Académique Documents
Professionnel Documents
Culture Documents
Dtme Mepov8 Keep Calm Carry On
Transféré par
Naresh NaniCopyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Dtme Mepov8 Keep Calm Carry On
Transféré par
Naresh NaniDroits d'auteur :
Formats disponibles
Keep calm
You think you have discovered
a fraud. What do you do?
Despite recent surveys pointing to fraud
being on the increase, the discovery of a
suspected fraud within any organization is
not an everyday occurrence for most people
and initial reactions may include shock and
surprise. However, action taken in the first
few hours and days after discovery will
significantly impact the course and/or
outcome of a full investigation and may
even make it or break it.
12 | Spring 2012 | A Middle East Point of View
Fraud
and carry on.
Most organizations have controls in place to prevent and
detect fraud being committed against them from the
outside. In the banking industry in particular, external fraud When a potential fraud is first
is an expected occurrence and banks employ sophisticated
processes and technology to prevent and detect such discovered, the following few
occurrences. The bigger problem occurs when fraud has
been committed from within. Apart from the cost involved,
hours or days can be very
there is always some collateral damage caused including loss
of reputation, brand damage and reduced employee morale.
confusing and stressful if the
Seniority of the suspect is also a factor, the more senior the
employee, the more serious the damage.
organization is unprepared
History shows that, in the absence of any structured
response plan, the amount of time and effort it takes for For example, in a recent fraud incident occurring in the UAE,
management to respond, particularly in the initial weeks, is an employee who was in charge of procurement for a
excessive and severely impacts the normal business activity of certain organization also operated a supply and contracting
the organization. When a potential fraud is first discovered, company which had been paid in excess of Dhs 3,000,000
the following few hours or days can be very confusing and by his employer’s company, all ordered and authorised by
stressful if the organization is unprepared. In the absence of him. The suspect, once discovered, was dismissed but was
a Fraud Response Plan, experience has shown that managers given a month’s grace period during which time he
handle the same problem in different ways - sometimes with destroyed a large number of incriminating documents.
disastrous consequences such as destroying the evidentiary
value of information by inappropriate handling processes, In another incident, it became widely known throughout an
inadvertently tipping off the suspect, enabling them to organization that a fraud had been uncovered. However,
destroy incriminating evidence, failing to keep the matter that particular incident, which became public knowledge,
confidential and taking inappropriate action caused by was only a small part of a much larger conspiracy between a
having insufficient information. number of employees and suppliers. By failing to keep the
A Middle East Point of View | Spring 2012 | 13
Fraudsters rarely restrict their activities
to only one modus operandi or method.
Therefore, every effort should be made
to obtain as much information as
possible before anyone is questioned,
confronted or interviewed.
matter confidential, the company management enabled
the conspirators to destroy incriminating records,
electronic data and to dispose of stolen property, which
rendered any future investigation futile. The identities of
the suspects were not confirmed, meaning that the
company may still be employing people who are actively
seeking ways to defraud it.
A Fraud Response Plan ensures that incidents are
handled in a systematic and efficient manner, not only
to conclude a successful investigation, but also to show
that the organization acted in a prudent and lawful
manner. And that it does not tolerate fraud.
The Fraud Response Plan should outline how far an
individual line manager should go in collecting initial
information before invoking the Response Plan. The
key is to provide the line manager with an effective
framework to resolve concerns, rather than leave such
resolution to individual initiative.
14 | Spring 2012 | A Middle East Point of View
Fraud
Initial Action
It is important to remember that when fraud is first
suspected, the matter may well be more serious than it It is vital that all allegations of fraud
may initially appear. This is because fraudsters rarely
restrict their activities to only one modus operandi or are treated seriously and that
method. Therefore, every effort should be made to
obtain as much information as possible before anyone
responsibility for handling fraud
is questioned, confronted or interviewed. This is
particularly important in organizations or business units
incidents is assigned to a senior,
with a close working environment, where there may be
a strong temptation to simply question an employee as
trusted individual or collection of
soon as suspicion is raised. individuals
It is also important to be aware that larger scale frauds
are often international in nature. Therefore, any fraud
Initial responsibility designation
contingency planning must include measures for taking
Fraud investigation is, by necessity, a confidential
legal and investigative action across jurisdictions.
