Académique Documents
Professionnel Documents
Culture Documents
6408AL Mod1-1 Trainer
Transféré par
Toyin Wise-SulaimanDescription originale:
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
6408AL Mod1-1 Trainer
Transféré par
Toyin Wise-SulaimanDroits d'auteur :
Formats disponibles
INSTRU CTOR
NOTES
MICROSOFT OFFICIAL DISTANCE LEARNING
6408AL
Getting Started with Server Management in Windows Server 2008
ii
Information in this document, including URL and other Internet Web site references, is subject to change without notice. Unless otherwise noted, the example companies, organizations, products, domain names, e-mail addresses, logos, people, places, and events depicted herein are fictitious, and no association with any real company, organization, product, domain name, e-mail address, logo, person, place or event is intended or should be inferred. Complying with all applicable copyright laws is the responsibility of the user. Without limiting the rights under copyright, no part of this document may be reproduced, stored in or introduced into a retrieval system, or transmitted in any form or by any means (electronic, mechanical, photocopying, recording, or otherwise), or for any purpose, without the express written permission of Microsoft Corporation. The names of manufacturers, products, or URLs are provided for informational purposes only and Microsoft makes no representations and warranties, either expressed, implied, or statutory, regarding these manufacturers or the use of the products with any Microsoft technologies. The inclusion of a manufacturer or product does not imply endorsement of Microsoft of the manufacturer or product. Links are provided to third party sites. Such sites are not under the control of Microsoft and Microsoft is not responsible for the contents of any linked site or any link contained in a linked site, or any changes or updates to such sites. Microsoft is not responsible for webcasting or any other form of transmission received from any linked site. Microsoft is providing these links to you only as a convenience, and the inclusion of any link does not imply endorsement of Microsoft of the site or the products contained therein. Microsoft may have patents, patent applications, trademarks, copyrights, or other intellectual property rights covering subject matter in this document. Except as expressly provided in any written license agreement from Microsoft, the furnishing of this document does not give you any license to these patents, trademarks, copyrights, or other intellectual property. 2008 Microsoft Corporation. All rights reserved. Microsoft, PowerPoint, Windows Media, Windows, and XBOX are either registered trademarks or trademarks of Microsoft Corporation in the United States and/or other countries. All other trademarks are property of their respective owners.
Lesson 1: Server Management Overview
Instructor Notes
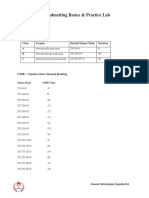
Introduction Students should have reviewed the Live Meeting Orientation recording prior to class. This section provides a refresher and practice session. 1. Describe Audio 2. Ask everyone to Restore the Default Layout by choosing Restore Default Layout from the View menu. This way, the Seating Chart and the Question Pan display for the students. 3. Ask students if they can hear you and can see the seating chart, to change their seat color to Red. Explain that Red indicates raising your hand and green indicates that you are ready to proceed or you are finished with an activity. If you encounter a color blind student who cannot distinguish between the colors red and green, explain that the student will be able to use the Ask Question pane to communicate the same information to you. 4. Explain how students can ask questions. Type a question into the Question field at the bottom right of the Live Meeting screen and click Ask. 5. Describe Question Management
Explain that questions only go to you Explain that you can answer individually or to the group.
6. If your class has over 6 students in it, a recommended practice is to break up student names into teams.
BLUE Team <Insert Student Names Here> GOLD Team <Insert Student Names Here> PURPLE Team <Insert Student Names Here>
7. Remind students that if they have not already done so, they should add Personal Information section to introduce themselves to the class. They can find the Personal Information by selecting User Preferences from the Tools menu. 8. Remind students to put their phones on MUTE when they are not talking. Mute is *6 and Unmute is #6. 9. Make sure the following Attendee Permissions are checked:
ASK QUESTIONS ANNOTATE INTERACT (NO CHAT) Ctrl-H (with Menus) F5 (without Menus)
10. Explain the Expanded View and ask the students to test both Expanded View options:
11. Explain how the Live Meeting Whiteboard works and ask students to experiment with the following ANNOTATION tools:
HIGHLIGHT SHAPES AND FREEHAND STAMP
12. Demonstrate the portal. You can put a screenshot of your actual portal in the slide if you want to. 13. Describe the Course At a Glance. Make sure to update the dates and times to reflect the actual dates. 14. Show a quick demonstration of the Day in the Life Lab Scenario environment. 15. Use an ice breaker. You can use your own fun getting to know you activity or use the activity provided. Ask each student to answer the questions above, using text annotation, in the box below their name.
Getting Started with Server Management in Windows Server 2008
Module 1-1
Getting Started with Server Management in Windows Server 2008
Module Contents:
Lesson 1: Server Management Overview Lesson 2: Server Core Lesson 3: Windows PowerShell Lesson 4: Windows Remote Management 1-1 1-28 1-41 1-58
Module 1-1: Getting Started with Server Management in Windows Server 2008
Windows Server 2008 eases the task of managing and securing multiple server roles in an enterprise with a variety of new features and technologies. The key message of this course is to provide information regarding benefits, technical details, and implementation of the management technologies and tools that Windows Server 2008 includes.
Module Description
This module provides information regarding the ways in which Windows Server 2008 eases the tasks of managing and securing multiple server roles in an enterprise by using a variety of new features and technologies.
Module 1-1 Objectives
After completing this module, you will be able to: Identify the Server Management improvements that have been made to Windows Server 2008. Identify when to use Server Core installation and list the benefits to your organization of implementing Server Core. Explain how Windows PowerShell command-line interface can simplify server administration. Explain Windows Remote Management and list the benefits to your organization of implementing Windows Remote Management.
Lesson 1: Server Management Overview
Introduction
Windows Server 2008 provides new tools, technologies, and installation options to improve the management experience.
Topic: Overview of Server Management
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
For local administration of a single server, Server Manager is an integrated Microsoft Management Console (MMC) that offers information technology (IT) professionals a seamless, integrated experience for adding, removing, and configuring server roles, role services, and features. It also acts as a portal for ongoing server management, monitoring, and operations by exposing key management tasks that are based on server role, and providing access to advanced administration tools.
Lesson Contents:
Topic: Overview of Server Management Lecture: Overview of Server Management Topic: Primary Management Tools Matching Type: Which Primary Management Tool? Topic: Alternative Management Tools Brainstorm: List the Alternative Management Tools Matching Type: Which Alternative Management Tool? Topic: Print Management Short Answer Poll: Print Management Brainstorm: What Are the Benefits of E-Mail Notifications? Topic: Technical Background Matching Type: Initial Configuration Tasks or Server Manager? Short Answer Poll: Permissions for Initial Configuration Tasks Short Answer Poll: Initial Configuration Tasks Demonstration: How to Use the Initial Configuration Tasks Window Game: Assigning Tasks in the Initial Configuration Tasks Window Brainstorm: List and Describe the Server Roles in Windows Server 2008 Demonstration: Configuring and Managing Server Roles Topic: Implementation/Usage Scenarios Lecture: Implementation/Usage Scenarios Topic: Recommendations Brainstorm: List the Recommendations for Performing Server Management by Using Windows Server 2008 Topic: Summary Lecture: Summary
Topic: Overview of Server Management
DISCUSS
Overview of Server Management
Instructor Notes This is a lecture topic.
Topic: Overview of Server Management
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
Student Workbook Content There are various utilities in Windows Server 2008 that are designed to allow easy, efficient management. This section provides an overview of the primary and secondary management tools that are available, in addition to improvements to assist with printer management.
Topic: Primary Management Tools
PARTICIPATE
Matching: Which Primary Management Tool?
In the table below, match the appropriate tool to the specified management task.
Initial Configuration Tasks
Task Determine server status Define servers domain membership Add a server role Set administrator password Stop a service Configure server network settings
Server Manager console
Instructor Notes This is a matching activity. Allow your students to discuss the topic, and then encourage individual students to annotate the slide with the appropriate answers.
Answers
Task
Initial Configuration Tasks
Server Manager console
Determine server status Define servers domain membership Add a server role Set administrator password
Topic: Primary Management Tools
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
Task
Initial Configuration Tasks
Server Manager console
Stop a service Configure server network settings
Student Workbook Content Initial Configuration Tasks and Server Manager are the primary features of Windows Server 2008 that are useful to IT professionals who are responsible for computer management and security throughout their organization: Initial Configuration Tasks. Initial Configuration Tasks is a new feature that is designed to guide IT administrators through the process of configuring a new server. Before Windows Server 2008, the setup for Windows server-class operating systems paused for administrators to provide administrator account, domain, and network information. Feedback indicated that this practice slowed the operating system and server deployment process because the completion of operating system installation was delayed until administrators responded to the prompts and provided this information. Initial Configuration Tasks enables administrators to postpone these tasks until installation is complete, which causes fewer interruptions during installation.
Note: Product activation can occur in a grace period (typically 30 days), and is not critical for the initial configuration of the server. Therefore, the Activate Your Server command, which was present on the Manage Your Server window in Windows Server 2003, does not appear in Initial Configuration Tasks.
Server Manager. Server Manager is a new MMC snap-in that provides a consolidated view of the server, including information about server configuration, status of installed roles, and links for adding and removing roles and features. Server Manager makes server administration more efficient by providing a single tool for administrators to do the following: View and make changes to server roles and features that are installed on the server. Perform management tasks that are associated with the operational life cycle of the server, such as starting or stopping services, and managing local user accounts. Perform management tasks that are associated with the operational life cycle of roles installed on the server. Determine server status, identify critical events, and analyze and troubleshoot configuration issues or failures.
Note: Server Manager replaces a number of features in Windows Server 2003, such as Manage Your Server, Configure Your Server, and Add or Remove Windows Components.
Topic: Primary Management Tools
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
Benefits of Using Initial Configuration Tasks/Server Manager
An administrator benefits from using Initial Configuration Tasks and Server Manager because they: Provide an easy, systematic way to complete important configuration tasks for a new server through a single interface. After you complete these tasks, your server should be able to perform its intended server role (for example, as a file server or print server). Provide a method to add and remove server roles and features more securely and reliably. Provide a single local management tool to examine server role status, perform key management tasks, and access advanced management tools. Ensure that service prerequisites are met.
Topic: Alternative Management Tools
PARTICIPATE
Brainstorm: List the Alternative Management Tools
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Answers Suggested answers include: ServerManagerCmd.exe Windows PowerShell Windows Remote Manager Windows Remote Shell Event Subscriptions Task Scheduling based on Events Microsoft System Center Student Workbook Content Consider the following question. Then, when your instructor prompts you, write your answers on the slide. What alternative management tools are available in Windows Server 2008?
Topic: Alternative Management Tools
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
PARTICIPATE
Matching: Which Alternative Management Tool?
In the table below, match the appropriate tool to the specified management task.
Server Manager Cmd
Task Automate the deployment of a server role Edit the registry from the command line Obtain data about local and remote computer objects such as disks Use with an XML file to automate role removal Access the certificate store from the command line
Windows PowerShell
Remote Management
Instructor Notes This is a matching activity. Allow your students to discuss the topic, and then encourage individual students to annotate the slide with the appropriate answers.
Answers
Topic: Alternative Management Tools
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
Task
Windows PowerShell
Remote Management
Server Manager Cmd
Automate the deployment of a server role Edit the registry from the command line Obtain data about local and remote computer objects such as disks Use with an XML file to automate role removal Access the certificate store from the command line
Student Workbook Content Windows Server 2008 gives you various alternative tools for managing your servers more effectively: ServerManagerCmd.exe. This command-line tool enables you to automate the deployment of server roles and features in Windows Server 2008. The tool accepts parameters to display a list of all roles, role services, and features that are both installed and available for installation; you can use parameters to install/uninstall server roles with their default settings. You can also use ServerManagerCmd.exe with an XML file to expedite automated installations and to add/remove roles and features. Windows PowerShell. Windows PowerShell is a new command-line shell and task-based scripting technology that gives IT administrators comprehensive control and automation of system administration tasks, increasing administrator productivity. Windows PowerShell includes numerous system administration utilities, consistent syntax and naming conventions, and improved navigation of common management data such as the registry, certificate store, or Windows Management Instrumentation (WMI). Windows PowerShell also includes an intuitive scripting language that is specifically designed for IT administration. Remote Management. Windows Remote Manager. Windows Remote Manager is the Microsoft implementation of WS-Management Protocol, a standard SOAP-based protocol that allows hardware and operating systems to interoperate. Unlike DCOM-based remote access, Windows Remote Management and WS-Management use standard, fixed ports, which provide an elevated level of security. You can use Windows Remote Management scripting objects, the Windows Remote Management command-line tool, or the Windows Remote Shell command-line tool to obtain management data from local and remote computers about objects (disks, network adapters, services, or processes). Windows Remote Shell (WinSH). You can use this tool to remotely manage servers or to obtain management data through Windows Remote Management (WinRM) and WMI objects on remote servers.
Topic: Alternative Management Tools
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
Event subscriptions. Event Viewer enables you to view events on a single remote computer. However, troubleshooting an issue may require you to examine a set of events that is stored in multiple logs on multiple computers. Windows Server 2008 and Windows Vista operating systems include the ability to collect copies of events from multiple remote computers and store them locally. To specify which events to collect, you create an event subscription. Among other details, the subscription specifies exactly which events will be collected and in which log they will be stored locally. After a subscription is active and events are being collected, you can view and manipulate these forwarded events as you would any other locally stored events. Using the eventcollecting feature requires that you configure both the forwarding and the collecting computers. The functionality depends on the WinRM service and the Windows Event Collector (Wecsvc) service. Both of these services must be running on computers that are participating in the forwarding and collecting process. Task scheduling based on events. The Windows Server 2008 Task Scheduler MMC snap-in helps you schedule automated tasks. It maintains a library of all scheduled tasks, which provides an organized, convenient point of access for managing them. The two key concepts that are involved in scheduling a task are triggers and actions. In Windows Server 2008, the triggers that you can use to initiate an action have been expanded to include on an event. This trigger causes the task to run when specific event entries are added to an event log. You can choose between specifying basic event trigger settings or custom event trigger settings. If you choose the basic event trigger settings, a single event from a specific event log will trigger the task. You specify the event log that contains the event, the event publisher name, and the event identifier. If you choose the custom event trigger settings, you can specify an XML event query or a custom event filter to query for events that will trigger the task. Microsoft System Center. By using the System Center family of IT management solutions, you have the power to more effectively and easily manage all of the components that define IT, enabling you to focus more on delivering new business value for your organization.
Topic: Print Management
PARTICIPATE
Poll: Print Management
Instructor Notes
Ask the students to vote by using the polling slide that is provided. After an appropriate amount of time has passed or all of the students have voted, close the polls and show the results. In certain cases, you may want to ask students to explain their answers before you show the results. Discuss the poll results.
Answers Suggested answer:
Topic: Print Management
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
False. Printers that are deployed by using this method appear in the Deployed Printers object of the Print Management tree when the print server to which they are connected is being monitored. Student Workbook Content
Consider the following poll question and, when the instructor opens the poll, cast your vote. Be prepared to join any discussion about the poll results that the instructor chooses to initiate.
True or false? Printers that are deployed by using group policies appear in the Printers object of the Print Management tree when the print server to which they are connected is being monitored. True False
PARTICIPATE
Brainstorm: What Are the Benefits of E-Mail Notifications?
