Académique Documents
Professionnel Documents
Culture Documents
Sa Service Idp Interoperability
Transféré par
Oskr KrvajalCopyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Sa Service Idp Interoperability
Transféré par
Oskr KrvajalDroits d'auteur :
Formats disponibles
Junos Pulse Secure Access Service
Intrusion Detection and Prevention Sensors
Release
8.0
Published: 2013-11-15
Copyright © 2013, Juniper Networks, Inc.
Juniper Networks, Inc.
1194 North Mathilda Avenue
Sunnyvale, California 94089
USA
408-745-2000
www.juniper.net
Copyright © 2013, Juniper Networks, Inc. All rights reserved.
Juniper Networks, Junos, Steel-Belted Radius, NetScreen, and ScreenOS are registered trademarks of Juniper Networks, Inc. in the United
States and other countries. The Juniper Networks Logo, the Junos logo, and JunosE are trademarks of Juniper Networks, Inc. All other
trademarks, service marks, registered trademarks, or registered service marks are the property of their respective owners.
Juniper Networks assumes no responsibility for any inaccuracies in this document. Juniper Networks reserves the right to change, modify,
transfer, or otherwise revise this publication without notice.
Products made or sold by Juniper Networks or components thereof might be covered by one or more of the following patents that are
owned by or licensed to Juniper Networks: U.S. Patent Nos. 5,473,599, 5,905,725, 5,909,440, 6,192,051, 6,333,650, 6,359,479, 6,406,312,
6,429,706, 6,459,579, 6,493,347, 6,538,518, 6,538,899, 6,552,918, 6,567,902, 6,578,186, and 6,590,785.
Junos Pulse Secure Access Service Intrusion Detection and Prevention Sensors
Release 8.0
Copyright © 2013, Juniper Networks, Inc.
All rights reserved.
The information in this document is current as of the date on the title page.
YEAR 2000 NOTICE
Juniper Networks hardware and software products are Year 2000 compliant. Junos OS has no known time-related limitations through the
year 2038. However, the NTP application is known to have some difficulty in the year 2036.
END USER LICENSE AGREEMENT
The Juniper Networks product that is the subject of this technical documentation consists of (or is intended for use with) Juniper Networks
software. Use of such software is subject to the terms and conditions of the End User License Agreement (“EULA”) posted at
http://www.juniper.net/support/eula.html. By downloading, installing or using such software, you agree to the terms and conditions of
that EULA.
ii Copyright © 2013, Juniper Networks, Inc.
Table of Contents
About the Documentation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
Documentation and Release Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
Supported Platforms . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
Documentation Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
Documentation Feedback . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xi
Requesting Technical Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xi
Self-Help Online Tools and Resources . . . . . . . . . . . . . . . . . . . . . . . . . . . xii
Opening a Case with JTAC . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xii
Part 1 Overview
Chapter 1 IDP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3
About IDP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3
IDP Deployment Scenarios . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4
Part 2 Configuration
Chapter 2 IDP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Configuring the Secure Access Service to Interoperate with IDP . . . . . . . . . . . . . . . 9
Interaction Between the IC Series and IDP . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Configuring IDP Sensor Policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10
Part 3 Administration
Chapter 3 Quarantined Users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Identifying and Managing Quarantined Users Manually . . . . . . . . . . . . . . . . . . . . . 15
Chapter 4 Sensor Event Polices . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
Defining Automatic Response Sensor Event Policies . . . . . . . . . . . . . . . . . . . . . . . 17
Part 4 Index
Index . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Copyright © 2013, Juniper Networks, Inc. iii
Intrusion Detection and Prevention Sensors
iv Copyright © 2013, Juniper Networks, Inc.
List of Figures
Part 1 Overview
Chapter 1 IDP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3
Figure 1: Secure Access Service and IDP Topology Scenario 1 . . . . . . . . . . . . . . . . . 4
Figure 2: Secure Access Service and IDP Topology Scenario 2 . . . . . . . . . . . . . . . . . 5
Part 3 Administration
Chapter 3 Quarantined Users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Figure 3: Managing Quarantined Users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
Copyright © 2013, Juniper Networks, Inc. v
Intrusion Detection and Prevention Sensors
vi Copyright © 2013, Juniper Networks, Inc.
