Académique Documents
Professionnel Documents
Culture Documents
A Grid-Based Mobile Agent Collaborative Virtual Environment
Transféré par
John SmithDescription originale:
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
A Grid-Based Mobile Agent Collaborative Virtual Environment
Transféré par
John SmithDroits d'auteur :
Formats disponibles
A Grid-Based Mobile Agent Collaborative Virtual Environment
Hoon Kang Neo1 , QingPing Lin2 and Kim Meow Liew1
1 2
School of Mechanical & Aerospace Engineering
Information Communication Institute of Singapore, School of Electrical & Electronic Engineering Nanyang Technological University 50 Nanyang Avenue, Singapore 639798. Emails: mhkneo@ntu.edu.sg, iqplin@ntu.edu.sg, mkmliew@ntu.edu.sg
Abstract
This paper describes a large-scale collaborative virtual environment architecture that has the capability of scaling across multiple geographically dispersed resources. The architecture consists of distributed mobile agents working cooperatively in supporting and managing the virtual environments. The mobile agents tasks include managing persistency and consistency of the virtual worlds, maintaining reliability and efciency of user interactions, ensuring security and integrity of data and systems, and so on. The mobile agents are autonomous and has the ability of migrating among hosts to maximize resource utilizations. Grid technologies and concepts are introduced into the architecture. These improvements allow the mobile agents to execute and communicate securely in multiple administrative domains. Grid-based scheduling components and polices are integrated to provide intelligent resource optimizations. Furthermore, a better load-balancing can be achieved by utilizing additional or more accurate information like data-user proximity and hosts workload invariance etc. The result will be a more scalable and robust mobile agent architecture.
or received simultaneously. However, in most practical implementations of Large-scale Collaborative Virtual Environments (LCVE), this feat requires tremendous amount of network capacity and computational power. Most LCVE systems are distributed in order to overcome the limited resources of a single hosting entity. However, when a LCVE system is implemented in distributed fashion, scalability is one of the primary problems. Large amount of communications are required between the distributed components in order to coordinate and share data. The amount of communication can increase exponentially as the number of users or size of virtual world grow. Although widely researched, scalability has always remained as one of the main challenges in LCVE systems. Over the years, various approaches and techniques have been researched and developed. They can be vaguely grouped into two classes: interest management and communication architecture. In interest management, the spatial division of virtual space and introduction of entity auras are among some of the popular methods. They are aimed at reducing the message exchanges without harming the shared context and interactive performance [8]. On the other hand, the communication architecture approach adopts different network topologies and protocols in dealing with scalability issues. Peer-to-peer, federated peer-to-peer [12], clientserver, and multicasting [6] are among some of the popular methods. In peer-to-peer architectures, databases are usually duplicated entirely on all participating hosts to prevent workload and communication bottlenecks [10]. In clientserver architectures, workload are distributed among multiple servers. The work in [10] has highlighted a need for exible approach to the scalability problem. Mobile agent paradigm
1. Introduction
Collaborative Virtual Environment technology is used in numerous application domains for users to experience shared sense of space and presence. It provides additional dimensions of communications [13], offering users the ability to interact with each other in a common context [10]. The changes and information propagated are experienced
Proceedings of the 2005 International Conference on Cyberworlds (CW05) 0-7695-2378-1/05 $20.00 2005
IEEE
has been identied as the possible solution. It is based on the idea of mobile codes or processes that can migrate from one host to another, continuing its executions after the migrations [3]. These codes have the ability of migrating to hosts with the desired resources and services, which significantly increases the overall performance, parallelism and resilience of the system. The network trafc is reduced, and the components are less coupled and more robust [1]. Using a mobile agent oriented approach, the LCVE can be constructed using exible and agile agents. These agents are assigned with different and overlapping tasks like user interactions, system maintenances, and resource managements etc. They work cooperatively to maintain the virtual worlds and the system. The mobile agent approach also offers robustness through duplication of tasks and data, and increased responsiveness through strategic assignments of user interaction agents. A Mobile Agent based Collaborative Virtual Environment (MACVE) has been proposed in [10]. While Mobile Agent systems are exible and agile, the Grid will be able to provide additional reliability and scalability needed [2]. Grid tools and concepts have been introduced into the MACVE architecture in view the following practical needs: The ability to scale across multiple administrative domains as the workload surpasses capacity of a single hosting domain. To guarantee a reasonable and well-balanced level of service to users who are geographically dispersed. To have a reliable distributed resource discovery mechanism in the heterogeneous environment. The need for a uniform resource referencing or naming system in the heterogeneous environment. To have a reliable and standardized security where authorizations, authentications and policies enforcement can take place easily in multiple administrative domains. A common communication infrastructure and protocol between the components. The need for an appropriate Grid-based scheduling framework and algorithms.