task and is a sensitive matter for the vast majority of
organizations. It is vital that all allegations of fraud are
In addition, most frauds involve the use of a computer
treated seriously and that responsibility for handling
at some stage in the planning or execution of the fraud.
fraud incidents is assigned to a senior, trusted individual
This is particularly evident in today’s environment, when
or collection of individuals. In many organizations, that
the majority of white collar employees are allocated a
responsibility is handed to a corporate security advisor,
computer by their employer. Business is conducted by
internal audit manager or risk management director.
computer and correspondence normally involves a
In other organizations, the responsibility is shared
computer through the widespread use of corporate
between members of senior management or an audit
e-mail. The pervasive involvement of the computer into
committee and the organization’s human resources
most facets of corporate life means that electronic
personnel and corporate lawyers are involved from
evidence is often vital to investigating corporate fraud.
a very early point. Fraud incident management
Obtaining that electronic piece of evidence is a specialist
responsibility is an important role and those chosen to
skill which should be discussed with your forensic
administer the role must come from the appropriate
specialists.
legal and management level to authorise investigative
actions and to co-ordinate the organization’s overall
Initial actions are crucial to the eventual outcome of an
response to fraud incidents.
investigation and, if a proper strategy is put in place and
adhered to, the extent of fraudulent activity can usually
be assessed and action taken to resolve the matter
successfully. This usually means assimilating sufficient
evidence to dismiss errant staff and to commence civil
and/or criminal proceedings against those concerned in
the fraud, or claims against insurers, if so desired.
A Middle East Point of View | Spring 2012 | 15
As part of their overall fraud control plan, organizations or explosion), so it is not uncommon to take a similar
should assign responsibility for fraud incident approach in a Fraud Response Plan. Typically, this means
management to an appropriate person(s) as a forming a Fraud Incident Management Team, comprising
precursor to adopting an incident management plan. essential members and co-opted members.
Consideration should also be given to the appropriate
level of involvement by corporate lawyers and human In some types of fraud, the victim may only have a few
resource personnel. hours to take action to freeze funds which have been
illicitly transferred. It is essential that contact numbers
for essential service providers are established
beforehand, including internal support departments,
Most frauds involve the use of a such as legal, corporate security, insurance external
lawyers, police and telecommunications agencies,
computer at some stage in the forensic accountants and investigators.
planning or execution of the fraud. Receipt and initial assessment of suspicion,
allegation or ‘tip off’
This is particularly evident in today’s Fraud investigations are often initiated after an
allegation or a tip-off (often anonymous) is received.
environment, when the majority of This will usually be sourced from inside the organization,
although external tip-offs are not uncommon. Many
white collar employees are allocated a fraud incidents are initially discovered by accident,
computer by their employer. perhaps as a result of an audit, job change or
resignation. Very few frauds are discovered as part
of a deliberate attempt to uncover fraud, as very few
organizations implement a proactive fraud detection
Fraud Response Team program.
Some Fraud Response Plans only deal with situations
where an employee discovers a fraud and hands it over The checklist on the right/left highlights initial actions to
to an investigation department to follow up. However, be taken (or not) upon the discovery of fraud or tip-off.
some frauds have impacts far beyond the remit of the
investigation department to deal with (such as when the At the conclusion of this stage, a decision must be
organization’s liquidity is threatened). The Plan also made as to whether the allegation or suspicion warrants
should cater for these eventualities. investigation or is implausible or vexatious. However,
this decision must be made carefully. If an allegation
Most large organizations have formed crisis management cannot be quickly dismissed as false, further action
committees to respond to major incidents (such as a fire should be taken.
