Académique Documents
Professionnel Documents
Culture Documents
Cisco Exam
Transféré par
Bart WetzelsDescription originale:
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Cisco Exam
Transféré par
Bart WetzelsDroits d'auteur :
Formats disponibles
Q.1 Which command is used to view the RIP routing protocol settings and configuration?
show version show ip route show interface show ip protocols
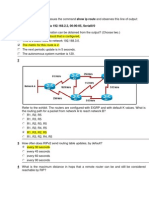
Q.2 Refer to the exhibit. What is the maximum number of RIP routers that could separate HostA and HostB and still leave the hosts with connectivity to each other? 14 15 16 17
Q.3 In which situation would a company register for its own autonomous system number (ASN)? when the company's ISP adds connection points to the Internet when additional routers are added to the corporate internetwork when more than one interior routing protocol is used when the company uses two or more ISPs
Q.4 Consider this routing table entry R 172.16.1.0/24 [120/1] via 200.1.1.1 00:00:27 Serial0/1 What type of route is this? a static route a default route a RIP route an OSPF route an EIGRP route a directly-connected route
Q.5 What is the difference between interior and exterior routing protocols? Exterior routing protocols are only used by large ISPs. Interior routing protocols are used by small ISPs. Interior routing protocols are used to route on the Internet. Exterior routing protocols are used inside organizations. Exterior routing protocols are used to administer a single autonomous system. Interior routing protocols are used to administer several domains.
Interior routing protocols are used to communicate within a single autonomous system. Exterior routing protocols are used to communicate between multiple autonomous systems.
Q.6 What information is included in RIPv2 routing updates that is not included in RIPv1 updates? metric subnet mask area identification hop count autonomous system number
Q.7 Which routing protocol is used to exchange data between two different ISPs? BGP EIGRP OSPF RIP v2
Q.8 Refer to the exhibit. Which configuration command or commands contributed to the output that is shown? routerA(config-router)# no version 2 routerA(config)# interface fa0/0 routerA(config-if)# ip address 172.19.0.0 255.255.0.0 routerA(config-router)# network 192.168.3.0 routerA(config)# no ip default-gateway
Q.9 Refer to the exhibit. If all routers are running RIP and network 10.0.0.0 goes down, when will R3 learn that the network is no longer available? in 30 seconds in 60 seconds in 90 seconds Immediately
Q.10 What statement is true regarding an AS number? AS numbers are controlled and registered for Internet use. Interior routing protocols require registered AS numbers. ISPs require all customers to have registered AS numbers. All routers at an ISP must be assigned the same AS number. Q.11 What is the purpose of the network command used when configuring RIP? to specify whether RIPv1 or RIPv2 will be used as the routing protocol to allow the router to monitor RIP updates that occur on other routers to identify which networks on the router will send and receive RIP updates to configure the IP address on an interface that will use RIP to identify all of the remote networks that should be reachable from the router
Q.12 Which command would a network administrator use to determine if the routers in an enterprise have learned about a newly added network? router# show ip address router# show ip route router# show ip networks router# show ip interface brief router# debug ip protocol router# debug rip update
Q.13 What is the purpose of a routing protocol? It is used to build and maintain ARP tables. It provides a method for segmenting and reassembling data packets. It allows an administrator to devise an addressing scheme for the network. It allows a router to share information about known networks with other routers. It provides a procedure for encoding and decoding data into bits for packet forwarding.
Q.14 What device enables an ISP to connect with other ISPs to transfer data? border gateway router DSLAM web server interior router
Q.15 Which command will display RIP routing updates as they are sent and received? show ip route show ip rip debug ip rip show ip protocols show ip rip database
Q.16 Which part of an IP packet does the router use to make routing decisions? source IP address source MAC address destination IP address destination MAC address
Q.17 What two types of businesses would benefit from registering as their own autonomous systems? (Choose two.) a home business with one ISP connection a global business with connections to multiple local ISPs a medium-sized nationwide business with Internet connectivity through different ISPs a large enterprise with two connections to the same ISP a small ISP with a single Internet connection through a larger ISP
Q.18 Which command will display RIP activity as it occurs on a router? debug ip rip show ip route show ip interface show ip protocols debug ip rip config show ip rip database
Q.19 Why is fast convergence desirable in networks that use dynamic routing protocols? Routers will not allow packets to be forwarded until the network has converged. Hosts are unable to access their gateway until the network has converged. Routers may make incorrect forwarding decisions until the network has converged. Routers will not allow configuration changes to be made until the network has converged.
Q.20 Which two statements describe static routes? (Choose two.) They are created in interface configuration mode. They require manual reconfiguration to accommodate network changes. They automatically become the default gateway of the router. They are identified in the routing table with the prefix S
They are automatically updated whenever an interface is reconfigured or shutdown.
Q.21 Which two statements or sets of statements describe differences between link-state and distance vector routing protocols? (Choose two.) Link-state routing protocols routinely use more bandwidth for updates than do distance vector routing protocols. Distance vector routing protocols update all routers at one time. Link-state routing protocols update one router at a time. Link-state routers only know about directly connected routers. Distance vector routers know about every router in the network. Link-state routing protocols update when a change is made. A network using distance vector routing protocols only updates at a specific interval. Distance vector routing protocols have limited information about the entire network. Link state routing protocols know about all routers in the network. In case of similar topologies, networks using link-state routing protocols typically converge more rapidly than do networks using distance vector routing protocols.
Q.22 Which protocol is an exterior routing protocol? BGP EIGRP OSPF RIP
Q.23 Hosts on two separate subnets cannot communicate. The network administrator suspects a missing route in one of the routing tables. Which three commands can be used to help troubleshoot Layer 3 connectivity issues? (Choose three.) Ping show arp Traceroute show ip route show interface show cdp neighbor detail
Q.24 What term refers to a group of networks that uses the same internal routing policies and is controlled by a single administrative authority? Internet intranet virtual private network autonomous system
Q.1 Which two statements are true about the OSI and TCP/IP models? (Choose two.) The two bottom layers of the TCP/IP model make up the bottom layer of the OSI model.
The TCP/IP model is a theoretical model and the OSI model is based on actual protocols. The OSI network layer is comparable to the Internet layer of the TCP/IP model. The TCP/IP model specifies protocols for the physical network interconnection. The TCP/IP model is based on four layers and the OSI model is based on seven layers.
Q.2 To meet customer expectations, an ISP must guarantee a level of service that is based on what two factors? (Choose two.) accessibility adaptability availability reliability scalability
Q.3 User1 is sending an e-mail to User2@cisco.com. What are two characteristics of the process of sending this data? (Choose two.) It utilizes TCP port 110. A TCP connection is established directly between the User1 and User2 client computers in order to send the e-mail message. It utilizes a store and forward process. The same application layer protocol is used to send the e-mail and retrieve it from the destination server. SMTP is used to send the e-mail message to the mail servers.
Q.4 Refer to the exhibit. Host1 is in the process of setting up a TCP session with Host2. Host1 has sent a SYN message to begin session establishment. What happens next? Host1 sends an ACK message to Host2. Host1 sends a SYN message to Host2. Host1 sends a SYN-ACK message to Host2. Host2 sends an ACK message to Host1. Host2 sends a SYN message to Host1. Host2 sends a SYN-ACK message to Host1.
Q.5 What are three characteristics of network reliability? (Choose three.) Redundant hardware provides enhanced reliability. Reliability is measured as a percent. Reliability is the responsibility of the ISP customers. Fault tolerance is a measure of reliability.
The longer the MTBF, the greater the reliability.
Q.6 Which two statements describe the FTP protocol? (Choose two.) It uses well-known port 23. The protocol interpreter is responsible for the data transfer function. In passive data connections, the FTP client initiates the transfer of data. It requires two connections between client and server. FTP servers open a well-known port on the client machine.
Q.7 What is the function of the TCP three-way handshake? It enables the synchronization of port numbers between source and destination hosts. It immediately triggers the retransmission of lost data. It synchronizes both ends of a connection by allowing both sides to agree upon initial sequence numbers. It identifies the destination application on the receiving host.
Q.8 What are three characteristics of HTTPS? (Choose three.) It uses a different client request-server response process than HTTP uses. It specifies additional rules for passing data between the application and data link layers. It supports authentication. It allows more simultaneous connections than HTTP allows. It encrypts packets with SSL. It requires additional server processing time.
Q.9 Which DNS zone resolves an IP address to a qualified domain name? dynamic lookup forward lookup resolution lookup reverse lookup
Q.10 What type of update allows client computers to register and update their resource records with a DNS server whenever changes occur? dynamic zone transfer local recursive query root domain query top-level domain query
Q.11 Refer to the exhibit. Which two statements are true about this file? (Choose two.) If the gateway address changes, the file will be updated dynamically. The command ping fileserv will use IP address 172.16.5.10. If the ping www.cisco.com command is issued, the file will be checked for the Cisco web server IP address before DNS is queried. The file must be created by the user if it is to be used by a workstation. Name to IP address mappings are added to the file after they are received from DNS.
Q.12 Which two tasks are the responsibility of the local DNS server? (Choose two.) maintaining a large number of cached DNS entries maintaining the ISP server mapping name-to-IP addresses for internal hosts forwarding name resolution requests to a caching-only server forwarding all name resolution requests to root servers on the Internet
Q.13 What are three unique characteristics of UDP? (Choose three.) connection oriented full-duplex operation low overhead no flow control no error-recovery function reliable transmission
Q.14 A manufacturing company is looking into subscribing to services from a new ISP. The company requires hosted world wide web, file transfer, and e-mail services. Which three protocols represent the key application services that are required by the company? (Choose three.) FTP HTTP ICMP PPP Telnet
SMTP
Q.15 Which two options correctly match protocol and well-known port number? (Choose two.) DNS - 25 FTP - 110 HTTP - 80 POP3 - 25 SMTP - 25
Q.16 Within TCP, what combination makes up a socket pair? source port with destination port source IP address with destination port source IP address and destination IP address source IP address and port with a destination IP address and port
Q.17 Which protocol is used to send e-mail, either from a client to a server or from a server to another server? SNMP FTP SMTP HTTPS
Q.18 Refer to the exhibit. The PC is requesting HTTP data from the server. What is a valid representation of source and destination sockets for this request? Source - 192.168.1.17:80 ; Destination - 192.168.2.39:80 Source - 192.168.1.17:80 ; Destination - 192.168.2.39:1045 Source - 192.168.1.17:1045 ; Destination - 192.168.2.39:80 Source - 192.168.1.17:1045 ; Destination - 192.168.2.39:1061
Q.19 What type of DNS server is typically maintained by an ISP? caching-only root second-level top-level
Q.20 A client is communicating with a server on a different segment of the network. How does the server determine what service is being requested by the client? The server will apply the default service configured in directory services. The server will use ARP to discover the appropriate service from the local router. The server will send a request to the client asking for the appropriate service. The server will determine the appropriate service from the destination port field.
Q.21 When a host is communicating with multiple applications on the same server at the same time, which of the following will have the same value for each session? (Choose two.) IP address MAC address session number sequence number 1 Which AAA service reduces IT operating costs by providing detailed reporting and monitoring of network user behavior, and also by keeping a record of every access connection and device configuration change across the network? authentication accreditation accounting authorization
2 Which three items are normally included when a log message is generated by a syslog client and forwarded to a syslog server? (Choose three.) date and time of message ID of sending device length of message message ID checksum field community ID
3 What is the advantage of using WPA to secure a wireless network? It uses a 128-bit pre-shared hexadecimal key to prevent unauthorized wireless access. It uses an advanced encryption key that is never transmitted between host and access point. It is supported on older wireless hardware, thus providing maximum compatibility with enterprise equipment. It requires the MAC address of a network device that is requesting wireless access to be on a list of approved MAC addresses.
4 A company wants to configure a firewall to monitor all channels of communication and allow only traffic that is part of a known connection. Which firewall configuration should be deployed? packet filtering proxy stateful packet inspection stateless packet inspection
5 A server log includes this entry: User student accessed host server ABC using Telnet yesterday for 10 minutes. What type of log entry is this? authentication authorization accounting accessing
6 What two measures help to verify that server backups have been reliably completed? (Choose two.) reviewing backup logs performing trial backups performing full backups only replacing tape backup with hard disk-based backup using an autoloader when backups require more than one tape
7 Which means of communication does an SNMP network agent use to provide a network management station with important but unsolicited information? query broadcast ICMP ping trap poll
8 Which three protocols are used for in-band management? (Choose three.) FTP HTTP SNMP Telnet TFTP DHCP
9 A hacker has gained access to sensitive network files. In analyzing the attack, it is found that the hacker gained access over a wireless segment of the network. It is further discovered that the only security measure in place on the wireless network is MAC Address Filtering. How is it likely that the hacker gained access to the network? The hacker used a software tool to crack the shared hexadecimal wireless key. The hacker obtained the MAC address of a permitted host, and cloned it on his wireless laptop NIC. The attacker mounted a denial of service attack to overwhelm the firewall before penetrating the wireless LAN. The hacker gained wireless access to the MAC address database and added his own MAC address to the list of permitted addresses.
10 A network administrator is assigning network permissions to new groups of users and employing the principle of least privilege. Which two actions should the administrator take? (Choose two.) Provide users with only the access to resources required to do their jobs. Provide the minimum level of permissions required for users to do their jobs. Remove all permissions from the users and grant permissions as they are requested. Allow users to decide how much permission they need to accomplish their job tasks. Provide full access to the users and gradually remove privileges over time.
11 Which three protocols describe methods that can be used to secure user data for transmission across the internet? (Choose three.) SMTP IPSEC SSL HTTPS FTP TFTP
12 Which benefit does SSH offer over Telnet when remotely managing a router? encryption TCP usage authorization connection using six VTY lines
13 Which of the following does SNMP use to hold information collected about the network?
network management station network management database management information base database information agent
14 What are two potential problems with using tape media to back up server data? (Choose two.) Tape is not a cost-effective means of backing up data. Data tapes are difficult to store offsite. Data tapes are prone to failure and must be replaced often. Tape drives require regular cleaning to maintain reliability. Backup logs are not available with tape backup solutions.
15 What is the term for the public network between the boundary router and the firewall? "clean" LAN intranet DMZ extranet
16 Which two characteristics of network traffic are being monitored if a network technician configures the company firewall to operate as a packet filter? (Choose two.) applications physical addresses packet size ports protocols
17 When is the use of out-of-band network management necessary? when a server needs to be monitored across the network when the management interface of a device is not reachable across the network when enhanced monitoring features are required to gain an overall view of the entire network when it is desirable to use the information that is provided by SNMP
18 What network layer security protocol can secure any application layer protocol used for communication? HTTPS
IMAP FTPS IPSEC TLS
19 Before a technician upgrades a server, it is necessary to back up all data. Which type of backup is necessary to ensure that all data is backed up? daily differential full incremental partial
20 What AAA component assigns varying levels of rights to users of network resources? auditing accounting authorization access control authentication acknowledgement
Q.1 A company is developing an Internet store for its website. Which protocol should be used to transfer credit card information from customers to the company web server ? FTPS HTTP HTTPS WEP2 TFTP
Q.2. Refer to the exhibit. A new branch office has been added to the corporate network and anew router is to be installed to allow branch office users to access the database server at headquarters. How should the serial 0/0/0 interface of the new branch office router be configured to connect to the headquarters router ? branch_23(config-if)# ip address 192.168.5.19 255.255.255.240 branch_23(config-if)# no shutdown branch_23(config-if)# encapsulation hdlc branch_23(config-if)# ip address 192.168.5.25 255.255.255.240 branch_23(config-if)# no shutdown branch_23(config-if)# encapsulation ppp branch_23(config-if)# no shutdown branch_23(config-if)# encapsulation ppp branch_23(config-if)# ip address 192.168.5.33 255.255.255.240 branch_23(config-if)# encapsulation ppp branch_23(config-if)# ip address 192.168.5.21 255.255.255.240 branch_23(config-if)# no shutdown
Q.3 Which two commands ensure that any password that permits access to the privileged EXEC mode is not shown in plain text when the configuration files are displayed ? (Choose two.) Router(config)# enable secret cisco Router(config)# enable cisco Router(config)# encryption-password all Router(config)# enable login encrypted Router(config)# enable password encryption Router(config)# service password-encryption
Q.4 A new network is to be configured on a router. Which of the following tasks must be completed to configure this interface and implement dynamic IP routing for the new network? (Choose three.) Select the routing protocol to be configured. Assign an IP address and subnet mask to the interface Update the ip host configuration information with the device name and new interface IP address. Configure the routing protocol with the new network IP address. Configure the routing protocol with the new interface IP address and subnet mask. Configure the routing protocol in use on all other enterprise routers with the new network information.
Q.5 How does TCP ensure the reliable transfer of data ? If data segments are not received from the source, the destination requests that the segments be resent. If an acknowledgment of the transmitted segments is not received from the destination in a predetermined amount of the time, the source resends the data. TCP uses the SYN-ACK portion of the three-way handshake to ensure that all data has been received The TCP Protocol Interpreter process verifies the transmitted data at source and destination.
Q.6 A network administrator is asked to design a system to allow simultaneous access to the Internet for 250 users. The ISP for this network can only supply five public IPs. What can be used to accomplish this task ? routable translation dynamic translation static translation port address translation
Q.7 What is the most commonly used exterior routing protocol ? BGP RIP OSPF EIGRP
Q.8 Refer to the exhibit. The network administrator needs to configure the router with a name. Which command will the administrator use to configure the router name ? Router# ip hostname Boise Router# enable hostname Boise Router(config-line)# name Boise Router(config)# hostname Boise Router(config)# ip hostname Boise
Q.9 Why are port numbers included in the TCP header of a segment ? to indicate the correct router interface that should be used to forward a segment to identify which switch ports should receive or forward the segment to determine which Layer 3 protocol should be used to encapsulate the data to enable a receiving host to forward the data to the appropriate application to allow the receiving host to assemble the packet in the proper order
Q.10 What is the purpose of the routing process ? to encapsulate data that is used to communicate across a network to select the paths that are used to direct traffic to destination networks to convert a URL name into an IP address to provide secure Internet file transfer to forward traffic on the basis of MAC addresses Q.11 Which two statements are true about the use of the debug ip rip command on a Cisco router? (Choose two.) The debug ip rip command displays RIP routing activity in real time. The debug ip rip command can be issued at the user EXEC configuration mode. The debug ip rip command displays a combination of the information that is displayed by the show ip route and show ip protocols commands. Because of router processor usage, the debug ip rip command should be used only when necessary. The debug ip rip command should be used instead of the show ip route command whenever possible.
Q.12 What minimum configurations must be set on a host to allow a request to be sent to http://www.cisco.com/? (Choose four.) DNS server WINS server IP address NetBIOS subnet mask default gateway
Q.13 A Catalyst 2960 switch has been taken out of storage to be used as a temporary replacement for another switch that needs to be repaired. About a minute after the switch has started, the SYST LED on the front of the switch transitions from blinking green to amber. What is the meaning of the amber SYST LED ? The switch has no configuration file in NVRAM. The switch has failed POST and must be sent for service. The switch is functioning properly. The switch is in half-duplex mode.
