Académique Documents
Professionnel Documents
Culture Documents
Access Management Secure Access Saml Server Instance Configuring NSM
Transféré par
Jyotirmoy SundiDescription originale:
Titre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Access Management Secure Access Saml Server Instance Configuring NSM
Transféré par
Jyotirmoy SundiDroits d'auteur :
Formats disponibles
Configuring a Secure Access SAML Server Instance (NSM Procedure)
The Secure Access device accepts authentication assertions generated by an SAML authority using either an artifact profile or a POST profile. This feature allows a user to sign in to a source site or portal without going through the Secure Access device first, and then to access the Secure Access device with single sign-on (SSO) through the SAML consumer service. To configure a new SAML server instance:
1. 2. 3.
In the NSM navigation tree, select Device Manager > Devices. Click the Device Tree tab, and then double-click the Secure Access device for which you want to configure an SAML server instance. Click the Configuration tab and select Authentication > Auth Servers. The corresponding workspace appears.
NOTE: If you want to update an existing server instance, click the appropriate link in the Auth Server Name box, and perform the Steps 5 through 8. Click the New button. The New dialog box appears. In the Auth Server Name list, specify a name to identify the server instance. Select SAML Server from the Auth Server Type list. Configure the server using the settings described in Table 1 on page 1. Click one:
4. 5. 6. 7. 8.
OKSaves the changes. CancelCancels the modifications.
Table 1: SAML Server Instance Configuration Details
Option Function Your Action
SAML Settings > Basic Settings tab
Source Site Inter-Site Transfer Service URL Issuer Value for Source Site
Specifies the source site inter-site transfer service URL.
Enter the URL.
Specifies the issuer value for the source site.
Enter the URL or hostname of the issuer of the assertion. Enter the string.
User Name Template
Specifies the user name template, which is a mapping string from the SAML assertion to a Secure Access user realm. Determines the maximum allowed difference in time between the Secure Access device clock and the source site clock.
Allow Clock Skew (minutes)
Enter the allowed clock skew value.
Configuring a Secure Access SAML Server Instance (NSM Procedure)
Table 1: SAML Server Instance Configuration Details (continued)
Option Function Your Action
SAML Settings > Artifact SSO tab
Source ID
Specifies the 20- byte identifier that the Secure Access device uses to recognize an assertion from a given source site. Specifies the source SOAP responder service URL.
Enter the Source ID.
Source SOAP Responder Service URL
Enter a URL. NOTE: You should specify this URL in the form of an HTTPS: protocol.
SOAP Client Authentication Username
Specifies the SOAP client authentication.
Select either HTTP Basic or SSL Client Certificate. Enter the username.
Specifies the username for SOAP client authentication. Specifies password for SOAP client authentication. Specifies the device certificate.
Password
Enter the password.
Device Certificate
Select a device certificate the drop-down list.
SAML Settings > POST SSO tab
Response Signing Certificate
Specifies the response signing cerificate for the SAML response signature verification. This is the PEM-formatted signing certificate, which is loaded for the SAML response signature verification. The certificate you select should be the same certificate used for signing the SAML response at the source site. The source site may send this certificate along with the SAML response, depending on the source site configuration. By default, the system performs signature verification of the SAML response first on the locally configured certificate. If a certificate is not configured locally in the SAML authentication server, then the system performs the signature verification on the certificate included in the SAML response from the source site.
Enter the name or browse to locate the response signing certificate.
Issued To
Displays name and attributes of the entity to whom the certificate is issued. Displays name and attributes of the entity that issued the certificate. Displays the time range that the certificate is valid.
Issued To details is displayed. Issued By details is displayed. Certificate valid time range is displayed.
Issued By
Valid
Configuring a Secure Access SAML Server Instance (NSM Procedure)
Table 1: SAML Server Instance Configuration Details (continued)
Option Function Your Action
Enable Signing Certificate status checking
Allows the Secure Access device to check the validity of the signing certificate configured in the SAML authentication server POST profile.
Select SAML Settings > POST SSO > Enable Signing Certificate status checking to enable this feature.
Server Catalog > Expressions tab
Name
Specifies a name for the user expression in the Certificate server user directory. Specifies a value for the user expression in the Certificate server user directory.
Enter the name.
Value
Enter the value.
