Académique Documents
Professionnel Documents
Culture Documents
Project Synopsis 12
Transféré par
Akhil Kumar GuptaDescription originale:
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Project Synopsis 12
Transféré par
Akhil Kumar GuptaDroits d'auteur :
Formats disponibles
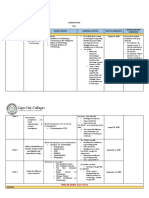
SHRI RAMMURTI SMARAK COLLEGE OF ENGINEERING & TECHNOLOGY.
BAREILLY-243101(U.P)
Synopsis
On
CREDIT CARD FRAUD DETECTION SYSTEM USING HIDDEN MARKOV MODEL
Group No: 11
SUBMITTED TO: Ms. Jyoti Agarwal PROJECT GUIDE: Ms. Priya Agarwal
SUMITTED BY: Abrar Ahmad (080004) Akhil Kr. Gupta (080006) Rudraansh Sethi (080085) Manoj Kr. Kannaujiya (080051)
September 14, 2011
[SYNOPSIS
CREDIT CARD FRAUD DETECTION SYSTEM]
CONTENTS
1. TITLE 2. OBJECTIVE OF PROJECT 3. REQUIREMENT SPECIFICATION 3.1 3.2 HARDWARE SOFTWARE
4. FEASIBILTY AND FUNTIONALITY 5. METHODOLOGY 6. ADVANTAGES OF PROJECT 7. PROJECT APPLICATION 8. PROJECT RISK 9. FUTURE ENHANCEMENTS 10. PROJECT LIMITATIONS 11.REFERNCES 12.SIGNATORY
September 14, 2011
[SYNOPSIS
CREDIT CARD FRAUD DETECTION SYSTEM]
1. Title: CREDIT CARD FRAUD DETECTION SYSTEM USING HIDDEN MARKOV MODEL
2. Objective of the Project: The objective of this application is as follows:
Creating an application to detect fraud Credit Cards. Implementing Hidden Markov model. Creating database containing all relevant information of Customer. Providing security to the customers at the time of transaction. Implementing firewall to restrict entry outside the Network.
3. Requirement Specification:
3.1) Software Requirement: Operating System: Windows XP/VISTA/2000/7 Application: Net Beans 6.5 Platform: JRE/JDK
September 14, 2011
[SYNOPSIS
CREDIT CARD FRAUD DETECTION SYSTEM]
3.2) Hardware Requirement:
RAM Requirement: 2 GB or above Processor : Dual Core/ Core 2 Duo/core i3/i5 Above 2.00 GHz 10GB or more
Processing speed : Hard Drive :
4. Features and Functionality
This project is based upon Hidden Markov Model. HMMs can be applied to the gesture-recognition problem. It is primarily concerned with empirically picking the HMM parameters from some sample data. Detects fraud to analyze the spending patterns on every card and to figure out any inconsistency with respect to the usual spending patterns. Fraud detection system is based on the analysis of existing purchase data of cardholder
It is a promising way to reduce the rate of successful credit card
frauds.
September 14, 2011
[SYNOPSIS
CREDIT CARD FRAUD DETECTION SYSTEM]
5. Methodology:
This project is developed under JAVA and applet as front end, so methodology adopted in this software is based on object oriented concept.
6. Advantage of the Project:
Proper security provisions are made from malicious threats and hacking tools so that user account cannot be harmed intentionally or non intentionally from frauds. Proper hierarchy of the users is maintained as per authority to access the data and use the services provided by the authority. Track all the necessary details during transaction process. In case of the existing system even the original card holder is also checked for fraud detection. But in this system no need to check the original user as we maintain a log. The log which is maintained will also be a proof for the bank for the transaction made. This reduces the tedious work of an employee in the bank. We can find the most accurate detection using this technique.
September 14, 2011
[SYNOPSIS
CREDIT CARD FRAUD DETECTION SYSTEM]
7. Project Applications:
The different areas where we can use this application are : It can be used on the server of any organization providing financial transactions. It can also be used in banks and modifications can be easily done according to requirements.
8. Project Risks:
Proper network security is necessary.
Frauds can be done using SQL injection.
9. Future Enhancements:
Speed of the software can be enhanced by implementation of
algorithms of less complexity. Inter mail server can be implemented using the same concept.
September 14, 2011
[SYNOPSIS
CREDIT CARD FRAUD DETECTION SYSTEM]
10. Project Limitations:
It works only on windows XP/2000/vista/7.
Proper Document hierarchy should be maintained for accessing the required credit card.
Files and folders of a user deleted accidently can not be
recovered.
September 14, 2011
[SYNOPSIS
CREDIT CARD FRAUD DETECTION SYSTEM]
REFERNCES
Data Compression by Khalid Sayood http://www.wikipedia.com http://www. ieeexplore.ieee.org
September 14, 2011
[SYNOPSIS
CREDIT CARD FRAUD DETECTION SYSTEM]
Group No: 12 Group Members: Abrar Ahmad.. Akhil Kr. Gupta. Manoj Kr. Kannaujiya Rudraansh Sethi .
