Académique Documents
Professionnel Documents
Culture Documents
Dimensions of Cyber-Attacks: Cultural, Social, Economic, and Political
Transféré par
ndaru_Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Dimensions of Cyber-Attacks: Cultural, Social, Economic, and Political
Transféré par
ndaru_Droits d'auteur :
Formats disponibles
© ISTOCK
Social, Political,
Economic, and Cultural
ROBIN GANDHI, ANUP SHARMA, WILLIAM MAHONEY,
WILLIAM SOUSAN, QIUMING ZHU, AND PHILLIP LAPLANTE
Digital Object Identifier 10.1109/MTS.2011.940293
Date of publication: 8 March 2011
28 | 1932-4529/11/$26.00©2011IEEE IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011
E
ssential systems pro- taxonomy and analysis of these at- ments, and outrage against acts
viding water, elec- tacks along the SPEC dimensions. related to physical violence.
tr icity, healthca re, We do not attempt to analyze why
finance, food, and past SPEC events have triggered Protesting Political/
transportation are now cyber-attacks, nor do we propose Government Actions
increasingly software dependent, solutions to reduce or prevent them. June 1998, India, attack on an
distributed, and interconnected. atomic research center – Hackers
The detrimental consequences of Categorical Record of Cases from the United States, England,
this growing dependence become Cyber-attacks cover a wide range the Netherlands, and New Zealand
apparent during times of politi- of actions, including defacing a (calling themselves “Milworm”)
cal conflict, social instability, and website and stealing valuable infor- attacked the website of India’s
other traumatic events. The Inter- mation. Howard [21] defines a cy- Bhabha Atomic Research Center
net has made information exchange ber-attack as an “event that occurs (BARC) to protest nuclear testing.
easier and more efficient, but it has on a computer or network that is The attackers posted text to the
also created a new space in which intended to result in something that web site and destroyed data [4].
criminals and terrorists can oper- is not authorized to happen.” Such September 1998, Indonesia, at-
ate almost undetected. No longer is attacks can affect data, processing, tack on websites to protest against
modern human conflict confined to and programs, and the network en- human right abuse in East Timor –
the physical world; it has spread to vironment [17]. We define a cyber- Portuguese hackers modified the
cyberspace. attack as any act by an insider or websites from 40 Indonesian serv-
Cyberspace is a massive socio- an outsider that compromises the ers to protest against human right
technical system of systems [25], security expectations of an individ- abuses in East Timor. The hack-
with a significant component be- ual, organization, or nation. ers posted the slogan “Free East
ing the humans involved. Current To thoroughly understand a Timor” on the websites [4].
anomaly detection models focus cyber-attack, we study the nature October 1998 , Mexico, the
primarily on analyzing network of the attack and the motivation website of president attacked –
traffic to prevent malicious activi- behind it. Some attacks are due to The website of Mexican president
ties [13], [24], [27], [35], but it has political conflict, while others are Ernesto Zedillo was attacked to
been shown that such approaches triggered by social tension. Some demonstrate against colonization,
fail to account for human behaviors attacks occur because of religious genocide, and racism throughout
behind the anomalies. Evidence is belief and extremism and others the world [32].
growing that more cyber-attacks are the result of revenge and anger. June 1999, Cologne, Germany,
are associated with social, politi- In the following we summarize cyber-attack to protest against the
cal, economic, and cultural (SPEC) some of the typical SPEC-related G8 summit – Hackers from Indo-
conflicts [34], [39], [42]. It is also cyber-attacks in a few of these cat- nesia, Israel, Germany, and Canada
now known that cyber-attackers’ egories. The discussed events are reportedly launched 10 000 cyber-
level of socio-technological so- by no means exhaustive, as it will attacks over five hours on various
phistication, their backgrounds, be impossible to enumerate them companies protesting the G8 meet-
and their motivations, are essential all; our selection is only meant to ing in Cologne. The attackers in-
components to predicting, prevent- highlight the types of attacks that tended to disrupt financial centers,
ing, and tracing cyber-attacks [28], can occur. banking districts, and multination-
[36]. Thus, SPEC factors have the al corporate power bases [4].
potential to be early predictors for Politically Motivated Attacks 1999, Serbia, Kosovo war –
outbreaks of anomalous activities, Cyber criminals involved in po- Serbian hackers attacked U.S. and
hostile attacks, and other security litically motivated attacks can be NATO sites using a “fraggle attack”
breaches in cyberspace. members of extremist groups who (when large numbers of packets are
We believe analyzing potential use cyberspace to spread propagan- sent to paralyze a system) [10].
correlations between historical/ da, attack websites and networks of The attackers disrupted services
current SPEC events and cyber- their political enemies, steal money on several government computers
attacks may provide valuable in- to fund their activities, or plan and and websites to object to NATO
sights regarding the origin, agents, coordinate physical-world crime and Yugoslav aggression [4]. The
means, motives, and potential tar- [10]. Based on the nature of an at- hackers also used cyberspace to
gets of future cyber-attacks. To- tack, politically motivated attacks share text, images, and video clips
wards this goal, we describe how can be further subdivided as: pro- to reach an international audience.
several SPEC events have led to tests against political actions, pro- December 2008, Beijing, website
cyber-attacks, and then present a tests against laws or public docu- of French Embassy attacked – The
IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011 | 29
French embassy website came was placed in the home page of An attack was also launched on the
under attack by Chinese hackers the U.S. Embassy in Beijing, and homepage of Yasukuni Shrine, which
immediately after the meeting of the Department of Interior web site is dedicated to Japanese war dead
French President Nicolas Sarkozy showed images of three journalists and is a constant source of friction
with the Dalai Lama [18]. killed during the bombing [4]. between these two countries [19].
August 1999, China/Taiwan, April 2007, Estonia /Russia ,
Dissatisfaction with the cyber conflict – The political con- DoS Attack – World War II
Launch of a Public Document, flicts between China and Taiwan monument conflict – A botnet at-
Policy, or Law led to cyber warfare. Chinese hack- tack was launched upon the Esto-
December 1995, France, cyber- ers took several Taiwanese and nian Government and commercial
attack against French Govern- government websites under their websites by Russian hackers caus-
ment websites – A group called control, placing inflammatory mes- ing a DoS [10]. About one million
the “Strano Network” launched an sages. Taiwanese hackers placed an computers worldwide were used to
hour-long Net strike attack against anti-communist message on a Chi- conduct the attack on the govern-
government web sites to protest nese high-tech internet site [4]. ment and corporate websites [14].
Over three weeks these attacks shut
down Estonia’s cyber infrastructure.