List of Tables
About the Documentation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
Table 1: Notice Icons . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . x
Table 2: Text and Syntax Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . x
Copyright © 2013, Juniper Networks, Inc. vii
Intrusion Detection and Prevention Sensors
viii Copyright © 2013, Juniper Networks, Inc.
About the Documentation
• Documentation and Release Notes on page ix
• Supported Platforms on page ix
• Documentation Conventions on page ix
• Documentation Feedback on page xi
• Requesting Technical Support on page xi
Documentation and Release Notes
®
To obtain the most current version of all Juniper Networks technical documentation,
see the product documentation page on the Juniper Networks website at
http://www.juniper.net/techpubs/.
If the information in the latest release notes differs from the information in the
documentation, follow the product Release Notes.
Juniper Networks Books publishes books by Juniper Networks engineers and subject
matter experts. These books go beyond the technical documentation to explore the
nuances of network architecture, deployment, and administration. The current list can
be viewed at http://www.juniper.net/books.
Supported Platforms
For the features described in this document, the following platforms are supported:
• MAG Series
• SA Series
Documentation Conventions
Table 1 on page x defines notice icons used in this guide.
Copyright © 2013, Juniper Networks, Inc. ix
Intrusion Detection and Prevention Sensors
Table 1: Notice Icons
Icon Meaning Description
Informational note Indicates important features or instructions.
Caution Indicates a situation that might result in loss of data or hardware damage.
Warning Alerts you to the risk of personal injury or death.
Laser warning Alerts you to the risk of personal injury from a laser.
Table 2 on page x defines the text and syntax conventions used in this guide.
Table 2: Text and Syntax Conventions
Convention Description Examples
Bold text like this Represents text that you type. To enter configuration mode, type the
configure command:
user@host> configure
Fixed-width text like this Represents output that appears on the user@host> show chassis alarms
terminal screen.
No alarms currently active
Italic text like this • Introduces or emphasizes important • A policy term is a named structure
new terms. that defines match conditions and
• Identifies guide names. actions.
• Junos OS CLI User Guide
• Identifies RFC and Internet draft titles.
• RFC 1997, BGP Communities Attribute
Italic text like this Represents variables (options for which Configure the machine’s domain name:
you substitute a value) in commands or
configuration statements. [edit]
root@# set system domain-name
domain-name
Text like this Represents names of configuration • To configure a stub area, include the
statements, commands, files, and stub statement at the [edit protocols
directories; configuration hierarchy levels; ospf area area-id] hierarchy level.
or labels on routing platform • The console port is labeled CONSOLE.
components.
< > (angle brackets) Encloses optional keywords or variables. stub <default-metric metric>;
x Copyright © 2013, Juniper Networks, Inc.
About the Documentation
Table 2: Text and Syntax Conventions (continued)
Convention Description Examples
| (pipe symbol) Indicates a choice between the mutually broadcast | multicast
exclusive keywords or variables on either
side of the symbol. The set of choices is (string1 | string2 | string3)
often enclosed in parentheses for clarity.
# (pound sign) Indicates a comment specified on the rsvp { # Required for dynamic MPLS only
same line as the configuration statement
to which it applies.
[ ] (square brackets) Encloses a variable for which you can community name members [
substitute one or more values. community-ids ]
Indention and braces ( { } ) Identifies a level in the configuration [edit]
hierarchy. routing-options {
static {
route default {
; (semicolon) Identifies a leaf statement at a
nexthop address;
configuration hierarchy level.
retain;
}
}
}
GUI Conventions
Bold text like this Represents graphical user interface (GUI) • In the Logical Interfaces box, select
items you click or select. All Interfaces.
• To cancel the configuration, click
Cancel.
> (bold right angle bracket) Separates levels in a hierarchy of menu In the configuration editor hierarchy,
selections. select Protocols>Ospf.
