Académique Documents
Professionnel Documents
Culture Documents
Introduction
Transféré par
Khairi AzmiDescription originale:
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Introduction
Transféré par
Khairi AzmiDroits d'auteur :
Formats disponibles
9/11/2011
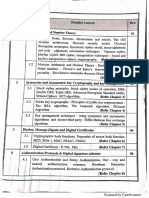
IntroductiontoCryptography SCR3443 Semester1,2011/12
By:
AssociateProf.DrMazleenaSalleh
DepartmentofComputerSystem&Communication FacultyofComputerScienceandInformationSystems
mazleena@utm.my 075532006/32369
AssociateProfDrMazleenaSalleh
Module1:Introduction
CourseLearningOutcome
Attheendofthecourse,studentsshouldhavethefollowing knowledge,skillsandattitudeto:
Illustratethefundamentalconceptsincryptography. Applythenecessarytheorytoperformencryptionanddecryption processes. Differentiatetechniquesusedincryptographywhichrelatetotheir differentuses. Recommendtools,techniquesandtrendscryptographyfordata security. Formulatedatasecuritystrategiesusinglatestcryptography technique.
AssociateProfDrMazleenaSalleh
Module1:Introduction
9/11/2011
References
HonorCode Collaborationonhomeworkwithotherstudentsencouraged. However,writealoneandgivecredit.
Module1:Introduction
AssociateProfDrMazleenaSalleh
InformationSecurity
Confidentiality/Privacy keepinginformationsecretfromallbutthosewhoare authorizedtoseeit. DataIntegrity ensuringinformationhasnotbeenalteredby unauthorizedorunknownmeans. maintainingdataconsistency EntityAuthentication/Identification corroborationoftheidentityofanentity(e.g.,aperson,a computerterminal,acreditcard,etc.)
AssociateProfDrMazleenaSalleh
Module1:Introduction
9/11/2011
...InformationSecurity
Messageauthentication corroboratingthesourceofinformation;alsoknownas dataoriginauthentication. Signature ameanstobindinformationtoanentity. Authorization conveyance,toanotherentity,ofofficialsanctiontodoor besomething. Validation ameanstoprovidetimelinessofauthorizationtouseor manipulateinformationorresources.
AssociateProfDrMazleenaSalleh Module1:Introduction 5
...InformationSecurity
Accesscontrol restrictingaccesstoresourcestoprivilegedentities. unauthorizedusersarekeptout Certification endorsementofinformationbyatrustedentity. Timestamping recordingthetimeofcreationorexistenceofinformation. Originatorofcommunicationscantdenyitlater
AssociateProfDrMazleenaSalleh
Module1:Introduction
9/11/2011
...InformationSecurity
Witnessing verifyingthecreationorexistenceofinformationbyan entityotherthanthecreator. Nonrepudiation preventingthedenialofpreviouscommitmentsoractions. Availability Legitimateusershaveaccesswhentheyneedit Someobjectivesarecombined: Userauthenticationusedforaccesscontrolpurposes Nonrepudiationcombinedwithauthentication
AssociateProfDrMazleenaSalleh Module1:Introduction 7
SecurityThreats
Informationdisclosure/informationleakage Integrityviolation Masquerading Denialofservice Illegitimateuse Genericthreat:Backdoors,trojanhorses,insiderattacks MostInternetsecurityproblemsareaccesscontrolor authenticationones Denialofserviceisalsopopular,butmostlyanannoyance
AssociateProfDrMazleenaSalleh
Module1:Introduction
9/11/2011
MainClassesOfThreats
Interruptionanassetsis lost/unavailable/cannot beutilizedeg:databaseis delete Interceptionanauthorized party(person/program)has gainedaccesstoanasseteg: wiretapping
AssociateProfDrMazleenaSalleh
Module1:Introduction
MainClassesOfThreats
Modification:an unauthorizedparty (person/program)hasgained accessandtamperedaround it,eg:modifyinganitemof database. Fabrication:Productionof counterfeitobjectsfor computingsystem,eg repeatingafinancial transaction
AssociateProfDrMazleenaSalleh
Module1:Introduction
10
9/11/2011
TypesofAttack
Passive attack can only observe communications or data Active attack can actively modify communications or data Often difficult to perform, but very powerful Mail forgery/modification TCP/IP spoofing/session hijacking
AssociateProfDrMazleenaSalleh
Module1:Introduction
11
SecurityMechanism
SecurityMechanism Physicalprotection Cryptography AccessControl Authorization Auditing Cryptographyisonlyasmallpartofprotectionneeded forabsolutesecrecy.