Related Topics
Configuring a Secure Access Active Directory or NT Domain Instance (NSM Procedure) Configuring a Secure Access NIS Server Instance (NSM Procedure) Configuring a Secure Access Certificate Server Instance (NSM Procedure)
Configuring a Secure Access SAML Server Instance (NSM Procedure)
Configuring a Secure Access SAML Server Instance (NSM Procedure)
Vous aimerez peut-être aussi
- Project Name System Verification Document: Company LogoDocument11 pagesProject Name System Verification Document: Company LogoFahad RustamPas encore d'évaluation
- ARCON PAM ITSM IntegrationDocument9 pagesARCON PAM ITSM Integrationquyetpv144Pas encore d'évaluation
- 123Document1 page123Vimal SoniPas encore d'évaluation
- Configuring OAM 11g Server in CERT ModeDocument3 pagesConfiguring OAM 11g Server in CERT ModeDenem OrhunPas encore d'évaluation
- Horizon View True Sso Enrollment Server Diagnostics Tool-2-2Document14 pagesHorizon View True Sso Enrollment Server Diagnostics Tool-2-2Haroon mehmoodPas encore d'évaluation
- Cyberoam SSL VPN Quick Start Guide For ApplianceDocument14 pagesCyberoam SSL VPN Quick Start Guide For AppliancedanashriPas encore d'évaluation
- DotLoop Single Sign OnDocument9 pagesDotLoop Single Sign OnArchil GogorishviliPas encore d'évaluation
- Deploying Web Server Certificate For Site SystemsDocument18 pagesDeploying Web Server Certificate For Site SystemsLaeeqSiddiquiPas encore d'évaluation
- SPNEGO Based Single Sign-On Using Secure Login Server X.509 Client CertificatesDocument26 pagesSPNEGO Based Single Sign-On Using Secure Login Server X.509 Client CertificatesJason CraigPas encore d'évaluation
- Certificate Profile: Table 36 Trusted Certificate Authorities Settings Field DescriptionDocument1 pageCertificate Profile: Table 36 Trusted Certificate Authorities Settings Field DescriptionDippiPas encore d'évaluation
- SAML Integration GuideDocument13 pagesSAML Integration GuideDaren DarrowPas encore d'évaluation
- ReferenceGuide SOASecurityDocument15 pagesReferenceGuide SOASecuritylordquesitoPas encore d'évaluation
- SOA Data Validation Framework: by Kathiravan UdayakumarDocument10 pagesSOA Data Validation Framework: by Kathiravan Udayakumarnaveen reddyPas encore d'évaluation
- Configuring RADIUS: Layer 3 SolutionsDocument36 pagesConfiguring RADIUS: Layer 3 SolutionsBrian FrenchPas encore d'évaluation
- Spnego Single Sign-On Using Secure Login Server X.509 Client CertificatesDocument25 pagesSpnego Single Sign-On Using Secure Login Server X.509 Client CertificatesRodrigo XavierPas encore d'évaluation
- Web Services and QTP-Part 3: Adding Web Service Test ObjectDocument8 pagesWeb Services and QTP-Part 3: Adding Web Service Test ObjectSibajit LenkaPas encore d'évaluation
- Pet ExplainedDocument11 pagesPet ExplainedTommy CookseyPas encore d'évaluation
- People Soft SAML SecurityDocument20 pagesPeople Soft SAML SecuritySean WitczakPas encore d'évaluation
- 456Document3 pages456Vimal SoniPas encore d'évaluation
- OneNote 2016 Tips Tricks (Sugerencias y Trucos)Document4 pagesOneNote 2016 Tips Tricks (Sugerencias y Trucos)tonyPas encore d'évaluation
- 76-LDAP IntegrationDocument12 pages76-LDAP IntegrationArun SomashekarPas encore d'évaluation
- J Radius SimulatorDocument13 pagesJ Radius SimulatorAmanda LewisPas encore d'évaluation
- AaaDocument12 pagesAaaRavi PandeyPas encore d'évaluation
- CTAS Installation Guide PDFDocument6 pagesCTAS Installation Guide PDFtimkrashPas encore d'évaluation
- Configurating SAML AuthenticationDocument6 pagesConfigurating SAML AuthenticationkrishnamurthyyadavPas encore d'évaluation
- Learn SOADocument403 pagesLearn SOAGyan SharmaPas encore d'évaluation
- Single Sign On - ServiceNowDocument7 pagesSingle Sign On - ServiceNowammuluPas encore d'évaluation
- 3 ADFS Installation and ConfigurationDocument14 pages3 ADFS Installation and ConfigurationIngrid CardenasPas encore d'évaluation
