Académique Documents
Professionnel Documents
Culture Documents
Raport Plagiat Mang
Transféré par
OmRauDescription originale:
Titre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Raport Plagiat Mang
Transféré par
OmRauDroits d'auteur :
Formats disponibles
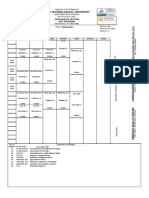
Turnitin Originality Report
Page 1
Turnitin Originality Report mang by Mang Mang
Image
From Quick Submit (Quick Submit) Processed on 09-May-2012 5:42 AM PDT ID: 248361119 Word Count: 1843 Similarity Index 63% Similarity by Source Internet Sources: 11% Publications: 62% Student Papers: 12%
sources: 1
51% match (publications) C.H. Lin. "A new public-key cipher system based upon the diophantine equations", IEEE Transactions on Computers, 1995
2% match (student papers from 06/10/03) Submitted to CSU, San Jose State University on 2003-06-10
2% match (Internet) http://hades.ph.tn.tudelft.nl/Internal/PHServices/Documentation/MathWorld/math/math/a/ a137.htm
1% match (publications) Morgos, Lucian. "Considerations about the Modeling of Software Defined Radio for Mobile Communications Networks", Journal of Electrical & Electronics Engineering/18446035, 20090601
1% match (Internet from 11/3/05) http://intro.gemplus.com/smart/rd/publications/ps/Pai99phd.ps.gz
1% match (Internet from 4/8/12) http://arxiv.org/pdf/1005.0781.pdf
1% match (Internet from 10/28/10) http://fsl.cs.uiuc.edu/pubs/rosu-2007-tr.pdf
1% match (student papers from 05/04/11) Submitted to Higher Education Commission Pakistan on 2011-05-04
1% match (Internet from 6/20/03) http://valle.fciencias.unam.mx/libros/criptografia/references.pdf
10
1% match (Internet from 2/13/07) http://www.azbet.com/sttot/topbets.aspx?id=7020
11
1% match (publications) Shaarawy, M.. "An improved public-key cipher system based upon diophantine equation",
file://localhost/D:/raport_plagiat_mang.html
09.05.2012 15:48:40
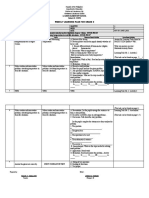
Turnitin Originality Report
Shaarawy, M.. "An improved public-key cipher system based upon diophantine equation", Computers & Industrial Engineering, 199812
Page 2
12
< 1% match (publications) Zhong Hong. "An Efficient (t, n)-Threshold Multi-Secret Sharing Scheme", First International Workshop on Knowledge Discovery and Data Mining (WKDD 2008), 01/2008
13
< 1% match (Internet from 10/10/10) http://oak.cs.ucla.edu/~cho/papers/cho-sampling.pdf
14
< 1% match (publications) Cusick, T.W.. "Cryptanalysis of a public key system based on Diophantine equations", Information Processing Letters, 19951027
paper text:
PUBLIC-KEY CRYPTOSYSTEM BASED ON THE DIOPHANTINE EQUATIONS Ioan Mang, Erica Mang
4Department of Computers, University of Oradea, Faculty of Electrical
Engineering and Information Technology, 1, Universitatii St., 410087 Oradea, Romania, E-mail: emang@keysys .ro Abstract This study analyses the
mathematical aspects of diophantic equations and the
potential of using them in cipher public-key systems. There are also presented the algorithms written in C language that were used for implementing such a system Keywords: public-key algorithms, Diophantine equation, cryptosystem, encryption. I. INTRODUCTION
1In this paper, a new public-key cipher scheme is proposed. By the use of
our scheme, the generating steps of keys are simple. Both the encryption and decryption procedures can be completed efficiently. Our cipher scheme is based upon the Diophantine equations. In general, a Diophantine equation is defined as follows: We are given a polynomial equation f(x
1 ,x 2 ,...,x n ) -
10 with integer coefficients and we are asked to find rational or integral