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Answers Suggested answers include: E-mail message notifications can be set up to alert administrators when a printer requires attention. This is especially useful when your organization has printers at multiple locations and different people are responsible for managing them. By using an automated system to notify the IT staff when a printer or print server is not working, the problem may be resolved sooner, which reduces the impact of printer and print server problems. Student Workbook Content Consider the following question. Then, when your instructor prompts you, write your answers on the slide. What are the benefits of e-mail notifications?
Topic: Print Management
Lesson 1: Server Management Overview
10
Getting Started with Server Management in Windows Server 2008
Print Management Overview
Effective print management can save you a significant amount of time when you install printers on client computers, and manage and monitor printers. Windows Server 2008 includes Print Management, which is an MMC snap-in that enables you to manage, monitor, and troubleshoot all of the printers in your organization from a single interface, even those in remote locations such as branch offices.
Note: Print Management provides centralized administration of all of the printers in the organization from any computer running Windows Server 2003 R2, Windows Vista, or Windows Server 2008 operating systems. Print Management is also available for Windows XP clients (x86 and x64).
Print Management provides up-to-the-minute details about the status of all printers and print servers on the network from one console. Print Management can help find printers that have error conditions, and can also send e-mail notifications, or run scripts when a printer or print server needs attention. On printer models that provide a Web interface, Print Management can access this additional data, which enables information such as toner and paper levels to be managed easily. By using Print Management in conjunction with the Configure Your Server Wizard and Terminal Services, you can automatically search for and install network printers on a local print server in branch offices. This is helpful when branch office personnel are not trained in administrative duties.
Integration with Group Policy
Rather than having to install and configure printer connections on individual computers, Print Management can be used with Group Policy to automatically add printer connections to the Printers and Faxes folder on the client computers, saving you time. A printer connection setting can be automatically added to an existing Group Policy object (GPO) in Active Directory directory service. When Group Policy processing runs on client computers, the printer connection settings are applied to the users or computers that are associated with the GPO. Printers that are deployed by using this method appear in the Deployed Printers object of the Print Management tree when the print server to which they are connected is being monitored. This method of installing a printer is useful in laboratory, classroom, or branch office settings where every computer in the room or office requires access to the same printer. It is also useful in large organizations, where computers and printers are often separated by function, workgroup, or department. A printer connection that has been installed by using a connection for each user is available to the user, no matter what computer the user logs on to. A printer connection that has been
Topic: Print Management
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
11
installed by using a connection for each computer appears in the Printers and Faxes folder and is available to any user of that computer.
Troubleshooting Printers
Print Management has several features that may help identify and resolve printer problems, even in remote locations: Setting predefined filters enables you to easily find all of the printers that are not in Ready status or that have print jobs waiting in a queue.
Note: Many devices, regardless of their manufacturer, provide rich status information, which is readily available to Print Management. By closely monitoring the printers in the organization, you may be able to resolve problems before they happen, such as identifying when paper or toner is low.
E-mail message notifications can be set up to alert administrators when a printer requires attention. This is especially useful when your organization has printers at multiple locations and different people are responsible for managing them. By using an automated system to notify the IT staff when a printer or print server is not working, the problem may be resolved sooner, which reduces the impact of printer and print server problems.
Topic: Technical Background
PARTICIPATE
Matching: Initial Configuration Tasks or Server Manager?
In the table below, match the management tool to the specified management tasks. Complete the entire table, but only annotate the slide with the information that is specified in the team space for your team.
Initial Configuration Tasks
Task Define domain Set time zone Remove features View features summary Add roles Configure firewall Install updates View roles summary
Server Manager console
Topic: Technical Background
Lesson 1: Server Management Overview
12
Getting Started with Server Management in Windows Server 2008
Task View system information
Initial Configuration Tasks
Server Manager console
Instructor Notes This is a team matching type activity. Allow your students to discuss the topic in teams, and then encourage a team leader to annotate the slide with the appropriate answers.
Answers
Task
Initial Configuration Tasks
Server Manager console
Define domain Set time zone Remove features View features summary Add roles Configure firewall Install updates View roles summary View system information
PARTICIPATE
Poll: Permissions for Initial Configuration Tasks
Instructor Notes
Ask the students to vote by using the polling slide that is provided. After an appropriate amount of time has passed or all of the students have voted, close the polls and show the results. In certain cases, you may want to ask students to explain their answers before you show the results. Discuss the poll results.
Topic: Technical Background
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
13
Answers Suggested answer: Local Administrator. Student Workbook Content Consider the following poll question and, when the instructor opens the poll, cast your vote. Be prepared to join any discussion about the poll results that the instructor chooses to initiate.
What permissions must you have to run Initial Configuration Tasks? Domain Admins Enterprise Admins Local Administrator Power User
PARTICIPATE
Poll: Initial Configuration Tasks
Instructor Notes
Ask the students to vote by using the polling slide that is provided. After an appropriate amount of time has passed or all of the students have voted, close the polls and show the results. In certain cases, you may want to ask students to explain their answers before you show the results. Discuss the poll results.
Answers Suggested answer: Add an administrator account. Student Workbook Content Consider the following poll question and, when the instructor opens the poll, cast your vote. Be prepared to join any discussion about the poll results that the instructor chooses to initiate.
Which of the following cannot be completed by using Initial Configuration Tasks? Add features Remove roles Configure networking Enable remote desktop
Topic: Technical Background
Lesson 1: Server Management Overview
14
Getting Started with Server Management in Windows Server 2008
Which of the following cannot be completed by using Initial Configuration Tasks? Configure Windows Firewall Add an administrator account
Initial Configuration Tasks
After the setup for Windows Server 2008 is complete, Initial Configuration Tasks guides you through the procedures that are necessary to configure a new server, such as specifying the administrator password, the computer name, the domain, and desired server roles. Initial Configuration Tasks replaces the Post-Setup Security Updates feature that was introduced in Windows Server 2003 Service Pack 1 (SP1). Initial Configuration Tasks extends the functionality of Post-Setup Security Updates by guiding you through all of the tasks that you must complete to configure a new server, not just those tasks that are related to security. By using Initial Configuration Tasks, it is much easier to configure a new server with Windows Server 2008 than it was to configure a new server with Windows Server 2003. For example, during setup, you are asked for only minimal information, such as product key information and an acceptance of the Microsoft Software License Terms. After you have installed the operating system, you can then use Initial Configuration Tasks to configure the server. Setup assigns default values for other configurations unless you specify otherwise. For example, by default, network cards are configured to obtain an Internet Protocol (IP) address that is assigned by Dynamic Host Configuration Protocol (DHCP). Also, by default, the server is a member of a workgroup.
Note: To use Initial Configuration Tasks, you must be logged on to the computer as an administrator. When you first install the operating system, you will automatically be logged on as an administrator and the administrator password will be blank until you configure it.
You can perform the following tasks by using Initial Configuration Tasks: Create an administrator password. Set time zone. Configure networking. Provide computer name and domain. Enable automatic updating and feedback. Download and install updates. Add roles. Add features. Enable remote desktop. Configure Windows Firewall.
Server Manager
Server Manager is designed to guide administrators through the process of installing, configuring, and managing server roles and features that are part of the Windows Server 2008 release. Although adding and removing server roles and features is not new, Server Manager unifies the functionality of multiple earlier tools in a single, simple, MMC-based user interface.
Topic: Technical Background
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
15
Server Manager is launched automatically after you complete the tasks that are listed in Initial Configuration Tasks. After that, it is also launched automatically when an administrator logs on to the server. At any time, Server Manager can be started by using the following methods: On the Start menu. On the Start menu, right-click Computer, and then click Manage. On the Start menu, point to Administrative Tools, and then click Server Manager. Quick Launch bar available on the Windows desktop.
Note: Server Manager is installed by default as part of the Windows Server 2008 setup process. To use Server Manager, you must be logged on to the computer as an administrator.
The main window of the Server Manager console contains the following four collapsible sections: Server Summary. This section includes two subsections, System Information and Security Summary: System Information displays the computer name, domain, local administrator account name, network connections, and the product ID of the operating system. Commands in the System Information subsection enable you to edit this information. Security Summary displays whether Windows Update and Windows Firewall are enabled. Commands in the Security Summary subsection allow you to edit these settings or view advanced options.
Roles Summary. This section contains a table that indicates which roles are installed on the server. Commands in this section allow you to add or remove roles, or go to a more detailed console in which you can manage a specific role. Features Summary. This section contains a table that indicates which features are installed on the server. Commands in this section allow you to add or remove features. Resources and Support. This section displays whether this server is participating in the feedback programs, Windows Server CEIP and Windows Error Reporting. Resources and Support is also designed to be a launch point for joining topical newsgroups, or for locating additional Help and research topics that are available online.
Server Manager Wizards
The Server Manager collection of wizards enables you to add, remove, or augment multiple roles in a single session, streamlining the task of deploying servers in your enterprise by reducing the time required. Role configurations are configured with recommended security settings by default; there is no requirement to run the Security Configuration Wizard following role or feature installation unless it is necessary to modify security defaults. Earlier versions of Windows Server required you to use Configure Your Server, Manage Your Server, or Add or Remove Windows Components to add or remove server roles or other software. Dependency checks were limited, and Add or Remove Windows Components limited administrators to the installation of only one role at a time. Before you could add more roles, installation of each role had to complete. Windows Server 2008 performs dependency checks as you progress through the
Topic: Technical Background
Lesson 1: Server Management Overview
16
Getting Started with Server Management in Windows Server 2008
Server Manager wizards, ensuring that all of the roles and role services that are required by a role that you select are installed, and none are removed that might still be required by remaining roles or role services. In addition to Initial Configuration Tasks, Server Manager is composed of the elements that are listed in the following table, each with a corresponding wizard.
Role Add Roles Wizard Description Use this wizard to add one or more roles to the server. This wizard automatically checks for dependencies between roles, and ensures that all of the required roles and features are installed based on user selections. For some roles, such as Terminal Services and Active Directory Certificate Services, the Add Roles Wizard also provides configuration pages that allow the user to specify how the role should be configured as part of the installation process. Some roles, such as File Server, Terminal Services, and Active Directory Certificate Services, are composed of multiple subelements, which are identified as role services in the Server Manager interface. After a role is installed, you can add further role services by using the Add Role Services Wizard. Similar to the Add Roles Wizard, this wizard enables you to install features on the server. Use this wizard to remove a role that is no longer required on the computer. Use this wizard to remove a role service that is no longer required on the computer. Use this wizard to remove a feature that is no longer required on the computer. When Server Manager is started, it scans the computer and detects which roles are currently installed. For each installed role, a role management home page is added to Server Manager. These home pages provide a high-level view of the status of each role (for example, which services are running and which errors were found in the event log) in addition to links to role-specific tools and Help content.
Add Role Services Wizard
Add Features Wizard
Remove Roles Wizard
Remove Role Services Wizard
Remove Features Wizard
Role management home pages
PARTICIPATE
Demonstration: How to Use the Initial Configuration Tasks Window
Instructor Notes
You will use the following recorded demonstration: clin5939ae_01_01_03_dem01.swf. The estimated time for this demonstration is five minutes. After the demonstration, you should ask the students if they have any questions. Be prepared to discuss any issues raised with the class.
Topic: Technical Background
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
17
Transcript
This demonstration shows how to use the Initial Configuration Tasks window and how to perform key administrative tasks. It also explains how to set the administrator password, enable Windows Automatic Update, and add features to Windows Server 2008. To complete the installation process of Windows Server 2008, you will need to perform key administrative tasks. To do this, use the Initial Configuration Tasks window, which opens by default when you log on. The Initial Configuration Tasks window is divided into three configuration areas: Provide Computer Information, Update This Server, and Customize This Server. To set the local administrators password, use the option under Provide Computer Information. To secure this server, rename the Administrators account with a complex name that is not recognizable. Administrator is an overused default account name in Windows. Log off to reset the name. After you have logged back on, Initial Configuration Tasks will reopen, and you can then reset the password. To reset the password, Initial Configuration Tasks displays a message that the password has already been set; you must change the password. Recommended practice is to use a strong password that has at least seven characters and include uppercase and lowercase letters, numbers, and symbols. You can see an example of a complex password on the screen. Other tasks that you could configure include setting the time zone and providing a computer name and domain. Use the options under Update This Server to configure settings for Windows Update. You can automatically receive updates from the Microsoft Windows Update Web site and participate in the Windows Server Customer Improvement Program by enabling feedback. It is a good idea to visit the Microsoft Windows Update Web site on a regular basis to get optional updates such as recommended software and hardware updates that improve the performance of your server(s). The final configuration area of Initial Configuration Tasks is Customize This Server. Configure settings for server roles and Windows Firewall, and enable remote desktop. The Add Features option replaces Add Windows Components. Here you will see a list of additional services and features that you can add to the server. A new feature in Windows Server 2008 is Microsoft BitLocker Drive Encryption, which is a hardware-based security feature to protect data on a volume. Before you select Install, a summary of information gives you the option to go back to the previous dialog box to add or remove features. After you have completed the initial configuration tasks of Windows Server 2008, select the check box to not show the next time you log on. This demonstration explained how to use the Initial Configuration Tasks window to perform key administrative tasks. It also explained how to set the administrator password, enable Windows Automatic Update, and add features to Windows Server 2008.
Student Workbook Content This demonstration explains how to use the Initial Configuration Tasks window to perform key administrative tasks. It also explains how to set the administrator password, enable Windows Automatic Update, and add features to Windows Server 2008. PLAY
Sorting: Assigning Tasks in the Initial Configuration Tasks Window
Instructor Notes
Allow students time to complete the sorting exercise in the Student Workbook. Then launch the game and discuss the results of the game. The game file is: clin5939ae_01_01_04_act01.swf. The estimated time for this activity is three minutes.
Topic: Technical Background
Lesson 1: Server Management Overview
18
Getting Started with Server Management in Windows Server 2008
Answers
Provide computer information
Update this server Download and install updates
Customize this server
Add features Enable remote desktop Configure Windows Firewall Set administrators password Provide computer name and domain
Student Workbook Content In the table below, sort the features that are listed below into the appropriate columns. Set administrators password Provide computer name and domain Add features Enable remote desktop Download and install updates Configure Windows Firewall
Update this server Customize this server
Provide computer information
Topic: Technical Background
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
19
PARTICIPATE
Brainstorm: List and Describe the Server Roles in Windows Server 2008
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Answers Suggested answers include: Active Directory Certificate Services (Active Directory CS) Active Directory Domain Services (Active Directory DS) Active Directory Federation Services (Active Directory FS) Active Directory Lightweight Directory Services (Active Directory LDS) Active Directory Rights Management Services (Active Directory RMS) Application Server DHCP Server Domain Name System (DNS) Server Fax Server File Services Network Policy & Access Services Print Services Terminal Services Universal Description, Discovery, and Integration (UDDI) Services Web Server (IIS) Windows Deployment Services (WDS) Windows SharePoint Services
Refer to the student workbook in this topic for further information regarding the function of each role.
Student Workbook Content Consider the following question. Then, when your instructor prompts you, write your answers on the slide. What are the Windows Server 2008 server roles and what does each role do?
Topic: Technical Background
Lesson 1: Server Management Overview
20
Getting Started with Server Management in Windows Server 2008
What Are Server Roles?