Q.14 Refer to the exhibit. Which combination of cables and symbols is correct ?
A - crossover, B - straight-through, C - straight-through A - crossover, B - rollover, C - straight-through A - straight-through, B - crossover, C - straight-through A - straight-through, B - straight-through, C - straight-through A - straight-through, B - straight-through, C - crossover
A - rollover, B - straight-through, C - straight-through
Q.15 After an unsuccessful ping to the local router, the technician decides to investigate the router. The technician observes that the lights and fan on the router are not operational. In which layer of the OSI model is the problem most likely occurring ? transport network data link physical
Q.16 What are three characteristics of the TCP protocol ? (Choose three.) exchanges datagrams unreliably is used to send IP error messages forces the retransmission of unacknowledged packets creates a virtual session between end-user applications carries the IP address of the destination host in the TCP header is responsible for breaking messages into segments and reassembling them at their destination
Q.17 Refer to the exhibit. The network shown is connected using services from the same ISP. How will the Fohi router dynamically learn routes to the 192.168.16.16/28, 192.168.16.32/28, and 192.168.16.64/28 subnetworks ? with BGP with a static route with a directly connected route with an interior routing protocol
Q.18 Refer to the exhibit. Which type of UTP cable should be used to connect Host A to Switch1 ? rollover console crossover straight-through
Q.19 When customers use credit cards to make purchases at a small business, a modem is heard dialing a telephone number to transfer the transaction data to the central office. What type of WAN serial connection is in use ? leased line packet switched circuit switched point-to-point
Q.20 A user reports being unable to access the Internet. The help desk technician employs a bottom-up approach to troubleshooting. The technician first has the user check the patch cable connection from the PC to the wall, and then has the user verify that the NIC has a green link light. What will the technician have the user do next ? Enter an IP address into the WWW browser address bar to see if DNS is at fault. Use traceroute to identify the device along the path to the ISP that may be at fault.
Verify the IP address, subnet, and gateway settings using ipconfig on the PC. Connect to the user home router to check firewall settings for blocked TCP ports.
Q.21 A ping 192.1.1.20 command is issued on workstation A to determine if workstation B can be reached. What events will occur if this command is successful ? (Choose two.) The router will block the ping request message. The router will reply to the echo request with a proxy ping response. Workstation A will send a UDP ping request message to workstation B. Workstation B will send a UDP ping reply message to workstation A. Workstation A will send an ICMP echo request message to workstation B. Workstation B will send an ICMP echo reply message to workstation A.
Q.22 How does a router know of paths to destination networks? (Choose two.) inspection of the destination IP address in data packets ARP requests from connected routers manual configuration of routes updates from other routers DHCP information broadcasts updates from the SMTP management information base
Q.23 Refer to the exhibit. Which two statements describe the data conversation shown ? (Choose two.) The data conversation was started by the HTTP application process running on the client. The data conversation is identified by TCP port 80 on the client. The user started the data conversation by sending an e-mail. The IP address of the Internet server is 192.168.17.43. The Internet server will send data to port 8547 on the client.
Q.24 What is one purpose of the TCP three-way handshake ? sending echo requests from the source to the destination host to establish the presence of the destination determining the IP address of the destination host in preparation for data transfer requesting the destination to transfer a binary file to the source synchronizing sequence numbers between source and destination in preparation for data transfer
Q.25 Which type of address is 192.168.17.111/28 ? host address network address broadcast address multicast address
Q.26 A customer reports connectivity problems to an ISP technician. Upon questioning the customer, the technician discovers that all network applications are functioning except for FTP. What should the technician suspect is the problem ? misconfigured firewall bad port on switch or hub misconfigured IP addressing on the customer's workstation wrong DNS server configured on the customer's workstation
wrong default gateway configured on the customer's workstation
Q.27 The show ip route command was executed on one of the routers shown in the graphic and the following output was displayed : C 192.168.4.0/24 is directly connected, Serial0/0 R 192.168.5.0/24 [120/1] via 192.168.4.2, 00:00:19, Serial0/0 R 192.168.1.0/24 [120/2] via 192.168.3.1, 00:00:20, Serial0/1 R 192.168.2.0/24[120/2] via 192.168.3.1, 00:00:20, Serial0/1 C 192.168.3.0/24 is directly connected, Serial0/1 From which router was this command executed ? A B C D
Q.28 Refer to the exhibit. Which two sets of commands are required to configure passwords for all management ports on a Catalyst 2960 switch ? (Choose two.) ALSwitch(config)# interface vlan 1 ALSwitch(config-if)# password cisco ALSwitch(config-if)# login ALSwitch(config)# line vty 0 4 ALSwitch(config-line)# password cisco ALSwitch(config-line)# login ALSwitch(config)# line vty 0 15 ALSwitch(config-line)# password cisco ALSwitch(config-line)# login ALSwitch(config)# enable secret class ALSwitch(config)# enable password cisco ALSwitch(config)# interface fa0/1 ALSwitch(config-if)# password cisco ALSwitch(config-if)# no shutdown ALSwitch(config)# line cons 0 ALSwitch(config-line)# password cisco ALSwitch(config-line)# login
Q.29 A user reports being able to access the Internet but not being able to download e-mail from the mail server at the ISP. What should the user check on the user workstation ? the POP3 and SMTP server settings in the e-mail application the patch cable connections at the back of the workstation and at the wall plate the DHCP settings in the operating system the IP address, mask, and default gateway values the NIC drivers
Q.30 Refer to the graphic. Which command will configure a static route on Router A to direct traffic from LAN A that is destined for LAN C ? RouterA(config)# ip route 192.168.4.0 255.255.255.0 192.168.5.2 RouterA(config)# ip route 192.168.4.0 255.255.255.0 192.168.3.2 RouterA(config)# ip route 192.168.5.0 255.255.255.0 192.168.3.2 RouterA(config)# ip route 192.168.3.0 255.255.255.0 192.168.3.1
RouterA(config)# ip route 192.168.3.2 255.255.255.0 192.168.4.0
Q.31 Which subnet masks could be used when subnetting a Class B IP address? (Choose two.) 255.255.255.240 255.255.192.0 255.255.0.0 255.192.0.0 240.0.0.0 255.0.0.0
Q.32 Refer to the exhibit. The network administrator has configured the RTA and RTB interfaces. In order to allow hosts that are attached to RTA to reach the server that is attached to RTB, a static route from RTA to the server LAN and a default route from RTB back to RTA need to be configured. Which two commands will the administrator use to accomplish these tasks on the two routers? (Choose two.) RTA(config)# ip route 255.255.255.252 10.16.10.6 RTA(config)# ip route 0.0.0.0 0.0.0.0 10.16.10.6 RTA(config)# ip route 10.16.10.96 255.255.255.252 10.16.10.6 RTB(config)# ip route 10.16.10.6 255.255.255.248 10.16.10.6 RTB(config)# ip route 0.0.0.0 0.0.0.0 S0/0/1 RTB(config)# ip route 0.0.0.0 0.0.0.0 10.16.10.6
Q.33 How do port filtering and access lists help provide network security ? They prevent specified types of traffic from reaching specified network destinations. They alert network administrators to various type of denial of service attacks as they occur. They prevent viruses, worms, and Trojans from infecting host computers and servers. They enable encryption and authentication of confidential data communications.
Q.34 Refer to the exhibit. The network administrator of the building in the graphic needs to choose the type of cable best suited to add ServerB to the network. Which cable type is the best choice ? STP UTP coaxial fiber optic
Q.35 What is used by a routing protocol to determine the best path to include in the routing table ? Convergence time Default distance Metric Type of router
Q.36 Refer to the exhibit. Which IP addresses could be assigned to the hosts in the diagram ? (Choose two.) 192.168.65.31 192.168.65.32
192.168.65.35 192.168.65.60 192.168.65.63 192.168.65.64
Q.37 Given the network 192.168.25.0 shown in the graphic, which subnet mask would accommodate the number of hosts in each subnet ? 255.255.0.0 255.255.224.0 255.255.255.0 255.255.255.224 255.255.255.240 255.255.255.248
Q.38 Which two protocols allow network devices to report their status and events to a centralized network management device ? (Choose two.) Syslog Telnet HTTP HTTPS SNMP
Q.39 What is true regarding the differences between NAT and PAT ? PAT uses the word "overload" at the end of the access-list statement to share a single registered address. Static NAT allows an unregistered address to map to multiple registered addresses. Dynamic NAT allows hosts to receive the same global address each time external access is required. PAT uses unique source port numbers to distinguish between translations.
Q.40 Refer to the exhibit. The graphic shows the output of a command issued on router RTB. According to the output, what two statements are true of router RTB ? (Choose two.) The router is connected to a router named Boise. Router RTB is connected to a Cisco 1841 router. Router RTB is directly connected to two other routers. The IP address of the router interface connected to router RTB is 192.168.2.6. The RTB router is connected to two Cisco devices by Fast Ethernet links.
Q.41 Refer to the exhibit. The network administrator uses the command below to configure a default route to the ISP network : RTB(config)# ip route 0.0.0.0 0.0.0.0 10.1.1.6 A ping issued from the ISP is successful to router RTB. However, ping echo request packets arrive at a host that is attached to the Fa0/0 interface of RTB, and the replies do not make it back to the ISP router. What will fix this problem ? The ISP must be configured to forward packets from the 192.168.1.0 network. The ip route command needs to be edited so that the next hop address is 10.1.1.5. The ip route command needs to be edited so that the 192.168.1.1 address is the next hop address. The ip route command should be removed from the RTB router configuration.
Q.42 A network technician is using anetwork management station to gather data about the performance of devices and links within the ISP. Which application layer protocol makes this possible ? SNMP FTP DHCP SMTP
Q.43 What are two purposes of DNS ? (Choose two.) to dynamically assign IP addressing information to network hosts to simplify the administration of host and default gateway addressing on client computers to assign TCP port numbers to hosts as part of the data transfer process to resolve human-readable domain names to numeric IP addresses to replace the static HOSTS file with a more practical dynamic system
Q.44 A hacker attempts to reach confidential information that is stored on a server inside the corporate network. A network security solution inspects the entire packet, determines that it is a threat, and blocks the packet from entering the inside network. Which security measure protected the network ? an IDS an IPS a host-based firewall Anti-X software
Q.45 How many host addresses may be assigned on each subnetwork when using the 130.68.0.0 network address with a subnet mask of 255.255.248.0 ? 30 256 2046 2048 4094 4096
Q.46 In an IPv4 environment, what information is used by the router to forward data packets from one interface of a router to another ? destination network address source network address source MAC address well known port destination address
Q.47 A small tire retailer requires a low-cost WAN connection to its headquarters in order to manage its inventory and process customer sales in real time. Which WAN connection type is best suited to its needs ? Sonet T3 dialup DSL leased line Q.48 The command copy tftp running-config has been entered on the router. What will this command do ?
copy the configuration in RAM to a server copy the configuration file from a server to RAM copy the configuration file in NVRAM to RAM copy the configuration file in NVRAM to a server copy the configuration file from a server to NVRAM
Q.49 Refer to the exhibit. The network administrator needs to configure the Fa0/0 interface of RTB so that hosts from RTA can connect to the server that is attached to RTB. Which two commands will the administrator use to accomplish this task ? (Choose two.) RTB# ipaddress 192.168.102.98 255.255.255.248 RTB(config-if)# ip address 192.168.102.99 255.255.255.252 RTB(config)# ip address 192.168.102.97 255.255.255.252 RTB(config)# no shutdown RTB(config-if)# no shutdown RTB(config-if)# ip address 192.168.102.97 255.255.255.252
Q.50 Refer to the exhibit. A NOC technician at an ISP enters the command shown. What are two reasons to use this command ? (Choose two.) to map the path to 192.168.1.7 to test reachability to 192.168.1.7 to locate connectivity problems along the route to 192.168.1.7 to identify the ISPs that interconnect the NOC with the remote host with the address 192.168.1.7 to measure the time that packets take to reach 192.168.1.7 and return to the technician's workstation
1. Refer to the exhibit. What are two possible causes for the interface status? (Choose two.) The loopback address is not set. *The encapsulation type is mismatched. A cable is not attached to the interface. *Keepalive messages are not being received. The interface is administratively shut down. 2. A network administrator is upgrading a Cisco 1841 router by adding a WIC-2T module card. Which show command can the administrator use to verify that the module is correctly recognized by the router? show flash: *show version show ip route show startup-configuration 3. Which two conditions identify issues that are confined to Layer 1? (Choose two.) *cables that exceed maximum length encapsulation errors viruses and worms that create excessive broadcast traffic *poor termination of cables receiving "line protocol down" messages on the router console 4. Refer to the exhibit. Which three statements are true about the output of the show ip interface brief command? (Choose three.) *FastEthernet0/0 is functioning correctly. *The shutdown command has been applied on Serial0/0. FastEthernet0/0 was configured by the startup-config at bootup. Serial0/0 is experiencing a Layer 1 network problem. *FastEthernet0/1 is experiencing a Layer 2 network problem.
Because the port is down, Serial0/1 has an IP address that does not show in the output. 5. A network administrator plugs a new PC into a switch port. The LED for that port changes to solid green. What statement best describes the current status of the port? There is a duplex mismatch error. There is a link fault error. This port is unable to forward frames. *The port is operational and ready to transmit packets. This port has been disabled by management and is unable to forward frames. The flash memory is busy. 6. A user is having trouble accessing the Internet. A network administrator begins by verifying that the IP address of the PC is correctly configured. Next the administrator pings the default gateway. Based on this information, what type of troubleshooting method is the administrator employing? top-down bottom-up *divide-and-conquer impossible to determine from this information 7. A user can access any web page on the Internet but cannot access e-mail. What troubleshooting method would be most efficient for troubleshooting this issue? *top-down bottom-up divide-and-conquer impossible to determine from this information 8. Which problem is associated with Layer 4 of the OSI model? *A firewall is blocking Telnet packets to a host. A host has an incorrect IP address. A router has no route to a host. A host sent a malformed HTTP request. 9. An administrator is creating a lab to simulate a WAN connection. During the setup, the administrator notices that there are different encapsulation types on each end of the serial connection. At what layer of the OSI model is this problem occurring? *Layer 2 Layer 4 Layer 5 Layer 6 10. A PC is able to reach devices that are located both inside and outside the network. However, when trying to reach an FTP server that is located on the same subnet, the PC fails to make a connection. The administrator has several other PCs that are located in the same subnet try a connection to the FTP server and they are successful. Which troubleshooting tool can be used to determine the problem between the PC and the FTP server? cable tester digital multimeter *protocol analyzer network analyzer 11. Refer to the exhibit. Which IP address is misconfigured and is causing connectivity problems between hosts and servers? HostA HostB Server1 *Server2 R1 Fa0/0 R1 Fa0/1 12. Refer to the exhibit. Users on the 10.12.10.0/24 network are unable to access anyone on
the 10.10.10.0/24 network. What two problems exist in the network? (Choose two.) *R2 is using a different version of RIP. *R2 has a missing network statement. R1 has an incorrect network statement. R3 has an incorrect network statement. A routing loop is occurring between all three routers. 13. Refer to the exhibit. A netwrk administrator is upgrading a Cisco 1841 router by adding a WIC-2T module card. Which show command can the administrator use to verifys in the process of sending a preconfigured text file to a router. When the administrator pastes the configuration into the router, an error message appears. What is the problem with the IP addressing scheme? Serial0/0 is configured with a network address. The IP address on FastEthernet0/0 overlaps with the IP on FastEthernet0/1. Serial0/1 is configured with a broadcast address. *The IP address on FastEthernet0/0 overlaps with the IP on Serial0/1. 14. Refer to the exhibit. Host H1 on the LAN is not able to access the FTP server across the Internet. Which two configuration statements are causing this problem? (Choose two.) There is no route to the Internet. The IP address on Fa0/0 is incorrect. The IP address on S0/0/0 is incorrect. *The NAT command on the Fa0/0 interface is applied in the wrong direction. *The NAT command on the S0/0/0 interface is applied in the wrong direction. 15. Refer to the exhibit. The PC is trying to ping router B at 192.168.2.2, but it fails. What is the problem? The PC is on the wrong subnet. *The default gateway on the PC should be 192.168.1.1. The default gateway should be 192.168.2.2. The DNS server is incorrect. The IP address for Fa0/0 on router A is incorrect. 16. How many usable host addresses does the 192.168.1.0/25 subnet provide? 254 128 127 *126 64 17. A network technician has isolated a problem at the transport layer of the OSI model. Which question would provide further information about the problem? *Do you have a firewall that is configured on your PC? Do you have a link light on your network card? Is your PC configured to obtain addressing information using DHCP? What default gateway address is configured in your TCP/IP settings? Can you ping www.cisco.com?
coaxial *fiber-optic 32. Refer to the exhibit. Which cable path segments require the use of crossover cables? A, D, F B, C, E *B, D, E A, C, F 33. Refer to the exhibit. Router R1 has been configured with the commands that are displayed. Which password will be used to access the EXEC privileged mode of the router? password1
*password2 password3 password4 34. Refer to the exhibit. Host A is unable to ping R1. Which two configuration steps should be performed on R1 to solve this problem? (Choose two.) Configure the appropriate line password to access the router. Configure the speed of the interface. *Enable the interface administratively. Configure a dynamic routing protocol on the router. *Configure the subnet mask on the router correctly. 35. Refer to the exhibit. Host A is unable to ping host B. What can be done to solve this problem? (Choose two.) Configure a default route on R1 with the use of exit interface Fa0/0. Configure a default route on R2 by using the exit interface Fa0/0. Configure a static route on R1 with 192.168.0.1/24 as the next hop address. *Configure a static route for network 10.1.2.0/24 on R2 and use exit interface S0/0/0. *Configure a static route for network 10.1.1.0/24 on R1 with the next hop address as the IP address of the serial interface of R2. 36. What are two reasons for issuing the show ip route command on a router? (Choose two.) It displays the routing activity in real time. It displays the length of time until the next routing update. *It displays the directly connected networks. It displays all of the routing protocols that are configured on the neighboring routers. *It displays the routing protocol that is receiving updates from the neighboring routers. 37. When a router learns two paths to the same destination network, which two factors determine the path that will be included in the routing table? (Choose two.) *route metric the MAC address of the neighboring router the source IP address in data packets the IP address of the next hop router *administrative distance 38.Refer to the exhibit. A network technician issues the tracert 192.168.2.99 command successfully on host A. What are two consequences of running this command? (Choose two.) The traceroute packet is broadcast to the network. The command output will display the IP address of both the inbound and outbound router interfaces that the packet passes through. *The command output will display all routers through which the packet has passed. All successful hops between host A and host B will reply to the echo request with a proxy ICMP response. *The command will calculate the time between when the packet is sent and when a reply is received from a router. 39. A host has been properly cabled and configured with a unique hostname and valid IP address. Which two additional components should be configured to enable the host to access remote resources? (Choose two.) *the subnet mask the MAC address *the default gateway the loopback IP address the DHCP server IP address 40. Refer to the exhibit. What two addresses are the broadcast addresses for network A and network B? (Choose two.) Network A broadcast address 192.168.1.32 *Network A broadcast address 192.168.1.47
Network A broadcast address 192.168.1.15 *Network B broadcast address 192.168.1.207 Network B broadcast address 192.168.1.240 Network B broadcast address 192.168.1.192 41. A network administrator has designed a Class B network with a 255.255.254.0 mask. Which two statements are true for this network? (Choose two.) *There are 128 subnets. There are 256 subnets. There are 512 subnets. There are 126 usable hosts per subnet. There are 254 usable hosts per subnet. *There are 510 usable hosts per subnet. 42. Refer to the exhibit. R1 and R2 are configured with the commands that are displayed. All interfaces are properly configured, but neither router is receiving routing updates. What two things can be done to solve the problem? (Choose two.) *Configure the routing protocol on R1 for network 10.0.0.0. *Configure the routing protocol on R2 for network 10.0.0.0. Configure the routing protocol on R1 for network 192.168.4.0. Configure the routing protocol on R1 for network 192.168.2.0. Configure the routing protocol on R2 for network 192.168.1.0. Configure the routing protocol on R2 for network 192.168.3.0. 43. Which two statements are correct about the ICMP packet that is used by the ping command? (Choose two.) It guarantees datagram delivery. *It verifies Layer 3 connectivity. It acknowledges the receipt of TCP segments. It determines where a packet is lost on the path from the source to the destination. *It measures the time that elapses between when the request packet is sent and the response packet is received. 44. What is the effect of issuing the banner login #Unauthorized login prohibited# command on a router? *It will display the message "Unauthorized login prohibited" before the router prompts for a user name. It replaces the banner motd command. It causes the router to prompt for login credentials for any user who is attempting to connect to the router. It causes the message "Unauthorized access prohibited" to display when a HyperTerminal connection is idle. 45. Refer to the exhibit. What fact can be determined from the exhibited output? PPP is enabled on this router. The bandwidth setting of the interfaces is consistent with a T1 connection. The serial0/0/0 interface is administratively down. *The default encapsulation is set for the serial0/0/0 interface. Subnet mask 255.255.255.255 has been configured for the serial0/0/0 interface. 46. In order to load an initial configuration on a new switch, a network administrator has connected a laptop to the switch via the use of a console cable. About a minute after the network administrator powers on the switch, the SYST LED on the front of the switch changes from blinking green to amber. What does this indicate? The network administrator has made an improper physical connection to the switch. The switch is ready to have a configuration file loaded. A port on the switch is bad. *The switch failed POST. 47. What occurs during a static NAT translation?
