Académique Documents
Professionnel Documents
Culture Documents
Mcafee Email Gateway Best Practices
Transféré par
testCopyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Mcafee Email Gateway Best Practices
Transféré par
testDroits d'auteur :
Formats disponibles
Best Practices
Revision A
McAfee Email Gateway 7.x Appliances
COPYRIGHT
Copyright 2012 McAfee, Inc. Do not copy without permission.
TRADEMARK ATTRIBUTIONS
McAfee, the McAfee logo, McAfee Active Protection, McAfee AppPrism, McAfee Artemis, McAfee CleanBoot, McAfee DeepSAFE, ePolicy Orchestrator,
McAfee ePO, McAfee EMM, McAfee Enterprise Mobility Management, Foundscore, Foundstone, McAfee NetPrism, McAfee Policy Enforcer, Policy Lab,
McAfee QuickClean, Safe Eyes, McAfee SECURE, SecureOS, McAfee Shredder, SiteAdvisor, SmartFilter, McAfee Stinger, McAfee Total Protection,
TrustedSource, VirusScan, WaveSecure, WormTraq are trademarks or registered trademarks of McAfee, Inc. or its subsidiaries in the United States and
other countries. Other names and brands may be claimed as the property of others.
LICENSE INFORMATION
License Agreement
NOTICE TO ALL USERS: CAREFULLY READ THE APPROPRIATE LEGAL AGREEMENT CORRESPONDING TO THE LICENSE YOU PURCHASED, WHICH SETS
FORTH THE GENERAL TERMS AND CONDITIONS FOR THE USE OF THE LICENSED SOFTWARE. IF YOU DO NOT KNOW WHICH TYPE OF LICENSE YOU
HAVE ACQUIRED, PLEASE CONSULT THE SALES AND OTHER RELATED LICENSE GRANT OR PURCHASE ORDER DOCUMENTS THAT ACCOMPANY YOUR
SOFTWARE PACKAGING OR THAT YOU HAVE RECEIVED SEPARATELY AS PART OF THE PURCHASE (AS A BOOKLET, A FILE ON THE PRODUCT CD, OR A
FILE AVAILABLE ON THE WEBSITE FROM WHICH YOU DOWNLOADED THE SOFTWARE PACKAGE). IF YOU DO NOT AGREE TO ALL OF THE TERMS SET
FORTH IN THE AGREEMENT, DO NOT INSTALL THE SOFTWARE. IF APPLICABLE, YOU MAY RETURN THE PRODUCT TO MCAFEE OR THE PLACE OF
PURCHASE FOR A FULL REFUND.
2 McAfee Email Gateway 7.x Appliances Best Practices
Contents
Preface 5
About this guide . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5
Audience . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5
Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5
What's in this guide . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6
Find product documentation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6
1 Introduction 7
How to use this guide . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7
Using the McAfee Email Gateway 7.x troubleshooting tree . . . . . . . . . . . . . . . . . . 7
2 Installation and initial configuration considerations 9
Pre-installation considerations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Considerations for operating modes . . . . . . . . . . . . . . . . . . . . . . . 9
Considerations for cluster installations . . . . . . . . . . . . . . . . . . . . . . 15
Considerations for blade server installations . . . . . . . . . . . . . . . . . . . . 16
Considerations for virtual appliances . . . . . . . . . . . . . . . . . . . . . . . 16
Migrating from other products or versions . . . . . . . . . . . . . . . . . . . . 17
Initial installation and setup considerations . . . . . . . . . . . . . . . . . . . . . . . 18
Initial configuration considerations . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
3 Securing the appliance 21
Physically secure the hardware . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Setting up users and user roles . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Defining password policy . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
Restricting remote access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
Securing the Mail Transfer Agent (MTA) . . . . . . . . . . . . . . . . . . . . . . . . 23
4 Policy best practices 25
About policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25
Policy order . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26
Scanning order . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26
Email Configuration options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 27
Configuring policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 27
Designing inbound and outbound policies . . . . . . . . . . . . . . . . . . . . . 28
Create user groups for inbound and outbound policies . . . . . . . . . . . . . . . 29
Setting Protocol presets for inbound email messages . . . . . . . . . . . . . . . . 30
Configuring LDAP for use with inbound mail . . . . . . . . . . . . . . . . . . . . 30
Anti-virus considerations . . . . . . . . . . . . . . . . . . . . . . . . . . . 31
Anti-spam considerations . . . . . . . . . . . . . . . . . . . . . . . . . . . 31
Data Loss Prevention considerations . . . . . . . . . . . . . . . . . . . . . . . 31
Compliance dictionary considerations . . . . . . . . . . . . . . . . . . . . . . . 32
5 Encryption best practices 33
Server-to-server encryption . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
McAfee Email Gateway 7.x Appliances Best Practices 3
Contents
6 System logging best practices 35
System logging best practices . . . . . . . . . . . . . . . . . . . . . . . . . . . . 35
7 Using McAfee Email Gateway with other McAfee products 37
Using McAfee Email Gateway with McAfee ePolicy Orchestrator . . . . . . . . . . . . . . . 37
Using McAfee Email Gateway with McAfee Quarantine Manager . . . . . . . . . . . . . . . 37
Index 39
4 McAfee Email Gateway 7.x Appliances Best Practices
Preface
This guide provides you with information about best practices for setting up and configuring your
McAfee Email Gateway appliance.
Contents
About this guide
Find product documentation
About this guide
This information describes the guide's target audience, the typographical conventions and icons used
in this guide, and how the guide is organized.
Audience
McAfee documentation is carefully researched and written for the target audience.
The information in this guide is intended primarily for:
Administrators People who implement and enforce the company's security program.
Security officers People who determine sensitive and confidential data, and define the
corporate policy that protects the company's intellectual property.
Conventions
This guide uses the following typographical conventions and icons.
Book title or Emphasis Title of a book, chapter, or topic; introduction of a new term; emphasis.
Bold Text that is strongly emphasized.
User input or Path Commands and other text that the user types; the path of a folder or
program.
Code A code sample.
User interface Words in the user interface including options, menus, buttons, and dialog
boxes.
Hypertext blue A live link to a topic or to a website.
Note: Additional information, like an alternate method of accessing an
option.
Tip: Suggestions and recommendations.
McAfee Email Gateway 7.x Appliances Best Practices 5
Preface
Find product documentation
Important/Caution: Valuable advice to protect your computer system,
software installation, network, business, or data.
Warning: Critical advice to prevent bodily harm when using a hardware
product.
What's in this guide
This guide is organized to help you find the information you need.
This guide contains the following sections:
Introduction
Installation and initial configuration considerations
Securing the appliance
Policy considerations
Encryption best practices
Reporting and system logging best practices
Using McAfee Email Gateway with other McAfee products
Find product documentation
McAfee provides the information you need during each phase of product implementation, from
installation to daily use and troubleshooting. After a product is released, information about the product
is entered into the McAfee online KnowledgeBase.
Task
1 Go to the McAfee Technical Support ServicePortal at http://mysupport.mcafee.com.
2 Under Self Service, access the type of information you need:
To access... Do this...
User documentation 1 Click Product Documentation.
2 Select a product, then select a version.
3 Select a product document.
KnowledgeBase Click Search the KnowledgeBase for answers to your product questions.
Click Browse the KnowledgeBase for articles listed by product and version.
6 McAfee Email Gateway 7.x Appliances Best Practices
1 Introduction
This guide contains a collection of information, tips and techniques that can be considered "best
practice" in relation to McAfee Email Gateway.
The information is targeted at McAfee Email Gateway 7.0 and later. Some of the information contained
within this guide does not apply to McAfee Email Gateway 6.7, and should not be applied to these
systems.
Contents
How to use this guide
Using the McAfee Email Gateway 7.x troubleshooting tree
How to use this guide
This guide is divided into chapters and topics around specific stages of installation and configuration,
or around individual features or functions within McAfee Email Gateway.
These chapters and topics deal with specific recommendations, and so may not necessarily be
applicable in all cases. You should consider each suggestion in relation to your own requirements,
networks, systems and configurations before implementing any changes to your McAfee Email
Gateway.
Using the McAfee Email Gateway 7.x troubleshooting tree
McAfee support has published a troubleshooting tree to assist you in resolving issues that you might
experience with your McAfee Email Gateway.
Download the McAfee Email Gateway 7.x troubleshooting tree from KnowledgeBase article PD23748.
McAfee Email Gateway 7.x Appliances Best Practices 7
1
Introduction
Using the McAfee Email Gateway 7.x troubleshooting tree
8 McAfee Email Gateway 7.x Appliances Best Practices
2 Installation and initial configuration
considerations
Find best practice information relating to processes, configuration and tasks that you are likely to need
during the installation and initial configuration stages of setting up your McAfee Email Gateway
appliances.
