Académique Documents
Professionnel Documents
Culture Documents
Annapoorana Engineering College, Salem
Transféré par
deepa0 évaluation0% ont trouvé ce document utile (0 vote)
16 vues1 pagebank
Titre original
Mobile Computing
Copyright
© © All Rights Reserved
Formats disponibles
DOC, PDF, TXT ou lisez en ligne sur Scribd
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentbank
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme DOC, PDF, TXT ou lisez en ligne sur Scribd
0 évaluation0% ont trouvé ce document utile (0 vote)
16 vues1 pageAnnapoorana Engineering College, Salem
Transféré par
deepabank
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme DOC, PDF, TXT ou lisez en ligne sur Scribd
Vous êtes sur la page 1sur 1
ANNAPOORANA ENGINEERING COLLEGE, SALEM B.E/B.
TECH DEGREE INTERNAL EXAMINATION I: Feb 2017
B.E/B.TECH DEGREE INTERNAL EXAMINATION I: Feb 2017 REGULATIONS: 2013
REGULATIONS: 2013 VI-SEMESTER: CSE
VI-SEMESTER: CSE IT6601- Mobile Computing
IT6601- Mobile Computing DATE: 16/02/2017 Max: 50 Marks
DATE: 16/02/2017 Max: 50 Marks TIME: 09.25 am to 10.55 am
TIME: 09.25 am to 10.55 am PART- A (7X 2 = 14)
ANSWER ALL QUESTIONS
PART- A (7X 2 = 14) 1. What are the applications of mobile computing?
ANSWER ALL QUESTIONS 2. Define mobile computing.
1. What are the applications of mobile computing? 3. Differentiate VANET and MANET.
2. Define mobile computing. 4. What are the characteristics of mobile computing?
3. Differentiate VANET and MANET. 5. What do you mean by tunneling?
4. What are the characteristics of mobile computing? 6. Differentiate Bluetooth and WIFI.
5. What do you mean by tunneling? 7. What is bandwidth?
6. Differentiate Bluetooth and WIFI.
7. What is bandwidth? PART- B (3X12 = 36)
ANSWER ALL QUESTIONS
PART- B (3X12 = 36) 8. a. (i) Explain about wireless MAC issues and reservation
ANSWER ALL QUESTIONS based schemes.(8)
8. a. (i) Explain about wireless MAC issues and reservation (ii) Explain about ALOHA technique.(4)
based schemes.(8) (or)
(ii) Explain about ALOHA technique.(4) b. (i) What are the types of CSMA and explain it?(6)
(or) (ii) Explain structure of mobile computing with diagram.(6)
b. (i) What are the types of CSMA and explain it?(6)
(ii) Explain structure of mobile computing with diagram.(6) 9. a. Explain about the fixed assignment schemes.(12)
(or)
9. a. Explain about the fixed assignment schemes.(12) b. (i) Explain about MAC protocol.(8)
(or) (ii) Differentiate wireless and mobile computing.(4)
b. (i) Explain about MAC protocol.(8)
(ii) Differentiate wireless and mobile computing.(4) 10. a. (i) What do you know about TCP, IP & UDP (6)
(ii) Explain about the term Ad-Hoc, physical layer & collision
10. a. (i) What do you know about TCP, IP & UDP (6) (6)
(ii) Explain about the term Ad-Hoc, physical layer & collision (or)
(6) b. (i) Explain about the terms Ethernet, RTO & Buffer.(6)
(or) (ii) Write in your own way about the packet transmission
b. (i) Explain about the terms Ethernet, RTO & Buffer.(6) process from sender to receiver in mobile computing.(6)
(ii) Write in your own way about the packet transmission
process from sender to receiver in mobile computing.(6)
ANNAPOORANA ENGINEERING COLLEGE, SALEM
Vous aimerez peut-être aussi
- Answer All The Questions Networking: (Subject With Code)Document4 pagesAnswer All The Questions Networking: (Subject With Code)gunaPas encore d'évaluation
- IT6601 MC AU QP Reg 2013Document11 pagesIT6601 MC AU QP Reg 2013bhuvangatesPas encore d'évaluation
- CCNA Interview Questions You'll Most Likely Be AskedD'EverandCCNA Interview Questions You'll Most Likely Be AskedPas encore d'évaluation