Multiple local addresses are mapped to one global address. The host device is configured with a permanent outside global address. *A one-to-one mapping is created between an inside local and outside global address. The router is forced to return the inside global address to the address pool when a session ends. 48. Refer to the exhibit. What is used to exchange routing information between routers within each AS? static routing *IGP routing protocols EGP routing protocols default routing 49. Why do the static routes fail to appear in the routing table? The default route has not been configured on the routers. A dynamic routing protocol has not been configured. *The router interfaces are administratively down. The serial interfaces must be configured with an address in the 10.14.14.0 network. 50. Refer to the exhibit. While configuring the serial interface of a router, the network administrator sees the highlighted error message. What is the reason for this? The serial interface is administratively down. The serial interface is already configured with an IP address. *The network administrator has attempted to configure the serial interface with a broadcast address. The same IP address has been configured on another interface. 51. Refer to the exhibit. R2 is connected to the Serial0/0/1 interface of R1 and is properly configured to share routing updates with R1. Which network will R2 exclude from installing in its routing table? R 192.168.10.0/24 [120/2] via 192.168.1.2, 00:00:10, Serial0/0/1 R 192.168.7.0/24 [120/1] via 192.168.1.2, 00:00:10, Serial0/0/1 *R 192.168.6.0/24 [120/15] via 192.168.3.2, 00:00:10, Serial0/0/0 R 192.168.8.0/24 [120/2] via 192.168.3.2, 00:00:10, Serial0/0/0 52. How does an SNMP trap aid network monitoring and management? It reports to the management station by responding to polls. It collects information for the management station by using polling devices. *It sends an alert message to the management station when a threshold is reached. It flags attempts to begin a DoS attack on the network. 53. Refer to the exhibit. Which statement is true based on the exhibited information? The router is using a link-state routing protocol. *The router will get routing updates on the FastEthernet0/0 interface. The router will not forward routing updates from the Serial0/0/0 interface. The network for Fa0/1 will be included in the routing updates that are sent from this router. 54. Different hosts connect to the same switch port at different times. If the switch port is configured with dynamic port security, how does it process the MAC addresses? The addresses are manually assigned with the use of the switchport command. *The addresses are dynamically learned and stored in the address table. The addresses are dynamically configured and saved in the running configuration. The addresses are stored in the address table and added to the running configuration.
1. A client is communicating with a server on a different segment of the network. How does the server determine what service is being requested by the client? applies the default service configured in directory services uses ARP to discover the appropriate service from the local router sends a request to the client asking for the appropriate service
*identifies the appropriate service from the destination port field 2. What is the function of the TCP three-way handshake? It enables the synchronization of port numbers between source and destination hosts. It immediately triggers the retransmission of lost data. *It synchronizes both ends of a connection by allowing both sides to agree upon initial sequence numbers. It identifies the destination application on the receiving host. 3. What are three unique characteristics of UDP? (Choose three.) connection oriented full-duplex operation *low overhead *no flow control *no error-recovery function reliable transmission 4. Within TCP, what combination makes up a socket pair? source port with destination port source IP address with destination port source IP address and destination IP address *source IP address and port with a destination IP address and port 5. What type of update allows client computers to register and update their resource records with a DNS server whenever changes occur? *dynamic zone transfer local recursive query root domain query top-level domain query 6. Which DNS zone resolves an IP address to a qualified domain name? dynamic lookup forward lookup resolution lookup *reverse lookup 7. Which two tasks are the responsibility of the local DNS server? (Choose two.) maintaining a large number of cached DNS entries maintaining the ISP server *mapping name-to-IP addresses for internal hosts *forwarding name resolution requests to a caching-only server forwarding all name resolution requests to root servers on the Internet 8. Which protocol is used to send e-mail, either from a client to a server or from a server to another server? SNMP FTP *SMTP HTTPS 9. A manufacturing company subscribes to certain hosted services from their ISP. The services
required include hosted world wide web, file transfer, and e-mail. Which protocols represent these three key applications? (Choose three.) *FTP *HTTP DNS SNMP DHCP *SMTP 10. To meet customer expectations, an ISP must guarantee a level of service that is based on what two factors? (Choose two.) accessibility adaptability *availability *reliability scalability 11. Which two statements are true about the OSI and TCP/IP models? (Choose two.) The two bottom layers of the TCP/IP model make up the bottom layer of the OSI model. The TCP/IP model is a theoretical model and the OSI model is based on actual protocols. *The OSI network layer is comparable to the Internet layer of the TCP/IP model. The TCP/IP model specifies protocols for the physical network interconnection. *The TCP/IP model is based on four layers and the OSI model is based on seven layers. 12. What type of DNS server is typically maintained by an ISP? *caching-only root second-level top-level 13. Which two options correctly match protocol and well-known port number? (Choose two.) DNS - 25 FTP - 110 *HTTP - 80 POP3 - 25 *SMTP - 25 14. What are three characteristics of HTTPS? (Choose three.) It uses a different client request-server response process than HTTP uses. It specifies additional rules for passing data between the application and data link layers. *It supports authentication. It allows more simultaneous connections than HTTP allows. *It encrypts packets with SSL. *It requires additional server processing time. 15. User1 is sending an e-mail to User2@cisco.com. What are two characteristics of the process of sending this data? (Choose two.) It utilizes TCP port 110. A TCP connection is established directly between the User1 and User2 client computers in order to send the e-mail message. *It utilizes a store and forward process. The same application layer protocol is used to send the e-mail and retrieve it from the destination
server. *SMTP is used to send the e-mail message to the mail servers. 16. Which three fields do a TCP header and a UDP header have in common? (Choose three.) *source port window *checksum *destination port acknowledgment number sequence number 17. When a host is communicating with multiple applications on the same server at the same time, which two values will likely be the same in all packets for each session? (Choose two.) *IP address *MAC address session number sequence number 18. What are three characteristics of network reliability? (Choose three.) *Redundant hardware provides enhanced reliability. Reliability is measured based on the number of applications in use on the network. The longer the MTTR, the greater the reliability. *Fault tolerance is a measure of reliability. *The longer the MTBF, the greater the reliability. An ISP guarantees the same level of reliability to all of its customers. 19. Refer to the exhibit. Host1 is in the process of setting up a TCP session with Host2. Host1 has sent a SYN message to begin session establishment. What happens next? Host1 sends an ACK message to Host2. Host1 sends a SYN message to Host2. Host1 sends a SYN-ACK message to Host2. Host2 sends an ACK message to Host1. Host2 sends a SYN message to Host1. *Host2 sends a SYN-ACK message to Host1. 20. Refer to the exhibit. The PC is requesting HTTP data from the server. What is a valid representation of source and destination sockets for this request? Source - 192.168.1.17:80 ; Destination - 192.168.2.39:80 Source - 192.168.1.17:80 ; Destination - 192.168.2.39:1045 *Source - 192.168.1.17:1045 ; Destination - 192.168.2.39:80 Source - 192.168.1.17:1045 ; Destination - 192.168.2.39:1061 21. Refer to the exhibit. Which two statements are true about this file? (Choose two.) If the gateway address changes, the file will be updated dynamically. *The command ping fileserv will use IP address 172.16.5.10. *If the ping www.cisco.com command is issued, the file will be checked for the Cisco web server IP address before DNS is queried. The command ping mypc will use IP address 172.16.5.1. Name to IP address mappings are added to the file after they are received from DNS.
1. What is the purpose of a routing protocol? It is used to build and maintain ARP tables. It provides a method for segmenting and reassembling data packets. It allows an administrator to devise an addressing scheme for the network. *It allows a router to share information about known networks with other routers. It provides a procedure for encoding and decoding data into bits for packet forwarding. 2. Why is fast convergence desirable in networks that use dynamic routing protocols? Routers will not allow packets to be forwarded until the network has converged. Hosts are unable to access their gateway until the network has converged. *Routers may make incorrect forwarding decisions until the network has converged. Routers will not allow configuration changes to be made until the network has converged. 3. In which situation would a company register for its own autonomous system number (ASN)? when the company's ISP adds connection points to the Internet when additional routers are added to the corporate internetwork when more than one interior routing protocol is used *when the company uses two or more ISPs 4. What term refers to a group of networks that uses the same internal routing policies and is controlled by a single administrative authority? Internet intranet virtual private network *autonomous system 5. Which protocol is an exterior routing protocol? *BGP EIGRP OSPF RIP 6. What device enables an ISP to connect with other ISPs to transfer data? *border gateway router DSLAM web server interior router 7. Which part of an IP packet does the router use to make routing decisions? source IP address source MAC address *destination IP address destination MAC address 8. What statement is true regarding an AS number? *AS numbers are controlled and registered for Internet use. Interior routing protocols require registered AS numbers. ISPs require all customers to have registered AS numbers. All routers at an ISP must be assigned the same AS number. 9. Which routing protocol is used to exchange data between two different ISPs? *BGP
EIGRP OSPF RIP v2 10. Consider this routing table entry: R 172.16.1.0/24 [120/1] via 200.1.1.1 00:00:27 Serial0/1 What type of route is this? a static route a default route *a RIP route an OSPF route an EIGRP route a directly-connected route 11. Refer to the exhibit. If all routers are running RIP and network 10.0.0.0 goes down, when will R3 learn that the network is no longer available? in 30 seconds in 60 seconds in 90 seconds *immediately 12. What information is included in RIPv2 routing updates that is not included in RIPv1 updates? metric *subnet mask area identification hop count autonomous system number 13. What two types of businesses would benefit from registering as their own autonomous systems? (Choose two.) a home business with one ISP connection *a global business with connections to multiple local ISPs *a medium-sized nationwide business with Internet connectivity through different ISPs a large enterprise with two connections to the same ISP a small ISP with a single Internet connection through a larger ISP 14. Which two statements describe static routes? (Choose two.) They are created in interface configuration mode. *They require manual reconfiguration to accommodate network changes. They automatically become the default gateway of the router. *They are identified in the routing table with the prefix S They are automatically updated whenever an interface is reconfigured or shutdown. 15. What is the difference between interior and exterior routing protocols? Exterior routing protocols are only used by large ISPs. Interior routing protocols are used by small ISPs. Interior routing protocols are used to route on the Internet. Exterior routing protocols are used inside organizations. Exterior routing protocols are used to administer a single autonomous system. Interior routing protocols are used to administer several domains.
*Interior routing protocols are used to communicate within a single autonomous system. Exterior routing protocols are used to communicate between multiple autonomous systems. 16. Refer to the exhibit. Which configuration command or commands contributed to the output that is shown? routerA(config-router)# no version 2 routerA(config)# interface fa0/0 routerA(config-if)# ip address 172.19.0.0 255.255.0.0 *routerA(config-router)# network 192.168.3.0 routerA(config)# no ip default-gateway 17. Refer to the exhibit. All of the routers are running RIP. There are two paths from router A to the 192.168.3.0 network. Based on the output of the show ip route command on router A, which route was entered into the routing table and why? A,B,C,D because it has the lowest administrative distance A,E,F,G,D because it has the lowest administrative distance *A,B,C,D because it has the lowest metric A,E,F,G,D because it has the lowest metric 18. What is the purpose of the network command in configuring RIP? to specify whether RIPv1 or RIPv2 will be used as the routing protocol to allow the router to monitor RIP updates that occur on other routers *to identify the directly connected networks that will be announced in RIP updates to configure the IP address on an interface that will use RIP to identify all of the remote networks that should be reachable from the router 19. Refer to the exhibit. If connectivity between the two hosts is maintained, what is the maximum number of RIP routers that can be in the path from HostA to HostB? 14 *15 16 17 20. Refer to the exhibit. Router B receives a packet with a destination address of 10.16.1.97. What will router B do? drop the packet forward the packet via the route to 10.16.1.0 forward the packet via the route to 10.16.1.64 *use the default route 1. What is the correct command sequence to configure a router host name to "LAB_A"? *Router> enable Router# configure terminal Router(config)# hostname LAB_A Router> enable Router# hostname LAB_A Router> enable Router# configure router Router(config)# hostname LAB_A Router> enable Router(config)# host name LAB_A
2. Passwords can be used to restrict access to all or parts of the Cisco IOS. Select the modes and interfaces that can be protected with passwords. (Choose three.) *VTY interface *console interface Ethernet interface secret EXEC mode *privileged EXEC mode router configuration mode 3. A network administrator needs to configure a router. Which of the following connection methods requires network functionality to be accessible? console AUX *Telnet modem 4. Which tasks can be accomplished by using the command history feature? (Choose two.) View a list of commands entered in a previous session. Recall up to 15 command lines by default. *Set the command history buffer size. *Recall previously entered commands. Save command lines in a log file for future reference. 5. A router has a valid operating system and a configuration stored in NVRAM. When the router boots up, which mode will display? global configuration mode setup mode ROM monitor mode *user EXEC mode 6. Which function is a unique responsibility of the DCE devices shown in the exhibit? transmission of data reception of data *clocking for the synchronous link noise cancellation in transmitted data 7. In what two ways does SDM differ from the IOS CLI? (Choose two.) *SDM is used for in-band management only. The IOS CLI can be used for in-band and out-of-band management. SDM is accessed through a Telnet application. The IOS CLI is accessed through a web browser. SDM is available for all router platforms. The IOS CLI is available for a limited number of Cisco devices. *SDM utilizes GUI buttons and text boxes. The IOS CLI requires the use of text-based commands. SDM is used for advanced configuration tasks. The IOS CLI is preferred for initial basic device configuration. 8. What three settings can be made in the SDM Express basic configuration screen? (Choose three.) *host name DHCP options *domain name interface IP addresses
*enable secret password DNS server IP addresses 9. Which three encapsulation types can be set on a serial interface by an administrator who is using SDM Express? (Choose three.) ATM CHAP *Frame Relay *HDLC PAP *PPP 10. What option within Cisco SDM Express must be configured to allow hosts that receive IP address settings from the router to resolve names on the network or Internet? host name domain name DHCP address pool *DNS server IP address 11. To save time, IOS commands may be partially entered and then completed by typing which key or key combination? *Tab Ctrl-P Ctrl-N Up Arrow Right Arrow Down Arrow 12. How does the SYST LED on the catalyst 2960 switch indicate a POST failure? blinks rapidly amber blinks rapidly green *steady amber steady green 13. Refer to the exhibit. From the router console, an administrator is unable to ping a Catalyst switch that is located in another building. What can the administrator do from her location to check the IP configuration of the attached switch? Open an SDM session with the switch from her desktop. Telnet to the switch from the router console. *Use the show cdp neighbors detail command from the router console. The administrator must go to the switch location and make a console connection to check these settings. 14. Which three pieces of information about a neighbor device can be obtained by the show cdp neighbors command? (Choose three.) *platform routing protocol *connected interface of neighbor device *device ID IP addresses of all interfaces enable mode password 15. Refer to the exhibit. Which series of commands will correctly configure the serial interface
on Router2? Router2(config)# interface S0/0/0 Router2(config-if)# ip address 192.168.6.11 255.255.255.252 Router2(config-if)# clock rate 64000 Router2(config-if)# no shutdown Router2(config)# interface S0/0/0 Router2(config-if)# ip address 192.168.6.11 255.255.255.252 Router2(config-if)# no shutdown Router2(config)# interface S0/0/0 Router2(config-if)# ip address 192.168.6.9 255.255.255.252 Router2(config-if)# clock rate 64000 Router2(config-if)# no shutdown *Router2(config)# interface S0/0/0 Router2(config-if)# ip address 192.168.6.9 255.255.255.252 Router2(config-if)# no shutdown 16. When utilizing SDM Express, which two configuration options allow a router serial interface to obtain an IP address without manually configuring it? (Choose two.) Static IP Address Frame Relay encapsulation *IP Negotiated HDLC encapsulation *IP Unnumbered 17. Refer to the exhibit. A company always uses the last valid IP address in a subnetwork as the IP address of the router LAN interface. A network administrator is using a laptop to configure switch X with a default gateway via the switch console port. The switch VLAN 1 interface is assigned IP address 192.168.5.68/26. What command will the administrator use to assign a default gateway to the switch? X(config)# ip default-gateway 192.168.5.1 *X(config)# ip default-gateway 192.168.5.126 X(config)# ip default-gateway 192.168.5.190 X(config)# ip route 0.0.0.0 0.0.0.0 192.168.5.192 X(config)# ip route 192.168.5.0 255.255.255.192 192.168.5.1 18. Refer to the exhibit. Users on both SW1 and SW2 report that they are unable to communicate with each other. A network administrator issues show ip interface brief commands on both routers to troubleshoot the connectivity between the two networks. What action will correct the connectivity issue? Configure a default route on router RA pointing to router RB. Modify the network address of the serial link from a /30 to a /24. Issue a clock rate command on the s0/0/0 interface on router RA. *Issue a no shutdown command on the s0/0/0 interface on router RB. Issue a debug ip rip on both routers to verify that the routing protocol is functioning properly. 19. Refer to the exhibit. Based on the output of the show port-security interface fastethernet0/1 command on the switch, which statement about the switch port is true? The port has been shut down. Only three unique MAC addresses are permitted to use this port. *There are ten devices with different MAC addresses connected to this port. Port security has been violated seven times on this port.
