Académique Documents
Professionnel Documents
Culture Documents
Yaredo
Transféré par
ላቨ ኪያTitre original
Copyright
Formats disponibles
Partager ce document
Partager ou intégrer le document
Avez-vous trouvé ce document utile ?
Ce contenu est-il inapproprié ?
Signaler ce documentDroits d'auteur :
Formats disponibles
Yaredo
Transféré par
ላቨ ኪያDroits d'auteur :
Formats disponibles
DAM BREACH MODELLING AND FLOOD
INUNDATION MAPPING:
A CASE STUDY OF KESEM DAM
By
Yared Michael Gebregziabher
Advisor:
Nigussie Teklie (Dr.Ing.)
An Msc Thesis Proposal
Submitted to
The School of Post Graduate Studies
Arba Minch University
July 16, 2014
Contents
List of Ta b I e s..-·-·-·-·-·-·-..-·...-·-·-·-·-..-·-·-·-·-..·..-·-·-·-·-....-·-·-·-·-·-·-··..-·-·-·-·-·-·-·-·-·-..-·-·-·-·-·-·-··..-·-·-·-·-·-..-·-·-·-·--..·..-·-·-·-·-..-·-·-·-·-·-..·..-·-·-........-..i i
Li st of Fig u r es ··---··-----··---·-------·-----·-----··----·-----··-----·-----··----··----··---ii
L'1 st of Abb rev .1 at 1. on s -·-·-·- -·-·-·- ..·..-·-·-·- _ _._ --.- _ _._ _._,_ _.._ _._ - ·-·-·- - -·-·-·-·- -- ...
111
L I ntr oducti o n,, - ·-·-·-·..·-·-·-·-·-·-·-·..····-·-·..·-···-···-·-·-- _,_, _ ---·-·-·-·-·- -----·-···- ---·-·-·- 1
1 .1 Bae kg round_··-----·-----·-----··----··-----·----··-----·-----··----·------·-----··---- 1
1.2 Statement of the Problem __ ····---···---····--···---····--···----···--······----···---··-3
1 .3 Obi ective of the st udi-·-·-·-·-·-·-·-·-·-·-..-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-....-·-·-·-·-..-·-·-·-·-·-..·..-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-·-··3
1.4 Scope of the Thesis·····---···---···----···--···-----··---··-----··---····-----·-·-··-··----4
1 .5 Research questions ··---·-------·-----------·-----·-----··-----------·-----·-----··- 4
z. Lite rat u re rev i e w..-·-·- -·-·-·- -·-·-·-·- ..·..-·-·-·- -·-·-·- ..·..-·-·-·-·- -·-·-·-·-·-·- -·-·- -..-·-·-·-·-·- -·-·- - ·-·-·-·-·- -·-·-·- ..·..-·-· 5
2. 1 Mode of Fa i I u re._._ - -·-·- -·-·-·-·- _.- _._ _._ - - _ _ _ _,_ _ ,_. 5
2. 2 Dam Break An a lysi s------------·-----------·-------·-----------·-----------··----·----6
2.3 Modeling the propagation of flood caused by structural failure _ -·-·-···-·-·- 8
3. Mat eri a Is and Method o I og i es -·-·- -·-·- - -·-·- - _,_ _,_ _,_ _,_.. l O
3.1 Description of the Study Area and the Dam under Analysis l0
3. 2 Material s - 13
3. 3 Met hodo I og i es._ _._,__,_,_,_,_,_ _._,_,_,_ _ __,_,_,_,_,_ _._,_, ,_,_,_,_,_.._,_,_,_, ,_,_,_,_ _.._,_,_, ,__, l 8
3.3. l Data collection 18
3. 3. 2 Data an a I ysi s-----··----·-----···----·-----··----·-----···---···---···-----·----··-· 18
.1: Significance of the Stu dy~.- - _ _ - _ - 21
5. Expected Outputs ··-------··- ··-------··-··-------··-··-------··--·-------··-··-·---21
6. Time sch ed u I e ·----···---···----····-· ···--·--··--- ··-----··--- ···----···-- 22
L Fin a nc i a I Br ea k Down_ - _,__, 23
AMU, School of PG, MSc Thesis Proposal ii
Dam Breach Modeling and Flood Mapping
Bi b I i o g rap h Y-·····-·-·-·-·-·-········-·-·-····-·-·-·-·-·-········-·-·-····-····-·-·-·-·-·····-·-·-····-··-·-·-·-·-·-········-·-·-·-·····-·-·-·-·-·-·····-·-·-·-·····-····-·-·-·-·····-·-·-·-·-·-·····-·-·-·-········-·-2 4
List of Tables
Table l: Breach Parameter Relations Based on Dam-Failure Case Studies ...•·-···-·-·-···-···-·-···········-·-·-···J 3
Table 2: Physically-based embankment dam breach models (Tony L. Wahl, l 998) J4
Table 3: Time Schedule for Conducting the Research. ·-·-·-·-·-···········-·-····-··-·-·-·-·-···········-·-····-··-·-·-·-·-···········-·-····-··-·-·-·-·22
Table 4: Financial Breakdown Required to Accomplish the Study ·--·--- --·--·-·· 23
List of Figures
Figure l: Location map of the study area ·-·-·-·---·-·-···- ---·-·- -•.- lO
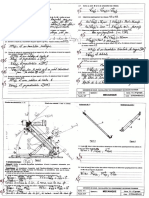
Figure 2 Typical Cross Section of the Main Dam··-·-·-········-·-·-·-···········-·-·-·-········-·-·-····-·····-·-·-·-···········-·-·-····-··-·-·-·-···········-·-·-····-·12
Figure 3: Conceptua I Framework. 20
AMU, School of PG, MSc Thesis Proposal ii
Dam Breach Modeling and Flood Mapping
List of Abbreviations
BEED Breach Erosion of Embankment Dams
BRDAM BReach DAM
DAMBRK DAM BReaK
EMA Ethiopian Mapping Agency
EAP Emergency Action Plan
Geo RAS Geographic River Analysis System
GIS Geographical Information System
ICOLD International Committee on Large Dams
m.a.s.l mean above sea level
MoWIE Ministry of Water, Irrigation and Energy
PMF probable maximum flood
-RAS Hydrologic Engineering Center - River Analysis System
NWS The National Weather Service
USBR United States Bureau of Reclamation
USACE United States Army Corps of Engineers
WWDSE Water Works Design and Supervision Enterprise
AMU, School of PG, MSc Thesis Proposal iii
Dam Breach Modeling and Flood Mapping
AMU, School of PG, MSc Thesis Proposal iv
Dam Breach Modeling and Flood Mapping
Approval Page
Submitted By:
Yared Michael
Student Signature Date
Approved By:
l. Dr. Nigussie Teklie
Major Advisor Signature Date
2. Mr. Zerihun Leggese
Co-Advisor Signature Date
3. Dr. Adane Abebe
Examiner Signature Date
4. Mr. Guta Wakbulcho
Chair Person Signature Date
5. Mr. Elias
Department Head Signature Date
AMU, School of PG, MSc Thesis Proposal iv
Dam Breach Modeling and Flood Mapping
1. Introduction
1 .1 Background
Construction of dams is highly essential in developing countries. Nowadays there are more
than 800,000 dams constructed around the world for different purposes: flood control (the
most common purpose), irrigation, electricity generation, water supply, recreation, etc ..
