Académique Documents
Professionnel Documents
Culture Documents
Cyber Crime
Transféré par
nainjaneDescription originale:
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Cyber Crime
Transféré par
nainjaneDroits d'auteur :
Formats disponibles
What is Cybercrime?
Online activities are just as vulnerable to crime and can compromise personal safety just
as effectively as common everyday crimes. Lawmakers, law enforcement, and
individuals need to know how to protect themselves and the persons for which they are
responsible. You can see by the explanations of various cybercrimes below that the
crimes have existed long before computers and the internet were made available to the
general public. The only difference involves the tools used to commit the crime.
Types of Cybercrime
Assault by Threat – threatening a person with fear for their lives or the lives of their
families or persons whose safety they are responsible for (such as employees or
communities) through the use of a computer network such as email, videos, or phones.
Child Pornography – the use of computer networks to create, distribute, or access
materials that sexually exploit underage children.
Cyber Contraband – transferring illegal items through the internet (such as encryption
technology) that is banned in some locations.
Cyberlaundering – electronic transfer of illegally-obtained monies with the goal of hiding
its source and possibly its destination.
Cyberstalking – express or implied physical threats that creates fear through the use of
computer technology such as email, phones, text messages, webcams, websites or videos.
Cyberterrorism – premeditated, usually politically-motivated violence committed against
civilians through the use of, or with the help of, computer techology.
Cybertheft – using a computer to steal. This includes activities related to: breaking and
entering, DNS cache poisoning, embezzlement and unlawful appropriation, espionage,
identity theft, fraud, malicious hacking, plagiarism, and piracy. Examples include:
1. Advertising or soliciting prostitution through the internet. It is against the law
to access prostitution through the internet (including in the state of Nevada in the
United States) because the process of accessing the internet crosses state and
sometimes national borders. This is a violation of the federal Digital Millennium
Copyright Act http://www.copyright.gov/legislation/dcma.pdf.
2. Drug Sales. Both illegal and prescription drug sales through the internet are
illegal except as a customer through a state licensed pharmacy based in the United
States http://www.fda.gov.
3. Computer-based fraud. Fraud is different from theft because the victim
voluntarily and knowingly gives the money or property to the criminal but would
not have if the criminal did not misrepresent themselves or their offering. Fraud is
a lie. If someone leads you on or allows you to believe something that is false to
benefit them, they are lying and this is fraud. You become a victim when you
voluntarily surrender monies or property based on their misrepresentation or lie.
Losing money from computer crime can be especially devastating because often it
is very difficult to get the money back. Examples are: scams and altering data to
get a benefit, suchas removing arrest records from the police station server,
changing grades on the school computer system or deleting speeding tickets from
driving records.
4. Online Gambling. Gambling over the internet is a violation of American law
because the gambling service providers require electronic payment for gambling
through the use of credit cards, debit cards, electronic fund transfers which is
illegal with the Unlawful Internet Gambling Enforcement Act
http://frwebgate.access.gpo.gov/cgi-bin/getdoc.cgi?
dbname=109_cong_bills&docid=f:h4411eh.txt.pdf.
Cybertresspass – someone accesses a computer’s or network’s resources without the
authorization or permission of the owner but does not alter, disturb, misuse, or damage
the data or system. This is hacking for the purpose of entering an electronic network
without permission. Examples might include:
1. Using a wireless internet connection at a hotel at which you are staying and
accessing the hotel’s private files without disturbing them because they are
available.
2. Reading email, files, or noting which programs are installed on a third-party's
computer system without permission just for fun, because you can. This is
sometimes called Snooping.
Cybervandalism - Damaging or destroying data rather than stealing or misusing them (as
with cybertheft) is called cybervandalism. This can include a situation where network
services are disrupted or stopped. This deprives the computer/network owners and
authorized users (website visitors, employees) of the network itself and the data or
information contained on the network. Examples:
• Entering a network without permission and altering, destroying, or deleting data
or files.
• Deliberately entering malicious code (viruses, Trojans) into a computer network
to monitor, follow, disrupt, stop, or perform any other action without the
permission of the owner of the network.
• Attacking the server of the computer network (DDoS attack) so the server does
not perform properly or prevents legitimate website visitors from accessing the
network resources with the proper permissions.