- Client Credentials FlowDocument10 pagesClient Credentials FlowAnonymous 1U2FukcPas encore d'évaluation
- ScepDocument6 pagesScepAndres Barrios SaenzPas encore d'évaluation
- Configure Multi-FactorDocument27 pagesConfigure Multi-FactorTran ThangPas encore d'évaluation
- Setup Citrix Access Gateway Enterprise Edition (Netscaler) For Use of Multiple Authentication MethodsDocument32 pagesSetup Citrix Access Gateway Enterprise Edition (Netscaler) For Use of Multiple Authentication MethodsBerrezeg MahieddinePas encore d'évaluation
- SSORead MeDocument5 pagesSSORead MeTATWORTHPas encore d'évaluation
- Openssl PDFDocument17 pagesOpenssl PDFAhmed OsmanPas encore d'évaluation
- RSA For 3rd Party AccessDocument9 pagesRSA For 3rd Party AccessParitosh KadamPas encore d'évaluation
- RSA For 3rd Party AccessDocument9 pagesRSA For 3rd Party AccessParitosh KadamPas encore d'évaluation
- 这篇文档是我当时部署 CHEVRON 中国区 802.1X 的设计实施文档, 由本人领导项目, 带领团 队执行, 事后书写成文. 每个企业环境不尽相同, 大家可供参考!Document41 pages这篇文档是我当时部署 CHEVRON 中国区 802.1X 的设计实施文档, 由本人领导项目, 带领团 队执行, 事后书写成文. 每个企业环境不尽相同, 大家可供参考!wanglinPas encore d'évaluation
- SSO Portal To SystemDocument12 pagesSSO Portal To Systemmahussain456Pas encore d'évaluation
- Chapter 3: AAADocument82 pagesChapter 3: AAARyanb378Pas encore d'évaluation
- AMC2 Installation Note EnUS 1354133899Document27 pagesAMC2 Installation Note EnUS 1354133899andrey_buckoPas encore d'évaluation
- OktaDocument17 pagesOktaMansoor AhmedPas encore d'évaluation
- Aruba Mac FIlterDocument3 pagesAruba Mac FIlterANAND ANTONYPas encore d'évaluation
- Consuming Web ServiceDocument20 pagesConsuming Web ServiceNageswar VattikutiPas encore d'évaluation
- PegaDocument3 pagesPegaVimal SoniPas encore d'évaluation
- 213922-Configure-Mac-Authentication-Ssid-On-Cis C9800Document15 pages213922-Configure-Mac-Authentication-Ssid-On-Cis C9800JavierPas encore d'évaluation
- TS Gateway 2008 & RSADocument16 pagesTS Gateway 2008 & RSAdtlsixeoc148250% (2)
- Configuring A Console Station: Related TopicsDocument4 pagesConfiguring A Console Station: Related TopicsAnonymous OYLvnCxPas encore d'évaluation
- Logging in To The Juniper SA SSL VPN Through User (Browser) CertificatesDocument12 pagesLogging in To The Juniper SA SSL VPN Through User (Browser) CertificatesmuttbarkerPas encore d'évaluation
- Convoxccs 3.2 Product Installation ManualDocument13 pagesConvoxccs 3.2 Product Installation Manualprasad saiPas encore d'évaluation
- ClearPass Deployment Guide - Mobility Access Switch Configuration For 802.1X Wired AuthenticationDocument4 pagesClearPass Deployment Guide - Mobility Access Switch Configuration For 802.1X Wired AuthenticationruphydPas encore d'évaluation
- AAM Integrated Windows Authentication/ Basic NTLM: How To Deploy A10 Networks AAM NTLM Feature Within Thunder ADCDocument8 pagesAAM Integrated Windows Authentication/ Basic NTLM: How To Deploy A10 Networks AAM NTLM Feature Within Thunder ADCPham Van NamPas encore d'évaluation
- Technical Brief Enabling NTLM AuthenticationDocument4 pagesTechnical Brief Enabling NTLM AuthenticationsasPas encore d'évaluation
- Setting Up 802.1x AuthentiactionDocument4 pagesSetting Up 802.1x AuthentiactionruletriplexPas encore d'évaluation
- How To Configure SM59Document8 pagesHow To Configure SM59GirishPas encore d'évaluation
- iTWO 4.0 Docu - WebAPIDocument6 pagesiTWO 4.0 Docu - WebAPIphil_turboPas encore d'évaluation
- Central Web Authentication On The WLC and ISE Configuration ExampleDocument12 pagesCentral Web Authentication On The WLC and ISE Configuration ExamplephamvanhaPas encore d'évaluation
- Intact Technology Definitive SSL Tso GuideDocument20 pagesIntact Technology Definitive SSL Tso GuideHoly Wayne 'Trinity' ChuaPas encore d'évaluation
- Securing .NET Web Services with SSL: How to Protect “Data in Transit” between Client and Remote ServerD'EverandSecuring .NET Web Services with SSL: How to Protect “Data in Transit” between Client and Remote ServerPas encore d'évaluation