consistencies, user interactions, scenes updating, and graphics rendering etc. Moreover, the agents are also tasked with resource discovery, scheduling, and monitoring roles. In this paper, we will take a brief look at ve main areas of the Grid-based MACVE architecture: 1. Mobile agent lookup services. 2. Grid-based mobile agent environment. 3. Resource discovery and monitoring. 4. Resource scheduling and load balancing. 5. Security.
2.1. Mobile Agent Lookup
One of the primary issues in large-scale mobile agent systems is determining the locations of agents. The system needs to have accurate and up-to-date knowledge of the locations in order to manage and operate efciently. This information is needed for tasks like message deliveries and resource scheduling. However, due the mobility of the agents and the dynamic nature of the Grid resources, keeping track of the agents locations can be difcult. There is no xed collection of hosts in the Grid-based MACVE environment. Hosts can join or leave the resource pool any time due to reasons like system crashes, network lost, system maintenances, and user quitting etc. Moreover, slow information propagation in the geographically dispersed and administratively diversied environment will contributed to incompatible views. As a result, contradicting decisions might be made by components of the system. The proposed solution is a distributed mobile agent lookup service. A distributed directory service will maintain and provide up-to-date information about the location of all the mobile agents in the Grid-based MACVE. Utilizing scalable and robust Peer-to-Peer distributed hash tables (DHTs), information are stored in different locations or nodes within the Grid-based MACVE environment. The node that stores the targeted data item can be located efciently using the mobile agents ID and one of the many DHT lookup or routing algorithms. Chord [15] is among the many P2P DHT algorithms explored in this work. In the Chord algorithm, the information nodes are virtually arranged in a ring geometry. The algorithm is based on a variant of consistent hashing [9], which allows Chord to adapt efciently as nodes leaves or join the network. Minimum rearrangement of data item is required when this happens. As pointed out in [15], with high probability, O(log2 N ) messages are needed to re-establish the necessary information when a node joins or leaves. On the other hand, consistent hashing also allows the Chord to load-balance efciently, with each node responsible for
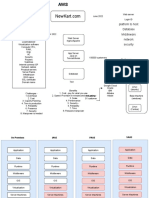
2. Grid-based MACVE Architecture
The Grid-based MACVE has the capability of scaling and adapting in a Grid environment. The mobile agents will be able to migrate among resources that are located in different administrative domains. The agents tasks includes LCVE supporting roles like maintaining database
Proceedings of the 2005 International Conference on Cyberworlds (CW05) 0-7695-2378-1/05 $20.00 2005
IEEE
(1 + )K/N keys where is proven to be of O(log N ) [15]. On top of scalability, graceful degrading and loadbalancing capability, the protocol is also characterized by its efcient lookup. Assuming a N-node Chord network, a query will be routed through a sequence of O(log N) nodes before its destination [15].