Read more: http://www.brighthub.com/internet/security-
privacy/articles/3435.aspx#ixzz19TXADLTr
Vous aimerez peut-être aussi
- Digital Dangers: Navigating the Perils of Online Safety and Piracy. Protecting Yourself and Your Content in the Digital AgeD'EverandDigital Dangers: Navigating the Perils of Online Safety and Piracy. Protecting Yourself and Your Content in the Digital AgePas encore d'évaluation
- Classification of Cyber CrimeDocument3 pagesClassification of Cyber Crimenanidefran100% (1)
- Cybercrime LessonDocument27 pagesCybercrime LessonXivaughn SebastianPas encore d'évaluation
- Cyber Law Introduction: We Can Categorize Cyber Crimes in Two WaysDocument6 pagesCyber Law Introduction: We Can Categorize Cyber Crimes in Two WaysAnushka Bansal 12G SNPas encore d'évaluation
- Lecture 01Document11 pagesLecture 01Sahim SalemPas encore d'évaluation
- We Can Categorize Cyber Crimes in Two WaysDocument33 pagesWe Can Categorize Cyber Crimes in Two Waysjeet1245Pas encore d'évaluation
- Cyber Law of IndiaDocument14 pagesCyber Law of IndiaSatya KumarPas encore d'évaluation
- Practical 1 AIM: Study Practical On Cyber Crime and Generation of Hash Values On File System. Theory: 1) Cyber CrimeDocument4 pagesPractical 1 AIM: Study Practical On Cyber Crime and Generation of Hash Values On File System. Theory: 1) Cyber CrimeSneha DasPas encore d'évaluation
- Socilogy Assignment PDFDocument4 pagesSocilogy Assignment PDFNEERAJ SHARMAPas encore d'évaluation
- What Is Cyber CrimeDocument3 pagesWhat Is Cyber CrimeJackson DavidPas encore d'évaluation
- Cyber Law of IndiaDocument16 pagesCyber Law of IndiaLitwin carmalPas encore d'évaluation
- Cyber World Crime ActsDocument63 pagesCyber World Crime ActsPity AgarwalPas encore d'évaluation
- Subject Notes Unit - 1: Introduction of Cyber CrimeDocument94 pagesSubject Notes Unit - 1: Introduction of Cyber CrimeayushPas encore d'évaluation
- Cybercrime Act R.A 10175Document11 pagesCybercrime Act R.A 10175Luis MasangkayPas encore d'évaluation
- The Cybercrime and Internet ThreatsDocument9 pagesThe Cybercrime and Internet ThreatsDiana Mark AndrewPas encore d'évaluation
- What Is CybercrimeDocument4 pagesWhat Is CybercrimeKartik Mehta SEC-C 2021Pas encore d'évaluation
- Unit 1 - Cyber Security - WWW - Rgpvnotes.inDocument7 pagesUnit 1 - Cyber Security - WWW - Rgpvnotes.inIndrajeet kumarPas encore d'évaluation
- Computer Crime ProjectDocument11 pagesComputer Crime ProjectankushbestPas encore d'évaluation
- Why Cyberlaw in IndiaDocument8 pagesWhy Cyberlaw in IndiaSaurabh KhannaPas encore d'évaluation
- I.T CSEC Computer Security and CybersecurityDocument54 pagesI.T CSEC Computer Security and Cybersecuritybrownavia9Pas encore d'évaluation
- Teknologi Maklumat Dalam Pendidikan: Computer Security, Ethic and PrivacyDocument70 pagesTeknologi Maklumat Dalam Pendidikan: Computer Security, Ethic and PrivacyFattihi EkhmalPas encore d'évaluation
- Cyber Crimes and The Law: CybercrimeDocument6 pagesCyber Crimes and The Law: CybercrimeAman GautamPas encore d'évaluation
- LESSON 1-CybercrimeDocument22 pagesLESSON 1-CybercrimeVamee AsuncionPas encore d'évaluation
- Cyber CrimesDocument11 pagesCyber CrimesHarshini JJWPas encore d'évaluation
- Unit 3 - Cyber SecurityDocument7 pagesUnit 3 - Cyber SecurityPradmohan Singh TomarPas encore d'évaluation
- National Persepctive IT ACTDocument13 pagesNational Persepctive IT ACTkingchamp00755Pas encore d'évaluation
- Business Ethics: Institute of Management Mba (Full Time) 2020-2022 (Nirma University)Document10 pagesBusiness Ethics: Institute of Management Mba (Full Time) 2020-2022 (Nirma University)ram avtar BansalPas encore d'évaluation