Contents
Pre-installation considerations
Initial installation and setup considerations
Initial configuration considerations
Pre-installation considerations
Give consideration to the following areas before you start installing McAfee Email Gateway.
Although some decisions that you make during the installation of your McAfee Email Gateway can be
easily changed or adapted postinstallation, others may require significant or fundamental changes. It
is best to understand the impact of some these significant changes before installing your McAfee Email
Gateway.
Before installing your McAfee Email Gateway, it is important to plan the installation and deployment.
Consider the following:
General guidelines to prepare your site.
Overviews of general site requirements to prepare your computer room for the McAfee Email
Gateway. This should include how you intend controlling the physical security of the McAfee Email
Gateway, including access to the hardware on which the McAfee Email Gateway is running.
Environmental requirements.
Information on environmental site requirements, including temperature, airflow, and space
requirements
Power requirements and considerations.
Power requirements and electrical factors that must be considered before installation
Operating modes.
How the McAfee Email Gateway connects into your network.
Considerations for operating modes
McAfee Email Gateway can be configured to work in one of several operating, or network modes.
Before you install and configure your McAfee Email Gateway, you must decide which network mode to
use. The mode you choose determines how you physically connect your appliance to your network.
McAfee Email Gateway 7.x Appliances Best Practices 9
2
Installation and initial configuration considerations
Pre-installation considerations
You can choose from the following network modes:
Transparent bridge mode The device acts as an Ethernet bridge.
Transparent router mode The device acts as a router.
Explicit proxy mode The device acts as a proxy server and a mail relay.
Architectural considerations about network modes
The main considerations regarding the network modes are:
Whether communicating devices are aware of the existence of the device. That is, if the device is
operating in one of the transparent modes.
How the device physically connects to your network.
The configuration needed to incorporate the device into your network.
Where the configuration takes place in the network.
Considerations before changing network modes
In explicit proxy and transparent router modes, you can set up the device to sit on more than one
network by setting up multiple IP addresses for the LAN1 and LAN2 ports.
If you change to transparent bridge mode from explicit proxy or transparent router mode, only the
enabled IP addresses for each port are carried over.
After you select a network mode, McAfee recommends not changing it unless you move the device or
restructure your network.
Transparent bridge mode
Use this information to better understand Transparent bridge mode on your McAfee Email Gateway.
In transparent bridge mode, the communicating servers are unaware of the device the devices
operation is transparent to the servers.
Figure 2-1 Transparent bridge mode apparent data path
In the figure, the external mail server (A) sends email messages to the internal mail server (C). The
external mail server is unaware that the email message is intercepted and scanned by the device (B).
The external mail server seems to communicate directly with the internal mail server the path is
shown as a dotted line. In reality, traffic might pass through several network devices and be
intercepted and scanned by the device before reaching the internal mail server.
What the device does in transparent bridge mode
In transparent bridge mode, the device connects to your network using the LAN1 and LAN2 ports. The
device scans the traffic it receives, and acts as a bridge connecting two network segments, but treats
them as a single logical network.
10 McAfee Email Gateway 7.x Appliances Best Practices
2
Installation and initial configuration considerations
Pre-installation considerations
Configuration in transparent bridge mode
Transparent bridge mode requires less configuration than transparent router and explicit proxy modes.
You do not need to reconfigure all your clients, default gateway, MX records, Firewall NAT or mail
servers to send traffic to the device. Because the device is not a router in this mode, you do not need
to update a routing table.
Where to place the device when using transparent bridge mode
For security reasons, you must use the device inside your organization, behind a firewall.
Figure 2-2 Positioning in Transparent bridge mode
In transparent bridge mode, position the device between the firewall and your router, as shown.
In this mode, you physically connect two network segments to the device, and the device treats them
as one logical network. Because the devices firewall, device, and router are on the same logical
network, they must all have compatible IP addresses on the same subnet.
Devices on one side of the bridge (such as a router) that communicate with devices on the other side
of the bridge (such as a firewall) are unaware of the bridge. They are unaware that traffic is
intercepted and scanned, therefore the device is said to operate as a transparent bridge.
Figure 2-3 Network structure Transparent bridge mode
McAfee Email Gateway 7.x Appliances Best Practices 11
2
Installation and initial configuration considerations
Pre-installation considerations
Transparent router mode
Use this information to better understand Transparent router mode on your McAfee Email Gateway.
In transparent router mode, the device scans email traffic between two networks. The device has one
IP address for outgoing scanned traffic, and must have one IP address for incoming traffic.
The communicating network servers are unaware of the intervention of the device the devices
operation is transparent to the devices.
What the device does in transparent router mode
In transparent router mode, the device connects to your networks using the LAN1 and LAN2 ports.
The device scans the traffic it receives on one network, and forwards it to the next network device on
a different network. The device acts as a router, routing the traffic between networks, based on the
information held in its routing tables.
Configuration in transparent router mode
Using transparent router mode, you do not need to explicitly reconfigure your network devices to send
traffic to the device. You need only configure the routing table for the device, and modify some routing
information for the network devices on either side of it (the devices connected to its LAN1 and LAN2
ports). For example, you might need to make the device your default gateway.
In transparent router mode, the device must join two networks. The device must be positioned inside
your organization, behind a firewall.
Transparent router mode does not support Multicast IP traffic or nonIP protocols, such as NETBEUI and
IPX.
Firewall rules
In transparent router mode, the firewall connects to the physical IP address for the LAN1/LAN2
connection to the management blade.
12 McAfee Email Gateway 7.x Appliances Best Practices
2
Installation and initial configuration considerations
Pre-installation considerations
Where to place the device
Use the device in transparent router mode to replace an existing router on your network.
If you use transparent router mode and you do not replace an existing router, you must reconfigure part
of your network to route traffic correctly through the device.
Figure 2-4 Network structure Transparent bridge mode
You need to:
Configure your client devices to point to the default gateway.
Configure the device to use the Internet gateway as its default gateway.
Ensure your client devices can deliver email messages to the mail servers within your organization.
Explicit proxy mode
Use this information to better understand explicit proxy mode on your McAfee Email Gateway.
In explicit proxy mode, some network devices must be set up explicitly to send traffic to the device.
The device then works as a proxy or relay, processing traffic on behalf of the devices.
Figure 2-5 Explicit proxy mode apparent data path
Explicit proxy mode is best suited to networks where client devices connect to the device through a
single upstream and downstream device.
This might not be the best option if several network devices must be reconfigured to send traffic to the
device.
McAfee Email Gateway 7.x Appliances Best Practices 13
2
Installation and initial configuration considerations
Pre-installation considerations
Network and device configuration
If the device is set to explicit proxy mode, you must explicitly configure your internal mail server to
relay email traffic to the device. The device scans the email traffic before forwarding it, on behalf of
the sender, to the external mail server. The external mail server then forwards the email message to
the recipient.
In a similar way, the network must be configured so that incoming email messages from the Internet
are delivered to the device, not the internal mail server.
The device scans the traffic before forwarding it, on behalf of the sender, to the internal mail server for
delivery, as shown.
For example, an external mail server can communicate directly with the device, although traffic might
pass through several network servers before reaching the device. The perceived path is from the
external mail server to the device.
Protocols
To scan a supported protocol, SMTP, POP3 or McAfee Secure Web Mail, you must configure your other
network servers or client computers to route that protocol through the device, so that no traffic
bypasses the device.
Firewall rules
Explicit proxy mode invalidates any firewall rules set up for client access to the Internet. The firewall
sees only the physical IP address information for the device, not the IP addresses of the clients, so the
firewall cannot apply its Internet access rules to the clients.
Ensure that your firewall rules are updated. The firewall must accept traffic from McAfee Email
Gateway, but must not accept traffic that comes directly from the client devices.
Set up firewall rules to prevent unwanted traffic entering your organization.
Where to place the device
Configure the network devices so that traffic needing to be scanned is sent to the McAfee Email
Gateway. This is more important than the location of the McAfee Email Gateway.
The router must allow all users to connect to the McAfee Email Gateway.
Figure 2-6 Positioning in Explicit proxy mode
The McAfee Email Gateway must be positioned inside your organization, behind a firewall, as shown
in Figure 6: Explicit proxy configuration.
14 McAfee Email Gateway 7.x Appliances Best Practices
2
Installation and initial configuration considerations
Pre-installation considerations
Typically, the firewall is configured to block traffic that does not come directly from the device. If you
are unsure about your networks topology and how to integrate the device, consult your network
expert.
Use this configuration if:
The device is operating in explicit proxy mode.
You are using email (SMTP).
For this configuration, you must:
Configure the external Domain Name System (DNS) servers or Network Address Translation (NAT)
on the firewall so that the external mail server delivers mail to the device, not to the internal mail
server.
Configure the internal mail servers to send email messages to the device. That is, the internal mail
servers must use the device as a smart host. Ensure that your client devices can deliver email
messages to the mail servers within your organization.