Project Incharge:
Ms. Jyoti Agarwal Project Guide:
Ms. Priya Agarwal
HOD Of CS Deptt:
Mr. L.S. Maurya
Vous aimerez peut-être aussi
- Credit Card Fraud Detection Using Hidden Markov Model-A SurveyDocument3 pagesCredit Card Fraud Detection Using Hidden Markov Model-A SurveypayoxPas encore d'évaluation
- Anshika Project ReportDocument36 pagesAnshika Project ReportLakshaya TeotiaPas encore d'évaluation
- Body of SynopsisDocument34 pagesBody of Synopsisjigyasha oarmarPas encore d'évaluation
- Synopsis SukeshDocument9 pagesSynopsis Sukeshsukeshbhalke10Pas encore d'évaluation
- SEPA Final2Document54 pagesSEPA Final2The Ketan SenapatiPas encore d'évaluation
- Project Report On ATM SystemDocument56 pagesProject Report On ATM SystemKumar Siva72% (116)
- Project Report On ATM SystemDocument54 pagesProject Report On ATM Systemdavidcooper0250% (1)
- Online Blood Bank System SynopsisDocument30 pagesOnline Blood Bank System SynopsisVipul RajputPas encore d'évaluation
- P Venkata Ayyappa 111520205034 V Rahul E Prasanth 111520205058 111520205010Document13 pagesP Venkata Ayyappa 111520205034 V Rahul E Prasanth 111520205058 111520205010Ganesh BoggavarapuPas encore d'évaluation
- Downloads Papers N5aa3923a44894Document4 pagesDownloads Papers N5aa3923a44894Imran KhanPas encore d'évaluation
- Profundity Net Banking: Kunal Govani Alpesh Harsoda Nirav KariaDocument35 pagesProfundity Net Banking: Kunal Govani Alpesh Harsoda Nirav KariaJay_1991Pas encore d'évaluation
- Credit Card Fraud Analysis Using Predictive ModelingDocument31 pagesCredit Card Fraud Analysis Using Predictive ModelingChaitanya kumarPas encore d'évaluation
- Cs2357 Ooad Lab ManualDocument240 pagesCs2357 Ooad Lab ManualheyramzzPas encore d'évaluation
- Atm Management SystemDocument40 pagesAtm Management SystemDada KhalandarPas encore d'évaluation
- PZ Ssa 8 J5 NJ G2 V 1 I T6 FWJ STB SXZKs U6 X WFK 34 R WDWDocument5 pagesPZ Ssa 8 J5 NJ G2 V 1 I T6 FWJ STB SXZKs U6 X WFK 34 R WDWAshlesha HataglePas encore d'évaluation
- AtmmachineprojectpdfDocument14 pagesAtmmachineprojectpdfYogiraj GautamPas encore d'évaluation
- Presented By:: Redg - No Guided byDocument13 pagesPresented By:: Redg - No Guided byalokray11Pas encore d'évaluation
- AssingmentDocument4 pagesAssingmentZain IjazPas encore d'évaluation
- Project Report On 2factor AuthenticationDocument47 pagesProject Report On 2factor Authenticationkuldeep0511100% (9)
- Project Report On ATM SystemDocument55 pagesProject Report On ATM SystemJaydip Patel100% (3)
- A Methodological Study of Digital E-Memo For RTO (Road Transport Authority) Using Image RenderingDocument9 pagesA Methodological Study of Digital E-Memo For RTO (Road Transport Authority) Using Image RenderingIJRASETPublicationsPas encore d'évaluation
- FINAL PROJECT REPORT - Rohit SinghalDocument31 pagesFINAL PROJECT REPORT - Rohit Singhalkaya DiwaanPas encore d'évaluation
- Bank Management System MCA Final ProjectDocument51 pagesBank Management System MCA Final ProjectDisha KokanePas encore d'évaluation
- Credit Card Fraud Detection Based On Ontology GraphDocument12 pagesCredit Card Fraud Detection Based On Ontology GraphijsptmPas encore d'évaluation
- Criminal Managemt System 1Document9 pagesCriminal Managemt System 1GUNDA LAXMISAIPas encore d'évaluation
- Fingerprint Based ATM System: This Document Is Prepared in Support of ProjectDocument13 pagesFingerprint Based ATM System: This Document Is Prepared in Support of Projectحسنین احمدPas encore d'évaluation
- Index: S.No. Particulars Page NoDocument30 pagesIndex: S.No. Particulars Page NoAnuj TiwariPas encore d'évaluation
- BATCH - 6 Mini Project FinalDocument39 pagesBATCH - 6 Mini Project FinalBanthalapati S Lavakumar RajuPas encore d'évaluation
- Report Kb1Document21 pagesReport Kb1sf4432tPas encore d'évaluation
- Taxi Booking Application: Mustafa Khuzembhai Alirajpurwala (21MCA058)Document30 pagesTaxi Booking Application: Mustafa Khuzembhai Alirajpurwala (21MCA058)Mustafa AlirajpurwalaPas encore d'évaluation