20. What step must be completed before port security can be enabled on an interface? The interface must be shut down. *The interface must be in access mode. The maximum number of MAC addresses must be configured. The violation mode must be configured. 21. Which three sets of commands are required to enable administrators to connect to a switch on the same LAN via Telnet for configuration and management? (Choose three.) Switch1(config)# interface fa0/1 Switch1(config-if)# ip address 192.168.2.64 255.255.255.192 Switch1(config)# ip default-gateway 192.168.2.1 Switch1(config)# exit *Switch1(config)# interface vlan 1 Switch1(config-if)# ip address 192.168.2.126 255.255.255.192 Switch1(config-if)# no shutdown Switch1(config)# line con 0 Switch1(config-line)# enable password cisco Switch1(config-line)# login *Switch1(config)# line vty 0 15 Switch1(config-line)# password cisco Switch1(config-line)# login *Switch1(config)# enable secret class 22. Which two statements are true regarding the user EXEC mode? (Choose two.) All router commands are available. Global configuration mode can be accessed by entering the enable command. *This is the default mode on an unconfigured router when first powered up. Interfaces and routing protocols can be configured. *Only some aspects of the router configuration can be viewed. 23. Which of the following identifies the correct items needed to initially configure a router? 1) DB-9-to-RJ-45 on the PC's serial port 2) a straight through cable 3) the router's console port 1) PC's Ethernet port 2) a crossover cable 3) the router's Ethernet port 1) DB-9-to-RJ-45 on the PC's serial port 2) a rollover cable 3) the router's Ethernet port 1) PC's Ethernet port 2) a rollover cable 3) the router's console port *1) DB-9-to-RJ-45 on the PC's serial port 2) a rollover cable 3) the router's console port 1) PC's Ethernet port 2) a rollover cable 3) the router's Ethernet port 24. An administrator enters the show ip route command into a router. What type of information will be displayed?
the current configuration stored in RAM *the networks learned from other neighbors the encapsulation and bandwidth of every interface the private IP addresses translated to public IP addresses Switch1(config)# exit 25.A network technician is attempting to add an older workstation to a Cisco switched LAN. The technician has manually configured the workstation to full-duplex mode in order to enhance the network performance of the workstation. However, when the device is attached to the network, performance degrades and excess collision are detected. What is the cause of this problem? The host is configured in a different subnet from the subnet of the switch. *There is a duplex mismatch between the workstation and switch port. The switch port is running at a different speed from the speed of the workstation NIC. The host has been configured with a default gateway that is different from that of the switch. 1. In an 8 bit binary number, what is the total number of combinations of the eight bits? 128 254 255 *256 512 1024 2. Convert the decimal number 231 into its binary equivalent. Select the correct answer from the list below. 11110010 11011011 11110110 *11100111 11100101 11101110 3. How many usable hosts are available given a Class C IP address with the default subnet mask? *254 255 256 510 511 512 4. What is the network broadcast address for a Class C address of 192.168.32.0 with the default subnet mask? 192.168.0.0 192.168.0.255 192.168.32.0 192.168.32.254 *192.168.32.255 5. Company XYZ uses a network address of 192.168.4.0. It uses the mask of 255.255.255.224 to create subnets. What is the maximum number of usable hosts in each subnet? 6
14 *30 62 6. Which IPv4 class provides the highest number of host addresses per network? *Class A Class B Class C Class D Class E 7. Which statement accurately describes public IP addresses? Public addresses cannot be used within a private network. *Public IP addresses must be unique across the entire Internet. Public addresses can be duplicated only within a local network. Public IP addresses are only required to be unique within the local network. Network administrators are free to select any public addresses to use for network devices that access the Internet. 8. Refer to the exhibit. Host A is connected to the LAN, but it cannot get access to any resources on the Internet. The configuration of the host is shown in the exhibit. What could be the cause of the problem? The host subnet mask is incorrect. The default gateway is a network address. The default gateway is a broadcast address. *The default gateway is on a different subnet from the host. 9. What are two reasons that NAT was developed? (Choose two.) *to preserve registered public IP addresses to allow users on the public Internet to access local networks *to provide a method for privately addressed LANs to participate in the Internet to make routing protocols operate more efficiently to allow private addresses to be routed on the public Internet to reduce overhead and CPU usage on gateway routers 10. IPv6 increases the IP address size from 32 bits to how many bits? 64 96 *128 192 256 512 11. Which two statements describe classful IP addresses? (Choose two.) It is possible to determine which class an address belongs to by reading the first bit. *The number of bits used to identify the hosts is fixed by the class of the network. Only Class A addresses can be represented by high-order bits 100. Up to 24 bits can make up the host portion of a Class C address. *All subnets in a network are the same size. Three of the five classes of addresses are reserved for multicasts and experimental use. 12. Which statement describes NAT overload or PAT?
Each internal address is dynamically translated to an individual external IP address. A single internal address is always translated to the same unique external IP address. *Many internal addresses can be translated to a single IP address using different port assignments. Many internal addresses are statically assigned a single IP address and port to use for communications. 13. What must happen for a privately addressed host on an inside local network to be able to communicate with an outside destination host on the Internet? The host IP address must be translated to an outside private address. The host IP address must be translated to an inside local address. The host IP address must be translated to an outside local address. *The host IP address must be translated to an inside global address. 14. What is the range of the first octet in a Class B address? 127 to 191 127 to 192 *128 to 191 128 to 192 15. Which option shows the proper notation for an IPv6 address? 2001,0db8,3c55,0015,abcd,ff13 2001-0db8-3c55-0015-abcd-ff13 2001.0db8.3c55.0015.abcd.ff13 *2001:0db8:3c55:0015::abcd:ff13 16. Refer to the exhibit. Which range of IP addresses would allow hosts that are connected to the Router1 Fa0/0 interface to access outside networks? 192.168.1.0 through 192.168.1.95 *192.168.1.66 through 192.168.1.94 192.168.1.66 through 192.168.1.96 192.168.1.0 through 192.168.1.127 192.168.1.66 through 192.168.1.128 17. Static NAT works by mapping a specific inside local IP address to what other specific address type? *inside global outside local outside global private IP address 18. Which port numbers are used by PAT to create unique global addresses? 255 and below 1023 and below *1024 and above 64,000 and above 19. Refer to the exhibit. R1 is performing NAT for the 10.1.1.0/24 inside network. HostA has sent a request to the web server. What is the destination IP address of the return packet from the web server? 10.1.1.2 172.30.20.1
*172.30.20.10 192.168.1.1 1. A network technician is assigned to perform a site visit to a customer location to determine the requirements for a network upgrade. In addition to the currently installed equipment inventory, what other information about the hosts and networking devices should the technician obtain from the customer? the cost of the currently installed equipment all product keys for site license software *any planned growth anticipated in the near future the memory requirements for installed application software 2. Which three issues should be noted on the technician's site survey report? (Choose three.) *unlabeled cables only two power outlets per wall in each room *poor physical security of network devices horizontal cabling runs under 100 meters *lack of UPS for critical devices two users sharing the same computer 3. What three things are included in a logical topology document? (Choose three.) the location of cables, computers, and other peripherals *the path that the data takes through a network the wireless signal coverage area the wiring closet and access point locations *the device names and Layer 3 addressing information *the location of routing, network address translation, and firewall filtering 4. When designing a network upgrade, which two tasks should the onsite technician perform? (Choose two.) configure the servers and routers prior to delivery upgrade the network operating system and all client operating systems *investigate and document the physical layout of the premises document the final design for approval by the customer *perform a site survey to document the existing network structure 5. What must be added when a network expands beyond the coverage area of the current telecommunications room? MDF POP *IDF IXP 6. Which three items are typically found in an MDF? (Choose three.) user workstations *switches and routers fax machines *network equipment racks *the point of presence copier 7. Which device has the ability to break up broadcast and collision domains?
repeater hub *router switch 8. Refer to the exhibit. Which type of twisted pair cable is used between each device? A=console, B=straight, C=crossover, D= crossover, E=straight A=straight, B=straight, C=straight, D=crossover, E=console A=crossover, B=straight, C=straight, D=crossover, E=crossover *A=console, B=straight, C=straight, D=crossover, E=crossover A=console, B=crossover, C=crossover, D=straight, E=straight 9. Why is it important to review the results of an on-site survey report with the customer before beginning the network design? to inform the customer of how much time the upgrade will take to discuss the implementation schedule for the new equipment *to verify that the report accurately describes the current network and any plans for expansion to review the new network design and discuss possible equipment upgrades and replacements 10. Which two benefits can be gained by locating network equipment in a telecommunications closet, rather than in a user area? (Choose two.) faster communication speeds *improved physical security more resistant to hacker attempts *centralized cable management less electrical usage 11. What does the use of redundant network components supply to a network? scalability manageability compatibility *reliability 12. Which type of cable has a solid copper core with several protective layers including PVC, braided wire shielding, and a plastic covering? STP UTP *coaxial fiber optic 13. What is the term for the location at the customer premise where the customer network physically connects to the Internet through a telecommunications service provider? backbone area *point of presence network distribution facility intermediate distribution frame 14. In what two ways will entering into a managed service agreement with an ISP for a network upgrade affect the costs that are incurred by the customer? (Choose two.) Customer IT training costs will increase to enable operation of the new equipment. The cost of hardware repairs and support will become the responsibility of the customer. *Network upgrade and maintenance costs will become predictable.
Staffing costs will increase because the customer will need to hire additional IT staff to complete the upgrade. *The company will not need to spend a large amount of money to purchase the equipment upfront. 15. What is the benefit for a company to use an ISR router? *An ISR provides the functionality of a switch, router, and firewall in one device. ISRs use a PC operating system for routing traffic, thus simplifying configuration and management. An ISR is immune to security attacks by hackers and so replaces all other network security measures. ISRs make routing decisions at OSI Layer 7, thus providing more intelligence to the network than do other routers. 16. It is said that the goal for availability of a communications system is "five-9s". What is meant by this? A down time of .00001% is unacceptable. *A network needs to be available 99.999% of the time. Five percent of all network expense covers 99% of user requirements. The most critical time for network availability is from 9:00 to 5:00 p.m. five days a week. The best time to do maintenance on a network is from 5:00 p.m. to 9:00 a.m. five days a week. 17. A client requires a networking device that is capable of expansion to accomodate growing network demands. What characteristic must this device have to meet this requirement? ability to monitor operation and change the settings for a device *modular physical configuration ability to manage the device remotely ports that can be activated and deactivated 18. Refer to the exhibit. To allow IP communication between the two networks, what type of device is required? hub *router switch access point 19. What are two advantages of having ISP-managed services? (Choose two.) do not require leasing costs for the services *predictable billing eliminate the need for data backup *increase availability of help desk services do not require a Service Level Agreement 1. The DHCP server in a lab environment is down when multiple DHCP clients in the lab are booted for the first time. Which two statements describe how the DHCP clients will be affected by the absence of a DHCP server during boot? (Choose two.) The clients will not boot completely until the DHCP server resumes functioning. The clients will attempt via the use of the IP address 127.0.0.1 to communicate with the other clients. *All clients with link-local addresses will communicate with each other in a peer-to-peer manner. *A link-local address will be automatically assigned to the hosts by the operating system.
A link-local process will use a DNS query to determine if any other device uses the same linklocal address. 2. Which is a function of the transport layer of the OSI model? routes data between networks converts data to bits for transmission *delivers data reliably across the network using TCP formats and encodes data for transmission transmits data to the next directly connected device 3. Which statement describes the process of escalating a help desk trouble ticket? The help desk technican resolves the customer problem over the phone and closes the trouble ticket. Remote desktop utilities enable the help desk technician to fix a configuration error and close the trouble ticket. *After trying unsuccessfully to fix a problem, the help desk technician sends the trouble ticket to the onsite support staff. When the problem is solved, all information is recorded on the trouble ticket for future reference. 4. Which two functions are provided by the upper layers of the OSI model? (Choose two.) placing electrical signals on the medium for transmission *initiating the network communication process *encrypting and compressing data for transmission segmenting and identifying data for reassembly at the destination choosing the appropriate path for the data to take through the network 5. Which scenario represents a problem at Layer 4 of the OSI model? An incorrect IP address on the default gateway. A bad subnet mask in the host IP configuration. *A firewall filtering traffic addressed to TCP port 25 on an email server. An incorrect DNS server address being given out by DHCP. 6. A customer calls to report a problem accessing an e-commerce web site. The help desk technician begins troubleshooting using a top-down approach. Which question would the technician ask the customer first? *Can you access other web sites? Is there a firewall installed on your computer? What is your IP address? Is the link light lit on your NIC card? 7. What are two primary goals of the ISP help desk? (Choose two.) conserving support resources *network optimization competitive scalability *customer retention 8. What are two basic procedures of incident management? (Choose two.) *opening a trouble ticket using diagnostic tools to identify the problem surveying network conditions for further analysis configuring new equipment and software upgrades
*adhering to a problem-solving strategy e-mailing a problem resolution to the customer 9. Which three command line utilities are most commonly used to troubleshoot issues at Layer 3? (Choose three.) *ping a packet sniffer Telnet *ipconfig *traceroute 10. What is the correct encapsulation order when data is passed from Layer 1 up to Layer 4 of the OSI model? *bits, frames, packets, segments frames, bits, packets, segments packets, frames, segments, bits segments, packets, frames, bits 11. What are two functions of the physical layer of the OSI model? (Choose two.) adding the hardware address *converting data to bits encapsulating data into frames *signal generation routing packets 12. A customer calls the help desk about setting up a new PC and cable modem and being unable to access the Internet. What three questions would the technician ask if the bottom-up troubleshooting approach is used? (Choose three.) *Is the NIC link light blinking? What is the IP address and subnet mask? Can the default gateway be successfully pinged? *Is the network cable properly attached to the modem? *Is the Category 5 cable properly connected to the network slot on the PC? Can you access your e-mail account? 13. A customer calls the ISP help desk after setting up a new PC with a cable modem but being unable to access the Internet. After the help desk technician has verified Layer 1 and Layer 2, what are three questions the help desk technician should ask the customer? (Choose three.) *What is your subnet mask? *What is your IP address? Is the NIC link light blinking? *Can you ping the default gateway? Is the network cable properly attached to the cable modem? Is the network cable correctly connected to the network port on the PC? 14.Which address is used by the router to direct a packet between networks? source MAC address destination MAC address source IP address *destination IP address 15. What is the first step that is used by a help desk technician in a systematic approach to
helping a customer solve a problem? identify and prioritize alternative solutions isolate the cause of the problem *define the problem select an evaluation process 16. While troubleshooting a connectivity issue on a host, a network administrator issues the ping 127.0.0.1 command. The pings are unsuccessful. What is most likely the problem? *The TCP/IP stack is not loaded properly. The default gateway is down. ARP is not functioning correctly. An IP address has not been assigned to the host. 17. An accounting firm experiencing connectivity issues requires Level 3 support from the ISP. Which function requires Level 3 or higher support? the diagnosis of basic network connectivity the use of diagnostic tools to identify problems *the installation and configuration of new equipment the documentation of basic user issues 18. What Layer 1 problem can cause a user to lose Internet connectivity? wrong subnet mask wrong default gateway *loose network cable wrong MAC address faulty printer cable 19. In what three ways do Level 1 and Level 2 help desk technicians attempt to identify a customer's problems? (Choose three.) *talking to the customer on the telephone upgrading hardware and software *using various web tools making an onsite visit installing new equipment *with remote desktop sharing applications 1. When does a host device issue an ICMP echo request? *to initiate a ping to determine if a destination address is reachable to respond to a DNS name query to broadcast its identity to its locally connected neighbors to request the MAC address of a destination IP address 2. What is the maximum T1 transmission speed? 56 kbps 128 kbps *1.544 Mbps 2.4 Mbps 3. At which point do individuals and small businesses connect directly to the ISP network to obtain Internet access? *at a POP at an IXP at a Metro Ethernet link
on the ISP extranet 4. Which network support services team is responsible for testing a new customer connection and for monitoring the ongoing operation of the link? customer service help desk network operations on-site installation 5. Which network support services team identifies whether the client site has existing network hardware and circuits installed? customer service help desk network operations *planning and provisioning 6. What are three main types of high-bandwidth connection options used by medium- to largesized businesses? (Choose three.) DSL cable modem Ethernet *metro Ethernet *T1 *T3 7. What feature enables network devices to be scalable? a fixed number of interfaces ease of repair *modularity low maintenance requirements low cost 8. Which statement describes a function of a Tier 1 ISP? *peers with other similarly sized ISPs to form the global Internet backbone uses the services of Tier 3 ISPs to connect to the global Internet backbone pays Tier 2 ISPs for transit services to connect across continents limits the offered services to small geographic areas 9. Which two things can be determined by using the ping command? (Choose two.) the number of routers between the source and destination device the IP address of the router nearest the destination device *the average time it takes a packet to reach the destination and for the response to return to the source *whether or not the destination device is reachable through the network the average time it takes each router in the path between source and destination to respond 10. The IT manager of a medium-sized business wishes to house the company-owned web servers in a facility that offers round-the-clock controlled access, redundant power, and highbandwidth Internet access. Which ISP service will fulfill this need? web hosting planning and provisioning application hosting
*equipment collocation Tier 1 ISP services 11. What was the original purpose of the Internet? voice communication marketing *research commerce 12. What is the purpose of an RFC? to provide the connection point for multiple ISPs to the Internet *to document the development and approval of an Internet standard to indicate a contract that a customer signs when purchasing co-location services to document agreements between an ISP and the customer 13. What units are used to measure Internet bandwidth? *bits per second bytes per second hertz megabytes per second packets per second 14. What three support service teams are commonly found within an ISP? (Choose three.) *help desk computer support application readiness *network operations center *planning and provisioning implementation and documentation 15. Which ISP network support systems team will typically contact the customer once a new circuit is ready and guide the customer in setting up passwords and other account information? *help desk customer service network operations center on-site installation team planning and provisioning 16. What interconnects the Internet backbone? MDFs *IXPs POPs satellite dishes 17. Refer to the exhibit. A host is having problems maintaining a connection to a server at 192.168.100.2. Which statement best describes the output of the ping command? The server is shut down. The server has no route back to the host. Two routers along the path are not responding to pings. *Some packets made it to the destination. 18. Refer to the exhibit. Host A cannot connect to the web server at 192.168.100.2. Based on
the output of the tracert command, which device is most likely causing the problem? Router A Router B Router C Router D Router E *Router F 19. Which network utility helps determine the location of network problems and identifies routers that packets travel across? ping ipconfig *tracert netstat nslookup Ping services are not supported on the destination. Q.1 Which three statements are true about local and network applications? (Choose three.) A local application is loaded in a local computer and can be accessed by a remote computer on the network. A network application is loaded in a local computer and accessed from a remote computer. A local application is loaded in a local computer and accessed only by the local computer. A network application is loaded in a local computer and accessed only by the local computer. An example of a local application is e-mail. An example of a network application is instant messaging.