Ensure that your firewall rules are updated. The firewall must accept traffic from the device, but
must not accept traffic that comes directly from the client devices. Set up rules to prevent
unwanted traffic entering your organization.
Considerations for cluster installations
Setting up and configuring clusters of McAfee Email Gateway appliances requires some special
considerations.
What is a cluster?
McAfee Email Gateway can be configured so that several appliances can function as a single scanning
system. This can be used to increase capacity, and can also provide improved redundancy in the event
of hardware failure.
Configuring a group of appliances as a cluster
When configuring a group of appliances as a cluster, you need an IP address for each appliance, as
well as a "virtual" address that is used to communicate with the currently active master appliance.
Once operational, you should use the virtual IP address to communicate with the cluster.
Configure all appliances within the cluster to use the same Cluster Identifier. If you are setting up multiple
clusters on the same subnet, use the Cluster Identifier to specify the appliances within each cluster.
Patch and hotfix versions for cluster installations
All McAfee Email Gateway appliances within a cluster must be maintained with the same software,
patch and hotfix versions.
Apply updates to the failover master appliance, then the master appliance, and then to each scanning
appliance in turn.
Configuring master and failover master appliances to scan email traffic
If you have more than three McAfee Email Gateway appliances configured within a cluster of
appliances, McAfee recommends that you disable scanning on the master appliances.
McAfee Email Gateway 7.x Appliances Best Practices 15
2
Installation and initial configuration considerations
Pre-installation considerations
Considerations for blade server installations
Setting up and configuring McAfee Content Security Blade Server requires some special
considerations.
The McAfee Email Gateway software can be installed onto a blade server system, to provide increased
scanning capacity and redundancy or High Availability (HA) capabilities.
When configuring a blade server, you will need an IP address for the master and the failover master
blades, as well as a "virtual" address that is used by the currently active master blade. Once
operational, you should use the virtual IP address to communicate with the blade server.
Blade Server DHCP
The scanning blades must all receive their IP addresses from the DHCP server within the blade server.
Lock down the DHCP server within the blade chassis so that it only issues IP addresses to scanning
blades with specified MAC addresses.
To prevent any DHCP servers on your network from issuing IP addresses for the scanning blades,
within the blade server, configure an Access Control List (ACL255) that drops all DHCP packets leaving
the blade server.
To prevent the onboard DHCP server from issuing IP addresses to devices outside of the blade server,
configure a second ACL (ACL256) to drop all DHCP packets entering the blade server.
Set up the Access Control Lists by logging into the web interface for the blade server interconnect
modules.
Placement of blades within the blade server enclosure
When installing blades into the blade server enclosure, the master management blade must be
installed in slot 1, and the failover management blade must be installed in slot 2.
When installing the scanning blades into the blade server enclosure, they should be placed in order,
using first slot 3, then slot 4 and slot 5 until all your scanning blades are installed.
Considerations for virtual appliances
Setting up and configuring virtual instances of McAfee Email Gateway requires some special
considerations.
When considering the installation of virtual versions of McAfee Email Gateway, be aware of the
following:
McAfee Email Gateway Virtual Appliance works in the following virtual environments:
VMware vSphere 4.x
VMware vSphere Hypervisor (ESXi) 4.x
VMware vSphere Hypervisor 5.x
Ensure that your hardware meets the minimum specifications for running your virtual environment.
See the VMware Knowledge Base article 1003661 available from http://www.vmware.com to get
the minimum system requirements for VMware vSphere or VMware vSphere Hypervisor 4.x. You
need a computer that has a 64bit x86 CPU.
16 McAfee Email Gateway 7.x Appliances Best Practices
2
Installation and initial configuration considerations
Pre-installation considerations
Ensure that the virtual machine for each McAfee Email Gateway Virtual Appliance meets the
following minimum specification.
Item Specification
Processor Two virtual processors
Available virtual memory 2 GB
Free hard disk space 80 GB
Ensure you have sufficient physical network interfaces for your chosen operating mode. These
connections should be dedicated for use by the McAfee Email Gateway Virtual Appliance.
Migrating from other products or versions
You can migrate settings from McAfee Email and Web Security appliances version 5.6 and from McAfee
Email Gateway version 6.7.x.
Migration paths are available, allowing you to migrate from either McAfee Email and Web Security
appliances version 5.6 or from McAfee Email Gateway version 6.7.x software, to McAfee Email
Gateway version 7.x.
Migrating from McAfee Email and Web Security appliances version 5.6
There are several supported methods that you can choose from to manage the process in the way that
is best suited to your organization:
From a McAfee Email Gateway 7.0 installation CD, perform a new installation and restore a
configuration file from a previous version.
From a McAfee Email Gateway 7.0 installation CD, perform an upgrade from a previous version
retaining configuration and log files.
To perform the upgrade from another location, obtain the McAfee Email Gateway 7.0 ISO image
and upload it on to an McAfee Email and Web Security Appliance 5.6 using the Rescue Image feature
(System | System Administration | Rescue Image.)
Ensure you have the latest McAfee Email and Web Security Appliance 5.6 patch installed before
migrating to McAfee Email Gateway 7.0.
Migrating from McAfee Email Gateway 6.7.x
Refer to McAfee Email Gateway 6.7.2 to 7.0.0 Migration Guide for detailed information about
migrating from McAfee Email Gateway version 6.7.x.
Differences between products
View a brief summary of the differences between the products.
Some of the major differences between McAfee Email and Web Security appliances, McAfee Email
Gateway version 6.7.x and McAfee Email Gateway version 7.x are summarized in the following table:
McAfee Email and Web McAfee Email Gateway McAfee Email Gateway
Security appliances version version 6.7.x version 7.x
5.6
Email and web scanning Dedicated email scanning Dedicated email scanning
capabilities
No secure web mail Secure Web Mail available Secure Web Mail available
Basic McAfee ePO support Basic McAfee ePO support Enhanced McAfee ePO support
Blade server support No blade server support Blade server support
McAfee Email Gateway 7.x Appliances Best Practices 17
2
Installation and initial configuration considerations
Initial installation and setup considerations
McAfee Email and Web McAfee Email Gateway McAfee Email Gateway
Security appliances version version 6.7.x version 7.x
5.6
No servertosever S/MIME and Servertosever S/MIME and Servertosever S/MIME and PGP
PGP encryption PGP encryption encryption
No 2nd AV engine 2nd AV engine is a purchasable No 2nd AV engine available in
option McAfee Email Gateway 7.0
Initial installation and setup considerations
Consider the physical installation requirements relating to McAfee Email Gateway.
Depending on the choices made at the time McAfee Email Gateway was ordered, you might need to
install physical hardware appliances, a blade server, or simply install a virtual McAfee Email Gateway
appliance within your existing virtualized server environment.
If you are installing physical hardware, observe all safety warnings and local and company procedures
regarding the lifting of heavy equipment.
Ensure that you secure access to any physical hardware that is used to host the McAfee Email
Gateway software.
Update the software
McAfee Email Gateway hardware has the software preinstalled on the machine. However, the software
may not be up to date. McAfee recommends that you download the latest version of the McAfee Email
Gateway software and install this on the appliance before you start configuring your system and
policies.
Setup wizard
The initial setup is either carried out by logging into the user interface, or by running through the
console from the monitor and keyboard attached to the appliance. Both methods provide you with the
same options and choices.
Select the most relevant setup path. The available options are:
Standard Setup configures your McAfee Email Gateway in Transparent Bridge mode, selecting the
mostused options for you.
Custom Setup provides you with additional options, such as selecting the required operating mode.
Restore from a File you can export a configuration file from an existing McAfee Email Gateway
appliance and use it as the basis for a new installation.
ePO Managed Setup configure your McAfee Email Gateway appliance to be managed by McAfee
ePolicy Orchestrator (McAfee ePO).
Encryption Only Setup configure a McAfee Email Gateway appliance to act as an encryption server for
other McAfee Email Gateway appliances.
On the Password page of the setup wizard, make sure that you change the password from its default
value.
18 McAfee Email Gateway 7.x Appliances Best Practices
2
Installation and initial configuration considerations
Initial configuration considerations
Initial configuration considerations
After you have installed your appliance and completed the initial setup steps, either from the console
or within the setup wizard, ensure that you give consideration to the following initial configuration
settings.
Reverse lookup of the sender IP address
By default, McAfee Email Gateway has the option to carry out the reverse lookup of the sender IP
addresses disabled.
Although enabling the reverse lookup of sender IP addresses can assist in confirming the identity of
the message, carrying out this lookup introduces delays as McAfee Email Gateway queries the Domain
Name Service (DNS) server to establish the sender IP address. If you encounter performance issues
with your McAfee Email Gateway, ensure that reverse lookup of the sender IP address is disabled.
The reverse lookup settings are found at: Email | Email Configuration | Receiving Email | Permit and Deny Lists.