- Automobile Service Management SystemDocument4 pagesAutomobile Service Management SystemsurePas encore d'évaluation
- AtmMachine Report Software EngineeringDocument12 pagesAtmMachine Report Software EngineeringminiPas encore d'évaluation
- Credit Card Fraud Detection Using Machine LearningDocument82 pagesCredit Card Fraud Detection Using Machine Learningshanmugaraja85100% (1)
- Crime Reporting System Project ReportDocument106 pagesCrime Reporting System Project ReportUma Shanker69% (13)
- Big Data Framework: Credit Card Fraud Detection UsingDocument6 pagesBig Data Framework: Credit Card Fraud Detection UsingDaud QwertyPas encore d'évaluation
- Fraud Detection FinalRreportDocument11 pagesFraud Detection FinalRreportShubham RaktatePas encore d'évaluation
- Obcs 2Document19 pagesObcs 2Sneh SankaliaPas encore d'évaluation
- An Approach For Eliciting Software Requirements and Its Prioritization Using Analytic Hierarchy ProcessDocument6 pagesAn Approach For Eliciting Software Requirements and Its Prioritization Using Analytic Hierarchy Processjaved501Pas encore d'évaluation
- Synopsis - FormatDocument18 pagesSynopsis - FormatkahalabhinavPas encore d'évaluation
- ATM PROJECT AbcDocument46 pagesATM PROJECT AbcHannah MisganawPas encore d'évaluation
- Mobile Based Feedback RailwayDocument38 pagesMobile Based Feedback Railwaymansha99Pas encore d'évaluation
- Fingerprint Driving License Verification System To Be Used by MttuDocument15 pagesFingerprint Driving License Verification System To Be Used by MttuNick Owusu-debrahPas encore d'évaluation
- Synopsis Major Project CreditCardFraudDetectionDocument16 pagesSynopsis Major Project CreditCardFraudDetectionRohit RanjanPas encore d'évaluation
- DocumentationDocument4 pagesDocumentationSanikaPas encore d'évaluation
- Irjet V7i8271Document6 pagesIrjet V7i8271Darshil ShahPas encore d'évaluation
- Atm With An EyeDocument25 pagesAtm With An EyeKiran StridesPas encore d'évaluation
- An Atm With An Eye: Submitted in Partial Fulfillment of The Requirements For Award of The Degree ofDocument15 pagesAn Atm With An Eye: Submitted in Partial Fulfillment of The Requirements For Award of The Degree ofNikhilaPas encore d'évaluation
- Secure Photo Sharing in Social NetworksDocument51 pagesSecure Photo Sharing in Social Networksshanmugaraja85Pas encore d'évaluation
- FINAL YEAR PROJECT REPORT CRIMINAL FACE DETECTION SYSTEM-PDF Converted - Shiva TamrkarDocument24 pagesFINAL YEAR PROJECT REPORT CRIMINAL FACE DETECTION SYSTEM-PDF Converted - Shiva TamrkarSafalya Gghosh RoyPas encore d'évaluation
- Lab ManualDocument38 pagesLab ManualAnvay JainPas encore d'évaluation
- Online Society Tracking: A Project Report OnDocument187 pagesOnline Society Tracking: A Project Report OnمحذPas encore d'évaluation
- EndUser Accusation DocumentationDocument126 pagesEndUser Accusation DocumentationVijay KapuPas encore d'évaluation
- On Line Crime Records Management System: A Case of PakistanDocument10 pagesOn Line Crime Records Management System: A Case of Pakistandereje bekelePas encore d'évaluation
- UPI Fraud DetectionDocument5 pagesUPI Fraud DetectionpachoryPas encore d'évaluation
- Credit Cards Fraud Detection System SynopsisDocument18 pagesCredit Cards Fraud Detection System SynopsisGaurav Chouksey100% (1)
- Crime Automation and Reporting SystemDocument3 pagesCrime Automation and Reporting SystemGoki KumarPas encore d'évaluation
- Safe Card: Infosys.110 Business Systems: Deliverable 2: Business Section 2014Document10 pagesSafe Card: Infosys.110 Business Systems: Deliverable 2: Business Section 2014HeidiStrajnarPas encore d'évaluation
- Face Detection and Recognition on Mobile DevicesD'EverandFace Detection and Recognition on Mobile DevicesÉvaluation : 1 sur 5 étoiles1/5 (1)