While planning and implementing dams, taking a good care of their safety is currently
becoming an important issue since lots of dams have been breached out in history in different
corners of the world and have resulted in a catastrophic damage to human lives, property and
the environment. A good example is the world's worst dam disaster occurred in Henan
province in China, in August 1975, when the Banqiao Dam and the Shimantan Dam failed
catastrophically due to the overtopping caused by torrential rains. Approximately 85,000
people died from flooding and many more died during subsequent epidemics and starvation;
millions of residents lost their homes.
Since the failure phenomena is unexpected and an abrupt one, an immediate mitigation
measures cannot be taken to hinder the breaching process. Hence, evacuating the
downstream residing people after the failure process has already commenced may not be
possible to save lives and property due to the aggressive nature of the wave front.
Various studies have been carried out to investigate the causes of dam failure, comprehend
the actual breaching process and determine the magnitude of out flowing water. Previously,
the approaches followed to prevent or minimize the catastrophes of dam failures were design
and construction of giant structures that can withstand the loads and accommodate floods of
high magnitude having long return period. This technique of flood prevention definitely renders
a tremendous amount of investment and the chance of prevention is not absolute. Therefore,
the method is currently being replaced by flood management approaches which focus on
reducing the consequences of disastrous events on downstream people and property by
assessing the risk of dam break and the flood that would inundate downstream field.
Assessing flood risk includes; identifying the failure modes and events that would trigger
breaching, quantifying the amount of flood that will propagate downstream and evaluating the
AMU, School of PG, MSc Thesis Proposal l
Dam Breach Modeling and Flood Mapping
socioeconomic and environmental threats it would result in.
Forecasting the possible dam break flood and formulating its temporal and areal distribution
on the downstream helps to develop disaster management plans such as demarking safe
building areas, constructing flood protection dykes, structuring evacuation techniques,
transmitting inundation information and setting early warning systems. This approach was
valid during Baldwin Hill and San Fernando dam failures where thousands of lives could be
evacuated.
The dam break can be triggered by overtopping, piping or foundation failure depending on the
type of dam, its constituent construction materials, hydrodynamic movements in the reservoir
and/or on the dam, magnitude of inflow, performance of the dam and its appurtenance
structures, operation of gates on times of peak floods and many more. Therefore, the dam
break analysis should consider these factors.
Different organizations and researchers have contributed their findings in the analysis of dam
break and its consequences. They have derived regression equations based on data from
historical dam failure events that are used in predicting the breach geometry. These include;
the United States Bureau of Reclamation (USBR) and MacDonald and Langridge equations.
Development of analytical models using the principles of hydraulics and sediment transport
are also useful in simulating the breach process and downstream flooding. Some of the
models are; The National Weather Service (NWS) models such as DAMBRK, SMPDBK and
FLDWAV. Using these equations and models, pre event analyses have been made on various
dams throughout the world and formulation of Emergency Action Plan (EAP) could be possible.
In Ethiopia the number of dams being constructed is increasing, ranging from small micro
earth dams built to fulfill community demands such as food and water supply to mega projects
as that of The Great Ethiopian Renaissance Dam, being implemented to boost the nation's
economy.
Kesem dam is one of the earth fill dams being constructed in different parts of the country
intended for impounding water to irrigate sugar cane plantation and feed the new sugar
AMU, School of PG, MSc Thesis Proposal 2
Dam Breach Modeling and Flood Mapping
factories under construction. The dam is a rock fill type dam with impervious clay core at the
middle covered by adjacent transition fill material and sand filters on both sides with a
purpose of preventing finer materials from migration.
Apart from constructing dams in Ethiopia, much has not been heard on pre event dam break
analysis and its consequences. Hence, the intention of this study is to model a breaching
process on Kesem Dam under different scenarios of inflow, failure mode, breach morphology
and analyze the consequences that will happen on downstream.
This research is expected to contribute some useful information to Kesem Dam administrating
body regarding to dam safety issues that should be considered, precautions to bear in mind
while implementing infrastructures on downstream areas and input data in preparing EAP.
Moreover, designers, consultants and contractors engaged on dam works may gain an input
data for their work.
AMU, School of PG, MSc Thesis Proposal 3
Dam Breach Modeling and Flood Mapping
1.2 Statement of the Problem
Thousands of dams have been constructed throughout the world and hundreds of these have
failed resulting in catastrophic consequences, such as loss of many lives, distraction of homes
and damage to various infrastructures. In Ethiopia, in contrary to the development of dams,
such pre event analysis is not being carried out by designers or researchers. Hence, dam
breach modelling is vital to identify the possible causes of dam failure, simulate the breaching
process so that design parameters can be reviewed, map the area that shall be flooded in
order to demarcate prone areas while planning the downstream area for various
infrastructures, alert concerned bodies to take a precaution on dam safety plans and formulate
a hazard management system.
Kesem Dam which is a rock fill dam with clay core is selected for this analysis since different
indicators of failure have been observed during and after construction of the dam. Some of
these are; spring out of hot water on dam site area during construction period and seepage of
water on downstream side of the abutments.
This pre event dam break analysis is therefore aimed to model the possible breaching process
of the embankment dam and to delineate the area that would be flooded out due to the
hazardous wave front. The problems that might envisage are summarized as follows:
l. Ruining out of the embankment and its appurtenant structures which are constructed
with high investment.
2. Loss of impounded water that has been accumulated for years and could irrigate an
enormous area of land.
3. Inundation of downstream area causing loss of human life and property.
4. Flooding of the Kesem sugar cane plantation which is the main purpose of constructing
the dam.
5. Drowning of the sugar processing factory.
AMU, School of PG, MSc Thesis Proposal 3
Dam Breach Modeling and Flood Mapping
Efforts will be made to assess gaps of previous experiences in breach modelling and flood
inundation mapping and different considerations with detail study shall be carried out to fill
some gaps as much as possible. provided that conditions in the case study area allow in doing
so.
1 .3 Objective of the study
The general objective of this study is to model the dam breach process, apply it to the case of
Kesem dam and map the downstream area to be inundated by the flood.
The specific objectives are:
1. To simulate the breach process applying different breach parameters that shall be set
up based on regression equations which are developed by various scholars using
historical dam break data.
2. To run the model for different catastrophic scenarios and analyze the consequences of
the most hazardous one.
3. To predict the outflow hydrograph just at the outlet of the breach.
4. To route the peak outflow hydrograph on downstream channel and map the area that
shall be flooded.
5. To prepare various types of maps such as area. velocity, depth with time that can
describe the nature of flood propagation and coverage.
1.4 Scope of the Thesis
This thesis shall cover determination of dam breach parameters through which the
catastrophic peak outflow passes. Different scenarios of inflow, mode of failure and breach
location will be considered and the one giving a worst condition shall be selected for further
downstream routing and flooding.
AMU. School of PG, MSc Thesis Proposal 4
Dam Breach Modeling and Flood Mapping
One dimensional flood simulation model which is based on unsteady flow equations will be
used for analysis.
From the known modes of failures, seismic type will not be considered in this study due to the
rare chance of occurrence during reservoir full condition. Sediment transport during erosion of
dam material will not be considered, since the selected model, HEC-RAS, simulates only clear
water flow.
1.5 Research questions
The following questions can be raised to initiate this study
l. What predominant mode of failure would the dam probably manifest?
2. What are the breach parameters defining the cross section of the breach?
3. What are the different scenarios that would cause the dam break and which of these is
the most catastrophic?
4. How long would it take for the breach process to complete and for the inflow flood
together with the reservoir water to evacuate?