Do not allow null senders, as valid senders usually have a genuine MAIL FROM:
address
To block messages that do not contain any sender information, go to Email | Email Configuration |
Protocol Configuration | Protocol Settings (SMTP). Deselect Allow null senders.
Be aware that bounced messages might be rejected because they potentially have a null sender
address.
Do not scan messages that come from blacklisted IP addresses
Enabling realtime blackhole list (RBL) checks prevents email messages that originate from blacklisted
IP addresses from being scanned. McAfee recommends that you Reject, close and deny (Block) any
messages that fail the RBL checks.
The RBL settings are found at: Email | Email Policies | Spam | Sender Authentication | RBL Configuration.
Third party realtime blackhole lists
You can configure your McAfee Email Gateway to use realtime blackhole lists provided by third
parties. However, be careful of using multiple RBL lists, as it will slow the performance as each email
address is checked against all of your configured RBL lists in turn.
The RBL settings are found at: Email | Email Policies | Spam | Sender Authentication | RBL Configuration.
Configuring Permit and Deny Lists
If you configure long lists of permitted and blocked connections and senders, the time that the McAfee
Email Gateway takes to resolve all the listed domain names and also carry out RBL checks on the
client IP addresses will increase. If this time causes to great a delay, disable Resolve permitted / blocked
hostnames to IP addresses from within Permitted and blocked senders.
Permit and Deny lists are found at: Email | Email Configuration | Receiving Email | Permit and Deny Lists
McAfee Email Gateway 7.x Appliances Best Practices 19
2
Installation and initial configuration considerations
Initial configuration considerations
20 McAfee Email Gateway 7.x Appliances Best Practices
3 Securing the appliance
As the role of your McAfee Email Gateway is to secure your email traffic, it makes sense that you
must first secure the McAfee Email Gateway to protect it.
Contents
Physically secure the hardware
Setting up users and user roles
Defining password policy
Restricting remote access
Securing the Mail Transfer Agent (MTA)
Physically secure the hardware
Before turning your attention to securing access to the user interface for McAfee Email Gateway,
ensure that you have secured access to the hardware.
You should lockdown access to the hardware that is used to run McAfee Email Gateway. This applies
whether you are using a physical hardware appliance, a blade server, or if you are using a virtualized
environment to run a McAfee Email Gateway Virtual Appliance.
This can be achieved by locating the hardware in accesscontrolled server rooms, or by locating it in
cabinets that have doors on both the front and rear of the units that are kept locked.
Setting up users and user roles
Configure user and role access to the McAfee Email Gateway user interface.
To secure access to the McAfee Email Gateway user interface, the software provides rolebased access
control. This is achieved by defining required user roles, and then applying these user roles to
individual users.
Users and User Roles are managed from System | Users | Users and Roles.
McAfee Email Gateway 7.x Appliances Best Practices 21
3
Securing the appliance
Defining password policy
User roles
McAfee Email Gateway includes the following administrator roles by default:
Super Administrator The Super Administrator role has access to all areas and settings within the
McAfee Email Gateway user interface.
Email Administrator The Email Administrator can access areas of the McAfee Email Gateway user
interface concerned with emailbased settings and email queues. By default, Email Administrators
can see the Dashboard, Reports, Email and Troubleshoot tabs within the user interface.
Reports Administrator The Reports Administrator role only has access to areas of the user interface
that allow the definition and running of reports. By default, the Reports Administrator can only see
the Dashboard and Reports tabs within the user interface.
You can create additional administrator roles, and can define the access rights for each new role.
Users
McAfee Email Gateway includes an admin user account. This default user account has full Super
Administrator rights.
McAfee recommends that you create additional Users, with access restricted to specific areas of
functionality within McAfee Email Gateway. At a minimum, create an Email Administrator user, and a
Reports Administrator user, using the default user roles.
You can create additional Users and User Roles as required within your organization.
Defining password policy
Configure the required level of password complexity and change control when accessing McAfee Email
Gateway.
Many organizations have standards for the required levels of password complexity and requirements
for changing passwords on a regular basis for critical infrastructure systems. McAfee Email Gateway
enables you to define the required levels of password complexity and how often passwords are
changed for the appliance.
These password complexity and change control settings are found at System | Users | Password
Management.
Configure these settings in line with your own corporate policies.
Restricting remote access
Lock down how administrators access the McAfee Email Gateway user interface.
In addition to creating Users and User Roles to restrict access to different areas of the McAfee Email
Gateway user interface, McAfee also recommends that you restrict how administrators remotely
access the appliance.
Settings relating to restricting remote access are found at System | Appliance Management | Remote
Access.
22 McAfee Email Gateway 7.x Appliances Best Practices
3
Securing the appliance
Securing the Mail Transfer Agent (MTA)
Using Secure Shell (SSH)
You can specify that administrators must use a Secure Shell client to access McAfee Email Gateway. In
addition, you can either allow SSH access from all hosts or networks, or to restrict access to specific
hosts or networks.
Using User interface access configuration restrictions
By default, access to McAfee Email Gateway is restricted to a management port, by default 10443,
from any host or network that can reach the appliance.
You can configure access so that only specific hosts or networks can be used to access McAfee Email
Gateway.
Using outofband (OOB) management
If your organization uses a separate management network to manage and control security devices,
you can configure outofband management. In this configuration, the management of McAfee Email
Gateway is carried out on a separate network to the ones used to carry email traffic to be scanned by
the appliance.
Before you enable outofband management, ensure that you have connected your McAfee Email
Gateway to the management network using either the dedicated outofband Network Interface on the
appliance (if applicable) or via a USBEthernet adaptor. Failure to connect the appliance to the defined
management network could result in you being unable to access the McAfee Email Gateway user
interface.
Securing the Mail Transfer Agent (MTA)
McAfee Email Gateway includes an inbuilt Mail Transfer Agent (MTA). Take steps to secure the MTA to
prevent the appliance being used to send out spam messages.
Configure antirelay
Configure the antirelay settings for your McAfee Email Gateway to prevent your appliance from being
used as an open relay by third parties to send spam messages.
Antirelay settings are found at Email | Email Configuration | Receiving Email | AntiRelay Settings.
Ensure that you define your local domains, as well as the domains from which you want to permit
email relaying, and that you want to deny email relaying. Defining a domain as a Permitted domain
ensures that email traffic from that domain is always allowed to be relayed.
Defining a domain as a Denied domain ensures that email traffic from that domain is not allowed to be
relayed, unless overridden by the Permitted connections list.
Defining a domain as a Local domain ensures that email traffic from that domain is always allowed to be
relayed, unless overridden by the Denied connections list.
McAfee Email Gateway 7.x Appliances Best Practices 23
3
Securing the appliance
Securing the Mail Transfer Agent (MTA)
24 McAfee Email Gateway 7.x Appliances Best Practices
4 Policy best practices
Find best practice information relating to configuring policies within McAfee Email Gateway.
Contents
About policies
Scanning order
Email Configuration options
Configuring policies
About policies
McAfee Email Gateway uses policies to enable you to define your scanning requirements.
Two classes of policy are used within McAfee Email Gateway:
Scanning policies
Protocol presets
Scanning policies use both connection attributes and conversation attributes, whereas protocol presets
only use connection attributes to match against.
About scanning polices
You can create multiple scanning policies, which are applied in a topdown order until a match is found
against either connection or conversation attributes of the email message being scanned.
When a match is found, the actions configured within the matching policy are applied. If no match is
found, the email message then passes to the next listed policy. If no other policies match, the actions
configured within the default policy are applied.
Like protocol presets, scanning policies are initially determined at connection. However, scanning
policies are then reevaluated at points during the SMTP conversation, including the MAIL FROM, RCPT
TO and DATA phases of the conversation.
When the McAfee Email Gateway receives and email message that is being sent to multiple recipients
within the organization, the appliance checks the policies that apply to each recipient. If different
policies apply to different recipients, the email message is split, so that the correct policies are applied
to the message for each recipient.
About protocol presets
Protocol presets enable you to create policies against the connection attributes for each email
message. These policies are useful for creating rules for particular offices or groups within your
organization. For example, they allow you to configure one policy for your marketing department, and
a different policy for your sales team.
McAfee Email Gateway 7.x Appliances Best Practices 25
4
Policy best practices
Scanning order
Using protocol presets, you can create individual settings for email coming to or from different
domains, IP addresses or other connection criteria. For example, you can configure address
masquerading and aliases, based on the domain or IP address.
Policy order
The order in which the scanning policies appear within the McAfee Email Gateway user interface
dictates the order that they are used to scan email messages.
McAfee Email Gateway uses a "topdown" approach when scanning email messages; policy attributes
are evaluated, starting at the topmost policy and working down the policy list until a complete match
is found. The settings for the matching policy are then applied.