A server role describes the primary function of the server. Administrators may choose to dedicate an entire server to one role, or install multiple server roles on a single computer. Each role may include one or more role services, or optionally installable elements of the role.
Note: No server roles are installed by default.
Server Manager provides a single point of access to management snap-ins for all installed roles. Adding a role automatically creates a management console home page in Server Manager for that role, which displays events and service status for all services that are part of the role. Role services, or subcomponents of a role, are listed in a section of this page. Administrators can open wizards to add or remove role services by using commands on this home page. The roles that are listed in the following table are available in Windows Server 2008 and can be installed and managed through Server Manager.
Role Active Directory Certificate Services (Active Directory CS) Active Directory Domain Services (Active Directory DS) Description Enables creation and management of digital certificates for users, computers, and organizations as part of a public key infrastructure. Stores information about objects on the network and makes this information available to users and network administrators. Uses domain controllers to give network users access to permitted resources anywhere on the network. Active Directory Federation Services (Active Directory FS) Active Directory Lightweight Directory Services (Active Directory LDS) Provides simplified, encrypted identity federation and Web single sign on (SSO) capabilities. Provides a store for application-specific data, for directory-enabled applications that do not require the infrastructure of Active Directory Domain Services. Multiple instances of Active Directory LDS can exist on a single server, each of which can have its own schema. Information protection technology that works to help safeguard
Active Directory Rights Management
Topic: Technical Background
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
21
Role Services (Active Directory RMS) Application Server
Description digital information from unauthorized use. Provides central management and hosting of high-performance, distributed business applications such as those built with Enterprise Services and the .NET Framework 3.0. Enables the central provisioning, configuration, and management of temporary IP addresses and related information for client computers. Translates domain and computer DNS names to IP addresses. DNS is easier to manage when it is installed on the same server as Active Directory Domain Services. Sends and receives faxes and enables you to manage fax resources such as jobs, settings, reports, and fax devices on this computer or on the network. Provides technologies for storage management, file replication, distributed namespace management, fast file searching, and streamlined client access to files. Provides support for routing local area network (LAN) and wide area network (WAN) network traffic, creating and enforcing network access policies, and accessing network resources over virtual private network (VPN) and dial-up connections. Provides access to and manages network printers and printer drivers. Provides technologies that enable access to a server running Windows-based programs or the full Windows desktop. Users can connect to a terminal server to run programs, save files, and use network resources on that server. Provides UDDI capabilities for sharing information about Web services in an organizations intranet or between business partners on an extranet. Organizes and catalogs Web services and other programmatic resources. A UDDI Services site consists of a UDDI Web Application connected to a UDDI Database. Provides a reliable, manageable, and scalable Web application infrastructure. Provides a simplified, secure means of rapidly deploying Windows operating systems to computers by using network-based installation, without the need for an administrator to work directly on each computer, or install Windows components from CD or DVD media. Helps organizations increase productivity by creating Web sites where users can collaborate on documents, tasks, and events and easily share contacts and other information.
DHCP Server
Domain Name System (DNS) Server
Fax Server
File Services
Network Policy & Access Services
Print Services
Terminal Services
Universal Description, Discovery, and Integration (UDDI) Services
Web Server (IIS)
Windows Deployment Services (WDS)
Windows SharePoint Services
Topic: Technical Background
Lesson 1: Server Management Overview
22
Getting Started with Server Management in Windows Server 2008
What Are Features?
A feature does not generally describe the primary function of the server. Instead, it describes an auxiliary or supporting function. Consequently, an administrator typically installs a feature not as the primary function of the server, but to augment the functionality of an installed role. For example, Failover Clustering is a feature that administrators can choose to install after installing specific roles, such as File Server, in order to make the File Server role more redundant. The following table lists the features that are available in Windows Server 2008 and can be installed by using Server Manager.
Feature .NET Framework 3.0 [contains subcategories] Description Combines the power of the .NET Framework 2.0 application programming interfaces (APIs) with new technologies for building applications that offer appealing user interfaces, protect your customers personal identity information, enable seamless and secure communication, and provide the ability to model a range of business processes. A hardware-based security feature to protect data via full volume encryption. Enables a BITS server to receive files that client computers upload. This feature is not necessary for client computers to download files from the BITS server. Generates Connection Manager profiles.
Microsoft BitLocker Drive Encryption Background Intelligent Transfer Service (BITS) Server Extensions
Connection Manager Administration Kit Desktop Experience
Installs features of Windows Vista, such as Windows Media Player, desktop themes, and photo management. Ensures high availability of server roles and applications that have persistent states, such as File Services and Microsoft SQL Server, database software by utilizing failover technology based on shared disks. Enables clients to use Hypertext Transfer Protocol (HTTP) to connect to printers on Web print servers. Processes registration requests, de-registration requests, and queries from iSCSI devices. Allows printing to devices attached to UNIX-based computers.
Failover Clustering
Internet Printing Client
Internet Storage Naming Server (iSNS) Line Printer Remote (LPR) Port Monitor Message Queuing (also known as MSMQ) [contains subcategories]
Enables applications that are running at different times to communicate across heterogeneous networks and systems that may be temporarily offline. Message Queuing provides guaranteed message delivery, efficient routing, security, and priority-based messaging. Provides support for utilizing multiple data paths to a storage device. Distributes incoming application requests among the group of servers that host instances of the application.
Multipath I/O
Network Load Balancing
Topic: Technical Background
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
23
Feature Peer Name Resolution Protocol
Description Allows applications to register and resolve names on your computer so that other computers can communicate with these applications. Quality Windows Audio Video Experience (qWave) is a networking platform for audio/video (A/V) streaming applications on IP home networks. qWave enhances A/V streaming performance and reliability by ensuring network quality-of-service (QOS) for A/V applications. Allows a remote user to connect to this computer and correct any problems directly. Enables role and feature management tools so that you can target them at another server running Windows Server 2008 for remote administration. This feature will not set up the core binaries for the selected components but only their administration tools. Manages and catalogs removable media and operates automated removable media devices. Relays RPC traffic from client applications over HTTP to the server as an alternative to clients accessing the server over a VPN connection. Simple TCP/IP Services Supports the transfer of electronic mail between servers.
Quality Windows Audio Video Experience
Remote Assistance
Remote Server Administration Tools [contains subcategories]
Removable Storage Manager
RPC over HTTP Proxy
Simple TCP/IP Services Simple Mail Transfer Protocol (SMTP) Server SNMP Services [contains subcategories] Storage Manager for Storage Area Networks (SANs) Subsystem for UNIX-based Applications (SUA)
Simple Network Management Protocol (SNMP) includes the SNMP Service and SNMP WMI Provider. Configures and provisions VDS-compliant SANs.
Together with a package of support utilities that is available for download from the Microsoft Web site, enables you to run UNIXbased programs, and perform system administration tasks from within a UNIX-based command-line environment. Uses the Telnet protocol to connect to a remote Telnet server and run applications on that server. Allows remote users to perform command-line administration and run programs by using a Telnet client, including UNIX-based clients. Enables transferring files by using a TFTP server.
Telnet Client
Telnet Server
Trivial File Transfer Protocol (TFTP) Client Windows Internal Database
Uses SQL Server 2005 Embedded Edition (Windows) as a relational data store for Windows-based roles and features only, such as Windows SharePoint Services, Active Directory Rights Management Services, UDDI Services, or Windows Server Update. A command-line shell and scripting language that helps IT professionals achieve greater productivity. It provides a new
Windows PowerShell
Topic: Technical Background
Lesson 1: Server Management Overview
24
Getting Started with Server Management in Windows Server 2008
Feature
Description administration-focused scripting language and more than 130 standard command-line tools to enable easy system administration and accelerated automation.
Windows Process Activation Service (WPAS) Windows Recovery Disc
Enables support for the .NET process environment and configuration APIs. Allows you to restore your computer by using system recovery options if you do not have a Windows installation disc or cannot access recovery options that were provided by your computers manufacturer. Allows recovery of operating system state, files, folders, and application data by periodically creating snapshots of the full server or selected volumes. Helps ensure equitable servicing of Web server traffic and multiple roles or workloads. Allows computers running Windows to find other computers by using NetBIOS across subnets. Configures wireless connections and wireless LAN profiles.
Windows Server Backup
Windows System Resource Manager
Windows Internet Name Service (WINS) Server Wireless Networking
New Management Group Policy Settings
You can use Group Policy to control the behavior of Initial Configuration Tasks and Server Manager at startup by enabling the following policies: Do not open Initial Configuration Tasks window automatically at logon. Do not open Server Manager automatically at logon.
PARTICIPATE
Demonstration: Configuring and Managing Server Roles
Instructor Notes
You will use the following recorded demonstration: clin5939ae_01_02_04_dem01.swf. The estimated time for this demonstration is five minutes. After the demonstration, you should ask the students if they have any questions. Be prepared to discuss any issues raised with the class.
Transcript
This demonstration shows how to configure Windows Server 2008 as a file server by using the Add Roles Wizard. This demonstration also explains how to administer server roles by using the Manage Roles area of Server Manager. Add a role to Windows Server 2008. Select the role that your server will be adopting. In this case, select the File Server role. The Add Roles Wizard provides introduction information for the role that the service will provide. Add Role Services to provide additional functionality.
Topic: Technical Background
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
25
Windows Search Service enables fast file searches and indexed content. Select which volume on which to install the Windows Search Engine. Select the default option. A final summary of information is provided with the option to go back to the previous step. This completes the installation of the File Server role. To manage this role after it has been installed, use the Manage Roles area of Server Manager. You can see that a subcategory for the role has been created, which is called File Server. By using Server Manager, you can view events relating to the role, such as Stop and Start Services, and you can install additional role services. View events relating to the role of file server. ServerRoles enables you to further filter the information if required. View individual events in Server Manager; highlight the event in the summary. View details about the event to help you with troubleshooting. View the details as XML or a friendly view. A key task for managing your server role is to add additional role services. From the Role Services area, you can add additional requirements. For the File Server role, you can select additional services, such as Distributed File System (DFS) or Single Instance Store, to extend the functionality of your file server. When you select the role service of DFS, the wizard displays a message that further configuration of DFS is required after this service is installed. By using Manage Roles in Server Manager, you can view the role status and role services that you have installed in a summary pane. This demonstration showed how to configure Windows Server 2008 as a file server by using the Add Roles Wizard. It also explained how to manage the role by using the Manage Roles area of Server Manager.
Student Workbook Content This demonstration shows how to configure Windows Server 2008 as a file server by using the Add Roles Wizard. This demonstration also explains how to administer server roles by using the Manage Roles area of Server Manager.
Topic: Implementation/Usage Scenarios
DISCUSS
Implementation/Usage Scenarios
Instructor Notes This is a lecture topic.
Student Workbook Content
Improved New Server Deployment and Configuration
Windows Server 2008 installation procedures enable administrators to postpone nonessential tasks until the installation is complete, which means that there are fewer interruptions during the installation.
Topic: Implementation/Usage Scenarios
Lesson 1: Server Management Overview
26
Getting Started with Server Management in Windows Server 2008
Initial Configuration Tasks provides an easy, secure way to complete important configuration tasks and guides IT administrators through the process of configuring a new server, ensuring that required tasks are performed.
Improved Security
Roles and features installed by using Server Manager are secure by default. Administrators can subsequently run the Security Configuration Wizard to change the default settings.
Improved Server Administration
The Server Manager console provides a single interface to: Provide a consolidated view of the server, including information about server configuration, status of installed roles and features. Provide a method to add or remove roles and features from a server. Perform management tasks associated with the operational life cycle of the server, such as starting or stopping services, and managing local user accounts. Determine server status, identify critical events, and analyze and troubleshoot configuration issues or failures.
ServerManagerCmd.exe allows you to automate the deployment of server roles and features in Windows Server 2008. It can also be used with an XML file to expedite automated unattended installations and to add and remove roles and features.
Topic: Recommendations
PARTICIPATE
Brainstorm: List the Recommendations for Performing Server Management by Using Windows Server 2008
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Answers Suggested answers include: For single server administration, use Server Manager. To manage roles from a command prompt, use ServerManagerCmd.exe.
Topic: Recommendations
Lesson 1: Server Management Overview
Getting Started with Server Management in Windows Server 2008
27
For multiple server administration, use Windows PowerShell. For Remote Management, use Windows Remote Management (based on WS-Management Standard). Use Event Subscriptions to collect Event Viewer logs from multiple servers. Use System Center for enterprise-wide management. Student Workbook Content
Consider the following question. Then, when your instructor prompts you, write your answers on the slide. List the recommendations for performing server management with Windows Server 2008.
Administrators should use Server Manager to manage single servers, but for multiple server management or for remote management, they should use Windows PowerShell and Windows Remote Management. Administrators should take advantage of the new Event Subscription capabilities in Windows Server 2008 for collecting data from Event Viewer event logs on multiple servers. The Microsoft System Center family of tools should be used for enterprise-wide management.
Topic: Summary
DISCUSS
Summary
Instructor Notes This is a lecture topic.
Student Workbook Content The Windows Server 2008 installation process postpones nonessential tasks until after initial installation completes and then launches Initial Configuration Tasks to guide an administrator
Topic: Summary
Lesson 1: Server Management Overview
28
Getting Started with Server Management in Windows Server 2008
through the process of configuring a new server. After Initial Configuration Tasks is complete, Server Manager provides a consolidated, single interface to manage all aspects of a server, including roles, features, security, networking, and other aspects. ServerManagerCmd.exe enables you to automate the deployment of server roles in Windows Server 2008 from a command-line environment. Windows PowerShell is a new command-line shell and task-based scripting technology that gives IT administrators comprehensive control and automation of system administration tasks, increasing productivity. Windows Remote Management provides administrators with a technology to remotely manage servers or to obtain management data through WinRM or WMI. Both Windows PowerShell and Windows Remote Management are excellent for multiple-server management scenarios. Windows Server 2008 and Windows Vista include the ability to collect copies of events from multiple remote computers and store them locally.
Lesson 2: Server Core
Introduction
This lesson provides an overview of the new Server Core capabilities of Windows Server 2008 and assists you in understanding how to implement Server Core to reduce management and maintenance overheads while improving security.
Lesson Contents:
Topic: Overview Brainstorm: List the Server Roles Supported by a Windows Core Server Short Answer Poll: Overview of Server Core Topic: Technical Background Short Answer Poll: Core Server Commands Short Answer Poll: Configuring a Core Server Matching Type: Which Configuration Command? Demonstration: Installing a Server Core Topic: Implementation/Usage Scenarios Lecture: Implementation/Usage Scenarios Topic: Recommendations Brainstorm: List the Recommendations for Implementing the Best Possible Server Core Environment by Using Windows Server 2008 Topic: Summary Lecture: Summary
Topic: Summary
Lesson 2: Server Core
Getting Started with Server Management in Windows Server 2008
29
Topic: Overview
PARTICIPATE
Brainstorm: List the Server Roles Supported by a Windows Core Server
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Answers Suggested answers include: Active Directory Domain Services Active Directory Lightweight Directory Services DHCP Server DNS Server File Services Print Services Windows Media Services Windows Virtualization Services Student Workbook Content Consider the following question. Then, when your instructor prompts you, write your answers on the slide. List the server roles supported by a Windows Core server.