5. How much area would the emerging flood hydrograph covers in the downstream until it
attenuates?
2. Literature review
Dams are designed to withstand different loads such as; upstream hydrostatic pressure load,
self weight. seismic load and other minor loads like the wind load. The greater the chance of
loss of life or damage to valuable property in case of the failure event. the safer the design
should be. Despite this fact, dams do frequently fail. In the case of embankment dams. failure
or breaching is merely erosion or sloughing of the dam material, which may be induced by
overtopping, piping, foundation seepage or seismic action.
AMU, School of PG, MSc Thesis Proposal 5
Dam Breach Modeling and Flood Mapping
2.1 Mode of Failure
Overtopping is one of the most common failure modes for earthfill dams. It can be triggered by
inflows higher than the design inflow, malfunctioning or a mistake in the operation of the
spillway or outlet structure, inadequate carrying capacity of spillways, settlement of the dam or
as a result of landslides into the reservoir. The overtopping flow can be computed by the broad
crested weir equation:
q = CH15
where; q - flow over the dam per unit length of the dam.
C - weir coefficient with a value of 2.6 for broad crested and 3.2 for sharp crested
H - head over the crest
Piping failure is a failure mode caused by water penetrating through the dam's body, carrying
with it small particles of dam material, continuously widening the gap. If the initial piping can
be detected before it reaches the critical condition, remedy might be possible. Penetration of
water in the dam body can cause slope failure. To prevent this type of failure, appropriate
instrumentation is needed to estimate the rate of infiltration within an embankment. Flow
through the pipe is computed by the orifice formula;
Q= C dA../ (2gH)
Where; Cd - coefficient of discharge with value 0.5- 0.6 for inefficient pipe entrance
Seepage failure or foundation failure occurs due to the saturation of the foundation material
leading to either washout of the material or a weakening of the rock towards a sliding failure.
The flow of water through a pervious foundation produces seepage forces as a result of the
friction between the percolating water and the walls of the pores of the soil through which it
flows.
Seismic failure is a dam one mode of dam failure triggered by earthquake which can result in
catastrophic effects, even though it rarely happens. It can cause either landslide in the
reservoir that induces a wave towards downstream overtopping the dam crest or liquefaction
AMU, School of PG, MSc Thesis Proposal 6
Dam Breach Modeling and Flood Mapping
of the fill material to fail in shear and thereby breach develops.
2.2 Dam Break Analysis
The primary tasks in dam break analysis are predicting the out flow hydrograph and routing
the flood through the downstream river channel and flood plain. To predict the outflow
hydrograph the parameters of the breach through which the reservoir water escapes have to
be determined initially.
2.2. l Breach Parameter Estimation
Breach parameters can be estimated using regression equations that are developed based on
historical dam failure data, see Table 1. Due to insufficient data on breach formation time,
spatial breach development during the failure phenomena and inadequate number of large
dams and reservoirs in the domain of analysis, these equations hold uncertainties .
Another technique to determine the breach parameters is using analytical models. The model
BREACH is one of the available mathematical models that can predict the breach
characteristics which are the size, shape and time of formation. This physically based model is
developed based on the principles of hydraulics, sediment transport, soil mechanics,
geometric and material properties of the dam, and the reservoir properties .
From soil mechanics principles, cohesive soils and rock fill dams with cohesive cores fail
through head cutting or sloughing mode of failure whereas the non cohesive ones through
erosion. On dam breach process, the embankment fill material may fail in sloughing either
laterally or longitudinally and geotechnical slope failure. The limitation of the model BREACH
and other physically based models such as BRDAM, BEED, FLOW SI Ml and FLOW SIM2 is that
they are developed considering tractive-stress based erosion in contrary to the general failure
mode of embankments which is head cutting .
The breaching process is accomplished in two time phases. The initiation phase is the initial
time at which overtopping or piping flow is observed the dam. During this phase, the flowing
water can be stopped and hence the dam can be saved from failure. In no measures are taken
to stop the water, erosion of embankment material will be triggered and any mitigation actions
that are undertaken to stop will be value less, this phase is called breach formation time.
AMU, School of PG, MSc Thesis Proposal 7
Dam Breach Modeling and Flood Mapping
It was observed from the collected historical dam failure events that in most of the cases the
ultimate breach shape is of trapezoidal shape. They concluded that for embankment dams, the
breach shape can be assumed to be triangular up to the time that the base of the embankment
is reached. Once the apex of the triangle reaches the foundation level, the breach develops
forming a trapezoidal section extending due to lateral erosion .
In spite of the incomplete understanding of breach formation processes and the limited
capabilities of mathematical description of dam breaching mechanisms. various breach
parameters estimation techniques are developed based on several assumptions. Some of
these, along with their limitations .. are discussed here under.
1. Experimental method: For better understanding the processes involved and to correctly
describe the complex phenomena of embankment breaching. various field and laboratory
experiments are carried out modeling gradual failure of dams and obtain data for
calibration and validation of mathematical models. These field and laboratory results lead
to extensive validation of the numerical models being used and under development .
11. Comparative Analysis: If the dam under consideration is very similar in size and
construction to a dam that failed, and the failure is well documented, appropriate
breach parameters or peak outflows may be determined by comparison. This method
is not highly reliable for large dams such as Kesem Dam, the case study of this
research which is 96m high. because of lack of accurate and comprehensive case
study data on large dam .
iii. Empirical equations: these equations are obtained from regression analysis of historical
dam failure events. Their application to a particular dam should be used cautiously making
sure that dam and reservoir characteristics are within the range of the dataset upon which
the empirical equation is based. The drawback of this method is the high uncertainties of
the data used to derive regression equations. The basic equations are provided in Table 1 ..
iv. Analytical models: these are physically based dam breach simulation models used to
predict breach parameters. This has special advantages such as prediction of breach
AMU. School of PG, MSc Thesis Proposal 8
Dam Breach Modeling and Flood Mapping
initiation time and intermediate breach dimensions as well as ultimate breach parameters.
BREACH is a widely used parameter prediction model .
2.2.2 Outflow Hydrograph Prediction
The breach outflow hydrograph is of crucially important for the assessment of flooding
characteristics in the downstream areas. As in the case of parameter estimation, there are also
regression equations developed in order to predict the amount of outflow through the breach
using dimensions of the dam and reservoir. An equation most relevant to the dam under study
is chosen and the peak out flow is computed.
Currently, numerous physically based models of predicting peak outflow are available. Some of
the models are listed in the methodology section under Table 2 and their detail description and
technical background is discussed in the paragraphs following the table. These models
simulate flow through the breach channel using either the orifice equation (at the initial phase
of piping failure) and the weir equation, or the one dimensional de Saint-Ven ant equations.
Various scenarios triggering dam failure such as variable inflow, different gate operations,
seismic loads and sunny day failure are set and the selected model is simulated to predict the
outflow hydrograph. The highest flood of the different scenarios is selected as a catastrophic
one.
2.3 Modeling the propagation of flood caused by structural failure
Having determined the breach parameters and peak outflow the next task is to route the most
catastrophic outflow hydrograph over the downstream channel and flood plain and prepare an
inundation map.
Inundation maps show the flood contour for natural floods of certain return periods, in most
cases up to PMF, and flood contours of potential dam break floods caused by a "sunny day
failure" and a failure superimposed over certain natural "base flood conditions".
This inundation maps are used to control building activities, develop necessary warning and
evacuation plans, conduct consequence assessment and are implemented into infrastructure
planning of the flood areas below the dam.
