Académique Documents
Professionnel Documents
Culture Documents
Tabla de Host
Transféré par
EloiGarciaCliment0 évaluation0% ont trouvé ce document utile (0 vote)
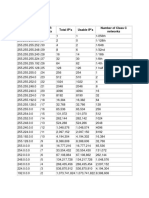
9 vues2 pagesThe document contains three tables that show how IP addresses from class A, B and C can be subnetted by borrowing bits from the host portion. Each table lists the number of bits borrowed, the corresponding subnet mask, the effective number of subnets created and number of hosts per subnet. Borrowing more bits from the host portion results in more effective subnets but fewer hosts per subnet.
Description originale:
Titre original
Tabla de host.docx
Copyright
© © All Rights Reserved
Formats disponibles
DOCX, PDF, TXT ou lisez en ligne sur Scribd
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentThe document contains three tables that show how IP addresses from class A, B and C can be subnetted by borrowing bits from the host portion. Each table lists the number of bits borrowed, the corresponding subnet mask, the effective number of subnets created and number of hosts per subnet. Borrowing more bits from the host portion results in more effective subnets but fewer hosts per subnet.
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme DOCX, PDF, TXT ou lisez en ligne sur Scribd
0 évaluation0% ont trouvé ce document utile (0 vote)
9 vues2 pagesTabla de Host
Transféré par
EloiGarciaClimentThe document contains three tables that show how IP addresses from class A, B and C can be subnetted by borrowing bits from the host portion. Each table lists the number of bits borrowed, the corresponding subnet mask, the effective number of subnets created and number of hosts per subnet. Borrowing more bits from the host portion results in more effective subnets but fewer hosts per subnet.
Droits d'auteur :
© All Rights Reserved
Formats disponibles
Téléchargez comme DOCX, PDF, TXT ou lisez en ligne sur Scribd
Vous êtes sur la page 1sur 2
Tabla de host/subred de clase A
Class A
Number of
Bits Borrowed Subnet Effective Number of Number of Subnet
from Host Portion Mask Subnets Hosts/Subnet Mask Bits
------- --------------- --------- ------------- -------------
1 255.128.0.0 2 8388606 /9
2 255.192.0.0 4 4194302 /10
3 255.224.0.0 8 2097150 /11
4 255.240.0.0 16 1048574 /12
5 255.248.0.0 32 524286 /13
6 255.252.0.0 64 262142 /14
7 255.254.0.0 128 131070 /15
8 255.255.0.0 256 65534 /16
9 255.255.128.0 512 32766 /17
10 255.255.192.0 1024 16382 /18
11 255.255.224.0 2048 8190 /19
12 255.255.240.0 4096 4094 /20
13 255.255.248.0 8192 2046 /21
14 255.255.252.0 16384 1022 /22
15 255.255.254.0 32768 510 /23
16 255.255.255.0 65536 254 /24
17 255.255.255.128 131072 126 /25
18 255.255.255.192 262144 62 /26
19 255.255.255.224 524288 30 /27
20 255.255.255.240 1048576 14 /28
21 255.255.255.248 2097152 6 /29
22 255.255.255.252 4194304 2 /30
23 255.255.255.254 8388608 2* /31
Host clase B/Tabla de subnet
Class B Subnet Effective Effective Number of Subnet
Bits Mask Subnets Hosts Mask Bits
------- --------------- --------- --------- -------------
1 255.255.128.0 2 32766 /17
2 255.255.192.0 4 16382 /18
3 255.255.224.0 8 8190 /19
4 255.255.240.0 16 4094 /20
5 255.255.248.0 32 2046 /21
6 255.255.252.0 64 1022 /22
7 255.255.254.0 128 510 /23
8 255.255.255.0 256 254 /24
9 255.255.255.128 512 126 /25
10 255.255.255.192 1024 62 /26
11 255.255.255.224 2048 30 /27
12 255.255.255.240 4096 14 /28
13 255.255.255.248 8192 6 /29
14 255.255.255.252 16384 2 /30
15 255.255.255.254 32768 2* /31
Tabla de Host clase C/Subred
Class C Subnet Effective Effective Number of Subnet
Bits Mask Subnets Hosts Mask Bits