solutions [6]. Throughout this paper, we shall assume that the solutions are nonnegative. For instance, consider the following equation: 3x 1
+ 4x 2 + 7x 3 + 5x 4 = 78. (1) The
1above equation is a Diophantine equation if we have to find a nonnegative
solution for this equation. In fact, our
solution is (x
101 , x 2 , x 3 , x 4 )=(2, 5, 1, 9). (2)
1A famous Diophantine equation problem is Hilbert's tenth problem, which
is defined as follows: Given a system of polynomials Pi(
file://localhost/D:/raport_plagiat_mang.html
09.05.2012 15:48:40
Turnitin Originality Report
Page 3
1A famous Diophantine equation problem is Hilbert's tenth problem, which
is defined as follows: Given a system of polynomials Pi(
x1, x2, ..., xn), 1 i m,
1with integer coefficients, deter-mine whether it has a nonnegative integer
solution or not. In and, it was shown that the Hilbert problem is undecidable for polynomials with degree 4. It was shown in that the Hilbert problem is undecidable for polynomials with 13 variables [1]. Gurari and Ibarra also proved that several Diophantine equations are in NP- complete class.
II. THE UNDERLYING MATHEMATICS
1Let w be some positive integer and the domain D be a set of positive
integers in the range of [0, w]. Let w = 2 b - 1, where b is some positive integer. Assume that a sending message M with length NB bits is broken up into n pieces of submessages, namely m1, m2, and mn. Each submessage is of length b bits. In other words, we can represent each submessage by a decimal number mi and mi in D. Suppose that n pairs of integers (q 1 , k 1 ), (q 2 , k 2 ), ... and (q n , kn) are chosen such that the following conditions hold: 1) qi's are pairwise relative primes; i.e. 1. (q i ,q j ) = 1 for
i j. 2. 2) k 1 >
2w for i = 1,2, ..., n. 3. 3) qi > kiw(qi mod ki), and qi mod ki 0, for i
11, 2, ..., n. These n integer pairs (qi, ki)'s will be kept secret and used to
decrypt messages. For convenience, we name the above three conditions the DK-conditions since they will be used as deciphering keys. Note that for the generating of pairwise relatively primes, one can consult. Furthermore, the following numbers are computed. First, compute Ri = qi mod ki and compute Pi's such that two conditions are satisfied: 1) Pi mod qi = Ri, and 2) Pj mod qi = 0 if i = j. Since qu's are pairwise relatively primes, one solution for Pi's satisfying the above two conditions is that Pi = Qibi with Qi
qi i j and bi
1is chosen such that Qibi modqi =Ri. Since Qi and qi are relatively prime, bi's
can be found by using the extended Euclid's algorithm. Note that the average number of divisions performed by the extended Euclid's algorithm for finding bi is approximately 0.843. ln (qi) + 1.47. Secondly, compute
Ni = qi /(kiRi )
file://localhost/D:/raport_plagiat_mang.html
09.05.2012 15:48:40
Turnitin Originality Report
Page 4
1for i = 1, 2, ..., n. Finally, compute n si = PiNi mod Q
where Q qi (3) i 1
1That is, we have a vector S = (s1, s2, ..., sn) with each
component computed as above. After this, S
2can be used as the enciphering key for encrypting messages. By
conducting a vector product between M = (m1, m2, ..., mn) and S = (s1, s2, ..., sn); i .e., n C = E(S ,M) = M*
S = misi (4) i 1
1a message M is transformed to its ciphertext C, where * denotes the vector
product operation. Conversely, the ith component mi, in M can be revealed by the following operation: mi = D(( qi,ki ),C)
= kiC/ qi
1for i = 1, 2, ..., n (5) Theorem 2.1 shows that (5) is the inverse function of (4).