- Mobile Computing Model Exam Question PapersDocument3 pagesMobile Computing Model Exam Question PapersSamy KmPas encore d'évaluation
- CE15-R4 Mobile Computing 2 PagesDocument26 pagesCE15-R4 Mobile Computing 2 PagesKhushi JainPas encore d'évaluation
- Building the Internet of Things with IPv6 and MIPv6: The Evolving World of M2M CommunicationsD'EverandBuilding the Internet of Things with IPv6 and MIPv6: The Evolving World of M2M CommunicationsPas encore d'évaluation
- Gujarat Technological UniversityDocument1 pageGujarat Technological UniversityJigarPas encore d'évaluation
- Assignment Wireless TechnologyDocument5 pagesAssignment Wireless TechnologyRyan JeePas encore d'évaluation
- IT6601-Mobile Computing Question Bank: Unit I Part ADocument7 pagesIT6601-Mobile Computing Question Bank: Unit I Part ANaveenTummidiPas encore d'évaluation
- Stucor Qp-Ec8702Document5 pagesStucor Qp-Ec8702diamond puppyPas encore d'évaluation
- CS8601 Mobile ComputigDocument3 pagesCS8601 Mobile ComputigAparna durairajPas encore d'évaluation
- Assessment 2 Ques PaperDocument4 pagesAssessment 2 Ques PaperKaviya TamilPas encore d'évaluation
- Gujarat Technological UniversityDocument1 pageGujarat Technological UniversityVrundaPas encore d'évaluation
- Question Paper Code:: Reg. No.Document2 pagesQuestion Paper Code:: Reg. No.Vijayarasu ThirunavukkarasuPas encore d'évaluation
- CLOUDoldqnpapersDocument9 pagesCLOUDoldqnpapersSurìyáPas encore d'évaluation
- Question Paper of Computer NetworkDocument1 pageQuestion Paper of Computer NetworkBhesh Chaudhary100% (1)
- WIRELESS+AND+MOBILE+NETWORKING Seme2 2006Document2 pagesWIRELESS+AND+MOBILE+NETWORKING Seme2 2006api-26171521Pas encore d'évaluation
- WSN June 2019 QPDocument1 pageWSN June 2019 QPtempPas encore d'évaluation
- Model Questionpaper - Paper2Document3 pagesModel Questionpaper - Paper2Shubhra DixitPas encore d'évaluation
- Mobile Adhoc Networks QPDocument2 pagesMobile Adhoc Networks QPDr.chitra ECEPas encore d'évaluation
- Mobile ComputingDocument5 pagesMobile Computingmichael.ferraris100% (1)
- Computer Networks ModelDocument2 pagesComputer Networks ModelMahendran MahePas encore d'évaluation
- Switching Theory and Logic Design - June-2015Document55 pagesSwitching Theory and Logic Design - June-2015Rama HarithaPas encore d'évaluation
- 2019 May IT462-A - Ktu QbankDocument2 pages2019 May IT462-A - Ktu QbankMukesh BathrePas encore d'évaluation
- Question BankDocument9 pagesQuestion BankK R OFFSET PRINTERSPas encore d'évaluation
- Adhoc Wireless and Sensor Networks: M. Tech II Semester Supplementary Examinations, February - 2014Document26 pagesAdhoc Wireless and Sensor Networks: M. Tech II Semester Supplementary Examinations, February - 2014Sreekanth PagadapalliPas encore d'évaluation
- CNALLQSTIONSDocument14 pagesCNALLQSTIONScodesearch1996Pas encore d'évaluation
- Fundamentals of IoT SET 1Document1 pageFundamentals of IoT SET 1Manjot KaurPas encore d'évaluation
- Question Paper Code:: Reg. No.Document2 pagesQuestion Paper Code:: Reg. No.rajkumarsacPas encore d'évaluation
- Anna University QP Iot 2022 mc4302Document2 pagesAnna University QP Iot 2022 mc4302Kanimozhi LPas encore d'évaluation
- Cs9251 Mobile ComputingDocument13 pagesCs9251 Mobile ComputingSenthil KumarPas encore d'évaluation
- Iot Question PaperDocument1 pageIot Question Paperdhanesh.mukkamPas encore d'évaluation
- Question Paper Code:: (10×2 20 Marks)Document2 pagesQuestion Paper Code:: (10×2 20 Marks)Ponraj Park100% (4)
- 13.606.4 PROFESSIONAL ETHICS (AT) (Elective II) Question PaperDocument1 page13.606.4 PROFESSIONAL ETHICS (AT) (Elective II) Question PaperpkcdubPas encore d'évaluation