Documentation Feedback
We encourage you to provide feedback, comments, and suggestions so that we can
improve the documentation. You can send your comments to
techpubs-comments@juniper.net, or fill out the documentation feedback form at
https://www.juniper.net/cgi-bin/docbugreport/ . If you are using e-mail, be sure to include
the following information with your comments:
• Document or topic name
• URL or page number
• Software release version (if applicable)
Requesting Technical Support
Technical product support is available through the Juniper Networks Technical Assistance
Center (JTAC). If you are a customer with an active J-Care or JNASC support contract,
Copyright © 2013, Juniper Networks, Inc. xi
Intrusion Detection and Prevention Sensors
or are covered under warranty, and need post-sales technical support, you can access
our tools and resources online or open a case with JTAC.
• JTAC policies—For a complete understanding of our JTAC procedures and policies,
review the JTAC User Guide located at
http://www.juniper.net/us/en/local/pdf/resource-guides/7100059-en.pdf.
• Product warranties—For product warranty information, visit
http://www.juniper.net/support/warranty/.
• JTAC hours of operation—The JTAC centers have resources available 24 hours a day,
7 days a week, 365 days a year.
Self-Help Online Tools and Resources
For quick and easy problem resolution, Juniper Networks has designed an online
self-service portal called the Customer Support Center (CSC) that provides you with the
following features:
• Find CSC offerings: http://www.juniper.net/customers/support/
• Search for known bugs: http://www2.juniper.net/kb/
• Find product documentation: http://www.juniper.net/techpubs/
• Find solutions and answer questions using our Knowledge Base: http://kb.juniper.net/
• Download the latest versions of software and review release notes:
http://www.juniper.net/customers/csc/software/
• Search technical bulletins for relevant hardware and software notifications:
https://www.juniper.net/alerts/
• Join and participate in the Juniper Networks Community Forum:
http://www.juniper.net/company/communities/
• Open a case online in the CSC Case Management tool: http://www.juniper.net/cm/
To verify service entitlement by product serial number, use our Serial Number Entitlement
(SNE) Tool: https://tools.juniper.net/SerialNumberEntitlementSearch/
Opening a Case with JTAC
You can open a case with JTAC on the Web or by telephone.
• Use the Case Management tool in the CSC at http://www.juniper.net/cm/.
• Call 1-888-314-JTAC (1-888-314-5822 toll-free in the USA, Canada, and Mexico).
For international or direct-dial options in countries without toll-free numbers, see
http://www.juniper.net/support/requesting-support.html.
xii Copyright © 2013, Juniper Networks, Inc.
PART 1
Overview
• IDP on page 3
Copyright © 2013, Juniper Networks, Inc. 1
Intrusion Detection and Prevention Sensors
2 Copyright © 2013, Juniper Networks, Inc.
CHAPTER 1
IDP
• About IDP on page 3
• IDP Deployment Scenarios on page 4
About IDP
Securing intranet work application and resource traffic is vital to protecting your network
from hostile outside intrusion. You can add levels of application security to your remote
access network by integrating a Juniper Networks Secure Access Service with a Juniper
Networks Intrusion Detection and Prevention (IDP) Sensor. The IDP device may provide
the following types of protection in this solution (some forms of protection depend upon
the specific configuration):
The IDP sensor monitors the network on which the IDP system is installed. The sensor’s
primary task is to detect suspicious and anomalous network traffic based on specific
rules defined in IDP rulebases.
The IDP device provides the following types of protection (some forms of protection
depend upon the specific configuration):
• Protects against attacks from user to application and from application to user (from
a server-side endpoint)
• Detects and blocks most network worms based on software vulnerabilities
• Detects and blocks non-file-based Trojan Horses
• Detects and blocks effects of spyware. adware, and key loggers
• Detects and blocks many types of malware
• Detects and blocks zero day attacks through the use of anomaly detection
NOTE: An IDP Sensor can send logs to one Secure Access Service only.
However, the Secure Access Service can receive logs from more than one
IDP Sensor.
You do not need a special license from Juniper Networks to enable interaction between
the Secure Access Service and the IDP.
Copyright © 2013, Juniper Networks, Inc. 3
Intrusion Detection and Prevention Sensors
Using the Secure Access Service admin console, you can configure and manage interaction
attributes between the Secure Access Service and an IDP, including the following:
• Global configuration parameters such as the IDP hostname or IP address, the TCP port
over which the sensor communicates with the Secure Access Service, and the one-time
password the Secure Access Service and IDP use to authenticate with one another.