------- --------------- --------- --------- --------------
1 255.255.255.128 2 126 /25
2 255.255.255.192 4 62 /26
3 255.255.255.224 8 30 /27
4 255.255.255.240 16 14 /28
5 255.255.255.248 32 6 /29
6 255.255.255.252 64 2 /30
7 255.255.255.254 128 2* /31
Vous aimerez peut-être aussi
- IPv4 - Subnetting CheatsheetDocument1 pageIPv4 - Subnetting CheatsheetKeith Crawford100% (2)
- Subnet Mask Cheat SheetDocument4 pagesSubnet Mask Cheat SheetAhmad YahyaPas encore d'évaluation
- IPv4 Subnet Cheat Sheet PDFDocument1 pageIPv4 Subnet Cheat Sheet PDFShanzida Anika MimPas encore d'évaluation
- Tabla de Host/subred de Clase ADocument2 pagesTabla de Host/subred de Clase AEloiGarciaClimentPas encore d'évaluation
- Class A HostDocument2 pagesClass A Hostjzre24Pas encore d'évaluation
- Subnet Mask Network Bits Host Bits SubnetsDocument1 pageSubnet Mask Network Bits Host Bits SubnetsIbrahimPas encore d'évaluation
- Cidr - Classless Interdomain Routing: Monday, February 22, 1999 Isp/Ixp Networking WorkshopDocument2 pagesCidr - Classless Interdomain Routing: Monday, February 22, 1999 Isp/Ixp Networking WorkshopUser NamePas encore d'évaluation
- Ipv4 Cidr Chart - 2015Document1 pageIpv4 Cidr Chart - 2015Nataša AleksićPas encore d'évaluation
- Subnet Cheat SheetDocument2 pagesSubnet Cheat SheetrajeshjhajhraPas encore d'évaluation
- Subnet MaskDocument1 pageSubnet MaskFulvio100% (1)
- Subnetting / Fixed Subnet (N+) (H-) CIDR / Supernet (N-) (H+)Document2 pagesSubnetting / Fixed Subnet (N+) (H-) CIDR / Supernet (N-) (H+)thuralwin85Pas encore d'évaluation
- Subnet WorkbookDocument6 pagesSubnet Workbooklunar_plaguePas encore d'évaluation
- CIDRDocument2 pagesCIDRKayode EmmanuelPas encore d'évaluation
- CIDRDocument2 pagesCIDRKayode EmmanuelPas encore d'évaluation
- Subnet Cheat Sheet: Guide To Sub-Class C BlocksDocument4 pagesSubnet Cheat Sheet: Guide To Sub-Class C BlocksFariz RenggaPas encore d'évaluation
- Tabla de Host/subred de Clase ADocument3 pagesTabla de Host/subred de Clase ABrianIvan27Pas encore d'évaluation
- Variable Length Subnet Mask (VLSM) Subnetting: By: Fritzie S. EstradaDocument29 pagesVariable Length Subnet Mask (VLSM) Subnetting: By: Fritzie S. EstradaAntonettePas encore d'évaluation
- Subnet Cheat Sheet: Guide To Sub-Class C BlocksDocument3 pagesSubnet Cheat Sheet: Guide To Sub-Class C Blocksmazc13Pas encore d'évaluation
- 04 - 04 Subnetting Reference TablesDocument2 pages04 - 04 Subnetting Reference Tablesssgt69Pas encore d'évaluation
- Subnetting GuruDocument1 pageSubnetting GuruSimran ThapaPas encore d'évaluation
- Subnet CheatSheetDocument4 pagesSubnet CheatSheetSai SudhakarPas encore d'évaluation
- Subnet Mask Cheat Sheet: Guide To Sub-Class C BlocksDocument3 pagesSubnet Mask Cheat Sheet: Guide To Sub-Class C Blockspriyanka joshiPas encore d'évaluation
- Subnet Mask Cheat SheetDocument4 pagesSubnet Mask Cheat Sheetlouiegi001Pas encore d'évaluation
- Subnet Mask Cheat Sheet: Guide To Sub-Class C BlocksDocument4 pagesSubnet Mask Cheat Sheet: Guide To Sub-Class C BlocksJulie BennettPas encore d'évaluation
- Subnet Mask Cheat SheetDocument4 pagesSubnet Mask Cheat SheetjkickliPas encore d'évaluation
- CCNA SubnetsRevisitedDocument1 pageCCNA SubnetsRevisitedSjanUKPas encore d'évaluation
- Subnet MaskDocument1 pageSubnet MaskLuis Gerardo MendozaPas encore d'évaluation
- Subnet Mask Cheat SheetDocument4 pagesSubnet Mask Cheat Sheetreji50Pas encore d'évaluation
- How To Calculate Subnet Mask From IP AddressDocument7 pagesHow To Calculate Subnet Mask From IP AddressVivekananda GNPas encore d'évaluation
- Subnet IP Ranges Cheat Sheet: by ViaDocument1 pageSubnet IP Ranges Cheat Sheet: by ViaW BurPas encore d'évaluation