To thoroughly understand a cyber- The Estonian government blamed
attack, we study the nature of the Russian hackers for this attack; the
Russian government denied involve-
attack and the motivation behind it. ment. Security experts speculated
that the hackers were protesting the
the French Government’s nuclear November 2000, Israel/Pal- Estonian government’s decision to
and social policy. Attack organiz- estine, cyber-attack on Lucent move a popular monument [14].
ers encouraged protestors to point Technology, – Lucent Technology,
their browsers at the government a company doing business with Is- Socio-Cultural Conflict
website, which generated a high rael, was targeted by a Palestinian Triggered Attacks
volume of web traffic and rendered group called Unity [10]. In the fall Socio-cultural conflict can be
it unavailable for other users [4]. of 2000, cyber warfare between viewed as competition between
1996, U.S., attack on a De- pro-Israeli and pro-Palestinian individuals or groups over incom-
partment of Justice (DOJ) web- groups resulted in a server crash patible goals, scarce resources, or
site – When the Communications that caused the Israeli stock market power, including the denial of con-
Decency Act was passed several to decline by 8% [26]. trol to others [5]. Cross-cultural
protestors were involved in delet- April 2001, U.S. /China, spy conflict can also manifest as ethnic
ing the contents from the U.S. DOJ plane crisis – Immediately follow- conflict. Cyber conflicts incited for
website [10]. ing the crash of a U.S. spy plane, cultural reasons include conflicts
March 2001, South Korea/Ja- numerous website defacing inci- between Taiwan-China (August
pan, attack on Japanese Education dents were reported in the U.S. 1999), Russia-Estonia (2007) and
Ministry’s website – South Korean and China. From April 28 to May Russia-Georgia (2008). Similarly,
hackers attacked the Japanese Edu- 8, Chinese “hactivists” defaced The Israel-Palestine cyber conflict,
cation Ministry’s website to protest almost 1000 U.S. websites and where national symbols – the Israe-
the publication of controversial his- launched a distributed denial-of- li flag, Hebrew text, and a record-
tory textbooks, which they felt did service (DDoS) attack against the ing of the Israeli national anthem –
not fairly address past Japanese White House and the Central Intel- were put into Hezbollah home page
military aggression. All of these ligence Agency [15]. These attacks [23], belongs in this category.
hackers were later identified as uni- on the U.S. government’s websites
versity students [7]. were highly sophisticated and bold. Land Dispute Triggered Attacks
Three hactivist groups – the Hack- 2000, India/Pakistan, attack on
Outrage against Acts er Union of China, China Eagle, Indian websites to protest con-
Related to Physical Violence and the Green Army Corps – were flict in Kashmir – Pakistani hack-
May 1999, Belgrade, Chinese Em- suspected of having launched these ers – the Muslim online Syndicate
bassy bombing – Chinese hackers attacks [10], [46]. (MOS) – attacked more than 500
attacked U.S. government sites for August 2001, China/Japan, Ya- websites in India to protest against
accidentally bombing the Chinese sukuni shrine conflict – Chinese the conflict in Kashmir [4].
embassy in Belgrade. A Chinese hackers routinely attacked the web- March 2005, Indonesia/Malay-
slogan “down with barbarians” sites and Internet Services in Japan. sia, Ambalat conflict – Indonesia
30 | IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011
and Malaysia dispute ownership of ternet infrastructure. This incident wrote a portion of the hard drive
Ambalat and East Ambalat, leading reveals an emerging trend of cyber Symantec reported that as many
to military posturing and attacks activity as a new dimension to con- as one million Korean computers
on government websites. Attacks ventional war [11]. were affected, resulting in more
escalated dramatically against Ma- December 2008, Israel/Pales- than $250 million in damages [44].
laysian government’s website dur- tine conflict – Since the start of the April 2008, Belarus/Eastern
ing the weeks of increased tension Gaza campaign, hacking groups Europe, DoS attack – Radio Free
over the Ambalat issue [46]. from Morocco, Lebanon, Turkey Europe/Radio Liberty in Belarus re-
March 2005, Korea /Japan, and Iran have attacked Israeli web- ported that their websites came under
‘Dokdo/Takeshima’ territorial con- sites; a Moroccan Islamic group a sustained DDoS attack. These at-
flict – The dispute over the Dokdo hacked into the registration system tacks coincided with the anniversary
and Takeshima islets, claimed server of “domainthenet.com” and of Chernobyl disaster and the 2007
by Japan but controlled by South defaced more than 300 websites cyber-attack against Estonia [2].
Korea, caused an outbreak of cy- including banks, weather channels, April 1, 2009, April fool’s day,
ber warfare. The homepage of the and news. While trying to access Conficker worm – Widespread
Japanese Foreign Ministry came these sites, visitors were rerouted to panic surrounded the discovery of
under attack, making access to a website featuring images of casu- the Conficker worm, also known
the site erratic. Japanese hactivists alties from the Israeli offense against as “Downadup”, “Kido”, and
retaliated by attacking the homep- Gaza, and anti-Israeli anti-U.S. mes- “Confick” [1]. The worm, a vari-
age of South Korea’s Ministry of sages. Israeli students retaliated by ant of “win32/d”, would trigger on
Foreign Affairs and Trade. The at- attacking Hamas websites [3]. April 1. As of this writing no such
tack prompted South Korea’s gov- issues have been reported.
ernment to issue a cyberterrorism Specific Anniversaries or
warning for all its overseas diplo- Historic Events Triggered Attacks Economically
matic missions [9], [46]. April 1999 CIH/Chernobyl – The Motivated Attacks
August 2008, Russia/Georgia, CIH/Chernobyl, a timed virus, was Economic situations and personal
conflict resulting in cyber-attacks spread over the Internet, causing or corporate financial greed often
– The outbreak of the Russia-Geor- great damage to business and home provide motives for cyber-attacks.
gia war over land disputes spilled computer users. These specific vi- Cyber mercenaries and organized
into cyberspace; Russian Internet ruses activated on a predefined date cartels also operate in cyber space.
forums were used for a coordinated on the anniversary of Chernobyl 2008-2009, China, IT Profession-
cyber-attack against Georgia’s In- nuclear disaster [10], and over- als attracted towards cybercrime
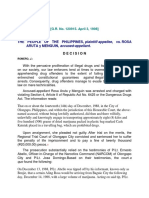
1998, India, BARC
1995, France, Web Attack 1999, Germany, G8 Summit
1999, China/Taiwan, Cyber conflict
1996, USA, DoJ Website Attack 2000, India / Pakistan, Kashmir Conflict
1998, Indonesia, East Timor conflict 2000, Israel/Palestine, Lucent Tech.
