Académique Documents
Professionnel Documents
Culture Documents
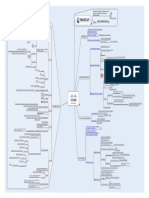
MindCert Wireshark MindMap
Transféré par
acehussainDescription originale:
Titre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
MindCert Wireshark MindMap
Transféré par
acehussainDroits d'auteur :
Formats disponibles
Motivation and Study Techniques to help you learn, remember, and pass your technical exams!
Can follow TCP, UDP, and SSL Streams
Cisco CISSP CEH More coming soon...
Wireshark can reassemble a specic session and display is in various formats
Great for debugging
Handy for viewing all the data about a stream in ASCII or RAW formats
Visit us
www.mindcert.com
Captures network traffic from the network interface.
Following Streams
Usage
Right click a TCP session and select Follow TCP Stream You can create a display filter from the selected stream
Wireshark is a network analyzer or sniffer
Can work for any connected interface Can capture in promiscuous mode Similar data format to TCPDUMP
Overview
Wireshark was formerly known as Ethereal Can open standard PCAP les for further investigation
Display lters restrict the output based on the ler
Larger capture file Capture everything
Capture lters are used to restrict the packets that are captured from the network
Reduces the size of the capture file If you are sure of the data to collect it is better than using a display filter
Display what you want to see
They are used on a capture le to show the data you want to see
Display filters can be defined and saved or just used when viewing a capture Capture filters can be defined and saved or used at the time of capture
Usage Usage
Define under the Capture menu item Use when capturing from an interface The display filter is shown in the main capture window Uses a different syntax to capture filters Only display packets sent to or received from 192.168.1.1 Same command ip.addr == 192.168.1.1 To or From ip.src == 192.168.1.1 or ip.dst == 192.168.1.1 Only display packets sent to 192.168.1.1 Only capture to or from a specific host
Wireshark Network Analyzer
host
host 192.168.1.1
Only capture from 192.168.1.1
To or From network
Only capture to or from a specific network net 192.168.1.0/24 Only captures from 192.168.1.0/24 Alternative
net 192.168.1.0 mask 255.255.255.0 ip.dst == 192.168.1.1 ip.src == 192.168.1.1 To (dst) host To (dst) dst host 192.168.1.1
Only capture to specific host
Only display packets sent from 192.168.1.1
Display Filters
From (src)
Capture Filters
From (src)
network
dst net 192.168.1.0/24
Only capture to specific network
Only display TCP port 80 packets Only display TCP port 80 or UDP port 53 packets
tcp.port eq 80 Ports
host
src host 192.168.1.1
Only capture from specific host
tcp.port eq 80 or udp.port eq 53 ip.addr != 192.168.1.1 arp
Display packets from all but 192.168.1.1
network Negating
src net 192.168.1.0/24
Only capture from specific network
Common Filters
Only display ARP traffic Only display ARP or DNS traffic
Common Filters
port 53
Only captures port 53 traffic To or From Only captures TCP ports 1-1024
arp or dns !arp Protocols port
tcp portrange 1-1024 dst port 80
Display all but ARP Display all apart from ARP and DNS Checks for POP passwords
Captures traffic destined to port 80 Captures traffic to port 80 or port 443 Only captures Telnet traffic to and from 192.168.1.1
!arp and !dns