Module1:Introduction 12
AssociateProfDrMazleenaSalleh
9/11/2011
Cryptography
Essentialtoolformakingsecurecomputingsystems. Badlydesignedprotocolsareeasilyexploitedtobreakinto computersystems,toeavesdroponphonecalls,tosteal services,andsoforth. Designishard. Itiseasytounderestimatethetaskandquicklycomeup withadhocprotocolsthatlaterturnouttobewrong. thenecessarytimeandexpertiseforproperprotocol designistypicallyunderestimated,oftenatfuturecost. takesknowledge,effortandingenuitytodothejobright.
AssociateProfDrMazleenaSalleh Module1:Introduction 13
Overview Field of Cryptology
AssociateProfDrMazleenaSalleh
Module1:Introduction
14
9/11/2011
Cryptography
Crytographyisthescienceofsecretwriting.MattBlaze Cryptographyisthestudyofsecret(crypto)writing(graphy) concernedwithdevelopingalgorithmswhichmaybeusedto provide(goals): secrecy authenticatethatamessagehasnotchangedintransit (integrity) implicitlyauthenticatethesender Cryptographyisdefensiveandcanprotectordinarycommerce andordinarypeople.
AssociateProfDrMazleenaSalleh
Module1:Introduction
15
SupportforSecurityMechanisms
Threebasicbuildingblocksareused: Encryptionisusedtoprovideconfidentiality,canprovide authenticationandintegrityprotection. Digitalsignaturesareusedtoprovideauthentication,integrity protection,andnonrepudiation. Checksums/hashalgorithmsareusedtoprovideintegrity protection,canprovideauthentication Oneormoresecuritymechanismsarecombinedtoprovidea securityservice.
AssociateProfDrMazleenaSalleh
Module1:Introduction
16
9/11/2011
FundamentalIdeaofCryptography
Possibletotransformplaintextintociphertextin whichinformationispresentbuthidden.Wecan releasethetransformedmessagewithoutexposing theinformationitrepresent. Differenttransformationscreatedifferentciphertext fortheexactsamemessage. Forperfectciphers,anyciphertextcanbeinterpreted asanymessage.
AssociateProfDrMazleenaSalleh
Module1:Introduction
17
WhatCryptographyCanDo
Itcanprotectprivacy. Itseparatesthesecurityofamessagefromthesecurityof themedia. Itcanauthorizesomeone. Itcanfacilitatetrust. Itcanallowfordigitalcredentials(authentication). Itcanvalidatetheintegrityofinformation. Itcanensurethefairnessoffinancialtransactions. Itcanprovideanaudittrailforlaterdisputeresolution. Cryptographystopslyingandcheating.
AssociateProfDrMazleenaSalleh Module1:Introduction 18
9/11/2011
OtherUsesofCryptography
Morespecializeduses: Digitalsignatures Undeniabledigitalsignatures Allornothingdisclosureofsecrets Zeroknowledgeproofs Oblivioustransfer Simultaneousexchangeofsecrets Secureelections Digitalcash
AssociateProfDrMazleenaSalleh Module1:Introduction 19
ThingsthatCryptographyCannotDo
Cryptographycanonlyhideinformationafteritisencrypted andwhileitremainsencrypted. Secretinformationgenerallydoesnotstartoutencrypted, sothereisnormallyanoriginalperiodwhichthesecretare notprotected. Secretinformationgenerallyisnotusedinencrypted form,soitisagainoutsidethecryptographicenvelope everytimethesecretisused. Cryptographycannotprotectagainstinformants,undercover spying,bugs,photographicevidenceortestimony.