The following lemmas are helpful in the proof of the theorem. Lemma 2.1: Let a and b be some positive integers where b > a. Then for all
x,
8a x / b < x if x ab/(b -a). Proof: Let Then x/b x / b
1c for some integer c. c <(x/b
+ 1). We have ac < ax/(b + a). (6) On the other hand, if x ab / (b-a), then (b-a) x ab; that is,
1Let mi's, ki's and qi's be chosen such that the DK - conditions are satisfied. Let Ri = qi mod ki. Then
k =mi. (11) iRimi qi /(kiRi) / qi Proof: Let = k iRimi qi /(kiRi) / qi = mi.
1It can be easily seen that the following two inequalities hold: and < iRim i(qi /
(kiRi)
1)/ qi k = mi (12) k = mi. (13) iRim i (qi /(kiRi ))/ qi
1Furthermore, the right-hand side of (13) is identical to m i and that of (12) is mi kiRimi / qi . On the other hand, since mi is an integer and kiRimi / qi <1, the
right-hand side in
=mi.
file://localhost/D:/raport_plagiat_mang.html
09.05.2012 15:48:40
Turnitin Originality Report
Page 5
1Furthermore, the right-hand side of (13) is identical to m i and that of (12) is mi kiRimi / qi . On the other hand, since mi is an integer and kiRimi / qi <1, the
right-hand side in (12) becomes m =mi.
(14) i kiRimi / qi
1Combining these two inequalities. we obtain that m i mi. Finally, we have =
mi, since is an integer.
Theorem 2.1: Let (q 1 , k 1 ),
1(q 2 , k 2 ), ..., and (q n ,k n ) be n pairs of positive integers satisfying the DK-
conditions. Let the vector S be computed by applying (1). Then (3) is the inverse function of (2). that is, a
message enciphered by (2) can be decrypted by (3). Proof:
1Let us prove the theorem by the following two
steps. First, from (1), define si = PiNi' we have a vector Let s = (s1,s2,...,sn); i.e., si =
12si mod Q, for i = 1,2,...,n. (ax/b + a)
x. (7) C' = M*S = m m i 1 misi i1 miPiNi. (15) Combining (6) and (7), we have that a Lemma 2.2: Let Ri = qi mod ki. Then x / b < x if x ab / (b-a). (8) kiRimi qi /(kiRi) mod kiqi = kiRimi qi /(kiRi) (9) Proof: Let a = Ri mi, b + ki Ri,
1and x = qi. Since qi > ki Ri w, we know that qi > ki Ri2 mi / (Ri (ki - mi)). That is, x
ab / (b- a) is satisfied. By applying Lemma 2.1, it can be seen that
Rimi qi /(kiRi) < qi. Therefore, ki Ri mi qi /(kiRi) mod ki qi = ki Ri mi qi /(kiRi) (10) Lemma 2.3: Since
1Pi's satisfy the following two conditions: 1)
Pimodqi=qimodki=Ri;and
12) Pj mod qi = 0 if i j j, n kiC' mod
kiqi = (ki i 1 mi Pi Ni )mod kiqi= =kimiRi qi /(kiRi )modkiqi. (16) Furthermore, by Lemma 2.2, kimiRi qi /(kiRi ) mod kiqi = kimiRi qi /(kiRi ) (17) That is, kiC mod kiqi = kimiRi qi /(kiRi )
1for i=1,2,...,n. In other words,
kiC=yikiqi+kimiRi qi /(kiRi ) . (18) for some integers yi. Moreover, Hence kiC'/ qi yiki kiC/qi=yiki+kimiRi qi / (kiRi ) /qi. (19) yiki kimiRiqi/(kiRi) kimiRi qi/(kiRi) /qi By applying Lemma 2.3, we have Thus Second, let then iC' / q i / q i (20) k = yiki + mi. (21) mi=modki. (22) n Qqi. (23) i 1 n C mod Q = ( i 1 m i si ) mod Q = ((m 1 s 1
file://localhost/D:/raport_plagiat_mang.html
09.05.2012 15:48:40
Turnitin Originality Report
