and being authenticated, the user enters the cloud desktop.
4.4 AD Smartcard Authentication
The USB key is a smartcard. Each USB key has hardware and personal identification number
(PIN) protection functions. A user can connect to the system only after obtaining both the
USB key and the PIN. If a user's PIN is leaked out, the user identity cannot be forged as long
as the USB key is not stolen. Also, if user A has the USB key of user B but does not know the
PIN of the key, user A cannot forge user B's identity.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 13
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 4 Identity Authentication and Access Management Security
Figure 1-6 Authentication for USB key non-single sign-on (SSO) login
4. After the authentication succeeds, obtain the
WI/HDC domain account and name from the certificate, AD/CA
and then send them to the AD over the WI to
check their validity.
3. Conduct the bidirectional authentication
1. Initiate the connection to the VM.
5.Return the VM list to the user.
between the WI and the USB key.
successful, users can log in to the VM.
7. Certificate authentication by the AD
2. Display the PIN text box.
is performed. After authentication is
6. Select one VM, click login, and then
enter the PIN number of the USB key.
Desktop Cloud User User VMs
The USB key non-SSO login and authentication process is as follows:
1 The user inserts the smartcard or USB key into the TC, run Internet Explorer, enter the
URL to log in to the WI (if the LB function is provided by the SVN, enter the URL of
the SVN), and then press Enter.
2. A PIN window is displayed. Enter the PIN of the USB key and press Enter.
3. Conduct the bidirectional authentication between the WI and the USB key.
4. After certificate is authenticated, the WI can obtain the VM list owned by the user.
5. The WI sends the VM list to the TC.
6. The user logs in to one of the VMs and enables the HDP connection. A PIN window is
displayed in the Windows. Then the user enters the PIN and clicks Login.
7. The USB key is authenticated by the administrator. After the USB key passes the
authentication, the user can log in to the VM OS.
The system can also be configured with the USB key SSO authentication. Insert the USB key
into the TC, log in to the WI, AND enter the PIN. You do not need to enter the PIN
again when logging in to the VM.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 14
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 4 Identity Authentication and Access Management Security
4.5 Third-Party Digital Certificate Authentication
For industries that have higher security requirements, when users migrate from PCs to
desktop clouds, the security login and audit software in the PCs is also applied to VMs. A
terminal security login module is usually included in this software and a USB key is used to
log in to the PC. A USB key is also used to log in to the desktop cloud. SSO login mode is
supported and you need to enter the PIN only once.
Huawei desktop cloud solutions provide integration with a third-party digital certificate
authentication to allow the USB key SSO login mode and one-time only PIN entering for
logging in to TCs, WIs, and VMs.
4.6 Dynamic Password Two-factor Authentication
In a verification system using traditional static passwords, passwords are set at a time and
used for multiple times. Users do not need to take other measures to obtain passwords.
Repeatedly used passwords raise the risks of password loss and decryption, making the
system more vulnerable to security risks.
Therefore, an identity verification system is required with changeable and ease-to-obtain
passwords. To meet the requirement, a physical factor is added to generate dynamic
passwords. A user must be authenticated with static and dynamic passwords before logging in
to the system.
Dynamic password two-factor authentication supports the generic hardware/software dynamic
password token cards and short message system (SMS)-based dynamic password
authentication.
Generic hardware/software dynamic password token cards: When users are logging in to the
WI, enter the domain account, domain password, and dynamic passwords on the login screen.
Users can log in to the WI and view the VM list only after both the domain password and the
dynamic password are authenticated.
WI AD
OTP
Server
1. The user enters the domain 2. The WI sends the domain password to 3. Af ter the authentication 4. Click the icon of one VM
account, password, and dynamic the AD and then sends the dynamic succeeds, the user can and click login to log in to
password, and then clicks login. password to the OTP server if the AD see the VM list. the VM.
authentication succeeds.
SMS-based dynamic password authentication: A mobile phone is used to receive the dynamic
password. The administrator registers the user account and mobile phone number in advance
on the dynamic password authentication server. The user enters the domain password when
logging in to the WI. After the password is authenticated, the WI sends the domain account
information to the server, then the server generates a dynamic password and sends it to the
registered mobile phone. The user copies the password to the WI within the required time.
After the password is authenticated, the WI sends the VM list to the user.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 15
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 4 Identity Authentication and Access Management Security
WI AD WI AD
OTP OTP
Server Server
1. The user enters the domain 2. The WI sends the domain 3. The OTP server creates a 5. A VM list is
4. The WI sends the domain
account and password and then password to the AD and then dynamic password and sends it to displayed. Click
password to the AD and then
obtains the dynamic password requires a dynamic password the user's cell phone over SMS one VM to log in to
sends the dynamic password
icon. from the OTP server if the AD gateway. The user enters the the VM.
to the OTP server if the AD
authentication succeeds. dynamic password and clicks login. authentication succeeds.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 16
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 5 Network Security
5 Network Security
5.1 Transmission Security
Data transfer may be interrupted, and data may be replicated, modified, forged, intercepted, or
monitoring during transfer. Therefore, it is necessary to ensure the integrity, confidentiality,
and validity of data during network transfer. The security of Huawei's desktop cloud data
transfer is ensured by the following methods:
Administrators access management systems using HTTPS, and data transfer channels are
encrypted using secure socket layer (SSL).
HTTPS is used for users to log in to the WI.
The desktop protocol (HDP) between TCs and VMs deploys vAG or SVN security
gateway of hardware and implements SSL transmission. AES 128 is adopted as the
encryption algorithm
The components (including the WI, HDC, ITA, license server, VNCGate, and HDA) in
the service system communicate with each other over HTTPS, and transmission channels
are encrypted over SSL.
The HTTPS provides encrypted data transfer and identity authentication. HTTPS encrypts
data using SSL, which has the following functions:
Authenticates users and servers and ensures that data is sent to the correct clients and
servers.
Encrypts data to prevent it from being intercepted during transfer.
Ensures data integrity and intactness during transfer.
5.2 Network Isolation
5.2.1 DHCP Quarantine
The FusionSphere security solution provides the Dynamic Host Configuration Protocol
(DHCP) quarantine function for VMs. Enabling the DHCP quarantine of the VM ports
prevents the corresponding VM from affecting other VMs if unauthorized DHCP software is
installed. The DHCP software allocates IP address to other VMs and will conflict with the
HDCP servers in the desktop cloud system.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 17
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 5 Network Security
5.2.2 DHCP Snooping
DHCP Snooping is a security feature that filters messages from untrusted sources by setting
up and maintaining the DHCP Snooping binding database. The DHCP Snooping feature
performs the following activities: Intercepts and parses DHCP ACK messages received from
virtual ports. Saves the IP addresses assigned by DHCP servers to the IP address and MAC
address binding database that is associated with virtual ports. The IP address and MAC
address binding is enabled by intelligent network interface cards (iNICs) or Elastic Virtual
Switches (EVSs).