2.2. Grid-based Mobile Agent Environment
The mobile agent environments (MAEs) are essentially agent servers residing in all participating nodes in the MACVE Grid. They are holistic environments where the mobile agents can execute securely in. Besides providing execution management services, the environments also enables the mobile agents to do things like accessing local resources, migrating to other MAEs and sending messages etc. The following is a list of the services the MAEs provide: Resource access and control based on agents credentials and ownerships. Mobile agent management services which can be invoked by mobile agents on themselves or others. Mobile agent migration handling, where the mobile agents can do a sender-initiated and secured transfer to desired destinations. Two types of communication channel between the agents. One for data streaming and the other for message passing. Monitoring of agents execution, where information about individual agents and their resource usage can be provided. In the Grid-based MACVE, MAEs exists in the forms of WSRF (Web Service Resource Framework) Grid services. There will be MAE daemons running on every participating hosts. The MAE services and functions are exposed to the mobile agents and peer MAEs via the WSRF. Two main services are identied: the Message Service and Agent Service. An overview of the Grid-based MAE services can be found in gure 1. In the Grid-based MACVE environment, communication is a critical part of the system. The mobile agents need an efcient, reliable and secured communication infrastructure for purposes like maintaining the virtual worlds, managing resources and co-ordinations. This infrastructure has to support data streaming and messaging. A guaranteed level of service is needed where time-critical data is concerned. Figure 2 shows a simple messaging service in the Gridbased MACVE environment. The service is implemented Figure 2. Messaging Service. On the other hand, agent management tasks are covered by the Agent Service and Agent Manager components. The main tasks include: Send an agents code segment or class to remote destination. Receive an agents code segment or class. Launch or instantiate an agent locally. Pause a running agent. Resume a paused agent. Kill a running agent. Figure 1. Overview of MAE Services. in the form of WSRF Grid service. There are two main elements: the Message Manager and Message Service. The Message Manager is part of the MAE daemon, listening to and servicing requests from the stateless instances of Message Service. The Message Manager can located by a service instance during its creation, using the MAE Resource Home. A new instance of Message Service is created each time the service interface is invoked. Mobile agents will post messages to the local Message Manager. The message will be delivered straight to the receiver agent if it resides in the same host. Otherwise, the Message Manager will try to locate the destination using the mobile agent lookup service described in section 2.1.
Proceedings of the 2005 International Conference on Cyberworlds (CW05) 0-7695-2378-1/05 $20.00 2005
IEEE
The agent management portion of the architecture has an identical design with the messaging service. It is shown in gure 3. There are two elements: the Agent Manager and Agent Service. The Agent Service instances are stateless and reside in the service container. A new instance of the Agent Service is created at every invocation of the service interface. The new instance will locate the Agent Manager using the Resource Home. In gure 1, the return of the retrieve() result is done by another service call from the service provider (Host A) to the consumer (Host B). This scheme allows the process to avoid session timeout before the transaction completes. The amount of time it takes for searching and transferring agents depends on factors like size of agent database, network latency, and the size of agent class etc. Therefore we are unable to determine whether the Web Service session will timeout before the transaction nishes.
Figure 4. Information Services and Resource Discovery.
Figure 3. Agent Management.
Manager Agent will seek resource information from its peers residing on other VOs. Historical data are also stored in the Group Manager Agents, which can be used for more efcient and intelligence resource management. On the other hand, additional non-static information are gathered from distributed systems monitoring tools like the NWS and Ganglia. Information such as the predicted resource parameters from the NWS can be utilized in the scheduling and load balancing algorithms.
3. Resource Scheduling & Load Balancing
2.3. Resource Discovery and Monitoring
Resource discovery, in MACVEs context, means the detection of new nodes and services. On the other hand, resource monitoring also involves keeping watch on the status of the services, mobile agents, and the nodes. In the Grid-based MACVE, these information can come from a few sources: the Grid infrastructures Information Services, monitoring tools like Network Weather Service (NWS) [11] or Ganglia [4], and the mobile agents. In the Globus Toolkit 4.0 (GT4) [5] implementation, the main discovery and monitoring component of the toolkit is called the Monitoring & Discovery System 4 (MDS4). Index Services implemented within the MDS4 allows the discovery and monitoring of Grid services. To utilize this framework, an agent (the Group Manager Agent) is tasked to nd out and monitor the individual nodes resources conditions from the Index Services, as shown in gure below. In every Virtual Organization (VO), there will be a representative Index Service where the Group Manager will be subscribed to. When new services or resources are available, it is the Group Manager Agents job to seek and nd out more about the resource. If the need arises, the Group The problem of scheduling and load balancing in the Grid-based MACVE can be viewed as a simple case of trying to assign n number of mobile agents with different workloads, to m number of hosts with different capacities. Optimization schemes and algorithms can be utilized to do this. However, in the real world, things are much more complicated than this. It is obvious that the effectiveness of the scheduling and load balancing algorithms will depend on the accuracy of the capacities and workloads calculations. In the Grid environment, it is relatively easy to capture, through information services, a hosts static information such as CPU frequency, memory size, network bandwidth, disk space etc. However, these information cannot realistically represent a grid resources capacity because it is a shared environment. Moreover, the measurement of the workload of the individual agent will be a complex task. It might not be a worthwhile effort after all. The closest we can get to real measurements are through historical data from similar mobile agents. Similar method has been used in [16] and [14], where the predicted execution time of a task is the average execution time of previous similar tasks in the past.