AMU, School of PG, MSc Thesis Proposal 9
Dam Breach Modeling and Flood Mapping
Various models have been developed to execute the flood inundation mapping process.
HEC-RAS is an example of one dimensional models analyzing downstream flow using
unsteady flow equations. The FESWMS (finite element surface water modelling system) is a
two dimensional model developed by FEMA to simulate movement of water in rivers, estuaries
and coastal waters. While the 1-0 models require cross sectional data of flow channels with
sufficient extension on both left and right direction, the 2-0 models use topographical data in
the form of a continuous surface represented by finite element mesh. Case studies comparing
1 D and 20 could show that the 20 models represent more accurate flow in the flood plain due
to both lateral and longitudinal movement of water.
In spite of the timely improvements of flood routing models, the predictive accuracy of such
models can be subject to significant error (2 feet or more in the crest profile) due to inaccuracy
in the computed reservoir inflow, breach parameter estimation and dynamics, downstream
cross section properties, flow resistance coefficients both in channels and flood plains, effect
of sediment transport and flow constrictions in channel and the complex flow patterns that are
not adequately described by one-dimensional flow equations.
One-dimensional models are best suited to geographic regions with moderate to steep slopes
whereby flood waters are contained within a relatively narrow flood plain and generally flow in
single stream direction. Whereas two dimensional models can route both channel flow which
is one-dimensional and two dimensional overland flows on flat terrain .
To correctly estimate the consequences derived from a structural failure modeling of flood
propagation should be of highly accurate. Identification of the inundated areas, inundation
depth, speed and duration, as well as the impact that flood water characteristics (salt,
freshwater, contaminated water, etc.) can have on the inundated areas, are very important for
decision making, emergency evacuation and early warning.
Most of the research on modeling dam break flood wave propagation has been focused on the
movement of clear water in the downstream valley, excluding debris flows and sediment
transport. Clear water dam break floods have been studied extensively experimentally,
analytically and numerically.
AMU, School of PG, MSc Thesis Proposal 1 O
Dam Breach Modeling and Flood Mapping
The De Saint-Venant equations or shallow water equations are used for modeling dam break
flood propagation. These equations consist of the mass and momentum conservation
equations, and assume that the vertical velocities are much smaller than the horizontal
velocities, which leads to hydrostatic pressure distribution in a channel cross section .
3. Materials and Methodologies
3.1 Description of the Study Area and the Dam under Analysis
The Kesem Dam and its Reservoir is located within Sabure and Boloyta Kebele of Awash
Fentale Wereda, Zone 3 of the Afar Regional State at a ground distance of about 215km
south-east of Addis Ababa, on the asphalt highway from Addis Ababa to Harar and is close to
the town Metahara.
AMU, School of PG, MSc Thesis Proposal 11
Dam Breach Modeling and Flood Mapping
The Kesem river catchment. at upstream of Kesem dam site, covers about 3,000 km2 and
extends from an altitude of almost 3600 m down to 860 m m.a.s.l (mean above sea level). It
rises on the high Ethiopian plateau and descends the western scrap of the Great Rift Valley to
join the Awash River at its middle stretch. Kesem dam is constructed on Kesem River. The dam
site is geographically located at 9°8'45" Latitude and 39°53'31" Longitude, as shown in Figure l
below.
35'1Tere «l"G'O"e 45'0'ere
15'0'er
A 5'0'0"H
~ !l!l'()'O''E .tO"O'O"!
''
10'0'er
~ ...1AWASH
O'O'erN
10"0'0- .......
5'0'0
KESEM WA~RS.HED
BASINS OF ETHIOPIA
O'O'O" '()"
... •
0 1060
ere
'°"'"'"'' ere
W O''E
•
Figure l: Location map of the study area
The dam is a zoned (clay core rock fill) embankment type dam, as shown on Figure 2 below,
with crest length of 720m and crest width of l Om. Its height is 95m at river bed section having
the dam crest level at 941 m and river bed level at 846m. m.a.s.l. the upstream slope is l :2. 5
whereas downstream is with slope of l :2.
The reservoir is intended to accommodate a total of 500 million cubic meter of water, covering
a total surface area of 3-4km2• The area to be flooded by the reservoir is estimated to be
AMU, School of PG, MSc Thesis Proposal 12
Dam Breach Modeling and Flood Mapping
around 3000ha. The overall dam reservoir and the spillway is designed to accommodate a
l 0,000 year PMF (probable maximum flood) of 9237m3/s and the PMF level is 939.5m. The
spillway is ungated type having a total length of l OOm. The dam is provided a bottom outlet
with discharge capacity of 300 m3/s.
AMU. School of PG, MSc Thesis Proposal 13
Dam Breach Modeling and Flood Mapping
f
~ll'it•l ... m I$ 'J Al.s'I\
(l)tcrt•I~
"'"''"''lr! •:1.W•·••.L-. .. C/.i!Ol~I<IOClfill
(»r.11 filtr
31c,,..., ~"~
1'~~."(~Nt
(SO••• ry w:till!
Coone &lkr,,,_...,1
1pllll'V\&I: ll\ ~ r.11
I
L'fllmm blar~c '-
'- .
(t1fRrd.t1' ~'
,_.. . .
-----------....
','()o,o\""" ... ' .i. .i.----
"?~::·-----------------.
;.. __,
!JM" 0\1< fol'
'
'
t .........
.::._ --- ---~\----------
--------------1-;J~- --·---·-~-----
---------------------------- ...""°"'- ·---------
SCH.! 1,l3't
·----------
Tl',.CAL llAJCIMUll CROSS SECTION ATlllvtll lED
Figure 2 Typical Cross Section of the Main Dam
AMU, School of PG, MSc Thesis Proposal 14
Dam Breach Modeling and Flood Mapping
3.2 Materials
3.2.1 Model Selection
Analytical models are developed for the simulation of earthdam breach erosion. Using a
reservoir water-mass depletion equation, broad-crested weir hydraulics and a breach-erosion
relation, solutions are derived for rectangular, triangular and trapezoidal shaped breaches .
Dimensions of the breach are determined using relations developed from case studies as
shown on Table 1 below.
Table 1: Breach Parameter Relations Based on Dam-Failure Case Studies
Reference Number of I Relations Pronosed
Case studies (S.I. units, meters, m3/s, hours)
Johnson and Illes (1976) 0.5hd sBs3hd for earthfill dams
sinoh and Snorrason 11982 20 2hd <B<5hd
1984) 0.15 m s dovtop s0.61 m
0.25 hr stfsl .0 hr
Maclioneld .d.2 Earthfill dams:
Ve = 0.0261 ( Vout•hli?,-·
and Langridge-Monopolis r •• [best-fit)
(1984) tf= 0.0179(Vet}"·· [upper envelope]
Non-earthfill dams:
Ver= 0.00348( Vout•hw/··· [best fit)
FERC 11987\ Bis normallv 2-4 times hd
Bean ranoe from 1-5 times hd
Z= 0.25 to 1.0 [engineered, compacted dams]
Z= 1to2 I [non-enoineered, slao or refuse dams]
tf= 0.1-1 hours [en aineered, comoacted earth dam]
tf= 0.1-0.5 hours [non-engineered, poorly
compacted]
Froehlich (1987) 43 -
) :n A71( • 0.2'
II
r '
Ko= 1.4 overtopoinq: 1.0 otherwise
Z-0.75~ (fr )1.57 -;; ")0.1
Kc= 0.6 with corewall: 1.0 without a corewall
n- =79(s)" ..