You should order your policies so that the most specific policies are listed at the top of the page, and
then reduce down to the default policy, which is the least specific.
You cannot change the position of the default policy in the policy list.
Scanning order
To get the most from your McAfee Email Gateway, it helps to understand the order in which scanning
happens.
To get maximum performance from your McAfee Email Gateway, it's important to block as many
messages as possible before the scanning phase. Resourceintensive checks like antivirus scanning,
content scanning and antispam scanning all occur at later stages in the scanning process.
There are a number of options that you can set to reduce the number of messages that are passed for
scanning.
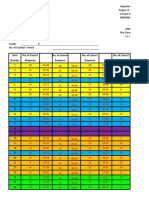
Figure 4-1 Order of phases and checks performed before scanning takes place
Using all these checks provides optimum protection and usage of the appliance's resources because
most of the bad content and messages are dropped or blocked before the scanning phase.
26 McAfee Email Gateway 7.x Appliances Best Practices
4
Policy best practices
Email Configuration options
Email Configuration options
McAfee Email Gateway provides many options for configuring email settings. These are grouped into
Protocol Configuration options, Receiving Email options and Sending Email options.
Protocol Configuration Timeouts
Usually, you do not need to change any of the values for the Timeouts settings.
However, if, for example, you find that you experience issues with email messages timing out when
being sent from a remote office, or from a home worker that has a slow internet connection, you can
create a protocol preset based on the IP address (or range of IP addresses) used by that office, and
can then increase the timeout values for messages coming from the specified connections.
Prevent connections to the firewall being blocked
In some network layouts, it is possible that the connection between McAfee Email Gateway and your
firewall can be blocked.
To prevent this issue, navigate to: Email | Email Configuration | Receiving Email | Permit and Deny Lists. Add
the IP address for your firewall to the Permitted connections list.
Define the NonDelivery Report (NDR) period
By default, the NDR period configured within McAfee Email Gateway is 108 hours (4.5 days.)
To change this NDR period, navigate to Email | Email Configuration | Sending Email | Queued email delivery.
Adjust Time before an NDR is issued to an appropriate interval to suit your requirements.
Configuring policies
When setting up the scanning policies for McAfee Email Gateway, give consideration to what you are
trying to achieve.
Where possible, keep your policies simple. Use the optional Description fields to document the reasons
and objectives for creating each policy; this helps when trying to diagnose problems with policies not
working as you expect.
McAfee Email Gateway enables you to create policies for Inbound and Outbound email messages. You can
create multiple policies of each type, and then order them so that the most specific policies appear at
the top of the list of policies, and the least specific (the Default policy) appears at the bottom of the
list.
See also
How McAfee Email Gateway processes mail traffic through your network on page 29
McAfee Email Gateway 7.x Appliances Best Practices 27
4
Policy best practices
Configuring policies
Designing inbound and outbound policies
Create policies to protect both your inbound and outgoing email messages.
Inbound policy connections
When designing policies to protect your inbound email messages, depending on your network and
McAfee Email Gateway configurations, you base them on the following connections:
Source IP address Incoming network connection
Destination IP address Outgoing network connection
Sender email address Source host name
Masqueraded sender email address Destination host name
Recipient email address Source network group
Recipient email address list Destination network group
Aliased recipient email address User group
Aliased recipient email address list LDAP Query
VLAN identifier Policy rules
Not all of these options make sense when creating generalpurpose policies, but may be useful when
dealing with, for example, specific types of unsolicited bulk email (spam) messages.
Outbound policy connections
When designing policies to protect your outgoing email messages, you typically have different
concerns than when designing inbound policies. You are less likely to be concerned about outgoing
spam messages, but may be worried about important company documents being sent outside of your
organization without the relevant approval. You can configure policies for Data Loss Prevention (DLP)
to stop this happening.
You have a similar list of connection types to those you use for your inbound connections.
28 McAfee Email Gateway 7.x Appliances Best Practices
4
Policy best practices
Configuring policies
How McAfee Email Gateway processes mail traffic through your network
This information describes how McAfee Email Gateway processes mail traffic through your internal and
external networks.
Mail traffic flow
Within McAfee Email Gateway, all email messages originating from outside of your organization are
considered Inbound, and all messages leaving your organization are considered to be Outbound.
Figure 4-2 Email flow into and out of your organization
Create user groups for inbound and outbound policies
You create users groups within McAfee Email Gateway that can be applied to your policies.
Creating user groups is a simple way of providing input information to your policies. By creating
different user groups, you can then create policies that can be tailored to the requirements of each
group.
For example, for outbound policies, you could decide to create user groups for specific teams or
functions within your organization. You may have a group for your marketing team, another group for
your sales team, and further groups for your Customer Support and Purchasing teams. Once you have
defined your user groups, you can then create policies for each.
McAfee Email Gateway 7.x Appliances Best Practices 29
4
Policy best practices
Configuring policies
User groups can be created from within the Email | Email Policies | Add Policy... dialog box, or from
Email | Group Management | Email Senders and Recipients.
You can define your user groups by Sender Email Address, Recipient Email Address or, if configured, by LDAP
Query. In addition to basing your user groups of these criteria, you can choose from several different
types of match logic. These include:
is
is not
is like
is not like
Using the "not" values allow you create exception rules; rules that apply to users not included in other
groups.
Setting Protocol presets for inbound email messages
Using protocol presets for your inbound email traffic allows you to tailor your recipient authentication
for specific inbound connection types.
Protocol presets are a special type of policy that is only concerned with information relating to the
connection settings of incoming email messages, not their content or other information.
Protocol presets can be configured from Email | Email Configuration | Receiving Email | Recipient
Authentication.
Depending on the configuration of your McAfee Email Gateway and your network, the following
connection types are available for you to use to define protocol presets:
Source IP address Source host name
Destination IP address Destination host name
VLAN Identifier Source network group
Incoming network connection Destination network group
Outgoing network connection Policy rules
Configuring LDAP for use with inbound mail
By querying a Lightweight Directory Access Protocol (LDAP) server, you can configure policies to
ensure that you only receive inbound email for genuine users within your organization.
Use the Directory Service wizard to set up a connection between the appliance and an LDAP server so that
the attributes in the LDAP server define behavior in your email flow. You can therefore define policies,
and update your LDAP to change email behavior. You can modify the following features in the
appliance to work with LDAP:
Recipient Authentication
Address Masquerading
Policy selection
Delivery routes
30 McAfee Email Gateway 7.x Appliances Best Practices
4
Policy best practices
Configuring policies
Custom queries can be created for use in policy selection using the Add Query option in the Add Directory
Service wizard.
Configure the LDAP servers to be queried by your McAfee Email Gateway from Email | Group
Management | Directory Services
Anti-virus considerations
For most applications, keeping the majority of the antivirus settings at their default values will give
the best security and performance balance.
McAfee carefully tune the antivirus settings on all their products to give the best balance between
security and performance. McAfee recommends that you do not change these settings unless advised
by your McAfee support representative.
Anti-spam considerations
Antispam settings can be tuned to better suit your specific requirements within your own email
environment.
Apply the following best practices when configuring your antispam settings.
Track spam email messages using spam score indicators
Add spam score indicator to all messages, and attach a spam report to all messages. They help track
messages and determine your action against spam messages.
Drop spam email messages
Drop items with a spam score of 10 or higher. Such items are almost certainly spam email messages.
Limit the spam scores when quarantining messages
If you want to quarantine items, limit the spam score to no more than 10. Spam scores over 10 are
almost certainly spam messages, and quarantining them increases the disk usage needed by the
quarantine database.
Do not change the default maximum message size parameters
Keep the default maximum message size for scanning. Increasing the maximum message size
increases the scanning resources used by McAfee Email Gateway, decreasing the overall system
performance.
Data Loss Prevention considerations
Follow the suggestions when configuring and using Data Loss Prevention (DLP).
Apply the following best practices when configuring your Data Loss Prevention settings.
Email | DLP and Compliance
Regularly back up your configuration
When using Data Loss Prevention within yourMcAfee Email Gateway, ensure that you regularly back
up your McAfee Email Gateway. Ensure that you include the DLP database in your backups.
McAfee Email Gateway 7.x Appliances Best Practices 31
4
Policy best practices
Configuring policies
Configure DLP for outbound policies
DLP is concerned with preventing important or confidential information from leaving your corporate
environment. Only configure the DLP settings within outbound policies.
Configure multiple policies
When using DLP, it is easier to create separate policies for each user group, than it is to design a
single policy that caters for the needs of several groups of users.
Tune the Document match percentage
You can specify the percentage of the original registered document which must be seen in order to
trigger DLP. For example, if the Document match percentage is set to 80% (the default setting), a
100page document will need to match at least 80 pages before it is detected as a match. Using the
same setting, a 10page document needs to match eight pages to be detected as a match.
If the Document match percentage is set too low, you increase the number of detections made, and
also increase the number of false positive detections.