AssociateProfDrMazleenaSalleh Module1:Introduction 20
10
9/11/2011
Adversaries
Hackers:informalandinstitutional Insiders Lonecriminals Commercialespionage Press Organizedcrime Terrorists Nationalintelligence
Module1:Introduction 21
AssociateProfDrMazleenaSalleh
CriminalAttacks
HowcanIacquirethemaximumfinancialreturnby attackingthesystem? Forgery,misrepresentation,replay,repudiation Generallyopportunistic Minimumnecessaryresources Focusesonlowtechflaws Focusesontheweakestsystems Mediumrisktolerance:willingtoriskjoborjailtime.
AssociateProfDrMazleenaSalleh Module1:Introduction 22
11
9/11/2011
ComponentsofaCryptosystem
Plaintextmessagespace,P Cipertextmessagespace,C Keyspace,K Asetofencryptionalgorithms,Ek Asetofdecryptionalgorithms,Dk
C
C=E(P,K)
AssociateProfDrMazleenaSalleh Module1:Introduction
P=D(C,K)
23
EncryptionandDecryption
Encryption Processofencodinganinformationsothatitsmeaningis notunderstood. Decryption Processofdecodingtheencryptedmessagetogetback theoriginalinformation.
Original Plaintext or Cleartext
AssociateProfDrMazleenaSalleh
Encrypt or Encipher
Ciphertext
Decrypt or Decipher
Recovered Plaintext or Cleartext
24
Module1:Introduction
12
9/11/2011
KeylessandKeyedCryptosystem
KeylesscryptosystemperformsE/Dwithoutusing anykey. Symmetrickey:Key1=Key2 Asymmetrickey:Key1Key2
Ciphertext Plaintext Encrypt Decrypt Plaintext
Key1
AssociateProfDrMazleenaSalleh Module1:Introduction
Key2
25
AlgorithmE/D
Plaintext,P=[p1,p2,..,pn] Ciphertext,C=[c1,c2,..,cn] IfEandDaretheencryptionandthedecryption algorithmsrespectively,then C=E(P) P=D(C) Cryptosystemshouldbehaveasfollows: P=D(E(P))orP=D(Key2,E(Key1,P))
AssociateProfDrMazleenaSalleh Module1:Introduction 26
13
9/11/2011
FeaturesofaGoodCryptosystem
EandDalgorithmsmustbeefficient. Thesystemmustbeeasytoused. Thesecurityofthesystemmustdependonthe secrecyofthekeysandNOTonthesecrecyoftheE andDalgorithms. Thesizeoftheciphertextisnotunnecessarylarger thantheplaintext.
AssociateProfDrMazleenaSalleh
Module1:Introduction
27
Confidentiality
Keepingthecontentsofamessageconfidential:during transmissionorstorage. IfAsendsamessagetoB,buttheenemyinterceptsit,Amust makesurethatthisenemywillneverunderstandsthecontent ofthemessage.
K
Transmitted (or Stored) Ciphertext,
Original Plaintext,
Encrypt,
E (K, P)
Decrypt,
D (K,C)
Recovered Plaintext,
AssociateProfDrMazleenaSalleh
Module1:Introduction
28
14
9/11/2011
Integrity
Provingthatthecontentsofamessagehave remainedunchanged.
Secret channel for keys
P E(K, P)
Seal
D(K, C)
Seal
C
Seal
Verify?
AssociateProfDrMazleenaSalleh
Module1:Introduction
29
Authenticity/NonRepudiation
Provingthatamessagecomesfromthedeclared,authenticsource Preventinganauthenticsourcefromlaterdenying(orrepudiate) theauthenticityofthemessage.
Private Key Public Key TTP Certification Authority
Sign
Digital Signature
Unsign
P P
AssociateProfDrMazleenaSalleh Module1:Introduction
Verify?