- Cyber CrimeDocument37 pagesCyber Crimerajanityagi23Pas encore d'évaluation
- 03 Ict 136 Unit 2 Lesson 1Document39 pages03 Ict 136 Unit 2 Lesson 1Kimberly LopinesPas encore d'évaluation
- Chapter 2Document19 pagesChapter 2Instead RepentPas encore d'évaluation
- Disadvantage of ICTDocument18 pagesDisadvantage of ICTAldwin Rex A. FranciscoPas encore d'évaluation
- Cyber SecurityDocument10 pagesCyber SecurityAmit ThubePas encore d'évaluation
- Cyber Crime in BangladeshDocument9 pagesCyber Crime in Bangladeshapi-291831560Pas encore d'évaluation
- Unit 1 - Cyber SecurityDocument6 pagesUnit 1 - Cyber Securitymysadidvd009Pas encore d'évaluation
- Fundamentals of The CybercrimesDocument8 pagesFundamentals of The CybercrimesMaki MakiPas encore d'évaluation
- Cyber LawDocument7 pagesCyber LawJyoti BhutiaPas encore d'évaluation
- Cyber Laws - Unit 1Document47 pagesCyber Laws - Unit 1Aradhana SinghPas encore d'évaluation
- Cyber Crime and Its Categories - PDF 39Document5 pagesCyber Crime and Its Categories - PDF 39Radical GracePas encore d'évaluation
- Unit 1 - Cyber SecurityDocument5 pagesUnit 1 - Cyber SecurityjinkhatimaPas encore d'évaluation
- Investigation of Cyber CrimesDocument27 pagesInvestigation of Cyber CrimesThamizhmani RathnamPas encore d'évaluation
- DICEDocument9 pagesDICEsarPas encore d'évaluation
- Unit 5 Cyber CrimeDocument35 pagesUnit 5 Cyber CrimeDeborahPas encore d'évaluation
- Violation of Privacy in Computers and It'S Prevention: by I ArchanaDocument7 pagesViolation of Privacy in Computers and It'S Prevention: by I ArchanaArchanaPas encore d'évaluation
- DF Unit-1Document18 pagesDF Unit-1UNALLOYED GAMINGPas encore d'évaluation
- Cyber Crime Forensic InvestigationDocument31 pagesCyber Crime Forensic InvestigationS.m. Jafar100% (1)
- Chapter 1 - Cyber SecurityDocument20 pagesChapter 1 - Cyber SecurityAnurag Parate100% (1)
- Mapeh PresentationDocument16 pagesMapeh PresentationEdward Joseph AmbrosioPas encore d'évaluation
- Cyber Law: Legal Environment of BusinessDocument24 pagesCyber Law: Legal Environment of BusinessImtiaz SkPas encore d'évaluation
- Nature Definition On Cyber CrimeDocument15 pagesNature Definition On Cyber Crimesailegummegister_768100% (1)
- Crimes Related To IT 27.03Document35 pagesCrimes Related To IT 27.03Hitesh PhulwaniPas encore d'évaluation
- The Disadvantage S of ICT: Group 2Document22 pagesThe Disadvantage S of ICT: Group 2Agnes MisamisPas encore d'évaluation
- Cybercrime Laws 1Document7 pagesCybercrime Laws 1Anime AddictPas encore d'évaluation
- Cyber Crime & Cyber LawDocument50 pagesCyber Crime & Cyber LawCA Monika PorwalPas encore d'évaluation
- Chapter 1 - Cyber SecurityDocument31 pagesChapter 1 - Cyber Securityorangesareamazing46100% (1)
- Digital LawsDocument19 pagesDigital LawsAIAH RIZPAH SOLIVAPas encore d'évaluation
- Internal Assessment ReportDocument14 pagesInternal Assessment Reportmanmeet chuggaPas encore d'évaluation
- Assignment 2 SitaDocument4 pagesAssignment 2 SitaNaveen PurohitPas encore d'évaluation
- Cybercrime: Intentionally Harm TheDocument7 pagesCybercrime: Intentionally Harm Thesuper quotes newPas encore d'évaluation
- Sop Takeover PJ SPJ PNPJDocument11 pagesSop Takeover PJ SPJ PNPJJeremie TisoyPas encore d'évaluation
- Ratan Lal Vs The State of Madhya Pradesh On 17 December, 1970Document4 pagesRatan Lal Vs The State of Madhya Pradesh On 17 December, 1970ghisaramPas encore d'évaluation