- Adhoc & Sensor Networks - EL IDocument1 pageAdhoc & Sensor Networks - EL IDr-Samson ChepuriPas encore d'évaluation
- III b.tech-II Sem Question BankDocument35 pagesIII b.tech-II Sem Question BankMukesh BathrePas encore d'évaluation
- Part - A (15 2 30) : Carrier Sense Multiple Access / Collision Detection (Csma / CD)Document2 pagesPart - A (15 2 30) : Carrier Sense Multiple Access / Collision Detection (Csma / CD)sandra karunysPas encore d'évaluation
- 52 FjbjfeDocument2 pages52 FjbjfeDiboresh SahaPas encore d'évaluation
- Mobile Computing Feb 2020Document1 pageMobile Computing Feb 2020Harish SarkiPas encore d'évaluation
- Gujarat Technological UniversityDocument2 pagesGujarat Technological Universityyicef37689Pas encore d'évaluation
- CS2402 QB mpc2Document10 pagesCS2402 QB mpc2Prabhavathi AadhiPas encore d'évaluation
- CN Imp QuestionsDocument3 pagesCN Imp QuestionsSuresh ManchikantiPas encore d'évaluation
- Mobile Computing Assignment MARCH 2024Document2 pagesMobile Computing Assignment MARCH 2024victorsebstarPas encore d'évaluation
- April 2011Document2 pagesApril 2011KalirajanPas encore d'évaluation
- Question BankDocument12 pagesQuestion BankMahu DPas encore d'évaluation
- Io T2Document6 pagesIo T2Rupesh MarathePas encore d'évaluation
- Question Bank For Mobile Computing Regulation 2013Document9 pagesQuestion Bank For Mobile Computing Regulation 2013PRIYA RAJI100% (1)
- 2019 May EE472-B - Ktu QbankDocument2 pages2019 May EE472-B - Ktu QbankMukesh BathrePas encore d'évaluation
- Sample of Mobile Computing Exam (June 2006) - UK University BSC Final YearDocument3 pagesSample of Mobile Computing Exam (June 2006) - UK University BSC Final YearTDiscover100% (4)
- 5 Years Anna University Question PaperDocument13 pages5 Years Anna University Question PaperG. SIVARANJANI Associate ProfessorPas encore d'évaluation
- Drona - VII Sem CSE Nov Dec 2020 QPDocument15 pagesDrona - VII Sem CSE Nov Dec 2020 QPManimegalaiPas encore d'évaluation
- Electronics and Communication Engineering: Question Paper Code: X10366Document4 pagesElectronics and Communication Engineering: Question Paper Code: X10366krithikgokul selvam100% (1)
- P16MCAE6Document2 pagesP16MCAE6SYED IBRAHIMPas encore d'évaluation
- Now and Get: Best VTU Student Companion App You Can GetDocument16 pagesNow and Get: Best VTU Student Companion App You Can GetMOHAMMED IYANUDDINPas encore d'évaluation
- V.M.K.V Engineering College Vinayaka Missions University Department of Information Technology IV YEAR (BATCH - 2006-2010) Mobile ComputingDocument5 pagesV.M.K.V Engineering College Vinayaka Missions University Department of Information Technology IV YEAR (BATCH - 2006-2010) Mobile ComputingpocketoxyPas encore d'évaluation
- WSN Question Bank 2017-2018Document6 pagesWSN Question Bank 2017-2018Kommisetty Murthyraju100% (1)
- Be Winter 2019Document1 pageBe Winter 2019Madhav janiPas encore d'évaluation
- CG Qu BankDocument24 pagesCG Qu Banktbuvaneswari2176Pas encore d'évaluation
- Full Outer JoinDocument1 pageFull Outer JoindeepaPas encore d'évaluation
- CP Int OneDocument2 pagesCP Int OnedeepaPas encore d'évaluation
- Works LabDocument46 pagesWorks LabMeena SasikumarPas encore d'évaluation
- Lab Open SourceDocument3 pagesLab Open SourcedeepaPas encore d'évaluation
- Ge6263 Computer Programming Laboratory SylDocument1 pageGe6263 Computer Programming Laboratory SyldeepaPas encore d'évaluation
- Lab Open SourceDocument3 pagesLab Open SourcedeepaPas encore d'évaluation
- Eee Oops Lab SyllabusDocument1 pageEee Oops Lab SyllabusdeepaPas encore d'évaluation