Topic: Overview
Lesson 2: Server Core
30
Getting Started with Server Management in Windows Server 2008
PARTICIPATE
Poll: Overview of Server Core
Instructor Notes
Ask the students to vote by using the polling slide that is provided. After an appropriate amount of time has passed or all of the students have voted, close the polls and show the results. In certain cases, you may want to ask students to explain their answers before you show the results. Discuss the poll results.
Answers Suggested answer: Yes, because Server Core is not an application platform; therefore, you cannot run or develop server applications on a Server Core installation. Student Workbook Content Consider the following poll question and, when the instructor opens the poll, cast your vote. Be prepared to join any discussion about the poll results that the instructor chooses to initiate.
Must I change my code to work with Windows Server 2008? Yes No
Server Core Installation
Server Core is not a separate version of Windows Server 2008; rather, it is a new installation option that provides a minimal environment for running specific server roles, reducing the maintenance and management requirements and the attack surface for those servers. No changes to your environment or infrastructure are required. A Server Core installation supports the following server roles: Active Directory Domain Services Active Directory Lightweight Directory Services DHCP Server
Lesson 2: Server Core
Topic: Overview
Getting Started with Server Management in Windows Server 2008
31
DNS Server File Services Print Services Windows Media Services Windows Virtualization Services
Note: You can run Windows Server virtualization (WSv) by using a Server Core installation of Windows Server 2008 as a host system. This enables you to benefit from Server Cores reduced software maintenance and file management needs and its smaller footprint (less than 1 GB of disk space is required for operating system installation).
The Server Core installation option installs only the subset of the Server binaries that are required by the above server roles. For example, the Explorer shell is not installed as part of a Server Core installation. Instead, the default user interface for a server running a Server Core installation is the command prompt. A Server Core installation is ideal in situations where you want to: Increase server stability. Reduce server management. Reduce the attack surface of a server. Reduce software maintenance. Reduce hardware requirements.
Benefits
A Server Core installation of Windows Server 2008 provides the following benefits: A Server Core installation installs only what is required to run the supported server roles, so: Less servicing is required than on a full installation of Windows Server 2008 and the server is more stable. Less maintenance is required than on a full installation of Windows Server 2008.
Fewer applications run on the server, so: The attack surface of the server is decreased. There is less to manage.
Hardware requirements are reduced because a Server Core installation requires less disk space.
Must I change my code to work with Windows Server 2008?
Server Core is not an application platform; therefore, you cannot run or develop server applications on a Server Core installation. You can only use a Server Core installation to run the supported server roles and management tools. Server Core does, however, support development of management tools and agents, which can be divided into two categories:
Topic: Overview
Lesson 2: Server Core
32
Getting Started with Server Management in Windows Server 2008
Remote Management tools. These tools do not require any changes, as long as they use one of the protocols that are supported in Server Core to communicate with the remote management workstation, such as RPC. Local Management tools and agents. These tools may require changes to work with Server Core because they cannot have any shell or user interface dependencies, nor use managed code.
Note: The Windows Server "Longhorn" software development kit (SDK) includes a list of APIs that are supported on Server Core. You must verify that all of the APIs that are called by your code are listed, and you must also test your code on a Server Core installation to ensure that it behaves as expected.
Topic: Technical Background
PARTICIPATE
Poll: Core Server Commands
Instructor Notes
Ask the students to vote by using the polling slide that is provided. After an appropriate amount of time has passed or all of the students have voted, close the polls and show the results. In certain cases, you may want to ask students to explain their answers before you show the results. Discuss the poll results.
Answers Suggested answer: Yes. Student Workbook Content Consider the following poll question and, when the instructor opens the poll, cast your vote. Be prepared to join any discussion about the poll results that the instructor chooses to initiate.
Are commands that are entered on a Core Server case sensitive? Yes No
Topic: Technical Background
Lesson 2: Server Core
Getting Started with Server Management in Windows Server 2008
33
PARTICIPATE
Poll: Configuring a Core Server
Instructor Notes
Ask the students to vote by using the polling slide that is provided. After an appropriate amount of time has passed or all of the students have voted, close the polls and show the results. In certain cases, you may want to ask students to explain their answers before you show the results. Discuss the poll results.
Answers Suggested answer:
netsh interface ipv4 set address name=2 source=static address=192.168.1.50 mask=255.255.255.0
Student Workbook Content Consider the following poll question and, when the instructor opens the poll, cast your vote. Be prepared to join any discussion about the poll results that the instructor chooses to initiate.
Which of the following is the correct syntax for configuring the IP address of a Core Server? netsh interface ip set address name=2 source=static address=192.168.1.50 mask=255.255.255.0 netsh interface ipv4 set address name=2 source=static address=192.168.1.50 mask=255.255.255.0 netsh interface ipv4 add address name=2 source=static address=192.168.1.50 mask=255.255.255.0 netsh interface ip add address name=2 source=static address=192.168.1.50 mask=255.255.255.0
PARTICIPATE
Matching: Which Configuration Command?
In the table below, match the required Core Server role with the appropriate configuration command. Complete the entire table, but only annotate the slide with the information that is specified in the team space for your team.
Role DNS DHCP DFS FRS Active Directory DS Setup command Dcpromo /unattend:Unattendfile Start /w ocsetup DFSN-Server Start /w ocsetup MediaServer Start /w ocsetup FRS-Infrastructure Start /w ocsetup DNS-Server-Core-Role
Topic: Technical Background
Lesson 2: Server Core
34
Getting Started with Server Management in Windows Server 2008
Role Media Services
Setup command Start /w ocsetup DHCPServerCore
Instructor Notes This is a team matching type activity. Allow your students to discuss the topic in teams, and then encourage a team leader to annotate the slide with the appropriate answers.
Answers
Role
Setup command
DNS DHCP DFS FRS Active Directory DS Media Services
Start /w ocsetup DNS-Server-Core-Role Start /w ocsetup DHCPServerCore Start /w ocsetup DFSN-Server Start /w ocsetup FRS-Infrastructure Dcpromo /unattend:Unattendfile Start /w ocsetup MediaServer
Prerequisites for Deploying a Server Core Installation
An installation of Windows Server 2008 Server Core requires the following: Windows Server 2008 media. A valid product key. A computer on which you can do a clean installation of Server Core.
Note: Only clean installations of Windows Server 2008 Server Core are supported. There is no way to upgrade from a previous version of the Windows Server operating system to a Server Core installation. There is no way to upgrade from a full installation of Windows Server 2008 to a Server Core installation. There is no way to upgrade from a Server Core installation to a full installation of Windows Server 2008.
Administrative credentialsif you are going to join the Server Core installation to an existing Windows domain, you must have a user name and password for an account that has the credentials to join a computer to the domain.
Topic: Technical Background
Lesson 2: Server Core
Getting Started with Server Management in Windows Server 2008
35
Deploying a Server Core Installation
A Server Core installation does not include the Windows user interface, so there is no "Out-of-Box Experience" to enable you to complete the configuration of the server. Instead you must manually complete the configuration by using the command-line tools or by performing an unattended installation by using an unattend.xml file.
Note: All commands in Server Core are case sensitive.
In addition to benefits that are typical of using an unattend file, performing an unattended installation of Server Core also provides the following benefits: It is not necessary to perform the initial configuration by using command-line tools. You can include the settings in the unattend file to enable remote administration as soon as setup is complete. You can configure settings that cannot be easily modified from the command line, such as display resolution.
The steps that are required for configuring a Server Core installation are as follows: Set the password for the local administrator account.
Note: In the command prompt, type net user administrator * and then press ENTER. Type the administrator password and then press ENTER.
Set a static IP address by using standard NETSH commands (if you are not using DHCP).
Note: In the command prompt, type ipconfig /all and then press ENTER. (The default setting for the network configuration is displayed. By default Windows Server 2008 Server Core uses DHCP configuration.) In the command prompt, type netsh interface IPv4 show interface and then press ENTER. (The list of network interfaces for the server are now shown. Note the Idx value for the Local Area Connection.) In the command prompt, type netsh interface ipv4 set address name=2 source=static address=192.168.1.50 mask=255.255.255.0 and then press ENTER. In the command prompt, type ipconfig /all and then press ENTER. (The network interface idx value was used as the name in the previous command. In addition, the setting for the gateway may be required in most circumstances. The return of the ipconfig command reflects the new settings.) In the command prompt, type netsh interface ipv4 add dnsserver name=2 address=192.168.1.1 index=1 and then press ENTER. (The DNS Server setting has been added to the interface. To add additional DNS server addresses, repeat the command and increment the index value by 1.)
Join a domain (if the server will be a member) and activate the server.
Note: In the command prompt, type netdom join NYC-CORE-01 /domain:woodgroovebank.com /userd:administrator /passwordD:* and then press ENTER.
Topic: Technical Background
Lesson 2: Server Core
36
Getting Started with Server Management in Windows Server 2008
When prompted, type the administrator password and then press ENTER. In a production environment, it would also be necessary to activate the server. From the command line, this can be done by using: Slmgr.vba ato. To complete the configuration, reboot the server.
View/Configure the Firewall.
Note: In the command prompt, type netsh and then press Enter. Type advfirewall and then press ENTER. In the command prompt, type show mode and then press ENTER. The returned value indicates that the firewall is currently turned on. You can configure rules via the netsh advfirewall firewall prompt.
Server Roles on a Server Core Installation
After the Server Core installation is complete and the server is configured for use, you can then install one or more of the supported server roles and associated features. DNS Server. To install the DNS server role: From the command, type: Start /w ocsetup DNS-Server-Core-Role
Note: You can also uninstall roles and features by using the ocsetup command, for example: start /w ocsetup DNS-Server-Core-Role /uninstall
DHCP Server. To install at the command prompt, type: Start /w ocsetup DHCPServerCore Configure a DHCP scope from the command line by using netsh, or remotely by using the DHCP snap-in.
Note: If the DHCP server is installed in an Active Directory domain, remember to authorize it in Active Directory.
File Server. This role is installed by default; however, there are a number of features that you can install from the command line as follows: File Replication Service (FRS): start /w ocsetup FRS-Infrastructure Distributed File System (DFS): start /w ocsetup DFSN-Server Distributed File System Replication (DFSR): start /w ocsetup DFSR-Infrastructure-ServerEdition Network File System (NFS): start /w ocsetup ServerForNFS-Base
Topic: Technical Background
Lesson 2: Server Core
Getting Started with Server Management in Windows Server 2008
37
Note: DFSR is a brand new replication engine. FRS still exists in Windows Server 2008 and is used by default for SYSVOL replication. After clients have established a Windows Server 2008 Domain Functional Mode, they can utilize DFSR and remove FRS.
Media Services. To install this role, at the command prompt, type: start /w ocsetup MediaServer
Note: After installation, use the Media Services MMC to remotely configure media services.
Active Directory Domain Services. To install this role, at the command prompt, type: Dcpromo /unattend:Unattendfile where Unattendfile is the name of a dcpromo unattend file.
Optional Features on a Server Core Installation
After the installation is complete and the server is configured for use, you can install optional features. The Server Core installation of Windows Server 2008 supports the following optional features, which can be installed from a command prompt by typing: Start /w ocsetup featurename (where featurename is the name shown in the following table):
Feature Backup BitLocker Drive Encryption Failover Cluster Multipath IO Network Load Balancing Removable Storage Management Feature name WindowsServerBackup BitLocker FailoverCluster-Core Microsoft-Windows-Multipathio NetworkLoadBalancingHeadlessServer Microsoft-WindowsRemovableStorageManagementCore SNMP-SC
Simple Network Management Protocol (SNMP) Subsystem for UNIX-based applications Telnet Client Windows Internet Naming Service (WINS)
SUACore TelnetClient WINS-SC
Note: The following optional features require appropriate hardware: Failover Cluster, Network Load Balancing, Multipath I/O, Removable Storage and Bitlocker Drive Encryption.
Managing a Server Core Installation
A Server Core installation requires initial configuration from the command line, because it does not include the traditional full graphical user interface. After it is configured, the server can be managed in the following ways:
Topic: Technical Background
Lesson 2: Server Core
38
Getting Started with Server Management in Windows Server 2008
Remotely via Terminal Server. By using another computer, you can use the Terminal Server client to connect to the server running the Server Core installation and manage it remotely. The shell in the Terminal Server session is the command prompt.
Note: To enable you to run cmd.exe in a window on your local computer instead of in the full terminal services client, publish cmd.exe by using Terminal Services Remote Programs.
Remotely via Windows Remote Shell. By using another computer running Windows Vista or Windows Server 2008, you can use Windows Remote Shell to run command-line tools and scripts on the Server Corebased server. Remotely via MMC. By using an MMC snap-in, you can connect to a server running a Server Core installation as you would any other computer running Windows. Locally and remotely via the Command Prompt window. By using the Windows command-line tools at the command prompt, you can manage servers running a Server Core installation.
Not all tasks can be performed from the command line or remotely through an MMC snap-in. To enable you to configure these settings, a script is included with the Server Core installation of Windows Server 2008 that can be used to: Enable automatic updates. Enable error reporting. Enable Terminal Server Remote Admin Mode. Enable Terminal Server client computers on previous versions of Windows to connect to a computer running Windows Server Core. Enable remote management of IPSec. Configure DNS SRV record weight and priority. View a list of common command-line tools.
Note: The script, scregedit.wsf, is located in the \Windows\System32 folder of the server running the Server Core installation.
PARTICIPATE
Demonstration: Installing a Server Core
Instructor Notes
You will use the following recorded demonstration: clin5937ae_01_02_03_dem01.swf. The estimated time for this demonstration is five minutes. After the demonstration, you should ask the students if they have any questions. Be prepared to discuss any issues raised with the class.
Topic: Technical Background
Lesson 2: Server Core
Getting Started with Server Management in Windows Server 2008
39
Transcript
Windows Server 2008 includes a new installation option called Server Core. Server Core is a minimal version of the operating system. In this demonstration, you will see how to install Server Core and how to configure it by using the command prompt. Select the Server Core option in the installation process. Continue through the installation process as normal. Notice that a Server Core installation does not have a Start button or any administration tools. Use the command prompt to manage the server. If you accidentally close the command prompt, use Task Manager to start a new one. As an example to install the DNS service, run ocsetup with the DNS Server Core Role switch. After you have installed the service, you can manage it from the command line by using the dnscmd utility, or use the DNS MMC snap-in on a remote computer. Use the shutdown command to shut down the Server Core system. Server Core is a limited functionality installation of Windows Server 2008. It is useful for branch office environments because its limited attack surface, service functionality, and management options minimize administration requirements and decrease the likelihood of compromise or failure.
Student Workbook Content In this demonstration, you will see how to install and configure a Server Core.
Topic: Implementation/Usage Scenarios
DISCUSS
Implementation/Usage Scenarios
Instructor Notes This is a lecture topic.
Student Workbook Content
Reduced Maintenance
A Server Core installation installs only what is required to run the supported server roles, so less maintenance is required than on a full installation of Windows Server 2008.
Reduced Attack Surface
Because server core is a minimal installation, there are fewer applications run on the server, thereby decreasing the attack surface.
Reduced Management
Fewer applications and services are installed on a server running the Server Core installation, so there is less to manage.
Topic: Implementation/Usage Scenarios
Lesson 2: Server Core
40
Getting Started with Server Management in Windows Server 2008
Less Disk Space Required
Less disk space is required for a Server Core installation.