2001, Japan, Education Ministry Website
1998, Mexico, Presidential Website 2001, China/Japan, Yasukuni Shrine
1999, Serbia, Kosovo War 2007, Estonia / Russia, DoS Attack
1999, Belgrade, Chinese Embassy 2008, Russia / Georgia Conflict
2001, USA /China, Spy Plane 2008, China, French Embassy Web
Politically
Motivated Socio-cultural
Motivation
2003, USA, Titan Rain
1999, CIH/Chernobyl Virus
2008, USA / China Strategic Info. 2005, Indonesia/Malaysia, Ambalat
2009, USA, Spies on Electrical Grid 2005, Korea/Japan, terratorial conflict
2009, China, GhostNet 2008, Belarus/Eastern Europe,
Economically DoS Attack
2008-9, 2008, Israel / Palestine conflict
China IT Professionals to Cybercrime Motivated
2009, E-Crime Survey 2009, April Fools Conflicker worm
2009, Ukraine IT Professionals to Cybercrime
2009, Health records, Virginia, USA
Fig. 1. The distribution of cyber-attacks across CSEP dimensions.
IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011 | 31
due to economic recessions – The specifications and flight-planning that could be gained from a more
Economic slowdown has affected software [23], [38]. comprehensive record. In Fig. 1
many countries. Many IT profes- 2008, U.S./China, Government note the large number of cyber-at-
sionals lost significant amounts of trying to steal strategic informa- tacks identified as politically and
money in the stock market, par- tion – The U.S. and Chinese gov- socially motivated; these types of
ticularly in China, where some IT ernments exchanged accusations attacks have been occurring for
professionals are turning to cyber- of launching hacking campaigns some time. Conversely, there is a
crime [29]. aimed at stealing strategic infor- relative dearth of attacks motivat-
2009, Ukraine, IT professionals mation [20]. ed principally by economics; such
in cybercrime – Some IT profes- 2009, China, GhostNet – Re- attacks seem to be a relatively re-
sionals employ cybercrime because searchers uncovered a cyber-espi- cent phenomenon. Attacks clas-
it pays. For example, Ukrainian onage network named GhostNet, sified as purely political (without
cyber criminals were able to steal suspected of being used by the socio-cultural or economic mo-
$172,000 in goods and services Chinese Government to extract in- tives) in nature seem to be dimin-
over a 16-day period [31]. formation from the Dalai Lama’s ishing or are less publicized, with
2009, Health records held hos- computer. The investigation led to the most recent high-profile event
tage for ransom, Virginia, U.S. – the discovery of infected machines reported in 2001.
Vulnerabilities in the website of in Britain, U.S., Indonesia, Iran, Another way to gain insights
the Virginia Department of Health the Philippines, and Laos [8]. into the attacks is via a world map
Professions were exploited by 2009, U.S., Spies on electricity (Fig. 2). Note the lack of attacks in
hackers to gain access to eight mil- grid – U.S. national security offi- some regions, such as Australia and
lion patient records. The hackers cials claimed that cyber spies from South America with a relatively
encrypted the records in the data- China and Russia penetrated the stable political and cultural envi-
base and later deleted the plaintext U.S. electrical grid, searching for ronment. This observation seems
copy. A ten million dollar ransom vulnerabilities and leaving behind to reinforce the notion that attacks
was demanded for the password to malware. These allegations were are strongly positively correlated to
decrypt the data [22]. not confirmed [16]. political and cultural conflicts. In
the case of Africa, a poor computer
Espionage (Political/ Visualizing Cyber-Attacks infrastructure could account for the
Economic) Related Attacks We organized the cases discussed lack of attacks.
September 2003, U.S., Titan Rain above as a Venn diagram (Fig. Fig. 3 presents a timeline of
cyber espionage issue – In an inci- 1). While these cases are by no the cyber-attacks previously de-
dent code-named Titan Rain, hack- means complete or representa- scribed. Inspection of the figure
ers penetrated NASA and other tive of their subsets, our analysis reveals that over time the types of
networks, and retrieved aviation demonstrates the kinds of insights attacks have been changing. Early
2009,
Ukraine IT Professionals to Cybercrime
1999, Belgrade, Chinese Embassy 2008, Belarus/Eastern Europe, DoS Attack
1999, Serbia, Kosovo War 2007, Estonia / Russia, DoS Attack
1999, Germany, G8 Summit 2008, Russia / Georgia Conflict
1995, France, Web Attack 1999, CIH/Chernobyl Virus
2001, Japan, Education Ministry Website
1996, USA, 2005, Korea/Japan, terratorial conflict
DoJ Website Attack
1999, China/Taiwan, Cyber conflict
2001, USA/China, Spy Plane 2001, China/Japan, Yasukuni Shrine
2003, USA, Titan Rain 2008, China, French Embassy Web
2008, USA/China Strategic Info. 2008-9, China IT Professionals
2009, USA, 2000, Israel/Palestine, 2009, China, GhostNet
Spies on Electrical Grid 2005, Indonesia/Malaysia, Ambalat
2009, USA, Lucent Tech.
Medical Records Hostage 2008, Israel / Palestine conflict 1998, Indonesia, East Timor conflict
1998, India, BARC
1998, Mexico, 2000, India / Pakistan, Kashmir
Presidential Website
2009, April Fools Conflicker worm
2009, E-Crime Survey
Fig. 2. Country-wise distribution of Cyber-attacks from CSEP dimensions.
32 | IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011
cyber-attacks tended to be against spans “human networks” across in- be classified into two categories: 1)
web sites, such as the French gov- ternational borders and cultures. Non-organized /Non-coordinated;
ernment and East Timor attacks. Below we give some insights and 2) Organized/Coordinated.