Reclamation 11988\ B= (3\hw I
tf= (0.01 l)B
Sinon and scarlatos 119881 52 Breacn aeometrv an: time o tauure tendencies
Btop/Bbottom averages 1.
29
Von Thun and Gillette (1990) 57 B, z, tfouidance see discussion)
Dewey and Gillette (1993) 57 Breach initiation model; B z, tfauidance
AMU, School of PG, MSc Thesis Proposal 13
Dam Breach Modeling and Flood Mapping
;:I Kovv..l 19
=0.00254Vw0.53hb i·v •• ,
KCF 1.4 for overtopping; 1.0 otherwise
Table 2: Physically-based embankment dam breach models (Tony L. Wahl, 1998)
Sediment Breach Other
Model and Year Transport Morphology Parameters Features
Constant
Empirical breach Angle of
Cristofano (1965) formula Width repose, others
Harris and Wagner (1967); Breach
BRDAM (Brown and Rogers, Schoklitsch Parabolic dimensions,
1977) formula breach shape sediments
Linear pre- Rectangular, Breach
determined triangular, or dimensions. Tailwater
erosion trapezoidal Others Effects
DAMBRK (Fread, 1977)
Meyer-Peter Critical shear
Lou (1981 ); and Muller Regime type stress, Tailwater
Ponce and Tsivoglou (1981) formula Relation Sediment Effects
Meyer-Peter Tailwater
and Muller Rectangular, effects, dry
modified by triangular, or Critical shear, slope
Smart trapezoidal Sediment stability
BREACH (Fread, 1988)
Tailwater
effects,
Einstein- Saturated
BEED (Singh and Scarlatos, Brown Rectangular or Sediments, slope
1985) formula trapezoidal Others stability
AMU, School of PG, MSc Thesis Proposal 14
Dam Breach Modeling and Flood Mapping
Sediment Breach Other
Model and Year Transport Morphology Parameters Features
Linear pre-
determined
erosion;
Schoklitsch Rectangular. Breach
FLOW SIM l and FLOW SIM 2 formula triangular. or dimensions.
(Bodine, undated) option trapezoidal sediments
di mens ions.
-!EC-RAS Clear water User defined rme
The previous Table 2and the following paragraphs discuss comparison on the technical
background of the physically based models. made by .
BRDAM (BReach DAM) was developed applying the Schoklitsch sediment transport equation to
dam breach flows. It was assumed breach erosion to begin immediately upon overtopping. and
to proceed until the breach reached the bottom of the dam.
The model developed by Lou, Ponce and Tsivoglou links the Meyer-Peter and MUiier sediment
transport equation to the one-dimensional differential equations of unsteady flow and
sediment conservation. The differential equations were solved with a four-point implicit finite
difference scheme that was computationally complex and prone to problems of numerical
instability. Flow resistance in the breach channel was represented using Manning's n. The
breach width was empirically related to the flow through the breach. The model accounted for
reservoir storage depletion in its upstream boundary condition.
BREACH: Fread (1988) developed the physically-based BREACH model to more realistically
simulate breaches initiated by overtopping or piping .. The model permits specification of three
different embankment materials: an inner core. an outer portion (downstream shell). and a
vegetated cover or riprap protective layer on the downstream face of the dam. Flow through
the breach section is determined by orifice or weir equations. and flow down the face of the
dam is modeled as a quasi-steady uniform flow with roughness determined from the Strickler
AMU. School of PG, MSc Thesis Proposal 15
Dam Breach Modeling and Flood Mapping
equation for Manning's n. The model introduces two structural mechanisms that may
contribute to breach formation: the breach shape may be impacted by slope stability of the
breach side slopes, and possible collapse of the upper portion of the dam by shear and sliding
is analyzed.
HEC-RAS (Hydrologic Engineering Center - River Analysis System): the HEC-RAS breach
hydraulic computations include both overtopping and piping failure modes. It requires a
breach location along the crest. breach shape parameters and breach formation time to be
provided after estimating outside of the model using general guidance, empirical methods or
from the results of process model applications.
Hence, as a summary for the comparison, the model BREACH seems to be more sound and
reliable since it uses the Meyer-Peter and MUiier sediment transport equation as modified by
Smart for steep channels. The equation was set up based on extensive experimental works
executed by the researchers .. The model looks for all possible breach morphology which can
be rectangular, trapezoidal and triangular. The parameters of the breach are estimated based
on the critical shear stress of the dam material and finally it takes into consideration the tail
water effect during simulation. Hence the model BREACH is more powerful in modelling the
breach process.
3.2.2 Description of Selected Models
3.2.2.1 HEC-RAS
A comparison is done among mostly used physically based numerical models in the previous
section. It is clearly stated that the BREACH model is highly suitable in that it takes many
aspects into consideration as described in detail in the section. However, due to financial
constraint and the availability of the model free of cost, HEC-RAS is going to be used in this
study.
This model is developed by the USACE (United States Army Corps of Engineers) and is used for
modeling the breach of the dam and predicting the catastrophic outflow hydrograph. It can be
used both for overtopping and piping failure breaches for earthen dams and for instantaneous
failure of gravity dams. The resulting flood wave is routed downstream using unsteady flow
AMU, School of PG, MSc Thesis Proposal 16
Dam Breach Modeling and Flood Mapping
equations. Upstream reservoir area can be modeled using cross section data and then
performing full unsteady flow routing through the reservoir pool and downstream of the dam. It
can also be modeled using a storage area. In this case level pool routing through the lake is
conducted followed by unsteady flow routing downstream of the dam.
To use this software, the modeler must estimate the maximum breach parameters and breach
formation time initially based on different sets of regression equations and come up with a
matrix of potential breach parameters and time. These ranges of estimated breach parameters
shall be run as separate trials in the model in order to test the sensitivity of the results. The
model gives different outflow hydrograph for each breach parameter estimated. These various
hydrographs are then routed downstream to identify the most hazardous flood.
HEC-RAS gives several plots, tables, cross sections, profiles and 30 plots for evaluating the
results of a dam break analysis. The hydrograph can be viewed at any desired location.
The model is based on an implicit finite difference solution of the complete one-dimensional
continuity and momentum equations for unsteady flow.
The basic unsteady flow equations used in the physically based model to route the flood wave
are:
Conservation of continuity,
Rate of Rate of Rate of Lateral
change mass mass mass flow
= - +
of mass inflow outflow
Simplifying,
Conservation of momentum,
AMU, School of PG, MSc Thesis Proposal 17
Dam Breach Modeling and Flood Mapping
Rate of Net rate of + Sum of all external forces
accumulati momentu
(Pressure F. + Gravitational F. +
on of = m
Drag F.)
momentum entering/fl
ux
Simplifying,
3.2.2.2 HEC-GeoRAS
HEC-GeoRAS (Geographic River Analysis System) is an ArcGIS extension developed by the
HEC. This model contains a set of tools specifically designed to process geospatial data to
support hydraulic model development and analysis of water surface profile results. It assists in
creating data sets in GIS to extract information essential for hydraulic modeling .
After steady or unsteady flow simulation, HEC-RAS results can be exported for processing in
the GIS (Geographical Information System) by GeoRAS. The user can read the HEC-RAS results
into the HEC-GeoRAS and perform the flood inundation mapping . Moreover, a pre-processing
of data is done in HEC-GeoRAS/ArcGIS and imported to HEC-RAS to generate geo-spatial
based output data for post-processing in HEC-GeoRAS once again to produce flood inundation
map.