Topic: Recommendations
PARTICIPATE
Brainstorm: List the Recommendations for Implementing the Best Possible Server Core Environment by Using Windows Server 2008
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Answers Suggested answers include: Use Server Core whenever possible. Publish cmd.exe by using Terminal Services RemoteApp to enable you to run cmd.exe in a window on your local computer rather than in the full terminal services client computer. Minimize administrative access to the system. Ensure physical security of the server. Implement BitLocker Drive Encryption. Student Workbook Content Consider the following question. Then, when your instructor prompts you, write your answers on the slide. List the recommendations for implementing the best possible Server Core environment by using Windows Server 2008.
Topic: Recommendations
Lesson 2: Server Core
Getting Started with Server Management in Windows Server 2008
41
To implement the best possible Server Core environment, you should keep the following in mind: Use Server Core whenever possible. Publish cmd.exe by using Terminal Services RemoteApp to enable you to run cmd.exe in a window on your local computer rather than in the full terminal services client. Minimize administrative access to the system. Ensure physical security of the server. Implement BitLocker Drive Encryption.
Topic: Summary
DISCUSS
Summary
Instructor Notes This is a lecture topic.
Student Workbook Content Server Core provides a minimal installation option for deploying Windows Server 2008 with a smaller footprint and attack surface, reducing management and maintenance needs. Initial installation of Server Core must be completed by utilizing command-line tools or through an unattended installation process; however, ongoing administration can be managed locally and remotely through the command line or remotely via MMC, Terminal Services, or the Windows Remote Shell tools. Server Core provides a script for configuring settings that cannot be configured through a command line or an MMC snap-in.
Lesson 3: Windows PowerShell
Introduction
Windows PowerShell is a new command-line shell and task-based scripting technology that gives IT administrators comprehensive control and automation of system administration tasks, increasing administrator productivity.
Topic: Summary
Lesson 3: Windows PowerShell
42
Getting Started with Server Management in Windows Server 2008
Windows PowerShell includes numerous system administration utilities, consistent syntax and naming conventions, and improved navigation of common management data such as the registry, certificate store, or WMI. Windows PowerShell also includes an intuitive scripting language that is specifically designed for IT administration.
Lesson Contents:
Topic: Overview Brainstorm: What Can I Do with Windows PowerShell? Short Answer Poll: PowerShell Installation Lecture: Benefits of Windows PowerShell Topic: Technical Background Matching Type: Which Cmdlet Type? Short Answer Poll: File Extensions for PowerShell Scripts Brainstorm: What Is the Pipeline, and What Does It Do? Short Answer Poll: Working with Drives Demonstration: Configuring Windows Server Core by Using Windows PowerShell Topic: Implementation/Usage Scenarios Lecture: Implementation/Usage Scenarios Topic: Recommendations Brainstorm: List the Recommendations for Implementing Windows PowerShell to Get the Greatest Benefits Topic: Summary Lecture: Summary
Topic: Overview
PARTICIPATE
Brainstorm: What Can I Do with Windows PowerShell?
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Answers Suggested answers include: Automate administration of multiple servers through a task-oriented scripting language.
Topic: Overview
Lesson 3: Windows PowerShell
Getting Started with Server Management in Windows Server 2008
43
Accelerate script authoring, testing, and debugging and write customer tools in a new command shell environment. Utilize new scripts and cmdlets. Manage command-line services, processes, registry, and WMI data. Manage and/or automate administration tasks for server roles such as IIS and Active Directory. Automate Terminal Server configuration changes by means of Windows PowerShell scripts, and examine configuration similarities and differences across a Terminal Server farm. Manage an Internet Information Services 7.0 environment. Remotely manage servers. Student Workbook Content
Consider the following question. Then, when your instructor prompts you, write your answers on the slide. What can I do with Windows PowerShell?
What Is Windows PowerShell?
Windows PowerShell is a new Windows command-line shell that is designed especially for system administrators. The shell includes an interactive prompt and a scripting environment that can be used independently or in combination. In Windows Server 2008, it is installed as a feature. Windows PowerShell is considered to be the new standard for command line and scripting for administrators. Future tools will be built around it and will generate scripts for you to use. Windows PowerShell provides an easier way for you to perform administrative tasks. For example, in the past, if you wanted to make a change to the registry, you would need to import or export files. By using Windows PowerShell, you can simply write to the registry as if it were any other file.
Note: Although Windows PowerShell is considered to be the new standard, it is not a replacement for existing mechanisms such as Microsoft Visual Basic, Scripting Edition (VBScript) or WMI scripting.
Topic: Overview
Lesson 3: Windows PowerShell
44
Getting Started with Server Management in Windows Server 2008
What Are Windows PowerShell Cmdlets?
Windows PowerShell can still run any external command-line utilities that you are familiar with using. This means that you can use it immediately, taking advantage of the knowledge and experience that you already have while learning to use the new power that Windows PowerShell provides. Windows PowerShell introduces the concept of a cmdlet (pronounced "command-let"), which is a single-feature command that manipulates objects in Windows PowerShell. You can use each cmdlet separately, but their power is realized when you use these simple tools in combination to perform complex tasks. Like many shells, Windows PowerShell gives you access to the file system on the computer. In addition, Windows PowerShell providers enable you to access other data stores, such as the registry and the digital signature certificate stores, as easily as you access the file system. You can recognize cmdlets by their name formata verb and noun separated by a dash (-), such as Get-Help, Get-Process, and Start-Service.
Note: Windows PowerShell includes more than 100 basic core cmdlets; in addition, you can write your own cmdlets and share them with other users.
What Can I Do with Windows PowerShell?
By using Windows PowerShell, you can: Automate administration of multiple servers through a task-oriented scripting language. Accelerate script authoring, testing, and debugging, and write customer tools in a new command shell environment. Utilize new scripts and cmdlets. Manage command-line services, processes, registry, and WMI data. Manage and/or automate administration tasks for server roles such as IIS and Active Directory. Automate Terminal Server configuration changes by means of Windows PowerShell scripts, and examine configuration similarities and differences across a Terminal Server farm. Manage an Internet Information Services 7.0 environment. Remotely manage servers.
PARTICIPATE
Poll: PowerShell Installation
Instructor Notes
Ask the students to vote by using the polling slide that is provided. After an appropriate amount of time has passed or all of the students have voted, close the polls and show the results. In certain cases, you may want to ask students to explain their answers before you show the results. Discuss the poll results.
Answers Suggested answer:
Topic: Overview
True.
Lesson 3: Windows PowerShell
Getting Started with Server Management in Windows Server 2008
45
Student Workbook Content Consider the following poll question and, when the instructor opens the poll, cast your vote. Be prepared to join any discussion about the poll results that the instructor chooses to initiate.
True or false? If you have a previous version of Windows PowerShell installed, you must uninstall it before installing a newer version. True False
Prerequisites
Windows PowerShell requires the following programs: Windows XP Service Pack 2, Windows 2003 Service Pack 1, or later versions of Windows. Microsoft .NET Framework 2.0.
Note: If any version of Windows PowerShell is already installed on the computer, use Add or Remove Programs in Control Panel to uninstall it before installing a new version.
DISCUSS
Benefits of Windows PowerShell
Instructor Notes This is a lecture topic.
Student Workbook Content
Benefits
Windows PowerShell is designed to improve the command-line and scripting environment by eliminating long-standing problems and adding new features: Discoverability. Windows PowerShell makes it easy to discover its new features by typing simple commands. Consistency. Managing systems can be a complex endeavor and tools that have a consistent interface help to control the inherent complexity. Unfortunately, neither command-line tools nor scriptable COM objects have been known for their consistency. The consistency of Windows PowerShell is one of its primary assets. For example, if you learn how to use the Sort-Object cmdlet, you can use that knowledge to sort the output of any cmdlet. You do not have to learn the various sorting routines of each cmdlet. In addition, developers of cmdlets do not have to design sorting features for their cmdlets. Windows PowerShell gives them a framework that provides the basic features and forces them to be consistent about many aspects of the interface. The framework eliminates some of the choices
Topic: Overview
Lesson 3: Windows PowerShell
46
Getting Started with Server Management in Windows Server 2008
that are typically left to the developer, but, in return, it makes the development of robust and easyto-use cmdlets much simpler. Interactive and scripting environments. Windows PowerShell is a combined interactive and scripting environment that gives you access to command-line tools and COM objects, and also enables you to use the power of the .NET Framework Class Library (FCL). This environment improves upon the Windows Command Prompt, which provides an interactive environment with multiple command-line tools. It also improves upon Windows Script Host (WSH) scripts, which enable you to use multiple command-line tools and COM automation objects, but do not provide an interactive environment. By combining access to all of these features, Windows PowerShell extends the ability of the interactive user and the script writer, and makes system administration more manageable. Object orientation. Although you interact with Windows PowerShell by typing commands in text, Windows PowerShell is based on objects, not text. The output of a command is an object. You can send the output object to another command as its input. As a result, Windows PowerShell provides a familiar interface to people who are experienced with other shells, while introducing a new and powerful command-line paradigm. It extends the concept of sending data between commands by enabling you to send objects, rather than text. Easy transition to scripting. Windows PowerShell makes it easy to transition from typing commands interactively to creating and running scripts. You can type commands at the Windows PowerShell command prompt to discover the commands that perform a task. Then, you can save those commands in a transcript or a history before copying them to a file for use as a script. Security. Windows PowerShell provides for increased security because: Scripts cannot be run by default. Scripts can be configured only if they are digitally signed. Scripts are not permitted to hijack a command name. While the PS1 filename extension is assigned to Windows PowerShell scripts, by default, it is not associated with Windows PowerShell. If you double-click a .ps1 file, it opens in Notepad rather than launching in Windows PowerShell. Windows PowerShell security is centrally controllable. An Administrative (ADM) template adds Windows PowerShell options to a GPO.
Topic: Technical Background
PARTICIPATE
Matching: Which Cmdlet Type?
In the table below, match the cmdlet type to the function that it performs.
Topic: Technical Background
Lesson 3: Windows PowerShell
Getting Started with Server Management in Windows Server 2008
47
Function Change data Retrieve data Format output
Cmdlet type Get Set Format
Instructor Notes This is a matching type activity. Allow your students to discuss the topic, and then encourage individual students to annotate the slide with the appropriate answers.
Answers
Function
Cmdlet type
Change data Retrieve data Format output
Set Get Format
Student Workbook Content
Native Support for Various Type Systems
Windows PowerShell adapts WMI, XML, ASDI, ADO, and COM objects to provide a common syntax to access their properties and methods.
Working with Cmdlets
You can run Windows command-line programs in Windows PowerShell, and you can start Windows programs that have a graphical user interface, such as Notepad and Calculator, in the shell. You can also capture the text that programs generate and use that text in the shell, in much the same way you would in Cmd.exe. In traditional shells, commands are executable programs that range from the very simple (such as attrib.exe) to the very complex (such as netsh.exe). In Windows PowerShell, most cmdlets are very simple, and they are designed to be used in combination with other cmdlets. For example, the get cmdlets only retrieve data, the set cmdlets only establish or change data, the format cmdlets only format data, and the out cmdlets only direct the output to a specified destination. Each cmdlet has a help file that you can access by typing: get-help <cmdlet-name> -detailed The detailed view of the cmdlet help file includes a description of the cmdlet, the command syntax, descriptions of the parameters, and example that demonstrate use of the cmdlet.
Topic: Technical Background
Lesson 3: Windows PowerShell
48
Getting Started with Server Management in Windows Server 2008
PARTICIPATE
Poll: File Extensions for PowerShell Scripts
Instructor Notes
Ask the students to vote by using the polling slide that is provided. After an appropriate amount of time has passed or all of the students have voted, close the polls and show the results. In certain cases, you may want to ask students to explain their answers before you show the results. Discuss the poll results.
Answers Suggested answer: False. The extension is PS1. Student Workbook Content Consider the following poll question, and when the instructor opens the poll, cast your vote. Be prepared to join any discussion about the poll results that the instructor chooses to initiate.
True or false? Windows PowerShell scripts have a PS extension. True False
PARTICIPATE
Brainstorm: What Is the Pipeline, and What Does It Do?
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Answers Suggested answers include: To create a pipeline in Windows PowerShell, you connect commands together with the pipe operator "|" and the output of each command is used as input to the next command. Student Workbook Content Consider the following question. Then, when your instructor prompts you, write your answers on the slide.
Topic: Technical Background
Lesson 3: Windows PowerShell
Getting Started with Server Management in Windows Server 2008
49
What is the pipeline, and what does it do?
A New Scripting Language
If you run particular commands or command sequences repeatedly, or if you develop a series of commands to perform a complex task, you will want to save your commands in a file and execute the command file, instead of typing commands at the prompt. A file of commands is called a script. Windows PowerShell uses its own language for scripting, rather than reusing existing languages, for the following reasons: Windows PowerShell needed a language for managing.NET objects. The language needed to provide a consistent environment for using cmdlets. The language needed to support complex tasks, without making simple tasks more complex. The language needed to be consistent with higher-level languages used in .NET programming, such as C#.
Note: In Windows PowerShell, script files have a .ps1 file name extension.
Important PowerShell Concepts
The Windows PowerShell design integrates concepts from many different environments. Several of them are familiar to people with experience in specific shells or programming environments, but very few people will know about all of them. Looking at some of these concepts provides a useful overview of the shell. Commands are not text-based. Unlike traditional command-line interface commands, Windows PowerShell cmdlets are designed to deal with objectsstructured information that is more than just a string of characters appearing on the screen. Command output always carries along extra information that you can use if you need it. If you have used text-processing tools to process command-line data in the past, you will find that they behave differently if you try to use them in Windows PowerShell. In most cases, you do not need text-processing tools to extract specific information. You can access portions of the data directly by using standard Windows PowerShell object manipulation commands.
Topic: Technical Background
Lesson 3: Windows PowerShell
50
Getting Started with Server Management in Windows Server 2008
The command family is extensible. Interfaces such as Cmd.exe do not provide a way for you to directly extend the built-in command set. You can create external command-line tools that run in Cmd.exe, but these external tools do not have services, such as help integration, and Cmd.exe does not automatically know that they are valid commands. The native binary commands in Windows PowerShell can be augmented by cmdlets that you create and that you add to Windows PowerShell by using snap-ins. Windows PowerShell snap-ins are compiled, just like binary tools in any other interface. You can use them to add Windows PowerShell providers to the shell, as well as new cmdlets. Windows PowerShell can run commands other than cmdlets. It supports scripts that are analogous to Cmd.exe batch files, but have a .ps1 file name extension. Windows PowerShell also allows you to create internal functions that can be used directly in the interface or in scripts.
Windows PowerShell handles console input and display. When you type a command, Windows PowerShell always processes the command-line input directly. It also formats the output that you see on the screen. This is significant because it reduces the work required of each cmdlet and ensures that you can always do things the same way regardless of which cmdlet you are using.
Note: If you run a graphic application in Windows PowerShell, the window for the application opens. Windows PowerShell intervenes only when processing the command-line input you supply or the application output returned to the console window; it does not affect how the application works internally.