Proceedings of the 2005 International Conference on Cyberworlds (CW05) 0-7695-2378-1/05 $20.00 2005
IEEE
Characterized by high migration cost of the Grid, we wanted to make sure that the performance gains would overshadow the migration penalties in any situation. Therefore, we are looking at adopting a scheduling strategy that gain maximum performance and at the same time minimizes the mobile agents movements. Load balancing via spread minimization, proposed by Kleinberg and Leighton in [7], is explored. The consistent load balancing used in [7] is motivated by the idea of consistent hashing [9] which minimize the changes to the environment during every adjustment. Furthermore, the dependencies between the mobile agents must be correctly captured to ensure the effectiveness of the scheduling and load balancing.
resources. This architecture is designed to be exible, autonomous and scalable. The development work for this architecture is still underway during the writing of this paper.
References
[1] W. R. Cockayne and M. Zyda. Mobile Agents. Manning Publications Co, 1997. [2] I. Foster, N. R. Jennings, and C. Kesselman. Brain meets brawn: Why grid and agents need each other. In Third International Joint Conference on Autonomous Agents and Multiagent Systems, volume 1, pages 815, 2004. [3] I. E. Foukarakis, A. I. Kostaridis, C. G. Biniaris, D. I. Kaklamani, and I. S. Venieris. Implementation of a mobile agent platform based on web services. In MATA, pages 190199, 2003. [4] Ganglia. Ganglia. http://ganglia.sourceforge.net/. [5] GT4. Globus toolkit 4.0. http://wwwunix.globus.org/toolkit/docs/development/4.0drafts/GT4Facts/index.html. [6] C. Joslin, T. D. Giacomo, and N. Magnenat-Thalmann. Collaborative virtual enivronments: From birth to standardization. IEEE Communication Magazine, Special Issue on Networked Virtual Environments, 42(4):6574, Apr 2004. [7] R. Kleinberg and T. Leighton. Consistent load balancing via spread minimization. In STOC 03: Proceedings of the thirty-fth annual ACM symposium on Theory of computing, pages 565574. ACM Press, 2003. [8] D. Lee, M. Lim, and S. Han. Atlas a scalable network framework for distributed virtual environments. In Proceeding of the 4th International Conference on Collaborative Virtual Environments, pages 4754, 2002. [9] D. M. Lewin. Consistent hashing and random trees: Algorithms for caching in distributed networks., 1998. Available at http://thesis.mit.edu/. [10] Z. Liang, L. Qingping, and C. T. Fook. Mobile agent-based architecture for large-scale cve. In CW, pages 6977, 2003. [11] NWS. Network weather service. http://nws.cs.ucsb.edu/. [12] S. Rooney, D. Bauer, and R. Deydier. A federated peerto-peer network game architecture. IEEE Communications Magazine, 42(5):11422, 2004. [13] S. Singhal and M. Zyda. Networked Virtual Environments Design and Implementation. Addison-Wesley, 1999. [14] W. Smith, I. T. Foster, and V. E. Taylor. Predicting application run times using historical information. In JSSPP, pages 122142, 1998. [15] I. Stoica, R. Morris, D. Liben-Nowell, D. R. Karger, M. F. Kaashoek, F. Dabek, and H. Balakrishnan. Chord: a scalable peer-to-peer lookup protocol for internet applications. IEEE/ACM Trans. Netw., 11(1):1732, 2003. [16] L. Yang, J. M. Schopf, and I. Foster. Conservative scheduling: Using predicted variance to improve scheduling decisions in dynamic environments. In Supercomputing 2003, Nov 2003.