5.2.3 Plane Isolation
The desktop cloud system has three network communication planes: the service plane, storage
plane, and management plane. Administrators cannot access the service plane.
The planes ensure that users do not corrupt basic platforms.
Service plane
The service plane provides service channels for users and enables the communication
planes of the virtual network interface cards (NICs) of VMs to provide services.
Storage plane
The storage plane works as the communication plane for storage over the Internet Small
Computer Systems Interface (ISCSI) and provides storage resources for VMs. The
storage plane communicates with VMs over the virtualization platform.
Management plane
The management plane works as the communication plane for cloud computing system
management, service deployment, and system loading.
The BMC plane is responsible for server management. It can either be isolated from the
management plane or not.
Figure 1-7 shows the software architecture of the Huawei FusionCloud solution
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 18
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 5 Network Security
Figure 1-7 Plane isolation provided by the FusionSphere solution
Terminal user
Service plane
Management
plane
Storage plane
Administrator
Computing nodes, management nodes Storage nodes
5.3 Security Area Isolation
Security domains are categorized by Huawei FusionCloud as follows:
Untrusted domain: a domain to which cloud terminals and administrators belong. Many
types of users need to access this domain, which results in high security risks.
Demilitarized zone (DMZ) domain: a domain where the access gateway vLB/vAG or
SVN is deployed. TCs and software clients (SCs) are used to access user VMs from this
zone.
User domain: a domain where user VMs are located. The user domain must be separated
from the management domain to prevent user VMs from accessing the management
network.
Management and platform domain: a domain where the management components for
FusionAccess, FusionCompute, and FusionManager are deployed.
Figure 1-8 shows the security domain division.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 19
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 5 Network Security
Figure 1-8 Security domain division
Untrust Untrust area
area Operation and maintenance
DMZ area
terminals
TCM
NetScaler
Firewall
Management and platform area
SVN
DNS DHCP AD
VNC GW
WI HDC ITA
Firewall Firewall
License DB
User area
Loggetter WSUS
User VMs
VM VM
VM VM FusionCompute FusionManager
Cloud
computing
terminals
Some functions and features provided by Huawei FusionCloud solution require
communication between the management plane and the service plane. To reduce management
plane vulnerability, different networking modes are recommended in the following scenarios:
In high-security scenarios, it is recommended to adopt the layer 2 networking mode,
in which case, the management plane cannot communicate with the service plane in the
layer 2 network. If the communication between the two planes is required, they can
communicate with each other in the lay 3 of the user's network, and therefore the user
must take high security measures, such as firewalls.
In common security scenarios, it is recommended to adopt layer 3 networking mode,
in which case, the management plane communicates with the service plane by default. To
ensure the isolation security of the management plane from the service plane, the access
control list (ACL) policy can be configured on the layer 3 switch.
5.4 Anti-Counterfeit of IPs and MAC
Binding an IP address to a MAC address prevents users from initiating IP address or MAC
address spoofing attacks after changing the IP address or MAC address of a network packet,
and therefore enhances the network security of user VMs. With this policy enabled, an IP
address is bound to an MAC address using DHCP snooping feature, and then the packets from
untrusted sources are filtered through IP Source Guard and dynamic ARP inspection (DAI).
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 20
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 5 Network Security
5.5 Fixed IP Addresses Supported for VMs
For industries that require high security, IP addresses of VMs are mapped with user identities
correspondingly. Therefore, the IP addresses of VMs are fixed and no dynamic IP address
setting over the HDCP server is allowed. The administrator of Huawei FusionCloud Desktop
specifies an IP address from the ITA to create a VM and then associates the VM with a user.
The IP address is not changed from then on.
5.6 Security Group
Security groups provide network isolation and access control functions for public cloud
tenants and private cloud users. (VMs are added to security groups, and access rules are set
for the security groups.) Security groups function as a virtual firewall (vFW) that is deployed
on the network egress of each VM to control access to the VM, improving VM security.
You can add some IP addresses of VMs to a security group and set access rules between
security groups. Random IP addresses are allowed in a security group.
Inter-group access rules support the following configurations:
Allow or forbid requests from another security group to access the security group
through specified protocols and interfaces.
Allow or forbid requests from a specified IP segment to access the security group
through specified protocols and interfaces.
The VMs within the same security group can access each other. You can forbid VMs within
the same security group from accessing each other.
For example, VMs in the same department are added to the same VLAN. VMs of different
project teams should not communicate with each other, but each VM should
communicate with the server. To implement this, add project teams 1 and 2 to security groups
1 and 2, respectively, and configure the following ACL rules for both security groups:
All packets that do not meet ACL rules are intercepted by default.
Service IP segments can be used to access the security group.
The Huawei FusionCloud Desktop Solution adopts the security group capabilities of the cloud platform
to implement the security group function. If virtual desktops require security groups, FusionManager is
used to provision VMs, and FusionAccess is used to manage the VMs.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 21
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 6 Virtualization Isolation
6 Virtualization Isolation
The Hypervisor isolates VMs running on the same physical machine to prevent data theft and
malicious attacks. Users can only use VMs to access resources belonging to their own VMs,
such as hardware and software resources and data. Figure 1-9 shows the VM isolation.
Figure 1-9 VM isolation
6.1.1.1 Physical and Virtual Resources Are Isolated
The Hypervisor ensures that each VM obtains independent physical resources. The
Hypervisor also ensures that the crash of one VM does not affect the Hypervisor and other
VMs.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 22
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 6 Virtualization Isolation
6.1.1.2 Virtual CPU (VCPU) Scheduling Is Used to Isolate the OS from
Applications
The Huawei cloud computing platform uses x86 architecture servers. The x86 architecture
offers 4 privilege levels ranging from ring 0 which is the most privileged, to ring 3 which is
the least privileged. OS core runs in ring 0. OS services run in ring 2, and user applications
run in ring 3. The Hypervisor schedules instructions to be executed and manages resources to
prevent conflicts from occurring. The Hypervisor prevents the Guest OS of VMs from
executing all the privileged instructions and isolates the OS from applications.