Windows PowerShell Pipeline
Pipelines act like a series of connected segments of pipe. Items moving along the pipeline pass through each segment. To create a pipeline in Windows PowerShell, you connect commands together with the pipe operator "|" and the output of each command is used as input to the next command. Pipelines are arguably the most valuable concept used in command-line interfaces. Properly used, pipelines not only reduce the effort involved in entering complex commands, but also make it easier to see the flow of work in the commands. A related useful characteristic of pipelines is that because they operate on each item separately, you do not have to modify them based on whether you will have zero, one, or many items in the pipeline. Furthermore, each command in a pipeline (called a pipeline element) usually passes its output to the next command in the pipeline item by item. This usually reduces the resource demand of complex commands and enables you to begin getting the output immediately. Processing objects. Technically, a .NET object is an instance of a .NET class that consists of data and the operations associated with that data. But you can think of an object as a data entity that has properties, which are like characteristics, and methods, which are actions that you can perform on the object. For example, when you get a service in Windows PowerShell, you are really getting an object that represents the service. When you view information about a service, you are viewing the properties of its service object. And, when you start a service, that is, when you change the Status property of the service to "started," you are using a method of the service object. All objects of the same type have the same properties and methods, but each instance of an object can have different values for the properties. For example, every service object has a Name and Status property. However, each service can have a different name and a different status.
Topic: Technical Background
Lesson 3: Windows PowerShell
Getting Started with Server Management in Windows Server 2008
51
PARTICIPATE
Poll: Working with Drives
Instructor Notes
Ask the students to vote by using the polling slide that is provided. After an appropriate amount of time has passed or all of the students have voted, close the polls and show the results. In certain cases, you may want to ask students to explain their answers before you show the results. Discuss the poll results.
Answers Suggested answer: False. You must specify the appropriate registry path; for example, HKCU: or HKLM: Student Workbook Content Consider the following poll question and, when the instructor opens the poll, cast your vote. Be prepared to join any discussion about the poll results that the instructor chooses to initiate.
True or false? You can access the registry directly from a Windows PowerShell script by using the Registry: drive. True False
Using Familiar Command Names (Aliasing)
By using a mechanism called aliasing, Windows PowerShell enables you to refer to commands by alternate names. Aliasing enables users who have experience in other shells to reuse common command names that they already know to perform similar operations in Windows PowerShell. Aliasing associates a command name that you type with another command. For example, Windows PowerShell has an internal function named Clear-Host that clears the output window. If you type either the cls or clear command at a command prompt, Windows PowerShell interprets that this is an alias for the Clear-Host function and runs the Clear-Host function. Aliasing helps you to learn Windows PowerShell. First, most users have a large repertoire of commands that users already know by name, and although the Windows PowerShell equivalents may not produce identical results, they are close enough in form that users can use them to do work without having to first memorize the Windows PowerShell names. Secondly, the major source of frustration in learning a new shell when the user is already familiar with another shell is the errors that are caused by "finger memory." If you have used Cmd.exe for years, when you have a screen full of output and want to clean it up, you would reflexively type the cls command and then press ENTER. Without the alias to the Clear-Host function in Windows PowerShell, you would simply get the error message "'cls' is not recognized as a cmdlet, function, operable program, or script file" and be left with no idea of what to do to clear the output.
Topic: Technical Background
Lesson 3: Windows PowerShell
52
Getting Started with Server Management in Windows Server 2008
Windows PowerShell Navigation
Folders, or directories as they are more commonly known, are a useful concept for organizing files and other directories. This approach does not ensure that the content is readable or usable by particular applications, but it does make it simpler to find specific items. Tools that enumerate or search through files and folders work with these devices as well. You can also address a specific item by using the path to the file that represents it. Analogously, the Windows PowerShell infrastructure supports exposing virtually anything that can be navigated like a standard Windows disk drive as a Windows PowerShell drive. A Windows PowerShell drive does not necessarily represent a real drive, either locally or on the network.
Note: This section primarily discusses navigation for file systems, but the concepts apply to Windows PowerShell drives that are not associated with file systems.
Managing the current location in Windows PowerShell. When navigating folder systems in Windows Explorer, you usually have a specific working locationnamely, the current open folder. Items in the current folder can be manipulated easily by clicking them. For command-line interfaces such as Cmd.exe, when you are in the same folder as a particular file, you can access it by specifying a relatively short name, rather than needing to specify the entire path to the file. The current directory is called the working directory. Windows PowerShell uses the noun Location to refer to the working directory, and implements a family of cmdlets to examine and manipulate your location.
Managing Windows PowerShell Drives. A Windows PowerShell drive is a data store location that you can access like a file system drive in Windows PowerShell. The Windows PowerShell providers create some drives for you, such as the file system drives (including C: and D:), the registry drives (HKCU: and HKLM:), and the certificate drive (Cert:), and you can create your own Windows PowerShell drives.
Note: These drives are very useful, but they are available only in Windows PowerShell. You cannot access them by using other Windows tools such as Windows Explorer or Cmd.exe.
Windows PowerShell uses the noun PSDrive for commands that work with Windows PowerShell drives. Working with files, folders, and registry keys. Windows PowerShell uses the noun Item to refer to things found on a Windows PowerShell drive. When dealing with the Windows PowerShell FileSystem provider, an Item might be a file, a folder, or the Windows PowerShell drive. Manipulating items directly. The elements that you see in Windows PowerShell drives, such as the files and folders in the file system drives, and the registry keys in the Windows PowerShell registry drives, are called items in Windows PowerShell. By using Windows PowerShell, you can create, rename, move, copy, delete, and execute items. Working with objects. The power of objects is that they provide you with access to a lot of complex data and it is already correlated. By using some simple techniques in Windows PowerShell, you can further manipulate objects to do even more work.
Topic: Technical Background
Lesson 3: Windows PowerShell
Getting Started with Server Management in Windows Server 2008
53
Using Windows PowerShell for Administration
The fundamental goal of Windows PowerShell is providing better, easier administrative control over systems, either interactively or from script. Windows PowerShell administrative capabilities include: Managing local processes. There are only two core Process cmdlets, Get-Process and StopProcess. Because it is possible to inspect and filter processes using either parameters or the Object cmdlets, you can perform some complex tasks by using only these two cmdlets. Managing local services. There are eight core Service cmdlets, designed for a wide range of service tasks. You can get a list of Service cmdlets by using Get-Help *-Service, and you can find information about each Service cmdlet by using Get-Help<Cmdlet-Name>, such as Get-Help NewService. Collecting information about computers. Get-WmiObject is the most important cmdlet for general system management tasks. All critical subsystem settings are exposed via WMI. Furthermore, WMI treats data as objects that are in collections of one or more items. Because Windows PowerShell also works with objects and has a pipeline that allows you to treat single or multiple objects in the same way, generic WMI access enables you to perform some advanced tasks with very little work. Working with software installations. Applications correctly designed to use the Windows Installer can be accessed through WMI's Win32_Product class, but not all applications in use today use the Windows Installer. Applications that are installed by copying the application files must be managed by using the techniques for managing files and folders. Changing computer state: locking, logging off, shutting down, and rebooting. You can reset a computer in various ways from Windows PowerShell, but in the initial release, you must use either a standard command-line tool or WMI. Working with printers. Printer management tasks can be performed in Windows PowerShell by using both WMI and the WScript.Network COM object from WSH. Performing networking tasks. Most low-level network protocol administration tasks involve TCP/IP, because TCP/IP is the most commonly used network protocol. A variety of network tasks can be performed in Windows PowerShell: IP Configuration tasks DHCP Configuration tasks Working with network shares
Working with files and folders. Navigating through Windows PowerShell drives and manipulating the items on them is similar to manipulating files and folders on Windows physical disk drives. Working with registry keys and entries. Because registry keys are items on Windows PowerShell drives, working with them is very similar to working with files and folders. One critical difference is that every item on a registry-based Windows PowerShell drive is a container, just like a folder on a file system drive. However, registry entries and their associated values are properties of the items, not distinct items.
Topic: Technical Background
Lesson 3: Windows PowerShell
54
Getting Started with Server Management in Windows Server 2008
Windows PowerShell Security
Scripting is a very powerful tool, but it can be misused for malicious purposes. To protect user data and the integrity of the operating system, Windows PowerShell includes several security features, among which are the execution policy and Windows PowerShell profiles: Execution policy. The Windows PowerShell execution policy determines whether scripts are allowed to run and, if they can run, whether they must be digitally signed. It also determines whether configuration files can be loaded. The default execution policy, Restricted, is the most secure of the execution policies. It does not permit any scripts to run, and it does not permit any configuration files, including a Windows PowerShell profile, to be loaded. You can still use Windows PowerShell interactively; however, if you wanted to run scripts or load configuration files, you would have to change the execution policy on your system. Windows PowerShell profiles. When you add aliases, functions, and variables to Windows PowerShell, you are actually adding them only to the current Windows PowerShell session. If you exit the session or close Windows PowerShell, the changes are lost. To retain these changes, you can create a Windows PowerShell profile and add the aliases, functions, and variables to the profiles. The profile is loaded every time that Windows PowerShell starts.
Note: To load a profile, your Windows PowerShell execution policy must permit you to load configuration files. If it does not, the attempt to load the profile fails and Windows PowerShell displays an error message.
You can have four different profiles in Windows PowerShell. The profiles are listed in load order. The most specific profiles have precedence over less specific profiles where they apply: %windir%\system32\WindowsPowerShell\v1.0\profile.ps1 (This profile applies to all users and all shells.) %windir%\system32\WindowsPowerShell\v1.0\ Microsoft.PowerShell_profile.ps1 (This profile applies to all users, but only to the Microsoft.PowerShell shell.) %UserProfile%\My Documents\WindowsPowerShell\profile.ps1 (This profile applies only to the to the current user, but affects all shells.) %UserProfile%\\MyDocuments\WindowsPowerShell\Microsoft.PowerShell_profile.ps1 (This profile applies only to the current user and the Microsoft.PowerShell shell.)
Note: You can create, share, and distribute profiles to enforce a consistent view of Windows PowerShell in a larger enterprise. Note: The profiles are not created automatically. To create a profile, create a text file with the specified name in the specified location.
Topic: Technical Background
Lesson 3: Windows PowerShell
Getting Started with Server Management in Windows Server 2008
55
PARTICIPATE
Demonstration: Configuring Windows Server Core by Using Windows PowerShell
Instructor Notes
You will use the following recorded demonstration: 5939ae_01_04_04_dem01.swf. The estimated time for this demonstration is five minutes. After the demonstration, you should ask the students if they have any questions. Be prepared to discuss any issues raised with the class.
Transcript
In this demonstration, you will see how to display information for WMI objects, using Windows PowerShell and the Get-WmiObject cmdlet. You will also review how to add extended information and format this data into a list. WMI is a core technology to help you identify a wide range of information in a uniform manner. By using Windows PowerShell, you can access WMI objects and display their properties. First, open Windows PowerShell. By using Windows PowerShell, the first command to run is the Get-WmiObject command to retrieve a list of the WMI classes available on the local computer. Depending on your computer, this will return different information. In this example, you can see the WMI class of Win32_Operating System. If you already know the name of the WMI namespace, you can use it to get information immediately. If you want to retrieve information from the Win32_Operating System WMI class, use the following command, using the Get-WmiObject cmdlet. This will output information such as the System Directory of the Operating System, Build Number, Registered User, Serial Number, and Version. The Win32_Operating System class has many more properties than those displayed. Using the GetWmiObject cmdlet and the Get-Member cmdlet, you can see all of the properties, and you will see extended information of the WMI class displayed, such as Boot Device properties. If you want information contained in the Win32_Operating System class that is not displayed by default, you can display it by using the Format cmdlet, adding additional data you want to display such as available memory data. You can add additional data for Total Virtual Memory, Total Visible Memory, Free Physical Memory, and Free Space in Paging Files. The output returns the values of each property in byte value. To see the same information in a more readable format, use the same command with the Format-List cmdlet. The memory data is more readable if you format it as a list. You can then see each line individually. By using Windows Powershell, you can enumerate WMI objects and their related properties. In this demonstration, you saw how to display information for WMI objects by using Windows PowerShell and the Get-WmiObject cmdlet. You also reviewed how to add extended information and format this data into a list.
Student Workbook Content In this demonstration, you will see how to display information for WMI objects by using Windows PowerShell and the Get-WmiObject cmdlet. You will also review how to add extended information and format this data into a list.
Topic: Technical Background
Lesson 3: Windows PowerShell
56
Getting Started with Server Management in Windows Server 2008
Topic: Implementation/Usage Scenarios
DISCUSS
Implementation/Usage Scenarios
Instructor Notes This is a lecture topic.
Student Workbook Content
Command-Line Services, Processes, Registry, and WMI Data Management
Common as-needed server administration tasks such as identifying running services or processes, viewing the registry, and reading and changing settings stored in WMI are easier than ever with the built-in command-line tools (cmdlets) get-service, get-process, get-wmiobject, and the registry provider for Windows PowerShell.
Server Management
Windows PowerShell enables you to manage specific Windows Server 2008 roles such as Active Directory, Internet Information Services (IIS) 7.0, and Terminal Server, in addition to Exchange Server 2007 and Microsoft Operations Manager 2007. In addition, a number of partners have provided Windows PowerShell commands that improve network management, and provide rich charting and gauge capabilities. Terminal Server management. Because Terminal Server stores a wealth of data in WMI, administrators can automate Terminal Server configuration changes by means of Windows PowerShell scripts, and examine configuration similarities and differences across a Terminal Server farm. There are numerous script examples in Microsofts TechNet ScriptCenter. Internet Information Services 7.0. Windows PowerShell is ideally suited to managing IIS 7.0, including deploying and configuring IIS 7.0 across a Web farm.
Topic: Recommendations
PARTICIPATE
Brainstorm: List the Recommendations for Implementing Windows PowerShell to Get the Greatest Benefits
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class.
Topic: Implementation/Usage Scenarios
Lesson 3: Windows PowerShell
Getting Started with Server Management in Windows Server 2008
57
Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Answers Suggested answers include: Start using Windows PowerShell immediately. Existing batch files and scripts will all still run in the Windows PowerShell environment. Dont forget the power of the wildcard character. Only deploy Windows PowerShell on administrator machines where it will be utilized. Immediately deploy a Group Policy object to centrally control security settings for Windows PowerShell. Student Workbook Content Consider the following question. Then, when your instructor prompts you, write your answers on the slide. List the recommendations for implementing Windows PowerShell to get the greatest benefits.
To get the greatest benefits from Windows PowerShell, administrators should keep the following in mind: Start using Windows PowerShell immediately. Because it is backward-compatible, existing knowledge and experience can be used while learning to use the new cmdlets and scripting language. Dont throw anything away! Existing batch files and scripts will all still run in the Windows PowerShell environment. When using cmdlets, dont forget the power of the wildcard character. While security was a design priority of Windows PowerShell, like any other powerful administrative tool, it should only be deployed on administrator machines where it will be utilized.
Topic: Recommendations
Lesson 3: Windows PowerShell
58
Getting Started with Server Management in Windows Server 2008
Immediately deploy a Group Policy object to centrally control security settings for Windows PowerShell, even if Windows PowerShell is not yet being used in the organization.
Topic: Summary
DISCUSS
Summary
Instructor Notes This is a lecture topic.