kiC=yikiqi+kimiRi qi /(kiRi ) . (18) for some integers yi. Moreover, Hence kiC'/ qi yiki kiC/qi=yiki+kimiRi qi / (kiRi ) /qi. (19) yiki kimiRiqi/(kiRi) kimiRi qi/(kiRi) /qi By applying Lemma 2.3, we have Thus Second, let then iC' / q i / q i (20) k = yiki + mi. (21) mi=modki. (22) n Qqi. (23) i 1 n C mod Q = ( i 1 m i si ) mod Q = ((m 1 s 1
Page 6
1mod Q) + ... + (mnsn mod Q)) mod Q = (m1 (s1 mod Q)
+ ... n + mn(sn
1mod Q))mod Q = ( m i s i ) mod Q
= C mod Q. i 1 That
1is, C = C(mod Q). Let C = C + zQ, for some positive
1integer z. We have k iC/ q i mod ki =( k i (C'
zQ)/ qi mod ki = = ( k iC' / qi kizQi ) mod ki = mod ki (24) Therefore, a vector n Q qi (27) i
131 S=(s 1 ,s 2 , . . . ,s n
) is obtained. There the
1n-tuple S of intgers is published and used as the public key
of the cryptosystem for enciphering messages. The chosen parameters
7(q 1 ,k 1 ), (q 2 ,k 2 ), ..., (q n ,k n
) are
1kept and used as the private key to decipher messages received.
1Specifically, let user A be the sender and user B be the
1receiver, and let A be sending a message represented by
M = (m 1 , m 2 ,...,m n ), where mi
1is a b-bits submessage represented by a decimal
1number in the range of [0, 2b -1]. Then (m 1 ,m 2 ,...,m n ) is enciphered by (4)
into an integer C. Afterward, the integer C
file://localhost/D:/raport_plagiat_mang.html
09.05.2012 15:48:40
Turnitin Originality Report
Page 7
1number in the range of [0, 2b -1]. Then (m 1 ,m 2 ,...,m n ) is enciphered by (4)
into an integer C. Afterward, the integer C
1is sent to user B as the ciphertext of the original message M.
1On the receiving of integer C user B is able to convert C into (m
1 ,m 2 ,...,m n ) by applying (5). IV. CONCLUSION AND DISCUSSION
1A new public-key cryptosystem is investigated in this paper. The
motivation of this attempt is trying to use real numbers for its dense property. However, if real numbers are used as keys, several disturbing problems, such as representation and precision will be encountered. With the help of integer functions, the possibility of using an integer as a key is increased significantly. That is, for a cryptanalyst who tries to break the cipher, he has to conduct an exhaustive search on a long list of integer numbers.
In other words, mi= k modki. iC' / qi III. THE CONSTRUCTION OF THE CRYPTOSYSTEM In this section, the
1algorithms for constructing the cryptosystem, encrypting
messages, respectively, are presented.
1First, each user picks n pairs of parameters
6(q 1 ,k 1 ), (q 2 ,k 2 ),..., and (q n ,k n ) such that the
DK-conditions are satisfied. Afterward, and Q (25) q j j i Ni qi /(ki (qi modki )) (26) are computed, and bis are integers chosen
11such that Qibi mod qi = qi mod ki, for i = 1,2, . . . n.
Let Pi = Qibi and si = PiNi
14mod Q, for i = 1,2,...,n, where
Fig.
11. Key Generating for Each User
Fig.
file://localhost/D:/raport_plagiat_mang.html
09.05.2012 15:48:40
Turnitin Originality Report
Page 8
12. - Encryption Procedure for Sender A
Fig. 3. - Decryption Procedure for Receiver B REFERENCES [1]
3D.E. Knuth: The Art of Computer Programming. Vol. 1: Fundamental
Algorithms, second ed. Reading, MA: Addison-Wesley, (1980). [2] D.E. Knuth: The Art of Computer Programming. Vol. 2: Seminumerical Algorithms, 2nd ed. Reading, MA: Addison-Wesley, (1981).