16 | Spring 2012 | A Middle East Point of View
Fraud
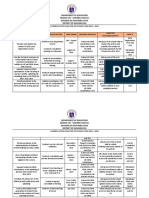
Checklist fraud:
n discovering a potential
Initial action checklist upo gat ion or
nt manager that an alle
1. Alert the fraud incide
suspicion exists
and details of initial
A typical Fraud Response Plan contains: 2. Document date, time
report/discovery if
• purpose of the plan, ervations and actions –
• policy statement, 3. Take notes of all obs e, it is worth
ing a me nta l not
something is worth tak
• definition of fraud,
a written note) ple who
• roles and responsibilities including lity (only inform those peo
4. Maintain confidentia rran ted
fraud response team, suspected act). Unwa
need to know about the ces sfu l
• objectives including civil and damage potential suc
disclosure can seriously
criminal response, front the suspect.
investigations. Do not con
• reporting of suspicions and collection pec ted act or wrongdoing
and preservation of evidence. 5. Write out in full the sus
including:
e occurred
• What is alleged to hav
e committed the act
• Who is alleged to hav
• Is the activity continu ing
• Where did it occur
loss or potential loss
• What is the value of the
As part of their overall • Who knows of the act
ivity
fraud control plan, 6. Identify all document
ary and other evidence
y
connected to the activit
organizations should assign • Invoices
responsibility for fraud • Contracts
• Purchase orders
incident management to an • Cheques
• Computers
appropriate person(s) as a • Credit card statement
s
ly
precursor to adopting an 7. Obtain evidence and
place in a secure area. (on
t alerting any sus pec ts)
where it is possible withou
incident management plan 8. Protect evidence from
dam age or contamination
uisition
ually taking note of acq
9. List each item individ
ation) and where the item
(incl. time, date and loc
by David Clements, director, Forensic and Dispute was securely stored
witnesses
Services, Deloitte Corporate Finance Ltd 10. Identify all potential
den ce is in the process of
11. Unless electronic evi t
go into the suspect/targe
being destroyed do not
computer systems ess
/or remove suspect’s acc
12. If possible, secure and w IT
tems. Do not allo
to relevant computers/sys
min e com puter
department to exa
ent ial sus pec ts and extent of fraud
13. Consider other pot
A Middle East Point of View | Spring 2012 | 17
Vous aimerez peut-être aussi
- IT Induction and Information Security Awareness: A Pocket GuideD'EverandIT Induction and Information Security Awareness: A Pocket GuidePas encore d'évaluation
- Exactech Newsletter APRIL 2019Document2 pagesExactech Newsletter APRIL 2019Mario FazekasPas encore d'évaluation
- Fraud Risk Management Second EditionDocument1 pageFraud Risk Management Second EditionAstalapulos ListestosPas encore d'évaluation
- The Secret To Creating A Cybersecurity-Aware Organization EbookDocument13 pagesThe Secret To Creating A Cybersecurity-Aware Organization EbookgamallofPas encore d'évaluation
- IAPP Top MistakesDocument3 pagesIAPP Top MistakesAnaPas encore d'évaluation
- This Study Resource Was: Individual Assignment Contemporary Issues of AuditingDocument5 pagesThis Study Resource Was: Individual Assignment Contemporary Issues of AuditingThuy LinhPas encore d'évaluation
- Unmasking The Enemy Within 110391Document15 pagesUnmasking The Enemy Within 110391Andrew Richard ThompsonPas encore d'évaluation
- Sep3701 PortifolioDocument9 pagesSep3701 Portifoliothandogumede RebecaPas encore d'évaluation
- Accist Reviewer 2Document8 pagesAccist Reviewer 2Cathryn SolitoPas encore d'évaluation
- Veriato - Three Steps To Spotting Insider ThreatsDocument12 pagesVeriato - Three Steps To Spotting Insider ThreatsRSME DubaiPas encore d'évaluation