• Dynamically changing the IDP configuration from the Secure Access Service and alerting
the IDP of changes in the IP address pool available to remote users.
• Various levels of attack severity warnings.
The IDP sits behind the Secure Access Service on your internal network and monitors
traffic flowing from the Secure Access Service into the LAN. Any abnormal events detected
by the IDP Sensor are reported to the Secure Access Service, which you configure to take
appropriate action based on the severity level of the reported events. The IDP Sensor
performs reporting functions in addition to any normal logging the IDP has been configured
to undertake.
You can use an IDP Sensor on the Secure Access Service cluster, if the cluster is configured
with a virtual IP (VIP) address.
Related • IDP Deployment Scenarios on page 4
Documentation
• Configuring the Secure Access Service to Interoperate with IDP on page 9
• Configuring IDP Sensor Policies on page 10
IDP Deployment Scenarios
The two most likely deployment scenarios are as follows:
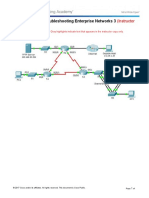
• Customer use of the Secure Access Service for extended enterprise access and IDP
for security of all perimeter traffic including but not limited to traffic from the Secure
Access Service. The following figure illustrates this scenario, in which the Secure Access
Service is deployed in the DMZ or on the LAN and the IDP is deployed in-line behind
the firewall and in front of the LAN.
Figure 1: Secure Access Service and IDP Topology Scenario 1
4 Copyright © 2013, Juniper Networks, Inc.
Chapter 1: IDP
• In the second deployment scenario, IDP is only used to protect traffic that comes
through the Secure Access Service but not in-line with other perimeter traffic. The
following figure illustrates this deployment scenario.
Figure 2: Secure Access Service and IDP Topology Scenario 2
Related • About IDP on page 3
Documentation
• Configuring the Secure Access Service to Interoperate with IDP on page 9
Copyright © 2013, Juniper Networks, Inc. 5
Intrusion Detection and Prevention Sensors
6 Copyright © 2013, Juniper Networks, Inc.
PART 2
Configuration
• IDP on page 9
Copyright © 2013, Juniper Networks, Inc. 7
Intrusion Detection and Prevention Sensors
8 Copyright © 2013, Juniper Networks, Inc.
CHAPTER 2
IDP
• Configuring the Secure Access Service to Interoperate with IDP on page 9
• Configuring IDP Sensor Policies on page 10
Configuring the Secure Access Service to Interoperate with IDP
The IDP Sensor is a powerful tool to counter users who initiate attacks. Integration with
the Secure Access Service allows you to configure automatic responses as well as
manually monitor and manage users.
To configure the Secure Access Service to interoperate with an associated standalone
IDP Sensor, you must first ensure the IDP has been configured according to the instructions
described in the Signaling Setup appendix of IDP Series Concepts and Examples Guide,
Version 5.1rX.
Once the IDP Sensor has been set up, you can specify the events you want the IDP to
watch for and the actions that the Secure Access Service takes once a particular event
has been noted and reported.
There are two locations on the Secure Access Service where you can specify actions to
be taken in response to users that perform attacks:
• Sensor Event policies page—Define the policy on this page to generate an automatic
response to users who perform attacks.
• Users page—Manually identify and quarantine or disable users on the System > Status
> Active Users page, which lists users who have performed attacks.
Interaction Between the IC Series and IDP
The Secure Access Service reads attack information as it is being sent by the IDP sensor.
The Secure Access Service receives the source and destination IP addresses and port
numbers of the attacking host and the resource against which the attack was launched,
along with the attack identifier, severity of the attack, and the time at which the attack
was launched.
The Secure Access Service incorporates and displays the attack information received
from the IDP sensor on the System > Status > Active Users page. Based on the attackers
Copyright © 2013, Juniper Networks, Inc. 9
Intrusion Detection and Prevention Sensors
IP address and port number, the Secure Access Service can uniquely identify the user’s
session.
You can choose automatic or manual actions for attacks detected by the IDP sensor. For
manual action, you look up the information available on the Active Users page and decide
on an action. For automatic action, you configure the action in advance when you define
your IDP policies.