- Ni K3 Ku IGht JBX PVIDocument1 pageNi K3 Ku IGht JBX PVISagar jPas encore d'évaluation
- SkuDocument20 pagesSkuJLee CarpioPas encore d'évaluation
- Preparation: Snc/identity/as P:CN IDS, OU IT, O CSW, C DEDocument8 pagesPreparation: Snc/identity/as P:CN IDS, OU IT, O CSW, C DEspicychaituPas encore d'évaluation
- Sap Security and Authorisation QDocument12 pagesSap Security and Authorisation QSimbarashe MarisaPas encore d'évaluation
- Spotify CookiesDocument7 pagesSpotify CookiesSwaroop hcPas encore d'évaluation
- Troubleshoot AD FS Issues in Azure Active Directory and Office 365Document16 pagesTroubleshoot AD FS Issues in Azure Active Directory and Office 365awslab8100% (1)
- Government of Manipur X-10: Employment Exchange Identity CardDocument1 pageGovernment of Manipur X-10: Employment Exchange Identity CardNongmaithem Bilash SinghPas encore d'évaluation
- Deploying Eap Chaining With Anyconnect Nam and Cisco Ise: Secure Access How - To Guides SeriesDocument51 pagesDeploying Eap Chaining With Anyconnect Nam and Cisco Ise: Secure Access How - To Guides SeriesReven The savagePas encore d'évaluation
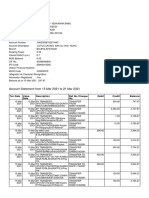
- Account Statement From 1 Jun 2022 To 30 Jun 2022: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDocument8 pagesAccount Statement From 1 Jun 2022 To 30 Jun 2022: TXN Date Value Date Description Ref No./Cheque No. Debit Credit Balancekiran gemsPas encore d'évaluation
- Veni AolDocument2 pagesVeni AolsusanPas encore d'évaluation
- Bank StatementDocument4 pagesBank Statementvenkatarammana99Pas encore d'évaluation
- PBL ProjhbghDocument4 pagesPBL ProjhbghKaushal PathakPas encore d'évaluation
- Role-Based Access Control (Rbac) 1Document16 pagesRole-Based Access Control (Rbac) 1sri nunePas encore d'évaluation
- One Time Password Authentication Integration Approach: IndroductionDocument2 pagesOne Time Password Authentication Integration Approach: Indroductionpuneet mishraPas encore d'évaluation
- THR Lebaran 2011 p2Document25 pagesTHR Lebaran 2011 p2Sanata BangunPas encore d'évaluation
- Erd Kettle Repository PDFDocument1 pageErd Kettle Repository PDFAndy Torres UtraPas encore d'évaluation
- Chapters 1 2Document36 pagesChapters 1 2radhe shamPas encore d'évaluation
- NO Answer: FAQ On DigitalmeDocument8 pagesNO Answer: FAQ On DigitalmeSyeida AlliPas encore d'évaluation
- All Accounts InformationDocument4 pagesAll Accounts InformationiltamasjaatPas encore d'évaluation
- Sentry LaravelDocument65 pagesSentry LaravelXhiko TanakaPas encore d'évaluation
- CISSP Prep CH 6. Identity and Access ManagementDocument68 pagesCISSP Prep CH 6. Identity and Access ManagementManish AgarwalPas encore d'évaluation
- GIIlz F3 o 4 A Svwda KDocument3 pagesGIIlz F3 o 4 A Svwda KVENKANNA BABU GUDDATIPas encore d'évaluation
- Dot1x Fail - Mab Success DebugDocument3 pagesDot1x Fail - Mab Success Debugshadab umairPas encore d'évaluation
- Secure Lock Manager Easy Quick Start GuideDocument61 pagesSecure Lock Manager Easy Quick Start GuideEd ArenasPas encore d'évaluation
- 5000 Fresh Hits AccountDocument1 362 pages5000 Fresh Hits AccountreezereturnsPas encore d'évaluation
- Hardware and Network Servicing: LO 1: Ensure User Accounts Are ControlledDocument3 pagesHardware and Network Servicing: LO 1: Ensure User Accounts Are ControlledSami NurPas encore d'évaluation
- About Dot1x From Cisco Myanmar FB GroupDocument2 pagesAbout Dot1x From Cisco Myanmar FB GroupAung Kyaw ThuPas encore d'évaluation
- Ipass Reference GuideDocument8 pagesIpass Reference Guidemagdy_gadoPas encore d'évaluation
- Ahoi MFA End User Teaser SlidesDocument8 pagesAhoi MFA End User Teaser SlidesAlexander LupskiPas encore d'évaluation
- CDS - 2012 03 12.00000Document3 pagesCDS - 2012 03 12.00000veldurthibuntyPas encore d'évaluation