- Cs6511 Case Tools Laboratory L T P CDocument1 pageCs6511 Case Tools Laboratory L T P CdeepaPas encore d'évaluation
- AICTE Published Free Open Source Software List Instead of Commercial Software For AcademicsDocument3 pagesAICTE Published Free Open Source Software List Instead of Commercial Software For AcademicsdeepaPas encore d'évaluation
- Zenerdiodes and Voltage RegulatorsDocument93 pagesZenerdiodes and Voltage RegulatorsSumanta BhattacharyyaPas encore d'évaluation
- Cadence Virtuso Layout EditorDocument18 pagesCadence Virtuso Layout EditorKrishna ChaitanyaPas encore d'évaluation
- Lab 1 RCDocument7 pagesLab 1 RCilet09Pas encore d'évaluation
- Fibre OpticsDocument51 pagesFibre OpticsAtanda Babatunde MutiuPas encore d'évaluation
- ZE500KL RF Hardware Trouble Shooting GuideDocument59 pagesZE500KL RF Hardware Trouble Shooting GuideWilliam SequeraPas encore d'évaluation
- PotentiometerDocument12 pagesPotentiometerkarthikeyan19470% (1)
- MAC Project Report - OBDDocument75 pagesMAC Project Report - OBDManoj PrabhakarPas encore d'évaluation
- Machine Architecture 14 Cache Memory Principles Elements of Cache DesignDocument34 pagesMachine Architecture 14 Cache Memory Principles Elements of Cache DesignAbul Asar Sayyad100% (1)
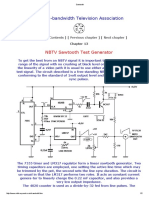
- Narrow Bandwidth Television Association: NBTV Sawtooth Test GeneratorDocument2 pagesNarrow Bandwidth Television Association: NBTV Sawtooth Test GeneratorSebastian CostaPas encore d'évaluation
- Jimma ThesisDocument65 pagesJimma ThesisMintesnot AlemuPas encore d'évaluation
- Different Types of Fuses and Its ApplicationsDocument10 pagesDifferent Types of Fuses and Its ApplicationsAhmet MehmetPas encore d'évaluation
- Wittek Stereo Surround PDFDocument43 pagesWittek Stereo Surround PDFАлександр СидоровPas encore d'évaluation
- Experiment 3: Channel Effects Elazegui, Diann Claire L.: Equation 1Document5 pagesExperiment 3: Channel Effects Elazegui, Diann Claire L.: Equation 1Diann ElazeguiPas encore d'évaluation
- SatNetCom ProductDocument6 pagesSatNetCom Producteko_suwarsonoPas encore d'évaluation
- Kathrein 739624Document2 pagesKathrein 739624anna.bPas encore d'évaluation
- MSD6886 US Service Manual V1.0 2019-7-11-6Document105 pagesMSD6886 US Service Manual V1.0 2019-7-11-6Tena y EstebanPas encore d'évaluation
- Cemento Conductor PDFDocument8 pagesCemento Conductor PDFLiz GutierrezPas encore d'évaluation
- Catalogo Tecnico 2018Document26 pagesCatalogo Tecnico 2018rene david villacis orqueraPas encore d'évaluation
- NM B661 EG431 EG532 - MB - V10 - 20180302 Lenovo IdeaPad 330-14IGMDocument60 pagesNM B661 EG431 EG532 - MB - V10 - 20180302 Lenovo IdeaPad 330-14IGMСемен СолдатовPas encore d'évaluation
- PhilipsDocument29 pagesPhilipsodilonsouzaPas encore d'évaluation
- 2.aruba JL682ADocument4 pages2.aruba JL682Anambi.kumresan1Pas encore d'évaluation
- NJW0281 NJW0302 Audio 250V 15A 150WDocument6 pagesNJW0281 NJW0302 Audio 250V 15A 150WRaduPas encore d'évaluation
- KORG N264 N364 Service ManualDocument14 pagesKORG N264 N364 Service Manualjfinnegan87Pas encore d'évaluation
- PVR7K User Manual (Release 2.7) PDFDocument226 pagesPVR7K User Manual (Release 2.7) PDFAgus KsPas encore d'évaluation
- Agwgimometria 2Document10 pagesAgwgimometria 2SupolPas encore d'évaluation
- Ds Esprimo Mobile v6535Document4 pagesDs Esprimo Mobile v6535kasem_bePas encore d'évaluation
- JBL Quantum Duo QSG MultilingualDocument20 pagesJBL Quantum Duo QSG MultilingualzoooooorePas encore d'évaluation
- TechDaten Man 7SS85 V0400 enDocument32 pagesTechDaten Man 7SS85 V0400 enLuis Miguel DíazPas encore d'évaluation
- C12-Electromagnetic WavesDocument74 pagesC12-Electromagnetic WavesGerald S. FernandezPas encore d'évaluation