dst port 80 or dst port 443
pop.request.command == PASS Useful ftp.request.command
tcp port 23 and host 192.168.1.1
Displays FTP commands including USER and PASS Displays all packets with the word PASS in them Handy for POP, IMAP and FTP Passwords
To negate a command use the not command before the filter Negating port not 53 not arp All but port 53 All traffic apart from ARP
frame contains 50:41:53:53
Only captures IP traffic Protocols ip Gets rid of layer 2 traffic ARP STP
Wireshark.mmap - 05/01/2010 - Andrew Mason
Vous aimerez peut-être aussi
- Powershell Cheat Sheet: Setting Security PolicyDocument2 pagesPowershell Cheat Sheet: Setting Security Policybf10l2Pas encore d'évaluation
- Layer MapDocument15 pagesLayer MapRodrigo PontesPas encore d'évaluation
- Network Segmentation Strategy A Complete Guide - 2020 EditionD'EverandNetwork Segmentation Strategy A Complete Guide - 2020 EditionPas encore d'évaluation
- CISSP Telecommunications and Network SecurityDocument1 pageCISSP Telecommunications and Network SecurityonlysubasPas encore d'évaluation
- Lesson 8: IPSecDocument61 pagesLesson 8: IPSecMahmmoud MahdiPas encore d'évaluation
- Security operations center A Complete Guide - 2019 EditionD'EverandSecurity operations center A Complete Guide - 2019 EditionPas encore d'évaluation
- Domain 1 PDFDocument22 pagesDomain 1 PDFKrish krishPas encore d'évaluation
- Cryptography, Network Security, and CyberlawDocument234 pagesCryptography, Network Security, and Cyberlaw1am17ec014 ashnal ahmedPas encore d'évaluation
- WildFire Administrator Guide-8.0Document189 pagesWildFire Administrator Guide-8.0Ryanb378Pas encore d'évaluation
- Network Documentation A Complete Guide - 2020 EditionD'EverandNetwork Documentation A Complete Guide - 2020 EditionPas encore d'évaluation
- File Integrity Monitoring Best PracticesDocument8 pagesFile Integrity Monitoring Best Practicestester checker100% (1)
- Lab Exercise: SubnettingDocument27 pagesLab Exercise: SubnettingMahmmoud MahdiPas encore d'évaluation
- Maturing Security Operations Centers A Complete Guide - 2021 EditionD'EverandMaturing Security Operations Centers A Complete Guide - 2021 EditionPas encore d'évaluation
- CHEAT SHEET PowerShell Commands For The MCSA 70Document4 pagesCHEAT SHEET PowerShell Commands For The MCSA 70Fletcher Mutukwa100% (1)
- MindCert Cisco IPsec MindMap PDFDocument1 pageMindCert Cisco IPsec MindMap PDFzinzinPas encore d'évaluation
- Cisco ChecklistDocument6 pagesCisco ChecklistDema PermanaPas encore d'évaluation
- ISO 9001: 2008 Certified CompanyDocument50 pagesISO 9001: 2008 Certified CompanyUnni KrishnanPas encore d'évaluation
- PowerShell Cheat SheetDocument2 pagesPowerShell Cheat SheetFederico MarzulloPas encore d'évaluation
- NShield Connect DsDocument2 pagesNShield Connect DssuhasinibPas encore d'évaluation
- Presented By: Intrusion Detection SysytemDocument15 pagesPresented By: Intrusion Detection SysytemRagala VishwatejaPas encore d'évaluation
- Chapter 1: Architectural Concepts Domain 1,2,6 NIST 800-145 Cloud Computing DefinitionDocument1 pageChapter 1: Architectural Concepts Domain 1,2,6 NIST 800-145 Cloud Computing DefinitionSherif_SalamhPas encore d'évaluation
- Mind MapDocument1 pageMind MapShu ShengPas encore d'évaluation
- CEH v9 Notes - Dads Man CaveDocument17 pagesCEH v9 Notes - Dads Man CaveJeshal PatelPas encore d'évaluation