Over a period of time, you should tune the Document match percentage so that you achieve an
acceptable balance between the number of genuine detections and the number of false positive
detections being made.
Tune the number of consecutive signatures needed to trigger a detection
By configuring the number of consecutive signatures within the Data Loss Prevention settings, you can
tune how McAfee Email Gateway detects small sections of original content, regardless of the size of
the documents.
The algorithms used in DLP involve text normalization, common word removal, and signature
generation. An approximate guide is that one signature represents eight words of text after common
words have been removed. These figures offer a guideline only.
By default, this is disabled.
Compliance dictionary considerations
McAfee Email Gateway includes a number of compliance dictionaries that assist you in enforcing
regulatory compliance.
Use compliance scanning to assist with conformance to regulatory compliance and corporate operating
compliance. You can choose from a library of predefined compliance dictionaries, or create your own
dictionaries and rules specific to your organization.
When searching the default set of compliance dictionaries, you can use the Language dropdown list to
sort the list into your preferred language.
This causes any compliance dictionaries that are languagespecific to be sorted into that language order.
It does not add or remove dictionaries that appear in different languages.
Before creating your own dictionaries and rules, check that suitable dictionaries do not already exist
within McAfee Email Gateway.
32 McAfee Email Gateway 7.x Appliances Best Practices
5 Encryption best practices
McAfee Email Gateway includes several forms of encryption. Configure the options most suited to
your corporate requirements.
McAfee Email Gateway can be configured to provide servertoserver encryption using Transport Layer
Security (TLS).
It can also be configured to encrypt the content of email messages using Secure Multipurpose Internet
Mail Extensions (S/MIME), PGP, and Secure Web Mail using either Push or Pull encryption.
Most forms of encryption require the exchanging of certificates to enable both parties to encrypt/
decrypt either the servertoserver communications, or the email messages themselves.
Encryptiononly McAfee Email Gateway
If you require all of your outgoing email traffic to be encrypted, consider setting up a McAfee Email
Gateway as an encryptiononly appliance.
In this configuration, you direct the output of all your emailscanning appliances to the encryptiononly
appliance. This has the benefit of removing the load of both encryption and scanning from a single
appliance.
Server-to-server encryption
Use TLS to secure your servertoserver communications.
McAfee Email Gateway uses SMTP over TLS to secure the communication layer between email
servers.
Transport Layer Security works by communicating a set of parameters known as the handshake
at the start of the connection process. Once these parameters have been defined, the communications
that follow within that session are secure, in that they cannot be decoded by servers that did not
partake in the handshake. The process includes steps to discuss the ciphers to be used during the
communications, and also authentication steps to prove the identity of the servers taking part in the
communications.
The handshake process includes the following main steps:
The McAfee Email Gateway requests a secure connection to the receiving email server and presents
a list of cipher suites to the receiving email server.
The receiving email server then selects the strongest supported cipher from that list, and then
notifies the McAfee Email Gateway of the chosen cipher.
The servers then use Public Key Infrastructure (PKI) to establish their authenticity. This is achieved
by the exchanging of digital certificates. On occasions, these digital certificates may be validated
against the Certificate Authority (CA) that issued the certificates.
McAfee Email Gateway 7.x Appliances Best Practices 33
5
Encryption best practices
Server-to-server encryption
Using the server's public key, McAfee Email Gateway generates a random number as a session key,
and sends it to the receiving email server. The receiving server then decrypts this session key using
its private key.
Both the McAfee Email Gateway and the receiving email server then use this encrypted session key
to set up communications, completing the handshake process.
Once the handshake has been completed, the secure connection is used to transfer the email
messages. The connection remains secure until the connection is closed.
Configuring TLS
Email | Encryption | TLS
When configuring communications between email servers that you know to use TLS, select Always from
the Use TLS dropdown list. This will typically be used between different email servers within your own
organization, or with customers, partners or suppliers that you have regular contact with.
To set up TLS, you must exchange TLS certificates and import them into McAfee Email Gateway.
34 McAfee Email Gateway 7.x Appliances Best Practices
6 System logging best practices
System logging enables you to monitor your McAfee Email Gateway, so that you can take any required
remedial actions to ensure that optimal performance is maintained.
System logging best practices
Understand the benefits and limitations of system logging on McAfee Email Gateway.
Logging system events is a useful way of ensuring that your McAfee Email Gateway is performing at
optimal levels. It is also useful when diagnosing and rectifying issues with your McAfee Email Gateway.
Use an offbox syslog server
McAfee Email Gateway can be configured to hold system logs of a limited size on its own hard disk
drives. Due to these size limits, the appliance only holds a relatively small amount of log information
before it starts overwriting the oldest data.
Configuring the McAfee Email Gateway to use an offbox system logging server enables you to hold
more detailed information covering longer time periods. Also, this information can be easily analyzed
by third party system monitoring software.
Configure offbox logging from: System | Logging, Alerting and SNMP | System Log Settings
What events to log
You should configure your logging so that you can monitor the basic functioning of your McAfee Email
Gateway. McAfee recommends you log high severity protocol and communication events under normal
circumstances.
Then, if you suspect that your McAfee Email Gateway is performing at less than its optimal level, you
should enable more detailed logging to assist you in identifying and correcting any issues that may
occur. Depending on your circumstances, you can increase the logging levels to either middle and high
severity protocol and communication events or all protocol and communication events.
Lowering the level of logging displays a notification warning you that increasing the number of events
being logged could have a negative impact on system performance.
Select the events to log at: System | Logging, Alerting and SNMP | Logging Configuration
McAfee Email Gateway 7.x Appliances Best Practices 35
6
System logging best practices
System logging best practices
36 McAfee Email Gateway 7.x Appliances Best Practices
7 Using McAfee Email Gateway with other
McAfee products
McAfee Email Gateway is designed to work alongside other McAfee products, including McAfee
ePolicy Orchestrator and McAfee Quarantine Manager.
Contents
Using McAfee Email Gateway with McAfee ePolicy Orchestrator
Using McAfee Email Gateway with McAfee Quarantine Manager
Using McAfee Email Gateway with McAfee ePolicy Orchestrator
McAfee ePolicy Orchestrator provides a convenient method of managing and monitoring many of
your McAfee products, including McAfee Email Gateway.
Do not modify the default dashboards or queries within McAfee ePO
If you want to change the way that a particular dashboard or query works within McAfee ePO, rather
than modifying the existing item, you should create a new dashboard or query based on the settings
from the existing dashboard or query.
The McAfee Email Gateway dashboards and queries installed on McAfee ePO are designed to be
compatible with the dashboards and reports found within McAfee Email Gateway. If you modify these
items, they may no longer show information consistent with that found on the McAfee Email Gateway.
Also, any modified dashboards or queries are likely to be overwritten if you install a newer version of
the McAfee Email Gateway extension for McAfee ePO.
Using McAfee Email Gateway with McAfee Quarantine Manager
McAfee Quarantine Manager consolidates the quarantine and antispam management functionality of
multiple McAfee products, including McAfee Email Gateway.
Best practices relating to setting up McAfee Quarantine Manager
Ensure that you follow the installation information and recommendations given in the McAfee
Quarantine Manager Product Guide for your version of McAfee Quarantine Manager.
Observe minimum disk space requirements
The drive used to host the McAfee Quarantine Manager database should have a minimum free space of
150% of your predicted maximum database size.
McAfee Email Gateway 7.x Appliances Best Practices 37
7
Using McAfee Email Gateway with other McAfee products
Using McAfee Email Gateway with McAfee Quarantine Manager
Schedule tasks
To prevent tasks running slowly, do not run simultaneous tasks on the same domains within McAfee
Quarantine Manager.
Allow scripts to run on your email client
Since the digest email is set as an attachment by default, ensure that scripts are allowed to run in the
attachment on your email client. Failure to enable scripts will prevent the digest actions being taken.
Do not change the default communications protocol and port
Do not change the default communication protocol and port (HTTP over port 80) between McAfee
Email Gateway 7.0 and McAfee Quarantine Manager.
Integrated Windows Authentication
If Integrated Windows Authentication is used for user authentication, ensure that McAfee Quarantine
Manager server is in the same domain as the Active Directory.
Install McAfee Quarantine Manager on a standalone server
Install McAfee Quarantine Manager on a standalone machine, where other McAfee products, Mail
Servers or other software are not installed.
Using MSSQL for McAfee Quarantine Manager
When MSSQL is used as McAfee Quarantine Manager database, ensure that "SQL Native Client" driver
is installed in McAfee Quarantine Manager machine.
Data Manipulation Language
Do not run any Data Manipulation Language (Insert, Update, and Delete) queries on the McAfee
Quarantine Manager database backend.
Firewall ports
Open up port 80 or 49500 for both directions on any firewalls between McAfee Email Gateway and
McAfee Quarantine Manager.