6.1.1.3 Virtual Memories of Different VMs Are Isolated from Each Other
The VM uses the Memory Virtualization technology to virtualize the physical memory and
isolate the virtual memory. This technology introduces a new address concept, physical
address, based on the existing mapping between virtual addresses and the machine addresses
of clients. The OS on a VM translates the virtual address into the physical address. The
Hypervisor first transfers the physical address of a client into a machine address, and then
sends the machine address to the physical server.
Virtual address (VA) is provided by the client OS for its applications.
Physical address (PA) is created by the Hypervisor on a VM.
Machine address (MA) is the address signal of the address bus.
6.1.1.4 Internal Networks Are Isolated
The Hypervisor provides the virtual private network (VPN) routing and forwarding (VRF).
Each guest VM has one or more virtual interfaces (VIFs) logically associated with the
VFR. Data packets sent from a VM first reach domain 0. Domain 0 filters the data packets,
checks the integrity of the data packets, adds or deletes rules, includes certificates, and sends
the data packets to the destination VM. Then the destination VM checks the certificates to
determine whether to accept the data packets.
6.1.1.5 The I/O Operations of Hard Disks Are Isolated
The Hypervisor intercepts and processes all input/output operations of a VM to ensure that a
VM only visits the allocated hard disks.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 23
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 7 Data Storage Security
7 Data Storage Security
7.1 User Data Isolation
Huawei Hypervisor (UVP) uses the separating device driver model to implement the I/O
virtualization. The model divides the device driver into the front-end driver, back-end driver,
and original driver. The front-end driver runs in Domain U whereas the back-end driver and
original driver run in Domain 0.
The front-end driver transfers the I/O request in Domain U to the back-end driver in Domain
0. The back-end driver resolves the I/O request, maps the request to a physical device, and
submits the request to the corresponding device driver control hardware.
The hardware performs I/O operations. In short, all I/O activities of VM are intercepted and
processed by VMM. VMM ensures that the VMs only visit the appointed space, thereby
ensuring the hard disk isolation.
7.2 Data Access Control
Volume storage: In the FusionCompute, access to each volume is controlled. Only users have
the access permission can access a volume, and different volumes are isolated from each
other.
7.3 Residual Information Protection
When the system reclaims resources, it rewrites the physical bits of logic volumes with
0s to ensure data security.
After the physical disks of the data center are replaced, the system administrator of the
data center degausses them or physically destroys them to prevent data leakage.
7.4 Data Backup
In Huawei's SingleCloud solution, one or more copies of backup data are stored so that data is
not lost and services are not affected even if storage devices such as hard disks become faulty.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 24
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 7 Data Storage Security
The system performs a bit- or byte-based verification on data stored in disks, and distributes
verification information to each disk in a disk array. During the distribution, the system makes
sure that a data block and its verification information are stored on different disks. In this way,
damaged data can be reconstructed based on other data blocks and corresponding verification
information after a disk is damaged.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 25
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 8 Management Security
8 Management Security
8.1 Log Management
8.1.1 Log Type
Logs of the FusionAccess portal record the system running status and operations, facilitating
behavior auditing and problem locating. Logs are classified into operation logs and running
logs. Operation logs records system security information.
Operation logs are related to system security. They are used for tracing, auditing, and
determining whether the system is attacked or operated on inappropriately.
8.1.2 Log Backup
The system backs up operation logs periodically. After logs are backed up successfully, the
system deletes them. Log Display and Query
Hypertext Transfer Protocol (HTTP) is used to display logs on the management systems. The
following security measures are taken for viewing logs:
The super administrator can view all logs, whereas common administrators can only
view logs recording their own operations.
Logs cannot be modified or deleted on the management systems.
Only administrators who have the permission to query logs can export them.
Logs are exported in *.xls format.
8.1.3 Log Format
Operation logs record information such as performed operations, user information, and the
operation time. With operation logs, administrators can recognize operations that potentially
affect the system or have already caused problems and then take appropriate measures to
improve system security.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 26
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 8 Management Security
8.2 Account and Password Security
8.2.1 Account and Default Password
Initial and default accounts and passwords are used to maintain hardware devices and systems.
It is recommended that administrators change default passwords when they log in to the
system for the first time. The passwords must meet the requirement for password complexity.
Administrators must change passwords periodically to ensure the password security.
8.2.2 Password Encryption and Changing Principles
Table 8-1 shows the principles for encrypting, setting, and changing passwords for accounts.
Table 8-1 Principles for encrypting, setting, and changing passwords for accounts
Item Principles
Initial password The default password must be changed when the system is logged in
setting to for the first time. For details about how to change the password,
see associated account password changing guide.
The password is set according to the password policy.
Password All passwords are encrypted before they are stored.
encryption Passwords are not displayed in plain texts.
Password Only authenticated users can change passwords.
changing Old passwords must be verified before they are changed.
After the password validity period expires, the system requires users
to change the passwords when they log in.
Administrator passwords must be changed at most every 180 days.
Password policy A password policy table is generated during system installation.
changing Only the system administrator has the permission to modify the
password policy table.
After the password policy table is modified, users can successfully
log in to the system using passwords set according to the old
password policy.
8.3 Rights- and Domain-Based Management
Administrators of different permission levels are allowed to access different ranges of data to
ensure system security. The following management systems support permission management:
Role-based management
Role-based management allows user operation rights to be controlled based on the user's role.
A role can be granted one or more operation rights, and a user can be assigned one or more
roles. Therefore, the rights of a user are determined by the roles of the user. A user who is
assigned multiple roles has the combined operation rights of all these roles. Huawei's desktop
cloud solution supports flexible role and rights configuration.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 27
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 8 Management Security
Domain-based management
Domain-based management allows the administrator to manage only resources assigned in its
domain.
For some large-scale enterprises or units, a second-level maintenance administrator is
assigned for each department or branch office. The first-level administrator divides the
management domains according to the enterprise organization structures and creates VMs
accordingly. The second-level administrator logs in to the desktop management system and
can only manage the VMs in its domain.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 28
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 8 Management Security
8.4 Role-Based Management
A high-security mode can be adopted and the role-based management is supported. There are
three types of administrators, system administrator, security administrator, and security
auditor. No super user is allowed in the system perform all operations without limitation.
