Académique Documents
Professionnel Documents
Culture Documents
K2 BP 101 IGuide 00 K2101 Roadmap
Transféré par
jhonnsonDescription originale:
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
K2 BP 101 IGuide 00 K2101 Roadmap
Transféré par
jhonnsonDroits d'auteur :
Formats disponibles
Introduction to K2 blackpearl 101
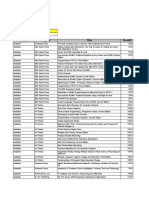
K2 BLACKPEARL 101: COURSE ROADMAP
PRESENTED BY:
WWW.K2.COM
WWW.K2.COM
INTRODUCTIONS
>
Lets start by getting to know one another > Your Name > Your Company or Organization Affiliation > Title and Job Function > Job Responsibility > Workflow Experience > K2 Experience > Expectations for the Course
CONFIDENTIAL
WWW.K2.COM
COURSE MATERIALS
>
>
>
Student Manual > Includes detailed reference information for you to take with you > Includes Step-by-Step Labs Student DVD > Includes the K2 blackpearl 101 VPC for use with the Labs Course Evaluation
CONFIDENTIAL
WWW.K2.COM
COURSE OUTLINE
>
26 Modules over three days > Day One > Introduction > K2 Fundamentals and Building Blocks > SmartObjects > K2 Designer for Visual Studio > K2 Workspace > Day Two > K2 Web Designer for SharePoint > K2 Designer for Visio > Collaborative Process Design > InfoPath > SharePoint Administration > Day Three > SharePoint Content Management > Business Data Catalog
CONFIDENTIAL
WWW.K2.COM
COURSE LOGISTICS
> >
>
> > > >
>
> >
Course Hours Building Hours Parking Restrooms Meals Phones Internet Access Messages Smoking Recycling
CONFIDENTIAL
WWW.K2.COM
ADDITIONAL RESOURCES BEYOND THIS COURSE
>
>
>
>
K2.com (www.k2.com) > Powered by K2 blackpearl, built on SmartObjects > Check out the case study to learn more > Content includes videos, white papers, technical briefs, case studies, events and more K2 Underground (www.k2underground.com) > Powered by the K2 community > K2 blackmarket for code and solution sharing > 3000+ registered users > Active forums and blogs > Content includes podcasts, videos, white papers, and discussions Portal (portal.k2workflow.com) > Content includes the Knowledge Base, downloads for additional documentation > Sign up for the RSS feed to be notified of new KB articles Product Documentation > Includes the Getting Started Guide, User Guide, Tutorials, SDK > Also available from the button within the product
CONFIDENTIAL
WWW.K2.COM
PROCESS-DRIVEN APPLICATIONS. FAST.
> >
>
> >
K2 is a platform for building process-driven applications Automate and manage business processes Reuse existing components, code and processes Enabling business people with visual tools and technical people with tools they know. Everything is visual, declarative, reusable and intuitive.
CONFIDENTIAL
WWW.K2.COM
WE HAVE A GLOBAL PRESENCE; AND WE ARE GROWING
> >
>
> > > >
>
> >
Founded in 2000 More than 300 employees Headquarters in Redmond, Washington Offices in Africa, Australia, Canada, China, Europe, New Zealand and Singapore Increased revenues 200 percent from 2005 to 2007 Customers in more than 40 countries 15 percent of Fortune 100 companies 1,500 customers More than 1 million users 3.9 percent share of the total BPMS market and an 8 percent share of the Windows-based BPMS market
CONFIDENTIAL
WWW.K2.COM
WE HAVE A STRONG COMMUNITY
>
K2 Underground with more than 3,000 users > People who use and sell our software, offer help and share insight and solutions. K2 Insiders > Hand-selected, global leaders in the K2 community drive conversation and content on the Underground.
>
CONFIDENTIAL
WWW.K2.COM
OUR PARTNERS MAKE US BETTER
> >
>
Our partner ties are strong, varied and extensive Partners include: Avanade, Bearing Point, Dimension Data, HP Strong relationship with Microsoft > One of only 30 ISVs managed by the Global ISV Team > Deeply involved in collaboration, research and development > Strategic product and go-to-market initiatives across many verticals
CONFIDENTIAL
WWW.K2.COM
WE ARE FANATICAL ABOUT CUSTOMER SATISFACTION
These are my trusty partners when I have trouble. I call them up and they help me solve business problems.