This trend may be caused in part gained from analyzing the record Non-organized attacks are not dis-
by the lack of security in earlier of cases. Our analysis has helped organized. Instead, we mean that
versions of web infrastructure soft- identify and categorize several di- the attacks could be implicitly,
ware, providing easy targets for in- mensions of a cyber-attack (Fig. semi-, or auto-organized. The mass-
dividuals and small groups. More 4). Appropriate metrics for defin- ing effect of the attack occurs once
recent attacks are different. These ing and modeling cyber-attacks in other individuals become aware of
are frequently DDoS attacks, in- the SPEC dimensions need to be an attack taking place. Non-orga-
volving a sophisticated group tak- developed, and we hope that our nized groups leverage nationalism,
ing over large numbers of com- analysis will provide new insights patriotism, and sensitive issues to
puters (“bots”) to attack political in that direction. motivate participation. Such groups
adversaries. Examples include the are loosely linked using social net-
Russia/Georgia conflict and the Attack Dimensions working tools such as chat rooms,
Estonia DoS attack. Other recent forums, and blogs. The recruits
attacks involve stealthy, targeted, Attack Agents participate in a large scale and dis-
and sophisticated attacks; for ex- While the direct participants (at- tributed attacks that rely on several
ample the Chinese infiltration of tackers and victims) in a cyber-at- individuals performing different
the U.S. electrical grid. tack are computer systems, behind tasks or overwhelming the target by
each attack is a human agent with DDoS. A mass email attack on the
Insights from the Record a motivation. The attacker type is Yasukuni Shrine web host in Japan
Our record of historic cases clearly a fundamental component in the [19], allegedly from China, is an ex-
demonstrates that over time more cyber-attack dimension, as these ample of such an attack. During the
cyber-attacks can be directly attrib-
uted to some form of SPEC events.
Furthermore, the origination of ac-
Cyber-attacks are strongly correlated
tive malware content has shown to to political and cultural conflicts.
vary significantly across different
countries and geophysical regions, human agents are the first transition Russia and Georgia conflict [11],
and in some instances is largely point between events in the physi- reports indicated that step-by-step
disproportionate to the number of cal world and events in the cyber instructions for launching a cyber-
Internet users [30]. world. Understanding the existence attack against the Georgia cyber
Interesting questions for infor- and closely monitoring variances in infrastructure were actively distrib-
mation security research arise. Can the possible numbers of a particular uted on web forums to voluntarily
the awareness of SPEC dimensions attacker type due to SPEC events mobilize Russian loyalists.
across geographical borders facili- can be used as a key predictor for a Conversely, organized attacks
tate early detection and prevention of cyber-attack. involve highly coordinated ac-
attacks on cyber systems? Are SPEC The human agents that perpetrate tivities among a close group of
factors correlated with the efficient a cyber-attack can be broadly clas- individuals working together co-
and sustainable operations of a cy- sified into four categories: 1) script vertly. These groups include crime
ber system? Can future anomalous kiddies (hacking for fun, low skill); syndicates or groups of individuals
activities in cyberspace be predicted 2) mercenaries (hacking for money, recruited by a military or govern-
based on SPEC events? Which SPEC organized and skilled); 3) social ment especially for the purpose of
factors can serve as strong predictors protestors (hacktivists, loosely orga- launching attacks.
of an impending cyber-attack, the nized); and 4) nation states (hacking
means that will be used to carry it under orders for a purpose, highly Attack origin and attribution
out, and the potential targets? skilled and well funded). A more “Attribution” is a significant chal-
Answers to these questions will elaborate list of attackers and their lenge for cyber security. Current
require organizing SPEC factors motives has been developed [40]. technology allows for only the
into an integrated model of trustwor- speculative location of attackers.
thy cyber system operations. Such a Attack Coordination Decentralized peer-to-peer com-
study reaches beyond the traditional Massive cyber-attacks are often mand and control networks (“zom-
transmission or network models of linked to groups of human agents bies”) obscure the origin of a cyber-
cyber security [29] and provides a working in unison. From a collabo- attack. For example, many months
more holistic perspective that also ration dimension, cyber-attacks can after the Russia-Georgia conflict,
IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011 | 33
Countries such as the U.S and significant number of victimized
computers or zombies that are used
China have a significant number to launch an attack [37]. The last
thing we want to see is a triggering
of victimized computers or zombies of conflicts between nations in both
that are used to launch an attack. the cyber and physical world based
on misinformation.
a possible link was discovered to launching an attack with irrefut- Attack Motive
a botnet services provider. Yet it able evidence [6]. Investigators The compiled record suggests that
may still be impossible to trace the often have to follow a breadcrumb many cyber-attacks are somehow
human network that is ultimately trail in both the cyber and physical motivated by deeply-rooted so-
responsible for planning and co- worlds to substantiate any claims cio-cultural issues. Attacks can
ordination. Unless certain groups with evidence. also be politically motivated or
take responsibility, it is difficult Studies show that countries used to influence government
to accuse a nation or individual of such as the U.S and China have a policy [12], [14].
October 2000:
1998: India/
Mexico, Pakistan,
Websites of May 1999 attack on April 2001:
president Indian
Belgrade, Websites U.S./China,
attacked Chinese to protest spy plane
Embassy conflict in crisis
bombing Kashmir
September
1998: March
Indonesia, June 2001:
December 1999:
1995: attack on South September
Websites Cologne, Korea/ 2003:
France, web to protest Germany, Japan,
attack against cyber attack on Titan Rain
against human attack to Japanese cyber-
French right protest Education espionage
Government abuse in against G8 Ministry’s issue, U.S.
Websites East Timor summit Website
1995 1996 1998 1999 2000 2001 2003
June April August
1998: 1999: 1999:
1996: August
India, CIH/ China/ November
USA, attack 2001:
Website chernobyl Taiwan, 2000:
on cyber Israel/ China/
of DOJ atomic Japan,
attack conflict Palestine,
research cyber Yasukuni
center attack on shrine
(BARC) Lucent conflict
Technology
1999:
Serbia,
Kosovo war
Fig. 3. A timeline of cyber-attacks from the CSEP dimensions during 1995–2009.
34 | IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011
In some cases the motivation
is ethical, i.e., a fight for social
The last thing we want to see is a
justice, and human rights. This conflict triggered between nations in
was the case in attacks launched
against the Indonesian and Mexi- both the cyber and physical worlds
can governments [4], [32], [46]. based on misinformation.
Financial gain is a significant
motive for criminal gangs to at-
tempt breaking into financial Attack Timing attack on a region; the movements
institutions. Cyber-attacks of- When cyber-attacks are used in pro- of Russian troops in Georgia were
ten involve anger and revenge. test they are often launched imme- correlated with cyber-attacks on
Many of the cyber-attacks we diately following a triggering event the Georgian communications in-
reviewed involve groups or in- in the physical world. In contrast, frastructure and defacement of
dividuals who were harmed by many attacks (coordinated and un- government websites. Cyber-at-
a government, another group, or coordinated) have been launched tacks are also timed to express out-
industrial entity. prior to or in sync with a military rage, or for revenge over, specific
dates or anniversaries; a Burmese
Web site came under devastating
cyber-attack on the anniversary of
2008-2009 last year’s failed uprising against
the Burmese junta. There has also
China, IT
2008: professionals been speculation about the planting
U.S.- China, attracted of malicious software in systems
Government towards
trying to cybercrime that control critical infrastructure
steal due to 2009: [16]. Such malicious software is
strategic Economic
March Recessions suspected to activate in a time of
2005: information Ukraine,
IT crisis or in coordination with ag-
Indonesia professionals
/Malaysia, August
gressive military operations.
in cybercrime
Ambalat 2008:
conflict
Korea/ Russia/ April 1, Attack Means
Japan, Georgia, 2009: History shows that DoS attacks are
‘Dokdo/ conflict April
Takeshina’ resulting fool’s day,
a favored means to compromise the
territorial in cyber Conficker availability of services or to esca-
conflict attacks worm late a hacker’s privileges in order
to deface websites and steal data.