Q.2 A wireless DHCP client cannot connect to the Internet through a Linksys integrated router. When you type ipconfig on the host, no IP address, subnet mask, or default gateway shows. What are two of the first things you will check? (Choose two.) SSID if the wireless client is configured for DHCP the cable between client and integrated router the firewall configuration on the integrated router if the correct default gateway is configured on the client if the correct default gateway is configured on the integrated router
Q.3 Refer to the graphic. Assume that the command output is from a wireless DHCP client that is connected to a Linksys integrated router. What can be deduced from the output? The wireless connection is good.
The WEP key or SSID needs to be checked. The DHCP configuration on the router needs to be checked. The wireless NIC driver or the NIC itself needs to be reinstalled.
Q.4 What measurement is commonly used to describe communication speed when transferring data? bps cps Hz MB
Q.5 What is an accurate description of network devices in the distribution layer? They are designed to interconnect individual hosts. They are designed to interconnect multiple companies. They are designed to interconnect local network segments. They are designed to switch data packets as fast as possible.
Q.6 When acting as a DHCP server, an integrated router can provide what three types of information to a client? (Choose three.) physical address MAC address default gateway static IP address dynamic IP address DNS server address Q.7 Where do ISPs get the public addresses that they assign to end users? ISPs create the addresses themselves. ISPs are assigned addresses through the RFC. ISPs obtain their addresses automatically. ISPs obtain address blocks from registry organizations.
Q.8 Refer to the graphic. What is the effect of setting the security mode to WEP on the Linksys integrated router? It identifies the wireless LAN. It allows the access point to inform clients of its presence. It translates IP addresses into easy-to-remember domain names. It encrypts data between the wireless client and the access point. It ensures that only authorized users are allowed access to the WLAN. It translates an internal address or group of addresses into an outside, public address.
Q.9 When are leased lines typically used?
when low bandwidth is required for home and small business connectivity when a dedicated digital data line is necessary as a less expensive option to cable and DSL modem service
Q.10 Which wireless protocol is used for encryption? EAP Open PSK WEP Q.11 The area covered by a single AP is known as what? ad-hoc network basic service set independent basic service set extended service set distribution system
Q.12 Which installation option should be chosen when the current operating system is too damaged to work properly? upgrade multi-boot clean install virtualization
Q.13 What layer is the first point of entry for a host into the network? core layer access layer network layer distribution layer
Q.14 What two commands can be used to form a new binding if client information does not agree with the DHCP client table? (Choose two.) ipconfig /release ipconfig /all ipconfig /flushdns ipconfig /renew ipconfig
15. What are two advantages of purchasing a custom-built computer? (Choose two.) usually a lower cost no waiting period for assembly user can specify higher performance components supports higher-end graphics and gaming applications fewer components to replace
Q.16 What information within a data packet does a router use, by default, to make forwarding decisions?
the destination MAC address the destination IP address the destination host name the destination service requested
Q.17 What is a service pack? an access policy an agreement between a company and a vendor a piece of code created to fix one specific problem a collection of patches and updates released by a vendor a small piece of software designed specifically for security issues
Q.18 What is an ISP? It is a standards body that develops cabling and wiring standards for networking. It is a protocol that establishes how computers within a local network communicate. It is an organization that allows individuals and businesses to connect to the Internet. It is a networking device that combines the functionality of several different networking devices in one.
Q.19 Which two statements correctly describe Media Access Control (MAC) addresses? (Choose two.) MAC addresses are used to identify a specific NIC. MAC addresses are physical addresses. MAC addresses contain a network number and unique host identification. MAC addresses are always assigned to network devices by a network administrator. MAC addresses can be dynamically assigned.
Q.20 What is the name for the contract between a customer and an ISP that specifies requirements for uptime and service response time? DSL IAB NAP SLA
Q.21 What are two ways that a user can interact with an operating system shell? (Choose two.) CLI OS GUI NIC kernel
Q.22 Select the connection that would require a straight-through cable. a switch to a hub a router to a switch a switch to a switch a router to a router
23. Choose the option that shows the correct sequence of steps in the encapsulation of TCP/IP data that is passed from a source to a destination host? A. converts data to bits for transmission
B. packages the data for end to end transport C. adds the data-link header and trailer D. adds the network IP address to the header of the frame A,B,C,D A,C,D,B B,D,C,A B,C,D,A D,C,B,A
Q.24 What is specified by the network number in an IP address? the network to which the host belongs the physical identity of the computer on the network the node of the subnetwork which is being addressed the broadcast identity of subnetwork
Q.25 Refer to the graphic. What is the purpose of assigning a Network Name of Academy? It identifies the wireless LAN. It translates IP addresses into easy-to-remember domain names. It encrypts data between the wireless client and the access point. It allows access to the AP configuration GUI by name rather than address. It translates an internal address or group of addresses into an outside, public address.
Q.26 Which of the following statements best describes DNS? DNS servers are used to map an IP address to a physical address. DNS servers are used to map a name to an IP address. DNS servers are used to configure logical address information for host computers. DNS servers are used to translate from private addresses to public addresses.
Q.27 Which of the following are the address ranges of the private IP addresses? (Choose three.) 10.0.0.0 to 10.255.255.255 200.100.50.0 to 200.100.25.255 150.150.0.0 to 150.150.255.255 172.16.0.0 to 172.31.255.255 192.168.0.0 to 192.168.255.255 127.16.0.0 to 127.31.255.255
Q.28 Which protocol is used to transfer files among network devices and perform file-management functions? DNS FTP HTML HTTP
Q.29 Select three statements that correctly describe how DHCP services may be provided. (Choose three.) An integrated router provides IP configurations for most ISPs. An integrated router can act as both DHCP server and DHCP client. A home PC using a static IP address obtained that address from a DHCP server. Most home network integrated routers receive an IP configuration directly from their ISP. A variety of devices can act as DHCP servers, as long as they run DHCP service software. A home PC is required by standards to obtain an IP address and default gateway from a DHCP server (usually the ISP).
Q.30 Refer to the graphic. Based on the information that is shown, what statement is true? This configuration would be commonly found in an ad hoc wireless network. Any wireless client that is attached to this access point would have the same IP address and SSID. All wireless devices that are connected to this access point must have an assigned SSID of Academy. In addition to accepting wireless client requests, this access point must connect to the wired network. Q.31 Identify two causes of physical layer network problems. (Choose two.) logical addressing issues improperly terminated cables cables plugged into wrong ports incorrect MAC address assigned packets received out of sequence incorrect subnet mask on an interface
Q.32 Which part of the electromagnetic spectrum is commonly used to exchange data between a PDA and a computer? FM radar infrared ultraviolet
Q.33 Which of the following are transport layer protocols of the TCP/IP model? (Choose two.) FTP
UDP SMTP TFTP TCP
Q.34 For the second time in a week, workstations on a LAN are not able to log into the server. The technician fixed the problem the first time, but cannot remember the steps taken to solve it. What aspect of the troubleshooting process has the technician neglected? identifying the problem asking end-users questions documenting the troubleshooting process using structured techniques to solve a problem
Q.35 What action will a router take when it receives a frame with a broadcast MAC address? It will not forward the frame to another network. It forwards the frame back to the sending host with its IP address as a response. It forwards the frame out of all interfaces except the interface where the frame was received. It forwards the frame back out the receiving interface to insure all hosts on the local network receive it.
Q.36 A network host is accessing a web server. What two protocols are most likely being used as the TCP/IP model application layer protocol and the internetwork layer protocol? (Choose two.) IP FTP TCP DHCP HTTP
Q.37 Which statement is true concerning stateful packet inspection? Access is permitted based on IP addresses of the source and destination devices. Access is permitted based on the MAC addresses of the source and destination devices. Access is permitted only if the type of application that is attempting to reach the internal host is allowed. Access is permitted only if it is a legitimate response to a request from an internal host.
Q.38 What does the term "attenuation" mean in data communication? loss of signal strength as distance increases time for a signal to reach its destination leakage of signals from one cable pair to another strengthening of a signal by a networking device
39. What is the default subnet mask for a class B address? 255.0.0.0 255.255.0.0 255.255.255.0 255.255.255.255
Q.40 Refer to the graphic. Based on the configuration information that is shown, which three types of 802.11 networks are allowed access to the WLAN? (Choose three.) 802.11a 802.11b 802.11e 802.11g 802.11n 802.11x
Q.41 Within a local network, which two items must be unique on a computer for it to successfully connect to the network? (Choose two.) IP address subnet mask computer name default gateway address operating system version
Q.42 When considering the purchase of a new operating system, what is meant by "Total Cost of Ownership?" applications and support costs hardware and support costs hardware and software costs hardware, software, and support costs hardware, operating system, and applications costs
Q.43 A computer joins the network and announces itself to all hosts on the LAN. What type of message does the computer send out? broadcast simulcast multicast unicast
Q.44 Refer to the graphic. What feature can be installed on the Linksys integrated router to convert private IP addresses to Internet-routable addresses? authentication DHCP encryption firewall NAT WEP
Q.45 When terminating UTP cabling, why is it important to untwist only a small amount of each wire pair? minimizes crosstalk makes installation faster ensures wires are in correct order makes it easier to fit wires into connector
Q.46 A host sent a message that all other hosts on the local network received and processed. What type of domain are all these hosts a part of? local domain multicast domain collision domain broadcast domain
Q.47 Your school network blocks all websites related to online gaming. What type of security policy is being applied? identification and authentication remote access acceptable use incident handling
Q.48 Refer to the graphic. Assume that the exhibited output is from a host that is connected to a Linksys integrated router. What is one of the first things you should check? IP address on the host IP address on the router subnet mask on the host
default gateway on the host link status LED on the front of the router
Q.49 How does a crossover cable make it possible for two "like devices" (for example, two switches) to communicate? The transmit pins are disconnected and only the receive pins are used. The transmit pins on one device are connected to the transmit pins on the other device. The receive pins on one device are connected to the receive pins on the other device. The transmit pins on one device are connected to the receive pins on the other device.
50. What are two examples of storage peripheral devices? (Choose two.) printer flash drive headphones external DVD barcode reader
Q.51 What are the two possible values for a digital bit? (Choose two.) 0 1 A F # 9
Q.52 What type of computer would most likely use a docking station? laptop server desktop mainframe workstation
Q.1. A user types www.cisco.com into a web browser address textbox. What does www.cisco.com represent? the IP address of a web server a physical network address the closest router interface to the source the source IP address in the data transmission
Q.2. What type of server would use IMAP? DNS DHCP e-mail FTP Telnet web
Q.3. Which type of server would most likely be used first by a network client in a corporate environment? DNS DHCP e-mail FTP Telnet web
Q.4. Which protocol is used by FTP to transfer files over the Internet? TCP SMTP UDP SNMP
Q.5. Which protocols are TCP/IP application layer protocols? (Choose two.) UDP FTP IP SMTP TCP
Q.6. Which of the following are layers of the TCP/IP model? (Choose three.) Application Physical Internet Network Access Presentation
Q.7. You are creating a network-based video game. What influences your decision about which transport protocol to use for the application? UDP will not disrupt the game to retransmit dropped packets. TCP provides extra acknowledgements that will ensure smooth video delivery. Both TCP and UDP can be used simultaneously to ensure speed and guaranteed delivery. Both TCP and UDP may slow transmission and disrupt game operation, so no transport protocol should be used.
Q.8. Whenever e-mail clients send letters, what device is used to translate the domain names into their associated IP addresses? Uniform Resource Locator Network redirector server SNMP server DNS server
Q.9. Which application is most likely used to translate www.cisco.com to 198.133.219.25? DHCP DNS FTP HTTP POP SMTP
Q.10. Refer to the graphic. Which protocol is used to access this website? IM FTP HTTP SNMP VoIP
Q.11. Which port number is used by SMTP? 20 21 25 26 110
Q.12. Which protocol is used by e-mail servers to communicate with each other? FTP HTTP TFTP SMTP POP SNMP Q.13. What client software enables logged in users to communicate with other logged in users in real time? blog e-mail
web mail instant messaging
Q.14. An Internet server is running both FTP and HTTP services. How does the server know which of these applications should handle an incoming segment? The packet header identifies it as an HTTP or FTP packet. The data in the segment is specially formatted for either HTTP or FTP. The segment destination port number identifies the application that should handle it. The source port number is associated with one of these well known server applications.
Q.15. What term is used to describe how TCP/IP protocols are layered and interact to format, address, and transmit information across a network? protocol hierarchy protocol modeling protocol stack protocol layering
Q.16. What three items are contained in an Ethernet frame? (Choose three.) source IP address source MAC address destination IP address destination MAC address error-checking information Q.17. What information is contained in an IP header? source and destination IP addresses source and destination MAC addresses only destination IP and MAC addresses both source and destination IP and MAC addresses Q.18. Cabling issues are associated with which OSI layer? 4 2 1 3 Q.19. A device receives an Ethernet frame and recognizes the MAC address as its own. What does the device do to the message to get to the encapsulated data? removes the IP header removes the TCP header passes data to the application layer removes the Ethernet header and trailer Q.20. A client has decoded a frame and started the de-encapsulation process. In which order does the de-encapsulation process occur? 1) remove IP header 2) remove Ethernet header and trailer 3) remove TCP header 4) pass data to the application 1) add TCP header to data 2) add an IP header 3) add frame header and trailer 4) encode the frame into bits 1) remove Ethernet header and trailer 2) remove IP header 3) remove TCP header 4) pass data to the application 1) add TCP header to data
2) add Ethernet header and trailer 3) add an IP header 4) encode the frame into bits
Q.21. What is an advantage of the use of layers in the OSI reference model? It breaks network communications into larger parts. It increases complexity. It prevents changes in one layer from affecting other layers. It requires the use of single-vendor equipment for hardware and software communications.
Q.22. What is the correct order of the layers of the OSI reference model, starting at the lowest layer and working up the model? data link, physical, transport, network, presentation, session, application physical, data link, network, session, transport, presentation, application physical, data link, network, transport, presentation, session, application physical, data link, network, transport, session, presentation, application application, session, presentation, transport, data link, network, physical
Q.1 Which command is used to view the RIP routing protocol settings and configuration? show version show ip route show interface show ip protocols
Q.2 Refer to the exhibit. What is the maximum number of RIP routers that could separate HostA and HostB and still leave the hosts with connectivity to each other? 14 15 16 17
Q.3 In which situation would a company register for its own autonomous system number (ASN)? when the company's ISP adds connection points to the Internet when additional routers are added to the corporate internetwork when more than one interior routing protocol is used when the company uses two or more ISPs
Q.4 Consider this routing table entry R 172.16.1.0/24 [120/1] via 200.1.1.1 00:00:27 Serial0/1 What type of route is this? a static route a default route a RIP route
an OSPF route an EIGRP route a directly-connected route
Q.5 What is the difference between interior and exterior routing protocols? Exterior routing protocols are only used by large ISPs. Interior routing protocols are used by small ISPs. Interior routing protocols are used to route on the Internet. Exterior routing protocols are used inside organizations. Exterior routing protocols are used to administer a single autonomous system. Interior routing protocols are used to administer several domains. Interior routing protocols are used to communicate within a single autonomous system. Exterior routing protocols are used to communicate between multiple autonomous systems.
Q.6 What information is included in RIPv2 routing updates that is not included in RIPv1 updates? metric subnet mask area identification hop count autonomous system number
Q.7 Which routing protocol is used to exchange data between two different ISPs? BGP EIGRP OSPF RIP v2
Q.8 Refer to the exhibit. Which configuration command or commands contributed to the output that is shown? routerA(config-router)# no version 2 routerA(config)# interface fa0/0 routerA(config-if)# ip address 172.19.0.0 255.255.0.0 routerA(config-router)# network 192.168.3.0 routerA(config)# no ip default-gateway
Q.9 Refer to the exhibit. If all routers are running RIP and network 10.0.0.0 goes down, when will R3 learn that the network is no longer available? in 30 seconds in 60 seconds in 90 seconds Immediately
Q.10 What statement is true regarding an AS number? AS numbers are controlled and registered for Internet use. Interior routing protocols require registered AS numbers. ISPs require all customers to have registered AS numbers. All routers at an ISP must be assigned the same AS number. Q.11 What is the purpose of the network command used when configuring RIP? to specify whether RIPv1 or RIPv2 will be used as the routing protocol to allow the router to monitor RIP updates that occur on other routers to identify which networks on the router will send and receive RIP updates to configure the IP address on an interface that will use RIP to identify all of the remote networks that should be reachable from the router
Q.12 Which command would a network administrator use to determine if the routers in an enterprise have learned about a newly added network? router# show ip address router# show ip route router# show ip networks router# show ip interface brief router# debug ip protocol router# debug rip update
Q.13 What is the purpose of a routing protocol? It is used to build and maintain ARP tables. It provides a method for segmenting and reassembling data packets. It allows an administrator to devise an addressing scheme for the network. It allows a router to share information about known networks with other routers. It provides a procedure for encoding and decoding data into bits for packet forwarding.
Q.14 What device enables an ISP to connect with other ISPs to transfer data? border gateway router DSLAM web server interior router
Q.15 Which command will display RIP routing updates as they are sent and received? show ip route show ip rip debug ip rip show ip protocols show ip rip database
Q.16 Which part of an IP packet does the router use to make routing decisions? source IP address source MAC address destination IP address destination MAC address
Q.17 What two types of businesses would benefit from registering as their own autonomous systems? (Choose two.) a home business with one ISP connection a global business with connections to multiple local ISPs a medium-sized nationwide business with Internet connectivity through different ISPs a large enterprise with two connections to the same ISP a small ISP with a single Internet connection through a larger ISP
Q.18 Which command will display RIP activity as it occurs on a router? debug ip rip show ip route show ip interface show ip protocols debug ip rip config show ip rip database
Q.19 Why is fast convergence desirable in networks that use dynamic routing protocols? Routers will not allow packets to be forwarded until the network has converged. Hosts are unable to access their gateway until the network has converged. Routers may make incorrect forwarding decisions until the network has converged. Routers will not allow configuration changes to be made until the network has converged.
Q.20 Which two statements describe static routes? (Choose two.) They are created in interface configuration mode. They require manual reconfiguration to accommodate network changes. They automatically become the default gateway of the router. They are identified in the routing table with the prefix S They are automatically updated whenever an interface is reconfigured or shutdown.
Q.21 Which two statements or sets of statements describe differences between link-state and distance vector routing protocols? (Choose two.) Link-state routing protocols routinely use more bandwidth for updates than do distance vector routing protocols.
Distance vector routing protocols update all routers at one time. Link-state routing protocols update one router at a time. Link-state routers only know about directly connected routers. Distance vector routers know about every router in the network. Link-state routing protocols update when a change is made. A network using distance vector routing protocols only updates at a specific interval. Distance vector routing protocols have limited information about the entire network. Link state routing protocols know about all routers in the network. In case of similar topologies, networks using link-state routing protocols typically converge more rapidly than do networks using distance vector routing protocols.