- Application Design: Key Principles For Data-Intensive App SystemsD'EverandApplication Design: Key Principles For Data-Intensive App SystemsPas encore d'évaluation
- McCluskey vs. University of Utah Federal LawsuitDocument51 pagesMcCluskey vs. University of Utah Federal LawsuitJessica McBridePas encore d'évaluation
- EyDocument33 pagesEyyajur_nagiPas encore d'évaluation
- Nishithdesai Prevention of Corruption Act 2018 AmendmentsDocument5 pagesNishithdesai Prevention of Corruption Act 2018 Amendmentsqubrex1Pas encore d'évaluation
- Partial Committee Report BRC COA DOH Final Formatted 31jan2022 330PM RJG SignedDocument113 pagesPartial Committee Report BRC COA DOH Final Formatted 31jan2022 330PM RJG SignedRappler100% (1)
- 1 05 Lab Crime Scene Sketch GADocument2 pages1 05 Lab Crime Scene Sketch GAthis is hardly gonna be usedPas encore d'évaluation
- Gurwinder Singh v. State of Punjab PDFDocument14 pagesGurwinder Singh v. State of Punjab PDFHURI BABAPas encore d'évaluation
- Zn6f Best Practice Guidance For Restorative Practice 2011Document42 pagesZn6f Best Practice Guidance For Restorative Practice 2011Maya MayaPas encore d'évaluation
- Help The Denver Post and Crime StoppersDocument1 pageHelp The Denver Post and Crime Stoppersapi-26046374Pas encore d'évaluation
- The California Child Abuse & Neglect Reporting Law: Issues and Answers For Mandated ReportersDocument57 pagesThe California Child Abuse & Neglect Reporting Law: Issues and Answers For Mandated Reportersmary engPas encore d'évaluation
- Sim Gill Letter To Bluffdale CityDocument2 pagesSim Gill Letter To Bluffdale CityKUTV 2NewsPas encore d'évaluation
- Https Campus - TcsDocument5 pagesHttps Campus - TcsAvi NashPas encore d'évaluation
- Plaintiff-Appellee Accused Accused-AppellantDocument9 pagesPlaintiff-Appellee Accused Accused-AppellantValerie AlcasidPas encore d'évaluation
- Warrantless ArrestDocument6 pagesWarrantless ArrestGigiRuizTicarPas encore d'évaluation
- CRB Research Brief - Asj FinalDocument17 pagesCRB Research Brief - Asj FinalGazetteonlinePas encore d'évaluation
- Print Edition: 20 March 2014Document21 pagesPrint Edition: 20 March 2014Dhaka TribunePas encore d'évaluation
- Constitutional Law II Assigned Cases 2Document5 pagesConstitutional Law II Assigned Cases 2Dewm DewmPas encore d'évaluation
- What Are The Ethical Challenges That Uber Faces in Using App-Based Peer-To-Sharing Technology?Document2 pagesWhat Are The Ethical Challenges That Uber Faces in Using App-Based Peer-To-Sharing Technology?Aina AguirrePas encore d'évaluation
- People VS PrajesDocument1 pagePeople VS PrajesGLORILYN MONTEJOPas encore d'évaluation
- Balkissoon Roodal V The StateDocument43 pagesBalkissoon Roodal V The StateKerry-ann LevenePas encore d'évaluation
- MANUSCRIPTDocument39 pagesMANUSCRIPTSophia Ann RegalarioPas encore d'évaluation
- ZinaDocument23 pagesZinaNurHafizahNasirPas encore d'évaluation
- Cyber Security GovernanceDocument20 pagesCyber Security GovernanceOlalekan SamuelPas encore d'évaluation
- Cattle Trespass ActDocument8 pagesCattle Trespass ActVenugopal BandaPas encore d'évaluation
- Indentured Servants and SlavesDocument10 pagesIndentured Servants and SlavesRachel Torres100% (1)
- CaseMine Judgement - Mithilesh KumarDocument24 pagesCaseMine Judgement - Mithilesh KumarpuneetastroPas encore d'évaluation
- Dangerous Drugs CasesDocument22 pagesDangerous Drugs CaseseibasPas encore d'évaluation
- Anabolic Steroid Guide Part 1Document9 pagesAnabolic Steroid Guide Part 1MarcelBorgesPinheiro100% (1)
- US v. Sweet 1 Phil. 18 (1901)Document3 pagesUS v. Sweet 1 Phil. 18 (1901)G-one Paisones100% (1)
- Lipa City Colleges: Recall and Describe The Evolution and Development of CriminologyDocument6 pagesLipa City Colleges: Recall and Describe The Evolution and Development of CriminologyMagr EscaPas encore d'évaluation
- Spring2018 Student Parent Acknowledgement FormDocument7 pagesSpring2018 Student Parent Acknowledgement FormMartha HillPas encore d'évaluation