In the role-based management, the system administrator, security administrator, and security
auditor enjoy independent rights while mutually constrain each other. The system
administrator takes charge of daily operation and maintenance (O&M), configures and
manages services, and manages alarms and logs. Rights management is not allowed for the
system administrator. The security administrator manages accounts and rights (accounts and
roles), reviews and approves user creations, manages domains and password policies. No
service management is allowed for the security administrator. The security auditor supervises
the operations of the system administrator and the security administrator and can only views
and exports logs. The security administrator and the security auditor cannot be assigned to one
person.
8.5 Certificate Snap-ins
8.5.1 Communication Certificate Snap-ins Between Components
To ensure secure communication between desktop cloud components, two-way SSL-based
HTTPS certification authentication is implemented for each desktop cloud component
(including the WI, HDC, License, VNCGate, and ITA), and an encrypted transmission
channel is created between the components. After each component is installed during
FusionAccess deployment, each component comes with a certificate by default. The
certificate is used for authenticating server and client certificates. If customers want to replace
certificates of each component in the management system, they can use their own Certificate
Authority (CA) system to issue certificates that can be used for client and server
authentication, and manually replace certificates of components. Alternatively, they can use
the certificate replacement tool provided by FusionAccess to generate new certificates which
automatically substitute for original certificates.
8.5.2 Unified O&M and Auditing
To address challenges to system and network security, IT O&M, and internal control and
external auditing of IT system, effective technologies are required to perform dedicated
management, subsequent tracking and auditing, and real-time supervision and alarm report in
accordance with the standards of the industry. A unified IT core resource O&M and auditing
platform, that is, a bastion host, can be set up to centrally manage and control the accounts,
certification, authentication, and auditing of all IT resources in the desktop cloud service
systems, other service systems, OS, databases, and network devices.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 29
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 8 Management Security
Disabled Desktop cloud
system A
O&M Disabled
personnel Other entries
Desktop cloud
management and data
server
User A
Service system B
Bastion Host UMAs Core services and
User B (Huawei UMA) data servers
Service system C
Core services and
Cooperator
data servers
Centralized monitoring
and audit
Unified maintenance portal
A unified security O&M access platform is set up to provide a unified O&M portal for
core service systems and SSO logins.
Centralized account management
Centralized and role-based master and slave account management is allowed, mappings
between users and device accounts are set up, device accounts are centrally managed,
and passwords are regularly modified.
Strict control of rights
Reasonable resource allocation is implemented according to users' service requirements.
Access to different resources by different users is allowed and illegal and unauthorized
access is prevented.
Comprehensive security auditing
The security auditing provides tracking and recording of the entire O&M process, saves
complete O&M logs, calculates accesses to the resources, locates faults and tracks
responsibilities in case of security incidents, and audits logins and operations of users.
Hence, a comprehensive auditing of users-to-resources is enabled and an auditing
platform and audit data is available for supervision departments.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 30
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 9 Infrastructure Security
9 Infrastructure Security
9.1 Web Security
Huawei's desktop cloud solution provides the following web security functions, which are
basic functions of the solution:
Automatically redirects users' access requests to Hypertext Transfer Protocol Secure
(HTTPS) links.
The web service platform automatically redirect users' access request to HTTPS links.
When users access a web service platform by using the HTTP, the web service platform
automatically redirects the users' access requests to HTTPS links to enhance access
security.
Prevents cross-site scripting
Cross-site scripting is a type of computer vulnerability typically found in Web
applications, which enables attackers to inject client-side scripts into Web pages viewed
by other users.
Prevents SQL injection
Structured Query Language (SQL) injection is done by including portions of SQL
statements in a Web form entry field in an attempt to get the website to pass a newly
formed rogue SQL command.
Prevents cross-site request forgery
Cross-site request forgery is a type of malicious exploit of a website whereby
unauthorized commands are transmitted from a user that the website trusts. For example,
a user logs in to the website A and then logs in to the website B that contains the attack
programs, when the session does not time out. In this case, attackers obtain the session
ID of website A and then log in to website A to intercept private information.
Protects sensitive information
The web service platform can protect sensitive information from being obtained by
attackers.
Limits the uploading and downloading of files
The Web service platform sets user restrictions on uploading or downloading files to
prevent files with high security level and insecure files from being uploaded or
downloaded.
Prevents uniform resource locator (URL) form overriding
Certain rights are granted to each type of users to prevent users form perform
unauthorized operations on systems.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 31
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 9 Infrastructure Security
Supports graphic verification code
On the login page of each web service platform, the system generates verification code
randomly. Users can log in to the system only when the username, password, and
verification code entered are all entered correctly.
Account password
Web accounts and passwords must meet specified complexity requirements.
9.2 OS Security
9.2.1 Windows 2008 OS Security Hardening
With Huawei FusionCloud Desktop solution, the AD, ITA, TCM, and log servers for
FusionAccess are all deployed in VMs that run Windows Server 2008 R2. To ensure the
security these VMs, basic OS security hardening is required. The OS security is hardened in
following aspects:
System installation
Legal copies of OS installation software are installed on VMs. System software and
application software are installed on different disks. System patches are installed in a
timely manner. BIOS passwords can be set. File system adopts the NTFS format
Account password
Strong account passwords are used and changed periodically.
System service
Use of the remote access service is not allowed. Use of unnecessary ports is prohibited.
Security auditing
The maximum number of security logs is configured to prevent important logs from
being replaced. Successful and failed user logins are audited.
File system
Important system files are protected, and they have a high security level. Registry
permission is controlled. System file integrity is verified.
System access control
Default sharing is deleted. The system cannot be powered off before a successful login.
System kernel
To improve security configuration efficiency, the Huawei desktop cloud solution
provides the SetWin tool and execution scripts to harden OS security quickly.
9.2.2 SUSE Linux OS Security Hardening
In Huawei FusionCloud Desktop solution, components in FusionAccess, such as the WI,
HDC, GaussDB, license server, and VNCGate, and the computing, storage, and management
nodes of FusionCompute use the SUSE Linux Soto ensure their security, basic security
configurations are required. The basic security configurations are provided as the basic
security functions of the solution, which are as follows:
Shut down unnecessary services, such as Telnet and FTP services.
Control access permissions on files and directories.
Manage user passwords.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 32
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 9 Infrastructure Security
9.3 Security Patch
Software design defects cause many system loopholes. Regular installation of system security
patches can eliminate system loopholes and prevent viruses, worms, and hackers from using
these loopholes to attack the system. Huawei's desktop cloud solution provides the following
security patches:
Patches for the virtual desktop infrastructure (VDI), such as the AD and ITA servers
FusionAccess VDI components AD and ITA are installed in servers that run Windows
server 2008 R2. It is recommended that apart from the foregoing servers, customers
deploy the Windows patch server and run periodic patch update tasks on the Windows
patch server to install the latest patches.