Student Workbook Content Windows PowerShell is a command-line shell and scripting environment that brings the power of the .NET Framework to command-line users and script writers. It introduces a number of powerful new concepts that enable you to extend the knowledge you have gained and the scripts you have created within the Windows Command Prompt and Windows Script Host environments. Windows PowerShell is ready to use now, but is backward-compatible with the command-line environment you are currently using. Because Windows PowerShell packs its own unique power in the form of object-oriented cmdlets, you do not need to script to take advantage of it. Windows PowerShell is the new standard for command-line management. It is the foundation for many new Microsoft products.
Lesson 4: Windows Remote Management
Introduction
Windows Remote Management is one component of Windows Hardware Management features that manage server hardware locally and remotely. These features include a service that implements the WS-Management protocol, hardware diagnosis and control through Baseboard Management Controllers (BMCs), and a COM API and scripting objects that enable you to write applications that communicate remotely through the WS-Management protocol. This lesson provides an overview of Windows Remote Management in Windows Server 2008 and how administrators can use it to streamline management of servers across the enterprise.
Lesson Contents:
Topic: Overview Lecture: Overview Topic: Technical Background Case Study: Enabling Windows Remote Management Case Study: Securing Windows Remote Management Demonstration: Windows Remote Management
Topic: Summary
Lesson 4: Windows Remote Management
Getting Started with Server Management in Windows Server 2008
59
Topic: Implementation/Usage Scenarios Brainstorm: List the Recommended Implementation Scenarios for Windows Remote Management Topic: Recommendations Brainstorm: List the Best Practices for Using Windows Remote Management Topic: Summary Lecture: Summary
Topic: Overview
DISCUSS
Overview
Instructor Notes This is a lecture topic.
Student Workbook Content
Remote Hardware Management
Windows Remote Management hardware management is intended to reduce overall IT administration costs by providing monitoring and control of remote hardware components, especially before the system is started and after an operating system failure. Original Equipment Manufacturers (OEMs) have developed a common architecture to address the need for hardware management. An important piece of this architecture is the baseboard management controller (BMC). A BMC is a specialized device that monitors the state of the server computer. The BMC provides remote control of server hardware, retrieves status data, and receives notifications about critical errors and other hardware state changes. A script or application that is monitoring a remote server can obtain data from the server either in-band, through the remote operating system, or out-of-band, directly from the BMC. A BMC has sensors that can detect, for example, when the server computer is overheating or when voltage is out of the acceptable range. Several standards exist to define the architecture of BMC. The Intelligent Platform Management Interface (IPMI) is one such standard that is used frequently. However, despite the IPMI standard, management access to server hardware is proprietary and requires use of management tools supplied by OEMs. Also, remote access to a BMC is provided using a specialized wire protocol, Remote Management Control Protocol (RMCP), which has non-standard security mechanisms for authentication of access. The Microsoft IPMI provider and IPMI driver, enable you to obtain BMC data from remote server computers through a standard WMI provider with WMI classes. While you can write a normal WMI script that obtains remote data through DCOM, in many cases the preferred method of obtaining IPMI data is through the WinRM command-line utility, the WinRM Scripting API, or WinRM C++ API. The BMC also has an event database called the System Event Log (SEL) which records events in the monitored computer. You cannot subscribe to have these events delivered to a script as you can with WMI event classes. However, you can use the Wecutil.exe command line tool to subscribe to them.
Topic: Overview
Lesson 4: Windows Remote Management
60
Getting Started with Server Management in Windows Server 2008
Windows Remote Management
Windows Remote Management (WinRM) is the Windows implementation of WS-Management, an industry-standard Web servicesbased protocol. Windows Remote Management provides a secure, efficient way for management applications and scripts to communicate with local and remote computers. The Windows service that Windows Remote Management installs and uses is called WinRM. When a server is connected to a BMC that supports the WS-Management standard, applications and scripts can use Windows Remote Management to communicate directly with the BMC, even when the operating system is offline (pre-boot or post-failure). When a server is not connected to a BMC, Windows Remote Management can still be used to connect to WMI remotely in situations where DCOM communication is impeded (for example, across a firewall). This is possible because the WS-Management standard is firewall-friendly and uses a single port configurable by the system administrator. Windows Remote Management exposes its own API for scripting, which can be used by scripts written in any Windows Script Hostcompatible language. The scripting API communicates with WMI using syntax different from standard WMI scripts. WinRM syntax is documented in the WinRM software development kit. Hardware Management uses a WMI plug-in to expose WMI classes to WinRM. WS-Management is based on the following standard specifications: HTTPS, SOAP over HTTP (WS-I profile), SOPA 1.2, WS-Addressing, ES-Transfer, WS-Enumeration, and WS Eventing.
WinRM Command-Line Tool (Winrm.cmd)
The command-line tool provided as the primary administrative interface for managing WinRM is a batch file (Winrm.cmd) that runs a Visual Basic, Scripting Edition script named Winrm.vbs. Because it is a script, you can open it as a text file and view the code to learn how it works. You can also write your own VBScript scripts that take advantage of the WinRM scripting API. Winrm.vbs runs under Cscript.exe, the command-line scripting engine of Windows Script Host. Winrm.vbs enables system administrators to configure and manage WinRM. Because WSManagement is a Web service that uses XML as its message format, Winrm.vbs output is natively XML as well. The tool provides switches to output more readable XML or plain text.
Prerequisites
WinRM is part of the operating system. However, to obtain data from remote computers, you must configure a WinRM listener. If a BMC is detected at system startup, then the IPMI provider loads; otherwise, the WinRM scripting objects and the WinRM command-line tool are still available.
Note: Windows Server 2003 R2: WinRM is not installed by default, but is available as the Hardware Management feature through the Add/Remove System Components feature in Control Panel under Management and Monitoring Tools. Note: Windows Server 2003 and Windows XP/2000/NT: WinRM is not available.
WinRM is dependent on WinHttp but no other services. If the IIS Admin Service is installed on the same computer, you may see messages that indicate WinRM cannot be loaded before IIS. However, WinRM does not actually depend on IIS: these messages occur because the load order ensures that IIS service starts before the HTTP service. WinRM does require that WinHTTP.dll be registered.
Benefits
By using Windows Remote Management, you can:
Topic: Overview
Lesson 4: Windows Remote Management
Getting Started with Server Management in Windows Server 2008
61
Perform local and remote server management by accessing multiple data management stores such as WMI, ADSI, COM, Certificates, Registry, and XML configuration files. Automate the management of local and remote servers. Obtain management data from local and remote computers that may have baseboard management controllers (BMCs). Utilize WMI on Windows systems. Utilize WS-Management Protocol for systems that are not Windows-based.
Topic: Technical Background
PARTICIPATE
Case Study: Enabling Windows Remote Management
Instructor Notes
This is a team Case Study activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Encourage students to use the course workbookand then, in the team space provided, write their answers to the questions on the slide. Ask each team in turn to consider their question, to discuss as a group, and then to indicate their answer in the team box provided.
Answers Suggested answer: By using Windows Server 2008 and Windows Vista, you can enable the WS-Management protocol on the local computer and set up the default configuration for remote management by using one command: winrm quickconfig
Student Workbook Content
Scenario:
Woodgrove Bank has deployed Windows Server 2008 throughout its organization. You need to enable Windows Remote Management on a number of servers in the New York offices. You are sitting in front of NYC-SVR1, and need to enable Windows Remote Management as quickly as possible. Answer the following question that also appears on the slide. Then, when prompted by your instructor, and working as a team, record your answer in the box provided on the slide.
Topic: Technical Background
Lesson 4: Windows Remote Management
62
Getting Started with Server Management in Windows Server 2008
Question What do you need to do to enable and configure Windows Remote Management quickly?
Answer
Remote Management Architecture
The following components and features are supplied by WinRM and hardware monitoring: WinRM scripting API. This scripting API enables you to obtain data from remote computers by using scripts that perform WS-Management protocol operations. Winrm.cmd. This command-line tool for system management is implemented in a Visual Basic, Scripting Edition file (Winrm.vbs) written using the WinRM scripting API. This tool allows an administrator to configure WinRM and to get data or manage resources.
Note: Windows Server 2003 R2: For this command to work, the Hardware Management feature had to be installed through Add/Remove System Components under Management and Monitoring Tools in Control Panel.
Winrs.exe. This command-line tool enables administrators to remotely execute most Cmd.exe commands by using the WS-Management protocol. For more information, see the online help provided by the command line Winrs /?.
Note: Windows Server 2003 R2: This command is not available.
Intelligent Platform Management Interface (IPMI) driver and WMI provider. Hardware management through the IPMI provider and driver allows you to control and diagnose remote server hardware through BMCs when the operating system is not running or deployed. WMI service. The WMI service continues to run side by side with WinRM and provides requested data or control through the WMI plug-in. You can continue to obtain data from standard WMI classes, such as Win32_Process, as well as IPMI-supplied data. WS-Management protocol. WS-Management protocol, a SOAP-based, firewall-friendly protocol, was designed for systems to locate and exchange management information. The intention of the WS-Management protocol specification is to provide interoperability and consistency for enterprise systems that have computers running on a variety of operating systems from different vendors.
Note: WS-Management protocol is based on the following standard Web service specifications: HTTPS, SOAP over HTTP (WS-I profile), SOAP 1.2, WS-Addressing, WS-Transfer, WS-Enumeration, and WS-Eventing.
Topic: Technical Background
Lesson 4: Windows Remote Management
Getting Started with Server Management in Windows Server 2008
63
Remote Management Installation
If Windows Remote Management is not installed and configured, WinRM scripts do not run and the WinRM command-line tool is unable to carry out data operations. The Windows Remote Shell command-line tool, WinRS, and event forwarding also depend on WinRM configuration. Default Configuration WinRM and IPMI WMI provider components are installed by default with Windows Server 2008 and the WinRM service starts automatically.
Note: On Windows Vista, the service must be started manually. Note: On Windows Server 2003 R2, WinRM is not installed by default but is available as the Hardware Management feature through the Add/Remove System Components feature in the Control Panel under Management and Monitoring Tools.
By default, no WinRM listener is configured. Even if the WinRM service is running, WSManagement protocol messages that request data cannot be received or sent. Internet Connection Firewall (ICF) blocks access to ports.
Note: You can use the Winrm command to locate listeners and the addresses by typing the following command at a command prompt: winrm e winrm/config/listener To check the state of configuration settings, type this command: winrm get winrm/config
Quick Default Configuration By using Windows Server 2008 and Windows Vista, you can enable the WS-Management protocol on the local computer and set up the default configuration for remote management with one command: winrm quickconfig
Note: Windows Server 2003 R2: The winrm quickconfig command is not available.
The winrm quickconfig command (or the abbreviated version) winrm qc, performs the following actions: Starts the WinRM service and sets the service startup type to auto-start. Configures a listener for the ports that send and receive WS-Management protocol messages by using either HTTP or HTTPS on any IP address. Defines ICF exceptions for the WinRM service and opens the ports for HTTP and HTTPS.
Note: You can get information on customizing configuration by typing winrm help config at a command prompt.
Topic: Technical Background
Lesson 4: Windows Remote Management
64
Getting Started with Server Management in Windows Server 2008
To Configure WinRM with Default Settings Run the following command at a command prompt: Winrm quickconfig
Note: If you are not running under the local computer Administrator account, you must either select Run as Administrator from the Start menu or use the Runas command at a command prompt.
When the tool displays Make these changes [y/n]?, type y If configuration is successful, you will see this output: WinRM has been updated for remote management. WinRM service type changed to delayed auto start. WinRM service started. Created a WinRM listener on HTTP://* to accept WS-Man requests to any IP on this machine.
You can either leave the default settings for client and server components of WinRM or customize them. For example, you may need to add certain remote computers to the client configuration TrustedHosts list.
Note: A trusted hosts list should be set up when mutual authentication cannot be established. Kerberos protocol allows mutual authentication but cannot be used in workgroups, only domains. A best practice in setting up trusted hosts for a workgroup is that the list should be as restricted as possible.
You can create an HTTPS listener by using the following command: winrm quickconfig - transport:https.
Note: Be aware that you must open Port 443 for HTTPS transport to work.
Windows Firewall and WinRM Ports The default listener ports configured by winrm quickconfig are Port 80 for HTTP transport and Port 443 for HTTPS. If you configure a custom port for a listener, you must open the port before WinRM can send and receive messages. The following example uses the netsh firewall command to open Port 3190 for a listener who uses that port: netsh firewall add portopening TCP 3190 "Port 3190" Configuring a Proxy Server for WinRM WinRM uses HTTP and HTTPS to send messages between the client and server computers. By default, the WinRM client is not configured to use a proxy server and sends messages directly to the WinRM server computer. Be aware that the WinRM client does not use the Internet Explorer proxy settings. If a proxy is required to reach the server computer, the WinRM proxy configuration can be changed by using the ProxyCfg.exe tool.
Topic: Technical Background
Lesson 4: Windows Remote Management
Getting Started with Server Management in Windows Server 2008
65
Scripting in WinRM
The Scripting API in WinRM and the accompanying COM API for C++ are designed to reflect closely the operations of the WS-Management protocol. The WinRM Scripting API in Windows Remote Management supports all of the WS-Management protocol operations except one. It does not allow subscriptions to events. To subscribe to events from the BMC System Event Log, you must use the Wecutil or Wevtutil command-line tools. The WinRM Scripting API is called by Winrm.vbs, a command-line tool, which is written in Visual Basic, Scripting Edition. Winrm.vbs provides examples of how to use the WinRM Scripting API. Using WSman Compared to Using WMI Scripting WMI connects to remote computers through DCOM, which requires the configuration described in Connecting to WMI on a Remote Computer. WinRM does not use DCOM to connect to a remote computer. Instead, the WS-Management protocol sends SOAP messages and the service uses a single port for HTTP and a port for HTTPS transport. Unlike the WinRM command-line tool, scripts must provide the XML required to pass to the WS-Management protocol messages. They must also provide URIs. The WMI Scripting API works with objects, such as instances of Win32_LogicalDisk, which represent resources on a computer. This WMI class is defined in Managed Object Format (MOF) files, which are stored in binary form in the WMI repository. In WMI, a Get operation for a single resource or a query for multiple instances returns WMI objects. A WinRM script does not return objects, but rather streams of XML text. WinRM Script and Winrm.cmd Output The output from a WinRM script is encoded in Unicode. If you create a FileSystemObject and write a file from the script, the resulting file is Unicode. However, if you redirect the output to a file, the encoding is ANSI. If you redirect the output to an XML file and there are Unicode characters in the output, the XML will be invalid. Be aware that the winrm command-line tool outputs ANSI.
Note: Windows Server 2003 R2: If a WMI class name, method, or property name contains non-ASCII characters, then the data cannot be retrieved by WinRM. However, the instance data can contain non-ASCII characters.
PARTICIPATE
Case Study: Securing Windows Remote Management
Instructor Notes
This is a team Case Study activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Encourage students to use the course workbook and then, in the Team space provided, write their answers to the questions on the slide. Ask each team in turn to consider their question, to discuss as a group, and then to indicate their answer in the team box provided.
Answers Suggested answer:
Topic: Technical Background
Lesson 4: Windows Remote Management
66
Getting Started with Server Management in Windows Server 2008
To allow all accounts in the Administrators group to access the service, set the following registry key to 1: HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\system\LocalAccountToken FilterPolicy
Student Workbook Content
Scenario:
Woodgrove Bank has deployed Windows Server 2008 throughout its organization. You are sitting in front of NYC-SVR1, a server in a workgroup, and must configure authentication to allow all members of the local administrators group to use WinRM to manage the server. Answer the following question that also appears on the slide. Then, when prompted by your instructor, and working as a team, record your answer in the box provided on the slide.