- Workplace Frauds: Fraud: Criminal Deception Swindle Imposture Pilferage: Steal in Small Quantities Swindle: CheatDocument5 pagesWorkplace Frauds: Fraud: Criminal Deception Swindle Imposture Pilferage: Steal in Small Quantities Swindle: CheatAnuj GoelPas encore d'évaluation
- KPMG Fraud Survey (Ch3)Document38 pagesKPMG Fraud Survey (Ch3)joyanto.roy7079Pas encore d'évaluation
- Goals of Auditing and Risk AssessmentDocument7 pagesGoals of Auditing and Risk Assessmentjoshua chegePas encore d'évaluation
- Computer Fraud and Security: Suggested Answers To Discussion QuestionsDocument22 pagesComputer Fraud and Security: Suggested Answers To Discussion QuestionsMikay TorioPas encore d'évaluation
- Computer Fraud and Security: Suggested Answers To Discussion QuestionsDocument22 pagesComputer Fraud and Security: Suggested Answers To Discussion QuestionsCelestaire LeePas encore d'évaluation
- Computer Fraud and Security: Suggested Answers To Discussion QuestionsDocument22 pagesComputer Fraud and Security: Suggested Answers To Discussion QuestionsMikay TorioPas encore d'évaluation
- An Inside Track On Insider Threats: You Can't Take It With YouDocument11 pagesAn Inside Track On Insider Threats: You Can't Take It With YouEvan Chronixx TomlixPas encore d'évaluation
- Recognizing The Many Faces of Insider ThreatsDocument14 pagesRecognizing The Many Faces of Insider ThreatskhaderPas encore d'évaluation
- The Marketing Finance Interface: Cgma ReportDocument48 pagesThe Marketing Finance Interface: Cgma ReportChristie RochaPas encore d'évaluation
- Pindi Yulinar Rosita - 008201905023 - Session 5Document7 pagesPindi Yulinar Rosita - 008201905023 - Session 5Pindi YulinarPas encore d'évaluation
- 04 - Fraud Risk Management A Guide To GOOD PRACTICEDocument48 pages04 - Fraud Risk Management A Guide To GOOD PRACTICEEd Gonzales GonzalesPas encore d'évaluation
- Rais12 SM CH05Document35 pagesRais12 SM CH05Anton VitaliPas encore d'évaluation
- Sisfo Jawaban KasusDocument36 pagesSisfo Jawaban KasuspnharyonoPas encore d'évaluation
- How To Conduct A Fraud Investigation (HR Advisor 2003) PDFDocument5 pagesHow To Conduct A Fraud Investigation (HR Advisor 2003) PDFAsim DarPas encore d'évaluation
- Exactech Newsletter Spring 2019Document2 pagesExactech Newsletter Spring 2019Mario FazekasPas encore d'évaluation
- Red Team Assessments EbookDocument8 pagesRed Team Assessments Ebookjesus_yustasPas encore d'évaluation
- Accist Reviewer 2Document6 pagesAccist Reviewer 2Angelie SaavedraPas encore d'évaluation
- Top Takeaways: Realize That We Have Been Breached?" and "Have We Taken The Appropriate Steps ToDocument2 pagesTop Takeaways: Realize That We Have Been Breached?" and "Have We Taken The Appropriate Steps Tojuki_7Pas encore d'évaluation
- FraudDocument10 pagesFraudHershey ReyesPas encore d'évaluation
- Countering The 10 Most Common Excuses For Corrupt Behaviour: A Pocket Guide For Business PractitionersDocument32 pagesCountering The 10 Most Common Excuses For Corrupt Behaviour: A Pocket Guide For Business PractitionersFrancheska VillamilPas encore d'évaluation
- Business Ethics - Bribery PPT-students'Document13 pagesBusiness Ethics - Bribery PPT-students'Susana Cordice100% (3)
- Assignment - Ipremier Case StudyDocument5 pagesAssignment - Ipremier Case StudyPranathi SepuriPas encore d'évaluation
- Computer Fraud: Chapter 3 - Custom Version of Textbook - Full Version of TextbookDocument33 pagesComputer Fraud: Chapter 3 - Custom Version of Textbook - Full Version of TextbookJoel Christian MascariñaPas encore d'évaluation