Non-coordinated attacks using
Internet forums, chat rooms, and
blogs to recruit attackers also dis-
2005 2007 2008 2009
tribute attack code injection scripts
December
2008: 2009: and lists of vulnerable targets, as
April part of attack mobilization efforts
2007: April Beijing, Spies on
2008: Website U.S. coupled with propaganda. Malware
Estonia/ electricity
Belarus/ of French
Russia,
Embassy grid that can amass a large bot army are
Dos Attack Eastern
- World Europe, attacked GhostNet, forms of DDoS, which is difficult
War II DoS Israel/ China to protect against. Zero-day ex-
monument attack Palestine
conflict conflict 2009: ploits could be potentially amassed
E-Crime as weapons which can be exploited
survey, in time of conflict.
Employee
involvement
in Attack Outcomes
cybercrime
Virginia,
US Health Attack Victims
records held
hostage for Individuals are not usually the tar-
ransom get of mass cyber-attacks [43], [44].
Infrastructure is usually the target,
and the after-effects can be far
IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011 | 35
Many cyber-attacks are motivated by promise of individuals. Massive
botnets composed of covertly vic-
deeply-rooted socio-cultural issues. timized machines are used to pre-
vent attribution and generate large
reaching. For example, it has been In contrast to mass cyber-at- amounts of attack traffic in order to
estimated that a mass cyber-attack tacks, small scale attacks target launch a cyber-attack.
could leave 70 percent of the U.S. users who are unaware of technical Governments and military es-
in total darkness without electrical system vulnerabilities [13]. Such tablishments are often victimized
power for six months [45]. In times users can be naïve, disabled, dis- for espionage, theft of intellectual
of conflict, cyber-attacks have been advantaged, desperate, lonely, or property, or exposure of secret in-
primarily targeted towards govern- emotionally weak [10]. Symantec formation. Such attacks are cov-
ment or military installations. But estimates that about 93 percent of ert in nature and are only discov-
as witnessed during the recent Rus- the non-organized cyber crimi- ered upon vigilant monitoring and
sia-Georgia and Estonia conflicts, nals target home users [43]. Data tracking of cyber activities. In most
financial institutions and banks are breaches at financial institutions cases investigators can only specu-
also attractive targets [33]. ultimately lead to the identity com- late on the activities of the attackers
Script Kiddies
Social protestors (hactivists)
Attack Agent
Mercenaries
Nation states
Cybermilitia
Organized attacks
Cyber Mafia organized crime
Chat rooms and Forum recuritment Un-organized Attack Co-ordination
attacks
Cybervigilante
Malware victims
Attack Origin
Malicious agents
Dissatisfaction Protest Political or Government Actions
against the launch of a Public Document, Policy or Law
Retaliation against acts of aggresion or physical attacks Political factors
Cyberespionage
Political
Land and Cultural disputes Socio-Cultural Attack Motive Cyber Attacks
factors
Anniversaries of historic events
Financial gain
Economic recession Economic factors
Greed
Immediately following an attack in the physical world
Preceeding an attack in the physical world
In parallel with an attack in the physical world Attack Timing
Uncorrelated with events in the physical world
Logical or timed activation of planted malware
Spread of Malware
Denial of Service
SQL or Code injection
Attack Means
Escalation of Priviledge
Zero-day exploits
Distribution of Attack Scripts
Fig. 4. Categorization of cyber-attack dimensions.
36 | IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011
after the attacks have taken place
[8], [16], [23], [38]. In some cases the motivation
for an attack is ethical.
Attack Consequences
The consequences of a cyber-attack critical assets, which imposes addi- Estonia, whose removal sparked the
are as diverse as the SPEC dimen- tional costs on taxpayers and con- cyber-attacks.
sions. Along the technological di- sumers. Consequences along the dimen-
mensions, a cyber-attack can leave Psychological effects can be sions of financial, information,
users distrustful of services such as significant, spreading widespread and physical losses are the more
banking, healthcare, and finance. fear. Consider the panic among the tangible and direct outcomes of a
The objective is similar in concept people of Estonia when significant cyber-attack. Physical loss in most
to spreading fear by conducting parts of their cyber infrastructure instances occurs when the cyber
terrorist activities against a trans- were inaccessible due to DoS at- world is tightly integrated with the
portation infrastructure. Another tacks. Such panic may also induce physical world, as in the case of
consequence of a cyber-attack is policy changes, as observed with the systems that control the distribu-
increased spending on securing restoration of the bronze statue in tion of power, gas, water, sewage,
oil, and critical services.
Pathology of SPEC-Triggered
Cyber-Attacks
Attacks triggered by SPEC events
have pathology similar to biologi-
cal pandemics [25], where each
outbreak develops in stages over
its life cycle [41]. Therefore it is
critical to identify features that
can be observed or discovered
as early predictors or indicators,
Individuals/Civilians
and monitor these factors before
the actual attack takes place or
Government
propagates.
Attack Victims Bussinesses
Cyber-defense is harder than
Critical Infrastructure
cyber-offense, and technological
Military Loss of confidence in
mechanisms alone are never suf-
technology
Technological effects ficient. To build appropriate exper-
Security budget increase
Mass panic
tise, understanding is needed in a
Psychological effects broad range of issues related to the
Induce Policy Changes
Lost productivity and time global cyber environment. We need
Financial loss to investigate a full range of factors
Attack Consequences Monetary loss
Loss of National/Business Secrets that shape and alter the cyber secu-
Indentify theft rity environment including social,
Information loss Privacy Loss
Personal Information political, economic, cultural, and
Intellectual Disclosure technological trends.
Physical system loss Property Loss Achieving global cyber security
is a matter of strategic economic
interest for all nations. Developing
a global culture of cyber security
also means assisting developing
economies in adopting the “tech-
nology, processes, and people” of
cyber security.