Processes to exclude from antivirus scans
Configure your antivirus (and any other monitoring software) to exclude following processes:
RPCServ.exe MySQLd.exe (if using MySQL)
SAFeService.exe RunAlert.exe (if using MSCS)
RunScheduled.exe
If you are using any backup software on your McAfee Email Gateway server, the MySQL install folder
should be excluded.
38 McAfee Email Gateway 7.x Appliances Best Practices
Index
A explicit proxy mode 13
about this guide 5
anti-spam settings 31
F
anti-virus settings 31 firewall connections being blocked 27
firewall rules
B explicit proxy mode 13
best practice
McAfee ePolicy Orchestrator 37 G
McAfee Quarantine Manager 37 groups
MQM 37 user 29
blade server considerations 16
H
C
hardware
change policy order 26
securing 21
cluster considerations 15
how to use this guide 7
compliance dictionaries 32
configuring NDR 27
I
configuring non-delivery reports 27
configuring the policy order 26 initial configuration 19
configuring timeouts 27
considerations
L
pre-installation 9 ldap 30
virtual appliance 16
conventions and icons used in this guide 5 M
mail traffic
D flow of 29
data loss prevention settings 31 mail transfer agent
define securing 23
role 21 McAfee Email and Web Security appliances
user 21 migrating from 17
designing McAfee Email Gateway
inbound policies 28 migrating from 17
outbound policies 28 McAfee ServicePortal, accessing 6
DLP settings 31 migration
documentation McAfee Email and Web Security appliances 17
audience for this guide 5 McAfee Email Gateway 17
product-specific, finding 6 MTA, securing 23
typographical conventions and icons 5
N
E network modes
encryption 33 explicit proxy mode 13
enforcing regulatory compliance 32 transparent bridge mode 10
transparent router mode 12
McAfee Email Gateway 7.x Appliances Best Practices 39
Index
O ServicePortal, finding product documentation 6
settings
online troubleshooting resource 7
anti-spam 31
operating modes
anti-virus 31
explicit proxy mode 13
data loss prevention 31
transparent bridge mode 10
DLP 31
transparent router mode 12
syslog 35
order of scanning 26
system logging 35
P
T
password complexity 22
Technical Support, finding product information 6
physical installation 18
tls 33
physical security 21
transparent bridge mode 10
policies 25
transparent router mode 12
configuring 27
transport layer security 33
designing inbound 28
Troubleshooting Tree 7
designing outbound 28
Troubleshooting, using the online tree 7
policy order 26
product differences 17
protocol presets 30
U
unblocking firewall connections 27
R user groups 29
using this guide 7
regulatory compliance
enforcing 32
restrict access
V
using IP address restrictions 22 virtual appliance
using out-of-band management 22 considerations 16
using secure shell/ssh 22
using user accounts 21 W
using user roles 21
what's in this guide 6
restricting access to McAfee Email Gateway 21, 22
S
scanning order 26
40 McAfee Email Gateway 7.x Appliances Best Practices
0A00
Vous aimerez peut-être aussi
- Mcafee Virusscan Enterprise 8.8 Software: Installation GuideDocument34 pagesMcafee Virusscan Enterprise 8.8 Software: Installation GuidesuderPas encore d'évaluation
- Mcafee NSP Guide 9.1Document457 pagesMcafee NSP Guide 9.1amitsignup100Pas encore d'évaluation
- UrBackup Server ServerAdminGuide v2.1 2Document35 pagesUrBackup Server ServerAdminGuide v2.1 2Andrea MoranoPas encore d'évaluation
- Linux - McAfee Antivirus InstallationDocument22 pagesLinux - McAfee Antivirus Installationsamvora2008997850% (2)
- ServerAdminGuide-v1 4Document28 pagesServerAdminGuide-v1 4GerardoPas encore d'évaluation
- Supercluster T5-8 DocumentDocument178 pagesSupercluster T5-8 Documentreddy.abhishek2190Pas encore d'évaluation
- Replace A Faulty FMOD On ExadataDocument6 pagesReplace A Faulty FMOD On ExadataThu Thủy Đào ThịPas encore d'évaluation
- Solaris 10 - HardeningDocument3 pagesSolaris 10 - HardeningfirestojPas encore d'évaluation
- OVM Command Line Interface User GuideDocument166 pagesOVM Command Line Interface User GuideJulio Cesar Flores NavarroPas encore d'évaluation
- BIG-IP Link Controller ImplementationsDocument80 pagesBIG-IP Link Controller ImplementationsmlaazimaniPas encore d'évaluation
- Clustered Data ONTAP 83 MetroCluster InstallationDocument215 pagesClustered Data ONTAP 83 MetroCluster InstallationAhmed HaggarPas encore d'évaluation
- Oci 100Document11 pagesOci 100Dharmesh BPas encore d'évaluation
- Clearing The Stop Fault Flag in Sun Cluster 3.xDocument4 pagesClearing The Stop Fault Flag in Sun Cluster 3.xBalachandar KrishnaswamyPas encore d'évaluation
- Oracle Database Appliance: ODA X8 19.11 Hands-On Lab Manual (OCI)Document84 pagesOracle Database Appliance: ODA X8 19.11 Hands-On Lab Manual (OCI)juliocon2104Pas encore d'évaluation
- BCEFE in A Nutshell Study Guide For Exam 150-610: Global Education Services Revision 0111Document70 pagesBCEFE in A Nutshell Study Guide For Exam 150-610: Global Education Services Revision 0111Walter BlokPas encore d'évaluation
- NetBackup81 AdminGuide VMwareDocument359 pagesNetBackup81 AdminGuide VMwarekhursheed4u3590Pas encore d'évaluation
- How To Use Zpool Split To Split Rpool in Solaris 11 x86x64Document18 pagesHow To Use Zpool Split To Split Rpool in Solaris 11 x86x64vijayen123Pas encore d'évaluation
- Solaris Cluster Failover LDom Resource Creation Fails With Master-Slave Dependency Between Primary Domain and Guest Domain Does Not ExistDocument3 pagesSolaris Cluster Failover LDom Resource Creation Fails With Master-Slave Dependency Between Primary Domain and Guest Domain Does Not ExistcresmakPas encore d'évaluation
- Oracle Solaris Cluster Data Service For Oracle GuideDocument118 pagesOracle Solaris Cluster Data Service For Oracle GuidemadhusribPas encore d'évaluation
- IBM XIV Implemetation PDFDocument488 pagesIBM XIV Implemetation PDFPrasadValluraPas encore d'évaluation
- IEM Relevance GuideDocument76 pagesIEM Relevance Guidesrivatsan_ecePas encore d'évaluation
- HP NG1 Bookmarked2Document68 pagesHP NG1 Bookmarked2enco123encoPas encore d'évaluation
- Imperva - END - Pilot - (Virtual Appliances Only) v0319Document2 pagesImperva - END - Pilot - (Virtual Appliances Only) v0319Alessandro PazPas encore d'évaluation
- Revision 1208: Introduction To FC LayersDocument27 pagesRevision 1208: Introduction To FC LayersTerry ChenPas encore d'évaluation
- Fabricattached MetroCluster Systems BrocadeDocument34 pagesFabricattached MetroCluster Systems BrocadeAlemseged HabtamuPas encore d'évaluation
- HPE FlexNetwork Stacking Firmware Upgrade v1.0Document5 pagesHPE FlexNetwork Stacking Firmware Upgrade v1.0Anton SoPas encore d'évaluation
- SANCOOCKBOOKDocument144 pagesSANCOOCKBOOKBetty AnghelPas encore d'évaluation
- Solaris 10 Handbook PDFDocument198 pagesSolaris 10 Handbook PDFChRamakrishnaPas encore d'évaluation
- Whats Up GoldDocument30 pagesWhats Up GoldValerie GardnerPas encore d'évaluation
- APIC 2-1 WalkMe Demo GuideDocument7 pagesAPIC 2-1 WalkMe Demo GuideintikhabmPas encore d'évaluation
- Fos 801 PwrecoverynotesDocument23 pagesFos 801 PwrecoverynotesHam Za0% (1)
- ES524CPX00074 - VxRail Installation and Implementation - Classroom - Participant Guide PDFDocument507 pagesES524CPX00074 - VxRail Installation and Implementation - Classroom - Participant Guide PDFSalome MarimbaPas encore d'évaluation
- Hands-On Keyboard 5 - WiresharkDocument16 pagesHands-On Keyboard 5 - Wiresharkpenumudi233Pas encore d'évaluation
- Time Navigator - Command Line - 4.2Document250 pagesTime Navigator - Command Line - 4.2unixjon100% (1)