- Exactech Newsletter June 2019Document2 pagesExactech Newsletter June 2019Mario FazekasPas encore d'évaluation
- 5 Steps For Better Risk Assessments Ebook LogicManagerDocument15 pages5 Steps For Better Risk Assessments Ebook LogicManagerSANJAY KUMAR M APas encore d'évaluation
- In Fa Building Effective Internal Financial Controls NoexpDocument14 pagesIn Fa Building Effective Internal Financial Controls NoexpFelix Peralta LalanePas encore d'évaluation
- Content Fraud BrainstormingDocument6 pagesContent Fraud BrainstormingCreanga GeorgianPas encore d'évaluation
- Fraud Detection in Non-Cash Transactions Using Information System Audit (A Case Study of Government Bank in Bandung Indonesia)Document6 pagesFraud Detection in Non-Cash Transactions Using Information System Audit (A Case Study of Government Bank in Bandung Indonesia)Wisanggeni RatuPas encore d'évaluation
- Fraud Investigation and Control Summit 2011Document3 pagesFraud Investigation and Control Summit 2011abidalidossa100% (1)
- Cisos-Under-The-Spotlight-Security-Whitepaper FDocument16 pagesCisos-Under-The-Spotlight-Security-Whitepaper FMariuxi S. PérezPas encore d'évaluation
- How To See It Coming: Linking Risk and Performance ManagementDocument12 pagesHow To See It Coming: Linking Risk and Performance Managementsunnykapoor3Pas encore d'évaluation
- WEF - Compliance (2020)Document14 pagesWEF - Compliance (2020)GDIAZPas encore d'évaluation
- Internal Audit: Key Risks & Focus Areas 2021Document7 pagesInternal Audit: Key Risks & Focus Areas 2021Trần Minh QuangPas encore d'évaluation
- Fraud Policy Template-Pdf-2Document13 pagesFraud Policy Template-Pdf-2Ranjeet DongrePas encore d'évaluation
- Dynamic: Near Miss ReportingDocument19 pagesDynamic: Near Miss ReportingObie86 BahhierPas encore d'évaluation
- Digital Asset Identification: Seen Primary ReasonDocument6 pagesDigital Asset Identification: Seen Primary ReasonJoshua MusilaPas encore d'évaluation
- PWC 2022 Flagship Piece - How Technology Can Enable Proactive Risk ManagementDocument9 pagesPWC 2022 Flagship Piece - How Technology Can Enable Proactive Risk ManagementGuy YgalPas encore d'évaluation
- Workplace Misconduct ColDocument8 pagesWorkplace Misconduct ColHugo Ceo PerúPas encore d'évaluation
- Whitepaper Product Building Robust DefensesDocument9 pagesWhitepaper Product Building Robust DefensesIonut JulaPas encore d'évaluation
- Dsa 102 Lesson 1Document16 pagesDsa 102 Lesson 1shadowlord468Pas encore d'évaluation
- Organizations, Employees and Computer Crimes: PHD Student Dana Ramona AndrişescuDocument12 pagesOrganizations, Employees and Computer Crimes: PHD Student Dana Ramona AndrişescuOtilia BadeaPas encore d'évaluation
- PwC-Pulling Money Laundering Out of The ShadowDocument108 pagesPwC-Pulling Money Laundering Out of The ShadowAdrian octo pratamaPas encore d'évaluation
- 2023 Phishing by Industry Benchmarking ReportDocument35 pages2023 Phishing by Industry Benchmarking Reportoria001Pas encore d'évaluation
- Cyber Security: Incident Management GuideDocument44 pagesCyber Security: Incident Management GuideOusmane NdourPas encore d'évaluation
- Forensic Services and Global Experience: The Intelligent Connection - EY IndiaDocument8 pagesForensic Services and Global Experience: The Intelligent Connection - EY IndiaBharat SinhaPas encore d'évaluation
- Five Steps To Risk ReductionDocument5 pagesFive Steps To Risk ReductionJordan PopovskiPas encore d'évaluation
- Ways To Improve: Staff Cyber Security AwarenessDocument9 pagesWays To Improve: Staff Cyber Security AwarenessconorgigelPas encore d'évaluation
- WoB AMLCTFDocument46 pagesWoB AMLCTFMorphuesPas encore d'évaluation