Author Information
Robin Gandhi, Anup Sharma, Wil-
liam Mahoney, William Sousan,
and Qiuming Zhu are with the
IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011 | 37
University of Nebraska at Omaha, [14] J. Germain, “The art of cyber warfare, networkworld.com/news/2009/032309-ukrai-
Omaha, NE. Part 1: The digital battlefield,” TechNews- nian-cybercriminals.html?page=1.
World, 2008; http://www.technewsworld.com/
Phillip Laplante is with the [32] M. Manion and A. Goodrum, “Terror-
rsstory/62779.html.
ism or civil disobedience: Toward a hacktivist
School of Graduate Professional [15] G. Gilmore, “Navy aircraft not a ‘spy ethic,” Computers and Society, 2000.
Studies, Penn State University, plane,’ DoD says,” American Forces Press Ser-
[33] J. Miks, “Asian countries looking to
30 East Swedesford Road, Mal- vice, 2001, http://www.defenselink.mil/news/
bolster cyber defenses,” World Politics Rev.
newsarticle.aspx?id=45042.
vern, PA 19355; email: plaplante@ Exclusive, 2008, http://www.worldpoliticsre-
[16] S. Gorman, “Electricity grid in U.S. view.com/articlePrint.aspx?ID=2576.
gv.psu.edu. penetrated by spies,” Wall Street J., Apr.
[34] M. Myers and F. Tan, “Beyond models
8, 2009; http://online.wsj.com/article/
of national culture in information systems re-
SB123914805204099085.html.
References search,” Advanced Topics in Global Informa-
[1] R. Adhikari, “Security sleuths work over- [17] R. Hundley and R. Anderson, “Emerging tion Management, ch. 1, 2003.
time to confound Conficker,” TechNews- challenge: Security and safety in cyberspace,”
[35] X. Peng and H. Zhao, “A framework of at-
World, Mar. 30, 2009; http://www.technews- IEEE Technology & Society Mag., vol. 14,
tacker centric cyber-attack behavior analysis,”
world.com/story/66666.html. no. 4, pp. 19-28, 1996.
in Proc. IEEE Int. Conf. on Communications,
[2] A. Amirzai, “Belarus: A telling cyberat- [18] M. Handelman, “French embassy in Bei- 2007, pp. 1449 –1454.
tack,” Stratfor Global Intelligence, 2008; jing under cyber-attack,” infosecurity.us, Dec.
[36] G. Rasche, E. Allwein et al. “Model-
http://www.stratfor.com/analysis/belarus_ 12, 2008; http://infosecurity.us/?p=4408.
based cyber security,” in Proc. 14th Ann.
telling_cyberattack. [19] S. Herman, “VOA’s Steve Herman reports IEEE Int. Conf. and Workshops on the Engi-
[3] M. Amona, “Cyberwar emerges amid from Tokyo,” Globalsecurity.org, 2005; http:// neering of Computer-Based Systems, 2007,
the Israeli-Palestinian conflict in Gaza,” www.globalsecurity.org/security/ library/ pp. 405–412.
h t t p : / / cyberstrategies.wordpress.com/, news/2005/01/sec-050106-3f7c3184.htm.
[37] SecureWorks, “Compromised U.S. and
Jan. 4, 2009; http://cyberstrategies.wordpress. [20] M. Hines, “Cyber-espionage moves into Chinese Computers Launch Greatest Number of
com/2009/01/14/cyberwar-emerges-amid-the- B2B,” InfoWorld, Jan. 15, 2008; http://www.in- Cyber-attacks,” 2008, http://www. securework s
israeli-palestinian-conflict-in-gaza/. foworld.com/t/business/cyber-espionage-moves- .com /media /press_releases/20080922-attacks.
[4] J. Arquilla and D. Ronfeldt, Networks and b2b-546?page=0,0.
[38] E. Shannon, “The invasion of the Chinese
Netwars: The Future of Terror, Crime, and [21] J. Howard and T. Longstaff, “A common cyberspies,” Time, 2005.
Militancy. Rand, 2001. language for computer security incidents,”
[39] J. Slay, “IS security, trust and culture: a
[5] K. Avruch, “Cross-cultural conflict” Sandia Labs, SAND98-8667, 1998.
theoretical framework for managing IS securi-
(Conflict Resolution), in Encyclopedia of [22] HSdailyWire.com, “Virginia medical ty in multicultural settings,” J. Campus-Wide
Life Support Systems (EOLSS). Oxford, U.K.: records hijacking;” May 8, 2009; http:// Information Systems, 2003, vol. 20, no. 3,
Eolss, 2002. homelandsecuritynewswire.com /virginia- pp. 98-104.
[6] M.A. Caloyannides, “Forensics is so ‘yes- medical-records-hijacking-update.
[40] S. Redwine, Ed., Secure Software Assur-
terday’,” IEEE Security & Privacy, vol. 7, [23] Athina Karatzogianni, Cyber-Conflict ance: A Guide to the Common Body of Knowl-
no. 2, pp. 18-25, 2009. and Global Politics, Routledge, 2008 edge to Produce, Acquire, and Sustain Secure
[7] CNN, “Japanese textbook dispute sparks Software, Version 1.1, Department of Home-
[24] M.E. Kuhl, J. Kistner, et al. “Cyber-
cyber-attack,” CNN.com, Mar. 31, 2001; land Security, SEI/CMU, 2006.
attack modeling and simulation for network
http://edition.cnn.com/2001/WORLD/asiap- security analysis,” in Proc. Winter Simulation [41] World Health Organization, Centers for
cf/east/03/31/japan.korea.website/index.html. Conf., 2007, pp. 1180 –1188. Disease Control and Prevention, “Stages of an
[8] CNN, “China analysts dismiss cyber- influenza pandemic,” June 11, 2009; https://
[25] P. Laplante, B. Michael, and J. Voas,
espionage claims,” CNN.com, 2009, http:// www.health.harvard.edu/flu-resource-center/
“Cyberpandemics: History, inevitability, re-
www.cnn.com/2009/TECH/03/30/ghostnet. stages-of-an-influenza-pandemic.htm.
sponse,” IEEE Security & Privacy, vol. 7, no. 1,
cyber.espionage/. pp. 63-67, 2009. [42] Strategypage.com, “Information War-
[9] CCRC staff, “Japan declared a cyberwar fare Article Index: Cyber War as the Ultimate
[26] J. Laprise, “Cyber warfare seen through a
against S. Korea,” Computer Crime Research Weapon,” Jan. 5, 2008; http://www.strat-
mariner’s spyglass,” IEEE Technology & So-
Center, Mar. 22, 2005; http://www.crime- egypage.com/htmw/htiw/articles/20080105.
ciety Mag., 2005.
research.org/news/22.03.2005/1067/. aspx.