Q.22 Which protocol is an exterior routing protocol? BGP EIGRP OSPF RIP
Q.23 Hosts on two separate subnets cannot communicate. The network administrator suspects a missing route in one of the routing tables. Which three commands can be used to help troubleshoot Layer 3 connectivity issues? (Choose three.) Ping show arp Traceroute show ip route show interface show cdp neighbor detail
Q.24 What term refers to a group of networks that uses the same internal routing policies and is controlled by a single administrative authority? Internet intranet virtual private network autonomous system
Q.1 In what two ways does SDM differ from the IOS CLI? (Choose two.) SDM is used for in-band management only. The IOS CLI can be used for in-band and out-of-band management. SDM is accessed through a Telnet application. The IOS CLI is accessed through a web browser. SDM is available for all router platforms. The IOS CLI is available for a limited number of Cisco devices. SDM utilizes GUI buttons and text boxes. The IOS CLI requires the use of text-based commands. SDM is used for advanced configuration tasks. The IOS CLI is preferred for initial basic device configuration.
Q.2 Which mode will a configured router display at login? global configuration mode setup mode ROM monitor mode user EXEC mode
Q.3 Refer to the exhibit. Which password or passwords will be encrypted as a result of the configuration that is shown? virtual terminal only enable mode only console and virtual terminal only enable mode and virtual terminal only the service password all configured passwords
Q.4 Refer to the exhibit. Which three sets of commands are required to enable administrators to connect to the Switch1 console over Telnet for configuration and management? (Choose three.) Switch1(config)# interface fa0/1 Switch1(config-if)# ip address 192.168.2.64 255.255.255.192 Switch1(config)# interface fa0/1 Switch1(config-if)# ip address 192.168.2.66 255.255.255.192 Switch1(config)# interface vlan 1 Switch1(config-if)# ip address 192.168.2.126 255.255.255.192 Switch1(config-if)# no shutdown Switch1(config)# line vty 0 4 Switch1(config-line)# enable password cisco Switch1(config-line)# login Switch1(config)# line vty 0 15 Switch1(config-line)# password cisco Switch1(config-line)# login Switch1(config)# ip default-gateway 192.168.2.65
Q.5 How does the SYST LED on the catalyst 2960 switch indicate a POST failure? blinks rapidly amber blinks rapidly green steady amber steady green
Q.6 Refer to the exhibit. A company always uses the last valid IP address in a subnetwork as the IP address of the router LAN interface. A network administrator is using a laptop to configure switch X with a default gateway. Assuming that the switch IP address is 192.168.5.147/24, what command will the administrator use to assign a default gateway to the switch? X(config)# ip default-gateway 192.168.5.254 X(config)# ip gateway 192.168.5.1 X(config)# ip route 0.0.0.0 0.0.0.0 192.168.5.1 X(config)# ip default-route 192.168.5.1 X(config)# ip route 192.168.5.254 255.255.255.0 fastethernet 0/0
Q.7 A technician has made changes to the configuration of a router. What command will allow the technician to view the current configuration before he saves the changes? router# show running-config router# show startup-config router# show flash router# show version
Q.8 Passwords can be used to restrict access to all or parts of the Cisco IOS. Select the modes and interfaces that can be protected with passwords. (Choose three.) VTY interface console interface Ethernet interface secret EXEC mode privileged EXEC mode router configuration mode
Q.9 To save time, IOS commands may be partially entered and then completed by typing which key or key combination? Tab Ctrl-P
Ctrl-N Up Arrow Right Arrow Down Arrow Q.10 What is the correct command sequence to configure a router host name to 'LAB_A'? Router> enable Router# configure terminal Router(config)# hostname LAB_A Router> enable Router# hostname LAB_A Router> enable Router# configure router Router(config)# hostname LAB_A Router> enable Router(config)# host name LAB_A
Q.11 Refer to the exhibit. From the router console, an administrator is unable to ping a Catalyst switch that is located in another building. What can the administrator do from her location to check the IP configuration of the attached switch? Open an SDM session with the switch from her desktop. Telnet to the switch from the router console. Use the show cdp neighbors detail command from the router console. The administrator must go to the switch location and make a console connection to check these settings.
Q.12 Which two options must be selected in SDM Express to enable a router serial interface to obtain an IP address automatically? (Choose two.) Easy IP (IP negotiated) IP unnumbered No IP address HDLC encapsulation Frame Relay encapsulation PPP encapsulation
Q.13 What three settings can be made in the SDM Express basic configuration screen? (Choose three.) host name DHCP options domain name interface IP addresses enable secret password DNS server IP addresses
Q.14 Which tasks can be accomplished by using the command history feature? (Choose two.) View a list of commands entered in a previous session. Recall up to 15 command lines by default. Set the command history buffer size. Recall previously entered commands. Save command lines in a log file for future reference.
Q.15 What option within Cisco SDM Express must be configured to allow hosts that receive IP address settings from the router to resolve names on the network or Internet? host name domain name DHCP address pool DNS server IP address
Q.16 Which three encapsulation types can be set on a serial interface by an administrator who is using SDM Express? (Choose three.) ATM CHAP Frame Relay HDLC PAP PPP
Q.17 Which command will display routing table information about all known networks and subnetworks? Router# show ip interfaces Router# show ip connections Router# show ip route Router# show ip networks
Q.18 A network administrator needs to configure a router. Which of the following connection methods requires network functionality to be accessible? console AUX Telnet modem
Q.19 Which three pieces of information about a neighbor device can be obtained by the show cdp neighbors command? (Choose three.) platform routing protocol connected interface of neighbor device device ID IP addresses of all interfaces enable mode password
Q.20 Which function is a unique responsibility of the DCE devices shown in the exhibit?
transmission of data reception of data clocking for the synchronous link noise cancellation in transmitted data
Q.21 Which of the following are functions of NVRAM? (Choose two.) stores the routing table retains contents when power is removed stores the startup configuration file contains the running configuration file stores the ARP table
Q.22 Refer to the exhibit. Which series of commands will enable users who are attached to Router1 to access the remote server? Router1(config)# interface S0/0/0 Router1(config-if)# ip address 64.100.0.129 255.255.255.252 Router1(config-if)# clock rate 64000 Router1(config-if)# no shutdown Router1(config)# interface S0/0/0 Router1(config-if)# ip address 64.100.0.125 255.255.255.252 Router1(config-if)# no shutdown Router1(config)# interface S0/0/0 Router1(config-if)# ip address 64.100.0.125 255.255.255.252 Router1(config-if)# clock rate 64000 Router1(config-if)# no shutdown Router1(config)# interface S0/0/0 Router1(config-if)# ip address 64.100.0.129 255.255.255.252 Router1(config-if)# no shutdown
Q.23 A network technician is attempting to add an older workstation to a Cisco switched LAN. The technician has manually configured the workstation to full-duplex mode in order to enhance the network performance of the workstation. However, when the device is attached to the network, performance degrades and excess collision are detected. What is the cause of this problem? The host is configured in a different subnet from the subnet of the switch. There is a duplex mismatch between the workstation and switch port. The switch port is running at a different speed from the speed of the workstation NIC. The host has been configured with a default gateway that is different from that of the switch.
Q.24 Which of the following statements are true regarding the user EXEC mode? (Choose two.)
All router commands are available. Global configuration mode can be accessed by entering the enable command. A password can be entered to allow access to other modes. Interfaces and routing protocols can be configured. Only some aspects of the router configuration can be viewed.
Q.25 Which command turns on a router interface? Router(config-if)# enable Router(config-if)# no down Router(config-if)# s0 active Router(config-if)# interface up Router(config-if)# no shutdown
Q.1 In an 8 bit binary number, what is the total number of combinations of the eight bits? 128 254 255 256 512 1024
Q.2 Convert the decimal number 231 into its binary equivalent. Select the correct answer from the list below. 11110010 11011011 11110110 11100111 11100101 11101110
Q.3 How many usable hosts are available given a Class C IP address with the default subnet mask? 254 255 256 510 511 512
Q.4 Which statement describes NAT overload or PAT? Each internal address is dynamically translated to an individual external IP address. A single internal address is always translated to the same unique external IP address. Many internal addresses can be translated to a single IP address using different port assignments. Many internal addresses are statically assigned a single IP address and port to use for communications.
Q.5 Which IPv4 class of addresses provides the most networks? Class A Class B Class C
Class D Class E
Q.6 Which statement accurately describes public IP addresses? Public addresses cannot be used within a private network. Public IP addresses must be unique across the entire Internet. Public addresses can be duplicated only within a local network. Public IP addresses are only required to be unique within the local network. Network administrators are free to select any public addresses to use for network devices that access the Internet.
Q.7 Which two statements describe classful IP addresses? (Choose two.) It is possible to determine which class an address belongs to by reading the first bit. The number of bits used to identify the hosts is fixed by the class of the network. Only Class A addresses can be represented by high-order bits 100. Up to 24 bits can make up the host portion of a Class C address. Up to 24 bits can be used to identify unique networks. Three of the five classes of addresses are reserved for multicasts and experimental use.
Q.8 Company XYZ uses a network address of 192.168.4.0. It uses the mask of 255.255.255.224 to create subnets. What is the maximum number of usable hosts in each subnet? 6 14 30 62
Q.9 hat is the network broadcast address for a Class C address of 192.168.32.0 with the default subnet mask? 192.168.0.0 192.168.0.255 192.168.32.0 192.168.32.254 192.168.32.255
Q.10 Refer to the exhibit. Host A is connected to the LAN, but it cannot get access to any resources on the Internet. The configuration of the host is shown in the exhibit. What could be the cause of the problem? The host subnet mask is incorrect. The default gateway is a network address. The default gateway is a broadcast address. The default gateway is on a different subnet from the host. Q.11 IPv6 increases the IP address size from 32 bits to how many bits? 64 96 128 192 256 512
Q.12 What is the range of the first octet in a Class B address? 127 to 191 127 to 192 128 to 191 128 to 192
Q.13 Which IPv4 class provides the highest number of host addresses per network? Class A Class B Class C Class D Class E
Q.14 refer to the exhibit. Which range of IP addresses would allow hosts that are connected to the Router1 Fa0/0 interface to access outside networks? 192.168.1.0 through 192.168.1.95 192.168.1.66 through 192.168.1.94 192.168.1.66 through 192.168.1.96 192.168.1.0 through 192.168.1.127 192.168.1.66 through 192.168.1.128
Q.15 Which option shows the proper notation for an IPv6 address? 2001,0db8,3c55,0015,abcd,ff13 2001-0db8-3c55-0015-abcd-ff13 2001.0db8.3c55.0015.abcd.ff13 2001:0db8:3c55:0015::abcd:ff13
Q.16 What are two reasons that NAT was developed? (Choose two.) to preserve registered public IP addresses to allow users on the public Internet to access local networks to provide a method for privately addressed LANs to participate in the Internet to make routing protocols operate more efficiently to allow private addresses to be routed on the public Internet to reduce overhead and CPU usage on gateway routers
Q.17 What must happen for a privately addressed host on an inside local network to be able to communicate with an outside destination host on the Internet? The host IP address must be translated to an outside private address. The host IP address must be translated to an inside local address. The host IP address must be translated to an outside local address. The host IP address must be translated to an inside global address.
Q.18 Which port numbers are used by PAT to create unique global addresses? 255 and below 1024 and below 1025 and above 64,000 and above
Q.19 Static NAT works by mapping a specific inside local IP address to what other specific address type? inside global outside local outside global private IP address
Q.20 What are three advantages of NAT implementations? (Choose three.) improved security improved router performance decreased processor load improved scalability universal application compatibility sharing few public IP addresses with many hosts
Q.1 Which two benefits can be gained by locating network equipment in a telecommunications closet, rather than in a user area? (Choose two.) faster communication speeds improved physical security more resistant to hacker attempts centralized cable management less electrical usage
Q.2 Which three issues should be noted on the technician's site survey report? (Choose three.) unlabeled cables
only two power outlets per wall in each room poor physical security of network devices horizontal cabling runs under 100 meters lack of UPS for critical devices two users sharing the same computer
Q.3 Which two types of cable are used for initial router configuration? (Choose two.) serial cable rollover cable straight-through cable crossover cable patch cable console cable
Q.4 In addition to the inventory sheet, what other information about the hosts and networking equipment should be documented by the on-site technician while performing the site survey? any obsolete office equipment being stored all product keys for site license software any planned growth anticipated in the near future the memory requirements for installed application software
Q.5 Refer to the exhibit. What type of device is used to connect two networks? hub router switch access point
Q.6 It is said that the goal for availability of a communications system is "five-9s". What is meant by this? A down time of .00001% is unacceptable. A network needs to be available 99.999% of the time. Five percent of all network expense covers 99% of user requirements. The most critical time for network availability is from 9:00 to 5:00 p.m. five days a week. The best time to do maintenance on a network is from 5:00 p.m. to 9:00 a.m. five days a week.
Q.7 What three things are included in a logical topology document? (Choose three.) the location of cables, computers, and other peripherals the path that the data takes through a network the wireless signal coverage area the wiring closet and access point locations the device names and Layer 3 addressing information the location of routing, network address translation, and firewall filtering
Q.8. Which device has the ability to break up broadcast and collision domains? repeater hub router switch
Q.9 Why is it important to review the results of an on-site survey report with the customer before beginning the network design? to inform the customer of how much time the upgrade will take to discuss the implementation schedule for the new equipment to verify that the report accurately describes the current network and any plans for expansion to layout the new network design and discuss possible equipment upgrades and replacements
Q.10 A client requires a networking device that is capable of expansion to suit growing network demands. What type of device will suit this requirement? a networking device with ports that can be activated and deactivated a networking device with a modular physical configuration a networking device with the ability to be turned off remotely a networking device with a cost per port that is as high as possible
Q.11 What does the use of redundant network components supply to a network? scalability manageability compatibility reliability
Q.12 What is the benefit for a company to use an ISR router? An ISR provides the functionality of a switch, router, and firewall in one device. ISRs use a PC operating system for routing traffic, thus simplifying configuration and management. An ISR is immune to security attacks by hackers and so replaces all other network security measures. ISRs make routing decisions at OSI Layer 7, thus providing more intelligence to the network than do other routers.
Q.13 Which three items are typically found in an MDF? (Choose three.) user workstations switches and routers fax machines network equipment racks the point of presence copier
Q.14 What are two advantages of having ISP-managed services? (Choose two.) does not require leasing costs for service can guarantee up to 99.999% availability eliminates the need for data backup
increases availability of help desk services does not require a Service Level Agreement
Q.15 A manufacturing company is in the process of a network upgrade. Which two statements are true about the phases of the upgrade process? (Choose two.) Phase 1 is used to determine network requirements. Phase 2 includes creating an analysis report. Phase 3 is based on an implementation schedule that allows extra time for unexpected events. Phase 4 is where prototypes are created and tested. Phase 5 includes identifying and addressing any weaknesses in the design.
Q.16 When designing a network upgrade, which two tasks should the onsite technician perform? (Choose two.) configure the servers and routers prior to delivery upgrade the network operating system and all client operating systems investigate and document the physical layout of the premises document the final design for approval by the customer perform a site survey to document the existing network structure
Q.17 What is the term for the location at the customer premise where the customer network physically connects to the Internet through a telecommunications service provider? backbone area point of presence network distribution facility intermediate distribution frame
Q.18 Refer to the exhibit. Which type of twisted pair cable is used between each device? A=console, B=straight, C=crossover, D= crossover, E=straight A=straight, B=straight, C=straight, D=crossover, E=console A=crossover, B=straight, C=straight, D=crossover, E=crossover A=console, B=straight, C=straight, D=crossover, E=crossover A=console, B=crossover, C=crossover, D=straight, E=straight
Q.19 In what two ways will entering into a managed service agreement with an ISP for a network upgrade affect the costs that are incurred by the customer? (Choose two.) Customer IT training costs will increase to enable operation of the new equipment. The cost of hardware repairs and support will become the responsibility of the customer. Network upgrade and maintenance costs will become predictable. Staffing costs will increase because the customer will need to hire additional IT staff to complete the upgrade.
The company will not need to spend a large amount of money to purchase the equipment upfront.
Q.20 Which type of cable has a solid copper core with several protective layers including PVC, braided wire shielding, and a plastic covering? STP UTP coaxial fiber optic
Q.21 What must be added when a network expands beyond the coverage area of the current telecommunications room? MDF POP IDF IXP
Q.1 Which two functions are provided by the upper layers of the OSI model? (Choose two.) placing electrical signals on the medium for transmission initiating the network communication process encrypting and compressing data for transmission segmenting and identifying data for reassembly at the destination choosing the appropriate path for the data to take through the network
Q.2 Which is a function of the transport layer of the OSI model? routes data between networks converts data to bits for transmission delivers data reliably across the network using TCP formats and encodes data for transmission transmits data to the next directly connected device
Q.3 Which common Layer 1 problem can cause a user to lose connectivity? incorrect subnet mask incorrect default gateway loose network cable NIC improperly installed
Q.4 Which three command line utilities are most commonly used to troubleshoot issues at Layer 3? (Choose three.) ping a packet sniffer Telnet ipconfig Traceroute
Q.5 Which address is used by the router to direct a packet between networks? source MAC address
destination MAC address source IP address destination IP address
Q.6 What is the correct encapsulation order when data is passed from Layer 1 up to Layer 4 of the OSI model? bits, frames, packets, segments frames, bits, packets, segments packets, frames, segments, bits segments, packets, frames, bits
Q.7 What are two goals of the ISP help desk? (Choose two.) conserving support resources network optimization competitive scalability customer retention sales of network services
Q.8 In what two ways do Level 1 and Level 2 help desk technicians attempt to solve a customer's problems? (Choose three.) talking to the customer on the telephone upgrading hardware and software using various web tools making an onsite visit installing new equipment with remote desktop sharing applications
Q.9 A customer calls the help desk about setting up a new PC and cable modem and being unable to access the Internet. What three questions would the technician ask if the bottom-up troubleshooting approach is used? (Choose three.) Is the NIC link light blinking? What is the IP address and subnet mask? Can the default gateway be successfully pinged? Is the network cable properly attached to the modem? Is the Category 5 cable properly connected to the network slot on the PC? Can you access your e-mail account?
Q.10 A customer calls to report a problem accessing an e-commerce web site. The help desk technician begins troubleshooting using a top-down approach. Which question would the technician ask the customer first? Can you access other web sites? Is there a firewall installed on your computer? What is your IP address? Is the link light lit on your NIC card?
Q.11 Which statement describes the process of escalating a help desk trouble ticket? The help desk technican resolves the customer problem over the phone and closes the trouble ticket.
Remote desktop utilities enable the help desk technician to fix a configuration error and close the trouble ticket. After trying unsuccessfully to fix a problem, the help desk technician sends the trouble ticket to the onsite support staff. When the problem is solved, all information is recorded on the trouble ticket for future reference.