3.2.2.3 ArcGIS
The GIS is a system capable of capturing, storing, analyzing and displaying geographically
referenced information. Hence, in our context, this model with its HEC-GeoRAS extension shall
be used to study the areal distribution of the flood on downstream reach and to delineate the
boundary of inundation.
3.3 Methodologies
3.3. l Data collection
Primary data:
The primary data to be collected include:
AMU, School of PG, MSc Thesis Proposal 18
Dam Breach Modeling and Flood Mapping
:;... Surveying data to be collected along the cross section of the river at downstream of the
dam on every chainage that will be sufficient for the flood mapping process.
:;.. Physical observation and measurement on leakages and weak zones, if there are any
visible ones.
:;... Land use land cover data of the area prone to flooding. This can vary from land surface
formation type that will be used to estimate the manning's roughness 'n' to land use
pattern to evaluate the economic value that the area has rendered the inhabitants.
:;.. Relevant photos shall be taken on site that would be essential for the study.
:;.. Detail topographical and other relevant data shall be taken on downstream existing
obstructions, river confluences and other visible conditions there exist.
Secondary data:
All necessary secondary data such as:
';. salient features of the dam
-,. salient features of the reservoir
> reservoir area-elevation-volume curves
';. Topographical map from EMA (Ethiopian Mapping Agency)
> Geotechnical information on the composition of the dam and foundation.
> hydrological data(full PMF inflow hydrograph for which the dam and spillway are
designed.) and all necessary information shall be gathered from the MoWIE (Ministry of
Water, Irrigation and Energy) and from WWDSE (Water Works Design and Supervision
Enterprise) who designed and is supervising the Kesem dam and irrigation
construction project.
3.3.2 Data analysis
:;... Initially the possible failure mode of the dam, either overtopping or piping, shall be
AMU, School of PG, MSc Thesis Proposal 19
Dam Breach Modeling and Flood Mapping
selected from historical failure experiences and susceptibility of the dam to these
modes based on current observable failure indicators.
:;.. Breach parameters shall be determined using regression equations and used as input
for the HEC-RAS model. Sensitivity analysis will be conducted using the different
parameters obtained from the regression equations and parameters giving the worst
condition, within reasonable limit, will be selected for further simulation.
:;... These sensitivity analyses shall be carried out for different scenarios of failure which
are classified based on; inflow magnitude, breach location, breach morphology and so
on.
:;.. This sensitivity analysis shall also be carried out for the different catastrophic
scenarios.
:;... Outflow hydrograph will be determined using the worst condition.
:;... The outflow hydrograph will be used and routed to downstream channel to investigate
the areal extent of the flood and thereby flood inundation model is prepared using
HEC-GeoRAS and GIS.
AMU, School of PG, MSc Thesis Proposal 20
Dam Breach Modeling and Flood Mapping
AMU, School of PG, MSc Thesis Proposal 21
Dam Breach Modeling and Flood Mapping
<-----'
Figure 3: Conceptual Framework
AMU, School of PG, MSc Thesis Proposal 22
Dam Breach Modeling and Flood Mapping
4. Significance of the Study
Preparing dam safety plans and hazard management strategies are unquestionably vital, since
lots of human lives have been lost and tremendous amount of economic crisis have been
recorded from dam failure events throughout the world in history. Setting out risk management,
emergency action plans or evacuation planning system to protect both lives and materials
during sudden dam failure phenomena and resulting flood waves is highly essential as it has
been found to be effective when applied during Baldwin Hill and San Fernando dam failures
occurred in Los Angeles, California USA where thousands could be evacuated.
Hence conducting pre event analysis of Kesem dam break and its consequences and
forwarding the hazard extent to public offices have great significances among which some are
listed below:
1. On time maintenance actions can be taken if the dam is susceptible to piping failure
mode.
2. Flood early warning system can be developed after the disastrous dam breaching flood
has been identified.
3. Downstream settlement of inhabitants can be planned in such a way that evacuation of
the people during dam breach can be done rapidly saving as much lives as possible.
4. Protection dikes can be provided at both downstream banks with their top level
considerably higher than the propagating flood level, especially on the stretches along
residence areas and factory plants.
5. The thesis paper can be used as a reference for further detailed researches on the
study area.
5. Expected Outputs
After conducting this thesis, the following outputs are expected:
1. The most feasible mode of failure will be selected
AMU, School of PG, MSc Thesis Proposal 23
Dam Breach Modeling and Flood Mapping
2. The dam breach parameters will be determined
3. The dam breach model will be simulated using the determined parameters
4. Outflow hydrograph will be plotted for different scenarios of inflow hydrograph and dam
operation
5. The resulting outflow hydrograph will be routed towards downstream and the
inundating flood will be mapped to see the area it covers.
6. Time schedule
Table 3: Time Schedule for Conducting the Research
Time Duration (in the year 2014) Remark
No. Description Of Work Jul Aug Sep Oct Nov. Dec.
l Literature review
2 Data collection
3 Breach parameter
estimation
4 PMF hydrograph
analysis
Holiday
5 HEC-RAS model setup
•
6 Model simulation and
sensitivity analysis
7 Preparing flood
inundation model,
HEC-GeoRAS
8 Mapping the flood
inundated area
AMU, School of PG, MSc Thesis Proposal 24
Dam Breach Modeling and Flood Mapping
9 Results and discussion
with conclusion and
recommendation
10 Compiling and
submitting the report
7. Financial Break Down
Table 4: Financial Breakdown Required to Accomplish the Study
No. Description Unit Quantity Unit Price Amount Remark
(Birr)
I. Consumable Material
1 Stationery l.s 1 200 200
2 Flash disc Pcs. 1 250 250 8 GB capacity
3 Compact disc, CD pac 1 200 200
k
4 External hard disc, 1 TB Pcs. 1 2500 2500
5 Digital camera Pcs. 1 5000 5000
6 1 :50,000 EMA MAP No. 6 100 600
Sub total 8,750
II Services
1 Internet hrs. 41.67 12 500
2 Report writing and pag 3x120 4 1440
AMU, School of PG, MSc Thesis Proposal 25
Dam Breach Modeling and Flood Mapping
printing e
3 Photocopying set 4 90 360
4 Binding set 5 10 50
Sub total 2350
111 Running cost
l Car rent(with fuel + day 5 3000 15000
driver) s
2 Surveyor with day 5 3000 15000
instrument and s
assistants
3 Per diem day 10 300 3000
s
4 Travel to Addis Ababa trip 4 300 1200
Sub total 34,550
Grand Total 45,320
Bibliography
Brunner, G. W. (2002). HEC-RAS, River Analysis System Hydraulic Reference Manual Davis: US
ARMY CORPS OF ENGINEERS.
Brunner, G. W. (2006). HEC-RAS, River Analysis Systme User's Manual Davis: US ARMY
CORPS OF ENGINEERS HYDROLOGIC ENGINEERING CENTER (HEC).
Cameron T. Ackerman and Gary W. Brunner. (not dated). Dam Failure Analysis Using HEC-RAS
and HEC-GeoRAS.
Cook, A. C. (2008, May). Comparison of one-dimensional HEC-RAS with two-dimensional
FESWMS model in flood inundation mapping. West Lafayette, Indiana. USA.
FEMA. (2013). Federal Guidelines for Inundation Mapping of Flood Risks Associated with Dam
Incidents and Fatlures.
Fread, D. (1991 ). BREACH: An Erosion Model for Earthen Dam Failures.