[3] S
1.P. Tung: Computational complexities of diophnatine equations with
parameters, J. Algorithms, vol. 8, pp. 324- 336,
(1987). [4]
5H.C. Williams: A modification of the RSA public-key encryption procedure,
IEEE Trans. Information Theory, vol. 26, pp. 726-729 (1980).
[5]
9L.J. Hoffman: Modern Methods for Computer Security and Privacy, second edition, Printice -Hall,
(1987) [6] Waclaw Sierpinski, Elementary Theory of numbers, Warszawa (1964)
file://localhost/D:/raport_plagiat_mang.html
09.05.2012 15:48:40
Vous aimerez peut-être aussi
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (121)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (588)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (400)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (895)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- Geometry (Part 1) Lines and AnglesDocument15 pagesGeometry (Part 1) Lines and Anglesunknown :)Pas encore d'évaluation
- Mathematics: Quarter 1 - Module 9Document33 pagesMathematics: Quarter 1 - Module 9Denmark Santos75% (4)
- Gn3-Na3-t4-Ufs104 Geant Network Recommedations For Ict RoomsDocument26 pagesGn3-Na3-t4-Ufs104 Geant Network Recommedations For Ict RoomsterramocoPas encore d'évaluation
- Aanklacht Tegen VolkswagenDocument6 pagesAanklacht Tegen VolkswagenAnonymous Hnv6u54HPas encore d'évaluation
- Contract Marissa Mayer YahooDocument12 pagesContract Marissa Mayer YahooOmRauPas encore d'évaluation
- Barbulescu RomaniaDocument3 pagesBarbulescu RomaniaOmRauPas encore d'évaluation
- Raport Plagiat UdreaDocument1 pageRaport Plagiat UdreaOmRauPas encore d'évaluation
- 2013 Boston Bombing Criminal ComplaintDocument11 pages2013 Boston Bombing Criminal ComplaintOmRauPas encore d'évaluation
- Two Different Architectures For The Hardware Implementation of The Rijndael AlgorithmDocument7 pagesTwo Different Architectures For The Hardware Implementation of The Rijndael AlgorithmRaluca PantaziPas encore d'évaluation
- Articolul Semnat Ioan MangDocument6 pagesArticolul Semnat Ioan MangRaluca PantaziPas encore d'évaluation
- Ioan Mang Raport Plagiat ucv-IC10Document14 pagesIoan Mang Raport Plagiat ucv-IC10OmRauPas encore d'évaluation
- Articol Plagiat MangDocument4 pagesArticol Plagiat MangOmRauPas encore d'évaluation
- Ioan Mang Raport Plagiat ucv-IC11Document12 pagesIoan Mang Raport Plagiat ucv-IC11OmRauPas encore d'évaluation
- NitratesDocument4 pagesNitratesOmRauPas encore d'évaluation
- National Contaminants Level EPADocument6 pagesNational Contaminants Level EPAMohamed WahbyPas encore d'évaluation
- Coca Cola Methylimidazole Nih CancerDocument21 pagesCoca Cola Methylimidazole Nih CancerOmRauPas encore d'évaluation
- The Innovation Union's Performance Scoreboard For Research and InnovationDocument101 pagesThe Innovation Union's Performance Scoreboard For Research and InnovationOmRauPas encore d'évaluation
- Not Found: Cebu Technological UniversityDocument1 pageNot Found: Cebu Technological UniversityKaren Joyce LabajoPas encore d'évaluation
- Math Pattern Task 16thDocument2 pagesMath Pattern Task 16thaPas encore d'évaluation