- CCNA Security Module 1 100%Document4 pagesCCNA Security Module 1 100%Akbal Larios100% (1)
- MindCert Cisco IPsec MindMapDocument1 pageMindCert Cisco IPsec MindMapcpawan_69Pas encore d'évaluation
- Install DLP Forcepoint PDFDocument59 pagesInstall DLP Forcepoint PDFneoaltPas encore d'évaluation
- Networ SecurityDocument113 pagesNetwor Securityloffy hackerPas encore d'évaluation
- Encryption Cheat SheetDocument3 pagesEncryption Cheat SheetbabuPas encore d'évaluation
- Understanding How DNS WorksDocument8 pagesUnderstanding How DNS WorksEduardo Andrés Loaiza MataPas encore d'évaluation
- Lab10 - DirbusterDocument15 pagesLab10 - DirbusterSaw GyiPas encore d'évaluation
- Commands To Check Memory Usage On LinuxDocument5 pagesCommands To Check Memory Usage On LinuxAnonymous gfw31FXbLvPas encore d'évaluation
- Study Guide: Check Point Security AdministrationDocument20 pagesStudy Guide: Check Point Security Administrationchakki100% (1)
- Oracle Baseline Security ChecklistDocument15 pagesOracle Baseline Security ChecklistChidi OkerekePas encore d'évaluation
- Symantec Lab ExerciseDocument136 pagesSymantec Lab Exercisedsunte100% (1)
- Wireless Hacking and Penetratin TestingDocument81 pagesWireless Hacking and Penetratin TestingbabuPas encore d'évaluation
- CCNP Switch: Network ManagementDocument83 pagesCCNP Switch: Network ManagementJe RelPas encore d'évaluation
- Lab3 SE161942Document15 pagesLab3 SE161942Nguyen Giang Nam (K16 HCM)Pas encore d'évaluation
- DHCP Implementation Guide - 0.1Document18 pagesDHCP Implementation Guide - 0.1Manaf Al OqlahPas encore d'évaluation
- CEH NotesDocument7 pagesCEH NotesKelvin Danso EffahPas encore d'évaluation
- Toolkit Reference For The Microsoft Deployment Toolkit PDFDocument1 191 pagesToolkit Reference For The Microsoft Deployment Toolkit PDFAaron SemoPas encore d'évaluation
- Host HardeningDocument28 pagesHost HardeningYonGodePas encore d'évaluation
- Internet Gateway Best PracticesDocument38 pagesInternet Gateway Best PracticesDavid XinPas encore d'évaluation
- Experience With Tripwire: Using Integrity Checkers For Intrusion DetectionDocument37 pagesExperience With Tripwire: Using Integrity Checkers For Intrusion DetectionSiva TejaPas encore d'évaluation
- Tripwire ReportDocument34 pagesTripwire ReportSanjeev Yadav75% (4)
- Submitted By-Anurag Deyasi Information Technology SSEC, BhilaiDocument39 pagesSubmitted By-Anurag Deyasi Information Technology SSEC, BhilaiAnonymous kbmKQLe0JPas encore d'évaluation
- Configuring F5 Advanced WAF (Previously Licensed As ASM)Document6 pagesConfiguring F5 Advanced WAF (Previously Licensed As ASM)IMEDITA INDIAPas encore d'évaluation
- Arp ProtocolDocument38 pagesArp ProtocolArivazhagan ChinnamadhuPas encore d'évaluation
- Information Security Policies - TEMPLATEDocument659 pagesInformation Security Policies - TEMPLATEugwakPas encore d'évaluation
- CPPMDocument28 pagesCPPMhem777Pas encore d'évaluation
- CCNA Sec 01Document11 pagesCCNA Sec 01Aissa ChaabiPas encore d'évaluation
- Domain 4 Communication and Network SecurityDocument9 pagesDomain 4 Communication and Network Securitysrivatsan_ecePas encore d'évaluation
- ESA-Resources Cheat SheetDocument5 pagesESA-Resources Cheat SheetSanjin ZuhricPas encore d'évaluation
- Gao It AuditDocument601 pagesGao It AuditbenjaminbofPas encore d'évaluation
- Cybrary SOC Analyst Level 1 Syllabus 1Document10 pagesCybrary SOC Analyst Level 1 Syllabus 1Mohana DatlaPas encore d'évaluation