30
15
9/11/2011
SymmetricKeyCryptosystem
Asinglekeysharedbybothsenderandreceiver. Advantages: Fastencryption/decryptionprocess,efficientforlong messages Weakness: Requiresestablishmentofasecurechannelforkeyexchange. Ifthiskeyisdisclosed,communicationsarecompromised. Suppose3personsA,B,Cwanttocommunicatetoeachotherin A B private, K
KAC
AssociateProfDrMazleenaSalleh Module1:Introduction
AB
KBC
31
Asymmetric/PublicKeyCryptosystem
Keythatisusedtoencryptthemessageisdifferenttothekey usedtodecryptthemessage. Publickeywidelyavailableanyonewantingtosendthema messageusesthealgorithmandtherecipientspublickeyto doso. Onlytherecipient,withtheirprivatekeycandecryptthe message. Weakness computationallyintensive,encryptionanddecryptiontake longer. Notsuitableforencryptinglongmessages
AssociateProfDrMazleenaSalleh Module1:Introduction 32
16
9/11/2011
Hashing
Cryptographichashfunctionisadeterministicprocedurethat takesanarbitraryblockofdataandreturnsafixedsizebit string,the(cryptographic)hashvalue. Idealcryptographichashfunctionhasfourmainorsignificant properties: itiseasytocomputethehashvalueforanygivenmessage, itisinfeasibletogenerateamessagethathasagivenhash, itisinfeasibletomodifyamessagewithouthashbeing changed, itisinfeasibletofindtwodifferentmessageswiththe samehash.
AssociateProfDrMazleenaSalleh Module1:Introduction 33
Hashing
Acryptographichash function(specifically, SHA1)atwork.Note thatevensmallchanges inthesourceinput(here intheword"over") drasticallychangethe resultingoutput,bythe socalledavalanche effect.
AssociateProfDrMazleenaSalleh
Module1:Introduction
34
17
9/11/2011
BlockCipher
Encryptsagroupofplaintext symbolsasoneblock. Decryptionissimplythereverseof theencryptionprocessusingthe samesecretkey. Differentplaintextblocks,usually64 bits,aremappedtodifferent ciphertextblocks;ablockcipher effectivelyprovidesapermutation ofthesetofallpossiblemessages. Theactualpermutationproduced duringanyparticularoperationis secret,anddeterminedbyakey.
AssociateProfDrMazleenaSalleh Module1:Introduction
Plaintext Block
Encrypt
Ciphertext Block
35
BlockCipher
Advantages: informationfromtheplaintextisdiffusedintoseveralciphertext symbol. immunitytoinsertionssinceasingleinsertionintoablockwould resultanincorrectlengthandthuscouldbedetectedduring decryption. Disadvantages: blockciphermustwaituntilanentireblockofplaintexthasbeen receivedbeforestartingtheencryptionprocess;thisresultinslowness ofencryption. errorpropagationwherebyasingleerrorwillaffectthetransformation ofallothercharactersinthesameblock.
AssociateProfDrMazleenaSalleh
Module1:Introduction
36
18
9/11/2011
StreamCipher
Astreamcipherbreakstheplaintextintounits,normallya singlecharacter.Itencryptsthenthunitoftheplaintextwith thenthunitofthekeystream. Streamcipherscanbedesignedtobeexceptionallyfast. Eachcharacterisencryptedwithoutregardforanyother plaintextcharacter,eachcharactercanbeencryptedassoon asitisread. Streamcipherhaslowerrorpropagationsinceeachcharacter isseparatelyencoded.Errorencounteronlyaffectsthat particularcharacter.
Module1:Introduction
AssociateProfDrMazleenaSalleh
37
StreamCipher
Runabout10timesfasterthancomparableblockciphers Disadvantages: lowdiffusionwherebyallinformationofthatparticular characteroftheplaintextisretainedinthecharacterof theciphertext. susceptibilitytomaliciousinsertionandmodification
key (optional) ISSOPMI plaintext
AssociateProfDrMazleenaSalleh
wdhuw... ciphertext
38
Module1:Introduction
19
9/11/2011
Cryptanalysis
Processofattemptingtodiscovertheplaintextorthe keyused. Strategydependonthenatureoftheencryption schemeandtheinformationavailable. However,anencryptionschemeisunconditionally secureiftheciphertextgenerateddoesnotcontain enoughinformationtodeterminethecorresponding plaintext.
Reading:Forouzan,pg5660
AssociateProfDrMazleenaSalleh
Module1:Introduction
39
AssociateProfDrMazleenaSalleh
Module1:Introduction
40
20
9/11/2011
CiphertextOnly
Cryptanalysthasonlytheciphertextfromwhichtodeterminethe plaintext. Noknowledgewhatsoeveroftheactualmessage Thecryptoanalysthastheciphertextofoneorseveralmessages. wanttorecovertheplaintextor(better)thekey. Given:C1=E(P1),C2=E(P2),...,Ci=E(Pi) Deduce: EitherP1,P2,...,Pi,K; oranalgorithmtoinferPi+1fromCi+1=E(Pi+1).