- Ubnetting: Subnet Chart Decimal To BinaryDocument1 pageUbnetting: Subnet Chart Decimal To Binaryopexxx100% (4)
- Ere Are The ChartsDocument1 pageEre Are The Chartssimin jadaPas encore d'évaluation
- TCPIP SubnettingDocument16 pagesTCPIP SubnettingRafael A Couto CabralPas encore d'évaluation
- IPv4 Subnet Cheat SheetDocument1 pageIPv4 Subnet Cheat SheetDanny EvansPas encore d'évaluation
- CIDR Subnet TableDocument4 pagesCIDR Subnet TableAnonymous 2zqZO1rZPas encore d'évaluation
- RFC 1817 RFC 1812: Class ADocument9 pagesRFC 1817 RFC 1812: Class AYousif AlgulaidiPas encore d'évaluation
- Sub NettingDocument9 pagesSub NettingLorido, Eraño R.Pas encore d'évaluation
- SUBNETTINGDocument9 pagesSUBNETTINGLorido, Eraño R.Pas encore d'évaluation
- IPv4 Subnetting Reference ChartDocument1 pageIPv4 Subnetting Reference ChartBook_UPas encore d'évaluation
- IPv4 Subnetting Reference ChartDocument1 pageIPv4 Subnetting Reference ChartAlejandro FernandezPas encore d'évaluation
- IPv4 Subnetting Reference Chart PDFDocument1 pageIPv4 Subnetting Reference Chart PDFumermansoor715Pas encore d'évaluation
- IP Addressing Practice 1: A. Identifying Network AddressesDocument5 pagesIP Addressing Practice 1: A. Identifying Network AddressesKieran HollisPas encore d'évaluation
- Subnet Mask Cheat Sheet - CidrDocument3 pagesSubnet Mask Cheat Sheet - CidrLarry TembuPas encore d'évaluation
- IPAddressingGuide PDFDocument1 pageIPAddressingGuide PDFKulbir SinghPas encore d'évaluation
- Subnet Cheat SheetDocument2 pagesSubnet Cheat Sheetgehmanedam oaschPas encore d'évaluation
- CIDR Subnetting CheatsheetDocument1 pageCIDR Subnetting CheatsheetMostafa HafidPas encore d'évaluation
- Subnetting TableDocument1 pageSubnetting Tablebaraynavab100% (22)
- Subnet GuideDocument4 pagesSubnet Guidetahazzad hossainPas encore d'évaluation
- The Cyber Mentor's Subnetting SheetDocument4 pagesThe Cyber Mentor's Subnetting SheetgagrrsdPas encore d'évaluation
- Profile of the Worldwide Semiconductor Industry - Market Prospects to 1997: Market Prospects to 1997D'EverandProfile of the Worldwide Semiconductor Industry - Market Prospects to 1997: Market Prospects to 1997Pas encore d'évaluation
- Technical Tables for Schools and Colleges: The Commonwealth and International Library Mathematics DivisionD'EverandTechnical Tables for Schools and Colleges: The Commonwealth and International Library Mathematics DivisionPas encore d'évaluation
- Implementing 802.11 with Microcontrollers: Wireless Networking for Embedded Systems DesignersD'EverandImplementing 802.11 with Microcontrollers: Wireless Networking for Embedded Systems DesignersPas encore d'évaluation
- CCTV Surveillance: Video Practices and TechnologyD'EverandCCTV Surveillance: Video Practices and TechnologyÉvaluation : 4 sur 5 étoiles4/5 (1)
- Triple Play: Building the converged network for IP, VoIP and IPTVD'EverandTriple Play: Building the converged network for IP, VoIP and IPTVPas encore d'évaluation
- StarLAN Technology ReportD'EverandStarLAN Technology ReportÉvaluation : 3 sur 5 étoiles3/5 (1)
- GIBS Information BrochureDocument6 pagesGIBS Information BrochureshazebkhannPas encore d'évaluation
- Openssl Aes.cDocument3 pagesOpenssl Aes.cschttPas encore d'évaluation
- Brian Kernighan and Dennis Ritchie - The C Programming Language-Prentice Hall PTR (1988)Document289 pagesBrian Kernighan and Dennis Ritchie - The C Programming Language-Prentice Hall PTR (1988)AjdernizPas encore d'évaluation
- Nimmitha IntenshipDocument28 pagesNimmitha IntenshipNimmitha SPas encore d'évaluation
- Sample Cover Letter Job Application Human ResourcesDocument9 pagesSample Cover Letter Job Application Human Resourcesrqaeibifg100% (1)