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPND'EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNÉvaluation : 5 sur 5 étoiles5/5 (1)
- The Compete Ccna 200-301 Study Guide: Network Engineering EditionD'EverandThe Compete Ccna 200-301 Study Guide: Network Engineering EditionÉvaluation : 5 sur 5 étoiles5/5 (4)
- Microsoft Certified Azure Fundamentals Study Guide: Exam AZ-900D'EverandMicrosoft Certified Azure Fundamentals Study Guide: Exam AZ-900Pas encore d'évaluation
- Concise Guide to OTN optical transport networksD'EverandConcise Guide to OTN optical transport networksÉvaluation : 4 sur 5 étoiles4/5 (2)
- Alcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsD'EverandAlcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsPas encore d'évaluation
- Cybersecurity: A Simple Beginner’s Guide to Cybersecurity, Computer Networks and Protecting Oneself from Hacking in the Form of Phishing, Malware, Ransomware, and Social EngineeringD'EverandCybersecurity: A Simple Beginner’s Guide to Cybersecurity, Computer Networks and Protecting Oneself from Hacking in the Form of Phishing, Malware, Ransomware, and Social EngineeringÉvaluation : 5 sur 5 étoiles5/5 (40)
- AWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamD'EverandAWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamPas encore d'évaluation
- PHP BLUEPRINT: An Essential Beginners Guide to Learn the Realms of PHP From A-ZD'EverandPHP BLUEPRINT: An Essential Beginners Guide to Learn the Realms of PHP From A-ZPas encore d'évaluation
- Unlock Any Roku Device: Watch Shows, TV, & Download AppsD'EverandUnlock Any Roku Device: Watch Shows, TV, & Download AppsPas encore d'évaluation
- Hacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.D'EverandHacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.Évaluation : 5 sur 5 étoiles5/5 (2)
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsD'EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsÉvaluation : 5 sur 5 étoiles5/5 (1)
- Networking Fundamentals: Develop the networking skills required to pass the Microsoft MTA Networking Fundamentals Exam 98-366D'EverandNetworking Fundamentals: Develop the networking skills required to pass the Microsoft MTA Networking Fundamentals Exam 98-366Pas encore d'évaluation
- Azure Networking: Command Line Mastery From Beginner To ArchitectD'EverandAzure Networking: Command Line Mastery From Beginner To ArchitectPas encore d'évaluation
- Hacking: A Beginners Guide To Your First Computer Hack; Learn To Crack A Wireless Network, Basic Security Penetration Made Easy and Step By Step Kali LinuxD'EverandHacking: A Beginners Guide To Your First Computer Hack; Learn To Crack A Wireless Network, Basic Security Penetration Made Easy and Step By Step Kali LinuxÉvaluation : 4.5 sur 5 étoiles4.5/5 (67)
- Software-Defined Networks: A Systems ApproachD'EverandSoftware-Defined Networks: A Systems ApproachÉvaluation : 5 sur 5 étoiles5/5 (1)
- Microsoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsD'EverandMicrosoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsPas encore d'évaluation
- Computer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityD'EverandComputer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityÉvaluation : 4.5 sur 5 étoiles4.5/5 (13)
- Designing and Building Security Operations CenterD'EverandDesigning and Building Security Operations CenterÉvaluation : 3 sur 5 étoiles3/5 (3)
- AWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamD'EverandAWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamÉvaluation : 5 sur 5 étoiles5/5 (1)