- FALLSEM2021-22 CSE3501 ETH VL2021220103880 Reference Material II 18-10-2021 Key Incident Management RolesDocument4 pagesFALLSEM2021-22 CSE3501 ETH VL2021220103880 Reference Material II 18-10-2021 Key Incident Management RolesSHARANYA MUKHERJEE 19BCE2676Pas encore d'évaluation
- Fraud PolicyDocument8 pagesFraud PolicyAkpenPas encore d'évaluation
- IPO Ordinance 2005Document13 pagesIPO Ordinance 2005Altaf SheikhPas encore d'évaluation
- Business Environment Analysis - Saudi ArabiaDocument24 pagesBusiness Environment Analysis - Saudi ArabiaAmlan JenaPas encore d'évaluation
- Specialty Arc Fusion Splicer: FSM-100 SeriesDocument193 pagesSpecialty Arc Fusion Splicer: FSM-100 SeriesSFTB SoundsFromTheBirdsPas encore d'évaluation
- TEVTA Fin Pay 1 107Document3 pagesTEVTA Fin Pay 1 107Abdul BasitPas encore d'évaluation
- Electrical ConnectorsDocument5 pagesElectrical ConnectorsRodrigo SantibañezPas encore d'évaluation
- Micron Interview Questions Summary # Question 1 Parsing The HTML WebpagesDocument2 pagesMicron Interview Questions Summary # Question 1 Parsing The HTML WebpagesKartik SharmaPas encore d'évaluation
- Lactobacillus Acidophilus - Wikipedia, The Free EncyclopediaDocument5 pagesLactobacillus Acidophilus - Wikipedia, The Free Encyclopediahlkjhlkjhlhkj100% (1)
- American AccentDocument40 pagesAmerican AccentTimir Naha67% (3)
- Action Plan Lis 2021-2022Document3 pagesAction Plan Lis 2021-2022Vervie BingalogPas encore d'évaluation
- Cancellation of Deed of Conditional SalDocument5 pagesCancellation of Deed of Conditional SalJohn RositoPas encore d'évaluation
- Aircraftdesigngroup PDFDocument1 pageAircraftdesigngroup PDFsugiPas encore d'évaluation
- GL 186400 Case DigestDocument2 pagesGL 186400 Case DigestRuss TuazonPas encore d'évaluation
- HRD DilemmaDocument4 pagesHRD DilemmaAjay KumarPas encore d'évaluation
- Missouri Courts Appellate PracticeDocument27 pagesMissouri Courts Appellate PracticeGenePas encore d'évaluation
- 199437-Unit 4Document36 pages199437-Unit 4Yeswanth rajaPas encore d'évaluation
- Dike Calculation Sheet eDocument2 pagesDike Calculation Sheet eSaravanan Ganesan100% (1)
- Deed of Assignment CorporateDocument4 pagesDeed of Assignment CorporateEric JayPas encore d'évaluation
- Gabby Resume1Document3 pagesGabby Resume1Kidradj GeronPas encore d'évaluation
- CSEC Jan 2011 Paper 1Document8 pagesCSEC Jan 2011 Paper 1R.D. KhanPas encore d'évaluation
- Calibration CertificateDocument1 pageCalibration CertificateSales GoldClassPas encore d'évaluation
- Edita's Opertionalization StrategyDocument13 pagesEdita's Opertionalization StrategyMaryPas encore d'évaluation
- MSDS - Tuff-Krete HD - Part DDocument6 pagesMSDS - Tuff-Krete HD - Part DAl GuinitaranPas encore d'évaluation
- What Caused The Slave Trade Ruth LingardDocument17 pagesWhat Caused The Slave Trade Ruth LingardmahaPas encore d'évaluation
- HandloomDocument4 pagesHandloomRahulPas encore d'évaluation
- Brochure Ref 670Document4 pagesBrochure Ref 670veerabossPas encore d'évaluation
- Manual 40ku6092Document228 pagesManual 40ku6092Marius Stefan BerindePas encore d'évaluation
- Enerparc - India - Company Profile - September 23Document15 pagesEnerparc - India - Company Profile - September 23AlokPas encore d'évaluation
- Hotel Reservation SystemDocument36 pagesHotel Reservation SystemSowmi DaaluPas encore d'évaluation
- SME-Additional Matter As Per Latest Syllabus Implementation WorkshopDocument14 pagesSME-Additional Matter As Per Latest Syllabus Implementation WorkshopAvijeet BanerjeePas encore d'évaluation
- Algorithmique Et Programmation en C: Cours Avec 200 Exercices CorrigésDocument298 pagesAlgorithmique Et Programmation en C: Cours Avec 200 Exercices CorrigésSerges KeouPas encore d'évaluation