9.4 Antivirus
9.4.1 Antivirus Software for Cloud Computing Platform
Components
Infrastructure VM
A hardened Linux system is adopted by the WI, HDC, License server, and VRM to
reduce the threats of virus infection. Hence no antivirus software is required.
Deploy the Trend Micro antivirus software on Windows Server 2008 ITA VMs to protect
infrastructure VMs from viruses by setting scheduled tasks for scanning and removal of
viruses.
If a customer does not use the Trend Micro antivirus software but use other antivirus software, the
software must pass Huawei's compatibility test.
Computing node and storage node
It is unnecessary to deploy antivirus software because of the following reasons:
The computing node and storage node run the reinforced Linux OS.
The computing nodes and storage nodes are in the closed network, and they do not
provide an external operation platform.
9.4.2 User VM Antivirus Software
An antivirus server can be deployed to provide antivirus software for user VMs. Virus
detection and removal tasks run on the server to protect user VMs from viruses. Users can
determine whether to install antivirus software based on VM security needs in an actual
situation.
To ensure VM security, it is recommended that antivirus software be installed. The following
antivirus products are compatible with the OSs of user VMs:
Trend antivirus
Kaspersky antivirus
Kingsoft antivirus
Rising antivirus
Jiangmin antivirus
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 33
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 9 Infrastructure Security
360 antivirus
Norton antivirus
McAfee antivirus
Symantec antivirus software
The preceding antivirus software products have passed Huawei's compatibility tests, and therefore are
recommended for installation. To prevent antivirus storms brought by the simultaneous disk virus
scanning and client updates, it is recommended that users use the software version optimized in virtual
environments, such as the Symantec SEP 12.1 or later versions, the network version of Rising Antivirus
optimized in virtual environments.
9.5 Database Security
9.5.1 Database Security Configuration
Huawei FusionCloud Desktop solution uses the GaussDB, which is a PostgreSQL9.2-based
relational database system developed by Huawei. Basic security configurations are required
for databases to ensure their secure operation. The security configurations for each type of
database are provided as the basic security functions of the solution, which are as follows:
GaussDB:
Strong passwords are required.
Database operation logs are recorded.
9.5.2 Data Backup
The active and standby GaussDB solution is available to enable data backup and enhance the
database serviceability and the data security. Besides, other data backup and recovery
solutions are also supported by the GaussDB to protect you data.
9.6 Physical Security
Physical security refers to the security of the physical devices in Huawei's desktop cloud
solution and their environments.
Device security
Devices must be deployed in a closed environment with door access control system to
prevent unauthorized personnel from entering the data center and unauthorized
storage devices from connecting to the data center.
Monitoring devices must be installed in equipment rooms, and entry-exist registration
must be implemented.
When the monitoring system generates an alarm, administrators must eliminate
security hazards in a timely manner.
Environment security
Installation environment: The temperature, humidity, and power supply must meet the
requirements of device installation.
Operation environment: Power supply, fans, and environment of the system must be
monitored in real time.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 34
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 10 User VM Security
10 User VM Security
10.1 Terminal Security Management
The terminal security management (TSM) system provides the following functions for
enterprises on desktop cloud:
Virtual desktop compliance management
Network access control
Staff activity monitoring
Software distribution
USB flash drive management.
The core rule of the TSM is to set up the network access control mechanism. The basic rules
are security check, access control, and security problem fixing. The TSM effectively controls
the increasing number of access points, including the network access from intranet staff,
visitors, partners, and temporary employees. It detects and isolates terminal hosts with threats,
thereby improving the network's attack defense capability.
10.1.1 Virtual Desktop Compliance Management
The desktop cloud solution enables users to log in to virtual desktops in the cloud using TCs
or software clients (SCs) to perform service operations, including receiving and sending
emails, completing daily work, and connecting to the Internet.
Virtual desktops are used to access cloud servers. If they are infected by viruses or Trojan,
they will impose great security threats to the entire cloud service resources and other virtual
desktops in the same access area. With the virtual desktop compliance management function,
the security of the access area is ensured.
10.1.2 Network Access Control
This function is used to control whether an end user can access the network resources.
Security access control is used with virtual desktop compliance management to deny
access requests from terminal hosts that do not meet security requirements and to force
the terminal hosts to fix security problems.
Security access control enables the TSM to control the rights for end users to access the
network. The TSM grants only the minimum network access rights to end users based on
the user roles and services to be implemented, thereby ensuring application security.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 35
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 10 User VM Security
10.1.3 Staff Activity Monitoring
This function enables the system to monitor the activities of an end user, so that it is easy to
find out whether a staff is online chatting, browsing a website, or handling personal affairs.
This protects corporate network resources against improper use. It also helps minimize the
possibility of law violation caused by staffs' personal online activities.
10.1.4 Patch Management
The vulnerabilities of the Windows OS pose great risks to local area networks (LANs). If a
large number of terminals without key patches installed exist, the virus attack and network
congestion risks of LANs are high. If the number of the vulnerable terminals is reduced by
installing security patches on them in time, the risk of virus spreading in a large area of the
network will be reduced.
10.1.5 Software Distribution
Terminal security management (TSM) servers enable IT administrators to push software
packages remotely so that software can be installed on or uninstalled from user VMs. This
function helps improve the IT management efficiency. The administrators can
determine whether to distribute software to specific user VMs or to all user VMs.
10.1.6 USB Flash Drive Management
This function enables the system to monitor and control the use of the USB flash drive. The
TSM supports the following control policies:
Restricts the use of the USB flash drive.
Grants only read permission to the USB flash drive. In this scenario, files cannot be
copied to the USB flash drive.
Grants read and write permission to the USB flash drive but records an audit event when
a file is copied to the USB flash drive.
Grants read and write permission to the USB flash drive but encrypts the file that is
copied to the USB flash drive. The file can be read and decrypted using only the user
VM of the same company.
The TSM server has private keys. The encrypted files can be read and decrypted using
the user VM on which the TSM Agent is installed.
Differentiates internal and external USB flash drives in some industries and flexibly
controls USB usage with the USB monitoring function of the TSM system. These
functions ensure that enterprise internal data is exchanged securely.