AssociateProfDrMazleenaSalleh Module1:Introduction 41
KnownPlaintextAttack
Inknownplaintextattacktheattackerhaspairs (x,e(x)),butthechoiceofxisnotunderthe attacker'scontrol.
AssociateProfDrMazleenaSalleh
Module1:Introduction
42
21
9/11/2011
ChosenPlaintext
Attackerhaspairs(x,e(x))andxischosenbytheattacker. capabilitytofindtheciphertextcorrespondingtoan arbitraryplaintextmessageofhisorherownchoosing. Thelikelihoodofthistypeofattackbeingpossibleisnotmuch. Codeswhichcansurvivethisattackareconsideredtobevery secure. Adaptivechosenplaintextattack,thecryptanalystcan determinetheciphertextofchosenplaintextsinaniterative processbasedonpreviousresults.Thisisthegeneralnamefora methodofattackingproductcipherscalled"differential cryptanalysis.
AssociateProfDrMazleenaSalleh Module1:Introduction 43
ChosenPlaintextAttack
Wanttorecoverthekey. Given:P1,P2,...,Pi,C1=E(P1),C2=E(P2),...,Ci=E(Pi) wherewecanselectP1,P2,...,Pi. Deduce:EitherKoranalgorithmtoinferPi+1from Ci+1=E(Pi+1).
AssociateProfDrMazleenaSalleh
Module1:Introduction
44
22
9/11/2011
ChosenCiphertext
Cryptanalystcanchooseanarbitraryciphertextand findthecorrespondingdecryptedplaintext. Thisattackcanbeusedinpublickeysystems,where itmayrevealtheprivatekey. Chosetheciphertexttobedecrypted. Given:C1,C2,...,Ci,P1=D(C1),P2=D(C2),...,Pi=D(Ci) Deduce:K
AssociateProfDrMazleenaSalleh
Module1:Introduction
45
BreakableCipher
Thereisanalgorithmknowntobeabletheoretically breakthecipher. Abreakableciphermaynotbefeasiblebroken exceptbyusingcurrenttechnology. Exampleusingbruteforcewhichrequire1030 operations. Cipherisbreakablebutinfeasible! Cryptanalysisishard,tedious,repetitiveandvery expensive.Successisneverassured.
AssociateProfDrMazleenaSalleh Module1:Introduction 46
23
9/11/2011
Kerckhoffs'Principle
AlsocalledKerckhoffs'assumption,axiomorlaw State:Acryptosystemshouldbesecureevenifeverythingaboutthe system,exceptthekey,ispublicknowledge. Majorityofciviliancryptographymakesuseofpubliclyknownalgorithms Butciphersusedtoprotectclassifiedgovernmentormilitary informationareoftenkeptsecret. Theresistanceoftheciphertoattackmustbebasedonlyonthesecrecy ofthekey. Keydomainforeachalgorithmissolargethatitmakesitdifficultforthe adversarytofindthekey.
AssociateProfDrMazleenaSalleh Module1:Introduction 47
Conclusions
Theproblemwithbadcryptographyisthatitlooksjustlike goodcryptography. Successfulattacksareoftenkeptsecret.Unlessattackers publicize. Weneedtobeproactive. Understandtherealthreatstoasystem Designsystemswithstrongcryptography Buildcryptographyintosystemsatthebeginning Perfectsolutionsarenotrequired,butsystemsthatcanbe brokencompletelyareunacceptable.