- DSP 10 Marks Assignment Compulsory For All PDFDocument2 pagesDSP 10 Marks Assignment Compulsory For All PDFrajPas encore d'évaluation
- Mototrbo Xir P3688 Portable Radio: You'Re Simply More EfficientDocument4 pagesMototrbo Xir P3688 Portable Radio: You'Re Simply More EfficientIndra GunawanPas encore d'évaluation
- ODocument164 pagesOJONICHIPas encore d'évaluation
- Health Care Data Privacy and Compliance: Navigating Regulatory LandscapeDocument13 pagesHealth Care Data Privacy and Compliance: Navigating Regulatory LandscapeCentral Asian StudiesPas encore d'évaluation
- Process Dynamics and Control: BITS PilaniDocument30 pagesProcess Dynamics and Control: BITS PilaniShubham ChoudharyPas encore d'évaluation
- 5.2 STATCOM System Functional RequirementsDocument34 pages5.2 STATCOM System Functional RequirementsYinwu ZhaoPas encore d'évaluation
- The Box Above Contains Words That Pertain To The Computer or The Computer Itself. Below Are The Operational Definitions of The WordsDocument4 pagesThe Box Above Contains Words That Pertain To The Computer or The Computer Itself. Below Are The Operational Definitions of The WordsMarkie Dela CruzPas encore d'évaluation
- Format of Lab ReportDocument3 pagesFormat of Lab ReportNirbhayPas encore d'évaluation
- Fine Woodworking Winter 2023 2024Document84 pagesFine Woodworking Winter 2023 2024Jorge LichtscheidlPas encore d'évaluation
- ClonixDocument8 pagesClonixNelson MartinsPas encore d'évaluation
- Philips+MRD 100 78Document35 pagesPhilips+MRD 100 78ald1968Pas encore d'évaluation
- Philips (Chassis L04L AB) Manual de ServicioDocument84 pagesPhilips (Chassis L04L AB) Manual de ServicioAlexis ColmenaresPas encore d'évaluation
- Understanding and Classifying Local, Distortional and Global Buckling in Open Thin-Walled MembersDocument56 pagesUnderstanding and Classifying Local, Distortional and Global Buckling in Open Thin-Walled MembersDaniela Mihaiela BocaPas encore d'évaluation
- Cba and CBQ: C1 Rxlev - Rxlev - Access - Min - Rxlev: Average Receive Level of The Ms in The Unit of DBMDocument3 pagesCba and CBQ: C1 Rxlev - Rxlev - Access - Min - Rxlev: Average Receive Level of The Ms in The Unit of DBMTadele TekaPas encore d'évaluation
- CMMS D-FW 2014-04 8034520g1Document246 pagesCMMS D-FW 2014-04 8034520g1Nelson KempPas encore d'évaluation
- Using Slic3r With The XYZprinting DaVinci 1.0Document5 pagesUsing Slic3r With The XYZprinting DaVinci 1.0anonymoose471Pas encore d'évaluation
- Berhanemeskel Reda PDF Anti Communism Far Left PoliticsDocument1 pageBerhanemeskel Reda PDF Anti Communism Far Left PoliticsAlula AbrahaPas encore d'évaluation
- NotesDocument12 pagesNotesaPas encore d'évaluation
- 1 N 52 XXBDocument2 pages1 N 52 XXB81968Pas encore d'évaluation
- Open For Feedback Till 24-07-2017: Visvesvaraya Technological University, Belagavi B.E (CBCS) Open Electives ListsDocument5 pagesOpen For Feedback Till 24-07-2017: Visvesvaraya Technological University, Belagavi B.E (CBCS) Open Electives Listsabdul.azeezPas encore d'évaluation
- ITC - Multi-Hazard Risk Ass..Document4 pagesITC - Multi-Hazard Risk Ass..Seher Banu Sencer KemeçPas encore d'évaluation
- Baan Query Tool 2.7: User Guide - Baan LNDocument28 pagesBaan Query Tool 2.7: User Guide - Baan LNmoughabatPas encore d'évaluation
- 63180en 01Document157 pages63180en 01Samuel MarquezPas encore d'évaluation
- Nokia Airscale Wi-Fi Module Ac210M, Release 17ADocument26 pagesNokia Airscale Wi-Fi Module Ac210M, Release 17Aprashant gauravPas encore d'évaluation
- Table of Specifications: Region Division School NameDocument19 pagesTable of Specifications: Region Division School Namecharissa quitorasPas encore d'évaluation