Q.12 What are two functions of the physical layer of the OSI model? (Choose two.) adding the hardware address converting data to bits encapsulating data into frames signal generation routing packets
Q.13 A customer calls the ISP help desk after setting up a new PC with a cable modem but being unable to access the Internet. After the help desk technician has verified Layer 1 and Layer 2, what are three questions the help desk technician should ask the customer? (Choose three.) What is your subnet mask? What is your IP address? Is the NIC link light blinking? Can you ping the default gateway? Is the network cable properly attached to the cable modem? Is the network cable correctly connected to the network port on the PC?
Q.14 Which scenario represents a problem at Layer 4 of the OSI model? An incorrect IP address on the default gateway. A bad subnet mask in the host IP configuration. A firewall filtering traffic addressed to TCP port 25 on an email server. An incorrect DNS server address being given out by DHCP.
Q.15 What are two basic procedures of incident management? (Choose two.) opening a trouble ticket using diagnostic tools to identify the problem surveying network conditions for further analysis configuring new equipment and software upgrades adhering to a problem-solving strategy e-mailing a problem resolution to the customer
Q.16 Which level of support is supplied by an ISP when providing managed services? Level 1 Level 2 Level 3 Level 4
Q.17 What is the first step that is used by a help desk technician in a systematic approach to helping a customer solve a problem? identify and prioritize alternative solutions isolate the cause of the problem define the problem select an evaluation process
Q.18 A network technician has isolated a problem at the transport layer of the OSI model. Which question would provide further information about the problem? Do you have a firewall that is configured on your PC? Do you have a link light on your network card? Is your PC configured to obtain addressing information using DHCP? What default gateway address is configured in your TCP/IP settings? Can you ping http://www.cisco.com?
Q.19 An ISP help desk technician receives a call from a customer who reports that no one at their business can reach any websites, or get their e-mail. After testing the communication line and finding everything fine, the technician instructs the customer to run nslookup from the command prompt. What does the technician suspect is causing the customer's problem? improper IP address configuration on the host hardware failure of the ISR used to connect the customer to the ISP bad cables or connections at the customer site failure of DNS to resolve names to IP addresses
Q.20 Which layers of the OSI model are commonly referred to as the upper layers? application, presentation, session application, session, network presentation, transport, network presentation, network, data link session, transport, network
Q.1 Which two things can be determined by using the ping command? (Choose two.) the number of routers between the source and destination device the IP address of the router nearest the destination device the average time it takes a packet to reach the destination and for the response to return to the source whether or not the destination device is reachable through the network the average time it takes each router in the path between source and destination to respond
Q.2 What are three main types of high-bandwidth connection options used by medium- to large-sized businesses? (Choose three.) DSL cable modem Ethernet metro Ethernet T1 T3
Q.3 What is the maximum T1 transmission speed? 56 kbps 128 kbps 1.544 Mbps 2.4 Mbps
Q.4 Which of the following start the test of destination reachability? echo request issued by source echo reply issued by source echo request issued by destination echo reply issued by destination
Q.5 Which statement describes a function of a Tier 1 ISP? peers with other similarly sized ISPs to form the global Internet backbone uses the services of Tier 3 ISPs to connect to the global Internet backbone pays Tier 2 ISPs for transit services to connect across continents limits the offered services to small geographic areas
Q.6 At which point do individuals and small businesses connect directly to the ISP network to obtain Internet access? at a POP at an IXP at a Metro Ethernet link on the ISP extranet
Q.7 What information is contained in the numbered RFCs maintained by the IETF? the rules for acceptable use of websites and e-mail the descriptions of various hardware components that connect to the Internet the specifications and rules for how devices communicate over an IP network the standards for cabling and wiring for local Ethernet networks
Q.8 Which network support services team is responsible for testing a new customer connection and for monitoring the ongoing operation of the link?" customer service help desk network operations on-site installation
Q.9 Which network support services team identifies whether the client site has existing network hardware and circuits installed? customer service help desk network operations planning and provisioning
Q.10 Which ISP network support systems team will typically contact the customer once a new circuit is ready and guide the customer in setting up passwords and other account information? help desk customer service network operations center on-site installation team planning and provisioning
Q.11 What feature allows network devices to be scalable? a fixed number of interfaces ease of repair modularity low maintenance requirements low cost
Q.12 Which command generated this output? 1 12.0.0.2 4 msec 4 msec 4 msec 2 23.0.0.3 20 msec 16 msec 16 msec 3 34.0.0.4 16 msec 18 msec 16 msec Router# traceroute 34.0.0.4 Router# nslookup 34.0.0.4 Router# ping 34.0.0.4 Router# telnet 34.0.0.4
Q.13 Which network utility helps determine the location of network problems and identifies routers that packets travel across? ping ipconfig traceroute ixp
Q.14 What interconnects the Internet backbone? gateway routers IXPs POPs satellite dishes
Q.15 What units are used to measure Internet bandwidth? bits per second bytes per second hertz megabytes per second packets per second
Q.16 The IT manager of a medium-sized business wishes to house the company-owned web servers in a facility that offers round-the-clock controlled access, redundant power, and high-bandwidth Internet access. Which ISP service will fulfill this need? web hosting planning and provisioning application hosting equipment colocation Tier 1 ISP services
Q.17 What is the purpose of an RFC? to provide the connection point for multiple ISPs to the Internet
to document the development and approval of an Internet standard to connect a business to an ISP to provide data communication services to ISP customers to monitor network performance and connection status of ISP clients
Q.18 When did the Internet become available for use by businesses and consumers? 1979 1984 1991 1999 2000
Q.19 What was the original purpose of the Internet? voice communication marketing research commerce
Q.20 What three support service teams are commonly found within an ISP? (Choose three.) help desk computer support application readiness network operations center planning and provisioning implementation and documentation
1 Which AAA service reduces IT operating costs by providing detailed reporting and monitoring of network user behavior, and also by keeping a record of every access connection and device configuration change across the network? authentication accreditation accounting authorization
2 Which three items are normally included when a log message is generated by a syslog client and forwarded to a syslog server? (Choose three.) date and time of message ID of sending device length of message message ID checksum field community ID
3 What is the advantage of using WPA to secure a wireless network? It uses a 128-bit pre-shared hexadecimal key to prevent unauthorized wireless access. It uses an advanced encryption key that is never transmitted between host and access point.
It is supported on older wireless hardware, thus providing maximum compatibility with enterprise equipment. It requires the MAC address of a network device that is requesting wireless access to be on a list of approved MAC addresses.
4 A company wants to configure a firewall to monitor all channels of communication and allow only traffic that is part of a known connection. Which firewall configuration should be deployed? packet filtering proxy stateful packet inspection stateless packet inspection
5 A server log includes this entry: User student accessed host server ABC using Telnet yesterday for 10 minutes. What type of log entry is this? authentication authorization accounting accessing
6 What two measures help to verify that server backups have been reliably completed? (Choose two.) reviewing backup logs performing trial backups performing full backups only replacing tape backup with hard disk-based backup using an autoloader when backups require more than one tape
7 Which means of communication does an SNMP network agent use to provide a network management station with important but unsolicited information? query broadcast ICMP ping trap poll
8 Which three protocols are used for in-band management? (Choose three.) FTP HTTP SNMP Telnet TFTP DHCP
9 A hacker has gained access to sensitive network files. In analyzing the attack, it is found that the hacker
gained access over a wireless segment of the network. It is further discovered that the only security measure in place on the wireless network is MAC Address Filtering. How is it likely that the hacker gained access to the network? The hacker used a software tool to crack the shared hexadecimal wireless key. The hacker obtained the MAC address of a permitted host, and cloned it on his wireless laptop NIC. The attacker mounted a denial of service attack to overwhelm the firewall before penetrating the wireless LAN. The hacker gained wireless access to the MAC address database and added his own MAC address to the list of permitted addresses.
10 A network administrator is assigning network permissions to new groups of users and employing the principle of least privilege. Which two actions should the administrator take? (Choose two.) Provide users with only the access to resources required to do their jobs. Provide the minimum level of permissions required for users to do their jobs. Remove all permissions from the users and grant permissions as they are requested. Allow users to decide how much permission they need to accomplish their job tasks. Provide full access to the users and gradually remove privileges over time.
11 Which three protocols describe methods that can be used to secure user data for transmission across the internet? (Choose three.) SMTP IPSEC SSL HTTPS FTP TFTP
12 Which benefit does SSH offer over Telnet when remotely managing a router? encryption TCP usage authorization connection using six VTY lines
13 Which of the following does SNMP use to hold information collected about the network? network management station network management database management information base database information agent
14 What are two potential problems with using tape media to back up server data? (Choose two.) Tape is not a cost-effective means of backing up data. Data tapes are difficult to store offsite. Data tapes are prone to failure and must be replaced often.
Tape drives require regular cleaning to maintain reliability. Backup logs are not available with tape backup solutions.
15 What is the term for the public network between the boundary router and the firewall? "clean" LAN intranet DMZ extranet
16 Which two characteristics of network traffic are being monitored if a network technician configures the company firewall to operate as a packet filter? (Choose two.) applications physical addresses packet size ports protocols
17 When is the use of out-of-band network management necessary? when a server needs to be monitored across the network when the management interface of a device is not reachable across the network when enhanced monitoring features are required to gain an overall view of the entire network when it is desirable to use the information that is provided by SNMP
18 What network layer security protocol can secure any application layer protocol used for communication? HTTPS IMAP FTPS IPSEC TLS
19 Before a technician upgrades a server, it is necessary to back up all data. Which type of backup is necessary to ensure that all data is backed up? daily differential full incremental partial
20 What AAA component assigns varying levels of rights to users of network resources? auditing
accounting authorization access control authentication acknowledgement
1 What is a feature of PAT? It maps IP addresses to URLs. It displays private IP addresses to public networks. It sends acknowledgments of received packets. It allows multiple hosts on a single LAN to share globally unique IP addresses.
2 An administrator wishes to protect a router by encrypting the console access password noaccess. Which command should be used?
Router(config)# enable secret noaccess Router(config)# enable password noaccess Router(config-line)# password noaccess Router(config)# service password-encryption
Refer to the graphic. Which command will configure a static route on Router A to direct traffic from LAN A that is destined for LAN C?
RouterA(config)# ip route 192.168.4.0 255.255.255.0 192.168.5.2 RouterA(config)# ip route 192.168.4.0 255.255.255.0 192.168.3.2 RouterA(config)# ip route 192.168.5.0 255.255.255.0 192.168.3.2 RouterA(config)# ip route 192.168.3.0 255.255.255.0 192.168.3.1 RouterA(config)# ip route 192.168.3.2 255.255.255.0 192.168.4.0
4. When using NAT on a router, what is the term for the IP address of an inside host as it appears to the outside network? inside local inside global outside local outside global 5 A network engineer is asked to specify the type of cable for a new network installation. The engineer plans horizontal cable runs of less than 90 feet (27.4 meters) using cable that is not expensive and is easy to implement. It will be positioned away from electrically noisy areas to avoid EMI. Which cable should the engineer choose? STP UTP coaxial fiber optic
Refer to the exhibit. Which subnet mask would accommodate the number of hosts shown for each subnetwork with the least amount of IP addresses wasted? 255.255.0.0 255.255.255.192 255.255.255.224 255.255.255.240 255.255.255.248 7
Refer to the exhibit. Which two IP addresses could be assigned to the hosts in the diagram? (Choose two.) 192.168.65.31 192.168.65.32 192.168.65.35 192.168.65.60 192.168.65.63 192.168.65.64
8. A user is able to ping an FTP server across a WAN but is unable to download files from the server. What should be checked to resolve this problem? the NIC drivers the IP configuration the LED status of the NIC firewall settings 9. What is a characteristic of Syslog? It requires users to prove their identity with the use of a username and password before users can access network resources. It listens to network traffic and sends an alert to a management station to track which applications are used and the length of time for which they are used. It enables devices to send information to a daemon that runs on a management station. It provides users the rights to access specific resources and perform specific tasks.
10.
Refer to the exhibit. What does the highlighted value 120 represent? the number of hops between the router and network 10.0.5.0 the administrative distance of the routing protocol the UDP port number that is used for forwarding traffic the bandwidth that is allocated to the serial interface
Refer to the exhibit. A new router has been configured for the first time with the commands that are
displayed. Which two facts can be determined about the interface of this router? (Choose two.)
It will act as a DCE device.
It is administratively down.
It will operate at a speed of 6.4 Mb/s.
It is the first interface on slot 0 of controller 1.
Because MOTD is not configured, the interface will not work.
Refer to the exhibit. What effect will the commands have when entered on R2?
The cisco1 file will be copied to NVRAM.
The commands will not work because a password has not been set on the TFTP server.
The running configuration will be copied from R2 to the TFTP server. The cisco1 file will be copied from the TFTP server to the running configuration of R2.
3 The command copy tftp running-config has been entered on the router. What will this command do?
copy the configuration in RAM to a server
copy the configuration file from a server to RAM
copy the configuration file in NVRAM to RAM
copy the configuration file in NVRAM to a server
copy the configuration file from a server to NVRAM
4 A small company has contracted with its ISP for web hosting. Which two items would be included in the SLA for this service? (Choose two.)
performance
web server cost
service availability
operating system on the web server
web server model and configuration
Refer to the exhibit. Which combination of cables and symbols is correct?
A crossover, B straight-through, C straight-through
A crossover, B rollover, C straight-through
A straight-through, B -crossover, C straight-through
A straight-through, B -straight-through, C straight-through
A straight-through, B straight-through, C crossover
A rollover, B straight-through, C straight-through
6 Which statement is true about the reverse lookup DNS zone?
It is most commonly experienced when users are surfing the Internet.
It is the backup for the forward lookup zone.
It dynamically updates the resource records.
It resolves an IP address to a fully qualified domain name.
7 A user reports being unable to access the Internet. The help desk technician employs a bottom-up approach to troubleshooting. The technician first has the user check the patch cable connection from the PC to the wall, and then has the user verify that the NIC has a green link light. What will the technician have the user do next?
Enter an IP address into the WWW browser address bar to see if DNS is at fault.
Use traceroute to identify the device along the path to the ISP that may be at fault.
Verify the IP address, subnet, and gateway settings using ipconfig on the PC.
Connect to the user home router to check firewall settings for blocked TCP ports.
8 What is the purpose of the routing process?
to encapsulate data that is used to communicate across a network
to select the paths that are used to direct traffic to destination networks
to convert a URL name into an IP address
to provide secure Internet file transfer
to forward traffic on the basis of MAC addresses
Refer to the exhibit. A ping 192.168.1.20 command is issued on workstation A to determine if workstation B
can be reached. What two events will occur if this command is successful? (Choose two.)
The router will reply to the echo request with a proxy ping response.
Workstation A will send a UDP ping request message to workstation B.
The router will send a TCP acknowledgment message to workstation A.
Workstation B will send a UDP ping reply message to the router.
Workstation A will send an ICMP echo request message to workstation B.
Workstation B will send an ICMP echo reply message to workstation A.
10
Refer to the exhibit. Router Left is unable to ping router Right. The show interfaces serial 0/0/0 command
indicates that the interface is up but the line protocol is down on both routers. Which action could be taken to establish connectivity between the two routers?
Configure S0/0/1 instead of S0/0/0 on router Right.
Enter the encapsulation hdlc command on router Right.
Contact the service provider to report that the circuit is down.
Contact the service provider to enable PPP on the WAN circuit.
Enter the no encapsulation ppp command on router Left S0/0/0.
11 Which combination of network address and subnet mask allows 62 hosts to be connected in a single subnet?
Network address 10.1.1.4 Subnet mask 255.255.255.240
Network address 10.1.1.0 Subnet mask 255.255.255.252
Network address 10.1.1.0 Subnet mask 255.255.255.192
Network address 10.1.1.4 Subnet mask 255.255.255.248
12 Which type of cable is used to connect a computer to the wall plate in the work area of a user?
patch cable
vertical cable
console cable
horizontal cable
13 Refer to the exhibit. A network administrator is troubleshooting the serial connection between R1 and R2. There is no communication between R1 and R2. Based on the output of the show ip interface brief command, what is the cause of the problem?
There is a misconfiguration of IP addresses.
There is a mismatch of encapsulation methods.
The no shutdown command should be issued on R2.
The routing protocols are not compatible.
14 In a structured cable system, which term describes the cable that connects the wall jack in the user work area to the patch panel in the wiring closet?
patch cable
vertical cable
horizontal cable
backbone cable
15 Refer to the exhibit. Which two statements describe the data conversation shown? (Choose two.)
The data conversation was started by the HTTP application process running on the client.
The data conversation is identified by TCP port 80 on the client.
The user started the data conversation by sending an e-mail.
The IP address of the Internet server is 192.168.17.43.
The Internet server will send data to port 8547 on the client.
16
The show ip route command was executed on one of the routers shown in the graphic and the following
output was displayed:
C 192.168.4.0/24 is directly connected, Serial0/0
R 192.168.5.0/24 [120/1] via 192.168.4.2, 00:00:19, Serial0/0
R 192.168.1.0/24 [120/2] via 192.168.3.1, 00:00:20, Serial0/1
R 192.168.2.0/24 [120/2] via 192.168.3.1, 00:00:20, Serial0/1
C 192.168.3.0/24 is directly connected, Serial0/1
From which router was this command executed?
17 What can be gained by using a caching-only DNS server?
The DNS server will use more WAN bandwidth.
The DNS server will only answer recursive queries.
The DNS server will be authoritative for only one zone.
The DNS server will resolve most queries more quickly.
18 A technician is trying to troubleshoot an e-mail client that is configured with invalid POP and SMTP server information. At which layers of the OSI model is this network issue occurring?
Layers 1-2
Layers 2-3
Layers 2-4
Layers 5-7
19 Refer to the exhibit. What does the ^ symbol indicate?
It marks the end of an error message and an insert point for a new command.
It marks the beginning of an error message and an insert point for a new command.
It marks a point in the command string where there is an incorrect or unrecognized character.
It marks a point in the command string where a parameter has to be entered to complete the command configuration.
20 What is a characteristic of a scalable network?
100% uptime
redundant links
easy expansion
multiple backup devices
21
Refer to the exhibit. Devices need to connect to the file server from remote networks. What method should
be used to provide the file server with an IP address to allow these connections?
static NAT
static PAT
dynamic NAT
dynamic PAT
22 Which transport layer protocol will allow segments to be exchanged between two hosts with low overhead and no mechanism for retransmission?
IP
FTP
TCP
UDP
SMTP
23 A building has experienced a power outage. When the power returns, none of the devices on one floor can access the Internet. The network administrator checks the switch in the IDF that these devices are connected to and notes that the SYST LED on the front of the switch is amber.
What is a possible cause of this problem?
The switch is functioning properly.
The switch has failed POST.
The switch configuration file was not saved to NVRAM.
The connection between the switch and the server did not autonegotiate speed and duplex properly.
24 What is a feature of PAT?
It maps IP addresses to URLs.
It displays private IP addresses to public networks.
It sends acknowledgments of received packets.
It allows multiple hosts on a single LAN to share globally unique IP addresses.