Related • Configuring IDP Sensor Policies on page 10
Documentation
Configuring IDP Sensor Policies
The Sensors tab allows you to specify the system settings the Secure Access Service
uses to establish a connection to a Juniper Network’s Intrusion Detection and Prevention
(IDP) device.
Use the System > Configuration > Sensors > Sensors tab to perform a number of tasks
related to configuring and managing interaction between the Secure Access Service and
an IDP Sensor. The main Sensor page displays the sensor, the network address, the state
(enabled), the version, and the status of any configured sensors.
Creating a New IDP Sensor Entry In IDP versions prior to 5.0, the Secure Access Service
sends only the user IP address. With version 5.0, the Secure Access Service sends session
information including the user, user role and IP address.
To enable or disable existing IDP Sensor entries on the Secure Access Service:
1. In the admin console, choose System > Configuration > Sensors.
NOTE: To use the IDP sensor with the Secure Access Service you must
enable logging for the applicable policies.
2. Click New Sensor. The admin console displays the New Sensor page.
3. Under Sensor Properties, specify the following information:
• Name—A name the Secure Access Service uses to identify the new connection
entry
• Hostname—The hostname or IP address of the IDP Sensor to which the Secure
Access Service connects in order to receive application and resource attack alert
messages
• Port—The TCP port on the IDP Sensor to which the Secure Access Service listens
when receiving application and resource attack alert messages
• One-time password—The encrypted password the Secure Access Service uses
when conducting the initial Transport Layer Security (TLS) handshake with the IDP
Sensor. You must enter the encrypted Secure Access Service OTP password as
displayed on the IDP ACM configuration summary screen.
10 Copyright © 2013, Juniper Networks, Inc.
Chapter 2: IDP
NOTE: The hostname, TCP port, and one-time password must already
be configured on the IDP Sensor before this configuration can be
successful.
4. Under Monitoring Options, specify IP addresses to monitor and the minimum alert
severity level the IDP Sensor will record and submit to the Secure Access Service:
• In the Addresses to Monitor field, specify individual IP addresses and address ranges,
one entry per line. IDP reports attack information only for the IP addresses that you
specify. If you want IDP to report all events to the Secure Access Service, enter
0.0.0.0/0. If you want IDP to report only selected events, enter <default> to permit
IDP to report events for events with source IPs that have an active user session on
the Secure Access Service, and /or enter one or more addresses or address ranges
for any endpoint that you want the IDP sensor to report.
• Select one of the severity options available in the Severity filter drop down list. The
severity level is a number on a scale from 1 to 5, where 1 is informational and 5 is
critical. This option represents the severity of messages the IDP should send to the
Secure Access Service.
5. Click Save Changes.
Enabling or Disabling IDP Sensors
To enable or disable existing IDP Sensor entries on the Secure Access Service:
1. In the admin console, choose System > Configuration > Sensors.
2. Select the checkbox next to one or more IDP Sensor entries you want to enable or
disable.
3. Click Enable or Disable to enable or disable the specified IDP Sensor entries,
respectively.
You can delete existing IDP Sensor entries that define a connection between the Secure
Access Service and an IDP Sensor.
To delete one or more existing IDP Sensor entries from the Secure Access Service:
1. In the admin console, choose System > Configuration > Sensors.
2. Select the checkbox next to the IDP Sensor entry or entries you want to delete.
3. Click Delete and then confirm that you want to delete the sensor entry or entries.
Reconnecting to an IDP Sensor
When the connection to an IDP Sensor is down, you can use the admin console on the
Secure Access Service to re-establish the connection. You can also use the admin console
to refresh the status of existing connections between the Secure Access Service and the
IDP Sensor.
Copyright © 2013, Juniper Networks, Inc. 11
Intrusion Detection and Prevention Sensors
If you need to re-establish communication with an IDP Sensor, you must generate a new
One-time Password.
To reconnect to an associated IDP Sensor:
1. In the admin console, choose System > Configuration > Sensors.
2. Select the checkbox next to the IDP Sensor to which you want to reconnect.
3. Click Reconnect.
The admin console displays a message informing you that the Secure Access Service
is currently attempting to re-establish connection to the specified IDP Sensor. This
page automatically refreshes each second during the reconnection process. Otherwise,
the connection status page automatically refreshes once every 30 seconds.