AMU, School of PG, MSc Thesis Proposal 26
Dam Breach Modeling and Flood Mapping
Fread. D. (1981). Some Limitaions of Dam-Breach Flood Routing Models. American Society of
Civil Engineers.
Gee, M. (2010). Use of Breach Processes Models to Estimate HEC-RAS Dam Breach
Parameters. 2ndJointFederal!nteragencyConference, Las Vega.s; NV. June21-Ju/y 7, 2070.
Guner, B. &. (2001 ). Pre-Event Dam Failure Analysis for Emergency Management. Turk J Engin
Environ Sci.
ICOLD. C. 0. (1998). DAM-BREAK FLOOD ANA YSIS. Paris: International Committee on Large
Dams.
Rijn, L. C. (1993). Principles of Sediment Transport in River.s; Estuaries and Coastal Seas.
Amsterdam. The Netherlands: Aqua Publications.
Singh, V. a. (1998). Retrieved June 27, 2014, from American Society of Civil Engineers: http:/ /dx.
doi.org/l 0.1061/(ASCE)0733-9429(1988)ll4:l (21)
Wahl, T. L. (1997). Predicting Embankment Dam Breach Parametrs-A Needs Assessment. JAHR
Congress.
Wahl, T. L. (1998). Prediction of Embankment Dam Breach Psrmeters. U.S. Department of the
Interior Bureauof Reclamation .
WWDSE. (2005). Final Dam Design Report. Addis Ababa: Water Works Design and Supervision
Enterprise.
Zagonjolli, M. (2007). Dam break Modelling, Risk Assessment and Uncertainity Analysis for
Flood Mitigation. ISBN 9 18047 5 455941 (Taylor & Francis Group). London, UK: Taylor &
Francis.
AMU. School of PG, MSc Thesis Proposal 27
Vous aimerez peut-être aussi
- E-Relev - N - 005 (Partenaire N - 00000000433499) - 157351309 PDFDocument5 pagesE-Relev - N - 005 (Partenaire N - 00000000433499) - 157351309 PDFJose GonzalezPas encore d'évaluation
- Tendances b2 Guide Corrig Transcrip (Respuestas)Document43 pagesTendances b2 Guide Corrig Transcrip (Respuestas)Wilber Rosas100% (1)
- The Lattice Boltzmann EquationDocument299 pagesThe Lattice Boltzmann EquationGanesh Chithambalam As100% (1)
- Cuento-Pablito-y-los-números-para Colorear PDFDocument12 pagesCuento-Pablito-y-los-números-para Colorear PDFAntonio Robaldi Vazquez100% (1)
- Libro Del Ascenso y Descenso Del Entendimiento PDFDocument84 pagesLibro Del Ascenso y Descenso Del Entendimiento PDFjaranibar_12Pas encore d'évaluation
- Ue0 Pompes TD Correction PDFDocument5 pagesUe0 Pompes TD Correction PDFFouad DimanePas encore d'évaluation
- Court Manual PDFDocument198 pagesCourt Manual PDFLesther CalabiasPas encore d'évaluation
- Uas Perencanaan Geometrik Jalan Syakhshiyah Islami A010319030 3a Teknik SipilDocument8 pagesUas Perencanaan Geometrik Jalan Syakhshiyah Islami A010319030 3a Teknik SipilSyakhshiyah IslamiPas encore d'évaluation
- Letra Himno A San MartinDocument4 pagesLetra Himno A San MartinJosé Luis Trigoso Paredes100% (1)
- Morsecode LipsumDocument2 pagesMorsecode LipsumIcecream lover101Pas encore d'évaluation
- Morsecode - The Hell Is ThisDocument1 pageMorsecode - The Hell Is ThisKairue Fans HardiPas encore d'évaluation
- 1689789334 (1)Document2 pages1689789334 (1)JackaxelPas encore d'évaluation
- Piping Design Part 2Document20 pagesPiping Design Part 2yesuplus2Pas encore d'évaluation
- Biological Effects of Electromagnetic Radiation-Radiowaves and Microwaves-Eurasian Communist CountriesDocument35 pagesBiological Effects of Electromagnetic Radiation-Radiowaves and Microwaves-Eurasian Communist CountriesM Del Mar RosaPas encore d'évaluation
- Corrigé Mécanique T1 GP1 2021Document6 pagesCorrigé Mécanique T1 GP1 2021kara baPas encore d'évaluation
- Bendi B3-30 Operators Manual F-492-0608Document112 pagesBendi B3-30 Operators Manual F-492-0608ИванPas encore d'évaluation
- Morsecode LipsumDocument1 pageMorsecode LipsumAnthony Ch'ngPas encore d'évaluation
- Pu"Blic of Ke:' - Ya: .RoelDocument1 pagePu"Blic of Ke:' - Ya: .RoelPeter OlooPas encore d'évaluation
- RoboCon 2016 RuleBookDocument39 pagesRoboCon 2016 RuleBookaakash30jan100% (1)
- (应用统计学丛书) 邵军 - 数理统计 (第二版) -高等教育出版社 (2018)Document581 pages(应用统计学丛书) 邵军 - 数理统计 (第二版) -高等教育出版社 (2018)YuanxingPas encore d'évaluation
- Fakoly DjembeDocument2 pagesFakoly DjembeDrew MakepeacePas encore d'évaluation
- Solutions To Sample QuestionsDocument8 pagesSolutions To Sample QuestionsbeefyboiwithahPas encore d'évaluation
- Unit 3Document4 pagesUnit 3Hazem MezoPas encore d'évaluation
- Adobe Scan 21 Jun 2022Document2 pagesAdobe Scan 21 Jun 2022Aput PupuPas encore d'évaluation
- Afunctional Approach Toward Sentence Connectives in EnglishDocument254 pagesAfunctional Approach Toward Sentence Connectives in EnglishthangdaotaoPas encore d'évaluation
- Questão 1 - ResoluçãoDocument1 pageQuestão 1 - ResoluçãoVictor SantosPas encore d'évaluation
- GOI DoT StationeryDocument1 pageGOI DoT Stationeryabc_dPas encore d'évaluation
- Theme: Afghan Film MagazineDocument48 pagesTheme: Afghan Film MagazineKDK FactoryPas encore d'évaluation
- Amines XIIDocument18 pagesAmines XIIarmandeeps100Pas encore d'évaluation
- D NG 1 LTDocument3 pagesD NG 1 LTAn BảoPas encore d'évaluation
- Drexel SL30!40!50 SE Operators Manual F-447-0308Document114 pagesDrexel SL30!40!50 SE Operators Manual F-447-0308marjan mircevskiPas encore d'évaluation
- MSC 2 Graph U1 Connectivity PartDocument12 pagesMSC 2 Graph U1 Connectivity PartTeertha SomanPas encore d'évaluation
- SOCIOBAS1P1C2T2KSRDocument3 pagesSOCIOBAS1P1C2T2KSRAagya DubeyPas encore d'évaluation
- Bendi AC Operators Manual F-522-0709Document114 pagesBendi AC Operators Manual F-522-0709Christian BedoyaPas encore d'évaluation
- DSA NotesDocument44 pagesDSA NotesGon FrecsPas encore d'évaluation
- Cálculo 1 - Regras de DerivaçãoDocument2 pagesCálculo 1 - Regras de DerivaçãoPablo BusattoPas encore d'évaluation
- 中科大少年班数学分析讲义Document243 pages中科大少年班数学分析讲义wwq10201999Pas encore d'évaluation