4. Security
Transparent authentication, authorization and local policy enforcement is important when the MACVE scales across heterogeneous systems in multiple administrative domains. The ultimate goal of the system is to enable the agents to migrate freely among all the hosts they have permissions to. The Grid Security Infrastructure (GSI) from GT4 supports authentication, authorization and delegation using X.509 certicates and public keys. Authorization policy is congured both on the service and client side. Therefore, the services (Agent Service and Message Service) provided by all the participating nodes are implemented in the form of secured services. On the other hand, the consumer components (in Agent Manager, Message Manager, and Agent Service) will either have authorization mechanisms or use security descriptors. The messages exchanged between the services will be secured using GT4s transport-level security. The transport-level security utilizing X.509 proxy certicates is based on the modied HTTP over SSL protocol (HTTPs). One of the many security threats identied in the Gridbased MACVE environment is the hacking or stealing of the agent codes through methods like code reverse engineering and code modication. Code level protection can be enforced with code obfuscators like Bolands Crema and Jschrink by Eastrifge Technology. These obfuscators work mainly by removing unused code and data, and obfuscating symbolic names, replacing them with non-intuitive alternatives. The obfuscating process makes the code resilience to decompilations.
5. Conclusion
In this paper, we have introduced a Grid-based collaborative virtual environment architecture that has the capability of scaling reliably across multiple geographically dispersed
Proceedings of the 2005 International Conference on Cyberworlds (CW05) 0-7695-2378-1/05 $20.00 2005
IEEE
Vous aimerez peut-être aussi
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5795)
- Registration Rooms, Lobbies, and Portals Interconnecting Large-ScaleNetworked Virtual Environments and CollaborationsDocument1 pageRegistration Rooms, Lobbies, and Portals Interconnecting Large-ScaleNetworked Virtual Environments and CollaborationsJohn SmithPas encore d'évaluation
- Collaborative VEDocument7 pagesCollaborative VEJohn SmithPas encore d'évaluation
- AdapTIVE An Intelligent Virtual Environment and Its Application in ECommerceDocument7 pagesAdapTIVE An Intelligent Virtual Environment and Its Application in ECommerceJohn SmithPas encore d'évaluation
- A Local Perception Filter For Distributed Virtual EnvironmentsDocument8 pagesA Local Perception Filter For Distributed Virtual EnvironmentsJohn SmithPas encore d'évaluation
- A Collaborative Virtual Environment For Industrial TrainingDocument1 pageA Collaborative Virtual Environment For Industrial TrainingJohn SmithPas encore d'évaluation
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (588)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (74)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (895)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (400)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2259)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (266)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (121)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- ABAP - PO HistoryDocument4 pagesABAP - PO HistoryinasapPas encore d'évaluation
- Banggood IRF 530 PA Instructions V1.4Document16 pagesBanggood IRF 530 PA Instructions V1.4Jorge MarinPas encore d'évaluation
- Lecture 04 - Machine Language (FULL)Document25 pagesLecture 04 - Machine Language (FULL)Hunter HaggardPas encore d'évaluation
- Overview of JSP: JSP Technology: Module 2 - JSP and Controlling The Structure of Generated ServletsDocument14 pagesOverview of JSP: JSP Technology: Module 2 - JSP and Controlling The Structure of Generated ServletsNayana GowdaPas encore d'évaluation