Refreshing and Displaying the Connection Status
To refresh and display the connection status for the specified IDP Sensor:
1. In the admin console, choose System > Configuration > Sensors.
2. Select the checkbox next to one or more IDP Sensor entries for which you want to
display current connection status.
3. Click Refresh.
Related • About IDP on page 3
Documentation
• Configuring the Secure Access Service to Interoperate with IDP on page 9
12 Copyright © 2013, Juniper Networks, Inc.
PART 3
Administration
• Quarantined Users on page 15
• Sensor Event Polices on page 17
Copyright © 2013, Juniper Networks, Inc. 13
Intrusion Detection and Prevention Sensors
14 Copyright © 2013, Juniper Networks, Inc.
CHAPTER 3
Quarantined Users
• Identifying and Managing Quarantined Users Manually on page 15
Identifying and Managing Quarantined Users Manually
When the Secure Access Service quarantines a user based on an attack, you can display
and manage the states by locating the user link in the System > Status > Active Users
page.
• A small warning icon displayed in front of the user name.
• The hyperlinked user name.
• An enabled Quarantined option button on the specific user’s page. If the user is not
quarantined, the option button is disabled.
You can manage quarantined users from either the admin GUI or by logging in as a user
with administrative rights on the local authentication server.
To manage quarantined users:
1. Identify quarantined users at System > Status > Active Users.
2. Locate the quarantined user from the Authentication > Auth. Servers > System Local
on the admin GUI or from the Admin Users window on the local authentication server.
You must be logged in to the local authentication server as an administrator user in
order to see the Admin User option.
3. Click the username link. The user page opens, showing a number of options.
Copyright © 2013, Juniper Networks, Inc. 15
Intrusion Detection and Prevention Sensors
Figure 3: Managing Quarantined Users
4. Click Disabled to disallow a user from authenticating.
5. Click Quarantined to leave a user in a quarantined state. The Quarantined option is
only enabled if the user is already quarantined.
NOTE: The Secure Access Service assigns quarantined users to the
quarantined role, regardless of their login realm.
6. Click Save Changes.
7. To re-enable previously quarantined or disabled users, select Authentication > Auth.
Servers > Select Server > Users and click the link for the given user.
NOTE: You can also disable users from this location.
8. Click Enabled to release the user from quarantine.
9. Click Save Changes.
All Sensor events are logged at System > Log/Monitoring > Sensors > Log.
Related • Defining Automatic Response Sensor Event Policies on page 17
Documentation
• Displaying Active Users
16 Copyright © 2013, Juniper Networks, Inc.
CHAPTER 4
Sensor Event Polices
• Defining Automatic Response Sensor Event Policies on page 17
Defining Automatic Response Sensor Event Policies
Use the System > Configuration > Sensors > Sensor Event Policies tab to specify one or
more rules that specify the action(s) the Secure Access Service takes when it receives
attack alert messages from an IDP Sensor.
To create a new IDP rule:
1. In the admin console, select System > Configuration > Sensors > Sensor Event Policies.
2. On the Sensor Event Policies page, click New Rules.
3. On the Juniper IDP Rule page, in the Rule: On Receiving... section:
• Select an existing event from the Event drop-down list.
• Click Events to edit an existing event or create a new type of event and add it to the
options in the Events drop-down list:
a. Specify a name for the event.
b. Populate the Expressions field by manually entering expressions or by selecting
one or more clauses from the Expressions Dictionary and clicking Insert Expression.
For example, to check for all critical/highest severity level attacks, enter the
following expression:
idp.severity >= 4
To check for all critical/highest severity level attacks for HTTP traffic, enter the
following expression:
idp.severity >= 4 AND idp.attackStr = “*HTTP*”
c. When you have finished entering the expressions you want to apply to this event,
click Add Expression.
d. Click Close.
4. In the Count this many times section, specify a number between 1 and 256 to determine
the number of times an event must occur before action is taken.
Copyright © 2013, Juniper Networks, Inc. 17
Intrusion Detection and Prevention Sensors
5. In the ...then perform this action section, specify one of the following actions:
• Ignore (just log the event)—Specifies that the Secure Access Service should log
the event, but take no further action against the user profile to which this rule applies.