- CIS Oracle Solaris 10 Benchmark v5.2.0Document156 pagesCIS Oracle Solaris 10 Benchmark v5.2.0alex perezPas encore d'évaluation
- Solaris 11 Systems Fault Analysis AssessmentDocument29 pagesSolaris 11 Systems Fault Analysis AssessmentstaojrPas encore d'évaluation
- Oracle VM Release Notes For 3.4.6Document170 pagesOracle VM Release Notes For 3.4.6SamratPas encore d'évaluation
- Manual Iboss EnterpriseDocument184 pagesManual Iboss Enterprisejbjrjaen4792100% (1)
- User Guide: Ibm Qradar User Behavior Analytics (Uba) AppDocument294 pagesUser Guide: Ibm Qradar User Behavior Analytics (Uba) AppLuka JussPas encore d'évaluation
- SOP NetApp CDOT ShutdownDocument3 pagesSOP NetApp CDOT ShutdownShailesh SinghPas encore d'évaluation
- Junos Space Security DirectorDocument346 pagesJunos Space Security DirectorZhivko GeorgievPas encore d'évaluation
- WhatsConnected 22 User GuideDocument79 pagesWhatsConnected 22 User GuideandreysmithPas encore d'évaluation
- Compellent Enterprise Manager Administrators GuideDocument436 pagesCompellent Enterprise Manager Administrators Guidebogdan_asdasdPas encore d'évaluation
- Getting Started BIG-IP Part2 AppDelivery Lab Guide PDFDocument23 pagesGetting Started BIG-IP Part2 AppDelivery Lab Guide PDFzxcdPas encore d'évaluation
- Docu 96752Document396 pagesDocu 96752Belu IonPas encore d'évaluation
- Oracle® Goldengate: Troubleshooting and Tuning GuideDocument158 pagesOracle® Goldengate: Troubleshooting and Tuning Guidekarthik76Pas encore d'évaluation
- Data Ontap 7-Mode CLI CommandsDocument15 pagesData Ontap 7-Mode CLI CommandsPurushothama GnPas encore d'évaluation
- EMC AX4-5 Hardware Installation and Troubleshooting GuideDocument60 pagesEMC AX4-5 Hardware Installation and Troubleshooting GuideShivam ChawlaPas encore d'évaluation
- Lab Guide CFP300 Rev0114 LG - LDocument118 pagesLab Guide CFP300 Rev0114 LG - LdipeshPas encore d'évaluation
- Dell PowerEdge RAID Controller (PERC) H200 and 6Gbps SAS HBA User S GuideDocument92 pagesDell PowerEdge RAID Controller (PERC) H200 and 6Gbps SAS HBA User S GuideAnonymous kbmKQLe0JPas encore d'évaluation
- Solaris System Performance Management - SA-400 - Student GuideDocument700 pagesSolaris System Performance Management - SA-400 - Student GuideamsreekuPas encore d'évaluation
- CIS Oracle Linux 7 Benchmark v2.0.0Document302 pagesCIS Oracle Linux 7 Benchmark v2.0.0Carolus GazaPas encore d'évaluation
- Install Oracle Application Multi-NodeDocument12 pagesInstall Oracle Application Multi-NodemaswananadrillPas encore d'évaluation
- How To Pvmove RHELDocument2 pagesHow To Pvmove RHELJhun PogiPas encore d'évaluation
- LogRhythm Overview 2009 04Document2 pagesLogRhythm Overview 2009 04testPas encore d'évaluation
- Tunnel Comparison Between Generic Routing Encapsulation (Gre) and Ip Security (Ipsec)Document37 pagesTunnel Comparison Between Generic Routing Encapsulation (Gre) and Ip Security (Ipsec)testPas encore d'évaluation
- DCC Release Notes: DSL-2730UDocument1 pageDCC Release Notes: DSL-2730UtestPas encore d'évaluation
- 2015ebook SDN NFV Ch1Document33 pages2015ebook SDN NFV Ch1Kaka NarcissePas encore d'évaluation
- Seagrass-Watch Seagrass-Watch: RisingDocument16 pagesSeagrass-Watch Seagrass-Watch: RisingtestPas encore d'évaluation
- Kpi Juniper Appliances Network-Management PDFDocument1 002 pagesKpi Juniper Appliances Network-Management PDFtestPas encore d'évaluation
- PA5200 SpecsheetDocument2 pagesPA5200 SpecsheettestPas encore d'évaluation
- Web Forensic Tools ThesisDocument204 pagesWeb Forensic Tools ThesistestPas encore d'évaluation
- Hankinson - Location Branding - A Study of The Branding Practices of 12 English CitiesDocument16 pagesHankinson - Location Branding - A Study of The Branding Practices of 12 English CitiesNatalia Ney100% (1)
- PropertycasesforfinalsDocument40 pagesPropertycasesforfinalsRyan Christian LuposPas encore d'évaluation
- Slides 99 Netslicing Georg Mayer 3gpp Network Slicing 04Document13 pagesSlides 99 Netslicing Georg Mayer 3gpp Network Slicing 04malli gaduPas encore d'évaluation
- For FDPB Posting-RizalDocument12 pagesFor FDPB Posting-RizalMarieta AlejoPas encore d'évaluation
- Spice Processing UnitDocument3 pagesSpice Processing UnitKSHETRIMAYUM MONIKA DEVIPas encore d'évaluation
- Astm D1895 17Document4 pagesAstm D1895 17Sonia Goncalves100% (1)
- Damodaram Sanjivayya National Law University VisakhapatnamDocument6 pagesDamodaram Sanjivayya National Law University VisakhapatnamSuvedhya ReddyPas encore d'évaluation
- KB000120-MRK456-01-HR SamplingDocument15 pagesKB000120-MRK456-01-HR SamplingMiguel Zuniga MarconiPas encore d'évaluation
- Activity-Based Management (ABM) Is A Systemwide, Integrated Approach That FocusesDocument4 pagesActivity-Based Management (ABM) Is A Systemwide, Integrated Approach That FocusestogarikalPas encore d'évaluation
- 6401 1 NewDocument18 pages6401 1 NewbeeshortPas encore d'évaluation
- Death and The King's Horseman AnalysisDocument2 pagesDeath and The King's Horseman AnalysisCelinaPas encore d'évaluation
- Book Review On PandeymoniumDocument2 pagesBook Review On PandeymoniumJanhavi ThakkerPas encore d'évaluation
- Dye-Sensitized Solar CellDocument7 pagesDye-Sensitized Solar CellFaez Ahammad MazumderPas encore d'évaluation
- Item AnalysisDocument7 pagesItem AnalysisJeff LestinoPas encore d'évaluation
- BSBHRM405 Support Recruitment, Selection and Induction of Staff KM2Document17 pagesBSBHRM405 Support Recruitment, Selection and Induction of Staff KM2cplerkPas encore d'évaluation
- (IME) (Starfinder) (Acc) Wildstorm IndustriesDocument51 pages(IME) (Starfinder) (Acc) Wildstorm IndustriesFilipe Galiza79% (14)
- Walt Whitman Video Worksheet. CompletedDocument1 pageWalt Whitman Video Worksheet. CompletedelizabethannelangehennigPas encore d'évaluation
- Green Campus Concept - A Broader View of A Sustainable CampusDocument14 pagesGreen Campus Concept - A Broader View of A Sustainable CampusHari HaranPas encore d'évaluation
- Holophane Denver Elite Bollard - Spec Sheet - AUG2022Document3 pagesHolophane Denver Elite Bollard - Spec Sheet - AUG2022anamariePas encore d'évaluation
- Ev Wireless Charging 5 PDFDocument27 pagesEv Wireless Charging 5 PDFJP GUPTAPas encore d'évaluation
- Fix List For IBM WebSphere Application Server V8Document8 pagesFix List For IBM WebSphere Application Server V8animesh sutradharPas encore d'évaluation
- Catalogue 2021Document12 pagesCatalogue 2021vatsala36743Pas encore d'évaluation
- Verb To Be ExerciseDocument6 pagesVerb To Be Exercisejhon jairo tarapues cuaycalPas encore d'évaluation
- Curriculum Vitae: Personal InformationDocument2 pagesCurriculum Vitae: Personal InformationtyasPas encore d'évaluation
- Proposal For Real Estate Asset Management and Brokerage ServicesDocument2 pagesProposal For Real Estate Asset Management and Brokerage ServicesTed McKinnonPas encore d'évaluation
- Task 1: MonologueDocument4 pagesTask 1: MonologueLaura Cánovas CabanesPas encore d'évaluation
- Novedades Jaltest CV en 887Document14 pagesNovedades Jaltest CV en 887Bruce LyndePas encore d'évaluation
- Sheet PilesDocument5 pagesSheet PilesolcayuzPas encore d'évaluation
- Science Technology and SocietyDocument46 pagesScience Technology and SocietyCharles Elquime GalaponPas encore d'évaluation
- Simple Past and Past Continuous Notes and ExercisesDocument5 pagesSimple Past and Past Continuous Notes and ExercisesConstantina KouverianosPas encore d'évaluation