Jonathan Wynn
Manager of Advanced Technology and Collaborative Services Del Monte Foods
CONFIDENTIAL
WWW.K2.COM
ORDER
STAFF
SALES
SUPPORT
PLANT
MANUFACTURING GOODS RECEIVABLE
CUSTOMERS
PAYROLL
PRODUCT
INVOICE COLLECTION DELIVERY LOGISTICS
SUPPLIER
BANK
WAREHOUSE
PAYMENT
CONFIDENTIAL
WWW.K2.COM
ORDER
STAFF PERFORMANCE
REVIEW SALES SUPPORT
PLANT
EXPENSE MANUFACTURING GOODS ABSENCE RECEIVABLE REQUEST
CUSTOMERS
PAYROLL ORDER SALES INVOICE COLLECTION
FINANCE SALES PAYMENT SUPPORT HR PRODUCT
INVOICE COLLECTION DELIVERY LOGISTICS
SUPPLIER
ISSUE LOGGING RETURNS
ISSUE RESOLVING WAREHOUSE BANK CUSTOMERS SUPPORT
PAYMENT
CONFIDENTIAL
WWW.K2.COM
FORMS
> PAPER > INFOPATH > WEB > SHAREPOINT LISTS > ADOBE
ACTIONS
> APPROVE > REJECT > DELEGATE
INFORMATION
> SAP & SIEBEL > DATABASE:SQL AND ORACLE > DOCUMENTS:SHAREPOINT > NEW DATA:NEED TO CREATE
REPORTS
> OUT-OF-THE-BOX > FOR BUSINESS USERS > FOR TECHNICAL USERS
PEOPLE
> ROLES > INFORMATION EXISTS > STATE
EVENT MONITORING
> INTERNAL EVENTS > EXTERNAL EVENTS
POLICIES
> CUSTOMER DISCOUNT > TASK DELIVERY > SLA > EXPENSE CLAIM LIMIT
PROCESS
> DESIGN > ASSEMBLE > EXECUTE > MONITOR > OPTIMIZE
WWW.K2.COM
FORMS
ACTIONS
START
INFORMATION REPORTS
CHANGE PROCESS
ACT1
PEOPLE
ACT2
EVENT MONITORING
POLICIES
PROCESS
1400
2000
1800
OUT OF OFFICE
> 5000
WWW.K2.COM
QUESTIONS?
CONFIDENTIAL
Vous aimerez peut-être aussi
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryD'EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryÉvaluation : 3.5 sur 5 étoiles3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)D'EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Évaluation : 4.5 sur 5 étoiles4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItD'EverandNever Split the Difference: Negotiating As If Your Life Depended On ItÉvaluation : 4.5 sur 5 étoiles4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaD'EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaÉvaluation : 4.5 sur 5 étoiles4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingD'EverandThe Little Book of Hygge: Danish Secrets to Happy LivingÉvaluation : 3.5 sur 5 étoiles3.5/5 (399)
- Grit: The Power of Passion and PerseveranceD'EverandGrit: The Power of Passion and PerseveranceÉvaluation : 4 sur 5 étoiles4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyD'EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyÉvaluation : 3.5 sur 5 étoiles3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeD'EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeÉvaluation : 4 sur 5 étoiles4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnD'EverandTeam of Rivals: The Political Genius of Abraham LincolnÉvaluation : 4.5 sur 5 étoiles4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeD'EverandShoe Dog: A Memoir by the Creator of NikeÉvaluation : 4.5 sur 5 étoiles4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerD'EverandThe Emperor of All Maladies: A Biography of CancerÉvaluation : 4.5 sur 5 étoiles4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreD'EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreÉvaluation : 4 sur 5 étoiles4/5 (1090)
- Her Body and Other Parties: StoriesD'EverandHer Body and Other Parties: StoriesÉvaluation : 4 sur 5 étoiles4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersD'EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersÉvaluation : 4.5 sur 5 étoiles4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceD'EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceÉvaluation : 4 sur 5 étoiles4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureD'EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureÉvaluation : 4.5 sur 5 étoiles4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaD'EverandThe Unwinding: An Inner History of the New AmericaÉvaluation : 4 sur 5 étoiles4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)D'EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Évaluation : 4 sur 5 étoiles4/5 (98)