10.2 Document Security Management
To secure the files on the user VMs, customers can deploy document security management
system and file security cases.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 36
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 11 Summary of Huawei's Desktop Cloud Solution
11 Summary of Huawei's Desktop Cloud
Solution
Huawei's desktop cloud solution systematically prevents unauthenticated users and malicious
system administrators from accessing the desktop cloud data center.
That is, unauthenticated users cannot access the system. Even if an unauthenticated user
accesses the system, the user cannot copy data or read confidential data. The system logs all
operations of the unauthenticated user to ensure that the unauthenticated user has to be
responsible for unauthorized operations. In addition, system data and user data can be
properly protected based on some encryption and data redundancy mechanisms.
Figure 11-1 Summary of Huawei's desktop cloud solution
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 37
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 11 Summary of Huawei's Desktop Cloud Solution
11.1.1 For Unauthenticated Users
11.1.1.1 Access Control
Users access desktop cloud with two-factor authentication such as fingerprint, USB key,
and token. With an intercepted password, an unauthenticated user still cannot access the
VM if he has no USB key or token.
802.1 X authentication is required for TC to access networks. Illegal TCs cannot access
the desktop cloud.
In high-security scenarios where only TCs at specified physical addresses can access
desktop cloud, the desktop cloud system can specify TCs with specified MAC addresses
to access the desktop.
Transmission between the TC and access gateway is encrypted using SSL to prevent
password interception or playback attack. Remote access can use SSL VPN.
The solution uses firewalls for isolation. Only specified HTTPS ports are available on
the user side.
11.1.1.2 Security Control
Information is controlled in the cloud in a centralized manner. Huawei desktop cloud
terminals are separated from information. The desktop and data are stored and processed
on the background. Only encrypted instructions about the desktop screen, keyboard, and
mouse are transmitted to terminals.
Delicacy control is performed for peripherals (such as USB ports and parallel ports) of
TCs and VM redirection. For example, peripherals are forbidden or set to read only so
that data cannot be copied.
Writable storage is unavailable on TCs and screen information cannot be recorded.
11.1.1.3 Rights Control
The DSM feature is used to encrypt confidential and sensitive files and control rights.
11.1.1.4 Operation Audit
The access gateway, authentication system, and VM of desktop cloud make records of user
access for accident responsibility tracing.
11.1.1.5 Data Protection
When the system retrieves resources, data is removed. When the space is allocated to
another user, the disk data of the former user cannot be recovered with disk data
recovery tools.
Highly available disaster recovery and data backup solutions are provided to desktop
cloud.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 38
Copyright Huawei Technologies Co., Ltd.
Huawei FusionCloud Desktop Solution 5.2
Security Technical White Paper 11 Summary of Huawei's Desktop Cloud Solution
11.1.2 For Malicious Administrator
11.1.2.1 Access Control
Management platform security is hardened with security patches and system hardening
to reduce attack risks. Malicious administrators cannot access the system through normal
channels.
Rights- and domain-based management is used for administrators to manage devices and
services. The management complies with the RBAC model of NIST and can create roles
and administrators flexibly to prevent administrators from override management.
In the role-based management, the system administrator, security administrator, and
security auditor enjoy independent rights while mutually constrain each other.
Accounts are managed in a centralized manner and passwords are changed periodically
to prevent malicious administrators use other accounts of higher rights to access the
system.
11.1.2.2 Security Control
A bastion host can be deployed to the only access port of the management platform. External
maintenance networks cannot interwork with nodes on the cloud platform, and malicious
administrators cannot copy user data to maintenance networks directly, for example, copy
users' disk volume files in dd command mode.
11.1.2.3 Rights Control
On VMs with important data, VM disk encryption can be used to prevent confidential
data leakage even if a malicious system administrator copies disk files or takes the
physical disk.
Sensitive information (such as account passwords) on the cloud platform is
encrypted with AES 128 or AES 256. Passwords that do not need to be restored are
encrypted with SHA256. The encryption prevents malicious administrators from
obtaining internal accounts to log in to the system and evading audit.
11.1.2.4 Operation Audit
Service portals of desktop cloud management, OS, and hardware devices all provide logs
of all administrator operations. Logs are stored for three months for audit.
As the only access port to the management platform, the bastion host stores logs and
records of all operations on the management system.
11.1.2.5 Data Protection
VM disk encryption or storage system encryption are used so that data does not leak out even
if a malicious system administrator takes disks out of the central data equipment room.
Issue 01 (2014-12-01) Huawei Proprietary and Confidential 39
Copyright Huawei Technologies Co., Ltd.
Vous aimerez peut-être aussi
- CompTIA Security+ Certification Study Guide: Exam SY0-201 3ED'EverandCompTIA Security+ Certification Study Guide: Exam SY0-201 3EPas encore d'évaluation
- Huawei Flash StorageDocument97 pagesHuawei Flash StorageRasika Kumara SudasinghePas encore d'évaluation
- Portafolio Huawei StorageDocument30 pagesPortafolio Huawei StorageFernando CalderonPas encore d'évaluation