- Data Center Topology With Cisco Nexus, HP Virtual Connect and VMware - Andrea DaineseDocument1 pageData Center Topology With Cisco Nexus, HP Virtual Connect and VMware - Andrea DaineseacehussainPas encore d'évaluation
- Core DDI Adavanced Troubleshooting CDAT CourseDocument1 pageCore DDI Adavanced Troubleshooting CDAT CourseacehussainPas encore d'évaluation
- Connecting An External Entity To Cisco ACI (External L3Out) - Andrea DaineseDocument1 pageConnecting An External Entity To Cisco ACI (External L3Out) - Andrea DaineseacehussainPas encore d'évaluation
- Dynamic DNS Configuration For OpenDNS - DynDNS On Cisco IOS Routers - Andrea DaineseDocument1 pageDynamic DNS Configuration For OpenDNS - DynDNS On Cisco IOS Routers - Andrea DaineseacehussainPas encore d'évaluation
- NICABM LindaGraham Brain2014Document21 pagesNICABM LindaGraham Brain2014acehussainPas encore d'évaluation
- NSX 63 TroubleshootingDocument232 pagesNSX 63 TroubleshootingacehussainPas encore d'évaluation
- NICABM JohnArden Brain2014Document22 pagesNICABM JohnArden Brain2014acehussain100% (1)
- NICABM BruceLipton Brain2014Document34 pagesNICABM BruceLipton Brain2014acehussainPas encore d'évaluation
- ISE TACACS+ Configuration Guide For Cisco ASA: Secure Access How-To User SeriesDocument22 pagesISE TACACS+ Configuration Guide For Cisco ASA: Secure Access How-To User SeriesacehussainPas encore d'évaluation
- NICABM RickHanson Brain2014 QuickStartDocument11 pagesNICABM RickHanson Brain2014 QuickStartacehussain100% (1)
- NICABM DanielAmen Brain2014 QuickStartDocument8 pagesNICABM DanielAmen Brain2014 QuickStartacehussainPas encore d'évaluation
- NICABM HelenFisher Brain2014 v2Document29 pagesNICABM HelenFisher Brain2014 v2acehussainPas encore d'évaluation
- NICABM RickHanson Brain2014Document31 pagesNICABM RickHanson Brain2014acehussain100% (3)
- How-To 89 CA-signed PxGridISEnode CAsigned PxGridclientDocument22 pagesHow-To 89 CA-signed PxGridISEnode CAsigned PxGridclientacehussainPas encore d'évaluation
- NICABM BruceLiptonQS Brain2014Document11 pagesNICABM BruceLiptonQS Brain2014acehussainPas encore d'évaluation
- Ise Content TableDocument12 pagesIse Content TableacehussainPas encore d'évaluation
- B Ise InstallationGuide21 Chapter 0101Document14 pagesB Ise InstallationGuide21 Chapter 0101acehussainPas encore d'évaluation
- How-To 89 CA-signed PxGridISEnode CAsigned PxGridclientDocument22 pagesHow-To 89 CA-signed PxGridISEnode CAsigned PxGridclientacehussainPas encore d'évaluation
- HowTo-30-IsE Profiling Design GuideDocument142 pagesHowTo-30-IsE Profiling Design GuideacehussainPas encore d'évaluation
- Brkcol 1985Document93 pagesBrkcol 1985acehussainPas encore d'évaluation
- Renaissance Securities (Cyprus) Limited Professional Clients & Eligible CounterpartiesDocument34 pagesRenaissance Securities (Cyprus) Limited Professional Clients & Eligible CounterpartiesacehussainPas encore d'évaluation
- 1 0 EAP TLSv2WhitePaperDocument88 pages1 0 EAP TLSv2WhitePaperacehussainPas encore d'évaluation
- L3 VPNConDocument81 pagesL3 VPNConacehussainPas encore d'évaluation
- Clarety PID TemplateDocument29 pagesClarety PID TemplateHarshal ChoksiPas encore d'évaluation
- EDU CC 70405 ch04 - TakeawayDocument15 pagesEDU CC 70405 ch04 - TakeawayMES BetisePas encore d'évaluation