- Bendi Series IV SE Operators Manual F-505-0608Document114 pagesBendi Series IV SE Operators Manual F-505-0608ИванPas encore d'évaluation
- John Brennan NotesDocument2 pagesJohn Brennan NotesChuck Ross50% (2)
- Enclosure 1 Brennan Notes UDocument2 pagesEnclosure 1 Brennan Notes UJamie WhitePas encore d'évaluation
- Ratcliffe - Declassified Brennan NotesDocument2 pagesRatcliffe - Declassified Brennan NotesWashington ExaminerPas encore d'évaluation
- Enclosure 1 (Brennan Notes) - UDocument2 pagesEnclosure 1 (Brennan Notes) - UThe Epoch Times67% (6)
- ENCLOSURE 1 Brennan Notes U PDFDocument2 pagesENCLOSURE 1 Brennan Notes U PDFdiPas encore d'évaluation
- HANGCHA Spec 5324518cc81da1141Document99 pagesHANGCHA Spec 5324518cc81da1141greek_tester100% (1)
- Final Tariff Book FY 202223Document27 pagesFinal Tariff Book FY 202223DIRK HARDINGPas encore d'évaluation
- Rosa2000 DiguesDocument34 pagesRosa2000 DiguesomarbossPas encore d'évaluation
- AO 46-2022-P5 - Etudes de L Agressivite Des SolsDocument16 pagesAO 46-2022-P5 - Etudes de L Agressivite Des SolsRabii El HadratiPas encore d'évaluation
- Rec Dce95Document52 pagesRec Dce95Serge KamandaPas encore d'évaluation
- Mejoramiento de Complejo DeportivoDocument76 pagesMejoramiento de Complejo DeportivoGerson Rojas FloresPas encore d'évaluation
- CH 17 Forest Our Lifeline PDFDocument1 pageCH 17 Forest Our Lifeline PDFDARSH BHANDARIPas encore d'évaluation
- Rosa2000 Structures MétalliquesDocument37 pagesRosa2000 Structures MétalliquesomarbossPas encore d'évaluation
- Modelo SG-SST ImplementaciónDocument1 pageModelo SG-SST ImplementaciónDANIELA ALEXANDRA RANGEL RUBIOPas encore d'évaluation
- Practice QuestionDocument3 pagesPractice QuestionUtsav GaharwarPas encore d'évaluation
- Limite D'atterbergDocument30 pagesLimite D'atterbergEL BOUHADDIOUIPas encore d'évaluation
- Rec Alb97Document25 pagesRec Alb97Serge KamandaPas encore d'évaluation
- Exp 4Document2 pagesExp 4topic2knowPas encore d'évaluation
- Ouvrage en Site Aquatique - Talus Et PentesDocument35 pagesOuvrage en Site Aquatique - Talus Et PentesYouyou YanisPas encore d'évaluation
- Hydrologie DE LA Région DE SAN Pédro: Autorite Pour L'Amenagement DE La Region DU Sud - OuestDocument84 pagesHydrologie DE LA Région DE SAN Pédro: Autorite Pour L'Amenagement DE La Region DU Sud - OuestfouziPas encore d'évaluation
- Epreuve Et Corrige Bac 2022 LV1 Anglais Series A1 A2 Cote D'ivoireDocument11 pagesEpreuve Et Corrige Bac 2022 LV1 Anglais Series A1 A2 Cote D'ivoireGoueti bi100% (1)
- Traité d'économétrie financière: Modélisation financièreD'EverandTraité d'économétrie financière: Modélisation financièrePas encore d'évaluation
- Affichage Liste Admis Def2023 AekoulikoroDocument66 pagesAffichage Liste Admis Def2023 AekoulikoroSéga DIARRAH100% (1)
- 955 PDFDocument28 pages955 PDFdknewsPas encore d'évaluation
- Adjectifs de CouleurDocument2 pagesAdjectifs de CouleurOthmane MKPas encore d'évaluation
- MemoireDocument8 pagesMemoireDorra CheikhrouhouPas encore d'évaluation
- TOGOLA AdamaDocument91 pagesTOGOLA AdamaNasrallah ManesouriPas encore d'évaluation
- Rs - Unilever Ci - Exercice 2011Document2 pagesRs - Unilever Ci - Exercice 2011Anne Marie ApedohPas encore d'évaluation
- Etat Des Lieux CONGO Int - WebDocument80 pagesEtat Des Lieux CONGO Int - WebMichel Tolima kitokoPas encore d'évaluation
- Bec 0373-6237 1999 Num 157 1 450961Document72 pagesBec 0373-6237 1999 Num 157 1 450961Pedro PereiraPas encore d'évaluation
- 1 Activité1 PFG CORDocument1 page1 Activité1 PFG CORg.gyumikeyPas encore d'évaluation
- ExtraitDocument8 pagesExtraitogmios_94Pas encore d'évaluation
- Live SchoolDocument11 pagesLive SchoolOdingha WATTOPas encore d'évaluation
- Combien Coûte Un Comptable? Tarif de Comptable - GGLBDocument11 pagesCombien Coûte Un Comptable? Tarif de Comptable - GGLBGGLB CPAPas encore d'évaluation
- 2 FACplan Ob 3 H11Document99 pages2 FACplan Ob 3 H11rememguardPas encore d'évaluation
- Bibliographie Catholique Tome 12Document145 pagesBibliographie Catholique Tome 12Jorge Candido da Silva100% (1)
- La Théorie de Coût de TransactionDocument8 pagesLa Théorie de Coût de TransactionHanane Aya100% (1)
- PDF Paramettre de PaieDocument6 pagesPDF Paramettre de PaieOrdie Dana MAYINZA100% (1)
- Programme de Delestage Snel 2023Document18 pagesProgramme de Delestage Snel 2023Cartouche MougueroPas encore d'évaluation
- Mémoire Finalisã© Zouaoui Sabrina (SDL)Document61 pagesMémoire Finalisã© Zouaoui Sabrina (SDL)Razi AminePas encore d'évaluation
- CinemaDocument1 pageCinemaarrouasPas encore d'évaluation
- Cahier Des Charges Essais Sonique D'Intégrité Des Pieux PR Pk23+070Document27 pagesCahier Des Charges Essais Sonique D'Intégrité Des Pieux PR Pk23+070Secretariat KAFIPas encore d'évaluation
- Feminisation Decrets Gouvernementaux BelgesDocument19 pagesFeminisation Decrets Gouvernementaux BelgesSite Commune LanguePas encore d'évaluation
- Crise Covid Et Changement Social Potentialités Et ImpassesDocument2 pagesCrise Covid Et Changement Social Potentialités Et ImpassesMorgane BalsamoPas encore d'évaluation
- Mondialisation Et FM AIT SOUDANE Sept 22Document28 pagesMondialisation Et FM AIT SOUDANE Sept 22zinebPas encore d'évaluation
- Tsge Passage Cor Var 2Document6 pagesTsge Passage Cor Var 2Youssef BourzakPas encore d'évaluation
- Mode de FinancementDocument22 pagesMode de Financementmarwitos100% (1)
- Module Sur Les EnquetesDocument44 pagesModule Sur Les EnquetesAbdoulkadri DjibrillaPas encore d'évaluation
- Soy Luna (OST) - Paroles de Quiero Verte Sonreír + Traduction en FrançaisDocument6 pagesSoy Luna (OST) - Paroles de Quiero Verte Sonreír + Traduction en FrançaisfyhluciePas encore d'évaluation