- Huawei FusionCloud Desktop Solution Overview Presentation (For Financial)Document55 pagesHuawei FusionCloud Desktop Solution Overview Presentation (For Financial)HUMANMANPas encore d'évaluation
- Huawei FusionSphere 5.1 Brochure (Server Virtualization)Document2 pagesHuawei FusionSphere 5.1 Brochure (Server Virtualization)Anthony ThomasPas encore d'évaluation
- Huawei OceanStor Dorado V3 All Flash Storage Technical White Paper PDFDocument43 pagesHuawei OceanStor Dorado V3 All Flash Storage Technical White Paper PDFDiana HernandezPas encore d'évaluation
- HUAWEI CloudEngine 6800 Switch DatasheetDocument12 pagesHUAWEI CloudEngine 6800 Switch DatasheetHussein DhafanPas encore d'évaluation
- Legal Aspects Ra9266 ReportDocument41 pagesLegal Aspects Ra9266 ReportArmie Jay dela CruzPas encore d'évaluation
- Accounting Changes//: Accounting Estimate Accounting PolicyDocument2 pagesAccounting Changes//: Accounting Estimate Accounting PolicyFaye RagosPas encore d'évaluation
- Huawei OceanStor 9000 Technical PresentationDocument57 pagesHuawei OceanStor 9000 Technical PresentationHUMANMANPas encore d'évaluation
- Huawei OceanStor S2200T&S2600T&S5500T&S5600T&S5800T&S6800 Storage System Product DescriptionDocument79 pagesHuawei OceanStor S2200T&S2600T&S5500T&S5600T&S5800T&S6800 Storage System Product DescriptionMenganoFulanoPas encore d'évaluation
- wd013-062.3 Gis 101 Challenge ExamDocument7 pageswd013-062.3 Gis 101 Challenge Examnguyenduy1133Pas encore d'évaluation
- Interconnection To Other Operators, International GatewayDocument13 pagesInterconnection To Other Operators, International GatewayBenny LuoPas encore d'évaluation
- Sales Superstore DatasetDocument737 pagesSales Superstore DatasetLoik-mael NysPas encore d'évaluation
- ABA Model Rules of Professional Conduct USPTO Rules of Professional ConductDocument58 pagesABA Model Rules of Professional Conduct USPTO Rules of Professional ConductansarixxxPas encore d'évaluation
- ENVS211 GIS Prac Manual 2017Document77 pagesENVS211 GIS Prac Manual 2017Johnson Todowede50% (2)
- Oceanspace Cloud Storage SystemDocument2 pagesOceanspace Cloud Storage SystemUtopia MediaPas encore d'évaluation
- Aspect® Unified IP® 7.4 SP1 Aspect® Unified IP® - Advanced List Management 7.4 ™ SP1 Product Release NotesDocument29 pagesAspect® Unified IP® 7.4 SP1 Aspect® Unified IP® - Advanced List Management 7.4 ™ SP1 Product Release NotesAbPas encore d'évaluation
- PortalsDocument160 pagesPortalsapi-26037880100% (1)
- Lecture Cbs of Huawei July2012Document31 pagesLecture Cbs of Huawei July2012artsan3100% (2)
- Excel-Based Toolset For Financial Reporting GuideDocument18 pagesExcel-Based Toolset For Financial Reporting GuideSunnyDrePas encore d'évaluation
- JD Edwards World Product Costing and Manufacturing Accounting A91 GuideDocument306 pagesJD Edwards World Product Costing and Manufacturing Accounting A91 Guide'Emraan Tahir'100% (1)
- Administering Avaya Proactive ContactDocument472 pagesAdministering Avaya Proactive Contactflat88Pas encore d'évaluation
- Test 6Document32 pagesTest 6Santosh JagtapPas encore d'évaluation
- Application IntegrationDocument15 pagesApplication IntegrationJovit FondevillaPas encore d'évaluation
- Term Paper - Virtualization in Cloud ComputingDocument10 pagesTerm Paper - Virtualization in Cloud ComputingSudipPas encore d'évaluation
- IPOFFICE Embedded Voicemail User enDocument26 pagesIPOFFICE Embedded Voicemail User enOctavio PuentePas encore d'évaluation
- OCS DCC Interface Reference (Multimedia Message Charging Process EventID ... 2Document38 pagesOCS DCC Interface Reference (Multimedia Message Charging Process EventID ... 2mikePas encore d'évaluation
- Virtualization in Cloud ComputingDocument5 pagesVirtualization in Cloud ComputingadamPas encore d'évaluation
- CRS Report On ICANN and Internet GovernanceDocument26 pagesCRS Report On ICANN and Internet GovernanceBennet Kelley50% (2)
- CIV531Document39 pagesCIV531syed.imamPas encore d'évaluation
- BIESG OBIEE SystemAdmin PDFDocument470 pagesBIESG OBIEE SystemAdmin PDFmpullareddyPas encore d'évaluation
- City Planning Decision Jessen PondsDocument7 pagesCity Planning Decision Jessen PondsDominic BaezPas encore d'évaluation
- Types of Computer Networks Advantages and DisadvantagesDocument6 pagesTypes of Computer Networks Advantages and DisadvantagesPatrickPas encore d'évaluation
- Oracle Argus Safety: Administration Guide Release 8.2.2Document258 pagesOracle Argus Safety: Administration Guide Release 8.2.2Arjun TalwakarPas encore d'évaluation
- Technical Specification Document-1Document4 pagesTechnical Specification Document-1Gaurav TandonPas encore d'évaluation
- Installing A FortiGate in Transparent ModeDocument5 pagesInstalling A FortiGate in Transparent Modepchauhan100% (1)
- VMware HealthAnalyzer Install and User Guide v5.5.2Document62 pagesVMware HealthAnalyzer Install and User Guide v5.5.2emcviltPas encore d'évaluation
- Access Control ProposalDocument9 pagesAccess Control ProposalsupportPas encore d'évaluation
- P Comm ServerDocument117 pagesP Comm ServercmeplantPas encore d'évaluation
- QStar - Technical SpecificationDocument25 pagesQStar - Technical SpecificationJad El FarranPas encore d'évaluation
- JD Edwards World Advanced Pricing A91 GuideDocument229 pagesJD Edwards World Advanced Pricing A91 GuidestrikerjaxPas encore d'évaluation
- Centers For Medicare & Medicaid ServicesDocument23 pagesCenters For Medicare & Medicaid ServicesLightning LamboPas encore d'évaluation
- J Armour, H Hansmann, R Kraakman The Essential Elements of CorporateDocument37 pagesJ Armour, H Hansmann, R Kraakman The Essential Elements of Corporatefsadfsdfsdf100% (1)
- Admin Guide OAMDocument190 pagesAdmin Guide OAMCristina XifraPas encore d'évaluation
- Acceptable Use Policy For CommunicationsDocument11 pagesAcceptable Use Policy For CommunicationsElizabeth ScheinbergPas encore d'évaluation
- Interactive Reporting Capacity Planning Report - IR 11.1.1 WindowsDocument31 pagesInteractive Reporting Capacity Planning Report - IR 11.1.1 WindowsRamChaitanyaPas encore d'évaluation