25 Which type of WAN connection uses a circuit-switched network?
ISDN
Frame Relay
DSL
Cable
26 To protect the data of its customers, an ISP applies the security principle of least privilege within its organization and network. What is the principle of least privilege?
Encrypt only mission-critical data.
Give employees access only to the resources that they need.
Restrict file and folder access to system administrators only.
Use the smallest possible number of servers to share files and folders.
27 Which question provides troubleshooting information about a problem at Layer 1 or Layer 2 of the OSI model?
Can the server be reached through Telnet?
Is there a firewall that is configured on the PC?
Is there a link light on the network card?
What addresses are configured in the TCP/IP settings?
28 A user is able to ping IP addresses but is unable to ping hosts by domain name. What should be checked at the workstation of the user?
the device driver configuration of NIC
the LED status of the NIC
the DNS configuration
the firewall settings
29 Which service team in an ISP is responsible for determining if the new customer has hardware that will support the new WAN connection and if new WAN circuits need to be installed?
customer service
onsite installation
planning and provisioning
network operations center
30 What is the maximum unrepeated distance set by industry standards for UTP cable?
10 meters
75 meters
100 meters
325 meters
31 A network engineer has been asked to design a new structured cable system. What should be the first step in the project?
Obtain an accurate floor plan.
Identify all potential sources of EMI.
Sketch the proposed network design.
Determine the locations of all network devices.
32 Refer to the exhibit. A new branch office has been added to the corporate network and a new router is to be installed to allow branch office users to access the database server at headquarters. How should the serial 0/0/0 interface of the new branch office router be configured to connect to the headquarters router?
branch_23(config-if)# ip address 192.168.5.19 255.255.255.240
branch_23(config-if)# no shutdown
branch_23(config-if)# encapsulation hdlc
branch_23(config-if)# ip address 192.168.5.25 255.255.255.240
branch_23(config-if)# no shutdown
branch_23(config-if)# encapsulation ppp
branch_23(config-if)# no shutdown
branch_23(config-if)# encapsulation ppp
branch_23(config-if)# ip address 192.168.5.33 255.255.255.240
branch_23(config-if)# encapsulation ppp
branch_23(config-if)# ip address 192.168.5.21 255.255.255.240
branch_23(config-if)# no shutdown
33 Refer to the exhibit. The network administrator of the building in the graphic needs to choose the type of cable best suited to add ServerB to the network. Which cable type is the best choice?
STP
UTP
coaxial
fiber optic
34 What is a characteristic of UDP?
It is a reliable transport protocol.
It requires the source host to resend packets that are not acknowledged.
It adds a minimal amount of overhead to the data to be transmitted.
It is a connection-oriented protocol.
35
Refer to the exhibit. Users at the branch office complain that they cannot download files from the FTP
server that is located at the company headquarters (HQ). Which three troubleshooting steps would be appropriate, in the order from first step to the last, if a technician troubleshoots the problem by using the divideand-conquer method?
steps 1, 3, and 6
steps 1, 4, and 6
steps 2, 3, and 7
steps 4, 5, and 6
36
Refer to the exhibit. Host H1 is sending a datagram to host H2 across the Internet. NAT will be configured
on RTRC. Which address is considered the inside local address?
10.1.1.1
10.1.1.6
209.165.201.2
209.165.201.17
209.165.200.226
37 What are three features of the TCP protocol? (Choose three.)
It provides retransmission of data packets if they are lost during transmission.
It is a connectionless protocol.
It uses a three-way handshake between the sending and receiving systems to establish each conversation.
It specifies how messages are reassembled at the destination host.
It requires only 8 bytes of overhead.
It breaks the data packet into datagrams.
38 To manage a Cisco switch using Telnet, where would the management IP address be configured on the switch?
VLAN 1 interface
first vty port
first trunk port
console port
FastEthernet 0/1 interface
39 What is the default encapsulation for serial interfaces on Cisco routers?
PPP
SLIP
HDLC
Frame Relay
40 When would TFTP in ROM monitor mode be used to restore a Cisco IOS image to a router?
when a console connection is the only available connection to the router
when the TFTP server software is incompatible with the router IOS version
when the router is set to boot from flash, but the Cisco IOS image in flash is corrupt or has been erased
when the current Cisco IOS on the router requires a feature upgrade
41 What is the effect of issuing the hostname RouterA command on a router?
A description will be configured on the router interfaces identifying them as belonging to RouterA.
The router will attempt to establish a connection to the host with the name RouterA.
The router will map an IP address to the domain name RouterA.
The router prompt will change from Router(config)# to RouterA(config)#
42 A network technician wants to restore a backup copy of the saved configuration file on a router from a TFTP server. After restoring the file from the TFTP server, the technician reloads the router and finds that it still has the old configuration file instead of the restored file. What could have caused this?
The technician entered the command delete flash: before reloading the router.
The technician entered the command boot system rom before reloading the router.
The technician entered the command erase startup-config before reloading the router.
The technician failed to enter the command copy running-config startup-config before reloading the router.
43
Refer to the exhibit. Which subnet mask would accommodate the number of hosts shown for each
subnetwork with the least amount of IP addresses wasted?
255.255.0.0
255.255.255.192
255.255.255.224
255.255.255.240
255.255.255.248
44 What is used by a routing protocol to determine the best path to include in the routing table?
Convergence time
Default distance
Metric
Type of router
45 A company functions from Monday to Friday each week. Their backup strategy calls for full backups each Friday night, with differential backups on all other weekday nights. If an administrator is asked to restore a server hard drive to its Wednesday morning state, how many backups must be used?
46 Which encapsulation method supports automatic IP address assignment via the option IP Negotiated, when SDM is used to configure WAN connections on a router?
PPP
HDLC
Ethernet
Frame Relay
47 How do port filtering and access lists help provide network security?
They prevent specified types of traffic from reaching specified network destinations.
They alert network administrators to various type of denial of service attacks as they occur.
They prevent viruses, worms, and Trojans from infecting host computers and servers.
They enable encryption and authentication of confidential data communications.
48
Refer to the exhibit. What does the highlighted value 120 represent?
the number of hops between the router and network 10.0.5.0
the administrative distance of the routing protocol
the UDP port number that is used for forwarding traffic
the bandwidth that is allocated to the serial interface
49 In the relationship between an ISP and a customer, what is the purpose of an SLA?
It shows bandwidth utilization over time.
It documents expectations and obligations of both parties.
It helps technicians locate sources of service interruptions.
It provides performance baselines for network troubleshooting.
50 Refer to the exhibit. Which statement correctly identifies the OSI layer and possible reason that Serial 0/0/0 is down?
Layer 1 cable is not plugged in correctly
Layer 1 no shutdown command not entered
Layer 2 clock rate not set
Layer 2 incorrect encapsulation is configured on the WAN link
Layer 3 incorrect IP addresses was configured on the interface
Layer 3 network statement is missing from the routing protocol configuration
51 Which protocol allows secure in-band management so that a network administrator can monitor and configure network devices without fear of any passwords being compromised?
SSH
HTTP
SNMP
Telnet
52 Which cable type is used to interconnect the FastEthernet interfaces of two routers?
straight-through
crossover
console
rollover
Vous aimerez peut-être aussi
- Serial Port Complete: COM Ports, USB Virtual COM Ports, and Ports for Embedded SystemsD'EverandSerial Port Complete: COM Ports, USB Virtual COM Ports, and Ports for Embedded SystemsÉvaluation : 3.5 sur 5 étoiles3.5/5 (9)
- Cisco 1 Reviewer For Final ExamDocument9 pagesCisco 1 Reviewer For Final ExamAlPas encore d'évaluation
- TCP/IP Networking Interview Questions, Answers, and Explanations: TCP/IP Network Certification ReviewD'EverandTCP/IP Networking Interview Questions, Answers, and Explanations: TCP/IP Network Certification ReviewÉvaluation : 4.5 sur 5 étoiles4.5/5 (2)
- Private Security Industry ReportDocument40 pagesPrivate Security Industry ReportkarndePas encore d'évaluation
- Dep 32.32.00.11-Custody Transfer Measurement Systems For LiquidDocument69 pagesDep 32.32.00.11-Custody Transfer Measurement Systems For LiquidDAYOPas encore d'évaluation
- Data Science Machine LearningDocument15 pagesData Science Machine LearningmagrinraphaelPas encore d'évaluation
- CCST Cisco Certified Support Technician Study Guide: Networking ExamD'EverandCCST Cisco Certified Support Technician Study Guide: Networking ExamPas encore d'évaluation
- Managerial Accounting and Cost ConceptsDocument67 pagesManagerial Accounting and Cost ConceptsTristan AdrianPas encore d'évaluation
- Banking Finance Agile TestingDocument4 pagesBanking Finance Agile Testinganil1karnatiPas encore d'évaluation
- Alcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsD'EverandAlcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsPas encore d'évaluation
- TG Comply With WP Hygiene Proc 270812 PDFDocument224 pagesTG Comply With WP Hygiene Proc 270812 PDFEmelita MendezPas encore d'évaluation
- Module 1 (Social Innovation)Document7 pagesModule 1 (Social Innovation)Marinette Medrano50% (2)
- CCNA Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesD'EverandCCNA Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesPas encore d'évaluation
- ROUTE Chapter 4 - CCNP ROUTE (Version 6.0)Document12 pagesROUTE Chapter 4 - CCNP ROUTE (Version 6.0)AS2205100% (5)
- Versatile Routing and Services with BGP: Understanding and Implementing BGP in SR-OSD'EverandVersatile Routing and Services with BGP: Understanding and Implementing BGP in SR-OSPas encore d'évaluation
- Practical Guide to LTE-A, VoLTE and IoT: Paving the way towards 5GD'EverandPractical Guide to LTE-A, VoLTE and IoT: Paving the way towards 5GPas encore d'évaluation
- Ccna 2 Module 6Document9 pagesCcna 2 Module 6shkarkoddl100% (4)
- DsmbISP Final Exam - CCNA Dicovery Working at A Small-To-Medium Business or ISP (Version 4.1) Final 2Document13 pagesDsmbISP Final Exam - CCNA Dicovery Working at A Small-To-Medium Business or ISP (Version 4.1) Final 2JesusforgivemePas encore d'évaluation
- Ewan Final ADocument31 pagesEwan Final Amoky_roPas encore d'évaluation
- CHAPTER - 3 Introduction To Dynamic Routing ProtocolDocument5 pagesCHAPTER - 3 Introduction To Dynamic Routing ProtocolAlexandrosAristeridisPas encore d'évaluation
- Ccna 3 Chapter 5 (Version 4.0)Document8 pagesCcna 3 Chapter 5 (Version 4.0)_mika_Pas encore d'évaluation
- Semester II. - Chapter 3Document6 pagesSemester II. - Chapter 3KlokanPas encore d'évaluation
- 20.05.2010 XX%Document9 pages20.05.2010 XX%jjw234080862Pas encore d'évaluation
- CCNA4 Practice FinalDocument13 pagesCCNA4 Practice Finalrastha7Pas encore d'évaluation
- CCNA 2 Final Exam Question Ans AnswerDocument100 pagesCCNA 2 Final Exam Question Ans AnswerTú BéoPas encore d'évaluation
- Ewan Final Exam 1Document8 pagesEwan Final Exam 1Kathlyn MercadoPas encore d'évaluation
- Take Assessment - DsmbISP Final Exam - CCNA Discovery - Working at A Small-To-Medium Business or ISP (Version 4.1)Document8 pagesTake Assessment - DsmbISP Final Exam - CCNA Discovery - Working at A Small-To-Medium Business or ISP (Version 4.1)Manjula RathnathilakePas encore d'évaluation
- CCNA Exploration2: Routing Protocols - Chapter 3 Exam: Distance of EIGRP Is Lower Than RIPDocument5 pagesCCNA Exploration2: Routing Protocols - Chapter 3 Exam: Distance of EIGRP Is Lower Than RIPsayedahmedPas encore d'évaluation
- G0/1.2 Will Be in A Down/down State. G0/1.1 Will Be in An Administratively Down StateDocument33 pagesG0/1.2 Will Be in A Down/down State. G0/1.1 Will Be in An Administratively Down Stateivan martinez robledoPas encore d'évaluation
- Chapter 3 Routing Protocol QuestionsDocument6 pagesChapter 3 Routing Protocol QuestionsYash RamlugunPas encore d'évaluation
- Remember: Use The Pop Quiz Feature To Test Your Understanding Throughout This CourseDocument17 pagesRemember: Use The Pop Quiz Feature To Test Your Understanding Throughout This CourseSathis Kumar ShanmugamPas encore d'évaluation
- Ccna2 Final Versi 1Document20 pagesCcna2 Final Versi 1Agus T SetiawanPas encore d'évaluation
- Cisco Discovery - Drsent Module 6: Selectionner Un Langage: Exam ModeDocument6 pagesCisco Discovery - Drsent Module 6: Selectionner Un Langage: Exam ModedomsonPas encore d'évaluation
- CCNA 1 RS Introduction To Networks Final Exam v50 2013Document15 pagesCCNA 1 RS Introduction To Networks Final Exam v50 2013daniel_afpPas encore d'évaluation
- CCNA Exploration2 - Routing Protocols and Concepts - Chapter 3 ExamDocument6 pagesCCNA Exploration2 - Routing Protocols and Concepts - Chapter 3 Examchocolat4Pas encore d'évaluation
- CCNA Semester 4 Review Voucher 3.1 (92%)Document7 pagesCCNA Semester 4 Review Voucher 3.1 (92%)4gen_1Pas encore d'évaluation
- CCNA1 Chapter 3Document8 pagesCCNA1 Chapter 3wahyuPas encore d'évaluation
- CCNA2 - Rounting Protocols and ConceptsDocument69 pagesCCNA2 - Rounting Protocols and Conceptsjmk78426Pas encore d'évaluation
- Final CCNA 4 (May 2010)Document10 pagesFinal CCNA 4 (May 2010)Liam MaiPas encore d'évaluation
- CCNA 1 FINAL Exam Answers v5.0 2013Document0 pageCCNA 1 FINAL Exam Answers v5.0 2013CCNA5.NETPas encore d'évaluation
- EWAN Final ExamDocument18 pagesEWAN Final Examadri_stanPas encore d'évaluation
- CCNA 1 v5.0 R&S ITN Final Exam Answers 2014Document22 pagesCCNA 1 v5.0 R&S ITN Final Exam Answers 2014jonmicPas encore d'évaluation
- Ccna 2 Final ExamDocument12 pagesCcna 2 Final Examshkarkoddl83% (12)
- ROUTING INFORMATION PROTOCOL: RIP DYNAMIC ROUTING LAB CONFIGURATIOND'EverandROUTING INFORMATION PROTOCOL: RIP DYNAMIC ROUTING LAB CONFIGURATIONPas encore d'évaluation
- First Hop Redundancy Protocol: Network Redundancy ProtocolD'EverandFirst Hop Redundancy Protocol: Network Redundancy ProtocolPas encore d'évaluation
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkD'EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkPas encore d'évaluation
- LEARN MPLS FROM SCRATCH PART-B: A Beginners guide to next level of networkingD'EverandLEARN MPLS FROM SCRATCH PART-B: A Beginners guide to next level of networkingPas encore d'évaluation
- Internet of Things: Architectures, Protocols and StandardsD'EverandInternet of Things: Architectures, Protocols and StandardsPas encore d'évaluation
- WAN TECHNOLOGY FRAME-RELAY: An Expert's Handbook of Navigating Frame Relay NetworksD'EverandWAN TECHNOLOGY FRAME-RELAY: An Expert's Handbook of Navigating Frame Relay NetworksPas encore d'évaluation
- The Effects of Traffic Structure on Application and Network PerformanceD'EverandThe Effects of Traffic Structure on Application and Network PerformancePas encore d'évaluation
- Autocad 2016Document59 pagesAutocad 2016Kaye OleaPas encore d'évaluation
- ADVOCACY AND LOBBYING NDocument7 pagesADVOCACY AND LOBBYING NMwanza MaliiPas encore d'évaluation
- Stock Futures Are Flat in Overnight Trading After A Losing WeekDocument2 pagesStock Futures Are Flat in Overnight Trading After A Losing WeekVina Rahma AuliyaPas encore d'évaluation
- Vaccination Management System of Brgy 6 (Table of Contents)Document8 pagesVaccination Management System of Brgy 6 (Table of Contents)Ryan Christian MenorPas encore d'évaluation
- Efectele Crizei Economice Asupra Politicilor Pietei Muncii Din RomaniaDocument24 pagesEfectele Crizei Economice Asupra Politicilor Pietei Muncii Din Romaniacristian_incaltarauPas encore d'évaluation
- Alvarez vs. COMELECDocument5 pagesAlvarez vs. COMELECvanessa3333333Pas encore d'évaluation
- Direct FileActDocument17 pagesDirect FileActTAPAN TALUKDARPas encore d'évaluation
- Draft SemestralWorK Aircraft2Document7 pagesDraft SemestralWorK Aircraft2Filip SkultetyPas encore d'évaluation
- Rural Perception of SUV CarsDocument29 pagesRural Perception of SUV CarsritusinPas encore d'évaluation
- Holmes 1993Document8 pagesHolmes 1993Rumaisa KrubaPas encore d'évaluation
- Fuel Pumps Left in Off PositionDocument7 pagesFuel Pumps Left in Off PositionherbuelPas encore d'évaluation
- Lfa Sop 00067Document6 pagesLfa Sop 00067Ahmed IsmaillPas encore d'évaluation
- Đề Số 1 - Đề Phát Triển Đề Minh Họa 2023Document20 pagesĐề Số 1 - Đề Phát Triển Đề Minh Họa 2023Maru KoPas encore d'évaluation
- EzraCohen TVMasterclass 2.0Document10 pagesEzraCohen TVMasterclass 2.0Pete PetittiPas encore d'évaluation
- Service Manual: DCR-DVD150E/DVD450E/DVD650/ DVD650E/DVD850/DVD850EDocument71 pagesService Manual: DCR-DVD150E/DVD450E/DVD650/ DVD650E/DVD850/DVD850EJonathan Da SilvaPas encore d'évaluation
- Everything You Need to Know About Distribution TransformersDocument2 pagesEverything You Need to Know About Distribution TransformersDONNYMUCKTEEPas encore d'évaluation
- Brexit Essay - Jasraj SinghDocument6 pagesBrexit Essay - Jasraj SinghJasraj SinghPas encore d'évaluation
- What Is Propaganda DeviceDocument3 pagesWhat Is Propaganda DeviceGino R. Monteloyola100% (1)
- Url Profile Results 200128191050Document25 pagesUrl Profile Results 200128191050Wafiboi O. EtanoPas encore d'évaluation
- 2018 Price List: Account NumberDocument98 pages2018 Price List: Account NumberPedroPas encore d'évaluation
- GSR Azure High Level ArchitectureDocument4 pagesGSR Azure High Level ArchitectureCSKPas encore d'évaluation
- Research Paper About Cebu PacificDocument8 pagesResearch Paper About Cebu Pacificwqbdxbvkg100% (1)
- Circulation in Vacuum Pans: January 2004Document18 pagesCirculation in Vacuum Pans: January 2004REMINGTON SALAYAPas encore d'évaluation