[27] Z. Liu, C. Wang, and S. Chen; “Correlat-
[10] M. Cross, Scene of the Cybercrime. Syn- [43] Symantec.com, “Symantec’s Internet
ing multi-step attack and constructing attack
gress, 2008, pp. 443–450. Security Threat Report,” vol. XII, 2007, vol.
scenarios based on attack pattern modeling,”
XIII, 2008; http://www.symantec.com/busi-
[11] D. Danchev, “Coordinated Russia vs in Proc. Int. Conf. Information Security and
ness/theme.jsp?themeid=threatreport.
Georgia cyber-attack in progress,” Zero Assurance, 2008, pp. 214–219.
Day, Aug. 11, 2008; http://blogs.zdnet.com/ [44] Symantec Security Response, W95
[28] J. Markoff, “Internet attacks seen as
security/?p=1670. CIH,” accessed Feb. 2010; http://www.sy-
more potent and complex,” 2008, http:/ /
mantec.com /secur ity_ response /wr iteup.
[12] D. Denning, “Activism, hacktivism, and www.iht.com/articles /2008/11/10/
jsp?docid=2000-122010-2655-99.
cyberterrorism: The Internet as a tool for in- technology/10attacks.php.
fluencing foreign policy”, presented at,” In- [45] T. Reid, Times Online, “China’s cyber
[29] R. McMillan, “China becoming the world’s
ternet and International Systems: Information army is preparing to march on America,”
malware factory,” Network World, 2009, http://
Technology and American Foreign Policy De- Sept. 8, 2007; http://technology.timesonline.
www.networkworld.com/news /2009/032409-
cisionmaking Workshop, 1999; http://faculty. co.uk/tol/news/tech_and_web/the_web/ar-
china-becoming-theworlds-malware.html.
nps.edu /dedennin /publications /activism- ticle2409865.ece.
hacktivism-cyberterrorism.pdf. [30] “MessageLabs Intelligence: 2008 An-
[46] M. Zubir, “Exchange of ‘cyberfire’ dur-
nual Security Report,” 2009; http://www.
[13] J. Eom, Y. Han, et al. “Active Cyber-at- ing the Malaysia-Indonesia Ambalat Dis-
messagelabs.com/intelligence.aspx.
tack model for network system’s vulnerability pute: A lesson for the future,” Centre for
assessment,” in Proc. Int. Conf. Information [31] E. Messmer“Ukrainian cybercrimi- Maritime Security and Diplomacy, MIMA,
Science and Security, 2008, pp. 153-158. nals raked in $10K/day,” 2009, http://www. 2005.
38 | IEEE TECHNOLOGY AND SOCIETY MAGAZINE | SPRING 2011
Vous aimerez peut-être aussi
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- MILITAR, EUA - ARN16448 - FM 3-57 Final - Civil Affairs OperationsDocument144 pagesMILITAR, EUA - ARN16448 - FM 3-57 Final - Civil Affairs OperationsbrunoPas encore d'évaluation
- FROM DICTATORSHIP TO DEMOCRACY by Gene SharpDocument101 pagesFROM DICTATORSHIP TO DEMOCRACY by Gene Sharpndaru_100% (1)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- Crim Pro ChecklistDocument9 pagesCrim Pro ChecklistKeith Dyer100% (1)
- Carl Schmitt - The Crisis of Parliamentary DemocracyDocument223 pagesCarl Schmitt - The Crisis of Parliamentary Democracyndaru_94% (16)
- Triple Cross Illustrated TimelineDocument32 pagesTriple Cross Illustrated TimelinePeter LancePas encore d'évaluation
- Soviet Role in The Korean War PDFDocument183 pagesSoviet Role in The Korean War PDFGreg JacksonPas encore d'évaluation
- CIA Activities in IndonesiaDocument19 pagesCIA Activities in IndonesiaVan kim Hoang Ha100% (1)
- Industrial Security ManagementDocument7 pagesIndustrial Security ManagementWilliam Bryle Pertos100% (2)
- CEH v5 Module 00 Student IntroductionDocument19 pagesCEH v5 Module 00 Student IntroductionDennis Quispe PuchocPas encore d'évaluation
- The Most Secret List of Soe Agents: MDocument133 pagesThe Most Secret List of Soe Agents: MeliahmeyerPas encore d'évaluation
- Cyber Infrastructure ProtectionDocument324 pagesCyber Infrastructure ProtectionSSI-Strategic Studies Institute-US Army War CollegePas encore d'évaluation
- MCTP 3-01BDocument210 pagesMCTP 3-01BDavid MarcoePas encore d'évaluation
- People Vs RomDocument2 pagesPeople Vs RomMacPas encore d'évaluation
- Internet History and Growth: William F. Slater, III Chicago Chapter of The Internet Society September 2002Document50 pagesInternet History and Growth: William F. Slater, III Chicago Chapter of The Internet Society September 2002janga1988Pas encore d'évaluation
- APrIGF Joint Statement FINALDocument4 pagesAPrIGF Joint Statement FINALndaru_Pas encore d'évaluation
- NetFPGA Status Update at GEC3Document10 pagesNetFPGA Status Update at GEC3ndaru_Pas encore d'évaluation
- ASEAN Intergovernmental Commission On Human Rights (AICHR) Regional BookletDocument44 pagesASEAN Intergovernmental Commission On Human Rights (AICHR) Regional BookletNisrina Nadhifah RahmanPas encore d'évaluation
- 2011 Global Civil Society Representatives Statement On Internet GovernanceDocument1 page2011 Global Civil Society Representatives Statement On Internet Governancendaru_Pas encore d'évaluation
- Amnesty International Urges United States To Not Be A Spectator As Malaysian Authorities Attack Peaceful ProtestorsDocument1 pageAmnesty International Urges United States To Not Be A Spectator As Malaysian Authorities Attack Peaceful Protestorsndaru_Pas encore d'évaluation
- Justice For Chiranuch Premchaiporn & Other Thai NetizensDocument2 pagesJustice For Chiranuch Premchaiporn & Other Thai Netizensndaru_Pas encore d'évaluation
- Notable Cases in Thailand Regarding Freedom of Expression OnlineDocument3 pagesNotable Cases in Thailand Regarding Freedom of Expression Onlinendaru_Pas encore d'évaluation
- Techniques For Restoring Telecom After Disasters & OutagesDocument45 pagesTechniques For Restoring Telecom After Disasters & Outagesndaru_Pas encore d'évaluation