- 15.1.3 Lab - Path Control Using PBRDocument14 pages15.1.3 Lab - Path Control Using PBRjosePas encore d'évaluation
- IP Packet Switching: COS 461: Computer Networks Spring 2006 (MW 1:30-2:50 in Friend 109)Document35 pagesIP Packet Switching: COS 461: Computer Networks Spring 2006 (MW 1:30-2:50 in Friend 109)ajazahmednet3946Pas encore d'évaluation
- Dynamic Host Configuration Protocol::, Modified by Prof. M. VeeraraghavanDocument39 pagesDynamic Host Configuration Protocol::, Modified by Prof. M. VeeraraghavanPablo Lorenzo Muños SanchesPas encore d'évaluation
- VPC LabDocument4 pagesVPC LabsaketsjPas encore d'évaluation
- Getting Started With Aws in NodeDocument137 pagesGetting Started With Aws in Node8detectPas encore d'évaluation
- LogDocument20 pagesLogNugroho Hade YuntaPas encore d'évaluation
- CHAPTER ONE MPLS FundamentalsDocument23 pagesCHAPTER ONE MPLS Fundamentalstienpq150987Pas encore d'évaluation
- Ip Rule Discard PostroutingDocument43 pagesIp Rule Discard Postroutinglamkakaka100% (1)
- ITM 6.1 Firewall ImplementaionDocument9 pagesITM 6.1 Firewall ImplementaionAliPas encore d'évaluation
- GPON Multicast-MVR Configuration and TroubleshootingDocument16 pagesGPON Multicast-MVR Configuration and Troubleshootingrico orensePas encore d'évaluation
- CEH Port NumbersDocument37 pagesCEH Port Numberskumusha123Pas encore d'évaluation
- Datasheet Maipu SM3120-Series 20161011Document11 pagesDatasheet Maipu SM3120-Series 20161011Ismael Ali AbdoulayePas encore d'évaluation
- 3PAR RDA Network DocumentDocument4 pages3PAR RDA Network DocumentGolamPas encore d'évaluation
- OSPF TroubleshootingDocument93 pagesOSPF TroubleshootingAnupama267100% (1)
- Huawei CloudEngine S5736-S Series Multi-GE Switches DatasheetDocument29 pagesHuawei CloudEngine S5736-S Series Multi-GE Switches DatasheetFABIO VICTORINOPas encore d'évaluation
- Outlook For Cloud Security PDFDocument32 pagesOutlook For Cloud Security PDFscott tangPas encore d'évaluation
- Linode: A Developer's ParadiseDocument4 pagesLinode: A Developer's ParadiseJohn CenaPas encore d'évaluation
- 331 Study 1Document6 pages331 Study 1kossydaniel2021Pas encore d'évaluation
- BIND 9 DevelopmentHuntOARC32Document38 pagesBIND 9 DevelopmentHuntOARC32Nb A DungPas encore d'évaluation
- Adsl Router User ManualDocument34 pagesAdsl Router User ManualRolando NoroñaPas encore d'évaluation
- Chapter 10: Application Layer: Instructor MaterialsDocument39 pagesChapter 10: Application Layer: Instructor MaterialsleyleyPas encore d'évaluation
- 001 Vlan LinkstarDocument3 pages001 Vlan Linkstargerson846Pas encore d'évaluation
- 340 - Questions - CCNA - CCNA 200-301 - Billy CalvertDocument176 pages340 - Questions - CCNA - CCNA 200-301 - Billy Calvertjrchangir89100% (4)
- Cisco Data Center Spine-And-Leaf Architecture - Design Overview White PaperDocument17 pagesCisco Data Center Spine-And-Leaf Architecture - Design Overview White PaperAsifPas encore d'évaluation
- NSX 63 TroubleshootingDocument238 pagesNSX 63 TroubleshootingAlessandroPas encore d'évaluation
- Modem vs. RouterDocument2 pagesModem vs. RouterPappu KhanPas encore d'évaluation
- Cloud - Computing UNIT-3 Material .Document17 pagesCloud - Computing UNIT-3 Material .kavists20Pas encore d'évaluation
- AWS Training ObjectivesDocument3 pagesAWS Training Objectivespdvprasad_obieePas encore d'évaluation
- Midterm Exam - Attempt ReviewDocument14 pagesMidterm Exam - Attempt Reviewkatherine anne ortiz100% (1)