- Ep-160016 ManualDocument342 pagesEp-160016 ManualJohn PoncePas encore d'évaluation
- C 2.1.5 Huawei Global Corporate Fact Sheet AnnexDocument4 pagesC 2.1.5 Huawei Global Corporate Fact Sheet AnnexHassanghasemiPas encore d'évaluation
- Cloud Computing Assignment-1 (Virtualization)Document18 pagesCloud Computing Assignment-1 (Virtualization)DarshpreetKaurPas encore d'évaluation
- ORAchk Collection Manger User Guide v121026Document66 pagesORAchk Collection Manger User Guide v121026Taufique HafeezPas encore d'évaluation
- Sap Data Center 01 01 PDF en v3Document4 pagesSap Data Center 01 01 PDF en v3quangteo2009Pas encore d'évaluation
- CSE Idatabase Management System Report PDFDocument18 pagesCSE Idatabase Management System Report PDFNehaPas encore d'évaluation
- Software AgreementDocument9 pagesSoftware AgreementYeh DavidPas encore d'évaluation
- 7 - Net Support SchoolDocument21 pages7 - Net Support SchoolAbdul AzizPas encore d'évaluation
- Huawei Desktop Cloud SolutionDocument4 pagesHuawei Desktop Cloud SolutionDmitriy BaybulatovPas encore d'évaluation
- Skybox ReferenceGuide V10!0!300Document460 pagesSkybox ReferenceGuide V10!0!300pisanij123Pas encore d'évaluation
- Zenoss Core Installation 04 072010 3.0 v02Document38 pagesZenoss Core Installation 04 072010 3.0 v02Patricio A. Palacios Maureira100% (1)
- Huawei OceanStor Dorado All-Flash Storage 6.1.0 Technical White PaperDocument186 pagesHuawei OceanStor Dorado All-Flash Storage 6.1.0 Technical White PaperFernandoPas encore d'évaluation
- Huawei FusionSphere 6.5.0 Technical White Paper (Server Virtualization)Document26 pagesHuawei FusionSphere 6.5.0 Technical White Paper (Server Virtualization)Myo Lwin SoePas encore d'évaluation
- 5 Paragraph EssayDocument2 pages5 Paragraph EssayGabriel DarkPas encore d'évaluation
- Chargeback SurveyDocument12 pagesChargeback SurveyGabriel DarkPas encore d'évaluation
- Unified Computing System - ArtDocument123 pagesUnified Computing System - ArtGabriel DarkPas encore d'évaluation
- Enterprise Network Product Visio Stencils User Guide PDFDocument2 pagesEnterprise Network Product Visio Stencils User Guide PDFGabriel DarkPas encore d'évaluation
- Demystifying NFV in Carrier NetworksDocument8 pagesDemystifying NFV in Carrier NetworksGabriel DarkPas encore d'évaluation
- Health Post - Exploring The Intersection of Work and Well-Being - A Guide To Occupational Health PsychologyDocument3 pagesHealth Post - Exploring The Intersection of Work and Well-Being - A Guide To Occupational Health PsychologyihealthmailboxPas encore d'évaluation
- Executive Summary-P-5 181.450 To 222Document14 pagesExecutive Summary-P-5 181.450 To 222sat palPas encore d'évaluation
- Quarter 1 - Module 1Document31 pagesQuarter 1 - Module 1Roger Santos Peña75% (4)
- Evolution Army 3 R DadDocument341 pagesEvolution Army 3 R DadStanisław DisęPas encore d'évaluation
- Assistant Cook Learner Manual EnglishDocument152 pagesAssistant Cook Learner Manual EnglishSang Putu Arsana67% (3)
- Rana2 Compliment As Social StrategyDocument12 pagesRana2 Compliment As Social StrategyRanaPas encore d'évaluation
- Catedral de SevillaDocument28 pagesCatedral de SevillaAnonymous LkgNmKePas encore d'évaluation
- Chapter 2Document13 pagesChapter 2Kumkumo Kussia KossaPas encore d'évaluation
- Technology Based Project: Special Track 1)Document14 pagesTechnology Based Project: Special Track 1)Kim ChiquilloPas encore d'évaluation
- Fundamentals of Public Health ManagementDocument3 pagesFundamentals of Public Health ManagementHPMA globalPas encore d'évaluation
- Notes:: Reinforcement in Manhole Chamber With Depth To Obvert Greater Than 3.5M and Less Than 6.0MDocument1 pageNotes:: Reinforcement in Manhole Chamber With Depth To Obvert Greater Than 3.5M and Less Than 6.0Mسجى وليدPas encore d'évaluation
- My Mother at 66Document6 pagesMy Mother at 66AnjanaPas encore d'évaluation
- Bolt Grade Markings and Strength ChartDocument2 pagesBolt Grade Markings and Strength ChartGregory GaschteffPas encore d'évaluation
- Tutorial 5 SolvedDocument3 pagesTutorial 5 SolvedAshutoshKumarPas encore d'évaluation
- Anemia in PregnancyDocument5 pagesAnemia in PregnancycfgrtwifhPas encore d'évaluation
- BSC HTM - TourismDocument4 pagesBSC HTM - Tourismjaydaman08Pas encore d'évaluation
- Delusion in SocietyDocument2 pagesDelusion in SocietyGasimovskyPas encore d'évaluation
- Peer PressureDocument13 pagesPeer PressuremightymarcPas encore d'évaluation
- 1 in 8.5 60KG PSC Sleepers TurnoutDocument9 pages1 in 8.5 60KG PSC Sleepers Turnoutrailway maintenancePas encore d'évaluation
- Promotion-Mix (: Tools For IMC)Document11 pagesPromotion-Mix (: Tools For IMC)Mehul RasadiyaPas encore d'évaluation
- Cyber Briefing Series - Paper 2 - FinalDocument24 pagesCyber Briefing Series - Paper 2 - FinalMapacheYorkPas encore d'évaluation
- Continue Practice Exam Test Questions Part 1 of The SeriesDocument7 pagesContinue Practice Exam Test Questions Part 1 of The SeriesKenn Earl Bringino VillanuevaPas encore d'évaluation
- Student Exploration: Inclined Plane - Simple MachineDocument9 pagesStudent Exploration: Inclined Plane - Simple MachineLuka MkrtichyanPas encore d'évaluation
- A Survey On Security and Privacy Issues of Bitcoin-1Document39 pagesA Survey On Security and Privacy Issues of Bitcoin-1Ramineni HarshaPas encore d'évaluation
- Cisco UCS Adapter TroubleshootingDocument90 pagesCisco UCS Adapter TroubleshootingShahulPas encore d'évaluation
- How To Configure PowerMACS 4000 As A PROFINET IO Slave With Siemens S7Document20 pagesHow To Configure PowerMACS 4000 As A PROFINET IO Slave With Siemens S7kukaPas encore d'évaluation
- Apexi Powerfc Instruction ManualDocument15 pagesApexi Powerfc Instruction ManualEminence Imports0% (2)
- Shakespeare Sonnet EssayDocument3 pagesShakespeare Sonnet Essayapi-5058594660% (1)
- Biblical World ViewDocument15 pagesBiblical World ViewHARI KRISHAN PALPas encore d'évaluation
- Enochian Dragon Ritual PDFDocument4 pagesEnochian Dragon Ritual PDFDenis NantelPas encore d'évaluation