This option is best used to deal with very minor “informational” attack alert messages
that come from the IDP Sensor.
• Terminate User Session—Specifies that the Secure Access Service should
immediately terminate the user session and require the user to sign in to the Secure
Access Service again.
• Disable user account—Specifies that the Secure Access Service should disable the
user profile associated with this attack alert message, thus rendering the client
unable to sign in to the Secure Access Service until the administrator re-enables
the user account. (This option is only applicable for users who have a local Secure
Access Service user account.)
• Replace user’s role with this one—Specifies that the role applied to this user’s
profile should change to the role you select from the associated dropdown list. This
new role remains assigned to the user profile until the session terminates. This
feature allows you to assign a user to a specific controlled role of your choice, based
on specific IDP events. For example, if the user performs attacks, you might assign
the user to a restricted role that limits the user’s access and activities.
• Choose to make this role assignment:
• Permanent—User remains in the quarantined state across subsequent logins
until the administrator releases the user from the quarantined state.
• For this session only—Default. User can log in to another session.
6. In the Roles section, specify:
• Policy applies to ALL roles—To apply this policy to all users.
• Policy applies to SELECTED roles—To apply this policy only to users who are
mapped to roles in the Selected roles list. Make sure to add roles to this list from
the Available roles list.
• Policy applies to all roles OTHER THAN those selected below—To apply this policy
to all users except for those who are mapped to the roles in the Selected roles list.
Make sure to add roles to this list from the Available roles list.
7. Click Save Changes.
Related • Configuring the Secure Access Service to Interoperate with IDP on page 9
Documentation
18 Copyright © 2013, Juniper Networks, Inc.
PART 4
Index
• Index on page 21
Copyright © 2013, Juniper Networks, Inc. 19
Intrusion Detection and Prevention Sensors
20 Copyright © 2013, Juniper Networks, Inc.
M
manuals
comments on....................................................................xi
P
Index parentheses, in syntax descriptions..................................xi
S
sensor policies for IDP, configuring...................................10
Symbols
support, technical See technical support
#, comments in configuration statements.....................xi
syntax conventions...................................................................x
( ), in syntax descriptions.......................................................xi
< >, in syntax descriptions......................................................x
T
[ ], in configuration statements...........................................xi
technical support
{ }, in configuration statements..........................................xi
contacting JTAC................................................................xi
| (pipe), in syntax descriptions............................................xi
B
braces, in configuration statements..................................xi
brackets
angle, in syntax descriptions.........................................x
square, in configuration statements.........................xi
C
comments, in configuration statements.........................xi
conventions
text and syntax...................................................................x
curly braces, in configuration statements.......................xi
customer support.....................................................................xi
contacting JTAC................................................................xi
D
documentation
comments on....................................................................xi
F
font conventions........................................................................x
I
IDP configuration.......................................................................3
IDP deployment examples....................................................4
IDP interaction............................................................................9
IDP sensor policies..................................................................10
IDP, automatic response........................................................17
IDP, interoperability..................................................................9
IDP, quarantining users manually......................................15
IDP, using with UAC...................................................................3