- On Fire: The (Burning) Case for a Green New DealD'EverandOn Fire: The (Burning) Case for a Green New DealÉvaluation : 4 sur 5 étoiles4/5 (73)
- Microsoft 70-346: ExamCollection Premimum FileDocument69 pagesMicrosoft 70-346: ExamCollection Premimum Filericha sonber100% (2)
- P6 EPPM Administrator's Guide - Oracle DatabaseDocument417 pagesP6 EPPM Administrator's Guide - Oracle DatabasemadhusribPas encore d'évaluation
- Zoho FactsheetDocument6 pagesZoho FactsheetRohan KapoorPas encore d'évaluation
- PowerShell For SharePoint Admins PDFDocument26 pagesPowerShell For SharePoint Admins PDFprincemailid143Pas encore d'évaluation
- APM Compatibility Guide 10.2Document780 pagesAPM Compatibility Guide 10.2vamsikolliPas encore d'évaluation
- Solutions: What's New: Developing Solutions For Microsoft Dynamics NAV 6.0Document38 pagesSolutions: What's New: Developing Solutions For Microsoft Dynamics NAV 6.0Welington SilvaPas encore d'évaluation
- Content Matrix Console Advanced Installation GuideDocument48 pagesContent Matrix Console Advanced Installation GuidesteinfieldPas encore d'évaluation
- Guidelines For Anti-Virus ExclusionsDocument13 pagesGuidelines For Anti-Virus ExclusionsadrianfzPas encore d'évaluation
- Netwrix Auditor Installation Configuration GuideDocument202 pagesNetwrix Auditor Installation Configuration Guideluckman212Pas encore d'évaluation
- Web Content Management System: June 2011Document13 pagesWeb Content Management System: June 2011Pankaj SinghPas encore d'évaluation
- Work Without WallsDocument18 pagesWork Without WallsKhairul Amri Md SohodPas encore d'évaluation
- Sharepoint Developer EbookDocument41 pagesSharepoint Developer Ebookiampalaniyandi7463100% (1)
- WikiNinjas Guide To SharePoint 2013 - Part II PDFDocument407 pagesWikiNinjas Guide To SharePoint 2013 - Part II PDFPierre PucheuPas encore d'évaluation
- Groove 2007 at A GlanceDocument5 pagesGroove 2007 at A GlanceLeids LumenPas encore d'évaluation
- Keeya ResumeDocument4 pagesKeeya ResumeSatishKumarSinhaPas encore d'évaluation
- Vmware Data Protection Administration Guide 61Document218 pagesVmware Data Protection Administration Guide 61billmarc1978Pas encore d'évaluation
- NetBackup 7.7.1 Licensing GuideDocument47 pagesNetBackup 7.7.1 Licensing GuidesparctusharPas encore d'évaluation
- HTTPS://WWW - Scribd.com/presentation/447809227/6 Distributed File SystemsDocument12 pagesHTTPS://WWW - Scribd.com/presentation/447809227/6 Distributed File SystemsDhikesh RjPas encore d'évaluation
- Help Desk (ERP) Manage Requests and Task of An EnterpriseDocument6 pagesHelp Desk (ERP) Manage Requests and Task of An EnterpriseTheDigitalGroupPas encore d'évaluation
- book24x7書單2008 111Document916 pagesbook24x7書單2008 111crampingpaulPas encore d'évaluation
- Microsoft Office 2007 Serial KeyDocument2 pagesMicrosoft Office 2007 Serial Keyapi-3798612100% (1)
- Install Sharepoint Server 2007Document38 pagesInstall Sharepoint Server 2007asimalampPas encore d'évaluation
- Veeam Backup 6 1 Release Notes PDFDocument14 pagesVeeam Backup 6 1 Release Notes PDFsorachut1989Pas encore d'évaluation
- BlackBerry Workspaces DatasheetDocument6 pagesBlackBerry Workspaces DatasheetPrasad KshirsagarPas encore d'évaluation
- E-Services Within Estonia. Wilfried Grommen, RTO Microsoft CEEDocument39 pagesE-Services Within Estonia. Wilfried Grommen, RTO Microsoft CEEEdmund Laugasson0% (1)
- Performance Management For Public Sector Organisations in ScotlandDocument8 pagesPerformance Management For Public Sector Organisations in ScotlandCharteris Plc100% (1)
- Exam 70-662 Microsoft Exchange Server 2010, Configuring Install and Config Exchange ServersDocument6 pagesExam 70-662 Microsoft Exchange Server 2010, Configuring Install and Config Exchange Serversviti_93Pas encore d'évaluation
- Veeam Basics: Intro To Veeam Products: Product DemoDocument11 pagesVeeam Basics: Intro To Veeam Products: Product DemolindaPas encore d'évaluation
- Microsoft Transporter SuiteDocument185 pagesMicrosoft Transporter SuitelocomaurePas encore d'évaluation