AssociateProfDrMazleenaSalleh Module1:Introduction 48
24
Vous aimerez peut-être aussi
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (588)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (400)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (345)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (74)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2259)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (121)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- Paxson Spring 2011 CS 161 Computer Security Final Exam: (Last) (First)Document18 pagesPaxson Spring 2011 CS 161 Computer Security Final Exam: (Last) (First)Bertin BidiasPas encore d'évaluation
- PS129 EncryptionDocument5 pagesPS129 Encryptionmraiyan4590Pas encore d'évaluation
- Chapter 01 - Security PrincipalsDocument18 pagesChapter 01 - Security PrincipalsJaye 99Pas encore d'évaluation
- Thales Protect Server 3 Network Hsms PBDocument3 pagesThales Protect Server 3 Network Hsms PBTrầnTuấnThànhNhânPas encore d'évaluation
- Ise LogsDocument168 pagesIse LogsDenis EgusquizaPas encore d'évaluation
- KaranjitDocument21 pagesKaranjitVikash SinghPas encore d'évaluation
- T215B Emad-Ameen MTA Summary V2Document12 pagesT215B Emad-Ameen MTA Summary V2Christina FingtonPas encore d'évaluation
- White Paper: AES EncryptionDocument5 pagesWhite Paper: AES EncryptionelyiasaPas encore d'évaluation
- SHA - 1 Hash: Practical:11 AIM: - Perform Techniques SHA-1 Hash and Digital Signature Algorithm With CryptoolDocument11 pagesSHA - 1 Hash: Practical:11 AIM: - Perform Techniques SHA-1 Hash and Digital Signature Algorithm With Cryptooljhyter54rdPas encore d'évaluation
- Icis 2016 7550955Document4 pagesIcis 2016 7550955Laxman JakatiPas encore d'évaluation
- Decrypting SSL/TLS Traffic For Hidden Threats Detection: Conference PaperDocument5 pagesDecrypting SSL/TLS Traffic For Hidden Threats Detection: Conference Paperlai khoiPas encore d'évaluation
- Unit-2 Security Threats To E-Business-15 May 2011Document16 pagesUnit-2 Security Threats To E-Business-15 May 201177ranga100% (1)
- Presented By:-Rahul Kumar Preeti SachdevaDocument30 pagesPresented By:-Rahul Kumar Preeti SachdevataariyPas encore d'évaluation
- (Slides) Authenticated Encryption GCM - CCMDocument48 pages(Slides) Authenticated Encryption GCM - CCMProject Symphony Collection100% (1)
- Constant Time Cryptoghraphic Library: ELE3001 Final ReportDocument25 pagesConstant Time Cryptoghraphic Library: ELE3001 Final ReportPriSimPas encore d'évaluation
- CRYPTOGRAPHYDocument18 pagesCRYPTOGRAPHYTawki BakiPas encore d'évaluation
- CSS TechmaxDocument392 pagesCSS TechmaxRushi Shah100% (5)
- Configure Eap Tls Flow With IseDocument24 pagesConfigure Eap Tls Flow With IseKash BarlasPas encore d'évaluation
- IS FileDocument39 pagesIS File55 ManviPas encore d'évaluation
- Sysadmin Magazine April 2023Document18 pagesSysadmin Magazine April 2023sylvain rosePas encore d'évaluation
- د. محمد يونسClassical Encryption TechniquesDocument51 pagesد. محمد يونسClassical Encryption TechniquesMohammed Al-RadwanPas encore d'évaluation
- Authentication of Iot Device and Iot Server Using Secure VaultsDocument6 pagesAuthentication of Iot Device and Iot Server Using Secure Vaultsrmsaqib1Pas encore d'évaluation
- Cryptology For SmartiesDocument101 pagesCryptology For Smartiessquared9Pas encore d'évaluation
- An 10922Document26 pagesAn 10922scr1bd9917Pas encore d'évaluation
- Finalpptslides 1662001123996Document33 pagesFinalpptslides 1662001123996Sushil VishwakarmaPas encore d'évaluation
- EAadhaar xxxxxxxx3861 09072021190322 173015Document1 pageEAadhaar xxxxxxxx3861 09072021190322 173015ABDUL RAZZAKPas encore d'évaluation
- Anexos PDFDocument21 pagesAnexos PDFfelsuquiPas encore d'évaluation
- Lecture 14Document29 pagesLecture 14Abrham GidayPas encore d'évaluation
- Secure Hash AlgorithmDocument1 pageSecure Hash AlgorithmAmulyaPas encore d'évaluation
- Epassport APIDocument2 pagesEpassport APIMario CostaPas encore d'évaluation