- 56 Edmund Sydeco Y Sionzon, Petitioner, vs. People of The PHILIPPINES, RespondentDocument2 pages56 Edmund Sydeco Y Sionzon, Petitioner, vs. People of The PHILIPPINES, RespondentHannah Sy100% (1)
- 7-People Vs RaveloDocument10 pages7-People Vs RaveloEvelynBeaPas encore d'évaluation
- KTVU StoryDocument2 pagesKTVU StoryErin SherbertPas encore d'évaluation
- Case of Gogitidze and Others v. GeorgiaDocument37 pagesCase of Gogitidze and Others v. GeorgiaSteve BacharidisPas encore d'évaluation
- Mondaiji-Tachi Ga Isekai Kara Kuru Sou Desu Yo Volume 1 - Yes! Kuro Usagi Called You!Document252 pagesMondaiji-Tachi Ga Isekai Kara Kuru Sou Desu Yo Volume 1 - Yes! Kuro Usagi Called You!Rackas Rackas100% (1)
- Essay On Death PenaltyDocument2 pagesEssay On Death PenaltyMoniruzzaman JurorPas encore d'évaluation
- Punishment and Different Forms of Violation of Human RightsDocument30 pagesPunishment and Different Forms of Violation of Human Rightsarnel jr. daquilaPas encore d'évaluation
- PP V Goh Eng SingDocument33 pagesPP V Goh Eng SingNoorPas encore d'évaluation
- People vs. Dela PiedraDocument2 pagesPeople vs. Dela PiedraKimberly RamosPas encore d'évaluation
- Sample Format of CSI Form 1: First Responder's FormDocument4 pagesSample Format of CSI Form 1: First Responder's Formarianne ayala100% (1)
- Violation Against WomenDocument10 pagesViolation Against WomenAyesha RehmanPas encore d'évaluation
- Joseph Mitchell PC StatementDocument2 pagesJoseph Mitchell PC StatementMcKenzie StaufferPas encore d'évaluation
- Rosas Vs Montor 204105Document16 pagesRosas Vs Montor 204105Anonymous OzIYtbjZPas encore d'évaluation
- Magistrate Report DominguezDocument54 pagesMagistrate Report DominguezInjustice WatchPas encore d'évaluation
- Ramiscal V SandiganbayanDocument2 pagesRamiscal V SandiganbayanAron PanturillaPas encore d'évaluation
- Cases Crimpro LastDocument4 pagesCases Crimpro LastJona MayPas encore d'évaluation
- Development Project Management Planning Tools and Techniques Final Project ReportDocument8 pagesDevelopment Project Management Planning Tools and Techniques Final Project ReportRupam Pratikshya100% (1)
- Anticipatory BailDocument14 pagesAnticipatory BailAishaPas encore d'évaluation
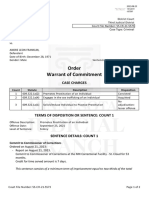
- Warrant of CommitmentDocument2 pagesWarrant of CommitmentMark WassonPas encore d'évaluation
- Chillicothe Police Reports For May 8th 2014Document79 pagesChillicothe Police Reports For May 8th 2014Andrew AB BurgoonPas encore d'évaluation
- Active Shooter PosterDocument1 pageActive Shooter PosterJO HN Scuba-rPas encore d'évaluation
- Rohan SahaiDocument20 pagesRohan SahaiMERCY LAWPas encore d'évaluation
- Cyber Laws in Pakistan: Presented byDocument26 pagesCyber Laws in Pakistan: Presented bySajjadPas encore d'évaluation
- Criminal Case No. 26558 People of The Philippines v. Joseph Ejercito Estrada Et. Al. by Justice Teresita Leondardo-De CastroDocument226 pagesCriminal Case No. 26558 People of The Philippines v. Joseph Ejercito Estrada Et. Al. by Justice Teresita Leondardo-De CastroHornbook Rule0% (1)
- SS 302 Theory On Differential Association (Constantino, Dansalan)Document7 pagesSS 302 Theory On Differential Association (Constantino, Dansalan)Rodrick Sonajo RamosPas encore d'évaluation
- Cyber Crimes. Pratap Full PaperDocument14 pagesCyber Crimes. Pratap Full PaperPratap C.EPas encore d'évaluation
- Government's Motion For Pre-Trial Detention, Vast Mexican Cartel Meth Ring in USDocument13 pagesGovernment's Motion For Pre-Trial Detention, Vast Mexican Cartel Meth Ring in USBrandon DarbyPas encore d'évaluation
- Jasleen K OberoiDocument19 pagesJasleen K Oberoisunshine4u5Pas encore d'évaluation