- OopsDocument49 pagesOopssenthil2uinPas encore d'évaluation
- Hardware User Manual: Digital CinemaDocument16 pagesHardware User Manual: Digital CinemaHendovaAlAzharPas encore d'évaluation
- Platform Support Ansys 14.5 Detailed SummaryDocument22 pagesPlatform Support Ansys 14.5 Detailed SummaryklashincoviskyPas encore d'évaluation
- How To Install SecurePlatform - Gaia From A USB Device On Check Point Appliance and Open ServersDocument3 pagesHow To Install SecurePlatform - Gaia From A USB Device On Check Point Appliance and Open ServersshikhaxohebkhanPas encore d'évaluation
- DeadlockDocument21 pagesDeadlockRam TamangPas encore d'évaluation
- Set Up Cisco ISE in A Distributed Environment: Cisco Identity Services Engine Administrator Guide, Release 2.1Document26 pagesSet Up Cisco ISE in A Distributed Environment: Cisco Identity Services Engine Administrator Guide, Release 2.1juan carlos alvarez rojasPas encore d'évaluation
- Vlsi-Chip Input and Output CircuitsDocument27 pagesVlsi-Chip Input and Output CircuitsSrilatha KolliPas encore d'évaluation
- Configuration PDFDocument118 pagesConfiguration PDFthassio gomesPas encore d'évaluation
- Using The AT89C2051 MCU As Virtual MachineDocument11 pagesUsing The AT89C2051 MCU As Virtual MachineplcmanaPas encore d'évaluation
- DCV NexusDocument217 pagesDCV NexusRatheesh Ravindran100% (1)
- Analysis of Quality of Object Oriented Systems Using Object Oriented MetricsDocument4 pagesAnalysis of Quality of Object Oriented Systems Using Object Oriented Metricsmeena meenakshiPas encore d'évaluation
- Software Manual-Soxtherm Manager SX PCDocument44 pagesSoftware Manual-Soxtherm Manager SX PCAnonymous SiO8gwwRto100% (1)
- SANGFOR - WANO - v9.5.3 - Associate - 05 - IPSEC VPN Multiline and Certificate Based AuthDocument33 pagesSANGFOR - WANO - v9.5.3 - Associate - 05 - IPSEC VPN Multiline and Certificate Based Authwendy yohanesPas encore d'évaluation
- 8051 Instruction SetDocument98 pages8051 Instruction SetSmt.N.Vasantha Gowri Assistant ProfessorPas encore d'évaluation
- DSP Attainment 2020-2021.Xlsx Send - XLSX TestDocument41 pagesDSP Attainment 2020-2021.Xlsx Send - XLSX TestManjula BMPas encore d'évaluation
- Laf 630 - 800 - 1250 - 1600 DC - 0740801008Document36 pagesLaf 630 - 800 - 1250 - 1600 DC - 0740801008BaptistePas encore d'évaluation
- Cisco Secure Network Server Ordering GuideDocument7 pagesCisco Secure Network Server Ordering GuideAlonso Sal y RosasPas encore d'évaluation
- IVMS-4200 AC Client Software Datasheet V1.0.1 20190712Document4 pagesIVMS-4200 AC Client Software Datasheet V1.0.1 20190712HEHHPas encore d'évaluation
- RTL 8186Document50 pagesRTL 8186Maria Alejandra DalcolmoPas encore d'évaluation
- ManualDocument3 pagesManualThawin LaithongPas encore d'évaluation
- Yamaha rx-v530 rx-v430 SCHDocument59 pagesYamaha rx-v530 rx-v430 SCHJulio Alberto Cabrera RodriguezPas encore d'évaluation
- Data TypesDocument13 pagesData TypesIshaanPas encore d'évaluation
- Platform To Host Database Middleware Network Security: Data CenterDocument32 pagesPlatform To Host Database Middleware Network Security: Data CenterDinesh SehgalPas encore d'évaluation
- Vibration Analysis For Large-Scale Wind Turbine Blade Bearing Fault Detection With An Empirical Wavelet Thresholding MethodDocument24 pagesVibration Analysis For Large-Scale Wind Turbine Blade Bearing Fault Detection With An Empirical Wavelet Thresholding MethodAkash RockPas encore d'évaluation
- Webinar - Log/File Outputs: Processes - /var/log/dme/logDocument6 pagesWebinar - Log/File Outputs: Processes - /var/log/dme/logBhudev Kumar SahuPas encore d'évaluation
- Esquire sm5Document21 pagesEsquire sm5mishanama85Pas encore d'évaluation