Copyright © 2013, Juniper Networks, Inc. 21
Intrusion Detection and Prevention Sensors
22 Copyright © 2013, Juniper Networks, Inc.
Vous aimerez peut-être aussi
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (400)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (266)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (74)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (121)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- Piano Marvel LogDocument2 pagesPiano Marvel LogAshish AroraPas encore d'évaluation
- Tegra2 Embedded Controller Interface Specification 20111117Document128 pagesTegra2 Embedded Controller Interface Specification 20111117Vivek ChandPas encore d'évaluation
- Cis-Audit SHDocument28 pagesCis-Audit SHrotiliojpaPas encore d'évaluation
- A Combined MCQ PDFDocument43 pagesA Combined MCQ PDFDhairyaraj Ataliya100% (1)
- Cisco Start Catalog 1704ap LDSL 0416Document205 pagesCisco Start Catalog 1704ap LDSL 0416Myo Lwin HtunPas encore d'évaluation
- CSS111 Information Sheet No. 4 Static and Dynamic IP AddressDocument3 pagesCSS111 Information Sheet No. 4 Static and Dynamic IP AddressNovel GabmulPas encore d'évaluation
- 02-C Ethernet RMON Performance ListDocument4 pages02-C Ethernet RMON Performance ListShakeb AmirPas encore d'évaluation
- 15CS833 Module-5 PDFDocument7 pages15CS833 Module-5 PDFsuryaPas encore d'évaluation
- Overview of Saturne As MDC - 2009-08 - en FinalDocument22 pagesOverview of Saturne As MDC - 2009-08 - en FinalyamezianePas encore d'évaluation
- Installation: Sun Storage 7110, 7210, 7410 Unified Storage System Installation Service United States 1 ScopeDocument4 pagesInstallation: Sun Storage 7110, 7210, 7410 Unified Storage System Installation Service United States 1 ScopeJainy RajPas encore d'évaluation
- archivetempTVLog PDFDocument24 pagesarchivetempTVLog PDFJuan Manuel Vázquez LeguizamónPas encore d'évaluation
- Deployment Guide-KEMP LoadMaster UC-APL Compliant 7 1 35Document23 pagesDeployment Guide-KEMP LoadMaster UC-APL Compliant 7 1 35CromPas encore d'évaluation
- GCSE (J277) Keywords For GcseDocument16 pagesGCSE (J277) Keywords For GcseEmma StevensPas encore d'évaluation
- MTN Radio UMTS Baseline PA12 21-May 20Document24 pagesMTN Radio UMTS Baseline PA12 21-May 20AjayPas encore d'évaluation
- Ques VAPTDocument9 pagesQues VAPTTanayyPas encore d'évaluation
- 640-822 ICND1 Exam TopicsDocument4 pages640-822 ICND1 Exam TopicsZoltan LedererPas encore d'évaluation
- DNS Interview Questions and AnswersDocument6 pagesDNS Interview Questions and Answersasinha08Pas encore d'évaluation
- Automated Application Visibility For The Software-Defined Data CenterDocument2 pagesAutomated Application Visibility For The Software-Defined Data CenterVal VegePas encore d'évaluation
- Netflix Openconnect: Appliance Deployment GuideDocument38 pagesNetflix Openconnect: Appliance Deployment GuidePranovePas encore d'évaluation
- 8.2.4.14 Packet Tracer - Troubleshooting Enterprise Networks 3 Instructions - ILMDocument13 pages8.2.4.14 Packet Tracer - Troubleshooting Enterprise Networks 3 Instructions - ILMIngrid RodriguezPas encore d'évaluation
- Schematic KIT PIC V3 MinhHaGroupDocument2 pagesSchematic KIT PIC V3 MinhHaGroupTrần MạnhPas encore d'évaluation
- Push TechnologyDocument21 pagesPush TechnologyPrasanth Naik0% (1)
- Cisco Unified IP Phone 9971Document9 pagesCisco Unified IP Phone 9971Daniela Monar VasconezPas encore d'évaluation
- Bussystem AS-Interface - Katalog Deutsch 2008/2009Document282 pagesBussystem AS-Interface - Katalog Deutsch 2008/2009ifm electronicPas encore d'évaluation
- Installing Multi Node Cluster - Handbook 2.0Document2 pagesInstalling Multi Node Cluster - Handbook 2.0aadifxPas encore d'évaluation
- 4 - Introduction To Dynamic Routing & DV Vs LsDocument26 pages4 - Introduction To Dynamic Routing & DV Vs Lsfauzi endraPas encore d'évaluation
- (OpenWrt Wiki) Unlocking The Netgear Telnet ConsoleDocument12 pages(OpenWrt Wiki) Unlocking The Netgear Telnet ConsoleLee HomeusePas encore d'évaluation
- Conext Combox Owners GuideDocument140 pagesConext Combox Owners GuideronaldmarcellePas encore d'évaluation
- EDS 508A Series - Moxa Eds 508a Series Firmware v3.8 - Software Release HistoryDocument10 pagesEDS 508A Series - Moxa Eds 508a Series Firmware v3.8 - Software Release Historysebascast77Pas encore d'évaluation
- Lesson PlanDocument6 pagesLesson PlanFaruk MohamedPas encore d'évaluation