Question What must you do to allow members of the administrators group to use WinRM to manage NYCSVR1? Answer
Authentication for Remote Connections
Windows Remote Management maintains security for communication between computers by supporting several standard methods of authentication and message encryption. The default credentials, user name and password, are the credentials for the logged-on user account that runs the script. Kerberos. Kerberos is the default method when the client is in a domain and the remote destination string is not one of the following: localhost, 127.0.0.1, or [::1]. Negotiate. Negotiate is the default method when the client is not in a domain. Negotiate is also the default method when the client is in a domain, but the remote destination string is one of the following: localhost, 127.0.0.1, or [::1].
Note: For more information about the authentication types that are enabled in the default configuration settings, see Installation and Configuration for Windows Remote Management [ http://msdn2.microsoft.com/enus/library/aa384372.aspx].
You can control the authentication method being used by WinRM: Basic authentication. Basic authentication is disabled in the default configuration settings for both WinRM client and WinRM server. To explicitly establish Basic authentication in the call to WSMan.CreateSession, set the WSManFlagUseBasic and WSManFlagCredUserNamePassword flags in the flags parameter. Digest authentication. To explicitly establish Digest authentication in the call to WSMan.CreateSession, set the WSManFlagUseDigest flag in the flags parameter. Digest is not supported, which means it cannot be configured, for the WinRM server component.
Topic: Technical Background
Lesson 4: Windows Remote Management
Getting Started with Server Management in Windows Server 2008
67
Negotiate authentication. To explicitly establish Negotiate authentication, also known as Windows Integrated Authentication, in the call to WSMan.CreateSession, set the WSManFlagUseNegotiate flag in the flags parameter. With Windows Server 2008 and Windows Vista, User Account Control (UAC) affects access to the WinRM service. When Negotiate authentication is used in a workgroup, only the built-in Administrator account can access the service. To allow all accounts in the Administrators group to access the service, set the following registry key to 1: HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\system\LocalAccountTokenFilt erPolicy
Kerberos authentication. To explicitly establish Kerberos authentication in the call to WSMan, set the WSManFlagUseKerberos flag in the flags parameter. Both the client and the server computers must be joined to a domain. If you use Kerberos as the authentication method, you cannot use an IP address in the call to WSMan.CreateSession or IWSMan::CreateSession.
Note: Windows Server 2003 R2: This type of authentication is not available.
Enabling Authentication Options The default authentication option at system installation is Kerberos. If your script or application requires a specific authentication method that is not enabled, you must change the configuration to allow that. This change can be made using the Winrm command-line tool or through Group Policy for the Windows Remote Management Group Policy Object. You may also choose to disable certain methods of authentication. PARTICIPATE
Demonstration: Windows Remote Management
Instructor Notes
You will use the following recorded demonstration: 6408AL_01_04_01.wmv. The estimated time for this demonstration is three minutes. After the demonstration, you should ask the students if they have any questions. Be prepared to discuss any issues raised with the class.
Transcript
At the NYC-SVR2 Server Core, WinRM is initially not configured to listen for remote management commands on any network interface. To configure WinRM to listen to remote management commands on NYC-SVR2, we must configure a listener on at least one interface. In this task we will use the WINRM QuickConfig command to create a default HTTP listener, which listens on all interfaces. Switching to the NYC-DC1 domain controller, and an open command prompt, we use the winrm get command to retrieve information about the WinRM service on NYC-SVR2. Next, we perform an enumerate operation. The WS-Management Enumerate operation returns a collection of objects. The resulting output will be similar to that of a GET operation, but instead of listing the information of a single object, it will list all of the objects. Here we enumerate information about the logical disks installed on NYC-SVR2. We can scroll up the output to see the detailed information returned. Next, we use an invoke operation to stop and start services. The WS-Management Invoke operation executes methods on the target object.
Topic: Technical Background
Lesson 4: Windows Remote Management
68
Getting Started with Server Management in Windows Server 2008
I can use the get operation to check the status of the service we just stopped. Next, we start the service modifying a previous command in the keyboard buffer for speed. Again, we can check the service status. It is now running. Finally, the WS-Management Remote Shell operation allows certain noninteractive commands to be executed in the CMD shell on the remote machine. This is very useful for performing remote operations. We will use this facility to check the hostname and IP configuration of NYC-SVR2. This concludes the demonstration.
Student Workbook Content In this demonstration, you will see how to configure the WinRM service on a Server Core. You will also see how to perform remote management of the server by using both WinRM and WinRS.
Topic: Implementation/Usage Scenarios
PARTICIPATE
Brainstorm: List the Recommended Implementation Scenarios for Windows Remote Management
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Answers Suggested answers include: Perform local and remote server management by accessing multiple data management stores such as WMI, ADSI, COM, Certificates, Registry, and XML configuration files. Automate the management of local and remote servers. Obtain management data from local and remote computers that may have baseboard management controllers (BMCs). Utilize WMI on Windows systems. Utilize WS-Management Protocol for systems that are not Windows-based. Monitor PC health by forwarding events to a central collector.
Student Workbook Content Consider the following question. Then, when your instructor prompts you, write your answers on the slide.
Topic: Implementation/Usage Scenarios
Lesson 4: Windows Remote Management
Getting Started with Server Management in Windows Server 2008
69
List the recommended implementation scenarios for Windows Remote Management.
Windows Server 2008 administrators must manage PCs in restricted environments, collect information for asset and configuration management, remotely manage servers, and monitor PC health. By using Windows Remote Management, you can do all of these things. You can: Perform local and remote server management by accessing multiple data management stores such as WMI, ADSI, COM, Certificates, Registry, and XML configuration files. Automate the management of local and remote servers. Obtain management data from local and remote computers that may have baseboard management controllers (BMCs). Utilize WMI on Windows systems. Utilize WS-Management Protocol for systems that are not Windows-based. Monitor PC health by forwarding events to a central collector.
Topic: Recommendations
PARTICIPATE
Brainstorm: List the Best Practices for Using Windows Remote Management
Instructor Notes
This is a brainstorming activity. Remind students that the Annotation tools are on the upper-right corner of the Live Meeting console. The icon labeled ab is the typing tool. Remind them to click that icon and then move their cursor into one of the boxes on the slide. When they type and press ENTER, the text that they type appears for everyone in the class. Discuss the topic with the students by using the Instructor Slide and Student Workbook Content (below), and then encourage students to annotate the slide with their suggestions.
Topic: Recommendations
Lesson 4: Windows Remote Management
70
Getting Started with Server Management in Windows Server 2008
Answers Suggested answers include: Enable Windows Remote Management to manage Windows Vista client computers. Remotely collect WMI properties to bolster your asset and inventory system. Use Event Forwarding to monitor client health by focusing only on Critical or Error events in the Application and System event logs. Use Event Forwarding to monitor client security by collecting Audit Failure events.
Student Workbook Content Consider the following question. Then, when your instructor prompts you, write your answers on the slide. List the best practices for using Windows Remote Management.
The following should be considered best practices for Windows Remote Management: Enable Windows Remote Management to manage Windows Vista client computers. Remotely collect WMI properties to bolster your asset and inventory system. Use Event Forwarding to monitor client health by focusing only on Critical or Error events in the Application and System event logs. Use Event Forwarding to monitor client security by collecting Audit Failure events.
Topic: Recommendations
Lesson 4: Windows Remote Management
Getting Started with Server Management in Windows Server 2008
71
Topic: Summary
DISCUSS
Summary
Instructor Notes This is a lecture topic.
Student Workbook Content Hardware Management in Windows Server 2008 comprises a set of features designed to improve management of server hardware. These features enable system administrators to securely manage remote server hardware across a firewall, using a standard Web servicebased protocol. Working with Baseboard Management Controller (BMC) hardware attached to a server that supports WSManagement, the Windows Hardware Management components can communicate with the remote system even if the Windows operating system has not yet booted or has failed. Windows Remote Management (WinRM) uses a new command-line tool, Winrm.cmd, to perform its operations. These operations include Get, Put, Invoke, and Enumerate. The command-line tool also has several switches to allow for remote operations, credentials, and hash tables. Windows Remote Management can utilize a WMI plug-in that exposes WMI classes, methods, and properties to Windows Remote Management. DISCUSS
Module Summary
Windows Server 2008 provides new tools, technologies, and installation options to improve the management experience. Initial Configuration Tasks guides an administrator through the process of configuring a new server. For local administration of a single server, Server Manager is an integrated MMC that offers IT professionals a seamless, integrated experience for adding, removing, and configuring server roles, role services, and features. It also acts as a portal for ongoing server management, monitoring, and operations, by exposing key management tasks based on server role, and providing access to advanced administration tools. Server Core provides a minimal installation option for certain server roles, offering a smaller server footprint and attack surface to reduce management and servicing needs. Windows PowerShell is a new command-line shell and task-based scripting technology that gives IT administrators comprehensive control and automation of system administration tasks, increasing administrator productivity. Windows PowerShell includes numerous system administration utilities, consistent syntax and naming conventions, and improved navigation of common management data such as the registry, certificate store, or WMI. Windows PowerShell also includes an intuitive scripting language specifically designed for IT administration.
Topic: Summary
Lesson 4: Windows Remote Management
72
Getting Started with Server Management in Windows Server 2008
Windows Remote Management hardware management is intended to reduce overall IT administration costs by providing monitoring and control of remote hardware components, especially before the system is started and after an operating system failure. In this module you learned how to: Identify the Server Management improvements that have been made to Windows Server 2008. Identify when to use Server Core installation and list the benefits to your organization of implementing Server Core. Explain how Windows PowerShell can simplify server administration. Explain Windows Remote Management and list the benefits to your organization of implementing Windows Remote Management.
Follow these links to access the additional content for this course: Link to Expand content: Course 5939, Introducing Server Management in Microsoft Windows Server Code Name "Longhorn" (Beta 3). This course is available here: https://www.microsoftelearning.com/eLearning/courseDetail.aspx?courseId=76475 Link to Apply content: TechNet Virtual Lab, Managing Windows Server 2008 Beta 3 using New Management Technologies. This lab is available here: http://msevents.microsoft.com/CUI/WebCastEventDetails.aspx?EventID=1032345257&EventCa tegory=3&culture=en-US&CountryCode=US
There are no assignments in this course.
Topic: Summary
Lesson 4: Windows Remote Management
Vous aimerez peut-être aussi
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (895)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (400)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (588)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (74)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (345)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2259)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (121)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- Question #1: Ans: BDocument25 pagesQuestion #1: Ans: BHiren KumarPas encore d'évaluation
- Userguide Motorola Mototrbo Dr3000Document31 pagesUserguide Motorola Mototrbo Dr3000dot16ePas encore d'évaluation
- 1014-Form4 HelpDocument2 pages1014-Form4 Helpapi-247514190Pas encore d'évaluation
- Integration WorkbookDocument20 pagesIntegration WorkbookShekhar GadewarPas encore d'évaluation
- Amicus With PIC18F25K22 and DS30 BootloaderDocument3 pagesAmicus With PIC18F25K22 and DS30 BootloaderHectorLopez100% (2)
- Blackout Survival GuideDocument24 pagesBlackout Survival GuideGeorgetta88% (17)
- Pepsi Lipton Number WorkDocument16 pagesPepsi Lipton Number WorkSachin KamraPas encore d'évaluation
- Facture PDFDocument2 pagesFacture PDFVinsonPas encore d'évaluation
- SubNetting Practice LabDocument3 pagesSubNetting Practice LabOdoch HerbertPas encore d'évaluation
- Red Hat Linux 6.2 Reference GuideDocument375 pagesRed Hat Linux 6.2 Reference GuideNikunjBhattPas encore d'évaluation
- Process-to-Process Delivery: Udp and TCP: (Chapter 23)Document41 pagesProcess-to-Process Delivery: Udp and TCP: (Chapter 23)Giri Tharan RockPas encore d'évaluation
- Assignment02 NahidurDocument5 pagesAssignment02 NahidurMD Nahidur RahmanPas encore d'évaluation
- Schneider Electric Wiser Energy MGMT SystemDocument2 pagesSchneider Electric Wiser Energy MGMT SystemebrahimPas encore d'évaluation
- Cisco San PDFDocument364 pagesCisco San PDFhema_rao2250100% (1)
- HNS Level III COC Knowledge Test-1Document8 pagesHNS Level III COC Knowledge Test-1Alem Girma100% (1)
- VoIP Testing With TEMS Investigation PC-based ClientsDocument18 pagesVoIP Testing With TEMS Investigation PC-based ClientsDavid Fonseca VieiraPas encore d'évaluation
- Krishna Avtar Part-4 of 8 (Gurmukhi, Punjabi Meanings)Document53 pagesKrishna Avtar Part-4 of 8 (Gurmukhi, Punjabi Meanings)nss1234567890Pas encore d'évaluation
- Delta Airlines Style Guide 2009Document127 pagesDelta Airlines Style Guide 2009dktakahashi25% (4)
- Application Layer: A Note On The Use of These PPT SlidesDocument76 pagesApplication Layer: A Note On The Use of These PPT SlidesShobhit GuptaPas encore d'évaluation
- #MH11 Day 1 May 3 - Healthcare Twitter TranscriptDocument93 pages#MH11 Day 1 May 3 - Healthcare Twitter TranscriptericasholtPas encore d'évaluation
- VERITAS Cluster Server Commands: VCS OperationsDocument3 pagesVERITAS Cluster Server Commands: VCS Operationsdeepaksaini420Pas encore d'évaluation
- In The Matter Of:: Tricia Mezzacappa,: Requester:: V.: Docket No.: AP 2020-1482: West Easton Borough,: RespondentDocument3 pagesIn The Matter Of:: Tricia Mezzacappa,: Requester:: V.: Docket No.: AP 2020-1482: West Easton Borough,: RespondentTricia PhillipsPas encore d'évaluation
- 8.1 Software Replacement Procedure (For PLC)Document17 pages8.1 Software Replacement Procedure (For PLC)LEVENT ÖZGALPas encore d'évaluation
- New UrDocument13 pagesNew UrHoney Thakur100% (1)
- DFL-260E+860E A1 QIG v1.00 PDFDocument32 pagesDFL-260E+860E A1 QIG v1.00 PDFFurio91Pas encore d'évaluation
- RTA Punto Revue TechniqueDocument194 pagesRTA Punto Revue TechniqueJustine DuboretPas encore d'évaluation
- Evolution of Social Media MarketingDocument6 pagesEvolution of Social Media MarketingAmanda MeisandyPas encore d'évaluation
- Ds-2Cd2047G1-L 4 MP Colorvu Fixed Bullet Network CameraDocument5 pagesDs-2Cd2047G1-L 4 MP Colorvu Fixed Bullet Network CameraNazih Ben JemaaPas encore d'évaluation
- Format of Thesis Report WritingDocument5 pagesFormat of Thesis Report Writinggj9fmkqd100% (1)
- The Torrent Guide For Everyone - 24 Pages PDFDocument24 pagesThe Torrent Guide For Everyone - 24 Pages PDFGlen GadowskiPas encore d'évaluation