- What Is A DDOS Attack?: How Do They Do It?Document6 pagesWhat Is A DDOS Attack?: How Do They Do It?ndaru_Pas encore d'évaluation
- "Upholding Online Anonymity in Internet Governance: Affordances, Ethical Frameworks, and Regulatory Practices" by Robert BodleDocument11 pages"Upholding Online Anonymity in Internet Governance: Affordances, Ethical Frameworks, and Regulatory Practices" by Robert Bodlendaru_Pas encore d'évaluation
- Joint Solidarity Statement and Action On July 1st On 09:00-12:00 in Front of Malaysian Embassy in JakartaDocument3 pagesJoint Solidarity Statement and Action On July 1st On 09:00-12:00 in Front of Malaysian Embassy in Jakartandaru_Pas encore d'évaluation
- EUTRALITY, PRIVACY AND SECURITY: THE EXAMPLE OF THE FILTERING MEASURES by Charlotte BoguszDocument14 pagesEUTRALITY, PRIVACY AND SECURITY: THE EXAMPLE OF THE FILTERING MEASURES by Charlotte Boguszndaru_Pas encore d'évaluation
- Content Controls, Freedom of Expression and ISP Liability On The InternetDocument20 pagesContent Controls, Freedom of Expression and ISP Liability On The Internetndaru_Pas encore d'évaluation
- 20110315165308Document3 pages20110315165308ndaru_Pas encore d'évaluation
- Government Access To Private-Sector DataDocument5 pagesGovernment Access To Private-Sector Datandaru_Pas encore d'évaluation
- 2011 Southeast Asia Civil Society Statement On Internet GovernanceDocument3 pages2011 Southeast Asia Civil Society Statement On Internet Governancendaru_Pas encore d'évaluation
- Migrant Care Report RB CaseDocument1 pageMigrant Care Report RB Casendaru_Pas encore d'évaluation
- Digital Artifacts For Remembering and Storytelling: Post History and Social Network FragmentsDocument10 pagesDigital Artifacts For Remembering and Storytelling: Post History and Social Network Fragmentsndaru_Pas encore d'évaluation
- Malaysian Employers Should Pay For All Medical, Hospitalization & Surgical Cost of Their WorkersDocument2 pagesMalaysian Employers Should Pay For All Medical, Hospitalization & Surgical Cost of Their Workersndaru_Pas encore d'évaluation
- Launching The DNS War: Dot-Com Privatization and The Rise of Global Internet GovernanceDocument473 pagesLaunching The DNS War: Dot-Com Privatization and The Rise of Global Internet GovernanceCraig Simon100% (1)
- Asahi Kosei (M) Sdn. BHD Must Respect Human Rights and Worker Rights Reinstate Thiha Soe and Aung San Without Loss of BenefitsDocument3 pagesAsahi Kosei (M) Sdn. BHD Must Respect Human Rights and Worker Rights Reinstate Thiha Soe and Aung San Without Loss of Benefitsndaru_Pas encore d'évaluation
- Migrant Care Report RB CaseDocument1 pageMigrant Care Report RB Casendaru_Pas encore d'évaluation
- Developing A 'Protection of Civilians' Agenda For Southeast Asia by Melly Caballero-AnthonyDocument22 pagesDeveloping A 'Protection of Civilians' Agenda For Southeast Asia by Melly Caballero-Anthonyndaru_Pas encore d'évaluation
- Migrant Care Report RB CaseDocument1 pageMigrant Care Report RB Casendaru_Pas encore d'évaluation
- 25 Point Implementation Plan To Reform Federal ITDocument40 pages25 Point Implementation Plan To Reform Federal ITChristopher DorobekPas encore d'évaluation
- Telecoms Liberalization 2nd EditionDocument48 pagesTelecoms Liberalization 2nd Editionndaru_100% (1)
- StandyDocument179 pagesStandycomanflaviusPas encore d'évaluation
- Lessons on interview and interrogation techniquesDocument23 pagesLessons on interview and interrogation techniquesHelen OfracioPas encore d'évaluation
- Humans-The Weakest Link-Group 4Document33 pagesHumans-The Weakest Link-Group 4MadMagga0% (1)
- Cyber TerrorismDocument23 pagesCyber Terrorismsaurabh_parikh27100% (10)
- Watching The Watchers - Conducting Ethnographic Research On Covert Police Investigation in The UKDocument16 pagesWatching The Watchers - Conducting Ethnographic Research On Covert Police Investigation in The UKIleana MarcuPas encore d'évaluation
- Iran's Security SectorDocument27 pagesIran's Security SectorShafat YousufPas encore d'évaluation
- SOP Police by SSP CiDocument40 pagesSOP Police by SSP CiNanda Win LwinPas encore d'évaluation
- Cyber Offences, IT Act 2000Document9 pagesCyber Offences, IT Act 2000Rishi TharianiPas encore d'évaluation
- Ch15Crypto6e Userauth Nemo2Document43 pagesCh15Crypto6e Userauth Nemo2highway2prakasPas encore d'évaluation
- Deadly Force Justified in Roosevelt Police ShootingDocument6 pagesDeadly Force Justified in Roosevelt Police ShootingGeoff LiesikPas encore d'évaluation
- AUS12414360154Document3 pagesAUS12414360154Ashoka Senani HewagePas encore d'évaluation
- Hastings FBI WMDocument32 pagesHastings FBI WMKy Henderson100% (1)
- (PDF) Karol Łopatecki, Mapy W Planowaniu Działań 4Document3 pages(PDF) Karol Łopatecki, Mapy W Planowaniu Działań 4Burak Cengo tvPas encore d'évaluation
- People vs. ArutaDocument17 pagesPeople vs. ArutaGeanelleRicanorEsperonPas encore d'évaluation
- Bortun 2012 - Country Image ManagementDocument5 pagesBortun 2012 - Country Image ManagementAlice Rose Marie DumitrachePas encore d'évaluation
- Sir Aquim 2Document14 pagesSir Aquim 2Jomar Agtarap CarlosPas encore d'évaluation
- Marriii 20407 Robert Wiley Marr III Federal ResumeDocument5 pagesMarriii 20407 Robert Wiley Marr III Federal Resumeapi-27353430Pas encore d'évaluation
- Final ETI Micro Project ReportDocument17 pagesFinal ETI Micro Project ReportAkhilesh0% (1)
- Globalization and Nigeria Border Security - Issues and ChallengesDocument8 pagesGlobalization and Nigeria Border Security - Issues and ChallengesAlexander DeckerPas encore d'évaluation