- Discrete Dynamical Systems and The Logistic Map: An Easy IntroductionDocument34 pagesDiscrete Dynamical Systems and The Logistic Map: An Easy IntroductionMichael GreenPas encore d'évaluation
- Solving Reynolds Equation Using Pseudospectral MethodDocument19 pagesSolving Reynolds Equation Using Pseudospectral MethodKiranmayee KolluruPas encore d'évaluation
- Xercise: Single Correct (Objective Questions)Document16 pagesXercise: Single Correct (Objective Questions)Adharshan NPas encore d'évaluation
- Russell: Paradox and Type Theory: Dr. James Studd FRW Lecture 4. Friday Wk. 4, HT14Document9 pagesRussell: Paradox and Type Theory: Dr. James Studd FRW Lecture 4. Friday Wk. 4, HT14anti ramirezPas encore d'évaluation
- Cluster 4Document34 pagesCluster 4Gary SPas encore d'évaluation
- Rational and Radical Function - Domain and Range PDFDocument9 pagesRational and Radical Function - Domain and Range PDFNystea MagdayaoPas encore d'évaluation
- Melcs Day Objectives Topic/s Classroom-Based Activities Home-Based Activities 1Document2 pagesMelcs Day Objectives Topic/s Classroom-Based Activities Home-Based Activities 1Raquel CarteraPas encore d'évaluation
- Elliot Cartee: Current PositionDocument2 pagesElliot Cartee: Current PositionVadim CatărăuPas encore d'évaluation
- Shivansh Gaba X-C Roll No: 34Document12 pagesShivansh Gaba X-C Roll No: 34Sahil BajajPas encore d'évaluation
- Coca AssignmentDocument8 pagesCoca AssignmentAmieliaPas encore d'évaluation
- 9th Class Annual Plan Final With Lesson PlanDocument7 pages9th Class Annual Plan Final With Lesson PlanAchanta PrakashPas encore d'évaluation
- Don Bosco 12-MATHS-PRE - BOARD-2023-24Document6 pagesDon Bosco 12-MATHS-PRE - BOARD-2023-24nhag720207Pas encore d'évaluation
- Question 1Document9 pagesQuestion 1mwidaniPas encore d'évaluation
- MMW - Problem Set 1 Module 2Document5 pagesMMW - Problem Set 1 Module 2John Rave Manuel GonzalesPas encore d'évaluation
- G52lac Notes 2up PDFDocument84 pagesG52lac Notes 2up PDFBaponPas encore d'évaluation
- EEE324 Digital Signal Processing 09-01-2017Document180 pagesEEE324 Digital Signal Processing 09-01-2017Abdul BasitPas encore d'évaluation
- 2 Linear TransformationsDocument32 pages2 Linear TransformationsShanPas encore d'évaluation
- Exterior Angles-Answer KeyDocument1 pageExterior Angles-Answer KeyWalaa MagdyPas encore d'évaluation
- Fraction - Practice Worksheet - 3Document3 pagesFraction - Practice Worksheet - 3Sahaj GhaiPas encore d'évaluation
- PDADocument52 pagesPDAIbrahim AnsariPas encore d'évaluation
- Ujian Bulanan 1 2020Document6 pagesUjian Bulanan 1 2020Helmi TarmiziPas encore d'évaluation
- TGMT Revision Guide HigherDocument84 pagesTGMT Revision Guide HigherChestha KundanPas encore d'évaluation
- AccountingResearchMethodsSSRN Id1921192 PDFDocument41 pagesAccountingResearchMethodsSSRN Id1921192 PDFasaPas encore d'évaluation
- Report Shooting MethodDocument7 pagesReport Shooting MethodahmedPas encore d'évaluation
- Time Series.Document97 pagesTime Series.Pranav Khanna100% (1)
- Elementary Algebra Textbook Solutions Manual PDFDocument517 pagesElementary Algebra Textbook Solutions Manual PDFAriel Ombajen Mentawan100% (1)